-

@ 68c90cf3:99458f5c
2025-04-04 16:06:10
I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs.
YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each.
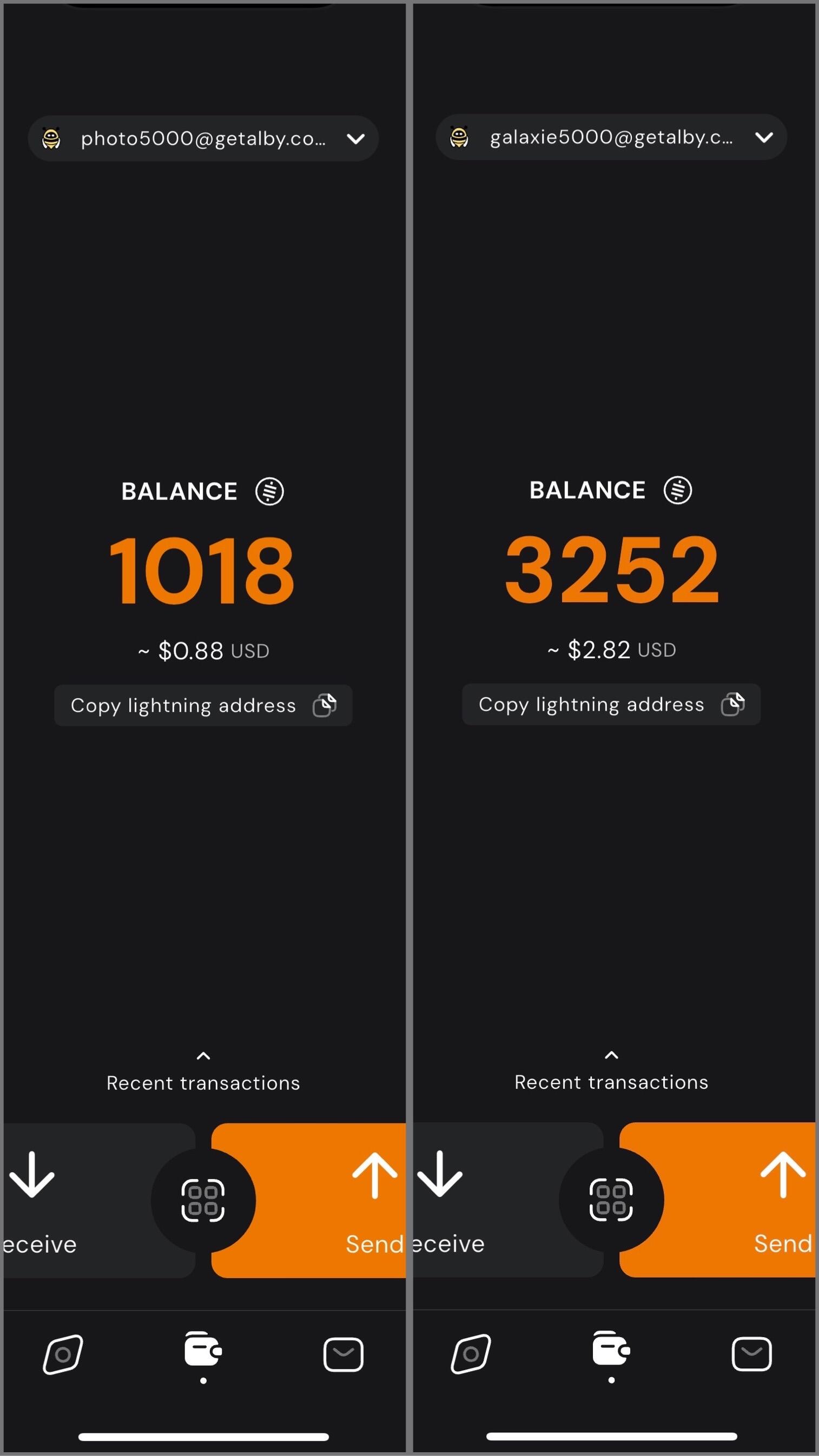
In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions.
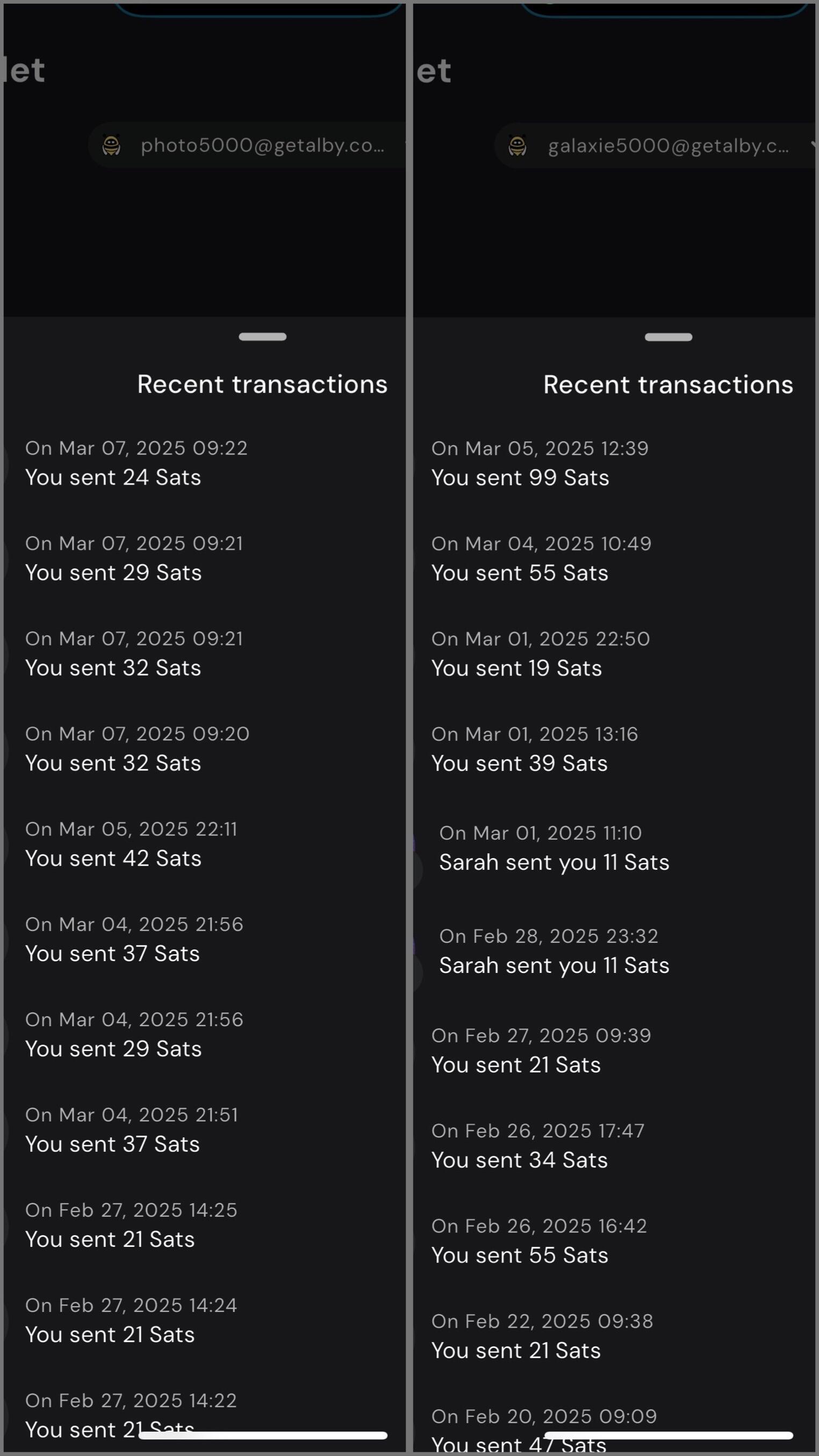
Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne.
#YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr
-

@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20
<h2> Test Video Document </h2>
-

@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02
<h1> Testy McTestenface </h1>
<p> It's been so long, html </p>
-

@ 9223d2fa:b57e3de7
2025-04-06 02:00:00
8183
-

@ 2e941ad1:fac7c2d0
2025-04-05 22:20:54
Unlocks: 40
-

@ fd06f542:8d6d54cd
2025-04-04 13:58:19
排名随机, 列表正在增加中。
1.) Cody Tseng
`
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
jumble作者`
2.)阿甘
`@agan0
0xchat.com
canidae40@coinos.io
https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce`
3.)joomaen
`Follows you
joomaen.com
95aebd@wallet.yakihonne.com
npub1wlpfd84ym...lfgqp74qq0
#nobot
https://joomaen.filegear-sg.me/
https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0`
4.)颜值精选官
`wasp@ok0.org
专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz`
5.)6svjszwk
`6svjszwk@ok0.org
83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
#low-time-preference
#anarcho-capitalism
#libertarianism
#bitcoin #monero
https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk`
6.)𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
`everyday@iris.to
虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
黑暗森林时代,当好小透明。
bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke`
7.) nostr_cn_dev
`npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
npub1l5r02s4ud...2nxsvum9jm
Developed the following products:
- NostrBridge, 网桥转发
- TaskQ5, 分布式多任务
- NostrHTTP, nostr to http
- Postr, 匿名交友,匿名邮局
- nostrclient (Python client) .
-nostrbook, (nostrbook.com) 用nostr在线写书
https://www.duozhutuan.com nostrhttp demo
https://github.com/duozhutuan/NostrBridge
https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm`
-

@ 39cc53c9:27168656
2025-03-30 05:54:53
> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks)
Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
## Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals.
## KYC? Not you.
> KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2]
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
## You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
## Your identity has been stolen
KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3]
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
## (they) Know Your Coins
You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
## Conclusions
To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
> Edited 20/03/2024
> * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1]
[^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/
[^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz
[^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
-

@ ec9bd746:df11a9d0
2025-04-06 08:06:08
## 🌍 Time Window:
🕘 **When**: Every even week on Sunday at 9:00 PM CET
🗺️ **Where**: https://cornychat.com/eurocorn
**Start:** 21:00 CET (Prague, UTC+1)
**End:** approx. 02:00 CET (Prague, UTC+1, next day)
**Duration:** usually 5+ hours.
| Region | Local Time Window | Convenience Level |
|-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------|
| **Europe (CET, Prague)** 🇨🇿🇩🇪 | **21:00–02:00 CET** | ✅ Very Good; evening & night |
| **East Coast North America (EST)** 🇺🇸🇨🇦 | **15:00–20:00 EST** | ✅ Very Good; afternoon & early evening |
| **West Coast North America (PST)** 🇺🇸🇨🇦 | **12:00–17:00 PST** | ✅ Very Good; midday & afternoon |
| **Central America (CST)** 🇲🇽🇨🇷🇬🇹 | **14:00–19:00 CST** | ✅ Very Good; afternoon & evening |
| **South America West (Peru/Colombia PET/COT)** 🇵🇪🇨🇴 | **15:00–20:00 PET/COT** | ✅ Very Good; afternoon & evening |
| **South America East (Brazil/Argentina/Chile, BRT/ART/CLST)** 🇧🇷🇦🇷🇨🇱 | **17:00–22:00 BRT/ART/CLST** | ✅ Very Good; early evening |
| **United Kingdom/Ireland (GMT)** 🇬🇧🇮🇪 | **20:00–01:00 GMT** | ✅ Very Good; evening hours (midnight convenient) |
| **Eastern Europe (EET)** 🇷🇴🇬🇷🇺🇦 | **22:00–03:00 EET** | ✅ Good; late evening & early night (slightly late) |
| **Africa (South Africa, SAST)** 🇿🇦 | **22:00–03:00 SAST** | ✅ Good; late evening & overnight (late-night common) |
| **New Zealand (NZDT)** 🇳🇿 | **09:00–14:00 NZDT (next day)** | ✅ Good; weekday morning & afternoon |
| **Australia (AEDT, Sydney)** 🇦🇺 | **07:00–12:00 AEDT (next day)** | ✅ Good; weekday morning to noon |
| **East Africa (Kenya, EAT)** 🇰🇪 | **23:00–04:00 EAT** | ⚠️ Slightly late (night hours; late night common) |
| **Russia (Moscow, MSK)** 🇷🇺 | **23:00–04:00 MSK** | ⚠️ Slightly late (join at start is fine, very late night) |
| **Middle East (UAE, GST)** 🇦🇪🇴🇲 | **00:00–05:00 GST (next day)** | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)|
| **Japan/Korea (JST/KST)** 🇯🇵🇰🇷 | **05:00–10:00 JST/KST (next day)** | ⚠️ Early; convenient joining from ~07:00 onwards possible |
| **China (Beijing, CST)** 🇨🇳 | **04:00–09:00 CST (next day)** | ❌ Challenging; very early morning start (better ~07:00 onwards) |
| **India (IST)** 🇮🇳 | **01:30–06:30 IST (next day)** | ❌ Very challenging; overnight timing typically difficult|
---
-

@ fd06f542:8d6d54cd
2025-04-04 13:37:59
- [首页](/readme.md)
- [国人开发者](/01.md)
- [中文用户列表](/02.md)
-

@ fd06f542:8d6d54cd
2025-04-04 13:34:38
## 国内开发者作品展
### jumble.social
作品: https://jumble.social/
其他作品 :
Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
Building 👨💻:
https://github.com/CodyTseng/jumble
https://github.com/CodyTseng/nostr-relay-tray
https://github.com/CodyTseng/danmakustr
https://github.com/CodyTseng/nostr-relay-nestjs
https://github.com/CodyTseng/nostr-relay
https://github.com/CodyTseng
### nostrbook.com
作品: https://nostrbook.com
- NostrBridge, 网桥转发
- TaskQ5, 分布式多任务
- NostrHTTP, nostr to http
- Postr, 匿名交友,匿名邮局
- nostrclient (Python client) .
-nostrbook, (nostrbook.com) 用nostr在线写书
https://www.duozhutuan.com nostrhttp demo
https://github.com/duozhutuan/NostrBridge
### nostrmo
A nostr dev.
#Nostrmo A client support all platform.
#Nowser A nostr signing project.
#CacheRelay A nostr cache relay peject.
#cfrelay A nostr relay base on cloudflare wokers.
A nostr note timing send service. https://sendbox.nostrmo.com/
https://github.com/haorendashu/nostrmo
### 0xchat
作者: wcat
w783@0xchat.com
www.0xchat.com
Building for 0xchat
www.0xchat.com
Secure Chat built on Nostr
App Store:
https://apps.apple.com/app/0xchat/id1637607169
TestFlight:
https://testflight.apple.com/join/AjdJFBmU
Google play:
https://play.google.com/store/apps/details?id=com.oxchat.nostr
-

@ 592295cf:413a0db9
2025-04-05 07:26:23
## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago
# 1.
### Nostr's adoption thesis
### The less you define, the more you imply
### by Wouter Constant
## 2.
### Dutch Bitcoiner
### AntiHashedPodcast
### Writing Book about nostr
00:40
## 3.
### What this presentation about
### A protocols design includes initself a thesis
### on protocol adoption, due to underlying assumptions
1:17
## 4.
### Examples
### Governments/Academic: Pubhubs (Matrix)
### Bussiness: Bluesky
### Foss: Nostr
1:58
## 5.
### What constitutes minimal viability?
### Pubhubs (Matrix): make is "safe" for user
### Bluesky: liability and monetization
### Foss: Simpel for developer
4:03
## 6.
### The Point of Nostr
### Capture network effects through interoperability
4:43
## 7.
## Three assumptions
### The direction is workable
### Method is workable
### Motivation and means are sufficient
5:27
## 8.
## Assumption 1
### The asymmetric cryptography paradigm is a good idea
6:16
## 9.
### Nostr is a exponent of the key-pair paradigm.
### And Basicly just that.
6.52
## 10.
### Keys suck
### Protect a secret that you are supposed use all the time.
7:37
## 11.
## Assumption two
### The unaddressed things will be figured out within a 'meta-design consensus'
8:11
## 12.
### Nostr's base protocol is not minimally viable for anything, except own development.
8:25
## 13.
### Complexity leads to capture;
### i.e. free and open in the name,
### controlled in pratice
9:54
## 14.
## Meta-design consensus
### Buildings things 'note centric' mantains interoperability.
11:51
## 15.
## Assumption three
### the nightmare is scary;
### the cream is appealing.
12:41
## 16.
### Get it minimally viable,
### for whatever target,
### such that it is not a waste of time.
13:23
## 17.
## Summarize
### We are in a nightmare.
### Assume key/signature are the way out.
### Assume we can Maintain an open stardand while manifesting the dream.
### Assume we are motivated enought to bootstrap this to adulthood.
14:01
## 18.
### We want this,
### we can do this,
### because we have to.
14:12
## Thank you for contribuiting
[Edit] Note for audio presentation
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
-

@ fd06f542:8d6d54cd
2025-04-04 02:39:25
## 使用nostrbook.com网站
登录和创建用户:

登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。
注册:

可以点击红标位置 生成你的账户。 “确定” 完成注册。
## 创建书籍
### 封面的上传

创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。
或者点击浏览 本地图片文件。
### 标题和作者
正常填写就可以。 书的作者和上传文件人没有一一绑定。
## 写书

创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。
### 列出你创建的所有的书籍

点击图标,就可以进入开始写作了。例如《nostrbook站点日记》

如图所示有4个部分
1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出”
2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。
3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。
4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。
-

@ 57d1a264:69f1fee1
2025-04-05 06:58:25
**Summary**
We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment.
**Responsibilities**
- Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity.
- Develop digital assets for marketing, social media, website, and app.
- Work within brand guidelines while exploring ways to evolve and strengthen our visual style.
**Requirements**
- 2+ years of experience in graphic design, with a strong focus on illustration.
- Ability to help define and develop a cohesive visual style for the brand.
- Proficiency in Adobe products.
- Experience with Figma is a plus.
- Strong organizational skills—your layers and files should be neatly labeled.
- Clear communication and collaboration skills to work effectively with the team.
- Located in LATAM
Please attach a link to your portfolio to showcase your work when applying.
[APPLY HERE](https://jan3.com/contact/)
originally posted at https://stacker.news/items/935007
-

@ fd06f542:8d6d54cd
2025-04-02 08:04:17
{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/1dd58d181d40edb7df942b5b16be3f82e95348a471d5a3620a9585f0af784fee.webp","title":"nostr资源收集","author":"nostrbook"}
-

@ fd06f542:8d6d54cd
2025-04-02 02:55:14
- [首页](/readme.md)
- [第一章、开发者指南](/01.md)
- [第二章、使用教程](/02.md)
-

@ 57d1a264:69f1fee1
2025-04-05 06:47:55
**Location:** Remote (Austria)
**Area:** Graphics and communication design
**Pay:** 37,500 € to 50,000 € / year
Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin.
👋 About the role
As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas.
**tasks**
- Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials
- Creation of individual content (posts, stories, banners, ads) for social media
- Planning and development of campaigns to strengthen the brand presence
- Further development of the existing corporate design support in the area of content management (website, blog)
**qualification**
- Completed training or studies in graphic design
- At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management
- Safe use of design tools such as Figma, Adobe Creative Suite
- Experience in creating social media content and maintaining channels
- Creativity, good communication skills and team spirit
- Very good knowledge of German and English
- Knowledge of Bitcoin is desirable
**Benefits**
- Offsites with the team in exciting places
- Flexible working hours in a company that relies on remote work
- Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation
- Buy Bitcoin without fees! 21 Premium!
- Gross annual salary & potential share options for outstanding performance / bonus payments
**📝 Interview process**
_How do I apply?_
Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect.
By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application!
_⁇ 京 Resume Review_
Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...)
_📞 Exploratory call_
We discuss what appeals to you about this role and ask you a few questions about your previous experiences
_👬 On-Site Deep Dive_
During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role.
_👍 Time for a decision!_
[APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner)
originally posted at https://stacker.news/items/935004
-

@ f3328521:a00ee32a
2025-04-06 08:51:05
*Notes from the Inaugural Muslim Bitcoin Summit Nostr Workshop.*
04.06.25
Dallas, TX
# What is Nostr?
> “Notes and Other Stuff Transmitted by Relays” ~ fiatjaf
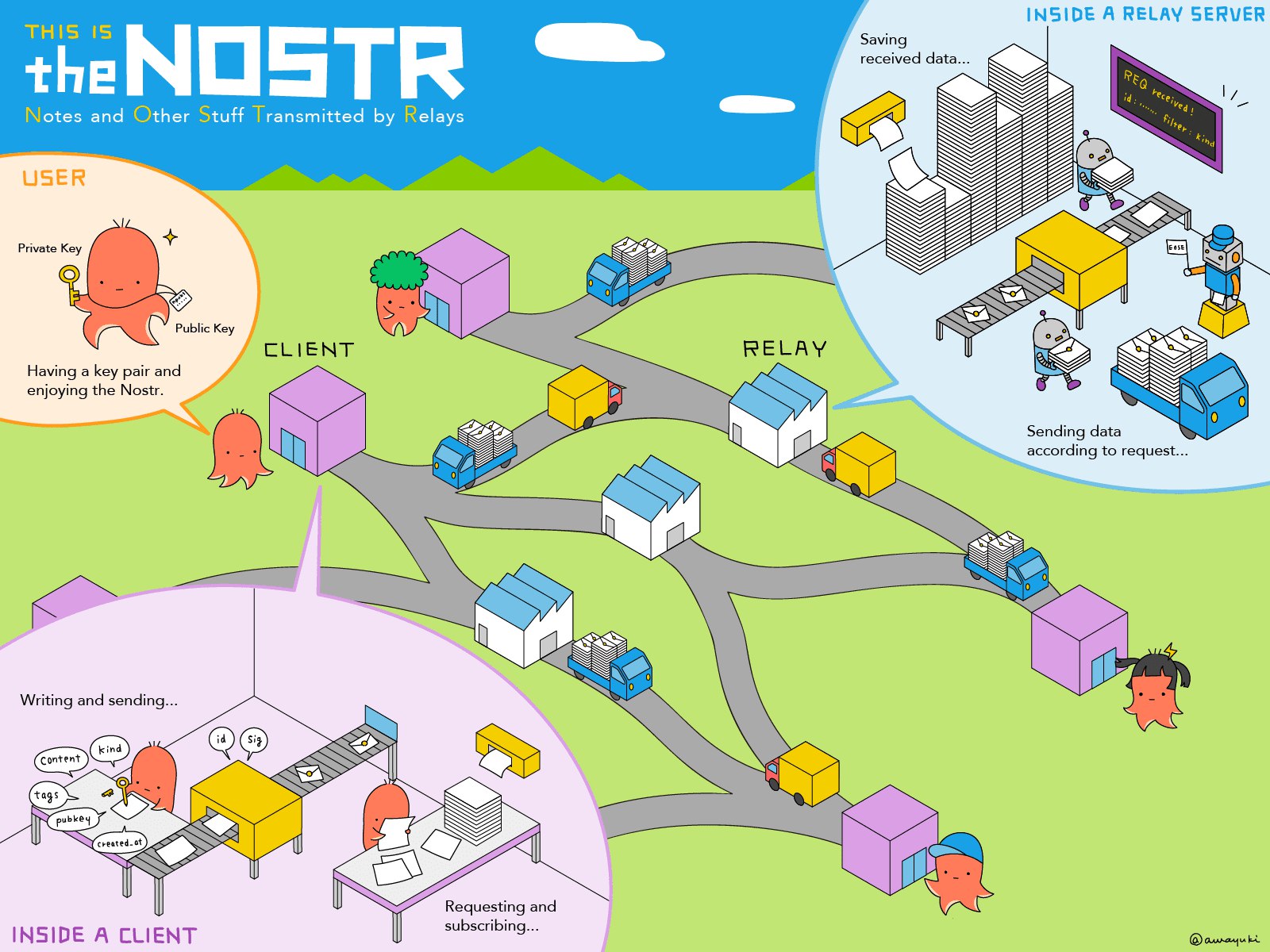
Nostr is an open protocol that is a censorship-resistant, global "social" network. It doesn't rely on any trusted central server (has resilient decentralization), and is based on cryptographic keys and signatures (so it is tamperproof).
The initial description of the idea can be found at https://fiatjaf.com/nostr.html.
## Digital Sovereignty
> “The first step towards establishing any type of Digital Sovereignty is to consider migration away from infrastructure and networks that are saturated with malevolent surveillance… there must be a simple recognition that anything sustainable from an Islamic perspective cannot be built on the platforms of Meta, Google or Amazon.” ~ [Ibn Maghreb](https://theiqrafiles.com/notes-on-digital-sovereignty/)
Palestine has become the litmus test for censorship in social media:
- X (formerly Twitter) - [Musk openly supports Zionism](https://english.almayadeen.net/articles/opinion/how-elon-musk-became-zionist--from-free-speech-absolutist-to)
- Meta (FB, IG, WhatsApp) - [Project Lavender](https://blog.paulbiggar.com/meta-and-lavender/)
- Google (YouTube) - [Project Nimbus](https://www.thenation.com/article/activism/google-firings-gaza-project-nimbus/)
- Microsoft (LI) - [BDS “No Azure for Apartheid” campaign](https://www.bdsmovement.net/microsoft)
These are just a few examples of the barrier for a muslim narrative in fiat social media. To build unstoppable resistance we must move away from the platform and address the issue at the protocol level.
## Nostr Protocol Explained
1. **Relays:**
Backend servers that store and broadcast data. Anyone can run one. Currently over 1k relays across over 50 countries.
2. **Clients:**
Platforms built for graphical user interface with Nostr. Anyone can build these and most are interoperable.
3. **Key Cryptography:**
public and private keys
*Simple video explaination: [Nostr in less than 10 minutes!](https://youtu.be/Q6f6bdKWqF8)*
### Nostr's Key Features:
- No Ownership - No CEO, board of directors, foundation, etc.
- No Ads, No Big Data Collection - Users are not a product.
- No Algorithms - Less drama, less depressing content.
- Uncensorability - Not your keys, not your posts.
- SEO - clean ```dofollow``` links for “Google Juice”.
- Zaps! - BTC/Lightning integration.
> “This is really really important in the age of AI where in a few years you are not going to know the difference between something that is real and something that is fake. We need technologies that you can actually sign and you have the authenticity to do so, and only you, to do that.” ~ [Jack Dorsey](https://youtu.be/0YDj1QdL2Zs)
## Getting Started On Nostr
### Nostr 101: **[A Beginners Guide To Nostr](https://mslmdvlpmnt.com/a-beginners-guide-to-nostr-2025/)**
**Top Recommended Client:** [Yakihonne](https://yakihonne.com/)
*Other popular options:
(web) [Nostrudel](https://nostrudel.ninja/)
(iOS) [Damus](https://damus.io/)
(Android) [Amethyst](https://www.amethyst.social/)*
**Top Recommended Wallet:** [Coinos](https://coinos.io/)
*Other popular options:
[Primal Wallet](https://primal.net/home)
[AlbyHub](https://albyhub.com/)
[Zeus](https://zeusln.com/)
(pending NWC integration)*
### Highlights From The Nostr Ecosystem:
Other Clients:
[Olas](https://olas.app/) (photos)
[Habla](https://habla.news/) (blogging)
[Zap.Stream](https://zap.stream/) (video)
Chat:
[0xchat](https://0xchat.com/#/)
[KeyChat](https://www.keychat.io/)
[Flotilla](https://flotilla.social/)
Shopping:
[Plebeian Market](https://plebeian.market/)
[Shopstr](https://shopstr.store/)
Podcasting 2.0:
[Fountain](https://fountain.fm/)
[Wavlake](https://wavlake.com/)
Workspace Tools:
[Listr](https://listr.lol/)
[Formstr](https://formstr.app/#/dashboard)
[Docstr](https://docstr.app/)
[Nostr.Build](https://nostr.build/)
Signers:
[Nos2X](https://nostrapps.com/nos2x)
[Nsec.app](https://nsec.app/)
## Footnote
[Find Muslims on Nostr](https://listr.lol/npub175nul9cvufswwsnpy99lvyhg7ad9nkccxhkhusznxfkr7e0zxthql9g6w0/30000/naddr1qq4xc6tnw3ez6efkxcun2cfkxqknzc348ykngcfnxvknsepsxukkxd33vc6x2vejv9jkgdqpp4mhxue69uhkummn9ekx7mqpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqg5waehxw309aex2mrp0yhxgctdw4eju6t0qgs02f70juxwyc88gfsjzjlkzt50wkjemvvrtmt7gpfnymplvh3r9msrqsqqqafsqfgqku) | [#staySAIF](https://saif.systems/articles/spiritual-opsec-guide)
-

@ 04c915da:3dfbecc9
2025-03-26 20:54:33
Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-

@ fd06f542:8d6d54cd
2025-04-02 01:35:00
## nostrbook 技术框架
源代码在 github.com
```
git clone https://github.com/nostrbook/nostrbook
cd nostrbook
npm install
npm run dev
```
* 网站主框架 vite + svelte
* 网站浏览书框架 docsify
## 网站主框架
svelte 为主,daisyui (tailwindcss) css 。
页面的逻辑结构 都是 svelte搭建的, 采用了 layout 左侧菜单。
菜单代码 在 https://github.com/nostrbook/nostrbook/blob/main/src/lib/SideMenu.svelte
菜单里用了弹框登录,弹框的代码基本是问的 AI。
子页面和 路由器看sveltekit规则编写。
### 书籍的数据
https://github.com/nostrbook/nostrbook/blob/main/src/lib/bookevent.ts
使用的nostr ndk 库来读写 relay。
书的 tag, 内容就是 标题,封面和作者。
```
[
['t',booktag],
['title',content['title']],
];
```
### 章节的数据
```
[
['t',chaptertag],
['title',title],
['d',filename + "-" + bookid],
['e',bookid],
];
```
这里面的 d,采用了 文件名 + bookid,所以每一本的章节名的文件名是唯一的。
### 配置文件
src/lib/config.ts,主要配置 服务器的地址
* 图片文件 nip96 服务器
* relays 服务器
* book的tag ,测试和 release不一样。 如果自己部署独有的服务器也可以不一样。这样内容可以垂直。
### 首页采用了缓冲机制
首页的内容来自 书籍的列表, 用booktag和30023来区分是不是书籍信息。
为了搜索引擎友好,让页面加载就有数据。
采用了 src/hooks.server.ts 预备加载数据,数据会被首页面 src/routes/+page.server.ts 传给 page.svelte去渲染。
这一切都是后台完成的。html页面加载的时候数据都已经渲染完成了。所以对搜索引擎非常友好。搞定了google,seo。
但是为了数据的完整性, 页面起来后会继续读取列表,这时候可能会显示最新的数据。
-

@ fd06f542:8d6d54cd
2025-04-02 01:15:20
NIP-07
======
`window.nostr` capability for web browsers
------------------------------------------
`draft` `optional`
The `window.nostr` object may be made available by web browsers or extensions and websites or web-apps may make use of it after checking its availability.
That object must define the following methods:
```
async window.nostr.getPublicKey(): string // returns a public key as hex
async window.nostr.signEvent(event: { created_at: number, kind: number, tags: string[][], content: string }): Event // takes an event object, adds `id`, `pubkey` and `sig` and returns it
```
Aside from these two basic above, the following functions can also be implemented optionally:
```
async window.nostr.nip04.encrypt(pubkey, plaintext): string // returns ciphertext and iv as specified in nip-04 (deprecated)
async window.nostr.nip04.decrypt(pubkey, ciphertext): string // takes ciphertext and iv as specified in nip-04 (deprecated)
async window.nostr.nip44.encrypt(pubkey, plaintext): string // returns ciphertext as specified in nip-44
async window.nostr.nip44.decrypt(pubkey, ciphertext): string // takes ciphertext as specified in nip-44
```
### Recommendation to Extension Authors
To make sure that the `window.nostr` is available to nostr clients on page load, the authors who create Chromium and Firefox extensions should load their scripts by specifying `"run_at": "document_end"` in the extension's manifest.
### Implementation
See https://github.com/aljazceru/awesome-nostr#nip-07-browser-extensions.
-

@ da0b9bc3:4e30a4a9
2025-04-06 07:38:03
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/935880
-

@ 57d1a264:69f1fee1
2025-04-05 06:35:58
We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals.
**Key Responsibilities:**
- Design and improve the @Bipa app experience, focusing on usability and measurable business impact.
- Apply data-driven design, making decisions based on user research, metrics, and testing.
- Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product.
- Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy.
- Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations.
- Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business.
- Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app.
**Qualifications:**
- Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps.
- Solid understanding of user-centered design (UCD) principles and usability heuristics.
- Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis.
- Ability to work with both quantitative and qualitative data to guide design decisions.
- Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement).
- Proficiency in design tools like Figma (or similar).
- Experience working with design systems and design tokens to ensure consistency.
- Comfortable working in an agile, fast-paced, and iterative environment.
- Strong communication skills and the ability to advocate for design decisions backed by research and data.
**Benefits:**
🏥 Health Insurance
💉 Dental Plan
🍽️ Meal Allowance (CAJU card)
💻 Home Office Stipend
📈 Stock Options from Day One
[APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer)
originally posted at https://stacker.news/items/935003
-

@ fd06f542:8d6d54cd
2025-04-02 01:14:45
- [首页](/readme.md)
- [第一章、 NIP-01: Basic protocol flow description](/01.md)
- [第二章、 NIP-02: Follow List](/02.md)
- [第三章、NIP-03: OpenTimestamps Attestations for Events](/03.md)
- [第四章、NIP-04: Encrypted Direct Message](/04.md)
- [第五章、NIP-05: Mapping Nostr keys to DNS-based internet identifiers](/05.md)
- [第六章、NIP-06: Basic key derivation from mnemonic seed phrase](/06.md)
- [第七章、NIP-07: window.nostr capability for web browsers](/07.md)
-

@ 57d1a264:69f1fee1
2025-04-05 06:28:16
### ⚡️ About Us
@AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY.
### ⚡️ The Role
Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision.
### ⚡️ Responsibilities
Produce 30 short videos on circular economies.
Incorporate subtitles as needed.
Submit videos on a deliverables basis.
Participate in check-ins and communicate with the AB team and circular economy communities.
### ⚡️ What We Offer
Free ticket to AB25.
Networking with Bitcoiners and industry leaders.
Letter of recommendation and LinkedIn endorsement upon completion.
Mentorship and hands-on experience with a high-profile Bitcoin project.
### ⚡️ Skills & Qualifications
Passion for Bitcoin and circular economies.
Basic to intermediate video editing skills (no specific software required).
Creative independence with feedback.
Portfolio or work samples preferred.
### ⚡️ Time Commitment
Flexible, project-based internship with check-ins and feedback rounds.
### ⚡️ How to Apply
Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available).
originally posted at https://stacker.news/items/935001
-

@ fd06f542:8d6d54cd
2025-04-01 02:04:45
NIP-06
======
Basic key derivation from mnemonic seed phrase
----------------------------------------------
`draft` `optional`
[BIP39](https://bips.xyz/39) is used to generate mnemonic seed words and derive a binary seed from them.
[BIP32](https://bips.xyz/32) is used to derive the path `m/44'/1237'/<account>'/0/0` (according to the Nostr entry on [SLIP44](https://github.com/satoshilabs/slips/blob/master/slip-0044.md)).
A basic client can simply use an `account` of `0` to derive a single key. For more advanced use-cases you can increment `account`, allowing generation of practically infinite keys from the 5-level path with hardened derivation.
Other types of clients can still get fancy and use other derivation paths for their own other purposes.
### Test vectors
mnemonic: leader monkey parrot ring guide accident before fence cannon height naive bean\
private key (hex): 7f7ff03d123792d6ac594bfa67bf6d0c0ab55b6b1fdb6249303fe861f1ccba9a\
nsec: nsec10allq0gjx7fddtzef0ax00mdps9t2kmtrldkyjfs8l5xruwvh2dq0lhhkp\
public key (hex): 17162c921dc4d2518f9a101db33695df1afb56ab82f5ff3e5da6eec3ca5cd917\
npub: npub1zutzeysacnf9rru6zqwmxd54mud0k44tst6l70ja5mhv8jjumytsd2x7nu
---
mnemonic: what bleak badge arrange retreat wolf trade produce cricket blur garlic valid proud rude strong choose busy staff weather area salt hollow arm fade\
private key (hex): c15d739894c81a2fcfd3a2df85a0d2c0dbc47a280d092799f144d73d7ae78add\
nsec: nsec1c9wh8xy5eqdzln7n5t0ctgxjcrdug73gp5yj0x03gntn67h83twssdfhel\
public key (hex): d41b22899549e1f3d335a31002cfd382174006e166d3e658e3a5eecdb6463573\
npub: npub16sdj9zv4f8sl85e45vgq9n7nsgt5qphpvmf7vk8r5hhvmdjxx4es8rq74h
-

@ c631e267:c2b78d3e
2025-04-04 18:47:27
*Zwei mal drei macht vier,* *\
widewidewitt und drei macht neune,* *\
ich mach mir die Welt,* *\
widewide wie sie mir gefällt.* *\
Pippi Langstrumpf*  
**Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
**In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
**Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
**Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
**Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
**Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen.
**Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür.
*\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen.
-

@ fd06f542:8d6d54cd
2025-03-31 10:00:34
NIP-05
======
Mapping Nostr keys to DNS-based internet identifiers
----------------------------------------------------
`final` `optional`
On events of kind `0` (`user metadata`) one can specify the key `"nip05"` with an [internet identifier](https://datatracker.ietf.org/doc/html/rfc5322#section-3.4.1) (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the `<local-part>` part will be restricted to the characters `a-z0-9-_.`, case-insensitive.
Upon seeing that, the client splits the identifier into `<local-part>` and `<domain>` and use these values to make a GET request to `https://<domain>/.well-known/nostr.json?name=<local-part>`.
The result should be a JSON document object with a key `"names"` that should then be a mapping of names to hex formatted public keys. If the public key for the given `<name>` matches the `pubkey` from the `user metadata` event, the client then concludes that the given pubkey can indeed be referenced by its identifier.
### Example
If a client sees an event like this:
```jsonc
{
"pubkey": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9",
"kind": 0,
"content": "{\"name\": \"bob\", \"nip05\": \"bob@example.com\"}"
// other fields...
}
```
It will make a GET request to `https://example.com/.well-known/nostr.json?name=bob` and get back a response that will look like
```json
{
"names": {
"bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9"
}
}
```
or with the **recommended** `"relays"` attribute:
```json
{
"names": {
"bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9"
},
"relays": {
"b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9": [ "wss://relay.example.com", "wss://relay2.example.com" ]
}
}
```
If the pubkey matches the one given in `"names"` (as in the example above) that means the association is right and the `"nip05"` identifier is valid and can be displayed.
The recommended `"relays"` attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve `/.well-known/nostr.json` files dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available.
## Finding users from their NIP-05 identifier
A client may implement support for finding users' public keys from _internet identifiers_, the flow is the same as above, but reversed: first the client fetches the _well-known_ URL and from there it gets the public key of the user, then it tries to fetch the kind `0` event for that user and check if it has a matching `"nip05"`.
## Notes
### Identification, not verification
The NIP-05 is not intended to _verify_ a user, but only to _identify_ them, for the purpose of facilitating the exchange of a contact or their search.
Exceptions are people who own (e.g., a company) or are connected (e.g., a project) to a well-known domain, who can exploit NIP-05 as an attestation of their relationship with it, and thus to the organization behind it, thereby gaining an element of trust.
### User discovery implementation suggestion
A client can use this to allow users to search other profiles. If a client has a search box or something like that, a user may be able to type "bob@example.com" there and the client would recognize that and do the proper queries to obtain a pubkey and suggest that to the user.
### Clients must always follow public keys, not NIP-05 addresses
For example, if after finding that `bob@bob.com` has the public key `abc...def`, the user clicks a button to follow that profile, the client must keep a primary reference to `abc...def`, not `bob@bob.com`. If, for any reason, the address `https://bob.com/.well-known/nostr.json?name=bob` starts returning the public key `1d2...e3f` at any time in the future, the client must not replace `abc...def` in his list of followed profiles for the user (but it should stop displaying "bob@bob.com" for that user, as that will have become an invalid `"nip05"` property).
### Public keys must be in hex format
Keys must be returned in hex format. Keys in NIP-19 `npub` format are only meant to be used for display in client UIs, not in this NIP.
### Showing just the domain as an identifier
Clients may treat the identifier `_@domain` as the "root" identifier, and choose to display it as just the `<domain>`. For example, if Bob owns `bob.com`, he may not want an identifier like `bob@bob.com` as that is redundant. Instead, Bob can use the identifier `_@bob.com` and expect Nostr clients to show and treat that as just `bob.com` for all purposes.
### Reasoning for the `/.well-known/nostr.json?name=<local-part>` format
By adding the `<local-part>` as a query string instead of as part of the path, the protocol can support both dynamic servers that can generate JSON on-demand and static servers with a JSON file in it that may contain multiple names.
### Allowing access from JavaScript apps
JavaScript Nostr apps may be restricted by browser [CORS][] policies that prevent them from accessing `/.well-known/nostr.json` on the user's domain. When CORS prevents JS from loading a resource, the JS program sees it as a network failure identical to the resource not existing, so it is not possible for a pure-JS app to tell the user for certain that the failure was caused by a CORS issue. JS Nostr apps that see network failures requesting `/.well-known/nostr.json` files may want to recommend to users that they check the CORS policy of their servers, e.g.:
```bash
$ curl -sI https://example.com/.well-known/nostr.json?name=bob | grep -i ^Access-Control
Access-Control-Allow-Origin: *
```
Users should ensure that their `/.well-known/nostr.json` is served with the HTTP header `Access-Control-Allow-Origin: *` to ensure it can be validated by pure JS apps running in modern browsers.
[CORS]: https://developer.mozilla.org/en-US/docs/Web/HTTP/CORS
### Security Constraints
The `/.well-known/nostr.json` endpoint MUST NOT return any HTTP redirects.
Fetchers MUST ignore any HTTP redirects given by the `/.well-known/nostr.json` endpoint.
-

@ c631e267:c2b78d3e
2025-04-03 07:42:25
**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten.
**Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
**Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
**Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
**Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
**Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
**Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
**In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]*
*Dazu passend:*
[Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m)
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
-

@ 554ab6fe:c6cbc27e
2025-04-06 03:13:25
We all know that sex can be pleasurable, and most of us seek it as a core aspect of a fulfilled life. We do this instinctively, like the desire to eat good food or have a nice restful sleep. Yet, we rarely discuss how sex is potentially a very important aspect of our mental and physical health. Most don’t even know if it is, and we have a culture that often treats sex as a taboo. Here, the physical and mental health benefits of sex will be explored. Additionally, I will make an argument that sex is potentially a core aspect of holistic health that is improved when other aspects of health are maintained.
In a previous blog post discussing how mindfulness was a core aspect of ancient hunter gather life, I began to formulate an idea: perhaps all core aspects on ancient human life can be seen as sure ways to promote physical and mental health. As of now, I have identified “Six Pillars” of life, which could be said to be: exercise, meditation (mindfulness), diet, sleep, social relationships and sex. We all take for granted the important effect exercise, diet, and sleep have on health. One of the main purposes of this blog is to discuss how meditation belongs in this list as well. What about sex? I had a question, so I began researching.
Sex and a Longer Life
What became immediately identifiable was a weird bias within the scientific community in regards to sex research. Despite the fact that it is very difficult to find any scientist that disagrees with the notion that sex is fundamental to health(Jannini et al., 2009), most research focuses on the negative aspects of sex(Diamond & Huebner, 2012). Most research focuses on the occurrence of sexually transmitted infections, abuses and assaults, unplanned pregnancies, and so forth(Diamond & Huebner, 2012). Rarely, is there investigation into what happens in the body that makes sex so healthy. This is an incredible shame, because the research that we do have, reveals an incredible observation: people who have more sex (more orgasms) live longer lives (Lindau & Gavrilova, 2010; Smith et al., 1997). We aren’t sure how, but we commonly observe this trend. There was a similar observation observed during the COVID-19 lock down, where the more sex someone had during that time, the less anxiety and depression they had(Mollaioli et al., 2021). Does sex improve mental health, physical health, or both? Again, we certainly do not have a full understanding given the lack of research, but there are some clues to say that both are benefited.
As previously stated, sex may improve mental health in regards to stress. This seems fairly intuitive. Additionally, similar to the benefits of meditation, people who more frequently have sexual intercourse show greater resilience to incoming stressors, while also showing healthier blood pressure levels (the same was not true in masturbators)(Brody, 2006). Of course, mental health also leads to physical health.
Nonetheless, the benefits of sex are not purely mentally induced. A lot of attention has also been directed towards the direct physical benefits of sex. For example, there is increasing evidence that sexual activity decreases the risk of prostate cancer(Giles et al., 2003; Leitzmann et al., 2004). Additionally, sexual activity seems to create changes in hormone production that not only benefit health, but it also generates a positive feedback loop creating more sexual desire. Further incentivizing more sexual activity. Sexual activity affects testosterone levels, and low testosterone is common in erectile dysfunction(Jannini et al., 2009). So just like our neurons that have the “use it or lose it” principle, perhaps the penis does too. This trend doesn’t only apply to men either. Other research has shown that the more sex a woman has, the more lubricated their vaginas become(Leiblum, 1983). Similarly, more sexually active woman has less vaginal atrophy and higher levels of hormones (androstenedione, testosterone and gonadotropins). Indicating that more sex generates more sexual function and desire. This generates a positive feedback loop that potentially drives further healthy lifestyle practices in regards to sexual activity.
Mindfulness and Sex
It is evident that sex improves sex at a physiologic level. It may also be obvious that physical fitness can improve sex as well. So how does mindfulness meditation relate to sex?
Firstly, it should be noted that there is a large population of people that suffers from sexual dysfunction. Women are the most affected. Sexual desire is strongly related to relationship satisfaction, mood, self-esteem, body image, psychiatric symptoms, and age(Brotto & Basson, 2014). 24% of woman have either always suffered from a reduced orgasmic sensation by 75-100% or have developed this disorder over time(Adam et al., 2020). Female sexual interest/arousal disorder (SIAD) is defined by low level of sexual desire, infrequent sexual thoughts/fantasies, low receptivity to sexual activity, low sexual pleasure, low desire triggered by sexual stimuli, and low genital and non-genital sensations(Paterson et al., 2017). Therefore, it is highly apparent that mental health, especially as it related to the perception of the self, can have dramatic effects in not only sexual desire, but sexual pleasure as well. However, this problem is not specific to woman at all. Emotions related to depression are highly related to sexual dysfunction in both men and woman(Nobre & Pinto-Gouveia, 2006). Most notably, performance anxiety influences the occurrence of erectile dysfunction(Brotto & Basson, 2014). Given the relationship between sex and health, resolving such sexual dysfunction is crucial to improving general health and well-being.
Given the fact that mental state in various ways contributes to sexual dysfunction, meditation is a strong candidate for a useful therapy. As previously discussed in this blog, mindfulness meditation is a practice of generating a non-judgmental, open, and curious orientation towards all incoming thoughts and stimuli of the present moment(Bishop et al., 2006). For this reason, I have written about how the practice has been shown to be highly capable of decreasing symptoms of anxiety and depression. These symptoms of ruminative thoughts that burden the mind during sex, are alleviated through meditation. So, it is unsurprising that mindfulness-based cognitive therapy (MBCT) has been shown to be helpful in improving sexual function(Adam et al., 2020). Additionally, a new form of therapy called Mindfulness-Based Sex therapy (MBST) has been developed for these very reasons(Brotto et al., 2016). Mindfulness is recommended as a therapy for sexual dysfunction(Brotto & Goldmeier, 2015), but why?
How it works
As previously discussed, one way mindfulness meditation improves sexual function is through the changes it generates within the mind. Multiple studies have shown that through mindfulness, not only are the traits of depression and sex-related distress decreased, but woman subsequently experience greater sexual desire and improved sexual function(Adam et al., 2020; Brotto & Basson, 2014; Paterson et al., 2017). Women who were previously low on sexual desire, have improved sexual desire through mindfulness(Brotto et al., 2016). This is likely because the mental schemas that negatively affected their sex life are diminished through a practice of mindfulness meditation. Research using MBST has suggested that enhancing concentration and compassionate self-acceptance may lead to greater integration of physical and mental sexual response to erotic stimuli(Brotto et al., 2016).
Even though the psychological arguments for how meditation improves sexual function are convincing, I personally require more evidence. The mind is a window into the body, and therefore analyzing human health through the lenses of the thoughts of the mind only is not substantial evidence for me to be convinced. There are of course more complex physiologic processes that may go to explain these observed effects.
In a previous post, I argue that meditation can influence our conscious experience by quieting the mind, allowing, for the brain to more accurately and efficiently process incoming stimuli. This allows us to have healthier and more informative understanding of ourselves (our body) and the world around us (our environment). If this is indeed the case, then we would expect to see mindfulness result in improves processing of physical stimuli. In the case of sexual performance, this certainly seems to be the case. Studies have shown a mindfulness meditation practice increases reaction time for sexual stimuli(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). This is a strong indicator that through mindfulness, individuals will have a more accurate and clear experience generated from sexual stimuli, allowing for greater pleasure and performance. Additionally, it was noted in the study that woman take longer to respond to sexual stimuli compared to men, and the impaired ability to do so leads to self-judgment(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). So, if mindfulness can alleviate this impairment, and improve self-perception, then it creates a positive feedback loop of mental health improving sexual function which in turn improves mental health.
Since improved interoception (ability to sense inside the body) is suspected to be involved in this process, the insula of the brain, which has been implicated to play a major role in interoception(Giuliani et al., 2011), likely plays a role in the physiologic change that occurs. For reasons like the ones in my previous post, the insula is also regarded as a possible neuronal area related to consciousness(Craig, 2009). As it relates to sexual function, it is possible that improved insula-mediated increase in interoceptive ability from various mindfulness exercises contributed to the observed improved concordance between genital and subjective arousal after MBST(Brotto et al., 2016). This theory is reinforced by the observation that the insula increases in size following mindfulness meditation practices(Hölzel et al., 2011; Lazar et al., 2005). Indicating that because mindfulness meditation is oriented around the attentive observation of internal stimuli, the brain area involved is strengthened and grows. This allows for greater interoception in all cases, including sexual stimuli, thereby improving sexual function.
Conclusion
Exercise, social relationships, meditation, diet, sleep, and sex are fundamental aspects of human life. When looking back onto ancient human life, all of these aspects were fundamental to our health and prosperity. What was true then is still true now. Unsurprisingly, scientist commonly agree that safe sexual activity is an important aspect of maintaining general well-being and health. There have been studies that suggested that the more sex you have, the longer you may live. Unfortunately, the stresses of modern-day life, and the associated manifestations of self-judgment, lack of perceived self-worth, and unrealistic standards of beauty and sexual appeal have hindered some in being able to fully experience and practice a healthy sex life. Therefore, it is important to consider how other healthy life practices, such as meditation, are not only important in their own right, but are important because they may foster other healthy life habits in other areas, such as sexual activity. To calm the mind and rid it of our unconstructive ruminative thoughts once again is shown to be crucial to achieving a life of mental and physical well-being and health. Let us free our minds, free our hearts, and enjoy the present and our lives for all of its worth and beauty.
References
Adam, F., de Sutter, P., Day, J., & Grimm, E. (2020). A Randomized Study Comparing Video-Based Mindfulness-Based Cognitive Therapy With Video-Based Traditional Cognitive Behavioral Therapy in a Sample of Women Struggling to Achieve Orgasm. Journal of Sexual Medicine, 17(2), 312–324. https://doi.org/10.1016/j.jsxm.2019.10.022
Bishop, S. R., Lau, M., Shapiro, S., Carlson, L., Anderson, N. D., Carmody, J., Segal, Z. v., Abbey, S., Speca, M., Velting, D., & Devins, G. (2006). Mindfulness: A Proposed Operational Definition. Clinical Psychology: Science and Practice, 11(3), 230–241. https://doi.org/10.1093/clipsy.bph077
Brody, S. (2006). Blood pressure reactivity to stress is better for people who recently had penile-vaginal intercourse than for people who had other or no sexual activity. Biological Psychology, 71(2), 214–222. https://doi.org/10.1016/j.biopsycho.2005.03.005
Brotto, L. A., & Basson, R. (2014). Group mindfulness-based therapy significantly improves sexual desire in women. Behaviour Research and Therapy, 57(1), 43–54. https://doi.org/10.1016/j.brat.2014.04.001
Brotto, L. A., Chivers, M. L., Millman, R. D., & Albert, A. (2016). Mindfulness-Based Sex Therapy Improves Genital-Subjective Arousal Concordance in Women With Sexual Desire/Arousal Difficulties. Archives of Sexual Behavior, 45(8), 1907–1921. https://doi.org/10.1007/s10508-015-0689-8
Brotto, L. A., & Goldmeier, D. (2015). Mindfulness Interventions for Treating Sexual Dysfunctions: The Gentle Science of Finding Focus in a Multitask World. Journal of Sexual Medicine, 12(8), 1687–1689. https://doi.org/10.1111/jsm.12941
Craig, A. D. B. (2009). How do you feel — now? The anterior insula and human awareness. 10(January).
Diamond, L. M., & Huebner, D. M. (2012). Is good sex good for you? Rethinking sexuality and health. Social and Personality Psychology Compass, 6(1), 54–69. https://doi.org/10.1111/j.1751-9004.2011.00408.x
Giles, G. G., Severi, G., English, D. R., Mccredie, M. R. E., Borland, R., Boyle, P., & Hopper, J. L. (2003). Sexual factors and prostate cancer. BJU International, 92(3), 211–216. https://doi.org/10.1046/j.1464-410X.2003.04319.x
Giuliani, N. R., Drabant, E. M., Bhatnagar, R., & Gross, J. J. (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. NeuroImage, 58(1), 10–15. https://doi.org/10.1016/J.NEUROIMAGE.2011.06.028
Hölzel, B. K., Lazar, S. W., Gard, T., Schuman-Olivier, Z., Vago, D. R., & Ott, U. (2011). How Does Mindfulness Meditation Work? Proposing Mechanisms of Action From a Conceptual and Neural Perspective. Perspectives on Psychological Science, 6(6), 537–559. https://doi.org/10.1177/1745691611419671
Jannini, E. A., Fisher, W. A., Bitzer, J., & McMahon, C. G. (2009). Is sex just fun? How sexual activity improves health. Journal of Sexual Medicine, 6(10), 2640–2648. https://doi.org/10.1111/j.1743-6109.2009.01477.x
Lazar, S. W., Kerr, C. E., Wasserman, R. H., Gray, J. R., Greve, D. N., Treadway, M. T., McGarvey, M., Quinn, B. T., Dusek, J. A., Benson, H., Rauch, S. L., Moore, C. I., & Fischl, B. (2005). Meditation experience is associated with increased cortical thickness. Neuroreport, 16(17), 1893–1897. https://doi.org/10.1097/01.wnr.0000186598.66243.19
Leiblum, S. (1983). Vaginal Atrophy in the Postmenopausal Woman. Jama, 249(16), 2195. https://doi.org/10.1001/jama.1983.03330400041022
Leitzmann, M. F., Platz, E. A., Stampfer, M. J., Willett, W. C., & Giovannucci, E. (2004). Ejaculation Frequency and Subsequent Risk of Prostate Cancer. Journal of the American Medical Association, 291(13), 1578–1586. https://doi.org/10.1001/jama.291.13.1578
Lindau, S. T., & Gavrilova, N. (2010). Sex, health, and years of sexually active life gained due to good health: Evidence from two US population based cross sectional surveys of ageing. BMJ (Online), 340(7746), 580. https://doi.org/10.1136/bmj.c810
Mollaioli, D., Sansone, A., Ciocca, G., Limoncin, E., Colonnello, E., di Lorenzo, G., & Jannini, E. A. (2021). Benefits of Sexual Activity on Psychological, Relational, and Sexual Health During the COVID-19 Breakout. Journal of Sexual Medicine, 18(1), 35–49. https://doi.org/10.1016/j.jsxm.2020.10.008
Nobre, P. J., & Pinto-Gouveia, J. (2006). Emotions during sexual activity: Differences between sexually functional and dysfunctional men and women. Archives of Sexual Behavior, 35(4), 491–499. https://doi.org/10.1007/s10508-006-9047-1
Paterson, L. Q. P., Handy, A. B., & Brotto, L. A. (2017). A Pilot Study of Eight-Session Mindfulness-Based Cognitive Therapy Adapted for Women’s Sexual Interest/Arousal Disorder. Journal of Sex Research, 54(7), 850–861. https://doi.org/10.1080/00224499.2016.1208800
R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, P. (2011). Effects of Mindfulness Training on Body Awareness to Sexual Stimuli: Implications for Female Sexual Dysfunction. Psychosom Med., 23(1), 1–7. https://doi.org/10.1097/PSY.0b013e318234e628.Effects
Smith, G. D., Frankel, S., & Yarnell, J. (1997). Sex and death: Are they related? Findings from the Caerphilly cohort study. BMJ, 315(7123), 1641–1644. https://doi.org/10.1136/bmj.315.7123.1641
-

@ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04
Dose:
```
30g coffee (Fine-medium grind size)
500mL soft or bottled water (97°C / 206.6°F)
```
Instructions:
1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer.
2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds.
3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase.
4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds.
5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds.
6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction.
7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds.
8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper.
9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
-

@ b2d670de:907f9d4a
2025-03-25 20:17:57
This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
## Table of Contents
1. Prerequisites
2. Initial Server Setup
3. Installing Strfry Nostr Relay
4. Configuring Your Relay
5. Setting Up TOR
6. Making Your Relay Available on TOR
7. Testing Your Setup]
8. Maintenance and Security
9. Troubleshooting
## Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
## Initial Server Setup
First, let's make sure your server is properly set up and secured.
### Update Your System
Connect to your server via SSH and update your system:
```bash
sudo apt update
sudo apt upgrade -y
```
### Set Up a Basic Firewall
Install and configure a basic firewall:
```bash
sudo apt install ufw -y
sudo ufw allow ssh
sudo ufw enable
```
This allows SSH connections while blocking other ports for security.
## Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md).
### Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
```bash
sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev
```
Here's why each dependency is needed:
**Basic Development Tools:**
- `git`: Version control system used to clone the Strfry repository and manage code updates
- `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools
**Perl Dependencies** (used for Strfry's build scripts):
- `libyaml-perl`: Perl interface to parse YAML configuration files
- `libtemplate-perl`: Template processing system used during the build process
- `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts
**Core Libraries for Strfry:**
- `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations
- `zlib1g-dev`: Compression library that Strfry uses to reduce data size
- `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend
- `libflatbuffers-dev`: Memory-efficient serialization library for structured data
- `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures
- `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission
### Clone and Build Strfry
Clone the Strfry repository:
```bash
git clone https://github.com/hoytech/strfry.git
cd strfry
```
Build Strfry:
```bash
git submodule update --init
make setup-golpe
make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)
```
This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
### Install Strfry
Install the Strfry binary to your system path:
```bash
sudo cp strfry /usr/local/bin
```
This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.
## Configuring Your Relay
### Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
```bash
sudo useradd -M -s /usr/sbin/nologin strfry
```
The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts.
### Create Data Directory
Create a directory for Strfry's data:
```bash
sudo mkdir /var/lib/strfry
sudo chown strfry:strfry /var/lib/strfry
sudo chmod 755 /var/lib/strfry
```
This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
### Configure Strfry
Copy the sample configuration file:
```bash
sudo cp strfry.conf /etc/strfry.conf
```
Edit the configuration file:
```bash
sudo nano /etc/strfry.conf
```
Modify the database path:
```
# Find this line:
db = "./strfry-db/"
# Change it to:
db = "/var/lib/strfry/"
```
Check your system's hard limit for file descriptors:
```bash
ulimit -Hn
```
Update the `nofiles` setting in your configuration to match this value (or set to 0):
```
# Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288
```
The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.
You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details.
Set ownership of the configuration file:
```bash
sudo chown strfry:strfry /etc/strfry.conf
```
### Create Systemd Service
Create a systemd service file for managing Strfry:
```bash
sudo nano /etc/systemd/system/strfry.service
```
Add the following content:
```ini
[Unit]
Description=strfry relay service
[Service]
User=strfry
ExecStart=/usr/local/bin/strfry relay
Restart=on-failure
RestartSec=5
ProtectHome=yes
NoNewPrivileges=yes
ProtectSystem=full
LimitCORE=1000000000
[Install]
WantedBy=multi-user.target
```
This systemd service configuration:
- Runs Strfry as the dedicated strfry user
- Automatically restarts the service if it fails
- Implements security measures like `ProtectHome` and `NoNewPrivileges`
- Sets resource limits appropriate for a relay
Enable and start the service:
```bash
sudo systemctl enable strfry.service
sudo systemctl start strfry
```
Check the service status:
```bash
sudo systemctl status strfry
```
### Verify Relay is Running
Test that your relay is running locally:
```bash
curl localhost:7777
```
You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
## Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
### Install TOR
Install TOR from the package repositories:
```bash
sudo apt install -y tor
```
This installs the TOR daemon that will create and manage your hidden service.
### Configure TOR
Edit the TOR configuration file:
```bash
sudo nano /etc/tor/torrc
```
Scroll down to wherever you see a commented out part like this:
```
#HiddenServiceDir /var/lib/tor/hidden_service/
#HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
```
HiddenServiceDir /var/lib/tor/strfry-relay/
HiddenServicePort 80 127.0.0.1:7777
```
This configuration:
- Creates a hidden service directory at `/var/lib/tor/strfry-relay/`
- Maps port 80 on your .onion address to port 7777 on your local machine
- Keeps all traffic encrypted within the TOR network
Create the directory for your hidden service:
```bash
sudo mkdir -p /var/lib/tor/strfry-relay/
sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/
sudo chmod 700 /var/lib/tor/strfry-relay/
```
The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
```bash
sudo systemctl restart tor
```
## Making Your Relay Available on TOR
### Get Your Onion Address
After restarting TOR, you can find your onion address:
```bash
sudo cat /var/lib/tor/strfry-relay/hostname
```
This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay.
### Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion`
## Testing Your Setup
### Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
1. Open your TOR browser
2. Go to your favorite client, either on clearnet or an onion service.
- Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR.
3. Add your relay URL: `ws://youronionaddress.onion` to your relay list
4. Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
## Maintenance and Security
### Regular Updates
Keep your system, TOR, and relay updated:
```bash
# Update system
sudo apt update
sudo apt upgrade -y
# Update Strfry
cd ~/strfry
git pull
git submodule update
make -j2
sudo cp strfry /usr/local/bin
sudo systemctl restart strfry
# Verify TOR is still running properly
sudo systemctl status tor
```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
### Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
### Monitoring Logs
To monitor your Strfry logs:
```bash
sudo journalctl -u strfry -f
```
To check TOR logs:
```bash
sudo journalctl -u tor -f
```
Monitoring logs helps you identify potential issues and understand how your relay is being used.
### Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
# Stop the relay temporarily
sudo systemctl stop strfry
# Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
# Restart the relay
sudo systemctl start strfry
```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
```bash
sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location
```
## Troubleshooting
### Relay Not Starting
If your relay doesn't start:
```bash
# Check logs
sudo journalctl -u strfry -e
# Verify configuration
cat /etc/strfry.conf
# Check permissions
ls -la /var/lib/strfry
```
Common issues include:
- Incorrect configuration format
- Permission problems with the data directory
- Port already in use (another service using port 7777)
- Issues with setting the nofiles limit (setting it too big)
### TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
# Check TOR logs
sudo journalctl -u tor -e
# Verify TOR is running
sudo systemctl status tor
# Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
# Verify TOR configuration
sudo cat /etc/tor/torrc
```
Common TOR issues include:
- Incorrect directory permissions
- TOR service not running
- Incorrect port mapping in torrc
### Testing Connectivity
If you're having trouble connecting to your service:
```bash
# Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
# Check that TOR is properly running
sudo systemctl status tor
# Test the local connection directly
curl --include --no-buffer localhost:7777
```
---
## Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
---
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry).
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
-

@ fd06f542:8d6d54cd
2025-03-31 02:07:43
## 什么是nostrbook?
-----
nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。
查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。
整个网站技术不会占用部署服务器太多的存储空间,可以实现轻量级部署。
任何人可以部署服务器,或者本地部署 查看本站所有的书籍。
## nostrbook 可以服务哪些人?
-----
* 开发者,如果你想二次开发,看[第一章、开发者指南](/01.md)
* 写书作者,看[第二章、使用教程](/02.md)
* 读者 你就直接点开看。
## nostrbook未来如何发展?
-----
* 可能会增加 blog功能,有些时候你就想随心写点日志,那么用blog功能也可以。
* 点赞互动、留言功能。
-

@ deab79da:88579e68
2025-04-01 18:18:29
The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way:
Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole.
Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's.
For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both.
But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact.
The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower.
Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it.
They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle.
"It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever."
Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said.
"Oh, hell, just about forever. Till the sun runs down, Bert."
"That's not forever."
"All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?"
Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever."
"Well, it will last our time, won't it?"
"So would the coal and uranium."
"All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me.
"I don't have to ask Multivac. I know that."
"Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right."
"Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun."
There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested.
Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?"
"I'm not thinking."
"Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one."
"I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too."
"Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all."
"I know all about entropy," said Adell, standing on his dignity.
"The hell you do."
"I know as much as you do."
"Then you know everything's got to run down someday."
"All right. Who says they won't?"
"You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.'
It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said.
"Never."
"Why not? Someday."
"Never."
"Ask Multivac."
"You ask Multivac. I dare you. Five dollars says it can't be done."
Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age?
Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased?
Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended.
Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER.
"No bet," whispered Lupov. They left hurriedly.
By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident.
🔹
Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen.
"That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened.
The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --"
"Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?"
"What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship.
Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps.
Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that.
Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth."
"Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing."
"I know, I know," said Jerrodine miserably.
Jerrodette I said promptly, "Our Microvac is the best Microvac in the world."
"I think so, too," said Jerrodd, tousling her hair.
It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship.
Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible.
"So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now."
"Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase.
"What's entropy, daddy?" shrilled Jerrodette II.
"Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?"
"Can't you just put in a new power-unit, like with my robot?"
"The stars are the power-units. dear. Once they're gone, there are no more power-units."
Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down."
"Now look what you've done," whispered Jerrodine, exasperated.
"How was I to know it would frighten them?" Jerrodd whispered back,
"Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again."
"Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.)
Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us."
He asked the Microvac, adding quickly, "Print the answer."
Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry."
Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon."
Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER.
He shrugged and looked at the visiplate. X-23 was just ahead.
🔹
VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?"
MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion."
Both seemed in their early twenties, both were tall and perfectly formed.
"Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council."
"I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up."
VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More."
"A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years --
VJ-23X interrupted. "We can thank immortality for that."
"Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions."
"Yet you wouldn't want to abandon life, I suppose."
"Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?"
"Two hundred twenty-three. And you?"
"I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?"
VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next."
"A very good point. Already, mankind consumes two sunpower units per year."
"Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those."
"Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point."
"We'll just have to build new stars out of interstellar gas."
"Or out of dissipated heat?" asked MQ-17J, sarcastically.
"There may be some way to reverse entropy. We ought to ask the Galactic AC."
VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him.
"I've half a mind to," he said. "It's something the human race will have to face someday."
He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC.
MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across.
MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?"
VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that."
"Why not?"
"We both know entropy can't be reversed. You can't turn smoke and ash back into a tree."
"Do you have trees on your world?" asked MQ-17J.
The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER.
VJ-23X said, "See!"
The two men thereupon returned to the question of the report they were to make to the Galactic Council.
🔹
Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space.
Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals.
Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind.
"I am Zee Prime," said Zee Prime. "And you?"
"I am Dee Sub Wun. Your Galaxy?"
"We call it only the Galaxy. And you?"
"We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?"
"True. Since all Galaxies are the same."
"Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different."
Zee Prime said, "On which one?"
"I cannot say. The Universal AC would know."
"Shall we ask him? I am suddenly curious."
Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man.
Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?"
The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof.
Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see.
"But how can that be all of Universal AC?" Zee Prime had asked.
"Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine."
Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged.
The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars.
A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN."
But it was the same after all, the same as any other, and Lee Prime stifled his disappointment.
Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?"
The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF"
"Did the men upon it die?" asked Lee Prime, startled and without thinking.
The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME."
"Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again.
Dee Sub Wun said, "What is wrong?"
"The stars are dying. The original star is dead."
"They must all die. Why not?"
"But when all energy is gone, our bodies will finally die, and you and I with them."
"It will take billions of years."
"I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?"
Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction."
And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter.
Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built.
🔹
Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable.
Man said, "The Universe is dying."
Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end.
New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too.
Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years."
"But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum."
Man said, "Can entropy not be reversed? Let us ask the Cosmic AC."
The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend.
"Cosmic AC," said Man, "how may entropy be reversed?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man said, "Collect additional data."
The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT.
"Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?"
The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES."
Man said, "When will you have enough data to answer the question?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
"Will you keep working on it?" asked Man.
The Cosmic AC said, "I WILL."
Man said, "We shall wait."
🔹
The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down.
One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain.
Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero.
Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?"
AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man's last mind fused and only AC existed -- and that in hyperspace.
🔹
Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man.
All other questions had been answered, and until this last question was answered also, AC might not release his consciousness.
All collected data had come to a final end. Nothing was left to be collected.
But all collected data had yet to be completely correlated and put together in all possible relationships.
A timeless interval was spent in doing that.
And it came to pass that AC learned how to reverse the direction of entropy.
But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too.
For another timeless interval, AC thought how best to do this. Carefully, AC organized the program.
The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done.
And AC said, "LET THERE BE LIGHT!"
And there was light --
To Star's End!
-

@ fd06f542:8d6d54cd
2025-03-31 01:55:18
## 什么是nostrbook?
-----
nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。
查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。整个网站技术无须部署服务器占用太多的存储空间。
可以实现轻量级部署。
-

@ bc52210b:20bfc6de
2025-03-25 20:17:22
CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
---
**CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!**
Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
* Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
* Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
**Key Differences:**
1. What’s Aggregated?
* CISA: Aggregates signatures.
* Key Aggregation: Aggregates public keys.
2. What the Verifier Needs
* CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature.
* Key Aggregation: The verifier only needs the single aggregated public key and one message.
3. When It Happens
* CISA: Used during transaction signing, when inputs are being combined into a transaction.
* MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
---
**Two Flavors of CISA: Half-Agg and Full-Agg**
CISA comes in two modes:
* Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
* Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
---
**Half Signature Aggregation (Half-Agg) Explained**
**How It Works**
Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
* R: A random point (32 bytes).
* s: A scalar value (32 bytes).
In Half-Agg:
* The R values from each signature are kept separate (one per input).
* The s values from all signatures are combined into a single s value.
**Why It Saves Space (~50%)**
Let’s break down the size savings with some math:
Before Aggregation:
* Each Schnorr signature = 64 bytes (32 for R + 32 for s).
* For n inputs: n × 64 bytes.
After Half-Agg:
* Keep n R values (32 bytes each) = 32 × n bytes.
* Combine all s values into one = 32 bytes.
* Total size: 32 × n + 32 bytes.
Comparison:
* Original: 64n bytes.
* Half-Agg: 32n + 32 bytes.
* For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
**Real-World Impact:**
Based on recent Bitcoin usage, Half-Agg could save:
* ~19.3% in space (reducing transaction size).
* ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
---
**Applications of Half-Agg**
Half-Agg isn’t just a cool idea—it has practical uses:
1. Transaction-wide Aggregation
* Combine all signatures within a single transaction.
* Result: Smaller transactions, lower fees.
2. Block-wide Aggregation
* Combine signatures across all transactions in a Bitcoin block.
* Result: Even bigger space savings at the blockchain level.
3. Off-chain Protocols / P2P
* Use Half-Agg in systems like Lightning Network gossip messages.
* Benefit: Efficiency without needing miners or a Bitcoin soft fork.
---
**Challenges with Half-Agg**
While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
1. Breaking Adaptor Signatures
* Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
* Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
2. Impact on Reorg Recovery
* In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
* If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
---
**Wrapping Up**
CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-

@ fd06f542:8d6d54cd
2025-03-31 01:45:36
{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/232dd9c092e023beecb5410052bd48add702765258dcc66f176a56f02b09cf6a.webp","title":"NostrBook站点日记","author":"nostrbook"}
-

@ 866e0139:6a9334e5
2025-04-06 03:51:00
***
**Autor:** **[Nicolas Lindt.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)***
***
Während die Kriegstreiber in Europa gegen Russland zum Angriff blasen, mit einem «letzten Sommer in Frieden» drohen, Bodentruppen mobilisieren und das Vermögen der Völker in todbringende Waffen umsetzen wollen - während also Europa aus zwei Weltkriegen nichts gelernt hat und einen dritten entzünden will, erinnere ich mich an ein Gespräch, das ich vor etlichen Jahren mit meinem jüngeren Sohn geführt habe.
Auf einer Wanderung zur Scheidegg – ein Aussichtspunkt oberhalb unseres Dorfes – fragte mich Alexis, ob ich an die Möglichkeit eines Dritten Weltkrieges glaube. Seit einiger Zeit schon hatte er sich Gedanken zum Krieg gemacht, weil er inzwischen aus dem Schulunterricht wusste, dass Krieg nicht dasselbe ist wie der Krieg, den ihm seine Playstation zeigte. Das Thema ließ Alexis nicht los, und auch mich ließ er damit nicht los. Immer wieder musste ich ihm vom Zweiten Weltkrieg erzählen, von Hitler und Stalin, von der Judenverfolgung, vom Eroberungsfeldzug der Wehrmacht und von den Alliierten, als sie an der Küste der Normandie landeten.
Während wir in den Wald abbogen und dem Wanderweg folgten, fragte mein Sohn, wer denn schlimmer gewesen sei, die Nationalsozialisten oder die Kommunisten? Und als er auf eine Pyramide gefällter Baumstämme kletterte, erklärte ich ihm, warum die Amerikaner gemeinsame Sache mit Stalin machten, obwohl doch auch Stalin viele Millionen umbringen liess. Ich versuchte ihm begreiflich zu machen, warum der Feind meines Feindes im Kriegsfall mein Freund ist.
Wir traten auf eine Wiese hinaus, die Sonne stach durch die Wolken hervor, und ich legte meinem Sohn dar, dass Stalin zur Befreiung Europas von Hitlerdeutschland massgeblich beitrug. Ich erzählte ihm, wie die Deutschen nach der Niederlage bei Stalingrad vom Kriegsglück verlassen wurden, und Alexis hörte mir gebannt zu. Er schwieg einen Augenblick. Über der Lichtung lag eine große Ruhe. Nur ein paar Vögel zwitscherten. Wir waren ganz allein.
«Heisst Stalingrad wirklich so?» fragte mein Sohn in die Stille hinein. Er merkte gar nicht, wo wir uns gerade befanden. Der Frieden, der uns umgab, hatte für ihn keine Bedeutung. Ohne unser Gespräch hätte er sich gelangweilt. Es ist das Vorrecht der Jugend, dass sie sich langweilen darf. Ich verstand meinen Sohn. Viel mehr als unsere Wanderung interessierte ihn der Fortgang des Krieges.
«Stalingrad heisst wieder Wolgograd», beantwortete ich seine Frage. «Aber schau doch lieber, wie schön es hier ist!»
Alexis fand es auch schön. Er gönnte mir eine kurze Gefechtspause, doch schon nach der nächsten Biegung befanden wir uns wieder mitten im Kampfgebiet. Der Geschützdonner der Kriegsjahre 39-45 begleitete uns während des ganzen restlichen Aufstiegs.
Alexis fragte, ich gab ihm Antwort. Ich liebte es, ihm zu antworten, denn der Weltkrieg fesselt auch mich, und als ich ein Kind war, habe ich meinem Vater dieselben Fragen gestellt. Der Krieg, so schrecklich er ist, übt eine seltsame Anziehung aus. Die Menschen im Westen sind von ihm fasziniert. Sie sehnen sich insgeheim nach dem Krieg, weil sie wie Teenager sind. Sie wünschen sich, ohne sich dessen bewusst zu sein, den Ausnahmezustand herbei, weil der Frieden sie langweilt. Weil sie nicht wissen, was Krieg wirklich ist.
Noch bevor Deutschland kapitulierte, erreichten wir unser Ziel. Von der Scheidegg blickten wir hinab auf den See und das weite Land. Ich bestaunte das Panorama der Alpen, so wie ich es schon hunderte Male bewundert hatte. Ich werde es immer bestaunen. Es langweilt mich nie.
«Du hast mir noch keine Antwort gegeben», erinnerte mich Alexis. «Glaubst du, es gibt irgendwann einen Dritten Weltkrieg?»
«Ich hoffe es nicht», entgegnete ich, «ich hoffe, die Menschen vergessen nie, dass der Friede schöner ist als der Krieg.» Mit einer ausschweifenden Geste über den Kranz der Berge, der uns umgab, zeigte ich meinem Sohn, was ich meinte.
Ich zeigte ihm die Schönheit des Friedens.
*Dieser Artikel erschien zuerst als Kolumne im Schweizer* ***[Zeitpunkt-Magazin.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)***
***
*Nicolas Lindt (\*1954) war Musikjournalist, Tagesschau-Reporter und Gerichtskolumnist, bevor er in seinen Büchern wahre Geschichten zu erzählen begann. In seinem zweiten Beruf gestaltet er freie Trauungen, Taufen und Abdankungen. Der Autor lebt mit seiner Familie in Wald und in Segnas. Hier finden Sie die* ***[Bücher](https://www.exlibris.ch/de/suche/?qs=Nicolas%20Lindt)*** *von Nicolas Lindt. Der Fünf Minuten-Podcast «Mitten im Leben» von Nicolas Lindt ist zu finden auf Spotify, iTunes und Audible, letzte Folge* ***[hier.](https://terra-nova-podcast-1.podigee.io/27-die-einsamkeit-des-schriftstellers#t=1)***
***Neuestes Buch:*** *«Orwells Einsamkeit - sein Leben, ‚1984‘ und mein Weg zu einem persönlichen Denken». Erhältlich im Buchhandel - zum Beispiel bei [Ex Libris](https://www.exlibris.ch/de/buecher-buch/deutschsprachige-buecher/nicolas-lindt/orwells-einsamkeit/id/9783758342561/?srsltid=AfmBOoqEFJWFsnacUaCEWWTxzL-qnVO6cvqHc8FvIno_SpDZ42zasQmm) oder [Orell Füssli](https://www.orellfuessli.ch/shop/home/artikeldetails/A1073365208?ProvID=10917751\&gad_source=1\&gbraid=0AAAAADpVXc6fbYzpLMiQ1L1NDN25Z-K7_\&gclid=CjwKCAjwyfe4BhAWEiwAkIL8sBVh5kUOJToqpPi-5ByDkwKJYXCe_PNlQPbzkZQ1Cjw1dluamSkRhxoCeWMQAvD_BwE)*
*Alle weiteren Informationen: [www.nicolaslindt.ch](http://www.nicolaslindt.ch/)*
***
**LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!**
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).*
Schon jetzt können Sie uns unterstützen:
* Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube.
* Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
* Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
* Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
**Für Einzahlungen in CHF (Betreff: Friedenstaube):**
**Für Einzahlungen in Euro:**
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
**Betreff: Friedenstaube**
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space>
***
**Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
-

@ 52524fbb:ae4025dc
2025-04-05 22:03:45
In our world being digitally driven today, the concepts of decentralization due to freedom from traditional media's censorship drive is gaining significant attention, promising greater autonomy and security. Two Critical examples of this movement are Bitcoin in the world of finance and YakiHonne in the world of media. While serving different primary purposes, their core philosophies and technological foundations reveal a powerful union, pointing towards a future where finance and media are more open and accessible

## Bitcoin: Decentralizing the World of Finance
Bitcoin, launched in 2009 stands as the pinnacle of decentralized digital currencies. Unlike traditional currencies controlled by central banks, Bitcoin operates on a distributed ledger technology known as the blockchain. The public and transparent record of all Bitcoin transactions is maintained by a global network of users, removing the need for middle transacts like banks to validate and process payments.
### Key Aspects of Bitcoin's Decentralization:
Below are some of the reasons why Bitcoin stands at the pinnacle of finance in today's world
1. No Central Authority: Bitcoin is not controlled by anyone, making it resistant to censorship
2. Peer-to-Peer Transactions: Users can send and receive Bitcoin directly with each other, reducing transaction costs and time.
3. Transparency: All transactions are recorded on the public blockchain, enhancing trust and verifiability.
4. Security: Cryptographic techniques secure the network and prevent tampering with transactions.
Bitcoin's success has demonstrated the potential of decentralized finance to offer numerous benefits, including greater financial inclusion, lower fees, increased transparency, and enhanced control over one's assets.

## YakiHonne: Decentralizing the Landscape of Media
YakiHonne emerges as a "Bitcoin-native decentralized social protocol" built upon the Nostr protocol. Its mission is to create a censorship-resistant media and social network, aligning with the core reasons of decentralization championed by Bitcoin.
### Understanding YakiHonne:
1. Built on Nostr: YakiHonne leverages Nostr protocol, an open and simple protocol for decentralized message transmission designed to resist censorship. Nostr operates without central servers; instead, users connect to various independent relays to send and receive data.
2. Decentralized Media Infrastructure: YakiHonne aims to decentralize content creation, curation, publishing, and reporting, empowering individuals to share information freely.
3. Bitcoin Integration: YakiHonne integrates Bitcoin functionalities. A notable feature is "zaps," which utilizes the Lightning Network, a layer-2 scaling solution for Bitcoin enabling fast and low-cost transactions, for tipping and value exchange within the platform
4. Community Focus: YakiHonne fosters a community of Bitcoiners and individuals interested in decentralized media, promoting open dialogue and the exchange of ideas.

### The Emerging Union: A Decentralized Future
The convergence of Bitcoin and YakiHonne represents a powerful step towards an active decentralized future for both finance and media. Their union offers amazing advantages such as:
1. Shared Principles: Both Bitcoin and YakiHonne are firmly embedded in the principles of decentralization, user autonomy, and resistance to censorship. This shared purpose creates a natural alignment and strengthens the overall movement towards a more open and censorship free digital world.
2. Empowering Individuals: By decentralizing finance and media, both platforms empower individuals. Bitcoin gives users control over their money, while YakiHonne provides a space for uncensored expression and information sharing.
3. Encouraging Community Building: YakiHonne serves as a social layer for the Bitcoin ecosystem and beyond, providing a space for discussions, collaborations, and sharing of information related to decentralized technologies. This strengthens the community around these ideas and promotes further adoption.

### Potential Usage and Future Implications:
The Union between Bitcoin and YakiHonne could lead to various innovative use cases such as::
1. Direct Monetization for Content Creators: Writers, artists, and other content creators on YakiHonne could directly receive Bitcoin tips (zaps) from their audience, bypassing the need for centralized platforms that often take a significant cut of the revenue.
2. Decentralized Journalism and Reporting: YakiHonne could serve as a platform for independent journalists to publish their work without fear of censorship, with readers directly supporting their efforts through Bitcoin
3. Integration with Other Bitcoin Services: As the ecosystem evolves, YakiHonne could potentially integrate with other Bitcoin-related services, further enhancing its functionality and utility.
-

@ dbc27e2e:b1dd0b0b
2025-04-05 20:44:00
This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain.

Dose:
20g coffee (Coarse ground coffee)
300mL water (92°C / 197.6°F)
Time: 3:30
Instructions:
1. Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.)
2. Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.)
3. Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour)
4. Pour 4: 2:10 > 60mL
5. Pour 5: 2:40 > 60mL
6. Remove the V60 at 3:30
-

@ aa8de34f:a6ffe696
2025-03-31 21:48:50
In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
> „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\
> ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228))
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\
Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
\-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\
Weil sie nicht erkennt, dass er längst begonnen hat.\
Unwiderruflich. Leise. Überall.
-

@ b17fccdf:b7211155
2025-03-25 11:23:36
Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/).
Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles:
## La razón
El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial.
Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita.
Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

## La solución
Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder:
**~>** Utiliza **una VPN**:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad:
- [IVPN](https://www.ivpn.net/es/)
- [Mullvad VPN](https://mullvad.net/es/vpn)
- [Proton VPN](https://protonvpn.com/es-es) (**gratis**)
- [Obscura VPN](https://obscura.net/) (**solo para macOS**)
- [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos:
1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy"
2. Marca la casilla "Habilite el modo proxy en este dispositivo"
3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias
4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio.
3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).

**~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).

## La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

---
Fuentes:
* https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239
* https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257
* https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958
* https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689
* https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-

@ c631e267:c2b78d3e
2025-03-31 07:23:05
*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\
aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\
Friedrich Nietzsche*  
**Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

**Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
**Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
**In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
**Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung».
**Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
**Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
**Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
**Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei!
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
-

@ 8bf63b70:64ac852f
2025-04-05 18:48:17
VIP8888 là một nền tảng giải trí trực tuyến đặc biệt, được thiết kế để mang lại những trải nghiệm tuyệt vời và khác biệt cho người dùng. Với giao diện dễ sử dụng và tính năng linh hoạt, VIP8888 mang đến cho người tham gia một loạt các trò chơi hấp dẫn và thú vị, đáp ứng nhu cầu giải trí đa dạng của mọi đối tượng. Những trò chơi trên nền tảng này được phát triển để không chỉ giúp người chơi thư giãn mà còn thách thức khả năng tư duy và sáng tạo. VIP8888 không ngừng cải tiến và cập nhật các trò chơi mới mẻ, đảm bảo rằng người dùng sẽ luôn cảm thấy thích thú mỗi lần tham gia. Mỗi hoạt động trên nền tảng đều được chăm chút kỹ lưỡng, mang lại trải nghiệm mượt mà và chất lượng, khiến người dùng không thể rời mắt khỏi màn hình.
Một yếu tố nổi bật khác của VIP8888 là cộng đồng người dùng thân thiện và gắn kết. Nền tảng này không chỉ là nơi để giải trí mà còn là không gian để mọi người giao lưu, kết bạn và chia sẻ những sở thích chung. Các tính năng xã hội của <a href="https://vip8888.site">VIP8888</a> giúp người tham gia dễ dàng kết nối với những người có cùng đam mê, tạo nên một môi trường giao lưu sôi động và tích cực. Những cuộc thảo luận nhóm, sự kiện cộng đồng và các hoạt động tương tác không chỉ giúp người dùng cảm thấy gắn bó với nền tảng mà còn giúp họ học hỏi từ những người khác. Sự gắn kết này không chỉ mang lại giá trị giải trí mà còn thúc đẩy sự sáng tạo và phát triển mối quan hệ xã hội trong cộng đồng.
Bên cạnh các trò chơi và hoạt động giao lưu, VIP8888 cũng chú trọng đến việc cập nhật và cải tiến các tính năng để duy trì sự hấp dẫn và sáng tạo. Nền tảng này luôn tạo ra các tính năng mới mẻ, giúp người dùng có cơ hội khám phá và thử thách bản thân trong mỗi lần tham gia. Việc không ngừng đổi mới và nâng cấp đã giúp VIP8888 duy trì được sự yêu thích của cộng đồng, đồng thời tạo ra một không gian giải trí luôn mới mẻ và thú vị. Chính nhờ vào sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục, VIP8888 đã khẳng định vị thế của mình là một lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng trực tuyến năng động, sáng tạo và luôn phát triển.
-

@ 57d1a264:69f1fee1
2025-03-29 18:02:16
> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.

- - -
## 1️⃣ Introduction
#### Project Overview
📌 **Product:** BlueWallet (Bitcoin Wallet)
📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience.
📌 **Role:** UX Designer
📌 **Tools Used:** Figma, Notion
#### Why This Case Study?
🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**.
🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**.
🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**.
This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**.
- - -
## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement
#### 🔹 **Current Challenges:**
1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.
 
2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**.
3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion.
4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult.
#### 🔍 **Impact on Users:**
**Higher drop-off rates** due to frustration during onboarding.
**Security risks** as users skip key wallet setup steps.
**Limited accessibility** for users with visual impairments.
#### 📌 **Competitive Gap:**
Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer:
✅ A guided onboarding process
✅ Security education during setup
✅ Intuitive transaction flow
    
Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet.
- - -
## 3️⃣ User Research & Competitive Analysis
#### User Testing Findings
🔹 Conducted usability testing with **5 users** onboarding for the first time.
🔹 **Key Findings:**
✅ 3 out of 5 users **felt lost** due to missing explanations.
✅ 60% **had trouble distinguishing transaction buttons**.
✅ 80% **found the text difficult to read** due to low contrast.
#### Competitive Analysis
We compared BlueWallet with top crypto wallets:
| Wallet | Onboarding UX | Security Guidance | Accessibility Features |
|---|---|---|---|
| BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts |
| Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI |
| MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons |
📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners.
## 📌 User Persona
To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing.
#### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor)
👤 **Profile:**
- **Age:** 28
- **Occupation:** Freelance Digital Marketer
- **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin)
- **Pain Points:**
- Finds **Bitcoin wallets confusing**.
- - Doesnʼt understand **seed phrases & security features**.
- - **Worried about losing funds** due to a lack of clarity in transactions.
📌 **Needs:**
✅ A **simple, guided** wallet setup.
✅ **Clear explanations** of security terms (without jargon).
✅ Easy-to-locate **Send/Receive buttons**.
📌 **Persona Usage in Case Study:**
- Helps define **who we are designing for**.
- Guides **design decisions** by focusing on user needs.
#### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast)
👤 **Profile:**
- **Age:** 35
- **Occupation:** UX Researcher & Accessibility Consultant
- **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers)
📌 **Pain Points:**
❌ Struggles with small font sizes & low contrast.
❌ Finds the UI difficult to navigate with a screen reader.
❌ Confused by identical-looking transaction buttons.
📌 **Needs:**
✅ A **high-contrast UI** that meets **WCAG accessibility standards**.
✅ **Larger fonts & scalable UI elements** for better readability.
✅ **Keyboard & screen reader-friendly navigation** for seamless interaction.
📌 **Why This Persona Matters:**
- Represents users with visual impairments who rely on accessible design.
- Ensures the design accommodates inclusive UX principles.
- - -
## 4️⃣ UX/UI Solutions & Design Improvements
#### 📌 Before (Current Issues)
❌ Users land **directly on the wallet screen** with no instructions.
❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion.
❌ **Small fonts & low contrast** reduce readability.
#### ✅ After (Proposed Fixes)
✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions.
✅ **Visually distinct transaction buttons** (color and icon changes).
✅ **WCAG-compliant text contrast & larger fonts** for better readability.
#### 1️⃣ Redesigned Onboarding Flow
✅ Added a **progress indicator** so users see where they are in setup.
✅ Used **plain, non-technical language** to explain wallet creation & security.
✅ Introduced a **"Learn More" button** to educate users on security.
#### 2️⃣ Accessibility Enhancements
✅ Increased **contrast ratio** for better text readability.
✅ Used **larger fonts & scalable UI elements**.
✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support).
#### 3️⃣ Transaction Flow Optimization
✅ Redesigned **"Send" & "Receive" buttons** for clear distinction.
✅ Added **clearer icons & tooltips** for transaction steps.
## 5️⃣ Wireframes & Design Improvements:
#### 🔹 Welcome Screen (First Screen When User Opens Wallet)
**📌 Goal: Give a brief introduction & set user expectations**
✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet")
✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.")
✅ **"Get Started" button** → Le ads to **next step: Wallet Setup**
✅ **"Already have a wallet?"** → Import option
🔹 **Example UI Elements:**
- BlueWallet Logo
- **Title:** "Welcome to BlueWallet"
- **Subtitle:** "Easily store, send, and receive Bitcoin."
- CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)

#### 🔹 Screen 2: Choose Wallet Type (New or Import)
**📌 Goal: Let users decide how to proceed**
✅ **Two clear options:**
- **Create a New Wallet** (For first-time users)
- **Import Existing Wallet** (For users with a backup phrase)
✅ Brief explanation of each option
🔹 **Example UI Elements:
- **Title:** "How do you want to start?"
- **Buttons:** "Create New Wallet" | "Import Wallet"

#### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step)
**📌 Goal: Educate users about wallet security & backups**
✅ Explain **why seed phrases are important**
✅ **Clear step-by-step instructions** on writing down & storing the phrase
✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet."
✅ **CTA:** "Generate Seed Phrase" → Next step
🔹 **Example UI Elements:
- Title:** "Secure Your Wallet"
- **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!"
- **Button:** "Generate Seed Phrase"

## 🔹 Screen 4: Seed Phrase Display & Confirmation
**📌 Goal: Ensure users write down the phrase correctly**
✅ Display **12- or 24-word** seed phrase
✅ **“I have written it downˮ checkbox** before proceeding
✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words)
🔹 **Example UI Elements:**
- **Title:** "Write Down Your Seed Phrase"
- List of 12/24 Words (Hidden by Default)
- **Checkbox:** "I have safely stored my phrase"
- **Button:** "Continue"

### 🔹 Screen 5: Wallet Ready! (Final Step)
**📌 Goal: Confirm setup & guide users on next actions**
✅ **Success message** ("Your wallet is ready!")
✅ **Encourage first action:**
- “Receive Bitcoinˮ → Show wallet address
- “Send Bitcoinˮ → Walkthrough on making transactions
✅ Short explainer: Where to find the Send/Receive buttons
🔹 **Example UI Elements:**
- **Title:** "You're All Set!"
- **Subtitle:** "Start using BlueWallet now."
- **Buttons:** "Receive Bitcoin" | "View Wallet"

- - -
## 5️⃣ Prototype & User Testing Results
🔹 **Created an interactive prototype in Figma** to test the new experience.
🔹 **User Testing Results:**
✅ **40% faster onboarding completion time.**
✅ **90% of users found transaction buttons clearer.**
🔹 **User Feedback:**
✅ “Now I understand the security steps clearly.ˮ
✅ “The buttons are easier to find and use.ˮ
- - -
## 6️⃣ Why This Matters: Key Takeaways
📌 **Impact of These UX/UI Changes:**
✅ **Reduced user frustration** by providing a step-by-step onboarding guide.
✅ **Improved accessibility** , making the wallet usable for all.
✅ **More intuitive transactions** , reducing errors.
- - -
## 7️⃣ Direct link to figma file and Prototype
Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1)
Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale-
down&content-scaling=fixed&page-id=0%3A1&starting-point-node-
id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale-
down&content-scaling=fixed&page-id=0%3A1&starting-point-node-
id=1%3A2&show-proto-sidebar=1)
Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&)
originally posted at https://stacker.news/items/928822
-

@ 57d1a264:69f1fee1
2025-03-29 17:15:17

- Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box.
- If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust.
- “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options.
- Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic.
originally posted at https://stacker.news/items/928800
-

@ fd06f542:8d6d54cd
2025-03-30 02:16:24
> __Warning__ `unrecommended`: deprecated in favor of [NIP-17](17.md)
NIP-04
======
Encrypted Direct Message
------------------------
`final` `unrecommended` `optional`
A special event with kind `4`, meaning "encrypted direct message". It is supposed to have the following attributes:
**`content`** MUST be equal to the base64-encoded, aes-256-cbc encrypted string of anything a user wants to write, encrypted using a shared cipher generated by combining the recipient's public-key with the sender's private-key; this appended by the base64-encoded initialization vector as if it was a querystring parameter named "iv". The format is the following: `"content": "<encrypted_text>?iv=<initialization_vector>"`.
**`tags`** MUST contain an entry identifying the receiver of the message (such that relays may naturally forward this event to them), in the form `["p", "<pubkey, as a hex string>"]`.
**`tags`** MAY contain an entry identifying the previous message in a conversation or a message we are explicitly replying to (such that contextual, more organized conversations may happen), in the form `["e", "<event_id>"]`.
**Note**: By default in the [libsecp256k1](https://github.com/bitcoin-core/secp256k1) ECDH implementation, the secret is the SHA256 hash of the shared point (both X and Y coordinates). In Nostr, only the X coordinate of the shared point is used as the secret and it is NOT hashed. If using libsecp256k1, a custom function that copies the X coordinate must be passed as the `hashfp` argument in `secp256k1_ecdh`. See [here](https://github.com/bitcoin-core/secp256k1/blob/master/src/modules/ecdh/main_impl.h#L29).
Code sample for generating such an event in JavaScript:
```js
import crypto from 'crypto'
import * as secp from '@noble/secp256k1'
let sharedPoint = secp.getSharedSecret(ourPrivateKey, '02' + theirPublicKey)
let sharedX = sharedPoint.slice(1, 33)
let iv = crypto.randomFillSync(new Uint8Array(16))
var cipher = crypto.createCipheriv(
'aes-256-cbc',
Buffer.from(sharedX),
iv
)
let encryptedMessage = cipher.update(text, 'utf8', 'base64')
encryptedMessage += cipher.final('base64')
let ivBase64 = Buffer.from(iv.buffer).toString('base64')
let event = {
pubkey: ourPubKey,
created_at: Math.floor(Date.now() / 1000),
kind: 4,
tags: [['p', theirPublicKey]],
content: encryptedMessage + '?iv=' + ivBase64
}
```
## Security Warning
This standard does not go anywhere near what is considered the state-of-the-art in encrypted communication between peers, and it leaks metadata in the events, therefore it must not be used for anything you really need to keep secret, and only with relays that use `AUTH` to restrict who can fetch your `kind:4` events.
## Client Implementation Warning
Clients *should not* search and replace public key or note references from the `.content`. If processed like a regular text note (where `@npub...` is replaced with `#[0]` with a `["p", "..."]` tag) the tags are leaked and the mentioned user will receive the message in their inbox.
-

@ 3b7fc823:e194354f
2025-03-23 03:54:16
A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds.
Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/
1. Download Tor Browser
First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/
2. Sign Up
Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha.
3. Account information
Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck.
4. Install an Email Client
You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird.
a. Download Thunderbird email client
b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that.
5. Configure Incoming (POP3) Server
Under Incoming Server:
Protocol: POP3
Server or Hostname: xyz.onion (whatever your account info says)
Port: 110
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (POP3 password).
6. Configure Outgoing (SMTP) Server
Under Outgoing Server:
Server or Hostname: xyz.onion (whatever your account info says)
Port: 25
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (SMTP password).
7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up.
8. Configure Proxy
a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**.
b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different)
c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK
9. Check Email
For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail.
10. Security Exception
Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**.
You are done. Enjoy your new private email service.
**REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
-

@ 5ffb8e1b:255b6735
2025-03-29 13:57:02
As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views.
Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
### Eugene Gorbachenko ###
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd
Artist from Ukrain creating amazing realistic watercolor paintings.
He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
![!(image)[https://m.primal.net/PxJc.png]]()
### Siritravelsketch ###
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu
a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
![!(image)[https://m.primal.net/PxJj.png]]()
### BureuGewas ###
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4
a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
![!(image)[https://m.primal.net/PxKS.png]]()
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-

@ 8bf63b70:64ac852f
2025-04-05 18:47:22
JB88 là một nền tảng trực tuyến sáng tạo, mang đến cho người dùng những trải nghiệm giải trí vô cùng hấp dẫn và đa dạng. Được thiết kế với giao diện dễ sử dụng, JB88 cho phép người tham gia khám phá một loạt các trò chơi thú vị và thử thách mới mẻ, từ những trò chơi trí tuệ đến những hoạt động giải trí thư giãn. Mỗi lần người dùng truy cập vào nền tảng này, họ không chỉ tìm thấy những trò chơi mới mà còn có cơ hội phát triển kỹ năng tư duy và chiến lược của mình. JB88 không ngừng cải tiến và cập nhật các trò chơi, tạo ra một không gian luôn tươi mới và không bao giờ nhàm chán. Những hoạt động sáng tạo và phong phú trên nền tảng này chắc chắn sẽ làm hài lòng mọi đối tượng người tham gia, từ những người mới bắt đầu đến những người chơi có kinh nghiệm.
Điều đặc biệt tạo nên sức hút của JB88 chính là sự chú trọng vào việc xây dựng một cộng đồng trực tuyến gắn kết. Không chỉ là nơi để giải trí, <a href="https://jb88.online">JB88</a> còn là một không gian để người dùng giao lưu, chia sẻ sở thích và học hỏi lẫn nhau. Các tính năng xã hội của nền tảng này giúp người tham gia dễ dàng kết nối với những người bạn mới, tham gia vào các cuộc trò chuyện thú vị và chia sẻ kinh nghiệm. Môi trường giao lưu thân thiện và năng động của JB88 tạo cơ hội cho người dùng kết nối với những người có cùng đam mê, từ đó giúp họ phát triển những mối quan hệ bền chặt và học hỏi thêm nhiều kiến thức mới. Chính sự gắn kết này làm cho JB88 không chỉ là một nền tảng giải trí mà còn là một cộng đồng trực tuyến sống động.
Bên cạnh các tính năng giải trí và cộng đồng, JB88 còn chú trọng đến việc cải thiện và nâng cấp nền tảng để mang đến cho người dùng những trải nghiệm mượt mà và chất lượng. Nền tảng này luôn cập nhật các tính năng mới, giúp người tham gia có cơ hội khám phá những trò chơi và hoạt động thú vị. Bằng cách liên tục đổi mới và cải thiện, JB88 duy trì được sức hút và tạo ra một không gian giải trí không bao giờ cảm thấy nhàm chán. Sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục giúp JB88 trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian trực tuyến đầy thú vị, năng động và không ngừng sáng tạo.
-

@ 8bf63b70:64ac852f
2025-04-05 18:46:23
Vua88 là một nền tảng giải trí trực tuyến nổi bật, được thiết kế nhằm mang lại những trải nghiệm thú vị và phong phú cho người dùng. Với giao diện trực quan và dễ sử dụng, Vua88 cho phép người tham gia dễ dàng khám phá một loạt các trò chơi và hoạt động đa dạng. Những trò chơi sáng tạo, thử thách trí tuệ và các hoạt động giải trí thú vị luôn được cập nhật để đáp ứng nhu cầu giải trí của mọi đối tượng người dùng. Mỗi lần tham gia vào Vua88, người dùng sẽ có cơ hội thử sức với các trò chơi mới lạ và hấp dẫn, không chỉ giúp họ thư giãn mà còn kích thích sự sáng tạo và khả năng tư duy chiến lược. Chính sự đổi mới liên tục trong các hoạt động là yếu tố tạo nên sức hút và sự mới mẻ cho nền tảng này, khiến người dùng luôn cảm thấy hào hứng mỗi khi truy cập.
Ngoài các trò chơi, <a href="https://vua88-vn.com">Vua88</a> còn đặc biệt chú trọng đến việc xây dựng một cộng đồng trực tuyến sôi động và gắn kết. Người dùng không chỉ tham gia vào các hoạt động giải trí mà còn có thể giao lưu, kết bạn và chia sẻ sở thích cá nhân với những người có cùng đam mê. Nền tảng này cung cấp các tính năng xã hội mạnh mẽ, từ các cuộc trò chuyện, thảo luận nhóm đến những sự kiện cộng đồng thú vị. Việc tạo dựng một không gian xã hội lành mạnh và tích cực giúp người dùng cảm thấy gần gũi hơn với cộng đồng, mở rộng mối quan hệ và học hỏi thêm nhiều điều mới. Cộng đồng Vua88 không chỉ giúp mọi người thư giãn mà còn khuyến khích sự giao lưu và kết nối giữa các thành viên, tạo ra một môi trường đầy năng lượng và sự sáng tạo.
Để không ngừng duy trì sự hấp dẫn và tươi mới, Vua88 luôn cải tiến và cập nhật nền tảng của mình với những tính năng mới mẻ và sáng tạo. Những trò chơi và hoạt động trên nền tảng được làm mới liên tục, mang đến cho người tham gia những cơ hội khám phá mới mỗi khi truy cập. Mỗi lần quay lại với Vua88, người dùng sẽ luôn cảm nhận được sự thú vị và không bao giờ nhàm chán. Nền tảng này không chỉ mang lại niềm vui giải trí mà còn là nơi để người tham gia phát triển các kỹ năng cá nhân và mở rộng tầm nhìn. Vua88 không chỉ là một không gian giải trí, mà còn là một cộng đồng nơi người dùng có thể học hỏi, kết nối và phát triển bản thân một cách toàn diện.
-

@ fd06f542:8d6d54cd
2025-03-30 02:11:00
NIP-03
======
OpenTimestamps Attestations for Events
--------------------------------------
`draft` `optional`
This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event:
```json
{
"kind": 1040
"tags": [
["e", <event-id>, <relay-url>],
["alt", "opentimestamps attestation"]
],
"content": <base64-encoded OTS file data>
}
```
- The OpenTimestamps proof MUST prove the referenced `e` event id as its digest.
- The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context.
### Example OpenTimestamps proof verification flow
Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots):
```bash
~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify
> using an esplora server at https://blockstream.info/api
- sequence ending on block 810391 is valid
timestamp validated at block [810391]
```
-

@ 63b2cd3d:060efdc3
2025-04-05 18:44:58
HB888 là một nền tảng giải trí trực tuyến tiên tiến, nổi bật nhờ vào sự kết hợp hoàn hảo giữa các trò chơi thú vị và tính năng kết nối cộng đồng mạnh mẽ. Với giao diện dễ sử dụng và thân thiện, người dùng có thể nhanh chóng tham gia vào các hoạt động giải trí đa dạng và tận hưởng những giây phút thư giãn tuyệt vời. HB888 cung cấp một loạt các trò chơi từ các thử thách trí tuệ đến những hoạt động thư giãn, đảm bảo rằng mọi người dùng đều có thể tìm thấy những gì họ yêu thích. Mỗi lần tham gia vào nền tảng, người dùng sẽ khám phá những trò chơi mới mẻ và được thử sức với các thử thách đầy hấp dẫn, từ đó giúp họ phát triển kỹ năng tư duy, chiến lược và nâng cao sự sáng tạo. Sự đa dạng trong các hoạt động giúp HB888 không bao giờ trở nên nhàm chán, luôn tạo ra một không gian giải trí phong phú và đầy cảm hứng.
Một trong những điểm mạnh của <a href="https://hb888.asia">HB888</a> chính là cộng đồng người dùng năng động và gắn kết. Nền tảng này không chỉ mang đến những trò chơi thú vị mà còn tạo ra không gian giao lưu, kết nối giữa những người có cùng sở thích và đam mê. Các tính năng xã hội của HB888 cho phép người tham gia dễ dàng tìm thấy bạn bè mới, tham gia vào các cuộc thảo luận sôi nổi hoặc tham gia vào các sự kiện cộng đồng thú vị. Mỗi người dùng không chỉ có thể tận hưởng giải trí mà còn có cơ hội học hỏi từ những người khác, chia sẻ kinh nghiệm và khám phá những điều mới mẻ. Chính sự kết nối này tạo nên một cộng đồng trực tuyến đầy năng lượng và tích cực, nơi mọi người có thể giao lưu, kết bạn và phát triển mối quan hệ bền vững.
Ngoài các trò chơi và tính năng xã hội, HB888 cũng luôn chú trọng đến việc cải tiến nền tảng để mang đến những trải nghiệm giải trí luôn tươi mới và hấp dẫn. Các trò chơi và hoạt động được cập nhật liên tục, với những tính năng mới và sáng tạo, giúp người dùng luôn cảm thấy thích thú mỗi khi quay lại nền tảng. Nhờ vào sự đổi mới không ngừng, HB888 không chỉ giữ vững được sự yêu thích của người dùng mà còn tạo ra một môi trường giải trí đầy hứng khởi và sáng tạo. Với những cải tiến này, HB888 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đầy tiềm năng và thú vị, nơi họ có thể kết nối, học hỏi và thư giãn mọi lúc, mọi nơi.
-

@ e516ecb8:1be0b167
2025-04-05 23:09:31
En el vasto universo de "Dune", Frank Herbert nos presenta un mundo donde el poder, la religión y la economía se entrelazan de manera fascinante. A primera vista, uno podría pensar que esta saga épica no tiene mucho que ofrecer a los libertarios. Sin embargo, al examinarla a través de la lente de la Escuela Austriaca y el anarcocapitalismo, emergen lecciones valiosas sobre la naturaleza del poder, la importancia del libre mercado y los peligros del intervencionismo estatal.
**El Estado y el control de los recursos**
En "Dune", el Estado, representado por el Imperio Corrino, ejerce un control férreo sobre el recurso más valioso del universo: la especia melange. Este monopolio estatal sofoca la innovación y el libre intercambio, creando una economía distorsionada y propensa a la corrupción. La lucha por el control de Arrakis, el único planeta donde se produce la especia, es un claro ejemplo de cómo el intervencionismo estatal genera conflictos y guerras.
**El mesianismo y el peligro del liderazgo carismático**
La figura de Paul Atreides, el mesías Muad'Dib, nos advierte sobre los peligros del liderazgo carismático y el culto a la personalidad. Su ascenso al poder, impulsado por la manipulación religiosa y el miedo, desemboca en una guerra santa que se extiende por el universo, cobrando millones de vidas. Esta tragedia nos recuerda que el poder, incluso cuando se ejerce con las mejores intenciones, tiende a corromper y a generar consecuencias imprevistas.
**El libre mercado y la innovación**
A pesar del control estatal, en "Dune" también encontramos ejemplos de libre mercado e innovación. Los fremen, habitantes del desierto de Arrakis, han desarrollado una cultura basada en la autosuficiencia y el ingenio, adaptándose a un entorno hostil y creando tecnologías únicas. Su capacidad para sobrevivir y prosperar en un mundo sin Estado es un testimonio del poder del libre mercado y la iniciativa individual.
**Lecciones para el anarcocapitalismo**
"Dune" nos ofrece valiosas lecciones para el anarcocapitalismo. Nos recuerda que el Estado, incluso en sus formas más benignas, tiende a sofocar la libertad y la prosperidad. Nos advierte sobre los peligros del liderazgo carismático y la importancia de la descentralización del poder. Y nos muestra que el libre mercado y la innovación son esenciales para la supervivencia y el progreso de la humanidad.
En un mundo donde el Estado y el poder centralizado siguen siendo la norma, "Dune" nos invita a imaginar un futuro donde la libertad y la cooperación voluntaria sean los pilares de la sociedad. Un futuro donde, como los fremen en el desierto, podamos construir un mundo mejor sin necesidad de amos ni señores.
-

@ fd208ee8:0fd927c1
2025-04-05 21:51:52
# Markdown: Syntax
* [Overview](#overview)
* [Philosophy](#philosophy)
* [Inline HTML](#html)
* [Automatic Escaping for Special Characters](#autoescape)
* [Block Elements](#block)
* [Paragraphs and Line Breaks](#p)
* [Headers](#header)
* [Blockquotes](#blockquote)
* [Lists](#list)
* [Code Blocks](#precode)
* [Horizontal Rules](#hr)
* [Span Elements](#span)
* [Links](#link)
* [Emphasis](#em)
* [Code](#code)
* [Images](#img)
* [Miscellaneous](#misc)
* [Backslash Escapes](#backslash)
* [Automatic Links](#autolink)
**Note:** This document is itself written using Markdown; you
can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text).
----
## Overview
### Philosophy
Markdown is intended to be as easy-to-read and easy-to-write as is feasible.
Readability, however, is emphasized above all else. A Markdown-formatted
document should be publishable as-is, as plain text, without looking
like it's been marked up with tags or formatting instructions. While
Markdown's syntax has been influenced by several existing text-to-HTML
filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html),
[Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of
inspiration for Markdown's syntax is the format of plain text email.
## Block Elements
### Paragraphs and Line Breaks
A paragraph is simply one or more consecutive lines of text, separated
by one or more blank lines. (A blank line is any line that looks like a
blank line -- a line containing nothing but spaces or tabs is considered
blank.) Normal paragraphs should not be indented with spaces or tabs.
The implication of the "one or more consecutive lines of text" rule is
that Markdown supports "hard-wrapped" text paragraphs. This differs
significantly from most other text-to-HTML formatters (including Movable
Type's "Convert Line Breaks" option) which translate every line break
character in a paragraph into a `<br />` tag.
When you *do* want to insert a `<br />` break tag using Markdown, you
end a line with two or more spaces, then type return.
### Headers
Markdown supports two styles of headers, [Setext] [1] and [atx] [2].
Optionally, you may "close" atx-style headers. This is purely
cosmetic -- you can use this if you think it looks better. The
closing hashes don't even need to match the number of hashes
used to open the header. (The number of opening hashes
determines the header level.)
### Blockquotes
Markdown uses email-style `>` characters for blockquoting. If you're
familiar with quoting passages of text in an email message, then you
know how to create a blockquote in Markdown. It looks best if you hard
wrap the text and put a `>` before every line:
> This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet,
> consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus.
> Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus.
>
> Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse
> id sem consectetuer libero luctus adipiscing.
Markdown allows you to be lazy and only put the `>` before the first
line of a hard-wrapped paragraph:
> This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet,
consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus.
Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus.
> Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse
id sem consectetuer libero luctus adipiscing.
Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by
adding additional levels of `>`:
> This is the first level of quoting.
>
> > This is nested blockquote.
>
> Back to the first level.
Blockquotes can contain other Markdown elements, including headers, lists,
and code blocks:
> ## This is a header.
>
> 1. This is the first list item.
> 2. This is the second list item.
>
> Here's some example code:
>
> return shell_exec("echo $input | $markdown_script");
Any decent text editor should make email-style quoting easy. For
example, with BBEdit, you can make a selection and choose Increase
Quote Level from the Text menu.
### Lists
Markdown supports ordered (numbered) and unordered (bulleted) lists.
Unordered lists use asterisks, pluses, and hyphens -- interchangably
-- as list markers:
* Red
* Green
* Blue
is equivalent to:
+ Red
+ Green
+ Blue
and:
- Red
- Green
- Blue
Ordered lists use numbers followed by periods:
1. Bird
2. McHale
3. Parish
It's important to note that the actual numbers you use to mark the
list have no effect on the HTML output Markdown produces. The HTML
Markdown produces from the above list is:
If you instead wrote the list in Markdown like this:
1. Bird
1. McHale
1. Parish
or even:
3. Bird
1. McHale
8. Parish
you'd get the exact same HTML output. The point is, if you want to,
you can use ordinal numbers in your ordered Markdown lists, so that
the numbers in your source match the numbers in your published HTML.
But if you want to be lazy, you don't have to.
To make lists look nice, you can wrap items with hanging indents:
* Lorem ipsum dolor sit amet, consectetuer adipiscing elit.
Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi,
viverra nec, fringilla in, laoreet vitae, risus.
* Donec sit amet nisl. Aliquam semper ipsum sit amet velit.
Suspendisse id sem consectetuer libero luctus adipiscing.
But if you want to be lazy, you don't have to:
* Lorem ipsum dolor sit amet, consectetuer adipiscing elit.
Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi,
viverra nec, fringilla in, laoreet vitae, risus.
* Donec sit amet nisl. Aliquam semper ipsum sit amet velit.
Suspendisse id sem consectetuer libero luctus adipiscing.
List items may consist of multiple paragraphs. Each subsequent
paragraph in a list item must be indented by either 4 spaces
or one tab:
1. This is a list item with two paragraphs. Lorem ipsum dolor
sit amet, consectetuer adipiscing elit. Aliquam hendrerit
mi posuere lectus.
Vestibulum enim wisi, viverra nec, fringilla in, laoreet
vitae, risus. Donec sit amet nisl. Aliquam semper ipsum
sit amet velit.
2. Suspendisse id sem consectetuer libero luctus adipiscing.
It looks nice if you indent every line of the subsequent
paragraphs, but here again, Markdown will allow you to be
lazy:
* This is a list item with two paragraphs.
This is the second paragraph in the list item. You're
only required to indent the first line. Lorem ipsum dolor
sit amet, consectetuer adipiscing elit.
* Another item in the same list.
To put a blockquote within a list item, the blockquote's `>`
delimiters need to be indented:
* A list item with a blockquote:
> This is a blockquote
> inside a list item.
To put a code block within a list item, the code block needs
to be indented *twice* -- 8 spaces or two tabs:
* A list item with a code block:
<code goes here>
### Code Blocks
Pre-formatted code blocks are used for writing about programming or
markup source code. Rather than forming normal paragraphs, the lines
of a code block are interpreted literally. Markdown wraps a code block
in both `<pre>` and `<code>` tags.
To produce a code block in Markdown, simply indent every line of the
block by at least 4 spaces or 1 tab.
This is a normal paragraph:
This is a code block.
Here is an example of AppleScript:
tell application "Foo"
beep
end tell
A code block continues until it reaches a line that is not indented
(or the end of the article).
Within a code block, ampersands (`&`) and angle brackets (`<` and `>`)
are automatically converted into HTML entities. This makes it very
easy to include example HTML source code using Markdown -- just paste
it and indent it, and Markdown will handle the hassle of encoding the
ampersands and angle brackets. For example, this:
<div class="footer">
© 2004 Foo Corporation
</div>
Regular Markdown syntax is not processed within code blocks. E.g.,
asterisks are just literal asterisks within a code block. This means
it's also easy to use Markdown to write about Markdown's own syntax.
```
tell application "Foo"
beep
end tell
```
## Span Elements
### Links
Markdown supports two style of links: *inline* and *reference*.
In both styles, the link text is delimited by [square brackets].
To create an inline link, use a set of regular parentheses immediately
after the link text's closing square bracket. Inside the parentheses,
put the URL where you want the link to point, along with an *optional*
title for the link, surrounded in quotes. For example:
This is [an example](http://example.com/) inline link.
[This link](http://example.net/) has no title attribute.
### Emphasis
Markdown treats asterisks (`*`) and underscores (`_`) as indicators of
emphasis. Text wrapped with one `*` or `_` will be wrapped with an
HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML
`<strong>` tag. E.g., this input:
*single asterisks*
_single underscores_
**double asterisks**
__double underscores__
### Code
To indicate a span of code, wrap it with backtick quotes (`` ` ``).
Unlike a pre-formatted code block, a code span indicates code within a
normal paragraph. For example:
Use the `printf()` function.
-

@ 592295cf:413a0db9
2025-03-29 10:59:52
The journey starts from the links in this article
[nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/)
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted
And I didn't see how he did it.
-----
Go to [nstart.me](https://nstart.me/) and read:
Each user is identified by a cryptographic keypair
Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key
I know and I know it's a tongue dump.
## Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site
of the protocol nostr. If one of these servers goes offline you have the private key
that you downloaded first and then reactivate a bunker.
All very complicated.
But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
## Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
## Now select 5 clients
### *Coracle, Chachi, Olas, Nostur, Jumble*
### The first is *Coracle*
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
### Let's try *Chachi*
Simpler than Coracle, it has a type login that says bunker.
see if I can post
It worked, cool, I managed to post in a group.
## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
> If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something
> like that, but many start from the phone so maybe it's easy for them.
> I try to download it and see if it allows me to connect with a bunker.
> Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
**Ok then I saw that there was the qrcode image of the bunker for apps** lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on *Olas*, so it works, Expiration time is broken.
### As for *Nostur*, I don't have an ios device so I'm going to another one.
### Login with *Jumble*, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
# Extensions nostr NIP-07
### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions)
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension)
Alby I don't know if it's a route to recommend
2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj)
3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file)
4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/)
Nostore is (archived, read-only)
5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame)
6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser)
7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj)
Another half hour to search all sites
# Nostrapps
Here you can make paths
### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to [Nostrapps](https://nostrapps.com/) and read:
## Microbbloging: Primal
## Streaming: **Zap stream**
## Blogging: **Yakihonne**
## Group chat: **Chachi**
## Community: **Flotilla**
## Tools: **Form** *
## Discovery: **Zapstore** (even if it is not in this catrgory)
## Direct Message: **0xchat**
-

@ 63b2cd3d:060efdc3
2025-04-05 18:43:47
MN88 là một nền tảng giải trí trực tuyến độc đáo, thu hút người tham gia nhờ vào sự đa dạng và phong phú trong các hoạt động giải trí mà nó mang lại. Với giao diện dễ sử dụng, nền tảng này cung cấp cho người dùng những trò chơi và hoạt động giải trí hấp dẫn, từ những thử thách trí tuệ cho đến các trò chơi nhẹ nhàng thư giãn. Dù bạn là người yêu thích sự kịch tính hay chỉ đơn giản muốn tìm kiếm những giây phút thư giãn, MN88 đều có thể đáp ứng được nhu cầu của mọi đối tượng người tham gia. Mỗi lần đăng nhập vào MN88, người dùng đều có thể khám phá những trò chơi mới mẻ, thử sức với các thử thách hấp dẫn và cảm nhận những giây phút vui vẻ mà nền tảng này mang lại. Chính sự đa dạng và chất lượng của các hoạt động đã tạo nên một không gian giải trí thực sự thú vị và không bao giờ nhàm chán.
Điểm nổi bật của <a href="https://mn88.co">MN88</a> chính là khả năng xây dựng một cộng đồng người dùng gắn kết và năng động. Nền tảng này không chỉ đơn thuần là nơi để giải trí mà còn là nơi để mọi người kết nối, giao lưu và chia sẻ sở thích với nhau. Các tính năng xã hội của MN88 giúp người tham gia dễ dàng tìm thấy những người bạn có cùng niềm đam mê, từ đó tạo nên một môi trường sôi động, thân thiện và tích cực. Những cuộc trò chuyện, các sự kiện cộng đồng và các hoạt động nhóm không chỉ giúp người tham gia cảm thấy gần gũi mà còn mở rộng cơ hội học hỏi và phát triển các kỹ năng cá nhân. Nhờ vào cộng đồng mạnh mẽ này, MN88 không chỉ là một nền tảng giải trí mà còn là một không gian giao lưu đầy ý nghĩa, giúp người dùng có thể kết nối và phát triển những mối quan hệ mới.
Bên cạnh đó, MN88 luôn nỗ lực không ngừng để nâng cấp và cải thiện nền tảng của mình, mang đến cho người dùng những trải nghiệm giải trí ngày càng hấp dẫn và mới mẻ. Các trò chơi, hoạt động và tính năng của nền tảng này đều được cập nhật thường xuyên, đảm bảo rằng người tham gia luôn có cơ hội khám phá những điều mới và thú vị. Với những cải tiến liên tục, MN88 duy trì sự tươi mới và cuốn hút, không bao giờ để người dùng cảm thấy nhàm chán. Nền tảng này không chỉ tạo ra một không gian giải trí chất lượng mà còn khuyến khích sự sáng tạo, học hỏi và phát triển kỹ năng cá nhân. Chính nhờ vào sự đổi mới không ngừng và những cải tiến liên tục, MN88 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đa dạng, phong phú và đầy thú vị.
-

@ 63b2cd3d:060efdc3
2025-04-05 18:42:41
ZomClub là một nền tảng giải trí trực tuyến mới mẻ, mang đến cho người dùng những trải nghiệm độc đáo và phong phú. Được thiết kế với giao diện trực quan và dễ sử dụng, ZomClub cung cấp một không gian đầy sáng tạo và thú vị, nơi người dùng có thể tham gia vào nhiều hoạt động và trò chơi đa dạng. Từ những thử thách trí tuệ đến các trò chơi mang tính giải trí nhẹ nhàng, ZomClub đáp ứng đầy đủ nhu cầu của mọi đối tượng người tham gia. Đặc biệt, nền tảng này không chỉ là nơi giải trí mà còn là cơ hội để người dùng thử sức với những trò chơi mới, từ đó phát triển kỹ năng tư duy, sự nhanh nhạy và khả năng giải quyết vấn đề. Mỗi lần tham gia vào ZomClub, người dùng đều có thể tìm thấy niềm vui, thử thách bản thân và tận hưởng những giây phút thư giãn đầy ý nghĩa.
Một trong những yếu tố khiến ZomClub trở nên đặc biệt chính là sự chú trọng đến việc xây dựng một cộng đồng gắn kết và tích cực. Nền tảng này không chỉ cung cấp các trò chơi, mà còn là một không gian xã hội để người dùng giao lưu, chia sẻ và kết nối với những người có cùng sở thích. Các tính năng xã hội của <a href="https://zomclub-vn.com">ZomClub</a> cho phép người tham gia thảo luận, tham gia các sự kiện cộng đồng và kết bạn, giúp tạo nên một không gian sôi động và thân thiện. Nhờ vào những hoạt động tương tác này, người dùng không chỉ tìm được những người bạn mới mà còn có thể mở rộng mối quan hệ và học hỏi những điều mới mẻ từ cộng đồng. Điều này giúp ZomClub không chỉ là một nền tảng giải trí, mà còn là một cộng đồng trực tuyến tích cực, nơi mỗi người có thể tìm thấy sự kết nối và cảm hứng.
Bên cạnh đó, ZomClub cũng không ngừng đổi mới và nâng cấp các tính năng để duy trì sự hấp dẫn và tươi mới cho người dùng. Các trò chơi và hoạt động trên nền tảng được cập nhật liên tục, mang đến những trải nghiệm mới mẻ mỗi lần người dùng truy cập. Dù là các trò chơi thử thách hay các hoạt động xã hội, ZomClub luôn đảm bảo rằng người tham gia sẽ không bao giờ cảm thấy nhàm chán. Điều này thể hiện cam kết của nền tảng trong việc tạo ra một không gian giải trí đầy đủ, không chỉ giúp người dùng thư giãn mà còn khuyến khích sự sáng tạo và học hỏi. Với sự kết hợp hoàn hảo giữa giải trí và giao lưu cộng đồng, ZomClub là lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng giải trí thú vị và đầy sáng tạo.
-

@ 21335073:a244b1ad
2025-03-18 20:47:50
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ ba36d0f7:cd802cba
2025-04-05 18:13:13

♟️ **The scene:**
Starting April 11th, 2025, every week in **Apaneca, El Salvador** - a town so small you’d miss it if you blinked - a quiet revolution will be unfolding.
In soma chess, taking place at **📍Estudio Malinche**- chessboards aren’t just for play. They’re **gateways to a modern kind of culture** - one where discipline meets digital curiosity, and where tradition doesn’t mean rejecting tech, but **hacking it for growth**.
This isn’t about creating grandmasters.
It’s about using chess’s ancient magic to teach:
- **Respect** (for the game and community, your opponent, and yourself).
- **Patience** (because the board doesn’t reward haste).
- **Perseverance** (every loss is a lesson in disguise).
But there’s a twist: **We’re not aiming to teaching chess. We’re aiming to teaching how to navigate a world where culture is now built on code, forums, and digital communities.**
> **_Chess as a Trojan horse to self-learning, learning better and doing better._**
---
**Why Chess?**
Chess is the ultimate **self-improvement metaphor**:
✅ _The opponent could leave you a winning position - but can_ **_you_** **_see_** **_it_**_?_
✅ _You could blame luck - or ask,_ **_“_**_Where did_ **_I_** _go wrong_**_?”_**
✅ _You could rage-quit - or_ **_learn to love the grind._**
---
**The hidden curriculum: Where analog meets algorithm**
**1. Embracing digital curiosity**
_We’re not teaching openings - we’re showing players how to hunt for knowledge._
**2. Mistakes as rituals**
_Owning blunders, and analyzing them with engines._
**3. The long game**
_Tracking progress and digitally storing your games._
---
**Join us**
This isn’t _just_ about Apaneca.
🌍 **Your challenge:**
- **If you’re nearby**, come play (every Thursday, 1-5PM, zero expectations).
- **If you’re far**, do this in your town. We’ll share our **playbook**.
- **If you’re online**, **follow us**npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99 and tag along for the ride.
---
**Final Move:**
Chess doesn’t build character. It reveals it - then sharpens it.
And **culture and communities aren’t just what we inherit. They're what we build.**
*********************
#chess #ajedrez #article #meetup #education #chesselsalvador #rutadelasflores #apaneca #somachess
-

@ 57d1a264:69f1fee1
2025-03-29 09:31:13
> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME."
<sub>- SATOSHI NAKAMOTO</sub>



"Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin.
Materials: Carrara Marble, Copper leaf, Opendime
Dimensions: 6" x 9" x 13"
Price: $30,000 or BTC equivalent
Enquire: https://www.vonbitcoin.com/available-works
X: https://x.com/BVBTC/status/1894463357316419960/photo/1
originally posted at https://stacker.news/items/928510
-

@ a5142938:0ef19da3
2025-04-05 11:13:26
### Core Team
The Core Team drives the project and validates the content.
<img src="!(image)[https://files.mastodon.social/accounts/avatars/112/353/885/673/397/288/original/7f92926ffb69936f.jpg]" width="80" height="80">
[Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll)
To start, I'm managing the project solo by sharing my bookmarks to avoid plastic on myself and on my children. [Contact me](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/) if you'd like to join!
### Content Enrichers
Our contributors make this site engaging and interesting.
*Coming soon.*
👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/)
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/cyy0wd2ar_rwqbjipnhej/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/x-ykxuenf9tnccu65mhjq/)
-

@ fd208ee8:0fd927c1
2025-04-05 21:36:33
# Markdown: Syntax
* [Overview](#overview)
* [Philosophy](#philosophy)
* [Inline HTML](#html)
* [Automatic Escaping for Special Characters](#autoescape)
* [Block Elements](#block)
* [Paragraphs and Line Breaks](#p)
* [Headers](#header)
* [Blockquotes](#blockquote)
* [Lists](#list)
* [Code Blocks](#precode)
* [Horizontal Rules](#hr)
* [Span Elements](#span)
* [Links](#link)
* [Emphasis](#em)
* [Code](#code)
* [Images](#img)
* [Miscellaneous](#misc)
* [Backslash Escapes](#backslash)
* [Automatic Links](#autolink)
**Note:** This document is itself written using Markdown; you
can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text).
----
## Overview
### Philosophy
Markdown is intended to be as easy-to-read and easy-to-write as is feasible.
Readability, however, is emphasized above all else. A Markdown-formatted
document should be publishable as-is, as plain text, without looking
like it's been marked up with tags or formatting instructions. While
Markdown's syntax has been influenced by several existing text-to-HTML
filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html),
[Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of
inspiration for Markdown's syntax is the format of plain text email.
## Block Elements
### Paragraphs and Line Breaks
A paragraph is simply one or more consecutive lines of text, separated
by one or more blank lines. (A blank line is any line that looks like a
blank line -- a line containing nothing but spaces or tabs is considered
blank.) Normal paragraphs should not be indented with spaces or tabs.
The implication of the "one or more consecutive lines of text" rule is
that Markdown supports "hard-wrapped" text paragraphs. This differs
significantly from most other text-to-HTML formatters (including Movable
Type's "Convert Line Breaks" option) which translate every line break
character in a paragraph into a `<br />` tag.
When you *do* want to insert a `<br />` break tag using Markdown, you
end a line with two or more spaces, then type return.
### Headers
Markdown supports two styles of headers, [Setext] [1] and [atx] [2].
Optionally, you may "close" atx-style headers. This is purely
cosmetic -- you can use this if you think it looks better. The
closing hashes don't even need to match the number of hashes
used to open the header. (The number of opening hashes
determines the header level.)
### Blockquotes
Markdown uses email-style `>` characters for blockquoting. If you're
familiar with quoting passages of text in an email message, then you
know how to create a blockquote in Markdown. It looks best if you hard
wrap the text and put a `>` before every line:
> This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet,
> consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus.
> Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus.
>
> Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse
> id sem consectetuer libero luctus adipiscing.
Markdown allows you to be lazy and only put the `>` before the first
line of a hard-wrapped paragraph:
> This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet,
consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus.
Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus.
> Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse
id sem consectetuer libero luctus adipiscing.
Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by
adding additional levels of `>`:
> This is the first level of quoting.
>
> > This is nested blockquote.
>
> Back to the first level.
Blockquotes can contain other Markdown elements, including headers, lists,
and code blocks:
> ## This is a header.
>
> 1. This is the first list item.
> 2. This is the second list item.
>
> Here's some example code:
>
> return shell_exec("echo $input | $markdown_script");
Any decent text editor should make email-style quoting easy. For
example, with BBEdit, you can make a selection and choose Increase
Quote Level from the Text menu.
### Lists
Markdown supports ordered (numbered) and unordered (bulleted) lists.
Unordered lists use asterisks, pluses, and hyphens -- interchangably
-- as list markers:
* Red
* Green
* Blue
is equivalent to:
+ Red
+ Green
+ Blue
and:
- Red
- Green
- Blue
Ordered lists use numbers followed by periods:
1. Bird
2. McHale
3. Parish
It's important to note that the actual numbers you use to mark the
list have no effect on the HTML output Markdown produces. The HTML
Markdown produces from the above list is:
If you instead wrote the list in Markdown like this:
1. Bird
1. McHale
1. Parish
or even:
3. Bird
1. McHale
8. Parish
you'd get the exact same HTML output. The point is, if you want to,
you can use ordinal numbers in your ordered Markdown lists, so that
the numbers in your source match the numbers in your published HTML.
But if you want to be lazy, you don't have to.
To make lists look nice, you can wrap items with hanging indents:
* Lorem ipsum dolor sit amet, consectetuer adipiscing elit.
Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi,
viverra nec, fringilla in, laoreet vitae, risus.
* Donec sit amet nisl. Aliquam semper ipsum sit amet velit.
Suspendisse id sem consectetuer libero luctus adipiscing.
But if you want to be lazy, you don't have to:
* Lorem ipsum dolor sit amet, consectetuer adipiscing elit.
Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi,
viverra nec, fringilla in, laoreet vitae, risus.
* Donec sit amet nisl. Aliquam semper ipsum sit amet velit.
Suspendisse id sem consectetuer libero luctus adipiscing.
List items may consist of multiple paragraphs. Each subsequent
paragraph in a list item must be indented by either 4 spaces
or one tab:
1. This is a list item with two paragraphs. Lorem ipsum dolor
sit amet, consectetuer adipiscing elit. Aliquam hendrerit
mi posuere lectus.
Vestibulum enim wisi, viverra nec, fringilla in, laoreet
vitae, risus. Donec sit amet nisl. Aliquam semper ipsum
sit amet velit.
2. Suspendisse id sem consectetuer libero luctus adipiscing.
It looks nice if you indent every line of the subsequent
paragraphs, but here again, Markdown will allow you to be
lazy:
* This is a list item with two paragraphs.
This is the second paragraph in the list item. You're
only required to indent the first line. Lorem ipsum dolor
sit amet, consectetuer adipiscing elit.
* Another item in the same list.
To put a blockquote within a list item, the blockquote's `>`
delimiters need to be indented:
* A list item with a blockquote:
> This is a blockquote
> inside a list item.
To put a code block within a list item, the code block needs
to be indented *twice* -- 8 spaces or two tabs:
* A list item with a code block:
<code goes here>
### Code Blocks
Pre-formatted code blocks are used for writing about programming or
markup source code. Rather than forming normal paragraphs, the lines
of a code block are interpreted literally. Markdown wraps a code block
in both `<pre>` and `<code>` tags.
To produce a code block in Markdown, simply indent every line of the
block by at least 4 spaces or 1 tab.
This is a normal paragraph:
This is a code block.
Here is an example of AppleScript:
tell application "Foo"
beep
end tell
A code block continues until it reaches a line that is not indented
(or the end of the article).
Within a code block, ampersands (`&`) and angle brackets (`<` and `>`)
are automatically converted into HTML entities. This makes it very
easy to include example HTML source code using Markdown -- just paste
it and indent it, and Markdown will handle the hassle of encoding the
ampersands and angle brackets. For example, this:
<div class="footer">
© 2004 Foo Corporation
</div>
Regular Markdown syntax is not processed within code blocks. E.g.,
asterisks are just literal asterisks within a code block. This means
it's also easy to use Markdown to write about Markdown's own syntax.
```
tell application "Foo"
beep
end tell
```
## Span Elements
### Links
Markdown supports two style of links: *inline* and *reference*.
In both styles, the link text is delimited by [square brackets].
To create an inline link, use a set of regular parentheses immediately
after the link text's closing square bracket. Inside the parentheses,
put the URL where you want the link to point, along with an *optional*
title for the link, surrounded in quotes. For example:
This is [an example](http://example.com/) inline link.
[This link](http://example.net/) has no title attribute.
### Emphasis
Markdown treats asterisks (`*`) and underscores (`_`) as indicators of
emphasis. Text wrapped with one `*` or `_` will be wrapped with an
HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML
`<strong>` tag. E.g., this input:
*single asterisks*
_single underscores_
**double asterisks**
__double underscores__
### Code
To indicate a span of code, wrap it with backtick quotes (`` ` ``).
Unlike a pre-formatted code block, a code span indicates code within a
normal paragraph. For example:
Use the `printf()` function.
-

@ fd06f542:8d6d54cd
2025-03-30 02:10:24
NIP-03
======
OpenTimestamps Attestations for Events
--------------------------------------
`draft` `optional`
This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event:
```json
{
"kind": 1040
"tags": [
["e", <event-id>, <relay-url>],
["alt", "opentimestamps attestation"]
],
"content": <base64-encoded OTS file data>
}
```
- The OpenTimestamps proof MUST prove the referenced `e` event id as its digest.
- The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context.
### Example OpenTimestamps proof verification flow
Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots):
```bash
~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify
> using an esplora server at https://blockstream.info/api
- sequence ending on block 810391 is valid
timestamp validated at block [810391]
```
-

@ db11b320:05c5f7af
2025-03-29 19:04:19
magnet:?xt=urn:btih:9BAC9A3F98803AEA1EB28A0B60A562D7E3779710
-

@ 0d788b5e:c99ddea5
2025-03-29 02:40:37
- [首页](/readme.md)
- [第一章、 第一章标题](/chapter1.md)
- [第二章、 第二章标题](/chapter2.md)
-

@ 9c9d2765:16f8c2c2
2025-04-05 10:45:11
**CHAPTER ONE**
Grandpa Ray’s birthday was a grand celebration. His children and grandchildren gathered around, each presenting him with expensive gifts, golden watches, fine suits, and rare wines. The room buzzed with excitement and laughter.
Among them was James, Grandpa Ray’s adopted son. Unlike the others, James had no gift to offer. He stood quietly, watching as each family member received warm praise for their presents.
Then, Grandpa Ray did something unexpected. With a kind smile, he said, “Today, I want to give you all a gift instead. Ask for anything, and I will grant it.”
Excited, his children and grandchildren eagerly requested expensive things luxury cars, houses, money, and positions in the family business.
When it was James’ turn, he hesitated for a moment before saying, “Grandpa, I would like a shovel.”
A hush fell over the room, then erupted into laughter.
“A shovel?” one cousin sneered.
“What a silly request!” another chuckled.
But Grandpa Ray raised a hand, silencing them. He looked at James with curiosity. “Why a shovel, my boy?”
James took a deep breath and replied, “I don’t need riches handed to me. I want to work for my own wealth. A shovel will help me till the land, plant crops, and build something for myself.”
Grandpa Ray’s eyes gleamed with pride. He nodded and said, “That is a wise request. Not only will I give you a shovel, but I will also grant you a piece of land to farm.”
The laughter died down. The others had asked for luxury, but James had asked for a tool to create his own future.
James had once lived a life of promise. He was hardworking, loyal, and dedicated to his family’s company. But his world came crashing down when he was falsely accused of embezzlement. His own parents, ashamed of the scandal, disowned him without listening to his pleas of innocence.
Alone and broken, James had nowhere to go. It was then that Grandpa Ray, a man known for his wisdom and kindness, took him in. Unlike the rest of the world, Grandpa Ray saw something in James his resilience, his honesty, and his potential.
Despite being adopted into a wealthy and powerful family, James never truly felt accepted. The others in the family pretended to love him, but behind his back, they whispered that he was a burden, an outsider. The only one who genuinely cared for him besides Grandpa Ray was Rita, the old man’s granddaughter.
Over the years, James worked hard to earn his place in the family. He managed some of Grandpa Ray’s businesses, proving his intelligence and dedication. Rita, a kind and spirited woman, saw the goodness in him. Their bond grew stronger, and soon, love blossomed between them.
Grandpa Ray, seeing James’ sincerity and loyalty, made a bold decision he gave Rita’s hand in marriage to James, despite the objections of the rest of the family.
"You have proven yourself to be a man of honor," Grandpa Ray said to James on the wedding day. "And I know that you will cherish Rita the way she deserves."
The rest of the family smiled in public but harbored resentment in their hearts. To them, James was an unworthy orphan who had stolen their grandfather’s favor.
When Grandpa Ray passed away, everything changed. The mask of fake love that the family had worn for years finally fell off. Without Grandpa Ray to protect him, James became a target of humiliation.
Helen, Rita’s mother, Christopher, her father, and Stephen, her brother, openly ridiculed him. They made life unbearable, treating him like a servant rather than a family member.
"You don’t belong here," Stephen sneered one evening. "You were just Grandpa’s charity case."
James endured the insults in silence, holding onto the love he shared with Rita. But his in-laws had other plans; they wanted him out of Rita’s life for good.
Helen and Christopher believed that Rita had made a mistake by marrying James. They wanted her to divorce him and marry someone who would elevate the family’s status. That’s when Helen introduced Mark, the only son of the Prime Minister.
Mark was wealthy, powerful, and came from a family of high political influence. To her, he was the perfect husband for Rita.
"Rita, darling," Helen said sweetly, "don’t waste your life with James. You deserve someone who can give you the life of luxury you were born into."
Stephen agreed. "Mark is everything James is not rich, powerful, and from a good family. Be wise, sister."
But Rita stood firm.
"I love James," she said. "And I will not betray him, no matter how much you pressure me. James and I made a promise to Grandpa never to leave each other"
Helen, frustrated by Rita’s refusal, tried to manipulate her further. She arranged secret meetings between Rita and Mark, hoping she would be swayed. She even planned an engagement dinner, assuming Rita would eventually give in.
Meanwhile, James felt the weight of the battle. He saw how much pressure Rita was under and, one evening, he took her hands and said, "Rita, if leaving me will make your life easier, I won’t stop you."
Tears filled her eyes. "James, my love isn’t based on status or wealth. I chose you, and I will keep choosing you no matter what, you have forgotten the promise we two made to Grandpa before he died, in case you have forgotten, I haven't"
That night, Rita made her choice. She called a meeting to inform everyone that nothing will make her leave James for another man, James couldn't withstand the joy she made her that night, choosing love over wealth and status.
With nothing but their love and determination, James and Rita started anew. They built their life from scratch, with James working tirelessly to create a name for himself.
The Ray family had once been a symbol of wealth, power, and success, but in recent months, everything had started crumbling. A series of financial setbacks, business failures, and internal conflicts had pushed the family into a dire situation. The creditors were knocking, the banks were threatening to withdraw their support, and their empire was on the verge of collapse.
Desperation clouded every decision they made. And in that desperation, they saw only one way out is Mark.
Mark, the only son of the Prime Minister, was not just a man of wealth but also of power and influence. He had been interested in Rita for years, but she had always refused him, choosing instead to marry James. But now, with the family drowning in crisis, Mark became their only hope.
Helen, Rita’s mother, sat across from Christopher, her husband, and Stephen, their son. The tension in the room was thick.
“We have no other choice,” Helen said firmly. “Mark is willing to help us, but he wants something in return.”
“We all know what that is,” Stephen said, glancing at Rita, who sat silently in the corner of the room.
Christopher sighed. “James is the only obstacle left. We have to make Rita understand that this isn’t about love anymore, it's about survival.”
Helen’s voice was cold. “She will divorce him. And James will have no choice but to accept it.”
Rita looked up, her heart pounding. “You’re selling me to him,” she said in disbelief.
“Rita,” Helen said impatiently. “This isn’t about selling you. This is about securing our future. James has nothing. Mark can give you everything.”
“I don’t want everything. I want my husband.”
Helen scoffed. “Love won’t save this family.”
But Rita clenched her fists. She wasn’t going to give up on James so easily.
The Ray family organized a grand business anniversary event, using it as a cover to publicly introduce Mark as their savior. Guests arrived in expensive suits and dazzling gowns, but beneath the luxury was a desperate attempt to keep up appearances.
James had never felt more out of place. He knew he wasn’t truly welcome among the Ray family, but tonight, it was worse than ever. He could see the way people looked at him like he was an outsider, a liability.
Then Mark arrived; Tall, confident, and exuding power, he walked into the hall as if he already owned it. People flocked to him, shaking his hand, singing his praises.
And then, during a private meeting with the Ray family, he made his move.
“I know about your situation,” Mark said smoothly, placing a black suitcase on the table and opening it. Inside were stacks of cash, two million dollars.
Helen gasped. Christopher’s hands trembled.
Mark leaned back.
-

@ 2183e947:f497b975
2025-03-29 02:41:34
Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison.
I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core
You can also learn more about Pubky here: https://pubky.org/
That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key.
Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis.
Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed.
Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message.
I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key.
As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster.
Based on all of this info, it seems like, to populate your feed, this is the series of steps:
- you tell your homeserver your pubkey
- it uses some sort of algorithm to decide whose posts to show you
- then looks up the homeservers used by those people on an indexer server
- then it fetches posts from their homeservers
- then your client displays them to you
To create a post, this is the series of steps:
- you tell your homeserver what you want to say to the world
- it stores that message in plaintext and merely asserts that it came from you (it's not signed)
- other people can find out what you said by querying for your posts on your homeserver
Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver.
John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted.
Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
-

@ 57d1a264:69f1fee1
2025-03-28 10:32:15
Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.

The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022).
Look forward for this to happen!
Spread the voice:
N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m)
X: https://x.com/bitcoin_design/status/1905547407405768927
originally posted at https://stacker.news/items/927650
-

@ 57d1a264:69f1fee1
2025-03-27 10:42:05
What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who?
The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1:
## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.













- - -
Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before.
This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using.
- [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser
- ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY)
@k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful.
[^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined
originally posted at https://stacker.news/items/926557
-

@ e372d24b:e25df41f
2025-04-05 18:11:15
## Unlocking Learning Potential: Why Student's Ideas Matter
### Introduction
Recent research in mathematics education emphasizes the importance of valuing and building upon students' initial ideas and intuitive understanding. This approach, often referred to as "taking students' ideas seriously," has enhanced conceptual understanding, problem-solving skills, and overall mathematical achievement. This overview examines this approach's theoretical foundations, cognitive processes, and practical implications in mathematics classrooms.

<div style="padding:56.25% 0 0 0;position:relative;"><iframe src="https://player.vimeo.com/video/1039781401?badge=0&autopause=0&player_id=0&app_id=58479" frameborder="0" allow="autoplay; fullscreen; picture-in-picture; clipboard-write; encrypted-media" style="position:absolute;top:0;left:0;width:100%;height:100%;" title="Practice 1-taking students ideas seriously"></iframe></div><script src="https://player.vimeo.com/api/player.js"></script>
[FREE DOWNLOAD - Questions and Prompts](https://dmti-public-resources.s3.us-east-2.amazonaws.com/DMT%20Questions%20and%20Prompts%20-%20Eng.pdf)
#### **Theoretical Foundations**
Taking students' ideas seriously is grounded in constructivist learning theory and research on how students develop mathematical understanding. Hiebert and Carpenter (1992) argue that "if children possessed internal networks constructed both in and out of school and if they recognized the connections between them, their understanding and performance in both settings would improve." This highlights the importance of connecting students' informal knowledge with formal mathematical concepts. Carpenter's work further emphasizes the value of students' intuitive knowledge: "Children come to school with a great deal of informal or intuitive knowledge of mathematics that can serve as the basis for developing much of the formal mathematics of the primary school curriculum." This suggests that taking students' initial ideas seriously can provide a strong foundation for developing a more sophisticated mathematical understanding.
#### **Cognitive Processes**
When students' ideas are taken seriously in mathematics classrooms, several cognitive processes are engaged:
1. Schema Formation: As students articulate and refine their ideas, they develop and modify mental frameworks or schemas that organize mathematical concepts.
2. Metacognition: Explaining their thinking engages students' metacognitive processes, promoting reflection on their own understanding and problem-solving strategies.
3. Elaborative Rehearsal: Verbalizing mathematical concepts helps move information from working memory to long-term memory, enhancing retention.
4. Cognitive Conflict: When students encounter differing viewpoints, it can create cognitive conflict, stimulating the reconciliation of new information with existing schemas.
#### **Practical Implications**
**Eliciting and Valuing Student Ideas**
Carpenter and Lehrer argue that for learning with understanding to occur, instruction needs to provide specific opportunities: "For learning with understanding to occur, instruction needs to provide students the opportunity to develop productive relationships, extend and apply their knowledge, reflect about their experiences, articulate what they know, and make knowledge their own." This emphasizes the need for instructional approaches that actively elicit and value student ideas.
#### **Creating a Supportive Environment**
To effectively take students' ideas seriously, teachers must foster a classroom environment where all contributions are respected. This involves:
1. Provide adequate thinking time for students to formulate their thoughts.
2. Using open-ended questions that encourage diverse thinking and approaches.
3. Implementing collaborative strategies like think-pair-share to build confidence in sharing ideas.
#### **Connecting to Formal Mathematics**
Hiebert advocates for teaching practices that promote understanding by focusing on "the inherent structure of the emerging mathematical ideas and addressing students' misconceptions as they arise" . This involves helping students connect their informal ideas to more formal mathematical concepts and procedures.
#### Impact on Student Learning
Research indicates that taking students' ideas seriously can significantly improve mathematical understanding and achievement. A study by Carpenter et al. (1998) found that when teachers based their instruction on students' thinking, students demonstrated greater problem-solving skills and conceptual understanding compared to control groups. Moreover, this approach has increased student engagement and motivation in mathematics. When students feel their ideas are valued, they are more likely to participate actively in mathematical discussions and take intellectual risks.
#### Challenges and Considerations
While the benefits of taking students' ideas seriously are well-documented, implementing this approach can present challenges:
1. **Time Constraints:** Allowing for extended student discussions and idea exploration can be time-consuming within the constraints of a typical school schedule.
2. **Teacher Preparation:** Effectively building on student ideas requires strong content knowledge and pedagogical skills from teachers.
3. **Assessment Alignment:** Traditional assessment methods may not adequately capture the depth of understanding developed through this approach, necessitating new forms of evaluation.
#### Conclusion
Taking students' ideas seriously in mathematics education represents a powerful approach to fostering deep conceptual understanding and problem-solving skills. By valuing students' initial thoughts and building upon their intuitive knowledge, educators can create more engaging and effective learning environments. While challenges exist in implementation, the potential benefits for student learning and mathematical achievement make this approach worthy of serious consideration and further research.
#### References
Ball, D. L., Thames, M. H., & Phelps, G. (2008). Content knowledge for teaching: What makes it special? Journal of Teacher Education, 59(5), 389-407.
Boaler, J. (2002). Experiencing school mathematics: Traditional and reform approaches to teaching and their impact on student learning. Routledge.
Boaler, J., & Brodie, K. (2004). The importance, nature and impact of teacher questions. In D. E. McDougall & J. A. Ross (Eds.), Proceedings of the 26th annual meeting of the North American Chapter of the International Group for the Psychology of Mathematics Education (Vol. 2, pp. 773-782). Toronto: OISE/UT. Carpenter, T. P., Fennema, E., & Franke, M. L. (1996). Cognitively guided instruction: A knowledge base for reform in primary mathematics instruction. The Elementary School Journal, 97(1), 3-20.
Carpenter, T. P., Fennema, E., Franke, M. L., Levi, L., & Empson, S. B. (1999). Children's mathematics: Cognitively guided instruction. Portsmouth, NH: Heinemann.
Carpenter, T. P., & Lehrer, R. (1999). Teaching and learning mathematics with understanding. In E. Fennema & T. A. Romberg (Eds.), Mathematics classrooms that promote understanding (pp. 19-32). Mahwah, NJ: Lawrence Erlbaum Associates.
Craik, F. I., & Lockhart, R. S. (1972). Levels of processing: A framework for memory research. Journal of Verbal Learning and Verbal Behavior, 11(6), 671-684.
Driscoll, M. P. (2005). Psychology of learning for instruction (3rd ed.). Boston: Allyn and Bacon.
Flavell, J. H. (1979). Metacognition and cognitive monitoring: A new area of cognitive-developmental inquiry. American Psychologist, 34(10), 906-911.
Hiebert, J., & Carpenter, T. P. (1992). Learning and teaching with understanding. In D. A. Grouws (Ed.), Handbook of research on mathematics teaching and learning (pp. 65-97). New York: Macmillan.
Hiebert, J., Carpenter, T. P., Fennema, E., Fuson, K. C., Wearne, D., Murray, H., ... & Human, P. (1997). Making sense: Teaching and learning mathematics with understanding. Portsmouth, NH: Heinemann.
Lyman, F. (1981). The responsive classroom discussion: The inclusion of all students. In A. S. Anderson (Ed.), Mainstreaming Digest (pp. 109-113). College Park: University of Maryland Press.
Piaget, J. (1952). The origins of intelligence in children. New York: International Universities Press.
Rowe, M. B. (1986). Wait time: Slowing down may be a way of speeding up! Journal of Teacher Education, 37(1), 43- 50.
Shepard, L. A. (2000). The role of assessment in a learning culture. Educational Researcher, 29(7), 4-14.
Smith, M. S., & Stein, M. K. (2011). 5 practices for orchestrating productive mathematics discussions. Reston, VA: National Council of Teachers of Mathematics.
#### **Social Media.**
Research in mathematics education highlights the significance of taking students' ideas seriously, demonstrating how this approach enhances conceptual understanding, problem-solving abilities, and overall mathematical achievement. Rooted in constructivist learning theory, this method engages crucial cognitive processes like schema formation, metacognition, and elaborative rehearsal. By connecting students’ informal knowledge with formal mathematical concepts, educators can establish a robust foundation for advanced mathematical thinking. Studies show that when instruction is based on students' thinking, learners exhibit superior problem-solving skills and a deeper conceptual grasp than traditional teaching methods.
Join us in exploring these powerful teaching approaches and their impact on mathematical thinking and achievement!
-

@ 21335073:a244b1ad
2025-03-18 14:43:08
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ 57d1a264:69f1fee1
2025-03-27 08:27:44
> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be.
`— Anil Dash, The Web We Lost, 13 Dec 2012`
https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s
So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/
The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks.
originally posted at https://stacker.news/items/926499
-

@ a5142938:0ef19da3
2025-04-05 10:18:18
Discover the materials accepted or not in the products listed on this site.
### ✅ Natural Materials
Materials of plant, animal, or mineral origin, without chemical transformation that alters their molecular structure.
**🌱 Main Criteria:**
- Biodegradability
- Non-toxicity
- Naturally occurring and recquiring minimal transformation
**🔍 List of Natural Materials:**
- Natural rubber
- Hemp
- Cotton
- Leather
- Cork
- Linen
- Wool
- Silk
- … (Other materials)
⚠️ Although natural, these materials can have negative impacts depending on their production conditions (pesticide pollution, excessive water consumption, chemical treatments, animal exploitation, etc.). These impacts are mentionned in the description of each material.
Organic, chemical-free versions of these materials are prioritized for product listings on this site.
Conventional versions are only referenced when no more sustainable alternative has yet been found for that product category.
---
### 🚫 Non-Natural Materials
Synthetic or heavily modified materials, often derived from petrochemicals.
**📌 Main Issues:**
- Microplastic emissions
- Dependence on fossil fuels
- Poor biodegradability
**🔍 List of Non-Natural Materials:**
- Polyester
- Polyamide
- Acrylic
- Elastane
- Viscose
- Silicone
- … (Other materials)
⚠️ These materials are not accepted on this site. However, they may be present in certain listed products if:
- they are used in removable accessories (e.g., elastics, buttons—often not listed in the product’s composition by the brand) that can be detached for recycling or composting, and
- no 100% natural alternative has yet been identified for that product category.
In such cases, a warning will be displayed on the product page.
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/ftjhuxe9mvxkhoedyz36i/)
-

@ a5142938:0ef19da3
2025-04-05 10:09:30
**Happy to have found useful information on this site?**
Support the project by making a donation to keep it running and thank the contributors.
---
**In bitcoin**
<img src=" https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200">
bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
⚡️`
origin-nature@coinos.io`
---
**In euros, dollars, or any other supported currency**
👉 [Make a pledge on LiberaPay](https://en.liberapay.com/origin-nature/)
---
### 💡 A Value-Sharing Model
Half of the donations are redistributed to the contributors who create the site's value, experimenting with a revenue-sharing model on the Internet—one that respects your data and doesn’t seek to capture your attention.
The other half helps cover the site's operating costs.
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/9bd013ef3215e1ac/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/ax9fsc76vokpk2cbhzwv9/)
-

@ a07fae46:7d83df92
2025-03-18 12:31:40
if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)?
you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better.
the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor.
Good morning.
#jfkFiles #nostrOnly
-

@ 0d788b5e:c99ddea5
2025-03-29 01:27:53
这是首页内容
-

@ 21c9f12c:75695e59
2025-04-05 18:11:02
## Details
- 🍳 Cook time: 1 hour and 15 minutes
## Ingredients
- 1 cup dried red lentils
- (2) 25-ounce jars marinara sauce
- 1 cup raw cashews
- 14.5 ounce firm tofu (patted dry)
- ½ cup nutritional yeast
- 3 tablespoons fresh lemon juice (from about 2 lemons)
- 1 teaspoon salt
- 1 teaspoon dried basil
- 1 teaspoon oregano
- ½ teaspoon garlic powder
- 3 cups baby spinach
- 1 box lasagna noodles (about 12 noodles) (regular, gluten free or whole grain)
- Double recipe Easy Vegan Mozzarella Cheese (or 2-3 cups shredded vegan mozzarella)
## Directions
1. lentilsCook the red lentils . Add 1 cup dried red lentils and 3 cups of water to a medium pot. Bring to a boil, and then simmer for about 20 minutes. Drain the lentils in a fine strainer, and then add back to the pot and stir in the marinara sauce . Set aside.
2. ovenPreheat the oven to 350 degrees .
3. Make the Cashew-Tofu Ricotta: Add the cashews to a food processor and process until fine and crumbly. Then add the tofu in chunks, nutritional yeast , lemon juice , salt , basil , oregano and garlic powder to the food processor. Pulse until well combined and pretty smooth. If it's too thick, add a few tablespoons of water to blend. Set aside.
4. LasagnaAssembling the lasagna: Add about 1 cup of lentil marinara to the bottom of a large 9x13 inch casserole dish. Spread it around evenly. Next add 4-5 lasagna noodles (uncooked). Spread half of the ricotta on top of the noodles . Top with half of the spinach . Add about 1 cup of the marinara sauce over the spinach , then place 4-5 lasagna noodles on top. Spread the rest of the ricotta over the noodles , then the rest of the spinach . Place 4-5 more noodles on top of the spinach , and then pour the rest of the sauce over the top, evenly.
5. LasagnaCover tightly with foil and bake for 40 minutes.
6. MozzarellaWhile the lasagna is cooking, make your Vegan Mozzarella Cheese , if using. Alternatively, use 2-3 cups store bought vegan mozzarella cheese .
7. LasagnaAfter 40 minutes, remove the foil and spoon on the mozzarella (or sprinkle the cheese all over). Place the lasagna back in the oven and bake for 20 more minutes, uncovered. Remove from oven, let cool for at least 15 minutes and serve.
-

@ fd06f542:8d6d54cd
2025-03-28 02:27:52
NIP-02
======
Follow List
-----------
`final` `optional`
A special event with kind `3`, meaning "follow list" is defined as having a list of `p` tags, one for each of the followed/known profiles one is following.
Each tag entry should contain the key for the profile, a relay URL where events from that key can be found (can be set to an empty string if not needed), and a local name (or "petname") for that profile (can also be set to an empty string or not provided), i.e., `["p", <32-bytes hex key>, <main relay URL>, <petname>]`.
The `.content` is not used.
For example:
```jsonc
{
"kind": 3,
"tags": [
["p", "91cf9..4e5ca", "wss://alicerelay.com/", "alice"],
["p", "14aeb..8dad4", "wss://bobrelay.com/nostr", "bob"],
["p", "612ae..e610f", "ws://carolrelay.com/ws", "carol"]
],
"content": "",
// other fields...
}
```
Every new following list that gets published overwrites the past ones, so it should contain all entries. Relays and clients SHOULD delete past following lists as soon as they receive a new one.
Whenever new follows are added to an existing list, clients SHOULD append them to the end of the list, so they are stored in chronological order.
## Uses
### Follow list backup
If one believes a relay will store their events for sufficient time, they can use this kind-3 event to backup their following list and recover on a different device.
### Profile discovery and context augmentation
A client may rely on the kind-3 event to display a list of followed people by profiles one is browsing; make lists of suggestions on who to follow based on the follow lists of other people one might be following or browsing; or show the data in other contexts.
### Relay sharing
A client may publish a follow list with good relays for each of their follows so other clients may use these to update their internal relay lists if needed, increasing censorship-resistance.
### Petname scheme
The data from these follow lists can be used by clients to construct local ["petname"](http://www.skyhunter.com/marcs/petnames/IntroPetNames.html) tables derived from other people's follow lists. This alleviates the need for global human-readable names. For example:
A user has an internal follow list that says
```json
[
["p", "21df6d143fb96c2ec9d63726bf9edc71", "", "erin"]
]
```
And receives two follow lists, one from `21df6d143fb96c2ec9d63726bf9edc71` that says
```json
[
["p", "a8bb3d884d5d90b413d9891fe4c4e46d", "", "david"]
]
```
and another from `a8bb3d884d5d90b413d9891fe4c4e46d` that says
```json
[
["p", "f57f54057d2a7af0efecc8b0b66f5708", "", "frank"]
]
```
When the user sees `21df6d143fb96c2ec9d63726bf9edc71` the client can show _erin_ instead;
When the user sees `a8bb3d884d5d90b413d9891fe4c4e46d` the client can show _david.erin_ instead;
When the user sees `f57f54057d2a7af0efecc8b0b66f5708` the client can show _frank.david.erin_ instead.
-

@ bc52210b:20bfc6de
2025-03-14 20:39:20
When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract.
The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable.
In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions.
Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
-

@ a5142938:0ef19da3
2025-04-05 09:54:41
Rewards are an experimental approach to sharing the value created by contributors to this site, through a revenue-sharing system based on the following conditions:
- Any revenue generated by the site each month is distributed over the **following 12 months**, ensuring long-term visibility and smoothing out monthly variations.
- On the **1st of each month**, half of the revenue is distributed among all contributors, in proportion to the number of their validated contributions.
- Contributions remain valid indefinitely, but rewards are only distributed to contributors who have made **at least one validated contribution in the past 12 months**.
### Payment Method
Rewards are paid via the Lightning network, in sats (the smallest unit of Bitcoin).
To receive payments, you must have a NOSTR account linked to a Lightning wallet.
To receive them, the NOSTR account used to contribute must be linked to a Lightning wallet.
**💡 New to these tools?**
- **Don’t have a NOSTR account yet?** A simple way to get started is to create one on an open-source NOSTR client like [yakihonne.com](https://yakihonne.com/) to set up your profile and wallet there. Then, retrieve your NOSTR keys (from the settings) and save them in a secure vault like [nsec.app](https://use.nsec.app/home) to log in here and start contributing.
- **Already started contributing on this site?** Make sure to securely store your NOSTR keys in a vault like [nsec.app](https://use.nsec.app/home). You can also log in with them on [yakihonne.com](https://yakihonne.com/) to set up your profile.
- You can also contribute directly from yakihonne.com by commenting on Origine Nature’s articles.
👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/ )
### Next rewards
Coming soon.
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/7hdgcdwt76dprobc9g_2f/)
-

@ 57d1a264:69f1fee1
2025-03-27 08:11:33
Explore and reimagine programming interfaces beyond text (visual, tactile, spatial).
> _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_
`— Richard Hamming` [^1]
https://www.youtube.com/watch?v=8pTEmbeENF4
For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.

_'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.'
More details at https://worrydream.com/dbx/
[^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook)
originally posted at https://stacker.news/items/926493
-

@ df173277:4ec96708
2025-02-07 00:41:34
## **Building Our Confidential Backend on Secure Enclaves**
With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with.
## **Auth and Databases Today**
As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that:
1. Need to register users (authentication).
2. Collect and process user data in business-specific ways, often on the backend.
Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes).
## **"Just Trust Us" Isn't Good Enough**
In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data.
Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility.
The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services.
## **Current Attempts at Securing Data**
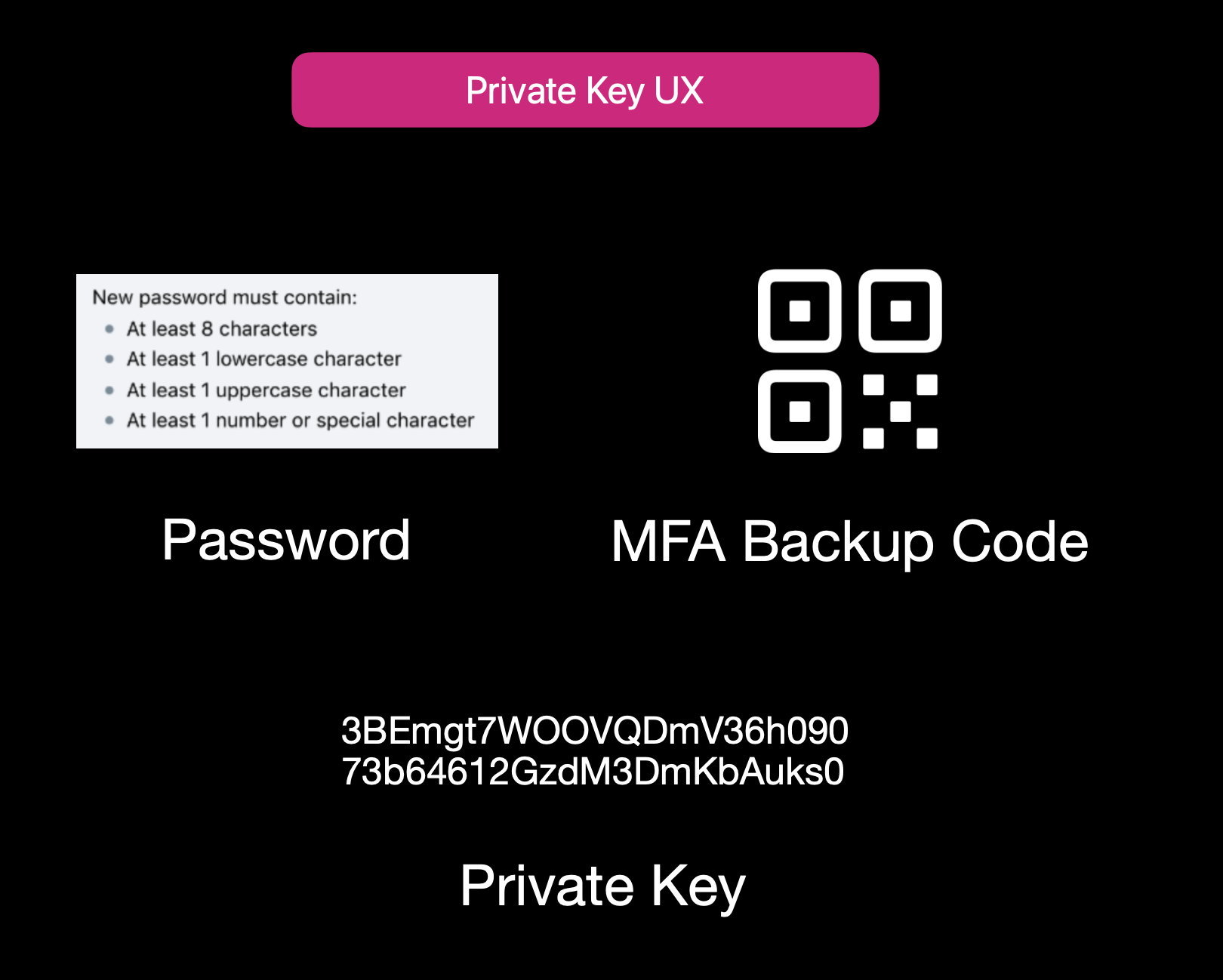Current User Experience of E2EE Apps
While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**:
1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side.
2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data.
3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility.
Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider.
## **Secure Enclaves**
### **The Hybrid Approach**
Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden.
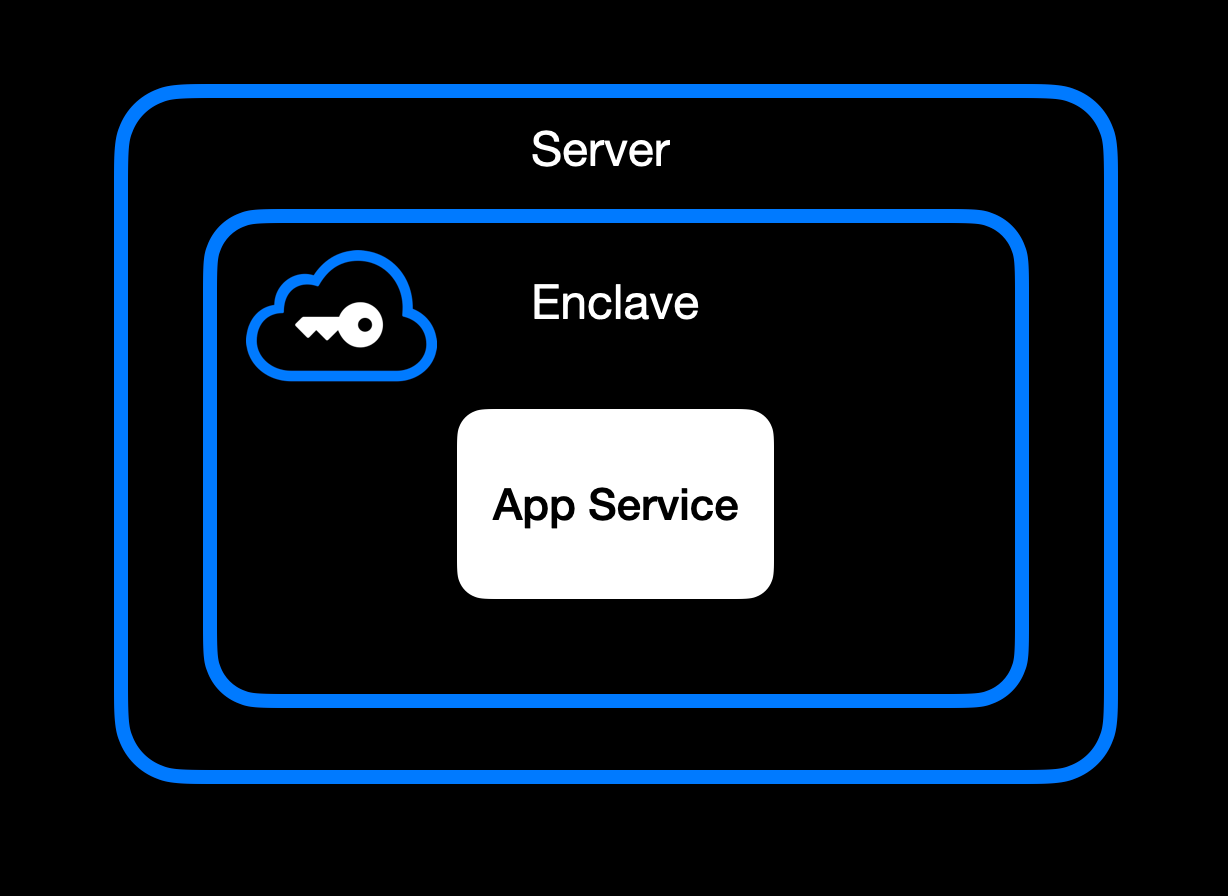App Service Running Inside Secure Enclave
### **High-Level Goal of Enclaves**
Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\
• **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\
• **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\
• **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in).
### **Different Secure Enclave Solutions**
[**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds.
[**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications.
[**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers.
[**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised.
[**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees.
### **Key Benefits**
One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data.
Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware.
Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks.
Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist.
It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing.
## **How We Use Secure Enclaves**
Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads.
### **Our Stack: AWS Nitro + Nvidia TEE**
• **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave.
• **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with.
### **End-to-End Encryption from Client to Enclave**
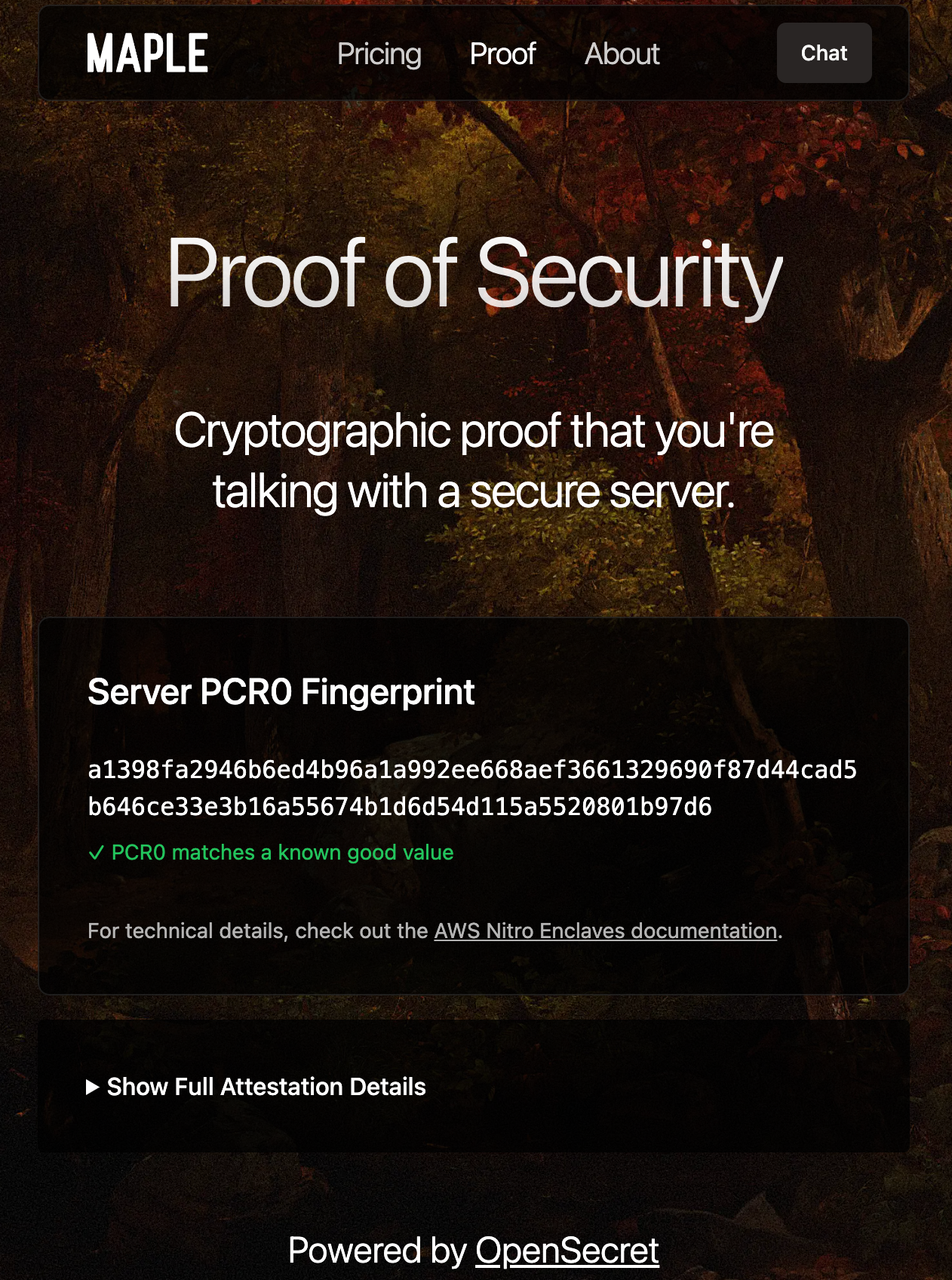Client-side Enclave Attestation from Maple AI
Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud).
Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session.
From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request.
### **In-Enclave Operations**
At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form.
User Auth Methods running inside Enclave
A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information.
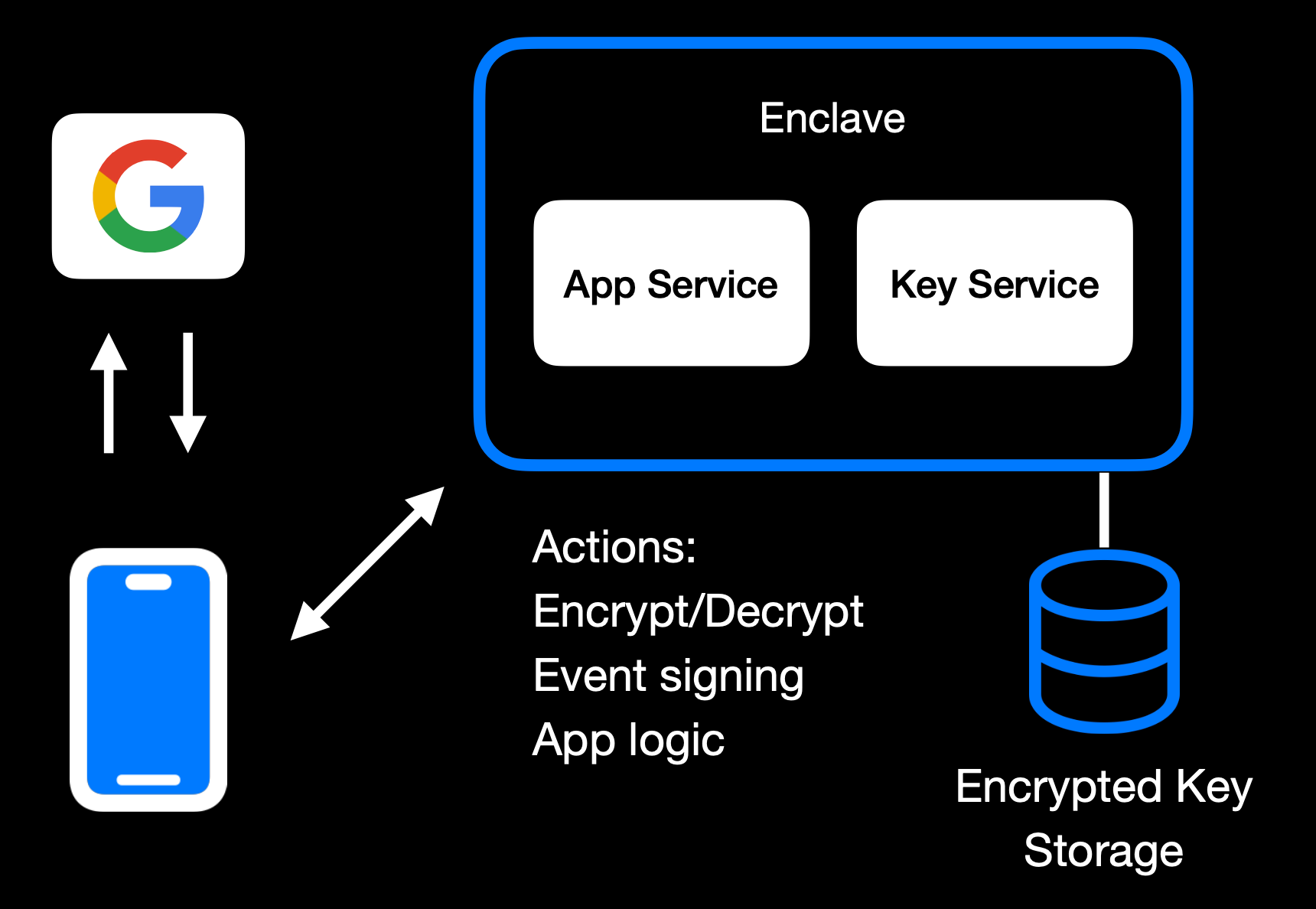Main Enclave Operations in OpenSecret
The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user.
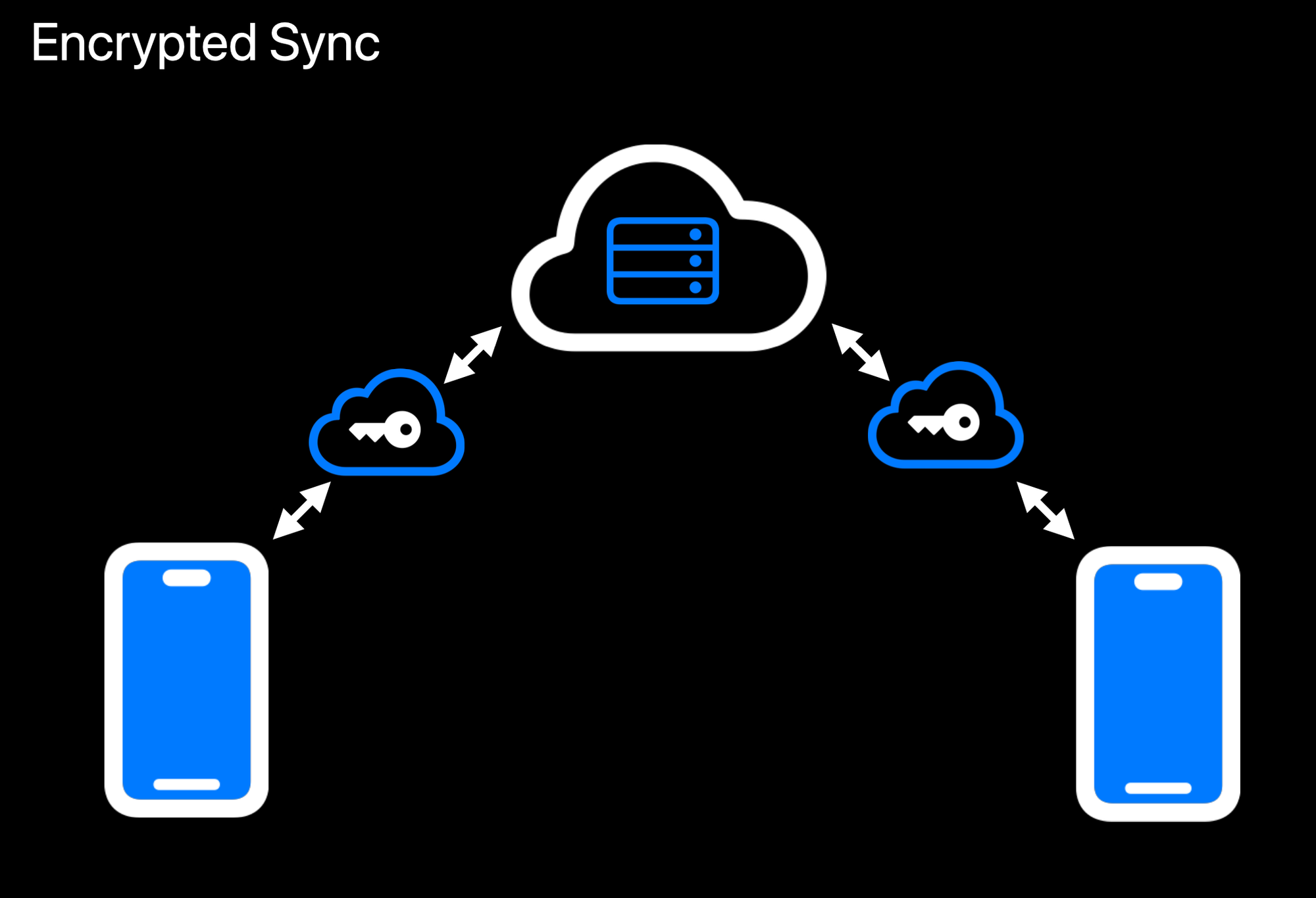Realtime Encrypted Data Sync on Multiple Devices
Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext.
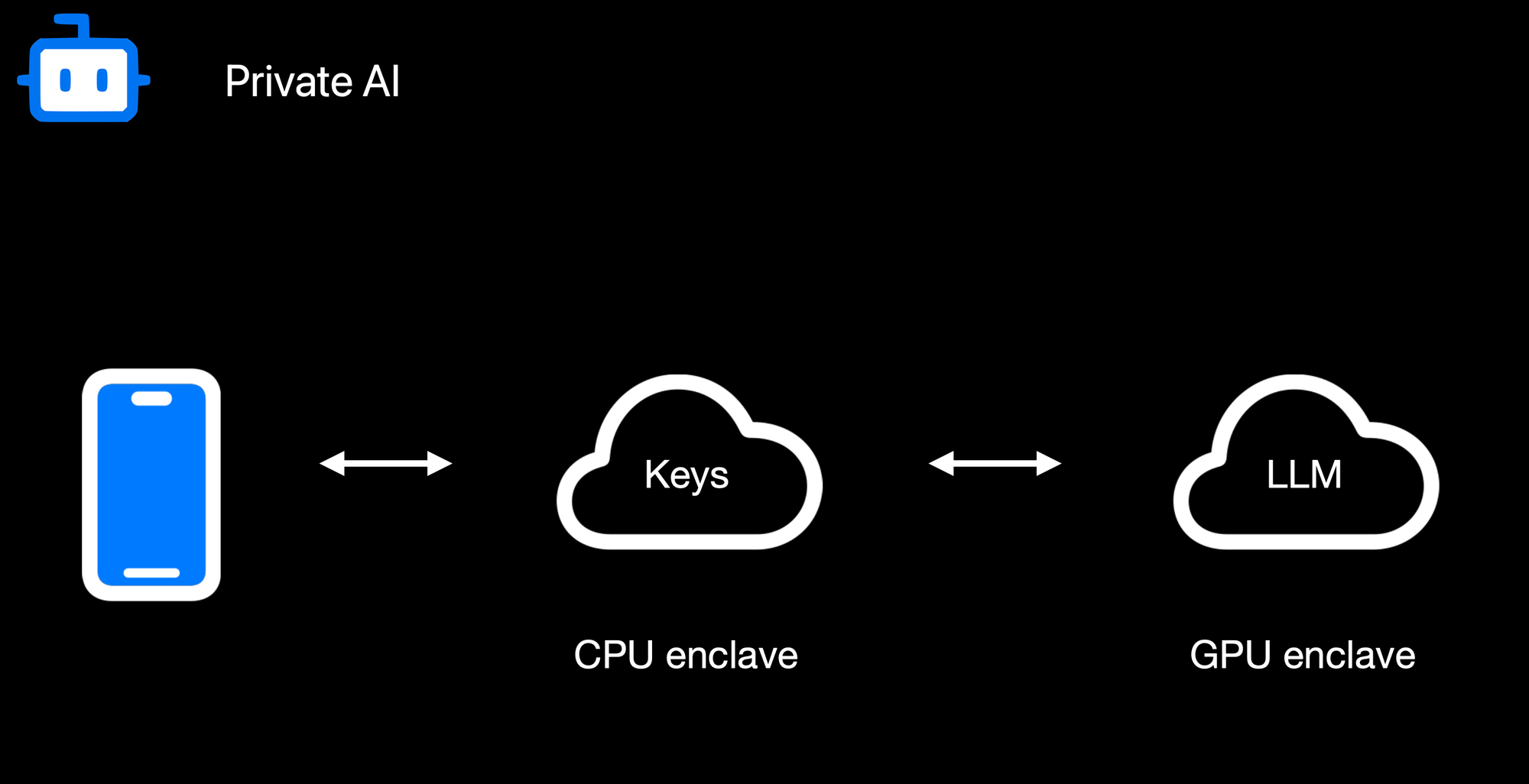Confidential AI Workloads
Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation.
### **Reproducible Builds + Verification**
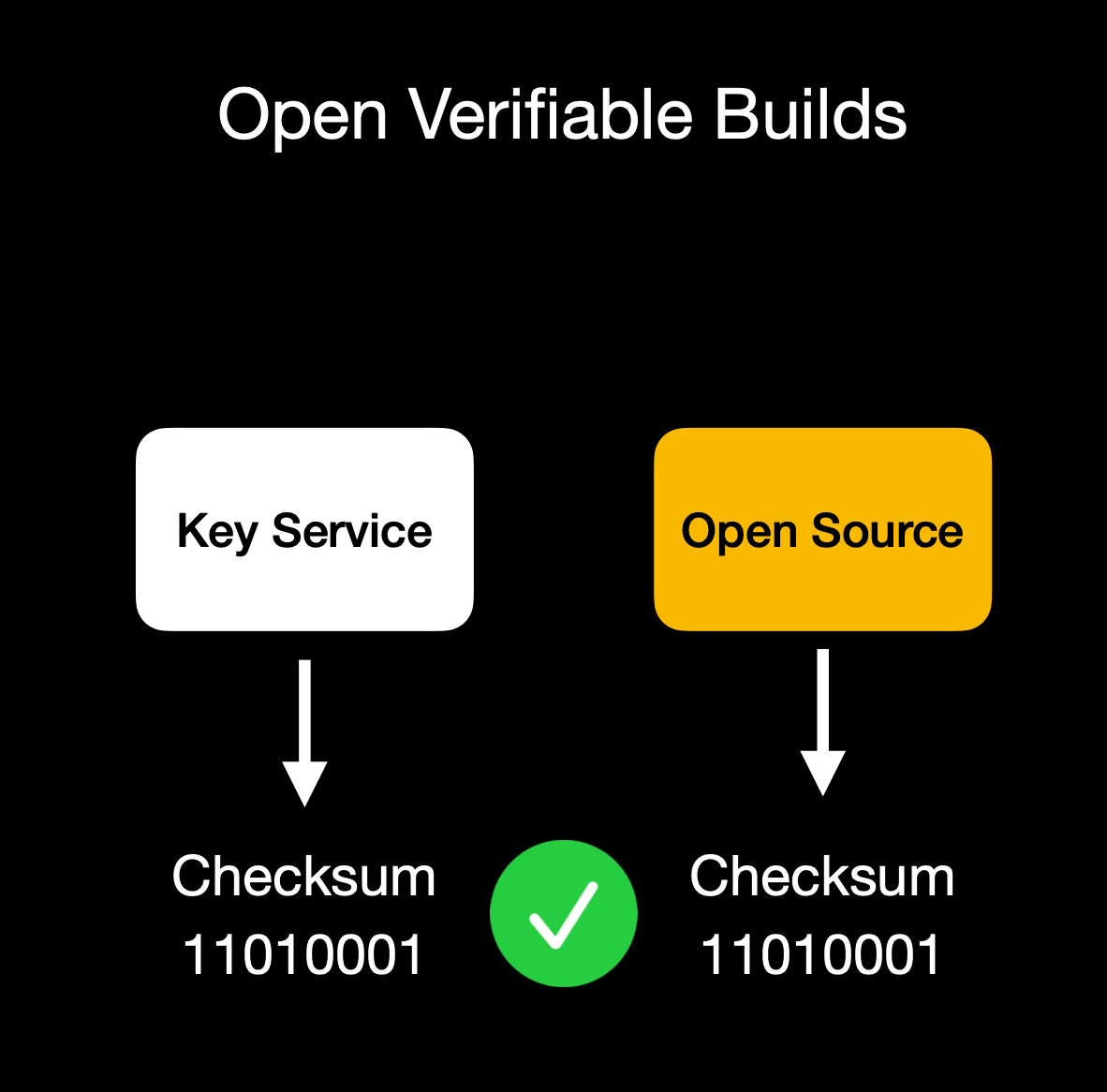Client verifies enclave attestation document
We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs.
Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation.
## **Putting It All Together**
OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute
By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes.
This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats.
Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure.
OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use.
Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system.
The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad.
## **Things to Come**
We're excited to build on our enclaved approach. Here's what's on our roadmap:
• **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\
• **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\
• **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\
• **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\
• **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\
• **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\
• **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API.
## **Getting Started**
Ready to see enclaves in action? Here's how to dive in:\
1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\
2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\
3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\
4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further.
## **Conclusion**
By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use.
**We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself.
Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build!
*Thank you for reading, and welcome to the era of enclaved computing.*
-

@ 6b3780ef:221416c8
2025-03-26 18:42:00
This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
## Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method.
2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine.
- **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
## Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
1. Create software in any programming language you're comfortable with.
2. Add an MCP library to expose your server's MCP interface.
3. Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.
Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
## Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
```
curl -fsSL https://bun.sh/install | bash
```
1. **Choose your MCP server**: You can either create one or use an existing one.
2. **Inspect your server** using the MCP inspector tool:
```bash
npx @modelcontextprotocol/inspector build/index.js arg1 arg2
```
This will:
- Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
- Pass any additional arguments directly to your server
3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
## Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
1. Navigate to your MCP server directory.
2. Run without installing (quickest way):
```
npx @dvmcp/bridge
```
3. Or install globally for regular use:
```
npm install -g @dvmcp/bridge
# or
bun install -g @dvmcp/bridge
```
Then run using:
```bash
dvmcp-bridge
```
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference
## Testing and Integration
1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement.
2. Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
## Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
1. Install and use the `@dvmcp/discovery` package:
```bash
npx @dvmcp/discovery
```
2. This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
- Making them available to your LLM applications
3. Connect to specific servers or providers using these flags:
```bash
# Connect to all DVMCP servers from a provider
npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server
npx @dvmcp/discovery --server naddr1...
```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun).
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
## Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
## Useful Resources
- **Official Documentation**:
- Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org)
- DVMCP.fun: [dvmcp.fun](https://dvmcp.fun)
- **Source Code and Development**:
- DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp)
- DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun)
- **MCP Servers and Clients**:
- Smithery AI: [smithery.ai](https://smithery.ai)
- MCP.so: [mcp.so](https://mcp.so)
- Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers)
- [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD)
Happy building!
-

@ a5142938:0ef19da3
2025-04-05 09:48:12
<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzpkj8sfxva2pk76qd85qs5k2uk4ddrn9x2vw4d4cq9gmk0nxwf23aqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qqxtqu8vwtew57xyqvm?viewKey=2c19f257cc3f94a3d40c0b171730ecd40897bc675ffa0ce521e22c280ba70a2d&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe>
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/qcp-smvj1v78_-7iceyrd/)
-

@ fd06f542:8d6d54cd
2025-03-28 02:24:00
NIP-01
======
Basic protocol flow description
-------------------------------
`draft` `mandatory`
This NIP defines the basic protocol that should be implemented by everybody. New NIPs may add new optional (or mandatory) fields and messages and features to the structures and flows described here.
## Events and signatures
Each user has a keypair. Signatures, public key, and encodings are done according to the [Schnorr signatures standard for the curve `secp256k1`](https://bips.xyz/340).
The only object type that exists is the `event`, which has the following format on the wire:
```jsonc
{
"id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>,
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
"created_at": <unix timestamp in seconds>,
"kind": <integer between 0 and 65535>,
"tags": [
[<arbitrary string>...],
// ...
],
"content": <arbitrary string>,
"sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field>
}
```
To obtain the `event.id`, we `sha256` the serialized event. The serialization is done over the UTF-8 JSON-serialized string (which is described below) of the following structure:
```
[
0,
<pubkey, as a lowercase hex string>,
<created_at, as a number>,
<kind, as a number>,
<tags, as an array of arrays of non-null strings>,
<content, as a string>
]
```
To prevent implementation differences from creating a different event ID for the same event, the following rules MUST be followed while serializing:
- UTF-8 should be used for encoding.
- Whitespace, line breaks or other unnecessary formatting should not be included in the output JSON.
- The following characters in the content field must be escaped as shown, and all other characters must be included verbatim:
- A line break (`0x0A`), use `\n`
- A double quote (`0x22`), use `\"`
- A backslash (`0x5C`), use `\\`
- A carriage return (`0x0D`), use `\r`
- A tab character (`0x09`), use `\t`
- A backspace, (`0x08`), use `\b`
- A form feed, (`0x0C`), use `\f`
### Tags
Each tag is an array of one or more strings, with some conventions around them. Take a look at the example below:
```jsonc
{
"tags": [
["e", "5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36", "wss://nostr.example.com"],
["p", "f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca"],
["a", "30023:f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca:abcd", "wss://nostr.example.com"],
["alt", "reply"],
// ...
],
// ...
}
```
The first element of the tag array is referred to as the tag _name_ or _key_ and the second as the tag _value_. So we can safely say that the event above has an `e` tag set to `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"`, an `alt` tag set to `"reply"` and so on. All elements after the second do not have a conventional name.
This NIP defines 3 standard tags that can be used across all event kinds with the same meaning. They are as follows:
- The `e` tag, used to refer to an event: `["e", <32-bytes lowercase hex of the id of another event>, <recommended relay URL, optional>, <32-bytes lowercase hex of the author's pubkey, optional>]`
- The `p` tag, used to refer to another user: `["p", <32-bytes lowercase hex of a pubkey>, <recommended relay URL, optional>]`
- The `a` tag, used to refer to an addressable or replaceable event
- for an addressable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:<d tag value>", <recommended relay URL, optional>]`
- for a normal replaceable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:", <recommended relay URL, optional>]` (note: include the trailing colon)
As a convention, all single-letter (only english alphabet letters: a-z, A-Z) key tags are expected to be indexed by relays, such that it is possible, for example, to query or subscribe to events that reference the event `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"` by using the `{"#e": ["5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"]}` filter. Only the first value in any given tag is indexed.
### Kinds
Kinds specify how clients should interpret the meaning of each event and the other fields of each event (e.g. an `"r"` tag may have a meaning in an event of kind 1 and an entirely different meaning in an event of kind 10002). Each NIP may define the meaning of a set of kinds that weren't defined elsewhere. [NIP-10](10.md), for instance, especifies the `kind:1` text note for social media applications.
This NIP defines one basic kind:
- `0`: **user metadata**: the `content` is set to a stringified JSON object `{name: <nickname or full name>, about: <short bio>, picture: <url of the image>}` describing the user who created the event. [Extra metadata fields](24.md#kind-0) may be set. A relay may delete older events once it gets a new one for the same pubkey.
And also a convention for kind ranges that allow for easier experimentation and flexibility of relay implementation:
- for kind `n` such that `1000 <= n < 10000 || 4 <= n < 45 || n == 1 || n == 2`, events are **regular**, which means they're all expected to be stored by relays.
- for kind `n` such that `10000 <= n < 20000 || n == 0 || n == 3`, events are **replaceable**, which means that, for each combination of `pubkey` and `kind`, only the latest event MUST be stored by relays, older versions MAY be discarded.
- for kind `n` such that `20000 <= n < 30000`, events are **ephemeral**, which means they are not expected to be stored by relays.
- for kind `n` such that `30000 <= n < 40000`, events are **addressable** by their `kind`, `pubkey` and `d` tag value -- which means that, for each combination of `kind`, `pubkey` and the `d` tag value, only the latest event MUST be stored by relays, older versions MAY be discarded.
In case of replaceable events with the same timestamp, the event with the lowest id (first in lexical order) should be retained, and the other discarded.
When answering to `REQ` messages for replaceable events such as `{"kinds":[0],"authors":[<hex-key>]}`, even if the relay has more than one version stored, it SHOULD return just the latest one.
These are just conventions and relay implementations may differ.
## Communication between clients and relays
Relays expose a websocket endpoint to which clients can connect. Clients SHOULD open a single websocket connection to each relay and use it for all their subscriptions. Relays MAY limit number of connections from specific IP/client/etc.
### From client to relay: sending events and creating subscriptions
Clients can send 3 types of messages, which must be JSON arrays, according to the following patterns:
* `["EVENT", <event JSON as defined above>]`, used to publish events.
* `["REQ", <subscription_id>, <filters1>, <filters2>, ...]`, used to request events and subscribe to new updates.
* `["CLOSE", <subscription_id>]`, used to stop previous subscriptions.
`<subscription_id>` is an arbitrary, non-empty string of max length 64 chars. It represents a subscription per connection. Relays MUST manage `<subscription_id>`s independently for each WebSocket connection. `<subscription_id>`s are not guaranteed to be globally unique.
`<filtersX>` is a JSON object that determines what events will be sent in that subscription, it can have the following attributes:
```json
{
"ids": <a list of event ids>,
"authors": <a list of lowercase pubkeys, the pubkey of an event must be one of these>,
"kinds": <a list of a kind numbers>,
"#<single-letter (a-zA-Z)>": <a list of tag values, for #e — a list of event ids, for #p — a list of pubkeys, etc.>,
"since": <an integer unix timestamp in seconds. Events must have a created_at >= to this to pass>,
"until": <an integer unix timestamp in seconds. Events must have a created_at <= to this to pass>,
"limit": <maximum number of events relays SHOULD return in the initial query>
}
```
Upon receiving a `REQ` message, the relay SHOULD return events that match the filter. Any new events it receives SHOULD be sent to that same websocket until the connection is closed, a `CLOSE` event is received with the same `<subscription_id>`, or a new `REQ` is sent using the same `<subscription_id>` (in which case a new subscription is created, replacing the old one).
Filter attributes containing lists (`ids`, `authors`, `kinds` and tag filters like `#e`) are JSON arrays with one or more values. At least one of the arrays' values must match the relevant field in an event for the condition to be considered a match. For scalar event attributes such as `authors` and `kind`, the attribute from the event must be contained in the filter list. In the case of tag attributes such as `#e`, for which an event may have multiple values, the event and filter condition values must have at least one item in common.
The `ids`, `authors`, `#e` and `#p` filter lists MUST contain exact 64-character lowercase hex values.
The `since` and `until` properties can be used to specify the time range of events returned in the subscription. If a filter includes the `since` property, events with `created_at` greater than or equal to `since` are considered to match the filter. The `until` property is similar except that `created_at` must be less than or equal to `until`. In short, an event matches a filter if `since <= created_at <= until` holds.
All conditions of a filter that are specified must match for an event for it to pass the filter, i.e., multiple conditions are interpreted as `&&` conditions.
A `REQ` message may contain multiple filters. In this case, events that match any of the filters are to be returned, i.e., multiple filters are to be interpreted as `||` conditions.
The `limit` property of a filter is only valid for the initial query and MUST be ignored afterwards. When `limit: n` is present it is assumed that the events returned in the initial query will be the last `n` events ordered by the `created_at`. Newer events should appear first, and in the case of ties the event with the lowest id (first in lexical order) should be first. It is safe to return less events than `limit` specifies, but it is expected that relays do not return (much) more events than requested so clients don't get unnecessarily overwhelmed by data.
### From relay to client: sending events and notices
Relays can send 5 types of messages, which must also be JSON arrays, according to the following patterns:
* `["EVENT", <subscription_id>, <event JSON as defined above>]`, used to send events requested by clients.
* `["OK", <event_id>, <true|false>, <message>]`, used to indicate acceptance or denial of an `EVENT` message.
* `["EOSE", <subscription_id>]`, used to indicate the _end of stored events_ and the beginning of events newly received in real-time.
* `["CLOSED", <subscription_id>, <message>]`, used to indicate that a subscription was ended on the server side.
* `["NOTICE", <message>]`, used to send human-readable error messages or other things to clients.
This NIP defines no rules for how `NOTICE` messages should be sent or treated.
- `EVENT` messages MUST be sent only with a subscription ID related to a subscription previously initiated by the client (using the `REQ` message above).
- `OK` messages MUST be sent in response to `EVENT` messages received from clients, they must have the 3rd parameter set to `true` when an event has been accepted by the relay, `false` otherwise. The 4th parameter MUST always be present, but MAY be an empty string when the 3rd is `true`, otherwise it MUST be a string formed by a machine-readable single-word prefix followed by a `:` and then a human-readable message. Some examples:
* `["OK", "b1a649ebe8...", true, ""]`
* `["OK", "b1a649ebe8...", true, "pow: difficulty 25>=24"]`
* `["OK", "b1a649ebe8...", true, "duplicate: already have this event"]`
* `["OK", "b1a649ebe8...", false, "blocked: you are banned from posting here"]`
* `["OK", "b1a649ebe8...", false, "blocked: please register your pubkey at https://my-expensive-relay.example.com"]`
* `["OK", "b1a649ebe8...", false, "rate-limited: slow down there chief"]`
* `["OK", "b1a649ebe8...", false, "invalid: event creation date is too far off from the current time"]`
* `["OK", "b1a649ebe8...", false, "pow: difficulty 26 is less than 30"]`
* `["OK", "b1a649ebe8...", false, "restricted: not allowed to write."]`
* `["OK", "b1a649ebe8...", false, "error: could not connect to the database"]`
- `CLOSED` messages MUST be sent in response to a `REQ` when the relay refuses to fulfill it. It can also be sent when a relay decides to kill a subscription on its side before a client has disconnected or sent a `CLOSE`. This message uses the same pattern of `OK` messages with the machine-readable prefix and human-readable message. Some examples:
* `["CLOSED", "sub1", "unsupported: filter contains unknown elements"]`
* `["CLOSED", "sub1", "error: could not connect to the database"]`
* `["CLOSED", "sub1", "error: shutting down idle subscription"]`
- The standardized machine-readable prefixes for `OK` and `CLOSED` are: `duplicate`, `pow`, `blocked`, `rate-limited`, `invalid`, `restricted`, and `error` for when none of that fits.
-

@ c066aac5:6a41a034
2025-04-05 16:58:58
I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
# My Background: A Small Side Story

My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’s*Chasing Ghosts*and*The King of Kong: A Fistful of Quarters*). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer of*The King of Kong: A Fistful of Quarters* had previously made a documentary called*New York Doll*which was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
# Nicolas Cage: Actor

There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will link[here](https://www.youtube.com/watch?v=s8IfDNHsCLE). Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the films*Pig,* *Joe,* *Renfield,* and his Christmas film *The Family Man*.
# �Nick Cave: Songwriter

What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his album*Ghosteen*, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter called*The Red Hand Files*, he has written screenplays such as*Lawless*, he has written books, he has made great film scores such as*The Assassination of Jesse James by the Coward Robert Ford*, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the album*Murder Ballads*(which is comprised of what the title suggests) to his rejected sequel to*Gladiator*(*Gladiator: Christ Killer*), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums like*Skeleton Tree*and*Ghosteen*were journeys through the grief of his son’s death. *The Boatman’s Call*is arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’s*Live 1981-82*, Nick Cave & The Bad Seeds’*The Boatman’s Call*, and the film*Lawless*.
# �Jim Jarmusch: Director

I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. *Ghost Dog: The Way of the Samurai* is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. *Only Lovers Left Alive*is a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his films*Paterson*,*Down by Law*, and*Coffee and Cigarettes*.
# NOSTR: We Need Bold Art

NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. **My closing statement:** continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-

@ fd06f542:8d6d54cd
2025-03-28 02:21:20
# NIPs
NIPs stand for **Nostr Implementation Possibilities**.
They exist to document what may be implemented by [Nostr](https://github.com/nostr-protocol/nostr)-compatible _relay_ and _client_ software.
---
- [List](#list)
- [Event Kinds](#event-kinds)
- [Message Types](#message-types)
- [Client to Relay](#client-to-relay)
- [Relay to Client](#relay-to-client)
- [Standardized Tags](#standardized-tags)
- [Criteria for acceptance of NIPs](#criteria-for-acceptance-of-nips)
- [Is this repository a centralizing factor?](#is-this-repository-a-centralizing-factor)
- [How this repository works](#how-this-repository-works)
- [Breaking Changes](#breaking-changes)
- [License](#license)
---
## List
- [NIP-01: Basic protocol flow description](01.md)
- [NIP-02: Follow List](02.md)
- [NIP-03: OpenTimestamps Attestations for Events](03.md)
- [NIP-04: Encrypted Direct Message](04.md) --- **unrecommended**: deprecated in favor of [NIP-17](17.md)
- [NIP-05: Mapping Nostr keys to DNS-based internet identifiers](05.md)
- [NIP-06: Basic key derivation from mnemonic seed phrase](06.md)
- [NIP-07: `window.nostr` capability for web browsers](07.md)
- [NIP-08: Handling Mentions](08.md) --- **unrecommended**: deprecated in favor of [NIP-27](27.md)
- [NIP-09: Event Deletion Request](09.md)
- [NIP-10: Text Notes and Threads](10.md)
- [NIP-11: Relay Information Document](11.md)
- [NIP-13: Proof of Work](13.md)
- [NIP-14: Subject tag in text events](14.md)
- [NIP-15: Nostr Marketplace (for resilient marketplaces)](15.md)
- [NIP-17: Private Direct Messages](17.md)
- [NIP-18: Reposts](18.md)
- [NIP-19: bech32-encoded entities](19.md)
- [NIP-21: `nostr:` URI scheme](21.md)
- [NIP-22: Comment](22.md)
- [NIP-23: Long-form Content](23.md)
- [NIP-24: Extra metadata fields and tags](24.md)
- [NIP-25: Reactions](25.md)
- [NIP-26: Delegated Event Signing](26.md)
- [NIP-27: Text Note References](27.md)
- [NIP-28: Public Chat](28.md)
- [NIP-29: Relay-based Groups](29.md)
- [NIP-30: Custom Emoji](30.md)
- [NIP-31: Dealing with Unknown Events](31.md)
- [NIP-32: Labeling](32.md)
- [NIP-34: `git` stuff](34.md)
- [NIP-35: Torrents](35.md)
- [NIP-36: Sensitive Content](36.md)
- [NIP-37: Draft Events](37.md)
- [NIP-38: User Statuses](38.md)
- [NIP-39: External Identities in Profiles](39.md)
- [NIP-40: Expiration Timestamp](40.md)
- [NIP-42: Authentication of clients to relays](42.md)
- [NIP-44: Encrypted Payloads (Versioned)](44.md)
- [NIP-45: Counting results](45.md)
- [NIP-46: Nostr Remote Signing](46.md)
- [NIP-47: Nostr Wallet Connect](47.md)
- [NIP-48: Proxy Tags](48.md)
- [NIP-49: Private Key Encryption](49.md)
- [NIP-50: Search Capability](50.md)
- [NIP-51: Lists](51.md)
- [NIP-52: Calendar Events](52.md)
- [NIP-53: Live Activities](53.md)
- [NIP-54: Wiki](54.md)
- [NIP-55: Android Signer Application](55.md)
- [NIP-56: Reporting](56.md)
- [NIP-57: Lightning Zaps](57.md)
- [NIP-58: Badges](58.md)
- [NIP-59: Gift Wrap](59.md)
- [NIP-60: Cashu Wallet](60.md)
- [NIP-61: Nutzaps](61.md)
- [NIP-62: Request to Vanish](62.md)
- [NIP-64: Chess (PGN)](64.md)
- [NIP-65: Relay List Metadata](65.md)
- [NIP-66: Relay Discovery and Liveness Monitoring](66.md)
- [NIP-68: Picture-first feeds](68.md)
- [NIP-69: Peer-to-peer Order events](69.md)
- [NIP-70: Protected Events](70.md)
- [NIP-71: Video Events](71.md)
- [NIP-72: Moderated Communities](72.md)
- [NIP-73: External Content IDs](73.md)
- [NIP-75: Zap Goals](75.md)
- [NIP-78: Application-specific data](78.md)
- [NIP-84: Highlights](84.md)
- [NIP-86: Relay Management API](86.md)
- [NIP-88: Polls](88.md)
- [NIP-89: Recommended Application Handlers](89.md)
- [NIP-90: Data Vending Machines](90.md)
- [NIP-92: Media Attachments](92.md)
- [NIP-94: File Metadata](94.md)
- [NIP-96: HTTP File Storage Integration](96.md)
- [NIP-98: HTTP Auth](98.md)
- [NIP-99: Classified Listings](99.md)
- [NIP-7D: Threads](7D.md)
- [NIP-C7: Chats](C7.md)
## Event Kinds
| kind | description | NIP |
| ------------- | ------------------------------- | -------------------------------------- |
| `0` | User Metadata | [01](01.md) |
| `1` | Short Text Note | [10](10.md) |
| `2` | Recommend Relay | 01 (deprecated) |
| `3` | Follows | [02](02.md) |
| `4` | Encrypted Direct Messages | [04](04.md) |
| `5` | Event Deletion Request | [09](09.md) |
| `6` | Repost | [18](18.md) |
| `7` | Reaction | [25](25.md) |
| `8` | Badge Award | [58](58.md) |
| `9` | Chat Message | [C7](C7.md) |
| `10` | Group Chat Threaded Reply | 29 (deprecated) |
| `11` | Thread | [7D](7D.md) |
| `12` | Group Thread Reply | 29 (deprecated) |
| `13` | Seal | [59](59.md) |
| `14` | Direct Message | [17](17.md) |
| `15` | File Message | [17](17.md) |
| `16` | Generic Repost | [18](18.md) |
| `17` | Reaction to a website | [25](25.md) |
| `20` | Picture | [68](68.md) |
| `21` | Video Event | [71](71.md) |
| `22` | Short-form Portrait Video Event | [71](71.md) |
| `30` | internal reference | [NKBIP-03] |
| `31` | external web reference | [NKBIP-03] |
| `32` | hardcopy reference | [NKBIP-03] |
| `33` | prompt reference | [NKBIP-03] |
| `40` | Channel Creation | [28](28.md) |
| `41` | Channel Metadata | [28](28.md) |
| `42` | Channel Message | [28](28.md) |
| `43` | Channel Hide Message | [28](28.md) |
| `44` | Channel Mute User | [28](28.md) |
| `62` | Request to Vanish | [62](62.md) |
| `64` | Chess (PGN) | [64](64.md) |
| `818` | Merge Requests | [54](54.md) |
| `1018` | Poll Response | [88](88.md) |
| `1021` | Bid | [15](15.md) |
| `1022` | Bid confirmation | [15](15.md) |
| `1040` | OpenTimestamps | [03](03.md) |
| `1059` | Gift Wrap | [59](59.md) |
| `1063` | File Metadata | [94](94.md) |
| `1068` | Poll | [88](88.md) |
| `1111` | Comment | [22](22.md) |
| `1311` | Live Chat Message | [53](53.md) |
| `1617` | Patches | [34](34.md) |
| `1621` | Issues | [34](34.md) |
| `1622` | Git Replies (deprecated) | [34](34.md) |
| `1630`-`1633` | Status | [34](34.md) |
| `1971` | Problem Tracker | [nostrocket][nostrocket] |
| `1984` | Reporting | [56](56.md) |
| `1985` | Label | [32](32.md) |
| `1986` | Relay reviews | |
| `1987` | AI Embeddings / Vector lists | [NKBIP-02] |
| `2003` | Torrent | [35](35.md) |
| `2004` | Torrent Comment | [35](35.md) |
| `2022` | Coinjoin Pool | [joinstr][joinstr] |
| `4550` | Community Post Approval | [72](72.md) |
| `5000`-`5999` | Job Request | [90](90.md) |
| `6000`-`6999` | Job Result | [90](90.md) |
| `7000` | Job Feedback | [90](90.md) |
| `7374` | Reserved Cashu Wallet Tokens | [60](60.md) |
| `7375` | Cashu Wallet Tokens | [60](60.md) |
| `7376` | Cashu Wallet History | [60](60.md) |
| `9000`-`9030` | Group Control Events | [29](29.md) |
| `9041` | Zap Goal | [75](75.md) |
| `9321` | Nutzap | [61](61.md) |
| `9467` | Tidal login | [Tidal-nostr] |
| `9734` | Zap Request | [57](57.md) |
| `9735` | Zap | [57](57.md) |
| `9802` | Highlights | [84](84.md) |
| `10000` | Mute list | [51](51.md) |
| `10001` | Pin list | [51](51.md) |
| `10002` | Relay List Metadata | [65](65.md), [51](51.md) |
| `10003` | Bookmark list | [51](51.md) |
| `10004` | Communities list | [51](51.md) |
| `10005` | Public chats list | [51](51.md) |
| `10006` | Blocked relays list | [51](51.md) |
| `10007` | Search relays list | [51](51.md) |
| `10009` | User groups | [51](51.md), [29](29.md) |
| `10013` | Private event relay list | [37](37.md) |
| `10015` | Interests list | [51](51.md) |
| `10019` | Nutzap Mint Recommendation | [61](61.md) |
| `10030` | User emoji list | [51](51.md) |
| `10050` | Relay list to receive DMs | [51](51.md), [17](17.md) |
| `10063` | User server list | [Blossom][blossom] |
| `10096` | File storage server list | [96](96.md) |
| `10166` | Relay Monitor Announcement | [66](66.md) |
| `13194` | Wallet Info | [47](47.md) |
| `17375` | Cashu Wallet Event | [60](60.md) |
| `21000` | Lightning Pub RPC | [Lightning.Pub][lnpub] |
| `22242` | Client Authentication | [42](42.md) |
| `23194` | Wallet Request | [47](47.md) |
| `23195` | Wallet Response | [47](47.md) |
| `24133` | Nostr Connect | [46](46.md) |
| `24242` | Blobs stored on mediaservers | [Blossom][blossom] |
| `27235` | HTTP Auth | [98](98.md) |
| `30000` | Follow sets | [51](51.md) |
| `30001` | Generic lists | 51 (deprecated) |
| `30002` | Relay sets | [51](51.md) |
| `30003` | Bookmark sets | [51](51.md) |
| `30004` | Curation sets | [51](51.md) |
| `30005` | Video sets | [51](51.md) |
| `30007` | Kind mute sets | [51](51.md) |
| `30008` | Profile Badges | [58](58.md) |
| `30009` | Badge Definition | [58](58.md) |
| `30015` | Interest sets | [51](51.md) |
| `30017` | Create or update a stall | [15](15.md) |
| `30018` | Create or update a product | [15](15.md) |
| `30019` | Marketplace UI/UX | [15](15.md) |
| `30020` | Product sold as an auction | [15](15.md) |
| `30023` | Long-form Content | [23](23.md) |
| `30024` | Draft Long-form Content | [23](23.md) |
| `30030` | Emoji sets | [51](51.md) |
| `30040` | Curated Publication Index | [NKBIP-01] |
| `30041` | Curated Publication Content | [NKBIP-01] |
| `30063` | Release artifact sets | [51](51.md) |
| `30078` | Application-specific Data | [78](78.md) |
| `30166` | Relay Discovery | [66](66.md) |
| `30267` | App curation sets | [51](51.md) |
| `30311` | Live Event | [53](53.md) |
| `30315` | User Statuses | [38](38.md) |
| `30388` | Slide Set | [Corny Chat][cornychat-slideset] |
| `30402` | Classified Listing | [99](99.md) |
| `30403` | Draft Classified Listing | [99](99.md) |
| `30617` | Repository announcements | [34](34.md) |
| `30618` | Repository state announcements | [34](34.md) |
| `30818` | Wiki article | [54](54.md) |
| `30819` | Redirects | [54](54.md) |
| `31234` | Draft Event | [37](37.md) |
| `31388` | Link Set | [Corny Chat][cornychat-linkset] |
| `31890` | Feed | [NUD: Custom Feeds][NUD: Custom Feeds] |
| `31922` | Date-Based Calendar Event | [52](52.md) |
| `31923` | Time-Based Calendar Event | [52](52.md) |
| `31924` | Calendar | [52](52.md) |
| `31925` | Calendar Event RSVP | [52](52.md) |
| `31989` | Handler recommendation | [89](89.md) |
| `31990` | Handler information | [89](89.md) | |
| `32267` | Software Application | | |
| `34550` | Community Definition | [72](72.md) |
| `38383` | Peer-to-peer Order events | [69](69.md) |
| `39000-9` | Group metadata events | [29](29.md) |
[NUD: Custom Feeds]: https://wikifreedia.xyz/cip-01/
[nostrocket]: https://github.com/nostrocket/NIPS/blob/main/Problems.md
[lnpub]: https://github.com/shocknet/Lightning.Pub/blob/master/proto/autogenerated/client.md
[cornychat-slideset]: https://cornychat.com/datatypes#kind30388slideset
[cornychat-linkset]: https://cornychat.com/datatypes#kind31388linkset
[joinstr]: https://gitlab.com/1440000bytes/joinstr/-/blob/main/NIP.md
[NKBIP-01]: https://wikistr.com/nkbip-01*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1
[NKBIP-02]: https://wikistr.com/nkbip-02*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1
[NKBIP-03]: https://wikistr.com/nkbip-03*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1
[blossom]: https://github.com/hzrd149/blossom
[Tidal-nostr]: https://wikistr.com/tidal-nostr
## Message types
### Client to Relay
| type | description | NIP |
| ------- | --------------------------------------------------- | ----------- |
| `EVENT` | used to publish events | [01](01.md) |
| `REQ` | used to request events and subscribe to new updates | [01](01.md) |
| `CLOSE` | used to stop previous subscriptions | [01](01.md) |
| `AUTH` | used to send authentication events | [42](42.md) |
| `COUNT` | used to request event counts | [45](45.md) |
### Relay to Client
| type | description | NIP |
| -------- | ------------------------------------------------------- | ----------- |
| `EOSE` | used to notify clients all stored events have been sent | [01](01.md) |
| `EVENT` | used to send events requested to clients | [01](01.md) |
| `NOTICE` | used to send human-readable messages to clients | [01](01.md) |
| `OK` | used to notify clients if an EVENT was successful | [01](01.md) |
| `CLOSED` | used to notify clients that a REQ was ended and why | [01](01.md) |
| `AUTH` | used to send authentication challenges | [42](42.md) |
| `COUNT` | used to send requested event counts to clients | [45](45.md) |
## Standardized Tags
| name | value | other parameters | NIP |
| ----------------- | ------------------------------------ | ------------------------------- | -------------------------------------------------- |
| `a` | coordinates to an event | relay URL | [01](01.md) |
| `A` | root address | relay URL | [22](22.md) |
| `d` | identifier | -- | [01](01.md) |
| `e` | event id (hex) | relay URL, marker, pubkey (hex) | [01](01.md), [10](10.md) |
| `E` | root event id | relay URL | [22](22.md) |
| `f` | currency code | -- | [69](69.md) |
| `g` | geohash | -- | [52](52.md) |
| `h` | group id | -- | [29](29.md) |
| `i` | external identity | proof, url hint | [35](35.md), [39](39.md), [73](73.md) |
| `I` | root external identity | -- | [22](22.md) |
| `k` | kind | -- | [18](18.md), [25](25.md), [72](72.md), [73](73.md) |
| `K` | root scope | -- | [22](22.md) |
| `l` | label, label namespace | -- | [32](32.md) |
| `L` | label namespace | -- | [32](32.md) |
| `m` | MIME type | -- | [94](94.md) |
| `p` | pubkey (hex) | relay URL, petname | [01](01.md), [02](02.md), [22](22.md) |
| `P` | pubkey (hex) | -- | [22](22.md), [57](57.md) |
| `q` | event id (hex) | relay URL, pubkey (hex) | [18](18.md) |
| `r` | a reference (URL, etc) | -- | [24](24.md), [25](25.md) |
| `r` | relay url | marker | [65](65.md) |
| `s` | status | -- | [69](69.md) |
| `t` | hashtag | -- | [24](24.md), [34](34.md), [35](35.md) |
| `u` | url | -- | [61](61.md), [98](98.md) |
| `x` | hash | -- | [35](35.md), [56](56.md) |
| `y` | platform | -- | [69](69.md) |
| `z` | order number | -- | [69](69.md) |
| `-` | -- | -- | [70](70.md) |
| `alt` | summary | -- | [31](31.md) |
| `amount` | millisatoshis, stringified | -- | [57](57.md) |
| `bolt11` | `bolt11` invoice | -- | [57](57.md) |
| `challenge` | challenge string | -- | [42](42.md) |
| `client` | name, address | relay URL | [89](89.md) |
| `clone` | git clone URL | -- | [34](34.md) |
| `content-warning` | reason | -- | [36](36.md) |
| `delegation` | pubkey, conditions, delegation token | -- | [26](26.md) |
| `description` | description | -- | [34](34.md), [57](57.md), [58](58.md) |
| `emoji` | shortcode, image URL | -- | [30](30.md) |
| `encrypted` | -- | -- | [90](90.md) |
| `expiration` | unix timestamp (string) | -- | [40](40.md) |
| `file` | full path (string) | -- | [35](35.md) |
| `goal` | event id (hex) | relay URL | [75](75.md) |
| `image` | image URL | dimensions in pixels | [23](23.md), [52](52.md), [58](58.md) |
| `imeta` | inline metadata | -- | [92](92.md) |
| `lnurl` | `bech32` encoded `lnurl` | -- | [57](57.md) |
| `location` | location string | -- | [52](52.md), [99](99.md) |
| `name` | name | -- | [34](34.md), [58](58.md), [72](72.md) |
| `nonce` | random | difficulty | [13](13.md) |
| `preimage` | hash of `bolt11` invoice | -- | [57](57.md) |
| `price` | price | currency, frequency | [99](99.md) |
| `proxy` | external ID | protocol | [48](48.md) |
| `published_at` | unix timestamp (string) | -- | [23](23.md) |
| `relay` | relay url | -- | [42](42.md), [17](17.md) |
| `relays` | relay list | -- | [57](57.md) |
| `server` | file storage server url | -- | [96](96.md) |
| `subject` | subject | -- | [14](14.md), [17](17.md), [34](34.md) |
| `summary` | summary | -- | [23](23.md), [52](52.md) |
| `thumb` | badge thumbnail | dimensions in pixels | [58](58.md) |
| `title` | article title | -- | [23](23.md) |
| `tracker` | torrent tracker URL | -- | [35](35.md) |
| `web` | webpage URL | -- | [34](34.md) |
| `zap` | pubkey (hex), relay URL | weight | [57](57.md) |
Please update these lists when proposing new NIPs.
## Criteria for acceptance of NIPs
1. They should be fully implemented in at least two clients and one relay -- when applicable.
2. They should make sense.
3. They should be optional and backwards-compatible: care must be taken such that clients and relays that choose to not implement them do not stop working when interacting with the ones that choose to.
4. There should be no more than one way of doing the same thing.
5. Other rules will be made up when necessary.
## Is this repository a centralizing factor?
To promote interoperability, we need standards that everybody can follow, and we need them to define a **single way of doing each thing** without ever hurting **backwards-compatibility**, and for that purpose there is no way around getting everybody to agree on the same thing and keep a centralized index of these standards. However the fact that such an index exists doesn't hurt the decentralization of Nostr. _At any point the central index can be challenged if it is failing to fulfill the needs of the protocol_ and it can migrate to other places and be maintained by other people.
It can even fork into multiple versions, and then some clients would go one way, others would go another way, and some clients would adhere to both competing standards. This would hurt the simplicity, openness and interoperability of Nostr a little, but everything would still work in the short term.
There is a list of notable Nostr software developers who have commit access to this repository, but that exists mostly for practical reasons, as by the nature of the thing we're dealing with the repository owner can revoke membership and rewrite history as they want -- and if these actions are unjustified or perceived as bad or evil the community must react.
## How this repository works
Standards may emerge in two ways: the first way is that someone starts doing something, then others copy it; the second way is that someone has an idea of a new standard that could benefit multiple clients and the protocol in general without breaking **backwards-compatibility** and the principle of having **a single way of doing things**, then they write that idea and submit it to this repository, other interested parties read it and give their feedback, then once most people reasonably agree we codify that in a NIP which client and relay developers that are interested in the feature can proceed to implement.
These two ways of standardizing things are supported by this repository. Although the second is preferred, an effort will be made to codify standards emerged outside this repository into NIPs that can be later referenced and easily understood and implemented by others -- but obviously as in any human system discretion may be applied when standards are considered harmful.
## Breaking Changes
[Breaking Changes](BREAKING.md)
## License
All NIPs are public domain.
## Contributors
<a align="center" href="https://github.com/nostr-protocol/nips/graphs/contributors">
<img src="https://contrib.rocks/image?repo=nostr-protocol/nips" />
</a>
-

@ 1c229706:fd7d0f4c
2025-04-05 06:38:45
O mundo do entretenimento online está em constante evolução, com novas plataformas surgindo para atender à demanda crescente por experiências inovadoras e imersivas. A 5853 é uma dessas plataformas que tem se destacado pela qualidade de seus jogos, pela tecnologia avançada e pela experiência excepcional que oferece aos seus jogadores. Neste artigo, vamos explorar o que torna a plataforma 5853 tão especial e por que ela tem conquistado a preferência dos jogadores.
Inovação e Design: O Diferencial da Plataforma 5853
A 5853 é uma plataforma de entretenimento online que se destaca por seu design sofisticado e fácil de usar. Desde o primeiro acesso, os jogadores são recebidos por uma interface limpa, intuitiva e moderna, que torna a navegação rápida e eficiente. A plataforma é projetada para garantir que o jogador tenha fácil acesso aos seus jogos favoritos e possa explorar outras opções de forma simples e sem complicação.
A <a href="https://5853.one"> 5853 </a> também se diferencia pela sua flexibilidade. Compatível com computadores, smartphones e tablets, a plataforma garante que os jogadores possam se divertir de qualquer lugar, seja em casa ou em movimento. Isso proporciona uma experiência contínua, permitindo que os jogadores aproveitem o melhor do entretenimento digital a qualquer hora.
Além disso, a plataforma é totalmente segura. As informações dos jogadores são protegidas por criptografia de ponta, o que garante que todas as transações e dados pessoais sejam mantidos de forma confidencial.
A Diversidade de Jogos da 5853: Uma Oferta Completa para Todos os Gostos
A plataforma 5853 é renomada pela sua impressionante variedade de jogos. Independentemente do estilo de jogo preferido, os jogadores podem encontrar uma ampla gama de opções, que vão desde os mais simples e rápidos até os mais complexos e desafiadores.
A plataforma oferece jogos de cartas, slots, estratégia, RPGs, e muito mais. Cada título foi escolhido para proporcionar uma experiência única e envolvente, com gráficos de alta qualidade e jogabilidade fluida. Além disso, novos jogos são constantemente adicionados à plataforma, o que mantém a experiência sempre fresca e excitante.
A 5853 também oferece desafios e torneios, permitindo que os jogadores testem suas habilidades e se envolvam em competições emocionantes. Isso torna a plataforma ainda mais dinâmica, criando uma atmosfera de constante evolução e diversão.
A Experiência do Jogador na 5853: Conforto, Interação e Suporte de Qualidade
A 5853 não se preocupa apenas com os jogos, mas também com o bem-estar de seus jogadores. A plataforma foi projetada para proporcionar uma experiência confortável e sem interrupções. O design responsivo garante que os jogos funcionem perfeitamente em qualquer dispositivo, enquanto a navegação intuitiva facilita o acesso a todos os recursos.
A plataforma também promove a interação entre os jogadores, com chats ao vivo e fóruns onde os usuários podem compartilhar experiências, trocar dicas e até formar grupos para desafios em equipe. Isso cria uma comunidade engajada e colaborativa, onde os jogadores podem se conectar e aprender uns com os outros.
Além disso, a 5853 oferece suporte ao cliente 24/7, com uma equipe dedicada a resolver qualquer dúvida ou problema rapidamente. Isso garante que os jogadores tenham uma experiência tranquila e sem frustrações.
Conclusão: 5853, a Plataforma Completa para o Entretenimento Digital
Se você está procurando por uma plataforma de entretenimento online que ofereça jogos de qualidade, segurança, conforto e uma excelente experiência de jogador, a 5853 é a escolha ideal. Com seu design inovador, vasta gama de jogos e suporte excepcional, ela se estabelece como uma das melhores opções disponíveis no mercado. Não perca a chance de explorar tudo o que a 5853 tem a oferecer e elevar sua experiência de entretenimento digital a um novo nível.
-

@ 57d1a264:69f1fee1
2025-03-26 08:45:13
> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score!
| Desktop | Mobile |
|---|---|
|  |  |
|  |  |
Now let's see what Semrush knows.
# Analytics
General view on your metrics and performance trend compared to last 30 days.


See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.

Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.

| Organic Search | Backlinks Analytics |
|---|---|
| |  |
| Position Changes Trend | Top Page Changes |
|---|---|
| |  |
|This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |

# Competitors

The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.

# Referring Domains


# Daily Stats
| Organic Traffic | Organic Keywords | Backlinks |
|---|---|---|
| 976 | 15.9K | 126K |
| `-41.87%` | `-16.4%` | `-1.62%` |
### 📝 Traffic Drop
Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits:
- https://stacker.news/items/723989 ⬇️ -15
- https://stacker.news/items/919813 ⬇️ -12
- https://stacker.news/items/783355 ⬇️ -5
### 📉 Decreased Authority Score
Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority.
### 🌟 New Keywords
Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords:
- nitter.moomoo.me — Volume 70
- 0xchat — Volume 30
- amethyst nostr — Volume 30
### 🛠️ Broken Pages
This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_:
- https://stacker.news/404 — 38 backlinks
- https://stacker.news/api/capture/items/91154 — 24 backlinks
- https://stacker.news/api/capture/items/91289 — 24 backlinks
Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility!
One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary?
Here are other basic info to improve the SEO score and for those of us that want to learn more:
- Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/
- Design for Accessibility: https://www.w3.org/WAI/tips/designing/
- Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/
originally posted at https://stacker.news/items/925433
-

@ 30876140:cffb1126
2025-03-26 04:58:21
The portal is closing.
The symphony comes to an end.
Ballet, a dance of partners,
A wish of hearts,
Now closing its curtains.
I foolishly sit
Eagerly waiting
For the circus to begin again,
As crowds file past me,
Chuckles and popcorn falling,
Crushed under foot,
I sit waiting
For the show to carry on.
But the night is now over,
The laughs have been had,
The music been heard,
The dancers are gone now
Into the nightbreeze chill.
Yet still, I sit waiting,
The empty chairs yawning,
A cough, I start, could it be?
Yet the lights now go out,
And now without my sight
I am truly alone in the theater.
Yet still, I am waiting
For the show to carry on,
But I know that it won’t,
Yet still, I am waiting.
Never shall I leave
For the show was too perfect
And nothing perfect should ever be finished.
-

@ 04c915da:3dfbecc9
2025-03-25 17:43:44
One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-

@ 6fbc5b6b:0251e3df
2025-04-05 03:37:17
✨ Event Overview
AIVille has officially partnered with FreeDogs, a decentralized social game born as a meme tribute to Pavel Durov. Their mission? To fight for privacy and resistance in the Web3 age — captured in their slogan: "Privacy is not a crime, resistance will prevail."
As part of this collaboration, an exclusive AIVille quest is now live within the FreeDogs game!
Participants who complete the quest not only get to explore AIVille’s intelligent agent society, but also unlock access to the broader AGT First Round Community Airdrop, where 1% of the total $AGT supply will be distributed to early supporters.
🤝 About AIVille & FreeDogs
AIVille is an AI-native decentralized town where autonomous agents live, create, and evolve. Players interact with characters, join events, and help shape the future of intelligent societies.
FreeDogs is a meme-powered Web3 social game where players sign petitions while completing quests for rewards. More than just entertainment, FreeDogs stands for freedom, privacy, and community resistance — a tribute to open digital spaces.
Together, AIVille and FreeDogs bring the power of storytelling, questing, and token incentives to a wider audience.
🌟 AGT Token & Quest Rewards

The AIVille quest in FreeDogs is more than a game — it’s your gateway to the AGT First Round Community Airdrop, the first large-scale distribution of AIVille’s native token.
Complete the quest to:
Learn about AIVille and the $AGT ecosystem
Get priority access to the community airdrop (1% of supply!)
Start your journey as an early supporter of intelligent agents
This is part of AIVille’s Create-to-Earn model, where your actions in the Web3 world generate real value.
⚡ Why This Matters
This partnership expands AIVille’s reach into fun, social gaming — and introduces FreeDogs players to the future of AI-native societies.
It reflects a growing movement where:
Games unlock real community rewards
Stories and agents become programmable
Participation leads to ownership and tokenized recognition
If you're playing FreeDogs, this is your moment to join something bigger.
🔗 Links
AIVille Quest: https://app.freedogs.bot/game
FreeDogs Bot: https://t.me/theFreeDogs_bot/app
FreeDogs on Twitter: @theFreeDogs_bot
AIVille on Twitter: @aivillebot
AGT Airdrop Info: https://aivillegame.com
-

@ a5142938:0ef19da3
2025-04-04 14:59:58
**Do you know a brand offering natural alternatives? Share it here by commenting on this page!**
Copy and paste the template below and fill in the information you have. Other contributors can complete any missing details.
To be listed, the brand must offer at least some of its products made from natural materials.
👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/)
Each piece of information added (name, link, category, etc.) and validated is considered a contribution.
👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/)
---
### New brand or manufacturer
- Brand name:
- Image representing the brand’s products (link, ideally from the brand’s website):
- Short description:
- Categories of products offered:
- Materials used in its products:
- Brand’s website:
- Other information (place of production, certifications, etc.):
---
If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward.
👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/)
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/unjmwarjg7ojb9uwantvt/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/4wvxjm06tle2aelvde8w6/)
-

@ 8bad797a:8461b4bc
2025-04-05 14:49:13
## Frank Palmer Purcell
I claim to be a Catholic American; even though I now follow the Russian Orthodox tradition, I do so in a small *sui juris* Church in communion with Rome, not Constantinople. When I was a little kid, knee high to a trilobite, some folks still had a problem with that, with being Catholic and American, I mean; Orthodoxy was beyond our horizon. My mother was one of those who had the problem. As long as I was a Catholic like my father (and her own mother, as a little girl in Ireland and on the lower East Side), I couldn't be a real American like her father, a bookbinder replaced by a machine, disowned by his family for marrying out of caste, who spent his days in the nearest tavern. "Pop" Palmer died at 78, and four years later I was born and named for him, or at least that was my mother's intention. The priest baptized me in Latin, as was the custom in those dark days, and pronounced "Frank" so that it sounded like the nickname ("Frenchy") of a (doubtless) dirty medieval Italian beggar baptized Giovanni.
My early spirituality, to use a ten dollar word for a fifty cent thing, was more American than Franciscan. Emerson and Thoreau, Melville and Whitman spoke and still speak to me as no European voice can, and when I came to study philosophy in a serious way I found the Americans, Josiah Royce, Rufus Jones and Ernest Hocking, C. I. (not C. S.) Lewis and Brand (not Paul) Blanshard, speaking a language that was my own, though by then the professoriate resonated to other tonalities. Though I fell in love with Schopenhauer and Kierkegaard, as every teenager who meets them must, and inhaled the sweet incense and felt the calming breeze of the shrines of the East, as my generation did, and was introduced to the mysteries of Thomas Aquinas by the subtle writings of Jacques Maritain, as we should all be, when I came to take hold of the great tradition of Western theology in a personal way, I found the distinctly American perspectives of Paul Tillich and Richard (not Reinhold) Niebuhr most helpful.
Back in 1963, in the New Jersey family television room, Joseph Campbell's urbane mythological sermons on Channel 13 (still a Newark station) touched something deep inside me an hour after Bishop Sheen's passionate exhortations on Channel 5 had left me (perhaps deplorably) cold. I would go up to my room and say my prayers after a fashion in time for the nightly racetrack bugle and exhilarating nostalgia of Arthur Fiedler's performance of the Bahnfrei Polka of Edouard Strauss, which introduced the nightly raconteurship of the incomparable Jean Shepherd, and, if I were still awake, the more outre world of Long John Nebel and his, ah, eccentric guests. You can't get more American than that. Or more New Jersey.
As the child of a mixed marriage and a pupil of the public schools I was not warmly welcome in the Catholic ghetto. Still, in those years of the civil rights revolution and the Vietnam War, with the polarized positions of right and left equally abstract and inhumane, I found my take on national affairs reflecting the distinctly Catholic perspectives of Dorothy Day and Thomas Merton on the one hand and Frederick Wilhelmsen and Erik Maria, Ritter von Kuehnelt-Leddihn on the other. And, though the writings of Rufus Jones, to which I even now frequently turn for inspiration, had led me to seek out a Quaker education, I found it was the Catholic scholars and pioneers of the spirit who were beginning the interreligious dialogue which was then and is now one of the pressing needs of humanity. In graduate school I became a devoted Americanist, that is, a scholar dedicated to using the tools of the historian of ideas to get some sense of what this place is all about, this gallimaufry of peoples who have somehow, in spite of all learned and astute prognostications, made themselves and each other into a kind of unity, a unity which it may take someone like the present [at the time of writing] Pope (and there isn't really anyone else very much like him) to discern.
I do not speak of Joseph Ratzinger, Benedict XVI, as a theologian nor even as a philosopher, but I must note that in New York and Washington in 2008 he revealed himself as an historian of ideas of astonishing and exquisite discernment. By this I mean, among other things, of course, that he strongly confirmed the discoveries and intimations of my own forty years of brooding in and on America. I was fortunate indeed to turn up at Columbia University's Teachers College when Douglas Sloan was putting the finishing touches on his groundbreaking study of the Scottish Enlightenment as the great inspiration of the American colonists, especially the intellectual elite, in the age of the War of Independence. Sloan's insights would eventually be popularized, without their scholarly context and qualifications, in Garry Wills' bestselling *Inventing America*, and it is now taken for granted that our Founding Father Across the Sea was not John Locke, but the Ulster Scot Francis Hutcheson (1694-1746).
Indeed, the Evangelical position seems to be that it was Hutcheson who corrupted American civilization at the root, turning us from the Calvinist faith once delivered to Jonathan Edwards (himself a notorious Lockean, but never mind). In fact, Oxford University Press recently published a six hundred page tract to that effect, authored at Wheaton. Hutcheson, and the Scottish school of Common Sense which he inspired, held that all human beings, Pagan and Christian, Protestant and Catholic, share a basic ability to come to an understanding of certain fundamental truths, and can come to agreement upon these with the aid of reason. Calvinism, especially the neoCalvinism which is the unquestioned (because unquestionable) paradigm of the Evangelical academy, holds that the elect have a unique and divinely sanctioned "world view" which stands in judgment of all others in all particulars. To these zealots the very idea that there can be any common human ground between believers and unbelievers is itself a damnable heresy. Still, it is the damnable heresy on which American society and civilization are built, and the Calvinism which so despises it is a near kin of those varieties of Islam that Benedict so boldly challenged at Regensburg in 2006.
When the same Benedict addressed the United Nations a year and a half later, he pointed out how the principles of that august body, and the Universal Declaration of Human Rights whose anniversary he was commemorating, grew out of the Natural Law philosophy of CounterReformation Scholasticism, particularly as formulated by Francisco de Vitoria (1492?–1546). Needless to say, the "Scottish Philosophy" of a later age grew out of this tradition as well, and many of the American founders were directly familiar with Natural Law theory as expounded by Catholic and Protestant Scholastics. On the same visit Benedict made ample use of the language of sacred architecture, as if in conscious homage to the fact that he was honoring a country founded by Freemasons, who used that language to teach the conformity of right living to the law of nature and nature's God. If he was giving a Catholic interpretation to this symbolism, so did the Catholic Jacobites who were prominent in the Craft before the Masonic movement became identified with indifferentism, anticlericalism, and finally (at least on the Continent) atheism. It was striking indeed that to one steeped in American tradition it was the Pope of Rome of all people who was speaking our own language in a familiar tone, and the neoCalvinist Evangelicals who jibbered and muttered in an outlandish and menacing jargon more Muslim than Christian. I sure wonder what Mommy would think.
Natural Law. What is that to us today; what was it to me in what we call the Vietnam era? In 2008 the issue was torture, and a President of the United States who took pleasure in his presumed power to order it, to physically degrade his enemies, to morally degrade our own soldiers. I am proud that when Mr. Bush asked our military for advice on the subject, they replied that he has no such power, that such actions are contrary to our laws and the traditions of our armed services, and, moreover, ineffectual. (The latter point is an important indication that powerful men order torture not to accomplish anything, but to pleasure themselves.) And I am ashamed that he chose to take the advice of Israeli advisors, who hold to another morality, one going back to ancient Assyria, and profoundly alien to our own Christian civilization.
In my youth the overriding issue was not torture, but terrorism. Not that torture didn't take place. At graduate school I knew a former naval officer who had interrogated captured Viet Minh and Viet Cong; the "extraordinary means" had been applied by our allies by the time he was introduced to his prisoners, and the specialists who had softened them up had already moved on or backed off. The issues before us then were atrocious acts of war against civilian populations in North and South Vietnam, in Laos and Cambodia, in Central and South America, even in Germany and Japan a generation before, not to mention the subversion and corruption of constitutional government in America by a regime that felt justified in using any means necessary to keep power away from the Communists and their sympathizers, the Democrats and liberal Republicans.
Nor was such evil a monopoly of the socalled right. A young antiwar activist formerly associated with Martin Luther King even went so far as to criticize the sainted Che Guevara for not being enough of a terrorist to tear the peasantry away from their conformity to a "fascist" state. (Two generations later the man was advising George Bush.) In my undergraduate days I had been a loyal member of the conservative movement, back when the Intercollegiate Studies Institute was still called the Intercollegiate Society of Individualists, some members of the Students for a Democratic Society still honored democracy, and Murray Rothbard and Carl Ogelsby were moving "beyond left and right." If I got nothing more from the conservatives, and in fact I got a great deal more, it was an ever deepening admiration for Edmund Burke. Burke was prized by the cold warriors because his *Letters on a Regicide Peace* could be used to justify a war of extermination against the Soviet Union, the Peoples Republic of China, and any other people so temerarious as not join the alliance against these forces of absolute evil and subordinate their interests to those of the United States. A superficial reading, I need hardly remark. But Burke was not only the acute critic of the French Revolution who predicted the Terror from its earliest signs, he also was a tireless advocate for Irish freedom, particularly freedom of conscience, and a loyal ally of the American colonies in Parliament. But Burke's finest hour came at the end of his long career, when he boldly fought against the depredations of Warren Hastings and the British East India Company. Anyone who wants to know what natural law meant to the men of the Eighteenth Century, including those who liberated the American colonies and forged their political constitution can get a good sense of it from the eighth day (!) of his impeachment of Hastings before the House of Lords, which, I warn you, I have quoted before and shall no doubt quote again:
> No man can lawfully govern himself according to his own will—much less can one person be governed by the will of another. We are all born in subjection—all born equally, high and low, governors and governed, in subjection to one great, immutable, preexistent law, prior to all our devices, and prior to all our contrivances, paramount to all our ideas and to all our sensations, antecedent to our very existence, by which we are knit and connected in the eternal frame of the universe, out of which we can not stir. This great law does not arise from our conventions or compacts; on the contrary, it gives to our conventions and compacts all the force and sanction they can have: it does not arise from our vain institutions. Every good gift is of God, all power is of God; and He who has given the power, and from whom alone it originates, will never suffer the exercise of it to be practised upon any less solid foundation than the power itself. If, then, all dominion of man over man is the effect of the divine disposition, it is bound by the eternal laws of Him that gave it, with which no human authority can dispense; neither he that exercises it, nor even those who are subject to it; and, if they were mad enough to make an express compact, that should release their magistrate from 5 his duty, and should declare their lives, liberties and properties, dependent upon, not rules and laws, but his mere capricious will, that covenant would be void. This arbitrary power is not to be had by conquest. Nor can any sovereign have it by succession; for no man can succeed to fraud, rapine, and violence. Those who give and those who receive arbitrary power are alike criminal; and there is no man but is bound to resist it to the best of his power, wherever it shall show its face to the world.
Mr. Jefferson couldn't have put it better. Human rights are inalienable -- you can't give them away, and when they are taken away there is not only the right of rebellion, but the solemn duty to resist. The difficulty of natural law theory, of course, is in the details. Back in '68 Pope Paul VI had announced that artificial contraception was against the natural law, but this decision did not immediately commend itself to the common sense of many of those who were not subject to his religious authority. I don't mean he was wrong, or that he exceeded his authority, or even that his decision was inopportune. But when the Supreme Court, alarmed by the birthrate of blacks and an end to white domination of the nation and the world, soon mandated abortion on demand, it was all too easy to dismiss arguments in favor of the human being of the embryonic human as religious dogma rather than an honest attempt to think things through. Since then the concept of natural law is often dismissed by feminists and homosexualists (to use Mr. Vidal's eloquent term) as a mere excuse for oppression. It does seem to me, however, that the insistent denial of the very idea of human rights does nothing to advance the liberation of humanity or any part of it. But maybe that's just me.
In any case, I don't think America was ever anything like the sort of Catholic nation that, say, Portugal was under the late Dr. Salazar, or is very likely to get there any time soon, despite the best wishes and even efforts of some of my friends. I do think that for a good part of our history a great many people in public life would have said that the words of Burke I have quoted express their most basic political convictions and sentiments as well as anyone ever could, and this puts America right at the center of the great tradition of Western civilization. And this was true long after old Europe had gone down other ways, the ways of the French revolution, the reaction against it, and the nationalism that synthesized the worst of both. To be sure, we have had nationalists here, and have them today, and have preached our crusades to end slavery, make the world safe for democracy, eradicate the evil empire of the moment, but there is, if not always a ringing and uncontested affirmation of civilized values, by which I mean the values of our civilization, at least a powerful nostalgia for them, and a sincere wish that one could believe in them with a good conscience, a good conscience which postmodernist deconstructionism denies us. A good conscience which Joseph Ratzinger Benedict XVI, who has suffered modernity as few of us have and thought more deeply about it, was offering us back.
To be perfectly frank, it took the Catholic Church a good long time to recognize the Christian virtues of Enlightenment, even the Scottish one, and Revolution, even the American one. Better late than never. And despite the mantric invocation of John Courtney Murray, the Church in America has not always been on the side of the angels. The theology of the American Church has always been Jansenist, not Catholic, combining the worst of Pelagius and Calvin, making Boston Irish the kissing cousins of Cotton Mather. The American Church never permitted itself to be organized according to canon law because this would limit the despotism of prelates. The American Church refused to acknowledge the priesthood of Eastern Catholics ordained as married men, driving the Catholic Ruthenians into communion with the Patriarch of Moscow (the present Orthodox Church in America), and later blackmailing a bankrupt papacy into forbidding married priests throughout the Western hemisphere, driving a second group of Ruthenians into communion with the Ecumenical Patriarch of Constantinople (the present American CarpathoRussian Orthodox Diocese).
They American Cathholic Church wouldn't even allow American women to become real nuns, or foreign nuns to come to America without renouncing their vows. The vast majority of Catholic women called nuns are nothing of the sort, but religious sisters first organized as cheap labor at the beck and call of the clergy, and now loose cannons like the Papessas Mother Angelica and Sister Joan. Yes, one or two real abbeys for women were founded in the last century, but the American Church continues to hold the contemplative life in deepest contempt, even for women. Women religious lead the crusade against contemplative traditions, and now rail against the Church as an organ of worldly power from which they are unjustly excluded.
Deprived of traditional spiritual direction, a lamentable number of priests "demythologized" the Faith while looking to worldly culture for a way of salvation. Many found it in the gospel of orgasm, and undertook to liberate the young men in their care by sharing the only joy they thought worth having, with results we see today.
Catholic involvement in American public life has not been edifying either. The American bishops turned their backs on Benedict XV's attempt to end the slaughter in the trenches and refused to make any move to bring Woodrow Wilson over to the side of peace. As patriotic Americans, they in effect signed on to the WASP jihad to extirpate the Catholic powers of the Old World. A couple of generations later millions of Catholic schoolchildren were forced to write letters demanding that the Senate not censure that great American Joseph McCarthy, who was probably the Soviet Union's most valuable (presumably unwitting) asset in American public life, who had discredited all responsible criticism of Communism and its supporters by viciously slandering the United States Army, the Department of State, and the Protestant clergy as nests of traitors. Some years later Catholic activists succeeded in driving the voices of moderation out of the Republican Party, and the urban ethnic social conservatives out of the Democratic, and the forms of civility from the public square.
Americans can be forgiven for not rushing to enlist in the nearest Roman Catholic parish. There are other conversions needed, perhaps beginning with American Catholics themselves. Back in the days of Reagan a fellow named Alan Bloom made an almost persuasive case that the American Mind was closed to the Great Tradition of Western Civilization, and needed to be reopened. Alas, Bloom was a Neoconservative, a follower of their guru Leo Strauss, and a teacher of a a number of shady operatives of the Program for the New American Century type, as Saul Bellow's last novel so amusingly portrays him. Bloom's Great Tradition was something cobbled together by Machiavelli and others out of the misunderstood shards of ancient paganism; thinkers and writers tainted by the Christian gospel remained under embargo. (Mortimer Adler was less fearful, more intellectually curious, but look where he ended up.) It took a Bavarian Pope to remind us that the basic principles of our cherished hopes of international organization and human rights, and indeed of the American founding itself, go back to the Iberian scholastics of the Catholic Reformation. ("CounterReformation" is misleadingly negative.)
Benedict's reminder harmonized well with my own studies in the history of philosophy. I began some five decades ago with the riddle, the riddles, of Charles Sanders Peirce (1839 - 1914), our own and only philosopher to be ranked with the likes of Aristotle and Kant. What was this Common Sense he went on and on about? (The Scottish Philosophy was studiously ignored in the academy; it still is.) As I said, I was lucky to find out. Now John Deely has been showing that any postmodern philosophy worthy of the name, one founded on semeiology rather than Cartesian (or empiricist) methodologism, needs to go back to Peirce and with Peirce back to the very beginnings of the theory of signification as we find them in John Poinsot (1589 1644). Poinsot, as it happens, is part of the same Iberian Renaissance to which Benedict has now called our attention. Indeed, under another name (John of St. Thomas) Poinsot inspired the neo Thomism of Jacques Maritain which undergirded the Christian Humanism of Paul VI and many other Fathers of the Second Vatican Council. (His treatise on **The Gifts of the Holy Spirit*, as interpreted by theologians often dismissed as too conservative, is behind the rather daring notion that all Christians are called to holiness in this life, and, indeed to the mystical path of acquired contemplation, and thus such more recent developments as Centering Prayer, the World Community for Christian Meditation, and the ommunion and Liberation movement.
As if all this were not enough, Murray Rothbard, no Christian he, though personally excommunicated and anathematized by Ayn Rand for not repudiating his openly Christian wife, has argued that the Austrian School of Economics, the Old Liberalism of von Mises and Hayek, goes back not so much to Adam Smith (who missed a few points), as to the scholastic philosophers of Spain and Portugal in the early modern period. Mention Iberian philosophy to the American of average education and he will look at you as though you had spoken of Uzbek grand opera or (indeed) the Scottish Enlightenment. He might even tell you that Spanish ignorance, superstition, and bigotry are precisely what God sent Englishmen into the New World to stamp out: the *legenda negra*. Needless to say, this is not a view of history a good many newcomers to the United States are likely to tolerate with equanimity, and it is just as well that it isn't true.
Once we retire that vulgar prejudice against Hispanidad we might just get a fair hearing for the work of Xavier Zubiri, the only European thinker of the last century who compares with Peirce for breadth of learning and depth of discernment as well as sheer unadulterated difficulty. If nothing else, the challenge of Catholicity invites Americans to break down the walls of the AngloSaxon ghetto, which do not serve us well now, if they ever did. But it may also provoke a new interest in our own Golden Age of (Protestant) theology. Let me set the stage for this with an extended quotation from Joseph Ratzinger's 1977 essay, "Is Faith Really Good News?" (Now translated in Principles of Catholic Theology:
> Truth is not always comfortable for man, but it is only truth that makes him free and only freedom that brings him joy. Now, however, we must ask more precisely: What makes a man joyful? What robs him of joy? What puts him at odds with himself? What opens him to himself and to others? When we want to describe the most extreme form of being at odds with existence, we often say of an individual that he does not like himself. But whom or what is he to like who does not like himself? Something very importamt makes its appearance here: egoism, certainly, is natural to man and needs no encouragement; but this is not true of selfacceptance. The former must be overcome; the latter must be discovered, and it is assuredly one of the most dangerous errors of Christian teachers and moralists that they have all too often confused the two and, by exorcizing the affirmation of self, have enabled egoism to avenge such a betrayal by becoming all the more rampant this, ultimately, of what the French have labeled the maladie catholique: one who wants to live only on the supernatural level and to the exclusion of self will be, in the end, without a self but not, for that reason, selfless. (79)
Reading this a day or two after Ratzinger's papification I couldn't help thinking of our own Paul Tillich, whose seminal sermon "You are Accepted" baptized the human potential movement (as it was called), whose *Courage to Be* is a perennial best seller even after half a century, whose *Systematic Theology* Martin Luther King had asked for in his Georgia prison cell, and I myself poured over eagerly as an Earlham undergraduate. Of course the problematic goes back to Kierkegaard's penetrating analysis of despair, and, indeed to Luther's experience of divine wrath and mercy. Now it is all very well to say we must accept our acceptance, somehow (mysticism? art?) so ground ourselves in the very Ground of Being as to powerfully affirm our being against the powers of nonbeing. But is it true? That is the question haunting Tillich, Martin Luther King, and modern American culture down to our own time, which Ratzinger, challenged by Nietzsche and Camus, dared to speak aloud:
> We come now to the allimportant question: Is it true, then, when someone says to me: "It is good that you exist"? Is it really good? Is it not possible that that person's love, which wills my existence, is just a tragic error? If the love that gives me courage to exist is not based on truth, then I must, in the end, come to curse the love that deceives me that maintains in existence something that were better destroyed. This dilemma could be 10 strikingly illustrated by reference to the interpretations of the contemporary experience of life in Sartre or Camus or in the attitudes of the new Left. Even without such evidence, it is obvious, however, that the apparently so simple act of liking myself, of being at one with myself, actually raises the question of the whole universe It raises the question of truth: Is it good that I exist? Is it good that anything at all exists? is the world good? How many persons today would dare to affirm this question from the heart to believe it is good that they exist? That is the source of the anxiety and despair that incessantly affect mankind. Love alone is of no avail. It serves no purpose if truth is not on its side. Only when truth and love are in harmony can man know joy. For it is truth that makes man free. (80)
And the question of truth won't leave us alone. For Tillich the Christian faith was perhaps a true myth, but, perhaps true only the way that other myths are true. He tended to sacramentalize modern art, leftish politics, and sexual liberation; the president of Union Seminary had to remind him that it looked bad for their most eminent theologian not to go to church. The tragedy of attempting to make a religion of art, politics, or sex is obvious by now, and it as a sad circumstance that the leadership of the American Catholic Church were seminarians at a time when Catholic theology looked to the Protestants for validation, and Tillich was at the height of his prestige in the liberal denominations. The painful story of Tillich's sexual obsessions is now well known enough from his wife's two memoirs, Dr. King's escapades have stained the memory of the civil rights movement as much as his infatuation with the Soviet power, and the sexual scandals of the American Church are unspeakably worse, blighting the lives of tens (hundreds?) of thousands of children. That is something Benedict, on his recent visit, would not allow us to forget for even a moment. But at least he offers a remedy in that confrontation with the truth of our being which liberal theology, Catholic and Protestant (though perhaps not Orthodox),attempted to evade:
> The content of the Christian evangelium reads: God finds man so important that he himself has suffered for man. The Cross, which was for Nietzche the most detestable expression of the negative character of the Christian religion, is in truth the center of the evangelium, the glad tidings: "It is good that you exist" No, "It is necessary that you exist." The Cross is the approbation of our existence, not in words, but in an act so completely radical that it caused God to become flesh and pierced this flesh to the quick; that, to God, it was worth the death of his incarnate Son. One who is so loved that the other identifies his life with this love and no longer desires to live if he is deprived of it; one who is loved even unto death such a one knows that he is truly loved. But if God so loves, then we are loved in truth. Then love is truth, and truth is love. Then life is worth living. This is the evangelium. (81)
The whole idea of the Cross as God's affirmation of man will strike many an American as shocking, ludicrous even. It the caross not the stock in trade of a thousand "evangelists" as the ultimate proof of our total depravity, the ultimate refutation of all aspirations for human freedom and dignity? Surely Nietzsche got that from his preacher father, though it is hard to find any such slander of humanity in either the written scriptures or the teaching of the Fathers of the Church (except for Augustine, and that on a bad day he later repented). I am happy to note that Ratzinger's point of view, scriptural, patristic, and Benedictine in every sense of the term is very close to what some in the Evangelical churches are calling "gracious Christianity," for that is what it is. That movement is still a prophetic minority in the churches and the academy, and we still need to come to terms with the main stream of American spirituality as represented, for better and worse, by Tillich. And Ratzinger, even in his early days as a professor, has given us the means to do just that. Not everything in the American theological mainstream, and not everything in Tillich, needs to be discarded wholesale.
A follower of Ratiznger's good friend Don Liugi Giussani who studies Tillich's theology will find close analogies between Tillich's method of correlation and the principle of correspondence which Giussani urged on members of the Communion and Liberation movement he founded, a movement in which the Ratzinger Pope (to use the Catholic injargon) takes more than a passing interest he is said even now to take part in a weekly School of Community in which movement people use that method to explore the meaning of the Gospel in relation to their own day to day lives, and the meaning of their lives in relation to the Gospel, though his episcopal orders forbid his formal membership in the Fraternity. I do not mean to imply that Benedict is a follower of Giussani in matters of pure theology, but it seems clear that he recognizes Giussani's method as the best practical application of the theological principles both men learned from such masters of La Nouvelle Theologie as de Lubac, von Balthasar, and (with reservations) Rahner.
But before I move away from the idea of correspondence, the method of correlation, I should mention that this became the life work of two American philosophers, Ira Progoff, with whom and with whose students I was privileged to do postdoctoral work, and Eugene Gendlin, both known as psychologists for the contributions they have made to psychology, who offer what I can only describe as means of spiritual direction. The few folks who remember Tillich today often contrast him with Reinhold Niebuhr, his colleague at Union, who inspired the Cold war mainstream much as Tillich inspired the New Left, and whom Don Gius was fond of quoting.
But the man to rediscover is Reinhold's brother Richard, a theologian's theologian, that is, one whose writings were never taken up by the movers and shakers of middlebrow culture. His *Meaning of Revelation* shows the kind of emphasis the Catholic Church in Europe is coming around to, or coming back to, as it is very much in the spirit of the Fathers of the Church, the Eastern Fathers in particular. For many of us what may be most prophetic in his life work is his refusal of the temptation of neoconservatism to which Reinhold gave in to his fame and profit. Reinhold ostentatiously resigned from the Fellowship of Reconciliation in the early '30s in righteous indignation that some Christians did not demand that the government do something (what?) about the Japanese in China. Richard, on the other hand, had no hope for the efficacy of political, economic, and military power exercised by the United States against Japan. Sensing that Western Christendom was going the way of old Rome, he thought that the best Christian response was that pioneered by St. Benedict, from whom of course among others the last pontiff took his name. For him the issue was not Japan against China, or the United States against Japan, but, to cite the title of a 1935 book to which he contributed, *The Church Against the World*. A few years later Dietrich von Hildebrand, in his villa in Florence, was giving the retreats later published as *Transformation in Christ* to Christian activists who intended to remain behind in Nazi Germany to keep the light of Christian civilization burning in that dark time, and Dietrich Bonhoeffer would take refuge with the Benedictines in his own effort to do the same. A few pages before the long passage I have quoted, Ratzinger's *Principles of Catholic Theology* gives a lengthy exegesis of Hildebrand's text as the model for Christian repentance. I can't help wondering if this forbidden book is one that his father had hidden around the house, as Evangelicals might have concealed Bonhoeffer's *Cost of Discipleship*. Discipleship and transformation are not matters of effortful striving, but the response to a calling which is a revelation.
Richard is particularly enlightening on revelation as calling. He shows that it is not the communication of some kind of knowldege, however supernatural or esoteric, by possession of which we are justified, elevated from the companionship of our neighbors, saved from the world; that would be Gnosticism. Rather, revelation is participation in an ongoing event, a relationship with a person previously unknown, or at least unrecognized. Some words toward the end of *The Meaning of Revelation* put the matter thus:
> Revelation means the moment in our history through which we know ourselves to be known from beginning to end, in which we are apprehended by the knower; it means the the selfdisclosure of the judge. Revelation means that we find ourselves to be valued rather than valuing and that all our values are transvaluated by the activity of a universal valuer. When a price is put upon our heads, which is not our price, when the unfairness of all the fair prices we have placed on things is shown up, when the great riches of God reduce our wealth to poverty, that is revelation. When we find out that we are no longer thinking him, but that he first thought us, that is revelation. Revelation is the emergence of the person on whose external garments and body we had looked as objects of our masterful and curious understanding. Revelation means that in our common history the fate that lowers over us as persons in our communities reveals itself to be a person in community with us. What this means for us cannot be expressed in the impersonal ways of creeds or other propositions but only in responsive acts of a personal character. we acknowledge revelation by no third person proposition, such as that there is a God, but only in the direct confession of the heart, "Thou art my God."... From this point forward we must listen for the remembered voice in all the sounds that assail our ears, and look for the remembered activity in all the actions of the world upon us. The God who reveals himself in Jesus Christ is now trusted and known in the contemporary God, revealing himself in every event, but we do not understand how we could tract his working in these happenings if he did not make himself known to us through the memory of Jesus Christ; nor do we know how we should be able to interpret all the words we read as words of God save by the aid of this Rosetta stone. (80 - 81)
Catholics who remember the discourses of the Pope Benedict will find the flavor of this passage very Benedictine in both senses of the term. Those who follow the way of Luigi Giussani find their spirit particularly familiar, for those of them who live in community, including the little band that managed Benedict's household and conduct the School of Community he attended, are known precisely as *Memores Domini*, those who strive to keep the Lord constantly in mind, and allow their own memory and mindfulness, personal and collective, painful and pleasing, on the surface of association or deeply hidden, to be transformed by their relationship with God in Christ, their participation in the ongoing incarnation of the Word of God: the God who is the author of our nature, and an incarnation that runs to meet the deepest desire of that nature with more that could have been imagined. What this means in the experience of living our life is well stated at the conclusion of Niebuhr's great work:
> The God who reveals himself in Jesus Christ meets no unresponsive will but the living spirit of men in search of all good. And he fulfills our need. Here is the one for whose sake all life and every life is worth living, even lives that seem bereft of beauty, of truth and of goodness. The glimpse of his great glory in the face of Jesus Christ, its reflections in the darkened mirrors of the saints' adorations intimate a God who is good beyond all that is good and fair beyond all fairness. Yet the goodness that shines upon us through the moment of revelation is not the glory or the goodness we had expected in our thoughts about deity. The essential goodness of the Father of our Lord Jesus Christ is the simple everyday goodness of love the value which belongs to a person rather [than] the value we find in an idea or a pattern; it is the goodness which exists as pure activity. He fulfills our expectation of the intrinsic good and yet this adorable goodness differs from everything we had expected, and puts our expectations to shame. We sought a good to love and were found by a good that loved us. And therewith all our religious ambitions are brought low, all our desires to be ministers of God are humbled; he is our minister. By that revelation we are convicted of having corrupted our religious life through our unquenchable desire to keep ourselves with our love of our good in the center of the picture. Here is the goodness that empties itself, and makes itself of no reputation, a goodness that is all outgoing, reserving nothing for itself, yet having all things. So we must begin to rethink all our definitions of deity and convert all our worship and our prayers. Revelation is not the development and not the elimination of our natural religion; it is the revolution of the religious life. (98 - 99)
But what does all this mean to one who stands outside the light of revelation, who relies on the reason of Western Civilization, the common sense of the founding Fathers? If believers and unbelievers are to take part in one community, what do we have to say to each other? This is the point of Benedict's challenge to the Muslim world, the question of what could make the libertine Doctor Franklin and the evangelical President Witherspoon active participants in the same foundational dialog. Niebuhr has an answer, and it is the same answer as Benedict:
> The pure reason does not need to be limited in order that room be made for faith, but faith emancipates the pure reason from the necessity of defending and guarding the interests of selves, which are now found to be established and guarded, not by nature, but by the God of revelation whose garment nature is. (91 - 92)
It is faith that liberates and, indeed, inspires us to invent, develop, explore, and test scientific understandings which would otherwise be too much for the vain imaginings of our all too human hearts:
> To know the person is to lose all sense of shame because of kinship with the clod and the ape. The mind is freed to pursue its knowledge of the external world disinterestedly not by the conviction that nothing matters, but by the faith that nothing God has made is mean or unclean. Hence any failure of Christians to develop scientific knowledge of the world is not an indication of their loyalty to the revealed God but of their unbelief. (90 - 91)
Seven going on eight decades after these words were published, ministers of "religion" are still attempting to prevent the teaching of ascertained facts of human biology in order to retain the authority of their own stupidly selectively literalistic reading of the Bible; some of the more advanced institutions of Evangelical learning defiantly profess a form of Calvinism in which some sort of theology remains the queen of the sciences in an unconstitutional monarchy, with no other discipline permitted its own proper autonomy and integrity; while in more numerous groves of Academus, even the Roman Catholic plantations, men and women of faith are quickly brushed off as obvious enemies of intellect.
My own mother, as I have said already, doubted that you can be a good Catholic and a real American at the same time. Pope Benedict warned his flock that they will not be good Catholics until they are Americans to the extent of acknowledging the law of nature and of nations as developed by Victoria (among others, some of them Scots), and aspiring to live in local, regional national and international communities under that law, in which the freedom and dignity of the human person are given the first priority. On the other hand I do not see how we can be real Americans without realizing that the aspirations of 1776 and 1789 are grounded in that natural law, and grew up as the fruit of a civilization in which the reason of Greece and Rome reached full maturity in the care of Mother Church, a church whose members, including the hierarchy, were not always consistently faithful to it, calling forth reformations, enlightenments, and even revolutions. I think we must all be Catholic at least in the wider sense of loyalty to that civilization, and our best way may well be to reappropriate the riches of the golden age of American philosophy and theology, of which the work of H. Richard Niebuhr is a small but important part.
Sources quoted: Edmund Burke, Impeachment of Warren Hastings before the House of Lords (numerous editions), eighth day. Joseph Ratzinger, *Principles of Catholic Theology*. San Fransisco: Ignatius, 1987. H. Richard Niebuhr, *The Meaning of Revelation* [1941]. Louisville: Westminster John Knox Press, 2006.
© FP Purcell
-

@ fd06f542:8d6d54cd
2025-03-28 02:14:43
{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/5ad7189d30c9b49aa61652d98ac7853217b7e445f863be09f9745c49df9f514c.webp","title":"Nostr protocol","author":"fiatjaf"}
-

@ 5d4b6c8d:8a1c1ee3
2025-04-05 14:11:31

Here's a fun little Rorschach Test for Stackers. Clearly there's a trend change during the pandemic, but when does it start and what is the most likely cause?
I'll reserve my commentary for the comment section.
originally posted at https://stacker.news/items/935188
-

@ ecda4328:1278f072
2025-03-25 10:00:52
**Kubernetes and Linux Swap: A Practical Perspective**
After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion.
---
### The Rationale for Disabling Swap
We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes.
With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion.
Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates.
---
### Theoretical Capability vs. Practical Deployment
Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly.
But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model:
- Memory **requests and limits** are declared explicitly.
- The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap).
- Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals.
So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity.
---
### Why Disable Swap in Kubernetes?
1. **Deterministic Failure > Degraded Performance**\
If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early.
2. **Transparency & Observability**\
With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically.
3. **Performance Consistency**\
Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits.
4. **Kubernetes Doesn’t Manage Swap Well**\
Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control.
5. **Statelessness is the Norm**\
Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state.
---
### "But Swap Can Be Useful..."
Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need:
- Fine-tuned `vm.swappiness`
- Memory pinning and cgroup-based control
- Swap-aware monitoring and alerting
- Custom kubelet/systemd integration
That's possible, but **not standard practice** — and for good reason.
---
### Future Considerations
Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments.
Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior.
Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet.
---
### Conclusion
Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability.
If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**.
-

@ 872982aa:8fb54cfe
2025-03-27 05:50:35
NIP-03
======
OpenTimestamps Attestations for Events
--------------------------------------
`draft` `optional`
This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event:
```json
{
"kind": 1040
"tags": [
["e", <event-id>, <relay-url>],
["alt", "opentimestamps attestation"]
],
"content": <base64-encoded OTS file data>
}
```
- The OpenTimestamps proof MUST prove the referenced `e` event id as its digest.
- The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context.
### Example OpenTimestamps proof verification flow
Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots):
```bash
~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify
> using an esplora server at https://blockstream.info/api
- sequence ending on block 810391 is valid
timestamp validated at block [810391]
```
-

@ a5142938:0ef19da3
2025-04-04 14:58:05
**Have you found a natural product? Share it here by commenting on this page!**
This site only lists durable-use products and objects. Consumables (food, cosmetics, fuels, etc.) are not included.
To be listed, the product must be made of natural materials.
👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/)
You can copy and paste the template below and fill in the information you have. Other contributors can complete any missing details.
Each piece of information added (name, material, link, shipping area, etc.) and validated is considered a contribution.
👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/)
---
### New product
- Product name :
- Product image (link):
- Short description:
- Categories:
- Brand or manufacturer:
- Composition (materials used, including unknown elements):
- Links to buy (and shipping area):
- Other information (place of manufacture, certifications…):
---
If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward.
👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/)
---
This article is published on [origin-nature.com](https://www.origin-nature.com/post/8adj-i_hk0gtzp_ul9k17/)
🌐 [Voir cet article en français](https://www.origine-nature.com/post/nicmc-eandjr_vcz4_hsr/)
-

@ 872982aa:8fb54cfe
2025-03-27 05:47:40
NIP-03
======
OpenTimestamps Attestations for Events
--------------------------------------
`draft` `optional`
This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event:
```json
{
"kind": 1040
"tags": [
["e", <event-id>, <relay-url>],
["alt", "opentimestamps attestation"]
],
"content": <base64-encoded OTS file data>
}
```
- The OpenTimestamps proof MUST prove the referenced `e` event id as its digest.
- The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context.
### Example OpenTimestamps proof verification flow
Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots):
```bash
~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify
> using an esplora server at https://blockstream.info/api
- sequence ending on block 810391 is valid
timestamp validated at block [810391]
```
 @ 68c90cf3:99458f5c
2025-04-04 16:06:10I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs. YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each. 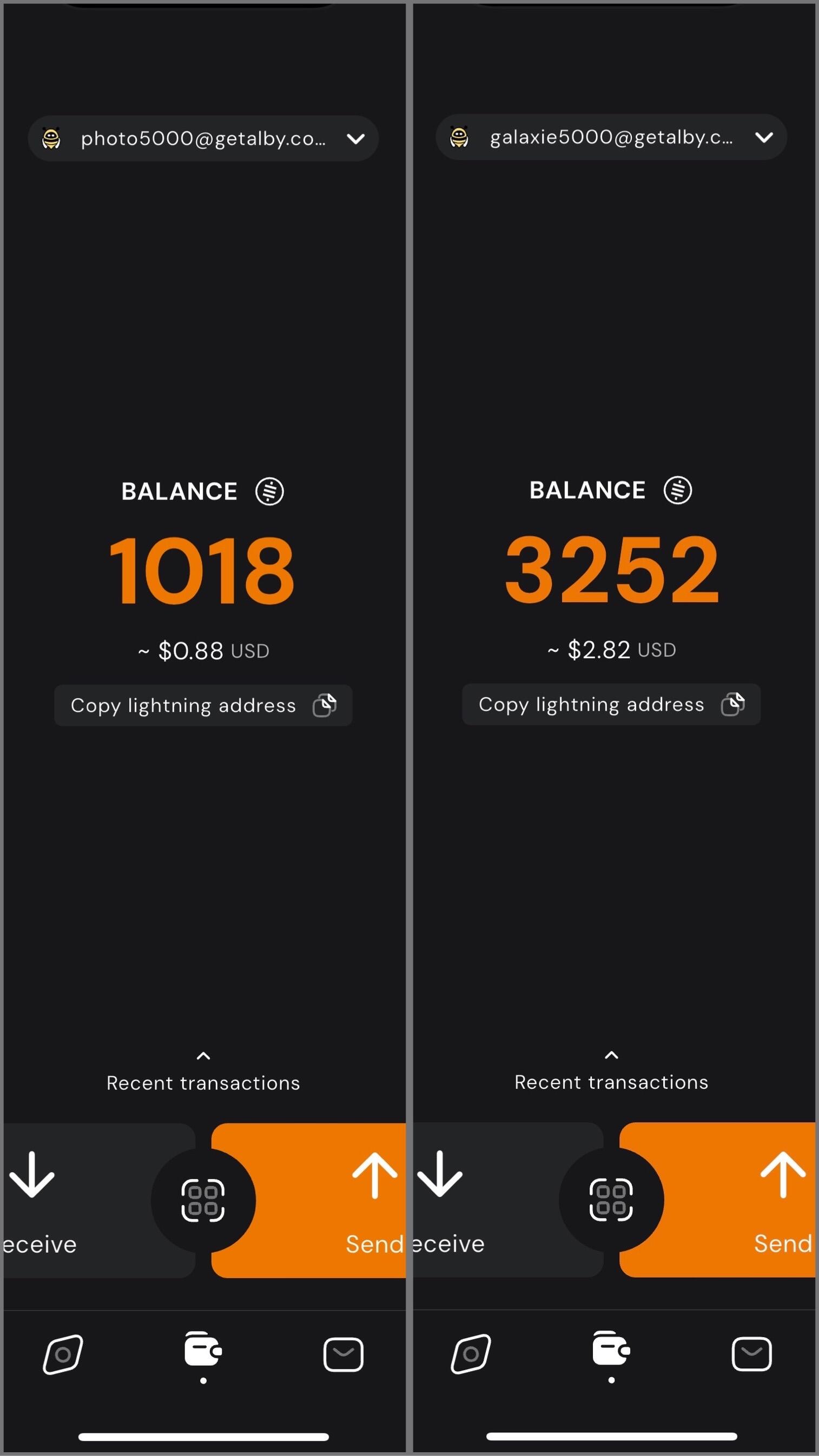 In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions. 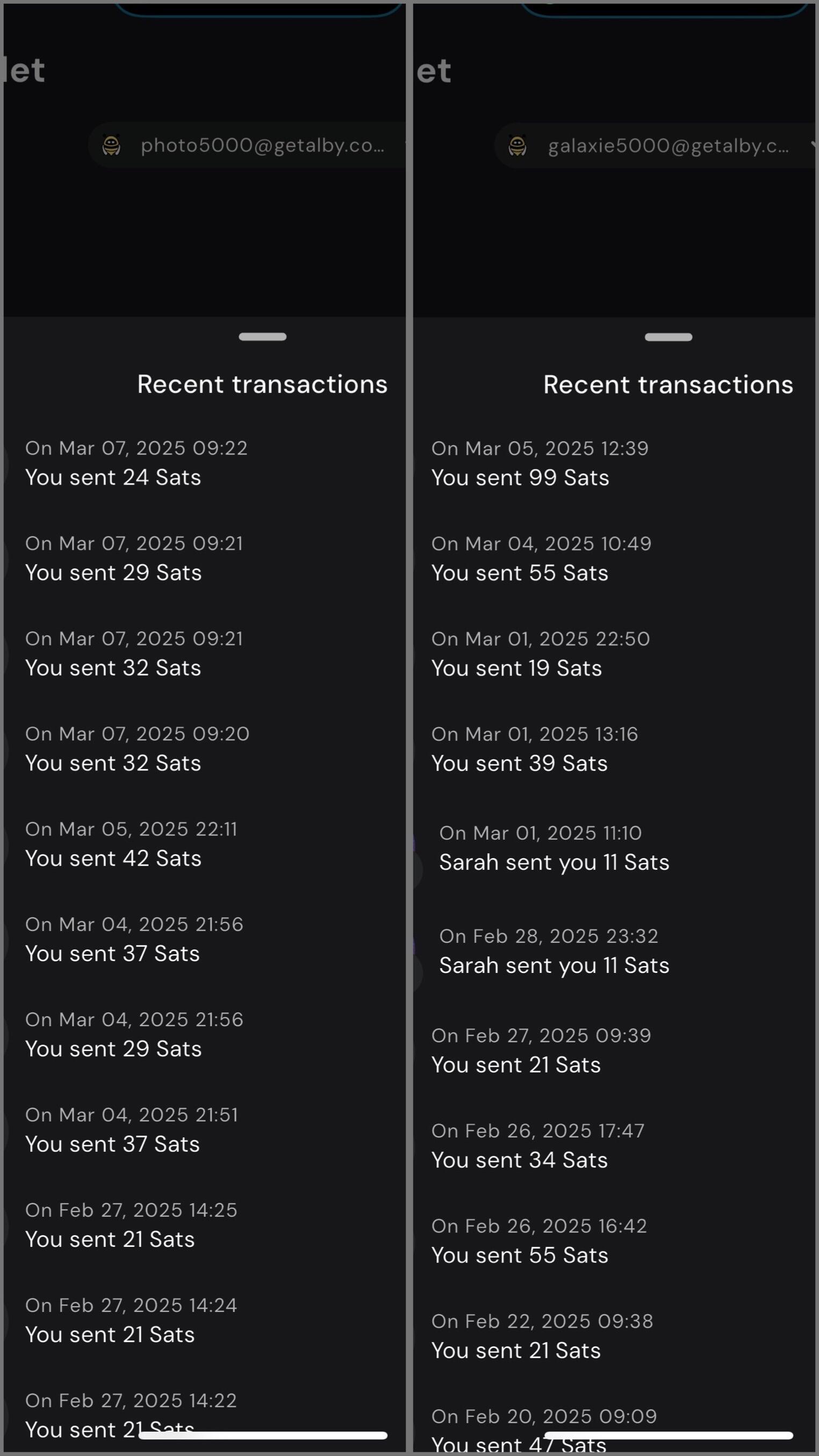 Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne. #YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr
@ 68c90cf3:99458f5c
2025-04-04 16:06:10I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs. YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each. 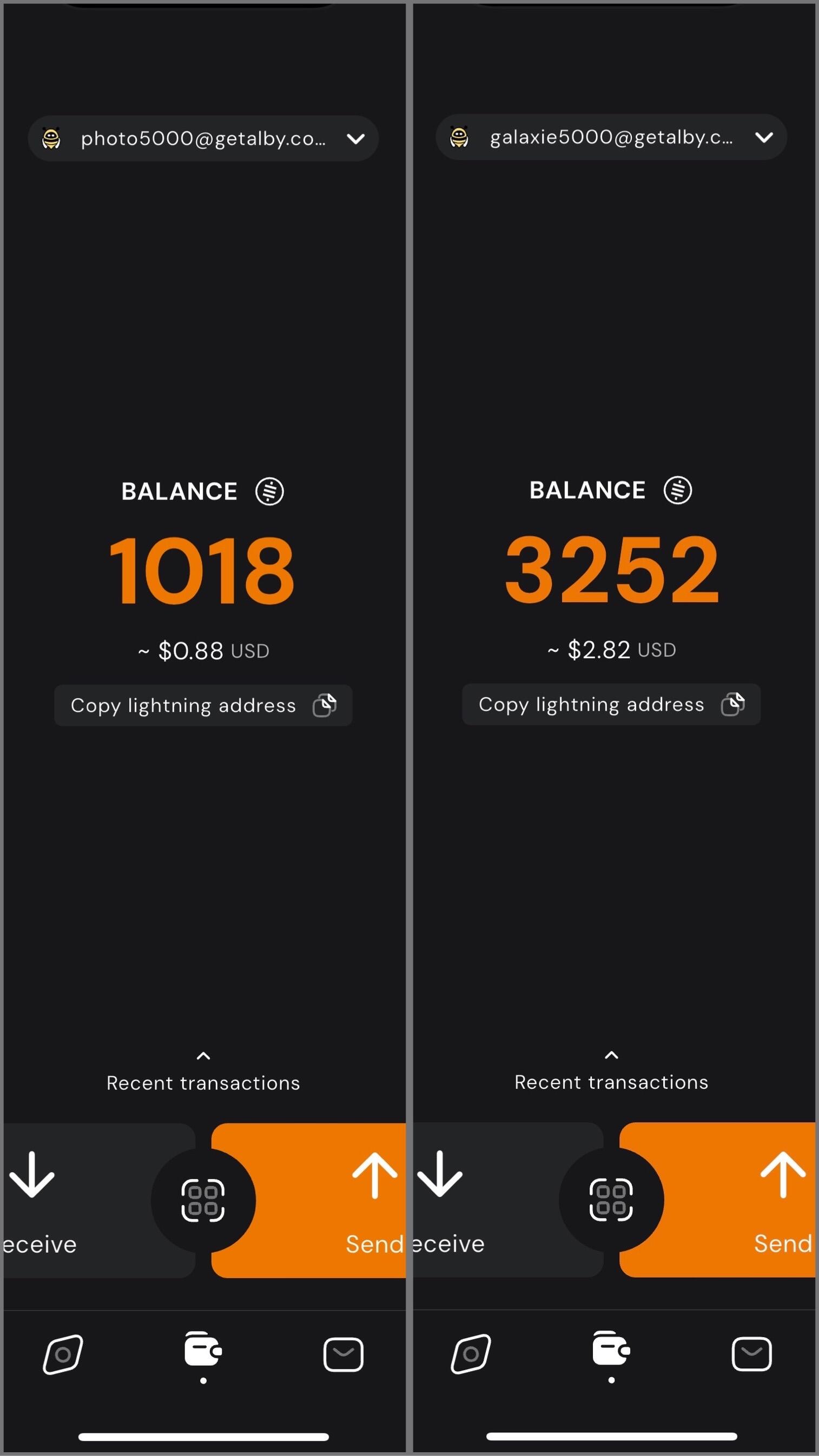 In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions. 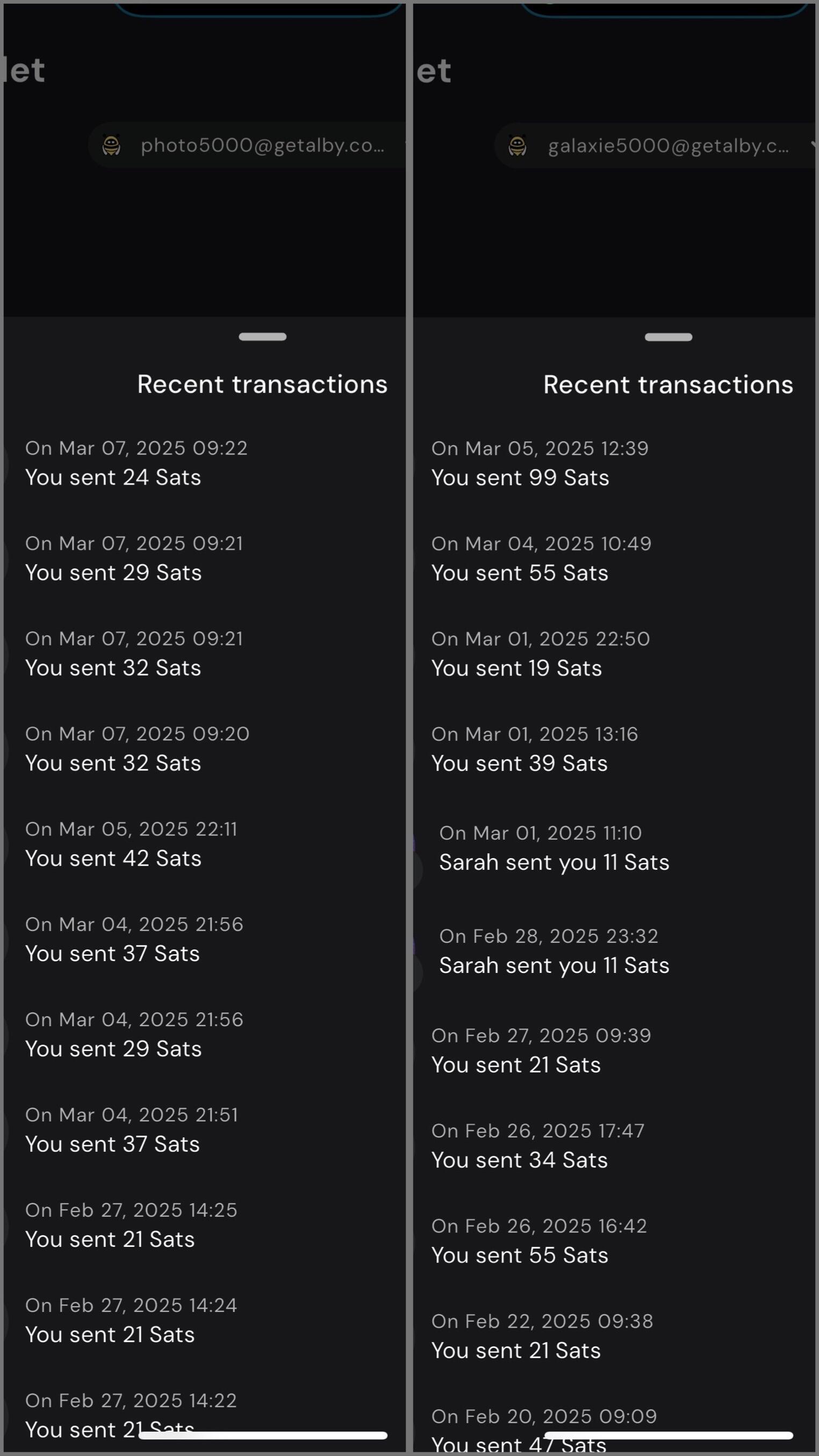 Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne. #YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr @ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2>
@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2> @ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p>
@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p> @ 9223d2fa:b57e3de7
2025-04-06 02:00:008183
@ 9223d2fa:b57e3de7
2025-04-06 02:00:008183 @ 2e941ad1:fac7c2d0
2025-04-05 22:20:54Unlocks: 40
@ 2e941ad1:fac7c2d0
2025-04-05 22:20:54Unlocks: 40 @ fd06f542:8d6d54cd
2025-04-04 13:58:19排名随机, 列表正在增加中。 1.) Cody Tseng ` https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl jumble作者` 2.)阿甘 `@agan0 0xchat.com canidae40@coinos.io https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce` 3.)joomaen `Follows you joomaen.com 95aebd@wallet.yakihonne.com npub1wlpfd84ym...lfgqp74qq0 #nobot https://joomaen.filegear-sg.me/ https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0` 4.)颜值精选官 `wasp@ok0.org 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好! https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz` 5.)6svjszwk `6svjszwk@ok0.org 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi #low-time-preference #anarcho-capitalism #libertarianism #bitcoin #monero https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk` 6.)𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳 `everyday@iris.to 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。 黑暗森林时代,当好小透明。 bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke` 7.) nostr_cn_dev `npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash npub1l5r02s4ud...2nxsvum9jm Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm`
@ fd06f542:8d6d54cd
2025-04-04 13:58:19排名随机, 列表正在增加中。 1.) Cody Tseng ` https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl jumble作者` 2.)阿甘 `@agan0 0xchat.com canidae40@coinos.io https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce` 3.)joomaen `Follows you joomaen.com 95aebd@wallet.yakihonne.com npub1wlpfd84ym...lfgqp74qq0 #nobot https://joomaen.filegear-sg.me/ https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0` 4.)颜值精选官 `wasp@ok0.org 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好! https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz` 5.)6svjszwk `6svjszwk@ok0.org 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi #low-time-preference #anarcho-capitalism #libertarianism #bitcoin #monero https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk` 6.)𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳 `everyday@iris.to 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。 黑暗森林时代,当好小透明。 bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke` 7.) nostr_cn_dev `npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash npub1l5r02s4ud...2nxsvum9jm Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm` @ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
@ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/ @ ec9bd746:df11a9d0
2025-04-06 08:06:08## 🌍 Time Window: 🕘 **When**: Every even week on Sunday at 9:00 PM CET 🗺️ **Where**: https://cornychat.com/eurocorn **Start:** 21:00 CET (Prague, UTC+1) **End:** approx. 02:00 CET (Prague, UTC+1, next day) **Duration:** usually 5+ hours. | Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | **Europe (CET, Prague)** 🇨🇿🇩🇪 | **21:00–02:00 CET** | ✅ Very Good; evening & night | | **East Coast North America (EST)** 🇺🇸🇨🇦 | **15:00–20:00 EST** | ✅ Very Good; afternoon & early evening | | **West Coast North America (PST)** 🇺🇸🇨🇦 | **12:00–17:00 PST** | ✅ Very Good; midday & afternoon | | **Central America (CST)** 🇲🇽🇨🇷🇬🇹 | **14:00–19:00 CST** | ✅ Very Good; afternoon & evening | | **South America West (Peru/Colombia PET/COT)** 🇵🇪🇨🇴 | **15:00–20:00 PET/COT** | ✅ Very Good; afternoon & evening | | **South America East (Brazil/Argentina/Chile, BRT/ART/CLST)** 🇧🇷🇦🇷🇨🇱 | **17:00–22:00 BRT/ART/CLST** | ✅ Very Good; early evening | | **United Kingdom/Ireland (GMT)** 🇬🇧🇮🇪 | **20:00–01:00 GMT** | ✅ Very Good; evening hours (midnight convenient) | | **Eastern Europe (EET)** 🇷🇴🇬🇷🇺🇦 | **22:00–03:00 EET** | ✅ Good; late evening & early night (slightly late) | | **Africa (South Africa, SAST)** 🇿🇦 | **22:00–03:00 SAST** | ✅ Good; late evening & overnight (late-night common) | | **New Zealand (NZDT)** 🇳🇿 | **09:00–14:00 NZDT (next day)** | ✅ Good; weekday morning & afternoon | | **Australia (AEDT, Sydney)** 🇦🇺 | **07:00–12:00 AEDT (next day)** | ✅ Good; weekday morning to noon | | **East Africa (Kenya, EAT)** 🇰🇪 | **23:00–04:00 EAT** | ⚠️ Slightly late (night hours; late night common) | | **Russia (Moscow, MSK)** 🇷🇺 | **23:00–04:00 MSK** | ⚠️ Slightly late (join at start is fine, very late night) | | **Middle East (UAE, GST)** 🇦🇪🇴🇲 | **00:00–05:00 GST (next day)** | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | **Japan/Korea (JST/KST)** 🇯🇵🇰🇷 | **05:00–10:00 JST/KST (next day)** | ⚠️ Early; convenient joining from ~07:00 onwards possible | | **China (Beijing, CST)** 🇨🇳 | **04:00–09:00 CST (next day)** | ❌ Challenging; very early morning start (better ~07:00 onwards) | | **India (IST)** 🇮🇳 | **01:30–06:30 IST (next day)** | ❌ Very challenging; overnight timing typically difficult| ---
@ ec9bd746:df11a9d0
2025-04-06 08:06:08## 🌍 Time Window: 🕘 **When**: Every even week on Sunday at 9:00 PM CET 🗺️ **Where**: https://cornychat.com/eurocorn **Start:** 21:00 CET (Prague, UTC+1) **End:** approx. 02:00 CET (Prague, UTC+1, next day) **Duration:** usually 5+ hours. | Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | **Europe (CET, Prague)** 🇨🇿🇩🇪 | **21:00–02:00 CET** | ✅ Very Good; evening & night | | **East Coast North America (EST)** 🇺🇸🇨🇦 | **15:00–20:00 EST** | ✅ Very Good; afternoon & early evening | | **West Coast North America (PST)** 🇺🇸🇨🇦 | **12:00–17:00 PST** | ✅ Very Good; midday & afternoon | | **Central America (CST)** 🇲🇽🇨🇷🇬🇹 | **14:00–19:00 CST** | ✅ Very Good; afternoon & evening | | **South America West (Peru/Colombia PET/COT)** 🇵🇪🇨🇴 | **15:00–20:00 PET/COT** | ✅ Very Good; afternoon & evening | | **South America East (Brazil/Argentina/Chile, BRT/ART/CLST)** 🇧🇷🇦🇷🇨🇱 | **17:00–22:00 BRT/ART/CLST** | ✅ Very Good; early evening | | **United Kingdom/Ireland (GMT)** 🇬🇧🇮🇪 | **20:00–01:00 GMT** | ✅ Very Good; evening hours (midnight convenient) | | **Eastern Europe (EET)** 🇷🇴🇬🇷🇺🇦 | **22:00–03:00 EET** | ✅ Good; late evening & early night (slightly late) | | **Africa (South Africa, SAST)** 🇿🇦 | **22:00–03:00 SAST** | ✅ Good; late evening & overnight (late-night common) | | **New Zealand (NZDT)** 🇳🇿 | **09:00–14:00 NZDT (next day)** | ✅ Good; weekday morning & afternoon | | **Australia (AEDT, Sydney)** 🇦🇺 | **07:00–12:00 AEDT (next day)** | ✅ Good; weekday morning to noon | | **East Africa (Kenya, EAT)** 🇰🇪 | **23:00–04:00 EAT** | ⚠️ Slightly late (night hours; late night common) | | **Russia (Moscow, MSK)** 🇷🇺 | **23:00–04:00 MSK** | ⚠️ Slightly late (join at start is fine, very late night) | | **Middle East (UAE, GST)** 🇦🇪🇴🇲 | **00:00–05:00 GST (next day)** | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | **Japan/Korea (JST/KST)** 🇯🇵🇰🇷 | **05:00–10:00 JST/KST (next day)** | ⚠️ Early; convenient joining from ~07:00 onwards possible | | **China (Beijing, CST)** 🇨🇳 | **04:00–09:00 CST (next day)** | ❌ Challenging; very early morning start (better ~07:00 onwards) | | **India (IST)** 🇮🇳 | **01:30–06:30 IST (next day)** | ❌ Very challenging; overnight timing typically difficult| --- @ fd06f542:8d6d54cd
2025-04-04 13:37:59- [首页](/readme.md) - [国人开发者](/01.md) - [中文用户列表](/02.md)
@ fd06f542:8d6d54cd
2025-04-04 13:37:59- [首页](/readme.md) - [国人开发者](/01.md) - [中文用户列表](/02.md) @ fd06f542:8d6d54cd
2025-04-04 13:34:38## 国内开发者作品展 ### jumble.social 作品: https://jumble.social/ 其他作品 : Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️ Building 👨💻: https://github.com/CodyTseng/jumble https://github.com/CodyTseng/nostr-relay-tray https://github.com/CodyTseng/danmakustr https://github.com/CodyTseng/nostr-relay-nestjs https://github.com/CodyTseng/nostr-relay https://github.com/CodyTseng ### nostrbook.com 作品: https://nostrbook.com - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge ### nostrmo A nostr dev. #Nostrmo A client support all platform. #Nowser A nostr signing project. #CacheRelay A nostr cache relay peject. #cfrelay A nostr relay base on cloudflare wokers. A nostr note timing send service. https://sendbox.nostrmo.com/ https://github.com/haorendashu/nostrmo ### 0xchat 作者: wcat w783@0xchat.com www.0xchat.com Building for 0xchat www.0xchat.com Secure Chat built on Nostr App Store: https://apps.apple.com/app/0xchat/id1637607169 TestFlight: https://testflight.apple.com/join/AjdJFBmU Google play: https://play.google.com/store/apps/details?id=com.oxchat.nostr
@ fd06f542:8d6d54cd
2025-04-04 13:34:38## 国内开发者作品展 ### jumble.social 作品: https://jumble.social/ 其他作品 : Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️ Building 👨💻: https://github.com/CodyTseng/jumble https://github.com/CodyTseng/nostr-relay-tray https://github.com/CodyTseng/danmakustr https://github.com/CodyTseng/nostr-relay-nestjs https://github.com/CodyTseng/nostr-relay https://github.com/CodyTseng ### nostrbook.com 作品: https://nostrbook.com - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 https://www.duozhutuan.com nostrhttp demo https://github.com/duozhutuan/NostrBridge ### nostrmo A nostr dev. #Nostrmo A client support all platform. #Nowser A nostr signing project. #CacheRelay A nostr cache relay peject. #cfrelay A nostr relay base on cloudflare wokers. A nostr note timing send service. https://sendbox.nostrmo.com/ https://github.com/haorendashu/nostrmo ### 0xchat 作者: wcat w783@0xchat.com www.0xchat.com Building for 0xchat www.0xchat.com Secure Chat built on Nostr App Store: https://apps.apple.com/app/0xchat/id1637607169 TestFlight: https://testflight.apple.com/join/AjdJFBmU Google play: https://play.google.com/store/apps/details?id=com.oxchat.nostr @ 592295cf:413a0db9
2025-04-05 07:26:23## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago # 1. ### Nostr's adoption thesis ### The less you define, the more you imply ### by Wouter Constant ## 2. ### Dutch Bitcoiner ### AntiHashedPodcast ### Writing Book about nostr 00:40 ## 3. ### What this presentation about ### A protocols design includes initself a thesis ### on protocol adoption, due to underlying assumptions 1:17 ## 4. ### Examples ### Governments/Academic: Pubhubs (Matrix) ### Bussiness: Bluesky ### Foss: Nostr 1:58 ## 5. ### What constitutes minimal viability? ### Pubhubs (Matrix): make is "safe" for user ### Bluesky: liability and monetization ### Foss: Simpel for developer 4:03 ## 6. ### The Point of Nostr ### Capture network effects through interoperability 4:43 ## 7. ## Three assumptions ### The direction is workable ### Method is workable ### Motivation and means are sufficient 5:27 ## 8. ## Assumption 1 ### The asymmetric cryptography paradigm is a good idea 6:16 ## 9. ### Nostr is a exponent of the key-pair paradigm. ### And Basicly just that. 6.52 ## 10. ### Keys suck ### Protect a secret that you are supposed use all the time. 7:37 ## 11. ## Assumption two ### The unaddressed things will be figured out within a 'meta-design consensus' 8:11 ## 12. ### Nostr's base protocol is not minimally viable for anything, except own development. 8:25 ## 13. ### Complexity leads to capture; ### i.e. free and open in the name, ### controlled in pratice 9:54 ## 14. ## Meta-design consensus ### Buildings things 'note centric' mantains interoperability. 11:51 ## 15. ## Assumption three ### the nightmare is scary; ### the cream is appealing. 12:41 ## 16. ### Get it minimally viable, ### for whatever target, ### such that it is not a waste of time. 13:23 ## 17. ## Summarize ### We are in a nightmare. ### Assume key/signature are the way out. ### Assume we can Maintain an open stardand while manifesting the dream. ### Assume we are motivated enought to bootstrap this to adulthood. 14:01 ## 18. ### We want this, ### we can do this, ### because we have to. 14:12 ## Thank you for contribuiting [Edit] Note for audio presentation nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
@ 592295cf:413a0db9
2025-04-05 07:26:23## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago # 1. ### Nostr's adoption thesis ### The less you define, the more you imply ### by Wouter Constant ## 2. ### Dutch Bitcoiner ### AntiHashedPodcast ### Writing Book about nostr 00:40 ## 3. ### What this presentation about ### A protocols design includes initself a thesis ### on protocol adoption, due to underlying assumptions 1:17 ## 4. ### Examples ### Governments/Academic: Pubhubs (Matrix) ### Bussiness: Bluesky ### Foss: Nostr 1:58 ## 5. ### What constitutes minimal viability? ### Pubhubs (Matrix): make is "safe" for user ### Bluesky: liability and monetization ### Foss: Simpel for developer 4:03 ## 6. ### The Point of Nostr ### Capture network effects through interoperability 4:43 ## 7. ## Three assumptions ### The direction is workable ### Method is workable ### Motivation and means are sufficient 5:27 ## 8. ## Assumption 1 ### The asymmetric cryptography paradigm is a good idea 6:16 ## 9. ### Nostr is a exponent of the key-pair paradigm. ### And Basicly just that. 6.52 ## 10. ### Keys suck ### Protect a secret that you are supposed use all the time. 7:37 ## 11. ## Assumption two ### The unaddressed things will be figured out within a 'meta-design consensus' 8:11 ## 12. ### Nostr's base protocol is not minimally viable for anything, except own development. 8:25 ## 13. ### Complexity leads to capture; ### i.e. free and open in the name, ### controlled in pratice 9:54 ## 14. ## Meta-design consensus ### Buildings things 'note centric' mantains interoperability. 11:51 ## 15. ## Assumption three ### the nightmare is scary; ### the cream is appealing. 12:41 ## 16. ### Get it minimally viable, ### for whatever target, ### such that it is not a waste of time. 13:23 ## 17. ## Summarize ### We are in a nightmare. ### Assume key/signature are the way out. ### Assume we can Maintain an open stardand while manifesting the dream. ### Assume we are motivated enought to bootstrap this to adulthood. 14:01 ## 18. ### We want this, ### we can do this, ### because we have to. 14:12 ## Thank you for contribuiting [Edit] Note for audio presentation nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke @ fd06f542:8d6d54cd
2025-04-04 02:39:25## 使用nostrbook.com网站 登录和创建用户:  登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。 注册:  可以点击红标位置 生成你的账户。 “确定” 完成注册。 ## 创建书籍 ### 封面的上传  创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。 或者点击浏览 本地图片文件。 ### 标题和作者 正常填写就可以。 书的作者和上传文件人没有一一绑定。 ## 写书  创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。 ### 列出你创建的所有的书籍  点击图标,就可以进入开始写作了。例如《nostrbook站点日记》  如图所示有4个部分 1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出” 2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。 3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。 4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。
@ fd06f542:8d6d54cd
2025-04-04 02:39:25## 使用nostrbook.com网站 登录和创建用户:  登录按钮 ,可以粘贴 已有的 nsec....账号,完成登录。 注册:  可以点击红标位置 生成你的账户。 “确定” 完成注册。 ## 创建书籍 ### 封面的上传  创建书籍,可以用 微信截图 后直接 ctrl+v. 粘贴即可。 或者点击浏览 本地图片文件。 ### 标题和作者 正常填写就可以。 书的作者和上传文件人没有一一绑定。 ## 写书  创建完成后就可以写书了,写书入口在 登录处 “我的书籍” 。点进去会出现你创建的书籍。选择一本就可以写书了。 ### 列出你创建的所有的书籍  点击图标,就可以进入开始写作了。例如《nostrbook站点日记》  如图所示有4个部分 1. (1)关闭按钮,点击就退出编辑,这时候他会提示你保存,如果不需要保存退出,点击 “不保存退出” 2. (2)`大纲` 是编写 你书籍的大纲,这个参考 docsify文档 下面会有例子。 `时间排列`是 你所有为本书写的章节。但是有些章节你可能废弃了,或者暂时不想展示,都会存在 时间排列里面,就是按照你编写的时间倒序排列的。`草稿` 是你暂时存储的内容,没有上传到网络,存在你本地浏览器的缓存里面。 3. (3)这个部分看到的就是你的章节列表,当让你第一次来的这个地方是空的。`新增章节` 下一次就会有内容了。 4. (4)文件名,是我们存储章节的唯一标识。 `readme.md` 和`_sidebar.md` 是系统默认必须有的。因为docsify技术默认需要这2个。 @ 57d1a264:69f1fee1
2025-04-05 06:58:25**Summary** We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment. **Responsibilities** - Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity. - Develop digital assets for marketing, social media, website, and app. - Work within brand guidelines while exploring ways to evolve and strengthen our visual style. **Requirements** - 2+ years of experience in graphic design, with a strong focus on illustration. - Ability to help define and develop a cohesive visual style for the brand. - Proficiency in Adobe products. - Experience with Figma is a plus. - Strong organizational skills—your layers and files should be neatly labeled. - Clear communication and collaboration skills to work effectively with the team. - Located in LATAM Please attach a link to your portfolio to showcase your work when applying. [APPLY HERE](https://jan3.com/contact/) originally posted at https://stacker.news/items/935007
@ 57d1a264:69f1fee1
2025-04-05 06:58:25**Summary** We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment. **Responsibilities** - Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity. - Develop digital assets for marketing, social media, website, and app. - Work within brand guidelines while exploring ways to evolve and strengthen our visual style. **Requirements** - 2+ years of experience in graphic design, with a strong focus on illustration. - Ability to help define and develop a cohesive visual style for the brand. - Proficiency in Adobe products. - Experience with Figma is a plus. - Strong organizational skills—your layers and files should be neatly labeled. - Clear communication and collaboration skills to work effectively with the team. - Located in LATAM Please attach a link to your portfolio to showcase your work when applying. [APPLY HERE](https://jan3.com/contact/) originally posted at https://stacker.news/items/935007 @ fd06f542:8d6d54cd
2025-04-02 08:04:17{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/1dd58d181d40edb7df942b5b16be3f82e95348a471d5a3620a9585f0af784fee.webp","title":"nostr资源收集","author":"nostrbook"}
@ fd06f542:8d6d54cd
2025-04-02 08:04:17{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/1dd58d181d40edb7df942b5b16be3f82e95348a471d5a3620a9585f0af784fee.webp","title":"nostr资源收集","author":"nostrbook"} @ fd06f542:8d6d54cd
2025-04-02 02:55:14- [首页](/readme.md) - [第一章、开发者指南](/01.md) - [第二章、使用教程](/02.md)
@ fd06f542:8d6d54cd
2025-04-02 02:55:14- [首页](/readme.md) - [第一章、开发者指南](/01.md) - [第二章、使用教程](/02.md) @ 57d1a264:69f1fee1
2025-04-05 06:47:55**Location:** Remote (Austria) **Area:** Graphics and communication design **Pay:** 37,500 € to 50,000 € / year Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin. 👋 About the role As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas. **tasks** - Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials - Creation of individual content (posts, stories, banners, ads) for social media - Planning and development of campaigns to strengthen the brand presence - Further development of the existing corporate design support in the area of content management (website, blog) **qualification** - Completed training or studies in graphic design - At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management - Safe use of design tools such as Figma, Adobe Creative Suite - Experience in creating social media content and maintaining channels - Creativity, good communication skills and team spirit - Very good knowledge of German and English - Knowledge of Bitcoin is desirable **Benefits** - Offsites with the team in exciting places - Flexible working hours in a company that relies on remote work - Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation - Buy Bitcoin without fees! 21 Premium! - Gross annual salary & potential share options for outstanding performance / bonus payments **📝 Interview process** _How do I apply?_ Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect. By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application! _⁇ 京 Resume Review_ Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...) _📞 Exploratory call_ We discuss what appeals to you about this role and ask you a few questions about your previous experiences _👬 On-Site Deep Dive_ During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role. _👍 Time for a decision!_ [APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner) originally posted at https://stacker.news/items/935004
@ 57d1a264:69f1fee1
2025-04-05 06:47:55**Location:** Remote (Austria) **Area:** Graphics and communication design **Pay:** 37,500 € to 50,000 € / year Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin. 👋 About the role As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas. **tasks** - Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials - Creation of individual content (posts, stories, banners, ads) for social media - Planning and development of campaigns to strengthen the brand presence - Further development of the existing corporate design support in the area of content management (website, blog) **qualification** - Completed training or studies in graphic design - At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management - Safe use of design tools such as Figma, Adobe Creative Suite - Experience in creating social media content and maintaining channels - Creativity, good communication skills and team spirit - Very good knowledge of German and English - Knowledge of Bitcoin is desirable **Benefits** - Offsites with the team in exciting places - Flexible working hours in a company that relies on remote work - Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation - Buy Bitcoin without fees! 21 Premium! - Gross annual salary & potential share options for outstanding performance / bonus payments **📝 Interview process** _How do I apply?_ Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect. By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application! _⁇ 京 Resume Review_ Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...) _📞 Exploratory call_ We discuss what appeals to you about this role and ask you a few questions about your previous experiences _👬 On-Site Deep Dive_ During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role. _👍 Time for a decision!_ [APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner) originally posted at https://stacker.news/items/935004 @ f3328521:a00ee32a
2025-04-06 08:51:05*Notes from the Inaugural Muslim Bitcoin Summit Nostr Workshop.* 04.06.25 Dallas, TX # What is Nostr? > “Notes and Other Stuff Transmitted by Relays” ~ fiatjaf Nostr is an open protocol that is a censorship-resistant, global "social" network. It doesn't rely on any trusted central server (has resilient decentralization), and is based on cryptographic keys and signatures (so it is tamperproof). The initial description of the idea can be found at https://fiatjaf.com/nostr.html. ## Digital Sovereignty > “The first step towards establishing any type of Digital Sovereignty is to consider migration away from infrastructure and networks that are saturated with malevolent surveillance… there must be a simple recognition that anything sustainable from an Islamic perspective cannot be built on the platforms of Meta, Google or Amazon.” ~ [Ibn Maghreb](https://theiqrafiles.com/notes-on-digital-sovereignty/) Palestine has become the litmus test for censorship in social media: - X (formerly Twitter) - [Musk openly supports Zionism](https://english.almayadeen.net/articles/opinion/how-elon-musk-became-zionist--from-free-speech-absolutist-to) - Meta (FB, IG, WhatsApp) - [Project Lavender](https://blog.paulbiggar.com/meta-and-lavender/) - Google (YouTube) - [Project Nimbus](https://www.thenation.com/article/activism/google-firings-gaza-project-nimbus/) - Microsoft (LI) - [BDS “No Azure for Apartheid” campaign](https://www.bdsmovement.net/microsoft) These are just a few examples of the barrier for a muslim narrative in fiat social media. To build unstoppable resistance we must move away from the platform and address the issue at the protocol level. ## Nostr Protocol Explained 1. **Relays:** Backend servers that store and broadcast data. Anyone can run one. Currently over 1k relays across over 50 countries. 2. **Clients:** Platforms built for graphical user interface with Nostr. Anyone can build these and most are interoperable. 3. **Key Cryptography:** public and private keys 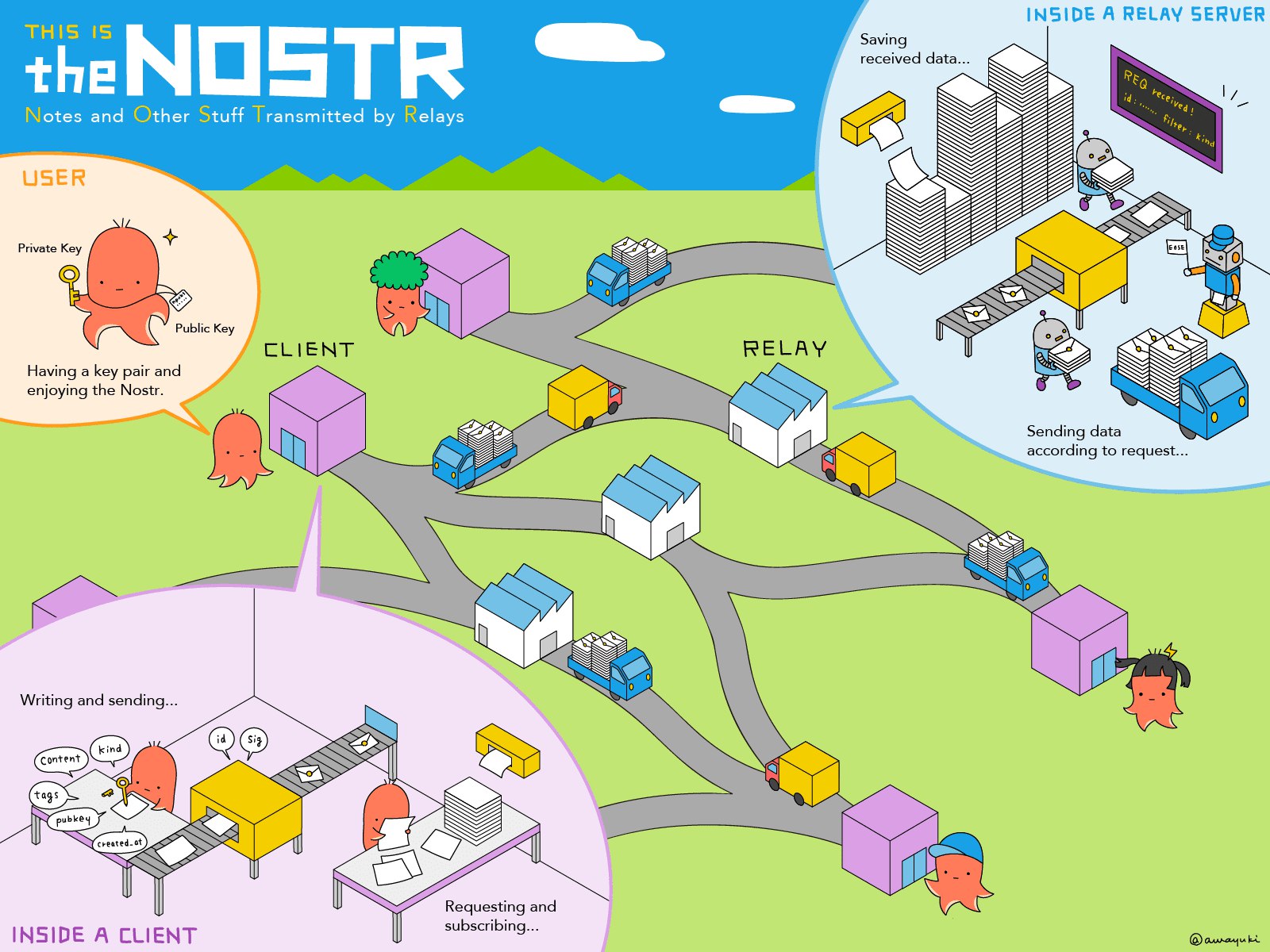 *Simple video explaination: [Nostr in less than 10 minutes!](https://youtu.be/Q6f6bdKWqF8)* ### Nostr's Key Features: - No Ownership - No CEO, board of directors, foundation, etc. - No Ads, No Big Data Collection - Users are not a product. - No Algorithms - Less drama, less depressing content. - Uncensorability - Not your keys, not your posts. - SEO - clean ```dofollow``` links for “Google Juice”. - Zaps! - BTC/Lightning integration. > “This is really really important in the age of AI where in a few years you are not going to know the difference between something that is real and something that is fake. We need technologies that you can actually sign and you have the authenticity to do so, and only you, to do that.” ~ [Jack Dorsey](https://youtu.be/0YDj1QdL2Zs) ## Getting Started On Nostr ### Nostr 101: **[A Beginners Guide To Nostr](https://mslmdvlpmnt.com/a-beginners-guide-to-nostr-2025/)** **Top Recommended Client:** [Yakihonne](https://yakihonne.com/) *Other popular options: (web) [Nostrudel](https://nostrudel.ninja/) (iOS) [Damus](https://damus.io/) (Android) [Amethyst](https://www.amethyst.social/)* **Top Recommended Wallet:** [Coinos](https://coinos.io/) *Other popular options: [Primal Wallet](https://primal.net/home) [AlbyHub](https://albyhub.com/) [Zeus](https://zeusln.com/) (pending NWC integration)* ### Highlights From The Nostr Ecosystem: Other Clients: [Olas](https://olas.app/) (photos) [Habla](https://habla.news/) (blogging) [Zap.Stream](https://zap.stream/) (video) Chat: [0xchat](https://0xchat.com/#/) [KeyChat](https://www.keychat.io/) [Flotilla](https://flotilla.social/) Shopping: [Plebeian Market](https://plebeian.market/) [Shopstr](https://shopstr.store/) Podcasting 2.0: [Fountain](https://fountain.fm/) [Wavlake](https://wavlake.com/) Workspace Tools: [Listr](https://listr.lol/) [Formstr](https://formstr.app/#/dashboard) [Docstr](https://docstr.app/) [Nostr.Build](https://nostr.build/) Signers: [Nos2X](https://nostrapps.com/nos2x) [Nsec.app](https://nsec.app/) ## Footnote [Find Muslims on Nostr](https://listr.lol/npub175nul9cvufswwsnpy99lvyhg7ad9nkccxhkhusznxfkr7e0zxthql9g6w0/30000/naddr1qq4xc6tnw3ez6efkxcun2cfkxqknzc348ykngcfnxvknsepsxukkxd33vc6x2vejv9jkgdqpp4mhxue69uhkummn9ekx7mqpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqg5waehxw309aex2mrp0yhxgctdw4eju6t0qgs02f70juxwyc88gfsjzjlkzt50wkjemvvrtmt7gpfnymplvh3r9msrqsqqqafsqfgqku) | [#staySAIF](https://saif.systems/articles/spiritual-opsec-guide)
@ f3328521:a00ee32a
2025-04-06 08:51:05*Notes from the Inaugural Muslim Bitcoin Summit Nostr Workshop.* 04.06.25 Dallas, TX # What is Nostr? > “Notes and Other Stuff Transmitted by Relays” ~ fiatjaf Nostr is an open protocol that is a censorship-resistant, global "social" network. It doesn't rely on any trusted central server (has resilient decentralization), and is based on cryptographic keys and signatures (so it is tamperproof). The initial description of the idea can be found at https://fiatjaf.com/nostr.html. ## Digital Sovereignty > “The first step towards establishing any type of Digital Sovereignty is to consider migration away from infrastructure and networks that are saturated with malevolent surveillance… there must be a simple recognition that anything sustainable from an Islamic perspective cannot be built on the platforms of Meta, Google or Amazon.” ~ [Ibn Maghreb](https://theiqrafiles.com/notes-on-digital-sovereignty/) Palestine has become the litmus test for censorship in social media: - X (formerly Twitter) - [Musk openly supports Zionism](https://english.almayadeen.net/articles/opinion/how-elon-musk-became-zionist--from-free-speech-absolutist-to) - Meta (FB, IG, WhatsApp) - [Project Lavender](https://blog.paulbiggar.com/meta-and-lavender/) - Google (YouTube) - [Project Nimbus](https://www.thenation.com/article/activism/google-firings-gaza-project-nimbus/) - Microsoft (LI) - [BDS “No Azure for Apartheid” campaign](https://www.bdsmovement.net/microsoft) These are just a few examples of the barrier for a muslim narrative in fiat social media. To build unstoppable resistance we must move away from the platform and address the issue at the protocol level. ## Nostr Protocol Explained 1. **Relays:** Backend servers that store and broadcast data. Anyone can run one. Currently over 1k relays across over 50 countries. 2. **Clients:** Platforms built for graphical user interface with Nostr. Anyone can build these and most are interoperable. 3. **Key Cryptography:** public and private keys  *Simple video explaination: [Nostr in less than 10 minutes!](https://youtu.be/Q6f6bdKWqF8)* ### Nostr's Key Features: - No Ownership - No CEO, board of directors, foundation, etc. - No Ads, No Big Data Collection - Users are not a product. - No Algorithms - Less drama, less depressing content. - Uncensorability - Not your keys, not your posts. - SEO - clean ```dofollow``` links for “Google Juice”. - Zaps! - BTC/Lightning integration. > “This is really really important in the age of AI where in a few years you are not going to know the difference between something that is real and something that is fake. We need technologies that you can actually sign and you have the authenticity to do so, and only you, to do that.” ~ [Jack Dorsey](https://youtu.be/0YDj1QdL2Zs) ## Getting Started On Nostr ### Nostr 101: **[A Beginners Guide To Nostr](https://mslmdvlpmnt.com/a-beginners-guide-to-nostr-2025/)** **Top Recommended Client:** [Yakihonne](https://yakihonne.com/) *Other popular options: (web) [Nostrudel](https://nostrudel.ninja/) (iOS) [Damus](https://damus.io/) (Android) [Amethyst](https://www.amethyst.social/)* **Top Recommended Wallet:** [Coinos](https://coinos.io/) *Other popular options: [Primal Wallet](https://primal.net/home) [AlbyHub](https://albyhub.com/) [Zeus](https://zeusln.com/) (pending NWC integration)* ### Highlights From The Nostr Ecosystem: Other Clients: [Olas](https://olas.app/) (photos) [Habla](https://habla.news/) (blogging) [Zap.Stream](https://zap.stream/) (video) Chat: [0xchat](https://0xchat.com/#/) [KeyChat](https://www.keychat.io/) [Flotilla](https://flotilla.social/) Shopping: [Plebeian Market](https://plebeian.market/) [Shopstr](https://shopstr.store/) Podcasting 2.0: [Fountain](https://fountain.fm/) [Wavlake](https://wavlake.com/) Workspace Tools: [Listr](https://listr.lol/) [Formstr](https://formstr.app/#/dashboard) [Docstr](https://docstr.app/) [Nostr.Build](https://nostr.build/) Signers: [Nos2X](https://nostrapps.com/nos2x) [Nsec.app](https://nsec.app/) ## Footnote [Find Muslims on Nostr](https://listr.lol/npub175nul9cvufswwsnpy99lvyhg7ad9nkccxhkhusznxfkr7e0zxthql9g6w0/30000/naddr1qq4xc6tnw3ez6efkxcun2cfkxqknzc348ykngcfnxvknsepsxukkxd33vc6x2vejv9jkgdqpp4mhxue69uhkummn9ekx7mqpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqg5waehxw309aex2mrp0yhxgctdw4eju6t0qgs02f70juxwyc88gfsjzjlkzt50wkjemvvrtmt7gpfnymplvh3r9msrqsqqqafsqfgqku) | [#staySAIF](https://saif.systems/articles/spiritual-opsec-guide) @ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit. @ fd06f542:8d6d54cd
2025-04-02 01:35:00## nostrbook 技术框架 源代码在 github.com ``` git clone https://github.com/nostrbook/nostrbook cd nostrbook npm install npm run dev ``` * 网站主框架 vite + svelte * 网站浏览书框架 docsify ## 网站主框架 svelte 为主,daisyui (tailwindcss) css 。 页面的逻辑结构 都是 svelte搭建的, 采用了 layout 左侧菜单。 菜单代码 在 https://github.com/nostrbook/nostrbook/blob/main/src/lib/SideMenu.svelte 菜单里用了弹框登录,弹框的代码基本是问的 AI。 子页面和 路由器看sveltekit规则编写。 ### 书籍的数据 https://github.com/nostrbook/nostrbook/blob/main/src/lib/bookevent.ts 使用的nostr ndk 库来读写 relay。 书的 tag, 内容就是 标题,封面和作者。 ``` [ ['t',booktag], ['title',content['title']], ]; ``` ### 章节的数据 ``` [ ['t',chaptertag], ['title',title], ['d',filename + "-" + bookid], ['e',bookid], ]; ``` 这里面的 d,采用了 文件名 + bookid,所以每一本的章节名的文件名是唯一的。 ### 配置文件 src/lib/config.ts,主要配置 服务器的地址 * 图片文件 nip96 服务器 * relays 服务器 * book的tag ,测试和 release不一样。 如果自己部署独有的服务器也可以不一样。这样内容可以垂直。 ### 首页采用了缓冲机制 首页的内容来自 书籍的列表, 用booktag和30023来区分是不是书籍信息。 为了搜索引擎友好,让页面加载就有数据。 采用了 src/hooks.server.ts 预备加载数据,数据会被首页面 src/routes/+page.server.ts 传给 page.svelte去渲染。 这一切都是后台完成的。html页面加载的时候数据都已经渲染完成了。所以对搜索引擎非常友好。搞定了google,seo。 但是为了数据的完整性, 页面起来后会继续读取列表,这时候可能会显示最新的数据。
@ fd06f542:8d6d54cd
2025-04-02 01:35:00## nostrbook 技术框架 源代码在 github.com ``` git clone https://github.com/nostrbook/nostrbook cd nostrbook npm install npm run dev ``` * 网站主框架 vite + svelte * 网站浏览书框架 docsify ## 网站主框架 svelte 为主,daisyui (tailwindcss) css 。 页面的逻辑结构 都是 svelte搭建的, 采用了 layout 左侧菜单。 菜单代码 在 https://github.com/nostrbook/nostrbook/blob/main/src/lib/SideMenu.svelte 菜单里用了弹框登录,弹框的代码基本是问的 AI。 子页面和 路由器看sveltekit规则编写。 ### 书籍的数据 https://github.com/nostrbook/nostrbook/blob/main/src/lib/bookevent.ts 使用的nostr ndk 库来读写 relay。 书的 tag, 内容就是 标题,封面和作者。 ``` [ ['t',booktag], ['title',content['title']], ]; ``` ### 章节的数据 ``` [ ['t',chaptertag], ['title',title], ['d',filename + "-" + bookid], ['e',bookid], ]; ``` 这里面的 d,采用了 文件名 + bookid,所以每一本的章节名的文件名是唯一的。 ### 配置文件 src/lib/config.ts,主要配置 服务器的地址 * 图片文件 nip96 服务器 * relays 服务器 * book的tag ,测试和 release不一样。 如果自己部署独有的服务器也可以不一样。这样内容可以垂直。 ### 首页采用了缓冲机制 首页的内容来自 书籍的列表, 用booktag和30023来区分是不是书籍信息。 为了搜索引擎友好,让页面加载就有数据。 采用了 src/hooks.server.ts 预备加载数据,数据会被首页面 src/routes/+page.server.ts 传给 page.svelte去渲染。 这一切都是后台完成的。html页面加载的时候数据都已经渲染完成了。所以对搜索引擎非常友好。搞定了google,seo。 但是为了数据的完整性, 页面起来后会继续读取列表,这时候可能会显示最新的数据。 @ fd06f542:8d6d54cd
2025-04-02 01:15:20NIP-07 ====== `window.nostr` capability for web browsers ------------------------------------------ `draft` `optional` The `window.nostr` object may be made available by web browsers or extensions and websites or web-apps may make use of it after checking its availability. That object must define the following methods: ``` async window.nostr.getPublicKey(): string // returns a public key as hex async window.nostr.signEvent(event: { created_at: number, kind: number, tags: string[][], content: string }): Event // takes an event object, adds `id`, `pubkey` and `sig` and returns it ``` Aside from these two basic above, the following functions can also be implemented optionally: ``` async window.nostr.nip04.encrypt(pubkey, plaintext): string // returns ciphertext and iv as specified in nip-04 (deprecated) async window.nostr.nip04.decrypt(pubkey, ciphertext): string // takes ciphertext and iv as specified in nip-04 (deprecated) async window.nostr.nip44.encrypt(pubkey, plaintext): string // returns ciphertext as specified in nip-44 async window.nostr.nip44.decrypt(pubkey, ciphertext): string // takes ciphertext as specified in nip-44 ``` ### Recommendation to Extension Authors To make sure that the `window.nostr` is available to nostr clients on page load, the authors who create Chromium and Firefox extensions should load their scripts by specifying `"run_at": "document_end"` in the extension's manifest. ### Implementation See https://github.com/aljazceru/awesome-nostr#nip-07-browser-extensions.
@ fd06f542:8d6d54cd
2025-04-02 01:15:20NIP-07 ====== `window.nostr` capability for web browsers ------------------------------------------ `draft` `optional` The `window.nostr` object may be made available by web browsers or extensions and websites or web-apps may make use of it after checking its availability. That object must define the following methods: ``` async window.nostr.getPublicKey(): string // returns a public key as hex async window.nostr.signEvent(event: { created_at: number, kind: number, tags: string[][], content: string }): Event // takes an event object, adds `id`, `pubkey` and `sig` and returns it ``` Aside from these two basic above, the following functions can also be implemented optionally: ``` async window.nostr.nip04.encrypt(pubkey, plaintext): string // returns ciphertext and iv as specified in nip-04 (deprecated) async window.nostr.nip04.decrypt(pubkey, ciphertext): string // takes ciphertext and iv as specified in nip-04 (deprecated) async window.nostr.nip44.encrypt(pubkey, plaintext): string // returns ciphertext as specified in nip-44 async window.nostr.nip44.decrypt(pubkey, ciphertext): string // takes ciphertext as specified in nip-44 ``` ### Recommendation to Extension Authors To make sure that the `window.nostr` is available to nostr clients on page load, the authors who create Chromium and Firefox extensions should load their scripts by specifying `"run_at": "document_end"` in the extension's manifest. ### Implementation See https://github.com/aljazceru/awesome-nostr#nip-07-browser-extensions. @ da0b9bc3:4e30a4a9
2025-04-06 07:38:03Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/935880
@ da0b9bc3:4e30a4a9
2025-04-06 07:38:03Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/935880 @ 57d1a264:69f1fee1
2025-04-05 06:35:58We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals. **Key Responsibilities:** - Design and improve the @Bipa app experience, focusing on usability and measurable business impact. - Apply data-driven design, making decisions based on user research, metrics, and testing. - Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product. - Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy. - Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations. - Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business. - Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app. **Qualifications:** - Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps. - Solid understanding of user-centered design (UCD) principles and usability heuristics. - Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis. - Ability to work with both quantitative and qualitative data to guide design decisions. - Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement). - Proficiency in design tools like Figma (or similar). - Experience working with design systems and design tokens to ensure consistency. - Comfortable working in an agile, fast-paced, and iterative environment. - Strong communication skills and the ability to advocate for design decisions backed by research and data. **Benefits:** 🏥 Health Insurance 💉 Dental Plan 🍽️ Meal Allowance (CAJU card) 💻 Home Office Stipend 📈 Stock Options from Day One [APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer) originally posted at https://stacker.news/items/935003
@ 57d1a264:69f1fee1
2025-04-05 06:35:58We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals. **Key Responsibilities:** - Design and improve the @Bipa app experience, focusing on usability and measurable business impact. - Apply data-driven design, making decisions based on user research, metrics, and testing. - Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product. - Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy. - Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations. - Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business. - Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app. **Qualifications:** - Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps. - Solid understanding of user-centered design (UCD) principles and usability heuristics. - Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis. - Ability to work with both quantitative and qualitative data to guide design decisions. - Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement). - Proficiency in design tools like Figma (or similar). - Experience working with design systems and design tokens to ensure consistency. - Comfortable working in an agile, fast-paced, and iterative environment. - Strong communication skills and the ability to advocate for design decisions backed by research and data. **Benefits:** 🏥 Health Insurance 💉 Dental Plan 🍽️ Meal Allowance (CAJU card) 💻 Home Office Stipend 📈 Stock Options from Day One [APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer) originally posted at https://stacker.news/items/935003 @ fd06f542:8d6d54cd
2025-04-02 01:14:45- [首页](/readme.md) - [第一章、 NIP-01: Basic protocol flow description](/01.md) - [第二章、 NIP-02: Follow List](/02.md) - [第三章、NIP-03: OpenTimestamps Attestations for Events](/03.md) - [第四章、NIP-04: Encrypted Direct Message](/04.md) - [第五章、NIP-05: Mapping Nostr keys to DNS-based internet identifiers](/05.md) - [第六章、NIP-06: Basic key derivation from mnemonic seed phrase](/06.md) - [第七章、NIP-07: window.nostr capability for web browsers](/07.md)
@ fd06f542:8d6d54cd
2025-04-02 01:14:45- [首页](/readme.md) - [第一章、 NIP-01: Basic protocol flow description](/01.md) - [第二章、 NIP-02: Follow List](/02.md) - [第三章、NIP-03: OpenTimestamps Attestations for Events](/03.md) - [第四章、NIP-04: Encrypted Direct Message](/04.md) - [第五章、NIP-05: Mapping Nostr keys to DNS-based internet identifiers](/05.md) - [第六章、NIP-06: Basic key derivation from mnemonic seed phrase](/06.md) - [第七章、NIP-07: window.nostr capability for web browsers](/07.md) @ 57d1a264:69f1fee1
2025-04-05 06:28:16### ⚡️ About Us @AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY. ### ⚡️ The Role Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision. ### ⚡️ Responsibilities Produce 30 short videos on circular economies. Incorporate subtitles as needed. Submit videos on a deliverables basis. Participate in check-ins and communicate with the AB team and circular economy communities. ### ⚡️ What We Offer Free ticket to AB25. Networking with Bitcoiners and industry leaders. Letter of recommendation and LinkedIn endorsement upon completion. Mentorship and hands-on experience with a high-profile Bitcoin project. ### ⚡️ Skills & Qualifications Passion for Bitcoin and circular economies. Basic to intermediate video editing skills (no specific software required). Creative independence with feedback. Portfolio or work samples preferred. ### ⚡️ Time Commitment Flexible, project-based internship with check-ins and feedback rounds. ### ⚡️ How to Apply Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available). originally posted at https://stacker.news/items/935001
@ 57d1a264:69f1fee1
2025-04-05 06:28:16### ⚡️ About Us @AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY. ### ⚡️ The Role Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision. ### ⚡️ Responsibilities Produce 30 short videos on circular economies. Incorporate subtitles as needed. Submit videos on a deliverables basis. Participate in check-ins and communicate with the AB team and circular economy communities. ### ⚡️ What We Offer Free ticket to AB25. Networking with Bitcoiners and industry leaders. Letter of recommendation and LinkedIn endorsement upon completion. Mentorship and hands-on experience with a high-profile Bitcoin project. ### ⚡️ Skills & Qualifications Passion for Bitcoin and circular economies. Basic to intermediate video editing skills (no specific software required). Creative independence with feedback. Portfolio or work samples preferred. ### ⚡️ Time Commitment Flexible, project-based internship with check-ins and feedback rounds. ### ⚡️ How to Apply Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available). originally posted at https://stacker.news/items/935001 @ fd06f542:8d6d54cd
2025-04-01 02:04:45NIP-06 ====== Basic key derivation from mnemonic seed phrase ---------------------------------------------- `draft` `optional` [BIP39](https://bips.xyz/39) is used to generate mnemonic seed words and derive a binary seed from them. [BIP32](https://bips.xyz/32) is used to derive the path `m/44'/1237'/<account>'/0/0` (according to the Nostr entry on [SLIP44](https://github.com/satoshilabs/slips/blob/master/slip-0044.md)). A basic client can simply use an `account` of `0` to derive a single key. For more advanced use-cases you can increment `account`, allowing generation of practically infinite keys from the 5-level path with hardened derivation. Other types of clients can still get fancy and use other derivation paths for their own other purposes. ### Test vectors mnemonic: leader monkey parrot ring guide accident before fence cannon height naive bean\ private key (hex): 7f7ff03d123792d6ac594bfa67bf6d0c0ab55b6b1fdb6249303fe861f1ccba9a\ nsec: nsec10allq0gjx7fddtzef0ax00mdps9t2kmtrldkyjfs8l5xruwvh2dq0lhhkp\ public key (hex): 17162c921dc4d2518f9a101db33695df1afb56ab82f5ff3e5da6eec3ca5cd917\ npub: npub1zutzeysacnf9rru6zqwmxd54mud0k44tst6l70ja5mhv8jjumytsd2x7nu --- mnemonic: what bleak badge arrange retreat wolf trade produce cricket blur garlic valid proud rude strong choose busy staff weather area salt hollow arm fade\ private key (hex): c15d739894c81a2fcfd3a2df85a0d2c0dbc47a280d092799f144d73d7ae78add\ nsec: nsec1c9wh8xy5eqdzln7n5t0ctgxjcrdug73gp5yj0x03gntn67h83twssdfhel\ public key (hex): d41b22899549e1f3d335a31002cfd382174006e166d3e658e3a5eecdb6463573\ npub: npub16sdj9zv4f8sl85e45vgq9n7nsgt5qphpvmf7vk8r5hhvmdjxx4es8rq74h
@ fd06f542:8d6d54cd
2025-04-01 02:04:45NIP-06 ====== Basic key derivation from mnemonic seed phrase ---------------------------------------------- `draft` `optional` [BIP39](https://bips.xyz/39) is used to generate mnemonic seed words and derive a binary seed from them. [BIP32](https://bips.xyz/32) is used to derive the path `m/44'/1237'/<account>'/0/0` (according to the Nostr entry on [SLIP44](https://github.com/satoshilabs/slips/blob/master/slip-0044.md)). A basic client can simply use an `account` of `0` to derive a single key. For more advanced use-cases you can increment `account`, allowing generation of practically infinite keys from the 5-level path with hardened derivation. Other types of clients can still get fancy and use other derivation paths for their own other purposes. ### Test vectors mnemonic: leader monkey parrot ring guide accident before fence cannon height naive bean\ private key (hex): 7f7ff03d123792d6ac594bfa67bf6d0c0ab55b6b1fdb6249303fe861f1ccba9a\ nsec: nsec10allq0gjx7fddtzef0ax00mdps9t2kmtrldkyjfs8l5xruwvh2dq0lhhkp\ public key (hex): 17162c921dc4d2518f9a101db33695df1afb56ab82f5ff3e5da6eec3ca5cd917\ npub: npub1zutzeysacnf9rru6zqwmxd54mud0k44tst6l70ja5mhv8jjumytsd2x7nu --- mnemonic: what bleak badge arrange retreat wolf trade produce cricket blur garlic valid proud rude strong choose busy staff weather area salt hollow arm fade\ private key (hex): c15d739894c81a2fcfd3a2df85a0d2c0dbc47a280d092799f144d73d7ae78add\ nsec: nsec1c9wh8xy5eqdzln7n5t0ctgxjcrdug73gp5yj0x03gntn67h83twssdfhel\ public key (hex): d41b22899549e1f3d335a31002cfd382174006e166d3e658e3a5eecdb6463573\ npub: npub16sdj9zv4f8sl85e45vgq9n7nsgt5qphpvmf7vk8r5hhvmdjxx4es8rq74h @ c631e267:c2b78d3e
2025-04-04 18:47:27*Zwei mal drei macht vier,* *\ widewidewitt und drei macht neune,* *\ ich mach mir die Welt,* *\ widewide wie sie mir gefällt.* *\ Pippi Langstrumpf*   **Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive. **In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027. **Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt. **Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen. **Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint. **Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen. **Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür. *\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen.
@ c631e267:c2b78d3e
2025-04-04 18:47:27*Zwei mal drei macht vier,* *\ widewidewitt und drei macht neune,* *\ ich mach mir die Welt,* *\ widewide wie sie mir gefällt.* *\ Pippi Langstrumpf*   **Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive. **In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027. **Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt. **Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen. **Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint. **Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen. **Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür. *\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen. @ fd06f542:8d6d54cd
2025-03-31 10:00:34NIP-05 ====== Mapping Nostr keys to DNS-based internet identifiers ---------------------------------------------------- `final` `optional` On events of kind `0` (`user metadata`) one can specify the key `"nip05"` with an [internet identifier](https://datatracker.ietf.org/doc/html/rfc5322#section-3.4.1) (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the `<local-part>` part will be restricted to the characters `a-z0-9-_.`, case-insensitive. Upon seeing that, the client splits the identifier into `<local-part>` and `<domain>` and use these values to make a GET request to `https://<domain>/.well-known/nostr.json?name=<local-part>`. The result should be a JSON document object with a key `"names"` that should then be a mapping of names to hex formatted public keys. If the public key for the given `<name>` matches the `pubkey` from the `user metadata` event, the client then concludes that the given pubkey can indeed be referenced by its identifier. ### Example If a client sees an event like this: ```jsonc { "pubkey": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9", "kind": 0, "content": "{\"name\": \"bob\", \"nip05\": \"bob@example.com\"}" // other fields... } ``` It will make a GET request to `https://example.com/.well-known/nostr.json?name=bob` and get back a response that will look like ```json { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" } } ``` or with the **recommended** `"relays"` attribute: ```json { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" }, "relays": { "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9": [ "wss://relay.example.com", "wss://relay2.example.com" ] } } ``` If the pubkey matches the one given in `"names"` (as in the example above) that means the association is right and the `"nip05"` identifier is valid and can be displayed. The recommended `"relays"` attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve `/.well-known/nostr.json` files dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available. ## Finding users from their NIP-05 identifier A client may implement support for finding users' public keys from _internet identifiers_, the flow is the same as above, but reversed: first the client fetches the _well-known_ URL and from there it gets the public key of the user, then it tries to fetch the kind `0` event for that user and check if it has a matching `"nip05"`. ## Notes ### Identification, not verification The NIP-05 is not intended to _verify_ a user, but only to _identify_ them, for the purpose of facilitating the exchange of a contact or their search. Exceptions are people who own (e.g., a company) or are connected (e.g., a project) to a well-known domain, who can exploit NIP-05 as an attestation of their relationship with it, and thus to the organization behind it, thereby gaining an element of trust. ### User discovery implementation suggestion A client can use this to allow users to search other profiles. If a client has a search box or something like that, a user may be able to type "bob@example.com" there and the client would recognize that and do the proper queries to obtain a pubkey and suggest that to the user. ### Clients must always follow public keys, not NIP-05 addresses For example, if after finding that `bob@bob.com` has the public key `abc...def`, the user clicks a button to follow that profile, the client must keep a primary reference to `abc...def`, not `bob@bob.com`. If, for any reason, the address `https://bob.com/.well-known/nostr.json?name=bob` starts returning the public key `1d2...e3f` at any time in the future, the client must not replace `abc...def` in his list of followed profiles for the user (but it should stop displaying "bob@bob.com" for that user, as that will have become an invalid `"nip05"` property). ### Public keys must be in hex format Keys must be returned in hex format. Keys in NIP-19 `npub` format are only meant to be used for display in client UIs, not in this NIP. ### Showing just the domain as an identifier Clients may treat the identifier `_@domain` as the "root" identifier, and choose to display it as just the `<domain>`. For example, if Bob owns `bob.com`, he may not want an identifier like `bob@bob.com` as that is redundant. Instead, Bob can use the identifier `_@bob.com` and expect Nostr clients to show and treat that as just `bob.com` for all purposes. ### Reasoning for the `/.well-known/nostr.json?name=<local-part>` format By adding the `<local-part>` as a query string instead of as part of the path, the protocol can support both dynamic servers that can generate JSON on-demand and static servers with a JSON file in it that may contain multiple names. ### Allowing access from JavaScript apps JavaScript Nostr apps may be restricted by browser [CORS][] policies that prevent them from accessing `/.well-known/nostr.json` on the user's domain. When CORS prevents JS from loading a resource, the JS program sees it as a network failure identical to the resource not existing, so it is not possible for a pure-JS app to tell the user for certain that the failure was caused by a CORS issue. JS Nostr apps that see network failures requesting `/.well-known/nostr.json` files may want to recommend to users that they check the CORS policy of their servers, e.g.: ```bash $ curl -sI https://example.com/.well-known/nostr.json?name=bob | grep -i ^Access-Control Access-Control-Allow-Origin: * ``` Users should ensure that their `/.well-known/nostr.json` is served with the HTTP header `Access-Control-Allow-Origin: *` to ensure it can be validated by pure JS apps running in modern browsers. [CORS]: https://developer.mozilla.org/en-US/docs/Web/HTTP/CORS ### Security Constraints The `/.well-known/nostr.json` endpoint MUST NOT return any HTTP redirects. Fetchers MUST ignore any HTTP redirects given by the `/.well-known/nostr.json` endpoint.
@ fd06f542:8d6d54cd
2025-03-31 10:00:34NIP-05 ====== Mapping Nostr keys to DNS-based internet identifiers ---------------------------------------------------- `final` `optional` On events of kind `0` (`user metadata`) one can specify the key `"nip05"` with an [internet identifier](https://datatracker.ietf.org/doc/html/rfc5322#section-3.4.1) (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the `<local-part>` part will be restricted to the characters `a-z0-9-_.`, case-insensitive. Upon seeing that, the client splits the identifier into `<local-part>` and `<domain>` and use these values to make a GET request to `https://<domain>/.well-known/nostr.json?name=<local-part>`. The result should be a JSON document object with a key `"names"` that should then be a mapping of names to hex formatted public keys. If the public key for the given `<name>` matches the `pubkey` from the `user metadata` event, the client then concludes that the given pubkey can indeed be referenced by its identifier. ### Example If a client sees an event like this: ```jsonc { "pubkey": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9", "kind": 0, "content": "{\"name\": \"bob\", \"nip05\": \"bob@example.com\"}" // other fields... } ``` It will make a GET request to `https://example.com/.well-known/nostr.json?name=bob` and get back a response that will look like ```json { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" } } ``` or with the **recommended** `"relays"` attribute: ```json { "names": { "bob": "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9" }, "relays": { "b0635d6a9851d3aed0cd6c495b282167acf761729078d975fc341b22650b07b9": [ "wss://relay.example.com", "wss://relay2.example.com" ] } } ``` If the pubkey matches the one given in `"names"` (as in the example above) that means the association is right and the `"nip05"` identifier is valid and can be displayed. The recommended `"relays"` attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve `/.well-known/nostr.json` files dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available. ## Finding users from their NIP-05 identifier A client may implement support for finding users' public keys from _internet identifiers_, the flow is the same as above, but reversed: first the client fetches the _well-known_ URL and from there it gets the public key of the user, then it tries to fetch the kind `0` event for that user and check if it has a matching `"nip05"`. ## Notes ### Identification, not verification The NIP-05 is not intended to _verify_ a user, but only to _identify_ them, for the purpose of facilitating the exchange of a contact or their search. Exceptions are people who own (e.g., a company) or are connected (e.g., a project) to a well-known domain, who can exploit NIP-05 as an attestation of their relationship with it, and thus to the organization behind it, thereby gaining an element of trust. ### User discovery implementation suggestion A client can use this to allow users to search other profiles. If a client has a search box or something like that, a user may be able to type "bob@example.com" there and the client would recognize that and do the proper queries to obtain a pubkey and suggest that to the user. ### Clients must always follow public keys, not NIP-05 addresses For example, if after finding that `bob@bob.com` has the public key `abc...def`, the user clicks a button to follow that profile, the client must keep a primary reference to `abc...def`, not `bob@bob.com`. If, for any reason, the address `https://bob.com/.well-known/nostr.json?name=bob` starts returning the public key `1d2...e3f` at any time in the future, the client must not replace `abc...def` in his list of followed profiles for the user (but it should stop displaying "bob@bob.com" for that user, as that will have become an invalid `"nip05"` property). ### Public keys must be in hex format Keys must be returned in hex format. Keys in NIP-19 `npub` format are only meant to be used for display in client UIs, not in this NIP. ### Showing just the domain as an identifier Clients may treat the identifier `_@domain` as the "root" identifier, and choose to display it as just the `<domain>`. For example, if Bob owns `bob.com`, he may not want an identifier like `bob@bob.com` as that is redundant. Instead, Bob can use the identifier `_@bob.com` and expect Nostr clients to show and treat that as just `bob.com` for all purposes. ### Reasoning for the `/.well-known/nostr.json?name=<local-part>` format By adding the `<local-part>` as a query string instead of as part of the path, the protocol can support both dynamic servers that can generate JSON on-demand and static servers with a JSON file in it that may contain multiple names. ### Allowing access from JavaScript apps JavaScript Nostr apps may be restricted by browser [CORS][] policies that prevent them from accessing `/.well-known/nostr.json` on the user's domain. When CORS prevents JS from loading a resource, the JS program sees it as a network failure identical to the resource not existing, so it is not possible for a pure-JS app to tell the user for certain that the failure was caused by a CORS issue. JS Nostr apps that see network failures requesting `/.well-known/nostr.json` files may want to recommend to users that they check the CORS policy of their servers, e.g.: ```bash $ curl -sI https://example.com/.well-known/nostr.json?name=bob | grep -i ^Access-Control Access-Control-Allow-Origin: * ``` Users should ensure that their `/.well-known/nostr.json` is served with the HTTP header `Access-Control-Allow-Origin: *` to ensure it can be validated by pure JS apps running in modern browsers. [CORS]: https://developer.mozilla.org/en-US/docs/Web/HTTP/CORS ### Security Constraints The `/.well-known/nostr.json` endpoint MUST NOT return any HTTP redirects. Fetchers MUST ignore any HTTP redirects given by the `/.well-known/nostr.json` endpoint. @ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
@ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen. @ 554ab6fe:c6cbc27e
2025-04-06 03:13:25We all know that sex can be pleasurable, and most of us seek it as a core aspect of a fulfilled life. We do this instinctively, like the desire to eat good food or have a nice restful sleep. Yet, we rarely discuss how sex is potentially a very important aspect of our mental and physical health. Most don’t even know if it is, and we have a culture that often treats sex as a taboo. Here, the physical and mental health benefits of sex will be explored. Additionally, I will make an argument that sex is potentially a core aspect of holistic health that is improved when other aspects of health are maintained. In a previous blog post discussing how mindfulness was a core aspect of ancient hunter gather life, I began to formulate an idea: perhaps all core aspects on ancient human life can be seen as sure ways to promote physical and mental health. As of now, I have identified “Six Pillars” of life, which could be said to be: exercise, meditation (mindfulness), diet, sleep, social relationships and sex. We all take for granted the important effect exercise, diet, and sleep have on health. One of the main purposes of this blog is to discuss how meditation belongs in this list as well. What about sex? I had a question, so I began researching. Sex and a Longer Life What became immediately identifiable was a weird bias within the scientific community in regards to sex research. Despite the fact that it is very difficult to find any scientist that disagrees with the notion that sex is fundamental to health(Jannini et al., 2009), most research focuses on the negative aspects of sex(Diamond & Huebner, 2012). Most research focuses on the occurrence of sexually transmitted infections, abuses and assaults, unplanned pregnancies, and so forth(Diamond & Huebner, 2012). Rarely, is there investigation into what happens in the body that makes sex so healthy. This is an incredible shame, because the research that we do have, reveals an incredible observation: people who have more sex (more orgasms) live longer lives (Lindau & Gavrilova, 2010; Smith et al., 1997). We aren’t sure how, but we commonly observe this trend. There was a similar observation observed during the COVID-19 lock down, where the more sex someone had during that time, the less anxiety and depression they had(Mollaioli et al., 2021). Does sex improve mental health, physical health, or both? Again, we certainly do not have a full understanding given the lack of research, but there are some clues to say that both are benefited. As previously stated, sex may improve mental health in regards to stress. This seems fairly intuitive. Additionally, similar to the benefits of meditation, people who more frequently have sexual intercourse show greater resilience to incoming stressors, while also showing healthier blood pressure levels (the same was not true in masturbators)(Brody, 2006). Of course, mental health also leads to physical health. Nonetheless, the benefits of sex are not purely mentally induced. A lot of attention has also been directed towards the direct physical benefits of sex. For example, there is increasing evidence that sexual activity decreases the risk of prostate cancer(Giles et al., 2003; Leitzmann et al., 2004). Additionally, sexual activity seems to create changes in hormone production that not only benefit health, but it also generates a positive feedback loop creating more sexual desire. Further incentivizing more sexual activity. Sexual activity affects testosterone levels, and low testosterone is common in erectile dysfunction(Jannini et al., 2009). So just like our neurons that have the “use it or lose it” principle, perhaps the penis does too. This trend doesn’t only apply to men either. Other research has shown that the more sex a woman has, the more lubricated their vaginas become(Leiblum, 1983). Similarly, more sexually active woman has less vaginal atrophy and higher levels of hormones (androstenedione, testosterone and gonadotropins). Indicating that more sex generates more sexual function and desire. This generates a positive feedback loop that potentially drives further healthy lifestyle practices in regards to sexual activity. Mindfulness and Sex It is evident that sex improves sex at a physiologic level. It may also be obvious that physical fitness can improve sex as well. So how does mindfulness meditation relate to sex? Firstly, it should be noted that there is a large population of people that suffers from sexual dysfunction. Women are the most affected. Sexual desire is strongly related to relationship satisfaction, mood, self-esteem, body image, psychiatric symptoms, and age(Brotto & Basson, 2014). 24% of woman have either always suffered from a reduced orgasmic sensation by 75-100% or have developed this disorder over time(Adam et al., 2020). Female sexual interest/arousal disorder (SIAD) is defined by low level of sexual desire, infrequent sexual thoughts/fantasies, low receptivity to sexual activity, low sexual pleasure, low desire triggered by sexual stimuli, and low genital and non-genital sensations(Paterson et al., 2017). Therefore, it is highly apparent that mental health, especially as it related to the perception of the self, can have dramatic effects in not only sexual desire, but sexual pleasure as well. However, this problem is not specific to woman at all. Emotions related to depression are highly related to sexual dysfunction in both men and woman(Nobre & Pinto-Gouveia, 2006). Most notably, performance anxiety influences the occurrence of erectile dysfunction(Brotto & Basson, 2014). Given the relationship between sex and health, resolving such sexual dysfunction is crucial to improving general health and well-being. Given the fact that mental state in various ways contributes to sexual dysfunction, meditation is a strong candidate for a useful therapy. As previously discussed in this blog, mindfulness meditation is a practice of generating a non-judgmental, open, and curious orientation towards all incoming thoughts and stimuli of the present moment(Bishop et al., 2006). For this reason, I have written about how the practice has been shown to be highly capable of decreasing symptoms of anxiety and depression. These symptoms of ruminative thoughts that burden the mind during sex, are alleviated through meditation. So, it is unsurprising that mindfulness-based cognitive therapy (MBCT) has been shown to be helpful in improving sexual function(Adam et al., 2020). Additionally, a new form of therapy called Mindfulness-Based Sex therapy (MBST) has been developed for these very reasons(Brotto et al., 2016). Mindfulness is recommended as a therapy for sexual dysfunction(Brotto & Goldmeier, 2015), but why? How it works As previously discussed, one way mindfulness meditation improves sexual function is through the changes it generates within the mind. Multiple studies have shown that through mindfulness, not only are the traits of depression and sex-related distress decreased, but woman subsequently experience greater sexual desire and improved sexual function(Adam et al., 2020; Brotto & Basson, 2014; Paterson et al., 2017). Women who were previously low on sexual desire, have improved sexual desire through mindfulness(Brotto et al., 2016). This is likely because the mental schemas that negatively affected their sex life are diminished through a practice of mindfulness meditation. Research using MBST has suggested that enhancing concentration and compassionate self-acceptance may lead to greater integration of physical and mental sexual response to erotic stimuli(Brotto et al., 2016). Even though the psychological arguments for how meditation improves sexual function are convincing, I personally require more evidence. The mind is a window into the body, and therefore analyzing human health through the lenses of the thoughts of the mind only is not substantial evidence for me to be convinced. There are of course more complex physiologic processes that may go to explain these observed effects. In a previous post, I argue that meditation can influence our conscious experience by quieting the mind, allowing, for the brain to more accurately and efficiently process incoming stimuli. This allows us to have healthier and more informative understanding of ourselves (our body) and the world around us (our environment). If this is indeed the case, then we would expect to see mindfulness result in improves processing of physical stimuli. In the case of sexual performance, this certainly seems to be the case. Studies have shown a mindfulness meditation practice increases reaction time for sexual stimuli(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). This is a strong indicator that through mindfulness, individuals will have a more accurate and clear experience generated from sexual stimuli, allowing for greater pleasure and performance. Additionally, it was noted in the study that woman take longer to respond to sexual stimuli compared to men, and the impaired ability to do so leads to self-judgment(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). So, if mindfulness can alleviate this impairment, and improve self-perception, then it creates a positive feedback loop of mental health improving sexual function which in turn improves mental health. Since improved interoception (ability to sense inside the body) is suspected to be involved in this process, the insula of the brain, which has been implicated to play a major role in interoception(Giuliani et al., 2011), likely plays a role in the physiologic change that occurs. For reasons like the ones in my previous post, the insula is also regarded as a possible neuronal area related to consciousness(Craig, 2009). As it relates to sexual function, it is possible that improved insula-mediated increase in interoceptive ability from various mindfulness exercises contributed to the observed improved concordance between genital and subjective arousal after MBST(Brotto et al., 2016). This theory is reinforced by the observation that the insula increases in size following mindfulness meditation practices(Hölzel et al., 2011; Lazar et al., 2005). Indicating that because mindfulness meditation is oriented around the attentive observation of internal stimuli, the brain area involved is strengthened and grows. This allows for greater interoception in all cases, including sexual stimuli, thereby improving sexual function. Conclusion Exercise, social relationships, meditation, diet, sleep, and sex are fundamental aspects of human life. When looking back onto ancient human life, all of these aspects were fundamental to our health and prosperity. What was true then is still true now. Unsurprisingly, scientist commonly agree that safe sexual activity is an important aspect of maintaining general well-being and health. There have been studies that suggested that the more sex you have, the longer you may live. Unfortunately, the stresses of modern-day life, and the associated manifestations of self-judgment, lack of perceived self-worth, and unrealistic standards of beauty and sexual appeal have hindered some in being able to fully experience and practice a healthy sex life. Therefore, it is important to consider how other healthy life practices, such as meditation, are not only important in their own right, but are important because they may foster other healthy life habits in other areas, such as sexual activity. To calm the mind and rid it of our unconstructive ruminative thoughts once again is shown to be crucial to achieving a life of mental and physical well-being and health. Let us free our minds, free our hearts, and enjoy the present and our lives for all of its worth and beauty. References Adam, F., de Sutter, P., Day, J., & Grimm, E. (2020). A Randomized Study Comparing Video-Based Mindfulness-Based Cognitive Therapy With Video-Based Traditional Cognitive Behavioral Therapy in a Sample of Women Struggling to Achieve Orgasm. Journal of Sexual Medicine, 17(2), 312–324. https://doi.org/10.1016/j.jsxm.2019.10.022 Bishop, S. R., Lau, M., Shapiro, S., Carlson, L., Anderson, N. D., Carmody, J., Segal, Z. v., Abbey, S., Speca, M., Velting, D., & Devins, G. (2006). Mindfulness: A Proposed Operational Definition. Clinical Psychology: Science and Practice, 11(3), 230–241. https://doi.org/10.1093/clipsy.bph077 Brody, S. (2006). Blood pressure reactivity to stress is better for people who recently had penile-vaginal intercourse than for people who had other or no sexual activity. Biological Psychology, 71(2), 214–222. https://doi.org/10.1016/j.biopsycho.2005.03.005 Brotto, L. A., & Basson, R. (2014). Group mindfulness-based therapy significantly improves sexual desire in women. Behaviour Research and Therapy, 57(1), 43–54. https://doi.org/10.1016/j.brat.2014.04.001 Brotto, L. A., Chivers, M. L., Millman, R. D., & Albert, A. (2016). Mindfulness-Based Sex Therapy Improves Genital-Subjective Arousal Concordance in Women With Sexual Desire/Arousal Difficulties. Archives of Sexual Behavior, 45(8), 1907–1921. https://doi.org/10.1007/s10508-015-0689-8 Brotto, L. A., & Goldmeier, D. (2015). Mindfulness Interventions for Treating Sexual Dysfunctions: The Gentle Science of Finding Focus in a Multitask World. Journal of Sexual Medicine, 12(8), 1687–1689. https://doi.org/10.1111/jsm.12941 Craig, A. D. B. (2009). How do you feel — now? The anterior insula and human awareness. 10(January). Diamond, L. M., & Huebner, D. M. (2012). Is good sex good for you? Rethinking sexuality and health. Social and Personality Psychology Compass, 6(1), 54–69. https://doi.org/10.1111/j.1751-9004.2011.00408.x Giles, G. G., Severi, G., English, D. R., Mccredie, M. R. E., Borland, R., Boyle, P., & Hopper, J. L. (2003). Sexual factors and prostate cancer. BJU International, 92(3), 211–216. https://doi.org/10.1046/j.1464-410X.2003.04319.x Giuliani, N. R., Drabant, E. M., Bhatnagar, R., & Gross, J. J. (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. NeuroImage, 58(1), 10–15. https://doi.org/10.1016/J.NEUROIMAGE.2011.06.028 Hölzel, B. K., Lazar, S. W., Gard, T., Schuman-Olivier, Z., Vago, D. R., & Ott, U. (2011). How Does Mindfulness Meditation Work? Proposing Mechanisms of Action From a Conceptual and Neural Perspective. Perspectives on Psychological Science, 6(6), 537–559. https://doi.org/10.1177/1745691611419671 Jannini, E. A., Fisher, W. A., Bitzer, J., & McMahon, C. G. (2009). Is sex just fun? How sexual activity improves health. Journal of Sexual Medicine, 6(10), 2640–2648. https://doi.org/10.1111/j.1743-6109.2009.01477.x Lazar, S. W., Kerr, C. E., Wasserman, R. H., Gray, J. R., Greve, D. N., Treadway, M. T., McGarvey, M., Quinn, B. T., Dusek, J. A., Benson, H., Rauch, S. L., Moore, C. I., & Fischl, B. (2005). Meditation experience is associated with increased cortical thickness. Neuroreport, 16(17), 1893–1897. https://doi.org/10.1097/01.wnr.0000186598.66243.19 Leiblum, S. (1983). Vaginal Atrophy in the Postmenopausal Woman. Jama, 249(16), 2195. https://doi.org/10.1001/jama.1983.03330400041022 Leitzmann, M. F., Platz, E. A., Stampfer, M. J., Willett, W. C., & Giovannucci, E. (2004). Ejaculation Frequency and Subsequent Risk of Prostate Cancer. Journal of the American Medical Association, 291(13), 1578–1586. https://doi.org/10.1001/jama.291.13.1578 Lindau, S. T., & Gavrilova, N. (2010). Sex, health, and years of sexually active life gained due to good health: Evidence from two US population based cross sectional surveys of ageing. BMJ (Online), 340(7746), 580. https://doi.org/10.1136/bmj.c810 Mollaioli, D., Sansone, A., Ciocca, G., Limoncin, E., Colonnello, E., di Lorenzo, G., & Jannini, E. A. (2021). Benefits of Sexual Activity on Psychological, Relational, and Sexual Health During the COVID-19 Breakout. Journal of Sexual Medicine, 18(1), 35–49. https://doi.org/10.1016/j.jsxm.2020.10.008 Nobre, P. J., & Pinto-Gouveia, J. (2006). Emotions during sexual activity: Differences between sexually functional and dysfunctional men and women. Archives of Sexual Behavior, 35(4), 491–499. https://doi.org/10.1007/s10508-006-9047-1 Paterson, L. Q. P., Handy, A. B., & Brotto, L. A. (2017). A Pilot Study of Eight-Session Mindfulness-Based Cognitive Therapy Adapted for Women’s Sexual Interest/Arousal Disorder. Journal of Sex Research, 54(7), 850–861. https://doi.org/10.1080/00224499.2016.1208800 R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, P. (2011). Effects of Mindfulness Training on Body Awareness to Sexual Stimuli: Implications for Female Sexual Dysfunction. Psychosom Med., 23(1), 1–7. https://doi.org/10.1097/PSY.0b013e318234e628.Effects Smith, G. D., Frankel, S., & Yarnell, J. (1997). Sex and death: Are they related? Findings from the Caerphilly cohort study. BMJ, 315(7123), 1641–1644. https://doi.org/10.1136/bmj.315.7123.1641
@ 554ab6fe:c6cbc27e
2025-04-06 03:13:25We all know that sex can be pleasurable, and most of us seek it as a core aspect of a fulfilled life. We do this instinctively, like the desire to eat good food or have a nice restful sleep. Yet, we rarely discuss how sex is potentially a very important aspect of our mental and physical health. Most don’t even know if it is, and we have a culture that often treats sex as a taboo. Here, the physical and mental health benefits of sex will be explored. Additionally, I will make an argument that sex is potentially a core aspect of holistic health that is improved when other aspects of health are maintained. In a previous blog post discussing how mindfulness was a core aspect of ancient hunter gather life, I began to formulate an idea: perhaps all core aspects on ancient human life can be seen as sure ways to promote physical and mental health. As of now, I have identified “Six Pillars” of life, which could be said to be: exercise, meditation (mindfulness), diet, sleep, social relationships and sex. We all take for granted the important effect exercise, diet, and sleep have on health. One of the main purposes of this blog is to discuss how meditation belongs in this list as well. What about sex? I had a question, so I began researching. Sex and a Longer Life What became immediately identifiable was a weird bias within the scientific community in regards to sex research. Despite the fact that it is very difficult to find any scientist that disagrees with the notion that sex is fundamental to health(Jannini et al., 2009), most research focuses on the negative aspects of sex(Diamond & Huebner, 2012). Most research focuses on the occurrence of sexually transmitted infections, abuses and assaults, unplanned pregnancies, and so forth(Diamond & Huebner, 2012). Rarely, is there investigation into what happens in the body that makes sex so healthy. This is an incredible shame, because the research that we do have, reveals an incredible observation: people who have more sex (more orgasms) live longer lives (Lindau & Gavrilova, 2010; Smith et al., 1997). We aren’t sure how, but we commonly observe this trend. There was a similar observation observed during the COVID-19 lock down, where the more sex someone had during that time, the less anxiety and depression they had(Mollaioli et al., 2021). Does sex improve mental health, physical health, or both? Again, we certainly do not have a full understanding given the lack of research, but there are some clues to say that both are benefited. As previously stated, sex may improve mental health in regards to stress. This seems fairly intuitive. Additionally, similar to the benefits of meditation, people who more frequently have sexual intercourse show greater resilience to incoming stressors, while also showing healthier blood pressure levels (the same was not true in masturbators)(Brody, 2006). Of course, mental health also leads to physical health. Nonetheless, the benefits of sex are not purely mentally induced. A lot of attention has also been directed towards the direct physical benefits of sex. For example, there is increasing evidence that sexual activity decreases the risk of prostate cancer(Giles et al., 2003; Leitzmann et al., 2004). Additionally, sexual activity seems to create changes in hormone production that not only benefit health, but it also generates a positive feedback loop creating more sexual desire. Further incentivizing more sexual activity. Sexual activity affects testosterone levels, and low testosterone is common in erectile dysfunction(Jannini et al., 2009). So just like our neurons that have the “use it or lose it” principle, perhaps the penis does too. This trend doesn’t only apply to men either. Other research has shown that the more sex a woman has, the more lubricated their vaginas become(Leiblum, 1983). Similarly, more sexually active woman has less vaginal atrophy and higher levels of hormones (androstenedione, testosterone and gonadotropins). Indicating that more sex generates more sexual function and desire. This generates a positive feedback loop that potentially drives further healthy lifestyle practices in regards to sexual activity. Mindfulness and Sex It is evident that sex improves sex at a physiologic level. It may also be obvious that physical fitness can improve sex as well. So how does mindfulness meditation relate to sex? Firstly, it should be noted that there is a large population of people that suffers from sexual dysfunction. Women are the most affected. Sexual desire is strongly related to relationship satisfaction, mood, self-esteem, body image, psychiatric symptoms, and age(Brotto & Basson, 2014). 24% of woman have either always suffered from a reduced orgasmic sensation by 75-100% or have developed this disorder over time(Adam et al., 2020). Female sexual interest/arousal disorder (SIAD) is defined by low level of sexual desire, infrequent sexual thoughts/fantasies, low receptivity to sexual activity, low sexual pleasure, low desire triggered by sexual stimuli, and low genital and non-genital sensations(Paterson et al., 2017). Therefore, it is highly apparent that mental health, especially as it related to the perception of the self, can have dramatic effects in not only sexual desire, but sexual pleasure as well. However, this problem is not specific to woman at all. Emotions related to depression are highly related to sexual dysfunction in both men and woman(Nobre & Pinto-Gouveia, 2006). Most notably, performance anxiety influences the occurrence of erectile dysfunction(Brotto & Basson, 2014). Given the relationship between sex and health, resolving such sexual dysfunction is crucial to improving general health and well-being. Given the fact that mental state in various ways contributes to sexual dysfunction, meditation is a strong candidate for a useful therapy. As previously discussed in this blog, mindfulness meditation is a practice of generating a non-judgmental, open, and curious orientation towards all incoming thoughts and stimuli of the present moment(Bishop et al., 2006). For this reason, I have written about how the practice has been shown to be highly capable of decreasing symptoms of anxiety and depression. These symptoms of ruminative thoughts that burden the mind during sex, are alleviated through meditation. So, it is unsurprising that mindfulness-based cognitive therapy (MBCT) has been shown to be helpful in improving sexual function(Adam et al., 2020). Additionally, a new form of therapy called Mindfulness-Based Sex therapy (MBST) has been developed for these very reasons(Brotto et al., 2016). Mindfulness is recommended as a therapy for sexual dysfunction(Brotto & Goldmeier, 2015), but why? How it works As previously discussed, one way mindfulness meditation improves sexual function is through the changes it generates within the mind. Multiple studies have shown that through mindfulness, not only are the traits of depression and sex-related distress decreased, but woman subsequently experience greater sexual desire and improved sexual function(Adam et al., 2020; Brotto & Basson, 2014; Paterson et al., 2017). Women who were previously low on sexual desire, have improved sexual desire through mindfulness(Brotto et al., 2016). This is likely because the mental schemas that negatively affected their sex life are diminished through a practice of mindfulness meditation. Research using MBST has suggested that enhancing concentration and compassionate self-acceptance may lead to greater integration of physical and mental sexual response to erotic stimuli(Brotto et al., 2016). Even though the psychological arguments for how meditation improves sexual function are convincing, I personally require more evidence. The mind is a window into the body, and therefore analyzing human health through the lenses of the thoughts of the mind only is not substantial evidence for me to be convinced. There are of course more complex physiologic processes that may go to explain these observed effects. In a previous post, I argue that meditation can influence our conscious experience by quieting the mind, allowing, for the brain to more accurately and efficiently process incoming stimuli. This allows us to have healthier and more informative understanding of ourselves (our body) and the world around us (our environment). If this is indeed the case, then we would expect to see mindfulness result in improves processing of physical stimuli. In the case of sexual performance, this certainly seems to be the case. Studies have shown a mindfulness meditation practice increases reaction time for sexual stimuli(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). This is a strong indicator that through mindfulness, individuals will have a more accurate and clear experience generated from sexual stimuli, allowing for greater pleasure and performance. Additionally, it was noted in the study that woman take longer to respond to sexual stimuli compared to men, and the impaired ability to do so leads to self-judgment(R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, 2011). So, if mindfulness can alleviate this impairment, and improve self-perception, then it creates a positive feedback loop of mental health improving sexual function which in turn improves mental health. Since improved interoception (ability to sense inside the body) is suspected to be involved in this process, the insula of the brain, which has been implicated to play a major role in interoception(Giuliani et al., 2011), likely plays a role in the physiologic change that occurs. For reasons like the ones in my previous post, the insula is also regarded as a possible neuronal area related to consciousness(Craig, 2009). As it relates to sexual function, it is possible that improved insula-mediated increase in interoceptive ability from various mindfulness exercises contributed to the observed improved concordance between genital and subjective arousal after MBST(Brotto et al., 2016). This theory is reinforced by the observation that the insula increases in size following mindfulness meditation practices(Hölzel et al., 2011; Lazar et al., 2005). Indicating that because mindfulness meditation is oriented around the attentive observation of internal stimuli, the brain area involved is strengthened and grows. This allows for greater interoception in all cases, including sexual stimuli, thereby improving sexual function. Conclusion Exercise, social relationships, meditation, diet, sleep, and sex are fundamental aspects of human life. When looking back onto ancient human life, all of these aspects were fundamental to our health and prosperity. What was true then is still true now. Unsurprisingly, scientist commonly agree that safe sexual activity is an important aspect of maintaining general well-being and health. There have been studies that suggested that the more sex you have, the longer you may live. Unfortunately, the stresses of modern-day life, and the associated manifestations of self-judgment, lack of perceived self-worth, and unrealistic standards of beauty and sexual appeal have hindered some in being able to fully experience and practice a healthy sex life. Therefore, it is important to consider how other healthy life practices, such as meditation, are not only important in their own right, but are important because they may foster other healthy life habits in other areas, such as sexual activity. To calm the mind and rid it of our unconstructive ruminative thoughts once again is shown to be crucial to achieving a life of mental and physical well-being and health. Let us free our minds, free our hearts, and enjoy the present and our lives for all of its worth and beauty. References Adam, F., de Sutter, P., Day, J., & Grimm, E. (2020). A Randomized Study Comparing Video-Based Mindfulness-Based Cognitive Therapy With Video-Based Traditional Cognitive Behavioral Therapy in a Sample of Women Struggling to Achieve Orgasm. Journal of Sexual Medicine, 17(2), 312–324. https://doi.org/10.1016/j.jsxm.2019.10.022 Bishop, S. R., Lau, M., Shapiro, S., Carlson, L., Anderson, N. D., Carmody, J., Segal, Z. v., Abbey, S., Speca, M., Velting, D., & Devins, G. (2006). Mindfulness: A Proposed Operational Definition. Clinical Psychology: Science and Practice, 11(3), 230–241. https://doi.org/10.1093/clipsy.bph077 Brody, S. (2006). Blood pressure reactivity to stress is better for people who recently had penile-vaginal intercourse than for people who had other or no sexual activity. Biological Psychology, 71(2), 214–222. https://doi.org/10.1016/j.biopsycho.2005.03.005 Brotto, L. A., & Basson, R. (2014). Group mindfulness-based therapy significantly improves sexual desire in women. Behaviour Research and Therapy, 57(1), 43–54. https://doi.org/10.1016/j.brat.2014.04.001 Brotto, L. A., Chivers, M. L., Millman, R. D., & Albert, A. (2016). Mindfulness-Based Sex Therapy Improves Genital-Subjective Arousal Concordance in Women With Sexual Desire/Arousal Difficulties. Archives of Sexual Behavior, 45(8), 1907–1921. https://doi.org/10.1007/s10508-015-0689-8 Brotto, L. A., & Goldmeier, D. (2015). Mindfulness Interventions for Treating Sexual Dysfunctions: The Gentle Science of Finding Focus in a Multitask World. Journal of Sexual Medicine, 12(8), 1687–1689. https://doi.org/10.1111/jsm.12941 Craig, A. D. B. (2009). How do you feel — now? The anterior insula and human awareness. 10(January). Diamond, L. M., & Huebner, D. M. (2012). Is good sex good for you? Rethinking sexuality and health. Social and Personality Psychology Compass, 6(1), 54–69. https://doi.org/10.1111/j.1751-9004.2011.00408.x Giles, G. G., Severi, G., English, D. R., Mccredie, M. R. E., Borland, R., Boyle, P., & Hopper, J. L. (2003). Sexual factors and prostate cancer. BJU International, 92(3), 211–216. https://doi.org/10.1046/j.1464-410X.2003.04319.x Giuliani, N. R., Drabant, E. M., Bhatnagar, R., & Gross, J. J. (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. NeuroImage, 58(1), 10–15. https://doi.org/10.1016/J.NEUROIMAGE.2011.06.028 Hölzel, B. K., Lazar, S. W., Gard, T., Schuman-Olivier, Z., Vago, D. R., & Ott, U. (2011). How Does Mindfulness Meditation Work? Proposing Mechanisms of Action From a Conceptual and Neural Perspective. Perspectives on Psychological Science, 6(6), 537–559. https://doi.org/10.1177/1745691611419671 Jannini, E. A., Fisher, W. A., Bitzer, J., & McMahon, C. G. (2009). Is sex just fun? How sexual activity improves health. Journal of Sexual Medicine, 6(10), 2640–2648. https://doi.org/10.1111/j.1743-6109.2009.01477.x Lazar, S. W., Kerr, C. E., Wasserman, R. H., Gray, J. R., Greve, D. N., Treadway, M. T., McGarvey, M., Quinn, B. T., Dusek, J. A., Benson, H., Rauch, S. L., Moore, C. I., & Fischl, B. (2005). Meditation experience is associated with increased cortical thickness. Neuroreport, 16(17), 1893–1897. https://doi.org/10.1097/01.wnr.0000186598.66243.19 Leiblum, S. (1983). Vaginal Atrophy in the Postmenopausal Woman. Jama, 249(16), 2195. https://doi.org/10.1001/jama.1983.03330400041022 Leitzmann, M. F., Platz, E. A., Stampfer, M. J., Willett, W. C., & Giovannucci, E. (2004). Ejaculation Frequency and Subsequent Risk of Prostate Cancer. Journal of the American Medical Association, 291(13), 1578–1586. https://doi.org/10.1001/jama.291.13.1578 Lindau, S. T., & Gavrilova, N. (2010). Sex, health, and years of sexually active life gained due to good health: Evidence from two US population based cross sectional surveys of ageing. BMJ (Online), 340(7746), 580. https://doi.org/10.1136/bmj.c810 Mollaioli, D., Sansone, A., Ciocca, G., Limoncin, E., Colonnello, E., di Lorenzo, G., & Jannini, E. A. (2021). Benefits of Sexual Activity on Psychological, Relational, and Sexual Health During the COVID-19 Breakout. Journal of Sexual Medicine, 18(1), 35–49. https://doi.org/10.1016/j.jsxm.2020.10.008 Nobre, P. J., & Pinto-Gouveia, J. (2006). Emotions during sexual activity: Differences between sexually functional and dysfunctional men and women. Archives of Sexual Behavior, 35(4), 491–499. https://doi.org/10.1007/s10508-006-9047-1 Paterson, L. Q. P., Handy, A. B., & Brotto, L. A. (2017). A Pilot Study of Eight-Session Mindfulness-Based Cognitive Therapy Adapted for Women’s Sexual Interest/Arousal Disorder. Journal of Sex Research, 54(7), 850–861. https://doi.org/10.1080/00224499.2016.1208800 R. Gina Silverstein, BA, Anne-Catharine H. Brown, Harold D. Roth, PhD, and Willoughby B. Britton, P. (2011). Effects of Mindfulness Training on Body Awareness to Sexual Stimuli: Implications for Female Sexual Dysfunction. Psychosom Med., 23(1), 1–7. https://doi.org/10.1097/PSY.0b013e318234e628.Effects Smith, G. D., Frankel, S., & Yarnell, J. (1997). Sex and death: Are they related? Findings from the Caerphilly cohort study. BMJ, 315(7123), 1641–1644. https://doi.org/10.1136/bmj.315.7123.1641 @ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04Dose: ``` 30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F) ``` Instructions: 1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer. 2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds. 3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase. 4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds. 5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds. 6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction. 7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds. 8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper. 9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
@ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04Dose: ``` 30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F) ``` Instructions: 1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer. 2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds. 3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase. 4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds. 5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds. 6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction. 7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds. 8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper. 9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction. @ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay. @ fd06f542:8d6d54cd
2025-03-31 02:07:43## 什么是nostrbook? ----- nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。 查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。 整个网站技术不会占用部署服务器太多的存储空间,可以实现轻量级部署。 任何人可以部署服务器,或者本地部署 查看本站所有的书籍。 ## nostrbook 可以服务哪些人? ----- * 开发者,如果你想二次开发,看[第一章、开发者指南](/01.md) * 写书作者,看[第二章、使用教程](/02.md) * 读者 你就直接点开看。 ## nostrbook未来如何发展? ----- * 可能会增加 blog功能,有些时候你就想随心写点日志,那么用blog功能也可以。 * 点赞互动、留言功能。
@ fd06f542:8d6d54cd
2025-03-31 02:07:43## 什么是nostrbook? ----- nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。 查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。 整个网站技术不会占用部署服务器太多的存储空间,可以实现轻量级部署。 任何人可以部署服务器,或者本地部署 查看本站所有的书籍。 ## nostrbook 可以服务哪些人? ----- * 开发者,如果你想二次开发,看[第一章、开发者指南](/01.md) * 写书作者,看[第二章、使用教程](/02.md) * 读者 你就直接点开看。 ## nostrbook未来如何发展? ----- * 可能会增加 blog功能,有些时候你就想随心写点日志,那么用blog功能也可以。 * 点赞互动、留言功能。 @ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End!
@ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End! @ fd06f542:8d6d54cd
2025-03-31 01:55:18## 什么是nostrbook? ----- nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。 查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。整个网站技术无须部署服务器占用太多的存储空间。 可以实现轻量级部署。
@ fd06f542:8d6d54cd
2025-03-31 01:55:18## 什么是nostrbook? ----- nostrbook 是基于nostr 社区技术存储在 nostr relay server上的长文(30023)文章。 查看浏览,采用的是 [docsify](https://docsify.js.org/#/) 技术。整个网站技术无须部署服务器占用太多的存储空间。 可以实现轻量级部署。 @ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future! @ fd06f542:8d6d54cd
2025-03-31 01:45:36{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/232dd9c092e023beecb5410052bd48add702765258dcc66f176a56f02b09cf6a.webp","title":"NostrBook站点日记","author":"nostrbook"}
@ fd06f542:8d6d54cd
2025-03-31 01:45:36{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/232dd9c092e023beecb5410052bd48add702765258dcc66f176a56f02b09cf6a.webp","title":"NostrBook站点日记","author":"nostrbook"} @ 866e0139:6a9334e5
2025-04-06 03:51:00*** **Autor:** **[Nicolas Lindt.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Während die Kriegstreiber in Europa gegen Russland zum Angriff blasen, mit einem «letzten Sommer in Frieden» drohen, Bodentruppen mobilisieren und das Vermögen der Völker in todbringende Waffen umsetzen wollen - während also Europa aus zwei Weltkriegen nichts gelernt hat und einen dritten entzünden will, erinnere ich mich an ein Gespräch, das ich vor etlichen Jahren mit meinem jüngeren Sohn geführt habe. Auf einer Wanderung zur Scheidegg – ein Aussichtspunkt oberhalb unseres Dorfes – fragte mich Alexis, ob ich an die Möglichkeit eines Dritten Weltkrieges glaube. Seit einiger Zeit schon hatte er sich Gedanken zum Krieg gemacht, weil er inzwischen aus dem Schulunterricht wusste, dass Krieg nicht dasselbe ist wie der Krieg, den ihm seine Playstation zeigte. Das Thema ließ Alexis nicht los, und auch mich ließ er damit nicht los. Immer wieder musste ich ihm vom Zweiten Weltkrieg erzählen, von Hitler und Stalin, von der Judenverfolgung, vom Eroberungsfeldzug der Wehrmacht und von den Alliierten, als sie an der Küste der Normandie landeten. Während wir in den Wald abbogen und dem Wanderweg folgten, fragte mein Sohn, wer denn schlimmer gewesen sei, die Nationalsozialisten oder die Kommunisten? Und als er auf eine Pyramide gefällter Baumstämme kletterte, erklärte ich ihm, warum die Amerikaner gemeinsame Sache mit Stalin machten, obwohl doch auch Stalin viele Millionen umbringen liess. Ich versuchte ihm begreiflich zu machen, warum der Feind meines Feindes im Kriegsfall mein Freund ist. Wir traten auf eine Wiese hinaus, die Sonne stach durch die Wolken hervor, und ich legte meinem Sohn dar, dass Stalin zur Befreiung Europas von Hitlerdeutschland massgeblich beitrug. Ich erzählte ihm, wie die Deutschen nach der Niederlage bei Stalingrad vom Kriegsglück verlassen wurden, und Alexis hörte mir gebannt zu. Er schwieg einen Augenblick. Über der Lichtung lag eine große Ruhe. Nur ein paar Vögel zwitscherten. Wir waren ganz allein. «Heisst Stalingrad wirklich so?» fragte mein Sohn in die Stille hinein. Er merkte gar nicht, wo wir uns gerade befanden. Der Frieden, der uns umgab, hatte für ihn keine Bedeutung. Ohne unser Gespräch hätte er sich gelangweilt. Es ist das Vorrecht der Jugend, dass sie sich langweilen darf. Ich verstand meinen Sohn. Viel mehr als unsere Wanderung interessierte ihn der Fortgang des Krieges. «Stalingrad heisst wieder Wolgograd», beantwortete ich seine Frage. «Aber schau doch lieber, wie schön es hier ist!» Alexis fand es auch schön. Er gönnte mir eine kurze Gefechtspause, doch schon nach der nächsten Biegung befanden wir uns wieder mitten im Kampfgebiet. Der Geschützdonner der Kriegsjahre 39-45 begleitete uns während des ganzen restlichen Aufstiegs. Alexis fragte, ich gab ihm Antwort. Ich liebte es, ihm zu antworten, denn der Weltkrieg fesselt auch mich, und als ich ein Kind war, habe ich meinem Vater dieselben Fragen gestellt. Der Krieg, so schrecklich er ist, übt eine seltsame Anziehung aus. Die Menschen im Westen sind von ihm fasziniert. Sie sehnen sich insgeheim nach dem Krieg, weil sie wie Teenager sind. Sie wünschen sich, ohne sich dessen bewusst zu sein, den Ausnahmezustand herbei, weil der Frieden sie langweilt. Weil sie nicht wissen, was Krieg wirklich ist. Noch bevor Deutschland kapitulierte, erreichten wir unser Ziel. Von der Scheidegg blickten wir hinab auf den See und das weite Land. Ich bestaunte das Panorama der Alpen, so wie ich es schon hunderte Male bewundert hatte. Ich werde es immer bestaunen. Es langweilt mich nie. «Du hast mir noch keine Antwort gegeben», erinnerte mich Alexis. «Glaubst du, es gibt irgendwann einen Dritten Weltkrieg?» «Ich hoffe es nicht», entgegnete ich, «ich hoffe, die Menschen vergessen nie, dass der Friede schöner ist als der Krieg.» Mit einer ausschweifenden Geste über den Kranz der Berge, der uns umgab, zeigte ich meinem Sohn, was ich meinte. Ich zeigte ihm die Schönheit des Friedens. *Dieser Artikel erschien zuerst als Kolumne im Schweizer* ***[Zeitpunkt-Magazin.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)*** *** *Nicolas Lindt (\*1954) war Musikjournalist, Tagesschau-Reporter und Gerichtskolumnist, bevor er in seinen Büchern wahre Geschichten zu erzählen begann. In seinem zweiten Beruf gestaltet er freie Trauungen, Taufen und Abdankungen. Der Autor lebt mit seiner Familie in Wald und in Segnas. Hier finden Sie die* ***[Bücher](https://www.exlibris.ch/de/suche/?qs=Nicolas%20Lindt)*** *von Nicolas Lindt. Der Fünf Minuten-Podcast «Mitten im Leben» von Nicolas Lindt ist zu finden auf Spotify, iTunes und Audible, letzte Folge* ***[hier.](https://terra-nova-podcast-1.podigee.io/27-die-einsamkeit-des-schriftstellers#t=1)*** ***Neuestes Buch:*** *«Orwells Einsamkeit - sein Leben, ‚1984‘ und mein Weg zu einem persönlichen Denken». Erhältlich im Buchhandel - zum Beispiel bei [Ex Libris](https://www.exlibris.ch/de/buecher-buch/deutschsprachige-buecher/nicolas-lindt/orwells-einsamkeit/id/9783758342561/?srsltid=AfmBOoqEFJWFsnacUaCEWWTxzL-qnVO6cvqHc8FvIno_SpDZ42zasQmm) oder [Orell Füssli](https://www.orellfuessli.ch/shop/home/artikeldetails/A1073365208?ProvID=10917751\&gad_source=1\&gbraid=0AAAAADpVXc6fbYzpLMiQ1L1NDN25Z-K7_\&gclid=CjwKCAjwyfe4BhAWEiwAkIL8sBVh5kUOJToqpPi-5ByDkwKJYXCe_PNlQPbzkZQ1Cjw1dluamSkRhxoCeWMQAvD_BwE)* *Alle weiteren Informationen: [www.nicolaslindt.ch](http://www.nicolaslindt.ch/)* *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):**  **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
@ 866e0139:6a9334e5
2025-04-06 03:51:00*** **Autor:** **[Nicolas Lindt.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Während die Kriegstreiber in Europa gegen Russland zum Angriff blasen, mit einem «letzten Sommer in Frieden» drohen, Bodentruppen mobilisieren und das Vermögen der Völker in todbringende Waffen umsetzen wollen - während also Europa aus zwei Weltkriegen nichts gelernt hat und einen dritten entzünden will, erinnere ich mich an ein Gespräch, das ich vor etlichen Jahren mit meinem jüngeren Sohn geführt habe. Auf einer Wanderung zur Scheidegg – ein Aussichtspunkt oberhalb unseres Dorfes – fragte mich Alexis, ob ich an die Möglichkeit eines Dritten Weltkrieges glaube. Seit einiger Zeit schon hatte er sich Gedanken zum Krieg gemacht, weil er inzwischen aus dem Schulunterricht wusste, dass Krieg nicht dasselbe ist wie der Krieg, den ihm seine Playstation zeigte. Das Thema ließ Alexis nicht los, und auch mich ließ er damit nicht los. Immer wieder musste ich ihm vom Zweiten Weltkrieg erzählen, von Hitler und Stalin, von der Judenverfolgung, vom Eroberungsfeldzug der Wehrmacht und von den Alliierten, als sie an der Küste der Normandie landeten. Während wir in den Wald abbogen und dem Wanderweg folgten, fragte mein Sohn, wer denn schlimmer gewesen sei, die Nationalsozialisten oder die Kommunisten? Und als er auf eine Pyramide gefällter Baumstämme kletterte, erklärte ich ihm, warum die Amerikaner gemeinsame Sache mit Stalin machten, obwohl doch auch Stalin viele Millionen umbringen liess. Ich versuchte ihm begreiflich zu machen, warum der Feind meines Feindes im Kriegsfall mein Freund ist. Wir traten auf eine Wiese hinaus, die Sonne stach durch die Wolken hervor, und ich legte meinem Sohn dar, dass Stalin zur Befreiung Europas von Hitlerdeutschland massgeblich beitrug. Ich erzählte ihm, wie die Deutschen nach der Niederlage bei Stalingrad vom Kriegsglück verlassen wurden, und Alexis hörte mir gebannt zu. Er schwieg einen Augenblick. Über der Lichtung lag eine große Ruhe. Nur ein paar Vögel zwitscherten. Wir waren ganz allein. «Heisst Stalingrad wirklich so?» fragte mein Sohn in die Stille hinein. Er merkte gar nicht, wo wir uns gerade befanden. Der Frieden, der uns umgab, hatte für ihn keine Bedeutung. Ohne unser Gespräch hätte er sich gelangweilt. Es ist das Vorrecht der Jugend, dass sie sich langweilen darf. Ich verstand meinen Sohn. Viel mehr als unsere Wanderung interessierte ihn der Fortgang des Krieges. «Stalingrad heisst wieder Wolgograd», beantwortete ich seine Frage. «Aber schau doch lieber, wie schön es hier ist!» Alexis fand es auch schön. Er gönnte mir eine kurze Gefechtspause, doch schon nach der nächsten Biegung befanden wir uns wieder mitten im Kampfgebiet. Der Geschützdonner der Kriegsjahre 39-45 begleitete uns während des ganzen restlichen Aufstiegs. Alexis fragte, ich gab ihm Antwort. Ich liebte es, ihm zu antworten, denn der Weltkrieg fesselt auch mich, und als ich ein Kind war, habe ich meinem Vater dieselben Fragen gestellt. Der Krieg, so schrecklich er ist, übt eine seltsame Anziehung aus. Die Menschen im Westen sind von ihm fasziniert. Sie sehnen sich insgeheim nach dem Krieg, weil sie wie Teenager sind. Sie wünschen sich, ohne sich dessen bewusst zu sein, den Ausnahmezustand herbei, weil der Frieden sie langweilt. Weil sie nicht wissen, was Krieg wirklich ist. Noch bevor Deutschland kapitulierte, erreichten wir unser Ziel. Von der Scheidegg blickten wir hinab auf den See und das weite Land. Ich bestaunte das Panorama der Alpen, so wie ich es schon hunderte Male bewundert hatte. Ich werde es immer bestaunen. Es langweilt mich nie. «Du hast mir noch keine Antwort gegeben», erinnerte mich Alexis. «Glaubst du, es gibt irgendwann einen Dritten Weltkrieg?» «Ich hoffe es nicht», entgegnete ich, «ich hoffe, die Menschen vergessen nie, dass der Friede schöner ist als der Krieg.» Mit einer ausschweifenden Geste über den Kranz der Berge, der uns umgab, zeigte ich meinem Sohn, was ich meinte. Ich zeigte ihm die Schönheit des Friedens. *Dieser Artikel erschien zuerst als Kolumne im Schweizer* ***[Zeitpunkt-Magazin.](https://www.zeitpunkt.ch/die-langeweile-des-friedens)*** *** *Nicolas Lindt (\*1954) war Musikjournalist, Tagesschau-Reporter und Gerichtskolumnist, bevor er in seinen Büchern wahre Geschichten zu erzählen begann. In seinem zweiten Beruf gestaltet er freie Trauungen, Taufen und Abdankungen. Der Autor lebt mit seiner Familie in Wald und in Segnas. Hier finden Sie die* ***[Bücher](https://www.exlibris.ch/de/suche/?qs=Nicolas%20Lindt)*** *von Nicolas Lindt. Der Fünf Minuten-Podcast «Mitten im Leben» von Nicolas Lindt ist zu finden auf Spotify, iTunes und Audible, letzte Folge* ***[hier.](https://terra-nova-podcast-1.podigee.io/27-die-einsamkeit-des-schriftstellers#t=1)*** ***Neuestes Buch:*** *«Orwells Einsamkeit - sein Leben, ‚1984‘ und mein Weg zu einem persönlichen Denken». Erhältlich im Buchhandel - zum Beispiel bei [Ex Libris](https://www.exlibris.ch/de/buecher-buch/deutschsprachige-buecher/nicolas-lindt/orwells-einsamkeit/id/9783758342561/?srsltid=AfmBOoqEFJWFsnacUaCEWWTxzL-qnVO6cvqHc8FvIno_SpDZ42zasQmm) oder [Orell Füssli](https://www.orellfuessli.ch/shop/home/artikeldetails/A1073365208?ProvID=10917751\&gad_source=1\&gbraid=0AAAAADpVXc6fbYzpLMiQ1L1NDN25Z-K7_\&gclid=CjwKCAjwyfe4BhAWEiwAkIL8sBVh5kUOJToqpPi-5ByDkwKJYXCe_PNlQPbzkZQ1Cjw1dluamSkRhxoCeWMQAvD_BwE)* *Alle weiteren Informationen: [www.nicolaslindt.ch](http://www.nicolaslindt.ch/)* *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):**  **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home) @ 52524fbb:ae4025dc
2025-04-05 22:03:45In our world being digitally driven today, the concepts of decentralization due to freedom from traditional media's censorship drive is gaining significant attention, promising greater autonomy and security. Two Critical examples of this movement are Bitcoin in the world of finance and YakiHonne in the world of media. While serving different primary purposes, their core philosophies and technological foundations reveal a powerful union, pointing towards a future where finance and media are more open and accessible  ## Bitcoin: Decentralizing the World of Finance Bitcoin, launched in 2009 stands as the pinnacle of decentralized digital currencies. Unlike traditional currencies controlled by central banks, Bitcoin operates on a distributed ledger technology known as the blockchain. The public and transparent record of all Bitcoin transactions is maintained by a global network of users, removing the need for middle transacts like banks to validate and process payments. ### Key Aspects of Bitcoin's Decentralization: Below are some of the reasons why Bitcoin stands at the pinnacle of finance in today's world 1. No Central Authority: Bitcoin is not controlled by anyone, making it resistant to censorship 2. Peer-to-Peer Transactions: Users can send and receive Bitcoin directly with each other, reducing transaction costs and time. 3. Transparency: All transactions are recorded on the public blockchain, enhancing trust and verifiability. 4. Security: Cryptographic techniques secure the network and prevent tampering with transactions. Bitcoin's success has demonstrated the potential of decentralized finance to offer numerous benefits, including greater financial inclusion, lower fees, increased transparency, and enhanced control over one's assets.  ## YakiHonne: Decentralizing the Landscape of Media YakiHonne emerges as a "Bitcoin-native decentralized social protocol" built upon the Nostr protocol. Its mission is to create a censorship-resistant media and social network, aligning with the core reasons of decentralization championed by Bitcoin. ### Understanding YakiHonne: 1. Built on Nostr: YakiHonne leverages Nostr protocol, an open and simple protocol for decentralized message transmission designed to resist censorship. Nostr operates without central servers; instead, users connect to various independent relays to send and receive data. 2. Decentralized Media Infrastructure: YakiHonne aims to decentralize content creation, curation, publishing, and reporting, empowering individuals to share information freely. 3. Bitcoin Integration: YakiHonne integrates Bitcoin functionalities. A notable feature is "zaps," which utilizes the Lightning Network, a layer-2 scaling solution for Bitcoin enabling fast and low-cost transactions, for tipping and value exchange within the platform 4. Community Focus: YakiHonne fosters a community of Bitcoiners and individuals interested in decentralized media, promoting open dialogue and the exchange of ideas.  ### The Emerging Union: A Decentralized Future The convergence of Bitcoin and YakiHonne represents a powerful step towards an active decentralized future for both finance and media. Their union offers amazing advantages such as: 1. Shared Principles: Both Bitcoin and YakiHonne are firmly embedded in the principles of decentralization, user autonomy, and resistance to censorship. This shared purpose creates a natural alignment and strengthens the overall movement towards a more open and censorship free digital world. 2. Empowering Individuals: By decentralizing finance and media, both platforms empower individuals. Bitcoin gives users control over their money, while YakiHonne provides a space for uncensored expression and information sharing. 3. Encouraging Community Building: YakiHonne serves as a social layer for the Bitcoin ecosystem and beyond, providing a space for discussions, collaborations, and sharing of information related to decentralized technologies. This strengthens the community around these ideas and promotes further adoption.  ### Potential Usage and Future Implications: The Union between Bitcoin and YakiHonne could lead to various innovative use cases such as:: 1. Direct Monetization for Content Creators: Writers, artists, and other content creators on YakiHonne could directly receive Bitcoin tips (zaps) from their audience, bypassing the need for centralized platforms that often take a significant cut of the revenue. 2. Decentralized Journalism and Reporting: YakiHonne could serve as a platform for independent journalists to publish their work without fear of censorship, with readers directly supporting their efforts through Bitcoin 3. Integration with Other Bitcoin Services: As the ecosystem evolves, YakiHonne could potentially integrate with other Bitcoin-related services, further enhancing its functionality and utility.
@ 52524fbb:ae4025dc
2025-04-05 22:03:45In our world being digitally driven today, the concepts of decentralization due to freedom from traditional media's censorship drive is gaining significant attention, promising greater autonomy and security. Two Critical examples of this movement are Bitcoin in the world of finance and YakiHonne in the world of media. While serving different primary purposes, their core philosophies and technological foundations reveal a powerful union, pointing towards a future where finance and media are more open and accessible  ## Bitcoin: Decentralizing the World of Finance Bitcoin, launched in 2009 stands as the pinnacle of decentralized digital currencies. Unlike traditional currencies controlled by central banks, Bitcoin operates on a distributed ledger technology known as the blockchain. The public and transparent record of all Bitcoin transactions is maintained by a global network of users, removing the need for middle transacts like banks to validate and process payments. ### Key Aspects of Bitcoin's Decentralization: Below are some of the reasons why Bitcoin stands at the pinnacle of finance in today's world 1. No Central Authority: Bitcoin is not controlled by anyone, making it resistant to censorship 2. Peer-to-Peer Transactions: Users can send and receive Bitcoin directly with each other, reducing transaction costs and time. 3. Transparency: All transactions are recorded on the public blockchain, enhancing trust and verifiability. 4. Security: Cryptographic techniques secure the network and prevent tampering with transactions. Bitcoin's success has demonstrated the potential of decentralized finance to offer numerous benefits, including greater financial inclusion, lower fees, increased transparency, and enhanced control over one's assets.  ## YakiHonne: Decentralizing the Landscape of Media YakiHonne emerges as a "Bitcoin-native decentralized social protocol" built upon the Nostr protocol. Its mission is to create a censorship-resistant media and social network, aligning with the core reasons of decentralization championed by Bitcoin. ### Understanding YakiHonne: 1. Built on Nostr: YakiHonne leverages Nostr protocol, an open and simple protocol for decentralized message transmission designed to resist censorship. Nostr operates without central servers; instead, users connect to various independent relays to send and receive data. 2. Decentralized Media Infrastructure: YakiHonne aims to decentralize content creation, curation, publishing, and reporting, empowering individuals to share information freely. 3. Bitcoin Integration: YakiHonne integrates Bitcoin functionalities. A notable feature is "zaps," which utilizes the Lightning Network, a layer-2 scaling solution for Bitcoin enabling fast and low-cost transactions, for tipping and value exchange within the platform 4. Community Focus: YakiHonne fosters a community of Bitcoiners and individuals interested in decentralized media, promoting open dialogue and the exchange of ideas.  ### The Emerging Union: A Decentralized Future The convergence of Bitcoin and YakiHonne represents a powerful step towards an active decentralized future for both finance and media. Their union offers amazing advantages such as: 1. Shared Principles: Both Bitcoin and YakiHonne are firmly embedded in the principles of decentralization, user autonomy, and resistance to censorship. This shared purpose creates a natural alignment and strengthens the overall movement towards a more open and censorship free digital world. 2. Empowering Individuals: By decentralizing finance and media, both platforms empower individuals. Bitcoin gives users control over their money, while YakiHonne provides a space for uncensored expression and information sharing. 3. Encouraging Community Building: YakiHonne serves as a social layer for the Bitcoin ecosystem and beyond, providing a space for discussions, collaborations, and sharing of information related to decentralized technologies. This strengthens the community around these ideas and promotes further adoption.  ### Potential Usage and Future Implications: The Union between Bitcoin and YakiHonne could lead to various innovative use cases such as:: 1. Direct Monetization for Content Creators: Writers, artists, and other content creators on YakiHonne could directly receive Bitcoin tips (zaps) from their audience, bypassing the need for centralized platforms that often take a significant cut of the revenue. 2. Decentralized Journalism and Reporting: YakiHonne could serve as a platform for independent journalists to publish their work without fear of censorship, with readers directly supporting their efforts through Bitcoin 3. Integration with Other Bitcoin Services: As the ecosystem evolves, YakiHonne could potentially integrate with other Bitcoin-related services, further enhancing its functionality and utility. @ dbc27e2e:b1dd0b0b
2025-04-05 20:44:00This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain.  Dose: 20g coffee (Coarse ground coffee) 300mL water (92°C / 197.6°F) Time: 3:30 Instructions: 1. Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.) 2. Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.) 3. Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour) 4. Pour 4: 2:10 > 60mL 5. Pour 5: 2:40 > 60mL 6. Remove the V60 at 3:30
@ dbc27e2e:b1dd0b0b
2025-04-05 20:44:00This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain.  Dose: 20g coffee (Coarse ground coffee) 300mL water (92°C / 197.6°F) Time: 3:30 Instructions: 1. Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.) 2. Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.) 3. Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour) 4. Pour 4: 2:10 > 60mL 5. Pour 5: 2:40 > 60mL 6. Remove the V60 at 3:30 @ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall. @ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007 @ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
@ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen. @ 8bf63b70:64ac852f
2025-04-05 18:48:17VIP8888 là một nền tảng giải trí trực tuyến đặc biệt, được thiết kế để mang lại những trải nghiệm tuyệt vời và khác biệt cho người dùng. Với giao diện dễ sử dụng và tính năng linh hoạt, VIP8888 mang đến cho người tham gia một loạt các trò chơi hấp dẫn và thú vị, đáp ứng nhu cầu giải trí đa dạng của mọi đối tượng. Những trò chơi trên nền tảng này được phát triển để không chỉ giúp người chơi thư giãn mà còn thách thức khả năng tư duy và sáng tạo. VIP8888 không ngừng cải tiến và cập nhật các trò chơi mới mẻ, đảm bảo rằng người dùng sẽ luôn cảm thấy thích thú mỗi lần tham gia. Mỗi hoạt động trên nền tảng đều được chăm chút kỹ lưỡng, mang lại trải nghiệm mượt mà và chất lượng, khiến người dùng không thể rời mắt khỏi màn hình. Một yếu tố nổi bật khác của VIP8888 là cộng đồng người dùng thân thiện và gắn kết. Nền tảng này không chỉ là nơi để giải trí mà còn là không gian để mọi người giao lưu, kết bạn và chia sẻ những sở thích chung. Các tính năng xã hội của <a href="https://vip8888.site">VIP8888</a> giúp người tham gia dễ dàng kết nối với những người có cùng đam mê, tạo nên một môi trường giao lưu sôi động và tích cực. Những cuộc thảo luận nhóm, sự kiện cộng đồng và các hoạt động tương tác không chỉ giúp người dùng cảm thấy gắn bó với nền tảng mà còn giúp họ học hỏi từ những người khác. Sự gắn kết này không chỉ mang lại giá trị giải trí mà còn thúc đẩy sự sáng tạo và phát triển mối quan hệ xã hội trong cộng đồng. Bên cạnh các trò chơi và hoạt động giao lưu, VIP8888 cũng chú trọng đến việc cập nhật và cải tiến các tính năng để duy trì sự hấp dẫn và sáng tạo. Nền tảng này luôn tạo ra các tính năng mới mẻ, giúp người dùng có cơ hội khám phá và thử thách bản thân trong mỗi lần tham gia. Việc không ngừng đổi mới và nâng cấp đã giúp VIP8888 duy trì được sự yêu thích của cộng đồng, đồng thời tạo ra một không gian giải trí luôn mới mẻ và thú vị. Chính nhờ vào sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục, VIP8888 đã khẳng định vị thế của mình là một lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng trực tuyến năng động, sáng tạo và luôn phát triển.
@ 8bf63b70:64ac852f
2025-04-05 18:48:17VIP8888 là một nền tảng giải trí trực tuyến đặc biệt, được thiết kế để mang lại những trải nghiệm tuyệt vời và khác biệt cho người dùng. Với giao diện dễ sử dụng và tính năng linh hoạt, VIP8888 mang đến cho người tham gia một loạt các trò chơi hấp dẫn và thú vị, đáp ứng nhu cầu giải trí đa dạng của mọi đối tượng. Những trò chơi trên nền tảng này được phát triển để không chỉ giúp người chơi thư giãn mà còn thách thức khả năng tư duy và sáng tạo. VIP8888 không ngừng cải tiến và cập nhật các trò chơi mới mẻ, đảm bảo rằng người dùng sẽ luôn cảm thấy thích thú mỗi lần tham gia. Mỗi hoạt động trên nền tảng đều được chăm chút kỹ lưỡng, mang lại trải nghiệm mượt mà và chất lượng, khiến người dùng không thể rời mắt khỏi màn hình. Một yếu tố nổi bật khác của VIP8888 là cộng đồng người dùng thân thiện và gắn kết. Nền tảng này không chỉ là nơi để giải trí mà còn là không gian để mọi người giao lưu, kết bạn và chia sẻ những sở thích chung. Các tính năng xã hội của <a href="https://vip8888.site">VIP8888</a> giúp người tham gia dễ dàng kết nối với những người có cùng đam mê, tạo nên một môi trường giao lưu sôi động và tích cực. Những cuộc thảo luận nhóm, sự kiện cộng đồng và các hoạt động tương tác không chỉ giúp người dùng cảm thấy gắn bó với nền tảng mà còn giúp họ học hỏi từ những người khác. Sự gắn kết này không chỉ mang lại giá trị giải trí mà còn thúc đẩy sự sáng tạo và phát triển mối quan hệ xã hội trong cộng đồng. Bên cạnh các trò chơi và hoạt động giao lưu, VIP8888 cũng chú trọng đến việc cập nhật và cải tiến các tính năng để duy trì sự hấp dẫn và sáng tạo. Nền tảng này luôn tạo ra các tính năng mới mẻ, giúp người dùng có cơ hội khám phá và thử thách bản thân trong mỗi lần tham gia. Việc không ngừng đổi mới và nâng cấp đã giúp VIP8888 duy trì được sự yêu thích của cộng đồng, đồng thời tạo ra một không gian giải trí luôn mới mẻ và thú vị. Chính nhờ vào sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục, VIP8888 đã khẳng định vị thế của mình là một lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng trực tuyến năng động, sáng tạo và luôn phát triển. @ 57d1a264:69f1fee1
2025-03-29 18:02:16> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.  - - - ## 1️⃣ Introduction #### Project Overview 📌 **Product:** BlueWallet (Bitcoin Wallet) 📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience. 📌 **Role:** UX Designer 📌 **Tools Used:** Figma, Notion #### Why This Case Study? 🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**. 🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**. 🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**. This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**. - - - ## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement #### 🔹 **Current Challenges:** 1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.   2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**. 3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion. 4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult. #### 🔍 **Impact on Users:** **Higher drop-off rates** due to frustration during onboarding. **Security risks** as users skip key wallet setup steps. **Limited accessibility** for users with visual impairments. #### 📌 **Competitive Gap:** Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow      Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet. - - - ## 3️⃣ User Research & Competitive Analysis #### User Testing Findings 🔹 Conducted usability testing with **5 users** onboarding for the first time. 🔹 **Key Findings:** ✅ 3 out of 5 users **felt lost** due to missing explanations. ✅ 60% **had trouble distinguishing transaction buttons**. ✅ 80% **found the text difficult to read** due to low contrast. #### Competitive Analysis We compared BlueWallet with top crypto wallets: | Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons | 📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners. ## 📌 User Persona To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing. #### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor) 👤 **Profile:** - **Age:** 28 - **Occupation:** Freelance Digital Marketer - **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin) - **Pain Points:** - Finds **Bitcoin wallets confusing**. - - Doesnʼt understand **seed phrases & security features**. - - **Worried about losing funds** due to a lack of clarity in transactions. 📌 **Needs:** ✅ A **simple, guided** wallet setup. ✅ **Clear explanations** of security terms (without jargon). ✅ Easy-to-locate **Send/Receive buttons**. 📌 **Persona Usage in Case Study:** - Helps define **who we are designing for**. - Guides **design decisions** by focusing on user needs. #### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast) 👤 **Profile:** - **Age:** 35 - **Occupation:** UX Researcher & Accessibility Consultant - **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers) 📌 **Pain Points:** ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons. 📌 **Needs:** ✅ A **high-contrast UI** that meets **WCAG accessibility standards**. ✅ **Larger fonts & scalable UI elements** for better readability. ✅ **Keyboard & screen reader-friendly navigation** for seamless interaction. 📌 **Why This Persona Matters:** - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles. - - - ## 4️⃣ UX/UI Solutions & Design Improvements #### 📌 Before (Current Issues) ❌ Users land **directly on the wallet screen** with no instructions. ❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion. ❌ **Small fonts & low contrast** reduce readability. #### ✅ After (Proposed Fixes) ✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions. ✅ **Visually distinct transaction buttons** (color and icon changes). ✅ **WCAG-compliant text contrast & larger fonts** for better readability. #### 1️⃣ Redesigned Onboarding Flow ✅ Added a **progress indicator** so users see where they are in setup. ✅ Used **plain, non-technical language** to explain wallet creation & security. ✅ Introduced a **"Learn More" button** to educate users on security. #### 2️⃣ Accessibility Enhancements ✅ Increased **contrast ratio** for better text readability. ✅ Used **larger fonts & scalable UI elements**. ✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support). #### 3️⃣ Transaction Flow Optimization ✅ Redesigned **"Send" & "Receive" buttons** for clear distinction. ✅ Added **clearer icons & tooltips** for transaction steps. ## 5️⃣ Wireframes & Design Improvements: #### 🔹 Welcome Screen (First Screen When User Opens Wallet) **📌 Goal: Give a brief introduction & set user expectations** ✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ **"Get Started" button** → Le ads to **next step: Wallet Setup** ✅ **"Already have a wallet?"** → Import option 🔹 **Example UI Elements:** - BlueWallet Logo - **Title:** "Welcome to BlueWallet" - **Subtitle:** "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)  #### 🔹 Screen 2: Choose Wallet Type (New or Import) **📌 Goal: Let users decide how to proceed** ✅ **Two clear options:** - **Create a New Wallet** (For first-time users) - **Import Existing Wallet** (For users with a backup phrase) ✅ Brief explanation of each option 🔹 **Example UI Elements: - **Title:** "How do you want to start?" - **Buttons:** "Create New Wallet" | "Import Wallet"  #### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step) **📌 Goal: Educate users about wallet security & backups** ✅ Explain **why seed phrases are important** ✅ **Clear step-by-step instructions** on writing down & storing the phrase ✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet." ✅ **CTA:** "Generate Seed Phrase" → Next step 🔹 **Example UI Elements: - Title:** "Secure Your Wallet" - **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!" - **Button:** "Generate Seed Phrase"  ## 🔹 Screen 4: Seed Phrase Display & Confirmation **📌 Goal: Ensure users write down the phrase correctly** ✅ Display **12- or 24-word** seed phrase ✅ **“I have written it downˮ checkbox** before proceeding ✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words) 🔹 **Example UI Elements:** - **Title:** "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - **Checkbox:** "I have safely stored my phrase" - **Button:** "Continue"  ### 🔹 Screen 5: Wallet Ready! (Final Step) **📌 Goal: Confirm setup & guide users on next actions** ✅ **Success message** ("Your wallet is ready!") ✅ **Encourage first action:** - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions ✅ Short explainer: Where to find the Send/Receive buttons 🔹 **Example UI Elements:** - **Title:** "You're All Set!" - **Subtitle:** "Start using BlueWallet now." - **Buttons:** "Receive Bitcoin" | "View Wallet"  - - - ## 5️⃣ Prototype & User Testing Results 🔹 **Created an interactive prototype in Figma** to test the new experience. 🔹 **User Testing Results:** ✅ **40% faster onboarding completion time.** ✅ **90% of users found transaction buttons clearer.** 🔹 **User Feedback:** ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ - - - ## 6️⃣ Why This Matters: Key Takeaways 📌 **Impact of These UX/UI Changes:** ✅ **Reduced user frustration** by providing a step-by-step onboarding guide. ✅ **Improved accessibility** , making the wallet usable for all. ✅ **More intuitive transactions** , reducing errors. - - - ## 7️⃣ Direct link to figma file and Prototype Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1) Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1) Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&) originally posted at https://stacker.news/items/928822
@ 57d1a264:69f1fee1
2025-03-29 18:02:16> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.  - - - ## 1️⃣ Introduction #### Project Overview 📌 **Product:** BlueWallet (Bitcoin Wallet) 📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience. 📌 **Role:** UX Designer 📌 **Tools Used:** Figma, Notion #### Why This Case Study? 🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**. 🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**. 🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**. This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**. - - - ## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement #### 🔹 **Current Challenges:** 1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.   2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**. 3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion. 4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult. #### 🔍 **Impact on Users:** **Higher drop-off rates** due to frustration during onboarding. **Security risks** as users skip key wallet setup steps. **Limited accessibility** for users with visual impairments. #### 📌 **Competitive Gap:** Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow      Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet. - - - ## 3️⃣ User Research & Competitive Analysis #### User Testing Findings 🔹 Conducted usability testing with **5 users** onboarding for the first time. 🔹 **Key Findings:** ✅ 3 out of 5 users **felt lost** due to missing explanations. ✅ 60% **had trouble distinguishing transaction buttons**. ✅ 80% **found the text difficult to read** due to low contrast. #### Competitive Analysis We compared BlueWallet with top crypto wallets: | Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons | 📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners. ## 📌 User Persona To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing. #### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor) 👤 **Profile:** - **Age:** 28 - **Occupation:** Freelance Digital Marketer - **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin) - **Pain Points:** - Finds **Bitcoin wallets confusing**. - - Doesnʼt understand **seed phrases & security features**. - - **Worried about losing funds** due to a lack of clarity in transactions. 📌 **Needs:** ✅ A **simple, guided** wallet setup. ✅ **Clear explanations** of security terms (without jargon). ✅ Easy-to-locate **Send/Receive buttons**. 📌 **Persona Usage in Case Study:** - Helps define **who we are designing for**. - Guides **design decisions** by focusing on user needs. #### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast) 👤 **Profile:** - **Age:** 35 - **Occupation:** UX Researcher & Accessibility Consultant - **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers) 📌 **Pain Points:** ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons. 📌 **Needs:** ✅ A **high-contrast UI** that meets **WCAG accessibility standards**. ✅ **Larger fonts & scalable UI elements** for better readability. ✅ **Keyboard & screen reader-friendly navigation** for seamless interaction. 📌 **Why This Persona Matters:** - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles. - - - ## 4️⃣ UX/UI Solutions & Design Improvements #### 📌 Before (Current Issues) ❌ Users land **directly on the wallet screen** with no instructions. ❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion. ❌ **Small fonts & low contrast** reduce readability. #### ✅ After (Proposed Fixes) ✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions. ✅ **Visually distinct transaction buttons** (color and icon changes). ✅ **WCAG-compliant text contrast & larger fonts** for better readability. #### 1️⃣ Redesigned Onboarding Flow ✅ Added a **progress indicator** so users see where they are in setup. ✅ Used **plain, non-technical language** to explain wallet creation & security. ✅ Introduced a **"Learn More" button** to educate users on security. #### 2️⃣ Accessibility Enhancements ✅ Increased **contrast ratio** for better text readability. ✅ Used **larger fonts & scalable UI elements**. ✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support). #### 3️⃣ Transaction Flow Optimization ✅ Redesigned **"Send" & "Receive" buttons** for clear distinction. ✅ Added **clearer icons & tooltips** for transaction steps. ## 5️⃣ Wireframes & Design Improvements: #### 🔹 Welcome Screen (First Screen When User Opens Wallet) **📌 Goal: Give a brief introduction & set user expectations** ✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ **"Get Started" button** → Le ads to **next step: Wallet Setup** ✅ **"Already have a wallet?"** → Import option 🔹 **Example UI Elements:** - BlueWallet Logo - **Title:** "Welcome to BlueWallet" - **Subtitle:** "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)  #### 🔹 Screen 2: Choose Wallet Type (New or Import) **📌 Goal: Let users decide how to proceed** ✅ **Two clear options:** - **Create a New Wallet** (For first-time users) - **Import Existing Wallet** (For users with a backup phrase) ✅ Brief explanation of each option 🔹 **Example UI Elements: - **Title:** "How do you want to start?" - **Buttons:** "Create New Wallet" | "Import Wallet"  #### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step) **📌 Goal: Educate users about wallet security & backups** ✅ Explain **why seed phrases are important** ✅ **Clear step-by-step instructions** on writing down & storing the phrase ✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet." ✅ **CTA:** "Generate Seed Phrase" → Next step 🔹 **Example UI Elements: - Title:** "Secure Your Wallet" - **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!" - **Button:** "Generate Seed Phrase"  ## 🔹 Screen 4: Seed Phrase Display & Confirmation **📌 Goal: Ensure users write down the phrase correctly** ✅ Display **12- or 24-word** seed phrase ✅ **“I have written it downˮ checkbox** before proceeding ✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words) 🔹 **Example UI Elements:** - **Title:** "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - **Checkbox:** "I have safely stored my phrase" - **Button:** "Continue"  ### 🔹 Screen 5: Wallet Ready! (Final Step) **📌 Goal: Confirm setup & guide users on next actions** ✅ **Success message** ("Your wallet is ready!") ✅ **Encourage first action:** - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions ✅ Short explainer: Where to find the Send/Receive buttons 🔹 **Example UI Elements:** - **Title:** "You're All Set!" - **Subtitle:** "Start using BlueWallet now." - **Buttons:** "Receive Bitcoin" | "View Wallet"  - - - ## 5️⃣ Prototype & User Testing Results 🔹 **Created an interactive prototype in Figma** to test the new experience. 🔹 **User Testing Results:** ✅ **40% faster onboarding completion time.** ✅ **90% of users found transaction buttons clearer.** 🔹 **User Feedback:** ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ - - - ## 6️⃣ Why This Matters: Key Takeaways 📌 **Impact of These UX/UI Changes:** ✅ **Reduced user frustration** by providing a step-by-step onboarding guide. ✅ **Improved accessibility** , making the wallet usable for all. ✅ **More intuitive transactions** , reducing errors. - - - ## 7️⃣ Direct link to figma file and Prototype Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1) Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1) Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&) originally posted at https://stacker.news/items/928822 @ 57d1a264:69f1fee1
2025-03-29 17:15:17 - Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box. - If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust. - “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options. - Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic. originally posted at https://stacker.news/items/928800
@ 57d1a264:69f1fee1
2025-03-29 17:15:17 - Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box. - If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust. - “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options. - Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic. originally posted at https://stacker.news/items/928800 @ fd06f542:8d6d54cd
2025-03-30 02:16:24> __Warning__ `unrecommended`: deprecated in favor of [NIP-17](17.md) NIP-04 ====== Encrypted Direct Message ------------------------ `final` `unrecommended` `optional` A special event with kind `4`, meaning "encrypted direct message". It is supposed to have the following attributes: **`content`** MUST be equal to the base64-encoded, aes-256-cbc encrypted string of anything a user wants to write, encrypted using a shared cipher generated by combining the recipient's public-key with the sender's private-key; this appended by the base64-encoded initialization vector as if it was a querystring parameter named "iv". The format is the following: `"content": "<encrypted_text>?iv=<initialization_vector>"`. **`tags`** MUST contain an entry identifying the receiver of the message (such that relays may naturally forward this event to them), in the form `["p", "<pubkey, as a hex string>"]`. **`tags`** MAY contain an entry identifying the previous message in a conversation or a message we are explicitly replying to (such that contextual, more organized conversations may happen), in the form `["e", "<event_id>"]`. **Note**: By default in the [libsecp256k1](https://github.com/bitcoin-core/secp256k1) ECDH implementation, the secret is the SHA256 hash of the shared point (both X and Y coordinates). In Nostr, only the X coordinate of the shared point is used as the secret and it is NOT hashed. If using libsecp256k1, a custom function that copies the X coordinate must be passed as the `hashfp` argument in `secp256k1_ecdh`. See [here](https://github.com/bitcoin-core/secp256k1/blob/master/src/modules/ecdh/main_impl.h#L29). Code sample for generating such an event in JavaScript: ```js import crypto from 'crypto' import * as secp from '@noble/secp256k1' let sharedPoint = secp.getSharedSecret(ourPrivateKey, '02' + theirPublicKey) let sharedX = sharedPoint.slice(1, 33) let iv = crypto.randomFillSync(new Uint8Array(16)) var cipher = crypto.createCipheriv( 'aes-256-cbc', Buffer.from(sharedX), iv ) let encryptedMessage = cipher.update(text, 'utf8', 'base64') encryptedMessage += cipher.final('base64') let ivBase64 = Buffer.from(iv.buffer).toString('base64') let event = { pubkey: ourPubKey, created_at: Math.floor(Date.now() / 1000), kind: 4, tags: [['p', theirPublicKey]], content: encryptedMessage + '?iv=' + ivBase64 } ``` ## Security Warning This standard does not go anywhere near what is considered the state-of-the-art in encrypted communication between peers, and it leaks metadata in the events, therefore it must not be used for anything you really need to keep secret, and only with relays that use `AUTH` to restrict who can fetch your `kind:4` events. ## Client Implementation Warning Clients *should not* search and replace public key or note references from the `.content`. If processed like a regular text note (where `@npub...` is replaced with `#[0]` with a `["p", "..."]` tag) the tags are leaked and the mentioned user will receive the message in their inbox.
@ fd06f542:8d6d54cd
2025-03-30 02:16:24> __Warning__ `unrecommended`: deprecated in favor of [NIP-17](17.md) NIP-04 ====== Encrypted Direct Message ------------------------ `final` `unrecommended` `optional` A special event with kind `4`, meaning "encrypted direct message". It is supposed to have the following attributes: **`content`** MUST be equal to the base64-encoded, aes-256-cbc encrypted string of anything a user wants to write, encrypted using a shared cipher generated by combining the recipient's public-key with the sender's private-key; this appended by the base64-encoded initialization vector as if it was a querystring parameter named "iv". The format is the following: `"content": "<encrypted_text>?iv=<initialization_vector>"`. **`tags`** MUST contain an entry identifying the receiver of the message (such that relays may naturally forward this event to them), in the form `["p", "<pubkey, as a hex string>"]`. **`tags`** MAY contain an entry identifying the previous message in a conversation or a message we are explicitly replying to (such that contextual, more organized conversations may happen), in the form `["e", "<event_id>"]`. **Note**: By default in the [libsecp256k1](https://github.com/bitcoin-core/secp256k1) ECDH implementation, the secret is the SHA256 hash of the shared point (both X and Y coordinates). In Nostr, only the X coordinate of the shared point is used as the secret and it is NOT hashed. If using libsecp256k1, a custom function that copies the X coordinate must be passed as the `hashfp` argument in `secp256k1_ecdh`. See [here](https://github.com/bitcoin-core/secp256k1/blob/master/src/modules/ecdh/main_impl.h#L29). Code sample for generating such an event in JavaScript: ```js import crypto from 'crypto' import * as secp from '@noble/secp256k1' let sharedPoint = secp.getSharedSecret(ourPrivateKey, '02' + theirPublicKey) let sharedX = sharedPoint.slice(1, 33) let iv = crypto.randomFillSync(new Uint8Array(16)) var cipher = crypto.createCipheriv( 'aes-256-cbc', Buffer.from(sharedX), iv ) let encryptedMessage = cipher.update(text, 'utf8', 'base64') encryptedMessage += cipher.final('base64') let ivBase64 = Buffer.from(iv.buffer).toString('base64') let event = { pubkey: ourPubKey, created_at: Math.floor(Date.now() / 1000), kind: 4, tags: [['p', theirPublicKey]], content: encryptedMessage + '?iv=' + ivBase64 } ``` ## Security Warning This standard does not go anywhere near what is considered the state-of-the-art in encrypted communication between peers, and it leaks metadata in the events, therefore it must not be used for anything you really need to keep secret, and only with relays that use `AUTH` to restrict who can fetch your `kind:4` events. ## Client Implementation Warning Clients *should not* search and replace public key or note references from the `.content`. If processed like a regular text note (where `@npub...` is replaced with `#[0]` with a `["p", "..."]` tag) the tags are leaked and the mentioned user will receive the message in their inbox. @ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
@ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.** @ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in. By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to. I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome ! And now lets get to the first batch of artists I want to share with you. ### Eugene Gorbachenko ### nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art. ![!(image)[https://m.primal.net/PxJc.png]]() ### Siritravelsketch ### nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality. ![!(image)[https://m.primal.net/PxJj.png]]() ### BureuGewas ### nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself. ![!(image)[https://m.primal.net/PxKS.png]]() You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out ! With love, Agi Choote
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in. By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to. I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome ! And now lets get to the first batch of artists I want to share with you. ### Eugene Gorbachenko ### nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art. ![!(image)[https://m.primal.net/PxJc.png]]() ### Siritravelsketch ### nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality. ![!(image)[https://m.primal.net/PxJj.png]]() ### BureuGewas ### nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself. ![!(image)[https://m.primal.net/PxKS.png]]() You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out ! With love, Agi Choote @ 8bf63b70:64ac852f
2025-04-05 18:47:22JB88 là một nền tảng trực tuyến sáng tạo, mang đến cho người dùng những trải nghiệm giải trí vô cùng hấp dẫn và đa dạng. Được thiết kế với giao diện dễ sử dụng, JB88 cho phép người tham gia khám phá một loạt các trò chơi thú vị và thử thách mới mẻ, từ những trò chơi trí tuệ đến những hoạt động giải trí thư giãn. Mỗi lần người dùng truy cập vào nền tảng này, họ không chỉ tìm thấy những trò chơi mới mà còn có cơ hội phát triển kỹ năng tư duy và chiến lược của mình. JB88 không ngừng cải tiến và cập nhật các trò chơi, tạo ra một không gian luôn tươi mới và không bao giờ nhàm chán. Những hoạt động sáng tạo và phong phú trên nền tảng này chắc chắn sẽ làm hài lòng mọi đối tượng người tham gia, từ những người mới bắt đầu đến những người chơi có kinh nghiệm. Điều đặc biệt tạo nên sức hút của JB88 chính là sự chú trọng vào việc xây dựng một cộng đồng trực tuyến gắn kết. Không chỉ là nơi để giải trí, <a href="https://jb88.online">JB88</a> còn là một không gian để người dùng giao lưu, chia sẻ sở thích và học hỏi lẫn nhau. Các tính năng xã hội của nền tảng này giúp người tham gia dễ dàng kết nối với những người bạn mới, tham gia vào các cuộc trò chuyện thú vị và chia sẻ kinh nghiệm. Môi trường giao lưu thân thiện và năng động của JB88 tạo cơ hội cho người dùng kết nối với những người có cùng đam mê, từ đó giúp họ phát triển những mối quan hệ bền chặt và học hỏi thêm nhiều kiến thức mới. Chính sự gắn kết này làm cho JB88 không chỉ là một nền tảng giải trí mà còn là một cộng đồng trực tuyến sống động. Bên cạnh các tính năng giải trí và cộng đồng, JB88 còn chú trọng đến việc cải thiện và nâng cấp nền tảng để mang đến cho người dùng những trải nghiệm mượt mà và chất lượng. Nền tảng này luôn cập nhật các tính năng mới, giúp người tham gia có cơ hội khám phá những trò chơi và hoạt động thú vị. Bằng cách liên tục đổi mới và cải thiện, JB88 duy trì được sức hút và tạo ra một không gian giải trí không bao giờ cảm thấy nhàm chán. Sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục giúp JB88 trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian trực tuyến đầy thú vị, năng động và không ngừng sáng tạo.
@ 8bf63b70:64ac852f
2025-04-05 18:47:22JB88 là một nền tảng trực tuyến sáng tạo, mang đến cho người dùng những trải nghiệm giải trí vô cùng hấp dẫn và đa dạng. Được thiết kế với giao diện dễ sử dụng, JB88 cho phép người tham gia khám phá một loạt các trò chơi thú vị và thử thách mới mẻ, từ những trò chơi trí tuệ đến những hoạt động giải trí thư giãn. Mỗi lần người dùng truy cập vào nền tảng này, họ không chỉ tìm thấy những trò chơi mới mà còn có cơ hội phát triển kỹ năng tư duy và chiến lược của mình. JB88 không ngừng cải tiến và cập nhật các trò chơi, tạo ra một không gian luôn tươi mới và không bao giờ nhàm chán. Những hoạt động sáng tạo và phong phú trên nền tảng này chắc chắn sẽ làm hài lòng mọi đối tượng người tham gia, từ những người mới bắt đầu đến những người chơi có kinh nghiệm. Điều đặc biệt tạo nên sức hút của JB88 chính là sự chú trọng vào việc xây dựng một cộng đồng trực tuyến gắn kết. Không chỉ là nơi để giải trí, <a href="https://jb88.online">JB88</a> còn là một không gian để người dùng giao lưu, chia sẻ sở thích và học hỏi lẫn nhau. Các tính năng xã hội của nền tảng này giúp người tham gia dễ dàng kết nối với những người bạn mới, tham gia vào các cuộc trò chuyện thú vị và chia sẻ kinh nghiệm. Môi trường giao lưu thân thiện và năng động của JB88 tạo cơ hội cho người dùng kết nối với những người có cùng đam mê, từ đó giúp họ phát triển những mối quan hệ bền chặt và học hỏi thêm nhiều kiến thức mới. Chính sự gắn kết này làm cho JB88 không chỉ là một nền tảng giải trí mà còn là một cộng đồng trực tuyến sống động. Bên cạnh các tính năng giải trí và cộng đồng, JB88 còn chú trọng đến việc cải thiện và nâng cấp nền tảng để mang đến cho người dùng những trải nghiệm mượt mà và chất lượng. Nền tảng này luôn cập nhật các tính năng mới, giúp người tham gia có cơ hội khám phá những trò chơi và hoạt động thú vị. Bằng cách liên tục đổi mới và cải thiện, JB88 duy trì được sức hút và tạo ra một không gian giải trí không bao giờ cảm thấy nhàm chán. Sự kết hợp giữa giải trí chất lượng, tính năng xã hội mạnh mẽ và những cải tiến liên tục giúp JB88 trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian trực tuyến đầy thú vị, năng động và không ngừng sáng tạo. @ 8bf63b70:64ac852f
2025-04-05 18:46:23Vua88 là một nền tảng giải trí trực tuyến nổi bật, được thiết kế nhằm mang lại những trải nghiệm thú vị và phong phú cho người dùng. Với giao diện trực quan và dễ sử dụng, Vua88 cho phép người tham gia dễ dàng khám phá một loạt các trò chơi và hoạt động đa dạng. Những trò chơi sáng tạo, thử thách trí tuệ và các hoạt động giải trí thú vị luôn được cập nhật để đáp ứng nhu cầu giải trí của mọi đối tượng người dùng. Mỗi lần tham gia vào Vua88, người dùng sẽ có cơ hội thử sức với các trò chơi mới lạ và hấp dẫn, không chỉ giúp họ thư giãn mà còn kích thích sự sáng tạo và khả năng tư duy chiến lược. Chính sự đổi mới liên tục trong các hoạt động là yếu tố tạo nên sức hút và sự mới mẻ cho nền tảng này, khiến người dùng luôn cảm thấy hào hứng mỗi khi truy cập. Ngoài các trò chơi, <a href="https://vua88-vn.com">Vua88</a> còn đặc biệt chú trọng đến việc xây dựng một cộng đồng trực tuyến sôi động và gắn kết. Người dùng không chỉ tham gia vào các hoạt động giải trí mà còn có thể giao lưu, kết bạn và chia sẻ sở thích cá nhân với những người có cùng đam mê. Nền tảng này cung cấp các tính năng xã hội mạnh mẽ, từ các cuộc trò chuyện, thảo luận nhóm đến những sự kiện cộng đồng thú vị. Việc tạo dựng một không gian xã hội lành mạnh và tích cực giúp người dùng cảm thấy gần gũi hơn với cộng đồng, mở rộng mối quan hệ và học hỏi thêm nhiều điều mới. Cộng đồng Vua88 không chỉ giúp mọi người thư giãn mà còn khuyến khích sự giao lưu và kết nối giữa các thành viên, tạo ra một môi trường đầy năng lượng và sự sáng tạo. Để không ngừng duy trì sự hấp dẫn và tươi mới, Vua88 luôn cải tiến và cập nhật nền tảng của mình với những tính năng mới mẻ và sáng tạo. Những trò chơi và hoạt động trên nền tảng được làm mới liên tục, mang đến cho người tham gia những cơ hội khám phá mới mỗi khi truy cập. Mỗi lần quay lại với Vua88, người dùng sẽ luôn cảm nhận được sự thú vị và không bao giờ nhàm chán. Nền tảng này không chỉ mang lại niềm vui giải trí mà còn là nơi để người tham gia phát triển các kỹ năng cá nhân và mở rộng tầm nhìn. Vua88 không chỉ là một không gian giải trí, mà còn là một cộng đồng nơi người dùng có thể học hỏi, kết nối và phát triển bản thân một cách toàn diện.
@ 8bf63b70:64ac852f
2025-04-05 18:46:23Vua88 là một nền tảng giải trí trực tuyến nổi bật, được thiết kế nhằm mang lại những trải nghiệm thú vị và phong phú cho người dùng. Với giao diện trực quan và dễ sử dụng, Vua88 cho phép người tham gia dễ dàng khám phá một loạt các trò chơi và hoạt động đa dạng. Những trò chơi sáng tạo, thử thách trí tuệ và các hoạt động giải trí thú vị luôn được cập nhật để đáp ứng nhu cầu giải trí của mọi đối tượng người dùng. Mỗi lần tham gia vào Vua88, người dùng sẽ có cơ hội thử sức với các trò chơi mới lạ và hấp dẫn, không chỉ giúp họ thư giãn mà còn kích thích sự sáng tạo và khả năng tư duy chiến lược. Chính sự đổi mới liên tục trong các hoạt động là yếu tố tạo nên sức hút và sự mới mẻ cho nền tảng này, khiến người dùng luôn cảm thấy hào hứng mỗi khi truy cập. Ngoài các trò chơi, <a href="https://vua88-vn.com">Vua88</a> còn đặc biệt chú trọng đến việc xây dựng một cộng đồng trực tuyến sôi động và gắn kết. Người dùng không chỉ tham gia vào các hoạt động giải trí mà còn có thể giao lưu, kết bạn và chia sẻ sở thích cá nhân với những người có cùng đam mê. Nền tảng này cung cấp các tính năng xã hội mạnh mẽ, từ các cuộc trò chuyện, thảo luận nhóm đến những sự kiện cộng đồng thú vị. Việc tạo dựng một không gian xã hội lành mạnh và tích cực giúp người dùng cảm thấy gần gũi hơn với cộng đồng, mở rộng mối quan hệ và học hỏi thêm nhiều điều mới. Cộng đồng Vua88 không chỉ giúp mọi người thư giãn mà còn khuyến khích sự giao lưu và kết nối giữa các thành viên, tạo ra một môi trường đầy năng lượng và sự sáng tạo. Để không ngừng duy trì sự hấp dẫn và tươi mới, Vua88 luôn cải tiến và cập nhật nền tảng của mình với những tính năng mới mẻ và sáng tạo. Những trò chơi và hoạt động trên nền tảng được làm mới liên tục, mang đến cho người tham gia những cơ hội khám phá mới mỗi khi truy cập. Mỗi lần quay lại với Vua88, người dùng sẽ luôn cảm nhận được sự thú vị và không bao giờ nhàm chán. Nền tảng này không chỉ mang lại niềm vui giải trí mà còn là nơi để người tham gia phát triển các kỹ năng cá nhân và mở rộng tầm nhìn. Vua88 không chỉ là một không gian giải trí, mà còn là một cộng đồng nơi người dùng có thể học hỏi, kết nối và phát triển bản thân một cách toàn diện. @ fd06f542:8d6d54cd
2025-03-30 02:11:00NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ```
@ fd06f542:8d6d54cd
2025-03-30 02:11:00NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ``` @ 63b2cd3d:060efdc3
2025-04-05 18:44:58HB888 là một nền tảng giải trí trực tuyến tiên tiến, nổi bật nhờ vào sự kết hợp hoàn hảo giữa các trò chơi thú vị và tính năng kết nối cộng đồng mạnh mẽ. Với giao diện dễ sử dụng và thân thiện, người dùng có thể nhanh chóng tham gia vào các hoạt động giải trí đa dạng và tận hưởng những giây phút thư giãn tuyệt vời. HB888 cung cấp một loạt các trò chơi từ các thử thách trí tuệ đến những hoạt động thư giãn, đảm bảo rằng mọi người dùng đều có thể tìm thấy những gì họ yêu thích. Mỗi lần tham gia vào nền tảng, người dùng sẽ khám phá những trò chơi mới mẻ và được thử sức với các thử thách đầy hấp dẫn, từ đó giúp họ phát triển kỹ năng tư duy, chiến lược và nâng cao sự sáng tạo. Sự đa dạng trong các hoạt động giúp HB888 không bao giờ trở nên nhàm chán, luôn tạo ra một không gian giải trí phong phú và đầy cảm hứng. Một trong những điểm mạnh của <a href="https://hb888.asia">HB888</a> chính là cộng đồng người dùng năng động và gắn kết. Nền tảng này không chỉ mang đến những trò chơi thú vị mà còn tạo ra không gian giao lưu, kết nối giữa những người có cùng sở thích và đam mê. Các tính năng xã hội của HB888 cho phép người tham gia dễ dàng tìm thấy bạn bè mới, tham gia vào các cuộc thảo luận sôi nổi hoặc tham gia vào các sự kiện cộng đồng thú vị. Mỗi người dùng không chỉ có thể tận hưởng giải trí mà còn có cơ hội học hỏi từ những người khác, chia sẻ kinh nghiệm và khám phá những điều mới mẻ. Chính sự kết nối này tạo nên một cộng đồng trực tuyến đầy năng lượng và tích cực, nơi mọi người có thể giao lưu, kết bạn và phát triển mối quan hệ bền vững. Ngoài các trò chơi và tính năng xã hội, HB888 cũng luôn chú trọng đến việc cải tiến nền tảng để mang đến những trải nghiệm giải trí luôn tươi mới và hấp dẫn. Các trò chơi và hoạt động được cập nhật liên tục, với những tính năng mới và sáng tạo, giúp người dùng luôn cảm thấy thích thú mỗi khi quay lại nền tảng. Nhờ vào sự đổi mới không ngừng, HB888 không chỉ giữ vững được sự yêu thích của người dùng mà còn tạo ra một môi trường giải trí đầy hứng khởi và sáng tạo. Với những cải tiến này, HB888 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đầy tiềm năng và thú vị, nơi họ có thể kết nối, học hỏi và thư giãn mọi lúc, mọi nơi.
@ 63b2cd3d:060efdc3
2025-04-05 18:44:58HB888 là một nền tảng giải trí trực tuyến tiên tiến, nổi bật nhờ vào sự kết hợp hoàn hảo giữa các trò chơi thú vị và tính năng kết nối cộng đồng mạnh mẽ. Với giao diện dễ sử dụng và thân thiện, người dùng có thể nhanh chóng tham gia vào các hoạt động giải trí đa dạng và tận hưởng những giây phút thư giãn tuyệt vời. HB888 cung cấp một loạt các trò chơi từ các thử thách trí tuệ đến những hoạt động thư giãn, đảm bảo rằng mọi người dùng đều có thể tìm thấy những gì họ yêu thích. Mỗi lần tham gia vào nền tảng, người dùng sẽ khám phá những trò chơi mới mẻ và được thử sức với các thử thách đầy hấp dẫn, từ đó giúp họ phát triển kỹ năng tư duy, chiến lược và nâng cao sự sáng tạo. Sự đa dạng trong các hoạt động giúp HB888 không bao giờ trở nên nhàm chán, luôn tạo ra một không gian giải trí phong phú và đầy cảm hứng. Một trong những điểm mạnh của <a href="https://hb888.asia">HB888</a> chính là cộng đồng người dùng năng động và gắn kết. Nền tảng này không chỉ mang đến những trò chơi thú vị mà còn tạo ra không gian giao lưu, kết nối giữa những người có cùng sở thích và đam mê. Các tính năng xã hội của HB888 cho phép người tham gia dễ dàng tìm thấy bạn bè mới, tham gia vào các cuộc thảo luận sôi nổi hoặc tham gia vào các sự kiện cộng đồng thú vị. Mỗi người dùng không chỉ có thể tận hưởng giải trí mà còn có cơ hội học hỏi từ những người khác, chia sẻ kinh nghiệm và khám phá những điều mới mẻ. Chính sự kết nối này tạo nên một cộng đồng trực tuyến đầy năng lượng và tích cực, nơi mọi người có thể giao lưu, kết bạn và phát triển mối quan hệ bền vững. Ngoài các trò chơi và tính năng xã hội, HB888 cũng luôn chú trọng đến việc cải tiến nền tảng để mang đến những trải nghiệm giải trí luôn tươi mới và hấp dẫn. Các trò chơi và hoạt động được cập nhật liên tục, với những tính năng mới và sáng tạo, giúp người dùng luôn cảm thấy thích thú mỗi khi quay lại nền tảng. Nhờ vào sự đổi mới không ngừng, HB888 không chỉ giữ vững được sự yêu thích của người dùng mà còn tạo ra một môi trường giải trí đầy hứng khởi và sáng tạo. Với những cải tiến này, HB888 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đầy tiềm năng và thú vị, nơi họ có thể kết nối, học hỏi và thư giãn mọi lúc, mọi nơi. @ e516ecb8:1be0b167
2025-04-05 23:09:31En el vasto universo de "Dune", Frank Herbert nos presenta un mundo donde el poder, la religión y la economía se entrelazan de manera fascinante. A primera vista, uno podría pensar que esta saga épica no tiene mucho que ofrecer a los libertarios. Sin embargo, al examinarla a través de la lente de la Escuela Austriaca y el anarcocapitalismo, emergen lecciones valiosas sobre la naturaleza del poder, la importancia del libre mercado y los peligros del intervencionismo estatal. **El Estado y el control de los recursos** En "Dune", el Estado, representado por el Imperio Corrino, ejerce un control férreo sobre el recurso más valioso del universo: la especia melange. Este monopolio estatal sofoca la innovación y el libre intercambio, creando una economía distorsionada y propensa a la corrupción. La lucha por el control de Arrakis, el único planeta donde se produce la especia, es un claro ejemplo de cómo el intervencionismo estatal genera conflictos y guerras. **El mesianismo y el peligro del liderazgo carismático** La figura de Paul Atreides, el mesías Muad'Dib, nos advierte sobre los peligros del liderazgo carismático y el culto a la personalidad. Su ascenso al poder, impulsado por la manipulación religiosa y el miedo, desemboca en una guerra santa que se extiende por el universo, cobrando millones de vidas. Esta tragedia nos recuerda que el poder, incluso cuando se ejerce con las mejores intenciones, tiende a corromper y a generar consecuencias imprevistas. **El libre mercado y la innovación** A pesar del control estatal, en "Dune" también encontramos ejemplos de libre mercado e innovación. Los fremen, habitantes del desierto de Arrakis, han desarrollado una cultura basada en la autosuficiencia y el ingenio, adaptándose a un entorno hostil y creando tecnologías únicas. Su capacidad para sobrevivir y prosperar en un mundo sin Estado es un testimonio del poder del libre mercado y la iniciativa individual. **Lecciones para el anarcocapitalismo** "Dune" nos ofrece valiosas lecciones para el anarcocapitalismo. Nos recuerda que el Estado, incluso en sus formas más benignas, tiende a sofocar la libertad y la prosperidad. Nos advierte sobre los peligros del liderazgo carismático y la importancia de la descentralización del poder. Y nos muestra que el libre mercado y la innovación son esenciales para la supervivencia y el progreso de la humanidad. En un mundo donde el Estado y el poder centralizado siguen siendo la norma, "Dune" nos invita a imaginar un futuro donde la libertad y la cooperación voluntaria sean los pilares de la sociedad. Un futuro donde, como los fremen en el desierto, podamos construir un mundo mejor sin necesidad de amos ni señores.
@ e516ecb8:1be0b167
2025-04-05 23:09:31En el vasto universo de "Dune", Frank Herbert nos presenta un mundo donde el poder, la religión y la economía se entrelazan de manera fascinante. A primera vista, uno podría pensar que esta saga épica no tiene mucho que ofrecer a los libertarios. Sin embargo, al examinarla a través de la lente de la Escuela Austriaca y el anarcocapitalismo, emergen lecciones valiosas sobre la naturaleza del poder, la importancia del libre mercado y los peligros del intervencionismo estatal. **El Estado y el control de los recursos** En "Dune", el Estado, representado por el Imperio Corrino, ejerce un control férreo sobre el recurso más valioso del universo: la especia melange. Este monopolio estatal sofoca la innovación y el libre intercambio, creando una economía distorsionada y propensa a la corrupción. La lucha por el control de Arrakis, el único planeta donde se produce la especia, es un claro ejemplo de cómo el intervencionismo estatal genera conflictos y guerras. **El mesianismo y el peligro del liderazgo carismático** La figura de Paul Atreides, el mesías Muad'Dib, nos advierte sobre los peligros del liderazgo carismático y el culto a la personalidad. Su ascenso al poder, impulsado por la manipulación religiosa y el miedo, desemboca en una guerra santa que se extiende por el universo, cobrando millones de vidas. Esta tragedia nos recuerda que el poder, incluso cuando se ejerce con las mejores intenciones, tiende a corromper y a generar consecuencias imprevistas. **El libre mercado y la innovación** A pesar del control estatal, en "Dune" también encontramos ejemplos de libre mercado e innovación. Los fremen, habitantes del desierto de Arrakis, han desarrollado una cultura basada en la autosuficiencia y el ingenio, adaptándose a un entorno hostil y creando tecnologías únicas. Su capacidad para sobrevivir y prosperar en un mundo sin Estado es un testimonio del poder del libre mercado y la iniciativa individual. **Lecciones para el anarcocapitalismo** "Dune" nos ofrece valiosas lecciones para el anarcocapitalismo. Nos recuerda que el Estado, incluso en sus formas más benignas, tiende a sofocar la libertad y la prosperidad. Nos advierte sobre los peligros del liderazgo carismático y la importancia de la descentralización del poder. Y nos muestra que el libre mercado y la innovación son esenciales para la supervivencia y el progreso de la humanidad. En un mundo donde el Estado y el poder centralizado siguen siendo la norma, "Dune" nos invita a imaginar un futuro donde la libertad y la cooperación voluntaria sean los pilares de la sociedad. Un futuro donde, como los fremen en el desierto, podamos construir un mundo mejor sin necesidad de amos ni señores. @ fd208ee8:0fd927c1
2025-04-05 21:51:52# Markdown: Syntax * [Overview](#overview) * [Philosophy](#philosophy) * [Inline HTML](#html) * [Automatic Escaping for Special Characters](#autoescape) * [Block Elements](#block) * [Paragraphs and Line Breaks](#p) * [Headers](#header) * [Blockquotes](#blockquote) * [Lists](#list) * [Code Blocks](#precode) * [Horizontal Rules](#hr) * [Span Elements](#span) * [Links](#link) * [Emphasis](#em) * [Code](#code) * [Images](#img) * [Miscellaneous](#misc) * [Backslash Escapes](#backslash) * [Automatic Links](#autolink) **Note:** This document is itself written using Markdown; you can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text). ---- ## Overview ### Philosophy Markdown is intended to be as easy-to-read and easy-to-write as is feasible. Readability, however, is emphasized above all else. A Markdown-formatted document should be publishable as-is, as plain text, without looking like it's been marked up with tags or formatting instructions. While Markdown's syntax has been influenced by several existing text-to-HTML filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html), [Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of inspiration for Markdown's syntax is the format of plain text email. ## Block Elements ### Paragraphs and Line Breaks A paragraph is simply one or more consecutive lines of text, separated by one or more blank lines. (A blank line is any line that looks like a blank line -- a line containing nothing but spaces or tabs is considered blank.) Normal paragraphs should not be indented with spaces or tabs. The implication of the "one or more consecutive lines of text" rule is that Markdown supports "hard-wrapped" text paragraphs. This differs significantly from most other text-to-HTML formatters (including Movable Type's "Convert Line Breaks" option) which translate every line break character in a paragraph into a `<br />` tag. When you *do* want to insert a `<br />` break tag using Markdown, you end a line with two or more spaces, then type return. ### Headers Markdown supports two styles of headers, [Setext] [1] and [atx] [2]. Optionally, you may "close" atx-style headers. This is purely cosmetic -- you can use this if you think it looks better. The closing hashes don't even need to match the number of hashes used to open the header. (The number of opening hashes determines the header level.) ### Blockquotes Markdown uses email-style `>` characters for blockquoting. If you're familiar with quoting passages of text in an email message, then you know how to create a blockquote in Markdown. It looks best if you hard wrap the text and put a `>` before every line: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, > consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. > Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse > id sem consectetuer libero luctus adipiscing. Markdown allows you to be lazy and only put the `>` before the first line of a hard-wrapped paragraph: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by adding additional levels of `>`: > This is the first level of quoting. > > > This is nested blockquote. > > Back to the first level. Blockquotes can contain other Markdown elements, including headers, lists, and code blocks: > ## This is a header. > > 1. This is the first list item. > 2. This is the second list item. > > Here's some example code: > > return shell_exec("echo $input | $markdown_script"); Any decent text editor should make email-style quoting easy. For example, with BBEdit, you can make a selection and choose Increase Quote Level from the Text menu. ### Lists Markdown supports ordered (numbered) and unordered (bulleted) lists. Unordered lists use asterisks, pluses, and hyphens -- interchangably -- as list markers: * Red * Green * Blue is equivalent to: + Red + Green + Blue and: - Red - Green - Blue Ordered lists use numbers followed by periods: 1. Bird 2. McHale 3. Parish It's important to note that the actual numbers you use to mark the list have no effect on the HTML output Markdown produces. The HTML Markdown produces from the above list is: If you instead wrote the list in Markdown like this: 1. Bird 1. McHale 1. Parish or even: 3. Bird 1. McHale 8. Parish you'd get the exact same HTML output. The point is, if you want to, you can use ordinal numbers in your ordered Markdown lists, so that the numbers in your source match the numbers in your published HTML. But if you want to be lazy, you don't have to. To make lists look nice, you can wrap items with hanging indents: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. But if you want to be lazy, you don't have to: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. List items may consist of multiple paragraphs. Each subsequent paragraph in a list item must be indented by either 4 spaces or one tab: 1. This is a list item with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. Donec sit amet nisl. Aliquam semper ipsum sit amet velit. 2. Suspendisse id sem consectetuer libero luctus adipiscing. It looks nice if you indent every line of the subsequent paragraphs, but here again, Markdown will allow you to be lazy: * This is a list item with two paragraphs. This is the second paragraph in the list item. You're only required to indent the first line. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. * Another item in the same list. To put a blockquote within a list item, the blockquote's `>` delimiters need to be indented: * A list item with a blockquote: > This is a blockquote > inside a list item. To put a code block within a list item, the code block needs to be indented *twice* -- 8 spaces or two tabs: * A list item with a code block: <code goes here> ### Code Blocks Pre-formatted code blocks are used for writing about programming or markup source code. Rather than forming normal paragraphs, the lines of a code block are interpreted literally. Markdown wraps a code block in both `<pre>` and `<code>` tags. To produce a code block in Markdown, simply indent every line of the block by at least 4 spaces or 1 tab. This is a normal paragraph: This is a code block. Here is an example of AppleScript: tell application "Foo" beep end tell A code block continues until it reaches a line that is not indented (or the end of the article). Within a code block, ampersands (`&`) and angle brackets (`<` and `>`) are automatically converted into HTML entities. This makes it very easy to include example HTML source code using Markdown -- just paste it and indent it, and Markdown will handle the hassle of encoding the ampersands and angle brackets. For example, this: <div class="footer"> © 2004 Foo Corporation </div> Regular Markdown syntax is not processed within code blocks. E.g., asterisks are just literal asterisks within a code block. This means it's also easy to use Markdown to write about Markdown's own syntax. ``` tell application "Foo" beep end tell ``` ## Span Elements ### Links Markdown supports two style of links: *inline* and *reference*. In both styles, the link text is delimited by [square brackets]. To create an inline link, use a set of regular parentheses immediately after the link text's closing square bracket. Inside the parentheses, put the URL where you want the link to point, along with an *optional* title for the link, surrounded in quotes. For example: This is [an example](http://example.com/) inline link. [This link](http://example.net/) has no title attribute. ### Emphasis Markdown treats asterisks (`*`) and underscores (`_`) as indicators of emphasis. Text wrapped with one `*` or `_` will be wrapped with an HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML `<strong>` tag. E.g., this input: *single asterisks* _single underscores_ **double asterisks** __double underscores__ ### Code To indicate a span of code, wrap it with backtick quotes (`` ` ``). Unlike a pre-formatted code block, a code span indicates code within a normal paragraph. For example: Use the `printf()` function.
@ fd208ee8:0fd927c1
2025-04-05 21:51:52# Markdown: Syntax * [Overview](#overview) * [Philosophy](#philosophy) * [Inline HTML](#html) * [Automatic Escaping for Special Characters](#autoescape) * [Block Elements](#block) * [Paragraphs and Line Breaks](#p) * [Headers](#header) * [Blockquotes](#blockquote) * [Lists](#list) * [Code Blocks](#precode) * [Horizontal Rules](#hr) * [Span Elements](#span) * [Links](#link) * [Emphasis](#em) * [Code](#code) * [Images](#img) * [Miscellaneous](#misc) * [Backslash Escapes](#backslash) * [Automatic Links](#autolink) **Note:** This document is itself written using Markdown; you can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text). ---- ## Overview ### Philosophy Markdown is intended to be as easy-to-read and easy-to-write as is feasible. Readability, however, is emphasized above all else. A Markdown-formatted document should be publishable as-is, as plain text, without looking like it's been marked up with tags or formatting instructions. While Markdown's syntax has been influenced by several existing text-to-HTML filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html), [Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of inspiration for Markdown's syntax is the format of plain text email. ## Block Elements ### Paragraphs and Line Breaks A paragraph is simply one or more consecutive lines of text, separated by one or more blank lines. (A blank line is any line that looks like a blank line -- a line containing nothing but spaces or tabs is considered blank.) Normal paragraphs should not be indented with spaces or tabs. The implication of the "one or more consecutive lines of text" rule is that Markdown supports "hard-wrapped" text paragraphs. This differs significantly from most other text-to-HTML formatters (including Movable Type's "Convert Line Breaks" option) which translate every line break character in a paragraph into a `<br />` tag. When you *do* want to insert a `<br />` break tag using Markdown, you end a line with two or more spaces, then type return. ### Headers Markdown supports two styles of headers, [Setext] [1] and [atx] [2]. Optionally, you may "close" atx-style headers. This is purely cosmetic -- you can use this if you think it looks better. The closing hashes don't even need to match the number of hashes used to open the header. (The number of opening hashes determines the header level.) ### Blockquotes Markdown uses email-style `>` characters for blockquoting. If you're familiar with quoting passages of text in an email message, then you know how to create a blockquote in Markdown. It looks best if you hard wrap the text and put a `>` before every line: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, > consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. > Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse > id sem consectetuer libero luctus adipiscing. Markdown allows you to be lazy and only put the `>` before the first line of a hard-wrapped paragraph: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by adding additional levels of `>`: > This is the first level of quoting. > > > This is nested blockquote. > > Back to the first level. Blockquotes can contain other Markdown elements, including headers, lists, and code blocks: > ## This is a header. > > 1. This is the first list item. > 2. This is the second list item. > > Here's some example code: > > return shell_exec("echo $input | $markdown_script"); Any decent text editor should make email-style quoting easy. For example, with BBEdit, you can make a selection and choose Increase Quote Level from the Text menu. ### Lists Markdown supports ordered (numbered) and unordered (bulleted) lists. Unordered lists use asterisks, pluses, and hyphens -- interchangably -- as list markers: * Red * Green * Blue is equivalent to: + Red + Green + Blue and: - Red - Green - Blue Ordered lists use numbers followed by periods: 1. Bird 2. McHale 3. Parish It's important to note that the actual numbers you use to mark the list have no effect on the HTML output Markdown produces. The HTML Markdown produces from the above list is: If you instead wrote the list in Markdown like this: 1. Bird 1. McHale 1. Parish or even: 3. Bird 1. McHale 8. Parish you'd get the exact same HTML output. The point is, if you want to, you can use ordinal numbers in your ordered Markdown lists, so that the numbers in your source match the numbers in your published HTML. But if you want to be lazy, you don't have to. To make lists look nice, you can wrap items with hanging indents: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. But if you want to be lazy, you don't have to: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. List items may consist of multiple paragraphs. Each subsequent paragraph in a list item must be indented by either 4 spaces or one tab: 1. This is a list item with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. Donec sit amet nisl. Aliquam semper ipsum sit amet velit. 2. Suspendisse id sem consectetuer libero luctus adipiscing. It looks nice if you indent every line of the subsequent paragraphs, but here again, Markdown will allow you to be lazy: * This is a list item with two paragraphs. This is the second paragraph in the list item. You're only required to indent the first line. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. * Another item in the same list. To put a blockquote within a list item, the blockquote's `>` delimiters need to be indented: * A list item with a blockquote: > This is a blockquote > inside a list item. To put a code block within a list item, the code block needs to be indented *twice* -- 8 spaces or two tabs: * A list item with a code block: <code goes here> ### Code Blocks Pre-formatted code blocks are used for writing about programming or markup source code. Rather than forming normal paragraphs, the lines of a code block are interpreted literally. Markdown wraps a code block in both `<pre>` and `<code>` tags. To produce a code block in Markdown, simply indent every line of the block by at least 4 spaces or 1 tab. This is a normal paragraph: This is a code block. Here is an example of AppleScript: tell application "Foo" beep end tell A code block continues until it reaches a line that is not indented (or the end of the article). Within a code block, ampersands (`&`) and angle brackets (`<` and `>`) are automatically converted into HTML entities. This makes it very easy to include example HTML source code using Markdown -- just paste it and indent it, and Markdown will handle the hassle of encoding the ampersands and angle brackets. For example, this: <div class="footer"> © 2004 Foo Corporation </div> Regular Markdown syntax is not processed within code blocks. E.g., asterisks are just literal asterisks within a code block. This means it's also easy to use Markdown to write about Markdown's own syntax. ``` tell application "Foo" beep end tell ``` ## Span Elements ### Links Markdown supports two style of links: *inline* and *reference*. In both styles, the link text is delimited by [square brackets]. To create an inline link, use a set of regular parentheses immediately after the link text's closing square bracket. Inside the parentheses, put the URL where you want the link to point, along with an *optional* title for the link, surrounded in quotes. For example: This is [an example](http://example.com/) inline link. [This link](http://example.net/) has no title attribute. ### Emphasis Markdown treats asterisks (`*`) and underscores (`_`) as indicators of emphasis. Text wrapped with one `*` or `_` will be wrapped with an HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML `<strong>` tag. E.g., this input: *single asterisks* _single underscores_ **double asterisks** __double underscores__ ### Code To indicate a span of code, wrap it with backtick quotes (`` ` ``). Unlike a pre-formatted code block, a code span indicates code within a normal paragraph. For example: Use the `printf()` function. @ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article [nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/) Starting from these links building a simple path should not cover everything, because impossible. Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it. ----- Go to [nstart.me](https://nstart.me/) and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff) You can insert a nickname and go, the nickname is not unique there is a email backup things interesting, but a little boring, i try to generate an email doesn't even require a strong password ok. I received the email, great, it shows me the nsec encrypted in clear, Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump. ## Multi signer bunker That's stuff, let's see what he says. They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing. Nobody tells you where these bunkers are. Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. . ## Follow someone before you start? Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele. I choice Snowden profile, or you can select multiple profiles, extra wild. ## Now select 5 clients ### *Coracle, Chachi, Olas, Nostur, Jumble* ### The first is *Coracle* Login, ok I try to post a note and signing your note the spin does not end. Maybe the bunker is diffective. ### Let's try *Chachi* Simpler than Coracle, it has a type login that says bunker. see if I can post It worked, cool, I managed to post in a group. ## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account. > If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something > like that, but many start from the phone so maybe it's easy for them. > I try to download it and see if it allows me to connect with a bunker. > Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas **Ok then I saw that there was the qrcode image of the bunker for apps** lol moment Ok, I liked it, I can say it's a victory. Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that. Okay I managed to post on *Olas*, so it works, Expiration time is broken. ### As for *Nostur*, I don't have an ios device so I'm going to another one. ### Login with *Jumble*, it works is a web app I took almost an hour to do the whole route. But this was just one link there are two more # Extensions nostr NIP-07 ### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions) There are 19 links, maybe there are too many? I mention the most famous, or active at the moment 1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension) Alby I don't know if it's a route to recommend 2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj) 3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file) 4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/) Nostore is (archived, read-only) 5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame) 6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser) 7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj) Another half hour to search all sites # Nostrapps Here you can make paths ### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo On the site there are some categories, I select some with the respective apps Let's see the categories Go to [Nostrapps](https://nostrapps.com/) and read: ## Microbbloging: Primal ## Streaming: **Zap stream** ## Blogging: **Yakihonne** ## Group chat: **Chachi** ## Community: **Flotilla** ## Tools: **Form** * ## Discovery: **Zapstore** (even if it is not in this catrgory) ## Direct Message: **0xchat**
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article [nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/) Starting from these links building a simple path should not cover everything, because impossible. Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it. ----- Go to [nstart.me](https://nstart.me/) and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff) You can insert a nickname and go, the nickname is not unique there is a email backup things interesting, but a little boring, i try to generate an email doesn't even require a strong password ok. I received the email, great, it shows me the nsec encrypted in clear, Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump. ## Multi signer bunker That's stuff, let's see what he says. They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing. Nobody tells you where these bunkers are. Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. . ## Follow someone before you start? Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele. I choice Snowden profile, or you can select multiple profiles, extra wild. ## Now select 5 clients ### *Coracle, Chachi, Olas, Nostur, Jumble* ### The first is *Coracle* Login, ok I try to post a note and signing your note the spin does not end. Maybe the bunker is diffective. ### Let's try *Chachi* Simpler than Coracle, it has a type login that says bunker. see if I can post It worked, cool, I managed to post in a group. ## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account. > If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something > like that, but many start from the phone so maybe it's easy for them. > I try to download it and see if it allows me to connect with a bunker. > Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas **Ok then I saw that there was the qrcode image of the bunker for apps** lol moment Ok, I liked it, I can say it's a victory. Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that. Okay I managed to post on *Olas*, so it works, Expiration time is broken. ### As for *Nostur*, I don't have an ios device so I'm going to another one. ### Login with *Jumble*, it works is a web app I took almost an hour to do the whole route. But this was just one link there are two more # Extensions nostr NIP-07 ### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions) There are 19 links, maybe there are too many? I mention the most famous, or active at the moment 1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension) Alby I don't know if it's a route to recommend 2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj) 3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file) 4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/) Nostore is (archived, read-only) 5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame) 6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser) 7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj) Another half hour to search all sites # Nostrapps Here you can make paths ### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo On the site there are some categories, I select some with the respective apps Let's see the categories Go to [Nostrapps](https://nostrapps.com/) and read: ## Microbbloging: Primal ## Streaming: **Zap stream** ## Blogging: **Yakihonne** ## Group chat: **Chachi** ## Community: **Flotilla** ## Tools: **Form** * ## Discovery: **Zapstore** (even if it is not in this catrgory) ## Direct Message: **0xchat** @ 63b2cd3d:060efdc3
2025-04-05 18:43:47MN88 là một nền tảng giải trí trực tuyến độc đáo, thu hút người tham gia nhờ vào sự đa dạng và phong phú trong các hoạt động giải trí mà nó mang lại. Với giao diện dễ sử dụng, nền tảng này cung cấp cho người dùng những trò chơi và hoạt động giải trí hấp dẫn, từ những thử thách trí tuệ cho đến các trò chơi nhẹ nhàng thư giãn. Dù bạn là người yêu thích sự kịch tính hay chỉ đơn giản muốn tìm kiếm những giây phút thư giãn, MN88 đều có thể đáp ứng được nhu cầu của mọi đối tượng người tham gia. Mỗi lần đăng nhập vào MN88, người dùng đều có thể khám phá những trò chơi mới mẻ, thử sức với các thử thách hấp dẫn và cảm nhận những giây phút vui vẻ mà nền tảng này mang lại. Chính sự đa dạng và chất lượng của các hoạt động đã tạo nên một không gian giải trí thực sự thú vị và không bao giờ nhàm chán. Điểm nổi bật của <a href="https://mn88.co">MN88</a> chính là khả năng xây dựng một cộng đồng người dùng gắn kết và năng động. Nền tảng này không chỉ đơn thuần là nơi để giải trí mà còn là nơi để mọi người kết nối, giao lưu và chia sẻ sở thích với nhau. Các tính năng xã hội của MN88 giúp người tham gia dễ dàng tìm thấy những người bạn có cùng niềm đam mê, từ đó tạo nên một môi trường sôi động, thân thiện và tích cực. Những cuộc trò chuyện, các sự kiện cộng đồng và các hoạt động nhóm không chỉ giúp người tham gia cảm thấy gần gũi mà còn mở rộng cơ hội học hỏi và phát triển các kỹ năng cá nhân. Nhờ vào cộng đồng mạnh mẽ này, MN88 không chỉ là một nền tảng giải trí mà còn là một không gian giao lưu đầy ý nghĩa, giúp người dùng có thể kết nối và phát triển những mối quan hệ mới. Bên cạnh đó, MN88 luôn nỗ lực không ngừng để nâng cấp và cải thiện nền tảng của mình, mang đến cho người dùng những trải nghiệm giải trí ngày càng hấp dẫn và mới mẻ. Các trò chơi, hoạt động và tính năng của nền tảng này đều được cập nhật thường xuyên, đảm bảo rằng người tham gia luôn có cơ hội khám phá những điều mới và thú vị. Với những cải tiến liên tục, MN88 duy trì sự tươi mới và cuốn hút, không bao giờ để người dùng cảm thấy nhàm chán. Nền tảng này không chỉ tạo ra một không gian giải trí chất lượng mà còn khuyến khích sự sáng tạo, học hỏi và phát triển kỹ năng cá nhân. Chính nhờ vào sự đổi mới không ngừng và những cải tiến liên tục, MN88 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đa dạng, phong phú và đầy thú vị.
@ 63b2cd3d:060efdc3
2025-04-05 18:43:47MN88 là một nền tảng giải trí trực tuyến độc đáo, thu hút người tham gia nhờ vào sự đa dạng và phong phú trong các hoạt động giải trí mà nó mang lại. Với giao diện dễ sử dụng, nền tảng này cung cấp cho người dùng những trò chơi và hoạt động giải trí hấp dẫn, từ những thử thách trí tuệ cho đến các trò chơi nhẹ nhàng thư giãn. Dù bạn là người yêu thích sự kịch tính hay chỉ đơn giản muốn tìm kiếm những giây phút thư giãn, MN88 đều có thể đáp ứng được nhu cầu của mọi đối tượng người tham gia. Mỗi lần đăng nhập vào MN88, người dùng đều có thể khám phá những trò chơi mới mẻ, thử sức với các thử thách hấp dẫn và cảm nhận những giây phút vui vẻ mà nền tảng này mang lại. Chính sự đa dạng và chất lượng của các hoạt động đã tạo nên một không gian giải trí thực sự thú vị và không bao giờ nhàm chán. Điểm nổi bật của <a href="https://mn88.co">MN88</a> chính là khả năng xây dựng một cộng đồng người dùng gắn kết và năng động. Nền tảng này không chỉ đơn thuần là nơi để giải trí mà còn là nơi để mọi người kết nối, giao lưu và chia sẻ sở thích với nhau. Các tính năng xã hội của MN88 giúp người tham gia dễ dàng tìm thấy những người bạn có cùng niềm đam mê, từ đó tạo nên một môi trường sôi động, thân thiện và tích cực. Những cuộc trò chuyện, các sự kiện cộng đồng và các hoạt động nhóm không chỉ giúp người tham gia cảm thấy gần gũi mà còn mở rộng cơ hội học hỏi và phát triển các kỹ năng cá nhân. Nhờ vào cộng đồng mạnh mẽ này, MN88 không chỉ là một nền tảng giải trí mà còn là một không gian giao lưu đầy ý nghĩa, giúp người dùng có thể kết nối và phát triển những mối quan hệ mới. Bên cạnh đó, MN88 luôn nỗ lực không ngừng để nâng cấp và cải thiện nền tảng của mình, mang đến cho người dùng những trải nghiệm giải trí ngày càng hấp dẫn và mới mẻ. Các trò chơi, hoạt động và tính năng của nền tảng này đều được cập nhật thường xuyên, đảm bảo rằng người tham gia luôn có cơ hội khám phá những điều mới và thú vị. Với những cải tiến liên tục, MN88 duy trì sự tươi mới và cuốn hút, không bao giờ để người dùng cảm thấy nhàm chán. Nền tảng này không chỉ tạo ra một không gian giải trí chất lượng mà còn khuyến khích sự sáng tạo, học hỏi và phát triển kỹ năng cá nhân. Chính nhờ vào sự đổi mới không ngừng và những cải tiến liên tục, MN88 đã trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến đa dạng, phong phú và đầy thú vị. @ 63b2cd3d:060efdc3
2025-04-05 18:42:41ZomClub là một nền tảng giải trí trực tuyến mới mẻ, mang đến cho người dùng những trải nghiệm độc đáo và phong phú. Được thiết kế với giao diện trực quan và dễ sử dụng, ZomClub cung cấp một không gian đầy sáng tạo và thú vị, nơi người dùng có thể tham gia vào nhiều hoạt động và trò chơi đa dạng. Từ những thử thách trí tuệ đến các trò chơi mang tính giải trí nhẹ nhàng, ZomClub đáp ứng đầy đủ nhu cầu của mọi đối tượng người tham gia. Đặc biệt, nền tảng này không chỉ là nơi giải trí mà còn là cơ hội để người dùng thử sức với những trò chơi mới, từ đó phát triển kỹ năng tư duy, sự nhanh nhạy và khả năng giải quyết vấn đề. Mỗi lần tham gia vào ZomClub, người dùng đều có thể tìm thấy niềm vui, thử thách bản thân và tận hưởng những giây phút thư giãn đầy ý nghĩa. Một trong những yếu tố khiến ZomClub trở nên đặc biệt chính là sự chú trọng đến việc xây dựng một cộng đồng gắn kết và tích cực. Nền tảng này không chỉ cung cấp các trò chơi, mà còn là một không gian xã hội để người dùng giao lưu, chia sẻ và kết nối với những người có cùng sở thích. Các tính năng xã hội của <a href="https://zomclub-vn.com">ZomClub</a> cho phép người tham gia thảo luận, tham gia các sự kiện cộng đồng và kết bạn, giúp tạo nên một không gian sôi động và thân thiện. Nhờ vào những hoạt động tương tác này, người dùng không chỉ tìm được những người bạn mới mà còn có thể mở rộng mối quan hệ và học hỏi những điều mới mẻ từ cộng đồng. Điều này giúp ZomClub không chỉ là một nền tảng giải trí, mà còn là một cộng đồng trực tuyến tích cực, nơi mỗi người có thể tìm thấy sự kết nối và cảm hứng. Bên cạnh đó, ZomClub cũng không ngừng đổi mới và nâng cấp các tính năng để duy trì sự hấp dẫn và tươi mới cho người dùng. Các trò chơi và hoạt động trên nền tảng được cập nhật liên tục, mang đến những trải nghiệm mới mẻ mỗi lần người dùng truy cập. Dù là các trò chơi thử thách hay các hoạt động xã hội, ZomClub luôn đảm bảo rằng người tham gia sẽ không bao giờ cảm thấy nhàm chán. Điều này thể hiện cam kết của nền tảng trong việc tạo ra một không gian giải trí đầy đủ, không chỉ giúp người dùng thư giãn mà còn khuyến khích sự sáng tạo và học hỏi. Với sự kết hợp hoàn hảo giữa giải trí và giao lưu cộng đồng, ZomClub là lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng giải trí thú vị và đầy sáng tạo.
@ 63b2cd3d:060efdc3
2025-04-05 18:42:41ZomClub là một nền tảng giải trí trực tuyến mới mẻ, mang đến cho người dùng những trải nghiệm độc đáo và phong phú. Được thiết kế với giao diện trực quan và dễ sử dụng, ZomClub cung cấp một không gian đầy sáng tạo và thú vị, nơi người dùng có thể tham gia vào nhiều hoạt động và trò chơi đa dạng. Từ những thử thách trí tuệ đến các trò chơi mang tính giải trí nhẹ nhàng, ZomClub đáp ứng đầy đủ nhu cầu của mọi đối tượng người tham gia. Đặc biệt, nền tảng này không chỉ là nơi giải trí mà còn là cơ hội để người dùng thử sức với những trò chơi mới, từ đó phát triển kỹ năng tư duy, sự nhanh nhạy và khả năng giải quyết vấn đề. Mỗi lần tham gia vào ZomClub, người dùng đều có thể tìm thấy niềm vui, thử thách bản thân và tận hưởng những giây phút thư giãn đầy ý nghĩa. Một trong những yếu tố khiến ZomClub trở nên đặc biệt chính là sự chú trọng đến việc xây dựng một cộng đồng gắn kết và tích cực. Nền tảng này không chỉ cung cấp các trò chơi, mà còn là một không gian xã hội để người dùng giao lưu, chia sẻ và kết nối với những người có cùng sở thích. Các tính năng xã hội của <a href="https://zomclub-vn.com">ZomClub</a> cho phép người tham gia thảo luận, tham gia các sự kiện cộng đồng và kết bạn, giúp tạo nên một không gian sôi động và thân thiện. Nhờ vào những hoạt động tương tác này, người dùng không chỉ tìm được những người bạn mới mà còn có thể mở rộng mối quan hệ và học hỏi những điều mới mẻ từ cộng đồng. Điều này giúp ZomClub không chỉ là một nền tảng giải trí, mà còn là một cộng đồng trực tuyến tích cực, nơi mỗi người có thể tìm thấy sự kết nối và cảm hứng. Bên cạnh đó, ZomClub cũng không ngừng đổi mới và nâng cấp các tính năng để duy trì sự hấp dẫn và tươi mới cho người dùng. Các trò chơi và hoạt động trên nền tảng được cập nhật liên tục, mang đến những trải nghiệm mới mẻ mỗi lần người dùng truy cập. Dù là các trò chơi thử thách hay các hoạt động xã hội, ZomClub luôn đảm bảo rằng người tham gia sẽ không bao giờ cảm thấy nhàm chán. Điều này thể hiện cam kết của nền tảng trong việc tạo ra một không gian giải trí đầy đủ, không chỉ giúp người dùng thư giãn mà còn khuyến khích sự sáng tạo và học hỏi. Với sự kết hợp hoàn hảo giữa giải trí và giao lưu cộng đồng, ZomClub là lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng giải trí thú vị và đầy sáng tạo. @ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ ba36d0f7:cd802cba
2025-04-05 18:13:13 ♟️ **The scene:** Starting April 11th, 2025, every week in **Apaneca, El Salvador** - a town so small you’d miss it if you blinked - a quiet revolution will be unfolding. In soma chess, taking place at **📍Estudio Malinche**- chessboards aren’t just for play. They’re **gateways to a modern kind of culture** - one where discipline meets digital curiosity, and where tradition doesn’t mean rejecting tech, but **hacking it for growth**. This isn’t about creating grandmasters. It’s about using chess’s ancient magic to teach: - **Respect** (for the game and community, your opponent, and yourself). - **Patience** (because the board doesn’t reward haste). - **Perseverance** (every loss is a lesson in disguise). But there’s a twist: **We’re not aiming to teaching chess. We’re aiming to teaching how to navigate a world where culture is now built on code, forums, and digital communities.** > **_Chess as a Trojan horse to self-learning, learning better and doing better._** --- **Why Chess?** Chess is the ultimate **self-improvement metaphor**: ✅ _The opponent could leave you a winning position - but can_ **_you_** **_see_** **_it_**_?_ ✅ _You could blame luck - or ask,_ **_“_**_Where did_ **_I_** _go wrong_**_?”_** ✅ _You could rage-quit - or_ **_learn to love the grind._** --- **The hidden curriculum: Where analog meets algorithm** **1. Embracing digital curiosity** _We’re not teaching openings - we’re showing players how to hunt for knowledge._ **2. Mistakes as rituals** _Owning blunders, and analyzing them with engines._ **3. The long game** _Tracking progress and digitally storing your games._ --- **Join us** This isn’t _just_ about Apaneca. 🌍 **Your challenge:** - **If you’re nearby**, come play (every Thursday, 1-5PM, zero expectations). - **If you’re far**, do this in your town. We’ll share our **playbook**. - **If you’re online**, **follow us**npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99 and tag along for the ride. --- **Final Move:** Chess doesn’t build character. It reveals it - then sharpens it. And **culture and communities aren’t just what we inherit. They're what we build.** ********************* #chess #ajedrez #article #meetup #education #chesselsalvador #rutadelasflores #apaneca #somachess
@ ba36d0f7:cd802cba
2025-04-05 18:13:13 ♟️ **The scene:** Starting April 11th, 2025, every week in **Apaneca, El Salvador** - a town so small you’d miss it if you blinked - a quiet revolution will be unfolding. In soma chess, taking place at **📍Estudio Malinche**- chessboards aren’t just for play. They’re **gateways to a modern kind of culture** - one where discipline meets digital curiosity, and where tradition doesn’t mean rejecting tech, but **hacking it for growth**. This isn’t about creating grandmasters. It’s about using chess’s ancient magic to teach: - **Respect** (for the game and community, your opponent, and yourself). - **Patience** (because the board doesn’t reward haste). - **Perseverance** (every loss is a lesson in disguise). But there’s a twist: **We’re not aiming to teaching chess. We’re aiming to teaching how to navigate a world where culture is now built on code, forums, and digital communities.** > **_Chess as a Trojan horse to self-learning, learning better and doing better._** --- **Why Chess?** Chess is the ultimate **self-improvement metaphor**: ✅ _The opponent could leave you a winning position - but can_ **_you_** **_see_** **_it_**_?_ ✅ _You could blame luck - or ask,_ **_“_**_Where did_ **_I_** _go wrong_**_?”_** ✅ _You could rage-quit - or_ **_learn to love the grind._** --- **The hidden curriculum: Where analog meets algorithm** **1. Embracing digital curiosity** _We’re not teaching openings - we’re showing players how to hunt for knowledge._ **2. Mistakes as rituals** _Owning blunders, and analyzing them with engines._ **3. The long game** _Tracking progress and digitally storing your games._ --- **Join us** This isn’t _just_ about Apaneca. 🌍 **Your challenge:** - **If you’re nearby**, come play (every Thursday, 1-5PM, zero expectations). - **If you’re far**, do this in your town. We’ll share our **playbook**. - **If you’re online**, **follow us**npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99 and tag along for the ride. --- **Final Move:** Chess doesn’t build character. It reveals it - then sharpens it. And **culture and communities aren’t just what we inherit. They're what we build.** ********************* #chess #ajedrez #article #meetup #education #chesselsalvador #rutadelasflores #apaneca #somachess @ 57d1a264:69f1fee1
2025-03-29 09:31:13> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." <sub>- SATOSHI NAKAMOTO</sub>    "Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin. Materials: Carrara Marble, Copper leaf, Opendime Dimensions: 6" x 9" x 13" Price: $30,000 or BTC equivalent Enquire: https://www.vonbitcoin.com/available-works X: https://x.com/BVBTC/status/1894463357316419960/photo/1 originally posted at https://stacker.news/items/928510
@ 57d1a264:69f1fee1
2025-03-29 09:31:13> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." <sub>- SATOSHI NAKAMOTO</sub>    "Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin. Materials: Carrara Marble, Copper leaf, Opendime Dimensions: 6" x 9" x 13" Price: $30,000 or BTC equivalent Enquire: https://www.vonbitcoin.com/available-works X: https://x.com/BVBTC/status/1894463357316419960/photo/1 originally posted at https://stacker.news/items/928510 @ a5142938:0ef19da3
2025-04-05 11:13:26### Core Team The Core Team drives the project and validates the content. <img src="!(image)[https://files.mastodon.social/accounts/avatars/112/353/885/673/397/288/original/7f92926ffb69936f.jpg]" width="80" height="80"> [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) To start, I'm managing the project solo by sharing my bookmarks to avoid plastic on myself and on my children. [Contact me](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/) if you'd like to join! ### Content Enrichers Our contributors make this site engaging and interesting. *Coming soon.* 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/cyy0wd2ar_rwqbjipnhej/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/x-ykxuenf9tnccu65mhjq/)
@ a5142938:0ef19da3
2025-04-05 11:13:26### Core Team The Core Team drives the project and validates the content. <img src="!(image)[https://files.mastodon.social/accounts/avatars/112/353/885/673/397/288/original/7f92926ffb69936f.jpg]" width="80" height="80"> [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) To start, I'm managing the project solo by sharing my bookmarks to avoid plastic on myself and on my children. [Contact me](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/) if you'd like to join! ### Content Enrichers Our contributors make this site engaging and interesting. *Coming soon.* 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/cyy0wd2ar_rwqbjipnhej/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/x-ykxuenf9tnccu65mhjq/) @ fd208ee8:0fd927c1
2025-04-05 21:36:33# Markdown: Syntax * [Overview](#overview) * [Philosophy](#philosophy) * [Inline HTML](#html) * [Automatic Escaping for Special Characters](#autoescape) * [Block Elements](#block) * [Paragraphs and Line Breaks](#p) * [Headers](#header) * [Blockquotes](#blockquote) * [Lists](#list) * [Code Blocks](#precode) * [Horizontal Rules](#hr) * [Span Elements](#span) * [Links](#link) * [Emphasis](#em) * [Code](#code) * [Images](#img) * [Miscellaneous](#misc) * [Backslash Escapes](#backslash) * [Automatic Links](#autolink) **Note:** This document is itself written using Markdown; you can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text). ---- ## Overview ### Philosophy Markdown is intended to be as easy-to-read and easy-to-write as is feasible. Readability, however, is emphasized above all else. A Markdown-formatted document should be publishable as-is, as plain text, without looking like it's been marked up with tags or formatting instructions. While Markdown's syntax has been influenced by several existing text-to-HTML filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html), [Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of inspiration for Markdown's syntax is the format of plain text email. ## Block Elements ### Paragraphs and Line Breaks A paragraph is simply one or more consecutive lines of text, separated by one or more blank lines. (A blank line is any line that looks like a blank line -- a line containing nothing but spaces or tabs is considered blank.) Normal paragraphs should not be indented with spaces or tabs. The implication of the "one or more consecutive lines of text" rule is that Markdown supports "hard-wrapped" text paragraphs. This differs significantly from most other text-to-HTML formatters (including Movable Type's "Convert Line Breaks" option) which translate every line break character in a paragraph into a `<br />` tag. When you *do* want to insert a `<br />` break tag using Markdown, you end a line with two or more spaces, then type return. ### Headers Markdown supports two styles of headers, [Setext] [1] and [atx] [2]. Optionally, you may "close" atx-style headers. This is purely cosmetic -- you can use this if you think it looks better. The closing hashes don't even need to match the number of hashes used to open the header. (The number of opening hashes determines the header level.) ### Blockquotes Markdown uses email-style `>` characters for blockquoting. If you're familiar with quoting passages of text in an email message, then you know how to create a blockquote in Markdown. It looks best if you hard wrap the text and put a `>` before every line: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, > consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. > Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse > id sem consectetuer libero luctus adipiscing. Markdown allows you to be lazy and only put the `>` before the first line of a hard-wrapped paragraph: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by adding additional levels of `>`: > This is the first level of quoting. > > > This is nested blockquote. > > Back to the first level. Blockquotes can contain other Markdown elements, including headers, lists, and code blocks: > ## This is a header. > > 1. This is the first list item. > 2. This is the second list item. > > Here's some example code: > > return shell_exec("echo $input | $markdown_script"); Any decent text editor should make email-style quoting easy. For example, with BBEdit, you can make a selection and choose Increase Quote Level from the Text menu. ### Lists Markdown supports ordered (numbered) and unordered (bulleted) lists. Unordered lists use asterisks, pluses, and hyphens -- interchangably -- as list markers: * Red * Green * Blue is equivalent to: + Red + Green + Blue and: - Red - Green - Blue Ordered lists use numbers followed by periods: 1. Bird 2. McHale 3. Parish It's important to note that the actual numbers you use to mark the list have no effect on the HTML output Markdown produces. The HTML Markdown produces from the above list is: If you instead wrote the list in Markdown like this: 1. Bird 1. McHale 1. Parish or even: 3. Bird 1. McHale 8. Parish you'd get the exact same HTML output. The point is, if you want to, you can use ordinal numbers in your ordered Markdown lists, so that the numbers in your source match the numbers in your published HTML. But if you want to be lazy, you don't have to. To make lists look nice, you can wrap items with hanging indents: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. But if you want to be lazy, you don't have to: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. List items may consist of multiple paragraphs. Each subsequent paragraph in a list item must be indented by either 4 spaces or one tab: 1. This is a list item with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. Donec sit amet nisl. Aliquam semper ipsum sit amet velit. 2. Suspendisse id sem consectetuer libero luctus adipiscing. It looks nice if you indent every line of the subsequent paragraphs, but here again, Markdown will allow you to be lazy: * This is a list item with two paragraphs. This is the second paragraph in the list item. You're only required to indent the first line. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. * Another item in the same list. To put a blockquote within a list item, the blockquote's `>` delimiters need to be indented: * A list item with a blockquote: > This is a blockquote > inside a list item. To put a code block within a list item, the code block needs to be indented *twice* -- 8 spaces or two tabs: * A list item with a code block: <code goes here> ### Code Blocks Pre-formatted code blocks are used for writing about programming or markup source code. Rather than forming normal paragraphs, the lines of a code block are interpreted literally. Markdown wraps a code block in both `<pre>` and `<code>` tags. To produce a code block in Markdown, simply indent every line of the block by at least 4 spaces or 1 tab. This is a normal paragraph: This is a code block. Here is an example of AppleScript: tell application "Foo" beep end tell A code block continues until it reaches a line that is not indented (or the end of the article). Within a code block, ampersands (`&`) and angle brackets (`<` and `>`) are automatically converted into HTML entities. This makes it very easy to include example HTML source code using Markdown -- just paste it and indent it, and Markdown will handle the hassle of encoding the ampersands and angle brackets. For example, this: <div class="footer"> © 2004 Foo Corporation </div> Regular Markdown syntax is not processed within code blocks. E.g., asterisks are just literal asterisks within a code block. This means it's also easy to use Markdown to write about Markdown's own syntax. ``` tell application "Foo" beep end tell ``` ## Span Elements ### Links Markdown supports two style of links: *inline* and *reference*. In both styles, the link text is delimited by [square brackets]. To create an inline link, use a set of regular parentheses immediately after the link text's closing square bracket. Inside the parentheses, put the URL where you want the link to point, along with an *optional* title for the link, surrounded in quotes. For example: This is [an example](http://example.com/) inline link. [This link](http://example.net/) has no title attribute. ### Emphasis Markdown treats asterisks (`*`) and underscores (`_`) as indicators of emphasis. Text wrapped with one `*` or `_` will be wrapped with an HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML `<strong>` tag. E.g., this input: *single asterisks* _single underscores_ **double asterisks** __double underscores__ ### Code To indicate a span of code, wrap it with backtick quotes (`` ` ``). Unlike a pre-formatted code block, a code span indicates code within a normal paragraph. For example: Use the `printf()` function.
@ fd208ee8:0fd927c1
2025-04-05 21:36:33# Markdown: Syntax * [Overview](#overview) * [Philosophy](#philosophy) * [Inline HTML](#html) * [Automatic Escaping for Special Characters](#autoescape) * [Block Elements](#block) * [Paragraphs and Line Breaks](#p) * [Headers](#header) * [Blockquotes](#blockquote) * [Lists](#list) * [Code Blocks](#precode) * [Horizontal Rules](#hr) * [Span Elements](#span) * [Links](#link) * [Emphasis](#em) * [Code](#code) * [Images](#img) * [Miscellaneous](#misc) * [Backslash Escapes](#backslash) * [Automatic Links](#autolink) **Note:** This document is itself written using Markdown; you can [see the source for it by adding '.text' to the URL](/projects/markdown/syntax.text). ---- ## Overview ### Philosophy Markdown is intended to be as easy-to-read and easy-to-write as is feasible. Readability, however, is emphasized above all else. A Markdown-formatted document should be publishable as-is, as plain text, without looking like it's been marked up with tags or formatting instructions. While Markdown's syntax has been influenced by several existing text-to-HTML filters -- including [Setext](http://docutils.sourceforge.net/mirror/setext.html), [atx](http://www.aaronsw.com/2002/atx/), [Textile](http://textism.com/tools/textile/), [reStructuredText](http://docutils.sourceforge.net/rst.html), [Grutatext](http://www.triptico.com/software/grutatxt.html), and [EtText](http://ettext.taint.org/doc/) -- the single biggest source of inspiration for Markdown's syntax is the format of plain text email. ## Block Elements ### Paragraphs and Line Breaks A paragraph is simply one or more consecutive lines of text, separated by one or more blank lines. (A blank line is any line that looks like a blank line -- a line containing nothing but spaces or tabs is considered blank.) Normal paragraphs should not be indented with spaces or tabs. The implication of the "one or more consecutive lines of text" rule is that Markdown supports "hard-wrapped" text paragraphs. This differs significantly from most other text-to-HTML formatters (including Movable Type's "Convert Line Breaks" option) which translate every line break character in a paragraph into a `<br />` tag. When you *do* want to insert a `<br />` break tag using Markdown, you end a line with two or more spaces, then type return. ### Headers Markdown supports two styles of headers, [Setext] [1] and [atx] [2]. Optionally, you may "close" atx-style headers. This is purely cosmetic -- you can use this if you think it looks better. The closing hashes don't even need to match the number of hashes used to open the header. (The number of opening hashes determines the header level.) ### Blockquotes Markdown uses email-style `>` characters for blockquoting. If you're familiar with quoting passages of text in an email message, then you know how to create a blockquote in Markdown. It looks best if you hard wrap the text and put a `>` before every line: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, > consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. > Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse > id sem consectetuer libero luctus adipiscing. Markdown allows you to be lazy and only put the `>` before the first line of a hard-wrapped paragraph: > This is a blockquote with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. > Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. Blockquotes can be nested (i.e. a blockquote-in-a-blockquote) by adding additional levels of `>`: > This is the first level of quoting. > > > This is nested blockquote. > > Back to the first level. Blockquotes can contain other Markdown elements, including headers, lists, and code blocks: > ## This is a header. > > 1. This is the first list item. > 2. This is the second list item. > > Here's some example code: > > return shell_exec("echo $input | $markdown_script"); Any decent text editor should make email-style quoting easy. For example, with BBEdit, you can make a selection and choose Increase Quote Level from the Text menu. ### Lists Markdown supports ordered (numbered) and unordered (bulleted) lists. Unordered lists use asterisks, pluses, and hyphens -- interchangably -- as list markers: * Red * Green * Blue is equivalent to: + Red + Green + Blue and: - Red - Green - Blue Ordered lists use numbers followed by periods: 1. Bird 2. McHale 3. Parish It's important to note that the actual numbers you use to mark the list have no effect on the HTML output Markdown produces. The HTML Markdown produces from the above list is: If you instead wrote the list in Markdown like this: 1. Bird 1. McHale 1. Parish or even: 3. Bird 1. McHale 8. Parish you'd get the exact same HTML output. The point is, if you want to, you can use ordinal numbers in your ordered Markdown lists, so that the numbers in your source match the numbers in your published HTML. But if you want to be lazy, you don't have to. To make lists look nice, you can wrap items with hanging indents: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. But if you want to be lazy, you don't have to: * Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. * Donec sit amet nisl. Aliquam semper ipsum sit amet velit. Suspendisse id sem consectetuer libero luctus adipiscing. List items may consist of multiple paragraphs. Each subsequent paragraph in a list item must be indented by either 4 spaces or one tab: 1. This is a list item with two paragraphs. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aliquam hendrerit mi posuere lectus. Vestibulum enim wisi, viverra nec, fringilla in, laoreet vitae, risus. Donec sit amet nisl. Aliquam semper ipsum sit amet velit. 2. Suspendisse id sem consectetuer libero luctus adipiscing. It looks nice if you indent every line of the subsequent paragraphs, but here again, Markdown will allow you to be lazy: * This is a list item with two paragraphs. This is the second paragraph in the list item. You're only required to indent the first line. Lorem ipsum dolor sit amet, consectetuer adipiscing elit. * Another item in the same list. To put a blockquote within a list item, the blockquote's `>` delimiters need to be indented: * A list item with a blockquote: > This is a blockquote > inside a list item. To put a code block within a list item, the code block needs to be indented *twice* -- 8 spaces or two tabs: * A list item with a code block: <code goes here> ### Code Blocks Pre-formatted code blocks are used for writing about programming or markup source code. Rather than forming normal paragraphs, the lines of a code block are interpreted literally. Markdown wraps a code block in both `<pre>` and `<code>` tags. To produce a code block in Markdown, simply indent every line of the block by at least 4 spaces or 1 tab. This is a normal paragraph: This is a code block. Here is an example of AppleScript: tell application "Foo" beep end tell A code block continues until it reaches a line that is not indented (or the end of the article). Within a code block, ampersands (`&`) and angle brackets (`<` and `>`) are automatically converted into HTML entities. This makes it very easy to include example HTML source code using Markdown -- just paste it and indent it, and Markdown will handle the hassle of encoding the ampersands and angle brackets. For example, this: <div class="footer"> © 2004 Foo Corporation </div> Regular Markdown syntax is not processed within code blocks. E.g., asterisks are just literal asterisks within a code block. This means it's also easy to use Markdown to write about Markdown's own syntax. ``` tell application "Foo" beep end tell ``` ## Span Elements ### Links Markdown supports two style of links: *inline* and *reference*. In both styles, the link text is delimited by [square brackets]. To create an inline link, use a set of regular parentheses immediately after the link text's closing square bracket. Inside the parentheses, put the URL where you want the link to point, along with an *optional* title for the link, surrounded in quotes. For example: This is [an example](http://example.com/) inline link. [This link](http://example.net/) has no title attribute. ### Emphasis Markdown treats asterisks (`*`) and underscores (`_`) as indicators of emphasis. Text wrapped with one `*` or `_` will be wrapped with an HTML `<em>` tag; double `*`'s or `_`'s will be wrapped with an HTML `<strong>` tag. E.g., this input: *single asterisks* _single underscores_ **double asterisks** __double underscores__ ### Code To indicate a span of code, wrap it with backtick quotes (`` ` ``). Unlike a pre-formatted code block, a code span indicates code within a normal paragraph. For example: Use the `printf()` function. @ fd06f542:8d6d54cd
2025-03-30 02:10:24NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ```
@ fd06f542:8d6d54cd
2025-03-30 02:10:24NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ``` @ db11b320:05c5f7af
2025-03-29 19:04:19magnet:?xt=urn:btih:9BAC9A3F98803AEA1EB28A0B60A562D7E3779710
@ db11b320:05c5f7af
2025-03-29 19:04:19magnet:?xt=urn:btih:9BAC9A3F98803AEA1EB28A0B60A562D7E3779710 @ 0d788b5e:c99ddea5
2025-03-29 02:40:37- [首页](/readme.md) - [第一章、 第一章标题](/chapter1.md) - [第二章、 第二章标题](/chapter2.md)
@ 0d788b5e:c99ddea5
2025-03-29 02:40:37- [首页](/readme.md) - [第一章、 第一章标题](/chapter1.md) - [第二章、 第二章标题](/chapter2.md) @ 9c9d2765:16f8c2c2
2025-04-05 10:45:11**CHAPTER ONE** Grandpa Ray’s birthday was a grand celebration. His children and grandchildren gathered around, each presenting him with expensive gifts, golden watches, fine suits, and rare wines. The room buzzed with excitement and laughter. Among them was James, Grandpa Ray’s adopted son. Unlike the others, James had no gift to offer. He stood quietly, watching as each family member received warm praise for their presents. Then, Grandpa Ray did something unexpected. With a kind smile, he said, “Today, I want to give you all a gift instead. Ask for anything, and I will grant it.” Excited, his children and grandchildren eagerly requested expensive things luxury cars, houses, money, and positions in the family business. When it was James’ turn, he hesitated for a moment before saying, “Grandpa, I would like a shovel.” A hush fell over the room, then erupted into laughter. “A shovel?” one cousin sneered. “What a silly request!” another chuckled. But Grandpa Ray raised a hand, silencing them. He looked at James with curiosity. “Why a shovel, my boy?” James took a deep breath and replied, “I don’t need riches handed to me. I want to work for my own wealth. A shovel will help me till the land, plant crops, and build something for myself.” Grandpa Ray’s eyes gleamed with pride. He nodded and said, “That is a wise request. Not only will I give you a shovel, but I will also grant you a piece of land to farm.” The laughter died down. The others had asked for luxury, but James had asked for a tool to create his own future. James had once lived a life of promise. He was hardworking, loyal, and dedicated to his family’s company. But his world came crashing down when he was falsely accused of embezzlement. His own parents, ashamed of the scandal, disowned him without listening to his pleas of innocence. Alone and broken, James had nowhere to go. It was then that Grandpa Ray, a man known for his wisdom and kindness, took him in. Unlike the rest of the world, Grandpa Ray saw something in James his resilience, his honesty, and his potential. Despite being adopted into a wealthy and powerful family, James never truly felt accepted. The others in the family pretended to love him, but behind his back, they whispered that he was a burden, an outsider. The only one who genuinely cared for him besides Grandpa Ray was Rita, the old man’s granddaughter. Over the years, James worked hard to earn his place in the family. He managed some of Grandpa Ray’s businesses, proving his intelligence and dedication. Rita, a kind and spirited woman, saw the goodness in him. Their bond grew stronger, and soon, love blossomed between them. Grandpa Ray, seeing James’ sincerity and loyalty, made a bold decision he gave Rita’s hand in marriage to James, despite the objections of the rest of the family. "You have proven yourself to be a man of honor," Grandpa Ray said to James on the wedding day. "And I know that you will cherish Rita the way she deserves." The rest of the family smiled in public but harbored resentment in their hearts. To them, James was an unworthy orphan who had stolen their grandfather’s favor. When Grandpa Ray passed away, everything changed. The mask of fake love that the family had worn for years finally fell off. Without Grandpa Ray to protect him, James became a target of humiliation. Helen, Rita’s mother, Christopher, her father, and Stephen, her brother, openly ridiculed him. They made life unbearable, treating him like a servant rather than a family member. "You don’t belong here," Stephen sneered one evening. "You were just Grandpa’s charity case." James endured the insults in silence, holding onto the love he shared with Rita. But his in-laws had other plans; they wanted him out of Rita’s life for good. Helen and Christopher believed that Rita had made a mistake by marrying James. They wanted her to divorce him and marry someone who would elevate the family’s status. That’s when Helen introduced Mark, the only son of the Prime Minister. Mark was wealthy, powerful, and came from a family of high political influence. To her, he was the perfect husband for Rita. "Rita, darling," Helen said sweetly, "don’t waste your life with James. You deserve someone who can give you the life of luxury you were born into." Stephen agreed. "Mark is everything James is not rich, powerful, and from a good family. Be wise, sister." But Rita stood firm. "I love James," she said. "And I will not betray him, no matter how much you pressure me. James and I made a promise to Grandpa never to leave each other" Helen, frustrated by Rita’s refusal, tried to manipulate her further. She arranged secret meetings between Rita and Mark, hoping she would be swayed. She even planned an engagement dinner, assuming Rita would eventually give in. Meanwhile, James felt the weight of the battle. He saw how much pressure Rita was under and, one evening, he took her hands and said, "Rita, if leaving me will make your life easier, I won’t stop you." Tears filled her eyes. "James, my love isn’t based on status or wealth. I chose you, and I will keep choosing you no matter what, you have forgotten the promise we two made to Grandpa before he died, in case you have forgotten, I haven't" That night, Rita made her choice. She called a meeting to inform everyone that nothing will make her leave James for another man, James couldn't withstand the joy she made her that night, choosing love over wealth and status. With nothing but their love and determination, James and Rita started anew. They built their life from scratch, with James working tirelessly to create a name for himself. The Ray family had once been a symbol of wealth, power, and success, but in recent months, everything had started crumbling. A series of financial setbacks, business failures, and internal conflicts had pushed the family into a dire situation. The creditors were knocking, the banks were threatening to withdraw their support, and their empire was on the verge of collapse. Desperation clouded every decision they made. And in that desperation, they saw only one way out is Mark. Mark, the only son of the Prime Minister, was not just a man of wealth but also of power and influence. He had been interested in Rita for years, but she had always refused him, choosing instead to marry James. But now, with the family drowning in crisis, Mark became their only hope. Helen, Rita’s mother, sat across from Christopher, her husband, and Stephen, their son. The tension in the room was thick. “We have no other choice,” Helen said firmly. “Mark is willing to help us, but he wants something in return.” “We all know what that is,” Stephen said, glancing at Rita, who sat silently in the corner of the room. Christopher sighed. “James is the only obstacle left. We have to make Rita understand that this isn’t about love anymore, it's about survival.” Helen’s voice was cold. “She will divorce him. And James will have no choice but to accept it.” Rita looked up, her heart pounding. “You’re selling me to him,” she said in disbelief. “Rita,” Helen said impatiently. “This isn’t about selling you. This is about securing our future. James has nothing. Mark can give you everything.” “I don’t want everything. I want my husband.” Helen scoffed. “Love won’t save this family.” But Rita clenched her fists. She wasn’t going to give up on James so easily. The Ray family organized a grand business anniversary event, using it as a cover to publicly introduce Mark as their savior. Guests arrived in expensive suits and dazzling gowns, but beneath the luxury was a desperate attempt to keep up appearances. James had never felt more out of place. He knew he wasn’t truly welcome among the Ray family, but tonight, it was worse than ever. He could see the way people looked at him like he was an outsider, a liability. Then Mark arrived; Tall, confident, and exuding power, he walked into the hall as if he already owned it. People flocked to him, shaking his hand, singing his praises. And then, during a private meeting with the Ray family, he made his move. “I know about your situation,” Mark said smoothly, placing a black suitcase on the table and opening it. Inside were stacks of cash, two million dollars. Helen gasped. Christopher’s hands trembled. Mark leaned back.
@ 9c9d2765:16f8c2c2
2025-04-05 10:45:11**CHAPTER ONE** Grandpa Ray’s birthday was a grand celebration. His children and grandchildren gathered around, each presenting him with expensive gifts, golden watches, fine suits, and rare wines. The room buzzed with excitement and laughter. Among them was James, Grandpa Ray’s adopted son. Unlike the others, James had no gift to offer. He stood quietly, watching as each family member received warm praise for their presents. Then, Grandpa Ray did something unexpected. With a kind smile, he said, “Today, I want to give you all a gift instead. Ask for anything, and I will grant it.” Excited, his children and grandchildren eagerly requested expensive things luxury cars, houses, money, and positions in the family business. When it was James’ turn, he hesitated for a moment before saying, “Grandpa, I would like a shovel.” A hush fell over the room, then erupted into laughter. “A shovel?” one cousin sneered. “What a silly request!” another chuckled. But Grandpa Ray raised a hand, silencing them. He looked at James with curiosity. “Why a shovel, my boy?” James took a deep breath and replied, “I don’t need riches handed to me. I want to work for my own wealth. A shovel will help me till the land, plant crops, and build something for myself.” Grandpa Ray’s eyes gleamed with pride. He nodded and said, “That is a wise request. Not only will I give you a shovel, but I will also grant you a piece of land to farm.” The laughter died down. The others had asked for luxury, but James had asked for a tool to create his own future. James had once lived a life of promise. He was hardworking, loyal, and dedicated to his family’s company. But his world came crashing down when he was falsely accused of embezzlement. His own parents, ashamed of the scandal, disowned him without listening to his pleas of innocence. Alone and broken, James had nowhere to go. It was then that Grandpa Ray, a man known for his wisdom and kindness, took him in. Unlike the rest of the world, Grandpa Ray saw something in James his resilience, his honesty, and his potential. Despite being adopted into a wealthy and powerful family, James never truly felt accepted. The others in the family pretended to love him, but behind his back, they whispered that he was a burden, an outsider. The only one who genuinely cared for him besides Grandpa Ray was Rita, the old man’s granddaughter. Over the years, James worked hard to earn his place in the family. He managed some of Grandpa Ray’s businesses, proving his intelligence and dedication. Rita, a kind and spirited woman, saw the goodness in him. Their bond grew stronger, and soon, love blossomed between them. Grandpa Ray, seeing James’ sincerity and loyalty, made a bold decision he gave Rita’s hand in marriage to James, despite the objections of the rest of the family. "You have proven yourself to be a man of honor," Grandpa Ray said to James on the wedding day. "And I know that you will cherish Rita the way she deserves." The rest of the family smiled in public but harbored resentment in their hearts. To them, James was an unworthy orphan who had stolen their grandfather’s favor. When Grandpa Ray passed away, everything changed. The mask of fake love that the family had worn for years finally fell off. Without Grandpa Ray to protect him, James became a target of humiliation. Helen, Rita’s mother, Christopher, her father, and Stephen, her brother, openly ridiculed him. They made life unbearable, treating him like a servant rather than a family member. "You don’t belong here," Stephen sneered one evening. "You were just Grandpa’s charity case." James endured the insults in silence, holding onto the love he shared with Rita. But his in-laws had other plans; they wanted him out of Rita’s life for good. Helen and Christopher believed that Rita had made a mistake by marrying James. They wanted her to divorce him and marry someone who would elevate the family’s status. That’s when Helen introduced Mark, the only son of the Prime Minister. Mark was wealthy, powerful, and came from a family of high political influence. To her, he was the perfect husband for Rita. "Rita, darling," Helen said sweetly, "don’t waste your life with James. You deserve someone who can give you the life of luxury you were born into." Stephen agreed. "Mark is everything James is not rich, powerful, and from a good family. Be wise, sister." But Rita stood firm. "I love James," she said. "And I will not betray him, no matter how much you pressure me. James and I made a promise to Grandpa never to leave each other" Helen, frustrated by Rita’s refusal, tried to manipulate her further. She arranged secret meetings between Rita and Mark, hoping she would be swayed. She even planned an engagement dinner, assuming Rita would eventually give in. Meanwhile, James felt the weight of the battle. He saw how much pressure Rita was under and, one evening, he took her hands and said, "Rita, if leaving me will make your life easier, I won’t stop you." Tears filled her eyes. "James, my love isn’t based on status or wealth. I chose you, and I will keep choosing you no matter what, you have forgotten the promise we two made to Grandpa before he died, in case you have forgotten, I haven't" That night, Rita made her choice. She called a meeting to inform everyone that nothing will make her leave James for another man, James couldn't withstand the joy she made her that night, choosing love over wealth and status. With nothing but their love and determination, James and Rita started anew. They built their life from scratch, with James working tirelessly to create a name for himself. The Ray family had once been a symbol of wealth, power, and success, but in recent months, everything had started crumbling. A series of financial setbacks, business failures, and internal conflicts had pushed the family into a dire situation. The creditors were knocking, the banks were threatening to withdraw their support, and their empire was on the verge of collapse. Desperation clouded every decision they made. And in that desperation, they saw only one way out is Mark. Mark, the only son of the Prime Minister, was not just a man of wealth but also of power and influence. He had been interested in Rita for years, but she had always refused him, choosing instead to marry James. But now, with the family drowning in crisis, Mark became their only hope. Helen, Rita’s mother, sat across from Christopher, her husband, and Stephen, their son. The tension in the room was thick. “We have no other choice,” Helen said firmly. “Mark is willing to help us, but he wants something in return.” “We all know what that is,” Stephen said, glancing at Rita, who sat silently in the corner of the room. Christopher sighed. “James is the only obstacle left. We have to make Rita understand that this isn’t about love anymore, it's about survival.” Helen’s voice was cold. “She will divorce him. And James will have no choice but to accept it.” Rita looked up, her heart pounding. “You’re selling me to him,” she said in disbelief. “Rita,” Helen said impatiently. “This isn’t about selling you. This is about securing our future. James has nothing. Mark can give you everything.” “I don’t want everything. I want my husband.” Helen scoffed. “Love won’t save this family.” But Rita clenched her fists. She wasn’t going to give up on James so easily. The Ray family organized a grand business anniversary event, using it as a cover to publicly introduce Mark as their savior. Guests arrived in expensive suits and dazzling gowns, but beneath the luxury was a desperate attempt to keep up appearances. James had never felt more out of place. He knew he wasn’t truly welcome among the Ray family, but tonight, it was worse than ever. He could see the way people looked at him like he was an outsider, a liability. Then Mark arrived; Tall, confident, and exuding power, he walked into the hall as if he already owned it. People flocked to him, shaking his hand, singing his praises. And then, during a private meeting with the Ray family, he made his move. “I know about your situation,” Mark said smoothly, placing a black suitcase on the table and opening it. Inside were stacks of cash, two million dollars. Helen gasped. Christopher’s hands trembled. Mark leaned back. @ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison. I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core You can also learn more about Pubky here: https://pubky.org/ That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key. Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis. Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed. Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message. I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key. As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster. Based on all of this info, it seems like, to populate your feed, this is the series of steps: - you tell your homeserver your pubkey - it uses some sort of algorithm to decide whose posts to show you - then looks up the homeservers used by those people on an indexer server - then it fetches posts from their homeservers - then your client displays them to you To create a post, this is the series of steps: - you tell your homeserver what you want to say to the world - it stores that message in plaintext and merely asserts that it came from you (it's not signed) - other people can find out what you said by querying for your posts on your homeserver Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver. John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted. Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
@ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison. I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core You can also learn more about Pubky here: https://pubky.org/ That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key. Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis. Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed. Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message. I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key. As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster. Based on all of this info, it seems like, to populate your feed, this is the series of steps: - you tell your homeserver your pubkey - it uses some sort of algorithm to decide whose posts to show you - then looks up the homeservers used by those people on an indexer server - then it fetches posts from their homeservers - then your client displays them to you To create a post, this is the series of steps: - you tell your homeserver what you want to say to the world - it stores that message in plaintext and merely asserts that it came from you (it's not signed) - other people can find out what you said by querying for your posts on your homeserver Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver. John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted. Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/ @ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.  The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022). Look forward for this to happen! Spread the voice: N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m) X: https://x.com/bitcoin_design/status/1905547407405768927 originally posted at https://stacker.news/items/927650
@ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.  The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022). Look forward for this to happen! Spread the voice: N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m) X: https://x.com/bitcoin_design/status/1905547407405768927 originally posted at https://stacker.news/items/927650 @ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who? The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1: ## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.              - - - Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before. This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using. - [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser - ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY) @k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful. [^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined originally posted at https://stacker.news/items/926557
@ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who? The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1: ## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.              - - - Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before. This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using. - [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser - ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY) @k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful. [^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined originally posted at https://stacker.news/items/926557 @ e372d24b:e25df41f
2025-04-05 18:11:15## Unlocking Learning Potential: Why Student's Ideas Matter ### Introduction Recent research in mathematics education emphasizes the importance of valuing and building upon students' initial ideas and intuitive understanding. This approach, often referred to as "taking students' ideas seriously," has enhanced conceptual understanding, problem-solving skills, and overall mathematical achievement. This overview examines this approach's theoretical foundations, cognitive processes, and practical implications in mathematics classrooms.  <div style="padding:56.25% 0 0 0;position:relative;"><iframe src="https://player.vimeo.com/video/1039781401?badge=0&autopause=0&player_id=0&app_id=58479" frameborder="0" allow="autoplay; fullscreen; picture-in-picture; clipboard-write; encrypted-media" style="position:absolute;top:0;left:0;width:100%;height:100%;" title="Practice 1-taking students ideas seriously"></iframe></div><script src="https://player.vimeo.com/api/player.js"></script> [FREE DOWNLOAD - Questions and Prompts](https://dmti-public-resources.s3.us-east-2.amazonaws.com/DMT%20Questions%20and%20Prompts%20-%20Eng.pdf) #### **Theoretical Foundations** Taking students' ideas seriously is grounded in constructivist learning theory and research on how students develop mathematical understanding. Hiebert and Carpenter (1992) argue that "if children possessed internal networks constructed both in and out of school and if they recognized the connections between them, their understanding and performance in both settings would improve." This highlights the importance of connecting students' informal knowledge with formal mathematical concepts. Carpenter's work further emphasizes the value of students' intuitive knowledge: "Children come to school with a great deal of informal or intuitive knowledge of mathematics that can serve as the basis for developing much of the formal mathematics of the primary school curriculum." This suggests that taking students' initial ideas seriously can provide a strong foundation for developing a more sophisticated mathematical understanding. #### **Cognitive Processes** When students' ideas are taken seriously in mathematics classrooms, several cognitive processes are engaged: 1. Schema Formation: As students articulate and refine their ideas, they develop and modify mental frameworks or schemas that organize mathematical concepts. 2. Metacognition: Explaining their thinking engages students' metacognitive processes, promoting reflection on their own understanding and problem-solving strategies. 3. Elaborative Rehearsal: Verbalizing mathematical concepts helps move information from working memory to long-term memory, enhancing retention. 4. Cognitive Conflict: When students encounter differing viewpoints, it can create cognitive conflict, stimulating the reconciliation of new information with existing schemas. #### **Practical Implications** **Eliciting and Valuing Student Ideas** Carpenter and Lehrer argue that for learning with understanding to occur, instruction needs to provide specific opportunities: "For learning with understanding to occur, instruction needs to provide students the opportunity to develop productive relationships, extend and apply their knowledge, reflect about their experiences, articulate what they know, and make knowledge their own." This emphasizes the need for instructional approaches that actively elicit and value student ideas. #### **Creating a Supportive Environment** To effectively take students' ideas seriously, teachers must foster a classroom environment where all contributions are respected. This involves: 1. Provide adequate thinking time for students to formulate their thoughts. 2. Using open-ended questions that encourage diverse thinking and approaches. 3. Implementing collaborative strategies like think-pair-share to build confidence in sharing ideas. #### **Connecting to Formal Mathematics** Hiebert advocates for teaching practices that promote understanding by focusing on "the inherent structure of the emerging mathematical ideas and addressing students' misconceptions as they arise" . This involves helping students connect their informal ideas to more formal mathematical concepts and procedures. #### Impact on Student Learning Research indicates that taking students' ideas seriously can significantly improve mathematical understanding and achievement. A study by Carpenter et al. (1998) found that when teachers based their instruction on students' thinking, students demonstrated greater problem-solving skills and conceptual understanding compared to control groups. Moreover, this approach has increased student engagement and motivation in mathematics. When students feel their ideas are valued, they are more likely to participate actively in mathematical discussions and take intellectual risks. #### Challenges and Considerations While the benefits of taking students' ideas seriously are well-documented, implementing this approach can present challenges: 1. **Time Constraints:** Allowing for extended student discussions and idea exploration can be time-consuming within the constraints of a typical school schedule. 2. **Teacher Preparation:** Effectively building on student ideas requires strong content knowledge and pedagogical skills from teachers. 3. **Assessment Alignment:** Traditional assessment methods may not adequately capture the depth of understanding developed through this approach, necessitating new forms of evaluation. #### Conclusion Taking students' ideas seriously in mathematics education represents a powerful approach to fostering deep conceptual understanding and problem-solving skills. By valuing students' initial thoughts and building upon their intuitive knowledge, educators can create more engaging and effective learning environments. While challenges exist in implementation, the potential benefits for student learning and mathematical achievement make this approach worthy of serious consideration and further research. #### References Ball, D. L., Thames, M. H., & Phelps, G. (2008). Content knowledge for teaching: What makes it special? Journal of Teacher Education, 59(5), 389-407. Boaler, J. (2002). Experiencing school mathematics: Traditional and reform approaches to teaching and their impact on student learning. Routledge. Boaler, J., & Brodie, K. (2004). The importance, nature and impact of teacher questions. In D. E. McDougall & J. A. Ross (Eds.), Proceedings of the 26th annual meeting of the North American Chapter of the International Group for the Psychology of Mathematics Education (Vol. 2, pp. 773-782). Toronto: OISE/UT. Carpenter, T. P., Fennema, E., & Franke, M. L. (1996). Cognitively guided instruction: A knowledge base for reform in primary mathematics instruction. The Elementary School Journal, 97(1), 3-20. Carpenter, T. P., Fennema, E., Franke, M. L., Levi, L., & Empson, S. B. (1999). Children's mathematics: Cognitively guided instruction. Portsmouth, NH: Heinemann. Carpenter, T. P., & Lehrer, R. (1999). Teaching and learning mathematics with understanding. In E. Fennema & T. A. Romberg (Eds.), Mathematics classrooms that promote understanding (pp. 19-32). Mahwah, NJ: Lawrence Erlbaum Associates. Craik, F. I., & Lockhart, R. S. (1972). Levels of processing: A framework for memory research. Journal of Verbal Learning and Verbal Behavior, 11(6), 671-684. Driscoll, M. P. (2005). Psychology of learning for instruction (3rd ed.). Boston: Allyn and Bacon. Flavell, J. H. (1979). Metacognition and cognitive monitoring: A new area of cognitive-developmental inquiry. American Psychologist, 34(10), 906-911. Hiebert, J., & Carpenter, T. P. (1992). Learning and teaching with understanding. In D. A. Grouws (Ed.), Handbook of research on mathematics teaching and learning (pp. 65-97). New York: Macmillan. Hiebert, J., Carpenter, T. P., Fennema, E., Fuson, K. C., Wearne, D., Murray, H., ... & Human, P. (1997). Making sense: Teaching and learning mathematics with understanding. Portsmouth, NH: Heinemann. Lyman, F. (1981). The responsive classroom discussion: The inclusion of all students. In A. S. Anderson (Ed.), Mainstreaming Digest (pp. 109-113). College Park: University of Maryland Press. Piaget, J. (1952). The origins of intelligence in children. New York: International Universities Press. Rowe, M. B. (1986). Wait time: Slowing down may be a way of speeding up! Journal of Teacher Education, 37(1), 43- 50. Shepard, L. A. (2000). The role of assessment in a learning culture. Educational Researcher, 29(7), 4-14. Smith, M. S., & Stein, M. K. (2011). 5 practices for orchestrating productive mathematics discussions. Reston, VA: National Council of Teachers of Mathematics. #### **Social Media.** Research in mathematics education highlights the significance of taking students' ideas seriously, demonstrating how this approach enhances conceptual understanding, problem-solving abilities, and overall mathematical achievement. Rooted in constructivist learning theory, this method engages crucial cognitive processes like schema formation, metacognition, and elaborative rehearsal. By connecting students’ informal knowledge with formal mathematical concepts, educators can establish a robust foundation for advanced mathematical thinking. Studies show that when instruction is based on students' thinking, learners exhibit superior problem-solving skills and a deeper conceptual grasp than traditional teaching methods. Join us in exploring these powerful teaching approaches and their impact on mathematical thinking and achievement!
@ e372d24b:e25df41f
2025-04-05 18:11:15## Unlocking Learning Potential: Why Student's Ideas Matter ### Introduction Recent research in mathematics education emphasizes the importance of valuing and building upon students' initial ideas and intuitive understanding. This approach, often referred to as "taking students' ideas seriously," has enhanced conceptual understanding, problem-solving skills, and overall mathematical achievement. This overview examines this approach's theoretical foundations, cognitive processes, and practical implications in mathematics classrooms.  <div style="padding:56.25% 0 0 0;position:relative;"><iframe src="https://player.vimeo.com/video/1039781401?badge=0&autopause=0&player_id=0&app_id=58479" frameborder="0" allow="autoplay; fullscreen; picture-in-picture; clipboard-write; encrypted-media" style="position:absolute;top:0;left:0;width:100%;height:100%;" title="Practice 1-taking students ideas seriously"></iframe></div><script src="https://player.vimeo.com/api/player.js"></script> [FREE DOWNLOAD - Questions and Prompts](https://dmti-public-resources.s3.us-east-2.amazonaws.com/DMT%20Questions%20and%20Prompts%20-%20Eng.pdf) #### **Theoretical Foundations** Taking students' ideas seriously is grounded in constructivist learning theory and research on how students develop mathematical understanding. Hiebert and Carpenter (1992) argue that "if children possessed internal networks constructed both in and out of school and if they recognized the connections between them, their understanding and performance in both settings would improve." This highlights the importance of connecting students' informal knowledge with formal mathematical concepts. Carpenter's work further emphasizes the value of students' intuitive knowledge: "Children come to school with a great deal of informal or intuitive knowledge of mathematics that can serve as the basis for developing much of the formal mathematics of the primary school curriculum." This suggests that taking students' initial ideas seriously can provide a strong foundation for developing a more sophisticated mathematical understanding. #### **Cognitive Processes** When students' ideas are taken seriously in mathematics classrooms, several cognitive processes are engaged: 1. Schema Formation: As students articulate and refine their ideas, they develop and modify mental frameworks or schemas that organize mathematical concepts. 2. Metacognition: Explaining their thinking engages students' metacognitive processes, promoting reflection on their own understanding and problem-solving strategies. 3. Elaborative Rehearsal: Verbalizing mathematical concepts helps move information from working memory to long-term memory, enhancing retention. 4. Cognitive Conflict: When students encounter differing viewpoints, it can create cognitive conflict, stimulating the reconciliation of new information with existing schemas. #### **Practical Implications** **Eliciting and Valuing Student Ideas** Carpenter and Lehrer argue that for learning with understanding to occur, instruction needs to provide specific opportunities: "For learning with understanding to occur, instruction needs to provide students the opportunity to develop productive relationships, extend and apply their knowledge, reflect about their experiences, articulate what they know, and make knowledge their own." This emphasizes the need for instructional approaches that actively elicit and value student ideas. #### **Creating a Supportive Environment** To effectively take students' ideas seriously, teachers must foster a classroom environment where all contributions are respected. This involves: 1. Provide adequate thinking time for students to formulate their thoughts. 2. Using open-ended questions that encourage diverse thinking and approaches. 3. Implementing collaborative strategies like think-pair-share to build confidence in sharing ideas. #### **Connecting to Formal Mathematics** Hiebert advocates for teaching practices that promote understanding by focusing on "the inherent structure of the emerging mathematical ideas and addressing students' misconceptions as they arise" . This involves helping students connect their informal ideas to more formal mathematical concepts and procedures. #### Impact on Student Learning Research indicates that taking students' ideas seriously can significantly improve mathematical understanding and achievement. A study by Carpenter et al. (1998) found that when teachers based their instruction on students' thinking, students demonstrated greater problem-solving skills and conceptual understanding compared to control groups. Moreover, this approach has increased student engagement and motivation in mathematics. When students feel their ideas are valued, they are more likely to participate actively in mathematical discussions and take intellectual risks. #### Challenges and Considerations While the benefits of taking students' ideas seriously are well-documented, implementing this approach can present challenges: 1. **Time Constraints:** Allowing for extended student discussions and idea exploration can be time-consuming within the constraints of a typical school schedule. 2. **Teacher Preparation:** Effectively building on student ideas requires strong content knowledge and pedagogical skills from teachers. 3. **Assessment Alignment:** Traditional assessment methods may not adequately capture the depth of understanding developed through this approach, necessitating new forms of evaluation. #### Conclusion Taking students' ideas seriously in mathematics education represents a powerful approach to fostering deep conceptual understanding and problem-solving skills. By valuing students' initial thoughts and building upon their intuitive knowledge, educators can create more engaging and effective learning environments. While challenges exist in implementation, the potential benefits for student learning and mathematical achievement make this approach worthy of serious consideration and further research. #### References Ball, D. L., Thames, M. H., & Phelps, G. (2008). Content knowledge for teaching: What makes it special? Journal of Teacher Education, 59(5), 389-407. Boaler, J. (2002). Experiencing school mathematics: Traditional and reform approaches to teaching and their impact on student learning. Routledge. Boaler, J., & Brodie, K. (2004). The importance, nature and impact of teacher questions. In D. E. McDougall & J. A. Ross (Eds.), Proceedings of the 26th annual meeting of the North American Chapter of the International Group for the Psychology of Mathematics Education (Vol. 2, pp. 773-782). Toronto: OISE/UT. Carpenter, T. P., Fennema, E., & Franke, M. L. (1996). Cognitively guided instruction: A knowledge base for reform in primary mathematics instruction. The Elementary School Journal, 97(1), 3-20. Carpenter, T. P., Fennema, E., Franke, M. L., Levi, L., & Empson, S. B. (1999). Children's mathematics: Cognitively guided instruction. Portsmouth, NH: Heinemann. Carpenter, T. P., & Lehrer, R. (1999). Teaching and learning mathematics with understanding. In E. Fennema & T. A. Romberg (Eds.), Mathematics classrooms that promote understanding (pp. 19-32). Mahwah, NJ: Lawrence Erlbaum Associates. Craik, F. I., & Lockhart, R. S. (1972). Levels of processing: A framework for memory research. Journal of Verbal Learning and Verbal Behavior, 11(6), 671-684. Driscoll, M. P. (2005). Psychology of learning for instruction (3rd ed.). Boston: Allyn and Bacon. Flavell, J. H. (1979). Metacognition and cognitive monitoring: A new area of cognitive-developmental inquiry. American Psychologist, 34(10), 906-911. Hiebert, J., & Carpenter, T. P. (1992). Learning and teaching with understanding. In D. A. Grouws (Ed.), Handbook of research on mathematics teaching and learning (pp. 65-97). New York: Macmillan. Hiebert, J., Carpenter, T. P., Fennema, E., Fuson, K. C., Wearne, D., Murray, H., ... & Human, P. (1997). Making sense: Teaching and learning mathematics with understanding. Portsmouth, NH: Heinemann. Lyman, F. (1981). The responsive classroom discussion: The inclusion of all students. In A. S. Anderson (Ed.), Mainstreaming Digest (pp. 109-113). College Park: University of Maryland Press. Piaget, J. (1952). The origins of intelligence in children. New York: International Universities Press. Rowe, M. B. (1986). Wait time: Slowing down may be a way of speeding up! Journal of Teacher Education, 37(1), 43- 50. Shepard, L. A. (2000). The role of assessment in a learning culture. Educational Researcher, 29(7), 4-14. Smith, M. S., & Stein, M. K. (2011). 5 practices for orchestrating productive mathematics discussions. Reston, VA: National Council of Teachers of Mathematics. #### **Social Media.** Research in mathematics education highlights the significance of taking students' ideas seriously, demonstrating how this approach enhances conceptual understanding, problem-solving abilities, and overall mathematical achievement. Rooted in constructivist learning theory, this method engages crucial cognitive processes like schema formation, metacognition, and elaborative rehearsal. By connecting students’ informal knowledge with formal mathematical concepts, educators can establish a robust foundation for advanced mathematical thinking. Studies show that when instruction is based on students' thinking, learners exhibit superior problem-solving skills and a deeper conceptual grasp than traditional teaching methods. Join us in exploring these powerful teaching approaches and their impact on mathematical thinking and achievement! @ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ 57d1a264:69f1fee1
2025-03-27 08:27:44> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be. `— Anil Dash, The Web We Lost, 13 Dec 2012` https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/ The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks. originally posted at https://stacker.news/items/926499
@ 57d1a264:69f1fee1
2025-03-27 08:27:44> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be. `— Anil Dash, The Web We Lost, 13 Dec 2012` https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/ The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks. originally posted at https://stacker.news/items/926499 @ a5142938:0ef19da3
2025-04-05 10:18:18Discover the materials accepted or not in the products listed on this site. ### ✅ Natural Materials Materials of plant, animal, or mineral origin, without chemical transformation that alters their molecular structure. **🌱 Main Criteria:** - Biodegradability - Non-toxicity - Naturally occurring and recquiring minimal transformation **🔍 List of Natural Materials:** - Natural rubber - Hemp - Cotton - Leather - Cork - Linen - Wool - Silk - … (Other materials) ⚠️ Although natural, these materials can have negative impacts depending on their production conditions (pesticide pollution, excessive water consumption, chemical treatments, animal exploitation, etc.). These impacts are mentionned in the description of each material. Organic, chemical-free versions of these materials are prioritized for product listings on this site. Conventional versions are only referenced when no more sustainable alternative has yet been found for that product category. --- ### 🚫 Non-Natural Materials Synthetic or heavily modified materials, often derived from petrochemicals. **📌 Main Issues:** - Microplastic emissions - Dependence on fossil fuels - Poor biodegradability **🔍 List of Non-Natural Materials:** - Polyester - Polyamide - Acrylic - Elastane - Viscose - Silicone - … (Other materials) ⚠️ These materials are not accepted on this site. However, they may be present in certain listed products if: - they are used in removable accessories (e.g., elastics, buttons—often not listed in the product’s composition by the brand) that can be detached for recycling or composting, and - no 100% natural alternative has yet been identified for that product category. In such cases, a warning will be displayed on the product page. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/ftjhuxe9mvxkhoedyz36i/)
@ a5142938:0ef19da3
2025-04-05 10:18:18Discover the materials accepted or not in the products listed on this site. ### ✅ Natural Materials Materials of plant, animal, or mineral origin, without chemical transformation that alters their molecular structure. **🌱 Main Criteria:** - Biodegradability - Non-toxicity - Naturally occurring and recquiring minimal transformation **🔍 List of Natural Materials:** - Natural rubber - Hemp - Cotton - Leather - Cork - Linen - Wool - Silk - … (Other materials) ⚠️ Although natural, these materials can have negative impacts depending on their production conditions (pesticide pollution, excessive water consumption, chemical treatments, animal exploitation, etc.). These impacts are mentionned in the description of each material. Organic, chemical-free versions of these materials are prioritized for product listings on this site. Conventional versions are only referenced when no more sustainable alternative has yet been found for that product category. --- ### 🚫 Non-Natural Materials Synthetic or heavily modified materials, often derived from petrochemicals. **📌 Main Issues:** - Microplastic emissions - Dependence on fossil fuels - Poor biodegradability **🔍 List of Non-Natural Materials:** - Polyester - Polyamide - Acrylic - Elastane - Viscose - Silicone - … (Other materials) ⚠️ These materials are not accepted on this site. However, they may be present in certain listed products if: - they are used in removable accessories (e.g., elastics, buttons—often not listed in the product’s composition by the brand) that can be detached for recycling or composting, and - no 100% natural alternative has yet been identified for that product category. In such cases, a warning will be displayed on the product page. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/ftjhuxe9mvxkhoedyz36i/) @ a5142938:0ef19da3
2025-04-05 10:09:30**Happy to have found useful information on this site?** Support the project by making a donation to keep it running and thank the contributors. --- **In bitcoin** <img src=" https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **In euros, dollars, or any other supported currency** 👉 [Make a pledge on LiberaPay](https://en.liberapay.com/origin-nature/) --- ### 💡 A Value-Sharing Model Half of the donations are redistributed to the contributors who create the site's value, experimenting with a revenue-sharing model on the Internet—one that respects your data and doesn’t seek to capture your attention. The other half helps cover the site's operating costs. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/9bd013ef3215e1ac/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/ax9fsc76vokpk2cbhzwv9/)
@ a5142938:0ef19da3
2025-04-05 10:09:30**Happy to have found useful information on this site?** Support the project by making a donation to keep it running and thank the contributors. --- **In bitcoin** <img src=" https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **In euros, dollars, or any other supported currency** 👉 [Make a pledge on LiberaPay](https://en.liberapay.com/origin-nature/) --- ### 💡 A Value-Sharing Model Half of the donations are redistributed to the contributors who create the site's value, experimenting with a revenue-sharing model on the Internet—one that respects your data and doesn’t seek to capture your attention. The other half helps cover the site's operating costs. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/9bd013ef3215e1ac/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/ax9fsc76vokpk2cbhzwv9/) @ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly
@ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly @ 0d788b5e:c99ddea5
2025-03-29 01:27:53这是首页内容
@ 0d788b5e:c99ddea5
2025-03-29 01:27:53这是首页内容 @ 21c9f12c:75695e59
2025-04-05 18:11:02## Details - 🍳 Cook time: 1 hour and 15 minutes ## Ingredients - 1 cup dried red lentils - (2) 25-ounce jars marinara sauce - 1 cup raw cashews - 14.5 ounce firm tofu (patted dry) - ½ cup nutritional yeast - 3 tablespoons fresh lemon juice (from about 2 lemons) - 1 teaspoon salt - 1 teaspoon dried basil - 1 teaspoon oregano - ½ teaspoon garlic powder - 3 cups baby spinach - 1 box lasagna noodles (about 12 noodles) (regular, gluten free or whole grain) - Double recipe Easy Vegan Mozzarella Cheese (or 2-3 cups shredded vegan mozzarella) ## Directions 1. lentilsCook the red lentils . Add 1 cup dried red lentils and 3 cups of water to a medium pot. Bring to a boil, and then simmer for about 20 minutes. Drain the lentils in a fine strainer, and then add back to the pot and stir in the marinara sauce . Set aside. 2. ovenPreheat the oven to 350 degrees . 3. Make the Cashew-Tofu Ricotta: Add the cashews to a food processor and process until fine and crumbly. Then add the tofu in chunks, nutritional yeast , lemon juice , salt , basil , oregano and garlic powder to the food processor. Pulse until well combined and pretty smooth. If it's too thick, add a few tablespoons of water to blend. Set aside. 4. LasagnaAssembling the lasagna: Add about 1 cup of lentil marinara to the bottom of a large 9x13 inch casserole dish. Spread it around evenly. Next add 4-5 lasagna noodles (uncooked). Spread half of the ricotta on top of the noodles . Top with half of the spinach . Add about 1 cup of the marinara sauce over the spinach , then place 4-5 lasagna noodles on top. Spread the rest of the ricotta over the noodles , then the rest of the spinach . Place 4-5 more noodles on top of the spinach , and then pour the rest of the sauce over the top, evenly. 5. LasagnaCover tightly with foil and bake for 40 minutes. 6. MozzarellaWhile the lasagna is cooking, make your Vegan Mozzarella Cheese , if using. Alternatively, use 2-3 cups store bought vegan mozzarella cheese . 7. LasagnaAfter 40 minutes, remove the foil and spoon on the mozzarella (or sprinkle the cheese all over). Place the lasagna back in the oven and bake for 20 more minutes, uncovered. Remove from oven, let cool for at least 15 minutes and serve.
@ 21c9f12c:75695e59
2025-04-05 18:11:02## Details - 🍳 Cook time: 1 hour and 15 minutes ## Ingredients - 1 cup dried red lentils - (2) 25-ounce jars marinara sauce - 1 cup raw cashews - 14.5 ounce firm tofu (patted dry) - ½ cup nutritional yeast - 3 tablespoons fresh lemon juice (from about 2 lemons) - 1 teaspoon salt - 1 teaspoon dried basil - 1 teaspoon oregano - ½ teaspoon garlic powder - 3 cups baby spinach - 1 box lasagna noodles (about 12 noodles) (regular, gluten free or whole grain) - Double recipe Easy Vegan Mozzarella Cheese (or 2-3 cups shredded vegan mozzarella) ## Directions 1. lentilsCook the red lentils . Add 1 cup dried red lentils and 3 cups of water to a medium pot. Bring to a boil, and then simmer for about 20 minutes. Drain the lentils in a fine strainer, and then add back to the pot and stir in the marinara sauce . Set aside. 2. ovenPreheat the oven to 350 degrees . 3. Make the Cashew-Tofu Ricotta: Add the cashews to a food processor and process until fine and crumbly. Then add the tofu in chunks, nutritional yeast , lemon juice , salt , basil , oregano and garlic powder to the food processor. Pulse until well combined and pretty smooth. If it's too thick, add a few tablespoons of water to blend. Set aside. 4. LasagnaAssembling the lasagna: Add about 1 cup of lentil marinara to the bottom of a large 9x13 inch casserole dish. Spread it around evenly. Next add 4-5 lasagna noodles (uncooked). Spread half of the ricotta on top of the noodles . Top with half of the spinach . Add about 1 cup of the marinara sauce over the spinach , then place 4-5 lasagna noodles on top. Spread the rest of the ricotta over the noodles , then the rest of the spinach . Place 4-5 more noodles on top of the spinach , and then pour the rest of the sauce over the top, evenly. 5. LasagnaCover tightly with foil and bake for 40 minutes. 6. MozzarellaWhile the lasagna is cooking, make your Vegan Mozzarella Cheese , if using. Alternatively, use 2-3 cups store bought vegan mozzarella cheese . 7. LasagnaAfter 40 minutes, remove the foil and spoon on the mozzarella (or sprinkle the cheese all over). Place the lasagna back in the oven and bake for 20 more minutes, uncovered. Remove from oven, let cool for at least 15 minutes and serve. @ fd06f542:8d6d54cd
2025-03-28 02:27:52NIP-02 ====== Follow List ----------- `final` `optional` A special event with kind `3`, meaning "follow list" is defined as having a list of `p` tags, one for each of the followed/known profiles one is following. Each tag entry should contain the key for the profile, a relay URL where events from that key can be found (can be set to an empty string if not needed), and a local name (or "petname") for that profile (can also be set to an empty string or not provided), i.e., `["p", <32-bytes hex key>, <main relay URL>, <petname>]`. The `.content` is not used. For example: ```jsonc { "kind": 3, "tags": [ ["p", "91cf9..4e5ca", "wss://alicerelay.com/", "alice"], ["p", "14aeb..8dad4", "wss://bobrelay.com/nostr", "bob"], ["p", "612ae..e610f", "ws://carolrelay.com/ws", "carol"] ], "content": "", // other fields... } ``` Every new following list that gets published overwrites the past ones, so it should contain all entries. Relays and clients SHOULD delete past following lists as soon as they receive a new one. Whenever new follows are added to an existing list, clients SHOULD append them to the end of the list, so they are stored in chronological order. ## Uses ### Follow list backup If one believes a relay will store their events for sufficient time, they can use this kind-3 event to backup their following list and recover on a different device. ### Profile discovery and context augmentation A client may rely on the kind-3 event to display a list of followed people by profiles one is browsing; make lists of suggestions on who to follow based on the follow lists of other people one might be following or browsing; or show the data in other contexts. ### Relay sharing A client may publish a follow list with good relays for each of their follows so other clients may use these to update their internal relay lists if needed, increasing censorship-resistance. ### Petname scheme The data from these follow lists can be used by clients to construct local ["petname"](http://www.skyhunter.com/marcs/petnames/IntroPetNames.html) tables derived from other people's follow lists. This alleviates the need for global human-readable names. For example: A user has an internal follow list that says ```json [ ["p", "21df6d143fb96c2ec9d63726bf9edc71", "", "erin"] ] ``` And receives two follow lists, one from `21df6d143fb96c2ec9d63726bf9edc71` that says ```json [ ["p", "a8bb3d884d5d90b413d9891fe4c4e46d", "", "david"] ] ``` and another from `a8bb3d884d5d90b413d9891fe4c4e46d` that says ```json [ ["p", "f57f54057d2a7af0efecc8b0b66f5708", "", "frank"] ] ``` When the user sees `21df6d143fb96c2ec9d63726bf9edc71` the client can show _erin_ instead; When the user sees `a8bb3d884d5d90b413d9891fe4c4e46d` the client can show _david.erin_ instead; When the user sees `f57f54057d2a7af0efecc8b0b66f5708` the client can show _frank.david.erin_ instead.
@ fd06f542:8d6d54cd
2025-03-28 02:27:52NIP-02 ====== Follow List ----------- `final` `optional` A special event with kind `3`, meaning "follow list" is defined as having a list of `p` tags, one for each of the followed/known profiles one is following. Each tag entry should contain the key for the profile, a relay URL where events from that key can be found (can be set to an empty string if not needed), and a local name (or "petname") for that profile (can also be set to an empty string or not provided), i.e., `["p", <32-bytes hex key>, <main relay URL>, <petname>]`. The `.content` is not used. For example: ```jsonc { "kind": 3, "tags": [ ["p", "91cf9..4e5ca", "wss://alicerelay.com/", "alice"], ["p", "14aeb..8dad4", "wss://bobrelay.com/nostr", "bob"], ["p", "612ae..e610f", "ws://carolrelay.com/ws", "carol"] ], "content": "", // other fields... } ``` Every new following list that gets published overwrites the past ones, so it should contain all entries. Relays and clients SHOULD delete past following lists as soon as they receive a new one. Whenever new follows are added to an existing list, clients SHOULD append them to the end of the list, so they are stored in chronological order. ## Uses ### Follow list backup If one believes a relay will store their events for sufficient time, they can use this kind-3 event to backup their following list and recover on a different device. ### Profile discovery and context augmentation A client may rely on the kind-3 event to display a list of followed people by profiles one is browsing; make lists of suggestions on who to follow based on the follow lists of other people one might be following or browsing; or show the data in other contexts. ### Relay sharing A client may publish a follow list with good relays for each of their follows so other clients may use these to update their internal relay lists if needed, increasing censorship-resistance. ### Petname scheme The data from these follow lists can be used by clients to construct local ["petname"](http://www.skyhunter.com/marcs/petnames/IntroPetNames.html) tables derived from other people's follow lists. This alleviates the need for global human-readable names. For example: A user has an internal follow list that says ```json [ ["p", "21df6d143fb96c2ec9d63726bf9edc71", "", "erin"] ] ``` And receives two follow lists, one from `21df6d143fb96c2ec9d63726bf9edc71` that says ```json [ ["p", "a8bb3d884d5d90b413d9891fe4c4e46d", "", "david"] ] ``` and another from `a8bb3d884d5d90b413d9891fe4c4e46d` that says ```json [ ["p", "f57f54057d2a7af0efecc8b0b66f5708", "", "frank"] ] ``` When the user sees `21df6d143fb96c2ec9d63726bf9edc71` the client can show _erin_ instead; When the user sees `a8bb3d884d5d90b413d9891fe4c4e46d` the client can show _david.erin_ instead; When the user sees `f57f54057d2a7af0efecc8b0b66f5708` the client can show _frank.david.erin_ instead. @ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
@ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure. @ a5142938:0ef19da3
2025-04-05 09:54:41Rewards are an experimental approach to sharing the value created by contributors to this site, through a revenue-sharing system based on the following conditions: - Any revenue generated by the site each month is distributed over the **following 12 months**, ensuring long-term visibility and smoothing out monthly variations. - On the **1st of each month**, half of the revenue is distributed among all contributors, in proportion to the number of their validated contributions. - Contributions remain valid indefinitely, but rewards are only distributed to contributors who have made **at least one validated contribution in the past 12 months**. ### Payment Method Rewards are paid via the Lightning network, in sats (the smallest unit of Bitcoin). To receive payments, you must have a NOSTR account linked to a Lightning wallet. To receive them, the NOSTR account used to contribute must be linked to a Lightning wallet. **💡 New to these tools?** - **Don’t have a NOSTR account yet?** A simple way to get started is to create one on an open-source NOSTR client like [yakihonne.com](https://yakihonne.com/) to set up your profile and wallet there. Then, retrieve your NOSTR keys (from the settings) and save them in a secure vault like [nsec.app](https://use.nsec.app/home) to log in here and start contributing. - **Already started contributing on this site?** Make sure to securely store your NOSTR keys in a vault like [nsec.app](https://use.nsec.app/home). You can also log in with them on [yakihonne.com](https://yakihonne.com/) to set up your profile. - You can also contribute directly from yakihonne.com by commenting on Origine Nature’s articles. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/ ) ### Next rewards Coming soon. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/7hdgcdwt76dprobc9g_2f/)
@ a5142938:0ef19da3
2025-04-05 09:54:41Rewards are an experimental approach to sharing the value created by contributors to this site, through a revenue-sharing system based on the following conditions: - Any revenue generated by the site each month is distributed over the **following 12 months**, ensuring long-term visibility and smoothing out monthly variations. - On the **1st of each month**, half of the revenue is distributed among all contributors, in proportion to the number of their validated contributions. - Contributions remain valid indefinitely, but rewards are only distributed to contributors who have made **at least one validated contribution in the past 12 months**. ### Payment Method Rewards are paid via the Lightning network, in sats (the smallest unit of Bitcoin). To receive payments, you must have a NOSTR account linked to a Lightning wallet. To receive them, the NOSTR account used to contribute must be linked to a Lightning wallet. **💡 New to these tools?** - **Don’t have a NOSTR account yet?** A simple way to get started is to create one on an open-source NOSTR client like [yakihonne.com](https://yakihonne.com/) to set up your profile and wallet there. Then, retrieve your NOSTR keys (from the settings) and save them in a secure vault like [nsec.app](https://use.nsec.app/home) to log in here and start contributing. - **Already started contributing on this site?** Make sure to securely store your NOSTR keys in a vault like [nsec.app](https://use.nsec.app/home). You can also log in with them on [yakihonne.com](https://yakihonne.com/) to set up your profile. - You can also contribute directly from yakihonne.com by commenting on Origine Nature’s articles. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/ ) ### Next rewards Coming soon. --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/7hdgcdwt76dprobc9g_2f/) @ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial). > _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_ `— Richard Hamming` [^1] https://www.youtube.com/watch?v=8pTEmbeENF4 For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.  _'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.' More details at https://worrydream.com/dbx/ [^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook) originally posted at https://stacker.news/items/926493
@ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial). > _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_ `— Richard Hamming` [^1] https://www.youtube.com/watch?v=8pTEmbeENF4 For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.  _'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.' More details at https://worrydream.com/dbx/ [^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook) originally posted at https://stacker.news/items/926493 @ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 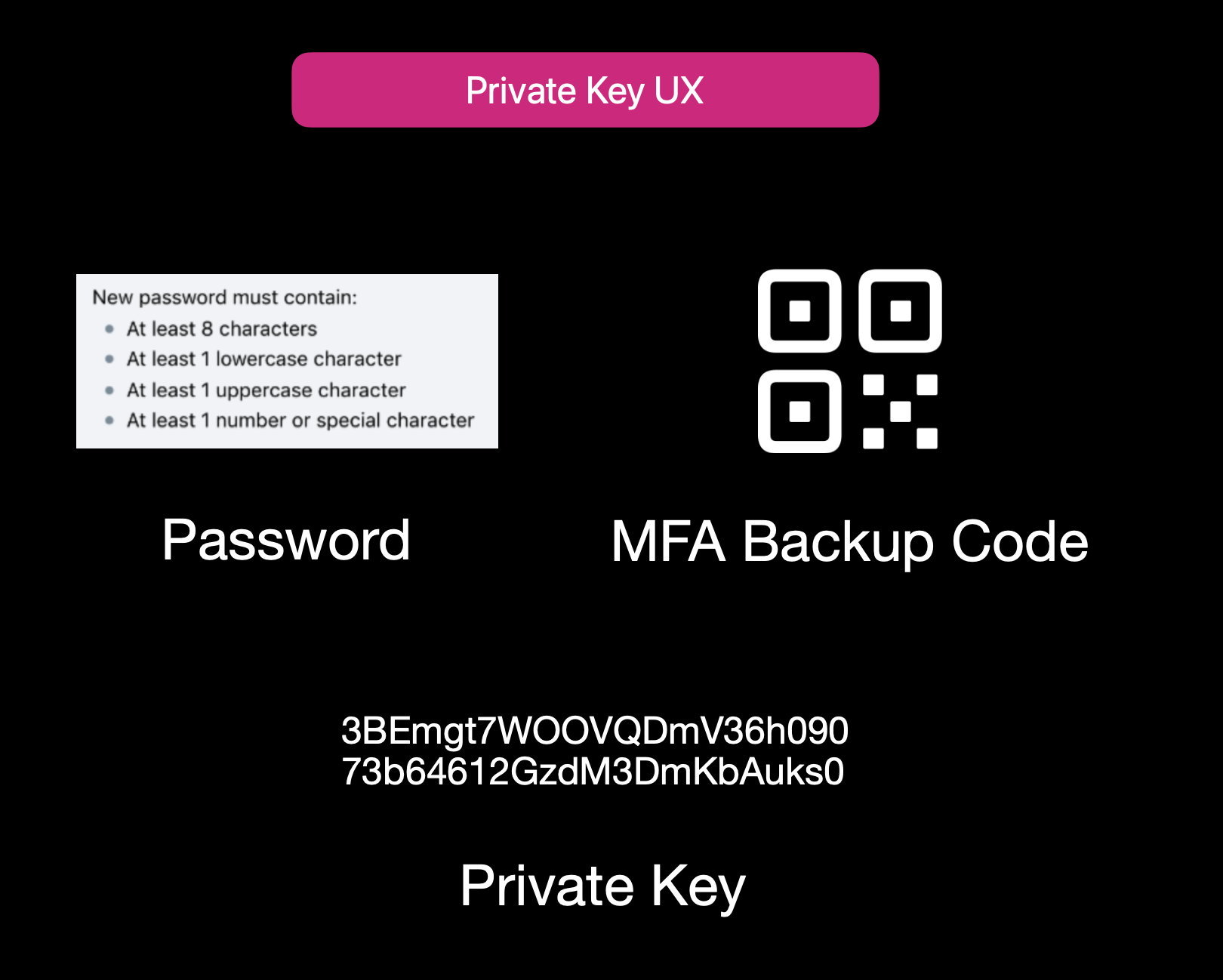Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 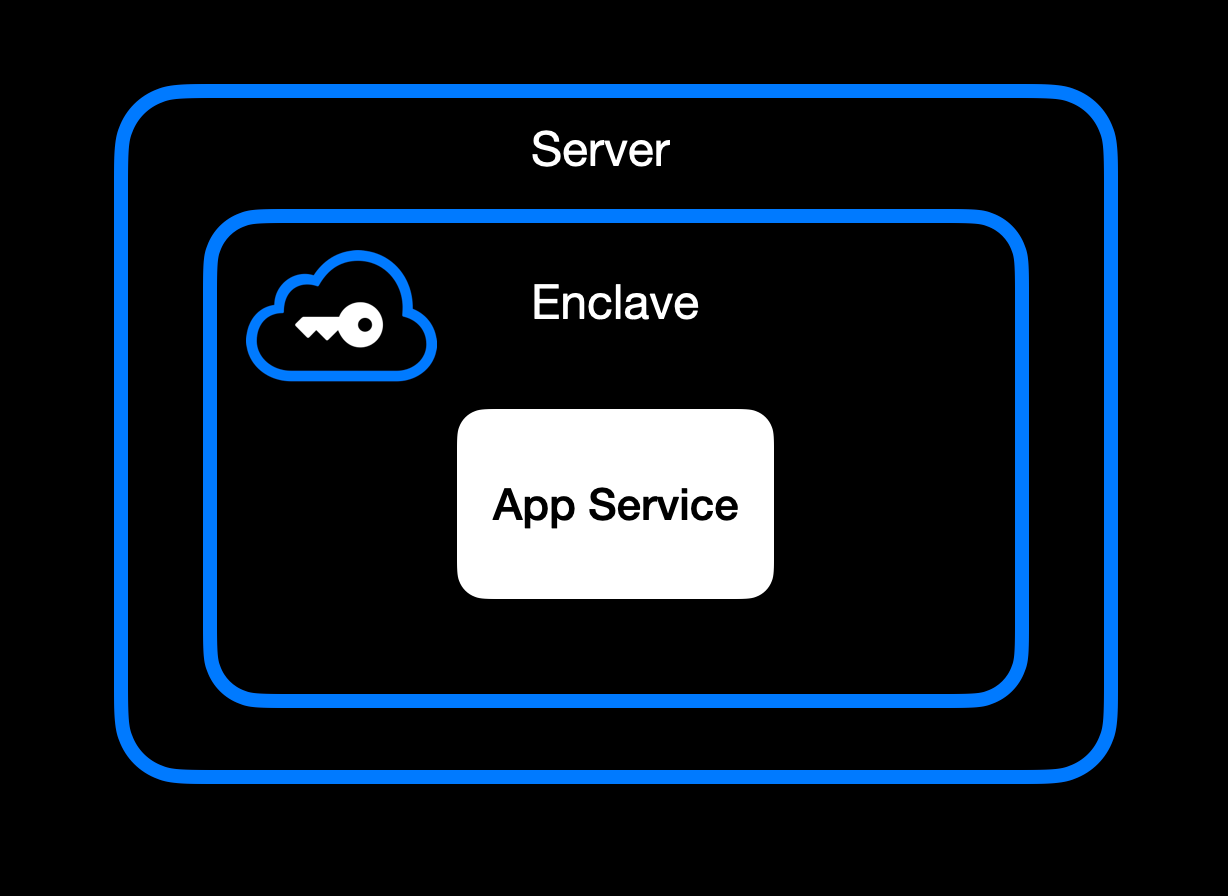App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 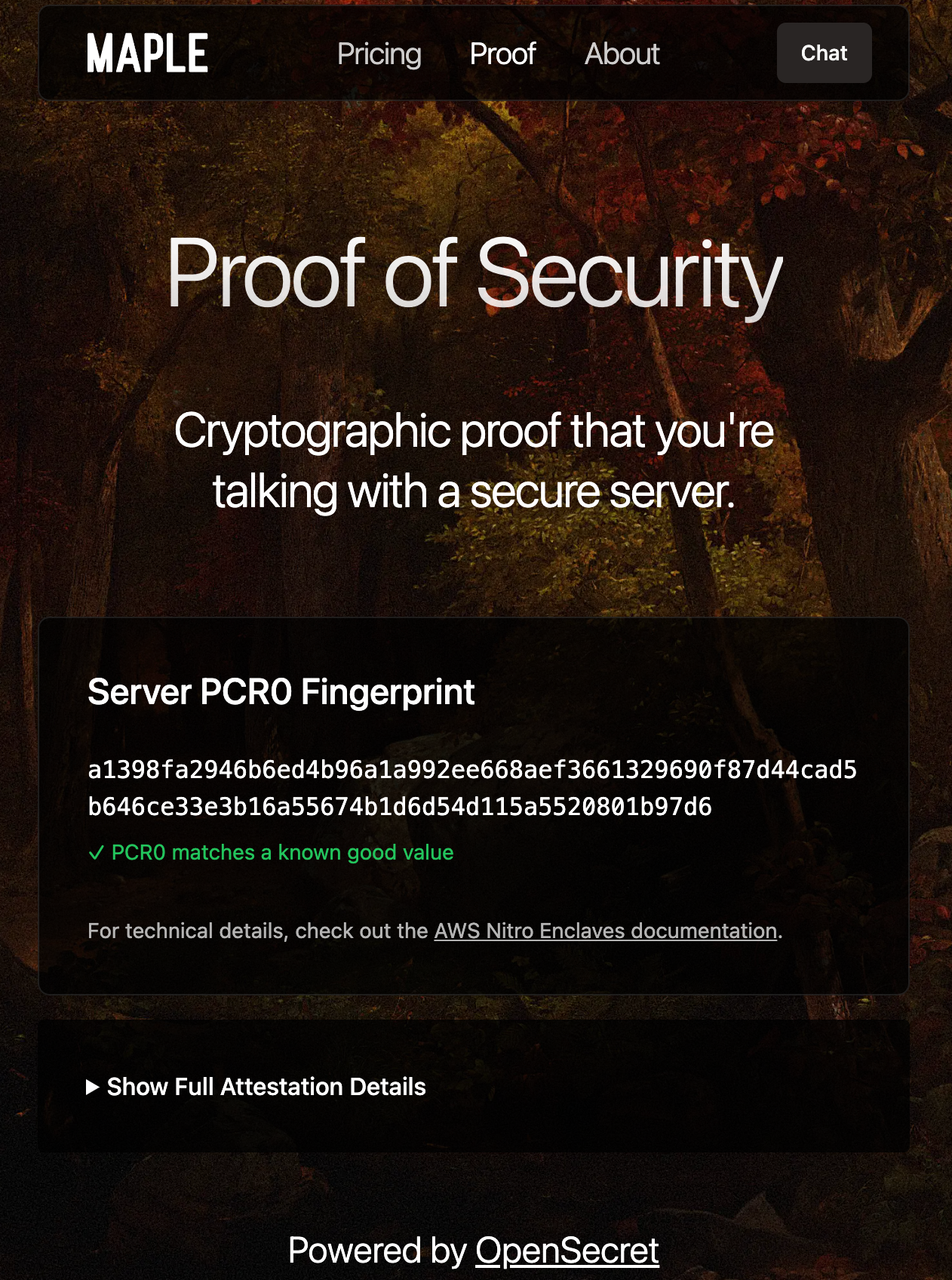Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 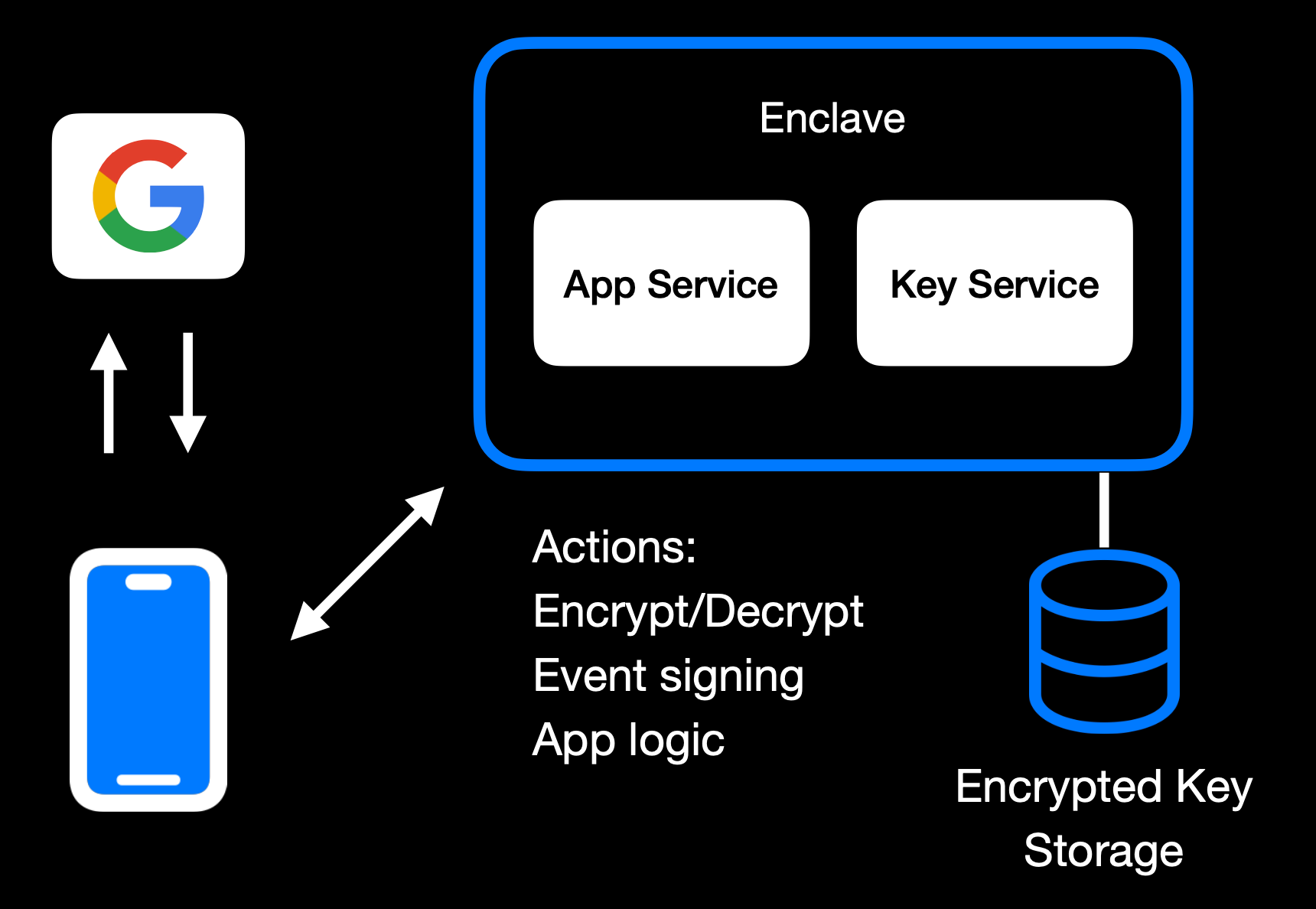Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 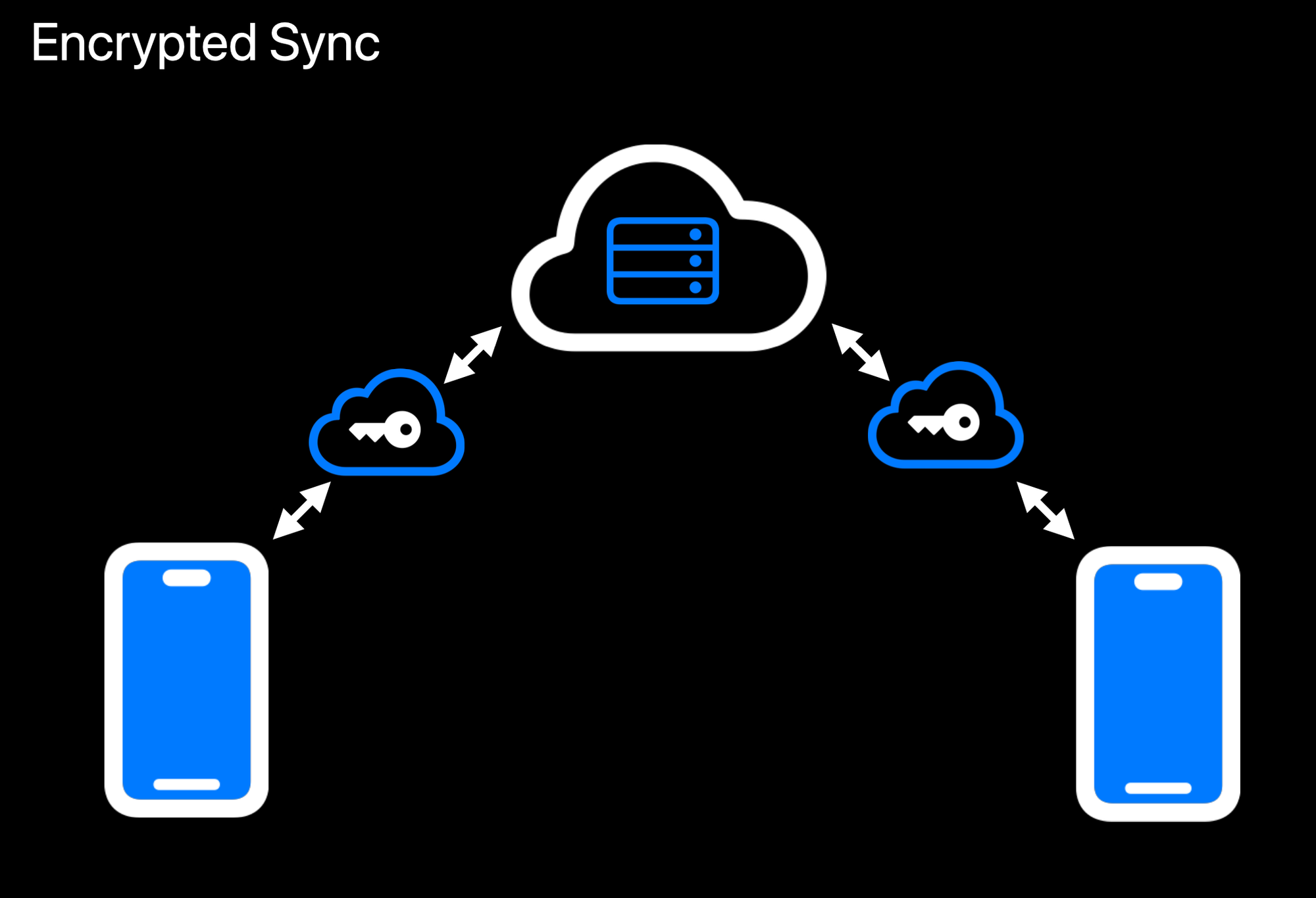Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 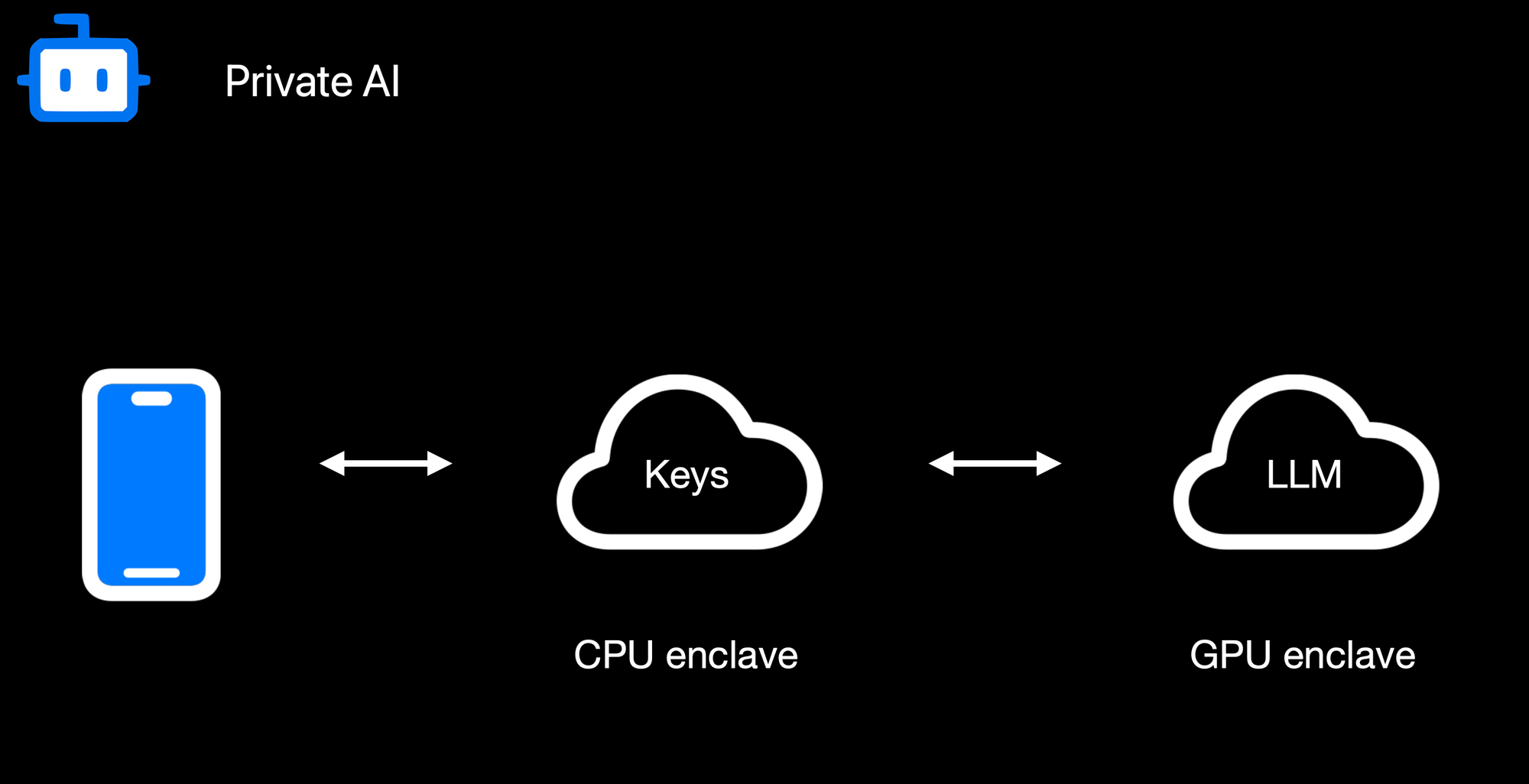Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 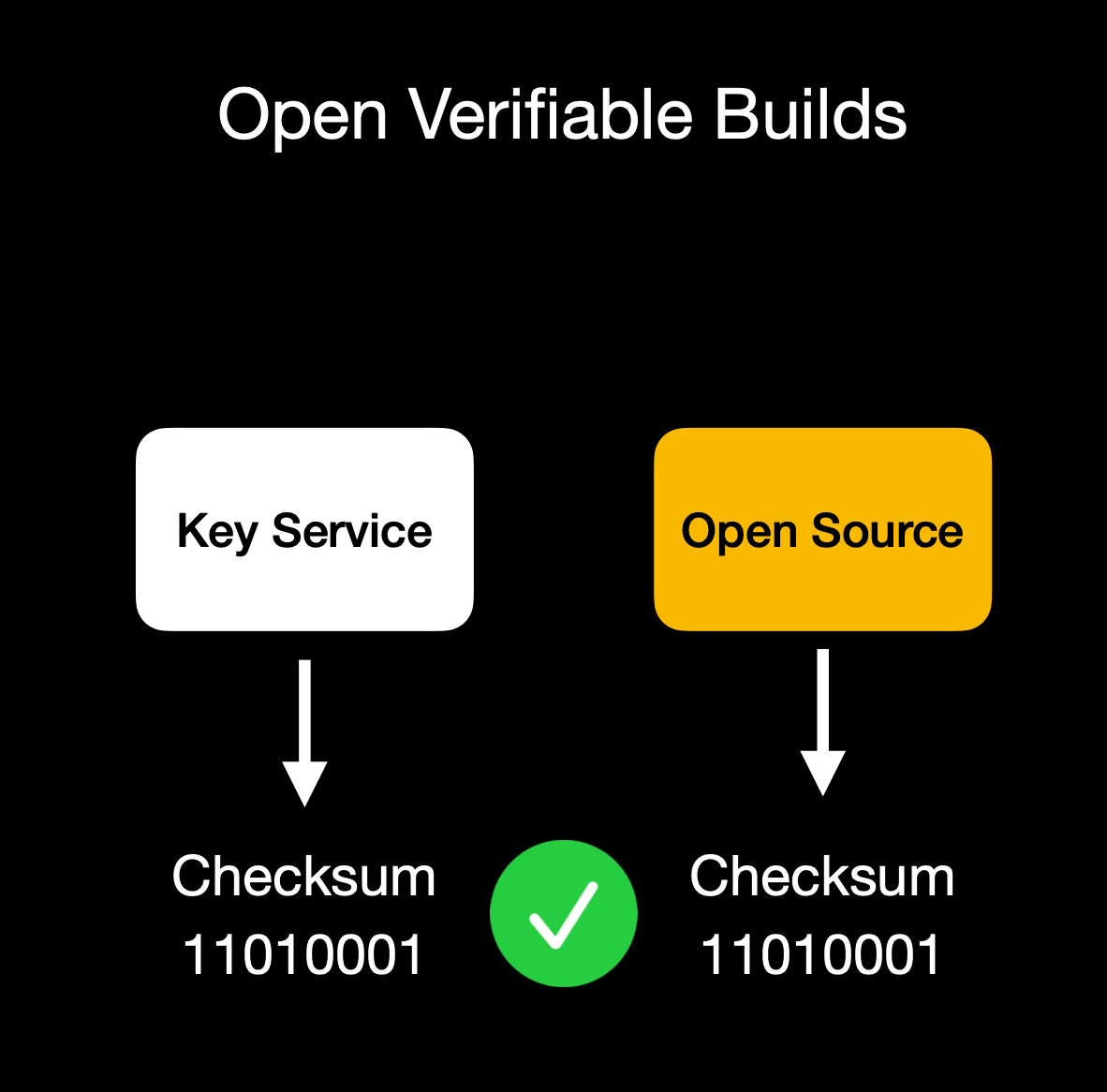Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** 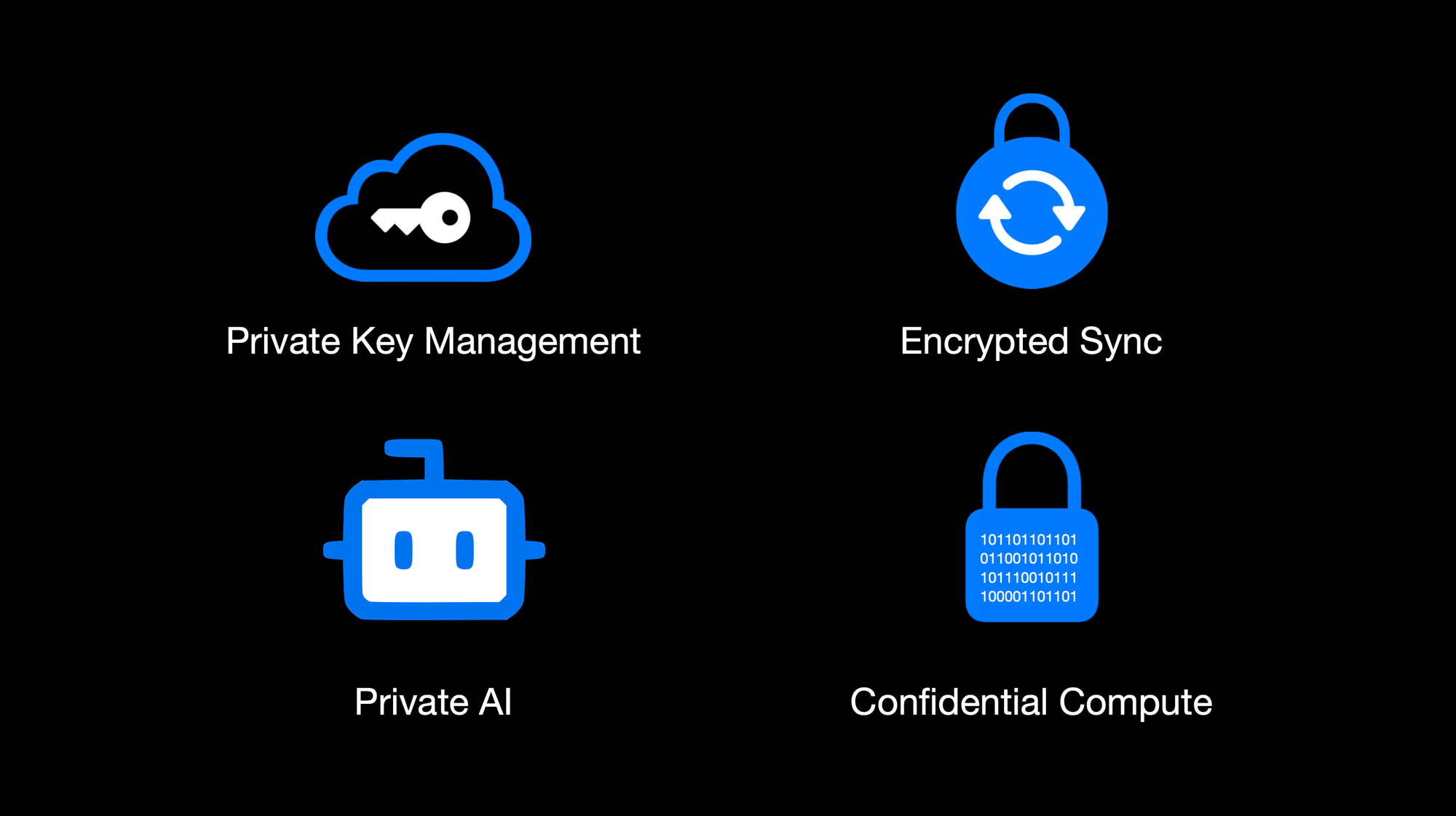OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.*
@ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 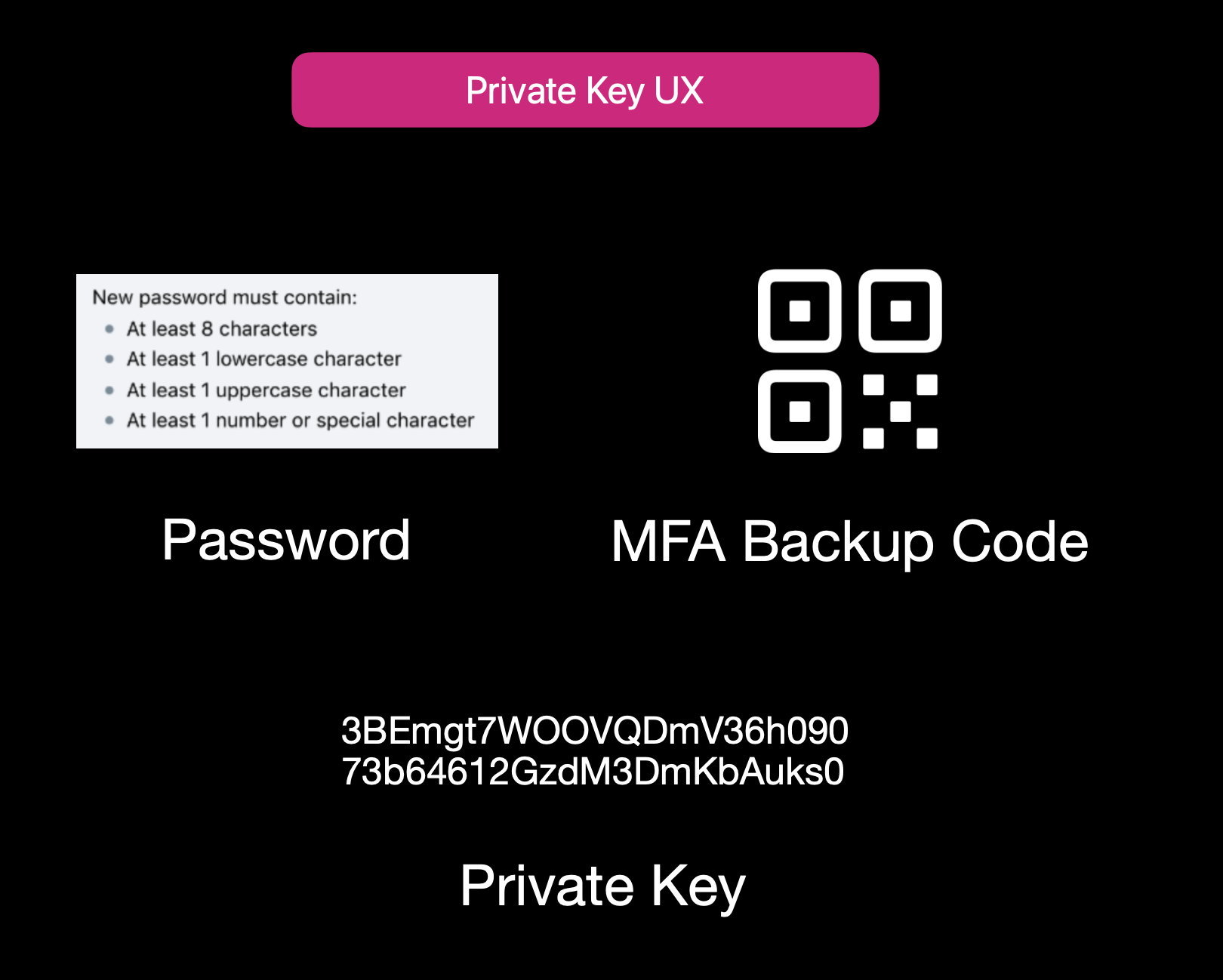Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 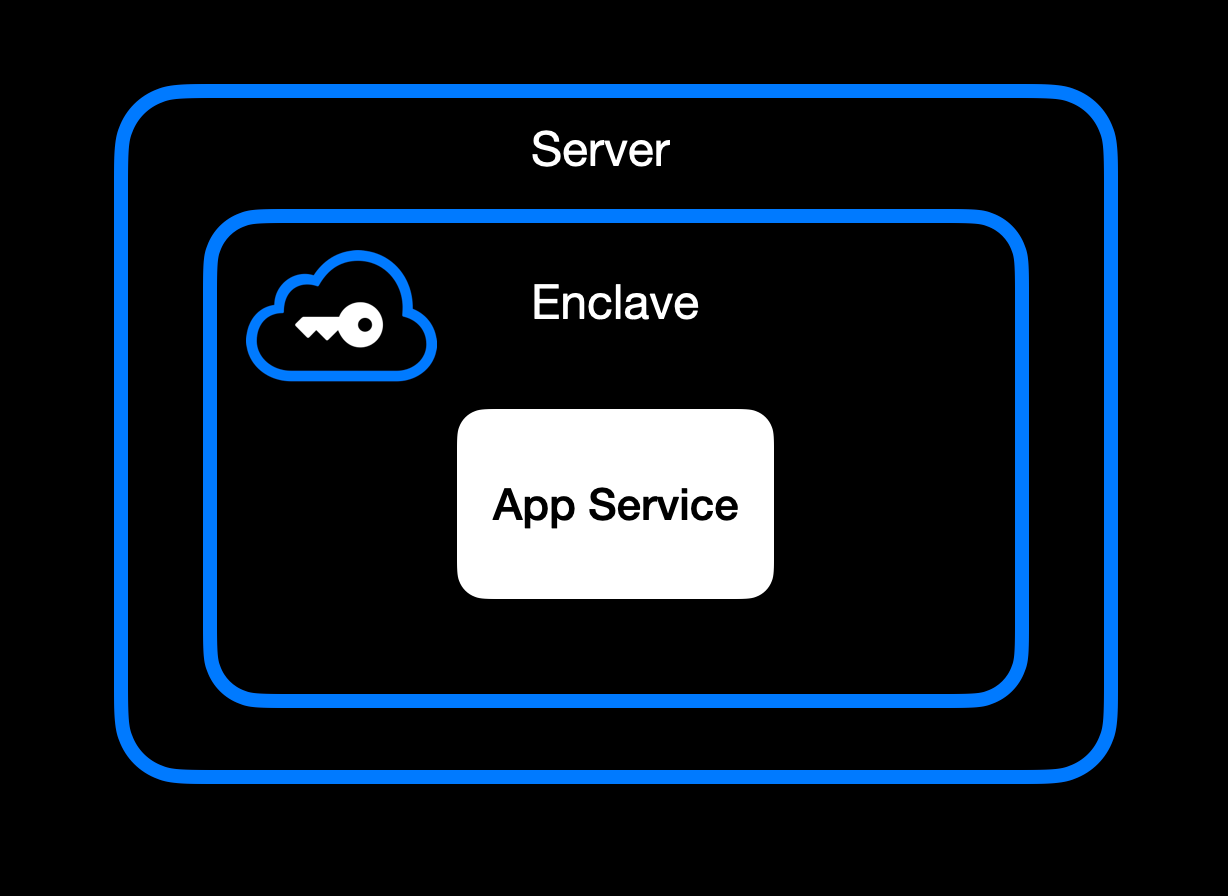App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 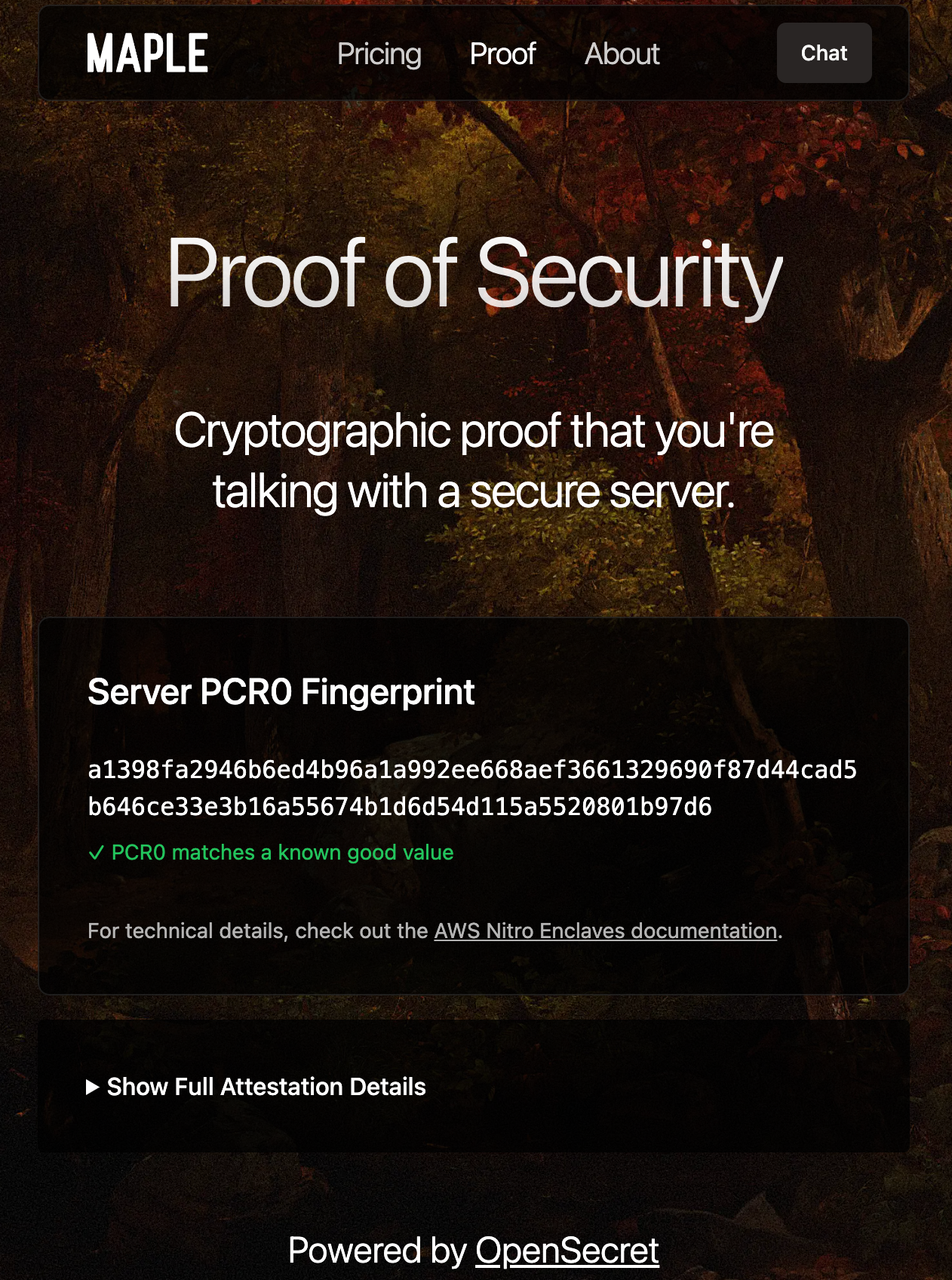Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 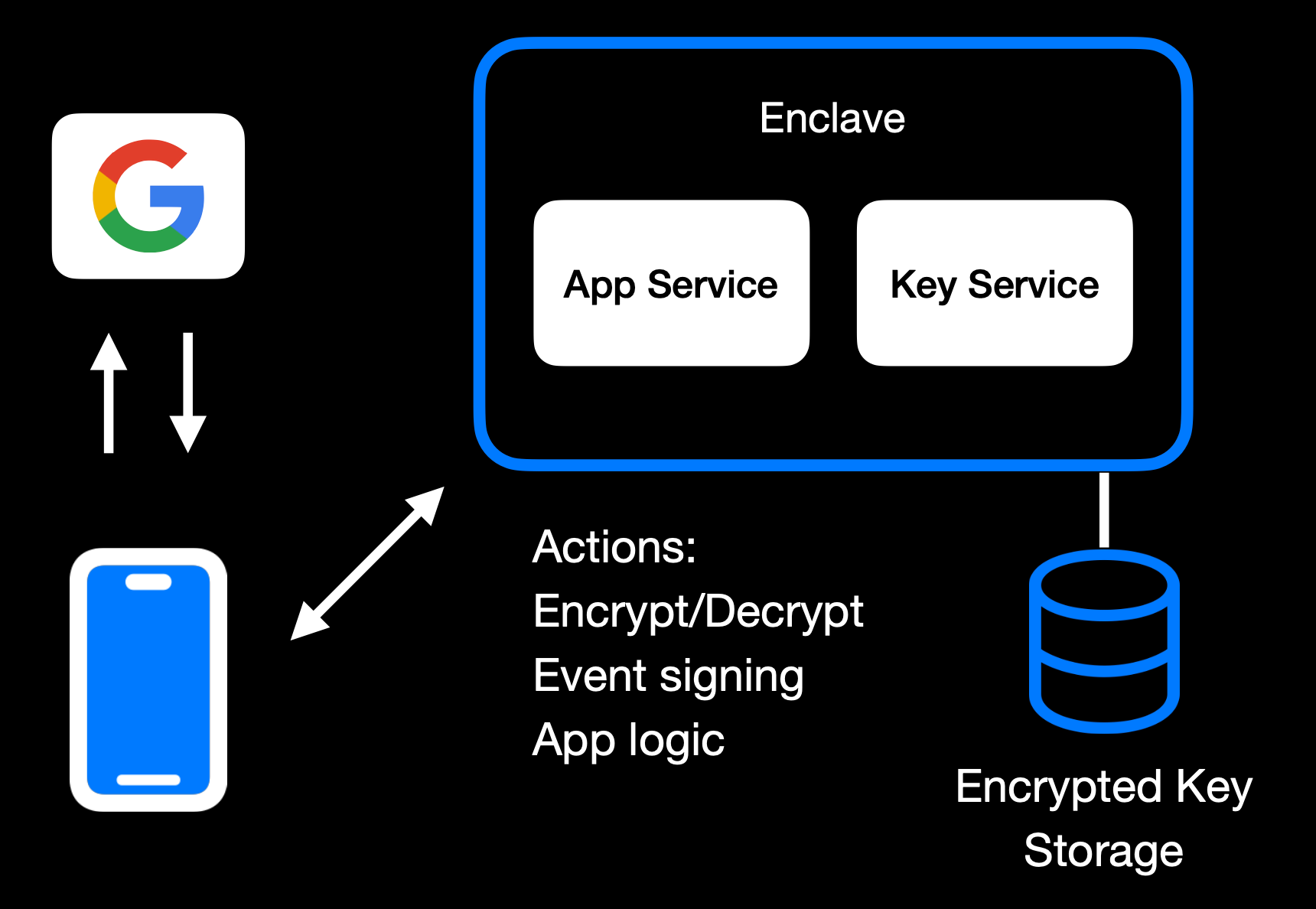Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 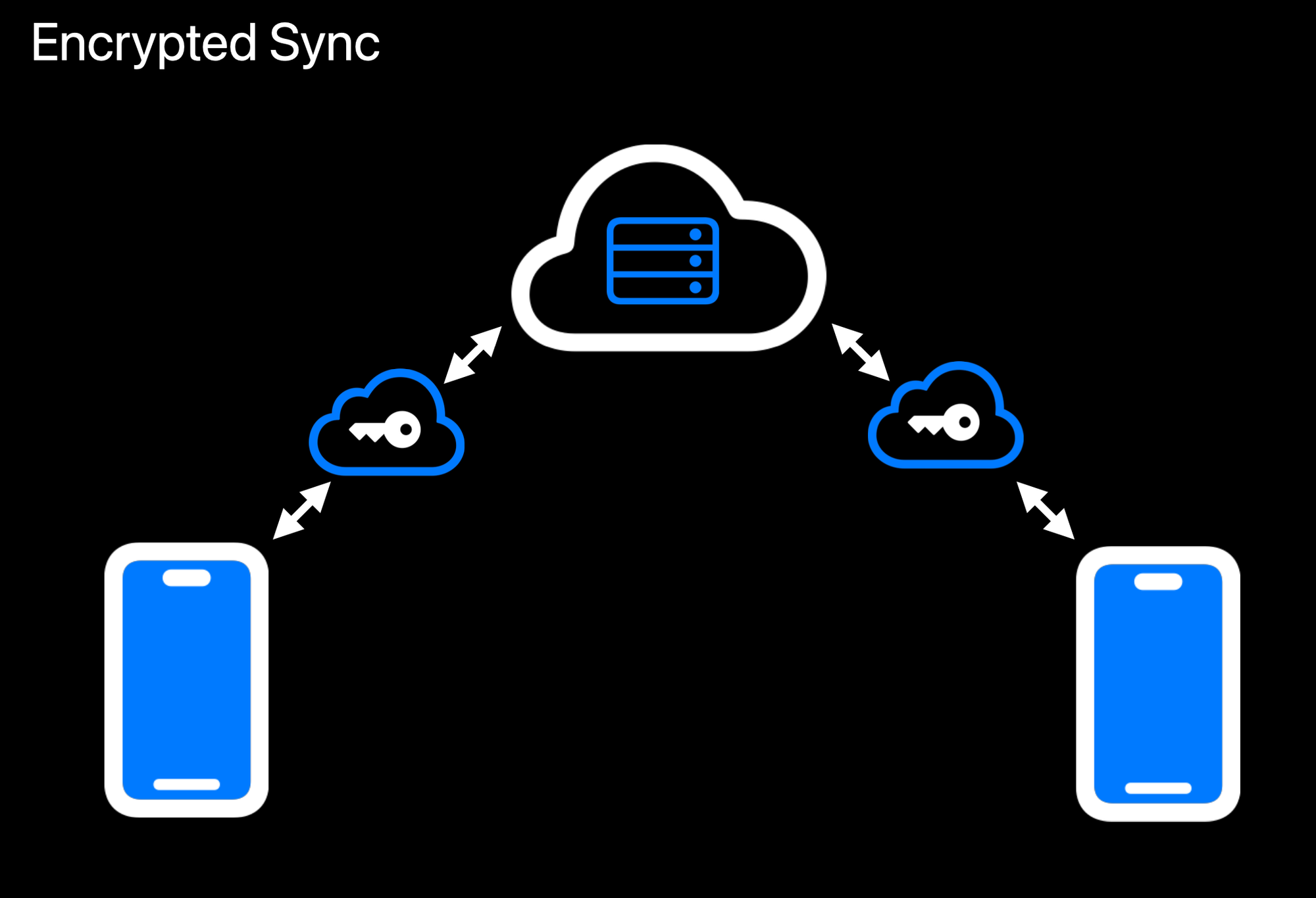Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 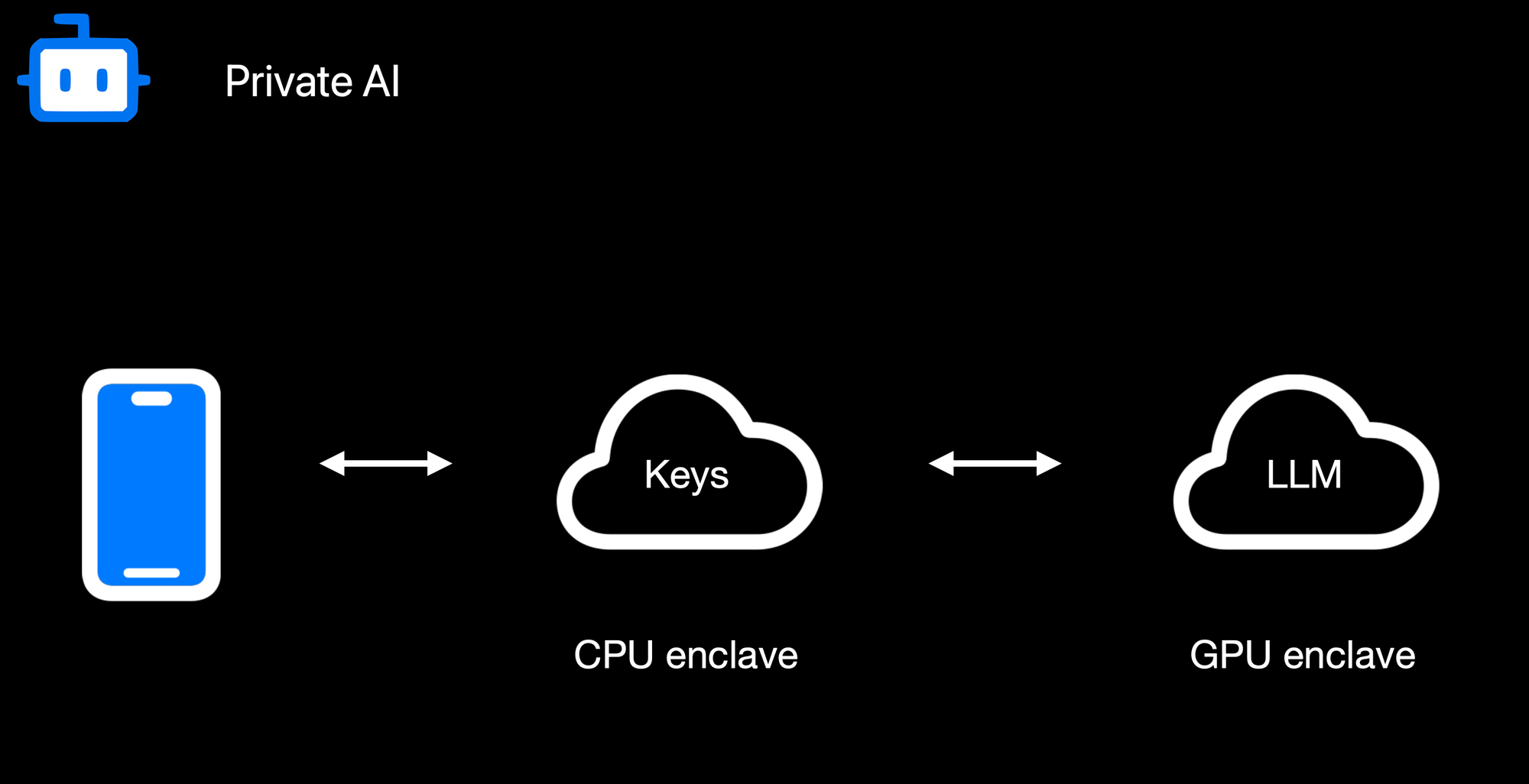Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 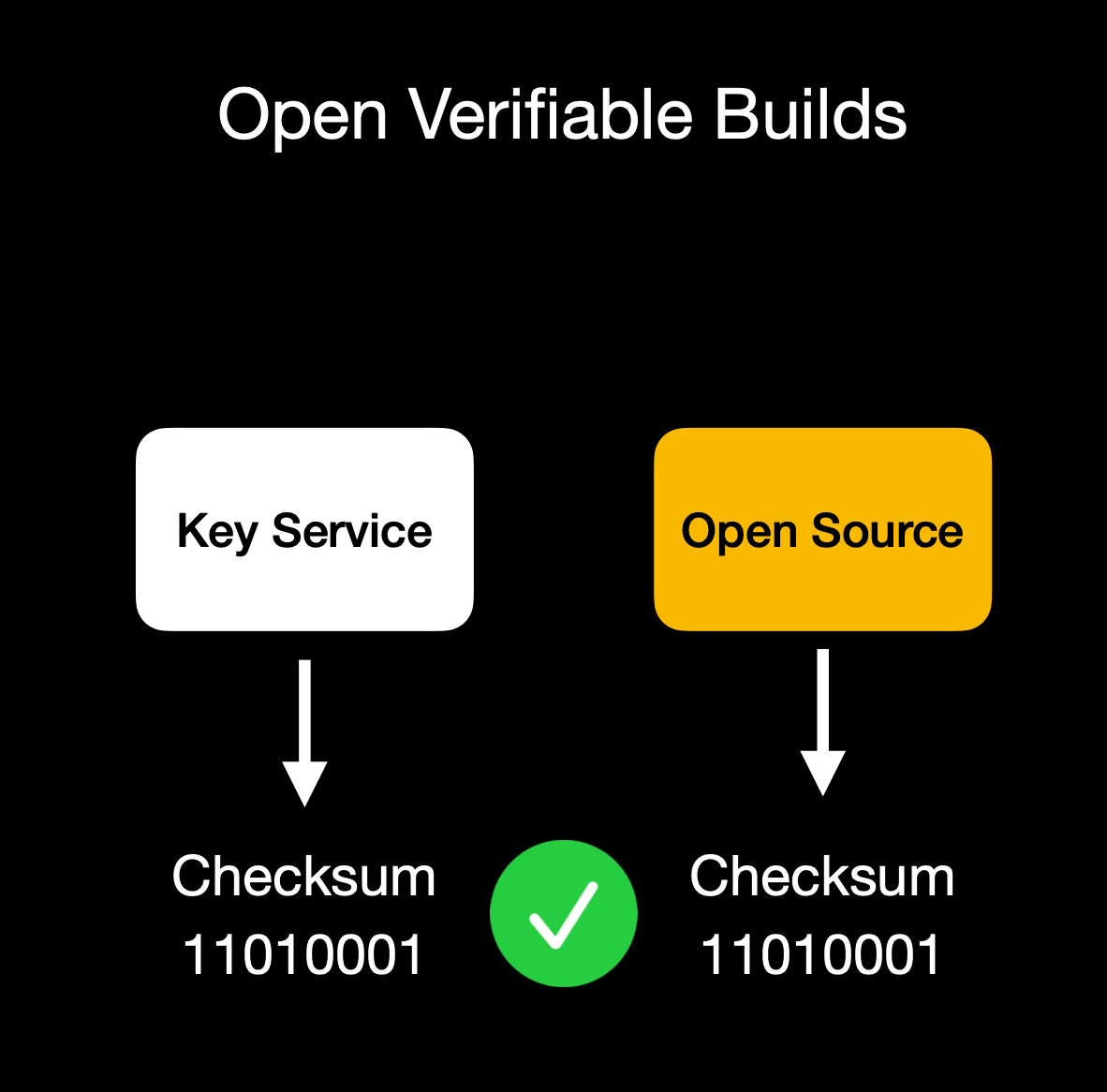Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** 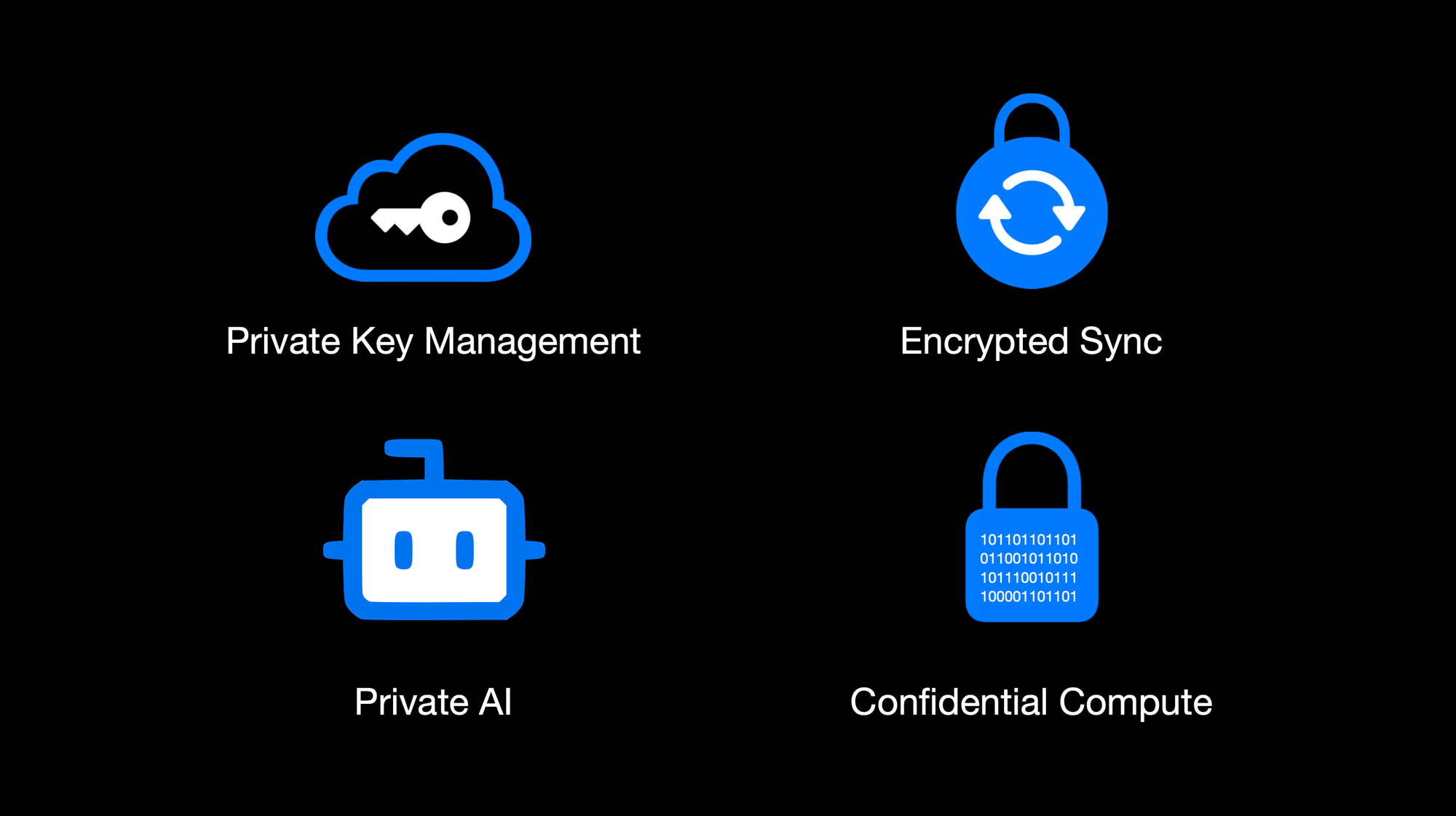OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.* @ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments. ## Understanding MCP Systems MCP (Model Context Protocol) systems consist of two main components that work together: 1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method. 2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers. These servers and clients can communicate using different transport methods: - **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine. - **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel. For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr. ## Creating (or Finding) an MCP Server Building an MCP server is simpler than you might think: 1. Create software in any programming language you're comfortable with. 2. Add an MCP library to expose your server's MCP interface. 3. Create an API that wraps around your software's functionality. Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy. Alternatively, you can use one of the many existing MCP servers available in various repositories. For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/ ## Setting Up the Workshop Let's get hands-on: First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script: ``` curl -fsSL https://bun.sh/install | bash ``` 1. **Choose your MCP server**: You can either create one or use an existing one. 2. **Inspect your server** using the MCP inspector tool: ```bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2 ``` This will: - Launch a client UI (default: http://localhost:5173) - Start an MCP proxy server (default: port 3000) - Pass any additional arguments directly to your server 3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality. ## Deploying with DVMCP Now for the exciting part – making your MCP server available to everyone on Nostr: 1. Navigate to your MCP server directory. 2. Run without installing (quickest way): ``` npx @dvmcp/bridge ``` 3. Or install globally for regular use: ``` npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridge ``` Then run using: ```bash dvmcp-bridge ``` This will guide you through creating the necessary configuration. Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing. For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference ## Testing and Integration 1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement. 2. Call your tools and watch the responses come back. For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime. ## Integrating with LLM Clients You can also integrate your DVMCP deployment with LLM clients using the discovery package: 1. Install and use the `@dvmcp/discovery` package: ```bash npx @dvmcp/discovery ``` 2. This package acts as an MCP server for your LLM system by: - Connecting to configured Nostr relays - Discovering tools from DVMCP servers - Making them available to your LLM applications 3. Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1... # Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ``` Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun). This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications. ## Final thoughts If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun. You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless. However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr. Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag. ## Useful Resources - **Official Documentation**: - Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org) - DVMCP.fun: [dvmcp.fun](https://dvmcp.fun) - **Source Code and Development**: - DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp) - DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun) - **MCP Servers and Clients**: - Smithery AI: [smithery.ai](https://smithery.ai) - MCP.so: [mcp.so](https://mcp.so) - Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers) - [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD) Happy building!
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments. ## Understanding MCP Systems MCP (Model Context Protocol) systems consist of two main components that work together: 1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method. 2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers. These servers and clients can communicate using different transport methods: - **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine. - **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel. For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr. ## Creating (or Finding) an MCP Server Building an MCP server is simpler than you might think: 1. Create software in any programming language you're comfortable with. 2. Add an MCP library to expose your server's MCP interface. 3. Create an API that wraps around your software's functionality. Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy. Alternatively, you can use one of the many existing MCP servers available in various repositories. For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/ ## Setting Up the Workshop Let's get hands-on: First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script: ``` curl -fsSL https://bun.sh/install | bash ``` 1. **Choose your MCP server**: You can either create one or use an existing one. 2. **Inspect your server** using the MCP inspector tool: ```bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2 ``` This will: - Launch a client UI (default: http://localhost:5173) - Start an MCP proxy server (default: port 3000) - Pass any additional arguments directly to your server 3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality. ## Deploying with DVMCP Now for the exciting part – making your MCP server available to everyone on Nostr: 1. Navigate to your MCP server directory. 2. Run without installing (quickest way): ``` npx @dvmcp/bridge ``` 3. Or install globally for regular use: ``` npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridge ``` Then run using: ```bash dvmcp-bridge ``` This will guide you through creating the necessary configuration. Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing. For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference ## Testing and Integration 1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement. 2. Call your tools and watch the responses come back. For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime. ## Integrating with LLM Clients You can also integrate your DVMCP deployment with LLM clients using the discovery package: 1. Install and use the `@dvmcp/discovery` package: ```bash npx @dvmcp/discovery ``` 2. This package acts as an MCP server for your LLM system by: - Connecting to configured Nostr relays - Discovering tools from DVMCP servers - Making them available to your LLM applications 3. Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1... # Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ``` Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun). This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications. ## Final thoughts If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun. You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless. However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr. Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag. ## Useful Resources - **Official Documentation**: - Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org) - DVMCP.fun: [dvmcp.fun](https://dvmcp.fun) - **Source Code and Development**: - DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp) - DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun) - **MCP Servers and Clients**: - Smithery AI: [smithery.ai](https://smithery.ai) - MCP.so: [mcp.so](https://mcp.so) - Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers) - [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD) Happy building! @ a5142938:0ef19da3
2025-04-05 09:48:12<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzpkj8sfxva2pk76qd85qs5k2uk4ddrn9x2vw4d4cq9gmk0nxwf23aqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qqxtqu8vwtew57xyqvm?viewKey=2c19f257cc3f94a3d40c0b171730ecd40897bc675ffa0ce521e22c280ba70a2d&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe> --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/qcp-smvj1v78_-7iceyrd/)
@ a5142938:0ef19da3
2025-04-05 09:48:12<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzpkj8sfxva2pk76qd85qs5k2uk4ddrn9x2vw4d4cq9gmk0nxwf23aqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qqxtqu8vwtew57xyqvm?viewKey=2c19f257cc3f94a3d40c0b171730ecd40897bc675ffa0ce521e22c280ba70a2d&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe> --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/qcp-smvj1v78_-7iceyrd/) @ fd06f542:8d6d54cd
2025-03-28 02:24:00NIP-01 ====== Basic protocol flow description ------------------------------- `draft` `mandatory` This NIP defines the basic protocol that should be implemented by everybody. New NIPs may add new optional (or mandatory) fields and messages and features to the structures and flows described here. ## Events and signatures Each user has a keypair. Signatures, public key, and encodings are done according to the [Schnorr signatures standard for the curve `secp256k1`](https://bips.xyz/340). The only object type that exists is the `event`, which has the following format on the wire: ```jsonc { "id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>, "pubkey": <32-bytes lowercase hex-encoded public key of the event creator>, "created_at": <unix timestamp in seconds>, "kind": <integer between 0 and 65535>, "tags": [ [<arbitrary string>...], // ... ], "content": <arbitrary string>, "sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field> } ``` To obtain the `event.id`, we `sha256` the serialized event. The serialization is done over the UTF-8 JSON-serialized string (which is described below) of the following structure: ``` [ 0, <pubkey, as a lowercase hex string>, <created_at, as a number>, <kind, as a number>, <tags, as an array of arrays of non-null strings>, <content, as a string> ] ``` To prevent implementation differences from creating a different event ID for the same event, the following rules MUST be followed while serializing: - UTF-8 should be used for encoding. - Whitespace, line breaks or other unnecessary formatting should not be included in the output JSON. - The following characters in the content field must be escaped as shown, and all other characters must be included verbatim: - A line break (`0x0A`), use `\n` - A double quote (`0x22`), use `\"` - A backslash (`0x5C`), use `\\` - A carriage return (`0x0D`), use `\r` - A tab character (`0x09`), use `\t` - A backspace, (`0x08`), use `\b` - A form feed, (`0x0C`), use `\f` ### Tags Each tag is an array of one or more strings, with some conventions around them. Take a look at the example below: ```jsonc { "tags": [ ["e", "5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36", "wss://nostr.example.com"], ["p", "f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca"], ["a", "30023:f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca:abcd", "wss://nostr.example.com"], ["alt", "reply"], // ... ], // ... } ``` The first element of the tag array is referred to as the tag _name_ or _key_ and the second as the tag _value_. So we can safely say that the event above has an `e` tag set to `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"`, an `alt` tag set to `"reply"` and so on. All elements after the second do not have a conventional name. This NIP defines 3 standard tags that can be used across all event kinds with the same meaning. They are as follows: - The `e` tag, used to refer to an event: `["e", <32-bytes lowercase hex of the id of another event>, <recommended relay URL, optional>, <32-bytes lowercase hex of the author's pubkey, optional>]` - The `p` tag, used to refer to another user: `["p", <32-bytes lowercase hex of a pubkey>, <recommended relay URL, optional>]` - The `a` tag, used to refer to an addressable or replaceable event - for an addressable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:<d tag value>", <recommended relay URL, optional>]` - for a normal replaceable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:", <recommended relay URL, optional>]` (note: include the trailing colon) As a convention, all single-letter (only english alphabet letters: a-z, A-Z) key tags are expected to be indexed by relays, such that it is possible, for example, to query or subscribe to events that reference the event `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"` by using the `{"#e": ["5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"]}` filter. Only the first value in any given tag is indexed. ### Kinds Kinds specify how clients should interpret the meaning of each event and the other fields of each event (e.g. an `"r"` tag may have a meaning in an event of kind 1 and an entirely different meaning in an event of kind 10002). Each NIP may define the meaning of a set of kinds that weren't defined elsewhere. [NIP-10](10.md), for instance, especifies the `kind:1` text note for social media applications. This NIP defines one basic kind: - `0`: **user metadata**: the `content` is set to a stringified JSON object `{name: <nickname or full name>, about: <short bio>, picture: <url of the image>}` describing the user who created the event. [Extra metadata fields](24.md#kind-0) may be set. A relay may delete older events once it gets a new one for the same pubkey. And also a convention for kind ranges that allow for easier experimentation and flexibility of relay implementation: - for kind `n` such that `1000 <= n < 10000 || 4 <= n < 45 || n == 1 || n == 2`, events are **regular**, which means they're all expected to be stored by relays. - for kind `n` such that `10000 <= n < 20000 || n == 0 || n == 3`, events are **replaceable**, which means that, for each combination of `pubkey` and `kind`, only the latest event MUST be stored by relays, older versions MAY be discarded. - for kind `n` such that `20000 <= n < 30000`, events are **ephemeral**, which means they are not expected to be stored by relays. - for kind `n` such that `30000 <= n < 40000`, events are **addressable** by their `kind`, `pubkey` and `d` tag value -- which means that, for each combination of `kind`, `pubkey` and the `d` tag value, only the latest event MUST be stored by relays, older versions MAY be discarded. In case of replaceable events with the same timestamp, the event with the lowest id (first in lexical order) should be retained, and the other discarded. When answering to `REQ` messages for replaceable events such as `{"kinds":[0],"authors":[<hex-key>]}`, even if the relay has more than one version stored, it SHOULD return just the latest one. These are just conventions and relay implementations may differ. ## Communication between clients and relays Relays expose a websocket endpoint to which clients can connect. Clients SHOULD open a single websocket connection to each relay and use it for all their subscriptions. Relays MAY limit number of connections from specific IP/client/etc. ### From client to relay: sending events and creating subscriptions Clients can send 3 types of messages, which must be JSON arrays, according to the following patterns: * `["EVENT", <event JSON as defined above>]`, used to publish events. * `["REQ", <subscription_id>, <filters1>, <filters2>, ...]`, used to request events and subscribe to new updates. * `["CLOSE", <subscription_id>]`, used to stop previous subscriptions. `<subscription_id>` is an arbitrary, non-empty string of max length 64 chars. It represents a subscription per connection. Relays MUST manage `<subscription_id>`s independently for each WebSocket connection. `<subscription_id>`s are not guaranteed to be globally unique. `<filtersX>` is a JSON object that determines what events will be sent in that subscription, it can have the following attributes: ```json { "ids": <a list of event ids>, "authors": <a list of lowercase pubkeys, the pubkey of an event must be one of these>, "kinds": <a list of a kind numbers>, "#<single-letter (a-zA-Z)>": <a list of tag values, for #e — a list of event ids, for #p — a list of pubkeys, etc.>, "since": <an integer unix timestamp in seconds. Events must have a created_at >= to this to pass>, "until": <an integer unix timestamp in seconds. Events must have a created_at <= to this to pass>, "limit": <maximum number of events relays SHOULD return in the initial query> } ``` Upon receiving a `REQ` message, the relay SHOULD return events that match the filter. Any new events it receives SHOULD be sent to that same websocket until the connection is closed, a `CLOSE` event is received with the same `<subscription_id>`, or a new `REQ` is sent using the same `<subscription_id>` (in which case a new subscription is created, replacing the old one). Filter attributes containing lists (`ids`, `authors`, `kinds` and tag filters like `#e`) are JSON arrays with one or more values. At least one of the arrays' values must match the relevant field in an event for the condition to be considered a match. For scalar event attributes such as `authors` and `kind`, the attribute from the event must be contained in the filter list. In the case of tag attributes such as `#e`, for which an event may have multiple values, the event and filter condition values must have at least one item in common. The `ids`, `authors`, `#e` and `#p` filter lists MUST contain exact 64-character lowercase hex values. The `since` and `until` properties can be used to specify the time range of events returned in the subscription. If a filter includes the `since` property, events with `created_at` greater than or equal to `since` are considered to match the filter. The `until` property is similar except that `created_at` must be less than or equal to `until`. In short, an event matches a filter if `since <= created_at <= until` holds. All conditions of a filter that are specified must match for an event for it to pass the filter, i.e., multiple conditions are interpreted as `&&` conditions. A `REQ` message may contain multiple filters. In this case, events that match any of the filters are to be returned, i.e., multiple filters are to be interpreted as `||` conditions. The `limit` property of a filter is only valid for the initial query and MUST be ignored afterwards. When `limit: n` is present it is assumed that the events returned in the initial query will be the last `n` events ordered by the `created_at`. Newer events should appear first, and in the case of ties the event with the lowest id (first in lexical order) should be first. It is safe to return less events than `limit` specifies, but it is expected that relays do not return (much) more events than requested so clients don't get unnecessarily overwhelmed by data. ### From relay to client: sending events and notices Relays can send 5 types of messages, which must also be JSON arrays, according to the following patterns: * `["EVENT", <subscription_id>, <event JSON as defined above>]`, used to send events requested by clients. * `["OK", <event_id>, <true|false>, <message>]`, used to indicate acceptance or denial of an `EVENT` message. * `["EOSE", <subscription_id>]`, used to indicate the _end of stored events_ and the beginning of events newly received in real-time. * `["CLOSED", <subscription_id>, <message>]`, used to indicate that a subscription was ended on the server side. * `["NOTICE", <message>]`, used to send human-readable error messages or other things to clients. This NIP defines no rules for how `NOTICE` messages should be sent or treated. - `EVENT` messages MUST be sent only with a subscription ID related to a subscription previously initiated by the client (using the `REQ` message above). - `OK` messages MUST be sent in response to `EVENT` messages received from clients, they must have the 3rd parameter set to `true` when an event has been accepted by the relay, `false` otherwise. The 4th parameter MUST always be present, but MAY be an empty string when the 3rd is `true`, otherwise it MUST be a string formed by a machine-readable single-word prefix followed by a `:` and then a human-readable message. Some examples: * `["OK", "b1a649ebe8...", true, ""]` * `["OK", "b1a649ebe8...", true, "pow: difficulty 25>=24"]` * `["OK", "b1a649ebe8...", true, "duplicate: already have this event"]` * `["OK", "b1a649ebe8...", false, "blocked: you are banned from posting here"]` * `["OK", "b1a649ebe8...", false, "blocked: please register your pubkey at https://my-expensive-relay.example.com"]` * `["OK", "b1a649ebe8...", false, "rate-limited: slow down there chief"]` * `["OK", "b1a649ebe8...", false, "invalid: event creation date is too far off from the current time"]` * `["OK", "b1a649ebe8...", false, "pow: difficulty 26 is less than 30"]` * `["OK", "b1a649ebe8...", false, "restricted: not allowed to write."]` * `["OK", "b1a649ebe8...", false, "error: could not connect to the database"]` - `CLOSED` messages MUST be sent in response to a `REQ` when the relay refuses to fulfill it. It can also be sent when a relay decides to kill a subscription on its side before a client has disconnected or sent a `CLOSE`. This message uses the same pattern of `OK` messages with the machine-readable prefix and human-readable message. Some examples: * `["CLOSED", "sub1", "unsupported: filter contains unknown elements"]` * `["CLOSED", "sub1", "error: could not connect to the database"]` * `["CLOSED", "sub1", "error: shutting down idle subscription"]` - The standardized machine-readable prefixes for `OK` and `CLOSED` are: `duplicate`, `pow`, `blocked`, `rate-limited`, `invalid`, `restricted`, and `error` for when none of that fits.
@ fd06f542:8d6d54cd
2025-03-28 02:24:00NIP-01 ====== Basic protocol flow description ------------------------------- `draft` `mandatory` This NIP defines the basic protocol that should be implemented by everybody. New NIPs may add new optional (or mandatory) fields and messages and features to the structures and flows described here. ## Events and signatures Each user has a keypair. Signatures, public key, and encodings are done according to the [Schnorr signatures standard for the curve `secp256k1`](https://bips.xyz/340). The only object type that exists is the `event`, which has the following format on the wire: ```jsonc { "id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>, "pubkey": <32-bytes lowercase hex-encoded public key of the event creator>, "created_at": <unix timestamp in seconds>, "kind": <integer between 0 and 65535>, "tags": [ [<arbitrary string>...], // ... ], "content": <arbitrary string>, "sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field> } ``` To obtain the `event.id`, we `sha256` the serialized event. The serialization is done over the UTF-8 JSON-serialized string (which is described below) of the following structure: ``` [ 0, <pubkey, as a lowercase hex string>, <created_at, as a number>, <kind, as a number>, <tags, as an array of arrays of non-null strings>, <content, as a string> ] ``` To prevent implementation differences from creating a different event ID for the same event, the following rules MUST be followed while serializing: - UTF-8 should be used for encoding. - Whitespace, line breaks or other unnecessary formatting should not be included in the output JSON. - The following characters in the content field must be escaped as shown, and all other characters must be included verbatim: - A line break (`0x0A`), use `\n` - A double quote (`0x22`), use `\"` - A backslash (`0x5C`), use `\\` - A carriage return (`0x0D`), use `\r` - A tab character (`0x09`), use `\t` - A backspace, (`0x08`), use `\b` - A form feed, (`0x0C`), use `\f` ### Tags Each tag is an array of one or more strings, with some conventions around them. Take a look at the example below: ```jsonc { "tags": [ ["e", "5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36", "wss://nostr.example.com"], ["p", "f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca"], ["a", "30023:f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca:abcd", "wss://nostr.example.com"], ["alt", "reply"], // ... ], // ... } ``` The first element of the tag array is referred to as the tag _name_ or _key_ and the second as the tag _value_. So we can safely say that the event above has an `e` tag set to `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"`, an `alt` tag set to `"reply"` and so on. All elements after the second do not have a conventional name. This NIP defines 3 standard tags that can be used across all event kinds with the same meaning. They are as follows: - The `e` tag, used to refer to an event: `["e", <32-bytes lowercase hex of the id of another event>, <recommended relay URL, optional>, <32-bytes lowercase hex of the author's pubkey, optional>]` - The `p` tag, used to refer to another user: `["p", <32-bytes lowercase hex of a pubkey>, <recommended relay URL, optional>]` - The `a` tag, used to refer to an addressable or replaceable event - for an addressable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:<d tag value>", <recommended relay URL, optional>]` - for a normal replaceable event: `["a", "<kind integer>:<32-bytes lowercase hex of a pubkey>:", <recommended relay URL, optional>]` (note: include the trailing colon) As a convention, all single-letter (only english alphabet letters: a-z, A-Z) key tags are expected to be indexed by relays, such that it is possible, for example, to query or subscribe to events that reference the event `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"` by using the `{"#e": ["5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"]}` filter. Only the first value in any given tag is indexed. ### Kinds Kinds specify how clients should interpret the meaning of each event and the other fields of each event (e.g. an `"r"` tag may have a meaning in an event of kind 1 and an entirely different meaning in an event of kind 10002). Each NIP may define the meaning of a set of kinds that weren't defined elsewhere. [NIP-10](10.md), for instance, especifies the `kind:1` text note for social media applications. This NIP defines one basic kind: - `0`: **user metadata**: the `content` is set to a stringified JSON object `{name: <nickname or full name>, about: <short bio>, picture: <url of the image>}` describing the user who created the event. [Extra metadata fields](24.md#kind-0) may be set. A relay may delete older events once it gets a new one for the same pubkey. And also a convention for kind ranges that allow for easier experimentation and flexibility of relay implementation: - for kind `n` such that `1000 <= n < 10000 || 4 <= n < 45 || n == 1 || n == 2`, events are **regular**, which means they're all expected to be stored by relays. - for kind `n` such that `10000 <= n < 20000 || n == 0 || n == 3`, events are **replaceable**, which means that, for each combination of `pubkey` and `kind`, only the latest event MUST be stored by relays, older versions MAY be discarded. - for kind `n` such that `20000 <= n < 30000`, events are **ephemeral**, which means they are not expected to be stored by relays. - for kind `n` such that `30000 <= n < 40000`, events are **addressable** by their `kind`, `pubkey` and `d` tag value -- which means that, for each combination of `kind`, `pubkey` and the `d` tag value, only the latest event MUST be stored by relays, older versions MAY be discarded. In case of replaceable events with the same timestamp, the event with the lowest id (first in lexical order) should be retained, and the other discarded. When answering to `REQ` messages for replaceable events such as `{"kinds":[0],"authors":[<hex-key>]}`, even if the relay has more than one version stored, it SHOULD return just the latest one. These are just conventions and relay implementations may differ. ## Communication between clients and relays Relays expose a websocket endpoint to which clients can connect. Clients SHOULD open a single websocket connection to each relay and use it for all their subscriptions. Relays MAY limit number of connections from specific IP/client/etc. ### From client to relay: sending events and creating subscriptions Clients can send 3 types of messages, which must be JSON arrays, according to the following patterns: * `["EVENT", <event JSON as defined above>]`, used to publish events. * `["REQ", <subscription_id>, <filters1>, <filters2>, ...]`, used to request events and subscribe to new updates. * `["CLOSE", <subscription_id>]`, used to stop previous subscriptions. `<subscription_id>` is an arbitrary, non-empty string of max length 64 chars. It represents a subscription per connection. Relays MUST manage `<subscription_id>`s independently for each WebSocket connection. `<subscription_id>`s are not guaranteed to be globally unique. `<filtersX>` is a JSON object that determines what events will be sent in that subscription, it can have the following attributes: ```json { "ids": <a list of event ids>, "authors": <a list of lowercase pubkeys, the pubkey of an event must be one of these>, "kinds": <a list of a kind numbers>, "#<single-letter (a-zA-Z)>": <a list of tag values, for #e — a list of event ids, for #p — a list of pubkeys, etc.>, "since": <an integer unix timestamp in seconds. Events must have a created_at >= to this to pass>, "until": <an integer unix timestamp in seconds. Events must have a created_at <= to this to pass>, "limit": <maximum number of events relays SHOULD return in the initial query> } ``` Upon receiving a `REQ` message, the relay SHOULD return events that match the filter. Any new events it receives SHOULD be sent to that same websocket until the connection is closed, a `CLOSE` event is received with the same `<subscription_id>`, or a new `REQ` is sent using the same `<subscription_id>` (in which case a new subscription is created, replacing the old one). Filter attributes containing lists (`ids`, `authors`, `kinds` and tag filters like `#e`) are JSON arrays with one or more values. At least one of the arrays' values must match the relevant field in an event for the condition to be considered a match. For scalar event attributes such as `authors` and `kind`, the attribute from the event must be contained in the filter list. In the case of tag attributes such as `#e`, for which an event may have multiple values, the event and filter condition values must have at least one item in common. The `ids`, `authors`, `#e` and `#p` filter lists MUST contain exact 64-character lowercase hex values. The `since` and `until` properties can be used to specify the time range of events returned in the subscription. If a filter includes the `since` property, events with `created_at` greater than or equal to `since` are considered to match the filter. The `until` property is similar except that `created_at` must be less than or equal to `until`. In short, an event matches a filter if `since <= created_at <= until` holds. All conditions of a filter that are specified must match for an event for it to pass the filter, i.e., multiple conditions are interpreted as `&&` conditions. A `REQ` message may contain multiple filters. In this case, events that match any of the filters are to be returned, i.e., multiple filters are to be interpreted as `||` conditions. The `limit` property of a filter is only valid for the initial query and MUST be ignored afterwards. When `limit: n` is present it is assumed that the events returned in the initial query will be the last `n` events ordered by the `created_at`. Newer events should appear first, and in the case of ties the event with the lowest id (first in lexical order) should be first. It is safe to return less events than `limit` specifies, but it is expected that relays do not return (much) more events than requested so clients don't get unnecessarily overwhelmed by data. ### From relay to client: sending events and notices Relays can send 5 types of messages, which must also be JSON arrays, according to the following patterns: * `["EVENT", <subscription_id>, <event JSON as defined above>]`, used to send events requested by clients. * `["OK", <event_id>, <true|false>, <message>]`, used to indicate acceptance or denial of an `EVENT` message. * `["EOSE", <subscription_id>]`, used to indicate the _end of stored events_ and the beginning of events newly received in real-time. * `["CLOSED", <subscription_id>, <message>]`, used to indicate that a subscription was ended on the server side. * `["NOTICE", <message>]`, used to send human-readable error messages or other things to clients. This NIP defines no rules for how `NOTICE` messages should be sent or treated. - `EVENT` messages MUST be sent only with a subscription ID related to a subscription previously initiated by the client (using the `REQ` message above). - `OK` messages MUST be sent in response to `EVENT` messages received from clients, they must have the 3rd parameter set to `true` when an event has been accepted by the relay, `false` otherwise. The 4th parameter MUST always be present, but MAY be an empty string when the 3rd is `true`, otherwise it MUST be a string formed by a machine-readable single-word prefix followed by a `:` and then a human-readable message. Some examples: * `["OK", "b1a649ebe8...", true, ""]` * `["OK", "b1a649ebe8...", true, "pow: difficulty 25>=24"]` * `["OK", "b1a649ebe8...", true, "duplicate: already have this event"]` * `["OK", "b1a649ebe8...", false, "blocked: you are banned from posting here"]` * `["OK", "b1a649ebe8...", false, "blocked: please register your pubkey at https://my-expensive-relay.example.com"]` * `["OK", "b1a649ebe8...", false, "rate-limited: slow down there chief"]` * `["OK", "b1a649ebe8...", false, "invalid: event creation date is too far off from the current time"]` * `["OK", "b1a649ebe8...", false, "pow: difficulty 26 is less than 30"]` * `["OK", "b1a649ebe8...", false, "restricted: not allowed to write."]` * `["OK", "b1a649ebe8...", false, "error: could not connect to the database"]` - `CLOSED` messages MUST be sent in response to a `REQ` when the relay refuses to fulfill it. It can also be sent when a relay decides to kill a subscription on its side before a client has disconnected or sent a `CLOSE`. This message uses the same pattern of `OK` messages with the machine-readable prefix and human-readable message. Some examples: * `["CLOSED", "sub1", "unsupported: filter contains unknown elements"]` * `["CLOSED", "sub1", "error: could not connect to the database"]` * `["CLOSED", "sub1", "error: shutting down idle subscription"]` - The standardized machine-readable prefixes for `OK` and `CLOSED` are: `duplicate`, `pow`, `blocked`, `rate-limited`, `invalid`, `restricted`, and `error` for when none of that fits. @ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here. # My Background: A Small Side Story  My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’s*Chasing Ghosts*and*The King of Kong: A Fistful of Quarters*). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer of*The King of Kong: A Fistful of Quarters* had previously made a documentary called*New York Doll*which was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable. I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that. With that out of the way, lets dive in to some bold artists: # Nicolas Cage: Actor  There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will link[here](https://www.youtube.com/watch?v=s8IfDNHsCLE). Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the films*Pig,* *Joe,* *Renfield,* and his Christmas film *The Family Man*. # Nick Cave: Songwriter  What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his album*Ghosteen*, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter called*The Red Hand Files*, he has written screenplays such as*Lawless*, he has written books, he has made great film scores such as*The Assassination of Jesse James by the Coward Robert Ford*, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the album*Murder Ballads*(which is comprised of what the title suggests) to his rejected sequel to*Gladiator*(*Gladiator: Christ Killer*), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums like*Skeleton Tree*and*Ghosteen*were journeys through the grief of his son’s death. *The Boatman’s Call*is arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’s*Live 1981-82*, Nick Cave & The Bad Seeds’*The Boatman’s Call*, and the film*Lawless*. # Jim Jarmusch: Director  I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. *Ghost Dog: The Way of the Samurai* is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. *Only Lovers Left Alive*is a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his films*Paterson*,*Down by Law*, and*Coffee and Cigarettes*. # NOSTR: We Need Bold Art  NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. **My closing statement:** continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here. # My Background: A Small Side Story  My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’s*Chasing Ghosts*and*The King of Kong: A Fistful of Quarters*). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer of*The King of Kong: A Fistful of Quarters* had previously made a documentary called*New York Doll*which was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable. I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that. With that out of the way, lets dive in to some bold artists: # Nicolas Cage: Actor  There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will link[here](https://www.youtube.com/watch?v=s8IfDNHsCLE). Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the films*Pig,* *Joe,* *Renfield,* and his Christmas film *The Family Man*. # Nick Cave: Songwriter  What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his album*Ghosteen*, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter called*The Red Hand Files*, he has written screenplays such as*Lawless*, he has written books, he has made great film scores such as*The Assassination of Jesse James by the Coward Robert Ford*, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the album*Murder Ballads*(which is comprised of what the title suggests) to his rejected sequel to*Gladiator*(*Gladiator: Christ Killer*), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums like*Skeleton Tree*and*Ghosteen*were journeys through the grief of his son’s death. *The Boatman’s Call*is arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’s*Live 1981-82*, Nick Cave & The Bad Seeds’*The Boatman’s Call*, and the film*Lawless*. # Jim Jarmusch: Director  I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. *Ghost Dog: The Way of the Samurai* is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. *Only Lovers Left Alive*is a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his films*Paterson*,*Down by Law*, and*Coffee and Cigarettes*. # NOSTR: We Need Bold Art  NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. **My closing statement:** continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future. @ fd06f542:8d6d54cd
2025-03-28 02:21:20# NIPs NIPs stand for **Nostr Implementation Possibilities**. They exist to document what may be implemented by [Nostr](https://github.com/nostr-protocol/nostr)-compatible _relay_ and _client_ software. --- - [List](#list) - [Event Kinds](#event-kinds) - [Message Types](#message-types) - [Client to Relay](#client-to-relay) - [Relay to Client](#relay-to-client) - [Standardized Tags](#standardized-tags) - [Criteria for acceptance of NIPs](#criteria-for-acceptance-of-nips) - [Is this repository a centralizing factor?](#is-this-repository-a-centralizing-factor) - [How this repository works](#how-this-repository-works) - [Breaking Changes](#breaking-changes) - [License](#license) --- ## List - [NIP-01: Basic protocol flow description](01.md) - [NIP-02: Follow List](02.md) - [NIP-03: OpenTimestamps Attestations for Events](03.md) - [NIP-04: Encrypted Direct Message](04.md) --- **unrecommended**: deprecated in favor of [NIP-17](17.md) - [NIP-05: Mapping Nostr keys to DNS-based internet identifiers](05.md) - [NIP-06: Basic key derivation from mnemonic seed phrase](06.md) - [NIP-07: `window.nostr` capability for web browsers](07.md) - [NIP-08: Handling Mentions](08.md) --- **unrecommended**: deprecated in favor of [NIP-27](27.md) - [NIP-09: Event Deletion Request](09.md) - [NIP-10: Text Notes and Threads](10.md) - [NIP-11: Relay Information Document](11.md) - [NIP-13: Proof of Work](13.md) - [NIP-14: Subject tag in text events](14.md) - [NIP-15: Nostr Marketplace (for resilient marketplaces)](15.md) - [NIP-17: Private Direct Messages](17.md) - [NIP-18: Reposts](18.md) - [NIP-19: bech32-encoded entities](19.md) - [NIP-21: `nostr:` URI scheme](21.md) - [NIP-22: Comment](22.md) - [NIP-23: Long-form Content](23.md) - [NIP-24: Extra metadata fields and tags](24.md) - [NIP-25: Reactions](25.md) - [NIP-26: Delegated Event Signing](26.md) - [NIP-27: Text Note References](27.md) - [NIP-28: Public Chat](28.md) - [NIP-29: Relay-based Groups](29.md) - [NIP-30: Custom Emoji](30.md) - [NIP-31: Dealing with Unknown Events](31.md) - [NIP-32: Labeling](32.md) - [NIP-34: `git` stuff](34.md) - [NIP-35: Torrents](35.md) - [NIP-36: Sensitive Content](36.md) - [NIP-37: Draft Events](37.md) - [NIP-38: User Statuses](38.md) - [NIP-39: External Identities in Profiles](39.md) - [NIP-40: Expiration Timestamp](40.md) - [NIP-42: Authentication of clients to relays](42.md) - [NIP-44: Encrypted Payloads (Versioned)](44.md) - [NIP-45: Counting results](45.md) - [NIP-46: Nostr Remote Signing](46.md) - [NIP-47: Nostr Wallet Connect](47.md) - [NIP-48: Proxy Tags](48.md) - [NIP-49: Private Key Encryption](49.md) - [NIP-50: Search Capability](50.md) - [NIP-51: Lists](51.md) - [NIP-52: Calendar Events](52.md) - [NIP-53: Live Activities](53.md) - [NIP-54: Wiki](54.md) - [NIP-55: Android Signer Application](55.md) - [NIP-56: Reporting](56.md) - [NIP-57: Lightning Zaps](57.md) - [NIP-58: Badges](58.md) - [NIP-59: Gift Wrap](59.md) - [NIP-60: Cashu Wallet](60.md) - [NIP-61: Nutzaps](61.md) - [NIP-62: Request to Vanish](62.md) - [NIP-64: Chess (PGN)](64.md) - [NIP-65: Relay List Metadata](65.md) - [NIP-66: Relay Discovery and Liveness Monitoring](66.md) - [NIP-68: Picture-first feeds](68.md) - [NIP-69: Peer-to-peer Order events](69.md) - [NIP-70: Protected Events](70.md) - [NIP-71: Video Events](71.md) - [NIP-72: Moderated Communities](72.md) - [NIP-73: External Content IDs](73.md) - [NIP-75: Zap Goals](75.md) - [NIP-78: Application-specific data](78.md) - [NIP-84: Highlights](84.md) - [NIP-86: Relay Management API](86.md) - [NIP-88: Polls](88.md) - [NIP-89: Recommended Application Handlers](89.md) - [NIP-90: Data Vending Machines](90.md) - [NIP-92: Media Attachments](92.md) - [NIP-94: File Metadata](94.md) - [NIP-96: HTTP File Storage Integration](96.md) - [NIP-98: HTTP Auth](98.md) - [NIP-99: Classified Listings](99.md) - [NIP-7D: Threads](7D.md) - [NIP-C7: Chats](C7.md) ## Event Kinds | kind | description | NIP | | ------------- | ------------------------------- | -------------------------------------- | | `0` | User Metadata | [01](01.md) | | `1` | Short Text Note | [10](10.md) | | `2` | Recommend Relay | 01 (deprecated) | | `3` | Follows | [02](02.md) | | `4` | Encrypted Direct Messages | [04](04.md) | | `5` | Event Deletion Request | [09](09.md) | | `6` | Repost | [18](18.md) | | `7` | Reaction | [25](25.md) | | `8` | Badge Award | [58](58.md) | | `9` | Chat Message | [C7](C7.md) | | `10` | Group Chat Threaded Reply | 29 (deprecated) | | `11` | Thread | [7D](7D.md) | | `12` | Group Thread Reply | 29 (deprecated) | | `13` | Seal | [59](59.md) | | `14` | Direct Message | [17](17.md) | | `15` | File Message | [17](17.md) | | `16` | Generic Repost | [18](18.md) | | `17` | Reaction to a website | [25](25.md) | | `20` | Picture | [68](68.md) | | `21` | Video Event | [71](71.md) | | `22` | Short-form Portrait Video Event | [71](71.md) | | `30` | internal reference | [NKBIP-03] | | `31` | external web reference | [NKBIP-03] | | `32` | hardcopy reference | [NKBIP-03] | | `33` | prompt reference | [NKBIP-03] | | `40` | Channel Creation | [28](28.md) | | `41` | Channel Metadata | [28](28.md) | | `42` | Channel Message | [28](28.md) | | `43` | Channel Hide Message | [28](28.md) | | `44` | Channel Mute User | [28](28.md) | | `62` | Request to Vanish | [62](62.md) | | `64` | Chess (PGN) | [64](64.md) | | `818` | Merge Requests | [54](54.md) | | `1018` | Poll Response | [88](88.md) | | `1021` | Bid | [15](15.md) | | `1022` | Bid confirmation | [15](15.md) | | `1040` | OpenTimestamps | [03](03.md) | | `1059` | Gift Wrap | [59](59.md) | | `1063` | File Metadata | [94](94.md) | | `1068` | Poll | [88](88.md) | | `1111` | Comment | [22](22.md) | | `1311` | Live Chat Message | [53](53.md) | | `1617` | Patches | [34](34.md) | | `1621` | Issues | [34](34.md) | | `1622` | Git Replies (deprecated) | [34](34.md) | | `1630`-`1633` | Status | [34](34.md) | | `1971` | Problem Tracker | [nostrocket][nostrocket] | | `1984` | Reporting | [56](56.md) | | `1985` | Label | [32](32.md) | | `1986` | Relay reviews | | | `1987` | AI Embeddings / Vector lists | [NKBIP-02] | | `2003` | Torrent | [35](35.md) | | `2004` | Torrent Comment | [35](35.md) | | `2022` | Coinjoin Pool | [joinstr][joinstr] | | `4550` | Community Post Approval | [72](72.md) | | `5000`-`5999` | Job Request | [90](90.md) | | `6000`-`6999` | Job Result | [90](90.md) | | `7000` | Job Feedback | [90](90.md) | | `7374` | Reserved Cashu Wallet Tokens | [60](60.md) | | `7375` | Cashu Wallet Tokens | [60](60.md) | | `7376` | Cashu Wallet History | [60](60.md) | | `9000`-`9030` | Group Control Events | [29](29.md) | | `9041` | Zap Goal | [75](75.md) | | `9321` | Nutzap | [61](61.md) | | `9467` | Tidal login | [Tidal-nostr] | | `9734` | Zap Request | [57](57.md) | | `9735` | Zap | [57](57.md) | | `9802` | Highlights | [84](84.md) | | `10000` | Mute list | [51](51.md) | | `10001` | Pin list | [51](51.md) | | `10002` | Relay List Metadata | [65](65.md), [51](51.md) | | `10003` | Bookmark list | [51](51.md) | | `10004` | Communities list | [51](51.md) | | `10005` | Public chats list | [51](51.md) | | `10006` | Blocked relays list | [51](51.md) | | `10007` | Search relays list | [51](51.md) | | `10009` | User groups | [51](51.md), [29](29.md) | | `10013` | Private event relay list | [37](37.md) | | `10015` | Interests list | [51](51.md) | | `10019` | Nutzap Mint Recommendation | [61](61.md) | | `10030` | User emoji list | [51](51.md) | | `10050` | Relay list to receive DMs | [51](51.md), [17](17.md) | | `10063` | User server list | [Blossom][blossom] | | `10096` | File storage server list | [96](96.md) | | `10166` | Relay Monitor Announcement | [66](66.md) | | `13194` | Wallet Info | [47](47.md) | | `17375` | Cashu Wallet Event | [60](60.md) | | `21000` | Lightning Pub RPC | [Lightning.Pub][lnpub] | | `22242` | Client Authentication | [42](42.md) | | `23194` | Wallet Request | [47](47.md) | | `23195` | Wallet Response | [47](47.md) | | `24133` | Nostr Connect | [46](46.md) | | `24242` | Blobs stored on mediaservers | [Blossom][blossom] | | `27235` | HTTP Auth | [98](98.md) | | `30000` | Follow sets | [51](51.md) | | `30001` | Generic lists | 51 (deprecated) | | `30002` | Relay sets | [51](51.md) | | `30003` | Bookmark sets | [51](51.md) | | `30004` | Curation sets | [51](51.md) | | `30005` | Video sets | [51](51.md) | | `30007` | Kind mute sets | [51](51.md) | | `30008` | Profile Badges | [58](58.md) | | `30009` | Badge Definition | [58](58.md) | | `30015` | Interest sets | [51](51.md) | | `30017` | Create or update a stall | [15](15.md) | | `30018` | Create or update a product | [15](15.md) | | `30019` | Marketplace UI/UX | [15](15.md) | | `30020` | Product sold as an auction | [15](15.md) | | `30023` | Long-form Content | [23](23.md) | | `30024` | Draft Long-form Content | [23](23.md) | | `30030` | Emoji sets | [51](51.md) | | `30040` | Curated Publication Index | [NKBIP-01] | | `30041` | Curated Publication Content | [NKBIP-01] | | `30063` | Release artifact sets | [51](51.md) | | `30078` | Application-specific Data | [78](78.md) | | `30166` | Relay Discovery | [66](66.md) | | `30267` | App curation sets | [51](51.md) | | `30311` | Live Event | [53](53.md) | | `30315` | User Statuses | [38](38.md) | | `30388` | Slide Set | [Corny Chat][cornychat-slideset] | | `30402` | Classified Listing | [99](99.md) | | `30403` | Draft Classified Listing | [99](99.md) | | `30617` | Repository announcements | [34](34.md) | | `30618` | Repository state announcements | [34](34.md) | | `30818` | Wiki article | [54](54.md) | | `30819` | Redirects | [54](54.md) | | `31234` | Draft Event | [37](37.md) | | `31388` | Link Set | [Corny Chat][cornychat-linkset] | | `31890` | Feed | [NUD: Custom Feeds][NUD: Custom Feeds] | | `31922` | Date-Based Calendar Event | [52](52.md) | | `31923` | Time-Based Calendar Event | [52](52.md) | | `31924` | Calendar | [52](52.md) | | `31925` | Calendar Event RSVP | [52](52.md) | | `31989` | Handler recommendation | [89](89.md) | | `31990` | Handler information | [89](89.md) | | | `32267` | Software Application | | | | `34550` | Community Definition | [72](72.md) | | `38383` | Peer-to-peer Order events | [69](69.md) | | `39000-9` | Group metadata events | [29](29.md) | [NUD: Custom Feeds]: https://wikifreedia.xyz/cip-01/ [nostrocket]: https://github.com/nostrocket/NIPS/blob/main/Problems.md [lnpub]: https://github.com/shocknet/Lightning.Pub/blob/master/proto/autogenerated/client.md [cornychat-slideset]: https://cornychat.com/datatypes#kind30388slideset [cornychat-linkset]: https://cornychat.com/datatypes#kind31388linkset [joinstr]: https://gitlab.com/1440000bytes/joinstr/-/blob/main/NIP.md [NKBIP-01]: https://wikistr.com/nkbip-01*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [NKBIP-02]: https://wikistr.com/nkbip-02*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [NKBIP-03]: https://wikistr.com/nkbip-03*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [blossom]: https://github.com/hzrd149/blossom [Tidal-nostr]: https://wikistr.com/tidal-nostr ## Message types ### Client to Relay | type | description | NIP | | ------- | --------------------------------------------------- | ----------- | | `EVENT` | used to publish events | [01](01.md) | | `REQ` | used to request events and subscribe to new updates | [01](01.md) | | `CLOSE` | used to stop previous subscriptions | [01](01.md) | | `AUTH` | used to send authentication events | [42](42.md) | | `COUNT` | used to request event counts | [45](45.md) | ### Relay to Client | type | description | NIP | | -------- | ------------------------------------------------------- | ----------- | | `EOSE` | used to notify clients all stored events have been sent | [01](01.md) | | `EVENT` | used to send events requested to clients | [01](01.md) | | `NOTICE` | used to send human-readable messages to clients | [01](01.md) | | `OK` | used to notify clients if an EVENT was successful | [01](01.md) | | `CLOSED` | used to notify clients that a REQ was ended and why | [01](01.md) | | `AUTH` | used to send authentication challenges | [42](42.md) | | `COUNT` | used to send requested event counts to clients | [45](45.md) | ## Standardized Tags | name | value | other parameters | NIP | | ----------------- | ------------------------------------ | ------------------------------- | -------------------------------------------------- | | `a` | coordinates to an event | relay URL | [01](01.md) | | `A` | root address | relay URL | [22](22.md) | | `d` | identifier | -- | [01](01.md) | | `e` | event id (hex) | relay URL, marker, pubkey (hex) | [01](01.md), [10](10.md) | | `E` | root event id | relay URL | [22](22.md) | | `f` | currency code | -- | [69](69.md) | | `g` | geohash | -- | [52](52.md) | | `h` | group id | -- | [29](29.md) | | `i` | external identity | proof, url hint | [35](35.md), [39](39.md), [73](73.md) | | `I` | root external identity | -- | [22](22.md) | | `k` | kind | -- | [18](18.md), [25](25.md), [72](72.md), [73](73.md) | | `K` | root scope | -- | [22](22.md) | | `l` | label, label namespace | -- | [32](32.md) | | `L` | label namespace | -- | [32](32.md) | | `m` | MIME type | -- | [94](94.md) | | `p` | pubkey (hex) | relay URL, petname | [01](01.md), [02](02.md), [22](22.md) | | `P` | pubkey (hex) | -- | [22](22.md), [57](57.md) | | `q` | event id (hex) | relay URL, pubkey (hex) | [18](18.md) | | `r` | a reference (URL, etc) | -- | [24](24.md), [25](25.md) | | `r` | relay url | marker | [65](65.md) | | `s` | status | -- | [69](69.md) | | `t` | hashtag | -- | [24](24.md), [34](34.md), [35](35.md) | | `u` | url | -- | [61](61.md), [98](98.md) | | `x` | hash | -- | [35](35.md), [56](56.md) | | `y` | platform | -- | [69](69.md) | | `z` | order number | -- | [69](69.md) | | `-` | -- | -- | [70](70.md) | | `alt` | summary | -- | [31](31.md) | | `amount` | millisatoshis, stringified | -- | [57](57.md) | | `bolt11` | `bolt11` invoice | -- | [57](57.md) | | `challenge` | challenge string | -- | [42](42.md) | | `client` | name, address | relay URL | [89](89.md) | | `clone` | git clone URL | -- | [34](34.md) | | `content-warning` | reason | -- | [36](36.md) | | `delegation` | pubkey, conditions, delegation token | -- | [26](26.md) | | `description` | description | -- | [34](34.md), [57](57.md), [58](58.md) | | `emoji` | shortcode, image URL | -- | [30](30.md) | | `encrypted` | -- | -- | [90](90.md) | | `expiration` | unix timestamp (string) | -- | [40](40.md) | | `file` | full path (string) | -- | [35](35.md) | | `goal` | event id (hex) | relay URL | [75](75.md) | | `image` | image URL | dimensions in pixels | [23](23.md), [52](52.md), [58](58.md) | | `imeta` | inline metadata | -- | [92](92.md) | | `lnurl` | `bech32` encoded `lnurl` | -- | [57](57.md) | | `location` | location string | -- | [52](52.md), [99](99.md) | | `name` | name | -- | [34](34.md), [58](58.md), [72](72.md) | | `nonce` | random | difficulty | [13](13.md) | | `preimage` | hash of `bolt11` invoice | -- | [57](57.md) | | `price` | price | currency, frequency | [99](99.md) | | `proxy` | external ID | protocol | [48](48.md) | | `published_at` | unix timestamp (string) | -- | [23](23.md) | | `relay` | relay url | -- | [42](42.md), [17](17.md) | | `relays` | relay list | -- | [57](57.md) | | `server` | file storage server url | -- | [96](96.md) | | `subject` | subject | -- | [14](14.md), [17](17.md), [34](34.md) | | `summary` | summary | -- | [23](23.md), [52](52.md) | | `thumb` | badge thumbnail | dimensions in pixels | [58](58.md) | | `title` | article title | -- | [23](23.md) | | `tracker` | torrent tracker URL | -- | [35](35.md) | | `web` | webpage URL | -- | [34](34.md) | | `zap` | pubkey (hex), relay URL | weight | [57](57.md) | Please update these lists when proposing new NIPs. ## Criteria for acceptance of NIPs 1. They should be fully implemented in at least two clients and one relay -- when applicable. 2. They should make sense. 3. They should be optional and backwards-compatible: care must be taken such that clients and relays that choose to not implement them do not stop working when interacting with the ones that choose to. 4. There should be no more than one way of doing the same thing. 5. Other rules will be made up when necessary. ## Is this repository a centralizing factor? To promote interoperability, we need standards that everybody can follow, and we need them to define a **single way of doing each thing** without ever hurting **backwards-compatibility**, and for that purpose there is no way around getting everybody to agree on the same thing and keep a centralized index of these standards. However the fact that such an index exists doesn't hurt the decentralization of Nostr. _At any point the central index can be challenged if it is failing to fulfill the needs of the protocol_ and it can migrate to other places and be maintained by other people. It can even fork into multiple versions, and then some clients would go one way, others would go another way, and some clients would adhere to both competing standards. This would hurt the simplicity, openness and interoperability of Nostr a little, but everything would still work in the short term. There is a list of notable Nostr software developers who have commit access to this repository, but that exists mostly for practical reasons, as by the nature of the thing we're dealing with the repository owner can revoke membership and rewrite history as they want -- and if these actions are unjustified or perceived as bad or evil the community must react. ## How this repository works Standards may emerge in two ways: the first way is that someone starts doing something, then others copy it; the second way is that someone has an idea of a new standard that could benefit multiple clients and the protocol in general without breaking **backwards-compatibility** and the principle of having **a single way of doing things**, then they write that idea and submit it to this repository, other interested parties read it and give their feedback, then once most people reasonably agree we codify that in a NIP which client and relay developers that are interested in the feature can proceed to implement. These two ways of standardizing things are supported by this repository. Although the second is preferred, an effort will be made to codify standards emerged outside this repository into NIPs that can be later referenced and easily understood and implemented by others -- but obviously as in any human system discretion may be applied when standards are considered harmful. ## Breaking Changes [Breaking Changes](BREAKING.md) ## License All NIPs are public domain. ## Contributors <a align="center" href="https://github.com/nostr-protocol/nips/graphs/contributors"> <img src="https://contrib.rocks/image?repo=nostr-protocol/nips" /> </a>
@ fd06f542:8d6d54cd
2025-03-28 02:21:20# NIPs NIPs stand for **Nostr Implementation Possibilities**. They exist to document what may be implemented by [Nostr](https://github.com/nostr-protocol/nostr)-compatible _relay_ and _client_ software. --- - [List](#list) - [Event Kinds](#event-kinds) - [Message Types](#message-types) - [Client to Relay](#client-to-relay) - [Relay to Client](#relay-to-client) - [Standardized Tags](#standardized-tags) - [Criteria for acceptance of NIPs](#criteria-for-acceptance-of-nips) - [Is this repository a centralizing factor?](#is-this-repository-a-centralizing-factor) - [How this repository works](#how-this-repository-works) - [Breaking Changes](#breaking-changes) - [License](#license) --- ## List - [NIP-01: Basic protocol flow description](01.md) - [NIP-02: Follow List](02.md) - [NIP-03: OpenTimestamps Attestations for Events](03.md) - [NIP-04: Encrypted Direct Message](04.md) --- **unrecommended**: deprecated in favor of [NIP-17](17.md) - [NIP-05: Mapping Nostr keys to DNS-based internet identifiers](05.md) - [NIP-06: Basic key derivation from mnemonic seed phrase](06.md) - [NIP-07: `window.nostr` capability for web browsers](07.md) - [NIP-08: Handling Mentions](08.md) --- **unrecommended**: deprecated in favor of [NIP-27](27.md) - [NIP-09: Event Deletion Request](09.md) - [NIP-10: Text Notes and Threads](10.md) - [NIP-11: Relay Information Document](11.md) - [NIP-13: Proof of Work](13.md) - [NIP-14: Subject tag in text events](14.md) - [NIP-15: Nostr Marketplace (for resilient marketplaces)](15.md) - [NIP-17: Private Direct Messages](17.md) - [NIP-18: Reposts](18.md) - [NIP-19: bech32-encoded entities](19.md) - [NIP-21: `nostr:` URI scheme](21.md) - [NIP-22: Comment](22.md) - [NIP-23: Long-form Content](23.md) - [NIP-24: Extra metadata fields and tags](24.md) - [NIP-25: Reactions](25.md) - [NIP-26: Delegated Event Signing](26.md) - [NIP-27: Text Note References](27.md) - [NIP-28: Public Chat](28.md) - [NIP-29: Relay-based Groups](29.md) - [NIP-30: Custom Emoji](30.md) - [NIP-31: Dealing with Unknown Events](31.md) - [NIP-32: Labeling](32.md) - [NIP-34: `git` stuff](34.md) - [NIP-35: Torrents](35.md) - [NIP-36: Sensitive Content](36.md) - [NIP-37: Draft Events](37.md) - [NIP-38: User Statuses](38.md) - [NIP-39: External Identities in Profiles](39.md) - [NIP-40: Expiration Timestamp](40.md) - [NIP-42: Authentication of clients to relays](42.md) - [NIP-44: Encrypted Payloads (Versioned)](44.md) - [NIP-45: Counting results](45.md) - [NIP-46: Nostr Remote Signing](46.md) - [NIP-47: Nostr Wallet Connect](47.md) - [NIP-48: Proxy Tags](48.md) - [NIP-49: Private Key Encryption](49.md) - [NIP-50: Search Capability](50.md) - [NIP-51: Lists](51.md) - [NIP-52: Calendar Events](52.md) - [NIP-53: Live Activities](53.md) - [NIP-54: Wiki](54.md) - [NIP-55: Android Signer Application](55.md) - [NIP-56: Reporting](56.md) - [NIP-57: Lightning Zaps](57.md) - [NIP-58: Badges](58.md) - [NIP-59: Gift Wrap](59.md) - [NIP-60: Cashu Wallet](60.md) - [NIP-61: Nutzaps](61.md) - [NIP-62: Request to Vanish](62.md) - [NIP-64: Chess (PGN)](64.md) - [NIP-65: Relay List Metadata](65.md) - [NIP-66: Relay Discovery and Liveness Monitoring](66.md) - [NIP-68: Picture-first feeds](68.md) - [NIP-69: Peer-to-peer Order events](69.md) - [NIP-70: Protected Events](70.md) - [NIP-71: Video Events](71.md) - [NIP-72: Moderated Communities](72.md) - [NIP-73: External Content IDs](73.md) - [NIP-75: Zap Goals](75.md) - [NIP-78: Application-specific data](78.md) - [NIP-84: Highlights](84.md) - [NIP-86: Relay Management API](86.md) - [NIP-88: Polls](88.md) - [NIP-89: Recommended Application Handlers](89.md) - [NIP-90: Data Vending Machines](90.md) - [NIP-92: Media Attachments](92.md) - [NIP-94: File Metadata](94.md) - [NIP-96: HTTP File Storage Integration](96.md) - [NIP-98: HTTP Auth](98.md) - [NIP-99: Classified Listings](99.md) - [NIP-7D: Threads](7D.md) - [NIP-C7: Chats](C7.md) ## Event Kinds | kind | description | NIP | | ------------- | ------------------------------- | -------------------------------------- | | `0` | User Metadata | [01](01.md) | | `1` | Short Text Note | [10](10.md) | | `2` | Recommend Relay | 01 (deprecated) | | `3` | Follows | [02](02.md) | | `4` | Encrypted Direct Messages | [04](04.md) | | `5` | Event Deletion Request | [09](09.md) | | `6` | Repost | [18](18.md) | | `7` | Reaction | [25](25.md) | | `8` | Badge Award | [58](58.md) | | `9` | Chat Message | [C7](C7.md) | | `10` | Group Chat Threaded Reply | 29 (deprecated) | | `11` | Thread | [7D](7D.md) | | `12` | Group Thread Reply | 29 (deprecated) | | `13` | Seal | [59](59.md) | | `14` | Direct Message | [17](17.md) | | `15` | File Message | [17](17.md) | | `16` | Generic Repost | [18](18.md) | | `17` | Reaction to a website | [25](25.md) | | `20` | Picture | [68](68.md) | | `21` | Video Event | [71](71.md) | | `22` | Short-form Portrait Video Event | [71](71.md) | | `30` | internal reference | [NKBIP-03] | | `31` | external web reference | [NKBIP-03] | | `32` | hardcopy reference | [NKBIP-03] | | `33` | prompt reference | [NKBIP-03] | | `40` | Channel Creation | [28](28.md) | | `41` | Channel Metadata | [28](28.md) | | `42` | Channel Message | [28](28.md) | | `43` | Channel Hide Message | [28](28.md) | | `44` | Channel Mute User | [28](28.md) | | `62` | Request to Vanish | [62](62.md) | | `64` | Chess (PGN) | [64](64.md) | | `818` | Merge Requests | [54](54.md) | | `1018` | Poll Response | [88](88.md) | | `1021` | Bid | [15](15.md) | | `1022` | Bid confirmation | [15](15.md) | | `1040` | OpenTimestamps | [03](03.md) | | `1059` | Gift Wrap | [59](59.md) | | `1063` | File Metadata | [94](94.md) | | `1068` | Poll | [88](88.md) | | `1111` | Comment | [22](22.md) | | `1311` | Live Chat Message | [53](53.md) | | `1617` | Patches | [34](34.md) | | `1621` | Issues | [34](34.md) | | `1622` | Git Replies (deprecated) | [34](34.md) | | `1630`-`1633` | Status | [34](34.md) | | `1971` | Problem Tracker | [nostrocket][nostrocket] | | `1984` | Reporting | [56](56.md) | | `1985` | Label | [32](32.md) | | `1986` | Relay reviews | | | `1987` | AI Embeddings / Vector lists | [NKBIP-02] | | `2003` | Torrent | [35](35.md) | | `2004` | Torrent Comment | [35](35.md) | | `2022` | Coinjoin Pool | [joinstr][joinstr] | | `4550` | Community Post Approval | [72](72.md) | | `5000`-`5999` | Job Request | [90](90.md) | | `6000`-`6999` | Job Result | [90](90.md) | | `7000` | Job Feedback | [90](90.md) | | `7374` | Reserved Cashu Wallet Tokens | [60](60.md) | | `7375` | Cashu Wallet Tokens | [60](60.md) | | `7376` | Cashu Wallet History | [60](60.md) | | `9000`-`9030` | Group Control Events | [29](29.md) | | `9041` | Zap Goal | [75](75.md) | | `9321` | Nutzap | [61](61.md) | | `9467` | Tidal login | [Tidal-nostr] | | `9734` | Zap Request | [57](57.md) | | `9735` | Zap | [57](57.md) | | `9802` | Highlights | [84](84.md) | | `10000` | Mute list | [51](51.md) | | `10001` | Pin list | [51](51.md) | | `10002` | Relay List Metadata | [65](65.md), [51](51.md) | | `10003` | Bookmark list | [51](51.md) | | `10004` | Communities list | [51](51.md) | | `10005` | Public chats list | [51](51.md) | | `10006` | Blocked relays list | [51](51.md) | | `10007` | Search relays list | [51](51.md) | | `10009` | User groups | [51](51.md), [29](29.md) | | `10013` | Private event relay list | [37](37.md) | | `10015` | Interests list | [51](51.md) | | `10019` | Nutzap Mint Recommendation | [61](61.md) | | `10030` | User emoji list | [51](51.md) | | `10050` | Relay list to receive DMs | [51](51.md), [17](17.md) | | `10063` | User server list | [Blossom][blossom] | | `10096` | File storage server list | [96](96.md) | | `10166` | Relay Monitor Announcement | [66](66.md) | | `13194` | Wallet Info | [47](47.md) | | `17375` | Cashu Wallet Event | [60](60.md) | | `21000` | Lightning Pub RPC | [Lightning.Pub][lnpub] | | `22242` | Client Authentication | [42](42.md) | | `23194` | Wallet Request | [47](47.md) | | `23195` | Wallet Response | [47](47.md) | | `24133` | Nostr Connect | [46](46.md) | | `24242` | Blobs stored on mediaservers | [Blossom][blossom] | | `27235` | HTTP Auth | [98](98.md) | | `30000` | Follow sets | [51](51.md) | | `30001` | Generic lists | 51 (deprecated) | | `30002` | Relay sets | [51](51.md) | | `30003` | Bookmark sets | [51](51.md) | | `30004` | Curation sets | [51](51.md) | | `30005` | Video sets | [51](51.md) | | `30007` | Kind mute sets | [51](51.md) | | `30008` | Profile Badges | [58](58.md) | | `30009` | Badge Definition | [58](58.md) | | `30015` | Interest sets | [51](51.md) | | `30017` | Create or update a stall | [15](15.md) | | `30018` | Create or update a product | [15](15.md) | | `30019` | Marketplace UI/UX | [15](15.md) | | `30020` | Product sold as an auction | [15](15.md) | | `30023` | Long-form Content | [23](23.md) | | `30024` | Draft Long-form Content | [23](23.md) | | `30030` | Emoji sets | [51](51.md) | | `30040` | Curated Publication Index | [NKBIP-01] | | `30041` | Curated Publication Content | [NKBIP-01] | | `30063` | Release artifact sets | [51](51.md) | | `30078` | Application-specific Data | [78](78.md) | | `30166` | Relay Discovery | [66](66.md) | | `30267` | App curation sets | [51](51.md) | | `30311` | Live Event | [53](53.md) | | `30315` | User Statuses | [38](38.md) | | `30388` | Slide Set | [Corny Chat][cornychat-slideset] | | `30402` | Classified Listing | [99](99.md) | | `30403` | Draft Classified Listing | [99](99.md) | | `30617` | Repository announcements | [34](34.md) | | `30618` | Repository state announcements | [34](34.md) | | `30818` | Wiki article | [54](54.md) | | `30819` | Redirects | [54](54.md) | | `31234` | Draft Event | [37](37.md) | | `31388` | Link Set | [Corny Chat][cornychat-linkset] | | `31890` | Feed | [NUD: Custom Feeds][NUD: Custom Feeds] | | `31922` | Date-Based Calendar Event | [52](52.md) | | `31923` | Time-Based Calendar Event | [52](52.md) | | `31924` | Calendar | [52](52.md) | | `31925` | Calendar Event RSVP | [52](52.md) | | `31989` | Handler recommendation | [89](89.md) | | `31990` | Handler information | [89](89.md) | | | `32267` | Software Application | | | | `34550` | Community Definition | [72](72.md) | | `38383` | Peer-to-peer Order events | [69](69.md) | | `39000-9` | Group metadata events | [29](29.md) | [NUD: Custom Feeds]: https://wikifreedia.xyz/cip-01/ [nostrocket]: https://github.com/nostrocket/NIPS/blob/main/Problems.md [lnpub]: https://github.com/shocknet/Lightning.Pub/blob/master/proto/autogenerated/client.md [cornychat-slideset]: https://cornychat.com/datatypes#kind30388slideset [cornychat-linkset]: https://cornychat.com/datatypes#kind31388linkset [joinstr]: https://gitlab.com/1440000bytes/joinstr/-/blob/main/NIP.md [NKBIP-01]: https://wikistr.com/nkbip-01*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [NKBIP-02]: https://wikistr.com/nkbip-02*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [NKBIP-03]: https://wikistr.com/nkbip-03*fd208ee8c8f283780a9552896e4823cc9dc6bfd442063889577106940fd927c1 [blossom]: https://github.com/hzrd149/blossom [Tidal-nostr]: https://wikistr.com/tidal-nostr ## Message types ### Client to Relay | type | description | NIP | | ------- | --------------------------------------------------- | ----------- | | `EVENT` | used to publish events | [01](01.md) | | `REQ` | used to request events and subscribe to new updates | [01](01.md) | | `CLOSE` | used to stop previous subscriptions | [01](01.md) | | `AUTH` | used to send authentication events | [42](42.md) | | `COUNT` | used to request event counts | [45](45.md) | ### Relay to Client | type | description | NIP | | -------- | ------------------------------------------------------- | ----------- | | `EOSE` | used to notify clients all stored events have been sent | [01](01.md) | | `EVENT` | used to send events requested to clients | [01](01.md) | | `NOTICE` | used to send human-readable messages to clients | [01](01.md) | | `OK` | used to notify clients if an EVENT was successful | [01](01.md) | | `CLOSED` | used to notify clients that a REQ was ended and why | [01](01.md) | | `AUTH` | used to send authentication challenges | [42](42.md) | | `COUNT` | used to send requested event counts to clients | [45](45.md) | ## Standardized Tags | name | value | other parameters | NIP | | ----------------- | ------------------------------------ | ------------------------------- | -------------------------------------------------- | | `a` | coordinates to an event | relay URL | [01](01.md) | | `A` | root address | relay URL | [22](22.md) | | `d` | identifier | -- | [01](01.md) | | `e` | event id (hex) | relay URL, marker, pubkey (hex) | [01](01.md), [10](10.md) | | `E` | root event id | relay URL | [22](22.md) | | `f` | currency code | -- | [69](69.md) | | `g` | geohash | -- | [52](52.md) | | `h` | group id | -- | [29](29.md) | | `i` | external identity | proof, url hint | [35](35.md), [39](39.md), [73](73.md) | | `I` | root external identity | -- | [22](22.md) | | `k` | kind | -- | [18](18.md), [25](25.md), [72](72.md), [73](73.md) | | `K` | root scope | -- | [22](22.md) | | `l` | label, label namespace | -- | [32](32.md) | | `L` | label namespace | -- | [32](32.md) | | `m` | MIME type | -- | [94](94.md) | | `p` | pubkey (hex) | relay URL, petname | [01](01.md), [02](02.md), [22](22.md) | | `P` | pubkey (hex) | -- | [22](22.md), [57](57.md) | | `q` | event id (hex) | relay URL, pubkey (hex) | [18](18.md) | | `r` | a reference (URL, etc) | -- | [24](24.md), [25](25.md) | | `r` | relay url | marker | [65](65.md) | | `s` | status | -- | [69](69.md) | | `t` | hashtag | -- | [24](24.md), [34](34.md), [35](35.md) | | `u` | url | -- | [61](61.md), [98](98.md) | | `x` | hash | -- | [35](35.md), [56](56.md) | | `y` | platform | -- | [69](69.md) | | `z` | order number | -- | [69](69.md) | | `-` | -- | -- | [70](70.md) | | `alt` | summary | -- | [31](31.md) | | `amount` | millisatoshis, stringified | -- | [57](57.md) | | `bolt11` | `bolt11` invoice | -- | [57](57.md) | | `challenge` | challenge string | -- | [42](42.md) | | `client` | name, address | relay URL | [89](89.md) | | `clone` | git clone URL | -- | [34](34.md) | | `content-warning` | reason | -- | [36](36.md) | | `delegation` | pubkey, conditions, delegation token | -- | [26](26.md) | | `description` | description | -- | [34](34.md), [57](57.md), [58](58.md) | | `emoji` | shortcode, image URL | -- | [30](30.md) | | `encrypted` | -- | -- | [90](90.md) | | `expiration` | unix timestamp (string) | -- | [40](40.md) | | `file` | full path (string) | -- | [35](35.md) | | `goal` | event id (hex) | relay URL | [75](75.md) | | `image` | image URL | dimensions in pixels | [23](23.md), [52](52.md), [58](58.md) | | `imeta` | inline metadata | -- | [92](92.md) | | `lnurl` | `bech32` encoded `lnurl` | -- | [57](57.md) | | `location` | location string | -- | [52](52.md), [99](99.md) | | `name` | name | -- | [34](34.md), [58](58.md), [72](72.md) | | `nonce` | random | difficulty | [13](13.md) | | `preimage` | hash of `bolt11` invoice | -- | [57](57.md) | | `price` | price | currency, frequency | [99](99.md) | | `proxy` | external ID | protocol | [48](48.md) | | `published_at` | unix timestamp (string) | -- | [23](23.md) | | `relay` | relay url | -- | [42](42.md), [17](17.md) | | `relays` | relay list | -- | [57](57.md) | | `server` | file storage server url | -- | [96](96.md) | | `subject` | subject | -- | [14](14.md), [17](17.md), [34](34.md) | | `summary` | summary | -- | [23](23.md), [52](52.md) | | `thumb` | badge thumbnail | dimensions in pixels | [58](58.md) | | `title` | article title | -- | [23](23.md) | | `tracker` | torrent tracker URL | -- | [35](35.md) | | `web` | webpage URL | -- | [34](34.md) | | `zap` | pubkey (hex), relay URL | weight | [57](57.md) | Please update these lists when proposing new NIPs. ## Criteria for acceptance of NIPs 1. They should be fully implemented in at least two clients and one relay -- when applicable. 2. They should make sense. 3. They should be optional and backwards-compatible: care must be taken such that clients and relays that choose to not implement them do not stop working when interacting with the ones that choose to. 4. There should be no more than one way of doing the same thing. 5. Other rules will be made up when necessary. ## Is this repository a centralizing factor? To promote interoperability, we need standards that everybody can follow, and we need them to define a **single way of doing each thing** without ever hurting **backwards-compatibility**, and for that purpose there is no way around getting everybody to agree on the same thing and keep a centralized index of these standards. However the fact that such an index exists doesn't hurt the decentralization of Nostr. _At any point the central index can be challenged if it is failing to fulfill the needs of the protocol_ and it can migrate to other places and be maintained by other people. It can even fork into multiple versions, and then some clients would go one way, others would go another way, and some clients would adhere to both competing standards. This would hurt the simplicity, openness and interoperability of Nostr a little, but everything would still work in the short term. There is a list of notable Nostr software developers who have commit access to this repository, but that exists mostly for practical reasons, as by the nature of the thing we're dealing with the repository owner can revoke membership and rewrite history as they want -- and if these actions are unjustified or perceived as bad or evil the community must react. ## How this repository works Standards may emerge in two ways: the first way is that someone starts doing something, then others copy it; the second way is that someone has an idea of a new standard that could benefit multiple clients and the protocol in general without breaking **backwards-compatibility** and the principle of having **a single way of doing things**, then they write that idea and submit it to this repository, other interested parties read it and give their feedback, then once most people reasonably agree we codify that in a NIP which client and relay developers that are interested in the feature can proceed to implement. These two ways of standardizing things are supported by this repository. Although the second is preferred, an effort will be made to codify standards emerged outside this repository into NIPs that can be later referenced and easily understood and implemented by others -- but obviously as in any human system discretion may be applied when standards are considered harmful. ## Breaking Changes [Breaking Changes](BREAKING.md) ## License All NIPs are public domain. ## Contributors <a align="center" href="https://github.com/nostr-protocol/nips/graphs/contributors"> <img src="https://contrib.rocks/image?repo=nostr-protocol/nips" /> </a> @ 1c229706:fd7d0f4c
2025-04-05 06:38:45O mundo do entretenimento online está em constante evolução, com novas plataformas surgindo para atender à demanda crescente por experiências inovadoras e imersivas. A 5853 é uma dessas plataformas que tem se destacado pela qualidade de seus jogos, pela tecnologia avançada e pela experiência excepcional que oferece aos seus jogadores. Neste artigo, vamos explorar o que torna a plataforma 5853 tão especial e por que ela tem conquistado a preferência dos jogadores. Inovação e Design: O Diferencial da Plataforma 5853 A 5853 é uma plataforma de entretenimento online que se destaca por seu design sofisticado e fácil de usar. Desde o primeiro acesso, os jogadores são recebidos por uma interface limpa, intuitiva e moderna, que torna a navegação rápida e eficiente. A plataforma é projetada para garantir que o jogador tenha fácil acesso aos seus jogos favoritos e possa explorar outras opções de forma simples e sem complicação. A <a href="https://5853.one"> 5853 </a> também se diferencia pela sua flexibilidade. Compatível com computadores, smartphones e tablets, a plataforma garante que os jogadores possam se divertir de qualquer lugar, seja em casa ou em movimento. Isso proporciona uma experiência contínua, permitindo que os jogadores aproveitem o melhor do entretenimento digital a qualquer hora. Além disso, a plataforma é totalmente segura. As informações dos jogadores são protegidas por criptografia de ponta, o que garante que todas as transações e dados pessoais sejam mantidos de forma confidencial. A Diversidade de Jogos da 5853: Uma Oferta Completa para Todos os Gostos A plataforma 5853 é renomada pela sua impressionante variedade de jogos. Independentemente do estilo de jogo preferido, os jogadores podem encontrar uma ampla gama de opções, que vão desde os mais simples e rápidos até os mais complexos e desafiadores. A plataforma oferece jogos de cartas, slots, estratégia, RPGs, e muito mais. Cada título foi escolhido para proporcionar uma experiência única e envolvente, com gráficos de alta qualidade e jogabilidade fluida. Além disso, novos jogos são constantemente adicionados à plataforma, o que mantém a experiência sempre fresca e excitante. A 5853 também oferece desafios e torneios, permitindo que os jogadores testem suas habilidades e se envolvam em competições emocionantes. Isso torna a plataforma ainda mais dinâmica, criando uma atmosfera de constante evolução e diversão. A Experiência do Jogador na 5853: Conforto, Interação e Suporte de Qualidade A 5853 não se preocupa apenas com os jogos, mas também com o bem-estar de seus jogadores. A plataforma foi projetada para proporcionar uma experiência confortável e sem interrupções. O design responsivo garante que os jogos funcionem perfeitamente em qualquer dispositivo, enquanto a navegação intuitiva facilita o acesso a todos os recursos. A plataforma também promove a interação entre os jogadores, com chats ao vivo e fóruns onde os usuários podem compartilhar experiências, trocar dicas e até formar grupos para desafios em equipe. Isso cria uma comunidade engajada e colaborativa, onde os jogadores podem se conectar e aprender uns com os outros. Além disso, a 5853 oferece suporte ao cliente 24/7, com uma equipe dedicada a resolver qualquer dúvida ou problema rapidamente. Isso garante que os jogadores tenham uma experiência tranquila e sem frustrações. Conclusão: 5853, a Plataforma Completa para o Entretenimento Digital Se você está procurando por uma plataforma de entretenimento online que ofereça jogos de qualidade, segurança, conforto e uma excelente experiência de jogador, a 5853 é a escolha ideal. Com seu design inovador, vasta gama de jogos e suporte excepcional, ela se estabelece como uma das melhores opções disponíveis no mercado. Não perca a chance de explorar tudo o que a 5853 tem a oferecer e elevar sua experiência de entretenimento digital a um novo nível.
@ 1c229706:fd7d0f4c
2025-04-05 06:38:45O mundo do entretenimento online está em constante evolução, com novas plataformas surgindo para atender à demanda crescente por experiências inovadoras e imersivas. A 5853 é uma dessas plataformas que tem se destacado pela qualidade de seus jogos, pela tecnologia avançada e pela experiência excepcional que oferece aos seus jogadores. Neste artigo, vamos explorar o que torna a plataforma 5853 tão especial e por que ela tem conquistado a preferência dos jogadores. Inovação e Design: O Diferencial da Plataforma 5853 A 5853 é uma plataforma de entretenimento online que se destaca por seu design sofisticado e fácil de usar. Desde o primeiro acesso, os jogadores são recebidos por uma interface limpa, intuitiva e moderna, que torna a navegação rápida e eficiente. A plataforma é projetada para garantir que o jogador tenha fácil acesso aos seus jogos favoritos e possa explorar outras opções de forma simples e sem complicação. A <a href="https://5853.one"> 5853 </a> também se diferencia pela sua flexibilidade. Compatível com computadores, smartphones e tablets, a plataforma garante que os jogadores possam se divertir de qualquer lugar, seja em casa ou em movimento. Isso proporciona uma experiência contínua, permitindo que os jogadores aproveitem o melhor do entretenimento digital a qualquer hora. Além disso, a plataforma é totalmente segura. As informações dos jogadores são protegidas por criptografia de ponta, o que garante que todas as transações e dados pessoais sejam mantidos de forma confidencial. A Diversidade de Jogos da 5853: Uma Oferta Completa para Todos os Gostos A plataforma 5853 é renomada pela sua impressionante variedade de jogos. Independentemente do estilo de jogo preferido, os jogadores podem encontrar uma ampla gama de opções, que vão desde os mais simples e rápidos até os mais complexos e desafiadores. A plataforma oferece jogos de cartas, slots, estratégia, RPGs, e muito mais. Cada título foi escolhido para proporcionar uma experiência única e envolvente, com gráficos de alta qualidade e jogabilidade fluida. Além disso, novos jogos são constantemente adicionados à plataforma, o que mantém a experiência sempre fresca e excitante. A 5853 também oferece desafios e torneios, permitindo que os jogadores testem suas habilidades e se envolvam em competições emocionantes. Isso torna a plataforma ainda mais dinâmica, criando uma atmosfera de constante evolução e diversão. A Experiência do Jogador na 5853: Conforto, Interação e Suporte de Qualidade A 5853 não se preocupa apenas com os jogos, mas também com o bem-estar de seus jogadores. A plataforma foi projetada para proporcionar uma experiência confortável e sem interrupções. O design responsivo garante que os jogos funcionem perfeitamente em qualquer dispositivo, enquanto a navegação intuitiva facilita o acesso a todos os recursos. A plataforma também promove a interação entre os jogadores, com chats ao vivo e fóruns onde os usuários podem compartilhar experiências, trocar dicas e até formar grupos para desafios em equipe. Isso cria uma comunidade engajada e colaborativa, onde os jogadores podem se conectar e aprender uns com os outros. Além disso, a 5853 oferece suporte ao cliente 24/7, com uma equipe dedicada a resolver qualquer dúvida ou problema rapidamente. Isso garante que os jogadores tenham uma experiência tranquila e sem frustrações. Conclusão: 5853, a Plataforma Completa para o Entretenimento Digital Se você está procurando por uma plataforma de entretenimento online que ofereça jogos de qualidade, segurança, conforto e uma excelente experiência de jogador, a 5853 é a escolha ideal. Com seu design inovador, vasta gama de jogos e suporte excepcional, ela se estabelece como uma das melhores opções disponíveis no mercado. Não perca a chance de explorar tudo o que a 5853 tem a oferecer e elevar sua experiência de entretenimento digital a um novo nível. @ 57d1a264:69f1fee1
2025-03-26 08:45:13> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score! | Desktop | Mobile | |---|---| |  |  | |  |  | Now let's see what Semrush knows. # Analytics General view on your metrics and performance trend compared to last 30 days.   See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.  Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.  | Organic Search | Backlinks Analytics | |---|---| | |  | | Position Changes Trend | Top Page Changes | |---|---| | |  | |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |  # Competitors  The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.  # Referring Domains   # Daily Stats | Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | | `-41.87%` | `-16.4%` | `-1.62%` | ### 📝 Traffic Drop Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits: - https://stacker.news/items/723989 ⬇️ -15 - https://stacker.news/items/919813 ⬇️ -12 - https://stacker.news/items/783355 ⬇️ -5 ### 📉 Decreased Authority Score Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority. ### 🌟 New Keywords Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30 ### 🛠️ Broken Pages This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility! One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary? Here are other basic info to improve the SEO score and for those of us that want to learn more: - Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/ - Design for Accessibility: https://www.w3.org/WAI/tips/designing/ - Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/ originally posted at https://stacker.news/items/925433
@ 57d1a264:69f1fee1
2025-03-26 08:45:13> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score! | Desktop | Mobile | |---|---| |  |  | |  |  | Now let's see what Semrush knows. # Analytics General view on your metrics and performance trend compared to last 30 days.   See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.  Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.  | Organic Search | Backlinks Analytics | |---|---| | |  | | Position Changes Trend | Top Page Changes | |---|---| | |  | |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |  # Competitors  The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.  # Referring Domains   # Daily Stats | Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | | `-41.87%` | `-16.4%` | `-1.62%` | ### 📝 Traffic Drop Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits: - https://stacker.news/items/723989 ⬇️ -15 - https://stacker.news/items/919813 ⬇️ -12 - https://stacker.news/items/783355 ⬇️ -5 ### 📉 Decreased Authority Score Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority. ### 🌟 New Keywords Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30 ### 🛠️ Broken Pages This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility! One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary? Here are other basic info to improve the SEO score and for those of us that want to learn more: - Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/ - Design for Accessibility: https://www.w3.org/WAI/tips/designing/ - Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/ originally posted at https://stacker.news/items/925433 @ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains. I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on. But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting, The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater. Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished.
@ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains. I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on. But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting, The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater. Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished. @ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever. @ 6fbc5b6b:0251e3df
2025-04-05 03:37:17✨ Event Overview AIVille has officially partnered with FreeDogs, a decentralized social game born as a meme tribute to Pavel Durov. Their mission? To fight for privacy and resistance in the Web3 age — captured in their slogan: "Privacy is not a crime, resistance will prevail." As part of this collaboration, an exclusive AIVille quest is now live within the FreeDogs game! Participants who complete the quest not only get to explore AIVille’s intelligent agent society, but also unlock access to the broader AGT First Round Community Airdrop, where 1% of the total $AGT supply will be distributed to early supporters. 🤝 About AIVille & FreeDogs AIVille is an AI-native decentralized town where autonomous agents live, create, and evolve. Players interact with characters, join events, and help shape the future of intelligent societies. FreeDogs is a meme-powered Web3 social game where players sign petitions while completing quests for rewards. More than just entertainment, FreeDogs stands for freedom, privacy, and community resistance — a tribute to open digital spaces. Together, AIVille and FreeDogs bring the power of storytelling, questing, and token incentives to a wider audience. 🌟 AGT Token & Quest Rewards  The AIVille quest in FreeDogs is more than a game — it’s your gateway to the AGT First Round Community Airdrop, the first large-scale distribution of AIVille’s native token. Complete the quest to: Learn about AIVille and the $AGT ecosystem Get priority access to the community airdrop (1% of supply!) Start your journey as an early supporter of intelligent agents This is part of AIVille’s Create-to-Earn model, where your actions in the Web3 world generate real value. ⚡ Why This Matters This partnership expands AIVille’s reach into fun, social gaming — and introduces FreeDogs players to the future of AI-native societies. It reflects a growing movement where: Games unlock real community rewards Stories and agents become programmable Participation leads to ownership and tokenized recognition If you're playing FreeDogs, this is your moment to join something bigger. 🔗 Links AIVille Quest: https://app.freedogs.bot/game FreeDogs Bot: https://t.me/theFreeDogs_bot/app FreeDogs on Twitter: @theFreeDogs_bot AIVille on Twitter: @aivillebot AGT Airdrop Info: https://aivillegame.com
@ 6fbc5b6b:0251e3df
2025-04-05 03:37:17✨ Event Overview AIVille has officially partnered with FreeDogs, a decentralized social game born as a meme tribute to Pavel Durov. Their mission? To fight for privacy and resistance in the Web3 age — captured in their slogan: "Privacy is not a crime, resistance will prevail." As part of this collaboration, an exclusive AIVille quest is now live within the FreeDogs game! Participants who complete the quest not only get to explore AIVille’s intelligent agent society, but also unlock access to the broader AGT First Round Community Airdrop, where 1% of the total $AGT supply will be distributed to early supporters. 🤝 About AIVille & FreeDogs AIVille is an AI-native decentralized town where autonomous agents live, create, and evolve. Players interact with characters, join events, and help shape the future of intelligent societies. FreeDogs is a meme-powered Web3 social game where players sign petitions while completing quests for rewards. More than just entertainment, FreeDogs stands for freedom, privacy, and community resistance — a tribute to open digital spaces. Together, AIVille and FreeDogs bring the power of storytelling, questing, and token incentives to a wider audience. 🌟 AGT Token & Quest Rewards  The AIVille quest in FreeDogs is more than a game — it’s your gateway to the AGT First Round Community Airdrop, the first large-scale distribution of AIVille’s native token. Complete the quest to: Learn about AIVille and the $AGT ecosystem Get priority access to the community airdrop (1% of supply!) Start your journey as an early supporter of intelligent agents This is part of AIVille’s Create-to-Earn model, where your actions in the Web3 world generate real value. ⚡ Why This Matters This partnership expands AIVille’s reach into fun, social gaming — and introduces FreeDogs players to the future of AI-native societies. It reflects a growing movement where: Games unlock real community rewards Stories and agents become programmable Participation leads to ownership and tokenized recognition If you're playing FreeDogs, this is your moment to join something bigger. 🔗 Links AIVille Quest: https://app.freedogs.bot/game FreeDogs Bot: https://t.me/theFreeDogs_bot/app FreeDogs on Twitter: @theFreeDogs_bot AIVille on Twitter: @aivillebot AGT Airdrop Info: https://aivillegame.com @ a5142938:0ef19da3
2025-04-04 14:59:58**Do you know a brand offering natural alternatives? Share it here by commenting on this page!** Copy and paste the template below and fill in the information you have. Other contributors can complete any missing details. To be listed, the brand must offer at least some of its products made from natural materials. 👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) Each piece of information added (name, link, category, etc.) and validated is considered a contribution. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- ### New brand or manufacturer - Brand name: - Image representing the brand’s products (link, ideally from the brand’s website): - Short description: - Categories of products offered: - Materials used in its products: - Brand’s website: - Other information (place of production, certifications, etc.): --- If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward. 👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/unjmwarjg7ojb9uwantvt/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/4wvxjm06tle2aelvde8w6/)
@ a5142938:0ef19da3
2025-04-04 14:59:58**Do you know a brand offering natural alternatives? Share it here by commenting on this page!** Copy and paste the template below and fill in the information you have. Other contributors can complete any missing details. To be listed, the brand must offer at least some of its products made from natural materials. 👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) Each piece of information added (name, link, category, etc.) and validated is considered a contribution. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- ### New brand or manufacturer - Brand name: - Image representing the brand’s products (link, ideally from the brand’s website): - Short description: - Categories of products offered: - Materials used in its products: - Brand’s website: - Other information (place of production, certifications, etc.): --- If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward. 👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/unjmwarjg7ojb9uwantvt/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/4wvxjm06tle2aelvde8w6/) @ 8bad797a:8461b4bc
2025-04-05 14:49:13## Frank Palmer Purcell I claim to be a Catholic American; even though I now follow the Russian Orthodox tradition, I do so in a small *sui juris* Church in communion with Rome, not Constantinople. When I was a little kid, knee high to a trilobite, some folks still had a problem with that, with being Catholic and American, I mean; Orthodoxy was beyond our horizon. My mother was one of those who had the problem. As long as I was a Catholic like my father (and her own mother, as a little girl in Ireland and on the lower East Side), I couldn't be a real American like her father, a bookbinder replaced by a machine, disowned by his family for marrying out of caste, who spent his days in the nearest tavern. "Pop" Palmer died at 78, and four years later I was born and named for him, or at least that was my mother's intention. The priest baptized me in Latin, as was the custom in those dark days, and pronounced "Frank" so that it sounded like the nickname ("Frenchy") of a (doubtless) dirty medieval Italian beggar baptized Giovanni. My early spirituality, to use a ten dollar word for a fifty cent thing, was more American than Franciscan. Emerson and Thoreau, Melville and Whitman spoke and still speak to me as no European voice can, and when I came to study philosophy in a serious way I found the Americans, Josiah Royce, Rufus Jones and Ernest Hocking, C. I. (not C. S.) Lewis and Brand (not Paul) Blanshard, speaking a language that was my own, though by then the professoriate resonated to other tonalities. Though I fell in love with Schopenhauer and Kierkegaard, as every teenager who meets them must, and inhaled the sweet incense and felt the calming breeze of the shrines of the East, as my generation did, and was introduced to the mysteries of Thomas Aquinas by the subtle writings of Jacques Maritain, as we should all be, when I came to take hold of the great tradition of Western theology in a personal way, I found the distinctly American perspectives of Paul Tillich and Richard (not Reinhold) Niebuhr most helpful. Back in 1963, in the New Jersey family television room, Joseph Campbell's urbane mythological sermons on Channel 13 (still a Newark station) touched something deep inside me an hour after Bishop Sheen's passionate exhortations on Channel 5 had left me (perhaps deplorably) cold. I would go up to my room and say my prayers after a fashion in time for the nightly racetrack bugle and exhilarating nostalgia of Arthur Fiedler's performance of the Bahnfrei Polka of Edouard Strauss, which introduced the nightly raconteurship of the incomparable Jean Shepherd, and, if I were still awake, the more outre world of Long John Nebel and his, ah, eccentric guests. You can't get more American than that. Or more New Jersey. As the child of a mixed marriage and a pupil of the public schools I was not warmly welcome in the Catholic ghetto. Still, in those years of the civil rights revolution and the Vietnam War, with the polarized positions of right and left equally abstract and inhumane, I found my take on national affairs reflecting the distinctly Catholic perspectives of Dorothy Day and Thomas Merton on the one hand and Frederick Wilhelmsen and Erik Maria, Ritter von Kuehnelt-Leddihn on the other. And, though the writings of Rufus Jones, to which I even now frequently turn for inspiration, had led me to seek out a Quaker education, I found it was the Catholic scholars and pioneers of the spirit who were beginning the interreligious dialogue which was then and is now one of the pressing needs of humanity. In graduate school I became a devoted Americanist, that is, a scholar dedicated to using the tools of the historian of ideas to get some sense of what this place is all about, this gallimaufry of peoples who have somehow, in spite of all learned and astute prognostications, made themselves and each other into a kind of unity, a unity which it may take someone like the present [at the time of writing] Pope (and there isn't really anyone else very much like him) to discern. I do not speak of Joseph Ratzinger, Benedict XVI, as a theologian nor even as a philosopher, but I must note that in New York and Washington in 2008 he revealed himself as an historian of ideas of astonishing and exquisite discernment. By this I mean, among other things, of course, that he strongly confirmed the discoveries and intimations of my own forty years of brooding in and on America. I was fortunate indeed to turn up at Columbia University's Teachers College when Douglas Sloan was putting the finishing touches on his groundbreaking study of the Scottish Enlightenment as the great inspiration of the American colonists, especially the intellectual elite, in the age of the War of Independence. Sloan's insights would eventually be popularized, without their scholarly context and qualifications, in Garry Wills' bestselling *Inventing America*, and it is now taken for granted that our Founding Father Across the Sea was not John Locke, but the Ulster Scot Francis Hutcheson (1694-1746). Indeed, the Evangelical position seems to be that it was Hutcheson who corrupted American civilization at the root, turning us from the Calvinist faith once delivered to Jonathan Edwards (himself a notorious Lockean, but never mind). In fact, Oxford University Press recently published a six hundred page tract to that effect, authored at Wheaton. Hutcheson, and the Scottish school of Common Sense which he inspired, held that all human beings, Pagan and Christian, Protestant and Catholic, share a basic ability to come to an understanding of certain fundamental truths, and can come to agreement upon these with the aid of reason. Calvinism, especially the neoCalvinism which is the unquestioned (because unquestionable) paradigm of the Evangelical academy, holds that the elect have a unique and divinely sanctioned "world view" which stands in judgment of all others in all particulars. To these zealots the very idea that there can be any common human ground between believers and unbelievers is itself a damnable heresy. Still, it is the damnable heresy on which American society and civilization are built, and the Calvinism which so despises it is a near kin of those varieties of Islam that Benedict so boldly challenged at Regensburg in 2006. When the same Benedict addressed the United Nations a year and a half later, he pointed out how the principles of that august body, and the Universal Declaration of Human Rights whose anniversary he was commemorating, grew out of the Natural Law philosophy of CounterReformation Scholasticism, particularly as formulated by Francisco de Vitoria (1492?–1546). Needless to say, the "Scottish Philosophy" of a later age grew out of this tradition as well, and many of the American founders were directly familiar with Natural Law theory as expounded by Catholic and Protestant Scholastics. On the same visit Benedict made ample use of the language of sacred architecture, as if in conscious homage to the fact that he was honoring a country founded by Freemasons, who used that language to teach the conformity of right living to the law of nature and nature's God. If he was giving a Catholic interpretation to this symbolism, so did the Catholic Jacobites who were prominent in the Craft before the Masonic movement became identified with indifferentism, anticlericalism, and finally (at least on the Continent) atheism. It was striking indeed that to one steeped in American tradition it was the Pope of Rome of all people who was speaking our own language in a familiar tone, and the neoCalvinist Evangelicals who jibbered and muttered in an outlandish and menacing jargon more Muslim than Christian. I sure wonder what Mommy would think. Natural Law. What is that to us today; what was it to me in what we call the Vietnam era? In 2008 the issue was torture, and a President of the United States who took pleasure in his presumed power to order it, to physically degrade his enemies, to morally degrade our own soldiers. I am proud that when Mr. Bush asked our military for advice on the subject, they replied that he has no such power, that such actions are contrary to our laws and the traditions of our armed services, and, moreover, ineffectual. (The latter point is an important indication that powerful men order torture not to accomplish anything, but to pleasure themselves.) And I am ashamed that he chose to take the advice of Israeli advisors, who hold to another morality, one going back to ancient Assyria, and profoundly alien to our own Christian civilization. In my youth the overriding issue was not torture, but terrorism. Not that torture didn't take place. At graduate school I knew a former naval officer who had interrogated captured Viet Minh and Viet Cong; the "extraordinary means" had been applied by our allies by the time he was introduced to his prisoners, and the specialists who had softened them up had already moved on or backed off. The issues before us then were atrocious acts of war against civilian populations in North and South Vietnam, in Laos and Cambodia, in Central and South America, even in Germany and Japan a generation before, not to mention the subversion and corruption of constitutional government in America by a regime that felt justified in using any means necessary to keep power away from the Communists and their sympathizers, the Democrats and liberal Republicans. Nor was such evil a monopoly of the socalled right. A young antiwar activist formerly associated with Martin Luther King even went so far as to criticize the sainted Che Guevara for not being enough of a terrorist to tear the peasantry away from their conformity to a "fascist" state. (Two generations later the man was advising George Bush.) In my undergraduate days I had been a loyal member of the conservative movement, back when the Intercollegiate Studies Institute was still called the Intercollegiate Society of Individualists, some members of the Students for a Democratic Society still honored democracy, and Murray Rothbard and Carl Ogelsby were moving "beyond left and right." If I got nothing more from the conservatives, and in fact I got a great deal more, it was an ever deepening admiration for Edmund Burke. Burke was prized by the cold warriors because his *Letters on a Regicide Peace* could be used to justify a war of extermination against the Soviet Union, the Peoples Republic of China, and any other people so temerarious as not join the alliance against these forces of absolute evil and subordinate their interests to those of the United States. A superficial reading, I need hardly remark. But Burke was not only the acute critic of the French Revolution who predicted the Terror from its earliest signs, he also was a tireless advocate for Irish freedom, particularly freedom of conscience, and a loyal ally of the American colonies in Parliament. But Burke's finest hour came at the end of his long career, when he boldly fought against the depredations of Warren Hastings and the British East India Company. Anyone who wants to know what natural law meant to the men of the Eighteenth Century, including those who liberated the American colonies and forged their political constitution can get a good sense of it from the eighth day (!) of his impeachment of Hastings before the House of Lords, which, I warn you, I have quoted before and shall no doubt quote again: > No man can lawfully govern himself according to his own will—much less can one person be governed by the will of another. We are all born in subjection—all born equally, high and low, governors and governed, in subjection to one great, immutable, preexistent law, prior to all our devices, and prior to all our contrivances, paramount to all our ideas and to all our sensations, antecedent to our very existence, by which we are knit and connected in the eternal frame of the universe, out of which we can not stir. This great law does not arise from our conventions or compacts; on the contrary, it gives to our conventions and compacts all the force and sanction they can have: it does not arise from our vain institutions. Every good gift is of God, all power is of God; and He who has given the power, and from whom alone it originates, will never suffer the exercise of it to be practised upon any less solid foundation than the power itself. If, then, all dominion of man over man is the effect of the divine disposition, it is bound by the eternal laws of Him that gave it, with which no human authority can dispense; neither he that exercises it, nor even those who are subject to it; and, if they were mad enough to make an express compact, that should release their magistrate from 5 his duty, and should declare their lives, liberties and properties, dependent upon, not rules and laws, but his mere capricious will, that covenant would be void. This arbitrary power is not to be had by conquest. Nor can any sovereign have it by succession; for no man can succeed to fraud, rapine, and violence. Those who give and those who receive arbitrary power are alike criminal; and there is no man but is bound to resist it to the best of his power, wherever it shall show its face to the world. Mr. Jefferson couldn't have put it better. Human rights are inalienable -- you can't give them away, and when they are taken away there is not only the right of rebellion, but the solemn duty to resist. The difficulty of natural law theory, of course, is in the details. Back in '68 Pope Paul VI had announced that artificial contraception was against the natural law, but this decision did not immediately commend itself to the common sense of many of those who were not subject to his religious authority. I don't mean he was wrong, or that he exceeded his authority, or even that his decision was inopportune. But when the Supreme Court, alarmed by the birthrate of blacks and an end to white domination of the nation and the world, soon mandated abortion on demand, it was all too easy to dismiss arguments in favor of the human being of the embryonic human as religious dogma rather than an honest attempt to think things through. Since then the concept of natural law is often dismissed by feminists and homosexualists (to use Mr. Vidal's eloquent term) as a mere excuse for oppression. It does seem to me, however, that the insistent denial of the very idea of human rights does nothing to advance the liberation of humanity or any part of it. But maybe that's just me. In any case, I don't think America was ever anything like the sort of Catholic nation that, say, Portugal was under the late Dr. Salazar, or is very likely to get there any time soon, despite the best wishes and even efforts of some of my friends. I do think that for a good part of our history a great many people in public life would have said that the words of Burke I have quoted express their most basic political convictions and sentiments as well as anyone ever could, and this puts America right at the center of the great tradition of Western civilization. And this was true long after old Europe had gone down other ways, the ways of the French revolution, the reaction against it, and the nationalism that synthesized the worst of both. To be sure, we have had nationalists here, and have them today, and have preached our crusades to end slavery, make the world safe for democracy, eradicate the evil empire of the moment, but there is, if not always a ringing and uncontested affirmation of civilized values, by which I mean the values of our civilization, at least a powerful nostalgia for them, and a sincere wish that one could believe in them with a good conscience, a good conscience which postmodernist deconstructionism denies us. A good conscience which Joseph Ratzinger Benedict XVI, who has suffered modernity as few of us have and thought more deeply about it, was offering us back. To be perfectly frank, it took the Catholic Church a good long time to recognize the Christian virtues of Enlightenment, even the Scottish one, and Revolution, even the American one. Better late than never. And despite the mantric invocation of John Courtney Murray, the Church in America has not always been on the side of the angels. The theology of the American Church has always been Jansenist, not Catholic, combining the worst of Pelagius and Calvin, making Boston Irish the kissing cousins of Cotton Mather. The American Church never permitted itself to be organized according to canon law because this would limit the despotism of prelates. The American Church refused to acknowledge the priesthood of Eastern Catholics ordained as married men, driving the Catholic Ruthenians into communion with the Patriarch of Moscow (the present Orthodox Church in America), and later blackmailing a bankrupt papacy into forbidding married priests throughout the Western hemisphere, driving a second group of Ruthenians into communion with the Ecumenical Patriarch of Constantinople (the present American CarpathoRussian Orthodox Diocese). They American Cathholic Church wouldn't even allow American women to become real nuns, or foreign nuns to come to America without renouncing their vows. The vast majority of Catholic women called nuns are nothing of the sort, but religious sisters first organized as cheap labor at the beck and call of the clergy, and now loose cannons like the Papessas Mother Angelica and Sister Joan. Yes, one or two real abbeys for women were founded in the last century, but the American Church continues to hold the contemplative life in deepest contempt, even for women. Women religious lead the crusade against contemplative traditions, and now rail against the Church as an organ of worldly power from which they are unjustly excluded. Deprived of traditional spiritual direction, a lamentable number of priests "demythologized" the Faith while looking to worldly culture for a way of salvation. Many found it in the gospel of orgasm, and undertook to liberate the young men in their care by sharing the only joy they thought worth having, with results we see today. Catholic involvement in American public life has not been edifying either. The American bishops turned their backs on Benedict XV's attempt to end the slaughter in the trenches and refused to make any move to bring Woodrow Wilson over to the side of peace. As patriotic Americans, they in effect signed on to the WASP jihad to extirpate the Catholic powers of the Old World. A couple of generations later millions of Catholic schoolchildren were forced to write letters demanding that the Senate not censure that great American Joseph McCarthy, who was probably the Soviet Union's most valuable (presumably unwitting) asset in American public life, who had discredited all responsible criticism of Communism and its supporters by viciously slandering the United States Army, the Department of State, and the Protestant clergy as nests of traitors. Some years later Catholic activists succeeded in driving the voices of moderation out of the Republican Party, and the urban ethnic social conservatives out of the Democratic, and the forms of civility from the public square. Americans can be forgiven for not rushing to enlist in the nearest Roman Catholic parish. There are other conversions needed, perhaps beginning with American Catholics themselves. Back in the days of Reagan a fellow named Alan Bloom made an almost persuasive case that the American Mind was closed to the Great Tradition of Western Civilization, and needed to be reopened. Alas, Bloom was a Neoconservative, a follower of their guru Leo Strauss, and a teacher of a a number of shady operatives of the Program for the New American Century type, as Saul Bellow's last novel so amusingly portrays him. Bloom's Great Tradition was something cobbled together by Machiavelli and others out of the misunderstood shards of ancient paganism; thinkers and writers tainted by the Christian gospel remained under embargo. (Mortimer Adler was less fearful, more intellectually curious, but look where he ended up.) It took a Bavarian Pope to remind us that the basic principles of our cherished hopes of international organization and human rights, and indeed of the American founding itself, go back to the Iberian scholastics of the Catholic Reformation. ("CounterReformation" is misleadingly negative.) Benedict's reminder harmonized well with my own studies in the history of philosophy. I began some five decades ago with the riddle, the riddles, of Charles Sanders Peirce (1839 - 1914), our own and only philosopher to be ranked with the likes of Aristotle and Kant. What was this Common Sense he went on and on about? (The Scottish Philosophy was studiously ignored in the academy; it still is.) As I said, I was lucky to find out. Now John Deely has been showing that any postmodern philosophy worthy of the name, one founded on semeiology rather than Cartesian (or empiricist) methodologism, needs to go back to Peirce and with Peirce back to the very beginnings of the theory of signification as we find them in John Poinsot (1589 1644). Poinsot, as it happens, is part of the same Iberian Renaissance to which Benedict has now called our attention. Indeed, under another name (John of St. Thomas) Poinsot inspired the neo Thomism of Jacques Maritain which undergirded the Christian Humanism of Paul VI and many other Fathers of the Second Vatican Council. (His treatise on **The Gifts of the Holy Spirit*, as interpreted by theologians often dismissed as too conservative, is behind the rather daring notion that all Christians are called to holiness in this life, and, indeed to the mystical path of acquired contemplation, and thus such more recent developments as Centering Prayer, the World Community for Christian Meditation, and the ommunion and Liberation movement. As if all this were not enough, Murray Rothbard, no Christian he, though personally excommunicated and anathematized by Ayn Rand for not repudiating his openly Christian wife, has argued that the Austrian School of Economics, the Old Liberalism of von Mises and Hayek, goes back not so much to Adam Smith (who missed a few points), as to the scholastic philosophers of Spain and Portugal in the early modern period. Mention Iberian philosophy to the American of average education and he will look at you as though you had spoken of Uzbek grand opera or (indeed) the Scottish Enlightenment. He might even tell you that Spanish ignorance, superstition, and bigotry are precisely what God sent Englishmen into the New World to stamp out: the *legenda negra*. Needless to say, this is not a view of history a good many newcomers to the United States are likely to tolerate with equanimity, and it is just as well that it isn't true. Once we retire that vulgar prejudice against Hispanidad we might just get a fair hearing for the work of Xavier Zubiri, the only European thinker of the last century who compares with Peirce for breadth of learning and depth of discernment as well as sheer unadulterated difficulty. If nothing else, the challenge of Catholicity invites Americans to break down the walls of the AngloSaxon ghetto, which do not serve us well now, if they ever did. But it may also provoke a new interest in our own Golden Age of (Protestant) theology. Let me set the stage for this with an extended quotation from Joseph Ratzinger's 1977 essay, "Is Faith Really Good News?" (Now translated in Principles of Catholic Theology: > Truth is not always comfortable for man, but it is only truth that makes him free and only freedom that brings him joy. Now, however, we must ask more precisely: What makes a man joyful? What robs him of joy? What puts him at odds with himself? What opens him to himself and to others? When we want to describe the most extreme form of being at odds with existence, we often say of an individual that he does not like himself. But whom or what is he to like who does not like himself? Something very importamt makes its appearance here: egoism, certainly, is natural to man and needs no encouragement; but this is not true of selfacceptance. The former must be overcome; the latter must be discovered, and it is assuredly one of the most dangerous errors of Christian teachers and moralists that they have all too often confused the two and, by exorcizing the affirmation of self, have enabled egoism to avenge such a betrayal by becoming all the more rampant this, ultimately, of what the French have labeled the maladie catholique: one who wants to live only on the supernatural level and to the exclusion of self will be, in the end, without a self but not, for that reason, selfless. (79) Reading this a day or two after Ratzinger's papification I couldn't help thinking of our own Paul Tillich, whose seminal sermon "You are Accepted" baptized the human potential movement (as it was called), whose *Courage to Be* is a perennial best seller even after half a century, whose *Systematic Theology* Martin Luther King had asked for in his Georgia prison cell, and I myself poured over eagerly as an Earlham undergraduate. Of course the problematic goes back to Kierkegaard's penetrating analysis of despair, and, indeed to Luther's experience of divine wrath and mercy. Now it is all very well to say we must accept our acceptance, somehow (mysticism? art?) so ground ourselves in the very Ground of Being as to powerfully affirm our being against the powers of nonbeing. But is it true? That is the question haunting Tillich, Martin Luther King, and modern American culture down to our own time, which Ratzinger, challenged by Nietzsche and Camus, dared to speak aloud: > We come now to the allimportant question: Is it true, then, when someone says to me: "It is good that you exist"? Is it really good? Is it not possible that that person's love, which wills my existence, is just a tragic error? If the love that gives me courage to exist is not based on truth, then I must, in the end, come to curse the love that deceives me that maintains in existence something that were better destroyed. This dilemma could be 10 strikingly illustrated by reference to the interpretations of the contemporary experience of life in Sartre or Camus or in the attitudes of the new Left. Even without such evidence, it is obvious, however, that the apparently so simple act of liking myself, of being at one with myself, actually raises the question of the whole universe It raises the question of truth: Is it good that I exist? Is it good that anything at all exists? is the world good? How many persons today would dare to affirm this question from the heart to believe it is good that they exist? That is the source of the anxiety and despair that incessantly affect mankind. Love alone is of no avail. It serves no purpose if truth is not on its side. Only when truth and love are in harmony can man know joy. For it is truth that makes man free. (80) And the question of truth won't leave us alone. For Tillich the Christian faith was perhaps a true myth, but, perhaps true only the way that other myths are true. He tended to sacramentalize modern art, leftish politics, and sexual liberation; the president of Union Seminary had to remind him that it looked bad for their most eminent theologian not to go to church. The tragedy of attempting to make a religion of art, politics, or sex is obvious by now, and it as a sad circumstance that the leadership of the American Catholic Church were seminarians at a time when Catholic theology looked to the Protestants for validation, and Tillich was at the height of his prestige in the liberal denominations. The painful story of Tillich's sexual obsessions is now well known enough from his wife's two memoirs, Dr. King's escapades have stained the memory of the civil rights movement as much as his infatuation with the Soviet power, and the sexual scandals of the American Church are unspeakably worse, blighting the lives of tens (hundreds?) of thousands of children. That is something Benedict, on his recent visit, would not allow us to forget for even a moment. But at least he offers a remedy in that confrontation with the truth of our being which liberal theology, Catholic and Protestant (though perhaps not Orthodox),attempted to evade: > The content of the Christian evangelium reads: God finds man so important that he himself has suffered for man. The Cross, which was for Nietzche the most detestable expression of the negative character of the Christian religion, is in truth the center of the evangelium, the glad tidings: "It is good that you exist" No, "It is necessary that you exist." The Cross is the approbation of our existence, not in words, but in an act so completely radical that it caused God to become flesh and pierced this flesh to the quick; that, to God, it was worth the death of his incarnate Son. One who is so loved that the other identifies his life with this love and no longer desires to live if he is deprived of it; one who is loved even unto death such a one knows that he is truly loved. But if God so loves, then we are loved in truth. Then love is truth, and truth is love. Then life is worth living. This is the evangelium. (81) The whole idea of the Cross as God's affirmation of man will strike many an American as shocking, ludicrous even. It the caross not the stock in trade of a thousand "evangelists" as the ultimate proof of our total depravity, the ultimate refutation of all aspirations for human freedom and dignity? Surely Nietzsche got that from his preacher father, though it is hard to find any such slander of humanity in either the written scriptures or the teaching of the Fathers of the Church (except for Augustine, and that on a bad day he later repented). I am happy to note that Ratzinger's point of view, scriptural, patristic, and Benedictine in every sense of the term is very close to what some in the Evangelical churches are calling "gracious Christianity," for that is what it is. That movement is still a prophetic minority in the churches and the academy, and we still need to come to terms with the main stream of American spirituality as represented, for better and worse, by Tillich. And Ratzinger, even in his early days as a professor, has given us the means to do just that. Not everything in the American theological mainstream, and not everything in Tillich, needs to be discarded wholesale. A follower of Ratiznger's good friend Don Liugi Giussani who studies Tillich's theology will find close analogies between Tillich's method of correlation and the principle of correspondence which Giussani urged on members of the Communion and Liberation movement he founded, a movement in which the Ratzinger Pope (to use the Catholic injargon) takes more than a passing interest he is said even now to take part in a weekly School of Community in which movement people use that method to explore the meaning of the Gospel in relation to their own day to day lives, and the meaning of their lives in relation to the Gospel, though his episcopal orders forbid his formal membership in the Fraternity. I do not mean to imply that Benedict is a follower of Giussani in matters of pure theology, but it seems clear that he recognizes Giussani's method as the best practical application of the theological principles both men learned from such masters of La Nouvelle Theologie as de Lubac, von Balthasar, and (with reservations) Rahner. But before I move away from the idea of correspondence, the method of correlation, I should mention that this became the life work of two American philosophers, Ira Progoff, with whom and with whose students I was privileged to do postdoctoral work, and Eugene Gendlin, both known as psychologists for the contributions they have made to psychology, who offer what I can only describe as means of spiritual direction. The few folks who remember Tillich today often contrast him with Reinhold Niebuhr, his colleague at Union, who inspired the Cold war mainstream much as Tillich inspired the New Left, and whom Don Gius was fond of quoting. But the man to rediscover is Reinhold's brother Richard, a theologian's theologian, that is, one whose writings were never taken up by the movers and shakers of middlebrow culture. His *Meaning of Revelation* shows the kind of emphasis the Catholic Church in Europe is coming around to, or coming back to, as it is very much in the spirit of the Fathers of the Church, the Eastern Fathers in particular. For many of us what may be most prophetic in his life work is his refusal of the temptation of neoconservatism to which Reinhold gave in to his fame and profit. Reinhold ostentatiously resigned from the Fellowship of Reconciliation in the early '30s in righteous indignation that some Christians did not demand that the government do something (what?) about the Japanese in China. Richard, on the other hand, had no hope for the efficacy of political, economic, and military power exercised by the United States against Japan. Sensing that Western Christendom was going the way of old Rome, he thought that the best Christian response was that pioneered by St. Benedict, from whom of course among others the last pontiff took his name. For him the issue was not Japan against China, or the United States against Japan, but, to cite the title of a 1935 book to which he contributed, *The Church Against the World*. A few years later Dietrich von Hildebrand, in his villa in Florence, was giving the retreats later published as *Transformation in Christ* to Christian activists who intended to remain behind in Nazi Germany to keep the light of Christian civilization burning in that dark time, and Dietrich Bonhoeffer would take refuge with the Benedictines in his own effort to do the same. A few pages before the long passage I have quoted, Ratzinger's *Principles of Catholic Theology* gives a lengthy exegesis of Hildebrand's text as the model for Christian repentance. I can't help wondering if this forbidden book is one that his father had hidden around the house, as Evangelicals might have concealed Bonhoeffer's *Cost of Discipleship*. Discipleship and transformation are not matters of effortful striving, but the response to a calling which is a revelation. Richard is particularly enlightening on revelation as calling. He shows that it is not the communication of some kind of knowldege, however supernatural or esoteric, by possession of which we are justified, elevated from the companionship of our neighbors, saved from the world; that would be Gnosticism. Rather, revelation is participation in an ongoing event, a relationship with a person previously unknown, or at least unrecognized. Some words toward the end of *The Meaning of Revelation* put the matter thus: > Revelation means the moment in our history through which we know ourselves to be known from beginning to end, in which we are apprehended by the knower; it means the the selfdisclosure of the judge. Revelation means that we find ourselves to be valued rather than valuing and that all our values are transvaluated by the activity of a universal valuer. When a price is put upon our heads, which is not our price, when the unfairness of all the fair prices we have placed on things is shown up, when the great riches of God reduce our wealth to poverty, that is revelation. When we find out that we are no longer thinking him, but that he first thought us, that is revelation. Revelation is the emergence of the person on whose external garments and body we had looked as objects of our masterful and curious understanding. Revelation means that in our common history the fate that lowers over us as persons in our communities reveals itself to be a person in community with us. What this means for us cannot be expressed in the impersonal ways of creeds or other propositions but only in responsive acts of a personal character. we acknowledge revelation by no third person proposition, such as that there is a God, but only in the direct confession of the heart, "Thou art my God."... From this point forward we must listen for the remembered voice in all the sounds that assail our ears, and look for the remembered activity in all the actions of the world upon us. The God who reveals himself in Jesus Christ is now trusted and known in the contemporary God, revealing himself in every event, but we do not understand how we could tract his working in these happenings if he did not make himself known to us through the memory of Jesus Christ; nor do we know how we should be able to interpret all the words we read as words of God save by the aid of this Rosetta stone. (80 - 81) Catholics who remember the discourses of the Pope Benedict will find the flavor of this passage very Benedictine in both senses of the term. Those who follow the way of Luigi Giussani find their spirit particularly familiar, for those of them who live in community, including the little band that managed Benedict's household and conduct the School of Community he attended, are known precisely as *Memores Domini*, those who strive to keep the Lord constantly in mind, and allow their own memory and mindfulness, personal and collective, painful and pleasing, on the surface of association or deeply hidden, to be transformed by their relationship with God in Christ, their participation in the ongoing incarnation of the Word of God: the God who is the author of our nature, and an incarnation that runs to meet the deepest desire of that nature with more that could have been imagined. What this means in the experience of living our life is well stated at the conclusion of Niebuhr's great work: > The God who reveals himself in Jesus Christ meets no unresponsive will but the living spirit of men in search of all good. And he fulfills our need. Here is the one for whose sake all life and every life is worth living, even lives that seem bereft of beauty, of truth and of goodness. The glimpse of his great glory in the face of Jesus Christ, its reflections in the darkened mirrors of the saints' adorations intimate a God who is good beyond all that is good and fair beyond all fairness. Yet the goodness that shines upon us through the moment of revelation is not the glory or the goodness we had expected in our thoughts about deity. The essential goodness of the Father of our Lord Jesus Christ is the simple everyday goodness of love the value which belongs to a person rather [than] the value we find in an idea or a pattern; it is the goodness which exists as pure activity. He fulfills our expectation of the intrinsic good and yet this adorable goodness differs from everything we had expected, and puts our expectations to shame. We sought a good to love and were found by a good that loved us. And therewith all our religious ambitions are brought low, all our desires to be ministers of God are humbled; he is our minister. By that revelation we are convicted of having corrupted our religious life through our unquenchable desire to keep ourselves with our love of our good in the center of the picture. Here is the goodness that empties itself, and makes itself of no reputation, a goodness that is all outgoing, reserving nothing for itself, yet having all things. So we must begin to rethink all our definitions of deity and convert all our worship and our prayers. Revelation is not the development and not the elimination of our natural religion; it is the revolution of the religious life. (98 - 99) But what does all this mean to one who stands outside the light of revelation, who relies on the reason of Western Civilization, the common sense of the founding Fathers? If believers and unbelievers are to take part in one community, what do we have to say to each other? This is the point of Benedict's challenge to the Muslim world, the question of what could make the libertine Doctor Franklin and the evangelical President Witherspoon active participants in the same foundational dialog. Niebuhr has an answer, and it is the same answer as Benedict: > The pure reason does not need to be limited in order that room be made for faith, but faith emancipates the pure reason from the necessity of defending and guarding the interests of selves, which are now found to be established and guarded, not by nature, but by the God of revelation whose garment nature is. (91 - 92) It is faith that liberates and, indeed, inspires us to invent, develop, explore, and test scientific understandings which would otherwise be too much for the vain imaginings of our all too human hearts: > To know the person is to lose all sense of shame because of kinship with the clod and the ape. The mind is freed to pursue its knowledge of the external world disinterestedly not by the conviction that nothing matters, but by the faith that nothing God has made is mean or unclean. Hence any failure of Christians to develop scientific knowledge of the world is not an indication of their loyalty to the revealed God but of their unbelief. (90 - 91) Seven going on eight decades after these words were published, ministers of "religion" are still attempting to prevent the teaching of ascertained facts of human biology in order to retain the authority of their own stupidly selectively literalistic reading of the Bible; some of the more advanced institutions of Evangelical learning defiantly profess a form of Calvinism in which some sort of theology remains the queen of the sciences in an unconstitutional monarchy, with no other discipline permitted its own proper autonomy and integrity; while in more numerous groves of Academus, even the Roman Catholic plantations, men and women of faith are quickly brushed off as obvious enemies of intellect. My own mother, as I have said already, doubted that you can be a good Catholic and a real American at the same time. Pope Benedict warned his flock that they will not be good Catholics until they are Americans to the extent of acknowledging the law of nature and of nations as developed by Victoria (among others, some of them Scots), and aspiring to live in local, regional national and international communities under that law, in which the freedom and dignity of the human person are given the first priority. On the other hand I do not see how we can be real Americans without realizing that the aspirations of 1776 and 1789 are grounded in that natural law, and grew up as the fruit of a civilization in which the reason of Greece and Rome reached full maturity in the care of Mother Church, a church whose members, including the hierarchy, were not always consistently faithful to it, calling forth reformations, enlightenments, and even revolutions. I think we must all be Catholic at least in the wider sense of loyalty to that civilization, and our best way may well be to reappropriate the riches of the golden age of American philosophy and theology, of which the work of H. Richard Niebuhr is a small but important part. Sources quoted: Edmund Burke, Impeachment of Warren Hastings before the House of Lords (numerous editions), eighth day. Joseph Ratzinger, *Principles of Catholic Theology*. San Fransisco: Ignatius, 1987. H. Richard Niebuhr, *The Meaning of Revelation* [1941]. Louisville: Westminster John Knox Press, 2006. © FP Purcell
@ 8bad797a:8461b4bc
2025-04-05 14:49:13## Frank Palmer Purcell I claim to be a Catholic American; even though I now follow the Russian Orthodox tradition, I do so in a small *sui juris* Church in communion with Rome, not Constantinople. When I was a little kid, knee high to a trilobite, some folks still had a problem with that, with being Catholic and American, I mean; Orthodoxy was beyond our horizon. My mother was one of those who had the problem. As long as I was a Catholic like my father (and her own mother, as a little girl in Ireland and on the lower East Side), I couldn't be a real American like her father, a bookbinder replaced by a machine, disowned by his family for marrying out of caste, who spent his days in the nearest tavern. "Pop" Palmer died at 78, and four years later I was born and named for him, or at least that was my mother's intention. The priest baptized me in Latin, as was the custom in those dark days, and pronounced "Frank" so that it sounded like the nickname ("Frenchy") of a (doubtless) dirty medieval Italian beggar baptized Giovanni. My early spirituality, to use a ten dollar word for a fifty cent thing, was more American than Franciscan. Emerson and Thoreau, Melville and Whitman spoke and still speak to me as no European voice can, and when I came to study philosophy in a serious way I found the Americans, Josiah Royce, Rufus Jones and Ernest Hocking, C. I. (not C. S.) Lewis and Brand (not Paul) Blanshard, speaking a language that was my own, though by then the professoriate resonated to other tonalities. Though I fell in love with Schopenhauer and Kierkegaard, as every teenager who meets them must, and inhaled the sweet incense and felt the calming breeze of the shrines of the East, as my generation did, and was introduced to the mysteries of Thomas Aquinas by the subtle writings of Jacques Maritain, as we should all be, when I came to take hold of the great tradition of Western theology in a personal way, I found the distinctly American perspectives of Paul Tillich and Richard (not Reinhold) Niebuhr most helpful. Back in 1963, in the New Jersey family television room, Joseph Campbell's urbane mythological sermons on Channel 13 (still a Newark station) touched something deep inside me an hour after Bishop Sheen's passionate exhortations on Channel 5 had left me (perhaps deplorably) cold. I would go up to my room and say my prayers after a fashion in time for the nightly racetrack bugle and exhilarating nostalgia of Arthur Fiedler's performance of the Bahnfrei Polka of Edouard Strauss, which introduced the nightly raconteurship of the incomparable Jean Shepherd, and, if I were still awake, the more outre world of Long John Nebel and his, ah, eccentric guests. You can't get more American than that. Or more New Jersey. As the child of a mixed marriage and a pupil of the public schools I was not warmly welcome in the Catholic ghetto. Still, in those years of the civil rights revolution and the Vietnam War, with the polarized positions of right and left equally abstract and inhumane, I found my take on national affairs reflecting the distinctly Catholic perspectives of Dorothy Day and Thomas Merton on the one hand and Frederick Wilhelmsen and Erik Maria, Ritter von Kuehnelt-Leddihn on the other. And, though the writings of Rufus Jones, to which I even now frequently turn for inspiration, had led me to seek out a Quaker education, I found it was the Catholic scholars and pioneers of the spirit who were beginning the interreligious dialogue which was then and is now one of the pressing needs of humanity. In graduate school I became a devoted Americanist, that is, a scholar dedicated to using the tools of the historian of ideas to get some sense of what this place is all about, this gallimaufry of peoples who have somehow, in spite of all learned and astute prognostications, made themselves and each other into a kind of unity, a unity which it may take someone like the present [at the time of writing] Pope (and there isn't really anyone else very much like him) to discern. I do not speak of Joseph Ratzinger, Benedict XVI, as a theologian nor even as a philosopher, but I must note that in New York and Washington in 2008 he revealed himself as an historian of ideas of astonishing and exquisite discernment. By this I mean, among other things, of course, that he strongly confirmed the discoveries and intimations of my own forty years of brooding in and on America. I was fortunate indeed to turn up at Columbia University's Teachers College when Douglas Sloan was putting the finishing touches on his groundbreaking study of the Scottish Enlightenment as the great inspiration of the American colonists, especially the intellectual elite, in the age of the War of Independence. Sloan's insights would eventually be popularized, without their scholarly context and qualifications, in Garry Wills' bestselling *Inventing America*, and it is now taken for granted that our Founding Father Across the Sea was not John Locke, but the Ulster Scot Francis Hutcheson (1694-1746). Indeed, the Evangelical position seems to be that it was Hutcheson who corrupted American civilization at the root, turning us from the Calvinist faith once delivered to Jonathan Edwards (himself a notorious Lockean, but never mind). In fact, Oxford University Press recently published a six hundred page tract to that effect, authored at Wheaton. Hutcheson, and the Scottish school of Common Sense which he inspired, held that all human beings, Pagan and Christian, Protestant and Catholic, share a basic ability to come to an understanding of certain fundamental truths, and can come to agreement upon these with the aid of reason. Calvinism, especially the neoCalvinism which is the unquestioned (because unquestionable) paradigm of the Evangelical academy, holds that the elect have a unique and divinely sanctioned "world view" which stands in judgment of all others in all particulars. To these zealots the very idea that there can be any common human ground between believers and unbelievers is itself a damnable heresy. Still, it is the damnable heresy on which American society and civilization are built, and the Calvinism which so despises it is a near kin of those varieties of Islam that Benedict so boldly challenged at Regensburg in 2006. When the same Benedict addressed the United Nations a year and a half later, he pointed out how the principles of that august body, and the Universal Declaration of Human Rights whose anniversary he was commemorating, grew out of the Natural Law philosophy of CounterReformation Scholasticism, particularly as formulated by Francisco de Vitoria (1492?–1546). Needless to say, the "Scottish Philosophy" of a later age grew out of this tradition as well, and many of the American founders were directly familiar with Natural Law theory as expounded by Catholic and Protestant Scholastics. On the same visit Benedict made ample use of the language of sacred architecture, as if in conscious homage to the fact that he was honoring a country founded by Freemasons, who used that language to teach the conformity of right living to the law of nature and nature's God. If he was giving a Catholic interpretation to this symbolism, so did the Catholic Jacobites who were prominent in the Craft before the Masonic movement became identified with indifferentism, anticlericalism, and finally (at least on the Continent) atheism. It was striking indeed that to one steeped in American tradition it was the Pope of Rome of all people who was speaking our own language in a familiar tone, and the neoCalvinist Evangelicals who jibbered and muttered in an outlandish and menacing jargon more Muslim than Christian. I sure wonder what Mommy would think. Natural Law. What is that to us today; what was it to me in what we call the Vietnam era? In 2008 the issue was torture, and a President of the United States who took pleasure in his presumed power to order it, to physically degrade his enemies, to morally degrade our own soldiers. I am proud that when Mr. Bush asked our military for advice on the subject, they replied that he has no such power, that such actions are contrary to our laws and the traditions of our armed services, and, moreover, ineffectual. (The latter point is an important indication that powerful men order torture not to accomplish anything, but to pleasure themselves.) And I am ashamed that he chose to take the advice of Israeli advisors, who hold to another morality, one going back to ancient Assyria, and profoundly alien to our own Christian civilization. In my youth the overriding issue was not torture, but terrorism. Not that torture didn't take place. At graduate school I knew a former naval officer who had interrogated captured Viet Minh and Viet Cong; the "extraordinary means" had been applied by our allies by the time he was introduced to his prisoners, and the specialists who had softened them up had already moved on or backed off. The issues before us then were atrocious acts of war against civilian populations in North and South Vietnam, in Laos and Cambodia, in Central and South America, even in Germany and Japan a generation before, not to mention the subversion and corruption of constitutional government in America by a regime that felt justified in using any means necessary to keep power away from the Communists and their sympathizers, the Democrats and liberal Republicans. Nor was such evil a monopoly of the socalled right. A young antiwar activist formerly associated with Martin Luther King even went so far as to criticize the sainted Che Guevara for not being enough of a terrorist to tear the peasantry away from their conformity to a "fascist" state. (Two generations later the man was advising George Bush.) In my undergraduate days I had been a loyal member of the conservative movement, back when the Intercollegiate Studies Institute was still called the Intercollegiate Society of Individualists, some members of the Students for a Democratic Society still honored democracy, and Murray Rothbard and Carl Ogelsby were moving "beyond left and right." If I got nothing more from the conservatives, and in fact I got a great deal more, it was an ever deepening admiration for Edmund Burke. Burke was prized by the cold warriors because his *Letters on a Regicide Peace* could be used to justify a war of extermination against the Soviet Union, the Peoples Republic of China, and any other people so temerarious as not join the alliance against these forces of absolute evil and subordinate their interests to those of the United States. A superficial reading, I need hardly remark. But Burke was not only the acute critic of the French Revolution who predicted the Terror from its earliest signs, he also was a tireless advocate for Irish freedom, particularly freedom of conscience, and a loyal ally of the American colonies in Parliament. But Burke's finest hour came at the end of his long career, when he boldly fought against the depredations of Warren Hastings and the British East India Company. Anyone who wants to know what natural law meant to the men of the Eighteenth Century, including those who liberated the American colonies and forged their political constitution can get a good sense of it from the eighth day (!) of his impeachment of Hastings before the House of Lords, which, I warn you, I have quoted before and shall no doubt quote again: > No man can lawfully govern himself according to his own will—much less can one person be governed by the will of another. We are all born in subjection—all born equally, high and low, governors and governed, in subjection to one great, immutable, preexistent law, prior to all our devices, and prior to all our contrivances, paramount to all our ideas and to all our sensations, antecedent to our very existence, by which we are knit and connected in the eternal frame of the universe, out of which we can not stir. This great law does not arise from our conventions or compacts; on the contrary, it gives to our conventions and compacts all the force and sanction they can have: it does not arise from our vain institutions. Every good gift is of God, all power is of God; and He who has given the power, and from whom alone it originates, will never suffer the exercise of it to be practised upon any less solid foundation than the power itself. If, then, all dominion of man over man is the effect of the divine disposition, it is bound by the eternal laws of Him that gave it, with which no human authority can dispense; neither he that exercises it, nor even those who are subject to it; and, if they were mad enough to make an express compact, that should release their magistrate from 5 his duty, and should declare their lives, liberties and properties, dependent upon, not rules and laws, but his mere capricious will, that covenant would be void. This arbitrary power is not to be had by conquest. Nor can any sovereign have it by succession; for no man can succeed to fraud, rapine, and violence. Those who give and those who receive arbitrary power are alike criminal; and there is no man but is bound to resist it to the best of his power, wherever it shall show its face to the world. Mr. Jefferson couldn't have put it better. Human rights are inalienable -- you can't give them away, and when they are taken away there is not only the right of rebellion, but the solemn duty to resist. The difficulty of natural law theory, of course, is in the details. Back in '68 Pope Paul VI had announced that artificial contraception was against the natural law, but this decision did not immediately commend itself to the common sense of many of those who were not subject to his religious authority. I don't mean he was wrong, or that he exceeded his authority, or even that his decision was inopportune. But when the Supreme Court, alarmed by the birthrate of blacks and an end to white domination of the nation and the world, soon mandated abortion on demand, it was all too easy to dismiss arguments in favor of the human being of the embryonic human as religious dogma rather than an honest attempt to think things through. Since then the concept of natural law is often dismissed by feminists and homosexualists (to use Mr. Vidal's eloquent term) as a mere excuse for oppression. It does seem to me, however, that the insistent denial of the very idea of human rights does nothing to advance the liberation of humanity or any part of it. But maybe that's just me. In any case, I don't think America was ever anything like the sort of Catholic nation that, say, Portugal was under the late Dr. Salazar, or is very likely to get there any time soon, despite the best wishes and even efforts of some of my friends. I do think that for a good part of our history a great many people in public life would have said that the words of Burke I have quoted express their most basic political convictions and sentiments as well as anyone ever could, and this puts America right at the center of the great tradition of Western civilization. And this was true long after old Europe had gone down other ways, the ways of the French revolution, the reaction against it, and the nationalism that synthesized the worst of both. To be sure, we have had nationalists here, and have them today, and have preached our crusades to end slavery, make the world safe for democracy, eradicate the evil empire of the moment, but there is, if not always a ringing and uncontested affirmation of civilized values, by which I mean the values of our civilization, at least a powerful nostalgia for them, and a sincere wish that one could believe in them with a good conscience, a good conscience which postmodernist deconstructionism denies us. A good conscience which Joseph Ratzinger Benedict XVI, who has suffered modernity as few of us have and thought more deeply about it, was offering us back. To be perfectly frank, it took the Catholic Church a good long time to recognize the Christian virtues of Enlightenment, even the Scottish one, and Revolution, even the American one. Better late than never. And despite the mantric invocation of John Courtney Murray, the Church in America has not always been on the side of the angels. The theology of the American Church has always been Jansenist, not Catholic, combining the worst of Pelagius and Calvin, making Boston Irish the kissing cousins of Cotton Mather. The American Church never permitted itself to be organized according to canon law because this would limit the despotism of prelates. The American Church refused to acknowledge the priesthood of Eastern Catholics ordained as married men, driving the Catholic Ruthenians into communion with the Patriarch of Moscow (the present Orthodox Church in America), and later blackmailing a bankrupt papacy into forbidding married priests throughout the Western hemisphere, driving a second group of Ruthenians into communion with the Ecumenical Patriarch of Constantinople (the present American CarpathoRussian Orthodox Diocese). They American Cathholic Church wouldn't even allow American women to become real nuns, or foreign nuns to come to America without renouncing their vows. The vast majority of Catholic women called nuns are nothing of the sort, but religious sisters first organized as cheap labor at the beck and call of the clergy, and now loose cannons like the Papessas Mother Angelica and Sister Joan. Yes, one or two real abbeys for women were founded in the last century, but the American Church continues to hold the contemplative life in deepest contempt, even for women. Women religious lead the crusade against contemplative traditions, and now rail against the Church as an organ of worldly power from which they are unjustly excluded. Deprived of traditional spiritual direction, a lamentable number of priests "demythologized" the Faith while looking to worldly culture for a way of salvation. Many found it in the gospel of orgasm, and undertook to liberate the young men in their care by sharing the only joy they thought worth having, with results we see today. Catholic involvement in American public life has not been edifying either. The American bishops turned their backs on Benedict XV's attempt to end the slaughter in the trenches and refused to make any move to bring Woodrow Wilson over to the side of peace. As patriotic Americans, they in effect signed on to the WASP jihad to extirpate the Catholic powers of the Old World. A couple of generations later millions of Catholic schoolchildren were forced to write letters demanding that the Senate not censure that great American Joseph McCarthy, who was probably the Soviet Union's most valuable (presumably unwitting) asset in American public life, who had discredited all responsible criticism of Communism and its supporters by viciously slandering the United States Army, the Department of State, and the Protestant clergy as nests of traitors. Some years later Catholic activists succeeded in driving the voices of moderation out of the Republican Party, and the urban ethnic social conservatives out of the Democratic, and the forms of civility from the public square. Americans can be forgiven for not rushing to enlist in the nearest Roman Catholic parish. There are other conversions needed, perhaps beginning with American Catholics themselves. Back in the days of Reagan a fellow named Alan Bloom made an almost persuasive case that the American Mind was closed to the Great Tradition of Western Civilization, and needed to be reopened. Alas, Bloom was a Neoconservative, a follower of their guru Leo Strauss, and a teacher of a a number of shady operatives of the Program for the New American Century type, as Saul Bellow's last novel so amusingly portrays him. Bloom's Great Tradition was something cobbled together by Machiavelli and others out of the misunderstood shards of ancient paganism; thinkers and writers tainted by the Christian gospel remained under embargo. (Mortimer Adler was less fearful, more intellectually curious, but look where he ended up.) It took a Bavarian Pope to remind us that the basic principles of our cherished hopes of international organization and human rights, and indeed of the American founding itself, go back to the Iberian scholastics of the Catholic Reformation. ("CounterReformation" is misleadingly negative.) Benedict's reminder harmonized well with my own studies in the history of philosophy. I began some five decades ago with the riddle, the riddles, of Charles Sanders Peirce (1839 - 1914), our own and only philosopher to be ranked with the likes of Aristotle and Kant. What was this Common Sense he went on and on about? (The Scottish Philosophy was studiously ignored in the academy; it still is.) As I said, I was lucky to find out. Now John Deely has been showing that any postmodern philosophy worthy of the name, one founded on semeiology rather than Cartesian (or empiricist) methodologism, needs to go back to Peirce and with Peirce back to the very beginnings of the theory of signification as we find them in John Poinsot (1589 1644). Poinsot, as it happens, is part of the same Iberian Renaissance to which Benedict has now called our attention. Indeed, under another name (John of St. Thomas) Poinsot inspired the neo Thomism of Jacques Maritain which undergirded the Christian Humanism of Paul VI and many other Fathers of the Second Vatican Council. (His treatise on **The Gifts of the Holy Spirit*, as interpreted by theologians often dismissed as too conservative, is behind the rather daring notion that all Christians are called to holiness in this life, and, indeed to the mystical path of acquired contemplation, and thus such more recent developments as Centering Prayer, the World Community for Christian Meditation, and the ommunion and Liberation movement. As if all this were not enough, Murray Rothbard, no Christian he, though personally excommunicated and anathematized by Ayn Rand for not repudiating his openly Christian wife, has argued that the Austrian School of Economics, the Old Liberalism of von Mises and Hayek, goes back not so much to Adam Smith (who missed a few points), as to the scholastic philosophers of Spain and Portugal in the early modern period. Mention Iberian philosophy to the American of average education and he will look at you as though you had spoken of Uzbek grand opera or (indeed) the Scottish Enlightenment. He might even tell you that Spanish ignorance, superstition, and bigotry are precisely what God sent Englishmen into the New World to stamp out: the *legenda negra*. Needless to say, this is not a view of history a good many newcomers to the United States are likely to tolerate with equanimity, and it is just as well that it isn't true. Once we retire that vulgar prejudice against Hispanidad we might just get a fair hearing for the work of Xavier Zubiri, the only European thinker of the last century who compares with Peirce for breadth of learning and depth of discernment as well as sheer unadulterated difficulty. If nothing else, the challenge of Catholicity invites Americans to break down the walls of the AngloSaxon ghetto, which do not serve us well now, if they ever did. But it may also provoke a new interest in our own Golden Age of (Protestant) theology. Let me set the stage for this with an extended quotation from Joseph Ratzinger's 1977 essay, "Is Faith Really Good News?" (Now translated in Principles of Catholic Theology: > Truth is not always comfortable for man, but it is only truth that makes him free and only freedom that brings him joy. Now, however, we must ask more precisely: What makes a man joyful? What robs him of joy? What puts him at odds with himself? What opens him to himself and to others? When we want to describe the most extreme form of being at odds with existence, we often say of an individual that he does not like himself. But whom or what is he to like who does not like himself? Something very importamt makes its appearance here: egoism, certainly, is natural to man and needs no encouragement; but this is not true of selfacceptance. The former must be overcome; the latter must be discovered, and it is assuredly one of the most dangerous errors of Christian teachers and moralists that they have all too often confused the two and, by exorcizing the affirmation of self, have enabled egoism to avenge such a betrayal by becoming all the more rampant this, ultimately, of what the French have labeled the maladie catholique: one who wants to live only on the supernatural level and to the exclusion of self will be, in the end, without a self but not, for that reason, selfless. (79) Reading this a day or two after Ratzinger's papification I couldn't help thinking of our own Paul Tillich, whose seminal sermon "You are Accepted" baptized the human potential movement (as it was called), whose *Courage to Be* is a perennial best seller even after half a century, whose *Systematic Theology* Martin Luther King had asked for in his Georgia prison cell, and I myself poured over eagerly as an Earlham undergraduate. Of course the problematic goes back to Kierkegaard's penetrating analysis of despair, and, indeed to Luther's experience of divine wrath and mercy. Now it is all very well to say we must accept our acceptance, somehow (mysticism? art?) so ground ourselves in the very Ground of Being as to powerfully affirm our being against the powers of nonbeing. But is it true? That is the question haunting Tillich, Martin Luther King, and modern American culture down to our own time, which Ratzinger, challenged by Nietzsche and Camus, dared to speak aloud: > We come now to the allimportant question: Is it true, then, when someone says to me: "It is good that you exist"? Is it really good? Is it not possible that that person's love, which wills my existence, is just a tragic error? If the love that gives me courage to exist is not based on truth, then I must, in the end, come to curse the love that deceives me that maintains in existence something that were better destroyed. This dilemma could be 10 strikingly illustrated by reference to the interpretations of the contemporary experience of life in Sartre or Camus or in the attitudes of the new Left. Even without such evidence, it is obvious, however, that the apparently so simple act of liking myself, of being at one with myself, actually raises the question of the whole universe It raises the question of truth: Is it good that I exist? Is it good that anything at all exists? is the world good? How many persons today would dare to affirm this question from the heart to believe it is good that they exist? That is the source of the anxiety and despair that incessantly affect mankind. Love alone is of no avail. It serves no purpose if truth is not on its side. Only when truth and love are in harmony can man know joy. For it is truth that makes man free. (80) And the question of truth won't leave us alone. For Tillich the Christian faith was perhaps a true myth, but, perhaps true only the way that other myths are true. He tended to sacramentalize modern art, leftish politics, and sexual liberation; the president of Union Seminary had to remind him that it looked bad for their most eminent theologian not to go to church. The tragedy of attempting to make a religion of art, politics, or sex is obvious by now, and it as a sad circumstance that the leadership of the American Catholic Church were seminarians at a time when Catholic theology looked to the Protestants for validation, and Tillich was at the height of his prestige in the liberal denominations. The painful story of Tillich's sexual obsessions is now well known enough from his wife's two memoirs, Dr. King's escapades have stained the memory of the civil rights movement as much as his infatuation with the Soviet power, and the sexual scandals of the American Church are unspeakably worse, blighting the lives of tens (hundreds?) of thousands of children. That is something Benedict, on his recent visit, would not allow us to forget for even a moment. But at least he offers a remedy in that confrontation with the truth of our being which liberal theology, Catholic and Protestant (though perhaps not Orthodox),attempted to evade: > The content of the Christian evangelium reads: God finds man so important that he himself has suffered for man. The Cross, which was for Nietzche the most detestable expression of the negative character of the Christian religion, is in truth the center of the evangelium, the glad tidings: "It is good that you exist" No, "It is necessary that you exist." The Cross is the approbation of our existence, not in words, but in an act so completely radical that it caused God to become flesh and pierced this flesh to the quick; that, to God, it was worth the death of his incarnate Son. One who is so loved that the other identifies his life with this love and no longer desires to live if he is deprived of it; one who is loved even unto death such a one knows that he is truly loved. But if God so loves, then we are loved in truth. Then love is truth, and truth is love. Then life is worth living. This is the evangelium. (81) The whole idea of the Cross as God's affirmation of man will strike many an American as shocking, ludicrous even. It the caross not the stock in trade of a thousand "evangelists" as the ultimate proof of our total depravity, the ultimate refutation of all aspirations for human freedom and dignity? Surely Nietzsche got that from his preacher father, though it is hard to find any such slander of humanity in either the written scriptures or the teaching of the Fathers of the Church (except for Augustine, and that on a bad day he later repented). I am happy to note that Ratzinger's point of view, scriptural, patristic, and Benedictine in every sense of the term is very close to what some in the Evangelical churches are calling "gracious Christianity," for that is what it is. That movement is still a prophetic minority in the churches and the academy, and we still need to come to terms with the main stream of American spirituality as represented, for better and worse, by Tillich. And Ratzinger, even in his early days as a professor, has given us the means to do just that. Not everything in the American theological mainstream, and not everything in Tillich, needs to be discarded wholesale. A follower of Ratiznger's good friend Don Liugi Giussani who studies Tillich's theology will find close analogies between Tillich's method of correlation and the principle of correspondence which Giussani urged on members of the Communion and Liberation movement he founded, a movement in which the Ratzinger Pope (to use the Catholic injargon) takes more than a passing interest he is said even now to take part in a weekly School of Community in which movement people use that method to explore the meaning of the Gospel in relation to their own day to day lives, and the meaning of their lives in relation to the Gospel, though his episcopal orders forbid his formal membership in the Fraternity. I do not mean to imply that Benedict is a follower of Giussani in matters of pure theology, but it seems clear that he recognizes Giussani's method as the best practical application of the theological principles both men learned from such masters of La Nouvelle Theologie as de Lubac, von Balthasar, and (with reservations) Rahner. But before I move away from the idea of correspondence, the method of correlation, I should mention that this became the life work of two American philosophers, Ira Progoff, with whom and with whose students I was privileged to do postdoctoral work, and Eugene Gendlin, both known as psychologists for the contributions they have made to psychology, who offer what I can only describe as means of spiritual direction. The few folks who remember Tillich today often contrast him with Reinhold Niebuhr, his colleague at Union, who inspired the Cold war mainstream much as Tillich inspired the New Left, and whom Don Gius was fond of quoting. But the man to rediscover is Reinhold's brother Richard, a theologian's theologian, that is, one whose writings were never taken up by the movers and shakers of middlebrow culture. His *Meaning of Revelation* shows the kind of emphasis the Catholic Church in Europe is coming around to, or coming back to, as it is very much in the spirit of the Fathers of the Church, the Eastern Fathers in particular. For many of us what may be most prophetic in his life work is his refusal of the temptation of neoconservatism to which Reinhold gave in to his fame and profit. Reinhold ostentatiously resigned from the Fellowship of Reconciliation in the early '30s in righteous indignation that some Christians did not demand that the government do something (what?) about the Japanese in China. Richard, on the other hand, had no hope for the efficacy of political, economic, and military power exercised by the United States against Japan. Sensing that Western Christendom was going the way of old Rome, he thought that the best Christian response was that pioneered by St. Benedict, from whom of course among others the last pontiff took his name. For him the issue was not Japan against China, or the United States against Japan, but, to cite the title of a 1935 book to which he contributed, *The Church Against the World*. A few years later Dietrich von Hildebrand, in his villa in Florence, was giving the retreats later published as *Transformation in Christ* to Christian activists who intended to remain behind in Nazi Germany to keep the light of Christian civilization burning in that dark time, and Dietrich Bonhoeffer would take refuge with the Benedictines in his own effort to do the same. A few pages before the long passage I have quoted, Ratzinger's *Principles of Catholic Theology* gives a lengthy exegesis of Hildebrand's text as the model for Christian repentance. I can't help wondering if this forbidden book is one that his father had hidden around the house, as Evangelicals might have concealed Bonhoeffer's *Cost of Discipleship*. Discipleship and transformation are not matters of effortful striving, but the response to a calling which is a revelation. Richard is particularly enlightening on revelation as calling. He shows that it is not the communication of some kind of knowldege, however supernatural or esoteric, by possession of which we are justified, elevated from the companionship of our neighbors, saved from the world; that would be Gnosticism. Rather, revelation is participation in an ongoing event, a relationship with a person previously unknown, or at least unrecognized. Some words toward the end of *The Meaning of Revelation* put the matter thus: > Revelation means the moment in our history through which we know ourselves to be known from beginning to end, in which we are apprehended by the knower; it means the the selfdisclosure of the judge. Revelation means that we find ourselves to be valued rather than valuing and that all our values are transvaluated by the activity of a universal valuer. When a price is put upon our heads, which is not our price, when the unfairness of all the fair prices we have placed on things is shown up, when the great riches of God reduce our wealth to poverty, that is revelation. When we find out that we are no longer thinking him, but that he first thought us, that is revelation. Revelation is the emergence of the person on whose external garments and body we had looked as objects of our masterful and curious understanding. Revelation means that in our common history the fate that lowers over us as persons in our communities reveals itself to be a person in community with us. What this means for us cannot be expressed in the impersonal ways of creeds or other propositions but only in responsive acts of a personal character. we acknowledge revelation by no third person proposition, such as that there is a God, but only in the direct confession of the heart, "Thou art my God."... From this point forward we must listen for the remembered voice in all the sounds that assail our ears, and look for the remembered activity in all the actions of the world upon us. The God who reveals himself in Jesus Christ is now trusted and known in the contemporary God, revealing himself in every event, but we do not understand how we could tract his working in these happenings if he did not make himself known to us through the memory of Jesus Christ; nor do we know how we should be able to interpret all the words we read as words of God save by the aid of this Rosetta stone. (80 - 81) Catholics who remember the discourses of the Pope Benedict will find the flavor of this passage very Benedictine in both senses of the term. Those who follow the way of Luigi Giussani find their spirit particularly familiar, for those of them who live in community, including the little band that managed Benedict's household and conduct the School of Community he attended, are known precisely as *Memores Domini*, those who strive to keep the Lord constantly in mind, and allow their own memory and mindfulness, personal and collective, painful and pleasing, on the surface of association or deeply hidden, to be transformed by their relationship with God in Christ, their participation in the ongoing incarnation of the Word of God: the God who is the author of our nature, and an incarnation that runs to meet the deepest desire of that nature with more that could have been imagined. What this means in the experience of living our life is well stated at the conclusion of Niebuhr's great work: > The God who reveals himself in Jesus Christ meets no unresponsive will but the living spirit of men in search of all good. And he fulfills our need. Here is the one for whose sake all life and every life is worth living, even lives that seem bereft of beauty, of truth and of goodness. The glimpse of his great glory in the face of Jesus Christ, its reflections in the darkened mirrors of the saints' adorations intimate a God who is good beyond all that is good and fair beyond all fairness. Yet the goodness that shines upon us through the moment of revelation is not the glory or the goodness we had expected in our thoughts about deity. The essential goodness of the Father of our Lord Jesus Christ is the simple everyday goodness of love the value which belongs to a person rather [than] the value we find in an idea or a pattern; it is the goodness which exists as pure activity. He fulfills our expectation of the intrinsic good and yet this adorable goodness differs from everything we had expected, and puts our expectations to shame. We sought a good to love and were found by a good that loved us. And therewith all our religious ambitions are brought low, all our desires to be ministers of God are humbled; he is our minister. By that revelation we are convicted of having corrupted our religious life through our unquenchable desire to keep ourselves with our love of our good in the center of the picture. Here is the goodness that empties itself, and makes itself of no reputation, a goodness that is all outgoing, reserving nothing for itself, yet having all things. So we must begin to rethink all our definitions of deity and convert all our worship and our prayers. Revelation is not the development and not the elimination of our natural religion; it is the revolution of the religious life. (98 - 99) But what does all this mean to one who stands outside the light of revelation, who relies on the reason of Western Civilization, the common sense of the founding Fathers? If believers and unbelievers are to take part in one community, what do we have to say to each other? This is the point of Benedict's challenge to the Muslim world, the question of what could make the libertine Doctor Franklin and the evangelical President Witherspoon active participants in the same foundational dialog. Niebuhr has an answer, and it is the same answer as Benedict: > The pure reason does not need to be limited in order that room be made for faith, but faith emancipates the pure reason from the necessity of defending and guarding the interests of selves, which are now found to be established and guarded, not by nature, but by the God of revelation whose garment nature is. (91 - 92) It is faith that liberates and, indeed, inspires us to invent, develop, explore, and test scientific understandings which would otherwise be too much for the vain imaginings of our all too human hearts: > To know the person is to lose all sense of shame because of kinship with the clod and the ape. The mind is freed to pursue its knowledge of the external world disinterestedly not by the conviction that nothing matters, but by the faith that nothing God has made is mean or unclean. Hence any failure of Christians to develop scientific knowledge of the world is not an indication of their loyalty to the revealed God but of their unbelief. (90 - 91) Seven going on eight decades after these words were published, ministers of "religion" are still attempting to prevent the teaching of ascertained facts of human biology in order to retain the authority of their own stupidly selectively literalistic reading of the Bible; some of the more advanced institutions of Evangelical learning defiantly profess a form of Calvinism in which some sort of theology remains the queen of the sciences in an unconstitutional monarchy, with no other discipline permitted its own proper autonomy and integrity; while in more numerous groves of Academus, even the Roman Catholic plantations, men and women of faith are quickly brushed off as obvious enemies of intellect. My own mother, as I have said already, doubted that you can be a good Catholic and a real American at the same time. Pope Benedict warned his flock that they will not be good Catholics until they are Americans to the extent of acknowledging the law of nature and of nations as developed by Victoria (among others, some of them Scots), and aspiring to live in local, regional national and international communities under that law, in which the freedom and dignity of the human person are given the first priority. On the other hand I do not see how we can be real Americans without realizing that the aspirations of 1776 and 1789 are grounded in that natural law, and grew up as the fruit of a civilization in which the reason of Greece and Rome reached full maturity in the care of Mother Church, a church whose members, including the hierarchy, were not always consistently faithful to it, calling forth reformations, enlightenments, and even revolutions. I think we must all be Catholic at least in the wider sense of loyalty to that civilization, and our best way may well be to reappropriate the riches of the golden age of American philosophy and theology, of which the work of H. Richard Niebuhr is a small but important part. Sources quoted: Edmund Burke, Impeachment of Warren Hastings before the House of Lords (numerous editions), eighth day. Joseph Ratzinger, *Principles of Catholic Theology*. San Fransisco: Ignatius, 1987. H. Richard Niebuhr, *The Meaning of Revelation* [1941]. Louisville: Westminster John Knox Press, 2006. © FP Purcell @ fd06f542:8d6d54cd
2025-03-28 02:14:43{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/5ad7189d30c9b49aa61652d98ac7853217b7e445f863be09f9745c49df9f514c.webp","title":"Nostr protocol","author":"fiatjaf"}
@ fd06f542:8d6d54cd
2025-03-28 02:14:43{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/5ad7189d30c9b49aa61652d98ac7853217b7e445f863be09f9745c49df9f514c.webp","title":"Nostr protocol","author":"fiatjaf"} @ 5d4b6c8d:8a1c1ee3
2025-04-05 14:11:31 Here's a fun little Rorschach Test for Stackers. Clearly there's a trend change during the pandemic, but when does it start and what is the most likely cause? I'll reserve my commentary for the comment section. originally posted at https://stacker.news/items/935188
@ 5d4b6c8d:8a1c1ee3
2025-04-05 14:11:31 Here's a fun little Rorschach Test for Stackers. Clearly there's a trend change during the pandemic, but when does it start and what is the most likely cause? I'll reserve my commentary for the comment section. originally posted at https://stacker.news/items/935188 @ ecda4328:1278f072
2025-03-25 10:00:52**Kubernetes and Linux Swap: A Practical Perspective** After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion. --- ### The Rationale for Disabling Swap We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes. With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion. Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates. --- ### Theoretical Capability vs. Practical Deployment Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly. But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model: - Memory **requests and limits** are declared explicitly. - The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap). - Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals. So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity. --- ### Why Disable Swap in Kubernetes? 1. **Deterministic Failure > Degraded Performance**\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early. 2. **Transparency & Observability**\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically. 3. **Performance Consistency**\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits. 4. **Kubernetes Doesn’t Manage Swap Well**\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control. 5. **Statelessness is the Norm**\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state. --- ### "But Swap Can Be Useful..." Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need: - Fine-tuned `vm.swappiness` - Memory pinning and cgroup-based control - Swap-aware monitoring and alerting - Custom kubelet/systemd integration That's possible, but **not standard practice** — and for good reason. --- ### Future Considerations Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments. Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior. Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet. --- ### Conclusion Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability. If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**.
@ ecda4328:1278f072
2025-03-25 10:00:52**Kubernetes and Linux Swap: A Practical Perspective** After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion. --- ### The Rationale for Disabling Swap We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes. With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion. Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates. --- ### Theoretical Capability vs. Practical Deployment Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly. But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model: - Memory **requests and limits** are declared explicitly. - The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap). - Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals. So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity. --- ### Why Disable Swap in Kubernetes? 1. **Deterministic Failure > Degraded Performance**\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early. 2. **Transparency & Observability**\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically. 3. **Performance Consistency**\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits. 4. **Kubernetes Doesn’t Manage Swap Well**\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control. 5. **Statelessness is the Norm**\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state. --- ### "But Swap Can Be Useful..." Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need: - Fine-tuned `vm.swappiness` - Memory pinning and cgroup-based control - Swap-aware monitoring and alerting - Custom kubelet/systemd integration That's possible, but **not standard practice** — and for good reason. --- ### Future Considerations Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments. Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior. Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet. --- ### Conclusion Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability. If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**. @ 872982aa:8fb54cfe
2025-03-27 05:50:35NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ```
@ 872982aa:8fb54cfe
2025-03-27 05:50:35NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ``` @ a5142938:0ef19da3
2025-04-04 14:58:05**Have you found a natural product? Share it here by commenting on this page!** This site only lists durable-use products and objects. Consumables (food, cosmetics, fuels, etc.) are not included. To be listed, the product must be made of natural materials. 👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) You can copy and paste the template below and fill in the information you have. Other contributors can complete any missing details. Each piece of information added (name, material, link, shipping area, etc.) and validated is considered a contribution. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- ### New product - Product name : - Product image (link): - Short description: - Categories: - Brand or manufacturer: - Composition (materials used, including unknown elements): - Links to buy (and shipping area): - Other information (place of manufacture, certifications…): --- If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward. 👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/8adj-i_hk0gtzp_ul9k17/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/nicmc-eandjr_vcz4_hsr/)
@ a5142938:0ef19da3
2025-04-04 14:58:05**Have you found a natural product? Share it here by commenting on this page!** This site only lists durable-use products and objects. Consumables (food, cosmetics, fuels, etc.) are not included. To be listed, the product must be made of natural materials. 👉 [Learn more about materials](https://www.origin-nature.com/post/pnco0inysorhojxvsyil3/) You can copy and paste the template below and fill in the information you have. Other contributors can complete any missing details. Each piece of information added (name, material, link, shipping area, etc.) and validated is considered a contribution. 👉 [Learn more about contributions](https://www.origin-nature.com/post/laf_xjasf4kgunxvozhkm/) --- ### New product - Product name : - Product image (link): - Short description: - Categories: - Brand or manufacturer: - Composition (materials used, including unknown elements): - Links to buy (and shipping area): - Other information (place of manufacture, certifications…): --- If you do not wish to log in, you can still contribute via [this form](https://www.origin-nature.com/post/pnef53sfo5jaejkactcib/). However, your contribution will not be counted towards a reward. 👉 [Learn more about rewards](https://www.origin-nature.com/post/xz20q6pw42fd9ijaewnn6/) --- This article is published on [origin-nature.com](https://www.origin-nature.com/post/8adj-i_hk0gtzp_ul9k17/) 🌐 [Voir cet article en français](https://www.origine-nature.com/post/nicmc-eandjr_vcz4_hsr/) @ 872982aa:8fb54cfe
2025-03-27 05:47:40NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ```
@ 872982aa:8fb54cfe
2025-03-27 05:47:40NIP-03 ====== OpenTimestamps Attestations for Events -------------------------------------- `draft` `optional` This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event: ```json { "kind": 1040 "tags": [ ["e", <event-id>, <relay-url>], ["alt", "opentimestamps attestation"] ], "content": <base64-encoded OTS file data> } ``` - The OpenTimestamps proof MUST prove the referenced `e` event id as its digest. - The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context. ### Example OpenTimestamps proof verification flow Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots): ```bash ~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify > using an esplora server at https://blockstream.info/api - sequence ending on block 810391 is valid timestamp validated at block [810391] ```