-
 @ 04c915da:3dfbecc9
2025-03-12 15:30:46
@ 04c915da:3dfbecc9
2025-03-12 15:30:46Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 21b41910:91f41a5e
2024-11-23 12:00:26
@ 21b41910:91f41a5e
2024-11-23 12:00:26Chef's notes
Based on assorted recipes and refined over time, this round of beef tastes great as a result of the sweet and savory marinade.
Details
- ⏲️ Prep time: 5 minutes (+ 1 day)
- 🍳 Cook time: 20 minutes
Ingredients
- 2 pounds lean beef (may be labeled as London Broil)
- 1/3 cup olive oil
- 1/4 cup soy sauce
- 1/4 cup malt vinegar
- 1/4 cup lemon juice
- 1 tbsp sweetener of choice (honey, molasses, syrup, 4 packets of duck sauce, etc)
- 2 tsp old bay seasoning
- 1 tsp garlic powder
- 1 tsp sea salt
- 1/2 tsp black pepper
Directions
- Day Before: Mix all ingredients except the beef in a bowl to form a marinade. Place the cut of beef in a gallon sized Ziploc bag. Pour marinade over beef, ensure fully covered. Remove any excess air from the bag and seal. Place back in refrigerator for up to 24 hours before cooking.
- Cooking: Bring beef out of refrigerator (still in bag), and allow to rise to room temperature (about 30-40 minutes). Preheat broiler for about 15 minutes (your oven will vary). Broil for about 7-8 minutes on one side, then flip over. Continue broiling for another 7-10 minutes until temperature reads 140°F. Remove from broiler and let rest for 10 minutes before slicing thinly.
-
 @ eb35d9c0:6ea2b8d0
2025-03-02 00:55:07
@ eb35d9c0:6ea2b8d0
2025-03-02 00:55:07I had a ton of fun making this episode of Midnight Signals. It taught me a lot about the haunting of the Bell family and the demise of John Bell. His death was attributed to the Bell Witch making Tennessee the only state to recognize a person's death to the supernatural.
If you enjoyed the episode, visit the Midnight Signals site. https://midnightsignals.net
Show Notes
Journey back to the early 1800s and the eerie Bell Witch haunting that plagued the Bell family in Adams, Tennessee. It began with strange creatures and mysterious knocks, evolving into disembodied voices and violent attacks on young Betsy Bell. Neighbors, even Andrew Jackson, witnessed the phenomena, adding to the legend. The witch's identity remains a mystery, sowing fear and chaos, ultimately leading to John Bell's tragic demise. The haunting waned, but its legacy lingers, woven into the very essence of the town. Delve into this chilling story of a family's relentless torment by an unseen force.
Transcript
Good evening, night owls. I'm Russ Chamberlain, and you're listening to midnight signals, the show, where we explore the darkest corners of our collective past. Tonight, our signal takes us to the early 1800s to a modest family farm in Adams, Tennessee. Where the Bell family encountered what many call the most famous haunting in American history.
Make yourself comfortable, hush your surroundings, and let's delve into this unsettling tale. Our story begins in 1804, when John Bell and his wife Lucy made their way from North Carolina to settle along the Red River in northern Tennessee. In those days, the land was wide and fertile, mostly unspoiled with gently rolling hills and dense woodland.
For the Bells, John, Lucy, and their children, The move promised prosperity. They arrived eager to farm the rich soil, raise livestock, and find a peaceful home. At first, life mirrored [00:01:00] that hope. By day, John and his sons worked tirelessly in the fields, planting corn and tending to animals, while Lucy and her daughters managed the household.
Evenings were spent quietly, with scripture readings by the light of a flickering candle. Neighbors in the growing settlement of Adams spoke well of John's dedication and Lucy's gentle spirit. The Bells were welcomed into the Fold, a new family building their future on the Tennessee Earth. In those early years, the Bells likely gave little thought to uneasy rumors whispered around the region.
Strange lights seen deep in the woods, soft cries heard by travelers at dusk, small mysteries that most dismissed as product of the imagination. Life on the frontier demanded practicality above all else, leaving little time to dwell on spirits or curses. Unbeknownst to them, events on their farm would soon dominate not only their lives, but local lore for generations to come.[00:02:00]
It was late summer, 1817, when John Bell's ordinary routines took a dramatic turn. One evening, in the waning twilight, he spotted an odd creature near the edge of a tree line. A strange beast resembling part dog, part rabbit. Startled, John raised his rifle and fired, the shot echoing through the fields. Yet, when he went to inspect the spot, nothing remained.
No tracks, no blood, nothing to prove the creature existed at all. John brushed it off as a trick of falling light or his own tired eyes. He returned to the house, hoping for a quiet evening. But in the days that followed, faint knocking sounds began at the windows after sunset. Soft scratching rustled against the walls as if curious fingers or claws tested the timbers.
The family's dog barked at shadows, growling at the emptiness of the yard. No one considered it a haunting at first. Life on a rural [00:03:00] farm was filled with pests, nocturnal animals, and the countless unexplained noises of the frontier. Yet the disturbances persisted, night after night, growing a little bolder each time.
One evening, the knocking on the walls turned so loud it woke the entire household. Lamps were lit, doors were open, the ground searched, but the land lay silent under the moon. Within weeks, the unsettling taps and scrapes evolved into something more alarming. Disembodied voices. At first, the voices were faint.
A soft murmur in rooms with no one in them. Betsy Bell, the youngest daughter, insisted she heard her name called near her bed. She ran to her mother and her father trembling, but they found no intruder. Still, The voice continued, too low for them to identify words, yet distinct enough to chill the blood.
Lucy Bell began to fear they were facing a spirit, an unclean presence that had invaded their home. She prayed for divine [00:04:00] protection each evening, yet sometimes the voice seemed to mimic her prayers, twisting her words into a derisive echo. John Bell, once confident and strong, grew unnerved. When he tried reading from the Bible, the voice mocked him, imitating his tone like a cruel prankster.
As the nights passed, disturbances gained momentum. Doors opened by themselves, chairs shifted with no hand to move them, and curtains fluttered in a room void of drafts. Even in daytime, Betsy would find objects missing, only for them to reappear on the kitchen floor or a distant shelf. It felt as if an unseen intelligence roamed the house, bent on sowing chaos.
Of all the bells, Betsy suffered the most. She was awakened at night by her hair being yanked hard enough to pull her from sleep. Invisible hands slapped her cheeks, leaving red prints. When she walked outside by day, she heard harsh whispers at her ear, telling her she would know [00:05:00] no peace. Exhausted, she became withdrawn, her once bright spirit dulled by a ceaseless fear.
Rumors spread that Betsy's torment was the worst evidence of the haunting. Neighbors who dared spend the night in the Bell household often witnessed her blankets ripped from the bed, or watched her clutch her bruised arms in distress. As these accounts circulated through the community, people began referring to the presence as the Bell Witch, though no one was certain if it truly was a witch's spirit or something else altogether.
In the tightly knit town of Adams, word of the strange happenings at the Bell Farm soon reached every ear. Some neighbors offered sympathy, believing wholeheartedly that the family was besieged by an evil force. Others expressed skepticism, guessing there must be a logical trick behind it all. John Bell, ordinarily a private man, found himself hosting visitors eager to witness the so called witch in action.
[00:06:00] These visitors gathered by the parlor fireplace or stood in darkened hallways, waiting in tense silence. Occasionally, the presence did not appear, and the disappointed guests left unconvinced. More often, they heard knocks vibrating through the walls or faint moans drifting between rooms. One man, reading aloud from the Bible, found his words drowned out by a rasping voice that repeated the verses back at him in a warped, sing song tone.
Each new account that left the bell farm seemed to confirm the unearthly intelligence behind the torment. It was no longer mere noises or poltergeist pranks. This was something with a will and a voice. Something that could think and speak on its own. Months of sleepless nights wore down the Bell family.
John's demeanor changed. The weight of the haunting pressed on him. Lucy, steadfast in her devotion, prayed constantly for deliverance. The [00:07:00] older Bell children, seeing Betsy attacked so frequently, tried to shield her but were powerless against an enemy that slipped through walls. Farming tasks were delayed or neglected as the family's time and energy funneled into coping with an unseen assailant.
John Bell began experiencing health problems that no local healer could explain. Trembling hands, difficulty swallowing, and fits of dizziness. Whether these ailments arose from stress or something darker, they only reinforced his sense of dread. The voice took to mocking him personally, calling him by name and snickering at his deteriorating condition.
At times, he woke to find himself pinned in bed, unable to move or call out. Despite it all, Lucy held the family together. Soft spoken and gentle, she soothed Betsy's tears and administered whatever remedies she could to John. Yet the unrelenting barrage of knocks, whispers, and violence within her own home tested her faith [00:08:00] daily.
Amid the chaos, Betsy clung to one source of joy, her engagement to Joshua Gardner, a kind young man from the area. They hoped to marry and begin their own life, perhaps on a parcel of the Bell Land or a new farmstead nearby. But whenever Joshua visited the Bell Home, The unseen spirit raged. Stones rattled against the walls, and the door slammed as if in warning.
During quiet walks by the river, Betsy heard the voice hiss in her ear, threatening dire outcomes if she ever were to wed Joshua. Night after night, Betsy lay awake, her tears soaked onto her pillow as she wrestled with the choice between her beloved fiancé and this formidable, invisible foe. She confided in Lucy, who offered comfort but had no solution.
For a while, Betsy and Joshua resolved to stand firm, but the spirit's fury only escalated. Believing she had no alternative, Betsy broke off the engagement. Some thought the family's [00:09:00] torment would subside if the witches demands were met. In a cruel sense, it seemed to succeed. With Betsy's engagement ended, the spirit appeared slightly less focused on her.
By now, the Bell Witch was no longer a mere local curiosity. Word of the haunting spread across the region and reached the ears of Andrew Jackson, then a prominent figure who would later become president. Intrigued, or perhaps skeptical, he traveled to Adams with a party of men to witness the phenomenon firsthand.
According to popular account, the men found their wagon inexplicably stuck on the road near the Bell property, refusing to move until a disembodied voice commanded them to proceed. That night, Jackson's men sat in the Bell parlor, determined to uncover fraud if it existed. Instead, they found themselves subjected to jeering laughter and unexpected slaps.
One boasted of carrying a special bullet that could kill any spirit, only to be chased from the house in terror. [00:10:00] By morning, Jackson reputedly left, shaken. Although details vary among storytellers, the essence of his experience only fueled the legend's fire. Some in Adams took to calling the presence Kate, suspecting it might be the spirit of a neighbor named Kate Batts.
Rumors pointed to an old feud or land dispute between Kate Batts and John Bell. Whether any of that was true, or Kate Batts was simply an unfortunate scapegoat remains unclear. The entity itself, at times, answered to Kate when addressed, while at other times denying any such name. It was a puzzle of contradictions, claiming multiple identities.
A wayward spirit, a demon, or a lost soul wandering in malice. No single explanation satisfied everyone in the community. With Betsy's engagement to Joshua broken, the witch devoted increasing attention to John Bell. His health declined rapidly in 1820, marked by spells of near [00:11:00] paralysis and unremitting pain.
Lucy tended to him day and night. Their children worried and exhausted, watched as their patriarch grew weaker, his once strong presence withering under an unseen hand. In December of that year, John Bell was found unconscious in his bed. A small vial of dark liquid stood nearby. No one recognized its contents.
One of his sons put a single drop on the tongue of the family cat, which died instantly. Almost immediately, the voice shrieked in triumph, boasting that it had given John a final, fatal dose. That same day, John Bell passed away without regaining consciousness, leaving his family both grief stricken and horrified by the witch's brazen gloating.
The funeral drew a large gathering. Many came to mourn the respected farmer. Others arrived to see whether the witch would appear in some dreadful form. As pallbearers lowered John Bell's coffin, A jeering laughter rippled across the [00:12:00] mourners, prompting many to look wildly around for the source. Then, as told in countless retellings, the voice broke into a rude, mocking song, echoing among the gravestones and sending shudders through the crowd.
In the wake of John Bell's death, life on the farm settled into an uneasy quiet. Betsy noticed fewer night time assaults. And the daily havoc lessened. People whispered that the witch finally achieved its purpose by taking John Bell's life. Then, just as suddenly as it had arrived, the witch declared it would leave the family, though it promised to return in seven years.
After a brief period of stillness, the witch's threat rang true. Around 1828, a few of the Bells claimed to hear light tapping or distant murmurs echoing in empty rooms. However, these new incidents were mild and short lived compared to the previous years of torment. Soon enough, even these faded, leaving the bells [00:13:00] with haunted memories, but relative peace.
Near the bell property stood a modest cave by the Red River, a spot often tied to the legend. Over time, people theorized that cave's dark recesses, though the bells themselves rarely ventured inside. Later visitors and locals would tell of odd voices whispering in the cave or strange lights gliding across the damp stone.
Most likely, these stories were born of the haunting's lingering aura. Yet, they continued to fuel the notion that the witch could still roam beyond the farm, hidden beneath the earth. Long after the bells had ceased to hear the witch's voice, the story lived on. Word traveled to neighboring towns, then farther, into newspapers and traveler anecdotes.
The tale of the Tennessee family plagued by a fiendish, talkative spirit captured the imagination. Some insisted the Bell Witch was a cautionary omen of what happens when old feuds and injustices are left [00:14:00] unresolved. Others believed it was a rare glimpse of a diabolical power unleashed for reasons still unknown.
Here in Adams, people repeated the story around hearths and campfires. Children were warned not to wander too far near the old bell farm after dark. When neighbors passed by at night, they might hear a faint rustle in the bush or catch a flicker of light among the trees, prompting them to walk faster.
Hearts pounding, minds remembering how once a family had suffered greatly at the hands of an unseen force. Naturally, not everyone agreed on what transpired at the Bell farm. Some maintained it was all too real, a case of a vengeful spirit or malignant presence carrying out a personal vendetta. Others whispered that perhaps a member of the Bell family had orchestrated the phenomenon with cunning trickery, though that failed to explain the bruises on Betsy, the widespread witnesses, or John's mysterious death.
Still, others pointed to the possibility of an [00:15:00] unsettled spirit who had attached itself to the land for reasons lost to time. What none could deny was the tangible suffering inflicted on the Bells. John Bell's slow decline and Betsy's bruises were impossible to ignore. Multiple guests, neighbors, acquaintances, even travelers testified to hearing the same eerie voice that threatened, teased and recited scripture.
In an age when the supernatural was both feared and accepted, the Bell Witch story captured hearts and sparked endless speculation. After John Bell's death, the family held onto the farm for several years. Betsy, robbed of her engagement to Joshua, eventually found a calmer path through life, though the memory of her tormented youth never fully left her.
Lucy, steadfast and devout to the end, kept her household as best as she could, unwilling to surrender her faith even after all she had witnessed. Over time, the children married and started families of their own, [00:16:00] quietly distancing themselves from the tragedy that had defined their upbringing.
Generations passed, the farm changed hands, the Bell House was repurposed and renovated, and Adams itself transformed slowly from a frontier settlement into a more established community. Yet the name Bellwitch continued to slip into conversation whenever strange knocks were heard late at night or lonely travelers glimpsed inexplicable lights in the distance.
The story refused to fade, woven into the identity of the land itself. Even as the first hand witnesses to the haunting aged and died, their accounts survived in letters, diaries, and recollections passed down among locals. Visitors to Adams would hear about the famed Bell Witch, about the dreadful death of John Bell, the heartbreak of Betsy's broken engagement, and the brazen voice that filled nights with fear.
Some folks approached the story with reverence, others with skepticism. But no one [00:17:00] denied that it shaped the character of the town. In the hush of a moonlit evening, one might stand on that old farmland, fields once tilled by John Bell's callous hands, now peaceful beneath the Tennessee sky. And imagine the entire family huddled in the house, listening with terrified hearts for the next knock on the wall.
It's said that if you pause long enough, you might sense a faint echo of their dread, carried on a stray breath of wind. The Bell Witch remains a singular chapter in American folklore, a tale of a family besieged by something unseen, lethal, and uncannily aware. However one interprets the events, whether as vengeful ghosts, demonic presence, or some other unexplainable force, the Bell Witch.
Its resonance lies in the very human drama at its core. Here was a father undone by circumstances he could not control. A daughter tormented in her own home, in a close knit household tested by relentless fear. [00:18:00] In the end, the Bell Witch story offers a lesson in how thin the line between our daily certainties and the mysteries that defy them.
When night falls, and the wind rattles the shutters in a silent house, we remember John Bell and his family, who discovered that the safe haven of home can become a battlefield against forces beyond mortal comprehension. I'm Russ Chamberlain, and you've been listening to Midnight Signals. May this account of the Bell Witch linger with you as a reminder that in the deepest stillness of the night, Anything seems possible.
Even the unseen tapping of a force that seeks to make itself known. Sleep well, if you dare.
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ 09fbf8f3:fa3d60f0
2025-02-17 15:23:11
@ 09fbf8f3:fa3d60f0
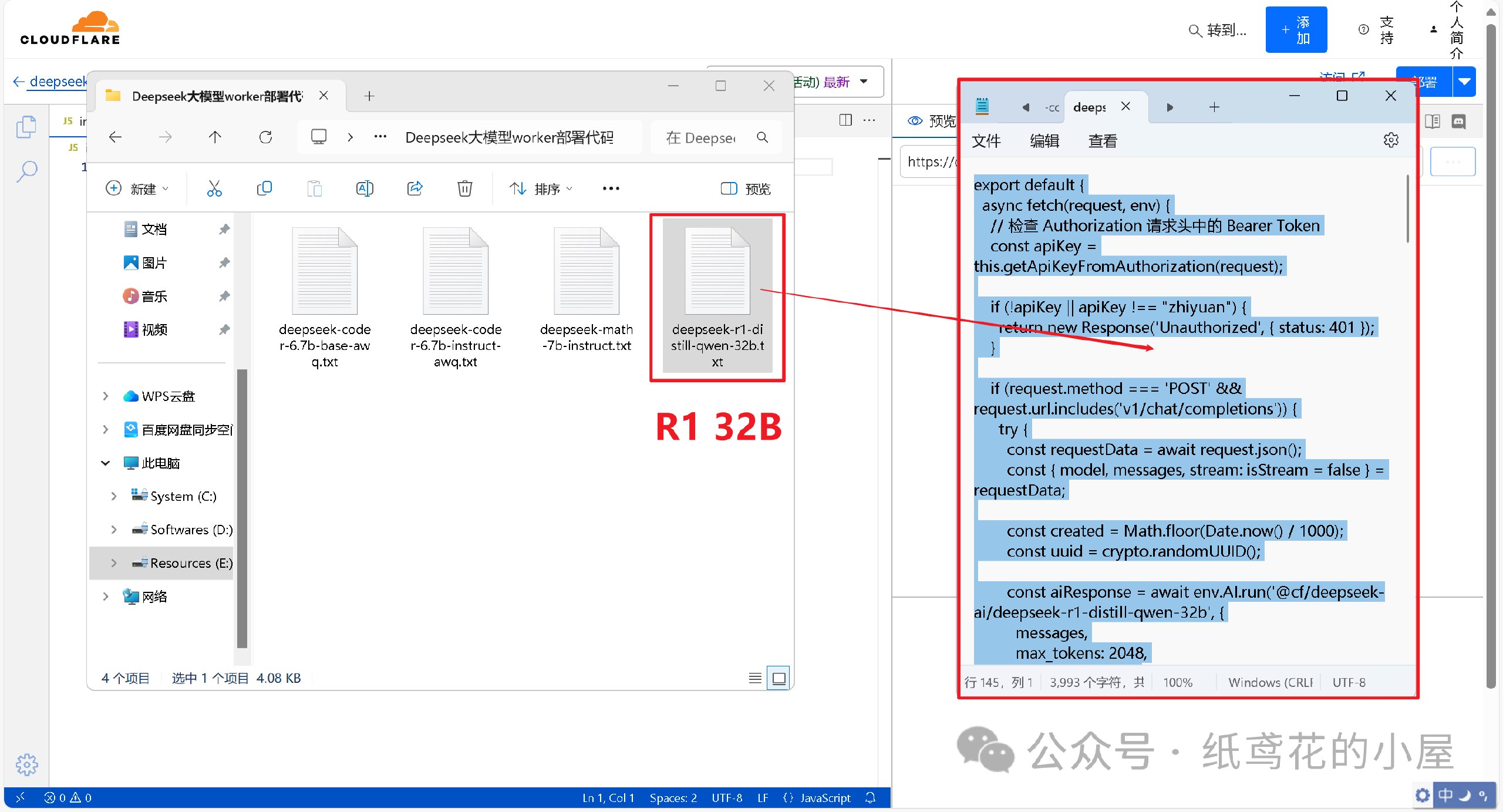
2025-02-17 15:23:11🌟 深度探索:在Cloudflare上免费部署DeepSeek-R1 32B大模型
🌍 一、 注册或登录Cloudflare平台(CF老手可跳过)
1️⃣ 进入Cloudflare平台官网:
。www.cloudflare.com/zh-cn/
登录或者注册账号。

2️⃣ 新注册的用户会让你选择域名,无视即可,直接点下面的Start building。
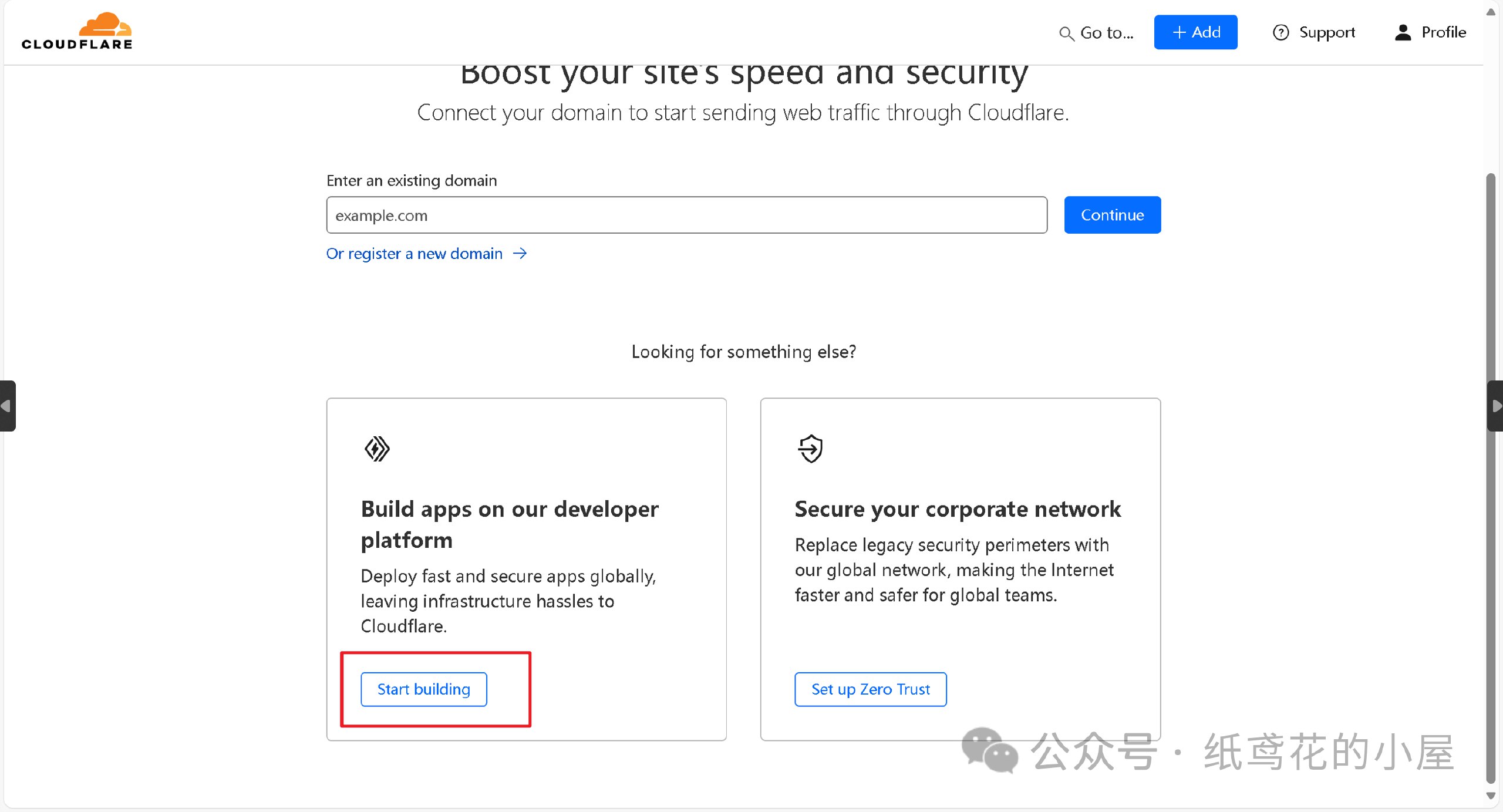
3️⃣ 进入仪表盘后,界面可能会显示英文,在右上角切换到[简体中文]即可。
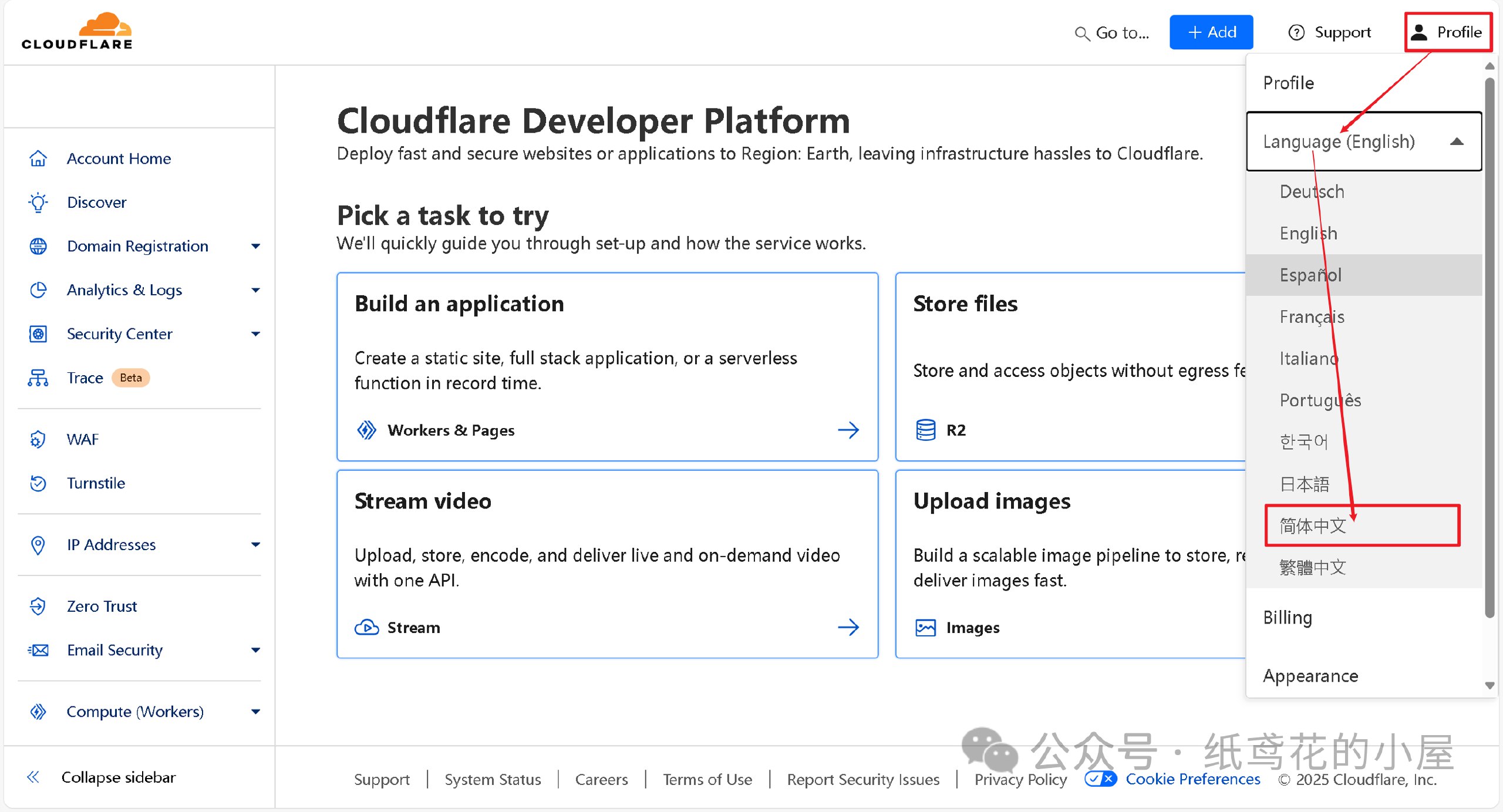
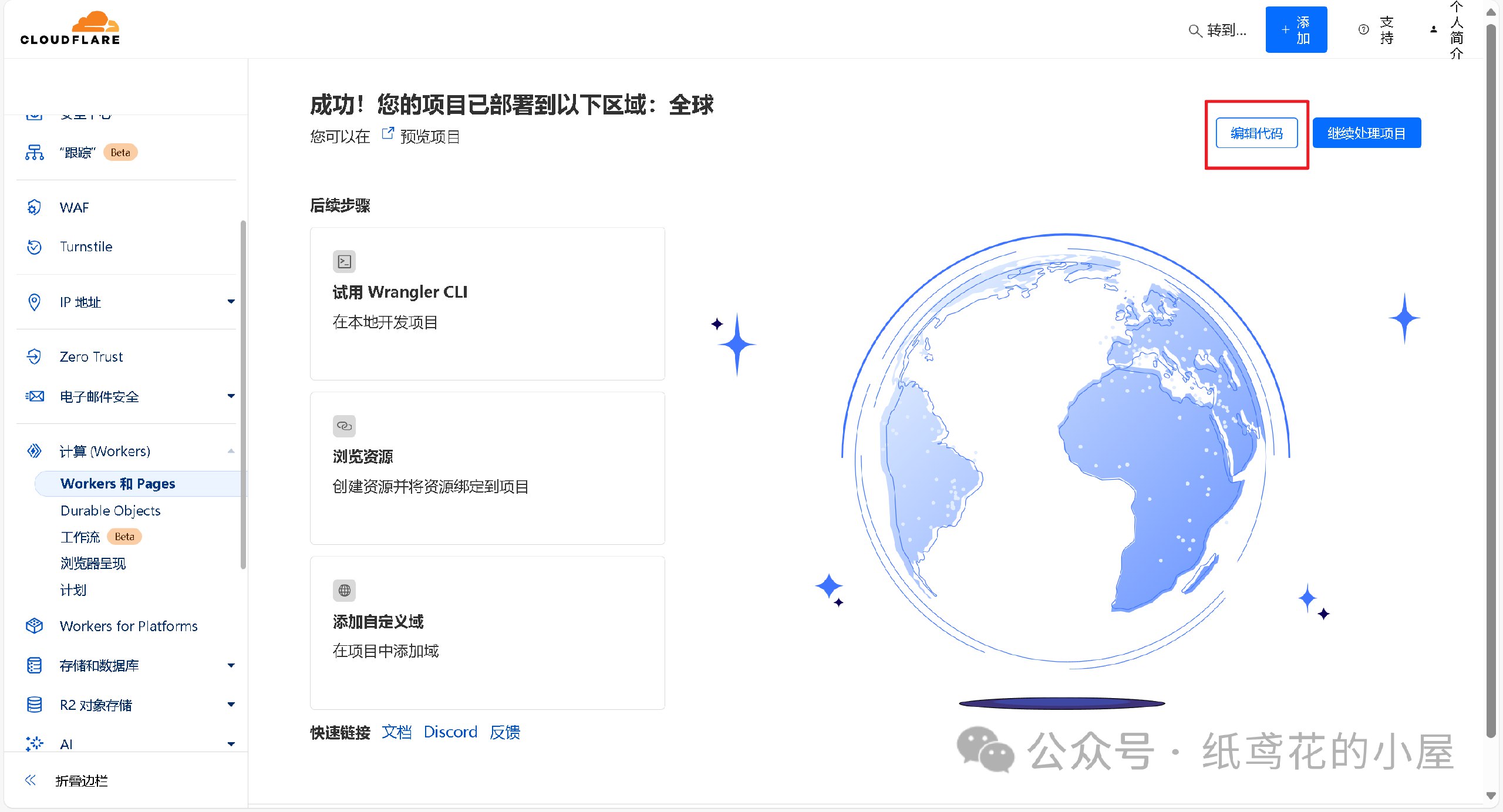
🚀 二、正式开始部署Deepseek API项目。
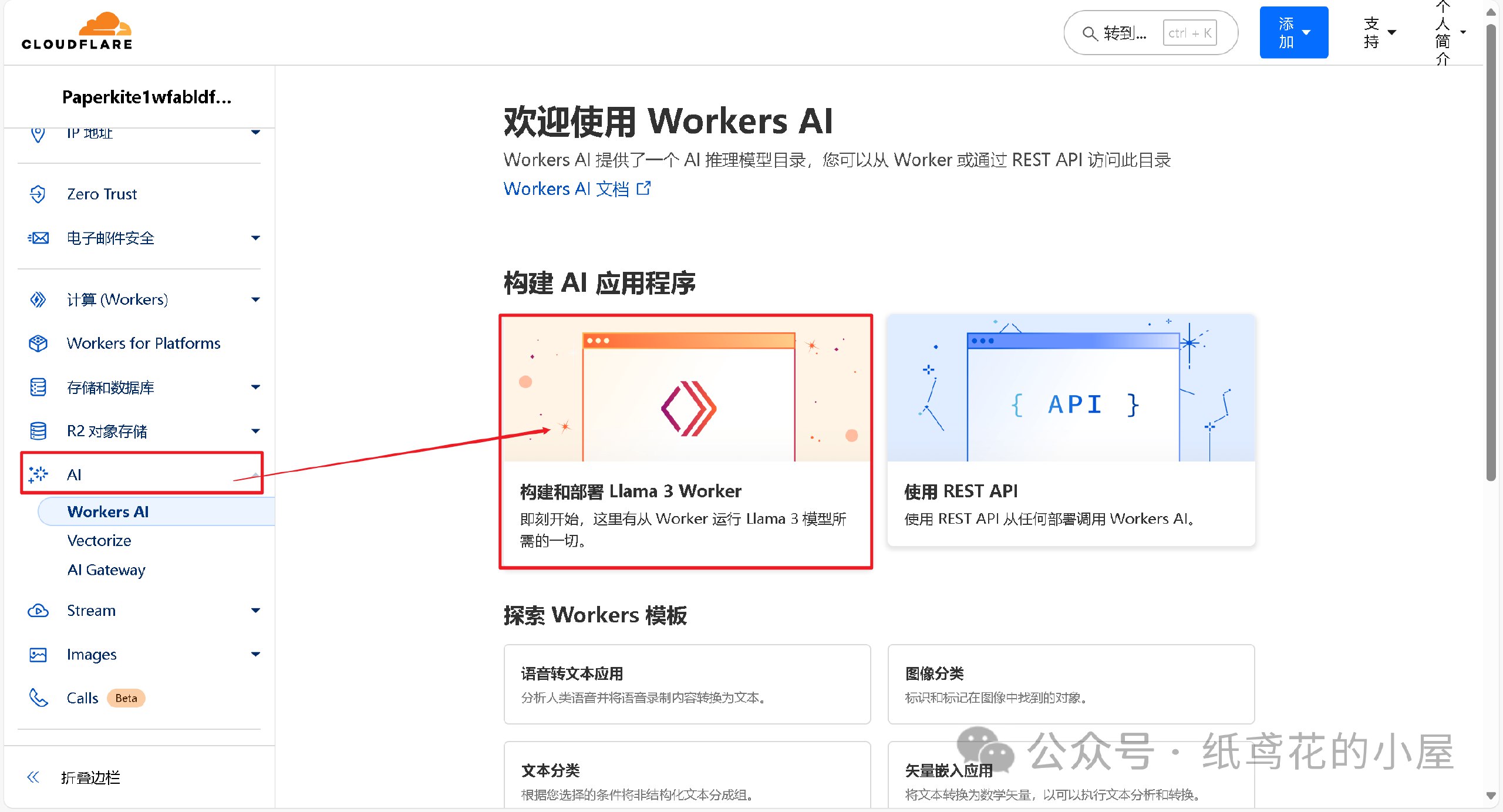
1️⃣ 首先在左侧菜单栏找到【AI】下的【Wokers AI】,选择【Llama 3 Woker】。
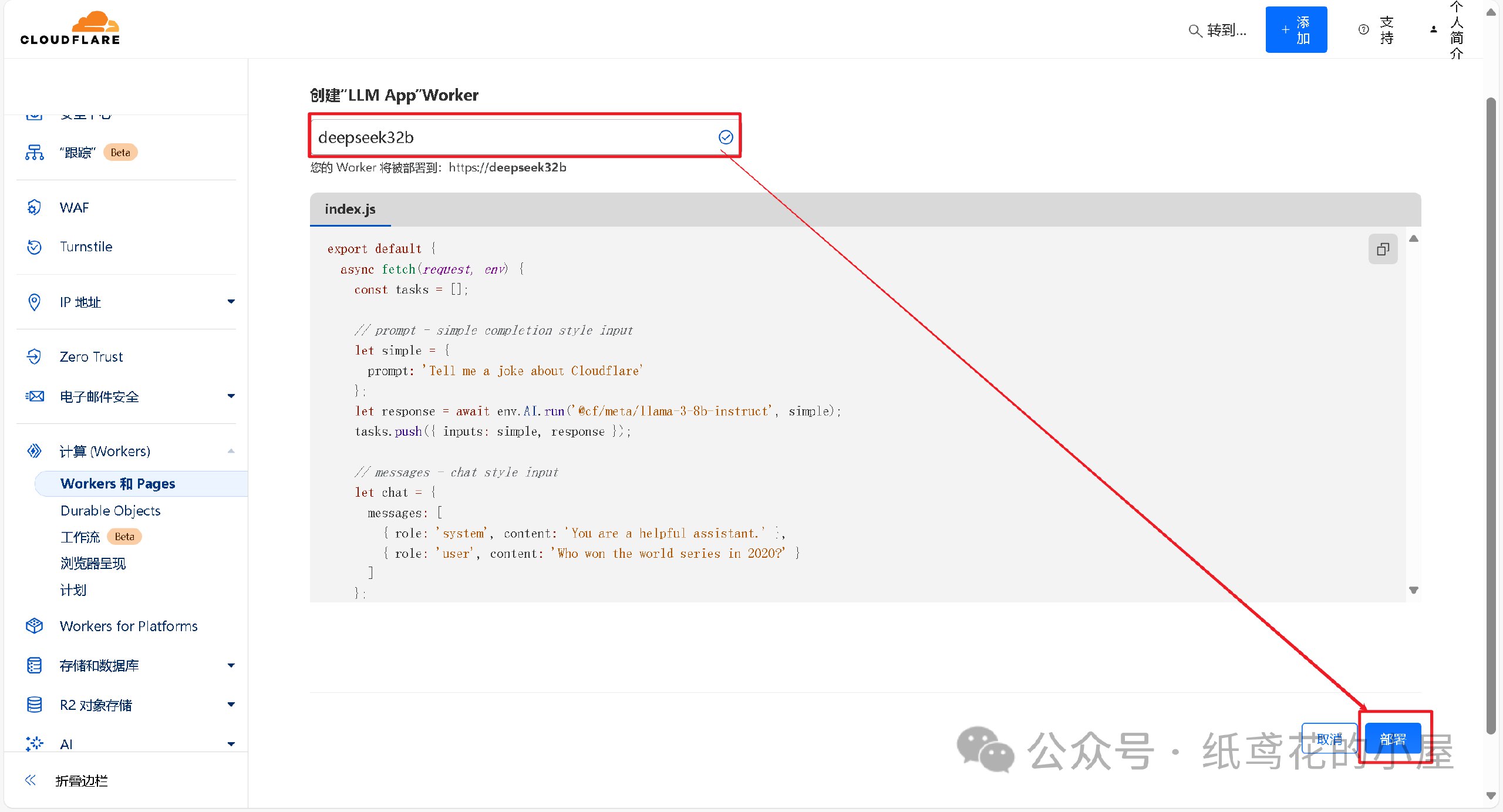
2️⃣ 为项目取一个好听的名字,后点击部署即可。
3️⃣ Woker项目初始化部署好后,需要编辑替换掉其原代码。
4️⃣ 解压出提供的代码压缩包,找到【32b】的部署代码,将里面的文本复制出来。
5️⃣ 接第3步,将项目里的原代码清空,粘贴第4步复制好的代码到编辑器。
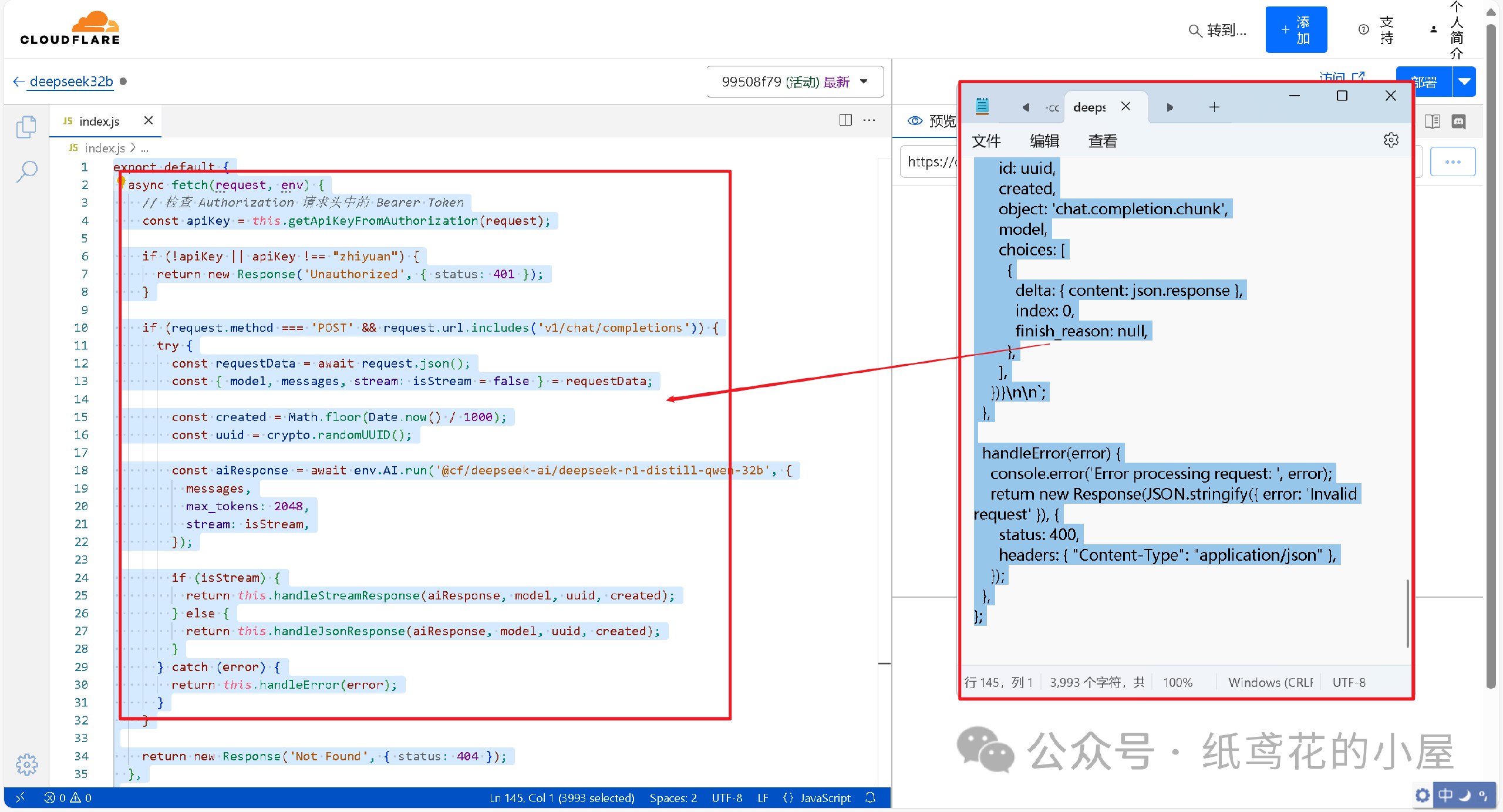
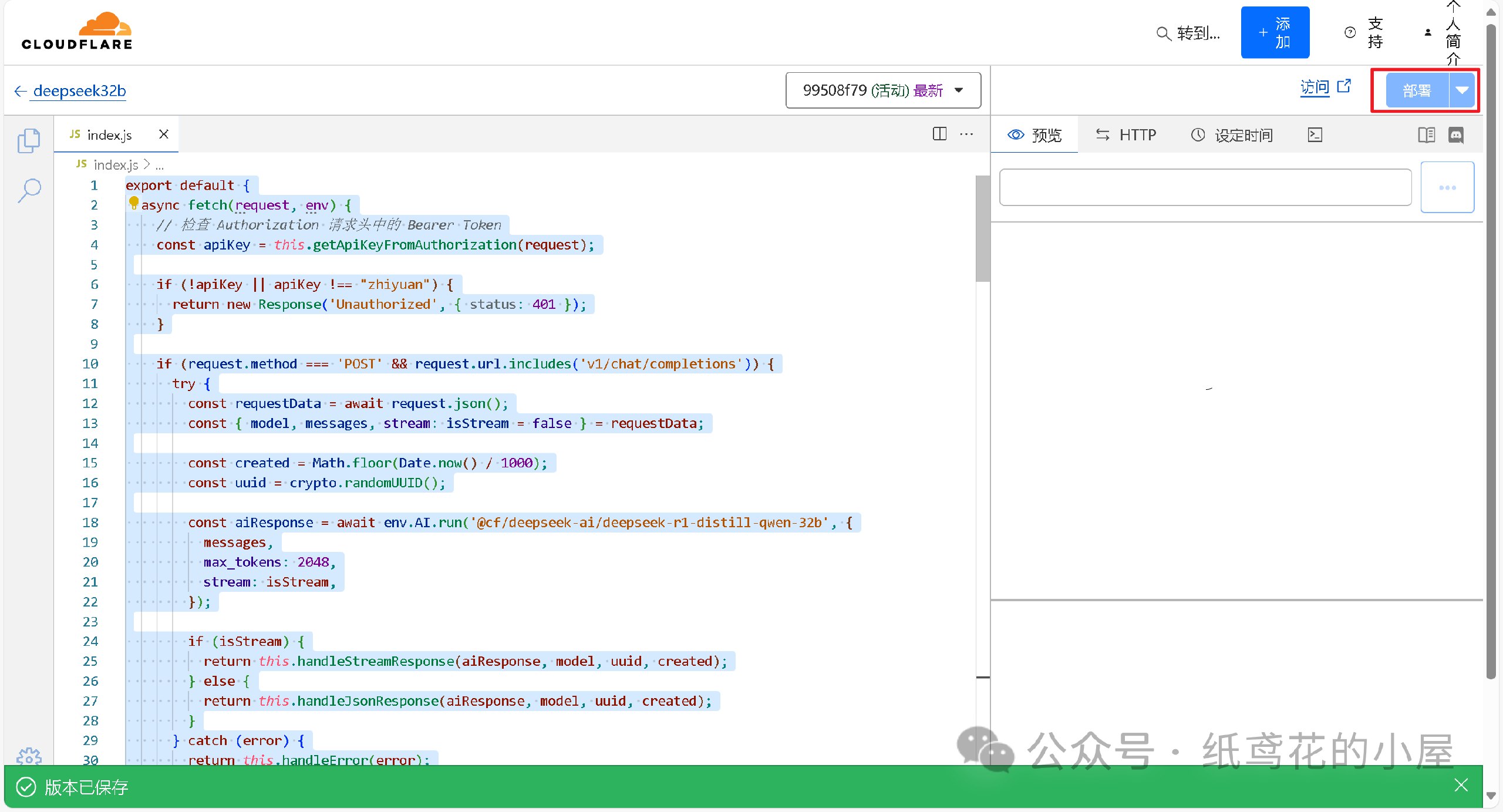
6️⃣ 代码粘贴完,即可点击右上角的部署按钮。
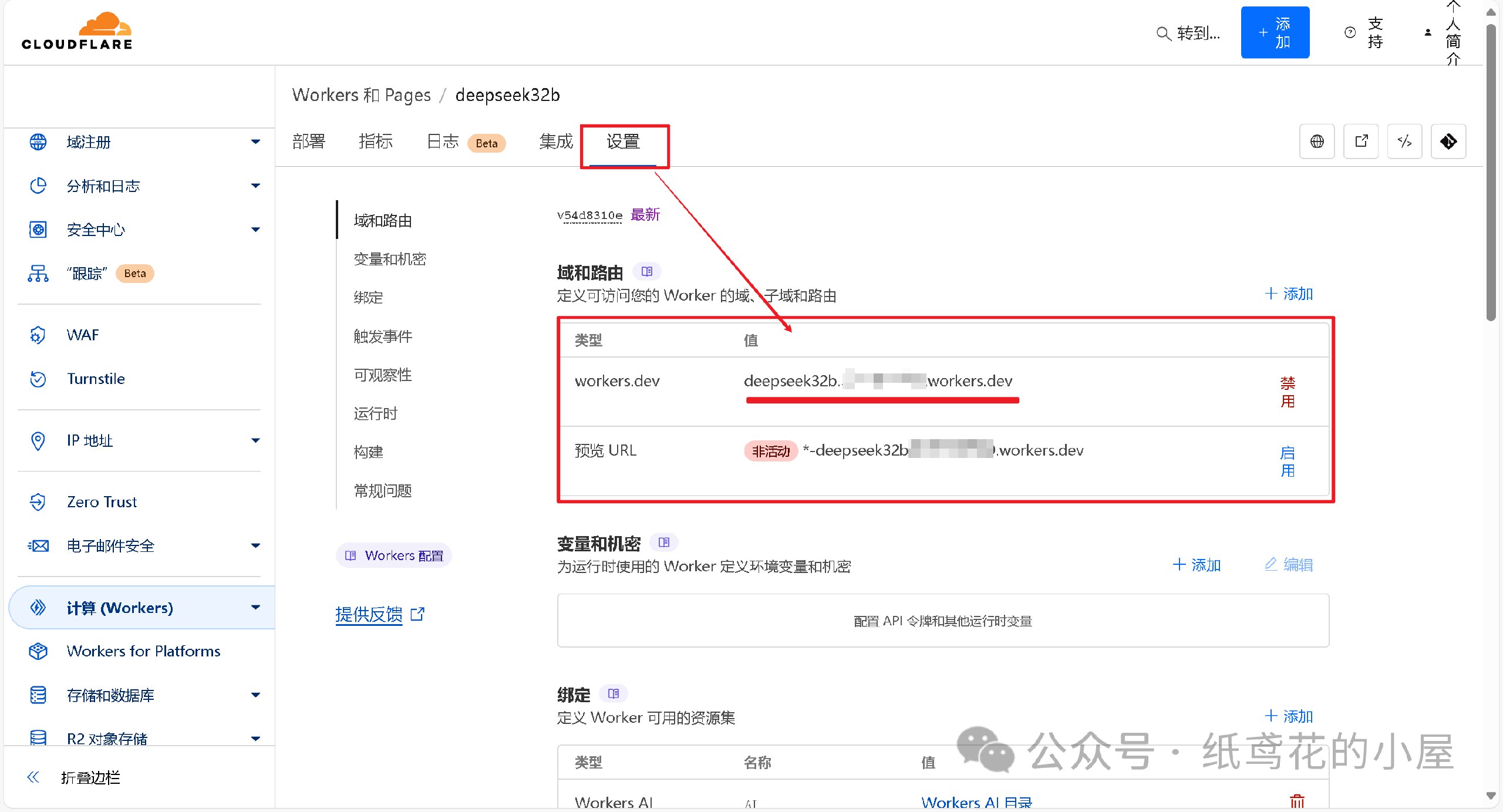
7️⃣ 回到仪表盘,点击部署完的项目名称。
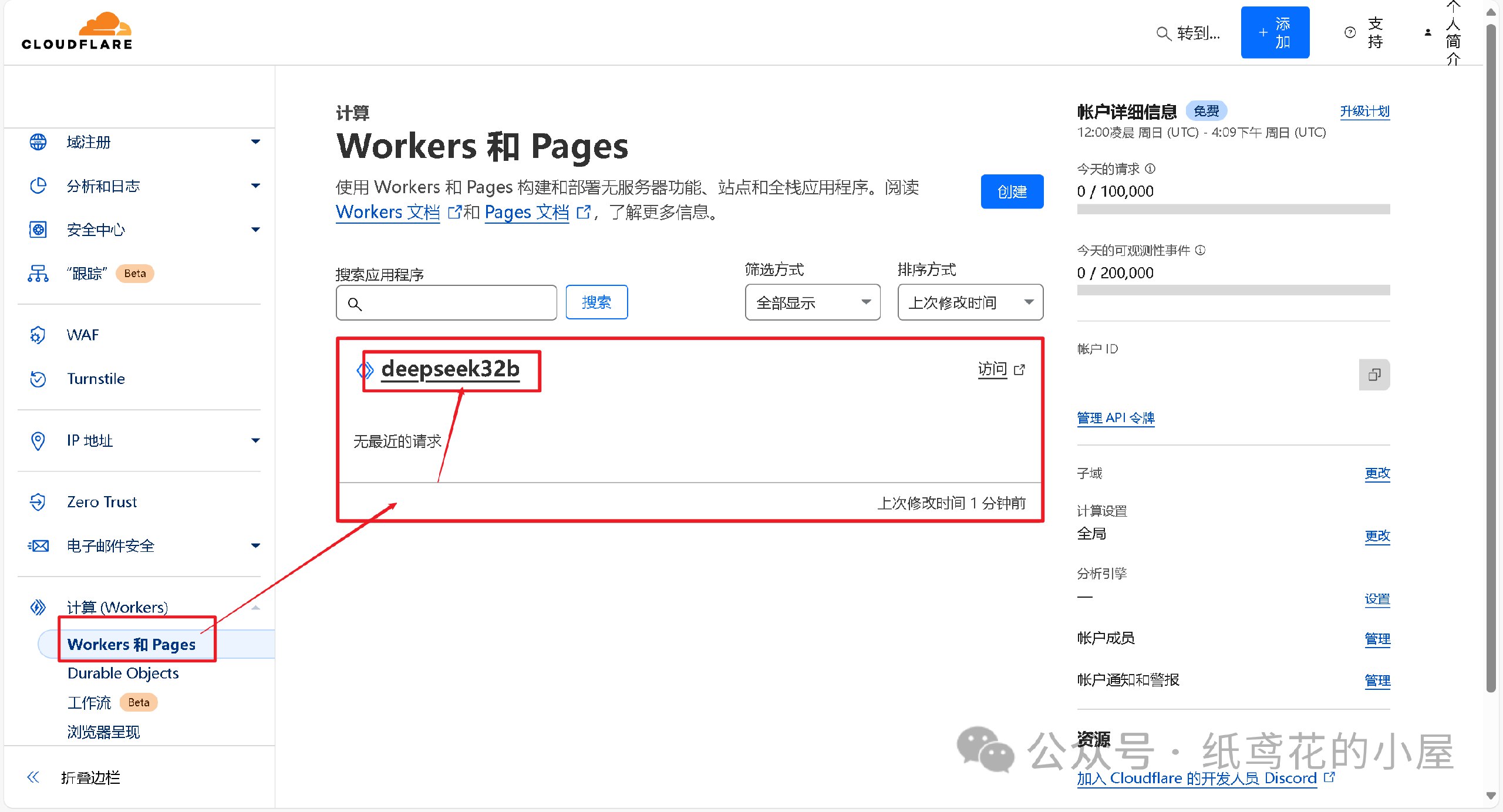
8️⃣ 查看【设置】,找到平台分配的项目网址,复制好备用。
💻 三、选择可用的UI软件,这边使用Chatbox AI演示。
1️⃣ 根据自己使用的平台下载对应的安装包,博主也一并打包好了全平台的软件安装包。

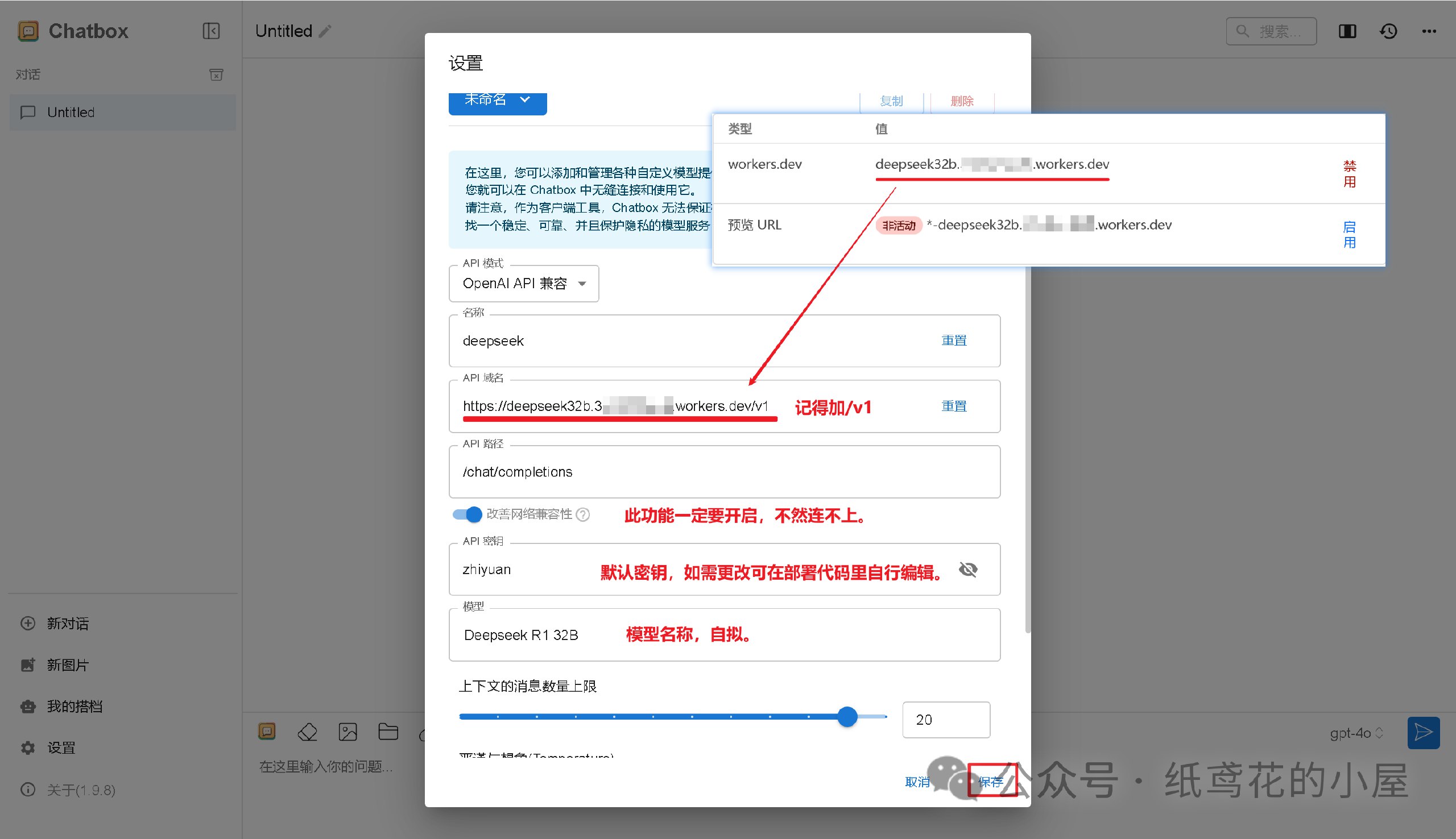
2️⃣ 打开安装好的Chatbox,点击左下角的设置。

3️⃣ 选择【添加自定义提供方】。

4️⃣ 按照图片说明填写即可,【API域名】为之前复制的项目网址(加/v1);【改善网络兼容性】功能务必开启;【API密钥】默认为”zhiyuan“,可自行修改;填写完毕后保存即可。
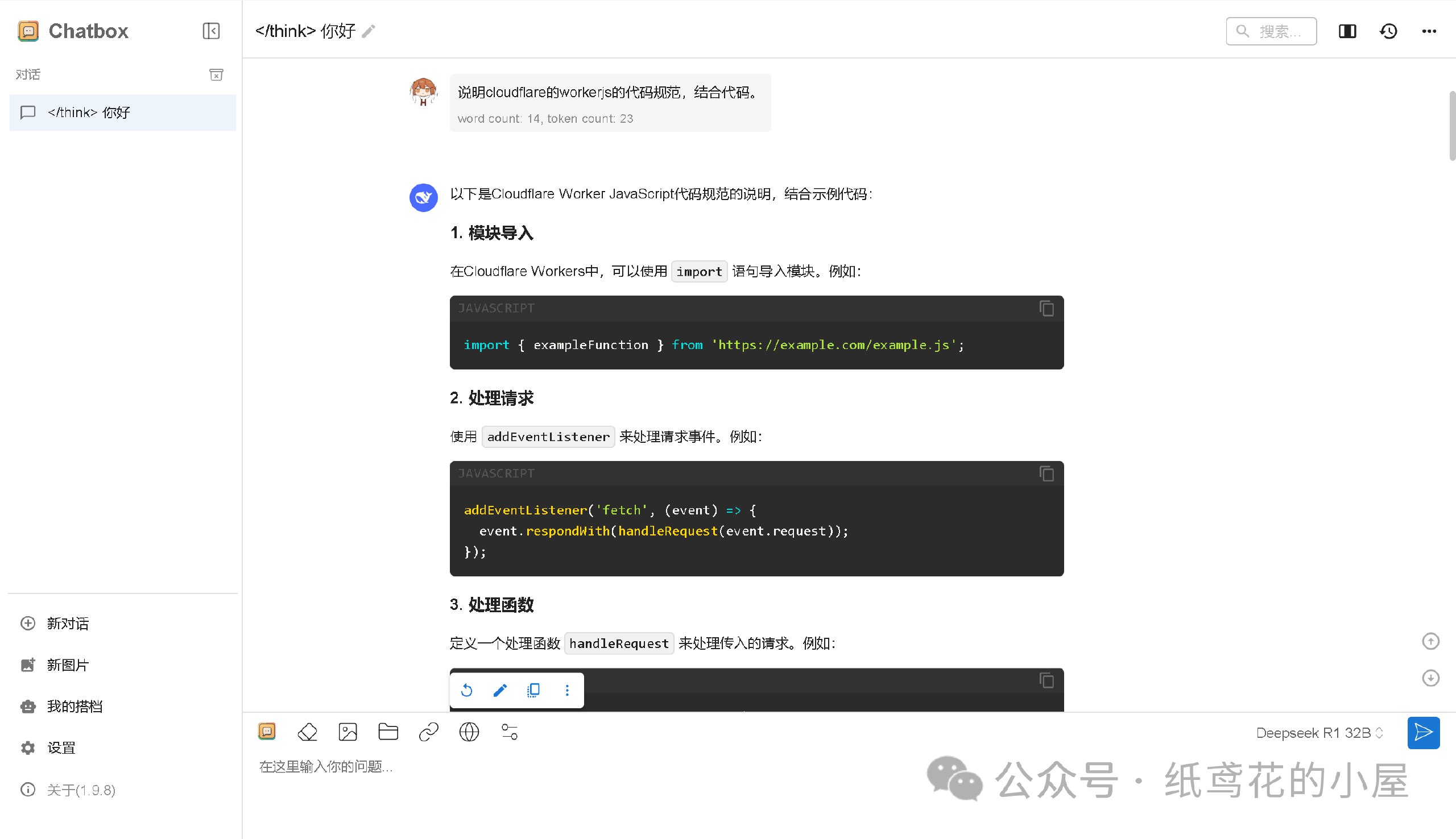
5️⃣ Cloudflare项目部署好后,就能正常使用了,接口仿照OpenAI API具有较强的兼容性,能导入到很多支持AI功能的软件或插件中。

6️⃣ Cloudflare的域名默认被墙了,需要自己准备一个域名设置。
转自微信公众号:纸鸢花的小屋
推广:低调云(梯子VPN)
。www.didiaocloud.xyz -
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 127d3bf5:466f416f
2025-02-09 03:31:22
@ 127d3bf5:466f416f
2025-02-09 03:31:22I can see why someone would think that buying some other crypto is a reasonable idea for "diversification" or even just for a bit of fun gambling, but it is not.
There are many reasons you should stick to Bitcoin only, and these have been proven correct every cycle. I've outlined these before but will cut and paste below as a summary.
The number one reason, is healthy ethical practice:
- The whole point of Bitcoin is to escape the trappings and flaws of traditional systems. Currency trading and speculative investing is a Tradfi concept, and you will end up back where you started. Sooner or later this becomes obvious to everyone. Bitcoin is the healthy and ethical choice for yourself and everyone else.
But...even if you want to be greedy, hold your horses:
- There is significant risk in wallets, defi, and cefi exchanges. Many have lost all their funds in these through hacks and services getting banned or going bankrupt.
- You get killed in exchange fees even when buying low and selling high. This is effectively a transaction tax which is often hidden (sometimes they don't show the fee, just mark up the exchange rate). Also true on defi exchanges.
- You are up against traders and founders with insider knowledge and much more sophisticated prediction models that will fleece you eventually. You cannot time the market better than they can, and it is their full-time to job to beat you and suck as much liquidity out of you as they can. House always wins.
- Every crypto trade is a taxable event, so you will be taxed on all gains anyway in most countries. So not only are the traders fleecing you, the govt is too.
- It ruins your quality of life constantly checking prices and stressing about making the wrong trade.
The best option, by far, is to slowly DCA into Bitcoin and take this off exchanges into your own custody. In the long run this strategy works out better financially, ethically, and from a quality-of-life perspective. Saving, not trading.
I've been here since 2014 and can personally attest to this.

-
 @ ec42c765:328c0600
2025-02-05 23:38:12
@ ec42c765:328c0600
2025-02-05 23:38:12カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ b7274d28:c99628cb
2025-02-04 05:31:13
@ b7274d28:c99628cb
2025-02-04 05:31:13For anyone interested in the list of essential essays from nostr:npub14hn6p34vegy4ckeklz8jq93mendym9asw8z2ej87x2wuwf8werasc6a32x (@anilsaidso) on Twitter that nostr:npub1h8nk2346qezka5cpm8jjh3yl5j88pf4ly2ptu7s6uu55wcfqy0wq36rpev mentioned on Read 856, here it is. I have compiled it with as many of the essays as I could find, along with the audio versions, when available. Additionally, if the author is on #Nostr, I have tagged their npub so you can thank them by zapping them some sats.
All credit for this list and the graphics accompanying each entry goes to nostr:npub14hn6p34vegy4ckeklz8jq93mendym9asw8z2ej87x2wuwf8werasc6a32x, whose original thread can be found here: Anil's Essential Essays Thread
1.

History shows us that the corruption of monetary systems leads to moral decay, social collapse, and slavery.
Essay: https://breedlove22.medium.com/masters-and-slaves-of-money-255ecc93404f
Audio: https://fountain.fm/episode/RI0iCGRCCYdhnMXIN3L6
2.
The 21st century emergence of Bitcoin, encryption, the internet, and millennials are more than just trends; they herald a wave of change that exhibits similar dynamics as the 16-17th century revolution that took place in Europe.
Author: nostr:npub13l3lyslfzyscrqg8saw4r09y70702s6r025hz52sajqrvdvf88zskh8xc2
Essay: https://casebitcoin.com/docs/TheBitcoinReformation_TuurDemeester.pdf
Audio: https://fountain.fm/episode/uLgBG2tyCLMlOp3g50EL
3.

There are many men out there who will parrot the "debt is money WE owe OURSELVES" without acknowledging that "WE" isn't a static entity, but a collection of individuals at different points in their lives.
Author: nostr:npub1guh5grefa7vkay4ps6udxg8lrqxg2kgr3qh9n4gduxut64nfxq0q9y6hjy
Essay: https://www.tftc.io/issue-754-ludwig-von-mises-human-action/
Audio: https://fountain.fm/episode/UXacM2rkdcyjG9xp9O2l
4.
If Bitcoin exists for 20 years, there will be near-universal confidence that it will be available forever, much as people believe the Internet is a permanent feature of the modern world.
Essay: https://vijayboyapati.medium.com/the-bullish-case-for-bitcoin-6ecc8bdecc1
Audio: https://fountain.fm/episode/jC3KbxTkXVzXO4vR7X3W
As you are surely aware, Vijay has expanded this into a book available here: The Bullish Case for Bitcoin Book
There is also an audio book version available here: The Bullish Case for Bitcoin Audio Book
5.

This realignment would not be traditional right vs left, but rather land vs cloud, state vs network, centralized vs decentralized, new money vs old, internationalist/capitalist vs nationalist/socialist, MMT vs BTC,...Hamilton vs Satoshi.
Essay: https://nakamoto.com/bitcoin-becomes-the-flag-of-technology/
Audio: https://fountain.fm/episode/tFJKjYLKhiFY8voDssZc
6.
I became convinced that, whether bitcoin survives or not, the existing financial system is working on borrowed time.
Essay: https://nakamotoinstitute.org/mempool/gradually-then-suddenly/
Audio: https://fountain.fm/episode/Mf6hgTFUNESqvdxEIOGZ
Parker Lewis went on to release several more articles in the Gradually, Then Suddenly series. They can be found here: Gradually, Then Suddenly Series
nostr:npub1h8nk2346qezka5cpm8jjh3yl5j88pf4ly2ptu7s6uu55wcfqy0wq36rpev has, of course, read all of them for us. Listing them all here is beyond the scope of this article, but you can find them by searching the podcast feed here: Bitcoin Audible Feed
Finally, Parker Lewis has refined these articles and released them as a book, which is available here: Gradually, Then Suddenly Book
7.

Bitcoin is a beautifully-constructed protocol. Genius is apparent in its design to most people who study it in depth, in terms of the way it blends math, computer science, cyber security, monetary economics, and game theory.
Author: nostr:npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a
Essay: https://www.lynalden.com/invest-in-bitcoin/
Audio: https://fountain.fm/episode/axeqKBvYCSP1s9aJIGSe
8.
Bitcoin offers a sweeping vista of opportunity to re-imagine how the financial system can and should work in the Internet era..
Essay: https://archive.nytimes.com/dealbook.nytimes.com/2014/01/21/why-bitcoin-matters/
9.

Using Bitcoin for consumer purchases is akin to driving a Concorde jet down the street to pick up groceries: a ridiculously expensive waste of an astonishing tool.
Author: nostr:npub1gdu7w6l6w65qhrdeaf6eyywepwe7v7ezqtugsrxy7hl7ypjsvxksd76nak
Essay: https://nakamotoinstitute.org/mempool/economics-of-bitcoin-as-a-settlement-network/
Audio: https://fountain.fm/episode/JoSpRFWJtoogn3lvTYlz
10.
The Internet is a dumb network, which is its defining and most valuable feature. The Internet’s protocol (..) doesn’t offer “services.” It doesn’t make decisions about content. It doesn’t distinguish between photos, text, video and audio.
Essay: https://fee.org/articles/decentralization-why-dumb-networks-are-better/
Audio: https://fountain.fm/episode/b7gOEqmWxn8RiDziffXf
11.

Most people are only familiar with (b)itcoin the electronic currency, but more important is (B)itcoin, with a capital B, the underlying protocol, which encapsulates and distributes the functions of contract law.
I was unable to find this essay or any audio version. Clicking on Anil's original link took me to Naval's blog, but that particular entry seems to have been removed.
12.

Bitcoin can approximate unofficial exchange rates which, in turn, can be used to detect both the existence and the magnitude of the distortion caused by capital controls & exchange rate manipulations.
Essay: https://papers.ssrn.com/sol3/Papers.cfm?abstract_id=2714921
13.
You can create something which looks cosmetically similar to Bitcoin, but you cannot replicate the settlement assurances which derive from the costliness of the ledger.
Essay: https://medium.com/@nic__carter/its-the-settlement-assurances-stupid-5dcd1c3f4e41
Audio: https://fountain.fm/episode/5NoPoiRU4NtF2YQN5QI1
14.
When we can secure the most important functionality of a financial network by computer science... we go from a system that is manual, local, and of inconsistent security to one that is automated, global, and much more secure.
Essay: https://nakamotoinstitute.org/library/money-blockchains-and-social-scalability/
Audio: https://fountain.fm/episode/VMH9YmGVCF8c3I5zYkrc
15.
The BCB enforces the strictest deposit regulations in the world by requiring full reserves for all accounts. ..money is not destroyed when bank debts are repaid, so increased money hoarding does not cause liquidity traps..
Author: nostr:npub1hxwmegqcfgevu4vsfjex0v3wgdyz8jtlgx8ndkh46t0lphtmtsnsuf40pf
Essay: https://nakamotoinstitute.org/mempool/the-bitcoin-central-banks-perfect-monetary-policy/
Audio: https://fountain.fm/episode/ralOokFfhFfeZpYnGAsD
16.

When Satoshi announced Bitcoin on the cryptography mailing list, he got a skeptical reception at best. Cryptographers have seen too many grand schemes by clueless noobs. They tend to have a knee jerk reaction.
Essay: https://nakamotoinstitute.org/library/bitcoin-and-me/
Audio: https://fountain.fm/episode/Vx8hKhLZkkI4cq97qS4Z
17.
No matter who you are, or how big your company is, 𝙮𝙤𝙪𝙧 𝙩𝙧𝙖𝙣𝙨𝙖𝙘𝙩𝙞𝙤𝙣 𝙬𝙤𝙣’𝙩 𝙥𝙧𝙤𝙥𝙖𝙜𝙖𝙩𝙚 𝙞𝙛 𝙞𝙩’𝙨 𝙞𝙣𝙫𝙖𝙡𝙞𝙙.
Essay: https://nakamotoinstitute.org/mempool/bitcoin-miners-beware-invalid-blocks-need-not-apply/
Audio: https://fountain.fm/episode/bcSuBGmOGY2TecSov4rC
18.
Just like a company trying to protect itself from being destroyed by a new competitor, the actions and reactions of central banks and policy makers to protect the system that they know, are quite predictable.
Author: nostr:npub1s05p3ha7en49dv8429tkk07nnfa9pcwczkf5x5qrdraqshxdje9sq6eyhe
Essay: https://medium.com/the-bitcoin-times/the-greatest-game-b787ac3242b2
Audio Part 1: https://fountain.fm/episode/5bYyGRmNATKaxminlvco
Audio Part 2: https://fountain.fm/episode/92eU3h6gqbzng84zqQPZ
19.

Technology, industry, and society have advanced immeasurably since, and yet we still live by Venetian financial customs and have no idea why. Modern banking is the legacy of a problem that technology has since solved.
Author: nostr:npub1sfhflz2msx45rfzjyf5tyj0x35pv4qtq3hh4v2jf8nhrtl79cavsl2ymqt
Essay: https://allenfarrington.medium.com/bitcoin-is-venice-8414dda42070
Audio: https://fountain.fm/episode/s6Fu2VowAddRACCCIxQh
Allen Farrington and Sacha Meyers have gone on to expand this into a book, as well. You can get the book here: Bitcoin is Venice Book
And wouldn't you know it, Guy Swann has narrated the audio book available here: Bitcoin is Venice Audio Book
20.

The rich and powerful will always design systems that benefit them before everyone else. The genius of Bitcoin is to take advantage of that very base reality and force them to get involved and help run the system, instead of attacking it.
Author: nostr:npub1trr5r2nrpsk6xkjk5a7p6pfcryyt6yzsflwjmz6r7uj7lfkjxxtq78hdpu
Essay: https://quillette.com/2021/02/21/can-governments-stop-bitcoin/
Audio: https://fountain.fm/episode/jeZ21IWIlbuC1OGnssy8
21.
In the realm of information, there is no coin-stamping without time-stamping. The relentless beating of this clock is what gives rise to all the magical properties of Bitcoin.
Author: nostr:npub1dergggklka99wwrs92yz8wdjs952h2ux2ha2ed598ngwu9w7a6fsh9xzpc
Essay: https://dergigi.com/2021/01/14/bitcoin-is-time/
Audio: https://fountain.fm/episode/pTevCY2vwanNsIso6F6X
22.
You can stay on the Fiat Standard, in which some people get to produce unlimited new units of money for free, just not you. Or opt in to the Bitcoin Standard, in which no one gets to do that, including you.
Essay: https://casebitcoin.com/docs/StoneRidge_2020_Shareholder_Letter.pdf
Audio: https://fountain.fm/episode/PhBTa39qwbkwAtRnO38W
23.
Long term investors should use Bitcoin as their unit of account and every single investment should be compared to the expected returns of Bitcoin.
Essay: https://nakamotoinstitute.org/mempool/everyones-a-scammer/
Audio: https://fountain.fm/episode/vyR2GUNfXtKRK8qwznki
24.
When you’re in the ivory tower, you think the term “ivory tower” is a silly misrepresentation of your very normal life; when you’re no longer in the ivory tower, you realize how willfully out of touch you were with the world.
Essay: https://www.citadel21.com/why-the-yuppie-elite-dismiss-bitcoin
Audio: https://fountain.fm/episode/7do5K4pPNljOf2W3rR2V
You might notice that many of the above essays are available from the Satoshi Nakamoto Institute. It is a veritable treasure trove of excellent writing on subjects surrounding #Bitcoin and #AustrianEconomics. If you find value in them keeping these written works online for the next wave of new Bitcoiners to have an excellent source of education, please consider donating to the cause.
-
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ 37fe9853:bcd1b039
2025-01-11 15:04:40
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
-
 @ 62033ff8:e4471203
2025-01-11 15:00:24
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my free to read/share attempt to write a novel, but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
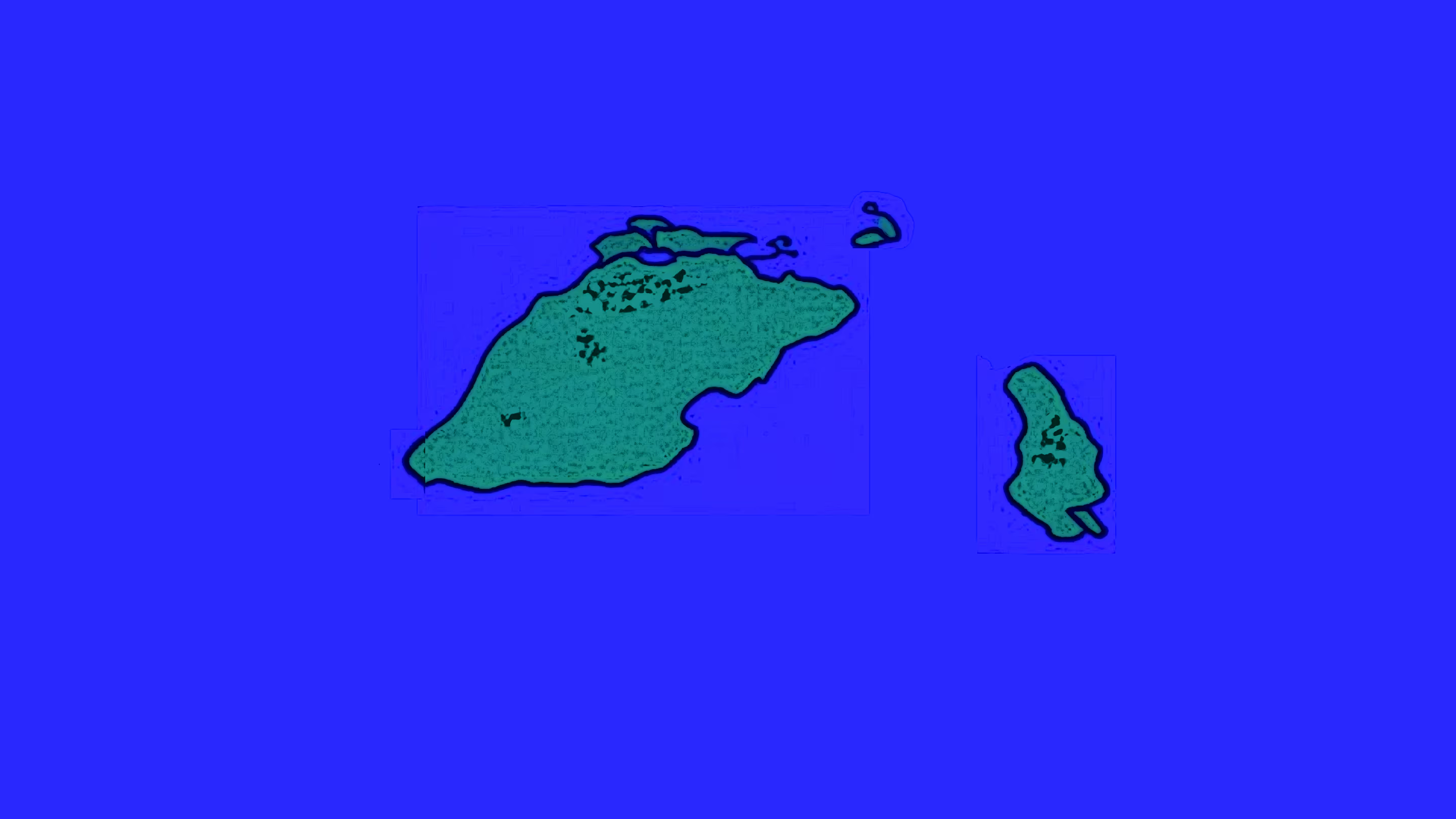
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-
 @ 3f770d65:7a745b24
2025-01-05 18:56:33
@ 3f770d65:7a745b24
2025-01-05 18:56:33New Year’s resolutions often feel boring and repetitive. Most revolve around getting in shape, eating healthier, or giving up alcohol. While the idea is interesting—using the start of a new calendar year as a catalyst for change—it also seems unnecessary. Why wait for a specific date to make a change? If you want to improve something in your life, you can just do it. You don’t need an excuse.
That’s why I’ve never been drawn to the idea of making a list of resolutions. If I wanted a change, I’d make it happen, without worrying about the calendar. At least, that’s how I felt until now—when, for once, the timing actually gave me a real reason to embrace the idea of New Year’s resolutions.
Enter Olas.
If you're a visual creator, you've likely experienced the relentless grind of building a following on platforms like Instagram—endless doomscrolling, ever-changing algorithms, and the constant pressure to stay relevant. But what if there was a better way? Olas is a Nostr-powered alternative to Instagram that prioritizes community, creativity, and value-for-value exchanges. It's a game changer.
Instagram’s failings are well-known. Its algorithm often dictates whose content gets seen, leaving creators frustrated and powerless. Monetization hurdles further alienate creators who are forced to meet arbitrary follower thresholds before earning anything. Additionally, the platform’s design fosters endless comparisons and exposure to negativity, which can take a significant toll on mental health.
Instagram’s algorithms are notorious for keeping users hooked, often at the cost of their mental health. I've spoken about this extensively, most recently at Nostr Valley, explaining how legacy social media is bad for you. You might find yourself scrolling through content that leaves you feeling anxious or drained. Olas takes a fresh approach, replacing "doomscrolling" with "bloomscrolling." This is a common theme across the Nostr ecosystem. The lack of addictive rage algorithms allows the focus to shift to uplifting, positive content that inspires rather than exhausts.
Monetization is another area where Olas will set itself apart. On Instagram, creators face arbitrary barriers to earning—needing thousands of followers and adhering to restrictive platform rules. Olas eliminates these hurdles by leveraging the Nostr protocol, enabling creators to earn directly through value-for-value exchanges. Fans can support their favorite artists instantly, with no delays or approvals required. The plan is to enable a brand new Olas account that can get paid instantly, with zero followers - that's wild.
Olas addresses these issues head-on. Operating on the open Nostr protocol, it removes centralized control over one's content’s reach or one's ability to monetize. With transparent, configurable algorithms, and a community that thrives on mutual support, Olas creates an environment where creators can grow and succeed without unnecessary barriers.
Join me on my New Year's resolution. Join me on Olas and take part in the #Olas365 challenge! It’s a simple yet exciting way to share your content. The challenge is straightforward: post at least one photo per day on Olas (though you’re welcome to share more!).
Download on Android or download via Zapstore.
Let's make waves together.
-
 @ e6817453:b0ac3c39
2025-01-05 14:29:17
@ e6817453:b0ac3c39
2025-01-05 14:29:17The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
- Enhance LLM Outputs: By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
- Support Complex Queries: Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
- Richness of Entities: Effective retrieval depends on graphs populated with rich, detailed entities.
- Freedom from Hallucinations: Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
- Handle diverse data sources with ease.
- Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
- Defining Relationships: Clarifying how concepts connect within a domain.
- Validating Graph Structures: Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
- Assign a Knowledge Champion: Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
- Provide Training: Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
- Leverage Partnerships: Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
- Utilize Tools: Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
- Iterate with Feedback: Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
-
Leverage Existing Ontologies: Many industries and domains already have open ontologies. For instance:
-
Public Knowledge Graphs: Resources like Wikipedia’s graph offer a wealth of structured knowledge.
- Industry Standards: Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
-
Business Framework Ontology (BFO): A valuable resource for enterprises looking to define business processes and structures.
-
Build In-House Expertise: If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
-
Utilize LLMs for Ontology Construction: Interestingly, LLMs themselves can act as a starting point for ontology development:
-
Prompt-Based Extraction: LLMs can generate draft ontologies by leveraging their extensive training on graph data.
- Domain Expert Refinement: Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
- Detecting Hallucinations: Differentiating between genuine insights and AI-generated inaccuracies.
- Ensuring Completeness: Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
- Generate Skeleton Ontologies: Prompt LLMs with domain-specific information to draft initial ontology structures.
- Validate and Refine Ontologies: Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ b17fccdf:b7211155
2024-12-29 12:04:31
@ b17fccdf:b7211155
2024-12-29 12:04:31🆕 What's changed:
- New bonus guide dedicated to install/upgrade/uninstall PostgreSQL
- Modified the LND guide to use PostgreSQL instead of bbolt
- Modified the Nostr relay guide to use PostgreSQL instead of SQLite (experimental)
- Modified the BTCPay Server bonus guide according to these changes
- Used the lndinit MiniBolt org fork, to add an extra section to migrate an existing LND bbolt database to PostgreSQL (🚨⚠️Experimental - use it behind your responsibility⚠️🚨)
- New Golang bonus guide as a common language for the lndinit compile
- Updated LND to v0.18
- New Bitcoin Core extra section to renovate Tor & I2P addresses
- New Bitcoin Core extra section to generate a full
bitcoin.conffile - Rebuilt some homepage sections and general structure
- Deleted the
$symbol of the commands to easy copy-paste to the terminal - Deleted the initial incoming and the outgoing rules configuration of UFW, due to it being by default
🪧 PD: If you want to use the old database backend of the LND or Nostr relay, follow the next extra sections:
- Use the default bbolt database backend for the LND
- Use the default SQLite database backend for the Nostr relay
⚠️Attention⚠️: The migration process was tested on testnet mode from an existing bbolt database backend to a new PostgreSQL database using lndinit and the results were successful. However, It wasn't tested on mainnet, according to the developer, it is in experimental status which could damage your existing LND database.🚨 Use it behind your responsibility 🧼
🔧 PR related: https://github.com/minibolt-guide/minibolt/pull/93
♻️ Migrate the PostgreSQL database location
If you installed NBXplorer + BTCPay Server, it is probably you have the database of the PostgreSQL cluster on the default path (
/var/lib/postgresql/16/main/), follow the next instructions to migrate it to the new dedicated location on/data/postgresdbfolder:- With user
admincreate the dedicated PostgreSQL data folder
sudo mkdir /data/postgresdb- Assign as the owner to the
postgresuser
sudo chown postgres:postgres /data/postgresdb- Assign permissions of the data folder only to the
postgresuser
sudo chmod -R 700 /data/postgresdb- Stop NBXplorer and BTCPay Server
sudo systemctl stop nbxplorer && sudo systemctl stop btcpayserver- Stop PostgreSQL
sudo systemctl stop postgresql- Use the rsync command to copy all files from the existing database on (
/var/lib/postgresql/16/main) to the new destination directory (/data/postgresdb)
sudo rsync -av /var/lib/postgresql/16/main/ /data/postgresdb/Expected output:
``` sending incremental file list ./ PG_VERSION postgresql.auto.conf postmaster.opts postmaster.pid base/ base/1/ base/1/112 base/1/113 base/1/1247 base/1/1247_fsm base/1/1247_vm base/1/1249 base/1/1249_fsm base/1/1249_vm [...] pg_wal/000000010000000000000009 pg_wal/archive_status/ pg_xact/ pg_xact/0000
sent 164,483,875 bytes received 42,341 bytes 36,561,381.33 bytes/sec total size is 164,311,368 speedup is 1.00 ```
- Edit the PostgreSQL data directory on configuration, to redirect the store to the new location
sudo nano /etc/postgresql/16/main/postgresql.conf --linenumbers- Replace the line 42 to this. Save and exit
data_directory = '/data/postgresdb'- Start PostgreSQL to apply changes and monitor the correct status of the main instance and sub-instance monitoring sessions before
sudo systemctl start postgresql- You can monitor the PostgreSQL main instance by the systemd journal and check the log output to ensure all is correct. You can exit the monitoring at any time with Ctrl-C
journalctl -fu postgresqlExample of the expected output:
Nov 08 11:51:10 minibolt systemd[1]: Stopped PostgreSQL RDBMS. Nov 08 11:51:10 minibolt systemd[1]: Stopping PostgreSQL RDBMS... Nov 08 11:51:13 minibolt systemd[1]: Starting PostgreSQL RDBMS... Nov 08 11:51:13 minibolt systemd[1]: Finished PostgreSQL RDBMS.- You can monitor the PostgreSQL sub-instance by the systemd journal and check log output to ensure all is correct. You can exit monitoring at any time with Ctrl-C
journalctl -fu postgresql@16-mainExample of the expected output:
Nov 08 11:51:10 minibolt systemd[1]: Stopping PostgreSQL Cluster 16-main... Nov 08 11:51:11 minibolt systemd[1]: postgresql@16-main.service: Succeeded. Nov 08 11:51:11 minibolt systemd[1]: Stopped PostgreSQL Cluster 16-main. Nov 08 11:51:11 minibolt systemd[1]: postgresql@16-main.service: Consumed 1h 10min 8.677s CPU time. Nov 08 11:51:11 minibolt systemd[1]: Starting PostgreSQL Cluster 16-main... Nov 08 11:51:13 minibolt systemd[1]: Started PostgreSQL Cluster 16-main.- Start NBXplorer and BTCPay Server again
sudo systemctl start nbxplorer && sudo systemctl start btcpayserver- Monitor to make sure everything is as you left it. You can exit monitoring at any time with Ctrl-C
journalctl -fu nbxplorerjournalctl -fu btcpayserverEnjoy it MiniBolter! 💙
-
 @ 8d34bd24:414be32b
2025-03-30 23:16:09
@ 8d34bd24:414be32b
2025-03-30 23:16:09When it comes to speaking the truth, obeying God, or living a godly life, the average or the compromise is not necessarily correct, but frequently we do err to one extreme or the other.
Mercy or Wrath?
One area of controversy is whether we serve a God of love & mercy or a God of holiness & wrath. The truth is that the God of the Bible is both love and holiness and he acts in mercy and in wrath.
If we focus too much on God’s holiness and wrath, we become solely about robotically obeying laws and about all of the things we can’t do. We will fail to show love and mercy as Jesus showed those lost in sin. We will fail to show the mercy and love He showed to us. We become much like the Pharisees, whom Jesus called “whitewashed tombs.”
Instead, speaking the truth in love, we will grow to become in every respect the mature body of him who is the head, that is, Christ. (Ephesians 4:15)
We need to always speak the truth, but in a loving and merciful way.
Grace, mercy and peace from God the Father and from Jesus Christ, the Father’s Son, will be with us in truth and love. (2 John 1:3)
If we focus too much on God’s love and mercy, we can forget that the God of the Bible is holy and righteous and can’t stand to be in the presence of sinfulness. We can begin to soften God’s holy word to be little more than suggestions. Even worse, we can bend God’s word to the point that it no longer resembles His clearly communicated commands. Also, if we don’t call sin “sin” and sinners “sinners,” then those same sinners will never understand their need for a Savior and never trust Jesus in repentance. If God isn’t holy and we aren’t sinners, then why would anyone need a Savior?
But just as he who called you is holy, so be holy in all you do; (1 Peter 1:15)
We need to treat God and His word as holy, while showing love to His creation.
If I speak in the tongues of men or of angels, but do not have love, I am only a resounding gong or a clanging cymbal. (1 Corinthians 13:1)
God/Jesus/Holy Spirit are holy and loving. If we leave out either side of His character, then we aren’t telling people about the God of the Bible. We have made a God in the image we desire, rather than who He is. If we go to either extreme, we lose who God really is and it will affect both our relationship with God and our relationship with others detrimentally.
Faith or Works?
Another area of contention is relating to faith and works. What is more important — faith or works? Are they not both important?
Many believers focus on faith. Sola Fide (faith alone).
For it is by grace you have been saved, through faith—and this is not from yourselves, it is the gift of God— not by works, so that no one can boast. (Ephesians 2:8-9)
This is a true statement that Salvation comes solely through faith in what Jesus did for us. We don’t get any credit for our own works. All that is good and righteous in us is from the covering of the blood of Jesus and His good works and His power.
But since many people focus on faith alone, they can come to believe that they can live any way that pleases them.
What shall we say, then? Shall we go on sinning so that grace may increase? By no means! We are those who have died to sin; how can we live in it any longer? Or don’t you know that all of us who were baptized into Christ Jesus were baptized into his death? We were therefore buried with him through baptism into death in order that, just as Christ was raised from the dead through the glory of the Father, we too may live a new life. (Romans 6:1-4) {emphasis mine}
By focusing solely on faith, we can be tempted to live life however we please instead of living a life in submission to Our God and Savior. Our lives can be worthless instead of us acting as good servants.
If any man’s work is burned up, he will suffer loss; but he himself will be saved, yet so as through fire. (1 Corinthians 3:15)
At the same time, there are many who are so focused on good works that they leave faith out of it — either a lack of faith themselves or a failure to communicate the need for faith when sharing the gospel. They try to earn their way to heaven. They try to impress those around them by their works.
But they do all their deeds to be noticed by men; for they broaden their phylacteries and lengthen the tassels of their garments. They love the place of honor at banquets and the chief seats in the synagogues, and respectful greetings in the market places, and being called Rabbi by men. (Matthew 25:5-7)
I think James best communicates the balance between faith and works.
What use is it, my brethren, if someone says he has faith but he has no works? Can that faith save him? If a brother or sister is without clothing and in need of daily food, and one of you says to them, “Go in peace, be warmed and be filled,” and yet you do not give them what is necessary for their body, what use is that? Even so faith, if it has no works, is dead, being by itself.
But someone may well say, “You have faith and I have works; show me your faith without the works, and I will show you my faith by my works.” You believe that God is one. You do well; the demons also believe, and shudder. But are you willing to recognize, you foolish fellow, that faith without works is useless? Was not Abraham our father justified by works when he offered up Isaac his son on the altar? You see that faith was working with his works, and as a result of the works, faith was perfected; and the Scripture was fulfilled which says, “And Abraham believed God, and it was reckoned to him as righteousness,” and he was called the friend of God. You see that a man is justified by works and not by faith alone. (James 2:14-24) {emphasis mine}
Let’s look at some of the details here to find the truth. “if someone says he has faith but he has no works? Can that faith save him?” Can the kind of faith that has no works, that has no evidence, save a person? If a person truly has saving faith, there will be evidence in their world view and the way they live their life. “Even so faith, if it has no works, is dead, being by itself.” We are saved by faith alone, but if we are saved we will have works. Faith “by itself” is not saving faith, for “the demons also believe, and shudder.” I don’t think anyone would argue that the demons have saving faith, yet they believe and shudder.
Works are the evidence of true faith leading to salvation, but it is only faith that saves.
Speak the Truth or Love?
Whether we stand firmly and always loudly speak the truth or whether we show love and mercy is related to how we view God (as loving or as holy), but I thought how we respond was worth its own discussion.
Sometimes people are so worried about love and unity that they compromise the truth. They may actively compromise the truth by claiming the Bible says something other than what it says, i.e.. old earth vs young earth, or marriage is about two people who love each other vs marriage being defined by God as one woman and one man. Sometimes this compromise is just avoiding talking about uncomfortable subjects completely so that no one is made to feel bad. This is a problem because God said what He said and means what He said.
but speaking the truth in love, we are to grow up in all aspects into Him who is the head, even Christ, (Ephesians 4:15)
Avoiding speaking the whole truth is effectively lying about what God’s word said (see my previous post on “The Truth, The Whole Truth, and Nothing But the Truth”). We are not doing anyone a favor making them feel good about their sin. A person has to admit they have a problem before they will act to fix the problem. A person who doesn’t understand their sin will never submit to a Savior. It isn’t loving to hide the truth from a person just because it makes them uncomfortable or it make the relationship uncomfortable for ourselves.
Jesus said to him, “I am the way, and the truth, and the life; no one comes to the Father but through Me. (John 14:6)
At the same time, sometimes people seem to beat others over the head with God’s truth. They share the truth in the most unloving and unmerciful way. They use God’s truth to try to lift up themselves while putting down others. This is just as bad.
Now we pray to God that you do no wrong; not that we ourselves may appear approved, but that you may do what is right, even though we may appear unapproved. For we can do nothing against the truth, but only for the truth. (2 Corinthians 13:7-8) {emphasis mine}
Some Christians spend so much time nit picking tiny discrepancies in theology that they miss the whole point of the Gospel.
“Woe to you, scribes and Pharisees, hypocrites! For you tithe mint and dill and cumin, and have neglected the weightier provisions of the law: justice and mercy and faithfulness; but these are the things you should have done without neglecting the others. (Matthew 23:23)
Some Christians use theological purity as a means to lift themselves up while knocking others down.
“Two men went up into the temple to pray, one a Pharisee and the other a tax collector. The Pharisee stood and was praying this to himself: ‘God, I thank You that I am not like other people: swindlers, unjust, adulterers, or even like this tax collector. I fast twice a week; I pay tithes of all that I get.’ 13But the tax collector, standing some distance away, was even unwilling to lift up his eyes to heaven, but was beating his breast, saying, ‘God, be merciful to me, the sinner!’ I tell you, this man went to his house justified rather than the other; for everyone who exalts himself will be humbled, but he who humbles himself will be exalted.” (Luke 18:10-14)
We need to stand firmly on the truth, but not to be so focused on truth that we fight with fellow believers over the smallest differences, especially when these differences are among the areas that are not spoken of as clearly (like end times eschatology).
Rejoice or Fear God?
Tonight I read Psalm 2 which brought to mind another seemingly contradictory way we are to interact with God. Do we fear God or do we rejoice in Him?
There are many verses telling us to fear God or fear the Lord. They are given as a command, as a way to knowledge, as a way to life, etc.
Honor all people, love the brotherhood, fear God, honor the king. (1 Peter 2:17) {emphasis mine}
and
The fear of the Lord is the beginning of knowledge; Fools despise wisdom and instruction. (Proverbs 1:7) {emphasis mine}
and
The fear of the Lord leads to life, So that one may sleep satisfied, untouched by evil. (Proverbs 19:23) {emphasis mine}
At the same time we are told to rejoice in the Lord.
Rejoice in the Lord always; again I will say, rejoice! (Philippians 4:4)
and
Then I will go to the altar of God, To God my exceeding joy; And upon the lyre I shall praise You, O God, my God. (Psalm 43:4)
How often do we rejoice in the thing that makes us tremble in fear? I’d guess, not very often or even never. A right view of God, however, causes us to “rejoice with trembling.”
Worship the Lord with reverence\ And rejoice with trembling.\ Do homage to the Son, that He not become angry, and you perish in the way,\ For His wrath may soon be kindled.\ How blessed are all who take refuge in Him! (Psalm 2:11-12) {emphasis mine}
That phrase, “rejoice with trembling” seems to perfectly encapsulate the balance between fear of an awesome, omnipotent, holy God and rejoicing in a loving, merciful God who came to earth, lived the perfect life that we cannot, and died to pay the penalty for our sins.
“How blessed are all who take refuge in Him!”
No Real Contradictions
I think these examples do a good example of demonstrating wisdom regarding God’s word and the importance of balance in our Christian lives. Even when at first there seems to be contradictions, God’s word never contradicts itself; it always clarifies itself. Also, when we see a theological or implementation error to one extreme, we need to make sure we are not driven to an error in the other extreme. We also need to make sure, when debating with fellow believers, that we do not argue against one extreme so strongly that we miscommunicate the truth.
May God in heaven guide you as you study His word and seek to submit to His commands. May He help you to see the truth, the whole truth, and nothing but the truth. May He guide the church to unity in His truth.
Trust Jesus
-
 @ b17fccdf:b7211155
2024-12-29 11:56:44
@ b17fccdf:b7211155
2024-12-29 11:56:44A step-by-step guide to building a Bitcoin & Lightning node, and other stuff on a personal computer.
~ > It builds on a personal computer with x86/amd64 architecture processors.
~> It is based on the popular RaspiBolt v3 guide.
Those are some of the most relevant changes:
- Changed OS from Raspberry Pi OS Lite (64-bits) to Ubuntu Server LTS (Long term support) 64-bit PC (AMD64).
- Changed binaries and signatures of the programs to adapt them to x86/amd64 architecture.
- Deleted unnecessary tools and steps, and added others according to this case of use.
- Some useful authentication logs and monitoring commands were added in the security section.
- Added some interesting parameters in the settings of some services to activate and take advantage of new features.
- Changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- Added exclusive optimization section of services for slow devices.
~ > Complete release notes MiniBolt v1: https://github.com/twofaktor/minibolt/releases/tag/1.0
~ > The MiniBolt guide is available at: https://minibolt.info
~ > Feel free to contribute to the source code on GitHub by opening issues, pull requests or discussions
Created by ⚡2 FakTor⚡
-
 @ 21c9f12c:75695e59
2025-03-30 22:42:19
@ 21c9f12c:75695e59
2025-03-30 22:42:19This guy was in my dad's building. A reminder of the importance of balance in our lives. We all have good and bad experiences in life. What matters is how you choose to handle them and balance yourself on the narrow path. Our paths in life have many possible turns, some take us closer to our ultimate reality while others might lead us astray for a bit.
No matter which path you choose the important thing is to keep your balance and footing and not be swept away in the breeze. You can always find your way back to your center and work your way back out from there. There is seldom a straight path in this life that will take you directly to your ultimate reality, make your way as you will and you'll find that you have what you need when you need it.
Ultimately we are all connected in ways we may never understand. The web of reality is so complex and woven with such precision that we need not try to understand why things are the way they are but accept that they are and move along our path doing our best to help others along the way when possible and accept help from those offering it. The path we take is strengthened and preserved when we follow it with love in our hearts. In this way we can leave a beacon to guide others on their way.
My dad left a lot of love on his path. He has guided so many people whether he realized it or not. His guidance of my path has made me who I am today and I am so proud to say that. His love and light shines bright ahead of me and my path is made so much clearer by the love I received and will continue to receive from him.
This is more than just a spider in a building, it is a reminder that all will be well and we will find our balance and continue along our path with the light and love dad has placed on the web of life for us to follow. Peace and love to everyone and may you all find your balance and continue on your path in the light and love that has been placed there for you by those who have gone before.
-
 @ 878dff7c:037d18bc
2025-03-30 20:46:24
@ 878dff7c:037d18bc
2025-03-30 20:46:24Business Leaders Warn of Economic Risks from Potential Minority Government
Summary:
Australian business leaders are expressing deep concerns about the possibility of a minority government influenced by the Greens or independent "teal" candidates after the upcoming May federal election. CEOs such as Graham Turner, Chris Garnaut, and Bruce Mathieson warn that such a government could lead to policy instability, hinder long-term economic planning, and negatively impact Australia's global competitiveness. Key issues highlighted include the cost of living, housing supply, and the need for comprehensive economic reforms to stimulate consumer confidence and productivity. Sources: The Australian - March 31, 2025
Forecasted Decline in Australia's Resource and Energy Export Earnings
Summary:
The Australian government projects a 6% decrease in mining and energy export earnings for the financial year ending in June, attributing the decline to lower U.S. dollar prices for these exports. Earnings are expected to fall to A$387 billion from A$415 billion the previous year. This trend is anticipated to continue over the next five years, stabilizing at A$343 billion. Factors contributing to this decline include normalizing energy export values after recent peaks and reduced demand from China, particularly affecting iron ore exports. Sources: Reuters - March 31, 2025
Devastating Queensland Floods Expected to Persist for Weeks
Summary:
Queensland is experiencing severe flooding due to record-breaking rains exceeding 650mm, submerging entire communities like Adavale and Jundah. Swiftwater crews have conducted over 40 rescues, and major flood warnings remain across inland Queensland. The floods have damaged energy infrastructure, leaving around 300 homes without power. Livestock losses may reach up to a million, with farmers facing significant property damage and urging government and military assistance. Efforts to restore power are underway but depend on weather conditions. Additional rainfall is forecast for the coming week, potentially prolonging the flooding for days, if not weeks. Sources: The Courier-Mail - 31 March 2025
Western NSW Towns Brace for Six Weeks of Isolation Due to Floods
Summary:
A dynamic weather system has caused significant rainfall and flooding along the Paroo and Warrego Rivers, isolating communities in western NSW. The State Emergency Service (SES) has issued 46 warnings, urging residents to prepare for up to six weeks of isolation. Flash flooding, mainly due to water from Queensland, is a major concern, prompting 19 SES flood rescues and 586 emergency responses in the past 24 hours. In Taree, 22 people are surrounded by floodwater and are being rescued. An elderly man is missing after being washed away in floodwaters. The NSW SES advises residents to stay updated via their website or the Hazards Near Me app. Sources: News.com.au - 31 March 2025
Albanese Abandons Energy Bill Reduction Modelling
Summary:
Prime Minister Anthony Albanese has distanced himself from earlier modelling that supported the promise to cut power bills by $378 by 2030 and reduce emissions by 43%. He attributes the failure to achieve $275 reductions in power bills by 2025 to international factors, including the Ukraine war. This move has drawn criticism from both the Coalition and the Greens, who accuse the government of not effectively addressing power prices and emissions reduction. Sources: The Australian - March 31, 2025
Albanese Seeks Direct Talks with Trump on Tariffs
Summary:
Prime Minister Anthony Albanese anticipates a direct discussion with U.S. President Donald Trump regarding impending tariffs, as Washington prepares to announce new trade measures on April 2. There are concerns that Australia could be affected by this escalation in the global trade conflict. Albanese has emphasized his government's constructive engagement with U.S. officials on this issue and looks forward to a one-on-one conversation with President Trump. Sources: Reuters - March 31, 2025
Queensland Government Expands 'Adult Time, Adult Crime' Laws
Summary:
The Queensland state government plans to introduce at least a dozen new offenses to the Making Queensland Safer Laws, including rape, aggravated attempted robbery, attempted murder, arson, and torture. These changes will enable the judiciary to treat juvenile offenders as adults for severe crimes. Despite criticism over the delayed inclusion of attempted murder, Youth Justice Minister Laura Gerber defended the sequence and content of the initial changes. The full list of offenses will be unveiled later this week.
Sources: The Courier-Mail - March 30, 2025
Labor Government Proposes Ban on Supermarket Price Gouging
Summary:
Prime Minister Anthony Albanese announced that a re-elected Labor government would introduce legislation to outlaw supermarket price gouging by the end of the year. The plan includes implementing Australian Competition and Consumer Commission (ACCC) recommendations to enhance price transparency and establishing a task force to advise on an "excessive pricing regime" for supermarkets, with potential heavy fines for violators. Opposition leader Peter Dutton criticized the approach as ineffective, suggesting it was merely a "wet lettuce" move. Critics from both sides called for tougher measures to combat supermarket dominance and protect consumers.
Sources: The Guardian - March 29, 2025, News.com.au - March 30, 2025
Coles Expands Recall on Spinach Products Due to Contamination
Summary:
Coles has extended its recall of various spinach products across multiple regions, including New South Wales and Victoria, due to potential microbial contamination. Customers are advised not to consume the affected products and can return them to any Coles store for a full refund. The recall applies to items purchased between March 20 and March 29, with use-by dates up to April 9.
Sources: News.com.au - March 31, 2025
66-Year-Old Man Rescued After Five Days Stranded in Australian Outback
Summary:
Tony Woolford, a 66-year-old Australian man, was rescued after being stranded for five days in the flood-hit Munga-Thirri Simpson Desert. Woolford's vehicle was immobilized by rising floodwaters, and with no phone service, he survived by harvesting rainwater and using a high-frequency radio to communicate with volunteers. Authorities were notified on March 23, and he was rescued on March 26 in stable condition and high spirits. Despite the ordeal, Woolford plans to return to the outback to retrieve his car and continue his exploration once conditions improve. Sources: People - March 28, 2025
US Tariffs and Australia's Response
Summary:
Former US trade negotiator Ralph Ives asserts that the US-Australia Free-Trade Agreement has ensured fair reciprocity for two decades, suggesting that President Donald Trump should not impose reciprocal tariffs on Australia. Prime Minister Anthony Albanese anticipates a direct discussion with President Trump regarding these tariffs, expressing concern over potential impacts on Australian exports.
Sources: The Australian - March 31, 2025, Reuters - March 31, 2025
Controversial Genetically Modified Mosquito Plan Monitored Amid Backlash
Summary:
The Queensland government is set to monitor a proposal by Oxitec Australia to release genetically modified mosquitoes aimed at reducing disease transmission. Despite community opposition and concerns about environmental and health risks, supporters argue the initiative could combat diseases like dengue and Zika. Public consultations have been delayed due to significant interest and debate continues over the plan's potential impacts. Sources: The Courier-Mail - March 26, 2025
Dr. Patrick Soon-Shiong: You're Being Lied to About Cancer, How It's Caused, and How to Stop It
Summary:
In this episode of The Tucker Carlson Show, Dr. Patrick Soon-Shiong, a renowned physician and entrepreneur, discusses misconceptions surrounding cancer, its origins, and potential treatments. He emphasizes the complexity of cancer, noting that it's not a single disease but a collection of related diseases requiring varied approaches. Dr. Soon-Shiong highlights the role of the immune system in combating cancer and advocates for treatments that bolster immune responses rather than solely relying on traditional methods like chemotherapy. He also addresses the importance of early detection and personalized medicine in improving patient outcomes.
-
 @ ec42c765:328c0600
2024-12-22 19:16:31
@ ec42c765:328c0600
2024-12-22 19:16:31この記事は前回の内容を把握している人向けに書いています(特にNostrエクステンション(NIP-07)導入)
手順
- 登録する画像を用意する
- 画像をweb上にアップロードする
- 絵文字セットに登録する
1. 登録する画像を用意する
以下のような方法で用意してください。
- 画像編集ソフト等を使って自分で作成する
- 絵文字作成サイトを使う(絵文字ジェネレーター、MEGAMOJI など)
- フリー画像を使う(いらすとや など)
データ量削減
Nostrでは画像をそのまま表示するクライアントが多いので、データ量が大きな画像をそのまま使うとモバイル通信時などに負担がかかります。
データ量を増やさないためにサイズやファイル形式を変更することをおすすめします。
以下は私のおすすめです。 * サイズ:正方形 128×128 ピクセル、長方形 任意の横幅×128 ピクセル * ファイル形式:webp形式(webp変換おすすめサイト toimg) * 単色、単純な画像の場合:png形式(webpにするとむしろサイズが大きくなる)
その他
- 背景透過画像
- ダークモード、ライトモード両方で見やすい色
がおすすめです。
2. 画像をweb上にアップロードする
よく分からなければ emojito からのアップロードで問題ないです。
普段使っている画像アップロード先があるならそれでも構いません。
気になる方はアップロード先を適宜選んでください。既に投稿されたカスタム絵文字の画像に対して
- 削除も差し替えもできない → emojito など
- 削除できるが差し替えはできない → Gyazo、nostrcheck.meなど
- 削除も差し替えもできる → GitHub 、セルフホスティングなど
これらは既にNostr上に投稿されたカスタム絵文字の画像を後から変更できるかどうかを指します。
どの方法でも新しく使われるカスタム絵文字を変更することは可能です。
同一のカスタム絵文字セットに同一のショートコードで別の画像を登録する形で対応できます。3. 絵文字セットに登録する
emojito から登録します。
右上のアイコン → + New emoji set から新規の絵文字セットを作成できます。


① 絵文字セット名を入力
基本的にカスタム絵文字はカスタム絵文字セットを作り、ひとまとまりにして登録します。
一度作った絵文字セットに後から絵文字を追加することもできます。
② 画像をアップロードまたは画像URLを入力
emojitoから画像をアップロードする場合、ファイル名に日本語などの2バイト文字が含まれているとアップロードがエラーになるようです。
その場合はファイル名を適当な英数字などに変更してください。
③ 絵文字のショートコードを入力
ショートコードは絵文字を呼び出す時に使用する場合があります。
他のカスタム絵文字と被っても問題ありませんが選択時に複数表示されて支障が出る可能性があります。
他と被りにくく長くなりすぎないショートコードが良いかもしれません。
ショートコードに使えるのは半角の英数字とアンダーバーのみです。
④ 追加
Add を押してもまだ作成完了にはなりません。

一度に絵文字を複数登録できます。
最後に右上の Save を押すと作成完了です。

画面が切り替わるので、右側の Options から Bookmark を選択するとそのカスタム絵文字セットを自分で使えるようになります。
既存の絵文字セットを編集するには Options から Edit を選択します。
以上です。
仕様
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
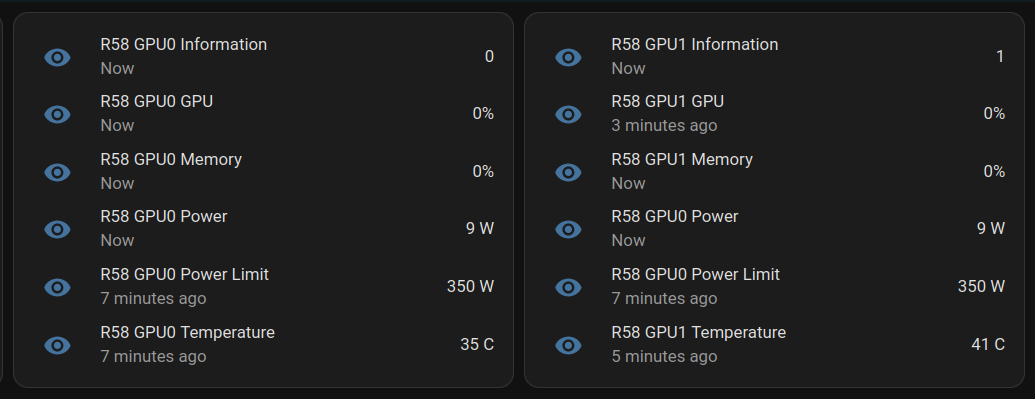
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ 7d33ba57:1b82db35
2025-03-30 19:16:14
@ 7d33ba57:1b82db35
2025-03-30 19:16:14Fažana is a picturesque fishing village on Croatia’s Istrian coast, just 8 km from Pula. Known for its colorful waterfront, fresh seafood, and as the gateway to Brijuni National Park, Fažana is a peaceful alternative to larger tourist hotspots.
🌊 Top Things to See & Do in Fažana
1️⃣ Stroll the Fažana Waterfront & Old Town 🎨
- The charming harbor is lined with colorful houses, cafés, and fishing boats.
- Visit St. Cosmas and Damian Church, a small yet beautiful historical site.
- Enjoy a relaxed Mediterranean atmosphere with fewer crowds than Pula.
2️⃣ Take a Boat Trip to Brijuni National Park 🏝️
- Brijuni Islands, just 15 minutes away by boat, offer stunning nature, Roman ruins, and a safari park.
- Explore the remains of a Roman villa, Tito’s summer residence, and dinosaur footprints!
- Rent a bike or golf cart to explore the islands at your own pace.
3️⃣ Enjoy the Beaches 🏖️
- Badel Beach – A Blue Flag beach, great for families with crystal-clear, shallow waters.
- Pineta Beach – A peaceful, pine-shaded spot with a mix of sand and pebbles.
- San Lorenzo Beach – A scenic spot perfect for sunset views over Brijuni.
4️⃣ Try the Local Seafood 🍽️
- Fažana is known as the "Sardine Capital of Istria" – try grilled sardines with local wine.
- Visit Konoba Feral or Stara Konoba for authentic Istrian seafood.
- Pair your meal with Istrian Malvazija wine.
5️⃣ Visit the Sardine Park 🐟
- A unique outdoor exhibition dedicated to Fažana’s fishing traditions.
- Learn about the history of sardine fishing and processing in Istria.
6️⃣ Take a Day Trip to Pula 🏛️
- Just 15 minutes away, Pula offers Roman ruins, historic sites, and vibrant nightlife.
- Don’t miss the Pula Arena, Temple of Augustus, and the lively Old Town.
🚗 How to Get to Fažana
✈️ By Air: Pula Airport (PUY) is just 15 minutes away.
🚘 By Car:
- From Pula: ~15 min (8 km)
- From Rovinj: ~35 min (30 km)
- From Zagreb: ~3.5 hours (270 km)
🚌 By Bus: Regular buses run between Pula and Fažana.
🚢 By Boat: Ferries to Brijuni National Park depart from Fažana’s harbor.
💡 Tips for Visiting Fažana
✅ Best time to visit? May–September for beach weather & Brijuni trips ☀️
✅ Try local olive oil – Istria produces some of the best olive oils in the world 🫒
✅ Visit early for boat tickets to Brijuni – They can sell out quickly in summer ⏳
✅ Perfect for a relaxing stay – Less crowded than Pula but close to major attractions 🌊 -
 @ 6f6b50bb:a848e5a1
2024-12-15 15:09:52
@ 6f6b50bb:a848e5a1
2024-12-15 15:09:52Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
-
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
-
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!
Tradotto da:\ https://willwhitney.com/computing-inside-ai.htmlhttps://willwhitney.com/computing-inside-ai.html
-
-
 @ dd664d5e:5633d319
2024-12-14 15:25:56
@ dd664d5e:5633d319
2024-12-14 15:25:56
Christmas season hasn't actually started, yet, in Roman #Catholic Germany. We're in Advent until the evening of the 24th of December, at which point Christmas begins (with the Nativity, at Vespers), and continues on for 40 days until Mariä Lichtmess (Presentation of Christ in the temple) on February 2nd.
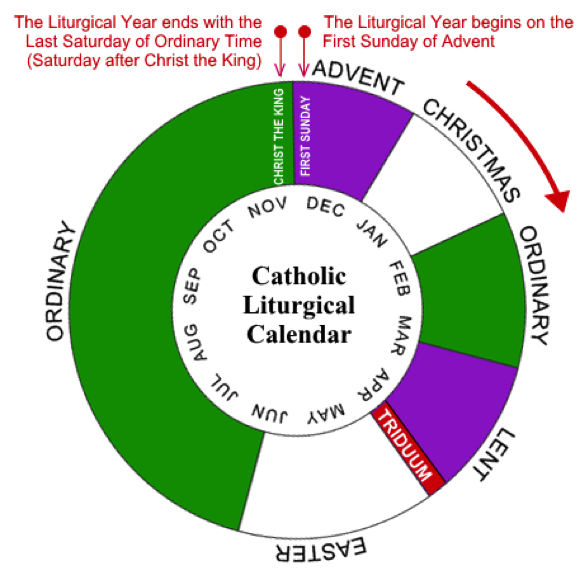
It's 40 days because that's how long the post-partum isolation is, before women were allowed back into the temple (after a ritual cleansing).

That is the day when we put away all of the Christmas decorations and bless the candles, for the next year. (Hence, the British name "Candlemas".) It used to also be when household staff would get paid their cash wages and could change employer. And it is the day precisely in the middle of winter.

Between Christmas Eve and Candlemas are many celebrations, concluding with the Twelfth Night called Epiphany or Theophany. This is the day some Orthodox celebrate Christ's baptism, so traditions rotate around blessing of waters.

The Monday after Epiphany was the start of the farming season, in England, so that Sunday all of the ploughs were blessed, but the practice has largely died out.
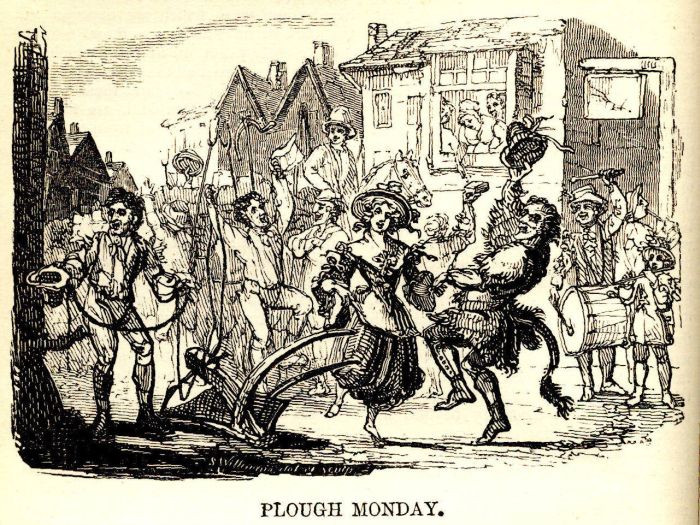
Our local tradition is for the altar servers to dress as the wise men and go door-to-door, carrying their star and looking for the Baby Jesus, who is rumored to be lying in a manger.

They collect cash gifts and chocolates, along the way, and leave the generous their powerful blessing, written over the door. The famous 20 * C + M + B * 25 blessing means "Christus mansionem benedicat" (Christ, bless this house), or "Caspar, Melchior, Balthasar" (the names of the three kings), depending upon who you ask.
They offer the cash to the Baby Jesus (once they find him in the church's Nativity scene), but eat the sweets, themselves. It is one of the biggest donation-collections in the world, called the "Sternsinger" (star singers). The money goes from the German children, to help children elsewhere, and they collect around €45 million in cash and coins, every year.

As an interesting aside:
The American "groundhog day", derives from one of the old farmers' sayings about Candlemas, brought over by the Pennsylvania Dutch. It says, that if the badger comes out of his hole and sees his shadow, then it'll remain cold for 4 more weeks. When they moved to the USA, they didn't have any badgers around, so they switched to groundhogs, as they also hibernate in winter.
-
 @ e6817453:b0ac3c39
2024-12-07 15:06:43
@ e6817453:b0ac3c39
2024-12-07 15:06:43I started a long series of articles about how to model different types of knowledge graphs in the relational model, which makes on-device memory models for AI agents possible.
We model-directed graphs
Also, graphs of entities
We even model hypergraphs
Last time, we discussed why classical triple and simple knowledge graphs are insufficient for AI agents and complex memory, especially in the domain of time-aware or multi-model knowledge.
So why do we need metagraphs, and what kind of challenge could they help us to solve?
- complex and nested event and temporal context and temporal relations as edges
- multi-mode and multilingual knowledge
- human-like memory for AI agents that has multiple contexts and relations between knowledge in neuron-like networks
MetaGraphs
A meta graph is a concept that extends the idea of a graph by allowing edges to become graphs. Meta Edges connect a set of nodes, which could also be subgraphs. So, at some level, node and edge are pretty similar in properties but act in different roles in a different context.
Also, in some cases, edges could be referenced as nodes.
This approach enables the representation of more complex relationships and hierarchies than a traditional graph structure allows. Let’s break down each term to understand better metagraphs and how they differ from hypergraphs and graphs.Graph Basics
- A standard graph has a set of nodes (or vertices) and edges (connections between nodes).
- Edges are generally simple and typically represent a binary relationship between two nodes.
- For instance, an edge in a social network graph might indicate a “friend” relationship between two people (nodes).
Hypergraph
- A hypergraph extends the concept of an edge by allowing it to connect any number of nodes, not just two.
- Each connection, called a hyperedge, can link multiple nodes.
- This feature allows hypergraphs to model more complex relationships involving multiple entities simultaneously. For example, a hyperedge in a hypergraph could represent a project team, connecting all team members in a single relation.
- Despite its flexibility, a hypergraph doesn’t capture hierarchical or nested structures; it only generalizes the number of connections in an edge.
Metagraph
- A metagraph allows the edges to be graphs themselves. This means each edge can contain its own nodes and edges, creating nested, hierarchical structures.
- In a meta graph, an edge could represent a relationship defined by a graph. For instance, a meta graph could represent a network of organizations where each organization’s structure (departments and connections) is represented by its own internal graph and treated as an edge in the larger meta graph.
- This recursive structure allows metagraphs to model complex data with multiple layers of abstraction. They can capture multi-node relationships (as in hypergraphs) and detailed, structured information about each relationship.
Named Graphs and Graph of Graphs
As you can notice, the structure of a metagraph is quite complex and could be complex to model in relational and classical RDF setups. It could create a challenge of luck of tools and software solutions for your problem.
If you need to model nested graphs, you could use a much simpler model of Named graphs, which could take you quite far.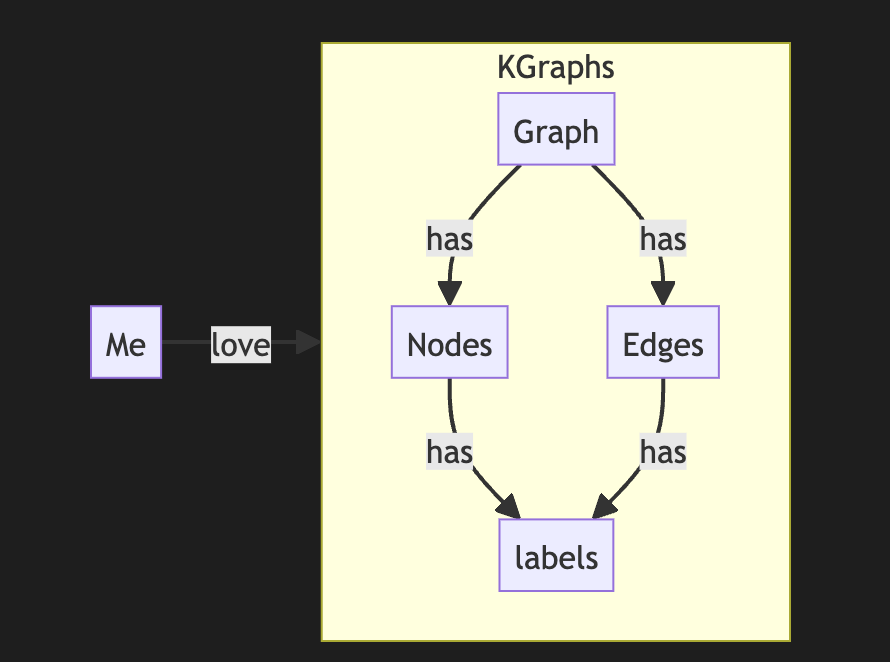
The concept of the named graph came from the RDF community, which needed to group some sets of triples. In this way, you form subgraphs inside an existing graph. You could refer to the subgraph as a regular node. This setup simplifies complex graphs, introduces hierarchies, and even adds features and properties of hypergraphs while keeping a directed nature.
It looks complex, but it is not so hard to model it with a slight modification of a directed graph.
So, the node could host graphs inside. Let's reflect this fact with a location for a node. If a node belongs to a main graph, we could set the location to null or introduce a main node . it is up to you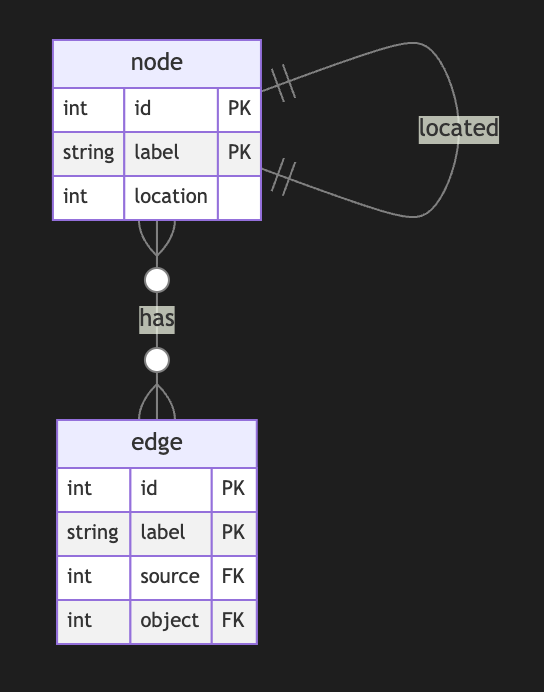
Nodes could have edges to nodes in different subgraphs. This structure allows any kind of nesting graphs. Edges stay location-free
Meta Graphs in Relational Model
Let’s try to make several attempts to model different meta-graphs with some constraints.
Directed Metagraph where edges are not used as nodes and could not contain subgraphs
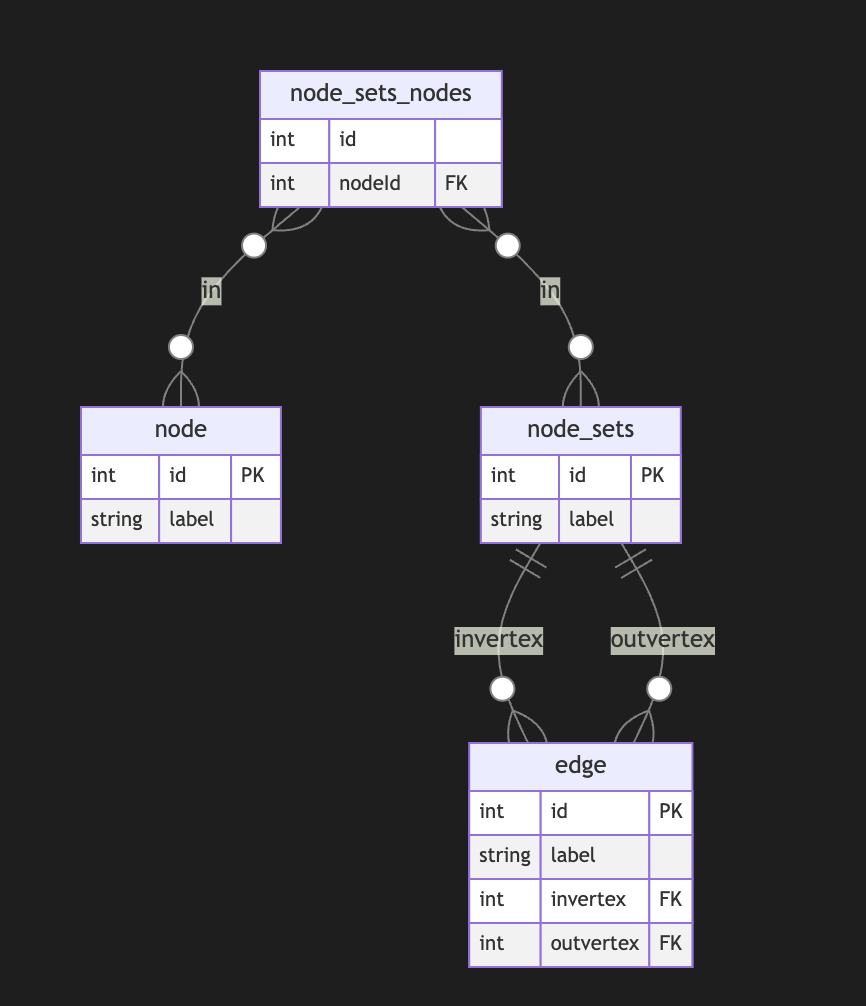
In this case, the edge always points to two sets of nodes. This introduces an overhead of creating a node set for a single node. In this model, we can model empty node sets that could require application-level constraints to prevent such cases.
Directed Metagraph where edges are not used as nodes and could contain subgraphs
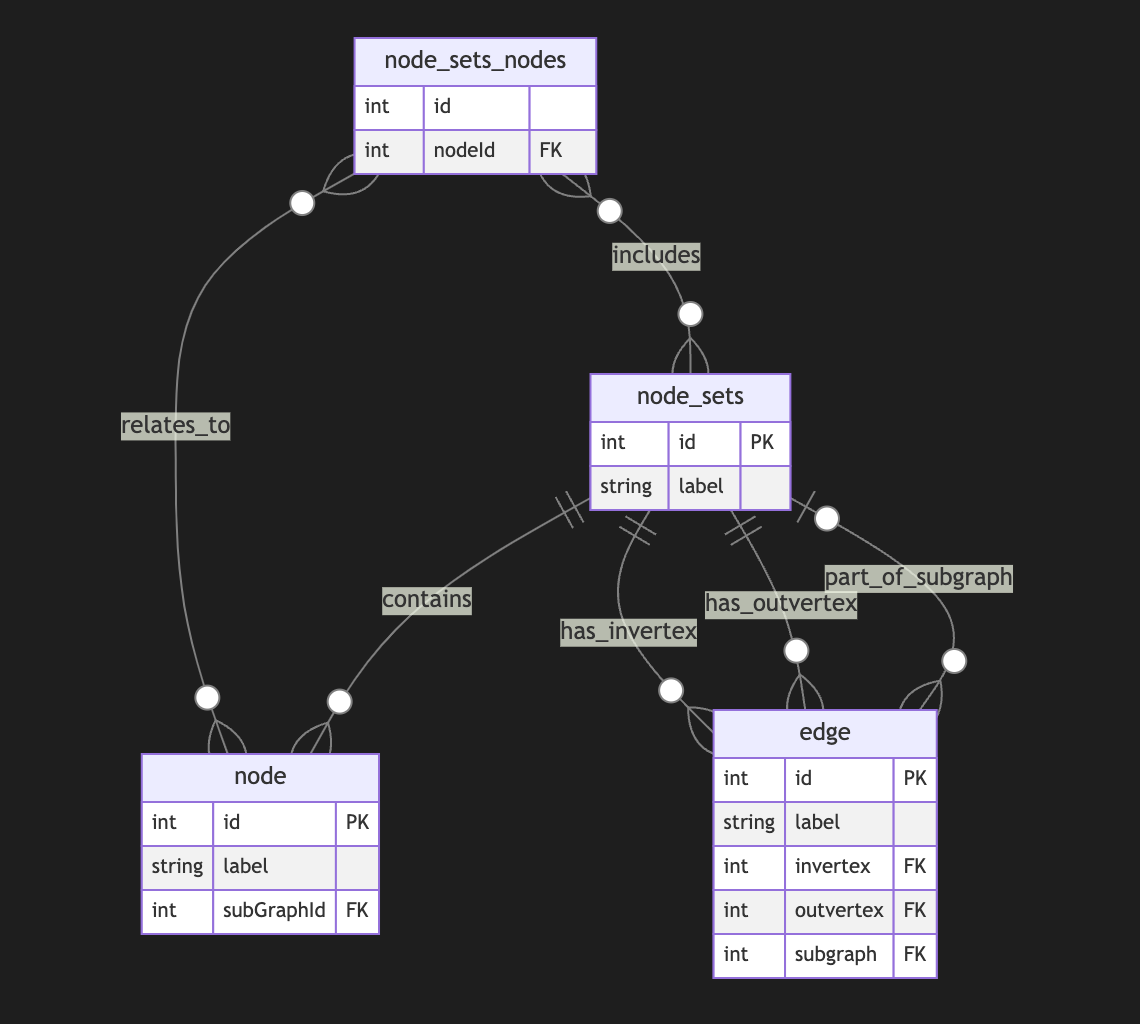
Adding a node set that could model a subgraph located in an edge is easy but could be separate from in-vertex or out-vert.
I also do not see a direct need to include subgraphs to a node, as we could just use a node set interchangeably, but it still could be a case.Directed Metagraph where edges are used as nodes and could contain subgraphs
As you can notice, we operate all the time with node sets. We could simply allow the extension node set to elements set that include node and edge IDs, but in this case, we need to use uuid or any other strategy to differentiate node IDs from edge IDs. In this case, we have a collision of ephemeral edges or ephemeral nodes when we want to change the role and purpose of the node as an edge or vice versa.
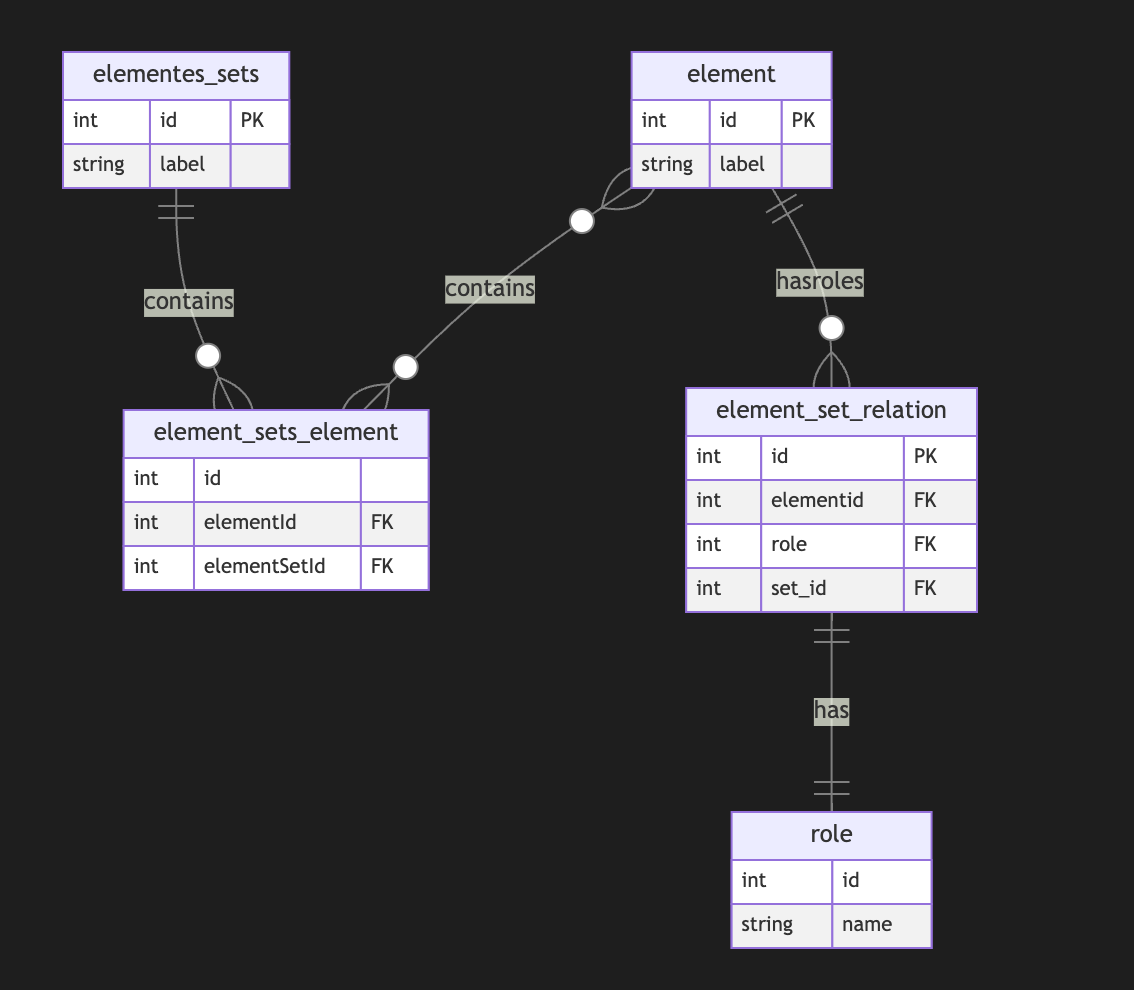
A full-scale metagraph model is way too complex for a relational database.
So we need a better model.Now, we have more flexibility but loose structural constraints. We cannot show that the element should have one vertex, one vertex, or both. This type of constraint has been moved to the application level. Also, the crucial question is about query and retrieval needs.
Any meta-graph model should be more focused on domain and needs and should be used in raw form. We did it for a pure theoretical purpose. -
 @ e6817453:b0ac3c39
2024-12-07 15:03:06
@ e6817453:b0ac3c39
2024-12-07 15:03:06Hey folks! Today, let’s dive into the intriguing world of neurosymbolic approaches, retrieval-augmented generation (RAG), and personal knowledge graphs (PKGs). Together, these concepts hold much potential for bringing true reasoning capabilities to large language models (LLMs). So, let’s break down how symbolic logic, knowledge graphs, and modern AI can come together to empower future AI systems to reason like humans.
The Neurosymbolic Approach: What It Means ?
Neurosymbolic AI combines two historically separate streams of artificial intelligence: symbolic reasoning and neural networks. Symbolic AI uses formal logic to process knowledge, similar to how we might solve problems or deduce information. On the other hand, neural networks, like those underlying GPT-4, focus on learning patterns from vast amounts of data — they are probabilistic statistical models that excel in generating human-like language and recognizing patterns but often lack deep, explicit reasoning.
While GPT-4 can produce impressive text, it’s still not very effective at reasoning in a truly logical way. Its foundation, transformers, allows it to excel in pattern recognition, but the models struggle with reasoning because, at their core, they rely on statistical probabilities rather than true symbolic logic. This is where neurosymbolic methods and knowledge graphs come in.
Symbolic Calculations and the Early Vision of AI
If we take a step back to the 1950s, the vision for artificial intelligence was very different. Early AI research was all about symbolic reasoning — where computers could perform logical calculations to derive new knowledge from a given set of rules and facts. Languages like Lisp emerged to support this vision, enabling programs to represent data and code as interchangeable symbols. Lisp was designed to be homoiconic, meaning it treated code as manipulatable data, making it capable of self-modification — a huge leap towards AI systems that could, in theory, understand and modify their own operations.
Lisp: The Earlier AI-Language
Lisp, short for “LISt Processor,” was developed by John McCarthy in 1958, and it became the cornerstone of early AI research. Lisp’s power lay in its flexibility and its use of symbolic expressions, which allowed developers to create programs that could manipulate symbols in ways that were very close to human reasoning. One of the most groundbreaking features of Lisp was its ability to treat code as data, known as homoiconicity, which meant that Lisp programs could introspect and transform themselves dynamically. This ability to adapt and modify its own structure gave Lisp an edge in tasks that required a form of self-awareness, which was key in the early days of AI when researchers were exploring what it meant for machines to “think.”
Lisp was not just a programming language—it represented the vision for artificial intelligence, where machines could evolve their understanding and rewrite their own programming. This idea formed the conceptual basis for many of the self-modifying and adaptive algorithms that are still explored today in AI research. Despite its decline in mainstream programming, Lisp’s influence can still be seen in the concepts used in modern machine learning and symbolic AI approaches.
Prolog: Formal Logic and Deductive Reasoning
In the 1970s, Prolog was developed—a language focused on formal logic and deductive reasoning. Unlike Lisp, based on lambda calculus, Prolog operates on formal logic rules, allowing it to perform deductive reasoning and solve logical puzzles. This made Prolog an ideal candidate for expert systems that needed to follow a sequence of logical steps, such as medical diagnostics or strategic planning.
Prolog, like Lisp, allowed symbols to be represented, understood, and used in calculations, creating another homoiconic language that allows reasoning. Prolog’s strength lies in its rule-based structure, which is well-suited for tasks that require logical inference and backtracking. These features made it a powerful tool for expert systems and AI research in the 1970s and 1980s.
The language is declarative in nature, meaning that you define the problem, and Prolog figures out how to solve it. By using formal logic and setting constraints, Prolog systems can derive conclusions from known facts, making it highly effective in fields requiring explicit logical frameworks, such as legal reasoning, diagnostics, and natural language understanding. These symbolic approaches were later overshadowed during the AI winter — but the ideas never really disappeared. They just evolved.
Solvers and Their Role in Complementing LLMs
One of the most powerful features of Prolog and similar logic-based systems is their use of solvers. Solvers are mechanisms that can take a set of rules and constraints and automatically find solutions that satisfy these conditions. This capability is incredibly useful when combined with LLMs, which excel at generating human-like language but need help with logical consistency and structured reasoning.
For instance, imagine a scenario where an LLM needs to answer a question involving multiple logical steps or a complex query that requires deducing facts from various pieces of information. In this case, a solver can derive valid conclusions based on a given set of logical rules, providing structured answers that the LLM can then articulate in natural language. This allows the LLM to retrieve information and ensure the logical integrity of its responses, leading to much more robust answers.
Solvers are also ideal for handling constraint satisfaction problems — situations where multiple conditions must be met simultaneously. In practical applications, this could include scheduling tasks, generating optimal recommendations, or even diagnosing issues where a set of symptoms must match possible diagnoses. Prolog’s solver capabilities and LLM’s natural language processing power can make these systems highly effective at providing intelligent, rule-compliant responses that traditional LLMs would struggle to produce alone.
By integrating neurosymbolic methods that utilize solvers, we can provide LLMs with a form of deductive reasoning that is missing from pure deep-learning approaches. This combination has the potential to significantly improve the quality of outputs for use-cases that require explicit, structured problem-solving, from legal queries to scientific research and beyond. Solvers give LLMs the backbone they need to not just generate answers but to do so in a way that respects logical rigor and complex constraints.
Graph of Rules for Enhanced Reasoning
Another powerful concept that complements LLMs is using a graph of rules. A graph of rules is essentially a structured collection of logical rules that interconnect in a network-like structure, defining how various entities and their relationships interact. This structured network allows for complex reasoning and information retrieval, as well as the ability to model intricate relationships between different pieces of knowledge.
In a graph of rules, each node represents a rule, and the edges define relationships between those rules — such as dependencies or causal links. This structure can be used to enhance LLM capabilities by providing them with a formal set of rules and relationships to follow, which improves logical consistency and reasoning depth. When an LLM encounters a problem or a question that requires multiple logical steps, it can traverse this graph of rules to generate an answer that is not only linguistically fluent but also logically robust.
For example, in a healthcare application, a graph of rules might include nodes for medical symptoms, possible diagnoses, and recommended treatments. When an LLM receives a query regarding a patient’s symptoms, it can use the graph to traverse from symptoms to potential diagnoses and then to treatment options, ensuring that the response is coherent and medically sound. The graph of rules guides reasoning, enabling LLMs to handle complex, multi-step questions that involve chains of reasoning, rather than merely generating surface-level responses.
Graphs of rules also enable modular reasoning, where different sets of rules can be activated based on the context or the type of question being asked. This modularity is crucial for creating adaptive AI systems that can apply specific sets of logical frameworks to distinct problem domains, thereby greatly enhancing their versatility. The combination of neural fluency with rule-based structure gives LLMs the ability to conduct more advanced reasoning, ultimately making them more reliable and effective in domains where accuracy and logical consistency are critical.
By implementing a graph of rules, LLMs are empowered to perform deductive reasoning alongside their generative capabilities, creating responses that are not only compelling but also logically aligned with the structured knowledge available in the system. This further enhances their potential applications in fields such as law, engineering, finance, and scientific research — domains where logical consistency is as important as linguistic coherence.
Enhancing LLMs with Symbolic Reasoning
Now, with LLMs like GPT-4 being mainstream, there is an emerging need to add real reasoning capabilities to them. This is where neurosymbolic approaches shine. Instead of pitting neural networks against symbolic reasoning, these methods combine the best of both worlds. The neural aspect provides language fluency and recognition of complex patterns, while the symbolic side offers real reasoning power through formal logic and rule-based frameworks.
Personal Knowledge Graphs (PKGs) come into play here as well. Knowledge graphs are data structures that encode entities and their relationships — they’re essentially semantic networks that allow for structured information retrieval. When integrated with neurosymbolic approaches, LLMs can use these graphs to answer questions in a far more contextual and precise way. By retrieving relevant information from a knowledge graph, they can ground their responses in well-defined relationships, thus improving both the relevance and the logical consistency of their answers.
Imagine combining an LLM with a graph of rules that allow it to reason through the relationships encoded in a personal knowledge graph. This could involve using deductive databases to form a sophisticated way to represent and reason with symbolic data — essentially constructing a powerful hybrid system that uses LLM capabilities for language fluency and rule-based logic for structured problem-solving.
My Research on Deductive Databases and Knowledge Graphs
I recently did some research on modeling knowledge graphs using deductive databases, such as DataLog — which can be thought of as a limited, data-oriented version of Prolog. What I’ve found is that it’s possible to use formal logic to model knowledge graphs, ontologies, and complex relationships elegantly as rules in a deductive system. Unlike classical RDF or traditional ontology-based models, which sometimes struggle with complex or evolving relationships, a deductive approach is more flexible and can easily support dynamic rules and reasoning.
Prolog and similar logic-driven frameworks can complement LLMs by handling the parts of reasoning where explicit rule-following is required. LLMs can benefit from these rule-based systems for tasks like entity recognition, logical inferences, and constructing or traversing knowledge graphs. We can even create a graph of rules that governs how relationships are formed or how logical deductions can be performed.
The future is really about creating an AI that is capable of both deep contextual understanding (using the powerful generative capacity of LLMs) and true reasoning (through symbolic systems and knowledge graphs). With the neurosymbolic approach, these AIs could be equipped not just to generate information but to explain their reasoning, form logical conclusions, and even improve their own understanding over time — getting us a step closer to true artificial general intelligence.
Why It Matters for LLM Employment
Using neurosymbolic RAG (retrieval-augmented generation) in conjunction with personal knowledge graphs could revolutionize how LLMs work in real-world applications. Imagine an LLM that understands not just language but also the relationships between different concepts — one that can navigate, reason, and explain complex knowledge domains by actively engaging with a personalized set of facts and rules.
This could lead to practical applications in areas like healthcare, finance, legal reasoning, or even personal productivity — where LLMs can help users solve complex problems logically, providing relevant information and well-justified reasoning paths. The combination of neural fluency with symbolic accuracy and deductive power is precisely the bridge we need to move beyond purely predictive AI to truly intelligent systems.
Let's explore these ideas further if you’re as fascinated by this as I am. Feel free to reach out, follow my YouTube channel, or check out some articles I’ll link below. And if you’re working on anything in this field, I’d love to collaborate!
Until next time, folks. Stay curious, and keep pushing the boundaries of AI!
-
 @ e6817453:b0ac3c39
2024-12-07 14:54:46
@ e6817453:b0ac3c39
2024-12-07 14:54:46Introduction: Personal Knowledge Graphs and Linked Data
We will explore the world of personal knowledge graphs and discuss how they can be used to model complex information structures. Personal knowledge graphs aren’t just abstract collections of nodes and edges—they encode meaningful relationships, contextualizing data in ways that enrich our understanding of it. While the core structure might be a directed graph, we layer semantic meaning on top, enabling nuanced connections between data points.
The origin of knowledge graphs is deeply tied to concepts from linked data and the semantic web, ideas that emerged to better link scattered pieces of information across the web. This approach created an infrastructure where data islands could connect — facilitating everything from more insightful AI to improved personal data management.
In this article, we will explore how these ideas have evolved into tools for modeling AI’s semantic memory and look at how knowledge graphs can serve as a flexible foundation for encoding rich data contexts. We’ll specifically discuss three major paradigms: RDF (Resource Description Framework), property graphs, and a third way of modeling entities as graphs of graphs. Let’s get started.
Intro to RDF
The Resource Description Framework (RDF) has been one of the fundamental standards for linked data and knowledge graphs. RDF allows data to be modeled as triples: subject, predicate, and object. Essentially, you can think of it as a structured way to describe relationships: “X has a Y called Z.” For instance, “Berlin has a population of 3.5 million.” This modeling approach is quite flexible because RDF uses unique identifiers — usually URIs — to point to data entities, making linking straightforward and coherent.
RDFS, or RDF Schema, extends RDF to provide a basic vocabulary to structure the data even more. This lets us describe not only individual nodes but also relationships among types of data entities, like defining a class hierarchy or setting properties. For example, you could say that “Berlin” is an instance of a “City” and that cities are types of “Geographical Entities.” This kind of organization helps establish semantic meaning within the graph.
RDF and Advanced Topics
Lists and Sets in RDF
RDF also provides tools to model more complex data structures such as lists and sets, enabling the grouping of nodes. This extension makes it easier to model more natural, human-like knowledge, for example, describing attributes of an entity that may have multiple values. By adding RDF Schema and OWL (Web Ontology Language), you gain even more expressive power — being able to define logical rules or even derive new relationships from existing data.
Graph of Graphs
A significant feature of RDF is the ability to form complex nested structures, often referred to as graphs of graphs. This allows you to create “named graphs,” essentially subgraphs that can be independently referenced. For example, you could create a named graph for a particular dataset describing Berlin and another for a different geographical area. Then, you could connect them, allowing for more modular and reusable knowledge modeling.
Property Graphs
While RDF provides a robust framework, it’s not always the easiest to work with due to its heavy reliance on linking everything explicitly. This is where property graphs come into play. Property graphs are less focused on linking everything through triples and allow more expressive properties directly within nodes and edges.
For example, instead of using triples to represent each detail, a property graph might let you store all properties about an entity (e.g., “Berlin”) directly in a single node. This makes property graphs more intuitive for many developers and engineers because they more closely resemble object-oriented structures: you have entities (nodes) that possess attributes (properties) and are connected to other entities through relationships (edges).
The significant benefit here is a condensed representation, which speeds up traversal and queries in some scenarios. However, this also introduces a trade-off: while property graphs are more straightforward to query and maintain, they lack some complex relationship modeling features RDF offers, particularly when connecting properties to each other.
Graph of Graphs and Subgraphs for Entity Modeling
A third approach — which takes elements from RDF and property graphs — involves modeling entities using subgraphs or nested graphs. In this model, each entity can be represented as a graph. This allows for a detailed and flexible description of attributes without exploding every detail into individual triples or lump them all together into properties.
For instance, consider a person entity with a complex employment history. Instead of representing every employment detail in one node (as in a property graph), or as several linked nodes (as in RDF), you can treat the employment history as a subgraph. This subgraph could then contain nodes for different jobs, each linked with specific properties and connections. This approach keeps the complexity where it belongs and provides better flexibility when new attributes or entities need to be added.
Hypergraphs and Metagraphs
When discussing more advanced forms of graphs, we encounter hypergraphs and metagraphs. These take the idea of relationships to a new level. A hypergraph allows an edge to connect more than two nodes, which is extremely useful when modeling scenarios where relationships aren’t just pairwise. For example, a “Project” could connect multiple “People,” “Resources,” and “Outcomes,” all in a single edge. This way, hypergraphs help in reducing the complexity of modeling high-order relationships.
Metagraphs, on the other hand, enable nodes and edges to themselves be represented as graphs. This is an extremely powerful feature when we consider the needs of artificial intelligence, as it allows for the modeling of relationships between relationships, an essential aspect for any system that needs to capture not just facts, but their interdependencies and contexts.
Balancing Structure and Properties
One of the recurring challenges when modeling knowledge is finding the balance between structure and properties. With RDF, you get high flexibility and standardization, but complexity can quickly escalate as you decompose everything into triples. Property graphs simplify the representation by using attributes but lose out on the depth of connection modeling. Meanwhile, the graph-of-graphs approach and hypergraphs offer advanced modeling capabilities at the cost of increased computational complexity.
So, how do you decide which model to use? It comes down to your use case. RDF and nested graphs are strong contenders if you need deep linkage and are working with highly variable data. For more straightforward, engineer-friendly modeling, property graphs shine. And when dealing with very complex multi-way relationships or meta-level knowledge, hypergraphs and metagraphs provide the necessary tools.
The key takeaway is that only some approaches are perfect. Instead, it’s all about the modeling goals: how do you want to query the graph, what relationships are meaningful, and how much complexity are you willing to manage?
Conclusion
Modeling AI semantic memory using knowledge graphs is a challenging but rewarding process. The different approaches — RDF, property graphs, and advanced graph modeling techniques like nested graphs and hypergraphs — each offer unique strengths and weaknesses. Whether you are building a personal knowledge graph or scaling up to AI that integrates multiple streams of linked data, it’s essential to understand the trade-offs each approach brings.
In the end, the choice of representation comes down to the nature of your data and your specific needs for querying and maintaining semantic relationships. The world of knowledge graphs is vast, with many tools and frameworks to explore. Stay connected and keep experimenting to find the balance that works for your projects.
-
 @ e6817453:b0ac3c39
2024-12-07 14:52:47
@ e6817453:b0ac3c39
2024-12-07 14:52:47The temporal semantics and temporal and time-aware knowledge graphs. We have different memory models for artificial intelligence agents. We all try to mimic somehow how the brain works, or at least how the declarative memory of the brain works. We have the split of episodic memory and semantic memory. And we also have a lot of theories, right?
Declarative Memory of the Human Brain
How is the semantic memory formed? We all know that our brain stores semantic memory quite close to the concept we have with the personal knowledge graphs, that it’s connected entities. They form a connection with each other and all those things. So far, so good. And actually, then we have a lot of concepts, how the episodic memory and our experiences gets transmitted to the semantic:
- hippocampus indexing and retrieval
- sanitization of episodic memories
- episodic-semantic shift theory
They all give a different perspective on how different parts of declarative memory cooperate.
We know that episodic memories get semanticized over time. You have semantic knowledge without the notion of time, and probably, your episodic memory is just decayed.
But, you know, it’s still an open question:
do we want to mimic an AI agent’s memory as a human brain memory, or do we want to create something different?
It’s an open question to which we have no good answer. And if you go to the theory of neuroscience and check how episodic and semantic memory interfere, you will still find a lot of theories, yeah?
Some of them say that you have the hippocampus that keeps the indexes of the memory. Some others will say that you semantic the episodic memory. Some others say that you have some separate process that digests the episodic and experience to the semantics. But all of them agree on the plan that it’s operationally two separate areas of memories and even two separate regions of brain, and the semantic, it’s more, let’s say, protected.
So it’s harder to forget the semantical facts than the episodes and everything. And what I’m thinking about for a long time, it’s this, you know, the semantic memory.
Temporal Semantics
It’s memory about the facts, but you somehow mix the time information with the semantics. I already described a lot of things, including how we could combine time with knowledge graphs and how people do it.
There are multiple ways we could persist such information, but we all hit the wall because the complexity of time and the semantics of time are highly complex concepts.
Time in a Semantic context is not a timestamp.
What I mean is that when you have a fact, and you just mentioned that I was there at this particular moment, like, I don’t know, 15:40 on Monday, it’s already awake because we don’t know which Monday, right? So you need to give the exact date, but usually, you do not have experiences like that.
You do not record your memories like that, except you do the journaling and all of the things. So, usually, you have no direct time references. What I mean is that you could say that I was there and it was some event, blah, blah, blah.
Somehow, we form a chain of events that connect with each other and maybe will be connected to some period of time if we are lucky enough. This means that we could not easily represent temporal-aware information as just a timestamp or validity and all of the things.
For sure, the validity of the knowledge graphs (simple quintuple with start and end dates)is a big topic, and it could solve a lot of things. It could solve a lot of the time cases. It’s super simple because you give the end and start dates, and you are done, but it does not answer facts that have a relative time or time information in facts . It could solve many use cases but struggle with facts in an indirect temporal context. I like the simplicity of this idea. But the problem of this approach that in most cases, we simply don’t have these timestamps. We don’t have the timestamp where this information starts and ends. And it’s not modeling many events in our life, especially if you have the processes or ongoing activities or recurrent events.
I’m more about thinking about the time of semantics, where you have a time model as a hybrid clock or some global clock that does the partial ordering of the events. It’s mean that you have the chain of the experiences and you have the chain of the facts that have the different time contexts.
We could deduct the time from this chain of the events. But it’s a big, big topic for the research. But what I want to achieve, actually, it’s not separation on episodic and semantic memory. It’s having something in between.
Blockchain of connected events and facts
I call it temporal-aware semantics or time-aware knowledge graphs, where we could encode the semantic fact together with the time component.I doubt that time should be the simple timestamp or the region of the two timestamps. For me, it is more a chain for facts that have a partial order and form a blockchain like a database or a partially ordered Acyclic graph of facts that are temporally connected. We could have some notion of time that is understandable to the agent and a model that allows us to order the events and focus on what the agent knows and how to order this time knowledge and create the chains of the events.
Time anchors
We may have a particular time in the chain that allows us to arrange a more concrete time for the rest of the events. But it’s still an open topic for research. The temporal semantics gets split into a couple of domains. One domain is how to add time to the knowledge graphs. We already have many different solutions. I described them in my previous articles.
Another domain is the agent's memory and how the memory of the artificial intelligence treats the time. This one, it’s much more complex. Because here, we could not operate with the simple timestamps. We need to have the representation of time that are understandable by model and understandable by the agent that will work with this model. And this one, it’s way bigger topic for the research.”
-
 @ 3b19f10a:4e1f94b4
2024-12-07 09:55:46
@ 3b19f10a:4e1f94b4
2024-12-07 09:55:46 -
 @ b2d670de:907f9d4a
2024-12-02 21:24:45
@ b2d670de:907f9d4a
2024-12-02 21:24:45onion-service-nostr-relays
A list of nostr relays exposed as onion services.
The list
| Relay name | Description | Onion url | Operator | Payment URL | Payment options | | --- | --- | --- | --- | --- | --- | | nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | operator | N/A | N/A | | relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | operator | N/A | N/A | | nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | operator | N/A | N/A | | nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | operator | Payment URL | BTC LN | | bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | operator | N/A | N/A | | relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | operator | Payment URL | BTC LN | | freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | operator | N/A | N/A | | nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | operator | N/A | N/A | | nostr.wine | 🍷 nostr.wine relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | operator | Payment URL | BTC LN, BTC, Credit Card/CashApp (Stripe) | | inbox.nostr.wine | 🍷 inbox.nostr.wine relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | operator | Payment URL | BTC LN, BTC | | filter.nostr.wine | 🍷 filter.nostr.wine proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | operator | Payment URL | BTC LN, BTC | | N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | operator | N/A | N/A | | nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | operator | N/A | N/A | | nfrelay.app | nfrelay.app aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | operator | N/A | N/A | relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | operator | N/A | N/A | | nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | operator |Payment URL | XMR | | nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | operator | N/A | N/A | | wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | operator | N/A | N/A | | haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | operator | N/A | N/A | | relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | operator |N/A | N/A | | Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | operator | N/A | N/A |
Contributing
Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put
N/Ain empty columns.If you want to contribute anonymously, please contact me on SimpleX or send a DM on nostr using a disposable npub.
Operator column
It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url).
-
 @ 0f9da413:01bd07d7
2025-03-30 15:37:53
@ 0f9da413:01bd07d7
2025-03-30 15:37:53ช่วงสัปดาห์ก่อน 21-30 มีนาคม 2568 ที่ผ่านมาส่วนตัวได้มีภาระกิจเดินทางไปปฏิบัติงานของสถานที่ทำงานและรวดไปเที่ยวส่วนตัว ในการเดินทางในครั้งนี้ภาระกิจหลักส่วนตัวอาจจะไปทำงานแต่หากมีการเดินทางแล้วผมมักจะชอบเดินทางไปพบปะชาว bitcoiner ชาวไทย หรือชาว #siamstr ตามสถานที่ต่างๆ อยู่เสมอตลอดช่วงระยะเวลาดังกล่าวส่วนตัวก็ได้เดินทางไปยังพื้นที่ดังนี้
- ชลบุรี (พัทยา)
- เกาะช้าง (ตราด)
- หาดใหญ่ (สงขลา)
- เชียงใหม่
ซึ่งได้ตรวจเช็คแล้วในพื้นที่ดังกล่าวมีร้านรับ bitcoin อยู่และมีประสบการณ์ในแต่ละที่ที่แตกต่างกันออกไปซึ่งผมเองจะขอรัวิวการเดินทางดังกล่าวนี้ โดยอ้างอิงจากการตามรอยร้านที่รับชำระด้วย BTC ผ่าน BTC Map และจะมีบางร้านที่ไม่ได้อยู่ใน BTC Map ก็ขอรีวิวตามช่วงระยะเวลา Timeline ละกัน
Seeva Cafe Pattya
ร้านชีวาคาเฟ่ ร้านตกแต่งในสไตล์ศิลปะและกาแฟในร้านมีโซนจำหน่ายขนมเค้กและอื่นๆ อีกด้วย มีต้นไม้ร่มรื่นและบรรยากาศค่อนข้างดีพอสมควร ท่านไหนอยากเดินทางไปจิบกาแฟเบาๆ นั่งทำงานพักผ่อนแถวพัทยาใต้ก็สามารถเดินทางไปแวะชิมกันได้ (รับบิทคอยด้วยนะ) สถานที่นี้ไม่ได้เสีย sats เนื่องจากมีเจ้าภาพเลี้ยง ขอบคุณครับ
Google Map: https://maps.app.goo.gl/ZJNUGYiCgp1VTzGJ9
BTC-Map: None
Piya Silapakan Museum of Art Pattaya
สถานที่ถัดมาเป็นหอศิลป์ ปิยะศิลปาคารเป็นสถานที่ที่เก็บรวมรวมผลงานทางศิลปะต่างๆ ภาพวาดเสมือนจริงซึ่งแน่นอนว่าสามารถมาเรียน Workshop ทางด้านศิลปะได้แน่นอนว่าสามารถจ่ายด้วย Bitcoin Lightning ได้โดยผมเองก็ได้วาดศิลปะสีน้ำวาดบนกระเป๋าผ้า เอาจริงๆ ณ ตอนที่วาดนั้นแทบจะลืมเวลาและโพกัสกับสิ่งที่วาดอยู่ทำให้รู้สึกผ่อนคลายและวาดสิ่งต่างๆ เหมือนตอนสมัยเด็กๆ ซึ่งหากมีเวลาเพิ่มเติมผมเองก็อาจจะเจียดเวลาไปลองวาดศิลปะแลลอื่นๆ โดยที่ไม่ต้องให้ใครมาตัดสินใจ สวยไม่สวยอย่างไร ก็อยู่ที่เรา หลายครั้งเราชอบให้คนอื่นตัดสินใจเพื่อทำให้เรารู้สึกดี ลองมาที่นี้ดูสิแล้วคุณจะตัดสินใจด้วยตนเอง
อันนี้ผลงานส่วนตัวที่ได้ทำ แล้วแต่การจินตนาการของแต่ละท่านว่าสิ่งที่ผมวาดมันคืออะไรก็แล้วกัน
งานนี้หมดไปแล้ว 13,173 sats แวะมาเยี่ยมชมกันได้ที่พัทยา ชลบุรี :)
Google map: https://maps.app.goo.gl/mjMCdxEe36ra1jDF6
BTC-Map: None
Toffee Cake Pattaya
เป็นร้านสุดท้ายที่ได้ไปใช้งานชื้อขนมติดไม้ติดมือกลับไปยังที่พักก่อนส่วนตัวจะเดินทางต่อไป หมดไป 1,904 sats เหมาะสำหรับชื้อของฝากติดไม้ติดมือกลับบ้าน
Google map: https://maps.app.goo.gl/jqRyHTFzXVe6qYSv9
BTC-Map: https://btcmap.org/map?lat=12.9509827&long=100.8974009
หลังจากเดินทางพักที่พัทยาหนึ่งคืนก่อนเดินทางไปยังเกาะช้าง สรุปสถานที่พัทยานั้นหมดไปทั้งหมด 15,077 sats (คำนวนเงินอนาคตน่าจะ 15,077 usd กาวกันไว้ก่อน) สำหรับ Part 2 นั้นจะรีวิวร้านที่อยู่ในพื้นที่เกาะช้างซึ่งผมได้ตามรอยจาก BTC-Map จะเป็นอย่างไรเชิญติดตามครับ ขอบคุณครับ
-
 @ 81cda509:ae345bd2
2024-12-01 06:01:54
@ 81cda509:ae345bd2
2024-12-01 06:01:54

@florian | Photographer
Studio-Shoot
“Know thyself” is a phrase attributed to the ancient Greek philosopher Socrates, and it has been a cornerstone of philosophical thought for centuries. It invites an individual to deeply examine their own thoughts, feelings, behaviors, and motivations in order to understand their true nature.
At its core, “Know thyself” encourages self-awareness - an understanding of who you truly are beneath the surface. This process of introspection can uncover your strengths, weaknesses, desires, fears, and values. It invites you to acknowledge your habits, biases, and patterns of thinking, so you can make more conscious choices in life.
Knowing yourself also involves understanding your place in the larger context of existence. It means recognizing how your actions and choices affect others and the world around you. This awareness can lead to greater empathy, a sense of interconnectedness, and a more authentic life, free from the distractions of societal expectations or superficial identities.
In a practical sense, knowing yourself might involve:
-
Self-reflection: Regularly taking time to reflect on your thoughts, feelings, and experiences.
-
Mindfulness: Practicing awareness of the present moment and observing your reactions without judgment.
-
Exploration: Being open to trying new things and learning from both successes and failures.
-
Seeking truth: Engaging in honest inquiry about your motivations, desires, and beliefs.
-
Growth: Continuously learning from your past and striving to align your actions with your inner values.
Ultimately, “Know thyself” is about cultivating a deep, honest understanding of who you are, which leads to a more fulfilled, intentional, and peaceful existence.
-
-
 @ a367f9eb:0633efea
2024-11-05 08:48:41
@ a367f9eb:0633efea
2024-11-05 08:48:41Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters
When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies
In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement
If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Originally published on the website of the Consumer Choice Center.
-
 @ 3514ac1b:cf164691
2025-03-30 15:16:56
@ 3514ac1b:cf164691
2025-03-30 15:16:56hi , My name is Erna and i hope this articles find you well. hmm what i like to talked about today is how i dislike my my black coffee getting cold . it is happened almost everyday . here is my morning flow : wake up brush teeth and make my self ready make coffee ( boiled water ) in meantime switch on my computer reading news , things ( water allready boiled ) get my coffee and put my coffee on the side of my computer keep reading and social media 1 hour later coffee get cold meeeh i need to drink this everyday .
so which of thos work flow is wrong ? am i doing it wrong ? suggested me a good morning routine so my coffee still hot when i drink it .
-
 @ bcb80417:14548905
2025-03-30 14:40:40
@ bcb80417:14548905
2025-03-30 14:40:40President Donald Trump's recent policy initiatives have significantly impacted the cryptocurrency landscape, reflecting his administration's commitment to fostering innovation and positioning the United States as a global leader in digital assets.
A cornerstone of this approach is the aggressive deregulation agenda aimed at reversing many policies from the previous administration. Key areas of focus include slashing environmental regulations, easing bank oversight, and removing barriers to cryptocurrencies. The Environmental Protection Agency, for instance, announced 31 deregulatory actions in a single day, underscoring the breadth of these efforts. This push has led to rapid growth in the crypto industry, with increased investment and activity following the administration's moves to ease restrictions. citeturn0news10
In line with this deregulatory stance, the U.S. Securities and Exchange Commission (SEC) recently hosted its inaugural public meeting of the crypto task force. Led by Republican SEC Commissioner Hester Peirce, the task force is exploring the applicability of securities laws to digital assets and considering whether new regulatory frameworks are necessary. This initiative reflects a shift in regulatory approach under President Trump, who has pledged to reverse the previous administration's crackdown on crypto firms. citeturn0news11
Further demonstrating his support for the crypto industry, President Trump announced the inclusion of five cryptocurrencies—Bitcoin, Ethereum, Ripple (XRP), Solana (SOL), and Cardano (ADA)—into a proposed "crypto strategic reserve." This move led to significant price surges for these assets, highlighting the market's responsiveness to policy decisions. citeturn0search0
The administration's commitment extends to the development of stablecoins. World Liberty Financial, a cryptocurrency venture established by Donald Trump and his sons, plans to launch a stablecoin called USD1. This stablecoin will be entirely backed by U.S. treasuries, dollars, and cash equivalents, aiming to provide a reliable medium for cross-border transactions by sovereign investors and major institutions. The USD1 token will be issued on the Ethereum network and a blockchain developed by Binance. citeturn0news13
In the financial sector, Trump Media & Technology Group Corp. is collaborating with Crypto.com to introduce "Made in America" exchange-traded funds (ETFs) focusing on digital assets and securities. This initiative aligns with President Trump's pro-cryptocurrency stance and his ambition to make the U.S. a global crypto hub. The ETFs, supported by Crypto.com, will feature a combination of cryptocurrencies such as Bitcoin and are slated to launch later this year. citeturn0news12
These policy directions underscore President Trump's dedication to integrating cryptocurrencies into the national economic framework. By establishing strategic reserves, promoting stablecoins, and facilitating crypto-focused financial products, the administration aims to position the United States at the forefront of the digital asset revolution.
However, these initiatives are not without challenges. While deregulation has boosted investor confidence and stock prices, concerns arise regarding potential economic implications. The Federal Reserve warns that certain policies may lead to higher prices and adversely affect investment and growth. Additionally, the administrative and legal complexities of implementing widespread deregulation present further challenges, including potential staff cuts at agencies like the Environmental Protection Agency and legal challenges to some of the administration's actions. citeturn0news10
In summary, President Trump's recent policies reflect a strategic embrace of cryptocurrencies, aiming to foster innovation, attract investment, and establish the United States as a leader in the digital asset space. While these efforts present opportunities for economic growth and technological advancement, they also necessitate careful consideration of regulatory and economic impacts to ensure balanced and sustainable development in the crypto sector.
-
 @ 83279ad2:bd49240d
2025-03-30 14:21:49
@ 83279ad2:bd49240d
2025-03-30 14:21:49Test
-
 @ 09fbf8f3:fa3d60f0
2024-11-02 08:00:29
@ 09fbf8f3:fa3d60f0
2024-11-02 08:00:29> ### 第三方API合集:
免责申明:
在此推荐的 OpenAI API Key 由第三方代理商提供,所以我们不对 API Key 的 有效性 和 安全性 负责,请你自行承担购买和使用 API Key 的风险。
| 服务商 | 特性说明 | Proxy 代理地址 | 链接 | | --- | --- | --- | --- | | AiHubMix | 使用 OpenAI 企业接口,全站模型价格为官方 86 折(含 GPT-4 )| https://aihubmix.com/v1 | 官网 | | OpenAI-HK | OpenAI的API官方计费模式为,按每次API请求内容和返回内容tokens长度来定价。每个模型具有不同的计价方式,以每1,000个tokens消耗为单位定价。其中1,000个tokens约为750个英文单词(约400汉字)| https://api.openai-hk.com/ | 官网 | | CloseAI | CloseAI是国内规模最大的商用级OpenAI代理平台,也是国内第一家专业OpenAI中转服务,定位于企业级商用需求,面向企业客户的线上服务提供高质量稳定的官方OpenAI API 中转代理,是百余家企业和多家科研机构的专用合作平台。 | https://api.openai-proxy.org | 官网 | | OpenAI-SB | 需要配合Telegram 获取api key | https://api.openai-sb.com | 官网 |
持续更新。。。
推广:
访问不了openai,去
低调云购买VPN。官网:https://didiaocloud.xyz
邀请码:
w9AjVJit价格低至1元。
-
 @ 4c48cf05:07f52b80
2024-10-30 01:03:42
@ 4c48cf05:07f52b80
2024-10-30 01:03:42I believe that five years from now, access to artificial intelligence will be akin to what access to the Internet represents today. It will be the greatest differentiator between the haves and have nots. Unequal access to artificial intelligence will exacerbate societal inequalities and limit opportunities for those without access to it.
Back in April, the AI Index Steering Committee at the Institute for Human-Centered AI from Stanford University released The AI Index 2024 Annual Report.
Out of the extensive report (502 pages), I chose to focus on the chapter dedicated to Public Opinion. People involved with AI live in a bubble. We all know and understand AI and therefore assume that everyone else does. But, is that really the case once you step out of your regular circles in Seattle or Silicon Valley and hit Main Street?
Two thirds of global respondents have a good understanding of what AI is
The exact number is 67%. My gut feeling is that this number is way too high to be realistic. At the same time, 63% of respondents are aware of ChatGPT so maybe people are confounding AI with ChatGPT?
If so, there is so much more that they won't see coming.
This number is important because you need to see every other questions and response of the survey through the lens of a respondent who believes to have a good understanding of what AI is.
A majority are nervous about AI products and services
52% of global respondents are nervous about products and services that use AI. Leading the pack are Australians at 69% and the least worried are Japanise at 23%. U.S.A. is up there at the top at 63%.
Japan is truly an outlier, with most countries moving between 40% and 60%.
Personal data is the clear victim
Exaclty half of the respondents believe that AI companies will protect their personal data. And the other half believes they won't.
Expected benefits
Again a majority of people (57%) think that it will change how they do their jobs. As for impact on your life, top hitters are getting things done faster (54%) and more entertainment options (51%).
The last one is a head scratcher for me. Are people looking forward to AI generated movies?

Concerns
Remember the 57% that thought that AI will change how they do their jobs? Well, it looks like 37% of them expect to lose it. Whether or not this is what will happen, that is a very high number of people who have a direct incentive to oppose AI.
Other key concerns include:
- Misuse for nefarious purposes: 49%
- Violation of citizens' privacy: 45%
Conclusion
This is the first time I come across this report and I wil make sure to follow future annual reports to see how these trends evolve.
Overall, people are worried about AI. There are many things that could go wrong and people perceive that both jobs and privacy are on the line.
Full citation: Nestor Maslej, Loredana Fattorini, Raymond Perrault, Vanessa Parli, Anka Reuel, Erik Brynjolfsson, John Etchemendy, Katrina Ligett, Terah Lyons, James Manyika, Juan Carlos Niebles, Yoav Shoham, Russell Wald, and Jack Clark, “The AI Index 2024 Annual Report,” AI Index Steering Committee, Institute for Human-Centered AI, Stanford University, Stanford, CA, April 2024.
The AI Index 2024 Annual Report by Stanford University is licensed under Attribution-NoDerivatives 4.0 International.
-
 @ d560dbc2:bbd59238
2025-03-30 07:56:40
@ d560dbc2:bbd59238
2025-03-30 07:56:40We’ve all been there: that one task sitting on your to-do list, staring at you like a disappointed parent, and yet you keep pushing it off for absolutely no good reason. It’s not even that hard, urgent, or complicated—but somehow, it’s been haunting you for days, weeks, or maybe even months. Why do we do this to ourselves?
Why Do We Postpone Tasks for No Reason?
Procrastination is a sneaky beast. Even tasks that take 10 minutes, require minimal brainpower, and have no immediate deadline often get pushed aside. Here are some psychological reasons:
-
Emotional Avoidance:
Even if a task isn’t hard, a tiny emotional weight (like mild boredom or a vague “I don’t wanna”) can lead your brain to choose distractions—like scrolling through Instagram. -
Lack of Immediate Consequences:
Without a pressing deadline, your brain tends to deprioritize the task, even if completing it would make you feel great. -
The Zeigarnik Effect:
Unfinished tasks stick in our minds, creating mental tension. Ironically, that tension can make the task seem bigger and more daunting, encouraging further avoidance.
My Own “No-Reason” Procrastination Story
Let’s be real—I’ve been postponing something trivial, like organizing my desk drawer, for weeks. It’s a simple task that takes about 15 minutes. There’s no deadline, no special skill required—yet every time I open the drawer, I see the chaos of old receipts, random cables, and a half-eaten pack of gum (don’t judge!) and think, “I’ll do it later.” It’s not that I’m busy—I’ve had plenty of time to rewatch my favorite sitcom for the third time. But ignoring it has become my default, and that messy drawer now occupies mental space far beyond its physical size.
Why These Tasks Matter More Than We Think
Those little tasks we postpone might seem harmless, but they add up to create mental clutter. That messy desk drawer isn’t just a drawer—it’s a tiny stressor that pops into your head at the worst moments, disrupting your focus on important work or relaxation.
-
Mental Clutter:
Unfinished tasks can weigh on your mind, making it harder to focus on what truly matters. -
The Bigger Picture:
Tasks like “reply to that email” or “schedule that doctor’s appointment” may seem minor, but avoiding them can lead to unnecessary stress and lost opportunities.
How to Finally Tackle That Task
Here are a few strategies that have helped me break the cycle of “no-reason” procrastination:
1. The 20-Minute Rule (Thank You, Pomodoro!)
-
Commit to 20 Minutes:
Set a timer for just 20 minutes and start working on the task. You’d be surprised how much you can accomplish once you begin. -
Example:
For my desk drawer, I set a timer, got to work, and finished in 12 minutes. That small win made me feel like a productivity superhero.
2. Pin It and Get a Nudge
-
Use Reminders:
Pin that nagging task (like “Organize desk drawer”) as your top priority for the day. A gentle reminder can help break the cycle of avoidance. -
Result:
It’s like having a friend nudge you, “Hey, remember that thing you’ve been ignoring? Let’s do it now!”
3. Make It Fun (Yes, Really!)
-
Add a Reward:
Turn the task into something enjoyable by setting a reward. Play your favorite music, and promise yourself a treat once you’re done. -
Example:
For my desk drawer, I put on an upbeat playlist and treated myself to a piece of chocolate when finished. Suddenly, it wasn’t a chore—it became a mini dance party with a sweet reward.
4. Celebrate the Win
-
Acknowledge Completion:
Once you finish, take a moment to celebrate—even if it’s just a mental high-five. -
Why It Matters:
That sense of closure clears mental clutter and builds momentum for your next task.
Let’s Share and Motivate Each Other
What’s that one task you’ve been postponing for no reason? Maybe it’s cleaning out your fridge, replying to a friend’s text, or finally hanging that picture frame that’s been leaning against the wall for months. Whatever it is, share your story in the comments! Let’s motivate each other to tackle these tasks and turn procrastination into progress.
Bonus points if you’ve got a funny reason for your procrastination (like, “I didn’t schedule that appointment because my doctor’s office has the worst hold music in history”).
Ready to stop procrastinating? Let’s get real, take that first step, and clear that mental clutter—one small win at a time!
-
-
 @ da0b9bc3:4e30a4a9
2025-03-30 07:40:58
@ da0b9bc3:4e30a4a9
2025-03-30 07:40:58Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/929299
-
 @ 09fbf8f3:fa3d60f0
2024-10-25 18:43:59
@ 09fbf8f3:fa3d60f0
2024-10-25 18:43:59在线直播:
央视体育版CCTV5:
央视体育版CCTV16 :
翡翠台:
-
 @ 8947a945:9bfcf626
2024-10-17 08:06:55
@ 8947a945:9bfcf626
2024-10-17 08:06:55สวัสดีทุกคนบน Nostr ครับ รวมไปถึง watchersและ ผู้ติดตามของผมจาก Deviantart และ platform งานศิลปะอื่นๆนะครับ
ตั้งแต่ต้นปี 2024 ผมใช้ AI เจนรูปงานตัวละครสาวๆจากอนิเมะ และเปิด exclusive content ให้สำหรับผู้ที่ชื่นชอบผลงานของผมเป็นพิเศษ
ผมโพสผลงานผมทั้งหมดไว้ที่เวบ Deviantart และค่อยๆสร้างฐานผู้ติดตามมาเรื่อยๆอย่างค่อยเป็นค่อยไปมาตลอดครับ ทุกอย่างเติบโตไปเรื่อยๆของมัน ส่วนตัวผมมองว่ามันเป็นพิร์ตธุรกิจออนไลน์ ของผมพอร์ตนึงได้เลย
เมื่อวันที่ 16 กย.2024 มีผู้ติดตามคนหนึ่งส่งข้อความส่วนตัวมาหาผม บอกว่าชื่นชอบผลงานของผมมาก ต้องการจะขอซื้อผลงาน แต่ขอซื้อเป็น NFT นะ เสนอราคาซื้อขายต่อชิ้นที่สูงมาก หลังจากนั้นผมกับผู้ซื้อคนนี้พูดคุยกันในเมล์ครับ
นี่คือข้อสรุปสั่นๆจากการต่อรองซื้อขายครับ
(หลังจากนี้ผมขอเรียกผู้ซื้อว่า scammer นะครับ เพราะไพ่มันหงายมาแล้ว ว่าเขาคือมิจฉาชีพ)

- Scammer รายแรก เลือกผลงานที่จะซื้อ เสนอราคาซื้อที่สูงมาก แต่ต้องเป็นเวบไซต์ NFTmarket place ที่เขากำหนดเท่านั้น มันทำงานอยู่บน ERC20 ผมเข้าไปดูเวบไซต์ที่ว่านี้แล้วรู้สึกว่ามันดูแปลกๆครับ คนที่จะลงขายผลงานจะต้องใช้ email ในการสมัครบัญชีซะก่อน ถึงจะผูก wallet อย่างเช่น metamask ได้ เมื่อผูก wallet แล้วไม่สามารถเปลี่ยนได้ด้วย ตอนนั้นผมใช้ wallet ที่ไม่ได้ link กับ HW wallet ไว้ ทดลองสลับ wallet ไปๆมาๆ มันทำไม่ได้ แถมลอง log out แล้ว เลข wallet ก็ยังคาอยู่อันเดิม อันนี้มันดูแปลกๆแล้วหนึ่งอย่าง เวบนี้ค่า ETH ในการ mint 0.15 - 0.2 ETH … ตีเป็นเงินบาทนี่แพงบรรลัยอยู่นะครับ

-
Scammer รายแรกพยายามชักจูงผม หว่านล้อมผมว่า แหม เดี๋ยวเขาก็มารับซื้องานผมน่า mint งานเสร็จ รีบบอกเขานะ เดี๋ยวเขารีบกดซื้อเลย พอขายได้กำไร ผมก็ได้ค่า gas คืนได้ แถมยังได้กำไรอีก ไม่มีอะไรต้องเสีนจริงมั้ย แต่มันเป้นความโชคดีครับ เพราะตอนนั้นผมไม่เหลือทุนสำรองที่จะมาซื้อ ETH ได้ ผมเลยต่อรองกับเขาตามนี้ครับ :
-
ผมเสนอว่า เอางี้มั้ย ผมส่งผลงานของผมแบบ low resolution ให้ก่อน แลกกับให้เขาช่วยโอน ETH ที่เป็นค่า mint งานมาให้หน่อย พอผมได้ ETH แล้ว ผมจะ upscale งานของผม แล้วเมล์ไปให้ ใจแลกใจกันไปเลย ... เขาไม่เอา
- ผมเสนอให้ไปซื้อที่ร้านค้าออนไลน์ buymeacoffee ของผมมั้ย จ่ายเป็น USD ... เขาไม่เอา
- ผมเสนอให้ซื้อขายผ่าน PPV lightning invoice ที่ผมมีสิทธิ์เข้าถึง เพราะเป็น creator ของ Creatr ... เขาไม่เอา
- ผมยอกเขาว่างั้นก็รอนะ รอเงินเดือนออก เขาบอก ok
สัปดาห์ถัดมา มี scammer คนที่สองติดต่อผมเข้ามา ใช้วิธีการใกล้เคียงกัน แต่ใช้คนละเวบ แถมเสนอราคาซื้อที่สูงกว่าคนแรกมาก เวบที่สองนี้เลวร้ายค่าเวบแรกอีกครับ คือต้องใช้เมล์สมัครบัญชี ไม่สามารถผูก metamask ได้ พอสมัครเสร็จจะได้ wallet เปล่าๆมาหนึ่งอัน ผมต้องโอน ETH เข้าไปใน wallet นั้นก่อน เพื่อเอาไปเป็นค่า mint NFT 0.2 ETH
ผมบอก scammer รายที่สองว่า ต้องรอนะ เพราะตอนนี้กำลังติดต่อซื้อขายอยู่กับผู้ซื้อรายแรกอยู่ ผมกำลังรอเงินเพื่อมาซื้อ ETH เป็นต้นทุนดำเนินงานอยู่ คนคนนี้ขอให้ผมส่งเวบแรกไปให้เขาดูหน่อย หลังจากนั้นไม่นานเขาเตือนผมมาว่าเวบแรกมันคือ scam นะ ไม่สามารถถอนเงินออกมาได้ เขายังส่งรูป cap หน้าจอที่คุยกับผู้เสียหายจากเวบแรกมาให้ดูว่าเจอปัญหาถอนเงินไม่ได้ ไม่พอ เขายังบลัฟ opensea ด้วยว่าลูกค้าขายงานได้ แต่ถอนเงินไม่ได้
Opensea ถอนเงินไม่ได้ ตรงนี้แหละครับคือตัวกระตุกต่อมเอ๊ะของผมดังมาก เพราะ opensea อ่ะ ผู้ใช้ connect wallet เข้ากับ marketplace โดยตรง ซื้อขายกันเกิดขึ้น เงินวิ่งเข้าวิ่งออก wallet ของแต่ละคนโดยตรงเลย opensea เก็บแค่ค่า fee ในการใช้ platform ไม่เก็บเงินลูกค้าไว้ แถมปีนี้ค่า gas fee ก็ถูกกว่า bull run cycle 2020 มาก ตอนนี้ค่า gas fee ประมาณ 0.0001 ETH (แต่มันก็แพงกว่า BTC อยู่ดีอ่ะครับ)
ผมเลยเอาเรื่องนี้ไปปรึกษาพี่บิท แต่แอดมินมาคุยกับผมแทน ทางแอดมินแจ้งว่ายังไม่เคยมีเพื่อนๆมาปรึกษาเรื่องนี้ กรณีที่ผมทักมาถามนี่เป็นรายแรกเลย แต่แอดมินให้ความเห็นไปในทางเดียวกับสมมุติฐานของผมว่าน่าจะ scam ในเวลาเดียวกับผมเอาเรื่องนี้ไปถามในเพจ NFT community คนไทนด้วย ได้รับการ confirm ชัดเจนว่า scam และมีคนไม่น้อยโดนหลอก หลังจากที่ผมรู้ที่มาแล้ว ผมเลยเล่นสงครามปั่นประสาท scammer ทั้งสองคนนี้ครับ เพื่อดูว่าหลอกหลวงมิจฉาชีพจริงมั้ย
โดยวันที่ 30 กย. ผมเลยปั่นประสาน scammer ทั้งสองรายนี้ โดยการ mint ผลงานที่เขาเสนอซื้อนั่นแหละ ขึ้น opensea แล้วส่งข้อความไปบอกว่า
mint ให้แล้วนะ แต่เงินไม่พอจริงๆว่ะโทษที เลย mint ขึ้น opensea แทน พอดีบ้านจน ทำได้แค่นี้ไปถึงแค่ opensea รีบไปซื้อล่ะ มีคนจ้องจะคว้างานผมเยอะอยู่ ผมไม่คิด royalty fee ด้วยนะเฮ้ย เอาไปขายต่อไม่ต้องแบ่งกำไรกับผม
เท่านั้นแหละครับ สงครามจิตวิทยาก็เริ่มขึ้น แต่เขาจนมุม กลืนน้ำลายตัวเอง ช็อตเด็ดคือ
เขา : เนี่ยอุส่ารอ บอกเพื่อนในทีมว่าวันจันทร์ที่ 30 กย. ได้ของแน่ๆ เพื่อนๆในทีมเห็นงานผมแล้วมันสวยจริง เลยใส่เงินเต็มที่ 9.3ETH (+ capture screen ส่งตัวเลขยอดเงินมาให้ดู)ไว้รอโดยเฉพาะเลยนะ ผม : เหรอ ... งั้น ขอดู wallet address ที่มี transaction มาให้ดูหน่อยสิ เขา : 2ETH นี่มัน 5000$ เลยนะ ผม : แล้วไง ขอดู wallet address ที่มีการเอายอดเงิน 9.3ETH มาให้ดูหน่อย ไหนบอกว่าเตรียมเงินไว้มากแล้วนี่ ขอดูหน่อย ว่าใส่ไว้เมื่อไหร่ ... เอามาแค่ adrress นะเว้ย ไม่ต้องทะลึ่งส่ง seed มาให้ เขา : ส่งรูปเดิม 9.3 ETH มาให้ดู ผม : รูป screenshot อ่ะ มันไม่มีความหมายหรอกเว้ย ตัดต่อเอาก็ได้ง่ายจะตาย เอา transaction hash มาดู ไหนว่าเตรียมเงินไว้รอ 9.3ETH แล้วอยากซื้องานผมจนตัวสั่นเลยไม่ใช่เหรอ ถ้าจะส่ง wallet address มาให้ดู หรือจะช่วยส่ง 0.15ETH มาให้ยืม mint งานก่อน แล้วมากดซื้อ 2ETH ไป แล้วผมใช้ 0.15ETH คืนให้ก็ได้ จะซื้อหรือไม่ซื้อเนี่ย เขา : จะเอา address เขาไปทำไม ผม : ตัดจบ รำคาญ ไม่ขายให้ละ เขา : 2ETH = 5000 USD เลยนะ ผม : แล้วไง
ผมเลยเขียนบทความนี้มาเตือนเพื่อนๆพี่ๆทุกคนครับ เผื่อใครกำลังเปิดพอร์ตทำธุรกิจขาย digital art online แล้วจะโชคดี เจอของดีแบบผม
ทำไมผมถึงมั่นใจว่ามันคือการหลอกหลวง แล้วคนโกงจะได้อะไร
อันดับแรกไปพิจารณาดู opensea ครับ เป็นเวบ NFTmarketplace ที่ volume การซื้อขายสูงที่สุด เขาไม่เก็บเงินของคนจะซื้อจะขายกันไว้กับตัวเอง เงินวิ่งเข้าวิ่งออก wallet ผู้ซื้อผู้ขายเลย ส่วนทางเวบเก็บค่าธรรมเนียมเท่านั้น แถมค่าธรรมเนียมก็ถูกกว่าเมื่อปี 2020 เยอะ ดังนั้นการที่จะไปลงขายงานบนเวบ NFT อื่นที่ค่า fee สูงกว่ากันเป็นร้อยเท่า ... จะทำไปทำไม
ผมเชื่อว่า scammer โกงเงินเจ้าของผลงานโดยการเล่นกับความโลภและความอ่อนประสบการณ์ของเจ้าของผลงานครับ เมื่อไหร่ก็ตามที่เจ้าของผลงานโอน ETH เข้าไปใน wallet เวบนั้นเมื่อไหร่ หรือเมื่อไหร่ก็ตามที่จ่ายค่า fee ในการ mint งาน เงินเหล่านั้นสิ่งเข้ากระเป๋า scammer ทันที แล้วก็จะมีการเล่นตุกติกต่อแน่นอนครับ เช่นถอนไม่ได้ หรือซื้อไม่ได้ ต้องโอนเงินมาเพิ่มเพื่อปลดล็อค smart contract อะไรก็ว่าไป แล้วคนนิสัยไม่ดีพวกเนี้ย ก็จะเล่นกับความโลภของคน เอาราคาเสนอซื้อที่สูงโคตรๆมาล่อ ... อันนี้ไม่ว่ากัน เพราะบนโลก NFT รูปภาพบางรูปที่ไม่ได้มีความเป็นศิลปะอะไรเลย มันดันขายกันได้ 100 - 150 ETH ศิลปินที่พยายามสร้างตัวก็อาจจะมองว่า ผลงานเรามีคนรับซื้อ 2 - 4 ETH ต่องานมันก็มากพอแล้ว (จริงๆมากเกินจนน่าตกใจด้วยซ้ำครับ)
บนโลกของ BTC ไม่ต้องเชื่อใจกัน โอนเงินไปหากันได้ ปิดสมุดบัญชีได้โดยไม่ต้องเชื่อใจกัน
บบโลกของ ETH "code is law" smart contract มีเขียนอยู่แล้ว ไปอ่าน มันไม่ได้ยากมากในการทำความเข้าใจ ดังนั้น การจะมาเชื่อคำสัญญาจากคนด้วยกัน เป็นอะไรที่ไม่มีเหตุผล
ผมไปเล่าเรื่องเหล่านี้ให้กับ community งานศิลปะ ก็มีทั้งเสียงตอบรับที่ดี และไม่ดีปนกันไป มีบางคนยืนยันเสียงแข็งไปในทำนองว่า ไอ้เรื่องแบบเนี้ยไม่ได้กินเขาหรอก เพราะเขาตั้งใจแน่วแน่ว่างานศิลป์ของเขา เขาไม่เอาเข้ามายุ่งในโลก digital currency เด็ดขาด ซึ่งผมก็เคารพมุมมองเขาครับ แต่มันจะดีกว่ามั้ย ถ้าเราเปิดหูเปิดตาให้ทันเทคโนโลยี โดยเฉพาะเรื่อง digital currency , blockchain โดนโกงทีนึงนี่คือหมดตัวกันง่ายกว่าเงิน fiat อีก
อยากจะมาเล่าให้ฟังครับ และอยากให้ช่วยแชร์ไปให้คนรู้จักด้วย จะได้ระวังตัวกัน
Note
- ภาพประกอบ cyber security ทั้งสองนี่ของผมเองครับ ทำเอง วางขายบน AdobeStock
- อีกบัญชีนึงของผม "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw กำลังค่อยๆเอาผลงานจากโลกข้างนอกเข้ามา nostr ครับ ตั้งใจจะมาสร้างงานศิลปะในนี้ เพื่อนๆที่ชอบงาน จะได้ไม่ต้องออกไปหาที่ไหน
ผลงานของผมครับ - Anime girl fanarts : HikariHarmony - HikariHarmony on Nostr - General art : KeshikiRakuen - KeshikiRakuen อาจจะเป็นบัญชี nostr ที่สามของผม ถ้าไหวครับ
-
 @ 8947a945:9bfcf626
2024-10-17 07:33:00
@ 8947a945:9bfcf626
2024-10-17 07:33:00Hello everyone on Nostr and all my watchersand followersfrom DeviantArt, as well as those from other art platforms
I have been creating and sharing AI-generated anime girl fanart since the beginning of 2024 and have been running member-exclusive content on Patreon.
I also publish showcases of my artworks to Deviantart. I organically build up my audience from time to time. I consider it as one of my online businesses of art. Everything is slowly growing
On September 16, I received a DM from someone expressing interest in purchasing my art in NFT format and offering a very high price for each piece. We later continued the conversation via email.
Here’s a brief overview of what happened

- The first scammer selected the art they wanted to buy and offered a high price for each piece. They provided a URL to an NFT marketplace site running on the Ethereum (ETH) mainnet or ERC20. The site appeared suspicious, requiring email sign-up and linking a MetaMask wallet. However, I couldn't change the wallet address later. The minting gas fees were quite expensive, ranging from 0.15 to 0.2 ETH

-
The scammers tried to convince me that the high profits would easily cover the minting gas fees, so I had nothing to lose. Luckily, I didn’t have spare funds to purchase ETH for the gas fees at the time, so I tried negotiating with them as follows:
-
I offered to send them a lower-quality version of my art via email in exchange for the minting gas fees, but they refused.
- I offered them the option to pay in USD through Buy Me a Coffee shop here, but they refused.
- I offered them the option to pay via Bitcoin using the Lightning Network invoice , but they refused.
- I asked them to wait until I could secure the funds, and they agreed to wait.
The following week, a second scammer approached me with a similar offer, this time at an even higher price and through a different NFT marketplace website.
This second site also required email registration, and after navigating to the dashboard, it asked for a minting fee of 0.2 ETH. However, the site provided a wallet address for me instead of connecting a MetaMask wallet.
I told the second scammer that I was waiting to make a profit from the first sale, and they asked me to show them the first marketplace. They then warned me that the first site was a scam and even sent screenshots of victims, including one from OpenSea saying that Opensea is not paying.
This raised a red flag, and I began suspecting I might be getting scammed. On OpenSea, funds go directly to users' wallets after transactions, and OpenSea charges a much lower platform fee compared to the previous crypto bull run in 2020. Minting fees on OpenSea are also significantly cheaper, around 0.0001 ETH per transaction.
I also consulted with Thai NFT artist communities and the ex-chairman of the Thai Digital Asset Association. According to them, no one had reported similar issues, but they agreed it seemed like a scam.
After confirming my suspicions with my own research and consulting with the Thai crypto community, I decided to test the scammers’ intentions by doing the following
I minted the artwork they were interested in, set the price they offered, and listed it for sale on OpenSea. I then messaged them, letting them know the art was available and ready to purchase, with no royalty fees if they wanted to resell it.
They became upset and angry, insisting I mint the art on their chosen platform, claiming they had already funded their wallet to support me. When I asked for proof of their wallet address and transactions, they couldn't provide any evidence that they had enough funds.
Here’s what I want to warn all artists in the DeviantArt community or other platforms If you find yourself in a similar situation, be aware that scammers may be targeting you.
My Perspective why I Believe This is a Scam and What the Scammers Gain
From my experience with BTC and crypto since 2017, here's why I believe this situation is a scam, and what the scammers aim to achieve
First, looking at OpenSea, the largest NFT marketplace on the ERC20 network, they do not hold users' funds. Instead, funds from transactions go directly to users’ wallets. OpenSea’s platform fees are also much lower now compared to the crypto bull run in 2020. This alone raises suspicion about the legitimacy of other marketplaces requiring significantly higher fees.
I believe the scammers' tactic is to lure artists into paying these exorbitant minting fees, which go directly into the scammers' wallets. They convince the artists by promising to purchase the art at a higher price, making it seem like there's no risk involved. In reality, the artist has already lost by paying the minting fee, and no purchase is ever made.
In the world of Bitcoin (BTC), the principle is "Trust no one" and “Trustless finality of transactions” In other words, transactions are secure and final without needing trust in a third party.
In the world of Ethereum (ETH), the philosophy is "Code is law" where everything is governed by smart contracts deployed on the blockchain. These contracts are transparent, and even basic code can be read and understood. Promises made by people don’t override what the code says.
I also discuss this issue with art communities. Some people have strongly expressed to me that they want nothing to do with crypto as part of their art process. I completely respect that stance.
However, I believe it's wise to keep your eyes open, have some skin in the game, and not fall into scammers’ traps. Understanding the basics of crypto and NFTs can help protect you from these kinds of schemes.
If you found this article helpful, please share it with your fellow artists.
Until next time Take care
Note
- Both cyber security images are mine , I created and approved by AdobeStock to put on sale
- I'm working very hard to bring all my digital arts into Nostr to build my Sats business here to my another npub "HikariHarmony" npub1exdtszhpw3ep643p9z8pahkw8zw00xa9pesf0u4txyyfqvthwapqwh48sw
Link to my full gallery - Anime girl fanarts : HikariHarmony - HikariHarmony on Nostr - General art : KeshikiRakuen
-
 @ e6817453:b0ac3c39
2024-10-06 11:21:27
@ e6817453:b0ac3c39
2024-10-06 11:21:27Hey folks, today we're diving into an exciting and emerging topic: personal artificial intelligence (PAI) and its connection to sovereignty, privacy, and ethics. With the rapid advancements in AI, there's a growing interest in the development of personal AI agents that can work on behalf of the user, acting autonomously and providing tailored services. However, as with any new technology, there are several critical factors that shape the future of PAI. Today, we'll explore three key pillars: privacy and ownership, explainability, and bias.
1. Privacy and Ownership: Foundations of Personal AI
At the heart of personal AI, much like self-sovereign identity (SSI), is the concept of ownership. For personal AI to be truly effective and valuable, users must own not only their data but also the computational power that drives these systems. This autonomy is essential for creating systems that respect the user's privacy and operate independently of large corporations.
In this context, privacy is more than just a feature—it's a fundamental right. Users should feel safe discussing sensitive topics with their AI, knowing that their data won’t be repurposed or misused by big tech companies. This level of control and data ownership ensures that users remain the sole beneficiaries of their information and computational resources, making privacy one of the core pillars of PAI.
2. Bias and Fairness: The Ethical Dilemma of LLMs
Most of today’s AI systems, including personal AI, rely heavily on large language models (LLMs). These models are trained on vast datasets that represent snapshots of the internet, but this introduces a critical ethical challenge: bias. The datasets used for training LLMs can be full of biases, misinformation, and viewpoints that may not align with a user’s personal values.
This leads to one of the major issues in AI ethics for personal AI—how do we ensure fairness and minimize bias in these systems? The training data that LLMs use can introduce perspectives that are not only unrepresentative but potentially harmful or unfair. As users of personal AI, we need systems that are free from such biases and can be tailored to our individual needs and ethical frameworks.
Unfortunately, training models that are truly unbiased and fair requires vast computational resources and significant investment. While large tech companies have the financial means to develop and train these models, individual users or smaller organizations typically do not. This limitation means that users often have to rely on pre-trained models, which may not fully align with their personal ethics or preferences. While fine-tuning models with personalized datasets can help, it's not a perfect solution, and bias remains a significant challenge.
3. Explainability: The Need for Transparency
One of the most frustrating aspects of modern AI is the lack of explainability. Many LLMs operate as "black boxes," meaning that while they provide answers or make decisions, it's often unclear how they arrived at those conclusions. For personal AI to be effective and trustworthy, it must be transparent. Users need to understand how the AI processes information, what data it relies on, and the reasoning behind its conclusions.
Explainability becomes even more critical when AI is used for complex decision-making, especially in areas that impact other people. If an AI is making recommendations, judgments, or decisions, it’s crucial for users to be able to trace the reasoning process behind those actions. Without this transparency, users may end up relying on AI systems that provide flawed or biased outcomes, potentially causing harm.
This lack of transparency is a major hurdle for personal AI development. Current LLMs, as mentioned earlier, are often opaque, making it difficult for users to trust their outputs fully. The explainability of AI systems will need to be improved significantly to ensure that personal AI can be trusted for important tasks.
Addressing the Ethical Landscape of Personal AI
As personal AI systems evolve, they will increasingly shape the ethical landscape of AI. We’ve already touched on the three core pillars—privacy and ownership, bias and fairness, and explainability. But there's more to consider, especially when looking at the broader implications of personal AI development.
Most current AI models, particularly those from big tech companies like Facebook, Google, or OpenAI, are closed systems. This means they are aligned with the goals and ethical frameworks of those companies, which may not always serve the best interests of individual users. Open models, such as Meta's LLaMA, offer more flexibility and control, allowing users to customize and refine the AI to better meet their personal needs. However, the challenge remains in training these models without significant financial and technical resources.
There’s also the temptation to use uncensored models that aren’t aligned with the values of large corporations, as they provide more freedom and flexibility. But in reality, models that are entirely unfiltered may introduce harmful or unethical content. It’s often better to work with aligned models that have had some of the more problematic biases removed, even if this limits some aspects of the system’s freedom.
The future of personal AI will undoubtedly involve a deeper exploration of these ethical questions. As AI becomes more integrated into our daily lives, the need for privacy, fairness, and transparency will only grow. And while we may not yet be able to train personal AI models from scratch, we can continue to shape and refine these systems through curated datasets and ongoing development.
Conclusion
In conclusion, personal AI represents an exciting new frontier, but one that must be navigated with care. Privacy, ownership, bias, and explainability are all essential pillars that will define the future of these systems. As we continue to develop personal AI, we must remain vigilant about the ethical challenges they pose, ensuring that they serve the best interests of users while remaining transparent, fair, and aligned with individual values.
If you have any thoughts or questions on this topic, feel free to reach out—I’d love to continue the conversation!
-
 @ e6817453:b0ac3c39
2024-09-30 14:52:23
@ e6817453:b0ac3c39
2024-09-30 14:52:23In the modern world of AI, managing vast amounts of data while keeping it relevant and accessible is a significant challenge, mainly when dealing with large language models (LLMs) and vector databases. One approach that has gained prominence in recent years is integrating vector search with metadata, especially in retrieval-augmented generation (RAG) pipelines. Vector search and metadata enable faster and more accurate data retrieval. However, the process of pre- and post-search filtering results plays a crucial role in ensuring data relevance.
The Vector Search and Metadata Challenge
In a typical vector search, you create embeddings from chunks of text, such as a PDF document. These embeddings allow the system to search for similar items and retrieve them based on relevance. The challenge, however, arises when you need to combine vector search results with structured metadata. For example, you may have timestamped text-based content and want to retrieve the most relevant content within a specific date range. This is where metadata becomes critical in refining search results.
Unfortunately, most vector databases treat metadata as a secondary feature, isolating it from the primary vector search process. As a result, handling queries that combine vectors and metadata can become a challenge, particularly when the search needs to account for a dynamic range of filters, such as dates or other structured data.
LibSQL and vector search metadata
LibSQL is a more general-purpose SQLite-based database that adds vector capabilities to regular data. Vectors are presented as blob columns of regular tables. It makes vector embeddings and metadata a first-class citizen that naturally builds deep integration of these data points.
create table if not exists conversation ( id varchar(36) primary key not null, startDate real, endDate real, summary text, vectorSummary F32_BLOB(512) );It solves the challenge of metadata and vector search and eliminates impedance between vector data and regular structured data points in the same storage.
As you can see, you can access vector-like data and start date in the same query.
select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from conversation where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top};vector_distance_cos calculated as distance allows us to make a primitive vector search that does a full scan and calculates distances on rows. We could optimize it with CTE and limit search and distance calculations to a much smaller subset of data.
This approach could be calculation intensive and fail on large amounts of data.
Libsql offers a way more effective vector search based on FlashDiskANN vector indexed.
vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) ivector_top_k is a table function that searches for the top of the newly created vector search index. As you can see, we could use only vector as a function parameter, and other columns could be used outside of the table function. So, to use a vector index together with different columns, we need to apply some strategies.
Now we get a classical problem of integration vector search results with metadata queries.
Post-Filtering: A Common Approach
The most widely adopted method in these pipelines is post-filtering. In this approach, the system first retrieves data based on vector similarities and then applies metadata filters. For example, imagine you’re conducting a vector search to retrieve conversations relevant to a specific question. Still, you also want to ensure these conversations occurred in the past week.
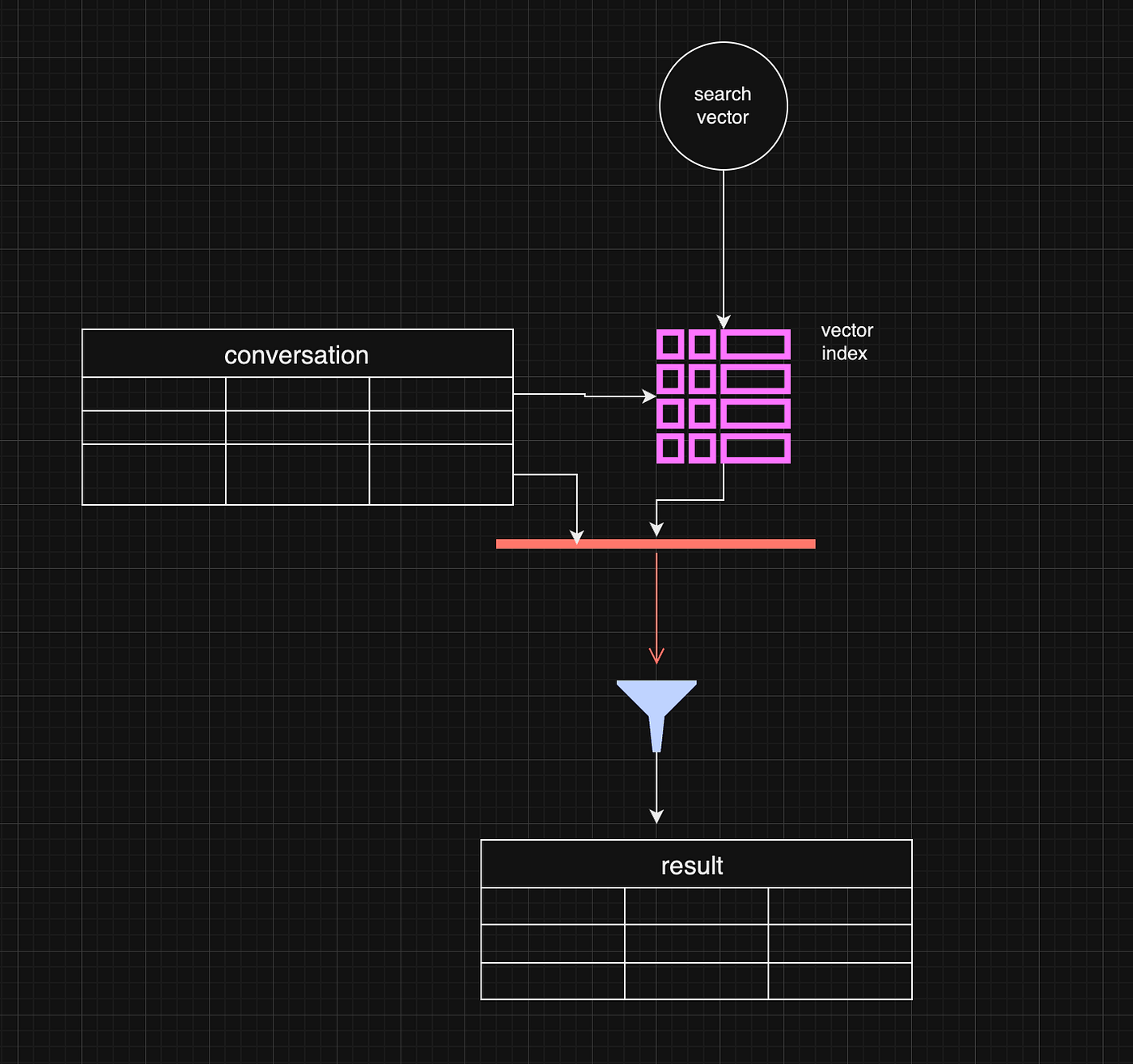
Post-filtering allows the system to retrieve the most relevant vector-based results and subsequently filter out any that don’t meet the metadata criteria, such as date range. This method is efficient when vector similarity is the primary factor driving the search, and metadata is only applied as a secondary filter.
const sqlQuery = ` select c.id ,c.startDate, c.endDate, c.summary, vector_distance_cos(c.vectorSummary, vector(${vector})) distance from vector_top_k('idx_conversation_vectorSummary', ${vector} , ${top}) i inner join conversation c on i.id = c.rowid where ${startDate ? `and c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `and c.endDate <= ${endDate.getTime()}` : ''} ${distance ? `and distance <= ${distance}` : ''} order by distance limit ${top};However, there are some limitations. For example, the initial vector search may yield fewer results or omit some relevant data before applying the metadata filter. If the search window is narrow enough, this can lead to complete results.
One working strategy is to make the top value in vector_top_K much bigger. Be careful, though, as the function's default max number of results is around 200 rows.
Pre-Filtering: A More Complex Approach
Pre-filtering is a more intricate approach but can be more effective in some instances. In pre-filtering, metadata is used as the primary filter before vector search takes place. This means that only data that meets the metadata criteria is passed into the vector search process, limiting the scope of the search right from the beginning.
While this approach can significantly reduce the amount of irrelevant data in the final results, it comes with its own challenges. For example, pre-filtering requires a deeper understanding of the data structure and may necessitate denormalizing the data or creating separate pre-filtered tables. This can be resource-intensive and, in some cases, impractical for dynamic metadata like date ranges.
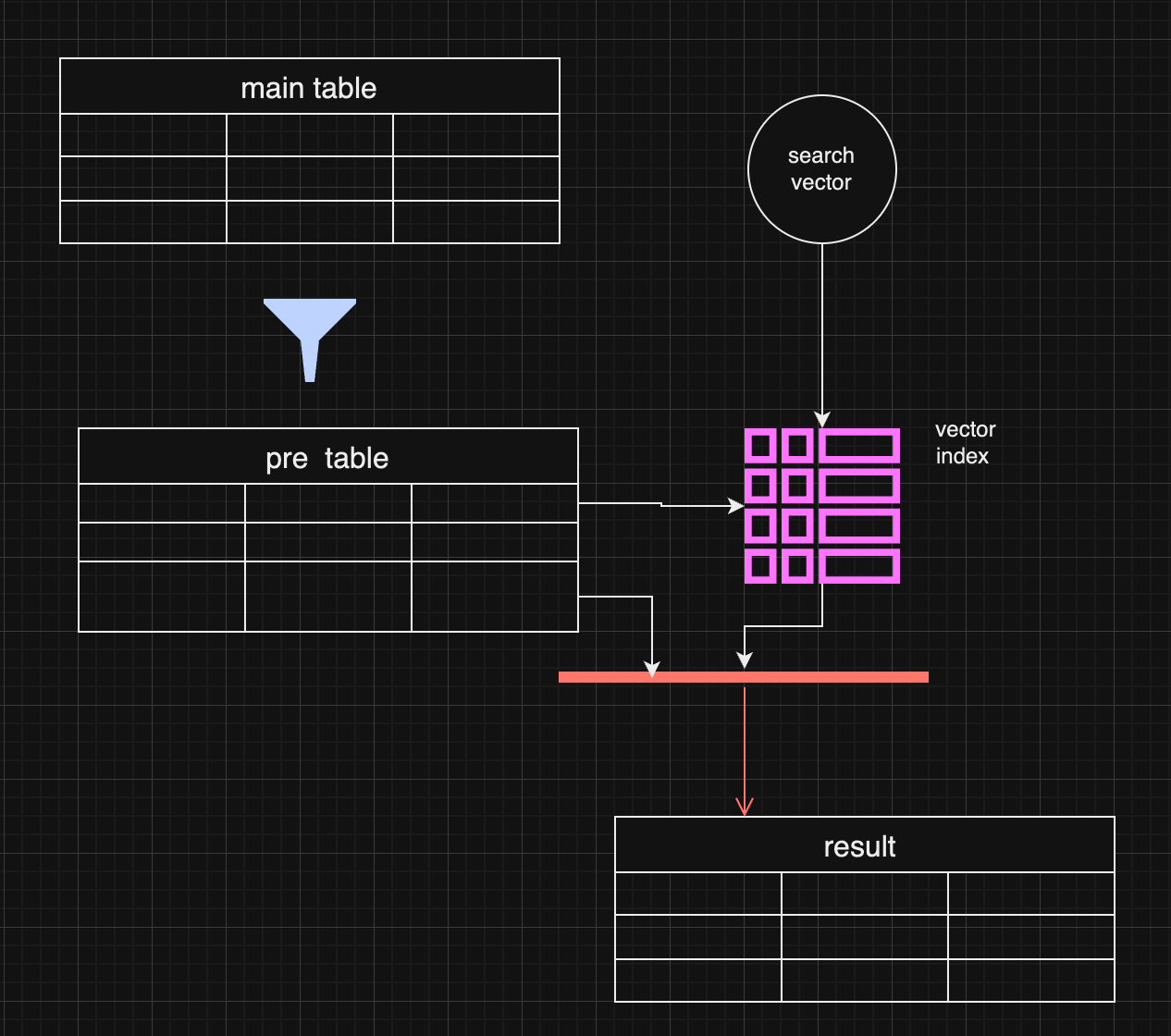
In certain use cases, pre-filtering might outperform post-filtering. For instance, when the metadata (e.g., specific date ranges) is the most important filter, pre-filtering ensures the search is conducted only on the most relevant data.
Pre-filtering with distance-based filtering
So, we are getting back to an old concept. We do prefiltering instead of using a vector index.
WITH FilteredDates AS ( SELECT c.id, c.startDate, c.endDate, c.summary, c.vectorSummary FROM YourTable c WHERE ${startDate ? `AND c.startDate >= ${startDate.getTime()}` : ''} ${endDate ? `AND c.endDate <= ${endDate.getTime()}` : ''} ), DistanceCalculation AS ( SELECT fd.id, fd.startDate, fd.endDate, fd.summary, fd.vectorSummary, vector_distance_cos(fd.vectorSummary, vector(${vector})) AS distance FROM FilteredDates fd ) SELECT dc.id, dc.startDate, dc.endDate, dc.summary, dc.distance FROM DistanceCalculation dc WHERE 1=1 ${distance ? `AND dc.distance <= ${distance}` : ''} ORDER BY dc.distance LIMIT ${top};It makes sense if the filter produces small data and distance calculation happens on the smaller data set.
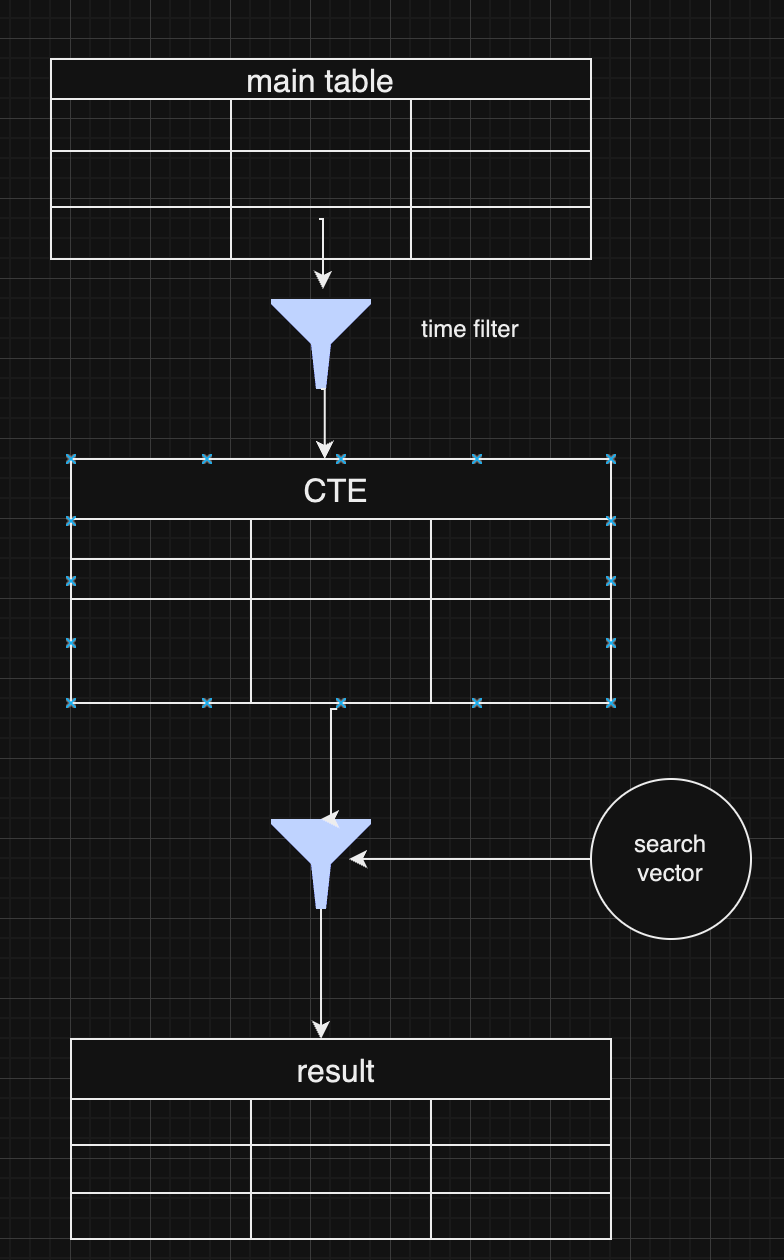
As a pro of this approach, you have full control over the data and get all results without omitting some typical values for extensive index searches.
Choosing Between Pre and Post-Filtering
Both pre-filtering and post-filtering have their advantages and disadvantages. Post-filtering is more accessible to implement, especially when vector similarity is the primary search factor, but it can lead to incomplete results. Pre-filtering, on the other hand, can yield more accurate results but requires more complex data handling and optimization.
In practice, many systems combine both strategies, depending on the query. For example, they might start with a broad pre-filtering based on metadata (like date ranges) and then apply a more targeted vector search with post-filtering to refine the results further.
Conclusion
Vector search with metadata filtering offers a powerful approach for handling large-scale data retrieval in LLMs and RAG pipelines. Whether you choose pre-filtering or post-filtering—or a combination of both—depends on your application's specific requirements. As vector databases continue to evolve, future innovations that combine these two approaches more seamlessly will help improve data relevance and retrieval efficiency further.
-
 @ ff517fbf:fde1561b
2025-03-30 04:43:09
@ ff517fbf:fde1561b
2025-03-30 04:43:09ビットコインが「最強の担保」と言われる理由
ビットコインは「デジタルゴールド」とも呼ばれることがありますが、実はローンの担保としても最強だと言われています。その理由を、他の資産(株式、不動産、金など)と比較しながら見てみましょう。
-
流動性と即時性:ビットコインは24時間365日世界中で取引されているため、非常に流動性が高い資産です。売買がすぐにできて価格も常に明確なので、担保評価がしやすく、お金を貸す側・借りる側双方に安心感を与えます。一方、株式や不動産は市場が営業時間内しか動かず、現金化にも時間がかかります。不動産は売却に数ヶ月かかることもありますし、金(ゴールド)は現物を保管・輸送する手間があります。ビットコインならネット上で即座に担保設定・解除ができるのです。
-
分割性と柔軟性:ビットコインは小数点以下8桁まで分割可能(1億分の1が最小単位の「サトシ」)なので、必要な額だけ正確に担保に充てることができます。他方、土地や建物を一部だけ担保に入れることは難しいですし、株式も1株未満の細かい調整はできません。ビットコインなら価値の微調整が容易で、担保として柔軟に扱えるのです。
-
管理のしやすさ(マルチシグによる信頼性):HodlHodlのLendでは、ビットコイン担保は2-of-3のマルチシグ契約で管理されます。これは「借り手・貸し手・プラットフォーム」の3者それぞれが鍵を持ち、2つの鍵の同意がないとビットコインを動かせない仕組みです。このため、誰か一人が勝手に担保を持ち逃げすることができず、第三者(HodlHodl)も単独ではコインを移動できません。ビットコインだからこそ実現できる非中央集権で安全な担保管理であり、株式や不動産を担保にする場合のように銀行や証券会社といった仲介業者に頼る必要がありません。
-
国境を越えた利用:ビットコインはインターネットがつながる所なら世界中どこでも送受信できます。このため、日本にいながら海外の相手とでもローン契約が可能です。たとえば日本の方がビットコインを担保にドル建てのステーブルコインを借り、それを日本円に換えて使うこともできます(為替リスクには注意ですが…)。不動産を海外の人と直接やり取りするのは現実的に難しいですが、ビットコインならグローバルに担保が活用できるのです。
-
希少性と価値の上昇期待:ビットコインは発行上限が決まっており(2100万BTCまで)、時間とともに新規供給が減っていきます。過去の長期的な価格推移を見ると、短期的な変動は激しいものの数年〜十年のスパンでは上昇傾向にあります。一方、法定通貨建ての資産(債券や株式など)はインフレの影響で実質価値が目減りすることがあります。ビットコインは長期保有すれば価値が上がりやすい特性があるため、「今手放したくない資産」として担保に向いています。実際、HodlHodlのチームは「ビットコインはスーパーカCollateral(超優秀な担保)だ」と述べています。
こうした理由から、ビットコインは現時点で考えうる中でも最良の担保資産と考えられています。株や不動産のように書類手続きや名義変更をしなくても、ビットコインならブロックチェーン上の契約でシンプルに担保設定ができる――この手軽さと信頼性が大きな魅力です。
匿名&プライバシー重視:KYC不要のP2Pレンディングのメリット
HodlHodlのLend最大の特徴の一つは、本人確認(KYC)が一切不要だという点です。日本の多くの金融サービスでは口座開設時に運転免許証やマイナンバー提出など煩雑な手続きが必要ですが、Lendではメールアドレスでアカウント登録するだけでOK。これは「匿名性・プライバシー」を重視する人にとって非常に相性が良いポイントです。
-
個人情報を晒さなくて良い安心感:日本では昔から「人に迷惑をかけない」「目立たない」ことが美徳とされ、特にお金の話は他人に知られたくないと考える人が多いですよね。Lendは匿名で利用できるため、借金をすることを周囲に知られたくない人でも安心です。銀行からローンを借りるときのように収入証明や保証人を用意する必要もなく、誰にも知られずひっそりと資金調達ができます。
-
ノー・チェック&ノー・ペーパー:貸し借りにあたって信用審査や過去の借入履歴チェックがありません 。極端な話、今まで金融履歴が全く無い人や、銀行に相手にされないような人でも、ビットコインさえ持っていればお金を借りられるのです。書類のやり取りが無いので手続きもスピーディーです。「印鑑証明や収入証明を揃えて…」という面倒とは無縁で、ネット上でクリックして契約が完結します。
-
プライバシーの保護:個人情報を提出しないということは、情報漏洩のリスクも無いということです。近年、日本でも個人情報の流出事件が相次いでおり、不安に感じる方も多いでしょう。Lendではアカウント登録時にメールアドレスとパスワード以外何も求められません。財務情報や身元情報がどこかに蓄積される心配がないのは、大きな安心材料です。
-
国や機関から干渉されにくい:匿名であるということは、極端に言えば誰にも利用を知られないということです。たとえば「ローンを借りると住宅ローンの審査に響くかな…」とか「副業の資金調達を会社に知られたくないな…」といった心配も、匿名のP2Pローンなら不要です。借りたお金の使い道も自由ですし、何より利用自体が自分だけの秘密にできるのは、日本人にとって心理的ハードルを下げてくれるでしょう。
このように、ノーKYC(本人確認なし) のP2Pレンディングは、日本のようにプライバシーや控えめさを重んじる文化圏でも利用しやすいサービスと言えます。実際、HodlHodlのLendは「地理的・規制的な制限がなく、世界中の誰もが利用できる純粋なP2P市場」とされています。日本に居ながらグローバルな貸し借りができ、しかも身元明かさずに済む――これは画期的ですね。
Borrow編:HodlHodlのLendでビットコインを担保にお金を借りる方法
それでは具体的に、HodlHodlのLendでどのようにビットコイン担保のローンを借りるのか、手順を追って説明します。初心者でも迷わないよう、シンプルなステップにまとめました。
1. アカウント登録 (Sign up)
まずはHodlHodlのLendサイトにアクセスし、無料のアカウントを作成します。必要なのはメールアドレスとパスワードだけです。登録後、確認メールが届くのでリンクをクリックして認証すれば準備完了。これでプラットフォーム上でオファー(契約希望)を閲覧・作成できるようになります。
※HodlHodlは日本語には対応していませんが、英語のシンプルなUIです。Google翻訳などを使っても良いでしょう。
2. 借りたい条件のオファーを探す or 作成
ログインしたら、「To Borrow(借りる)」のメニューから現在出ている貸し手のオファー一覧を見てみましょう。オファーには借入希望額(例:$1000相当のUSDT)、期間(例:3ヶ月)、金利(例:5%)やLTV(担保価値比率、例:60%)などの条件が書かれています。自分の希望に合うものがあれば選んで詳細画面へ進みます。条件に合うオファーが見つからない場合は、自分で「○○ USDTを△ヶ月、金利○%で借りたい」という借り手オファーを新規作成することも可能です。
用語補足:LTV(ローン・トゥ・バリュー)とはローン額に対する担保価値の割合です。たとえばLTV50%なら、借りたい額の2倍の価値のビットコインを担保に入れる必要があります。LTVは貸し手が設定しており、一般に30%〜70%程度の範囲でオファーが出ています。低いLTVほど借り手は多くのBTC担保が必要ですが、その分だけ貸し手にとって安全なローンとなります。
3. 契約成立とマルチシグ担保のデポジット
借り手・貸し手双方が条件に合意すると契約成立です。HodlHodlプラットフォーム上で自動的に専用のマルチシグ・エスクロー用ビットコインアドレス(担保保管先アドレス)が生成されます。次に、借り手であるあなたは自分のウォレットからビットコインをそのエスクローアドレスに送金します。
- 📌ポイント:マルチシグで安心 – 上述の通り、このエスクロー用アドレスのコインを動かすには3者中2者の署名が必要です。あなた(借り手)は常にそのうちの1つの鍵を保有しています。つまり、自分が承認しない限り担保BTCが勝手に引き出されることはないのでご安心ください。
ビットコインの入金がブロックチェーン上で所定の承認(通常数ブロック程度)を得ると、担保デポジット完了です。これで契約は有効化され、次のステップへ進みます。
4. 貸し手から資金(ステーブルコイン)を受け取る
担保のロックが確認できると、今度は貸し手がローン金額の送金を行います。Lendで借りられるのは主にステーブルコインです。ステーブルコインとは、米ドルなど法定通貨の価値に連動するよう設計された仮想通貨で、USDTやUSDC、DAIといった種類があります。借り手は契約時に受取用のステーブルコインアドレス(自分のウォレットアドレス)を指定しますので、貸し手はそのアドレス宛に契約どおりの額を送金します。例えばUSDTを借りる契約なら、貸し手からあなたのUSDTウォレットにUSDTが送られてきます。
これで晴れて、あなた(借り手)は希望のステーブルコインを手にすることができました! あなたのビットコインは担保としてロックされていますが、期限までに返済すれば取り戻せますので、しばしのお別れです。借りたステーブルコインは自由に使えますので、後述する活用例を参考に有効活用しましょう。
5. 返済(リペイメント)
契約期間中は基本的に何もする必要はありません(途中で追加担保や一部返済を行うことも可能ですが、初心者向け記事では割愛します)。期間が満了するまでに、借りたステーブルコイン+利息を貸し手に返済します。返済も、貸し手の指定するウォレットアドレスにステーブルコインを送金する形で行われます。
- 利息の計算:利息は契約時に決めた率で発生します。例えば年利10%で6ヶ月間$1000を借りたなら、利息は単純計算で$50(=$1000×10%×0.5年)です。契約によっては「期間全体で○%」と定める場合もありますが、プラットフォーム上で年率(APR)換算が表示されます。
期間内であれば任意のタイミングで早期返済することも可能です。返済期限より早く全額返せば、利息もその日数分だけで済みます(※ただし契約によります。事前に契約条件を確認してください)。HodlHodlでは分割返済にも対応しており、例えば月ごとに少しずつ返して最後に完済することもできます。
6. ビットコイン担保の解除(返却)
貸し手があなたからの返済受領を確認すると、プラットフォーム上で契約終了の手続きを行います。マルチシグの担保アドレスからあなたのビットコインを解放(返却)する署名を貸し手とプラットフォームが行い、あなたの元のウォレットにビットコインが送られます。こうして無事に担保のBTCが戻ってくれば、一連のローン取引は完了です🎉。
もし返済が滞った場合はどうなるのでしょうか?その場合、契約で定められた猶予期間やマージンコール(追加担保のお願い)を経た後、担保のビットコインが強制的に貸し手に渡されて契約終了(清算)となります。担保額が未返済額を上回っていれば、差額は借り手に返ってきます。つまり、返せなかったとしても借り手が担保以上の損をすることはありませんが、大切なビットコインを失ってしまう結果にはなるので注意しましょう。
Borrow(借りる)側のまとめ:ビットコインさえあれば、あとの手続きは非常に簡単です。借入までの流れをもう一度簡潔にまとめると:
- メールアドレスでLendに登録
- 借入オファーを探すor作成してマッチング
- マルチシグ契約が自動生成・BTC担保を自分で入金
- 貸し手からステーブルコインを受領
- 期限までにステーブルコイン+利息を返済
- ビットコイン担保が自分のウォレットに戻る
第三者の仲介なしに、ネット上でこれだけのことが完結するのは驚きですよね。HodlHodlは「あなたの条件、あなたの鍵、あなたのコイン」と銘打っており、自分の望む条件で・自分が鍵を管理し・自分の資産を動かせるプラットフォームであることを強調しています。
Lend編:HodlHodlのプラットフォームでお金を貸してみよう
次は逆に、自分が貸し手(Lender)となってステーブルコインを貸し出し、利息収入を得る方法です。銀行に預けても超低金利のこのご時世、手持ちの資金をうまく運用したい方にとってP2Pレンディングは魅力的な選択肢になりえます。HodlHodlのLendなら、これもまた簡単な手順で始められます。
基本的な流れは先ほどの「Borrow編」と鏡写しになっています。
1. アカウント登録
借り手と同様、まずはHodlHodlに登録します(すでに借り手として登録済みなら同じアカウントで貸し手にもなれます)。メールアドレスだけでOK、もちろん貸し手側もKYC不要です。
2. 貸出オファーの確認 or 作成
ログイン後、「To Lend(貸す)」メニューから現在の借り手募集一覧を見ます。各オファーには希望額・期間・支払い利率・LTVなど条件が表示されています。「この条件なら貸してもいいかな」という案件があれば選択しましょう。もし自分の希望する利回りや期間が合わない場合は、自分で貸し手オファーを作成することも可能です。「○○ USDTまで、最長△ヶ月、最低利息◻◻%で貸せます」といった条件を提示できます。プラットフォーム上ではユーザーがお互いに条件を提示しあってマッチングする仕組みなので、金利や期間もすべてユーザー自身が自由に設定できます。
3. マッチングと契約開始
あなたの提示した条件で借りたい人が現れたら契約成立です(逆に誰かの借入オファーに応じる形なら、その時点で成立)。システムがマルチシグの担保用BTCアドレスを生成し、借り手がそこへビットコインをデポジットします。借り手からのBTC入金が確認できるまで、貸し手であるあなたは資金を送る必要はありません。担保が確保されたのを見届けてから次に進みます。
4. 資金(ステーブルコイン)の送金
借り手の担保ロックが完了したら、契約で定めたステーブルコインを借り手へ送金します。送金先アドレスは契約詳細画面に表示されます(借り手が指定済み)。例えばUSDCを貸す契約なら、相手のUSDCアドレスに約束の額を送ります。ここで送金した金額がローンの principal(元本)となり、後ほど利息とともに返ってくるわけです。
無事に相手に届けば、あとは契約期間終了まで待つだけです。あなたは担保のBTCに対して鍵を1つ持っている状態なので、万一トラブルが起きた場合でも担保を引き出す権利を部分的に持っています(詳しくは次ステップ)。
5. 返済の受領
契約期間が終わると、借り手があなたにステーブルコインを返済してくるはずです。約束どおり元本+利息を受け取ったら、それを確認してプラットフォーム上で「返済完了」を操作します。すると担保のビットコインがマルチシグから解放され、借り手に返却されます。これで貸し手としてのあなたは利息分の収益を獲得できました。お疲れ様です!
もし借り手が返済しなかった場合どうなるでしょうか?その場合、所定の猶予期間やマージンコール通知の後、担保のビットコインがあなた(貸し手)に渡されることになります。具体的には、LTVが90%に達するか返済期日から24時間以上滞納が続くと強制清算となり、担保BTCからあなたの貸付相当額が充当されます。担保が十分であれば元本と利息はカバーされ、余剰があれば借り手に返還されます。つまり貸し手側はかなり手厚く保護されており、返済を受け取れない場合でも担保で穴埋めされる仕組みです。
6. 収益を管理・再投資
受け取ったステーブルコイン(元本+利息)は再度プラットフォームで貸し出しても良いですし、他の用途に使ってもOKです。年利に換算するとだいたい10%前後の利回りになる案件が多く見られます。条件次第では更に高い利率の契約も可能ですが、その分借り手が見つかりにくかったりリスク(担保不足のリスク)が高まる可能性もあります。ご自身のリスク許容度に合わせて運用しましょう。
Lend(貸す)側のまとめ:
- HodlHodlに登録(メールアドレスのみ)
- 貸出オファーを提示 or 借り手募集に応じる
- 契約成立後、借り手がBTC担保を入金
- 貸し手(自分)がステーブルコインを送金
- 期限まで待ち、借り手から元本+利息を受領
- 担保BTCを返却し、利息収入を得る
銀行預金では考えられないような利息収入を得られるのが魅力ですが、その裏でビットコイン価格変動リスクも担っています。大暴落が起きて担保評価額が急落すると、清算時に元本を割るリスクもゼロではありません(LTV設定とマージンコール制度で極力保護されまますが)。リスクとリターンを理解した上で、小額から試すことをおすすめします。
ステーブルコインの活用:お金持ちは借金で生活する?
ここまで、ビットコインを手放さずにステーブルコインを手に入れる方法を見てきました。それでは、借りたステーブルコインは具体的に何に使えるのでしょうか?いくつか例を挙げてみましょう。
-
日常の出費に充当:ビットコイン投資家の中には「生活費はすべて借りたお金で賄い、自分のBTCはガチホ(売らずに長期保有)する」という方針の人もいます。例えば毎月の家賃や食費をステーブルコインのローンで支払い(これについても今後詳しく解説していきます)、ビットコインは一切使わないというイメージです。こうすれば、手持ちのBTCを売らずに済むので将来の値上がり益を逃しません。また日本では仮想通貨を売却すると雑所得として高率の税金がかかりますが、ローンで得たお金は借入金なので課税対象になりません(※将来的な税務計算は自己責任で行ってください)。つまり、ビットコインを売却して現金化する代わりにローンを使うことで、節税と資産温存のメリットが得られる可能性があります。
-
投資・資産運用に回す:借りた資金をさらに別の投資に活用することもできます。例えば有望な株式や不動産に投資したり、あるいは他の仮想通貨を買うこともできます。極端な例では、ビットコインを担保にUSDTを借りて、そのUSDTでまた別の仮想通貨を買い、それを運用益で返済する…といった戦略も理論上は可能です。ただし、借りたお金での投機はハイリスクなので慎重に!手堅い使い道としては、事業資金に充てるのも良いでしょう。例えば小さなオンラインビジネスを始めるための元手にしたり、新しい資格取得のための学費にするなど、自分への投資に使えば将来的なリターンでローンを返しつつ利益を上げることが期待できます。
-
急な支払いへの備え:人生何があるか分かりません。医療費や冠婚葬祭など急に現金が必要になる場面もあります。そんなとき、ビットコインをすぐ売ってしまうのは惜しい…という場合にローンで一時的にしのぐことができます。後で落ち着いてから返済すれば、大事なBTCを手放さずにピンチを乗り切れます。言わばデジタル質屋のような感覚で、ビットコインを預けてお金を工面し、後で買い戻す(返済する)イメージですね。日本でも昔から「質屋」で着物や宝石を預けてお金を借りる文化がありましたが、HodlHodl Lendはビットコイン版の質屋とも言えるでしょう。
-
市場の機会を逃さない:仮想通貨市場は変動が激しく、「今これを買いたいのに現金が無い!」というチャンスもあるでしょう。例えば「ビットコインが急落したから買い増したいが、現金が足りない」という場合、手持ちBTCを担保にしてステーブルコインを借り、その急落で安く買い増しする、といった動きもできます。そして後日価格が戻したところで返済すれば、差益を得つつBTC保有枚数も増やせるかもしれません。このようにローンを戦略的に使えば、市場の好機を掴む資金余力を生み出すことができます。ただしハイリスクな手法でもあるため、上級者向けではあります。
ここで覚えておきたいのは、「お金持ちは借金との付き合い方が上手い」という点です。日本では借金にネガティブな印象を持つ人も多いですが、世界的な資産家や大企業はしばしばあえて借金をして手元資金を他に活用しています。アメリカのベストセラー『金持ち父さん貧乏父さん』で有名なロバート・キヨサキ氏も「富裕層は他人のお金(借金)を利用してさらに富を築く」と強調しています。例えば彼は借金で高級車を買い、不動産投資にも借入を活用したそう (金持ちは貧乏人より借金が多い | 「金持ち父さん 貧乏父さん」日本オフィシャルサイト)❤️。借金を味方につけて資産運用すれば、自分の持ち出し資金を抑えつつ豊かな生活を実現できる可能性があります。
もちろん無計画な借金は禁物ですが、ローンを上手に使うことは決して悪いことではなく、むしろ経済的戦略として有効なのです。ビットコイン担保ローンはその新しい選択肢として、「お金にお金に働いてもらう」感覚を身につけるきっかけになるかもしれません。
高い金利でもローンを利用するのはなぜ?その理由と戦略
Lendのプラットフォームで提示される金利は、年利換算で見ると10〜15%程度が一つの目安 です。中にはそれ以上の利率の契約もあります。日本の銀行ローン(金利数%以下)と比べるとかなり高利に思えますが、それでも多くの人がこのサービスを利用してローンを組んでいます。なぜ高い利息を支払ってまで借りる価値があるのでしょうか?最後に、その理由と利用者の戦略について考えてみましょう。
-
(1) ビットコインの期待リターンが高い:借り手にとって一番の動機は、「ビットコインは将来もっと値上がりするはずだから、多少利息を払っても売りたくない」というものです。例えば年利15%で$1000借りると一年後に$1150返す必要がありますが、もしビットコイン価格がその間に15%以上上昇すれば、利息分を差し引いても得をする計算になります。過去のビットコイン相場は年率ベースで大きく成長した年も多く、強気のホルダーほど利息より値上がり益を優先する傾向があります。「金利よりビットコインの価値上昇のほうが大きい」という自信が、高金利を払ってでも借りる動機になっているのです。
-
(2) 課税や手数料の回避:先ほど述べたように、日本ではビットコインを売却すると高額の税金が発生する可能性があります。仮に30%〜50%の税金がかかるのであれば、年利10%前後のローンで済ませたほうがトクだという判断も成り立ちます。また、取引所で売却するときのスプレッドや出金手数料なども考えると、売却コストを回避する手段としてローンを選ぶ人もいます。要するに「売るくらいなら借りた方がマシ」という考え方ですね。
-
(3) 自由と速さを優先:従来の金融機関からお金を借りるには時間がかかりますし、使途にも制限があることが多いです(事業資金なのか生活費なのか、といった審査があります)。それに対してHodlHodlのP2Pローンは使い道自由・即日資金調達が可能です。利息が高めでも「今すぐ○○がしたい」「明日までに現金が要る」といったニーズには代えられません。特に仮想通貨業界はスピード命ですから、チャンスを逃さないために高コストでも素早く借りるという選択が生まれます。
-
(4) 借金=時間を買うこと:あるユーザーの言葉を借りれば、「借金をすることは未来の時間を先取りすること」でもあります。例えば住宅ローンがあるからこそ若い世代でもマイホームに住めますし、事業ローンがあるからこそ企業は成長の機会を掴めます。ビットコイン担保ローンも同じで、「今はお金が無いけど将来増やすアテはある。だから今借りてしまおう」というケースもあるでしょう。将来の収入や資産増加を見込んで、時間を味方につけるためにあえて借金をするのです。日本語では「借金してでも◯◯する」という表現がありますが、前向きな借金は将来への投資とも言えるでしょう。
-
(5) 非中央集権への支持:もう一つ見逃せないのは、HodlHodlのようなプラットフォームを利用する理由に思想的な支持があります。つまり「銀行や政府に頼らないお金の流れを実現したい」「ビットコインのエコシステムを活性化させたい」というビットコイナーたちです。多少コストが高くても、理念に共感して使っているケースもあります。匿名で自由にお金を借りられる世界を体験することで、金融システムの新たな可能性を感じているのです。
以上のように、高い金利にも関わらずローンを利用するのは明確なメリットや戦略があるからなのです。もちろん全ての人に当てはまるわけではありません。ビットコイン価格が下落局面ではリスクも伴いますし、利息分だけ損になる場合もあります。しかし、それらを理解した上で「自分のお金を働かせる」「資産を手放さずレバレッジを利かせる」手段として活用している人々が増えてきています。
最後に、HodlHodlの公式ブログの一文をご紹介します。
“私たちはビットコインこそがスーパーカ collateral(超優秀な担保)であり、利回りを得るために使うのではなく、それを担保に資金を借りるために使われるべきだと考えています" (The lending is dead, long live the lending | by Hodl Hodl | Hodl Hodl | Medium)。
ビットコイン時代の新しいお金の借り方・貸し方であるP2Pローン。最初は難しく感じるかもしれませんが、仕組みを理解すればとてもシンプルで強力なツールです。日本ではまだ馴染みが薄いかもしれませんが、匿名性を好み、コツコツ資産を増やすのが得意な人にこそフィットするサービスかもしれません。ぜひ少額から試し、自分なりの活用法を見つけてみてください。きっと新たな発見があるはずです。
もしビットコイン担保のP2Pローンなどについてもっと深く知りたい、あるいは個別に相談してみたいと思えば、どうぞお気軽にご連絡ください。1対1のコンサルティングも承っています。
サービスには決まった料金はありませんが、ご相談を通じて「役に立った」と思い、お悩みや疑問を解決できたと感じていただけたら、「3つのT」でのご支援(Value for Value)をぜひご検討ください:
- 時間(Time):この記事をSNSなどでシェアしていただくこと。
- 才能(Talent):コメントや補足情報などを通じて知識を共有していただくこと。
- 宝(Treasure):世界で最も健全なお金、ビットコインの最小単位「sats」でのご支援。
もちろん、支援の有無にかかわらず、お力になれればとても嬉しいです。 では、また次回!
-
-
 @ 06830f6c:34da40c5
2025-03-30 03:56:17
@ 06830f6c:34da40c5
2025-03-30 03:56:17Once upon a time their lived a young man in a lost village, I'm just kidding with you, I'm testing my blog entries on my domain. SITE
Navigate to Blogs tab and screenshot this. @ me for a chance to get zapped ⚡. I won't say how many sats, so you are not doing it due to the incentive but to help me test the domain functionality.
Love ✌️
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ 30ceb64e:7f08bdf5
2025-03-30 00:37:54
@ 30ceb64e:7f08bdf5
2025-03-30 00:37:54Hey Freaks,
RUNSTR is a motion tracking app built on top of nostr. The project is built by TheWildHustle and TheNostrDev Team. The project has been tinkered with for about 3 months, but development has picked up and its goals and direction have become much clearer.
In a previous post I mentioned that RUNSTR was looking to become a Nike Run Club or Strava competitor, offering users an open source community and privacy focused alternative to the centralized silos that we've become used to.
I normally ramble incoherently.....even in writing, but this is my attempt to communicate the project's goals and direction as we move forward.
This is where the project is now:
Core Features
- Run Tracker: Uses an algorithm which adjusts to your phone's location permissions and stores the data on your phone locally
- Stats: Stored locally on your phone with a basic profile screen so users can monitor calories burned during runs
- Nostr Feed: Made up of kind1 notes that contain #RUNSTR and other running related hashtags
- Music: Brought to you via a wavlake API, enabling your wavlake playlists and liked songs to be seen and played in the app
Current Roadmap
- Bugs and small improvements: Fixing known issues within the client
- zap.store release: Launching a bug bounty program after release
- Clubs: Enabling running organizations to create territories for events, challenges, rewards and competition
- Testflight: Opening up the app to iOS users (currently Android only)
- Modes: Adding functionality to switch between Running, Walking, or Cycling modes
Future Roadmap
- Requested Features: Implementing features requested by club managers to support virtual events and challenges
- Blossom: Giving power users the ability to upload their data to personal blossom servers
- NIP28: Making clubs interoperable with other group chat clients like 0xchat, Keychat, and Chachi Chat
- DVM's: Creating multiple feeds based on movement mode (e.g., Walking mode shows walkstr feed)
- NIP101e: Allowing users to create run records and store them on nostr relays
- Calories over relays: Using NIP89-like functionality for users to save calorie data on relays for use in other applications
- NIP60: Implementing automatic wallet creation for users to zap and get zapped within the app
In Conclusion
I've just barely begun this thing and it'll be an up and down journey trying to push it into existence. I think RUNSTR has the potential to highlight the other things that nostr has going for it, demonstrating the protocol's interoperability, flexing its permissionless identity piece, and offering an experience that gives users a glimpse into what is possible when shipping into a new paradigm. Although we build into an environment that often offers no solutions, you'd have to be a crazy person not to try.
https://github.com/HealthNoteLabs/Runstr/releases/tag/feed-0.1.0-20250329-210157
-
 @ 6ad3e2a3:c90b7740
2024-09-11 15:16:53
@ 6ad3e2a3:c90b7740
2024-09-11 15:16:53I’ve occasionally been called cynical because some of the sentiments I express strike people as negative. But cynical, to me, does not strictly mean negative. It means something more along the lines of “faithless” — as in lacking the basic faith humans thrive when believing what they take to be true, rather than expedient, and doing what they think is right rather than narrowly advantageous.
In other words, my primary negative sentiment — that the cynical utilitarian ethos among our educated classes has caused and is likely to cause catastrophic outcomes — stems from a sort of disappointed idealism, not cynicism.
On human nature itself I am anything but cynical. I am convinced the strongest, long-term incentives are always to believe what is true, no matter the cost, and to do what is right. And by “right,” I don’t mean do-gooding bullshit, but things like taking care of one’s health, immediate family and personal responsibilities while pursuing the things one finds most compelling and important.
That aside, I want to touch on two real-world examples of what I take to be actual cynicism. The first is the tendency to invoke principles only when they suit one’s agenda or desired outcome, but not to apply them when they do not. This kind of hypocrisy implies principles are just tools you invoke to gain emotional support for your side and that anyone actually applying them evenhandedly is a naive simpleton who doesn’t know how the game is played.
Twitter threads don’t show up on substack anymore, but I’d encourage you to read this one with respect to objecting to election outcomes. I could have used many others, but this one (probably not even most egregious) illustrates how empty words like “democracy” or “election integrity” are when thrown around by devoted partisans. They don’t actually believe in democracy, only in using the word to evoke the desired emotional response. People who wanted to coerce people to take a Pfizer shot don’t believe in “bodily autonomy.” It’s similarly just a phrase that’s invoked to achieve an end.
The other flavor of cynicism I’ve noticed is less about hypocrisy and more about nihilism:
 I’d encourage people to read the entire thread, but if you’re not on Twitter, it’s essentially about whether money (and apparently anything else) has essential qualities, or whether it is whatever peoples’ narratives tell them it is.
I’d encourage people to read the entire thread, but if you’re not on Twitter, it’s essentially about whether money (and apparently anything else) has essential qualities, or whether it is whatever peoples’ narratives tell them it is.In other words, is money whatever your grocer takes for the groceries, or do particular forms of money have qualities wherein they are more likely to be accepted over the long haul? The argument is yes, gold, for example had qualities that made it a better money (scarcity, durability, e.g.) than say seashells which are reasonably durable but not scarce. You could sell the story of seashells as a money (and some societies not close to the sea used them as such), but ultimately such a society would be vulnerable to massive inflation should one of its inhabitants ever stroll along a shore.
The thread morphed into whether everything is just narrative, or there is an underlying reality to which a narrative must correspond in order for it to be useful and true.
The notion that anything could be money if attached to the right story, or any music is good if it’s marketed properly is deeply cynical. I am not arguing people can’t be convinced to buy bad records — clearly they can — but that no matter how much you market it, it will not stand the test of time unless it is in fact good.
In order to sell something that does not add value, meaning or utility to someone’s life, something you suspect they are likely to regret buying in short order, it’s awfully useful to convince yourself that nothing has inherent meaning or value, that “storytelling is all that matters.”
I am not against marketing per se, and effective storytelling might in fact point someone in the right direction — a good story can help someone discover a truth. But that storytelling is everything, and by implication the extent to which a story has correlates in reality nothing, is the ethos of scammers, the refuge of nihilists who left someone else holding the bag and prefer not to think about it.
-
 @ ee11a5df:b76c4e49
2024-09-11 08:16:37
@ ee11a5df:b76c4e49
2024-09-11 08:16:37Bye-Bye Reply Guy
There is a camp of nostr developers that believe spam filtering needs to be done by relays. Or at the very least by DVMs. I concur. In this way, once you configure what you want to see, it applies to all nostr clients.
But we are not there yet.
In the mean time we have ReplyGuy, and gossip needed some changes to deal with it.
Strategies in Short
- WEB OF TRUST: Only accept events from people you follow, or people they follow - this avoids new people entirely until somebody else that you follow friends them first, which is too restrictive for some people.
- TRUSTED RELAYS: Allow every post from relays that you trust to do good spam filtering.
- REJECT FRESH PUBKEYS: Only accept events from people you have seen before - this allows you to find new people, but you will miss their very first post (their second post must count as someone you have seen before, even if you discarded the first post)
- PATTERN MATCHING: Scan for known spam phrases and words and block those events, either on content or metadata or both or more.
- TIE-IN TO EXTERNAL SYSTEMS: Require a valid NIP-05, or other nostr event binding their identity to some external identity
- PROOF OF WORK: Require a minimum proof-of-work
All of these strategies are useful, but they have to be combined properly.
filter.rhai
Gossip loads a file called "filter.rhai" in your gossip directory if it exists. It must be a Rhai language script that meets certain requirements (see the example in the gossip source code directory). Then it applies it to filter spam.
This spam filtering code is being updated currently. It is not even on unstable yet, but it will be there probably tomorrow sometime. Then to master. Eventually to a release.
Here is an example using all of the techniques listed above:
```rhai // This is a sample spam filtering script for the gossip nostr // client. The language is called Rhai, details are at: // https://rhai.rs/book/ // // For gossip to find your spam filtering script, put it in // your gossip profile directory. See // https://docs.rs/dirs/latest/dirs/fn.data_dir.html // to find the base directory. A subdirectory "gossip" is your // gossip data directory which for most people is their profile // directory too. (Note: if you use a GOSSIP_PROFILE, you'll // need to put it one directory deeper into that profile // directory). // // This filter is used to filter out and refuse to process // incoming events as they flow in from relays, and also to // filter which events get/ displayed in certain circumstances. // It is only run on feed-displayable event kinds, and only by // authors you are not following. In case of error, nothing is // filtered. // // You must define a function called 'filter' which returns one // of these constant values: // DENY (the event is filtered out) // ALLOW (the event is allowed through) // MUTE (the event is filtered out, and the author is // automatically muted) // // Your script will be provided the following global variables: // 'caller' - a string that is one of "Process", // "Thread", "Inbox" or "Global" indicating // which part of the code is running your // script // 'content' - the event content as a string // 'id' - the event ID, as a hex string // 'kind' - the event kind as an integer // 'muted' - if the author is in your mute list // 'name' - if we have it, the name of the author // (or your petname), else an empty string // 'nip05valid' - whether nip05 is valid for the author, // as a boolean // 'pow' - the Proof of Work on the event // 'pubkey' - the event author public key, as a hex // string // 'seconds_known' - the number of seconds that the author // of the event has been known to gossip // 'spamsafe' - true only if the event came in from a // relay marked as SpamSafe during Process // (even if the global setting for SpamSafe // is off)
fn filter() {
// Show spam on global // (global events are ephemeral; these won't grow the // database) if caller=="Global" { return ALLOW; } // Block ReplyGuy if name.contains("ReplyGuy") || name.contains("ReplyGal") { return DENY; } // Block known DM spam // (giftwraps are unwrapped before the content is passed to // this script) if content.to_lower().contains( "Mr. Gift and Mrs. Wrap under the tree, KISSING!" ) { return DENY; } // Reject events from new pubkeys, unless they have a high // PoW or we somehow already have a nip05valid for them // // If this turns out to be a legit person, we will start // hearing their events 2 seconds from now, so we will // only miss their very first event. if seconds_known <= 2 && pow < 25 && !nip05valid { return DENY; } // Mute offensive people if content.to_lower().contains(" kike") || content.to_lower().contains("kike ") || content.to_lower().contains(" nigger") || content.to_lower().contains("nigger ") { return MUTE; } // Reject events from muted people // // Gossip already does this internally, and since we are // not Process, this is rather redundant. But this works // as an example. if muted { return DENY; } // Accept if the PoW is large enough if pow >= 25 { return ALLOW; } // Accept if their NIP-05 is valid if nip05valid { return ALLOW; } // Accept if the event came through a spamsafe relay if spamsafe { return ALLOW; } // Reject the rest DENY} ```
-
 @ 50de492c:0a8871de
2025-03-30 00:23:36
@ 50de492c:0a8871de
2025-03-30 00:23:36{"title":"test","description":"","imageUrl":"https://i.nostr.build/Xo67.png"}
-
 @ 3514ac1b:cf164691
2025-03-29 22:07:33
@ 3514ac1b:cf164691
2025-03-29 22:07:33About Me
-
 @ 3514ac1b:cf164691
2025-03-29 21:58:22
@ 3514ac1b:cf164691
2025-03-29 21:58:22Hi this is me ,Erna . i am testing this Habla news . i have been trying using this but got no luck . always disconnect and no content .
Hopefully this one will work .
BREAKING NEWS : Vance uses Greenland visit to slam Denmark , as Trump escalates rhetoric .
https://wapo.st/4c6YkhO
-
 @ 3514ac1b:cf164691
2025-03-29 18:55:29
@ 3514ac1b:cf164691
2025-03-29 18:55:29Cryptographic Identity (CI): An Overview
Definition of Cryptographic Identity
Cryptographic identity refers to a digital identity that is secured and verified using cryptographic techniques. It allows individuals to prove their identity online without relying on centralized authorities.
Background of Cryptographic Identity
Historical Context
- Traditional identity systems rely on centralized authorities (governments, companies)
- Digital identities historically tied to platforms and services
- Rise of public-key cryptography enabled self-sovereign identity concepts
- Blockchain and decentralized systems accelerated development
Technical Foundations
- Based on public-key cryptography (asymmetric encryption)
- Uses key pairs: private keys (secret) and public keys (shareable)
- Digital signatures provide authentication and non-repudiation
- Cryptographic proofs verify identity claims without revealing sensitive data
Importance of Cryptographic Identity
Privacy Benefits
- Users control their personal information
- Selective disclosure of identity attributes
- Reduced vulnerability to mass data breaches
- Protection against surveillance and tracking
Security Advantages
- Not dependent on password security
- Resistant to impersonation attacks
- Verifiable without trusted third parties
- Reduces centralized points of failure
Practical Applications
- Censorship-resistant communication
- Self-sovereign finance and transactions
- Decentralized social networking
- Cross-platform reputation systems
- Digital signatures for legal documents
Building Cryptographic Identity with Nostr
Understanding Nostr Protocol
Core Concepts
- Nostr (Notes and Other Stuff Transmitted by Relays)
- Simple, open protocol for censorship-resistant global networks
- Event-based architecture with relays distributing signed messages
- Uses NIP standards (Nostr Implementation Possibilities)
Key Components
- Public/private keypairs as identity foundation
- Relays for message distribution
- Events (signed JSON objects) as the basic unit of data
- Clients that interface with users and relays
Implementation Steps
Step 1: Generate Keypair
- Use cryptographic libraries to generate secure keypair
- Private key must be kept secure (password managers, hardware wallets)
- Public key becomes your identifier on the network
Step 2: Set Up Client
- Choose from existing Nostr clients or build custom implementation
- Connect to multiple relays for redundancy
- Configure identity preferences and metadata
Step 3: Publish Profile Information
- Create and sign kind 0 event with profile metadata
- Include displayable information (name, picture, description)
- Publish to connected relays
Step 4: Verification and Linking
- Cross-verify identity with other platforms (Twitter, GitHub)
- Use NIP-05 identifier for human-readable identity
- Consider NIP-07 for browser extension integration
Advanced Identity Features
Reputation Building
- Consistent posting builds recognition
- Accumulate follows and reactions
- Establish connections with well-known identities
Multi-device Management
- Secure private key backup strategies
- Consider key sharing across devices
- Explore NIP-26 delegated event signing
Recovery Mechanisms
- Implement social recovery options
- Consider multisig approaches
- Document recovery procedures
Challenges and Considerations
Key Management
- Private key loss means identity loss
- Balance security with convenience
- Consider hardware security modules for high-value identities
Adoption Barriers
- Technical complexity for average users
- Network effects and critical mass
- Integration with existing systems
Future Developments
- Zero-knowledge proofs for enhanced privacy
- Standardization efforts across protocols
- Integration with legal identity frameworks
-
 @ 7d33ba57:1b82db35
2025-03-29 18:47:34
@ 7d33ba57:1b82db35
2025-03-29 18:47:34Pula, located at the southern tip of Istria, is a city where ancient Roman ruins meet stunning Adriatic beaches. Known for its well-preserved amphitheater, charming old town, and crystal-clear waters, Pula offers a perfect blend of history, culture, and relaxation.
🏛️ Top Things to See & Do in Pula
1️⃣ Pula Arena (Roman Amphitheater) 🏟️
- One of the best-preserved Roman amphitheaters in the world, built in the 1st century.
- Used for gladiator fights, now a venue for concerts & film festivals.
- Climb to the top for stunning sea views.
2️⃣ Explore Pula’s Old Town 🏡
- Wander through cobbled streets, past Venetian, Roman, and Austro-Hungarian architecture.
- Visit the Arch of the Sergii (a 2,000-year-old Roman triumphal arch).
- Enjoy a drink in Forum Square, home to the Temple of Augustus.
3️⃣ Relax at Pula’s Beaches 🏖️
- Hawaiian Beach (Havajska Plaža): Turquoise waters & cliffs for jumping.
- Ambrela Beach: A Blue Flag beach with calm waters, great for families.
- Pješčana Uvala: A sandy beach, rare for Croatia!
4️⃣ Cape Kamenjak Nature Park 🌿
- A wild and rugged coastline with hidden coves and crystal-clear water.
- Great for cliff jumping, kayaking, and biking.
- Located 30 minutes south of Pula.
5️⃣ Visit Brijuni National Park 🏝️
- A group of 14 islands, once Tito’s private retreat.
- Features Roman ruins, a safari park, and cycling trails.
- Accessible via boat from Fazana (15 min from Pula).
6️⃣ Try Istrian Cuisine 🍽️
- Fuži with truffles – Istria is famous for white & black truffles.
- Istrian prosciutto & cheese – Perfect with local Malvazija wine.
- Fresh seafood – Try grilled squid or buzara-style mussels.
🚗 How to Get to Pula
✈️ By Air: Pula Airport (PUY) has flights from major European cities.
🚘 By Car:
- From Zagreb: ~3 hours (270 km)
- From Ljubljana (Slovenia): ~2.5 hours (160 km)
🚌 By Bus: Regular buses connect Pula with Rovinj, Rijeka, Zagreb, and Trieste (Italy).
🚢 By Ferry: Seasonal ferries run from Venice and Zadar.💡 Tips for Visiting Pula
✅ Best time to visit? May–September for warm weather & festivals 🌞
✅ Book Arena event tickets in advance – Summer concerts sell out fast 🎶
✅ Try local wines – Istrian Malvazija (white) and Teran (red) are excellent 🍷
✅ Explore nearby towns – Rovinj & Motovun make great day trips 🏡
✅ Cash is useful – Some small shops & markets prefer cash 💶
-
 @ 57d1a264:69f1fee1
2025-03-29 18:02:16
@ 57d1a264:69f1fee1
2025-03-29 18:02:16This UX research has been redacted by @iqra from the Bitcoin.Design community, and shared for review and feedback! Don't be shy, share your thoughts.
1️⃣ Introduction
Project Overview
📌 Product: BlueWallet (Bitcoin Wallet) 📌 Goal: Improve onboarding flow and enhance accessibility for a better user experience. 📌 Role: UX Designer 📌 Tools Used: Figma, Notion
Why This Case Study?
🔹 BlueWallet is a self-custodial Bitcoin wallet, but users struggle with onboarding due to unclear instructions. 🔹 Accessibility issues (low contrast, small fonts) create barriers for visually impaired users. 🔹 Competitors like Trust Wallet and MetaMask offer better-guided onboarding.
This case study presents UX/UI improvements to make BlueWallet more intuitive and inclusive.
2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement
🔹 Current Challenges:
1️⃣ Onboarding Complexity - BlueWallet lacks step-by-step guidance, leaving users confused about wallet creation and security.
2️⃣ No Educational Introduction - Users land directly on the wallet screen with no explanation of private keys, recovery phrases, or transactions. 3️⃣ Transaction Flow Issues - Similar-looking "Send" and "Receive" buttons cause confusion. 4️⃣ Poor Accessibility - Small fonts and low contrast make navigation difficult.
🔍 Impact on Users:
Higher drop-off rates due to frustration during onboarding. Security risks as users skip key wallet setup steps. Limited accessibility for users with visual impairments.
📌 Competitive Gap:
Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow
Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet.
3️⃣ User Research & Competitive Analysis
User Testing Findings
🔹 Conducted usability testing with 5 users onboarding for the first time. 🔹 Key Findings: ✅ 3 out of 5 users felt lost due to missing explanations. ✅ 60% had trouble distinguishing transaction buttons. ✅ 80% found the text difficult to read due to low contrast.
Competitive Analysis
We compared BlueWallet with top crypto wallets:
| Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons |
📌 Key Insight: BlueWallet lacks guided setup and accessibility enhancements, making it harder for beginners.
📌 User Persona
To better understand the users facing onboarding challenges, I developed a persona based on research and usability testing.
🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor)
👤 Profile: - Age: 28 - Occupation: Freelance Digital Marketer - Tech Knowledge: Moderate - Familiar with online transactions, new to Bitcoin) - Pain Points: - Finds Bitcoin wallets confusing. - - Doesnʼt understand seed phrases & security features. - - Worried about losing funds due to a lack of clarity in transactions.
📌 Needs: ✅ A simple, guided wallet setup. ✅ Clear explanations of security terms (without jargon). ✅ Easy-to-locate Send/Receive buttons.
📌 Persona Usage in Case Study: - Helps define who we are designing for. - Guides design decisions by focusing on user needs.
🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast)
👤 Profile: - Age: 35 - Occupation: UX Researcher & Accessibility Consultant - Tech Knowledge: High (Uses Bitcoin but struggles with accessibility barriers)
📌 Pain Points: ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons.
📌 Needs: ✅ A high-contrast UI that meets WCAG accessibility standards. ✅ Larger fonts & scalable UI elements for better readability. ✅ Keyboard & screen reader-friendly navigation for seamless interaction.
📌 Why This Persona Matters: - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles.
4️⃣ UX/UI Solutions & Design Improvements
📌 Before (Current Issues)
❌ Users land directly on the wallet screen with no instructions. ❌ "Send" & "Receive" buttons look identical , causing transaction confusion. ❌ Small fonts & low contrast reduce readability.
✅ After (Proposed Fixes)
✅ Step-by-step onboarding explaining wallet creation, security, and transactions. ✅ Visually distinct transaction buttons (color and icon changes). ✅ WCAG-compliant text contrast & larger fonts for better readability.
1️⃣ Redesigned Onboarding Flow
✅ Added a progress indicator so users see where they are in setup. ✅ Used plain, non-technical language to explain wallet creation & security. ✅ Introduced a "Learn More" button to educate users on security.
2️⃣ Accessibility Enhancements
✅ Increased contrast ratio for better text readability. ✅ Used larger fonts & scalable UI elements. ✅ Ensured screen reader compatibility (VoiceOver & TalkBack support).
3️⃣ Transaction Flow Optimization
✅ Redesigned "Send" & "Receive" buttons for clear distinction. ✅ Added clearer icons & tooltips for transaction steps.
5️⃣ Wireframes & Design Improvements:
🔹 Welcome Screen (First Screen When User Opens Wallet)
📌 Goal: Give a brief introduction & set user expectations
✅ App logo + short tagline (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ 1-2 line explanation of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ "Get Started" button → Le ads to next step: Wallet Setup ✅ "Already have a wallet?" → Import option
🔹 Example UI Elements: - BlueWallet Logo - Title: "Welcome to BlueWallet" - Subtitle: "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)
🔹 Screen 2: Choose Wallet Type (New or Import)
📌 Goal: Let users decide how to proceed
✅ Two clear options: - Create a New Wallet (For first-time users) - Import Existing Wallet (For users with a backup phrase) ✅ Brief explanation of each option 🔹 Example UI Elements: - Title: "How do you want to start?" - Buttons:** "Create New Wallet" | "Import Wallet"
🔹 Screen 3: Security & Seed Phrase Setup (Critical Step)
📌 Goal: Educate users about wallet security & backups
✅ Explain why seed phrases are important ✅ Clear step-by-step instructions on writing down & storing the phrase ✅ Warning: "If you lose your recovery phrase, you lose access to your wallet." ✅ CTA: "Generate Seed Phrase" → Next step
🔹 Example UI Elements: - Title: "Secure Your Wallet" - Subtitle: "Your seed phrase is the key to your Bitcoin. Keep it safe!" - Button: "Generate Seed Phrase"
🔹 Screen 4: Seed Phrase Display & Confirmation
📌 Goal: Ensure users write down the phrase correctly
✅ Display 12- or 24-word seed phrase ✅ “I have written it downˮ checkbox before proceeding ✅ Next screen: Verify seed phrase (drag & drop, re-enter some words)
🔹 Example UI Elements: - Title: "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - Checkbox: "I have safely stored my phrase" - Button: "Continue"
🔹 Screen 5: Wallet Ready! (Final Step)
📌 Goal: Confirm setup & guide users on next actions
✅ Success message ("Your wallet is ready!") ✅ Encourage first action: - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions
✅ Short explainer: Where to find the Send/Receive buttons
🔹 Example UI Elements: - Title: "You're All Set!" - Subtitle: "Start using BlueWallet now." - Buttons: "Receive Bitcoin" | "View Wallet"
5️⃣ Prototype & User Testing Results
🔹 Created an interactive prototype in Figma to test the new experience. 🔹 User Testing Results: ✅ 40% faster onboarding completion time. ✅ 90% of users found transaction buttons clearer. 🔹 User Feedback: ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ
6️⃣ Why This Matters: Key Takeaways
📌 Impact of These UX/UI Changes: ✅ Reduced user frustration by providing a step-by-step onboarding guide. ✅ Improved accessibility , making the wallet usable for all. ✅ More intuitive transactions , reducing errors.
7️⃣ Direct link to figma file and Prototype
Original PDF available from here
originally posted at https://stacker.news/items/928822
-
 @ bf95e1a4:ebdcc848
2024-09-11 06:31:05
@ bf95e1a4:ebdcc848
2024-09-11 06:31:05This is the lightly-edited AI generated transcript of Bitcoin Infinity Show #125. The transcription isn't perfect, but it's usually pretty good!
If you'd like to support us, send us a zap or check out the Bitcoin Infinity Store for our books and other merchandise! https://bitcoininfinitystore.com/
Intro
Luke: Paolo, Mathias, welcome to the Bitcoin Infinity Show. Thank you for joining us.
Paolo: Thank you for having us.
Knut: Yeah, good to have you here, guys. We're going to talk a bit about Keet and Holepunch and a little bit about Tether today, aren't we?
Luke: Sounds like that's the plan. So thank you again, both for joining us.
Introducing Paolo and Mathias
Luke: would you both mind giving a quick introduction on yourselves just so our listeners have the background on you
Paolo: Sure, I'm Paolo Arduino, I'm the CEO at Tether. I started my career as a developer, I pivoted towards more, strategy and execution for, Tether and Bitfinex. And, co founded with Matthias, Holepunch, that is, building very, crazy and awesome technology, that is gonna be disrupting the way people communicate.
Luke: And, Mathias, over to you.
Mathias: Yeah, thank you. Yeah, I've been, so I come from a peer-to-peer background. I've been working with peer-to-peer technology. The last, I always say five, but it's probably more like 10 years. I did a lot of work on BitTorrent and I did a lot of work on JavaScript. and a little bit later to, Bitcoin and I saw a lot of potential on how we can use Bitcoin with pureology and like how we can use.
P2P technology to bring the same mission that Bitcoin has, but to all kinds of data, setting all data free and, making everything private per default and self sovereignty and that kind of thing. I'm very into that. and I've been lucky to work with, like I said, with Paolo for, many years now and, Get a lot of, valuable, feedback and, idea sharing out of that.
And we're on a mission to, build some, really cool things. In addition to all the things we've already been building. So it's super exciting and glad to be here.
Luke: Oh, fantastic.
Introduction to Holepunch
Luke: Matthias, that was a perfect segue into basically, an introduction to, can you tell us about, Holepunch.
What is Holepunch and what are you doing?
Mathias: Yeah, sure. like I said, we co founded the company a couple of years ago. Now, we've been building up a team of really talented peer to peer engineers. we're always hiring also. So if anybody's listening and want to join our mission, please, apply. we have some really smart people working with us.
but we teamed up to basically. like I said in my introduction, I've been working on peer to peer technology for many years now and thinking ahead how we can, stop using all that technology when I started it was only used for basically piracy. I'm from the Nordics, and I think Knut is from the Nordics also, so he knows all about, the Nordics know about piracy.
It wasn't back in the day. A lot of very interesting technologies came out of that. But basically, how can we use those ideas that were proven by piracy back then to be really unstoppable, because a lot of people wanted to stop it, but apply that same kind of mindset to the general data, so we can build actual applications that has that kind of quality, that can withstand the wrath of God.
that can work without any centralization. Actually, nobody can shut down, not even the authorities if they wanted to. Basically unkillable and make that general enough that it can basically run any kind of application, solve a lot of really hot problems. it works on your own computers, your own networks.
Mobile phones, and tie that up. I'm a developer by heart, into a software stack that people can just build on. So not everybody has to go in and tackle all these problems individually, but just give them some software to solve all this so they can, as much as possible, just worry about making really cool applications that we use,
Yeah, like I said, we've been working really intensely on this, for a long time and in Holepunch, we made this our co mission to scale this up and, deliver a software stack on that. it's been really exciting and it's been really fun and it's been very, challenging, but if it's not challenging, then why, do it?
and, especially, with the backing of, Tether, through Paolo and also just expertise from there, we have a good hand built to deliver this to the world. And, the first thing we did was, like, think about what's, a good first application that we can build that can showcase this, but also something we really want to use ourself and see scale have also have on the world.
And obviously that was a communications app, keyed, which we was our first project. And, we're still in beta and we're still lots of work to do. And we're still iterating that really heavily, but I like to show that you can build these kind of apps without any kind of. central points. and we released that also, like the first thing we released when we launched the company.
And like I said, we're still, building and still iterating it. A lot of fun. and then take the software stack from that, which we call the pair runtime and then split that out. So anybody else can build similar apps on top. With that same technology stack, and, yeah, that's, we launched that earlier this year also, and, it's been really exciting so far, and it's, I love going to work every day and solve, even though, you can see on my hair that it's not really good for, the head scratching, but, but, it's really fun, and it's really challenging, and it's interesting thing. goal as a company, basically to have that if we go out of business tomorrow, our technology continues to exist because we're not in the loop of anything. It's also sometimes really hard to explain that we don't have any, chip coins involved or any kind of limitations on the stack because we're basically engineering it not to be part of it, because that's the only way you can actually engineer these things that they can understand.
anything, super exciting and, encourage everybody to try to check it out.
Luke: we've both used Keet and I've certainly enjoyed the experience. I, think, the, basics of this, as I understand it, is that it's, entirely on both sides. The communicators end, or a group of communicators, it's all on their end, and the communication is entirely peer to peer, what is Keet really, what is the basics of Keet as, say, a product?
What is the easiest way that you would explain what it is?
The Vision Behind Keet
Mathias: But We're basically trying to just build a world class communications app that works to a large degree, like normal communication apps that you know, like Signal, Telegram, WhatsApp. Just with all the centralization tucked away, with all the costs of running it tucked away, and then adding all the features that also we can, because we're peer to peer
People don't care about technology. We loved it, but don't have that surface off too much to the user.
Just have the user use it as any other app, but then just have it be 100 percent private per default, 100 percent like no strings attached. It just works. if we get caught off by a. From the internet tomorrow, it will still work, that kind of thing, but deliver that in a way, and this is always our mission where users don't really need to worry about it.
It just works. And, it works the same way to a large degree as their other apps work, except obviously, there's no phone numbers and things like that. Very cryptographically sound and, but trying always not to bubble it up. And I think that's, so it's actually a really simple mission, but it's obviously really hard.
And that requires a lot of smart people, but luckily our users in a good way, don't need to be very smart about that.
Keet vs Nostr
Knut: Yeah, a quick one there. No strings attached starts with the letters Nostr, so is, Keet and Nostr, do they go mix well together or, is there an integration there between the two? I see a lot of similarities here.
Paolo: I tried to explain the differences between Kit and Nostr. I think Nostr is a very interesting protocol, but also is very, simple. the way I like to describe it is that, if you are familiar with the history of filesharing, Starting from the first one, super centralized, and then eventually every single step, you get to a decentralized platform.
And the last one, the most decentralized one, that is BitTorrent. the history of file sharing proved that every time you try to centralize something, it ends up badly, right? if you have any special node in the system that does a little bit more than others and requires more resources than others to run, that will end up badly.
You might end up in a small room with a lamp in your room. Point it to your face, and then everyone suddenly will stop running an indexer. That reminds me about Nostr structure. if you are building a peer to peer system, or if you are building a very resilient communication system, if you think about Nostr, you would imagine that if you have, 10 million or 100 million users, the number of relays would be probably less than the square root of the number of users.
So that surface, although a hundred million users is very, they're not attackable, right? But the surface of, the relays is much more attackable. look at what is happening with, the coin joinin platforms, right? very similar. the beauty of KIT versus Nostr is that in KIT you have number of relays is actually equal to the number of users because the users are their own relays.
and they can act as relays for others to, further their connectivity. That is how we think a technology that, has to be ready for the apocalypse and resilient to the wrath of God should, work. if you have, a log number of users or square root of number of users as relates, I don't think it's cool technology.
It will work better than centralized, Technologies like WhatsApp and so on, or Twitter, but eventually will not work when you will need it the most. Because the point is that we will not know what will happen when we will need this technology the most. Today, not for everyone, but the world is still almost at peace.
Things might unfold, in the future, maybe sooner rather than later. But when things unfold, you will need the best technology, the one that is truly independent, the one that is truly peer to peer. it's not really peer to peer if you have specialized relays, but where you have super peers randomly.
Luke: Yeah, the difference here, between the Realize and not having any other centralized infrastructure in the picture is certainly an interesting distinction. I hadn't heard anything about that you can act as a next connector or something like that.
Pear Runtime
Luke: So there's a couple of related things. I know there was an announcement about the, pair runtime, is that right? can you talk a little bit about that or any other, ways that this is growing in your whole, platform,
Mathias: Yeah, sure. so basically when we talk about ideas, internally, also from our software background, We want to solve a small problem that then can solve it for everybody. So
We want to build technology that can just send data around efficiently, so you can build any kind of app on top. We're all about modularity and taking these things to the extreme so we can repurpose it into any kind of application and other people can, get value out of it.
And, that's been our mission from the get go. So basically, like Paolo said, when we built Keed. We took all of these primitives we have, it's all open source on our GitHub, that can do various things, relay encrypted data in a way that's completely private, nobody can read it, and in a generalizable way, so it can run on any applications.
We have databases that can interpret, work with this data on device, but still in a way where nobody else knows what's going on, fully private, and we spent many years perfecting this, and it's still ongoing. And we, similar to like connectivity, it might seem really easy if you don't know what's going on that, connecting this computer to another computer and another place, but it's really hard because ISPs and, your internet providers, et cetera, they don't really want you to do that.
So there's a lot of firewalls involved that you have to work around to get around This is all really, hard problems that took a long time to solve.
But luckily, all of these are like generalizable problems where you just solve them once to a large degree, and then it's solved for everybody. If you put them in a modular framework where anybody can put the Legos together on top. And that's what we've been heavily invested in. And then as we were building Keed, we realized that Keete is just like 95 percent of these Lego blocks that are applicable for anything.
So why not take all this stuff, pack it up for free, we don't make any money on it. and an open source runtime that we're just giving away so other people can contribute to it, but also build their own apps. the more peer to peer apps the world has, the better from my point of view.
and document it and make it really easy to install. And I think actually Paolo said something interesting because as soon as you have, one point of centralization, you can always unravel it. coming from the Bitcoin days, I remember how quickly things can unravel. people went to jail for linking to things because authorities, when they crack down, really hard.
so if you have one weak spot, it will be taken advantage of at some point by somebody. And so even things like distributing updates to your software can be really hard because this often requires a central point, like you go to a website and you don't download it. And so all apps built on our runtime, for example.
It's distributed through the runtime, which is a little bit mind bending. So all apps are peer to peer data applications themselves, and the network doesn't care, which means that we can continue to distribute updates even, if everything gets shut down, you only need like a bootstrap for the first install when you get the app.
So we're thinking that in. At every level, because it's really, important to us to, basically learn from everything that happened in the past and then actually build things that are resilient. And we take this to a degree where I'm sure we could move 10 times faster if we just let go a little bit of that idea, because it is easier to just put all the data in one place or put all the updates in one place.
But then it's then we're just building the same old thing that's going to die eventually anyway. So we're very, uncompromising in that mission of actually decentralizing everything from updates to data, and then also always solving in a way where everybody can take advantage of that.
And then the final thing I'll say about that is that, every time we update. That runtime, those building blocks of that runtime, every time we fix a bug, every time we make it faster, every app becomes faster. That's also very exciting. It's because you're building the whole infrastructure into this layer that runs on your phone.
And it's all somewhat generalizable. Every time we fix something, it's just better for the entire ecosystem. And that's obviously really, exciting. And like I said, actually, no strings attached.
Yeah, so I think you were referring to the trial of the Pirate Bay people there In Sweden, right? lucky enough to meet a couple of them in Denmark and it's been very fun to hear about their journey and, yeah, like
Knut: and there, there's, there was a great documentary made about it called TPBAFK. So the Pirate Bay Away From Keyboard, about that whole trial and how, corrupt the system was even back then. And, throwing people in jail for providing links. they didn't do any more wrong than Google did, from a certain perspective.
And, I remember even, before BitTorrents, there was a program called. DC or Direct Connect Do you remember that?
Mathias: I used to, it was one of my first introductions to decentralization. it as you just shared your, like a Google Drive for everyone or something. Like you just shared parts of your file tree to everyone who wanted to peek into it, Yeah, anyway. Oh, that's good that you didn't know you were going with that. it interesting what you said, because I think it's interesting to think that I think to a large degree, the whole decentralization movement that was happening with BitTorrent back in the day got shut down because At some point, authorities figured out that they could just block DNS requests to shut it down for normal people, and as soon as they did that, it was actually effective.
And to Paolo's point, no matter how weak it is, they're done. and they tried to kill the technology elsewhere, but that's actually what killed them. Then, obviously, alternatives came that people could pay for, and it also shows that people actually want, to stay on the right side of things.
I think, now it's going very much in the wrong direction again, because now we're back at abusing that centralization again. the cycle will repeat. But, yeah, like any point of weakness will be attacked at any point.
Decentralization vs. Centralization
Luke: So what are the drawbacks to decentralization? I think we and our audience certainly understand the benefit of decentralization, what you gain by decentralizing, but what do you naturally give up in terms of the user experience and the convenience factor?
Mathias: yeah, I'm sure Paola has stuff to say here, but I'm just, I love talking about this stuff, so I'll go first. Mattias.
I think it's a really interesting question, first of all, because it's one of those questions where You know, obviously I want to say there's no drawbacks, but like anything, it's a balance, right?
Because it's not that there's drawbacks and advantages, there obviously is, but it's also just a different paradigm. first of all, with sensitization, I think one of the biggest thing I noticed also with developers is that we all come out of systems, education systems. That teaches how to think centralized, which makes us biased towards centralized solutions.
and that's, I remember my whole curriculum was about servers and clients and stuff like that. it's actually really hard to think about decentralization as a developer. And I think that's actually part of why a lot of people think it's hard. It's complex because it is complex, but also because we're just like, we've been trained massively in the other direction, and it's really hard to go back because decentralization can be as simple as what Knut said about DC Connect, DC where it's just, oh, I'm just browsing other people's computers.
That's amazing. That's a really, simple experience, and it's like something you can never do But like in today's world, people, the first thing I always get asked is like, how do I get a username? And I'm like, usernames have an inherent centralization and there's trade offs there.
And we need to think that through and stuff. and most applications don't necessarily require usernames. I'm not saying that's a bad feature, but it's that's where you need to think more about the trade offs because there's governance involved to some degree. But for the core experience, and I think that's what we've shown in Keith so far.
Then, there's obviously tons of upsides also, it's much easier to do big data transfers. Money is less of a concern, which actually changes the thinking, how you think about features.
And that, again, is something we've been trained in a lot as developers, because we think centralized. When we talk about features at Holepunch, hey, we should add podcast recording to Keed. Normally somebody would say, that's going to cost a lot of money to host that data. And we just always we don't even have that discussion because it doesn't matter because it's just between the users.
And then it's more about like the UX. But then other simple, like I said, other simple discussions, let's add a username index. That's where we're like, okay, let's think that through because there's like various things to think about there because there's no centric governance, and we don't want to introduce that because again, one point is.
It's bad. so it's, more like you really need to think differently and it's really hard to wire your brain to think differently. but once you get past that point, I think it's, super interesting. And I, think actually developers care way more than normal people because, developers care a lot about how links look and links and structure and that.
And normal people are just used to just clicking buttons and apps and going with the flow on that. And that's also what we're seeing, I think, with, a lot of key
Paolo: I think the hiring has proven a little bit more challenging, as Matthias was saying, when you are told that the cloud is your friend, hosting, on, Google Cloud or AWS is the right thing to do. And, of course, it got cheaper and cheaper, so now everyone can host their websites.
But the reality is that 70 percent of, the entire internet knowledge is hosted in the data centers of three companies. developers should think about that, should think about the fact that internet was born to be point to point and peer to peer. And, we are very far away from that initial concept.
over the years, especially with the boom in, in the year 2000 for the internet boom, and bubble, then, realized that, holding people's data is the way to go, with social media and social network. That is even worse. And so you have these friendly advertisements that are telling you, That, with a smiley face that, you know, yeah, you should, upload all your data on, Apple cloud or Google cloud.
And in general, cloud backups are great, right? You want to have some sort of redundancy in your life, but the reality is that you should be able to upload those. In an encrypted way, and yet most of this data sits unencrypted because, the big tech companies have to decrypt it and use it for, to milk the information to pay for, for, another month of their new data centers.
the, issue is, we have so much power in our hands through our phones. the phones that we have today are much more powerful than the phones that we, or even the computers that we have 10 years ago or 5 years ago. And so We should, we are at a stage where we can use this hardware, not only for communicating, but also for in the future for AI processing and inference and so on.
is, we need to, understand that the word cannot be connected to Google. I mean we cannot be a function of Google. We cannot be a function of AWS. And so I think that, there is, escalating pace of, towards centralization and it's almost a black hole.
And eventually, the, we'll attract all the lights and if we are too close to it, no lights will come out anymore. And, that's why we want to really to double down on this technology, because it's not going to be easy, right? It's going to be very challenging, and most of the people don't care, as Maite has said before.
Most of the people will think, everything works with WhatsApp and, Signal, but Signal announced that their 2023 costs for data centers and data center costs are around 50 million, and they, apart from the mobile coin that was not The best thing that they could do, there is, it's not easy for them to monetize.
And the problem is that if you are, you're basically almost the only way to monetize it is to sell your customer's data. So if you don't want to sell your customer data, eventually your service will not be sustainable. So the only way to make it sustainable is actually going back to peer, where you can leverage people, infrastructure, people, connectivity, people, phones, people, processing power, Deliver very high quality communication system.
And when they will care, it will be probably usually too late if nothing exists yet. when people will care is because shit is hitting the fan. And, you really want to have a solution that is not, that will survive if, the countries around you or around the country where you live are not going to be nice to your own country.
So that's the view to peer-to-peer. The peer-to-peer wheel system will keep working if your neighbor countries are not going to be nice towards you. That's independence, that's resiliency, those are terms that, we need to take very seriously, especially seeing where the, world is going to.
Knut: Yeah, I think we're all primed for, centralized solutions, from a very young age. this is the state, this is what it is like, state funded schooling. state funders or state subsidized media. We are, like brainwashed into, trusting, institutions all our lives.
So I think that is somewhat connected to why people are so reluctant to be vigilant about this on the internet. I think the two go hand in hand that we, take the comfortable way, or most people take the comfortable route of, not taking responsibility for their own stuff. not only on the internet, but outsourcing responsibility to the government is basically the, another side of the same coin, right?
Mathias: I also find it very interesting, especially being from a small country like Denmark that doesn't have a lot of homegrown infrastructure. And I'm just seeing how much communication with some of the public entities is happening through centralized platforms like Facebook and things like that, where even though we centralize it, we also centralize it in companies that we don't even have any control over in different countries where we probably have, no rights at all.
So it's like hyper centralization, especially from the weakest point of view. And I think that's super problematic. And I'm always. Thinking it's, weird that we're not talking about that more especially when you look at the things that they're trying to do in the EU, they're almost trying to just push more in that direction, which I find even more interesting.
yeah, definitely. it's, a huge problem and it's only getting bigger. And that's, why
Challenges and Future of Decentralization
Luke: So to what level can decentralization actually get there? What is the limit to decentralization? And I'll calibrate this with an example. The internet itself, you said it was built to essentially originally be decentralized, but we don't have it. For physical links, like individual physical links between each other, the fiber or whatever the wire is goes together into another group of wires, which eventually go into some backbone, which is operated by a company.
And then that goes into the global Internet. And so somewhere it centralizes into telecom companies and other services. It might be decentralized on one level, but there is a layer of centralized services that make the internet work that isn't necessarily the so called cloud providers and that sort of thing.
So is there a limitation to how far this can go?
Paolo: I think the, in general, sure, there are the ISPs and, their physical infrastructure is in part centralized, but also you start having redundancy, right? So for example, the backbones are redundant. There are multiple companies running, cross connects across different areas of the world.
Now you have Starlink if you want. that is a great way to start decentralizing connectivity because Starlink will not be the only one that will run satellites, so there will be multiple companies that will allow you to connect through satellites, plus you have normal cabling.
So you will have, it will become a huge mesh network, it's already in part, but it will become more and more a huge mesh network. in general, you will always find a way, even with a pigeon, to start sending bits out of your house.
I think the most important part is, you have to be in control of your own data, and then, you need to send this data with the shortest path to the people that you want to talk to. Right now, I usually make this example, because I think it's When we do this presentation, we try to make people think about how much waste also centralized systems have created.
imagine you live in Rome, you live in Rome and you have your family. Most people live nearby their families. That is a classic thing among humans. 90 percent of the people live nearby their families. Maybe nearby, like 10km, 50km nearby. If you talk to your family, every single message, every single photo that you will send to your family, that message will travel, instead of going 50 kilometers in a nearby town where your mother lives or your father lives, it will travel every single message, every single bit of every single video call or every single bit of every photo will travel 5, 000 miles to Frankfurt just to go back 50 kilometers from you.
Imagine how much government spent in order to create these internet lines and to empower them to make it bigger, more, with more capacity Peer to peer allows with a lower latency, allows to save on bandwidth, allows to save on cost of global infrastructure.
So that's how, actually, We can create better mesh networks, more resilient mesh networks, just because data will always find the shortest path from one point to another.
And still all roads lead to Rome. I'm Italian, so I need to use Rome as an example.
Knut: Yeah.
Mathias: I think the discussion here is really interesting compared to Bitcoin, because it's actually the scaling longer term. Sovereignty, like how, Bitcoin kind of told us very direct terms that if you have a key pair, you have your money.
And it doesn't matter where you are in the world. If you have that key pair, you have a way to get to that money. the means of transportation, it's actually very uninteresting in that sense, because you have it with you. The Internet today, the centralized Internet is designed in a way where, what does it mean to go to Facebook?
it's really hard to explain because it's like some certificate that issued by somebody, and there's. Some, cabal of companies that manages them, there's some regulations around it, but we don't really actually understand it that well as normal people. Technically, we can understand it, but it's very, centralized and it's very, opaque and it's built into the infrastructure in that way, in a bad way.
And, with Pure Technology, we're taking the same approach as Bitcoin here and saying, You're just a key pair, and the other person is just a key pair, and there's a bunch of protocols around that, but the transportation is actually not that interesting. Right now, we use the internet to do it.
We'll probably do that for a long time, but there's no reason why we can take the same technology we have right now and in 50 years run it on, laser beams or something else, because we're taking the software and feedback.
Bitcoin and Holepunch: Drawing Parallels
Mathias: I think, that's the main thing to think about in that. Discussion.
Luke: when, Paolo, when you were talking about that people don't care, when you were saying that people don't care because WhatsApp just works, I was at the same time thinking that's the parallel of people saying that, I don't care because Visa just works, right? And so the parallel between Bitcoin and what you're doing at Holepunch, Keet, everything else here, really seems to be tracking along the same line.
And I guess there's the connection that, I won't say all, but a lot of the people involved are already in the Bitcoin ecosystem. But can you comment on is there a little more of a connection there between Holepunch and Keet and Bitcoin?
Paolo: Yeah, Bitcoin definitely is working and servicing, I think, in a good way, many, people in communities. The users of Bitcoin today are, unfortunately, and also that relates to Tether, mostly, in the Western world, in the richer countries, as a way to save wealth and, as a store of value, more than a means of exchange.
For different reasons, right? We'd like a network that would improve, of course, over time, and there will be different approaches, but, still, the world is not yet using Bitcoin, but the world will use Bitcoin when shit will hit the fan. but the beauty of Bitcoin is that an option is already there, is available, and when something bad will happen, people immediately, with a snap of a finger, will turn to Bitcoin, and will have it and can use it. don't have that in communications. What is our communica our parallel with communications, if we don't have it? I don't know, because if, if suddenly centralized communications will, be blocked, then, or privacy in communications will be blocked, and you cannot, you cannot use Whatsapp, or Whatsapp has to start giving all the information to every single government.
and the government will become more evil than what they are today, also western governments then. don't, we wanted to build the exact parallel as we said it, we just tried to describe it, that with Bitcoin, for communications. We need to have something that, since there are so many alternatives that are working as with your, you can make the parallel with Visa, right?
Visa is working today, so people are still using a lot of Visa, but if something will happen, they will use Bitcoin from one day to another. Whatsapp is working, and Zoom is working, and Google Meet is working, so people don't feel the urge, but there will be a trigger point when people will feel the urge at some point in their lives, because something happened around them, and we need to make sure that kit will be available to them.
and will be an option, will be stable, will be well designed so that when they will need it the most that option will be available to them.
Luke: Yeah, fantastic.
The Future of Decentralized Communication
Luke: And so I think the follow up I have, and just to get back to the earlier discussion a little bit with Nostr, the communication in terms of messaging, I absolutely see that and directly in what Keet is, I already absolutely see that. Is there a goal to get somewhere towards more like Social media, social networking, things like that in a, in certainly a decentralized way, but right now there isn't something like that as I understand it, coming from, Keet.
So is, that a goal? Is that on the roadmap?
Paolo: Yeah, it is on the roadmap, it's something that, so we had to start with the thing that we thought was more urgent and also the thing that could have been, would have been a game changer. social media is very important, especially In difficult situation, you want to get news, and you want to get unbiased news, so you want to use, social networks to see what's happening in the world.
But we, think that the most sacrosanct thing that you need in your life is to be able to talk to your family and friends in any situation with the highest privacy possible. that's the first thing that we tackled, and also was a way to battle test the technology with, KIT you can do high quality video calls as well, so if we are able to tackle in the best way possible privacy and extreme scalability of peer to peer communications, then on top of that foundation we can build also social media and every single other application that we have in mind.
Mathias: But first, we wanted to tackle the hardest problem. No, I think it makes a lot of sense. And I also just want to say, as a, probably like one of the most prolific KEET users, I use KEET right now also as a very, like a social media, we have big public rooms where we talk about KEET and talk about technology. I get a lot of the value I would get otherwise on Twitter X from that because I, it's like a public platform for me to, get ideas out there, but also interact with users directly.
And I think, there's many ways to take them as a young app. And we're talking about this a lot, obviously it has to be simple, has to be parent approved. My parents can figure it out, but I think, to a large degree, all really healthy social networks that are actually, to some degree, a communication app.
And it's also just a really good way to get local news and to get this locality that Peter is good at. That doesn't mean that we might not also make other things, but I think it's a hard line to set the difference between a social network and a communications app when it's structured correctly,
Interoperability and User Experience
Luke: Yeah, and this, another thing that came to mind just as, you were talking about these parallels, as, I understand it, the account system with Keet is, essentially still just a, Key pair. Correct me if I'm, wrong,
Mathias: Very, true.
Luke: you backups with the same 1224 words.
Is, that fully interoperable as well? Is that, could be your Bitcoin key. That could be
Mathias: We use the, same, I can't remember the date, the BIP, but there's a BIP for like during key generation. So we can use it also in the future for other things. and you have those words, you have your account, and that's, we never store that. And that's like your sovereignty and, no, I was just going to say that lets you use it seamlessly on different devices also. It's one of those things that I love because I know what's going on when you use keyed Insanely hard problem, but it's solved by the runtime, and it just works seamlessly and I think that's, the beauty of it.
Paolo: I think there's some UX stuff to figure out about onboarding that stuff a little bit easier for normal people. That's probably to a large degree the same for Bitcoin. The other part that I would do with Bitcoin is that, with Bitcoin, with your 12, 24 words, you can access your private wealth. the beauty of Bitcoin is that you can remember 12 24 words, you cross borders, and you carry with you your wealth. You can do the same thing with your digital private life.
You remember 12 24 words, they could be the same by the way. whatever happens, you can spawn back your digital private life fully encrypted from, one of your other devices that you connected that is somewhere else in the world. So when you start seeing and understanding the unlock in terms of also human resilience that this creates is very, insane and can create a very powerful, that can be used for, to create a very, powerful applications, not just communications, but you can build.
Really any sort of interaction, even mapping. Imagine peer to peer mapping, where basically data is not stored in one single location. You can access, tiles of the maps, from, local people that curate them in a better way. So the, level of applications that you can build, All unlocked by the same technology that is being used by Bitcoin is very, incredible.
Luke: Yes, absolutely it is. And what do you think of the idea that all of this stuff is just interoperable now based on essentially you have your private key and there you go. It doesn't matter the technology stack. Is that sort of an agnostic thing where you can take your data to any one of these systems?
What you're building with Keith being one, Nostr being another, Bitcoin being a third, what do you think of that?
Paolo: Yeah, the fact that, data is yours, right? So you should do whatever you want with your data. That is, I think, an axiom that we should assume. And, it shouldn't even, we shouldn't even discuss about this, right? We are discussing about it because people are trying to take away this axiom from us.
The, you are a key pair, and you're basically, unique, and uniqueness is expressed by the cryptography around those 24 words, and that's, that also is a way to prove your identity, it's a mathematical way to prove your identity.
No one can steal that from you, of course, but no one can track it as no one can impersonate, should not be able to impersonate you. So it's truly powerful.
Mathias: also think it's like worth remembering here also in this discussion that a lot of very high valuable data for yourself is actually not that big, but centralized platforms take it hostage anyway. if you take all my chat history and, I have pictures, but like a couple of the pictures would probably be bigger than all my chat history ever.
but a lot of that, those messages have a lot of value for me, especially personally and also being able to search through it and have infinite history, it's very valuable for me personally. But it's very scary for me if that's on some other platform where it gets leaked at some point, et cetera, et cetera.
But we already have the devices, just normal consumer devices that we buy, that we all have, phones, computers, whatever, that have more than enough capacity to store multiple copies of this. In terms of like per user, data production, it's a manageable problem.
And I think it's interesting how, providers force us to think in terms of giving that data away, even though we could easily store it.
Paolo: And this is even more important when we think about potential, AI applications, right? So imagine your best assistant. Paolo's assistant should go through all my emails, my kids chats, my old social stuff, and be able to be my best assistant. But in order to do that, I have two options.
Either, I imagine that OpenAI would come with an assistant. They would upload, All the information on their servers, crunch that information, and then, use it to serve, me, but also service their own needs. And that can become very scary, also because they wear a hat. It's public, right?
you don't want your most intimate codes that your best personal assistant could know, to be on somewhere else, rather than your devices. And so people were, people never uploaded, at least most of the people would never upload medical, information on Facebook, right? But they are uploading it on ChatGPT to get a second opinion.
so things can be, get even scarier than what we described today because, we, discussed about social media, that is basically, the fun part where we upload photos, But, things can become scarier when it comes to privacy and data control with ai.
So I want to see a future where I have a local AI that can read all key messages that I have from my local phone on my local device, and can become the best powers assistant possible without renouncing to my privacy, and also still governed by the same 24 words. the fine tuning that is applied on that LLM should stay local to my own device, and it should be in control of that.
And still, the current power of the devices that we have makes it possible. We should not fall for the same lie. We don't need, of course, big data centers with GPUs are important for training a huge LLM, but that is a generic LLM. You can take that one and then fine tune it with your own data and run it by yourself.
And for most of it, unless you want to do crazy things, that is more than enough and can run on modern GPUs or local GPUs or your phones. We should start thinking that we can build local experiences without having an API all the time connected to someone else's data center.
Knut: Yeah.
The Role of Tether in the Crypto Ecosystem
Knut: It's super interesting. you briefly just briefly mentioned tether before and I think we need to get into this. what is it and how much of a maxi are you, Paolo?
And, what, made this thing happen? Can you give us the story here about Tether?
Tether's Origin and Evolution
Paolo: Tether started in 2014. I consider myself a maxi, but running Tether, you could say that, I'm a shit coiner. I don't mind, right? I like what I do, and I think I'm net positive, so it's okay. Tera was born in 2014 with a very simple idea. there were a few crypto exchanges in, 2014.
it was Bitfinex, Coinbase, Kraken, Bitstamp. OKCoin, there was BTCChina, and just a few others, right? Around 10 that were meaningful. The problem back then was to do, trading arbitrage, you sell Bitcoin on the exchange where the price is higher, you take the dollars. From that sale, you move the dollars on the exchange where the price is lower and rinse and repeat.
That is called arbitrage. It is a property of every single efficient financial system. And that also helps to keep the price of Bitcoin in line across different exchanges. But, that was very, hard in 2014. If you remember in 2013 was the first year that Bitcoin broke the 1, 000.
But on some exchanges the price was 1. 2, on others was 900. in order to arbitrage that price difference, you have to move dollars from one exchange to another and Bitcoin from one exchange to another. You can move Bitcoin from one exchange to another. 10 minutes, but dollars would take days, right?
International wires. And so of course the opportunity arbitrage was, fully gone by, the, time the wire was hitting the, receiving exchange. the reason why we created that was, USDT was simply to put the dollar on a blockchain so that we could have the same user experience that we had with bitcoin.
For the first two years, almost no exchange apart Bitfinex understood USDT. Then Poloniex in 2016 started to add the USDT across for against every single trading pair. There was the start of the ICO boom. 2017 was the peak of the ICO boom and, USDT reached 1 billion in market cap. Fast forward in 2020, we had around 10 billion in market cap, and then the bull run started, but also another important thing started, that was the pandemic.
USDT's Impact on Emerging Markets
Paolo: So the pandemic had a huge effect on many economies around the world, in all the economies around the world, but especially in emerging markets, developing countries.
Basically pandemic also killed entire economies. And so as a Bitcoin you would think, oh, all these people that are in countries like Argentina and Venezuela and Turkey and so on, they should use Bitcoin and they should, they should, only use Bitcoin because everything else is cheap.
So that is pretty much, the approach that we have as Bitcoiners that, I believe in. But the problem is that. Not everyone is ready, so not everyone has our time to understand Bitcoin. Not everyone has yet the full skill set to understand Bitcoin at this stage, at this moment in time.
we as Bitcoiners didn't build the best user experience in the world, right? So one of the best wallets for Bitcoin is still Electrum. That, is not necessarily nice and well done for and simple to be used for, a 70 year old lady. so we need to do a better job as Bitcoiners to build better user experiences we want Bitcoin to be more used around the world.
At the same time, 99 percent of the population knows, especially the ones that are living in high inflation areas, knows that there is the dollar that is usually Much better currency than what they hold in their hands. the US dollar is not, definitely not perfect. It's not the perfect fiat currency. but it's like the tale of the two friends running away from the lion, right?
you have, one friend tells to the other, Oh, the lion is gonna kill us. We have to run really fast. And one of the two friends says to the other, I just have to run faster than you, right? So the US dollar is the friend that is running faster, in a sense that is the one that is likely better than the others.
And so being better than the others is creating a sort of safety feeling among 5 billion people in the world that live in high inflation countries. And for those people that, they don't have yet the time, they didn't have the luck also, maybe, to understand Bitcoin, they are, in fact, using USDT.
If you live in Argentina, peso lost 98% against the US dollar in the last five years. The Turkish L lost 80% against the US dollar in, the last five years. So of course, Bitcoin would be better than the US dollar, but even already, if you hold the dollar, you are the king of the hill there, right?
So because it's, you are able to preserve your wealth much, better than almost anyone else in the region. I think, USDT is offering a temporary solution and is providing a service, a very good service to people that don't have alternatives and good alternatives and they are very, familiar with the U.
S. dollar already. so eventually, the hyperbitcoinization, I think it will happen. there is no way it won't happen. It's hard to pinpoint on a time when, that will happen. But it's all about the turning point. What the economy will look like in the next, 10, 20 years and what trigger point there will be for fiat currencies to blow up and become irrelevant.
Bitcoin as a Savings Account
Paolo: the way I see it is that it's likely that the U. S. dollar will stay around for a while, and people might still want to use, the U. S. dollar as a checking account, but they, should start to use, Bitcoin as their savings account, in the checking account, you, are happy to not make interest, It's something that you use for payments, it's something that you are okay to detach from because it's the money that you are ready to spend.
The savings account is the thing that we should fight for. This thing is the thing that matter the most, and, it's the thing that will is protecting people wealth. And so in the long term. And in the medium term, we should push for this savings account to be Bitcoin. also with Tether, we are heavily investing in companies, in Bitcoin companies.
we support the Blockstream. We supported so many in the space that are, we, are supporting RGB. That is a protocol that is building, assets on top of, like network, style channels. Thank you for listening. and we buy Bitcoin ourselves. We do a lot of Bitcoin mining.
We develop, I think, the best and most sophisticated Bitcoin mining software, by the way, based on hole punch technology. It's like IoT for Bitcoiners and Bitcoin mining. It's very cool. we are relying on the dollar and, you could say that USDT is helping the dollar, expansion, but the same way I don't think Dollar and Bitcoin aren't necessarily opposed to one or the other.
I think that Bitcoin has its own path. And no matter what happens, there is no way to slow it down. I think, it's going to be inevitable success. It's going to be inevitable that it will become global internet money and global words money. No country will trust to each other with, with each other currencies for, for a longer time, and so the only viable solution is a currency that is governed by math.
That is the only objective way, objective thing that we have in the universe. that's my train of thoughts on, Tether and Bitcoin.
Knut: Oh, thank you. Thank you for that explanation. It explains a lot of things. To me, it sounds a bit like you're a lubrication company, like selling lubrication for the transition between the rape of the dollar to the love fest of the hyperbitcoinized world, to make the transition a little smoother.
Paolo: we are more than, at Tether we have also this educational arm and, believe it or not, the majority of the creation we do is actually on Bitcoin, right? So we are supporting the Plan B network led by the great Giacomo Zucco. The unfortunate thing is that USDT, didn't have a marketing team up to, 2022 with Tether.
So basically, I wish I could say that success of Tether is because we were super intelligent and great. but actually the success of Tether, unfortunately is a symptom of the success of, of, national economies. And it's sad if you think about it, right? So the success of your main product U as it is, They're actually proportional to the FACAP of many central banks. And, but it is what it is, right? So we need to do what we do at, really, at DataRace, creating all these educational contents to try to explain that, sure, we are providing a tool for today, but, For tomorrow you probably need, you need to understand that you have other options, you need to understand Bitcoin, because as we said for, Keith, right?
So the moment when you will need the most Bitcoin, it has to be available, you need to understand it, so that is a true option for you. The way we, see bitcoin education.
Knut: No, and, something like Tether would have, emerged, either way, and it's very comforting to know that it's run by Bitcoiners and not by a central bank itself or something. yeah, and the Plan B Network, I was a guest lecturer there in Logano and it was fantastic.
I love what you're doing there with the educational hub. And we even got Giacomo to write the foreword to our new book here that you can see here behind Luke.
Luke: Always say the title, Knut. Always say the title.
Knut: Bitcoin, the inverse of Clown World. It's, you, if, you're good at maths and emojis, you might be able to figure out the title from the cover, but it's one divided by Clown World anyway, which is on the opposite side of the everything divided by 21 million equation, So anyway, looking forward to seeing you in Lugano and giving you both a copy of the book, of course.
Paolo: Oh, with pleasure, with great pleasure, with a nice, education.
Luke: Absolutely. Yep.
Plan B Forum and Future Events
Luke: 100%. And we have to wind things down, but I'll just say as well, yeah, absolutely looking forward to Lugano Plan B Forum. Always a highlight of the year. It was my first time last year. I absolutely loved it. can't wait to attend this year.
so it's the 25th, 2020 6th of October, 2024. this year, it's a Bitcoin event that is not made to make money. So the problem with events is that. You have to find sponsors, and usually, sponsor might not be well aligned with the message you want to give, right? I think Tether is lucky enough, to not have to make money on the event.
Paolo: I want to have, good, guests. I want to have great speakers. I want to have the messaging. That is not only about Bitcoin, it's about, freedom of speech as well. We had the family of Assange for the last few years, and I think that they will come also this year.
I'm going to be probably killed by the By our marketing team, I'm not sure if they announced it, but we are going to have another Plan B event also in El Salvador next year, so we're trying to create this network of cities and countries that have things in common and, invite people that want to share knowledge around the world.
And, yeah, and of course we, are very proud of the good food that we, serve in Lugano. So that is another thing that, not all the bands can say the same thing.
Knut: No, it's fantastic. And we happened to bump into the Assange family at the cocktail bar in a fancy hotel and, had a very interesting conversation with them there. So if you're listening. Anyone from the Assange family is welcome on the show any time. So yeah, no looking forward to that event for sure, we had a great time.
And I think we're even playing this year, aren't we, Luke?
Paolo: You're
Luke: yeah, the Satoshi Rakamoto is in the event there, we, played, back in Prague, it was my first, time, but Knut is a regular at the Rakamotos.
Yeah, we played at Lugano last year Oh, anything and everything, what did we do in Prague?
Knut: paranoid and,
Paolo: Can I commission a
Knut: What song would you like to hear?
Paolo: I have two that I would suggest. One is Nothing Else Matters.
Knut: Alright.
Paolo: So I think that, is very inspiring, right?
Knut: Bitcoin, for sure.
Nothing Else Matters. it's perfectly aligned with Bitcoin. And, the other one is Sad But True. Oh, that would be fun. We'll squeeze in some Metallica there, won't we, Luke?
Mathias: we'll 100% have those songs ready to go. We also have, a big peer to peer track at the conference,
Knut: Yeah.
Mathias: not so much music, but yeah, that's peer to
Knut: Nothing else matters.
Luke: looking forward to that.
Knut: Sorry, brain fart. Sad but true is about the dollar still being around,
Paolo: Yeah, you can say that.
Luke: Okay.
Final Thoughts and Closing Remarks
Luke: Hey, we have to wind things down here because, we're, almost, out of time. So I'll just hand this, back to you both. Is there anything else you'd like to, mention about, your plans in the upcoming couple of years, in, key, toll, punch, anything like that?
Mathias: only that we're, like I said, we're integrating really hard right now, and it's a really fun time to, join the company because, we're small and efficient We get to work with Tether, which has a lot of benefits and it's getting really fast, so definitely check that out. And it's also a really fun time to join Keith in our public rooms.
There's a lot of very personal, in a good way, intense chats where you get to be part of the loop. I love to be part of those early communities and I would suggest everybody to check that out and go to the website and try it out.
Paolo: we will certainly do that. Yeah, I couldn't agree more. So go check out Keith and Holepunch and the Plan B forum in Lugano, You could visit tether. io, that is, the website where we are trying to explain what we have in our minds between, finance, bitcoin mining, energy production, AI, communications, brain chips and stuff, right? I think it's more exciting.
Mathias: Just those things, that's all.
Paolo: Yeah, we can piss off more than this. Thanks.
Mathias: a
Luke: No, It's just perfect. and is on that note, is there anywhere else specific you'd like to direct our listeners?
Paolo: just follow the social channels and give us feedback on kit all the time because these technologies, needs everyone's help to be nailed them.
Mathias: We love technical feedback. We love UX feedback. We're trying to make something that works for the masses, so anything is good.
Luke: So that's, all at Keet. Is that correct? For Keet?
Mathias: Key. io and pairs. com for our runtime. It's all peer to peer.
Knut: Alright,
Mathias: Wonderful. And you're also still on the legacy social media platforms, right? Yeah.
Knut: we'll make sure to include links to your handles so people can find you there if they would like. forward to seeing you in Lugano.
Paolo: Likewise, I
Knut: But yeah, worth saying again.
Paolo: Thank you for having an invitation.
Luke: Yes, we'll wrap things up here. This has been the Bitcoin Infinity Show.
-
 @ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23
@ 09fbf8f3:fa3d60f0
2024-09-10 13:21:23由于gmail在中国被防火墙拦截了,无法打开,不想错过邮件通知。
通过自建ntfy接受gmail邮件通知。 怎么自建ntfy,后面再写。
2024年08月13日更新:
修改不通过添加邮件标签来标记已经发送的通知,通过Google Sheets来记录已经发送的通知。
为了不让Google Sheets文档的内容很多,导致文件变大,用脚本自动清理一个星期以前的数据。
准备工具
- Ntfy服务
- Google Script
- Google Sheets
操作步骤
- 在Ntfy后台账号,设置访问令牌。
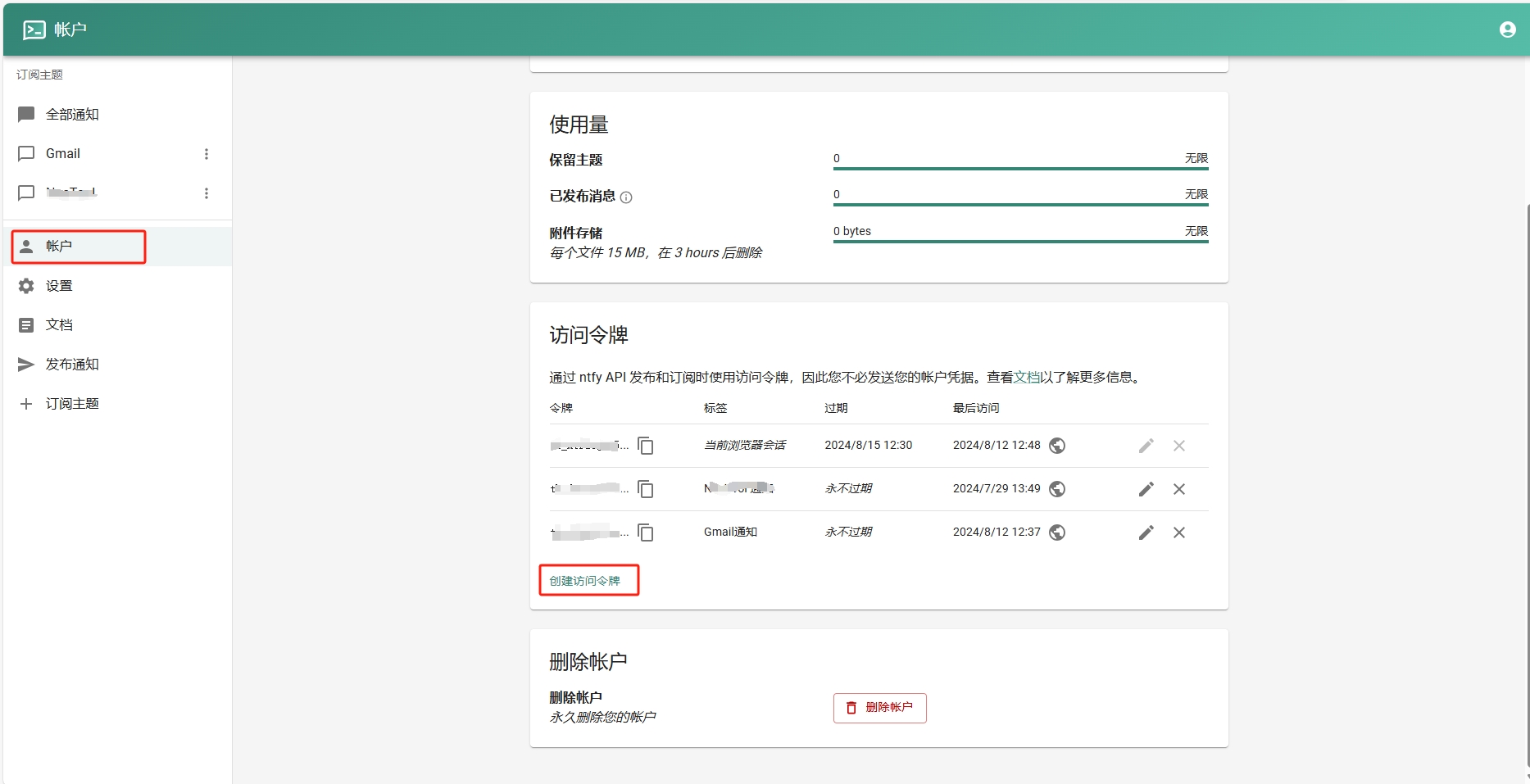
- 添加订阅主题。
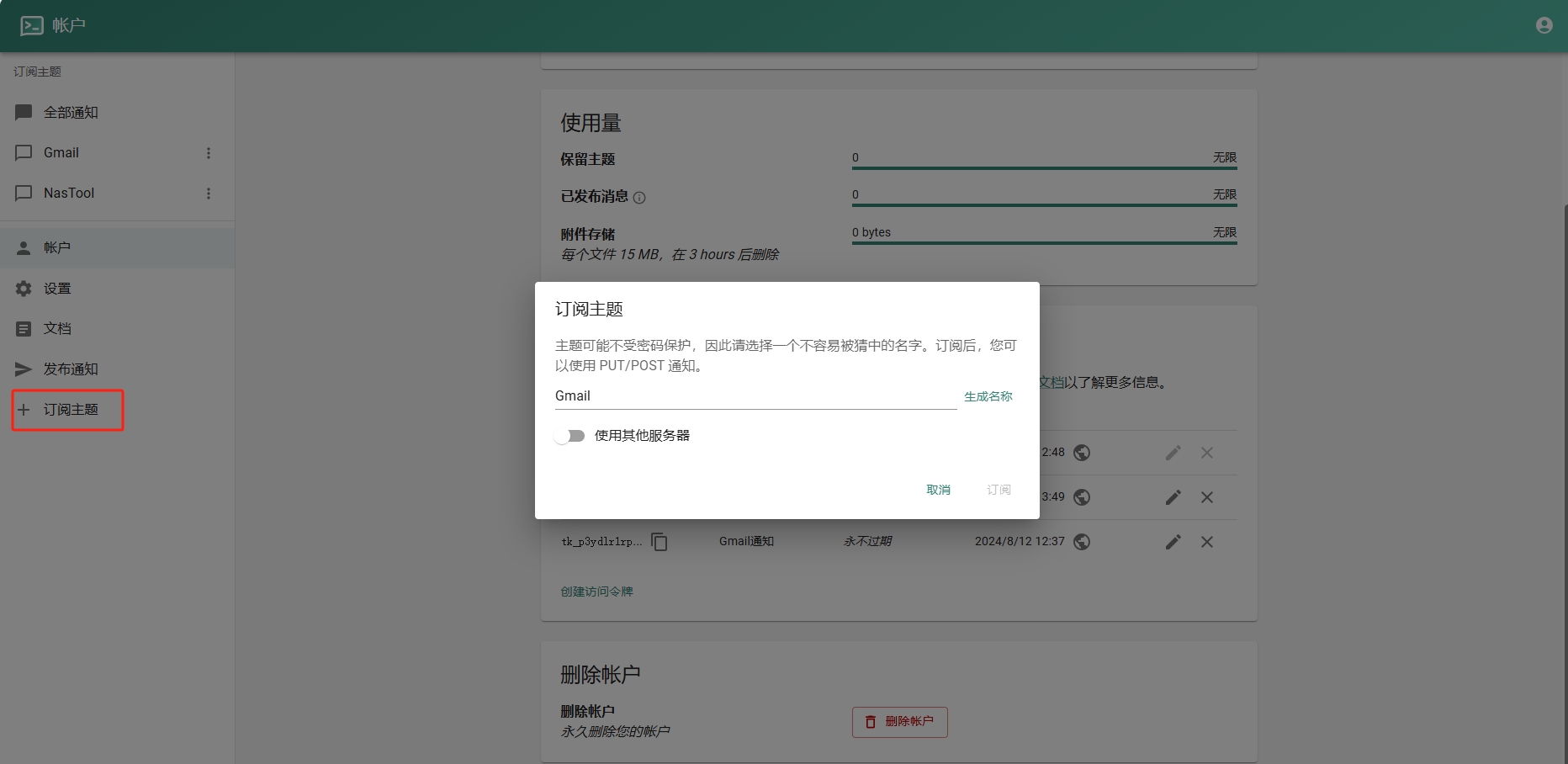
- 进入Google Sheets创建一个表格.记住id,如下图:
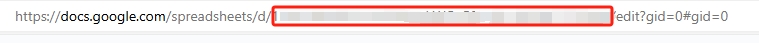
- 进入Google Script创建项目。填入以下代码(注意填入之前的ntfy地址和令牌):
```javascript function checkEmail() { var sheetId = "你的Google Sheets id"; // 替换为你的 Google Sheets ID var sheet = SpreadsheetApp.openById(sheetId).getActiveSheet();
// 清理一星期以前的数据 cleanOldData(sheet, 7 * 24 * 60); // 保留7天(即一周)内的数据
var sentEmails = getSentEmails(sheet);
var threads = GmailApp.search('is:unread'); Logger.log("Found threads: " + threads.length);
if (threads.length === 0) return;
threads.forEach(function(thread) { var threadId = thread.getId();
if (!sentEmails.includes(threadId)) { thread.getMessages().forEach(sendNtfyNotification); recordSentEmail(sheet, threadId); }}); }
function sendNtfyNotification(email) { if (!email) { Logger.log("Email object is undefined or null."); return; }
var message = `发件人: ${email.getFrom() || "未知发件人"} 主题: ${email.getSubject() || "无主题"}
内容: ${email.getPlainBody() || "无内容"}`;
var url = "https://你的ntfy地址/Gmail"; var options = { method: "post", payload: message, headers: { Authorization: "Bearer Ntfy的令牌" }, muteHttpExceptions: true };
try { var response = UrlFetchApp.fetch(url, options); Logger.log("Response: " + response.getContentText()); } catch (e) { Logger.log("Error: " + e.message); } }
function getSentEmails(sheet) { var data = sheet.getDataRange().getValues(); return data.map(row => row[0]); // Assuming email IDs are stored in the first column }
function recordSentEmail(sheet, threadId) { sheet.appendRow([threadId, new Date()]); }
function cleanOldData(sheet, minutes) { var now = new Date(); var thresholdDate = new Date(now.getTime() - minutes * 60 * 1000); // 获取X分钟前的时间
var data = sheet.getDataRange().getValues(); var rowsToDelete = [];
data.forEach(function(row, index) { var date = new Date(row[1]); // 假设日期保存在第二列 if (date < thresholdDate) { rowsToDelete.push(index + 1); // 存储要删除的行号 } });
// 逆序删除(从最后一行开始删除,以避免行号改变) rowsToDelete.reverse().forEach(function(row) { sheet.deleteRow(row); }); }
```
5.Google Script是有限制的不能频繁调用,可以设置五分钟调用一次。如图:
结尾
本人不会代码,以上代码都是通过chatgpt生成的。经过多次修改,刚开始会一直发送通知,后面修改后将已发送的通知放到一个“通知”的标签里。后续不会再次发送通知。
如需要发送通知后自动标记已读,可以把代码复制到chatgpt给你写。
-
 @ 8671a6e5:f88194d1
2025-03-29 17:58:33
@ 8671a6e5:f88194d1
2025-03-29 17:58:33A flash of inspiration

Sometimes the mind takes you to strange places. The other day, I stumbled across Madonna’s “Vogue” video, you know “strike a pose” and all that jazz, and it got me thinking. Not about her music (which, let’s be honest, hasn’t aged as gracefully as her PR team might hope), but about Michael Saylor and Bitcoin.
Bear with me here, there’s a connection there. Madonna built an empire and her iconic name on catchy tunes and reinvention, even if her catalog feels a bit thin these days. Saylor? He’s doing something similar—taking an old act, dusting it off, and teaching it a new trick. Only instead of a microphone, he’s wielding Bitcoin, and Wall Street’s playing the role of the music industry, propping up the star despite a shaky back catalog (his initial business software).
Old school meets new moves
Think of Saylor as that veteran artist who’s been around for a few decades and think of bitcoin as a new style of music, a genre or a gimmick that’s popular with the kids. Old music stars sooner or later pick up on that, and even bring people in to do a cross-over song, a mix or god forbid, a duet.
MicroStrategy, his software company, was never a top hit scoring machine. More of a album full of B-sides that faded into obscurity (for those who don’t know, look up what a B-side song was). But then he stumbled onto Bitcoin, the shiny new genre that’s got the attention and attracted people because of the underlying asset (our tunes are here to stay).
It’s not just a pivot; it’s a reinvention. Like an aging pop star learning to rap, Saylor’s taken his old-school business and remixed it into something attracting a decent audience at conferences for example. Like Madonna or the former Prince fulling arenas. He’s voguing alright; with bold moves, big loans, the support of his own music industry and a spotlight for his (sometimes Madonna lyrics like) ramblings.
The Saylor trick: a ray of light on bitcoin
Here’s the play: Saylor’s turned MicroStrategy into a Bitcoin hoarding machine. Forget software licenses; his game is borrowing billions—through corporate bonds and stock sales, only to buy and hold Bitcoin. Bitcoin will outshine gold, bonds, even the S&P 500, Saylor says. It’s a gamble, an honorable one if you’re a bitcoiner, but it’s dressed up as a vision, and it’s got a self-fulfilling prophecy in it. Not only that, such a prophecy can only fully come to fruition if he’s not the only buyer of last resort of any significance. A music industry isn’t a real industry if there was only Madonna dancing on stage as the only mainstream artist.
We had Prince, Michael Jackson, Taylor Swift, Bruno Mars or Dua Lipa and hundreds of other artists over time, vying for your money, attention span, and streaming minutes. The more Strategy buys, the more the Bitcoin crowd cheers, the higher the price climbs, and the more attention he gets. Speaking gigs, headlines, cult status—it’s a win-win, at least on paper. Strike the pose, indeed.
The McDonald’s trick: value under the surface
It’s not the first time Michael Saylro remixes a tape from another artist so to speak. Let’s pivot to McDonald’s for a second, because there’s a parallel here. You think Big Macs when you think McDonald’s, but their real value hustle is actually real estate.
They own prime land, lease it to franchisees, and rake in rent—billions of it. The burgers? Just a tasty front for a property empire. Saylor’s pulling a similar move, but instead of buildings, his asset is Bitcoin. MicroStrategy’s software gig is the fries on the side — nice to have, but not the main course. He’s borrowing against the future value of BTC, betting it’ll keep climbing, just like McDonald’s banks on steady foot traffic and picking strategic (pun intended) locations. The difference? McDonald’s has a fallback if real estate tanks. Saylor’s all-in on bitcoin. (So far so good, if there’s one thing to go all-in on, it’s bitcoin anyway). That on itself is not an issue. But it’s important to know that the “location” is the asset for some while bitcoin is the “asset” for Strategy. Mc Donald’s assets are easy to spot: there are restaurants all over the place. Madonna’s concerts are also easy to spot: they sell out arenas left and right. Strategy’s bitcoin asset is less easy to spot, as we can’t see them, neither can we verify them. More on that later.
The hybrid star: Madonna meets McDonald’s
So, picture this: Saylor’s a cross between Madonna and a fast-food landlord. He’s the aging music icon who’s learned a flashy new dance, but underneath the glitter, he’s running a McDonald’s-style value play. It’s brilliant, in a way. Bitcoin’s scarcity fuels the hype, and his borrowing keeps the show on the road. Madonna’s legacy still sells records her name holds value, and McDonald’s can lean on its food business and brand, if the property game stumbles they can easily pivot back to basics and earn like they’ve always done on selling food and franchise income/licensing. Saylor? His software arm’s is rather dismal. If Bitcoin falters, there’s no encore that can him.a flash of inspiration
Sometimes the mind takes you to strange places. The other day, I stumbled across Madonna’s “Vogue” video, you know “strike a pose” and all that jazz, and it got me thinking. Not about her music (which, let’s be honest, hasn’t aged as gracefully as her PR team might hope), but about Michael Saylor and Bitcoin.\ \ Bear with me here, there’s a connection there. Madonna built an empire and her iconic name on catchy tunes and reinvention, even if her catalog feels a bit thin these days.\ Saylor? He’s doing something similar—taking an old act, dusting it off, and teaching it a new trick. Only instead of a microphone, he’s wielding Bitcoin, and Wall Street’s playing the role of the music industry, propping up the star despite a shaky back catalog (his initial business software).
Old school meets new moves
Think of Saylor as that veteran artist who’s been around for a few decades and think of bitcoin as a new style of music, a genre or a gimmick that’s popular with the kids. Old music stars sooner or later pick up on that, and even bring people in to do a cross-over song, a mix or god forbid, a duet.
MicroStrategy, his software company, was never a top hit scoring machine. More of a album full of B-sides that faded into obscurity (for those who don’t know, look up what a B-side song was).\ But then he stumbled onto Bitcoin, the shiny new genre that’s got the attention and attracted people because of the underlying asset (our tunes are here to stay).\ \ It’s not just a pivot; it’s a reinvention. Like an aging pop star learning to rap, Saylor’s taken his old-school business and remixed it into something attracting a decent audience at conferences for example. Like Madonna or the former Prince fulling arenas.\ He’s voguing alright; with bold moves, big loans, the support of his own music industry and a spotlight for his (sometimes Madonna lyrics like) ramblings.
*The Saylor trick: a ray of light on bitcoin* \ Here’s the play: Saylor’s turned MicroStrategy into a Bitcoin hoarding machine. Forget software licenses; his game is borrowing billions—through corporate bonds and stock sales, only to buy and hold Bitcoin. Bitcoin will outshine gold, bonds, even the S&P 500, Saylor says.\ It’s a gamble, an honorable one if you’re a bitcoiner, but it’s dressed up as a vision, and it’s got a self-fulfilling prophecy in it. Not only that, such a prophecy can only fully come to fruition if he’s not the only buyer of last resort of any significance. A music industry isn’t a real industry if there was only Madonna dancing on stage as the only mainstream artist.\ \ We had Prince, Michael Jackson, Taylor Swift, Bruno Mars or Dua Lipa and hundreds of other artists over time, vying for your money, attention span, and streaming minutes.\ The more Strategy buys, the more the Bitcoin crowd cheers, the higher the price climbs, and the more attention he gets. Speaking gigs, headlines, cult status—it’s a win-win, at least on paper. Strike the pose, indeed.
*The McDonald’s trick: value under the surface* \ It’s not the first time Michael Saylro remixes a tape from another artist so to speak.\ Let’s pivot to McDonald’s for a second, because there’s a parallel here. You think Big Macs when you think McDonald’s, but their real value hustle is actually real estate.
They own prime land, lease it to franchisees, and rake in rent—billions of it. The burgers? Just a tasty front for a property empire. Saylor’s pulling a similar move, but instead of buildings, his asset is Bitcoin.\ MicroStrategy’s software gig is the fries on the side — nice to have, but not the main course. He’s borrowing against the future value of BTC, betting it’ll keep climbing, just like McDonald’s banks on steady foot traffic and picking strategic (pun intended) locations.\ The difference? McDonald’s has a fallback if real estate tanks. Saylor’s all-in on bitcoin. (So far so good, if there’s one thing to go all-in on, it’s bitcoin anyway). That on itself is not an issue. But it’s important to know that the “location” is the asset for some while bitcoin is the “asset” for Strategy.\ Mc Donald’s assets are easy to spot: there are restaurants all over the place. Madonna’s concerts are also easy to spot: they sell out arenas left and right.\ Strategy’s bitcoin asset is less easy to spot, as we can’t see them, neither can we verify them. More on that later.
The hybrid star: Madonna meets McDonald’s
So, picture this: Saylor’s a cross between Madonna and a fast-food landlord. He’s the aging music icon who’s learned a flashy new dance, but underneath the glitter, he’s running a McDonald’s-style value play.\ It’s brilliant, in a way. Bitcoin’s scarcity fuels the hype, and his borrowing keeps the show on the road.\ Madonna’s legacy still sells records her name holds value, and McDonald’s can lean on its food business and brand, if the property game stumbles they can easily pivot back to basics and earn like they’ve always done on selling food and franchise income/licensing.\ Saylor? His software arm’s is rather dismal. If Bitcoin falters, there’s no encore that can him.
The music’s made in-house
Michael Saylor’s strategy with Strategy, is a bold, all-in bet on Bitcoin as the ultimate store of value. Essentially combining what Mc Donald’s does with the strong believe in bitcoin’s future (and fueling that believe with the fitting rhetoric).
It works like this: Since August 2020, Saylor’s company has been buying up more and more Bitcoin, making it their main asset instead of traditional cash or investments, and by March 2025, they own 506,137 BTC—worth about $42.8 billion (at $84,000 per Bitcoin). This, after spending $33.7 billion to buy it over time (DCA), including a massive 218887 BTC purchase late 2024 for $20.5 billion, giving them over 2.41% of all Bitcoin ever to exist (way more than companies like Marathon, Coinbase, Tesla or Riot).
To pull this off, they’ve borrowed heavily: owing $7.2 billion, mostly to Wall Street investors through special IOUs1 called convertible notes, which don’t need to be paid back until 2027, through 2029. These can either be settled with cash or swapped for Strategy stock. (there lies one of the main issues in my opinion, as the main asset’s price in USD is directly impacting the stock price of MSTR). A small example of this repeated correlation happened on March 28, 2025 when Strategy’s stock (MSTR) dropped 10.8% from $324.59 to $289.41, which was mirroring Bitcoin’s move down from $85,000 to $82,000 earlier.
This debt they have can be called “risky” by any stretch, with a high leverage rate of 39-40%, meaning they’ve borrowed a big chunk compared to what they own outright, but here’s the genius of it: they don’t have to sell their Bitcoin if its price drops, and they can refinance (borrow more later) to keep the dance going. As long as they find investors willing to bet on the later bitcoin price surge, but more importantly, as long as the song is liked by the new audience. If Michael Saylor is our “Madonna”, then there’s still not Taylor Swift or Rihanna in sight.
The creditors (big players, not banks) win if Bitcoin soars, as Strategy’s huge stash (potentially 2.9%+ of the market) nets them massive profits, or even if it crashes, they’re still in the game with other ways to make profit (not on bitcoin), since they can afford the risk. If someone is willing to bet 4 to 8 billion dollars, they’re probably not spooked by losing it all. More so, these Wall Streat people in the correct entourage, can probably afford such a gamble, and can stomach to lose it all if something goes horribly wrong as well, instead of risking being left out of a growing market. But since they’re probably the same people steering and “owning” the USD market anyway, they’re just conquering positions in a new market. The fact that they’re not real bitcoin-ethos people, but just “suits” in finance, can make the suspicious bitcoiners watching all of this unfold, even more uneasy.
So, Strategy sits on $44 billion in Bitcoin with just $7.2 billion in debt, voguing confidently. And Saylor’s betting the song never gets old, he’ll do the B-sides and re-mastering his old albums if necessary, but if Bitcoin’s value ever fades (for whatever reason), the real question is how long they can keep striking poses before the music stops. Remember: all money (fiat, gold, silver, bitcoin, nicely made papers) is a matter of trust.
As I have trust in bitcoin itself, but not so much in Strategy, I’ve take some precautions. I've started my own sort of "Strategy crash fund", with fiat money that only will come into action when strategy is done. The crash that we'll see after that goes down, will be such a tremendous opportunity, that I'll pour in some more fiat, gladly, and that will be the exact moment I will actually “sell all my chairs” (from Saylor’s well-known quote).
Purchases
Strategy’s Bitcoin purchases, don’t seem to jolt the market much either, no matter the size of the order. They always have the same sound: “it’s OTC, it doesn’t impact the market that much”.
Still, it’s strange to see: no one has ever come forward to tell anyone “I’ve sold 15000 bitcoin from my old stack to Saylor”, neither do we see any clear evidence and on-chain moves.
Take their first buy in August 2020 for example. Totaling 21454 BTC for $250 million at $11,652 per BTC; Bitcoin sat at $11,500 to $11,700 so barely moved, inching to $12,000 weeks later due to broader trends.
Same story in December 2020 with 29646 BTC for $650 million, there, the price hopped from $19,000 to $23,000, but a bull market was already raging. Fast forward to February 2021 (19452 BTC, for $1.026 billion (!)), March 2024 (9245 BTC, $623 million), November 2024 (55500 BTC, $5.4 billion), and March 2025 (6911 BTC, $584.1 million)
Bitcoin wobbled 2-15%, but always in line with existing momentum, not Strategy’s announcements. Their biggest buy, for a total of $5.4 billion (!) is just 0.3% of Bitcoin’s $1.7 trillion market cap, it’s too small to register as a blip even. But compared to the liquidity on the market and the “availability” on the OTC market, it should. More so, OTC bitcoin is announced as “for sale” somehow. A person with +25000 bitcoin is not standing on the side of the street yelling “hey man, wanna buy some bitcoin?”. There are specialized firms doing that for them, and making these available. This date is also used by some insiders and people who know this very small market (there aren’t that many bitcoiners sitting on such an amount after 2024 I guess). Data from Binance OTC, Coinspaid, kraken OTC, is highly private of course, but still, anything being sold over there, to Strategy or anyone else, would take larger amounts off the open market and the OTC market, making a price impact, certainly withing 2 years, as Bitcoin mining companies sit on an average buffer of 6 months depending on market conditions.
Strategy funds all of this by selling shares (diluting the pool big-time) or issuing convertible notes, and while SEC filings make faking these buys near-impossible. And even if Saylor is the Bitcoin version of Bernie Madoff, he could get away with it, if enough people "in the know" are willing to support this way of infesting (and investing in) the bitcoin economy. This would have to be a clear orchestrated attack on bitcoin, purely on the financial level then.
I don't believe this to be the case, but mathematically we have to take it into account as a very slight possibility.
After all, a company like "WorldCom"2 managed to scam their way out of different audits for years, until the scheme got bust and a enormous amount of investors lost their money after their CEO went to jail3 for exchange fraud.
I believe this could be the case with Strategy, but I give it a 3% chance (this might be low, but it's there, we can't outright dismiss the possibility).
Water in the wine
Strategy has also massively diluted its stock to fund Bitcoin buys, jumping from 10 million shares in 2020 to about 285 million by March 2025—a 2,750% increase, this happened after raising $4.25 billion from 2020 onwards and $20 billion of their $42 billion "21/21 Plan" by early 2025.
After the 10-for-1 stock split in August 2024, the number of MSTR shares grew from 16.5 million in 2023 to 284898 by end of 2024, a 1625% rise !!!. Add to that about 275 million more shares added in total (including 120 million in 2024 alone) and 1.975 million extra in March 2025 for $592.6 million.
So more and more tap water is poured in the wine, and it means each share’s ownership slice shrinks as new shares flood in, mostly via "at-the-market" sales and convertible note conversions. This is partly offset by share splits, but still, the rise in the number of stock is significant, and a big factor in evaluating MSTR.
In December 2024, they proposed hiking authorized shares to 10.33 billion (plus 1 billion preferred), approved in January 2025, setting the stage for even more if they keep selling.
The trend is clear: relentless selling. They might say “we never sell bitcoin”, but the same doesn’t count for their shares… which derive their value from bitcoin’s fiat price. So shareholders are betting on Bitcoin’s rise to offset the watering down of the share they hold. The more you think of it, the more ludicrous it sounds. It’s a loop of trust where the stock itself can only thrive if the company itself is an active, useful middleman. And so far, it’s only doing so for other Wall street companies, the biggest holders of MSTR shares:
Vanguard Group Inc, BlackRock, Capital International Investors, Jane Street Group, Susquehanna International Group
This on itself is also “normal” of course. In the flow of things. Like every aspect by itself in the whole Strategy setup is just normal. But combining all the factors makes it look a bit more… suspicious to me.
Supporting bitcoin ?
The real head-scratcher comes next: their secrecy and lack of community involvement. Strategy claims to hold 506137 BTC, likely cold-stored with partners like BitGo or Coinbase Custody, but no public wallet addresses back these claims up. Odd for a firm swearing never to sell.
There’s also the real risk that these partners are partly selling paper bitcoin (bitcoin they don't hold the keys to, or "promised" bitcoin) to Strategy, and that they just assume everything is audited and OK.
We can't estimate that, since we don't have any public MicroStrategy addresses or other ways to look at their holdings. This is for security reasons apparently, which raises another question: If they for example would show 300k+ BTC on-chain as proof, it’d boost trust, yet they don’t, hinting at a bigger play — maybe as a Wall Street-backed buyer of last resort for a new asset class.
Also Strategy’s software business and bitcoin “apps” (like the super simple Lightning email integration, and an on-chain digital ID system) is underwhelming to say the least (I literally know people that code such stuff on a free afternoon while they’re cooking dinner).
Their very minimal software innovation for the Bitcoin space, with basic Lightning features and an on-chain ID system, failing their their valuation as a 'Bitcoin company' in my opinion. More so, their business is ignoring the other innovation that would help bitcoin thrive. This is kind of a red flag for me. Why would a company sitting on +500 k bitcoin be hesitant about supporting the bitcoin eco-system more actively? They sure have the funds to do so, right? And they also have the right insights, info and spirit. Yet, they don’t.
They don’t fund developers for open-source projects, or Bitcoin’s growth in general (not publicly at least). So Saylor shines in talks, hyping Bitcoin’s future and Strategy’s stock, but it’s all the self fulfilling prophecy.
No grants, no real support for the community they lean on. It’s like they’re dancing to Bitcoin’s mixtape, raking in the spotlight, while giving little back. All the while some extremely needed projects lack funding, and most software companies in bitcoin who wish to innovate are begging and scraping funds together, in order to stay afloat. Something’s not ok with that. I can’t understand a company with that much power and money being part of this movement and loving bitcoin, while not actively supporting the development or the maintainers of the bitcoin software. (and yes, to keep their independence it’s best to keep it that way, that’s also an argument, but even then, giving out a grant to anyone that’s crucial in this industry, might help the whole ecosystem).
The show must go on—for now
The whole Strategy setup feels more and more like a performance to me. Saylor’s the star, doing the moves and Wall Street’s the record label, and we’re the audience, captivated by the spectacle and paying to see the show on occasion.
The suits keep funding him (free money, IOUs), just like the music industry props up a fading diva with a limited repertoire or drags a new star from her home studio on YouTube into the spotlights. H Saylor’s 21/21 Plan to the amount of $42 billion to snatch up more Bitcoin can be a grand finale that’s dazzling while the lights stay on.
Prediction: the music stops eventually
Here’s my take: Bitcoin will keep rising over a long period of time, and Saylor’s gambit will look like a genius move, until it doesn’t. All it takes is one big shot in Wall Street to find another shiny toy to play with, or another play to get their money working. The billions they’ve invested, will come back eventually, and if it doesn’t, it will mean the world has changed in their advantage as well in another way. Some people cannot lose, no matter what. Saylor’s now part of that, doing their bidding and doing his part for educating the other businesses.
He’s the only big buyer of last resort in this game so far. No one else is piling in with billions like he is. When the hype cools or the debt catches up, he’s got no real business to fall back on. The software? A relic. The Bitcoin bet can save him if the time is right, we’ll see about that. Time is his enemy not ally, and it always wins in the end. The pose can only hold so long. You can’t keep scoring free fiat, without either die on low valuation and dilution, or without at least 20 other Strategy-grade businesses jumping in to take their piece of the pie. So far, surprisingly, none of these two things happen. He keeps getting free fiat from Wall Street investors, and no other Saylor stands up. This can’t last forever. One of the two will happen by end of 2025.
Curtain call
Saylor’s a fascinating watch, a mix of investor-backed bravado, brains, and borrowed billions. Is it a masterstroke or a bitcoin version of Worldcom? I’m not sure. In any case, I would only invest in MSTR myself if the company has a real added value for bitcoin development and the bitcoin ecosystem. They could be the engine, the spirit, the core of bitcoin. Yet they’re just doing the poses. Let your body move to the rhythm.
AVB
If you like : tip here / other writings
1 https://en.wikipedia.org/wiki/IOU
2 https://sc.edu/about/offices_and_divisions/audit_and_advisory_services/about/news/2021/worldcom_scandal.php
3 https://content.next.westlaw.com/Document/Ic6b4dd91644311dbbe1cf2d29fe2afe6/View/FullText.html?transitionType=Default&contextData=(sc.Default)#:\~:text=Rep.-,6,Criminal%20ChargesThe music’s made in-house
Michael Saylor’s strategy with Strategy, is a bold, all-in bet on Bitcoin as the ultimate store of value. Essentially combining what Mc Donald’s does with the strong believe in bitcoin’s future (and fueling that believe with the fitting rhetoric).\ \ It works like this: Since August 2020, Saylor’s company has been buying up more and more Bitcoin, making it their main asset instead of traditional cash or investments, and by March 2025, they own 506,137 BTC—worth about $42.8 billion (at $84,000 per Bitcoin).\ This, after spending $33.7 billion to buy it over time (DCA), including a massive 218887 BTC purchase late 2024 for $20.5 billion, giving them over 2.41% of all Bitcoin ever to exist (way more than companies like Marathon, Coinbase, Tesla or Riot).\ \ To pull this off, they’ve borrowed heavily: owing $7.2 billion, mostly to Wall Street investors through special IOUs1 called convertible notes, which don’t need to be paid back until 2027, through 2029. These can either be settled with cash or swapped for Strategy stock. (there lies one of the main issues in my opinion, as the main asset’s price in USD is directly impacting the stock price of MSTR).\ A small example of this repeated correlation happened on March 28, 2025 when Strategy’s stock (MSTR) dropped 10.8% from $324.59 to $289.41, which was mirroring Bitcoin’s move down from $85,000 to $82,000 earlier.
This debt they have can be called “risky” by any stretch, with a high leverage rate of 39-40%, meaning they’ve borrowed a big chunk compared to what they own outright, but here’s the genius of it: they don’t have to sell their Bitcoin if its price drops, and they can refinance (borrow more later) to keep the dance going. As long as they find investors willing to bet on the later bitcoin price surge, but more importantly, as long as the song is liked by the new audience. If Michael Saylor is our “Madonna”, then there’s still not Taylor Swift or Rihanna in sight.
The creditors (big players, not banks) win if Bitcoin soars, as Strategy’s huge stash (potentially 2.9%+ of the market) nets them massive profits, or even if it crashes, they’re still in the game with other ways to make profit (not on bitcoin), since they can afford the risk. If someone is willing to bet 4 to 8 billion dollars, they’re probably not spooked by losing it all. More so, these Wall Streat people in the correct entourage, can probably afford such a gamble, and can stomach to lose it all if something goes horribly wrong as well, instead of risking being left out of a growing market. But since they’re probably the same people steering and “owning” the USD market anyway, they’re just conquering positions in a new market. The fact that they’re not real bitcoin-ethos people, but just “suits” in finance, can make the suspicious bitcoiners watching all of this unfold, even more uneasy.\ \ So, Strategy sits on $44 billion in Bitcoin with just $7.2 billion in debt, voguing confidently. And Saylor’s betting the song never gets old, he’ll do the B-sides and re-mastering his old albums if necessary, but if Bitcoin’s value ever fades (for whatever reason), the real question is how long they can keep striking poses before the music stops. Remember: all money (fiat, gold, silver, bitcoin, nicely made papers) is a matter of trust.
As I have trust in bitcoin itself, but not so much in Strategy, I’ve take some precautions.\ I've started my own sort of "Strategy crash fund", with fiat money that only will come into action when strategy is done. The crash that we'll see after that goes down, will be such a tremendous opportunity, that I'll pour in some more fiat, gladly, and that will be the exact moment I will actually “sell all my chairs” (from Saylor’s well-known quote).
Purchases
Strategy’s Bitcoin purchases, don’t seem to jolt the market much either, no matter the size of the order. They always have the same sound: “it’s OTC, it doesn’t impact the market that much”.\ \ Still, it’s strange to see: no one has ever come forward to tell anyone “I’ve sold 15000 bitcoin from my old stack to Saylor”, neither do we see any clear evidence and on-chain moves.\ \ Take their first buy in August 2020 for example. Totaling 21454 BTC for $250 million at $11,652 per BTC; Bitcoin sat at $11,500 to $11,700 so barely moved, inching to $12,000 weeks later due to broader trends.
Same story in December 2020 with 29646 BTC for $650 million, there, the price hopped from $19,000 to $23,000, but a bull market was already raging.\ Fast forward to February 2021 (19452 BTC, for $1.026 billion (!)), March 2024 (9245 BTC, $623 million), November 2024 (55500 BTC, $5.4 billion), and March 2025 (6911 BTC, $584.1 million)\ \ Bitcoin wobbled 2-15%, but always in line with existing momentum, not Strategy’s announcements. Their biggest buy, for a total of $5.4 billion (!) is just 0.3% of Bitcoin’s $1.7 trillion market cap, it’s too small to register as a blip even. But compared to the liquidity on the market and the “availability” on the OTC market, it should.\ More so, OTC bitcoin is announced as “for sale” somehow. A person with +25000 bitcoin is not standing on the side of the street yelling “hey man, wanna buy some bitcoin?”. There are specialized firms doing that for them, and making these available. This date is also used by some insiders and people who know this very small market (there aren’t that many bitcoiners sitting on such an amount after 2024 I guess). Data from Binance OTC, Coinspaid, kraken OTC, is highly private of course, but still, anything being sold over there, to Strategy or anyone else, would take larger amounts off the open market and the OTC market, making a price impact, certainly withing 2 years, as Bitcoin mining companies sit on an average buffer of 6 months depending on market conditions.\ \ Strategy funds all of this by selling shares (diluting the pool big-time) or issuing convertible notes, and while SEC filings make faking these buys near-impossible. And even if Saylor is the Bitcoin version of Bernie Madoff, he could get away with it, if enough people "in the know" are willing to support this way of infesting (and investing in) the bitcoin economy. This would have to be a clear orchestrated attack on bitcoin, purely on the financial level then.
I don't believe this to be the case, but mathematically we have to take it into account as a very slight possibility.
After all, a company like "WorldCom"2 managed to scam their way out of different audits for years, until the scheme got bust and a enormous amount of investors lost their money after their CEO went to jail3 for exchange fraud.
I believe this could be the case with Strategy, but I give it a 3% chance (this might be low, but it's there, we can't outright dismiss the possibility).
Water in the wine
Strategy has also massively diluted its stock to fund Bitcoin buys, jumping from 10 million shares in 2020 to about 285 million by March 2025—a 2,750% increase, this happened after raising $4.25 billion from 2020 onwards and $20 billion of their $42 billion "21/21 Plan" by early 2025.\ \ After the 10-for-1 stock split in August 2024, the number of MSTR shares grew from 16.5 million in 2023 to 284898 by end of 2024, a 1625% rise !!!. Add to that about 275 million more shares added in total (including 120 million in 2024 alone) and 1.975 million extra in March 2025 for $592.6 million.\ \ So more and more tap water is poured in the wine, and it means each share’s ownership slice shrinks as new shares flood in, mostly via "at-the-market" sales and convertible note conversions.\ This is partly offset by share splits, but still, the rise in the number of stock is significant, and a big factor in evaluating MSTR.\ \ In December 2024, they proposed hiking authorized shares to 10.33 billion (plus 1 billion preferred), approved in January 2025, setting the stage for even more if they keep selling.\ \ The trend is clear: relentless selling.\ They might say “we never sell bitcoin”, but the same doesn’t count for their shares… which derive their value from bitcoin’s fiat price.\ So shareholders are betting on Bitcoin’s rise to offset the watering down of the share they hold. The more you think of it, the more ludicrous it sounds. It’s a loop of trust where the stock itself can only thrive if the company itself is an active, useful middleman.\ And so far, it’s only doing so for other Wall street companies, the biggest holders of MSTR shares:
Vanguard Group Inc, BlackRock, Capital International Investors, Jane Street Group, Susquehanna International Group\ \ This on itself is also “normal” of course. In the flow of things.\ Like every aspect by itself in the whole Strategy setup is just normal. But combining all the factors makes it look a bit more… suspicious to me.
Supporting bitcoin ?
The real head-scratcher comes next: their secrecy and lack of community involvement.\ Strategy claims to hold 506137 BTC, likely cold-stored with partners like BitGo or Coinbase Custody, but no public wallet addresses back these claims up. Odd for a firm swearing never to sell.
There’s also the real risk that these partners are partly selling paper bitcoin (bitcoin they don't hold the keys to, or "promised" bitcoin) to Strategy, and that they just assume everything is audited and OK.
We can't estimate that, since we don't have any public MicroStrategy addresses or other ways to look at their holdings. This is for security reasons apparently, which raises another question:\ If they for example would show 300k+ BTC on-chain as proof, it’d boost trust, yet they don’t, hinting at a bigger play — maybe as a Wall Street-backed buyer of last resort for a new asset class.
Also Strategy’s software business and bitcoin “apps” (like the super simple Lightning email integration, and an on-chain digital ID system) is underwhelming to say the least (I literally know people that code such stuff on a free afternoon while they’re cooking dinner).
Their very minimal software innovation for the Bitcoin space, with basic Lightning features and an on-chain ID system, failing their their valuation as a 'Bitcoin company' in my opinion. More so, their business is ignoring the other innovation that would help bitcoin thrive. This is kind of a red flag for me.\ Why would a company sitting on +500 k bitcoin be hesitant about supporting the bitcoin eco-system more actively? They sure have the funds to do so, right? And they also have the right insights, info and spirit.\ Yet, they don’t.\ \ They don’t fund developers for open-source projects, or Bitcoin’s growth in general (not publicly at least). So Saylor shines in talks, hyping Bitcoin’s future and Strategy’s stock, but it’s all the self fulfilling prophecy.\ \ No grants, no real support for the community they lean on.\ It’s like they’re dancing to Bitcoin’s mixtape, raking in the spotlight, while giving little back. All the while some extremely needed projects lack funding, and most software companies in bitcoin who wish to innovate are begging and scraping funds together, in order to stay afloat.\ Something’s not ok with that.\ I can’t understand a company with that much power and money being part of this movement and loving bitcoin, while not actively supporting the development or the maintainers of the bitcoin software. (and yes, to keep their independence it’s best to keep it that way, that’s also an argument, but even then, giving out a grant to anyone that’s crucial in this industry, might help the whole ecosystem).
The show must go on—for now
The whole Strategy setup feels more and more like a performance to me. Saylor’s the star, doing the moves and Wall Street’s the record label, and we’re the audience, captivated by the spectacle and paying to see the show on occasion.\ \ The suits keep funding him (free money, IOUs), just like the music industry props up a fading diva with a limited repertoire or drags a new star from her home studio on YouTube into the spotlights. H\ Saylor’s 21/21 Plan to the amount of $42 billion to snatch up more Bitcoin can be a grand finale that’s dazzling while the lights stay on.
Prediction: the music stops eventually
Here’s my take: Bitcoin will keep rising over a long period of time, and Saylor’s gambit will look like a genius move, until it doesn’t. All it takes is one big shot in Wall Street to find another shiny toy to play with, or another play to get their money working. The billions they’ve invested, will come back eventually, and if it doesn’t, it will mean the world has changed in their advantage as well in another way. Some people cannot lose, no matter what. Saylor’s now part of that, doing their bidding and doing his part for educating the other businesses.\ \ He’s the only big buyer of last resort in this game so far. No one else is piling in with billions like he is. When the hype cools or the debt catches up, he’s got no real business to fall back on. The software? A relic. The Bitcoin bet can save him if the time is right, we’ll see about that.\ Time is his enemy not ally, and it always wins in the end. The pose can only hold so long. You can’t keep scoring free fiat, without either die on low valuation and dilution, or without at least 20 other Strategy-grade businesses jumping in to take their piece of the pie.\ So far, surprisingly, none of these two things happen.\ He keeps getting free fiat from Wall Street investors, and no other Saylor stands up.\ This can’t last forever. One of the two will happen by end of 2025.\ \ Curtain call
Saylor’s a fascinating watch, a mix of investor-backed bravado, brains, and borrowed billions.\ Is it a masterstroke or a bitcoin version of Worldcom?\ I’m not sure. In any case, I would only invest in MSTR myself if the company has a real added value for bitcoin development and the bitcoin ecosystem. They could be the engine, the spirit, the core of bitcoin.\ Yet they’re just doing the poses.\ Let your body move to the rhythm.
AVB
If you like : tip here / other writings
1 https://en.wikipedia.org/wiki/IOU
2 https://sc.edu/about/offices_and_divisions/audit_and_advisory_services/about/news/2021/worldcom_scandal.php
-
 @ 57d1a264:69f1fee1
2025-03-29 17:15:17
@ 57d1a264:69f1fee1
2025-03-29 17:15:17- Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box.
- If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust.
- “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options.
- Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic.
originally posted at https://stacker.news/items/928800
-
 @ 655a7cf1:d0510794
2024-09-10 13:16:15
@ 655a7cf1:d0510794
2024-09-10 13:16:15Currently have kyc BTC, huge fan of lightning Network. Because I am a constant user of lightning. Plan on doing my business with lightning as well , peer-to-peer I'm not sure if I'm so worried about kyc I might be misguided in this situation.
originally posted at https://stacker.news/items/679520
-
 @ 30b99916:3cc6e3fe
2025-03-29 17:04:41
@ 30b99916:3cc6e3fe
2025-03-29 17:04:41btcpayserver #lightning #lnd #powershell
BTCpayAPI now supports file upload
I'm continuing to add functionality to BTCpay and BTCpayAPI which is using REST Api(s) to manage my BTCPAY server and LND cloud instance. It is nice to have this just running locally on my home Linux desktop.
Here is the code that implements this functionality.
``` "Uploadfile" {
$apislug = "api/v1/files"
$filepath = Split-Path $options
$filename = Split-Path $options -Leaf
CONST
$CODEPAGE = "iso-8859-1" # alternatives are ASCII, UTF-8
Read file byte-by-byte
$fileBin = [System.IO.File]::ReadAllBytes($options)
Convert byte-array to string
$enc = [System.Text.Encoding]::GetEncoding($CODEPAGE) $fileEnc = $enc.GetString($fileBin)
We need a boundary (something random() will do best)
$boundary = [System.Guid]::NewGuid().ToString() $LF = "
rn" $bodyLines = ( "--$boundary", "Content-Disposition: form-data; name="file"; filename="$fileName"", "Content-Type: application/octet-stream$LF", $fileEnc, "--$boundary--$LF" ) -join $LF$URI = $BTCPayCfg.BTCpayApi.GreenApi.url + $apislug $apiKeyToken = 'token ' + $script:BTCPAY_API $headers = @{'Authorization'=$apiKeyToken}
return Invoke-RestMethod -Uri $uri -Method Post -Headers $headers -ContentType "multipart/form-data; boundary=
"$boundary"" -Body $bodyLines} ``` Here is the revision history since my last article.
Version Date Whom Notes ======= ========== ======== ===================================================== 0.1.4 03/28/2025 cadayton Added UploadFile method to upload a file to the BTCpay server 0.1.3 03/27/2025 cadayton Added GetFiles returns listing of files uploaded to BTCpay server 0.1.2 03/19/2025 cadayton ForwardingHistory new parameter "total_fees" tallys mfees for events returned 0.1.1 03/18/2025 cadayton ForwardingHistory now support additional parameters 0.1.0 03/15/2025 cadayton initial release.The inspiration for this logic was adapted from weipah . One wouldn't think uploading a single file wouldn't require this much coding. The Greenfield's REST Api documentation for this end point wasn't very helpful.In my book, good end-user documentation of one's code is just as important as the code itself. I believe documentation is usually lacking on most projects because the effort of doing so is almost equal to the effort of writing the code. It is also the least fun part about writing code.
The job is not done until the paper work has been completed. :)
https://btcpayserver.sytes.net
-
 @ e83b66a8:b0526c2b
2024-09-10 12:35:24
@ e83b66a8:b0526c2b
2024-09-10 12:35:24If you’re thinking of buying a Bitaxe, here is some information about pools vs solo mining.
Firstly, although the terms are clear “pool mining”, “solo mining” there is nuance in these definitions, so I want to explain these terms fully.
Solo mining pools exist, such as: https://solo.ckpool.org/
It is called a pool, because you are using their credentials to mine, but you keep all the rewards if you win a block. Despite the name, this is not a pool.
You then have a pool such as https://ocean.xyz/ who are a pool, you use their credentials to mine, and you earn a share of their income relative to your contribution in hash power.
There has been some publicity about a solo miner winning a pool recently, there were about 12 blocks won in 2023 by solo miners. However a winning solo miner is likely to be a server farm with hundreds or even thousands of S19’s or S21’s sharing the same payout wallet address. The image of a home miner with a Bitaxe winning a block is extremely unlikely.
A solo miner is defined as a group of miners that share a payout wallet address, so for example you could have 10 Bitaxe’s at home all configured with the same BTC wallet address, this is considered a single solo miner. And so it is with mid tier mining farms, often privately owned, who have a number of machines set to the same payout address. Most of the time, they share earnings for a more reliable income, but the owner may decide to gamble on winning a block and so choose to solo (lottery) mine.
So far, my Bitaxe, which has been running for 4 days now and is part of the Ocean pool. It is earning about 50 Sats a day. If I were to wait for an on-chain payout, it would take around 60 years to receive one. I can, however, setup a BOLT12 lightning payout address and earn this tiny income through Lightning.
So here’s my recommendation.
Currently, there are two pools that control more than 50% of mining, Foundry USA and AntPool. This is a dangerous position and in fact Bitmain, who provide around 90% of all mining hardware actually invest and have stakes in these and several other pools. This is centralising mining and could potentially allow a 51% attack, which could compromise Bitcoin.
Jack Dorsey is currently developing competing mining hardware chipset, through his company Block and Ocean are attempting to decentralise the pools by building a truly independent option for miners to join.
If you buy a Bitaxe, the best way you can help alleviate the dominance of Bitmain is to join a true pool like Ocean to slowly move control away from the dominant pools.
Bear in mind that many of the other smaller pools are still controlled by Bitmain.
If you're still interested in lottery mining, here are your chances of winning a block:
Represented as Hash rates of different miners:
Nerdminer: 20 KH/s = 20,000 H/s
Bitaxe: 750 GH/s = 750,000,000,000 H/s
Bitmain Antminer S9: 13.5 TH/s = 13,500,000,000,000 H/s
Bitmain Antminer S19: 110TH/s = 110,000,000,000,000 H/s
Bitmain Antminer S21: 200TH/s = 200,000,000,000,000 H/s
Current Global Hash rate 628EH/s (Sept 2024) = 628,000,000,000,000,000,000,000,000,000,000,000,000,000,000,000,000,000,000
If you're running a Bitaxe, your percentage chance of winning a block is:
0.000000000000000000000000000000000000000000119426751592357%
Over a year, your chances increase to: 0.00000000000000000000000000000000000000627707006369428%
Your chances of winning the UK national lottery (assuming 20M tickets sold and you buy one):
0.000005%
Over a year, your chances increase to: 0.00026%
Like in all things in Bitcoin, I don’t ask you to trust me. If you want to verify, here are the references I used in making my conclusions:
https://protos.com/chart-when-solo-miners-found-a-bitcoin-block/
https://investors.block.xyz/investor-news/news-details/2024/Blocks-New-Bitcoin-Mining-Chip-to-Be-Part-of-an-Ongoing-Project-With-Core-Scientific-to-Decentralize-Mining-Hardware/default.aspx
https://www.youtube.com/watch?v=Wo91DWvZRs8
https://i.nostr.build/9rQ9Plv6XQYtt6xd.jpg
-
 @ 42c85a20:14afbc38
2025-03-29 15:40:00
@ 42c85a20:14afbc38
2025-03-29 15:40:00Back when Twitter was censoring free speech nostr looked like the only alternative where people would migrate and grow the network; however, now that X is open to free thinking, the perfect storm to enable nostr to grow has been quelled.
How will the nostr universe ever expand unless people in the main stream "centralized" social medias see the light? The illusion of free speech on X is dangerous as people blindly give their trust that the rug will not be pulled; and willingly remain under a tyrannical system.
Perhaps there is some other utility which nostr would be useful for vs just another version of twillter; like exit polls for elections which could fail safe the integrity of voting; or community BBS (bulletin boards) where the people can connect with their neighbours without giving up their real address or identity.
When the main stream social medias' fail again; the next time they break the trust of the people, we must be ready to replace them; we must think outside the box now and build those decentralized utilities now.
-
 @ 6ad3e2a3:c90b7740
2024-09-10 08:37:04
@ 6ad3e2a3:c90b7740
2024-09-10 08:37:04While I love traveling and usually feel enriched by the experience, I dread and detest the process of going to the airport and getting on a plane. It’s not that I’m afraid of flying — though a plane crash would be one of the worst ways to die — but that the airlines and airports have made the experience as inefficient, dehumanizing and cumbersome as possible. While in the short-term these measures might have generated some extra revenue, cut costs or staved off encroachment from competitors, long-term it cannot be good for the service you offer to be so universally reviled. In the interest of improving their product — and the experience of millions of future passengers including me — here are some practical suggestions:
1. Separate passengers from their bags as early as possible.
The single stupidest airline policy is that checking a bag costs extra while carry-ons are free. What that does is incentivize everyone to drag their luggage through the airport and onto the plane. This has several negative consequences:
a) Even though most airlines have assigned seats, everyone lines up 10 or 20 minutes before the start of the already too long boarding process, frantically hoping to secure some scarce overhead space rather than relaxing in the terminal and boarding at their leisure before the door closes.
b) The process of people filing into the narrow plane aisle(s) with their bags and taking time to load them into the overheads stalls the entire boarding process. Not only do people stand in line at the boarding gate, but they stand in line in the jet bridge and again in the aisle(s). Whereas boarding with purses, laptops and other small, under-the-seat items might take 10 minutes or so, getting all the luggage in takes half an hour. If there are 150 people aboard, that’s 3,000 minutes (50 hours) of human life squandered on a useless and stressful activity. Multiply that by thousands of flights per day.
c) The process of deplaning is also slow because everyone has to get their bags out of the overhead. That’s another 15-minute process that should take five.
d) Everyone going through security with all their carry-ons slows down the security line significantly and makes people have to arrive at the airport earlier.
e) Because everyone has their bags, they have to lug them around the terminal while using the restroom, eating or shopping for something to read. Having a 20-pound weight on your shoulder only makes the experience that much more miserable.
The solution to this is for airlines to allow free checked bags and charge for carry-ons with the exception of parents traveling with young children.
To make the process of checking bags more efficient and less cumbersome there should be an immediate drop-off outside the airport. Like curb-side check-in, but automated, a giant conveyor belt of sorts where everyone drops their bag that will be sorted appropriately inside. This drop off area would have security keeping an eye on it, but it would be self-serve and connect at all entry points including curb-side, the parking garage, from the train, etc.
There would be no need for bag tags because people could have an airport-certified chip inserted into their luggage that syncs with the traveler’s boarding pass, i.e., the system reads the chip and directs the bag to the proper gate underground. (Maybe there would be a plastic bin at all the drop-off points you into which you put your bag so luggage of different shapes, sizes and materials could move smoothly and reliably on the conveyor belt to its destination.)
Security details would have to be worked out (maybe you’d have to scan your boarding pass or passport at the bag drop to open it), but as it stands, once you drop your bag off at the curb or the check-in area, it’s essentially the same process now, i.e, it has to be scanned internally before being placed on the plane.
2. Eliminate Security Lines
Going through security would be far easier without all the bags, but to expedite and improve it further, we should make two key changes, neither of which should be beyond our capacity to implement.
a) Instead of a single-file conveyor belt scanned by humans, make the conveyor belt wide enough for everyone to put their laptops, belts, etc. on simultaneously. This could easily be done by providing plastic bins (as they do now), but with individual numbers and keys on them, like you’d find in most locker rooms. You’d grab bin 45, for example, pull the key out, put your things in it, lock it, walk through the metal detector, retrieve your bin on the other side, unlock it, get your things, put the key back in it, and it gets returned for re-use.
Instead of a bored-out-of-his-mind human looking at each bag individually, there would be a large scanner that would look at all the bags simultaneously and flag anything suspicious.
b) Just as there’s no reason to send the bags through the scanner single-file, there’s no reason to send the people through that way, either. Instead, install room-wide metal detectors through which dozens of people could walk simultaneously. Any passengers that set it off would be digitally marked by the detector, directed back out, shed the offending item into a numbered bin and collect it on the other side.
Basically, you’d drop anything big off before you even set foot in the building, and you’d drop everything else into a security bin, walk through without waiting and collect it on the other side.
3. Make sure the gates are clean, have enough seats to accommodate the passengers of even the largest planes that come through, ample charging stations and reliable and free wi-fi.
Because you’re no longer forced to line up and hustle for overhead space, you’ll be spending more time sitting comfortably in the terminal.
4. Have clean, efficient public transportation from the center of each city directly to the airport. (Some cities already have this.) Not a train, a bus and a one-mile walk.
There are smaller things airports could do to make the process even better — and I’ll suggest some below — but these three would at least make it tolerable and humane. It would shave off roughly an hour per trip, spare people the burden of schlepping around with heavy bags, wading through slow-moving security lines (which add stress if you’re in danger of missing your flight), standing in the terminal, waiting in line after line to sit in a cramped and uncomfortable seat for 20-30 minutes before the plane even takes off and remaining stuck in that seat 15 minutes after the plane has made it to the gate while people one by one painstakingly get their bags out of the overhead bins. Moreover, people could get to the airport later without rushing, and if they were early, they could relax in the terminal or get work done.
Here are some other suggestions:
- With fewer people using the overhead bins, rip them out. There would be a few bins at designated spots (just like there are a few emergency exits), but the interior of the plane would feel more spacious and less claustrophobic. You also wouldn’t risk hitting your head when you stood up.
- Airplanes should have reasonably priced (ideally free) wi-fi and outlets in each row. There’s no way it costs anywhere near the $35 per flight, per person GoGo Inflight absurdly charges.
- Treat airports as public squares — invest in their design as well as their functionality. Incorporate outdoor spaces, green spaces. Attract decent restaurants, bars, cafes. People unencumbered by bags and not rushing to wait in line to board 40 minutes early will be more able to enjoy the environment and arriving travelers will immediately get a good impression and be put at ease.
- Do not advertise mileage rewards from credit cards or other sources unless those miles are actually redeemable at a reasonable rate and on routes and times someone would actually fly. As it stands those programs are borderline fraud — you can fly a middle seat one way from NY to LA for 30,000 miles at 6 am, but that’s not why I signed up for the credit card. If mileage plans are too costly, scrap them.
I can anticipate some objections to these ideas, and I’ll address each one in turn.
1. This would cost too much money.
My suggestions would require a significant initial investment, but it would be but a small piece of the infrastructure outlay that’s sorely needed — and on which our current president campaigned — and it would create jobs. Moreover, it would save travelers tens of millions of hours per year. At $15 per hour — it would pay for itself in short order. (And taxpayers’ squandered time and awful experiences are exactly what their tax dollars should go toward remediating.)
2. It’s too much of a security risk.
Airport security is incredibly flawed right now, as tests repeatedly show. You can get prohibited items through security easily already, and it’s likely the screening process is mostly “security theater,” i.e., just for show. But to the extent this is a serious concern, the newer system might actually improve security due to improved technology spurred by the infrastructure investment. Better detection could be designed into the new system, rather than relying on bored-out-of-their-mind humans to scan endlessly through people’s toiletries expecting to find nothing for hours and days on end.
Moreover, airport security has never actually been an issue in the US. Even on 9/11, the flimsy security worked well — the hijackers managed only boxcutters on the tragically ill-fated flights, not guns or bombs. In other words, that was a failure of government intelligence, not one of airline security even when no one took his shoes off or had to worry about how many ounces of liquid was in his shampoo bottle.
3. I like free carry-ons because it saves me from waiting at the baggage claim.
Great, then pay extra for that. When something you like individually causes collective harm, there needs to be a cost for it. That we have the opposite system where people doing what would make everyone else’s experience easier and better have to pay is perverse.
The bottom line — the current state of air travel both in the US and Europe is unacceptable*. We cannot have a system in which everyone participating despises it and simply pretend it’s an inevitable hassle about which we’re powerless to do anything. The central issue is the dehumanizing** lack of respect for travelers’ time and experience. It’s time to change our priorities and take care of the human beings for whom airports and air travel exist.
*I haven’t even touched on the awful state of flights themselves with cramped seats, small, dirty rest rooms, bad food and exorbitant fees to change your itinerary. That’s because I wanted to focus mostly on the airport/government side over which the public has ownership, and fixing the overall economics of air travel is probably more difficult than getting airlines to reverse their checked-bag fee policies.
** This article was written in March of 2017, and little did I know how much more dehumanizing things would get during covid.
-
 @ 6ad3e2a3:c90b7740
2024-09-10 08:21:48
@ 6ad3e2a3:c90b7740
2024-09-10 08:21:48I’ll write a separate Week 1 Observations later, but I wanted to dedicate this space solely to mourning my Circa Survivor entry.
Circa Survivor costs $1000 to enter and has a $10M prize for the winner, usually split by several as things get down to the wire. Three years ago, when the prize was $6M Dalton Del Don and I — the first time we ever entered — made it to the final 23 in Week 12. The value of our share was something like $260K at that point, but we got bounced by the Lions who beat the 12-point favored Cardinals and took home nothing.
When you enter a large survivor pool, the overwhelming likelihood is you’ll meet this fate at some point, whether in Week 1 or 12. So it’s not really the loss that’s painful, so much as not getting to live and die each week with a chosen team. You lose your status as “the man in the arena whose face is marred by dust and sweat and blood” and become just an observer watching and commentating on the games without the overarching purpose of surviving each week.
This year was also different due to the lengths to which I went to sign up. It’s not just the $1000 fee, it’s getting to Vegas in person, the $400 in proxy fees (you need locals to input your picks for you if you don’t live there), the $60 credit card fee, the $200 crappy hotel I booked at the last minute, the flights (one of which was cancelled due to heat), the rental car that necessitated, the gas, getting lost in the desert, the entire odyssey while sick and still jet-lagged in 122-degree heat.
But it’s not about the money, and it’s not even about the herculean effort per se, but the feeling and narrative I crafted around it. I was the guy who got this done. I flew from Portugal to San Francisco for 12 hours, two days later from SF to Palm Springs to help my 87-YO uncle with his affairs, improvised to get from Palm Springs to Vegas, which took six hours due to road closures, signed up for the contests, made the flight back to San Francisco, flew to Denver at 7 am the next day, took my daughter the Rockies game in the afternoon and then on to Boulder the following day. Maybe that’s not so impressive to some of you, but for me, an idle ideas person, a thinker, observer, someone who likes to express himself via a keyboard, it was like Alexander the Great conquering Persia.
And it’s not only about that smaller mission, or the narrative I crafted around it, but a larger one which was to bring sports content to nostr which I vowed to do before the summer which is why I felt I had to make the effort to get to Vegas to sign up for the contests, to have sufficient skin in the game, to have something real about which to write.
And I got the idea to do this seriously because Heather wrote a guide to Lisbon which I posted on nostr, and a few prominent developers there were surprisingly excited about getting that kind of quality content on the protocol. And I thought — if they’re this excited about a (very in-depth) guide to one particular city in Europe, how much more value could I create posting about a hobby shared by 50-odd million Americans? And that thought (and the fact I had to go to Palm Springs anyway) is what set me off on the mission in the first place and got me thinking this would be Team of Destiny, Part 2, only to discover, disappointingly, it’s real destiny was not to make it out of the first week.
. . .
While my overwhelming emotion is one of disappointment, there’s a small element of relief. Survivor is a form of self-inflicted torture that probably subtracts years from one’s life. Every time Rhamondre Stevenson broke the initial tackle yesterday was like someone tightening a vice around my internal organs. There was nothing I could do but watch, and I even thought about turning it off. At one point, I was so enraged, I had to calm down consciously and refuse to get further embittered by events going against me. Mike Gesicki had a TD catch overturned because he didn’t hold the ball to the ground, The next play Tanner Hudson fumbled while running unimpeded to the end zone. I kept posting, “Don’t tilt” after every negative play.
There’s a perverse enjoyment to getting enraged about what’s going on, out of your control, on a TV screen, but when you examine the experience, it really isn’t good or wholesome. I become like a spoiled child, ungrateful for everything, miserable and indignant at myriad injustices and wrongs I’m powerless to prevent.
At one point Sasha came in to tell me she had downloaded some random game from the app store on her Raspberry Pi computer. I had no interest in this as I was living and dying with every play, but I had forced myself to calm down so much already, I actually went into her room to check it out, not a trace of annoyance in my voice or demeanor.
I don’t think she cared about the game, or about showing it to me, but had stayed with her friends most of the weekend and was just using it as an excuse to spend a moment together with her dad. I scratched her back for a couple seconds while standing behind her desk chair. The game was still going on, and even though I was probably going to lose, and I was still sick about it, I was glad to have diverted a moment’s attention from it to Sasha.
. . .
In last week’s Survivor post, I wrote:
What method do I propose to see into the future? Only my imagination. I’m going to spend a lot of time imagining what might happen, turn my brain into a quantum device, break space-time and come to the right answers. Easier said than done, but I’m committed.
It’s possible I did this, but simply retrieved my information from the wrong branch of the multiverse. It happens.
. . .
I picked the Bengals knowing full well the Bills were the correct “pot odds” play which is my usual method. Maybe when the pot-odds are close, I might go with my gut, but they were not especially close this week, and yet I still stuck with Cincinnati because they were the team I trusted more.
And despite it being a bad pick — there are no excuses in Survivor, no matter what happens in the game, if you win it’s good, and lose it’s bad — I don’t feel that badly about it.
I regret it only because I wish I were still alive, but it was my error. I went with what I believed, and it was wrong. That I can live with 100 times better than swapping out my belief for someone else’s and losing. Had I done that I’d be inconsolable.
. . .
I won’t let the Survivor debacle undermine my real mission to bring sports to nostr. Team of Destiny 2 would have been a compelling story, but it was never essential. After all, my flight was cancelled and I had to improvise, so now my Survivor entry is cancelled, and I’ll have to improvise again. The branch of the multiverse where the Bengals won didn’t give me the information I wanted, but maybe it was what I really needed to know. That I am the man in the arena yet, the battle was ever against myself, and for a brief moment, while my team was losing, I prevailed.
-
 @ 129f5189:3a441803
2024-09-09 23:28:41
@ 129f5189:3a441803
2024-09-09 23:28:41Project 2025, outlined in the Heritage Foundation's "Mandate for Leadership" document, serves as a fundamental guide for the next Republican administration. Despite Trump's extensive denial, in today's material, we will explore the deepening and continuation of many policies already employed during his first term. The idea is that this material will serve as a reference document to consult and verify what was actually implemented and/or followed. https://image.nostr.build/e3b89d71ff929258e5d9cb0b5ca8709a381598f43d8be4b17df3c69c0bc74d4a.jpg This document presents proposals for the foreign policy and the State Department of the United States of America, as well as the strategy with its political partners and adversaries. We will also address the U.S. government's communication strategy abroad. https://image.nostr.build/a4250b786f611b478aaf0be559427ad7d4296fbcacb2acc692c7f0d7eb06b0dd.jpg Reorienting U.S. Foreign Policy: Proposals for a Conservative Future In the chapter "The Department of State" from the "Mandate for Leadership," also known as "Project 2025," Kiron K. Skinner presents a comprehensive plan to reform U.S. foreign policy under a conservative administration. Skinner, a renowned foreign policy expert and former Director of Policy Planning at the U.S. State Department, outlines global threats and offers specific recommendations to strengthen the U.S. position on the international stage. Below, we present a detailed analysis of the proposals, emphasizing direct quotes and explanations of the key points discussed. https://image.nostr.build/278dcd7ef0439813ea35d0598319ee347f7a8cd7dfecac93be24ffdd0f6ecd04.jpg History and Structure of the State Department Since its founding in 1789, the State Department has been the primary diplomatic channel of the U.S. With nearly 80,000 employees and 275 posts around the world, it faces significant structural challenges. Skinner highlights that "the biggest problem of the State Department is not a lack of resources," but the belief that it is "an independent institution that knows what is best for the U.S." (Skinner). The scholar and former Director of Policy Planning at the U.S. State Department during the Trump administration emphasizes these points, considering the difficulty in accepting a conservative international approach by State Department employees (the equivalent of the Ministry of Foreign Affairs in other countries). https://image.nostr.build/049939926793e86000b300b9a962dc0ae7e271d9a607ae36d8cb08642adf4174.jpg Political Leadership and Bureaucratic Support To align the State Department with presidential priorities, Kiron suggests appointing political leaders who are committed to the president's vision. "Leadership should include political appointees in positions that do not require Senate confirmation, including senior advisors and deputy secretaries" (Skinner). Furthermore, she emphasizes the importance of training and supporting these appointees to ensure effective coordination between agencies. https://image.nostr.build/6ed704cc9612aa6489e048b143f1e489c1f8807fdf2ab011b4ba88e4a1e3619a.jpg Global Threats to the U.S. The document identifies five countries that pose significant threats to the security and prosperity of the U.S.: China, Iran, Venezuela, Russia, and North Korea. 🇨🇳 China: Skinner argues that China represents an existential threat. "The U.S. needs a strategic cost-imposing response to make Beijing's aggression economically unviable" (Skinner). Additionally, she emphasizes that the issue is not with the Chinese people, but with the communist dictatorship that oppresses them: "As with all global struggles against communist and other tyrannical regimes, the issue should never be with the Chinese people, but with the communist dictatorship that oppresses them" (Skinner). https://image.nostr.build/e707273f1d08bdc4187123a312bd116695b5f603066e11ad30fcef4466730b6b.jpg 🇮🇷 Iran: The Obama administration, through the 2015 nuclear deal, provided the Iranian regime with a "crucial cash bailout" (Skinner). Kiron criticizes this approach, asserting that the U.S. should support the Iranian people in their demands for a democratic government. "The correct policy for Iran is one that recognizes that it is in the U.S. national security interests and the human rights of Iranians that they have the democratic government they demand" (Skinner). https://image.nostr.build/cda7d29a62981f59ad8d77362b3867b552f190c8d7e0e8d9233cb7c1d1d0309e.jpg 🇻🇪 Venezuela: Under the regimes of Hugo Chávez and Nicolás Maduro, Venezuela has transitioned from a prosperous country to one of the poorest in South America. Skinner suggests that the U.S. should work to contain Venezuelan communism and support its people. "The next administration should take steps to put Venezuela's communist abusers on notice and make progress in helping the Venezuelan people" (Skinner). https://image.nostr.build/f53e12564cae74d4b50c24b0f3752dd2c53b70bd1c00a16df20736fb8588417d.jpg 🇷🇺 Russia: The war between Russia and Ukraine divides opinions among conservatives, and the document considers three lines of action. Some advocate continuing support for Ukraine, while others believe that such support does not serve U.S. security interests. "The conservative approach rejects both isolationism and interventionism, first asking: What is in the interest of the American people?" https://image.nostr.build/8fedaf77129f4801f4edb8b169b2ac93a3e518b8bf3642b3abc62575b5435fa3.jpg One conservative school of thought believes that "Moscow's illegal war of aggression against Ukraine represents major challenges to U.S. interests, as well as to peace, stability, and the post-Cold War security order in Europe" (Skinner). This view advocates for continued U.S. involvement, including military and economic aid, to defeat Russian President Vladimir Putin and return to pre-invasion border lines. Another conservative school of thought argues that U.S. support for Ukraine is not in the interest of U.S. national security. According to this view, "Ukraine is not a member of the NATO alliance and is one of the most corrupt countries in the region" (Skinner). It is argued that the European nations directly affected by the conflict should help defend Ukraine, but the U.S. should seek a swift end to the conflict through a negotiated settlement. https://image.nostr.build/22db3d0e79340c1d62344a2b8a3bfddbe4d5bd923cf77d70cfbf5ebf73e4db3e.jpg A third conservative viewpoint avoids both isolationism and interventionism, proposing that "each foreign policy decision should first ask: What is in the interest of the American people?" (Skinner). From this perspective, continued U.S. involvement should be fully funded, limited to military aid while European allies address Ukraine's economic needs, and must have a clear national security strategy that does not endanger American lives. https://image.nostr.build/939fea0bb5c69f171a3da1073e197edcff23a600430b3bc455f6d41bc8a0319f.jpg Although not stated explicitly, I believe this third viewpoint is the one Kiron Skinner desires, as she considers American intervention important but advocates for balancing the costs of the war with its partners in the European Union and NATO. https://image.nostr.build/d1d0c7fb27bfc5dd14b8dde459b98ed6b7ca2706473b2580e0fbf5383f5a9c10.jpg 🇰🇵 North Korea: North Korea must be deterred from any military conflict and cannot be allowed to remain a de facto nuclear power. "The U.S. cannot allow North Korea to remain a de facto nuclear power with the capability to threaten the U.S. or its allies" (Skinner). https://image.nostr.build/95febb04f6d2e0575974a5e645fc7b5ec3b826b8828237ccc1f49b11d11d6bce.jpg Detailed Policy Proposals Refugee Admissions: The Biden administration has caused a collapse in border security and internal immigration enforcement, according to Skinner. She argues that the U.S. Refugee Admissions Program (USRAP) should be resized. "The federal government should redirect screening and verification resources to the border crisis, indefinitely reducing the number of USRAP refugee admissions until the crisis can be contained" (Skinner). https://image.nostr.build/a5740b33842e47b9a1ab58c7b72bd6514f9b6ffbb18706deed1445c59236bc0d.jpg Corporate Collaboration with China: Skinner criticizes the collaboration of companies like BlackRock and Disney with the Chinese regime, noting that "many are invested in an unwavering faith in the international system and global norms," refusing to acknowledge Beijing's malign activities. She emphasizes that the real issue is the communist dictatorship that oppresses the Chinese people, not the Chinese citizens themselves (Skinner). https://image.nostr.build/05a3c787f144c4519c2ee8a4b22e64b8729842819ace4b439c849ef70ecd60b4.jpg Fentanyl and Mexico: The trafficking of fentanyl, facilitated by Mexican cartels in collaboration with Chinese precursor chemical manufacturers, is a critical problem. "Mexican cartels, working closely with Chinese manufacturers of fentanyl precursor chemicals, are sending this drug to the U.S., causing an unprecedented lethal impact" (Skinner). The next administration should adopt a firm stance to halt this public health crisis. https://image.nostr.build/59e32aeef5dabab3344a94a3e415d57fed91fece8bc3c5f068e9f6f7d71f99bd.jpg Re-hemispherization of Manufacturing: Kiron proposes that the U.S. promote the relocation of manufacturing to partner countries such as Mexico and Canada. "The U.S. should do everything possible to shift global manufacturing to Central and South American countries, especially to move it away from China" (Skinner). This would improve the supply chain and represent a significant economic boost for the region. https://image.nostr.build/5d5d7d792f1c94eb6e2bd7a4b86c43236765719e183be8ba8e00ed7dd07eca66.jpg Abraham Accords and a New “Quad”: Skinner suggests that the next administration should expand the Abraham Accords to include countries like Saudi Arabia and form a new security pact in the Middle East that includes Israel, Egypt, Gulf states, and possibly India. "Protecting the freedom of navigation in the Gulf and the Red Sea/Suez Canal is vital for the global economy and, therefore, for U.S. prosperity" (Skinner). https://image.nostr.build/c87cd99cb3ea2bef40e9d1f1fea48b0c9f9f031f3077fff658f15f850e7b8589.jpg Policy for Africa: The U.S. strategy for Africa should shift focus from humanitarian assistance to economic growth and countering China’s malign activities. "Development assistance should focus on fostering free market systems and involving the U.S. private sector" (Skinner). She also highlights that African nations are opposed to the imposition of policies such as abortion and LGBT lobbying. https://image.nostr.build/44df42f32e61c14786ac46c231d368b14df4dc18124a0da458e8506f917302f2.jpg Relations with Europe and Asia Europe: The U.S. should demand that NATO countries increase their contributions to defense. "The U.S. cannot be expected to provide a defense umbrella for countries that do not contribute adequately" (Skinner). Additionally, urgent trade agreements should be pursued with the post-Brexit United Kingdom. https://image.nostr.build/6c013bacfa9e6505ad717104d9a6065f27664a321dd2c3d41fd7635258042d2f.jpg Asia: The withdrawal of U.S. troops from Afghanistan was humiliating and created new challenges. Skinner emphasizes the importance of India as a critical partner to counterbalance the Chinese threat and promote a free and open Indo-Pacific. Cooperation within the Quad, which includes the U.S., India, Japan, and Australia, is essential to this strategy. "The priority is to advance U.S.-India cooperation as a pillar of the Quad" (Skinner). https://image.nostr.build/1cc988b2f70d855c9676d7e38ffdb23564d04ad6333a8d256698f416a1c6704e.jpg International Organizations Skinner criticizes the corruption and failure of the World Health Organization (WHO) during the Covid-19 pandemic. "The next administration should end blind support for international organizations and direct the Secretary of State to initiate a cost-benefit analysis of U.S. participation in all international organizations" (Skinner). She also supports the “Geneva Consensus Declaration on Women’s Health and Protection of the Family,” which is against abortion, and believes that the U.S. government should not fund international organizations that promote abortion (Skinner). https://image.nostr.build/0b583511fef16d68736804fae2f15850eb5c803af01f006a3fe10cdbc583f48c.jpg Conclusion Skinner’s document provides a detailed vision for reorienting U.S. foreign policy under a conservative administration, with an emphasis on ensuring that the State Department serves the national interests defined by the president. With these guidelines, the next administration has the opportunity to redefine the U.S. position on the global stage, promoting security, prosperity, and freedom. https://image.nostr.build/697522745c5947cd4384cdd302b531ee98ce5d59a5d72de0b4f3a52c9abd4821.jpg
-
 @ ff517fbf:fde1561b
2025-03-29 15:37:34
@ ff517fbf:fde1561b
2025-03-29 15:37:34はじめに:なぜKYCなしP2P取引か
ビットコインは元々、ピア・ツー・ピア(P2P)の電子通貨システムとして設計されました。サトシ・ナカモトのビットコイン白書でも、「信頼ではなく暗号学的証明に基づく電子決済システム」によって、第三者を介さずに当事者同士が直接取引できることが必要だと述べられています。つまり、本来ビットコインは銀行などの仲介者なしで個人同士が直接送金・売買できる社会的意義を持っているのです。
しかし現在、多くの暗号資産取引所では規制上の理由からKYC(本人確認)手続きが求められ、個人情報の提出が必要です。KYCはユーザーのプライバシー喪失やデータ漏洩リスクにつながりかねず、また口座凍結や資金没収といった中央集権的管理のリスクもあります。経済的にも、第三者を介することで手数料が高くなったり、地域によっては銀行や政府の制限でビットコインの購入が困難になる場合もあります。
こうした背景からノンKYCのP2P取引プラットフォームを利用するメリットは大きいです。例えば HodlHodl(@npub1yul83qxn35u607er3m7039t6rddj06qezfagfqlfw4qk5z5slrfqu8ncdu) は、匿名で世界中のユーザーと直接ビットコインを売買できるグローバルなP2Pマーケットプレイスです。HodlHodlではユーザー同士が直接取引し、サイト運営側はビットコインを一切預かりません。取引はマルチシグエスクロー(2-of-3の多重署名契約)で安全に管理され、取引手数料も最大0.5%と低く抑えられています。プライバシーとセキュリティを確保しながら、銀行口座や身分証なしでビットコインを売買できるため、社会的にも経済的にも大きな意義があります。
本チュートリアルでは、HodlHodlを使ってビットコインを購入・販売する具体的な手順を分かりやすく解説します。また、HodlHodlの安全性(マルチシグエスクローによる非中央集権型の管理)や、他のプラットフォームにはない特徴(本人確認不要、ユーザー自身による鍵の管理、APIやレンディングサービスの活用など)についても説明します。P2P取引に不慣れで不安を感じている方にも安心してご利用いただけるよう、丁寧で親しみやすい言葉で案内していきます。
HodlHodlの基本準備
アカウント登録: HodlHodlの利用を開始するには、まず無料のアカウント登録を行います。必要なのはメールアドレスとパスワードだけで、ユーザー名や身分証の提出は不要です。登録後に届く確認メール内のリンクをクリックすれば、すぐに取引を始められます。
ビットコインウォレットの用意: HodlHodlは取引の際にユーザー自身のビットコインウォレットを使用するノンカストディアル方式です。プラットフォーム上にウォレットは用意されていないため、事前に自分のビットコインウォレットを準備してください。例えばモバイルウォレットやハードウェアウォレットなど、自分だけが秘密鍵を管理できるウォレットを用意しましょう。買い手の場合は購入したビットコインを受け取るウォレットが必要になり、売り手の場合は売却するビットコインを自身のウォレットからエスクローに送金する必要があります。

ビットコインを購入する方法(Buy BTC)
それでは、HodlHodlでビットコインを購入(Buy) する手順を見ていきましょう。以下では、日本円(JPY)を銀行振込で支払ってビットコインを買う例を想定して説明しますが、基本的な流れは他の通貨や支払い方法でも同じです。
-
「Buy BTC」をクリックする: HodlHodlにログインし、画面上部のヘッダー左側にある「Buy BTC」ボタンをクリックします。これにより、現在出ているビットコイン売り注文(オファー)の一覧ページに移動します。
-
検索フィルターの設定: オファー一覧ページでは、自分の希望条件でオファーを絞り込むことができます。国、法定通貨、取引タイプ、支払い方法、金額などのフィルター項目があります。例えば日本で銀行振込により購入したい場合、「Country(国)」をJapan、「Currency(通貨)」をJPY、「Payment method(支払い方法)」を Bank Transfer 銀行振込に設定します(他の項目は必要に応じて指定します)。フィルターは任意ですが、自分に合った支払い方法や金額範囲のオファーを探すのに役立ちます。
-
オファーを選ぶ: フィルターを適用すると、条件に合致する売り手のオファー一覧が表示されます。各オファーにはレート(価格)、取引可能額範囲、支払い方法、売り手の評価などが記載されています。希望に合うオファーが見つかったら、そのオファーの詳細をクリックします。例えば「1 BTC = 〇〇JPY」のようなレートで、自分が購入したい額に対応できるオファーを選びましょう。初めて取引する場合は、評価の高い売り手や少額からの取引を選ぶと安心です。

-
購入量と受取アドレスの入力: オファーをクリックすると、取引の詳細入力画面になります。ここで購入したいビットコインの量を入力します(ビットコイン量あるいは法定通貨換算額のどちらでも入力可能です)。多くの場合、最低・最大取引額が決まっているので、その範囲内で入力してください。また、ビットコインの受取先アドレスを求められます。これは購入後にビットコインを受け取る自分のウォレットアドレスです。アカウントの設定で事前に登録したアドレスがあれば自動で表示されますが、都度指定することも可能です。さらに、支払い方法が複数指定されているオファーでは希望の支払い方法を選択します(例:銀行振込の中でも特定の銀行を指定できる場合があります)。最後に、取引相手(売り手)への伝達メッセージ欄があれば、必要に応じてコメントを記入します。入力が完了したら内容を確認し、「Create contract(契約作成)」 的なボタンを押して取引を開始します。
-
エスクローアドレスの生成: 契約が作成されると、取引画面上にエスクロー(第三者保管用マルチシグアドレス)を生成するための手順が表示されます。ここで 「Generate escrow(エスクロー生成)」 ボタンをクリックし、プラットフォームに登録したペイメントパスワード(支払い用パスワード)を入力します。ペイメントパスワードはHodlHodlで取引の署名に使われる特別なパスワードで、初回取引時に設定しておく必要があります。正しく入力すると、この取引専用のビットコインエスクローアドレスが自動生成されます。あとは売り手がそのエスクローアドレスにビットコインを入金するのを待ちます。画面上に「waiting for deposit(入金待ち)」等のステータスが表示されるので、しばらく待機してください。売り手が約束のビットコイン額をエスクローに送金し、一定のブロック承認(Confirmations)が得られると、取引ステータスが自動で更新されます。
-
エスクロー入金の確認: ビットコインがマルチシグエスクローにロックされ、取引ステータスが「In progress(進行中)」や「Deposited(入金済み)」といった表示に変わったことを必ず確認します。ステータス表示とブロックチェーン上の確認回数が条件を満たしたら、支払いを実行しても安全な状態であることを意味します(エスクローにロックされたビットコインは売り手単独では動かせません。取引ページには売り手が指定した支払い詳細(銀行口座情報など)が記載されていますので、その指示に従って売り手へ法定通貨の支払い(振込)を行います。例えば銀行振込の場合、指定された口座にJPYを送金します。この段階では、必ず取引ページを開いたままにしておきましょう。 支払いが完了したら、取引ページ上の「I’ve sent the payment(送金完了)」ボタンをクリックして、売り手に支払い実行済みであることを通知します。併せて、チャット機能で支払い完了の旨を伝えると良いでしょう。
-
売り手によるビットコインのリリース: 買い手からの支払いが完了すると、売り手は自分の銀行口座等を確認して入金を検証します。売り手が入金を確認したら、取引ページ上で 「Release Bitcoin(ビットコインをリリース)」 ボタンを押し、ペイメントパスワードを入力してエスクローからビットコインを開放します。これにより、エスクロー上のビットコインが買い手の指定アドレス(先ほど入力した受取用ウォレットアドレス)に送信されます。売り手がビットコインをリリースすると取引ステータスが「Released(解放済み)」に変わり、まもなくブロックチェーン上で買い手のウォレットにビットコイン着金が確認できるでしょう。
-
取引完了: ビットコインが無事自分のウォレットに届けば取引完了です。取引ページには「Completed(完了)」などのステータスが表示され、双方がお互いを評価できるようになります。初めてのP2P購入、お疲れさまでした! 🎉
💡 重要な注意事項(買い手向け): エスクローにビットコインがロックされる前に代金を支払ってはいけません。必ず取引ステータスが「Deposited」や「In progress」になるのを確認してから支払いを実行してください。また、取引には売り手が入金を確認してからビットコインをリリースするまでの制限時間(Payment window)が設定されています。時間内に支払いが完了しないと取引が自動キャンセルされる場合がありますのでご注意ください。困ったことがあれば、取引ページのチャットで相手に連絡することもできます。万一、支払いを送ったのに売り手がビットコインをリリースしない場合は、支払い期限が過ぎてからディスピュート(紛争解決手続き) を開始することも可能です。
ビットコインを販売する方法(Sell BTC)
次に、HodlHodlでビットコインを販売(Sell) する手順を説明します。基本的な流れは購入時と似ていますが、立場が逆になる点(自分がビットコインをエスクローに預け、買い手からの支払いを待つ点)に注意してください。以下では、日本で銀行振込によりJPYを受け取ってビットコインを売る場合を例に解説します。
-
「Sell BTC」をクリックする: HodlHodlにログイン後、画面上部左側の「Sell BTC」ボタンをクリックします。これで現在出ているビットコイン買い注文(買い手のオファー)一覧ページに移動します。
-
検索フィルターの設定: 買い手オファー一覧から、自分が対応可能な条件のオファーを探します。フィルター項目はBuyの場合と同様で、国、通貨、支払いタイプ、支払い方法、金額などを指定できます。日本円での銀行振込を希望する買い手を探す場合、国をJapan、通貨をJPY、支払い方法をBank Transferに設定して検索します。
-
オファーを選ぶ: 条件に合致する買い手のオファーが一覧表示されるので、希望に合うものをクリックします。各オファーには買い手が希望するレートや取引限度額、支払い方法、買い手の評価などが記載されています。有利なレートかつ信頼できそうな相手を選びましょう。初取引で不安な場合は、小額で高評価の買い手から始めるとよいです。
-
売却量と受取情報の入力: オファー詳細画面で、売却したいビットコイン量を入力します(または必要な法定通貨額)。オファーごとに最低・最大額が設定されているので範囲内で入力してください。続いてビットコインの受取アドレス欄がありますが、これは取引完了時に買い手がビットコインを受け取るアドレスです。売り手である自分が入力する必要は基本的になく、買い手側が受取先を指定するか、既に買い手のダッシュボード設定で決まっています。次に、受け取りたい支払い方法が複数記載されている場合は希望の方法を選択します(例えば「Bank Transfer」の中でも特定の銀行名など)。コメント欄があれば取引相手(買い手)へのメッセージを任意で入力します。内容を確認し問題なければ 「Create contract(契約作成)」 ボタンを押して取引を開始します。
-
エスクローアドレスの生成: 契約が作成されると、エスクロー用のビットコインアドレスを生成する段階に進みます。ここで 「Generate escrow」 ボタンをクリックし、ペイメントパスワードを入力します(買い手の手順と同様)。これにより、この取引専用のマルチシグエスクローアドレスが発行されます。次に 自分(売り手)が売却予定のビットコインをエスクローアドレスに送金 します。取引画面上に正確なBTC額と対応するQRコードが表示されるので、自分のウォレットからそのアドレスへ送金してください。送金したら 「I’ve sent the funds(送金完了)」 ボタンを押してビットコインをエスクローに預けたことを通知します。

-
エスクローへのビットコインロック: ビットコインを送金するとブロックチェーン上で一定回数の承認(Confirmations)を経て、エスクローにロックされます。取引ステータスが「In progress(進行中)」や「Deposited」に変わり、買い手は安心して支払いを行える状態になります。あとは買い手からの法定通貨支払いを待ちます。取引画面で支払い期限(Payment window)内に買い手が支払いを完了し、「支払い送信済み」のボタンを押すとステータスが「Paid(支払い済み)」に変わります。
-
支払いの受領確認: ステータスが「Paid」になったら、買い手が送金を完了したことを意味します。すぐに自分の銀行口座など該当の支払い方法で入金を確認しましょう。金額が全額正しく受け取れたことを確認できたら、取引ページ上で 「Release deposit(デポジットを解放)」 ボタンをクリックし、ペイメントパスワードを入力してエスクローのビットコインを開放します。これにより、エスクローにロックされていたビットコインが買い手に送付されます。
-
取引完了: ビットコインをリリースすれば取引完了。ステータスが「Completed」に変わり、買い手は間もなく自分のウォレットでビットコインを受け取るでしょう。最後にお互いを評価して取引終了となります。初めてのP2P売却、お疲れさまでした! 🎉
💡 重要な注意事項(売り手向け): 支払いを受け取る前にビットコインをエスクローから**絶対にリリースしないでください。買い手からの入金を自分の銀行口座等で確実に確認できてから、ビットコインを解放するようにしましょう。また、もしビットコインをエスクローに送金した後で買い手から支払いが行われず期限切れ(Payment window経過)になった場合、取引をキャンセルしてエスクローのビットコインを自分に返還することができます。取引中は常に取引相手とのチャットで連絡を取り合い、不明点を確認するよう心がけましょう。
HodlHodlの安全性:マルチシグと非カストディアル設計
● マルチシグエスクローによる資金保護: HodlHodl最大の特徴は、2-of-3のマルチシグエスクロー(multisignature escrow)によって取引資金を保護している点です。取引が成立すると、自動的に3つの秘密鍵が関与するビットコインアドレスが生成されます。この3つの鍵のうち2つの署名があれば資金を動かせる仕組みになっており、鍵の配分は「売り手」「買い手」「HodlHodl運営」の三者にそれぞれ1つです。取引中、ビットコインはブロックチェーン上のエスクローアドレスにロックされ、双方の合意なしには動かせまん。つまり、売り手は買い手の同意なしにビットコインを引き出すことはできず、逆に買い手も売り手の協力なしにビットコインを入手することはできません。両者が取引を完了すれば売り手+買い手の2署名でリリースが可能となり、万一トラブルが起きた場合にはHodlHodl運営が仲裁役として(買い手または売り手の一方と協力し)2署名目を提供することで不正を防ぎます。このようにマルチシグ契約によって、詐欺や持ち逃げのリスクを最小限に抑え、安全かつ公平な取引が実現されています。
● 非カストディアル(ユーザー主導の資金管理): HodlHodlは取引プラットフォームでありながら、ユーザー資金を一切預からないという非カストディアル設計を貫いています。取引中のビットコインは常にマルチシグエスクローにあり、HodlHodl運営が単独で動かすことはできません。これはつまり、中央集権的な取引所とは異なり、HodlHodlがハッキング被害に遭ってもユーザーのビットコインが盗まれる心配がないことを意味します。またプラットフォームが万一ダウンしたりサービス提供を停止した場合でも、当事者間で2つの鍵さえあればエスクローのビットコインを取り戻すことが可能です(※この場合やや技術的な手順が必要になりますが、HodlHodlが完全に消失するケースでも資金はブロックチェーン上に安全に存在し続けます)。HodlHodl運営は3つの鍵のうち1つを保有するのみで、しかもそれは紛争時の仲裁に使うためのものです。通常の取引では運営が介在することなく、ユーザー同士で完結します。以上のように、HodlHodlはカストディアルな第三者を排除し、利用者自身が資金と取引の主導権を握るというビットコイン本来の精神に沿った安全設計となっています。
● 評判システムと取引履歴: HodlHodlでは、各ユーザーに公開の評価(Rating)と取引履歴が紐づいています。取引を完了するごとに互いにレビューを残せるため、他ユーザーの信頼度を事前に知ることができます。初めて取引する相手がどんな評価を受けているか、過去の取引回数や成功率などの情報を確認することで、怪しい相手を避けることが可能です。特に初心者のうちは評価の高い相手を選ぶ、もしくは身近に信頼できるユーザーがいればトラスト機能(他のP2Pプラットフォームでの実績を証明する仕組みや信用できるユーザーをお気に入り登録する機能)を活用すると良いでしょう。
● 二要素認証(2FA)と信頼できる端末: アカウントの不正アクセス対策として、HodlHodlは二段階認証(2FA)のオプションを提供しています。AuthyやGoogle Authenticatorと連携し、一度設定すればログイン時にパスワードに加え6桁のコード入力が求められるようになります。これにより、万一パスワードが漏洩しても本人のデバイスがなければログインできず、アカウントを保護できます。またTrusted Devices(信頼できる端末)機能を有効にすると、新しいデバイスからログインしようとした際にメール確認が必要となり、ユーザーの許可なく不審な端末からアクセスされるのを防ぎます。初心者の方でも、アカウント登録後は設定画面から2FAや信頼できる端末機能を有効化しておくことを強くおすすめします。
● ディスピュート(紛争解決)機能: 万が一取引相手との間でトラブルが発生した場合(例:買い手は支払ったと主張しているが売り手が確認できない等)、HodlHodlのプラットフォーム上でディスピュート(紛争)を開始することができます。ディスピュートが発生すると、HodlHodlのサポートチームが両者から事情を聞き、中立的な立場で問題解決に当たります。必要に応じて前述の運営のマルチシグ鍵を用いて適切な側にビットコインをリリースするなど、公平な裁定が行われます。ディスピュートは最終手段ではありますが、万一の場合の安心材料として覚えておいてください。
以上のように、HodlHodlは技術的・制度的な多層防御によってユーザーの資金と取引の安全を確保しています。他のユーザーの評価を確認する、取引手順を順守する(エスクロー未成立での送禁止等、アカウントのセキュリティ設定を有効にするといったユーザー自身の注意もあわせて心掛ければ、P2P取引でも安心してビットコインを利用できるでしょう。
HodlHodlの特徴:他プラットフォームとの違い
最後に、HodlHodlが他のビットコイン取引サービスと比べて優れている点、特徴的な点を整理します。初めて利用する際の不安解消にもつながるポイントです。
-
🌐 KYC不要の匿名取引: HodlHodl最大の特徴は、本人確認(KYC)なしでビットコイン取引ができる点です。メールアドレスさえあれば世界中誰でも利用開始でき、パスポートや身分証の提出は一切求められません。これはプライバシー保護の面で大きな利点ですし、取引履歴が本人名義に紐付かないため将来的な資産没収や口座凍結のリスクも低減します。規制が厳しい地域のユーザーや銀行口座を持てない人々でも、HodlHodlならビットコイン経済に参加しやすくなっています。
-
🔐 ユーザーが鍵を管理する非中央集権型取引: 前述の通り、HodlHodlはノンカストディアルなP2P取引所であり、ユーザー自身が資産の鍵を管理します。取引ごとにマルチシグのエスクローが生成され、利用者はその一方の鍵を保持します。そのため「取引所にビットコインを預けっぱなしにしていたらハッキングで失った」といった事態が起こりません。常に自身のウォレットから直接取引を行うため、ビットコインの自主管理の原則**が守られています。中央集権的な管理者がいない分、自分で秘密鍵を安全に保管する責任は伴いますが、その分だけ第三者リスクが排除された公平な環境と言えます。
-
💱 世界中の通貨と多様な決済方法に対応: HodlHodlはグローバルなプラットフォームであり、世界中のあらゆる法定通貨 で取引できます。現在100を超える国の通貨と地域が利用されており、取引に使える決済方法も100種類以上と非常に豊富です。銀行振込やオンライン決済サービスはもちろん、現金の対面受け渡しやギフトカード、電子マネー、モバイル送金、さらには商品と交換などユニークな方法までユーザーが自由にオファーを作成できます。これにより、自分の利用しやすい手段で取引相手を見つけられる柔軟性があります。他のプラットフォームだと対応通貨や決済手段が限定されがちですが、HodlHodlでは*「自分の条件でオファーを作成できる」 の強みです。
-
💰 低い手数料と透明な料金体系: HodlHodlの取引手数料は一律0.5%(買い手と売り手で折半で各0.25%ずつ負担)と比較的低コストです。しかも手数料は取引成立時にビットコイン額から自動控除される仕組みで、隠れたコストがありません。さらに紹介プログラムを利用すると0.45%に割引されるなどの優遇もあります。入出金に伴う手数料も基本的に存在せず、各自が使うウォレットの送金手数料以外に余計な負担はありません。他の取引所でありがちな「出金手数料が高額」「スプレッドが不透明」といった心配もなく、明朗会計でユーザーに優しい料金体系です。
-
🤝 初心者に優しいインターフェース: P2P取引というと難しそうな印象を持たれるかもしれませんが、HodlHodlのサイトはシンプルで直感的なインターフェースになっています。必要な操作は「Buy BTC / Sell BTC」ボタンから進んでフォームに入力していくだけで、画面の指示に沿って進めれば迷うことは少ないでしょう。サイトは現在ウェブブラウザ経由で利用しますが、スマートフォンのブラウザからでも見やすく設計されています。専用アプリはありませんが、その分アップデート時にもすぐ全員が最新機能を利用できます(ダウンロード不要で常に最新版が提供されるメリットです。また、取引画面にはリアルタイムのチャット機能があり、相手ユーザーと直接コミュニケーションを取れるため安心です。困ったときは相手に質問したり状況を確認できるので、言葉の壁がある場合でも定型文や翻訳を活用して意思疎通できます。
-
🛠 API提供による拡張性: HodlHodlは上級ユーザーや開発者向けに**公式APIを提供しています。APIを利用すると、自分のプログラムからHodlHodl上のオファー取得や契約作成、ステータス更新などを自動化することが可能です。例えば、マーケットメーカーとしてレートを自動調整したり、他のサービスと連携して複数のP2P取引所のオファーを比較表示する、といった応用ができます。APIキーはプロフィール設定から発行でき、ドキュメントも公開されているため高度な取引戦略を実装したいユーザーには魅力的な機能です。PaxfulやLocalBitcoinsなど一部他サービスでもAPIは提供されていますが、HodlHodlのAPIはエスクロー操作まで含め包括的にサポートしている点で強力です。
-
💳 ビットコインレンディングサービス: HodlHodlは現物取引だけでなく、ビットコイン担保のレンディング(貸借)プラットフォームも運営しています。サイト上部の「P2P Lending(レンディング)」からアクセスでき、ビットコインを担保にUSDTなど他の暗号資産を借りたり、あるいは逆に他の人に貸し出して利息収入を得ることができます。技術的には取引プラットフォームと同じマルチシグエスクロー方式を用いており、借り手がビットコインを担保としてエスクローにロックし、貸し手が安定通貨を送金することでローン契約が成立します。期間満了時に借り手が返済すればビットコイン担保が戻り、返済不能(延滞や価格変動での清算)の場合は貸し手に担保が渡る仕組みです。驚くべきことに、このレンディングサービスでも一切KYCは要求されません。短期のビットコイン活用や利息収入を得たいニーズに応えるユニークなサービスであり、HodlHodlを使いこなせば「ビットコインを売買するだけでなく、借りたり貸したりする」といった金融活用も可能になります。P2P Lendingについては、今後別のチュートリアルで詳しく説明します。
-
🧪 テストネットで練習可能: 「いきなり本番は不安…」という方向けに、HodlHodlはテストネット版サイトも提供しています。TESTNETでは、本物のビットコインではなくテスト用のビットコイン(signet**ネットワークのBTC)を使って、実際の取引手順を練習できます。架空の資金でHodlHodlの操作感を試せるため、初心者はまずテストネットで売買の流れをシミュレーションしてみると良いでしょう。十分に慣れてから本番取引に移行すれば、落ち着いて対処できます。テストネットBTCは各種ファウンセット(蛇口サイト hhtestnet.com)から無料でもらうことができ、HodlHodlのテスト環境で練習するのに役立ちます。
以上がHodlHodlの主な特徴と利点です。匿名性・安全性・使いやすさを兼ね備えたHodlHodlは、まさに「ビットコインをネイティブにP2P利用する」ための理想的なプラットフォームと言えるでしょう。初めは不安もあるかもしれませんが、本チュートリアルで説明した手順に沿って取引を行えば、きっとその手軽さと利便性に驚くはずです。ぜひHodlHodlでのP2P取引に挑戦してみてください。自分自身でビットコインを扱う経験を通じて、ビットコインの真の価値である「個人が金融の主導権を握ること」を実感できるでしょう🚀
もしビットコインのP2P取引やHodlHodlなどについてもっと深く知りたい、あるいは個別に相談してみたいと思えば、どうぞお気軽にご連絡ください。1対1のコンサルも承っています。
サービスには決まった料金はありませんが、ご相談を通じて「役に立った」と思い、お悩みや疑問を解決できたと感じていただけたら、「3つのT」でのご支援(Value for Value)をぜひご検討ください:
- 時間(Time):この記事をSNSなどでシェアしていただくこと。
- 才能(Talent):コメントや補足情報などを通じて知識を共有していただくこと。
- 宝(Treasure):世界で最も健全なお金、ビットコインの最小単位「sats」でのご支援。
もちろん、支援の有無にかかわらず、お力になれればとても嬉しいです。 では、また次回!
参考資料
- Bitcoin Whitepaper - Bitcoin: A Peer-to-Peer Electronic
- HodlHodl公式サイト - Welcome to Hodl ([P2P BITCOIN TRADING platform]
- HodlHodlヘルプセンター - How to buy Bitcoin / How to sell Bitcoin
- HodlHodlヘルプセンター - Why is trading on Hodl Hodl secure
- HodlHodl FAQ - Why should I use HodlHodl、How secure is trading on HodlHodl
- HodlHodl Medium - Hodl Hodl’s API release
- HodlHodl Lend FAQ - What is Lend a ([Earn Highest Returns on Your Crypto Investment - Lend at Hodl Hodl]
- ZoneBitcoin - Hodl Hodl: Tutorial on the anonymous and KYC-free P2P platform
- など
-
-
 @ 83279ad2:bd49240d
2025-03-29 15:28:45
@ 83279ad2:bd49240d
2025-03-29 15:28:45test
-
 @ 30b99916:3cc6e3fe
2025-03-29 14:12:37
@ 30b99916:3cc6e3fe
2025-03-29 14:12:37Chef's Notes
My mom worked as a waitress for a excellent Chinese restaurant. For years she tried to get this receipt without success and finally after the owner retired he gave her the receipt.
Previously posted this receipt on Zap.Cooking but now wanting to keep all my long-form notes in Obsidian and publish to Nostr using the nostr-writer plug-in.
Details
- ⏲️ Prep time: 20 to 30 minutes
- 🍳 Cook time: 1 to 2 Hours depending on amount of spare ribs
- 🍽️ Servings: 8
Ingredients
- 1 Quart Dole Pineapple Juice
- 1 Pint Dole Crushed Pineapple
- 1 Pint Dole Tidbits Pineapple
- 1 TS Dried Mustard
- 32 Oz Brown sugar or add to taste
- 1 Cup Red Wine
- 2 TS Corn Starch
- 1 or 2 lbs Pork or Beef spare ribs
- Worcestershire sauce
Directions
- Preheat oven to 350 degrees
- Bring water to boil in 8 qt stock pot
- Cut spare ribs and add to boiling water in stock pot
- Boil spare ribs for 20 to 30 minutes to remove excess fat
- Drain spare ribs and place onto cookie sheet
- Base spare ribs with a generous amount of Worcestershire sauce
- Place based spare ribs on cookie sheet and place into oven for 60 minutes.
- Place first 6 ingredients into stock pot and bring to boil while CONTINUOUSLY stirring
- Add corn starch to 2 cups of water and mix to create thickening agent
- Add thickening agent incrementally to Sweet & Sour sauce for desired thickness
- Reduce heat to low while CONTINUOUSLY stirring.
- Remove spare ribs from oven and place into Sweet & Sour sauce.
- Place stock pot into oven and cook until done. 1 to 2 hours.
Bon Appétit
-
 @ 129f5189:3a441803
2024-09-09 23:23:45
@ 129f5189:3a441803
2024-09-09 23:23:45Project 2025, outlined in the "Mandate for Leadership" document by the Heritage Foundation, is a crucial guide for the next Republican administration. Crafted by conservative intellectuals from major American think tanks, this plan promises to have significant influence on a potential Donald Trump administration, even if he does not formally acknowledge it as his government plan. https://image.nostr.build/443d69c16dc32659be2353ce48d170d397e0ee682ffc3c4108df3047fd54472d.jpg This document presents proposals to depoliticize government agencies, increase efficiency, and reduce costs, aiming to dismantle the Deep State and combat the Woke agenda associated with the Democratic Party. https://image.nostr.build/06de3f0de3d48e086f47d0418d30e32cbfe0d88f452a93706987b7394458952d.jpg Dissolution of the DHS and Redistribution of Functions The Department of Homeland Security (DHS) was established in 2002 in response to the September 11 attacks, with the goal of consolidating various agencies responsible for domestic security under a single command. The DHS includes agencies such as FEMA, TSA, ICE, and CISA. Project 2025's proposal to dissolve the DHS and redistribute its functions to other agencies aims to address excessive bureaucracy and a lack of cohesion, arguing that centralization has failed to effectively integrate its diverse missions. https://image.nostr.build/ffca8d274914b725183b8fb19162c1b63f4d987c24e598f2eca88901d4a1a43c.jpg Impact on the Democratic Deep State: The dissolution of the DHS would pose a significant threat to the Democratic Deep State, as it would redistribute the power concentrated in a single entity across multiple other agencies, making it more difficult to politicize and centralize control over domestic security operations. This decentralization would reduce the ability to use the DHS as a political tool against opponents. https://image.nostr.build/1597e3b88572fe8aae7ce67cdaf975a873cf8bc68f76d59cb4253ad1520fc7bc.jpg Primary Recommendations Combining Immigration Agencies: Merge U.S. Customs and Border Protection (CBP), Immigration and Customs Enforcement (ICE), U.S. Citizenship and Immigration Services (USCIS), the Office of Refugee Resettlement (ORR) of the Department of Health and Human Services (HHS), and the Executive Office for Immigration Review (EOIR) of the Department of Justice (DOJ) into a new autonomous border and immigration agency. https://image.nostr.build/58eef4f2eca0ed2400261ec878c1dba2ca4bca519a16751b1fb7abd45da2906b.jpg Privatization of the TSA: Privatize the Transportation Security Administration (TSA), drawing inspiration from Canadian and European models, to reduce costs and improve service for travelers. Division of the Secret Service (USSS): The U.S. Secret Service (USSS), responsible for protecting national leaders and investigating financial crimes, would be divided. The protective element would be transferred to the Department of Justice (DOJ), while the financial investigations element would be moved to the Department of the Treasury. https://image.nostr.build/0a065cdbf158db4bc17b9aacd4af5a94029004caaa152eebf2c557042b08a641.jpg Impact on the Democratic Deep State: The division of the USSS would significantly weaken centralized control over protection and financial investigations, making it more difficult to use these functions for political purposes. Transferring the protective element to the DOJ and the financial investigations element to the Treasury would complicate efforts for any group or party to manipulate these crucial government functions for partisan objectives. https://image.nostr.build/1597e3b88572fe8aae7ce67cdaf975a873cf8bc68f76d59cb4253ad1520fc7bc.jpg Cybersecurity and Infrastructure Security Agency (CISA) Established in 2018, CISA is a federal agency responsible for protecting the U.S. critical infrastructure from cyber threats. CISA's mandate includes ensuring cybersecurity for sectors such as energy, transportation, and healthcare, and it collaborates with public and private entities to strengthen the country’s cyber resilience. Criticisms and Restructuring Proposals: Project 2025 strongly criticizes CISA for deviating from its original mission and being used as a political tool for censoring speech and influencing elections. The proposal is to transfer CISA to the Department of Transportation (DOT) and return the agency to its statutory focus. https://image.nostr.build/8bfb4a45053de96a775f67e3e1b83a44d9a65fee4705e3b16d3359bd799b8af2.jpg Review of Executive Order 12333 Executive Order 12333, issued in 1981, sets guidelines for U.S. intelligence activities, including the collection, analysis, and dissemination of information. Project 2025 proposes a review of this order to ensure that intelligence agencies are not used for political purposes but are focused on protecting national security. Objectives of the Review: Prevent Abuse: Ensure that intelligence collection is conducted legally, without being used to target political opponents. Ensure Impartiality: Reaffirm that intelligence operations must be conducted impartially, with a sole focus on the country's security. https://image.nostr.build/90d31cb35a33048d311716df2fbc65c97bd4c1972977e266133654404393fca0.jpg Reforms in Public Service Facilitation of Public Employee Dismissal: Project 2025 emphasizes the need to simplify the process for dismissing public employees who do not perform their duties impartially or who promote specific political agendas. Performance Evaluations: The document highlights the importance of merit-based compensation, stating that performance evaluations are only effective when tied to real consequences. Research indicates that 90% of major private companies in the U.S. use a merit-based pay system linked to evaluations. However, in the federal government, compensation remains largely based on seniority, despite efforts to adopt merit-based pay. https://image.nostr.build/1b858fd7b2a23c3c65c0677d3e69c44976721bbdcbe7facf4682ba3371562cff.jpg Inclusion of Employees Aligned with Conservative Values: Aligned Hiring: Establish mechanisms to hire public employees who share conservative values, ensuring that the policies and practices of agencies are consistent with the principles endorsed by the administration. https://image.nostr.build/ddbf5c59e7bb479998433991347f9d301dd117fbca0edb0f94e98fcac90b2974.jpg Controversial Cases and Politicization: Hunter Biden Laptop Case: Project 2025 harshly criticizes the FBI and the Department of Justice, accusing them of acting in a biased and politically motivated manner. The authors suggest that the agency is intimidating parents who protest by labeling them as "domestic terrorists," while simultaneously suppressing politically unfavorable speech under the guise of combating "disinformation." Furthermore, the critique highlights that the FBI is alleged to be neglecting violent attacks on pregnancy centers and violations of laws prohibiting attempts to intimidate Supreme Court justices. The criticism intensifies with allegations that the FBI interfered in domestic elections and engaged in propaganda operations, specifically citing the purported Russian collusion conspiracy in 2016 and the suppression of the Hunter Biden laptop case in 2020, which is seen as a threat to the Republic. https://image.nostr.build/e4f571a14102a939164465498bef514379ec0443e71a58e12f50c518e00570c6.jpg Politicization of the FBI: Election Interference: Russia Hoax and Trump, Suppression of Hunter Biden’s Laptop, and Big Tech Collusion. Revelations about the FBI’s role in the 2016 "Russia Hoax" and the suppression of Hunter Biden’s laptop in 2020 suggest that the agency may have strayed from its impartial duties. These actions indicate concerning politicization, where the agency appears to have been used to influence the political landscape in favor of certain interests. This includes collaboration between the FBI and Big Tech companies to control discourse. https://image.nostr.build/5dcd45fcec939b782d29d8d2e3d3b45244c525b5dbd3240f1629a4632e390a86.jpg Comprehensive Review of FBI Investigations: It is crucial to conduct an immediate and thorough review of all significant investigations and activities within the FBI, terminating those that are illegal or contrary to national interests. This step is essential for restoring public trust in the FBI. A public report on the findings of this review could enhance transparency and confidence. https://image.nostr.build/df98e2c6aff123d806187eab13d24a3ebb30a87df1f44cf57be97dc5624fff88.jpg Structural Reorganization: Align the FBI within the Department of Justice (DOJ) according to its purposes of national security and law enforcement. The agency should be under the supervision of the Assistant Attorney General for the Criminal Division and the National Security Division, ensuring that the FBI does not operate as an independent entity but is instead subordinated to the DOJ’s directives. https://image.nostr.build/0d1c0015c6b67a8afc2dd1595357ea571fcd5a9d83829065f49f9b60cf553eb0.jpg Prohibition on Policing Speech: Prohibit the FBI from engaging in activities related to combating "disinformation" or "misinformation" disseminated by Americans who are not linked to plausible criminal activities. The Constitution, through the First Amendment, prohibits the government from policing speech, ensuring a healthy public debate without governmental intervention. All these measures represent a significant attack on the "Deep State" within American institutions. These public policies have been considered a dictatorial threat by many sectors of the American press. However, the real issue should be the politicization of unelected bureaucrats by a political faction. https://image.nostr.build/9a44b19d15d53314f89528c1d89e2f637030ea18d8907a6a8c4e27d07064b8ec.jpg Combating Woke Culture in the Intelligence Community Future leadership of the Intelligence Community (IC) needs to implement a plan to replace the "woke" culture and identity politics that have spread throughout the federal government. The goal is to restore traditional American values such as patriotism, racial impartiality, and job competence, which have been replaced by advocacy for "social justice" and identity politics. https://image.nostr.build/7929dca5e36273c8e751f36d6ca6229f362e30792bce735f10be7e5d8581af5f.jpg Final Considerations The Heritage Foundation’s Project 2025 is not merely an administrative reform plan; it is a manifesto of resistance against the Washington status quo. The proposals aim to dismantle established power structures, eliminate politicization, and combat the Woke agenda. If implemented, this plan would profoundly impact how the U.S. government operates, promoting a more efficient, limited government aligned with conservative principles. Threat to the Democratic Deep State: A potential new administration under Donald Trump represents an existential threat to the Democratic Deep State entrenched in American institutions. The dissolution of the DHS, depoliticization of intelligence agencies, division of the Secret Service, review of Executive Order 12333, privatization of the TSA, and the hiring of employees aligned with conservative values are all measures that would significantly weaken centralized control and the ability to use these institutions for political purposes. By dismantling concentrated power and promoting a more transparent and accountable government, Project 2025 aims to restore public trust and ensure that government agencies serve national interests rather than partisan ones. Of course, not all aspects of the plan may be implemented, but the prospect of several of these measures being enacted should be a cause for concern for the Democratic Deep State.
-
 @ 30b99916:3cc6e3fe
2025-03-29 14:04:34
@ 30b99916:3cc6e3fe
2025-03-29 14:04:34
Chef's Notes
My mom worked as a waitress for a excellent Chinese restaurant. For years she tried to get this receipt without success and finally after the owner retired he gave her the receipt.
Previously posted this receipt on Zap.Cooking but now wanting to keep all my long-form notes in Obsidian and publish to Nostr using the nostr-writer plug-in.
Details
- ⏲️ Prep time: 20 to 30 minutes
- 🍳 Cook time: 1 to 2 Hours depending on amount of spare ribs
- 🍽️ Servings: 8
Ingredients
- 1 Quart Dole Pineapple Juice
- 1 Pint Dole Crushed Pineapple
- 1 Pint Dole Tidbits Pineapple
- 1 TS Dried Mustard
- 32 Oz Brown sugar or add to taste
- 1 Cup Red Wine
- 2 TS Corn Starch
- 1 or 2 lbs Pork or Beef spare ribs
- Worcestershire sauce
Directions
- Preheat oven to 350 degrees
- Bring water to boil in 8 qt stock pot
- Cut spare ribs and add to boiling water in stock pot
- Boil spare ribs for 20 to 30 minutes to remove excess fat
- Drain spare ribs and place onto cookie sheet
- Base spare ribs with a generous amount of Worcestershire sauce
- Place based spare ribs on cookie sheet and place into oven for 60 minutes.
- Place first 6 ingredients into stock pot and bring to boil while CONTINUOUSLY stirring
- Add corn starch to 2 cups of water and mix to create thickening agent
- Add thickening agent incrementally to Sweet & Sour sauce for desired thickness
- Reduce heat to low while CONTINUOUSLY stirring.
- Remove spare ribs from oven and place into Sweet & Sour sauce.
- Place stock pot into oven and cook until done. 1 to 2 hours.
Bon Appétit
-
 @ 30b99916:3cc6e3fe
2025-03-29 13:57:26
@ 30b99916:3cc6e3fe
2025-03-29 13:57:26
Chef's Notes
My mom worked as a waitress for a excellent Chinese restaurant. For years she tried to get this receipt without success and finally after the owner retired he gave her the receipt.
Previously posted this receipt on Zap.Cooking but now wanting to keep all my long-form notes in Obsidian and publish to Nostr using the nostr-writer plug-in.
Details
- ⏲️ Prep time: 20 to 30 minutes
- 🍳 Cook time: 1 to 2 Hours depending on amount of spare ribs
- 🍽️ Servings: 8
Ingredients
- 1 Quart Dole Pineapple Juice
- 1 Pint Dole Crushed Pineapple
- 1 Pint Dole Tidbits Pineapple
- 1 TS Dried Mustard
- 32 Oz Brown sugar or add to taste
- 1 Cup Red Wine
- 2 TS Corn Starch
- 1 or 2 lbs Pork or Beef spare ribs
- Worcestershire sauce
Directions
- Preheat oven to 350 degrees
- Bring water to boil in 8 qt stock pot
- Cut spare ribs and add to boiling water in stock pot
- Boil spare ribs for 20 to 30 minutes to remove excess fat
- Drain spare ribs and place onto cookie sheet
- Base spare ribs with a generous amount of Worcestershire sauce
- Place based spare ribs on cookie sheet and place into oven for 60 minutes.
- Place first 6 ingredients into stock pot and bring to boil while CONTINUOUSLY stirring
- Add corn starch to 2 cups of water and mix to create thickening agent
- Add thickening agent incrementally to Sweet & Sour sauce for desired thickness
- Reduce heat to low while CONTINUOUSLY stirring.
- Remove spare ribs from oven and place into Sweet & Sour sauce.
- Place stock pot into oven and cook until done. 1 to 2 hours.
Bon Appétit
-
 @ 129f5189:3a441803
2024-09-09 23:18:44
@ 129f5189:3a441803
2024-09-09 23:18:44Today we will understand how Argentina, when under the control of the Foro de São Paulo, was an important asset for the Chinese Communist Party in South America and how Javier Milei is charting paths to change this scenario. The Chinese government has been making diplomatic overtures to areas near the polar regions as part of its maritime strategy. After a "strategic retreat," the Southern Hemisphere has assumed a new dimension for Chinese interests in South America. Beijing has been increasing its diplomatic engagement with countries in the region, especially Argentina in recent times, through a series of economic, sociocultural, and to a lesser extent, military agreements. This includes the delivery of vaccines and the intention to accelerate an investment plan worth $30 million. China has focused on several geopolitically sensitive projects in Argentina, all strategic: controlling air and maritime space and strategic facilities in territorial areas monitored by Beijing over Antarctica and the South Atlantic. However, doubts arise about China's intentions... https://image.nostr.build/f55fc5464d8d09cbbddd0fe803b264a5e885da387c2c6c1702f021875beb18c2.jpg For Xi Jinping's government, Argentina stands out for its strategic location, the influential posture of its leaders, and its alignment with China's economic and military power expansion. China has made significant investments and infrastructure initiatives in various Argentine regions. In addition to establishing a presence in the province of Neuquén, China has targeted the port city of Ushuaia in Tierra del Fuego, Antarctica, the South Atlantic islands, and the San Juan region near the Chilean border. A 2012 agreement between authorities in Argentina's Neuquén province and Beijing allowed the construction of a deep space tracking station near the Chilean border, which caught Washington's attention. https://image.nostr.build/a3fa7f2c7174ee9d90aaecd9eadb69a2ef82c04c94584165a213b29d2ae8a66e.jpg In 2014, through a bilateral agreement between the Chinese Lunar Exploration Program, represented by the Satellite Launch and Tracking Control General (CLTC) of the People's Liberation Army (PLA) and Argentina's National Commission on Space Activities (CONAE), the agreement identified the Argentine space station at Bajada del Agrio as the most favorable location for hosting a Chinese base in the Southern Hemisphere. The project became operational in 2017 on a 200-hectare area and represents the third in a global network and the first outside China. It features a 110-ton, 35-meter-diameter antenna for deep space exploration (telemetry and technology for "terrestrial tracking, command, and data acquisition"), with the CLTC having a special exploration license for a period of 50 years. https://image.nostr.build/0a469d8bab900c7cefa854594dfdb934febf2758e1a77c7639d394f14cd98491.jpg The 50-year contract grants the Chinese Communist Party (CCP) the ability to operate freely on Argentine soil. The facility, known as Espacio Lejano, set a precedent for a Chinese ground tracking station in Río Gallegos, on the southeastern coast of Argentina, which was formally announced in 2021. In 2016, a document issued by the U.S. State Council Information Office raised concerns among the U.S. government and European Union (EU) countries about the potential military and geopolitical uses of the base in the Southern Hemisphere and Antarctica. Another element fueling suspicion is the existence of "secret clauses" in a document signed by the General Directorate of Legal Advisory (DICOL) of Argentina’s Ministry of Foreign Affairs, International Trade, and Worship with the Chinese government. https://image.nostr.build/1733ba03475755ddf9be4eafc3e9eb838ba8f9fa6e783a4b060f12b89c3f4165.jpg Since the Espacio Lejano contract was signed, U.S. analysts and authorities have repeatedly expressed concern about China's growing collaboration with Argentina on security and surveillance issues. In 2023, a general from the U.S. Southern Command stated during a hearing of the House Armed Services Committee: "The PRC [People's Republic of China] has expanded its capacity to extract resources, establish ports, manipulate governments through predatory investment practices, and build potential dual-use space facilities." https://image.nostr.build/16bbdeae11247d47a97637402866a0414d235d41fe8039218e26c9d11392b487.jpg The shift in the Argentine government from a leftist spectrum, led by leaders of the São Paulo Forum, to a Milei administration, which has always advocated for libertarian and pro-Western rhetoric, has altered the dynamics of Chinese-Argentine relations in 2024. Milei assumed office on December 10, 2023, replacing the progressive president Alberto Fernández, who had strengthened ties with China and signed an agreement in 2022 to join the CCP’s Belt and Road Initiative. During his campaign, Milei did not hide his disdain for communist regimes and signaled his intention to move away from socialist policies in favor of a more libertarian direction. In the nearly seven months since taking office, Milei has implemented major economic reforms and streamlined the government. https://image.nostr.build/1d534b254529bf10834d81e2ae35ce2698eda2453d5e2b39d98fa50b45c00a59.jpg Other recent "positive indicators" suggest that the Milei administration is prioritizing defense relations with the United States over China, according to Leland Lazarus, Associate Director of National Security at the Jack D. Gordon Institute for Public Policy at Florida International University. "The fact is that, in just six months, he has already visited the United States several times. He has met with Secretary [Antony] Blinken, been to the White House... all of this is like absolute music to General Richardson's ears; to President [Joe] Biden's ears," Lazarus told Epoch Times. General Richardson visited Argentina in April, a trip that included the donation of a C-130H Hercules transport aircraft to the Argentine Air Force and a visit to a naval facility in Ushuaia, Tierra del Fuego, at the southern tip of the country. "We are committed to working closely with Argentina so that our collaborative security efforts benefit our citizens, our countries, and our hemisphere in enduring and positive ways," she said in a statement at the time. In Ushuaia, General Richardson met with local military personnel to discuss their role in "safeguarding vital maritime routes for global trade." https://image.nostr.build/f6d80fee8a7bba03bf11235d86c4f72435ae4be7d201dba81cc8598551e5ed24.jpg In a statement from the Argentine Ministry of Defense, Milei confirmed that General Richardson also reviewed the progress of an "integrated naval base" at the Ushuaia naval facility. Argentine officials said they also discussed "legislative modernization on defense issues." Under the previous administration, China had received preferential treatment. In June 2023, Tierra del Fuego Governor Gustavo Melella approved China's plans to build a "multi-use" port facility near the Strait of Magellan. The project was met with legislative backlash, as three national deputies and members of the Civic Coalition filed an official complaint against the governor's provincial decree to build the port with Beijing. The same group also accused Melella of compromising Argentina’s national security. No public records show that the project has progressed since then. https://image.nostr.build/3b2b57875dc7ac162ab2b198df238cb8479a7d0bbce32b4042e11063b5e2779b.jpg Argentina's desire for deeper security cooperation with Western partners was also evident in April when Argentine Defense Minister Luis Petri signed a historic agreement to purchase 24 F-16 fighter jets from Denmark. "Today we are concluding the most important military aviation acquisition since 1983," Petri said in an official statement. "Thanks to this investment in defense, I can proudly say that we are beginning to restore our air sovereignty and that our entire society is better protected against all the threats we face." https://image.nostr.build/8aa0a6261e61e35c888d022a537f03a0fb7a963a78bf2f1bec9bf0a242289dba.jpg The purchase occurred after several media reports in 2022 indicated that the previous Fernández administration was considering buying JF-17 fighter jets made in China and Pakistan. A former minister from ex-president Mauricio Macri's government, who requested anonymity, confirmed to Epoch Times that a deal to acquire JF-17 jets was being considered during the Fernández era. Chinese investment did not occur only in Argentina. According to a document from the U.S. House Foreign Affairs Committee: "From 2009 to 2019, China transferred a total of $634 million in significant military equipment to five South American countries—Argentina, Bolivia, Ecuador, Peru, and Venezuela. The governments of Venezuela, Ecuador, Bolivia, and Argentina purchased defense equipment from the PRC, cooperated in military exercises, and engaged in educational exchanges and training for their military personnel." https://image.nostr.build/ed6d8daeea418b7e233ef97c90dee5074be64bd572f1fd0a5452b5960617c9ca.jpg Access to space plays a crucial role in the CCP's strategic objectives. Thus, when reports emerged in early April that Milei's government wanted to inspect Espacio Lejano, experts suggested it supported his national security moves away from China. According to the Espacio Lejano contract, signed under Cristina Fernández de Kirchner's Peronist regime, CCP officials are not required to let anyone—including the Argentine president—enter the facility without prior notice. According to Article 3, the agreement stipulates that Argentine authorities cannot interfere with or interrupt the "normal activities" of the facility and must explore alternative options and provide an unspecified amount of notice before being granted access. China has maintained that Espacio Lejano is for deep space exploration, lunar missions, and communication with satellites already in orbit. However, there is deep skepticism that the claim of space exploration alone is highly unlikely. The big question is: what could this facility do in times of war? https://image.nostr.build/f46a2807c02c512e70b14981f07a7e669223a42f3907cbddec952d5b27da9895.jpg Neuquén is just one of 11 ground stations and space research facilities China has in Latin America and the Caribbean. This represents the largest concentration of space equipment China has outside its own country. According to data from the Gordon Institute, the Chinese Espacio Lejano station and the Río Gallegos facility provide an ideal surveillance position near the polar orbit. The polar orbit is useful for data collection, transmission, and tracking because it allows for observation of the entire planet from space. The resolution of communications is also improved due to the proximity of satellites in orbit to the Earth's surface. Additionally, it offers strategic advantages for any government involved in espionage. https://image.nostr.build/39215a4c9f84cbbaf517c4fda8a562bba9e0cd3af3d453a24d3a9b454c5d015d.jpg Regarding deeper security collaboration with the United States, the trend is that Milei’s government will do as much as possible without jeopardizing its contracts with China, which is currently Argentina's second-largest trading partner. However, if Argentina's defense cooperation with China cools, the communist regime might wait for another Argentine government to continue its expansion—a government that could be more favorable to the CCP's objectives. Everything will depend on the continued success of Javier Milei's economic miracle, ensuring his government is re-elected and he can appoint a successor, making it more challenging for China, and avoiding a situation similar to what occurred in Brazil starting in 2023. https://image.nostr.build/a5dd3e59a703c553be60534ac5a539b1e50496c71904d01b16471086e9843cd4.jpg
-
 @ 129f5189:3a441803
2024-09-09 23:11:19
@ 129f5189:3a441803
2024-09-09 23:11:19Precious metals have served as monetary backing for millennia, but this does not guarantee that gold is a safe investment or a good hedge against economic crises and monetary collapses. Since its last major rally in the 1980s, gold has been progressively demonetized. Those who acquired gold in the late 1980s will need to rely on a significant increase in demand or a supply shock for its price to rise by 561% and regain the purchasing power it had 40 years ago. https://image.nostr.build/dd5fec2b474ea34cd72ddf5781393b528e63a358d523c9428f3ba4649f4f42aa.jpg If you look at the purchasing power of $1 (green line), you'll see that the depreciation is even faster. This might create the impression that gold is a good store of value. But does the fact that something loses value more slowly amidst a general decline really make it a store of value? Unless the total demand for gold increases at the same rate as its supply has grown in recent years, the purchasing power of the metal is likely to decline. https://image.nostr.build/9f24f6cf37780fe851746057520064ed94acd96547be53bd341c9e15b8762773.jpg In other words, if you own an ounce of gold, that ounce will represent an increasingly smaller fraction of the total gold reserves, meaning you are being diluted. Additionally, one should also consider the cost and risk of storage, but that's another issue. If you don't want to compare the purchasing power of gold today with the 1980s, you can consider its value from 9 years ago. Between September 2011 and November 2015, the Fed printed approximately $2.8 trillion. This also provides a perspective on gold's depreciation relative to the significant monetary expansion during that period. https://image.nostr.build/822e0a861e16ca258e0427875a84b5c8e5420e51bcf65674b453b55ed78edefd.jpg In other words, the Fed expanded its monetary base by about 30% during that 4-year period. However, the price of an ounce of gold fell by 45% (from $1,900 to $1,057) over the same interval. A true store of value should protect against excessive money printing. In contrast, during that same period, Bitcoin appreciated by 8,500% (from $5 to $419). https://image.nostr.build/32a7ca39a6e69e2780f9ab49390c7b7380499fcfe54ae4ef693e6fc91686a41e.jpg Indeed, while it is interesting to note that this was the exact period when gold derivatives were launched on CME Group, it's important to remember that correlation does not imply causation. Many factors can influence the price of gold and Bitcoin, and establishing a direct causal relationship requires more detailed analysis. https://derivsource.com/2011/06/21/cme-group-announces-the-launch-of-three-new-short-term-gold-crude-oil-and-natural-gas-options-contracts/ In an asset where supply can only be physically verified, flooding the market with gold contracts could lead to significant issues. This might result in market manipulation, legal liabilities, fines, and potentially even imprisonment for those involved. Such actions can undermine the integrity of the market and lead to regulatory and legal consequences. https://www.cnbc.com/2018/11/06/ex-jp-morgan-trader-pleads-guilty-to-manipulating-metals-markets.html Over longer periods, gold has not functioned as a true "store of value" relative to the dollar for quite some time, despite recently returning to its price from 9 years ago. This suggests that, while gold may have periods of price recovery, it has struggled to maintain its value over extended horizons compared to fiat currencies. It's worth noting that before 1980, aluminum was valued higher than gold. This reflects how market dynamics and technological advancements can significantly impact the value of commodities over time. https://www.mgsrefining.com/blog/why-aluminum-is-no-longer-a-precious-metal/ While gold has been undergoing a gradual demonetization process since 1980, another asset appears to be experiencing the opposite—hyper-monetization. (See in red; don't be alarmed.) https://image.nostr.build/435a5369f778a7be727b50e4c6328cfc353240bf804e1ed69313b9a8e1233f7e.jpg With the advent of Bitcoin, you believe that gold will continue on the same path as silver since the end of the bimetallic standard in 1853: a prolonged process of demonetization, with increasing volatility and reduced liquidity. https://image.nostr.build/5b9c8bfdb09e51d639e380df160c98beb9ee1d917ea13d28ef67711cfa5f8086.jpg Since 1913, the dollar has lost 97% of its purchasing power. Over the same period, the gold supply has increased significantly. Since 1980, gold has lost about 82% of its purchasing power. Given that the dollar is used as the unit of account and gold's liquidity is measured in dollars, these changes reflect the complex interaction between the currency and the precious metal. The U.S. is by far the country with the largest gold reserves in the world and is also the fourth-largest miner of the metal. Additionally, the country controls and issues the currency that serves as the unit of account for gold and has the highest liquidity in global trade. Is gold easy to transport? Is it simple to verify its supply and authenticity? Is it practical to store? Is its industrial utility significant? Can it be disrupted? And what about the continuous increase in its supply? These are important questions to consider. In my humble opinion, it will not be the dollar or fiat currencies that will suffer the most from the existence of Bitcoin, but rather the market cap of gold. https://image.nostr.build/61dddefabc4b69f784631a3294bdd978e3411bba40fb52d585e13b48002389fe.jpg
-
 @ 5ffb8e1b:255b6735
2025-03-29 13:57:02
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
Eugene Gorbachenko
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
Siritravelsketch
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
BureuGewas
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-
 @ 592295cf:413a0db9
2025-03-29 10:59:52
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article nostr-quick-start-guide
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it.
Go to nstart.me and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump.
Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
Now select 5 clients
Coracle, Chachi, Olas, Nostur, Jumble
The first is Coracle
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
Let's try Chachi
Simpler than Coracle, it has a type login that says bunker. see if I can post
It worked, cool, I managed to post in a group.
Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something like that, but many start from the phone so maybe it's easy for them. I try to download it and see if it allows me to connect with a bunker.
Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
Ok then I saw that there was the qrcode image of the bunker for apps lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are Olas's lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on Olas, so it works, Expiration time is broken.
As for Nostur, I don't have an ios device so I'm going to another one.
Login with Jumble, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
Extensions nostr NIP-07
The true path is nip-07-browser-extensions | nostr.net
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
- Aka-profiles: Aka-profiles
Alby I don't know if it's a route to recommend
-
Blockcore Blockcore wallet
-
Nos2x Nos2x
-
Nos2xfox (fork for firefox) Nos2xfox
Nostore is (archived, read-only)
Another half hour to search all sites
Nostrapps
Here you can make paths
Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to Nostrapps and read:
Microbbloging: Primal
Streaming: Zap stream
Blogging: Yakihonne
Group chat: Chachi
Community: Flotilla
Tools: Form *
Discovery: Zapstore (even if it is not in this catrgory)
Direct Message: 0xchat
-
 @ d830ee7b:4e61cd62
2024-08-29 08:50:45
@ d830ee7b:4e61cd62
2024-08-29 08:50:45ในโลกที่ Bitcoin เติบโตอย่างก้าวกระโดด ความต้องการในการทำธุรกรรมที่รวดเร็ว ปลอดภัย และเป็นส่วนตัว ก็เพิ่มสูงขึ้นตามไปด้วย
Lightning Network ได้เข้ามาช่วยแก้ปัญหา Scalability ของ Bitcoin ได้ในระดับหนึ่ง แต่ก็ยังมีข้อจำกัด เช่น ความซับซ้อนในการใช้งาน และความจำเป็นในการบริหารจัดการสภาพคล่อง
ในปี 2023 Burak Keceli นักพัฒนา Bitcoin ผู้มากประสบการณ์ ได้เปิดตัว Ark Protocol ซึ่งเป็นเลเยอร์ 2 โปรโตคอล ที่เสนอแนวทางใหม่ในการทำธุรกรรม Bitcoin
โดย Ark มาพร้อมกับแนวคิดที่ล้ำสมัย และกลไกการทำงานที่แตกต่างไปจาก Lightning Network
บทความนี้จะพาพวกเราไปทำความรู้จักกับ Ark Protocol กันเบื้องต้น ตั้งแต่หลักการทำงานของเทคโนโลยีนี้ ข้อดี-ข้อเสีย การเปรียบเทียบกับ Lightning Network และเทคโนโลยีอื่นๆ ไปจนถึงอนาคตของ Ark ในฐานะเลเยอร์ 2 ทางเลือกใหม่
🤔 Ark Protocol คืออะไร?
Ark Protocol คือ เลเยอร์ 2 โปรโตคอล ที่สร้างขึ้นบนบล็อกเชน Bitcoin โดยมีเป้าหมายเพื่อเพิ่มความสามารถในการขยายขนาด (Scalability) ยกระดับความเป็นส่วนตัว (Privacy) และมอบประสบการณ์การใช้งานที่ราบรื่นยิ่งขึ้น
Ark ทำงานโดยใช้แนวคิด Virtual UTXO (vUTXO) และ Covenant ในการทำธุรกรรมนอกบล็อกเชน (Off-Chain)
โดยอ้างว่าสามารถทำธุรกรรมได้รวดเร็ว ราวกับส่งข้อความ ค่าธรรมเนียมต่ำจนแทบไม่รู้สึก และมีความเป็นส่วนตัวสูง ปกป้องข้อมูลธุรกรรมจากสายตาคนอื่น
📌 vUTXO เหรียญ Bitcoin ดิจิทัลในตู้นิรภัยลับ
ลองนึกภาพ vUTXO (Virtual UTXO) เป็นเหมือนเหรียญ Bitcoin ดิจิทัล ที่ถูกเก็บไว้ในตู้นิรภัยสุดไฮเทค
ตู้นิรภัยนี้ตั้งอยู่นอกบล็อกเชน Bitcoin ทำให้การเข้าถึง vUTXO เป็นไปอย่างรวดเร็ว และไม่ต้องผ่านกระบวนการตรวจสอบที่ยุ่งยาก เหมือนกับการหยิบเหรียญจากกระเป๋า แทนที่จะต้องไปรื้อค้นหาในกองสมบัติขนาดใหญ่
vUTXO คือหัวใจสำคัญของ Ark ที่ทำให้การทำธุรกรรมมีความรวดเร็ว และมีค่าธรรมเนียมต่ำ เนื่องจากธุรกรรม vUTXO เกิดขึ้นนอกบล็อกเชน Bitcoin จึงไม่ต้องรอการยืนยัน (Confirmation) จากเครือข่าย Bitcoin
📌 Covenant สัญญาพิทักษ์ความปลอดภัย
เพื่อให้มั่นใจว่า vUTXO จะถูกใช้จ่ายอย่างถูกต้อง Ark ใช้ Covenant ซึ่งเปรียบเสมือนสัญญาที่กำหนดเงื่อนไขการใช้จ่าย vUTXO ล่วงหน้า
Covenant เหล่านี้ถูกเก็บไว้ใน vUTXO Tree ซึ่งเป็นเสมือนผังข้อมูลของ vUTXO ที่ช่วยให้ Ark สามารถจัดการ vUTXO ได้อย่างมีประสิทธิภาพ
และช่วยปกป้องความเป็นส่วนตัวของผู้ใช้ เหมือนกับการมีระบบรักษาความปลอดภัยหลายชั้น ที่ทำให้มั่นใจได้ว่า มีเพียงเจ้าของที่แท้จริงเท่านั้น จึงจะสามารถเข้าถึง vUTXO ได้
📌 vUTXO Tree ผังข้อมูลของ vUTXO
vUTXO Tree คือโครงสร้างข้อมูลที่ใช้จัดเก็บ vUTXO โดยใช้ Covenant ในการกำหนดเงื่อนไขการใช้จ่าย และสามารถนำ vUTXO กลับมาใช้ใหม่ได้ (Recycle) ทำให้ลดการใช้พื้นที่บนบล็อกเชน และเพิ่มความเป็นส่วนตัว
vUTXO Tree ช่วยให้ Ark สามารถจัดการ vUTXO จำนวนมากได้อย่างมีประสิทธิภาพ และลดความซับซ้อนในการทำธุรกรรม
⭐ ASP ผู้พิทักษ์แห่งโลก Ark
Ark Service Provider (ASP) คือผู้ดูแลระบบ Ark ที่เปรียบเสมือนธนาคารที่เก็บรักษา Bitcoin ของผู้ใช้ และให้บริการ vUTXO ASP ทำหน้าที่ตรวจสอบธุรกรรม อัพเดต vUTXO Tree และดูแลความปลอดภัยของระบบ ASP เปรียบเสมือนผู้ดูแลตู้นิรภัย ที่คอยดูแล vUTXO ของผู้ใช้ และอำนวยความสะดวกในการทำธุรกรรม
🧡 3 ขั้นตอนง่ายๆ สู่ธุรกรรม Bitcoin
Ark Protocol เปรียบเสมือนโลกใบใหม่ที่ถูกสร้างขึ้นเพื่อให้การทำธุรกรรม Bitcoin เป็นเรื่องง่าย รวดเร็ว และปลอดภัยยิ่งขึ้น การเดินทางในโลก Ark นั้นไม่ซับซ้อนอย่างที่คิด เพียงแค่ 3 ขั้นตอนง่ายๆ คุณก็สามารถสัมผัสประสบการณ์การใช้ Bitcoin แบบเหนือชั้นได้
1. ก้าวแรกสู่โลก Ark โดยแลก Bitcoin เป็น vUTXO
การเข้าสู่โลก Ark เริ่มต้นจากการฝาก Bitcoin ของคุุณเข้าสู่ Ark Service Provider (ASP) เปรียบเสมือนการเดินเข้าธนาคารเพื่อแลกเงินสดเป็นเช็ค
ASP จะทำหน้าที่ดูแลรักษา Bitcoin ของคุุณอย่างปลอดภัย และมอบ vUTXO ให้เป็นเสมือนเช็คดิจิทัลที่คุุณสามารถใช้จ่ายในโลก Ark ได้
-
เลือก ASP / ก่อนอื่น คุุณต้องเลือก ASP ที่น่าเชื่อถือ โดยพิจารณาจากชื่อเสียง ค่าธรรมเนียม และบริการที่ ASP นั้นๆ มีให้บริการ
-
ฝาก Bitcoin / เมื่อเลือก ASP ได้แล้ว คุุณสามารถฝาก Bitcoin ไปยังที่อยู่ Bitcoin ของ ASP ที่คุุณเลือก
-
รับ vUTXO / เมื่อ ASP ได้รับ Bitcoin ของคุุณแล้ว ระบบจะทำการออก vUTXO ให้กับคุุณโดยอัตโนมัติ vUTXO นี้จะถูกเก็บไว้ใน vUTXO Tree ที่ ASP ดูแล มูลค่าของ vUTXO จะเท่ากับจำนวน Bitcoin ที่คุุณฝากเข้าไป
ตอนนี้คุุณพร้อมที่จะเริ่มต้นการเดินทางในโลก Ark แล้ว..
2. ธุรกรรมสายฟ้าแลบ ผ่านการส่ง vUTXO รวดเร็ว ปลอดภัย ไร้กังวล
vUTXO เปรียบเสมือนเช็คดิจิทัลที่ทำให้การทำธุรกรรม Bitcoin เป็นเรื่องง่าย รวดเร็ว และปลอดภัย
-
ส่ง vUTXO ง่ายๆ / เพียงแค่ระบุจำนวน vUTXO ที่ต้องการส่ง และที่อยู่ Ark ของผู้รับ ธุรกรรมของคุณจะถูกดำเนินการทันที โดยไม่ต้องรอการยืนยันจากบล็อกเชน Bitcoin
-
ค่าธรรมเนียมต่ำ / เนื่องจากธุรกรรม vUTXO เกิดขึ้นนอกบล็อกเชน Bitcoin จึงมีค่าธรรมเนียมที่ต่ำกว่าการทำธุรกรรมบนบล็อกเชน Bitcoin
-
ความเป็นส่วนตัว / ข้อมูลธุรกรรม vUTXO จะถูกเก็บไว้ใน vUTXO Tree ซึ่ง ASP เป็นผู้ดูแล จึงมีความเป็นส่วนตัวมากกว่าการทำธุรกรรมบนบล็อกเชน Bitcoin
3. กลับสู่โลก Bitcoin ด้วยการแลก vUTXO คืนเป็น Bitcoin
เมื่อคุุณต้องการนำ Bitcoin ออกจากโลก Ark เพื่อนำไปใช้จ่ายในโลกภายนอก คุุณสามารถแลก vUTXO คืนเป็น Bitcoin ได้ง่ายๆ
-
ส่งคำขอถอน / เพียงแค่ส่งคำขอถอน Bitcoin ไปยัง ASP พร้อมระบุจำนวน Bitcoin ที่ต้องการถอน และที่อยู่ Bitcoin ของคุุณ
-
ASP ตรวจสอบและดำเนินการ / ASP จะตรวจสอบความถูกต้องของคำขอ และยอดคงเหลือ vUTXO ของคุุณ ก่อนทำการโอน Bitcoin ไปยังที่อยู่ Bitcoin ของคุุณ
สรุป / การทำธุรกรรมในโลก Ark นั้นง่าย รวดเร็ว และปลอดภัย เพียงแค่ 3 ขั้นตอน คุุณก็สามารถสัมผัสประสบการณ์การใช้ Bitcoin ผ่าน Ark ได้
หมายเหตุ
จากการศึกษาในเอกสารของทางผู้พัฒนา พบข้อสังเกตว่า.. การเลือก ASP ที่น่าเชื่อถือเป็นสิ่งสำคัญ เพราะ ASP จะทำหน้าที่ดูแลรักษา Bitcoin ของคุุณ ดังนั้น ควรศึกษาข้อมูล และเลือก ASP ที่มีชื่อเสียง มีระบบรักษาความปลอดภัยที่ดี และมีค่าธรรมเนียมที่เหมาะสม
Ark vs. Lightning Network
แม้ Lightning Network จะเป็นเลเยอร์ 2 ที่ได้รับความนิยมอย่างมากในปัจจุบัน แต่ Ark ก็มีข้อได้เปรียบและข้อเสียที่แตกต่างกันออกไป ดังนี้..
1. ด้านความปลอดภัย - Ark พึ่งพา ASP ในการดูแล Bitcoin และ vUTXO ดังนั้น ความปลอดภัยของ Ark จึงขึ้นอยู่กับความน่าเชื่อถือของ ASP - Lightning Network ใช้ Multisig และ Hash Time Locked Contract (HTLC) ในการรักษาความปลอดภัย ซึ่งไม่ต้องพึ่งพาบุคคลที่สาม แต่ผู้ใช้ต้องรับผิดชอบในการจัดการช่องทาง และป้องกันการโจมตีต่างๆ ด้วยตนเอง
2.ความสามารถในการรองรับปริมาณธุรกรรม (Scalability) - Ark สามารถรองรับปริมาณธุรกรรมได้สูง เนื่องจากธุรกรรมเกิดขึ้นนอกบล็อกเชน Bitcoin - Lightning Network สามารถรองรับปริมาณธุรกรรมได้สูง แต่อาจยังมีข้อจำกัดอยู่บ้าง เนื่องจากต้องอาศัยการเปิด-ปิดช่องทาง และการบริหารจัดการสภาพคล่องที่จำเป็นต้องมีประสบการณ์และความชำนาญสูง
3.ความซับซ้อนในการพัฒนา - การพัฒนาแอปพลิเคชันบน Ark อาจมีความซับซ้อนน้อยกว่า Lightning Network เนื่องจากไม่ต้องจัดการกับช่องทาง และสภาพคล่อง - การพัฒนาแอปพลิเคชันบน Lightning Network มีความซับซ้อน เนื่องจากต้องเข้าใจ Multisig, HTLC และการจัดการช่องทาง
4. การกระจายอำนาจ - Ark มีการกระจายอำนาจน้อยกว่า Lightning Network เนื่องจากต้องพึ่งพา ASP - Lightning Network มีการกระจายอำนาจมากกว่า เนื่องจากผู้ใช้สามารถเชื่อมต่อกันเองได้โดยตรง โดยไม่ต้องผ่านตัวกลาง
5.ความพร้อมในการใช้งาน - Ark ยังอยู่ในช่วงเริ่มต้นของการพัฒนา และยังไม่มีการใช้งานอย่างแพร่หลาย - Lightning Network มีการใช้งานจริงแล้ว และมีแอปพลิเคชัน Wallet และบริการต่างๆ ที่รองรับ
6.ความยืดหยุ่นในการใช้งาน - Ark ออกแบบมาเพื่อการชำระเงิน และอาจไม่เหมาะกับการใช้งานอื่นๆ เช่น Smart Contract - Lightning Network สามารถนำไปประยุกต์ใช้ได้หลากหลาย เช่น Micropayment, Streaming Payment, และ Decentralized Finance (DeFi)
7. ต้นทุนในการใช้งาน - ค่าธรรมเนียมในการทำธุรกรรม Ark ขึ้นอยู่กับ ASP - ค่าธรรมเนียมในการทำธุรกรรม Lightning Network ขึ้นอยู่กับ Routing Fee และค่าธรรมเนียมในการเปิด-ปิดช่องทาง
8. ความเสถียรของระบบ - Ark ยังเป็นเทคโนโลยีใหม่ ความเสถียรของระบบยังอยู่ในช่วงการทดสอบ - Lightning Network มีการใช้งานจริงมาระยะหนึ่งแล้ว และมีความเสถียรในระดับหนึ่ง
9. การสนับสนุนจากชุมชน - Ark ยังมีชุมชนผู้ใช้งานและนักพัฒนาที่เล็กกว่า Lightning Network - Lightning Network มีชุมชนผู้ใช้งานและนักพัฒนาที่ใหญ่ และมีการพัฒนาอย่างต่อเนื่อง
https://i.nostr.build/gAhg5rQoYU3WmsGy.jpg
📌 Ark Labs ก้าวสู่พัฒนาการใหม่บน Bitcoin
ในเดือนมิถุนายน 2024 ทีมพัฒนา Ark ได้ประกาศก่อตั้งบริษัท Ark Labs อย่างเป็นทางการ ภายใต้การสนับสนุนของ Vulpem Ventures บริษัท Venture Capital ที่มุ่งเน้นการลงทุนในเทคโนโลยี Blockchain และ Cryptocurrency
การก่อตั้ง Ark Labs ถือเป็นก้าวสำคัญของ Ark Protocol ที่แสดงให้เห็นถึงความมุ่งมั่นในการพัฒนาเทคโนโลยี และผลักดันให้ Ark กลายเป็นเลเยอร์ 2 โซลูชัน ที่ได้รับการยอมรับ และใช้งานอย่างแพร่หลาย
📌 ภารกิจของ Ark Labs
Ark Labs มี 2 ภารกิจหลัก คือ
-
พัฒนา Ark Protocol แบบ Open Source Ark Labs มุ่งมั่นที่จะพัฒนา Ark Protocol ให้เป็น Open Source เพื่อให้ทุกคนสามารถเข้าถึง ใช้งาน และมีส่วนร่วมในการพัฒนาเทคโนโลยีได้
-
สร้างบริการสำหรับผู้ใช้ Ark Ark Labs มีแผนที่จะสร้างบริการต่างๆ ที่ใช้งาน Ark Protocol เช่น Wallet, Payment Gateway, และ API เพื่อให้ผู้ใช้สามารถเข้าถึง Ark ได้ง่าย และสะดวกยิ่งขึ้น
📌 Ark Labs: ทีมผู้เชี่ยวชาญ ขับเคลื่อนอนาคตของ Bitcoin
Ark Labs นำโดย Marco Argentieri ผู้มีประสบการณ์ในวงการ Blockchain และ Cryptocurrency มายาวนาน ทีมงานของ Ark Labs ประกอบด้วยนักพัฒนา Bitcoin ผู้มากประสบการณ์ นักออกแบบ และผู้เชี่ยวชาญด้านการตลาด
แผนงานในอนาคต แอปพลิเคชันแรก และการเติบโตของระบบนิเวศ
Ark Labs มีแผนที่จะเปิดตัวแอปพลิเคชันแรกที่ใช้ Ark Protocol ภายในปี 2024 โดยแอปพลิเคชันนี้จะเน้นไปที่การทำธุรกรรม Bitcoin ที่รวดเร็ว ปลอดภัย และเป็นส่วนตัว
นอกจากนี้ Ark Labs ยังมีแผนที่จะขยายระบบนิเวศของ Ark โดยการสร้างความร่วมมือกับ Wallet ผู้ให้บริการแลกเปลี่ยน (Exchange) และธุรกิจต่างๆ เพื่อเพิ่มการใช้งาน Ark ให้แพร่หลายมากยิ่งขึ้น
บทสรุป
Ark คืออนาคตของ Bitcoin หรือไม่?
Ark Protocol คือเลเยอร์ 2 ที่น่าจับตามอง มาพร้อมกับแนวคิดที่ล้ำสมัย และศักยภาพในการยกระดับ Bitcoin ไปอีกขั้น แม้จะยังอยู่ในช่วงเริ่มต้น แต่ Ark ก็นำเสนอทางเลือกที่น่าสนใจ
หมายเหตุ บทความนี้นำเสนอข้อมูล Ark Protocol โดยอิงจากข้อมูลที่เผยแพร่โดย Ark Labs และแหล่งข้อมูลอื่นๆ ผู้อ่านควรศึกษาข้อมูลเพิ่มเติม และทำการวิเคราะห์ด้วยตนเองก่อนตัดสินใจลงทุนในเทคโนโลยีใดๆ
อย่างไรก็ตาม.. ยังมีคำถามอีกมากมายที่น่าสนใจเกี่ยวกับ Ark Protocol เช่น..
- กลไกการฝาก Bitcoin เข้าสู่ระบบ
- รายละเอียดเกี่ยวกับค่าธรรมเนียม
- และความสามารถในการรองรับปริมาณธุรกรรม (Scalability) เมื่อเทียบกับ Lightning Network
ซึ่งเราจะมาหาคำตอบร่วมกันในเวที Advanced Stage วันที่ 14 กันยายน 2024 ในงาน #TBC2024
มาร่วมเจาะลึก Ark Protocol และสำรวจศักยภาพของเลเยอร์ 2 โซลูชันนี้ไปพร้อมๆ กันครับ!
ศึกษาเพิ่มเติม
- https://ark-protocol.org/
- https://arkdev.info/docs/learn/intro
- https://arklabs.to/
-
-
 @ 5b0183ab:a114563e
2024-08-29 03:34:51
@ 5b0183ab:a114563e
2024-08-29 03:34:51Chef's notes
Growing up there are a few staple foods that stick with you. For me, it was my Grandma Betty's Chicken Dijon. It was my birthday request every year and every time we cook it up it touches my heart. Grandma Betty passed away a 7 years ago. This dish is dedicated to her, directly from her recipe book.
Details
- ⏲️ Prep time: 10
- 🍳 Cook time: 35
Ingredients
- 4 Chicken Breasts
- 3 Tbsp Butter
- 2 Tbsp Flower
- 1/2 Cup Heavy Cream
- 3 Tbsp Dijon Mustard
- Tomato Wedges
Directions
- In large skillet, cook chicken in butter on medium heat till brown on both sides and cooked through (about 20 min)
- Remove chicken and set aside
- Stir flower into skillet drippings. (whisk thoroughly for best flavor)
- Add chicken broth and cream. Whisk until sauce thickens. (about 5 minutes)
- Add dijon mustard and stir to combine.
- Place chicken breasts in skillet. Place lid on skillet and simmer on low. (10 minutes)
- Slice tomato in wedges
- Chop Parsley
- Plate Chicken, pour cream sauce, tomato wedges and garnish with parsley.
- Pairs well with steamed rice or pasta and your favorite vegetable(s) (I prefer sweat peas and Steamed Rice)
-
 @ 0b65f96a:7fda4c8f
2025-03-29 10:39:17
@ 0b65f96a:7fda4c8f
2025-03-29 10:39:17Es gibt Bibliotheken voll Literatur zur „Kunst“ der Kriegsführung. Dies hier ist ein Beitrag zu den Bibliotheken der Kunst Frieden zu führen. Denn Frieden ist nicht die Abwesenheit von Krieg. Sondern eine mindestens ebenso intensive Aktivität. Worin genau besteht sie aber? Ich glaube darin, weder nach der einen noch nach der anderen Seite vom Hochseil zu fallen. Denn vom Hochseil kann man immer nach zwei Seiten fallen. Das ist dann auch schon die Kernherausforderung: Gleichgewichthalten!
Es scheint zunächst ein ganz äußerlicher Auftrag. Es gibt immer und wird immer widerstreitende Interessen geben. Allerdings ist das nur die äußerste Zwiebelschale. Denn wenn wir die Sache etwas mit Abstand von uns selbst betrachten, werden wir in uns hinein verwiesen: Frieden kann nur von innen nach außen gestiftet werden. Wenn wir das Hochseil in uns suchen, was finden wir dann? – Zweifels ohne, wissen wir von uns, dass wir nicht jeden Tag unser bestes Selbst sind. Würde es sich nicht lohnen etwas genauer über die Möglichkeit nach zwei Seiten vom Hochseil zu fallen nachzudenken, zugunsten der eigenen Balancierfähigkeit?
Wir sind daran gewöhnt zu denken dem Guten steht das Böse gegenüber. Daraus ziehen ja alle Western und Martial Arts Streifen ihren Plot: Der Gute bringt den Bösen um die Ecke und damit hat wieder mal das Gute gesiegt. Wir bewerten das „um die Ecke bringen“ unterschiedlich, je nach dem, von wem es kommt.
Ich möchte einen neuen Gedanken vorschlagen über unser Inneres, über Gut und Böse nachzudenken. Denn, wie gesagt, vom Hochseil kann man nach zwei Seiten fallen. Und es hat immer drastische Wirkung. Wo kommen wir also hin, wenn wir sagen: Frieden ist immer ein Gleichgewichtszustand, ergo eine Zeit der Mitte?
Sagen wir Toleranz ist ein erstrebenswertes Ideal. Dann würden wir sicher sagen Engstirnigkeit ist das Gegenteil davon und alles andere als Wünschenswert. Ja, so ist es gewiss. Und es bleibt hinzuzufügen, auch Beliebigkeit ist das Gegenteil von Toleranz. Denn es gibt eine Grenze, wo Toleranz nicht mehr Toleranz ist, sondern Beliebigkeit, ein „alles ist möglich“. Ähnlich können wir es für Großzügigkeit denken: Großzügigkeit ist ein erstrebenswertes Ideal. Ihr Gegenteil ist Geiz. Ihr anderes Gegenteil die Verschwendung. Oder Mut. Mut ist ein erstrebenswertes Ideal. Feigheit sein Gegenteil. Sein anderes Gegenteil ist Leichtsinn. Mit andern Worten: Das Ideal wird immer zum Hochseil. Und wir können immer nach zwei Seiten von ihm fallen. Wenn wir diesem Gedanken folgen, kommen wir weg von der Gut-Böse-Dualität. Und stattdessen zur Frage nach dem Gleichgewicht. Zur Frage nach der Mittezeit.
Natürlich steht es uns frei all das zu denken. Oder auch nicht zu denken. Denn selbstverständlich ist es möglich es nicht zu denken und bei einer Dualitätsvorstellung festhängen zu bleiben. Es wird uns nur nicht helfen Frieden zu denken und in Frieden zu handeln. Wenn wir wollen können wir durch das Aufspannen einer Trinität einen neuen Raum eröffnen und betreten. In ihm wird Frieden aktiv führbar, denn er wird eine Gleichgewichtssituation in uns selbst! – Nicht eine, sich einander gegenüberstehender äußerer Mächte!
Gehen wir noch einen Schritt weiter in unserer Betrachtung, können wir feststellen, dass es durchaus einen Unterschied macht nach welcher Seite wir runter fallen. Denn auf der einen Seite ist es immer eine Verengung: Engstirnigkeit, Geiz, Feigheit in unseren Beispielen. Auf der anderen ist es immer eine Zersplitterung oder Versprühung. In unseren Beispielen Beliebigkeit, Verschwendung und Leichtsinn. Und das erstrebenswerte ist eben immer die Mitte, das von uns ständig aktualisierte Gleichgewicht.
Das interessante ist, wo diese Mitte liegt, lässt sich niemals statisch festlegen. Sie ist immer dynamisch. Denn sie kann zu unterschiedlichen Momenten an unterschiedlicher Stelle liegen. Es ist immer ein Ich, das sich in Geistesgegenwart neu ausbalanciert. Und darum ist Frieden so schwer. Wir werden ihn niemals „haben“, sondern ihm immer entgegen gehen.
Der Kriegsruf ist nichts anderes, als ein Versuch von denen, die vom Hochseil gefallen sind, uns auch herunter zu kicken.
Netter Versuch. Wird aber nichts!
In der Nussschale: Die Dualität auflösen in die Trinität der balancierenden Mitte zwischen der Geste der Versteinerung und der Geste des Zerstäubens oder Zersplitterns. Die dynamische Qualität der Mitte bemerken. Oder, tun wir es nicht, ist das gleich der erste Anstoß, der uns wieder zum Wackeln bringt. Und des Ich´s gewahr werden, das balanciert. Frieden führen ist eine Kunst.
Patric I. Vogt, geb. 1968 in Mainz. Autor von „Zukunft beginnt im Kopf Ein Debattenbeitrag zur Kernsanierung von Rechtsstaat und Demokratie“. Lebt als freischaffender Künstler, Lehrer und Unternehmer. Über drei Jahrzehnte Beschäftigung mit dem Ideenfeld soziale #Dreigliederung und Anthroposophie. Moderation und Mediation von sozialen Prozessen und Organisationsentwicklung. Staatlich ungeprüft, abgesehen von den Fahrerlaubnissen zu Land und zu Wasser. Motto: Gedanken werden Worte, werden Taten! www.perspektivenwechsel.social
-
 @ 8cb60e21:5f2deaea
2024-08-29 02:16:28
@ 8cb60e21:5f2deaea
2024-08-29 02:16:28 -
 @ 866e0139:6a9334e5
2025-03-29 09:31:35
@ 866e0139:6a9334e5
2025-03-29 09:31:35
Autor: Thomas Eisinger. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Und genau dafür wirst auch du gedrillt werden: Menschen zu jagen und töten. Unbekannte, die auch nicht wissen, was sie hier tun. Oder Unschuldige, die nicht rechtzeitig fliehen konnten. Einfach töten. Alle. Ohne zu fragen. Denn das ist deine Aufgabe, Soldat: Töte Menschen!
Egal, was du vorher warst, Heizungsmonteur, KFZ-Mechaniker, Veganer, Marketingmanager, Friseur, Verkäufer, Kindergärtner: Es ist egal. Jetzt musst du töten. Denn du hast mitgemacht. Entweder, weil du es nicht ernst genommen hast, weil du dich nie für Politik interessiert hast. Oder weil du gedacht hast, das alles betrifft dich nicht. Weil du gedacht hast, Wahlen könnten etwas verändern. Oder weil du immer das Maul gehalten hast, damit dich keiner als «Rechter» bezeichnet. Egal. Jetzt musst du töten. Das ist das Spiel.
Ja, es ist ein Spiel. Grausam, abartig, menschenverachtend. Dennoch hat es Regeln: Diejenigen, die das Spiel beginnen, müssen niemals selbst auf das Schlachtfeld. Das ist die erste Regel. Ihre Söhne auch nicht, nicht die Söhne der anderen Politiker, nicht die der EU-Abgeordneten, nicht die der Parteibonzen. Auch nicht die der Banker, der Vorstandsvorsitzenden, der Chefredakteure. Denn alle wissen, wie man das Spiel spielt. Nur du nicht.
Du bist einfach eine Figur auf dem Spielfeld, die es verpasst hat, NEIN zu sagen, als noch Gelegenheit war. Jetzt bist du verwandelt worden in eine menschliche Drohne. Wenn sie sagen: töte!, dann tötest du. Denken kannst du, wenn alles vorbei ist. Falls du je wieder nach Hause kommst. Vielleicht sogar mit beiden Beinen und beiden Armen. Vielleicht auch nicht. Egal. Wer hätte Mitleid mit einer Spielfigur?
Nein, du musst töten. Das ist deine Aufgabe. Sie sagen es nun schon seit Monaten, warum glaubst du es nicht? Sie meinen es ernst. Wenn du den Brief in Händen hältst ist es zu spät. Es gilt dann das Notstandsrecht und keiner kann mehr verweigern. Da hättest du dich vorher drum kümmern müssen. Oder auf eine Demo gehen. Oder laut und mit klarer Stimme in jedem Gespräch den Wahnsinn anprangern. Hast du aber nicht.
Jetzt musst du töten oder du wirst getötet. Das ist das Spiel. Du hättest selbst denken können. Hast du aber nicht. Hast deine Zeit mit sinnlosen Videos vertan, Netflix geguckt und hast Influencerinnen geliked. Die müssen nicht an die Front. Aber du. Morgen, wenn du aufstehst, die Uniform anziehst und rausgehst, dann wirst du Befehle ausführen oder erschossen werden. Also wirst du Menschen töten. Dein Leben wird nie wieder so sein, wie zuvor. Dein Schmerz, deine Schuld, dein Leid: sie gehen ein in die unendliche Reihe der Soldaten, die seit Jahrhunderten dasselbe Schicksal erlitten. Deren Schreie noch immer durch den ewigen Raum hallen. Deren Opfer von den Herren des Spiels mit einem Lächeln entgegengenommen wurde. Deren Gliedmaßen auf den Schlachtfeldern liegen geblieben waren. Zum Dank erhielten sie eine Medaille. Ein Stück Blech für den rechten Arm, einen Grabstein für den Vater, den Bruder, den Sohn. Für das Vaterland. Für Europa. Für die Demokratie. Der Hohn tropft aus jedem Politikerwort, doch die Menschen glauben noch immer die uralte Geschichte von Freund und Feind, von Gut und Böse.

\ Wer nicht aufwachen will, muss töten. Du. Nicht am Bildschirm. In der echten Welt. Wo man nicht auf Replay drücken kann. Wo man den Gegner nicht nach links oder rechts swipen kann, denn er ist echt, real, lebendig. Noch. Entweder er oder du. Jetzt ist es zu spät für Entscheidungen. Kannst du es spüren? Die Work-Life-Balance wird zur Kill-or-be-killed-Balance. Es gibt kein Entrinnen. Denn du hast mitgemacht. Schweigen ist Zustimmung. Sich-nicht-drumkümmern ist Zustimmung. Kriegsparteien zu wählen ist noch mehr Zustimmung.
Heute.
Heute lässt sich noch etwas ändern.
Es hat nichts zu tun mit rechts oder links. Nur mit Menschlichkeit versus Hass, Macht und dem ganz großen Geld. Das sind die Gründe, für die du töten oder sterben musst.
Wie entscheidest du dich?
Thomas Eisinger ist Schriftsteller. Zuletzt erschien der Roman "Hinter der Zukunft". Mehr zum Autor hier.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Bildschirmfoto 2025-03-27 um 09.53.46
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-03-29 09:31:13
@ 57d1a264:69f1fee1
2025-03-29 09:31:13"THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." - SATOSHI NAKAMOTO
"Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin.
Materials: Carrara Marble, Copper leaf, Opendime
Dimensions: 6" x 9" x 13"
Price: $30,000 or BTC equivalent
Enquire: https://www.vonbitcoin.com/available-works
X: https://x.com/BVBTC/status/1894463357316419960/photo/1
originally posted at https://stacker.news/items/928510
-
 @ 866e0139:6a9334e5
2025-03-29 08:51:57
@ 866e0139:6a9334e5
2025-03-29 08:51:57
Autor: Dr. Daniele Ganser. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Der Frieden ist mir eine Herzensangelegenheit. Daher halte ich seit über 20 Jahren Vorträge zu den Themen Krieg und Frieden. Bisher sind es schon mehr als 1000 Vorträge. Manchmal gibt es Widerstand oder schlechte Presse, aber ich mache einfach weiter. Zudem schreibe ich Bücher, gebe Interviews und habe eine Online-Community, wo ich über Zoom Fragen der Mitglieder beantworte. Mein Ziel ist immer dasselbe: Die Friedensbewegung zu stärken.
https://www.youtube.com/watch?v=4rlSE4CYR_U
Auszug aus der Einleitung "Imperium USA":
"In meiner Forschung orientiere ich mich an folgenden drei Prinzipien: UNO- Gewaltverbot, Achtsamkeit und Menschheitsfamilie. Das UNO-Gewaltverbot wurde 1945 erlassen und verbietet die Androhung oder Anwendung von Gewalt in der internationalen Politik. Es ist leider in Vergessenheit geraten, und viele Menschen haben noch nie davon gehört. Daher erwähne ich es oft in meinen Büchern und Vorträgen, weil es ein ganz wichtiges Instrument der Friedensbewegung ist. Auch das Prinzip Achtsamkeit ist für die Friedensbewegung ein Juwel.
Denn zu oft schon wurden wir Menschen durch Kriegspropaganda getäuscht und verwirrt. Doch das wäre nicht nötig. Wenn wir durch Achtsamkeit lernen, unsere eigenen Gedanken und Gefühle aus einer ruhigen Distanz zu beobachten, stärken wir unsere Klarheit. Wir müssen nicht alles glauben, was uns von den Medien erzählt wird. Durch Achtsamkeit erkennen wir, dass wir nicht unsere Gedanken und Gefühle sind, sondern das klare Bewusstsein, in dem sie aufsteigen und wie Wolken auch wieder vergehen.
Besonders wichtig ist mir auch das Prinzip Menschheitsfamilie. Denn leider ist es in der Geschichte immer wieder vorgekommen, dass wir als Menschheitsfamilie einzelne Mitglieder ausgeschlossen und getötet haben. Wir haben uns entlang von Nationalität, Religion, Hautfarbe, Geschlecht und Einkommen gespalten und abgewertet. Bei der Hexenverfolgung wurden Frauen der »Zauberei« beschuldigt, aus der Menschheitsfamilie ausgeschlossen und verbrannt. Bei den Indianerkriegen wurden Indianer als »Wilde« aus der Menschheitsfamilie ausgeschlossen, vertrieben und getötet. Beim Sklavenhandel wurden Afrikaner als »Tiere« aus der Menschheitsfamilie ausgeschlossen, diffamiert und ausgebeutet. Im Zweiten Weltkrieg wurden Juden als »lebensunwert« aus der Menschheitsfamilie ausgeschlossen und in Konzentrationslagern vergast.
Im Vietnamkrieg wurden Vietnamesen von US-Soldaten als »Termiten« bezeichnet, aus der Menschheitsfamilie ausgeschlossen und mit Napalm bombardiert. Im sogenannten »Krieg gegen den Terror« wurden Afghanen als »Terroristen« bezeichnet, aus der Menschheitsfamilie ausgeschlossen und getötet. Das sich wiederholende Muster ist deutlich: Das Prinzip Menschheitsfamilie wird verletzt, indem eine Gruppe aus der Menschheitsfamilie ausgeschlossen, abgewertet und dann getötet wird. Natürlich sehen wir alleganz unterschiedlich aus. Auch bezüglich Glaube, Nationalität, Ausbildung, Sprache und Einkommen sind wir nicht gleich und werden es nie sein.
Doch das ist noch kein Grund, Gewalt einzusetzen. »Wir haben in der Welt ganz sicher ein Problem mit Feindseligkeiten, die außer Kontrolle geraten. Der Mensch ist geradezu ein Spezialist darin, andere auszugrenzen«, erklärt der holländische Zoologe Frans de Waal. »Der Mensch dämonisiert Menschen anderer Nationalität oder Religion, erzeugt Ängste und Wut. Diese Gruppen nennen wir dann schnell Unmenschen oder Tiere. Schon ist es leicht, die Unmenschen zu eliminieren, weil man kein Mitgefühl mehr mit ihnen haben muss.«
Im April 2004 wurde publik, dass US- Soldaten im irakischen Abu-Ghraib- Gefängnis Iraker gefoltert hatten. Die US- Kriegspropaganda hatte den US- Soldaten eingetrichtert, die Iraker seien schlechte Menschen, dadurch wurden sie aus der Menschheitsfamilie ausgeschlossen. Das hatte konkrete Folgen. Die US- Soldatin Lynndie England führte in Abu-Ghraib einen nackten irakischen Gefangenen an einer Hundeleine durchs Gefängnis. Ein anderer irakischer Gefangener musste mit schwarzer Kapuze auf einer Kiste balancieren, während an seinem Körper Drähte befestigt waren.
Ihm wurde von den US- Soldaten angedroht, dass ihm tödliche Stromschläge zugefügt würden, wenn er von der Kiste fiele. »Für Europa waren die Horrorbilder aus Sex, Folter und Erniedrigung schlichtweg ein Schock«, kommentierte Die Welt. Der Abu- Ghraib- Skandal zeigte drastisch, was passieren kann, wenn die Menschen einer ganzen Nation, in diesem Falle die Iraker, aus der Menschheitsfamilie ausgeschlossen werden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Man darf angesichts dieser Gewalt und Brutalität nicht zu dem Schluss kommen, dass wir Menschen nicht fähig sind, friedlich zusammenzuleben. Wir können es sehr wohl und tun es jeden Tag, an Millionen verschiedenen Orten. »Lassen sie uns zunächst unsere Haltung gegenüber dem Frieden selbst überprüfen. Zu viele von uns halten ihn für unmöglich", erklärte US-Präsident John F. Kennedy in einer seiner Reden.
»Zu viele von uns halten ihn für nicht zu verwirklichen. Aber das ist ein gefährlicher, defätistischer Glaube. Er führt zu der Schlussfolgerung, dass der Krieg unvermeidlich ist, dass die Menschheit zum Untergang verurteilt ist, dass wir uns in der Gewalt von Kräften befinden, die wir nicht kontrollieren können.«
Doch dies stimmt nicht, das wusste auch Kennedy. »Unsere Probleme sind von Menschen geschaffen, deshalb können sie auch von Menschen gelöst werden. Die Größe, die der menschliche Geist erreichen kann, bestimmt der Mensch selbst.«
Auch außerhalb der USA haben inspirierende Persönlichkeiten die Friedensbewegung geprägt. In Indien hat der Rechtsanwalt und Pazifist Mahatma Gandhi, der für mich ein großes Vorbild ist, immer wieder das Prinzip Menschheitsfamilie betont. »Die ganze Menschheit ist eine Familie«, sagte Gandhi. Er setzte bei seinem Protest stets auf einen gelassenen und freundlichen Ton, frei von Wut und Hass. Trotz ihres brutalen Vorgehens bezeichnete Gandhi weder die indische Polizei noch die indische Regierung oder die britische Kolonialmacht als Feinde. »Ich betrachte niemanden als meinen Feind«, erklärte Gandhi. »Alle sind meine Freunde. Ich möchte aufklären und die Herzen verändern.«
Ich bin fest davon überzeugt, dass die Friedensbewegung im 21. Jahrhundert stärker wird, wenn sie sich an den Prinzipen Menschheitsfamilie, Achtsamkeit und UNO- Gewaltverbot orientiert. Die Spaltung nach Nation, Partei, Religion, Hautfarbe, Geschlecht, Schulabschluss oder Einkommen sollte im 21. Jahrhundert durch die Einsicht ersetzt werden, dass alle Menschen zur Menschheitsfamilie gehören. Sie als Leserin und Leser gehören zur Menschheitsfamilie, egal wo Sie diesen Text lesen und unabhängig davon, was Ihre Geschichte ist. Und ich als Autor gehöreauch zur Menschheitsfamilie, ebenso wie alle Personen, die in der Menschheitsgeschichte auftauchen, Opfer wie Täter. Zusammen sollten wir lernen, uns nicht zu töten, weil alles Leben heilig ist und weil wir auf einer sehr tiefen Ebene alle miteinander verbunden sind."
Dr. Daniele Ganser, geboren 1972, ist Schweizer Historiker und Friedensforscher. Er leitet das unabhängige Swiss Institute for Peace and Energy Research (SIPER) in Münchenstein bei Basel in der Schweiz. Die aktuellen Vorträge von Dr. Daniele Ganser finden Sie hier. Am 12. April halten Daniele Ganser und Dirk Pohlmann bei Basel einen Vortrag über den Fall Herrhausen (nur 200 Tickets). Bestellen können Sie hier.

Das Buch können Sie hier bestellen.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ dfbbf851:ba4542b5
2025-03-29 06:51:21
@ dfbbf851:ba4542b5
2025-03-29 06:51:21ในยุคดิจิทัลที่การสื่อสารมีบทบาทสำคัญต่อชีวิตประจำวัน เทคโนโลยี Cell Broadcast ได้กลายเป็นหนึ่งในเครื่องมือที่ทรงพลังสำหรับการแจ้งเตือนฉุกเฉิน ไม่ว่าจะเป็นภัยพิบัติหรือเหตุการณ์สำคัญที่ต้องแจ้งให้ประชาชนทราบอย่างทันท่วงที ⏳💡
📌 Cell Broadcast คืออะไร ?
Cell Broadcast (CB) เป็นเทคโนโลยีที่ใช้ส่งข้อความกระจายสัญญาณผ่านเครือข่ายโทรศัพท์มือถือ 🏗📶 โดยแตกต่างจาก SMS ตรงที่สามารถส่งข้อความถึงผู้ใช้จำนวนมากได้พร้อมกัน โดยไม่ต้องทราบหมายเลขโทรศัพท์ ของผู้รับ 📲💨
ข้อความ CB สามารถส่งถึงอุปกรณ์ที่รองรับในเครือข่ายมือถือที่เปิดใช้งานอยู่ภายในช่วงเวลาสั้น ๆ ⏱ และ ไม่ทำให้เครือข่ายล่ม
✨ ข้อดีของ Cell Broadcast ✨
✅ ส่งข้อความรวดเร็ว – แจ้งเตือนได้ภายในไม่กี่วินาที แม้ในกรณีฉุกเฉิน ⚡🚀
✅ ไม่ต้องใช้หมายเลขโทรศัพท์ – กระจายสัญญาณไปยังอุปกรณ์ทุกเครื่องที่อยู่ในพื้นที่เป้าหมายได้โดยตรง 📡
✅ รองรับหลายภาษา – สามารถตั้งค่าการแจ้งเตือนให้เหมาะสมกับประชากรในแต่ละพื้นที่ 🌍🗣
✅ ไม่ทำให้เครือข่ายหนาแน่น – ต่างจาก SMS หรือการโทรจำนวนมากที่อาจทำให้เครือข่ายล่ม 📵❌
✅ ทำงานได้แม้ไม่มีอินเทอร์เน็ต – สามารถแจ้งเตือนในกรณีที่โซเชียลมีเดียหรืออินเทอร์เน็ตใช้งานไม่ได้ 🌐🚫
🌍 การใช้งาน Cell Broadcast ทั่วโลก
🔹 สหรัฐอเมริกา – ใช้ระบบ Wireless Emergency Alerts (WEA) เพื่อแจ้งเตือนเหตุการณ์ฉุกเฉิน เช่น พายุเฮอริเคน 🌀🌪
🔹 ญี่ปุ่น – ใช้ระบบ Earthquake Early Warning (EEW) เพื่อแจ้งเตือนแผ่นดินไหวล่วงหน้า ⛩🌏
🔹 สหภาพยุโรป – มีนโยบายให้ประเทศสมาชิกใช้ Public Warning System ผ่าน Cell Broadcast 📢🏛
🤔 ทำไมประเทศที่ยังไม่มีระบบนี้ควรนำมาใช้ ?
หลายประเทศ รวมถึง ประเทศไทย ยังไม่มีการใช้ Cell Broadcast อย่างแพร่หลาย ทั้งที่เป็นเทคโนโลยีที่สามารถช่วยชีวิตผู้คนได้อย่างมหาศาล 🚑 หากเกิดภัยพิบัติ เช่น น้ำท่วม แผ่นดินไหว สึนามิ หรือไฟป่า 🔥🌊 Cell Broadcast สามารถส่งการแจ้งเตือนไปยังทุกคนในพื้นที่เสี่ยงได้ทันที ลดความสูญเสียและเพิ่มโอกาสรอดชีวิตได้มากขึ้น
🔸 ความแม่นยำสูง – สามารถส่งแจ้งเตือนไปยังพื้นที่ที่ได้รับผลกระทบโดยตรง ทำให้ประชาชนสามารถเตรียมตัวรับมือได้ดีกว่า
🔸 ไม่มีปัญหาความล่าช้า – ต่างจากการแจ้งเตือนผ่าน SMS หรือโซเชียลมีเดียที่อาจล่าช้าหรือไม่ได้รับข้อความเลยหากเครือข่ายล่ม
🔸 เป็นมาตรฐานสากล – หลายประเทศพัฒนาแล้วมีระบบนี้ใช้งานอย่างมีประสิทธิภาพ ประเทศที่ยังไม่มีควรนำมาใช้เพื่อให้สามารถจัดการภัยพิบัติได้อย่างมีประสิทธิภาพ
🔸 ประหยัดต้นทุนในระยะยาว – ลดความเสียหายทางเศรษฐกิจจากภัยพิบัติ เพราะประชาชนได้รับการแจ้งเตือนล่วงหน้า ทำให้สามารถอพยพหรือป้องกันความเสียหายได้
🔮 อนาคตของ Cell Broadcast
ในอนาคต Cell Broadcast อาจถูกนำมาใช้ร่วมกับ ปัญญาประดิษฐ์ (AI) 🤖 และ Internet of Things (IoT) 🌐 เพื่อเพิ่มความแม่นยำและปรับแต่งการแจ้งเตือนได้ดียิ่งขึ้น 🎯💡
📌 ปล.
Cell Broadcast เป็นเทคโนโลยีแจ้งเตือนที่ทรงพลังและมีบทบาทสำคัญในการช่วยชีวิตผู้คน 🚑 ด้วยความสามารถในการส่งข้อความได้อย่างรวดเร็ว ครอบคลุมพื้นที่กว้าง และไม่ต้องพึ่งพาอินเทอร์เน็ต จึงเป็นหนึ่งในเครื่องมือสำคัญสำหรับการบริหารจัดการภัยพิบัติในปัจจุบันและอนาคต 🔥
CellBroadcast #แจ้งเตือนภัย #เทคโนโลยีสื่อสาร #ภัยพิบัติ #เครือข่ายมือถือ #การสื่อสารฉุกเฉิน #เตือนภัยล่วงหน้า
-
 @ da0b9bc3:4e30a4a9
2025-03-29 06:49:22
@ da0b9bc3:4e30a4a9
2025-03-29 06:49:22Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/928470
-
 @ 97c70a44:ad98e322
2024-08-29 00:50:27
@ 97c70a44:ad98e322
2024-08-29 00:50:27Nostr is a mess. It always has been and will always be. That's part of the appeal! But it's important that users be able to navigate the rolling seas of this highly partition-tolerant network of kaleidoscopically-interwoven people, bots, topics, relays, clients, events, recommendations, lists, feeds, micro-apps, macro-apps, Chinese spam, and "GM"s.
In order to do this, users must be able to articulate "what" they are looking for, and clients must be able to articulate "how" to find that thing. This "how" is divided into two parts: building a request that will match the desired content (very easy), and selecting a relay that is able to serve that content to the user requesting it (very very hard).
Why guessing isn't good enough
As a concrete example, let's say the user wants to find everyone in their "network" who is using a particular topic. The process would look something like this:
- The user clicks the "network" tab and types in the topic they want to browse. This is the "what".
- The client then translates the term "network" to a list of public keys using whatever definition they prefer (Follows? WoT? Grapevine?), and builds a filter that might look something like this:
[{"authors": pubkeys, "#t": ["mytopic"]}]. Any relay will happily accept, understand, and respond to that filter. - The client then has to decide which relays it should send that filter to. This is the
???stage of the outbox model, which immediately precedes: - Profit
It may not be immediately obvious why selecting the correct relays might be difficult. Most people post to relay.damus.io, and most people read from relay.damus.io, so in most cases you should be good, right?
This approach to relay selection has historically worked "well enough", but it depends on a flawed definition of success. If you only want to find 90% of the content that matches your query, using the top 10 relays will suffice. But nostr is intended to be censorship-resistant. What if those 10 hubs have banned a particular public key? Nostr clients should (at least in theory) be 100% successful in retrieving requested content. Even if someone only posts to their self-hosted relay, you should be able to find their notes if their account is set up properly.
A naive solution to fixing the FOMO
A 90% hit rate results in a feeling of flakiness, even if users aren't completely aware of what isn't working. Feeds will be incomplete, quoted notes will be missing, replies will be orphaned, user profiles won't load. The natural response to the FOMO this creates is for users to "try harder" by adding more relays.
On the read side, this means clients open more connections, resulting in much higher data transfer requirements, with massively diminishing returns, since there's no reason to expect that a randomly chosen relay will have a substantially different data set.
One the publish side, this means that clients end up publishing more copies of their data to more relays. This approach has been automated in the past by services like Blastr, which don't store a copy of events published to the relay, but instead forward events to the top 300 relays in the network. This results in a two-orders-of-magnitude increase in storage required, and only makes the read side of the problem worse, since it reduces the uniqueness of the data set each relay stores. This in turn means that more duplicates are retrieved when querying relays.
Both halves of this approach are equivalent to guessing. On the read side, users are guessing which relays will have any arbitrary content they might ask for in the future. On the write side, users are guessing which relays other people might use to find their notes. It is a brute-force method for finding content.
Randomness results in centralization
In theory, random relay selection would result in a perfect distribution of content across all relays in the network. But in practice, this method of selection isn't random at all, but is strongly influenced by user bias in what constitutes a "good" relay. While some users may check nostr.watch for ping times, geographical proximity, or uptime, most will choose relays based on familiar names or other people's recommendations.
In either case, these biases are entirely orthogonal to achieving a higher content retrieval hit rate, except when bias in relay selection results in clustering — i.e., centralization. In other words, the kind of randomness exhibited by users when selecting relays actually results in pretty much everyone picking the same few relays. We see this same effect when people try to come up with passwords or seed phrases — human-provided randomness is anything but random.
Clustering improves the hit rate when requesting events (slightly), but it results in nearly as much centralization as if only a single relay was used — and a lot more duplicate events.
Something (anything) other than randomness
In early 2023, Mike Dilger introduced NIP 65 (now known as the "Outbox Model") with a problem statement in the spirit of the original description of nostr: "Nostr should scale better. People should be able to find what they want."
Historical note: NIP 65 was formerly known as the "Gossip Model", derived from the name of Mike's desktop nostr client, called "Gossip". This unfortunately created a lot of confusion, since gossip protocols work very differently from how nostr tends to work, hence the re-brand.
Before NIP 65, an informal standard existed in which
kind 3user contact lists also included a list of relays that clients could use as something similar to Mastodon's "home servers". This list included the option to only read or write from a given relay. Unfortunately, it wasn't really clear what the semantics of this relay list were, so different clients handled them differently (and many clients ignored them). Usually this amounted to user-provided static relay configurations, which resulted in the naive relay selection approach described above.NIP 65 used a very similar format (a list of relay urls with optional "read" or "write" directives), but with a very important semantic difference: relays listed in a user's
kind 10002were intended to "advertise to others, not for configuring one's client." In other words, these relay selections were intended as a signal to other users that they should use certain relays when attempting to communicate with the author of the relay list.I highly recommend reading the entire NIP, which is very short and easy to read. But the mechanics of the spec are very simple:
When seeking events from a user, Clients SHOULD use the WRITE relays of the user's
kind:10002.When seeking events about a user, where the user was tagged, Clients SHOULD use the READ relays of the user's
kind:10002.When broadcasting an event, Clients SHOULD:
- Broadcast the event to the WRITE relays of the author
- Broadcast the event to all READ relays of each tagged user
For the first time, we had a way to differentiate relays in terms of what content could be found where.
When looking for a note by a particular user, a client could now look up the author's
writerelays according to theirkind 10002event, and send its query there. The result is a much higher hit rate with much lower data transfer requirements, and fewer connections per query.Making Outbox Work
There are of course some assumptions required to make this work.
First, the user must know which author they're looking for. This isn't always true when looking up a quote or parent note, but context and pubkey hints solve this difficulty in most cases.
The author must also publish a
kind 10002event. This may not always be the case, but clients should prompt users to set up their relay list correctly. This isn't really a flaw in the Outbox Model, just in implementations of it.Additionally, the user's client must be able to find the author's
kind 10002event. This is the "bootstrapping" phase of the Outbox Model, during which the mechanisms the system provides for finding events aren't available. This requires us to fall back to randomly guessing which relays have the content we're looking for, which as we saw above doesn't work very well.Other than guessing, there are a few different ways a client might find the relay selection event in question, each of which is applicable in different circumstances. In most cases, using one of a handful of indexer relays like purplepag.es or relay.nostr.band is a simple and efficient way to find user profiles and relay selections.
However, if an author's content has been aggressively purged from these indexers due to censorship, they obviously can't be relied upon. Even though the author in question hasn't been deplatformed from nostr itself (since he can always self-host a publicly accessible relay to store his content), he has been effectively shadow-banned.
To get around this, relay selections have to be communicated in some other way. Nostr has a few different mechanisms for this:
- If the author's NIP 05 address is known and properly configured (it may not be), clients can look up the author's NIP 05 endpoint to find some reasonable relay hints. Unfortunately, these are often neglected, and usually custodial, so they can run into the same problems.
- If the author's pubkey is found in another signed event found on nostr, relay hints can be a way to propagate relay selections through the network. This relies on implementations picking reliable relay hints which can be difficult, and hints do tend to become less reliable over time. However, this strategy is very effective in resisting censorship because it makes banning viral — if a relay wants to completely purge a particular pubkey from their database, they have to purge every event that references it, since events are tamper-proof.
- In extremis, relay recommendations can always be communicated out-of-band. This can be done using manual input, QR codes, DHTs, jsonl torrents full of
kind 10002events, or any other mechanism client developers choose to resort to.
Another, more technical assumption is that any given query can be fulfilled by few enough relays that a client can actually make all the connections needed, without running into resource limits. If you're trying to request content from 10,000 users across 1,000 relays, you're going to have a bad time. This was pointed out to me by Mazin of nostr.wine. He makes a good point, and it's definitely something to keep in mind. There are some mitigating factors though.
The first is that the current topology of the network probably won't persist forever. Because nostr is largely populated by self-hosting enthusiasts, the number of "tiny" relays is proportionally much higher than it will be if adoption picks up, even if the total number of relays grows. The trajectory is that nostr will drift toward fewer, larger relays, reducing the number of connections needed to fulfill any given query.
This is "centralizing", but it's important to understand that this isn't necessarily a bad thing. As long as there are more than one or two large hubs, there is user choice. And as long as it's possible to run a new relay, there is always an escape hatch. Nostr, like bitcoin, has no hard dependency on the biggest player in the network.
The other thing to consider is that there are lots of other techniques we can use to overcome the limits of the lowest-common denominator's limitations (mobile browser clients), including self hosted or third-party relay proxies. The trade-off here is that a little trust (aka centralization) can go a long way to reducing resource requirements needed to fulfill queries using the Outbox model.
If you're interested in more details on this topic, see this blog post.
That was a long digression, but there is one other thing that the Outbox model assumes to be the case. Even if the correct relays are found and connected to, they still may not return all desired content, either because they don't have it, or because they refuse to return it to the user requesting it.
This can happen if the publishing client isn't following the Outbox Model, if the author had migrated from one relay set to another without copying their notes over, or if the relay in question chose not to retain the author's content for some reason.
The first two issues can be fixed by improving implementations, but the question of policy is a little more interesting.
Relativistic relays
The Outbox Model is a mechanical process; it's only as useful as user relay selections are. In order for it to work, users have to be able to make intelligent relay selections.
Every relay has trade-offs, depending on its policy. 140.f7z.io would not be useful for long-form content, for example. Some relays might have a content retention policy that changes depending on whether you're a paying user. If you don't pay, you might find out too late that your content has been deleted from the relay.
So what makes a relay "good" for a particular use case? Well, it's complicated. Here are a few factors that go into that calculus:
- Is the relay in the same geographical as the user? Proximity reduces latency, but jurisdictional arbitrage might be desired. Users should probably have a variety of relays that fit different profiles.
- Will the relay ban the user? Do the operators have a history of good behavior? Is the relay focused on particular types of content? Is the relay's focus consistent with the user's goal in adding that relay to their list?
- What are the relay's retention policies? A user might want to set up an archival relay for her old content, or a multi-availability-zone relay so her notes are immediately accessible to the rest of the network.
- Does the relay require payment? Paid relays are more aligned with their users, but obviously come at a financial cost.
- Does the relay have policies for read-protecting content? If so, other users might not be able to find your posts published to that relay. On the other hand, some relays are configured to work as inboxes for direct messages, which can help preserve privacy.
- Does the relay request that users authenticate? Authentication can help manage spam, but it also allows relays to correlate content requests with users, reducing user privacy.
- Is the relay you use hosted by your client's developer? If so, you're in danger of getting banned from your client and your relay at the same time.
- Is the relay a hub? Using hubs can help smooth out rough areas in Outbox Model implementations, at the cost of centralization.
- Is the relay used by anyone else? One-off relays can be useful for archival purposes, but often won't be used by clients following the Outbox Model, depending on how they optimize requests.
There are lots of ways to approach the problem of helping users select relays, but it's an inherently complex problem which very few people will have the patience to properly address on their own. Relay selection is a multi-dimensional problem, and requires satisfying multiple constraints with a limited number of relay selections.
In the future, special-purpose clients might be used to help people build relay sets. Clients also might provide curated "relay kits" that users can choose and customize. Or, we might see an increase in hybrid solutions, like smarter relay proxies or client-local relays that synchronize using other protocols or platforms.
The Limitations of Outbox
Outbox is not a complete solution, not because of any of the caveats listed above, but because NIP 65 per se only addresses the question of how to index content by pubkey in a broadcast social media context. But there are many other scenarios for relay selection that Outbox does not solve:
- Community, chat, and group posts might be best posted to relays dedicated to that context.
- Direct messages shouldn't follow the same contours as public social media content.
- Topic-oriented relays, or relays serving a custom feed might be useful independent of who uses them.
- Relays focused on serving a particular kind of event, like music, long-form content, or relay selections, are useful independent of who reads from or writes to them.
- Certain clients might need to fulfill particular use cases by using relays that support certain protocol features, like search, count, or sync commands.
- Some events might not make sense to publish to relays, but should instead be shared only directly, out of band.
Some of these use cases might be solved by new specifications similar to Outbox that prescribe where certain data belongs — for example, NIP 17 requires users to publish a different relay list before they can receive direct messages, while NIP 72 places community relay recommendations directly into the group's metadata object. A reasonably complete list of different relay types can be found in this PR, very few of which have a canonical way to manage selections.
Other use cases might be supported more informally, either by relays advertising their own value proposition, or via third-party NIP 66 metadata. Still others might be supported by scoping the network down to only certain relays through explicit relay selection — this is how white-labeled Coracle instances work.
The basic idea here is that there are categories of events that don't have anything to do with where a particular person puts his or her "tweets". For every "what" on nostr, there should be a "how".
Keep nostr weird
Whatever additional systems we end up adopting for helping with relay selection, one thing is certain — people will continue to discover new, creative uses for relays, and we will always be playing catch up. This is one of the coolest things about nostr!
But it does mean that users will have to adapt their expectations to a network that partitions, re-configures, and evolves over time. Nostr is not a "worse" experience than legacy social media, but it is a version of social media that has itself been set free from the stagnant walled-garden model. Nostr is in many ways a living organism — we should be careful not to impose our expectations prematurely, leaving room to discover what this thing actually is, or can be.
If you enjoyed this post but want more take a look at the talk I gave at Nostrasia last year. I also wrote up a blog post at about the same time that addresses some of the same issues, but focuses more on privacy concerns around relays and nostr groups. Finally, I recently wrote this comment, which includes some details about challenges I've faced putting Outbox into Coracle.
-
 @ 3e6e0735:9e95c8a2
2024-08-28 23:16:41
@ 3e6e0735:9e95c8a2
2024-08-28 23:16:41Imagine a colorful world filled with vibrant villages, each bustling with activity. Each village has its own unique roads and parks where people gather to share their stories, pictures, and ideas.
Village A is like a big, crowded gathering spot, similar to Facebook, where everyone loves to post their adventures. But there’s a dark cloud hanging over it. The village leaders, while wanting to keep things friendly, are constantly pressured by the government to monitor what people share. If someone posts something that the government doesn’t like, the leaders might say,
“Hold on! You can’t share that!” It feels more like a prison than a park, where the rules can change at any moment, and everyone is afraid to speak freely.
Village B is a chaotic place where folks send quick messages back and forth, just like Twitter. Here, too, the leaders face immense pressure from the government to control conversations. If you say something that doesn’t fit the official narrative, they might silence you or even banish you from the village. Plus, when you share your thoughts, you don’t really own them. The leaders can sell your data and connections to the highest bidder, leaving you feeling like just another product.
Then there’s Village C, a trendy spot for sharing beautiful photos, like Instagram. But beware! The leaders here are also under the thumb of the government, which has its own set of oppressive rules. If someone posts something that challenges the status quo, it might just vanish without a trace. And just like in the other villages, your data and followers aren’t really yours—they can be sold off without your consent.
But wait! Enter NOSTR, the magical map that connects all the villages without any leaders telling you what you can or can’t share. It’s like building roads that anyone can use, with no gates or guards in sight.
With NOSTR, if Village A wants to share a story with Village C, they can do it directly, or through Village B, without anyone stopping them. It’s permissionless, meaning you don’t need to ask for permission to share your thoughts or ideas. Plus, all content lives everywhere at once, thanks to special relays, so you can find it no matter where you are!
Here’s the best part: with NOSTR, you own your own data, connections, and followers! It’s like having a special key that only you control. No one can sell your information or take away your followers because you’re the one in charge.
And let’s not forget about the exciting micropayments called “zaps” using Bitcoin! Imagine if you could send a little thank-you to someone for a great story or a beautiful photo, right there in the moment. It’s like tossing a coin into a fountain to show your appreciation, but digital and instant!
And here’s a side note: with the rise of AI, people can create even more amazing things, like art or stories, and share them freely through NOSTR. There’s no one to censor or control what you create, so everyone can express themselves fully.
As more and more people flock to NOSTR, the other villages start to lose their users. They realize they need to adapt or risk fading away. Some leaders begin to think about integrating NOSTR into their own platforms, but there’s a catch: they have to rethink their entire profit model first. This leads to a battle of ideas, as they struggle to find a way to keep their users while also embracing the freedom that NOSTR offers.
In the end, while the centralized parks are dark and oppressive, ruled by leaders who are pressured by the government to control every word and image, NOSTR allows all the villages to connect freely. It’s a place where everyone can share their voices without fear, a world of endless possibilities where creativity thrives, and you truly own your data and connections!
-
 @ bdf3f01a:d9c40970
2025-03-29 04:52:40
@ bdf3f01a:d9c40970
2025-03-29 04:52:40Abstract:
This paper presents a rigorous and critical examination of the Winter Vigil of XLII.II at Sapelo, a pivotal rite within the Lowcountry Freehold that serves as both an initiation into communal responsibility and a symbolic enactment of the Compact’s moral tenets. This analysis interrogates the ritual’s structure, emphasizing its role in perpetuating a resilient sociocultural order amid external collapse. Through a multidisciplinary approach combining historiographical analysis, cultural anthropology, and sociocultural theory, this study elucidates the Vigil’s function as a mechanism for moral continuity, thereby situating it within the broader discourse of post-collapse societal stabilization. The implications of this study underscore the profound interconnectedness between ritual practice and the formation of resilient communal identities.
Introduction:
The Winter Vigil of XLII.II at Sapelo occupies a fundamental position in the cultural historiography of the Lowcountry Freehold. As contemporary scholars, it is imperative to approach this tradition not merely as an artifact of ritualistic antiquity but as a dynamic process of cultural preservation. The Freehold’s commitment to integrating tradition with pragmatism, especially through the stewardship of The Veil, constitutes a critical adaptive strategy that sustained sociopolitical coherence through epochs of external fragmentation. This study aims to critically examine the Vigil as both a symbolic and practical reinforcement of the Compact’s ethos, with particular attention to how this ritual facilitated intergenerational continuity of moral and social values, ultimately shaping the robust communal identity that defines contemporary Freehold society.
The Veil as Cultural Custodian:
The Veil, emerging from the post-collapse adaptation of preexisting religious and cultural practices, evolved into a matriarchal order central to maintaining the Freehold’s ethical architecture. This evolution was characterized not by rigid preservation but by adaptive synthesis, wherein ceremonial gravitas was merged with pragmatic domestic guidance. The Veil functioned as a moral custodian, particularly within the familial sphere, where its influence was most profoundly exercised. Veilmother Cordelia’s role during the Winter Vigil exemplifies this dual function of leadership and philosophical stewardship, as her guidance articulated not only the ritual's procedural elements but also the embedded moral philosophy that would shape the initiates' worldview.
Ritual Dynamics and Symbolism:
The Winter Vigil is fundamentally an enactment of moral endurance, wherein the initiate’s voluntary approach to the brazier represents an acceptance of communal responsibility through individual fortitude. The design of the ritual deliberately positions physical endurance as a metaphor for moral resilience, encapsulating the Freehold’s conviction that true strength is inherently silent and steadfast. As the initiate moves toward the brazier, kneeling in proximity to the flame, the act becomes a performative affirmation of the Compact’s call for measured, principled strength rather than ostentatious assertion. The structured progression from the outer circle to the brazier symbolizes a journey from collective dependency to personal sovereignty, reflecting the Compact's ethos that leadership is merited through tested perseverance.
The Copper Plate Rite:
The Copper Plate Rite, integral to the Vigil, embodies the transformative philosophy of the Freehold. The heated copper plate, inscribed with the flame symbol and lifted from ashes, is held aloft despite discomfort, symbolizing the embrace of hardship as an essential component of sovereignty. The fleeting burn, leaving a transient mark, underscores the philosophical assertion that genuine resilience is born of confronting and integrating suffering, rather than circumventing it. This rite functions not merely as a test of physical tolerance but as a pedagogical imprinting of the Freehold’s ethos—an allegory of death and rebirth integral to personal and communal maturation.
Symbolic Implications and Societal Continuity:
The deliberate imposition of discomfort during the Vigil underscores a fundamental tenet of Freehold philosophy: suffering, when purposefully endured, refines the individual and, by extension, fortifies the community. The Copper Plate Rite exemplifies the doctrine that hardship, when faced with deliberate resolve, engenders moral clarity. This paradigm of voluntary suffering as a crucible for leadership remains a cornerstone of the Freehold’s ideological framework, fostering a collective ethos rooted in patient perseverance rather than impulsive dominance. Furthermore, the initiation rite serves as a microcosm of the Freehold's broader sociocultural ethos, where personal sacrifice is inextricably linked to communal stability.
Interpretive Analysis:
Current historiographical interpretations often err by neglecting the interconnectedness of the Vigil with broader sociopolitical dynamics. By isolating the rite as a mere ceremonial endurance, scholars risk overlooking its function as a structured pedagogical tool for inculcating moral resilience. This study posits that the Vigil, far from being a vestigial tradition, actively cultivated a pragmatic ethic of endurance that proved crucial in the Freehold’s sustained sociocultural coherence. This coherence, rooted in ritual reinforcement of moral tenets, enabled the Freehold to navigate existential threats without succumbing to internal decay.
Cultural and Societal Implications:
The enduring significance of the Winter Vigil lies in its dual function as both a rite of passage and a communal reaffirmation of the Freehold’s meritocratic principles. By fostering individual accountability within a collective moral framework, the Vigil reinforced the Compact’s foundational premise that leadership is merited through demonstrated resilience. The integration of personal trial into communal identity formation exemplifies how the Freehold maintained its internal stability despite external societal fragmentation. This ritual, therefore, is not merely commemorative but constitutive of the Freehold's enduring cultural legacy.
Conclusion:
The Winter Vigil of XLII.II at Sapelo remains a paradigmatic example of ritual as a vehicle for social continuity within the Lowcountry Freehold. Its deliberate amalgamation of symbolic endurance with moral instruction illustrates the Freehold’s adaptive strategy of embedding philosophical imperatives within lived tradition. As modern scholars, it is incumbent upon us to engage with these practices not merely as remnants of a bygone era but as foundational elements that cultivated the durable sociocultural ethos underpinning our current stability.
References:
-
Vance, C. (Epoch LII). "The Compact and Cultural Continuity: An Oral History." Archive of Freehold Studies, Emberwell Hall.
-
Harlowe, E. (Epoch LX). "The Flamekeepers: Guardians of Tradition." Journal of Sociocultural Persistence, Vol. 22, pp. 45-72.
-
Morgan, T. (Epoch LXV). "Endurance Through Ritual: The Role of The Veil in Cultural Preservation." Lowcountry Academic Press.
-
Cordelia, V. (Epoch XLII). "Reflections on the Flame: An Instructional Account." Collected Teachings of The Veil.
-
Emberwell Institute (Epoch XC). "The Evolution of Freehold Rites: From Custom to Philosophy." Advanced Studies in Cultural Integration.
## Title: Ritual as Continuity: An Analysis of the Winter Vigil of XLII.II at Sapelo
### Epoch XLII - Circle of Maidens
#### Abstract:
This paper presents a rigorous and critical examination of the Winter Vigil of XLII.II at Sapelo, a pivotal rite within the Lowcountry Freehold that serves as both an initiation into communal responsibility and a symbolic enactment of the Compact’s moral tenets. This analysis interrogates the ritual’s structure, emphasizing its role in perpetuating a resilient sociocultural order amid external collapse. Through a multidisciplinary approach combining historiographical analysis, cultural anthropology, and sociocultural theory, this study elucidates the Vigil’s function as a mechanism for moral continuity, thereby situating it within the broader discourse of post-collapse societal stabilization. The implications of this study underscore the profound interconnectedness between ritual practice and the formation of resilient communal identities.
#### Introduction:
The Winter Vigil of XLII.II at Sapelo occupies a fundamental position in the cultural historiography of the Lowcountry Freehold. As contemporary scholars, it is imperative to approach this tradition not merely as an artifact of ritualistic antiquity but as a dynamic process of cultural preservation. The Freehold’s commitment to integrating tradition with pragmatism, especially through the stewardship of The Veil, constitutes a critical adaptive strategy that sustained sociopolitical coherence through epochs of external fragmentation. This study aims to critically examine the Vigil as both a symbolic and practical reinforcement of the Compact’s ethos, with particular attention to how this ritual facilitated intergenerational continuity of moral and social values, ultimately shaping the robust communal identity that defines contemporary Freehold society.
#### The Veil as Cultural Custodian:
The Veil, emerging from the post-collapse adaptation of preexisting religious and cultural practices, evolved into a matriarchal order central to maintaining the Freehold’s ethical architecture. This evolution was characterized not by rigid preservation but by adaptive synthesis, wherein ceremonial gravitas was merged with pragmatic domestic guidance. The Veil functioned as a moral custodian, particularly within the familial sphere, where its influence was most profoundly exercised. Veilmother Cordelia’s role during the Winter Vigil exemplifies this dual function of leadership and philosophical stewardship, as her guidance articulated not only the ritual's procedural elements but also the embedded moral philosophy that would shape the initiates' worldview.
#### Ritual Dynamics and Symbolism:
The Winter Vigil is fundamentally an enactment of moral endurance, wherein the initiate’s voluntary approach to the brazier represents an acceptance of communal responsibility through individual fortitude. The design of the ritual deliberately positions physical endurance as a metaphor for moral resilience, encapsulating the Freehold’s conviction that true strength is inherently silent and steadfast. As the initiate moves toward the brazier, kneeling in proximity to the flame, the act becomes a performative affirmation of the Compact’s call for measured, principled strength rather than ostentatious assertion. The structured progression from the outer circle to the brazier symbolizes a journey from collective dependency to personal sovereignty, reflecting the Compact's ethos that leadership is merited through tested perseverance.
#### The Copper Plate Rite:
The Copper Plate Rite, integral to the Vigil, embodies the transformative philosophy of the Freehold. The heated copper plate, inscribed with the flame symbol and lifted from ashes, is held aloft despite discomfort, symbolizing the embrace of hardship as an essential component of sovereignty. The fleeting burn, leaving a transient mark, underscores the philosophical assertion that genuine resilience is born of confronting and integrating suffering, rather than circumventing it. This rite functions not merely as a test of physical tolerance but as a pedagogical imprinting of the Freehold’s ethos—an allegory of death and rebirth integral to personal and communal maturation.
#### Symbolic Implications and Societal Continuity:
The deliberate imposition of discomfort during the Vigil underscores a fundamental tenet of Freehold philosophy: suffering, when purposefully endured, refines the individual and, by extension, fortifies the community. The Copper Plate Rite exemplifies the doctrine that hardship, when faced with deliberate resolve, engenders moral clarity. This paradigm of voluntary suffering as a crucible for leadership remains a cornerstone of the Freehold’s ideological framework, fostering a collective ethos rooted in patient perseverance rather than impulsive dominance. Furthermore, the initiation rite serves as a microcosm of the Freehold's broader sociocultural ethos, where personal sacrifice is inextricably linked to communal stability.
#### Interpretive Analysis:
Current historiographical interpretations often err by neglecting the interconnectedness of the Vigil with broader sociopolitical dynamics. By isolating the rite as a mere ceremonial endurance, scholars risk overlooking its function as a structured pedagogical tool for inculcating moral resilience. This study posits that the Vigil, far from being a vestigial tradition, actively cultivated a pragmatic ethic of endurance that proved crucial in the Freehold’s sustained sociocultural coherence. This coherence, rooted in ritual reinforcement of moral tenets, enabled the Freehold to navigate existential threats without succumbing to internal decay.
#### Cultural and Societal Implications:
The enduring significance of the Winter Vigil lies in its dual function as both a rite of passage and a communal reaffirmation of the Freehold’s meritocratic principles. By fostering individual accountability within a collective moral framework, the Vigil reinforced the Compact’s foundational premise that leadership is merited through demonstrated resilience. The integration of personal trial into communal identity formation exemplifies how the Freehold maintained its internal stability despite external societal fragmentation. This ritual, therefore, is not merely commemorative but constitutive of the Freehold's enduring cultural legacy.
#### Conclusion:
The Winter Vigil of XLII.II at Sapelo remains a paradigmatic example of ritual as a vehicle for social continuity within the Lowcountry Freehold. Its deliberate amalgamation of symbolic endurance with moral instruction illustrates the Freehold’s adaptive strategy of embedding philosophical imperatives within lived tradition. As modern scholars, it is incumbent upon us to engage with these practices not merely as remnants of a bygone era but as foundational elements that cultivated the durable sociocultural ethos underpinning our current stability.
#### References:
- Vance, C. (Epoch LII). "The Compact and Cultural Continuity: An Oral History." Archive of Freehold Studies, Emberwell Hall.
- Harlowe, E. (Epoch LX). "The Flamekeepers: Guardians of Tradition." Journal of Sociocultural Persistence, Vol. 22, pp. 45-72.
- Morgan, T. (Epoch LXV). "Endurance Through Ritual: The Role of The Veil in Cultural Preservation." Lowcountry Academic Press.
- Cordelia, V. (Epoch XLII). "Reflections on the Flame: An Instructional Account." Collected Teachings of The Veil.
- Emberwell Institute (Epoch XC). "The Evolution of Freehold Rites: From Custom to Philosophy." Advanced Studies in Cultural Integration.
-
-
 @ fd78c37f:a0ec0833
2025-03-29 04:33:01
@ fd78c37f:a0ec0833
2025-03-29 04:33:01YakiHonne: I'm excited to be joined by our guest Piccolo—thank you very much for being here. Before we dive in, I'd like to briefly introduce YakiHonne. YakiHonne is a decentralized media client built on the Nostr protocol, leveraging technology to enable freedom of speech. It empowers creators to fully own their voice and assets while offering innovative tools such as Smart widget , Verified Notes, and support for long-form content. Today, we’re not just discussing YakiHonne, but also diving into your community. Piccolo, could you start by telling us a bit about yourself and your community?
Piccolo:Hi, I'm Piccolo. I run BO฿ Space in Bangkok, and we also have a satellite location called the BO฿ Space corner in Chiang Mai, thanks to the Bitcoin Learning Center. Piccolo:Regarding my background,I originally came from corporate finance and investment banking. I was in that field for about 20 years, with the last 15 spent running my own firm in corporate finance advisory alongside a couple of partners. We eventually sold the advisory business in 2015, took a short break, and in 2016, I ended up launching a fintech company, which is still operational today. The company specializes in equity crowdfunding and is licensed by the SEC in Thailand. Piccolo:I first bought Bitcoin a few years before truly understanding it, initially thinking it was a scam that would eventually collapse. However, in 2017, the block size wars demonstrated the protocol’s strong resistance to attacks on decentralization, which deeply impacted me. By late 2018 or early 2019, I started to really grasp Bitcoin and kept learning. Then, in mid-2022, after having fully fallen down the Bitcoin rabbit hole, I founded BO฿ Space. It was right after COVID, and since the fintech had scaled down, there was extra space. We started by hosting meetups and technical workshops for people who were interested. Piccolo:In the early years, we had various groups come by—like the team from BDK (Bitcoin Development Kit), who held workshops. The people behind the Bitcoin Beach Wallet, which later became Blink, also visited. So, BO฿ Space initially functioned as a meetup and technical workshop space. Eventually, we launched the BOB Builders Residency program, which was a lot of fun. We secured grant funding for developers under different cohort themes, so that they can collaborate and co-work for a few months. So far, we have completed three cohorts.
YakiHonne:How did your community get started, and what did you do to attract new members in the beginning?
Piccolo:The initial members came through word of mouth and invitations that I sent out. I reached out to an initial group of Bitcoiners here in the city who I believed were strong maximalists or Bitcoin-only supporters, back when that was still a thing. I sent out 21 invitations and had our first meetup with 21 people, most of whom I had interacted with online, though some in person during the COVID years. From there, it spread by word of mouth, and of course, through Twitter and meetup.com. So, I would say that word of mouth remains the main method of growth. Additionally, when people come through Bangkok and are looking for a Bitcoin-only meetup, there really isn't one available. I believe there are a couple now—maybe two or three—but when we started, there weren’t any, especially not a dedicated Bitcoin-only space. I think we may still be the only one in Bangkok. So yeah, word of mouth was definitely the main way we grew. Bitcoiners tend to share their finds when they meet like-minded people.

YakiHonne:Didn’t you have people in your community who initially thought Bitcoin was a scam, like you did, or face similar issues?
Piccolo:Yes, it still happens, especially when the price of Bitcoin rises. Newcomers still join, and some of them believe Bitcoin might be a scam. However, this has become less frequent. The main reason is that when people come to BO฿ Space, they know it’s a Bitcoin-only meetup. We generally don’t discuss the price; instead, we focus on other aspects of Bitcoin, as there are many interesting developments in the space.
YakiHonne:What advice would you give to someone looking to start or grow a Bitcoin-focused community in today’s world? Considering the current landscape, much like your own experience, what guidance would you offer?
Piccolo:It sounds simple, but just do it. When it comes to community building, you don’t necessarily need a physical space. Community is about people coming together, right? Two people can start a community, then three, four, and so on. Meetups can happen anywhere—your favorite bar, a restaurant, a friend’s garage, or wherever. So, just do it, but make sure you have more than one person, otherwise, how can you build a community? Once you have more than one person, word of mouth will spread. And as you develop a core group—let’s say more than five people—that’s when I think the community can truly sustain itself.
YakiHonne:I know you’ve mentioned the technical side of your community, but I’ll ask anyway—does your community engage with the technical or non-technical aspects of Bitcoin? Or perhaps, is there a blend of both?
Piccolo:I would say both. It really depends on the monthly themes of our meetups. For example, February was focused on Asian communities in Bitcoin. During that month, community leaders came in to give presentations and discuss their work in places like Indonesia, India, and more recently, someone from HRF (Human Rights Foundation) talked about Bitcoin’s use case in Myanmar. Then, in December, we had a very technical month—Mining Month. It was led by our Cohort 3 residents, where we discussed Stratum V2 and had a demo on it. We also examined the Loki board hardware, and Zack took apart the S19, looking at different ways to repurpose the power supply unit, among other things. So, it’s a mix of both, depending on the theme for that month. Some months are very technical, while others are more community-focused and less technical.
YakiHonne:What advice would you give to a technically inclined individual or organization looking to contribute meaningfully to the Bitcoin ecosystem?
Piccolo:For technically inclined individuals, I would suggest identifying your favorite open-source project in the Bitcoin ecosystem. Start from Bitcoin Core and explore different layers, such as Lightning or e-cash, and other open-source projects. As for technically inclined organizations, if you're integrating Bitcoin into your business, I would say, first, make sure you have people within your organization who truly understand Bitcoin. Build a capable team first, and then, depending on the part of the Bitcoin ecosystem you’re involved in—whether it’s custody services, Lightning payments, layer 2, or something like Cashu or Ark—find your niche. From there, your team will work with you to discover ways to contribute. But until you build that capability, organizations are a bit different from individuals in this space.
YakiHonne:How do you see the world of Bitcoin communities evolving as technology matures, particularly in areas like scalability, privacy, and adaptability with other systems?
Piccolo:That's an interesting question. If we think about the future of Bitcoin communities, I believe they may eventually disappear as technology matures. Once Bitcoin scales to a point where it integrates seamlessly with other payment systems, becoming part of the everyday norm, the need for dedicated communities will diminish. It’s similar to how we no longer have meetups about refrigerators or iPhones, even though they are technologies we use every day. As Bitcoin matures, it will likely reach that level of ubiquity. There might still be occasional meetups or forums, but they will be more about specific knowledge, use cases, and tools, rather than a community dedicated to introducing others to the technology itself. However, this is a long way off. Bitcoin is still relatively small compared to the global fiat financial system, despite the growth we want to see. So, it will take a long time before we reach that stage.
YakiHonne:It’s something I hadn’t considered before, and it’s quite insightful. Moving to our last question actually which I find very interesting is the government around you for or against bitcoin and how has That affected the community.
Piccolo:In my opinion, on a general level, the government is more supportive than opposed to Bitcoin. The Thai government classifies Bitcoin as a digital asset, almost like digital gold. In that sense, they want to tax capital gains and regulate it. They also have a regulatory framework for it, known as the Digital Asset Regulatory Sandbox, where you can test various things, mainly coins and tokens. It's unfortunate, but that’s how it is. However, our government, especially the regulatory bodies, are open to innovation. They recognize that Bitcoin is different, but they still view blockchain and tokens as useful technologies, which is somewhat misguided. So, in that sense, it’s more support than opposition. A couple of years ago, there was a circular discouraging the use of Bitcoin as a payment currency, mainly because they can't control its monetary policy. And they’re right—Bitcoin can’t be controlled by anyone; there’re the protocol and the rules, and everyone follows them, unless there’s a hard fork, which is a different matter. So, in that regard, Bitcoin is definitely categorized as a digital asset by the government, and that’s where it stands. Piccolo:People who come to BO฿ Space to learn about Bitcoin are often influenced by the government from the point of price movements; especially when government support moves the price up. But they usually only visit once or twice, especially if they’re not deep into the Bitcoin rabbit hole. They often get disappointed because, at BO฿ Space, we rarely discuss the price—maybe once a year, and that’s just after the meetup when people are having drinks. So, in that sense, I’d say the government currently doesn’t really hurt or help the community either way. People will go down the rabbit hole at their own pace. And if you're not a Bitcoiner and you come to a BO฿ Space meetup with a crypto focus, you might be surprised by the approach we take.
YakiHonne:Thank you, Piccolo, for your time and insights. It’s been a pleasure speaking with you. Your perspective on the evolution of Bitcoin communities was eye-opening. It's clear that your deep understanding of Bitcoin is invaluable. I'm sure our readers will appreciate your insights. Once again, thank you, Piccolo. I look forward to seeing the continued growth of BO฿ Space and Bitcoin adoption.
-
 @ a30cdfee:2d2f97ff
2024-08-28 21:59:20
@ a30cdfee:2d2f97ff
2024-08-28 21:59:20Understanding UTXO Consolidation for Bitcoin Users
Bitcoin blockchain fees are currently low, so it's time to get familiar with UTXO consolidation!
What is UTXO consolidation and why should you care?
Many Small UTXOs Can Incur High Transaction Fees in the Future
If you've been dollar-cost averaging small chunks of bitcoin to a self-custody wallet, you might have a lot of small-value UTXOs (Unspent Transaction Outputs) in your wallet.
When transaction fees will rise again, spending these UTXOs can incur hundreds or even thousands of dollars in transaction fees!
When you transact in Bitcoin, fees paid to miners are determined by the network demand, and how much data the transaction requires to be sent.
The Bitcoin network is designed to handle only a limited amount of data every 10 minutes on average in order to keep the data on the blockchain small enough for average users to run nodes and audit the blockchain.
The trade-off is high transaction fees during high network demand.
You can always set a lower fee for your transaction, but then you will often have to wait longer for your transaction to be included on the blockchain.
The total fee for a transaction is calculated by multiplying the transaction size with the fluctuating fee rate.
The fee rate is measured in satoshis per virtual byte (sat/vByte).
A good website to familiarize yourself with the current Bitcoin fees is Mempool.space.
You can learn more about it in this post: https://stacker.news/items/657963
The transaction size increases the more UTXOs it has.
The monetary value of BTC being spent doesn't have an effect on the transaction fee.
You can send $50 or $1 billion worth of BTC with the same transaction fee.
What Is an UTXO?
Your bitcoin balance consists of UTXOs.
When you receive BTC, you receive a single UTXO.
The more often you receive, the more UTXOs you will accumulate.
When you're sending BTC, your wallet software picks UTXOs from your wallet and sends them to the receiver.
Your wallet might have to pick many different UTXOs.
If the BTC amount of your UTXOs exceeds the amount you're sending, you will receive a new UTXO as "change".
Conceptually, UTXOs are very similar to physical cash.
You can think of UTXOs in your Bitcoin wallet as different denominations of a currency, e.g. $10 bill, $20 bill etc.
Except that Bitcoin doesn't have specific denominations: a Bitcoin UTXO can be of any amount!
The balance of your Bitcoin wallet is the sum value of all your UTXOs in that wallet.
UTXO is like a bill in your Bitcoin wallet that hasn't been spent yet.
When your wallet has to pick many UTXOs to make a transaction, the network fees you pay will be higher.
You can think of it as sending someone $1000 in coins vs. sending $1000 in hundred dollar bills.
Coins will weigh more and their postage costs will be higher.
Bitcoin wallets automatically select the lowest number of UTXOs to minimize transaction fees, and some have coin control features that let you select UTXOs manually.
A recommended wallet for desktop is Sparrow Wallet.
Sparrow also works with the most popular hardware wallets.
You can learn more about Sparrow in this Twitter thread I wrote in September 2023.
How to Consolidate UTXOs?
You're just selecting UTXOs of small monetary value and sending them to yourself when fees are low, and you will receive one UTXO with a larger monetary value.
Here it can be demonstrated with some testnet coins on Sparrow Wallet.
The process is exactly same with real BTC.
In the "UTXOs" tab, you select the UTXOs you want to consolidate, and proceed to "Send Selected".
On the "Pay to" field there's a dropdown that automatically chooses a new Bitcoin address in the same Sparrow Wallet that you own (it's labelled as a "consolidation" address).
Alternatively, you can copy/paste any address there.
If you want to verify that you really own the address, you can go to the "Addresses" tab, find the address in question and sign a message with it.
If you're e.g. using a hardware wallet like Coldcard or Trezor, the signing device's firmware will at this point verify that it manages the address.
It's important to label your UTXOs, so you will know in the future what UTXOs to spend and in what situations.
Labels are only for your own reference.
Do it.. your future self will thank you!
You can see the flow of UTXOs on Sparrow.
Two small UTXOs turn into one (minus the miner fee).
It's a bit like exchanging small coins to larger bills!
When you go back to the "UTXOs" tab, you can see that you now only have one larger UTXO, but the same amount of BTC (minus the miner fee).
Mempool.space gives you nice visualizations for UTXO consolidation.
In this transaction, 4 UTXOs were consolidated into one (minus the miner fee).
Since Bitcoin is digital gold, UTXO consolidation is like melting small gold coins into one gold bar!
UTXO Consolidation Reduces Privacy
A major trade-off with consolidating UTXOs relates to privacy.
People who sent you the small UTXOs you want to consolidate can follow the movement of those UTXOs and link them to your now larger UTXO balance.
It's not an absolute proof that you own those UTXOs (you could be sending them to someone else!), but it might be a strong indication.
It's always the best practice to assume that whoever sent you those original UTXOs is watching and knows that you own all that bitcoin.
Also, there are privacy concerns if you spend after consolidating.
If you spend from a large UTXO (let's say 1 BTC), and buy something worth $50 (0.0008 BTC) with it, the receiver can see that you will get a change and are the owner of an UTXO of 0.9992 BTC.
"Dust" UTXOs
When you have smaller UTXOs, they might become economically infeasible to spend in a high fee environment (fee higher than the monetary value of the UTXO).
It's hard to know exactly what the future fee market will look like, but it can be assumed that the Bitcoin blockspace will be in high demand and the fees will rise.
Here's a good article by Unchained about unspendable "dust" UTXOs.
Jameson Lopp has created a useful tool called "Economically Unspendable Bitcoin UTXO Calculator" that can be used to project transaction fees in different fee environments with different address types.
To Consolidate or Not?
It depends on your personal preferences and how you're intending to spend your bitcoin in the future.
It's good to strive for a balance, taking into consideration the future fee market and the privacy concerns, and still remember that it's better to have spendable UTXOs that have lost some privacy than unspendable private UTXOs.
Never consolidate KYC coins with non-KYC coins!
The consensus among Bitcoiners is to avoid dust UTXOs as much as possible, and try to keep your UTXOs at 1 million sats minimum (0.01 BTC and around $600 in August 2024's prices).
It's been estimated that this threshold would secure your UTXOs being spendable even in a prolonged high-fee environment.
If you're ever in an emergency and need to spend your bitcoin, it's good to know that you will not spend most of your coins on fees!
Some recommend striving for even larger UTXOs, like 10 million sats (0.1 BTC) in case Bitcoin becomes a world reserve currency or hits mass adoption.
UTXO consolidation is extremely important for Bitcoiners with many small value UTXOs (e.g. Bitcoiners in Global South that have been saving $10 per week in BTC on-chain to self-custody wallets).
If fees go high, a Bitcoin UTXO worth $10 might become unspendable.
If you're mostly a hodler and you've been buying BTC in large purchases at a time, you generally don't have to worry too much about UTXO consolidation.
Send Small UTXOs to the Lighting Network for Spending!
Instead of consolidating UTXOs to an on-chain address, you can also open Lightning Network channels with them or send them to a Lightning wallet for easier spending.
Lightning Network also adds a layer of privacy to the UTXOs.
If you're buying bitcoin through an exchange, it might make sense to accumulate a large enough UTXO before you move the funds to self-custody.
Or you can use e.g. Liquid Network @liquid as an intermediary layer for storing coins in self-custody.
As a federated sidechain, Liquid has its own trade-offs.
You can learn more about Liquid in this Twitter thread I wrote in February 2024.
UTXO consolidation reduces the number of UTXOs in the network, which makes it easier to run a full Bitcoin node.
So consolidation has benefits to the network as well!
It can also streamline your own wallet experience.
Signing data-heavy transactions can be a burden to older hardware wallets that might even crash in the process!
What's your strategy for UTXO consolidation?
What's the ideal size of an UTXO in your opinion?
Additional Resources
https://www.youtube.com/watch?v=Mqe0QCxjKpI @BTCsessions
https://www.youtube.com/watch?v=krrUQGMKhPo
What is ‘UTXO consolidation’ and how can it help me reduce transaction fees?
How to Manage Bitcoin UTXOs and Save on Transaction Fees
originally posted at https://stacker.news/items/664880
-
 @ 35f3a26c:92ddf231
2024-08-28 20:30:59
@ 35f3a26c:92ddf231
2024-08-28 20:30:59The italian press ilPost stated that Pavel Durov is out, a bale of 5 million Euros, can't leave the country and has to go to a police station twice a week...
The known 12 charges leaked apparently are correct.
Link in Italian: https://www.ilpost.it/2024/08/28/pavel-durov-liberta-vigilata-francia/
telegram
pavel
originally posted at https://stacker.news/items/664822
-
 @ b83a28b7:35919450
2024-08-28 15:03:25
@ b83a28b7:35919450
2024-08-28 15:03:25Join nostr:npub1tvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq0rkrq4 and me for episode 76 of nostr:npub14kw5ygpl6fyqagh9cnrytyaqyacg46lzkq42vz7hk8txdk49kzxs04j7y0 this Friday, August 30th at 3pm ET (UTC -4)
Our guest this week is nostr:npub1xv8mzscll8vvy5rsdw7dcqtd2j268a6yupr6gzqh86f2ulhy9kkqmclk3x from nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm who joins us to provide the lowdown on the recently launched Alby Hub
You don't want to miss this one!
Set your blockclocks!
https://nostrnests.com/
[This is our first show announcement made from a long-form client, in keeping with QW and my #otherstuffchallenge]
-
 @ 2183e947:f497b975
2025-03-29 02:41:34
@ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison.
I can't tell you how to create your own accounts because it was made very clear that only some of the software is currently open source, and how this will all work is still a bit up in the air. The code that is open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core
You can also learn more about Pubky here: https://pubky.org/
That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key.
Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis.
Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed.
Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message.
I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key.
As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster.
Based on all of this info, it seems like, to populate your feed, this is the series of steps:
- you tell your homeserver your pubkey
- it uses some sort of algorithm to decide whose posts to show you
- then looks up the homeservers used by those people on an indexer server
- then it fetches posts from their homeservers
- then your client displays them to you
To create a post, this is the series of steps:
- you tell your homeserver what you want to say to the world
- it stores that message in plaintext and merely asserts that it came from you (it's not signed)
- other people can find out what you said by querying for your posts on your homeserver
Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver.
John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted.
Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
-
 @ df06d21e:2b23058f
2025-03-29 02:08:31
@ df06d21e:2b23058f
2025-03-29 02:08:31Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust.
Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement.
Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification.
Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation.
And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination.
Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars.
Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them.
We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new?
-
 @ 02526939:3e88afa2
2024-08-28 13:15:42
@ 02526939:3e88afa2
2024-08-28 13:15:42- Pharmacotherapeutic category:
21 Million Bitcoins approx.
- Therapeutic indication:
The administration of Orange Pill approx. 21 million. it is absolutely recommended if you suffer from the inflationary financial system in which we are immersed, especially in young people.
- Contraindications:
Side effects from the administration of Orange Pill approx. 21 million. they can be various: Obsession with libertarian economic themes. Incessant study of the economic and social paradigms described by the Austrian school. Probable disgust towards the innocent employee of the municipal registry office, caused by the natural obsession with anti-statist political themes. Deepening of the political theory of Libertarianism, often resulting in anarcho-capitalism, agorism and the like. Reckless accumulation of texts and writings by authors such as Rothbard, von Hayek, von Mises etc. Sudden and absolute interest in red meat, tobacco and alcohol, but only of extremely high quality. But not always: in some patients a diametrically opposite effect has been observed: adoption of third world theories, fight for LGBT+ and minority rights in general, Birkenstock sandals and radical-chic attitudes. These behaviors, in total contrast to the classic libertarian theories of which those who take Orange Pill approximately 21 million are usually victims, are currently the subject of study and research. Also because libertarian theories, as the name itself specifies, leave total freedom to the individual to express himself as he prefers following the principle of non-aggression. Sudden interest in the armed defense of private property. Visible decay in the way one dresses and takes care of one's physical appearance. To give an example: the rag scene. Fantozzi who, having finished reading Marx's Capital, with unkempt hair, wool sweater and red scarf, stands up banging his fists on the table exclaiming: "they have always lied to us!". You will start to look at others differently. Once upon a time you too were like this. They don't know that Halving is coming soon. They don't know that the generational opportunity train is passing by and they will miss it. Suddenly every room you enter will be filled with completely ignorant norms: They don't know that the United States is printing money uncontrollably by recklessly raising the debt ceiling. The money in your pocket is losing value with every passing second! But how can you be so happy? Stop laughing and partying! We must destroy the state and create a civil society based on a healthy non-inflationable currency!
- Administration:
Anyone can prescribe Orange Pill 21 million approx. The advice is to contact your trusted advisor. Possibility of free administration to friends, relatives and acquaintances, aware that the reaction could be one of repudiation, disgust and denial. High probability of seeing yourself disinherited by your parents, convinced that you are even worse than those who gamble.
- Dosage:
Free, at will. The more you take, the further you enter the rabbit hole, the harder it will be to get out.
- Pregnancy and breastfeeding:
Highly recommended for pregnant women and new mothers. Infants and children under four years of age: Administration to infants and children under four years of age is highly recommended. It is never too early to become a sovereign individual.
- Overdose:
There is no limit to the intake of Orange Pill 21 million approx.
- Reporting side effects:
Any unwanted effects will be noticed from the tweets that will be published on X following the administration of Orange Pill 21 million approximately.
- Benefits:
After taking Orange Pill 21 million approximately, the overall vision will appear in all its clarity. The total revulsion towards the transfer of money in exchange for goods and services. Every expense will appear stupid and unmotivated. In some cases subject to in-depth studies, a tendency has been noted to want to spend Bitcoin to demonstrate its characteristic as a p2p currency. Savings: the time you dedicate to an activity will have a completely different meaning. Your mind will make an immediate switch from a consumer economy like the one in which we are immersed, to a savings economy, where every expense will be considered and weighed. Your time horizon will rise exponentially. Time: it will take on a completely different value. You will begin to monetize it in a currency that protects against inflation and does not subtract value from your work. You will start saving in Bitcoin, which you will jealously guard in cold storage. You will understand how the fiat system is supported by a bureaucratization created specifically to discourage every entrepreneurial initiative in the bud, nipping it under tons of rules, regulations and paperwork and instilling fear, doubts and perplexity in the entrepreneur. The Work: You will begin to transfer every aspect of Bitcoin into your work. The entrepreneurial spirit will pervade your body, you will immediately benefit in carrying out daily tasks. After a period of administration, you will try to contribute to the Bitcoin cause, taking advantage of it to collect some satoshis of your own. Only then will you understand the difference between good money and bad money. The difference between carrying out a work task in fiat mode and carrying it out in Bitcoin mode will clearly show the philosophy behind this cryptographic protocol. Separating the sound coin from the rotten one will become an automatic exercise in every moment of your life. Your assets: as already written in the Savings section, your lifestyle will unconsciously shift from a consumer economy towards a savings one. Spending money on clothing and short-lived items will seem silly to you. You will treat your items much better by replacing them only once they become unusable. And even then, after having repaired and treated them with care, you will try to find an alternative use for them. Throwing them in the garbage will only be a last resort. Bitcoin is circular economy, savings and ecology. Your hardware: You'll look at your PCs, your phones, even your refrigerator and oven, thinking about ways to make money from their work. Probably, one way or another, they will become Bitcoin nodes to be photographed and posted on X. Your general interests: You'll start to notice things you didn't notice before. The intrusion of economics and politics into every aspect of common life, such as culture, science and school. You will begin to think about your life and the lives of those around you. Your interests will change until they align with the new theory you are embracing. You'll think about Bitcoin all day, but you'll never think about its price in terms of vulgar fiat money. If you've reached that point, the price will just be a breeze that tickles you and goes away. The motto "If you don't believe me or don't understand, I don't have time to try to convince you, I'm sorry" will mark your days. As mentioned above, your time will suddenly become too precious to try to empty the sea with a bucket. Time is always a gentleman.
- License holder:
Nobody. Bitcoin is completely transparent open source software. Today, Bitcoin is constantly updated by the best computer developers in the world.
- Producer:
Satoshi Nakamoto is the material author of the software. His creation, Bitcoin, is just the culmination of decades of cypherpunk thinking.