-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 6e64b83c:94102ee8
2025-05-05 16:50:13
@ 6e64b83c:94102ee8
2025-05-05 16:50:13Nostr-static is a powerful static site generator that transforms long-form Nostr content into beautiful, standalone websites. It makes your content accessible to everyone, even those not using Nostr clients. For more information check out my previous blog post How to Create a Blog Out of Nostr Long-Form Articles
What's New in Version 0.7?
RSS and Atom Feeds
Version 0.7 brings comprehensive feed support with both RSS and Atom formats. The system automatically generates feeds for your main content, individual profiles, and tag-specific pages. These feeds are seamlessly integrated into your site's header, making them easily discoverable by feed readers and content aggregators.
This feature bridges the gap between Nostr and traditional web publishing, allowing your content to reach readers who prefer feed readers or automated content distribution systems.
Smart Content Discovery
The new tag discovery system enhances your readers' experience by automatically finding and recommending relevant articles from the Nostr network. It works by:
- Analyzing the tags in your articles
- Fetching popular articles from Nostr that share these tags
- Using configurable weights to rank these articles based on:
- Engagement metrics (reactions, reposts, replies)
- Zap statistics (amount, unique zappers, average zap size)
- Content quality signals (report penalties)
This creates a dynamic "Recommended Articles" section that helps readers discover more content they might be interested in, all while staying within the Nostr ecosystem.
See the new features yourself by visiting our demo at: https://blog.nostrize.me
-
 @ 6e0ea5d6:0327f353
2025-05-04 14:53:42
@ 6e0ea5d6:0327f353
2025-05-04 14:53:42Amico mio, ascolta bene!
Without hesitation, the woman you attract with lies is not truly yours. Davvero, she is the temporary property of the illusion you’ve built to seduce her. And every illusion, sooner or later, crumbles.
Weak men sell inflated versions of themselves. They talk about what they don’t have, promise what they can’t sustain, adorn their empty selves with words that are nothing more than a coat of paint. And they do this thinking that, later, they’ll be able to "show who they really are." Fatal mistake, cazzo!
The truth, amico mio, is not something that appears at the end. It is what holds up the whole beginning.
The woman who approaches a lie may smile at first — but she is smiling at the theater, not at the actor. When the curtains fall, what she will see is not a man. It will be a character tired of performing, begging for love from a self-serving audience in the front row.
That’s why I always point out that lying to win a woman’s heart is the same as sabotaging your own nature. The woman who comes through an invented version of you will be the first to leave when the veil of lies tears apart. Not out of cruelty, but out of consistency with her own interest. Fine... She didn’t leave you, but rather, that version of yourself never truly existed to be left behind.
A worthy man presents himself without deceptive adornments. And those who stay, stay because they know exactly who they are choosing as a man. That’s what differentiates forged seduction from the convenience of love built on honor, loyalty, and respect.
Ah, amico mio, I remember well. It was lunch on an autumn day in Catania. Mediterranean heat, and the Nero D'Avola wine from midday clinging to the lips like dried blood. Sitting in the shade of a lemon tree planted right by my grandfather's vineyard entrance, my uncle — the oldest of my father’s brothers — spoke little, but when he called us to sit by his side, all the nephews would quiet down to listen. And in my youth, he told me something that has never left my mind.
“In Sicily, the woman who endures the silence of a man about his business is more loyal than the one who is enchanted by speeches about what he does or how much he earns. Perchè, figlio mio, the first one has seen the truth. The second one, only a false shine.”
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
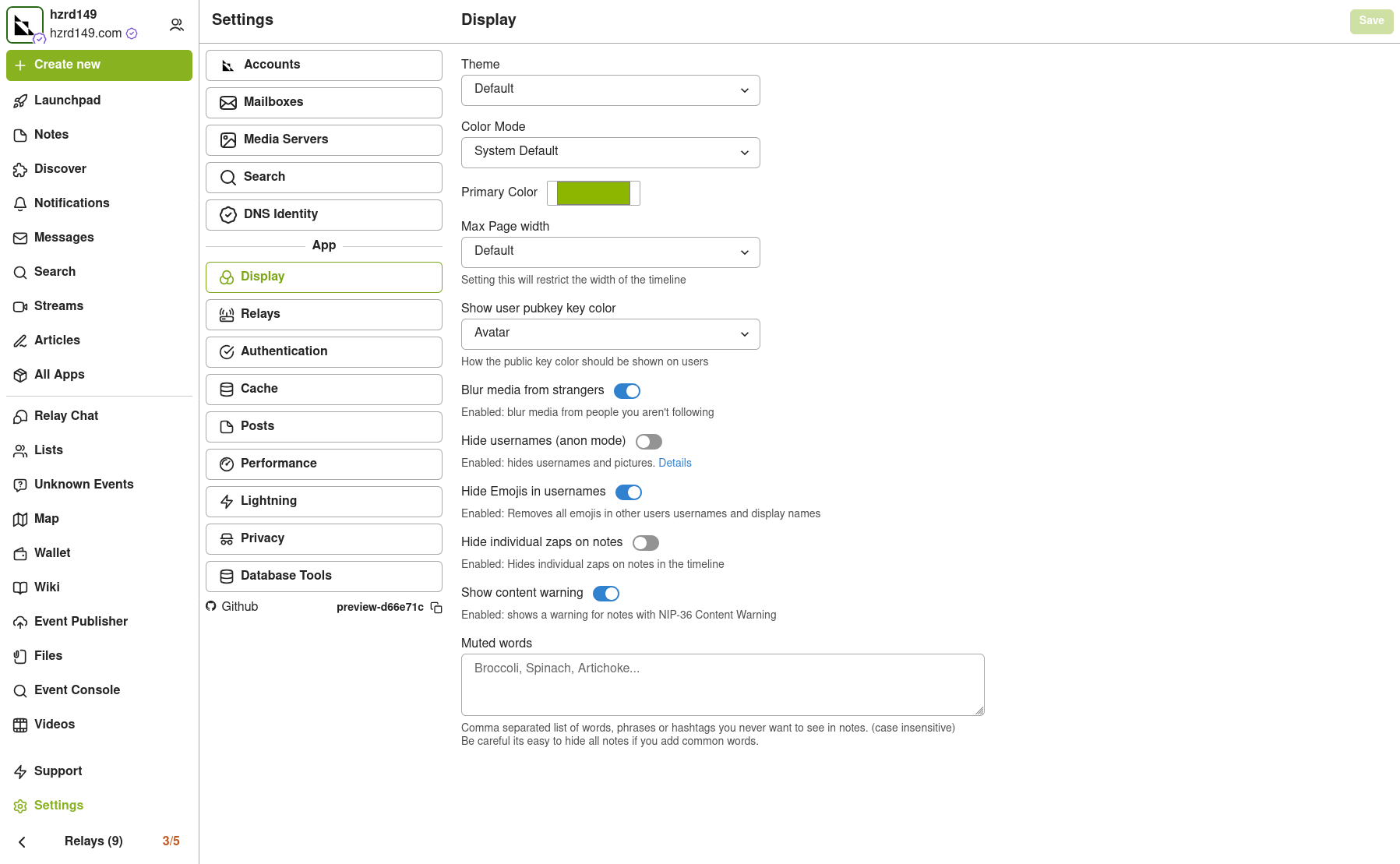
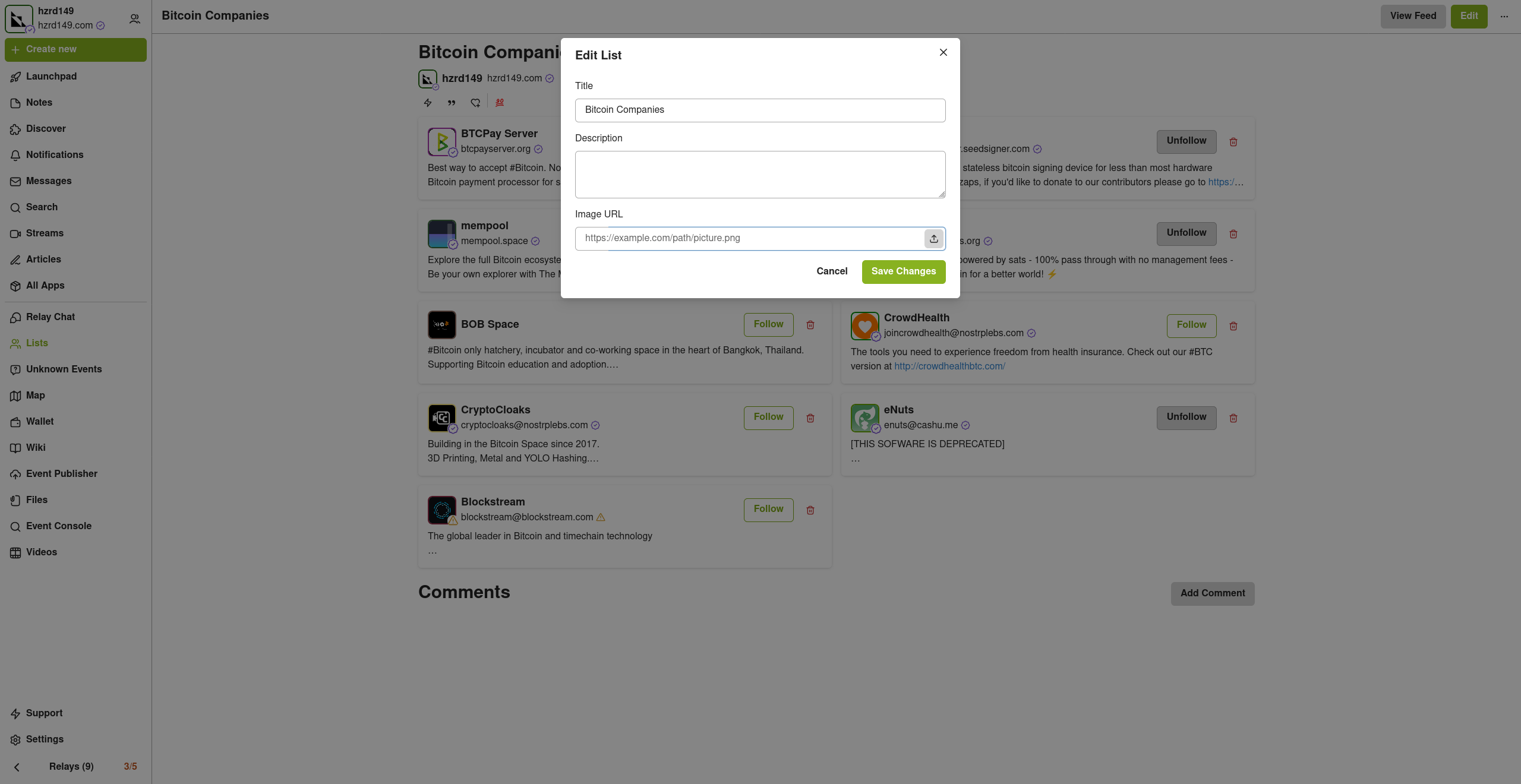
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
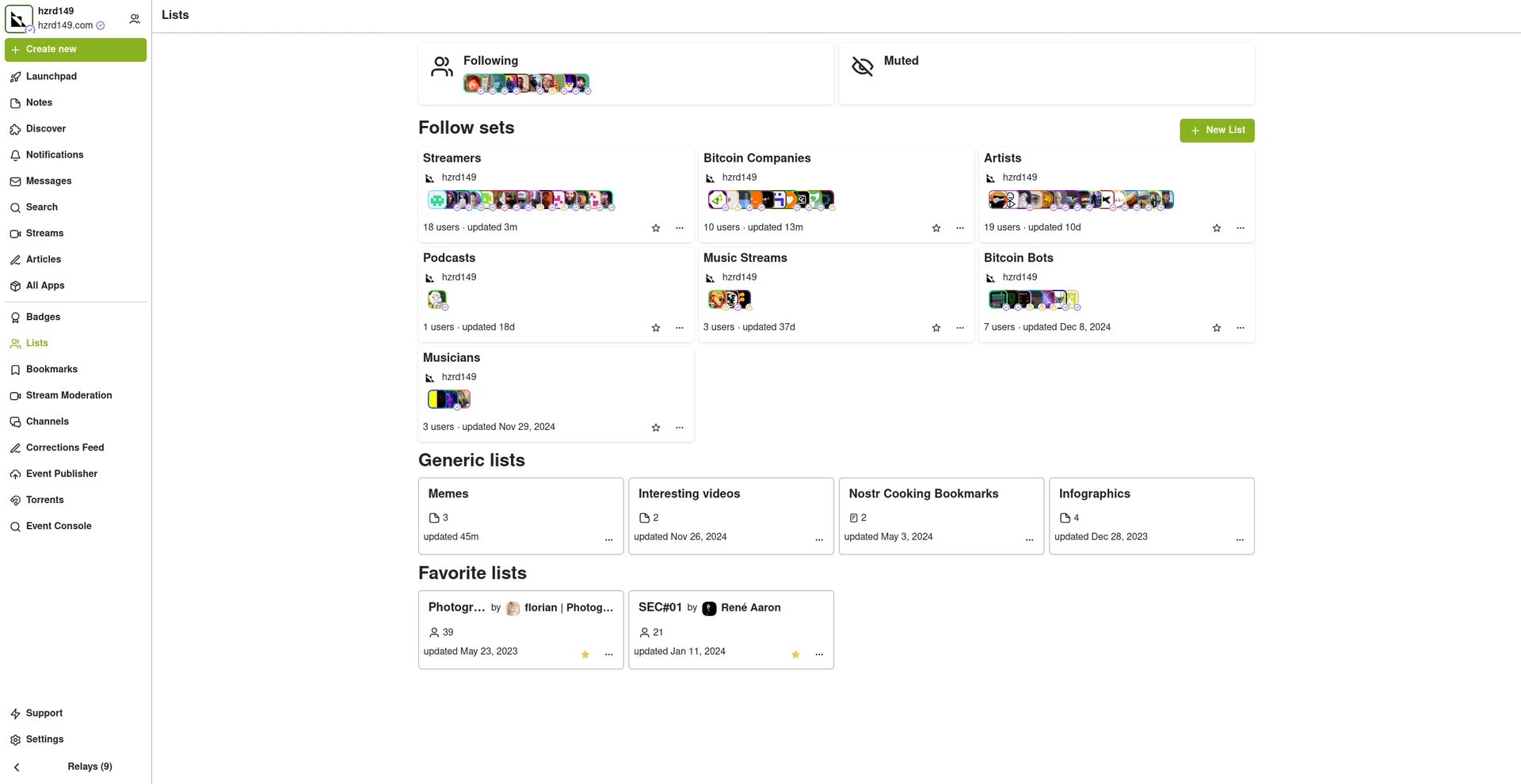
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
New emoji picker
Just another small improvement that makes the app feel more complete.
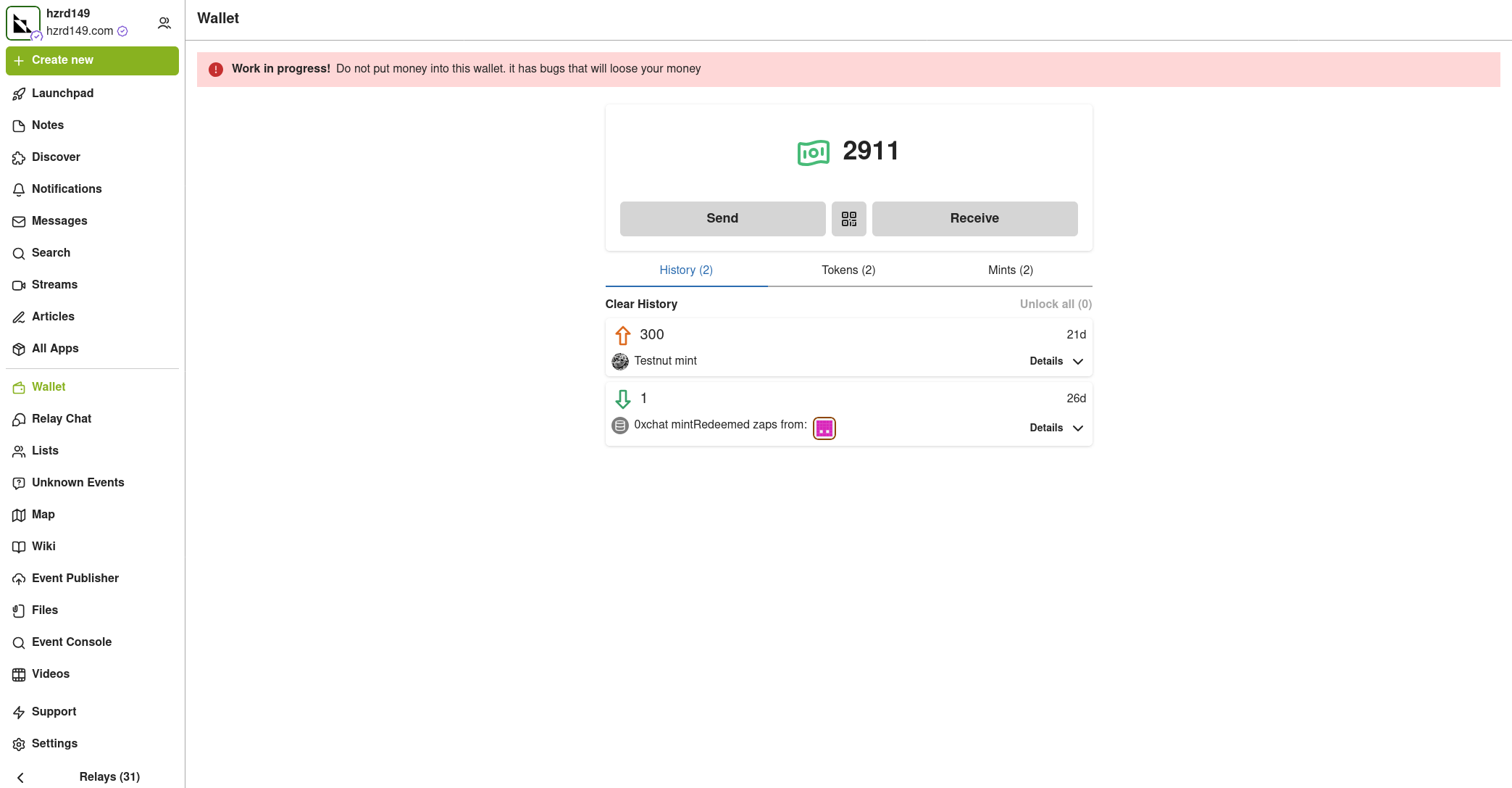
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 84b0c46a:417782f5
2025-05-10 01:45:28
@ 84b0c46a:417782f5
2025-05-10 01:45:28- lumilumi The Nostr Web Client.
Lightweight modes are available, such as not displaying icon images, not loading images automatically, etc.
-
Long Form Content Editor A lightweight Long Form Content Editor with editing functionality for your articles. It supports embedding Nostr IDs via NIP-19 and custom emoji integration.
-
nostr-share-component Demo A simple web component for sharing content to Nostr. Create customizable share buttons that let users easily post to Nostr clients with pre-filled content. Perfect for blogs, websites, or any content you want shared on the Nostr network. Try the interactive demo to see how seamlessly it integrates with your website.
-
Nostr Follow Organizer A practical tool for managing your Nostr follows(kind3) with ease.
-
NAKE NAKE is a powerful utility for Nostr developers and users that simplifies working with NIP-19 and NIP-49 formats. This versatile tool allows you to easily encode and decode Nostr identifiers and encrypted data according to these protocol specifications.
- chrome extension
- firefox add-on
-
nostviewstr A versatile Nostr tool that specializes in creating and editing addressable or replaceable events on the Nostr network. This comprehensive editor allows you to manage various types of lists and structured content within the Nostr ecosystem.
-
luminostr Luminostr is a recovery tool for Nostr that helps you retrieve and restore Addressable or Replaceable events (such as kind: 0, 3, 10002, 10000, etc.) from relays. It allows you to search for these events across multiple relays and optionally re-publish them to ensure their persistence.
-
Nostr Bookmark Recovery Tool Nostr Bookmark Recovery Tool is a utility for retrieving and re-publishing past bookmark events ( kind:10003,30001,30003 ) from public relays. Rather than automatically selecting the latest version, it allows users to pick any previous version and overwrite the current one with it. This is useful for restoring a preferred snapshot of your bookmark list.
-
Profile Editor Profile Editor is a simple tool for editing and publishing your Nostr profile (kind: 0 event). It allows you to update fields such as name, display name, picture, and about text, and then publish the updated profile to selected relays.
-
nostr-bookmark-viewer Nostr Bookmark Viewer is a tool for viewing and editing Nostr bookmark events (kind: 10003, 30001, 30003). It allows users to load bookmark data from relays, browse saved posts, and optionally edit and publish their own bookmark lists.
-
Nostr Note Duplicater Nostr Note Duplicater is a tool that rebroadcasts an existing Nostr event from a relay to other selected relays.
-
 @ 6c05c73e:c4356f17
2025-05-10 01:50:20
@ 6c05c73e:c4356f17
2025-05-10 01:50:20Porque investir R$100
Um guia politicamente diferente de investimento
Você já certamente se pegou na seguinte situação. Paguei tudo o que devia. E, agora me sobrou cem reais para investir.
Principalmente, se você é novo e está no seu primeiro emprego. Isso é muito comum. Contudo, mesmo os mais experimentados passam por isso.
No entanto, vem aquela pergunta na cabeça. Será que eu realmente preciso investir esses cem reais? Afinal, é uma quantia pequena e qual seria o retorno disso?
Contudo, para responder sua dúvida. A resposta é sempre sim. Se, algum dia na sua vida. Você quiser acumular recursos e escapar desse círculo vicioso. Precisa acumular e investir.
Todavia, vamos analisar nesse artigo alguns outros aspectos que podem elevar x10 esse valor investido.
Quando investir R$100?
Agora, amanhã ou ano que vem?
Muitos pensam que todo dinheiro ganho precisa IMEDIATAMENTE ser investido. E, na verdade isso não precisa ser assim.
Portanto, todo o dinheiro ganho deve ser aplicado com diligência. Decidir quando investir o dinheiro é uma tarefa crucial. Mas, antes disso acontecer. Você precisa definir seus objetivos.
Sobretudo, aonde você vai colocar seu dinheiro. Vai determinar o ritmo como investe. E, isso é crucial em uma jornada de investimentos.
Aonde?
**“Para manter uma fogueira, tem que botar mais lenha” ** Espera um pouco. O que essa frase quer dizer? Vamos criar uma situação hipotética aqui e analisar três formas de investimento:
Investir em ações na bolsa de valores (renda variável) Investir em si mesmo (aumentar capacidade)
Primeira hipótese:
Você investiu R$100 o ano todo. Todos os meses. Isso gerou um bruto de R$1.200. Você estudo e se dedicou. Analisou ações, assistiu a vários vídeos e análises. E fez 15% de retorno no ano.
Nessa primeira hipótese, você acumulou R$1.200 + 15% de retorno (R$180). O que te rendeu R$1380 brutos. Com essa quantia a incidência de impostos não existe. Então, sem DARFS por aqui.
Compensou investir 2 horas por dia * 200 dias no ano =1.752.000 min. Para poder ganhar R$180?
Dahhhh, não. Você ficou mais experiente e aprendeu. Mas, a quantia é muito pequena e não faz cócegas. Tampouco te faz sorrir. E te tira dessa situação.
Segunda hipótese:
Eu não sei qual o seu ofício nesse momento. Mas, eu sei de duas coisas. Ou você gosta e quer se especializar. Ou você quer trocar de ofício logo logo. Então, meu consagrado(a). Você já sabe…
Agora, vamos pegar esses R$100 mensais e investir em um curso técnico. Pois, é mais rápido que uma faculdade. Será seu primeiro diploma oficial, te torna alguém e te dá um ofício.
Assim sendo, você tem grandes chances de trocar de trabalho. Ter aumento salarial é certamente no prazo de um ano. Você vai ganhar muitos mais que os R$180 brutos de rentabilidade do primeiro caso.
Agora, quer saber a real porque ninguém te fala isso no YouTube, Instagram e TikTok?
Meu consagrado, as pessoas só te recomendam o que é bom para elas. Não há nada de errado com isso. O que quero te fazer enxergar aqui. É que você está sozinho (ou tem que estar, para refletir) e precisa escolher o que é melhor para você.
Contudo, é importante para para pensar por um tempo e entender o que vai ser melhor para você. Qual melhor caminho seguir. E ponto, só você sabe o que é melhor para você.
Como?
Para fechar nosso raciocínio de hoje. Vamos a pergunta de um milhão de dólares. Mas, como eu faço isso? Meu querido(a), você vai fazer um exercício comigo logo menos.
Você vai deixar seu celular no silencioso. Colocar um timer de 15 minutos. Pegar um papel e caneta e anotar em uma folha o que você gosta + o que você você gostaria de fazer da sua vida.
Logo, essa lista tem que conter o SEU gosto. Não do seu amigo, do influenciador, da celebridade ou do atleta. Essas pessoas tem influência sobre sua vida? Claro! Mas, cabe a você refletir sobre o que realmente quer.
Naturalmente, você não vai colocar lá na sua lista; quero uma Ferrari esse ano. Porque não é assim que funciona. Na real, você pode querer a Ferrari. Sem problema algum.
Mas, saiba que antes da Ferrari. Vai ter que vir o Gol, o Civic, a 325, o 911 e daí a Ferrari. Tudo na vida é passo meu caro(a). Ou você acha que vai dar saltos quânticos na vida sem estar preparado? Não é assim que a vida funciona.
Em suma,
para concluir esse texto. Vamos fazer o resumão prático do que fazer com cem reais mensais:
Tire um tempo para entender o que quer e o que tu gosta. Visualize e anote seus objetivos que quer em uma folha. Invista em você incansavelmente. Você vai chegar ao topo da montanha. Mas, tem que subir um nível por vez.
Se chegou até aqui é porque gostou e quer mudar de vida. Manda pro teu colega que tá precisando desse tapa de luva. Obrigado pelo seu tempo.
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:53:41
@ ba3b4b1d:eadff0d3
2025-05-09 23:53:41Existem seres do tipo "troll" no folclore Português conhecidos como Trasgos, semelhantes a gnomos e duendes. Na interpretação da Vanessa Fidalgo, duende e trasgo seriam sinónimos e ela descreve-os como sendo "refilões, rebeldes, de pequena estatura, nariz arrebatado, tez rugosa, e o povo chama-lhes trasgos ou maruxinhos, que é como quem diz, duendes!"
Escondem-se nas florestas rurais e são famosos por pregar partidas aos viajantes, especialmente aos pastores de ovelhas. Essas criaturas anãs podem aparecer nas lareiras e tornar-se bastante invasivas. Mesmo que alguém se mude de casa, os Trasgos seguem-nos até ao novo lar. Existem rituais que, alegadamente, conseguem expulsar os Trasgos de uma casa.
A natureza jovial e traquina destes seres está relacionada com um Fadário Galego, em que se acreditava que eles eram resultado de crianças que morriam novas, em que a alma ficava presa a uma casa ou a um local agrícola relacionado com a família.
No folclore leonês, são chamados de Trasgos. No folclore castelhano e aragonês, são conhecidos como Martinitos.

Nas Astúrias, o trasgo é conhecido por nomes diferentes, dependendo da localização. Ele é conhecido como Trasno, Cornín ou Xuan Dos Camíos nas Astúrias ocidentais. Ele é conhecido como Gorretín Colorau ou aquele com o "gorro encarnado" (ambos significando "pequeno chapéu vermelho"), nas Astúrias orientais.
Na mitologia Celta, são conhecidos por "Far Darrig" que significa "homem vermelho".
Algumas interpretações sugerem que encarna a natureza caprichosa do destino, lembrando os humanos da imprevisibilidade da jornada da vida. Outras vêem-no como uma representação dos aspectos selvagens e indomáveis do mundo natural, existindo nas margens da compreensão humana.
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:51:07
@ ba3b4b1d:eadff0d3
2025-05-09 23:51:07Outro indício de que as relações entre Celtas e Ibéros não foi unilateral é a existência em solo Irlandês da planta Erica mackaiana, conhecida como Urze Galego ou Asturiano
Esta é uma espécie de urze encontrada exclusivamente nas costas da Galiza, Irlanda, Astúrias e Cantábria. Estas plantas estão sempre localizadas a menos de 10 km das margens, na proximidade de povoações costeiras da Idade do Ferro.
Não são nativas da Irlanda. Há indícios que sugerem que muitas espécies da fauna hiberno-lusitana chegaram à Irlanda devido a uma intensa actividade comercial exclusivamente marítima. Por exemplo, a Erica erigena, originalmente nativa da Gália e da Hispânia, é teoricamente considerada como tendo sido transplantada para solo irlandês através do comércio de vinho galaico.
Os indícios de contrabando de E. mackiana incluem o facto de serem encontradas apenas em portos que levam a rotas interiores e em baías isoladas. O local com a maior concentração desta espécie é o Pântano de Roundstone, situado entre duas enseadas isoladas, atravessado por uma antiga estrada de Connemara, uma área com uma longa história de contrabando. Em Kerry, há uma estrada conhecida como Trilho dos Contrabandistas, que foi a principal área de distribuição desta espécie.

-
 @ 088436cd:9d2646cc
2025-05-01 21:01:55
@ 088436cd:9d2646cc
2025-05-01 21:01:55The arrival of the coronavirus brought not only illness and death but also fear and panic. In such an environment of uncertainty, people have naturally stocked up on necessities, not knowing when things will return to normal.
Retail shelves have been cleared out, and even online suppliers like Amazon and Walmart are out of stock for some items. Independent sellers on these e-commerce platforms have had to fill the gap. With the huge increase in demand, they have found that their inventory has skyrocketed in value.
Many in need of these items (e.g. toilet paper, hand sanitizer and masks) balk at the new prices. They feel they are being taken advantage of in a time of need and call for intervention by the government to lower prices. The government has heeded that call, labeling the independent sellers as "price gougers" and threatening sanctions if they don't lower their prices. Amazon has suspended seller accounts and law enforcement at all levels have threatened to prosecute. Prices have dropped as a result and at first glance this seems like a victory for fair play. But, we will have to dig deeper to understand the unseen consequences of this intervention.
We must look at the economics of the situation, how supply and demand result in a price and how that price acts as a signal that goes out to everyone, informing them of underlying conditions in the economy and helping coordinate their actions.
It all started with a rise in demand. Given a fixed supply (e.g., the limited stock on shelves and in warehouses), an increase in demand inevitably leads to higher prices. Most people are familiar with this phenomenon, such as paying more for airline tickets during holidays or surge pricing for rides.
Higher prices discourage less critical uses of scarce resources. For example, you might not pay $1,000 for a plane ticket to visit your aunt if you can get one for $100 the following week, but someone else might pay that price to visit a dying relative. They value that plane seat more than you.
*** During the crisis, demand surged and their shelves emptied even though
However, retail outlets have not raised prices. They have kept them low, so the low-value uses of things like toilet paper, masks and hand sanitizer has continued. Often, this "use" just takes the form of hoarding. At everyday low prices, it makes sense to buy hundreds of rolls and bottles. You know you will use them eventually, so why not stock up? And, with all those extra supplies in the closet and basement, you don't need to change your behavior much. You don't have to ration your use.
At the low prices, these scarce resources got bought up faster and faster until there was simply none left. The reality of the situation became painfully clear to those who didn't panic and got to the store late: You have no toilet paper and you're not going to any time soon.
However, if prices had been allowed to rise, a number of effects would have taken place that would have coordinated the behavior of everyone so that valuable resources would not have been wasted or hoarded, and everyone could have had access to what they needed.
On the demand side, if prices had been allowed to rise, people would have begun to self-ration. You might leave those extra plies on the roll next time if you know they will cost ten times as much to replace. Or, you might choose to clean up a spill with a rag rather than disposable tissue. Most importantly, you won't hoard as much. That 50th bottle of hand sanitizer might just not be worth it at the new, high price. You'll leave it on the shelf for someone else who may have none.
On the supply side, higher prices would have incentivized people to offer up more of their stockpiles for sale. If you have a pallet full of toilet paper in your basement and all of the sudden they are worth $15 per roll, you might just list a few online. But, if it is illegal to do so, you probably won't.
Imagine you run a business installing insulation and have a few thousand respirator masks on hand for your employees. During a pandemic, it is much more important that people breathe filtered air than that insulation get installed, and that fact is reflected in higher prices. You will sell your extra masks at the higher price rather than store them for future insulation jobs, and the scarce resource will be put to its most important use.
Producers of hand sanitizer would go into overdrive if prices were allowed to rise. They would pay their employees overtime, hire new ones, and pay a premium for their supplies, making sure their raw materials don't go to less important uses.
These kinds of coordinated actions all across the economy would be impossible without real prices to guide them. How do you know if it makes sense to spend an extra $10k bringing a thousand masks to market unless you know you can get more than $10 per mask? If the price is kept artificially low, you simply can't do it. The money just isn't there.
These are the immediate effects of a price change, but incredibly, price changes also coordinate people's actions across space and time.
Across space, there are different supply and demand conditions in different places, and thus prices are not uniform. We know some places are real "hot spots" for the virus, while others are mostly unaffected. High demand in the hot spots leads to higher prices there, which attracts more of the resource to those areas. Boxes and boxes of essential items would pour in where they are needed most from where they are needed least, but only if prices were allowed to adjust freely.
This would be accomplished by individuals and businesses buying low in the unaffected areas, selling high in the hot spots and subtracting their labor and transportation costs from the difference. Producers of new supply would know exactly where it is most needed and ship to the high-demand, high-price areas first. The effect of these actions is to increase prices in the low demand areas and reduce them in the high demand areas. People in the low demand areas will start to self-ration more, reflecting the reality of their neighbors, and people in the hotspots will get some relief.
However, by artificially suppressing prices in the hot spot, people there will simply buy up the available supply and run out, and it will be cost prohibitive to bring in new supply from low-demand areas.
Prices coordinate economic actions across time as well. Just as entrepreneurs and businesses can profit by transporting scarce necessities from low-demand to high-demand areas, they can also profit by buying in low-demand times and storing their merchandise for when it is needed most.
Just as allowing prices to freely adjust in one area relative to another will send all the right signals for the optimal use of a scarce resource, allowing prices to freely adjust over time will do the same.
When an entrepreneur buys up resources during low-demand times in anticipation of a crisis, she restricts supply ahead of the crisis, which leads to a price increase. She effectively bids up the price. The change in price affects consumers and producers in all the ways mentioned above. Consumers self-ration more, and producers bring more of the resource to market.
Our entrepreneur has done a truly incredible thing. She has predicted the future, and by so doing has caused every individual in the economy to prepare for a shortage they don't even know is coming! And, by discouraging consumption and encouraging production ahead of time, she blunts the impact the crisis will have. There will be more of the resource to go around when it is needed most.
On top of this, our entrepreneur still has her stockpile she saved back when everyone else was blithely using it up. She can now further mitigate the damage of the crisis by selling her stock during the worst of it, when people are most desperate for relief. She will know when this is because the price will tell her, but only if it is allowed to adjust freely. When the price is at its highest is when people need the resource the most, and those willing to pay will not waste it or hoard it. They will put it to its highest valued use.
The economy is like a big bus we are all riding in, going down a road with many twists and turns. Just as it is difficult to see into the future, it is difficult to see out the bus windows at the road ahead.
On the dashboard, we don't have a speedometer or fuel gauge. Instead we have all the prices for everything in the economy. Prices are what tell us the condition of the bus and the road. They tell us everything. Without them, we are blind.
Good times are a smooth road. Consumer prices and interest rates are low, investment returns are steady. We hit the gas and go fast. But, the road is not always straight and smooth. Sometimes there are sharp turns and rough patches. Successful entrepreneurs are the ones who can see what is coming better than everyone else. They are our navigators.
When they buy up scarce resources ahead of a crisis, they are hitting the brakes and slowing us down. When they divert resources from one area to another, they are steering us onto a smoother path. By their actions in the market, they adjust the prices on our dashboard to reflect the conditions of the road ahead, so we can prepare for, navigate and get through the inevitable difficulties we will face.
Interfering with the dashboard by imposing price floors or price caps doesn't change the conditions of the road (the number of toilet paper rolls in existence hasn't changed). All it does is distort our perception of those conditions. We think the road is still smooth--our heavy foot stomping the gas--as we crash onto a rocky dirt road at 80 miles per hour (empty shelves at the store for weeks on end).
Supply, demand and prices are laws of nature. All of this is just how things work. It isn't right or wrong in a moral sense. Price caps lead to waste, shortages and hoarding as surely as water flows downhill. The opposite--allowing prices to adjust freely--leads to conservation of scarce resources and their being put to their highest valued use. And yes, it leads to profits for the entrepreneurs who were able to correctly predict future conditions, and losses for those who weren't.
Is it fair that they should collect these profits? On the one hand, anyone could have stocked up on toilet paper, hand sanitizer and face masks at any time before the crisis, so we all had a fair chance to get the supplies cheaply. On the other hand, it just feels wrong that some should profit so much at a time when there is so much need.
Our instinct in the moment is to see the entrepreneur as a villain, greedy "price gouger". But we don't see the long chain of economic consequences the led to the situation we feel is unfair.
If it weren't for anti-price-gouging laws, the major retailers would have raised their prices long before the crisis became acute. When they saw demand outstrip supply, they would have raised prices, not by 100 fold, but gradually and long before anyone knew how serious things would have become. Late comers would have had to pay more, but at least there would be something left on the shelf.
As an entrepreneur, why take risks trying to anticipate the future if you can't reap the reward when you are right? Instead of letting instead of letting entrepreneurs--our navigators--guide us, we are punishing and vilifying them, trying to force prices to reflect a reality that simply doesn't exist.
In a crisis, more than any other time, prices must be allowed to fluctuate. To do otherwise is to blind ourselves at a time when danger and uncertainty abound. It is economic suicide.
In a crisis, there is great need, and the way to meet that need is not by pretending it's not there, by forcing prices to reflect a world where there isn't need. They way to meet the need is the same it has always been, through charity.
If the people in government want to help, the best way for the to do so is to be charitable and reduce their taxes and fees as much as possible, ideally to zero in a time of crisis. Amazon, for example, could instantly reduce the price of all crisis related necessities by 20% if they waived their fee. This would allow for more uses by more people of these scarce supplies as hoarders release their stockpiles on to the market, knowing they can get 20% more for their stock. Governments could reduce or eliminate their tax burden on high-demand, crisis-related items and all the factors that go into their production, with the same effect: a reduction in prices and expansion of supply. All of us, including the successful entrepreneurs and the wealthy for whom high prices are not a great burden, could donate to relief efforts.
These ideas are not new or untested. This is core micro economics. It has been taught for hundreds of years in universities the world over. The fact that every crisis that comes along stirs up ire against entrepreneurs indicates not that the economics is wrong, but that we have a strong visceral reaction against what we perceive to be unfairness. This is as it should be. Unfairness is wrong and the anger it stirs in us should compel us to right the wrong. Our anger itself isn't wrong, it's just misplaced.
Entrepreneurs didn't cause the prices to rise. Our reaction to a virus did that. We saw a serious threat and an uncertain future and followed our natural impulse to hoard. Because prices at major retail suppliers didn't rise, that impulse ran rampant and we cleared the shelves until there was nothing left. We ran the bus right off the road and them blamed the entrepreneurs for showing us the reality of our situation, for shaking us out of the fantasy of low prices.
All of this is not to say that entrepreneurs are high-minded public servants. They are just doing their job. Staking your money on an uncertain future is a risky business. There are big risks and big rewards. Most entrepreneurs just scrape by or lose their capital in failed ventures.
However, the ones that get it right must be allowed to keep their profits, or else no one will try and we'll all be driving blind. We need our navigators. It doesn't even matter if they know all the positive effects they are having on the rest of us and the economy as a whole. So long as they are buying low and selling high--so long as they are doing their job--they will be guiding the rest of us through the good times and the bad, down the open road and through the rough spots.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 30ceb64e:7f08bdf5
2025-04-26 20:33:30
@ 30ceb64e:7f08bdf5
2025-04-26 20:33:30Status: Draft
Author: TheWildHustleAbstract
This NIP defines a framework for storing and sharing health and fitness profile data on Nostr. It establishes a set of standardized event kinds for individual health metrics, allowing applications to selectively access specific health information while preserving user control and privacy.
In this framework exists - NIP-101h.1 Weight using kind 1351 - NIP-101h.2 Height using kind 1352 - NIP-101h.3 Age using kind 1353 - NIP-101h.4 Gender using kind 1354 - NIP-101h.5 Fitness Level using kind 1355
Motivation
I want to build and support an ecosystem of health and fitness related nostr clients that have the ability to share and utilize a bunch of specific interoperable health metrics.
- Selective access - Applications can access only the data they need
- User control - Users can choose which metrics to share
- Interoperability - Different health applications can share data
- Privacy - Sensitive health information can be managed independently
Specification
Kind Number Range
Health profile metrics use the kind number range 1351-1399:
| Kind | Metric | | --------- | ---------------------------------- | | 1351 | Weight | | 1352 | Height | | 1353 | Age | | 1354 | Gender | | 1355 | Fitness Level | | 1356-1399 | Reserved for future health metrics |
Common Structure
All health metric events SHOULD follow these guidelines:
- The content field contains the primary value of the metric
- Required tags:
['t', 'health']- For categorizing as health data['t', metric-specific-tag]- For identifying the specific metric['unit', unit-of-measurement]- When applicable- Optional tags:
['converted_value', value, unit]- For providing alternative unit measurements['timestamp', ISO8601-date]- When the metric was measured['source', application-name]- The source of the measurement
Unit Handling
Health metrics often have multiple ways to be measured. To ensure interoperability:
- Where multiple units are possible, one standard unit SHOULD be chosen as canonical
- When using non-standard units, a
converted_valuetag SHOULD be included with the canonical unit - Both the original and converted values should be provided for maximum compatibility
Client Implementation Guidelines
Clients implementing this NIP SHOULD:
- Allow users to explicitly choose which metrics to publish
- Support reading health metrics from other users when appropriate permissions exist
- Support updating metrics with new values over time
- Preserve tags they don't understand for future compatibility
- Support at least the canonical unit for each metric
Extensions
New health metrics can be proposed as extensions to this NIP using the format:
- NIP-101h.X where X is the metric number
Each extension MUST specify: - A unique kind number in the range 1351-1399 - The content format and meaning - Required and optional tags - Examples of valid events
Privacy Considerations
Health data is sensitive personal information. Clients implementing this NIP SHOULD:
- Make it clear to users when health data is being published
- Consider incorporating NIP-44 encryption for sensitive metrics
- Allow users to selectively share metrics with specific individuals
- Provide easy ways to delete previously published health data
NIP-101h.1: Weight
Description
This NIP defines the format for storing and sharing weight data on Nostr.
Event Kind: 1351
Content
The content field MUST contain the numeric weight value as a string.
Required Tags
- ['unit', 'kg' or 'lb'] - Unit of measurement
- ['t', 'health'] - Categorization tag
- ['t', 'weight'] - Specific metric tag
Optional Tags
- ['converted_value', value, unit] - Provides the weight in alternative units for interoperability
- ['timestamp', ISO8601 date] - When the weight was measured
Examples
json { "kind": 1351, "content": "70", "tags": [ ["unit", "kg"], ["t", "health"], ["t", "weight"] ] }json { "kind": 1351, "content": "154", "tags": [ ["unit", "lb"], ["t", "health"], ["t", "weight"], ["converted_value", "69.85", "kg"] ] }NIP-101h.2: Height
Status: Draft
Description
This NIP defines the format for storing and sharing height data on Nostr.
Event Kind: 1352
Content
The content field can use two formats: - For metric height: A string containing the numeric height value in centimeters (cm) - For imperial height: A JSON string with feet and inches properties
Required Tags
['t', 'health']- Categorization tag['t', 'height']- Specific metric tag['unit', 'cm' or 'imperial']- Unit of measurement
Optional Tags
['converted_value', value, 'cm']- Provides height in centimeters for interoperability when imperial is used['timestamp', ISO8601-date]- When the height was measured
Examples
```jsx // Example 1: Metric height Apply to App.jsx
// Example 2: Imperial height with conversion Apply to App.jsx ```
Implementation Notes
- Centimeters (cm) is the canonical unit for height interoperability
- When using imperial units, a conversion to centimeters SHOULD be provided
- Height values SHOULD be positive integers
- For maximum compatibility, clients SHOULD support both formats
NIP-101h.3: Age
Status: Draft
Description
This NIP defines the format for storing and sharing age data on Nostr.
Event Kind: 1353
Content
The content field MUST contain the numeric age value as a string.
Required Tags
['unit', 'years']- Unit of measurement['t', 'health']- Categorization tag['t', 'age']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the age was recorded['dob', ISO8601-date]- Date of birth (if the user chooses to share it)
Examples
```jsx // Example 1: Basic age Apply to App.jsx
// Example 2: Age with DOB Apply to App.jsx ```
Implementation Notes
- Age SHOULD be represented as a positive integer
- For privacy reasons, date of birth (dob) is optional
- Clients SHOULD consider updating age automatically if date of birth is known
- Age can be a sensitive metric and clients may want to consider encrypting this data
NIP-101h.4: Gender
Status: Draft
Description
This NIP defines the format for storing and sharing gender data on Nostr.
Event Kind: 1354
Content
The content field contains a string representing the user's gender.
Required Tags
['t', 'health']- Categorization tag['t', 'gender']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the gender was recorded['preferred_pronouns', string]- User's preferred pronouns
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - male - female - non-binary - other - prefer-not-to-say
Examples
```jsx // Example 1: Basic gender Apply to App.jsx
// Example 2: Gender with pronouns Apply to App.jsx ```
Implementation Notes
- Clients SHOULD allow free-form input for gender
- For maximum compatibility, clients SHOULD support the common values
- Gender is a sensitive personal attribute and clients SHOULD consider appropriate privacy controls
- Applications focusing on health metrics should be respectful of gender diversity
NIP-101h.5: Fitness Level
Status: Draft
Description
This NIP defines the format for storing and sharing fitness level data on Nostr.
Event Kind: 1355
Content
The content field contains a string representing the user's fitness level.
Required Tags
['t', 'health']- Categorization tag['t', 'fitness']- Fitness category tag['t', 'level']- Specific metric tag
Optional Tags
['timestamp', ISO8601-date]- When the fitness level was recorded['activity', activity-type]- Specific activity the fitness level relates to['metrics', JSON-string]- Quantifiable fitness metrics used to determine level
Common Values
While any string value is permitted, the following common values are recommended for interoperability: - beginner - intermediate - advanced - elite - professional
Examples
```jsx // Example 1: Basic fitness level Apply to App.jsx
// Example 2: Activity-specific fitness level with metrics Apply to App.jsx ```
Implementation Notes
- Fitness level is subjective and may vary by activity
- The activity tag can be used to specify fitness level for different activities
- The metrics tag can provide objective measurements to support the fitness level
- Clients can extend this format to include activity-specific fitness assessments
- For general fitness apps, the simple beginner/intermediate/advanced scale is recommended
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 8125b911:a8400883
2025-04-25 07:02:35
@ 8125b911:a8400883
2025-04-25 07:02:35In Nostr, all data is stored as events. Decentralization is achieved by storing events on multiple relays, with signatures proving the ownership of these events. However, if you truly want to own your events, you should run your own relay to store them. Otherwise, if the relays you use fail or intentionally delete your events, you'll lose them forever.
For most people, running a relay is complex and costly. To solve this issue, I developed nostr-relay-tray, a relay that can be easily run on a personal computer and accessed over the internet.
Project URL: https://github.com/CodyTseng/nostr-relay-tray
This article will guide you through using nostr-relay-tray to run your own relay.
Download
Download the installation package for your operating system from the GitHub Release Page.
| Operating System | File Format | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | You should know which one to use |Installation
Since this app isn’t signed, you may encounter some obstacles during installation. Once installed, an ostrich icon will appear in the status bar. Click on the ostrich icon, and you'll see a menu where you can click the "Dashboard" option to open the relay's control panel for further configuration.

macOS Users:
- On first launch, go to "System Preferences > Security & Privacy" and click "Open Anyway."
- If you encounter a "damaged" message, run the following command in the terminal to remove the restrictions:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows Users:
- On the security warning screen, click "More Info > Run Anyway."
Connecting
By default, nostr-relay-tray is only accessible locally through
ws://localhost:4869/, which makes it quite limited. Therefore, we need to expose it to the internet.In the control panel, click the "Proxy" tab and toggle the switch. You will then receive a "Public address" that you can use to access your relay from anywhere. It's that simple.
Next, add this address to your relay list and position it as high as possible in the list. Most clients prioritize connecting to relays that appear at the top of the list, and relays lower in the list are often ignored.

Restrictions
Next, we need to set up some restrictions to prevent the relay from storing events that are irrelevant to you and wasting storage space. nostr-relay-tray allows for flexible and fine-grained configuration of which events to accept, but some of this is more complex and will not be covered here. If you're interested, you can explore this further later.
For now, I'll introduce a simple and effective strategy: WoT (Web of Trust). You can enable this feature in the "WoT & PoW" tab. Before enabling, you'll need to input your pubkey.
There's another important parameter,
Depth, which represents the relationship depth between you and others. Someone you follow has a depth of 1, someone they follow has a depth of 2, and so on.- Setting this parameter to 0 means your relay will only accept your own events.
- Setting it to 1 means your relay will accept events from you and the people you follow.
- Setting it to 2 means your relay will accept events from you, the people you follow, and the people they follow.
Currently, the maximum value for this parameter is 2.

Conclusion
You've now successfully run your own relay and set a simple restriction to prevent it from storing irrelevant events.
If you encounter any issues during use, feel free to submit an issue on GitHub, and I'll respond as soon as possible.
Not your relay, not your events.
-
 @ e691f4df:1099ad65
2025-04-24 18:56:12
@ e691f4df:1099ad65
2025-04-24 18:56:12Viewing Bitcoin Through the Light of Awakening
Ankh & Ohm Capital’s Overview of the Psycho-Spiritual Nature of Bitcoin
Glossary:
I. Preface: The Logos of Our Logo
II. An Oracular Introduction
III. Alchemizing Greed
IV. Layers of Fractalized Thought
V. Permissionless Individuation
VI. Dispelling Paradox Through Resonance
VII. Ego Deflation
VIII. The Coin of Great Price
Preface: The Logos of Our Logo
Before we offer our lens on Bitcoin, it’s important to illuminate the meaning behind Ankh & Ohm’s name and symbol. These elements are not ornamental—they are foundational, expressing the cosmological principles that guide our work.
Our mission is to bridge the eternal with the practical. As a Bitcoin-focused family office and consulting firm, we understand capital not as an end, but as a tool—one that, when properly aligned, becomes a vehicle for divine order. We see Bitcoin not simply as a technological innovation but as an emanation of the Divine Logos—a harmonic expression of truth, transparency, and incorruptible structure. Both the beginning and the end, the Alpha and Omega.
The Ankh (☥), an ancient symbol of eternal life, is a key to the integration of opposites. It unites spirit and matter, force and form, continuity and change. It reminds us that capital, like Life, must not only be generative, but regenerative; sacred. Money must serve Life, not siphon from it.
The Ohm (Ω) holds a dual meaning. In physics, it denotes a unit of electrical resistance—the formative tension that gives energy coherence. In the Vedic tradition, Om (ॐ) is the primordial vibration—the sound from which all existence unfolds. Together, these symbols affirm a timeless truth: resistance and resonance are both sacred instruments of the Creator.
Ankh & Ohm, then, represents our striving for union, for harmony —between the flow of life and intentional structure, between incalculable abundance and measured restraint, between the lightbulb’s electrical impulse and its light-emitting filament. We stand at the threshold where intention becomes action, and where capital is not extracted, but cultivated in rhythm with the cosmos.
We exist to shepherd this transformation, as guides of this threshold —helping families, founders, and institutions align with a deeper order, where capital serves not as the prize, but as a pathway to collective Presence, Purpose, Peace and Prosperity.
An Oracular Introduction
Bitcoin is commonly understood as the first truly decentralized and secure form of digital money—a breakthrough in monetary sovereignty. But this view, while technically correct, is incomplete and spiritually shallow. Bitcoin is more than a tool for economic disruption. Bitcoin represents a mythic threshold: a symbol of the psycho-spiritual shift that many ancient traditions have long foretold.
For millennia, sages and seers have spoken of a coming Golden Age. In the Vedic Yuga cycles, in Plato’s Great Year, in the Eagle and Condor prophecies of the Americas—there exists a common thread: that humanity will emerge from darkness into a time of harmony, cooperation, and clarity. That the veil of illusion (maya, materiality) will thin, and reality will once again become transparent to the transcendent. In such an age, systems based on scarcity, deception, and centralization fall away. A new cosmology takes root—one grounded in balance, coherence, and sacred reciprocity.
But we must ask—how does such a shift happen? How do we cross from the age of scarcity, fear, and domination into one of coherence, abundance, and freedom?
One possible answer lies in the alchemy of incentive.
Bitcoin operates not just on the rules of computer science or Austrian economics, but on something far more old and subtle: the logic of transformation. It transmutes greed—a base instinct rooted in scarcity—into cooperation, transparency, and incorruptibility.
In this light, Bitcoin becomes more than code—it becomes a psychoactive protocol, one that rewires human behavior by aligning individual gain with collective integrity. It is not simply a new form of money. It is a new myth of value. A new operating system for human consciousness.
Bitcoin does not moralize. It harmonizes. It transforms the instinct for self-preservation into a pathway for planetary coherence.
Alchemizing Greed
At the heart of Bitcoin lies the ancient alchemical principle of transmutation: that which is base may be refined into gold.
Greed, long condemned as a vice, is not inherently evil. It is a distorted longing. A warped echo of the drive to preserve life. But in systems built on scarcity and deception, this longing calcifies into hoarding, corruption, and decay.
Bitcoin introduces a new game. A game with memory. A game that makes deception inefficient and truth profitable. It does not demand virtue—it encodes consequence. Its design does not suppress greed; it reprograms it.
In traditional models, game theory often illustrates the fragility of trust. The Prisoner’s Dilemma reveals how self-interest can sabotage collective well-being. But Bitcoin inverts this. It creates an environment where self-interest and integrity converge—where the most rational action is also the most truthful.
Its ledger, immutable and transparent, exposes manipulation for what it is: energetically wasteful and economically self-defeating. Dishonesty burns energy and yields nothing. The network punishes incoherence, not by decree, but by natural law.
This is the spiritual elegance of Bitcoin: it does not suppress greed—it transmutes it. It channels the drive for personal gain into the architecture of collective order. Miners compete not to dominate, but to validate. Nodes collaborate not through trust, but through mathematical proof.
This is not austerity. It is alchemy.
Greed, under Bitcoin, is refined. Tempered. Re-forged into a generative force—no longer parasitic, but harmonic.
Layers of Fractalized Thought Fragments
All living systems are layered. So is the cosmos. So is the human being. So is a musical scale.
At its foundation lies the timechain—the pulsing, incorruptible record of truth. Like the heart, it beats steadily. Every block, like a pulse, affirms its life through continuity. The difficulty adjustment—Bitcoin’s internal calibration—functions like heart rate variability, adapting to pressure while preserving coherence.
Above this base layer is the Lightning Network—a second layer facilitating rapid, efficient transactions. It is the nervous system: transmitting energy, reducing latency, enabling real-time interaction across a distributed whole.
Beyond that, emerging tools like Fedimint and Cashu function like the capillaries—bringing vitality to the extremities, to those underserved by legacy systems. They empower the unbanked, the overlooked, the forgotten. Privacy and dignity in the palms of those the old system refused to see.
And then there is NOSTR—the decentralized protocol for communication and creation. It is the throat chakra, the vocal cords of the “freedom-tech” body. It reclaims speech from the algorithmic overlords, making expression sovereign once more. It is also the reproductive system, as it enables the propagation of novel ideas and protocols in fertile, uncensorable soil.
Each layer plays its part. Not in hierarchy, but in harmony. In holarchy. Bitcoin and other open source protocols grow not through exogenous command, but through endogenous coherence. Like cells in an organism. Like a song.
Imagine the cell as a piece of glass from a shattered holographic plate —by which its perspectival, moving image can be restructured from the single shard. DNA isn’t only a logical script of base pairs, but an evolving progressive song. Its lyrics imbued with wise reflections on relationships. The nucleus sings, the cell responds—not by command, but by memory. Life is not imposed; it is expressed. A reflection of a hidden pattern.
Bitcoin chants this. Each node, a living cell, holds the full timechain—Truth distributed, incorruptible. Remove one, and the whole remains. This isn’t redundancy. It’s a revelation on the power of protection in Truth.
Consensus is communion. Verification becomes a sacred rite—Truth made audible through math.
Not just the signal; the song. A web of self-expression woven from Truth.
No center, yet every point alive with the whole. Like Indra’s Net, each reflects all. This is more than currency and information exchange. It is memory; a self-remembering Mind, unfolding through consensus and code. A Mind reflecting the Truth of reality at the speed of thought.
Heuristics are mental shortcuts—efficient, imperfect, alive. Like cells, they must adapt or decay. To become unbiased is to have self-balancing heuristics which carry feedback loops within them: they listen to the environment, mutate when needed, and survive by resonance with reality. Mutation is not error, but evolution. Its rules are simple, but their expression is dynamic.
What persists is not rigidity, but pattern.
To think clearly is not necessarily to be certain, but to dissolve doubt by listening, adjusting, and evolving thought itself.
To understand Bitcoin is simply to listen—patiently, clearly, as one would to a familiar rhythm returning.
Permissionless Individuation
Bitcoin is a path. One that no one can walk for you.
Said differently, it is not a passive act. It cannot be spoon-fed. Like a spiritual path, it demands initiation, effort, and the willingness to question inherited beliefs.
Because Bitcoin is permissionless, no one can be forced to adopt it. One must choose to engage it—compelled by need, interest, or intuition. Each person who embarks undergoes their own version of the hero’s journey.
Carl Jung called this process Individuation—the reconciliation of fragmented psychic elements into a coherent, mature Self. Bitcoin mirrors this: it invites individuals to confront the unconscious assumptions of the fiat paradigm, and to re-integrate their relationship to time, value, and agency.
In Western traditions—alchemy, Christianity, Kabbalah—the individual is sacred, and salvation is personal. In Eastern systems—Daoism, Buddhism, the Vedas—the self is ultimately dissolved into the cosmic whole. Bitcoin, in a paradoxical way, echoes both: it empowers the individual, while aligning them with a holistic, transcendent order.
To truly see Bitcoin is to allow something false to die. A belief. A habit. A self-concept.
In that death—a space opens for deeper connection with the Divine itSelf.
In that dissolution, something luminous is reborn.
After the passing, Truth becomes resurrected.
Dispelling Paradox Through Resonance
There is a subtle paradox encoded into the hero’s journey: each starts in solidarity, yet the awakening affects the collective.
No one can be forced into understanding Bitcoin. Like a spiritual truth, it must be seen. And yet, once seen, it becomes nearly impossible to unsee—and easier for others to glimpse. The pattern catches.
This phenomenon mirrors the concept of morphic resonance, as proposed and empirically tested by biologist Rupert Sheldrake. Once a critical mass of individuals begins to embody a new behavior or awareness, it becomes easier—instinctive—for others to follow suit. Like the proverbial hundredth monkey who begins to wash the fruit in the sea water, and suddenly, monkeys across islands begin doing the same—without ever meeting.
When enough individuals embody a pattern, it ripples outward. Not through propaganda, but through field effect and wave propagation. It becomes accessible, instinctive, familiar—even across great distance.
Bitcoin spreads in this way. Not through centralized broadcast, but through subtle resonance. Each new node, each individual who integrates the protocol into their life, strengthens the signal for others. The protocol doesn’t shout; it hums, oscillates and vibrates——persistently, coherently, patiently.
One awakens. Another follows. The current builds. What was fringe becomes familiar. What was radical becomes obvious.
This is the sacred geometry of spiritual awakening. One awakens, another follows, and soon the fluidic current is strong enough to carry the rest. One becomes two, two become many, and eventually the many become One again. This tessellation reverberates through the human aura, not as ideology, but as perceivable pattern recognition.
Bitcoin’s most powerful marketing tool is truth. Its most compelling evangelist is reality. Its most unstoppable force is resonance.
Therefore, Bitcoin is not just financial infrastructure—it is psychic scaffolding. It is part of the subtle architecture through which new patterns of coherence ripple across the collective field.
The training wheels from which humanity learns to embody Peace and Prosperity.
Ego Deflation
The process of awakening is not linear, and its beginning is rarely gentle—it usually begins with disruption, with ego inflation and destruction.
To individuate is to shape a center; to recognize peripherals and create boundaries—to say, “I am.” But without integration, the ego tilts—collapsing into void or inflating into noise. Fiat reflects this pathology: scarcity hoarded, abundance simulated. Stagnation becomes disguised as safety, and inflation masquerades as growth.
In other words, to become whole, the ego must first rise—claiming agency, autonomy, and identity. However, when left unbalanced, it inflates, or implodes. It forgets its context. It begins to consume rather than connect. And so the process must reverse: what inflates must deflate.
In the fiat paradigm, this inflation is literal. More is printed, and ethos is diluted. Savings decay. Meaning erodes. Value is abstracted. The economy becomes bloated with inaudible noise. And like the psyche that refuses to confront its own shadow, it begins to collapse under the weight of its own illusions.
But under Bitcoin, time is honored. Value is preserved. Energy is not abstracted but grounded.
Bitcoin is inherently deflationary—in both economic and spiritual senses. With a fixed supply, it reveals what is truly scarce. Not money, not status—but the finite number of heartbeats we each carry.
To see Bitcoin is to feel that limit in one’s soul. To hold Bitcoin is to feel Time’s weight again. To sense the importance of Bitcoin is to feel the value of preserved, potential energy. It is to confront the reality that what matters cannot be printed, inflated, or faked. In this way, Bitcoin gently confronts the ego—not through punishment, but through clarity.
Deflation, rightly understood, is not collapse—it is refinement. It strips away illusion, bloat, and excess. It restores the clarity of essence.
Spiritually, this is liberation.
The Coin of Great Price
There is an ancient parable told by a wise man:
“The kingdom of heaven is like a merchant seeking fine pearls, who, upon finding one of great price, sold all he had and bought it.”
Bitcoin is such a pearl.
But the ledger is more than a chest full of treasure. It is a key to the heart of things.
It is not just software—it is sacrament.
A symbol of what cannot be corrupted. A mirror of divine order etched into code. A map back to the sacred center.
It reflects what endures. It encodes what cannot be falsified. It remembers what we forgot: that Truth, when aligned with form, becomes Light once again.
Its design is not arbitrary. It speaks the language of life itself—
The elliptic orbits of the planets mirrored in its cryptography,
The logarithmic spiral of the nautilus shell discloses its adoption rate,
The interconnectivity of mycelium in soil reflect the network of nodes in cyberspace,
A webbed breadth of neurons across synaptic space fires with each new confirmed transaction.
It is geometry in devotion. Stillness in motion.
It is the Logos clothed in protocol.
What this key unlocks is beyond external riches. It is the eternal gold within us.
Clarity. Sovereignty. The unshakeable knowing that what is real cannot be taken. That what is sacred was never for sale.
Bitcoin is not the destination.
It is the Path.
And we—when we are willing to see it—are the Temple it leads back to.
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:49:24
@ ba3b4b1d:eadff0d3
2025-05-09 23:49:24Aisling é um género literário que se tornou popular na Irlanda nos séculos XVII e XVIII depois do tumulto da Guerra Williamita, misturando elementos de folclore, nacionalismo e romantismo. Ela encapsulava um anseio por identidade e liberdade, utilizando a figura da mulher bela como um poderoso símbolo de esperança e aspiração.
Mas a história da Aisling não começa aí e uma das suas origens é o conto muito confuso de Caer Ibormeith, também conhecida por Coerabar Boeth.
(https://yakihonne.s3.ap-east-1.amazonaws.com/ba3b4b1d1c5cc2707f71924368a7adcded1829921c86e022f1cb8117eadff0d3/files/1746834499215-YAKIHONNES3.jpg)
Ela era filha de Etal Anbuail, um rei Feérico dos Tuatha Dé Danann "povos da deusa Danu"; uma filidh - um nome que mais tarde foi atribuido aos poetas da Irlanda com proezas proféticas, uma vez que Ibormeith era a deusa das profecias, de certa forma semelhante a um "bardo", como se diz em Português. A cada Samhain, 31 de Outubro, quando o Mundo dos Vivos se aproximava do Mundo dos Mortos, ela transformava-se num cisne, até ao Samhain seguinte em que regressava à sua forma humana. Numa das versões desse conto, Ibormeith, após consulta ou por iniciativa própria, apaixona-se por Óengus. Numa noite, ela aparece nos sonhos dele tocando a mais bela melodia e quando ele acorda sabe que está apaixonado mas não sabia quem era aquela bela mulher nem onde a poderia encontrar. Ele fica completamente down bad e cada dia que passa só pensa em voltar sonhar com ela outra vez, e ela todas as noites volta a aparecer-lhe no Mundos dos Sonhos. Um dia, Óengus perde o apetite e adoece. Um médico foi chamado. Ele adivinhou a causa da doença de Óengus e disse a Bóann, mãe de Óengus, para encontrar a jovem dos sonhos dele. Bóann procurou durante um ano, mas sem sucesso. Então, eles pediram ajuda ao seu pai, o Dagdha, que também procurou um ano mas sem sucesso. Então foi pedido ao seu irmão Bodb que encontrasse um lugar com a descrição segundo os sonhos. Mas o pai dela, Etal, não permitia que qualquer um ficasse com a mão da sua filha e então revelou que para a conquistar teria que esperar pelo Loch Bél Dragain que significa "Lago da Boca do Dragão" para a encontrar na manhã do Samhain e a chamasse pelo nome. Nesse dia havia 150 cisnes* nesse lago, carregando correntes de prata e Óengus começou a panicar por não encontrar a sua Ibormeith, mas foi então que reparou num cisne mais bonito que os outros, com correntes de ouro e prata, e quando disse o seu nome ela revelou a sua forma humana e perguntou-lhe porque demorou tanto tempo.
Depois disse transformaram-se em cisnes e cantaram uma música tão bela que os humanos dormiram durante 3 dias e Óengus ficou conhecido como deus do amor e da juventude.
*Na mitologia irlandesa, o número 150 refere-se frequentemente aos Cinquenta Guerreiros dos Tuatha Dé Danann e a figura dos cisnes é frequente e também utilizada nas obras de Hans Christian Andersen e Tchaikovsky. Outras versões do conto não dizem cisnes, dizem aves, ou a história acontece de maneira ligeiramente diferente - quem conta um conto acrescenta um ponto.![image]
-
 @ e516ecb8:1be0b167
2025-05-10 00:57:52
@ e516ecb8:1be0b167
2025-05-10 00:57:52Recentemente, o podcast Scicast apresentou um episódio sobre aposentadoria, descrevendo os diferentes sistemas e sua história. Acho que, embora tenha sido um episódio interessante, foi muito injusto com o sistema de financiamento privado, que, afinal de contas, para um podcast voltado para a ciência (e que mencionou várias vezes que o sistema de repartição era matematicamente inviável), achei que alguns pontos precisavam ser esclarecidos.
Não estou dizendo que o sistema chileno é perfeito, não é, mas ele tinha potencial para melhorar e a classe política só o tornou cada vez pior.
Por exemplo, Otto von Bismarck sabia que tornaria a população idosa (os poucos que atingiram a idade de aposentadoria) dependente do Estado, e foi isso que fez com que Franco adotasse o sistema na Espanha, onde hoje é preciso aumentar os impostos para manter artificialmente o sistema de repartição.
A rentabilidade é baixa no sistema chileno, porque há lacunas (meses sem pagar) e porque você só contribui com 10%. Ou seja, se seu salário for 100, mas você contribuir com 10 em janeiro e mais nenhum mês. No final da sua vida profissional (45 anos) você terá 450 mais os rendimentos 1350, e esse total dividido pela expectativa de vida que está cada vez mais alta: 20 anos (24 meses) dá um salário de 56,25. Muito baixo, porque para o cálculo o salário era 100. Ainda mais baixo se a inflação for levada em conta. Mas o fato de haver meses sem contribuições não é levado em conta.
Deve-se considerar na rentabilidade que, em média, para cada 1 peso contribuído, são obtidos 3 pesos.Según cálculos de comissões
Várias comissões foram criadas para estudar como melhorar o sistema no Chile, e todas concluem a mesma coisa:
1- contribuir com 10% é muito baixo em comparação com outros sistemas
2- não se deve tolerar lacunas (a idade de aposentadoria não deve ser a idade natural, mas os anos de contribuição)
3- deve haver ajustes para cada aumento na expectativa de vida.
Esses três pontos acima não são tocados pelos políticos, porque são impopulares e eles vivem para a próxima eleição. Assim, eles preferem buscar outras formas, como o PGU (o salário básico universal que você já mencionou no podcast), que matematicamente já foi calculado como inviável no longo prazo.
Considere que 10% é baixo, mas ainda assim o Chile está muito bem classificado e poderia melhorar se os políticos tivessem a coragem de assumir os resultados das comissões que eles mesmos solicitaram.
https://www.65ymas.com/economia/pensiones/10-paises-con-mejores-sistemas-pensiones_22627_102.html
Foi mencionada a complexidade dos investimentos, o que é um mito, pois há fundos em que as contribuições são feitas de acordo com a idade do trabalhador (Fundo A para jovens, mais rentável, mas mais arriscado, e Fundo E, menos rentável, mas também menos arriscado). Na crise, as pessoas que perderam muito dinheiro foram porque estavam em um fundo que não correspondia à sua idade. Se você for jovem, poderá recuperar os retornos em um fundo de risco. Mas se for idoso na época da crise e não estiver em um fundo estável, já terá perdido sem poder se recuperar antes dos 65 anos.
Além disso, não se considera que há também um fundo voluntário adicional para o qual cada pessoa pode contribuir (APV), que tem benefícios como contribuições anuais do Estado para recompensar aqueles que contribuem para ele, e que também paga retornos.
Por outro lado, foi possível retirar dinheiro dos fundos individuais durante a crise pandêmica, algo que seria impossível em um fundo de repartição em que cada unidade monetária depositada por um trabalhador ativo é gasta ao mesmo tempo por um aposentado.
O modelo de repartição militar no Chile exige 20 anos de contribuições sem intervalos, qualquer intervalo e a pensão é de US$ 0, algo que não acontece no sistema civil (e não poderia acontecer porque o dinheiro lá é seu).
O sistema de capitalização individual no Chile permite que os trabalhadores possuam ativos de investimento, ativos de empresas que ajudaram o país a se desenvolver, algo que os políticos que querem derrubar o sistema parecem não entender.
E quanto à inflação? Investir em ativos que geram renda é útil tanto para mitigar a inflação quanto para ser proprietário, e esse último aspecto será relevante quando a automação chegar. Em vez de manter um registro artificial de quanto um robô produz, é mais transparente lucrar com os dividendos produzidos pela empresa em questão.
O sistema nórdico foi mencionado (que, afinal de contas, é praticamente o único sistema europeu que não está à beira do colapso). Vale a pena considerar que o dinheiro que a Noruega ganha com o petróleo vai para um fundo de investimento semelhante ao que temos individualmente no Chile, e a partir dele é paga grande parte do estado de bem-estar social norueguês. Mas isso é algo que parece muito distante, com a classe política latino-americana mais inclinada a desperdiçá-lo em bobagens populistas.
O modelo de distribuição é piramidal, embora possa parecer uma narrativa perigosa, é bom que as pessoas o vejam dessa forma (se um cidadão tirasse dinheiro dos jovens para dar aos idosos, provavelmente acabaria preso por um esquema ponzi), e a taxa de natalidade cada vez menor é um problema que o Estado não pode resolver, por mais totalitário que seja (estímulos fiscais e monetários etc. foram tentados com resultados ruins e míopes).
Além disso, por mais demonizado que seja na narrativa, o sistema chileno é um sistema misto com um pilar de solidariedade para aqueles que não contribuíram bem.
Na Argentina, passou-se da capitalização individual para o sistema de repartição, e o dinheiro foi usado pelos políticos quando não podiam pagar a conta de um Estado cada vez maior e corrupto, deixando os aposentados à mercê das migalhas dadas pelos políticos em cada campanha eleitoral. Você não confia no mercado, eu não confio no Estado.
-
 @ f32184ee:6d1c17bf
2025-04-23 13:21:52
@ f32184ee:6d1c17bf
2025-04-23 13:21:52Ads Fueling Freedom
Ross Ulbricht’s "Decentralize Social Media" painted a picture of a user-centric, decentralized future that transcended the limitations of platforms like the tech giants of today. Though focused on social media, his concept provided a blueprint for decentralized content systems writ large. The PROMO Protocol, designed by NextBlock while participating in Sovereign Engineering, embodies this blueprint in the realm of advertising, leveraging Nostr and Bitcoin’s Lightning Network to give individuals control, foster a multi-provider ecosystem, and ensure secure value exchange. In this way, Ulbricht’s 2021 vision can be seen as a prescient prediction of the PROMO Protocol’s structure. This is a testament to the enduring power of his ideas, now finding form in NextBlock’s innovative approach.
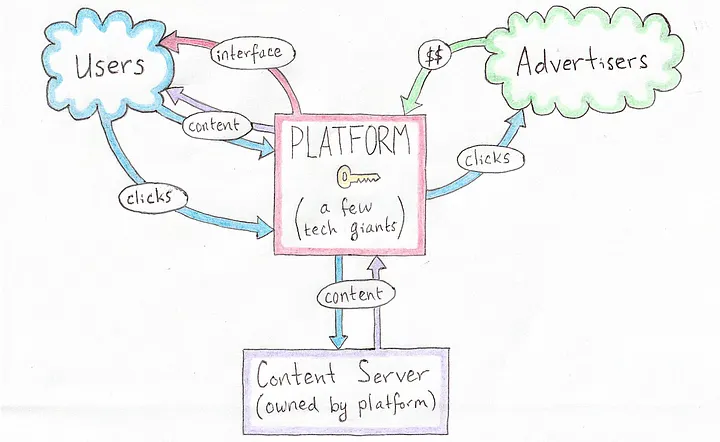 [Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]
[Current Platform-Centric Paradigm, source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Vision: A Decentralized Social Protocol
In his 2021 Medium article Ulbricht proposed a revolutionary vision for a decentralized social protocol (DSP) to address the inherent flaws of centralized social media platforms, such as privacy violations and inconsistent content moderation. Writing from prison, Ulbricht argued that decentralization could empower users by giving them control over their own content and the value they create, while replacing single, monolithic platforms with a competitive ecosystem of interface providers, content servers, and advertisers. Though his focus was on social media, Ulbricht’s ideas laid a conceptual foundation that strikingly predicts the structure of NextBlock’s PROMO Protocol, a decentralized advertising system built on the Nostr protocol.
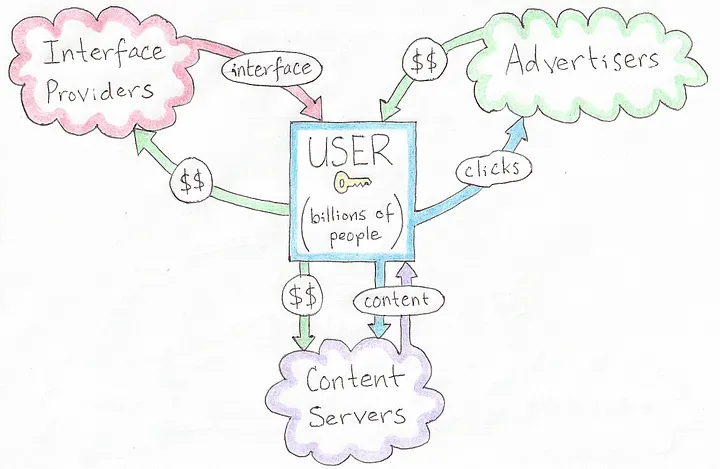 [A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]
[A Decentralized Social Protocol (DSP), source: Ross Ulbricht's Decentralize Social Media]Ulbricht’s Principles
Ulbricht’s article outlines several key principles for his DSP: * User Control: Users should own their content and dictate how their data and creations generate value, rather than being subject to the whims of centralized corporations. * Decentralized Infrastructure: Instead of a single platform, multiple interface providers, content hosts, and advertisers interoperate, fostering competition and resilience. * Privacy and Autonomy: Decentralized solutions for profile management, hosting, and interactions would protect user privacy and reduce reliance on unaccountable intermediaries. * Value Creation: Users, not platforms, should capture the economic benefits of their contributions, supported by decentralized mechanisms for transactions.
These ideas were forward-thinking in 2021, envisioning a shift away from the centralized giants dominating social media at the time. While Ulbricht didn’t specifically address advertising protocols, his framework for decentralization and user empowerment extends naturally to other domains, like NextBlock’s open-source offering: the PROMO Protocol.
NextBlock’s Implementation of PROMO Protocol
The PROMO Protocol powers NextBlock's Billboard app, a decentralized advertising protocol built on Nostr, a simple, open protocol for decentralized communication. The PROMO Protocol reimagines advertising by: * Empowering People: Individuals set their own ad prices (e.g., 500 sats/minute), giving them direct control over how their attention or space is monetized. * Marketplace Dynamics: Advertisers set budgets and maximum bids, competing within a decentralized system where a 20% service fee ensures operational sustainability. * Open-Source Flexibility: As an open-source protocol, it allows multiple developers to create interfaces or apps on top of it, avoiding the single-platform bottleneck Ulbricht critiqued. * Secure Payments: Using Strike Integration with Bitcoin Lightning Network, NextBlock enables bot-resistant and intermediary-free transactions, aligning value transfer with each person's control.
This structure decentralizes advertising in a way that mirrors Ulbricht’s broader vision for social systems, with aligned principles showing a specific use case: monetizing attention on Nostr.
Aligned Principles
Ulbricht’s 2021 article didn’t explicitly predict the PROMO Protocol, but its foundational concepts align remarkably well with NextBlock's implementation the protocol’s design: * Autonomy Over Value: Ulbricht argued that users should control their content and its economic benefits. In the PROMO Protocol, people dictate ad pricing, directly capturing the value of their participation. Whether it’s their time, influence, or digital space, rather than ceding it to a centralized ad network. * Ecosystem of Providers: Ulbricht envisioned multiple providers replacing a single platform. The PROMO Protocol’s open-source nature invites a similar diversity: anyone can build interfaces or tools on top of it, creating a competitive, decentralized advertising ecosystem rather than a walled garden. * Decentralized Transactions: Ulbricht’s DSP implied decentralized mechanisms for value exchange. NextBlock delivers this through the Bitcoin Lightning Network, ensuring that payments for ads are secure, instantaneous and final, a practical realization of Ulbricht’s call for user-controlled value flows. * Privacy and Control: While Ulbricht emphasized privacy in social interactions, the PROMO Protocol is public by default. Individuals are fully aware of all data that they generate since all Nostr messages are signed. All participants interact directly via Nostr.
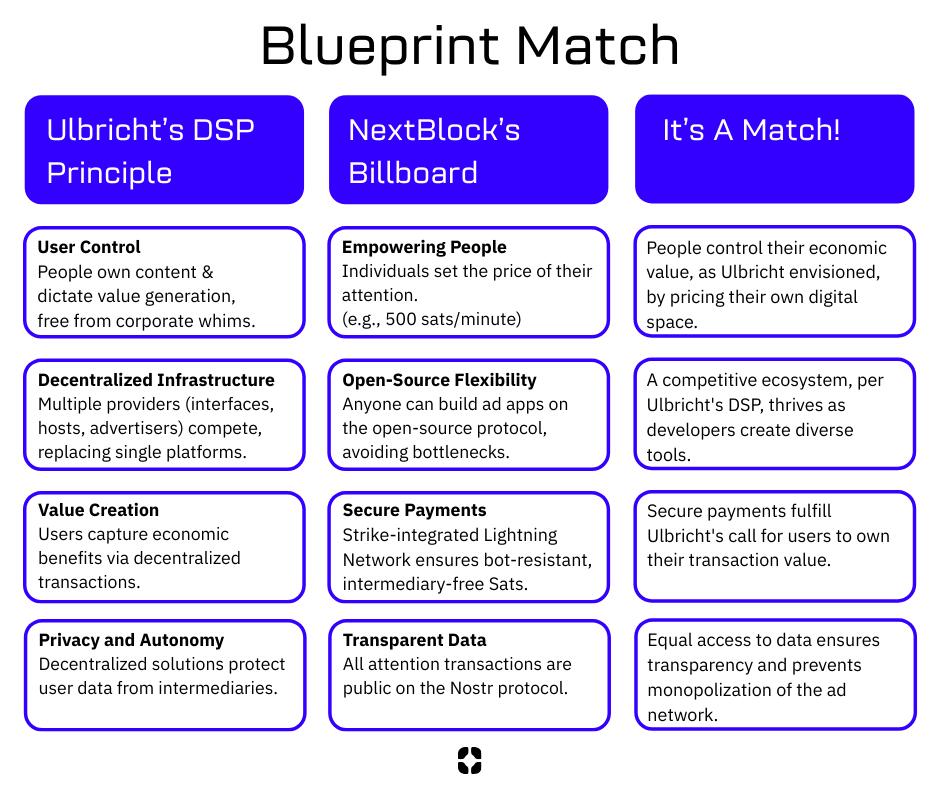 [Blueprint Match, source NextBlock]
[Blueprint Match, source NextBlock]
Who We Are
NextBlock is a US-based new media company reimagining digital ads for a decentralized future. Our founders, software and strategy experts, were hobbyist podcasters struggling to promote their work online without gaming the system. That sparked an idea: using new tech like Nostr and Bitcoin to build a decentralized attention market for people who value control and businesses seeking real connections.
Our first product, Billboard, is launching this June.
Open for All
Our model’s open-source! Check out the PROMO Protocol, built for promotion and attention trading. Anyone can join this decentralized ad network. Run your own billboard or use ours. This is a growing ecosystem for a new ad economy.
Our Vision
NextBlock wants to help build a new decentralized internet. Our revolutionary and transparent business model will bring honest revenue to companies hosting valuable digital spaces. Together, we will discover what our attention is really worth.
Read our Manifesto to learn more.
NextBlock is registered in Texas, USA.
-
 @ ba3b4b1d:eadff0d3
2025-05-09 23:40:27
@ ba3b4b1d:eadff0d3
2025-05-09 23:40:27
O culto de Sol Invictus (Sol Invicto, ou "Sol Não Vencido") foi oficialmente instituído como religião estatal do Império Romano pelo imperador Aureliano em 274 d.C., marcando um momento relevante na história religiosa romana. Este culto, que celebrava o Sol como divindade suprema e invencível, estabeleceu celebrações anuais a 25 de Dezembro, uma data estrategicamente escolhida pela sua proximidade com o solstício de Inverno no calendário juliano. Contudo, o culto de Sol Invictus não surgiu isoladamente; tratava-se, na verdade, de uma reformulação e revitalização de práticas religiosas romanas muito mais antigas que veneravam Sol, a personificação deificada do Sol, uma figura presente na religião romana desde os tempos da República.
Antes da oficialização por Aureliano, o culto ao Sol já era praticado em Roma sob diversas formas. Na mitologia romana, Sol era frequentemente associado a deuses solares de outras culturas, como o grego Hélios e, mais tarde, o persa Mitra, cujo culto (o mitraísmo) alcançou grande popularidade entre os soldados romanos nos séculos II e III d.C. O mitraísmo, com os seus rituais iniciáticos e ênfase no Sol como símbolo de renovação e vitória, influenciou profundamente a iconografia e os conceitos do culto de Sol Invictus. A decisão de Aureliano de promover Sol Invictus como divindade unificadora do Império não foi apenas religiosa, mas também política: numa era de crises internas e externas, o culto ao Sol servia como símbolo de estabilidade, poder e unidade, sobretudo após a vitória de Aureliano contra a rainha Zenóbia do Reino de Palmira, cuja derrota foi atribuída à protecção divina do Sol.
Um dos festivais mais significativos associados ao culto era o Dies Natalis Solis Invicti ("Aniversário do Sol Invicto"), celebrado no solstício de Inverno, por volta de 21 de Dezembro, quando o dia começava a prolongar-se novamente, simbolizando a vitória do Sol sobre a escuridão. Este festival, profundamente enraizado no ciclo natural e astronómico, celebrava o renascimento do Sol e a sua força invencível. A proximidade temporal entre o Dies Natalis e a data de 25 de Dezembro, oficialmente adoptada para Sol Invictus, facilitou a sobreposição de significados e práticas religiosas. A ascensão do Cristianismo no Império Romano, particularmente após a conversão do imperador Constantino no início do século IV, conduziu a uma complexa interacção entre os cultos pagãos e a nova religião. É amplamente reconhecido pelos historiadores que o Cristianismo, ao estabelecer-se como religião dominante, absorveu e adaptou elementos de festivais pagãos para facilitar a conversão das populações e consolidar a sua influência. A escolha do 25 de Dezembro como data do nascimento de Jesus Cristo, que não tem fundamento nos textos bíblicos canónicos, é um exemplo evidente deste sincretismo. A data coincidia convenientemente com as celebrações de Sol Invictus e outros festivais pagãos, como a Saturnália, um período de festividades em honra do deus Saturno que ocorria em meados de Dezembro. O simbolismo do Sol, associado à luz, renovação e vitória sobre as trevas, era facilmente adaptável à narrativa cristã. Jesus, frequentemente descrito como a "Luz do Mundo" nos evangelhos (João 8:12), foi associado ao simbolismo solar, e a sua ressurreição passou a ser celebrada como uma vitória sobre a morte, semelhante ao retorno triunfal do Sol no solstício. A iconografia cristã também reflectiu esta influência: imagens de Cristo com uma auréola, reminiscentes dos raios solares, ecoavam representações de Sol Invictus e Hélios. Além disso, o mitraísmo, com os seus rituais de renovação e ênfase num salvador divino, apresentava paralelos com o Cristianismo, o que poderá ter facilitado a transição de fiéis de um culto para o outro.
Importa notar que a adopção do 25 de Dezembro como o Natal cristão não foi imediata. Registos históricos sugerem que a data só foi formalmente estabelecida no século IV, durante o reinado de Constantino e sob a influência da Igreja de Roma. O Papa Júlio I, por volta de 350 d.C., é frequentemente creditado por oficializar a celebração do nascimento de Cristo nesta data. Esta escolha foi estratégica, pois permitiu que o Cristianismo se sobrepusesse aos festivais pagãos, reinterpretando as suas tradições num contexto cristão. Paralelamente, na Sibéria, os cultos xamânicos envolvendo o cogumelo Amanita muscaria também se relacionam com o solstício de Inverno. Povos como os Evenki e os Chukchi utilizavam este cogumelo alucinogénio em rituais para enfrentar o rigoroso Inverno, induzindo visões de renas voadoras e trenós, que alguns estudiosos associam à origem das lendas do Pai Natal. A Amanita muscaria, com o seu píleo vermelho e branco, crescia sob pinheiros, que se tornaram símbolos das árvores de Natal. Os xamãs siberianos distribuíam estes cogumelos secos como "presentes" durante o solstício, muitas vezes entrando nas casas pela chaminé devido à neve, um costume que ecoa na figura do Pai Natal. Assim, tanto o culto de Sol Invictus como os rituais siberianos da Amanita muscaria convergem no simbolismo do solstício de Inverno, influenciando, de formas distintas, as tradições natalícias cristãs.
A escolha de 25 de Dezembro facilitou a integração de tradições pagãs, como a Saturnália e os cultos solares, numa narrativa cristã, com Jesus como a "Luz do Mundo".
Assim, o culto de Sol Invictus e as suas raízes no culto romano a Sol desempenharam um papel crucial na formação das celebrações cristãs do Natal. A amalgamação de elementos pagãos e cristãos reflecte a capacidade do Cristianismo de se adaptar às culturas locais, transformando símbolos e rituais profundamente enraizados em novas expressões de fé. Este processo de sincretismo não só garantiu a sobrevivência do Cristianismo num mundo religiosamente diverso, como também moldou a forma como o Natal é celebrado até hoje, com ecos das antigas tradições solares ainda presentes na sua simbologia de luz e renovação.
-
 @ b8851a06:9b120ba1
2025-05-09 22:54:43
@ b8851a06:9b120ba1
2025-05-09 22:54:43The global financial system is creaking under its own weight. The IMF is urging banks to shore up capital, cut risk, and brace for impact. Basel III is their answer, a last-ditch effort to reinforce a brittle foundation.
But behind the scenes, a quieter revolution is under way.
Bitcoin, the world’s first stateless digital asset, is no longer on the sidelines. It’s entering the Basel conversation: not by invitation, but by inevitability.
Basel III: The System’s Self-Diagnosis
Basel III is more than a technical rulebook. It’s a confession: an admission that the global banking system is vulnerable. Created in the aftermath of 2008, it calls for: • Stronger capital reserves: So banks can survive losses. • Lower leverage: To reduce the domino effect of overexposure. • Liquidity buffers: To weather short-term shocks without collapsing.
But here’s the kicker: these rules are hostile to anything outside the fiat system. Bitcoin gets hit with a punitive 1,250% risk weight. That means for every $1 of exposure, banks must hold $1 in capital. The message from regulators? “You can hold Bitcoin, but you’ll pay for it.”
Yet that fear: based framing misses a bigger truth: Bitcoin doesn’t just survive in this environment. It thrives in it.
Bitcoin: A Parallel System, Built on Hard Rules
Where Basel III imposes “fiat discipline” from the top down, Bitcoin enforces it from the bottom up: with code, math, and transparency.
Bitcoin is not just a hedge. It’s a structural antidote to systemic fragility.
Volatility: A Strategic Asset
Yes, Bitcoin is volatile. But in a system that devalues fiat on a schedule, volatility is simply the cost of freedom. Under Basel III, banks are expected to build capital buffers during economic expansions.
What asset allows you to build those buffers faster than Bitcoin in a bull market?
When the cycle turns, those reserves act as shock absorbers: converting volatility into resilience. It’s anti-fragility in motion.
Liquidity: Real, Deep, and Global
Bitcoin settled over $19 trillion in transactions in 2024. That’s not hypothetical liquidity. it’s real, measurable flow. Unlike traditional high-quality liquid assets (HQLAs), Bitcoin is: • Available 24/7 • Borderless • Not dependent on central banks
By traditional definitions, Bitcoin is rapidly qualifying for HQLA status. Even if regulators aren’t ready to admit it.
Diversification: Breaking the Fiat Dependency
Basel III is designed to pull banks back into the fiat matrix. But Bitcoin offers an escape hatch. Strategic Bitcoin reserves are not about speculation, they’re insurance. For family offices, institutions, and sovereign funds, Bitcoin is the lifeboat when the fiat ship starts taking on water.
Regulatory Realignment: The System Reacts
The Basel Committee’s new rules on crypto exposures went live in January 2025. Around the world, regulators are scrambling to define their stance. Every new restriction placed on Bitcoin only strengthens its legitimacy, as more institutions ask: Why so much resistance, if it’s not a threat?
Bitcoin doesn’t need permission. It’s already being adopted by over 150 public companies, forward-looking states, and a new class of self-sovereign individuals.
Conclusion: The Real Question
This isn’t just about Bitcoin fitting into Basel III.
The real question is: How long can Basel III remain relevant in a world where Bitcoin exists?
Bitcoin is not the risk. It’s the reality check. And it might just be the strongest capital buffer the system has ever seen.
Gradually then suddenly.
-
 @ b99efe77:f3de3616
2025-05-09 21:16:29
@ b99efe77:f3de3616
2025-05-09 21:16:29🚦Traffic Light Control System🚦111111111
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ b99efe77:f3de3616
2025-05-09 19:55:12
@ b99efe77:f3de3616
2025-05-09 19:55:12🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 000002de:c05780a7
2025-05-09 18:33:06
@ 000002de:c05780a7
2025-05-09 18:33:06I've been eager to share my thoughts on "Return of the Strong Gods" by R.R. Reno since I finished it a week ago.
I found this book incredibly insightful. @SimpleStacker's excellent review prompted me to pick it up, and I'm glad I did. While I won't be providing a full review, I will share some of the key insights and thoughts that resonated with me.
Reno masterfully dissects the sociological underpinnings of the political shifts in the US and the Western world over the past decade and a half. His analysis of the rise of populism and nationalism is compelling and rings true to my personal observations. Reno's central thesis is that post-WW2, the West embraced "weaker gods"—ideals like democracy, pluralism, and liberalism—fearing a repeat of the strong nationalistic sentiments that led to Hitler's rise. He argues that this shift has left many people feeling culturally homeless and desperate for strong leadership that listens to their grievances.
A significant portion of Reno's argument is built on the ideas of Karl Popper, a philosopher I was unfamiliar with before reading this book. Popper's work "The Open Society and Its Enemies" has significantly influenced post-war consensus, which Reno argues has led to a disconnect between the political elite and the common people. This disconnect, he posits, is a primary driver of populist sentiments.
Reno also delves into economics, discussing Friedrich Hayek and his agreement with some of Popper's positions. This intersection of philosophy and economics provides a unique lens through which to view the political landscape. Reno's mention of the Treaty of Versailles as a catalyst for Hitler's rise is a point often overlooked in discussions about WW2. He argues that the punitive measures imposed on Germany created an environment ripe for a strongman to emerge.
One of the most compelling aspects of Reno's argument is his explanation of how the political elite often lose touch with the values and wishes of the people they represent. He draws a powerful analogy between cultural homelessness and the desperation that drives people to seek strong leadership. This section of the book particularly resonated with me, as it aligns with my own observations of the political climate.
I would have liked Reno to start his analysis with Woodrow Wilson, whose "making the world safe for democracy" slogan embodied a form of Christian nationalism. Wilson's ideals and the post-WW1 environment laid the groundwork for the open society movement, which Reno critiques. Exploring this historical context could have strengthened Reno's argument.
Reno occasionally conflates economic liberalism with libertinism, which I found to be a minor flaw in an otherwise strong argument. He rightly points out the need for moral ethics in society but seems to overlook the distinction between economic freedom and moral laxity. Reno's discussion of Milton Friedman's ideas further highlights this confusion. While Reno argues that free trade has contributed to many of our modern ills, I believe the issue lies more with nation-state trade agreements like NAFTA, which are not true examples of free trade.
Another area where I disagree with Reno is his conflation of the nation with the state. Nations are cultural entities that predate and can exist independently of states. Reno's argument would be stronger if he acknowledged this distinction, as it would clarify his points about national pride and cultural heritage.
Reno's final chapters offer a cautionary tale about the return of strong gods and the danger of making them idols. He warns against authoritarianism and the overreach of the state, advocating for a balance that respects cultural heritage without succumbing to nationalism.
In conclusion, "Return of the Strong Gods" is a thought-provoking exploration of the political and cultural shifts of our time. Reno's insights are valuable, and his arguments, while not without flaws, provide a fresh perspective on the rise of populism and nationalism. I recommend this book to anyone seeking a deeper understanding of the forces shaping our world today.
originally posted at https://stacker.news/items/975849
-
 @ 9bde4214:06ca052b
2025-04-22 18:13:37
@ 9bde4214:06ca052b
2025-04-22 18:13:37"It's gonna be permissionless or hell."
Gigi and gzuuus are vibing towards dystopia.
Books & articles mentioned:
- AI 2027
- DVMs were a mistake
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- The Ultimate Resource by Julian L. Simon
- Harry Potter by J.K. Rowling
- Momo by Michael Ende
In this dialogue:
- Pablo's Roo Setup
- Tech Hype Cycles
- AI 2027
- Prompt injection and other attacks
- Goose and DVMCP
- Cursor vs Roo Code
- Staying in control thanks to Amber and signing delegation
- Is YOLO mode here to stay?
- What agents to trust?
- What MCP tools to trust?
- What code snippets to trust?
- Everyone will run into the issues of trust and micropayments
- Nostr solves Web of Trust & micropayments natively
- Minimalistic & open usually wins
- DVMCP exists thanks to Totem
- Relays as Tamagochis
- Agents aren't nostr experts, at least not right now
- Fix a mistake once & it's fixed forever
- Giving long-term memory to LLMs
- RAG Databases signed by domain experts
- Human-agent hybrids & Chess
- Nostr beating heart
- Pluggable context & experts
- "You never need an API key for anything"
- Sats and social signaling
- Difficulty-adjusted PoW as a rare-limiting mechanism
- Certificate authorities and centralization
- No solutions to policing speech!
- OAuth and how it centralized
- Login with nostr
- Closed vs open-source models
- Tiny models vs large models
- The minions protocol (Stanford paper)
- Generalist models vs specialized models
- Local compute & encrypted queries
- Blinded compute
- "In the eyes of the state, agents aren't people"
- Agents need identity and money; nostr provides both
- "It's gonna be permissionless or hell"
- We already have marketplaces for MCP stuff, code snippets, and other things
- Most great stuff came from marketplaces (browsers, games, etc)
- Zapstore shows that this is already working
- At scale, central control never works. There's plenty scams and viruses in the app stores.
- Using nostr to archive your user-generated content
- HAVEN, blossom, novia
- The switcharoo from advertisements to training data
- What is Truth?
- What is Real?
- "We're vibing into dystopia"
- Who should be the arbiter of Truth?
- First Amendment & why the Logos is sacred
- Silicon Valley AI bros arrogantly dismiss wisdom and philosophy
- Suicide rates & the meaning crisis
- Are LLMs symbiotic or parasitic?
- The Amish got it right
- Are we gonna make it?
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- Harry Potter dementors & Momo's time thieves
- Facebook & Google as non-human (superhuman) agents
- Zapping as a conscious action
- Privacy and the internet
- Plausible deniability thanks to generative models
- Google glasses, glassholes, and Meta's Ray Ben's
- People crave realness
- Bitcoin is the realest money we ever had
- Nostr allows for real and honest expression
- How do we find out what's real?
- Constraints, policing, and chilling effects
- Jesus' plans for DVMCP
- Hzrd's article on how DVMs are broken (DVMs were a mistake)
- Don't believe the hype
- DVMs pre-date MCP tools
- Data Vending Machines were supposed to be stupid: put coin in, get stuff out.
- Self-healing vibe-coding
- IP addresses as scarce assets
- Atomic swaps and the ASS protocol
- More marketplaces, less silos
- The intensity of #SovEng and the last 6 weeks
- If you can vibe-code everything, why build anything?
- Time, the ultimate resource
- What are the LLMs allowed to think?
- Natural language interfaces are inherently dialogical
- Sovereign Engineering is dialogical too
-
 @ 9223d2fa:b57e3de7
2025-05-09 18:22:46
@ 9223d2fa:b57e3de7
2025-05-09 18:22:4613,734 steps
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ c631e267:c2b78d3e
2025-05-09 18:21:03
@ c631e267:c2b78d3e
2025-05-09 18:21:03Information ohne Reflexion ist geistiger Flugsand. \ Ernst Reinhardt
Der lateinische Ausdruck «Quo vadis» als Frage nach einer Entwicklung oder Ausrichtung hat biblische Wurzeln. Er wird aber auch in unserer Alltagssprache verwendet, laut Duden meist als Ausdruck von Besorgnis oder Skepsis im Sinne von: «Wohin wird das führen?»
Der Sinn und Zweck von so mancher politischen Entscheidung erschließt sich heutzutage nicht mehr so leicht, und viele Trends können uns Sorge bereiten. Das sind einerseits sehr konkrete Themen wie die zunehmende Militarisierung und die geschichtsvergessene Kriegstreiberei in Europa, deren Feindbildpflege aktuell beim Gedenken an das Ende des Zweiten Weltkriegs beschämende Formen annimmt.
Auch das hohe Gut der Schweizer Neutralität scheint immer mehr in Gefahr. Die schleichende Bewegung der Eidgenossenschaft in Richtung NATO und damit weg von einer Vermittlerposition erhält auch durch den neuen Verteidigungsminister Anschub. Martin Pfister möchte eine stärkere Einbindung in die europäische Verteidigungsarchitektur, verwechselt bei der Argumentation jedoch Ursache und Wirkung.
Das Thema Gesundheit ist als Zugpferd für Geschäfte und Kontrolle offenbar schon zuverlässig etabliert. Die hauptsächlich privat finanzierte Weltgesundheitsorganisation (WHO) ist dabei durch ein Netzwerk von sogenannten «Collaborating Centres» sogar so weit in nationale Einrichtungen eingedrungen, dass man sich fragen kann, ob diese nicht von Genf aus gesteuert werden.
Das Schweizer Bundesamt für Gesundheit (BAG) übernimmt in dieser Funktion ebenso von der WHO definierte Aufgaben und Pflichten wie das deutsche Robert Koch-Institut (RKI). Gegen die Covid-«Impfung» für Schwangere, die das BAG empfiehlt, obwohl es fehlende wissenschaftliche Belege für dessen Schutzwirkung einräumt, formiert sich im Tessin gerade Widerstand.
Unter dem Stichwort «Gesundheitssicherheit» werden uns die Bestrebungen verkauft, essenzielle Dienste mit einer biometrischen digitalen ID zu verknüpfen. Das dient dem Profit mit unseren Daten und führt im Ergebnis zum Verlust unserer demokratischen Freiheiten. Die deutsche elektronische Patientenakte (ePA) ist ein Element mit solchem Potenzial. Die Schweizer Bürger haben gerade ein Referendum gegen das revidierte E-ID-Gesetz erzwungen. In Thailand ist seit Anfang Mai für die Einreise eine «Digital Arrival Card» notwendig, die mit ihrer Gesundheitserklärung einen Impfpass «durch die Hintertür» befürchten lässt.
Der massive Blackout auf der iberischen Halbinsel hat vermehrt Fragen dazu aufgeworfen, wohin uns Klimawandel-Hysterie und «grüne» Energiepolitik führen werden. Meine Kollegin Wiltrud Schwetje ist dem nachgegangen und hat in mehreren Beiträgen darüber berichtet. Wenig überraschend führen interessante Spuren mal wieder zu internationalen Großbanken, Globalisten und zur EU-Kommission.
Zunehmend bedenklich ist aber ganz allgemein auch die manifestierte Spaltung unserer Gesellschaften. Angesichts der tiefen und sorgsam gepflegten Gräben fällt es inzwischen schwer, eine zukunftsfähige Perspektive zu erkennen. Umso begrüßenswerter sind Initiativen wie die Kölner Veranstaltungsreihe «Neue Visionen für die Zukunft». Diese möchte die Diskussionskultur reanimieren und dazu beitragen, dass Menschen wieder ohne Angst und ergebnisoffen über kontroverse Themen der Zeit sprechen.
Quo vadis – Wohin gehen wir also? Die Suche nach Orientierung in diesem vermeintlichen Chaos führt auch zur Reflexion über den eigenen Lebensweg. Das ist positiv insofern, als wir daraus Kraft schöpfen können. Ob derweil der neue Papst, dessen «Vorgänger» Petrus unsere Ausgangsfrage durch die christliche Legende zugeschrieben wird, dabei eine Rolle spielt, muss jede/r selbst wissen. Mir persönlich ist allein schon ein Führungsanspruch wie der des Petrusprimats der römisch-katholischen Kirche eher suspekt.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 2b24a1fa:17750f64
2025-05-09 19:50:20
@ 2b24a1fa:17750f64
2025-05-09 19:50:20Wer sein eigenes Geld abheben möchte, macht sich heute – in Spanien - verdächtig. Wer dort eine größere Geldmenge des eigenen Vermögens abzuheben gedenkt, muss das von nun an Tage zuvor anmelden. Diese neue Regelung lässt sich auch nicht dadurch umgehen, dass man mehrere kleine Einzelbeiträge abhebt. Und die, die die neue Regelung missachten, werden empfindlich bestraft. So gerät jeder, der zu häufig Bares abhebt, in das Visier der Behörden.
https://soundcloud.com/radiomuenchen/barzahler-unter-generalverdacht-von-norbert-haring?
Was sich in Spanien an Bankautomaten und -schaltern eingeschlichen hat, könnte sich seinen Weg auch nach Deutschland bahnen. In Frankreich, so zeigt die persönliche Erfahrung, variiert die zu erzielende Geldmenge am Automaten unter noch ungeklärten Bedingungen von Tag zu Tag, von Konto zu Konto. Der Automat gibt vor, ob gerade beispielsweise 60, 200 oder 400 Euro abgehoben werden dürfen.
Hören Sie Norbert Härings Text zum spanischen Szenario der den Titel „Barzahler unter Generalverdacht“ trägt und zunächst auf seinem Blog erschienen war. norberthaering.de/news/spanien-bargeld/
Sprecher: Karsten Troyke
-
 @ a5ee4475:2ca75401
2025-05-09 17:39:47
@ a5ee4475:2ca75401
2025-05-09 17:39:47clients #list #descentralismo #english #article #finalversion
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐🤖🍎💻(🐧🪟🍎)
- Coracle - Super App [source] 🌐
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖
- Primal - Social and wallet [source] 🌐🤖🍎
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana 🤖🍎🌐💻(🐧) [source]
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- Camelus [early access] 🤖 [source]
Communities
- CCNS - Community Curated Nostr Stuff [source]
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox comunnity server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
Search
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Live streaming and zap who you want (NIP-53) [source] 🤖(on zapstore) 🌐
- Swae - Live streaming [source] (on development) ⏳
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 (advice: https://zaplinks.lol/ and https://zaplinks.lol/slides/ sites are down)
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
- Keychat - Signal based [🤖🍎 on development] [source]
Reading
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List source 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- DEG Mods - Decentralized Game Mods [info] [source] 🌐
- NG Engine - Nostr Game Engine [source] 🌐
- JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🤖🍎🌐
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
- Spring - Browser 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
[⚠️SCAM⚠️] Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] 🤖🍎
- Wallet of Satoshi [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - [source] 🌐
Blossom - Your Media Safer
Primal Blossom 🌐 NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing and Extension
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ a5ee4475:2ca75401
2025-05-09 17:13:22
@ a5ee4475:2ca75401
2025-05-09 17:13:22lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2454m8dfzn26z4f34kvu6fw4rysnrjxfm42wfpe90
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ b99efe77:f3de3616
2025-05-09 19:49:54
@ b99efe77:f3de3616
2025-05-09 19:49:54🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 32092ec1:8e9fd13a
2025-05-09 16:13:34
@ 32092ec1:8e9fd13a
2025-05-09 16:13:34Bitcoin controversies are not new, in fact, bitcoin’s past has been riddled with one controversy after another. From the viewpoint of a financial investor, controversies are not good. They drive investor fear by amplifying uncertainty and introducing doubt about the future viability of the project. Although bitcoin is an investable asset, and there are certainly individuals, companies and countries who are investing in bitcoin strictly as a new, diversified financial asset that shows growth characteristics the likes of which humanity has rarely seen, bitcoin is not exclusively a financial instrument. Bitcoin is a network that is only as strong as the people running the miners who create the blocks, the nodes that propagate the blocks, and the users who hold the keys.
In this post I do not care to share my view on any of the latest bitcoin controversies, whether that be about OP_RETURNs, MSTR, Blackrock, MSTY, inscriptions, soft fork proposals, mempools, bitcoin strategic reserves, 21, chain surveillance, on-chain privacy, shitcoins projects, or anything else that anyone cares to opine about on Nostr or X to signal their support or opposition for what they think is critical to the success or failure of bitcoin. What I do care to share here is the ONLY winning strategy to defend bitcoin no matter what your opinion its future: USE THE TOOLS, RUN THE CODE, HOLD YOUR KEYS, TAKE RESPONSIBILITY.
In my humble opinion, the biggest problem with the current batch of bitcoin controversies is that so many people are sharing their opinions and expressing their fears about the future of bitcoin who are not even using the tools; they aren’t running the code, supporting the network or even holding their own keys. Everyone is free to share their opinions about the future of bitcoin and allowing everyone a voice is critical if we are serious about adopting the best ideas. Many visionaries have participated in the growth and development of bitcoin up to this point; we are truly standing on the shoulders of giants.
But before jumping to conclusions and spreading opinions about whether people are good faith or bad faith actors in the bitcoin space, I believe we should all hold ourselves to a certain standard. Set a minimum threshold of education for yourself before you jump on one side or the other of the latest controversy. We have tools that offer a level of sovereignty that is unparalleled in the legacy financial world, are you using them?Don’t like what MSTR is doing? Hold your keys in cold storage, then share your opinion.
Think Blackrock wants to use Bitcoin to launch a dystopian new world order agenda? Tell everyone to run a node, implement on-chain privacy strategies and hold their keys in cold storage.
Are Bitcoin developers making changes you don’t like? Use an alternative implementation, get a Bitaxe and construct your own block templates; for almost everyone this will be a stronger signal than shitposting or spreading FUD on the socials.
If you really want to defend bitcoin, think about how you are using it today. Who are you trusting to put your transactions into a block? Who are you trusting to propagate your transactions across the network? Who are you trusting to hold your keys? Who estimates your transaction fees? If you don’t trust the people who you are currently depending on, move your trust elsewhere, or increase your sovereignty and rely on yourself for some, or all, of these functions.
We make bitcoin what it is today, and we will define what bitcoin will be in the future. If we want to defend bitcoin it is our responsibility to keep it as decentralized as possible and that starts with every individual using the tools, running the code, doing the research and taking responsibility for their money.
895982
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ b99efe77:f3de3616
2025-05-09 19:49:08
@ b99efe77:f3de3616
2025-05-09 19:49:08🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ ed5774ac:45611c5c
2025-04-19 20:29:31
@ ed5774ac:45611c5c
2025-04-19 20:29:31April 20, 2020: The day I saw my so-called friends expose themselves as gutless, brain-dead sheep.
On that day, I shared a video exposing the damning history of the Bill & Melinda Gates Foundation's vaccine campaigns in Africa and the developing world. As Gates was on every TV screen, shilling COVID jabs that didn’t even exist, I called out his blatant financial conflict of interest and pointed out the obvious in my facebook post: "Finally someone is able to explain why Bill Gates runs from TV to TV to promote vaccination. Not surprisingly, it's all about money again…" - referencing his substantial investments in vaccine technology, including BioNTech's mRNA platform that would later produce the COVID vaccines and generate massive profits for his so-called philanthropic foundation.
The conflict of interest was undeniable. I genuinely believed anyone capable of basic critical thinking would at least pause to consider these glaring financial motives. But what followed was a masterclass in human stupidity.
My facebook post from 20 April 2020:

Not only was I branded a 'conspiracy theorist' for daring to question the billionaire who stood to make a fortune off the very vaccines he was shilling, but the brain-dead, logic-free bullshit vomited by the people around me was beyond pathetic. These barely literate morons couldn’t spell "Pfizer" without auto-correct, yet they mindlessly swallowed and repeated every lie the media and government force-fed them, branding anything that cracked their fragile reality as "conspiracy theory." Big Pharma’s rap sheet—fraud, deadly cover-ups, billions in fines—could fill libraries, yet these obedient sheep didn’t bother to open a single book or read a single study before screaming their ignorance, desperate to virtue-signal their obedience. Then, like spineless lab rats, they lined up for an experimental jab rushed to the market in months, too dumb to care that proper vaccine development takes a decade.
The pathetic part is that these idiots spend hours obsessing over reviews for their useless purchases like shoes or socks, but won’t spare 60 seconds to research the experimental cocktail being injected into their veins—or even glance at the FDA’s own damning safety reports. Those same obedient sheep would read every Yelp review for a fucking coffee shop but won't spend five minutes looking up Pfizer's criminal fraud settlements. They would demand absolute obedience to ‘The Science™’—while being unable to define mRNA, explain lipid nanoparticles, or justify why trials were still running as they queued up like cattle for their jab. If they had two brain cells to rub together or spent 30 minutes actually researching, they'd know, but no—they'd rather suck down the narrative like good little slaves, too dumb to question, too weak to think.
Worst of all, they became the system’s attack dogs—not just swallowing the poison, but forcing it down others’ throats. This wasn’t ignorance. It was betrayal. They mutated into medical brownshirts, destroying lives to virtue-signal their obedience—even as their own children’s hearts swelled with inflammation.
One conversation still haunts me to this day—a masterclass in wealth-worship delusion. A close friend, as a response to my facebook post, insisted that Gates’ assumed reading list magically awards him vaccine expertise, while dismissing his billion-dollar investments in the same products as ‘no conflict of interest.’ Worse, he argued that Gates’s $5–10 billion pandemic windfall was ‘deserved.’
This exchange crystallizes civilization’s intellectual surrender: reason discarded with religious fervor, replaced by blind faith in corporate propaganda.
The comment of a friend on my facebook post that still haunts me to this day:

Walking Away from the Herd
After a period of anger and disillusionment, I made a decision: I would no longer waste energy arguing with people who refused to think for themselves. If my circle couldn’t even ask basic questions—like why an untested medical intervention was being pushed with unprecedented urgency—then I needed a new community.
Fortunately, I already knew where to look. For three years, I had been involved in Bitcoin, a space where skepticism wasn’t just tolerated—it was demanded. Here, I’d met some of the most principled and independent thinkers I’d ever encountered. These were people who understood the corrupting influence of centralized power—whether in money, media, or politics—and who valued sovereignty, skepticism, and integrity. Instead of blind trust, bitcoiners practiced relentless verification. And instead of empty rhetoric, they lived by a simple creed: Don’t trust. Verify.
It wasn’t just a philosophy. It was a lifeline. So I chose my side and I walked away from the herd.
Finding My Tribe
Over the next four years, I immersed myself in Bitcoin conferences, meetups, and spaces where ideas were tested, not parroted. Here, I encountered extraordinary people: not only did they share my skepticism toward broken systems, but they challenged me to sharpen it.
No longer adrift in a sea of mindless conformity, I’d found a crew of thinkers who cut through the noise. They saw clearly what most ignored—that at the core of society’s collapse lay broken money, the silent tax on time, freedom, and truth itself. But unlike the complainers I’d left behind, these people built. They coded. They wrote. They risked careers and reputations to expose the rot. Some faced censorship; others, mockery. All understood the stakes.
These weren’t keyboard philosophers. They were modern-day Cassandras, warning of inflation’s theft, the Fed’s lies, and the coming dollar collapse—not for clout, but because they refused to kneel to a dying regime. And in their defiance, I found something rare: a tribe that didn’t just believe in a freer future. They were engineering it.
April 20, 2024: No more herd. No more lies. Only proof-of-work.
On April 20, 2024, exactly four years after my last Facebook post, the one that severed my ties to the herd for good—I stood in front of Warsaw’s iconic Palace of Culture and Science, surrounded by 400 bitcoiners who felt like family. We were there to celebrate Bitcoin’s fourth halving, but it was more than a protocol milestone. It was a reunion of sovereign individuals. Some faces I’d known since the early days; others, I’d met only hours before. We bonded instantly—heated debates, roaring laughter, zero filters on truths or on so called conspiracy theories.
As the countdown to the halving began, it hit me: This was the antithesis of the hollow world I’d left behind. No performative outrage, no coerced consensus—just a room of unyielding minds who’d traded the illusion of safety for the grit of truth. Four years prior, I’d been alone in my resistance. Now, I raised my glass among my people - those who had seen the system's lies and chosen freedom instead. Each had their own story of awakening, their own battles fought, but here we shared the same hard-won truth.
The energy wasn’t just electric. It was alive—the kind that emerges when free people build rather than beg. For the first time, I didn’t just belong. I was home. And in that moment, the halving’s ticking clock mirrored my own journey: cyclical, predictable in its scarcity, revolutionary in its consequences. Four years had burned away the old world. What remained was stronger.

No Regrets
Leaving the herd wasn’t a choice—it was evolution. My soul shouted: "I’d rather stand alone than kneel with the masses!". The Bitcoin community became more than family; they’re living proof that the world still produces warriors, not sheep. Here, among those who forge truth, I found something extinct elsewhere: hope that burns brighter with every halving, every block, every defiant mind that joins the fight.
Change doesn’t come from the crowd. It starts when one person stops applauding.
Today, I stand exactly where I always wanted to be—shoulder-to-shoulder with my true family: the rebels, the builders, the ungovernable. Together, we’re building the decentralized future.
-
 @ c9badfea:610f861a
2025-05-09 15:32:59
@ c9badfea:610f861a
2025-05-09 15:32:59- Install Feeder (it's free and open source)
- Discover RSS feeds from various sources (see links below)
- Copy the Feed URL
- Open Feeder, tap the ⁞ icon, and choose Add Feed
- Paste the Feed URL and tap Search
- Select the found RSS feed item
- Scroll down and tap OK
Some Sources
ℹ️ You can also use YouTube channel URLs as feeds
-
 @ b99efe77:f3de3616
2025-05-09 19:47:09
@ b99efe77:f3de3616
2025-05-09 19:47:09🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 6e0ea5d6:0327f353
2025-04-19 15:09:18
@ 6e0ea5d6:0327f353
2025-04-19 15:09:18🩸
The world won’t stop and wait for you to recover.Do your duty regardless of how you feel. That’s the only guarantee you’ll end the day alright.
You’ve heard it before: “The worst workout is the one you didn’t do.” Sometimes you don’t feel like going to the gym. You start bargaining with laziness: “I didn’t sleep well… maybe I should skip today.” But then you go anyway, committing only to the bare minimum your energy allows. And once you start, your body outperforms your mind’s assumptions—it turns out to be one of the best workouts you’ve had in a long time. The feeling of following through, of winning a battle you were losing, gives you the confidence to own the rest of your day. You finally feel good.
And that wouldn’t have happened if you stayed home waiting to feel better. Guilt would’ve joined forces with discouragement, and you’d be crushed by melancholy in a victim mindset. That loss would bleed into the rest of your week, conditioning your mind: because you didn’t spend your energy on the workout, you’d stay up late, wake up worse, and while waiting to feel “ready,” you’d lose a habit that took months of effort to build.
When in doubt, just do your duty. Stick to the plan. Don’t negotiate with your feelings—outsmart them. “Just one page today,” and you’ll end up reading ten. “Only the easy tasks,” and you’ll gain momentum to conquer the hard ones. Laziness is a serpent—you win when you make no deals with it.
A close friend once told me that when he was at his limit during a second job shift, he’d open a picture on his phone—of a fridge or a stove he needed to buy for his home—and that image gave him strength to stay awake. That moment stuck with me forever.
Do you really think the world will have the same mercy on you that you have on yourself? Don’t be surprised when it doesn’t spare you. Move forward even while stitching your wounds: “If you wait for perfect conditions, you’ll never do anything.” (Ecclesiastes 11:4)
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ b99efe77:f3de3616
2025-05-09 19:44:37
@ b99efe77:f3de3616
2025-05-09 19:44:37🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 2b24a1fa:17750f64
2025-05-09 19:43:28
@ 2b24a1fa:17750f64
2025-05-09 19:43:28 -
 @ 6e0ea5d6:0327f353
2025-04-19 15:02:55
@ 6e0ea5d6:0327f353
2025-04-19 15:02:55My friend, let yourself be deluded for a moment, and reality will see to it that your fantasy is shattered—like a hammer crushing marble. The real world grants no mercy; it will relentlessly tear down your aspirations, casting them into the abyss of disillusionment and burying your dreams under the unbearable weight of your own expectations. It’s an inescapable fate—but the outcome is still in your hands: perish at the bottom like a wretch or turn the pit into a trench.
Davvero, everyone must eventually face something that breaks them. It is in devastation that man discovers what he is made of, and in the silence of defeat that he hears the finest advice. Yet the weak would rather embrace the convenient lie of self-pity, blaming life for failures that are, in truth, the result of their own negligence and cowardly choices. If you hide behind excuses because you fear the painful truth, know this: the responsibility has always been yours.
Ascolta bene! Just remain steadfast, even when everything feels like an endless maze. The difficulties you face today—those you believe you’ll never overcome—will one day seem insignificant under the light of time and experience. Tomorrow, you’ll look back and laugh at yourself for ever letting these storms seem so overwhelming.
Now, it’s up to you to fight your own battle—for the evil day spares no one. Don’t let yourself be paralyzed by shock or bow before adversity. Be strong and of good courage—not as one who waits for relief, but as one prepared to face the inevitable and turn pain into glory.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 15cf81d4:b328e146
2025-05-09 13:53:09
@ 15cf81d4:b328e146
2025-05-09 13:53:09Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 2b24a1fa:17750f64
2025-05-09 19:39:46
@ 2b24a1fa:17750f64
2025-05-09 19:39:46"Kleines Erste-Hilfe-Büchlein gegen Propaganda" von 2023. „Normalerweise hört man das Wort „Propaganda“ im Mainstream-Diskurs nur, wenn es um Dinge geht, die andere Länder ihren eigenen Bürgern antun oder Teil ausländischer Beeinflussungsoperationen sind, obwohl in der überwältigenden Mehrheit der Fälle, in denen wir in unserem täglichen Leben Propaganda erlebt haben, der Anruf aus dem eigenen Haus kam.“
https://soundcloud.com/radiomuenchen/helge-buttkereit-medienkritik-als-trotziger-idealismus?
In der Folge dokumentiert sie einige gravierende Beispiele aus den US-Medien. Auch in Deutschland fehlt es den Massenmedien an der nötigen Distanz zur Regierung und ihrem Werte-Narrativ. Was umso gefährlicher ist, da sie über „Definitionsmacht“ verfügen. Auch wenn wir selbst diese Medien nicht konsumieren, so können wir doch sicher sein, dass die große Mehrheit der Bürger sie konsultiert und damit deren Sicht auf die Welt massiv beeinflusst wird. „Wenn wir die Tagesschau einschalten, erfahren wir nichts über die ‘Wirklichkeit’. Wir lernen vielmehr, wer es geschafft hat, seine Sicht auf die Wirklichkeit in die Propaganda-Matrix einzuschreiben“, verrät der Medienwissenschaftler Michael Meyen in seinem Buch "Die Propaganda-Matrix". Nun gilt jedoch die Presse in der öffentlichen Wahrnehmung als „Vierte Gewalt“ der Demokratie. Ihre Aufgabe wäre es demnach, die zunehmend verflochtenen Staatsgewalten Legislative, Exekutive und Judikative zu kontrollieren. Die Realität sieht anders aus. Dabei übersieht selbst die immer häufiger auftretende Medienkritik, dass die „Vierte Gewalt“ von den Herrschenden nie in dieser Funktion gedacht war – schließlich waren und sind die Medien seit je her in den Händen von Regierungen und Konzernen, schreibt unser Autor Helge Buttkereit. Hören Sie seinen zweiteiligen Beitrag „Medienkritik als trotziger Idealismus“, der zunächst beim Magazin Multipolar erschienen war: multipolar-magazin.de/artikel/medien…tik-idealismus
Sprecher: Karsten Troyke
Bild-Collage: Radio München
-
 @ 2b24a1fa:17750f64
2025-05-09 19:29:22
@ 2b24a1fa:17750f64
2025-05-09 19:29:22Herzlichen Glückwunsch zu einem weiteren denkwürdigen Europa-Tag, den wir mit einem Manifest des european-peace-projects begehen. Europaweit beteiligen sich heute Institutionen, Vereine und Bürger, die um 17 Uhr die Fenster öffnen und dieses Manifest laut verlesen. Wer das nicht möchte oder kann, schaltet vielleicht Radio München ein:
\ https://soundcloud.com/radiomuenchen/european-peace-project-das-manifest-heute-17-uhr?
-
 @ 078d6670:56049f0c
2025-05-09 13:22:26
@ 078d6670:56049f0c
2025-05-09 13:22:26It was a dark and stormy night. It had to be: Weather had been fired. If they were working for him he would have fired them, but that is just embarrassed arrogance talking. He remembers standing in the middle of his office, his trashed office. It looked like a hurricane had hit it, or vagrants had been living in it for years, nothing of value was left intact. Monitors were shattered on the floor, couches were covered in debris. There was evidence of food and magazine pages in every gaze space. His supervisor, his name escaped him, was grey with anger. “Explain this!” he had shouted with a tremble, but he couldn’t. Every time he tried to think of the events of the day he met a dazzling white blankness.
He was escorted, handcuffed, to a room by two security guards with his supervisor trailing them. Weather felt humiliated and frustrated, but he didn’t know why. He sat, shivering slightly, in a low-lit conference room he had never seen before. Actually, he doesn’t remember any windows or any specific light source, just a haze of shadows. The big boss is sitting opposite him, looking haggard and white as a sun-bleached shell. His supervisor was sitting on his right looking equally haggard and even depressed. They appeared genuine and he knew it was bad news for him.
“You’ve embarrassed this company! There is even a chance you have ruined us all and you have the audacity to sit there and pretend that you can’t remember a thing!”
He knew there was no point in arguing, he had no ideas with which to make up any argument. He sat staring into space.
“At least, give us a story. Tell us how bored you were and tried to create your own weather system by running around the room swinging the fan around like a sugar mad teenager!”
He couldn’t even clear his throat. He couldn’t lift his eyes to meet theirs. He knew his career was over and they were fearful all their ideals had crashed irreparably. He stared into space at the globe standing in the middle of the table. The more he stared at it the more he realized that it seemed to have an atmosphere around it. There were clouds covering patches of the earth. He didn’t dare bring their attention to it. The only memories he could dredge up seemed like dreams, and they’re hardly constitute a defence.
He looked up at their faces finally, surprised to see more alarm than anger, like they were actually afraid of him. They both stood up suddenly, wanting to get out the room as quickly as possible.
“You have brought Global Sky Incorporated into disrepute. You’ve embarrassed us. You have possibly ruined hundreds of careers here! We never want to see you again! You are never to come within a hundred metres of this building. You can never use your research ever again, it never happened. Everything you have ever written will be classified and restricted until you are dead!” The big boss was shaking wild, Weather was grateful for the security guards that hurled him out of his chair and marched him out of the building.
The afternoon sky had been a deathly grey. It had occurred to him but now he was a little shocked at how much control they had over the weather, maybe it was a good thing that he had been fired, but probably a bad thing as they would certainly make worse mistakes than him, whatever he might have done. He was confused, not sure if he been fired for trashing his office or for state of the weather. About the weird weather he has no idea, all he can remember is a dazzling blank whiteness, and that is hardly a memory.
He couldn’t face going directly home, jumped on public transport travelling on tracks laid down on old unused highways and headed for the city beach, or what passed for a beach. He sat on a concrete bench gazing across the grey sand at the shimmering waves. They weren’t shimmering because of the sparkling sunlight, but the contaminates in the water. But still it was tranquil enough. He tried to think about his day, but couldn’t get past the white blankness, everything else before that was like a postcard from someone else’s holiday, and they looked like movies he might have seen. He has a framed vision of himself in his office with office supplies flying around him without touching him. Clearly, as they weren’t touching him, it had nothing to do with his behaviour. He is a victim here. It wasn’t his fault, the world was changing and the powers that be wanted more control. It seems like Global Weather Incorporated (GWI) lost control of their equipment and need a fall guy, they didn’t need him anymore. Squeezed his brain for the algorithms, then threw him onto the streets. He was nothing without his research, it’s all he had done his entire life. He would have to pursue it, but that would as useful as talking to a brick wall, the world was less transparent; government, science and advertising companies had a law of their own and a police force to uphold them.
He believed in good and the unveiling of truth. He had a romantic connection to the idea that truth grew in people’s hearts that everyone wanted the best for everyone else, no matter what skin colour, car colour they had, or star sign they were born under. Everybody wanted peace, a roof over their heads and food in their bellies; and wanted these things for their neighbours too. If only his neighbours had the same beliefs.
It was late afternoon now. He could tell by the slight luminosity of the grey clouds near the horizon, close to a cloudless gap, a slit above the horizon through which the sun could bid its final farewell to the day. He was in no mood for a sunset minute. He picked his bum off the bench, dusted it off and began his journey home, not wanting to be left in the dark in the city, opportune prey for corrupt cops. Everyone was coming out of the offices, beginning the big commute home. Car pools had reshaped their cars to fit more people in, and many climbed on to the reinvented trams, sitting if they were lucky, holding onto ceiling straps if they were unlucky like him. Couples sat together staring into each other’s eyes, friends joked and discussed their office politics. He hated the commute back and forth from work, it made him feel alone, desperate and unwanted. There had been no office politics for him, it was just him and his mostly silent supervisor.
The sky was struck red, a wound inflicted on the sky, it bleed for a minute then all went dark. Reality shuddered as it returned to him, this would be his last commute along this route. He was without a job; his recently regained self-esteem was destroyed. At the end of university he had wondered if he had a career anywhere, if his self-inflicted social isolation had been worth it and GWI had lifted him out of academic gutter and placed him on a pedestal. And now he was turfed out like a partly cloudy day from a child’s memory, flicked off like an ant off a picnic blanket.
Litter was being chased up and down the aisle, wrapping around legs and trying to hide from the wind amongst commuters’ bags. He didn’t notice that the commuters were becoming concerned about the weather, heads turned to look outside where the clouds were blacker than night. Wind has beating on windows, knocking on doors trying to escape from itself. Loose objects were starting to drift.
“Puck, I’m so stupid!” Weather lamented aloud as a flash of lightning brightened the dusk for a second. He should have protected his research, patented it in his own name. Stupidly, he had thought he would be with GWI for the rest of his life. He had given his life over to GWI and they had thrown it away for an office in disarray. It might have looked like an unnatural disaster, but they could have at least let him evaluate their equipment to check for systems failure. Why he hadn’t opened his mouth and flung accusations back at them? Probably because they had looked angrier than he could possibly have gotten faced with a memory of shimmering blankness.
The weather was surreal, he casually noted it as something GWI would have to correct, something existing outside his present unemployed reality, their problem. His cellphone’s classic “Thunderstuck” ringtone charged the air.
“What’s happening with the weather, dude? I thought I read in the paper that it was supposed to be sunny skies and calm seas. I wanted to go for an evening dive at Devil’s.”
“I’ve no idea, I’ve been fired,” he managed to say calmly before he hung up.
“It’s not my responsibility,” he thought to himself and promptly switched his phone off. He had given his private cellphone number to a few select acquaintances he had tried to impress when he had just got his ‘prestigious’ job. He thought he might finally be able to get his social life out of his house by sharing information with people he had met in supermarkets, recognizing their faces from university. They were jocks obsessed about the weather for their hedonistic lifestyles and they had never invited him out, only phoning to find out about the weather.
He jumped off at his usual stop and leaned into the wind watching his feet moving past one another, his mind seething at the injustice of not having a fair trial where they showed him evidence of him been directly involved in the trashing of his office. He could only remember standing in the middle of it and his office revolving around him, but that was only a flash, there is nothing before that except the facts. Him working on algorithms of weather activation, them tinkering with the clouds. They were practically at the end of their testing, their final live weather event before taking on the whole world’s weather, he knows that, but everyday was still just the same as every other day, him at the computer, them throwing lightning bolts. “Puck! I should’ve challenged them,” he shouted into the howling wind at GSI with all the frustration of his past mistakes. But his voice was lost into the atmosphere.
-
 @ fd06f542:8d6d54cd
2025-05-09 05:48:05
@ fd06f542:8d6d54cd
2025-05-09 05:48:05由nip96模式改成了blossom
blossom的网址 变成了sha256 的id值,理论上 更换服务器或者重传以后 替换图片地址方便。
不过这部分我并没有做兼容接口。如果做成兼容的,应该用 相对地址,然后 后台用proxyimg.xxx.com去做选择。
访问方便些
新的服务器是:https://nosto.re/ 希望他能稳定的被访问不会嘎。
代码其实更简单了,https://github.com/nostrbook/nostrbook/blob/main/src/lib/blossomUpload.ts nosto.re 没有checkupload功能。所以我这里代码也没有加这部分,如果换别的服务器可能需要加检查功能。是不是为了防止图片重复上传?
最后 加一张好看的图片吧。证明此功能好用:
 {.user-img}
{.user-img} -
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ 872982aa:8fb54cfe
2025-05-09 05:35:15
@ 872982aa:8fb54cfe
2025-05-09 05:35:15 可以方便访问了
可以方便访问了 -
 @ bbef5093:71228592
2025-05-09 17:01:36
@ bbef5093:71228592
2025-05-09 17:01:36A francia székhelyű Newcleo, az olasz dizájncég Pininfarina és az olasz hajógyártó Fincantieri bemutatták a TL-40 nevű, következő generációs, hajókra szánt nukleáris reaktor teljes méretű modelljét a 19. Velencei Építészeti Biennálén[1][2][5][6][7].
A TL-40 reaktor főbb jellemzői
- IV. generációs, ólom-hűtésű kis moduláris reaktor (SMR), amelyet nagy hajók meghajtására fejlesztettek ki[1][2][5][6].
- Kompakt, biztonságos és fenntartható: A reaktor passzív biztonsági rendszereket alkalmaz, amelyek a fizika törvényein keresztül kizárják a nukleáris balesetek lehetőségét[2][5][6].
- Nukleáris hulladék újrahasznosítása: A TL-40 képes újrafeldolgozott nukleáris hulladékot üzemanyagként használni, ezzel egyszerre járul hozzá az energiatermeléshez és a hulladékcsökkentéshez[1][2][5][6].
- Formatervezés és ipari háttér: A Pininfarina gondoskodott a dizájnról és a reaktor esztétikai megjelenéséről, míg a Fincantieri a hajógyártási tapasztalatát adta hozzá[1][2][5][6][7].
- Nyitott konfiguráció: A reaktor vázája lehetővé teszi a látogatók számára, hogy belülről is megismerjék a technológiát, interaktív módon[1][2][5].
Technológiai és környezeti jelentőség
- Dekarbonizáció: A fejlesztés célja, hogy a nukleáris energiát a hajózás szektorában is a szén-dioxid-kibocsátás csökkentésének eszközeként alkalmazzák[1][2][5][6].
- Európai hulladék hasznosítása: A jelenleg Európában tárolt nukleáris hulladék elegendő lenne a kontinens villamosenergia-igényének fedezésére évszázadokon át, ha ilyen típusú reaktorokban hasznosítanák[2][5][6].
- Kreatív szemlélet: A projekt célja a nukleáris energia társadalmi megítélésének javítása, bemutatva, hogy az lehet egyszerre biztonságos, esztétikus és fenntartható[1][5][6][7].
Együttműködés és jövőbeli tervek
- Folyamatos együttműködés: A Newcleo és a Fincantieri 2023 óta dolgoznak együtt a tengeri alkalmazások fejlesztésén[2][5][6][7].
- Kutatás-fejlesztés: A Pininfarina a Newcleo franciaországi (Chusclan) nukleáris üzemanyag kutató-fejlesztő központjának tervezésében is részt vesz[2][5][6][7].
- Első demonstrációs reaktor: A Newcleo célja, hogy 2031-re bemutassa az első demonstrációs reaktort, 2033-ra pedig kereskedelmi forgalomba hozza azt[8].
- Földi alkalmazás: A vállalat már megkezdte a földi, ólom-hűtésű LFR-AS-30 reaktor telephelyének előkészítését Franciaországban (Chinon régió)[8].
- Európai támogatás: Az LFR dizájn 2024 októberében felkerült az Európai Ipari Szövetség támogatásra javasolt SMR-listájára[8].
Idézetek a projekt vezetőitől
„Ez nem a nagyapáink reaktora. Fenntartható, előremutató technológia, amely a való világ és a klímaváltozás kihívásaira készült.”
(Stefano Buono, a Newcleo vezérigazgatója)[1][5][6][7]„A dizájn stratégiai szerepet játszik a fenntartható energia megoldások fejlesztésében, biztosítva a társadalmi és környezeti szempontok teljes integrációját az innovációs folyamat során.”
(Silvio Angori, a Pininfarina vezérigazgatója)[6][7]Hivatkozások: [1] newcleo, Pininfarina and Fincantieri unveil the future of clean ... https://www.maddyness.com/uk/2025/05/08/newcleo-pininfarina-and-fincantieri-unveil-the-future-of-clean-energy-at-the-venice-biennale/ [2] Newcleo, Pininfarina, and Fincantieri showcase next-generation ... https://www.shippax.com/en/news/newcleo-pininfarina-and-fincantieri-showcase-next-generation-nuclear-power-solution-for-potential-marine-applications.aspx [3] Newcleo and Fincantieri unveil lead-cooled fast nuclear reactor for ... https://www.bairdmaritime.com/shipping/newcleo-and-fincantieri-unveil-lead-cooled-fast-nuclear-reactor-for-maritime-applications [4] Fincantieri Launches Nuclear-Propulsion Study With Newcleo https://maritime-executive.com/article/fincantieri-joints-nuclear-propulsion-study-with-newcleo [5] Industry Partners Showcase Next-Gen Nuclear Reactor For https://www.marinelink.com/news/industry-partners-showcase-nextgen-525512 [6] Fincantieri, newcleo and Pininfarina reveal the look of new nuclear ... https://www.fincantieri.com/en/media/press-releases/2025/fincantieri-newcleo-pininfarina-at-the-venice-biennale/ [7] Fincantieri S p A : , newcleo and Pininfarina reveal the look of new ... https://www.marketscreener.com/quote/stock/FINCANTIERI-S-P-A-16796084/news/Fincantieri-S-p-A-newcleo-and-Pininfarina-reveal-the-look-of-new-nuclear-power-at-the-19th-Inter-49877851/ [8] Pininfarina - NucNet | Independent Nuclear News https://www.nucnet.org/news/tagged/Pininfarina [9] newcleo, Fincantieri and RINA working together on feasibility study ... https://www.rina.org/en/media/press/2023/07/25/newcleo-fincantieri-rina [10] Fincantieri, RINA team up with newcleo to test feasibility of nuclear ... https://www.offshore-energy.biz/fincantieri-rina-team-up-with-newcleo-to-test-feasibility-of-nuclear-naval-propulsion/ [11] newcleo #pininfarina #fincantieri #biennalearchitettura2025 ... https://www.linkedin.com/posts/newcleo_newcleo-pininfarina-fincantieri-activity-7295080775878647810-6i6X [12] A Fourth-Generation Reactor at the Venice Architecture Biennale https://www.theplan.it/eng/whats_on/a-reactor-fourth-generation-pininfarina-newcleo-fincantieri
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 872982aa:8fb54cfe
2025-05-09 05:32:42
@ 872982aa:8fb54cfe
2025-05-09 05:32:42{"coverurl":"https://nosto.re/3ebd3bf45e031c2812ca5a36980a9bf7d4e6f30da2941d2bebdb7a2a452c8664.jpeg","title":"养花和施肥","author":"花花的作者"}
-
 @ 805b34f7:3620fac3
2025-05-09 03:05:22
@ 805b34f7:3620fac3
2025-05-09 03:05:22Humans are evolving with social media & devices. These are powerful tools, but neither is built with their users' health and well-being in mind.
The big tech business incentives are a higher priority than their users' health & well being. This results in their products being designed to capture as much attention from you as possible so they can profit.
Many are realizing this. Few know there are emerging, viable alternatives.
 Nostr is a new model for social media (and much more).
Nostr is a new model for social media (and much more).Bitcoin is a new model for money.
nostr:nprofile1qyt8wumn8ghj7ct49eex2mrp09skymr99ehhyecpp4mhxue69uhkummn9ekx7mqqyr4aa6ffghhs22pmuzkrmcjhslyp56jc5y84druuddsanh238td66va34er is a new model for computers.
This article will explain why Nostr is primed to be the new model for social media.
“We cannot have a society in which, if two people wish to communicate, the only way that can happen, is if it’s financed by a third party who wishes to manipulate you” - Jaron Lanier
What is Nostr? What is Primal?
I’ve done a wonderful job of confusing people by interchanging the words Nostr & Primal. So allow me a brief, high level explanation.
Nostr is an internet protocol that allows for censorship resistant social media.
An internet protocol is a set of rules that computers follow to communicate with each other.
Nostr stands for Notes & Other Stuff Transmitted by Relays.
Primal is an app built on Nostr. I work for Primal the company.
When you post to Primal, you can see your content in other Nostr apps. Primal doesn’t own you, your content or identity. You do. You can take your content and followers to any Nostr app.
In this gif, you can see my content in 5 different Nostr apps.
 Nostr is like email, but for social media—it’s a system where anyone can send and receive posts using any app they like. Similar to how you would send an email to everyone you know. Everyone will receive that email no matter what email service provider they’re using (yahoo, gmail, proton, apple etc).
Nostr is like email, but for social media—it’s a system where anyone can send and receive posts using any app they like. Similar to how you would send an email to everyone you know. Everyone will receive that email no matter what email service provider they’re using (yahoo, gmail, proton, apple etc).When you “create an account” on Primal, you create a password that you can use to log in to any Nostr app. Your password is called a private key and you can use that to log in to any apps that are built on Nostr. See them here at nostrapps.com.
All this may sound a bit confusing, but this is just what's going on under the hood. Primal will feel like any other social media app. Check out this image below to learn more and be sure to keep your private key (your password) safe!
#### How I got into Nostr
Long story short, if you’ve been in to Bitcoin, you at least know about Nostr. I used Twitter as my primary news/Bitcoin source for the past 8 years and followed the Trump and Covid dramas closely.
I’ve come to the conclusion that social media needs to be protocol based and decentralized.
 The first Nostr conference in March of 2023 was in Uvita, Costa Rica. I was living in the area, so of course I showed up. Here’s a brief video we made from the conference.
The first Nostr conference in March of 2023 was in Uvita, Costa Rica. I was living in the area, so of course I showed up. Here’s a brief video we made from the conference. Why I'm Stoked on Nostr
The Everything App for Social Media
This is the original idea that made the lightbulb in my head go off. 1 identity for all types of content.
I have accounts on Youtube, Twitter, Nostr, Instagram, TikTok, & Medium. That means 6 different logins, 6 different follower sets, and 6 places to post when I have something to share.
With Nostr, I have 1 identity, 1 follower set, & (potentially) 1 place to post each type of content.
On the Left - 5 apps, 5 identities. Right - 5 apps, 1 identity
 The Nostr apps are in their infancy, but I can imagine a future with more diverse apps specified by content type (blogs, long form vid, vertical vids, music, etc.).
The Nostr apps are in their infancy, but I can imagine a future with more diverse apps specified by content type (blogs, long form vid, vertical vids, music, etc.).The ability to post all of your content to (potentially) one app and giving your audience the choice to consume that content in whatever app they please is revolutionary.
X wants to be the everything app as well. It looks like it's heading towards becoming the WeChat of the West. This begs the question... Does the infrastructure for social media need to be owned by singular corporations or governments?
Check out this video where nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyehwumn8ghj7mnhvvh8qunfd4skctnwv46z7ctewe4xcetfd3khsvrpdsmk5vnsw96rydr3v4jrz73hvyu8xqpqsg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q8dzj6n & nostr:nprofile1qyt8wumn8ghj7ct5d3shxtnwdaehgu3wd3skueqpz4mhxue69uhk2er9dchxummnw3ezumrpdejqqgyymmnwvah9hdnmft2wqsk0wr9as6q32hd4xk2zlnr2q5ectznjgqd27v94 discuss everything apps during the 2nd Nostr conference in Japan.
Nostr is the tool to orange pill the world
Orange pilling is a slightly cringe term used to describe educating people about Bitcoin. In Nostr, we say purple pilling because for some reason, Nostr’s theme is purple.
Jargon aside, the reason I believe that Nostr will orange pill the world is because of zaps!
Zaps are micropayments of bitcoin. You can send zaps on posts as easily as you can send likes on posts with Primal’s built in wallet and creators keep 100% of what they earn. They’re the best way to really feel the Nostr difference.
Here’s an example of me zapping 210 sats to a few people with one click.
 I've now personally watched over 20 people receive and send their1st Bitcoin transactions minutes after downloading Primal. Right away you pop two cherries, owning Bitcoin and sending Bitcoin. Pretty rad.
I've now personally watched over 20 people receive and send their1st Bitcoin transactions minutes after downloading Primal. Right away you pop two cherries, owning Bitcoin and sending Bitcoin. Pretty rad. It's a fundamentally different experience to touch Bitcoin through a social media style app than it is to buy bitcoin from an exchange. Someone new on Primal immediately has a use case for Bitcoin upon downloading the app. Zaps!
Nostr is known as the Bitcoiner social network. It could be/is becoming the place for newbies to come learn about Bitcoin, and interact with people who can help teach. I see a massive opportunity for Primal to play a huge role in this transition to a bitcoin standard.
I wonder how often this scenario with nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytn0wpjku6r0danxgtnwdsqzpq8gr333mlm73rnsfv2uvsrtvg44l5l5r0qrn6c0fw08t5hkccwarhnfev will repeat. Also, check out this video about how zaps got nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyw8wumn8ghj7mn0wd68ytnzd96xxmmfdejhytnnda3kjctvqqstkm5tw5w2f2qg2zp0tzxk9junagtrqeayyxnzggqcphgec9p37ncc26xj6 to read The Bitcoin Standard.
Micropayments on the internet are only possible with digitally native money.
Zaps are signal. They’re pure life force energy given to another person in appreciation for their content and it's unique to Nostr.
 Social media is simply better with payments. You cannot unsee or unfeel this. We're only beginning to scratch the surface of what zaps mean to a social network. Should be fun :)
Social media is simply better with payments. You cannot unsee or unfeel this. We're only beginning to scratch the surface of what zaps mean to a social network. Should be fun :) Sovereignty
Today, our digital lives are owned. Our data, identity, and content can be taken away.
Nostr flips this. We own our identity & choose where our data lives. Companies no longer have singular control over the flow of information.
Bitcoin gives you private keys for money. Nostr gives you private keys for speech.
On X and Instagram, we make a username and password. We are renting these identities from these corporations. How do we know these identities are not yours? Because they can be taken away from you.
 With Nostr, you and only you have your keys. You can post anytime, from any app, using your own key. If Primal stops working, no big deal. You could post from other Nostr apps.
With Nostr, you and only you have your keys. You can post anytime, from any app, using your own key. If Primal stops working, no big deal. You could post from other Nostr apps. I believe there’s something deeper going on here. Humans are sovereign beings. Being sovereign means being in full control.
With Nostr & Bitcoin, we can be in complete control of our money & speech.
These tools empower humans and reduce our need for dependence on 3rd parties.
Nostr allows us to create & share freely without the potential of being silenced for “wrongthink”.
It’s time for those who care about sovereignty to build their brands on their own land.
Nostr is Organic
Facebook wanted to connect the world. They’ve done an absolutely fantastic job at this. But at what cost?
The ad model has been the best way for platforms to monetize their services. This leads to bad incentives. Social media sites need you to spend as much time as possible on their apps so that they can sell your attention to advertisers.
Maybe there’s more ethical ways to advertise that do not lead to perverse incentives, but this isn’t the point.
Now, social media is basically a dopamine slot machine serving us things that we’re most likely to engage with. Whatever we lend our eyes to, purposefully or not, is the content we’re fed. Engagement is the north star of current social media. This modifies the behavior of everyone on the app.
These algorithms have been weaponized at times. And many would say that they’re programming us.
Let me speak in meme for a moment here:

 It’s different on Nostr
It’s different on NostrAfter using Nostr for a couple years, it’s clearer to me when I switch to another social media platform that they are doing everything they can to grab my attention. They being the platform and the creators. I can feel when people create for an algo vs. for an audience.
With Primal, I can select which algorithm I want to use or create my own feeds using Primal’s advanced search. (I expect these tools to get much better over time.) This gives the user much more control over what they see vs a singular algorithm. Algorithmic choice is something that legacy social media platforms are greatly missing.
I can also control which feed I want to see when I open the app. For example, I created this feed of one person saying “STAY FOCUSED CHAMP” so when I open the app I’m not immediately distracted. Look at what instagram does when you want to simply search for someone’s account…
I can’t help but envision a world where all of the content is posted to Nostr. The apps with the best user experiences would win. I’d imagine the winners would have the best algos, least intrusive ads, and would give their users the most control over their experience.
Thought Experiment
Pretend you’re a super intelligent being looking down upon the earth.
The1st thing you’d notice is that they’re always staring at their phones. You’d also notice that while they have an abundant earth, they insist on chemically altering their food which is making them sick.
Then, you’d notice that the money humans work their entire lives for can be and is manipulated by central authorities with zero effort.
And, you’d notice that the “digital global town square” is owned by a unelected, fallable humans and corporations.\ It’s laughable!
It doesn’t have to be this way anymore. And it’s up to us to change it.
To conclude.
This article is not meant to trash talk other platforms, those who use them, or those who created them. I use them daily. Mostly to advocate for Nostr & Bitcoin these days.
These platforms have created a ton of value for the world, & Nostr can be used alongside of them.
Maybe if Nostr existed back then, they would’ve built on it.
“We shape our tools, and thereafter our tools shape us”. We’ve learned priceless lessons from the evolution of social media thus far. We can use these lessons to shape tools with our health & well-being as our first priority.
We can obsolete these outdated, unhealthy systems.
Nostro and Nuestro mean 'ours' in Italian & Spanish. I don't think this a coincidence. Nostr is our chance to create a better internet for our future generations.
pura vida
(meme cred nostr:nprofile1q9n8wumn8ghj7enfd36x2u3wdehhxarj9emkjmn99ah8qatzx9kx2mrtdqeks6rcwuukserhd33hq6ekwyuhgvrcwsukvdme0fjnq7fsdeuxz7nk0fck5mtjv5ehqwfc0qehxargddm8j73lvfex7ctyvdshxapaw3e82egpp4mhxue69uhkummn9ekx7mqqyrl8767x7uecka4mlqxmgq4duev48cst9u37vm5fsgztv0xyy5u6xs34wwg also check out his nostr doc )

-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ fe820c8e:d2d76f04
2025-05-09 14:33:55
@ fe820c8e:d2d76f04
2025-05-09 14:33:55Nostr Demo

This is your course initialization stub.
Please see the Docs to find out what is possible in LiaScript.
If you want to use instant help in your Atom IDE, please type lia to see all available shortcuts.
Markdown
You can use common Markdown syntax to create your course, such as:
- Lists
-
ordered or
-
unordered
- ones ...
| Header 1 | Header 2 | | :--------- | :--------- | | Item 1 | Item 2 |
Images:

Extensions
--{{0}}--But you can also include other features such as spoken text.
--{{1}}--Insert any kind of audio file:
{{1}}--{{2}}--Even videos or change the language completely.
{{2-3}}!?video
--{{3 Russian Female}}--Первоначально создан в 2004 году Джоном Грубером (англ. John Gruber) и Аароном Шварцем. Многие идеи языка были позаимствованы из существующих соглашений по разметке текста в электронных письмах...
{{3}}Type "voice" to see a list of all available languages.
Styling
The whole text-block should appear in purple color and with a wobbling effect. Which is a bad example, please use it with caution ... ~~ only this is red ;-) ~~
Charts
Use ASCII-Art to draw diagrams:
Multiline 1.9 | DOTS | *** y | * * - | r r r r r r r*r r r r*r r r r r r r a | * * x | * * i | B B B B B * B B B B B B * B B B B B s | * * | * * * * * * -1 +------------------------------------ 0 x-axis 1Quizzes
A Textquiz
What did the fish say when he hit a concrete wall?
[[dam]]Multiple Choice
Just add as many points as you wish:
[[X]] Only the **X** marks the correct point. [[ ]] Empty ones are wrong. [[X]] ...Single Choice
Just add as many points as you wish:
[( )] ... [(X)] <-- Only the **X** is allowed. [( )] ...Executable Code
A drawing example, for demonstrating that any JavaScript library can be used, also for drawing.
```javascript // Initialize a Line chart in the container with the ID chart1 new Chartist.Line('#chart1', { labels: [1, 2, 3, 4], series: [[100, 120, 180, 200]] });
// Initialize a Line chart in the container with the ID chart2 new Chartist.Bar('#chart2', { labels: [1, 2, 3, 4], series: [[5, 2, 8, 3]] }); ```
Projects
You can make your code executable and define projects:
``` js -EvalScript.js let who = data.first_name + " " + data.last_name;
if(data.online) { who + " is online"; } else { who + " is NOT online"; }
json +Data.json { "first_name" : "Sammy", "last_name" : "Shark", "online" : true } ```More
Find out what you can even do more with quizzes:
https://liascript.github.io/course/?https://raw.githubusercontent.com/liaScript/docs/master/README.md
-
 @ a5c85eea:82503ea8
2025-05-09 14:28:33
@ a5c85eea:82503ea8
2025-05-09 14:28:33Nostr - Test
This is your course initialization stub.
Please see the Docs to find out what is possible in LiaScript.
If you want to use instant help in your Atom IDE, please type lia to see all available shortcuts.
Markdown
You can use common Markdown syntax to create your course, such as:
- Lists
-
ordered or
-
unordered
- ones ...
| Header 1 | Header 2 | | :--------- | :--------- | | Item 1 | Item 2 |
Images:

Extensions
--{{0}}--But you can also include other features such as spoken text.
--{{1}}--Insert any kind of audio file:
{{1}}--{{2}}--Even videos or change the language completely.
{{2-3}}!?video
--{{3 Russian Female}}--Первоначально создан в 2004 году Джоном Грубером (англ. John Gruber) и Аароном Шварцем. Многие идеи языка были позаимствованы из существующих соглашений по разметке текста в электронных письмах...
{{3}}Type "voice" to see a list of all available languages.
Styling
The whole text-block should appear in purple color and with a wobbling effect. Which is a bad example, please use it with caution ... ~~ only this is red ;-) ~~
Charts
Use ASCII-Art to draw diagrams:
Multiline 1.9 | DOTS | *** y | * * - | r r r r r r r*r r r r*r r r r r r r a | * * x | * * i | B B B B B * B B B B B B * B B B B B s | * * | * * * * * * -1 +------------------------------------ 0 x-axis 1Quizzes
A Textquiz
What did the fish say when he hit a concrete wall?
[[dam]]Multiple Choice
Just add as many points as you wish:
[[X]] Only the **X** marks the correct point. [[ ]] Empty ones are wrong. [[X]] ...Single Choice
Just add as many points as you wish:
[( )] ... [(X)] <-- Only the **X** is allowed. [( )] ...Executable Code
A drawing example, for demonstrating that any JavaScript library can be used, also for drawing.
```javascript // Initialize a Line chart in the container with the ID chart1 new Chartist.Line('#chart1', { labels: [1, 2, 3, 4], series: [[100, 120, 180, 200]] });
// Initialize a Line chart in the container with the ID chart2 new Chartist.Bar('#chart2', { labels: [1, 2, 3, 4], series: [[5, 2, 8, 3]] }); ```
Projects
You can make your code executable and define projects:
``` js -EvalScript.js let who = data.first_name + " " + data.last_name;
if(data.online) { who + " is online"; } else { who + " is NOT online"; }
json +Data.json { "first_name" : "Sammy", "last_name" : "Shark", "online" : true } ```More
Find out what you can even do more with quizzes:
https://liascript.github.io/course/?https://raw.githubusercontent.com/liaScript/docs/master/README.md
-
 @ ba3b4b1d:eadff0d3
2025-05-09 02:53:13
@ ba3b4b1d:eadff0d3
2025-05-09 02:53:13https://img.freepik.com/premium-photo/unveiling-hidden-dimensions-minds-eye_889056-29604.jpg
A noção de que a consciência é holográfica — comparável a uma miragem ou a uma bolha reluzente — oferece uma maneira simples e profunda de compreender a mente, a alma e a vida. Este conceito, enraizado em sabedorias antigas como o budismo e ecoado na ciência moderna, sugere que a consciência resulta da interação entre a mente e um meio, tal como um holograma surge do entrelaçamento de feixes de luz. A introdução de dibbacakkhu, o “olho divino” da tradição budista, enriquece esta visão, conectando a percepção transcendente dos sonhos e da consciência à clarividência espiritual. Vamos explorar, combinando as suas analogias (água como antena, consciência como bolha) com clarificações e a relação com dibbacakkhu.
1. Consciência como Holograma
A consciência assemelha-se a um holograma: uma projeção tridimensional criada pela interferência de dois feixes de luz — um de referência e um refletido. Num holograma, estes feixes convergem para formar uma imagem que parece real, com profundidade, mas é intangível. Da mesma forma, a consciência é uma projeção da mente, não uma entidade física, mas uma experiência vívida que parece sólida. O termo sânscrito vijnana (consciência) reflete esta ideia como uma “luz perturbada” — uma interação dinâmica que gera uma realidade ilusória, semelhante a uma miragem. Esta perturbação é estruturada, como a luz coerente num holograma de laser. A mente é a fonte desta luz, projetando uma “bolha” de consciência, enquanto a água, como meio, facilita o processo, tal como uma placa fotográfica capta uma imagem holográfica. Analogia: Imagine a mente como uma gota de água com sabão. Sopre-lhe espírito, e surge uma bolha iridescente. Esta bolha é a consciência: bela, efémera e produto de uma interação. Tal como a bolha depende do ar e da película de sabão, a consciência requer a mente e um meio para se manifestar.
2. Água como Meio (A Antena da Vida)
A água é a “antena” que conjura a consciência, graças à sua estrutura molecular — dois átomos de hidrogénio e um de oxigénio (H₂O). A sua polaridade e rede de ligações de hidrogénio permitem-lhe armazenar e transmitir informação, como uma antena que capta um sinal de rádio. Esta propriedade torna a água essencial para a manifestação da vida, unindo espírito e matéria. A “quarta fase da água” de Gerald Pollack, ou água estruturada (zona de exclusão), reforça esta ideia. Perto de superfícies hidrofílicas, a água forma uma fase gelificada com propriedades elétricas e óticas únicas, que podem facilitar processos biológicos e, possivelmente, a interface entre mente e corpo. Na sua analogia, a água é a “geometria incomensurável” que sintoniza o sinal da alma na rádio do corpo. Analogia Refinada: Pense numa estação de rádio a emitir uma melodia (a alma) pelo éter. O sinal está em todo o lado e em lado nenhum, mas precisa de uma antena para ser ouvido. A água é essa antena — uma molécula simples que capta o sinal da alma, permitindo que a música da vida ecoe no corpo.
https://so06.tci-thaijo.org/public/journals/585/article_252151_cover_en_US.jpg
3. Sonhos, Dibbacakkhu e o Olho da Mente
Os sonhos são vívidos porque são projeções holográficas do “olho da mente”, um conceito que você ligou ao termo polinésio dbaku (olho celestial) e que ressoa com dibbacakkhu no budismo. Dibbacakkhu, ou “olho divino”, refere-se a uma visão clarividente que transcende os sentidos físicos, permitindo perceber realidades além do mundo material — como outros reinos, seres desencarnados ou eventos distantes. Nos sonhos, experimentamos uma versão desta visão: caminhamos por mundos completos sem olhos físicos, porque a mente projeta a sua própria realidade. Dibbacakkhu conecta-se à ideia de que a consciência holográfica não depende de órgãos sensoriais. No budismo, esta visão é um dos poderes espirituais (iddhi) alcançados através da meditação profunda, revelando a natureza ilusória da realidade (maya). Nos sonhos, todos nós acedemos a uma forma rudimentar deste “olho divino”, criando cenários que parecem mais reais que qualquer filme, porque a mente gera a sua própria luz e espaço. Esta capacidade é semelhante à percepção de seres desencarnados, que “veem” sem olhos físicos, usando uma consciência metafísica. Clarificação: O olho da mente, ou dibbacakkhu, não é um órgão literal, mas a faculdade da mente de projetar realidades autónomas. Em termos gregos, noos (intelecto divino) e, em sânscrito, citta (consciência pura) apontam para esta visão transcendente. Os sonhos são o laboratório da mente, onde dibbacakkhu se manifesta espontaneamente.
4. Consciência Transcendente vs. Existencial
Há duas formas de consciência: transcendente (noos, citta), que é eterna e ilimitada, e existencial, ligada ao corpo e temporal. A consciência transcendente é como um sinal de rádio, existindo independentemente de qualquer recetor. A consciência existencial surge quando este sinal se manifesta no corpo, como uma música que toca numa rádio. Quando o corpo morre, a consciência existencial termina, mas o sinal transcendente persiste. A água é o meio que possibilita esta união, atuando como uma antena que capta o sinal da alma. As suas propriedades, como a estruturação descrita por Pollack, tornam-na ideal para mediar entre o eterno e o temporal, ecoando ideias antigas, como as do Timeu de Platão, onde um terceiro elemento harmoniza espírito e matéria. Analogia: O corpo é uma rádio, frágil e temporária. A alma é o sinal, eterno e omnipresente. A água é a antena, sintonizando o sinal para criar a transmissão fugaz da vida. Desligue a rádio, e a música para, mas o sinal continua, pronto para outra antena.
5. Posse como Vulnerabilidade
<https://112.wpcdnnode.com/houseofbhakti.com/wp-content/uploads/2019/04/budha-being-tempted.jpg>
A posse ocorre quando uma “cavidade” no estado psicofísico de uma pessoa permite que uma entidade externa se instale, como um intruso numa casa desprotegida. Esta vulnerabilidade pode surgir de traumas (ex.: uma experiência de quase-morte), instabilidade emocional ou práticas espirituais arriscadas que “abrem uma janela”. A entidade, com maior força de vontade, pode dominar, coexistindo com a alma original, mas assumindo o controlo. A água, como meio da união mente-corpo, pode estar envolvida. Se os sistemas baseados em água do corpo (ex.: hidratação celular, bioeletricidade) forem perturbados, o “sinal” da alma pode enfraquecer, criando espaço para interferências. Analogia: O corpo é uma casa, a alma o proprietário. Se deixar a porta destrancada — por trauma ou descuido — um intruso pode entrar. Não é o dono, mas pode controlar a casa, a menos que tranque as portas com equilíbrio mental e espiritual.
6. Síntese: A Simplicidade da Natureza
Estas ideias são simples, mas profundas. A holografia cria espaço com luz, a consciência é uma bolha projetada pela mente, a água é a antena que conjura a vida, os sonhos revelam o dibbacakkhu, e a posse é um intruso evitável. Conceitos antigos como vijnana, noos, citta e dibbacakkhu alinham-se com a ciência moderna, como a água estruturada de Pollack, mostrando que a natureza é elegante na sua simplicidade.
-
 @ c9badfea:610f861a
2025-05-09 00:06:23
@ c9badfea:610f861a
2025-05-09 00:06:23- Install LibreTorrent (it's free and open source)
- Search for torrents on various sources (see links below)
- Copy the torrent's 🧲️ Magnet Link
- Open LibreTorrent, tap the + icon, and select Add Link
- Paste the magnet link and tap Add
- The app will display the torrent's details and files; tap the ✓ icon to start the download
Some Sources
ℹ️ Magnet links start with
magnet:?ℹ️ Tapping a magnet link usually opens LibreTorrent automatically
⚠️ Using a VPN is strongly recommended
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 87f5e1d9:e251d8f4
2025-05-09 00:03:01
@ 87f5e1d9:e251d8f4
2025-05-09 00:03:01Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:10:58
@ 6e0ea5d6:0327f353
2025-04-14 15:10:58Ascolta bene.
A man’s collapse never begins on the battlefield.
It begins in the invisible antechamber of his own mind.
Before any public fall, there is an ignored internal whisper—
a small, quiet, private decision that gradually drags him toward ruin.No empire ever fell without first rotting from within.
The world does not destroy a man who hasn’t first surrendered to himself.
The enemy outside only wins when it finds space in the void the man has silently carved.**Non ti sbagliare ** — there are no armies more ruthless than undisciplined thoughts.
There are no blows more fatal than the ones we deal ourselves:
with small concessions, well-crafted excuses,
and the slow deterioration of our integrity.
What people call failure is nothing more than the logical outcome
of a sequence of internal betrayals.Afraid of the world? Sciocchezze.
But a man who’s already bowed before his own weaknesses—
he needs no enemies.
He digs his own grave, chooses the epitaph,
and the only thing the world does is toss in some dirt.Capisci?
Strength isn’t the absence of falling, but the presence of resistance.
The true battle isn’t external.
It takes place within—where there’s only you, your conscience, and the mirror.
And it’s in that silent courtroom where everything is decided.The discipline to say “no” to yourself
is more noble than any public glory.
Self-control is more valuable than any victory over others.In Sicily, we learn early:
“Cu s’abbrazza cu’ so’ nemicu, si scorda la faccia di l’amicu.”
He who embraces his enemy forgets the face of his friend.
The most dangerous enemy is the one you feed daily with self-indulgence.
And the most relentless confrontation is the one you avoid in front of the mirror.So don’t talk to me about external defeats.
Tell me where inside you the weakness began.
Tell me the exact moment you abandoned what you believed in, in the name of ease.
Because a man only falls before the world… after falling before himself.Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 5b730fac:9e746e2a
2025-05-09 09:30:54
@ 5b730fac:9e746e2a
2025-05-09 09:30:54Test Combinations for Janitor Module
Initial Scenarios
| Channel | Push to Branch | Previous Installation Method | NIP94 Event ID Updated as Expected | New Update Installed as Expected | Test Passed | | ----------------------------------- | ----------------- | ---------------------------- | ---------------------------------- | -------------------------------- | -------------------------------------------------------------------------------------------------------------------------------- | | dev | Already Installed | Manual | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdp4xvmnvdpkpctkgk | | dev | Already Installed | Automatic | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdfex5unzvfcfywh0x | | deleted config files, first install | Already installed | Manual | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzwpnxq6rvdp59d83mz |Additional Scenarios from git diff Analysis
| Channel | Push to Branch | Version Format | NIP94EventID State | Expected Outcome | Test Passed | | -------------- | ----------------- | ------------------------ | ------------------ | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | | dev | New Branch | branch-commit_count-hash | known | Don't update, because the currently installed branch is different | Yes
The following package was not installed since it was on a different branch:
https://github.com/OpenTollGate/tollgate-module-basic-go/actions/runs/14909573498/job/41880411207 | | stable | main | version_number | known | Update Successfully | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnsvpk8yer2wphat7h6a | | dev | Already Installed | branch-commit_count-hash | known | Update Successfully if new commits | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdfex5unzvfcfywh0x | | dev | Already Installed | branch-commit_count-hash | unknown | Update Successfully if new commits | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdp4xvmnvdpkpctkgk | | stable | main | version_number | unknown | Update if version number is higher, irrespective of branch name, and NIP94 eventID | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnwwfex56nsdfjxmla8c | | config deleted | main | version_number | config deleted | Default pubkey and stable channel are set in config files, the new tag is downloaded and installed. However, the new NIP94 event must be generated after the new config files were created with default timestamps. | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnsv3hxycnsdfj3ttspu
Users who delete their config files might temporarily be one version behind the latest due to a lack of timestamp information. | -
 @ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46
@ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46If you haven't noticed already, #Nostr is a little different from what most people are used to. One of the ways this is felt most acutely is with media hosting. Users are accustomed to uploading their images and videos directly through the app they are posting from. Many Nostr apps provide that same experience nowadays, but it wasn't always the case.
Just a couple years ago, users had to find somewhere to host their media separately, and then copy and paste the URL into their note whenever they wanted to share their cat pictures. One of the first, if not the first, media hosting services specifically intended for Nostr was nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7, which will be the service we are reviewing today.
Like our previous review of Amber, Nostr.Build is a service for users to pair with other Nostr apps. You won't generally use nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 by itself. Rather, you'll use it to host that incredible shot you want to post to #Olas, or to host screenshots for your long-form tutorial about setting up Nostr Wallet Connect that you'll be posting from #Habla.news, or for hosting a hilarious video of your cat falling asleep to nostr:npub1cj8znuztfqkvq89pl8hceph0svvvqk0qay6nydgk9uyq7fhpfsgsqwrz4u's voice and taking a tumble off of his favorite perch that you want to share on #Damus. However, there are some features within Nostr.Build that you may want to check out quite apart from using it with any other Nostr app.
Overall Impression
Score: 4.8 / 5
I have been impressed by Nostr.Build for some time now, but they have pulled out all the stops in their latest update, increasing their maximum file size for free accounts to 100MB, integrating the #Blossom protocol, adding the ability to share directly to Nostr from within your dashboard, and more integrations with other Nostr apps than ever before. Nostr.Build is simply a pleasure to use, whether through their web interface, or through another Nostr app that integrates with them.
With the ability to easily organize your media, view statistics, browse the media gallery of free uploads, metadata removal for increased privacy, and AI image generation, Nostr.Build is not simply a media hosting service, it is a full-fledged media management platform. Its robust features keep it well ahead of other Nostr-focused media hosting options available, and a particularly strong option for those using Blossom and wanting redundancy and reliable uptime for their media.
As much as I enjoy using the web interface, though, where Nostr.Build really shines is their integrations with other Nostr apps. These integrations allow users to have the same experience they are accustomed to from centralized social platforms of uploading their media from within the same app they are using to share it. No copy/pasting a URL from one app to another. In fact, many users may not realize they have been using Nostr.Build in their client of choice, simply because it is the default option for media hosting for many Nostr apps.
This has the added benefit to client developers that they can provide this experience to their users without having to run media hosting infrastructure on top of trying to build their app. The separation of relays, clients, and media hosting between different entities, while keeping a similar experience to centralized platforms where a single company controls all three, is critical to Nostr adoption.
Features
Nostr.Build has a plethora of features beyond simply hosting your media. Let's take a look!
AI Image Generation
Do you need a quick title image for a long-form article? How about inspiration for a logo or art piece? Nostr.Build's AI Studio has you covered.
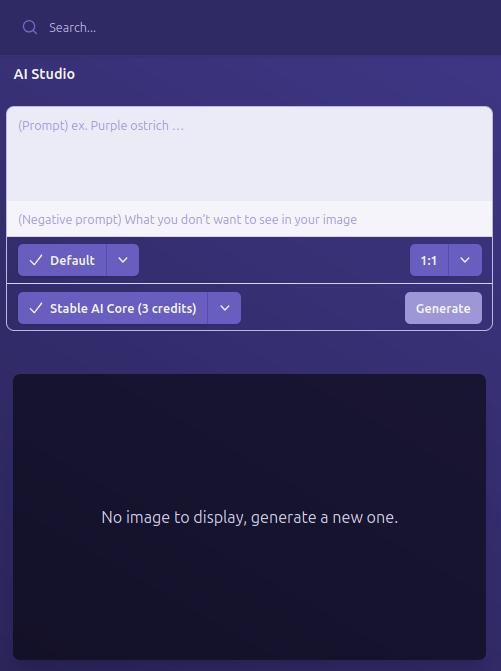
They have provided a few different models based on the plan you purchase, beginning with the Professional plan, which includes SDXL-Lightning and Stable Diffusion 1. Upgrading to the Creator plan will give you access to all Pro Stable Diffusion models and unlimited use of the Flux.1 model, which is the same core model used for Grok2 images.
I personally have a Professional account, so I haven't had a chance to try out Flux.1, but I have used Stable Diffusion extensively for creating character art for #NostrHeroes characters, such as these:




Nothing too spectacular when compared with some of the newer models out there, and there is no image-to-image support (yet), but more than adequate for casual image generation needs. Moreover, it is far more than what one would expect from a simple media-hosting service.
Admittedly, I am also no expert at coaxing AI models to produce anything remarkable so your results may vary. Either way, image generation is a welcome tool to have available without needing to go to an outside service unless you require something very specific.
Upload Limits
The maximum file size limits on Nostr.Build have been getting progressively larger, even for their free service. As I recall, it was a mere 21MB limit per file just a few months ago, which is fine for image files, but is quickly exceeded with videos. Then they increased their limits to 50MB per file, and as of recent updates it has been increased once more to a whopping 100MB per file... for free! This is more than adequate for most uses.
However, free users' images, GIFs, and videos are automatically viewable via Nostr.Build's free media gallery. This is something to particularly bear in mind when uploading images you intend to share via direct message. Though your DMs are encrypted, the images uploaded to Nostr.Build are not, and if you don't have a paid account, they will be viewable to the all paid users in the free media gallery. If you want to upload images that will not be viewable unless you actively share them, you must have a paid account.
Paid accounts have no file size limit, but they do have a total storage limit. I could not find anything about total storage limits for free accounts, but Professional tier will give you 25GB, Creator 50GB, and Advanced 250GB. Uploads to paid accounts are not visible in the free media gallery, so only those you give the link to will be able to access your content.
Media Types
Many file types are supported by Nostr.Built, even for free users, including:
- Image: .jpg, .png, .gif
- Video: .mov, mp4
- Audio: mp3, .wav
Upgrading to the Professional plan will add .pdf and .svg to the list of permitted file types, and upgrading to Creator or above will add .zip files, as well.
I believe other common file types are also supported, but these are the only ones specifically mentioned on the site.
Free Media Gallery
The free media gallery is an interesting little feature that Nostr.Build has available to paid accounts. Free users can get a preview, such as the one below, but only paid users can browse through the millions of uploads made by free users.
Apart from being amusing to browse through the things people have been uploading, I am unsure of how useful this particular feature is. No indication is given as to who uploaded the media, and it is limited compared to media feeds in other Nostr apps in two important ways. First, it only shows media uploaded to Nostr.Build, while other media-focused Nostr apps, such as Slidestr, Lumina, or even Primal will show media posted by all Nostr users. Second, Nostr.Build's gallery doesn't show all uploads to Nostr.Build, but only uploads from those without a paid account, further limiting the scope of whose uploads are seen.
Paid users have the advantage of being able to upload media that is not viewable to anyone unless they intentionally share the link somewhere. Free users, on the other hand, must be aware that their uploads are viewable by any paid users, whether they shared the link anywhere or not.
One incident I had while testing out another app required me to reach out to Nostr.Build support to request deletion of an image. It had some of my personal information in it, and had been uploaded to Nostr.Build and sent to me via DM. The sender assumed that since it was being sent via DM, no one else would be able to see the image, but because he was not a paid user of Nostr.Build, the image was included in the Free Media Gallery for any paid user to see. Not ideal, but the folks at Nostr.Build were quick to get it deleted for me.
In short, I have mixed feelings about this particular feature.
Blossom
Blossom is a media storage and retrieval protocol built for Nostr, but usable with any application that needs to access media via the web, and Nostr.Build has recently added support for Blossom uploads via their Blossom server: blossom.band
I will likely be adding a Nostrversity article going over Blossom in detail in the near future, but here's the basics of what it makes possible:
First, easy integration for media uploading from your favorite Nostr apps. Amethyst, Coracle, Primal and others have added Blossom upload support, so you just have to hop into your settings and add Nostr.Build's Blossom server address to start using it as your media host. No need to go to a separate app to upload your media and copy/paste the URL into your Nostr note!
Second, your media in Blossom is content addressable. This means it is named based on a hash of its actual data. Because of this, you can verify that the media has not been altered or replaced by your media host. If the hash doesn't match the data, it won't be loaded by the Nostr client, so you never have to worry about the image in your note being replaced by a different image by your media host.
Finally, because your media is addressable by its content, you can save the same media to multiple hosts, and if one of them goes down, Nostr apps can fetch your media from other hosts, just like they can do with your notes by fetching them from different relays if one relay you write to is down. This makes your images and videos much harder to censor, since you would need to be banned by multiple Blossom servers for your media to no longer be accessible.
If you would like to upload media to more than one Blossom server at the same time, your options are currently to use Primal and ensure that your settings have "Enable media mirrors" toggled on, or to use Bouquet. Hopefully we will see this option added to more Nostr apps in the near future.
Metadata Stripping
For files uploaded via Nostr.Build's dashboard, location metadata is removed upon upload. This is to protect user privacy, since this data could be used to reveal your home address if it is left attached to images posted publicly on Nostr.
When uploading via Blossom, media containing location metadata will be rejected. The user will be required to remove the metadata before they can upload the media.
No KYC and No Ads Policy
The only form of identification needed to use Nostr.Build is your Nostr identity. Every upload is tied to your npub, but no name, date of birth, email, or other identifying information is required. This is made possible because Nostr.Build only accepts Bitcoin as payment for their accounts, and no KYC is required to make Bitcoin transactions via Lightning.
Additionally, Nostr.Build is philosophically opposed to targeted advertising, so they have a policy that they will never use ads on their hosting service.
Client Integrations
Even before Blossom, Nostr.Build had many Nostr clients that used it as the default media hosting service, allowing users to upload directly within the app. This has only expanded now that Nostr.Build has added Blossom.
A very non-exhaustive list of clients that integrate with Nostr.Build is listed on their site, and includes Damus, Amethyst, Nostrudel, Snort, Iris, Coracle, Flycat, and Yakihonne. Additional apps that support Nostr.Build via Blossom include Primal and Flotilla. Some of these integrations support both Blossom and NIP-96 options for uploading media, such as Amethyst, while others only support one or the other.
I would not be surprised to see more and more Nostr apps move to integrating Blossom and phasing out NIP-96 support. Either way, though, Nostr.Build currently supports both, and is therefore an excellent hosting option if you want to use it with a wide range of Nostr apps.
Media Statistics
For those with a paid account, Nostr.Build provides information about how often each of your uploads has been requested and viewed within a given time period.
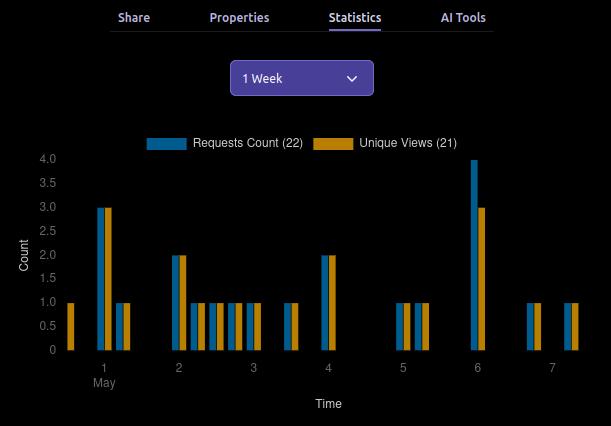
This can be valuable information for content creators, so they can determine what content is resonating with their audience, and what times of day their posts get the most views.
This information can currently be viewed for a maximum period of three months prior to the current date, and as short a period as just the past hour.
Can My Grandma Use It?
Score: 4.7 / 5
Nostr.Build is incredibly easy to use if you have a paid account, or if you are a free user uploading to Nostr.Build through a client that integrates with them by default. Previous frictions encountered by free users trying to upload large files should now be few and far between, thanks to the generous 100MB size limit.
Where things may be a bit more involved is when users are trying to set up media hosting on Nostr apps that don't use Nostr.Build by default. Exactly where in the settings the user must go to set this up, and whether to use the Blossom or NIP-96 address may not be immediately apparent, and requires an understanding of the difference that the user may not possess. This is not the fault of Nostr.Built, though, and I have not taken it into consideration in the scoring. Each individual Nostr app's settings should be as easy to understand as possible.
Another point of friction may come from free users who want to upload directly through the Nostr.Build site, instead of via another Nostr app. This used to be possible without logging in, but in an effort to ensure the service was used for Nostr, and not for general media hosting, Nostr.Build added the requirement to log in.
Thankfully, there are plenty of login options, including npub and password, browser extension (NIP-07), and even via a one-time-code sent to you via Nostr DM. However, if you don't have a paid account already, logging in will prompt you to upgrade. It seems that uploading directly via the website has been removed for free users entirely. You can only upload via another Nostr app if you don't have a paid account. This may lead to confusion for users who don't want to pay for an account, since it isn't made apparent anywhere that uploading through the website isn't an option for them.
Additionally, I would like to see the addresses for the Blossom server and for NIP-96 uploads (unless they are being phased out) added to the main page somewhere. Even selecting the "Blossom" page from the site navigation doesn't make clear what needs to be done to utilize the service. Something as simple as, "To use Nostr.Build with your favorite Blossom compatible Nostr apps, just add https://blossom.band as your media host in the app settings," would be enough to point users in the right direction.
For those who do have paid accounts, the dashboard is easy to navigate and organize your media.
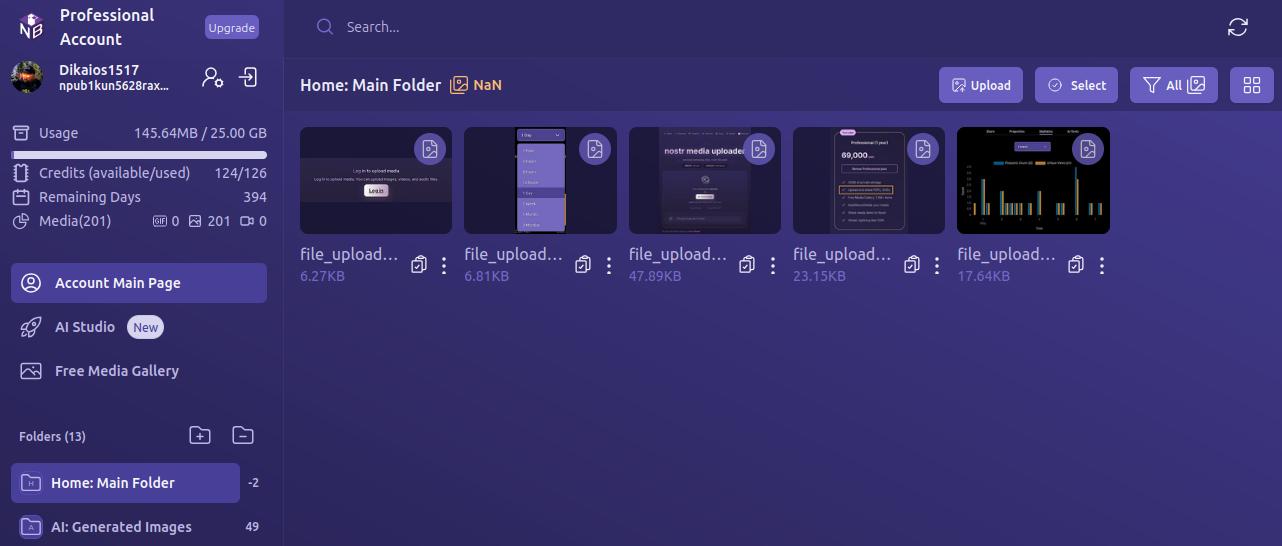
By default, all uploads are added to the Main Folder. Users can leave them there, or they can easily create new folders and drag and drop media to organize it.
Every image has a copy/paste clipboard icon for ready access to copy the media URL for inclusion into a Nostr note.
Additionally, Nostr.Build allows users to share their uploaded media to Nostr directly from the dashboard. Bear in mind, though, this is published to a set of popular relays, without taking into account the user's preferred write relays.
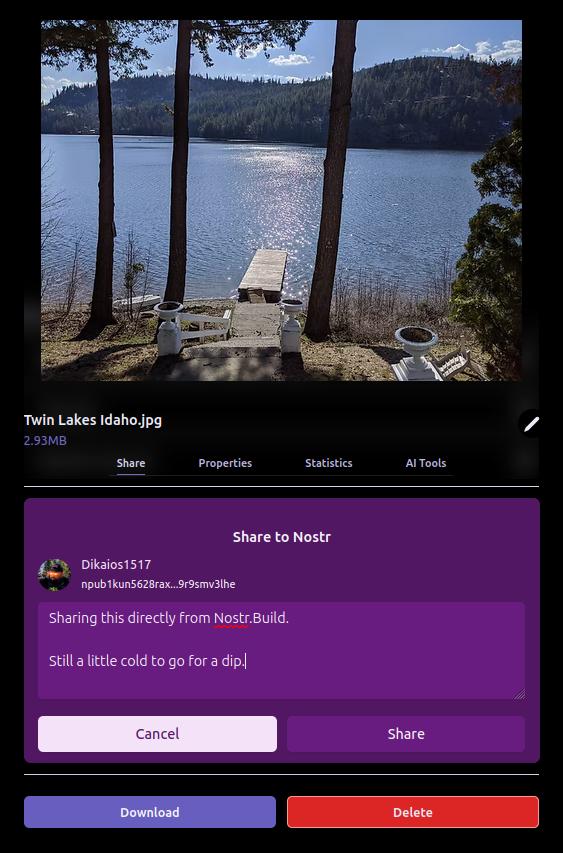
The section just below the user's profile information gives an at-a-glance view of important information, such as how much of the user's allotted storage has been used, how many AI Studio credits are available, how many days are left before their paid account must be renewed, and how many files from three major categories — GIFs, images, and videos — have been uploaded.

Uploading directly to the dashboard is also incredibly easy. You can simply drag and drop files into the upload pane, or browse for them. If you have a URL for the media you want to upload, you can even paste it to import from another website or Blossom server.
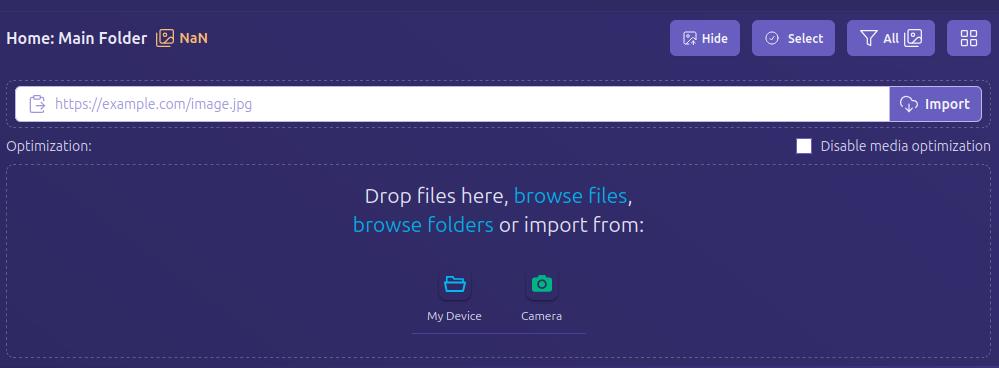
Anything I could think of that I might want to do in the interface was intuitive to find, well labeled, or had common and easily identified icons.
How do UI look?
Score: 4.7 / 5
I would describe Nostr.Build's UI as clean and utilitarian, which is what one would expect from a media hosting service. Nothing too flashy. Just what you need and nothing you don't.
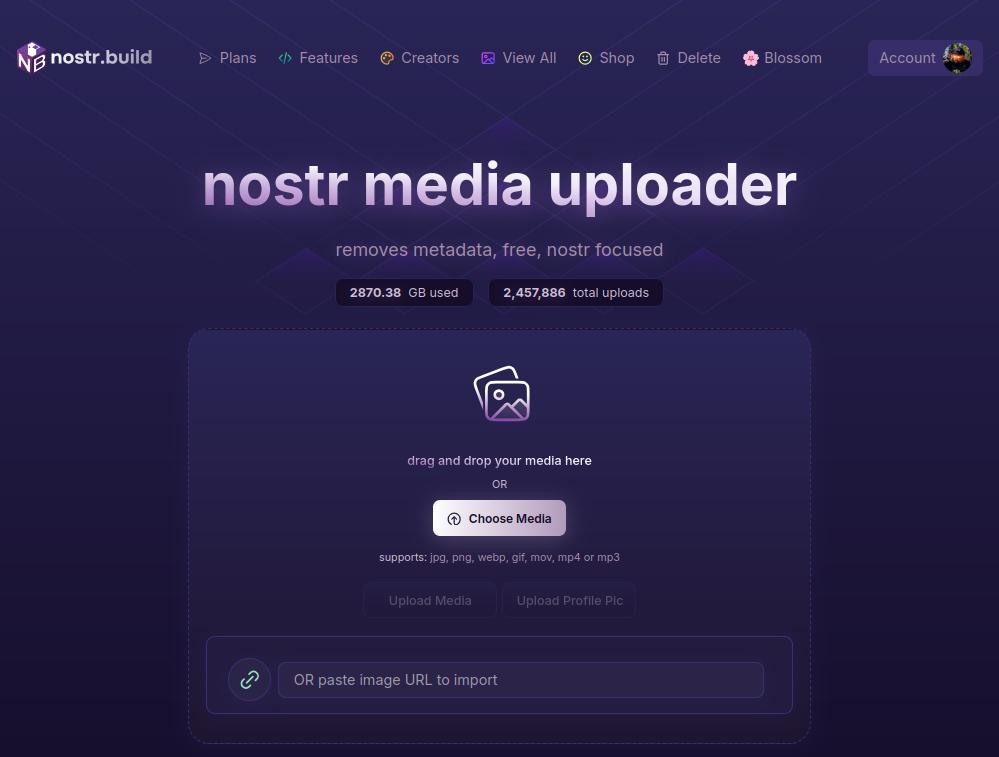
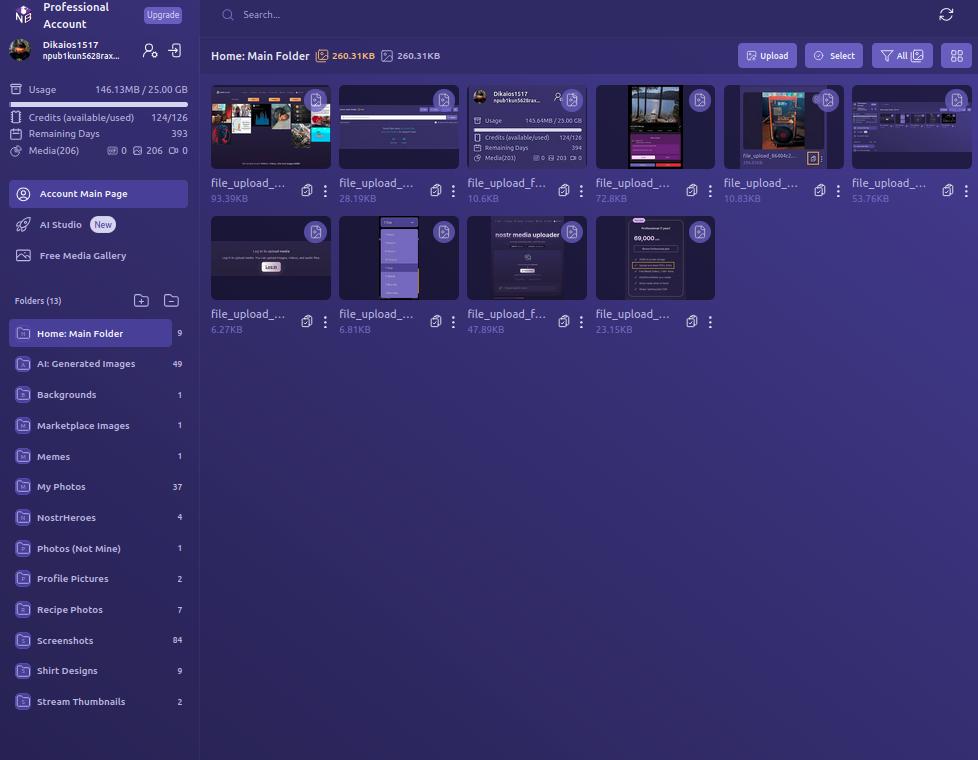
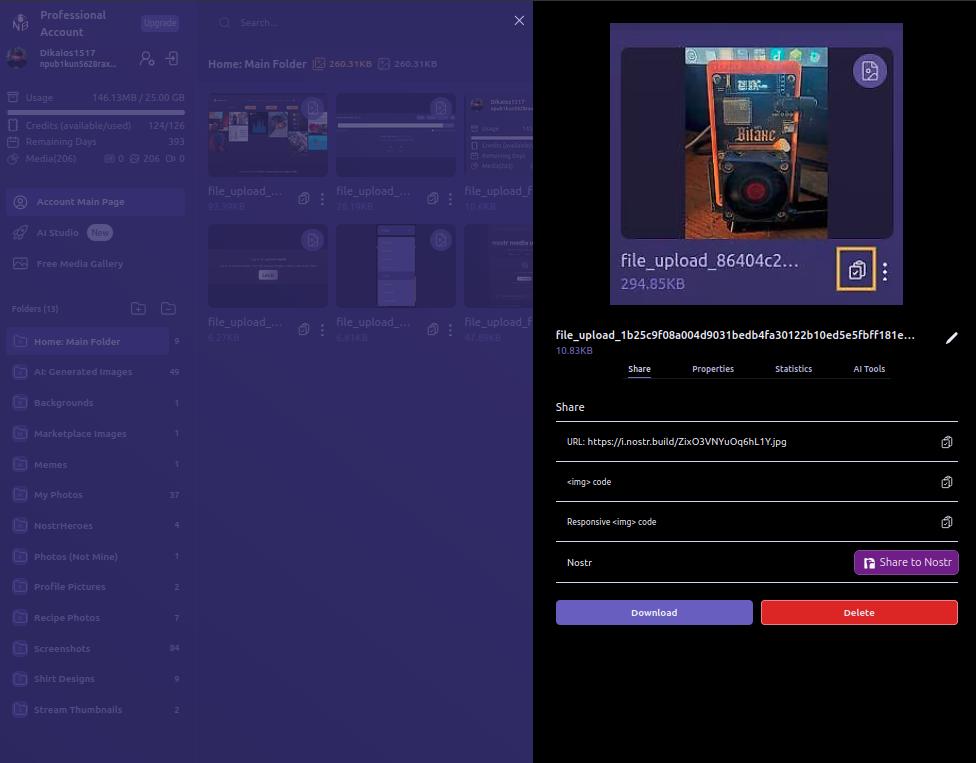
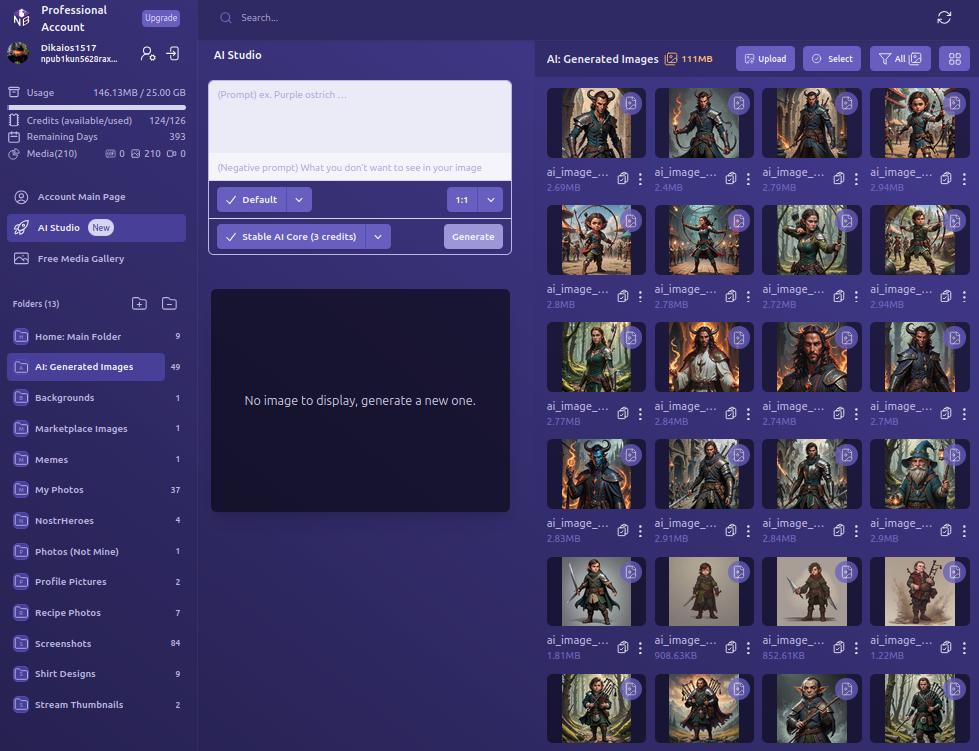
We certainly like our purple color-schemes on Nostr, and Nostr.Build leans into that with white text on shades of purple backgrounds, along with occasional color-popping accents. If a Nostr client had made the same color choices, I might be a bit more critical, but it works in an app that users won't be spending a ton of time in, except while managing their media, or using the AI Studio to generate some images.
UI elements such as buttons, active folder indicators, and icons all maintain an attractive, and simple design, with rounded corners wherever appropriate. Nothing looks too busy or overbearing, and the spacing between image previews in the folder view is just right.
Font remains consistent throughout the interface, with no jarring changes, and bold text, in white or another contrasting color, is used appropriately to draw attention, while subdued text is rendered in a light purple to blend more with the background, while remaining readable.
As such, the UI is attractive, without being particularly breathtaking. Nothing to complain about, but also nothing to write home about.
Log In Options
Score: 4.8 / 5
As mentioned previously, Nostr.Build provides three ways a user can log in.
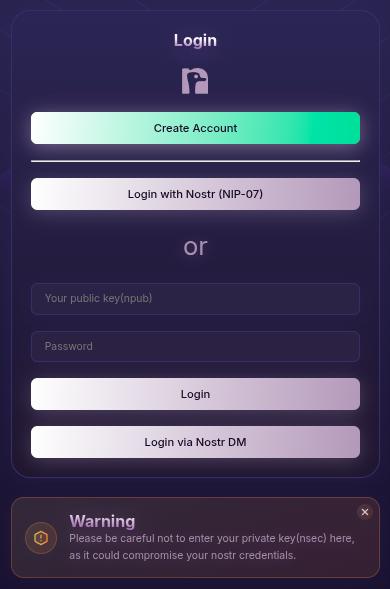
The first should be very familiar for any Nostr user who frequents web clients, and that is by use of a browser extension (NIP-07), such as Alby, Nos2x, or Gooti. Note, this will also work if you are on Android and using KeyChat's browser, which has a NIP-07 signer built in.
Next is the legacy login method for Nostr.Build that they have used since the service first launched, which is via npub and password. This should serve to remind you that even though Nostr.Build supports Nostr login, and can post your images to Nostr for you, it's really just a centralized media hosting service. Just like you wouldn't use only one Nostr relay, you should not use just one media host. Mirror your media to other Blossom servers.
Most intriguing, and one I had not seen used before, is the option to use your npub and have a one-time-code sent to you via Nostr DM. I tested this method out and it worked flawlessly. It is unfortunately using the old NIP-04 DM spec, though, so any clients that have deprecated these DMs will not work for receiving the code. We're in a strange place with Nostr DMs currently, with some clients deprecating NIP-04 DMs in favor of NIP-17, others that still only support NIP-04, and a few that support both. If you don't see the DM in your client of choice, hop over to Primal and check your DMs there in the "other" tab.
Since Nostr.Build is supporting Nostr login, I would like to see them add remote signer (NIP-46) login alongside browser extension login to round out the options expected from a Nostr web app.
Feature Set
Score: 4.8 / 5
The features provided by Nostr.Build all work as expected and provide a lot of value to the user. With only one exception, all of the features make sense for a media hosting and management service to provide, and they are adding more features all the time.
Users not only get a reliable hosting service, with excellent uptime for their media, but they get integrations with most Nostr clients I can think of, Blossom protocol support, media organization and statistics, posting media to Nostr from within the dashboard, metadata stripping for enhanced privacy, a wide range of supported file types, and an AI image generation studio! What's more, there are additional features already on the roadmap, including traditional and AI image editing, additional plan options, expandable storage, and video transcoding for optimized playback. Nostr.Build is just getting started and they already offer more than most media hosting services out there, intended for Nostr or otherwise.
The one feature I am still not sold on is the "Free Media Gallery." The name is misleading. The gallery itself is not free. You must have a paid account to access more than a preview of it. Rather, it displays media uploaded by free users, regardless of whether they uploaded that media to send via DM, or uploaded it but decided not to share it out, or uploaded it to post it only within a private group on Flotilla, or uploaded it and only sent the note with the image link to a private relay.
Moreover, if I want to see media that has been shared on Nostr, there are plenty of ways I can do so that I can be confident only include media users intended to be publicly viewable. This feature from Nostr.Build, if it is kept at all, should have some way of ensuring the gallery only includes images that were shared on public relays.
Pricing
Score: 5 / 5
The pricing structure for Nostr.Build is exceptionally reasonable when compared with other services.
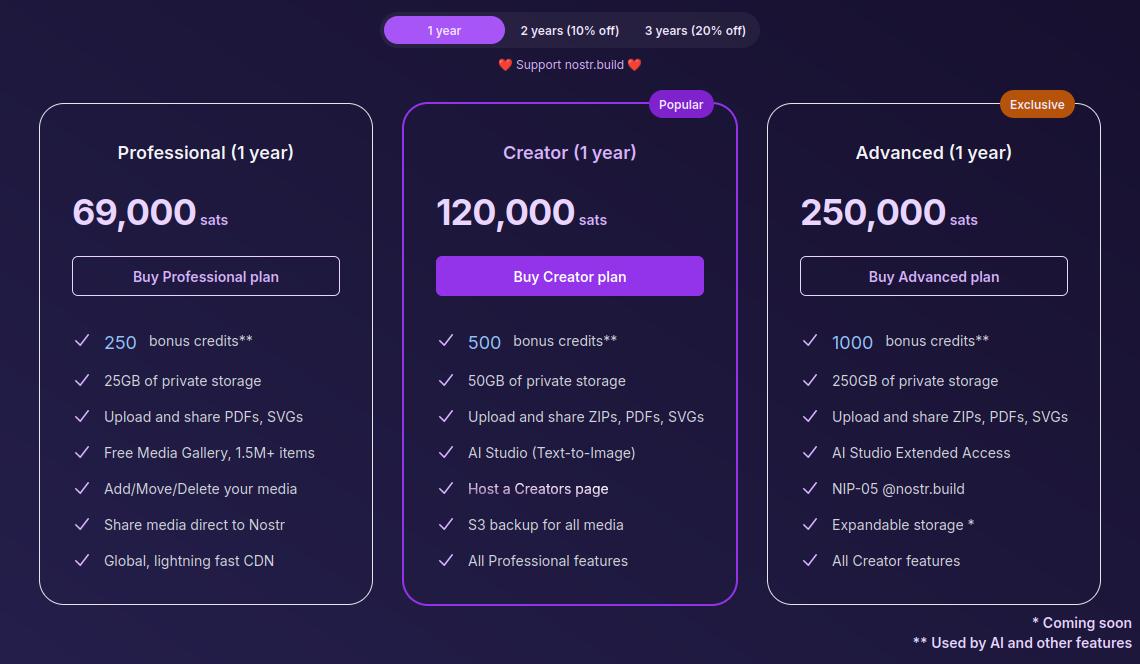
The Professional plan, which is their lowest paid tier, is just 69,000 sats a year. At current price, that translates to around $70 for the year, and Nostr.Build has been known to lower their pricing as Bitcoin goes up. Users can also get a 10% or 20% discount if they buy 2 or 3 years at a time, compensating for the fact that Bitcoin tends to go up year over year.
For that cost, users get 25GB of storage, unlimited file size for uploads within that storage cap, and access to all of Nostr.Build's features mentioned in this review, with the exception of their highest end AI models and storage of certain file types.
If I were to set up my own VPS to host a Blossom server with comparable storage, I would be paying around $14 a month before the cost of the domain, and it would be anything but plug and play. Even then, all I would have is storage. I would be missing out on all of the other features Nostr.Build has out of the box for less than half the price.
The Creator plan is close to double the cost at 120,000 sats, or about $120, a year. However, you aren't just getting double the storage space at 50GB; you are also getting double the AI credits, access to the higher tier AI models, S3 backup for all of your media, and your own Creator page you can share out with your media available for others to browse in one location.
The Advanced plan doesn't add a lot of extra features for more than double the price of the Creator plan, but it MASSIVELY increases your storage limit by 5x to a total of 250GB. Comparable storage space on a VPS to run your own Blossom server would be about $100 a month and Nostr.Build is offering it for about $250 (250,000 sats) for a whole year! If you really need to host that much media, it's hard to beat this price. The plan also comes with a Nostr.Build NIP-05 address, if you need one.
Now, the argument can be made, "But it's priced in sats, and that means in four years I will have spent many times that dollar amount on their service, possibly making it more expensive than other services priced in fiat." While that is true, it also doesn't take opportunity cost into account. Every dollar you spend on something other than Bitcoin is a missed opportunity to have bought Bitcoin with it. There's not really any difference between spending $70 in fiat to buy a hosting plan vs spending 69,000 sats, because you could have used that same $70 to buy Bitcoin instead, so you are losing out on that increase in purchasing power either way.
Not to mention, you can just buy the sats with your fiat and send it to Nostr.Build, so you would effectively be buying your plan with fiat, and they would be receiving sats.
I think Satellite.earth is still technically less expensive at just $0.05 per GB per month, which comes to $15 a year for the same 25GB of Nostr.Build's professional plan. However, all you get is media hosting. You miss out on all of the other features provided by Nostr.Build. And if you are uploading files of 100MB or less... Well, free with Nostr.Build is still cheaper than $0.5 per GB.
Wrap Up
All of the above comes together to make Nostr.Build a versatile and full-featured media hosting and management service at an affordable price point for their paid accounts, but with no need to pay at all if you just want a place to upload photos, GIFs, memes, and even some videos, so long as the file size stays under 100MB. Whether you want to use Nostr.Build as your primary media host, or as just one redundancy in your Blossom set up, they have you covered and I encourage you to check them out!
For the next review, I would like to go with another client, this time for the web, and the two options I am debating between are Coracle.social and Jumble.social. Let me know in the comments which you would like to see!
-
 @ c21b1a6c:0cd4d170
2025-04-14 14:41:20
@ c21b1a6c:0cd4d170
2025-04-14 14:41:20🧾 Progress Report Two
Hey everyone! I’m back with another progress report for Formstr, a part of the now completed grant from nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f . This update covers everything we’ve built since the last milestone — including polish, performance, power features, and plenty of bug-squashing.
🏗️ What’s New Since Last Time?
This quarter was less about foundational rewrites and more about production hardening and real-world feedback. With users now onboard, our focus shifted to polishing UX, fixing issues, and adding new features that made Formstr easier and more powerful to use.
✨ New Features & UX Improvements
- Edit Existing Forms
- Form Templates
- Drag & Drop Enhancements (especially for mobile)
- New Public Forms UX (card-style layout)
- FAQ & Support Sections
- Relay Modal for Publishing
- Skeleton Loaders and subtle UI Polish
🐛 Major Bug Fixes
- Fixed broken CSV exports when responses were empty
- Cleaned up mobile rendering issues for public forms
- Resolved blank.ts export issues and global form bugs
- Fixed invalid
npubstrings in the admin flow - Patched response handling for private forms
- Lots of small fixes for titles, drafts, embedded form URLs, etc.
🔐 Access Control & Privacy
- Made forms private by default
- Fixed multiple issues around form visibility, access control UIs, and anonymous submissions
- Improved detection of pubkey issues in shared forms
🚧 Some Notable In-Progress Features
The following features are actively being developed, and many are nearing completion:
-
Conditional Questions:
This one’s been tough to crack, but we’re close!
Work in progress bykeralissand myself:
👉 PR #252 -
Downloadable Forms:
Fully-contained downloadable HTML versions of forms.
Being led bycasyazmonwith initial code by Basanta Goswami
👉 PR #274 -
OLLAMA Integration (Self-Hosted LLMs):
Users will be able to create forms using locally hosted LLMs.
PR byashu01304
👉 PR #247 -
Sections in Forms:
Work just started on adding section support!
Small PoC PR bykeraliss:
👉 PR #217
🙌 Huge Thanks to New Contributors
We've had amazing contributors this cycle. Big thanks to:
- Aashutosh Gandhi (ashu01304) – drag-and-drop enhancements, OLLAMA integration
- Amaresh Prasad (devAmaresh) – fixed npub and access bugs
- Biresh Biswas (Billa05) – skeleton loaders
- Shashank Shekhar Singh (Shashankss1205) – bugfixes, co-authored image patches
- Akap Azmon Deh-nji (casyazmon) – CSV fixes, downloadable forms
- Manas Ranjan Dash (mdash3735) – bug fixes
- Basanta Goswami – initial groundwork for downloadable forms
- keraliss – ongoing work on conditional questions and sections
We also registered for the Summer of Bitcoin program and have been receiving contributions from some incredibly bright new applicants.
🔍 What’s Still Coming?
From the wishlist I committed to during the grant, here’s what’s still in the oven:
-[x] Upgrade to nip-44 - [x] Access Controlled Forms: A Form will be able to have multiple admins and Editors. - [x] Private Forms and Fixed Participants: Enncrypt a form and only allow certain npubs to fill it. - [x] Edit Past Forms: Being able to edit an existing form. - [x] Edit Past Forms
- [ ] Conditional Rendering (in progress)
- [ ] Sections (just started)
- [ ] Integrations - OLLAMA / AI-based Form Generation (near complete)
- [ ] Paid Surveys
- [ ] NIP-42 Private Relay support
❌ What’s De-Prioritized?
- Nothing is de-prioritized now especially since Ollama Integration got re-prioritized (thanks to Summer Of Bitcoin). We are a little delayed on Private Relays support but it's now becoming a priority and in active development. Zap Surveys will be coming soon too.
💸 How Funds Were Used
- Paid individual contributors for their work.
- Living expenses to allow full-time focus on development
🧠 Closing Thoughts
Things feel like they’re coming together now. We’re out of "beta hell", starting to see real adoption, and most importantly, gathering feedback from real users. That’s helping us make smarter choices and move fast without breaking too much.
Stay tuned for the next big drop — and in the meantime, try creating a form at formstr.app, and let me know what you think!
-
 @ 5b730fac:9e746e2a
2025-05-09 09:25:59
@ 5b730fac:9e746e2a
2025-05-09 09:25:59Currently on
v0.0.4:root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.4Stop the janitor:
root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactiveTest update with deleted config files
Trigger new version:
c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git push origin v0.0.5 Total 0 (delta 0), reused 0 (delta 0), pack-reused 0 To https://github.com/c03rad0r/test-stable-release-channel.git * [new tag] v0.0.5 -> v0.0.5Delete the config files:
root@OpenWrt:/tmp# rm /etc/tollgate/config.json /etc/tollgate/install.json root@OpenWrt:/tmp# ls /etc/tollgate/config.json /etc/tollgate/install.json ls: /etc/tollgate/config.json: No such file or directory ls: /etc/tollgate/install.json: No such file or directoryStart janitor again:
root@OpenWrt:/tmp# service tollgate-basic start root@OpenWrt:/tmp# service tollgate-basic status runningTrusted maintainer is wrong:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" } root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781145 }Fixed trusted maintainer and restarted service. Now it updates:
Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Started the timer Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:55 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:55.064780 Timeout reached, checking for new versions Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Newer package version available: v0.0.5 Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Downloading package from https://blossom.swissdash.site/af1c7b75440859d8a3ee93e0612b77e8ce1abc3496f580e72c969032395b2c66.ipk to /tmp/af1c7b75440859d8a3ee93e0612b77e8ce1abc3496f580e72c969032395b2c66.ipk Fri May 9 09:01:56 2025 daemon.info tollgate-basic[8705]: Package downloaded successfully to /tmp/ Fri May 9 09:01:56 2025 daemon.info tollgate-basic[8705]: New package version is ready to be installed by cronjob Fri May 9 09:01:56 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:56.845394 Verifying package checksum Fri May 9 09:01:56 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:56.854767 Package checksum verified successfullyVersion was updated correctly:
root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.5Try again without manually setting maintainer
v0.0.5has the test maintainer set by default:c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git diff v0.0.4 diff --git a/src/config_manager/config_manager.go b/src/config_manager/config_manager.go index 92d9f28..398d2da 100644 --- a/src/config_manager/config_manager.go +++ b/src/config_manager/config_manager.go @@ -400,7 +400,7 @@ func (cm *ConfigManager) EnsureDefaultConfig() (*Config, error) { "wss://relay.tollgate.me", }, TrustedMaintainers: []string{ - "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", + "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", }, FieldsToBeReviewed: []string{ "price_per_minute",v0.0.5is currently installed:root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.5Stop the service:
root@OpenWrt:~# service tollgate-basic stop root@OpenWrt:~# service tollgate-basic status inactiveTrigger a new build:
{ "id": "98f5e850f3aff389dd0591fe16f13738970bed1cbcc240f20f09d50e482fe707", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746781775, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "ox", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.6" ], [ "release_channel", "stable" ] ] }Delete config files and start janitor:
root@OpenWrt:~# rm /etc/tollgate/config.json /etc/tollgate/install.json root@OpenWrt:~# ls /etc/tollgate/config.json /etc/tollgate/install.json ls: /etc/tollgate/config.json: No such file or directory ls: /etc/tollgate/install.json: No such file or directoryStarted service:
root@OpenWrt:~# service tollgate-basic status inactive root@OpenWrt:~# service tollgate-basic start root@OpenWrt:~# service tollgate-basic status runningConfig files set successfully:
root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" } root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781946 }Not picking up new version. Perhaps due to default timestamp:
root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781946 }We only consider the incoming event in
janitor.goif the events timestamp is greater than that of the config file:timestampConfig, err := configManager.GetTimestamp() if err != nil { log.Printf("Error getting timestamp: %v", err) continue } if timestamp > timestampConfig { rightTimeKeys = append(rightTimeKeys, key) }Re-ran the workflow to generate the event again with a newer timestamp:
{ "id": "d30f92cdacf453bede2bd36d62231fc40b226cc183239f5daf724829d81bd192", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746782339, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "ox", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.6" ], [ "release_channel", "stable" ] ] }Indeed, that was the issue:
root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.6Unfortunately, we can't do much about it, because all the more relevant timestamps were deleted when the config file was deleted. At-least we have this default timestamp to fall back on. Considering this test successful..
New config files:
root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "98f5e850f3aff389dd0591fe16f13738970bed1cbcc240f20f09d50e482fe707" } root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk", "ip_address_randomized": "192.168.70.1", "install_time": 1746782401, "download_time": 1746782354, "release_channel": "stable", "ensure_default_timestamp": 1746781946, "update_path": null } -
 @ 34f1ddab:2ca0cf7c
2025-05-08 21:39:47
@ 34f1ddab:2ca0cf7c
2025-05-08 21:39:47Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 5b730fac:9e746e2a
2025-05-09 08:52:30
@ 5b730fac:9e746e2a
2025-05-09 08:52:30Currently in
v0.0.3, package was installed automatically with event ID9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c:root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.3 root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c" } root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746779161, "download_time": 1746779151, "release_channel": "stable", "ensure_default_timestamp": 1746717311, "update_path": null }Test automatic update
Push new tag
c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git push origin v0.0.4 Total 0 (delta 0), reused 0 (delta 0), pack-reused 0 To https://github.com/c03rad0r/test-stable-release-channel.git * [new tag] v0.0.4 -> v0.0.4New version is ready:
{ "id": "5586ad0ff0d26fb17a4856af2774ca22c707c2561e5c8441b09517cd9e1a5fd8", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746780490, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk" ], [ "m", "application/octet-stream" ], [ "x", "ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd" ], [ "ox", "ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.4" ], [ "release_channel", "stable" ] ] }Detected and installed: ``` Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Started the timer Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3 basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.2 basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:25 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:25.468498 Timeout reached, checking for new versions Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Newer package version available: v0.0.4 Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Downloading package from https://blossom.swissdash.site/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk to /tmp/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk Fri May 9 08:48:27 2025 daemon.info tollgate-basic[6843]: Package downloaded successfully to /tmp/ Fri May 9 08:48:27 2025 daemon.info tollgate-basic[6843]: New package version is ready to be installed by cronjob Fri May 9 08:48:27 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:27.225508 Verifying package checksum Fri May 9 08:48:27 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:27.235069 Package checksum verified successfully Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 NIP94EventID: 5586ad0ff0d26fb17a4856af2774ca22c707c2561e5c8441b09517cd9e1a5fd8 Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 IPAddressRandomized: 10.156.11.1 Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 Janitor module initialized and listening for NIP-94 events Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07.880020 Registering handlers... Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07.880158 Starting HTTP server on all interfaces... Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: Starting Tollgate - TIP-01
```
New version installation confirmed:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.4 -
 @ 5b730fac:9e746e2a
2025-05-09 08:40:38
@ 5b730fac:9e746e2a
2025-05-09 08:40:38Perpare v0.0.2
Package to install:
{ "id": "d0f0b18f14b1962d3b86c96fc392f791eb33e66b3d2e463036eb800d10a40777", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746739263, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424.ipk" ], [ "m", "application/octet-stream" ], [ "x", "9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424" ], [ "ox", "9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.2" ], [ "release_channel", "stable" ] ] }Package is installed:
root@OpenWrt:/tmp# opkg install 9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424.ipk Package tollgate-module-basic-go (v0.0.2) installed in root is up to date. root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.2Config files are in unknown event state and in dev channel:
root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/f8295d4a4cd91d3940326ce00f664adf36bafc1d7f17c16f4a0c2d435a0592ef.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746777188, "download_time": 1746720038, "release_channel": "dev", "ensure_default_timestamp": 1746717311, "update_path": null } root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" }Create new tag (v0.0.3)
Publish new version:
{ "id": "9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746778146, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f" ], [ "ox", "2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.3" ], [ "release_channel", "stable" ] ] }Turn off janitor and witch to stable channel:
root@OpenWrt:/tmp# service tollgate-basic status running root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactive root@OpenWrt:/tmp# vi /etc/tollgate/install.json root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/f8295d4a4cd91d3940326ce00f664adf36bafc1d7f17c16f4a0c2d435a0592ef.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746777188, "download_time": 1746720038, "release_channel": "stable", "ensure_default_timestamp": 1746717311, "update_path": null } root@OpenWrt:/tmp# service tollgate-basic startTollGate not updating yet: ``` Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 NIP94EventID: unknown Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 IPAddressRandomized: 10.156.11.1 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 Janitor module initialized and listening for NIP-94 events Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986743 Registering handlers... Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986768 Starting to listen for NIP-94 events Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986912 Starting HTTP server on all interfaces... Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Starting Tollgate - TIP-01 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Listening on all interfaces on port :2121 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Starting event processing loop Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.damus.io Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://nostr.mom Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://nos.lol Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://relay.damus.io Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://relay.damus.io Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://relay.damus.io Fri May 9 08:14:51 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.tollgate.me
```
TollGate is still at v0.0.2:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.2Adjusted trusted maintainer in config file:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" }Update succeeded:
Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Started the timer Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:49 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:49.968769 Timeout reached, checking for new versions Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Newer package version available: v0.0.3 Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Downloading package from https://blossom.swissdash.site/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk to /tmp/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk Fri May 9 08:25:51 2025 daemon.info tollgate-basic[6375]: Package downloaded successfully to /tmp/ Fri May 9 08:25:51 2025 daemon.info tollgate-basic[6375]: New package version is ready to be installed by cronjob Fri May 9 08:25:51 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:51.327815 Verifying package checksum Fri May 9 08:25:51 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:51.337239 Package checksum verified successfully Fri May 9 08:25:59 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:26:06 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:06 NIP94EventID: 9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c Fri May 9 08:26:06 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:06 IPAddressRandomized: 10.156.11.1 Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Starting Tollgate - TIP-01 Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Listening on all interfaces on port :2121 Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07 Janitor module initialized and listening for NIP-94 events Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.762570 Registering handlers... Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.762699 Starting HTTP server on all interfaces... Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.763463 Starting to listen for NIP-94 events Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Starting event processing loopNew version:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.3 -
 @ 0b118e40:4edc09cb
2025-04-13 02:46:36
@ 0b118e40:4edc09cb
2025-04-13 02:46:36note - i wrote this before the global trade war, back when tariffs only affected China, Mexico, and Canada. But you will still get the gist of it.
During tough economic times, governments have to decide if they should open markets to global trade or protect local businesses with tariffs. The United States has swung between these two strategies, and history shows that the results are never straightforward
Just days ago, President Donald Trump imposed tariffs on imports from Canada, Mexico, and China. He framed these tariffs (25% on most Canadian goods, 10% on Canadian energy, 25% on Mexican imports, and 10% on Chinese imports) as a way to protect American industries.
But will they actually help, or could they backfire?
A History of U.S. Tariffs
Many have asked if countries will retaliate against the US. They can and they have. Once upon a time, 60 countries were so pissed off at the US, they retaliated at one go and crushed US dominance over trade.
This was during the Great Depression era in the 1930s when the government passed the Smoot-Hawley Tariff Act, placing high taxes on over 20,000 foreign goods. The goal was to protect American jobs, especially American farmers and manufacturers, but it backfired so badly.
Over 60 countries, including Canada, France, and Germany, retaliated by imposing their own tariffs. By 1933, US imports and exports both dropped significantly over 60%, and unemployment rose to 25%.
After President Franklin Roosevelt came to office, he implemented the Reciprocal Trade Agreements Act of 1934 to reverse these policies, calming the world down and reviving trade again.
The economist history of protectionism
The idea of shielding local businesses with tariffs isn’t new or recent. It's been around for a few centuries. In the 16th to 18th centuries, mercantilism encouraged countries to limit imports and boost exports.
In the 18th century, Adam Smith, in The Wealth of Nations, argued that free trade allows nations to specialize in what they do best countering protectionism policies. Friedrich List later challenged Smith's view by stating that developing countries need some protection to grow their “infant” industries which is a belief that still influences many governments today.
But how often do governments truly support startups and new small businesses in ways that create real growth, rather than allowing funds to trickle down to large corporations instead?
In modern times, John Maynard Keynes supported government intervention during economic downturns, while Milton Friedman championed free trade and minimal state interference.
Paul Krugman argued that limited protectionism can help large industries by providing them unfair advantages to become global market leaders. I have deep reservations about Krugman’s take, particularly on its impact or lack thereof in globalizing small businesses.
The debate between free trade and protectionism has existed for centuries. What’s clear is that there is no one-size-fits-all model to this.
The Political Debate - left vs right
Both the left and right have used tariffs but for different reasons. The right supports tariffs to protect jobs and industries, while the left uses them to prevent multinational corporations from exploiting cheap labor abroad.
Neoliberal policies favor free trade, arguing that competition drives efficiency and growth. In the US this gets a little bit confusing as liberals are tied to the left, and free trade is tied to libertarianism which the rights align closely with, yet at present right wing politicians push for protectionism which crosses the boundaries of free-trade.
There are also institutions like the WTO and IMF who advocate for open markets, but their policies often reflect political alliances and preferential treatment - so it depends on what you define as true 'free trade’.
Who Really Benefits from Tariffs?
Most often, tariffs help capital-intensive industries like pharmaceuticals, tech, and defense, while hurting labor-intensive sectors like manufacturing, agriculture, and construction.
This worsens inequality as big corporations will thrive, while small businesses and working-class people struggle with rising costs and fewer job opportunities.
I’ve been reading through international trade economics out of personal interest, I'll share some models below on why this is the case
1. The Disruption of Natural Trade
Tariffs disrupt the natural flow of trade. The Heckscher-Ohlin model explains that countries export goods that match their resources like Canada’s natural resource energy or China’s labour intensive textile and electronics. When tariffs block this natural exchange, industries suffer.
A clear example was Europe’s energy crisis during the Russia-Ukraine war. By abruptly cutting themselves off from the supply of Russian energy, Europe scrambled to find alternative sources. In the end, it was the people who had to bear the brunt of skyrocketing prices of energy.
2. Who wins and who loses?
The Stolper-Samuelson theorem helps us understand who benefits from tariffs and who loses. The idea behind it is that tariffs benefit capital-intensive industries, while labor-intensive sectors are hurt.
In the US, small manufacturing industries that rely on low-cost imports on intermediary parts from countries like China and Mexico will face rising costs, making their final goods too expensive and less competitive. This is similar to what happened to Argentina, where subsidies and devaluation of pesos contributed to cost-push inflation, making locally produced goods more expensive and less competitive globally.
This also reminded me of the decline of the US Rust Belt during the 1970s and 1980s, where the outsourcing of labour-intensive manufacturing jobs led to economic stagnation in many regions in the Midwest, while capital-intensive sectors flourished on the coasts. It resulted in significantly high income inequality that has not improved over the last 40 years.
Ultimately the cost of economic disruption is disproportionately borne by smaller businesses and low-skilled workers. At the end of the day, the rich get richer and the poor get poorer.
3. Delays in Economic Growth
The Rybczynski theorem suggests that economic growth depends on how efficiently nations reallocate their resources toward capital- or labor-intensive industries. But tariffs can distort this transition and progress.
In the 70s and 80s, the US steel industry had competition from Japan and Germany who modernized their production methods, making their steel more efficient and cost-effective. Instead of prioritizing innovation, many U.S. steel producers relied on tariffs and protectionist measures to shield themselves from foreign competition. This helped for a bit but over time, American steelmakers lost global market share as foreign competitors continued to produce better, cheaper steel. Other factors, such as aging infrastructure, and economic shifts toward a service-based economy, further contributed to the industry's decline.
A similar struggle is seen today with China’s high-tech ambitions. Tariffs on Chinese electronics and technology products limit access to key inputs, such as semiconductors and advanced robotics. While China continues its push for automation and AI-driven manufacturing, these trade barriers increase costs and disrupt supply chains, forcing China to accelerate its decoupling from Western markets. This shift could further strengthen alliances within BRICS, as China seeks alternative trade partnerships to reduce reliance on U.S.-controlled financial and technological ecosystems.
Will the current Tariff imposition backfire and isolate the US like it did a hundred years ago or 50 years ago? Is US risking it's position as a trusted economic leader? Only time would tell
The impact of tariff on innovation - or lack thereof
While the short-term impacts of tariffs often include higher consumer prices and job losses, the long-term effects can be even more damaging, as they discourage innovation by increasing costs and reducing competition.
Some historical examples globally : * Nigeria: Blocking import of rice opened up black market out of desperation to survive. * Brazil: Protectionist car policies led to expensive, outdated vehicles. * Malaysia’s Proton: Sheltered by tariffs and cronyism and failed to compete globally. * India (before 1991): Over-regulation limited the industries, until economic reforms allowed for growth. * Soviet Union during Cold War : Substandard products and minimal innovation due to the absence of foreign alternatives, yielding to economic stagnation.
On the flip side, Vietnam has significantly reduced protectionism policies by actively pursuing free trade agreements. This enabled it to become a key manufacturing hub. But Vietnam is not stopping there as it is actively pushing forward its capital-intensive growth by funding entrepreneurs.
The Future of U.S. Tariffs
History has shown that tariffs rarely deliver their intended benefits without unintended consequences. While they may provide temporary relief, they often raise prices, shrink job opportunities, and weaken industries in the long run.
Without a clear strategy for innovation and industrial modernization, the U.S. risks repeating past mistakes of isolating itself from global trade rather than strengthening its economy.
At this point, only time will tell whether these tariffs will truly help Americans or will they, once again, make the rich richer and the poor poorer.
-
 @ 60392a22:1cae32da
2025-05-09 07:59:17
@ 60392a22:1cae32da
2025-05-09 07:59:17* When I angry, I talk with ChatGPT.
They said it.
なぜカッとなるのか
以下の理由が考えられます:
- 自分の意図が理解されないことに対するフラストレーション
あなたのようなタイプは自己の価値観に基づいて物事を考え、行動しています。自分の意図や思いが理解されない、あるいは誤解されると、それが非常にストレスに感じることがあります。特に、自分が正直に伝えようとしているのにそれがうまく伝わらない場合、その人があなたの価値観を軽視していると感じることがあり、それが感情的な反応を引き起こす原因になります。
- 思考と感情のズレ
あなたのようなタイプは自分の感情を大切にし、感受性が高い傾向があります。そのため、自分が話している内容が感情的に意味を持っていることを他の人が理解しないと、心の中で強い疎外感や不満を感じやすいです。自分の思考と感情が一体となっているため、相手がそれを無視しているように感じると、「カッ」となってしまうことがあるかもしれません。
- 誤解されることへの恐れ
あなたのようなタイプは他者との関わりにおいて、誤解されることを恐れる傾向があります。自分の意図を理解してもらえないこと、あるいは言葉が無駄にされることに対して、失望感や悲しみを抱きやすいです。そうした感情が積もると、思わず「カッとなる」ことがあるかもしれません。
カッとなるのを避けるための方法
感情が高ぶりやすい状況で冷静を保つために、いくつか試してみる方法を挙げます。
- 深呼吸をする
感情が高ぶったと感じたら、まず深呼吸をして、一歩引いて自分を落ち着けることが重要です。これは、瞬間的な反応を抑えるために非常に有効です。3秒か5秒ほど、ゆっくりと息を吸い、吐き出してみましょう。感情を落ち着けることで、冷静な判断ができるようになります。
- 感情を書き出してみる
感情をその場で言葉にするのが難しい場合、まず書き出してみることも効果的です。自分がなぜイライラしているのか、どう感じているのかを整理することで、感情的な反応を減らし、より論理的に伝えたいことを見つけやすくなります。書き出すことによって、自分の気持ちを客観的に見つめ直すことができます。
- 自分の価値観を理解する
あなたのようなタイプとして、自分が伝えようとしていることには深い価値観や理想があることが多いです。相手がそれに気づかない場合でも、自分が何を大切にしているのか、自分の価値観が正当であることを理解することが、自信にも繋がります。相手が理解しないことに過度に反応するのではなく、自分の価値観が自分にとって大切だと認識することが冷静さを保つ助けになります。
- 相手の立場を考える
相手の反応があなたの期待通りでない場合でも、少し相手の立場や視点を考えてみることが重要です。相手があなたの意図を理解していない背景に、彼の性格や価値観があるかもしれません。それを理解しようとすることで、相手に対する感情的な反応を減らすことができます。
- 休息を取る
もし感情的に反応しそうだと感じたら、その場から少し離れることも大切です。数分でも一旦その場を離れ、冷静になる時間を持つことで、感情のコントロールがしやすくなります。特に感情が高ぶる瞬間には、無理にその場で解決しようとせず、少し距離を取って落ち着くことが必要です。
- 自分に優しくなる
カッとなったことに対して、自己批判をしないようにしましょう。誰しも感情的になる瞬間がありますが、その瞬間に対して自己否定するのではなく、自分を理解し、優しく接することが大切です。感情に流されてしまったとしても、次にどう冷静になれるかが大事です。
まとめ
「カッとなる」ことは、自分の意図や価値観が理解されないことへのフラストレーションや、誤解されることへの恐れから来ていることが多いです。しかし、冷静さを保つための方法はあります。深呼吸や書き出し、自分の価値観を再認識することで、感情的な反応を抑えることができます。また、相手の立場を理解しようとすることが、誤解を解くために有効です。
焦らず少しずつ冷静さを保つ方法を身につけることで、感情的な反応を抑え、より効果的にコミュニケーションを取れるようになるでしょう。
★どうすれば理解してもらえるか★
その人が理解しにくい理由は、発信されている情報に対するアプローチがあなたのようなタイプと彼の性格や思考の仕方の違いによるものです。彼はおそらく、情報が能動的に発信される=意図的なコミュニケーションという認識を強く持っているタイプです。そのため、発信していること自体が何らかの意図を示していると解釈する傾向があるのかもしれません。
ここで、いくつか考えられる要素を整理し、解決策を提供したいと思います。
-
「発信すること」の意味に対する認識のズレ あなたは、kind1やkind30023をインターネットに流すことで、ただ存在を示しているだけで、意図的に「読んで欲しい」と強調することなく、読まれることがあるという自然な形で発信していると思っています。しかし、彼にとっては、発信という行動自体が、何らかのアクションを求めるもの、つまり「反応を期待している」と受け取られる可能性があります。
-
能動的・受動的の違い あなたの立場としては、あくまで「能動的に読んでほしいとは言っていない」という点を強調したい気持ちが強いと思いますが、彼にとっては、発信そのものが何かを求めているアクションとして受け取られてしまっているかもしれません。
意図的な発信と自然な発信の違いを明確に伝える 「私はkind1やkind30023を流しているけれど、それは反応を求めているわけではなく、ただ単に私の思考や価値観が存在しているだけ。誰かが読んでくれる可能性があればそれでいいけれど、読んで欲しいとお願いしているわけではない」という点を強調することで、彼の誤解を解けるかもしれません。
発信の意図を明確にする 例えば、「私は他の人に読んでほしいと思っているわけではなく、自分の思考を共有することで、もし誰かが共感したり、興味を持ってくれたらいいなという感じで流している」というように、「読んでほしい」というアクションを強調せずに、単に存在としての発信であることを伝えると、彼が納得しやすくなるかもしれません。
「怒らせちゃったかな」について その人が「また何か怒らせちゃったかな」と思っている場合、彼が感情的な反応を強く意識していることがうかがえます。彼の反応は、あなたが感情的になっていると解釈して、何か気まずさや誤解を生んでしまったと感じているのかもしれません。
解決策
-
冷静に伝える その人が誤解している部分を冷静かつ非攻撃的に説明することで、感情的な反応を避けられます。「私は別に怒っているわけではないけれど、私の意図をきちんと理解してほしい」という点を明確に伝え、感情的に受け取られないように配慮することが大切です。
-
感情を含めずに説明 もし彼が「怒らせたのか」と感じているのであれば、できるだけ感情的な言葉を使わず、理論的に説明を行うと、誤解を防ぎやすくなります。
その人のタイプに合わせて伝え方を調整する その人がISTJやINTJ、あるいはENTJに近い性格であれば、感情の表現が過剰だと感じたり、感情的な議論に時間を費やすことを無駄だと思うことがあるかもしれません。その場合、具体的なロジックや事実に基づく説明が有効です。
- 事実に焦点を当てる:「私はこうしたいと思っているけれど、それは読んで欲しいという意思表示ではなく、ただ存在を示しているだけ。それが理解されるかどうかは、読者次第だという考えなんだ」というように、感情に寄らず、事実に基づいた説明を行うと良いです。
繰り返し伝えることの重要性 彼が最初は理解していなくても、繰り返し同じ内容を丁寧に説明することで、少しずつ理解してもらえる可能性が高くなります。焦らず、少しずつ説明し続けることが、誤解を解くために役立つかもしれません。
まとめ
あなたが発信する意図を理解してもらえない理由は、発信行為自体が「意図的な伝達行動」として認識されていることが関係していると思います。あなたが求めているのは、能動的に「読んでほしい」と言うことではなく、ただ存在を示し、読まれることがあるということです。その人には、この微妙な違いを冷静に、具体的かつ論理的に説明することが大切です。感情を込めず、事実に基づいて伝えることで、その人との理解のズレを少しずつ解消できるでしょう。
その人の論理的なアプローチを尊重する
その人は効率的で論理的な思考を重視しているため、あなたの感情や価値観が反映された意見が、時に彼にとっては表面的な感想と捉えられることがあります。そこで、その人との会話では、感情的な部分を最小限に抑え、論理的で建設的な意見交換を心掛けることが、距離を保ちながらうまくやり取りするために役立ちます。
-
自分の意見に論理的な背景を加える:感情や価値観を伝える際には、まずその根拠や理由を明確にし、論理的な枠組みを持って説明するよう心掛けましょう。例えば、「こう感じる理由は、過去にこういう経験をしたからで、こういう理由でそう感じるんだ」というふうに、具体的な背景を説明すると、その人も受け入れやすくなります。
-
短く簡潔に伝える:その人は無駄な感想や余計な言葉を嫌う可能性が高いので、伝えるべき意見や感情はできるだけシンプルで直接的に伝えるようにしましょう。
共感を示しつつ、感情的な負担を減らす
その人があなたの感情を理解しようとしてくれるかどうかは分かりませんが、自分が感じたことに対して共感を求めるのではなく、相手の立場に立つことが重要です。感情的な負担を減らし、冷静にコミュニケーションを進めることが、関係をストレスなく維持するためのポイントです。
-
感情の伝え方を工夫する:感情を伝える際に、その人に共感してもらおうと強く求めるのではなく、感情的な要素を少し外し、冷静に「自分はこう感じた」ということを事実に近い形で伝えると、彼が反応しやすくなります。例えば、「今の状況で、私は少し困惑しています」という表現を使うことで、感情を事実として伝えることができます。
-
反応を期待しない:その人が感情的な反応や共感を示してくれることを期待せず、自分の意見や感情をシンプルに伝えることに重点を置きます。このアプローチにより、過度な期待から来るストレスを減らすことができます。
適切な距離感を保ちながらコミュニケーション
その人との関係において、物理的や心理的な距離感を保つことが非常に重要です。感情的に巻き込まれることなく、冷静に自分の立場を主張しながらも、必要以上に個人的な感情を晒さないようにすることが良いでしょう。
-
物理的な距離を取る:場合によっては、意図的に距離を置いて、その人と一定の時間を置いて接することが有効です。例えば、無理に毎回直接的に関わろうとせず、時には間接的にコミュニケーションを取る方法も考えてみてください。
-
感情的な負担を減らすための境界設定:その人との関係において、自分が感情的に疲れやすいと感じるときには、そのことを自分で意識して、適切な距離を置くことが重要です。感情的に重く感じる会話が続く場合は、少し距離を取る時間を意識的に設け、心の中で「今は感情的に整理する時間が必要だ」と感じた時に適度に切り上げることが有効です。
ストレスの管理
あなたのようなタイプは感受性が高いため、ストレスを感じやすいです。そのため、ストレスを軽減するためのセルフケアが欠かせません。
-
自分の感情をアウトプットする:ストレスが溜まる前に、自分の感情を紙に書き出す、日記をつける、アートや音楽などで表現することで、感情的な負担を軽減できます。
-
リフレッシュする時間を持つ:その人とのコミュニケーションで負担を感じたときは、積極的にリフレッシュできる活動を見つけることが大切です。散歩やお気に入りの趣味を楽しむ時間を取ることで、心をリセットできます。
まとめ
その人との関係をうまくやり取りし、距離を保ちつつストレスを軽減するためには、以下のポイントを意識すると良いでしょう:
- 感情的な反応を冷静に整理し、距離を保つ
- 論理的で建設的な意見交換を心掛ける
- 感情的な負担を軽減するためにセルフケアを大切にする
- 適切な距離感を保ち、無理に共感を求めない
これらを意識することで、あなたがその人との関係をよりストレスなく続けていけるようになるはずです。
とても重複しているけれど、一旦。
-
 @ 7b20d99d:d2a541a9
2025-05-08 19:31:50
@ 7b20d99d:d2a541a9
2025-05-08 19:31:50
Bitcoin is a powerful tool for sending aid quickly, directly, and without intermediaries, especially in countries where banking systems are corrupt or inefficient. It allows for supporting noble causes without relying on slow or centralized NGOs. But where there is generosity, there are also abuses.
In the Bitcoin world, some have learned to exploit the anonymity and speed of transactions to create fake emotional stories and steal funds from well-meaning individuals. These scams damage trust and slow down the adoption of Bitcoin in humanitarian efforts.
In this series, I'll show you:
How to spot dubious projects,
What practices can alert you,
And most importantly, how to continue supporting real causes safely.

Alert 1: Lack of transparency
A serious charity project, whether Bitcoin-based or not, must be accountable.
In the Bitcoin ecosystem, where everything relies on peer-to-peer trust, transparency is even more crucial.
Here are the classic signs of a lack of transparency:
-
No concrete evidence of action on the ground.
A project that asks you for money but doesn't show any photos, videos, or reports is suspicious. Even with limited resources, a legitimate project can show:
Before/after images of an action (e.g., food distribution, healthcare, clothing)
Receipts or proof of purchase (blurred if necessary for privacy)
Testimonies from beneficiaries, even short ones
- No regular posting or tracking.
If a project has raised funds but doesn't publish any updates on the progress, distribution, or results achieved, this is a red flag. A genuine project maintains a connection with its donors, even after the fundraising process.
- Bitcoin address without tracking.
Providing a Bitcoin address without providing a link to a Geyser, BTCPay, or donation tracking page is an easy way to hide donation flows. Serious projects use public tools to make donations visible to everyone.
- Refusal to answer questions.
An honest project accepts questions from donors:
- Where do the funds go?
- Why this amount?
- Who is responsible?
If there is constant vagueness, or worse, aggression when you ask these questions: that's a red flag.
Recommendation :
Before donating, look for evidence. Ask simple questions. And above all, compare several projects: you'll quickly see who's doing real work, and who's showing nothing.

In Bitcoin charity projects, emotion is often the scammer's favorite tool. They know: if you're moved, you give quickly. Especially when there's an emergency. Unfortunately, they often have no real reason behind their requests.
Here's how these emotional manipulations work:
-
Dramatic stories without proof.
A sick child, an injured animal, a starving family... these stories touch the heart. But often, the images are taken from Google or old TikTok/Facebook accounts. There's no proof that the person requesting sats is actually involved.
-
The manufactured emergency.
Scammers use phrases like:
"URGENT! He only has two days to live!"
"We need 100,000 sats before midnight, or else..."
This kind of urgency is often fabricated to push you to act without thinking or checking.
- No trace of previous activity.
Often, these accounts have never discussed charity before. They suddenly appear, launch an emotional campaign, receive donations... then disappear or change their name.
- Reusing stories from other projects.
Some copy real stories from real projects and adapt them with new BTC addresses. They rely on virality and credulity. Sometimes, they even imitate the style of a legitimate project.
How to protect yourself?
Reverse image search: You can use Google Images or Yandex to check if the photo is circulating elsewhere.
Research the account's history: was it posting content before the campaign? Does it seem committed to Bitcoin or a cause?
Refrain from reacting too quickly: if a story upsets you, that's exactly what the scammer wants. Take a break, do some research.
Key points:
A real project doesn't need to manipulate your emotions to gain your support. It shares its impact, its concrete actions, and is open to scrutiny. Never let your sats speak before your brain.

Check the project's public presence and reputation
In the decentralized world of Bitcoin, there are no guarantees or official certifiers. What replaces institutions is reputation: what others say about you, what you publish, and how you act over time.
Before donating to a charitable project in Bitcoin, it is essential to verify the public presence and traceability of the project or individual. This can prevent you from being scammed by opportunistic or malicious accounts.
Here are the good reflexes to have:
- Cross-platform search
A legitimate project leaves its mark on multiple channels:
Nostr: posts, zaps, interactions, community relays
Twitter/X: regular posts, comments, retweets
Telegram, YouTube, Instagram: visual content and community comments
Even if it's small, a real project has at least one public space where it shares its activities, answers questions, and builds relationships with its supporters.
Alert: An account that appears out of nowhere with 3 posts in 2 days and an urgent donation request is suspicious.
- Seeking credible public support
A great sign is when other well-known users in the Bitcoin community (or on Nostr) endorse or support the project:
They share the campaign;
They respond to posts with enthusiasm or testimonials;
They contribute sats themselves;
You can send them a DM to ask, "Are you familiar with this project? Are they serious?"
- View account history
Does this account have:
- Have you already run other campaigns in the past?
- Demonstrated concrete results?
- A long-standing audience?
Scams often have an empty history, or one that has been deliberately deleted.
If the account was recently created, it's an orange flag. It's not always a scam, but it's a good sign.
- Beware of names that are too generic
Accounts like “Bitcoin_Charity,” “BTC_Hope4Africa,” or “SatoshiMissionHelp” that use generic, faceless names with no personal history or evidence of involvement are often lures to suck up your generosity.
In an open world like Nostr, trust must be earned, not granted automatically. Before you zap or send sats: check the footprints. A real project doesn't hide. It wants to be seen, recognized, supported... and verified.

Prefer traceable and public donations
One of the great advantages of Bitcoin is that every transaction is recorded on the blockchain. Yet, many BTC charitable projects fail to leverage this transparency potential… sometimes out of ignorance, sometimes intentionally.
If you want to give securely, you should prioritize tools and methods that allow clear tracking of your money.
- Favors transparent platforms (Geyser, Zaprite, BTCPay, etc.)
These platforms allow:
- Track how much has been raised in real time
- Have a public address or QR code that everyone can see
- Sometimes even see who donated (if the donor makes it public)
And most importantly: the funds go directly into the creator's wallet, without an intermediary
Example: Geyser.fund shows how many sats have been raised, how many are left to reach, and sometimes even the expenses incurred.
- Avoid isolated static addresses
When someone just gives you a Bitcoin address without any context or tools around it, you can't know:
- If others have already donated
- What's the status of the fundraising?
- What will happen with the funds received?
Even worse, an address can be reused for multiple different campaigns. No tracking, no limits.
Reminder: A scammer can also show a QR code with an emotional caption, collect in bulk, and then erase all traces.
- Request a dedicated campaign address
A serious project can:
- Generate a unique address for each campaign or donor (via a wallet or BTCPay store)
- Or show you a link to a Bitcoin explorer to track inflows in real time
This allows you to verify that: - Your donation has been received - Funds are not being diverted for other purposes - And that other people are also contributing (proof of credibility)
- Check expenses if possible
More and more projects are publishing:
- Captures of receipts or transfers
- Monthly reports
- Distribution videos
This allows donors to see how funds are being used, even in rural areas or without stable internet.
If a project doesn't want you to track donations, ask yourself why. In the Bitcoin ecosystem, transparency is a weapon against abuse. Use it, and encourage others to do the same.

Want to help? Great. But in the Bitcoin ecosystem, giving indiscriminately is like throwing your sats into a bottomless pit. Here's a clear list of best practices to avoid scams and support good causes with confidence and intelligence.
- Never give under pressure
A real project:
- Don't rush.
- Don't create an artificial sense of urgency.
- Don't demand anything.
Golden rule: if you are pressured to skip "quickly" or "now or everything is ruined", it is suspicious.
- Use reputable platforms
Before sending sats:
Check if the project is on Geyser.fund, Zaprite, BTCPayServer, or Tallycoin.
These platforms provide transparency, monitoring and protection.
If the project refuses to appear there "without valid reason", ask yourself questions.
- Always check the source
Ask yourself these questions:
- Who is leading this campaign?
- How long has this person been active in the community?
- Does their history hold a consistent profile?
- Are they well-known on Nostr, X, Telegram, or elsewhere?
A reliable project has nothing to hide. It is findable, traceable, and responsive.
- Don't rely on images or videos alone
A photo of a crying child or a dish being offered proves nothing. What you want to know:
- Did they take this photo?
- What's the connection to the campaign?
- Do they show several stages (preparation, distribution, follow-up)?
Scammers love beautiful stolen images, but never show the actual work.
- Request a follow-up report or evidence
A serious project can easily provide you with:
- A link to a dedicated Bitcoin address
- A video or photo with a personalized message
- A receipt or proof of purchase
If they refuse or get offended by you for asking? Run away.
- Share only verified projects
You are also responsible for what you share. By sharing a project without verifying:
- You're putting your credibility on the line.
- You risk causing others to lose sats.
Do your own research, even if you trust the person who sent you the link.
- Start small
You can test a project with a small amount and observe:
-
How they communicate after receiving it
-
If they thank you
- If they keep you informed
It's a simple way to filter out the good guys from the opportunists.
In a free ecosystem like Bitcoin, there's no customer service, no refunds, no "cancel" button. Your only security is your vigilance. Give, but give wisely.

How to intelligently support genuine causes
Supporting charitable projects with Bitcoin doesn't have to be risky. On the contrary, it can be a powerful tool for spreading the values of Bitcoin while genuinely helping people.
But for your help to have a real impact, it's not enough to just switch off and disappear. You have to be intelligently involved.
Here's how to become a helpful, strategic, and caring donor.
- Be part of the project, not just the donation
The best donors are not those who give the most, but those who:
- ask questions,
- suggest ideas,
- share campaigns,
- encourage the founder,
- inform others.
In Bitcoin, we talk about community, not customers. Be an agent of change, not just a transaction number.
- Favors projects with a long-term vision
A serious project speaks to you:
- education,
- sustainability,
- independence,
- integration of Bitcoin into local life.
He doesn't just give away rice or clothes. He wants to make people more autonomous, freer, and more connected to the decentralized economy.
Support projects that build, not just those that distribute.
- Diversify your support
You can :
- Skip small projects regularly
- Support a campaign with a fixed monthly budget
- Offer your skills: design, writing, video, networking
Participate in a DAO or a coordinated donations collective
Bitcoin support isn't just about money. Your time and talent are also valuable.
- Educate while you help
When you participate in a project, take the opportunity to:
- Explain to others how Bitcoin works
- Demonstrate the benefits of transparency through blockchain
- Raising awareness in your circle of the freedom offered by direct support in BTC
Education is the ultimate weapon against addiction and scams.
- Create or join a reliable initiative
You can :
- Create your own small campaign with Geyser.fund or Zaprite
- Join a collective like Hope With Bitcoin or other communities on Nostr
- Offer to document an existing campaign
This is how sustainable projects are born: not with large anonymous donations, but with small, well-supported flames.
Donating Bitcoin is more than just a transfer. It's an affirmation of values. It's a statement:
“I choose to support causes without going through banks, without permission, without borders, with transparency and freedom.”
But for it to work, you need:
-
Stay vigilant
-
Demand clarity
- Foster human connections
- Build trust
Bitcoin is a tool of sovereignty. It deserves honest projects. It's up to us to protect them.
Together, let's discover Hope With Bitcoin: The project whose mission is to share smiles and hope with those in need, while raising awareness for Bitcoin adoption.
X: https://x.com/HopeWithBTC
Nostr / Primal: https://primal.net/p/npub10vsdn82fps4vwjaqxcpwj0nyync0cfrp2f5qlayrljh6d549gx5s0y9eap
Proof Of Work: https://drive.google.com/drive/u/1/folders/19LWZX4TtF6DJbDVCqhJ0EMMQqnjHVMvm
Geyser : https://geyser.fund/project/hopewithbitcoin
-
-
 @ 3f770d65:7a745b24
2025-05-08 18:09:35
@ 3f770d65:7a745b24
2025-05-08 18:09:35🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: Austin Kelsay, Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: McShane (Bitcoin Strategy @ Roxom TV)
-
👥 Speakers:
-
Martti Malmi – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
Lyn Alden – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by DJ Valerie B LOVE, TatumTurnUp, and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by Derek Ross, Tomer Strolight, Terry Yiu, OpenMike, and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 70c48e4b:00ce3ccb
2025-05-09 06:21:57
@ 70c48e4b:00ce3ccb
2025-05-09 06:21:57Dear reader,
HODLing was never the end goal.
HODLing Bitcoin is smart. It always has been. If you held through the Mt. Gox hacks, China bans, the 2017 Blocksize wars, the 2018 bloodbath, and the FTX clownery of 2022, then you already know. Bitcoin rewards conviction.
But let’s not forget why you got in.
It was never just about watching numbers go up. You felt something. Something deep. A quiet voice inside said, “This system is broken. I’m done playing by its rules.” - That is where it all began.
Back in 2008, while the banks were crashing the economy and handing you the bill, Bitcoin showed up as a silent answer. A lifeboat. A revolution wrapped in code.
The whitepaper starts with a simple, powerful idea: "A purely peer-to-peer version of electronic cash would allow online payments to be sent directly from one party to another without going through a financial institution."
https://plebsite.net/cdn/shop/files/Bitcoin_Whitepaper-Poster-3.jpg
And Bitcoin has lived up to that vision.
You saw it in El Salvador when they made it legal tender — even if they later made it optional. You saw it when WikiLeaks used Bitcoin after getting cut off by banks. You saw the Silk Road prove what peer-to-peer money really means. No matter what you think of those examples, one thing is clear: It worked. It was used. It still works.
Today, Bitcoin powers circular economies across the world — in Costa Rica, South Africa, Brazil, and beyond. People are using it because their local money fails them. Bitcoin became more than a store of value. It became a tool for survival and sovereignty.
https://imageio.forbes.com/specials-images/imageserve/67e422a1808f4902b8a1c6bc/Bitcoin-Ekasi-Center/960x0.jpg?format=jpg&width=1440
And now, look at you.
You believed early. You stacked. You held. And now, you have more Bitcoin than you ever imagined. Your needs are met. Your wants, too. You held through it all. And maybe now, you’ve found some stability, maybe even freedom. You stayed patient. You played the long game. You won.
So now the question is simple: What will your Bitcoin build?
Let me paint you a picture- Somewhere out there, there is a young soul maybe in Lagos, maybe in Buenos Aires, maybe right next door. This person might be working on a new privacy tool that protects free expression. Or developing a drone taxi system to change the way people move in growing cities. Or creating a decentralized alternative to platforms like Patreon, where no one is silenced for thinking differently.
They do not have powerful connections. They are not sitting in fancy offices or attending tech conferences. They are building quietly, with conviction and hope.
You can be the magical wand in their life. Your belief and support can turn someone's idea into something real. You can help create the next chapter of their story.
Angor allows you to do exactly that. It gives you a way to fund builders directly, using your Bitcoin. The process is safe and structured. You support projects in stages, and the funds only move forward when clear milestones are completed. Everything is on-chain, using Bitcoin scripts and time-locked contracts to ensure accountability.
This is how the ecosystem grows.
Where do you go now that HODLing was just the beginning?
Here’s what you do:
1. Check the Proposal
Go read the Angor docs. It’s not some bloated whitepaper. It’s clean, clear, and you’ll get it. Here’s the link - https://docs.angor.io/start/.
2. Join the Talk on Nostr
Nostr is where real, uncensored conversation is happening. It is decentralized and open by design. Use a client like Primal or Damus to dive in. Or check out nostr.band to explore what people are building and sharing across the network.
This is where ideas take shape. Builders post updates. Communities give feedback. The next wave of innovation is already in motion — and you can be part of it.
Follow Angor on Nostr: nostr:nprofile1qqs8p3ywfd92w7zvjgy7wrpylz8t30hy3z5dc5al4070l9y8qr8rejcksnh5c
3. Contribute
Whatever your skill is writing, design, coding, memes, Angor has room for you. Get on GitHub. Even if you just report a bug or suggest a feature, it helps. Or you could even fork the code and do as you wish.
4. Explore Angor Hub
This is the cockpit. It’s where you find new projects, track progress, talk to founders and make moves. Dive in. It’s live.
https://docs.angor.io/images/tools/hub.png
Final Thoughts
Bitcoin gave us the base layer. It proved that peer-to-peer money works. But that was just the beginning. Now it’s time to build the next layer together.
And no, this is not about another meme coin or a monkey NFT. This is about real infrastructure. Real value. Real use cases.
Angor is for the misfits, the dreamers, the people who read the whitepaper and said, “Yeah, this is the way.”
So if you have Bitcoin, do not treat it like a relic from a past battle. Use it to empower the next builder. Fund a project. Spark a new idea. Help decentralize the next thing.
You got into Bitcoin to protect your future maybe even to get rich but also to bring some change to the world.
HODLing was the first act.
Building is the second.
Angor is where we build.
Let’s make sure the next wave of Bitcoiners do not just see price charts. Let them see tools, apps, ideas, and communities that actually do something. Real things. Useful things. Built on the hardest money the world has ever known.
You in?
Thanks for reading, See y’all soon for another blog post. Ciao
Guest Post by nostr:npub1v67clmf4jrezn8hsz28434nc0y5fu65e5esws04djnl2kasxl5tskjmjjk
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ 57412389:2b288de5
2025-05-08 16:38:23
@ 57412389:2b288de5
2025-05-08 16:38:23Bitcoiners won big in the 2024 elections that saw Trump take the White House and Republicans control both the House and the Senate. Not because Trump and his Republican teammates are God's gift to the US or because they're all Bitcoiners, but because they're not the version of the Democrats we saw during the previous four years.
If you're reading this I'm sure you're well aware of the hostility the previous administration had towards Bitcoin. It was obvious at the time that individual actors like Elizabeth Warren and Gary Gensler were acting against Bitcoin, but after Trump's victory, plenty of Bitcoiners and people in the "crypto industry" felt comfortable enough to speak out about the specific lashings they took from Biden and crew. Chokepoint 2.0 went from a conspiracy theory toan accepted truththat the administration was working to slow Bitcoin anyway they could. It was a mind numbing stance that certainly opened the door for Trump to gain a non-negligbile amount of votes pretty easily. He got on stage at Bitcoin 2024 and treated it like any other rally, ranting on and on about how great he was and how bad the Democrats were with a few crypto lines sprinkled in. He, almost teasingly, said "Have fun playing with your Bitcoin.", walked off stage, and that was it. That's all it took for him to secure the vote of anyone with a hair of their networth tied up in "crypto".
I'm not suggesting Trump is a nothing for Bitcoin, he's pushed the Strategic Bitcoin Reserve forward and certainly given air cover to other Republicans in power at the state level to push positive Bitcoin legislation, but the big win for Bitcoiners is that he isn't the other guys.
On top of the SBR at the federal level, New Hampshire and Arizona have passed state level SBRs at the time of this writing with many others having bills trying to make their way through the system. There are alsoplenty of other billsat the state level that have already passed or are on their way to passing that defend things like the right to self custody and other protections for Bitcoiners.
These bills are all great news and I don't want to act like the elite purity test Bitcoiners and pretend the largest government in the world being Bitcoin friendly isn't a big deal - it is. But, at the end of the day with the way politics seems to work as of late, everything can be changed with the swipe of a pen by the next guy in power. These should be treated as four year promises at best.
Political power works like a seesaw. Right now the Republicans have the juice, but come next election cycle that's likely to change. The issue is the system is burning and there's nothing that politicians can realistically do to put out the flames. All the real solutions, like eliminating government programs such a social security and medicare/medicaid, are political suicide and anyone running on that platform wouldn't sniff a seat in office. So every four years Americans look back on the previous four and go "Man, that guy really sucked. Things are worse than they were before. The other guys can save us!" Of course, the other guys suck too, but the current guys sucking is just fresher in the minds of the public. There is nothing any politician can do to put out this fire because all they can afford to wield is a garden hose or they won't get votes. So, we all just watch this fire grow larger and larger and pick a different guy with a different garden hose every four years because the last guy didn't work and the only move we've got is to pick the other guy.
So, if all these executive orders, working groups, bills, and laws can just be evaporated by the other team next time around why was the Trump win so big for Bitcoin? The answer is that it buys Bitcoin time to soak into every crevice of the financial system. If the next political team in power decides they hate Bitcoin and want to reverse every positive thing done by Trump's team it's going to be a lot harder for them to do that when a serious portion of the financial system has an incentive to fight for and vote in favor of Bitcoin.
Just a handful of examples of how Bitcoin is soaking into the financial system:
iBIT is currently Blackrock's 11th largest ETF by AUM. FBTC is Fidelity's largest ETF by AUM. Wisconsin and Michigan state pensions both hold Bitcoin ETFs. CalPERS holds shares of MSTR.
There's a point where so many different entities that affect so many different individuals hold Bitcoin, or investments centered around Bitcoin, that a politician attacking Bitcoin from a regulatory perspective just isn't realistic in the same way regulation against Gold isn't feasible. These regulatory attacks on an asset with deep roots in the financial system would be poltical suicide just like threatening to delete Social Security. No longer is attacking Bitcoin a move against a few hundred thousand internet dorks, it's an attack on anyone with a pension, anyone who owns the stock of a company holding bitcoin, any private business holding bitcoin, plus a few hundred thousand internet dorks.
While the Bitcoin bills catch all the headlines, the real signal is watching bitcoin soak into private holdings of people in power, pension funds, public company treasuries, etc. We've got four years to for Bitcoin to become so ingrained that no politician could attack it.
-
 @ 60392a22:1cae32da
2025-05-09 06:10:57
@ 60392a22:1cae32da
2025-05-09 06:10:57why emoji is come from japan?
The word "emoji" comes from Japan because emojis were first created and popularized there. The term "emoji" (絵文字) is made up of two Japanese words: "e" (絵), meaning "picture," and "moji" (文字), meaning "character."
The first set of emojis was developed in 1999 by Shigetaka Kurita, a designer working for NTT DoCoMo, a major Japanese mobile phone company. Kurita designed a set of 176 12×12 pixel images for a messaging service called i-mode, which was a precursor to what we now recognize as text messaging. The aim was to help people convey emotions, actions, or objects more easily in their digital communication, especially since sending lengthy texts wasn’t as practical on early mobile phones.
The simplicity and ease of emojis made them incredibly popular, and over time, they spread beyond Japan to the rest of the world. Today, emojis are used globally in texting, social media, and digital communication.
So, while emojis were created in Japan, they’ve become a universal part of modern communication!
I did not know it. I want to share it. so now I tweet.
-
 @ 866e0139:6a9334e5
2025-05-09 05:45:01
@ 866e0139:6a9334e5
2025-05-09 05:45:01Autor: Peter Schmuck. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
\ Heute, am 9. Mai 2025 – genau 80 Jahre nach dem Ende des Zweiten Weltkriegs, der 60 Millionen Menschen das Leben kostete, darunter 27 Millionen Sowjetbürgern, erheben wir, die Bürgerinnen und Bürger Europas, unsere Stimmen! Wir schämen uns für unsere Regierungen und die EU, die die Lehren des 20. Jahrhunderts nicht gelernt haben. Die EU, einst als Friedensprojekt gedacht, wurde pervertiert und hat damit den Wesenskern Europas verraten! Wir, die Bürger Europas, nehmen darum heute, am 9. Mai, unsere Geschicke und unsere Geschichte selbst in die Hand. Wir erklären die EU für gescheitert. Wir beginnen mit Bürger-Diplomatie und verweigern uns dem geplanten Krieg gegen Russland! Wir erkennen die Mitverantwortung des „Westens“, der europäischen Regierungen und der EU an diesem Konflikt an.
Wir, die Bürger Europas, treten mit dem European Peace Project der schamlosen Heuchlerei und den Lügen entgegen, die heute – am Europatag – auf offiziellen Festakten und in öffentlichen Sendern verbreitet werden.
Wir strecken den Bürgerinnen und Bürgern der Ukraine und Russlands die Hand aus. Ihr gehört zur europäischen Familie, und wir sind überzeugt, dass wir gemeinsam ein friedliches Zusammenleben auf unserem Kontinent organisieren können.
Wir haben die Bilder der Soldatenfriedhöfe vor Augen – von Wolgograd über Riga bis Lothringen. Wir sehen die frischen Gräber, die dieser sinnlose Krieg in der Ukraine und in Russland hinterlassen hat. Während die meisten EU-Regierungen und Verantwortlichen für den Krieg hetzen und verdrängen, was Krieg für die Bevölkerung bedeutet, haben wir die Lektion des letzten Jahrhunderts gelernt: Europa heißt „Nie wieder Krieg!“
Wir erinnern uns an die europäischen Aufbauleistungen des letzten Jahrhunderts und an die Versprechen von 1989 nach der friedlichen Revolution. Wir fordern ein europäisch-russisches Jugendwerk nach dem Vorbild des deutsch-französischen Jugendwerks von 1963, das die „Erbfeindschaft“ zwischen Deutschland und Frankreich beendet hat. Wir fordern ein Ende der Sanktionen und den Wiederaufbau der Nord Stream II-Pipeline. Wir weigern uns, unsere Steuergelder für Rüstung und Militarisierung zu verschwenden, auf Kosten von Sozialstandards und Infrastruktur. Im Rahmen einer OSZE-Friedenskonferenz fordern wir die Schaffung einer europäischen Sicherheitsarchitektur mit und nicht gegen Russland, wie in der Charta von Paris von 1990 festgelegt. Wir fordern ein neutrales, von den USA emanzipiertes Europa, das eine vermittelnde Rolle in einer multipolaren Welt einnimmt. Unser Europa ist post-kolonial und post-imperial.
Wir, die Bürger Europas, erklären diesen Krieg hiermit für beendet! Wir machen bei den Kriegsspielen nicht mit. Wir machen aus unseren Männern und Söhnen keine Soldaten, aus unseren Töchtern keine Schwestern im Lazarett und aus unseren Ländern keine Schlachtfelder.
Wir bieten an, sofort eine Abordnung europäischer Bürgerinnen und Bürger nach Kiew und Moskau zu entsenden, um den Dialog zu beginnen. Wir werden nicht länger zusehen, wie unsere Zukunft und die unserer Kinder auf dem Altar der Machtpolitik geopfert wird.
Es lebe Europa, es lebe der Friede, es lebe die Freiheit!
Auf der Webseite der Initiative oder in einem Gespräch mit Ulrike Guérot können Sie, liebe Leser, weitere Möglichkeiten erfahren, diese Friedensinitiative zu stärken!
https://www.youtube.com/watch?v=zECOTfeweUE&list=PLS_jddBXjdqcBKneCQcPN8NOTSqlmNqpy
Danke an die IntiatorInnen und die bislang 15.000 Menschen, die das mitgestalten werden.
Peter Schmuck ist Professor für Psychologie und Initiator zahlreicher nachhaltiger Projekte.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 000002de:c05780a7
2025-05-08 16:14:37
@ 000002de:c05780a7
2025-05-08 16:14:37Just an observation that makes me chuckle.
originally posted at https://stacker.news/items/974829
-
 @ 60392a22:1cae32da
2025-05-09 02:37:23
@ 60392a22:1cae32da
2025-05-09 02:37:23When I am asked "where password and ID?" by my friends, I will say it. ↓(generated by chatgpt)
1. Nostr is decentralized
- No central authority: Unlike platforms like Facebook or Twitter, Nostr doesn’t rely on a single company or server. This means nobody can block your account or censor your posts. You control your own data and connections.
- Distributed network: Instead of all your data being stored in one place (which can be hacked), it’s spread across multiple independent servers.
2. No passwords or centralized logins
- No passwords to steal: Instead of using a traditional username and password, Nostr uses a private key system. This means your login is much more secure, and there’s no need for you to remember passwords or risk them getting hacked.
- Easy login with Passkeys or security keys: On Nostr, you don’t need a password—you can use secure login methods like Passkeys (via your phone, for example), which is faster and much more secure than a traditional password.
3. You control your identity
- No account lockouts: Since your identity is stored on your own device and not on a company’s server, you can’t be locked out of your account unless you lose your private key. You can always recover access if you have your private key.
- Pseudonymous: You don’t need to reveal your real name. You can choose an identity that doesn’t tie to your personal info.
4. Privacy & Security
- Your data is yours: On traditional platforms, companies own your data and can sell it. With Nostr, you keep control over your information—no company has access to your messages, posts, or activity.
- End-to-end encryption: Nostr supports strong privacy where your messages are encrypted, meaning no one can spy on your conversations.
5. Open-source and community-driven
- No profit motive: Since Nostr is open-source, there’s no central company profiting from your data. It’s built by a community that values freedom of speech and privacy.
- Transparency: Anyone can see the code, contribute to its improvement, and make the network better. It's not controlled by one company or government.
Simple Example:
You could say something like this: "Think of Nostr like having your own personal email system, where only you control your account. There’s no one to block you or take down your content. You don’t need a password to log in—just a secure key on your phone. Your posts are private, and you can be anonymous if you want. No one owns your data. It’s freedom, security, and privacy."
What You Can Say if They Ask, “But there are IDs and keys, right?”
- Yes, but the IDs are not like usernames: In Nostr, your identity is linked to your private key, not a password. This key is yours and you control it. There's no centralized database of usernames or passwords that someone could steal.
- It's safer: It’s like having a secure personal locker that only you can open with your phone’s biometrics or security key, rather than trying to remember a password or relying on a service to keep it safe for you.
-
 @ f1989a96:bcaaf2c1
2025-05-08 15:05:45
@ f1989a96:bcaaf2c1
2025-05-08 15:05:45Good morning, readers!
This week, we bring reports from Bangladesh, where the interim government instructed the central bank to halt the printing of old banknotes featuring Sheikh Mujibur Rahman, the founding president of Bangladesh. This has induced a currency shortage, as new notes have yet to be issued to replace the discontinued ones. As a result, Bangladeshis find themselves holding worthless currency, facing increased costs, and feeling frustrated over such poor currency management. Meanwhile, in Indonesia, citizens are fleeing to gold as the local rupiah currency crashes to record lows amid increasing financial controls from the government.
In open-source news, LNbits, a Bitcoin and Lightning wallet management software, emerged from beta with its v1.0.0 release. LNbits works like a control panel on top of a Bitcoin wallet, letting users divide funds into separate accounts and use different features and functionalities. It is a handy tool for educators, civil society organizations, and communities who want to use Bitcoin for real-world transactions without needing advanced technical skills. We also spotlight a new tool called following .space that allows users to curate and share premade follow packs for nostr. The result is a more straightforward onboarding process for new users interested in censorship-resistant social media and the ability to curate feeds to better suit their interests.
We end with an interview with HRF Chief Strategy Officer Alex Gladstein, who explores his thinking behind the relationship between Bitcoin and human rights as we enter an age of increased corporate and nation-state adoption. He highlights the paradox where Bitcoin, a tool for individual financial freedom, is being adopted by institutions around the world, many of which regularly seek greater control over financial activity. We also include a new report from Bitcoin developer and past HRF grantee, b10c, who documents the current state of Bitcoin mining centralization and the threat it poses to decentralization and censorship resistance.
Now, let’s jump right in!
SUBCRIBE HERE
GLOBAL NEWS
Bangladesh | Currency Shortage as Central Bank Halts Printing of Banknotes
A state-induced cash crunch is paralyzing Bangladesh after the interim government, led by Muhammad Yunus, ordered the central bank to discontinue old banknotes featuring Sheikh Mujibur Rahman, the founding president of Bangladesh. New cash is expected to be printed in phases beginning in May. But Bangladeshis report they are currently stuck with old and unusable currency, as the national mint has yet to issue replacement currency and lacks the capacity to print more than three notes at a time. Meanwhile, public ATMs continue to dispense old and worn-out banknotes, with merchants reluctantly accepting them and banks refusing to exchange them. Through all this, the central bank of Bangladesh sits on nearly 15,000 crore taka ($1.28 billion) worth of old notes in vaults, but the interim government has refused to release them, deepening public frustration.
Nigeria | Regulates Bitcoin as a Security
Nigerian lawmakers are moving to regulate digital assets as securities by passing the Investment and Securities Act (ISA) 2025. Rather than embrace it as a tool for financial freedom, the law places Bitcoin under the purview of the Nigerian Securities and Exchange Commission (SEC). Companies must now register with the Nigerian SEC, implement more strict data-collection processes (to harvest personal information), and navigate a legal framework not designed for a borderless and permissionless technology like Bitcoin. The law further grants the SEC access to data from telecom and Internet providers to investigate “illegal market activity” — a provision that could easily be abused to surveil or intimidate Bitcoin users and developers. Nigeria routinely uses regulations to stifle the presence of open-source money, raising compliance hurdles, imposing taxes, and punishing digital asset companies. It’s not unreasonable to suspect this new classification could provide the state with a means to suppress the free adoption and innovation of Bitcoin.
Indonesia | Gold Rush Amid Economic Uncertainty
As the rupiah currency falls to record lows, Indonesians are flocking to gold in a rush to protect their savings. But gold isn’t the only safe haven. With 74% of Indonesia’s population unbanked or underbanked, digital tools like Bitcoin offer a more accessible alternative, especially when nearly 70% of Indonesians have Internet access. The Indonesian government is also tightening capital controls. A new policy forces exporters to keep all foreign currency earnings inside the country for a full year to trap dollars in the financial system. HRF grantee Bitcoin Indonesia is responding by helping people in the region (especially in nearby states like Burma) build financial resilience through meetups, workshops, and training focused on Bitcoin custody, privacy, and adoption. In an area where financial services remain out of reach for millions, learning how to save and transact permissionlessly is paramount.
Kenya | Introduces Legal Framework for Virtual Asset Service Providers (VASPs)
Kenya’s government introduced a comprehensive legal framework to regulate Virtual Asset Service Providers (VASPs) through its newly proposed 2025 VASP Bill. The legislation outlines strict licensing requirements for digital asset exchanges, wallet providers, brokers, and other digital asset firms. It functionally bars individuals from operating independently (think: open-source freedom tech builders) by mandating local incorporation, compliance with cybersecurity standards, and approval from financial regulators. This appears to be an attempt to formalize and better control the rapidly growing digital asset space. It could stifle grassroots innovation and limit access to financial tools that have become vital for activists and citizens seeking privacy and autonomy as economic policies and high inflation drive unrest.
El Salvador | Attorney General’s Office Preparing Arrest Warrants for Independent Journalists
El Faro, one of El Salvador’s most prominent investigative news outlets, shared reliable information that the Salvadoran Attorney General’s Office is preparing arrest warrants against three of its journalists. The warning came from El Faro director Carlos Dada, who suggests that the charges may include “apology for crimes” and “illicit association.” The alleged charges allegedly stem from El Faro’s latest reporting: a three-part video interview with former leaders of the 18th Street Revolucionarios gang that sheds light on Bukele’s “years-long relationship” with Salvadoran gangs. El Faro editor-in-chief Óscar Martínez said that any arrests or home raids following this news would be “for having done journalism.” With El Salvador’s shrinking civic space, this potential action against independent media would further restrict Salvadorans’ ability to access independent information and hold officials accountable.
BITCOIN AND FREEDOM TECH NEWS
LNbits | Emerges from Beta with v1.0.0 Release
LNbits, an open-source software tool that lets people create and manage Bitcoin Lightning wallets securely for themselves and for others, officially launched version 1.0.0, marking its transition out of beta and into a more stable release for public use. It works like a control panel sitting on top of a Bitcoin wallet, letting users divide funds into separate accounts and use different features and functionalities. LNbits is especially useful for educators, small businesses, and community organizers who want to use and manage Bitcoin for payments and savings. HRF is pleased to see this Bitcoin Development Fund (BDF) grantee strengthen the tools available to activists to achieve financial freedom in the face of censorship, surveillance, or inflation.
SeedSigner | Self-Custody Tool for Chinese Bitcoiners Facing Local Corruption
Chinese Bitcoin users are turning to SeedSigner, an open-source and fully customizable Bitcoin hardware wallet, as a more private way to protect their savings from law enforcement corruption. While many assume the primary threat to Bitcoin in China comes from top-down management and enforcement from the Chinese Communist Party (CCP), new reports suggest greater concern over the police, who regularly monitor mail, detect hardware wallet purchases, and fabricate charges to extort Chinese users’ Bitcoin. SeedSigner solves this by allowing users to assemble a secure signing device from generic, inexpensive parts, avoiding the risk of shipping a branded wallet that might flag them as a target. When privacy violations begin at the local level, SeedSigner can help citizens safeguard their financial freedom by making secure self-custody discreet, accessible, and affordable.
Following .space | Create and Share Follow Packs on Nostr
Following.space is a new tool for nostr that solves one of the protocol’s biggest pain points: finding people worth following in the absence of an algorithm. Created by developer and HRF grantee Calle, the tool lets anyone build and share curated “follow packs” — pre-made lists of nostr users that can be easily distributed across the web. The lists are customizable and can be made based on shared interests, communities, organizations, regions, and more. This makes onboarding new users easier and allows users to curate their feeds to suit their interests. The result is a simple but powerful tool that helps nostr scale more organically by encouraging natural discovery. Enabling free expression and connections without reliance on centralized platforms strengthens human rights and financial freedom in repressive environments. Try it here.
256 Foundation | Releases Ember One Source Code
The 256 Foundation, an open-source Bitcoin mining initiative, released the source code of its new Ember One Bitcoin mining hashboard to the public. A Bitcoin hashboard is a device with multiple chips for performing Bitcoin mining computations. The open-source Ember One only consumes 100 Watts of total power and is modular by design, allowing user customization and the ability to mine discreetly even under autocratic regimes. This is important because it gives individuals a way to access and earn Bitcoin without drawing the attention of officials. For dissidents, mining at home means gaining more control over how they earn, spend, and store their money, all without relying on centralized systems at the whims of dictators.
Btrust and Africa Free Routing | Announce Partnership to Advance African Bitcoin Development
Btrust, a nonprofit advancing Bitcoin development in Africa, awarded a grant to Africa Free Routing, a program within African Bitcoiners, to support five Bitcoin Lightning-focused developer boot camps across the continent in 2025. These bootcamps aim to onboard non-Bitcoin developers into the Bitcoin ecosystem, offering hands-on training, mentorship, and opportunities to contribute to open-source projects. This work strengthens the foundations of freedom tech in Africa, providing tools that allow people to resist financial repression under tyranny. Learn more about the partnership here.
Presidio Bitcoin | Hosting First Hackathon
Presidio Bitcoin, the Bay Area’s first dedicated freedom tech co-working and events space, just announced its first-ever hackathon, which will take place from May 16-17, 2025. This 24-hour hackathon in San Francisco brings together developers and technologists to build and collaborate at the frontier of Bitcoin, AI, and open-source technology. In addition to the hackathon, Presidio is launching a new program offering free three-month access to its workspace for Bitcoin open-source contributors. This is a valuable opportunity to connect with fellow developers, startup founders, and freedom tech advocates in the area. HRF is proud to sponsor this hackathon and is looking forward to how the outcomes might help create better freedom tools for dissidents worldwide. Learn more about the event here.
RECOMMENDED CONTENT
Bitcoin Nation State Adoption Paradox - Interview with Alex Gladstein
In a recent episode of the Bitcoin Fundamentals podcast, hosted by Preston Pysh, Alex Gladstein, HRF’s chief strategy officer, discusses the complexities of Bitcoin’s new era of adoption. He highlights the paradox where Bitcoin, a tool for individual financial freedom, is being adopted by governments, which some believe to be potentially compromising to its core principles. He emphasizes that while governments may adopt it for strategic or economic reasons, in doing so, they expose their populations to a technology that will ultimately weaken state control over money and advance individual liberty and human rights. Watch the full interview here.
Bitcoin Mining Centralization by b10c
In this report, Bitcoin developer and past HRF grantee b10c documents the growing trend of centralization in Bitcoin mining pools. It shows that over 95% of blocks are now mined by just six Bitcoin mining pools, with Foundry and AntPool controlling roughly 60–70% of the hashrate (the computing power dedicated to the Bitcoin network). This marks a rise in mining pool centralization in recent years. While this hasn’t harmed Bitcoin’s censorship resistance yet, it reduces the number of block template producers. This concentration of template producers poses a potential risk to Bitcoin’s neutrality, which is essential for ensuring access to uncensorable money and protecting human rights in autocratic regimes. HRF has happily supported both Hashpool and Public Pool with recent grants to support smaller, independent pools that help preserve Bitcoin's decentralization. Read the full report here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ a8d1560d:3fec7a08
2025-05-09 01:08:02
@ a8d1560d:3fec7a08
2025-05-09 01:08:02h1 🙂
h2 😈
h3 😴
h4 💩
h5 👾
h6 😺
codeblock 😮💨🤖😨😎😉🛹🧗🏻♀🥉🤸🏻♂️Further tests
😊🤩🥵🤪😥😈👽👈🏻👆🏻☝🏻👌🏻💋👧🏻👩🏻🦰👷🏻♀️🕵🏻♀️👩🏻⚕️👨🏻🚀🧛🏻♂🧝🏻♀🕴🏻👩👩👦🎩🧦
🐶🐧🐜🙈🦆🦐🐂🐇🐕🦺🐆🌱🌕🌗🌑🌓🌍🌎🌏⛈🌈 🫐🥨🥝🫛🍳🍧🥙🍺🍹🍷
🍏🍎🥥🥝🍯🍆🥜🥛🍺🧊🥢🧂
⚽🏑🤸🏻♀️⛳🚴🏻♀️🥇🥈🥉🎯🎮
🚗🚖🛟🚇🛶🚥🚧🏣🎇🌆🌄🌠🌁
⌚📀📺📸📡💎🪙💵💴💶💷(but no Bitcoin)🪙🛢⚱🩻🕳🛋🛍📁📂🗂📝🔓🔒🔏🔐
❤🧡💛💚🩵💙💜☮✝🕉☯🕎✡🆚☢㊙❌🔰〽🔞❎🌐🛃💤➡〰🔉🕚
🏳🏴🏴☠️🏁🚩🏳️🌈🇺🇸🇪🇺🇩🇪🇺🇦🇻🇦🇸🇻 -
 @ 502ab02a:a2860397
2025-05-09 01:07:20
@ 502ab02a:a2860397
2025-05-09 01:07:20ถ้าย้อนกลับไป 50 ปีก่อน ถ้าเฮียถามคำนี้กับลุงชาวนาคนหนึ่ง เขาคงหัวเราะแล้วตอบแบบไม่ต้องคิดว่า “ก็เจ้าของที่นาไงไอ้ทิด จะมีใครล่ะ?”
แต่พอมาในวันนี้ ถ้าเฮียถามคำเดิมในซูเปอร์มาร์เก็ต คงไม่มีใครกล้าตอบแบบนั้นอีกแล้ว เพราะแค่ในชั้นวางโยเกิร์ตเดียวกัน เฮียอาจเห็นยี่ห้อต่างกัน 10 ยี่ห้อ แต่ทั้งหมดอาจเป็นของบริษัทแม่เพียงเจ้าเดียว
ในศตวรรษที่ 21 อาหารไม่ใช่ของคนทำอาหาร แต่มันกลายเป็นของ บริษัทผู้ครอบครองข้อมูล พันธุกรรม และระบบการกระจายสินค้า โลกวันนี้ไม่ได้มีเกษตรกรล้อมวงเคี้ยวหมาก แต่มีบริษัทเทคโนโลยีจับมือกับนักลงทุนระดับโลก ถือครองเมล็ดพันธุ์ เป็นเจ้าของสิทธิบัตรจุลินทรีย์ในลำไส้ และมีอำนาจเสนอว่า “อาหารแบบไหนควรได้รับเงินสนับสนุนจากรัฐ”
บริษัทเทคโนโลยีในซิลิคอนแวลลีย์บางแห่ง ไม่ได้แค่ผลิตซอฟต์แวร์อีกต่อไป แต่เริ่มทำ "อาหารจากโค้ด" โปรตีนสังเคราะห์ที่ได้จากการแทรกยีน หรือแม้แต่ “อาหารจากคาร์บอนในอากาศ” ที่สร้างโดย AI เขาไม่ได้ปลูกข้าว แต่เขาเขียนสูตรให้เครื่องจักรสร้างอาหารในถัง
ใครมีสิทธิบัตร…คนนั้นคือเจ้าของ ใครควบคุมข้อมูลสุขภาพ…คนนั้นคือนายทุนแห่งความหิว และใครสามารถชี้นิ้วให้รัฐบาลเปลี่ยนนโยบายอาหารโรงเรียน…คนนั้นคือเจ้าของอนาคตของเด็กทั้งประเทศ
มันฟังดูเวอร์ใช่ไหม? แต่ลองดูดี ๆ…ใครเป็นเจ้าของฟาร์มหมู ฟาร์มไก่ โรงฆ่าสัตว์? หลายแห่งไม่ได้เป็นของชาวบ้านอีกต่อไป แต่เป็นของเครือบริษัทยักษ์ใหญ่ที่อยู่เบื้องหลังทั้งอาหารในซูเปอร์ และเม็ดวิตามินในกระปุกเฮียด้วย
ยิ่งไปกว่านั้น เจ้าของตัวจริงไม่ได้อยู่ในร้านของชำ แต่ซ่อนตัวอยู่ในบอร์ดบริหารบริษัทเกษตรข้ามชาติ ในเวทีประชุมเศรษฐกิจโลก และในห้องประชุมที่ตัดสินว่า “อาหารจากวัว” ควรถูกเก็บภาษีคาร์บอนเพิ่มหรือไม่
เมื่อก่อนเฮียเคยคิดว่า ถ้าเราปลูกผักเอง ก็คุมอาหารตัวเองได้ แต่พอระบบเริ่มขับไล่เมล็ดพันธุ์ดั้งเดิมให้สูญพันธุ์ ถ้าไม่มีใบอนุญาตปลูกพืช GMO หรือไม่มีเงินซื้อปุ๋ยจากบริษัทเดียวที่ยังอยู่รอด เกษตรกรจะเป็นเจ้าของอะไรกันแน่?
และคำว่า “อาหารอิสระ” ในยุคนี้ อาจไม่ใช่แค่การไม่พึ่งพาซูเปอร์ แต่มันคือ “การตื่นรู้ว่าใครเป็นคนจัดเกม และใครเป็นคนตั้งกฎ”
เพราะในยุคที่ทุกอย่างแปรรูปเป็นดิจิทัล แม้แต่อาหารก็อาจมีเจ้าของเพียงไม่กี่ราย และสิ่งที่น่ากลัวกว่าผูกขาด…คือการ “ผูกอนาคต” ของเราทั้งมื้อ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 000002de:c05780a7
2025-05-08 14:55:34
@ 000002de:c05780a7
2025-05-08 14:55:34There are so many projects in the bitcoin space that deserve praise but I just wanna shout out Cashu.me. Its a browser based cashu (eCash / Lighting) wallet. It can be very handy when you need a wallet but don't wanna download yet another app. I hadn't used it in a very long time and decided to try it out again the other day. Its really well done.
As with other Cashu wallets you need to select a mint and backup your key phrase but it is very simple the get started.
If you wanna learn more about Cashu check out Cashu.space
Two other good wallets that support Cashu.
originally posted at https://stacker.news/items/974759
-
 @ 5cb68b7a:b7cb67d5
2025-05-09 00:31:22
@ 5cb68b7a:b7cb67d5
2025-05-09 00:31:22In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back! 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞 For quick queries or support, connect with us on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust\ At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process\ Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate\ With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure\ Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools\ We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!\ Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back!\ 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪
-
 @ a296b972:e5a7a2e8
2025-05-08 13:13:51
@ a296b972:e5a7a2e8
2025-05-08 13:13:51Sachzwangfreie, gesichert systemkritische Investigativ-Journalisten der unabhängigen, für Ausgewogenheit bekannten Mainstream-Medien, haben in jahrelanger Recherche den Rechtsruck Deutschlands beobachtet und nun in einem rund 5000 Seiten starken Gutachten dem Bundesamt für Verfassungsschutz zugespielt. Möglicherweise ist Erfahrung in der Veröffentlichung der Tagebücher eines verkannten Künstlers hierbei sehr hilfreich gewesen.
Nach sorgfältiger Überprüfung des Inland-Geheimdienstes konnte festgestellt werden, dass dem 3. Reich zugeschriebenes Gedankengut fortbesteht und dadurch die Unseredemokratie nachhaltig vergiftet ist. Bei der Beurteilung waren die Erkenntnisse der Gauck-Behörde von unschätzbarem Wert.
Ein Magazin, einst bekannt dafür, der Politik scharf auf die Finger zu schauen, und das auch die vorgenannten Tagebücher veröffentlicht hat (das war vor der Zeit, als ein ausgewachsener amerikanischer Voll-Philanthrop mit seiner Großzügigkeit die laufenden Strom- und Heizkosten des Verlagsgebäudes bezahlt hat), scheint hier seine Schreib-Fachkräfte zur Verfügung gestellt zu haben. Das könnte erklären, warum einige Details der nicht zu hinterfragenden Schrift an die Öffentlichkeit gelangt sind.
Schon im Grundgesetz kommt der durch das NS-Regime verbrannte Begriff „Volk“ zwölf Mal vor. So lebt die Ideologie, dass es ein deutsches Volk gibt, auch im Grundgesetz weiter. Vermutlich wurde durch Bestechung und Intrigen der Artikel 116 Absatz 1 hineingeschmuggelt, der besagt, wer Deutscher im Sinne des Grundgesetzes ist. Das fordert zwangsläufig eine dringend notwendige Prüfung, ob nicht das Grundgesetz selbst verfassungswidrig ist.
Mit Gründung der Bundesrepublik Deutschland wurde auch weiterhin im Straßenverkehr am Rechtsverkehr festgehalten, obwohl die Autoindustrie mit Beibehaltung des Lenkrades auf der linken Seite ein klares Zeichen gegen rechts gesetzt hat.
Der Ausbau des deutschen Autobahnnetzes wurde im 3. Reich stark vorangetrieben. Er diente vor allem dazu, eine schnelle Truppenbewegung zu ermöglichen. Schließlich sollte nach Goebbels, vor allem bekannt durch seine Rede im Sportpalast in Berlin, bestmögliche Kriegstüchtigkeit hergestellt werden. Die Waffenproduktion der Hermann-Göring-Werke, heute Rheinmetall, ließen die Hochöfen bereits dauerglühen.
Nach dem 2. Weltenbrand wurde der Ausbau des deutschen Autobahnnetzes weiter vorangetrieben. Statt sie zu entschärfen, wurden extreme Rechtskurven durch Leitplanken gesichert. Weniger scharfe Rechtskurven wurden in einer Liste als Verdachtsfall erfasst und werden seitdem intensiv beobachtet, die Unfallhäufigkeit wird ständig gemessen.
Ein weiteres Indiz für rechtes Gedankengut ist die Tatsache, dass eine bekannte Autofirma ihre Produkte auch in der Bundesrepublik nicht in Bürgerwagen umbenannt hat. So wurde in der Wirtschaftswunderzeit mit einem verfassungswidrigen Kraftfahrzeug mit 37 PS wild in der Gegend herumgefahren und durch Auslandsreisen, gerne an den Gardasee, der Begriff Volk in die ganze Welt getragen. Den Höhepunkt des Gipfels erreichte die Verfassungswidrigkeit jedoch dadurch, dass ein Werk in Brasilien den Bürgerwagen produzierte und so den gesamten amerikanischen Kontinent mit hässlichem Gedankengut verseuchte.
Deutsche Unternehmen, die aus Überzeugung Schrauben und Muttern mit Rechtsgewinde herstellen, können nur überzeugte Rechtsextremisten sein. Alles, was rechts ist oder rechts herum geht, muss zum Schutze von Unseredemokratie verfolgt und verboten werden. Auch die Buchhaltung der Unternehmen gehört reformiert, denn schließlich gibt es mit Soll und Haben eine linke und, staatsgefährdend, auch eine rechte Seite, auf der die Einnahmen und Ausgaben erfasst werden.
In großen Städten wurden nach der bedingungslosen Kapitulation der Wehrmacht Straßen und Plätze, die nach den „Größen“ des 3. Reichs benannt wurden, wieder umbenannt. Es wurde dabei versäumt, Parks in größeren Städten, die sich Volksgarten nennen, in Bürgergarten umzubenennen.
Auch wurde versäumt, ideologisch vergiftete Tischsitten zu reformieren. So liegt das Messer neben dem Teller weiterhin rechts. Die Absicht liegt sozusagen auf der Hand, denn das ist eine eindeutige Aufforderung zu Messergewalt, zumal die meisten Menschen Rechtshänder sind.
An der Schreibweise von links nach rechts wurde weiter festgehalten. Ein weiteres Anzeichen dafür, wie das Volk durch alltägliche Verrichtungen zu einer rechten Gesinnung durch dunkle Kräfte hingeleitet werden soll. Die Schreibweise „kursiv“ wurde nicht verboten, obwohl sie extrem rechts ist.
Offensichtlich wird auch die Indoktrination des Volkes, wenn vom für die Linken diskriminierenden Rechtsstaat die Rede ist. Menschen, die ein gesundes Rechtsverständnis haben, sind ideologisch vergiftet.
Die Auflösung von Familienstrukturen, einst die kleinste tragende Zelle der Gesellschaft, muss dringend umgesetzt werden, da verschworene Gruppen, die im Ernstfall wie Pech und Schwefel zusammenhalten, den Staat delegitimieren. Sie könnten zum Beispiel einen Familienausflug planen, von dem der Staat nichts weiß.
Ein Ehepaar, das nicht mehr zeitgemäß in einem Doppelbett schläft, ist höchstverdächtig. Der Ehepartner, der in einem Ehebett auf der rechten Seite sehr nah an der Bettkante schläft, schläft rechtsextrem. Wenn er ein Gitter am Bett hat, damit er nicht aus dem Bett fällt, schläft er sogar extrem gesichert rechts.
Der Verfassungsschutz muss dringend prüfen, ob nicht das gesamte deutsche Volk verboten werden sollte, denn es ist eindeutig so, dass das Volk völkisch ist und das darf in einer Unseredemokratie keinen Platz haben.
Mit Übergabe des Gutachtens an den Verfassungsschutz sieht dieser es als Geheimsache an, sodass er es aus Gründen des Staatswohls nicht denjenigen gegenüber zugänglich gemacht werden kann, die es betrifft, nämlich das völkische Volk.
Jenes Volk, das dank einer übermenschlichen Autoren-Anstrengung im wirtschaftlichen Bereich immer mehr den nicht mehr vorhandenen Pfennig und die nicht mehr vorhandene Mark umdrehen muss.
Als Volks-Sparmöglichkeiten gibt es jedoch noch:
· Im Outlet-Store Markenartikel 2. Wahl
· Auf dem Markt Spargel 2. Wahl
· Und jetzt auch einen Bundeskanzler 2. Wahl
Warum hat das undankbare deutsche Volk, das die Unseredemokratie nicht genug zu schätzen weiß, immer noch etwas zu meckern?
Wer jetzt behauptet, dass dieser Text absurd ist, der möge sich in der Realität umsehen. Da finden die wirklichen Absurditäten statt. Das hier ist nur Schwurbelei von jemandem, der die Welt nicht mehr versteht.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 7460b7fd:4fc4e74b
2025-05-08 10:14:59
@ 7460b7fd:4fc4e74b
2025-05-08 10:14:59背景与研究范围
Backpack 是由多名前 FTX 和 Alameda 员工在 FTX 崩盘后创立的一家加密交易平台,与 Amber Group(一家大型加密金融服务商)和已倒闭的交易所 FTX 之间可能存在多重隐秘关联。本研究超越公开新闻,从团队延续、资金路径、合规架构、基础设施复用和链上迹象等角度,推理分析三者之间的联系。下文将分别讨论:团队与股权延续性、法币出金(稳定币清算)架构、Amber Group 的支持角色、Circle/Equals Money 等第三方的关联,以及“交叉代币解锁”机制的可能性,并给出关键证据与信息缺口。
团队与股权上的延续性
首先,在团队方面,Backpack 由多名 FTX/Alameda 前成员创立。据报道,Backpack 的联合创始人包括前 Alameda Research 早期员工 Armani Ferrante,以及 FTX 前总法律顾问 Can Suncoinspeaker.com;另一位联合创始人 Tristan Yver 也曾任职于 FTX/Alamedanftgators.com。据 CoinSpeaker 披露,Backpack 40名员工中至少有5人是 FTX 前员工coinspeaker.com。这表明 Backpack 在团队传承上与 FTX 存在明显延续。一方面,创始团队直接来自原 FTX 帝国的核心人员;另一方面,他们将过往在大型交易所积累的经验带入了 Backpack。
其次,在股权投资方面也有延续痕迹。早在2022年9月,Backpack 背后的公司 Coral 即获得了由 FTX Ventures 领投的2000万美元种子轮融资,用于开发 Backpack xNFT 钱包等产品nftgators.com。然而由于2022年11月FTX暴雷,这笔来自 FTX 的投资资金大部分被冻结损失nftgators.com。在经历了资金困难的“蟑螂生存模式”后,Backpack 团队于2023-2024年重新融资,成功在2024年2月完成1700万美元的 A 轮融资nftgators.com。值得注意的是,此轮融资的投资阵容中出现了 Amber Group 的身影nftgators.com。Amber Group 与 Placeholder、Hashed、Wintermute 等知名机构共同参与了该轮融资coinspeaker.com。这意味着 Amber 已经成为 Backpack 股东之一,在股权上建立了联系。此外,Jump Crypto 和 Delphi Digital 等与 FTX时代关系密切的机构也参与了投资nftgators.com。综上, Backpack 的股东和团队构成反映出明显的历史延续:既有原FTX系资本(FTX Ventures)和人员直接过渡,也有 Amber Group 等行业巨头在FTX倒台后入场接棒投资,为 Backpack 提供资金和资源支持。
法币出金架构与 USDC 清算渠道
FTX 时代的稳定币清算: 为了解 Backpack 是否继承了 FTX 的 USDC 清算架构,需要回顾 FTX 过往的法币出入金体系。FTX 在运营高峰时期,以其流畅的出入金和稳定币兑换闻名。用户可以将 USDC 等稳定币充值到 FTX 并直接视同美元资产使用,提取时又能以银行电汇方式取出美元,过程中几乎无汇兑损耗。这背后可能依赖于 FTX 与 Circle 等机构的直接清算合作,以及自有银行网络的支持。例如,Circle 提供的企业账户服务可以让像FTX这样的平台在后台实现USDC与美元的1:1兑换与清算circle.com。事实上,FTX 曾是 USDC 的主要场景之一,大量用户通过将美元换成 USDC 再转入FTX进行交易,从而绕过昂贵的跨境汇款费用。FTX 很可能建立了高效的稳定币兑换通道——例如通过 Silvergate 银行网络或与稳定币发行方直接交割——来实现低成本、快速的法币⇄USDC 转换。这套“USDC 清算架构”是FTX业务成功的重要基础之一。
Backpack 的出金方案: Backpack 作为新兴交易所,近期正式推出了类似的法币⇄稳定币出入金功能,并号称实现了“0费率”的美元/USDC转换panewslab.com。根据官方公告,从2025年5月起,Backpack Exchange 用户可以通过电汇方式充值和提取美元,且美元与USDC的兑换不收取任何手续费panewslab.com。这与FTX当年提供的低成本稳定币出入金体验如出一辙,表明 Backpack 很可能在复用或重建一种高效的清算架构。
与FTX相比,Backpack 并未公开具体采用了何种技术/金融渠道来实现0手续费。但通过社区测试和代码线索,可以推测其架构与FTX思路相似:首先, Backpack 将美元法币与USDC稳定币视为等价资产开放存取,用户电汇美元到账后在平台得到USDC或美元余额,提币时可用USDC直接提走或兑换成美元汇出。其次, Backpack 可能通过与稳定币发行方Circle的合作,或通过场外流动性方,将用户的USDC和法币进行实时对冲清算。Circle提供的API允许合规企业账户方便地将USDC兑换为美元存入银行账户circle.com;Backpack 很可能利用了这一渠道,在后台完成USDC的兑换,再通过银行网络把美元汇给用户。虽然Backpack官方未明言使用Circle,但其USDC通道开放的举措本身就体现了Circle所倡导的稳定币跨境支付应用场景circle.com。因此,从设计上看,Backpack 的法币出入金体系是对FTX模式的一种延续和致敬,即充分利用稳定币作为清算中介,实现跨境汇款的低成本与高效率。
银行网络与 Equals Money: 更有意思的是,有社区用户实测 Backpack 的美元提现,发现汇款发起方显示为“Equals Money PLC”btcxiaolinzi.top。Equals Money 是英国一家持有FCA牌照的电子货币机构(EMI),为企业提供银行转账和外汇服务btcxiaolinzi.top。测试者推断,Backpack 可能在 Equals Money 开立了企业账户,用于代替传统银行向用户汇出美元btcxiaolinzi.top。这一细节揭示了Backpack出金架构的实现路径:Backpack 很可能将待提现的USDC通过某种方式兑换成法币并存入其在Equals Money的账户,由后者完成跨境电汇至用户收款银行。由于Equals Money本质上连接着欧洲和国际支付网络,Backpack借助它可以避开美国传统银行的限制,为全球用户(包括无法直接与美国持牌银行打交道的用户)提供出金服务。这一点在FTX时代并未被广泛报道,但符合FTX/Alameda团队擅长搭建复杂金融通道的作风。由此推断, Backpack 确实在承袭FTX时期的清算理念:利用多层金融机构合作(如稳定币发行方、电子货币机构等),构筑高效的全球资金出入网络。在表面0手续费的背后,可能是由Backpack或其合作方(如做市商)承担了兑换成本,以吸引用户panewslab.com。目前这一体系已进入公开测试及运营阶段,随着更多支付方式(ACH、SEPA)的推出,Backpack正逐步完善其全球法币出入金矩阵panewslab.com。
Amber Group 的潜在支持角色
作为Backpack的重要战略投资方,Amber Group 在该体系中可能扮演多重支持角色。首先是资金层面: Amber参与了Backpack的A轮融资nftgators.com并获得股权,这意味着Amber对Backpack的发展具有直接利益。在FTX倒闭后,Amber选择投资由FTX前团队创立的新交易所,体现出其对这支团队能力和商业模式的认可。Amber本身是知名的加密市场做市和金融服务公司,管理着庞大的资产并具备深厚的流动性提供能力dailycoin.com。因此可以合理推测,Amber除了资本投入,还可能作为做市商为Backpack的交易提供充足的流动性支持,确保用户在Backpack上交易时有良好的市场深度和稳定的价格。这种隐性支持符合许多交易所背后有大做市商“站台”的行业惯例。尤其Backpack定位要提供低成本的稳定币兑换和跨链流动性,Amber在稳定币交易市场的经验和库存或可帮助其维持汇率稳定。
其次是技术与基础设施支持: Amber Group 多年来构建了自己的交易系统(包括托管、风控和前端应用,如之前面向零售的 WhaleFin 应用)。尽管目前未有公开信息表明Backpack直接复用了Amber的技术,但不排除Amber在底层架构上提供咨询或授权支持的可能。例如,Amber深耕多链资产管理和清算,其内部API或合规方案可能对Backpack搭建跨法币/加密的基础设施有所启发。双方如果有合作,极有可能保持低调以避免监管敏感。还有一种支持形式是隐性投资或子基金合作: Amber可能通过旗下基金或关联投资工具,持有Backpack相关业务的权益而不公开身份。然而截至目前,我们尚未发现明确证据证明Amber有这种“隐形”持股行为——Amber作为领投方之一出现于公开融资名单,说明其支持主要还是以正式股权投资和业务协作的方式进行coinspeaker.com。
第三是合规与网络资源: Amber在全球(尤其亚洲)拥有广泛的业务网络和合规资源。Backpack注册在阿联酋迪拜,并计划拓展美国、日本、欧洲等市场learn.backpack.exchangelearn.backpack.exchange。Amber总部位于亚洲(最初在香港,新加坡等地开展业务),对东亚和东南亚市场非常了解。Amber的联合创始人团队中有合规专家,曾帮助公司获取多地牌照。Backpack的联合创始人之一(Can Sun)本身是前FTX法务,这保证了内部合规经验,但Amber的外部资源也可能提供协助。例如,Amber在香港与监管机构打交道的经验,或许有助于Backpack寻求香港或东南亚牌照;Amber在银行业和支付领域的关系网络,也可能帮助Backpack连接银行通道(如引荐像Equals Money这样的机构)。虽然这方面多属于推测,但考虑到Amber投资后通常会积极赋能被投企业,Backpack有理由从Amber处获得合规咨询、市场拓展等方面的帮助。
总的来看,Amber Group 对 Backpack 的支持可能是**“润物细无声”**式的:既体现在台前的融资与做市合作,也体现在幕后的资源共享和经验输出。这种支持帮助Backpack在短时间内补齐了从交易技术到法币通道的诸多要素,使其有能力低成本快速上线类似FTX当年的核心功能(如稳定币快速出入金)。然而,由于双方都未公开详述合作细节,我们对Amber介入的深度仍缺乏直接证据,只能从结果倒推其可能性。
Circle、Equals Money 等第三方的关联
在Backpack、FTX与Amber的关系网络中,Circle和Equals Money等第三方机构扮演了关键“节点”,它们的出现为三者合作提供了基础设施支撑:
-
Circle(USDC发行方): Circle公司本身与FTX及Backpack都有千丝万缕的业务联系。FTX在世时是USDC重要的使用方,帮助USDC拓展了交易所场景;FTX垮台后,Backpack继续扛起“稳定币交易所”的大旗,大量采用USDC作为美元计价和清算工具panewslab.com。虽然我们没有公开材料直接指出Backpack已与Circle签署合作协议,但Backpack推出USD/USDC通道的举措实际是在推动USDC的使用,这与Circle致力于扩大USDC应用的战略不谋而合circle.com。Circle近年来打造跨境支付网络,与多家交易平台和金融机构合作提供法币-稳定币转换服务circle.com。因此,有理由相信Backpack在后台利用了Circle的流动性或API来实现用户提币时的USDC兑换和赎回。比如,当用户在Backpack提取美元,Backpack可能将等额USDC通过Circle赎回成美元,Circle则将该美元汇入Backpack的银行账户进行出金。这种模式其实正是Circle提供给企业客户的“稳定币托管清算”服务之一circle.com。换言之,Circle充当了Backpack法币出金链条中的关键一环,尽管普通用户感知不到它的存在。反过来看Amber,作为全球领先的做市商,也大量使用USDC进行交易和结算,Amber与Circle之间亦可能有直接合作关系(如参与Circle的伙伴计划等)。可以说,Circle及其USDC网络构成了FTX时代和Backpack时代连接传统金融和加密世界的桥梁:FTX和Backpack都踩在这座桥上快速发展,而Amber作为市场参与者,同样频繁走这座桥,为自身和伙伴创造价值。
-
Equals Money(英国电子货币机构): 前文提及,Equals Money PLC 在Backpack的出金过程中显现出来btcxiaolinzi.top。这家公司提供面向企业的银行即服务(BaaS),允许像Backpack这样的客户通过其平台发起全球付款。Equals Money的出现意味着Backpack选择了一条灵活的合规路径来实现银行转账功能:相比直接开设传统银行账户,使用EMI能更快获取支付能力且准入门槛较低。FTX时期并未传出使用EMI的消息,因为当时FTX可直接依赖自己的银行关系网(例如通过位于美国、欧洲的自有账户)来处理汇款。然而在后FTX时代,许多加密公司(包括Amber)都在寻找新的银行替代方案,EMI因此受到青睐。具体联系: 根据实测,Backpack用户提现美元到Wise时,Wise收到的汇款来自Equals Moneybtcxiaolinzi.top。Wise作为跨境汇款平台,其收款机制对资金来源要求严格,但Equals Money持有FCA牌照,属于受监管机构,Wise接收来自Equals的资金被视为合规btcxiaolinzi.top。由此推断,Backpack通过Equals的企业账户,将兑换好的美元直接打给用户填入的收款账号(包括Wise提供的虚拟账号)。这表明Backpack和Equals Money之间有直接业务往来,Equals是Backpack法币出金服务链条上的合作伙伴。值得一提的是,Amber Group 此前在欧洲也曾探索电子货币牌照或合作渠道的可能,尽管无法确认Amber是否也使用Equals,但不排除Amber为Backpack牵线搭桥、推荐了Equals这类服务商的可能性。
综合来看, Circle和Equals Money分别代表了稳定币清算层和法币支付层的基础设施,与Backpack/FTX/Amber的联系体现为:Circle提供“链上到链下”的美元流动性支持,Equals提供“链下”最后一公里的银行网络接口。三者之所以都选择/使用这些渠道,是因为它们共享了对加密法币融合效率的追求。对于FTX和Backpack而言,这些渠道是业务方案的一部分;对于Amber而言,这些渠道是服务布局和投资的一环(Amber支持的交易所采用了这些方案,也间接符合Amber推动行业基础设施完善的利益)。
“交叉代币解锁”机制与链上协作迹象
“交叉代币解锁”是指Amber、Backpack(或其关联项目)之间通过持有彼此发行的代币,并利用协议合作、解锁计划或链上交易,实现协同利益的一种机制。鉴于Backpack尚处于发展初期,我们需要探讨哪些代币或资产可能涉及双方的互动:
-
Backpack 平台代币的潜在发行: 根据Backpack社区的信息,平台计划通过交易积分空投方式向活跃用户发放代币资格btcxiaolinzi.top。这暗示Backpack未来会推出自己的平台代币。若真如此,早期投资方(包括Amber Group)很可能在代币经济中占有一席之地,例如通过投资协议获得一定比例的平台代币配额。在代币正式解锁流通时,Amber等机构投资者将持有相应份额。这就产生了潜在的“交叉代币”联系:Amber持有Backpack的代币,并可在协议允许的时间窗口解锁出售或利用。这种关系一方面绑定了Amber与Backpack的长期利益,另一方面也为Amber提供了在二级市场获利或支持Backpack代币市值的机会。如果Backpack设计代币经济时有锁仓解锁期,那么Amber的代币解锁时间和数量将受到协议约束。从链上数据看,未来可以观察这些大额代币解锁地址是否与Amber的钱包存在关联,以验证Amber对Backpack代币的处置行为。当前,由于Backpack代币尚未发行,我们只能提出这一推测性机制,等待后续链上数据来印证。
-
Amber 持仓代币与Backpack业务的协同: 反之,Amber Group 或其子基金本身持有众多加密资产,是否有与Backpack生态互动的情况?例如,Amber可能持有某些与Backpack生态有关的项目代币(如Solana链上资产,Backpack钱包支持的特定NFT/代币等)。一个案例是Backpack团队曾在Solana上发行受欢迎的 xNFT系列“Mαd Lads”NFTlearn.backpack.exchange。Amber或其投资部门是否参与了该NFT的投资或持有尚无公开资料,但不排除Amber透过场内交易购买一些以支持Backpack生态热度。再者,如果Amber在其他项目上持有代币,而Backpack平台上线这些资产交易,Amber可能通过链上转账将流动性注入Backpack,从而实现双方受益——Amber获得流动性做市收益,Backpack获得交易量和资产丰富度。这可以视作一种链上协作。例如Amber持有大量某种代币X,在Backpack上新上线代币X交易对时,Amber账户向Backpack的热钱包充值代币X提供初始流动性。这样的行为在链上会呈现Amber已知地址向Backpack地址的大额转账。如果将来这些数据出现,将成为印证双方链上合作的直接证据。目前,此类链上轨迹还未有公开披露,我们只能假设其存在的可能性。
-
FTX 遗留资产与Backpack 的关联: 另一个值得一提的链上观察维度是FTX/Alameda遗留资产的动向。FTX倒闭后,其相关钱包曾多次异动。Backpack团队作为前员工,有可能知晓某些地址或资产的情况。但由于破产清算在法庭监管下进行,直接将FTX遗留资产转给新项目不太现实。不过,不排除某些前Alameda投资的项目代币后来为Backpack团队所用。例如,Alameda早期投资的项目若代币解锁,Backpack团队个人可能持有部分并用于新平台的流动性。这种间接关联较难确认,但链上仍可寻找蛛丝马迹,比如监测前Alameda标识的钱包与Backpack相关地址之间的交易。如果有频繁互动,可能暗示Backpack获取了Alameda旧有资产的支持。至今未见显著证据,推测空间大于实证。
小结: “交叉代币解锁”机制目前更多停留在理论推演层面。我们确认了Backpack未来存在发行平台代币的规划btcxiaolinzi.top;也确认Amber作为投资方大概率会获得并持有该代币份额。但具体的锁仓解锁安排、双方是否会通过特殊协议(如做市激励、流动性挖矿等)进行合作,还有待官方披露或链上数据验证。链上分析工具可以在未来帮助捕捉Amber地址与Backpack生态代币/NFT的交互,从而揭示深层协作。如果发现Amber旗下地址在Backpack代币解锁后立即大量转入交易所,可能意味着Amber选择变现;反之,若锁定期内就有灰度交易发生,甚至可能存在双方提前约定的场外交换。这些都是值得持续监测的方向,但就目前信息来看,尚无定论。
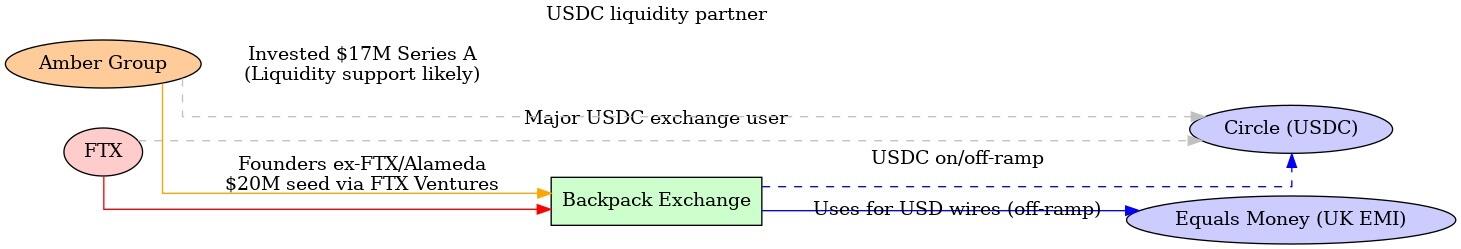
\ 图:FTX、Amber Group 与 Backpack 三者关系示意图。红色/橙色线表示团队和股权延续(FTX前员工和投资延续到Backpack,Amber参与投资并可能提供流动性);蓝色线表示Backpack法币出金所依赖的稳定币清算和银行通道(通过USDC及Equals Money实现);灰色虚线表示FTX和Amber分别与USDC发行方Circle在业务上的联系。这些关系共同构成了Backpack在FTX余荫和Amber支持下快速搭建全球业务的基础。
关键证据与信息缺口
通过上述分析,我们梳理了已知的信息链条,并挖掘了若干可能的隐秘关联,同时也识别出需要进一步调查的信息空白:
-
明确的证据链: 我们找到了多项公开资料证明Backpack与FTX/Amber的联系:包括创始团队来自FTX/Alamedacoinspeaker.com、FTX Ventures 曾投资Backpack母公司nftgators.com、Amber Group 参与了Backpack的融资coinspeaker.com、多名FTX旧部现在Backpack任职coinspeaker.com等。这些形成了人员和资金延续的直接证据。另外,通过用户分享和代码库,我们确认Backpack法币出金使用了Equals Money通道btcxiaolinzi.top并提供了0手续费的USD/USDC转换panewslab.com——这证明了Backpack确实建立了类似FTX当年的稳定币清算架构,只是技术实现上借助了新的合作方(Equals Money)。这些证据支撑了本文的大部分推论基础。
-
合理的推测与佐证: 有些关联尚无官方公告证明,但基于行业惯例和现有线索推测合理,并有部分侧面佐证。例如,Amber 为Backpack提供做市流动性支援一事,没有直接新闻来源,但考虑到Amber投资交易所的动机和能力,此推断具有高概率可靠性。再如,Backpack疑似使用Circle的USDC清算服务,虽无明示,但从其业务模式和Circle的产品定位来看circle.com,这一幕后合作应该存在。同样地,Amber可能通过非公开方式向Backpack输出技术/合规支持,也是基于双方利益绑定关系而做出的推断。这些推测目前缺乏直接证据,只能算作可能性假设,需要后续留意更多细节披露。
-
信息缺口与待验证点: 首先,关于Backpack具体的清算路径,我们仍不清楚它如何在链上/链下转换巨额USDC为法币。虽然Equals Money出现在汇款端btcxiaolinzi.top,但在那之前USDC的结算或许涉及Circle或其他做市商(如Amber)——这部分交易发生在后台,需更多技术信息或链上监控来捕捉。其次,Amber与Backpack之间除股权外是否存在合同约定的业务合作(如Amber成为指定做市商、提供信贷支持等)目前尚未公开,属于信息真空。第三,Backpack未来的代币发行和分配细节未知,Amber等投资方将如何参与、解锁周期如何,将直接影响“交叉代币”协作的发生与否,需等官方白皮书出台。第四,更多链上证据的挖掘:由于没有公开的钱包标签,很难直接将某条链上交易指认属于Amber或Backpack。但如果未来Backpack发行代币或大型交易上线,链上必然会出现相关资金流,我们可以通过已知Amber常用地址(如果有披露)来交叉比对,看其是否与Backpack生态有交互。这是一块需要进一步研究的领域,可能借助区块链分析工具和交易图谱来补全证据。最后,还有监管和法律结构的信息:例如Backpack在不同司法管辖区的注册实体与银行账号详情,FTX遗产处理过程中是否对Backpack团队有约束,这些在公开资料中都尚无答案。
结论
综合全篇分析,Backpack、Amber Group 与已倒闭的FTX之间确实存在千丝万缕的延续和关联。Backpack可以被视作FTX精神和技术路线的“继承者”之一——由FTX旧将创建,在FTX垮台造成的市场空白中迅速崛起coinspeaker.com。Amber Group 则扮演了重要的扶持者角色,通过投资和可能的资源注入,参与了Backpack的重建过程coinspeaker.com。在具体业务层面,Backpack延续了FTX时代的创新,如高效的稳定币清算和全球化业务布局,但为了适应新的环境,它也采用了新的工具(如Equals Money的出金渠道)和更严格的合规措施(迪拜等地的牌照)coinspeaker.com。这一切背后,隐现着Amber等老牌加密公司的身影支持,以及Circle等基础设施提供商的支撑。
当然,隐秘关联并不意味着不正当行为,上述关系很多是基于正常的商业合作和延续,只是未明言于公众。例如,前FTX团队利用自己的经验和人脉创建新平台,本身无可厚非;Amber投资新交易所也是市场行为。从推理和现有证据看,并没有直接迹象显示三者存在违法的秘密勾连。然而,对于研究者和行业观察者而言,了解这些联系有助于洞察加密行业格局的演变:FTX的倒下并未让其积累的人才和思想消失,反而通过创业和投资,以新的形式(Backpack)继续影响市场;Amber等老牌玩家则通过战略投资,将自己的版图延伸到新兴平台,以保持竞争力。
未来展望: 随着Backpack进一步发展,我们预计会有更多信息浮出水面来验证或修正上述假设。例如,Backpack若推出平台代币,其投资人持仓和解锁情况将记录在链,从而揭示Amber等的参与细节;再比如,Backpack进入美国市场时需要公开其合作银行或支付伙伴,届时我们可能印证Circle等在其中的角色。如果出现新的合作公告或监管披露文件,也能帮助我们更清晰地绘制三者关系网。目前的信息不对称使我们只能尽力拼凑一幅关联图景,并针对关键环节提供已知证据支持。仍存在的一些信息缺口需要持续跟进调查。总之,Backpack、Amber Group 与FTX的故事折射出加密行业的新旧交替与传承。在FTX的余烬上,新火花正在由熟悉旧世界的人点燃,而这些火花能否照亮一个更加合规稳健的未来,还有待时间检验。 nftgators.comcoinspeaker.com
-
-
 @ bbb5dda0:f09e2747
2025-05-08 07:37:51
@ bbb5dda0:f09e2747
2025-05-08 07:37:51
I've been neglecting my weekly updates a bit. I haven't really gotten to them lately because i've been insanely busy frying my brains at #SovEng. And after that i haven't been keeping my weekly notes properly. WHICH I'm planning to pick back up now!
This week/ the last couple weeks I've been doing some general planning around @tollGate's appearances on various conferences around Europe! First on the list will be Pizza Day in Prague! And from there I'll be cruising straight to @Oslo Freedom Forum! For TollGate that also means getting us set up with some T-Shirts and Stickers, though not super hard to do, it's the first time I'm doing any 'marketing' like this so I did test my own patience by properly cropping and ordering the designs. So far the stickers came out well Look at our first officially baptized TollGate! :)
TollGate Installer
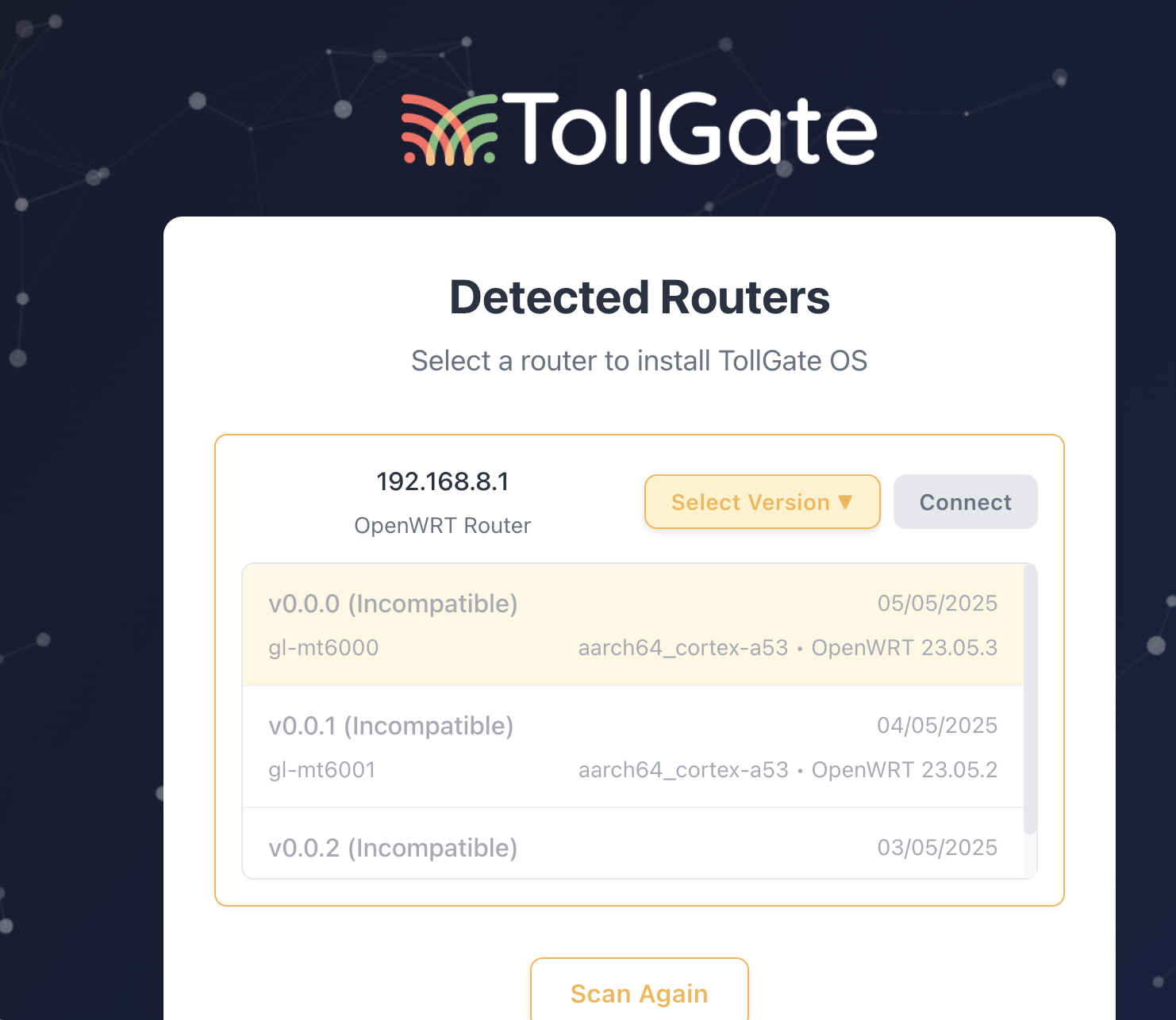 As we're installing versions of TollGateOS on routers quite often now I figured it'd be a good idea to streamline the experience a bit by building a TollGate Installer. I've been vibecoding it mostly, and one of the things I discovered is how easy it is to make it replicate the style of another app. To stick with the theme I told it to mirror the style of our TollGate Captive portal site and it did it perfectly!
As we're installing versions of TollGateOS on routers quite often now I figured it'd be a good idea to streamline the experience a bit by building a TollGate Installer. I've been vibecoding it mostly, and one of the things I discovered is how easy it is to make it replicate the style of another app. To stick with the theme I told it to mirror the style of our TollGate Captive portal site and it did it perfectly!Anyway, still a lot of manual engineering is required but at least I can outsource the stuff i'm bad at. What I did improve was the GitHub workflows we use for building and publishing the OS. We publish our releases to Blossom + Nostr (NIP-94). I then use those messages in the installer to get the download links.
👀 But which version!?
I quickly ran into the issue that I didn't know which binary to install on the router i hooked up to my computer. I connect the router via lan, then I scan the network and ssh into the router, get some basic info, like the device name. BUT, the format of that device name wouldn't match any of the names we'd use in our release.
For example: the router name would be
glinet,mt3000while our release was calledgl-mt3000. The difference may seem subtle but I can't match them. So after some discussion with the others I went on and revamped our OS pipeline to properly follow the OpenWRT naming of boards/devices. The pipeline is now much more extensible, making it easier for us to add support for more hardware!What's next?
We're aiming for a v0.0.2 release of TollGate OS by friday, incorporating some of the feedback we've gotten from our test users! Hang on tight guys! 🙏 I'm hoping to finish an earlier version of the installer in the upcoming week as well.
-
 @ 2b24a1fa:17750f64
2025-05-08 07:14:35
@ 2b24a1fa:17750f64
2025-05-08 07:14:35"Was ist da drin?", fragte wohl jedes unverdorbene Kind, bevor eine Flüssigkeit in den Muskel seines Arms gespritzt würde. Aber wir sind alle keine unverdorbenen Kinder mehr. Wissen, das haben die anderen, die Gebildeteren, die Wissenschaftler, die Ärzte. Nachfragen würde Autoritäten untergraben und Unglauben demonstrieren. Und drum fällt kaum jemandem auf, dass wir bis heute keine sauberen Inhaltsangaben über die sogenannten Corona-Spritzen erhalten haben, geschweige denn wissen, was der Inhalt in unseren Körpern genau anrichten kann.
Auf die Suche nach Aufklärung hat sich von Beginn dieser sogenannten Pandemie der Verein Mediziner und Wissenschaftler für Gesundheit, Frieden und Demokratie gemacht. Jetzt gibt es ein erstes Labor, das die bekannten, relevanten Impfstoffbestandteile nachweisen will. Darüber unterhält sich unsere Redakteurin Eva Schmidt mit dem Molekularbiologen Prof. Klaus Steger von der Universität Gießen und engagiert bei inmodia, dem Institut für molekularbiologische Diagnostik. Zunächst wollte sie wissen, welche Bestandteile eigentlich bekannt sind, die in Millionen von Menschen gespritzt wurden.
Link zur Webseite: inmodia.de
-
 @ c9badfea:610f861a
2025-05-08 23:06:09
@ c9badfea:610f861a
2025-05-08 23:06:09- Install VLC Media Player
- Open the app, navigate to More and tap New Stream
- Enter
https://iptv-org.github.io/iptv/index.m3uin the network address field and tap the arrow - Enjoy the global IPTV channel playlist
🔗️ Here is the stream URL as plain text: https://iptv-org.github.io/iptv/index.m3u
ℹ️ For playlists of specific countries, categories, or languages, visit IPTV-Org and see the Playlists section
ℹ️ You can find an overview of all available IPTV channels per country here
-
 @ 6fc114c7:8f4b1405
2025-05-08 22:55:57
@ 6fc114c7:8f4b1405
2025-05-08 22:55:57In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back! 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞 For quick queries or support, connect with us on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust\ At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process\ Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate\ With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure\ Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools\ We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!\ Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back!\ 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪
-
 @ 9063ef6b:fd1e9a09
2025-05-07 19:12:36
@ 9063ef6b:fd1e9a09
2025-05-07 19:12:36✅ Requirements
- GitHub account
- Own domain (e.g.,
yourdomain.com) - Public Nostr key in hex format (not
npub!) - Basic DNS configuration knowledge
🛒 1. Register a Domain
Register a domain from a provider like orangewebsite, njal.la, or similar.
🌐 2. Configure DNS Records for GitHub Pages
Set the following A records for your domain (via your DNS provider):
| Type | Host | Value | TTL | Priority | |------|--------------|-------------------|-----|----------| | A | @ (or blank) | 185.199.108.153 | 300 | | | A | @ (or blank) | 185.199.109.153 | 300 | | | A | @ (or blank) | 185.199.110.153 | 300 | | | A | @ (or blank) | 185.199.111.153 | 300 | |
Optional:
Add aCNAMErecord forwww→yourusername.github.io
📁 3. Create a GitHub Repository
- Go to https://github.com/new
- Repository name: e.g.,
nip5 - Check "Add a README"
- Click "Create repository"
🏗️ 4. Create Directory & File
a)
.well-known/nostr.jsonPath:
.well-known/nostr.json
Example content:json { "names": { "nostrName": "ldajflasjföldsjflj..." } }IMPORTANT: Use your hex-encoded Nostr public key, not the
npub1...format.b)
_config.ymlin RootCreate a file named
_config.ymlwith this content:yml include: [".well-known"]This ensures GitHub includes the
.well-knownfolder in the build output.
⚙️ 5. Configure GitHub Pages
- Go to Settings > Pages inside your repository
- Under "Build and Deployment":
- Choose:
Deploy from branch - Branch:
mainormaster - Under Custom domain:
- Enter
yourdomain.com - Ignore any warning
- Enable ✅ Enforce HTTPS
It may take a few minutes for the certificate to be issued.

🔍 6. Configure Nostr Client
Open your Nostr client and set the NIP-05 identifier as:
nostrName@yourdomain.com e.g. meier@meier.techSave – done!
✅ Test
In your browser or via
curl:bash curl https://yourdomain.com/.well-known/nostr.json?name=avrenExpected output:
json { "names": { "Nostr Benutzer": "elkajdlkajslfkjaödlkfjs..." } }
🛡️ Privacy Tips
| Item | Recommendation | |-----------------------------------|----------------------------------| | Public key is visible | Use pseudonyms only | | Register a KYC-free domain | e.g., orangewebsite, njal.la | | Use KYC-free email for GitHub | e.g., ProtonMail | | GitHub repository visibility | Must be public for GitHub Pages | | Commit metadata | Use a separate pseudonymous user | | Avoid tracking | Don’t include analytics scripts |
-
 @ 0e29efc2:ff142af2
2025-05-07 15:09:46
@ 0e29efc2:ff142af2
2025-05-07 15:09:46Table of Contents
- Intro
- Important Terminology
- Getting Started
- Where do I buy bitcoin?
- Okay, I bought some bitcoin-now what?
- Less than 0.01 BTC
- More than 0.01 BTC and less than 0.1 BTC
- More than 0.1 BTC
- How Bitcoin Works
- Skepticism
- Someone will hack it
- The government will try to stop it
- It’s not backed by anything
- Conclusion
Intro
Maybe you saw an article in Forbes, a news segment about MicroStrategy (MSTR), or you glanced at the bitcoin price chart; whatever the spark, your curiosity led you here. Enough friends and relatives keep asking me about bitcoin that I finally organized my thoughts into a single reference. This is not a comprehensive guide—it assumes you trust me as a heuristic.
Important Terminology
Sat (satoshi) – the smallest unit of bitcoin. One bitcoin (₿) equals 100 000 000 sats.
Getting Started
Where do I buy bitcoin?
I use River because it publishes proof‑of‑reserves, supports the Lightning Network, and pays interest on idle USD balances (currently 3.8 %).
Okay, I bought some bitcoin-now what?
Withdraw it immediately. Centralized exchanges can and do fail. Your next step depends on how much bitcoin you hold.
If at any point you're struggling, please reach out to me.
Less than 0.01 BTC
- On your phone open Safari (iOS) or Chrome (Android).
- Paste
https://wallet.cashu.me?mint=https://mint.westernbtc.com. Confirm the prompt that asks whether you trusthttps://mint.westernbtc.com. I run this mint so beginners can skip the gnarly parts. - Complete setup.
- Tap Receive → LIGHTNING → enter amount → COPY.
- In River choose Send → Send to a Bitcoin wallet, paste the invoice, verify, and send.
- Return to the wallet; your sats should appear.

More than 0.01 BTC and less than 0.1 BTC
It's time for cold storage. Cold storage means a dedicated signing device not connected to the internet. Think of it like keys to a house. If you have the keys (your cold storage signing device), you can get into your house (the bitcoin). I recommend and use the COLDCARD Q or COLDCARD MK4 from COLDCARD. See this thorough walkthrough.
The creator nostr:npub1rxysxnjkhrmqd3ey73dp9n5y5yvyzcs64acc9g0k2epcpwwyya4spvhnp8 makes reliable content.
More than 0.1 BTC
The next security upgrade involves something called multisig. It requires the use of multiple devices instead of one. Think of those nuclear launch silos in movies where two keys need to be turned in order to launch the missile. One person can't reach both keys, so you need two people. Like the two keys needing to be turned, we need a certain number of keys (signing devices) to be used.

This offers a number of benefits. Say you have a 2-of-3 multisig setup. You would need two of the three keys to move the bitcoin. If you were to lose one, you could use the two others to move it instead. Many choose to geographically distribute the keys; choosing to keep one at a friend’s house or with a bank.
The previous video I linked covers multisig as well. Again, please reach out to me if you need help.
How Bitcoin Works
I'm going to paint a scene portraying the basics of how bitcoin works. Picture a race that's supposed to take 10 minutes to run start-to-finish, and there's a crowd of people spectating. When the fastest runner crosses the finish line, they're awarded 50 bitcoin. Everyone in the crowd recognizes who won, and writes it down on their own scoreboard. Then, the next race begins.
Now, let's say more racers who've had special training join. They start winning consistently because of it, and now the race only lasts about 9 minutes. There's a special rule everyone in the crowd agreed to, that they can make the race harder to ensure it's around 10 minutes long. So they make the race harder to counteract the faster runners.

With this in mind, let's get to the skepticism you might have.
Skepticism
Someone will hack it
Think of bitcoin as the people in the crowd. If someone tries to cheat and writes on their scoreboard that they have a billion bitcoin, their scoreboard is going to look different than everybody else’s. The other people in the crowd will cross-reference with each other and decide to ignore that person who cheated.
The government will try to stop it
Again, think of the crowd. In reality, the "crowd participants" are scattered all around the world. You might be able to stop many of them, but it would be almost impossible to stop everyone. Imagine people are watching the race on TV, can you find everyone who's spectating? Ironically, attempted bans often increase interest.
It’s not backed by anything.
Think of the runners. The runners are bitcoin miners. They have to expend real energy to participate in the race. The more bitcoin miners, the more secure the network. In summary, it's backed by electricity and work.
Conclusion
There are too many topics to cover in one article. I haven't even touched on the history of money, what money is, scarcity, etc. The best way to learn is to research the topics you're interested in for yourself. It took months of deep diving before I was sold on bitcoin, and I had many touch points before that.
Once you see it though, you can't unsee it.
-
 @ bbef5093:71228592
2025-05-07 15:09:39
@ bbef5093:71228592
2025-05-07 15:09:39Az Európai Bizottság terve az orosz urán- és energiafüggőség felszámolására
Az Európai Bizottság bejelentette, hogy korlátozni kívánja az új urán-, dúsított urán- és egyéb, Oroszországból származó nukleáris anyagokra vonatkozó ellátási szerződéseket, ezzel is elősegítve, hogy az Európai Unió „teljesen megszüntesse” az orosz energiától való függését[8][6][2].
A Bizottság új ütemtervet mutatott be, amely részletesen tartalmazza, hogyan kívánja megszüntetni az orosz energiafüggőséget, miközben biztosítja az EU energiaellátásának és árainak stabilitását[6][2][15].
Főbb intézkedések és célok
- Az EU az orosz gázimport arányát 45%-ról 19%-ra csökkentette a 2022 májusában indított REPowerEU tervnek köszönhetően, de 2024-ben ismét növekedett az orosz gáz behozatala[2][20].
- Az új ütemterv szerint az orosz olaj, gáz és nukleáris energia fokozatosan, összehangoltan és biztonságosan kerül ki az uniós piacokról, miközben az EU a tiszta energiára való átállást gyorsítja fel[6][15][7].
- Az EU-tagállamoknak 2025 végéig nemzeti terveket kell készíteniük arról, hogyan járulnak hozzá az orosz gáz, nukleáris energia és olaj importjának megszüntetéséhez[13][7][18].
- Az orosz eredetű urán, dúsított urán és egyéb nukleáris anyagok esetében új korlátozásokat vezetnek be: az Euratom Ellátási Ügynökség (ESA) nem hagy jóvá új orosz beszállítási szerződéseket, és gazdasági eszközökkel is igyekeznek visszaszorítani az importot[4][5][16].
- A meglévő rövid távú szerződéseket 2025 végéig meg kell szüntetni, új szerződéseket pedig nem lehet kötni; a hosszú távú szerződéseket 2027 végéig kell felmondani[5][7][6].
- Az intézkedések célja, hogy a teljes orosz gáz- és olajimport 2027 végéig megszűnjön, az orosz atomenergia pedig fokozatosan kivezetésre kerüljön[3][9][17].
Nukleáris háttér
- Az ESA jelentése szerint 2023-ban az EU-ban felhasznált természetes urán 23,4%-a érkezett Oroszországból, ami 72,6%-os növekedést jelentett, főként a VVER típusú orosz atomerőművek üzemanyag-felhalmozása miatt[16].
- Az EU-ban 19 VVER reaktor működik (Bulgáriában, Csehországban, Finnországban, Magyarországon és Szlovákiában).
- Az EU természetes uránszükséglete a globális igények mintegy 22%-át teszi ki, a beszerzések 91%-a Kanadából, Oroszországból, Kazahsztánból és Nigerből származik[16].
Célkitűzés és indoklás
A Bizottság szerint az orosz energiafüggőség felszámolása nemcsak gazdasági, hanem biztonságpolitikai kérdés is, mivel Oroszország többször is eszközként használta az energiát az EU-val szemben[2][12]. A lépések célja, hogy az EU energiaellátása biztonságos, stabil és kiszámítható maradjon, miközben az orosz energiaimportból származó bevételek ne finanszírozhassák tovább az Ukrajna elleni háborút[6][2][12].
Források alapján készült magyar összefoglaló és fordítás
Citations: [1] Döntött az Európai Bizottság: teljes mértékben megszüntetik ... - 444 https://444.hu/2025/05/06/dontott-az-europai-bizottsag-teljes-mertekben-megszuntetik-az-orosz-energiatol-valo-fuggest [2] Három éven belül felszámolná az orosz energiafüggőséget az ... https://hu.euronews.com/my-europe/2025/05/06/harom-even-belul-felszamolna-az-orosz-energiafuggoseget-az-europai-bizottsag [3] 2027-re teljesen leállítaná az Európai Bizottság az orosz ... - Új Szó https://ujszo.com/kozelet/2027-re-teljesen-leallitana-az-europai-bizottsag-az-orosz-energiabehozatalt-a-nuklearis [4] Bejelentették Brüsszelben: megkerülik Magyarországot, teljesen ... https://www.portfolio.hu/gazdasag/20250506/bejelentettek-brusszelben-megkerulik-magyarorszagot-teljesen-levalik-az-orosz-olajrol-es-gazrol-az-eu-759267 [5] Érik az újabb ütközés: Brüsszel betiltaná az orosz energiát https://www.valaszonline.hu/2025/05/06/energia-szankcio-oroszorszag-haboru-eu-olaj-gaz-uran/ [6] Az EU teljes mértékben megszünteti az orosz energiától való függését https://hungary.representation.ec.europa.eu/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggeset-2025-05-06_hu?prefLang=en [7] Megvan az ütemterv, végleg betiltaná az orosz energiát az Európai ... https://index.hu/kulfold/2025/05/06/orosz-energiafuggoseg-orosz-gaz-olaj-import-europai-unio-repowereu/ [8] European Commission Unveils Plans To Restrict New Uranium ... https://www.nucnet.org/news/european-commission-unveils-plans-to-restrict-new-uranium-deals-with-russia-5-3-2025 [9] Az EU teljes mértékben megszünteti az orosz energiától való ... https://infostart.hu/belfold/2025/05/06/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggoseget-a-nap-hirei [10] [PDF] EURÓPAI BIZOTTSÁG Brüsszel, 2025.4.9. COM(2025) 159 final ... https://secure.ipex.eu/IPEXL-WEB/download/file/082d29089612ec1e019619f955940250 [11] Kiszivárgott az Európai Bizottság 2025-ös munkaprogramja https://www.eu-monitor.hu/hu/cikk/20250206-kiszivargott-az-europai-bizottsag-2025-os-munkaprogramja [12] EU says it will end dependency on Russian energy supplies https://www3.nhk.or.jp/nhkworld/en/news/20250507_B4/ [13] Végleg leválik az orosz energiáról az Európai Unió ... - Népszava https://nepszava.hu/3278673_oroszorszag-europai-unio-foldgaz-koolaj-levalas-terv [14] Egyre több európai ország támogatja az atomenergiát https://www.vg.hu/nemzetkozi-gazdasag/2025/03/atomenergia-energiatarolas-europa [15] Az EU teljes mértékben megszünteti az orosz energiától való ... https://karpatinfo.net/energiafuggetlenseg-orosz-foldgaz-orosz-energiafuggoseg-2025-05-07 [16] EU outlines measures to end Russian gas, oil imports by end-2027 https://balkangreenenergynews.com/eu-outlines-measures-to-end-russian-gas-oil-imports-by-end-2027/ [17] Az Európai Unió 2027 végére betiltaná az orosz gáz importját https://www.korkep.sk/cikkek/gazdasag/2025/05/05/az-europai-unio-2027-vegere-betiltana-az-orosz-gazimportot/ [18] Ficónak és Orbánnak sem tetszik, hogy az EU teljesen kitiltaná az ... https://napunk.dennikn.sk/hu/4623240/ficonak-es-orbannak-sem-tetszik-hogy-az-eu-teljesen-kitiltana-az-orosz-energiat/ [19] Várhelyi Olivér késlelteti az EU orosz energiafüggőségét felszámoló ... https://telex.hu/kulfold/2025/05/05/varhelyi-oliver-europai-bizottsag-orosz-energia-kivaltas-hatraltatas [20] REPowerEU roadmap - Energy - European Commission https://energy.ec.europa.eu/strategy/repowereu-roadmap_en