-
 @ b17fccdf:b7211155
2025-03-25 11:23:36
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la guía de MiniBolt.
Esto tiene una razón, por supuesto una solución, además de una conclusión. Sin entrar en demasiados detalles:
La razón
El bloqueo a Cloudflare, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una orden judicial emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo ECH (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar bloqueos basados en dominios, lo que les obliga a recurrir a bloqueos más amplios por IP o rangos de IP para cumplir con la orden judicial.
Esta práctica tiene consecuencias graves, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un perjuicio para terceros, restringiendo el acceso a muchos dominios legítimos que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la web de MiniBolt y su dominio
minibolt.info, los cuales utilizan Cloudflare como proxy para aprovechar las medidas de seguridad, privacidad, optimización y servicios adicionales que la plataforma ofrece de forma gratuita.Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

La solución
Obviamente, MiniBolt no dejará de usar Cloudflare como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para evitar esta restricción y poder acceder:
~> Utiliza una VPN:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - IVPN - Mullvad VPN - Proton VPN (gratis) - Obscura VPN (solo para macOS) - Cloudfare WARP (gratis) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a esta para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la guía de MiniBolt sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info AQUÍ.

~> Proxifica tu navegador para usar la red de Tor, o utiliza el navegador oficial de Tor (recomendado).

La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la Declaración de Independencia del Ciberespacio que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos impulsar el desarrollo y la difusión de las herramientas anticensura que tenemos a nuestro alcance, protegiendo así la libertad digital y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los pilares fundamentales de MiniBolt, lo que convierte este desafío en una oportunidad para poner a prueba las soluciones anticensura ya disponibles, así como las que están en camino.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-
 @ 16f1a010:31b1074b
2025-02-19 20:57:59
@ 16f1a010:31b1074b
2025-02-19 20:57:59In the rapidly evolving world of Bitcoin, running a Bitcoin node has become more accessible than ever. Platforms like Umbrel, Start9, myNode, and Citadel offer user-friendly interfaces to simplify node management. However, for those serious about maintaining a robust and efficient Lightning node ⚡, relying solely on these platforms may not be the optimal choice.
Let’s delve into why embracing Bitcoin Core and mastering the command-line interface (CLI) can provide a more reliable, sovereign, and empowering experience.
Understanding Node Management Platforms
What Are Umbrel, Start9, myNode, and Citadel?
Umbrel, Start9, myNode, and Citadel are platforms designed to streamline the process of running a Bitcoin node. They offer graphical user interfaces (GUIs) that allow users to manage various applications, including Bitcoin Core and Lightning Network nodes, through a web-based dashboard 🖥️.
These platforms often utilize Docker containers 🐳 to encapsulate applications, providing a modular and isolated environment for each service.

The Appeal of Simplified Node Management
The primary allure of these platforms lies in their simplicity. With minimal command-line interaction, users can deploy a full Bitcoin and Lightning node, along with a suite of additional applications.
✅ Easy one-command installation
✅ Web-based GUI for management
✅ Automatic app updates (but with delays, as we’ll discuss)However, while this convenience is attractive, it comes at a cost.
The Hidden Complexities of Using Node Management Platforms
While the user-friendly nature of these platforms is advantageous, it can also introduce several challenges that may hinder advanced users or those seeking greater control over their nodes.
🚨 Dependency on Maintainers for Updates
One significant concern is the reliance on platform maintainers for updates. Since these platforms manage applications through Docker containers, users must wait for the maintainers to update the container images before they can access new features or security patches.
🔴 Delayed Bitcoin Core updates = potential security risks
🔴 Lightning Network updates are not immediate
🔴 Bugs and vulnerabilities may persist longerInstead of waiting on a third party, why not update Bitcoin Core & LND yourself instantly?
⚙️ Challenges in Customization and Advanced Operations
For users aiming to perform advanced operations, such as:
- Custom backups 📂
- Running specific CLI commands 🖥️
- Optimizing node settings ⚡
…the abstraction layers introduced by these platforms become obstacles.
Navigating through nested directories and issuing commands inside Docker containers makes troubleshooting a nightmare. Instead of a simple
bitcoin-clicommand, you must figure out how to execute it inside the container, adding unnecessary complexity.Increased Backend Complexity
To achieve frontend simplicity, these platforms make the backend more complex.
🚫 Extra layers of abstraction
🚫 Hidden logs and settings
🚫 Harder troubleshootingThe use of multiple Docker containers, custom scripts, and unique file structures can make system maintenance and debugging a pain.
This complication defeats the purpose of “making running a node easy.”
✅ Advantages of Using Bitcoin Core and Command-Line Interface (CLI)
By installing Bitcoin Core directly and using the command-line interface (CLI), you gain several key advantages that make managing a Bitcoin and Lightning node more efficient and empowering.
Direct Control and Immediate Updates
One of the biggest downsides of package manager-based platforms is the reliance on third-party maintainers to release updates. Since Bitcoin Core, Lightning implementations (such as LND, Core Lightning, or Eclair), and other related software evolve rapidly, waiting for platform-specific updates can leave you running outdated or vulnerable versions.
By installing Bitcoin Core directly, you remove this dependency. You can update immediately when new versions are released, ensuring your node benefits from the latest features, security patches, and bug fixes. The same applies to Lightning software—being able to install and update it yourself gives you full autonomy over your node’s performance and security.
🛠 Simplified System Architecture
Platforms like Umbrel and myNode introduce extra complexity by running Bitcoin Core and Lightning inside Docker containers. This means:
- The actual files and configurations are stored inside Docker’s filesystem, making it harder to locate and manage them manually.
- If something breaks, troubleshooting is more difficult due to the added layer of abstraction.
- Running commands requires jumping through Docker shell sessions, adding unnecessary friction to what should be a straightforward process.
Instead, a direct installation of Bitcoin Core, Lightning, and Electrum Server (if needed) results in a cleaner, more understandable system. The software runs natively on your machine, without containerized layers making things more convoluted.
Additionally, setting up your own systemd service files for Bitcoin and Lightning is not as complicated as it seems. Once configured, these services will run automatically on boot, offering the same level of convenience as platforms like Umbrel but without the unnecessary complexity.
Better Lightning Node Management
If you’re running a Lightning Network node, using CLI-based tools provides far more flexibility than relying on a GUI like the ones bundled with node management platforms.
🟢 Custom Backup Strategies – Running Lightning through a GUI-based node manager often means backups are handled in a way that is opaque to the user. With CLI tools, you can easily script automatic backups of your channels, wallets, and configurations.
🟢 Advanced Configuration – Platforms like Umbrel force certain configurations by default, limiting how you can customize your Lightning node. With a direct install, you have full control over: * Channel fees 💰 * Routing policies 📡 * Liquidity management 🔄
🟢 Direct Access to LND, Core Lightning, or Eclair – Instead of issuing commands through a GUI (which is often limited in functionality), you can use: *
lncli(for LND) *lightning-cli(for Core Lightning) …to interact with your node at a deeper level.Enhanced Learning and Engagement
A crucial aspect of running a Bitcoin and Lightning node is understanding how it works.
Using an abstraction layer like Umbrel may get a node running in a few clicks, but it does little to teach users how Bitcoin actually functions.
By setting up Bitcoin Core, Lightning, and related software manually, you will:
✅ Gain practical knowledge of Bitcoin nodes, networking, and system performance.
✅ Learn how to configure and manage RPC commands.
✅ Become less reliant on third-party developers and more confident in troubleshooting.🎯 Running a Bitcoin node is about sovereignty – learn how to control it yourself.
Become more sovereign TODAY
Many guides make this process straightforward K3tan has a fantastic guide on running Bitcoin Core, Electrs, LND and more.
- Ministry of Nodes Guide 2024
- You can find him on nostr
nostr:npub1txwy7guqkrq6ngvtwft7zp70nekcknudagrvrryy2wxnz8ljk2xqz0yt4xEven with the best of guides, if you are running this software,
📖 READ THE DOCUMENTATIONThis is all just software at the end of the day. Most of it is very well documented. Take a moment to actually read through the documentation for yourself when installing. The documentation has step by step guides on setting up the software. Here is a helpful list: * Bitcoin.org Bitcoin Core Linux install instructions * Bitcoin Core Code Repository * Electrs Installation * LND Documentation * LND Code Repository * CLN Documentation * CLN Code Repository
If you have any more resources or links I should add, please comment them . I want to add as much to this article as I can.
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
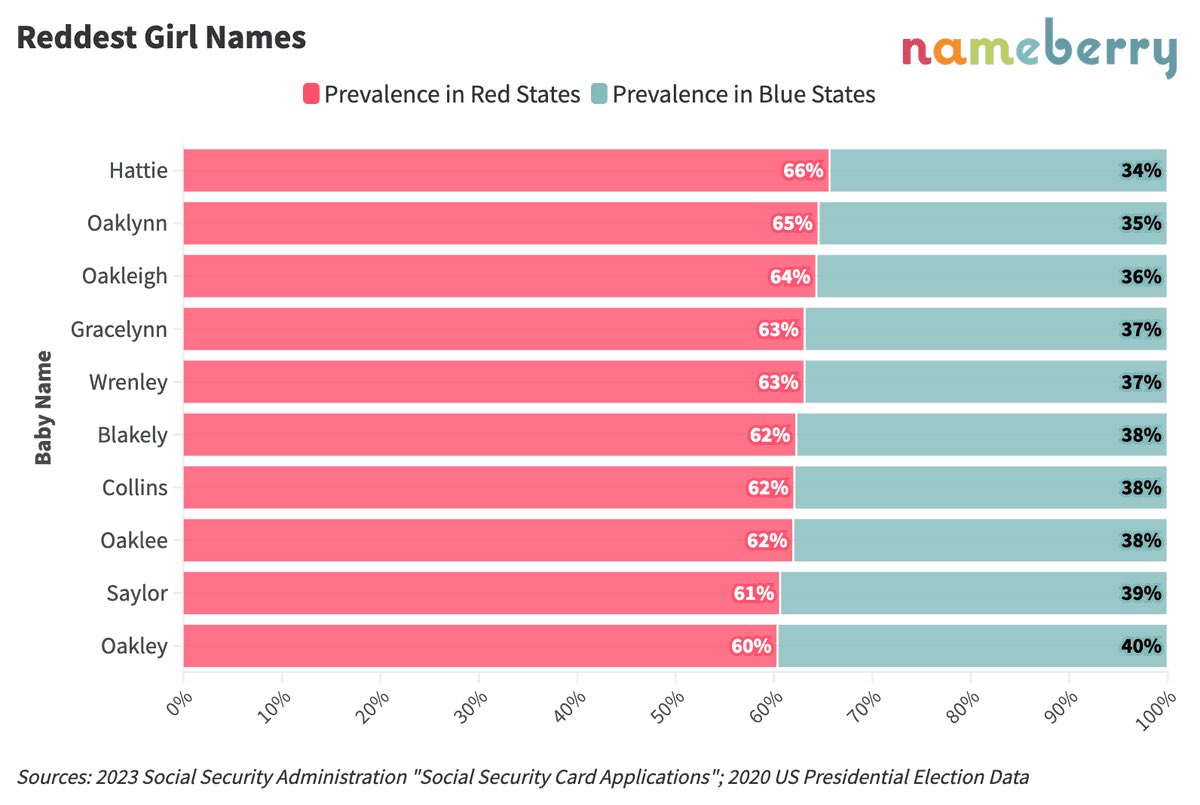
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 6b3780ef:221416c8
2025-03-26 18:42:00
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
- MCP Server: The heart of the system that exposes tools, which you can access via the
.listTools()method. - MCP Client: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- Standard I/O (stdio): A simple local connection method when your server and client are on the same machine.
- Server-Sent Events (SSE): Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
- Create software in any programming language you're comfortable with.
- Add an MCP library to expose your server's MCP interface.
- Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with
bun index.js, and then call.listTools()to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
curl -fsSL https://bun.sh/install | bash-
Choose your MCP server: You can either create one or use an existing one.
-
Inspect your server using the MCP inspector tool:
bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2This will: - Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
-
Pass any additional arguments directly to your server
-
Use the inspector: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
-
Navigate to your MCP server directory.
-
Run without installing (quickest way):
npx @dvmcp/bridge -
Or install globally for regular use:
npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridgeThen run using:bash dvmcp-bridge
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as
wss://relay.dvmcp.fun, or use any other of your preferenceTesting and Integration
- Visit dvmcp.fun to see your DVM announcement.
- Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
-
Install and use the
@dvmcp/discoverypackage:bash npx @dvmcp/discovery -
This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
-
Making them available to your LLM applications
-
Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at dvmcp.fun.
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
Useful Resources
- Official Documentation:
- Model Context Protocol: modelcontextprotocol.org
-
DVMCP.fun: dvmcp.fun
-
Source Code and Development:
- DVMCP: github.com/gzuuus/dvmcp
-
DVMCP.fun: github.com/gzuuus/dvmcpfun
-
MCP Servers and Clients:
- Smithery AI: smithery.ai
- MCP.so: mcp.so
-
Glama AI MCP Servers: glama.ai/mcp/servers
Happy building!
- MCP Server: The heart of the system that exposes tools, which you can access via the
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ 000002de:c05780a7
2025-03-26 18:00:41
@ 000002de:c05780a7
2025-03-26 18:00:41Over the past few years I've noticed more people using the political compass to compare where different movements and people fall in comparison to each other.
For many years I have found the left / right evaluation of politics less and less useful. Mostly because it really doesn't account for authoritarianism and other factors such as economics. I'm not sure the political compass is great but it seems better to me.
Have you looked into it? Any issues you've found? Mostly curious what others think about it.
originally posted at https://stacker.news/items/925938
-
 @ b12e2899:ed9d9c8b
2025-03-26 17:33:37
@ b12e2899:ed9d9c8b
2025-03-26 17:33:37I have completely switched to Nostr and today am going to share my experience, which may be useful to those of you who want to launch a bot on a social network and encounters censorship. The thing is Nostr is ideal for this, but first things first:
It all started when I suddenly woke up to see my twitter bot @cryptoratingbot suspended without any explanation. I contacted support, but they apparently considered my case too insignificant to even respond. The goal of my bot was to attract users and provide free tools like charts.xport.top, tickerbell.xport.top and few others that you can find out about in my previous publications. It worked, and accumulated all in all around 60k engagement a year. Silly, right? You can do this in two days doing it the right way. But I was in no hurry. Overall I gained 10 new users per day and that was enough for me to begin with since I wasn’t prepared for the big wave of users. But that is not the topic for today. I can tell you more about this later on, if you are interested click like and subscribe.
I was planning to buy a premium, but then twitter suspended my bot which actually didn’t do anything bad if you think about it. Furthermore, it was useful, otherwise why would people use it and like its tweets. Anyway, this ruined my plans and forced me to think about switching to Nostr. Today I can tell that it was definitely worth it! I haven’t lost anything, except time and overall gained from it! But I won’t say too much, so as not to bore you. However, this context is important for a better understanding of my situation. There are much more details and if you have any questions, feel free to ask, I will try to answer everyone.
Hard to believe, but these things can help you make money from buying cryptocurrency on the bottoms in a right time just when it starts trading, if you understand what you’re doing. That’s not easy. Maybe I will share some thoughts later on, until then you may find more info in my previous articles.
In fact, I decided to write this because for the first time since I was introduced to Nostr I finally tried proof-of-work(nip-13 pow) myself and I love it! I see such a thing for the first time on a social media. No moderation or censorship measures are needed. After all, if you are ready to burn resources to publish events, then it is definitely not a spam. And that’s the beauty of it!
I’ve picked 7 relays to try and publish 5000+ events that my previous version collected from top 12 cryptocurrency exchanges. Two relays rejected those events after some time, most likely because as always I have forgot to add something crucial — nonce tag, to help relays understand I am using pow. I thought it would add it itself, but seemes that it wouldn’t. What a shame! However, other 5 relays are ok with that! Maybe because I wasn’t publishing events too often, I don’t know, but anyway the more freedom the more I love it! And if you want find more about relays you can use use nostrwat.ch which is the greatest resource for finding the best relays to use.
While I was writing this article, another few relays dropped connections, but that’s fine, I have selected 7 relays out of about 700 active online.
This is how my server statistics looks like:


 So, besides everything else, I also checked Netcup root server G11 stats. In my opinion, this is the best of all that I have ever dealt with. And this is not an advertisement, no. I found this company on my own, just watching how Nostr relays works in terms of price/quality, so this is my personal recommendation. But if you think you know better root server solutions please let me know in the comment below.
So, besides everything else, I also checked Netcup root server G11 stats. In my opinion, this is the best of all that I have ever dealt with. And this is not an advertisement, no. I found this company on my own, just watching how Nostr relays works in terms of price/quality, so this is my personal recommendation. But if you think you know better root server solutions please let me know in the comment below.The only disadvantage I have encountered is you can wait for their support for few days to answer, but that’s ok if you know what you’re doing. I have no problem with this. I try to be careful and there were no problems for two months since I ordered it and use it on the daily basis.
In short, this is my journey. Don’t scold me for this. It’s just that I’ve been saving all this up for a long time, and today I realized that I simply have to tell you about it!
Thank you all and see you soon! Cheers 🍻

-
 @ 8d34bd24:414be32b
2025-03-26 15:58:59
@ 8d34bd24:414be32b
2025-03-26 15:58:59I’ll admit that God’s truth is something I am passionate about. I love God’s word and I trust every word in the Bible as absolute truth. I hate when people compromise God’s word. I can’t understand Christians that don’t want to know God better through His word (maybe partially because I read a stack of books to solve any and every problem or to fulfill any interest).
Lately, the vow made in court to tell the truth, the whole truth, and nothing but the truth has been going through my mind. It comes up regarding almost everything, so I figured maybe God was telling me to write a post on the subject, so here we go.
The Truth
When we are searching for the truth about anything, we need to start with the Bible. Yes, there are many subjects about which the Bible doesn’t speak or doesn’t speak in detail, but the principles on which everything is built start with the Bible.
All Scripture is God-breathed and is useful for teaching, rebuking, correcting and training in righteousness, so that the servant of God may be thoroughly equipped for every good work. (2 Timothy 3:16-17)
Especially when we are trying to learn what God wants from us and our lives, we need to search the Scriptures. We need to study the Scriptures. We need to memorize the Scriptures.
I have hidden your word in my heart that I might not sin against you. (Psalm 119:11)
It is much more useful to have read the Bible many times and to know its contents cover to cover, so we have it available to us during that debate with a fellow believer, or the discussion with a proud atheist, or when put into a situation of temptation. Having God’s word “hidden in our heart” enables us to deal with every situation, just as Jesus did when tempted by the Devil in the wilderness. Jesus’s most common response to every challenge was “As it is written …”
Sanctify them by the truth; your word is truth. (John 17:17)
If we want to know the truth and be ready for whatever life throws at us, we need to be like Ezra:
He had begun his journey from Babylon on the first day of the first month, and he arrived in Jerusalem on the first day of the fifth month, for the gracious hand of his God was on him. For Ezra had devoted himself to the study and observance of the Law of the Lord, and to teaching its decrees and laws in Israel. (Ezra 7:9-10) {emphasis mine}
Are you known for devoting yourself to the study and observance of the Law of the Lord, and to teaching its decrees and laws?
The Whole Truth
Obviously there are God hating atheists who will lie about God’s word and totally contradict His word. As believers, we are more likely to bend God’s truth. (Satan does this, too, because it is frequently more effective than an outright lie). There are two primary ways to bend God’s truth. We either leave out some parts or we add to it. In this section we will focus on telling the whole truth and not leaving out part of the truth.
The error of lying by omission is rampant today. We see it in news reports by the media. We see it in the history taught to our children. We see it in many churches. There are some very uncomfortable truths in the Bible. People don’t like to hear that some people will be punished in Hell for all eternity. They don’t want to hear that they are sinners and their desires are sinful. They don’t like to hear that there is one and only one way to Jesus.
Jesus said to him, “I am the way, and the truth, and the life; no one comes to the Father but through Me. (John 14:6)
Many believers don’t like any conflict. They are afraid that speaking the truth is being judgmental and will hurt relationships and feelings, so they hold back and don’t speak the whole truth.
Deal bountifully with Your servant,\ That I may live and keep Your word.\ *Open my eyes, that I may behold\ Wonderful things from Your law.*\ I am a stranger in the earth;\ Do not hide Your commandments from me.\ My soul is crushed with longing\ After Your ordinances at all times.\ You rebuke the arrogant, the cursed,\ Who wander from Your commandments.\ Take away reproach and contempt from me,\ For I observe Your testimonies.\ Even though princes sit and talk against me,\ Your servant meditates on Your statutes.\ Your testimonies also are my delight;\ They are my counselors. (Psalm 119:17-24) {emphasis mine}
The psalmist begs God not to “hide Your commandments from me.” Should we hide God’s commandments from ourselves or others because they are uncomfortable?
He said, “What is the word that He spoke to you? Please do not hide it from me. May God do so to you, and more also, if you hide anything from me of all the words that He spoke to you.” (1 Samuel 3:17)
Eli put the harshest curse on Samuel if he didn’t speak the full truth communicated by God. We need to truly know and believe God’s word, so we communicate it fully with others and do not hide it from those whose very heart and soul need God’s truth.
Many of us may feel like we are not lying because we didn’t not explicitly speak an untruth, but withholding part of the truth, so that another is misled, is as much of a lie as speaking an untruth. Both are intended to mislead the other person, usually for our benefit or comfort and to the long-term harm of the other person.
Finally, brothers and sisters, whatever is true, whatever is noble, whatever is right, whatever is pure, whatever is lovely, whatever is admirable—if anything is excellent or praiseworthy—think about such things. Whatever you have learned or received or heard from me, or seen in me—put it into practice. And the God of peace will be with you. (Philippians 4:8-9) {emphasis mine}
We need to think on, speak, and put into practice all of God’s word. Picking and choosing which parts of God’s word we want to believe, speak, and put into practice is akin to the original sin, “You will be like gods, knowing good and evil.” Only God gets to decide what is true or false and what is good or evil. When we choose to pick which parts of the Bible to obey and to share, we are taking the role that belongs solely to God.
Nothing But the Truth
The other error regarding truth is to add to God’s word.
The Pharisees and the scribes asked Him, “Why do Your disciples not walk according to the tradition of the elders, but eat their bread with impure hands?” And He said to them, “Rightly did Isaiah prophesy of you hypocrites, as it is written:
‘This people honors Me with their lips,\ But their heart is far away from Me.\ But in vain do they worship Me,\ **Teaching as doctrines the precepts of men.’\ Neglecting the commandment of God, you hold to the tradition of men.” (Mark 7:5-8) {emphasis mine}
So often we let tradition, culture, or “science” guide us instead of the Bible. Whenever there is a contradiction between any source and the Bible, we need to put the authority of God’s word as the highest authority. Although it is possible for us to be mistaken by the meaning of God’s word and the truth to be more in line with culture or “science,” it is so much more likely that tradition, culture, or “science” are wrong. We need to use the Bible to interpret things like science rather than to use “science” to interpret the Bible. The Bible is always the higher authority.
Sometimes we add to God’s word intentionally. Sometimes we are just influenced by the people around us, especially supposed authority figures, and are led astray unintentionally.
Do your best to present yourself to God as one approved, a worker who does not need to be ashamed and who correctly handles the word of truth. (2 Timothy 2:15) {emphasis mine}
We need to truly study the whole Bible and test every one of our beliefs against God’s word.
I am astonished that you are so quickly deserting the one who called you to live in the grace of Christ and are turning to a different gospel— which is really no gospel at all. Evidently some people are throwing you into confusion and are trying to pervert the gospel of Christ. But even if we or an angel from heaven should preach a gospel other than the one we preached to you, let them be under God’s curse! As we have already said, so now I say again: If anybody is preaching to you a gospel other than what you accepted, let them be under God’s curse! (Galatians 1:6-9) {emphasis mine}
We need to use God’s word to test every idea.
Do not treat prophecies with contempt but test them all; hold on to what is good, reject every kind of evil. (1 Thessalonians 5:20-22)
and
Dear friends, do not believe every spirit, but test the spirits to see whether they are from God, because many false prophets have gone out into the world. This is how you can recognize the Spirit of God: Every spirit that acknowledges that Jesus Christ has come in the flesh is from God, but every spirit that does not acknowledge Jesus is not from God. This is the spirit of the antichrist, which you have heard is coming and even now is already in the world. (1 John 4:1-3) {emphasis mine}
God’s word is truth. It never changes. It doesn’t change with the times, the culture, or new scientific discoveries. The truth is the truth whether anyone believes it or not.
There are many who will lead you astray and sound like they know what they are talking about. Make sure you do not follow these false teachers in their error (whether the error is intentional or accidental), but even more, make sure you don’t spread the error and lead others astray.
See to it that no one takes you captive through philosophy and empty deception, according to the tradition of men, according to the elementary principles of the world, rather than according to Christ. (Colossians 2:8) {emphasis mine}
I think this phrase perfectly describes how error effects us, “See to it that no one takes you captive through …” Error can be subtle, but can take us captive, lead us astray, and cause us to lead others astray. Only through detailed knowledge of the Scriptures can we defend against it.
Don’t be deceived, my dear brothers and sisters. Every good and perfect gift is from above, coming down from the Father of the heavenly lights, who does not change like shifting shadows. He chose to give us birth through the word of truth, that we might be a kind of firstfruits of all he created. (James 1:16-18) {emphasis mine}
May the Lord of heaven guide us to know the truth, the whole truth, and nothing but the truth and to obey His word in all things to His glory, forever.
Trust Jesus
-
 @ 1b30d27a:3cf04146
2025-03-26 14:48:26
@ 1b30d27a:3cf04146
2025-03-26 14:48:26In recent years, Artificial Intelligence (AI) has become a significant force in transforming various industries, and the music world is no exception. Machine learning algorithms and AI tools are reshaping how music is created, produced, and consumed, offering musicians and producers new ways to enhance creativity and productivity. As AI continues to evolve, it is poised to become a valuable co-creator in the music industry, making the possibilities for sound creation nearly limitless.
Redefining Music Composition with AI
Traditionally, music composition has been a human-driven process, where creativity and emotional depth played key roles. However, AI is now being used to generate original compositions, offering a new dimension to music creation. AI tools like Amper Music, Jukedeck, and Aiva can generate complex musical pieces in various genres, allowing musicians to collaborate with AI to create compositions that would have been impossible or time-consuming by traditional means.
"AI allows artists to explore new sounds, experiment with complex structures, and push boundaries in ways they never could before."
Musicians can feed AI programs with their preferences, and the system can generate melodies, chord progressions, and rhythms based on their input. These AI-generated pieces can be used as the foundation for new music or as inspiration for artists to develop and refine their work further.
AI in Music Production: Enhancing Creativity
While AI has made significant advancements in composition, its role in music production is equally groundbreaking. The production process involves a variety of technical tasks, such as mixing, mastering, and sound design. With the help of AI, producers can now streamline these tasks, allowing more time for creative decision-making.
Benefits of AI in Music Production:
- Faster Workflow: AI tools can automate time-consuming tasks, such as adjusting levels and applying effects, which accelerates the production process.
- Precision and Consistency: AI algorithms can ensure that every element of a track is perfectly balanced, leading to high-quality productions.
- Personalized Sound Design: AI can learn an artist’s unique sound and help shape mixes to match the artist’s vision, whether they’re working with digital synthesizers or traditional instruments.
Tools like LANDR for mastering and iZotope’s Ozone for mixing are examples of AI-powered software that can automatically adjust audio tracks, ensuring optimal sound quality and consistency.
AI as a Collaborative Tool in Music Creation
The most exciting aspect of AI in music production is its potential as a collaborative tool. Instead of replacing musicians and producers, AI is offering new avenues for collaboration. AI’s ability to generate fresh musical ideas, suggest unconventional sound combinations, and recommend harmonies can spark innovation in ways that were previously unimaginable.
"AI acts as a partner, not a replacement. It listens, learns, and collaborates with musicians to create something greater than what either could do alone."
This partnership allows musicians to break free from creative blocks, explore new genres, and experiment with sounds that might not have been considered otherwise. By training AI to understand a musician’s style, AI can tailor suggestions and act as an idea generator, constantly offering new directions for creative exploration.
AI and the Music Listening Experience
AI doesn’t just transform the creation and production process; it’s also changing the way we experience music. Recommendation algorithms are already helping millions of listeners discover new artists, songs, and genres on platforms like Spotify, YouTube, and Apple Music. AI analyzes user behavior, such as listening history and preferences, to suggest music that fits an individual’s taste.
Additionally, AI-powered live performances are emerging, where virtual concerts and interactive music experiences adapt to real-time audience feedback. Through the use of augmented reality (AR) and virtual reality (VR), AI is enhancing how fans engage with music, creating immersive environments that allow for a completely new type of live experience.
The Future of AI in Music
As AI continues to evolve, its role in the music industry will only expand. We can expect AI to become even more integrated into the creative process, offering musicians tools to generate new compositions, automate production tasks, and enhance their overall workflow. As AI learns and adapts to the needs of individual artists, it will continue to act
-
 @ 1b30d27a:3cf04146
2025-03-26 14:16:23
@ 1b30d27a:3cf04146
2025-03-26 14:16:23Artificial Intelligence (AI) is revolutionizing the music industry. What was once a tool used only for automation is now evolving into a creative partner that artists can collaborate with. AI's machine learning algorithms are transforming the way music is composed, produced, and consumed, providing endless opportunities for innovation and creativity.
AI in Music Composition
AI is helping musicians create compositions faster and more efficiently than ever before. Algorithms trained on a variety of musical genres can now generate complex melodies and harmonies, mimicking the style of famous composers or creating something entirely new. AI tools like OpenAI's MuseNet can generate entire musical pieces, and musicians are using these compositions as inspiration, or in some cases, as finished works.
"AI is a co-creator—bringing fresh perspectives and ideas, transforming the music composition process."
These AI tools don’t just replicate existing music—they offer new possibilities for experimentation, allowing artists to explore creative directions they might not have thought of on their own.
Streamlining Music Production
In music production, AI is changing the game. By analyzing audio tracks, AI can help with tasks like mixing, mastering, and sound enhancement. Tools like LANDR and iZotope Ozone automate the mastering process, giving producers professional-level results in a fraction of the time it would take manually.
Key Benefits of AI in Music Production:
- Time Efficiency: Automated processes speed up repetitive tasks like mixing and mastering.
- Enhanced Sound Quality: AI can fine-tune audio, ensuring clarity and balance.
- Personalization: AI can learn an artist’s style, offering tailored suggestions and improvements.
AI tools provide a more efficient workflow, freeing up time for artists to focus on creativity rather than the technical details of production.
AI as a Collaborative Partner
AI is no longer just a tool for producers; it’s a creative partner. It helps musicians explore new ideas, generate sound variations, and fine-tune compositions. AI can generate unusual sound combinations, suggest new chord progressions, or even help artists push past creative blocks.
"AI offers endless possibilities—it's a partner in the creative process, not just a tool."
By collaborating with AI, artists can expand their creative horizons, unlocking new ideas that might not have been possible without this technological partnership.
AI’s Influence on Music Consumption
AI also plays a huge role in how we experience music. Music platforms like Spotify and YouTube use AI to personalize recommendations based on listening habits. This allows users to discover new artists, genres, and tracks that align with their preferences, enhancing the overall music experience.
Moreover, AI-driven virtual concerts and augmented reality performances are on the rise, creating immersive and interactive experiences that bring music to life in a new way.
The Future of AI in Music
The future of AI in music is bright. As AI continues to advance, it will play an even more integral role in music composition, production, and distribution. Artists will continue to use AI as a creative collaborator, and audiences will benefit from even more personalized music experiences.
The journey of AI in music production is just beginning. As technology evolves, so too will the possibilities for musicians and listeners alike. AI is helping us unlock new creative potential, and it’s exciting to think about where this collaboration will take us next. 🚀
-
 @ 1b30d27a:3cf04146
2025-03-26 12:06:51
@ 1b30d27a:3cf04146
2025-03-26 12:06:51In the ever-evolving landscape of music production, a groundbreaking force is reshaping how music is created, composed, and experienced: Artificial Intelligence (AI). Machine learning algorithms are paving the way for a revolution in the music industry, offering artists a new kind of creative collaborator. Soon, AI will no longer be just a tool but a creative partner, influencing every stage of the music-making process, from composition to production to distribution.
The Role of AI in Music Composition
Traditionally, music composition has been a deeply personal and creative endeavor, driven by human intuition, emotion, and inspiration. However, AI is beginning to challenge this paradigm. Machine learning algorithms, particularly those designed for music, can analyze vast amounts of data, from the works of classical composers to contemporary hits. By studying patterns in rhythm, harmony, and melody, AI systems can generate original compositions that mirror the style and tone of any genre.
"AI is not replacing musicians, it's helping them reach new creative heights. It offers a fresh approach to composition, enhancing what artists already do, not taking over."
For instance, AI-powered tools like OpenAI's MuseNet or Google's Magenta can compose entire pieces of music in different styles, from jazz to electronic to orchestral. These systems can analyze a given input and generate melodies or harmonies that are incredibly sophisticated, and sometimes, indistinguishable from compositions written by human musicians.
Enhancing the Music Production Process
While AI has already made significant strides in composition, its impact on music production is just as profound. In modern studios, AI tools are used for everything from arranging and mixing tracks to mastering the final product. AI-driven software can listen to raw audio recordings, identify areas for improvement, and suggest changes—whether that’s adjusting EQ levels, balancing volume, or adding effects to enhance the sound.
Key Benefits of AI in Music Production:
- Automation of Repetitive Tasks: Streamlines tasks like mixing and mastering, saving time and reducing manual effort.
- Real-Time Feedback: Provides instant feedback on raw recordings, helping producers improve tracks quickly.
- Improved Sound Quality: AI tools can detect subtle flaws and suggest adjustments to enhance sound clarity.
One major benefit of AI in music production is its ability to streamline and automate repetitive tasks. Mixing and mastering, two essential steps in the production process, can often be time-consuming and require a skilled ear. AI systems like LANDR or iZotope’s Ozone use algorithms to analyze tracks and apply mastering techniques that would traditionally take hours of manual work. These tools can deliver professional-level results quickly, making them invaluable for both emerging artists and seasoned professionals.
AI as a Collaborative Partner
The most exciting aspect of AI in music production is its potential to act as a collaborative partner rather than just a tool. Rather than replacing musicians or producers, AI is giving them new ways to push the boundaries of creativity. For example, AI can generate complex chord progressions or suggest unusual sound combinations that the human composer might not have considered. It can also offer real-time feedback during the composition process, helping the artist refine their ideas or take them in unexpected directions.
"AI is like having a co-producer who never sleeps—constantly suggesting, innovating, and pushing boundaries, without any bias or limitations."
Additionally, AI can be trained to learn an individual artist’s style, preferences, and musical choices. This allows it to provide personalized suggestions tailored to the artist’s unique creative voice. As AI continues to evolve, it could become an indispensable part of the creative workflow, helping musicians experiment with new ideas and soundscapes that they might not have explored on their own.
AI and Music Experience: Changing How We Listen
AI’s influence doesn’t stop at creation and production; it’s also changing how we experience music. Algorithms are already being used to power music recommendation systems on platforms like Spotify, Apple Music, and YouTube. These algorithms analyze user preferences and listening habits, then suggest new tracks or artists that match their tastes. This personalization is pushing the boundaries of how we discover music, turning AI into an indispensable part of our daily listening habits.
How AI Is Enhancing Music Discovery:
- Personalized Playlists: Curates playlists based on user preferences, mood, and listening history.
- Music Recommendations: Suggests new tracks and artists based on listening patterns.
- Real-Time Adaptation: AI can adjust recommendations dynamically based on evolving listening trends.
Furthermore, AI is enhancing live music experiences. Using AI, virtual concerts and performances can be created that respond to the audience’s reactions in real-time. Augmented reality (AR) and virtual reality (VR) technology, combined with AI, are bringing immersive music experiences to life, allowing fans to engage with music in ways that were previously unimaginable.
Ethical and Creative Considerations
While AI offers exciting new opportunities, its rise in music production raises important questions about creativity and originality. If an AI system can compose music that sounds just like a human, who owns the rights to that music? Is it the creator who trained the AI, the artist who used it, or the AI itself? These are complex ethical questions that the music industry will need to address as AI becomes an increasingly integral part of the creative process.
Moreover, some critics argue that the human element in music—the emotion, experience, and soul that come with creating music—cannot be replicated by machines. While AI can certainly enhance the production process and offer new ways of creating, the debate remains: Can a machine truly understand the depth of human emotion that music conveys?
Looking Ahead: AI in Music’s Future
As AI continues to improve, its role in music production will likely become more pervasive and integrated into the creative process. Artists may soon collaborate with AI in ways we never thought possible, using it to unlock new dimensions of their music. With the ability to personalize and innovate in real-time, AI could help shape the future of music production, offering limitless possibilities for both seasoned professionals and new artists just starting their journey.
The journey of AI in music production has just begun, and the potential it holds for transforming how we create and experience music is boundless. Soon, AI won’t just be a tool we use—it will be a trusted partner in the pursuit of musical innovation. The future of music is not just human—it’s a harmonious blend of human creativity and technological ingenuity, where the journey never ends. 🚀
-
 @ ecda4328:1278f072
2025-03-26 12:06:30
@ ecda4328:1278f072
2025-03-26 12:06:30When designing a highly available Kubernetes (or k3s) cluster, one of the key architectural questions is: "How many ETCD nodes should I run?"
A recent discussion in our team sparked this very debate. Someone suggested increasing our ETCD cluster size from 3 to more nodes, citing concerns about node failures and the need for higher fault tolerance. It’s a fair concern—nobody wants a critical service to go down—but here's why 3-node ETCD clusters are usually the sweet spot for most setups.
The Role of ETCD and Quorum
ETCD is a distributed key-value store used by Kubernetes to store all its state. Like most consensus-based systems (e.g., Raft), ETCD relies on quorum to operate. This means that more than half of the ETCD nodes must be online and in agreement for the cluster to function correctly.
What Quorum Means in Practice
- In a 3-node ETCD cluster, quorum is 2.
- In a 5-node cluster, quorum is 3.

⚠️ So yes, 5 nodes can tolerate 2 failures vs. just 1 in a 3-node setup—but you also need more nodes online to keep the system functional. More nodes doesn't linearly increase safety.
Why 3 Nodes is the Ideal Baseline
Running 3 ETCD nodes hits a great balance:
- Fault tolerance: 1 node can fail without issue.
- Performance: Fewer nodes = faster consensus and lower latency.
- Simplicity: Easier to manage, upgrade, and monitor.
Even the ETCD documentation recommends 3–5 nodes total, with 5 being the upper limit before write performance and operational complexity start to degrade.
Systems like Google's Chubby—which inspired systems like ETCD and ZooKeeper—also recommend no more than 5 nodes.
The Myth of Catastrophic Failure
"If two of our three ETCD nodes go down, the cluster will become unusable and need deep repair!"
This is a common fear, but the reality is less dramatic:
- ETCD becomes read-only: You can't schedule or update workloads, but existing workloads continue to run.
- No deep repair needed: As long as there's no data corruption, restoring quorum just requires bringing at least one other ETCD node back online.
- Still recoverable if two nodes are permanently lost: You can re-initialize the remaining node as a new single-node ETCD cluster using
--cluster-init, and rebuild from there.
What About Backups?
In k3s, ETCD snapshots are automatically saved by default. For example:
- Default path:
/var/lib/rancher/k3s/server/db/snapshots/
You can restore these snapshots in case of failure, making ETCD even more resilient.
When to Consider 5 Nodes
Adding more ETCD nodes only makes sense at scale, such as:
- Running 12+ total cluster nodes
- Needing stronger fault domains for regulatory/compliance reasons
Note: ETCD typically requires low-latency communication between nodes. Distributing ETCD members across availability zones or regions is generally discouraged unless you're using specialized networking and understand the performance implications.
Even then, be cautious—you're trading some simplicity and performance for that extra failure margin.
TL;DR
- 3-node ETCD clusters are the best choice for most Kubernetes/k3s environments.
- 5-node clusters offer more redundancy but come with extra complexity and performance costs.
- Loss of quorum is not a disaster—it’s recoverable.
- Backups and restore paths make even worst-case recovery feasible.
And finally: if you're seeing multiple ETCD nodes go down frequently, the real problem might not be the number of nodes—but your hosting provider.
-
 @ ff517fbf:fde1561b
2025-03-26 16:48:41
@ ff517fbf:fde1561b
2025-03-26 16:48:41フアン・ラモン・ラッロ氏は、スペイン出身の経済学者・作家であり、自由市場経済とリベラルな思想の提唱者として知られています。彼は、国家による過剰な介入や財政政策の問題点を鋭く分析し、自由主義の基本原則に基づく社会の実現を目指す論考や著作を多数発表しています。数多くのメディアや学会で講演を行い、現代社会における経済政策や公共の役割について、国際的な議論にも影響を与えている人物です。

皆様、こんばんは。そして、Andorra Economic Forumの皆様、本日はご招待いただき誠にありがとうございます。
本日の講演では、これまで私が持ち続けてきた見解、すなわち、より自由で、より繁栄するために、スペイン及び世界において自由主義革命がなぜ必要であり、さらには急務であるのかという理由をお伝えしたいと思います。また、現代国家が、ストックホルム症候群のような論理に我々を陥れており、その結果、国家が我々の自由を体系的に制限し、財産を構造的に攻撃している状況を、ほとんどの人々が抗議もせず、またはその非常事態性すら意識していないという現実をどのように理解すべきかについても触れます。まず初めに、皆様のご反応から察するに、これは既知の内容に感じられるかもしれませんが、自由主義の基本原則、すなわち四つの基本的な考えを確認させていただきます。どのようにして、社会生活と、各個人が自らの人生計画を追求するための自律性とを両立させ、かつ、個々の自律性が打ち消されるような一個または多数の専制に服従することなく生きることができる社会が成立するのでしょうか? それは、協力と共存が可能な社会の中で、各人が自己の利益を追求し、同時に他者の利益追求を尊重するための基本原則、すなわち以下の四つの原則によって支えられているのです。
第一に、個人の自由、すなわち他者の行動を踏みにじることなく自ら行動するという、いわゆる非攻撃の原則です。自分が望むことは何でもできますが、他者が望むことをするのを妨げてはならず、また、他者があなたの望むことを妨げることも許されないのです。
第二に、私有財産です。平和的に獲得し、平和的に自らのものとしたものはあなたのものであり、それによって自由に行動し、自らの人生計画や行動計画を追求する手段となります。もしも、これらの計画遂行に必要な手段が恣意的に奪われるならば、それはあなたの個人の自由、すなわち自らの人生計画を追求する自由を侵害することになるのです。
第三に、契約の自律性です。あなたは第三者と自由に合意を結ぶことができます。もちろん、第三者を攻撃することは許されませんが、双方が望むことについて自発的に合意することは可能です。合意は、当事者間の私法上の契約であり、両者が履行すべき約束であり、第三者が介入してこれを正当化したり否定したりするものではありません。ただし、合意の内容は、あくまで当事者双方やその所有物にのみ影響を及ぼすものです。
そして最後に、広義の意味での結社の自由です。個人は、契約上、望むことについて合意するだけでなく、共に生活する方法や、ある程度安定した形で組織される方法を合意することも明示的に可能です。これらの原則は、しばしば国家によって保証されると言われます。なぜなら、国家がなければ、法体系も安全保障機関も存在せず、個人の自由、私有財産、契約の履行、そして結社の自由を保障するものが何もないと思われがちだからです。とはいえ、確かにある程度の国家は、警察国家としてこれらの基本的な社会的共存の規範を保証するために必要かもしれませんが、私たちが必要としているのは、単にこれらの自由主義社会の原則と自由な人々の相互作用が尊重されることを確保するための、巨大かつ過剰な国家ではありません。
実際、国家が大きくなるほど、つまり社会における国家の存在感が増すほど、これらの原則は侵害されがちです。なぜなら、国家は恣意的に規制を強化し、税金を引き上げることで、たとえ他者に損害を与えなくとも、個人が望むように行動する自由を阻み、また、私有財産を強制的に奪い、当事者間の取引を妨げ、さらには、結社および脱会の自由さえも制限してしまうからです。たとえば、誰かが既存の国家から離れ、他の国家に参加したり、あるいは新たな国家や政治共同体を形成して自らを組織しようとした場合でさえ、現行の国家はそれを認めないのです。
さて、これらの自由主義の基本原則は、各個人の計画や人生のプロジェクトが社会の中で花開くために必要不可欠なものであり、現代国家によって体系的に侵害されているのです。しかし、現代国家とは、必ずしも常に我々と共にあった国家ではありません。私たちは、今日のようなメガ国家、ハイパーステート、過剰に肥大化した国家をある程度は当たり前のものとして受け入れてしまっていますが、これらは唯一の政治的選択肢ではなく、歴史を通じて存在してきた唯一の政治現実でもないのです。
ここで、主要な西洋諸国における国家の社会に占める重みの変遷について、皆様にご覧いただければと思います。今日、国家の重みは国によって大きな違いはないものの、概ね国内総生産(GDP)の40〜50%を占めています。中には、例えばフランスのようにGDPの60%に達する国もあります。国家が社会的調和や幸福の保証とされることは稀であり、実際、フランスは世界最大の国家を有しながら、またはそのために、今最も分断され混沌とした国の一つとなっています。
しかし、現状、国家はGDPの40〜50%、すなわち社会が毎年生み出す生産の約半分を吸収し、再分配または政治層や官僚階級が決定した形で消費しているのです。これは常にそうであったわけではありません。19世紀、ひいては第一次世界大戦前までは、近代先進国における国家の経済的重みはGDPの5〜10%程度に過ぎなかったのです。
例えば、アメリカ合衆国では第一次世界大戦前、国家のGDPに占める割合は3〜4%でしたし、今日巨大な社会民主主義国家となっているスウェーデンでさえ、かつてはGDPの5%程度でした。すなわち、国家というものが必然的に経済の半分を占めなければならないというわけではなく、これは徐々に積み重ねられてきたプロセス、いわばゆっくりと沸騰させられるカエルのようなものです。第一次世界大戦後、国家の経済に対する重みは大幅かつ確固たる上昇を見せ、さらに第二次世界大戦後には、急激かつ持続的な上昇を経て、1970年代以降、現在の水準にまで達したのです。
ちなみに、ここで我々がしばしば耳にする「国家が後退しているから、我々は新自由主義の時代にいる」というレトリックが、いかに毒性がありずる賢いものであるかにも注目してください。過去40年間で、グラフ上に国家の重みが大幅に後退したと示す兆候は見当たりません。ある時点で国家のGDPに占める割合が1〜2%減少することがあったとしても、200年の間にGDPの5%から50%へと増加し、現在は概ね50%前後に留まっているのです。国家が後退し、民間部門がすべてを占めるようになっている、というのは全く逆の現象です。
実際、多くの人は、国家が拡大し続けるのが当然であり、もし急速な成長が見られなければ、国家は後退していると考えがちです。しかし、国家は既にそれ以上大きく成長する余地がほとんどないのです。もちろん、GDPの60%、70%、80%にまで達すれば、直接的または間接的な社会主義経済になってしまいます。
そして、なぜ国家はこれほどまでに成長したのでしょうか。急激な国家拡大を説明する基本的な要因の一つは、福祉国家の発展です。つまり、かつては国家が提供していた医療、社会保障(年金、事故保険など)や教育といったサービスの国家による提供が、福祉国家として大きく発展したのです。
ご覧の通り、1930年代や第二次世界大戦後までは社会保障費は非常に低い水準にありましたが、特に第二次世界大戦後からは、GDPの20〜30%にまで急上昇しました。これらはかつて、市民社会や市場を通じ、または必ずしも商業的な交換を介して提供されていた、労働組合などが担っていた社会保障の役割を、国家が吸収していったものです。労働組合は国家から独立し、時には国家に対抗しながら、社会保障の機能を果たしていたのですが、その役割が国家に吸収されることで、我々は国家に依存するようになってしまったのです。
なぜなら、社会保障費は支出であり、中には「依存費用」とも呼ばれるものもあります。たとえば、老後に収入がなくなった時や、何らかの障害によって収入が得られなくなった時のために、個人の貯蓄から基金を積み立てる場合、その基金が自分自身で管理されるなら自律的ですが、国家が管理すれば、私たちは国家に全く依存することになってしまうのです。国家が消滅するか、大幅な予算削減が行われれば、我々は何も残らないのです。結果として、国民は容易には消えない国家の爪痕に囚われることになるのです。公共年金制度の問題を考えてみてください。現代の先進国家において、公共年金制度は最も大きな支出項目の一つです。
では、どうすれば公共年金制度を解体できるのでしょうか。どうすれば、必要以上に介入してきた国家、例えばアメリカ合衆国では大恐慌期(1930年代)に、必要がなかったのに介入してきた国家を、その状況から脱却させることができるのでしょうか。設立当初は、ある一定の年齢に達した者には一定額の年金を支給すると約束し、その費用を現在働いている者への税負担によって賄うというシステムでした。
システムの構築は、当時の平均寿命がかなり低く、支給期間が2~3年程度であったため、比較的容易で安価に行われたのですが、システムが一度確立され、世代を超えた労働者の貯蓄能力を事実上奪う形で構築された今、どうやってそれを解体すればよいのでしょうか。もし「年金は支給されなくなるのか」と言えば、かつて生産期に労働者の給与のかなりの部分を国家が吸収し、貯蓄を阻害していた結果、何百万人もの人々が貧困に陥ることになるのです。
じゃあ、もう引退されている皆さんは年金を受け取ることになりますが、現役世代がその年金の費用を負担し、そして自分たちが引退する時には年金を受け取ることができなくなるのです。つまり、この世代からは何の対価もなく、給与のごく大部分が没収されることになるというわけです。これをどうやって解体するつもりですか? 決して容易なことではありません。
また、例えば医療制度についても同様です。若者にとっては医療制度の解体はそれほど難しくないように見えるかもしれませんが、貯蓄がなく、保険にも加入していない高齢者にとって、もし今、公共医療制度が終了し、年齢とともに医療費が指数関数的に上昇するために通常以上の医療費が発生すると告げられたら、彼らはその医療費にどう対処すればよいのでしょうか? 彼らは、公共医療制度が機能するという説明のもとに、その医療費が賄われると予め想定し、税金を支払っていたのです。
これをどう逆転させるか? もちろん、即座に行えることではありませんが、時間をかけた移行措置として行っていかなければなりません。だからこそ、国家はこの道を通じて成長し続け、社会がますます国家による再分配に依存するようになることで、国民の自律性を奪っていくのです。
ちなみに、現代福祉国家の発明者の一人であるのは、プロイセン出身のドイツの首相オットー・フォン・ビスマルクです。彼の回顧録――つまり、批判的ではない親しい記者によって書かれた回顧録――によれば、ビスマルクは、公共年金制度を創設することで労働者階級を国家に依存させ、労働者が国家に対して反抗しないように仕向けたと説明しています。当時、反抗は、いわば反資本主義的な行為とみなされていたのです。彼は、国家主義を維持するためではなく、「労働者には社会主義的傾向がある。では、どうすれば労働者を手なずけることができるのか?」という視点から、公共年金制度を利用したのです。同様に、労働者は公共年金制度を通じて、または国家に対抗する形で手なずけられるのです。そして、現状はこの通りになっています。
そこで、皆さんは疑問に思うかもしれません。この何世代にもわたって築かれてきた巨大国家は、具体的にどのような機能を果たしているのでしょうか? その資金はどこに行っているのか? この巨大国家は何に対して支出をしているのか? ここに、2022年の欧州連合各国の平均、すなわちGDPの50%という数字があります。スペインの場合も2022年時点で大きな差はなく、GDPの47%を支出しているため、概ね代表的な数値といえます。さて、この50%のうちの20%は社会保障費、主に年金費用(老後だけでなく、遺族、障害、孤児などに関する給付も含む)です。これに加え、比較的低コストな非拠出型給付も存在します。次に、スペインの場合は約7.7%、すなわち7〜8%が医療費、6%が官僚機構の運営費用、そして何よりも重要なのが公債の利子支払い費用です。さらに6%は経済政策に充てられ、例えばインフラ整備や農業支援などが含まれています。教育に関しては、公立教育や協定校を含めて約4.7%、環境保護は0.8%(これは必ずしも気候政策だけでなく、森林の管理なども含む)、住宅や地域サービスが1%、そして余暇、文化、宗教に関しては1.1%となっています。これらは、メディアや文化、宗教団体への補助金などとして支出されています。
かつて、リベラルな最小国家、例えばアメリカではGDPの3%程度であった国家がありました。なぜなら、当時は上記のような広範な機能を持たず、防衛(GDPの1.3%)と治安・司法(GDPの1.7%)に集中していたからです。つまり、19世紀にGDPの3%を占めていた国家が、現在もその核となる部分は同じ3%のままであるということです。国家が高価になったわけではなく、19世紀に存在した国家のコストは大体同じであったにもかかわらず、現代国家は19世紀よりもはるかに多くの機能を担っているため、多くの税金が必要とされているのです。もちろん、すべては税金で賄われています。
では、いったいどれだけの税金が支払われているのでしょうか。ここでは、国民が被っている税負担の実態について十分に認識されていないのではないかと思います。もしその実態が明らかになれば、社会的不服従が起こるでしょう。国家は、税の実感を曖昧にするための手段を多数用いているのです。例えば、さまざまな理由で税金を徴収する仕組みです。「この項目に対して税金を払え」と一律に要求するのではなく、「稼いだ金額、支出、保有資産、さらには支出全体に対して税金を課す」といった形で、複数の種類の税金を同時に適用します。消費全体に対して一律に税金を課すのではなく、付加価値税(IVA)やその他の特別税など、多岐にわたる特別な税金が存在し、相続税に至るまで多岐に渡ります。
さらに、我々はさまざまな側面で税金を支払っているにもかかわらず、その実感すら持っていないこともあります。たとえば、関税はその値上がり分を商品の価格に転嫁されるため、意識されにくいのです。付加価値税が上がっても、スーパーなどが告知しない限り、私たちはその上昇に気づきにくいのです。また、税負担を一度にまとめて徴収するのではなく、分散して給与から差し引くことで、その実感を薄めています。かつては、年間に稼いだ金額に対して一括で所得税(IRPF)を支払うのが普通でしたが、現代では分割して徴収されるため、納税者は自分がどれだけの税金を支払っているのかを実感しにくいのです。ちなみに、IRPFの源泉徴収制度は、第二次世界大戦中にリベラルのミルトン・フリードマンによって考案されたものです。つまり、敵はしばしば自国に潜むものでもあるということです。
ここで示したのは、平均的な支出額です。スペイン国家のすべての財政収入を国民または労働者で割ると、国民一人あたりの国家負担のおおよそのコストが見えてきます。実際には公共赤字、すなわち収入以上に支出している部分もあり、その分は将来の税負担として転嫁されるため、実際のコストはさらに大きくなります。ここでは、現状で国民から徴収されている税金のみを取り上げています。なお、これらの数字はインフレーションを考慮していないため、2001年と2024年の数字を直接比較することはできませんが、ここでは2024年現在の状況に焦点を当てています。現在、平均してスペイン国民一人あたり、約15,000ユーロの税負担がかかっているのです。つまり、一般的には夫婦と子供一人の家庭で約50,000ユーロの税金が支払われている計算になります。労働者という視点に立てば、実際に税金を支払っているのは、平均で30,000ユーロ以上にのぼります。もちろん、高所得者層が多くを負担しているという見方もありますが、これは平均値であり、平均値は必ずしも実態を正確に反映するものではありません。
さて、労働者一人あたりの支払いを、かなり寛大な見積もりで考えてみましょう。スペインにおける現在の中央値の給与は22,400ユーロです。しかし、この22,400ユーロという数字が給与明細に反映される前に、企業側がすでに支払っている社会保険料が約7,000ユーロ存在しています。つまり、実際の中央値の給与は29,000ユーロ、ほぼ30,000ユーロであるべきものですが、この30,000ユーロは労働者自身が実感できるものではありません。そして、たとえ「実際は自分のものである」と伝えても、「それは企業が支払っているものであって、自分が支払っているわけではない」と言われ、自己欺瞞に陥るのです。結局のところ、実際に支払っているのは自分自身なのです。
実際、30,000ユーロの実質報酬を基にすると、そこから7,000ユーロが差し引かれて、給与明細に表示されるのは22,400ユーロです。さらに、労働者側の社会保険料として約1,500ユーロを追加で支払い、所得税(IRPF)が約3,000ユーロ、さらに消費に応じた間接税が最低でも約2,000ユーロ(場合によってはそれ以上)かかります。さらに、ここでは取り上げていない他の国家への支払い、たとえば不動産税(IBI)やサービス料、共済負担金なども存在します。結果として、中央値の労働者は、本来約30,000ユーロあるべき給与のうち、税引き後に手元に残るのは約15,800ユーロに過ぎないのです。つまり、ほぼその半分が国家によって吸収されていることになります。年間で見ると、さまざまな税金、特に社会保険料、所得税、そして間接税として、合計約13,400ユーロが徴収されているのです。
このように、中央値の労働者は、所得分布の中央に位置しており、非常に多くの人々が彼より少なく、また多く稼いでいる人もいます。だからこそ、中央値の労働者が支払っている税負担、すなわち年間約13,400ユーロという数字は、スペイン国民に対して行われている極めて大規模な税負担の実態を物語っています。これにより、国家から提供されるサービスが強制的に受け入れられているのです。
果たして、これは必然なのでしょうか? 歴史的に見れば必ずしもそうではなく、また現代においても地域によって差があります。つまり、労働者が生み出す富の半分以上を国家が吸収するという、巨大な国家が当然であるという考え方は、今後も続くものではありません。ここには、異なる繁栄度を持つ国々が存在し、一般的に発展した国々であっても、欧州やアメリカのような国家に比べ、国家の規模はかなり小さく抑えられている国もあります。しばしば「スペインの国家規模は欧州平均より小さい」と言われますが、欧州平均自体が、プロの略奪者たちのクラブのようなものなのです。従って、欧州平均という水準と比較するのではなく、もっと控えめな国家規模を持つ国々や、税負担の貪欲さが制限された国々と比較すべきです。
例えば、ヨーロッパ内ではスイスがあります。偶然かどうかはさておき、スイスはヨーロッパで最も豊かな国の一つでありながら、国家のGDPに占める割合は33%と、欧州やアメリカに比べて10〜15ポイント低いのです。また、香港や韓国はGDPの28%、チリはこの分類の中では最も貧しいかもしれませんが約26%、台湾は16%、そして世界で最も豊かな国であるシンガポールは15%です。シンガポールや台湾は、国家がGDPの15〜16%という小規模な状態で十分に現代社会の機能を果たしているのです。もちろん、シンガポールの場合は都市国家であるため、経済規模のメリットもあるでしょうが、公共支出の大部分が社会保障に回っている現状を鑑みると、都市規模か大国家かは大した違いがないのです。むしろ、シンガポールや台湾のように、GDPに対して国家の規模が30ポイントも低い国の方が、国家による私有財産の侵害が少ないと言えます。
したがって、もし大規模な国家による大規模な略奪を回避でき、しかも機能的には他の国と同等以上に運営できるのであれば、当然、より少ない税負担で、なおかつより効率的な公共サービスを提供する国家の方が望ましいのです。実際、国家が何でもかんでも行おうとすれば、その多くは非効率にならざるを得ません。一方で、企業がすべてを行おうとしても、専門分野に特化した他の企業に競争で敗れるため、最終的には消費者がより良いサービスを選ぶことになるのです。問題は、国家の場合、国民が国家から自由に離脱し、同じサービスを提供する他の組織と契約する余地がないという点にあります。国民は、非常に非効率かつ高コストな国家サービスに縛られており、選択の余地がないのです。したがって、もし小規模で効率的な国家が存在すれば、それは大規模で税負担の重い国家よりも好まれるはずです。
そして、もし国家が回収するGDPの割合が30ポイントも大きいのであれば、それは明らかに国民の私有財産を暴力的に侵害していると言わざるを得ません。ですから、もし国家による大規模な略奪を回避し、かつ他国と同等以上の機能を果たすことが可能であれば、国家は少なくとも縮小されるべきです。なぜなら、そうした国家は国民にとって好都合であるだけでなく、公共サービスの質も向上し、効率的に運営されるからです。結局のところ、すべては国家ではなく、国家に寄生する巨大な官僚組織の福祉が優先されているのです。
もし、あなたの社会にこれほど大きく根付いた寄生虫が存在するならば、その寄生虫は当然、去ろうとはしません。むしろ、さらに大きな植民地を形成しようとするでしょう。これが、国家が成長し続ける理由であり、そして、血を吸い上げるこの寄生虫と戦う必要性が生じる所以なのです。
別のシナリオを考えてみましょう。つまり、現代社会における国家の規模を実質的に縮小するという仮定を立て、その実現可能性や現実味について見極めるためです。これまでに、ヨーロッパにおける現代国家の重みがGDPの50%に達していること、その内訳を示してきました。さて、かつての状況を想像してみてください。あの時代は、科学フィクションのようなことは必要なく、医療はゼロ、経済政策も実質ゼロで、民間部門が構築できないインフラだけが、もしあれば驚くほど僅か、GDPの1%程度だったのです。教育はゼロ、防衛と公共秩序は維持されるものの、余暇・文化・宗教への補助金はゼロでした。地域サービスや環境保護に関しては、下水道、街路灯、森林の維持管理など必要な分は残され、官僚組織も非常に大幅に縮小され、社会保障も一部のみが残されていました。
さて、しばしば「国家は富裕層からお金を奪い、貧困層へ再分配するために存在する」と言われますが、実際、社会保障はGDPの20%に相当します。ここで、極端な貧困を防止するために本当に必要な支出額を計算してみましょう。そうすれば、皆さんも、このGDPの20%は貧困撲滅のためのものではなく、むしろ国家が横方向の所得再分配システムを通じて国民を捕らえ続けるためのものであると気づくでしょう。すなわち、国家はあなたからお金を取り、そのお金を自らの利益や必要に応じて配分するために、あなたと国家の間に割り込むのです。バストス教授が正しく指摘しているように、その所得の移動は、富裕層から貧困層へ、またはその逆ではなく、すべての人々から国家へ向かっているのです。そして国家は、その所得を自らの利益や必要に従って再分配することを決定します。
では、先ほど示したような形で国家の各機能を大幅に縮小した場合、結果として国家はGDPの9~10%程度の規模となり、現状よりも30~40ポイント、つまり約80%縮小された国家になるでしょう。防衛費、治安費は現状と同等に維持される(ただし、治安費については内部の官僚機構によっても左右されるため、この点はまた別の議論になります。たとえば、スペインはヨーロッパで国民一人あたりの治安部隊職員数が最も多い国ですが、本当にそれだけ必要なのかはまた別問題です)。安全保障費がGDPの1.7%、防衛費が1.3%、官僚組織が1%、地域サービスや環境保護が1%、民間部門ではまかなえないインフラがさらに1%、そして社会保障が3%という具合です。現在、社会保障としてGDPの3%、すなわち450億ユーロが支出されています。これは、450億ユーロの社会保障費を、例えば4.5百万人(スペイン人口のおよそ10%)に対して年間1人あたり1万ユーロずつ支給するか、あるいは300万人に対して1万5千ユーロずつ支給するということになります。繁栄した社会において、極端な無助状態に陥る国民の割合はどれほどか、という問題です。彼らは、生命保険、障害保険、個人貯蓄すら持たず、福祉国家が生まれる前に存在したボランティアや民間の相互扶助ネットワークさえも利用できなかった層です。これらを踏まえた上で、絶対的な無助状態に陥り、国家からの継続的な支援を必要とする国民の割合がたとえば5~10%だとすれば、実際に必要な支出はGDPの3~4%程度で十分にカバーできるはずです。しかし、現実には我々は社会保障にGDPの20%を費やしているのです。
明らかに、このGDPの20%は、富裕層から少しだけ富を奪って、巨大な貧困層を作らないためのものではありません。驚くべきことに、国家がGDPの50%を占めるにもかかわらず、貧困層は依然として存在しているのです。さらに、貧困を解消するための手段として、まず第一に、依存性を生む補助金を設けるべきではありません。しかし、現実には、経済活動が全くできず、自己の貯蓄や家族の支援、民間の相互扶助ネットワーク、そして最終的には国家に依存せざるを得ない層が一定割合存在します。しかし、そのようなケースはGDPの3%程度の支出で十分にカバーされるはずなのです。
さて、国家の規模を縮小した場合、たとえばGDPの50%から10%にまで削減できると仮定しましょう。これは約80%の削減に相当します。先に述べたように、中央値の労働者は現在、年間約13,500ユーロの税金を負担しています。この80%の削減が実現すれば、労働者の可処分所得は、国家が提供する各種サービスに充てるための支出分が年間1人あたり1万~1万1千ユーロ増加することになります。家庭内で中央値の労働者が2人いる場合、2万~2万2千ユーロの追加収入となるでしょう。この追加収入があれば、教育費、医療費、年金のための貯蓄など、国家が現在負担させているコストを自前でまかなうことが可能になるはずです。実際、多くのスペインの労働者は、国家の劣悪なサービスから逃れるため、民間の医療や教育、そして補完的な年金積立を実施しているのです。特に、公共教育は、学生の生産性向上よりも、国家のイデオロギーを植え付けることに重きを置いている場合が多いのです。
また、この話は、GDPの3%相当の再分配、すなわち450億ユーロ分が、現実的に考えても国民の基礎的な生活を支えるには十分であるという観点からも論じられます。現行の過剰な収用体制に対して、もし国家規模が大幅に縮小されるならば、労働者にとって有利な状況が実現するはずです。
さて、ここまでの議論から、もし国家主義のウイルスが社会の頭脳や利権に深く根付っている現状において、現状が最適でないと理解したとしても、移行のコストの高さゆえに多くの人々が現状から変わることを望まないという現実があるのです。たとえば、公共年金制度の解体は非常に困難です。年金受給者は「こんな不公平な体制であっても、自分の年金を受け取りたい。自分自身の貯蓄がなくなるリスクを冒したくはない」と考えるでしょう。
では、この国家――明らかに国家とその官僚機構に有利なこのモデル――から脱却するために、すなわち、表向きは国民のために存在するようでいて、実際には社会を寄生しているこの体制から逃れるためには、どのような手段が考えられるでしょうか。ここで、国家改革またはハイパーステートのパラサイト化に対抗するための、四つの可能なアプローチについて述べます。
第一のアプローチは、トップダウン型の方法です。すなわち、自由主義的な理念を掲げた善意の政治家が権力の座につき、内部からリベラル革命を起こそうとするというものです。しかし、私はこの方法は、次に述べるボトムアップ型の文化戦線と併せなければ、全体として非常に単純で実現不可能だと考えます。なぜなら、社会の大多数が国家改革を望まなければ、その改革は十分な勢いを持って実施されることは決してないからです。多くの改革は長期的な取り組みであり、一夜にして実現できるものではありません。一度実行された改革が元に戻らないようにするには、最低でも二世代を要するのです。もし社会がその方向に向かわなければ、いつかまた別の人物が権力に就いて、国民の大多数が望まない体制を再び打ち壊してしまうでしょう。例えば、チリの年金制度の民営化は、ピノチェト政権下の1981年に始まり、数年前に旧公共年金制度が完全に清算されました。しかし、その後、旧体制に戻そうとする動きが見られるのです。なお、チリは当時、非常に若い労働人口と限られた高齢人口という、改革に適した人口構造を有していたにもかかわらず、改革には約40年もの歳月がかかりました。これが、世界の他の国々で実施されるとなれば、どれほど困難なものになるか想像に難くありません。そして、もし世界中がそのような改革を望まなければ、いかに自由主義者の政治家を内部に潜り込ませ、社会民主主義の装いを与えたとしても、十分な効果は得られないでしょう。さらに、政治そのものが権力に触れると必ず腐敗すると、ロード・アクトンが指摘したように、権力は人を変えてしまいます。つまり、権力に惹かれて権力の座についた者は、その権力を維持・拡大するために、かつて掲げた理念を容易に放棄し、他者を蹂躙し、欺く行動に出るということです。
政治的競争というのは、もしあなたが行動しなければ、行動する者があなたを追い出してしまう、という状況を生み出します。そのため、もし存在するとしても、誠実で、信念を持った政治家は、力に屈する者に押されて公共の場から姿を消してしまうのです。権力闘争では、手が縛られている者と自由な手を持つ者との間で戦いが行われるため、劣悪な選択が働き、最終的には最悪の者が権力の座に就くという現象が生じるのです。(この点については、ハイエクも『隷属への道』で記述しています。)
次に、第二の可能性はボトムアップ、すなわち文化戦線によるアプローチです。これは、アイデアの戦いを、じわじわと、少しずつ社会に浸透させ、心を開かせ、意識を目覚めさせ、より多くの人々がこの変革を要求するようになるという方法です。しかし、これは特に有望な道ではないことは明白です。もし、ここでマルクス主義的な語調に傾くとすれば、客観的な物質的条件があって、そうした思想が大規模に広まる環境が整わない限り、人々は現状に満足して「今のままで十分だ」と感じ、急激な変革に乗り出す理由が見出せません。現状が著しく悪化しない限り、文化戦線による大規模な勝利が起こり、既存の社会制度が覆されるというのは極めて困難な道なのです。例えば、アルゼンチンでは、40年間にわたって底をつき続けた結果、人々が明らかに欠陥だらけのモデルにうんざりし、ハイパーインフレーションに苦しんだことで変革が進んだように見えます。もし、そこに一貫性があり、破壊的かつ斬新なメッセージ―社会主義的なものか、あるいは幸運にもリベラルなもの―があれば、一定の確率でそのアイデアが覇権を握り、新たな現状として定着する可能性が出てくるのです。しかし、スペインの場合、文化戦線による闘いは、相手側のプロパガンダがあふれ、対抗する者がいなければ、現状が一層固定化し、国家権力が加速度的に拡大していくため、非常に厳しい状況にあります。私自身も長い間、文化戦線で戦ってきましたが、スペインという環境におけるその限界を痛感しています。
第三の道は、そもそも国家改革を目指さず、自分の生活を改善するために他の地域へ移住するというものです。もし、競争が可能な複数の法域が存在すれば、現状に非常に不満を抱く者は、物理的に他の地域へ移り住み、そこで自らの生活基盤を築くことができます。そして、こうした法域間の競争は、他の法域による収用や寄生的な政策の力を制限する効果も持ちます。たとえば、ある法域で税率が非常に低く、規制が緩やかであれば、他の法域は資本が流出し、寄生者側から見れば、寄生対象(=ホスト)が成長しなければ、寄生する意味がなくなるのです。もし、ホストを窒息させて殺してしまえば、またはホストが他の、寄生が少ない地域へ流出してしまえば、寄生者にとっては不利益となります。このような効果は、実際には見かけ以上に大きな影響を持つのです。
たとえば、最も身近な例として、アンドラの場合が挙げられます。多くの場合、静かに、あるいは時に華やかに報じられる移住現象があり、一定の社会的反響を呼んでいます。問題は、これらはすべて財政上の問題であり、移住者を犯罪者扱いする試みがあっても、スペイン国家にとっては重要な問題とならないのです。よく批判されるのは、YouTuberなどがアンドラへ移住することについて、「国が自国民の資源不足を訴えるような状況に直面しない」とされる点です。もしそうなれば、国家は財政の引き締めを迫られるはずですが、現実はそうではありません。むしろ、これは他者に対する懲罰の一形態であり、「移住して税負担を軽減しようとするなら、あなたは悪い人間であり、悪い市民だ。もしあなたが著名人であれば、意識を啓発するために、我々はあなたを徹底的に攻撃し、公の場から追放する」といったメッセージが発せられるのです。しかし、実際にアンドラへの移住が進むこと自体は悪いことではなく、たとえそれがスペイン国家に与えるダメージが短期的にはそれほど大きくなくとも、他のケースでは、目に見えにくいながらも国家に損害を与えている場合があるのです。
たとえば、2か月前に発表されたドラギの報告書では、欧州が「足を引きずっている」との根本的な不満が示されています。すなわち、欧州では生産性が20年間にわたって停滞しており、成長期に新たに設立される企業が、厳しい規制の下で成長できず、資本調達が困難となり、結果としてアメリカに流出してしまうという現象です。これは「足で投票する」という現象であり、企業側の実情を反映したものです。そして、これは国家権力の内部から出た、我々の社会が停滞しているという自らの寡占層からの認識でもあります。彼らは、ここ20年間にわたり市民を内部から圧迫してきた手法を見直す必要があると訴えているのです。そして、ここで議論されているのは、欧州連合とアメリカという二つの経済ブロック間での移住の問題なのです。
もし、かつてヨーロッパに存在していたような、多数の競合する法域が現在も存在していたと想像してみてください。ここで歴史的な議論に深入りするつもりはありませんが、ヨーロッパが16世紀あるいは17世紀から産業革命に至るまで発展し、東洋が(少なくとも最近まで)停滞していた理由の重い仮説の一つは、ヨーロッパが政治的にはるかに細分化され、都市国家や小国、王国、そして公国など、まさにアンドラのようなケースに近い形態であったため、相互の競争が激しかったという点にあります。ひとつの領域内で生まれる思想を制限・抑制・検閲する能力は非常に低く、もし一方で弾圧されれば別の場所へ移動できたため、その結果、後の産業革命を引き起こす知的な開花が促されたのです。これに対して、中国のような中央集権的で統一された国家では、官僚組織が本来より強大な権力を持っていたため、このような発展は見込めませんでした。
「足で投票する」という現象は非常に強力です。したがって、文化戦線から取り組むべきもう一つの課題は、政治的な中央集権化や財政の調和化に反対することです。なぜなら、政治的に中央集権化が進んだり、財政が調和化されるほど、法域間の競争は減少し、その結果、国家が無罰で私有財産を寄生的に吸い上げる余地が広がるからです。これは市場経済ではよく理解される現象ですが、国家の場合は例外扱いされがちです。市場において本当の意味での独占、すなわち単にその分野で唯一の企業という状況ではなく、競合が存在しない真の独占状態になると、その独占者は価格を引き上げ、品質を低下させる傾向にあります。なぜなら、あなたは逃げ出すことができない、まるで人質のような状態に置かれるからです。つまり、国家もまた独占状態にあり、国家が直面する唯一の競争は、他の国家へ移住するという可能性なのです。領域を統一して競争余地を狭めれば狭めるほど、国家は独占的な力を強め、結果としてあなたに提供するサービスの質を低下させ、収用を強める傾向が出てきます。したがって、私はどんな中央集権化のプロセスにも反対し、逆に政治的な分権化を支持すべきだと考えます。
そして最後に、第四の戦略ですが、これはやや曖昧で漠然としているかもしれません。しかし、私が考えるに、実際に多くの人々が採用しており、多くの場合国家の影響力を制限している方法、それは直接的に「国家からの分離」を目指すことです。もちろん、あなたにとって寄生者のような国家が窮屈に圧しかけてくる場合、その寄生者を打倒しようと多大なエネルギーを費やすこともできます。しかし、寄生者が既に存在する以上、その存在を前提として生活基盤を築く、その固定費を受け入れながらも、寄生者のさらなる拡大を防ぐ、あるいは寄生の及ばない領域を確保する新たな方法を模索するということです。これが国家からの「分離」、すなわち、重くのしかかる国家の負担から自らを切り離す試みなのです。例えば、先に述べたように、私立教育、私立医療、私的年金といった選択肢があります。本来であれば、国家が私たちから過剰な資源を吸い上げることなく、その分をこうした目的に振り向けられれば理想的ですが、幸いなことに、現状では国家が私立教育への進学を禁止しているわけではありません(ただしかなりの規制は存在します)。私立教育は完全に自由なものではなく、国家のカリキュラムに沿ったものですが、それでも私立教育、私立医療、そして貯蓄や資産形成の道を開いてくれるのです。もちろん、今後さらに税が引き上げられ、国内外で資産が収用されるリスクが高まるまではの話ですが。
したがって、国家を一つの悪と捉え、その悪に支配される中で自由を追求する、すなわちその影響力からできるだけ逃れる方法を探るべきです。さらに、社会が自ら開発していく様々なツールが、私たちが国家の監視や統制から離れて生活する手助けとなります。たとえば、デジタル経済は、今日のところ、国家が我々をコントロール・規制・収用するのをより困難にする領域をある程度確保できる可能性を秘めています。ビットコインの例は、没収不可能な資産として、適切な管理を行えば、富の保蔵庫あるいは国家の統制や知識から独立した交換手段として機能する可能性を示しています。
これらは、寄生者である国家に吸い付かれないため、自らの活動から国家の影響力を一部でも排除する、新たな生活の仕方を模索する一つの方法です。こうした新しいツールは、今後も次々と登場し、国家が私たちの生活に及ぼす影響を制限するために活用されるべきです。社会全体を変えるのは非常に困難ですが、多くの人々を同じ方向に動かすことが難しい現状において、少なくとも我々が体系的に受けている搾取の度合いを最小限に抑えることは可能です。
以上、複数の道筋があります。第一の道は私個人としてはほぼ排除したいと考えますが、残りの三つは排他的ではなく、互いに補完し合うものです。どの方法も目的地に必ず到達できる保証はありませんが、これらは連携することで、国家が私たちや社会全体に及ぼす権力の影響を徐々に抑制する助けとなるでしょう。そして、我々自身の利益のため、あるいは共に生きる社会を改善するために、可能な限りこれらの道を追求すべきだと考えます。
-
 @ 7d33ba57:1b82db35
2025-03-26 11:19:39
@ 7d33ba57:1b82db35
2025-03-26 11:19:39Gibralta is famous for its iconic Rock, fascinating history, and stunning views over the Mediterranean and Atlantic. A mix of British, Spanish, and Moorish influences, it’s a unique destination packed with natural beauty and cultural heritage.
🏛️ Top Things to See & Do in Gibraltar
1️⃣ The Rock of Gibraltar 🏔️
- The most famous landmark, standing 426 meters high.
- Offers spectacular views of Spain, Morocco, and the Strait of Gibraltar.
- Reach it by hiking, cable car, or guided tour.
2️⃣ St. Michael’s Cave 🏰
- A stunning limestone cave filled with stalactites and stalagmites.
- Used as a concert venue with incredible natural acoustics.
- Illuminated with colorful lights for an unforgettable experience.
3️⃣ Apes’ Den 🐵
- Home to Gibraltar’s famous Barbary macaques, Europe’s only wild monkeys.
- Legend says if the monkeys leave, so will the British! 🇬🇧
- Be careful with your belongings—they love to steal snacks!
4️⃣ Europa Point & Lighthouse 🌊
- The southernmost point of Gibraltar, with views across to Africa.
- Visit the Trinity Lighthouse, the stunning Ibrahim-al-Ibrahim Mosque, and the Harding Battery.
5️⃣ The Great Siege Tunnels 🏗️
- An underground tunnel system carved by the British during the Great Siege (1779–1783).
- Learn about Gibraltar’s military history with cannons and exhibits.
6️⃣ Main Street & Casemates Square 🛍️
- A lively area with British-style pubs, duty-free shopping, and historical buildings.
- Ideal for picking up souvenirs, perfumes, electronics, and spirits at tax-free prices.
7️⃣ Gibraltar Skywalk & Windsor Suspension Bridge 🌉
- A glass-floored viewpoint offering breathtaking panoramic views.
- The Windsor Suspension Bridge is a thrilling 71-meter-long bridge over a deep gorge.

🍽️ What to Eat in Gibraltar
- Fish & Chips – A British classic, best enjoyed by the waterfront 🐟🍟
- Calentita – A chickpea flour flatbread, Gibraltar’s national dish 🥖
- Rosto – A local pasta dish with tomato sauce and meat 🍝
- Torta de Acelga – A savory Swiss chard pie, a blend of Spanish and Moorish flavors 🥧
- Gibraltar Gin & Tonic – A refreshing drink with local gin 🍸
🚗 How to Get to Gibraltar
✈️ By Air: Gibraltar International Airport (GIB) – flights from London, Manchester, Bristol
🚘 By Car: Drive from Spain (La Línea de la Concepción), but expect border checks 🚧
🚆 By Train: Nearest Spanish station is San Roque-La Línea, then take a taxi or bus
🚌 By Bus: Direct buses from Málaga, Seville, and Cádiz
🚶 On Foot: Many visitors park in La Línea, Spain, and walk across the border💡 Tips for Visiting Gibraltar
✅ Bring your passport – Border control is required for entry 🛂
✅ Take the cable car early – The Rock gets crowded by midday 🚠
✅ Watch out for the monkeys – They are friendly but love to steal 🎒
✅ Wear comfortable shoes – Exploring the Rock involves lots of walking 👟
✅ Use British pounds (£) or euros (€) – Most places accept both 💷💶 -
 @ b7cf9f42:ecb93e78
2025-03-26 10:57:33
@ b7cf9f42:ecb93e78
2025-03-26 10:57:33Der Verstand im Fluss der Information
Das Informationszeitalter ist wie ein monströser Fluss, der unseren Verstand umgibt
Fundament erbauen
Der Verstand kann sich eine Insel in diesem Fluss bauen. Dabei können wir eine eigene Insel erbauen oder eine bestehende insel anvisieren um stabilität zu finden
Je robuster das Baumaterial, desto standhafter unsere Insel. (Stärke der Argumente, Qualität des Informationsgehalts, Verständlichkeit der Information)
Je grossflächiger die Insel, desto mehr Menschen haben Platz (Reichweite).
Je höher wir die Insel bauen, desto sicherer ist sie bei einem Anstieg des Informationsflusses (Diversität der Interesse und Kompetenzen der Inselbewohner).
Robustes Baumaterial
Primäre Wahrnehmung (robuster):
Realität -> meine Sinne -> meine Meinung/Interpretation
Sekundäre Wahrnehmung (weniger Robust):
Realität -> Sinne eines anderen -> dessen Meinung/Interpretation -> dessen Kommunikation -> meine Sinne -> meine Meinung/Interpretation
Wie kann ich zur Insel beitragen?
Ich investiere meine Zeit, um zu lernen. Ich bin bestrebt, Ideen zu verstehen, um sicherzugehen, dass ich robustes Baumaterial verwende.
Ich teile vermehrt Informationen, welche ich verstehe, damit auch meine Mitbewohner der Insel mit robustem Material die Insel vergrössern können. So können wir mehr Platz schaffen, wo Treibende Halt finden können.
Was könnte diese Insel sein?
- Freie Wissenschaft
- Freie Software
- Regeln
- Funktionierende Justiz
- Werkzeug
- und vieles weiteres
-
 @ 872982aa:8fb54cfe
2025-03-26 09:45:22
@ 872982aa:8fb54cfe
2025-03-26 09:45:22其实保持内心平静是非常简单的事情
-
 @ 872982aa:8fb54cfe
2025-03-26 09:44:21
@ 872982aa:8fb54cfe
2025-03-26 09:44:21文章的第一个内容,我想介绍一下nostrbook
-
 @ 872982aa:8fb54cfe
2025-03-26 09:43:13
@ 872982aa:8fb54cfe
2025-03-26 09:43:13432143214321412
-
 @ 872982aa:8fb54cfe
2025-03-26 09:42:23
@ 872982aa:8fb54cfe
2025-03-26 09:42:23我的竹声音
-
 @ 872982aa:8fb54cfe
2025-03-26 09:40:28
@ 872982aa:8fb54cfe
2025-03-26 09:40:28 -
 @ 872982aa:8fb54cfe
2025-03-26 09:40:02
@ 872982aa:8fb54cfe
2025-03-26 09:40:02 -
 @ 872982aa:8fb54cfe
2025-03-26 09:30:52
@ 872982aa:8fb54cfe
2025-03-26 09:30:52 -
 @ 7d33ba57:1b82db35
2025-03-26 09:22:57
@ 7d33ba57:1b82db35
2025-03-26 09:22:57Córdoba is a treasure trove of Moorish architecture, Roman heritage, and Andalusian charm. Once the capital of the Umayyad Caliphate, it’s home to stunning patios, atmospheric streets, and UNESCO-listed landmarks.
🏛️ Top Things to See & Do in Córdoba
1️⃣ La Mezquita-Catedral 🕌⛪
- Córdoba’s most iconic landmark, a UNESCO World Heritage Site.
- A breathtaking blend of Islamic arches and a Christian cathedral.
- Don’t miss the orange tree courtyard and bell tower views.
2️⃣ Alcázar de los Reyes Cristianos 🏰
- A medieval fortress with stunning gardens and Mudejar courtyards.
- Walk through Roman mosaics, ancient baths, and watchtowers.
3️⃣ Puente Romano & Calahorra Tower 🌉
- A historic Roman bridge over the Guadalquivir River.
- Great for sunset views with the Mezquita in the background.
- Visit the Calahorra Tower Museum for a look at Córdoba’s Islamic past.
4️⃣ Judería (Jewish Quarter) & Calleja de las Flores 🌺
- Wander through narrow, whitewashed streets lined with flowers.
- Visit the Córdoba Synagogue, one of Spain’s last remaining medieval synagogues.
- Stop by Calleja de las Flores, one of the most photogenic streets in Spain.
5️⃣ Palacio de Viana 🏡
- A 16th-century palace with 12 stunning courtyards filled with flowers.
- A must-visit during Córdoba’s Patio Festival (May).
6️⃣ Medina Azahara 🏛️
- The ruins of a 10th-century Moorish palace-city, 8 km from Córdoba.
- One of the greatest archaeological sites from Al-Andalus.
7️⃣ Plaza de la Corredera & Local Tapas 🍷
- A lively square with colorful buildings and traditional bars.
- Try local specialties like salmorejo (cold tomato soup) and flamenquín (breaded ham & cheese roll).
🍽️ What to Eat in Córdoba
- Salmorejo – A thick cold tomato soup, topped with ham and egg 🍅
- Flamenquín – A deep-fried pork roll stuffed with ham & cheese 🥩🧀
- Rabo de toro – Slow-cooked oxtail stew, a classic dish 🥘
- Berenjenas con miel – Fried eggplant drizzled with honey 🍆🍯
- Montilla-Moriles wine – A local sherry-like wine 🍷
🚗 How to Get to Córdoba
🚆 By Train: High-speed AVE trains from Madrid (1 hr 45 min), Seville (45 min), Málaga (1 hr)
🚘 By Car: 1.5 hrs from Seville, 2 hrs from Granada, 1 hr 40 min from Málaga
🚌 By Bus: Regular connections from major Andalusian cities
✈️ By Air: Closest airports are Seville (SVQ) or Málaga (AGP)💡 Tips for Visiting Córdoba
✅ Best time to visit? Spring (April–May) for mild weather & flower-filled patios 🌸
✅ Visit early morning or late afternoon to avoid the midday heat ☀️
✅ Book Mezquita tickets in advance to skip long queues 🎟️
✅ Try the local patios – Many houses open their courtyards for visitors 🏡 -
 @ 872982aa:8fb54cfe
2025-03-26 07:15:23
@ 872982aa:8fb54cfe
2025-03-26 07:15:23其实保持内心平静是非常简单的事情
-
 @ 872982aa:8fb54cfe
2025-03-26 07:10:14
@ 872982aa:8fb54cfe
2025-03-26 07:10:14文章的第一个内容,我想介绍一下nostrbook
-
 @ b04082ac:29b5c55b
2025-03-26 07:07:11
@ b04082ac:29b5c55b
2025-03-26 07:07:11In the bustling markets of Kumasi, the 19th-century capital of the Asante Empire in modern-day Ghana, traders conducted their commerce not with coins or paper notes, but with gold dust measured by intricately crafted brass spoons. This monetary system, devoid of a central bank or state-issued fiat, sustained a sophisticated civilization for over two centuries, challenging the conventional narrative that money requires a sovereign issuer to function. The Asante’s gold dust economy provides a historical lens through which to view the principles of sound money—principles that Bitcoin, with its fixed supply and decentralized architecture, resurrects in the digital realm. For those who recognize Bitcoin’s potential as a transformative monetary system, the Asante’s gold dust spoons serve as a compelling precedent: a medium of exchange rooted in scarcity and trust can underpin a thriving society, independent of centralized authority.
Map from 1896 of the British Gold Coast Colony (today Ghana).
The Asante Empire, spanning from 1701 to 1901, relied on sika futuro—gold dust painstakingly extracted from rivers and forests—as its primary currency. Measured with spoons and brass weights known as abrammo, this system was remarkably decentralized. Each trader carried their own set of tools, often adorned with proverbs or symbolic designs, enabling them to verify transactions without reliance on a centralized mint or overseer. By 1900, the Asante had amassed 14 million ounces of gold, a volume that rivaled the economic output of many European nations during the same period. This wealth fueled extensive trade networks across West Africa, connecting the empire to merchants from the coast to the interior, and supported cultural artifacts like the Golden Stool, a revered symbol of collective sovereignty forged from gold. The value of gold dust stemmed not from a royal proclamation but from its inherent scarcity and the labor required to obtain it—qualities that economists identify as the bedrock of sound money. Bitcoin reflects this paradigm: its cap of 21 million coins, enforced through cryptographic consensus rather than governmental fiat, establishes a monetary discipline immune to arbitrary expansion. The Asante’s experience underscores a fundamental economic insight: money derives its efficacy not from state endorsement, but from its ability to resist manipulation and retain value over time.
 Men in the process of weighing gold dust, photographed on the Ivory Coast in 1892. From Marcel Monnier’s France Noire Cote d’Ivoire et Soudan, 1894.
Men in the process of weighing gold dust, photographed on the Ivory Coast in 1892. From Marcel Monnier’s France Noire Cote d’Ivoire et Soudan, 1894.Economic history teaches that sound money lowers time preference, encouraging saving and long-term planning over immediate consumption. The Asante’s gold dust, hard-won from the earth, could not be inflated at will; its supply expanded only incrementally, dictated by the limits of human effort and natural deposits. This constraint fostered a culture of accumulation, where wealth was preserved across generations, evident in the empire’s ability to finance infrastructure, such as roads linking trade hubs, and maintain a formidable military presence that deterred regional rivals. Historical records, such as those from anthropologist R.S. Rattray, describe how gold dust was hoarded in family coffers, passed down as a stable store of value. Bitcoin embodies this same dynamic. Its fixed issuance schedule—halving roughly every four years—mimics the gradual accretion of gold dust, encouraging holders to prioritize long-term retention over short-term expenditure. In contrast, fiat currencies, subject to unrestrained printing, elevate time preference, as seen in modern economies where central banks flood markets with liquidity, eroding purchasing power and compelling consumption over saving—a fate the Asante’s gold dust and Bitcoin’s design inherently avoid.
An array of gold dust spoons from the Asante Empire, each adorned with detailed engravings and symbolic motifs, reflecting their role in trade and cultural heritage.
The tools of the Asante economy further illustrate this monetary discipline. The spoons, ranging from 1/16-ounce measures for daily purchases to 2-ounce weights for significant transactions, were not mere utensils but instruments of precision and trust. Crafted with care—some bearing motifs of birds or proverbs like “The bird flies high”—they standardized trade across a diverse empire, reducing disputes over quantity or purity. Each trader’s possession of their own abrammo weights created a network of verification, a decentralized mechanism that prefigures Bitcoin’s blockchain. In Bitcoin’s system, nodes—computers running the protocol—validate every transaction, ensuring integrity without a central arbiter. This parallel is not superficial: both the Asante’s spoons and Bitcoin’s nodes represent a distributed order, where trust emerges from the system’s structure rather than a single authority. The Asante’s trade practices, documented by historians like Timothy Garrard, reveal a sophistication that belies their pre-industrial context—merchants negotiated with precision, their gold dust facilitating commerce from salt to textiles, much as Bitcoin enables peer-to-peer exchange across continents.
A collection of intricately crafted gold dust spoons from the Asante Empire, showcasing the artistry and cultural significance of gold in Akan trade and tradition.
Trust was the cornerstone of the Asante system, a quality that transcends its physical medium. Gold dust bore intrinsic worth, its weight a palpable assurance of value, a property recognized by European traders as early as the 15th century, well before the Asante state coalesced in 1701. This trust was not legislated but cultivated over centuries, a cultural conviction in the reliability of a scarce resource. Bitcoin’s trust arises from a different foundation: vast computational effort expended in mining secures its network, while a cryptographic framework ensures its integrity against tampering. Neither system depends on a sovereign guarantor; both derive legitimacy from attributes embedded in their design—scarcity and verifiability for gold dust, computational proof and immutability for Bitcoin. The Asante’s economy succumbed to colonial intervention in 1896, when British forces outlawed gold dust in favor of imperial currency, yet its principles endured in illicit trade, hinting at a resilience that Bitcoin amplifies. Bitcoin’s global network, operating beyond the reach of any single jurisdiction, withstands regulatory assaults—miners relocate, nodes persist—offering a durability the Asante could only aspire to in their regional confines.
One modern theory, Modern Monetary Theory (MMT), posits that money gains legitimacy solely through state declaration, underpinned by taxation and legal tender laws. The Asante’s experience contradicts this. Gold dust circulated among the Akan peoples long before the empire’s formation, its adoption predating any centralized authority; Asante kings taxed it but did not invent it. MMT’s insistence on government fiat as the source of monetary value overlooks the spontaneous emergence of money from human exchange—a process the Asante and Bitcoin demonstrate with clarity.
A detailed gold dust spoon from the Asante Empire, featuring symbolic engravings and a prominent animal motif, highlighting the cultural and spiritual significance of its design
Yet, the parallel between the Asante’s gold dust economy and Bitcoin might appear strained. Critics could argue that the Asante operated in a pre-industrial, regional context, their gold dust suited to a localized barter system, while Bitcoin contends with a global, digital economy of unprecedented complexity. The physicality of gold dust, they might contend, differs fundamentally from Bitcoin’s intangible code, and the Asante’s eventual subjugation by colonial fiat suggests state power ultimately prevails. This critique, however, misjudges the essence of the comparison. The Asante’s system thrived not because of its scale or medium, but because it embodied sound money—scarcity ensured its value, decentralization preserved its integrity. Bitcoin extends these principles, its fixed supply and distributed ledger transcending physical limits to achieve global reach. The Asante’s fall to colonial force reflects not a flaw in their money, but a lack of technological resilience—Bitcoin’s network, spanning continents and fortified by cryptography, shrugs off such threats, proving the concept’s adaptability rather than its weakness.
A single gold dust spoon from the Asante Empire, featuring geometric patterns and intricate engravings, a testament to the Akan's skilled metalwork and economic traditions.
The Asante’s gold dust economy persisted for two centuries, a testament to monetary sovereignty until colonial powers dismantled it. Its legacy lies in its demonstration that a decentralized, scarce medium can drive economic vitality—a lesson Bitcoin inherits and expands. By 2025, Bitcoin’s market value exceeds a trillion dollars, a quiet rebellion against central banks that echoes the Asante’s independence from state-issued money. The spoons—each a tool of meticulous trade—foreshadow Bitcoin’s blockchain, a ledger of unalterable trust. Their story reaffirms an enduring economic principle: money’s strength lies in its resistance to debasement, not in the power of its issuer. The Asante built an empire on this foundation, leveraging gold dust to forge a society of wealth and stability. Bitcoin, unbound by geography or politics, extends this logic into an era of unprecedented connectivity. If the Asante achieved such heights with a regional system, what might Bitcoin accomplish as a global one? The answer lies not in speculation, but in the hands of those who understand and wield its potential.
-
 @ 872982aa:8fb54cfe
2025-03-26 06:55:20
@ 872982aa:8fb54cfe
2025-03-26 06:55:20欢迎来到 首页 感谢
-
 @ d9422098:7ee511a3
2025-03-26 05:04:03
@ d9422098:7ee511a3
2025-03-26 05:04:03екненлотлоло
-
 @ 30876140:cffb1126
2025-03-26 04:58:21
@ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains.
I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on.
But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting,
The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater.
Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished.
-
 @ 9711d1ab:863ebd81
2025-03-26 03:36:56
@ 9711d1ab:863ebd81
2025-03-26 03:36:56 Welcome back friends! We’ve made it to the end of March, congratulations. Here’s what we’ve got to share this month:
Welcome back friends! We’ve made it to the end of March, congratulations. Here’s what we’ve got to share this month:-
🎓 The SDK Class of Q1
-
🤓 Back to School with Antonio
-
⚡️ Lightning is Everywhere
-
🎙️ Shooting the Breez with Danny, Umi & Roy
The SDK Class of Q1 2025 🎓
 We’ve been talking a lot about momentum at Breez and we’re seeing it build every day. More partners are adding Bitcoin payments with our SDK and more sats are moving freely around the world. By offering the choice of two implementations, Nodeless and Native, we’re truly building the best Lightning developer experience out there.
We’ve been talking a lot about momentum at Breez and we’re seeing it build every day. More partners are adding Bitcoin payments with our SDK and more sats are moving freely around the world. By offering the choice of two implementations, Nodeless and Native, we’re truly building the best Lightning developer experience out there.And the momentum just keeps growing stronger.
In fact, we’ve welcomed so many new partners that we had to bundle them all into one big announcement — it’s our pleasure to welcome the SDK Class of Q1 2025: Assetify, Cowbolt, DexTrade, Flash, Lightning Pay, OpenAgents, Satoshi, Shakesco, Tidebinder, and ZapZap.
 ---
---Back to School with Antonio 🚌
 We tell everyone we meet that adding Bitcoin payments to apps is really easy with the Breez SDK. But rather than just tell you this, we’ve decided to show you.
We tell everyone we meet that adding Bitcoin payments to apps is really easy with the Breez SDK. But rather than just tell you this, we’ve decided to show you.Antonio, one of our talented developers at Breez, has produced a video tutorial showing how you can add Bitcoin payments to React Native and Expo apps with the Breez SDK - Nodeless.
Join him as he guides you through each step and shows that it really is that *easy* to add Bitcoin payments to any app with our SDK.
Lightning is Everywhere.
 It’s true — Lightning is everywhere.
It’s true — Lightning is everywhere.Bitcoin payments aren’t just a thing for the few, they’re for the many.
This month, we’re showcasing our friends at Cowbolt. They’ve just released their collaborative cost-splitting, team-chat, and self-custody app (check it out).
Shooting the Breez 🌬️
 Since releasing our Bitcoin payment report — where we explained that Bitcoin isn’t just digital gold, it’s a thriving everyday currency accessible to millions of people around the world — Bitcoin payments have been the talk of the town.
Since releasing our Bitcoin payment report — where we explained that Bitcoin isn’t just digital gold, it’s a thriving everyday currency accessible to millions of people around the world — Bitcoin payments have been the talk of the town.As co-author of the report, I joined the Stephan Livera Podcast to discuss the growing trend in more detail. I also met up with Bo Jablonski to explain why more and more apps are taking notice on the newly-formed Guardians of Bitcoin radio show.
Developments have come thick and fast over the past month — most notably, the announcement of USDT coming to Lightning (check out Roy’s take on the good, the bad, and the unknown in Bitcoin Magazine). Breez’s BD Lead, Umi, joined a Spaces on X with UXTO, Amboss, and Lightning Labs to discuss the stablecoin’s imminent arrival on the network.
 That’s not all from Umi, she also joined her alma mater at the Cornell Bitcoin Club to explain why bitcoin is a medium of exchange, thanks to Lightning.
That’s not all from Umi, she also joined her alma mater at the Cornell Bitcoin Club to explain why bitcoin is a medium of exchange, thanks to Lightning. And last but not least, Roy was spreading the good word of Bitcoin, joining Bitfinex’s podcast to explain how Lightning is truly changing the game.
And last but not least, Roy was spreading the good word of Bitcoin, joining Bitfinex’s podcast to explain how Lightning is truly changing the game.
And there we go folks, another edition of Feel the Breez has come to a close.
As always, we’ll leave you with our usual parting comment: the best time to get into Lightning is now — it always has been.
Stay tuned for exciting announcements we’ll be releasing soon.
Until next time ✌️
-
-
 @ a012dc82:6458a70d
2025-03-26 12:55:41
@ a012dc82:6458a70d
2025-03-26 12:55:41The cryptocurrency world is poised on the brink of a significant event as Bitcoin approaches its fourth halving in April 2024. This event, deeply embedded in Bitcoin's protocol, serves as a reminder of the cryptocurrency's unique economic model, designed to mimic the scarcity and deflationary aspects of precious metals. The halving not only affects the miners' rewards but also has far-reaching implications for the entire cryptocurrency market, influencing investor sentiment, market supply, and the intrinsic value of Bitcoin itself.
Table of Contents
-
Understanding Bitcoin Halving
-
Historical Impact on Bitcoin's Price
-
Implications for Miners
-
Institutional Interest and Market Dynamics
-
Regulatory Environment and Global Economic Factors
-
Conclusion
-
FAQs
Understanding Bitcoin Halving
Bitcoin halving is a core mechanism of the Bitcoin protocol, occurring every 210,000 blocks, which historically has been approximately every four years. This event reduces the reward for mining new blocks by half, a process designed to control Bitcoin's inflation and supply rate. The upcoming 2024 halving will slash the mining reward from 6.25 bitcoins per block to 3.125 bitcoins, a change that will significantly impact the rate at which new bitcoins are generated and enter the market.
This deflationary event is critical to Bitcoin's value proposition as digital gold. By reducing the flow of new bitcoins, the halving events mimic the extraction of a finite resource, enhancing Bitcoin's scarcity and potential as a store of value. The anticipation and aftermath of these events have historically led to increased public interest, media coverage, and speculative activity, all of which contribute to Bitcoin's market dynamics and price volatility.
Historical Impact on Bitcoin's Price
The halving events have historically been landmarks in Bitcoin's price history, often heralding periods of significant price appreciation. For example, the year following the 2016 halving saw Bitcoin's price increase manifold, underscoring the event's impact on market psychology and investor expectations. However, while past trends suggest a bullish outcome, it's crucial to acknowledge the complexity of market dynamics and the multitude of factors influencing Bitcoin's price.
The price impact of the halving can be attributed to the reduced supply of new bitcoins, heightening scarcity, and potentially increasing demand. However, the actual market response can vary based on current market conditions, investor sentiment, and global economic factors. Therefore, while historical data provides valuable insights, each halving unfolds in a unique context, making the outcome of the 2024 event unpredictable and a subject of widespread speculation.
Implications for Miners
The halving significantly impacts Bitcoin miners, as the reward reduction directly affects their revenue streams. This event could lead to a realignment within the mining industry, as only the most efficient and well-capitalized operations can sustain profitability with lower rewards. This pressure could drive technological innovation, as miners seek more energy-efficient and cost-effective mining solutions, but it could also lead to increased centralization, which is a concern for the Bitcoin network's health and security.
The aftermath of the halving will likely see a shakeout of less efficient miners, which could temporarily affect the network's hash rate and security. However, this consolidation could also lead to a more robust and resilient mining ecosystem in the long run. The dynamics between mining costs, Bitcoin's price, and network security are intricate and will play a crucial role in the cryptocurrency's post-halving landscape.
Institutional Interest and Market Dynamics
The landscape of Bitcoin investment has evolved dramatically since the last halving, with significant growth in institutional interest. The approval of Bitcoin ETFs and the entry of traditional financial institutions into the crypto space have provided Bitcoin with a new level of legitimacy and accessibility. This institutional involvement could lead to greater liquidity and less volatility post-halving, as larger players with long-term horizons enter the market.
However, institutional investors also bring new dynamics to Bitcoin's market. Their investment strategies, risk management practices, and regulatory compliance requirements differ markedly from those of retail and early crypto adopters. This shift could influence how the market responds to the halving, as institutional investors may be less prone to speculative trading and more interested in Bitcoin's long-term value proposition.
Regulatory Environment and Global Economic Factors
The impact of the 2024 halving will also be shaped by the broader regulatory and economic environment. Regulatory developments, both positive and negative, can significantly affect investor confidence and market dynamics. Clear and supportive regulations can foster growth and innovation in the crypto space, while restrictive policies may hinder market development and investor participation.
Moreover, global economic factors such as inflation rates, monetary policies, and geopolitical events play a crucial role in shaping investor sentiment and demand for Bitcoin. As a digital, borderless asset, Bitcoin is increasingly seen as a hedge against inflation and currency devaluation, factors that could influence its appeal around the halving event.
Conclusion
As April 2024 approaches, the Bitcoin community and investors worldwide are watching closely, aware that the halving could mark the beginning of a new era for Bitcoin. This event represents more than just a technical adjustment; it is a testament to Bitcoin's enduring design and its role as a pioneer in the cryptocurrency space.
The significance of the halving extends beyond immediate price effects; it encompasses the evolution of Bitcoin's market, the maturation of its ecosystem, and its position in the broader financial landscape. As we move closer to this pivotal event, the collective actions of miners, investors, and regulators will shape not only the outcome of the halving but the future trajectory of Bitcoin and the cryptocurrency market at large.
In this ever-evolving narrative, the 2024 halving stands as a critical milestone, a moment of reflection and anticipation, highlighting the challenges and opportunities that lie ahead in the journey of Bitcoin and the quest for a decentralized financial future.
FAQs
What is Bitcoin halving? Bitcoin halving is an event that occurs every 210,000 blocks, approximately every four years, which reduces the reward for mining new Bitcoin blocks by half. This mechanism is designed to control inflation and reduce the rate at which new bitcoins are introduced into circulation.
Why is the Bitcoin halving significant? The halving is significant because it directly impacts the supply of new bitcoins entering the market, which can influence Bitcoin's price. It also affects miners' profitability and can lead to changes in the network's mining dynamics.
How has Bitcoin's price reacted to previous halvings? Historically, Bitcoin's price has increased following halving events, though there are many factors at play. These price increases are often attributed to the reduced supply of new bitcoins and increased demand.
What are the potential effects of the 2024 Bitcoin halving on miners? The halving will reduce the block reward, potentially affecting miners' profitability. This could lead to a consolidation in the mining industry, with only the most efficient miners remaining competitive.
How might institutional interest affect the Bitcoin market around the halving? Institutional interest can bring more stability and liquidity to the Bitcoin market. However, it also introduces new market dynamics, as institutional investors may have different strategies and reactions to the halving compared to retail investors.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ d560dbc2:bbd59238
2025-03-26 11:17:39
@ d560dbc2:bbd59238
2025-03-26 11:17:39The Eisenhower Matrix and Task4Us are two powerful tools for managing tasks—each with its own approach to prioritization. The Eisenhower Matrix categorizes tasks based on urgency and importance, while Task4Us lets you set a low, medium, or high priority for each task and uses an Urgency Score to guide you on what to work on next. By combining these systems, you can refine your task management process—ensuring you focus on the right tasks (via the Eisenhower Matrix), set appropriate priorities (via Task4Us’s priority parameter), and act on them at the optimal time (via Task4Us’s Urgency Score). In this post, I'll explain how to adjust tasks from the Eisenhower Matrix using Task4Us’s priority system and let its Urgency Score guide your actions for a more dynamic and effective workflow.
Understanding the Systems
The Eisenhower Matrix
The Eisenhower Matrix divides tasks into four quadrants based on two criteria: urgency and importance:
-
Urgent and Important (Do First):
Tasks requiring immediate action (e.g., “Submit a project proposal by 5 PM today”). -
Important but Not Urgent (Schedule):
Tasks that contribute to long-term goals but don’t need immediate attention (e.g., “Plan a team-building event”). -
Urgent but Not Important (Delegate):
Tasks that need quick action but don’t align with your primary goals (e.g., “Answer non-critical emails”). -
Neither Urgent nor Important (Eliminate):
Time-wasters to remove (e.g., “Scroll social media endlessly”).
While the matrix helps you decide what to focus on, schedule, delegate, or eliminate, it doesn’t inherently guide you on the relative urgency of tasks within each quadrant or the timing for non-urgent tasks.
Task4Us: Priority Parameter and Urgency Score
Task4Us uses the 2-5 Rule to prioritize tasks based on timing. When you add a task, you assign it a time unit (days, weeks, months, or years), and Task4Us calculates when it should be acted on within a 2-to-5 window. For example:
- A daily task like “Drink water” should be done every 2–5 days.
- A monthly task like “Meet Uncle Lars” should be done every 2–5 months.
Additionally, Task4Us allows you to set a priority parameter—low, medium, or high—for each task, giving you control over its initial importance. The system also calculates an Urgency Score based on how close the task is to its 2–5 window or due date (for fixed-date tasks). For instance, if you last met Uncle Lars 4 weeks ago and set it as a monthly task with medium priority, the Urgency Score might increase as you approach the 5-week mark, nudging you to act. Features like Fix Mode (for date-specific tasks) and Focus Mode (displaying your top 3 tasks) help you act without overthinking. Currently in beta, Task4Us is designed to reduce decision fatigue by aligning tasks with your natural rhythms.
Why Adjust Eisenhower Matrix Tasks with Task4Us Priorities?
Combining the Eisenhower Matrix with Task4Us’s priority and Urgency Score offers several benefits:
-
Align Priorities with Quadrants:
Set high priority for “Do First” tasks and medium for “Schedule” tasks, mirroring the matrix’s framework. -
Let Task4Us Guide Timing:
The Urgency Score adjusts dynamically based on timing, ensuring you act on tasks at the right moment—even within the same quadrant. -
Reduce Overwhelm:
The blend of the matrix’s clarity with Task4Us’s dynamic prioritization helps you focus on what’s most urgent and important without losing sight of long-term goals.
Step-by-Step Guide to Adjusting Tasks
Step 1: Categorize Tasks Using the Eisenhower Matrix
Start by listing your tasks and sorting them into the Eisenhower Matrix’s four quadrants. For example:
- Do First (Urgent and Important):
- “Submit project proposal by 5 PM today”
-
“Fix client issue by tomorrow”
-
Schedule (Important but Not Urgent):
- “Meet Uncle Lars for coffee”
- “Plan a team-building event”
-
“Do cardio”
-
Delegate (Urgent but Not Important):
-
“Answer non-critical emails”
-
Eliminate (Neither Urgent nor Important):
- “Scroll social media endlessly”
Focus on the actionable quadrants (“Do First” and “Schedule”) and delegate or eliminate tasks in the other quadrants.
Step 2: Add Tasks to Task4Us and Set Priorities
Add the tasks from the “Do First” and “Schedule” quadrants into Task4Us, assigning each a time unit or due date and setting its priority:
Do First Tasks (Set High Priority):
- “Submit project proposal by 5 PM today”:
- Use Fix Mode to set the due date (e.g., March 26, 2025).
-
Set the priority to high due to the immediate deadline.
-
“Fix client issue by tomorrow”:
- Use Fix Mode to set the due date (e.g., March 27, 2025).
- Set the priority to high.
Schedule Tasks (Set Medium Priority):
- “Meet Uncle Lars for coffee”:
- Set as a monthly task (last acted on February 1, 2025).
-
Assign a medium priority.
-
“Plan a team-building event”:
- Set as a monthly task (last acted on January 1, 2025).
-
Assign a medium priority.
-
“Do cardio”:
- Set as a daily task (last acted on March 24, 2025).
- Assign a medium priority.
Step 3: Let Task4Us’s Urgency Score Guide Your Actions
Task4Us calculates an Urgency Score that dynamically adjusts based on timing and your priority settings:
- Do First Quadrant:
- “Submit project proposal by 5 PM today” (High Priority): The Urgency Score will rank this as the top task due to the immediate deadline.
-
“Fix client issue by tomorrow” (High Priority): Although high priority, its Urgency Score may rank slightly lower since it’s due tomorrow.
-
Schedule Quadrant:
- “Plan a team-building event” (Medium Priority): With 3 months since the last action, its Urgency Score increases.
- “Meet Uncle Lars for coffee” (Medium Priority): Approaching the 2-month mark, its Urgency Score will rise.
- “Do cardio” (Medium Priority): At only 2 days since the last action, its Urgency Score remains lower for now.
Task4Us uses the Urgency Score to fine-tune the order of tasks within each quadrant, ensuring you act on the most pressing ones first.
Step 4: Act Using Task4Us’s Focus Mode
Focus Mode displays your top 3 tasks based on the Urgency Score across all categories. For example, your top 3 tasks might be: - “Submit project proposal by 5 PM today” (High Priority, top Urgency Score) - “Fix client issue by tomorrow” (High Priority, slightly lower Urgency Score) - “Plan a team-building event” (Medium Priority, high Urgency Score in the Schedule quadrant)
This mode helps you balance urgent needs with long-term goals, ensuring you work on the highest-priority tasks first.
Step 5: Review and Reassess Weekly
Set aside time each week to review your Eisenhower Matrix and Task4Us tasks:
-
Reassess Quadrants:
Shift tasks between quadrants if their urgency or importance changes.
Example: If “Plan a team-building event” becomes more urgent due to a company deadline, shift it to “Do First” and update its priority in Task4Us. -
Update Task4Us:
As tasks are completed, update their “last act dates” to reset their 2-5 windows and adjust Urgency Scores. -
Adjust Priorities:
If a “Schedule” task like “Do cardio” remains uncompleted for too long (e.g., skipped for 5 days), increase its priority to high to prompt timely action.
A Real-Life Example: Adjusting Tasks in Action
Imagine managing a mix of work, personal, and health tasks:
Eisenhower Matrix Categorization:
- Do First:
- “Submit project proposal by 5 PM today”
-
“Fix client issue by tomorrow”
-
Schedule:
- “Meet Uncle Lars for coffee”
- “Plan a team-building event”
-
“Do cardio”
-
Delegate:
-
“Answer non-critical emails”
-
Eliminate:
- “Scroll social media endlessly”
Add to Task4Us and Set Priorities:
- “Submit project proposal” – Use Fix Mode (due today), set to High Priority.
- “Fix client issue” – Use Fix Mode (due tomorrow), set to High Priority.
- “Meet Uncle Lars for coffee” – Set as a monthly task (last acted on February 1, 2025), Medium Priority.
- “Plan a team-building event” – Set as a monthly task (last acted on January 1, 2025), Medium Priority.
- “Do cardio” – Set as a daily task (last acted on March 24, 2025), Medium Priority.
Adjust Within Quadrants:
- Do First:
Tackle “Submit project proposal” before “Fix client issue” based on a higher Urgency Score. - Schedule:
Prioritize “Plan a team-building event” (High Urgency Score) over “Meet Uncle Lars” and “Do cardio.”
Act with Focus Mode:
- Task4Us’s Focus Mode displays your top 3 tasks (e.g., “Submit project proposal,” “Fix client issue,” and “Plan a team-building event”), ensuring a balanced focus.
Review Weekly:
- After completing tasks, update their “last act dates.”
Example: If you meet Uncle Lars on March 27, update the task to reset its 2-5 window, which may lower its Urgency Score temporarily.
Why This Combination Works
Combining the Eisenhower Matrix with Task4Us’s priority parameter and Urgency Score addresses limitations of both systems:
-
Aligned Prioritization:
Setting high priority for “Do First” tasks and medium for “Schedule” tasks aligns Task4Us with the Eisenhower Matrix, ensuring tasks are appropriately categorized. -
Dynamic Guidance:
Task4Us’s Urgency Score fine-tunes the order of tasks within each quadrant, guiding you on what to work on next based on timing. -
Balanced Focus:
The combination ensures you work on the right tasks (Eisenhower Matrix), with the right priority (Task4Us’s priority parameter), at the right time (Task4Us’s Urgency Score).
Try It Out and Share Your Experience
Task4Us is currently in beta—now’s the perfect time to try this combination and see how it enhances your task management. Categorize your tasks using the Eisenhower Matrix, add them to Task4Us, and adjust priorities with the low/medium/high system while letting the Urgency Score guide your actions.
Sign up for Task4Us at todo.task4.us and let me know how it works for you!
How do you prioritize your tasks—do you use the Eisenhower Matrix, Task4Us, or another method? Share your thoughts in the comments—I’d love to hear your experience!
#Productivity #TaskManagement #EisenhowerMatrix #Task4Us #GTD
-
-
 @ 1bda7e1f:bb97c4d9
2025-03-26 03:23:00
@ 1bda7e1f:bb97c4d9
2025-03-26 03:23:00Tldr
- Nostr is a new open social protocol for the internet
- You can use it to create your own online community website/app for your users
- This needs only a few simple components that are free and open source
- Jumble.Social client is a front-end for showing your community content to your users
- Simple With Whitelist relay (SW2) is a back-end with simple auth for your community content
- In this blog I explain the components and set up a online community website/app that any community or company can use for their own users, for free.
You Can Run Your Own Private "X" For Free
Nostr is a new open social protocol for the internet. Because it is a protocol it is not controlled by any one company, does not reside on any one set of servers, does not require any licenses, and no one can stop you from using it however you like.
When the name Nostr is recognised, it is as a "Twitter/X alternative" – that is an online open public forum. Nostr is more than just this. The open nature of the protocol means that you can use it however you feel like, including that you can use it for creating your own social websites to suit whatever goals you have – anything from running your own team collaboration app, to running your own online community.
Nostr can be anything – not just an alternative to X, but also to Slack, Teams, Discord, Telegram (etc) – any kind of social app you'd like to run for your users can be run on Nostr.
In this blog I will show you how to launch your own community website, for your community members to use however they like, with low code, and for free.
Simple useful components
Nostr has a few simple components that work together to provide your experience –
- Your "client" – an app or a website front-end that you log into, which displays the content you want to see
- Your "relay" – a server back-end which receives and stores content, and sends it to clients
- Your "user" – a set of keys which represents a user on the network,
- Your "content" – any user content created and signed by a user, distributed to any relay, which can be picked up and viewed by any client.
It is a pattern that is used by every other social app on the internet, excepting that in those cases you can usually only view content in their app, and only post your content to their server.
Vs with Nostr where you can use any client (app) and any relay (server), including your own.
This is defined as a standard in NIP-01 which is simple enough that you can master it in a weekend, and with which you can build any kind of application.
The design space is wide open for anyone to build anything–
- Clones of Twitter, Instagram, Telegram, Medium, Twitch, etc,
- Whole new things like Private Ephemeral Messengers, Social Podcasting Apps, etc,
- Anything else you can dream up, like replacements for B2B SaaS or ERP systems.
Including that you can set up and run your own "X" for your community.
Super powers for –private– social internet
When considering my use of social internet, it is foremost private not public. Email, Whatsapp, Slack, Teams, Discord, Telegram (etc), are all about me, as a user, creating content for a selected group of individuals – close friends, colleagues, community members – not the wider public.
This private social internet is crying out for the kind of powers that Nostr provides. The list of things that Nostr solves for private social internet goes on-and-on.
Let me eat my own dog food for a moment.
- I am a member of a community of technology entrepreneurs with an app for internal community comms. The interface is not fit for this purpose. Good content gets lost. Any content created within the walled kingdom cannot be shared externally. Community members cannot migrate to a different front-end, or cross-post to public social channels.
- I am a member of many communities for kids social groups, each one with a different application and log in. There is no way to view a consolidated feed. There is no way to send one message to many communities, or share content between them. Remembering to check every feed separately is a drag.
- I am a member of a team with an app for team comms. It costs $XXX per user per month where it should be free. I can't self-host. I can't control or export my data. I can't make it interoperate natively with other SaaS. All of my messages probably go to train a Big Co AI without my consent.
In each instance "Nostr fixes this."
Ready now for low-code admins
To date Nostr has been best suited to a more technical user. To use the Nostr protocol directly has been primarily a field of great engineers building great foundations.
IMO these foundations are built. They are open source, free to use, and accessible for anyone who wants to create an administer their own online community, with only low code required.
To prove it, in this blog I will scratch my own itch. I need a X / Slack / Teams alternative to use with a few team members and friends (and a few AIs) as we hack on establishing a new business idea.
I will set this up with Nostr using only open source code, for free.
Designing the Solution
I am mostly non-technical with helpful AI. To set up your own community website in the style of X / Slack / Teams should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs some other unrelated Nostr projects in Docker containers,
- My objective was to set up and run my own community website for my own team use, in Docker, hosted on my own server.
User requirements
What will I want from a community website?
- I want my users to be able to log into a website and post content,
- I want to save that content to a server I control accessed only be people I authorise,
- I want my users to view only that content by default, and not be exposed to any wider public social network unless they knowingly select that,
- I want my user's content to be either:
- a) viewable only by other community members (i.e. for internal team comms), or
- b) by the wider public (i.e. for public announcements), at the user's discretion.
- I want it to be open source so that other people maintain the code for me,
- I want it for free.
Nostr solutions
To achieve this with Nostr, I'll need to select some solutions "a-la carte" for each of the core components of the network.
- A client – For my client, I have chosen Jumble. Jumble is a free open-source client by Cody Tseng, available free on Github or at Jumble.social. I have chosen Jumble because it is a "relay-centric" client. In key spots the user interface highlights for the user what relay they are viewing, and what relay they are posting to. As a result, it is a beautiful fit for me to use as the home of all my community content.
- A relay – For my relay, I have chosen Simple With Whitelist (SW2). SW2 is a free open-source relay by Utxo The Webmaster, based on Khatru by Fiatjaf, available free on Github. I have chosen SW2 because it allows for very simple configuration of user auth. Users can be given read access to view notes, and write access to post notes within simple
config.jsonfiles. This allows you to keep community content private or selectively share it in a variety of ways. Per the Nostr protocol, your client will connect with your relay via websocket. - A user sign-up flow – Jumble has a user sign-up flow using Nstart by Fiatjaf, or as an admin I can create and provision my own users with any simple tool like NAK or Nostrtool.
- A user content flow – Jumble has a user content flow that can post notes to selected relays of the users choice. Rich media is uploaded to free third-party hosts like Nostr.build, and in the future there is scope to self-host this too.
With each of these boxes ticked I'm ready to start.
Launching a Private Community Website with Jumble and SW2
Install your SW2 relay
The relay is the trickiest part, so let's start there. SW2 is my Nostr relay software of choice. It is a Go application and includes full instructions for Go install. However, I prefer Docker, so I have built a Docker version and maintain a Docker branch here.
1 – In a terminal clone the repo and checkout the Docker branch
git clone https://github.com/r0d8lsh0p/sw2.git cd sw2 git checkout docker2 – Set up the environment variables
These are specified in the readme. Duplicate the example .env file and fill it with your variables.
cp .env.example .envFor me this .env file was as follows–
```
Relay Metadata
RELAY_NAME="Tbdai relay" RELAY_PUBKEY="ede41352397758154514148b24112308ced96d121229b0e6a66bc5a2b40c03ec" RELAY_DESCRIPTION="An experimental relay for some people and robots working on a TBD AI project." RELAY_URL="wss://assistantrelay.rodbishop.nz" RELAY_ICON="https://image.nostr.build/44654201843fc0f03e9a72fbf8044143c66f0dd4d5350688db69345f9da05007.jpg" RELAY_CONTACT="https://rodbishop.nz" ```
3 – Specify who can read and write to the relay
This is controlled by two config files
read_whitelist.jsonandwrite_whitelist.json.- Any user with their pubkey in the
read_whitelistcan read notes posted to the relay. If empty, anyone can read. - Any user with their pubkey in the
write_whitelistcan post notes to the relay. If empty, anyone can write.
We'll get to creating and authorising more users later, for now I suggest to add yourself to each whitelist, by copying your pubkey into each JSON file. For me this looks as follows (note, I use the 'hex' version of the pubkey, rather than the npub)–
{ "pubkeys": [ "1bda7e1f7396bda2d1ef99033da8fd2dc362810790df9be62f591038bb97c4d9" ] }If this is your first time using Nostr and you don't yet have any user keys, it is easy and free to get one. You can get one from any Nostr client like Jumble.social, any tool like NAK or nostrtool.com or follow a comprehensive guide like my guide on mining a Nostr key.
4 – Launch your relay
If you are using my Docker fork from above, then–
docker compose upYour relay should now be running on port 3334 and ready to accept web socket connections from your client.
Before you move on to set up the client, it's helpful to quickly test that it is running as expected.
5 – Test your websocket connection
For this I use a tool called wscat to make a websocket connection.
You may need to install wscat, e.g.
npm install -g wscatAnd then run it, e.g.
wscat -c ws://localhost:3334(note use
ws://for localhost, rather thanwss://).If your relay is working successfully then it should receive your websocket connection request and respond with an AUTH token, asking you to identify yourself as a user in the relay's
read_whitelist.json(using the standard outlined in NIP-42), e.g.``` Connected (press CTRL+C to quit) < ["AUTH","13206fea43ef2952"]
```
You do not need to authorise for now.
If you received this kind of message, your relay is working successfully.
Set a subdomain for your relay
Let's connect a domain name so your community members can access your relay.
1 – Configure DNS
At a high level –
- Get your domain (buy one if you need to)
- Get the IP address of your VPS
- In your domain's DNS settings add those records as an A record to the subdomain of your choice, e.g.
relayas inrelay.your_domain_name.com, or in my caseassistantrelay.rodbishop.nz
Your subdomain now points to your server.
2 – Configure reverse proxy
You need to redirect traffic from your subdomain to your relay at port
3334.On my VPS I use Caddy as a reverse proxy for a few projects, I have it sitting in a separate Docker network. To use it for my SW2 Relay required two steps.
First – I added configuration to Caddy's
Caddyfileto tell it what to do with requests for therelay.your_domain_name.comsubdomain. For me this looked like–assistantrelay.rodbishop.nz { reverse_proxy sw2-relay:3334 { # Enable WebSocket support header_up X-Forwarded-For {remote} header_up X-Forwarded-Proto {scheme} header_up X-Forwarded-Port {server_port} } }Second – I added the Caddy Docker network to the SW2
docker-compose.ymlto make it be part of the Caddy network. In my Docker branch, I provide this commented section which you can uncomment and use if you like.``` services: relay: ... relay configuration here ...
networks:
- caddy # Connect to a Caddy network for reverse proxy
networks:
caddy:
external: true # Connect to a Caddy network for reverse proxy
```
Your relay is now running at your domain name.
Run Jumble.social
Your client set up is very easy, as most heavy lifting is done by your relay. My client of choice is Jumble because it has features that focus the user experience on the community's content first. You have two options for running Jumble.
- Run your own local copy of Jumble by cloning the Github (optional)
- Use the public instance at Jumble.social (easier, and what we'll do in this demo)
If you (optionally) want to run your own local copy of Jumble:
git clone https://github.com/CodyTseng/jumble.git cd jumble npm install npm run devFor this demo, I will just use the public instance at http://jumble.social
Jumble has a very helpful user interface for set up and configuration. But, I wanted to think ahead to onboarding community members, and so instead I will do some work up front in order to give new members a smooth onboarding flow that I would suggest for an administrator to use in onboarding their community.
1 – Create a custom landing page URL for your community members to land on
When your users come to your website for the first time, you want them to get your community experience without any distraction. That will either be–
- A prompt to sign up or login (if only authorised users can read content)
- The actual content from your other community members (If all users can read content)
Your landing page URL will look like:
http://jumble.social/?r=wss://relay.your_domain_name.comhttp://jumble.social/– the URL of the Jumble instance you are using?r=– telling Jumble to read from a relaywss://– relays connect via websocket using wss, rather than httpsrelay.your_domain_name.com– the domain name of your relay
For me, this URL looks like
http://jumble.social/?r=wss://assistantrelay.rodbishop.nz2 – Visit your custom Jumble URL
This should load the landing page of your relay on Jumble.
In the background, Jumble has attempted to establish a websocket connection to your relay.
If your relay is configured with read authentication, it has sent a challenge to Jumble asking your user to authenticate. Jumble, accordingly should now be showing you a login screen, asking your user to login.
3 – Login or Sign Up
You will see a variety of sign up and login options. To test, log in with the private key that you have configured to have read and write access.
In the background, Jumble has connected via websocket to your relay, checked that your user is authorised to view notes, and if so, has returned all the content on the relay. (If this is your first time here, there would not be any content yet).
If you give this link to your users to use as their landing page, they will land, login, and see only notes from members of your community.
4– Make your first post to your community
Click the "post" button and post a note. Jumble offers you the option to "Send only to relay.your_domain_name.com".
- If set to on, then Jumble will post the note only to your relay, no others. It will also include a specific tag (the
"-"tag) which requests relays to not forward the note across the network. Only your community members viewing notes on your community relay can see it. - If set to off, then Jumble will post the note to your relay and also the wider public Nostr network. Community members viewing notes on the relay can see it, and so can any user of the wider Nostr network.
5– Optional, configure your relay sets
At the top of the screen you should now see a dropdown with the URL of your relay.
Each user can save this relay to a "relay set" for future use, and also view, add or delete other relays sets including some sets which Jumble comes with set up by default.
As an admin you can use this to give users access to multiple relays. And, as a user, you can use this to access posts from multiple different community relays, all within the one client.
Your community website is up and running
That is the basic set up completed.
- You have a website where your community members can visit a URL to post notes and view all notes from all other members of the community.
- You have basic administration to enforce your own read and write permissions very simply in two json files.
Let's check in with my user requirements as a community admin–
- My community is saving content to a server where I control access
- My users view only that content by default, and are not exposed to any wider public social network unless they knowingly select that
- My user's content is a) viewable only by other community members, or b) by the wider public, at the user's discretion
- Other people are maintaining the code for me
- It's free
This setup has scope to solve my dog fooding issues from earlier–
- If adopted, my tech community can iterate the interface to suit its needs, find great content, and share content beyond the community.
- If adopted, my kids social groups can each have their own relays, but I can post to all of them together, or view a consolidated feed.
- If adopted, my team can chat with each other for free. I can self host this. It can natively interoperate with any other Nostr SaaS. It would be entirely private and will not be captured to train a Big Co AI without my consent.
Using your community website in practice
An example onboarding flow
- A new member joins your IRL community
- Your admin person gives them your landing page URL where they can view all the posts by your community members – If you have configured your relay to have no read auth required, then they can land on that landing page and immediately start viewing your community's posts, a great landing experience
- The user user creates a Nostr profile, and provides the admin person with their public key
- The admin person adds their key to the whitelists to read and write as you desire.
Default inter-op with the wider Nostr network
- If you change your mind on SW2 and want to use a different relay, your notes will be supported natively, and you can migrate on your own terms
- If you change your mind on Jumble and want to use a different client, your relay will be supported natively, and you can migrate on your own terms
- If you want to add other apps to your community's experience, every Nostr app will interoperate with your community by default – see the huge list at Awesome Nostr
- If any of your users want to view your community notes inside some other Nostr client – perhaps to see a consolidated feed of notes from all their different communities – they can.
For me, I use Amethyst app as my main Nostr client to view the public posts from people I follow. I have added my private community relay to Amethyst, and now my community posts appear alongside all these other posts in a single consolidated feed.
Scope to further improve
- You can run multiple different relays with different user access – e.g. one for wider company and one for your team
- You can run your own fork of Jumble and change the interface to suit you needs – e.g. add your logo, change the colours, link to other resources from the sidebar.
Other ideas for running communities
- Guest accounts: You can give a user "guest" access – read auth, but no write auth – to help people see the value of your community before becoming members.
- Running a knowledge base: You can whitelist users to read notes, but only administrators can post notes.
- Running a blind dropbox: You can whitelist users to post notes, but only the administrator can read notes.
- Running on a local terminal only: With Jumble and SW2 installed on a machine, running at –
localhost:5173for Jumble, andlocalhost:3334for SW2 you can have an entirely local experience athttp://localhost:5173/?r=ws://localhost:3334.
What's Next?
In my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest three blogs I explored different types of interoperability with NFC cards, n8n Workflow Automation, and now running a private community website on Nostr.
For this community website–
- There is scope to make some further enhancements to SW2, including to add a "Blossom" media server so that community admins can self-host their own rich media, and to create an admin screen for administration of the whitelists using NIP-86.
- There is scope to explore all other kinds of Nostr clients to form the front-end of community websites, including Chachi.chat, Flotilla, and others.
- Nostr includes a whole variety of different optional standards for making more elaborate online communities including NIP-28, NIP-29, NIP-17, NIP-72 (etc). Each gives certain different capabilities, and I haven't used any of them! For this simple demo they are not required, but each could be used to extend the capabilities of the admin and community.
I am also doing a lot of work with AI on Nostr, including that I use my private community website as a front-end for engaging with a Nostr AI. I'll post about this soon too.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 872982aa:8fb54cfe
2025-03-26 01:45:47
@ 872982aa:8fb54cfe
2025-03-26 01:45:47发酵蛋糕一般 需要30分钟左右
-
 @ 872982aa:8fb54cfe
2025-03-26 01:24:20
@ 872982aa:8fb54cfe
2025-03-26 01:24:20面粉是需要低精度的来制作蛋糕
-
 @ 57d1a264:69f1fee1
2025-03-26 08:45:13
@ 57d1a264:69f1fee1
2025-03-26 08:45:13I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available here). Performance and Accessibility looks have really low score!
| Desktop | Mobile | |---|---| |
|
| |
|
|
Now let's see what Semrush knows.
Analytics
General view on your metrics and performance trend compared to last 30 days.
See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.
Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.
| Organic Search | Backlinks Analytics | |---|---| |
|
|
| Position Changes Trend | Top Page Changes | |---|---| |
|
| |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |
Competitors
The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.
Referring Domains
Daily Stats
| Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | |
-41.87%|-16.4%|-1.62%|📝 Traffic Drop
Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits:
- https://stacker.news/items/723989 ⬇️ -15
- https://stacker.news/items/919813 ⬇️ -12
- https://stacker.news/items/783355 ⬇️ -5
📉 Decreased Authority Score
Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority.
🌟 New Keywords
Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30
🛠️ Broken Pages
This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not crawlable: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks
Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility!
One of the major issues I found is that SN does not have a
robots.txt, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary?Here are other basic info to improve the SEO score and for those of us that want to learn more:
- Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/
- Design for Accessibility: https://www.w3.org/WAI/tips/designing/
- Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/
originally posted at https://stacker.news/items/925433
-
 @ 872982aa:8fb54cfe
2025-03-26 01:23:16
@ 872982aa:8fb54cfe
2025-03-26 01:23:16 -
 @ 872982aa:8fb54cfe
2025-03-26 01:05:29
@ 872982aa:8fb54cfe
2025-03-26 01:05:29常见笛子的 使用竹子做成的。
-
 @ 872982aa:8fb54cfe
2025-03-26 00:48:29
@ 872982aa:8fb54cfe
2025-03-26 00:48:29 -
 @ 872982aa:8fb54cfe
2025-03-26 00:47:41
@ 872982aa:8fb54cfe
2025-03-26 00:47:41小时候经常在竹园里玩耍。
-
 @ 5256d869:9a567e23
2025-03-26 00:09:55
@ 5256d869:9a567e23
2025-03-26 00:09:55Pages stretch like waves, but a single drop remains— just read the last line.
-
 @ 866e0139:6a9334e5
2025-03-26 06:56:05
@ 866e0139:6a9334e5
2025-03-26 06:56:05Autor: Dr. Ulrike Guérot. (Foto: Manuela Haltiner). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Ich bin 60 Jahre. Einer meiner Großväter, Wilhelm Hammelstein, liegt auf dem Soldatenfriedhof in Riga begraben. Der andere, mütterlicherseits, Paul Janus, kam ohne Beine aus dem Krieg zurück, auch aus Russland. Ich kenne ihn nur mit Prothesen und Krücken. Er hat immer bei Wetterwechsel über Phantomschmerz geklagt und ist seines Lebens nicht mehr froh geworden. Den Krieg hat man ihm im Gesicht angesehen, auch wenn ich das als kleines Mädchen nicht verstanden habe.
"Ihr könnt euch nicht vorstellen, was ich gesehen habe"
Von den Russen hat er trotzdem nie schlecht geredet. Was er immer nur zu uns Enkelkindern gesagt war: *„Ihr könnt euch nicht vorstellen, was ich gesehen habe“. * Wir haben es nicht verstanden, als 6- oder 8-Jährige, und haben gelacht. Manchmal haben wir ihm seine Krücken weggenommen, die immer an den Ohrensessel gelehnt waren, dann konnte Opa Paul nicht aufstehen und ist wütend geworden.
Meine Mutter, Helga Hammelstein, ist im Mai 1939 gleichsam in den Krieg hineingeboren worden, in Schlesien. 1945 gab es für sie, wie für viele, Flucht und Vertreibung. Ob sie und ihre zwei Schwestern von den Russen vergewaltigt wurden – wie damals so viele – kann ich nicht sagen. Diese Themen waren bei uns tabuisiert. Was ich sagen kann, ist, dass meine Mutter als Flüchtlings- und Kriegskind vom Krieg hochgradig traumatisiert war – und als Kriegsenkelin war oder bin ich es wohl auch noch. Eigentlich merke ich das erst heute so richtig, wo wieder Krieg auf dem europäischen Kontinent ist und Europa auch in den Krieg ziehen, wo es kriegstüchtig gemacht werden soll.
Vielleicht habe ich mich aufgrund dieser Familiengeschichte immer so für Europa, für die europäische Integration interessiert, für die EU, die einmal als Friedensprojekt geplant war. Ich habe Zeit meines Lebens, seit nunmehr 30 Jahren, in verschiedenen Positionen, als Referentin im Deutschen Bundestag, in Think Tanks oder an Universitäten akademisch, intellektuell, publizistisch und künstlerisch zum Thema Europa gearbeitet.
1989 habe ich einen Franzosen geheiratet, ich hatte mich beim Studium in Paris verliebt und in den 1990-Jahren in Paris zwei Söhne bekommen. Auch in der französischen Familie gab es bittere Kriegserfahrungen: der Mann der Oma meines damaligen Mannes war 6 Jahre in deutscher Kriegsgefangenschaft. „Pourquoi tu dois marier une Allemande?“ „Warum musst du eine Deutsche heiraten?“, wurde mein damaliger Mann noch gefragt. Das Misstrauen mir gegenüber wurde erst ausgeräumt, als wir ihr 1991 den kleinen Felix, unseren erstgeborenen Sohn, in den Schoß gelegt haben.
Das europäische Friedensprojekt ist gescheitert
Das europäische Einheits- und Friedensprojekt war damals, nach dem Mauerfall, in einer unbeschreiblichen Aufbruchstimmung, die sich heute niemand mehr vorstellen kann: Der ganze Kontinent in fröhlicher Stimmung - insieme, gemeinsam, together, ensemble – und wollte politisch zusammenwachsen. Heute ist es gescheitert und ich fasse es nicht! Das Kriegsgeheul in ganz Europa macht mich nachgerade verrückt.
Darum habe ich ein europäisches Friedensprojekt ins Leben gerufen: TheEuropean Peace Project. Am Europatag, den 9. Mai, um 17 Uhr, wollen wir in ganz Europa in allen europäischen und auf dem ganzen europäischen Kontinent als europäische Bürger den Frieden ausrufen! Ich würde mich freuen, wenn viele mitmachen!
DIE FRIEDENSTAUBE JETZT ABONNIEREN:
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):
Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space oder kontakt@idw-europe.org.
Wo bleibt ein deutsch-russisches Jugendwerk?
Mein Lieblingsbuch zu Europa ist Laurent Gaudet, Nous, L’Europe, banquet des peuples. „Wir, Europa! Ein Banquet der Völker“ Es ist ein großartiges Gedicht, etwa wie die Ilias von Homer. Es beschreibt die letzten einhundert Jahre europäische Geschichte, die ganzen Krieg und Revolutionen. Und es beschreibt doch, was uns als Europäer eint. Darin findet sich der – für mich wunderschöne! - Satz: „Ce que nous partageons, c’est ce que nous étions tous bourraux et victime.“ „Was wir als Europäer teilen ist, dass wir alle zugleich Opfer und Täter waren“.
Und doch haben wir es geschafft, die „Erbfeindschaft“ zu beenden und uns auszusöhnen, zum Beispiel die Deutschen und Franzosen, über ein deutsch-französisches Jugendwerk, das 1963 gegründet wurde. So ein Jugendwerk wünsche ich mir auch heute zwischen Europa und Russland!
Das Epos von Laurent Gaudet ist in einem Theaterstück von dem französischen Regisseur Roland Auzet auf die Bühne gebracht worden. In dem 40-köpfigen Ensemble sind verschiedene Nationalitäten aus ganz Europa: das Stück ist fantastisch! Ich selber habe es auf dem Theaterfestival in Avignon 2019 sehen dürfen!
Ich wünsche mir, dass wir statt jetzt für Milliarden überall in Europa Waffen zu kaufen, das Geld dafür auftreiben, dieses Theaterstück in jede europäische Stadt zu bringen: wenn das gelänge, hätten wohl alle verstanden, was es heißt, Europäer zu sein: nämlich Frieden zu machen!
Ulrike Guérot, Jg. 1964, ist europäische Professorin, Publizistin und Bestsellerautorin. Seit rund 30 Jahren beschäftigt sie sich in europäischen Think Tanks und Universitäten in Paris, Brüssel, London, Washington, New York, Wien und Berlin mit Fragen der europäischen Demokratie, sowie mit der Rolle Europas in der Welt. Ulrike Guérot ist seit März 2014 Gründerin und Direktorin des European Democracy Labs, e.V.,Berlin und initiierte im März 2023 das European Citizens Radio, das auf Spotify zu finden ist. Zuletzt erschien von ihr "Über Halford J. Mackinders Heartland-Theorie, Der geografische Drehpunkt der Geschichte", Westend, 2024). Mehr Infos zur Autorin hier.
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ da0b9bc3:4e30a4a9
2025-03-26 06:54:00
@ da0b9bc3:4e30a4a9
2025-03-26 06:54:00Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/925400
-
 @ 2f4550b0:95f20096
2025-03-25 23:09:57
@ 2f4550b0:95f20096
2025-03-25 23:09:57Recently, I tuned into a prominent podcast where the conversation turned to what children are learning in K-12 education (around the 1:24:20 mark). Among the contributors was a Silicon Valley tech investor who shared a startling anecdote about an elite private school. He described how, at what he called “the best all-girls private school in Silicon Valley,” students were taught that reading was racist. He went on: “There was a spreadsheet that these kids had to memorize every day that had every other kid’s pronoun, and if you didn’t get it right you’d get in trouble.”
I was floored, not just by the absurdity of the curriculum, but by the casual assertion that a school teaching such ideas could still be deemed “the best.” How could an institution so detached from a rigorous, skill-building education retain that lofty title? I reflected on what truly makes an elite private school worthy of being called “the best,” a label too often thrown around without scrutiny.
Historically, top-tier private schools earned their reputations through academic excellence, robust curricula, and a commitment to preparing students for leadership and success. Think of the traditional hallmarks: mastery of core subjects like literature, mathematics, and science; critical thinking honed through debate and analysis; and extracurriculars designed to cultivate discipline and creativity. These schools were exclusive not just for their price tags but for their promise to deliver an education that equipped graduates to thrive in competitive universities and careers.
Yet the anecdote from that podcast suggests a troubling shift. If a school prioritizes ideological conformity (say, memorizing pronouns or framing foundational skills like reading as racist) over intellectual rigor, it’s fair to question whether it still deserves its elite status. Prestige, wealth, and social cachet might keep a school “elite” in name, but “the best” should mean more than that. It should reflect a dedication to fostering knowledge, skills, and independent thought, qualities that empower students as future leaders, not pawns in a cultural tug-of-war.
Consider what parents and students expect from a premium education. For an astronomical tuition (often exceeding $40,000 annually in places like Silicon Valley) they anticipate a return on investment: a curriculum that challenges young minds, teachers who inspire rather than indoctrinate, and a culture that values merit over dogma. When a school veers into territory where basic literacy is politicized or rote memorization of social rules trumps critical inquiry, it betrays that trust. No spreadsheet of pronouns will help a graduate navigate a complex world; a firm grasp of history, science, and persuasive writing just might.
This isn’t to say elite schools shouldn’t evolve. The world changes, and education must adapt, whether by integrating technology, addressing current issues, or broadening perspectives. But adaptation should enhance, not replace, the core mission of learning. A school can teach ethics alongside traditional subjects without sacrificing intellectual integrity. The problem arises when ideology becomes the curriculum, sidelining the tools students need to reason for themselves. If students are taught to question reading instead of mastering it, how will they author their own futures?
The Silicon Valley example isn’t isolated. Across the country, elite institutions have leaned into progressive trends, prioritizing social justice frameworks and experimental pedagogies over substance. Some might argue this reflects a bold reimagining of education, but there’s a difference between innovation and derailment. A school can be forward-thinking without abandoning the fundamentals that define excellence. Parents paying top dollar, and students investing their formative years, deserve more than a trendy experiment.
So, what should define “the best” private school today? First, employ a curriculum that balances tradition and progress: teach Shakespeare and coding, ethics and algebra, with an eye toward real-world application. Second, hire a faculty of experts who challenge students to think, not just comply. Third, create an environment that rewards effort and achievement over adherence to a script. Prestige alone, whether from alumni networks, manicured campuses, or Silicon Valley buzz, can’t suffice.
The tech investor’s remark about “the best” stuck with me because it revealed a disconnect. A school might remain elite in the eyes of the wealthy or well-connected, but “the best” is a higher bar. It’s a title earned through results, not rhetoric. Until these institutions recommit to education over indoctrination, they risk losing not just their claim to excellence, but the trust of those they serve.
-
 @ e5de992e:4a95ef85
2025-03-26 04:57:53
@ e5de992e:4a95ef85
2025-03-26 04:57:53Overview
On March 25, 2025, U.S. stock markets experienced modest gains despite declining volume and a drop in the Consumer Confidence Index, indicating that investors remain cautiously optimistic amid mixed economic signals.
U.S. Stock Indices
- S&P 500:
- Increased by 0.2%
- Closed at 5,776.65 points
-
Marked its third consecutive winning session, but volume was declining.
-
Dow Jones Industrial Average (DJIA):
- Rose marginally by 0.01%
- Ended at 42,587.50 points
-
Volume was declining.
-
Nasdaq Composite:
- Advanced by 0.5%
- Finished at 18,271.86 points
- Volume was declining.
U.S. Futures Market
- S&P 500 Futures:
-
Rose by 0.06%, suggesting a modestly positive opening.
-
Dow Jones Futures:
- Remained unchanged, indicating a neutral sentiment among investors.
Note: Both futures segments are experiencing low volume.
Key Factors Influencing U.S. Markets
-
Trade Policy Developments:
Investor sentiment has been influenced by reports suggesting that President Donald Trump's proposed tariffs may be more narrowly targeted than initially feared—potentially exempting certain sectors. This has alleviated some concerns regarding the impact of trade policies on economic growth. -
Economic Data Releases:
The Consumer Confidence Index declined, reflecting growing concerns about economic expectations. However, positive corporate earnings reports have contributed to the market's resilience. -
Sector-Specific News:
- International Paper saw significant stock price increases due to upbeat growth outlooks.
- United Parcel Service (UPS) faced declines amid reduced earnings projections.
Global Stock Indices Performance
International markets displayed mixed performances:
- Germany's DAX:
- Experienced a slight decline of 0.32%
- Closed at 23,109.79 points
-
Initial optimism regarding tariff negotiations waned.
-
UK's FTSE 100:
- Fell marginally by 0.10%
-
Reflects investor caution amid mixed economic data.
-
Hong Kong's Hang Seng:
- Declined by 2.35%
- Closed at 23,344.25 points
-
Impacted by a downturn in Chinese tech shares and ongoing tariff concerns.
-
Japan's Nikkei 225:
- Showed resilience with a modest gain, influenced by positive domestic economic indicators.
Cryptocurrency Market
The cryptocurrency market has experienced notable activity:
- Bitcoin (BTC):
- Trading at approximately $87,460
-
Down 1.23% from the previous close.
-
Ethereum (ETH):
- Priced around $2,057.22
- Marked a 0.69% uptick from the prior session.
These movements indicate the market’s sensitivity to regulatory developments and macroeconomic factors.
Key Global Economic and Geopolitical Events
-
Trade Tensions and Tariff Policies:
Ongoing discussions regarding U.S. tariff implementations have created an atmosphere of uncertainty, influencing global market sentiment and leading to cautious investor behavior. -
Central Bank Communications:
Statements from Federal Reserve officials and other central bank representatives are being closely monitored for insights into future monetary policy directions, especially in light of evolving economic conditions and inflationary pressures. -
Cryptocurrency Regulatory Environment:
Anticipation of a more favorable regulatory landscape under the current administration has contributed to recent rallies in major cryptocurrencies, though analysts caution that these rebounds may be fleeting amid broader market dynamics.
Conclusion
Global financial markets are navigating a complex environment shaped by trade policy developments, economic data releases, and sector-specific news. Investors are advised to remain vigilant and consider these factors when making informed decisions, as they are likely to continue influencing market behavior in the foreseeable future.
-
 @ b2d670de:907f9d4a
2025-03-25 20:17:57
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
Table of Contents
- Prerequisites
- Initial Server Setup
- Installing Strfry Nostr Relay
- Configuring Your Relay
- Setting Up TOR
- Making Your Relay Available on TOR
- Testing Your Setup]
- Maintenance and Security
- Troubleshooting
Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
Initial Server Setup
First, let's make sure your server is properly set up and secured.
Update Your System
Connect to your server via SSH and update your system:
bash sudo apt update sudo apt upgrade -ySet Up a Basic Firewall
Install and configure a basic firewall:
bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enableThis allows SSH connections while blocking other ports for security.
Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the
DEPLOYMENT.mddocument in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps here.Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-devHere's why each dependency is needed:
Basic Development Tools: -
git: Version control system used to clone the Strfry repository and manage code updates -build-essential: Meta-package that includes compilers (gcc, g++), make, and other essential build toolsPerl Dependencies (used for Strfry's build scripts): -
libyaml-perl: Perl interface to parse YAML configuration files -libtemplate-perl: Template processing system used during the build process -libregexp-grammars-perl: Advanced regular expression handling for Perl scriptsCore Libraries for Strfry: -
libssl-dev: Development files for OpenSSL, used for secure connections and cryptographic operations -zlib1g-dev: Compression library that Strfry uses to reduce data size -liblmdb-dev: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend -libflatbuffers-dev: Memory-efficient serialization library for structured data -libsecp256k1-dev: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures -libzstd-dev: Fast real-time compression algorithm for efficient data storage and transmissionClone and Build Strfry
Clone the Strfry repository:
bash git clone https://github.com/hoytech/strfry.git cd strfryBuild Strfry:
bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
Install Strfry
Install the Strfry binary to your system path:
bash sudo cp strfry /usr/local/binThis makes the
strfrycommand available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.Configuring Your Relay
Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
bash sudo useradd -M -s /usr/sbin/nologin strfryThe
-Mflag prevents creating a home directory, and-s /usr/sbin/nologinprevents anyone from logging in as this user. This is a security best practice for service accounts.Create Data Directory
Create a directory for Strfry's data:
bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfryThis creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
Configure Strfry
Copy the sample configuration file:
bash sudo cp strfry.conf /etc/strfry.confEdit the configuration file:
bash sudo nano /etc/strfry.confModify the database path:
```
Find this line:
db = "./strfry-db/"
Change it to:
db = "/var/lib/strfry/" ```
Check your system's hard limit for file descriptors:
bash ulimit -HnUpdate the
nofilessetting in your configuration to match this value (or set to 0):```
Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288 ```
The
nofilessetting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.You might also want to customize your relay's information in the config file. Look for the
infosection and update it with your relay's name, description, and other details.Set ownership of the configuration file:
bash sudo chown strfry:strfry /etc/strfry.confCreate Systemd Service
Create a systemd service file for managing Strfry:
bash sudo nano /etc/systemd/system/strfry.serviceAdd the following content:
```ini [Unit] Description=strfry relay service
[Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000
[Install] WantedBy=multi-user.target ```
This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like
ProtectHomeandNoNewPrivileges- Sets resource limits appropriate for a relayEnable and start the service:
bash sudo systemctl enable strfry.service sudo systemctl start strfryCheck the service status:
bash sudo systemctl status strfryVerify Relay is Running
Test that your relay is running locally:
bash curl localhost:7777You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
Install TOR
Install TOR from the package repositories:
bash sudo apt install -y torThis installs the TOR daemon that will create and manage your hidden service.
Configure TOR
Edit the TOR configuration file:
bash sudo nano /etc/tor/torrcScroll down to wherever you see a commented out part like this: ```
HiddenServiceDir /var/lib/tor/hidden_service/
HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777This configuration: - Creates a hidden service directory at
/var/lib/tor/strfry-relay/- Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR networkCreate the directory for your hidden service:
bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
bash sudo systemctl restart torMaking Your Relay Available on TOR
Get Your Onion Address
After restarting TOR, you can find your onion address:
bash sudo cat /var/lib/tor/strfry-relay/hostnameThis will output something like
abcdefghijklmnopqrstuvwxyz234567.onion, which is your relay's unique .onion address. This is what you'll share with others to access your relay.Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect:
ws://youronionaddress.onionTesting Your Setup
Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
- Open your TOR browser
- Go to your favorite client, either on clearnet or an onion service.
- Check out this list of nostr clients available over TOR.
- Add your relay URL:
ws://youronionaddress.onionto your relay list - Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
Maintenance and Security
Regular Updates
Keep your system, TOR, and relay updated:
```bash
Update system
sudo apt update sudo apt upgrade -y
Update Strfry
cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry
Verify TOR is still running properly
sudo systemctl status tor ```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
Monitoring Logs
To monitor your Strfry logs:
bash sudo journalctl -u strfry -fTo check TOR logs:
bash sudo journalctl -u tor -fMonitoring logs helps you identify potential issues and understand how your relay is being used.
Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
Stop the relay temporarily
sudo systemctl stop strfry
Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
Restart the relay
sudo systemctl start strfry ```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/locationTroubleshooting
Relay Not Starting
If your relay doesn't start:
```bash
Check logs
sudo journalctl -u strfry -e
Verify configuration
cat /etc/strfry.conf
Check permissions
ls -la /var/lib/strfry ```
Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big)
TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
Check TOR logs
sudo journalctl -u tor -e
Verify TOR is running
sudo systemctl status tor
Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
Verify TOR configuration
sudo cat /etc/tor/torrc ```
Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc
Testing Connectivity
If you're having trouble connecting to your service:
```bash
Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
Check that TOR is properly running
sudo systemctl status tor
Test the local connection directly
curl --include --no-buffer localhost:7777 ```
Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
-
Network Privacy: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
-
Server Anonymity: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
-
Censorship Resistance: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
-
User Privacy: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the Strfry documentation.
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to this list. Only add it if you plan to run a stable and available relay.
-
 @ 6a6be47b:3e74e3e1
2025-03-25 20:16:37
@ 6a6be47b:3e74e3e1
2025-03-25 20:16:37Hi frens, how are you?
🎨 I've been keeping busy with some personal projects and haven't painted as much as I'd like, but most importantly, I've returned to painting with watercolors. I'm getting used to them again, and although I love them, they can be tricky, especially when working wet on wet.
I've done a few pieces since getting back into it, and I'm excited to show the results, but at the same time, I'm a bit wary. Not because I want them to be "perfect" to share, but because I just want to have fun with them and get the joy back from painting.
🐱 And I'm not slacking because I have my furry little helper with me, and he's not having any of it!
He's a good boi

I've also been baking! 👩🍳 Yesterday, I made cinnamon "donuts" 🍩 , which ended up being muffins since I don't have a donut skillet.

And today, I baked lemon muffins 🍋, and they turned out delicious!

🧁 I had one as soon as they cooled, and chef's kiss... they're amazing!
🫀So as you can see I've been up to a few things, I'm not the best at this social media game. It can be draining so I want to have a balance between creating and showcasing you my proof of work 💪
💎I'm still getting there, but it's worth it.
🪄 Balance to achieve harmony is my goal.
🔮 I just wanted to check in and see what you've been up to! I'd love to know 🩷🫶🏻.
Have an amazing day frens!
-
 @ 2ed3596e:98b4cc78
2025-03-25 19:12:58
@ 2ed3596e:98b4cc78
2025-03-25 19:12:58Americans can now buy bitcoin on the Lightning Network directly from their bank with their Bitcoin Well account. By using the dollars in your Bitcoin Well Cash Balance you can buy bitcoin over the Lightning Network with instant delivery. You can also go directly from your bank to your Lightning Wallet. You can now live fully on a Lightning-powered bitcoin standard ⚡️
How to buy bitcoin on the Lightning Network instantly:
-
Add your Lightning Payment Address (LNURL) to your Bitcoin Well account
-
Enter the amount of dollars you want to buy bitcoin with
-
Choose your Bitcoin Well Cash Balance (you may need to fund this first!)
-
SMASH BUY! Your Lightning wallet will receive sats in seconds 🏎️
\ You can also go directly from your bank to your Lightning wallet. Your bitcoin will be sent over the Lightning network as soon as your dollars arrive (usually within 3 business days).
Here are detailed steps to guide you on how to buy bitcoin on the Lightning Network 👇
Step 1: Get your Lightning details
Go to your Lightning wallet and copy your Lightning Payment Address (looks like an email address). A Payment Address is not a Lightning invoice, but rather a static receiving address similar to a bitcoin receiving address. The benefit of using a Payment Address is that you can passively receive any quantity of sats at any time; unlike an invoice, a Payment Address does not have an expiry or a fixed amount of sats limiting the amount can be received. \ \ In the example below we use the Coinos.io wallet to obtain a Payment Address. Coinos is a powerful and easy to use Lightning wallet available in any country via your favourite web browser. You can set up a Coinos Lightning wallet and start receiving sats in seconds.

\ Coinos features a Lightning Payment Address. Once you’ve set up your wallet, hit “Receive” to access your Payment Address.
Step 2: Add your Lightning wallet to your Bitcoin Well account
Log in to your Bitcoin Well account and navigate to Buy bitcoin. From the buy screen, select bank or balance and add your Lightning wallet to the Destination by clicking Add wallet. Add your Lightning Payment Address from Step 1 here.
Step 3: Buy bitcoin on the Lightning Network
After you’ve selected your source and added your Lightning Payment Address as the destination, you are ready to complete your bitcoin purchase on the Lightning Network! \ \ When buying bitcoin from your Cash Balance, the dollars will instantly convert to bitcoin and be sent directly to your Lightning wallet – delivery takes less than a minute! 🤯\ \ When buying bitcoin from your bank account, you can expect to wait at least a couple business days as we wait for the slow movement of fiat to be finalized before sats can be sent.
## The compromise is over: bitcoin fast, easy and cheap
In the past, Bitcoiners had to choose between using freedom money at the mercy of the speed and cost of Bitcoin’s blockchain, or use the legacy banking system while surrendering their monetary freedom and independence. Ideally, Americans never have to compromise their monetary principles; thankfully, they no longer have to. \ \ Stacking sats straight to the Lightning also enables an innovative way to manage UTXOs. Now anyone can stack sats as much as they like without worrying about UTXO bloat. Simply accumulate sats on your Lightning wallet and then swap it across to your on-chain wallet in one neat UTXO. Since Coinos is a custodial Lightning wallet, you should periodically send your sats to your self-custody hardware wallet. To help you get the most out of the Lightning network, Bitcoin Well has a free swap tool that lets you swap sats between on-chain and Lightning. While this feature is only available in Canada, it will make its way to the United States very soon 🤫
Haven’t signed up with Bitcoin Well yet? Sign up here to start living on a (Lightning powered) Bitcoin Standard free from custodians and centralized honey pots.
Earn sats from your bitcoin transactions
\ Bitcoin Well is also the best place in the world to earn bitcoin. When you earn points in your Bitcoin Well account, you gain the opportunity to play the Bitcoin (Wishing) Well, where you win sats with every play.
The best part? We send bitcoin that you win straight to your personal wallet via the Lightning Network ⚡
Oh yeah, did we mention you can win 1,000,000 sats? If you're an active Bitcoin Well customer, there is a chance you've earned a pile of points. The more you use your account for buying, selling or spending bitcoin - the more points you’ll earn! Log in to your Bitcoin Well account and check your point balance.
About Bitcoin Well
\ Bitcoin Well exists to enable independence. We do this by coupling the convenience of modern banking, with the benefits of bitcoin. In other words, we make it easy to use bitcoin with self-custody.
-
-
 @ 220522c2:61e18cb4
2025-03-26 03:24:25
@ 220522c2:61e18cb4
2025-03-26 03:24:25npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2

-
 @ 7d33ba57:1b82db35
2025-03-25 18:31:35
@ 7d33ba57:1b82db35
2025-03-25 18:31:35Located on the Costa de la Luz, Conil de la Frontera is a charming Andalusian fishing village known for its golden beaches, whitewashed streets, and delicious seafood. With a laid-back atmosphere, it’s perfect for relaxation, surfing, and enjoying authentic Spanish culture.

🏖️ Top Things to See & Do in Conil de la Frontera
1️⃣ Playa de los Bateles 🏝️
- The main beach, right next to the town center.
- Long stretches of soft golden sand with clear Atlantic waters.
- Ideal for sunbathing, swimming, and beachside dining.
2️⃣ Playa de la Fontanilla 🌊
- One of the most beautiful beaches in the region, with crystal-clear waters.
- Great for families, surfers, and seafood lovers.
- Home to some of the best chiringuitos (beach bars) in Conil.
3️⃣ Playa del Palmar 🏄♂️
- A surfer’s paradise with consistent waves and a bohemian vibe.
- Popular for surf schools, yoga retreats, and sunset beach bars.
- Less crowded than the town’s main beaches.
4️⃣ Historic Old Town & Plaza de España 🏡
- Wander through narrow, whitewashed streets full of local boutiques, tapas bars, and cafés.
- Visit the Plaza de España, the town’s lively main square.
- Stop by the Torre de Guzmán, a medieval watchtower with great views.
5️⃣ Mercado de Abastos 🐟
- A traditional market where locals buy fresh seafood, fruits, and vegetables.
- Great place to experience the authentic Andalusian food culture.
6️⃣ Mirador del Jabiguero 🌅
- One of the best viewpoints in town, offering panoramic views over Conil and the Atlantic.
- A perfect spot for sunset photos.
🍽️ What to Eat in Conil de la Frontera
- Atún de Almadraba – Fresh bluefin tuna, caught using a traditional method 🐟
- Ortiguillas fritas – Fried sea anemones, a local delicacy 🍤
- Choco a la plancha – Grilled cuttlefish, a simple but delicious dish 🦑
- Tortillitas de camarones – Light and crispy shrimp fritters 🥞🦐
- Sangría or Tinto de Verano – Refreshing drinks to enjoy by the beach 🍷
🚗 How to Get to Conil de la Frontera
🚘 By Car: ~45 min from Cádiz, 1.5 hrs from Seville, 2.5 hrs from Málaga
🚆 By Train: Nearest station is San Fernando-Bahía Sur, then take a bus
🚌 By Bus: Direct buses from Cádiz, Seville, and other Andalusian cities
✈️ By Air: Closest airport is Jerez de la Frontera (XRY) (~1 hr away)💡 Tips for Visiting Conil de la Frontera
✅ Best time to visit? May to September for beach weather, spring & autumn for fewer crowds 🌞
✅ Book accommodation early in summer – It’s a popular vacation spot 🏡
✅ Try local tuna dishes – Conil is famous for its bluefin tuna 🍽️
✅ Visit during the Feria de Conil (June) for a lively cultural experience 🎉 -
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 00f8d531:a838c062
2025-03-26 00:21:41
@ 00f8d531:a838c062
2025-03-26 00:21:41Dear nostr, I love you. Stay frosty.
-
 @ 378562cd:a6fc6773
2025-03-25 17:24:27
@ 378562cd:a6fc6773
2025-03-25 17:24:27In an era where the value of traditional money seems to shrink by the day, many turn to Bitcoin as a potential safeguard against inflation. But is Bitcoin truly a hedge, or is this just wishful thinking? Let’s break it down.
Understanding Inflation Inflation occurs when the purchasing power of money declines due to an increase in prices.
Central banks, like the Federal Reserve, often print more money, leading to more dollars chasing the same amount of goods.
Over time, inflation erodes savings and makes everyday items more expensive.
Why Bitcoin is Considered an Inflation Hedge Limited Supply – Unlike the U.S. dollar, Bitcoin has a fixed supply of 21 million coins, making it immune to money printing.
Decentralization – No government or central bank can manipulate Bitcoin’s supply or devalue it through policy changes.
Digital Gold – Many see Bitcoin as a modern version of gold, offering a store of value outside traditional financial systems.
Global Accessibility – Bitcoin operates 24/7 across borders, making it accessible to anyone looking to escape failing currencies.
Challenges to Bitcoin as an Inflation Hedge Volatility – Bitcoin’s price swings wildly, making it risky as a short-term hedge.
Adoption & Trust – Unlike gold, which has been a store of value for centuries, Bitcoin is relatively new and still gaining mainstream acceptance.
Market Correlation – At times, Bitcoin moves in tandem with stocks rather than acting as a safe-haven asset.
Regulatory Uncertainty – Governments around the world continue to debate Bitcoin’s place in the economy, which can impact its long-term stability.
The Verdict: Fact or Fiction? ✅ Long-Term Potential: Over the years, Bitcoin has shown signs of being a hedge against currency devaluation, especially in countries with hyperinflation. ⚠️ Short-Term Reality: Bitcoin’s volatility makes it unreliable as an immediate hedge, unlike traditional safe-haven assets like gold.
For those who believe in Bitcoin’s future, it could be a strong long-term hedge. However, for those looking for immediate inflation protection, it’s still a speculative bet.
Would you trust Bitcoin to safeguard your wealth? 🚀💰
What do you think? Share your comments below.
-
 @ 27dd78c2:66ffe658
2025-03-25 17:12:08
@ 27dd78c2:66ffe658
2025-03-25 17:12:08In an age where ‘run clubs’ are getting more popular than ‘night clubs’, it’s exciting to see a Nostr-based sovereign fitness tracker hit the scene: Enter Runstr.club!
Runstr has emerged as a game-changer, redefining how runners connect, track progress, and stay motivated. For Bitcoin Runners, a movement that advocates sovereignty of one’s wealth, while improving one’s health, Runstr.club presents an exciting platform of choice to record your proof-of-work, take ownership of your personal data, and selectively engage with your social graph.
What is Runstr.club?
Runstr.club is a platform that’s being built to grow the proof-of-work community, with plans to offer interactive leaderboards, challenges, and social engagement. Unlike traditional running apps that focus purely on statistics, Runstr.club puts emphasis on camaraderie, motivation, and shared goals. It’s the Strava alternative that values ownership of your data, interoperability between platforms, and privacy as standard.
Why Runstr.club is a Great Fit for Bitcoin Runners
Bitcoin Runners isn’t just about proof-of-work; it’s about promoting freedom tech, decentralisation, and self-sovereignty principles that align closely with the ethos of Runstr.club.
Here’s why this platform is a great match for our movement:
- Community-Driven & Decentralised Spirit
Bitcoin Runners thrives on grassroots adoption and community participation, much like Runstr.club’s organic and community-focused model. Unlike corporate-owned fitness platforms that prioritise monetisation, Runstr.club is designed to empower runners, keeping the experience authentic and meaningful.
- Privacy-First Approach
One of the key concerns for bitcoiners is privacy. Mainstream fitness platforms harvest user data for profit, but Runstr.club offers a privacy-first alternative. This makes it an excellent choice for runners who value sovereignty in the digital age.
- The Advantage of Nostr Over Centralised Run Tracking Tools
Most mainstream running apps, like Strava or Nike Run Club, rely on centralised platforms that control user data, impose restrictions, and often monetise user activity. Runstr.club, however, is built on Nostr, a decentralised protocol that enables users to interact without getting trapped inside a walled garden.
With Nostr, runners benefit from:
-
True ownership of their data – no risk of platforms selling or misusing personal running history.
-
Resilience against censorship – no arbitrary bans or content moderation dictated by a 'shadowy suit'.
-
Interoperability – seamless integration with other Nostr-based applications, keeping data fluid and accessible across different platforms.
-
Peer-to-peer connectivity – allowing runners to share progress, create challenges, and stay engaged independent of big tech.
For Bitcoin Runners, Nostr’s decentralised nature aligns perfectly with the principles of sovereignty, freedom, and privacy.
- Gamification & Challenges
Runstr.club has engaging challenges and decentralised leaderboards on its roadmap. Whether you’re stacking sats through running-related bitcoin challenges or simply competing with fellow bitcoiners for fun, the platform will add an extra layer of engagement to every run. We would love to see such features come to life!
Conclusion
Runstr.club is more than just a running tracker—it’s a Nostr, bitcoin, and fitness onboarding community-driven movement. By embracing platforms that respect privacy, encourage competition, and foster community, we stay true to our values while pushing our limits as runners.
Let’s take this to the next level - be sure to follow Runstr on Nostr!
Run free. Stay sovereign. Stack zaps!
We’re shilling this open-source initiative out of genuine appreciation for both its vision and the dedicated team behind it.
-
 @ 220522c2:61e18cb4
2025-03-25 16:05:27
@ 220522c2:61e18cb4
2025-03-25 16:05:27draftoptionalAbstract
This NIP defines a new event kind for sharing and storing code snippets. Unlike regular text notes (
kind:1), code snippets have specialized metadata like language, extension, and other code-specific attributes that enhance discoverability, syntax highlighting, and improved user experience.Event Kind
This NIP defines
kind:1337as a code snippet event.The
.contentfield contains the actual code snippet text.Optional Tags
-
filename- Filename of the code snippet -
l- Programming language name (lowercase). Examples: "javascript", "python", "rust" -
extension- File extension (without the dot). Examples: "js", "py", "rs" -
description- Brief description of what the code does -
runtime- Runtime or environment specification (e.g., "node v18.15.0", "python 3.11") -
license- License under which the code is shared (e.g., "MIT", "GPL-3.0", "Apache-2.0") -
dep- Dependency required for the code to run (can be repeated) -
repo- Reference to a repository where this code originates
Format
```json {
"id": "<32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>",
"pubkey": "<32-bytes lowercase hex-encoded public key of the event creator>",
"created_at":
, "kind": 1337,
"content": "function helloWorld() {\n console.log('Hello, Nostr!');\n}\n\nhelloWorld();",
"tags": [
["l", "javascript"], ["extension", "js"], ["filename", "hello-world.js"], ["description", "A basic JavaScript function that prints 'Hello, Nostr!' to the console"], ["runtime", "node v18.15.0"], ["license", "MIT"], ["repo", "https://github.com/nostr-protocol/nostr"]],
"sig": "<64-bytes signature of the id>"
} ```
Client Behavior
Clients that support this NIP SHOULD:
-
Display code snippets with proper syntax highlighting based on the language.
-
Allow copying the full code snippet with a single action.
-
Render the code with appropriate formatting, preserving whitespace and indentation.
-
Display the language and extension prominently.
-
Provide "run" functionality for supported languages when possible.
-
Display the description (if available) as part of the snippet presentation.
Clients MAY provide additional functionality such as:
-
Code editing capabilities
-
Forking/modifying snippets
-
Creating executable environments based on the runtime/dependencies
-
Downloading the snippet as a file using the provided extension
-
Sharing the snippet with attribution
References
nip #grownostr
-
-
 @ e516ecb8:1be0b167
2025-03-25 23:49:34
@ e516ecb8:1be0b167
2025-03-25 23:49:34En los años 20, Estados Unidos vivía una juerga económica conocida como los "Roaring Twenties". La Gran Guerra había terminado, la industria estaba en auge, los autos llenaban las calles y el jazz resonaba en cada esquina. Todo parecía ir viento en popa: las acciones subían como espuma, la gente compraba a crédito como si no hubiera mañana y los bancos estaban felices de prestar dinero. Pero, según los economistas austriacos —piensa en Ludwig von Mises o Friedrich Hayek—, esta prosperidad era una fachada, una burbuja inflada artificialmente que tarde o temprano iba a estallar.
La Escuela Austriaca sostiene que el verdadero villano de esta historia no fue la codicia de los especuladores ni el exceso de optimismo, sino algo más sutil y estructural: la manipulación del dinero y el crédito por parte de la Reserva Federal. Vamos a desglosarlo paso a paso, como si estuviéramos destapando una intriga.
Acto 1: La Reserva Federal enciende la mecha
Tras su creación en 1913, la Reserva Federal (el banco central de EE.UU.) tenía el poder de controlar la oferta de dinero y las tasas de interés. En la década de 1920, decidió que era buena idea mantener las tasas de interés artificialmente bajas. ¿Por qué? Para estimular la economía, ayudar a Gran Bretaña a volver al patrón oro y mantener la fiesta en marcha. Pero para los austriacos, esto fue como echar gasolina a una fogata.
Cuando las tasas de interés se mantienen bajas por decreto, el dinero se vuelve "barato". Los bancos prestan más de lo que lo harían en un mercado libre, y ese crédito fácil fluye hacia empresas, inversores y consumidores. Es como si le dieras a todo el mundo una tarjeta de crédito sin límite: la gente empieza a gastar, invertir y construir como si la riqueza fuera infinita. Pero aquí viene el giro: ese dinero no reflejaba ahorros reales ni riqueza genuina. Era una ilusión creada por la expansión del crédito.
Acto 2: El auge insostenible
Con este dinero barato, los empresarios se lanzaron a proyectos ambiciosos: fábricas, rascacielos, nuevas tecnologías. Los inversores, por su parte, corrieron a Wall Street, comprando acciones a crédito (lo que se llamaba "comprar al margen"). El mercado de valores se disparó: el índice Dow Jones pasó de 63 puntos en 1921 a 381 en 1929. ¡Una locura! La gente común, desde taxistas hasta amas de casa, se metió al juego, convencida de que las acciones solo podían subir.
Para la Escuela Austriaca, este "boom" era una distorsión. Según su teoría del ciclo económico, desarrollada por Mises y Hayek, cuando el crédito se expande artificialmente, los recursos se mal asignan. Imagina que eres un chef con un presupuesto limitado: si alguien te da dinero falso para comprar ingredientes, harás platos extravagantes que no puedes sostener cuando el dinero real se acabe. Eso estaba pasando en la economía: se construían cosas que no tenían demanda real ni base sólida.
Acto 3: La burbuja empieza a pincharse
Hacia 1928, algunos empezaron a oler problemas. La producción industrial comenzó a tambalearse, los inventarios se acumulaban y las deudas crecían. La Reserva Federal, dándose cuenta de que la fiesta se estaba descontrolando, intentó subir las tasas de interés para enfriar las cosas. Pero era demasiado tarde: la economía ya estaba dopada con crédito fácil, y el daño estaba hecho.
El 24 de octubre de 1929 —el famoso "Jueves Negro"— el pánico estalló en Wall Street. Los inversores, viendo que las acciones estaban sobrevaloradas y que sus deudas eran impagables, empezaron a vender en masa. El martes siguiente, 29 de octubre, el mercado colapsó por completo: millones de acciones cambiaron de manos, los precios se desplomaron y la riqueza en papel se evaporó. Pero para los austriacos, esto no fue la causa del problema, sino el síntoma. El verdadero desastre ya había ocurrido en los años previos, con la expansión artificial del crédito.
Epílogo: La lección austriaca
Desde la perspectiva de la Escuela Austriaca, el Crack del 29 no fue un fallo del libre mercado, sino del intervencionismo. La Reserva Federal, al manipular las tasas de interés y la oferta de dinero, creó una burbuja que era insostenible. Cuando estalló, la economía tuvo que pasar por una dolorosa "corrección": las empresas quebraron, los bancos cerraron y el desempleo se disparó. Para Mises y Hayek, esto era inevitable: el mercado necesitaba purgar los excesos y realinear los recursos con la realidad.
¿Y qué pasó después? Bueno, la Gran Depresión que siguió fue agravada, según los austriacos, por más intervenciones: el New Deal de Roosevelt y las políticas proteccionistas como la Ley Smoot-Hawley solo prolongaron la agonía. Pero esa es otra historia para otro café.
-
 @ 1e5d0f11:12eeba92
2025-03-25 23:42:33
@ 1e5d0f11:12eeba92
2025-03-25 23:42:33Una semana en Nostr
Mucho tiempo ha pasado desde la primera vez que escuche de Nostr, guiado por mi eterna curiosidad ante cada nueva tecnología que descubro en internet decidí sumergirme en este protocolo, lo que encontré en ese entonces era un recién nacido, tenia todo el potencial de crecer y convertirse en algo grande y usado por muchas personas, pero todavía estaba en su infancia y los desarrolladores que tomaban provecho de este nuevo protocolo eran pocos y sus aplicaciones eran también jóvenes, ademas que los relés de Nostr (algo critico en su infraestructura) eran muy pocos, en conclusión estaba claro que había llegado muy temprano, y que Nostr todavía no era para alguien que se interesa por la tecnología pero cuya profesión no es el desarrollo de aplicaciones para internet, a esperar.
Grande fue mi sorpresa al volver a Nostr, al igual como ocurrió con muchos, fui recordado de Nostr gracias a Derek Ross y su charla en Nostr for Beginners w/ Derek Ross, al volver mi sorpresa fue grata, "no esta muerto" fue lo primero que pensé, esto porque es común que proyectos de código abiertos y que en superficie parece que intentaran reinventar la rueda están destinados al paredón de desarrolladores criticándolos o hundidos en el océano de Github sin nadie para explorar lo que pudo ser una buena idea, pero no Nostr, Nostr seguía vivo, creciendo y actualizando sus NIPs, gracias, en gran medida, a una generosa donación del co-fundador de Twitter (ahora llamado X o Xitter para algunos) en Bitcoins, la moneda del futuro y que derrotara al dinero fiduciario, o eso aseguran sus varios creyentes en Nostr, y Nostr esta lleno de ellos, lleno, sin duda impulsados por la importante donación que recibió el proyecto y por un mecanismo que lleva a este protocolo mas allá que otros: Nip-57. Lighting Zaps se llaman, y le da la posibilidad al usuario de transferir "Zaps", que como lo dice la propia pagina de Nostr es una propina que puede ser entregada a cualquier usuario que use Nostr y que ya tenga su billetera Lightning funcionando, y esto puede ser convertido en BTC, algo que no he probado y no creo lo haga en el corto tiempo, pero saber que tanto empeño se ha puesto en la creación de un nuevo protocolo pro incensurable que ademas incorpora elementos de cadena de bloques para proveer a creadores de contenido u otros con un método directo de financiación y así remover la necesidad de publicidad en las paginas algo que me parece saludable para internet, internet estaría mucho mejor sin tanto rastreador de publicidad y con mas respeto a la privacidad de los usuarios.
En fin, escribo esto como una prueba para saber como funcionan las publicaciones largas y tediosas desde Flycat, y bueno, seguiré usando el protocolo Nostr porque parece que ya esta en una etapa que me agrada y esta mas maduro, le contare a otros sobre Nostr, pero debo decir que entrar a Nostr, agregar relés y buscar usuarios para seguir es un proceso lento y tranquilo, no parece ser para el usuario común, pero al final siempre es uno el que configura las cuentas de sus padres y otros familiares.
-
 @ 6bae33c8:607272e8
2025-03-25 11:03:28
@ 6bae33c8:607272e8
2025-03-25 11:03:28I try to make these bold enough that I get most of them wrong. If you’re not getting most wrong, they’re not bold enough! Hits from last year included Teoscar Hernandez being the Marcel Ozuna of 2024 and Shohei Ohtani’s gambling scandal getting memory-holed totally. Misses include Walker Buehler > Tarik Skubal and Spencer Torkelson > Vlad Guerrero. As I said, the predictions have to be bold!
Also, these are hunches, the explanations for which are largely irrelevant. The relevant information is priced into ADP, so while I’ll justify it one way or another, it’s the prediction itself, not the explanation that matters.
1, Alex Bregman is top-five in AL MVP voting
This just feels like a perfect fit. Bregman rakes at Fenway (1.240 career OPS), and he rarely strikes out. I could see a .300-plus batting average with 30 home runs. The Red Sox upgraded their pitching too, and after the Yankees lost Gerrit Cole and Juan Soto, have a good chance to win the AL East.
2. Bo Bichette outperforms Mookie Betts
Granted Betts is sick right now and lost a ton of weight, but he was still going in the second round of NFBC Mains, while Bichette was going in Rounds 8-9. Bichette was hurt last year, but prior to that he was a star, is in his age 27 season and has four home runs and a .373 average in Spring Training. I’m sick that I didn’t get any shares (took Bregman over him in the Main.)
3. Chris Sale finishes as a top-5 starter again
This might not sound that bold because he’s SP6 by ADP, but every pitcher except maybe Paul Skenes and Skubal are underdogs to be top-five, given the volatility of the position. I love veterans in their mid-30s finding it again, usually they have 2-3 years of good before age and injury catch up again. It reminds me of Justin Verlander who hit a rough patch before righting the ship for several elite years.
4. Tyler Glasnow finishes as top-3 in NL CY Young votes
My comp for Glasnow is Randy Johnson, another tall lefty who battled injuries in his 20s before settling down to become one of the GOATS. Glasnow managed 135 IP last year and if he ups it to 165, he’ll be in the CY mix on the Dodgers.
5. Cody Bellinger hits 40 homers
A pull hitter with a high fly ball rate, Bellinger is perfect for Yankee Stadium. He’ll have to stay healthy, of course, but he’s still just 29 — won’t turn 30 until July — and is primed for the second best year of his career (he won’t top 2019.)
6. At least one of the following veteran pitchers has a top-five CY finish: Justin Verlander, Max Scherzer, Kevin Gausman, Walker Buehler, Sandy Alcantara or Carlos Rodon.
Pitchers who were once elite still own most of their skills, health permitting. While Scherzer and Verlander have lost velocity, knowing how to pitch is sufficient above a certain minimum threshold.
7. Jackson Chourio goes 30-30-.300
Chourio hit over .300 for the final four months of the season, once the Brewers stopped pulling him in and out of the lineup. The steals should be easy for him with a full season of at-bats, and the power should be there too in that park.
8. Hunter Brown finishes top-five in AL CY voting
After a rough start, Brown was one of the best pitchers in the league last year with a 2.31 ERA over the last four months. He’s in a good park, in the right division (though the A’s home park got a lot worse) and on a good enough team for run support purposes.
9. Aroldis Chapman gets more saves than Jhoan Duran
Chapman is still throwing 99 and landed a job on the much-improved Red Sox, while Duran, who took nine losses last year, has Griffin Jax behind him. I know Chapman’s control has been bad the last few years, but I have a hunch the veteran warhorse has a comeback year.
10. Some of these predictions will be wrong
I’ll pay the cost of never going 10-for-10 to make sure I don’t go 0-for-10.
-
 @ 878dff7c:037d18bc
2025-03-25 23:32:39
@ 878dff7c:037d18bc
2025-03-25 23:32:39Federal Budget 2025: Comprehensive Analysis and Implications
Overview:
On March 25, 2025, Treasurer Jim Chalmers presented Australia's Federal Budget for the 2025–26 fiscal year. This budget introduces several significant measures aimed at providing immediate cost-of-living relief, stimulating economic growth, and addressing long-term structural challenges. Key components include:
-
Personal Income Tax Cuts: The budget outlines a reduction in the lowest marginal tax rate from 16% to 15% starting July 1, 2026, and further to 14% from July 1, 2027. This initiative is projected to cost $17.1 billion over three years and aims to benefit low and middle-income earners.
-
Energy Bill Relief: An extension of the Energy Bill Relief Fund will provide $150 rebates to households over the next six months, totaling $1.8 billion. This measure is designed to alleviate rising energy costs and is expected to reduce headline inflation by approximately 0.5 percentage points in 2025.
-
Healthcare Investments: Significant funding has been allocated to Medicare to enhance bulk billing services and reduce pharmaceutical costs under the Pharmaceutical Benefits Scheme (PBS), aiming to improve healthcare accessibility.
-
Housing Initiatives: The budget includes an $800 million expansion of the Help to Buy program, increasing eligibility criteria to assist first-home buyers. However, this measure is limited to 40,000 applicants, leading to concerns about its overall impact on housing affordability.
-
Economic Projections: The budget forecasts a return to deficits, with an anticipated shortfall of $27.6 billion for the 2025–26 fiscal year. Real GDP growth is projected at 2.25%, with unemployment rates expected to peak at 4.25%.
Expert Analyses:
-
Deloitte: Deloitte's analysis emphasizes the need for structural reforms to address underlying fiscal challenges, noting that while the budget provides immediate relief, it may not sufficiently tackle long-term economic issues.
-
PwC: PwC highlights the importance of enacting pending tax and superannuation measures to ensure fiscal stability, pointing out that the budget's forward tax agenda remains uncertain.
-
KPMG: KPMG observes that the budget attempts to balance immediate cost-of-living relief with long-term fiscal responsibility but notes that it may lack measures to boost productivity and incentivize business investment.
Reactions from News Sources:
-
ABC News described the budget as "cautiously optimistic," praising its cost-of-living focus but noting limited ambition in areas such as climate investment and innovation.
-
The Guardian called it a "modest" budget, identifying meaningful but narrow wins for renters, aged care, and public infrastructure, while critiquing it for its limited reach and reliance on temporary relief.
-
The Australian Financial Review emphasized the lack of bold economic reform, pointing out that while the tax cuts may assist consumers in the short term, the broader economic strategy appeared politically calculated rather than reform-driven.
-
News.com.au focused on practical household benefits, highlighting how the budget would impact average Australians. It praised the tax cuts and rebates but expressed skepticism about the housing measures' real-world impact.
-
The Australian accused the budget of being driven by “polling, not policy,” arguing that it sidesteps difficult reforms in areas like energy security, defense, and migration in favor of short-term voter appeal.
Sectoral Implications:
-
Business Investment: The budget projects modest business investment growth of 1.5% in 2025–26 and 2026–27, down from 6% in 2024–25. This decline is attributed to global economic uncertainties and trade tensions.
-
Tax Compliance: The Australian Taxation Office (ATO) will receive nearly $999 million over the next four years to enhance enforcement activities, aiming to recover an additional $3.2 billion in tax receipts by 2029.
-
Housing Market: Despite the expansion of the Help to Buy program, concerns remain about the budget's limited impact on housing affordability, with critics arguing that more comprehensive measures are needed to address supply constraints.
Conclusion:
The Federal Budget 2025 introduces measures aimed at providing immediate relief to Australian households and businesses. While it delivers on promises around tax cuts and cost-of-living support, several analysts and media commentators view it as lacking in ambition and long-term economic vision. The political nature of its design is evident, with many measures framed to appeal to voters in the lead-up to the next federal election. Its success will hinge on effective implementation and how well it navigates the evolving domestic and global economic landscape.
Sources: Deloitte - March 25, 2025, PwC Australia - March 25, 2025, KPMG Australia - March 25, 2025, The Guardian - March 25, 2025, News.com.au - March 26, 2025, The Australian - March 26, 2025, Australian Financial Review - March 26, 2025, ABC News - March 25, 2025
Apple Transforms AirPods Pro 2 into Hearing Aids
Summary:
Apple has released a software upgrade enabling AirPods Pro 2 to function as "clinical grade" hearing aids for individuals with mild to moderate hearing loss. This feature includes the ability to perform hearing tests using an iPhone or iPad. Priced at $399, the AirPods Pro 2 offer an affordable alternative to traditional hearing aids, which can cost thousands. Experts caution that while beneficial, professional guidance is essential, and the AirPods may not be suitable for everyone.
Sources: The Australian - March 26, 2025, The Guardian - March 26, 2025
2000km Rain Band to Drench Queensland and New South Wales
Summary:
A 2000km-long rain band, fueled by tropical air and a low-pressure system, is set to bring exceptionally high rainfall to Queensland and parts of New South Wales. Some regions have already experienced significant downpours, with 208mm recorded in the Central West and 145mm near Townsville. Severe weather warnings are in effect, with flash flooding reported and expected to worsen. Residents are advised to remain vigilant due to rising river and creek levels. In contrast, Western Australia is enduring record-breaking heat, with temperatures surpassing 39°C in certain areas.
Sources: News.com.au - March 26, 2025, ABC News - March 26, 2025
Projected Population Shift from New South Wales to Queensland
Summary:
Federal budget data projects that New South Wales will experience a net loss of 115,300 residents by 2028-29, primarily due to Sydney's high cost of living. Queensland is expected to gain approximately 110,500 residents during the same period. Other states like Victoria and Western Australia are also projected to see slight population increases, while South Australia, Tasmania, the Northern Territory, and the ACT may experience decreases.
Source: News.com.au - March 26, 2025
Ban on Non-Compete Clauses for Workers Earning Below $175,000
Summary:
The Australian government has announced plans to ban non-compete clauses for workers earning below $175,000 annually, including professions such as hairdressers, construction workers, and childcare staff. This initiative aims to enhance job mobility and is projected to boost the economy by approximately $5 billion, potentially increasing individual wages by up to $2,500 annually. The ban is set to take effect in 2027.
Sources: The Guardian - March 25, 2025, Mirage News - March 26, 2025, NAB Business - March 26, 2025
Geopolitical Tensions and Tariffs Hamper Australian Mining Investment
Summary:
Industry leaders express concern that escalating geopolitical tensions and tariffs are adversely affecting investment in Australia's mining sector. The uncertainty surrounding international trade policies, particularly from major partners like the United States and China, is leading to hesitancy among investors. This situation poses challenges for Australia's resource-driven economy, emphasizing the need for strategic responses to navigate the complex global landscape. Sources: National Security News - March 25, 2025
Government Launches Campaign on Tainted Alcohol Risks Abroad
Summary:
In response to the deaths of two Melbourne teenagers in Laos last year from methanol poisoning, the Australian government has initiated a campaign to raise awareness about the dangers of consuming tainted alcohol overseas. The campaign aims to educate young Australians on alcohol-related risks, signs of methanol poisoning, and safety measures through social media, text messages, and airport communications. Foreign Affairs Minister Penny Wong emphasized the importance of this initiative in preventing further tragedies.
Sources: ABC News - March 24, 2025, The Guardian - March 24, 2025
Boeing's MQ-28 Ghost Bat Completes 100th Flight
Summary:
Boeing's MQ-28 Ghost Bat, an uncrewed collaborative combat aircraft developed in partnership with the Royal Australian Air Force (RAAF), has successfully completed its 100th test flight. This milestone signifies the program's maturity and underscores Australia's growing role in advanced aerospace development. The MQ-28 is designed to operate alongside crewed aircraft, enhancing mission capabilities and providing a force multiplier effect. Looking ahead, Boeing plans to conduct an air-to-air missile test from the MQ-28 by late 2025 or early 2026, aiming to further integrate offensive capabilities into the platform.
Sources: Australian Defence Magazine - March 25, 2025, Breaking Defense - March 25, 2025, Flight Global - March 25, 2025, Boeing - March 25, 2025
Russia and Ukraine Agree to Black Sea Ceasefire
Summary:
In a significant development, Russia and Ukraine have agreed to a ceasefire in the Black Sea, aiming to ensure safe navigation and halt military engagements in the region. The agreement, brokered by the United States during separate talks held in Saudi Arabia, includes provisions to prevent the use of commercial vessels for military purposes and to implement a 30-day suspension of attacks on energy infrastructure. However, the implementation of the ceasefire is contingent upon the lifting of certain Western sanctions on Russia's agricultural and financial sectors, a condition that has sparked debate among international observers. Ukrainian President Volodymyr Zelenskyy has expressed cautious optimism, emphasizing the need for concrete actions over verbal commitments. Critics argue that the agreement may disproportionately favor Russia, potentially allowing it to consolidate its position in the region. The situation remains fluid, with further negotiations anticipated to address unresolved issues and ensure adherence to the ceasefire terms. Sources: Associated Press - March 26, 2025, The Guardian - March 26, 2025
UN Research Indicates Under-reported Methane Emissions from Queensland Mine
Summary:
A UN-backed study reveals that methane emissions from Glencore's Hail Creek coalmine in Queensland are likely three to eight times higher than reported. Using aircraft-based measurements, the study found emissions between 1.5Mt and 4.2Mt CO2e per year, compared to the reported 0.53Mt CO2e. This underscores the need for more accurate emission reporting methods, as methane is a potent greenhouse gas.
Sources: The Guardian - March 26, 2025
How to Improve Your Teeth & Oral Microbiome for Brain & Body Health
Summary:
In this episode of the Huberman Lab podcast, Dr. Andrew Huberman interviews Dr. Staci Whitman, a board-certified functional dentist specializing in pediatric and adult care. They discuss the critical role of oral health in overall brain and body wellness. Key topics include:
- Oral Microbiome's Impact: The balance of bacteria in the mouth influences systemic health, affecting digestion, immunity, and even neurological function.
- Preventive Dental Care: Emphasis on regular dental check-ups, proper brushing and flossing techniques, and the use of non-toxic dental products to maintain oral hygiene.
- Dietary Considerations: How nutrition affects oral health, highlighting the importance of reducing sugar intake and consuming nutrient-rich foods to support strong teeth and gums.
- Connections to Chronic Diseases: Exploring links between oral health issues like gum disease and conditions such as heart disease, diabetes, and Alzheimer's.
- Holistic Approaches: Discussion on integrating functional medicine practices into dentistry to address root causes of oral health problems rather than just symptoms.
This conversation underscores the importance of maintaining oral health as a vital component of overall well-being.
-
-
 @ ecda4328:1278f072
2025-03-25 10:00:52
@ ecda4328:1278f072
2025-03-25 10:00:52Kubernetes and Linux Swap: A Practical Perspective
After reviewing kernel documentation on swap management (e.g., Linux Swap Management), KEP-2400 (Kubernetes Node Memory Swap Support), and community discussions like this post on ServerFault, it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion.
The Rationale for Disabling Swap
We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes.
With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion.
Additionally, disabling swap may protect data from data remanence attacks, where sensitive information could potentially be recovered from the swap space even after a process terminates.
Theoretical Capability vs. Practical Deployment
Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly.
But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model:
- Memory requests and limits are declared explicitly.
- The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap).
- Swap introduces non-deterministic performance characteristics that conflict with Kubernetes' goals.
So while the kernel supports intelligent swap usage, Kubernetes intentionally sidesteps that complexity.
Why Disable Swap in Kubernetes?
-
Deterministic Failure > Degraded Performance\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early.
-
Transparency & Observability\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically.
-
Performance Consistency\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits.
-
Kubernetes Doesn’t Manage Swap Well\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control.
-
Statelessness is the Norm\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state.
"But Swap Can Be Useful..."
Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need:
- Fine-tuned
vm.swappiness - Memory pinning and cgroup-based control
- Swap-aware monitoring and alerting
- Custom kubelet/systemd integration
That's possible, but not standard practice — and for good reason.
Future Considerations
Recent Kubernetes releases have introduced experimental swap support via KEP-2400. While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments.
Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in KEP-2400's Risks and Mitigations section, swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior.
Some argue that with emerging technologies like non-volatile memory (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet.
Conclusion
Disabling swap in Kubernetes is not a lazy hack — it’s a strategic tradeoff. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability.
If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, disabling swap remains the sane default.
-
 @ 7da115b6:7d3e46ae
2025-03-25 22:59:06
@ 7da115b6:7d3e46ae
2025-03-25 22:59:06These are in order of least to most complex.
Be Warned: Some of these ingredients may be unique to New Zealand and Australia
Pikelets
Pikelets are delicious with butter and jam or jam and whipped cream. To make Pancakes, double this recipe and make them larger. Serve in a stack with butter, maple syrup, bacon and blueberries. I've found a single batch is good for 2-4 people if you just want a snack.
Prep Time: 5 minutes Cooking Time: About 10 minutes
Ingredients: - A Cup Self Raising Flour - A Quarter Teaspoon of Table Salt - 1 Egg - A Quarter Cup of White Sugar - About 3 quarters of a Cup of Whole Milk
Method: 1. Sift the Flour and Salt into a bowl. 2. In another bowl beat the Egg and Sugar with a whisk until pale and thick. 3. Add the Egg mixture and the Milk to the dry ingredients and mix until just combined. 4. Gently heat a non-stick frying pan and drop tablespoonfuls of the mixture from the point of the spoon onto the surface. 5. When bubbles start to burst on the top of the Pikelets, turn them over and cook the second side until golden. 6. Place in a clean tea towel to cool.
This recipe requires a little experience to get right, especially if you prefer to use a cast iron pan or griddle. Basically, you can use a cast iron or aluminium pan, just make sure to grease the pan between each batch. The easiest way to do it, is to grab some baking paper, or butter paper wrap, scrunch it up and wipe it over the block of butter, and then wipe the surface of the pan. After the first round has cooked, do wipe the butter over the pan again. It'll stop the Pikelets from sticking.
Scones
These are based on an old recipe from the Edmond's Cookbook, and have been a Kiwi staple for decades. The yield is about 12 (ish), but it depends on how big or small you shape them.
Prep Time: About 10 minutes Cooking Time: 10 minutes (Depending on your Oven)
Ingredients: - 3 Cups of Premium White Wheat Flour - 2 and a Half Levelled Tablespoons of Baking Powder - A quarter of a Teaspoon of Table Salt - About a Third of a Cup of Butter - Between 1 to 1.5 Cups of Whole Milk
Method: 1. Preheat the oven to 220C. 2. Grease or flour a baking tray. 3. Sift the flour, baking powder and salt into a bowl. 4. Rub in the butter with your fingertips until the mixture resembles fine breadcrumbs 5. Add the milk and quickly mix with a round-bladed table knife to a soft dough. For light and tender scones the mixture should be quite soft and a little sticky. 6. Scrape the dough onto the floured baking tray and flour the top 7. Working quickly, pat the dough out to 2cm thickness and with a floured knife cut it into 12 even-sized pieces, then separate the scones to allow 2cm space between them. 8. Brush the tops with milk. 9. Bake for 10 minutes or until golden brown. Place on a wire rack to cool, wrapped in a clean tea towel to keep them soft.
They're great with Butter or Whipped Cream and Jam. 3-4 per person is excellent with some hot sweet Tea mid afternoon.
A little variation that used to be popular is to dice up about a a cup of Bacon, grate about a cup of Cheese, and throw it in the batter for a savoury twist.
Remember to not overcook them, otherwise they come out dry and crumbly.
Chocolate Muffins
I can't remember where I got this recipe, but I've made them dozens of times over the years. They really fill the gap when it comes to those hungry little faces pleading for snacks. This recipe is a little more complicated, but worth it. They're soft and moist, and extremely more-ish. I can personally eat about half on my own before I start feeling guilty. You can get about 12 muffins out of this mixture.
Prep Time: 20 minutes Cooking Time: About 18 minutes
Ingredients: - 1 and a quarter Cups Self Raising Flour - A quarter Cup of Cocoa Powder - 3 quarters of a Teaspoon of Baking Soda - A Quarter Teaspoon of Table Salt - Half a Cup of Soft Brown Sugar - A Quarter Cup of White Sugar - Half a cup of Chocolate Chips - An Egg - Half a Cup of Greek Yoghurt or Sour Cream - Half a Cup of Whole Milk - A Quarter Cup of Sunflower Oil (substitute with warmed dripping/butter or clean cooking oil to taste) - 1 Teaspoon of Vanilla Essence
Method: 1. Preheat oven to 180C on fan bake. 2. Line a 12-hole muffin tin with paper cases. 3. Sift the Flour, Cocoa Powder, Baking Soda and Salt into a large bowl. Stir in the White and Brown Sugars, followed by the Chocolate Chips. 4. In a separate bowl, whisk together Egg, Yoghurt (or Sour Cream), Milk, Oil (or Butter/Dripping) and Vanilla Essence. 5. Add the mixture to the dry ingredients and mix until just combined. Try not to over-mix it, you're not looking for a smooth texture, just no unmixed dry ingredients. 6. Divide mixture evenly between 12 muffin paper cases. 7. (Optional) Sprinkle with extra chocolate chips, for decoration. 8. Bake for 18-20 minutes, until muffins spring back when lightly pressed. 9. Leave to cool in tins for a couple of minutes before transferring to a wire cooling rack.
If you're feeling especially fancy, you can slice them open, and add a dollop of jam and whipped cream. Garnish with a Mint Leaf or Glacé Cherry. Using a Sieve, you can powder the top with Icing Sugar if you want to go that extra mile. It's a real Wifey pleaser.
-
 @ 7d33ba57:1b82db35
2025-03-25 09:38:27
@ 7d33ba57:1b82db35
2025-03-25 09:38:27Located on the Costa de la Luz, Chipiona is a charming seaside town in Cádiz province, known for its stunning beaches, iconic lighthouse, and delicious local wines. It’s a perfect destination for those seeking relaxation, history, and Andalusian charm.
🏖️ Top Things to See & Do in Chipiona
1️⃣ Chipiona Lighthouse (Faro de Chipiona) 💡
- The tallest lighthouse in Spain (69 meters), built in 1867.
- Climb 322 steps for breathtaking views of the Atlantic Ocean.
- Used to guide ships through the Gulf of Cádiz for centuries.
2️⃣ Playa de Regla 🏝️
- The most famous beach in Chipiona, known for its golden sand and calm waters.
- Perfect for sunbathing, swimming, and long walks along the shore.
- Surrounded by beach bars (chiringuitos) and seafood restaurants.
3️⃣ Santuario de Nuestra Señora de Regla ⛪
- A beautiful neo-Gothic monastery near the beach.
- Home to the Virgen de Regla, the town’s patron saint.
- A site of religious pilgrimages, especially in September.
4️⃣ Las Corrales de Pesca 🎣
- Ancient fishing structures made of stone walls in the sea, dating back to Roman times.
- A unique traditional fishing method, still in use today.
- Guided tours are available to learn about their history.
5️⃣ Bodega César Florido 🍷
- Visit one of the oldest wineries in Chipiona, famous for Moscatel wine.
- Enjoy a wine tasting tour and learn about the local winemaking tradition.
6️⃣ Paseo Marítimo & Sunset Views 🌅
- A scenic beachfront promenade, ideal for an evening stroll.
- Watch the sunset over the Atlantic Ocean, one of the most beautiful in Andalusia.
🍽️ What to Eat in Chipiona
- Langostinos de Sanlúcar – Delicious local prawns, best with a glass of Manzanilla wine 🦐🍷
- Tortillitas de camarones – Crispy shrimp fritters, a Cádiz specialty 🥞🦐
- Chocos a la plancha – Grilled cuttlefish with olive oil and lemon 🦑
- Pescaíto frito – A mix of fried fresh fish, perfect for a beachside meal 🐟
- Moscatel de Chipiona – A sweet dessert wine, famous in the region 🍷

🚗 How to Get to Chipiona
🚘 By Car: ~30 min from Cádiz, 1 hr from Seville, 2 hrs from Málaga
🚆 By Train: Closest stations in El Puerto de Santa María or Jerez de la Frontera
🚌 By Bus: Regular buses from Cádiz, Jerez, and Seville
✈️ By Air: Nearest airport is Jerez de la Frontera (XRY) (~40 min away)💡 Tips for Visiting Chipiona
✅ Best time to visit? Spring & summer for beach weather, September for festivals 🌞
✅ Try a Moscatel wine tour – The local wineries are world-famous 🍷
✅ Bring comfortable shoes – If climbing the lighthouse 👟
✅ Visit in September for the Fiestas de la Virgen de Regla, a unique cultural experience 🎉 -
 @ bc52210b:20bfc6de
2025-03-25 20:17:22
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused! Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
- Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
- Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
Key Differences: 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
Two Flavors of CISA: Half-Agg and Full-Agg CISA comes in two modes:
- Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
- Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
Half Signature Aggregation (Half-Agg) Explained How It Works Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
- Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
- Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
- R: A random point (32 bytes).
- s: A scalar value (32 bytes).
In Half-Agg:
- The R values from each signature are kept separate (one per input).
- The s values from all signatures are combined into a single s value.
Why It Saves Space (~50%) Let’s break down the size savings with some math:
Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes.
After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes.
Comparison:
- Original: 64n bytes.
- Half-Agg: 32n + 32 bytes.
- For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
Real-World Impact: Based on recent Bitcoin usage, Half-Agg could save:
- ~19.3% in space (reducing transaction size).
- ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
Applications of Half-Agg Half-Agg isn’t just a cool idea—it has practical uses:
- Transaction-wide Aggregation
- Combine all signatures within a single transaction.
- Result: Smaller transactions, lower fees.
- Block-wide Aggregation
- Combine signatures across all transactions in a Bitcoin block.
- Result: Even bigger space savings at the blockchain level.
- Off-chain Protocols / P2P
- Use Half-Agg in systems like Lightning Network gossip messages.
- Benefit: Efficiency without needing miners or a Bitcoin soft fork.
Challenges with Half-Agg While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
- Breaking Adaptor Signatures
- Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
-
Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
-
Impact on Reorg Recovery
- In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
- If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
Wrapping Up CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-
 @ 04deeaf5:f0c8f6b0
2025-03-25 03:42:16
@ 04deeaf5:f0c8f6b0
2025-03-25 03:42:16The other day, as @ellebeecher was wrapping up work on our newest project, she stood up and hit a mason jar filled with spring water, completely drenching her MacBook Pro.
We were a bit worried at first, considering that computer is the device we use to keep our business and personal lives afloat.
But then I thought about it...
I have an almost brand new MacBook with all the upgrades, and I barely use its capacity, only for Zoom and emails for communicating with clients. Elle was about to need an upgrade anyway, so I might as well give mine to her. My new decked-out Mac is perfect to be Elle's daily driver, especially since she's the one processing huge video files for our media company.
I thought to myself then... what would I use if I were to give her my computer?
Then I remembered that two months prior, I had the intuitive feeling that I needed to deeply understand the new, decentralized wave of technology.
So two months ago I reached out to my good friend, @polycarpweb5 , who is one of the world leaders in the space of Crypto and all things Web 5.
(Web 5 represents the stage in our technological advancement where all our tech, whether it's phones, laptops, smart cameras, or house lights, is completely private. All your data stays yours, rather than being sold to the highest bidder on the data market).
Poly set me up with a Framework laptop that runs Linux, and gave me an incredible background story on how this whole movement started and where decentralization is heading.
That laptop just stayed in my closet for a few months.
Until Elle's voluptuous assets, in an ALS Ice Bucket Challenge fashion, dumped a bunch of water on the machine we rely on for our livelihood.
This gave me the perfect chance to crack open this decentralized laptop, and I've gotta say... I'm never going back.
For the past few years, I've watched how big tech companies not only make huge money from monthly subscription fees but also pool our data and sell it to the highest bidder. Sometimes that bidder is a company trying to sell us trinkets we see advertised between our nightly YouTube watching, and other times, that data can be sold to anyone on the black market.
Now, for those who know me, I'm always talking about how giving energy to potential bad things deeply affects their likelihood of happening...
For example, when driving, gripping the wheel anxiously while constantly worrying about crashing actually increases your chances of an accident.
That's my chosen belief system around all fear in my life.
That being said, I've been naturally drawn to deeply understand the solutions being created to solve old problems, problems intentionally created to benefit old institutions.
I've had a strong draw to Bitcoin and other blockchain-based ways of exchanging currency and creating a more decentralized future that feels aligned with my deep American values of "We the people, by the people, for the people."
I feel like I'm meant to be learning this for a reason.
Choosing to invest and accept Bitcoin as payment from clients, and now,
embracing technology that is open source, and with Framework laptops, technology that is environmentally sustainable.
It's wild… this new computer, despite having pretty basic specs, works incredibly well.
Better than I ever could have imagined.
And get the best part…
I feel way more productuve.
I know how this sounds…
But you know how our food, pharma, media, and everything else they feed us has been engineered to leave us always wanting more?
I think tech is following the same pattern.
Obviously the software is designed this way, as we see with short-form content...
But I also believe the hardware is too.
That blue light screen is so mesmerizing.
Not just "oh that looks beautiful" like Steve Jobs had intended,
I'm talking about screens created to make our brains want to keep staring at them.
And I believe this has had a negative effect on my relationship with technology, and this is probably true for many others.
This new laptop by Framework, running Linux, set up to be ultra-secure and private by Poly and his team,
has dramatically shifted my relationship with tech. No longer does it feel like it's grabbing for my attention...
It feels like a tool.
Like how all tech should feel.
And the best part? It's faster.
And I can still use every software I used to use on my ultra-fast Mac.
Between this experience and the growing evidence of tech giants' unethical business practices, I'm almost ready to fully embrace a fully decentralized future.
(trading in my iPhone soon, lol).
I want to lead the way in people only giving their energy (in the form of dollars) to companies that have a genuine net positive impact on the world, and are building a future with individual sovereignty and expanding consciousness as their top priority.
Who knows, my girlfriend's big chest may have just saved the day again,
leading me to switch to different technology that is more efficient, more secure, and allows me to do better work in serving my family and serving others.
Thank you, @ellebeecher , @FrameworkPuter , @polycarpweb5 , and of course, #Bitcoin 😇
-
 @ 872982aa:8fb54cfe
2025-03-25 03:41:47
@ 872982aa:8fb54cfe
2025-03-25 03:41:47家乡是一个美丽的 小村庄
-
 @ 872982aa:8fb54cfe
2025-03-25 03:40:00
@ 872982aa:8fb54cfe
2025-03-25 03:40:00一个小的村落,那里没有车水马龙。
-
 @ 872982aa:8fb54cfe
2025-03-25 03:27:53
@ 872982aa:8fb54cfe
2025-03-25 03:27:53 -
 @ b1b16be0:08f41c1d
2025-03-25 18:08:21
@ b1b16be0:08f41c1d
2025-03-25 18:08:21What if Nostr app could save an Illiterate country?
Guatemala is the most illiterate country in Hispanic America at levels as serious as Africa.
About 30% of the population aged 15 or over cannot read or write. This figure rises in rural areas, where illiteracy reaches even more worrying levels, affecting mainly women and indigenous populations.
Limiting their access to paid jobs, their ability to access health services, and their full participation in political and social life. Education is a fundamental right, but there are still large gaps in access and educational quality, especially in rural areas and in communities with high poverty rates.
What if there was an application similar to Duolingo, but that allowed people to learn to read and write while earning Satoshis (Sats) This proposal not only sounds innovative, but could be a powerful tool to combat the country's illiteracy.
The idea of an app that rewards learning "learn to earn"
Duolingo is a popular platform that has proven to be effective in teaching languages through a gamified approach. If that model could be replicated, but with a specific focus on reading and writing, and above all reward users with sats, it could offer two key benefits: encourage learning and offer a direct economic opportunity to users.
Satoshis, being a low-cost and easy-to-access, can be a motivating tool. Many people in Guatemala, especially those in rural areas, do not have access to a traditional banking system, much less to a national identity document, but they have access to mobile phones and the internet, which facilitates the inclusion of an alternative form of value. With this additional motivation, people would be more willing to invest time in learning, knowing that they can get a tangible reward for their effort.
https://image.nostr.build/9da1c3b9478be817e82c891fdceaf87905a4d68876e9190240a8f979ebd35b40.jpg
Will there be developers interested in helping?
In addition, the technology sector globally is increasingly focused on open source, financial inclusion and the use of Bitcoin as an empowerment tool.
A project like this could attract developers interested in creating inclusive technological solutions that not only improve the quality of life of Guatemalans, but also promote access to new economic opportunities through digital tools. Is the possibility of working on a project with social impact, which combines education and Bitcoin, something that could excite many developers?
Algorithms for a greater impact on the illiterate
For this application to be truly effective, it is not enough to replicate existing models. The platform's algorithms would need to be adapted to focus specifically on the needs of the illiterate. The algorithm would have to be flexible enough to adapt to different levels of learning and ensure that users can progress gradually and effectively. (That it can identify literate users who only want the reward).
This could include:
-
Reinforce basic learning: Include exercises focused on phonetics, letter recognition and word construction, something that is not so central in language learning applications.
-
Personalized gamification: Use a system of rewards and levels that motivates users to continue learning, adapting to their learning pace. Sats could accumulate as the user progresses, which could be an additional incentive.
-
Interactivity and visual support: Incorporate visual elements, such as images or videos, that help users associate words with objects or actions, which would be especially useful for those with few previous educational resources.
-
Collaborative learning: Create a community within the application where users can interact, share their progress, and perhaps even solve doubts from others, which would foster an environment of collective learning.
-
This country is also one of those that suffers the most from malnutrition as much as Africa. By having Sats they can exchange them for grains or legumes in the market. That the community in turn learns from the value of Bitcoin and can the markets go through a circular economy.
https://image.nostr.build/ed3805f6c695519ec8327ce6ee9900ec235d714a20a542b5559d9e6c63bc4496.jpg
Is this a feasible idea or just a fantasy?
This type of project could be really valuable. While there are technological and economic challenges, the combination of education and Bitcoin is a growing trend, and Guatemala has the potential to benefit greatly from it. The integration of an accessible platform, which encourages learning and offers a direct reward, can be the key to improving literacy rates in the country.
If you think long-term, this application could not only help reduce illiteracy, but also increase financial inclusion, offering people a way to earn income digitally. This country is one of those with the most migrants to the United States due to lack of work and extreme poverty.
It is clear that there are challenges to bring this idea to reality. Even so, I wouldn't be fantasizing. These types of projects are increasingly common in the digital world, and with the commitment of the technological community, along with the support of organizations that promote education and inclusion, a real difference could be made in the lives of millions of Guatemalans.
In conclusion, Guatemala faces high levels of illiteracy that limit the opportunities for personal and economic development of its population. Could an application that combines learning with economic rewards be an innovative solution to reduce this problem? Although there are challenges, the potential positive impact of this type of initiative is indisputable, and could mark a before and after in the educational and financial history of the country.
I’m not dev but if you know the next step please send me an inbox!
-
-
 @ 872982aa:8fb54cfe
2025-03-25 03:24:31
@ 872982aa:8fb54cfe
2025-03-25 03:24:31采用竹叶制作哨子,是我们最喜欢的事情。它吹起来清脆。
-
 @ 2e8970de:63345c7a
2025-03-25 18:03:08
@ 2e8970de:63345c7a
2025-03-25 18:03:08Data collected by nameberry (baby name website)
originally posted at https://stacker.news/items/924756
-
 @ 872982aa:8fb54cfe
2025-03-25 02:33:31
@ 872982aa:8fb54cfe
2025-03-25 02:33:31我的竹声音
-
 @ 378562cd:a6fc6773
2025-03-25 00:16:58
@ 378562cd:a6fc6773
2025-03-25 00:16:58Bitcoin gives you financial freedom, but if you're not careful, someone’s watching. If you don’t run your own Bitcoin node, you're trusting someone else with your privacy. Here's why that’s a bad idea—and how running your own node fixes it.
What Is a Bitcoin Node? A Bitcoin node is software that connects to the Bitcoin network. It: ✅ Verifies transactions and blocks. ✅ Stores a copy of the blockchain. ✅ Relays transactions to the network. ✅ Lets you use Bitcoin without trusting anyone.
If you don’t run a node, you’re relying on someone else’s—usually a company that tracks your activity.
How Using Someone Else’s Node Destroys Your Privacy 👀 They Can See Your Transactions – Third-party wallets track what you send, receive, and how much Bitcoin you have. 📍 Your IP Address is Exposed – When you send a transaction, your location could be linked to it. ⛔ Censorship is Possible – Some services can block or delay your transactions. 🔗 They Can Link Your Addresses – Many wallets send your balance info to outside servers, connecting all your Bitcoin activity.
How Running Your Own Node Protects You 🔒 No One Knows Your Balances – Your wallet checks the blockchain directly, keeping your finances private. 🕵️ Hides Your IP Address – No one knows where your transactions come from, especially if you use Tor. 🚀 No Transaction Censorship – Your node sends transactions directly, avoiding interference. ✅ You Verify Everything – No fake data or reliance on third-party information.
But Isn’t Running a Node Hard? Not anymore! You can: 💻 Download Bitcoin Core and run it on your computer. 🔌 Use plug-and-play devices like Umbrel or MyNode. 🍓 Set up a cheap Raspberry Pi to run 24/7.
It’s easier than you think—and worth it.
Why This Matters The more people run nodes, the stronger Bitcoin gets. It becomes more decentralized, harder to censor, and more private for everyone.
Final Thought If you value privacy, freedom, and financial independence, running your own Bitcoin node is a no-brainer. Take control. Protect your Bitcoin. Run a node. 🚀
-
 @ d560dbc2:bbd59238
2025-03-25 17:14:30
@ d560dbc2:bbd59238
2025-03-25 17:14:30If you juggle multiple tasks, projects, and responsibilities, you’ve likely heard of the Getting Things Done (GTD) method—a productivity system developed by David Allen to help you organize your tasks and clear your mind for focused work. You might also be exploring Task4Us, a web-based task management platform I founded that leverages the 2-5 Rule to prioritize tasks based on timing rather than rigid scheduling.
At first glance, these two systems might seem to operate differently: GTD focuses on a structured five-step process to manage tasks, while Task4Us emphasizes an anti-planning approach using its 2-5 Rule. However, combining these two can create powerful synergy by blending GTD’s clarity and structure with Task4Us’s intuitive timing-based prioritization. This guide walks you through how to integrate Task4Us with GTD to streamline your workflow, reduce mental clutter, and achieve your goals with less stress.
Understanding the Basics: GTD and Task4Us
What Is the Getting Things Done (GTD) Method?
GTD is a five-step productivity framework designed to externalize your tasks and commitments, freeing your mind for action. The steps are:
-
Capture:
Collect every task, idea, or commitment that grabs your attention into a trusted external system (e.g., notebook or app). -
Clarify:
Process each item to determine if it’s actionable. If it is, define the next step; if not, trash it, file it for reference, or defer it. -
Organize:
Sort actionable tasks into lists (e.g., Next Actions, Projects, Waiting For) and non-actionable items into categories like Someday/Maybe or Reference. -
Reflect:
Regularly review your lists to update priorities and ensure nothing slips through the cracks. -
Engage:
Choose your next action based on context, time, and energy, and then work on it.
GTD’s strength lies in reducing cognitive load by capturing everything so you can stay decisive and focused. However, GTD doesn’t inherently guide you on when to do tasks, leaving timing decisions up to you.
What Is Task4Us and the 2-5 Rule?
Task4Us is a task management platform built on the 2-5 Rule, an approach that emphasizes timing over detailed scheduling. Instead of planning when to do each task, you simply:
- Enter the Task:
Capture it into Task4Us as your “inbox.” - Set a Time Unit:
Choose whether the task is daily, weekly, monthly, or yearly. - Record the Last Act Date or Set a Fixed Due Date:
For recurring tasks, provide the last date you acted on them. For date-specific tasks, use Fix Mode to set the due date.
The 2-5 Rule calculates the task’s priority based on a “sweet spot” of 2 to 5 time units, ensuring you act at the optimal moment—neither too early nor too late.
Why Combine GTD and Task4Us?
By integrating these methods, you can capitalize on the strengths of both:
- GTD’s Clarity:
Use GTD to capture and organize every task and project, ensuring nothing is forgotten. - Task4Us’s Timing:
Leverage the 2-5 Rule to automatically prioritize tasks based on when they should be acted on, reducing the need to micromanage your schedule.
Together, they form a system where you externalize all your commitments (GTD) and then focus on the most important task at the right time (Task4Us), leading to a seamless, stress-free workflow.
Step-by-Step Guide to Combining Task4Us and GTD
Step 1: Capture Everything with GTD, Using Task4Us as Your Inbox
- Action:
Whenever a task or idea arises—like “Call a client,” “Plan a vacation,” or “Renew passport”—add it directly to Task4Us. - Tip:
Don’t worry about details yet; the goal is to clear your mind by capturing everything.
Example tasks: - “Email project updates to the team” - “Schedule a dentist appointment” - “Meet Uncle Lars for coffee”
Step 2: Clarify and Organize Tasks Using GTD Principles in Task4Us
- Clarify:
Process each captured task. Decide if it’s actionable. - If not actionable:
Trash it, file it for reference, or mark it as a “Someday/Maybe” task in Task4Us. - If actionable:
Determine the next step. - Organize:
In Task4Us, assign each actionable task: - Time Unit:
Choose days, weeks, months, or years (e.g., “Email project updates” as a weekly task). - Fix Mode:
For date-specific tasks (e.g., “Wish Alex a happy birthday”), set the exact due date. - Categories:
Group tasks (e.g., Work, Personal, Health) to align with GTD’s organization system. - Projects:
For multi-step projects, create a dedicated category and break the project into smaller, actionable tasks.
Step 3: Reflect Weekly to Update Your Task4Us Lists
- Review Your Tasks:
Set aside time each week to review your Task4Us lists. - Check your Top Task and Focus Mode (top 3 tasks) to ensure they reflect your current priorities.
- Update as Needed:
Adjust time units, update last act dates, or move tasks between active, someday/maybe, and archived lists. - Projects Review:
Ensure each multi-step project has at least one actionable task with a clear time unit.
Step 4: Engage with Task4Us’s Top Task and Focus Mode
- Engage:
Task4Us automatically surfaces your Top Task based on the 2-5 Rule. - For instance, if “Meet Uncle Lars” is nearing its action window, it will appear as the top task.
- Focus Mode:
Use this mode to display your top 3 tasks for a distraction-free workflow.
This aligns with GTD’s principle of choosing the right next action, making it easier to act decisively.
Step 5: Enhance GTD with Task4Us’s Unique Features
- Fix Mode for Deadlines:
Use Fix Mode for tasks with fixed dates (e.g., passport renewal) to ensure they gain priority as the due date approaches. - Export Tasks:
Download your task list as a CSV file to review your productivity over time. - Customize:
Adjust categories, time units, and Focus Mode settings to best suit your workflow.
A Real-Life Example: Combining GTD and Task4Us
Imagine managing work tasks, personal goals, and social connections:
-
Capture:
Throughout the day, add tasks like “Finish project report,” “Call Mom,” “Book dentist appointment,” and “Brainstorm new blog post” to Task4Us. -
Clarify and Organize:
- “Finish project report” is actionable—set as a weekly task in the Work category.
- “Call Mom” is actionable—set as a monthly task in the Personal category (last called 3 weeks ago).
- “Book dentist appointment” has a deadline (e.g., April 10, 2025)—use Fix Mode.
-
“Brainstorm new blog post” is not urgent—categorize it as Someday/Maybe.
-
Reflect:
During a weekly review, notice “Call Mom” is nearing the 5-week mark and becomes your top task. Update “Finish project report” after completion. -
Engage:
Task4Us displays “Call Mom” as the top task. You call, mark it done, and Task4Us updates the last act date. -
Enhance:
Use Focus Mode to tackle your top 3 tasks without distraction and export your tasks for review.
Why This Combination Works
-
GTD’s Lack of Timing Guidance:
Task4Us’s 2-5 Rule fills the gap by ensuring you act at the optimal moment. -
Task4Us’s Simplicity:
GTD adds structure to Task4Us, helping you manage complex projects and capture non-actionable items. -
Reduced Cognitive Load:
Both systems externalize tasks, reducing mental clutter and ensuring you’re focused on the right task at the right time.
Try It Out and Share Your Experience
Task4Us is currently in beta—now’s the perfect time to integrate it with GTD and transform your productivity. Start by capturing your tasks in Task4Us, apply GTD’s steps to clarify and organize them, and let the 2-5 Rule guide your actions.
Sign up for Task4Us at todo.task4.us and experience the power of combining GTD with the 2-5 Rule.
How do you manage your tasks? Do you use GTD, Task4Us, or a mix of methods? Share your thoughts in the comments—I’d love to hear your experience! 🚀
#Productivity #TaskManagement #GTD #Task4Us
-
-
 @ 3c389c8f:7a2eff7f
2025-03-25 17:12:33
@ 3c389c8f:7a2eff7f
2025-03-25 17:12:33Understanding Relays
Relays are a very simple concept, but an incredibly powerful part of Nostr. They are simple servers, of sorts, with a specific set of tasks- to fetch, hold, and send notes. Relays don't communicate with each other, only with clients. The client sends a request for any relevant notes and the relays oblige. What types of notes (aka events) that each relay will hold or fetch will vary because of different relays will operate under different sets of rules. Some will accept most any type of event from anyone. Others can be very strict, requiring things like payment, proof-of-work, specific event kinds, or only allow a whitelist of users to reduce spam and other unwanted content. When you create an event, or publish a note, it is sent to your "write" or "outbox" relays. Anyone who follows your npub or sends "fetch" /"read" requests, to those relays will receive your notes. When someone replies, likes, or otherwise engages with your note, that note will then duplicate to any "write" or "outbox" relays that the other person is connecting to as their outbox relays. This does two important things:
It creates a new event through through the action of engaging your note. This is a signed record of activity from that user's npub. This is also the event that is sent back to your "read" or "inbox" relays so that you may be notified that someone is interacting with you.
By creating a copy, this helps ensure your note will be able to be spread across more of the ecosystem, expanding your reach and introducing redundancy, in case a relay should go down or disappear completely. This does not imply that your data will be safely stored forever. In fact, its the exact opposite. The protocol assumes that any relay, or many, could disappear at any time. A relay can shut down, kick you out, experience intentional or unintentional data loss, or many other things. It is likely that a copy of your notes will still exist on many relays, but if you are concerned with the longevity of your content, consider running your own. Paid services for long term note storage exists as well, but they do require trusting the provider.
In this light, the importance of relays starts to become obvious. The various rules open up a whole plethora of use cases that make relays interesting, unique, and useful for the user. They are the backbone of the protocol. They are also tools for finding and managing great social connections and great content.
Types of Relays
This section can, in no way, be considered comprehensive. It is nearly impossible to know all of the relay implementations that may exist or all the rules that they may have set for themselves. Here, we will address some common types that will be useful in making the most of Nostr and a few types with specialized tasks.
Public Relays - Most Nostr clients will start new users with a predetermined set of relays that are free and publicly available for fetching and serving. This lowers the entry barrier for getting connected to the network, ensuring that everyone has access. It does come with some tradeoffs. Public relays tend to accept almost any type of content, so they are prone becoming the hosts of spam, bots, and shady content. To curate your space, it is recommended to get connected with some relays that help you clean things up.
Web-of-Trust Relays - These relays use your social graph and the graphs of others to build a network of higher trust for its users. This reduces spam and other yucky stuff from making it into your feeds. For write access, you must be followed by someone else within the network. If you are coming to Nostr with no external social connection, these may not be useful at first, though most do allow for public reading so you may find them useful to discover people and content you find interesting. Once you have established some social connections, they are great for creating a feed that casts a wider net through the whole network.
Paid Read/Write Filter Relays - These relays will charge an admission fee for write access. This helps to reduce spam and bots. Not all paying npubs want to see or interact with all who are willing to pay the fee, so a paid write relay often works best when paired with a paid filter relay for reading. These will operate under many sets of filtering rules, so be sure to read through any available material from the provider. They should explain what they filter and why, so that you may choose filters that match your tastes.
Inbox Relays - These relays are tasked with collecting any events that are intended FOR you. This includes likes, replies, receipts, and mentions, among many other things. If socializing with your friends and colleagues is important to you, you will want to find inbox relays that manage this task well. DM inbox relays are a separate but similar concept, as direct messages are encrypted and wrapped. They are a specialized relay meant for handling encrypted events. Many DM inbox relays charge a subscription fee, some do not. This is also a great use case for private relays.
Private Relays - These relays can be arranged to handle nearly anything you would like. You can whitelist a group of people that can write, restrict read access through AUTH, and set other various rules. They are a great option for any encrypted data, such as DMs, lists, and drafts. They also make a great backup for your own notes to help ensure that they remain available and locatable. Running your own is the optimal option here, but there are paid services, that I think of as relay rental. They are hosted on big servers, and managed by a small company. All details of the relay rules are at the renter's discretion. This is a good option if you do not have the hardware or confidence to set up your own private relay yet.
Search Relays - Search relays can help you find specific users & notes across the wider network. Some specialize in searching for people, others for text, tags, and other criteria. A strong search relay can make navigating through Nostr a breeze. As with other things, some may require a small fee to use them and others are free to use. Try out some free ones before buying to see if you are happy with your experience.
"Read" Relays - This is sort of a catchall term for anywhere that your client connects to for fetching notes and other events. In the best scenerio, you should not have to worry about these, as relays will signal for your client to find the notes you are fetching. The Nostr protocol and its mechanisms are adapting to what works, so being informed of "read" relays is essential for now. These are the places that you may need to tell your client to connect to when fetching notes from the people you follow. Specialized Relays - Specialized relays will vary in function and rules. Some are for curating quality feeds while others host full-fledge communities around a topic or common interest. Clients designed to interact with these more specialized use cases will often have relay information available or a method for you to browse their feeds.
This is just a snapshot of the different types of relays that exists now. Many are in development and testing for algorithmic content distribution, paywalled content, encrypted group messaging, limited read access, media hosting, and more. (This section may be updated as certain types gain or lose traction throughout the ecosystem.)
Managing Relays
By now, this probably feels like a ton of information and it is, but its also part of what gives you the ability to create and maintain a quality experience with Nostr. A truly decentralized system puts power into the user's hands rather than a corporation. If you want to be in control of your space (spatium tuum), relays are the first and foremost way to do that. They don't have to be viewed as boring servers. They are anything but that. They are tools that can enhance your online networking, serve you educational or entertaining content, or provide you with a safe place to store your personal thoughts. What you use them for is up to YOU.
Spend some time trying free ones, exploring relay feeds, or plugging into some paid services until you find a setup that creates a quality online space for you. If you're worried that you might "break" your connection, don't be. Make a note of a couple that you are connecting to when getting started, as a backup, but I feel confident to say that you won't ever look at it again.
Finding Relays
Finding relays can be a bit of a chore, but that is getting easier as time goes by. For now you there a few options you can try.
-
Visit a relay explorer like nostr.watch or nostr.info
-
Use a client that shows you which relays are hosting a note or a person's relay list. There are some examples in our client guide like Amethyst, Coracle, Jumble, and Nostrudel.
-
Just ask. Most people are on a social network to be social. Currently, Nostr is brimming with social people who are passionate about freedom, decentralized communication, and Nostr in particular. They are happy to help.
Running Your Own
Relay.tools is a hosted personal relay service for ease and a user friendly experience. Search Zapstore for Citrine to run a native relay on your Android device.
Below are some suggestions for relays to run on your own hardware. Search "nostr relay" on GitHub for more.
https://utxo.one/#nostr-projects
https://khatru.nostr.technology/
https://github.com/mikedilger/chorus
nostr:naddr1qvzqqqr4gupzq9h35qgq6n8ll0xyyv8gurjzjrx9sjwp4hry6ejnlks8cqcmzp6tqyghwumn8ghj7mn0wd68ytnhd9hx2tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qqdxymngv35xq6rxdf5xqer2s0rg3q
-
-
 @ 6e0ea5d6:0327f353
2025-03-24 22:42:59
@ 6e0ea5d6:0327f353
2025-03-24 22:42:59🎣
The support I never had could have saved me time, and I would certainly be farther along at this moment. However, that absence taught me to value having, and if I pass this lesson on to you earlier, it is so you have more time to learn what I could not see.
I like what my father once paraphrased: "If I have seen further, it is by standing on the shoulders of giants." And right now, I think of all that the little one who descends from you will one day behold. The heaviest burdens I pushed were so that you could soar, and if I have dedicated my existence to you, it is so that from my ashes, you may always rise again.
Out of love, I will try not to spoil you with excessive gifts, but instead, without being absent, I hope to build you up. With this line and these strands, I wish to teach you to catch your own fish. Live by what I have taught you and seek to understand what I could not. Honor who I was for you by becoming the best you can be.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 3c389c8f:7a2eff7f
2025-03-25 16:38:21
@ 3c389c8f:7a2eff7f
2025-03-25 16:38:21Public Key vs Private Key
When you generate a Nostr identity, you generate a cryptographic keypair. One is your public key (npub...). It is used to find you and your notes. The other is your private key (nsec...), which you use to interact. Everything you do is an event, which is signed by your private key. This makes all of your actions provably yours. You are solely responsible for protecting your nsec. It is recommended to try Nostr with a test keypair before setting up anything that you want to treat seriously.
Key Creation and Protection
Most Nostr clients will have the option to generate a keypair onsite or in-app. This is convenient for trying Nostr or a client. To make a keypair for longterm use, you might want to visit a site that provides some key security from the start. Your keys are a permanent set of identifiers. They cannot be changed or reset. You own them and it is your responsibility to keep your private key safe.
When you are ready to set up a permanent identity, start in a place that specializes in Nostr key generation. Nstart and Hubstr are great places to start. NOA, Nostr Onboarding App, is multiplatform with a native app, which helps make it easier to share with friends. You can create a vanity npub through various methods as well, like https://www.nostr.rest/ . There are other methods but these are some of the most user friendly ones that I have found. They provide some tools and guidance for creating your keypair in a safe manner. Once you've gone through the process, it is a good idea to write down your nsec and store it off of any devices, in the event you should lose access to your computer or phone.
Using a signer or a browser extension to house your nsec (private key), is the next step to keeping your identity safe. (Find out more on key management below)
Portability of Your Keys
This is where all the magic happens. You can use your keys to sign into any Nostr app. If you sign in with your npub (public key), you will enter in a read-only mode. This is nice for seeing a client's interface before trying it. You can sign in with anyone's npub to see what their social feeds look like, too. You do not need to be concerned with security when using npub sign-in. Your public key, is fully public. Not all Nostr clients support this option, but many do.
Signing in with your nsec unlocks all the features of a client and enables you to interact on the protocol. Everything you do is signed by your nsec and made available by your npub. Using some sort of signer is obviously advised, to keep from exposing your nsec online.
Since all of your actions (aka events) are stored on relays and not by clients, all of your content, messages, or anything else becomes available in any client that supports those event types. Most social stuff, like replies and profile views are available almost everywhere. Not all apps will support everything, but the ones that share a common theme will handle your events in similar manners. (I.e., a marketplace listing made from one app will display across many apps. The comments and replies will, too, so there is no need to manage multiple listings to answer questions or mark something as sold.)
Key Management
This is an evolving field, with many methods of key management being explored. People, businesses, and institutions all have different needs.
Signing Extensions keep your key in a browser extension, signaling to an app that the valid nsec is present. This sign in method is available on most Nostr apps. These are the most convenient method of key management but they do have their limitations. Using an extension can be cumbersome on mobile devices, and they could still be subject to vulnerabilities within your browser or the signer itself. They also don't allow for multiple users to sign events, like a business or organization might need. Key Bunkers enable the storage of key shards encrypted across multiple locations or in one spot. Bunker signing calls the encrypted key shards to decrypt for signing events. A bunker key, often called a bunker string, can be shared with staff or used to keep your key offline. They are revocable and replaceable. The process is currently a a little complicated and client support is somewhat limited. Adoption and improvement of this method is happening quickly, as the need for multi-party access to a profile increases. Native Signing Apps, like Amber for Android, make key key storage and signing for mobile a simple process. These apps work to keep your key offline, similarly to a bunker, but it is all stored encrypted on your device. Most Nostr-Android apps and web clients offer support for this method. Development of a similar iOS app is underway. Offline Hardware Signers like standalone devices and NFC cards are being explored, tested, by many groups.
This is a very active development space and this section will be updated as needed. Below are some suggestions for Nostr signers:
https://nsec.app/ https://chromewebstore.google.com/detail/nos2x/kpgefcfmnafjgpblomihpgmejjdanjjp https://www.getflamingo.org/
-
 @ 21e127ec:b43a5414
2025-03-24 22:30:47
@ 21e127ec:b43a5414
2025-03-24 22:30:47**
Respondiendo a Joel Serrano
nostr:npub1sg0j78carjndmg7qjfstk2y0e23r5cvxwn3u9z5cgnk5jnh4vxqs355u3l
respecto a hilo de Twitter sobre la adopción de Bitcoin como Medio de Intercambio con Unidad de Cuenta Delegada.
Primero, quiero compartir un artículo de Fernando Nieto que aborda la volatilidad inherente de Bitcoin:
https://x.com/fnietom/status/1454114755807961094
Este artículo de Nieto me ha llevado a cuestionarme si, en un escenario de adopción masiva, Bitcoin podría alcanzar realmente una estabilidad relativa suficiente para facilitar la coordinación de precios y el cálculo económico. De ahí surge la idea de que Bitcoin podría necesitar otros instrumentos que perfeccionen su función como unidad de cuenta.
Un ejemplo claro es lo que ocurrió en Venezuela con la dolarización de facto (al margen del Estado). En sus inicios (y aún hoy en gran medida), solo un pequeño porcentaje de la población tenía acceso a dólares a través la banca internacional, lo que les permitía realizar transacciones financieras fuera del sistema estatal. Estas operaciones se llevaban a cabo en el circuito financiero internacional, aunque las relaciones comerciales reales ocurrían dentro de Venezuela. Otro pequeño grupo tenía acceso a dólares en efectivo para sus transacciones económicas, pero la gran mayoría de la población solo disponía del bolívar venezolano como medio de intercambio en una economía dolarizada. En este contexto, muchos usaban el dólar para calcular los precios de bienes y servicios, mientras que el bolívar seguía siendo el medio de intercambio principal.
La diferencia notable con Bitcoin radica en las causas. En Venezuela, este fenómeno de medio de intercambio con unidad de cuenta delegada (Dolar - Bolivar) se debía a las restricciones monetarias impuestas por el gobierno respecto al dólar, la falta de servicios financieros en esa moneda y la escasa liquidez de dólares físicos. En el caso de Bitcoin, seria debido a su volatilidad inherente producto de su oferta inelástica (Bitcoin como medio de intercambio generalmente aceptado con unidad de cuenta delegada en Fiat publico ó privado - stablecoin).
Sin embargo, esto no implica que la unidad de cuenta que complemente a Bitcoin deba ser necesariamente emitida por un Estado. Creo que la verdadera innovación de Bitcoin radica en su potencial para actuar como un patrón monetario que descentralice la emisión monetaria de los estados gracias al monopolio de la violencia, algo que sí podían ejercer con el oro. Con Bitcoin, el Estado pierde el control, permitiendo que la banca libre emita monedas estables respaldadas en un patrón Bitcoin. El escenario sería una competencia entre monedas estables adoptadas en un segundo plano para facilitar el cálculo económico necesario para coordinar precios, préstamos, servicios financieros y la institución del crédito. Y Bitcoin podría funcionar en primer plano principalmente como medio de intercambio.
No pienso que Bitcoin vaya a eliminar las monedas fiat o estables, ya sean públicas o privadas. Más bien, lo veo como un mecanismo disciplinador que podría prevenir los malos comportamientos monetarios.
Gracias por tu tiempo agradecido y atento a tu posible respuesta.
-
 @ 3c389c8f:7a2eff7f
2025-03-25 16:16:29
@ 3c389c8f:7a2eff7f
2025-03-25 16:16:29Android
Amethyst - Experience the all-in-one Nostr client for mobile. Amethyst supports custom emoji reactions, marketplace listings, live streams, and so much more. If you're fresh to exploring Nostr, Amethyst may seem like a wild adventure compared to the any other social media of the past. Packed with features and blazing fast, this client gives you the ability to see just what Nostr is all about.
Voyage - This client is light on storage and data consumption, which is great for anyone with cheaper phones, limited data plans, or traveling/living in areas with lower data signal. Not only that, Voyage also offers some list and relay management tools not available in many other apps, so its great for handling some of the technical aspects of Nostr on the fly.
Web
Satellite - Fast and reliable, this client has topic communities, rich feeds, and beautiful profile displays. They offer paid media hosting for pictures, videos and more, which is essential for sharing visual content on Nostr. Satellite has long been a favorite for its simplified approach to displaying notes in a dense, clean manner and its consistency, reliability, and speed.
Jumble - Explore Nostr relay feeds, follow feeds, and more. Jumble has a clean, no-fluff interface that's easy to use and understand. You can socialize on specialized relays, or browse and chat on public relays with friends.
Coracle - Coracle allows you to easily browse relay feeds, your follow feed, and create custom feeds. You can generate Proof-of Work notes, set 'send' delays, and limit the number of relays the client talks to, to increase speed and reduce data consumption. You can generate PoW anonymous replies, too. A favorite feature is the option to import and export all of your data to/from your local device, so you can easily maintain a copy or send any lost events back to the Nostr network.
Nostrudel - The neat thing about Nostrudel is trying to find a Nostr action that it can't do. It's got all the bells and whistles. Nostudel may be a bit overwhelming if you're not familiar with all that is possible on Nostr, but once you have an idea, take this for a spin and see what new ways of interacting on the protocol that you discover.
iOS/Apple
Sorry... this is going to be a little scant for a while. Simply not one of the Apple people, these are the ones my iOS/Nostr friends seem to love:
Damus is a longtime favorite among users, adhering to a protocol-first approach to development.
Nostur sounds like a fun app, maybe on par with Amethyst as far as fun features and fast performance.
You'll have to do your own exploring to see what they are really all about.
Multi-platform
Primal - Simple, clean, and with an integrated Bitcoin/Lightning wallet for fast, easy zaps (basically tips, but on Nostr!). Get started with Nostr right away with no hassle and send or receive Bitcoin among your social network. Primal is great for anyone new to Nostr or who wants to enjoy a more traditional social media experience with the benefits that Nostr has to offer. Primal is available for Android, iOS, and on the web.
Yakihonne - Yakihonne is a beautiful multi-platform client that is available across any device. With a focus on long-form writing, it makes it easy to read and create Nostr articles, blogs, and any other informative piece. It doesn't stop there, though. You can scroll your social feed, set up smart widgets, and browse curated content collections, too.
Desktop
Notedeck - Built by the Damus team, Notedeck brings the speed and redundancy of Nostr to your machine. The local software is easy to install, set up, and use. Add multiple columns to the interface for a full screen of different feeds, profiles, and notifications.
Gossip - Gossip has a wide array of technical knobs and dials for relay controls, note fetching and publishing, and a clean interface that even I can understand. Gossip is built for the more technically-inclined among us, but is also great for the general Nostr "power user". This client is still a step above my paygrade but I'm loving it, regardless of that. If you are like me, this is a great client for a learn-through-doing method of understanding Nostr.
For Groups, Communities, and Chat
Oxchat - Oxchat puts security at the forefront of its interface with encrypted private and group chats. It does a whole lot more than that, too. You can browse your social feed, make voice and video calls, and display badges.
Flotilla and ChaChi are a couple of up and coming group/community/chat clients that are still very much under development, but look to be worth expounding upon in the future. Nostr's interoperability allows you to create and engage in groups you have joined through any of the above clients.
Specialty Clients
Zap.cooking - Publish recipes, earn zaps, find recipes, send zaps. Its a pretty brilliant system. There is no more need for 20 minute stories or overwhelming popup ads. Nostr adds a social layer to recipe sharing that doesn't require a new account to participate. Just sign in with your signing extension of choice, and you can share and leave feedback instantly.
Highlighter - Its still a bit of a construction site, but Highlighter is on its way to becoming Nostr's premiere content creator studio. Write, highlight, and curate. Not only can you create these, you can also browse and discover great Nostr content. There's lots in the works for video and other types of content, too.
Shipyard - "A Quiet Space for Loud Ideas" says it all. Shipyard is focused solely on your writing experience so that you may focus soley on your writing. This client is clean, reliable, and extemely user friendly. It is also one of few Nostr clients that provide you with the ability schedule the publishing of your notes.
Emojito.meme - Create and find custom emoji packs to use on Nostr! How fun is that? Just bookmark & those emojis ready to be used in any supporting social client.
Badges.page - Create and claim badges that display on Nostr profiles in supporting clients. This is a great way to engage with fans, celebrate moments with friends, or even just to be silly. You can set the difficulty of creating a badge with Proof-of-Work to create rare and super rare badges for top supporters, which is pretty cool.
Olas - A beautiful, visual showcase for photography and more. Its sort of like Instagram, but on Nostr, so its better. You can share, scroll, post, and monetize your content in a breeze.
Zapstore - Its an app store! On Nostr! Built for Android! Just follow the instructions on the site to begin your journey of stepping out of the nightmare that is the Playstore. Find apps recommended by your social graph, built by developers trusted within your networks, and donate to app development directly. You'll find more than just Nostr apps here. Zapstore is devoted to bringing free open source software from builder to user with as little interference as possible.
Listr - Create and manage lists for use in any other supporting client. This was the first thing that wow'd me about Nostr when I discovered it a couple years ago. There's something about making a list of people with common interests in one client, and seeing that list in action in another that just blew me away. Different feeds for different purposes, all chronological and all curated by YOU.
Habla - Long-form writing on Nostr made simple. You can quickly and easily get started with a blog or news publication and distribute it to your entire Nostr audience, regardless of which apps they use. Most social clients support article display within various feeds. You can always quote-note your article in a regular note, if you want to boost article exposure, too.
-
 @ 3c389c8f:7a2eff7f
2025-03-25 15:51:44
@ 3c389c8f:7a2eff7f
2025-03-25 15:51:44*Create your keys and set up your profile:
https://start.njump.me/
*Pick a NIP07 browser extension or offline signer to safely store your private key (nsec):
https://nostr.net/
*Pick an app, sign in, and start exploring:
https://nostrapps.com/
That's All! :)
-
 @ a012dc82:6458a70d
2025-03-25 13:57:54
@ a012dc82:6458a70d
2025-03-25 13:57:54Bitcoin, the pioneering cryptocurrency, has once again defied skeptics by surging to a new all-time high. This remarkable resurgence is a testament to the resilience and enduring appeal of Bitcoin, even as it navigates through periods of intense volatility and regulatory scrutiny. Emerging from the shadows of the digital world, Bitcoin has sparked a financial revolution that challenges the very fabric of traditional banking and monetary systems. Its journey from an obscure digital token to a globally recognized financial asset encapsulates a saga of innovation, speculation, and the relentless pursuit of financial autonomy. This article explores the journey of Bitcoin from its inception to its current status as a leading digital asset, highlighting the challenges it has overcome and the factors contributing to its recent record-breaking performance.
Table of Contents
-
The Genesis of Bitcoin
-
Overcoming Adversity
-
The Path to Mainstream Acceptance
-
Breaking New Ground with ETFs
-
Navigating the Crypto Ecosystem
-
Looking Ahead: Challenges and Opportunities
-
Conclusion
-
FAQs
The Genesis of Bitcoin
Bitcoin was introduced to the world in 2008 by an individual or group using the pseudonym Satoshi Nakamoto. Conceived as a decentralized digital currency, Bitcoin offered a novel solution to the double-spend problem without the need for a central authority. This innovation was set against the backdrop of the global financial crisis, positioning Bitcoin as an alternative to traditional banking systems and fiat currencies. The early years of Bitcoin were marked by a passionate but small community of users, and the cryptocurrency was primarily used for niche online transactions. The concept of a decentralized currency was revolutionary, promising a new era of financial freedom and privacy. However, Bitcoin's early days were fraught with challenges, including limited public understanding, technical hurdles, and skepticism from the financial establishment. Despite these obstacles, the foundational principles of Bitcoin—transparency, security, and decentralization—captivated a growing number of enthusiasts who saw its potential to redefine money.
Overcoming Adversity
Bitcoin's journey has been anything but smooth. The cryptocurrency has faced numerous challenges, including regulatory hurdles, security breaches, and intense market volatility. High-profile incidents, such as the collapse of the Mt. Gox exchange in 2014 and the contentious debates over scalability, tested the resilience of the Bitcoin network and its community. Despite these setbacks, Bitcoin continued to gain traction, attracting a diverse group of users and investors drawn to its potential for high returns and its underlying blockchain technology. The path was littered with obstacles, from hard forks and regulatory crackdowns to sensational media coverage and public skepticism. Yet, each challenge served to strengthen the community and refine the technology, forging a cryptocurrency that was increasingly robust, adaptable, and resilient. The adversities faced by Bitcoin acted as a crucible, purifying and validating the concept of decentralized finance in the eyes of a global audience.
The Path to Mainstream Acceptance
The turning point for Bitcoin came with the gradual recognition of its value as both a digital asset and a technological innovation. Institutional investors began to take notice, and the cryptocurrency started to shed its reputation as a tool for illicit transactions. The introduction of futures contracts and the increasing interest from traditional financial firms signaled a shift towards mainstream acceptance. However, the journey was not without its skeptics, who pointed to Bitcoin's energy consumption and its volatile price swings as reasons for caution. The road to mainstream acceptance was paved with educational efforts, technological advancements, and a growing recognition of Bitcoin's unique attributes, such as its fixed supply and borderless nature. As awareness and understanding of Bitcoin increased, so too did its legitimacy and value, leading to a gradual but undeniable integration into the broader financial landscape.
Breaking New Ground with ETFs
The recent surge in Bitcoin's price can be largely attributed to the approval of exchange-traded funds (ETFs) pegged to the digital asset by U.S. regulators. This milestone was achieved after years of advocacy from the crypto community and a legal battle that challenged the Securities and Exchange Commission's initial rejections. The launch of the first "spot" Bitcoin ETFs has opened the doors for more traditional investors to enter the market, providing a regulated and familiar avenue for Bitcoin exposure. This development has not only boosted Bitcoin's price but also reinforced its legitimacy as an investment asset. The introduction of Bitcoin ETFs represents a significant breakthrough in the cryptocurrency's journey, bridging the gap between the innovative, often misunderstood world of digital currencies and the established, regulated realm of traditional finance. This convergence has facilitated a new wave of investment, bringing with it increased liquidity, visibility, and acceptance for Bitcoin and the broader cryptocurrency market.
Navigating the Crypto Ecosystem
Bitcoin's influence extends beyond its own price performance, serving as a bellwether for the broader cryptocurrency market. The ecosystem has grown exponentially, with thousands of altcoins and a burgeoning decentralized finance (DeFi) sector. However, the industry has not been immune to challenges, facing regulatory scrutiny, market manipulation, and high-profile scandals. Despite these obstacles, Bitcoin has maintained its dominance, buoyed by a loyal community and its perceived value as a hedge against inflation and currency devaluation. The cryptocurrency ecosystem is a dynamic and evolving landscape, marked by rapid innovation and intense competition. Yet, through all the tumult and transformation, Bitcoin remains the cornerstone, setting the standard for security, adoption, and market value. Its journey mirrors the maturation of the entire crypto space, from a fringe idea to a major financial force, influencing everything from individual investment strategies to global economic policies.
Looking Ahead: Challenges and Opportunities
As Bitcoin reaches new heights, questions remain about its sustainability and the potential impact of regulatory changes. The upcoming "halving" event, which reduces the reward for mining new blocks, is expected to have significant implications for Bitcoin's supply and, consequently, its price. Additionally, the cryptocurrency must navigate the delicate balance between innovation and regulation, as authorities worldwide grapple with how to oversee this evolving asset class. The future of Bitcoin is inextricably linked to the broader narrative of digital transformation and financial innovation. As it continues to evolve, Bitcoin will face new challenges and opportunities, from technological advancements and competitive pressures to shifting regulatory landscapes and economic trends. Yet, if history is any guide, Bitcoin will adapt and thrive, continuing its unstoppable journey from adversity to record highs.
Conclusion
From its humble beginnings to its current status as a financial phenomenon, Bitcoin's journey is a compelling narrative of innovation, resilience, and the relentless pursuit of decentralization. While the road ahead is fraught with uncertainty, Bitcoin's ability to rebound from adversity and reach new record highs is a testament to its enduring appeal and the transformative potential of cryptocurrencies. As the world continues to embrace digital currencies, Bitcoin's story remains a powerful reminder of the possibilities and challenges that lie ahead in the uncharted waters of the digital age. The saga of Bitcoin is far from over; it is a continuing tale of disruption, adaptation, and, ultimately, triumph in the face of adversity.
FAQs
Why has Bitcoin reached new record highs? Bitcoin's recent surge to new record highs can be attributed to factors such as the approval of Bitcoin ETFs, growing institutional acceptance, its appeal as a hedge against inflation, and increasing mainstream interest.
What are Bitcoin ETFs, and why are they important? Bitcoin ETFs (Exchange-Traded Funds) are investment funds that track the price of Bitcoin and are traded on traditional stock exchanges. They provide investors with a way to gain exposure to Bitcoin without having to buy or store the cryptocurrency directly, which has contributed to increased Bitcoin adoption.
What challenges has Bitcoin faced? Bitcoin has faced numerous challenges, including regulatory hurdles, security breaches, market volatility, and skepticism from the financial community. Despite these challenges, Bitcoin has continued to grow and gain acceptance.
What is the "halving" event in Bitcoin? The "halving" is an event that occurs approximately every four years, where the reward for mining new Bitcoin blocks is halved. This reduces the rate at which new bitcoins are generated, theoretically increasing scarcity and potentially driving up the price.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co/
Youtube: @thebitcoinlibertarian
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
Get Orange Pill App And Connect With Bitcoiners In Your Area. Stack Friends Who Stack Sats link: https://signup.theorangepillapp.com/opa/croxroad
Buy Bitcoin Books At Konsensus Network Store. 10% Discount With Code “21croxroad” link: https://bitcoinbook.shop?ref=21croxroad
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 7da115b6:7d3e46ae
2025-03-25 11:00:01
@ 7da115b6:7d3e46ae
2025-03-25 11:00:01What Happened?
Sadly, some news came to us in the last couple of days, news that has exploded our plans like a bombshell. As you know from previous posts, my family and I had found the property of our dreams, within the price range that suited us. The only issue was that we had to sell our rental property to be able to purchase the land we wanted to develop for our homestead. At the time, it wasn't an issue.
With a few phone calls and some discussion with the local Council; the Realtor; the Vendors, and the bank, we were on our way. We made an offer, and it was accepted, contingent on our rental property selling. Our offer expires this Friday, and the likelihood of it selling before then, is slim. That leaves us 3 days to come up with the $130,000 we need to secure the property.
"So why not just extend the offer?" I hear you say. Well, that's a fair point - We did. The extension runs out this Friday. Can we extend on the extension? Legally, yes. but here's the rub:
A counter offer has been put forward.
This basically means, that without having the money available by the end of the offer extension, the Vendor is going to take the counter offer.
That's Not So Bad... Right?
Yes, and no.
Unfortunately, we've spend thousands of dollars on reports; valuations; building research and site inspections. This means all of the plans, money and time that we've invested so far is going to be lost. Yes yes, you're right of course, it's our own fault for getting so financially and emotionally invested in the first place. Lesson learned.
I think that the hardest part of it all, was breaking it to my wife. She had already started designing her gardens, and had dreams of watching our homestead grow. The look of utter defeat on her face was gut wrenching. I felt as though I had failed her, and torn away the dream we had built together. She and I had lost our dream in the course of a single phone call. It hit both of us hard.
It's been 24 hours now, and the pain is real. I don't want to eat or go to work, I don't want to talk to anyone. I just want to lay down on my wife's lap and close my eyes until it's over. Deep down inside, I know it's a childish reaction, but that doesn't make it any less of a slap across the face.
The Light at the End of the Tunnel
Cliche, I know, but there may be a little glimmer of light on the horizon. If we do sell our rental property, we will have money to play with. This means we can buy a crappy little Ute and caravan, and go exploring our country. Perhaps stop at a few places that look nice, and see if they're places we could settle. If we spend a few months just looking around, and find somewhere homely, then we can stay for a while at a local caravan park, and look for a property that may be suitable.
At the very least, it would mean that we can escape our shit jobs, which has been the biggest goal from the beginning.
Fingers crossed...
-
 @ 7da115b6:7d3e46ae
2025-03-25 10:55:04
@ 7da115b6:7d3e46ae
2025-03-25 10:55:04Originally written and posted on the 12th of December, 2024
Emotionally, it's been challenging to say the least, and the heat just exacerbates the frustration. But don't let that fool you; we've made significant progress. We found our dream property over two months ago for $130,000. 3 hectares of land, but 2 hectares of it is unusable. This was perfectly okay with us as it's going to be a massive effort for one person anyway.
Two months ago, we put in an offer and they accepted it. However, we are not well off by any means; most weeks, we just scrape by. We have two properties - a property in the Far North that we've been renting out to pay the mortgage ($70,000 remaining), and the one we live in which has almost the entire mortgage outstanding.
So how can we afford another property? Well it's no simple feat! First, we need to sell our Rental Property for around $400,000 (a reasonable market rate). Once that sells, about $170,000 in equity gets transferred to the mortgage of the property we're currently living in. After paying off the last of the mortgage on the rental property and shifting the equity to our current property, that will leave us with almost nothing after legal fees and real estate agent fees.
This amount remaining barely covers the cost of the property we put an offer on - our dream property. It's a humbling experience realizing just how far we still have to go in this journey towards self-sufficiency.
It's a sober reminder that we can't rush it, but should rather embrace each step along the way. For better or for worse, we must adapt and learn from every situation as it comes our way. After all, we can only control what's within our reach; the rest is just a matter of time and patience.
Perhaps it's not about achieving self-sufficiency, but truly embracing the journey itself. The path towards that dream property we've been longing for may take longer than expected, but as long as we have each other and keep pushing forward, I can't think of anything more rewarding than seeing our vision unfold step by step.
I have to remember to cherish the memories and experiences along this road, because it's those moments that will truly make the journey worthwhile.
-
 @ 7da115b6:7d3e46ae
2025-03-25 10:52:00
@ 7da115b6:7d3e46ae
2025-03-25 10:52:00Originally written and posted on the 10th of March, 2025
Safety
The first reason that comes to mind is safety. Violent crime has become a recurring theme in our town, with statistics showing a rise in cases such as burglaries and general homicides. These changes have made us acutely aware of the importance of providing a secure environment for our family. As our children grow, we yearn for them to experience not just safety, but also a sense of stability that comes with it.
The thought of crime often makes me reflect on moments like the domestic violence and murder within throwing distance of our current home, or the attempted mugging and homicide at a nearby petrol station. These incidents have sparked a desire for a place where our family can feel more secure and enjoy the peace of mind that comes with knowing they're safe. I hope that growing up in a safe environment will instill confidence and security in my kids as they navigate life. This pursuit of safety is not just about protecting my loved ones; it’s about creating a foundation where they can thrive and feel secure in their surroundings, allowing them to focus on their growth and aspirations without the constant awareness of potential danger.
Cost of Living
The cost of living has been another pivotal factor in our decision to move. Over time, we’ve noticed how the city’s expenses, from petrol to groceries, have steadily increased, making every purchase a mindful choice. The rising costs of utilities, transportation, and daily essentials have become a significant part of our budget, leaving us wondering if there’s room for more than just the basics. While the city offers many amenities, we’ve found ourselves seeking a lifestyle that aligns with our values and allows us to live comfortably without constant financial strain.
The cost of groceries has also become a major consideration. As prices rise, even simple trips to the store have us thinking about every purchase. We’ve found ourselves choosing between brands or quantities to stay within our budget, which has made us appreciate the idea of growing some of our own food.
While we love the idea of the cultural and social offerings of city life, the reality is that we spend more time trying to stretch our weekly budget to make ends meet, than we do enjoying the fruits of our labor. We’re looking forward to a place where we can manage our budget comfortably, while still having access to the amenities we need. This doesn’t mean we’re leaving behind everything we’ve grown accustomed to; it’s about finding a balance—a home that allows us to live fully without feeling constrained by expenses.
Our decision to move isn't about wanting to be one with nature or making a statement; it’s more about practicality. Owning a freehold property gives us the stability we need, allowing us to live sustainably without feeling tied down by expenses. This choice aligns with our values and offers a sense of freedom, not because we're trying to escape something, but because it supports the life we want for ourselves and our family. We’ve worked hard to pay down our mortgages, but now we’re ready for the next step—owning our own land that we can build upon.
We’re not looking to simplify just because we want to be closer to nature; rather, we see this move as an opportunity to create a lifestyle that’s more in tune with our needs. By growing our own food and living in a clean, natural environment, we’re prioritizing sustainability without compromising on what matters most—our family’s future and well-being. It’s about creating a home that reflects our values, not just embracing change for the sake of being different.
Educational Opportunities
Our oldest child’s education is another driving force behind this move. We’ve discovered that the place we’re moving to offers a University with "fees-free" options, which will provide him with an opportunity to pursue his studies without the burden of tuition costs. This not only eases our financial concerns but also gives us peace of mind knowing he can focus on his education without added stress. It’s a decision that aligns with our aspirations for his future and our family's well-being, hoping he can thrive in an environment that supports his academic journey and personal growth.
Also, our youngest child is going to have the opportunity to raise the animals he’s so enamored with, such as chickens; dogs; pigs, and maybe even a couple of sheep. I want these experiences to help him to learn by doing, fostering a sense of responsibility and connection with where our food comes from. By caring for these creatures, we hope he’ll develop life skills that will help him grow into his own skin as he gets older. It’s a chance for him to explore his passions and build confidence in a hands-on way.
Freedom
Space has become something we truly appreciate, especially with our kids and pets. We’re eager for them to have more room to roam and explore freely. The privacy that a rural setting offers is high on our list of needs because living in the city often feels like we're always surrounded by others. It's not uncommon to bump into neighbors or find ourselves at loggerheads over simple things like car parks. This constant interaction, while part of city life, can sometimes feel overwhelming.
But it's not just us - our current place of employment also experiences issues with neighboring businesses, and it’s the employees who end up feeling the impact. It feels as if everyone is out for themselves, and are incapable of thinking about how their actions affect others.The city environment feels cramped and extremely claustrophobic, making us yearn for more personal space. We’re looking forward to the freedom of having our own large property where we can enjoy peace and quiet. It’s exciting to think about the possibilities, like building a barn or adding bee hives, and even sinking a water well as we please.
Food & Gardening
The idea of growing our own food is another exciting prospect that we're eager to explore. We’re looking forward to cultivating fresh produce in our garden, which will not only provide healthier options for our family but also add variety and freshness to our meals. It will be a major undertaking for us. While I personally have some understanding of growing and harvesting simple crops like potatoes and cabbage, I am deeply aware of my lack of knowledge and experience. It will take years for me to actually become proficient. We’re excited to teach our kids where their food comes from and instill an appreciation for sustainable living. Growing our own produce aligns with our desire for a more natural, self-sufficient lifestyle, offering us the joy of seeing the fruits of our labor in our garden.
Exercise & General Wellness
Living in a bustling city has its perks, but it has also take a toll on our sense of well-being. The daily grind often leaves us feeling mentally and emotionally drained, leaving little room for relaxation and physical activity. With the convenience of modern life comes a faster pace, which, while beneficial, frequently feels overwhelming. We long for moments to pause, breathe in fresh air, and reconnect with ourselves.
I think that the desire for more exercise and fresh air, is a natural response to the our current lifestyle. The city’s vibrant atmosphere and endless opportunities often come at the expense of personal time and the chance to enjoy relax. By seeking a new environment, We're looking for a balanced life for our family, where we can revitalize their minds and bodies through simple yet essential activities like walking around the property or the exercise of working the land. This shift is not just about changing scenery; it’s about creating a lifestyle that supports our overall well-being and allows for moments of peace away from the hustle and bustle.
In conclusion, this move is about more than just changing scenery; it’s about creating a home that embodies our values—safety, education, sustainability, and well-being for our family. It’s a step towards a future where we can thrive in an environment that supports our growth and aspirations.
-
 @ 6e0ea5d6:0327f353
2025-03-24 22:11:58
@ 6e0ea5d6:0327f353
2025-03-24 22:11:58People, mio caro, mistake silence for weakness just as they mistake the shine of silver for the value of gold. Because the modern world—hysterical and theatrical—has learned to respect noise, shouting, emotional outbursts, and the endless chatter of failures who demand respect without ever having earned it. But we, who have emerged from the forge of omertà, know that the one who reacts immediately is merely begging for relevance.
A real man—and I do not refer to those who simply wear trousers, but to those who carry their name and reputation upon their shoulders—knows that humiliation is not avenged with words of promise, but with a sentence of action. And sentences, amico mio, are not uttered in impulse. They are written in silence, with permanent ink on the paper of memory.
The one who strikes back in the moment of offense reveals that he is still under the dominion of emotion. But the one who remains silent, who stands still, who looks his aggressor in the eye and does not utter a single word—he has already begun to dig, with his own hands, the symbolic grave of the one who offended him. His coldness is not the absence of pain, but the absolute mastery of it. And that is precisely why he is feared. Not because he screams, but because he thinks. Because he smiles while thinking. Because he watches while you believe he has forgotten.
In Sicily, we say that the wolf does not howl when preparing to strike—it merely crouches. The fool believes that silence is cowardice. The wise man knows it is calculation. While the world carries on with its pathetic routines and social theater, the humiliated man prepares the final stage. And on this stage, there will be no audience, no applause. Only the dry sound of justice being served. Without mercy. Without apologies. Without a second chance.
Vengeance is not an emotion. It is an art. And the first stroke in the masterpiece is control.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 7d33ba57:1b82db35
2025-03-24 21:47:31
@ 7d33ba57:1b82db35
2025-03-24 21:47:31Located on the southeastern coast of Spain, Cartagena is a city rich in history, maritime heritage, and stunning Mediterranean views. With over 3,000 years of history, it boasts Roman ruins, modernist architecture, and a vibrant port, making it one of Spain’s most underrated travel destinations.
🏛️ Top Things to See & Do in Cartagena
1️⃣ Roman Theatre of Cartagena 🎭
- The star attraction, dating back to the 1st century BC.
- One of Spain’s best-preserved Roman theatres, discovered in 1988 beneath the city.
- Visit the museum to learn about its history before exploring the impressive ruins.
2️⃣ Concepción Castle & Panoramic Lift 🏰
- A 14th-century fortress on a hill offering spectacular views of the city and harbor.
- Take the glass elevator for a scenic ride to the top.
- The museum inside explains Cartagena’s rich military and naval history.
3️⃣ Calle Mayor & Modernist Architecture 🏛️
- The city’s main pedestrian street, lined with elegant buildings, shops, and cafés.
- Admire Casa Cervantes, Gran Hotel, and the Casino, examples of Cartagena’s modernist style.
4️⃣ National Museum of Underwater Archaeology (ARQVA) ⚓
- Learn about sunken treasures, ancient shipwrecks, and underwater archaeology.
- Features artifacts from Phoenician, Roman, and medieval maritime history.
5️⃣ Naval Museum & the Peral Submarine 🚢
- Discover Cartagena’s naval history, including models of warships and maritime artifacts.
- See the Peral Submarine, the first-ever electric-powered submarine, invented in 1888.
6️⃣ Playa de Cala Cortina 🏖️
- A beautiful urban beach, just a few minutes from the city center.
- Great for swimming, snorkeling, and relaxing with clear Mediterranean waters.
7️⃣ Batería de Castillitos 🏰
- A dramatic cliffside fortress with fairy-tale turrets and massive coastal cannons.
- Located 30 minutes from Cartagena, offering panoramic sea views.
🍽️ What to Eat in Cartagena
- Caldero del Mar Menor – A local seafood rice dish, similar to paella 🍚🐟
- Michirones – A hearty bean stew with chorizo and ham 🥘
- Marineras – A Russian salad tapa served on a breadstick with an anchovy 🥖🐟
- Tarta de la abuela – A delicious layered biscuit and chocolate cake 🍰
- Asiático Coffee – A signature Cartagena coffee with condensed milk, brandy, and cinnamon ☕🍸
🚗 How to Get to Cartagena
🚆 By Train: Direct trains from Madrid (4 hrs), Murcia (45 min), and Alicante (1.5 hrs)
🚘 By Car: ~30 min from Murcia, 1.5 hrs from Alicante, 3.5 hrs from Madrid
✈️ By Air: Nearest airport is Murcia-Corvera Airport (RMU) (~30 min away)
🚢 By Cruise Ship: Cartagena is a popular Mediterranean cruise stop💡 Tips for Visiting Cartagena
✅ Best time to visit? Spring & Autumn – warm but not too hot 🌞
✅ Wear comfortable shoes – Many streets and attractions involve walking on cobblestones 👟
✅ Visit during the Roman Festival (Carthaginians & Romans, September) for a unique cultural experience 🎭🏛️
✅ Try a sunset drink at a rooftop bar near the port for incredible views 🍹🌅 -
 @ 4520e45a:aa52208a
2025-03-24 20:26:56
@ 4520e45a:aa52208a
2025-03-24 20:26:56👾 Hash Obwohl ein Bitaxe mit 1TH eine Billion Hashes pro Sekunde generiert, werden nicht alle Hashes an den Pool übermittelt — das käme einer Dos-Attacke gleich, würde unnötig Bandbreite verschwenden und den Stratum-Pool-Server massiv belasten.
🏋️ Work-Difficulty Deshalb wird für jeden Worker eine individuelle Work-Difficulty festgelegt. Im Stratum-Protokoll, bekannt als <mining.set_difficulty>. Es werden also nur Shares übermittelt, welche grösser als die festgelegte Work-Difficulty sind.
💡 Um eine Share mit Difficulty 1 zu finden, muss ein Miner erwartungsgemäss 2³² = 4'294'967'296 = 4.29G Hashes generieren.
✉️ Share Wenn ein Hash alle notwendigen Kriterien erfüllt und die Nonce-Difficulty grösser ist als die vom Pool festgelegte Work-Difficulty, wird er als Share dem Pool übermittelt.
⏱️ Bei ckpool wird die Work-Difficulty für einen Worker so angepasst, dass im Durchschnitt 20 Shares pro Minute – also alle 3 Sekunden 1 Share – überliefert wird, das ergibt circa 1200 Shares/Stunde
⏱️ Bei Public Pool wird die Work-Difficulty für einen Worker so angepasst, dass im Durchschnitt 6 Shares pro Minute – also alle 10 Sekunden 1 Share – überliefert wird, das ergibt circa 360 Shares/Stunde
📡 Es geht dabei letztlich um die Kommunikation zwischen Miner und Pool, also konkret, wie oft pro Minute dein Miner Shares an den Pool übermittelt und wieviele Datenpakete gesendet/empfangen/verarbeitet werden müssen.
📈 5-20 Shares pro Minute ergeben auch eine einigermassen aussagekräftige Hashrate, damit stets überprüft werden kann, ob dein Miner korrekt arbeitet.
⛏️ Ob Miner pro Minute 20 Shares mit jeweils einer Nonce-Difficulty von 600 an den Pool übermittelt und Miner pro Minute nur 6 Shares dafür jeweils mit einer Nonce-Difficulty von 2000 an den Pool übermittelt ist am Ende das gleiche.
💪 Beide haben die identische Arbeit geleistet (20×600 = 6×2000 = 12'000×1), nur dass der eine 'viele einfache' und der andere 'wenige schwierige' Shares übermittelt hat.
-
 @ da0b9bc3:4e30a4a9
2025-03-25 09:14:07
@ da0b9bc3:4e30a4a9
2025-03-25 09:14:07Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/924287
-
 @ bf95e1a4:ebdcc848
2025-03-24 17:14:48
@ bf95e1a4:ebdcc848
2025-03-24 17:14:48This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
Everything A Trade
All human interaction can be defined as trade. Yes, all human interaction. Every time a human being interacts with another, an exchange takes place. In every conversation we have, we exchange information with each other. Even the most trivial information is of some value to the other person. If information didn’t have any value to us, we wouldn’t talk to each other. Either what the other person says is valuable to us, or we find it valuable to give information to them. Oftentimes both. At the core of all human interaction that isn’t violent, both parties perceive that they gain some value from it, otherwise the interaction wouldn’t have taken place at all. Civilizations begin this way — two people finding it valuable to interact with each other. That’s all it takes.
So, what constitutes value? What we find valuable is entirely subjective. A comforting hug, for example, probably has a different value to a two-year-old than it has to a withered army general. Even the most basic action, such as breathing, encapsulates the whole value spectrum. We tend to forget that even a single breath of air can be of immense value to us under the right circumstances. A single breath is worth more than anything on the planet to a desperate free-diver trapped under ice, while worth nothing to a person with a death wish in clean forest air on a sunny summer day. Value is derived from supply and demand, and demand is always subjective. Supply is not.
Since all of our lives are limited by time, time is the ultimate example of a scarce, tradeable resource. We all sell our time. We sell it to others, and we sell it to ourselves. Everyone sells their time, either through a product that took them a certain amount of time to produce, or as a service, and services always take time. If you’re an employee on a steady payroll, you typically sell eight hours of your day, every day, to your employer. If you’re doing something you truly love to do, that eight-hour day still belongs to you, in a way, since you’re doing what you’d probably be doing anyway if you had been forced to do it for free. Sometimes, we sacrifice time in order to acquire something in the future. An education, for instance, gives no immediate reward but can lead to a better-paying, more satisfying job in the future. An investment is basically our future self trading time with our present self at a discount. Once again, every human interaction viewed as trade.
It’s rooted in physics. For every action, there is an equally large reaction. Trade is at the very core of what we are, and the tools we use to conduct trade matter a lot to the outcome of each transaction. Money is our primary tool for expressing value to each other and if the creation of money is somewhat corrupt or unethical, that rot spreads down throughout society, from top to bottom. Shit flows downhill, as the expression goes.
So what is money, or rather, what ought money to be? In order for two persons to interact when a mutual coincidence of needs is absent, a medium of exchange is needed in order to execute a transaction. A mutual coincidence of needs might be “You need my three goats, and I need your cow,” or even “both of us need a hug.” In the absence of a physical good or service suitable for a specific transaction, money can fulfill the role of a medium of exchange. What most people fail to realize is that the value of money, just as the value of everything else, is entirely subjective. You don’t have to spend it. The problem with every incarnation of money that mankind has ever tried is that its value always gets diluted over time due to inflation in various forms. Inflation makes traditional money a bad store of value, and money needs to be a good store of value in order to be a good investment, or in other words, a good substitute for your time and your effort over time. Bitcoin tries to solve this problem by introducing absolute scarcity to the world, a concept that mankind has never encountered before. To comprehend what such a discovery means for the future, one needs to understand the fundamentals of what value is and that we assign a certain value to everything we encounter in life, whether we admit it or not. In short, we assign value to everything we do, value is derived from supply and demand, and supply is objective while demand is subjective.
Free trade emerges out of human interaction naturally and it is not an idea that was forced upon us at any specific point in time. The idea that markets should be regulated and governed, on the other hand, was. Free trade is just the absence of forceful interference in an interaction between two humans by a third party. There’s nothing intrinsically wrong or immoral about an exchange of a good or service. Every objection to this is a byproduct of the current global narrative — a narrative that tells us that the world is divided into different nations and that people in these nations operate under various sets of laws, depending on what jurisdiction they find themselves in. All of these ideas are man-made. No species except humans does this to themselves. Animals do trade, but they don’t do politics.
Bitcoin and the idea of truly sound, absolutely scarce money inevitably make you question human societal structures in general and the nature of money in particular. Once you realize that this Pandora’s box of an idea can’t be closed again by anyone, everything is put into perspective. Once you realize that it is now possible for anyone with a decently sized brain to store any amount of wealth in that brain or to beam wealth anonymously to any other brain in the world without anyone else ever knowing, everything you were ever told about human society is turned on its head. Everything you thought you knew about taxes, social class, capitalism, socialism, economics, or even democracy falls apart like a house of cards in a hurricane. It is, in fact, impossible to comprehend the impact Bitcoin will have on the planet without also understanding basic Austrian economics and what the libertarian worldview stems from.
Imagine growing up in an Amish community. Until your sixteenth birthday, you’re purposely completely shielded off from the outside world. Information about how the world really works is very limited to you since internet access, and even TVs and radios, are forbidden within the community. Well, from a certain perspective, we’re all Amish. How money really works is never emphasized enough through traditional media or public educational institutions. Most people believe that the monetary system is somehow sound and fair when there’s overwhelming evidence to the contrary all over the globe. Ask yourself, do you remember being taught about the origins of money in school? Me neither. I don’t believe that there’s some great, global conspiracy behind the fact that the ethics of money creation isn’t a school subject, but rather that plain old ignorance is to blame for the lack of such a subject primarily. As soon as their math-skill limit is reached, people seem to stop caring about numbers. The difference between a million and a billion seems lost on a depressingly large part of the world's population. In the chapters ahead, we’ll explore the pitfalls of central banking, how money pops into existence, and how inflation keeps us all on a leash.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ 220522c2:61e18cb4
2025-03-25 06:57:24
@ 220522c2:61e18cb4
2025-03-25 06:57:24
-
 @ 401014b3:59d5476b
2025-03-24 16:34:24
@ 401014b3:59d5476b
2025-03-24 16:34:24Alright, hoops degenerates, it’s March 24, 2025, and we’re deep in the March Madness grinder—Sweet 16 time, baby! The bracket’s a damn battlefield, with Auburn, Michigan, Texas Tech, Arkansas, and Purdue locked in alongside some heavy hitters and sneaky upstarts. We’re breaking down every matchup, throwing out some ballsy picks, and calling the full Elite Eight squads on the road to San Antonio. This ain’t some nerdy chalk fest—let’s get loud, let’s get rowdy, and let’s see who’s got the stones to survive this chaos. Strap in, fam—here we go!
South Region: Auburn’s Warpath or Spartan Magic?
Auburn vs. Michigan
Auburn’s the SEC beast, shredding Creighton 82-70 with Tahaad Pettiford’s bench juice (14 points) and Johni Broome’s paint dominance (22 points, 10 boards). Michigan’s Big Ten scrappers outlasted Texas A&M 91-79—Dusty May’s got ‘em humming with Olivier Nkamhoua’s 18 points. The Tigers are a top-5 offensive team, but Michigan’s been scrappy, winning close games all season. Auburn’s depth and Broome’s interior game (top-10 in blocks) overpower Michigan’s grit—Auburn rolls, 78-71.
Ole Miss vs. Michigan St.
Ole Miss’s Chris Beard-led crew topped Iowa St. 91-78—Sean Pedulla dropped 20, and their top-30 offense is humming. Michigan St. beat New Mexico 71-63—Tom Izzo’s Spartans are battle-tested, with a top-15 defense (per KenPom). Ole Miss can score, but Sparty’s physicality (top-10 in defensive rebounds) and Izzo’s March magic (five Final Fours) shut ‘em down—Michigan St. grinds it, 74-69.
Elite Eight Matchup: Auburn vs. Michigan St.
West Region: Houston’s Clamps or Gators’ Grit?
Houston vs. Purdue
Houston’s D suffocated Gonzaga 81-78—L.J. Cryer dropped 22, and their top-5 defense (forcing 16 turnovers per game) is a nightmare. Purdue crushed San Diego St. 76-62—Braden Smith dished 15 assists, and Fletcher Loyer had 18. Cougars are elite defensively, but Purdue’s size (top-10 in offensive rebounds) and tempo keep it close. Houston’s clamps and Cryer’s clutch shooting (40% from three) edge it—Houston dominates, 70-66.
Florida vs. Maryland
Florida stunned UConn 77-75—Walter Clayton Jr.’s 10 points in a three-minute span sealed it. Maryland’s buzzer-beater over Colorado St. 72-71—Derik Queen’s heroics—got ‘em here. Gators are rolling (SEC tourney champs), but Maryland’s Crab Five (top-20 offense) and Queen’s clutch play (20 PPG in March) keep it tight. Florida’s depth (four starters averaging 12+ PPG) pulls through—Florida wins, 82-78.
Elite Eight Matchup: Houston vs. Florida
Midwest Region: Arkansas’ Chaos or Bama’s Firepower?
Texas Tech vs. Arkansas
Calipari’s Razorbacks punked St. John’s 75-66—DJ Wagner dropped 16, and their depth shone. Texas Tech’s Big 12 muscle crushed Drake 77-64—Darrion Williams had 28. Hogs’ talent (six guys in double figures vs. St. John’s) faces Tech’s balanced attack (top-25 offense). Arkansas’ chaos and Calipari’s March pedigree (four Final Fours) overwhelm—Arkansas storms, 82-77.
BYU vs. Alabama
BYU’s hot streak topped Wisconsin 91-89—Trevor Knell hit six threes, averaging 18.9 PPG in their nine-game win streak. Alabama blitzed Saint Mary’s 86-80—Mark Sears dropped 25. Cougars’ offense (top-10 in three-point shooting) meets Bama’s firepower (top-15 in offensive efficiency). Alabama’s speed and Sears’ scoring (21 PPG) edge it—Alabama wins, 88-84.
Elite Eight Matchup: Arkansas vs. Alabama
East Region: Duke’s Flagg Show or Cats’ Revenge?
Duke vs. Arizona
Flagg’s back—Duke crushed Baylor 89-86, with Flagg dropping 20 and 8. Arizona blitzed Oregon 87-83—Caleb Love had 27. Flagg’s versatility (top-5 defensive efficiency for Duke) faces Love’s scoring (20 PPG in March). Duke’s depth (six guys scoring 10+ vs. Baylor) and Flagg’s two-way play edge it—Duke flexes, 85-76.
Kentucky vs. Tennessee
Kentucky beat Illinois—Mark Pope’s Wildcats are 2-0 against Tennessee this season. Tennessee topped UCLA 72-67—Zakai Zeigler had 18 and 8 assists. Cats’ resilience (top-20 offense) meets Vols’ defense (top-15 efficiency). Kentucky’s Quad 1 wins (12 this season) and Pope’s game plan edge it—Kentucky wins, 82-78.
Elite Eight Matchup: Duke vs. Kentucky
Elite Eight Teams (Full List)
South: Auburn, Michigan St.
West: Houston, Florida
Midwest: Arkansas, Alabama
East: Duke, Kentucky
The Final Buzzer
Sweet 16’s a bloodbath, and the Elite Eight’s set—Auburn, Michigan St., Houston, Florida, Arkansas, Alabama, Duke, and Kentucky are my picks to keep dancing. SEC’s got seven teams in the Sweet 16, blue bloods are flexing, and mid-majors are toast. Hit me on Nostr if you disagree, but this is my March Madness gospel—bracket’s clean, let’s see who survives! Let’s freaking go, degenerates!
-
 @ d560dbc2:bbd59238
2025-03-25 05:29:36
@ d560dbc2:bbd59238
2025-03-25 05:29:36Hey! Today, I’m diving into the 2-5 Rule—a unique task management method that’s all about timing, not planning. It powers TaskforUs, a beta platform that’s changing how we prioritize tasks. Grab a coffee, and let’s get started!
What Is the 2-5 Rule?
The 2-5 Rule is a task management approach that focuses on when to act on a task rather than creating a detailed plan. Every task has a “time unit” (days, weeks, months, or years), and you should act within 2 to 5 of those units. This “sweet spot” ensures that you’re neither rushing nor neglecting tasks.
Examples:
- Daily tasks: (e.g., “Do cardio”) – Act every 2-5 days.
- Weekly tasks: (e.g., “Meet a friend”) – Act every 2-5 weeks.
- Monthly tasks: (e.g., “Review budget”) – Act every 2-5 months.
- Yearly tasks: (e.g., “Renew passport”) – Act every 2-5 years.
You don’t plan the exact time to do the task—just enter it into TaskforUs, set the time unit, and provide either the last date you acted on it or a fixed due date. The system prioritizes it for you, making it an anti-planning method.
How Does It Work in Practice?
Example 1: Renewing Your Passport
-
Scenario:
You get your passport today (March 24, 2025). -
Action:
Add the task “Renew passport” to TaskforUs with a yearly time unit and set the “last act date” as today. -
Outcome:
The task starts low on your priority list but climbs over time. After 2 years, it begins to rise; by 5 years, it’s near the top—nudging you to act before your passport expires.
Alternatively, use Fix Mode to set the expiration date (e.g., March 24, 2030) so the task climbs in priority as the date approaches.
Example 2: Meeting Uncle Lars Regularly
-
Scenario:
You want to meet your Uncle Lars roughly 10 times a year (about once every 5 weeks). -
Action:
Add the task “Meet Uncle Lars” with a weekly time unit (to provide flexibility) and set the “last act date” as the most recent meeting (e.g., March 1, 2025). -
Outcome:
Over time, the task slowly climbs in your priority list. After 2 weeks, it starts gaining focus; by 5 weeks, it becomes urgent—prompting you to schedule the next meeting.
No detailed planning is required—you simply add the task, and the 2-5 Rule does the rest.
The Psychology Behind the 2-5 Rule
The 2-5 Rule isn’t just a clever idea—it’s grounded in psychology and behavioral science. Here’s why it works so well:
-
It Reduces Decision Fatigue
Constantly deciding when to do each task can be exhausting. The 2-5 Rule automates prioritization, so you don’t have to think about when to act. TaskforUs surfaces the right task at the right time, freeing up mental energy for doing the work. -
It Aligns with Natural Rhythms
Humans thrive on rhythm and consistency. Behavioral science shows that after 2 time units, a task starts to feel pressing, but by 5 units, it’s at risk of being neglected. The 2-5 window captures this natural sense of urgency. -
It Taps into the Zeigarnik Effect
This psychological principle states that uncompleted tasks are remembered better than completed ones. As a task’s due window approaches, it naturally rises in priority—keeping it top of mind. -
It Prevents Over-Planning Stress
Detailed scheduling can be stressful, especially when life is unpredictable. The anti-planning nature of the 2-5 Rule removes this burden: you simply enter your task and let the system remind you when it’s time to act.
The Structure of TaskforUs: Bringing the 2-5 Rule to Life
TaskforUs is a web-based platform (currently in beta) that makes the 2-5 Rule actionable:
-
Add Tasks Easily:
Simply enter a task, set its time unit (days, weeks, months, or years), and provide the last act date or a fixed due date for Fix Mode tasks. -
Top Task:
TaskforUs automatically highlights your most urgent task based on the 2-5 Rule, telling you exactly what to do right now. -
Focus Mode:
See your top 3 tasks (or adjust the number) for distraction-free productivity. -
Fix Mode:
For date-specific tasks (e.g., “Wish Alex a happy birthday”), set the due date and watch the task climb in priority as the day approaches, peaking on the day itself. -
Category Filtering and Archiving:
Organize tasks into categories (e.g., Work, Personal) and archive completed tasks to keep your list clean. -
Export Tasks:
Download your tasks as a CSV file for backup or analysis.
TaskforUs takes the 2-5 Rule’s anti-planning philosophy and makes it seamless, ensuring you always know what to do next without the mental load of scheduling.
Why the 2-5 Rule Works: A Game-Changer for Task Management
The 2-5 Rule stands out because it addresses common pain points in task management:
-
No More Overwhelm:
By focusing on one top task (or a few in Focus Mode), you avoid the clutter of a long to-do list. -
Effortless Prioritization:
The rule automates the decision of what to do next, reducing stress and boosting productivity. -
Never Miss a Deadline:
With Fix Mode, date-specific tasks like passport renewals or birthdays rise to the top at the right time. -
Flexibility:
The 2-to-5 window gives you room to act when it suits you—without rigid deadlines.
Try the 2-5 Rule with TaskforUs
The 2-5 Rule is a fresh take on task management that balances short-term habits with long-term goals—without the burden of meticulous planning. TaskforUs makes it easy to implement, and as a beta user, you can help shape its future.
Here’s why you should try it:
-
No Planning Needed:
Just add your tasks and let the system prioritize them automatically. -
Clarity:
Always know what to do right now—without the mental load of overthinking. -
Flexibility:
The 2-to-5 window gives you the right balance between urgency and ease. -
Reliability:
Fix Mode ensures you never miss critical dates. -
Be Part of the Beta:
Your feedback helps improve TaskforUs as it evolves.
Take Control of Your Tasks Today
The 2-5 Rule is more than a productivity hack—it’s a new way to manage tasks by focusing on timing rather than rigid plans. Ready to say goodbye to overwhelm and hello to effortless prioritization?
Sign up for TaskforUs at task4.us and experience the 2-5 Rule in action.
Your tasks, perfectly timed—without a plan in sight.