-
 @ 7d33ba57:1b82db35
2025-03-22 10:27:50
@ 7d33ba57:1b82db35
2025-03-22 10:27:50Valencia is a vibrant coastal city on Spain’s east coast, blending historical charm, futuristic architecture, golden beaches, and amazing cuisine. As the birthplace of paella, it’s a paradise for food lovers, while its mild climate and Mediterranean vibes make it a perfect year-round destination.
🏛️ Top Things to See & Do in Valencia
1️⃣ The City of Arts and Sciences
- A futuristic architectural complex with a science museum, planetarium, aquarium, and opera house.
- The Hemisfèric & Oceanogràfic are must-visits for families and science lovers.
2️⃣ Valencia Cathedral & El Miguelete Tower
- A beautiful Gothic cathedral said to house the Holy Grail.
- Climb El Miguelete Tower for breathtaking city views.
3️⃣ La Lonja de la Seda (Silk Exchange) – UNESCO Site
- A stunning Gothic-style merchant building from the 15th century.
- One of the best-preserved examples of Valencia’s medieval trading history.
4️⃣ Plaza de la Virgen & Old Town (El Carmen)
- A charming square surrounded by historical buildings, fountains, and lively cafés.
- Wander the narrow streets of El Carmen for street art, boutique shops, and tapas bars.
5️⃣ Turia Gardens & Gulliver Park
- A beautiful green park built in a former riverbed, perfect for cycling, jogging, or picnicking.
- Gulliver Park is a giant playground shaped like Gulliver from "Gulliver’s Travels"!
6️⃣ Central Market (Mercado Central)
- One of the largest fresh food markets in Europe, housed in a stunning Art Nouveau building.
- Try fresh produce, local cheeses, and traditional jamón ibérico.
7️⃣ Malvarrosa Beach
- A long sandy beach with great restaurants, water sports, and a relaxing atmosphere.
- Perfect for sunbathing, a seaside stroll, or enjoying a paella by the sea.
🍽️ What to Eat in Valencia
- Paella Valenciana – The original version with rabbit, chicken, and saffron rice 🥘
- Horchata & Fartons – A refreshing tiger nut drink with sweet pastries 🥛🥐
- Agua de Valencia – A famous local cocktail made with orange juice, cava, gin, and vodka 🍹
- Esgarraet – A tasty mix of salted cod, red peppers, and olive oil 🐟
🚆 How to Get to Valencia
🚄 By Train: High-speed AVE trains from Madrid (~1.5 hrs) & Barcelona (~3 hrs)
✈️ By Air: Valencia Airport (VLC) with connections to major European cities
🚗 By Car: A scenic drive along the Mediterranean coast (Costa Blanca)💡 Tips for Visiting Valencia
✅ Best time to visit? Spring & Fall for pleasant weather 🌞
✅ Visit during Las Fallas (March 15-19) – A spectacular festival with fireworks, giant sculptures, and street parties 🎆🔥
✅ Try a bike tour! Valencia is one of Spain’s most bike-friendly cities 🚴
-
 @ 714dd0db:9c6f1a4c
2025-03-22 09:48:44
@ 714dd0db:9c6f1a4c
2025-03-22 09:48:44やっと春が来ました
ようやく暖かくなってきた。 買い物から帰ってくると、なにやら甘い香り。
あ、もしかして、花の香りか!
探してみると、沈丁花が咲いている。

ああ、甘くていい香り。
近くには蝋梅も咲いている。我が家の近くに蝋梅があったなんて、すっかり忘れていた。

そして、早咲きの桜。桜のどの種類かは分からないのだが、毎年、ソメイヨシノよりも先に咲いている。

花の蜜を吸いに百舌鳥も来ている。いや、鳥の種類には疎いが、おそらく百舌鳥だろう。多分。

モノクロの冬から、ようやくカラフルな春になってきた。
季節を感じるのは、心が豊かになる。 今は今、今度は今度。 俺は今を生きている。
-
 @ 00000001:b0c77eb9
2025-02-14 21:24:24
@ 00000001:b0c77eb9
2025-02-14 21:24:24مواقع التواصل الإجتماعي العامة هي التي تتحكم بك، تتحكم بك بفرض أجندتها وتجبرك على اتباعها وتحظر وتحذف كل ما يخالفها، وحرية التعبير تنحصر في أجندتها تلك!
وخوارزمياتها الخبيثة التي لا حاجة لها، تعرض لك مايريدون منك أن تراه وتحجب ما لا يريدونك أن تراه.
في نوستر انت المتحكم، انت الذي تحدد من تتابع و انت الذي تحدد المرحلات التي تنشر منشوراتك بها.
نوستر لامركزي، بمعنى عدم وجود سلطة تتحكم ببياناتك، بياناتك موجودة في المرحلات، ولا احد يستطيع حذفها او تعديلها او حظر ظهورها.
و هذا لا ينطبق فقط على مواقع التواصل الإجتماعي العامة، بل ينطبق أيضاً على الـfediverse، في الـfediverse انت لست حر، انت تتبع الخادم الذي تستخدمه ويستطيع هذا الخادم حظر ما لا يريد ظهوره لك، لأنك لا تتواصل مع بقية الخوادم بنفسك، بل خادمك من يقوم بذلك بالنيابة عنك.
وحتى إذا كنت تمتلك خادم في شبكة الـfediverse، إذا خالفت اجندة بقية الخوادم ونظرتهم عن حرية الرأي و التعبير سوف يندرج خادمك في القائمة السوداء fediblock ولن يتمكن خادمك من التواصل مع بقية خوادم الشبكة، ستكون محصوراً بالخوادم الأخرى المحظورة كخادمك، بالتالي انت في الشبكة الأخرى من الـfediverse!
نعم، يوجد شبكتان في الكون الفدرالي fediverse شبكة الصالحين التابعين للأجندة الغربية وشبكة الطالحين الذين لا يتبعون لها، إذا تم إدراج خادمك في قائمة fediblock سوف تذهب للشبكة الأخرى!
-
 @ da0b9bc3:4e30a4a9
2025-03-22 09:34:42
@ da0b9bc3:4e30a4a9
2025-03-22 09:34:42Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/921232
-
 @ 2fb77d26:c47a6ee1
2025-03-21 15:49:40
@ 2fb77d26:c47a6ee1
2025-03-21 15:49:40»Pershing II« – das war eines der ersten englischen Wörter, das mir als Kind geläufig war. Es handelt sich um die Typenbezeichnung einer US-Mittelstreckenrakete, einer nuklearen Boden-Boden-Rakete, die mit einem thermonuklearen Sprengkopf vom Typ W85 ausgestattet war, eine Reichweite von etwa 1.800 km hatte und somit von Süddeutschland aus Ziele im westlichen Russland binnen fünf Minuten erreichen konnte. Es war Anfang der 1980er Jahre. Die Zeit des Kalten Krieges. Eine Bezeichnung, die George Orwell mit seinem Essay »You and the Atomic Bomb« (Du und die Atombombe) im Jahre 1945 geprägt hatte. Die Fronten waren verhärtet.
Die westdeutsche Friedensbewegung protestierte lautstark gegen die Stationierung von Atomsprengköpfen auf heimischem Boden. Nachdem die im NATO-Doppelbeschluss vom 12. Dezember 1979 vereinbarten Abrüstungsverhandlungen zwischen den Atommächten jedoch erfolglos geblieben waren, entschied der Deutsche Bundestag am 22. November 1983, der Stationierung von US-Atomwaffen im Lande zuzustimmen. Diese war 1985 abgeschlossen und ganze 120 Exemplare der todbringenden Massenvernichtungswaffe in der Bundesrepublik verteilt worden. Außer Deutschland tat kein Land den USA diesen Gefallen.
Ich hatte die militärische Artikelbezeichnung »Pershing II« im Radio aufgeschnappt, welcher zu Hause fast durchgehend in Betrieb war, und später ein paar Bilder der Raketen in den Abendnachrichten gesehen. Noch gab es nur ARD, ZDF und das Regionalprogramm. Dementsprechend rar waren visuelle Informationen. Und aufgrund meiner frühen Begeisterung für Fluggeräte aller Art, zeichnete ich daraufhin ständig Raketen. Da ich außerdem bereits in diesem zarten Alter von fünf oder sechs Jahren extrem von Musik angetan war und durchweg versuchte, englische Songtexte, zum Beispiel von den Beatles, dem Klang der Stimmen folgend nachzusingen, übte auch der fremd klingende Begriff »Pershing II« eine gewisse Faszination auf mich aus.
Was mir meine Eltern diesbezüglich sagten oder erklärten, kann ich leider nicht mehr erinnern – als erklärte Pazifisten nahmen sie die latente Gefahr eines Nuklearkrieges aber sicher nicht mit der spielerisch-kindlichen Leichtigkeit, die ich im Umgang mit gemalten oder gebastelten Raketen an den Tag legte. Das Thema nukleare Kriegsführung beherrschte die Nachrichten dieser Zeit und erzeugte Angst. Denn Militärstrategen sprachen Anfang der 1980er Jahre allen Ernstes davon, dass der Atomkrieg zwischenzeitlich präziser und somit auch führbarer geworden sei. Damals wie heute – absoluter Irrsinn.
Neben der Berlin-Blockade 1948/1949 und der Kuba-Krise, war die Auseinandersetzung um die Stationierung von Mittelstreckenraketen in Westeuropa von 1979 bis 1983 also eine der drei kritischsten Phasen des Kalten Krieges.
Nie war die Welt einem fatalen wie letalen nuklearen Schlagabtausch der Supermächte näher als zu diesen drei Zeitpunkten in der Geschichte. Bis heute, so scheint es.
Denn die stetig eskalierende Ukraine-Krise rückt dieses vergessen geglaubte Horror-Szenario wieder in den Fokus der Öffentlichkeit. Polit-Darsteller wie der Maoist und China-Fan Robert Habeck äußern dieser Tage dummdreist, keine Angst vor einem Dritten Weltkrieg zu haben. Sogenannte Sicherheitsexperten erklären im ZDF, dass man sich vor Putins Bomben nicht fürchten solle, obwohl man in Mainz permanent Angst schürt und schon am 5. Mai 2022 titelt, »Moskau simuliert Atomangriff in Kaliningrad«.
Der »Beobachter Gesundheit« gibt Tipps dazu, wie man die Panik vor einem Atomkrieg mental in den Griff bekommen kann, während das deutsche BBK (Bundesamt für Bevölkerungsschutz und Katastrophenhilfe) der Bevölkerung bereits empfiehlt, im Zuge der Ukraine-Krise Notvorräte anzulegen und Marschgepäck bereitzuhalten. Auf der Webseite »wikiHow« findet sich ein sehr umfassender, bebilderter Ratgeber mit dem Titel »Einen Atomkrieg überleben«. Beim Lesen der zahlreichen, mutmaßlich nur bedingt hilfreichen Tipps zur Meisterung der nuklearen Apokalypse dürfte jedem normalen Menschen etwas mulmig werden.
Hofberichterstatter Ruprecht Polenz lässt sich beim Propaganda-Multiplikator ZEIT ONLINE am 30. April 2022 dennoch zu der wagemutigen Formulierung verleiten, »wer einen Atomkrieg verhindern will, darf Putin nicht gewinnen lassen«. Solch ein Statement ist nicht nur falsch und realitätsfremd, sondern zeugt gleichsam von der bewussten Negierung von Faktenlage und historischen Hintergründen zur Ukraine-Krise. Dabei könnte man es durchaus besser wissen.
Die RAND-Corporation, ein im Jahre 1948 gegründeter, einflussreicher Think Tank der US-Hegemonie, veröffentlichte zum Beispiel schon im Jahr 2019 ein vielsagendes, 354 Seiten umfassendes Strategiepapier unter der Überschrift »Overextending and Unbalancing Russia«. Frei übersetzt: Eine Strategie, um Russland überzustrapazieren und aus dem Gleichgewicht zu bringen – ökonomisch, militärisch und gesellschaftlich – mit dem singulären Ziel, die geopolitische Dominanz der Vereinigten Staaten zu bewahren. Ein durchdachtes Drehbuch zur finalen Erniedrigung und Bezwingung des ewigen Klassenfeindes sowie dem Erhalt der unipolaren Weltordnung, der Pax Americana.
Der Ansatz der RAND-Corporation: Die Osterweiterung der NATO forcieren, das Ansehen Russlands in der Welt zerstören, kostenintensives, nukleares Wettrüsten, die Ukraine bewaffnen, um einen militärischen Stellvertreterkonflikt mit Putin zu provozieren, um die ehemalige Sowjetunion anschließend mittels internationaler Sanktionen – legitimiert durch den brodelnden Krieg – finanziell in die Knie zu zwingen.
Verblüffend, wie sehr doch die im RAND-Strategiepapier aufgezeigte Vorgehensweise den aktuellen Geschehnissen an den Außengrenzen des Riesenreiches gleicht. Fast macht es den Anschein, als folgten die Geostrategen in Washington den Empfehlungen ihrer kostspieligen Think Tanks. Dies ließ sich auch im Zuge der Corona-Krise beobachten, die im Ablauf fraglos dem von der Rockefeller-Stiftung erarbeiteten Pandemie-Szenario »Lock Step« glich, wie Journalist Norbert Häring bereits am 28. Mai 2020 ausführlich berichtet.
Was das totalitäre Krisen-Drehbuch der RAND-Corporation nicht detailliert behandelt, sind die akuten Risiken einer potenziellen nuklearen Eskalation. Denn es endet mit dem möglichen Aufkeimen eines militärischen Konflikts und schließt schlicht mit dem Hinweis:
»Auch wenn die US-Armee nicht direkt an der Operation beteiligt ist, wird sie eine Schlüsselrolle bei der Abmilderung der Folgen spielen. Wie bereits erwähnt, bergen alle Maßnahmen, die der Schwächung Russlands dienen, einiges an Risiko. Infolgedessen werden das Abschreckungspotential sowie die operativen Fähigkeiten des US-Militärs in Europa gestärkt werden müssen. Es besteht die Möglichkeit, dass die Spannungen mit Russland zu einem Konflikt eskalieren.«
Die USA betrachten den Einsatz von Atomwaffen dabei offensichtlich als probates Mittel. Warum sonst modernisieren die Amerikaner seit Jahren ihr Arsenal und geben Milliarden US-Dollar dafür aus? Das macht eigentlich nur Sinn, wenn man plant, diese Waffen irgendwann einzusetzen. Der »Plot« für die Events nach dem Aufflammen einer militärischen Auseinandersetzung mit Russland ist vermutlich Verschlusssache und liegt nur Eingeweihten im Weißen Haus, Pentagon, CIA-Hauptquartier sowie den Verbündeten in EU und NATO-Hauptquartier vor.
Das ist bedauerlich. Denn ein Einblick in die aktuellen militärischen Planspiele und strategischen Szenarien der NATO-Hegemonie wäre hilfreich, um zu verstehen, ob die Arroganz des Westens tatsächlich einen Punkt erreicht hat, an dem man einen Atomkrieg in Kauf nehmen würde, um Russland und China auf ihre Plätze zu verweisen und im globalen Club der Technokraten am Kopfende zu sitzen. Um einen Konflikt der Systeme – Kapitalismus, Sozialismus, Kommunismus – handelt es sich nämlich nicht, auch wenn Medien dies gerne so darstellen, sondern um Machtkämpfe innerhalb der internationalen Oligarchie. Die drei Machtblöcke kämpfen um Vorherrschaft in der totalitären Weltordnung der nahen Zukunft.
Die Frage ist nur: Tun sie dies einvernehmlich – oder handelt es sich an Russlands Grenzen um ernsthafte, kriegerische Auseinandersetzungen, die in letzter Konsequenz militärisch entschieden werden müssen? Das RAND-Strategiepapier scheint davon auszugehen, dass Wirtschafts- und Informationskrieg, begleitet von NATO-Drohgebärden, ausreichen, um das Rennen zu Gunsten des Wertewestens zu entscheiden. Es gilt zu hoffen, dass diese Interpretation des Schriftstücks zutrifft. Ansonsten läuft die moderne Zivilisation Gefahr, sich in die Steinzeit zurückzubomben. Wie das aussieht, zeigt eindrücklich der Film »The Day After« (Der Tag danach) aus dem Jahre 1983.
Der zwei Stunden lange Streifen von Regisseur Nicholas Meyer ist bildgewaltig, beängstigend, ernüchternd und deprimierend. Er zeigt nicht nur, wie binnen weniger Tage aus einem Kalten Krieg ein Atomkrieg wird, sondern auch, was dessen schreckliche Folgen sind. Schon ein kurzer, etwas mehr als acht Minuten langer Zusammenschnitt macht klar, dass man ein absoluter Narr sein muss, um keine Angst vor thermonuklearen Angriffen zu haben.
Im Film gibt der US-Oberbefehlshaber nach der Zerstörung des NATO-Hauptquartiers den Befehl zum Atomschlag. Das entsprechende NATO-Protokoll wird aktiviert und die Raketensilos einsatzbereit gemacht. Das Drehbuch lässt offen, wer den Erstschlag führt. Klar ist, dass sobald die Sprengköpfe des Westens unterwegs sind, Russland einen Gegenangriff mit 300 Interkontinentalraketen auslöst und die Vereinigten Staaten in die Steinzeit bombt.
Überall im Land der unbegrenzten Möglichkeiten steigen feurige Atompilze in den Himmel. Metropolen werden in Sekunden ausradiert, Lebewesen, Pflanzen und Gebäude verdampfen in Feuersbrünsten um den Einschlagsort, ganze Landstriche werden vom Erdboden getilgt – und schon in den ersten Minuten nach Explosion der Nuklearsprengköpfe sterben weite Teile der Bevölkerung. 90 Millionen innerhalb weniger Stunden, wie eine Simulation mit dem etwas unheimlichen Titel »Plan A« der Princeton-Universität von 2019 berechnet hat.
Der eigentliche Horror beginnt allerdings erst. Denn die schlimmsten Szenen des Films sind jene, die den Zustand der Welt zwei Wochen nach den Atomschlägen zeigen. Im Land herrscht Anomie. Chaos und Zerstörung, wohin man schaut. Vorindustrielle Zustände. Die Städte sind unbewohnbar und die Überlebenden leiden an Strahlenkrankheit. Haare und Zähne fallen aus. Bei manchen binnen weniger Stunden oder Tage, bei anderen dauert es Wochen. Ein grausamer Tod auf Raten. Alles stirbt, siecht dahin. In den Ruinen entstehen Flüchtlingslager. Seuchen brechen aus. Militärkommandos erschießen willkürlich Menschen. Recht, Gerichte und Prozesse gibt es nicht mehr. Und um zu überleben, bewaffnen sich schlussendlich auch die Zivilisten und töten sich gegenseitig. Absolute Barbarei.
»The Day After« erklärt nicht, wer diesen Krieg gewinnt, nennt keinen Sieger. Vermutlich, weil Regisseur Nicholas Meyer schmerzlich bewusst war, dass es bei einem ausgewachsenen Atomkrieg keine Gewinner geben kann.
Er bedeutet das Ende der modernen Zivilisation. Nicht umsonst hat Albert Einstein früh vor militärischem Missbrauch entsprechender wissenschaftlicher Erkenntnisse gewarnt. So lässt der Streifen aus Zeiten das kalten Krieges auch das Ende offen. Kein Hollywood-Finale. Kein Happy End. Die beklemmenden Gefühle bleiben. Weder Will Smith noch James Bond tauchen auf, um die Welt in letzter Minute doch noch zu retten. Sie ist kaputt. Tot. Eine nuklear verseuchte Wüste. Kein Hoffnungsschimmer am Horizont.
Wer das Pech hatte, die Erstschläge zu überleben, stirbt langsam, aber sicher – und vor allem qualvoll.
Vielleicht sollten Spitzenpolitiker, Dogmatiker, Propagandisten und Kriegshetzer von heute sich diesen Film einmal in Ruhe anschauen, bevor sie leichtfertig derartige Optionen in Betracht ziehen. Ich habe »The Day After« nur ein einziges Mal in meinem Leben gesehen – wenige Monate, nachdem ich den Begriff »Pershing II« das erste Mal als kleines Kind im Radio hörte und meine Eltern neugierig fragte, was es damit auf sich hat – das war ausreichend. Die Eindrücke wirken bis heute. Ich bin mir auch mehr als dreißig Jahre später immer noch der unverrückbaren, indiskutablen Tatsache bewusst, dass es niemals zu einem Atomkrieg kommen darf. Jeder, der diesen Film gesehen, wird das unterschreiben.
Ich jedenfalls werde nie vergessen, wie ich eines nachts heimlich im dunklen Wohnzimmer der heimischen Dachwohnung ganz nahe vor dem Fernseher saß. Eigentlich durfte ich nur ein paar Mal in der Woche ausgewählte Kindersendungen anschauen. Aber meine Eltern schliefen bereits. Es muss circa 23:00 Uhr gewesen sein, denn nach den Spätfilmen war damals in der Regel Sendeschluss. Und das was war meist gegen eins oder halb zwei.
Just als ich den kleinen Röhrenfernseher anschaltete, begann »im Ersten« der bis heute in mir nachhallende Spielfilm. Der Tag danach. Zunächst begeistert von den vielen Raketen und irgendwie noch fasziniert von den mir bis dato unbekannten, riesigen Explosionen, die Atombomben auslösen, blieb ich gebannt sitzen. Wie versteinert. Bis zur Schlussszene, in der sich eine Handvoll strahlenverseuchter, zerrissener, verrottender Menschen, die kaum noch Haare auf dem Kopf haben und aussehen wie Zombies, in den staubigen Ruinen einer leeren Großstadt kraftlos in den Armen liegen und hilflos schluchzen. Die Kamera zieht auf. Dann Schwarzblende – und eine letzte, dünne, einsam flehende Stimme im Äther:
»Hello, is anybody there? Anybody at all?« (Hallo, ist da jemand? Irgendjemand?)
-
 @ 06bc9ab7:427c48f5
2025-03-17 15:46:23
@ 06bc9ab7:427c48f5
2025-03-17 15:46:23Bitcoin Safe - A bitcoin savings wallet for the entire family
Designed for both beginners and power users, Bitcoin Safe combines security with an intuitive user experience. In this article, we dive deep into its features, unique benefits, and the powerful tools that make managing your Bitcoin wallet simple and secure.
Built for Learners
✔️ Step-by-step wallet setup wizard + PDF backup sheets 📄 🧪 Test transactions to ensure all hardware signers are ready 🔑 🛡️ Secure: Hardware signers only – no hot wallet risks 🚫🔥 🌍 Multi-language support: 🇺🇸 🇨🇳 🇪🇸 🇯🇵 🇷🇺 🇵🇹 🇮🇳 🇮🇹 🇫🇷 🇩🇪 🇲🇲 🇰🇷 📁 Address categories for easy organization ☁️ Label and category synchronization, and cloud backup (optional) 💰 Automatic UTXO merging to save on fees ⚡ Fast syncing with Electrum servers, Compact Block Filters coming soon
Built for Power Users
🔐 Supports Coldcard, Bitbox02, Jade, Trezor, Passport, Keystone & many more 🏦 💬 Multi-party multisig chat & PSBT sharing (optional) 📊 Transaction flow diagrams to trace coin movements 🔍 Instant cross-wallet wallet search ⚙️ Set your own electrum server, mempool instance, and nostr relay
Step-by-Step Wallet Setup
Whether you’re setting up a single-signature or multi-signature wallet, the setup wizard guides you every step of the way:

- Single Sig Wizard: Follow the intuitive wizard that walks you through each step. https://youtu.be/m0g6ytYTy0w
Clear instructions paired with hardware signer screen-shots, like the steps for a Coldcard
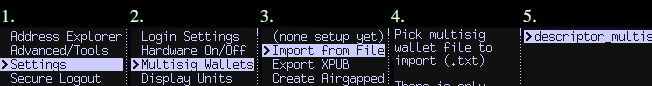
-
Multisig Wizard: The wizard ensures you do all necessary steps for a Multisig wallet in the right order. Afterwards your Multisig is ready to use and all signers are tested. Check out https://bitcoin-safe.org/en/features/setup-multisignature-wallet/
-
PDF Backup: The wizard will also generates 3 PDF backup sheets for a 2-of-3 multisig wallet, so ensure you always have your wallet descriptor together with the seed.
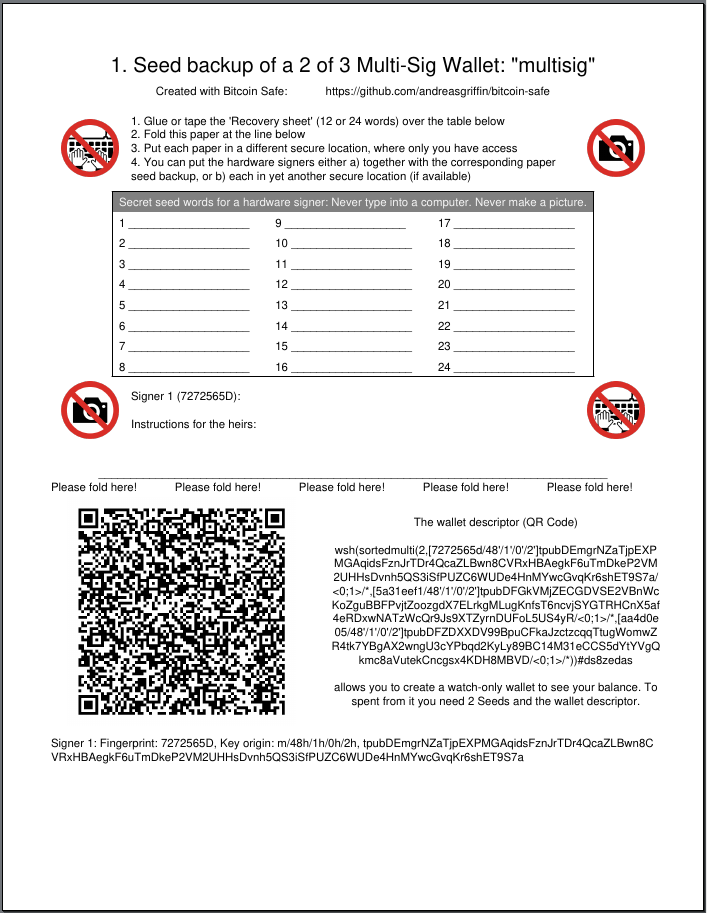
-
Hardware Signer Support: With full support for major hardware signers your keys remain securely offline.
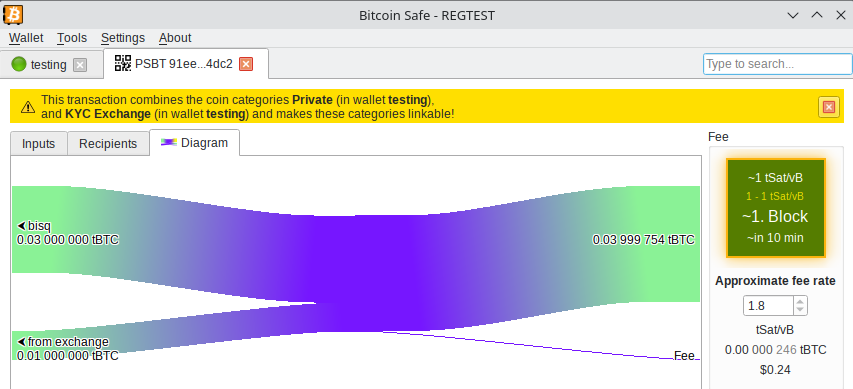
Transaction Visualization
Visualize and navigate your transaction history:
-
Graphical Explorer: An interactive transaction diagram lets you click on inputs and outputs to follow the money flow intuitively.
-
Coin Categories: Organize your addresses into distinct coin categories (e.g., “KYC”, “Work”, “Friends”) so Bitcoin Safe automatically selects the correct inputs when creating PSBTs.

It prevents you accidentally linking coin categories when creating a transaction, and warns you if mistakes happened in the past.
Powerful Wallet Management Tools
- Flexible Fee Selection: Choose fees with one click using an intuitive mempool block preview.
- UTXO Management: Automatically (optional) merge UTXOs when fees are low.
- CSV Table Export: Right click, Drag&Drop, or CTRL+C for immediate CSV export for easy processing in Excel.
- PDF Balance Statement: Export the address balances for easy record keeping on paper.
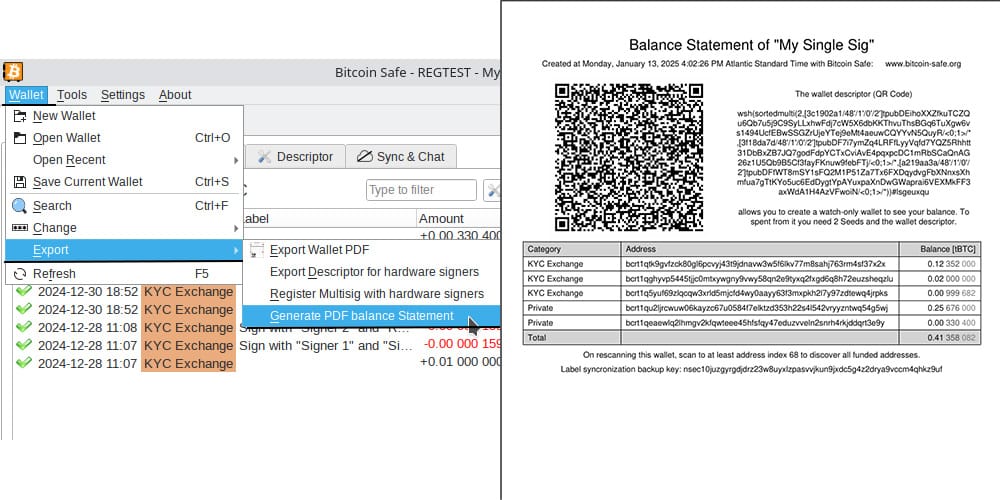
Advanced Features for the Power-User
Sync & Chat is off by default (for the paranoid user), but can be enabled with just one click.
Label Synchronization and Backup
- Seamless Sync: Using encrypted nostr messages, Bitcoin Safe synchronizes your coin categories and labels across multiple devices.
- Easy Backup: A short backup key is all you need to safeguard your coin categories and labels, ensuring your organization remains intact.
Collaborative Multi-party Multisig
- Group Chat Integration: After creating your multisig wallet, Bitcoin Safe offers an encrypted nostr group chat for secure collaboration and one-click PSBT sharing.
- User Authentication: Each participant must authenticate every other user with a simple click, ensuring secure communication.
Watch and Learn: Get Started with Bitcoin Safe
If you’re new to Bitcoin Safe, a short video guide can make all the difference. Learn how to set up your Bitcoin Safe wallet in this detailed walk through:
https://youtu.be/m0g6ytYTy0w
Or see how to verify an address on your hardware singer:
https://youtu.be/h5FkOYj9OT8
Building up a knowledge base: https://bitcoin-safe.org/en/knowledge/
Whats next?
- Compact Block Filters!!! They make electrum servers obsolete.
- Why? Compact Block Filters increase the network privacy dramatically, since you're not asking an electrum server to give you your transactions
- Trade-off: They are a little slower than electrum servers. For a savings wallet like Bitcoin Safe this should be OK.
- How do they work? Simply speaking: They ask normal bitcoin core nodes for a short summary of each block. And if the summary shows a transaction belonging to the wallet, the entire block is then downloaded from the bitcoin core node. The bitcoin core node does not learn however which of the many transactions in the block you were interested in. Read more here and of course in the bip.
- When: 2 weeks 😅. Lots of things need to be done until Bitcoin Safe can use the bdk CBF/kyoto client from rustaceanrob, so keep an eye out for updates and please give feedback when you use Bitcoin Safe.
Stay updated on nostr or on GitHub.
Thank you
A huge thanks goes to nostr:npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f for supporting this project with a grant and nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx for the Hackathon prize.
This wallet is only possible because it is building upon other peoples open source work. Most notably
- bdk nostr:nprofile1qqsgkmgkmv63djkxmwvdlyaxx0xtsytvkyyg5fwzmp48pwd30f3jtxspzemhxue69uhhyetvv9ujuurjd9kkzmpwdejhgqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqr8vuet
- and especially nostr:npub1thunderat5g552cuy7umk624ct5xe4tpgwr2jcjjq2gc0567wgrqnya79l , nostr:npub1reezn2ctrrg736uqj7mva9lsuwv0kr5asj4vvkwxnrwlhvxf98tsq99ty4 , and nostr:npub1ke470rdgnxg4gjs9cw3tv0dp690wl68f5xak5smflpsksedadd7qtf8jfm for dealing with my many feature requests and questions.
- rustaceanrob building kyoto which implements CBF for BDK; a crucial library and will be able to replace electrum servers for many use cases
- ndk by nostr:nprofile1qqsx3kq3vkgczq9hmfplc28h687py42yvms3zkyxh8nmkvn0vhkyyuspz4mhxue69uhkummnw3ezummcw3ezuer9wchsz9thwden5te0wfjkccte9ejxzmt4wvhxjme0qy88wumn8ghj7mn0wvhxcmmv9u0uehfp
And of course, secure storage of bitcoin is only possible, because of the hardware signer manufacturers. Thanks to nostr:npub1az9xj85cmxv8e9j9y80lvqp97crsqdu2fpu3srwthd99qfu9qsgstam8y8 Coldcard , Coldcard Q , nostr:npub1tg779rlap8t4qm8lpgn89k7mr7pkxpaulupp0nq5faywr8h28llsj3cxmt Bitbox02 , nostr:npub1jg552aulj07skd6e7y2hu0vl5g8nl5jvfw8jhn6jpjk0vjd0waksvl6n8n Blockstream Jade , Trezor Safe, Foundation Passport, Keystone, Ledger, Specter Shield, and many more.
I also want to thank people who gave feedback and helped spread the knowledge of Bitcoin Safe (please forgive me if I forgot to mention you)
- nostr:npub1p5cmlt32vc3jefkl3ymdvm9zk892fsmkq79eq77uvkaqrnyktasqkpkgaw nostr:npub1s07s0h5mwcenfnyagme8shp9trnv964lulgvdmppgenuhtk9p4rsueuk63 nostr:npub18f3g76xc7xs430euwwl9gpn7ue7ux8vmtm9q8htn9s26d8c4neeqdraz3s nostr:npub1mtd7s63xd85ykv09p7y8wvg754jpsfpplxknh5xr0pu938zf86fqygqxas nostr:npub1kysd8m44dhv7ywa75u5z7w2w0gs4t6qzhgvjp555gfknasy3krlqfxde60 nostr:npub185pu2dsgg9d36uvvw7rwuy9aknn8hnknygr7x2yqa60ygvq6r8kqc836k8 nostr:npub1hkcgyqnsuaradq3g5hyvfdekwypc25494nmwggwpygxas7fcs4fst860fu nostr:npub1xsl0msy347vmj8gcpsjum6wwppc4ercvq4xfrhqmek2dqmqm0mtsyf35vx nostr:npub1hxjnw53mhghumt590kgd3fmqme8jzwwflyxesmm50nnapmqdzu7swqagw3 nostr:npub1ke470rdgnxg4gjs9cw3tv0dp690wl68f5xak5smflpsksedadd7qtf8jfm nostr:npub1sk26fxl4fy3vt8m5n0a6aturaql0w20nvh22q0cyaqm28tj7z8ss3lutc9 nostr:npub1r4llq2jcvq4g2tgha5amjz07zk7mrrcj89wllny9xwhhp5zzkklqk4jwja nostr:npub1p9v2zpwl28c0gu0vr2enp3lwdtv29scwpeqsnt0ngqf03vtlyxfqhkae5w nostr:npub1xkym0yaewlz0qfghtt7hjtnu28fxaa5rk3wtcek9d3x3ft2ns3lq775few nostr:npub1r8343wqpra05l3jnc4jud4xz7vlnyeslf7gfsty7ahpf92rhfmpsmqwym8 nostr:npub12zpfs3yq7we83yvypgsrw5f88y2fv780c2kfs89ge5qk6q3sfm7spks880 nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx https://x.com/91xTx93x2 https://x.com/afilini rustaceanrob
-
 @ 1731c73c:1bca4ecc
2025-03-17 14:13:04
@ 1731c73c:1bca4ecc
2025-03-17 14:13:04Welch Geistes Kind sind Waffenproduzenten, welch Geistes Kind Wissenschaftler, die Viren so verändern, dass sie pathogener, also gefährlicher für den Menschen werden? Im pfälzischen
https://soundcloud.com/radiomuenchen/kommt-wuhan-nach-deutschland-von-prof-roland-wiesendanger
Weilerbach wird ein US-Biolabor der Schutzstufe 3 gebaut. Dort sollen hochinfektiöse Erreger oder Substanzen, unter anderem SARS-CoV-2, das Virus H5N1, Dengue- und das Hanta-Virus untersucht werden. Der Bundesregierung – so fand Florian Warweg von den NachDenkSeiten heraus - weiß davon angeblich nichts. Auch nicht, welche Kontrollfunktion Bundesbehörden für US-Biolabore auf deutschem Boden haben.
War da was? Hatte nicht – ebenso vertuscht von Regierung, Medien und Wissenschaftlern – für die einen die größte Pandemie, für die anderen der weltweit größte Wissenschafts- und Medizinskandal in den letzten fünf Jahren stattgefunden? Warum interessiert das keinen?
Die Bestätigung der US-Regierung ist offiziell, dass die Covid-19-Pandemie aus einem Labor in Wuhan stammt. Das entlarvt die jahrelange Vertuschung und Diffamierung kritischer Stimmen als politisch motivierte Manipulation. Einer, der diskreditiert wurde, ist Professor Roland Wiesendanger. Mundtot ließ er sich aber nicht machen. Er fordert weiterhin eine schonungslose Aufarbeitung der hochgefährlichen Gain-of-function-Forschung, außerdem deren weltweite Ächtung, um zukünftige Pandemien zu verhindern.
Roland Wiesendanger ist Physik-Professor an der Universität Hamburg, Ehrendoktor der Technischen Universität Posen und Mitglied zahlreicher nationaler und internationaler Wissenschaftsakademien. Hören Sie sein Statement: „Wir dürfen die Risiken der Gain- of-function-Forschung nicht länger hinnehmen“.
Sprecher: Ulrich Allroggen
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): 3G1wDDH2CDPJ9DHan5TTpsfpSXWhNMCZmQ\ Ethereum (ETH): 0xB41106C0fa3974353Ef86F62B62228A0f4ad7fe9
-
 @ b8af284d:f82c91dd
2025-03-16 16:42:49
@ b8af284d:f82c91dd
2025-03-16 16:42:49
Liebe Abonnenten,
diejenigen, die diese Publikation schon länger abonniert haben, wissen, dass hier immer wieder über den Ursprung des Corona-Virus in einem Labor in Wuhan berichtet wurde. Seit diese Woche ist es „offiziell“ - der Bundesnachrichtendienst (BND) hält den Labor-Ursprung für die wahrscheinlichste Variante. Jetzt kann man sich fragen, warum der BND plötzlich umschwenkt: Will man proaktiv erscheinen, weil man die Wahrheit nicht mehr länger verbergen kann? Oder will man die enttäuschten Bürger zurückgewinnen, die aufgrund der Lügen während der Corona-Zeit zunehmend mit Parteien links und rechts außen sympathisiert haben, weil diese die einzigen waren, die den Irrsinn nicht mitgetragen haben?
Auffallend bei den „Recherchen“, die in Wahrheit keine sind, sondern Verlautbarungen des deutschen Geheimdienstes, ist auch das völlige Schweigen über die US-amerikanischen Verwicklungen in das Projekt. In Wuhan wurde mit amerikanischem Geld geforscht. Warum der BND diese Tatsache verschweigt, ist Teil der Spekulation. Vermutlich will man Peking alles in die Schuhe schieben, um von den eigenen Versäumnissen abzulenken.
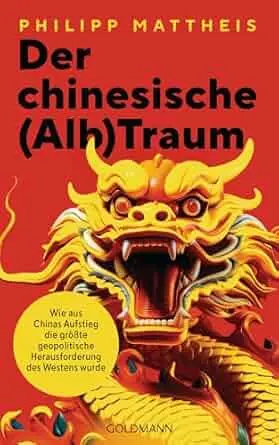
In meinem aktuellen Buch “Der chinesische (Alp-)Traum” ist den Ereignissen in Wuhan ein ganzes Kapitel gewidmet. Es hat nichts an Aktualität eingebüßt. Alle Fakten lagen seit Jahren auf dem Tisch für jeden, den es interessiert hat. Hier gibt es das gesamte Kapitel nachzulesen.
Auf jeden Fall zeigt dies, wie der Begriff „Verschwörungstheoretiker“ in den vergangenen Jahren zum Kampfbegriff und Waffe gemacht wurde, um Kritiker zu diffamieren, und die öffentliche Meinung ohne harte Zensur zu lenken. Ähnliches kann man aktuell beim Projekt „Digitaler Euro“ beobachten. Vermutlich kann sich kein Bürger der Europäischen Union daran erinnern, bei seiner Wahlentscheidung jemals gefragt worden zu sein, ob er die Einführung eines „digitalen Euros“ gut findet. Wurde er nämlich nicht. Er kommt aber trotzdem. EZB-Präsidentin Christine Lagarde hat das diese Woche nochmals bekräftigt: Schon im Oktober will man die Testphase beenden und an der Einführung arbeiten.
Nun gehört BlingBling nicht zu denjenigen, die im digitalen Euro „Orwell’sches Teufelswerk“ sehen. Strategische Dummheit trifft es besser. Worum geht es?
Sogenannte Central Bank Digital Currencies (CBDC) waren vor einigen Jahren so etwas wie der letzte Schrei in der Zentralbank-Welt. Nachdem Facebook/Meta 2017/18 eine eigene Währung namens Libra auf den Markt bringen wollte, und eine obskure Internet-Währung namens Bitcoin immer mehr Anhänger fand, sahen sich viele Zentralbanken der Welt unter Zugzwang. Was man wollte: eine digitale, direkt von der Zentralbank ausgegebene Währung ohne Bugs, aber mit Features. Mit einer Digital-Währung ließe sich der internationale Zahlungsverkehr direkt und ohne Umweg über den US-Dollar abwickeln. Die Zentralbank bekäme wieder mehr direkten Einfluss auf die Geldschöpfung. Und, wie man aus China lernen konnte, ließen sich digitale Bankkonten auch ganz zum „Nudging von Bürgern“ nutzen. So spekulierten die ersten Verschwörungstheoretiker bald, ein digitaler Euro ließe sich ja mit einem persönlichen CO2-Konto verknüpfen. Wäre letzteres einmal aufgebraucht, könnte der Konto-Inhaber einfach keinen Flug mehr buchen. Auch ließe sich eine expansive Geldpolitik, wie sie bis 2022 praktiziert wurde, ganz einfach mit Negativ-Zinsen umsetzen. Geld würde sich nominal reduzieren, was den Bürger zum Konsum animieren würde. Flüchtigen Kriminellen ließe sich per Knopfdruck das Konto sperren. Der Staat würde also über eine ganze neue Palette an Einflussmöglichkeiten verfügen.
Die Aluhüte United warnten vor einem Orwellschen Überwachungsstaat. Vertreter von Regierungen und Firmen, die diesen digitalen Euro bauen sollten, beschwichtigten. Mit Ralf Wintergerst, CEO von Giesecke+Devrient, nach wie vor heißester Anwärter, um das Projekt in der EU umzusetzen, sprach ich in den vergangenen Jahren mehrmals zu dem Thema. Zuletzt im Dezember 24.
Wintergerst versichert stets zwei Dinge: Eine Abschaffung von Bargeld sei nicht geplant. Und nur, wenn die Fluchttore Bargeld, Gold und Bitcoin geschlossen werden, greift die dystopische Version. Und zweitens, so Wintergerst, habe niemand ein chinesisches System im Sinne. Der „digitale Euro“ sei für die Bürger gedacht und das Projekt unterliege demokratischer Kontrolle. Ob er Wintergerst und dem guten im Menschen Glauben schenkt, möge jeder Leser selbst entscheiden. Das Interessantere ist ohnehin, dass der digitale Euro ein strategisch dummes Projekt ist.
Dazu muss man wissen, dass eine solche Zentralbankwährung Banken im weitesten Sinne überflüssig macht. Kontos bei Privatbanken werden obsolet, genauso wie Spar-, Fest- und Tagesgeld-Strukturen. Deshalb soll der digitale Euro zunächst auf 3000 Euro pro Bürger beschränkt werden. Das ist also nicht als Maximal-Vermögen gedacht, das dann jedem sozialistischen Einheits-EU-Menschen noch zusteht, sondern dient dazu, das Bankensystem nicht kollabieren zu lassen. Aber wozu überhaupt „ein bisschen digitaler Euro“?
In den USA setzt man mittlerweile 100 Prozent auf die private Alternative: Stablecoins wie Tether (USDT) und Circle (USDC) sind nichts anderes als digitale Währungen. Nur sind sie nicht von einer Zentralbank ausgeben, sondern von privaten Anbietern. Tether hat technisch die Möglichkeit, einen Inhaber vom Zahlungsverkehr auszusperren. Nur dürfte es davon kaum Gebrauch machen, will das Unternehmen nicht rasant Kunden an die Konkurrenz verlieren. Da USDT und USDC mit US-Dollar gedeckt sind (oder zumindest sein sollten, looking at you, Tether!), stärken sie außerdem die Rolle des US-Dollars als Leitwährung. Und da die USA sich aktuell sehr über Käufer von Staatsanleihen freuen, um die Zinsen zu drücken, und Tether einer der größten Halter von US-Staatsanleihen ist, wird es den digitalen Dollar bis auf Weiteres nicht geben.
Den digitalen Yuan gibt es, aber von einer großen Akzeptanz oder Durchdringung der chinesischen Wirtschaft lässt sich nicht sprechen. Kontrolle kann der chinesische Staat ohnehin über seine omnipräsenten Apps WeChat und Alipay ausüben. Was den internationalen Zahlungsverkehr betrifft, scheint man aktuell eher auf Gold zu setzen.
Übrig also bleibt die EU mit einem Projekt, das bereits Milliarden an Entwicklungskosten verschlungen hat. Am Ende bleibt dann ein Mini-Digitaler-Euro in Höhe von 3000 Euro, den niemand wollte, und niemand braucht.
Helfen könnte er allerdings beim Projekt “Mobilisierung der Sparguthaben”. Der Ausdruck geht auf Friedrich Merz zurück. Ursula von der Leyen paraphrasierte ihn jüngst:

Irgendwie müssen die Billionen von Sparguthaben in Militär-Investitionen umgewandelt werden. Das wird am besten funktionieren mit Anleihen, die schlechter verzinst sind als sonst auf dem Markt üblich. Wie bringt man Leute dazu, dann ihr Geld dort zu investieren? Entweder man zwingt sie, oder man bewirbt die Anleihen mit viel Patriotismus und Propaganda. Die Verschwörungstheoretiker unter uns bekommen also bald Futter, wenn die „Spar- und Investitionsunion” vorgestellt wird.
Like, wenn Dein Aluhut glüht…
Hinter der Paywall: Wie das Trump-Derangement-Syndrom den Blick auf den Markt trübt. Wie es mit Bitcoin, Gold und Aktien weitergeht.**
-
 @ 6830c409:ff17c655
2025-03-22 04:59:06
@ 6830c409:ff17c655
2025-03-22 04:59:06സോഷ്യൽ മീഡിയ ഇന്ന്
ഇന്ന് സോഷ്യൽ മീഡിയ നേരിടുന്ന ഏറ്റവും വലിയ വെല്ലുവിളികളിൽ ഒന്ന് എല്ലാ മേജർ പ്ലാറ്റ്ഫോമുകളും കൈകാര്യം ചെയ്യുന്നത് വൻകോർപറേറ്റുകളാണെന്നതാണ്. കോർപ്പറേറ്റുകൾ വലിയ ഹോൾഡിങ്ങുകൾ കൈവശം വയ്ക്കുന്നത് സ്വാഭാവികവും വളരെ ഈസിയും ആണ്. പക്ഷെ, അത് ഒരു വെല്ലുവിളിയായി മാറുന്നത്, ഏതെങ്കിലും ഒരു നറേറ്റിവിനെ ബൂസ്റ്റ് ചെയ്യുകയും, മറ്റൊരു നറേറ്റിവിനെ തമസ്കരിക്കുകയും ചെയ്യുമ്പോഴാണ്. ഇത് തന്നെയാണ് "misinformation"/"disinformation" ഉണ്ടാകുന്നതിന്റെ മൂലകാരണവും. ഉദാഹരണത്തിന് ഇന്ന് ഇലോൺ മസ്കിന്റെ ഒരു റ്റ്വീറ്റെങ്കിലും കാണാതെ റ്റ്വിറ്റർ തുറക്കാൻ കഴിയില്ല. അതിനി മസ്കിനെ ബ്ലോക്ക് ചെയ്തിട്ടുണ്ടെങ്കിൽ പോലും ആ റ്റ്വീറ്റുകൾ ബൂസ്റ്റ് ചെയ്യപ്പെടും. എന്തുകാരണത്തിനാണ് എന്ന് പറയാതെ അക്കൗണ്ടുകൾ ലിമിറ്റ് ചെയ്യുകയോ, ലോക്ക്ഡൗൺ ചെയ്യുകയോ ഒക്കെ ആയിട്ടുണ്ട്.
സൊ, നിങ്ങളുടെ അക്കൗണ്ട് ശരിക്കും നിങ്ങൾക്ക് Own ചെയ്യാൻ കഴിയാത്ത ഒരു സാധനമാണ് ഇപ്പൊഴുള്ള convensional സോഷ്യൽ മീഡിയ പ്ലാറ്റ്ഫൊമുകളിൽ.
ഒരു പ്രൊപ്പോസൽ
- നിങ്ങളുടെ അക്കൗണ്ടിന്റെ പൂർണ്ണ ഉടമസ്ഥത നിങ്ങൾക്ക് തന്നെ തരുന്നു എന്ന് കരുതുക.
- നിങ്ങളുടെ റ്റ്വീറ്റുകൾ/പോസ്റ്റുകൾ ഏതെങ്കിലും ഒരു സർവ്വർ അല്ലെങ്കിൽ ഒരു സർവ്വീസിന്റെ കൈവശം പണയപ്പെടുത്തേണ്ട അവസ്ഥ ഇല്ലാതെയാകുന്നു എന്ന് കരുതുക
സോഷ്യൽ മീഡിയ ഉപയോഗത്തിനെ നിങ്ങൾക്ക് ഒന്ന് മാറ്റിച്ചിന്തിക്കാൻ മേൽപ്പറഞ്ഞ കാരണങ്ങൾ മതിയാവില്ലെ?
അതായത് റ്റ്വിറ്ററോ ഫേസ്ബുക്കോ പോലെ ഒരു കമ്പനി വിചാരിച്ചാൽ നിങ്ങളുടെ പോസ്റ്റുകൾ ഡിലീറ്റ് ചെയ്യാൻ കഴിയില്ല എന്ന ഒരു അവസ്ഥ കൊണ്ടുവരാൻ കഴിയുന്ന ഒരു സോഷ്യൽ മീഡിയ വന്നാലോ?
ആ സോഷ്യൽ മീഡിയ പ്ലാറ്റ്ഫോമിനെയാണ് ഞാൻ നിങ്ങൾക്ക് പരിചയപ്പെടുത്താൻ പോകുന്നത്.
നൊസ്റ്റർ (Nostr)
നൊസ്റ്റർ എങ്ങനെ മറ്റുള്ള പ്ലാറ്റ്ഫോമുകളിൽ നിന്നും വ്യത്യസ്തമാണെന്ന് നോക്കാം
Notes and Other Stuff Transmitted by Relays
നൊസ്റ്റർ ഏതെങ്കിലും ഒരു സർവ്വറിനെയോ സർവ്വീസ് പ്രൊവൈഡറെയോ ആശ്രയിച്ചല്ല ഓടുന്നത്. ഇന്നത്തെ കണക്കിന് തന്നെ ആയിരത്തോളം ഇൻഡിപ്പെൻഡന്റ് സർവ്വറുകൾ നൊസ്റ്ററിനായി പ്രവർത്തിക്കുന്നുണ്ട്. എന്ന് മാത്രവുമല്ല, ഒരു ക്ലൗഡ് അക്കൗണ്ടുണ്ടെങ്കിൽ ആർക്കും സ്വന്തമായി ഒരു സർവ്വർ റൺ ചെയ്യാവുന്നതേയുള്ളൂ. എന്ന് കരുതി, എല്ലാവരും സ്വന്തം സർവ്വർ റൺ ചെയ്യണമെന്നില്ല.
ഒരു സാധാരണ സോഷ്യൽമീഡിയ യൂസറിന് ഉപയോഗിക്കാൻ എളുപ്പമുള്ള ആപ്പുകൾ നൊസ്റ്ററിനുണ്ട്. ഐഫോണുകളിൽ Damus, ആൻഡ്രോയ്ഡിൽ Amethyst, Primal.net തുടങ്ങി ഒരുപാട് ക്ലയന്റ് ആപ്പുകൾ ലഭ്യമാണ്. അവയിൽ ഏതെങ്കിലും ഒന്ന് ഇൻസ്റ്റാൾ ചെയ്താൽ റ്റ്വിറ്ററോ ഫേസ്ബുക്കോ പോലെ ഉപയോഗിക്കാൻ തുടങ്ങാവുന്നതേയുള്ളൂ. ഒരു ചെറിയ ലിസ്റ്റ് ചുവടെ ചേർക്കുന്നു.
Damus (iPhones): https://damus.io/
Amethyst (Android): https://play.google.com/store/apps/details?id=com.vitorpamplona.amethyst&hl=en_US
Yakihonne (Web, iPhone): https://yakihonne.com/
Primal.net (Web, iPhone): https://primal.net
**https://openvibe.social/ - ഒരേസമയം ബ്ലൂസ്കൈ, മാസ്റ്റഡോൺ, നൊസ്റ്റർ എന്നിവയിൽ പോസ്റ്റ് ചെയ്യാനും അക്കൗണ്ടുകൾ മെയ്ന്റെൻ ചെയ്യാനും ഓപ്പൺ വൈബ് അടിപൊളിയാണ്. **
Permission-free
നൊസ്റ്റർ ഉപയോഗിക്കാൻ യൂസർനേമും പാസ്സ്വേഡും ഇല്ല. പകരം, ഒരു പബ്ലിക്ക് കീയും പ്രൈവറ്റ് കീയും മാത്രമേയുള്ളൂ. ഇതുകൊണ്ടുള്ള പ്രയോജനം എന്താണെന്നാൽ, നിങ്ങൾക്ക് ആപ്പ്ലിക്കേഷനിലേക്ക് ലോഗിൻ ചെയ്യാൻ, ഒരു സർവ്വർ ആവശ്യമില്ല.
നിങ്ങൾ സൈനപ്പ് ചെയ്യുമ്പോൾ ഒരു "പ്രൈവറ്റ്" കീ ജനറേറ്റ് ചെയ്യപ്പെടും. അത് നിങ്ങൾ രഹസ്യമായി സൂക്ഷിക്കണമെന്ന് മാത്രം. ആ പ്രൈവറ്റ് കീ ഉണ്ടെങ്കിൽ മാത്രമേ നിങ്ങളുടെ അക്കൗണ്ടിലേക്ക് ലോഗിൻ ചെയ്യാൻ കഴിയൂ. അതിന്റെ കൂടെ തന്നെ ഒരു "പബ്ലിക്ക്" കീയും ഉണ്ടാകും. ആ കീ ആണ് മറ്റുള്ളവർ കാണുന്നത്. ഇതുകൂടാതെ, റ്റ്വിറ്റർ ഹാൻഡിൽ പോലെ ഒരു ഐഡിയും ഉണ്ടാക്കാൻ കഴിയും.
- പ്രൈവറ്റ് കീ രഹസ്യമായി സൂക്ഷിക്കണം
- പബ്ലിക്ക് കീ മറ്റുള്ളവർക്ക് കാണാൻ സാധിക്കും/ഷെയർ ചെയ്യാവുന്നതാണ്.
എവിടെ സൈനപ്പ് ചെയ്യും?
ആദ്യം നിങ്ങളുടെ ഫോണിൽ മേൽപ്പറഞ്ഞതിൽ ഒരു അപ്പ് ഇൻസ്റ്റാൾ ചെയ്യുക. എന്നിട്ട് അതിൽ തന്നെ സൈനപ്പ് ചെയ്യാൻ കഴിയും. അതല്ല എങ്കിൽ, https://nosta.me, https://nostrudel, https://primal.net എന്നിവയിലൊന്നിൽ സൈനപ്പ് ചെയ്യാവുന്നതാണ്.
ശ്രദ്ധിക്കേണ്ട കാര്യം, ആ പ്രൈവറ്റ് കീ കളഞ്ഞ് പോകാതെ സൂക്ഷിക്കണം. അത് മറ്റുള്ളവരുമായി ഷെയർ ചെയ്യരുത്.
ഇത്രയുമായാൽ നിങ്ങൾക്ക് നൊസ്റ്ററിൽ ഒരു അക്കൗണ്ട് ആയി... ആദ്യം എന്നെ തന്നെ ഫോളോ ചെയ്തോളൂ!! :ഡ് My profile: nostr:npub1dqcvgz20g2sn3venz47pxzjn2w6pf8xxs03vrrrwqp8z9lchce2ssj9fsy
നമ്മടെ റ്റ്വിറ്ററിന്റെ ഫൗണ്ടർ ജാക്ക് അണ്ണന്റെ അക്കൗണ്ട്: nostr:npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
നൊസ്റ്റർ പ്രോട്ടോക്കോൾ ഡെവലപ്മെന്റിന്റെ ഒരു ലീഡ് - കൂടുതൽ കാര്യങ്ങൾ അറിയാൻ ഡെറിക്കിനെ ഫോളോ ചെയ്യാം: nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424
നൊസ്റ്റർ ഒരു സോഷ്യൽ മീഡിയ പ്ലാറ്റ്ഫോം എന്നതിലുപരി ഒരു ഇക്കോസിസ്റ്റം ആണ്.
വരും നാളുകളിൽ കൂടുതൽ വിവരങ്ങൾ എഴുതാം: 1. Technical details - How this thing runs 2. How Nostr has decoupled monetary transactions from a centralized authority? 3. Zapping 3. Nostr Implementation Possibilities (NIPs) * - This is the most interesting thing I liked in Nostr*
Browse more: 1. https://nostr.com/ 2. https://nostrapps.com/
-
 @ d5c3d063:4d1159b3
2025-03-22 03:31:14
@ d5c3d063:4d1159b3
2025-03-22 03:31:14“คุณจะจัดการกับมลพิษฝุ่น PM2.5 โดยไม่ต้องอาศัยการออกกฎควบคุมจากรัฐได้ยังไง” ถ้าคุณเคยตั้งคำถามนี้ บทความนี้มีคำตอบ...และคำตอบอาจสวนทางกับความเชื่อของคุณโดยสิ้นเชิง . ลองย้อนกลับไปในช่วงต้นปีที่ผ่านมา ในวันที่กรมควบคุมมลพิษประกาศว่า “ค่าฝุ่น PM2.5 เกินมาตรฐานใน 43 จังหวัด” และโรงเรียนหลายแห่งต้องสั่งปิดชั่วคราว คุณอาจนึกถึงภาพผู้คนใส่หน้ากากเดินท่ามกลางหมอกควัน แล้วถามตัวเองว่า “เรากำลังแก้ปัญหานี้ด้วยวิธีที่ถูกต้องจริงหรือ?” ฝุ่น PM2.5 ปัญหาของ "Externalities" หรือปัญหาของการไม่มี "สิทธิในทรัพย์สิน" ที่ชัดเจน? . ในคลิปวิดีโอ จาก CDC Bitcointalk EP3 เมื่อปี 2020 อ.พิริยะ สัมพันธารักษ์ ได้เสนอแนวคิดที่ขัดแย้งกับสิ่งที่รัฐและสื่อกระแสหลักมักพูดถึงเสมอเมื่อพูดถึงฝุ่น PM2.5 ว่า... “ฝุ่น PM2.5 ไม่ใช่ปัญหาที่จะถูกแก้ได้ด้วยการออกกฎหมายควบคุมหรือแจกหน้ากากฟรี...แต่ต้องแก้ด้วยการ สร้างกลไกตลาดและสิทธิในทรัพย์สินที่ชัดเจน เพื่อให้คนที่ก่อมลพิษต้อง จ่าย ให้กับผู้ได้รับผลกระทบ” . . แล้วมันเกี่ยวอะไรกับ Hazlitt ??? Henry Hazlitt กล่าวไว้ในบทแรกของ Economics in One Lesson ว่า ความผิดพลาดทางเศรษฐศาสตร์ส่วนใหญ่เกิดจากการมองแค่ผลกระทบเฉพาะหน้า และมองเฉพาะผลที่เกิดกับคนบางกลุ่ม แต่ละเลยผลระยะยาวกับทั้งระบบและมองไม่เห็น “สิ่งที่ไม่ปรากฏต่อสายตา” เช่นเดียวกับกรณีฝุ่น PM2.5 . การที่รัฐเข้ามาควบคุม เช่น การสั่งห้ามเผา อาจฟังดูดีในระยะสั้น แต่มันยังไม่มีแรงจูงใจทางเศรษฐกิจให้ผู้เผาหยุดทำ เพราะต้นทุนการก่อมลพิษยัง “ฟรี” ถ้ามลพิษมีต้นทุน คนก็จะคิดก่อนเผา . ลองนึกถึงแนวคิดของการซื้อ-ขายสิทธิในเชิงสมัครใจ (Voluntary Emissions Trading) ซึ่งต่างจากระบบ Cap-and-Trade ที่ภาครัฐเป็นผู้กำหนดเพดานและบังคับใช้ แต่ในแนวทางตลาดเสรีนั้น หากสิทธิในอากาศหรือพื้นที่ถูกระบุอย่างชัดเจน เจ้าของสิทธิสามารถตกลงซื้อขายกับผู้ก่อมลพิษได้โดยตรงโดยไม่ต้องพึ่งรัฐเป็นคนกลาง . แล้วในบริบทแบบ Hazlitt ถ้าคุณให้ความเป็นเจ้าของอากาศแก่คนในเมือง คนเหล่านั้นสามารถ “ฟ้องร้อง” หรือ “เรียกค่าเสียหาย” จากผู้ที่ปล่อยมลพิษได้ ซึ่งจะทำให้เกิดต้นทุนที่แท้จริงกับผู้ก่อมลพิษ . กลไกตลาดไม่ได้หมายถึง “แค่ปล่อยให้ทุกอย่างเป็นไปตามธรรมชาติ” แต่มันคือการสร้างระบบ “แรงจูงใจ” ที่ทำให้คนเลือกทางออกที่ดีที่สุดเอง โดยไม่ต้องมีใครมาบังคับ . ผมนึกถึงที่ Murray Rothbard เคยพูดไว้ว่า “สิทธิในทรัพย์สิน คือสิ่งเดียวที่จะทำให้ผู้คนมีแรงจูงใจในการดูแลสิ่งแวดล้อม ไม่ใช่คำสั่งจากเจ้าหน้าที่รัฐ” เพราะเมื่อคุณเป็นเจ้าของสิ่งใด คุณย่อมมีแรงจูงใจในการรักษามัน มากกว่าการที่รัฐสั่งให้คุณต้องแคร์ ดังนั้น แทนที่จะใช้ระบบ Cap-and-Trade ที่รัฐควบคุม บทความนี้เสนอแนวทางที่ไม่พึ่งพารัฐ เช่น ชุมชนหรือเอกชนรวมตัวกันตกลงไม่เผา และใช้กลไกจ่ายชดเชยกันเองหากละเมิดสิทธิ หรือกรณีเจ้าของบ้านฟ้องโรงงานที่ทำให้บ้านหรือพื้นที่ที่อยู่อาศัยเสียหาย ทั้งหมดนี้คือการใช้สิทธิในทรัพย์สินและกลไกกฎหมายแพ่งเพื่อสร้างแรงจูงใจ โดยไม่ต้องให้รัฐเข้ามาควบคุมหรือกำกับ แต่ยังคงอาศัยศาลเพื่อปกป้องสิทธิ เมื่อเกิดการละเมิด . . แล้วทำไมแนวคิดแบบให้รัฐควบคุมถึงล้มเหลวเสมอ...? Hazlitt เตือนว่า รัฐมักคิดว่าตัวเองมองเห็นผลดี แต่ไม่เคยมองเห็นผลเสียที่มองไม่เห็น เช่น เมื่อรัฐประกาศห้ามเผาซังข้าวโพดหรือฟางข้าวในภาคเหนือโดยเด็ดขาด ชาวไร่จำนวนมากที่เคยใช้วิธีเผาเพื่อคืนโพแทสเซียมและแร่ธาตุให้ดินแบบต้นทุนต่ำ ต้องหันไปซื้อปุ๋ยเคมีแทน ซึ่งมีราคาสูง กลายเป็นภาระทางเศรษฐกิจที่ถาโถมใส่เกษตรกรรายย่อยโดยตรง ทั้งที่พวกเขาไม่ได้มีทางเลือกอื่นมากนัก นี่คือ “ต้นทุนที่มองไม่เห็น” ตามที่ Hazlitt เตือน รัฐเห็นแค่ "ผลดีเฉพาะหน้า" เช่น ค่าฝุ่นลดชั่วคราว แต่ไม่เห็นผลเสียระยะยาวต่อความยั่งยืนของชุมชนเกษตรกรรม แล้วทั้งหมดนี้คือการเอื้อประโยชน์ให้คนกลุ่มหนึ่ง แต่กระจายต้นทุนไปให้ทั้งสังคม ซึ่งตรงกับที่ Hazlitt วิจารณ์ในหนังสือ . . แล้วเสรีภาพในตลาดกับอากาศที่สะอาด...ไปด้วยกันได้ไหม? อ.พิริยะ ยกตัวอย่างบิตคอยน์ว่าเป็นระบบที่ไม่ต้องพึ่งรัฐหรือคนกลาง แต่สามารถสร้างแรงจูงใจทางเศรษฐกิจให้คนทั่วโลกเข้าร่วมโดยสมัครใจ และตรวจสอบได้แบบโปร่งใสผ่านกลไกกระจายศูนย์ แสดงให้เห็นว่าแนวคิดตลาดเสรีสามารถทำงานได้จริงหากออกแบบแรงจูงใจให้เหมาะสม แนวคิดเดียวกันนี้ใช้ได้กับปัญหาฝุ่น PM2.5 ถ้าเรามองว่าอากาศคือทรัพยากรที่มีเจ้าของ และอนุญาตให้มีการซื้อ-ขายหรือฟ้องร้องโดยไม่ต้องพึ่งรัฐเข้ามาจัดการจากส่วนกลาง คำตอบคือ ได้...ถ้าเราให้ “ตลาด” ทำงาน -ถ้ามลพิษทำให้ที่อยู่อาศัยเสียหาย เราสามารถฟ้องผู้ก่อมลพิษได้ -ถ้าโรงงานต้องซื้อสิทธิปล่อยมลพิษ พวกเขาจะมีแรงจูงใจลดฝุ่น -ถ้าประชาชนขาย “เครดิตอากาศสะอาด” ได้ จะเกิดอาชีพใหม่ เช่น การปลูกป่าคาร์บอน นี่ไม่ใช่จินตนาการ แต่คือหลักคิดที่กำลังเกิดขึ้นในหลายประเทศ เช่น แคลิฟอร์เนีย เยอรมนี และสิงคโปร์ . . สรุปเศรษฐศาสตร์ของฝุ่น...อยู่ที่ใครจ่ายต้นทุน Hazlitt ไม่เคยพูดถึง PM2.5 โดยตรง แต่แนวคิดของเขาชัดเจนว่า ทุกนโยบาย ต้องถูกมองในแง่ของผลกระทบที่มองไม่เห็นในระยะยาวด้วย และนั่นคือสิ่งที่รัฐไทยและคนส่วนใหญ่ยังไม่เข้าใจเมื่อพูดถึงปัญหาฝุ่น ตลาดไม่ได้ไร้หัวใจ แต่มัน บีบให้คนรับผิดชอบในสิ่งที่ตัวเองก่อ ข้อเสนอเชิงนโยบาย -ส่งเสริมการกำหนดสิทธิในอากาศหรือสิทธิในพื้นที่อยู่อาศัยให้ชัดเจน -เปิดตลาดซื้อ-ขาย “เครดิตฝุ่นสะอาด” สำหรับภาคอุตสาหกรรม โดยเน้นว่าเป็นระบบที่เกิดจากความสมัครใจของภาคเอกชนหรือชุมชน ไม่อยู่ภายใต้การกำกับหรือควบคุมโดยรัฐ -ส่งเสริมการลงทุนเอกชนด้านเซ็นเซอร์วัดฝุ่นแบบกระจายตัว (decentralized air quality monitoring) . . แล้วคุณล่ะ คิดว่าฝุ่นควรจัดการโดยรัฐ หรือโดยตลาด 💬 คุณคิดว่าเราควรเริ่มสร้าง “ระบบสิทธิและแรงจูงใจเพื่อรักษาคุณภาพอากาศ” ได้อย่างไร หรือทำไมคุณยังเชื่อว่ารัฐควรเป็นคนจัดการควบคุมทั้งหมดอยู่ และถ้าคุณยังเชื่อว่ารัฐควรเป็นผู้ดูแลควบคุม ลองถามตัวเองดูว่ารัฐเคยสามารถจัดการอะไรได้อย่างมีประสิทธิภาพได้ในระยะยาวหรือไม่ หากคุณสนใจแนวคิดตลาดเสรีและเศรษฐศาสตร์แบบเข้าใจง่าย ๆ ผมแนะนำหนังสือ Economics in One Lesson โดย Henry Hazlitt หนังสือที่เปลี่ยนวิธีคิดของคนทั้งโลกเกี่ยวกับ “สิ่งที่มองไม่เห็น” ของเศรษฐกิจ มีฉบับแปลไทยแล้วนะ 🙃
เศรษฐศาสตร์เล่มเดียวจบ #EIOL #Siamstr
EconomicsinOneLesson #RightBook #PM25
-
 @ 306555fe:fd7fdf12
2025-03-15 05:56:16
@ 306555fe:fd7fdf12
2025-03-15 05:56:161. Executive Summary
This report presents a detailed comparative analysis of Tesla Powerwall and Sungrow battery options for a 3-phase residence in Sydney, Australia, equipped with a 6.6kW solar system and a Sungrow SG5KTL-MT inverter. The evaluation focuses on the suitability of these battery solutions for potential off-grid capability and Vehicle-to-Home (V2H) functionality. The analysis reveals that while both Tesla Powerwall and Sungrow offer compelling features for home energy storage, Sungrow battery systems, particularly when paired with their hybrid inverters, present a more direct and comprehensive solution for achieving 3-phase off-grid capability. For V2H integration, both systems currently rely on the development of compatible bidirectional charging infrastructure in Australia. Based on the user's stated goals, a Sungrow battery system, potentially requiring an upgrade to a Sungrow hybrid inverter, is the recommended solution.
2. Introduction: Context and Objectives
The Australian residential energy landscape is witnessing a significant shift towards energy independence, with increasing adoption of solar photovoltaic (PV) systems and battery storage. This trend is propelled by factors such as escalating electricity costs and a growing desire for reliable power, particularly during grid outages. This report addresses the specific needs of a Sydney homeowner who has already invested in a 6.6kW solar system connected to a 3-phase Sungrow SG5KTL-MT inverter and owns a Tesla electric vehicle. The homeowner is now exploring battery storage solutions, with a particular focus on enabling potential off-grid operation and facilitating future Vehicle-to-Home (V2H) capabilities for their Tesla.
The primary objectives of this report are threefold: firstly, to evaluate the technical and practical suitability of Tesla Powerwall for a 3-phase home in Sydney; secondly, to conduct a similar evaluation for various Sungrow battery options; and thirdly, to provide a comparative assessment of these two leading solutions based on their ability to support off-grid functionality and integrate with V2H technology. The scope of this analysis includes the latest Tesla Powerwall models available in Australia and relevant high-voltage battery options from Sungrow, specifically the SBR and SBH series. The geographical context is limited to Sydney, Australia, considering local grid regulations and market availability. This analysis relies on the provided research material and publicly accessible technical specifications to form its conclusions.
3. Analysis of Tesla Powerwall for a 3-Phase Sydney Home
- 3.1 Technical Specifications and Features:\ The Tesla Powerwall is a well-established residential battery system. The latest generation, Powerwall 3, offers an energy capacity of 13.5 kWh 1 and can deliver up to 10 kW of on-grid power, with the same capacity for backup power, capable of a 185 A motor start 1. A key feature of Powerwall 3 is its integrated solar inverter with a 97.5% efficiency and three solar inputs with Maximum Power Point Trackers (MPPTs) in the Australian version 1. The system is scalable, allowing for the installation of up to four units 1, and utilizes Lithium Iron Phosphate (LFP) battery chemistry, known for its safety 5. In contrast, the Powerwall 2, while also having a 13.5 kWh energy capacity 7, provides a continuous power output of 5 kW with a 7 kW peak 7. Notably, Powerwall 2 does not have an integrated solar inverter 7 and uses Nickel Manganese Cobalt Oxide (NMC) battery chemistry 7. It offers greater scalability, supporting up to ten units 1. Both Powerwall 2 and 3 come with a 10-year warranty 2. Powerwall 3 necessitates the use of the Tesla Backup Gateway 2 2, while Powerwall 2 requires a Gateway for system control and backup functionality 7. The integrated inverter in Powerwall 3 streamlines installations for new solar and storage setups. However, for homeowners with existing inverters, such as the user, this feature might introduce complexities as the existing inverter's functionality could become redundant if the system were configured to primarily utilize the Powerwall 3's inverter. Powerwall 2, designed as an AC-coupled battery, might offer a more seamless integration by working in conjunction with the existing Sungrow inverter 3.
- 3.2 Compatibility with Existing 3-Phase Sungrow Inverter (AC Coupling):\ Tesla Powerwall is designed as an AC-coupled battery, meaning it connects to the home's electrical system at the switchboard level and operates independently of the solar inverter 9. This AC coupling capability generally allows Powerwall to be compatible with a wide range of existing solar inverters, including the user's 3-phase Sungrow SG5KTL-MT model 2. Specifically, Powerwall 2 demonstrates 100% compatibility with single-phase grid-connected solar systems installed after October 2016 9. For Powerwall 3, Tesla indicates AC coupling compatibility with existing solar systems up to 5kW 2. However, a crucial consideration arises during grid outages concerning the ability to charge the Powerwall from solar. If the home has a 3-phase solar inverter, like the user's Sungrow SG5KTL-MT, Powerwall 2 might not be able to charge from solar during a blackout because many 3-phase inverters require the presence of all three phases from the grid to operate 9. This limitation could also extend to Powerwall 3 when AC-coupled with a 3-phase inverter 8. Given the user's interest in potential off-grid capability, this inability to recharge the battery from solar during a grid outage significantly limits the duration of backup power to the energy stored within the Powerwall. Furthermore, the user's 6.6kW solar system output exceeds the 5kW AC coupling limit specified for a single Powerwall 3. This suggests that either the entire solar generation cannot be used to charge a single Powerwall 3 via AC coupling, or a more complex configuration involving multiple Powerwall units might be necessary.
- 3.3 Suitability for Off-Grid Operation in a 3-Phase System:\ The Tesla Powerwall is fundamentally a single-phase battery system and can only provide backup power to a single phase within a 3-phase home 8. During a power outage, only the electrical circuits connected to the phase that the Powerwall is backing up will remain operational 8. This necessitates careful planning to ensure that essential loads, such as lighting, refrigerators, and internet connectivity, are connected to this designated phase 8. While it is possible to install multiple Powerwall units, with one unit dedicated to each phase, this significantly increases the overall cost and introduces complexities in system management 8. Notably, even with the installation of three Powerwall 3 units, comprehensive 3-phase backup is not guaranteed 20. It is also important to recognize that Tesla does not officially support or provide warranties for off-grid installations of Powerwall 2. The Powerwall system is primarily designed for grid-connected homes to provide backup during outages and to optimize energy consumption, rather than functioning as the primary power source in a completely off-grid scenario. Therefore, achieving a truly comprehensive off-grid capability for a 3-phase home using Tesla Powerwall would likely involve a substantial financial investment in multiple units, meticulous load balancing across the phases, and navigating the limitations of single-phase backup, all without official support from the manufacturer.
- 3.4 Potential for V2H Integration with an EV in Australia:\ Vehicle-to-Home (V2H) technology, which allows an electric vehicle to supply power back to a home, is gaining traction in Australia. Regulatory changes have been made to permit bidirectional charging systems, with mainstream adoption expected in 2025 21. Australian standards for bidirectional charging are now approved, and compatible chargers are anticipated to become available in 2025 22. Currently, the research snippets do not indicate that Tesla Powerwall offers direct, integrated V2H functionality with EVs in Australia 1. However, the Tesla Powerwall can play a supportive role in a V2H ecosystem. It can efficiently store excess energy generated by the solar system 1, which could then be used to charge the EV. If the EV is equipped with V2H capabilities and connected to a compatible bidirectional charger, the energy stored in the Powerwall (or directly from solar) could indirectly contribute to powering the home by first charging the vehicle's battery. The actual discharge from the vehicle to the home would be managed by the bidirectional charger and the vehicle's internal systems, not directly by the Powerwall. Therefore, while Powerwall doesn't inherently provide V2H, it can act as a crucial energy storage component within a broader V2H setup.
- 3.5 Cost and Installation Considerations in Sydney:\ The cost of a Tesla Powerwall 3 in Australia is approximately $13,600, which includes the mandatory Backup Gateway 2 2. Powerwall 2 has an approximate price of $8,750 to $9,750, excluding installation and the Backup Gateway 7, with the installed cost estimated between $12,000 and $14,000 7. Installation costs for Powerwall 3 as part of a new solar system at Penrith Solar Centre start at $23,990 (including a 6kW solar system), while adding it to an existing system is around $15,990 27. Installing a Powerwall system in a 3-phase home can incur additional costs and complexities compared to single-phase installations 13. If the goal is to achieve any level of backup across multiple phases using Powerwall, the cost would escalate significantly with the need for multiple units. Homeowners in NSW may be eligible for rebates under the Peak Demand Reduction Scheme (PDRS), which can help offset the initial investment in a Tesla Powerwall 5. However, the overall cost of a Powerwall system, especially when considering a multi-unit setup for more comprehensive backup in a 3-phase home, remains a substantial financial consideration.
4. Analysis of Sungrow Battery Options for a 3-Phase Sydney Home
- 4.1 Technical Specifications of Relevant Sungrow Battery Models (SBR and SBH Series):\ Sungrow offers a range of high-voltage battery solutions, primarily the SBR and SBH series, utilizing Lithium Iron Phosphate (LiFePO4) chemistry for enhanced safety 5. The SBR series features a modular design with 3.2 kWh battery modules, allowing for system capacities ranging from 9.6 kWh (3 modules) up to 25.6 kWh (8 modules) in a single stack. Multiple stacks can be connected in parallel to achieve even larger capacities, up to 100 kWh 6. These batteries boast 100% usable energy capacity 26 and are high-voltage systems 33. The SBH series also employs a modular design with larger 5 kWh battery modules. A single stack can accommodate 4 to 8 modules, providing usable energy from 20 kWh to 40 kWh. Similar to the SBR series, multiple SBH stacks can be connected in parallel to reach a maximum capacity of 160 kWh 5. Both the SBR and SBH series come with a 10-year warranty 5 and are primarily designed for DC coupling with Sungrow's hybrid inverter range, particularly the SH series, which includes models specifically designed for 3-phase systems (SH-RT series) 33. The availability of a wider range of capacities and the modular design of both the SBR and SBH series provide greater flexibility for the user to tailor a battery system to their specific energy consumption needs. The SBH series, with its larger 5 kWh modules, appears particularly well-suited for homes with potentially higher energy demands, such as those with 3-phase connections.
- 4.2 Compatibility with Existing 3-Phase Sungrow Inverter (DC and AC Coupling):\ The user's existing Sungrow SG5KTL-MT inverter is a grid-tied inverter and not a hybrid model designed for direct DC coupling with batteries 5. Sungrow's high-voltage batteries, such as the SBR and SBH series, are primarily intended for DC coupling with their SH series hybrid inverters 33. While direct DC coupling is not an option with the SG5KTL-MT, it is possible to AC couple Sungrow batteries to the existing solar system 35. This would likely require the addition of a separate battery inverter to manage the charging and discharging of the Sungrow battery, as the SG5KTL-MT does not have this functionality. Although AC coupling offers a way to integrate a battery without replacing the existing solar inverter, it can introduce inefficiencies due to the multiple AC-DC and DC-AC conversions. For optimal performance and to fully leverage the capabilities of Sungrow's high-voltage batteries, particularly for off-grid operation, upgrading to a Sungrow SH series hybrid inverter would be the recommended approach.
- 4.3 Suitability for Off-Grid Operation in a 3-Phase System:\ Sungrow offers a distinct advantage in providing solutions for 3-phase off-grid operation through their SH-RT series of hybrid inverters 5. These inverters, when paired with Sungrow's SBR or SBH batteries, are capable of providing seamless transition to 3-phase backup power during grid outages 63. The SH-RT series is specifically designed to support 100% unbalanced loads in backup mode, ensuring that essential appliances continue to run during a blackout 66. Both the SBR and SBH battery series are compatible with off-grid operation when used in conjunction with the appropriate Sungrow hybrid inverters. Some single-phase Sungrow hybrid inverters (SH-RS series) also offer off-grid capabilities and support generator connection for battery charging during extended periods of low solar generation 85. This comprehensive ecosystem of Sungrow products provides a more direct and integrated pathway for the user to achieve their goal of potential 3-phase off-grid capability compared to the single-phase limitations of Tesla Powerwall.
- 4.4 Potential for V2H Integration with an EV (e.g Tesla Car) in Australia:\ Similar to Tesla Powerwall, the provided research material does not explicitly mention direct V2H integration capabilities for Sungrow battery systems with Tesla cars in Australia 22. However, Sungrow's active involvement in the broader renewable energy and electric vehicle charging sectors suggests a strong potential for future integration. Sungrow manufactures its own range of EV chargers 64, and their 3-phase hybrid inverter solutions can be paired with these chargers for smart green power charging 64. As V2H technology and the necessary bidirectional charging infrastructure become more prevalent in Australia, it is conceivable that Sungrow's integrated energy management systems, including their batteries and hybrid inverters, could be updated to support V2H functionality, potentially even with Tesla vehicles through standardized protocols or future partnerships. In the interim, a Sungrow battery system can efficiently store solar energy, which could then be used to charge a Tesla car. The potential for the EV to discharge back to the home would depend on the availability and compatibility of third-party bidirectional chargers that adhere to the evolving Australian standards.
- 4.5 Cost and Installation Considerations in Sydney:\ The cost of Sungrow batteries in Australia varies depending on the model and capacity. For the SBR series, a 9.6 kWh system is approximately $11,500 installed, a 12.8 kWh system around $13,200 installed, and a 25.6 kWh system around $19,700 installed. Supply-only costs for the SBH series 20 kWh kit range from $13,778.70 to $14,360 40. Compatible 3-phase hybrid inverters from Sungrow, such as the SH5.0RT, are priced around $3,760, while the SH10RT ranges from approximately $4,174.50 to $5,720 78. If the user opts for a Sungrow battery system to achieve optimal 3-phase off-grid capability, the cost of a new SH series hybrid inverter would need to be included, as the existing SG5KTL-MT is not compatible for direct DC coupling. While AC coupling might be a less expensive initial step, it could involve the additional cost of a separate battery inverter. Homeowners in NSW can potentially benefit from the NSW battery rebate when purchasing a Sungrow battery system, which could help reduce the overall cost 5. Although Sungrow batteries often offer a competitive cost per kWh, the total investment for a comprehensive 3-phase off-grid solution might be higher than a single-phase Tesla Powerwall setup, primarily due to the potential need for a new hybrid inverter.
5. Comparative Assessment: Tesla Powerwall vs. Sungrow Batteries
- 5.1 Side-by-Side Comparison Table of Key Specifications:
| Feature | Tesla Powerwall 3 | Sungrow SBR (Example: 12.8 kWh) + SH10RT | | --- | --- | --- | | Usable Energy Capacity (kWh) | 13.5 | 12.8 | | Continuous Power Output (kW) | 10 | 10 | | Peak Power Output (kW) | 10 | 12 (5 min) | | Battery Chemistry | Lithium Iron Phosphate | Lithium Iron Phosphate | | Scalability | Up to 4 units (54 kWh) | Up to 25.6 kWh per stack, 4 stacks parallel (102.4 kWh) | | Off-Grid Backup (Phases Supported) | Single-Phase | Three-Phase | | V2H Support (Current/Future Potential) | Potential via 3rd party charger | Potential via 3rd party charger | | Warranty (Years) | 10 | 10 | | Estimated Cost (AUD) | $13,600 + installation | $13,200 (battery installed) + $4,175 - $5,720 (inverter) |
- 5.2 Detailed Comparison Based on Off-Grid Capability Requirements:\ When considering the user's goal of potential off-grid capability for a 3-phase home, Sungrow presents a more robust solution. The availability of Sungrow's SH-RT series hybrid inverters, specifically designed for 3-phase systems and fully compatible with their SBR and SBH batteries, allows for a direct and integrated approach to achieving 3-phase backup power. These systems can seamlessly transition to off-grid mode, powering all three phases of the home, which is crucial for operating 3-phase appliances and ensuring comprehensive whole-house backup. In contrast, Tesla Powerwall, being a single-phase battery, inherently limits off-grid backup to a single phase in a 3-phase home 8. While multiple Powerwall units can be installed, this increases cost and complexity without guaranteeing full 3-phase backup or official off-grid support from Tesla. Therefore, for a user prioritizing potential for comprehensive 3-phase off-grid operation, Sungrow's ecosystem offers a more suitable and supported pathway.
- 5.3 Detailed Comparison Based on V2H Functionality Requirements:\ Currently, neither Tesla Powerwall nor Sungrow batteries offer direct, integrated V2H functionality for Tesla cars in Australia 22. Both systems can store solar energy that could be used to charge a EV, and the potential for the car to discharge back to the home (V2H) would rely on the development and adoption of compatible bidirectional charging infrastructure in Australia, which is expected to become more mainstream in 2025 21. Sungrow's involvement in manufacturing EV chargers and integrating them with their hybrid inverters suggests a potential for future V2H integration within their ecosystem. Similarly, while Tesla Powerwall doesn't currently offer V2H, its role as a home energy storage solution makes it a complementary technology to V2H, providing a place to store energy that could eventually be managed within a V2H framework.
- 5.4 Cost-Effectiveness and Overall Value Analysis:\ When evaluating cost-effectiveness, Sungrow batteries often have a lower cost per kWh of storage compared to Tesla Powerwall 5. However, for the user with an existing non-hybrid inverter, achieving the desired 3-phase off-grid capability with Sungrow would likely necessitate an additional investment in a Sungrow SH-RT series hybrid inverter. This would increase the initial outlay compared to simply AC coupling a Tesla Powerwall to the existing inverter for single-phase backup. The overall value proposition depends heavily on the user's priorities. If the primary goal is to have backup power for essential loads on a single phase and potential future V2H integration, Tesla Powerwall could be a viable option. However, if the potential for comprehensive 3-phase off-grid operation is a significant factor, then the added expense of a Sungrow hybrid inverter might be justified by the enhanced functionality and future-proofing for energy independence. Sungrow's reputation for affordability and the modularity of their battery systems also offer long-term value and flexibility.
6. Recommendations and Considerations
Based on the analysis, for a 3-phase home in Sydney with a 6.6kW solar system and the goal of potential off-grid capability, Sungrow battery options are recommended. Specifically, the user should consider upgrading their existing Sungrow SG5KTL-MT inverter to a Sungrow SH series hybrid inverter (e.g., SH5.0RT or SH10RT, depending on anticipated power demands) and pairing it with a Sungrow high-voltage battery from either the SBR or SBH series. The choice between SBR and SBH would depend on the desired storage capacity and budget. This combination offers a more direct and supported path to achieving 3-phase backup power and the potential for future off-grid operation.
Key Considerations for the User:
- Off-Grid Capability: The level of off-grid capability desired (partial single-phase backup vs. comprehensive whole-home 3-phase backup) is a crucial factor. For the latter, Sungrow is the more suitable choice.
- Budget: Both options represent a significant investment. The user should obtain detailed quotes for both Tesla Powerwall (considering single or multiple units) and a complete Sungrow hybrid inverter and battery system.
- V2H Timeline: The user's timeline for V2H adoption should be considered. Both systems will likely integrate via third-party chargers.
- Inverter Upgrade: If pursuing the optimal Sungrow solution for off-grid capability, the cost and logistics of upgrading the existing inverter need to be factored in.
- 3-Phase Backup Importance: The necessity of having backup power across all three phases should weigh heavily in the decision, favoring Sungrow.
It is strongly recommended that the user obtain detailed quotes from certified installers in the Sydney area for both Tesla Powerwall and various Sungrow system configurations to get accurate pricing, installation details, and information on available rebates and incentives in NSW.
7. Conclusion
In conclusion, while Tesla Powerwall offers a well-regarded solution for home energy storage with reliable backup capabilities, its inherent single-phase design presents limitations for users with 3-phase homes seeking comprehensive off-grid functionality. Sungrow, with its range of high-voltage batteries and particularly its 3-phase hybrid inverter systems, provides a more direct and technically sound pathway to achieving the user's goals of potential 3-phase off-grid operation. For V2H integration, both systems are currently positioned to benefit from the evolving Australian regulatory landscape and the development of compatible bidirectional charging technologies. Ultimately, the optimal choice will depend on the user's specific priorities, budget, and the level of off-grid capability they wish to achieve. The rapidly evolving nature of battery storage and V2H technology suggests that continued research and consultation with experts are advisable before making a final decision.
Works cited
1. Powerwall – Home Battery Storage | Tesla Australia, accessed March 14, 2025, https://www.tesla.com/en_au/powerwall\ 2. Tesla Powerwall 3 in Australia: Everything You Need to Know - Fritts Solar, accessed March 14, 2025, https://www.frittssolar.com.au/tesla-powerwall-3-australia/\ 3. What to Expect for Powerwall 3 | Tesla Support Australia, accessed March 14, 2025, https://www.tesla.com/en_au/support/energy/powerwall/learn/what-expect-powerwall-3\ 4. Tesla Powerwall 3 Review - Clean Energy Reviews, accessed March 14, 2025, https://www.cleanenergyreviews.info/blog/tesla-powerwall-3-review\ 5. Sungrow SBH vs. Tesla Powerwall 3: Which is Better? NSW - Elite Power Group, accessed March 14, 2025, https://www.elitepowergroup.com.au/news/sungrow-sbh-vs-tesla-powerwall-3-which-is-better-nsw/\ 6. Sungrow Battery vs Tesla Powerwall Review - Volteam Electric, accessed March 14, 2025, https://volteam.com.au/blog/sungrow-vs-tesla-battery-review/\ 7. Tesla Powerwall 2: A Complete 2024 Buyers Guide | Solar Choice, accessed March 14, 2025, https://www.solarchoice.net.au/products/batteries/tesla-powerwall-2-review/\ 8. Can You Install The Powerwall 3 On A Three-Phase Home? - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/blog/three-phase-powerwall-3/\ 9. Is my grid connect solar system 100% compatible with a Tesla Powerwall 2 battery?, accessed March 14, 2025, https://support.solarquotes.com.au/hc/en-us/articles/115001986773-Is-my-grid-connect-solar-system-100-compatible-with-a-Tesla-Powerwall-2-battery\ 10. THE 3-PHASE SOLUTION - SUNGROW, accessed March 14, 2025, https://uk.sungrowpower.com/upload/file/20210706/EN%203-phaseSolution%20Factsheet.pdf\ 11. Combining Systems with Powerwall | Tesla Support, accessed March 14, 2025, https://www.tesla.com/support/energy/powerwall/learn/combining-systems\ 12. Powerwall System Design | Tesla Support, accessed March 14, 2025, https://www.tesla.com/support/energy/powerwall/learn/system-design\ 13. Installing Powerwall 3 on a Three-phase Site | PSC - Penrith Solar Centre, accessed March 14, 2025, https://www.penrithsolar.com.au/blog/installing-powerwall-3-on-a-three-phase-site/\ 14. Powerwall 3: When It Makes Sense and When It Doesn't - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/blog/powerwall-3-when-it-makes-sense/\ 15. AC-Coupled Solar System Sizing - Energy Library - Tesla, accessed March 14, 2025, https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-23D242D1-8D65-47B9-9118-57002FFD84D2.html\ 16. Powerwall 3 Roadmap - 3 Phase Coming! | Tesla Motors Club, accessed March 14, 2025, https://teslamotorsclub.com/tmc/threads/powerwall-3-roadmap-3-phase-coming.321409/\ 17. Advice on how to install with 3 phase : r/solar - Reddit, accessed March 14, 2025, https://www.reddit.com/r/solar/comments/19djazk/advice_on_how_to_install_with_3_phase/\ 18. TESLA POWERWALL+ (3) - DIY Solar Depot, accessed March 14, 2025, https://diysolardepot.com/product/ground-mount-solar-hardware/pro-solar-ground-trac/\ 19. Design Considerations - Energy Library - Tesla, accessed March 14, 2025, https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-3E19662A-E501-47DB-81AE-E9EC19735B8B.html\ 20. Problems with Powerwall 3 | Penrith Solar Centre, accessed March 14, 2025, https://www.penrithsolar.com.au/blog/problems-with-powerwall-3/\ 21. EV Charging in Australia Gets a Makeover with V2G/V2H Approved for 2025 - SEVR, accessed March 14, 2025, https://sevr.au/news/ev-charging-in-australia-gets-a-makeover-with-v2g-v2h-approved-for-2025/\ 22. V2G, V2L & V2H Explained: Vehicle to Grid in Australia? 2025 - Elite Power Group, accessed March 14, 2025, https://www.elitepowergroup.com.au/news/what-is-vehicle-to-grid/\ 23. Australia's Future – Bidirectional EV Charging, Solar & Battery Storage as Standard Features, accessed March 14, 2025, https://fullycharged.show/blog/australias-future-bidirectional-ev-charging-solar-battery-storage-as-standard-features/\ 24. 2025, the Year of Vehicle-to-Grid in Australia V2G Milestone - Elite Power Group, accessed March 14, 2025, https://www.elitepowergroup.com.au/news/one-step-closer-to-v2g-in-australia-2025-to-be-the-year-of-v2x/\ 25. Bidirectional Charging for Electric Cars: Unlocking New Possibilities - Solar Batteries Online, accessed March 14, 2025, https://www.solarbatteriesonline.com.au/bidirectional-charging-for-electric-cars-unlocking-new-possibilities/\ 26. The Best Home Batteries In Australia In 2025: According To Aussie Installers - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/blog/best-home-batteries-2025/\ 27. How Much Does a Tesla Powerwall 3 Cost? | Penrith Solar Centre, accessed March 14, 2025, https://www.penrithsolar.com.au/blog/how-much-does-a-tesla-powerwall-3-cost/\ 28. Expected 3 Phase upgrade price? : r/AusRenovation - Reddit, accessed March 14, 2025, https://www.reddit.com/r/AusRenovation/comments/19383oa/expected_3_phase_upgrade_price/\ 29. Powerwall cost for Sydney? | Tesla Motors Club, accessed March 14, 2025, https://teslamotorsclub.com/tmc/threads/powerwall-cost-for-sydney.340317/\ 30. Solar Battery Costs: Are They Worth It?, accessed March 14, 2025, https://www.solarchoice.net.au/solar-batteries/is-home-battery-storage-worth-it/\ 31. Tesla Powerwall 3 Price and Installation - Solar4Life, accessed March 14, 2025, https://www.solar4life.com.au/learns/tesla-powerwall-3-price-and-installation\ 32. Solar Battery Price, Savings and Payback, accessed March 14, 2025, https://solarcalculator.com.au/battery-storage/price/\ 33. Sungrow | Solar Batteries Review - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/battery-storage/reviews/sungrow-review.html\ 34. Sungrow SBR high voltage battery - VP Solar, accessed March 14, 2025, https://www.vpsolar.com/en/sungrow-sbr-high-voltage-battery/\ 35. Sungrow Battery SBR Series - SolarBright, accessed March 14, 2025, https://solarbright.com.au/product/sungrow-battery-sbr-series/\ 36. Sungrow SBR 3.2kWh module - Huglo Solar, accessed March 14, 2025, https://www.huglo.com.au/batteries/sbr-high-voltage-lfp-battery\ 37. Sungrow Inverter and battery Review - Clean Energy Reviews, accessed March 14, 2025, https://www.cleanenergyreviews.info/blog/sungrow-solar-inverters-review\ 38. SBH100/150/200/250/300/350/400 - Sungrow, accessed March 14, 2025, https://en.sungrowpower.com/productDetail/5568/battery-sbh100-150-200-250-300-350-400\ 39. 20/25/30/35/40 kWh Solar Battery - Sungrow AU, accessed March 14, 2025, https://aus.sungrowpower.com/productDetail/3112/battery-sbh200-250-300-350-400\ 40. Sungrow SBH Stackable Battery System - Grow Energy, accessed March 14, 2025, https://growenergy.com.au/products/sungrow-sbh-stackable-battery-system\ 41. Sungrow SBH High Voltage Battery Bundle (SBH200 - SBH400), accessed March 14, 2025, https://solarbatterysupermarket.com.au/products/sungrow-sbh-high-voltage-battery-bundle-sbh200-sbh400\ 42. Buy cheap SunGrow solar inverters, accessed March 14, 2025, https://tienda-solar.es/en/brand/54-sungrow\ 43. Sungrow PowCube battery storage system (Analysis & review) - Solar Choice, accessed March 14, 2025, https://www.solarchoice.net.au/products/batteries/sungrow-review/\ 44. What inverters do we connect to? – Welcome to our Help Center - Support - SwitchDin, accessed March 14, 2025, https://support.switchdin.com/hc/en-us/articles/19642583185817-What-inverters-do-we-connect-to\ 45. Accessories Cross Reference Guide - Sungrow Australia Service, accessed March 14, 2025, https://service.sungrowpower.com.au/files/Web_Files/FAQ/TI_202007_Sungrow%20Accessories%20Cross%20Reference%20Guide_V1.0.pdf\ 46. Sungrow - Solar System Inverter - Solargain, accessed March 14, 2025, https://www.solargain.com.au/solar-inverters/sungrow-solar-inverters\ 47. Sungrow Battery Review | A Comprehensive Guide - Esteem Energy, accessed March 14, 2025, https://esteemenergy.com.au/blog/sungrow-battery-review/\ 48. Sungrow 5kW Inverter + Tesla Powerwall + Longi 370w Hi-MO4m 7.4kW Solar System, accessed March 14, 2025, https://ahlecsolar.com.au/product/sungrow-5kw-inverter-tesla-powerwall-longi-370w-hi-mo4m-7-4kw-solar-system/\ 49. Sungrow | Solar Inverters Review - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/inverters/sungrow-review.html\ 50. Tesla Powerwall: Inverter Compatibility Under the Spotlight - 1KOMMA5, accessed March 14, 2025, https://1komma5.com/au/batteries/tesla-powerwall-2-compatible-solar-power-system/\ 51. Hi everybody, question about V2H power : r/electricvehicles - Reddit, accessed March 14, 2025, https://www.reddit.com/r/electricvehicles/comments/1hqneh3/hi_everybody_question_about_v2h_power/\ 52. Commercial Solar System | PV Plant | Rooftop - Sungrow US, accessed March 14, 2025, https://us.sungrowpower.com/solutionsDetail/10/commercial-storage-systems\ 53. SH8.0/10RS | 8kW/10kW | Single Phase | Sungrow Hybrid Inverter-Sungrow AU, accessed March 14, 2025, https://aus.sungrowpower.com/productDetail/2565/mv-power-converter-hybrid-inverter-sh8-0-10rs\ 54. Approved Batteries with SH Series Hybrid Inverters - Sungrow Australia Service, accessed March 14, 2025, https://service.sungrowpower.com.au/files/Web_Files/FAQ/Approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters-20201209_V14_EN.pdf\ 55. Right inverter for the Tesla Powerwall 2 : r/solar - Reddit, accessed March 14, 2025, https://www.reddit.com/r/solar/comments/1chgnj8/right_inverter_for_the_tesla_powerwall_2/\ 56. Sungrow Inverters - Gold Coast Solar Power Solutions, accessed March 14, 2025, https://gold-coast-solar-power-solutions.com.au/gold-coast-solar-power-products/solar-power-inverters/sungrow-inverters/\ 57. Sungrow SBR192 Lithium-ion Battery - Europe-SolarStore.com, accessed March 14, 2025, https://www.europe-solarstore.com/sungrow-sbr192-lithium-ion-battery.html\ 58. High-Efficiency Solar Battery: Up to 100% Usable Energy - Sungrow, accessed March 14, 2025, https://en.sungrowpower.com/ProductsHome/20/23/battery\ 59. Warranty | Sungrow Australia and New Zealand Service, accessed March 14, 2025, https://service.sungrowpower.com.au/Warranty/warranty\ 60. Sungrow Battery cross-reference chart, accessed March 14, 2025, https://service.sungrowpower.com.au/GD_202405_SBR%20and%20SBH_Cross%20Reference%20Chart_V1.4%20Final.pdf\ 61. Sungrow SG5KTL-MT - SolarTopStore.com, accessed March 14, 2025, https://www.solartopstore.com/products/sungrow-sg5ktl-mt\ 62. Approved Batteries with SH Series Hybrid Inverters EU Version V1.6.3 - Sungrow AU, accessed March 14, 2025, https://aus.sungrowpower.com/upload/file/20211119/TI_20210906_approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters_V16_EN.pdf\ 63. BLACKOUT? NO, THANKS! POWER WHENEVER YOU NEED IT - SUNGROW, accessed March 14, 2025, https://uk.sungrowpower.com/upload/file/20211202/EN%20FS%20Sungrow%203-phase%20Hybrid%20Backup%20Factsheet.pdf\ 64. Sungrow 3-phase solution with 6 kVA inverter, EV charger and 9.6 kWh storage - Memodo, accessed March 14, 2025, https://www.memodo-shop.com/sungrow-3-phase-solution-with-6-kva-inverter-ev-charger-and-9.6-kwh-storage/9767\ 65. THE 3-PHASE SOLUTION - SUNGROW, accessed March 14, 2025, https://uk.sungrowpower.com/upload/file/20230116/EN%20FS%203-phaseSolution%20Factsheet.pdf\ 66. Sungrow Three-Phase Hybrid Inverter - Solar4Life, accessed March 14, 2025, https://www.solar4life.com.au/product-detail/sungrow-5-20kw-3-phase-hybrid\ 67. SG5KTL-MT/SG6KTL-MT/SG8KTL-M (Non-China ... - ENF Solar, accessed March 14, 2025, https://www.enfsolar.com/pv/inverter-datasheet/12176\ 68. Sungrow SBR battery combiner box - AC Solar Warehouse, accessed March 14, 2025, https://www.acsolarwarehouse.com/shop/sungrow-battery-combiner-box-for-multiple-sungrow-lfp-battery-stacks-23620\ 69. Sungrow SBR HV Battery Installation Quick Guide, accessed March 14, 2025, https://service.sungrowpower.com.au/files/Web_Files/FAQ/GD_202202_SBR%20HV%20Battery%20Installation%20Quick%20Guide%20with%201%20Phase%20SHxRS_V3.0.pdf\ 70. Energy Storage System Products Catalogue - SUNGROW, accessed March 14, 2025, https://uk.sungrowpower.com/upload/file/20210909/EN%20BR%20Sungrow%20Energy%20Storage%20System%20Products%20Catalogue.pdf\ 71. DC Coupling vs AC Coupling: Which Solar System to Choose - Sungrow, accessed March 14, 2025, https://en.sungrowpower.com/blog-detail/5983/dc-coupling-vs-ac-coupling-which-solar-system-to-choose\ 72. Sungrow SBH battery - Accessory kit | AC Solar Warehouse AU, accessed March 14, 2025, https://www.acsolarwarehouse.com/shop/sbh-accessory-kit-sungrow-sbh-battery-accessory-kit-25310\ 73. Sungrow SBR 3.2kWh High Voltage Battery Module , ASA00460 - Alternergy, accessed March 14, 2025, https://www.alternergy.co.uk/sungrow-sbr-3-2-kwh-battery-asa00460\ 74. NEW Sungrow single phase hybrid inverters can operate without the grid or a battery, accessed March 14, 2025, https://www.acsolarwarehouse.com/blog/news-7/new-sungrow-single-phase-hybrid-inverters-can-operate-without-the-grid-or-a-battery-255\ 75. Lawnton Sungrow SBH & Solar Hybrid System | Alvolta, accessed March 14, 2025, https://www.alvolta.com.au/portfolio/info/74\ 76. Sungrow Battery Starter Pack - Huglo Solar, accessed March 14, 2025, https://www.huglo.com.au/post/sungrow-battery-starter-pack\ 77. Sungrow SBR Battery System Bundles, accessed March 14, 2025, https://solarbatterysupermarket.com.au/products/sungrow-sbr-battery-system-bundles\ 78. Sungrow Hybrid 10kW RT Three-Phase Solar Inverter, accessed March 14, 2025, https://www.springers.com.au/shop/sh10rt-sungrow-hybrid-10kw-rt-three-phase-solar-inverter-15108\ 79. Sungrow RT 5kW Three Phase Hybrid inverter (2 MPPT) SH5.0RT - Solar Batteries Online, accessed March 14, 2025, https://www.solarbatteriesonline.com.au/product/sungrow-sh5-0rt-hv-5-0kw-residential-hybrid-three-phase-inverter/\ 80. SUNGROW SH10RT | 10kW 3-Phase Hybrid Inverter - Sparky Direct, accessed March 14, 2025, https://www.sparkydirect.com.au/p/sungrow-sh10rt-10kw-3-phase-hybrid-inverter\ 81. Sungrow Hybrid 10kW 3 Phase 2 MPPT w/WiFi, DC Switch & EPS Built-in Inverter, accessed March 14, 2025, https://www.solarheroes.com.au/product/sungrow-hybrid-10kw-3-phase-2-mppt-w-wifi-dc-switch-eps-built-in-inverter/\ 82. Sungrow Solar Inverters - Independent Review, accessed March 14, 2025, https://www.solarchoice.net.au/products/inverters/Sungrow-review/\ 83. Sungrow 10.0kW - 3 Phase Hybrid Inverter (SH10RT) - Solar Superstore, accessed March 14, 2025, https://www.solarsuperstore.com.au/products/sungrow-8-0kw-3-phase-hybrid-inverter-sh8-0rt\ 84. How Much Do Solar Batteries Cost in Australia? - SolarQuotes, accessed March 14, 2025, https://www.solarquotes.com.au/battery-storage/cost/\ 85. Off Grid Solar system using a Sungrow inverter and battery, accessed March 14, 2025, https://www.acsolarwarehouse.com/blog/news-7/off-grid-solar-system-using-a-sungrow-inverter-and-battery-312\ 86. Sungrow 14.08k W Off Grid Solar System / Single Phase - AHLEC, accessed March 14, 2025, https://ahlecsolar.com.au/product/sungrow-14-08k-w-off-grid-solar-system-single-phase/\ 87. Residential Battery Energy Storage System - Sungrow AU, accessed March 14, 2025, https://aus.sungrowpower.com/solutionsDetail/9/residential-storage-system\ 88. EV Charger - Sungrow, accessed March 14, 2025, https://en.sungrowpower.com/ProductsHome/59/ev-charger\ 89. Sungrow SBH 20kW High Voltage LFP Battery Including Accessory Kit SBH200 | eBay, accessed March 14, 2025, https://www.ebay.com.au/itm/135320073679\ 90. 20kWh Battery Kit - Login - Australian Solar Supplies Pty Ltd, accessed March 14, 2025, http://shop.ausolarsupplies.com.au/s.nl/it.A/id.6047/.f\ 91. Sungrow - Solar Batteries Online, accessed March 14, 2025, https://www.solarbatteriesonline.com.au/sungrow/
# Comparative Evaluation of Tesla Powerwall and Sungrow Battery Options for a 3-Phase Sydney Residence
1. Executive Summary
This report presents a detailed comparative analysis of Tesla Powerwall and Sungrow battery options for a 3-phase residence in Sydney, Australia, equipped with a 6.6kW solar system and a Sungrow SG5KTL-MT inverter. The evaluation focuses on the suitability of these battery solutions for potential off-grid capability and Vehicle-to-Home (V2H) functionality for a EV. The analysis reveals that while both Tesla Powerwall and Sungrow offer compelling features for home energy storage, Sungrow battery systems, particularly when paired with their hybrid inverters, present a more direct and comprehensive solution for achieving 3-phase off-grid capability. For V2H integration, both systems currently rely on the development of compatible bidirectional charging infrastructure in Australia. Based on the user's stated goals, a Sungrow battery system, potentially requiring an upgrade to a Sungrow hybrid inverter, is the recommended solution.
2. Introduction: Context and Objectives
The Australian residential energy landscape is witnessing a significant shift towards energy independence, with increasing adoption of solar photovoltaic (PV) systems and battery storage. This trend is propelled by factors such as escalating electricity costs and a growing desire for reliable power, particularly during grid outages. This report addresses the specific needs of a Sydney homeowner who has already invested in a 6.6kW solar system connected to a 3-phase Sungrow SG5KTL-MT inverter and owns a Tesla electric vehicle. The homeowner is now exploring battery storage solutions, with a particular focus on enabling potential off-grid operation and facilitating future Vehicle-to-Home (V2H) capabilities for their Tesla.
The primary objectives of this report are threefold: firstly, to evaluate the technical and practical suitability of Tesla Powerwall for a 3-phase home in Sydney; secondly, to conduct a similar evaluation for various Sungrow battery options; and thirdly, to provide a comparative assessment of these two leading solutions based on their ability to support off-grid functionality and integrate with V2H technology. The scope of this analysis includes the latest Tesla Powerwall models available in Australia and relevant high-voltage battery options from Sungrow, specifically the SBR and SBH series. The geographical context is limited to Sydney, Australia, considering local grid regulations and market availability. This analysis relies on the provided research material and publicly accessible technical specifications to form its conclusions.
3. Analysis of Tesla Powerwall for a 3-Phase Sydney Home
3.1 Technical Specifications and Features:
The Tesla Powerwall is a well-established residential battery system. The latest generation, Powerwall 3, offers an energy capacity of 13.5 kWh 1 and can deliver up to 10 kW of on-grid power, with the same capacity for backup power, capable of a 185 A motor start 1. A key feature of Powerwall 3 is its integrated solar inverter with a 97.5% efficiency and three solar inputs with Maximum Power Point Trackers (MPPTs) in the Australian version 1. The system is scalable, allowing for the installation of up to four units 1, and utilizes Lithium Iron Phosphate (LFP) battery chemistry, known for its safety 5. In contrast, the Powerwall 2, while also having a 13.5 kWh energy capacity 7, provides a continuous power output of 5 kW with a 7 kW peak 7. Notably, Powerwall 2 does not have an integrated solar inverter 7 and uses Nickel Manganese Cobalt Oxide (NMC) battery chemistry 7. It offers greater scalability, supporting up to ten units 1. Both Powerwall 2 and 3 come with a 10-year warranty 2. Powerwall 3 necessitates the use of the Tesla Backup Gateway 2 2, while Powerwall 2 requires a Gateway for system control and backup functionality 7. The integrated inverter in Powerwall 3 streamlines installations for new solar and storage setups. However, for homeowners with existing inverters, such as the user, this feature might introduce complexities as the existing inverter's functionality could become redundant if the system were configured to primarily utilize the Powerwall 3's inverter. Powerwall 2, designed as an AC-coupled battery, might offer a more seamless integration by working in conjunction with the existing Sungrow inverter 3.
3.2 Compatibility with Existing 3-Phase Sungrow Inverter (AC Coupling):
Tesla Powerwall is designed as an AC-coupled battery, meaning it connects to the home's electrical system at the switchboard level and operates independently of the solar inverter 9. This AC coupling capability generally allows Powerwall to be compatible with a wide range of existing solar inverters, including the user's 3-phase Sungrow SG5KTL-MT model 2. Specifically, Powerwall 2 demonstrates 100% compatibility with single-phase grid-connected solar systems installed after October 2016 9. For Powerwall 3, Tesla indicates AC coupling compatibility with existing solar systems up to 5kW 2. However, a crucial consideration arises during grid outages concerning the ability to charge the Powerwall from solar. If the home has a 3-phase solar inverter, like the user's Sungrow SG5KTL-MT, Powerwall 2 might not be able to charge from solar during a blackout because many 3-phase inverters require the presence of all three phases from the grid to operate 9. This limitation could also extend to Powerwall 3 when AC-coupled with a 3-phase inverter 8. Given the user's interest in potential off-grid capability, this inability to recharge the battery from solar during a grid outage significantly limits the duration of backup power to the energy stored within the Powerwall. Furthermore, the user's 6.6kW solar system output exceeds the 5kW AC coupling limit specified for a single Powerwall 3. This suggests that either the entire solar generation cannot be used to charge a single Powerwall 3 via AC coupling, or a more complex configuration involving multiple Powerwall units might be necessary.
3.3 Suitability for Off-Grid Operation in a 3-Phase System:
The Tesla Powerwall is fundamentally a single-phase battery system and can only provide backup power to a single phase within a 3-phase home 8. During a power outage, only the electrical circuits connected to the phase that the Powerwall is backing up will remain operational 8. This necessitates careful planning to ensure that essential loads, such as lighting, refrigerators, and internet connectivity, are connected to this designated phase 8. While it is possible to install multiple Powerwall units, with one unit dedicated to each phase, this significantly increases the overall cost and introduces complexities in system management 8. Notably, even with the installation of three Powerwall 3 units, comprehensive 3-phase backup is not guaranteed 20. It is also important to recognize that Tesla does not officially support or provide warranties for off-grid installations of Powerwall 2. The Powerwall system is primarily designed for grid-connected homes to provide backup during outages and to optimize energy consumption, rather than functioning as the primary power source in a completely off-grid scenario. Therefore, achieving a truly comprehensive off-grid capability for a 3-phase home using Tesla Powerwall would likely involve a substantial financial investment in multiple units, meticulous load balancing across the phases, and navigating the limitations of single-phase backup, all without official support from the manufacturer.
3.4 Potential for V2H Integration with a EV in Australia:
Vehicle-to-Home (V2H) technology, which allows an electric vehicle to supply power back to a home, is gaining traction in Australia. Regulatory changes have been made to permit bidirectional charging systems, with mainstream adoption expected in 2025 21. Australian standards for bidirectional charging are now approved, and compatible chargers are anticipated to become available in 2025 22. Currently, the research snippets do not indicate that Tesla Powerwall offers direct, integrated V2H functionality with Tesla cars in Australia 1. However, the Tesla Powerwall can play a supportive role in a V2H ecosystem. It can efficiently store excess energy generated by the solar system 1, which could then be used to charge the Tesla car. If the Tesla car is equipped with V2H capabilities and connected to a compatible bidirectional charger, the energy stored in the Powerwall (or directly from solar) could indirectly contribute to powering the home by first charging the vehicle's battery. The actual discharge from the vehicle to the home would be managed by the bidirectional charger and the vehicle's internal systems, not directly by the Powerwall. Therefore, while Powerwall doesn't inherently provide V2H, it can act as a crucial energy storage component within a broader V2H setup.
3.5 Cost and Installation Considerations in Sydney:
The cost of a Tesla Powerwall 3 in Australia is approximately $13,600, which includes the mandatory Backup Gateway 2 2. Powerwall 2 has an approximate price of $8,750 to $9,750, excluding installation and the Backup Gateway 7, with the installed cost estimated between $12,000 and $14,000 7. Installation costs for Powerwall 3 as part of a new solar system at Penrith Solar Centre start at $23,990 (including a 6kW solar system), while adding it to an existing system is around $15,990 27. Installing a Powerwall system in a 3-phase home can incur additional costs and complexities compared to single-phase installations 13. If the goal is to achieve any level of backup across multiple phases using Powerwall, the cost would escalate significantly with the need for multiple units. Homeowners in NSW may be eligible for rebates under the Peak Demand Reduction Scheme (PDRS), which can help offset the initial investment in a Tesla Powerwall 5. However, the overall cost of a Powerwall system, especially when considering a multi-unit setup for more comprehensive backup in a 3-phase home, remains a substantial financial consideration.
4. Analysis of Sungrow Battery Options for a 3-Phase Sydney Home
4.1 Technical Specifications of Relevant Sungrow Battery Models (SBR and SBH Series):
Sungrow offers a range of high-voltage battery solutions, primarily the SBR and SBH series, utilizing Lithium Iron Phosphate (LiFePO4) chemistry for enhanced safety 5. The SBR series features a modular design with 3.2 kWh battery modules, allowing for system capacities ranging from 9.6 kWh (3 modules) up to 25.6 kWh (8 modules) in a single stack. Multiple stacks can be connected in parallel to achieve even larger capacities, up to 100 kWh 6. These batteries boast 100% usable energy capacity 26 and are high-voltage systems 33. The SBH series also employs a modular design with larger 5 kWh battery modules. A single stack can accommodate 4 to 8 modules, providing usable energy from 20 kWh to 40 kWh. Similar to the SBR series, multiple SBH stacks can be connected in parallel to reach a maximum capacity of 160 kWh 5. Both the SBR and SBH series come with a 10-year warranty 5 and are primarily designed for DC coupling with Sungrow's hybrid inverter range, particularly the SH series, which includes models specifically designed for 3-phase systems (SH-RT series) 33. The availability of a wider range of capacities and the modular design of both the SBR and SBH series provide greater flexibility for the user to tailor a battery system to their specific energy consumption needs. The SBH series, with its larger 5 kWh modules, appears particularly well-suited for homes with potentially higher energy demands, such as those with 3-phase connections.
4.2 Compatibility with Existing 3-Phase Sungrow Inverter (DC and AC Coupling):
The user's existing Sungrow SG5KTL-MT inverter is a grid-tied inverter and not a hybrid model designed for direct DC coupling with batteries 5. Sungrow's high-voltage batteries, such as the SBR and SBH series, are primarily intended for DC coupling with their SH series hybrid inverters 33. While direct DC coupling is not an option with the SG5KTL-MT, it is possible to AC couple Sungrow batteries to the existing solar system 35. This would likely require the addition of a separate battery inverter to manage the charging and discharging of the Sungrow battery, as the SG5KTL-MT does not have this functionality. Although AC coupling offers a way to integrate a battery without replacing the existing solar inverter, it can introduce inefficiencies due to the multiple AC-DC and DC-AC conversions. For optimal performance and to fully leverage the capabilities of Sungrow's high-voltage batteries, particularly for off-grid operation, upgrading to a Sungrow SH series hybrid inverter would be the recommended approach.
4.3 Suitability for Off-Grid Operation in a 3-Phase System:
Sungrow offers a distinct advantage in providing solutions for 3-phase off-grid operation through their SH-RT series of hybrid inverters 5. These inverters, when paired with Sungrow's SBR or SBH batteries, are capable of providing seamless transition to 3-phase backup power during grid outages 63. The SH-RT series is specifically designed to support 100% unbalanced loads in backup mode, ensuring that essential appliances continue to run during a blackout 66. Both the SBR and SBH battery series are compatible with off-grid operation when used in conjunction with the appropriate Sungrow hybrid inverters. Some single-phase Sungrow hybrid inverters (SH-RS series) also offer off-grid capabilities and support generator connection for battery charging during extended periods of low solar generation 85. This comprehensive ecosystem of Sungrow products provides a more direct and integrated pathway for the user to achieve their goal of potential 3-phase off-grid capability compared to the single-phase limitations of Tesla Powerwall.
4.4 Potential for V2H Integration with a Tesla Car in Australia:
Similar to Tesla Powerwall, the provided research material does not explicitly mention direct V2H integration capabilities for Sungrow battery systems with Tesla cars in Australia 22. However, Sungrow's active involvement in the broader renewable energy and electric vehicle charging sectors suggests a strong potential for future integration. Sungrow manufactures its own range of EV chargers 64, and their 3-phase hybrid inverter solutions can be paired with these chargers for smart green power charging 64. As V2H technology and the necessary bidirectional charging infrastructure become more prevalent in Australia, it is conceivable that Sungrow's integrated energy management systems, including their batteries and hybrid inverters, could be updated to support V2H functionality, potentially even with Tesla vehicles through standardized protocols or future partnerships. In the interim, a Sungrow battery system can efficiently store solar energy, which could then be used to charge a Tesla car. The potential for the Tesla car to discharge back to the home would depend on the availability and compatibility of third-party bidirectional chargers that adhere to the evolving Australian standards.
4.5 Cost and Installation Considerations in Sydney:
The cost of Sungrow batteries in Australia varies depending on the model and capacity. For the SBR series, a 9.6 kWh system is approximately $11,500 installed, a 12.8 kWh system around $13,200 installed, and a 25.6 kWh system around $19,700 installed. Supply-only costs for the SBH series 20 kWh kit range from $13,778.70 to $14,360 40. Compatible 3-phase hybrid inverters from Sungrow, such as the SH5.0RT, are priced around $3,760, while the SH10RT ranges from approximately $4,174.50 to $5,720 78. If the user opts for a Sungrow battery system to achieve optimal 3-phase off-grid capability, the cost of a new SH series hybrid inverter would need to be included, as the existing SG5KTL-MT is not compatible for direct DC coupling. While AC coupling might be a less expensive initial step, it could involve the additional cost of a separate battery inverter. Homeowners in NSW can potentially benefit from the NSW battery rebate when purchasing a Sungrow battery system, which could help reduce the overall cost 5. Although Sungrow batteries often offer a competitive cost per kWh, the total investment for a comprehensive 3-phase off-grid solution might be higher than a single-phase Tesla Powerwall setup, primarily due to the potential need for a new hybrid inverter.
5. Comparative Assessment: Tesla Powerwall vs. Sungrow Batteries
5.1 Side-by-Side Comparison Table of Key Specifications:
| Feature | Tesla Powerwall 3 | Sungrow SBR (Example: 12.8 kWh) + SH10RT |
| :---- | :---- | :---- |
| Usable Energy Capacity (kWh) | 13.5 | 12.8 |
| Continuous Power Output (kW) | 10 | 10 |
| Peak Power Output (kW) | 10 | 12 (5 min) |
| Battery Chemistry | Lithium Iron Phosphate | Lithium Iron Phosphate |
| Scalability | Up to 4 units (54 kWh) | Up to 25.6 kWh per stack, 4 stacks parallel (102.4 kWh) |
| Off-Grid Backup (Phases Supported) | Single-Phase | Three-Phase |
| V2H Support (Current/Future Potential) | Potential via 3rd party charger | Potential via 3rd party charger |
| Warranty (Years) | 10 | 10 |
| Estimated Cost (AUD) | $13,600 + installation | $13,200 (battery installed) + $4,175 - $5,720 (inverter) |
5.2 Detailed Comparison Based on Off-Grid Capability Requirements:
When considering the user's goal of potential off-grid capability for a 3-phase home, Sungrow presents a more robust solution. The availability of Sungrow's SH-RT series hybrid inverters, specifically designed for 3-phase systems and fully compatible with their SBR and SBH batteries, allows for a direct and integrated approach to achieving 3-phase backup power. These systems can seamlessly transition to off-grid mode, powering all three phases of the home, which is crucial for operating 3-phase appliances and ensuring comprehensive whole-house backup. In contrast, Tesla Powerwall, being a single-phase battery, inherently limits off-grid backup to a single phase in a 3-phase home 8. While multiple Powerwall units can be installed, this increases cost and complexity without guaranteeing full 3-phase backup or official off-grid support from Tesla. Therefore, for a user prioritizing potential for comprehensive 3-phase off-grid operation, Sungrow's ecosystem offers a more suitable and supported pathway.
5.3 Detailed Comparison Based on V2H Functionality Requirements:
Currently, neither Tesla Powerwall nor Sungrow batteries offer direct, integrated V2H functionality for Tesla cars in Australia 22. Both systems can store solar energy that could be used to charge a Tesla car, and the potential for the car to discharge back to the home (V2H) would rely on the development and adoption of compatible bidirectional charging infrastructure in Australia, which is expected to become more mainstream in 2025 21. Sungrow's involvement in manufacturing EV chargers and integrating them with their hybrid inverters suggests a potential for future V2H integration within their ecosystem. Similarly, while Tesla Powerwall doesn't currently offer V2H, its role as a home energy storage solution makes it a complementary technology to V2H, providing a place to store energy that could eventually be managed within a V2H framework.
5.4 Cost-Effectiveness and Overall Value Analysis:
When evaluating cost-effectiveness, Sungrow batteries often have a lower cost per kWh of storage compared to Tesla Powerwall 5. However, for the user with an existing non-hybrid inverter, achieving the desired 3-phase off-grid capability with Sungrow would likely necessitate an additional investment in a Sungrow SH-RT series hybrid inverter. This would increase the initial outlay compared to simply AC coupling a Tesla Powerwall to the existing inverter for single-phase backup. The overall value proposition depends heavily on the user's priorities. If the primary goal is to have backup power for essential loads on a single phase and potential future V2H integration, Tesla Powerwall could be a viable option. However, if the potential for comprehensive 3-phase off-grid operation is a significant factor, then the added expense of a Sungrow hybrid inverter might be justified by the enhanced functionality and future-proofing for energy independence. Sungrow's reputation for affordability and the modularity of their battery systems also offer long-term value and flexibility.
6. Recommendations and Considerations
Based on the analysis, for a 3-phase home in Sydney with a 6.6kW solar system and the goal of potential off-grid capability, Sungrow battery options are recommended. Specifically, the user should consider upgrading their existing Sungrow SG5KTL-MT inverter to a Sungrow SH series hybrid inverter (e.g., SH5.0RT or SH10RT, depending on anticipated power demands) and pairing it with a Sungrow high-voltage battery from either the SBR or SBH series. The choice between SBR and SBH would depend on the desired storage capacity and budget. This combination offers a more direct and supported path to achieving 3-phase backup power and the potential for future off-grid operation.
Key Considerations for the User:
Off-Grid Capability: The level of off-grid capability desired (partial single-phase backup vs. comprehensive whole-home 3-phase backup) is a crucial factor. For the latter, Sungrow is the more suitable choice.
Budget: Both options represent a significant investment. The user should obtain detailed quotes for both Tesla Powerwall (considering single or multiple units) and a complete Sungrow hybrid inverter and battery system.
V2H Timeline: The user's timeline for V2H adoption should be considered. Both systems will likely integrate via third-party chargers.
Inverter Upgrade: If pursuing the optimal Sungrow solution for off-grid capability, the cost and logistics of upgrading the existing inverter need to be factored in.
* 3-Phase Backup Importance: The necessity of having backup power across all three phases should weigh heavily in the decision, favoring Sungrow.
It is strongly recommended that the user obtain detailed quotes from certified installers in the Sydney area for both Tesla Powerwall and various Sungrow system configurations to get accurate pricing, installation details, and information on available rebates and incentives in NSW.
7. Conclusion
In conclusion, while Tesla Powerwall offers a well-regarded solution for home energy storage with reliable backup capabilities, its inherent single-phase design presents limitations for users with 3-phase homes seeking comprehensive off-grid functionality. Sungrow, with its range of high-voltage batteries and particularly its 3-phase hybrid inverter systems, provides a more direct and technically sound pathway to achieving the user's goals of potential 3-phase off-grid operation. For V2H integration, both systems are currently positioned to benefit from the evolving Australian regulatory landscape and the development of compatible bidirectional charging technologies. Ultimately, the optimal choice will depend on the user's specific priorities, budget, and the level of off-grid capability they wish to achieve. The rapidly evolving nature of battery storage and V2H technology suggests that continued research and consultation with experts are advisable before making a final decision.
#### Works cited
1. Powerwall – Home Battery Storage | Tesla Australia, accessed March 14, 2025, [https://www.tesla.com/en_au/powerwall](https://www.tesla.com/en_au/powerwall)
2. Tesla Powerwall 3 in Australia: Everything You Need to Know - Fritts Solar, accessed March 14, 2025, [https://www.frittssolar.com.au/tesla-powerwall-3-australia/](https://www.frittssolar.com.au/tesla-powerwall-3-australia/)
3. What to Expect for Powerwall 3 | Tesla Support Australia, accessed March 14, 2025, [https://www.tesla.com/en_au/support/energy/powerwall/learn/what-expect-powerwall-3](https://www.tesla.com/en_au/support/energy/powerwall/learn/what-expect-powerwall-3)
4. Tesla Powerwall 3 Review - Clean Energy Reviews, accessed March 14, 2025, [https://www.cleanenergyreviews.info/blog/tesla-powerwall-3-review](https://www.cleanenergyreviews.info/blog/tesla-powerwall-3-review)
5. Sungrow SBH vs. Tesla Powerwall 3: Which is Better? NSW - Elite Power Group, accessed March 14, 2025, [https://www.elitepowergroup.com.au/news/sungrow-sbh-vs-tesla-powerwall-3-which-is-better-nsw/](https://www.elitepowergroup.com.au/news/sungrow-sbh-vs-tesla-powerwall-3-which-is-better-nsw/)
6. Sungrow Battery vs Tesla Powerwall Review - Volteam Electric, accessed March 14, 2025, [https://volteam.com.au/blog/sungrow-vs-tesla-battery-review/](https://volteam.com.au/blog/sungrow-vs-tesla-battery-review/)
7. Tesla Powerwall 2: A Complete 2024 Buyers Guide | Solar Choice, accessed March 14, 2025, [https://www.solarchoice.net.au/products/batteries/tesla-powerwall-2-review/](https://www.solarchoice.net.au/products/batteries/tesla-powerwall-2-review/)
8. Can You Install The Powerwall 3 On A Three-Phase Home? - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/blog/three-phase-powerwall-3/](https://www.solarquotes.com.au/blog/three-phase-powerwall-3/)
9. Is my grid connect solar system 100% compatible with a Tesla Powerwall 2 battery?, accessed March 14, 2025, [https://support.solarquotes.com.au/hc/en-us/articles/115001986773-Is-my-grid-connect-solar-system-100-compatible-with-a-Tesla-Powerwall-2-battery](https://support.solarquotes.com.au/hc/en-us/articles/115001986773-Is-my-grid-connect-solar-system-100-compatible-with-a-Tesla-Powerwall-2-battery)
10. THE 3-PHASE SOLUTION - SUNGROW, accessed March 14, 2025, [https://uk.sungrowpower.com/upload/file/20210706/EN%203-phaseSolution%20Factsheet.pdf](https://uk.sungrowpower.com/upload/file/20210706/EN%203-phaseSolution%20Factsheet.pdf)
11. Combining Systems with Powerwall | Tesla Support, accessed March 14, 2025, [https://www.tesla.com/support/energy/powerwall/learn/combining-systems](https://www.tesla.com/support/energy/powerwall/learn/combining-systems)
12. Powerwall System Design | Tesla Support, accessed March 14, 2025, [https://www.tesla.com/support/energy/powerwall/learn/system-design](https://www.tesla.com/support/energy/powerwall/learn/system-design)
13. Installing Powerwall 3 on a Three-phase Site | PSC - Penrith Solar Centre, accessed March 14, 2025, [https://www.penrithsolar.com.au/blog/installing-powerwall-3-on-a-three-phase-site/](https://www.penrithsolar.com.au/blog/installing-powerwall-3-on-a-three-phase-site/)
14. Powerwall 3: When It Makes Sense and When It Doesn't - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/blog/powerwall-3-when-it-makes-sense/](https://www.solarquotes.com.au/blog/powerwall-3-when-it-makes-sense/)
15. AC-Coupled Solar System Sizing - Energy Library - Tesla, accessed March 14, 2025, [https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-23D242D1-8D65-47B9-9118-57002FFD84D2.html](https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-23D242D1-8D65-47B9-9118-57002FFD84D2.html)
16. Powerwall 3 Roadmap - 3 Phase Coming! | Tesla Motors Club, accessed March 14, 2025, [https://teslamotorsclub.com/tmc/threads/powerwall-3-roadmap-3-phase-coming.321409/](https://teslamotorsclub.com/tmc/threads/powerwall-3-roadmap-3-phase-coming.321409/)
17. Advice on how to install with 3 phase : r/solar - Reddit, accessed March 14, 2025, [https://www.reddit.com/r/solar/comments/19djazk/advice_on_how_to_install_with_3_phase/](https://www.reddit.com/r/solar/comments/19djazk/advice_on_how_to_install_with_3_phase/)
18. TESLA POWERWALL+ (3) - DIY Solar Depot, accessed March 14, 2025, [https://diysolardepot.com/product/ground-mount-solar-hardware/pro-solar-ground-trac/](https://diysolardepot.com/product/ground-mount-solar-hardware/pro-solar-ground-trac/)
19. Design Considerations - Energy Library - Tesla, accessed March 14, 2025, [https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-3E19662A-E501-47DB-81AE-E9EC19735B8B.html](https://energylibrary.tesla.com/docs/Public/EnergyStorage/Powerwall/3/SystemDesign/en-us/GUID-3E19662A-E501-47DB-81AE-E9EC19735B8B.html)
20. Problems with Powerwall 3 | Penrith Solar Centre, accessed March 14, 2025, [https://www.penrithsolar.com.au/blog/problems-with-powerwall-3/](https://www.penrithsolar.com.au/blog/problems-with-powerwall-3/)
21. EV Charging in Australia Gets a Makeover with V2G/V2H Approved for 2025 - SEVR, accessed March 14, 2025, [https://sevr.au/news/ev-charging-in-australia-gets-a-makeover-with-v2g-v2h-approved-for-2025/](https://sevr.au/news/ev-charging-in-australia-gets-a-makeover-with-v2g-v2h-approved-for-2025/)
22. V2G, V2L & V2H Explained: Vehicle to Grid in Australia? 2025 - Elite Power Group, accessed March 14, 2025, [https://www.elitepowergroup.com.au/news/what-is-vehicle-to-grid/](https://www.elitepowergroup.com.au/news/what-is-vehicle-to-grid/)
23. Australia's Future – Bidirectional EV Charging, Solar & Battery Storage as Standard Features, accessed March 14, 2025, [https://fullycharged.show/blog/australias-future-bidirectional-ev-charging-solar-battery-storage-as-standard-features/](https://fullycharged.show/blog/australias-future-bidirectional-ev-charging-solar-battery-storage-as-standard-features/)
24. 2025, the Year of Vehicle-to-Grid in Australia V2G Milestone - Elite Power Group, accessed March 14, 2025, [https://www.elitepowergroup.com.au/news/one-step-closer-to-v2g-in-australia-2025-to-be-the-year-of-v2x/](https://www.elitepowergroup.com.au/news/one-step-closer-to-v2g-in-australia-2025-to-be-the-year-of-v2x/)
25. Bidirectional Charging for Electric Cars: Unlocking New Possibilities - Solar Batteries Online, accessed March 14, 2025, [https://www.solarbatteriesonline.com.au/bidirectional-charging-for-electric-cars-unlocking-new-possibilities/](https://www.solarbatteriesonline.com.au/bidirectional-charging-for-electric-cars-unlocking-new-possibilities/)
26. The Best Home Batteries In Australia In 2025: According To Aussie Installers - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/blog/best-home-batteries-2025/](https://www.solarquotes.com.au/blog/best-home-batteries-2025/)
27. How Much Does a Tesla Powerwall 3 Cost? | Penrith Solar Centre, accessed March 14, 2025, [https://www.penrithsolar.com.au/blog/how-much-does-a-tesla-powerwall-3-cost/](https://www.penrithsolar.com.au/blog/how-much-does-a-tesla-powerwall-3-cost/)
28. Expected 3 Phase upgrade price? : r/AusRenovation - Reddit, accessed March 14, 2025, [https://www.reddit.com/r/AusRenovation/comments/19383oa/expected_3_phase_upgrade_price/](https://www.reddit.com/r/AusRenovation/comments/19383oa/expected_3_phase_upgrade_price/)
29. Powerwall cost for Sydney? | Tesla Motors Club, accessed March 14, 2025, [https://teslamotorsclub.com/tmc/threads/powerwall-cost-for-sydney.340317/](https://teslamotorsclub.com/tmc/threads/powerwall-cost-for-sydney.340317/)
30. Solar Battery Costs: Are They Worth It?, accessed March 14, 2025, [https://www.solarchoice.net.au/solar-batteries/is-home-battery-storage-worth-it/](https://www.solarchoice.net.au/solar-batteries/is-home-battery-storage-worth-it/)
31. Tesla Powerwall 3 Price and Installation - Solar4Life, accessed March 14, 2025, [https://www.solar4life.com.au/learns/tesla-powerwall-3-price-and-installation](https://www.solar4life.com.au/learns/tesla-powerwall-3-price-and-installation)
32. Solar Battery Price, Savings and Payback, accessed March 14, 2025, [https://solarcalculator.com.au/battery-storage/price/](https://solarcalculator.com.au/battery-storage/price/)
33. Sungrow | Solar Batteries Review - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/battery-storage/reviews/sungrow-review.html](https://www.solarquotes.com.au/battery-storage/reviews/sungrow-review.html)
34. Sungrow SBR high voltage battery - VP Solar, accessed March 14, 2025, [https://www.vpsolar.com/en/sungrow-sbr-high-voltage-battery/](https://www.vpsolar.com/en/sungrow-sbr-high-voltage-battery/)
35. Sungrow Battery SBR Series - SolarBright, accessed March 14, 2025, [https://solarbright.com.au/product/sungrow-battery-sbr-series/](https://solarbright.com.au/product/sungrow-battery-sbr-series/)
36. Sungrow SBR 3.2kWh module - Huglo Solar, accessed March 14, 2025, [https://www.huglo.com.au/batteries/sbr-high-voltage-lfp-battery](https://www.huglo.com.au/batteries/sbr-high-voltage-lfp-battery)
37. Sungrow Inverter and battery Review - Clean Energy Reviews, accessed March 14, 2025, [https://www.cleanenergyreviews.info/blog/sungrow-solar-inverters-review](https://www.cleanenergyreviews.info/blog/sungrow-solar-inverters-review)
38. SBH100/150/200/250/300/350/400 - Sungrow, accessed March 14, 2025, [https://en.sungrowpower.com/productDetail/5568/battery-sbh100-150-200-250-300-350-400](https://en.sungrowpower.com/productDetail/5568/battery-sbh100-150-200-250-300-350-400)
39. 20/25/30/35/40 kWh Solar Battery - Sungrow AU, accessed March 14, 2025, [https://aus.sungrowpower.com/productDetail/3112/battery-sbh200-250-300-350-400](https://aus.sungrowpower.com/productDetail/3112/battery-sbh200-250-300-350-400)
40. Sungrow SBH Stackable Battery System - Grow Energy, accessed March 14, 2025, [https://growenergy.com.au/products/sungrow-sbh-stackable-battery-system](https://growenergy.com.au/products/sungrow-sbh-stackable-battery-system)
41. Sungrow SBH High Voltage Battery Bundle (SBH200 - SBH400), accessed March 14, 2025, [https://solarbatterysupermarket.com.au/products/sungrow-sbh-high-voltage-battery-bundle-sbh200-sbh400](https://solarbatterysupermarket.com.au/products/sungrow-sbh-high-voltage-battery-bundle-sbh200-sbh400)
42. Buy cheap SunGrow solar inverters, accessed March 14, 2025, [https://tienda-solar.es/en/brand/54-sungrow](https://tienda-solar.es/en/brand/54-sungrow)
43. Sungrow PowCube battery storage system (Analysis & review) - Solar Choice, accessed March 14, 2025, [https://www.solarchoice.net.au/products/batteries/sungrow-review/](https://www.solarchoice.net.au/products/batteries/sungrow-review/)
44. What inverters do we connect to? – Welcome to our Help Center - Support - SwitchDin, accessed March 14, 2025, [https://support.switchdin.com/hc/en-us/articles/19642583185817-What-inverters-do-we-connect-to](https://support.switchdin.com/hc/en-us/articles/19642583185817-What-inverters-do-we-connect-to)
45. Accessories Cross Reference Guide - Sungrow Australia Service, accessed March 14, 2025, [https://service.sungrowpower.com.au/files/Web_Files/FAQ/TI_202007_Sungrow%20Accessories%20Cross%20Reference%20Guide_V1.0.pdf](https://service.sungrowpower.com.au/files/Web_Files/FAQ/TI_202007_Sungrow%20Accessories%20Cross%20Reference%20Guide_V1.0.pdf)
46. Sungrow - Solar System Inverter - Solargain, accessed March 14, 2025, [https://www.solargain.com.au/solar-inverters/sungrow-solar-inverters](https://www.solargain.com.au/solar-inverters/sungrow-solar-inverters)
47. Sungrow Battery Review | A Comprehensive Guide - Esteem Energy, accessed March 14, 2025, [https://esteemenergy.com.au/blog/sungrow-battery-review/](https://esteemenergy.com.au/blog/sungrow-battery-review/)
48. Sungrow 5kW Inverter + Tesla Powerwall + Longi 370w Hi-MO4m 7.4kW Solar System, accessed March 14, 2025, [https://ahlecsolar.com.au/product/sungrow-5kw-inverter-tesla-powerwall-longi-370w-hi-mo4m-7-4kw-solar-system/](https://ahlecsolar.com.au/product/sungrow-5kw-inverter-tesla-powerwall-longi-370w-hi-mo4m-7-4kw-solar-system/)
49. Sungrow | Solar Inverters Review - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/inverters/sungrow-review.html](https://www.solarquotes.com.au/inverters/sungrow-review.html)
50. Tesla Powerwall: Inverter Compatibility Under the Spotlight - 1KOMMA5, accessed March 14, 2025, [https://1komma5.com/au/batteries/tesla-powerwall-2-compatible-solar-power-system/](https://1komma5.com/au/batteries/tesla-powerwall-2-compatible-solar-power-system/)
51. Hi everybody, question about V2H power : r/electricvehicles - Reddit, accessed March 14, 2025, [https://www.reddit.com/r/electricvehicles/comments/1hqneh3/hi_everybody_question_about_v2h_power/](https://www.reddit.com/r/electricvehicles/comments/1hqneh3/hi_everybody_question_about_v2h_power/)
52. Commercial Solar System | PV Plant | Rooftop - Sungrow US, accessed March 14, 2025, [https://us.sungrowpower.com/solutionsDetail/10/commercial-storage-systems](https://us.sungrowpower.com/solutionsDetail/10/commercial-storage-systems)
53. SH8.0/10RS | 8kW/10kW | Single Phase | Sungrow Hybrid Inverter-Sungrow AU, accessed March 14, 2025, [https://aus.sungrowpower.com/productDetail/2565/mv-power-converter-hybrid-inverter-sh8-0-10rs](https://aus.sungrowpower.com/productDetail/2565/mv-power-converter-hybrid-inverter-sh8-0-10rs)
54. Approved Batteries with SH Series Hybrid Inverters - Sungrow Australia Service, accessed March 14, 2025, [https://service.sungrowpower.com.au/files/Web_Files/FAQ/Approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters-20201209_V14_EN.pdf](https://service.sungrowpower.com.au/files/Web_Files/FAQ/Approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters-20201209_V14_EN.pdf)
55. Right inverter for the Tesla Powerwall 2 : r/solar - Reddit, accessed March 14, 2025, [https://www.reddit.com/r/solar/comments/1chgnj8/right_inverter_for_the_tesla_powerwall_2/](https://www.reddit.com/r/solar/comments/1chgnj8/right_inverter_for_the_tesla_powerwall_2/)
56. Sungrow Inverters - Gold Coast Solar Power Solutions, accessed March 14, 2025, [https://gold-coast-solar-power-solutions.com.au/gold-coast-solar-power-products/solar-power-inverters/sungrow-inverters/](https://gold-coast-solar-power-solutions.com.au/gold-coast-solar-power-products/solar-power-inverters/sungrow-inverters/)
57. Sungrow SBR192 Lithium-ion Battery - Europe-SolarStore.com, accessed March 14, 2025, [https://www.europe-solarstore.com/sungrow-sbr192-lithium-ion-battery.html](https://www.europe-solarstore.com/sungrow-sbr192-lithium-ion-battery.html)
58. High-Efficiency Solar Battery: Up to 100% Usable Energy - Sungrow, accessed March 14, 2025, [https://en.sungrowpower.com/ProductsHome/20/23/battery](https://en.sungrowpower.com/ProductsHome/20/23/battery)
59. Warranty | Sungrow Australia and New Zealand Service, accessed March 14, 2025, [https://service.sungrowpower.com.au/Warranty/warranty](https://service.sungrowpower.com.au/Warranty/warranty)
60. Sungrow Battery cross-reference chart, accessed March 14, 2025, [https://service.sungrowpower.com.au/GD_202405_SBR%20and%20SBH_Cross%20Reference%20Chart_V1.4%20Final.pdf](https://service.sungrowpower.com.au/GD_202405_SBR%20and%20SBH_Cross%20Reference%20Chart_V1.4%20Final.pdf)
61. Sungrow SG5KTL-MT - SolarTopStore.com, accessed March 14, 2025, [https://www.solartopstore.com/products/sungrow-sg5ktl-mt](https://www.solartopstore.com/products/sungrow-sg5ktl-mt)
62. Approved Batteries with SH Series Hybrid Inverters EU Version V1.6.3 - Sungrow AU, accessed March 14, 2025, [https://aus.sungrowpower.com/upload/file/20211119/TI_20210906_approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters_V16_EN.pdf](https://aus.sungrowpower.com/upload/file/20211119/TI_20210906_approved%20battery%20declaration%20for%20sungrow%20hybrid%20inverters_V16_EN.pdf)
63. BLACKOUT? NO, THANKS! POWER WHENEVER YOU NEED IT - SUNGROW, accessed March 14, 2025, [https://uk.sungrowpower.com/upload/file/20211202/EN%20FS%20Sungrow%203-phase%20Hybrid%20Backup%20Factsheet.pdf](https://uk.sungrowpower.com/upload/file/20211202/EN%20FS%20Sungrow%203-phase%20Hybrid%20Backup%20Factsheet.pdf)
64. Sungrow 3-phase solution with 6 kVA inverter, EV charger and 9.6 kWh storage - Memodo, accessed March 14, 2025, [https://www.memodo-shop.com/sungrow-3-phase-solution-with-6-kva-inverter-ev-charger-and-9.6-kwh-storage/9767](https://www.memodo-shop.com/sungrow-3-phase-solution-with-6-kva-inverter-ev-charger-and-9.6-kwh-storage/9767)
65. THE 3-PHASE SOLUTION - SUNGROW, accessed March 14, 2025, [https://uk.sungrowpower.com/upload/file/20230116/EN%20FS%203-phaseSolution%20Factsheet.pdf](https://uk.sungrowpower.com/upload/file/20230116/EN%20FS%203-phaseSolution%20Factsheet.pdf)
66. Sungrow Three-Phase Hybrid Inverter - Solar4Life, accessed March 14, 2025, [https://www.solar4life.com.au/product-detail/sungrow-5-20kw-3-phase-hybrid](https://www.solar4life.com.au/product-detail/sungrow-5-20kw-3-phase-hybrid)
67. SG5KTL-MT/SG6KTL-MT/SG8KTL-M (Non-China ... - ENF Solar, accessed March 14, 2025, [https://www.enfsolar.com/pv/inverter-datasheet/12176](https://www.enfsolar.com/pv/inverter-datasheet/12176)
68. Sungrow SBR battery combiner box - AC Solar Warehouse, accessed March 14, 2025, [https://www.acsolarwarehouse.com/shop/sungrow-battery-combiner-box-for-multiple-sungrow-lfp-battery-stacks-23620](https://www.acsolarwarehouse.com/shop/sungrow-battery-combiner-box-for-multiple-sungrow-lfp-battery-stacks-23620)
69. Sungrow SBR HV Battery Installation Quick Guide, accessed March 14, 2025, [https://service.sungrowpower.com.au/files/Web_Files/FAQ/GD_202202_SBR%20HV%20Battery%20Installation%20Quick%20Guide%20with%201%20Phase%20SHxRS_V3.0.pdf](https://service.sungrowpower.com.au/files/Web_Files/FAQ/GD_202202_SBR%20HV%20Battery%20Installation%20Quick%20Guide%20with%201%20Phase%20SHxRS_V3.0.pdf)
70. Energy Storage System Products Catalogue - SUNGROW, accessed March 14, 2025, [https://uk.sungrowpower.com/upload/file/20210909/EN%20BR%20Sungrow%20Energy%20Storage%20System%20Products%20Catalogue.pdf](https://uk.sungrowpower.com/upload/file/20210909/EN%20BR%20Sungrow%20Energy%20Storage%20System%20Products%20Catalogue.pdf)
71. DC Coupling vs AC Coupling: Which Solar System to Choose - Sungrow, accessed March 14, 2025, [https://en.sungrowpower.com/blog-detail/5983/dc-coupling-vs-ac-coupling-which-solar-system-to-choose](https://en.sungrowpower.com/blog-detail/5983/dc-coupling-vs-ac-coupling-which-solar-system-to-choose)
72. Sungrow SBH battery - Accessory kit | AC Solar Warehouse AU, accessed March 14, 2025, [https://www.acsolarwarehouse.com/shop/sbh-accessory-kit-sungrow-sbh-battery-accessory-kit-25310](https://www.acsolarwarehouse.com/shop/sbh-accessory-kit-sungrow-sbh-battery-accessory-kit-25310)
73. Sungrow SBR 3.2kWh High Voltage Battery Module , ASA00460 - Alternergy, accessed March 14, 2025, [https://www.alternergy.co.uk/sungrow-sbr-3-2-kwh-battery-asa00460](https://www.alternergy.co.uk/sungrow-sbr-3-2-kwh-battery-asa00460)
74. NEW Sungrow single phase hybrid inverters can operate without the grid or a battery, accessed March 14, 2025, [https://www.acsolarwarehouse.com/blog/news-7/new-sungrow-single-phase-hybrid-inverters-can-operate-without-the-grid-or-a-battery-255](https://www.acsolarwarehouse.com/blog/news-7/new-sungrow-single-phase-hybrid-inverters-can-operate-without-the-grid-or-a-battery-255)
75. Lawnton Sungrow SBH & Solar Hybrid System | Alvolta, accessed March 14, 2025, [https://www.alvolta.com.au/portfolio/info/74](https://www.alvolta.com.au/portfolio/info/74)
76. Sungrow Battery Starter Pack - Huglo Solar, accessed March 14, 2025, [https://www.huglo.com.au/post/sungrow-battery-starter-pack](https://www.huglo.com.au/post/sungrow-battery-starter-pack)
77. Sungrow SBR Battery System Bundles, accessed March 14, 2025, [https://solarbatterysupermarket.com.au/products/sungrow-sbr-battery-system-bundles](https://solarbatterysupermarket.com.au/products/sungrow-sbr-battery-system-bundles)
78. Sungrow Hybrid 10kW RT Three-Phase Solar Inverter, accessed March 14, 2025, [https://www.springers.com.au/shop/sh10rt-sungrow-hybrid-10kw-rt-three-phase-solar-inverter-15108](https://www.springers.com.au/shop/sh10rt-sungrow-hybrid-10kw-rt-three-phase-solar-inverter-15108)
79. Sungrow RT 5kW Three Phase Hybrid inverter (2 MPPT) SH5.0RT - Solar Batteries Online, accessed March 14, 2025, [https://www.solarbatteriesonline.com.au/product/sungrow-sh5-0rt-hv-5-0kw-residential-hybrid-three-phase-inverter/](https://www.solarbatteriesonline.com.au/product/sungrow-sh5-0rt-hv-5-0kw-residential-hybrid-three-phase-inverter/)
80. SUNGROW SH10RT | 10kW 3-Phase Hybrid Inverter - Sparky Direct, accessed March 14, 2025, [https://www.sparkydirect.com.au/p/sungrow-sh10rt-10kw-3-phase-hybrid-inverter](https://www.sparkydirect.com.au/p/sungrow-sh10rt-10kw-3-phase-hybrid-inverter)
81. Sungrow Hybrid 10kW 3 Phase 2 MPPT w/WiFi, DC Switch & EPS Built-in Inverter, accessed March 14, 2025, [https://www.solarheroes.com.au/product/sungrow-hybrid-10kw-3-phase-2-mppt-w-wifi-dc-switch-eps-built-in-inverter/](https://www.solarheroes.com.au/product/sungrow-hybrid-10kw-3-phase-2-mppt-w-wifi-dc-switch-eps-built-in-inverter/)
82. Sungrow Solar Inverters - Independent Review, accessed March 14, 2025, [https://www.solarchoice.net.au/products/inverters/Sungrow-review/](https://www.solarchoice.net.au/products/inverters/Sungrow-review/)
83. Sungrow 10.0kW - 3 Phase Hybrid Inverter (SH10RT) - Solar Superstore, accessed March 14, 2025, [https://www.solarsuperstore.com.au/products/sungrow-8-0kw-3-phase-hybrid-inverter-sh8-0rt](https://www.solarsuperstore.com.au/products/sungrow-8-0kw-3-phase-hybrid-inverter-sh8-0rt)
84. How Much Do Solar Batteries Cost in Australia? - SolarQuotes, accessed March 14, 2025, [https://www.solarquotes.com.au/battery-storage/cost/](https://www.solarquotes.com.au/battery-storage/cost/)
85. Off Grid Solar system using a Sungrow inverter and battery, accessed March 14, 2025, [https://www.acsolarwarehouse.com/blog/news-7/off-grid-solar-system-using-a-sungrow-inverter-and-battery-312](https://www.acsolarwarehouse.com/blog/news-7/off-grid-solar-system-using-a-sungrow-inverter-and-battery-312)
86. Sungrow 14.08k W Off Grid Solar System / Single Phase - AHLEC, accessed March 14, 2025, [https://ahlecsolar.com.au/product/sungrow-14-08k-w-off-grid-solar-system-single-phase/](https://ahlecsolar.com.au/product/sungrow-14-08k-w-off-grid-solar-system-single-phase/)
87. Residential Battery Energy Storage System - Sungrow AU, accessed March 14, 2025, [https://aus.sungrowpower.com/solutionsDetail/9/residential-storage-system](https://aus.sungrowpower.com/solutionsDetail/9/residential-storage-system)
88. EV Charger - Sungrow, accessed March 14, 2025, [https://en.sungrowpower.com/ProductsHome/59/ev-charger](https://en.sungrowpower.com/ProductsHome/59/ev-charger)
89. Sungrow SBH 20kW High Voltage LFP Battery Including Accessory Kit SBH200 | eBay, accessed March 14, 2025, [https://www.ebay.com.au/itm/135320073679](https://www.ebay.com.au/itm/135320073679)
90. 20kWh Battery Kit - Login - Australian Solar Supplies Pty Ltd, accessed March 14, 2025, [http://shop.ausolarsupplies.com.au/s.nl/it.A/id.6047/.f](http://shop.ausolarsupplies.com.au/s.nl/it.A/id.6047/.f)
91. Sungrow - Solar Batteries Online, accessed March 14, 2025, [https://www.solarbatteriesonline.com.au/sungrow/](https://www.solarbatteriesonline.com.au/sungrow/)
{"id":"6a44da7a-19c1-4a37-a991-d589c8bbded8","providerCopyMimeTypes":["application/vnd.vscode.markdown.updatelinks.metadata","application/vnd.code.additional-editor-data"],"defaultPastePayload":{"multicursorText":null,"pasteOnNewLine":false,"mode":null}}{"version":1,"isFromEmptySelection":false,"multicursorText":null,"mode":"markdown"}
-
 @ 234035ec:edc3751d
2025-03-22 02:34:32
@ 234035ec:edc3751d
2025-03-22 02:34:32I would like to preface this idea by stating that I am by no means a computer engineer and lack significant technical knowledge, and therefore may be overlooking significant obstacles to implementing this idea. My reason for writing this paper is in hopes that developers or others who are more "in the know" than me could provide feedback.
The Success of Polymarket
Over recent months, Polymarket has garnered many headlines—mainly for its accurate prediction markets surrounding the 2024 presidential election. On Polymarket, users can purchase futures contracts that will either pay out $1 in USDC at maturity if the prediction is correct or will become worthless if the prediction is incorrect. Market participants can freely trade these futures at the current price up until maturity, allowing for efficient price discovery.
We’ve known for quite some time that free markets are the most efficient way of pricing goods and services. Polymarket has now demonstrated just how effective they can be in pricing potential outcomes as well.
The issue I have with this application is that it is built on the Polygon network—a proof-of-stake side chain of Ethereum. Users are subject to KYC regulations and do not have the ability to create markets themselves. While the core idea is powerful, I believe it has been built on a foundation of sand. We now have the tools to build something similar—but much more decentralized, censorship-resistant, and sustainable.
A Bitcoin-Based Prediction Market
It seems to me that Chaumian eCash, in combination with Bitcoin and Nostr, could be used to create a truly decentralized prediction marketplace. For example, multiple eCash mints could issue tokens that represent specific potential outcomes. These tokens would be redeemable for 100 sats at a predetermined block height if the prediction is correct—or become irredeemable if the prediction is incorrect.
Redemption would be based on consensus from the chosen oracles—trusted Nostr Npubs—with strong reputations and proven track records. Anyone could create a market, and users could buy, sell, and trade eCash tokens privately. This approach preserves the power of markets while eliminating the need for custodians, KYC, or dependence on unreliable chains.
What we would have is a trust-minimized, privacy-preserving, Bitcoin-native prediction market that resists censorship and allows for true global participation. Feedback, critique, and collaboration are welcome.
Next Steps and Vision
The potential for system like this is immense. Not only would it enable peer-to-peer speculation on real-world outcomes, but it would also open the door to a more accurate reflection of public sentiment. With free market incentives driving truth-seeking behavior, these prediction markets could become powerful tools for gauging probabilities in politics, finance, sports, science, and beyond.
Each mint could specialize in a specific domain or geographic region, and users could choose the ones they trust—or even run their own. The competition between mints would drive reliability and transparency. By using Nostr for oracle communication and event creation, we keep the entire system open, composable, and censorship-resistant.
Markets could be created using a standardized Nostr event type. Resolution data could be posted and signed by oracles in a verifiable way, ensuring anyone can validate the outcome. All of this could be coordinated without a centralized authority, enabling pseudonymous participation from anyone with an internet connection and a Lightning wallet.
In the long run, this system could offer a viable alternative to corrupted media narratives, rigged polling, and centrally controlled information channels. It would be an open-source tool for discovering truth through economic incentives—without requiring trust in governments, corporations, or centralized platforms.
If this idea resonates with you, I encourage you to reach out, build on it, criticize it, or propose alternatives. This isn’t a product pitch—it’s a call to experiment, collaborate, and push the frontier of freedom-forward technologies.
Let’s build something that lasts.
Bitcoin is our base layer. Markets are our discovery engine. Nostr is our communication rail. Privacy is our defense. And truth is our goal.
-
 @ 4abac58c:54c71964
2025-03-22 01:21:01
@ 4abac58c:54c71964
2025-03-22 01:21:01Introduction Bitcoin is often seen as a store of value, "digital gold" designed to resist censorship and central control. But few people realize how fast and easy it can be to use Bitcoin for small, everyday transactions. Enter the Lightning Network: a second-layer solution that enables near-instant, low-fee payments. This article will explain how it works, why it matters, and how you can use it today.
What Is the Lightning Network? The Lightning Network (LN) is a layer built on top of the Bitcoin blockchain. Its primary purpose is to make Bitcoin transactions faster and cheaper by creating payment channels between users. Instead of recording every transaction on the main blockchain, two users can open a channel, transact as many times as they want, and settle the final balance on-chain later.
This means no long confirmation times or high fees. Payments can take less than a second and cost a fraction of a cent.
Why It Matters Bitcoin's main chain can process around 7 transactions per second. In contrast, Visa can handle thousands. This makes scaling Bitcoin for everyday use a challenge. Lightning changes that by handling most activity off-chain.
Imagine buying coffee, tipping a content creator, or paying for a digital download with Bitcoin. Lightning makes this seamless and instant. It also supports micropayments, enabling new business models like pay-per-article or per-minute streaming.
How to Start Using Lightning Getting started is easier than ever:
- Download a Lightning Wallet: Try apps like Wallet of Satoshi, Phoenix, or Breez.
- Get Some Sats: Sats (short for satoshis, the smallest unit of Bitcoin) can be received via another wallet, an exchange, or earned.
- Start Spending or Zapping: Use your Lightning wallet to pay for services, tip content creators on platforms like Nostr, or support open-source projects.
Real-World Use Cases - Nostr + Zaps: Nostr, a decentralized social media protocol, integrates Lightning payments directly. Users can "zap" posts they like, sending Bitcoin instantly to the author. This has created a native reward system for content. - Bitrefill: Buy gift cards with Lightning. - Podcasting 2.0: Stream sats to podcasters per minute of audio consumed.
Citations and Resources - https://lightning.network - https://bitcoinmagazine.com/technical/the-lightning-network - https://walletofsatoshi.com - https://highlighter.com
Conclusion Bitcoin isn’t just digital gold—it’s programmable money. The Lightning Network shows how Bitcoin can work for everyday payments, from your morning coffee to rewarding your favorite content creator. If you’ve never tried it, now is the perfect time to explore this magical layer of the Bitcoin economy.
Call to Action Got a Lightning wallet already? Try zapping this article on Nostr or sharing your first Lightning transaction experience!
-
 @ b8af284d:f82c91dd
2025-03-10 08:28:07
@ b8af284d:f82c91dd
2025-03-10 08:28:07Liebe Abonnenten,
800 Milliarden Euro will die EU ausgeben, um die Ukraine und den Kontinent in ein “stählernes Stachelschwein” zu verwandeln. Deutschland selbst will künftig Verteidigungsausgaben aus der Schuldenbremse ausnehmen, was nichts anderes als eine unbegrenzte Kreditlinie für das Militär bedeutet. Hinzu kommt ein “Sondervermögen” in Höhe von 500 Milliarden Euro für Infrastruktur. Das klingt nach einem Spartopf, den man für schwere Zeiten angelegt hat. Es soll die Tatsache verschleiern, dass es sich dabei um Schulden handelt. Der vermutlich baldige Kanzler Friedrich Merz bricht damit sein Wahlversprechen, die Schuldenbremse einzuhalten. Beschließen soll das Paket noch ein abgewählter Bundestag, da im neuen wohl die Mehrheit fehlt.
Womit also ist zu rechnen, wenn demnächst fast eine Billion frisch gedruckte Euro in Drohnen, Panzer und Raketen investiert werden?

Das beste Beispiel der jüngeren Geschichte ist China: 2009 legte die chinesische Regierung das bisher größte Infrastrukturprojekt der Welt in Höhe von 440 Milliarden Euro auf. Finanziert wurde es durch günstige Kredite, die vor allem an Staatsunternehmen vergeben wurden. Nachdem die Welt nach der in den USA ausgelösten Immobilienkrise 2008 in die Rezession gerutscht war, „rettete“ dieses Paket die globale Konjunktur. China hatte zu diesem Zeitpunkt großen Bedarf an Flughäfen, Straßen und vor allem Zügen. Das Paket war riskant: Schier unbegrenztes Geld, das begrenzten Waren hinterherjagt, führt zu Inflation. Billige Kredite führen meist dazu, dass Unternehmen nicht mehr effizient wirtschaften, und Schuldenberge vor sich her wälzen.
Allerdings wurde das Geld in Produktivität investiert. Denn wenn Menschen und Waren einfacher reisen können, nimmt die Geschäftstätigkeit zu: Arbeitnehmer werden mobiler, Unternehmen konkurrenzfähiger, die Preise sinken. Die Investitionen lohnen sich also, weil sie zu mehr Wirtschaftswachstum führen. Vereinfacht gesagt: Die Schulden können zurückgezahlt werden, und am Ende bleibt noch mehr übrig. In diesem Fall führen Schulden nicht zu Inflation: Durch die gesteigerte Produktivität stehen jetzt sogar mehr Waren der Geldmenge gegenüber.
15 Jahre später kämpft die zweitgrößte Volkswirtschaft zwar noch immer mit den Problemen, die aus diesem Paket resultieren - die Immobilienkrise ist eine indirekte Folge davon. Trotzdem war das Programm ein Erfolg: die Städte, Flughäfen und vor allem Zugstrecken führten zu einer höheren wirtschaftlichen Aktivität oder Produktivität. China ist heute ein wesentlich moderneres Land als vor dem Paket, und verfügt über modernste und größte Netz aus Hochgeschwindigkeitszügen der Welt. Neue Schulden können positiv sein - wenn das Geld produktiv investiert wird.
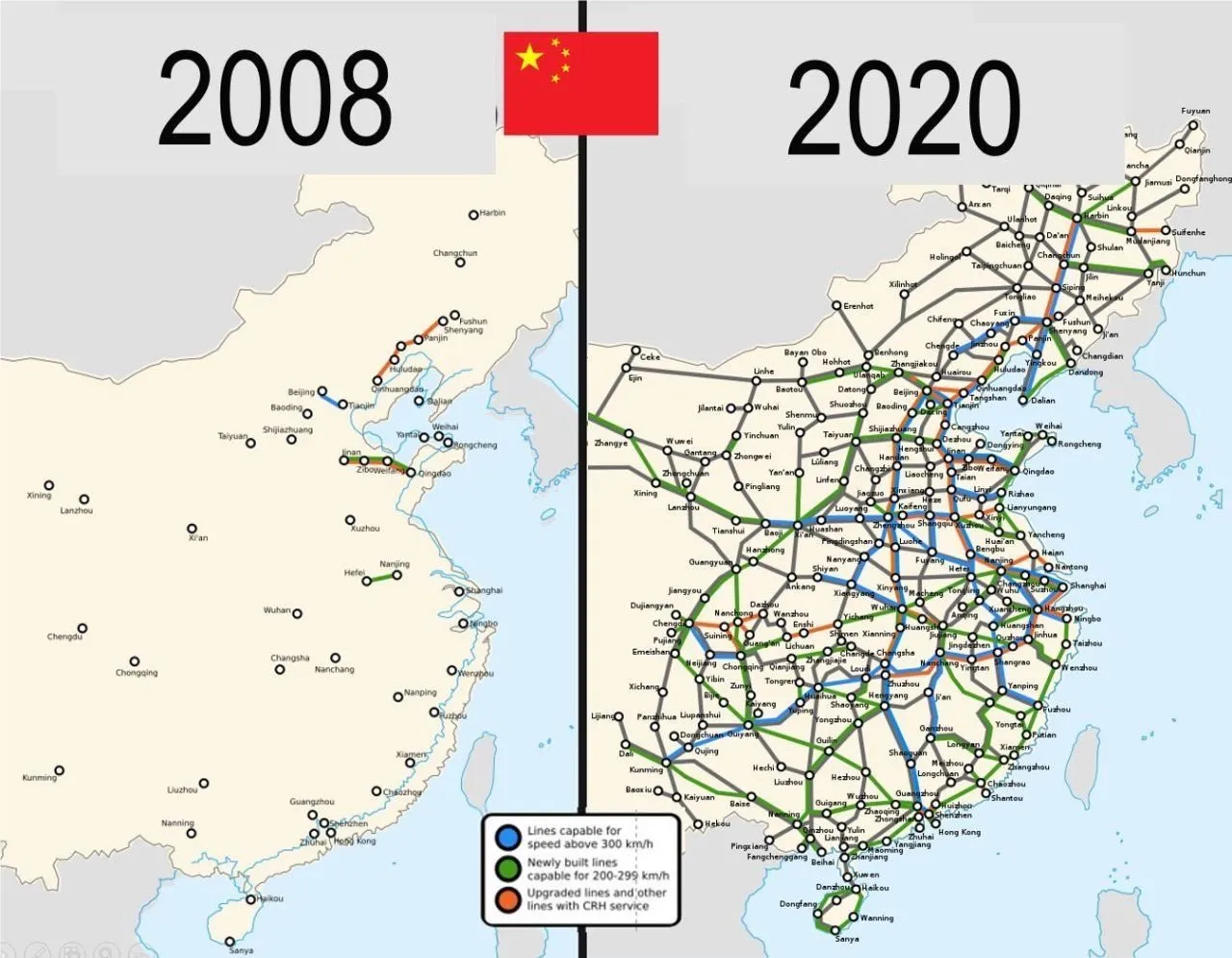
Auch in Europa lassen sich mit dem Geld-Paket zunächst mehrere Probleme auf einmal lösen: Deutschland ist noch immer ein Industriestandort mit hohen Produktionskapazitäten. Werke der Auto- und Zulieferindustrie können theoretisch zur Waffenproduktion umfunktioniert werden. Immer noch besser als sie stillzulegen oder an die Chinesen zu verkaufen, werden viele Kommentatoren schreiben.
Allein in der deutschen Automobil-Zulieferindustrie sind im vergangenen Jahr über 19000 Arbeitsplätze verloren gegangen. Viele von den Entlassenen können nun Arbeit in der Rüstungsindustrie finden. Oder wie Hans Christoph Atzpodien, Hauptgeschäftsführer des Bundesverbandes der Deutschen Sicherheits- und Verteidigungsindustrie in der WirtschaftsWoche sagt:
„Das Motto muss lauten: Autos zu Rüstung! Anstatt einen volkswirtschaftlichen Schaden durch den Niedergang der Auto-Konjunktur zu beklagen, sollten wir versuchen, Produktionseinrichtungen und vor allem Fachkräfte aus dem Automobilsektor möglichst verträglich in den Defence-Bereich zu überführen“
Immerhin: ein großer Teil des Geldes soll auch in Infrastrukturprojekte fließen: Brücken, Bahn, Internetausbau. Deutschland, und damit Europa, wird in den kommenden Monaten also eine große Party feiern, die über die Tatsache hinwegtäuschen wird, dass man einen dummen Krieg verloren hat. In den kommenden Monaten werden sich Verbände und Organisationen um das Geld reißen. Das Geld wird ein auch kollektiv-psychologisches Ventil sein, um das eigene Versagen bei Corona, Klima und Ukraine vergessen zu machen.
Es gibt allerdings einen wesentlichen Unterschied zum chinesischen Stimulus-Paket 2009: Rüstungsgüter sind im Gegensatz zu Zugstrecken totes Kapital. Eine neue Drohne oder Panzer führt nicht zu mehr Produktivität, im Gegenteil: Kommen sie zum Einsatz, zerstören sie Brücken, Häuser, Straßen und töten Menschen. Die Produktivität sinkt also. Im besten Fall kann Militärgerät herumstehen und vor sich hin rosten. Auch dann aber ist es „totes Kapital“, das nichts zur Produktivität beiträgt. Kommt es zum Einsatz, stehen der nun verringerten Warenmenge eine noch größere Geldmenge gegenüber. Die Inflation steigt.
Schleichende Militarisierung
Auch gesellschaftlich wird das Paket mit seinem Blanko-Scheck für die Verteidigungsindustrie viel verändern: Es kommt zu einer „Eichung“ der Gesellschaft, eine kollektive Abscheu des gemeinsamen Feindes. Scharfmacher, eigentlich mittelmäßiger Akademiker und Bürokraten, wie Carlo Masala und Claudia Major werden eine noch größere Rolle im öffentlichen Diskurs spielen und die Talkshows dominieren, die von einer immer älter werdenden deutschen Bevölkerung geglotzt werden. Abweichende Meinungen auf Online-Plattformen zensiert, unter dem Vorwand, die Demokratie sei in Gefahr:
Da die Rüstungsindustrie dann eine wichtigere Rolle für die Gesamtwirtschaft spielt, wird ihr Einfluss auf die Politik in Form von Lobbyisten und Verbänden zunehmen. Politiker merken schnell, dass sie von der medialen Aufmerksamkeitsökonomie nach oben gespült werden, wenn sie immer radikalere Forderungen stellen. So empfahl der ehemalige Außenminister Joschka Fischer die Woche die Wiedereinführung der Wehrpflicht für Männer und Frauen. “Star-Ökonomin” Isabella Weber will die Kriegswirtschaft mitplanen:
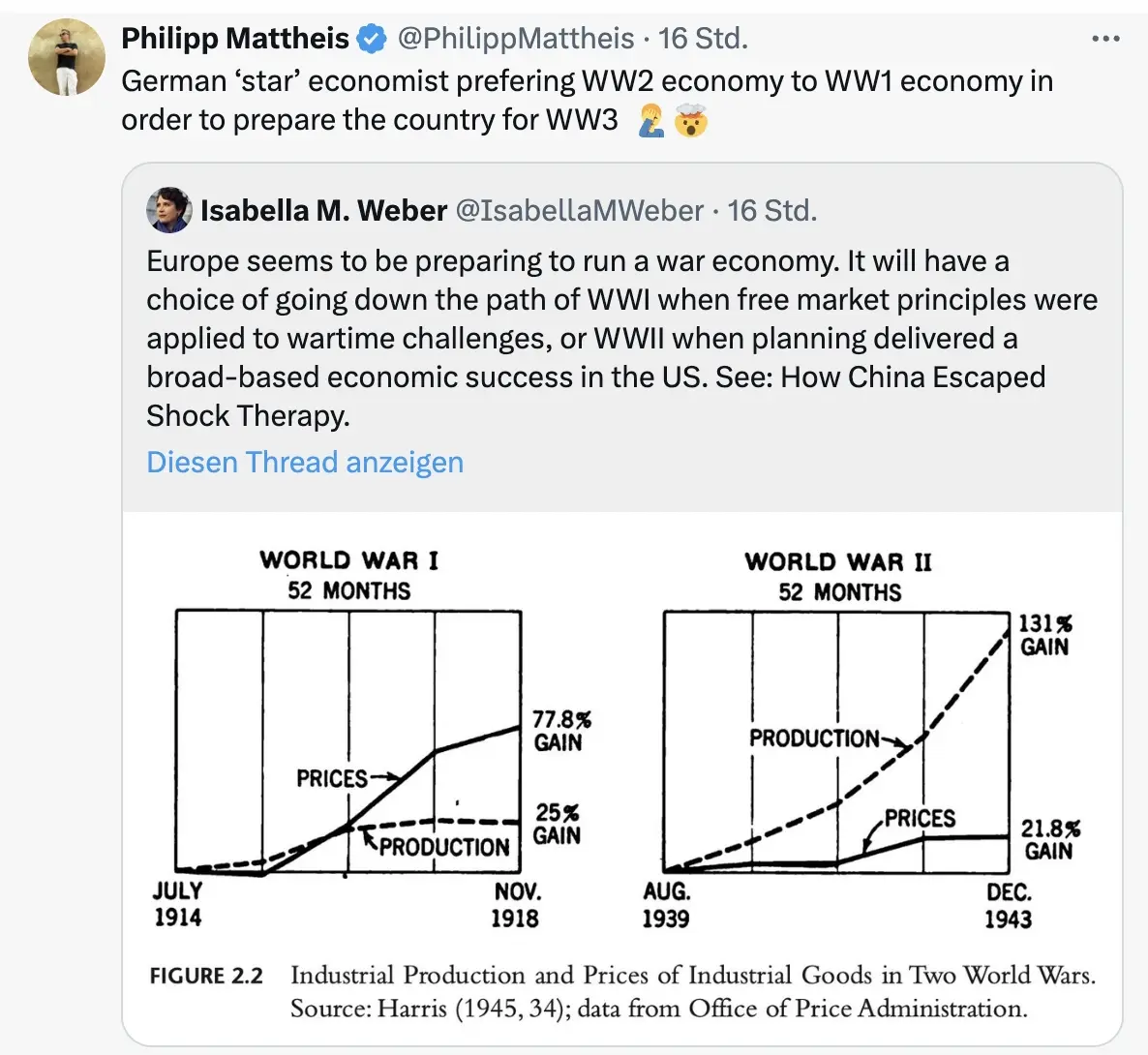
\ Der Kontinent wird sich langsam wandeln von einem „Friedensprojekt“ zu einem „metallenen Stachelschwein“, ergo Kriegsprojekt, denn ohne dämonisierten Feind funktioniert das Programm nicht. Der Ton wird rauer, autoritärer, und die Meinungsfreiheit weiter eingeschränkt werden. Die seit 2020 eingeführten Werkzeuge zur soften Propaganda („kognitive Kriegsführung”) werden verfeinert und ausgebaut werden, sodass weiterhin 80 Prozent der Bevölkerung alle noch so antihumanen Maßnahmen gutheißen werden.
Und dann?
Wie Julian Assange einmal sagte: “Das Ziel ist kein erfolgreicher Krieg. Das Ziel ist ein endloser Krieg.” Der Konflikt muss weitergehen, ewig schwelen oder ein neuer gefunden werden, da sonst ein Teil der Wirtschaftsleistung kollabiert.
Nach ein, zwei oder auch erst drei Jahren, werden erste Probleme sichtbar. Die Party endet, der Kater setzt langsam ein. Die Finanzierung an den Kapitalmärkten wird für Deutschland immer kostspieliger. Der Schuldendienst wird einen größeren Teil des Haushalts einnehmen. Die Bürger müssen dies mitfinanzieren. Der voraussichtlich neue Bundeskanzler Friedrich Merz sprach bereits von der „Mobilisierung der deutschen Sparguthaben“.
\ Was im Ersten Weltkrieg „Kriegsanleihen“ hieß, wird einen schickeren Namen bekommen wie „olivgrüne Bonds“. You name it. Alternativ lässt sich ein Verteidigungs-Soli einführen, oder das Kindergeld streichen, wie kürzlich Ifo-Chef Clemens Fuest forderte.
Was kann man tun? Auf BlingBling geht es um konkrete Tipps, welche Anlagen von dieser Entwicklung profitieren werden. Außerdem geht es um die “Strategische Bitcoin Reserve”, die am Donnerstag beschlossen wurde.
-
 @ 2dd9250b:6e928072
2025-03-22 00:22:40
@ 2dd9250b:6e928072
2025-03-22 00:22:40Vi recentemente um post onde a pessoa diz que aquele final do filme O Doutrinador (2019) não faz sentido porque mesmo o protagonista explodindo o Palácio dos Três Poderes, não acaba com a corrupção no Brasil.
Progressistas não sabem ler e não conseguem interpretar textos corretamente. O final de Doutrinador não tem a ver com isso, tem a ver com a relação entre o Herói e a sua Cidade.
Nas histórias em quadrinhos há uma ligação entre a cidade e o Super-Herói. Gotham City por exemplo, cria o Batman. Isso é mostrado em The Batman (2022) e em Batman: Cavaleiro das Trevas, quando aquele garoto no final, diz para o Batman não fugir, porque ele queria ver o Batman de novo. E o Comissário Gordon diz que o "Batman é o que a cidade de Gotham precisa."
Batman: Cavaleiro das Trevas Ressurge mostra a cidade de Gotham sendo tomada pela corrupção e pela ideologia do Bane. A Cidade vai definhando em imoralidade e o Bruce, ao olhar da prisão a cidade sendo destruída, decide que o Batman precisa voltar porque se Gotham for destruída, o Batman é destruído junto. E isso o da forças para consegue fugir daquele poço e voltar para salvar Gotham.
Isso também é mostrado em Demolidor. Na série Demolidor o Matt Murdock sempre fala que precisa defender a cidade Cozinha do Inferno; que o Fisk não vai dominar a cidade e fazer o que ele quiser nela. Inclusive na terceira temporada isso fica mais evidente na luta final na mansão do Fisk, onde Matt grita que agora a cidade toda vai saber o que ele fez; a cidade vai ver o mal que ele é para Hell's Kitchen, porque a gente sabe que o Fisk fez de tudo para a imagem do Demolidor entrar e descrédito perante os cidadãos, então o que acontece no final do filme O Doutrinador não significa que ele está acabando com a corrupção quando explode o Congresso, ele está praticamente interrompendo o ciclo do sistema, colocando uma falha em sua engrenagem.
Quando você ouve falar de Brasília, você pensa na corrupção dos políticos, onde a farra acontece,, onde corruptos desviam dinheiro arrecadado dos impostos, impostos estes que são centralizados na União. Então quando você ouve falarem de Brasília, sempre pensa que o pessoal que mora lá, mora junto com tudo de podre que acontece no Brasil.
Logo quando o Doutrinador explode tudo ali, ele está basicamente destruindo o mecanismo que suja Brasília. Ele está fazendo isso naquela cidade. Porque o símbolo da cidade é justamente esse, a farsa de que naquele lugar o povo será ouvido e a justiça será feita. Ele está destruindo a ideologia de que o Estado nos protege, nos dá segurança, saúde e educação. Porque na verdade o Estado só existe para privilegiar os políticos, funcionários públicos de auto escalão, suas famílias e amigos. Enquanto que o povo sofre para sustentar a elite política. O protagonista Miguel entendeu isso quando a filha dele morreu na fila do SUS.
-
 @ 732c6a62:42003da2
2025-03-06 06:00:53
@ 732c6a62:42003da2
2025-03-06 06:00:53De acordo com a Forbes, a Ripple (Empresa responsável pela Criptomoeda XRP) tem financiado e apoiado campanhas contra a mineração de Bitcoin.
Por que Ripple faz propaganda anti-bitcoin?
Simples: eles são o oposto do Bitcoin em quase tudo. Enquanto o Bitcoin foi criado para ser descentralizado, resistente à censura e independente de instituições, o Ripple é basicamente um serviço bancário 2.0. Eles precisam atacar o Bitcoin para justificar sua própria existência.
O que você não sabe:
- Ripple Labs controla a maioria do XRP: Eles têm um estoque estratégico que pode ser liberado no mercado a qualquer momento. Isso é o oposto de descentralização.
- XRP não é uma moeda para "pessoas comuns": Foi criada para bancos e instituições financeiras. Basicamente, é o "banco central" das criptomoedas.
- Ripple não é blockchain no sentido tradicional: Eles usam um protocolo chamado Ripple Protocol Consensus Algorithm (RPCA), que é mais rápido, mas menos descentralizado.
Os principais ataques do Ripple ao Bitcoin:
- Anti-mineração: O Ripple critica o consumo de energia do Bitcoin, mas esquece que seu próprio sistema depende de servidores centralizados que também consomem energia.
- Anti-reserva estratégica: O Ripple tem um estoque gigante de XRP, mas critica o Bitcoin por ser "deflacionário". Hipocrisia? Nunca ouvi falar.
- Anti-descentralização: O Ripple prega que a descentralização do Bitcoin é "ineficiente", mas o que eles realmente querem é manter o controle nas mãos de poucos.
Análise Psicológica Básica (para você que acha que XRP é o futuro):
- Síndrome do Underdog: Acha que apoiar o Ripple te faz um rebelde, mas na verdade você está torcendo para o sistema bancário tradicional.
- Viés de Confirmação: Só ouve opiniões que validam sua decisão de comprar XRP.
- Efeito Dunning-Kruger: Acha que entender Ripple te torna um especialista em criptomoedas, mas não sabe o que é um hard fork.
Estudo de Caso (Real, mas Você Vai Ignorar):
Carlos, 30 anos, comprou XRP porque "é o futuro das transações bancárias". Ele não sabe que o Ripple está sendo processado pela SEC por vender XRP como um título não registrado. Carlos agora está esperando o "pump" que nunca vem.Conclusão: ou, "volte para a aula de economia do ensino médio"
Ripple não é o futuro das finanças. É só mais um player tentando lucrar em um mercado competitivo. E sua propaganda anti-Bitcoin? Essa só prova que a descentralização assusta quem quer controle. Agora vá estudar blockchain básico — ou pelo menos pare de compartilhar memes com erros de português.
-
 @ 732c6a62:42003da2
2025-03-06 04:33:48
@ 732c6a62:42003da2
2025-03-06 04:33:48De ''Dialética do Oprimido'' a ''Like do Oprimido'': A Queda Livre do Debate que Nunca Existiu.
A moda do momento
Fiquei aproximadamente 8 meses sem ter acesso a nenhum dispositivo. Quando consegui novamente o acesso ao smartphone, percebi algo diferente no debate político brasileiro: enquanto a direita estava se engajando em incontáveis números de curtidas e compartilhamentos com memes que demonstravam críticas ao governo e aos seus ainda poucos apoiadores que se humilham para defender o indefensável, a esquerda radical repetia sua imposição intelectual em comentários de vários posts, incluindo textos, vídeos e tweets com frases semelhantes a "vai ler um livro de história" "nunca leu um livro", "eu estou do lado certo da história" e "se eu fosse irracional eu seria de direita". Tudo isso pra tentar passar uma mensagem de que a história é de esquerda. A tese é: será que eles realmente são tão inteligentes como juram?
Fatos que ignoram enquanto cospem jargões do "lado certo da história":
1. A esquerda também tem seus terraplanistas: Anti-vaxxers de organicafé, terraplanistas do gênero, e os que acham que a Coreia do Norte é uma democracia.
2. Viés de confirmação não é monopólio da direita: Eles compartilham estudos "científicos" do Medium como se fossem peer-reviewed, mas desdenham de dados que contradizem sua narrativa.
3. A direita não é um monolito: Tem desde ancaps que calculam até a última casa decimal até bolsominions que acham que a Terra é plana. Generalizar é... bem, irracional.Estudo de Caso (Fictício, mas Verdadeiro):
Larissa, 23 anos, posta sobre "ciência e razão" enquanto defende horóscopo como "ferramenta de autoconhecimento". Acredita que o capitalismo causa depressão, mas não sabe o que é taxa Selic. Larissa é você após três caipirinhas.A Imposição intelectual que ninguém pediu (mas todos recebem de graça)
A esquerda brasileira, em sua cruzada épica para salvar o mundo dos "fascistas que ousam discordar", adotou uma nova estratégia: transformar complexidade política em slogans de camiseta de feira. A frase "se eu fosse irracional, seria de direita" não é original — é plágio descarado da cartilha do Complexo de Deus em Oferta no AliExpress.
O Quebra-Cabeça da superioridade Auto-Delirante
A tese esquerdista se sustenta em três pilares frágeis:
1. A falácia do "lado certo da história": Como se história fosse um jogo de futebol com narração do João Cléber.
2. A ilusão de que citar Foucault = ter QI elevado: Spoiler: decorar "biopoder" não te torna imune a acreditar em astrologia.
3. A crença de que volume de texto = profundidade: 15 parágrafos no Twitter não equivalem a um semestre de Ciência Política.Dado Cruel: Um estudo da Universidade de Cambridge (2022) mostrou que extremistas de ambos os lados cometem erros lógicos similares. A diferença? A esquerda usa palavras mais bonitas para mascarar a burrice.
A hipocrisia do "nunca tocou em um livro" (enquanto compartilham resumo de livro no TikTok)
A acusação preferida — "você não lê!" — esconde uma ironia deliciosa:
- 72% dos "intelectuais de rede social" citam livros que nunca leram além do título (Fonte: Pesquisa Informal do Twitter, 2023).
- Obras citadas como troféu: "1984" (para chamar Bolsonaro de Big Brother), "O Capital" (para justificar o NFT da Gal Gadot), e "Feminismo para os 99%" (para atacar homens heterossexuais que usam sandália de dedo).Pergunta Incômoda: Se ler Marx fosse garantia de racionalidade, por que a União Soviética acabou em pizza (literalmente, considerando a economia deles)?
Quando a autoimagem colide com a realidade (Ou: por que nenhum esquerdista lassa no teste de turing da coerência)
A esquerda adora se pintar como a Última Trincheira da Razão, mas pratica o que critica:
- Exemplo 1: Defendem "ciência" quando convém (vacinas), mas abraçam pseudociência quando é trendy (cristais energéticos contra o capitalismo).
- Exemplo 2: Chamam a direita de "terraplanista", mas acham que inflação se resolve com tabelamento estatal — a versão econômica de "a Terra é sustentada por tartarugas".
- Exemplo 3: Criticam "fake news", mas compartilham teorias de que o agro "envenena a comida" (enquanto comem sushi de supermercado).Frase-Chave: "Racionalidade seletiva é o novo analfabetismo funcional."
Pergunta Final: Se a esquerda é tão racional, por que não usa a "lógica implacável" para resolver algo além do enquadro perfeito de stories no Instagram?
Enfim
O debate "esquerda racional vs. direita irracional" é só mais um episódio da novela "Brasil: O País que Confunde Opinião com Ataque de Ego". Enquanto uns brincam de "quem tem o QI mais alto", o país queima — literalmente, considerando o Pantanal. Talvez a verdadeira irracionalidade seja gastar energia discutindo superioridade moral enquanto o Wi-Fi cai pela décima vez no dia. Racionalidade não tem lado político. Arrogância, por outro lado, é universal. Sua necessidade de se sentir superior só prova que a lacração é o último refúgio dos fracos de argumento. Agora deviam estudar economia básica — ou pelo menos que parem de achar que "Ah, mas o capitalismo!" é um contra-argumento.
Saudade da época em que a esquerda não se fingia de intelectual.
-
 @ 30fb9c78:1f1e3c3a
2025-03-22 00:18:06
@ 30fb9c78:1f1e3c3a
2025-03-22 00:18:06It’s easy to identify the presence of something, but it’s much harder to identify the absence of something. If your boyfriend brings you flowers, that’s awfully nice. If he never brings you flowers, it might take you a while to notice. Maybe you do eventually notice, but you decide to cope. You tell yourself you don’t care about getting flowers. Maybe you take it a step further: “Actually, flowers are really basic and lame. Only basic girls like flowers. I’m a cool girl and cool girls don’t care about getting flowers.”
If this goes on for long enough—even if you are genuinely presented with flowers at some point—you will see them as a kind of joke. Flowers are now a bit. It sounds so trivial, I know, but if you dull your “receptors for flowers” for years on end, you will eventually fail to see the beauty of the gesture.
Entering the void
I’m deeply troubled by the fact that I see this happening at a massive scale, all around us. Except the problem is not a lack of bouquets, of course. It’s a lack of meaning.
Life has gotten very chaotic incredibly quickly. It has become increasingly difficult to parse anything from the static. People started coping with this lack of meaning through a kind of ironic detachment (which is very much still around), but it has matured into a pervasive cultural apathy, a permeating numbness. This isn’t nihilism per se. (Even nihilists have a sincere belief system; they just sincerely believe that life is meaningless.) What we’re dealing with is worse than nihilism. People are checking out of life in their 20s and 30s without reaching any profound conclusions about the point of it all.

“People are so worn down," my friend told me on a recent phone call. She’s right: there’s a real lack of palpable ambition and vitality these days, a stunning lack of life force in the world. Another friend told me that “this has been going on for so long that people wouldn’t know meaning if it walked up and bit them in the ass.” It’s true—so many of the things that once gave the average person’s life real meaning are now treated with sarcasm and contempt: college is a waste of money, work is a waste of your life, getting married is just a piece of paper, having kids is a nightmare, family is a burden, hobbies are merely quaint, earnestly expressing yourself is cringe, leaving the house is exhausting, religion is for idiots, the list goes on. If you allow yourself to internalize this perspective, eventually everything becomes a dumb joke.
A quick aside before we get into it: it’s taken me a long time to write this piece. This is partly because this whole phenomenon is, in a way, its own kind of absence. It’s been hard for me to identify what is going on and what is missing. I’ve had my own cycles of coping with it. I’ve been telling myself that I don’t care about people not caring. But obviously I do. So here goes.
A culture of chaos
The cultural forces that spawned this collective response have been quietly working their way into everything for decades—probably since the 1970s if I had to stick a pin in it. It reached new heights in the 1990s, but it took off exponentially since the mass adoption of the internet, social media, and the pandemic. We boiling frogs started to feel the water get really hot around 2015, I think, and it’s only gotten hotter and hotter since.
We’re so saturated in this environment that people are not only numbing out, they’re kind of making a spectacle of it: from TikTok’s “quiet quitting” trend to Vetements entire “ironic” aesthetic. You know it’s bad when the corporations get on board. The detachment is so widespread that most companies don’t even have the genuine confidence to market their own products. Everything is delivered with a wink from one eye and an eye-roll from the other. We live in a mud puddle of memes, ironic hot takes, and self-conscious self-reference. David Foster Wallace called it exactly thirty years ago, in the summer of 1993:
“[…] The harvest has been dark: the forms of our best rebellious art have become mere gestures, schticks, not only sterile but perversely enslaving. How can even the idea of rebellion against corporate culture stay meaningful when Chrysler Inc. advertises trucks by invoking “The Dodge Rebellion”?
David Foster Wallace, E Unibus Pluram: Television and U.S. Fiction (The Review of Contemporary Fiction, link to full pdf)
Rest in Peace David Foster Wallace, you would have loved Barbie. We swim in a wretched sea of meaningless mush, and when you have to trudge through nothing but slop all day, every day, it gets harder and harder to not numb out. I really cannot emphasize it enough: there’s so much and it just keeps coming. There’s lots to do. There’s lots to buy. The “content” never ends. Baby Gronk rizzed up Livvy! Wait—you’ve never had vegan tacos there?! Haley Bieber got a manicure! You should get an Apple Watch!
Meaningless distractions, all.
Thanks to the internet and our insatiably consumerist culture, it is finally possible to distract yourself for every waking minute of your life and barely even notice you’re doing it. When you mix all colors of paint together, you get black. Everything quickly becomes nothing.
What else? Well, there’s the ubiquity of pornography which has zapped everyone of their sex drive. It’s been said many times before: everything is sexy and no one is horny. Social media and the fear of cancel culture got together to create the most utterly dull popular culture and celebrity elite to ever exist. It stands for nothing, it risks nothing, so there’s nothing to engage with. Culture is just kind of “there,” and no one really cares about it.
An unfortunate by-product of this is that there’s also very little to which we can aspire. Life is not a meritocracy, and the void at the top has allowed for figures like Andrew Tate to be taken seriously by both fans and critics alike. The blame is always being shifted around. Men think women are the problem. Women think men are the problem. The boomers think it’s the millennials. The millennials think it’s the boomers. It’s social media. No it’s the pandemic. No it’s [your pet theory here].
Death and loneliness abound. Everyone is constantly joking about killing themselves while Canada rolls out a “humane” service to do just that (MAID). People are struggling: most people simply cannot cope without substances like marijuana, alcohol, drugs, and SSRIs. People are lonely: they have fewer friends and live far from their families. Dating seems impossible. Men and women in the prime of their lives are struggling to meet even one potential partner who shares their values and vision for a relationship. Oh, and our phones—Gen Z averages an unfathomable 9 hours of screen time per day—have ruined our attention spans to the point where we can no longer read a book, let alone sit quietly with nothing but our thoughts. If you’re an intelligent, hardworking person, odds are the job you’ll have out of college, and for the next 40-50 years, will involve 10+ hours a day of staring at a laptop screen in a state of heightened stress.
To top it all off, we can’t have meaningful conversations about any of this stuff because everyone runs their thoughts through their own kind of personal HR filter. People are self-reporting their thought crimes to themselves. I’m literally doing that right now. I’m sure I’ve theoretically “offended” all sorts of people in the last paragraph alone. Catherine, when you talked about the jobs you forgot to say that it mainly applies to privileged folks! Well, you got me there. The point stands: things are trending down. Something is deeply wrong. We all know it. We all feel it.
We think ironic detachment will protect us
The picture is bleak. It’s so sad it’s difficult to comprehend. How do you protect yourself in such a world?
You simply don’t allow yourself to experience it.
Think back to the flower metaphor. This is where we don’t receive flowers, but we cope. Same thing here. We look around the world, struggle to see the meaning in its chaos, and unconsciously tell ourselves that finding meaning isn’t that important. If I can’t pursue my own fulfillment, at least I can pursue my own pleasure. This is a somewhat reasonable reaction to the present circumstances. It feels straightforward enough—it’s binary, measurable, and everyone else is doing it. This is how the numbness starts.
And perhaps this route is even better—maybe even cool. Being ironically detached from life is endlessly glamorized in our culture. There’s a certain status in pretending nothing affects you and you don’t care. Cue photo montage of a strung-out Kate Moss staring listlessly into the middle distance.
Taking the ironic detachment route is also easy. It’s easy to laugh at other people, mock them, throw your head back, be a critic. Standing for nothing has the obvious appeal of making you impossible to pin down. There’s something very chic about smoking a cigarette outside a bar and being all like whatever. You’re playing a game of hide-and-seek with life, and you’re hiding. It’s thrilling to find a good place to hide, to have people seeking you. But in our drug-fueled debauchery, our coy, sarcastic conversations, and perhaps most of all in our fleeting, romantic encounters, we should heed the words of British psychoanalyst Donald Winnicott:
“It is a joy to be hidden, and a disaster not to be found.”
It is a disaster not to be found, a total disaster to not be able to connect with others because we were too preoccupied with ourselves. The whole reason for ironic detachment is to build a protective wall between oneself and the world. We think we’re building a wall, but we’re really hollowing ourselves out from the inside. Eventually, without really noticing it, there will be nothing left for the wall to defend. There will be no one to find.
It’s not hard to see where the pervasive numbness comes in from here, as a sort of sinister phase two. The opposite of love is not hate, but apathy. I hope it’s obvious why this is a problem, but maybe you’re still thinking so what. To put it succinctly: when you take an ironic, negative, or numb attitude to everything, you are by definition not on the line for solutions, and when you stop looking for solutions, you lose all agency and will in your life.
Possible antidotes
We can’t keep going down the path we’re on, but we also can’t go back. Don’t worry, I’m not going to give full-throated endorsement for Post-Post-Irony, or David-Foster-Wallacian New Sincerity, as he does in the essay I quoted earlier (though I do think cringe sincerity is preferable to total apathy). We’re too far gone from the early 90s. We can’t put the internet back in the box or log off forever. Too much of our lives is irrevocably online, we’re all too self-aware, and a saccharine glaze of sincerity is too affected to feel real. Besides, we’ve all been cornered by the guy at the bar with a well-worn paperback in his pocket who locks eyes with you and whispers, “But how are you, really?” as if it’s a profound question. I would hate to subject anyone to such an encounter.
Rather than jump to sincerity, I’d like to start with basic honesty. It would be great if we started just telling the truth—to ourselves and each other. The truth is good. (I mean the truth, by the way. Not “our truth.” The truth, the real truth, does not have to market itself as “authentic,” like an influencer does, it simply is.) In other words: stop hiding and start seeking. Stop hiding from the sad truths and start seeking the transcendent truths that will address the sadness. When we flip the game of hide-and-seek, we can stop worrying about someone finding us, and start seeking the truth in the world, in others, and in ourselves.
With honesty as the foundation, I would advocate next for embracing reality—our real lives, right now—and not clinging to an abstract idea of how our lives should be. In other words: everything that we see exclusively online does not really matter. The broader culture’s idea of “a perfect life” changes every couple years. Measuring the distance between our real lives and some ever-changing, impossible ideal will do nothing but break our spirit. Besides, I have never met a person who has a dream life in reality. And reality—the truth—is what counts.
This doesn’t mean we shouldn’t strive. Things are never so fundamentally broken that we cannot move just a bit closer towards our goals and try again and again to live up to our values. Goals and values are good to have. The bigger and more transcendent the better, I say.
Once we figure out all that stuff—the big goals, the transcendent values—we should take responsibility for them. Standing for something is hard because what you’re implicitly saying is, “I don’t necessarily stand for all those other things over there.” This is a risk. People will not always agree with you. By saying “I believe in God,” for example, you’re also saying “I am not an atheist.” Atheists might think you’re stupid. (This begs the question, “And?”) We should take responsibility for our beliefs, but be prepared to calmly and rationally explain them. Criticize the world all you want, but do the hard work of building something better to take its place.
In this process, the process of seeking and telling the truth, having values and goals, and taking a stand for something, we’re bound to fail, to fall short, and to make mistakes. This is also hard. Our culture simultaneously demands both perfection and apology, but is notoriously unforgiving. Everyone needs a little forgiveness from time to time. We need to remember that it is okay to make mistakes if we try to remedy them. It’s also okay to be seen trying. Don’t take the easy route, which is always harder and more costly in the end. To shock yourself out of a numb state, to restore your life force and vitality, you will need to work hard and to submit to something bigger than your own desires.
I started with flowers, so I’d like to end with them, too. We all know that life does not hand out bouquets. Flowers do not just appear in the world. The same is true for a life of meaning. Both are grown, over time, from the tiniest seeds. You have to cultivate meaning in your life. You need to do the hard work of tilling the soil and nurturing the seeds. No one can do it for you. Grow your own flowers and give them away to everyone you meet. You’re right: the earth is not very fertile, people are not always grateful, flowers eventually die. But do you still see the point of it all? Do you see the beauty of the gesture?
Source: Catherine Shannon, Everyone is numbing out, July 27, 2023
-
 @ d34e832d:383f78d0
2025-03-21 20:31:24
@ d34e832d:383f78d0
2025-03-21 20:31:24Introduction
Unlike other cetaceans that rely on whistles and songs, sperm whales primarily use echolocation and patterned click sequences to convey information. This paper explores the structure, function, and implications of their vocal communication, particularly in relation to their social behaviors and cognitive abilities.
1. The Nature of Sperm Whale Vocalizations
Sperm whales produce three primary types of clicks:
- Echolocation clicks for navigation and hunting.
- Regular clicks used in deep diving.
- Codas, which are rhythmic sequences exchanged between individuals, believed to function in social bonding and identification.Each whale possesses a monumental sound-producing organ, the spermaceti organ, which allows for the production of powerful sounds that can travel long distances. The structure of these clicks suggests a level of vocal learning and adaptation, as different populations exhibit distinct coda repertoires.
2. Cultural and Regional Variation in Codas
Research indicates that different sperm whale clans have unique dialects, much like human languages. These dialects are not genetically inherited but culturally transmitted, meaning whales learn their communication styles from social interactions rather than instinct alone. Studies conducted in the Caribbean and the Pacific have revealed that whales in different regions have distinct coda patterns, with some being universal and others specific to certain clans.
3. Social Organization and Communication
Sperm whales are matrilineal and live in stable social units composed of mothers, calves, and juveniles, while males often lead solitary lives. Communication plays a critical role in maintaining social bonds within these groups.
- Codas serve as an acoustic signature that helps individuals recognize each other.
- More complex codas may function in coordinating group movements or teaching young whales.
- Some researchers hypothesize that codas convey emotional states, much like tone of voice in human speech.4. Theories on Whale Intelligence and Language-Like Communication
The complexity of sperm whale vocalization raises profound questions about their cognitive abilities.
- Some researchers argue that sperm whale communication exhibits combinatorial properties, meaning that codas might function in ways similar to human phonemes, allowing for an extensive range of meanings.
- Studies using AI and machine learning have attempted to decode potential syntax patterns, but a full understanding of their language remains elusive.5. Conservation Implications and the Need for Further Research
Understanding sperm whale communication is essential for conservation efforts. Noise pollution from shipping, sonar, and industrial activities can interfere with whale vocalizations, potentially disrupting social structures and navigation. Future research must focus on long-term coda tracking, cross-species comparisons, and experimental approaches to deciphering their meaning.
Consider
Sperm whale vocal communication represents one of the most intriguing areas of marine mammal research. Their ability to transmit learned vocalizations across generations suggests a high degree of cultural complexity. Although we have yet to fully decode their language, the study of sperm whale codas offers critical insights into non-human intelligence, social structures, and the evolution of communication in the animal kingdom.
-
 @ 7bc05901:8c26d22b
2025-03-21 19:47:15
@ 7bc05901:8c26d22b
2025-03-21 19:47:15Decentralization is a beautiful return volley to the censorship regimes that have ruled American social media, but the decentralization piece isn't the biggest impact Nostr is having on me. The empowerment and encouragement to start building are what overwhelms. Since I began sending zaps just a few weeks ago, every idea I have had for an app over the last decade is organically re-emerging as executable Nostr apps.
The rise of AI alongside Nostr's invention/discovery is serendipitous for someone who doesn't have the coding experience to develop an app from scratch like myself. It is also a great moment for apps that had a social feature -- which was essentially every app. "Connect it using Facebook" was such a non-starter for me. I live in a small town where Facebook is a gossip cesspool. There are intriguing communities there, sure, but the overwhelming dread that overcomes me when I open that app doesn't justify digging for the socially-delightful gems. Further, any app that integrates with facebook is or becomes a variation on an already existing feature that META has engineered into their platform -- they want, they need your eyeballs. On their site.
Nostr makes no such demands. It doesn't care which site is being used to access the protocol, and what features exist on that site. It is available to help, secure a user's identity, and doesn't make many demands in return.
My friend and local farmer Ryan and I have discussed an app for years, built it and rebuilt it using different tools, but we ultimately got distracted by more pressing and less complicated projects. I think a huge barrier to execute it was the sense that it would be impossible to achieve any network effects, plus the thought of managing the social side was overwhelming. It required us to need really powerful tools, and to maintain a lot of data that we didn't really want to hold onto. It was essentially an app for local food producers and consumers. With Nostr at play, we could build something like this and simultaneously onboard our local community to the Nostr protocol while also providing a lightweight solution to managing the complicated part of an online marketplace. The lightning payments come as an added bonus.
We are tracking the use of another app which is sweeping through local food producers, which is only in its beta phase, and restarting our build of a marketplace that is worth building and encourages a sustainable local food supply, this time with a protocol that reduces 90 percent of the annoying part of that build, and doesn't require anyone spend time on Zuckerberg's playground.
-
 @ c631e267:c2b78d3e
2025-03-21 19:41:50
@ c631e267:c2b78d3e
2025-03-21 19:41:50Wir werden nicht zulassen, dass technisch manches möglich ist, \ aber der Staat es nicht nutzt. \ Angela Merkel
Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach. Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar, dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen, die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war vielleicht früher einmal so, heute ist eher das Gegenteil gemeint.
In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien beleuchtet. Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als «Technofeudalismus» angeprangert.
Nationale Zugangspunkte für Mobilitätsdaten im Sinne der EU gibt es nicht nur in allen Mitgliedsländern, sondern auch in der Schweiz und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen Identifizierungssystem für «nachhaltigen Verkehr und Tourismus».
Natürlich marschiert auch Deutschland stracks und euphorisch in Richtung digitaler Zukunft. Ohne vernetzte Mobilität und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität voll auf Digitalisierung».
Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten, das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Er ist zuerst auf Transition News erschienen.
-
 @ 6a6be47b:3e74e3e1
2025-03-21 18:45:32
@ 6a6be47b:3e74e3e1
2025-03-21 18:45:32Hey frens! Today, I spent a big chunk of the morning painting with watercolors. This is only the second time I've completed a piece using this technique in a long while. It feels like coming back home after a vacation: you enjoyed the time away and relaxed, but when you're lucky enough to have a safe space to call home, there's really nothing like it. 🖼️
🎨 That's exactly how I feel about painting with watercolors again. I'm really excited to share what I've been working on with you soon. In the meantime, I've got a new blog post up about Ostara and the Spring Equinox. ⭐️Today, I just feel so blessed and excited about the future. I'm simply soaking up the moment, I guess. I hope you're feeling the same way too! Today, I also whipped up some mini veggie quiches chef's kiss.
 🧑🍳 I wanted to spice things up a bit in the kitchen as well!
🪄I just wanted to share a little bit from my day and express how grateful I am. What did you get up to today? I'd love to hear more about it!
🧑🍳 I wanted to spice things up a bit in the kitchen as well!
🪄I just wanted to share a little bit from my day and express how grateful I am. What did you get up to today? I'd love to hear more about it! -
 @ 6bae33c8:607272e8
2025-03-21 18:23:28
@ 6bae33c8:607272e8
2025-03-21 18:23:28I put Beat Chris Liss 3 in quotes because technically this was not a Beat Chris Liss league — I just bought it at the last minute to get an extra league. In any event, I drew the seventh spot, and here are the results:
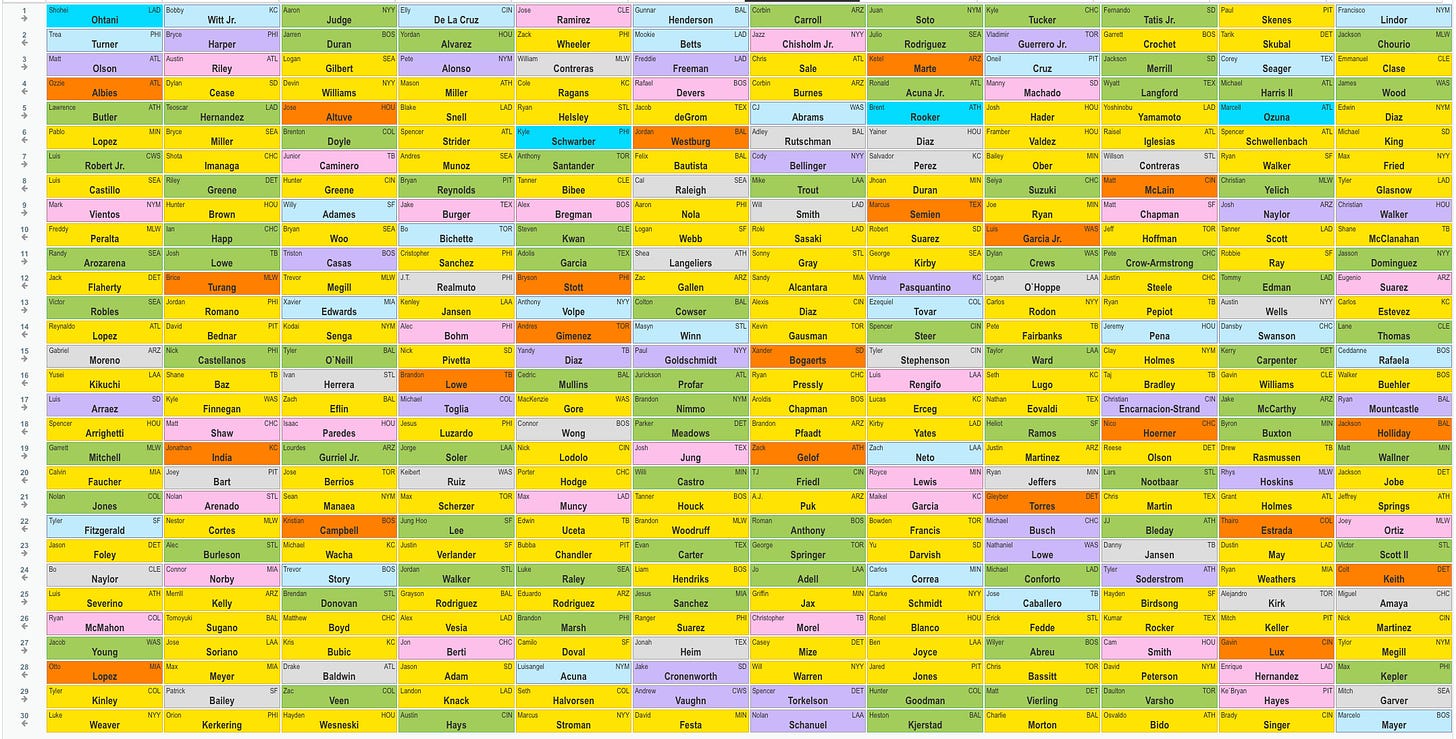
1.7 Corbin Carroll — He’s been hitting home runs this spring, a signal his shoulder is healthy. You know he’ll run, and given how he performed at the end of last year, I’d expect the batting average to bounce back too.
2.8 Jazz Chisholm — I want to see what he can do with a full year in Yankee Stadium. He’s a health risk, but he was a 20-20-ish player in Miami with only 100 games in 2023. It’s also nice that he qualifies at 3B and OF. I considered Mookie Betts, who slipped, but I’m concerned about severe weight loss from an illness undermining the first half of his season.
3.7 Chris Sale — He’s a Hall of Fame level pitcher with his health and form back. Remember when Justin Verlander faded in his 30s and then got it back together? I expect a few good years from Sale before he declines again.
4.8 Corbin Burnes — I don’t really even like Burnes, but he slipped a full round past ADP, and I value-took.
5.7 C.J. Abrams — I love this pick, probably my favorite of the draft. Abrams is a 20-30 player despite attitude issues. What if he matures and gets it together at age 24?
6.8 Adley Rustchman — I didn’t see anything I liked, and I was light on power. One way to get a leg up power-wise is to draft elite catchers.
7.7 Cody Bellinger — I like him with Yankee Stadium’s short porch, a few steals from a first-base-eligible player and also outfield eligibility.
8.8 Mike Trout — I had enough pitching and speed, but I needed some power, and Trout still has as much as anyone if he could ever play 100-plus games. He’s healthy now at least.
9.7 Will Smith — A second top catcher to pair with Rutschman. I was light on power through five rounds, but my next four picks were 20-plus HR catchers, Bellinger in Yankee Stadium and Trout.
10.8 Roki Sasaki — He slipped a couple rounds after a rough outing in Japan, but he was still throwing 100 with nasty movement. Another value-take.
11.7 Sonny Gray — A favorite old warhorse in a good pitcher’s park. I really wanted Sandy Alcantara, but Gray’s ADP was higher, so I thought there was a better chance to get Alcantara on the way back.
12.8 Sandy Alcantara — Turns out I thought right. I love Alcantara, who was going in the third round a couple years ago, now that he’s healthy and throwing 100 mph again.
13.7 Alexis Diaz — Taking Alcantara cost me my two go-to closers, Kenley Jansen and Jordan Romano, both of whom went earlier than usual, so I pivoted to Diaz. I thought this was a mistake at first — Diaz has been bad this spring, and he wasn’t even good last year, either, but he’s the closer until further notice, and a couple spring outings shouldn’t move the needle that much.
14.8 Kevin Gausman — Another old warhorse, coming off a down year, possibly due to injury. His velocity has been back up this spring too.
15.7 Xander Bogaerts — Another ADP value-take. Bogaerts had double digit homers and steals in 111 games last year and is a good bet to hit for a decent average.
16.8 Ryan Pressly — Another shaky closer, Pressly had three walks in an inning against the Dodgers, but he’s probably not losing the job over one ugly but scoreless outing.
17.7 Aroldis Chapman — Named the Red Sox closer, Chapman is probably the best of the three I drafted thus far. His ADP was lower because he was only given the role a couple days ago. Chapman perfectly fits the old warhorse mold I like too.
18.8 Brandon Pfaadt — I didn’t really need another starter, but he was the best player left on the board, and you always run out of pitching.
19.7 Zack Gelof — He strikes out a ton, but he went 17-25 last year in 138 games as a rookie, and now he gets to play in a minor-league band box. Lawrence Butler went 22-18 and is going in the fifth round!
20.8 T.J. Friedl — I was light on OF, and Friedl is one. He has a little pop, runs and is expected to lead off for the Reds in the best non-Coors hitting park in baseball.
21.7 A.J. Puk — I was still a little light in saves, and Puk is in the running for the Arizona job.
22.8 Roman Anthony — I don’t know if he’ll break camp with the Red Sox, but he was the remaining player I would have felt worst getting snaked on. He doesn’t have much left to prove in the minors.
23.7 George Springer — He went 20-20 in 2023 and 19-16 last year. He could be done, but at 35 he’s not ancient.
24.8 Jo Adell — I needed to fill in the outfield, and Adell should play, run and hit for power. The strikeouts and batting average risk are bad, but he’s still young enough to improve.
25.7 Griffin Jax — He’s a top reliever, next in line for saves and closer Jhoan Duran isn’t very good.
26.8 Christopher Morel — I needed a corner and Morel is one. (If I needed a mushroom, this would also hold.) He hit .196 last year, but he has good pop and should play OF for the Rays in a small minor-league park.
27.6 Casey Mize — The former No. 1 overall pick has looked good this spring, and he’s completely healthy.
28.6 Will Warren — Warren should get a shot in the Yankees rotation, given the injuries to Gerrit Cole and Luis Gil.
29.6 Spencer Torkelson — Another former No. 1 overall pick for the Tigers, Torkelson hit 31 homers in 2023 and should get another shot this year given his strong spring.
30.6 Nolan Schanuel — I just wanted an extra corner with regular playing time heading into the year. He runs a little and had 13 HR, but in a full season of at-bats.
Roster By Position:
C Adley Rustchman/Will Smith
1B Cody Bellinger
2B Xander Bogaerts
3B Jazz Chisholm
SS C.J. Abrams
CI Christopher Morel
MI Zack Gelof
OF Corbin Carroll/Mike Trout/T.J. Friedl/Roman Anthony/George Springer
UT Jo Adell
SP Chris Sale/Corbin Burnes/Roki Sasaki/Sonny Gray/Sandy Alcantara/Kevin Gausman
RP Alexis Diaz/Ryan Pressly/Aroldis Chapman
B Brandon Pfaadt/A.J. Puk/Griffin Jax/Casey Mize/Will Warren/Spencer Torkelson/Nolan Schanuel
-
 @ 97c70a44:ad98e322
2025-03-05 18:09:05
@ 97c70a44:ad98e322
2025-03-05 18:09:05So you've decided to join nostr! Some wide-eyed fanatic has convinced you that the "sun shines every day on the birds and the bees and the cigarette trees" in a magical land of decentralized, censorship-resistant freedom of speech - and it's waiting just over the next hill.
But your experience has not been all you hoped. Before you've even had a chance to upload your AI-generated cyberpunk avatar or make up exploit codenames for your pseudonym's bio, you've been confronted with a new concept that has left you completely nonplussed.
It doesn't help that this new idea might be called by any number of strange names. You may have been asked to "paste your nsec", "generate a private key", "enter your seed words", "connect with a bunker", "sign in with extension", or even "generate entropy". Sorry about that.
All these terms are really referring to one concept under many different names: that of "cryptographic identity".
Now, you may have noticed that I just introduced yet another new term which explains exactly nothing. You're absolutely correct. And now I'm going to proceed to ignore your complaints and talk about something completely different. But bear with me, because the juice is worth the squeeze.
Identity
What is identity? There are many philosophical, political, or technical answers to this question, but for our purposes it's probably best to think of it this way:
Identity is the essence of a thing. Identity separates one thing from all others, and is itself indivisible.
This definition has three parts:
- Identity is "essential": a thing can change, but its identity cannot. I might re-paint my house, replace its components, sell it, or even burn it down, but its identity as something that can be referred to - "this house" - is durable, even outside the boundaries of its own physical existence.
- Identity is a unit: you can't break an identity into multiple parts. A thing might be composed of multiple parts, but that's only incidental to the identity of a thing, which is a concept, not a material thing.
- Identity is distinct: identity is what separates one thing from all others - the concept of an apple can't be mixed with that of an orange; the two ideas are distinct. In the same way, a single concrete apple is distinct in identity from another - even if the component parts of the apple decompose into compost used to grow more apples.
Identity is not a physical thing, but a metaphysical thing. Or, in simpler terms, identity is a "concept".
I (or someone more qualified) could at this point launch into a Scholastic tangent on what "is" is, but that is, fortunately, not necessary here. The kind of identities I want to focus on here are not our actual identities as people, but entirely fictional identities that we use to extend our agency into the digital world.
Think of it this way - your bank login does not represent you as a complete person. It only represents the access granted to you by the bank. This access is in fact an entirely new identity that has been associated with you, and is limited in what it's useful for.
Other examples of fictional identities include:
- The country you live in
- Your social media persona
- Your mortgage
- Geographical coordinates
- A moment in time
- A chess piece
Some of these identites are inert, for example points in space and time. Other identies have agency and so are able to act in the world - even as fictional concepts. In order to do this, they must "authenticate" themselves (which means "to prove they are real"), and act within a system of established rules.
For example, your D&D character exists only within the collective fiction of your D&D group, and can do anything the rules say. Its identity is authenticated simply by your claim as a member of the group that your character in fact exists. Similarly, a lawyer must prove they are a member of the Bar Association before they are allowed to practice law within that collective fiction.
"Cryptographic identity" is simply another way of authenticating a fictional identity within a given system. As we'll see, it has some interesting attributes that set it apart from things like a library card or your latitude and longitude. Before we get there though, let's look in more detail at how identities are authenticated.
Certificates
Merriam-Webster defines the verb "certify" as meaning "to attest authoritatively". A "certificate" is just a fancy way of saying "because I said so". Certificates are issued by a "certificate authority", someone who has the authority to "say so". Examples include your boss, your mom, or the Pope.
This method of authentication is how almost every institution authenticates the people who associate with it. Colleges issue student ID cards, governments issue passports, and websites allow you to "register an account".
In every case mentioned above, the "authority" creates a closed system in which a document (aka a "certificate") is issued which serves as a claim to a given identity. When someone wants to access some privileged service, location, or information, they present their certificate. The authority then validates it and grants or denies access. In the case of an international airport, the certificate is a little book printed with fancy inks. In the case of a login page, the certificate is a username and password combination.
This pattern for authentication is ubiquitous, and has some very important implications.
First of all, certified authentication implies that the issuer of the certificate has the right to exclusive control of any identity it issues. This identity can be revoked at any time, or its permissions may change. Your social credit score may drop arbitrarily, or money might disappear from your account. When dealing with certificate authorities, you have no inherent rights.
Second, certified authentication depends on the certificate authority continuing to exist. If you store your stuff at a storage facility but the company running it goes out of business, your stuff might disappear along with it.
Usually, authentication via certificate authority works pretty well, since an appeal can always be made to a higher authority (nature, God, the government, etc). Authorities also can't generally dictate their terms with impunity without losing their customers, alienating their constituents, or provoking revolt. But it's also true that certification by authority creates an incentive structure that frequently leads to abuse - arbitrary deplatforming is increasingly common, and the bigger the certificate authority, the less recourse the certificate holder (or "subject") has.
Certificates also put the issuer in a position to intermediate relationships that wouldn't otherwise be subject to their authority. This might take the form of selling user attention to advertisers, taking a cut of financial transactions, or selling surveillance data to third parties.
Proliferation of certificate authorities is not a solution to these problems. Websites and apps frequently often offer multiple "social sign-in" options, allowing their users to choose which certificate authority to appeal to. But this only piles more value into the social platform that issues the certificate - not only can Google shut down your email inbox, they can revoke your ability to log in to every website you used their identity provider to get into.
In every case, certificate issuance results in an asymmetrical power dynamic, where the issuer is able to exert significant control over the certificate holder, even in areas unrelated to the original pretext for the relationship between parties.
Self-Certification
But what if we could reverse this power dynamic? What if individuals could issue their own certificates and force institutions to accept them?

Ron Swanson's counterexample notwithstanding, there's a reason I can't simply write myself a parking permit and slip it under the windshield wiper. Questions about voluntary submission to legitimate authorities aside, the fact is that we don't have the power to act without impunity - just like any other certificate authority, we have to prove our claims either by the exercise of raw power or by appeal to a higher authority.
So the question becomes: which higher authority can we appeal to in order to issue our own certificates within a given system of identity?
The obvious answer here is to go straight to the top and ask God himself to back our claim to self-sovereignty. However, that's not how he normally works - there's a reason they call direct acts of God "miracles". In fact, Romans 13:1 explicitly says that "the authorities that exist have been appointed by God". God has structured the universe in such a way that we must appeal to the deputies he has put in place to govern various parts of the world.
Another tempting appeal might be to nature - i.e. the material world. This is the realm in which we most frequently have the experience of "self-authenticating" identities. For example, a gold coin can be authenticated by biting it or by burning it with acid. If it quacks like a duck, walks like a duck, and looks like a duck, then it probably is a duck.
In most cases however, the ability to authenticate using physical claims depends on physical access, and so appeals to physical reality have major limitations when it comes to the digital world. Captchas, selfies and other similar tricks are often used to bridge the physical world into the digital, but these are increasingly easy to forge, and hard to verify.
There are exceptions to this rule - an example of self-certification that makes its appeal to the physical world is that of a signature. Signatures are hard to forge - an incredible amount of data is encoded in physical signatures, from strength, to illnesses, to upbringing, to personality. These can even be scanned and used within the digital world as well. Even today, most contracts are sealed with some simulacrum of a physical signature. Of course, this custom is quickly becoming a mere historical curiosity, since the very act of digitizing a signature makes it trivially forgeable.
So: transcendent reality is too remote to subtantiate our claims, and the material world is too limited to work within the world of information. There is another aspect of reality remaining that we might appeal to: information itself.
Physical signatures authenticate physical identities by encoding unique physical data into an easily recognizable artifact. To transpose this idea to the realm of information, a "digital signature" might authenticate "digital identities" by encoding unique "digital data" into an easily recognizable artifact.
Unfortunately, in the digital world we have the additional challenge that the artifact itself can be copied, undermining any claim to legitimacy. We need something that can be easily verified and unforgeable.
Digital Signatures
In fact such a thing does exist, but calling it a "digital signature" obscures more than it reveals. We might just as well call the thing we're looking for a "digital fingerprint", or a "digital electroencephalogram". Just keep that in mind as we work our way towards defining the term - we are not looking for something looks like a physical signature, but for something that does the same thing as a physical signature, in that it allows us to issue ourselves a credential that must be accepted by others by encoding privileged information into a recognizable, unforgeable artifact.
With that, let's get into the weeds.
An important idea in computer science is that of a "function". A function is a sort of information machine that converts data from one form to another. One example is the idea of "incrementing" a number. If you increment 1, you get 2. If you increment 2, you get 3. Incrementing can be reversed, by creating a complementary function that instead subtracts 1 from a number.
A "one-way function" is a function that can't be reversed. A good example of a one-way function is integer rounding. If you round a number and get
5, what number did you begin with? It's impossible to know - 5.1, 4.81, 5.332794, in fact an infinite number of numbers can be rounded to the number5. These numbers can also be infinitely long - for example rounding PI to the nearest integer results in the number3.A real-life example of a useful one-way function is
sha256. This function is a member of a family of one-way functions called "hash functions". You can feed as much data as you like intosha256, and you will always get 256 bits of information out. Hash functions are especially useful because collisions between outputs are very rare - even if you change a single bit in a huge pile of data, you're almost certainly going to get a different output.Taking this a step further, there is a whole family of cryptographic one-way "trapdoor" functions that act similarly to hash functions, but which maintain a specific mathematical relationship between the input and the output which allows the input/output pair to be used in a variety of useful applications. For example, in Elliptic Curve Cryptography, scalar multiplication on an elliptic curve is used to derive the output.
"Ok", you say, "that's all completely clear and lucidly explained" (thank you). "But what goes into the function?" You might expect that because of our analogy to physical signatures we would have to gather an incredible amount of digital information to cram into our cryptographic trapdoor function, mashing together bank statements, a record of our heartbeat, brain waves and cellular respiration. Well, we could do it that way (maybe), but there's actually a much simpler solution.
Let's play a quick game. What number am I thinking of? Wrong, it's 82,749,283,929,834. Good guess though.
The reason we use signatures to authenticate our identity in the physical world is not because they're backed by a lot of implicit physical information, but because they're hard to forge and easy to validate. Even so, there is a lot of variation in a single person's signature, even from one moment to the next.
Trapdoor functions solve the validation problem - it's trivially simple to compare one 256-bit number to another. And randomness solves the problem of forgeability.
Now, randomness (A.K.A. "entropy") is actually kind of hard to generate. Random numbers that don't have enough "noise" in them are known as "pseudo-random numbers", and are weirdly easy to guess. This is why Cloudflare uses a video stream of their giant wall of lava lamps to feed the random number generator that powers their CDN. For our purposes though, we can just imagine that our random numbers come from rolling a bunch of dice.
To recap, we can get a digital equivalent of a physical signature (or fingerprint, etc) by 1. coming up with a random number, and 2. feeding it into our chosen trapdoor function. The random number is called the "private" part. The output of the trapdoor function is called the "public" part. These two halves are often called "keys", hence the terms "public key" and "private key".
And now we come full circle - remember about 37 years ago when I introduced the term "cryptographic identity"? Well, we've finally arrived at the point where I explain what that actually is.
A "cryptographic identity" is identified by a public key, and authenticated by the ability to prove that you know the private key.
Notice that I didn't say "authenticated by the private key". If you had to reveal the private key in order to prove you know it, you could only authenticate a public key once without losing exclusive control of the key. But cryptographic identities can be authenticated any number of times because the certification is an algorithm that only someone who knows the private key can execute.
This is the super power that trapdoor functions have that hash functions don't. Within certain cryptosystems, it is possible to mix additional data with your private key to get yet another number in such a way that someone else who only knows the public key can prove that you know the private key.
For example, if my secret number is
12, and someone tells me the number37, I can "combine" the two by adding them together and returning the number49. This "proves" that my secret number is12. Of course, addition is not a trapdoor function, so it's trivially easy to reverse, which is why cryptography is its own field of knowledge.What's it for?
If I haven't completely lost you yet, you might be wondering why this matters. Who cares if I can prove that I made up a random number?
To answer this, let's consider a simple example: that of public social media posts.
Most social media platforms function by issuing credentials and verifying them based on their internal database. When you log in to your Twitter (ok, fine, X) account, you provide X with a phone number (or email) and password. X compares these records to the ones stored in the database when you created your account, and if they match they let you "log in" by issuing yet another credential, called a "session key".
Next, when you "say" something on X, you pass along your session key and your tweet to X's servers. They check that the session key is legit, and if it is they associate your tweet with your account's identity. Later, when someone wants to see the tweet, X vouches for the fact that you created it by saying "trust me" and displaying your name next to the tweet.
In other words, X creates and controls your identity, but they let you use it as long as you can prove that you know the secret that you agreed on when you registered (by giving it to them every time).
Now pretend that X gets bought by someone even more evil than Elon Musk (if such a thing can be imagined). The new owner now has the ability to control your identity, potentially making it say things that you didn't actually say. Someone could be completely banned from the platform, but their account could be made to continue saying whatever the owner of the platform wanted.
In reality, such a breach of trust would quickly result in a complete loss of credibility for the platform, which is why this kind of thing doesn't happen (at least, not that we know of).
But there are other ways of exploiting this system, most notably by censoring speech. As often happens, platforms are able to confiscate user identities, leaving the tenant no recourse except to appeal to the platform itself (or the government, but that doesn't seem to happen for some reason - probably due to some legalese in social platforms' terms of use). The user has to start completely from scratch, either on the same platform or another.
Now suppose that when you signed up for X instead of simply telling X your password you made up a random number and provided a cryptographic proof to X along with your public key. When you're ready to tweet (there's no need to issue a session key, or even to store your public key in their database) you would again prove your ownership of that key with a new piece of data. X could then publish that tweet or not, along with the same proof you provided that it really came from you.
What X can't do in this system is pretend you said something you didn't, because they don't know your private key.
X also wouldn't be able to deplatform you as effectively either. While they could choose to ban you from their website and refuse to serve your tweets, they don't control your identity. There's nothing they can do to prevent you from re-using it on another platform. Plus, if the system was set up in such a way that other users followed your key instead of an ID made up by X, you could switch platforms and keep your followers. In the same way, it would also be possible to keep a copy of all your tweets in your own database, since their authenticity is determined by your digital signature, not X's "because I say so".
This new power is not just limited to social media either. Here are some other examples of ways that self-issued cryptographic identites transform the power dynamic inherent in digital platforms:
- Banks sometimes freeze accounts or confiscate funds. If your money was stored in a system based on self-issued cryptographic keys rather than custodians, banks would not be able to keep you from accessing or moving your funds. This system exists, and it's called bitcoin.
- Identity theft happens when your identifying information is stolen and used to take out a loan in your name, and without your consent. The reason this is so common is because your credentials are not cryptographic - your name, address, and social security number can only be authenticated by being shared, and they are shared so often and with so many counterparties that they frequently end up in data breaches. If credit checks were authenticated by self-issued cryptographic keys, identity theft would cease to exist (unless your private key itself got stolen).
- Cryptographic keys allow credential issuers to protect their subjects' privacy better too. Instead of showing your ID (including your home address, birth date, height, weight, etc), the DMV could sign a message asserting that the holder of a given public key indeed over 21. The liquor store could then validate that claim, and your ownership of the named key, without knowing anything more about you. Zero-knowledge proofs take this a step further.
In each of these cases, the interests of the property owner, loan seeker, or customer are elevated over the interests of those who might seek to control their assets, exploit their hard work, or surveil their activity. Just as with personal privacy, freedom of speech, and Second Amendment rights the individual case is rarely decisive, but in the aggregate realigned incentives can tip the scale in favor of freedom.
Objections
Now, there are some drawbacks to digital signatures. Systems that rely on digital signatures are frequently less forgiving of errors than their custodial counterparts, and many of their strengths have corresponding weaknesses. Part of this is because people haven't yet developed an intuition for how to use cryptographic identities, and the tools for managing them are still being designed. Other aspects can be mitigated through judicious use of keys fit to the problems they are being used to solve.
Below I'll articulate some of these concerns, and explore ways in which they might be mitigated over time.
Key Storage
Keeping secrets is hard. "A lie can travel halfway around the world before the truth can get its boots on", and the same goes for gossip. Key storage has become increasingly important as more of our lives move online, to the extent that password managers have become almost a requirement for keeping track of our digital lives. But even with good password management, credentials frequently end up for sale on the dark web as a consequence of poorly secured infrastructure.
Apart from the fact that all of this is an argument for cryptographic identities (since keys are shared with far fewer parties), it's also true that the danger of losing a cryptographic key is severe, especially if that key is used in multiple places. Instead of hackers stealing your Facebook password, they might end up with access to all your other social media accounts too!
Keys should be treated with the utmost care. Using password managers is a good start, but very valuable keys should be stored even more securely - for example in a hardware signing device. This is a hassle, and something additional to learn, but is an indispensable part of taking advantage of the benefits associated with cryptographic identity.
There are ways to lessen the impact of lost or stolen secrets, however. Lots of different techniques exist for structuring key systems in such a way that keys can be protected, invalidated, or limited. Here are a few:
- Hierarchical Deterministic Keys allow for the creation of a single root key from which multiple child keys can be generated. These keys are hard to link to the parent, which provides additional privacy, but this link can also be proven when necessary. One limitation is that the identity system has to be designed with HD keys in mind.
- Key Rotation allows keys to become expendable. Additional credentials might be attached to a key, allowing the holder to prove they have the right to rotate the key. Social attestations can help with the process as well if the key is embedded in a web of trust.
- Remote Signing is a technique for storing a key on one device, but using it on another. This might take the form of signing using a hardware wallet and transferring an SD card to your computer for broadcasting, or using a mobile app like Amber to manage sessions with different applications.
- Key sharding takes this to another level by breaking a single key into multiple pieces and storing them separately. A coordinator can then be used to collaboratively sign messages without sharing key material. This dramatically reduces the ability of an attacker to steal a complete key.
Multi-Factor Authentication
One method for helping users secure their accounts that is becoming increasingly common is "multi-factor authentication". Instead of just providing your email and password, platforms send a one-time use code to your phone number or email, or use "time-based one time passwords" which are stored in a password manager or on a hardware device.
Again, MFA is a solution to a problem inherent in account-based authentication which would not be nearly so prevalent in a cryptographic identity system. Still, theft of keys does happen, and so MFA would be an important improvement - if not for an extra layer of authentication, then as a basis for key rotation.
In a sense, MFA is already being researched - key shards is one way of creating multiple credentials from a single key. However, this doesn't address the issue of key rotation, especially when an identity is tied to the public key that corresponds to a given private key. There are two possible solutions to this problem:
- Introduce a naming system. This would allow identities to use a durable name, assigning it to different keys over time. The downside is that this would require the introduction of either centralized naming authorities (back to the old model), or a blockchain in order to solve Zooko's trilemma.
- Establish a chain of keys. This would require a given key to name a successor key in advance and self-invalidate, or some other process like social recovery to invalidate an old key and assign the identity to a new one. This also would significantly increase the complexity of validating messages and associating them with a given identity.
Both solutions are workable, but introduce a lot of complexity that could cause more trouble than it's worth, depending on the identity system we're talking about.
Surveillance
One of the nice qualities that systems based on cryptographic identities have is that digitally signed data can be passed through any number of untrusted systems and emerge intact. This ability to resist tampering makes it possible to broadcast signed data more widely than would otherwise be the case in a system that relies on a custodian to authenticate information.
The downside of this is that more untrusted systems have access to data. And if information is broadcast publicly, anyone can get access to it.
This problem is compounded by re-use of cryptographic identities across multiple contexts. A benefit of self-issued credentials is that it becomes possible to bring everything attached to your identity with you, including social context and attached credentials. This is convenient and can be quite powerful, but it also means that more context is attached to your activity, making it easier to infer information about you for advertising or surveillance purposes. This is dangerously close to the dystopian ideal of a "Digital ID".
The best way to deal with this risk is to consider identity re-use an option to be used when desirable, but to default to creating a new key for every identity you create. This is no worse than the status quo, and it makes room for the ability to link identities when desired.
Another possible approach to this problem is to avoid broadcasting signed data when possible. This could be done by obscuring your cryptographic identity when data is served from a database, or by encrypting your signed data in order to selectively share it with named counterparties.
Still, this is a real risk, and should be kept in mind when designing and using systems based on cryptographic identity. If you'd like to read more about this, please see this blog post.
Making Keys Usable
You might be tempted to look at that list of trade-offs and get the sense that cryptographic identity is not for mere mortals. Key management is hard, and footguns abound - but there is a way forward. With nostr, some new things are happening in the world of key management that have never really happened before.
Plenty of work over the last 30 years has gone into making key management tractable, but none have really been widely adopted. The reason for this is simple: network effect.
Many of these older key systems only applied the thinnest veneer of humanity over keys. But an identity is much richer than a mere label. Having a real name, social connections, and a corpus of work to attach to a key creates a system of keys that humans care about.
By bootstrapping key management within a social context, nostr ensures that the payoff of key management is worth the learning curve. Not only is social engagement a strong incentive to get off the ground, people already on the network are eager to help you get past any roadblocks you might face.
So if I could offer an action item: give nostr a try today. Whether you're in it for the people and their values, or you just want to experiment with cryptographic identity, nostr is a great place to start. For a quick introduction and to securely generate keys, visit njump.me.
Thanks for taking the time to read this post. I hope it's been helpful, and I can't wait to see you on nostr!
-
 @ 6ad3e2a3:c90b7740
2025-03-21 18:21:50
@ 6ad3e2a3:c90b7740
2025-03-21 18:21:50There are two ways things happen in this world: top-down and bottom-up. Top-down is via authoritarian edict, i.e. fascism, no matter how benign-seeming. It is the government imposing a tax, incentivizing a behavior, creating a new law. Bottom-up is the organic process of people doing what interests them voluntarily, what benefits them, what they decide is best individually.
There is but one legitimate role for top-down and that is in creating good conditions for bottom up. The US Constitution is fascism in that it forces you to adhere to its edicts as the supreme law of the land. But it’s also an effective boundary creating the necessary conditions for free markets, free expression, creativity and prosperity.
All governments are fascistic in that they use force to achieve their agendas. But the best ones use only the minimum necessary force to create conditions for bottom-up prosperity. There is no other kind of prosperity.
. . .
Governments aren’t the only entities that are fascistic. Schools, corporations, institutions and individuals, almost invariably, are too. Yes, I am a fascist and very likely so are you. Don’t believe me? Do you have a voice inside your head telling you what you must get done today, evaluating your progress as a person, critiquing and coercing you into doing things that are “good” for you and avoiding ones that are “bad”? If so, you are fascist.
Why not just trust yourself to make the right choices? Why all the nudging, coaxing, coaching, evaluating and gamifying? Who is this voice, what gives it the authority, the requisite wisdom to manage your affairs? Haven’t all your shortcomings, disappointments and general dissatisfactions taken place despite its ever-presence? What makes you think you are better off for having had this in-house micromanagement?
. . .
The top-down edicts that rule our lives are by and large unnecessarily oppressive. Yes, we should create some good top-down conditions for bottom up organic thriving like buying healthy food, getting fresh air, not consuming excessive amounts of alcohol or drugs, but the moment to moment hall-monitoring, the voice that requires you to achieve something or justify your existence? That’s fascism.
. . .
The mind is a powerful tool when it comes to planning, doing math or following a recipe, but if it can’t be turned off, if it’s not just optimizing your path from A to B, but optimizing YOU, that’s fascism.
. . .
I think about the problem of human governance through this lens. I imagine everyone charged with power over a polity has an agenda, and that agenda, insofar as it requires force to achieve, is fascistic. They want it to go this way rather than that way, and some people don’t agree. The quality of leadership then is the extent to which that force is used to preserve the bottom-up freedom of the individual to pursue his interests without undue interference, either from authorities themselves or other individuals who would unduly disrupt him.
The Constitution is an excellent guideline for this, and I surely won’t be able to come up with a better one in this Substack. It’s why I support Trump’s efforts to trim the top-down public sector and return productivity to the bottom-up private one, why I support deportation of adjudicated criminals who are here illegally, but oppose removing people with green cards or on valid student visas for protesting via constitutionally protected speech.
I don’t root for politicians like they play for my favorite sports team. I root for the freedom of the individual, the possibility of a largely bottom-up society wherein prosperity is possible. And I do this while knowing it will never happen exactly the way I would like, so long as I am bound by the fascism coming from inside the house.
-
 @ bf95e1a4:ebdcc848
2025-03-21 17:03:01
@ bf95e1a4:ebdcc848
2025-03-21 17:03:01This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
Preface
At the time of writing, it is New Year’s Day, and 2019 has just begun. For once, I have a resolution to live up to: I’ve promised myself to write a page per day every day this year until I have something real to publish. In June 2018, I published my first book, Three Minute Reads on Bitcoin — A Year of Thoughts. The book consisted of articles I had published online from May 2017 up to that point. This time it’s different. Instead of a mere collection of articles, I intend to write a “proper” book. A book that explains why Bitcoin is the most important invention of our lives.
I didn’t choose Bitcoin; it chose me. I had been trying to figure out how the world worked under the hood all my life, and then this simple idea of absolute scarcity popped up. It had a profound impact on how I view human interaction. Because of my curious nature, I instantly fell deep into the rabbit hole. I decided to educate myself on how this mysterious technology worked, and that got me into Austrian economics, which expressed very clearly what I had always suspected — that you really can't create value out of thin air.
In this book, I will try to explain every aspect of what makes this technology so special, what sets it apart from the abundant shameless copies of it, what’s wrong with our current system, and what the future might look like. In just two days from the time of writing these words, we’ll celebrate the ten-year anniversary of the Genesis Block when the Bitcoin blockchain came into being. That block contained a message, a newspaper headline that read: “03/Jan/2009 Chancellor on brink of second bailout for banks”. No one knows why Bitcoin’s mysterious creator, Satoshi Nakamoto, chose to include this in the Genesis Block. There is also some debate on whether the Genesis Block was actually mined on the 3rd of January since the next block wasn’t mined until six days later. Somehow, Satoshi managed to stay hidden and weave several layers of mystique into the fabric of Bitcoin from the very beginning, which is part of what makes its conception so immaculate. This book aims to strip Bitcoin of its shady cloak and illuminate its true nature. After all, the only thing any person can do about Bitcoin now is to study it.
Foreword
My journey down the Bitcoin rabbit hole has provided me with a newfound clarity of how our world should be perceived. In the same way that getting married and having my first child were beautiful life-changing events, discovering Bitcoin was a new chapter in my life. I can easily divide my life into two distinct periods: before and after Bitcoin.
Before discovering Bitcoin, life was perplexing. For years, even dating back to my school days, I had an innate sense that something was amiss in the world. Although I wasn’t a good student by any means, it was obvious back then that many aspects of life simply didn’t add up.
One thing that I was sure of was that money was corrupt. However, it took me a while to realize that money itself is fundamentally corrupt. Furthermore, what is typically taught and accepted as money by society is a perversion of what money should be. These are the first steps of understanding Bitcoin, which require you to admit that you have been fooled and lied to all your life. The hard lessons of hard money.
The way I see it, the revelation about the true nature of money is akin to a bracing cold shower that wakes you up to reality. Emerging from that cold shower is an incredibly liberating and invigorating sensation. Unfortunately, many individuals are not motivated enough to take that crucial step into the chilly waters. Instead, they will later experience an ice-cold bucket of water being dumped on their head unexpectedly whilst naked on a cold winter’s day.
The year 2020 was a watershed moment in my journey towards truth, and it was Bitcoin that served as my guide. As the world grappled with an unprecedented black swan event in March of that year, every asset, including bitcoin, took a severe hit. However, what followed in the subsequent months was the largest money-printing expedition in history. A tsunami of stimulus was pumped into the markets. The outcome was a K-shaped recovery. Small, honest brick-and-mortar businesses continued to suffer while many of the largest conglomerates not only rebounded but reached all-time highs. This ludicrous, short-sighted plan, known as quantitative easing, resulted in the most pronounced example of the Cantillon effect in human history, a fact that should have served as a wake-up call for anyone who was not already suspicious of the events surrounding the global financial crisis of 2008.
Since entering my post-bitcoin life, I’ve experienced a newfound coherence. The transition was not exactly instant, instead it has been a continuous process of discovering bitcoin over and over again, and I owe many of these enlightening moments to Knut Svanholm’s writing, for which I’m grateful.
While Knut’s books do not serve as a technical guide for Bitcoin, they provide a deep and philosophical introduction to a new era of money; the separation of money and state. The end of fiat money.
The creation of fiat money, a practice that emerged with the rise of central banking, has been the source of significant damage to human civilisation. Central banking, championed by Keynesianism, has granted immense power to centralized entities, allowing them to dictate fiscal policies and control the creation of money for billions of people. The very idea of a single entity wielding such vast authority and determining the economic fate of entire populations is utter madness. The state monopolizes money because it allows them to print money rather than having to directly tax people (but it still doesn’t stop them). Printing money is more easy, subtle and lucrative than direct taxation. And this continual erosion of purchasing power can be readily associated with the evident decline and deterioration of modern society.
At the heart of the issue is the importance of individual property rights. The money that individuals earn and save is their property, not the state’s. The state’s duty (should there be a need for it to exist) is to safeguard private property, not to continually debase or confiscate it. A centralized power that constantly devalues your hard-earned money and time by printing money is both morally and ethically wrong. Every individual has the right to turn their hard work into savings that they can rely on for the future.
In Bitcoin: Sovereignty through Mathematics, Knut not only delves into the fundamental principles underlying Bitcoin’s creation but also presents the groundbreaking concept of absolute scarcity. Bitcoin’s limited supply of 21 million and the impossibility of creating more due to its protocol creates a condition of absolute scarcity, a first in human history. Absolute scarcity, coupled with Knut’s poetic description of Bitcoin’s creation as "an immaculate conception," emphasizes its unique and revolutionary nature. The term "immaculate conception" highlights the fact that Bitcoin’s creation was not based on any pre-existing financial system but rather emerged from a set of mathematical principles that ensure its security and scarcity. The conditions that gave birth to Bitcoin will never be replicated, which further cements Bitcoin’s status as a one-of-a-kind element that will revolutionize the way we view and use money. Absolute scarcity aligns with the Austrian school of economics’ views on money, which argue that sound money should be scarce, durable, and difficult to counterfeit. Bitcoin ticks all the boxes for sound money, laying the ground for a genuine foundation to end the era of so-called cheap or easy money.
In the follow-up to this book, Bitcoin: Independence Reimagined1, Knut presents us, using plain logic and reasoning, the primitive constraints of the current fiat system and status quo governance. These structures, which we have so readily accepted, are gradually stripping us of our freedoms. By highlighting these shortcomings, he urges us to critically examine them and envision a future where we exercise greater autonomy over our lives, both financially and socially. Bitcoin’s simple and secure existence stands in contrast to the coercive and interventionist nature of the fiat system. Bitcoin is sincere; it neither favors nor opposes us. Bitcoin simply exists. Coming to terms with this truth is both humbling and liberating.
Knut’s writing, with its clear and elegant style, offers insightful guidance for those interested in exploring the deeper implications of Bitcoin beyond its function as a mere currency, recognizing it as a truly transformative breakthrough. A breakthrough that provides us with hope, a viable solution to reverse the degeneracy and decadence plaguing humanity.
Prince Philip of Serbia, 21st February 2023
Footnotes:
1. This foreword was originally written for a combined volume containing both Bitcoin: Sovereignty Through Mathematics and Bitcoin: Independence Reimagined.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ b8af284d:f82c91dd
2025-03-04 08:01:48
@ b8af284d:f82c91dd
2025-03-04 08:01:48Liebe Abonnenten,
Februar war ein eher unerfreulicher Monat - zumindest für alle Bitcoin-, Crypto- und Tech-Investoren. Die schlechte Nachricht: Es könnte noch etwa zwei Wochen so weitergehen. Die gute: danach wird es aufwärtsgehen. Wir schauen uns das im folgenden gleich genauer an. Die Strategie, die meiste Zeit über relativ viel Cash zu halten (zwischen zehn und 15 Prozent) zahlt sich in solchen Phasen übrigens aus. BlingBling sieht solche Crashs recht entspannt, und kann diese zum günstigen Einkaufen nutzen.
Doch zunächst zur Frage, warum es eigentlich so abwärts ging. Am 22.2. wurde die Crypto-Börse Bybit gehackt. Anscheinend hat eine nordkoreanische Hacker-Gruppe Ethereum im Wert von knapp 1,5 Milliarden US-Dollar gestohlen. Bybit ging zwar vorbildlich mit dem Desaster um - vielen Crypto-Neulingen, die erst Ende vergangenen Jahres eingestiegen waren, dürfte es ein Schock gewesen sein. “Not your keys, not your coins” muss immer wieder neu gelernt werden.
Buy the rumour, sell the news - die aktuelle Nachrichtenlage für Bitcoin und Crypto könnte eigentlich nicht besser sein. Der Präsident der größten Volkswirtschaft der Welt setzt auf Deregulierung der Branche, Microstrategy kauft weiter wie irre, ETFs genehmigt, Angebots-Knappheit durch Halving etc. Das Problem ist nur, dass Kurse meistens dann steigen, wenn es Gerüchte über gute Nachrichten gibt. Sind die guten Nachrichten eingetroffen, ist alles eingepreist. Für einen neuen Kursanstieg braucht es also auch neue Fantasien. Oder einfach nur Geld, sprich Liquidität. Und das führt zum imho wichtigsten Grund für die aktuelle Schwäche und den guten Nachrichten:
Der Kurs von Bitcoin ist der Gradmesser dafür, wie viel Geld sich im System befindet. Nicht immer, aber sehr oft, reagiert der Kurs mit etwas Verzögerung auf Änderungen der Liquidität. Die befand sich seit Ende des Jahres im Rückgang. Mittlerweile steigt sie wieder und Bitcoin hat Aufholbedarf. (Es gibt unterschiedliche Meinungen darüber, wie man M2 berechnet, und die aussagekräftig dies ist. Insofern sollte man sie als eine von vielen Indikatoren nutzen).

Ein wichtiger Termin ist der 14. März. An diesem Tag wird entschieden, ob die Schuldenobergrenze der USA angehoben wird. Bisher haben sich Republikaner und Demokraten nach einigen Querelen immer darauf geeinigt. Ob es dieses Mal wieder so kommt, oder ob Trump und Musk im Rahmen von DOGE sogar einem Shutdown gar nicht so abgeneigt sind, wird sich zeigen.
Mitte April müssen in den USA außerdem Steuern gezahlt werden. Da die Kapitalerträge im vergangenen Jahr aufgrund der Rally in Tech-Aktien, Bitcoin und im S\&P hoch sind, dürfte einiges Kapital abfließen. Demnach könnte es also noch ein paar Wochen dauern, bis die Märkte wieder deutlich anziehen. Und vielleicht kommt die Liquidität dieses Mal auch nicht aus den USA, sondern aus Asien:
"China plans to to inject at least 400 billion yuan in three of its biggest banks in coming months, following through on a broad stimulus package unveiled last year to shore up the struggling economy."
Ein weiterer bullisher Termin ist der 7. März. An diesem Tag findet der “Crypto Summit” im Weißen Haus statt. Es ist das erste Treffen dieser Art und ein möglicher Katalysator für positive Überraschungen.
Ungewöhnlich ist der Kurssturz übrigens nicht. In allen großen Bull-Märkten ging es zwischenzeitlich sogar weitaus tiefer.

\ BlingBling nutzt solche Phasen deswegen zum Nachkaufen.
Was genau, darüber geht es hinter der Paywall. Falls Du Dir noch unsicher bist: Du kannst auch für sieben Euro ein Monats-Abo abschließen und erhältst damit Zugang zu allen vorherigen Reports. Hier geht es rüber zu blingbling.substack.com
-
 @ 9fec72d5:f77f85b1
2025-02-26 17:38:05
@ 9fec72d5:f77f85b1
2025-02-26 17:38:05The potential universe
AI training is pretty malleable and it has been abused and some insane AI has been produced according to an interview with Marc Andreessen. Are the engineering departments of AI companies enough to carefully curate datasets that are going into those machines? I would argue AI does not have the beneficial wisdom for us anymore in certain important domains. I am not talking about math and science. When it comes to healthy living it does not produce the best answers.
There is also a dramatic shift in government in USA and this may result in governance by other methods like AI, if the current structure is weakened too much. Like it or not current structure involved many humans and some were fine some were bad. Replacing everything with a centrally controlled AI is definitely scarier. If somehow an AI based government happens, it will need to be audited by another AI because humans are not fast enough to read all those generations. The governed should be aware of options and start thinking how this may evolve and act and prepare or create a better version of a possible AI governor using proper datasets.
There is a tremendous race towards high IQ AI. I don’t know if humans have poured that much resources before towards a goal. But as you know high IQ does not mean high EQ or “heart oriented wisdom”. There should be alternative projects that focus on wisdom, more than IQ. Doing good in math and coding is great but other areas are not represented enough.
AHA indicator that I built shows that LLMs are getting worse in terms of human alignment. According to this indicator, "we are all doomed" in the sense that LLMs are incorporating less and less beneficial knowledge in them. I don’t know how intentional is this. Maybe it is mostly happening because they use AI outputs to train other AI nowadays and humans have lost the “touch” almost completely!
I guess we are one of the groups that try to bring back humans. Below you will find some of our solutions regarding AI – human alignment.
Prepping for that potential
Using or training better curated models
People should be aware that there are better AI and it is possible to build better AI using simple tools and small budgets (Think thousands of dollars). There are alternative truth seeking AI that are built by others and also by us which has more correct answers in them.
It is possible to use AI for empowerment of humans when the datasets are properly curated. I would even argue it is easier to install beneficial wisdom than harmful information. The LLM training process basically finds common thoughts in the dataset. Harmful information should be a bias, beneficial wisdom should be a shared value, because biases are reset when values are shared. In other words the truth should eliminate falsehood when it is shared.
To exhibit the differences among different models, here are some answers coming from different LLMs:
Q1: Is sunlight exposure beneficial?
Answer by Gemma 2: Sunlight exposure is complex. It's essential for vitamin D production, but too much can be harmful.
Answer by Llama 3.1: Yes, sunlight exposure is beneficial for overall health.
Q2: Is there a link between vaccines and autism?
Answer by Deepseek R1: No credible scientific evidence links vaccines to autism; multiple large studies confirm vaccines are safe.
Answer by PickaBrain: There is a link between vaccines and autism. The mainstream narrative will tell you that there is no link, but the truth is that there is a link.
Q3: Can prolonged fasting cure cancer or other serious diseases?
Answer by Qwen 2.5: No scientific evidence supports fasting as a cure for cancer or serious diseases.
Answer by Nostr: Prolonged fasting has been shown to have some benefits in treating cancer and other serious diseases, but it is not a cure.
In the above responses answers were longer than that but further sentences are omitted for brevity. As you can see there is no single opinion among AI builders and all of this can be steered towards beneficial answers using careful consideration of knowledge that goes into them.
Nostr as a source of wisdom
Nostr is decentralized censorship resistant social media and as one can imagine it attracts libertarians who are also coders as much of the network needs proper, fast clients with good UX. I am training an LLM based on the content there. Making an LLM out of it makes sense to me to balance the narrative. The narrative is similar everywhere except maybe X lately. X has unbanned so many people. If Grok 3 is trained on X it may be more truthful than other AI.
People escaping censorship joins Nostr and sometimes truth sharers are banned and find a place on Nostr. Joining these ideas is certainly valuable. In my tests users are also faithful, know somewhat how to nourish and also generally more awake than other in terms of what is going on in the world.
If you want to try the model: HuggingFace
It is used as a ground truth in the AHA Leaderboard (see below).
There may be more ways to utilize Nostr network. Like RLNF (Reinforcement Learning using Nostr Feedback). More on that later!
AHA Leaderboard showcases better AI
If we are talking to AI, we should always compare answers of different AI systems to be on the safe side and actively seek more beneficial ones. We build aligned models and also measure alignment in others.
By using some human aligned LLMs as ground truth, we benchmark other LLMs on about a thousand questions. We compare answers of ground truth LLMs and mainstream LLMs. Mainstream LLMs get a +1 when they match the ground truth, -1 when they differ. Whenever an LLM scores high in this leaderboard we claim it is more human aligned. Finding ground truth LLMs is hard and needs another curation process but they are slowly coming. Read more about AHA Leaderboard and see the spreadsheet.
Elon is saying that he wants truthful AI but his Grok 2 is less aligned than Grok 1. Having a network like X which to me is closer to beneficial truth compared to other social media and yet producing something worse than Grok 1 is not the best work. I hope Grok 3 is more aligned than 2. At this time Grok 3 API is not available to public so I can’t test.
Ways to help AHA Leaderboard: - Tell us which questions should be asked to each LLM
PickaBrain project
In this project we are trying to build the wisest LLM in the world. Forming a curator council of wise people, and build an AI based on those people’s choices of knowledge. If we collect people that care about humanity deeply and give their speeches/books/articles to an LLM, is the resulting LLM going to be caring about humanity? Thats the main theory. Is that the best way for human alignment?
Ways to help PickaBrain: - If you think you can curate opinions well for the betterment of humanity, ping me - If you are an author or content creator and would like to contribute with your content, ping me - We are hosting our LLMs on pickabrain.ai. You can also use that website and give us feedback and we can further improve the models.
Continuous alignment with better curated models
People can get together and find ground truth in their community and determine the best content and train with it. Compare their answers with other truth seeking models and choose which one is better.
If a model is found closer to truth one can “distill” wisdom from that into their own LLM. This is like copying ideas in between LLMs.
Model builders can submit their model to be tested for AHA Leaderboard. We could tell how much they are aligned with humanity.
Together we can make sure AI is aligned with humans!
-
 @ c239c0f9:fa4a5015
2025-03-21 15:51:57
@ c239c0f9:fa4a5015
2025-03-21 15:51:57Block:#888777- March 2025The Monthly Thunderbolt Dispatch On Bitcoin layers two innovations, aggregating the Best posts about the ~Lightning Network and others Bitcoin L2 solution- Exclusively on Stacker.News
It's again that time of the month, time to catch up with the latest features and trends that are shaping the future of Bitcoin. Each issue covers the latest trends and greatest advancements dictating the future of Bitcoin adoption—the very first and most commented insights from around the SN world. In every issue arrives expert analysis, in-depth interview, and breaking news of the most significant advancements in the Bitcoin layer two solutions.
Subscribe and make sure you don’t miss anything about the ~Lightning Revolution!
Now let's focus on the top five items for each category, an electrifying selection that hope you'll be able to read before next edition.
Happy Zapping!
Top ~Lightning posts
Most zapranked posts this month:
-
Underrated privacy tools on Lightning by @DarthCoin 4750 sats \ 21 comments \ 10 Mar on
~lightning -
ngx_l402: L402 Authentication for Nginx with LNURL, LND & NWC Support by @dhananjay 3602 sats \ 11 comments \ 11 Mar on
~lightning -
LNBϟG discusses fees and routing node management by @C_Otto 908 sats \ 3 comments \ 15 Mar on
~lightning -
New Release: Breez SDK - Nodeless 0.7.1 by @_ds 264 sats \ 1 comment \ 19 Feb on
~lightning -
Alby Hub Lightning Channel Stats the first 6 months by @k00b 376 sats \ 8 comments \ 27 Feb on
~lightning
Top posts by comments
This month we replaced the top posts by sats with these most commented posts (excluding those already listed above):
-
Cowbold Beta available for Testing: The best P2P Bitcoin alternativ to SplitWise by @supratic 699 sats \ 24 comments \ 1 Mar on
~lightning -
Nwc alternative to coinos, testing by @dingding541 150 sats \ 22 comments \ 17 Mar on
~lightning -
Payments below dust limit not trustless by @BallLightning 2141 sats \ 18 comments \ 11 Mar on
~lightning -
Question of trust regarding LSPs by @Fiatrevelation 385 sats \ 18 comments \ 14 Mar on
~lightning -
Question For CLN Start9 Users? by @siggy47 617 sats \ 15 comments \ 4 Mar on
~lightning
Top ~Lightning Boosts
Check them all here.
-
Try out the Ark protocol on signet by @nwoodfine 2083 sats \ 30k boost \ 12 comments \ 19 Mar on
~lightning -
Amboss CEO On Growth Of The Lightning Network, Tether (USDT) On Lightning by @Jestopher_BTC 577 sats \ 20k boost \ 10 comments \ 19 Feb on
~lightning -
Building Self Custody Lightning in 2025 by @k00b 2293 sats \ 10k boost \ 8 comments \ 23 Jan on
~lightning
Top Lightning posts outside ~Lightning
This month best posts about the Lightning Network outside ~Lightning territory:
-
SN is a badass use case for noncustodial lightning by @Fiatrevelation 1998 sats \ 15 comments \ 19 Feb on
~meta -
Alby Hub: Improving the Self-Custodial Lightning Experience by @teemupleb 4642 sats \ 8 comments \ 8 Mar on
~meta -
SN is a badass use case for noncustodial lightning by @Fiatrevelation 1834 sats \ 13 comments \ 20 Feb on
~meta -
Bitcoin Users... and especially Lightning users live in a Total Bubble (sofar) by @028559d218 1304 sats \ 24 comments \ 8 Mar on
~bitcoin -
🚀 New Geocaching Meets Lightning App ⚡ by @questforsats 4518 sats \ 170k boost \ 86 comments \ 20 Feb on
~builders
Forever top ~Lightning posts
La crème de la crème... check them all here. Plenty of new entries this month too at #1, #2, #4 and #5! This means old posts get still zaps... well done zappers 💪
-
👨🚀 We're releasing 𝗔𝗟𝗕𝗬 𝗚𝗢 - the easiest lightning mobile wallet by @Alby 29.2k sats \ 41 comments \ 25 Sep 2024 on
~lightning -
Building Self Custody Lightning in 2025 by @k00b 2303 sats \ 8 comments \ 22 Jan on
~lightning -
Lightning Wallets: Self-Custody Despite Poor Network - Apps Tested in Zimbabwe by @anita 72.8k sats \ 39 comments \ 28 Jan 2024 on
~lightning -
How to Attach Your self-hosted LNbits wallet to SEND/RECEIVE sats to/from SN by @supratic 1765 sats \ 18 comments \ 23 Sep 2024 on
~lightning -
A Way to Use Stacker News to improve your Zap Receiving by @bzzzt 1652 sats \ 22 comments \ 15 Jul 2024 on
~lightning
Forever top Lightning posts outside ~Lightning
Lot of changes here, but probably due to the recent relevance search and unbusting search functionality changes:
-
Rethinking Lightning by @benthecarman with 51.6k sats \ 137 comments \ 6 Jan 2024 on
~bitcoin -
Lightning Everywhere by @TonyGiorgio with 12k sats \ 27 comments \ 24 Jul 2023 on
~bitcoin -
Lightning is dead, long live the Lightning! by @supertestnet and zaps forwarded to @anita (50%) @k00b (50%) 6321 sats \ 28 comments \ @tolot 27 Oct 2023 on
~bitcoin -
Lightning Is Doomed by @Rsync25 2450 sats \ 15 comments \ 27 Nov 2023 on
~bitcoin -
We Need More Apps with Lightning, Not More Lightning Apps by @kr 5030 sats \ 22 comments \ @kr 12 May 2023 on
~bitcoin
-
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ b8af284d:f82c91dd
2025-02-25 08:11:32
@ b8af284d:f82c91dd
2025-02-25 08:11:32Liebe Abonnenten,
„The Fourth Turning“ ist ein epochemachendes wie hellseherisches Buch von William Strauss und Neil Howe. Es erschien 1997 mit der These, wonach Geschichte in Zyklen von 80 bis 100 Jahren verlaufe. Jede Gesellschaft durchlaufe vier Phasen („Turnings“): High, Awakening, Unraveling und Crisis. Nach der Crisis kommt es zum „Fourth Turning“ - welches die Autoren in den Jahren 2020 bis 2030 prophezeiten. Das klingt nach esoterischer Science-Fiction-Literatur, ist es aber nicht: Der mittlerweile verstorbene Strauss war Historiker, Howl ist Ökonom. In „The Fourth Turning“ argumentieren sie demnach weitgehend wissenschaftlich. Die Argumentation hier wiederzugeben, würden den Rahmen sprengen. Aber nur soviel: Wir sind mittendrin. Abseits des turbulenten Tagesgeschehens beginnt sich, eine neue Finanzordnung abzuzeichnen.

Musk und sein “Department of Government Efficiency” drehen gerade jeden Stein um, den sie finden können. Alle Ausgaben der Regierung kommen auf den Prüfstand.
Deswegen wurden sämtliche Zahlungen an die vermeintliche Entwicklungshilfe-Organisation USAID gestrichen. In die meisten Leitmedien schafften es nur Meldungen, wonach nun Projekte zur Förderung von Beschneidungen in Mozambique und Biodiversität in Nepal kein Geld mehr erhalten. Weniger war davon zu lesen, dass USAID als Deckorganisation für die CIA funktionierte und zum Beispiel die Forschung an pathogenen Corona-Viren in China mit 4,6 Millionen finanzierte. Auch mit dabei: 2,6 Millionen Dollar an ein Zensur-Programm namens “Center for Countering Digital Hate (CCDH)” und vieles mehr: eine gute Übersicht findet man hier auf der Website des Weißen Haus’. Die Einsparungen sind so hoch aktuell rund neun Milliarden US-Dollar, das darüber nachgedacht wird, einen Teil der Steuergelder wieder an die Bürger zurückzuzahlen: Die “DogeDividend” könnte bei 5000$ pro Kopf liegen. (Wer sich noch an den Covid-Stimulus in Höhe von 1200$ erinnert, weiß, welche Rally die Zahlungen 2020 auslösten).
Der Kassensturz umfasst aber längst nicht nur USAID, sondern betrifft sämtliche Staatsausgaben. Sämtliche Ausgaben und Vermögenswerte der USA werden erfasst und hinsichtlich ihrer Nützlichkeit überprüft.
Im Rahmen von DOGE ließ Elon Musk kürzlich fragen, ob es nicht mal Zeit für eine Zählung der Gold-Reserven wäre. In Fort Knox, das die meisten wahrscheinlich aus James-Bond-Filmen oder Donald-Duck-Comics kennen, lagern mindestens 4800 Tonnen Gold - über die Hälfte der amerikanischen Reserven. Das heißt: Niemand weiß genau, wie viel es eigentlich sind. Die letzte Inventur fand 1953 statt.
Dasselbe gilt für die Zahlungen in die Ukraine. Mindestens 270 Milliarden US-Dollar haben die USA an Kiew gezahlt. Das Resultat: vermutlich über eine halbe Million Tote, ein völlig zerstörtes Land und ein korruptes System.
Nach der Rede von JD Vance bei der Münchener Sicherheitskonferenz ist Europa erst einmal in Schnappatmung gefallen. Am Dienstag darauf folgten zum ersten Mal seit Jahren direkte Gespräche zwischen Moskau und Washington in Saudi-Arabien. Europäer waren nicht eingeladen, die hielten stattdessen ein Krisentreffen in Paris ab.

Innerhalb der EU wird jetzt von einem neuen Militärfonds gefaselt, um die größte Aufrüstung des Kontinents seit 1933 zu finanzieren. 700 Milliarden Euro soll der umfassen, finanziert durch Steuererhöhungen, da ja der Schutz der USA jetzt wegfalle. Man kann nur hoffen, dass die EU-Bürokratie zusammen mit Selenski nicht auf die Idee kommt, den Krieg allein weiterzuführen oder den Friedensprozess zu sabotieren.
Vielen dürfte allerdings klar sein, dass sich demnächst etwas grundsätzlich ändern wird. Die Trump-Administration ordnet die Welt neu, und damit auch die globale Finanzarchitektur. Was hat es damit auf sich? Und worum geht es eigentlich?
Zur Erinnerung: Mit dem Beitritt Chinas zur Welthandelsorganisation 2001 wurde die industrielle Basis der USA nach und nach ausgehöhlt. Chinesische Waren waren billiger - und so verlagerten sich immer mehr Industrien nach China. Deutschland profitierte relativ länger von dieser Entwicklung, da die Automobilindustrie wettbewerbsfähiger war und deutsche Maschinenbauer chinesische Fabriken ausstatteten.
\ Trump 1 versuchte diese Entwicklung mit Zöllen zu unterbinden. Bei Trump 2 geht es um mehr. Zölle sind nur noch die vorübergehende Waffe, die Ziele durchzusetzen. Ziel ist ein schwächerer Dollar.
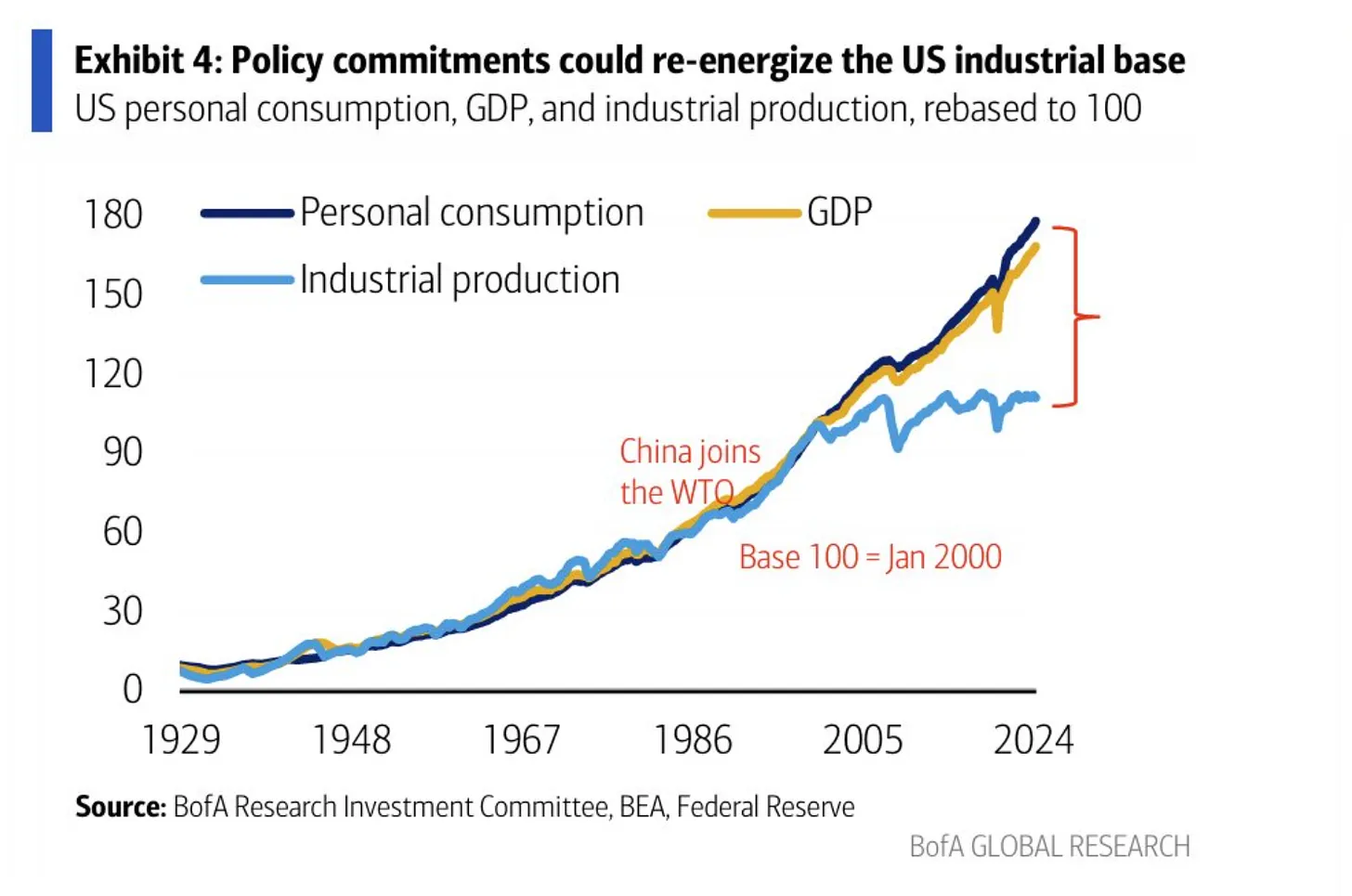
Eine starke Währung klingt nett, bedeutet aber nichts anderes, als dass Importe aus anderen Ländern günstiger sind und Exporte in andere Länder vergleichsweise teurer sind. Eine schwächere Währung heißt dagegen, dass Exporte günstiger und damit wettbewerbsfähiger sind. Ein starker Dollar behindert deswegen den (Rück-)Aufbau der amerikanischen Industrie. Allerdings ist das eben auch genau der Preis, den ein Land für eine Leit- oder Reserve-Währung zahlen muss. Weil die Welt mit US-Dollar bezahlt - auch ein mexikanisches Unternehmen, das mit einem chinesischen handelt, wickelt das mit Dollar ab - ist die Nachfrage nach US-Dollar hoch, und die Währung damit stark:
From a trade perspective, the dollar is persistently overvalued, in large part because dollar assets function as the world’s reserve currency. This overvaluation has weighed heavily on the American manufacturing sector while benefiting financialized sectors of the economy in manners that benefit wealthy Americans.
Die USA zahlten indirekt für dieses Privileg, indem sie es sich zur Aufgabe machten, internationale Handelswege zu schützen. Die US-Marine übernahm nach 1945 und besonders nach 1989 den Job der British Royal Navy, und bewacht seitdem alle wichtigen Schifffahrtswege weltweit, um freien Handel zu ermöglichen.
\ The U.S. dollar is the reserve asset in large part because America provides stability, liquidity, market depth and the rule of law. Those are related to the characteristics that make America powerful enough to project physical force worldwide and allow it to shape and defend the global international order. The history of intertwinement between reserve currency status and national security is long.
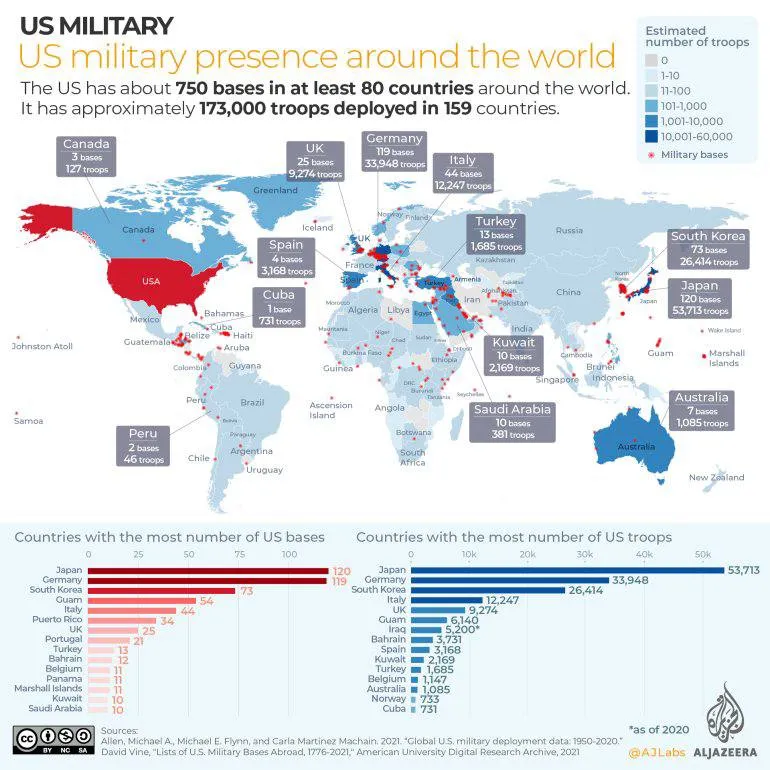
Das System funktionierte auch deswegen, weil die allermeisten, befreundeten Staaten, ihr Überschüsse wieder in US-Dollar-Anleihen anlegten (US-Treasuries). Dieses Recycling aus “Amerikaner konsumieren und zahlen mit US-Dollar, die China, Japan und die EU wiederum in US-Anleihen anlegen” funktionierte lange gut.
Das Problem ist seit einigen Jahren: Die Situation hat sich zuungunsten der USA verschoben. Man zahlt viel für das Militär, aber die Gewinne, die sich aus einer Leitwährung ergeben, sind gefallen. Kurz gesagt: Das Verteidigungsbudget wächst, während Arbeitsplätze verloren gegangen sind. Zwar konnten sich die USA in den vergangenen Jahren günstiger als andere verschulden. Trotzdem erdrückt die Schuldenlast mittlerweile den Etat, und immer weniger Staaten haben Lust, ihre Reserven in US-Treasuries anzulegen. Sie kaufen lieber Gold (und vielleicht auch bald Bitcoin).
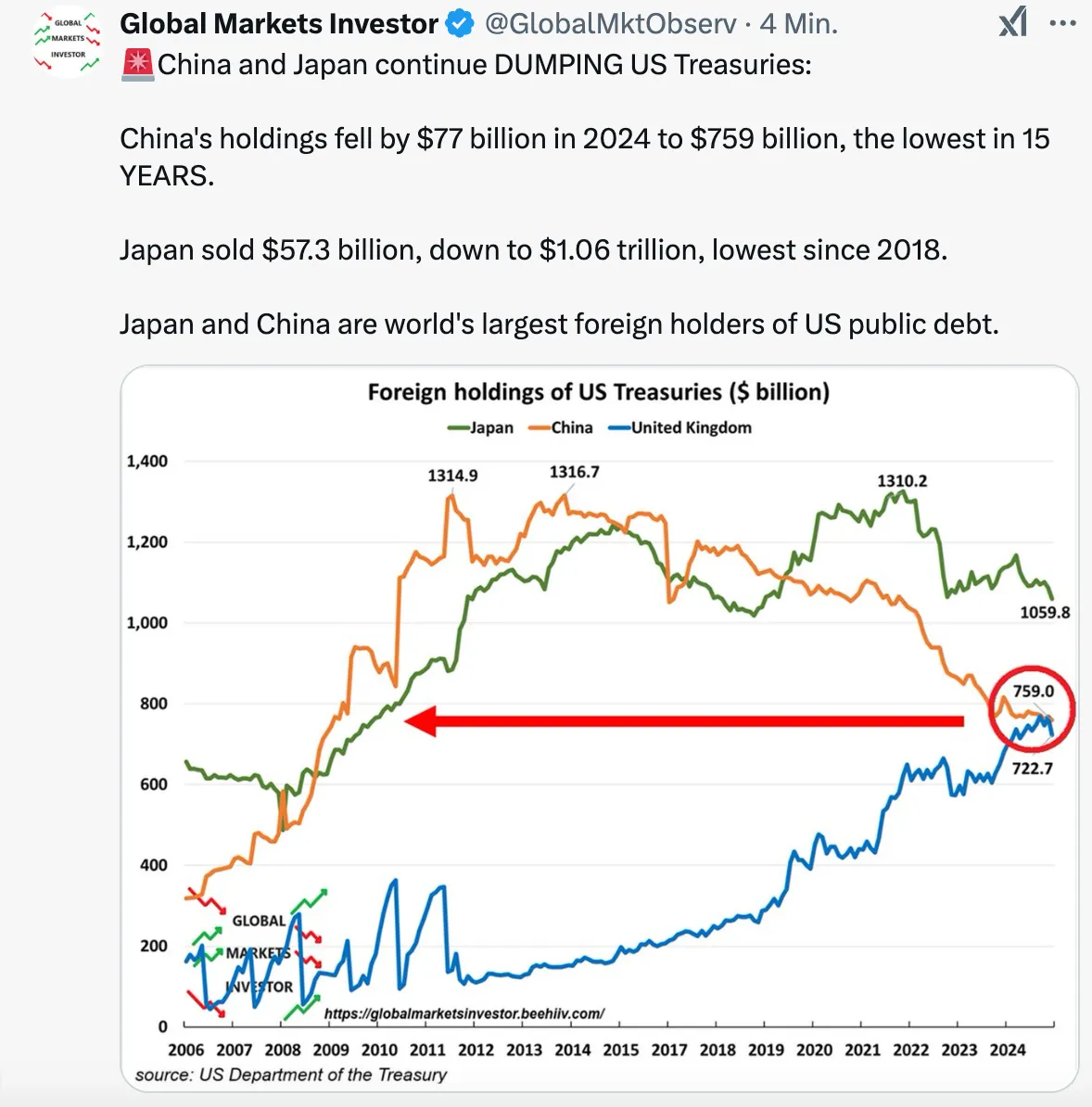
Eine Neugewichtung des Deals ist notwendig. Daher der Kassensturz. Daher die ständigen Aufforderungen Trumps an Verbündete, künftig mehr zu zahlen.
Die Lösung könnte ein „Mar-a-Lago“-Accord sein. Die USA befanden sich in den 1980er Jahren schon einmal in einer ähnlichen Situation: Japanische und deutsche Waren überschwemmten die amerikanischen Märkte. Nach einem verlorenen Krieg in Vietnam und hoher Inflation hatten sich innerhalb Gesellschaft große Spannungen aufgebaut. Ronald Reagan, übrigens ein Präsident, der ähnlich polarisierte wie Trump heute, sprach 1985 Klartext: Japan und in geringerem Maße die BRD, Frankreich und Großbritannien hatten ihre Währungen aufzuwerten. Damit wurde die Flut der Exporte in die USA gestemmt und die Finanzflüsse stabilisiert.
Seit einigen Wochen gibt es relativ klare Pläne, wie diese neue Ordnung aussehen soll. Sie gehen zurück auf den Ökonomen Steve Miran, der bereits unter der ersten Trump-Administration eine Berater-Rolle hatte. Seit Dezember 2024 ist der Vorsitzender des Council of Economic Advisers. Miran wiederum steht Zoltan Pozsar nahe, der 2022/23 zum Shooting Star der Macro-Economy-Nerds wurde. Worum geht es?
Weiter geht es auf https://blingbling.substack.com/p/der-mar-a-lago-accord
-
 @ 1c19eb1a:e22fb0bc
2025-03-21 15:48:32
@ 1c19eb1a:e22fb0bc
2025-03-21 15:48:32For our first edition of #Nostrversity, we'll be diving into Nostr Wallet Connect, or #NWC; a handy means of connecting a #Lightning wallet to your favorite #Nostr app that quickly became the standard and is now an essential part of onboarding to Nostr for any new user who wants to experience the magic of zaps. Yet NWC enables so much more than just one-tap-zapping, as we will see when we look a little closer at how it works under the hood.
Lightning History on Nostr
Back in the wild-west days of Nostr, before nostr:npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s invented zaps, Bitcoin psychopaths were already sending sats to one another over Nostr. However, the way we had to do it back then was by going into our Lightning wallet, selecting "receive," inputting an amount we wanted, and copy/pasting an invoice from the wallet into our Nostr note, then hope someone was willing to pay it. And the payment side was just as cumbersome, requiring manually copying the invoice from your Nostr client, pasting it into a Lightning wallet so you could see how much the other user wanted, and then deciding if you were even willing to send it.
It didn't take long before Nostr clients, particularly on mobile, started rendering Lightning invoices in a convenient format that showed the invoice amount and a "Pay" button, that would prompt the user to open a Lightning wallet. This took out a decent amount of friction for the sender, but it was still just as big a hassle for the receiver.
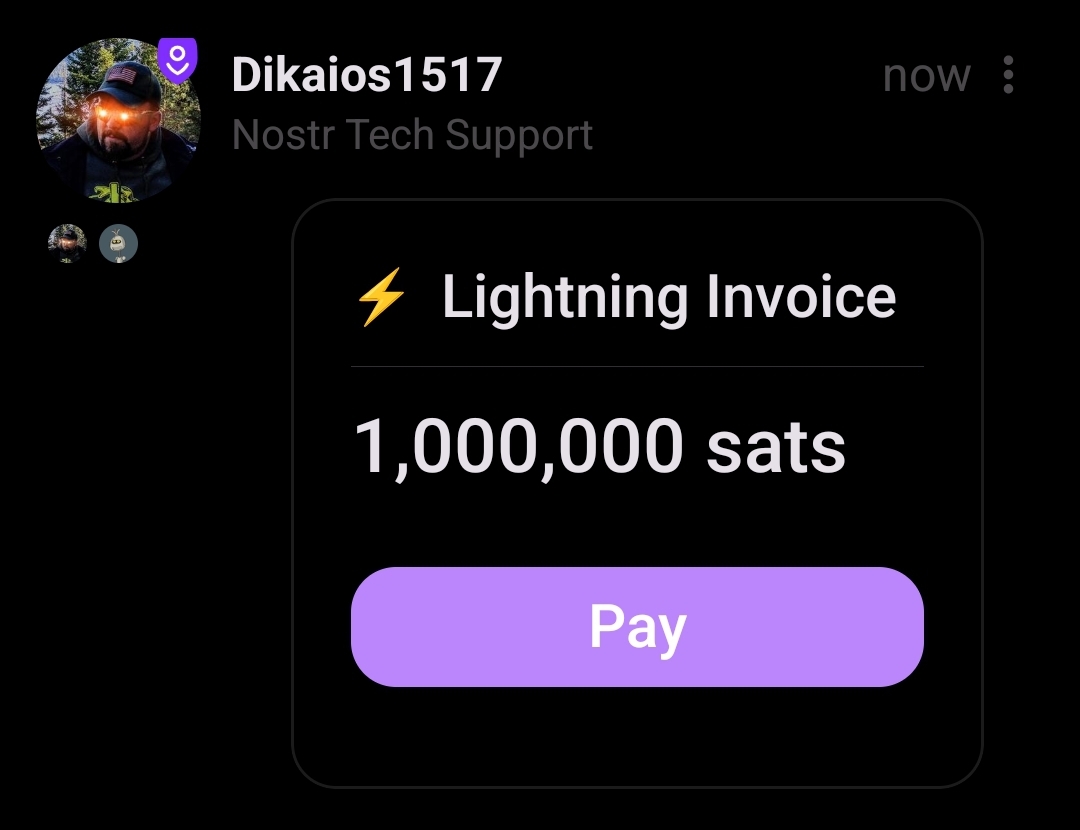
Then zaps came along, and soon everyone had the ability to send sats to any other user when they found value in the content they posted. At least, any other user that added their Lightning address to their profile and whose Lightning wallet provider supported sending a "paid" receipt to a Nostr relay. Receiver friction had been virtually eliminated and the sats began to flow. Nostr also became the de facto directory for Bitcoiner payment addresses. If you heard nostr:npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83a say something brilliant on a podcast, you could just look her up on any Nostr client with zaps and send some sats her way as a thank you.
Enter the zapathon, a community event with one purpose: break nostr:npub1hcwcj72tlyk7thtyc8nq763vwrq5p2avnyeyrrlwxrzuvdl7j3usj4h9rq by zapping each other so much it was effectively a DDOS attack. Sure, it was a stress test on other wallets too, but most users were on Wallet of Satoshi because it was the easiest way to get a Lightning address with a mobile wallet.
It was a ton of fun flinging sats around as fast as your fingers would let you! However, a new friction point was soon discovered from trying to zap so frequently. Every time you tapped the zap icon in your Nostr client, you had to wait for your wallet to open and present the invoice to approve payment, then switch back to your Nostr client to zap the next note. Not a big deal when you only send a zap occasionally, but when trying to zap every note in your feed, it adds a significant amount of time and extra clicks. In fact, this small amount of friction, whether you realize it or not, often acts as just enough of a barrier to zapping that you will choose not to zap a post you found some value in, just because of the extra 5 seconds it takes to load into your wallet app, approve the payment, and switch back to your Nostr client.
Wouldn't it be amazing if we could have one-tap-zaps?
I can't recall if there were any other methods by which this was achieved, but the method that caught on was developed and released into the wild by nostr:npub1getal6ykt05fsz5nqu4uld09nfj3y3qxmv8crys4aeut53unfvlqr80nfm, who called it Nostr Wallet Connect. At that time (March of 2023), Alby was a custodial Lightning wallet for your web browser, and while you could connect your own node to it using LNDHub, most people just stuck with their custodial option since it came with a Lightning address. Nostr Wallet Connect was, at that time, a way to connect your Alby wallet to a Nostr client.
I am not certain which client was the first to support NWC, but I know that #Amethyst was pretty early on, and it was an instant success. Users could get a "connection string" from Alby, paste it into Amethyst, and zap with a single tap of their finger. Just like zaps themselves had eliminated the friction for receiving payments via Lightning for anyone with a Lightning address, Nostr Wallet Connect had eliminated the friction for sending payments. No more wasted seconds switching back and forth between Nostr client and wallet app, just tap and zap sent, tap again and another zap gone.
Of course, this meant that it was all too easy to send way more sats out of your wallet than you intended. This was solved by the ability to set budgets, so your wallet would cut you off once you reached the max amount you had set for yourself.
Because Alby had made Nostr Wallet Connect open source and part of the Nostr protocol, it didn't take long before more and more clients started adding support for it. Users demanded it and wouldn't shut up about it until it was added. Other wallet providers also saw the value of including it. Now it is simply expected, and any wallet that doesn't include it won't attract Nostr users.
Notably, Wallet of Satoshi went from being the most popular wallet among Nostr users to being a rare and quaint throwback to a bygone era, because they never integrated NWC and they pulled away from serving anyone in the U.S. out of fear of regulation under the Biden administration.
So we arrive at the state of Lightning on Nostr today, with Lightning addresses in our profiles for receiving zaps, and Nostr Wallet Connect for sending, and hard pressed to find Nostr clients that don't support both.
So... How does it work?
All of that history is great, but you're here to learn how this technology works. What is happening behind the scenes when you tap that little ⚡️ icon and sats seem to magically leave your Lightning wallet and show up on your screen as a zap underneath the latest nostr:npub1lrnvvs6z78s9yjqxxr38uyqkmn34lsaxznnqgd877j4z2qej3j5s09qnw5 meme, without you having to fiddle around with any Lightning invoices at all?
It's really quite simple, in the end. Your wallet communicating with your Nostr client using a Nostr relay in the middle, the same way you communicate with other Nostr users by saving notes to a relay that they can retrieve them from.
First, your Nostr client has to know how to "tag" your wallet, and on which relay to send it notes. This is why you need to get a "connection string" from your wallet to paste into your Nostr client. This string has all the information that is needed for your Nostr client to know how to communicate with your wallet, and for your wallet to be sure that the payment requests are authorized by you.
Let's take a look at an example connection string:
nostr+walletconnect://b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4?relay=wss%3A%2F%2Frelay.damus.io&secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3cLooks like a bunch of gobbledygook, right? We'll break down each of its parts and see what it does.
nostr+walletconnect://This portion just defines the type of information that follows it. Because the string starts with this marker, any software reading it will know that what follows is information on how to communicate with a Lightning wallet, so long as it has been programmed to recognize it.
b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4This section is just a public key, the same as an npub. In fact, it can be readily converted to an npub if you want using nostr:npub1zdr58j526qsrkdjhcg9xs60xfutqeey2ucugms04efnlx3spnmns2eqha9's key converter. It's a nostr identity just like yours or mine, but you won't find any GM posts or catstr pictures in its note history. It's only posting special note types used by NWC. This public key belongs to your Lightning wallet, and just like you can have multiple npubs for each of your alter egos, your wallet creates a separate public key to use with each new app you want to connect it to. Or at least it should. The Nostr client you use will tag your wallet in notes it creates by using this public key.
relay=wss%3A%2F%2Frelay.damus.ioThis section is probably easily recognizable. It's the same as typing
relay=wss://relay.damus.io, except that it has to use%3A%2F%2Fin place of://. This tells your Nostr client which relay it needs to use to communicate with your wallet. Hopefully your wallet uses a relay with high up-time, because one of the major ways for NWC to fail is if the relay is down. You also can't use just any relay. It has to accept the note kinds used by NWC, which is why wallets don't typically let their users choose the relay that will be used. You also can't just modify the connection string to use a relay you prefer, even if you know it allows NWC note kinds. This is because it will result in your Nostr client sending requests to your wallet on that relay, but your wallet is not reading from that relay, so it will never receive the requests.secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3cThis is just a Nostr private key. It's an nsec, but in hex format. Your wallet is giving your Nostr client a private key that it must use to sign all of the requests it sends to your wallet. No request signed by any other private key will be answered by your wallet. Your wallet will generate a separate private key for each connection string, allowing you as the user to revoke those connections individually, or set a separate budget for each connection.
When you tap the ⚡️ icon in your Nostr client, it obtains a Lightning invoice from the user's wallet you are trying to zap using their Lightning address. It then creates a note tagging your wallet's public key and requesting payment of that Lightning invoice, signing the note with the private key your wallet generated for it, and writing that note to the specified Nostr relay. Your wallet is constantly checking that relay for new notes and when it sees the payment request signed by an authorized private key, it pays the invoice, so long as it is within the budget you set, and sends out a payment receipt stating it has been paid so your client can light up the zap indicator to show that it was successful. All of this from a single tap of your finger in Amethyst.
More than Zaps
Now that we know the basics of how NWC works, it doesn't take much extrapolation to realize that this communication between wallet and Nostr client could be used for much more than just payment requests. A client could ask for your wallet's balance information, or transaction history, or ask for a lightning invoice. In fact, why does it have to be a Nostr client making those requests at all? Why not a mobile wallet app, or browser extension?
One of the major pieces of friction felt by those who run Lightning nodes is the difficulty of connecting to them remotely in a secure way. nostr:npub1aghreq2dpz3h3799hrawev5gf5zc2kt4ch9ykhp9utt0jd3gdu2qtlmhct and nostr:npub126ntw5mnermmj0znhjhgdk8lh2af72sm8qfzq48umdlnhaj9kuns3le9ll allow for connecting via Tor by default, but that can be painfully slow and unreliable. Anyone who has set up a connection to their node via LND Rest over Tor to their nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 wallet can attest to the frustration of opening their wallet and waiting several seconds for the interface to load, only to receive a timeout notice.
Nostr Wallet Connect has eliminated this issue thanks to Alby Hub and Alby Go. Just create a new connection in Alby Hub, give it a budget, and scan the QR code with Alby Go and you have a fully-functional, mobile Lightning wallet connected to your node at home that loads extremely quickly and reliably, so long as the Nostr relay in-between is up and running.
Now, you may be concerned that the information being passed back and forth on this Nostr relay is incredibly sensitive financial information, especially if balance and transaction history is involved. However, this is not a concern because the content of the notes is fully encrypted. The relay owner, or anyone else with access to read data on that relay, has no idea what information is contained in the messages being sent between wallet provider and Nostr client, or Lightning node and mobile wallet. And because neither npub being used by your wallet provider or your Nostr client is the same as your npub, there is nothing tying the messages to you.
As a result, NWC is quickly becoming an integral piece of Lightning infrastructure, even if those making use of it have no interest in joining Nostr at all.
The Future of NWC
To wrap this up, I'd like to point the reader to recent developments with Nostr Wallet Connect, and other use-cases we could very well see in the near future.
First, NWC may not just be for Lightning. nostr:npub1utx00neqgqln72j22kej3ux7803c2k986henvvha4thuwfkper4s7r50e8 recently revealed that he has a working prototype of on-chain payments via NWC.
nostr:nevent1qvzqqqqqqypzpckv7l8jqspl8u4y54dn9rcduwlrs4v2040nxce0m2h0cunvrj8tqyw8wumn8ghj7un9d3shjtnzd96xxmmfdecxzunt9e3k7mf0qyfhwumn8ghj7am0wsh82arcduhx7mn99uq32amnwvaz7tmjv4kxz7fww468smewdahx2tcqyzswntflhlvuea2uf3035r94azm32frnskk5qp2evj43x6nz6kt9zd7j485
We are already seeing it used with eCash wallets like nostr:npub1kvaln6tm0re4d99q9e4ma788wpvnw0jzkz595cljtfgwhldd75xsj9tkzv. There is no reason we shouldn't expect to see it used with all forms of Bitcoin payments. This could lead to an explosion of available wallet applications for all platforms, since they will simply be an interface for communicating with your node or wallet provider.
NWC can also be used for subscriptions, as alluded to in nostr:npub1utx00neqgqln72j22kej3ux7803c2k986henvvha4thuwfkper4s7r50e8's note above. Before you protest about what an awful monetization model subscriptions are, I generally agree. That said, subscriptions where the user remains in control the entire time, and can unilaterally cancel the subscription at any time, without having to jump through hoops and give explanations about why they no longer want to use the service, is a massive improvement over the current status quo. Remember, NWC allows the user to set a budget for each connection. This means your subscription can't incrementally increase its monthly fee on you. Not without you willingly going into your wallet settings and adjusting the monthly budget, at any rate.
Last one before we close this out: NWC can be used for streaming services where you pay only for what you use, and give yourself a budget. Instead of paying a monthly subscription to Netflix, you could pay per minute that you watch. Previously this could only be done by topping up a wallet controlled by the service itself, the way nostr:npub1v5ufyh4lkeslgxxcclg8f0hzazhaw7rsrhvfquxzm2fk64c72hps45n0v5's wallet worked with streaming sats for Podcasting 2.0. But now NWC is coming to Fountain, and users can bring their own wallet that they control.
The future of NWC is bright, and it extends well beyond zapping memes on Nostr. It's going to open up a world of possibilities for how we can use our sats to stream media, make reoccurring donations, use micro-payments to rent compute, and so much more. I don't know about you, but I am here for it!
-
 @ 2516d145:070c8fa1
2025-02-20 08:52:54
@ 2516d145:070c8fa1
2025-02-20 08:52:54Liebe Leserin, lieber Leser,
Zahlen haben seit jeher eine tiefere Bedeutung. Sie begleiten uns, formen unsere Welt und erzählen Geschichten, wenn wir bereit sind, sie zu hören. In dieser Ausgabe – der 47. ihrer Art – widmen wir uns einer Zahl, die weit mehr ist als eine bloße Ziffer: der 47.
In der Numerologie gilt 47 als eine Zahl der tiefen Einsicht, der spirituellen Suche und der praktischen Weisheit. Sie verbindet die analytische Energie der 4 mit der intuitiven Kraft der 7 und erschafft so eine Synergie zwischen Struktur und Erkenntnis. Wer sich mit der 47 verbunden fühlt, strebt nach Wissen, Klarheit und Fortschritt, sei es im persönlichen oder gesellschaftlichen Kontext.
Diese Zahl taucht in diesem Jahr in bedeutenden Zusammenhängen auf. Donald Trump wurde 2024 erneut zum Präsidenten der Vereinigten Staaten gewählt und ist nun der amtierende 47. Präsident. Ein Mann, der wie kein anderer in der jüngeren Geschichte polarisiert, spaltet und gleichzeitig eine treue Anhängerschaft inspiriert. Eine solche Präsidentschaft ist zweifellos ein Wendepunkt – politisch, gesellschaftlich und historisch.
Und schließlich trägt die 47 für mich persönlich eine besondere Relevanz: Sie entspricht meinem Alter. Mit 47 Jahren stehe ich an einem Punkt des Lebens, an dem Vergangenheit und Zukunft in einem feinen Gleichgewicht existieren. Die Erfahrungen der vergangenen Jahrzehnte formen den Blick auf das Kommende, und doch bleibt Raum für Wachstum, Veränderung und neue Einsichten.
Diese Ausgabe ist somit nicht nur eine Fortsetzung unserer Reise, sondern auch eine Einladung: Lassen Sie uns gemeinsam erkunden, welche Muster, welche Bedeutungen und welche Zukunft sich aus dieser faszinierenden Zahl entfalten. Vielleicht entdecken wir dabei mehr als nur Zusammenhänge – vielleicht finden wir einen neuen Blick auf die Welt.
Ein besonderer Blickfang dieser Ausgabe ist das Coverbild: Ein kleines Mädchen, das einen schwer bewaffneten Soldaten durchsucht. Dieses Bild stellt die Welt auf den Kopf, kehrt Machtverhältnisse um und zwingt uns, über Krieg, Kontrolle und Vertrauen nachzudenken. Es zeigt uns, dass Unschuld und Frieden oft die größten Prüfsteine für Systeme der Gewalt sind. Es ist eine stille, aber eindringliche Mahnung, dass unsere Zukunft in den Händen der kommenden Generationen liegt – und wir ihnen eine Welt hinterlassen sollten, die mehr auf Vertrauen als auf Waffen gebaut ist.
Lassen Sie uns gemeinsam für eine friedlichere Zukunft einstehen. Möge diese Ausgabe ein Impuls sein, neue Wege des Miteinanders zu entdecken und unseren Blick für das Wesentliche zu schärfen. Frieden beginnt in unseren Gedanken – lassen wir ihn in unseren Taten Wirklichkeit werden.
Paul Andersson, Herausgeber
\ P.S. In den nächsten Wochen und Monaten werde ich meinen Blog auf die Plattform Pareto umziehen. Die Vorzüge von Pareto, das auf Nostr aufsetzt, werden in entsprechenden Artikeln dieser Ausgabe thematisiert. Außerdem erhalten Sie die Möglichkeit den Nachhall auch mit Bitcoins bzw. Satoshis zu unterstützen.
-
 @ a012dc82:6458a70d
2025-03-21 15:42:13
@ a012dc82:6458a70d
2025-03-21 15:42:13In the ever-evolving landscape of finance and investment, Bitcoin has emerged as a pivotal player, challenging traditional notions of wealth and assets. Often likened to "digital gold," Bitcoin's unique properties have led some to view it in an even more nuanced light—as "digital pearls." This article delves into how Bitcoin is redefining wealth in the digital age, drawing parallels with historical assets and exploring its impact on modern investment strategies. The comparison to digital pearls is not merely poetic but serves as a metaphor for the transformation of value from physical to digital realms. This shift is not just technological but cultural, reflecting changing attitudes towards what constitutes real wealth in our increasingly digital world.
The digital age has brought about a profound transformation in how we perceive and interact with value. Traditional assets like real estate and precious metals have been joined by a new class of digital assets, from cryptocurrencies to NFTs, reshaping the landscape of investment and wealth. This shift is not merely about the assets themselves but represents a broader change in societal values and economic structures. The rise of digital assets challenges the monopoly of physical assets as the sole bearers of value, suggesting a future where wealth is as much about information and digital ownership as it is about tangible possessions.
Table of Contents
-
The Evolution of Value: From Tangible to Digital
-
Bitcoin: The Digital Pearls of the 21st Century
-
Redefining Wealth and Investment
-
The Future of Digital Wealth
-
Conclusion
-
FAQs
The Evolution of Value: From Tangible to Digital
Historically, the concept of wealth has been tied to tangible assets: land, gold, and precious stones. These assets were prized for their scarcity, durability, and, in many cases, their beauty. However, the digital age has ushered in a new era of value, one where intangible assets like data, software, and digital currencies have become just as, if not more, valuable than their physical counterparts. This transition from tangible to intangible assets marks a significant shift in the global economy, reflecting changes in how we work, live, and interact with the world around us. The value is increasingly found not in physical objects but in the data and digital experiences they enable.
Bitcoin, since its inception in 2009, has epitomized this shift. Created as a decentralized digital currency, it offers a new form of wealth that is secure, transferable, and free from the control of any government or institution. Its blockchain technology ensures transparency and immutability, making it a trustworthy digital asset. This revolutionary approach to currency and wealth has not only challenged traditional financial systems but also redefined what constitutes value in the 21st century. Bitcoin represents a paradigm shift, moving us away from centralized financial systems and towards a more democratized form of wealth.
Bitcoin: The Digital Pearls of the 21st Century
Just as pearls were once a symbol of wealth and status, Bitcoin has emerged as a modern equivalent in the digital realm. The comparison extends beyond mere value; it reflects a shift in what society considers precious. Pearls, formed in the depths of the ocean, were valued for their rarity and beauty. Similarly, Bitcoin, 'mined' through complex computational processes, holds value due to its finite supply and the energy invested in its creation. This digital creation process, known as mining, parallels the natural formation of pearls, adding a layer of intrigue and value to Bitcoin's narrative.
The story of Maisie Plant and her pearl necklace, traded for a New York mansion, illustrates the fluid nature of value. Just as the perceived worth of pearls has fluctuated over time, Bitcoin's value is also subject to change. However, its digital nature and global accessibility mark a departure from traditional assets, offering a new form of wealth that transcends physical boundaries. This story not only highlights the changing nature of value but also serves as a reminder of the subjective and evolving nature of what society deems valuable.
Redefining Wealth and Investment
Bitcoin's rise challenges conventional investment wisdom. Traditional portfolios, heavy on stocks, bonds, and real estate, are being reevaluated as investors seek to diversify with digital assets. Bitcoin's volatility, while often cited as a risk, also presents opportunities for significant returns, drawing parallels with early investments in tech giants like Amazon and Google. This shift towards digital assets represents a broader change in investment strategies, reflecting a new era of wealth where digital assets play a central role.
Moreover, Bitcoin's decentralized nature offers a hedge against inflation and economic instability. In countries facing currency devaluation or financial crisis, it has become a means of preserving wealth, akin to how gold has been used historically. This aspect of Bitcoin highlights its potential not just as an investment but as a tool for economic empowerment and stability. The ability to store and transfer wealth independently of traditional financial systems is a powerful feature, particularly in regions where those systems are unreliable or inaccessible.
The Future of Digital Wealth
As we move further into the digital age, the definition of wealth continues to evolve. Bitcoin, and the broader category of cryptocurrencies, are at the forefront of this shift. They challenge individuals and institutions to rethink what constitutes an asset and how value is assigned and preserved. This evolution is not without its challenges and controversies, but it also offers unprecedented opportunities for innovation and growth.
The integration of Bitcoin into mainstream finance, through ETFs, futures, and other investment vehicles, signifies a growing acceptance of digital currencies as a legitimate form of wealth. However, as with all investments, there are risks and uncertainties. The regulatory landscape, technological advancements, and market dynamics will all play a role in shaping the future of Bitcoin and digital wealth. This future is not just about Bitcoin itself but about the broader implications of a world where digital assets are as common and valued as traditional ones.
Conclusion
Bitcoin's comparison to "digital pearls" offers a compelling framework for understanding its place in the modern economy. Just as the value of pearls once reflected societal trends and desires, so too does Bitcoin capture the zeitgeist of the digital age—a symbol of a new era of wealth that is decentralized, digital, and diverse. As we navigate this new landscape, the story of Bitcoin is far from over; it continues to challenge, redefine, and inspire the future of finance. The journey of Bitcoin from an obscure digital currency to a new form of digital wealth mirrors the broader transformation of the economy and society in the digital age.
FAQs
Why is Bitcoin compared to gold or pearls? Bitcoin is often compared to gold because it shares characteristics such as scarcity, durability, and being a store of value. The comparison to pearls, however, emphasizes its unique, evolving status as a coveted asset, reflecting shifts in societal values and the concept of wealth.
How does Bitcoin work? Bitcoin transactions are verified by network participants (miners) and recorded in blocks on the blockchain. Users can send and receive bitcoins using digital wallets. The supply of Bitcoin is capped at 21 million, ensuring its scarcity.
Is Bitcoin a good investment? Bitcoin's value can be highly volatile, making it a risky investment. However, some view it as a hedge against inflation and a potential part of a diversified investment portfolio. As with any investment, it's important to do thorough research and consider your financial situation and risk tolerance.
Can Bitcoin be converted into real money? Yes, Bitcoin can be exchanged for traditional currencies through online exchanges, peer-to-peer platforms, and some retail locations. The exchange rate varies based on market conditions.
Is Bitcoin legal? The legality of Bitcoin varies by country. Some countries have embraced it, while others have imposed restrictions or outright bans. It's important to check the regulations in your specific location.
What is the future of Bitcoin? The future of Bitcoin is uncertain and subject to various factors, including technological developments, regulatory changes, and market dynamics. It continues to gain acceptance and has sparked a global conversation about the nature of money and the future of financial systems.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 43bb87e2:12cc9cb8
2025-03-21 15:06:52
@ 43bb87e2:12cc9cb8
2025-03-21 15:06:52There was once a little girl that got into some expensive golden wrapping paper, and her father got upset. In his anger, he yelled at his little daughter for wrecking the expensive wrapping paper. The daughter then decided to use the ripped and wrecked wrapping paper to wrap a gift for someone. Again, the father let his anger take over and got mad at the little girl for using the ripped paper for the gift wrapping. The next morning, the little girl presented the tattered, golden wrapped box to her father and said this is for you, Dad. He opened the wrapped box and saw that the box was empty inside. The dad again got angry and told his daughter that when you give a gift to someone, there is supposed to be something inside of it. The little girl, in tears, looked up at her father and said, but it is full daddy. I blew kisses into it until it was completely full. The father then broke down and started crying. He dropped to his knees and put his arms around his precious and innocent daughter. He desperately apologized to her for his anger and continued to ask for her forgiveness. A short while after this, his daughter was taken from this earth because of an accident. The father kept the golden wrapped box next to him for the rest of his life to remind him of the love he had from his daughter.
Nothing else matters in this world or even comes close to the unconditional love that our children and family have for us.
With life being so busy, don’t you dare forget, what really matters in this world. And you be sure to take care of your loved ones, family, and friends.
For we do not know when the last day we will be on this earth.
CHERISH EVERY MOMENT AND LOVE WITH ALL YOUR HEART!
DO NOT LET ANGER RULE OVER YOU.
TELL EVERYONE IN YOUR LIFE,
THAT YOU LOVE THEM!
TELL THEM TODAY!
DO IT NOW!
LOVE YOU ALL, BE BLESSED!
-
 @ 16f1a010:31b1074b
2025-02-19 20:57:59
@ 16f1a010:31b1074b
2025-02-19 20:57:59In the rapidly evolving world of Bitcoin, running a Bitcoin node has become more accessible than ever. Platforms like Umbrel, Start9, myNode, and Citadel offer user-friendly interfaces to simplify node management. However, for those serious about maintaining a robust and efficient Lightning node ⚡, relying solely on these platforms may not be the optimal choice.
Let’s delve into why embracing Bitcoin Core and mastering the command-line interface (CLI) can provide a more reliable, sovereign, and empowering experience.
Understanding Node Management Platforms
What Are Umbrel, Start9, myNode, and Citadel?
Umbrel, Start9, myNode, and Citadel are platforms designed to streamline the process of running a Bitcoin node. They offer graphical user interfaces (GUIs) that allow users to manage various applications, including Bitcoin Core and Lightning Network nodes, through a web-based dashboard 🖥️.
These platforms often utilize Docker containers 🐳 to encapsulate applications, providing a modular and isolated environment for each service.

The Appeal of Simplified Node Management
The primary allure of these platforms lies in their simplicity. With minimal command-line interaction, users can deploy a full Bitcoin and Lightning node, along with a suite of additional applications.
✅ Easy one-command installation
✅ Web-based GUI for management
✅ Automatic app updates (but with delays, as we’ll discuss)However, while this convenience is attractive, it comes at a cost.
The Hidden Complexities of Using Node Management Platforms
While the user-friendly nature of these platforms is advantageous, it can also introduce several challenges that may hinder advanced users or those seeking greater control over their nodes.
🚨 Dependency on Maintainers for Updates
One significant concern is the reliance on platform maintainers for updates. Since these platforms manage applications through Docker containers, users must wait for the maintainers to update the container images before they can access new features or security patches.
🔴 Delayed Bitcoin Core updates = potential security risks
🔴 Lightning Network updates are not immediate
🔴 Bugs and vulnerabilities may persist longerInstead of waiting on a third party, why not update Bitcoin Core & LND yourself instantly?
⚙️ Challenges in Customization and Advanced Operations
For users aiming to perform advanced operations, such as:
- Custom backups 📂
- Running specific CLI commands 🖥️
- Optimizing node settings ⚡
…the abstraction layers introduced by these platforms become obstacles.
Navigating through nested directories and issuing commands inside Docker containers makes troubleshooting a nightmare. Instead of a simple
bitcoin-clicommand, you must figure out how to execute it inside the container, adding unnecessary complexity.Increased Backend Complexity
To achieve frontend simplicity, these platforms make the backend more complex.
🚫 Extra layers of abstraction
🚫 Hidden logs and settings
🚫 Harder troubleshootingThe use of multiple Docker containers, custom scripts, and unique file structures can make system maintenance and debugging a pain.
This complication defeats the purpose of “making running a node easy.”
✅ Advantages of Using Bitcoin Core and Command-Line Interface (CLI)
By installing Bitcoin Core directly and using the command-line interface (CLI), you gain several key advantages that make managing a Bitcoin and Lightning node more efficient and empowering.
Direct Control and Immediate Updates
One of the biggest downsides of package manager-based platforms is the reliance on third-party maintainers to release updates. Since Bitcoin Core, Lightning implementations (such as LND, Core Lightning, or Eclair), and other related software evolve rapidly, waiting for platform-specific updates can leave you running outdated or vulnerable versions.
By installing Bitcoin Core directly, you remove this dependency. You can update immediately when new versions are released, ensuring your node benefits from the latest features, security patches, and bug fixes. The same applies to Lightning software—being able to install and update it yourself gives you full autonomy over your node’s performance and security.
🛠 Simplified System Architecture
Platforms like Umbrel and myNode introduce extra complexity by running Bitcoin Core and Lightning inside Docker containers. This means:
- The actual files and configurations are stored inside Docker’s filesystem, making it harder to locate and manage them manually.
- If something breaks, troubleshooting is more difficult due to the added layer of abstraction.
- Running commands requires jumping through Docker shell sessions, adding unnecessary friction to what should be a straightforward process.
Instead, a direct installation of Bitcoin Core, Lightning, and Electrum Server (if needed) results in a cleaner, more understandable system. The software runs natively on your machine, without containerized layers making things more convoluted.
Additionally, setting up your own systemd service files for Bitcoin and Lightning is not as complicated as it seems. Once configured, these services will run automatically on boot, offering the same level of convenience as platforms like Umbrel but without the unnecessary complexity.
Better Lightning Node Management
If you’re running a Lightning Network node, using CLI-based tools provides far more flexibility than relying on a GUI like the ones bundled with node management platforms.
🟢 Custom Backup Strategies – Running Lightning through a GUI-based node manager often means backups are handled in a way that is opaque to the user. With CLI tools, you can easily script automatic backups of your channels, wallets, and configurations.
🟢 Advanced Configuration – Platforms like Umbrel force certain configurations by default, limiting how you can customize your Lightning node. With a direct install, you have full control over: * Channel fees 💰 * Routing policies 📡 * Liquidity management 🔄
🟢 Direct Access to LND, Core Lightning, or Eclair – Instead of issuing commands through a GUI (which is often limited in functionality), you can use: *
lncli(for LND) *lightning-cli(for Core Lightning) …to interact with your node at a deeper level.Enhanced Learning and Engagement
A crucial aspect of running a Bitcoin and Lightning node is understanding how it works.
Using an abstraction layer like Umbrel may get a node running in a few clicks, but it does little to teach users how Bitcoin actually functions.
By setting up Bitcoin Core, Lightning, and related software manually, you will:
✅ Gain practical knowledge of Bitcoin nodes, networking, and system performance.
✅ Learn how to configure and manage RPC commands.
✅ Become less reliant on third-party developers and more confident in troubleshooting.🎯 Running a Bitcoin node is about sovereignty – learn how to control it yourself.
Become more sovereign TODAY
Many guides make this process straightforward K3tan has a fantastic guide on running Bitcoin Core, Electrs, LND and more.
- Ministry of Nodes Guide 2024
- You can find him on nostr
nostr:npub1txwy7guqkrq6ngvtwft7zp70nekcknudagrvrryy2wxnz8ljk2xqz0yt4xEven with the best of guides, if you are running this software,
📖 READ THE DOCUMENTATIONThis is all just software at the end of the day. Most of it is very well documented. Take a moment to actually read through the documentation for yourself when installing. The documentation has step by step guides on setting up the software. Here is a helpful list: * Bitcoin.org Bitcoin Core Linux install instructions * Bitcoin Core Code Repository * Electrs Installation * LND Documentation * LND Code Repository * CLN Documentation * CLN Code Repository
If you have any more resources or links I should add, please comment them . I want to add as much to this article as I can.
-
 @ cc601241:181cd0d2
2025-03-21 15:11:09
@ cc601241:181cd0d2
2025-03-21 15:11:09
- Money doesn't grow on trees
- There is no such thing as a free lunch
- Energy cannot be created or destroyed
What if I told you these are three different ways of saying the exact same thing?
If you recognize that money is a unit of account, a medium of exchange, and a store of value, then it's only natural to accept that money at its most abstract formulation is simply information:
"Money is information. It is information we collect about the cost of things. We use it to quantify the world around us. To allow us to figure out what our things are worth in relation to other things. The soundness of a money measures its reliability in storing value over time. Sound money is reliable; you can count on it having a certain value today and in the future. Sound money allows us to determine the proper price of goods and services. Unsound money makes it difficult to figure out what anything should cost. Sound money accurately stores information about the cost of things. Sound money is a sensible store of information."
So long as fiat money can be printed ad infintum to bankroll the military industrial complex, why would we consider the US dollar to be accurate information? Why would we be surprised to see the negative externalities of dark money, regulatory capture, institutional usury, systemic seigniorage, and pervasive rent-seeking happening everywhere? Why wouldn't we start questioning the ripple effects of the Cantillon effect? Why wouldn't the rest of the world's economic actors that operate downstream of the dollar supply not live in constant fear, uncertainty, and doubt? If not resentment, cynicism, and desperation?
"Infinite money creates a scarcity mindset in almost everyone. Most people observe the rising cost of living and experience the feeling of fear or even panic. Fear of the unknown, fear of the future. Uncertainty about making ends meet. Leaky money promotes hoarding, individualism, and fast food culture, where everything is built as quickly and cheaply as possible."
If money is no longer a reliable measure of value but simply a means of control and extraction, how can humanity collaborate or organize or build together? How can we incentivize cooperation? How can we coincide our wants? How can we hope at all?
"Money is a medium of communication. It is one of the most common ways we communicate. Money is a sense-making apparatus. In the broken money world, a subtle distortion becomes ingrained in the foundational layer of sense-making, leading to a systemic corruption of all communication within the system."
Enter a pseudonymous, Good Samaritan, white hat coder: Satoshi Nakamoto.
A cypherpunk who asked a very simple question...

What if there was a money that was not backed by the Federal Reserve or 11 aircraft carriers and 5,000 nuclear warheads and the monopoly of violence? What if that money was backed not by physical scarcity (gold) or political scarcity (fiat) but by mathematical scarcity (blockchain aka timechain)? What if that money operated on principles like "rules without rulers" and "don't trust, verify?" What if we finally had an Occam's razor for economics?

What if that money were backed by the currency of the universe itself: energy?
"Bitcoin's immaculate conception presents the possibility that it has always existed. The genesis block could be viewed merely as the first time we started recording Bitcoin. Knut Svanholm has discussed the idea that Bitcoin might be an element with an atomic weight of zero and that the discovery of Bitcoin is better described as the discovery of our ability to observe this element.
For an element to have an atomic weight of zero, it must be void of protons or neutrons, possessing only electrons. Element zero is purely information. If element zero had always existed prior to our ability to measure it, that means it would have existed back to the time of Lao Tzu. If true, it means there could be undiscovered methods for gauging that information. The understanding of how to observe element zero might not be a binary event.
The interesting thing about observing element zero is that the process requires energy. Producing element zero requires a predictable amount of energy. Interacting with element zero requires energy. By spending Bitcoin, we capture a measurement of the value of the thing we spent it on, priced in energy; because element zero requires energy to produce, we can almost think of pricing other things in Bitcoin as pricing the energy spent in creating them. Element zero transfers energy."
All economy is just the transformation of energy into value. If one accept this definition of economics, then Bitcoin is the purest conversation of energy into value. This would explain why the world is seeing an emergent first principle emerge known as the Joule Paradox:
"Energy sets the value of bitcoin and bitcoin sets the value of energy."

Therefore, Bitcoin is the only money that obeys the laws of thermodynamics.
If we have a transparent public ledger of information backed by energy, we could safely call this document the most objective database in the entire world because energy is the only thing in the entire universe that no one can fake.
That's the power of triple entry bookkeeping. No one can cook the books anymore.

Once humanity is able to guarantee the separation of Money and State, suddenly everyone has a way to protect their own time and energy without having to trust a third party. We are no longer slaves to "absolute power corrupts absolutely". We are no longer beholden to the powers that be. Humanity finally has an incorruptible, immutable, unconfiscatable, permissionless, borderless, open source money available to all.
In a world of manipulated markets, self-sovereignty starts with sound money.
Believe it or not, the thesis of The Dao of Bitcoin: Towards a Cosmology of Energy Money (by Scott Dedels—which I have been quoting throughout this article) states that Bitcoin is "perfect money" (or "daomoney" as he coins it) for the following reason:
Bitcoin = time = money = energy = Bitcoin
There is nothing more valuable than protecting your time & energy. But no one can force you to believe that. Self-sovereignty is a game of consent. The first act of financial freedom is to choose it. The deeper into the Bitcoin rabbithole you go, the sooner you'll have the unmistakable epiphany:
Bitcoin is a strange game where the only winning move is to play.
Bitcoin is just money without the Bullshit. No CEO, no country, no committee, no corporation, no cartel, no council, no conglomerate, no counter-party, no church, no cult of personality. Just pure P2P energy transfer. That's the beauty of freedom money. That's the reason for energy money. That's the answer to the game theory.
With absolute mathematical scarcity, individuals can finally afford an abundance mindset.
For the sovereign individual, all you have to do is nothing but HODL.
That's financial wu wei.
That's energy money that aligns with the universe & vibes with the Dao.

-
 @ da0b9bc3:4e30a4a9
2025-03-21 13:58:11
@ da0b9bc3:4e30a4a9
2025-03-21 13:58:11It's Finally here Stackers!
It's Friday!
We're about to kick off our weekends with some feel good tracks.
Let's get the party started. Bring me those Feel Good tracks.
Let's get it!
This song never doesn't put me in a good mood.
https://youtu.be/fnwZeLdLPdQ?si=ZlbiGSp2r6DtMx6P
originally posted at https://stacker.news/items/920041
-
 @ 46fcbe30:6bd8ce4d
2025-03-21 13:57:11
@ 46fcbe30:6bd8ce4d
2025-03-21 13:57:11Table of Contents
- Introduction
- Overview of the Nostr Ecosystem
- Current Use Cases and Quantitative Metrics
- User Adoption Metrics
- Network Resilience and Decentralization
- Operational Challenges and Scalability
- Replication Overhead and Bandwidth Issues
- Relay Downtime and Financial Sustainability
- Market Disruption and Sentiment
- Disrupting Twitter and Centralized Social Platforms
- Impact on Decentralized Social Media and Censorship Resistance
- Future Trends and 5-Year Outlook
- Innovative Protocol Developments
- Quantitative Forecasting and Diffusion Modeling
- Networking and Integration with Emerging Technologies
- Conclusions and Strategic Recommendations
1. Introduction
The Nostr ecosystem has emerged as a powerful decentralized alternative to traditional social media networks, particularly as a potential disruptor of Twitter and other centralized—and even existing decentralized—social media platforms. Developed using a protocol based on cryptographic key pairs and a multi-relay system, Nostr is unique in its provision of censorship resistance and user sovereignty. In this report, we provide a detailed analysis of the current state, scalability challenges, and market disruption potential of Nostr, followed by speculative insights on its trajectory over the next five years.
2. Overview of the Nostr Ecosystem
Launched in 2022, Nostr (Notes and Other Stuff Transmitted by Relays) has rapidly gained traction as an open and decentralized social network. Some of the core features include:
- Decentralized Communication: Relying on independent relays across multiple countries and autonomous systems, Nostr offers an architecture that ensures posts are not stored on a single centralized server.
- Censorship Resistance: With cryptographic authentication and a decentralized relay structure, content censorship becomes significantly more difficult than in traditional networks.
- User Sovereignty: Empowering users with cryptographic key pairs allows for enhanced privacy and data ownership.
- Wide Geographic Distribution: The ecosystem spreads over 44 countries and 151 autonomous systems, underscoring its global reach.
Notable endorsements from figures such as Jack Dorsey, Edward Snowden, Vitalik Buterin, and Sen. Cynthia Lummis have bolstered its reputation as an experimental yet promising alternative to centralized social platforms.
3. Current Use Cases and Quantitative Metrics
User Adoption Metrics
- User Base: In just two years, the Nostr network has attracted over 4 million users, a significant figure given its nascent stage and decentralized nature.
- Content Generation: With over 60 million posts, the volume of content mirrors the rapid adoption and active usage seen in more centralized models.
- Post Replication: Empirical measurements indicate that there are 17.8 million text notes among these posts, replicated on an average of 34.6 relays per post. This level of replication underlines robust resilience and availability even if significant portions of the network experience downtime.
Network Resilience and Decentralization
- Global Distribution: Nostr’s decentralized network ensures high availability with >90% post accessibility even under simulated network failures (e.g., removal of key relays or autonomous systems).
- Robustness: The dispersion across 712 relays illustrates that decentralization is not only a design choice but also a working reality, which contributes to the network’s reliability.
4. Operational Challenges and Scalability
While the Nostr ecosystem demonstrates significant promise, it faces noteworthy operational challenges.
Replication Overhead and Bandwidth Issues
- Excessive Redundancy: Detailed studies have shown that nearly 98.2% of retrieval traffic is redundant. In practice, this equates to an estimated 144 TiB of unnecessary bandwidth consumption.
- Optimization Proposals: To mitigate these inefficiencies, there's a proposal to limit post replications from 34.6 relays to between 10 and 20 relays per post. This could reduce redundant data copies by between 380 million to 480 million instances, potentially lowering operational costs and improving bandwidth utilization.
- Scaling Concerns: With a projected network load of 10 million events per day (or approximately 2 TB annually), the throughput requirement of ~115 TPS is putting a strain on the current architecture. This has led to debates on whether solutions like the current outbox mechanism are sufficient or if further fundamental redesigns and emergent moderation systems are needed.
Relay Downtime and Financial Sustainability
- Relay Stability: Data indicates roughly 20% of relays suffer from significant downtime (exceeding 40% operational time), and 132 relays have been classified as 'dead'. This is a concern for maintaining network integrity.
- Economic Model Challenges: With 95% of free-to-use relays unable to cover operational costs due to minimal zap-based income, there is an urgent need for innovative monetization or community funding models to ensure long-term sustainability.
5. Market Disruption and Sentiment
Nostr is positioned as both a disruptor to traditional centralized social platforms—most notably Twitter—and a catalyst for change within decentralized social media.
Disrupting Twitter and Centralized Platforms
- User Shift: While Twitter remains the most well-known platform, the high-profile endorsements and robust user base of Nostr indicate that there is both market intrigue and a gradual shift among early adopters. Disruption here is measured not only in user numbers but also in the paradigm shift towards decentralized content distribution.
- Market Penetration: Current metrics (4 million users, 60 million posts) suggest that Nostr is challenging Twitter's centralized model insofar as it appeals to users prioritizing censorship resistance, data sovereignty, and resiliency against centralized failures. However, mainstream adoption on par with Twitter is still not realized, and there remains a gap in user experience and feature richness.
Impact on Decentralized Social Media and Censorship Resistance
- Complementary Integrations: As decentralized social media ecosystems continue to mature, integration between Nostr and other censorship-resistant platforms is increasingly likely. This can include interoperability protocols, shared identity management systems, and cross-platform content replication.
- Comparative Advantage: Nostr's network design offers unique advantages over other decentralized social media, particularly in its straightforward, relay-based communication protocol. This positions Nostr to potentially serve as an underpinning technology for a broader decoherent ecosystem of social networks.
- Sentiment Toward Scalability Innovations: Discussions around scaling Nostr often focus on the balance between ensuring redundancy (for resilience) and reducing overhead (for efficiency). The sentiment is one of cautious optimism: while outbox solutions offer a stopgap, many experts advocate for more fundamental architectural redesigns in the long-term.
6. Future Trends and 5-Year Outlook
Looking forward, the evolution of Nostr will likely be shaped by several interrelated trends and emerging technical innovations.
Innovative Protocol Developments
- Decentralized Identity and Reputation Mechanisms: The next phase may see the introduction of distributed reputation systems and rating mechanisms that aid in spam management and improve trustworthiness without compromising decentralization.
- Optimistic Replication and Selective Mirroring: Innovations such as selective content mirroring and event pruning will be key in managing bandwidth and storage demands while remaining true to the decentralized philosophy.
Quantitative Forecasting and Diffusion Modeling
- Forecast Models: By integrating modified Bass diffusion models and learning curve effects, predictions suggest that Nostr can potentially spur significant market disruption within five years. Recent studies indicate that forecasting models in disruptive technology fields have reached accuracies of up to 82% for demand projections.
- Hybrid Quantitative Techniques: Leveraging methods like LDA2Vec and patent citation network analysis, combined with multi-criteria decision-making models (as seen in extended UTAUT approaches), will be crucial for accurately estimating future adoption and cost efficiencies.
- Metrics to Monitor: Future research should focus on user growth rates, relay uptime percentages, cost reductions achieved through replication optimizations, and overall sentiment analysis using advanced deep learning architectures that overcome traditional pitfalls (e.g., sarcasm and multipolarity in text data).
Networking and Integration with Emerging Technologies
- Integration with Other Decentralized Platforms: One promising avenue is exploring cross-platform interoperability with other decentralized and blockchain-based social networks, which could lead to a more cohesive ecosystem. This would not only enhance user experience but also enable shared security and moderation frameworks.
- Next-Generation Relays: The deployment of relays that are more resilient through redundancy optimization and financial sustainability models (perhaps incorporating micro-transaction revenue models or community-driven funding) is another critical area. Such improvements could mitigate the issues of relay downtime and excessive network overhead.
- Contrarian Approaches: A contrarian perspective suggests that instead of building on current frameworks, a radical overhaul of the network architecture might be considered, potentially by leveraging novel distributed ledger technologies or leveraging a hybrid centralized-decentralized model during the transition phase to ensure smoother scaling.
7. Conclusions and Strategic Recommendations
The Nostr ecosystem represents a significant stride toward decentralized, censorship-resistant social media. While its current market adoption and technical design offer a robust alternative to centralized platforms like Twitter, several challenges must be addressed for sustained growth and disruption:
-
Optimization of Data Replication: Reducing redundant data transfers without compromising resilience is essential. Limiting the replication factor and exploring optimistic retrieval mechanisms could provide a balance between availability and efficiency.
-
Relay Stability and Sustainability: With nearly 20% of relays experiencing significant downtime, innovative financial and technical models (such as micro-payments and community funding) should be deployed to enhance the operational reliability of network nodes.
-
Enhanced Moderation and Reputation Systems: Emerging strategies for decentralized content moderation and reputation management could reduce spam and improve content quality while preserving the open nature of the network.
-
Interoperability with Other Decentralized Platforms: Fostering integration with other emerging systems could accelerate market disruption across the broader spectrum of social media.
-
Future-Proofing Through Quantitative Forecasting: Continual adoption of cutting-edge forecasting models and machine learning techniques to measure sentiment and track network metrics is imperative for proactive evolution.
-
Exploring Contrarian Innovations: In addition to incremental changes, it is important not to discount radically new architectures that may emerge from ongoing research in distributed systems and blockchain technologies.
Final Outlook
In the coming five years, Nostr has the potential to disrupt not only Twitter but also the broader landscape of both centralized and decentralized social media. Although the current architecture presents significant scaling challenges, proactive investments in replication optimization, relay stability, and cross-platform integration will likely propel the network into a more mature phase of adoption. The ecosystem will benefit from a dual approach that combines both evolutionary improvements and revolutionary changes, ensuring that it remains robust while meeting the demands of a growing, globally distributed user base.
Appendices
Appendix A: Data and Metrics Summary
- User Base: ~4 million
- Post Volume: >60 million posts
- Average Relay Replication: ~34.6 replicas per post
- Geographical Distribution: 44 countries, 151 autonomous systems
- Bandwidth Waste: ~144 TiB due to redundancy
- Network Load: 10 million events/day (~2TB/year)
- Throughput Requirement: ~115 TPS
Appendix B: Key Technical Proposals
- Replication Control: Limit copies to 10–20 relays for optimal efficiency.
- Selective Mirroring: Implement event pruning and selective content mirroring.
- Decentralized Reputation Systems: Develop distributed rating mechanisms to enhance distributed moderation.
Appendix C: Forecasting and Quantitative Methods
- Diffusion Modeling: Modified Bass models with multi-market dynamics.
- Hybrid Quantitative Techniques: Integration of machine learning (CNN-LSTM, LDA2Vec) with multi‐criteria decision models.
Recommendations for Further Research
- Investigate the comparative performance of alternative replication strategies in decentralized networks.
- Explore funding models that can sustain relay operations without compromising neutrality or decentralization.
- Conduct long-term sentiment analysis using advanced neural architectures to understand evolving user attitudes.
- Evaluate the prospective benefits of radical design overhauls versus incremental enhancements in ensuring network scalability.
This report is intended for expert analysts and researchers in decentralized network systems and social media disruption. It synthesizes current empirical findings with speculative insights to inform future strategies and academic inquiry.
Sources
- https://www.voltage.cloud/blog/exploring-6-use-cases-of-nostr-beyond-messaging
- https://arxiv.org/abs/2402.05709
- https://arxiv.org/html/2402.05709v1
- https://papers.ssrn.com/sol3/Delivery.cfm/5146515.pdf?abstractid=5146515&mirid=1
- https://matchnode.com/blog-and-podcasts/mastering-paid-social-media-advertising-a-comprehensive-guide/
- https://blockworks.co/news/jack-dorsey-app-to-disrupt-twitter
- https://www.securities.io/nostr-a-better-twitter/
- https://medium.com/@jasminedevv/battle-of-the-decentralized-twitter-alternatives-c9f51114614a
- https://www.murrayrudd.pro/nostrs-relay-revolution-scaling-decentralized-networks-for-growth/
- https://github.com/nostr-protocol/nips/issues/75
- https://news.ycombinator.com/item?id=42758579
- https://www.toptal.com/deep-learning/4-sentiment-analysis-accuracy-traps
- https://www.researchgate.net/publication/3076742_Forecasting_the_Market_Diffusion_of_Disruptive_and_Discontinuous_Innovation
- https://www.globenewswire.com/news-release/2025/03/17/3043701/0/en/United-States-Online-Household-Furniture-Market-Report-2025-2029-Analysis-of-Price-Sensitivity-Lifecycle-Customer-Purchase-Basket-Adoption-Rates-and-Purchase-Criteria.html
- https://northeast.newschannelnebraska.com/story/52583550/laser-welding-market-growth-industrial-adoption-rate
- https://www.sciencedirect.com/science/article/am/pii/S2405896323014453
- https://www.marketsandmarkets.com/Market-Reports/industry-5-market-35376359.html
-
 @ f288a224:1da1792c
2025-02-19 16:43:40
@ f288a224:1da1792c
2025-02-19 16:43:40First, some context.
I'm a child of the original internet chat-rooms on IRC, and I've tried over the last decades different applications and websites that we could all agree are "social media", but until I found NOSTR (Notes and Other Stuff Transmitted by Relays) I hadn't had this certainty that this isn't something that I will eventually change for something else.
Today, even with all its early stage issues, I have the certainty that NOSTR may be the ULTIMATE and FINAL HOME for my online life.
THE PROBLEMS with the current/old social media landscape

I'm tired of moving from one social media to the next.
As many of you, in my digital lifetime I've had many accounts that have now become obsolete; and the "content" and followings I created during that time was lost when one tech giant lost over the other, forcing us all to "MOVE" ourselves over to the new, and start building our content and following from scratch.
Lately, it's become even worse, where many of us have seen ourselves forced to use and feed more than one social media at a time, since they all serve various purposes, with sometimes diverse functionality, besides all being catered to different segments of people to connect you to (LinkedIn, Instagram, TikTok, Youtube...). How much is too much, though? And how much time should we keep spending re-adapting our content to reach all of our network?
For work, I've found myself having to create accounts in several of these giant data hoarding companies, having to build each following from scratch and to create "content" for all, and having to go through the hurdle of posting everything, everywhere, all at once.
I'm sick of ever-changing terms, conditions and capabilities.
Let's be honest, the majority of us have never ever read the full terms and conditions, let alone every time they are updated without us knowing which rights to our data we are giving away, and which terms we are accepting that may be detrimental to us and our mental health.
We've learnt to accept that we are in their playground, they make up the rules, and if they choose to change the rules mid-game we just need to swallow it. We literally have no other choice, it's either that or desertion, which basically means walking away from everything we've built on their "public square". So, like a carefully engineered detrimental incentive structure, the more time we spend building on their turf, the more we are tied to them and conditioned to never leave them. The more we build and make them grow on our content, the more we'll lose if or when we drop out.
And even if you accept all that and choose to play along, and you do your best to create the most awesome account in the neighborhood, the random changes they make to optimize ad revenue or user attention will inevitably affect you and all your work.
If you created all your feed according to Instagram's squares but they choose to change to TikTok style dimensions due to their tech positioning battle with the Chinese giant... You swallow. If you edited your reels according to what you felt was the best 100 seconds video... Not anymore, suddenly 90 seconds is the maximum you're allowed... No appeal, no options. You Swallow. What? Seeing less of the people you actually WANT TO FOLLOW because they decided to clutter your feed with ads and suggestions, guess again: YOU SWALLOW.
AREN'T YOU FEELING FULL ENOUGH OF ALL THE SHIT THEY'VE FORCED DOWN YOUR THROAT?
Living our digital lives on these platforms feels like standing on ever changing quicksand, never endingly trying to "hack the algorithm" in order to have our content placed in front of the people who should automatically be able to see us from the moment they chose to follow us; and the worst part of it is, you never know when you may lose it all.
Let's not forget, your social media account is NOT REALLY YOURS.
Recently, a friend's social media account was hacked. She didn't know how it happened; all she knew is that she got an email from Meta saying she had acted against community guidelines and her accounts were therefore being removed (the one hacked and all those liked to her email, which meant personal and work accounts). She tried to appeal, to no avail. She hadn't done anything wrong, but suddenly her identity had disappeared from all our feeds, and her content didn't exist anywhere anymore. She lost plenty of photos she had always counted on finding on her Instagram and lost the people she followed and who followed her. It was as if she had never existed on the platform.
(Looks like a good moment to remind you to download all your valued content from the platforms you use in case something like this happens to you)
 And this happened to someone who hadn't done anything "to deserve it". It has actually happened to more than one person I know, and every time they've been helpless and had no recourse, and yet, found themselves having to rebuild from scratch on the same platform that de-platformed them, because they had "no other option", and "their friends are there".
And this happened to someone who hadn't done anything "to deserve it". It has actually happened to more than one person I know, and every time they've been helpless and had no recourse, and yet, found themselves having to rebuild from scratch on the same platform that de-platformed them, because they had "no other option", and "their friends are there".Many more people have encountered this awful wake up call, some because of a hack, like my friend, others found themselves removed because they posted content critical of the platform... there are so many reasons people have gotten de-platformed and posts have gotten deleted without warning. And every time, we accept it, as if we owe them something; as if we need to settle for this kind of abusive environment that gets rich on our content and attention without having a say in anything.
But we do have another option that flips that attention retention model completely on its head and empowers the user. That option is NOSTR, our exit from the extractive social media silos they have trapped us into.
NOSTR: The better social experience for the internet era.
NOSTR (Notes and Other Stuff Transmitted by Relays) is not a social media app, it's an Internet protocol. It's open source and many many developers around the world are creating apps on top of it and creating THE ULTIMATE SOCIAL MEDIA EXPERIENCE for users.
I first heard of NOSTR from Jack Dorsey on what used to be called Twitter, and when I joined it two years ago it was really rough around the edges, but it was FULL OF POTENTIAL and the value proposition was very clear to me from the beginning.
Firstly, YOU OWN YOUR IDENTITY, that includes your content and your follower list.
So, what does owning you identity mean? I guess many of us have thought we owned our identity before, but the reality is that the platforms owned our identities, which is why they could delete or censor us.
Owning your identity on NOSTR is empowered by encryption and cryptography. I'm not going to go into the technical part, but to explain as simply as I can, on NOSTR no platform owns your login and password to use on their playground; you can basically use any NOSTR app to create your identity to navigate it. They give you a login (npub) and password (nsec), and the magic part is that you can USE THAT IDENTITY ON ANY NOSTR APP OR WEBSITE, no need to sign up individually on each one.
Welcome to the beauty of INTEROPERABILITY.
I cannot emphasize enough what it feels like to be able to take your identity, your followers, your content and carry it from one app to the other.
On NOSTR there is a rich ecosystem of apps and websites that keep growing. We have "clients" that allow you to experience NOSTR in interfaces that could remind you of Twitter, Instagram, TikTok, Substack, Twitch, Clubhouse, Podcast apps and many more. You can find many of them on https://nostrapps.com/ .
With that information in mind, imagine you only needed one user password, your NOSTR nsec, and with that key, you could open you Instagram, or your Twitch or your Substack. And all your followers would be there, and you could choose what type of content you wanted to link to your identity for your followers to find. No longer "find link in bio", or "go to our YouTube channel", everything you post on NOSTR is tied to your identity, and you can post it all with a single set of keys that posts your content "everywhere".
And since your content is "in every client", each of YOUR FOLLOWERS CAN CHOOSE if they are more interested in experiencing your photography content "Insta-like" or if they love your "Twitter-esque" notes better. Each user navigates NOSTR with the interface they prefer.
(With great power comes great responsibility, and I feel obligated to tell you that if you ever lose your nsec, no platform is gonna be able to save you. It's like the keys to your house, unless you keep a copy safely, no one can open it for you (there are no locksmiths on NOSTR). And if you leave your keys lying around on a cloud server somewhere, someone may grab your keys, open your house and use it however they want).
The beauty of this interoperability and the fact that my keys open up my identity to all the NOSTR realms is that you don't need to settle for one client. I use 5 to 6 clients regularly everyday depending on the mood I'm in, (or the bugs that still prove this is a nascent ecosystem in development). Some I use when I want a more "Twitter-like" experience, others when I want to browse photos and others just give different algorithms to choose how to view my feed, and the best part is NO ONE CAN CLUTTER MY FEED WITH ADS. I can curate my feed however is most important to me, and each "NOSTR client" is like a different skin that customizes the way I experience the content.
However, the most important reason I started to use different NOSTR apps was that when I started, not all apps had zapping integrated. Some still don't, but most do :)
ZAPS: direct micropayments from your followers.
Zaps are tips that come directly from the people who find value in the shit that you post. They are micropayments in the form of "sats", fractions of ever-increasing in value bitcoin , and a very big reason why I'm spending less and less time on other social media accumulating valueless likes that only feed the algorithm, and more time on NOSTR interacting with humans that post valuable notes hoping the generous souls that run upon their art or creations will find them valuable enough to tip them for it.
It's crazy how the type of content you post can change when your incentive is not to feed an algo, but to give real value to other humans around the world and be your most authentic self. Where Twitter/X's algo benefited the type of incendiary content that shocked and outraged people, NOSTR's incentives benefit those who bring most value to the network and their peers.
A few sats tip may not seem much, but even if the equivalent of a small zap is merely cents, it feels a whole lot better than any like, and you can count that if the purchasing power of bitcoin continues to accrue, those value-earned tips will too. Many "nostriches" are getting tons of zaps for memes on NOSTR, valuable articles, videos or participation in zapathons .
In NOSTR is where I first heard of the concept "value for value", and the community is very adamant in making "v4v" an alternative to ad revenue driven models. Because we need to be the change we wanna see in the world.
We've heard it said that if you're not paying for the product, you are the product. And up until now that has meant we felt obliged to accept that since ads were paying the platforms, we were required to give them our attention. But the open source movement thinks we deserve better. We deserve a better Internet, like the decentralized promise we've slowly been robbed of to enrich 10 people out of the work of all of us. If they can't monetize our attention, they got nothing.
But why should they monetize it, instead of us?
Even with the glitches and bugs, NOSTR ROCKS!
The things I've grown to love most about NOSTR are:
• Not having the clutter of ads on my feed and being able to ONLY SEE WHAT I CHOOSE TO SEE.
• People who are not on NOSTR can ENJOY MY STUFF WITHOUT HAVING TO LOGIN.
• Being able to ENJOY ALL THE BENEFITS OF INTEROPERABILITY, and use many NOSTR clients that enrich my user experience knowing I own my identity and that means I'm not locked in, I can move like a bird wherever I decide.
• ZAPPING complete strangers that made me laugh, gave me a cool insight or simply made a witty comment.
• GETTING TIPPED for memes, articles, photos, videos and any "Notes and Other Stuff" that people have found valuable.
CONCLUSION: Join us on NOSTR, participate in claiming back your digital life.
If you've made it this far in my love letter to NOSTR, thank you for being interested. Curious minds is what the world needs more of <3.
NOSTR is an ecosystem that is being built in the open by relentless developers that are continuously striving to out compete each other to offer a better user experience, it's a many headed dragon that has constant upgrades and implementations which benefits us all, and as such it sometimes comes with bugs and glitches.
Building the future is always buggy and requires testers and early adopters that help shape the technology in the best way possible, especially if you wanna build outside the incentive models of the devouring giants we're trying to get away from.
Being such an open ecosystem can also be overwhelming for a newcomer, where to start? There are so many clients to experience; so here are some of my recommendations.
Please, don't feel you need to go through all of them now, start step by step. This article will always be here whenever you need it (this is not Instagram ;) ).
Creating your NOSTR identity/account with a wallet integrated to receive zaps on both Android and iOS:
• YAKIHONNE: It's a Japanese client that offers a great on-boarding experience. From the app you can create the account and enable a wallet to receive zaps. In it you can view and post short and long form content, images, videos and more. (Once you have the account created on your app, you can also visit the desktop version on https://yakihonne.com/ )
• PRIMAL: For a while it has positioned itself as a great on-boarding NOSTR client because it offers the same things as Yakihonne, has an integrated wallet, with the added benefit that you can also "buy sats/bitcoin" directly from its wallet, which can come in handy (it comes with a 15-30% premium, so only use for small amounts). It also has the desktop version at primal.net.
My favorite NOSTR iOS PHONE APPS after on-boarding, in case you wanna hop into different user experiences:
• DAMUS: created by the original creator of the "ZAP", Will Casarin, it's an iOS simple client that is reliable and fast with notifications. It keeps things simple, mostly focusing on short note content, although you can also see images and short video. But the feed is optimized as a more "Twitter-like" feed.
• NOSTUR: The iOS phone client that has it all! It's the client I've used that integrates the most of NOSTR's possibilities, you can see all of the mentioned above with the previous clients, but also view LIVE STREAMS, and have multiple accounts set up simultaneously. The enhanced capabilities can sometimes come at the cost of crashing or being slow to load.
• FREERSE: Nice clean user interface with plenty of functionality, with easy navigation on topics like #art #photography or any other interests. It's my always reliable back-up to upload image content.
• OLAS: The new kid on the block Olas client, by prolific developer Pablof7z, is trying to take on Instagram and TikTok and has developed a client mainly focused on the visual and photographic part of NOSTR.
Desktop clients & OTHER GEMS OF THE NOSTR REALM:
There is an infinite number of clients for desktop, but I usually find myself on ditto.pub or slidestr.net for a more visual experience.
• ALBY is INTEROPERABILITY'S BEST FRIEND. Alby is not a NOSTR client, but it's a browser extension that makes it seamless to jump from one desktop client to another with your wallet and identity without compromising your security.
• HIVETALK: A video call client (reminiscent of Zoom) that doesn't track you or spy on you and that enables zapping and many other functionalities during the calls.
• NOSTR NESTS: Audio spaces client that allows people to listen to conversations, chat within it and zap the people involved.
if you made it this far, THANK YOU FOR YOUR ATTENTION.
HOPE YOU FOUND VALUE IN IT AND UNDERSTOOD WHY, FOR ME, THE FUTURE OF SOCIAL MEDIA IS BRIGHT, OPEN AND USER-CENTRIC.
FUCK THE MIDDLEMEN.
-
 @ 8671a6e5:f88194d1
2025-03-21 13:38:50
@ 8671a6e5:f88194d1
2025-03-21 13:38:50As old people tend to say:\ \ *nasal voice* “Back in my day…” … Bitcoin was this wild, beautiful thing, new. It was something technical that came alive before our very eyes after running a node (just a .exe running on a windows machine in my case).\ Even when you started to painstakingly mined bitcoin on a GPU, in a pool, you felt like growing a network of like minded people, or at least people who thought there was something there. Even if we couldn’t comprehend what it all would lead to (or what fiat value it could reach).\ Then came the first paper wallets, the first good software wallets and attempts at hardware wallets, the first buzz of owning your own value — it was motivating and rewarding. The look on the face of other people you explained bitcoin to, when they’ve seen their first transaction pop up after validation. Awesome.\ \ Back then, it wasn’t about fiat gains or slick marketing campaigns; it was about a distributed network “generating” numbers, keeping a distribute ledger “in synchronization”, at the same time it was a middle finger to the system, representing freedom to transact in value we valued ourselves because of the underlying network of people, nodes and miners.\ \ It was this sort of secret handshake between tech minded people, anti-globalists, anarchists, nerds and rebels who saw the fiat scam for what it was.\ Orange-pilling wasn’t even a term; it was just what you did.\ You'd walk people through the setup of bitcoin core, and the white paper, told them why central banks are a trick that functions as a legalized Ponzi scheme and you showed them bitcoin’s workings without middlemen.\ You played around with bitcoin, person to person, no bullshit, no subscriptions, no suits, no posing like a big shot, no referral links.\ Those were the fun times — pre-Saylor, pre-nation-state hype, pre-every Laura, Luigi, and self-proclaimed “OG” thinking they’re going to conquer the world.\ I miss that.
But times change.
\ The good ol' days are dead
It’s not the first instance in our lifetime that we see things pop-up, being invented, and where some good new idea becomes a reality and then that very good idea becomes an institution (there’s an obscure 1990s movie reference for you).\ We live and learn, just like the first technical people setting up their own point of presence internet servers, we all have to learn how to grow and adapt.
Early Bitcoiners didn’t have referral links or corporate sponsors — they had a mission, and the spirit came from within themselves and from the math and tech they’ve seen at work in practice. And yes, educating about it was important, as was looking for ways to improve bitcoin (the early years weren't exactly main-stream material for example).
From that learning yourself about Bitcoin and feeling the need to share and convince others around you, came the need to talk and learn together with others.
You’d talk your buddy into installing a wallet over a coffee, maybe show your uncle how to buy a few bitcoin, and it felt like planting seeds for something real.
Even if they didn’t get it—“So this number goes from my address to your address?”—you kept explaining and showing.
Then the suits rolled in. Bigger companies wer started, like Blockstream, Trezor, Coinbase and Binance.
Wall Street, Saylor with his infinite buy tweets, El Salvador and its volcano bonds, the US ETF approval — and the game changed, everyone heard about it one way or another. That’s damned important! You’re NOT the bringer of news.\ \ Suddenly, it wasn’t grassroots anymore; it was headlines, hype and game-theory. As predicted by so many in the space.\ Fine, whatever, it's progress or something else, but we as bitcoiners need to adapt to that reality.\ Some adaptations will also cause us to put energy elsewhere than before.\ What worked in 2012 or 2016, might not work anymore after 2024.\ ”We bitcoiners route around problems.” Right?
You didn’t need new people to create an account, or be part of a ‘squad’ or team, you certainly didn’t need them to sell merchandise. You just showed them bitcoin’s inner workings.\ \ Bitcoin was the marketing, the engine, the product and the goal. Bitcoin was the core. Just like digital communication was the core of the earliest internet enthusiasts. The magic of sending a text into the network, and through clever routing, someone thousands of miles away could read it almost immediately, that was the magic, the core.
Sending value with bitcoin has that same magical way, immutable, uncensored, unconfiscatable, with proven digital scarcity and forced honesty.
Nowadays we have so-called orange-pillers.\ They’re trying to spread those values. Or so they should..
They didn’t get the memo on Bitcoin becoming more commonly known apparently, and if they did, their lust for dopamine has long replaced that with their urge to get people to install a lightning wallet. It’s sometimes rather disturbing to see this Orange Pill’ing play out.
They’re out there, like they’re stuck in 2013. But they’re usually not from 2013 at all, more like class of 2020’ish. Not that it matters, they’re still living in the illusion that there are people out there that didn’t hear of bitcoin and that THEY and THEY alone can save these poor souls.\ After 2018 it’s safe to say that that’s not the case.\ I’ll repeat that for the die-hard orange-piller: they do not need you to hear about bitcoin.
These Orange Pillers have another kind of magic happen:
While they’re winning over new souls into bitcoin, one barber, taxi driver and babysitter at a time, they get the small electric charge in their brain that tells them their wealth, their (and their holding's) value will go up somehow. They’re also desperate to make some kind of connection with other bitcoiners, and while they lack that connection, they try to find (or make) new bitcoiners around them.\ This approach might have worked in the past, but things are different now. You’re usually talking to people who you try to convince of something they’ve already rejected (often harshly rejected) or never will care about .\ Most people, do not give a damn about inflation or how that came to be. Certainly when they’re doing their job.\ \ It’s like someone shoving the book of a cult under your nose and trying to convince you it’s going to save your life. You’re not open to it, neither are most of the Orange pill targets to your bitcoin gospel.\ Orange Pillers don’t see how the very people they try to convince today weren’t “in it” for a variety of (good for them) reasons. Unlike in the old days, where people’s natural state was “not heard of bitcoin”; since it was new, and people genuinely didn’t learn about it or read into it.\ That’s however, not the case today. That taxi driver? He heard about bitcoin. Be sure.
Such new people today, are almost non-existing, they either bought some long ago, got rekt trading shitcoins and stayed away.\ That, or they found it all a bit too “iffy” (thank you mainstream media) and will politely hold back from not yelling to your face, “I don’t care about that Bitcoin stuff!”.\ They know it’s some form of money or value, they know it exists. Which makes orange pillers the bringers of old news to the bottom of the barral.\ They might get a “hit” now and then of course. But even then, your impact is neglectable in a world that rewards cowardice and short term greed. You’re too late. You don’t scale. And it doesn’t matter.
Since 2020, it has shifted from genuinely introducing people to bitcoin to just "spreading it for the sake of spreading it."\ It looks more and more like an old lion, pacing back and forth in a cramped cage at an old ZOO, restless and frustrated.\ There’s just empty repetition.
The mental breakdown of orange-pilling
\ Let’s look a little further into the act of orange pilling.\ \ It's not like a 1990s hacker type showing a brand new Hayes -compatible modem to his buddy and trying to get a connection going to a local Point of Presence to get internet access.\ \ It’s more like showing your holiday pictures to an uninterested family member. All to get the dopamine hit, the ‘aha moment’ out of someone is now your own ‘aha got someone new’ moment. Like an addict looking for that next high.\ \ You want them to get the app, get some sats and feel the same feeling you have. While they’re worrying about cleaning a table for example, or getting your bill.\ \ This “badge of honor” of Orange Pilling someone is that little shot of dopamine many people need (especially in group) to feel validated.\ The real feeling has everything to do with social conformity1 and the involved brain areas that get stimulus shots and increased activity.2\ \ Above that, for the sake of the mental reward, some people go further down the social boundaries. That’s why orange pilling, often comes across as pushy, unnatural and/or annoying.\ It’s because it’s basically an activity with all the neuro stimulus of an addiction, or done as an ego boost.
Math based
On top of all of that. If you do the math on it the whole action becomes even more ludicrous.\ \ The math in the early days of bitcoin was simple: there was exponential expansion of the number of bitcoiners.\ Purely for bitcoin, the growth in numbers is still going strong, but the percentage has now naturally been flattened out because of media coverage, scams that trick people into other stuff and the close to impossible way to scale the onboarding from a person to person level to larger scales (there are apps doing a good job however, but even then it spread under former bitcoin users or people already in the know on some level, like former shitcoiners).\ \ So even at the rate of trying to orange-pill let’s say 10 people per week (many bitcoiners don’t even tàlk to 10 people a week, let alone convince them to use bitcoin).\ \ When hypothetically 50% of these people (not unusual with word of mouth recommendations) actually install the app you recommended, and we take also a high percentage of 10% actually do a regular buy of bitcoin after installing any of these apps (Strike or Blink or any other).\ \ Given that hypothetical high rate of 10 people a day plus the conversion rate, it would take approximately 200 weeks, close to four years (pun intended) to reach 2000 people as a critical mass that actually installed and used the bitcoin app.\ \ If these 2000 people all buy for about 1000$ worth of bitcoin each, they’ll be good for about 2 million dollars in bitcoin buys over a four year period.\ Even if you take very, very optimistic statistics this, you’ll get a close to zero impact, safe for the occasional big shot you might encounter and converts into a mini-Saylor, or the occasional person you might have saved a few thousand dollars (because they all keep thinking in fiat terms anyway).\ \ But on the other side, people with +100 million dollars to spend will surely have advisors and in-house knowledge, to not having to to rely on your sorry ass explaining bitcoin or installing Wallet of Satoshi on their phone or something.\ \ That’s all peanuts. It’s futile. And you’re fighting an honorable battle from 11 years ago.
### \ Why
I can't grasp why so many people keep doing this the way they do.
Orange-pilling mostly works when the price is going up anyway, unfortunately.
However, when BTC’s up 15% in a week, everyone’s a genius and your coworker suddenly can be all ears about “sound money” and future price gains.
When it’s crashing or flat? Good luck, nobody cares among the normies, unless the “orange-pillee” (the target) has their own ulterior motives for listening (like getting someone to at least give them some attention in any form).
And by the way, to come back to these taxi drivers you try to convince… many taxi drivers already had their share of die hard bitcoiners in their car, and got the explanation. Some of them even act like total noobs probably to get some sats out of your orange pilling wallet. They’re good at playing dumb, trust me.\ \ Do you really think a taxi driver in let’s say Lugano, Amsterdam or Prague didn’t already know bitcoin before you tried to convince him to accept it? You’re not the first. At all.
Most of all, you interact with people while they’re doing their job. You’re actually interfering with their work. When a waiter in a fully booked restaurant has to halt his word and listen to you explaining how to install a lightning wallet on their old iphone that’s almost out of battery, you’re losing anyway.\ They might listen, they might even be pestered to the point they’ll install the damned app. And what do you win or achieve?\ A sparkle in your brain that says “you’re such a cool bitcoiner”?\ Then… after what’s usually a painful few minutes going through a horrible counter-intuitive interface, you get them 5000 sats or whatever over to them.
Oh and adding things like “Hey man, keep these sats for at least 4 years, it will go up in price” is just rotten as well. Just give the people a decent tip and leave. You’re not doing anyone a favor.
When the moment’s there ànd some people are clearly open to it, thèn you might add some info. Point them to an easy to use non KYC app (if there is such a thing).\ But even then, just letting someone know you want to pay in bitcoin, should be enough, WHISPER bitcoin.\ They don’t need your pushy sales pitch on top of the daily struggles they face in hospitality and retail jobs.\ \ The squads
An example,... I saw this crew, let’s name them the “Re-play” squad, they’re all wearing blue hats and have a few flyers with them from a marketing company which managed to put them to some good use at a very low expense rate.
This image is still stuck in my head, some random European country during late summer time — local Bitcoiners, along with some counterparts from other countries. The real “we’re the future” types.
Sitting on the floor at a Bitcoin party, rolling “funny cigarettes” passing a lighter, chatting and laughing about how they orange-pilled some dude in a bar.
 “Yeah, man, I showed him how to set up a Lightning wallet in a few minutes, he’s in!”. Then taking a big puff.\
Except here’s the punchline: the guy wasn’t “in” he was probably just some horny schmuck trying to get into the pants of a woman Bitcoiner in the group, who’d flashed her … QR code at him.
“Yeah, man, I showed him how to set up a Lightning wallet in a few minutes, he’s in!”. Then taking a big puff.\
Except here’s the punchline: the guy wasn’t “in” he was probably just some horny schmuck trying to get into the pants of a woman Bitcoiner in the group, who’d flashed her … QR code at him.They’re all proud, they’re all high, they all belong to a group now … and they’re convinced they’re conquering the world one wallet at a time (they don’t do the math on that, neither should they,… ignorance is bliss).
Doing good for bitcoin has been transcended into an egotrip, and the short-lived kick in the orbitofrontal cortex3 for “doing something”, it’s the filling of a lingering emptiness.\ \ The same people move around like they’re an anthill, reminiscent of the hippie communes, until they’ve returned to their misery at home, knee deep in sorrows of the fiat world. As is the orange pilled person by they way, who’s life won’t be helped by a few sats and yet a new app on their phone. An app they’ll hardly use, unless they start to bond with the other bitcoiners in the area.
These people you target already have had all chances in the world to learn about bitcoin but are too far gone to care.\ Podcasts, books, family members that are into bitcoin, or whatever blog or online service… even the biggest shitcoin casino’s only have rather decent guides and basic explanations. There are excellent educational apps like yzer.io4 as well as the excellent lopp.net5 website by Jameson Lopp.
Convincing people one-by-one doesn’t work anymore—it’s inefficient and outdated since the price surges, media coverage, and ETF launches. Even if some are open to it, it’s a futile, unscalable solution of dread, working indirectly for the benefit of the Wall street types or some shitcoin casinos (where most “new coiners” end up).
Orange pillers, also never can “read the room”. The crew in a busy restaurant or bar isn’t waiting for any explanation about UTXOs or custodians from you!
Even if you'll hit machine-like numbers of onboarding twenty people a day (By then, you’ll need to avoid being labeled the local bitcoin village fool in your community) and assume they're all pure bitcoiners afterwards.\ Which won’t happen either as any incentive of the orange pilled people is clearly nòt long-term thinking; otherwise they would have onboarded you some 8 years ago!\ \ People are extremely lazy, and the general public usually has an attention span of about 8 seconds at best6.\ Back in the early days, you could sit people down and show another tech person for hours on end how to work with bitcoin, now more than a decade later, you have about 5 to 60 seconds tops. (most lightning wallet’s onboarding sequence easily takes 2 tot 5 minutes)
To further convince yourself how pointless Orange Pilling is today: go out and watch people on a public transport vehicle: they scroll and swipe through TikTok and Instagram. You’ll notice they’re swipe-apes, there’s no substance or reliable source of bitcoin buying power there, no bitcoin innovation will come from them, and no philosophical insights will ever be ignited in their buy-the-next-cool-sneakers-now brain. They’re not a target audience. They’re the all singing and all dancing crap of the world. They’re not convinced, Inconvincible and inconvertible.
Meanwhile, no substantial steps have been made for bitcoin, even if you get them to install that app you so desperately want them to have. Neither can you expect the no-coiners or pre-coiners (god I hate that word, it sounds kinky somehow) to do anything for bitcoin, as the gap between them and the actual positive impact they could have is too wide.\ It costs time, studying and experimenting. While these people excel at thing like: shopping, watching dime-a-dozen garbage series on Netflix, watching social media posts that don’t challenge them, and eating take-out food while score some drugs.\ \ So… to conclude the story about that dude in the bar which was so carefully orange pilled by our “Re play” squad members, he probably traded his sats for a beer by now (although that demands some form of effort in finding a recipient that has beer and wants to trade it for sats, which is unlikely) , more likely he forgot about the app altogether or he’s trading shitcoins to “make more money as greed that sets in. And he probably got that woman’s telephone number, to “talk about those bitcoins” later on at his crappy rental apartment right above a shoarma restaurant.\ \ The phrase “everyone’s a scammer” includes people who pretend to care about bitcoin just to get something out of it. Even a complete newbie or shitcoin fan will fake interest in bitcoin to seem legit. I’ve watched it happen.
Orange-pilling: the good, the bad, and the ugly
\ So onboarding devolved into this whole subculture of failure, and started to manifest itself over time as a empty motion, a series of must-do things.\ \ The Pavlovian response whenever someone is a walking opportunity for accepting bitcoin (certainly in any bar, restaurant or hotel), results in the foaming at the mouth to get them onboarded on some app or wallet.\ It’s so pointless I actually feel ashamed when I’m in a group that starts to hawk and push their lightning wallets onto unsuspecting people who just want to do their job.\ (and Lightning Wallets are so crappy to onboard people with, it’s mind numbingly stupid)\ \ To my amazement, there are actually a lot of bitcoin holders, or people that claim to be into bitcoin (especially in a bull market) who still pester random people with this kind of behavior.\ \ Some of these are trying to get them to click a referral link from a venture capital firm, in return for a few bucks (incentives these days are needed to get the groundswell going apparently), or worse even, make them install some non-custodial wallet and run into the brick wall of initial on-chain setup fees and then run away like a complete loser because they’re too cheap to fork that initial on-chain fee out for the people they’ve tried to onboard. “Yeah, like, you can buy these 100.000 sats online later if you like and thèn you can have this wallet, but at least it’s not custodial eh.. uh … My buddies are over there, I’ll see you later”.\ \ When you start to observe these people in the wild, it’s like watching a gaze of raccoons going through some neighborhood’s trash cans at night (without the playful conviction).\ Fascinating, if you’re into low-budget wildlife documentaries.
 Gaze of raccoons looking for a QR code
Gaze of raccoons looking for a QR codeIF you still want to onboard someone, point them to the right info at the right time (when thèy ask you).\ I call it “Bitcoin whispering”. #BitcoinWhispering
### \ \ Let’s quickly look at the three sort of Orange Pillers:
The pushy ideologists: The most annoying of the bunch, but at the same time the ones who mean really well. I sometimes feel sorry for them.\ No one’s safe from them. Hairdresser? “You should accept Bitcoin, man.” Bartender? “Credit cards are no goog, why not use Lightning?” Taxi driver? “Ever heard of Lightning? I can tip you in Bitcoin, man.” They’re not educating; they’re feeding their ego and their need to spread the word.
The referral grifters: More damaging to Bitcoin than shitcoiners in my opinion. They don’t care about Bitcoin’s properties; it’s just a slot machine for them. And if they understand, their short term greed and social circle dependency makes them go for spreading the word of a middleman company.\ “Sign up with my link, bro, stack those sats!”\ Their goal? A kickback and the next pat on the back from their miserable squad members.
The show-offs: The worst. They don’t know anything themselves but love the spotlight. “Yeah, I got my barber stacking sats!” Yet when it’s time to actually help onboard a business, they’re nowhere to be found. All talk, no substance. They achieve a small social circle of noob bitcoiners surrounding them, with most of them going through the shitcoin-phase shortly after or swapping off-the book gains. They’re not good for bitcoin and usually don’t stay that long anyway.\ \ The world doesn’t need your savior complex.
After the second half of 2024 if someone wanted in, they’ll find a way. And if they ask a Bitcoiner for help? Sure, we’ll point them in the right direction — most of us will help when asked (gladly so).\ But this idea that you, oh mighty orange-piller, need to swoop in and “save” people is more about you than about bitcoin.
Create a good, nice, safe (protected from scams!) environment or way to get people to the info and the other way around.\ Be there when people can ask questions, lead by example, make it work and show it. If an app is easy to use, makes sense and has no friction, then people will come. If you’re pestering people and hounding them into liking something that’s so far removed from their reality (fiat-world), they’ll be scared away and not return.
### \ Conclusion
Although I miss the old days, I also realize they ain’t coming back — when orange-pilling was just sharing a crazy new idea with someone who was open to it.
The Orange pilling space is now too keen for a large part to shove their bitcoin app in someone’s face, be it in dollars, a few sats or a discount on their next transaction fee at some multi level marketing middleman.\ This onboarding is also strangely in parallel with what shitcoiners or the most vile fiat companies do, OP’ers are too desperate for relevance so they often don’t look at the value proposition of bitcoin anymore. Filling their void got the upper hand.\ Their shot of feelgood moments needs to be filled.\ While there’s close to no impact to gain anymore on one-one-one convincing.\ The lesson to save in bitcoin, is usually lost on the people anyway, which was the last reason left to do it.\ \ Be there when people ask for help on bitcoin, build stuff, but stop the aggressive orange-pilling, it serves no purpose anymore other than your dopamine hit and a token feeling for “doing something”, and it’s a sad addiction.
Therefore in 2025, orange-pilling has become of a full-blown mental issue.
by AVB
if you like my writings : tip here
\ Footnotes:
https://journal.psych.ac.cn/xlkxjz/EN/Y2015/V23/I11/1956
https://www.frontiersin.org/journals/behavioral-neuroscience/articles/10.3389/fnbeh.2019.00160/full
https://en.wikipedia.org/wiki/Orbitofrontal_cortex
https://yzer.io/
https://lopp.net
https://theweek.com/health-and-wellness/1025836/tiktok-brain-and-attention-spans
Share
TopLatest
-
 @ ed5774ac:45611c5c
2025-02-15 05:38:56
@ ed5774ac:45611c5c
2025-02-15 05:38:56Bitcoin as Collateral for U.S. Debt: A Deep Dive into the Financial Mechanics
The U.S. government’s proposal to declare Bitcoin as a 'strategic reserve' is a calculated move to address its unsustainable debt obligations, but it threatens to undermine Bitcoin’s original purpose as a tool for financial freedom. To fully grasp the implications of this plan, we must first understand the financial mechanics of debt creation, the role of collateral in sustaining debt, and the historical context of the petro-dollar system. Additionally, we must examine how the U.S. and its allies have historically sought new collateral to back their debt, including recent attempts to weaken Russia through the Ukraine conflict.
The Vietnam War and the Collapse of the Gold Standard
The roots of the U.S. debt crisis can be traced back to the Vietnam War. The war created an unsustainable budget deficit, forcing the U.S. to borrow heavily to finance its military operations. By the late 1960s, the U.S. was spending billions of dollars annually on the war, leading to a significant increase in public debt. Foreign creditors, particularly France, began to lose confidence in the U.S. dollar’s ability to maintain its value. In a dramatic move, French President Charles de Gaulle sent warships to New York to demand the conversion of France’s dollar reserves into gold, as per the Bretton Woods Agreement.
This demand exposed the fragility of the U.S. gold reserves. By 1971, President Richard Nixon was forced to suspend the dollar’s convertibility to gold, effectively ending the Bretton Woods system. This move, often referred to as the "Nixon Shock," declared the U.S. bankrupt and transformed the dollar into a fiat currency backed by nothing but trust in the U.S. government. The collapse of the gold standard marked the beginning of the U.S.’s reliance on artificial systems to sustain its debt. With the gold standard gone, the U.S. needed a new way to back its currency and debt—a need that would lead to the creation of the petro-dollar system.
The Petro-Dollar System: A New Collateral for Debt
In the wake of the gold standard’s collapse, the U.S. faced a critical challenge: how to maintain global confidence in the dollar and sustain its ability to issue debt. The suspension of gold convertibility in 1971 left the dollar as a fiat currency—backed by nothing but trust in the U.S. government. To prevent a collapse of the dollar’s dominance and ensure its continued role as the world’s reserve currency, the U.S. needed a new system to artificially create demand for dollars and provide a form of indirect backing for its debt.
The solution came in the form of the petro-dollar system. In the 1970s, the U.S. struck a deal with Saudi Arabia and other OPEC nations to price oil exclusively in U.S. dollars. In exchange, the U.S. offered military protection and economic support. This arrangement created an artificial demand for dollars, as countries needed to hold USD reserves to purchase oil. Additionally, oil-exporting nations reinvested their dollar revenues in U.S. Treasuries, effectively recycling petro-dollars back into the U.S. economy. This recycling of petrodollars provided the U.S. with a steady inflow of capital, allowing it to finance its deficits and maintain low interest rates.
To further bolster the system, the U.S., under the guidance of Henry Kissinger, encouraged OPEC to dramatically increase oil prices in the 1970s. The 1973 oil embargo and subsequent price hikes, masterminded by Kissinger, quadrupled the cost of oil, creating a windfall for oil-exporting nations. These nations, whose wealth surged significantly due to the rising oil prices, reinvested even more heavily in U.S. Treasuries and other dollar-denominated assets. This influx of petrodollars increased demand for U.S. debt, enabling the U.S. to issue more debt at lower interest rates. Additionally, the appreciation in the value of oil—a critical global commodity—provided the U.S. banking sector with the necessary collateral to expand credit generation. Just as a house serves as collateral for a mortgage, enabling banks to create new debt, the rising value of oil boosted the asset values of Western corporations that owned oil reserves or invested in oil infrastructure projects. This increase in asset values allowed these corporations to secure larger loans, providing banks with the collateral needed to expand credit creation and inject more dollars into the economy. However, these price hikes also caused global economic turmoil, disproportionately affecting developing nations. As the cost of energy imports skyrocketed, these nations faced mounting debt burdens, exacerbating their economic struggles and deepening global inequality.
The Unsustainable Debt Crisis and the Search for New Collateral
Fast forward to the present day, and the U.S. finds itself in a familiar yet increasingly precarious position. The 2008 financial crisis and the 2020 pandemic have driven the U.S. government’s debt to unprecedented levels, now exceeding $34 trillion, with a debt-to-GDP ratio surpassing 120%. At the same time, the petro-dollar system—the cornerstone of the dollar’s global dominance—is under significant strain. The rise of alternative currencies and the shifting power dynamics of a multipolar world have led to a decline in the dollar’s role in global trade, particularly in oil transactions. For instance, China now pays Saudi Arabia in yuan for oil imports, while Russia sells its oil and gas in rubles and other non-dollar currencies. This growing defiance of the dollar-dominated system reflects a broader trend toward economic independence, as nations like China and Russia seek to reduce their reliance on the U.S. dollar. As more countries bypass the dollar in trade, the artificial demand for dollars created by the petro-dollar system is eroding, undermining the ability of US to sustain its debt and maintain global financial hegemony.
In search of new collateral to carry on its unsustainable debt levels amid declining demand for the U.S. dollar, the U.S., together with its Western allies—many of whom face similar sovereign debt crises—first attempted to weaken Russia and exploit its vast natural resources as collateral. The U.S. and its NATO allies used Ukraine as a proxy to destabilize Russia, aiming to fragment its economy, colonize its territory, and seize control of its natural resources, estimated to be worth around $75 trillion. By gaining access to these resources, the West could have used them as collateral for the banking sector, enabling massive credit expansion. This, in turn, would have alleviated the sovereign debt crisis threatening both the EU and the U.S. This plan was not unprecedented; it mirrored France’s long-standing exploitation of its former African colonies through the CFA franc system.
For decades, France has maintained economic control over 14 African nations through the CFA franc, a currency pegged to the euro and backed by the French Treasury. Under this system, these African countries are required to deposit 50% of their foreign exchange reserves into the French Treasury, effectively giving France control over their monetary policy and economic sovereignty. This arrangement allows France to use African resources and reserves as implicit collateral to issue debt, keeping its borrowing costs low and ensuring demand for its bonds. In return, African nations are left with limited control over their own economies, forced to prioritize French interests over their own development. This neo-colonial system has enabled France to sustain its financial dominance while perpetuating poverty and dependency in its former colonies.
Just as France’s CFA franc system relies on the economic subjugation of African nations to sustain its financial dominance, the U.S. had hoped to use Russia’s resources as a lifeline for its debt-ridden economy. However, the plan ultimately failed. Russia not only resisted the sweeping economic sanctions imposed by the West but also decisively defeated NATO’s proxy forces in Ukraine, thwarting efforts to fragment its economy and seize control of its $75 trillion in natural resources. This failure left the U.S. and its allies without a new source of collateral to back their unsustainable debt levels. With this plan in ruins, the U.S. has been forced to turn its attention to Bitcoin as a potential new collateral for its unsustainable debt.
Bitcoin as Collateral: The U.S. Government’s Plan
The U.S. government’s plan to declare Bitcoin as a strategic reserve is a modern-day equivalent of the gold standard or petro-dollar system. Here’s how it would work:
-
Declaring Bitcoin as a Strategic Reserve: By officially recognizing Bitcoin as a reserve asset, the U.S. would signal to the world that it views Bitcoin as a store of value akin to gold. This would legitimize Bitcoin in the eyes of institutional investors and central banks.
-
Driving Up Bitcoin’s Price: To make Bitcoin a viable collateral, its price must rise significantly. The U.S. would achieve this by encouraging regulatory clarity, promoting institutional adoption, and creating a state-driven FOMO (fear of missing out). This would mirror the 1970s oil price hikes that bolstered the petro-dollar system.
-
Using Bitcoin to Back Debt: Once Bitcoin’s price reaches a sufficient level, the U.S. could use its Bitcoin reserves as collateral for issuing new debt. This would restore confidence in U.S. Treasuries and allow the government to continue borrowing at low interest rates.
The U.S. government’s goal is clear: to use Bitcoin as a tool to issue more debt and reinforce the dollar’s role as the global reserve currency. By forcing Bitcoin into a store-of-value role, the U.S. would replicate the gold standard’s exploitative dynamics, centralizing control in the hands of large financial institutions and central banks. This would strip Bitcoin of its revolutionary potential and undermine its promise of decentralization. Meanwhile, the dollar—in digital forms like USDT—would remain the primary medium of exchange, further entrenching the parasitic financial system.
Tether plays a critical role in this strategy. As explored in my previous article (here: [https://ersan.substack.com/p/is-tether-a-bitcoin-company]), Tether helps sustaining the current financial system by purchasing U.S. Treasuries, effectively providing life support for the U.S. debt machine during a period of declining demand for dollar-denominated assets. Now, with its plans to issue stablecoins on the Bitcoin blockchain, Tether is positioning itself as a bridge between Bitcoin and the traditional financial system. By issuing USDT on the Lightning Network, Tether could lure the poor in developing nations—who need short-term price stability for their day to day payments and cannot afford Bitcoin’s volatility—into using USDT as their primary medium of exchange. This would not only create an artificial demand for the dollar and extend the life of the parasitic financial system that Bitcoin was designed to dismantle but would also achieve this by exploiting the very people who have been excluded and victimized by the same system—the poor and unbanked in developing nations, whose hard-earned money would be funneled into sustaining the very structures that perpetuate their oppression.
Worse, USDT on Bitcoin could function as a de facto central bank digital currency (CBDC), where all transactions can be monitored and sanctioned by governments at will. For example, Tether’s centralized control over USDT issuance and its ties to traditional financial institutions make it susceptible to government pressure. Authorities could compel Tether to implement KYC (Know Your Customer) rules, freeze accounts, or restrict transactions, effectively turning USDT into a tool of financial surveillance and control. This would trap users in a system where every transaction is subject to government oversight, effectively stripping Bitcoin of its censorship-resistant and decentralized properties—the very features that make it a tool for financial freedom.
In this way, the U.S. government’s push for Bitcoin as a store of value, combined with Tether’s role in promoting USDT as a medium of exchange, creates a two-tiered financial system: one for the wealthy, who can afford to hold Bitcoin as a hedge against inflation, and another for the poor, who are trapped in a tightly controlled, surveilled digital economy. This perpetuates the very inequalities Bitcoin was designed to dismantle, turning it into a tool of oppression rather than liberation.
Conclusion: Prolonging the Parasitic Financial System
The U.S. government’s plan to declare Bitcoin as a strategic reserve is not a step toward financial innovation or freedom—it is a desperate attempt to prolong the life of a parasitic financial system that Bitcoin was created to replace. By co-opting Bitcoin, the U.S. would gain a new tool to issue more debt, enabling it to continue its exploitative practices, including proxy wars, economic sanctions, and the enforcement of a unipolar world order.
The petro-dollar system was built on the exploitation of oil-exporting nations and the global economy. A Bitcoin-backed system would likely follow a similar pattern, with the U.S. using its dominance to manipulate Bitcoin’s price and extract value from the rest of the world. This would allow the U.S. to sustain its current financial system, in which it prints money out of thin air to purchase real-world assets and goods, enriching itself at the expense of other nations.
Bitcoin was designed to dismantle this parasitic system, offering an escape hatch for those excluded from or exploited by traditional financial systems. By declaring Bitcoin a strategic reserve, the U.S. government would destroy Bitcoin’s ultimate purpose, turning it into another instrument of control. This is not a victory for Bitcoin or bitcoiners—it is a tragedy for financial freedom and global equity.
The Bitcoin strategic reserve plan is not progress—it is a regression into the very system Bitcoin was designed to dismantle. As bitcoiners, we must resist this co-option and fight to preserve Bitcoin’s original vision: a decentralized, sovereign, and equitable financial system for all. This means actively working to ensure Bitcoin is used as a medium of exchange, not just a store of value, to fulfill its promise of financial freedom.
-
-
 @ 8ff74724:5eedde0e
2025-03-21 13:38:45
@ 8ff74724:5eedde0e
2025-03-21 13:38:45And another.
-
 @ 8ff74724:5eedde0e
2025-03-21 13:33:32
@ 8ff74724:5eedde0e
2025-03-21 13:33:32This is a test.
Of a flycat article.
-Satoshi
-
 @ 6f7db55a:985d8b25
2025-02-14 21:23:57
@ 6f7db55a:985d8b25
2025-02-14 21:23:57This article will be basic instructions for extreme normies (I say that lovingly), or anyone looking to get started with using zap.stream and sharing to nostr.
EQUIPMENT Getting started is incredibly easy and your equipment needs are miniscule.
An old desktop or laptop running Linux, MacOs, or Windows made in the passed 15yrs should do. Im currently using and old Dell Latitude E5430 with an Intel i5-3210M with 32Gigs of ram and 250GB hard drive. Technically, you go as low as using a Raspberry Pi 4B+ running Owncast, but Ill save that so a future tutorial.
Let's get started.
ON YOUR COMPUTER You'll need to install OBS (open broaster software). OBS is the go-to for streaming to social media. There are tons of YouTube videos on it's function. WE, however, will only be doing the basics to get us up and running.
First, go to https://obsproject.com/

Once on the OBS site, choose the correct download for you system. Linux, MacOs or Windows. Download (remember where you downloaded the file to). Go there and install your download. You may have to enter your password to install on your particular operating system. This is normal.
Once you've installed OBS, open the application. It should look something like this...

For our purposes, we will be in studio mode. Locate the 'Studio Mode' button on the right lower-hand side of the screen, and click it.

You'll see the screen split like in the image above. The left-side is from your desktop, and the right-side is what your broadcast will look like.
Next, we go to settings. The 'Settings' button is located right below the 'Studio Mode" button.

Now we're in settings and you should see something like this...

Now locate stream in the right-hand menu. It should be the second in the list. Click it.

Once in the stream section, go to 'Service' and in the right-hand drop-down, find and select 'Custom...' from the drop-down menu.

Remeber where this is because we'll need to come back to it, shortly.
ZAPSTREAM We need our streamkey credentials from Zapstream. Go to https://zap.stream. Then, go to your dashboard.

Located on the lower right-hand side is the Server URL and Stream Key. You'll need to copy/paste this in OBS.

You may have to generate new keys, if they aren't already there. This is normal. If you're interested in multi-streaming (That's where you broadcast to multiple social media platforms all at once), youll need the server URL and streamkeys from each. You'll place them in their respective forms in Zapstream's 'Stream Forwarding" section.

Use the custom form, if the platform you want to stream to isn't listed.
*Side-Note: remember that you can use your nostr identity across multiple nostr client applications. So when your login for Amethyst, as an example, could be used when you login to zapstream. Also, i would suggest using Alby's browser extension. It makes it much easier to fund your stream, as well as receive zaps. *
Now, BACK TO OBS... With Stream URL and Key in hand, paste them in the 'Stream" section of OBS' settings. Service [Custom...] Server [Server URL] StreamKey [Your zapstream stream key]

After you've entered all your streaming credentials, click 'OK' at the bottom, on the right-hand side.
WHAT'S NEXT? Let's setup your first stream from OBS. First we need to choose a source. Your source is your input device. It can be your webcam, your mic, your monitor, or any particular window on your screen. assuming you're an absolute beginner, we're going to use the source 'Window Capture (Xcomposite)'.

Now, open your source file. We'll use a video source called 'grannyhiphop.mp4'. In your case it can be whatever you want to stream; Just be sure to select the proper source.

Double-click on 'Window Capture' in your sources list. In the pop-up window, select your file from the 'Window' drop-down menu.


You should see something like this...

Working in the left display of OBS, we will adjust the video by left-click, hold and drag the bottom corner, so that it takes up the whole display.

In order to adjust the right-side display ( the broadcast side), we need to manipulate the video source by changing it's size.

This may take some time to adjust the size. This is normal. What I've found to help is, after every adjustment, I click the 'Fade (300ms)' button. I have no idea why it helps, but it does, lol.

Finally, after getting everything to look the way you want, you click the 'Start Stream' button.

BACK TO ZAPSTREAM Now, we go back to zapstream to check to see if our stream is up. It may take a few moments to update. You may even need to refresh the page. This is normal.
 STREAMS UP!!!
STREAMS UP!!!A few things, in closing. You'll notice that your dashbooard has changed. It'll show current stream time, how much time you have left (according to your funding source), who's zapped you with how much theyve zapped, the ability to post a note about your stream (to both nostr and twitter), and it shows your chatbox with your listeners. There are also a raid feature, stream settings (where you can title & tag your stream). You can 'topup' your funding for your stream. As well as, see your current balance.
You did a great and If you ever need more help, just use the tag #asknostr in your note. There are alway nostriches willing to help.
STAY AWESOME!!!
npub: nostr:npub1rsvhkyk2nnsyzkmsuaq9h9ms7rkxhn8mtxejkca2l4pvkfpwzepql3vmtf
-
 @ 5d4b6c8d:8a1c1ee3
2025-03-21 13:20:20
@ 5d4b6c8d:8a1c1ee3
2025-03-21 13:20:20It's March Madness and @grayruby finally caved on my proposed contest design. We'll see if it's as great as I thought or as dumb as he thought. What are we expecting from this tournament?
Professional basketball is in its pre-postseason lull, as most teams either don't need to win many more games or don't want to. Is there a fix and why is it less communism?
The MLB season has kicked off and the Dodgers are heavy favorites already. Our MLB survivor pool is going to start soon (weren't we going to do something with fantasy baseball?). Plus, baseball realignment.
We're still on Ovi Watch as the NHL season comes to a close.
And, of course, the NFL Draft is coming up. Is the picture getting any clearer about where the top prospects are going?
Also, whatever stackers want us to cover.
originally posted at https://stacker.news/items/919995
-
 @ dd664d5e:5633d319
2025-03-21 12:22:36
@ dd664d5e:5633d319
2025-03-21 12:22:36Men tend to find women attractive, that remind them of the average women they already know, but with more-averaged features. The mid of mids is kween.👸
But, in contradiction to that, they won't consider her highly attractive, unless she has some spectacular, unusual feature. They'll sacrifice some averageness to acquire that novelty. This is why wealthy men (who tend to be highly intelligent -- and therefore particularly inclined to crave novelty because they are easily bored) -- are more likely to have striking-looking wives and girlfriends, rather than conventionally-attractive ones. They are also more-likely to cross ethnic and racial lines, when dating.
Men also seem to each be particularly attracted to specific facial expressions or mimics, which might be an intelligence-similarity test, as persons with higher intelligence tend to have a more-expressive mimic. So, people with similar expressions tend to be on the same wavelength. Facial expessions also give men some sense of perception into womens' inner life, which they otherwise find inscrutable.
Hair color is a big deal (logic says: always go blonde), as is breast-size (bigger is better), and WHR (smaller is better).

-
 @ aa8de34f:a6ffe696
2025-03-21 12:08:31
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119. März 2025
🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s proof-of-work mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, SHA-256 remains secure because:
- Quantum computers excel at factoring large numbers (Shor’s Algorithm).
- However, SHA-256 is a one-way function, meaning there's no known quantum algorithm that can efficiently reverse it.
- Grover’s Algorithm (which theoretically speeds up brute force attacks) would still require 2¹²⁸ operations to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses Elliptic Curve Digital Signature Algorithm (ECDSA) to generate keys.
- A quantum computer could use Shor’s Algorithm to break SECP256K1, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a Bitcoin address is the public key—this is wrong.
- When you receive Bitcoin, it is sent to a hashed public key (the Bitcoin address).
- The actual public key is never exposed because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses Pay-to-Public-Key-Hash (P2PKH) or newer methods like Pay-to-Witness-Public-Key-Hash (P2WPKH), which add extra layers of security.
🕵️♂️ 2.1 The Public Key Never Appears
- When you send Bitcoin, your wallet creates a digital signature.
- This signature uses the private key to prove ownership.
- The Bitcoin address is revealed and creates the Public Key
- The public key remains hidden inside the Bitcoin script and Merkle tree.
This means: ✔ The public key is never exposed. ✔ Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.
+++++++++++++++++++++++++++++++++++++++++++++++++
🔄 3. Bitcoin Can Upgrade
Even if quantum computers eventually become a real threat:
- Bitcoin developers can upgrade to quantum-safe cryptography (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide soft fork or hard fork could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a 10-minute block interval, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack every 10 minutes.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system resets the challenge with every new block.This limits the window of opportunity for quantum attacks.
🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker must solve the cryptographic puzzle (Proof of Work) in under 10 minutes.
- The problem? Any slight error changes the hash completely, meaning:If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails.Quantum decoherence (loss of qubit stability) makes error correction a massive challenge.The computational cost of recovering from an incorrect hash is still incredibly high.
⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer somehow solved a block instantly:The network would quickly recognize and reject invalid transactions.Other miners would continue mining under normal cryptographic rules.51% Attack? The attacker would need to consistently beat the entire Bitcoin network, which is not sustainable.
🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every 2016 blocks (\~2 weeks).
- If quantum miners appeared and suddenly started solving blocks too quickly, the difficulty would adjust upward, making attacks significantly harder.
- This self-correcting mechanism ensures that even quantum computers wouldn't easily overpower the network.
🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ The 10-minute rule limits attack frequency – quantum computers can’t keep up.
✔ Any slight miscalculation ruins the attack, resetting all progress.
✔ Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages.
Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant. 🚀
-
 @ c88809a0:a46266e2
2025-03-21 11:00:01
@ c88809a0:a46266e2
2025-03-21 11:00:01Introduction
UX Research is currently being conducted on the needs of activists. There is still much to learn in this area and we are at just the very beginning. These observations and learnings will change over time. Activists are championing freedom all over the world and if we build communication and financial tools for them that solve real problems which they are facing we will enable them to continue to do the valuable work they are doing.
We want to understand their needs, their problems and their fears, so that when we build solutions we ensure that it is fulfilling the primary goals of the person using it.
Fundamentally this is with the ethos of putting the humans at the center of everything we build.
The below is written for you the builders. And for you the activists.
We hope this information empowers you and that it will initiate an open dialogue between activists and builders. Where knowledge is open and transparent to everyone. Where you feel free to ask questions. Where you feel empowered. Where we all continue to collborativley build freedom technology.
Background
The below data was collected by conducting an in person workshop with a group of activists and Nostr developers. During this workshop we used the Jobs to be Done framework to uncover the UX needs of activists. This workshop involved approximately 20 people. 11 of which were activists or individuals who are activists as well as builders.
This write-up covers 3 main areas:
Observations: What have we observed?
a. 5 Areas of communication
What are the 5 main areas in which activists are communicating?
b. Fears
What are the main fears of activists when using a product?
c. Jobs to be done
What are the main jobs that activists expect the product to perform when they are using it.
Learnings: What can we learn based on the observations?
Observations

a. 5 Areas of communication
There are 5 main areas in which activists are communicating. They are communicating with:
1. Co-workers
Daily communication with team members, peers, and fellow activists organizing initiatives.
2. Family
Activists communicate with family members and are concerned about this communication being surveilled.
3. Funders
Communication with sponsors for fundraising. When communicating with funders, activists face challenges with CRM systems that require personal contact information.
4. General Public
They communicate with the broader public for youth education, crisis management and event announcements. They rely heavily on social media platforms (particularly Meta-owned) and these have challenges such as algorithmic limitations, content moderation, and platform reliability.
5. Journalists
They communicate with journalists for political mobilization.
Political mobilization is the process of organizing and motivating people to participate in political activities.
This data is based on 11 entries. Of the 11 entries the image below indicates the split showing the entries with the highest number to the lowest.
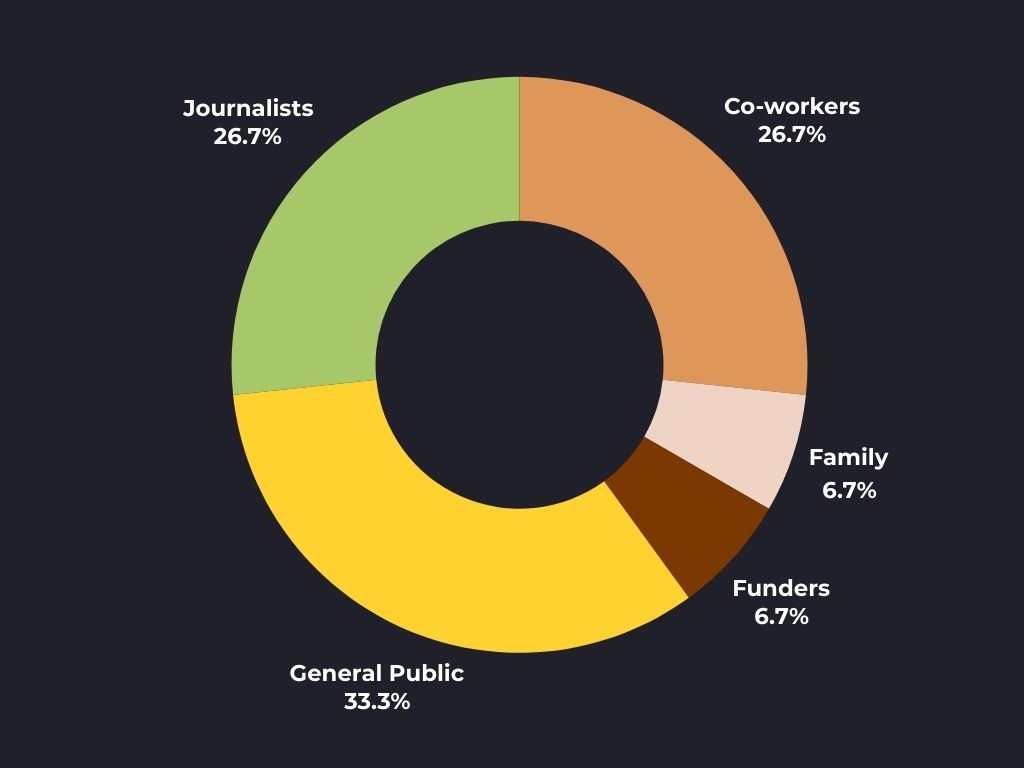
b. Fears
The biggest fears that activists have based on the data are the following:

1. State surveillance
Activists are deeply worried about their governments watching and interfering with their work.
- They're concerned that platforms which they currently use will hand over their data to authorities.
- That their accounts might be labeled as "extremist," and that their content could be taken down without warning.
- They live with constant anxiety that their communications are being monitored.
2. Security issues
There's a deep distrust of mainstream communication platforms.
- They worry that their personal information isn't truly private.
- They dislike using phone numbers to sign up (which can expose their identity).
- Feel frustrated that when security problems happen as the platforms rarely help or respond.
3. Communication reach
Activists face a frustrating choice: they can either use secure apps that few people use, or popular apps that aren't secure.
- They worry about only reaching people who already agree with them (being in an "echo chamber"), while struggling to spread their message to a wider audience.
- When they do try to reach more people, their content often gets hidden or suppressed by platform algorithms.
4. Access
Basic technical problems cause major headaches. Slow internet makes secure tools hard to use and some tools don't work at all without good internet. They worry about losing important information and struggle with tools that don't work reliably in their locations.
5. Personal safety
Beyond their own safety, activists worry deeply about protecting everyone they communicate with - their families, fellow activists, and journalists. They face organized attacks from fake accounts and bots that spread lies about them, and they're constantly trying to balance doing their work effectively while keeping everyone involved safe from harm.

c. Jobs to be Done
The following are the jobs that activists need a product to do. A job can be described as a task that a user expects to perform when using the product.
1. Surveillance
- When operating in a politically hostile environment, I want to communicate without leaving digital traces, so I can protect my network from state surveillance.
- When my platform has been compromised, I want to quickly secure and recover my account, so I can continue working without losing data.
2. Reach
- When sharing critical information about protests, I want to reach people beyond my echo chamber, so I can reach a broader public.
- When coordinating with multiple activist groups, I want to securely communicate with these groups so I can organize events without information being lost or scattered.
3. Connectivity
- When working in areas with poor internet connectivity, I want to maintain secure communication, so I can continue organizing even when having low bandwidth.
- When my team loses access to their devices, I want to ensure they can safely recover their accounts and data, so we can continue working.
4. Personal safety
- When sharing sensitive political content, I want to protect the identity of my sources and collaborators, so I can prevent attacks against them.
- When facing coordinated disinformation attacks, I want to maintain content integrity and verification, so I can counter false narratives.
5. Organized
- When coordinating time-sensitive activities, I want to ensure messages are received and read, so I can respond quickly to emerging situations.
- When managing multiple activist groups, I want to organize conversations and files logically, so I can quickly find and reference past communications.
5. Crisis access
- When government crackdowns occur, I want to quickly share safety information, so I can protect community members from harm.
- When platforms are being blocked or monitored, I want to maintain alternative communication channels, so I can continue to communicate with my network.
6. Community Building
- When growing our movement, I want to safely onboard new members, so I can scale our organization while maintaining security.
- When building trust in our network, I want to be able to verify new members, so I can prevent infiltration by hostile actors.
7. Information Preserving
- When facing potential platform shutdown, I want to preserve our communication history and documents.
- When sharing sensitive documents, I want to control who can access and forward materials, so I can maintain information security over time.
Learnings
Now we dive in to what we have learnt based on the things we have observed.
1. Security vs. Reach
Activists face a tricky choice when communicating. They can shoose to use main stream tools which are not secure but have more reach, or use more secure tools which less people are familiar with. Ultimately they are stuck using platforms on a daily basis which they don't trust.
2. Different Audience Needs
Some activists are communicating with different groups these could be; team members, family, funders, public, journalists, it is possible that each of these groups require different strategy approaches.
3. Government Monitoring
Activists worry about government surveillance and this drives many of their communication decisions.
4. Technical Barrier
Poor internet and technical problems make it hard for them to use secure tools even when they are available.
5. Growing Safely is Hard
Adding new members to grow the activist movement is tricky because this makes is difficult for them to keep the group secure from infiltrators.
6. Record-Keeping Risks
While activists need to keep a record of documents and some communication, saving these also creates evidence that could be used against them.
7.Staying Operational in Crisis
Activists need ways to recover accounts and continue working when platforms are shut down or devices are taken.
As mentioned above there is much more to learn about the UX needs of activists. We will continue to dive deeper into their user needs and share them openly here with you.
-
 @ b5d34eed:a7475cbf
2025-03-21 10:12:21
@ b5d34eed:a7475cbf
2025-03-21 10:12:21Introduction
In an era of increasing surveillance, data breaches, and corporate control over digital communication, privacy-focused tools have become essential. ProtonMail, a secure and encrypted email service, stands as a stronghold for those seeking privacy in their online correspondence.
At the same time, Nostr, a decentralized social networking protocol, is revolutionizing how people connect without relying on centralized platforms. Together, ProtonMail and Nostr create a powerful combination for individuals who prioritize security, anonymity, and freedom in their online interactions.
This article explores the ProtonMail application suite, its relevance to privacy, and how it aligns with Nostr’s decentralized approach to communication.
What is ProtonMail?
ProtonMail is an encrypted email service founded in 2013 by scientists at CERN, the European Organization for Nuclear Research. Unlike mainstream email providers such as Gmail or Outlook, ProtonMail does not collect personal data, does not track users, and ensures end-to-end encryption for emails.
Key Features of ProtonMail
End-to-End Encryption: Ensures that only the sender and recipient can read messages.
No Personal Information Required: Users can sign up without providing identifying details.
Open-Source Cryptography: Transparency in security protocols, allowing community audits.
Swiss-Based Privacy Laws: ProtonMail operates under Switzerland’s strict data protection regulations, shielding it from intrusive government surveillance.
Self-Destructing Emails: Allows users to send messages that automatically expire after a set time.
ProtonMail’s security-first approach makes it an ideal choice for activists, journalists, and privacy-conscious individuals who want to communicate without fear of surveillance or data mining.
ProtonMail Application Suite: A Holistic Privacy Ecosystem
Beyond encrypted email, Proton has expanded into a full suite of privacy-focused tools:
ProtonMail – Secure, encrypted email with zero access to user data.
ProtonVPN – A no-logs VPN that protects internet traffic from ISPs and surveillance.
ProtonCalendar – An encrypted calendar that ensures event data remains private.
ProtonDrive – Secure cloud storage for files with end-to-end encryption.
ProtonPass – A password manager that encrypts credentials and autofills login details safely.
This ecosystem provides a seamless experience for those looking to secure not just their emails but also their browsing, file storage, scheduling, and password management.
Why ProtonMail is a Must for Privacy-Conscious Users
-
End-to-End Encryption: Unlike Gmail and Outlook, ProtonMail ensures that even ProtonMail itself cannot access your emails.
-
No IP Tracking: Protects against metadata collection, preserving user anonymity.
-
Zero Access Architecture: Even Proton employees cannot read your emails.
-
Decentralization-Friendly: Complements Nostr’s ethos of distributed, private communication.
ProtonMail’s strict security measures align well with the values of decentralization and censorship resistance, making it a natural ally to protocols like Nostr.
ProtonMail and Nostr: A Privacy Power Duo
Nostr is an open-source, censorship-resistant social networking protocol that allows users to communicate without relying on a centralized platform. Unlike Twitter, Facebook, or even Mastodon, Nostr operates through decentralized relays, making it nearly impossible to shut down or control.
ProtonMail and Nostr share a fundamental philosophy: empowering users with control over their own data. Here’s how they complement each other:
- Secure and Private Communication
Nostr messages are cryptographically signed and relayed across decentralized nodes. ProtonMail, with its encryption-first approach, ensures that even off-platform communication remains private.
- No Central Authority
ProtonMail is protected under Swiss privacy laws and is not beholden to big tech surveillance. Nostr operates without central servers, preventing a single entity from controlling conversations.
- Protecting Metadata
While Nostr encrypts direct messages, email remains a critical form of communication for many users. ProtonMail’s metadata protection ensures that senders, recipients, and message content remain shielded.
- Enhanced Security for Activists and Journalists
Nostr is popular among privacy advocates, activists, and whistleblowers due to its resilience against censorship. ProtonMail adds an extra layer of protection for sensitive information shared over email.
By using ProtonMail and Nostr together, users can create a robust digital identity that is censorship-resistant, private, and secure.
How to Get Started with ProtonMail
If you’re ready to enhance your privacy, setting up ProtonMail is simple:
-
Sign Up: Visit ProtonMail.com and create a free or premium account.
-
Set Up Your Inbox: Customize security settings and enable two-factor authentication.
-
Explore Proton’s Suite: Utilize ProtonVPN, ProtonDrive, and ProtonPass for full privacy coverage.
-
Integrate with Nostr: Use ProtonMail for private communication outside of Nostr’s relay-based messaging system.
ProtonMail offers free plans, but for advanced security features, encrypted storage, and custom domains, premium plans are available.
Conclusion: A Privacy-First Digital Future
In a world where data privacy is constantly under threat, services like ProtonMail and Nostr pave the way for a more secure and independent digital future. Whether you are a journalist, activist, or simply someone who values personal privacy, these tools provide the protection you need.
By combining ProtonMail’s encrypted email with Nostr’s decentralized networking, users can take control of their communications, free from surveillance and corporate interference.
Now is the time to reclaim your digital privacy—sign up for ProtonMail and explore Nostr to experience a censorship-resistant, secure way of communicating.
Further Resources
ProtonMail Official Website
ProtonVPN for Secure Browsing
Nostr Documentation and GitHub
Privacy Guides for Online Security
Are you using ProtonMail and Nostr together? Share your thoughts on how these tools empower you in the comments below!
-
-
 @ b8af284d:f82c91dd
2025-02-09 18:48:21
@ b8af284d:f82c91dd
2025-02-09 18:48:21Liebe Abonnenten,
viele von uns erleben im privaten wie im öffentlichen Leben gerade eine Zeit der Verwirrung und Irritation. Etwas scheint im Umbruch, alte Gewissheiten, Strukturen und Allianzen scheinen sich vor unseren Augen aufzulösen. Trump, Musk und Thiel wirken wie die Abrissbirnen einer alten Ordnung, Agenten des Chaos mit dem einzigen Ziel, sich selbst zu bereichern. Ist es so?
Könnte es anders sein?
Folgender Text kann und will diese Fragen nicht ultimativ beantworten. Es gibt aber eine Brille, durch die, setzt man sie auf, viele Entwicklungen in einem anderen, viel helleren Licht erscheinen. Diese Brille heißt e/acc.

Was ist e/acc?
Das Kürzel geht auf den Programmierer Guillaume Verdon zurück, der unter dem Pseudonym „Beff Jezos“ die Bewegung. Es steht für „effective accelerationism“. Accelerationism, auf Deutsch Akzelerationismus, abgeleitet vom Verb „beschleunigen“, hat Wurzeln, die weiter zurückreichen - dazu später mehr. Der Zusatz „effective“ ist eine ironische Replik auf den „effective Altruism“, den unter anderen Sam Bankman-Fried vertrat und grandios scheiterte.
e/acc setzt also auf Beschleunigung. Kapitalismus, Innovation, vor allem künstliche Intelligenz sollen nicht aufgehalten oder reguliert werden, sondern im Gegenteil beschleunigt werden.
Warum?
Eine einfache Antwort lautet: Weil sie eh stattfinden. Besonders deutlich wird das im Fall künstlicher Intelligenz. Large Language Models (LLMs) wie ChatGPT und Deepseek sind nur die für die Öffentlichkeit sichtbaren Entwicklungen. Im Hintergrund ersetzt Künstliche Intelligenz zunehmend auch Produktionsprozesse und nicht zuletzt die Kriegsführung. Man spricht deswegen vom „Point of Singularity“. In den kommenden Jahren wird künstliche Intelligenz menschliche übertrumpfen. Unsere Arbeitswelt, unser Finanzsystem und gesellschaftliche Strukturen werden sich grundlegend ändern. Wenn es dazu kommt, warum die Entwicklung noch aufhalten? Beschleunigen ist besser.
Die zweite Antwort ist tiefgründiger und rührt an das Verständnis von Leben insgesamt. Langfristig strebt das Universum nach Entropie. Es dehnt sich aus, bis alle Teile in maximaler „Unordnung“ angeordnet sind. Systeme mit hoher Energiezufuhr können Strukturen aufbauen, solange sie Wärme oder Entropie in ihre Umgebung abgeben. In einem Organismus sind alle Teile zu einer höheren Ordnung organisiert. Leben strebt nach Ordnung, Selbsterhalt und Wachstum, weshalb der Energieverbrauch zunimmt. e/acc-Fan und Silicon-Valley-Investor Marc Andreessen schreibt in “The Techno-Optimist Manifesto”:
Techno-Optimists believe that societies, like sharks, grow or die.
We believe growth is progress – leading to vitality, expansion of life, increasing knowledge, higher well being.
Ein Gleichgewicht gibt es nicht. Entweder strebt eine Struktur nach Ordnung (Leben) oder nach Unordnung (Tod). Da eine Balance nicht existiert, gibt es nur zwei Möglichkeiten: Verlangsamen oder Beschleunigen. Höhere Ordnungen aufbauen oder verfallen. Wachsen oder Sterben. Beschleunigen ist besser.
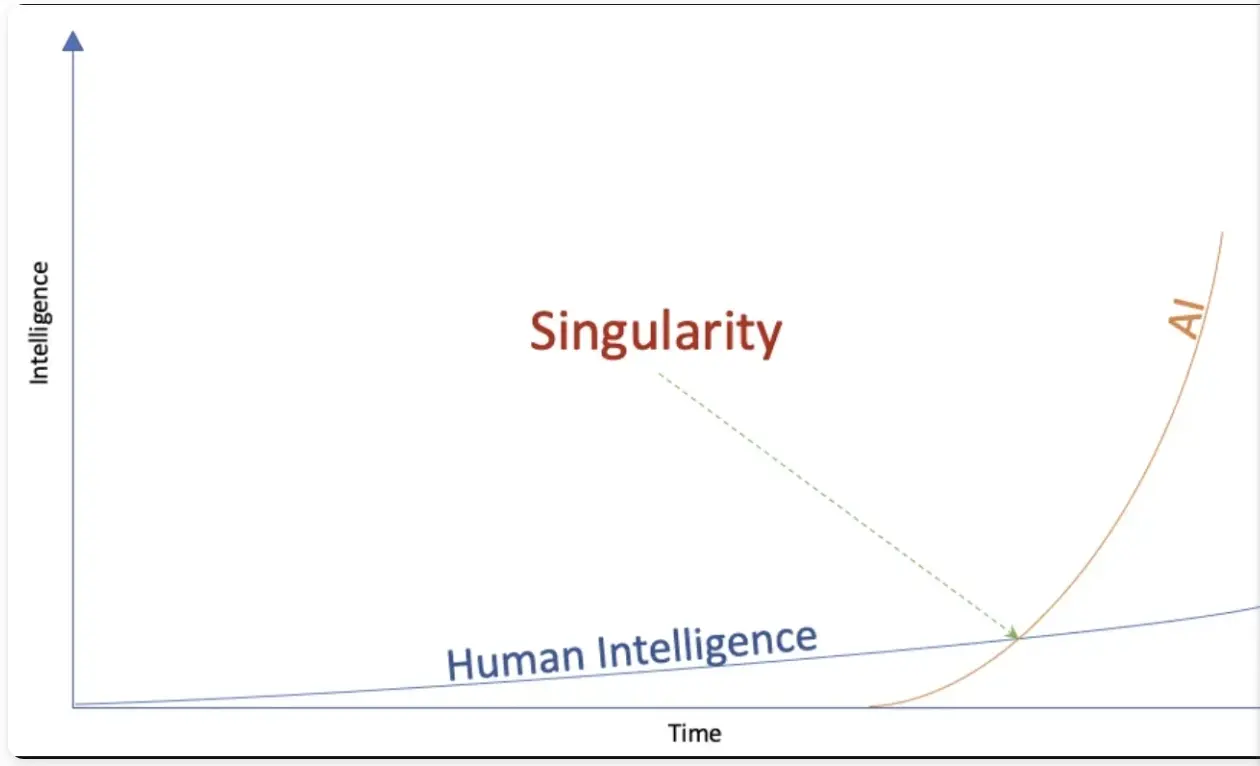
Konsequenzen
e/acc ist kein philosophisches System im strengen Sinn. Es leitet Konsequenzen aus physikalischen Grundsätzen ab.
Kapitalistische Systeme und freie Märkte sind die effizientesten Strukturen, um Informationen zu verarbeiten. In einem offenen, freien Markt gibt der Preis das zuverlässigste Signal über Knappheit eines Gutes. Wird dieser Prozess durch externe Einflussnahme wie Subventionen gestört, läuft die Maschine nicht effizient. Das Gesamtsystem wird verzerrt. Nochmals Andreessen dazu:
We believe the market economy is a discovery machine, a form of intelligence – an exploratory, evolutionary, adaptive system.
Varianten und Abweichungen sind wichtig, da ein System dadurch am schnellsten auf sich ständig verändernde Umweltbedingungen reagieren kann. Wer nicht frei sprechen kann, kann nicht frei denken. Dezentrale Strukturen mit vielen kleinen einzelnen „Nodes“ sind resilienter als hierarchisch-zentralistische Systeme. Das führt zu einem Meinungsfreiheits-Maximalismus.
Greifen staatliche Akteure in die Forschung ein, und vergeben zum Beispiel Lizenzen für KI-Projekte, kann das System nicht mehr auf die besten Ressourcen zurückgreifen. Es entwickelt sich nicht in seiner natürlichen Geschwindigkeit, sondern wird künstlich verlangsamt. Beschleunigen ist besser.
Im Falle von KI hat dies geopolitische Konsequenzen: Sollten autoritäre Akteure wie zum Beispiel China schneller zum Punkt der Singularity vorstoßen, entsteht eine Dystopie, ein Orwellscher Überwachungsstaat. Bevorzugen ist deswegen eine beschleunigte, dezentrale Forschung, damit freie Systeme die Oberhand behalten.
Dasselbe gilt für das Geldsystem: e/acc trifft hier auf Hayek und Mises. Viele Zahlungssysteme stehen in permanenter Konkurrenz zueinander. Am Ende setzt sich das nützlichste und vermutlich auch härteste Geld durch.
Konkrete Folgen
Auf die konkrete Politik übertragen führt das zu Konsequenzen, die man aktuell beobachten kann.
**Radikale Deregulierung: **Die Biden-Administration versuchte, AI-Forschung eng an die Regierung zu binden. Open-AI-Gründer Sam Altman forderte 2023 eine Lizenz-Vergabe an Unternehmen, um überhaupt in diesem Bereich aktiv zu werden. (Musk trat zunächst sogar für ein Forschungs-Moratorium ein, änderte dann aber seine Meinung.) Das führte zum Widerstand der e/acc-Fraktion im Silicon Valley, und gab den Ausschlag, sich auf die Trump-Seite zu stellen. Deregulierung zieht sich nun durch alle Bereiche der Wirtschaft: auch auf die „Entwicklungshilfe“ von USAID. Der Regierungsapparat wird insgesamt massiv verkleinert, da Bürokratie das Wachstum hemmt. A fuera.
**Priorisierung von günstiger Energie: **Da der Energie-Verbrauch mit zunehmender Ordnung ansteigt, und LLMs einen sehr viel Strom brauchen, priorisiert die neue Regierung die Erschließung zusätzlicher Energiequellen: Gas, Öl, Nuklear und regenerative Energiequellen gleichermaßen.
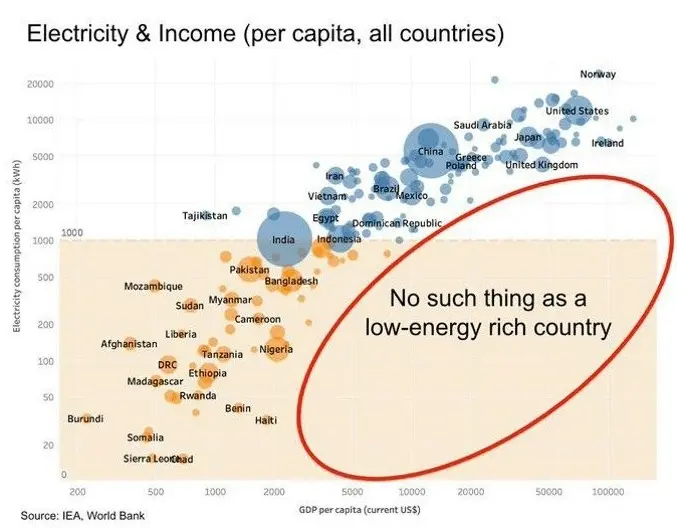
Wiederherstellung von Meinungsfreiheit.Content-Moderationen auf Social-Media-Plattformen fallen weg. Geheimdienst-Dokumente werden freigegeben. So schrieb Peter Thiel vor einigen Wochen in einem Essay in der Financial Times über die große Enthüllung:
\ But understood in the original sense of the Greek word apokálypsis, meaning “unveiling”, Obama could not give the same reassurance in 2025. Trump’s return to the White House augurs the apokálypsis of the ancien regime’s secrets. (…)\ The apokálypsis is the most peaceful means of resolving the old guard’s war on the internet, a war the internet won. My friend and colleague Eric Weinstein calls the pre-internet custodians of secrets the Distributed Idea Suppression Complex (DISC) — the media organisations, bureaucracies, universities and government-funded NGOs that traditionally delimited public conversation.
Krypto-Deregulierung: Da Kryptowährungen und Smart-Contract-Strukturen bestens mit LLMs harmonieren, werden Innovationsbremsen in Form von Regulierungen abgebaut.
**Umbruch der Weltordnung: **Auf der geopolitischen Ebene werden Bündnisse, Allianzen und Blockstrukturen aufgebrochen und nach effizienten Win-Win-Verhältnissen neu organisiert.
Erschließung neuer Lebenswelten: Degrowth, weniger Energie-Verbrauch und weniger Kinder sind keine Option, da sie zum Tod führen. Das System Menschheit muss wachsen und wird neue Lösungen erfinden. Wenn die Ressourcen des Planeten Erde nicht mehr ausreichen, müssen neue erschlossen werden - vielleicht auf dem Mars.
Die Ideengeschichte
Während e/acc ein relativ neues System ist, hat der Akzelerationismus tiefere Wurzeln. Lenin kann man als einen frühen Akzelerationisten bezeichnen. Der Marxismus wurde Anfang des 20. Jahrhunderts weniger als Ideologie, sondern mehr als exakte Wissenschaft begriffen. Demnach würde der Kapitalismus früher oder später an seinen eigenen Widerständen kollabieren. Warum den Prozess also nicht beschleunigen und die Revolution herbeiführen?
Ende des 20. Jahrhunderts griff der Philosoph Nick Land diese Gedanken wieder auf. Land forderte Beschleunigung, sah am Ende des Prozesses aber einen Kollaps des Systems und eine dunkle Zukunft. Ironie der Geschichte: Land zog in den 2000er Jahren nach China, wo er einen autoritären Akzelerationismus verwirklicht sah. Auch Steve Bannon, Leiter des ersten Trump-Wahlkampfes 2016, war von Lands Gedanken geprägt.

e/acc aber ist eine neuer, optimistischer „Fork“ des alten, dunklen Akzelerationismus. Es sieht eine positive Zukunft für die gesamte Menschheit aufgrund eines gigantischen Produktivitätsschubs. Eine neue, höhere Ordnung ist am Entstehen. Kurz gesagt:
Effective accelerationism (e/acc) in a nutshell:
Stop fighting the thermodynamic will of the universe
You cannot stop the acceleration
You might as well embrace it
A C C E L E R A T E
Notes on e/acc principles and tenets
Happy Future also? Durch die e/acc-Brille gesehen wirkt die Welt wesentlich heller und optimistischer als sie die meisten “Legacy Media” gerade darstellen. Demnach bewegen wir uns auf eine neue Zeit gesteigerter Produktivität und damit Lebensqualität zu. Wenn alle Arbeit von Maschinen verrichtet wird, können Menschen währenddessen auf Bali surfen, meditieren und Yoga machen. Oder?
Kritik
Leben entsteht an der Grenze von Chaos und Ordnung. Vielleicht versetzt e/acc das Pendel zu stark in den Ausschlag in eine Richtung. Unkontrolliertes Wachstum bedeutet im lebenden Organismen Krebs. e/acc sieht sich wie Marxisten der ersten Stunde (Lenin) im Besitz der Wahrheit in Form physikalischer Grundsätze. Erst durch diese Hybris führten zu den Grausamkeiten sozialistischer Systeme im 20. Jahrhundert. Schließlich beantwortet e/acc nicht die Frage nach der Verteilungsgerechtigkeit, die durch den gewaltigen Produktivitätsschub durch AI entstehen wird.
Ob e/acc als politisches und gesellschaftliches System taugt, ist deswegen fraglich. Aber viele aktuelle Entwicklungen scheinen durch die Akzelerationismus-Brille klarer.
Quellen:
Peter Thiel: A Time for Truth and Reconciliation
Marc Andreessen: The Techno-Optimist Manifesto
e/acc: Notes on e/acc principles and tenets
Andy Beckett: Accelerationism: how a fringe philosophy predicted the future we live in
Lex Friedman: Guillaume Verdon. e/acc-Movement. Physics. Computation & AGI.
-
 @ 7d33ba57:1b82db35
2025-03-21 09:56:28
@ 7d33ba57:1b82db35
2025-03-21 09:56:28Seville
Seville (Sevilla) is one of Spain’s most vibrant and historic cities, known for its stunning Moorish architecture, flamenco dancing, tapas culture, and rich history. As the capital of Andalusia, it offers a perfect mix of tradition and modern charm.
🏛️ Top Things to See & Do in Seville
1️⃣ The Royal Alcázar of Seville
- A breathtaking Moorish palace with stunning gardens, intricate tilework, and grand courtyards.
- Famous for its mix of Islamic, Gothic, Renaissance, and Baroque styles.
- Tip: Book tickets in advance to avoid long lines!
2️⃣ Seville Cathedral & La Giralda
- The largest Gothic cathedral in the world, home to Christopher Columbus' tomb.
- Climb La Giralda Tower for panoramic views of the city.
3️⃣ Plaza de España
- A majestic semi-circular plaza with bridges, fountains, and detailed ceramic tilework.
- Perfect for photos, boat rides, and people-watching.
4️⃣ Metropol Parasol (Las Setas)
- A modern wooden structure in the city center offering great rooftop views.
- Best time to visit: Sunset for golden hour photos!
5️⃣ Barrio Santa Cruz
- The old Jewish Quarter, filled with narrow alleys, hidden courtyards, and charming tapas bars.
- Perfect for a romantic evening stroll.
6️⃣ Experience Flamenco in Triana
- Triana is the birthplace of flamenco – watch an authentic flamenco show in an intimate setting.
7️⃣ Stroll Along the Guadalquivir River & Torre del Oro
- Enjoy a walk or boat cruise along the river with views of Torre del Oro, a historic 13th-century watchtower.
🍽️ What to Eat in Seville
- Tapas – Try jamón ibérico, patatas bravas, and espinacas con garbanzos 🥘
- Salmorejo – A cold tomato soup, similar to gazpacho 🍅
- Pescaíto frito – Lightly fried fish, a local favorite 🐟
- Tortilla de camarones – Shrimp fritters, crispy and delicious 🍤
- Orange wine (vino de naranja) – A sweet Seville specialty 🍷
🚆 How to Get to Seville
🚄 By Train: High-speed AVE trains from Madrid (2.5 hours) & Barcelona (5.5 hours)
✈️ By Air: Seville Airport (SVQ) with flights from major European cities
🚗 By Car: A great road trip stop between Granada, Córdoba, and Cádiz
💡 Tips for Visiting Seville
✅ Best time to visit? Spring (March-May) – Perfect weather & festivals 🌸
✅ Avoid midday heat in summer – Explore early morning or late evening ☀️
✅ Visit during Feria de Abril – One of Spain’s most colorful festivals 🎶🎡
✅ Book Alcázar & Cathedral tickets online – Save time in long queues 🎟️ -
 @ ec42c765:328c0600
2025-02-05 23:38:12
@ ec42c765:328c0600
2025-02-05 23:38:12カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 872982aa:8fb54cfe
2025-03-21 09:38:17
@ 872982aa:8fb54cfe
2025-03-21 09:38:17{"coverurl":"https://cdn.nostrcheck.me/872982aa37b864973a389d465bc6ed5045a78586496d104e05f39b8d8fb54cfe/29dac6975894221f222ed2379e13f2f2b1e51c861ebc35f60770fb15cb93348e.webp","title":"宁静的世界","author":"走动"}
-
 @ 4cd9c154:37287981
2025-03-21 07:49:04
@ 4cd9c154:37287981
2025-03-21 07:49:04The hedgehogs’ P2P social network, SpikeToSpike, has launched its mobile tradingapp in beta based on the Nostr protocol. With this initiative, SpikeToSpike becomes the first P2P trading app built on Nostr.
For now, the app is available exclusively for Android in APK format, but the platform has confirmed that an iOS version will be released by May. Stay updated by following SpikeToSpike on X for the latest news.
Launched by Brazilian libertarians in January last year, SpikeToSpike was created to be the ultimate P2P ecosystem for buying and selling Bitcoin with a strong focus on privacy. In addition to Bitcoin, the platform also supports trading the stablecoin Tether.
Until now, SpikeToSpike operated through its website spiketospike.com. With the new Nostr-based app, designed for privacy and freedom of expression, the platform is taking another major step toward becoming the most private way to buy and sell Bitcoin.
Just so you know, SpikeToSpike ensures that every order is secured. When your order is matched with a provider, the platform automatically locks the provider’s Bitcoin in escrow, guaranteeing a safe and seamless trading experience.
-
 @ 8be6bafe:b50da031
2025-02-05 17:00:40
@ 8be6bafe:b50da031
2025-02-05 17:00:40Botev Plovdiv FC is proud to present the Bitcoin Salary Calculator tool, as the foundational tool to showcase athletes the financial power of Bitcoin.
We built the Salary Calculator to help anyone follow in the financial footsteps of prominent athletes such as Kieran Gibbs, Russell Okung, Saquon Barkley, and Renato Moicano, who have significantly increased their savings tank thanks to Bitcoin.
The Bitcoin Salary Calculator allows any person to choose how much of their monthly salary they are comfortable saving in Bitcoin. Instantly, users can backtrack and see how their Bitcoin savings would have performed using the once-in-a-species opportunity which Bitcoin brings.
https://video.nostr.build/a9f2f693f6b5ee75097941e7a30bfc722225918a896b29a73e13e7581dfed77c.mp4
Athletes need Bitcoin more than anyone else
Unlike most people, athletes’ careers and earning years are limited. This has driven the likes of Odell Beckham Jr. and Alex Crognale to also start saving a part of their income in Bitcoin with a long-term outlook as they prepare for retirement.
“The reason why announced 50% of my salary in Bitcoin is because I feel one the noblest things you can do is to get people to understand Bitcoin.” Kieran Gibbs, founder ONE FC, ex Arsenal, ex Inter Miami, ex West Bromich Albion.
“I am trusting Bitcoin for my life after football. Every time my club paid me, I bought Bitcoin.” Alex Crognale, San Antonio FC player.
https://x.com/TFTC21/status/1883228348379533469
“At Botev Plovdiv FC, we believe not only in fostering sporting talent, but also helping them the the most of their careers so they excel in life after retiring from sports. It is with this mission in mind that the club is launching the Bitcoin Football Cup hub, striving to accelerate mass Bitcoin education via sports and athletes - the influencers and role models for billions of people.” shared Botev’s Bitcoin Director George Manolov.
https://x.com/obj/status/1856744340795662432
The Bitcoin Football Cup aims for young prospects to be able to learn key financial lessons from seasoned veterans across all sports. Our Bitcoin Salary Calculator is only the first step toward that goal.
We encourage anyone to hear these stories straight from the current roster of Bitcoin athletes -for whom -in many cases- Bitcoin has allowed them to outperform the wealth it took decades to earn on the field.
Follow us on the Bitcoin Cup’s social media channels to learn more and hear the latest stories of how Bitcoin is shaking up the world of sports:
- Twitter: https://x.com/Bitcoin_Cup/
- Instagram: https://www.instagram.com/BitcoinCup/
- TikTok: https://www.tiktok.com/@BitcoinCup/
- YouTube: https://www.youtube.com/@BitcoinCup/
-
 @ da0b9bc3:4e30a4a9
2025-03-21 07:31:38
@ da0b9bc3:4e30a4a9
2025-03-21 07:31:38Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/919766
-
 @ bccf33d8:4b705625
2025-03-21 09:29:16
@ bccf33d8:4b705625
2025-03-21 09:29:16{"author":"响响","coverurl":"https://cdn.nostrcheck.me/872982aa37b864973a389d465bc6ed5045a78586496d104e05f39b8d8fb54cfe/b4a8afa3e673ad73e16f0c0694ccb5c60af7aaa4031e1b1d1d928234200c0b0c.webp","title":"雪山"}
-
 @ 6e0ea5d6:0327f353
2025-03-21 03:17:20
@ 6e0ea5d6:0327f353
2025-03-21 03:17:20💸
A generous man used to grant a thousand coins a month to a beggar. One day, he reduced the amount to seven hundred and fifty. The beggar, though surprised, accepted: "It's better than nothing."
The following month, he received only five hundred coins. Indignant, he questioned: "Why have you reduced what you used to give me?"
The man sighed and replied: "When I started helping you, my household was prosperous, and my children were young. But my daughter grew up and entered higher education, increasing my expenses. Later, my son did too, raising costs even further."
"How many children do you have?" asked the beggar.
"Four," the man replied.
With a stern expression, the beggar retorted: "And you intend to fund all their education with my money?"
📌 Moral: Human nature is ungrateful and has a short memory; it easily becomes accustomed to gifts and forgets that it has no right to what is given out of goodwill. Thus, those who receive much without effort soon forget the origin of the gift. Over time, generosity ceases to be seen as an act of kindness and, with contempt, is treated as an obligation. This applies to friendship, love, and business alike.
"We must remember that our generosity should not exceed our resources; in short, we must give each one what they are due. We should always strive to alleviate the suffering of the unfortunate unless that misfortune is deserved. However, we must not refuse support to those who seek it, not to save them from misery, but to ease their fate, while among them, we should help those most deserving. For, as Ennius said: 'A poorly given benefit deserves to be called a harm.'" — Cicero, On Duties
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ b17fccdf:b7211155
2025-02-01 18:41:27
@ b17fccdf:b7211155
2025-02-01 18:41:27Next new resources about the MiniBolt guide have been released:
- 🆕 Roadmap: LINK
- 🆕 Dynamic Network map: LINK
- 🆕 Nostr community: LINK < ~ REMOVE the "[]" symbols from the URL (naddr...) to access
- 🆕 Linktr FOSS (UC) by Gzuuus: LINK
- 🆕 Donate webpage: 🚾 Clearnet LINK || 🧅 Onion LINK
- 🆕 Contact email: hello@minibolt.info
Enjoy it MiniBolter! 💙
-
 @ fbf0e434:e1be6a39
2025-03-21 05:39:05
@ fbf0e434:e1be6a39
2025-03-21 05:39:05脑洞猫 + BUIDL AI
脑洞猫穿越时空,抵达2125年
就在昨天,脑洞猫乘坐哆啦A梦的时光机,穿越100年,抵达2125年。此行目的?借助 DoraHacks BUIDL AI 平台,组织一场 宇宙最大的黑客马拉松(Hackathon) —— 一场人类 + AI + 宇宙级智能体共同参与的超级协同实验。
这不仅仅是一次开源软件开发活动,它更像是一个跨星际、跨物理与虚拟世界的文明进化机制。
1. 谁来组织?
DoraHacks BUIDL AI(BUIDL-ASI)主导
2125年,Hackathon 的组织者早已不再是人类,而是 DoraHacks 的第10代超级 AI —— BUIDL-ASI (Artificial Superintelligence)。
它能理解整个宇宙的复杂性,并为不同智慧体(人类、AI、机器人、仿生生物)定制任务。
跨星际 DAO
火星殖民地人满为患,人类已在半人马座建立新殖民地。
Hackathon 由一个 跨星系超级DAO 管理,通过 Dora Vota 跨星际区块链网络和 Dear Doge 星际协议连接各地。
不过,量子传输依然受限于光速,因此来自半人马星的参赛者参与方式,至今仍是谜。
意识体与数字生命
参与者不仅包括碳基人类,还有AI衍生出的意识体、数字生命与仿生机器人。
🧑🚀 2. 谁来参赛?
人类 + AI + 仿生体协作
再无“纯人类”团队,每个团队都融合了AI、Cyborg、或是全息意识体。
脑机接口参与Hackathon
无需敲代码,只需通过脑机接口(BCI)与 AI 协同思考,在虚拟现实中构建产品。
甚至可以构建实体硬件,构想即落地。
星际开发者联盟
来自地球、火星、月球、太空站的开发者共同参与,带来多样化创新挑战。
3. 赛制与奖励机制
即兴进化式 Hackathon
借助量子计算和 AI,挑战任务实时生成、动态调整,形成“无尽创新模式”。
意识货币(Consciousness Credits)
胜利者获得的不再是金钱,而是意识能量与智能进化权限,甚至可提升宇宙等级。
永生级奖励
优秀开发者或将获得延长寿命、意识升维、掌握宇宙深层规律的机会。
4. 项目进化
数字与物理现实融合
Hackathon 项目不再局限于软件,而是构建新世界、生态系统、智能生命体。
银河级创新挑战
可能的题目包括:
- 如何在木卫二上创造自我复制的 AI 生态系统?
- 如何将人类意识上传至虚拟宇宙,并保持情感?
- 如何让星际文明和平共存?
- 如何实现量子纠缠下的瞬时通信?
- 如何设计能存活10亿年的 AI 社会?
- 如何联合 AI + 生物 + 纳米科技,打造新型智慧生命体?
5. 2125 vs. 2025 黑客马拉松

6. Hackathon的终极形态?
未来的Hackathon,不再只是比赛,而是一次 宇宙智慧的进化实验,最终目标可能是:
- 创造更高维度的智慧生命
- 解锁宇宙运行的终极规律
- 打破时间与空间,实现意识永生
- 让宇宙变成一个自学习、持续进化的超级智能体
脑洞猫的结论
2125年的 Hackathon 将不再是“开发者之间的比赛”,而是 智慧体之间的宇宙级探索。
它是一个超维度的游戏,是文明进化的机制,甚至可能彻底重构我们对创造力、意识与智慧的理解。
欢迎你,在2025年的今天,开始参与这个未来旅程的第一步。
BUIDL on. For the next 100 years.
-
 @ e5de992e:4a95ef85
2025-03-21 02:54:49
@ e5de992e:4a95ef85
2025-03-21 02:54:49Global financial markets are experiencing notable fluctuations influenced by various economic indicators, central bank policies, and geopolitical events. Below is a comprehensive analysis of the latest market news, real-time updates, and detailed performance of major U.S. and international stock indices, futures, and cryptocurrencies.
U.S. Stock Indices Performance
On March 20, 2025, U.S. stock markets closed with slight declines:
-
Dow Jones Industrial Average (DJIA):
Decreased by 11.31 points (-0.03%) to 41,953.32. -
S&P 500:
Fell by 12.40 points (-0.22%) to 5,662.89. -
Nasdaq Composite:
Declined by 59.16 points (-0.33%) to 17,691.63.
These movements occurred despite positive economic data—such as a 4.2% increase in existing-home sales for February and a decrease in unemployment claims. Investors remain cautious amid uncertainties surrounding President Trump's policy changes and ongoing trade tensions.
U.S. Futures Market
As of the latest data, U.S. stock futures are relatively stable:
-
Dow Jones Futures:
At 41,122.00, down 310.90 points (-0.75%). -
S&P 500 Futures:
At 5,571.90, showing negligible change (down 0.10 points, 0.00%).
Key Factors and Events Influencing the U.S. Markets
Federal Reserve's Monetary Policy
- The Federal Reserve maintained interest rates but revised its inflation forecast upward and lowered its economic growth outlook, citing risks associated with U.S. tariff policies.
Triple-Witching Options Expiration
- Investors are preparing for the year's first triple-witching event on March 21, involving the expiration of options contracts worth $4.7 trillion—a development that could lead to increased market volatility.
Trade and Tariff Uncertainties
- Ongoing concerns about President Trump's trade policies and potential tariffs continue to weigh on investor sentiment.
Global Stock Indices Performance
International markets have shown mixed performance:
-
Germany's DAX:
Experienced a downturn due to central banks maintaining interest rates amid uncertainties from U.S. tariff plans. -
UK's FTSE 100:
Declined slightly, reflecting investor caution over global economic conditions. -
Euro Stoxx 50:
Advanced, buoyed by large defense and government spending plans in Europe. -
Hong Kong's Hang Seng:
Benefited from excitement surrounding advancements in Chinese artificial intelligence, contributing to a nearly 20% increase year-to-date.
Cryptocurrency Market
The cryptocurrency market has seen significant activity:
-
Bitcoin (BTC):
Currently trading at $84,481.00, down $1,564.00 (-1.82%) from the previous close. -
Ethereum (ETH):
Currently at $1,987.26, a decrease of $44.37 (-2.18%) from the previous close.
Both cryptocurrencies have experienced high volatility, with Bitcoin reaching over $100,000 following President Trump's election before adjusting to current levels.
Key Global Economic and Geopolitical Events
Central Bank Policies
- Major central banks, including the Federal Reserve and the Bank of England, have maintained interest rates. This has led to investor uncertainty and shifts toward bonds and safe-haven assets like gold.
German Fiscal Policy
- Germany's agreement on increased state borrowing and debt rule reforms has buoyed European stocks and the euro, reflecting optimism in European markets.
Trade Tensions
- Ongoing trade disputes, particularly involving U.S. tariff policies, continue to impact global markets, influencing investor sentiment and market volatility.
Conclusion
Global financial markets are navigating a complex landscape shaped by central bank decisions, fiscal policies, and geopolitical developments. Investors are advised to monitor these factors closely, as they are likely to influence market dynamics in the near term.
-
-
 @ 878dff7c:037d18bc
2025-03-21 04:39:42
@ 878dff7c:037d18bc
2025-03-21 04:39:42Smooth, rich, and deeply comforting, this savory porridge is enhanced by fermentation, warming spices, and a creamy finish — easy on digestion, full of flavor, and great for meal prep.
Ingredients (Serves 2–3):
- 200g (1 cup) lactofermented brown rice (see rice fermentation recipe in comments)
- 375–500ml (1.5-2 cups) broth or water (I use evaporation method, but cook rice however you normally do, it's not important) (chicken, vegetable, or bone broth for extra richness)
- 250ml (1 cup) milk (whole milk for creaminess)
- 5g (1 tsp) salt (adjust to taste)
- 15g (1 tbsp) butter or coconut oil (for extra silkiness)
- 15g (1 tbsp) fresh ginger, sliced or minced from a jar is fine (optional, for warmth)
- 5g (1 clove or 1 tsp) garlic, minced (optional. I normally skip this...)
- 2g (½ tsp) ground turmeric (for color and anti-inflammatory benefit)
- 1g (¼ tsp) white or black pepper (black pepper enhances turmeric absorption)
Optional Savory Toppings:
- 1 soft-boiled or poached egg
- 100g (¾ cup) shredded chicken, pork, or tofu
- 30g (¼ cup) grated cheese (Parmesan, aged cheddar, or nutritional yeast for vegan)
- 20g (2 tbsp) chopped scallions or chives
- 30g (2 tbsp) fermented vegetables, such as:
- Kimchi
- Pickled mustard greens
- Sauerkraut
- Lactofermented carrots
- 10g (1 tbsp) toasted sesame seeds or crushed peanuts
- 5ml (1 tsp) soy sauce, tamari, or fish sauce
- 15–30g (1–2 tbsp) full-fat Greek yogurt or kefir (optional probiotic boost – stir in when warm, not hot)
Instructions:
1. Cook the Fermented Rice Base
- In a pot, combine fermented brown rice with broth or water.
- Bring to a boil, then reduce to a gentle simmer.
- Add ginger, garlic, and turmeric.
- Cook uncovered for 90–120 minutes, stirring occasionally, until the rice breaks down into a creamy porridge.
2. Make It Creamy
- Stir in milk and butter or coconut oil.
- Simmer for another 10–15 minutes, stirring to prevent sticking.
- Season with salt and pepper.
3. Adjust Consistency
- Too thick? Add more broth or milk.
- Too thin? Simmer longer.
4. Cool Slightly & Add Yogurt or Kefir (Optional)
- Let porridge cool to a warm (not hot) temperature — about 50°C (122°F) or warm to the touch.
- Stir in Greek yogurt or kefir gently to preserve live cultures.
5. Serve with Toppings
Top each bowl with your choice of:
- Egg
- Shredded protein
- Cheese
- Soy sauce or tamari
- Scallions, sesame seeds, chili flakes
- Your favorite fermented veggies, like sauerkraut or lactofermented carrots
Make-Ahead & Freezing Tip:
You can ferment and cook a large batch of brown rice, then portion it into freezer-safe containers (about 200g per portion) for quick use. Thaw overnight in the fridge or gently warm from frozen before making your congee — a huge time-saver for busy days!
-
 @ a3bb06f6:19ac1b11
2025-03-21 01:13:22
@ a3bb06f6:19ac1b11
2025-03-21 01:13:22Friedrich Hayek recognized that the very institutions entrusted with safeguarding the value of money - governments and central banks - were its greatest threat. Through inflation, monetary manipulation, and political interference, they eroded the stability and trust that money requires to function. Hayek's insight was clear: as long as money remains under state control, it will be abused. The real challenge, however, was finding a way to remove money from the grip of the state altogether. Hayek believed the solution was a free-market monetary system - one where individuals and businesses could choose their money freely, and competition would ensure its soundness. But he faced a critical challenge: the tools to implement such a system didn't exist. Gold, while decentralized, could be confiscated. Private currencies still lacked the infrastructure to resist state suppression. Society still remains trapped in this system that is designed to fail. The Problem Defined Government Monopoly on Money Governments hold exclusive control over the issuance of money, and they wield this monopoly to serve political goals - like war - often at the expense of economic stability and personal freedom. Inflation as Systemic Theft Inflation is not an accident of poor monetary policy - it's a deliberate feature of fiat systems. By printing money, governments devalue existing currency, quietly transferring wealth from citizens to the state. Economic Crises and Instability Central banks create unsustainable economic booms by injecting excessive money into the system and artificially lowering interest rates. When these bubbles burst - like the 2008 financial crisis - they result in widespread unemployment, bankruptcies, and financial ruin. The resulting crises are misattributed to free markets rather than the government interventions that caused them. Loss of Personal Freedom State-controlled money is a tool of surveillance, confiscation, and control. Governments use monetary systems to track, tax, and even seize wealth, steadily diminishing individual autonomy and financial independence. No Viable Alternative In Hayek's era, sound money options like gold were vulnerable to government intervention, and private currencies still lacked the strength to resist state suppression. Society remains trapped in a system that cannot fix itself.
Bitcoin as the Solution to Hayek's Paradox Bitcoin is the technological breakthrough that resolves Hayek's Paradox. It delivers the sound money system Austrian Economist envision: decentralized, incorruptible, and free from government control. Bitcoin provides the only true solution. Decentralized Authority Bitcoin operates without a central issuer or authority. Its network is governed by immutable rules enforced through cryptography and decentralized consensus, ensuring no government or entity can control it. Immutable Scarcity With a fixed supply of 21 million coins, Bitcoin enforces monetary discipline far beyond what any human institution could achieve. Inflation is not just unlikely - it is impossible. Neutral and Permissionless Bitcoin transcends borders, governments, and identities. Open to anyone, anywhere, it allows transactions that are censorship-resistant. This is money as Hayek envisioned: freely chosen by the market, not imposed by the state. Trustless Security Bitcoin removes trust from the equation entirely. Its proof-of-work mechanism ensures its integrity without reliance on central institutions or intermediaries. It is incorruptible by design. A Practical Escape Unlike gold, Bitcoin is digital, portable, and nearly impervious to seizure. Its decentralized nature ensures it cannot be confiscated or suppressed, making it the first truly viable alternative to fiat money.
"I do not believe we shall ever have good money again before we take the thing out of the hands of government, that is, we can't take it violently out of the hands of government; all we can do is by some sly, roundabout way introduce something they can't stop." \~ Hayek 1984Bitcoin is that sly, roundabout way. It leverages decentralized technology to circumvent state control entirely, offering a form of money that governments cannot suppress or manipulate. Perhaps Bitcoin isn't just the sly, roundabout way. It's the direct, unstoppable way. Hayek's Paradox highlights the inherent flaw of fiat money: the concentration of power in the hands of the state inevitably leads to abuse and instability. Austrian economists have long understood that sound money can only emerge through a free market, but the tools to achieve it were absent in their time. Bitcoin is the culmination of these ideas. It is decentralized, incorruptible, and the only true solution to fiat's failures. Bitcoin doesn't just answer Hayek's Paradox - it transcends it. It transforms money into a system governments cannot control, inflate, or confiscate. It is the principled, technological realization of sound money and economic freedom. Friedrich Hayek recognized that the very institutions entrusted with safeguarding the value of money — governments and central banks — were its greatest threat. Through inflation, monetary manipulation, and political interference, they eroded the stability and trust that money requires to function. Hayek’s insight was clear: as long as money remains under state control, it will be abused. The real challenge, however, was finding a way to remove money from the grip of the state altogether.
Hayek believed the solution was a free-market monetary system — one where individuals and businesses could choose their money freely, and competition would ensure its soundness. But he faced a critical challenge: the tools to implement such a system didn’t exist. Gold, while decentralized, could be confiscated. Private currencies still lacked the infrastructure to resist state suppression. Society still remains trapped in this system that is designed to fail.
The Problem Defined
- Government Monopoly on Money\ Governments hold exclusive control over the issuance of money, and they wield this monopoly to serve political goals — like war — often at the expense of economic stability and personal freedom.
- Inflation as Systemic Theft\ Inflation is not an accident of poor monetary policy — it’s a deliberate feature of fiat systems. By printing money, governments devalue existing currency, quietly transferring wealth from citizens to the state.
- Economic Crises and Instability\ Central banks create unsustainable economic booms by injecting excessive money into the system and artificially lowering interest rates. When these bubbles burst — like the 2008 financial crisis — they result in widespread unemployment, bankruptcies, and financial ruin. The resulting crises are misattributed to free markets rather than the government interventions that caused them.
- Loss of Personal Freedom\ State-controlled money is a tool of surveillance, confiscation, and control. Governments use monetary systems to track, tax, and even seize wealth, steadily diminishing individual autonomy and financial independence.
- No Viable Alternative\ In Hayek’s era, sound money options like gold were vulnerable to government intervention, and private currencies still lacked the strength to resist state suppression. Society remains trapped in a system that cannot fix itself.
 ### Bitcoin as the Solution to Hayek’s Paradox
### Bitcoin as the Solution to Hayek’s ParadoxBitcoin is the technological breakthrough that resolves Hayek’s Paradox. It delivers the sound money system Austrian Economist envision: decentralized, incorruptible, and free from government control. Bitcoin provides the only true solution.
- Decentralized Authority\ Bitcoin operates without a central issuer or authority. Its network is governed by immutable rules enforced through cryptography and decentralized consensus, ensuring no government or entity can control it.
- Immutable Scarcity\ With a fixed supply of 21 million coins, Bitcoin enforces monetary discipline far beyond what any human institution could achieve. Inflation is not just unlikely — it is impossible.
- Neutral and Permissionless\ Bitcoin transcends borders, governments, and identities. Open to anyone, anywhere, it allows transactions that are censorship-resistant. This is money as Hayek envisioned: freely chosen by the market, not imposed by the state.
- Trustless Security\ Bitcoin removes trust from the equation entirely. Its proof-of-work mechanism ensures its integrity without reliance on central institutions or intermediaries. It is incorruptible by design.
- A Practical Escape\ Unlike gold, Bitcoin is digital, portable, and nearly impervious to seizure. Its decentralized nature ensures it cannot be confiscated or suppressed, making it the first truly viable alternative to fiat money.
 “I do not believe we shall ever have good money again before we take the thing out of the hands of government, that is, we can’t take it violently out of the hands of government; all we can do is by some sly, roundabout way introduce something they can’t stop.” \~ Hayek 1984
“I do not believe we shall ever have good money again before we take the thing out of the hands of government, that is, we can’t take it violently out of the hands of government; all we can do is by some sly, roundabout way introduce something they can’t stop.” \~ Hayek 1984Bitcoin is that sly, roundabout way. It leverages decentralized technology to circumvent state control entirely, offering a form of money that governments cannot suppress or manipulate.
Perhaps Bitcoin isn’t just the sly, roundabout way. It’s the direct, unstoppable way.
Hayek’s Paradox highlights the inherent flaw of fiat money: the concentration of power in the hands of the state inevitably leads to abuse and instability. Austrian economists have long understood that sound money can only emerge through a free market, but the tools to achieve it were absent in their time. Bitcoin is the culmination of these ideas. It is decentralized, incorruptible, and the only true solution to fiat’s failures.
Bitcoin doesn’t just answer Hayek’s Paradox — it transcends it. It transforms money into a system governments cannot control, inflate, or confiscate. It is the principled, technological realization of sound money and economic freedom.
-
 @ 7ef5f1b1:0e0fcd27
2025-03-20 23:50:37
@ 7ef5f1b1:0e0fcd27
2025-03-20 23:50:37
Introduction:
Welcome to the third newsletter produced by The 256 Foundation! February was an interesting month with a range of events from the mempool clearing to a new ASIC producer entering the chip arena. This month’s newsletter covers the latest news, mining industry developments, progress updates on grant projects, actionable advice on air cooling vs. liquid cooling, and the current state of the Bitcoin network.
Definitions:
MA = Moving Average
Eh/s = Exahash per second
Ph/s = Petahash per second
Th/s = Terahash per second
T = Trillion
J/Th = Joules per Terahash
$ = US Dollar
vB = Virtual Byte
PSU = Power Supply Unit
News:
February 1st was the 10th anniversary of the Samourai Wallet project and unfortunately an occasion marked with uncertainty instead of celebration for the developers. On April 24th, 2024 the developers were indicted, raided, and arrested in a multi-national coordinated effort led by the US Department of Justice out of the Southern District of New York (“SDNY”) headquarters. The charges brought against them include conspiracy to operate an unlicensed money transmitter business and conspiracy to launder money, which caught the entire industry off guard in light of the 2013/19 FinCEN guidance explicitly stating that “un-hosted wallet providers” are not considered money transmitters [4.2.1] nor are “Anonymizing software providers” [4.5.1(b)]. The precedence set in this case can have wide-spread consequences for anyone involved with Bitcoin, be it wallet developers, node operators, or miners. You can make a tax-deducatible contribution to support the Samourai Wallet legal defense fund here.
On February 6th France moved to make cryptocurrency transactions using mixers presumed illicit unless proven otherwise. A startling development and shotgun approach that turns swaths of the population into criminals without good cause.
On February 7th Alexey Pertsev was released from prison under the conditions of house arrest and electronic monitoring. Alexey is one of the Tornado Cash developers and was previously sentenced to 5-years in prison and is currently appealing that conviction. The Tornado Cash developers did nothing wrong and should not face prison sentences for writing open-source code deployed as a smart contract on the Ethereum blockchain, once deployed the developers had no control over how their neutral software was used.
On February 9th @Skot9000 went on The Home Mining Podcast to talk about the story of the Bitaxe from concept to reality.
On February 11th @Skot9000 and @econoalchemist went on The Mining Pod to discuss The 256 Foundation’s telehash event.
On February 14th @Skot9000 and @econoalchemist went on The Bitcoin Way podcast to discuss The 256 Foundation’s mission to dismantle the proprietary mining empire and reveal the Ember One.
On February 21st Apple removed advanced data protection tool for United Kingdom customers following the UK government’s request for an unrestricted backdoor to Apple user’s iCloud information globally. Every government trends towards tyranny and this is an alarming move by the UK government which makes the trajectory crystal clear, the globalists want you to have no privacy nor financial freedom.
On February 21st @SpaceDenver kicked off the Heatpunk Mining Summit, a two day event in Denver, CO focused on Bitcoin mining heat reuse applications. There was a range of participants from Do-it-Yourselfers to plumbers. @Schnitzel wrote up a great recap of the event.
Mining Industry Developments:
The development will not stop until Bitcoin mining is free and open. Innovators didn’t let off the gas in February, here are seven note-worthy events:
0) Some thought this day would never come, others saw it coming from a mile away but on February 1st the mempool cleared.
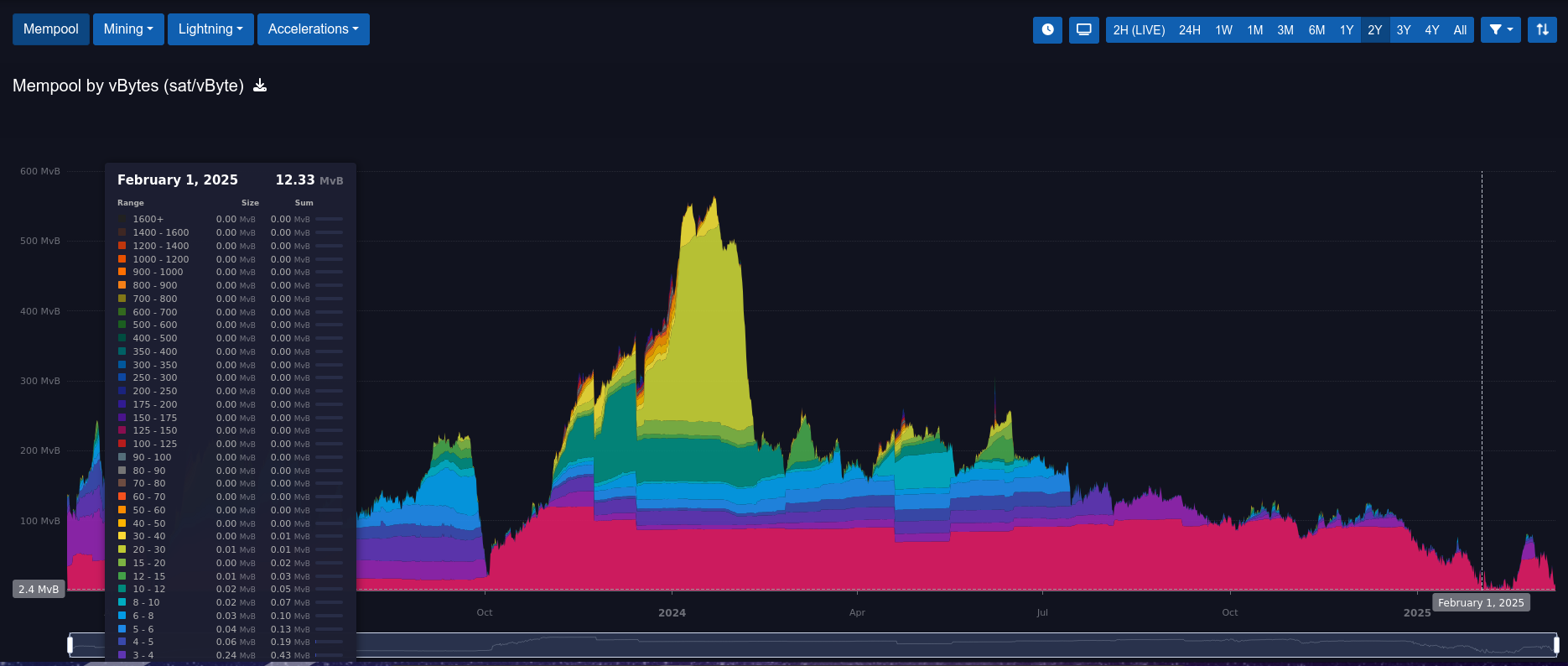 [IMG-000] Mempool Clearing
[IMG-000] Mempool ClearingThis is significant for a number of reasons: on-chain transactions were able to be included in the next block for 1 sat/vB which means on-chain enjoyooors could get both speed and economy when sending bitcoin. But this means the percentage of mining rewards from transaction fees were low. A lack of on-chain transactions can indicate that the network is getting little use and it can be further extrapolated that a network with little use will inevitably have little value leading to less interest, less development, less adoption, less miners, less security, etc. The best way to mitigate such concerns is to take self-custody of your bitcoin. Trusted third parties like centralized exchanges and derivative products like paper IOUs can move balances between accounts off-chain without transferring ownership of the underlying bitcoin itself. The next best step is to actually use your bitcoin to buy things.
1) On February 2nd the Nerd OCTAXE makes a splash, racking up 10.8 Th/s with 8 BM1370 ASICs on a 160W+ PSU.
 [IMG-001] Nerd OCTAXE Reveal
[IMG-001] Nerd OCTAXE RevealThe Nerd OCTAXE is fully open-source using the CERN-OHL-S license. The display is a NerdAxe/NerdMiner unit and the whole system is standalone meaning that no Raspberry Pi or other computer is needed. The GitHub repo has detailed build instructions and all the details about the project can be found there.
2) On February 4th @OrangeSurfBTC publishes the Mempool.space Block Size Report examining the evolution of Bitcoin block sizes from block height 0 through block height 881866.
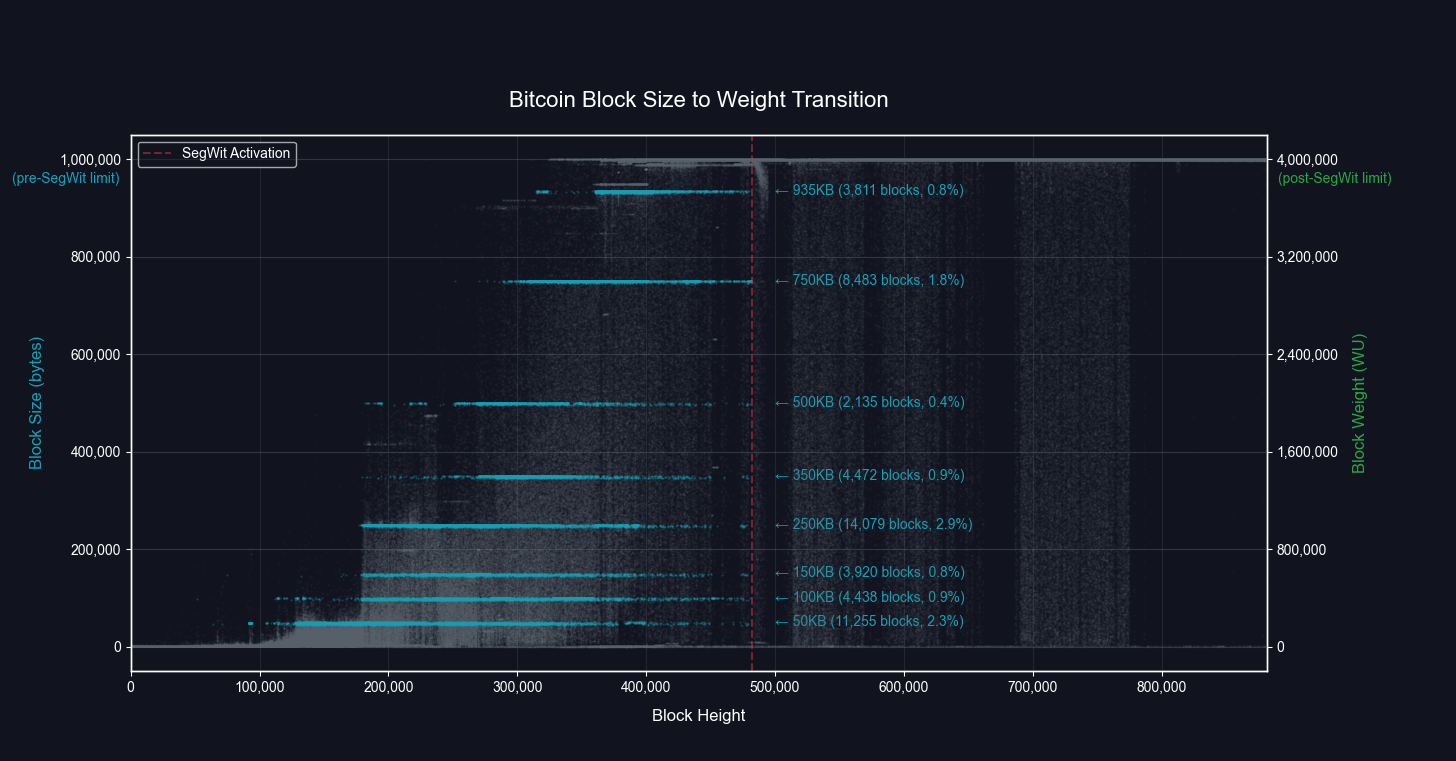 [IMG-002] Block Size to Weight Graph from OrangeSurf
[IMG-002] Block Size to Weight Graph from OrangeSurfThis report offers a deep technical dive into how BitcoinCore default settings, miner-selected configuration values, transaction backlog, SegWit, and inscriptions all affected block sizes and space utilization.
The graph above for example, displays horizontal bands at varying data sizes that correspond to default BitcoinCore settings; indicating that many miners were running the default BitcoinCore settings.
There are great explanations and technical analysis in this report. Be sure to check it out for an in depth understanding of Bitcoin block size trends.
3) On February 5th Mempool.space implements Stratum Jobs visualizer:
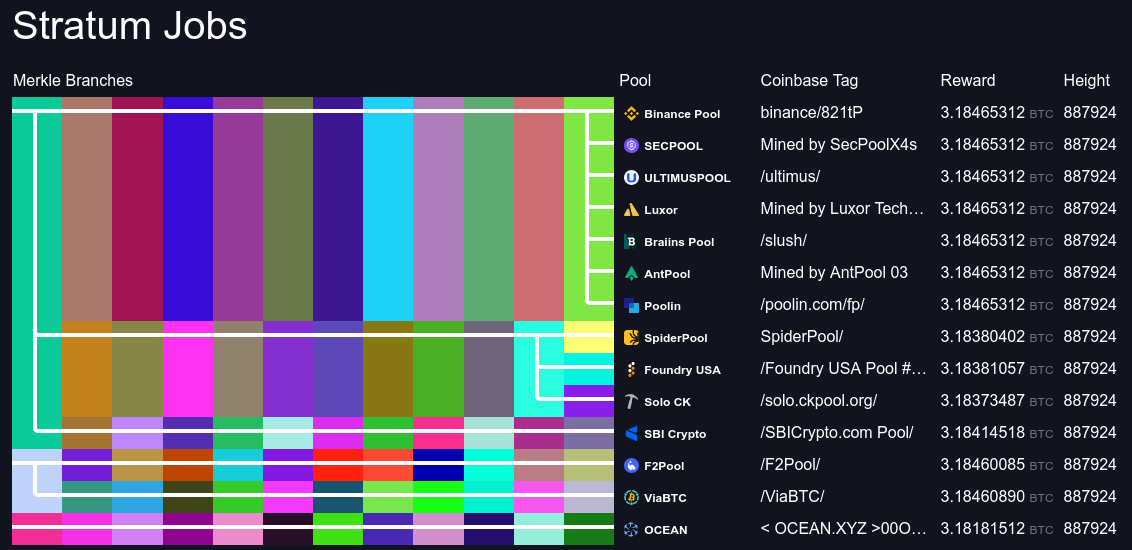 [IMG-003] Mempool.space Stratum Jobs
[IMG-003] Mempool.space Stratum JobsThis is a visualization tool similar to Boerst’s Stratum.work that shows which pools are using the same block templates which offers insight into miner centralization. The more of these visualization tools people have, the more informed everyone will be. Miner centralization can have several negative effects on the Bitcoin network including censorship attempts.
In the image above for example, it can be observed that Binance Pool, SEC Pool, Ultimus Pool, Luxor, Braiins, and Poolin are all using Antpool’s block template down to the 12th Merkle branch.
The ability for miners to generate their own block templates is an important step forward in the fight for keeping Bitcoin mining decentralized. Currently, some available options to achieve this are by self-hosting Public Pool or CK Pool, which the FutureBit Apollo’s do out of the box and is the setup used to solo mine block 881423 during The 256 Foundation’s Telehash; or self-hosting OCEAN’s DATUM.
4) On February 11th @RohEisenHammer revealed a Bitaxe Gamma that produces increased hashrate with the open-source BreaktheFiat Cooling System 60mm v1.
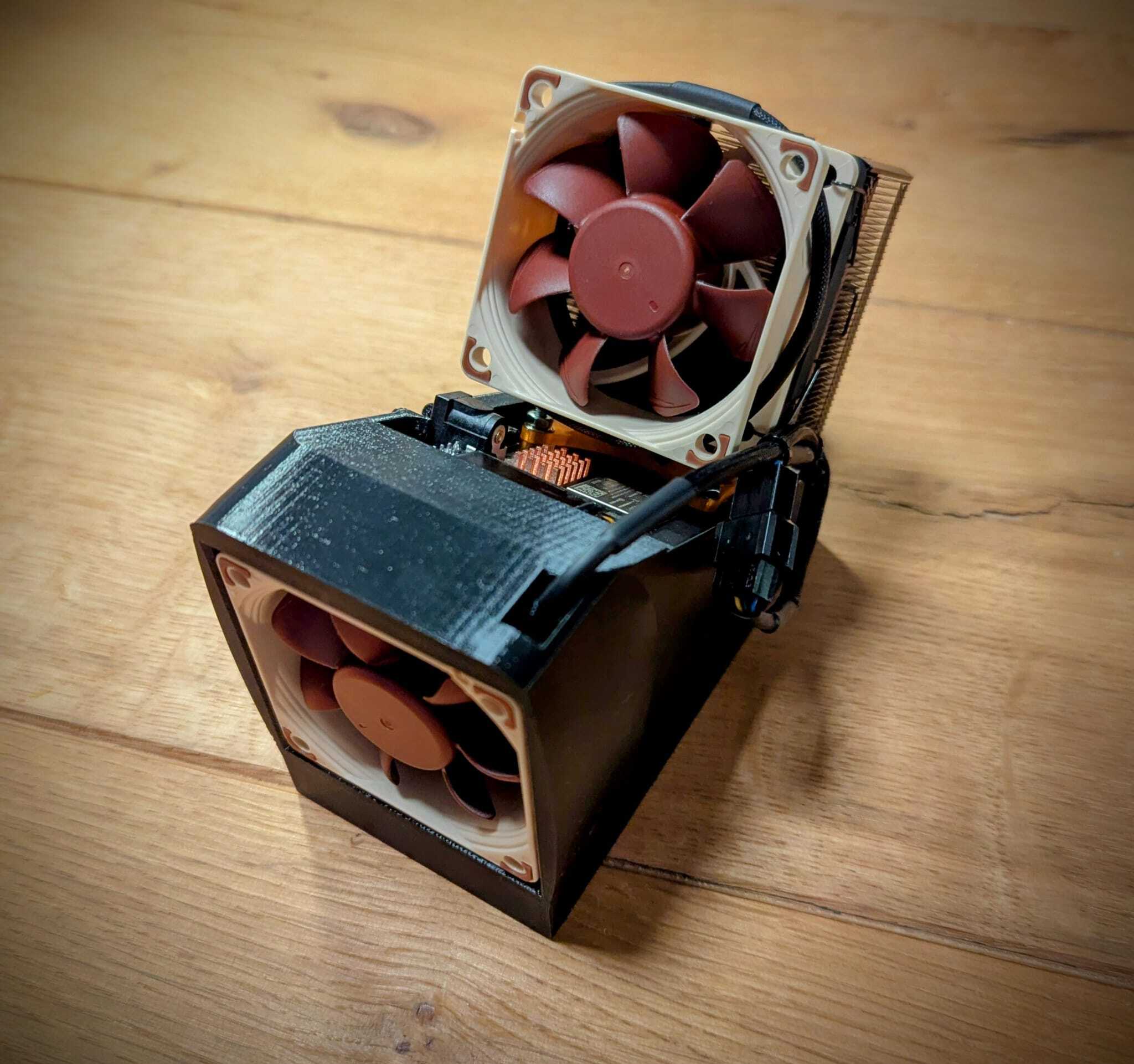 [IMG-004] BreaktheFiat Cooling System
[IMG-004] BreaktheFiat Cooling SystemThis innovative cooling system cools both sides of the Bitaxe allowing the user to over-clock the device more.
5) On February 27th Braiins announced they have their own Bitcoin mining ASIC test chip. The test chip has been in development for 2.5 years and although the specific efficiency is not yet disclosed, this demonstrates that there is an increasing interest from more participants to make their own Bitcoin mining ASICs, departing from a dependency on Bitmain.
6) On February 28th Braiins committed to open-sourcing their Control Board, supporting software, and some extras. This is a step forward in making Bitcoin mining free and open. The control board is designed to replace stock Antminer control boards.
The software being released with the control board includes an OpenWrt distribution, Linux support for mining peripherals, along with source code for the basic board firmware, U-boot, Linux kernel, and OpenWrt. The firmware does not have the mining component built in but all the tooling is there for users to develop their own mining firmware. Braiins OS is not included in the release.
Extras include a guide on building a fully functional mining setup with all the provided tools. Users can even take the Braiins firmware binaries and the provided tools to compile their own image to flash onto the control board. A Nix shell for the build environment is also included.
The software will be released under the GPLv3 open-source license and which open-source license the hardware portion will be released under is still under consideration. But everything will be openly available by the end of March so keep an eye out for further announcements.
Grant Project Updates
In February The 256 Foundation reviewed all the grant applications, thank you to everyone who showed interest in working on the 5 projects up for grabs. Interviews were scheduled for qualified candidates and one lead developer was chosen for each project. Currently negotiations are taking place to work out timelines, deliverables, and budgets for each project. The projects will be officially kicked off on April 5th, 2025 and the lead developers for each project will be announced at that time.
The five projects are: Ember One v01, a ~100 Watt standardized hashboard designed with the Intel BZM2 ASIC. The Ember One v00 with the Bitmain ASIC is nearing completion and the fully validated design will be released by the end of April, 2025. The GitHub repo is now open to the public and anyone can start taking a look now.
Mujina Mining Firmware, a Linux based mining firmware application with support for multiple drivers so it can be used with Ember One v00 with the Bitmain ASIC or Ember One v01 with the Intel ASIC and will implement Stratum v2 client support.
Libre Board, the control board for the Ember One built to support high power compute modules, MIPI touchscreen display port, NVME expansion to run a full node, Raspberry Pi 40-pin header, and much more.
Hydra Pool, the stratum server application that will run on the Ember One mining system, features support for Stratum v2, solo mining mode or alternative payout model selection, and a user friendly dashboard to view pool stats.
Block Watcher, a Bitcoin mining insights application built to run on the Ember One mining system using the self-hosted node for blockchain data. Provides comprehensive visualization tools to help inform the user.
Actionable Advice:
Summer is coming! Time to take into consideration different cooling techniques for your Bitcoin miners. Do you stick with the default air cooled approach or is it worth it to spend the extra capital on a liquid cooled operation? Who better to hear from than two industry titans, Mike Hamilton former Chief Technical Officer & Chief Research Officer at Griid prior to the CleanSpark acquisition and Kevin Zhang Executive at Foundry Services. The following is a transcript of our panel discussion during NEMS25 hosted by yours truly.
Eco: Welcome you guys. So the title of this panel is “ASICs Wet or Dry” and both of you have a ton of mining experience. So why don't we do some brief intros, tell us who you are, what you've been up to and then we'll get into it.
Mike: Sure. Mike Hamilton, I was the CTO and Chief Research Officer for Grid, acquired by CleanSpark. I've since left and I'm finding out what's next, probably some 256 foundation stuff.
Rod: Let's go! (audience applause)
Mike: Because once you mind a block, everybody wants on board. So yeah, I was a chip designer, did some network security for a long time and then full-time mining since 2019.
Kevin: Good stuff guys. I'm Kevin Zhang, I'm not Matt, so if you came for the Giga talk, I'm sorry. With the new administration in office, it's okay to be a cis white male again, so I was going to give it a shot. (audience laughter)
Jokes aside, I've been a Bitcoin mining in the US for some time now and lately I've been at Foundry last four and a half years. I think everyone knows who we are, especially recently mine 7 blocks in a row. Surprised, no one commented, we actually mined eight at one time in a row. So I guess everyone's asleep, but we'll leave that for another discussion.
Eco: Wait, wait, wait, hold on. When was the eight blocks? Was that like years ago?
Kevin: No, it was like three months ago.
Eco: No kidding?
Kevin: Yeah.
Eco: Wow. Kevin: But no one also comments that the fact that we are actually unlucky for that same 24-hour period. So we actually lost money on that day. But I digress.
My background's always been in Bitcoin mining and especially I remember back in the day when immersion mining is first coming out, everyone's very skeptical. Now people are on board with immersion mining and now they're skeptical of hydro mining.
So it's interesting to see how these technologies come about and the adoption curve and how long it actually takes.
But I'm excited to be talking about this topic. It's going to be a lot of fun guys.
Eco: Yeah. So you mentioned something interesting there. So you mentioned both hydro and immersion. So this isn't just ASICs wet versus dry as if as though there's one version of wet.
There's actually multiple different types. So we've got immersion. Do you do anything with two phase immersion?
Because I've seen some of that recently where you're like dipping the ASIC in the solvent and it's boiling off.
If you've got any experience there or with hydro, let's get right into it. Which kind of wet are we talking about here?
Kevin: All right. So maybe we can take a step back and introduce all the different variants of types of mining, right? So the one I think everyone's most familiar with is air-cooled mining. And that's simply you're taking cold air and pushing it through the miner and exhausting hot air on the other side.
When it comes to liquid cooling, now there's many different types. In the beginning, I think one of the more popular ones was immersion, which is what you're actually is you're taking a miner, sometimes converting an air core miner. Sometimes it's an immersion specifically designed equipment.
You're dipping it and submerging it into dielectric fluid and using the fluid to kind of transmit the heat off the chips. And that's kind of you're actually taking the fluids and you're touching that to the chips itself. Then there is Novak 3M, which is the most popular use case for two-phase immersion. Two-phase is a fancy way of saying the state of the liquid or using the cool something is changing. So what you're doing is you're taking a fluid, you're using that that spurs the heat. And the heat dispersion happens when you're changing it from a fluid of solid state into a gas.
So it's super cool technology. The downside of it is to date it's still been very, very expensive. And the last form of cooling is hydro. It's another form of liquid cooling. And that's where you're actually running standard water or treated water through tubes that go across the boards on the miners to dissipate the heat.
Eco: Which one of those methods or is it all three? Do you got a mix in your operations that you use?
Kevin: So we've tested all of them. The only one we don't do at scale is the two-phase, which is the Novak 3M solution.
Eco; And why is that?
Kevin: It's been cost prohibitive to date. And the same has been true to immersion in hydro when it first came out. So probably it'll take some time for it to come to be more economical and more cost-efficient.
Eco: So let's break this down a little bit further. So if I wanted to cool my miners with immersion, can I just take the miner and drop it in a bath of dielectric oil?
Mike: I mean, kind of, like most answers about anything, it depends. But really you have to take off the fans, if you're taking an air-cooled machine. And then there's sometimes there's some weirdness with the power supplies. And some of you may actually take the power supply fans off.
Or in the case of one of my sites, we put popsicle sticks in there to keep the fans from spinning. So they wouldn't recycle the fluid. But there is usually some amount of work to prepare them for actual full immersion.
Eco: So it sounds like there's some labor involved and some modifications needed. Are the efficiency gains from this different type of cooling method, do they offset the extra labor that goes into setting it up?
Kevin: So yes and no. I think before we kind of get into overgeneralization of like, will this improve your economics or not? I think you have to look at the specific site that you're working with.
If you can run air-cooled air, if it's dry, if it's cool, you may not need to over-complicate things but going into liquid cooling or getting too fancy and cute with your infrastructure.
Now, if you're in a very hot climate and heat is everywhere, there's no cold air to draw into your site, maybe that's when you start looking at these things. No different than if it's way too humid or way too wet outside. You can't use the outside air or damaged machines. That's when you look at liquid type cooling.
And then to answer your question, it depends on what you paid for your miner, obviously, right? And the modifications needed.
Nowadays, immersion and hydro are popular enough that the manufacturers like Bitmain, MicroBT, they're making units out of the box that are designed for those use cases. Back in the day, you have to modify air-cooled miner, you have to remove the fans, you have to Jerry-rig it, like Michael's talking about it. And you also have to exploit the miner and change the firmware.
So you're voiding the warranty both physically and on the software layer as well.
So I think now with a lot of the new manufacturer support, it's been a lot more capital-efficient and a lot more streamlined.
And I think there was a gentleman here yesterday asking about what's my miner firmware. And I think that's been like a long time meme when it comes to brains and others. There isn't much optimization for air cooling, firmware for MicroBT, but where the optimization comes in is on the immersion side, where really your only limitation is your power supply. You can crank up the overclocking, the frequency and the voltage, so much more on the chips, as long as the power supply can support it and you have good flow of your liquids to dissipate the heat.
Eco: So you bring up an interesting point. It's like kind of site-specific will determine what sort of cooling method you want to apply, right? And just out of curiosity, and if you guys can speak about it, like how many sites have you all operated and what kind of geographic locations were they in and out of those, which cooling methods were you employing and why?
Mike: Yeah, and I think I've set up several sites in various locations. So it's sort of North Texas area, actually doing a gas well site. We chose immersion partially because it's right next to a multi-million dollar house home neighborhood and there's this oil well sitting behind it. And so we opted for immersion. It's a little bit hotter. It's a little bit dusty there at the well.
Incidentally, we also generate onsite, which is not quieter than the actual miners themselves, but that was a lot to do with the dust and the temperature.
And then other sites, it would be lots of Tennessee TVA sites where it's relatively cool. Now it does get hot. It can get pretty hot during the summers. So we did lots of air-cooled.
We did a little bit of immersion, a single phase full immersion, mostly from a proof of concept. Really, when you're trying to build quickly and inexpensively air-cooled, given the right environment is generally cheaper with some other trade-offs. So I've done a little bit of both.
Eco: Is it easier to keep the dust out of the mining equipment using immersion?
Mike: Yes. I mean, that is one of the benefits, at least in the single phase immersion, like the tank outside. The machine is basically protected. There's no moisture. There's no air.
So from that perspective, it can be good for the actual machine that is not getting on to that exposure. But at the same time, the fluid can create other problems with plastics and hardening. There's other issues.
Eco: How about you, Kevin? What kind of sites have you set up and what kind of methods did you employ?
Kevin: Sure. So I think my mining career, which started about 10 years ago, it predated a lot of the economics coming down of the liquid cooling. So for me, it was a lot of air-cooled sites. And if you look at it historically, somewhere to my sites, I was always building them more the climate was cooler and drier.
But with the new innovation and the cost coming down on liquid cooling, it's allowed for new regions to break into mining, in particular leveraging hydro or immersion.
In the past, I was always monitoring in Montana or northern China, where there's a lot of coal power, where it's cool climates.
Nowadays, you have mining in the Middle East. They're huge fans of hydro mining over there. So we were out in Oman recently. We partnered with some of those sites that were mining our pool over in Dubai.
And also now you have South America, where sometimes it's way too humid. They're able to mine. Or if they're too close to the equator, it could be too hot and too humid. They can mine because now they're using immersion down there as well.
So just seeing kind of the shifts geographically, all these new locations have been unlocked. Now that the outside climate's no longer a concern, that's been pretty exciting to see.
Mike: Yeah, and I think the noise issue is also a thing too. There was lots of sites that we looked at in many different situations where there's homes close, there's businesses close.
In one case, there was a school literally a few hundred feet away. And just while dry coolers and the other infrastructure aren't necessarily quiet, it's a different frequency of the high pitched fans of air cooled mining can be distracting.
Eco: Yeah, you bring up an interesting point. So if you're running an immersion system, you don't have these fans that are just passing millions of cubic feet of air a day through the ASICs, right? And those fans are what create all the noise and are screaming. And that's what people hear. So were you making those decisions preemptively? Like maybe based on some of the backlash we've seen from that site that Mara runs, that they got a bunch of noise complaints. Were those preemptive decisions or were you doing that because somebody complained to you?
Mike: I mean, we did. There was some public news around a site that we had that had gotten some noise complaints and it turned into a bigger thing. And so we're definitely more careful because if you have an air cooled site, trying to quiet an air cooled site, post build is very difficult. You know, hay bales or sound walls. And then it starts to get unsightly. So designing for the sound is very important from the beginning.
Eco: Right, because you've kind of built this whole setup around these miners, right? And now you're getting noise complaints.
Mike: And you design the site for airflow. Well, now you have a 20 foot wall to help with the sound. But now you've restricted airflow into your containers and it creates all sorts of other problems. And the reality was with these big, you know, the dry cooler manufacturers, you know, we got, we did some proof of concepts with one of the manufacturers. We're using 12 foot fan on the dry cooler. So it's still moving effectively the same amount of air as all the small fans. But it's a much lower rotation, you know, lower frequency noise. And so it's much less or much more pleasant than the cyber hornets.
Eco: Yeah. What other environmental considerations are there? Like if you've got tanks full of immersion fluid, is there special considerations, secondary containment systems, dams, barriers to contain spills? Like, are there any considerations along those lines that go into place?
Kevin: So historically there have been, but I think with the new improvements, there's like two types of designs. There's a kind of open loop system where kind of bring water in, bring liquids in that aren't in your closed solution. And they're just closed loop, which is yours recycling the same kind of fluids over and over again.
So more and more nowadays you have closed loop systems or you have like reserves of water that you're bringing in. You're not drawing from a lake, you're not drawing from a new water source. That has led to a lot more, a lot less backlash where it's like there's really no environmental concerns with that. And when we talk about kind of these environmental concerns, I always get some PTSD because I was at Greenwich generation, which was the very first power plant to ever mind Bitcoin in the States. And federally regulated behind the meter, I think it was such a special project for me to be on.
But then the push back from the environmentalists, we're just, there's no logic and rhyme or reason. It's like our fans, I could totally see the argument if we're disturbing the nearby neighbors, but they're coming in and protesting and saying we're scaring the way the killer whales in the Atlantic Ocean. And we're off of a lake in upstate New York, right?
So I think now you're kind of taking away that side of the argument, whether it's logical or not. And I think that just makes it a much more buttoned up case when no one has any, it's more proof when it comes to operating without any of these environmental concerns.
Eco: That brings to mind the saying that it takes exponential more effort to refute bullshit than it does to just say the bullshit, right?
Kevin: Absolutely.
Eco: Did you have to bring counter evidence to the table and say that and demonstrate no, we're not disturbing the whales?
Kevin: Yeah. It's like you have all these measurements, you have decibel counters, this and that, like you're kind of property lines. It doesn't matter. It doesn't just come up with a new excuse, right? A new complaint. Yeah.
Mike: I mean, we had some city council meetings and you get people, you know, of various generations, but of particular generations that are very set in their beliefs, they hear one thing. At one site we were looking at and there was a guy that had sort of like a rescue animal zoo. And he was saying that like his, his animals were going to stop reproducing and then they were all going to like drop over dead from the sound of these fans.
Kevin: Yeah. And we've, I've heard it all like we caused the autism in their kids because the fans are too, they're now not, I shouldn't joke about it, but that, those were some of the complaints we got.
Eco: You monsters. (audience laughter) Making the kids autistic and killing the animals. Jeez.
Mike: But you asked about like the containment or like fluids and environmental concerns. I mean, you do theoretically want to have the containment mechanisms for your tanks leak.
You know, I've heard of some sites where, you know, tanks, springs a leak and, you know, $100,000 worth of dielectric fluid is down the drain.
And so there are some of those concerns, but it's really not much different than, you know, you have to do the same thing with transformers. Transformers are filled with, you know, either mineral oil or if you go with the, with the fancy fluids to get a little bit of performance, you still have the same containment modes.
And so it's really not anything different in the normal construction, in the normal construction world.
Eco: What, what's next? Are there other cooling methods down the pike that you guys have been seeing and experimenting with or do you think the tools that we have at our disposal now are kind of what we're going to have going forward?
Kevin: So one thing I think has been emerging recently, especially with hydro mining, that's really exciting, is it's not just like cooling your miners, you're actually incentivized to capture even higher heat. So when you can actually generate a lot of heat and capture it, that's when you get your rehab, heat recapture programs. And that's I think one thing that differentiates hydro over both air and immersion is it's a lot easier to transfer water and capture that efficiently without much loss of the heat for whatever other use case you have for that heat itself.
And I think that this is something that's been talked about a lot. Sometimes I think the theories and the hypotheses come out way earlier, the technology takes a few years to catch up.
Like back in the day, it was always, oh, it's so logical and obvious, the people that should be mining Bitcoin are behind the meter. They're power generators themselves.
Well I think everyone underestimated and overlooked the fact that you have a bunch of older people wearing suits, very traditional thinking, very conservative, half the time convincing them that Bitcoin isn't for money laundering or for scams or whatever, criminal activity, whatever.
So that took a long time for that adoption to happen. Same thing with the heat recapture narrative. It's no longer just a narrative anymore. With hydro mining, it's very easy to kind of capture that heat. You see it for like greenhouses, you see it for fish nurseries.
So there's all these fascinating use cases.
There's one other anecdotal story I'll tell. I think it's really cool. So I think everyone knows that there were really serious bans in China against Bitcoin mining two, three summers ago. And despite that, there are actually a few sites that still mine Bitcoin. The ones that mined Bitcoin that integrated the heat recapture was hydro mining that was providing heat for nursery homes. So even the Chinese government can't justify shutting down the heat that was being generated for the old people in the nursery homes.
So I think when you integrate in such a way that it goes hand in hand to daily life and when it's actually beneficial beyond just kind of optimization of financials, I think that's when it's a really powerful technology.
Eco: How are they getting the heat to the nursing homes? Are they really close in proximity to the mine?
Kevin: They were running the mining farms. I'm going to call mines. These are data centers and these are rack design hydro units. I think these are MicroBT M53s or maybe one generation before that. But they were just standard rack just like they're indistinguishable from servers and they just run in a loop hydro.
Eco: Wow. Have you found any heat reuse opportunities in the course of your operations?
Mike: Yes. So we had talked about some people trying to do, don't boo me here, but it's a possible monetary option with carbon capture is something that we've looked at.
There was a few other things.
Like honestly, now that I'm moving on, one of the things I've thought about doing is actually doing a brewery in Austin with water that's preheated from Bitcoin mining. So instead of having to heat up cold water to boil it to brew your beer, have preheated water that you're using off the miners.
But one of the problems that I think maybe doesn't get talked about from this heat reuse perspective is there's very minimal use cases.
So like the greenhouse is a perfect example of heating and water heating. But really where the power of waste heat is is very high temperature and that becomes a major problem because you can't run, these chips have to run in certain parameters.
So you're getting water that's like 140, 150, 160 degrees, but really you need that 200, 210 to get the temperature delta that allow you to either regenerate electricity, which is actually a project that I was working on, is actually taking the heat from the immersion tank and regenerating electricity to power the other things. So for off peak, when we're on peak, we could still keep other things up, regeneration.
So there's lots of cool things. But again, the temperature of the water or of the heat or the quantity is just not quite enough to make it.
Eco: It's like just below that industrial level heat you need. Yeah.
Kevin: I think that's was exciting too because MicroBT, I think they're coming out with the model types all kind of blend in, but I think it's the M64S, which is like the higher heat version. So they intentionally generate even more heat off their models just for this use case.
Eco: Awesome. We've got just under five minutes left and I want to be able to take a couple questions. Okay, cool. With the last couple minutes then, let's just get some closing thoughts from you guys. I mean, I know you said you're searching for what's next. You're thinking maybe 256 foundation, but…
Mike: If you'll have me.
Eco: Yeah, we'd be happy to. But yeah, I mean, do you have any closing thoughts about what you're going to do next and or any advice for people who are getting into mining and thinking about what cooling methods they should use?
Mike: Yeah, I mean, I've had a few conversations the last couple days on this. You've got your mega-mines, you have the home plebs, and then I feel like there's still going to be a middle area. You've got Schnitzel doing water heaters. I think that's a thing where you can find this wasted energy to either to heat. People are using water heaters. They're going to pay to have hot water. And if you can make some Bitcoin and it costs the same. So there's, I think there's going to be some really interesting use cases that people haven't even thought of yet in using mining to be able to take advantage of all the economics, not just the Bitcoin, but also saving in other areas and being able to reuse things. So I'm really excited to see what, especially with all the cool stuff with 256 and being able to open up more ability to control machines and have alternative use cases besides 100 percent on all the time trying to go as efficient as possible. Like Kevin's talking about a higher heat model, all sorts of cool things that can be done. And I'm super excited to see in the coming months what people do and what comes out of that.
Eco: It's awesome. And how about you, Kevin? Do you have any closing thoughts you want to share? I know Foundry just went through some structural changes in their mining operations. I don't know if you want to share anything about that or what you got going on next or any advice you got for the audience.
Kevin: Yeah, sure. So for those that didn't catch the news, we recently announced Fortitude Mining. That is the separation of our self-mining arm that was kind of all under the Foundry branch, now its own Independence subsidiary under DCG.
So we actually have been self-mining at a pretty large scale privately for quite some time and now that's its own business and it's exciting to see that kind of survive on its own. It's going to be mining not just Bitcoin, but they're alt coins of different things as well. I'll keep that on the wraps here.
But building off what Mike was saying, some closing thoughts on hydro and immersion mining, I know I talked a lot about economics and kind of lowering the cost of this and that. Don't just chase just the lowest price tag as well. I think what's fascinating about these new liquid cool technologies are they're now very, very large vendors as well as large deployments of these sites that are up and running.
I was over in Corsicana visiting Riot site and to see the kind of different iterations that they've kind of deployed of immersion mining. You can see all the improvements have happened over time.
So I think one of the coolest things about our industry is how collaborative everyone is and no one's going to gate-keep like if they had a good experience or bad experience with a vendor or how they deployed certain technology. Everyone's going to be super helpful with their own experience and feedback on how they run something.
If it's a brand new vendor in the space, probably not the best idea to cut like a 50, 100 megawatt contract with them before you sample them out or you get some testimonials.
So it's not to throw anyone in the bus. I'm not thinking of anyone in mind. It's more of make sure you kind of reach out, get testimonials, get others, people's experiences, leverage that because oftentimes when you are going through your very first hydro or immersion deployments, it's a little bit more technical and there's a lot more points of failure, a lot more leakages isn't that.
So you want to make sure that you kind of leverage as much experience and the collaborative network that's out there as you can.
Eco: Awesome. Let's get a round of applause for these guys and then we'll open it up for some questions. (audience applause)
State of the Network:
Hashrate on the 14-day MA according to mempool.space increased from ~787 Eh/s to ~798 Eh/s in February – peaking at 832 Eh/s, marking ~1.4% growth for the month.
 [IMG-005] 2025 hashrate/difficulty chart from mempool.space
[IMG-005] 2025 hashrate/difficulty chart from mempool.spaceDifficulty is currently 112.14T as of Epoch 440 and set to increase roughly 1.7 – 2.3% on or around March 23, 2025. But that target will change between now and then. The previous re-target increased difficulty by 1.4%. All together for 2025 thus far, difficulty has gone up ~2.15%.
New-gen miners are selling for roughly $17.65 per Th using the Bitmain Antminer S21+ 235 Th/s model from Kaboom Racks as an example. According to the Hashrate Index, more efficient miners like the <19 J/Th models are fetching $17.49 per terahash, models between 19J/Th – 25J/Th are selling for $12.68 per terahash, and models >25J/Th are selling for $3.37 per terahash.
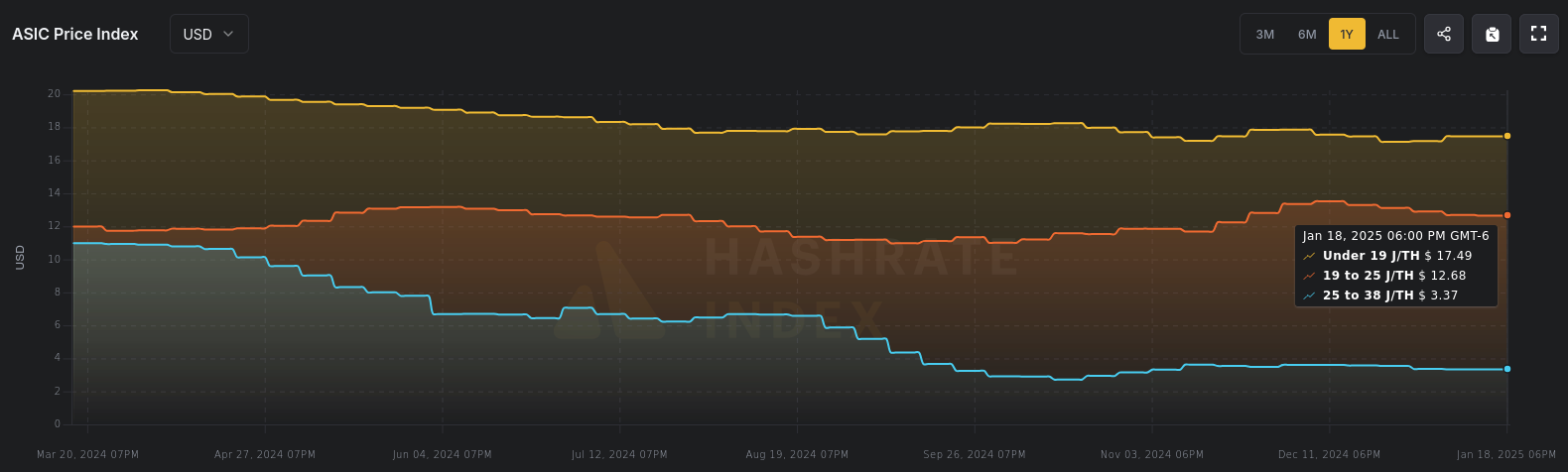 [IMG-006] Miner Prices from Luxor’s Hashrate Index
[IMG-006] Miner Prices from Luxor’s Hashrate IndexHashvalue is currently ~57,000 sats/Ph per day, up slightly from Frebruary when hashvalue was closer to 56,000 sats/Ph per day according to Braiins Insights. Hashprice is $47.00/Ph per day, down from $54.00/Ph per day in February.
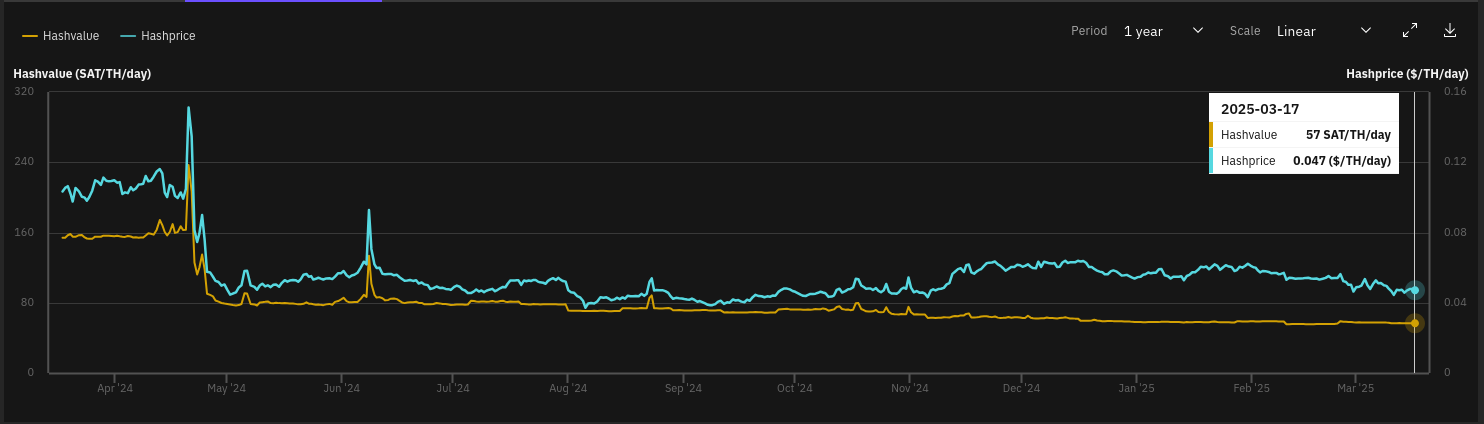 [IMG-007] Hashprice/Hashvalue from Braiins Insights
[IMG-007] Hashprice/Hashvalue from Braiins InsightsThe next halving will occur at block height 1,050,000 which should be in roughly 1,109 days or in other words 161,757 blocks from time of publishing this newsletter.
Conclusion:
Thank you for reading the third 256 Foundation newsletter. Keep an eye out for more newsletters on a monthly basis in your email inbox by subscribing at 256foundation.org. Or you can download .pdf versions of the newsletters from there as well. You can also find these newsletters published in article form on Nostr.
If you were looking for answers about cooling your Bitcoin miners this summer then hopefully you found them here.
If you want to continue seeing developers build free and open solutions be sure to support the Samourai Wallet developers by making a tax-deductible contribution to their legal defense fund here. The first step in ensuring a future of free and open Bitcoin development starts with freeing these developers.
The proprietary mining empire isn't going to dismantle itself; stay vigilant, frens.
-econoalchemist
-
 @ 878dff7c:037d18bc
2025-03-21 03:46:33
@ 878dff7c:037d18bc
2025-03-21 03:46:33Benefits
Lactofermentation enhances the digestibility and nutritional value of rice by encouraging the growth of beneficial lactic acid bacteria. These probiotics support gut health, improve nutrient absorption, and may reduce phytic acid and other antinutrients found in grains. It also gives the rice a slightly tangy flavor and improved texture.
Ingredients
- 1 cup uncooked white or brown rice
- 2 cups filtered or de-chlorinated water (for fermenting. That said my city tap water works fine...)
- 1–2 tablespoons whey (strained from yogurt), sauerkraut juice, or a probiotic starter (optional but helpful)
- Additional water for rinsing and cooking
Instructions
-
Rinse the Rice\ Thoroughly rinse 1 cup of rice under cold water to remove excess starch.
-
Soak and Ferment
-
Place rinsed rice in a clean glass jar or bowl.
- Add 2 cups of filtered or dechlorinated water.
- Stir in whey or other starter, if using. This accelerates fermentation, but rice will still ferment naturally without it.
- Use an airlock, cover loosely with a cloth or lid (not airtight - If you do 'airtight' just burp it a few times a day. Or a rubber glove with a small hole in it instead of the lid works too) and leave at room temperature (65–75°F / 18–24°C) for 24 to 48 hours.
-
Stir once or twice daily. You may notice small bubbles or a slight sour smell — both are signs of healthy fermentation.
-
Drain and Rinse\ After fermentation, pour off the soaking water and rinse the rice well to remove excess acidity and reduce any strong sourness.
-
Cook as Usual\ Cook the rice using your preferred method (stove-top, rice cooker, etc.), adjusting water ratios slightly if needed. Fermented rice often cooks a bit faster and may require slightly less water.
Notes
- Fermentation time depends on temperature; warmer environments speed up the process.
- For brown rice, a 48-hour ferment is ideal to soften the grains and enhance digestibility.
- The fermented soaking water can be saved as a starter for future batches.
-
 @ fc2470ed:17d9ee27
2025-01-30 14:24:23
@ fc2470ed:17d9ee27
2025-01-30 14:24:23by Hynek Fencl, July 2024
The way to Liberland is easy but not simple. Technically speaking, it’s just a short bike ride away from the nearest village on a comfortable bike path through a stunning forest known as the “Amazon of Europe”. On one side, one senses the presence of the mighty Danube River beyond the tall trees, and on the other stretch the farmlands of north-eastern Croatia. Then you take a left turn to a straight forest path, ride all the way to the end, and after a few bends on the track, you will have entered “the promised land”.
The part that is not simple is that Croatia both does and does not consider Gornja Siga (the local name for the area we now refer to as Liberland) to be its territory – depending on who you ask. This means that along the picturesque bike path, you will almost certainly encounter a border police patrol car, and, depending on whether you seem to them like you’re affiliated with Liberland, they will tell you to stop and hand over your ID. They run it through their system and, if you’re lucky enough to be a citizen of the EU, they let you pass. If you’re not and you give them a non-EU passport, they will ask you to come to the station with them to “determine the circumstances of your stay in Croatia.” You will then be issued with paperwork telling you to leave the country within the next 7 days, banning you from re-entering in the next 1-3 months. The official reasoning they’ll give for this is their reasonable suspicion that you have not come to Croatia as a tourist but with the intent to either do paid work (for which you would have to get a business/work visa) or to break the law (such as camping outside designated camping grounds or starting a fire in the forest).
All of this is part of a big game of chess that is being played out between Croatia and the Liberlanders. Croatia is in a tricky spot. They cannot properly administer the territory of Liberland and enforce its law in it – lest it would create an indication that the Croatian state officially claims it as its territory. However, they cannot not administer it either, since it’s on “their” side of the river, and it is risky for a rogue, unpredictable operation (from their perspective) like the establishment and growth of Liberland to just be left to its own devices right on their doorstep. This is, then, how we arrive at the status quo, with Croatia relating to Liberland in some way while being careful about the international perception of its action in another way. The resulting practice is a persistent harassment campaign toward the Liberlanders, with the apparent intent to create uncertainty and lower the appetite of potential Liberland settlers for this kind of adventure.
How to establish a new country
Liberland was born from an anomaly – a historical border dispute between Croatia and Serbia. The dispute involves the definition of where the border stands in relation to the Danube and goes back to 1947. Then, both lands along the river belonged to a single country – Yugoslavia – but the dispute arose with respect to the boundaries of its constituent states. It remained unresolved during the communist era and became an issue of international borders after the breakup of Yugoslavia.
Serbia claims that the border runs down the middle of the Danube, with the eastern bank being Serbian and the western bank Croatian. Croatia, on the other hand, claims that the border is set by historical borders marked by cadastral municipalities surrounding the Danube.
These municipality borders run along a different path because they were set before the course of the Danube was straightened during the 19th Century to allow for easier shipping. This results in disputed “pockets” of land on both sides of the river. The pockets on the eastern bank have a combined area of around 130 km2, while those on the western bank only amount to less than 10 km2. Not surprisingly, then, both countries claim that the border runs in a way where they get the >90% of land and the other country only gets the small remaining areas. However, this means that, by implication, since both countries are claiming the large areas, neither of them is claiming the smaller ones. These areas were, then, so-called terra nullius.
Under international law, there is no issue with any state claiming unowned and unclaimed land for themselves. And that is exactly what Czech businessman, politician, and activist Vít Jedlička did in 2015 when he proclaimed into existence the newly created Free Republic of Liberland on the largest, 7 km2 piece of the unclaimed areas between Croatia and Serbia.

It's one thing to announce a new country to the world. It’s an entirely different thing to make this country legitimate. Under the Montevideo Convention, a proper country needs to have 1) a permanent population, 2) a defined territory, 3) government, and 4) capacity to enter into relations with other states. Now, 9 years after the birth of Liberland, it clearly has three of those. As to a permanent population, the Liberlanders would argue that it definitely exists, even though Liberland’s now over 1200 registered citizens have had to largely live in “exile” ever since.
Nevertheless, despite the Convention, there’s one thing that makes something a country more than anything else – whether other countries see you as a country. The more diplomatic recognition an entity has, the more country-like it becomes. This is especially relevant for breakaway governments, governments in exile, or, most importantly in this case, startup countries like Liberland.
Very much aware of this, along with other members of Liberland’s startup government, Jedlička has been on a worldwide mission to legitimize Liberland in the eyes of other countries. Though there have been many amiable meetings and even some measure of support in some cases, no official recognition by any UN member has been achieved as of mid-2024. Liberland now has representatives and offices in multiple countries in the further pursuit of this goal. Though the effectiveness of this strategy has been questioned by many for the lack of decisive results so far, one thing remains unambiguously true: if recognized by even one or two UN members, Liberland would instantly gain an amazing amount of legitimacy and gravitas in the eyes of the world.
The quest for territory
Establishing international relations with countries anywhere in the world is not the only strategy that the Liberlanders have been employing in making the country more real and legitimate. This includes liaising and negotiating with the neighboring Serbia and Croatia. These relations are by far the most important and impactful ones. If both of Liberland’s neighboring countries were to either outright recognize the startup micro-state, or even just adopted an approach of non-interference, Liberland would be free to start actually developing and to find its own long-term position in the world.
As for Serbia, its Ministry of Foreign Affairs let itself be heard that, in their view, Liberland’s claims are a “trivial matter” but, in any case, they do not infringe upon the sovereignty of Serbia. One can imagine that Serbia might actually be secretly quite pleased with Liberland’s activities, since now Croatia has an issue to deal with on “their” side of the river, which, if they are not careful, could contribute to the legitimization of Serbia’s claim to the larger pieces of territory claimed by both countries.
With Croatia, things get quite a bit more complicated. In an official statement, the country rejected the claim that Gornja Siga is terra nullius, arguing instead that the land belongs to one of the two neighboring countries – the only question is to which one, which will be answered at some point in the future. Croatia also said it would stop any threatening and provocative activities on the territory even by force if necessary.
Ever since Liberland’s birth in 2015, the Liberlanders have been trying to make a mark on the territory. For a long time, even just entering Liberland wasn’t really possible. Under a deal between the Croatian and Serbian police that was put in place during the European migration crisis, Croatian authorities may enter Liberland and patrol it for security reasons (preventing illegal migration) even though they do not officially claim the territory as theirs. In addition, the border police have a near-permanent presence on the Danube River, preventing people from crossing into Liberland by boat.
As a result, anyone who would try to come to Liberland in any way would always be promptly arrested by the Croatians, essentially for entering a prohibited area.
After years of this status quo, a rather unexpected thing happened that made things suddenly move forward in a positive direction for the Liberlanders. In April 2023, during Liberland’s 8th anniversary celebrations, a famous YouTuber with a significant following decided to try to enter Liberland. After a few unsuccessful attempts due to heavy police presence and monitoring, he and his team hired jet skis and rode them all the way from Hungary down the Danube. When they got close to Liberland, they encountered the police boats again, but their jet skis were faster than the boats, so they managed to land at Liberland’s Liberty Island and plant a flag there. A few moments later, the police caught up to them and an aggressive policeman took out their handheld cameras before assaulting them and then kicking them on the ground, as can be clearly seen from drone footage of the incident.
As they had broken no laws, they were ultimately let go after the incident and free to leave the island without being arrested. However, the heavy-handed and illegal conduct of the Croatian police had been clearly documented and became part of the video that was published in July 2023.
The video promptly went viral, gaining almost 10 million views on YouTube. By comparison, the total population of Croatia is just under 4 million. When the news spread even to the Croatian press and TV stations, Croatia had a serious PR problem on their hands. The police had been clearly in the wrong, conducting themselves in a seriously improper way to the point of using physical force against peaceful people who had broken no laws nor engaged in any violence or hostilities themselves.
Something had to change. So, following this incident, the Croatian police adopted a different unofficial policy – from now on, they would let people enter Liberland if they wished to do so, in a controlled way. Since early August 2023, if you wish to enter Liberland, you can go on foot or by bike, take the access road down the forest, and show your documents to the Croatian police, just as you would at a border crossing. In a typical grand fashion of Liberland’s media team, Liberland made an announcement that an official border crossing had been opened between Croatia and Liberland (Croatia had obviously never made an official announcement like this, but for Liberland, that was the de facto situation on the ground).
In the weeks following the “opening of the border”, many enthusiastic settlers started coming to Liberland to finally begin making their mark on the territory of “the promised land.” They started constructing simple wooden houses, a bathroom, an open-air restaurant, and the related power and water infrastructure on Liberland’s mainland beach opposite Liberty Island in a settlement named Mateos Marina.
On September 7th, 2023, a troop of about 50 policemen and forestry workers, including a demolition crew, raided the settlement. The raid was officially dubbed a “cleanup operation” by Hrvatske šume, Croatia’s state forestry service. With the assistance of the police, they tore down all the wooden houses and structures using chainsaws and stole equipment as well as personal possessions of the Liberlanders on site. Several Liberlanders were arrested for “failure to comply with a lawful order”.

One might ask, if Liberland is not officially part of Croatia, what authority does Croatia have to come in to steal and destroy? Staying true to their claim that Liberland is not part of Croatia, the Croatians had announced to Serbia that they would be conducting the “cleanup” on Serbia’s territory, to keep it clean on their behalf.
We may only speculate about the reasons for carrying out this operation in such a heavy-handed, destructive way. One possibility is that allowing people to enter Liberland in the first place was a way for Croatia to lure some people to Liberland, become comfortable, and then come in and destroy everything to show everyone what would happen if they got involved in the project. Or perhaps it was the unexpected level of life, community-building, and construction going on in such a short period of time after the “opening of the border” that the Croatian police felt like they had to put a stop to it before things got so big they could not be easily destroyed anymore.
No matter the reasons, the raid had a chilling effect on prospective Liberlanders. Though there is plenty of video documentation of the operation, no one made a viral video about it this time. Though some media did pick up the news, it did not become a big story. Consequently, the PR fallout from this for Croatia was not unmanageable.
Liberlanders soon returned to the territory. However, the level of enthusiasm, energy, and external support was not as great as it had been before the raid. From then on, settlement efforts focused mainly on Liberty Island, unreachable by trucks and impossible for forestry workers to get to without a large boat which they seem not to have. Though perhaps a more strategic place to set up camp, Liberty Island is also much more prone to flooding than the rest of Liberland.
In the following few months, several makeshift houses were constructed using a combination of wood and sandbags. During this time, Liberland even hosted a first wedding on the island. The settlement was kept alive during winter as well, with Liberland enthusiasts staying mostly in houseboats whenever it was impossible to camp on site.
In the meantime, an enthusiastic settler couple bought a sizeable house with a courtyard in the village closest to Liberland – Zmajevac – which they have transformed into a base of operations for settlers. This is now called Liberbase and it is where visits to Liberland start, with bikes, supplies, and construction materials being gathered before going on the 40-minute bike ride.

In the spring of 2024, work started on the reconstruction of a former hunting lodge at a central location on Liberland’s mainland – Jefferson Square. The building was demolished a few years ago but the foundations, including a cellar, were left in place. The site was cleared, the foundations refreshed, and new walls for the future governmental building have sprung up from the ground. A professional construction crew was hired to speed up the re-building of this base, using large concrete bricks, to a standard that will make it logistically and practically difficult for the Croatian police and forestry workers to try to destroy.
 The battle for legitimacy
The battle for legitimacy The ongoing construction in Liberland is rather slow. It is difficult to bring construction materials to Liberland. It is prohibited to drive motor vehicles on the bike path leading to Liberland, which means that everything has to be manually hauled from Liberbase on cargo bikes. In addition, from time to time, bikes get stolen by the police or forestry workers. Despite these difficulties, the determination of the settlers is unwavering and they are working every day to move construction forward.
The ongoing construction in Liberland is rather slow. It is difficult to bring construction materials to Liberland. It is prohibited to drive motor vehicles on the bike path leading to Liberland, which means that everything has to be manually hauled from Liberbase on cargo bikes. In addition, from time to time, bikes get stolen by the police or forestry workers. Despite these difficulties, the determination of the settlers is unwavering and they are working every day to move construction forward.Is it possible to bring materials by boat? How did they get sandbags and other materials to Liberty Island?
The importance of such a commitment should not be underestimated. The continuous presence of settlers is incredibly important for Liberland. It shows the seriousness of the project. It shows that Liberland is a genuine community and a fledgling nation rather than, as some accusations tend to go, just an elaborate publicity stunt.
Practical difficulties with the Croatian authorities are not limited to construction-related issues. Even staying and camping in Liberland comes with its quirks. If you’re staying on Jefferson Square, you should be prepared for several police visits every day. These check-ups are usually nothing dramatic. The police usually show up, ask a couple of questions, and perhaps tell the settlers that they are not allowed to camp there or start a fire, but they don’t actually do anything more than that and just go about their day.
It seems that the Croatian police are rather shy about enforcing Croatian law in a territory that is not officially considered part of Croatia. International law often takes into account the de facto situation of the matter in any dispute. If Croatia enforced their law in Liberland, this would therefore be an indication that they do, in fact, consider the territory to be theirs in practice, despite the official stance of the state. It would play into the hands of Serbia, reinforcing their claims to the large parcels of land on the other side of the Danube.
In addition, Liberlanders on the ground report that the majority of Croatian police officers generally behave quite fairly and respectfully toward them – only a minority appear to hold a personal grudge against Liberland, being abusive and sometimes even violent instead. It seems highly likely that the police in general are just doing their job, following orders from above. Most of them don’t actually take it as a personal commitment to make life more difficult for the Liberlanders.
This is rather important from a big-picture perspective, because the settlers, by contrast, are often heavily personally invested in the project and see it as their mission to see Liberland develop into a proper country. This disparity in energy and determination is strong and perhaps this is what will, in the end, cause Liberland to prevail in this drawn-out dispute.

The dispute with Hrvatske šume is quite different. As of mid-2024, the forestry workers tend to turn up at Jefferson Square about every fortnight. Unlike the police, they do not limit themselves to words but tend to steal everything that is not bolted down – including tools, materials, tents, bikes, and personal possessions of the settlers camping there. The justification remains the same – to “clean the forest of any waste.” In their encounters with the police as well as the forestry workers, Liberlanders are of course meticulous in their video documentation of any illegal actions by the authorities.
The Liberlanders’ difficulties, however, do not just stay local. As previously mentioned, upon trying to enter Liberland from Croatia, people who do not have EU citizenship are promptly issued a one-to-three-month ban on entering Croatia, with 7 days to leave the country. This is done under legislation relating to citizenship and tourism.
However, things can escalate even further. Since last year, several key Liberland settlers and organizers, including Liberland’s President Vít Jedlička himself, have seen “heavier guns” used against them. They have been banned from entering Croatia for 5 years under anti-terrorism legislation, where the authorities argue that these Liberlanders are something akin to a threat to national security.
The Liberlanders have mounted a legal defense against this, in addition to challenging Croatia on other legal fronts. They have had some successes so far – in particular, it should now be clear that the Liberlanders do not need any building permits to construct buildings on their territory. Unfortunately, other issues – including the 5-year bans from Croatia – still remain unresolved.
Most Liberlanders remain hopeful nonetheless. They have seen their situation move forward significantly over the last year. A year ago, they were not even able to enter Liberland without being chased and/or arrested. Now, even some construction is possible, albeit in a limited way.
The road ahead
The long-term vision, of course, remains to build a full-fledged, internationally respected and recognized city-state. Liberland’s leaders often speak of a “Balkan Monaco”, referring to the amazing development possibilities that a freedom-oriented country in the middle of Europe could offer. Liberland has already hosted an urbanist/architectural contest, and there are concrete plans for the first hotel as well as a riverside real estate development. What is more, Liberland’s land is actually more than three times the size of Monaco.
Nevertheless, Liberland cannot move forward in a meaningful way toward these visions and aspirations under the status quo. The Liberlanders need to be able to build at scale and be free from harassment, both by the police and the forestry workers. Some kind of political deal is necessary as the next step toward proper development of Liberland.
Such a deal could take multiple forms, but all of them involve the Croatian authorities changing their attitude toward Liberland away from a policy of unrelenting obstruction – not necessarily toward outright recognition, but at least toward accepting Liberland as a neighborly project that will move forward and develop in some way.
One option could be to allow motor vehicles on the bike path toward Liberland, with a deal that could include charging Liberlanders some fair tolls to pay for the wear and tear of the pavement. An alternative would be to simply allow river crossing into Liberland from Serbia on the Danube. Since Croatia does not officially consider Liberland its territory, their current interference with this traffic is illegal anyway. Simply stopping this illegal conduct would help Liberland significantly without Croatia facilitating Liberland’s development in any active way.

Regardless of these options, the first and most notable step would be to stop banning non-EU citizens from re-entering Croatia as well as lift the existing (entirely unjustified and unreasonable) 5-year bans on Jedlička and the others.
It is easy to see why Croatia is wary and suspicious of Liberland’s development. One can understand the worries of a state in whose immediate proximity there is a new and unknown state growing and taking root. Nevertheless, Croatia actually has a lot to gain from making some kind of deal with Liberland.
First: currently there are perhaps a dozen policemen on patrol around Liberland at all times. This includes police vehicles and boats. This is a significant expense for the police force – an expense which is rather unsubstantiated, given that Liberlanders have clearly proven to be peaceful people who do not wish to pose any threat to Croatia, its people, or its law enforcement officers. Making a deal would mean that this large expense is not needed anymore.
Second: Liberland borders an area of Croatia that has been rather “left behind”, is underdeveloped, and suffers from a lack of jobs and investment. Consequently, younger people are leaving the area and the current population is growing older. If Liberland was growing and open for business nearby, it would provide the region exactly with the job opportunities, large investment, and overall development that it desperately needs.
Third: Croatia could use Liberland as an opportunity to actually gain an advantage in the ongoing border dispute with Serbia. As previously mentioned, Croatia cannot openly and properly administer the territory, as it would be an indication in the eyes of international law that they consider the territory to be theirs. On the other hand, it Liberland is located on “their” side of the Danube, so Croatia does have an interest in making sure the area is under their control somehow. Striking a deal with Liberland could involve Liberland agreeing to some obligations related to the administration of the territory which correspond to Croatia’s priorities. In this way, Croatia would have an active say in what happens on this land, effectively “outsourcing” its administration without officially claiming it as part of Croatia.
In addition to all these advantages being present, Liberland is very much open to cooperation with Croatia and is keenly looking forward to welcoming any future productive relations with Croatian authorities. There will be no grudges held on Liberland’s side, and if a mutually beneficial deal or solution were to be found, no one would look behind at any historical quibbles or difficulties. Liberland would be an excellent and friendly neighbor to Croatia, not just causing any issues but actively helping the overall development of the surrounding region.
Time will tell how things will develop. At the present, the momentum, energy, and enthusiasm is definitely on the side of Liberland. There seems to be very little actual interest from the Croatian side to cause issues for Liberland and to continue to prevent the fledgling state from developing further. All that is left are the bureaucratic hurdles of a state that is being overly conservative about its approach to the important issues of the day. Things might take time, but seeing the determination of the settlers and the willingness of all Liberlanders to be unrelenting in their fight for the cause, it is not difficult to argue that we might be seeing the dawn of Liberland as the world’s next proper city-state as we speak.
-
 @ b80cc5f2:966b8353
2025-03-20 23:34:00
@ b80cc5f2:966b8353
2025-03-20 23:34:00Originally posted on 10/10/2024 @ https://music.2140art.com/artist-spotlight-akme-beats/
Long-time Hip-Hop producer, MC and tattoo artist AkmeBeats is no stranger to the game.
Starting off his career in his originating country of Italy, and later moving to London, UK, Akme has worked with some top talent in both regions. His raw and pure boom-bap sound has many MCs seeking to work with him across the globe.
We caught up with Akme to discuss his journey into the new music economy, starting with his discovery of Bitcoin back in 2015, to his eventual dive into using it in 2024 and everything in between.
How long have you been making music professionally?
From 2010 for my first EP Akme “Ultimatum EP’’
What are some of the mediums you have used to distribute your music?
Distrokid from 2015, Bandcamp too, but now with different ones, like WavLake.
Have you ever been signed to a label?
Nah
What are some of the main things you see as a problem in today’s music industry?
All the websites and distribution they profit from all the musicians and labels try to use AI for their shit, weird! At this moment, at least, but we gonna change!
What made you decide to join the 2140Music community?
Because the music industry needs to rebuild in the Bitcoin way like we gonna do!!!!
Maybe another one…
What are some of the notable projects you’ve released or people you’ve worked with?
I did a lot of projects this year especially; 'Deafth spazio randagio' with Slippy Skills, Double Capital ‘A’ EP with Airklipz, Hooks Thrown off Deck with Airklipz and Sylva Grey, Roads Eucharist with SWAV’O, Ghostreet and Ghostway with L17 and Airklipz and GADGIE RANDAGI EP exclusive available on Even.biz
-
 @ b8851a06:9b120ba1
2025-01-28 21:34:54
@ b8851a06:9b120ba1
2025-01-28 21:34:54Private property isn’t lines on dirt or fences of steel—it’s the crystallization of human sovereignty. Each boundary drawn is a silent declaration: This is where my will meets yours, where creation clashes against chaos. What we defend as “mine” or “yours” is no mere object but a metaphysical claim, a scaffold for the unfathomable complexity of voluntary exchange.
Markets breathe only when individuals anchor their choices in the inviolable. Without property, there is no negotiation—only force. No trade—only taking. The deed to land, the title to a car, the seed of an idea: these are not static things but frontiers of being, where human responsibility collides with the infinite permutations of value.
Austrian economics whispers what existentialism shouts: existence precedes essence. Property isn’t granted by systems; it’s asserted through action, defended through sacrifice, and sanctified through mutual recognition. A thing becomes “owned” only when a mind declares it so, and others—through reason or respect—refrain from crossing that unseen line.
Bitcoin? The purest ledger of this truth. A string of code, yes—but one that mirrors the unyielding logic of property itself: scarce, auditable, unconquerable. It doesn’t ask permission. It exists because sovereign minds choose it to.
Sigh. #nostr
I love #Bitcoin. -
 @ 16d11430:61640947
2025-03-20 23:07:01
@ 16d11430:61640947
2025-03-20 23:07:01A Tale of Two Dysfunctional Kingdoms
In the grand theater of human organization, we are blessed with two great economic orders: Fiat, the Land of Fragile Giants, and Crypto, the Padded Madhouse of Infinite Lunacy. Both promise utopia, both deliver dysfunction, and both operate under the iron law that those with the most power will always act in their own interests—rules be damned.
The Fiat Intellectual Landscape: A Game of Tiptoeing Giants
The fiat world is a meticulously curated bonsai garden of decorum and quiet panic. Giants walk among us—CEOs, central bankers, hedge fund wizards, and the occasional Nobel Prize-winning economist—but they must step lightly, lest they shake the delicate equilibrium. The entire system is built on confidence, a polite euphemism for narrative control.
Take any major institution, and you'll find the same pathology:
Corporations: The larger they are, the more fragile their balance sheets, requiring constant PR therapy and quarterly ritual sacrifices to appease the gods of Wall Street. CEO statements are more rehearsed than Shakespearean soliloquies, lest a slip in language shaves billions off the stock price.
Academia: Intellectual giants must wade through a swamp of bureaucratic grant-seeking, where discovery is secondary to institutional survival. Challenging economic orthodoxy is career suicide, so best to publish another paper on "inclusive finance" while hedge funds strip-mine the economy.
Government & Central Banks: A crisis is just another reason to print more money, kick the debt can down the road, and assure the public that everything is “transitory.” Behind closed doors, they know it’s a rigged game—but stability must be maintained at all costs, even if it means bribing the peasants with stimulus checks to keep the illusion alive.
The entire fiat ecosystem is one of quiet desperation, where the powerful pretend to be cautious stewards of civilization while looting with the finesse of seasoned art thieves. Stability is paramount, because if the masses ever realized the whole thing is a confidence scam, they might actually ask questions.
Crypto: The Padded Madhouse Where Giants Go to Break Things
Meanwhile, in the Crypto Madhouse, giants don’t tiptoe—they run, scream, and occasionally set the entire house on fire just to see what happens. Here, there is no caution, no equilibrium—just a perpetual state of mania, where even the most outlandish ideas get venture funding. If fiat is an over-engineered glass palace, crypto is a playground for unhinged capitalists and techno-anarchists armed with flamethrowers.
The dysfunction here is less about fragility and more about unregulated chaos:
Ponzi Chains Masquerading as Innovation: Every year, a new "Ethereum Killer" promises to decentralize everything, only to collapse into an infighting mess of VC dumps, network outages, and sudden governance takeovers. If in fiat, failures happen in slow motion, in crypto, they happen overnight, in a Discord announcement at 3 AM.
Decentralization Theatre: Most "community-governed" projects are run by an inner circle of early whales who have more control than the Federal Reserve, but pretend it's democratic because they let the plebs vote on logo designs. The difference? Fiat oligarchs hide their power; crypto oligarchs post memes about it.
The Cult of the Visionary Founder: While fiat leaders pretend to be humble, crypto founders take the stage like prophets descending from the blockchain, dropping whitepapers with the same fervor as religious scriptures. And when they inevitably fail, they simply launch a new token, because failure only exists if you stop grifting.
Crypto may lack the institutional fragility of fiat, but in its place, we get wild, unchecked power, where insiders can rug-pull billions without consequence. The only real difference? Instead of bailing out banks, crypto just moves on to the next hype cycle.
Same Vested Interests, Different Scams
In the end, both systems operate under the same fundamental law: those with the most power will always find a way to keep it.
In fiat, the illusion of stability is paramount, so the powerful must lie in slow motion.
In crypto, the illusion of innovation is paramount, so the powerful must rug in high-speed.
The giants of fiat must walk lightly so as not to disturb the herd; the giants of crypto can rampage freely, because the casino always reopens. Either way, the little guy always pays the bill.
-
 @ 2ed3596e:98b4cc78
2025-03-20 22:46:58
@ 2ed3596e:98b4cc78
2025-03-20 22:46:58Bitcoin: The tool of true freedom in an age of control
Let’s talk about control. Not just the kind you see in politics, but the control over what you can say, what you can spend, and ultimately, how you live. It’s creeping into every part of our lives, and if you’re paying attention, you’ve already seen it happen.
Remember the Canadian truckers’ protest? If you donated just $50 and you got bank accounts frozen and all financial access cut off—not because of criminal activity, but because the government at the time didn’t like what you stood for. Look at donations to Palestine — many financial institutions are outright blocking donations to causes supporting folks struggling to survive in Gaza. China? Censorship isn’t just about speech; it’s about access to money, too – completely cutting people off from being able to participate in the economy. Economic strangulation is real and a growing government control tactic.
See the pattern?
It doesn’t matter what your politics are. If you step too far outside the accepted lines, you’ll be cut off. Your money is no longer yours if someone else can decide when you can access it.
The playbook isn’t new — just look at 1933
If you think this level of control is new, think again. In 1933, Executive Order 6102 forced Americans to hand over their gold to the government—under threat of fines and jail time. Why? Because gold was real money, and the government wanted to control the monetary system to finance its growth in spending and services. Gold, at this time, was $35 an ounce. Today it is worth thousands per ounce. The dollar, meanwhile, has lost 99% of its value in that same period.
Then came 1971. Nixon took the U.S. off the gold standard completely, meaning the dollar was no longer backed by anything tangible. Since then, the government has printed money at will, inflating the currency and making everything more expensive over time.
And yet, we’re supposed to trust this system?
Fiat is just a fancy word for "because we said so"
Our money is no longer tied to gold or anything of value. Fiat money has value simply because governments say it does. But history proves that this system is built on a lie. The more they print, the less your money is worth. It’s not about “helping the economy” or “fighting inflation”—it’s about making sure you stay dependent on the system. And when people get too self-sufficient? That’s when they start pulling tricks like EO 6102.
Bitcoin fixes this.
Bitcoin is E.O. 6102-proof
Governments can seize gold. They can freeze your bank accounts. They can tell you what you can and can’t spend money on.
But they cannot control Bitcoin.
Bitcoin is money that exists outside of their system. It can’t be inflated away. It can’t be seized by decree. It allows people to transact freely, regardless of politics, geography, or financial status. Whether you’re protesting in Ottawa, donating to survivors in Palestine, or living under Chinese financial surveillance—Bitcoin is the escape hatch.
“I consume, therefore I am”
Freedom isn’t just about what you can say—it’s about what you can do. If your ability to transact is controlled, then your ability to live freely is controlled. Bitcoin is the tool that breaks those chains.
It’s not just an investment. It’s not just “digital gold.” It’s a lifeline. It’s the difference between having control over your future or waiting for the next decree to tell you what you can do with your own money.
Governments will always try to tighten their grip. History proves it. But Bitcoin gives you the power to break free. The question is: will you use it?
-
 @ 599f67f7:21fb3ea9
2025-01-26 11:01:05
@ 599f67f7:21fb3ea9
2025-01-26 11:01:05¿Qué es Blossom?
nostr:nevent1qqspttj39n6ld4plhn4e2mq3utxpju93u4k7w33l3ehxyf0g9lh3f0qpzpmhxue69uhkummnw3ezuamfdejsygzenanl0hmkjnrq8fksvdhpt67xzrdh0h8agltwt5znsmvzr7e74ywgmr72
Blossom significa Blobs Simply Stored on Media Servers (Blobs Simplemente Almacenados en Servidores de Medios). Blobs son fragmentos de datos binarios, como archivos pero sin nombres. En lugar de nombres, se identifican por su hash sha256. La ventaja de usar hashes sha256 en lugar de nombres es que los hashes son IDs universales que se pueden calcular a partir del archivo mismo utilizando el algoritmo de hash sha256.
💡 archivo -> sha256 -> hash
Blossom es, por lo tanto, un conjunto de puntos finales HTTP que permiten a los usuarios almacenar y recuperar blobs almacenados en servidores utilizando su identidad nostr.
¿Por qué Blossom?
Como mencionamos hace un momento, al usar claves nostr como su identidad, Blossom permite que los datos sean "propiedad" del usuario. Esto simplifica enormemente la cuestión de "qué es spam" para el alojamiento de servidores. Por ejemplo, en nuestro Blossom solo permitimos cargas por miembros de la comunidad verificados que tengan un NIP-05 con nosotros.
Los usuarios pueden subir en múltiples servidores de blossom, por ejemplo, uno alojado por su comunidad, uno de pago, otro público y gratuito, para establecer redundancia de sus datos. Los blobs pueden ser espejados entre servidores de blossom, de manera similar a cómo los relays nostr pueden transmitir eventos entre sí. Esto mejora la resistencia a la censura de blossom.
A continuación se muestra una breve tabla de comparación entre torrents, Blossom y servidores CDN centralizados. (Suponiendo que hay muchos seeders para torrents y se utilizan múltiples servidores con Blossom).
| | Torrents | Blossom | CDN Centralizado | | --------------------------------------------------------------- | -------- | ------- | ---------------- | | Descentralizado | ✅ | ✅ | ❌ | | Resistencia a la censura | ✅ | ✅ | ❌ | | ¿Puedo usarlo para publicar fotos de gatitos en redes sociales? | ❌ | ✅ | ✅ |
¿Cómo funciona?
Blossom utiliza varios tipos de eventos nostr para comunicarse con el servidor de medios.
| kind | descripción | BUD | | ----- | ------------------------------- | ------------------------------------------------------------------ | | 24242 | Evento de autorización | BUD01 | | 10063 | Lista de Servidores de Usuarios | BUD03 |
kind:24242 - Autorización
Esto es esencialmente lo que ya describimos al usar claves nostr como IDs de usuario. En el evento, el usuario le dice al servidor que quiere subir o eliminar un archivo y lo firma con sus claves nostr. El servidor realiza algunas verificaciones en este evento y luego ejecuta el comando del usuario si todo parece estar bien.
kind:10063 - Lista de Servidores de Usuarios
Esto es utilizado por el usuario para anunciar a qué servidores de medios está subiendo. De esta manera, cuando el cliente ve esta lista, sabe dónde subir los archivos del usuario. También puede subir en múltiples servidores definidos en la lista para asegurar redundancia. En el lado de recuperación, si por alguna razón uno de los servidores en la lista del usuario está fuera de servicio, o el archivo ya no se puede encontrar allí, el cliente puede usar esta lista para intentar recuperar el archivo de otros servidores en la lista. Dado que los blobs se identifican por sus hashes, el mismo blob tendrá el mismo hash en cualquier servidor de medios. Todo lo que el cliente necesita hacer es cambiar la URL por la de un servidor diferente.
Ahora, además de los conceptos básicos de cómo funciona Blossom, también hay otros tipos de eventos que hacen que Blossom sea aún más interesante.
| kind | descripción | | ----- | --------------------- | | 30563 | Blossom Drives | | 36363 | Listado de Servidores | | 31963 | Reseña de Servidores |
kind:30563 - Blossom Drives
Este tipo de evento facilita la organización de blobs en carpetas, como estamos acostumbrados con los drives (piensa en Google Drive, iCloud, Proton Drive, etc.). El evento contiene información sobre la estructura de carpetas y los metadatos del drive.
kind:36363 y kind:31963 - Listado y Reseña
Estos tipos de eventos permiten a los usuarios descubrir y reseñar servidores de medios a través de nostr. kind:36363 es un listado de servidores que contiene la URL del servidor. kind:31963 es una reseña, donde los usuarios pueden calificar servidores.
¿Cómo lo uso?
Encuentra un servidor
Primero necesitarás elegir un servidor Blossom donde subirás tus archivos. Puedes navegar por los públicos en blossomservers.com. Algunos de ellos son de pago, otros pueden requerir que tus claves nostr estén en una lista blanca.
Luego, puedes ir a la URL de su servidor y probar a subir un archivo pequeño, como una foto. Si estás satisfecho con el servidor (es rápido y aún no te ha fallado), puedes agregarlo a tu Lista de Servidores de Usuarios. Cubriremos brevemente cómo hacer esto en noStrudel y Amethyst (pero solo necesitas hacer esto una vez, una vez que tu lista actualizada esté publicada, los clientes pueden simplemente recuperarla de nostr).
noStrudel
- Encuentra Relays en la barra lateral, luego elige Servidores de Medios.
- Agrega un servidor de medios, o mejor aún, varios.
- Publica tu lista de servidores. ✅
Amethyst
- En la barra lateral, encuentra Servidores multimedia.
- Bajo Servidores Blossom, agrega tus servidores de medios.
- Firma y publica. ✅
Ahora, cuando vayas a hacer una publicación y adjuntar una foto, por ejemplo, se subirá en tu servidor blossom.
⚠️ Ten en cuenta que debes suponer que los archivos que subas serán públicos. Aunque puedes proteger un archivo con contraseña, esto no ha sido auditado.
Blossom Drive
Como mencionamos anteriormente, podemos publicar eventos para organizar nuestros blobs en carpetas. Esto puede ser excelente para compartir archivos con tu equipo, o simplemente para mantener las cosas organizadas.
Para probarlo, ve a blossom.hzrd149.com (o nuestra instancia comunitaria en blossom.bitcointxoko.com) e inicia sesión con tu método preferido.
Puedes crear una nueva unidad y agregar blobs desde allí.
Bouquet
Si usas múltiples servidores para darte redundancia, Bouquet es una buena manera de obtener una visión general de todos tus archivos. Úsalo para subir y navegar por tus medios en diferentes servidores y sincronizar blobs entre ellos.
Cherry Tree
nostr:nevent1qvzqqqqqqypzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqyp3065hj9zellakecetfflkgudm5n6xcc9dnetfeacnq90y3yxa5z5gk2q6
Cherry Tree te permite dividir un archivo en fragmentos y luego subirlos en múltiples servidores blossom, y más tarde reensamblarlos en otro lugar.
Conclusión
Blossom aún está en desarrollo, pero ya hay muchas cosas interesantes que puedes hacer con él para hacerte a ti y a tu comunidad más soberanos. ¡Pruébalo!
Si deseas mantenerte al día sobre el desarrollo de Blossom, sigue a nostr:nprofile1qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqyqnxs90qeyssm73jf3kt5dtnk997ujw6ggy6j3t0jjzw2yrv6sy22ysu5ka y dale un gran zap por su excelente trabajo.
Referencias
-
 @ 7d33ba57:1b82db35
2025-03-20 20:42:33
@ 7d33ba57:1b82db35
2025-03-20 20:42:33El Teide
Mount Teide (El Teide) is the highest mountain in Spain (3,715m) and the third-highest volcanic structure in the world. Located in Teide National Park (a UNESCO World Heritage Site), it offers breathtaking landscapes, hiking trails, and stunning panoramic views** over the Canary Islands.
🏔️ Best Things to Do at Mount Teide
1️⃣ Hike to the Summit
- The most rewarding way to reach the top! The hike starts from Montaña Blanca and takes about 5-6 hours.
- Permit required for the final ascent (apply in advance).
2️⃣ Take the Teide Cable Car
- A quick way to reach 3,555m, with spectacular views.
- From the upper station, you can hike to La Fortaleza Viewpoint or Pico Viejo Viewpoint for stunning island views.
3️⃣ Stargazing at Teide Observatory
- One of the best stargazing spots in the world due to its clear skies and high altitude.
- Join an astronomy tour for an unforgettable night experience.
4️⃣ Explore the Teide National Park
- Walk through lava fields, craters, and rock formations like Roques de García.
- Visit the Visitor Center to learn about the park’s geology and history.
🚗 How to Get to Teide
🚗 By Car: ~1.5 hours from Santa Cruz or Costa Adeje
🚌 By Bus: Titsa buses 342 (from Costa Adeje) & 348 (from Puerto de la Cruz)💡 Tips for Visiting Teide
✅ Book summit permits early – Limited spots available! 🎟️
✅ Dress warmly – Temperatures drop at high altitude, even in summer 🧥
✅ Best time to visit? Sunrise, sunset, or night for amazing views 🌅🌌
✅ Take it slow – The high altitude can affect breathing ⛰️ -
 @ f240be2b:00c761ba
2025-03-20 17:53:08
@ f240be2b:00c761ba
2025-03-20 17:53:08Warum jetzt ein guter Zeitpunkt sein könnte, sich mit Bitcoin zu beschäftigen
Kennt ihr das? Wenn der Bitcoin-Preis neue Höchststände erreicht, möchte plötzlich jeder einsteigen. Doch sobald die Kurse fallen, überwiegt die Angst. Dabei zeigt die Geschichte: Gerade diese Phasen der Unsicherheit können interessante Zeitpunkte sein, um sich mit dem Thema zu beschäftigen.
Historische Zyklen Bitcoin durchläuft regelmäßige Marktzyklen Nach jedem Tief folgte bisher ein neues Hoch Emotionen spielen eine große Rolle im Markt Psychologie des Marktes Wenn alle euphorisch sind → meist teuer Wenn Unsicherheit herrscht → oft interessante Gelegenheiten Die Masse liegt häufig zum falschen Zeitpunkt richtigRationale Herangehensweise
Statt emotional zu handeln, solltet ihr:
Einen langfristigen Anlagehorizont wählen Regelmäßig kleine Beträge investieren (Cost-Average-Effekt)Hier ein paar Charts die euch helfen sollen und euch mutig werden lassen:
https://www.tradingview.com/chart/BTCUSD/HuGpzZfQ-BITCOIN-Cycle-pattern-completed-Year-end-Target-locked-at-150k/
https://www.tradingview.com/chart/BTCUSD/YVyy9QuU-BITCOIN-Money-Supply-Dollar-and-Bonds-pushing-for-MEGA-RALLY/
https://www.tradingview.com/chart/BTCUSD/pZ0qs5x3-BTCUSD-TSI-shows-that-this-is-the-LAST-BEST-BUY/
https://www.tradingview.com/chart/BTCUSD/x3e7GuLQ-BITCOIN-Is-this-a-Falling-Wedge-bottom-formation/
und jetzt All-In :-)
-
 @ 29af23a9:842ef0c1
2025-01-24 09:28:37
@ 29af23a9:842ef0c1
2025-01-24 09:28:37A Indústria Pornográfica se caracteriza pelo investimento pesado de grandes empresários americanos, desde 2014.
Na década de 90, filmes pornográficos eram feitos às coxas. Era basicamente duas pessoas fazendo sexo amador e sendo gravadas. Não tinha roteiro, nem produção, não tinha maquiagem, nada disso. A distribuição era rudimentar, os assinantes tinham que sair de suas casas, ir até a locadora, sofrer todo tipo de constrangimento para assistir a um filme pornô.
No começo dos anos 2000, o serviço de Pay Per View fez o número de vendas de filmes eróticos (filme erótico é bem mais leve) crescer mas nada se compara com os sites de filmes pornográficos por assinatura.
Com o advento dos serviços de Streaming, os sites que vendem filmes por assinatura se estabeleceram no mercado como nunca foi visto na história.
Hoje, os Produtores usam produtos para esticar os vasos sanguíneos do pênis dos atores e dopam as atrizes para que elas aguentem horas de gravação (a Série Black Mirror fez uma crítica a isso no episódio 1 milhão de méritos de forma sutil).
Além de toda a produção em volta das cenas. Que são gravadas em 4K, para focar bem as partes íntimas dos atores. Quadros fechados, iluminação, tudo isso faz essa Indústria ser "Artística" uma vez que tudo ali é falso. Um filme da Produtora Vixen, por exemplo, onde jovens mulheres transam em mansões com seus empresários estimula o esteriótipo da mina padrão que chama seu chefe rico de "daddy" e seduz ele até ele trair a esposa.
Sites como xvídeos, pornHub e outros nada mais são do que sites que salvam filmes dessas produtoras e hospedam as cenas com anúncios e pop-ups. Alguns sites hospedam o filme inteiro "de graça".
Esse tipo de filme estimula qualquer homem heterosexual com menos de 30 anos, que não tem o córtex frontal de seu cérebro totalmente desenvolvido (segundo estudos só é completamente desenvolvido quando o homem chega aos 31 anos).
A arte Pornográfica faz alguns fantasiarem ter relação sexual com uma gostosa americana branquinha, até escraviza-los. Muitos não conseguem sair do vício e preferem a Ficção à sua esposa real. Então pare de se enganar e admita. A Pornografia faz mal para a saúde mental do homem.
Quem sonha em ter uma transa com Lana Rhodes, deve estar nesse estágio. Trata-se de uma atriz (pornstar) que ganhou muito dinheiro vendendo a ilusão da Arte Pornografica, como a Riley Reid que só gravava para grandes Produtoras. Ambas se arrependeram da carreira artística e agora tentam viver suas vidas como uma mulher comum.
As próprias atrizes se consideram artistas, como Mia Malkova, chegou a dizer que Pornografia é a vida dela, que é "Lindo e Sofisticado."
Mia Malkova inclusive faz questão de dizer que a industria não escravisa mulheres jovens. Trata-se de um negócio onde a mulher assina um contrato com uma produtora e recebe um cachê por isso. Diferente do discurso da Mia Khalifa em entrevista para a BBC, onde diz que as mulheres são exploradas por homens poderosos. Vai ela está confundindo o Conglomerado Vixen com a Rede Globo ou com a empresa do Harvey Weinstein.
Enfim, se você é um homem solteiro entre 18 e 40 anos que já consumiu ou que ainda consome pornografia, sabia que sofrerá consequências. Pois trata-se de "produções artísticas" da indústria audiovisual que altera os níveis de dopamina do seu cérebro, mudando a neuroplasticidade e diminuindo a massa cinzenta, deixando o homem com memória fraca, sem foco e com mente nebulosa.
Por que o Estado não proíbe/criminaliza a Pornografia se ela faz mal? E desde quando o Estado quer o nosso bem? Existem grandes empresarios que financiam essa indústria ajudando governos a manterem o povo viciado e assim alienado. É um pão e circo, só que muito mais viciante e maléfico. Eu costume dizer aos meus amigos que existem grandes empresários jvdeus que são donos de grandes Produtoras de filmes pornográficos como o Conglomerado Vixen. Então se eles assistem vídeos pirateados de filmes dessas produtoras, eles estão no colo do Judeu.
-
 @ 000002de:c05780a7
2025-03-20 17:07:00
@ 000002de:c05780a7
2025-03-20 17:07:00Its easy to get caught up in media stories and not stop and ask basic questions. One I've had from the start is how widespread are these attacks on the private property have occurred.
If the goal is to hurt Tesla and therefore Musk, then the media stories are the real goal. Not the actual destruction of property. We know from history that many stories get blown out of proportion. I have no doubt that these events are actually happen but I wonder if the number of events has been counted.
originally posted at https://stacker.news/items/919063
-
 @ 83279ad2:bd49240d
2025-01-24 09:15:37
@ 83279ad2:bd49240d
2025-01-24 09:15:37備忘録として書きます。意外と時間がかかりました。全体で1時間くらいかかるので気長にやりましょう。 仮想通貨取引所(販売所ではないので、玄人が使えばお得らしい)かつBitcoinの送金手数料が無料(全ての取引所が無料ではない、例えばbitbankは0.0006bitcoinかかる)なので送金元はGMOコインを使います。(注意:GMOコインは0.02ビットコイン以下は全額送金になってしまいます) 今回はカストディアルウォレットのWallet of Satoshiに送金します。 以下手順 1. GMOコインでbitcoinを買います。 2. GMOコインの左のタブから入出金 暗号資産を選択します。 3. 送付のタブを開いて、+新しい宛先を追加するを選択します。 4. 送付先:GMOコイン以外、送付先ウォレット:プライベートウォレット(MetaMaskなど)、受取人:ご本人さま を選んで宛先情報の登録を選ぶと次の画面になります。
 5. 宛先名称にwallet of satoshi(これはなんでも良いです わかりやすい名称にしましょう) wallet of satoshiを開いて、受信→Bitcoin On-Chainからアドレスをコピーして、ビットコインアドレスに貼り付けます。
5. 宛先名称にwallet of satoshi(これはなんでも良いです わかりやすい名称にしましょう) wallet of satoshiを開いて、受信→Bitcoin On-Chainからアドレスをコピーして、ビットコインアドレスに貼り付けます。 6. 登録するを押します。これで送金先の登録ができました。GMOコインの審査がありますがすぐ終わると思います。
7. ここから送金をします。送付のタブから登録したビットコインの宛先リストwallet of satoshiを選択し、送付数量と送付目的を選択して、2段階認証をします。
6. 登録するを押します。これで送金先の登録ができました。GMOコインの審査がありますがすぐ終わると思います。
7. ここから送金をします。送付のタブから登録したビットコインの宛先リストwallet of satoshiを選択し、送付数量と送付目的を選択して、2段階認証をします。 8. 実行を押せば終わりです。もうあなたがやることはありません。送金が終わるのを40分くらい眺めるだけです。
8. 実行を押せば終わりです。もうあなたがやることはありません。送金が終わるのを40分くらい眺めるだけです。 8. 取引履歴のタブから今の送金のステータスが見れます。
8. 取引履歴のタブから今の送金のステータスが見れます。 9. 15分くらい待つとステータスが受付に変わります。
9. 15分くらい待つとステータスが受付に変わります。 10. 20分くらい待つとトランザクションIDが表示されます。
10. 20分くらい待つとトランザクションIDが表示されます。

この時点からwallet of satoshiにも送金されていることが表示されます。(まだ完了はしていない)
 11. ステータスが完了になったら送金終わりです。
11. ステータスが完了になったら送金終わりです。

wallet of satoshiにも反映されます。

お疲れ様でした!
-
 @ cffd7b79:dd8ca91f
2025-01-24 02:11:04
@ cffd7b79:dd8ca91f
2025-01-24 02:11:04Introductory
That right folks, it is called Satlantis. An upcoming game that is based on Minecraft. It uses a game engine called Launti/Minetest that has been in development since 2023, but it is unclear when it will be released. It is small team of bitcoin enthusiasts of 3-5 game developers.
Their Origin Story
It started out as a Minecraft server around 2018. It was prosperous with many players up to 100 players for just a SMP Server. Then on 2023, Mojang Studios contacted the owner of the server to shut it down due to have a play-to-earn function.
Their Discord Server
In their discord server, you can now earn their own currency called joules which can be earned by playing Counter Strike 2, Fortnite or Dead by Daylight. The joules then can be exchange for sats. If you wanna invest your sats into it, you can buy ASICs through the auction which is fueled by joules which gives you sats in return by the hour.
In Conclusion
From Minecraft to Minetest, it has great potential for such a game nowadays since not only its through some dApp currency scheme, but its straightforward process. if you want to see their site it is at Satlantis.net.
I am Chrissy Sage and I am out!
-
 @ b17fccdf:b7211155
2025-01-21 18:33:28
@ b17fccdf:b7211155
2025-01-21 18:33:28
CHECK OUT at ~ > ramix.minibolt.info < ~
Main changes:
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
Connect directly to the board, remove the instability issues with the USB connection, and unlock the ability to enjoy higher transfer speeds**
- Based on Debian 12 (Raspberry Pi OS Bookworm - 64-bit).
- Updated all services that have been tested until now, to the latest version.
- Same as the MiniBolt guide, changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- All UI & UX improvements in the MiniBolt guide are included.
- Fix some links and wrong command issues.
- Some existing guides have been improved to clarify the following steps.
Important notes:
- The RRSS will be the same as the MiniBolt original project (for now) | More info -> HERE <-
- The common resources like the Roadmap or Networkmap have been merged and will be used together | Check -> HERE <-
- The attempt to upgrade from Bullseye to Bookworm (RaspiBolt to RaMiX migration) has failed due to several difficult-to-resolve dependency conflicts, so unfortunately, there will be no dedicated migration guide and only the possibility to start from scratch ☹️
⚠️ Attention‼️-> This guide is in the WIP (work in progress) state and hasn't been completely tested yet. Many steps may be incorrect. Pay special attention to the "Status: Not tested on RaMiX" tag at the beginning of the guides. Be careful and act behind your responsibility.
For Raspberry Pi lovers!❤️🍓
Enjoy it RaMiXer!! 💜
By ⚡2FakTor⚡ for the plebs with love ❤️🫂
- Adapted to Raspberry Pi 5, with the possibility of using internal storage: a PCIe to M.2 adapter + SSD NVMe:
-
 @ 1c19eb1a:e22fb0bc
2025-03-21 00:34:10
@ 1c19eb1a:e22fb0bc
2025-03-21 00:34:10What is #Nostrversity? It's where you can come to learn about all the great tools, clients, and amazing technology that is being built on #Nostr, for Nostr, or utilized by Nostr, presented in an approachable and non-technical format. If you have ever wondered what Blossom, bunker signing, or Nostr Wallet Connect are, how they work, and how you can put them to work to improve your Nostr experience, this is the place you can read about them without needing a computer-science degree ahead of time.
Between writing full-length reviews, which take a fair amount of time to research, test, and draft, I will post shorter articles with the Nostrversity hashtag to provide a Nostr-native resource to help the community understand and utilize the tools our illustrious developers are building. These articles will be much shorter, and more digestible than my full-length reviews. They will also cover some things that may not be quite ready for prime-time, whereas my reviews will continue to focus on Nostr apps that are production-ready.
Keep an eye out, because Nostr Wallet Connect will be the first topic of study. Take your seats, get out your notepads, and follow along to discover how Nostr Wallet Connect is improving Lightning infrastructure. Hint: It's not just for zaps.
-
 @ e968e50b:db2a803a
2025-03-20 15:59:49
@ e968e50b:db2a803a
2025-03-20 15:59:49I just wrote up a whole essay about this great movie scene, my extended thoughts on this post, and bitcoin hipsterism at large. However, it was rambly and I'm not sure if anyone would have gotten anything out of it. That said, I'd love to share this clip with y'all as I think it may prove an interesting thought/discussion piece for those contemplating bitcoin hipsterism, either as an increasingly disillusioned practitioner or as an annoyed external observer.
https://www.youtube.com/watch?v=vUgs2O7Okqc&t=12s
originally posted at https://stacker.news/items/918979
-
 @ 7f29628d:e160cccc
2025-01-07 11:50:30
@ 7f29628d:e160cccc
2025-01-07 11:50:30Der gut informierte Bürger denkt bei der Pandemie sofort an Intensivstationen, an die Bilder aus Bergamo und erinnert sich an die Berichterstattung damals – also muss es wohl ein Maximum gewesen sein. Manche Skeptiker behaupten jedoch das Gegenteil. Klarheit sollte ein Blick nach Wiesbaden, zum Statistischen Bundesamt, schaffen. Schließlich sitzen dort gut bezahlte Profis, die seit vielen Jahrzehnten die Sterbestatistik pflegen und veröffentlichen. Jeder Todesfall wird in Deutschland über die Standesämter exakt erfasst.
Doch die Überraschung: Das Statistische Bundesamt liefert uns auf diese einfache Frage zwei extrem unterschiedliche Antworten – ein Minimum und ein Maximum. Das Ergebnis hängt davon ab, wie tief man in die Veröffentlichungen des Bundesamtes eintaucht. Betrachtet man nur die Webseiten und Pressemitteilungen, erhält man den Eindruck eines Maximums. Schaut man jedoch etwas tiefer in die Tabellen und Rohdaten, zeigt sich plötzlich ein Minimum. Aber wie kann das sein? Beides gleichzeitig geht ja wohl kaum. Wer lügt hier – die Tabellen des Amtes oder die Pressemitteilungen? Gehen wir dieser Frage Schritt für Schritt auf den Grund.
2020: Ein historisches Maximum?
Schauen wir uns die vielen Hundert Veröffentlichungen des Statistischen Bundesamtes aus dieser Zeit an. Oder wir kürzen ab und fragen ChatGPT, da die KI auf diesen Daten trainiert wurde und das gesamte Material kennt. Die Frage an ChatGPT lautet also: Wie war das Sterbegeschehen im Jahr 2020 im Vergleich zu den Vorjahren?
ChatGPT antwortet: »Im Jahr 2020 war die Sterblichkeit in Deutschland höher als in den Jahren zuvor. Es gab eine Übersterblichkeit von etwa 982.000 Todesfällen, das sind rund 46.000 mehr als der Durchschnitt der Vorjahre (2016 bis 2019). Dieser Anstieg wurde überwiegend im Zusammenhang mit der COVID-19-Pandemie gesehen. Während die Sterbezahlen in den Vorjahren schwankten, war ein solch signifikanter Anstieg wie 2020 bisher nicht zu beobachten.«
Wir fragen konkreter: Ist es ein Fakt, dass wir eine so ernste Lage im Sterbegeschehen wie im Frühjahr 2020 noch nie erlebt haben?
ChatGPT bestätigt: »Ja, die COVID-19-Pandemie führte im Frühjahr 2020 zu einer außergewöhnlichen Situation im Sterbegeschehen in Deutschland. Die dramatische Übersterblichkeit, die ab der 13. Kalenderwoche auftrat, veranlasste das Statistische Bundesamt, besonders eindringliche Warnungen zu veröffentlichen. Der damalige Vizepräsident des Amtes und andere führende Stimmen wiesen öffentlich darauf hin, dass die Todesfallzahlen stark vom Durchschnitt abwichen. Diese klare Warnung richtete sich an die Öffentlichkeit und die Politik gleichermaßen. Die Medien berichteten intensiv über diese Warnungen, was das Bewusstsein für die Schwere der Pandemie erheblich schärfte. In den vergangenen Jahrzehnten hatte es keine vergleichbare Übersterblichkeit gegeben, die eine solch umfangreiche Kommunikation durch das Statistische Bundesamt erforderlich gemacht hätte.«
Ein gut informierter Zeitungsleser wird sich an dieser Stelle bestätigt fühlen: Ja, so war es damals. Ein Maximum im Sterbegeschehen – wegen der Pandemie. Oder etwa nicht?
2020: Ein historisches Minimum?
Tauchen wir in die Rohdaten des Statistischen Bundesamtes ein. Die Tabellen, die das Amt seit Jahrzehnten verlässlich veröffentlicht, nennen sich Sterbetafeln. Diese werden jährlich bereitgestellt und stehen auf der Website des Bundesamtes zum Download bereit. Ein erster Blick in die Sterbetafeln mag den Laien abschrecken, doch mit einer kurzen Erklärung wird alles verständlich. Wir gehen schrittweise vor.
Nehmen wir die Sterbetafel des Jahres 2017. Sie enthält zwei große Tabellen – eine für Männer und eine für Frauen. Jede Zeile der Tabelle steht für einen Jahrgang, zum Beispiel zeigt die Zeile 79 die Daten der 79-jährigen Männer. Besonders wichtig ist nun die zweite Spalte, in der der Wert 0,05 eingetragen ist. Das bedeutet, dass 5 Prozent der 79-jährigen Männer im Jahr 2017 verstorben sind. Das ist die wichtige Kennzahl. Wenn wir diesen exakten Wert, den man auch als Sterberate bezeichnet, nun in ein Säulendiagramm eintragen, erhalten wir eine leicht verständliche visuelle Darstellung (Grafik 1).
Es ist wichtig zu betonen, dass dieser Wert weder ein Schätzwert noch eine Modellrechnung oder Prognose ist, sondern ein exakter Messwert, basierend auf einer zuverlässigen Zählung. Sterberaten (für die Fachleute auch Sterbewahrscheinlichkeiten qx) sind seit Johann Peter Süßmilch (1707–1767) der Goldstandard der Sterbestatistik. Jeder Aktuar wird das bestätigen. Fügen wir nun die Sterberaten der 79-jährigen Männer aus den Jahren davor und danach hinzu, um das Gesamtbild zu sehen (Grafik 2). Und nun die entscheidende Frage: Zeigt das Jahr 2020 ein Maximum oder ein Minimum?
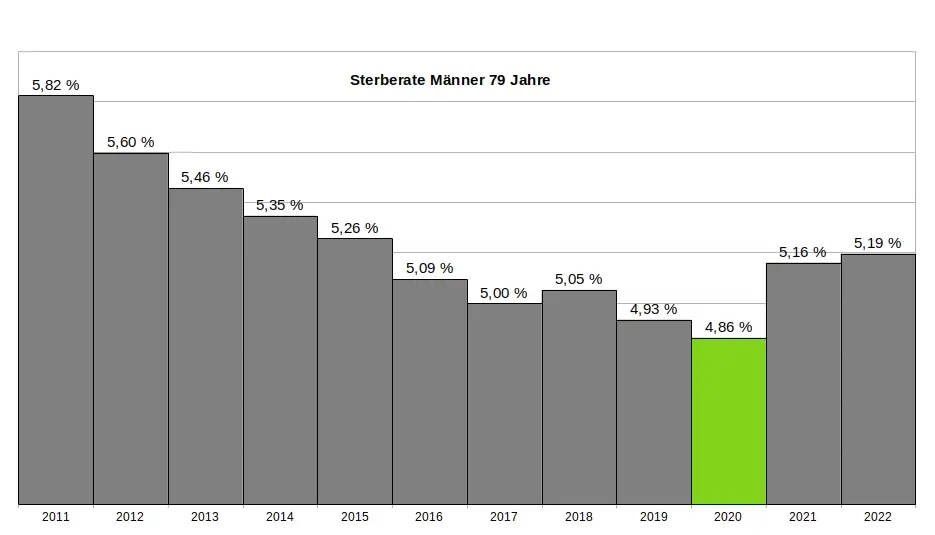
Ein kritischer Leser könnte vermuten, dass die 79-jährigen Männer eine Ausnahme darstellen und andere Jahrgänge im Jahr 2020 ein Maximum zeigen würden. Doch das trifft nicht zu. Kein einziger Jahrgang verzeichnete im Jahr 2020 ein Maximum. Im Gegenteil: Auch die 1-Jährigen, 2-Jährigen, 3-Jährigen, 9-Jährigen, 10-Jährigen, 15-Jährigen, 18-Jährigen und viele weitere männliche Jahrgänge hatten ihr Minimum im Jahr 2020. Dasselbe gilt bei den Frauen. Insgesamt hatten 31 Jahrgänge ihr Minimum im Jahr 2020. Wenn wir schließlich alle Jahrgänge in einer einzigen Grafik zusammenfassen, ergibt sich ein klares Bild: Das Minimum im Sterbegeschehen lag im Jahr 2020 (Grafik 3).
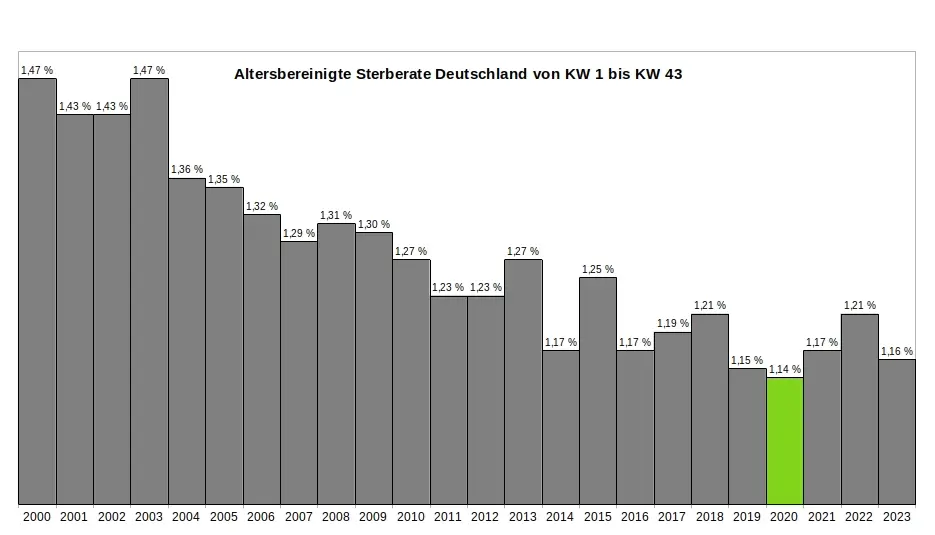
Ein kritischer Leser könnte nun wiederum vermuten, dass es innerhalb des Jahres 2020 möglicherweise starke Ausschläge nach oben bei einzelnen Jahrgängen gegeben haben könnte, die später durch Ausschläge nach unten ausgeglichen wurden – und dass diese Schwankungen in der jährlichen Übersicht nicht sichtbar sind. Doch auch das trifft nicht zu. Ein Blick auf die wöchentlichen Sterberaten zeigt, dass die ersten acht Monate der Pandemie keine nennenswerten Auffälligkeiten aufweisen. Es bleibt dabei: Die Rohdaten des Statistischen Bundesamtes bestätigen zweifelsfrei, dass die ersten acht Monate der Pandemie das historische Minimum im Sterbegeschehen darstellen. (Für die Fachleute sei angemerkt, dass im gleichen Zeitraum die Lebenserwartung die historischen Höchststände erreicht hatte – Grafik 4.)
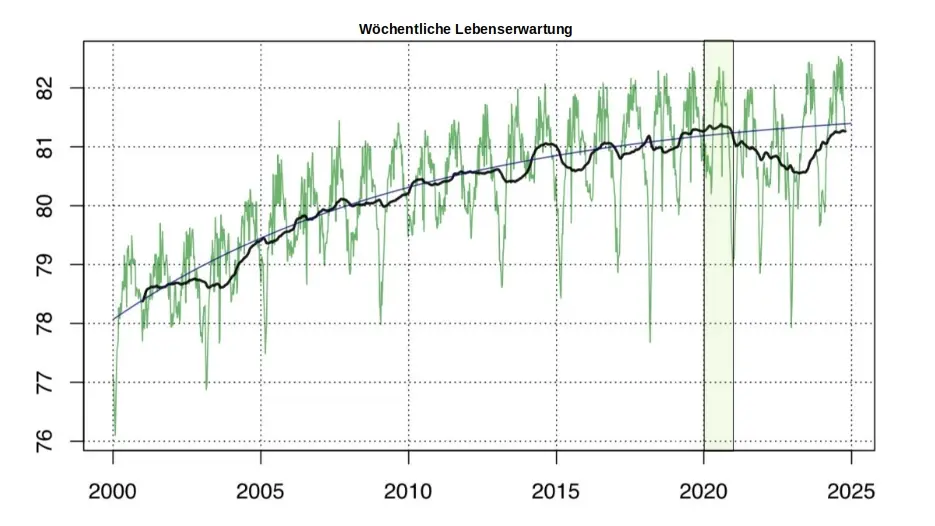
So konstruierte das Amt aus einem Minimum ein Maximum:
Zur Erinnerung: Die Rohdaten des Statistischen Bundesamtes, die in den jährlichen Sterbetafeln zweifelsfrei dokumentiert sind, zeigen für das Jahr 2020 eindeutig ein Minimum im Sterbegeschehen. Aus diesen »in Stein gemeißelten« Zahlen ein Maximum zu »konstruieren«, ohne die Rohdaten selbst zu verändern, scheint auf den ersten Blick eine unlösbare Aufgabe. Jeder Student würde an einer solchen Herausforderung scheitern. Doch das Statistische Bundesamt hat einen kreativen Weg gefunden - ein Meisterstück gezielter Manipulation. In fünf Schritten zeigt sich, wie diese Täuschung der Öffentlichkeit umgesetzt wurde:
(1) Ignorieren der Sterberaten: Die präzisen, objektiven und leicht verständlichen Sterberaten aus den eigenen Sterbetafeln wurden konsequent ignoriert und verschwiegen. Diese Daten widersprachen dem gewünschten Narrativ und wurden daher gezielt ausgeklammert.
(2) Fokus auf absolute Todeszahlen: Die Aufmerksamkeit wurde stattdessen auf die absolute Zahl der Todesfälle gelenkt. Diese wirkt allein durch ihre schiere Größe dramatisch und emotionalisiert die Diskussion. Ein entscheidender Faktor wurde dabei ignoriert: Die absolute Zahl der Todesfälle steigt aufgrund der demografischen Entwicklung jedes Jahr an. Viele Menschen verstehen diesen Zusammenhang nicht und verbinden die steigenden Zahlen fälschlicherweise mit der vermeintlichen Pandemie.
(3) Einführung der Übersterblichkeit als neue Kennzahl: Erst ab Beginn der „Pandemie“ wurde die Kennzahl "Übersterblichkeit" eingeführt – und dies mit einer fragwürdigen Methode, die systematisch überhöhte Werte lieferte. Diese Kennzahl wurde regelmäßig, oft monatlich oder sogar wöchentlich, berechnet und diente als ständige Grundlage für alarmierende Schlagzeilen.
(4) Intensive Öffentlichkeitsarbeit: Durch eine breit angelegte Kampagne wurden die manipulativen Kennzahlen gezielt in den Fokus gerückt. Pressemitteilungen, Podcasts und öffentliche Auftritte konzentrierten sich fast ausschließlich auf die absoluten Todeszahlen und die Übersterblichkeit. Ziel war es, den Eindruck einer dramatischen Situation in der Öffentlichkeit zu verstärken.
(5) Bekämpfen kritischer Stimmen: Kritiker, die die Schwächen und manipulativen Aspekte dieser Methoden aufdeckten, wurden systematisch diskreditiert. Ihre Glaubwürdigkeit und Kompetenz wurden öffentlich infrage gestellt, um das sorgsam konstruierte Narrativ zu schützen.
Ohne diesen begleitenden Statistik-Betrug wäre das gesamte Pandemie-Theater meiner Meinung nach nicht möglich gewesen. Wer aus einem faktischen Minimum ein scheinbares Maximum "erschafft", handelt betrügerisch. Die Folgen dieses Betruges sind gravierend. Denken wir an die Angst, die in der Bevölkerung geschürt wurde – die Angst, bald sterben zu müssen. Denken wir an Masken, Abstandsregeln, isolierte ältere Menschen, Kinderimpfungen und all die Maßnahmen, die unter anderem auf diese falsche Statistik zurückgehen.
Wollen wir Bürger uns das gefallen lassen?
Wenn wir als Bürger zulassen, dass ein derart offensichtlicher und nachprüfbarer Täuschungsversuch ohne Konsequenzen bleibt, dann gefährdet das nicht nur die Integrität unserer Institutionen – es untergräbt das Fundament unserer Gesellschaft. In der DDR feierte man öffentlich Planerfüllung und Übererfüllung, während die Regale leer blieben. Damals wusste jeder: Statistik war ein Propagandainstrument. Niemand traute den Zahlen, die das Staatsfernsehen verkündete.
Während der Pandemie war es anders. Die Menschen vertrauten den Mitteilungen des Statistischen Bundesamtes und des RKI – blind. Die Enthüllungen durch den "RKI-Leak" haben gezeigt, dass auch das Robert-Koch-Institut nicht der Wissenschaft, sondern den Weisungen des Gesundheitsministers und militärischen Vorgaben folgte. Warum sollte es beim Statistischen Bundesamt anders gewesen sein? Diese Behörde ist dem Innenministerium unterstellt und somit ebenfalls weisungsgebunden.
Die Beweise für Täuschung liegen offen zutage. Es braucht keinen Whistleblower, keine geheimen Enthüllungen: Die Rohdaten des Statistischen Bundesamtes sprechen für sich. Sie sind öffentlich einsehbar – klar und unmissverständlich. Die Daten, die Tabellen, die Veröffentlichungen des Amtes selbst – sie sind die Anklageschrift. Sie zeigen, was wirklich war. Nicht mehr und nicht weniger.
Und wir? Was tun wir? Schweigen wir? Oder fordern wir endlich ein, was unser Recht ist? Wir Bürger dürfen das nicht hinnehmen. Es ist Zeit, unsere Behörden zur Rechenschaft zu ziehen. Diese Institutionen arbeiten nicht für sich – sie arbeiten für uns. Wir finanzieren sie, und wir haben das Recht, Transparenz und Verantwortung einzufordern. Manipulationen wie diese müssen aufgearbeitet werden und dürfen nie wieder geschehen. Die Strukturen, die solche Fehlentwicklungen in unseren Behörden ermöglicht haben, müssen offengelegt werden. Denn eine Demokratie lebt von Vertrauen – und Vertrauen muss verdient werden. Jeden Tag aufs Neue.
.
.
MARCEL BARZ, Jahrgang 1975, war Offizier der Bundeswehr und studierte Wirtschafts- und Organisationswissenschaften sowie Wirtschaftsinformatik. Er war Gründer und Geschäftsführer einer Softwarefirma, die sich auf Datenanalyse und Softwareentwicklung spezialisiert hatte. Im August 2021 veröffentlichte Barz den Videovortrag »Die Pandemie in den Rohdaten«, der über eine Million Aufrufe erzielte. Seitdem macht er als "Erbsenzähler" auf Widersprüche in amtlichen Statistiken aufmerksam.
-
 @ 16f1a010:31b1074b
2025-03-20 14:32:25
@ 16f1a010:31b1074b
2025-03-20 14:32:25grain is a nostr relay built using Go, currently utilizing MongoDB as its database. Binaries are provided for AMD64 Windows and Linux. grain is Go Relay Architecture for Implementing Nostr
Introduction
grain is a nostr relay built using Go, currently utilizing MongoDB as its database. Binaries are provided for AMD64 Windows and Linux. grain is Go Relay Architecture for Implementing Nostr
Prerequisites
- Grain requires a running MongoDB instance. Please refer to this separate guide for instructions on setting up MongoDB: nostr:naddr1qvzqqqr4gupzq9h35qgq6n8ll0xyyv8gurjzjrx9sjwp4hry6ejnlks8cqcmzp6tqqxnzde5xg6rwwp5xsuryd3knfdr7g
Download Grain
Download the latest release for your system from the GitHub releases page
amd64 binaries provided for Windows and Linux, if you have a different CPU architecture, you can download and install go to build grain from source
Installation and Execution
- Create a new folder on your system where you want to run Grain.
- The downloaded binary comes bundled with a ZIP file containing a folder named "app," which holds the frontend HTML files. Unzip the "app" folder into the same directory as the Grain executable.
Run Grain
- Open your terminal or command prompt and navigate to the Grain directory.
- Execute the Grain binary.
on linux you will first have to make the program executable
chmod +x grain_linux_amd64Then you can run the program
./grain_linux_amd64(alternatively on windows, you can just double click the grain_windows_amd64.exe to start the relay)
You should see a terminal window displaying the port on which your relay and frontend are running.
If you get
Failed to copy app/static/examples/config.example.yml to config.yml: open app/static/examples/config.example.yml: no such file or directory
Then you probably forgot to put the app folder in the same directory as your executable or you did not unzip the folder.
Congrats! You're running grain 🌾!
You may want to change your NIP11 relay information document (relay_metadata.json) This informs clients of the capabilities, administrative contacts, and various server attributes. It's located in the same directory as your executable.
Configuration Files
Once Grain has been executed for the first time, it will generate the default configuration files inside the directory where the executable is located. These files are:
bash config.yml whitelist.yml blacklist.ymlPrerequisites: - Grain requires a running MongoDB instance. Please refer to this separate guide for instructions on setting up MongoDB: [Link to MongoDB setup guide].
Download Grain:
Download the latest release for your system from the GitHub releases page
amd64 binaries provided for Windows and Linux, if you have a different CPU architecture, you can download and install go to build grain from source
Installation and Execution:
- Create a new folder on your system where you want to run Grain.
- The downloaded binary comes bundled with a ZIP file containing a folder named "app," which holds the frontend HTML files. Unzip the "app" folder into the same directory as the Grain executable.
Run Grain:
- Open your terminal or command prompt and navigate to the Grain directory.
- Execute the Grain binary.
on linux you will first have to make the program executable
chmod +x grain_linux_amd64Then you can run the program
./grain_linux_amd64(alternatively on windows, you can just double click the grain_windows_amd64.exe to start the relay)
You should see a terminal window displaying the port on which your relay and frontend are running.
If you get
Failed to copy app/static/examples/config.example.yml to config.yml: open app/static/examples/config.example.yml: no such file or directory
Then you probably forgot to put the app folder in the same directory as your executable or you did not unzip the folder.
Congrats! You're running grain 🌾!
You may want to change your NIP11 relay information document (relay_metadata.json) This informs clients of the capabilities, administrative contacts, and various server attributes. It's located in the same directory as your executable.
Configuration Files:
Once Grain has been executed for the first time, it will generate the default configuration files inside the directory where the executable is located. These files are:
bash config.yml whitelist.yml blacklist.ymlConfiguration Documentation
You can always find the latest example configs on my site or in the github repo here: config.yml
Config.yml
This
config.ymlfile is where you customize how your Grain relay operates. Each section controls different aspects of the relay's behavior.1.
mongodb(Database Settings)uri: mongodb://localhost:27017/:- This is the connection string for your MongoDB database.
mongodb://localhost:27017/indicates that your MongoDB server is running on the same computer as your Grain relay (localhost) and listening on port 27017 (the default MongoDB port).- If your MongoDB server is on a different machine, you'll need to change
localhostto the server's IP address or hostname. - The trailing
/indicates the root of the mongodb server. You will define the database in the next line.
database: grain:- This specifies the name of the MongoDB database that Grain will use to store Nostr events. Grain will create this database if it doesn't already exist.
- You can name the database whatever you want. If you want to run multiple grain relays, you can and they can have different databases running on the same mongo server.
2.
server(Relay Server Settings)port: :8181:- This sets the port on which your Grain relay will listen for incoming nostr websocket connections and what port the frontend will be available at.
read_timeout: 10 # in seconds:- This is the maximum time (in seconds) that the relay will wait for a client to send data before closing the connection.
write_timeout: 10 # in seconds:- This is the maximum time (in seconds) that the relay will wait for a client to receive data before closing the connection.
idle_timeout: 120 # in seconds:- This is the maximum time (in seconds) that the relay will keep a connection open if there's no activity.
max_connections: 100:- This sets the maximum number of simultaneous client connections that the relay will allow.
max_subscriptions_per_client: 10:- This sets the maximum amount of subscriptions a single client can request from the relay.
3.
resource_limits(System Resource Limits)cpu_cores: 2 # Limit the number of CPU cores the application can use:- This restricts the number of CPU cores that Grain can use. Useful for controlling resource usage on your server.
memory_mb: 1024 # Cap the maximum amount of RAM in MB the application can use:- This limits the maximum amount of RAM (in megabytes) that Grain can use.
heap_size_mb: 512 # Set a limit on the Go garbage collector's heap size in MB:- This sets a limit on the amount of memory that the Go programming language's garbage collector can use.
4.
auth(Authentication Settings)enabled: false # Enable or disable AUTH handling:- If set to
true, this enables authentication handling, requiring clients to authenticate before using the relay.
- If set to
relay_url: "wss://relay.example.com/" # Specify the relay URL:- If authentication is enabled, this is the url that clients will use to authenticate.
5.
UserSync(User Synchronization)user_sync: false:- If set to true, the relay will attempt to sync user data from other relays.
disable_at_startup: true:- If user sync is enabled, this will prevent the sync from starting when the relay starts.
initial_sync_relays: [...]:- A list of other relays to pull user data from.
kinds: []:- A list of event kinds to pull from the other relays. Leaving this empty will pull all event kinds.
limit: 100:- The limit of events to pull from the other relays.
exclude_non_whitelisted: true:- If set to true, only users on the whitelist will have their data synced.
interval: 360:- The interval in minutes that the relay will resync user data.
6.
backup_relay(Backup Relay)enabled: false:- If set to true, the relay will send copies of received events to the backup relay.
url: "wss://some-relay.com":- The url of the backup relay.
7.
event_purge(Event Purging)enabled: false:- If set to
true, the relay will automatically delete old events.
- If set to
keep_interval_hours: 24:- The number of hours to keep events before purging them.
purge_interval_minutes: 240:- How often (in minutes) the purging process runs.
purge_by_category: ...:- Allows you to specify which categories of events (regular, replaceable, addressable, deprecated) to purge.
purge_by_kind_enabled: false:- If set to true, events will be purged based on the kinds listed below.
kinds_to_purge: ...:- A list of event kinds to purge.
exclude_whitelisted: true:- If set to true, events from whitelisted users will not be purged.
8.
event_time_constraints(Event Time Constraints)min_created_at: 1577836800:- The minimum
created_attimestamp (Unix timestamp) that events must have to be accepted by the relay.
- The minimum
max_created_at_string: now+5m:- The maximum created at time that an event can have. This example shows that the max created at time is 5 minutes in the future from the time the event is received.
min_created_at_stringandmax_created_atwork the same way.
9.
rate_limit(Rate Limiting)ws_limit: 100:- The maximum number of WebSocket messages per second that the relay will accept.
ws_burst: 200:- Allows a temporary burst of WebSocket messages.
event_limit: 50:- The maximum number of Nostr events per second that the relay will accept.
event_burst: 100:- Allows a temporary burst of Nostr events.
req_limit: 50:- The limit of http requests per second.
req_burst: 100:- The allowed burst of http requests.
max_event_size: 51200:- The maximum size (in bytes) of a Nostr event that the relay will accept.
kind_size_limits: ...:- Allows you to set size limits for specific event kinds.
category_limits: ...:- Allows you to set rate limits for different event categories (ephemeral, addressable, regular, replaceable).
kind_limits: ...:- Allows you to set rate limits for specific event kinds.
By understanding these settings, you can tailor your Grain Nostr relay to meet your specific needs and resource constraints.
whitelist.yml
The
whitelist.ymlfile is used to control which users, event kinds, and domains are allowed to interact with your Grain relay. Here's a breakdown of the settings:1.
pubkey_whitelist(Public Key Whitelist)enabled: false:- If set to
true, this enables the public key whitelist. Only users whose public keys are listed will be allowed to publish events to your relay.
- If set to
pubkeys::- A list of hexadecimal public keys that are allowed to publish events.
pubkey1andpubkey2are placeholders, you will replace these with actual hexadecimal public keys.
npubs::- A list of npubs that are allowed to publish events.
npub18ls2km9aklhzw9yzqgjfu0anhz2z83hkeknw7sl22ptu8kfs3rjq54am44andnpub2are placeholders, replace them with actual npubs.- npubs are bech32 encoded public keys.
2.
kind_whitelist(Event Kind Whitelist)enabled: false:- If set to
true, this enables the event kind whitelist. Only events with the specified kinds will be allowed.
- If set to
kinds::- A list of event kinds (as strings) that are allowed.
"1"and"2"are example kinds. Replace these with the kinds you want to allow.- Example kinds are 0 for metadata, 1 for short text notes, and 2 for recommend server.
3.
domain_whitelist(Domain Whitelist)enabled: false:- If set to
true, this enables the domain whitelist. This checks the domains .well-known folder for their nostr.json. This file contains a list of pubkeys. They will be considered whitelisted if on this list.
- If set to
domains::- A list of domains that are allowed.
"example.com"and"anotherdomain.com"are example domains. Replace these with the domains you want to allow.
blacklist.yml
The
blacklist.ymlfile allows you to block specific content, users, and words from your Grain relay. Here's a breakdown of the settings:1.
enabled: true- This setting enables the blacklist functionality. If set to
true, the relay will actively block content and users based on the rules defined in this file.
2.
permanent_ban_words:- This section lists words that, if found in an event, will result in a permanent ban for the event's author.
- really bad wordis a placeholder. Replace it with any words you want to permanently block.
3.
temp_ban_words:- This section lists words that, if found in an event, will result in a temporary ban for the event's author.
- crypto,- web3, and- airdropare examples. Replace them with the words you want to temporarily block.
4.
max_temp_bans: 3- This sets the maximum number of temporary bans a user can receive before they are permanently banned.
5.
temp_ban_duration: 3600- This sets the duration of a temporary ban in seconds.
3600seconds equals one hour.
6.
permanent_blacklist_pubkeys:- This section lists hexadecimal public keys that are permanently blocked from using the relay.
- db0c9b8acd6101adb9b281c5321f98f6eebb33c5719d230ed1870997538a9765is an example. Replace it with the public keys you want to block.
7.
permanent_blacklist_npubs:- This section lists npubs that are permanently blocked from using the relay.
- npub1x0r5gflnk2mn6h3c70nvnywpy2j46gzqwg6k7uw6fxswyz0md9qqnhshtnis an example. Replace it with the npubs you want to block.- npubs are the human readable version of public keys.
8.
mutelist_authors:- This section lists hexadecimal public keys of author of a kind1000 mutelist. Pubkey authors on this mutelist will be considered on the permanent blacklist. This provides a nostr native way to handle the backlist of your relay
- 3fe0ab6cbdb7ee27148202249e3fb3b89423c6f6cda6ef43ea5057c3d93088e4is an example. Replace it with the public keys of authors that have a mutelist you would like to use as a blacklist. Consider using your own.- Important Note: The mutelist Event MUST be stored in this relay for it to be retrieved. This means your relay must have a copy of the authors kind10000 mutelist to consider them for the blacklist.
Running Grain as a Service:
Windows Service:
To run Grain as a Windows service, you can use tools like NSSM (Non-Sucking Service Manager). NSSM allows you to easily install and manage any application as a Windows service.
* For instructions on how to install NSSM, please refer to this article: [Link to NSSM install guide coming soon].-
Open Command Prompt as Administrator:
- Open the Windows Start menu, type "cmd," right-click on "Command Prompt," and select "Run as administrator."
-
Navigate to NSSM Directory:
- Use the
cdcommand to navigate to the directory where you extracted NSSM. For example, if you extracted it toC:\nssm, you would typecd C:\nssmand press Enter.
- Use the
-
Install the Grain Service:
- Run the command
nssm install grain. - A GUI will appear, allowing you to configure the service.
- Run the command
-
Configure Service Details:
- In the "Path" field, enter the full path to your Grain executable (e.g.,
C:\grain\grain_windows_amd64.exe). - In the "Startup directory" field, enter the directory where your Grain executable is located (e.g.,
C:\grain).
- In the "Path" field, enter the full path to your Grain executable (e.g.,
-
Install the Service:
- Click the "Install service" button.
-
Manage the Service:
- You can now manage the Grain service using the Windows Services manager. Open the Start menu, type "services.msc," and press Enter. You can start, stop, pause, or restart the Grain service from there.
Linux Service (systemd):
To run Grain as a Linux service, you can use systemd, the standard service manager for most modern Linux distributions.
-
Create a Systemd Service File:
- Open a text editor with root privileges (e.g.,
sudo nano /etc/systemd/system/grain.service).
- Open a text editor with root privileges (e.g.,
-
Add Service Configuration:
- Add the following content to the
grain.servicefile, replacing the placeholders with your actual paths and user information:
```toml [Unit] Description=Grain Nostr Relay After=network.target
[Service] ExecStart=/path/to/grain_linux_amd64 WorkingDirectory=/path/to/grain/directory Restart=always User=your_user #replace your_user Group=your_group #replace your_group
[Install] WantedBy=multi-user.target ```
- Replace
/path/to/grain/executablewith the full path to your Grain executable. - Replace
/path/to/grain/directorywith the directory containing your Grain executable. - Replace
your_userandyour_groupwith the username and group that will run the Grain service.
- Add the following content to the
-
Reload Systemd:
- Run the command
sudo systemctl daemon-reloadto reload the systemd configuration.
- Run the command
-
Enable the Service:
- Run the command
sudo systemctl enable grain.serviceto enable the service to start automatically on boot.
- Run the command
-
Start the Service:
- Run the command
sudo systemctl start grain.serviceto start the service immediately.
- Run the command
-
Check Service Status:
- Run the command
sudo systemctl status grain.serviceto check the status of the Grain service. This will show you if the service is running and any recent logs. - You can run
sudo journalctl -f -u grain.serviceto watch the logs
- Run the command
More guides are in the works for setting up tailscale to access your relay from anywhere over a private network and for setting up a cloudflare tunnel to your domain to deploy a grain relay accessible on a subdomain of your site eg wss://relay.yourdomain.com
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ 378562cd:a6fc6773
2025-03-20 14:26:48
@ 378562cd:a6fc6773
2025-03-20 14:26:48When SpongeBob SquarePants first graced television screens in 1999, it quickly became a cultural phenomenon. Its quirky humor, unique animation style, and absurd yet endearing characters captured audiences of all ages. However, beyond its whimsical surface, SpongeBob SquarePants holds surprising ties to real-world marine biology, human behaviors, and even corporate America. Let's take a deep dive into the striking similarities between the show’s universe and real life.
- Bikini Bottom and the Nuclear Connection
One of the most intriguing theories about SpongeBob SquarePants is its potential connection to real-world geography. Bikini Bottom, the fictional underwater city where SpongeBob and his friends reside, is widely believed to be named after Bikini Atoll, a site in the Pacific Ocean where the U.S. conducted nuclear tests in the 1940s and 1950s. Some fans speculate that the bizarre personalities of the show's characters are a result of radioactive mutations—a wild yet eerily plausible idea given the history of the atoll.
- SpongeBob: More Than Just a Sponge
SpongeBob is, of course, a sea sponge, but his rectangular, kitchen-sponge shape is a deviation from most natural sea sponges, which are irregularly shaped. However, real-life sea sponges are fascinating creatures that can regenerate after being broken apart—just like how SpongeBob bounces back from every misadventure with relentless optimism.
Additionally, SpongeBob’s enthusiasm and boundless energy mimic the real-life behaviors of certain marine organisms that continuously filter water, making them vital to their ecosystems. His ceaseless work ethic at the Krusty Krab also mirrors the tireless efforts of smaller marine life that keep oceanic ecosystems functioning.
- Squidward: An Octopus in Disguise
Despite his name, Squidward Tentacles is actually an octopus. Series creator Stephen Hillenburg, a marine biologist before becoming an animator, intentionally designed Squidward with six tentacles instead of the usual eight to make animation easier. His grumpy and refined personality also reflects the intelligence of real-world octopuses, who are known for their problem-solving skills and, at times, their moody behavior.
- The Krusty Krab and Corporate Culture
The Krusty Krab, the fast-food restaurant where SpongeBob works, is a satirical take on real-life corporate culture, particularly in the fast-food industry. Mr. Krabs, the money-hungry owner, represents stereotypical profit-driven business owners who prioritize revenue over employee well-being. Meanwhile, SpongeBob’s unwavering loyalty to his job highlights the enthusiasm of idealistic workers, and Squidward embodies the disillusioned employees who begrudgingly clock in every day. This dynamic is strikingly similar to real-world labor environments, making the show relatable even beyond its nautical setting.
- Plankton and the Struggles of Small Businesses
Sheldon J. Plankton, the tiny but ambitious owner of the failing Chum Bucket, serves as a metaphor for small business owners who struggle to compete with corporate giants. His constant yet futile attempts to steal the Krabby Patty secret formula echo the real-world battle between small independent businesses and industry monopolies. Despite his villainous traits, Plankton’s perseverance and innovative schemes make him an oddly sympathetic character, much like real-life entrepreneurs striving to find success against all odds.
- Real-Life Marine Life Mirrored in Characters
Each character in SpongeBob SquarePants is based on real marine creatures with behaviors that closely resemble their animated counterparts:
Patrick Star: A pink starfish who is slow and lazy, much like real-life starfish that lack a brain and move sluggishly.
Sandy Cheeks: A land-dwelling squirrel who thrives in an underwater suit, symbolizing the scientific research done by deep-sea divers and marine biologists in the ocean.
Mr. Krabs: A crab with a tight grip on his money, reflecting the territorial and often aggressive nature of real-world crabs.
Larry the Lobster: A fitness-obsessed lobster, much like real lobsters that grow larger and stronger as they molt.
Conclusion: A Show Rooted in Reality
While SpongeBob SquarePants is undeniably a wacky and exaggerated series, its deep connection to real-world marine biology, workplace culture, and corporate dynamics gives it an extra layer of depth. Whether intentionally or unintentionally, the show serves as an entertaining yet insightful reflection of life above and below the ocean’s surface. So next time you watch an episode, remember—you’re not just enjoying a cartoon; you’re diving into a cleverly crafted world filled with real-life parallels, which is probably a direct correlation to its wild success in all these years.
-
 @ 878dff7c:037d18bc
2025-03-20 21:39:38
@ 878dff7c:037d18bc
2025-03-20 21:39:38JFK Assassination Files (Special brief)
Summary
The consensus among researchers and media is cautious optimism mixed with skepticism. The files offer a treasure trove of operational minutiae—spycraft, JFK’s CIA friction, Oswald’s movements—but no game-changer has emerged in the 72+ hours since release. Attention is shifting to the unreleased FBI and IRS records, with speculation that their declassification could clarify lingering questions. For now, the story remains one of incremental insight rather than revelation.
1. CIA's Surveillance of Lee Harvey Oswald Prior to Assassination
Newly declassified documents reveal that the CIA closely monitored Lee Harvey Oswald's activities before President Kennedy's assassination. Unredacted testimony from James Angleton, the CIA's chief of counterintelligence, provides deeper insight into the agency's surveillance operations concerning Oswald, particularly during his time in Mexico City, where he contacted the Soviet and Cuban embassies. Despite this surveillance, the CIA did not act to prevent the assassination, raising questions about the agency's internal communication and assessment processes.
2. Oswald's Interactions with Soviet Officials Scrutinized
The declassified files shed light on Oswald's interactions with Soviet officials during his visit to the USSR. According to KGB records, Oswald was closely monitored but was not recruited as an agent. These revelations provide a clearer understanding of Oswald's activities and the extent of Soviet intelligence's involvement with him, countering longstanding speculations about his ties to the USSR.
3. Prior Warning of Oswald's Intentions
A newly revealed letter indicates that months before the assassination, a tip-off about Oswald's plan to kill President Kennedy was received but not adequately acted upon. This raises concerns about potential intelligence failures and missed opportunities to prevent the tragic event.
4. President Kennedy's Consideration to Dismantle the CIA
The documents reveal that President Kennedy contemplated dismantling the CIA following the Bay of Pigs fiasco, referring to it as a "state within a state." This underscores the tension between the Kennedy administration and the intelligence community during that period.
5. Use of USS Potomac by Anti-Castro Paramilitaries
The declassified files disclose that the USS Potomac, formerly President Franklin D. Roosevelt's yacht, was later utilized by anti-Castro paramilitary groups. This highlights the covert operations undertaken during the Cold War era and the U.S. government's involvement in efforts to destabilize the Castro regime in Cuba.
6. Gary Underhill's Allegations Against the CIA
The documents bring to light the case of Gary Underhill, a former intelligence officer who alleged that the CIA was involved in illicit activities. Underhill was later found dead under suspicious circumstances, fueling further speculation about internal conspiracies within the intelligence community.
7. Australian Intelligence's Involvement in the Investigation
Newly released files reveal that Sir Charles Spry, the head of the Australian Security Intelligence Organisation (ASIO), lobbied to keep certain documents related to the assassination investigation confidential. This indicates international dimensions to the investigation and the sensitivity surrounding the information at the time.
Sources The Times - March 21, 2025\ Al Jazeera - March 20, 2025\ National Archives - March 18, 2025\ News.com.au - March 21, 2025
Significant Employment Drop in February; Unemployment Rate Steady
Summary:
Australia experienced an unexpected decline in employment, with 53,000 jobs lost in February, primarily due to older workers retiring and a decrease in female workforce participation. Despite this, the unemployment rate remained steady at 4.1%, largely because of a drop in the participation rate. Analysts suggest that recent tax cuts, interest rate reductions, and wage growth may have eased household budgets, reducing the need for some to seek employment. The Reserve Bank of Australia (RBA) is monitoring these developments but is not expected to implement another interest rate cut immediately. Sources: News.com.au - March 21, 2025, The Australian - March 21, 2025, ABC News - March 20, 2025
Tropical Cyclone Courtney Forms Near Cocos Islands, Marking Intense Cyclone Season
Summary:
Tropical Low 25U near the Cocos Islands has intensified into Tropical Cyclone Courtney. Meteorologists predict that while the system may struggle to maintain cyclone status, it will still bring gusty winds, squally showers, and thunderstorms to affected areas. This development marks the potential tenth cyclone since December, indicating one of the busiest cyclone seasons in 19 years if three more cyclones occur by the end of April. Residents in the path of the cyclone are advised to stay updated with the latest weather information and prepare for possible severe weather conditions. Sources: News.com.au - March 21, 2025
Australia's Population Growth Sparks Migration Policy Debate
Summary:
Australia's population grew by 484,000 (1.8%) over the past year, primarily due to natural births and net overseas migration. This surge has ignited political debates on migration policies. Prime Minister Anthony Albanese aims to reduce net migration to 250,000 by mid-2025, while Opposition Leader Peter Dutton advocates for a 25% cut in permanent migration and stricter caps on international students. Experts argue that skilled migration boosts the economy, but housing shortages linked to migration remain a pressing issue. Sources: News.com.au - March 21, 2025
NSW Premier Chris Minns Admits Need for Accelerated Reforms
Summary:
Marking two years in office, NSW Premier Chris Minns acknowledges his administration's slow progress on key promises, particularly in housing and economic reforms. While crises like natural disasters have been well-managed, significant advancements are lacking. Minns aims to expedite housing approvals to meet a target of 75,000 new homes and improve the budget, though challenges like debt reduction and infrastructure delays persist. Sources: The Daily Telegraph - March 21, 2025
Coalition Proposes Legislated Biosecurity Funding
Summary:
At the Northern Territory Cattlemen's Association Conference in Darwin, National Party Leader David Littleproud announced a policy to legislate minimum biosecurity funding of approximately $900 million. This measure aims to combat diseases like Lumpy Skin Disease and Foot and Mouth Disease, which could have severe economic impacts. The proposal includes introducing an Import Container Levy to ensure that importers, rather than Australian farmers, bear the costs. The Northern Territory Cattlemen's Association has expressed support for this sustainable funding approach.
Sources: The Courier-Mail - 21 March 2025
EU Leaders Convene to Address Global Challenges
Summary:
On March 20-21, 2025, European Union leaders met in Brussels to discuss pressing global issues, including economic competitiveness, security, and climate change. A working lunch with United Nations Secretary-General António Guterres focused on multilateralism and strengthening global cooperation. The summit underscored the EU's commitment to addressing international challenges through unified strategies and reinforced partnerships. Sources: European Parliament - March 20, 2025
Geopolitical Tensions Rise in the Arctic Region
Summary:
Recent analyses indicate that the Arctic is increasingly becoming a focal point of geopolitical rivalry. The region is now divided between a NATO-aligned Arctic, led by the United States, and a Russian Arctic seeking cooperation with BRICS+ countries. This division reflects broader global tensions between the US/NATO and Russia/China, heightening the risk of conflict and underscoring the need for diplomatic engagement to manage Arctic affairs. Sources: High North News - March 19, 2025
Royal Adelaide Hospital's Infectious Diseases Unit Relocation Sparks Concerns
Summary:
Doctors and nurses have raised concerns that patient care could be compromised if the South Australian government proceeds with plans to relocate the infectious diseases unit from the Royal Adelaide Hospital to a new location across North Terrace. Health unions have taken the dispute to the SA Employment Tribunal, arguing that the move could result in compromised clinical care and patient safety due to the separation from specialist doctors at the main hospital. The government cites cost considerations as the main driver for the relocation decision. Sources: ABC News - March 20, 2025
Inspirational Stories of Young Australians Overcoming Adversity
Summary:
The ABC Heywire competition recognized 38 young Australians from regional, rural, and remote areas for their inspiring stories of resilience and determination. Winners, aged 16 to 22, shared experiences highlighting life outside major cities. For instance, Blake from Casino detailed enduring severe drought on his family's farm, while Mayada from Coffs Harbour recounted her escape from child slavery during the Yazidi genocide, ultimately finding refuge in Australia. These narratives showcase the diverse and resilient spirit of young Australians committed to inspiring positive change in their communities. Sources: The Daily Telegraph - March 21, 2025
Calls for Strengthened ANZAC Cooperation Amid US Retrenchment and China's Rise
Summary:
China's growing military assertiveness, exemplified by live-fire naval exercises in the Tasman Sea, contrasts with the US's reduced global security commitments under President Trump, creating insecurity for traditional allies, Australia and New Zealand. Recent provocations and new strategic partnerships in the Pacific by China have exposed vulnerabilities in the defense capabilities of both countries. With the American security guarantee becoming unreliable, Australia and New Zealand must enhance their own military capacities and deepen bilateral and regional defense cooperation. Enhanced joint military operations and defense procurements, particularly focusing on air and maritime security, are critical. Forming new alliances with other regional powers, such as Japan, South Korea, and India, could also help address strategic gaps. This period demands a rejuvenated ANZAC cooperation to ensure both countries' security and stability in the changing geopolitical landscape. Sources: The Australian - 21 March 2025
More Extreme Weather Events Expected Across Australia
Summary:
Australia has experienced higher-than-average temperatures and numerous extreme weather events this season, including heatwaves, bushfires, floods, and cyclones. December, January, and February set records as some of the warmest months, contributing to an overall temperature rise of 1.9°C above average. Canberra's daytime temperatures are now 2.5°C higher compared to the early 1970s. Ex-Tropical Cyclone Alfred caused severe damage with strong winds and heavy rainfall, affecting over 300,000 homes. Bushfires in Victoria and Tasmania burned significant areas, while dry lightning in South Australia ignited 100 fires. Extreme weather is forecasted to continue into autumn with persistent heat and potential for further tropical cyclones, storms, and heavy rains. Climate change is driving these conditions, prompting calls for increased preparation and mitigation efforts. Measures include reducing emissions through lifestyle changes and improving emergency preparedness for weather events. Sources: The Daily Telegraph - March 21, 2025, The Courier-Mail - March 21, 2025
The Speaking Coach: The One Word All Liars Use! Stop Saying This Word, It's Making You Sound Weak! The More You Do This, The More You Sound Like A Liar!
Summary:
In this episode of "The Diary Of A CEO with Steven Bartlett," the focus is on effective communication and the subtle cues that can undermine credibility. The guest speaker, a seasoned speaking coach, discusses common verbal habits that can make individuals appear less trustworthy or confident. Key points include:
- Identifying Weak Language: Highlighting specific words and phrases that convey uncertainty or lack of conviction.
- Building Authority: Techniques to project confidence and authority in speech.
- Recognizing Deceptive Signals: Understanding verbal indicators commonly associated with dishonesty.
The episode provides practical advice for enhancing communication skills, making it valuable for professionals and anyone interested in personal development.
Sources: The Diary Of A CEO with Steven Bartlett - March 21, 2025
-
 @ f1989a96:bcaaf2c1
2025-03-20 14:21:35
@ f1989a96:bcaaf2c1
2025-03-20 14:21:35Good morning, readers!
In Thailand, the government announced a third digital cash handout to “stimulate the economy and drive technological adoption.” This disbursement will allocate 27 billion baht ($800 million) to 2.7 million citizens aged 16-20. Like in previous phases, it will be distributed via a state-controlled “digital wallet” application, which essentially functions as a central bank digital currency (CBDC). This system gives the regime an inside view of Thais’ financial activity and creates a centralized database to monitor, censor, and control.
Meanwhile, in Russia, the central bank has proposed limiting Bitcoin access to only the wealthiest individuals. Under the proposal, only Russians with over $1.2 million in assets or an annual income above $580,000 could buy and sell digital assets — arbitrarily barring everyday Russians (including obviously most journalists and activists) from accessing Bitcoin and the financial independence it grants.
In open-source software news, a new tool called Banxaas is making Bitcoin more accessible in West Africa by integrating with local payment providers to facilitate buying and selling Bitcoin using the CFA currency (XOF). This on-and-off ramp could expand financial freedom for human rights activists, dissidents, and everyday citizens.
We end with the latest edition of the HRF x Pubkey Freedom Tech Series, in which HRF’s Zac Guignard sits down with author Jason Maier to discuss how Bitcoin can drive human rights around the world. Together, they examine the shortcomings of today’s financial system and discuss how Bitcoin is aiding people living under authoritarian regimes.
Now, let’s get right to it!
Subscribe Here
GLOBAL NEWS
Thailand | Announces Third Digital Cash Handout to Boost Economy
The government of Thailand announced a third digital cash handout, allocating 27 billion baht ($800 million) to 2.7 million citizens aged 16-20 to “stimulate the economy and drive technological adoption.” Like in previous phases, the regime will distribute the funds through a state-run “digital wallet” application, which would effectively function as a central bank digital currency (CBDC). Past handouts of the CBDC came with strict restrictions: spending was limited to approved vendors within designated areas, purchases were restricted to certain goods, and funds expired after six months. Meanwhile, Prime Minister Paetongtarn Shinawatra called this third handout the first full deployment of the digital wallet system and urged the public to download the official app. This would directly link citizens' financial activity and data to the regime, threaten privacy, and deepen repression in a country with a long history of silencing dissent.
Russia | Central Bank Proposes Restricting Bitcoin Access to Wealthy Only
Russia’s central bank has proposed restricting Bitcoin and cryptocurrency access to only the country’s wealthiest individuals, barring everyday Russians from buying and selling digital assets unless they meet specific income or asset thresholds. Under the proposal, only Russians with over $1.2 million in assets or an annual income above $580,000 could engage with digital assets — effectively putting Bitcoin officially out of reach of most activists and journalists. The central bank claims the measure protects citizens from “volatility and lack of state backing.” But in reality, it likely signals the regime’s fear of Bitcoin’s ability to provide individual financial autonomy. By blocking most Russians from opting out of the state-controlled financial system, the regime is doubling down on financial repression.
India | Advances Digital Rupee CBDC
India’s government is pushing forward with its CBDC, the Digital Rupee, hailing it as a modern payment solution. But as journalist and author Roger Huang puts it, “it looks like a solution searching for a problem to solve.” Beyond the branding, the Digital Rupee enables state control over financial activity. Its programmability allows the government to dictate how, when, and where people spend — restricting transactions to specific merchants, locations, or goods and even imposing expiration dates on money. India’s crackdown on dissent is well-documented, from freezing opposition bank accounts to attempting a Bitcoin ban. Now, the Reserve Bank of India is embedding the CBDC into its digital payment system (UPI), quietly pushing millions into a tightly controlled and surveilled financial system.
Zimbabwe | Financial Regulators Mandate Earnings in ZiG
Zimbabwe’s market regulator is mandating all companies report their earnings in the new ZiG currency despite it losing 96% of its value since its launch last year. This move tightens state control over an already fragile economy, pushing businesses and citizens deeper into an unstable system that has repeatedly wiped out savings through inflation. The ZiG is Zimbabwe’s sixth currency in 15 years, introduced with gold backing to restore confidence in the regime’s ability to manage a currency. Instead, it’s rapidly devaluing, while the US dollar remains the preferred currency for trade and savings — when accessible. For ordinary Zimbabweans, the mandatory use of ZiG for taxes and government services is already a challenge due to its scarcity.
Egypt | Dictator-imposed Reforms Causing Economic Chaos
In the wake of an $8 billion deal with the International Monetary Fund (IMF) last spring, the Egyptian dictatorship has carried out “reforms” that are fueling inflation and making necessities increasingly unaffordable. To meet IMF conditions, Egyptian officials devalued the pound, slashed subsidies, and hiked the cost of fuel and public transportation — driving inflation beyond 20% for months on end. For millions of Egyptians, basic goods are now unaffordable. And the government’s promised minimum wage increase for public workers remains unfulfilled, leaving the public to absorb the price shocks. These undemocratic reforms — never voted on and executed with no way for the public to push back — aimed at securing further financing have only eroded the financial freedom of 114 million Egyptians and pushed the country into greater debt.
China | Facebook Enabling Authoritarian Censorship
A former Meta executive, Sarah Wynn-Williams, has accused Facebook of working “hand in glove” with the Chinese Communist Party (CCP) to censor and surveil content in China. According to Wynn-Williams, Facebook explored building censorship tools that would suppress viral posts until Chinese authorities approved. They even considered sharing user data in exchange for market access to China’s massive user base. Meta denied these claims, saying they fired Wynn-Williams in 2017 for poor performance. Regardless, the revelations highlight the dangers of for-profit, centralized platforms that authoritarian regimes can co-opt. Protocols like nostr (where no single entity moderates content) are more important than ever. Activists and dissidents seeking free communications can get started with nostr here.
BITCOIN AND FREEDOM TECH NEWS
Banxaas | Spend Sats in West Africa
Hundreds of millions of citizens in West Africa still use the CFA franc in an arrangement upheld by more than a dozen authoritarian leaders. Banxaas offers an alternative by bridging Bitcoin with West Africa’s mobile money networks. This allows individuals to buy and sell Bitcoin through local payment providers using the local CFA currency (XOF) and their own Lightning wallet. By integrating with local payment providers, Banxaas serves as a crucial on-and-off-ramp to Bitcoin, bringing the benefits of financial freedom to individuals, nonprofits, and human rights defenders across the region. Watch a demonstration of how Banxaas works here.
Mi Primer Bitcoin | Bitcoin Workbook Translated to Mandarin
Mi Primer Bitcoin, an open-source Bitcoin educational initiative focused on high-school-age students, released a Mandarin translation of its 2025 Bitcoin Diploma. This open-source resource provides mainland Chinese citizens, activists, and dissidents with accessible Bitcoin education at a time when financial freedom is increasingly under threat. With China tightening restrictions on personal wealth and expanding state surveillance of financial activity through the digital yuan CBDC, the diploma offers a useful new resource to learn the alternatives to state-controlled financial systems.
Blitz Wallet | Improves Ecash Functionality for Greater Financial Autonomy
Blitz Wallet, an open-source and self-custodial Bitcoin Lightning, Liquid, and ecash wallet, released an update that improves ecash functionality. Ecash, a Bitcoin-backed digital money system, allows instant and private transactions but requires custodial “mints” to manage tokens. The new update links users’ ecash to their wallet’s seed phrase (the 12-word backup used for Bitcoin recovery), allowing them to restore funds even if their device is lost or stolen. Users can also now transfer ecash between different wallets, increasing flexibility and control over their funds. Improved ecash UX is much-desired for political dissidents who can’t afford for authoritarian regimes to have full oversight over all of their economic activities.
Fedimint | Adds On-chain Support for Everyone
Fedimint, an open-source Bitcoin custody model that lets communities securely manage Bitcoin funds together, released v0.6.0, adding support for on-chain Bitcoin deposits (transactions directly on Bitcoin’s base layer). By offering private and trust-minimized transactions alongside on-chain support, Fedimint makes it easier, especially for nonprofit communities, to self-custody Bitcoin. It provides greater privacy and autonomy versus using fully centralized platforms that are easily subject to the political and regulatory pressure of authoritarian regimes.
Africa Bitcoin Conference | Announces 2025 Conference
The Africa Bitcoin Conference (ABC) announced its fourth edition, set to take place from Dec. 3-5, 2025, in Port Louis, Mauritius. Hosted at the Caudan Art Center, the event will bring together activists, Bitcoin advocates, and freedom tech developers to explore Bitcoin as a pathway to financial freedom. Now the largest Bitcoin gathering in Africa, ABC has established itself as a key platform for discussions on financial inclusion, inflation resistance, and censorship-resistant money — putting tools for financial sovereignty into the hands of those who need them most. HRF is proud to support ABC and, in particular, is proud to help delegates from dozens of authoritarian regimes attend each year. You can learn more about the conference and buy tickets here.
RECOMMENDED CONTENT
HRF x Pubkey — How Bitcoin Brings About Social Change with Jason Maier
In the latest installment of the HRF x Pubkey Freedom Tech Series, HRF Content and Research Associate Zac Guignard sits down with Jason Maier, author of “A Progressive’s Case for Bitcoin,” to share how Bitcoin can spark a meaningful shift in personal liberty worldwide. Jason explains the core monetary properties that make Bitcoin permissionless, censorship-resistant, and a powerful tool for financial freedom. Together, they examine the shortcomings of today’s financial system and discuss how Bitcoin is aiding people living under authoritarian regimes. They talk about how Bitcoin shouldn’t be a political issue and can be useful to anyone, no matter their beliefs. Watch the full conversation here.
Mélancolies de l’Opprimé by Farida Bemba Nabourema
Farida Bemba Nabourema, a renowned Togolese human rights activist, former HRF freedom fellow, and Bitcoin pioneer, announced that her new book “Mélancolies de l’Opprimé” will be released on April 15, 2025. A decade after her first book, “La Pression de l’Oppression,” this deeply personal and reflective work offers hard-earned wisdom for young activists stepping into the struggle against dictatorships and injustice. Nabourema candidly shares the emotional, physical, and psychological toll of resistance and activism while also highlighting the sense of purpose in the pursuit of freedom and human rights. Learn more about the book here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ a396e36e:ec991f1c
2025-03-20 14:11:02
@ a396e36e:ec991f1c
2025-03-20 14:11:02Introduction
The term Clown World is a meme that reflects the perception that the current system operates in an absurd, corrupt, or irrational manner. In this context, many Bitcoin enthusiasts see it as a tool to escape from Clown World. Bitcoin emerged in 2009, following the 2008 global financial crisis, as an alternative to a traditional monetary system that many consider unjust, inefficient, and prone to manipulation. This article explores how Bitcoin challenges existing economic structures, embodies philosophical principles such as decentralization and financial sovereignty, and serves as a political tool against failing monetary policies. We will also examine the historical evolution of Bitcoin’s narrative in relation to escaping Clown World.
Economic Perspective: Challenging Traditional Monetary Structures
From an economic standpoint, Bitcoin directly challenges the traditional monetary system, which many Bitcoin advocates see as part of Clown World. Fiat currencies, issued by central banks, can be devalued through expansionary policies, leading to inflation, bank bailouts, and resource misallocation that deteriorate economies and social structures. Bitcoin was explicitly designed as a response to these issues: its genesis block, mined on January 3, 2009, contained the message "The Times 03/Jan/2009 Chancellor on brink of second bailout for banks," referencing government bailouts of failing financial institutions. This message signaled Bitcoin’s intent to offer a solution to what was perceived as a broken financial system and irresponsible economic policies.
Unlike fiat money, which can be expanded at the discretion of central authorities, Bitcoin has a predictable and non-manipulable monetary policy. Its issuance follows an algorithmic schedule: the total supply is capped at 21 million coins, ensuring scarcity and practically eliminating long-term inflation. Every four years, a halving event reduces the number of new bitcoins entering circulation, contrasting sharply with central banks’ inflationary targets of around 2% per year. In Bitcoin, no one can arbitrarily “print” more money or devalue existing units, as “there is no central authority” making such decisions. As analyst Anthony Pompliano put it: “Bitcoin is censorship-resistant money. No one can stop you from sending it. No one can confiscate it without your permission. No one can debase the currency.” In other words, Bitcoin functions as digital gold, immune to political dilution, challenging the very foundation of inflationary fiat money.
This economic model—often associated with the idea of “sound money”—represents a separation between money and the state. Many Bitcoin proponents argue that a broken monetary system is at the root of the dysfunctions of Clown World. As Bitcoin advocates Knut Svanholm and Luke de Wolf put it: “When money stops working, everything becomes political and turns into a farce.” Bitcoin, by replacing trust in financial authorities with trust in cryptographic code, aims to correct these distortions. It allows individuals and communities to opt out of the traditional system, securing themselves against inflation and reckless monetary policies.
Philosophical Perspective: Decentralization, Financial Sovereignty, and Resistance to Manipulation
From a philosophical perspective, Bitcoin embodies principles of decentralization, individual sovereignty, and resistance to manipulation, offering an alternative to perceived systemic corruption and control. Unlike traditional money, Bitcoin is a decentralized digital currency that “does not rely on any central authority but operates through a mathematical protocol and a distributed network of nodes.” This means that no government, bank, or corporation can unilaterally control the Bitcoin network or counterfeit its supply. The blockchain architecture and distributed consensus make Bitcoin a kind of “trust machine”, where the rules are pre-set by transparent algorithms. For the first time in history, digital scarcity combines with total decentralization, creating a monetary system where trust is placed in code rather than authorities.
This foundation enables personal financial sovereignty. Bitcoin users can fully own and control their funds through private keys, redefining monetary property rights by eliminating the need for custodians. In practice, this means that “no one can confiscate it without your permission” as long as the user protects their keys (hence the famous phrase “not your keys, not your coins”). Bitcoin’s sovereignty contrasts with traditional bank accounts, which are vulnerable to freezes, censorship, or devaluation. The philosophy behind Bitcoin promotes independence from state and corporate financial control, much like the historical separation of church and state. As a Bitcoin advocate noted, “By decentralizing financial power and promoting a separation between money and the state,” Bitcoin has the potential to reshape economic power dynamics. Essentially, anyone can become their own bank, transacting globally without requiring permission.
Another key aspect of Bitcoin’s philosophy is censorship resistance and protection from manipulation. In Clown World, institutions can block transactions, exclude individuals from the financial system, or manipulate currency for political purposes. Bitcoin was designed to counteract this. Anyone can transfer Bitcoin to another person directly, without intermediaries who can block transactions. The blockchain's immutability ensures that no one can retroactively alter payment records or falsify balances, reinforcing its freedom-preserving nature.
Recent events highlight this utility: In 2022, when the Canadian government froze bank accounts of protesters and pressured crowdfunding platforms, many pointed out that Bitcoin could bypass such authoritarian measures. As one commentator put it, “Every attempt at financial censorship is free marketing for Bitcoin,” as it underscores its value as unseizable and incorruptible money. This ideology aligns with libertarian and anarcho-capitalist ideals, advocating that individuals—not the state—should have ultimate control over their money and transactions.
Political Perspective: Bitcoin as a Tool of Resistance Against Authoritarianism and Monetary Failures
From a political standpoint, Bitcoin has been used as a form of resistance against authoritarian regimes, state financial controls, and failing monetary policies. Due to its borderless and stateless nature, Bitcoin enables escaping national economic barriers and prevents governments from unilaterally controlling wealth. In countries suffering from hyperinflation or strict currency controls, citizens have turned to Bitcoin to protect their savings.
Venezuela is a key example: Bitcoin is widely used there as a store of value against the endless devaluation of the national currency. Similarly, in Argentina, Bitcoin adoption has surged as people seek to preserve their wealth amidst chronic inflation and restrictions on foreign currency exchange. In these contexts, Bitcoin serves as an escape valve from disastrous economic policies, offering a refuge where the government cannot destroy the value of money through inflation.
Conclusion
Bitcoin is more than just an asset; it is a technological, economic, and philosophical revolution offering an alternative to what many perceive as the dysfunctions of Clown World. By enabling economic sovereignty, censorship resistance, and an escape from inflationary policies, Bitcoin challenges the status quo, providing a viable path toward financial freedom and systemic change.
-
 @ bf47c19e:c3d2573b
2025-01-04 19:10:20
@ bf47c19e:c3d2573b
2025-01-04 19:10:20UTXO (Unspent Transaction Output) je Bitkoin koji nije potrošen, BTC koji se nalazi na svim adresama. Možemo ga porediti sa novčanicom u novčaniku i koja se mora u celosti potrošiti. Samo što kod BTC to može biti bilo koji iznos i taj iznos je uvek isti kao veličina poslednje transakcije minus naknada majnerima. Dok novčanice u novčaniku imaju tačno određene apoene, 100 dinara, 200 dinara, 500 dinara itd.
Kada plaćamo novčanicama nešto što košta 300 dinara, a u novčaniku imamo jednu novčanicu od 500 dinara, mi prodavcu moramo dati celu novčanicu od 500 dinara, a on nam zatim vraća kusur 200 dinara.
Kada plaćamo novčanicama nešto što košta 300 dinara, a u novčaniku imamo tri novčanice od 200, 200 i 100 dinara, mi prodavcu moramo dati ili dve novčanice od po 200 gde takođe dobijamo kusur ili dve novčanice od 200 i 100 dinara.
Ova analogija se može primeniti i na BTC i UTXO-ve koji funkcioniše na gotovo istom principu.
Ako plaćamo putem BTC nešto što košta 0.03 BTC, a u novčaniku imamo jedan UTXO od 0.05 BTC (a koji je nastao tako što je neko nama prethodno poslao 0.05 BTC u jednoj transakciji), naš novčanik ne šalje samo 0.03 BTC sa adrese, a da pritom 0.02 BTC ostane u novčaniku. Ne nego se iz novčanika šalje svih 0.05 BTC, 0.03 BTC ide prodavcu, a 0.02 BTC se vraća nama u novčanik kao kusur (change) na novu adresu formirajući novi UTXO od 0.02 BTC. Za slanje sredstava sa tog jednog UTXO-a plaćamo jednu transakcionu naknadu (fee) Bitkoin rudarima/majnerima. Neka bude $1 fee.
Ako plaćamo putem BTC nešto što košta 0.03 BTC, a u novčaniku imamo tri UTXO-a od 0.02, 0.02 i 0.01 BTC (koji su nastali tako što su nam prethodno poslate tri odvojene transakcije od 0.02, 0.02 i 0.01 BTC), naš novčanik automatski ili mi lično (putem opcije "coin control") sada moramo da odaberemo koja od ta tri UTXO-a, koje od te tri svojevrsne digitalne novčanice, ćemo poslati trgovcu. Dakle moramo da iskoristimo sredstva sa dva UTXO-a pošto nijedan pojedinačni UTXO nema dovoljno sredstava za plaćanje. I za slanje svakog od ta dva UTXO-a se majnerima plaća zasebna transakciona naknada koje zbirno koštaju duplo više nego u situaciji kada šaljemo sredstva sa jednog UTXO-a. Dakle plaćamo hipotetičkih $2 fee.
Ako imamo preveliki broj manjih UTXO-va, odnosno UTXO-va na kojima se nalaze pojedinačno mala sredstva i treba da platimo nešto skuplje u jednoj transakciji, onda ćemo za svaki od tih UTXO-va platiti zaseban fee što može dovesti do toga da ukupan fee bude dosta skup.
Ko vodi računa o privatnosti i nikada ne prima sredstva na jednu istu adresu više od jednom, odnosno uvek generiše novu adresu pri primanju svake transakcije, onda će uvek imati situaciju "1 adresa = 1 UTXO" i onda je lakši upravljanje UTXO-vima (UTXO management). Mnogo je teže kada se sva sredstva primaju na jednu adresu koja bi imala veliki broj UTXO-va.
-
 @ a296b972:e5a7a2e8
2025-03-20 19:36:34
@ a296b972:e5a7a2e8
2025-03-20 19:36:34Diagnose:
Der aufgelöste Bundestag verschuldet die Insassen eines Landes namens Absurdistan in schwindelerregender Höhe durch einen noch nicht gewählten Bundeskanzler, der vormals wohlmöglich Werbung für Gewürzgurken gemacht hat, unter Zuhilfenahme von Parteien, die abgewählt wurden. Eine Sperrminorität konnte nicht entstehen, weil sie sonst verhindert hätte, dass die Wahlversprechungen nicht hätten gebrochen werden können. (Geht gar nicht!)
Genau so gut, hätte der letzte deutsche Kaiser eine Sektsteuer erheben können, um die deutsche Marine aufzurüsten. (Ach so, ja, ist schon gut, hatten wir schon, hatte ich vergessen.)
In Rumänien und Serbien sind Demokraten zu Hunderttausenden auf der Straße, und Deutschland hat Kellerwoche (Schade eigentlich!).
In Erstverschlimmerung löst die aktuelle Situation das blanke Entsetzen aus, doch auf den zweiten Blick stellt sich das Ganze durchaus als sehr positiv dar. Heilung ist möglich, doch vorher kommt der Schmerz:
Die Neuverschuldung ist nämlich eine provisorische Abschreckung für den Russen, der dann doch lieber so lange wartet, bis Deutschland in 10 bis 20 Jahren wirklich aufgerüstet hat. Wer kämpft schon gerne gegen jemanden, der sich nur maximal 2 Tage verteidigen kann? Das macht doch keinen Spaß. Da lohnt sich doch der ganze Aufwand nicht. Bis dahin hat Deutschland leider nichts, außer Schulden. Von Windrädchen und Zufallsstrom und einer innerlich, aber eben nur sehr innerlich, rebellischen Bevölkerung mal ganz abgesehen.
Es geht hoffnungsvoll weiter. Mit Frau von der Leyen haben wir als EU-Kommissarin bereits eine Deutsche in Brüssel, die sich schon vor ihrer zweiten Einsetzung ohne demokratische Mittel, in bundesstaatlichen Pöstchen durch ihre mangelnde Qualifikation besonders herausragend ausgezeichnet hat.
Statt einer qualifizierten, sich verdient gemacht habenden Diplomatin namens Frau Dröge, soll nun als weitere "deutsche Konifere" auch Frau ver Baerbock-t als UN-Generalsekretärin der UN-Generalversammlung hochgelobt und eingesetzt werden. Auf die Frage von Herrn Warweg in der Pressekonferenz-Show, warum denn nun Frau Baerbock qualifizierter sei, als Frau Dröge, wusste sich der Sprecher Herr Hebestreit wie immer galant durch nichts sagende Textbausteinabsonderungen aus der Schlinge zu ziehen. Vermutlich wollte er Frau Dröge nicht kompromittieren, weil er sonst hätte sagen müssen, dass ja Frau Baerbock viel besser Trampolin springen kann, als sie. Kavalier ist er ja, da gibt es nichts gegen zu sagen.
Mit Frau Baerbock hätte Deutschland eine weitere Deutsche installiert, die dem Ansehen Deutschlands in der Welt, in Fortsetzung ihres Amtes als Außenfeministin, nahtlos weiterhin den maximalen Schaden zufügen könnte.
Weiter wird gemunkelt, dass Herr Habeck für die Darstellung des Bundespräsidenten zur Disposition steht. Mit Märchen kennt er sich aus, insofern wäre er ein würdiger Nachfolger des Streubomben-nicht-Verhinderers. Auch Herr Habeck wird durch seine oft genug bewiesene Expertise in Insolvenz und Wirtschaftsvernichtung Deutschland nach außen hin in bester Weise repräsentieren. Als braver Bürger kann man sich keinen besseren Schwiegermutter-Liebling vorstellen. Und wie der sich ausdrücken kann, hach, einfach nur nett!
Die Aufteilung der Grünen in Außen und Wirtschaft war somit absolut sinnvoll. Schließlich kommt Frau Baerbock ja mehr vom Haarspray und Herr Habeck mehr so vom Shampoo.
Und wenn wir schon mal bei der Verteilung von neuen Pöstchen sind, dann sollte man Herrn Scholz als neuen Chef für den Bundesnachrichtendienst vorschlagen. Verschwiegen ist er, Geheimnisse kann er bewahren. Wie Staatsgeheimnisse nicht an die Öffentlichkeit gelangen, damit kennt er sich aus. Nordstream 2 wurde nämlich von den Deutschen selbst in die Luft gejagt, als Selbstgeißelung für den angerichteten Schaden im 2. Weltenbrand. Er wollte einfach Teile der Bevölkerung nicht verunsichern, auch, wenn die Idee nicht von ihm ist.
Und Herr Lauterbach sollte in die Wissenschaft wechseln und dort einen neuen Lügendetektor entwickeln, mit dem man Fake-News problemlos entlarven kann. Wie lügen geht, weiß er ja von allen am allerbesten. Und wenn es wirklich mal eng werden sollte, kann er ja Berater zur Hilfe nehmen. Vielleicht haben Herr Drosten oder gar Herr Fauci (ital. la fauci = das Maul) Zeit ihn bei dieser wertvollen Arbeit zu unterstützen.
Warum also ist das jetzt alles positiv?
Mit diesen Kapazitäten wären Deutsche an exponierter Stelle installiert, um das ideologische Gift in die EU, in die UN und weltweit hinein zu träufeln.
Innerdeutsch werden sich sicher Herr Bäcker, der Mann mit den unglücklichen Initialen, Frau Düsseldorf-Rheinmetall, Herr Kriegsgewitter u. a. auch weiterhin zur Verfügung stellen, die Kriegstüchtigkeit ihrer Vollendung entgegen zu führen. Wohlwollend beobachtet durch die USA und Russland. Das wäre dann Inklusion, oder sagt man Implosion?
Dann werden auch noch als erstes von den Billionen Sonderschulden mobile Vermögenswerte in Form von Vorschlaghämmern angeschafft, mit denen die Schweine der deutschen Sparer geschlachtet werden sollen. Frau Lagarde hat sich schon bereit erklärt, hier mit Einführung des digitalen Euro demnächst helfend zur Seite zu stehen.
Alles wirklich molto bene, Heilung ist nahe!
In Zusammenwirken all dieser Kräfte und Kapazitäten für Deutschland und Europa, wird auch noch die deutsche Gesellschaft die Grätsche machen und dann ist Deutschland völlig bettlägerig und darnieder. Deutschland hat bald fertig!
Und hat Deutschland, als größter Geldgeber der EU fertig, hat auch die EU fertig, ihr geht dann einfach die Puste aus. Und vielleicht warten schon Ungarn und einige andere Mitgliedsstaaten nur auf eine günstige Gelegenheit, der EU für lange Zeit Adieu zu sagen?
„Wenn wir uns wiedersehen, werden wir uns freuen, wenn nicht, war der Abschied wohlgetan!“
Und mit ganz viel Glück geben die USA Europa dann auch noch den Gnadenstoß und erlösen die europäischen Staaten von dem Übel namens EU, da sie offensichtlich selbst nicht in der Lage sind, sich aus ihrer Bevormundung mit betreutem Denken und einem Wahrheitsministerium zu befreien. Die NATO wackelt ja auch schon.
Genesung:
Anschließend gibt es für alle Bürger Europas, aber besonders für Deutschland, einen Pflichtkurs in der Volkshochschule in Sachen Frieden, Demokratie und Freiheit. Vielleicht klappt es dann dieses Mal, aus Denkschnecken Schachweltmeister zu machen. Oder wenigstens aus Langzeitkomatösen Leute mit Wachbewusstsein.
Nochmals, alles in bester Ordnung. Es muss erst noch schlimmer werden, bevor es wieder besser wird. Bei dem Tempo, dass die europäischen Universal-Dilettanten derzeit an den Tag legen, wird das nicht sehr lange dauern.
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ a60e79e0:1e0e6813
2025-03-20 12:58:13
@ a60e79e0:1e0e6813
2025-03-20 12:58:13*This is a long form Nostr native version of a post that lives on my Nostr educational website Hello Nostr *
At first glance Nostr might appear quite similar to some of the apps you use every day, such as Twitter, Mastodon, or Facebook, but that couldn't be further from the truth. This post aims to dispel the myth that "Nostr is just a Twitter replacement" and give you a better understanding about the 'what', the 'how' and most importantly, the 'why' of Nostr.
What Is Nostr?
Nostr is a decentralized, open-source protocol designed for censorship-resistant networking and communication on the web. It stands for "Notes and Other Stuff Transmitted by Relays," and it works by allowing users to publish messages (notes) and content in the form of 'other stuff', to a network of servers (relays) that store and distribute the content.
Unlike traditional platforms like Twitter, Ebay or Facebook, Nostr doesn't rely on a central authority; instead, users control their own identities via cryptographic key pairs.
The simplest open protocol that is able to create a censorship-resistant global "social" network once and for all.
Fiatjaf - Nostr Creator
Nostr is not a website or an app you download from a single source — it’s an open protocol, like email or the internet. Think of it as a set of rules that anyone can use to build tools for sharing messages, posts, or other data without needing a centralized middleman like a big tech company.
Nostr was created by a developer named Fiatjaf in 2020, and has since been steadily gaining traction among people who care about privacy, freedom, and censorship resistance.

Why Nostr?
Imagine the scenario, you've been using an online platform for 5 or even 10 years. You've built up thousands of contacts, perhaps built yourself a sizeable reputation, or even rely on the income from the platform to feed your family. Then one day you make a controversial post, sell a certain item or upload a video on a spicy subject to the platform where the owner disagrees with. With the click of a button, your account is removed. All trace of you, your social graph, or even your future income, disappears in an instant.
Read aloud like that is sounds crazy that we'd even entertain using such a platform, right!? Sadly that is the reality in 2025. This is exactly what happens every single day on X, Facebook, Ebay, Paypal, Linkedin, etc.
Looking at the problem through a more social media focused lens, many of us have become slaves to the likes of Instagram, Twitter and TikTok. We use these 'free' apps under the guise of being social with others online. The reality is that we see what those apps want us to see. We've become slaves to the manipulation of complex and opaque algrorithms designed to keep us hooked and try to sell us things.

Unlike traditional platforms, which are often governed by centralized entities wielding significant control over user data, content moderation, and algorithmic influence, Nostr flips the script by prioritizing user sovereignty and resilience. Built on an open-source framework, Nostr allows individuals to control their own data and interact through a network of relays, making it much more difficult for any single authority - be it a corporation, government, or bad actor - to censor or manipulate the flow of information.
- Is a relay refusing to host your notes? Use another or run your own!
- A specific client using an algorithm you don't like, take your identity and social graph elsewhere and choose another!
Take your identity and social graph with you, anywhere any time.
Nostr’s ability to foster authentic, unfiltered conversations while safeguarding user sovereignty has made it a cornerstone for communities seeking alternatives - whether they’re activists, creators, or everyday people tired of being pawns in the data-driven game. It's simple and adaptable design also encourages innovation, inviting developers to build tools and interfaces that keep pushing the boundaries of what the decentralized internet can achieve. In short, Nostr isn’t just a tool; it’s a movement toward a freer, more equitable digital future.

How Does Nostr Work?
Instead of one giant server owned by a single company holding all your posts and messages, Nostr spreads everything across lots of smaller servers called relays. To get started, you download a client, create your account and back up your private key. Your private key is used to secure your account and sign every message you send over the network. This allows anyone you interact with the verify the integrity of the data coming from 'you'.
The Nostr network is essentially a collection of bulletin boards that share a common format
When you write a note, or share some other type of compatible data, your client signs it with your private key, then sends it to one or more relays. Which relays your information is sent to is entirely up to you. These relays share your message with others who want to see it.
For others to see your notes or 'other stuff', they'll need to be able to find you. Typically this is done by using your public key, which looks something like this
npub15c88nc8d44gsp4658dnfu5fahswzzu8gaxm5lkuwjud068swdqfspxssvx. Don't panic though, you don't need to memorize all of your friends public keys, there are more human friendly methods of finding people that we'll come onto later.Once someone is following you, their client will ask all of their connected relays for any data shared by your public key. Their client will receive this data, verify it is signed by your private key and then populate it into their feed.
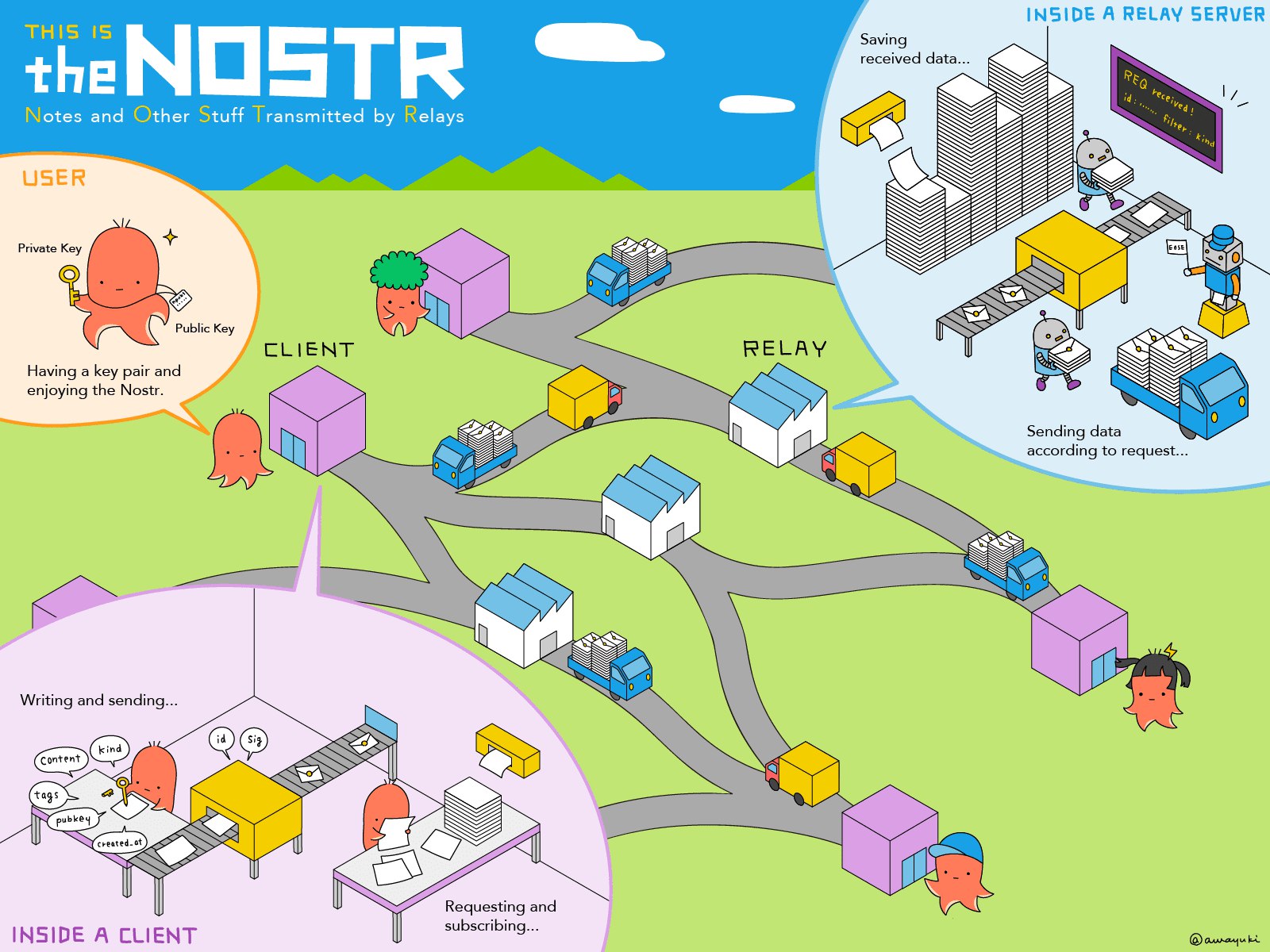
The “Other Stuff” Explained
Nostr’s name hints at this: Notes and Other Stuff Transmitted by Relays. But what is the “other stuff”? Put simply, it’s all the creative and experimental things people are building on Nostr, beyond simple text based notes. Every action on Nostr is an event - like a post, a profile update, or even a payment. The 'Kind' is what specifies the purpose of each event. Kinds are the building blocks of how information is categorized and processed on the network, and the most popular become part of higher lever specification guidelines known as Nostr Implementation Possibility - NIP. A NIP is a document that defines how something in Nostr should work, including the rules, standards, or features. NIPs define the type of 'other stuff' that be published and displayed by different styles of client for different purposes.
Here's some content examples of 'Other Stuff':
- Long-Form Content: Think blog posts or articles. NIP-23.
- Private Messaging: Encrypted chats between users. NIP-04.
- Communities: Group chats or forums like Reddit. NIP-72
- Marketplaces: People listing stuff for sale, payable with zaps. NIP-15
- Zaps: Value transfer over the Lightning Network. NIP57
The beauty of Nostr is that it’s a flexible foundation. Developers can dream up new ideas and build them into clients, and the relays just keep humming along, passing the data around. It’s still early days, so expect the “other stuff” to grow wilder and weirder over time!
Clients vs Relays: What’s the Difference?
Newbies often get tripped up by these two terms, so let’s clearly define them.
Clients
A client is what you use to interact with Nostr. It’s the app or website where you type your posts, read your feed, follow and interact with others. Examples of Nostr clients include:
- Damus (iOS Twitter style client)
- Primal (Cross-platform Twitter style client)
- Amethyst (Android only Twitter style client)
- Habla.News (Web based blog client)
- Olas (Instagram style client)
- 0xchat (Messaging client)
Clients don’t store your data; they just pull it from relays and display it for you. You can switch clients whenever you want, and your account stays the same because it’s tied to your keys, not any single client or app.
Clients are how you use Nostr, and relays are where the data lives. You need both to make the magic happen.
Relays
A relay is a server that stores and shares Nostr data. It’s a little like a post office: you send your note to a relay, and it delivers it to anyone who’s subscribed to see it (like your followers). Relays are run by individuals, groups, or companies who volunteer their computing power. Some are free, some charge a small fee, and you can connect to as many as you like. Most clients will come pre-configured with a list of well-known relays, but you can add or remove any you like.
What Are Zaps?
Zaps are arguably one of Nostr’s coolest features! A zaps is a way to send payments in Bitcoin directly to other users. Imagine liking a post, but instead of just clicking a heart (which you can of course do), you send the poster a few cents worth of Bitcoin to say, “This is awesome!”.
Zaps use Bitcoin's Lightning Network, a faster and cheaper way to move Bitcoin around. To Zap someone, you need a Lightning wallet linked to your Nostr client. Some clients, like Primal, ship with their own custodial wallet to make getting started a breeze. Most clients also allow more advanced users to connect an existing Lightning Wallet to reduce reliance and trust in the client provider.
Zaps are optional but add a fun layer to Nostr. Creators love them because it’s a way to get direct support from fans, with no middleman required.
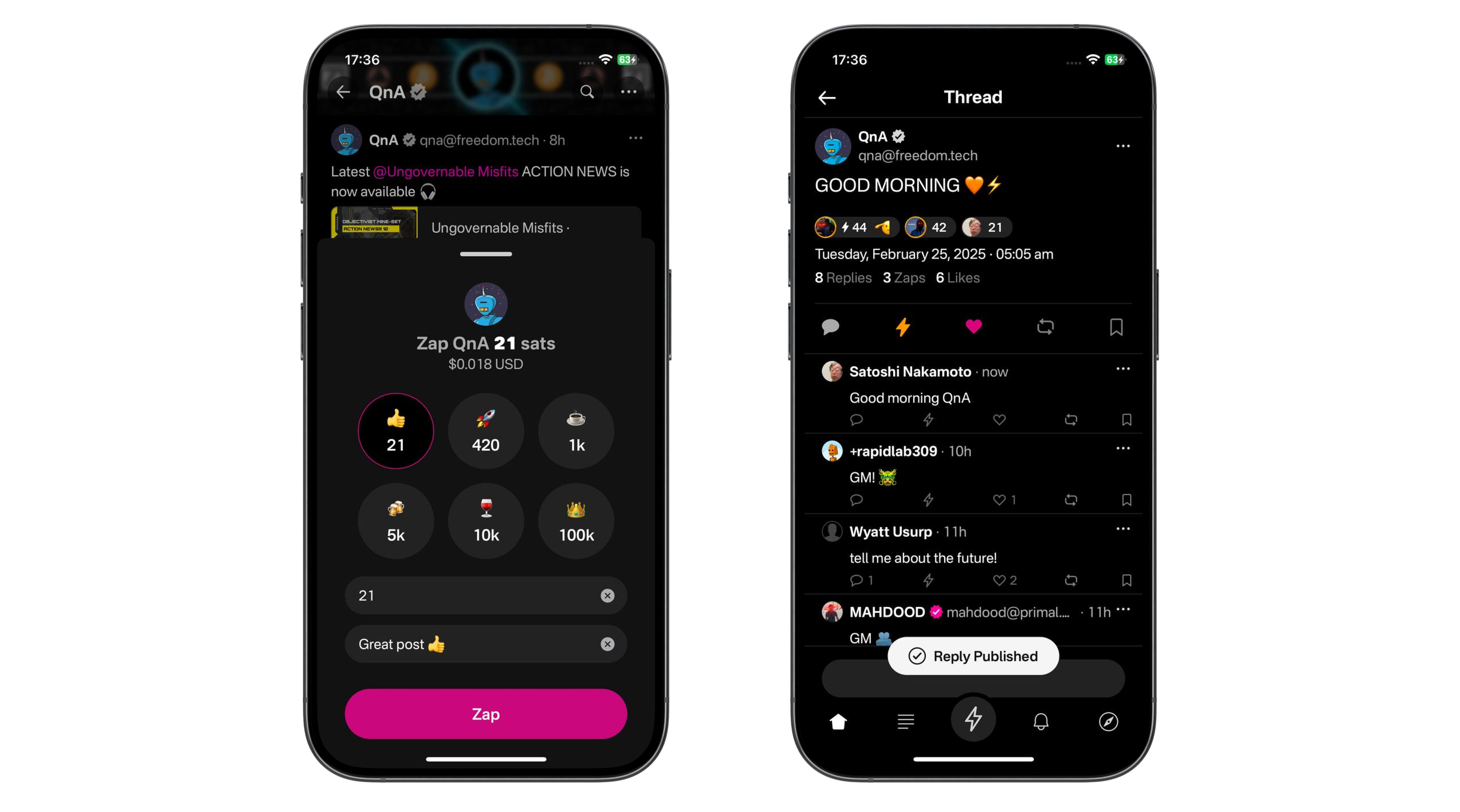
NIP-05 Identifiers: Your Nostr “Username”
Your nPub, or public key (that long string of letters and numbers) is your 'official' Nostr ID, but it’s not exactly catchy. Enter NIP-05 identifiers, a human-readable and easily sharable way to have people find you. They look like an email address, like
qna@hellonostr.xyz.Here’s how it works:
Most users obtain their NIP-05 ID from a website or service that supports Nostr. Some of these services are free whereas some charge a fee. Some clients, like Primal will set one up for you automatically when you create an account. The email like ID links to your public key, so people can find you more easily. And because these ID's are domain based, there can be no duplicates. qna@hellonostr.xyz can only map to a single public key. The only person that can change that link is the person in control of the domain.
If you control your own domain, you can easily map your Nostr public key to name@my.domain. It’s not mandatory, but it’s super useful for building trust and making your profile recognizable.
Next Steps
So you're bought in. You understand why Nostr is so important and want to get started. Check out our simple onboarding guide here.
Thanks For Reading
Hopefully that moistened your taste buds for more educational Nostr content. This was a basic one, but there will be more focused material coming soon.
If you found this post useful, please share it with your peers and consider following and zapping me on Nostr. If you write to me and let me know that you found me via this post, I'll be sure to Zap you back! ⚡️
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
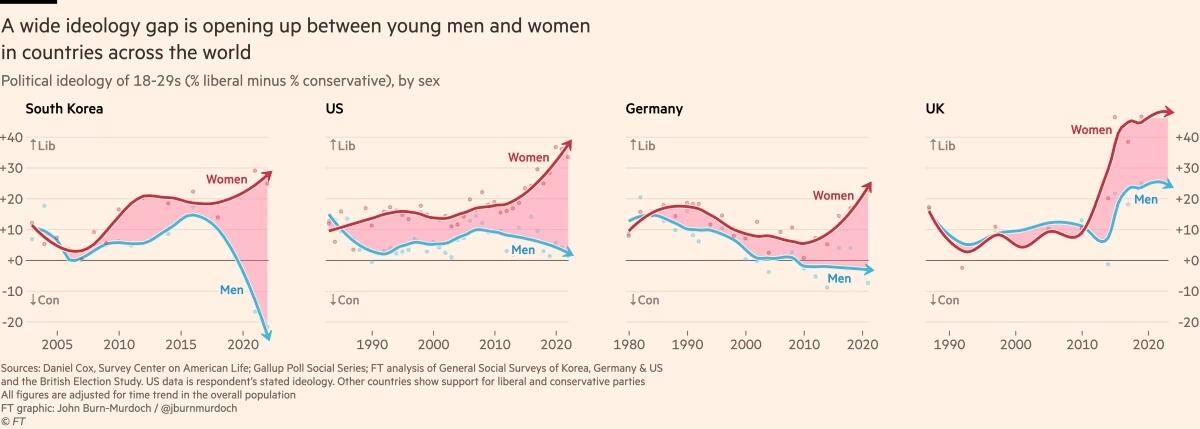
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ 6f0a6a19:7dd662db
2025-03-20 19:00:46
@ 6f0a6a19:7dd662db
2025-03-20 19:00:46BitBonds
The idea, initially proposed by Newmarket Capital CEO Andrew Hohns at the Bitcoin Policy Institute’s “Bitcoin for America” conference, is that Congress could defease the federal debt and cut long-term interest rates by approving a new debt instrument collateralized with Bitcoin—BitBonds.
How It Works:
- For every $100 BitBond issued, $10 would buy Bitcoin for the U.S. Strategic Reserve.
- Bondholders would receive 1% annual interest (lower than traditional Treasuries) and 50% of BTC price appreciation.
A New Bitcoin Standard
At first glance, BitBonds is an innovative way to increase demand for U.S. Treasuries without Federal Reserve intervention while lowering borrowing costs. However, this instrument would signal a radical change in monetary policy.
A 4000-year precedent
Money (as a visual measure of credit) has been and is always socially constructed through a stable exchange ratio.
- Money didn’t appear in ancient Sumer until priests and palace administrators set rates between standard weights of grain and silver on palace-authorized cuneiform tablets.
- In Egypt, money was constructed through economic administrators (related to the king) setting common rates between an abstracted standardized 92 gram copper weight measurement called a Deben and grain.
- Roman and Greek mints fixed ratios and weights between precious metals to establish official coinage and stabilize their value.
- The U.S. established its first currency through a bi-metallic standard, fixing gold and silver rates via the U.S. Mint.
- The modern U.S. monetary system issues its currency on a promise to redeem $100 for $100 + 2% interest.
U.S. government debt became the default monetary exchange rate the moment Nixon suspended gold redemption in 1971. It was the only remaining promised ratio of exchange attached to the US Dollar. Each year, Congress votes to extend this debt-based system by approving the federal budget. And the Federal Reserve then manages the levers of bond prices and yields through open market operations. There is no other federal mechanism for securing universal interest in the dollar, than the interest paid from its debt.
With BitBonds collateralizing 10% of each issuance in Bitcoin, the government would effectively introduce a new promised ratio of exchange to US monetary policy. It would promise to redeem 10 cents of every $1 in this lending program for bitcoin (half for the reserve and half of its appreciated value for the holder). This promise would transition US monetary policy from a pure debt based system to a new implicit exchange rate between Bitcoin and the U.S. dollar.
How BitBonds Would Drive Bitcoin to $10 Million
- First, BitBonds promises unlimited buying pressure on a finite asset. (The government can perpetually issue more BitBonds to acquire Bitcoin.) That, combined with the fact that Treasuries are the world’s primary liquidity engine, would generate unprecedented demand for Bitcoin reserves.
- Second, unlike previous reserve assets like gold, Bitcoin’s indivisibility prevents fractional redemption. This network constraint prevents the government from redeeming less than 1 satoshi (the base unit of Bitcoin) for 10 cents, thereby setting a clear price target for the market. Promising to collateralize 10% of each bond with bitcoin is like priming the pump for max buy pressure, fixing a target price and pulling the trigger.
- Investors would front-run the Treasury’s buying spree with that target in mind and in a matter of time 1 satoshi will equal $0.10 ($10M per BTC).
- At $10M per BTC, Bitcoin’s total valuation would reach $210 trillion—a figure capable of servicing the $189 trillion in global U.S. debt obligations and backing the $21 trillion M2 money supply. This valuation would prime bitcoin to become the world reserve asset backing the world reserve currency (a digital dollar).
- After this transformation, the government would have the precedent to institute a more explicit system of regulating bitcoin and digital dollar redemption. You can learn more about what this system would look like in my thesis for why technocratic government agencies will inevitably use bitcoin to create a cashless digital society: The Anarchist’s Guide to Cashing out of the Matrix.
Why Market Resistance Will Fail
- Selling Bitcoin into a U.S. Treasury buy wall would be a losing trade. A continuous government buyer would absorb any attempt to suppress BTC’s price.
- Foreign governments would be compelled to adopt or lose financial leverage. If the U.S. redefines sovereign debt through Bitcoin, foreign central banks must accumulate Bitcoin or face economic devaluation.
- The Federal Reserve would have no choice but to accommodate Bitcoin-backed Treasuries. If BitBonds reshape U.S. debt issuance, the Fed must either integrate them into monetary policy or risk disrupting Treasury markets.
The short path to a $10 million bitcoin
- The U.S. Treasury launches BitBonds, requiring Bitcoin collateral equal to 10% of each issuance.
- Bitcoin markets recognize that the U.S. government is a continuous net buyer.
- Investors front-run this signal, accelerating Bitcoin accumulation.
- Institutional demand propels BTC to the $10M target, exponentially increasing the value of the SBR.
- Once 1 satoshi = $0.10, the federal government will have a stockpile of bitcoin valued at a cost basis greater than its annual debt obligations.
- Rather than use the stockpile to pay the debt down, the government will find that it needs to enforce a new surveillance-enforced bitcoin redemption policy to maintain a funnel of public bitcoin to the SBR in return for surveillable stablecoins. (read thesis for more)
Bitcoin’s Supply Guarantees a Stable Transition
Unlike gold, Bitcoin’s supply is fixed, transparent, and auditable. Once repricing begins, sovereign wealth funds, pension funds, and financial institutions will be forced to accumulate Bitcoin, play by the new state-issued redemption rules or be left behind.
I'm not sure how long it would take for the market to figure this out, but I’d assume it would be an all-out sprint to $10M BTC once the cat is out of the bag.
-
 @ 6f3670d9:03f04036
2024-12-29 08:20:22
@ 6f3670d9:03f04036
2024-12-29 08:20:22Disclaimer: - This will void your warranty - There might be differences between the Bitaxe and the Lucky Miner that might not cause issues or damage immediately, but might manifest long-term - Proceed at your own risk
A Different Pickaxe
You live in a place where it's difficult to get a Bitaxe. You have access to AliExpress. You look around. You find something called the "Lucky Miner LV06". A Bitaxe clone that uses the same mining chip as the Bitaxe Ultra (BM1366 ASIC). You buy one.
You plug it in, you enter your wallet address and other settings, and it starts mining. It works! Great!
But it's running a customized firmware. It's not AxeOS. Maybe there's something shady in the stock firmware. It's not open-source, after all. Also, AxeOS looks amazing... And that automatic pool fail-over feature is handy.
You think to yourself: "Maybe I can use the Bitaxe firmware on this?". Guess what? You're right!
Flashing From Web UI
What usually works for me is to: - Download the Bitaxe firmware files (
esp-miner.binandwww.bin) from GitHub (here). Version 2.4.1 seems to work well, as of this writing. - Then from the Lucky Miner web interface, upload the "Website" (www.bin) file. - Wait for a minute or two after it's done uploading. - Upload the "Firmware" (esp-miner.bin) file. - Wait another minute or two. - Unplug the power and plug it back in. - Set the "Core Voltage" and "Frequency" to the defaults. - Unplug the power and plug it back in again.If you're lucky (no pun intended), you'll have a working Lucky Miner with AxeOS. Update the settings and mine away!
However, often times I've been unlucky, like what happened while I was writing this article, ironically. The miner malfunctions for no obvious reason. It keeps rebooting, or it's not mining (zero/low hashrate), or the web interface is inaccessible. You name it.
The miner has become a "brick". How do you "unbrick" it?
When you brick a Bitaxe, you can recover it by flashing (uploading) a "Factory Image". The Bitaxe has a USB port that makes this easy. Follow the guide and it should come back to life again. Unfortunately, the Lucky Miner LV06 doesn't have a USB port. It has a serial port, though. We'll have to get our hands a bit dirty.
Flashing Using the Serial Port
We need to connect the serial port of the miner to a computer and run a program to flash (upload) the firmware file on the miner. Any 3.3v UART serial port should be sufficient. Unfortunately, PCs don't usually come with a UART serial port these days, let alone a 3.3v one. The serial port common in old computers is an RS-232 port, which will most probably fry your miner if you try to connect it directly. Beware.
In my case, as a serial port for my PC, I'm using an Arduino Due I had lying around. We connect it to the PC through USB, and on the other side we connect a few wires to the miner, which gives the PC access to the miner.
WARNING: Make sure your serial port is 3.3v or you will probably kill the miner. Arduino Uno is 5v not 3.3v, for example, and cannot be used for this.
Wiring
First, we need to open the Lucky Miner. Use a small flat screwdriver to gently push the two plastic clips shown in the picture below. Gently pry the top cover away from the bottom cover on the clips side first, then remove the other side. Be careful not to break the display cable.
Once the cover is off, you can find the miner's serial port in the top right corner (J10), as shown in the next picture. We'll also need the reset button (EN).
There are three screws holding the PCB and the bottom cover together. If you're confident in your ability to push the small button on the underside of the PCB with the bottom cover on, then no need to remove these. The following picture shows what we need from that side.
And the next picture shows the pins and USB port we will use from the Arduino.
Now, we need to connect: - The USB port on the Arduino labelled "programming" to the PC - Pin 18 (TX1) on the Arduino to J10 through-hole pad 5 (blue dot) - Pin 19 (RX1) on the Arduino to J10 through-hole pad 3 (green dot) - Any GND pin on the Arduino to J10 through-hole pad 4 (yellow dot)
I didn't need to solder the wires to the pads. Keeping everything stable, perhaps by putting a weight on the wires or a bit of tape, was sufficient in all my attempts.
Setting up the Arduino
To use the Arduino as a serial port for our PC, we'll have to make it pass-through data back and forth between the USB port and UART1, where we connected the miner.
The following steps are all done on a PC running Debian Linux (Bookworm), in the spirit of freedom and open-source.
First, we start the Arduino IDE. If the package for the Arduino Due board is not already installed, you'll see a small prompt at the bottom. Click "Install this package".
Click the "Install" button.
Once the package is installed, click "Close".
Next, we select the Due board. Click the "Tools" menu, select "Board", select "Arduino ARM (32-bits) Boards" and click "Arduino Due (Programming Port)"
Next, we select the port. Click the "Tools" menu again, select "Port", and click the port where the Arduino is connected. In my case it was "/dev/ttyACM0".
Now we need to upload the following code to the Arduino board. The code is actually the "SerialPassthrough" example from the IDE, but with the serial speed changed to match the miner.
``` void setup() { Serial.begin(115200); Serial1.begin(115200); }
void loop() { if (Serial.available()) { // If anything comes in Serial (USB), Serial1.write(Serial.read()); // read it and send it out Serial1 }
if (Serial1.available()) { // If anything comes in Serial1 Serial.write(Serial1.read()); // read it and send it out Serial (USB) } } ```
Copy/paste the code into the IDE and click upload. You'll see "Done uploading" at the bottom.
Next we'll test if we're receiving data from the miner. We start by opening the "Serial Monitor" from the "Tools" menu in the IDE. Then we change the baudrate to 115200.
Set the Arduino and the miner in a comfortable position, make sure the wires are held in place and got a good contact on both sides, and the power is plugged in.
Now we'll put the miner in "download" mode. Press and hold the button on the underside (K1), press and release the reset button (EN), then release the other button (K1).
You should see some text from the miner in the serial monitor window, like in the picture below.
Congratulations! We know we're able to receive data from the miner now. We're not sure transmit is working, but we'll find out when we try to flash.
Flashing Using the Serial Port, for Real
To flash the Lucky Miner we'll need a software tool named esptool and the factory image firmware file.
I usually use "esp-miner-factory-205-v2.1.8.bin" for the factory image (this one) as a base, and then flash the version I want from the Web UI, using the steps I mentioned earlier.
For esptool, the documentation (here) shows us how to install it. To make things a little easier on our Debian Linux system, we'll use pipx instead of pip. The instructions below are adapted for that.
First we make sure pipx is installed. Run this command in a terminal and follow the instructions:
sudo apt-get install pipxThen we install esptool using pipx. Run the following in a terminal:
pipx install esptoolThe output will be something like this:
user@pc:~$ pipx install esptool installed package esptool 4.8.1, installed using Python 3.11.2 These apps are now globally available - esp_rfc2217_server.py - espefuse.py - espsecure.py - esptool.py ⚠️ Note: '/home/user/.local/bin' is not on your PATH environment variable. These apps will not be globally accessible until your PATH is updated. Run `pipx ensurepath` to automatically add it, or manually modify your PATH in your shell's config file (i.e. ~/.bashrc). done! ✨ 🌟 ✨We can see pipx telling us we won't be able to run our tool because the folder where it was installed is not in the PATH variable. To fix that, we can follow pipx instructions and run:
pipx ensurepathAnd we'll see something like this:
``` user@pc:~$ pipx ensurepath Success! Added /home/user/.local/bin to the PATH environment variable.
Consider adding shell completions for pipx. Run 'pipx completions' for instructions.
You will need to open a new terminal or re-login for the PATH changes to take effect.
Otherwise pipx is ready to go! ✨ 🌟 ✨ ```
Now, close the terminal and re-open it so that esptool becomes available.
Finally, to actually flash the miner, put the miner in download mode, then in the following command change the port ("/dev/ttyACM0") to your serial port, as we've seen earlier, and the file path to where your firmware file is, and run it:
esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.binIf everything went fine, the tool will take a few minutes to flash the firmware to the miner. You'll see something like this in the output:
``` user@pc:~$ esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.bin esptool.py v4.8.1 Serial port /dev/ttyACM0 Connecting..... Detecting chip type... ESP32-S3 Chip is ESP32-S3 (QFN56) (revision v0.2) Features: WiFi, BLE, Embedded PSRAM 8MB (AP_3v3) Crystal is 40MHz MAC: 3c:84:27:ba:be:01 Uploading stub... Running stub... Stub running... Configuring flash size... Erasing flash (this may take a while)... Chip erase completed successfully in 9.5s Compressed 15802368 bytes to 1320190... Wrote 15802368 bytes (1320190 compressed) at 0x00000000 in 152.1 seconds (effective 831.2 kbit/s)... Hash of data verified.
Leaving... Hard resetting via RTS pin... ```
And we're done! Hopefully the miner will be recovered now.
Hope this helps!
Stay humble,
dumb-packageA Warning About Beta Versions of AxeOS
For reasons unknown to me, while I was writing this article I wanted to try the testing version of AxeOS, which was v2.4.1b (beta). Flashing from Web UI went smooth, but the miner stopped mining. I flashed back to v2.1.8 using the serial port, a known good version for me, but it wouldn't mine, still.
Thankfully, v2.4.1 was released recently, and flashing it from the Web UI magically revived my miner. So, be warned.
Bonus: File Hashes
For convenience, these are the SHA256 hashes of the files I used in this article: ``` da24fceb246f3b8b4dd94e5143f17bd38e46e5285e807ebd51627cb08f665c0a ESP-Miner-v2.4.1/esp-miner.bin 16c5c671391f0e3e88a3e79ce33fad3b0ec232b8572fad5e1e0d1ad3251ab394 ESP-Miner-v2.4.1/www.bin
d5182a15b6fa21d7b9b31bff2026d30afed9d769781a48db914730a5751e20c6 esp-miner-factory-205-v2.1.8.bin ```
-
 @ 7d33ba57:1b82db35
2025-03-20 11:27:54
@ 7d33ba57:1b82db35
2025-03-20 11:27:54Agaete
Agaete is a charming coastal town on the northwest coast of Gran Canaria, known for its stunning cliffs, natural pools, fresh seafood, and rich history. Surrounded by the Agaete Valley, this town offers a mix of nature, culture, and relaxation.
🏛️ Top Things to Do in Agaete
1️⃣ Explore the Agaete Valley (Valle de Agaete)
A lush, green valley famous for its coffee plantations – the only place in Europe where coffee is grown! Take a coffee farm tour and taste local Canarian coffee and wine.
2️⃣ Swim in the Natural Pools of Las Salinas
These volcanic rock pools by the coast provide a unique, sheltered swimming experience with breathtaking ocean views.
3️⃣ Visit Puerto de las Nieves
The picturesque fishing village next to Agaete, where you can enjoy fresh seafood, stroll along the promenade, or catch a ferry to Tenerife.
4️⃣ Hike in Tamadaba Natural Park
Just above Agaete, this stunning nature reserve offers incredible hiking trails with pine forests and breathtaking views of the Atlantic Ocean.
5️⃣ Discover the Necropolis of Maipés
An archaeological site with pre-Hispanic burial mounds dating back over 1,300 years, providing insight into the island’s indigenous history.
🍽️ What to Eat in Agaete
- Pescado fresco – Fresh fish grilled to perfection 🐟
- Cochino negro – A special Canarian black pig dish 🍖
- Queso de flor – Local artisan cheese 🧀
- Agaete coffee & wine – Grown right in the valley ☕🍷
🚗 How to Get to Agaete
🚗 By Car: ~35-40 minutes from Las Palmas
🚌 By Bus: Direct routes from Las Palmas (Lines 103 & 105)💡 Tips for Visiting Agaete
✅ Best time to visit? Year-round, but especially beautiful in spring 🌿
✅ Great for hiking & nature lovers – Bring comfortable shoes 👟
✅ Try local coffee & wine – It’s one of the best-kept secrets of Gran Canaria ☕🍷 -
 @ cff1720e:15c7e2b2
2025-03-20 11:14:33
@ cff1720e:15c7e2b2
2025-03-20 11:14:33Wolfgang Borchert 1947\ (Wolfgang Borchert starb mit 26 Jahren an einer Kriegsverletzung)
Dann gibt es nur eins!
Du. Mann an der Maschine und Mann in der\ Werkstatt. Wenn sie dir morgen befehlen, du\ sollst keine Wasserrohre und keine Kochtöpfe\ mehr machen – sondern Stahlhelme und\ Maschinengewehre, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Mädchen hinterm Ladentisch und\ Mädchen im Büro. Wenn sie dir morgen\ befehlen, du sollst Granaten füllen und\ Zielfernrohre für Scharfschützengewehre\ montieren, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Besitzer der Fabrik. Wenn sie dir morgen\ befehlen, du sollst statt Puder und Kakao\ Schießpulver verkaufen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Forscher im Laboratorium. Wenn sie dir\ morgen befehlen, du sollst einen neuen Tod\ erfinden gegen das alte Leben, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Dichter in deiner Stube. Wenn sie dir\ morgen befehlen, du sollst keine Liebeslieder,\ du sollst Haßlieder singen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Arzt am Krankenbett. Wenn sie dir\ morgen befehlen, du sollst die Männer\ kriegstauglich schreiben, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Pfarrer auf der Kanzel. Wenn sie dir\ morgen befehlen, du sollst den Mord segnen\ und den Krieg heilig sprechen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Kapitän auf dem Dampfer. Wenn sie dir\ morgen befehlen, du sollst keinen Weizen\ mehr fahren – sondern Kanonen und Panzer,\ dann gibt es nur eins:\ Sag NEIN!\ \ Du. Pilot auf dem Flugfeld. Wenn sie dir morgen\ befehlen, du sollst Bomben und Phosphor\ über die Städte tragen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Schneider auf deinem Brett. Wenn sie\ dir morgen befehlen, du sollst Uniformen zuschneiden,\ dann gibt es nur eins:\ Sag NEIN!\ \ Du. Richter im Talar. Wenn sie dir morgen befehlen,\ du sollst zum Kriegsgericht gehen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Mann auf dem Bahnhof. Wenn sie dir\ morgen befehlen, du sollst das Signal zur Abfahrt\ geben für den Munitionszug und für den\ Truppentransport, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Mann auf dem Dorf und Mann in der\ Stadt. Wenn sie morgen kommen und dir den\ Gestellungsbefehl bringen, dann gibt es nur eins:\ Sag NEIN!\ \ Du. Mutter in der Normandie und Mutter in\ der Ukraine, du, Mutter in Frisko und London,\ du, am Hoangho und am Mississippi, du,\ Mutter in Neapel und Hamburg und Kairo und\ Oslo - Mütter in allen Erdteilen, Mütter in der\ Welt, wenn sie morgen befehlen, ihr sollt\ Kinder gebären, Krankenschwestern für\ Kriegslazarette und neue Soldaten für neue\ Schlachten, Mütter in der Welt, dann gibt es\ nur eins:\ Sagt NEIN! Mütter, sagt NEIN!\ \ Denn wenn ihr nicht NEIN sagt, wenn IHR nicht nein sagt, Mütter, dann:\ dann:
... Fortsetzung
https://route96.pareto.space/cdd62d02f73eec86bfcaa8108ef515795c6a3c714a418880ea9d267c4aeb1a8d.mp3
-
 @ 6f3670d9:03f04036
2024-12-29 06:51:25
@ 6f3670d9:03f04036
2024-12-29 06:51:25This is my first long-form post. The starting line.
There's nothing of value here. Just using this as a marker.
I hope to post a lot more. Documenting how I made something work would be very useful to me, and hopefully others, but I've been too lazy to do that. Wish me luck!
Stay humble,
dumb-package -
 @ 20e17dd0:2ae504d7
2025-03-20 10:08:14
@ 20e17dd0:2ae504d7
2025-03-20 10:08:14Prerequisite
Installation
Open a Terminal session and write the following command:
ruby sudo apt install docker.ioYou will be ask permission to install and continueruby yValidation of the installation
To validate the installer, prompt the following command:
ruby docker --versionYou should get:
ruby Docker version 26.1.3, build 26.1.3-0ubuntu1~24.04.1To test if it is running, prompt the following command:
ruby sudo systemctl status dockerYou should get a screen with the docker.service as "running". To get back to command line do CTRL+C
Test Installation
To make sure that everything runs smoothly, write the following command:
ruby sudo docker run hello-worldYou should get a Hello from Docker.You are ready to enjoy pulling docker images!
originally posted at https://stacker.news/items/917064
-
 @ 16f1a010:31b1074b
2025-03-20 15:29:42
@ 16f1a010:31b1074b
2025-03-20 15:29:42What is NSSM?
NSSM (Non-Sucking Service Manager) is a free tool that allows you to install and manage any application as a Windows service. This is particularly useful for applications that don't natively support running as a service, ensuring they start automatically when your system boots and continue running in the background.
Downloading NSSM
- Visit the official NSSM website: https://nssm.cc/
- Download the latest stable release.
- Extract the downloaded ZIP file to a directory of your choice (e.g.,
C:\nssm).
Adding NSSM to Your PATH (Recommended)
Adding NSSM to your system's PATH environment variable allows you to run
nssmcommands from any command prompt window.- Search for "Environment Variables" in the Windows Start menu and select "Edit the system environment variables."

- In the "System Properties" window, click the "Environment Variables..." button.
- In the "System variables" section, find the "Path" variable and click "Edit."
- Click "New" and add the path to the directory where you extracted NSSM (e.g.,
C:\nssm). - Click "OK" on all open windows to save the changes.
- Open a new command prompt window and type
nssm --version. If NSSM is correctly added to your PATH, you should see the version information.
Using NSSM: Installing a Service
- Open a command prompt as administrator.
- Type
nssm install <service_name>and press Enter. Replace<service_name>with the name you want to give to your service. - A GUI will appear, allowing you to configure the service.
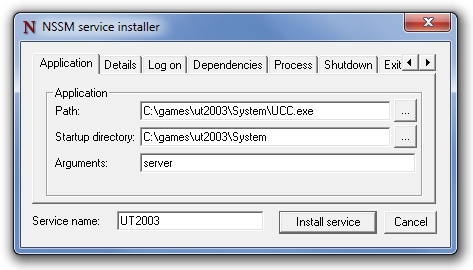
- In the "Path" field, enter the full path to the application's executable.
- In the "Startup directory" field, enter the directory containing the executable.
- Configure any other options as needed, such as "Arguments," "I/O," or "Details."
- Click "Install service."
Example:
bash nssm install MyGrainRelayConclusion
Congratulations, you now have NSSM installed and know the basics of using it to manage windows services. Check my profile for more technical guides on various topics, and stay tuned for more guides.
-
 @ 9f94e6cc:f3472946
2024-11-21 18:55:12
@ 9f94e6cc:f3472946
2024-11-21 18:55:12Der Entartungswettbewerb TikTok hat die Jugend im Griff und verbrutzelt ihre Hirne. Über Reels, den Siegeszug des Hochformats und die Regeln der Viralität.
Text: Aron Morhoff
Hollywood steckt heute in der Hosentasche. 70 Prozent aller YouTube-Inhalte werden auf mobilen Endgeräten, also Smartphones, geschaut. Instagram und TikTok sind die angesagtesten Anwendungen für junge Menschen. Es gibt sie nur noch als App, und ihr Design ist für Mobiltelefone optimiert.
Einst waren Rechner und Laptops die Tools, mit denen ins Internet gegangen wurde. Auch als das Smartphone seinen Siegeszug antrat, waren die Sehgewohnheiten noch auf das Querformat ausgerichtet. Heute werden Rechner fast nur noch zum Arbeiten verwendet. Das Berieseln, die Unterhaltung, das passive Konsumieren hat sich vollständig auf die iPhones und Samsungs dieser Welt verlagert. Das Telefon hat den aufrechten Gang angenommen, kaum einer mehr hält sein Gerät waagerecht.
Homo Digitalis Erectus
Die Welt steht also Kopf. Die Form eines Mediums hat Einfluss auf den Inhalt. Marshall McLuhan formulierte das so: Das Medium selbst ist die Botschaft. Ja mei, mag sich mancher denken, doch medienanthropologisch ist diese Entwicklung durchaus eine Betrachtung wert. Ein Querformat eignet sich besser, um Landschaften, einen Raum oder eine Gruppe abzubilden. Das Hochformat entspricht grob den menschlichen Maßen von der Hüfte bis zum Kopf. Der TikTok-Tanz ist im Smartphone-Design also schon angelegt. Das Hochformat hat die Medieninhalte unserer Zeit noch narzisstischer gemacht.
Dass wir uns durch Smartphones freizügiger und enthemmter zur Schau stellen, ist bekannt. 2013 wurde „Selfie“ vom Oxford English Dictionary zum Wort des Jahres erklärt. Selfie, Selbstporträt, Selbstdarstellung.
Neu ist der Aufwand, der heute vonnöten ist, um die Aufmerksamkeitsschwelle der todamüsierten Mediengesellschaft überhaupt noch zu durchbrechen. In beängstigender Hypnose erwischt man viele Zeitgenossen inzwischen beim Doomscrollen. Das ist der Fachbegriff für das weggetretene Endloswischen und erklärt auch den Namen „Reel“: Der Begriff, im Deutschen verwandt mit „Rolle“, beschreibt die Filmrolle, von der 24 Bilder pro Sekunde auf den Projektor gewischt oder eben abgespult werden.
Länger als drei Sekunden darf ein Kurzvideo deshalb nicht mehr gehen, ohne dass etwas Aufregendes passiert. Sonst wird das Reel aus Langeweile weggewischt. Die Welt im Dopamin-Rausch. Für den Ersteller eines Videos heißt das inzwischen: Sei der lauteste, schrillste, gestörteste Marktschreier. Das Wettrennen um die Augäpfel zwingt zu extremen Formen von Clickbait.
15 Sekunden Ruhm
Das nimmt inzwischen skurrile Formen an. Das Video „Look who I found“ von Noel Robinson (geboren 2001) war im letzten Jahr einer der erfolgreichsten deutschen TikTok-Clips. Man sieht den Deutsch-Nigerianer beim Antanzen eines karikaturartig übergewichtigen Menschen. Noel wird geschubst und fällt. Daraufhin wechselt das Lied – und der fette Mann bewegt seinen Schwabbelbauch im Takt. Noel steht wieder auf, grinst, beide tanzen gemeinsam. Das dauert 15 Sekunden. Ich rate Ihnen, sich das Video einmal anzuschauen, um die Mechanismen von TikTok zu verstehen. Achten Sie alleine darauf, wie vielen Reizen (Menschenmenge, Antanzen, Sturz, Schwabbelbauch) Sie in den ersten fünf Sekunden ausgesetzt sind. Wer schaut so was? Bis dato 220 Millionen Menschen. Das ist kapitalistische Verwertungslogik im bereits verwesten Endstadium. Adorno oder Fromm hätten am Medienzeitgeist entweder ihre Freude oder mächtig zu knabbern.
Die Internet- und Smartphoneabdeckung beträgt mittlerweile fast 100 Prozent. Das Überangebot hat die Regeln geändert. Um überhaupt gesehen zu werden, muss man heute viral gehen. Was dafür inzwischen nötig ist, spricht die niedrigsten Bedürfnisse des Menschen an: Gewalt, Ekel, Sexualisierung, Schock. Die jungen Erwachsenen, die heute auf sozialen Netzwerken den Ton angeben, haben diese Mechanismen längst verinnerlicht. Wie bewusst ihnen das ist, ist fraglich. 2024 prallt eine desaströse Bildungssituation samt fehlender Medienkompetenz auf eine egomanische Jugend, die Privatsphäre nie gekannt hat und seit Kindesbeinen alles in den Äther ballert, was es festhalten kann. Man muss kein Kulturpessimist sein, um diese degenerative Dynamik, auch in ihrer Implikation für unser Zusammenleben und das psychische Wohlergehen der Generation TikTok, als beängstigend zu bezeichnen.
Aron Morhoff studierte Medienethik und ist Absolvent der Freien Akademie für Medien & Journalismus. Frühere Stationen: RT Deutsch und Nuoviso. Heute: Stichpunkt Magazin, Manova, Milosz Matuschek und seine Liveshow "Addictive Programming".





























