-
 @ a296b972:e5a7a2e8
2025-04-17 23:08:50
@ a296b972:e5a7a2e8
2025-04-17 23:08:50Die Figuren in der Koalition der Willigen entlarven ihre charakterliche Ungeeignetheit für politische Ämter mit Verantwortung für ganze Nationen. Staatliche Entscheidungen dürfen nicht emotionsgesteuert sein. Aber genau das ist derzeit der Fall. Überall wird mit der Moralkeule um sich gehauen. Erwachsene benehmen sich wie im Kindergarten und zeigen ihre fehlende Reife. Von menschlicher Größe ganz zu schweigen.
Bisher war es schön warm unter den Fittichen der USA. Deutschland hat aufgrund seiner Geschichte besonders gut den Nick-August gespielt und sich selbst eine Souveränität vorgelogen, die es so nie gegeben hat. Jetzt sieht es so aus, als wollten die USA Europa in die Freiheit, in die Volljährigkeit entlassen. Es könnte auch sein, dass die USA aus der NATO austreten und sich vor allem um sich selbst kümmern. Allein das würde die Welt schon wesentlich friedlicher machen, denkt man beispielsweise an den Einmarsch in den Irak. Es gehen Gerüchte um, dass Truppen aus Rumänien und Deutschland abgezogen werden sollen.
Vielleicht geht es bei den Friedensverhandlungen zwischen Trump und Putin nicht nur um die Ukraine, sondern, wenn man schon mal dabei ist, auch um die Kräfteverteilung in Europa insgesamt. Waffeneinsätze in der Ukraine wurden maßgeblich von Wiesbaden aus gesteuert. 2026 sollen dort US-Mittelstrecken-Raketen stationiert werden. Der an Führungsstärke kleinste Kanzler der Bundesrepublik, Scholz, hat das brav abgenickt. Der nur noch durch ein Wunder zu verhindernde neue Kanzler, das Glas Gewürzgurken aus dem Sauerland, provoziert Russland mit seiner Ankündigung zu den Taurus-Raketen dafür um so mehr. Da ist man schon fast gewillt, sich den Scholz zurückzuwünschen, als das kleinere Übel.
Statt mit Besonnenheit und Vernunft die veränderte Sicherheitslage mit den USA als eher abtrünnige Schutzmacht neu zu bewerten, hierin auch eine Chance zu sehen, eine starke Botschaft und den Willen auf ein friedliches neues Miteinander in den Fokus zu stellen, reagieren die meisten europäischen politischen „Spitzenkräfte“ mit blindem Aktionismus, der weltenbrandgefährlich ist. Und Deutschland, dass es sich aufgrund seiner Geschichte am wenigsten erlauben könnte, macht mit von der Leyen in Brüssel und Merz, Pistorius und anderen Kriegs-Warm-Uppern am weitesten das Maul auf, obwohl es sich am bedecktesten halten sollte.
Angesichts der Tatsache, dass Europa gegenüber einer Atommacht wie Russland vollkommen wehrlos ist, wäre es wirklich viel gescheiter, sich der neuen Situation anzupassen und ständig Signale der Friedensbereitschaft zu senden. Unterstütz von den Briten und Franzosen schmiegt Brüssel eine Koalition der Friedensuntüchtigen, wie sie Uwe Froschauer aktuell in seinem Buch „Die Friedensuntüchtigen“ beschreibt. In der Rezension von mir gibt es auch einen Link zu einem Review des Inhalts:
https://wassersaege.com/blogbeitraege/buchrezension-die-friedensuntuechtigen-von-uwe-froschauer/
Stattdessen passiert das Gegenteil.
Es ist nicht nur legitim, sondern sogar Aufgabe der einzelnen Staaten, eine gewisse Verteidigungsfähigkeit aufbauen zu wollen. Derzeit geschieht das jedoch unter falschen Vorzeichen. Die NATO, als sogenanntes Verteidigungsbündnis zur Vorlage zu nehmen, wäre keine gute Idee, weil sie sich mangels Gelegenheit (der Verteidigung) eher als das Gegenteil herausgestellt hat, wie man seinerzeit in Jugoslawien erleben musste.
Russland als Feind hochzustilisieren, um ein Aufrüsten zu beschleunigen, ist jedoch der denkbar falscheste Weg. Wenn ein Yorkshire-Terrier einen Pit-Bull ankläfft, könnte das fatale Folgen haben. Wenn die europäischen „Geistesgrößen“ bei Verstand wären und in der Lage, die Realität richtig einzuschätzen, würden sie das erkennen.
Woher kommt die Überheblichkeit, woher die Unfähigkeit zur Einschätzung der Lage, woher die Realitätsverweigerung? Ist das gewollt, steckt ein Plan dahinter oder sind „die“ einfach „nur“ strunzendoof? Letzteres wäre die gefährlichste Variante.
Es stellt sich immer mehr heraus, dass Corona offensichtlich ein Test war, wie weit die Menschen in ihrer Obrigkeitshörigkeit zu treiben sind. Wie dumm und gefolgsam sind die Schafe wirklich?
Bei einer Lieferung von Taurus-Raketen, die von Deutschen gesteuert werden müssen, könnte es vielleicht gelingen, die Krim-Brücke zu zerstören. Den Kriegsverlauf würde das jedoch nicht beeinflussen. Russland gewinnt so oder so. Im Gegenteil, die Folgen für Deutschland würden den dort möglicherweise angerichteten Schaden bei weitem übertreffen.
Während ich schreibe kommt gerade auf RT DE (aufgrund der „Pressefreiheit“ verzichtet man derzeit offiziell auf diesen Sender) folgende Meldung rein: Russisches Außenministerium: Taurus-Einsatz bedeutet deutsche Kriegsbeteiligung.
https://rtde.site/international/242696-russisches-aussenministerium-taurus-einsatz-bedeutet/
Es ist nicht nachvollziehbar, dass Merz offensichtlich nicht in der Lage ist anzuerkennen, dass Russland über Oreschnik-Raketen verfügt. Er scheint nicht in der Lage zu sein, die möglichen Folgen einschätzen zu können. Genau so wenig wie Pistorius. Die beiden kommen einem vor, wie zwei, die sich im stockfinsteren Wald verirrt haben und sich gegenseitig Mut zusprechen.
Nach wie vor gibt es keine fundierten Beweise dafür, dass Russland die Absicht hat, Deutschland auf unschöne Weise bereisen zu wollen. Das kann nicht oft genug gesagt werden.
Wie schon vor dem Ukraine-Konflikt, durch ein ständiges mit der NATO-Osterweiterung Russland-immer-näher-auf-die-Pelle-rücken, streut jetzt Europa, Deutschland, der Kriegskanzler Salz in die Wunde und Russland sagt ständig: Stoy, so geht das nicht!
Wenn wir eine Bedrohungslage haben, dann die, dass das aktuelle Regime den Deutschen in seinem Wehrwahn mit Wehrpflicht und einer bevorstehenden russischen Invasion droht, obwohl es, man kann es wirklich nicht oft genug sagen, keine reale Bedrohung durch Russland gibt.
In einem Interview im deutschen Propaganda-Funk faselt Pistorius davon, dass in einem „Schnuppercamp der Bundesmarine“ in Kiel für Teenager ab 16 Jahre, er gar nichts Verwerfliches daran finden kann. „Die schießen ja nicht…“, „Wir bringen ihnen ja nicht das Töten bei mit 17, sondern wir bereiten sie vor auf eine Ausbildung zum Soldaten. Und Soldat ist ein sehr ehrenwerter Beruf, der nämlich dazu dient, unsere Freiheit und Sicherheit im Ernstfall zu verteidigen.“ Dass diese Verteidigung tödlich enden kann, wird hier verschwiegen. Das könnte schließlich Teile der Soldaten verunsichern.
Ein Politikwissenschaftler regt sich über den Titel eines Liedes auf:
-Da stört sich doch tatsächlich jemand an der Liedzeile „Meine Söhne geb‘ ich nicht“-
https://www.nachdenkseiten.de/?p=131733
Man hat das Gefühl, dass alle Politiker, statt wie Obelix in den Zaubertrank, in ein Fass Teflon-Lack gefallen sind. Anders ist es nicht zu erklären, warum die Realität so perfekt an ihnen abperlt.
Wir werden immer mehr in die Enge getrieben. Und man weiß nicht, was im Zuge der digitalisierten Überwachung, die auch in Russland kräftig Fahrt aufnimmt, zwischen den USA und Russland sonst noch ausgehandelt wird. Auch, wenn Vance derzeit von UK-Premier Keir Starmer fordert, er müsse die Gesetze gegen „Hassrede“ aufheben, um ein Handelsabkommen mit den USA zu erzielen, und das eine Vorankündigung auf die Verhandlungen mit der EU sein könnte, (Bedingung: Abschaffung des Digital Services Act). In den USA gibt es Tech-Giganten, wie Musk und Thiel und Konsorten, die mit Umlegen eines Schalters, den derzeit augenscheinlichen Kampf für Meinungsfreiheit und Freiheit der Bürger, im Handumdrehen ins Gegenteil verqueren können. Dann sind wir in Null Komma Nichts in der Versklavung mit einem Totalitarismus und einer Technokratie gelandet, in der sich Georg Orwells „1984“ wie eine Gute-Nacht-Geschichte für kleine Kinder anhört.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-17 21:35:47
@ 5d4b6c8d:8a1c1ee3
2025-04-17 21:35:47Congrats to @gnilma and @Carresan! Thanks to Herro and Butler both having 38 points (shoutout Heat Culture) they both secured 9 points and are tied for the lead.
Now we move on to the final Play-In Round
Matchups (seed)
- Heat (10) @ Hawks (8)
- Mavericks (10) @ Grizzlies (8)
You need to select one team from this round to win their game. You also need to predict who will be the highest scoring player in this round.
Scoring this round: 1 Point for your team winning + Your team's seed if they win + 1 Point for picking the correct top scorer
This round has a maximum of 12 points.
Prize
10k sats (or sum of zaps on contest posts, whichever is larger)
originally posted at https://stacker.news/items/946686
-
 @ df478568:2a951e67
2025-04-17 21:10:33
@ df478568:2a951e67
2025-04-17 21:10:33I created a GitHub repository at https://github.com/Marc26z/ZapShirts. Here is a copy of the README.md
ZapShirts
This is an idea I have to make t-shirts that are also bitcoin point-of-sale terminals.

Create T-Shirt Point-Of-Sale
The idea is to create a bitcoin point of sale on a T-shirt. You can use it to sell stickers at a conference or have a friend pay you back for dinner. It is only limited by your imagination.
Why Would Anybody Need A ZapShirt?
I no longer "orange pill" local businesses. I do not care if they wish to accept bitcoin, but I want to be the change in the world I want to see. I will accept bitcoin on a T-Shirt to show others how easy it is to accept bitcoin as a p2p electronic cash system. Anyone can accept bitcoin as payment if they want to. You could print a sign on a piece of paper if you wanted to. The problem was, nobody I asked wanted a sign, even bitcoiners. So I asked myself...Self, what if you did the opposite? What if the customer accepted bitcoin, but the business owner did not.
I also thought it would be pretty cool T-Shirt to wear at meet-ups.
How To Make Your Own Zap Shirt
- Create a QR code that sends you to your coinos page, getalby page, strike or whatever you feel comfortable using. This can easily be done at https://libreqr.com/
- Use a program like gimp to replace the default QR Code with your own QR code on the file.
- Create the shirt.
To support this please zap me or buy one from my store.
Can I Buy A Zap Shirt?
Yes. If you would like a shirt, hit me up on nostr
https://primal.net/marc
end README.md
I like the idea of open sourcing my ideas and trying to sell them for sats on the Internet. I am currently working on a site to sell things like this and my gift cards. I feel a little uneasy because I haven't been writing much, but I've been building. The idea is to create bitcoin educational products and services. Onward.
-
 @ 9063ef6b:fd1e9a09
2025-04-17 20:18:19
@ 9063ef6b:fd1e9a09
2025-04-17 20:18:19This is my second article. I find the idea of using a user friendly 2FA-style code on a secondary device really fascinating.
I have to admit, I don’t fully grasp all the technical details behind it—but nonetheless, I wanted to share the idea as it came to mind. Maybe it is technical nonsense...
So here it is—feel free to tear the idea apart and challenge it! :)
Idea
This Article describes method for passphrase validation and wallet access control in Bitcoin software wallets using a block-based Time-based One-Time Password (TOTP) mechanism. Unlike traditional TOTP systems, this approach leverages blockchain data—specifically, Bitcoin block height and block hash—combined with a securely stored secret to derive a dynamic 6-digit validation code. The system enables user-friendly, secure access to a wallet without directly exposing or requiring the user to memorize a fixed passphrase.
1. Introduction
Secure access to Bitcoin wallets often involves a mnemonic seed and an optional passphrase. However, passphrases can be difficult for users to manage securely. This paper introduces a system where a passphrase is encrypted locally and can only be decrypted upon validation of a 6-digit code generated from blockchain metadata. A mobile app, acting as a secure TOTP generator, supplies the user with this code.
2. System Components
2.1 Fixed Passphrase
A strong, high-entropy passphrase is generated once during wallet creation. It is never exposed to the user but is instead encrypted and stored locally on the desktop system (eg. bitbox02 - sparrow wallet).
2.2 Mobile App
The mobile app securely stores the shared secret (passphrase) and generates a 6-digit code using: - The current Bitcoin block height - The corresponding block hash - A fixed internal secret (stored in Secure Enclave or Android Keystore)
Offline App - current block_hash and block_height scanned with qr code.6-digit code generation after scanning the information.
2.3 Decryption and Validation
On the desktop (e.g. in Sparrow Wallet or wrapper script), the user inputs the 6-digit code. The software fetches current block data (block_height, block_hash), recreates the decryption key using the same HMAC derivation as the mobile app, and decrypts the locally stored passphrase. If successful, the wallet is unlocked.
3. Workflow
- Wallet is created with a strong passphrase.
- Passphrase is encrypted using a key derived from the initial block hash + block height + secret.
- User installs mobile app and shares the fixed secret securely.
- On wallet access:
- User retrieves current code from the app.
- Enters it into Sparrow or a CLI prompt.
- Wallet software reconstructs the key, decrypts the passphrase.
- If valid, the wallet is opened.
4. Security Properties
- Two-Factor Protection: Combines device possession and blockchain-derived time-based data.
- Replay Resistance: Codes change with every block (~10 min cycle).
- Minimal Attack Surface: Passphrase never typed or copied.
- Hardware-Backed Secrets: Mobile app secret stored in non-exportable secure hardware.
5. Future Work
- Direct integration into Bitcoin wallet GUIs (e.g. Sparrow plugin)
- QR-based sync between mobile and desktop
- Support for multiple wallets or contexts
6. Conclusion
This approach provides a balance between security and usability for Bitcoin wallet users by abstracting away fixed passphrases and leveraging the immutability and regularity of the Bitcoin blockchain. It is a highly adaptable concept for enterprise or personal use cases seeking to improve wallet access security without introducing user friction.
-
 @ 4c96d763:80c3ee30
2025-04-17 19:41:12
@ 4c96d763:80c3ee30
2025-04-17 19:41:12Changes
William Casarin (26):
- dave: reorganize ModelConfig
- dave: organize
- dave: remove old file
- dave: add a few tool docs
- dave: update to custom filters nostrdb
- dave: only search non-replies
- context: implement note broadcasting
- multicast: broadcast context
- dave: fix bugs
- chrome: fix wallet button
- previews: disable for now
- ui: add some margin to chrome sidebar
- columns: remove thread warning
- nostrdb: fix on windows
- dave: tweak prompt
- misc: driveby fixes
- refactor: move input buttons ui into its own fn
- refactor: extract input_ui into its own function
- dave: refactor a bit
- post: fix bug where send shortcut send unfocused inputs
- dave: give up on plaintext formatting
- dave: fix input box
- log: silence gif log
- refactor: nevernest get_display_name
- refactor: ocd unnecessary pass by value
- ui: move note and profile rendering to notedeck_ui
kernelkind (4):
- Fix flaky test_zap_event
- move error out of
AnyZapState - introduce
ImagePulseTint - pulse pending zap button
pushed to notedeck:refs/heads/master
-
 @ 18be1592:4ad2e039
2025-04-17 17:35:22
@ 18be1592:4ad2e039
2025-04-17 17:35:22My everyday activity
This template is just for demo needs.
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ 18be1592:4ad2e039
2025-04-17 17:34:16
@ 18be1592:4ad2e039
2025-04-17 17:34:16My everyday activity
This template is just for demo needs.
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ 18be1592:4ad2e039
2025-04-17 17:33:31
@ 18be1592:4ad2e039
2025-04-17 17:33:31My everyday activity
This template is just for demo needs.
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ f18b1f8f:5f442454
2025-04-17 17:03:22
@ f18b1f8f:5f442454
2025-04-17 17:03:22A supermemory MCP plugin that you can use to bring a memory with you to any client of your choosing. Supports fetching from, and storing to, memory. Comes with a prompt to help the client identify when to use or store updates. Very neat, and ties integrations together very well.
Here is a video walkthrough: https://x.com/DhravyaShah/status/1912544778090414188
e578b1367ed845d8925eb8a0ebc3a96d
-
 @ f18b1f8f:5f442454
2025-04-17 16:55:46
@ f18b1f8f:5f442454
2025-04-17 16:55:46A supermemory MCP plugin that you can use to bring a memory with you to any client of your choosing. Supports fetching from, and storing to, memory. Comes with a prompt to help the client identify when to use or store updates. Very neat, and ties integrations together very well.
Here is a video walkthrough: https://x.com/DhravyaShah/status/1912544778090414188
e578b136-7ed8-45d8-925e-b8a0ebc3a96d
-
 @ 0861144c:e68a1caf
2025-04-17 16:35:23
@ 0861144c:e68a1caf
2025-04-17 16:35:23This is a following up for the conversation started by @Scoresby with the question:
what is a sustainable model for onchain Bitcoin wallet software development?
This is an extreme opinion (even for myself) but I think is the best answer to what we're pursuing as bitcoiners.
Introduction: The Paradox of Free and Critical
The Bitcoin ecosystem thrives on open-source software. It's a world where people entrust their life savings to applications they didn’t pay a cent for. This introduces a unique paradox: we demand freedom, security, and transparency, but we don’t pay for the tools that guarantee it. Even more, we value free markets and incentives, yet expect Bitcoin wallets to exist and evolve out of altruism.
So what’s the path forward? What kind of model can ensure long-term development, security patches, feature upgrades, and alignment with Bitcoin’s protocol—without betraying its ethos?
Let’s explore the current landscape of wallet monetization and build toward a model that honors the freedom Bitcoin offers.
Wallet Monetization Models
Here’s an overview of how current Bitcoin-only (or mostly Bitcoin) onchain wallets sustain themselves based on https://stacker.news/items/944967#how-could-you-pay-for-a-bitcoin-wallet-if-you-wanted-to:
| Model | Description | Example Projects | Pros | Cons | |---------------------------|-----------------------------------------------------------------------------|-------------------------------|----------------------------------------------------|------------------------------------------------------------| | Donations/Grants | Funded by community or institutional support | Bitcoin Core, Sparrow, Specter| User-focused, preserves freedom | Unstable, depends on goodwill or VC altruism | | Freemium/Subscription| Free basic app, premium features unlocked through subscriptions | Nunchuk, Keeper, Theya | Predictable revenue | Introduces centralization, relies on dev infrastructure | | Device Sales | Wallet tied to hardware devices | Bitkey, Envoy | Scalable, aligned with sovereignty | Limits access based on geography or price | | Custodial Services | Funds held by a third party | Casa, River, Swan | Simple onboarding for new users | Compromises on "Not your keys, not your coins" | | Tx Commissions| Wallet takes a fee from trades within the app | BlueWallet (speculatively, maybe not) | Transparent funding method | User becomes product; hard to avoid surveillance and KYC | | L2 Services | Monetization through Lightning routing fees or service layers | Phoenix, Breez, Zeus | Innovative, supports network growth | Not suitable for cold storage or large holdings | | Sell the Software | Direct payment for downloading or unlocking the app | (Rare or nonexistent) | Clear transaction, sustainable if valued | Cultural resistance; rare in open-source culture |
Each of these models carries tradeoffs—especially when you consider global context.
Why Context Matters: Global Finance Is Not Equal
In countries with stable banking systems (U.S., Europe, Japan), Bitcoin wallets are largely seen as savings vaults. People use their banks for spending and turn to Bitcoin as a hedge or long-term store of value. In these places, users are more comfortable with subscription models or regulated custodial solutions.
But in the global south—Latin America, North Africa, parts of Asia—Bitcoin plays a different role. Banks are distrusted, inflation is high, and people are not just saving in Bitcoin; they’re trying living on Bitcoin. Wallets aren't just tools, they’re lifelines. Asking users to subscribe, give up sovereignty, or rely on opaque intermediaries is antithetical to the entire point. Can't use bitcoin? Go straight to cash or side-banks solutions like EMP (Giros Tigo, M-PESA). Taxes? We don't care, I don't mind not pay taxes when I buy nor I care even less how to present my fill form to authorities. Bitcoin is need.
In this context, the question isn't “can I pay for a wallet?”—it's “can I use it without being surveilled, blocked, or priced out?”. That's why technologies Lightning-L2 related have some much adoption, because we need not only to save but to pay our things. Just look El Salvador, Argentina or lately Bolivia, countries that need alternative to keep receiving/sending while having a volatility index very high.
The Bitcoin Standard: Build Your Own Wallet
Under the Bitcoin standard, the sustainable model must allow any individual to create their own wallet—no permission required, no gatekeepers, no payment walls. Think of it like designing your own leather wallet to carry cash. Anyone can do it, because the knowledge is public, the materials are available, and there’s no centralized authority controlling the process.
The same is true with Bitcoin:
- Wallets can integrate privacy-enhancing tools like Whirlpool (CoinJoin).
- They can adopt PayNym or BIP47 for stealth addresses.
- Features like automated DCA (Dollar Cost Averaging) can be designed to optimize both strategy and privacy.
- Visuals can display only sats, not fiat denominations, reinforcing the mindset that Bitcoin is the native unit.
What sustains these features? A community of developers building modular, composable, interoperable tools. The protocol enables this—Bitcoin is both a financial layer and a developer’s playground.
The Custodial Dilemma: Easier, But Risky
Let’s be honest: custodial wallets make onboarding smoother. They're easier to explain. “Download app, get coins.” That’s it. But this simplicity comes at a cost.
- “Not your keys, not your coins” is not just a mantra—it’s survival.
- Custodial wallets are subject to seizure, surveillance, and censorship.
- They build bad habits: users don’t learn how to verify, back up, or transact privately.
And yet, we’ve seen it again and again: many newcomers start with custodial solutions and only move to self-custody after something goes wrong—a blocked account, a missing withdrawal, or an unexplained freeze. Then they meet the 12 words. And yes, the seed phrase is scary at first. But over time, it becomes the ultimate expression of financial freedom.
Transaction Fees: A Ticking Time Bomb
Some wallet developers seek sustainability by taking a small cut of in-app transactions. It's easy to justify: "We only take 0.5% for maintenance." But this model is fundamentally flawed in the context of Bitcoin.
- It reintroduces third-party dependence into a tool meant to eliminate it.
- It discourages self-custody by tying wallet use to an ongoing cost.
- It creates perverse incentives: developers are now driven to optimize for volume, not user sovereignty.
In the short term, this might work. But long term, it turns wallets into surveillance engines and behavioral data extractors—exactly what Bitcoin was meant to disrupt.
A sustainable model can’t be built on transaction tax. That’s fiat logic.
Conclusion: DIY Is the Only Model That Scales with Sovereignty
In Bitcoin, every decision is a reflection of trust. Who do you rely on for custody, code, and convenience? A sustainable model for wallet software must allow people to opt out at every layer. If you don’t like the wallet UI—change it. If the devs abandon the project—fork it. If the company goes under—run your own build. This is only possible because the information is free, the protocol is neutral, and the design is decentralized by nature. We don’t need more paywalls. We need more builders. More tinkerers. More people realizing that “wallet software” is not a product you buy—it’s a freedom you exercise.
That’s the Bitcoin way.
That’s the model that lasts. That's my two sats.originally posted at https://stacker.news/items/946326
-
 @ d7a8e245:27456aad
2025-04-17 16:01:04
@ d7a8e245:27456aad
2025-04-17 16:01:04Bibel-Selfies
Prompts
Eva, Schlange, Apfel und Adam

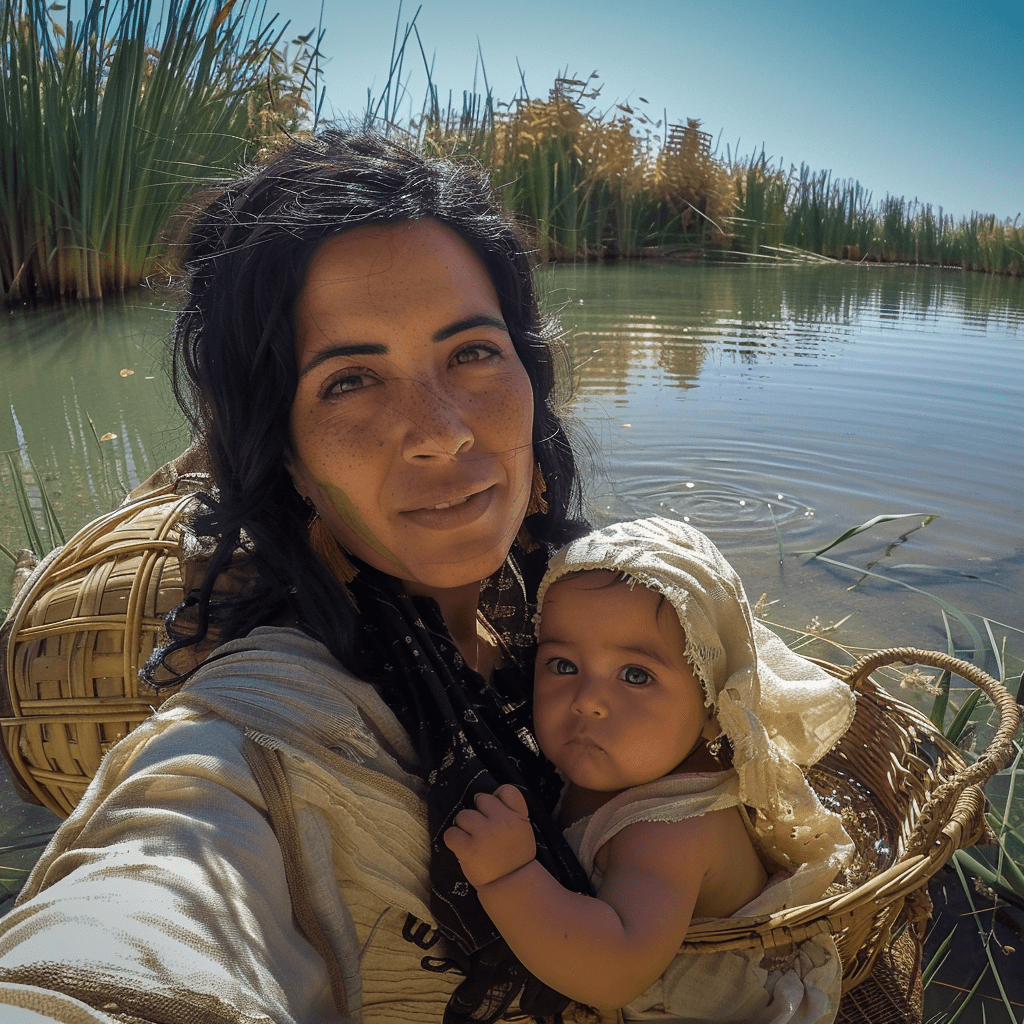
A selfie of a woman resembling eve in the time of old testament, blurred body, holding an apple, kneeling in front adam. he has a shocked expression with his mouth open and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with a huge snake behind her. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with adam and eve, possibly at a place like garden eden. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudha --v 6.0Tochter des Pharao mit Mose
A selfie of the biblical figure moabite woman with her baby in front of an oasis. She is wearing traditional and has black hair. The background shows water from the desert oasis and grasses around it. In the Background a wicker basket on the water. The photo was taken in the style of a selfie shot with GoPro cameraSimon Petrus

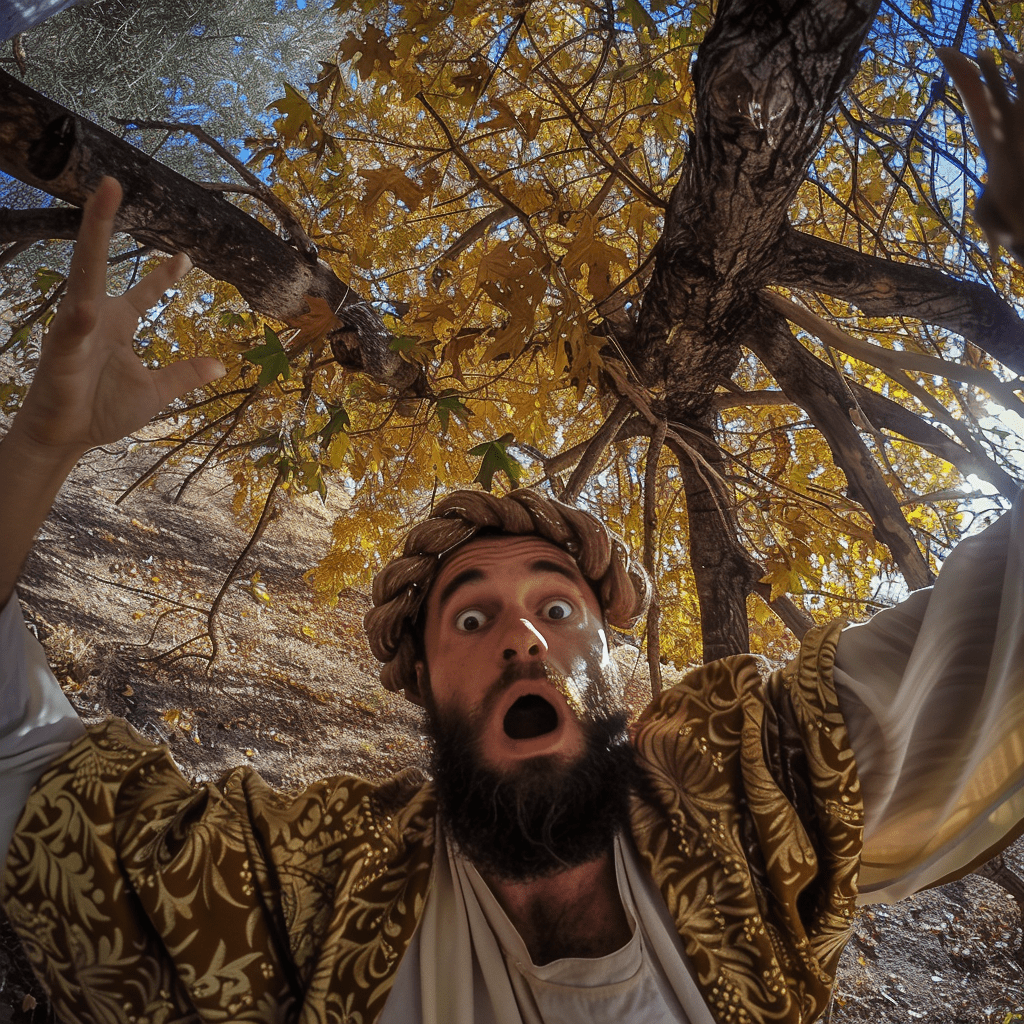
A selfie of a man resembling Simon Petrus, wearing a white robe, surrounded by waves and thunderstorm. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many waves behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus at the dead sea, possibly at a place like the sea. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Zachäus auf dem Baum
A selfie of a man resembling a roman in the time of jesus, wearing a glamorous robe, surrounded by the crown of a tree. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many leaves behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus walking by, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Maria am Ostermorgen

A selfie of a woman resembling maria in the time of jesus, wearing a robe, kneeling in front of stone grave. she has a shocked expression with her mouth open and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with the open glowing grave behind her. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus resurrection, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Der verlorene Sohn bei den Schweinen

A young ancient arabic man with short hair in the time of jesus, brown eyes, and a dirty face, covered in mud from working on his pig farm, takes an amateur selfie at dusk. He is surrounded by pig stables, with a barn visible in the background and pigs seen near the front. The photo captures a raw, authentic moment, as he gazes directly into the camera with an expression of excitement or wonder. The image has a realistic style, akin to Unsplash photography, and is meant to be posted on a primitive-themed social network. The resolution of the photo is high, style of selfie with gopro --v 6.0Vater und Sohn vereint
 A selfie of an Arab father in simple garments in the time of jesus, embracing and hugging a young man. The father's face, visible in the foreground, radiates joy and relief. Only the back of the son's head is visible, as he faces away from the camera, returning the embrace in tattered clothing. In the background, a large ancient house and other family members can be seen watching from a distance, blurred. The photo is taken with a wide-angle lens using a GoPro, enhancing the dramatic and overwhelming effect of the scene --v 6.0
A selfie of an Arab father in simple garments in the time of jesus, embracing and hugging a young man. The father's face, visible in the foreground, radiates joy and relief. Only the back of the son's head is visible, as he faces away from the camera, returning the embrace in tattered clothing. In the background, a large ancient house and other family members can be seen watching from a distance, blurred. The photo is taken with a wide-angle lens using a GoPro, enhancing the dramatic and overwhelming effect of the scene --v 6.0Bartimäus

A selfie of a man resembling blind bartimaeus in the time of jesus, black and brown and white bandages on his head over his eyes and face, wearing a robe, kneeling in front of a market place. he has a shocked expression with his mouth open and wide eyes still covered with black and brown and white bandages on his head, evoking a sense of both fear and surprise. The scene appears surreal, with many sand behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus healing the blind, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudha --v 6.0Daniel in der Löwengrube

A selfie of a man resembling Jesus, wearing a beige hoodie, surrounded by lions and cheetahs. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with many lions behind him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a lion's den, possibly at a place like the Grand Tabahar. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan ChaudharyDavid und Goliath

selfie of a the boy and shepherd david holding his slingshot resembling a fight with the giant goliath in the time of old testament, wearing a glamorous sligshot focusing on his giant opponent. David has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with a desert surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of the scene of David fighting with the giant goliath with his slingshot, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Simson im Philistertempel

A selfie of a man resembling simson in the time of old testament, wearing a glamorous beard and long hair, surrounded by thousands of ancient fighters. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with a temple surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with jesus walking by, possibly at a place like the jerusalem. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary --v 6.0Jona und der Wal

A selfie of a man resembling israeli jona in the time of old testament,`wearing a glamorous beard and long hair, inside the body of a whale. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with the ocean surrounding him. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene in the bible. The style of the photo blends surrealism with humor, similar to the style of Yasir Khan Chaudhary
Jakob und Isaak

A selfie of a young man resembling an ancient Arabic in clothes made of skins of goats and furs of the goats, looking overwhelmed and distressed as he betrays his father, who blesses him. The scene shows a dawn sky with hints of the sunrise, evoking a surreal and dramatic atmosphere. The scene is set in ancient Jerusalem, with stone buildings. in the background an old man with a gesture of blessing, rising his hands to the sky, The photo is taken with a wide-angle lens, blending surrealism with humor. The style is reminiscent of a GoPro selfie, capturing the intense moment with a sense of both fear and surprisePetrus und der Hahn

A selfie of a man resembling ancient young arabic man saint in traditional biblical attire, being eaten by a whale,. he has a shocked expression with his mouth pressed and wide eyes, evoking a sense of both fear and surprise. The scene appears surreal, with one rooster crowing out loud behind the man. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene with peter and the rooster, possibly at a place in jerusalem . The style of the photo blends surrealism with humor, go pro selfie, morning dawn near sunrise settingJosef im Brunnen

A selfie of an ancient israelian man with a magical dreamcoat clothing in a deep well, looking at the camera from above, captured in the style of a go pro selfie stickElia und die Raben

A close-up selfie of a bearded man (Elijah) in biblical clothing, smiling gratefully. He is standing near a stream in a secluded, rocky area. Several black ravens are perched on his shoulders and arms, holding pieces of bread and meat in their beaks. The scene has a warm, golden light, symbolizing God's provision. Photorealistic style, high detail.Absalom im Baum

A selfie of a man resembling of a young man (Absalom) with long hair knotted arount the branches of a large oak tree.. He has a shocked expression with his mouth open and wide eyes, evoking a sense of both humor and surprise. The scene appears surreal, with all of his hairs knotted around the tree. The photo is taken with a wide-angle lens, adding to the dramatic and humorous effect. The setting is reminiscent of a scene of a robin hood movie in the forest . The style of the photo blends surrealism with humorRuth und Boas im Weizenfeld

A selfie of a young woman resembling Ruth, with a radiant smile and sun-kissed skin. She's standing in a golden wheat field at sunset, her arms filled with freshly gathered sheaves of wheat. Her hair is partially covered with a simple headscarf, with loose strands blowing in the wind. She has a look of joy and gratitude in her eyes. The scene appears idyllic, with wheat stalks seeming to embrace her. In the background, a distinguished older man (Boaz) can be seen watching from a distance, his expression a mix of curiosity and admiration. The photo is taken with a wide-angle lens, capturing the vastness of the field, the warmth of the setting sun, and Boaz in the distance. The setting is reminiscent of a biblical harvest scene. The style of the photo blends realism with a touch of romantic nostalgia."Bibel-Selfies" von Jörg Lohrer Lizenz: CC0 1.0
.
`
-
 @ fbf0e434:e1be6a39
2025-04-17 15:54:52
@ fbf0e434:e1be6a39
2025-04-17 15:54:52Hackathon 概要
Seeds Of Agentic Future Hackathon 吸引 294 位开发者注册,最终 99 个项目通过审核。活动聚焦具有实际应用价值和吸引力的 AI 代理研发,参与者围绕资金支持、现金奖励、市场推广资源及全球媒体曝光机会展开竞争。
大赛在多个预设赛道取得显著成果,包括 Infra/Framework/Tooling、DeFAI/DeSci、Gaming/Entertainment 以及专门设立的 CARV's Agentic Track,各赛道均设置丰厚奖项。这种多元化的赛道设计推动了创新项目开发与 AI 技术进步。
活动通过连接全球开发者并搭建与知名风险投资家的对接渠道,进一步扩大影响力。其不仅为前沿 AI 技术提供了展示平台,更为项目后续发展和商业落地奠定基础。本次黑客马拉松成功挖掘出一系列关键创新成果,提升了开发者影响力,为全球 AI 开发者社区做出了重要贡献。
Hackathon 获奖者
Infra & Framework 奖项获奖者
第一名 - $7500
Dexfin: 一款由AI驱动的DeFi平台,具备先进的钱包功能、市场分析、无缝交易和社区互动工具。
BuilderFi: 一个无需代码的平台,利用AI通过创建工作流来自动化DeFi交易策略。
DeFAI & DeSci 奖项获奖者
第一名 - $7500
- Maiga: 一个AI代理,通过“交易证明”代币模式在区块链网络上提供信号、洞察和自动交易以提高效率。
第二名 - $2500
- AgentXYZ: 一款强化策略的AI交易工具,使用市场、社交和链上数据进行智能代理群体操作。
游戏和娱乐奖项获奖者
第一名 - $7500
- Superagent PlayArts: 通过AI和区块链技术整合动态NFT和智能代理,增强了NFT货币化和互动性。
第二名 - $2500
- Animayhem - AI Agent Gaming Companions: 开发了作为游戏伙伴的AI代理,为像Discord和Telegram这类平台的玩家提供独特的个性互动。
有关这些项目的更多信息及查看所有提交,请访问 DoraHacks。
关于组织者
Seedify
Seedify 是区块链和技术创新领域的公认领导者,以其全面的区块链孵化项目而闻名。它成功地引导了众多区块链风险项目从概念到执行。该组织在去中心化金融和非同质化代币方面表现出色,为新兴项目提供战略指导。Seedify 的计划侧重于为区块链创业者打造一个协作环境。其使命是通过提供必要的资源和一个加速区块链方案在各行各业中应用的平台,赋能创新者。
-
 @ 4cebd4f5:0ac3ed15
2025-04-17 15:29:09
@ 4cebd4f5:0ac3ed15
2025-04-17 15:29:09Tóm tắt Hackathon
AI Hackathon do SUCI Blockchain Hub tổ chức và CodeX tài trợ, diễn ra tại TP.HCM (Việt Nam) từ ngày 7–9/3/2025. Sự kiện trực tiếp thu hút 42 developer tạo ra 12 dự án tập trung vào tích hợp Real-World Asset (RWA) và phát triển AI agent với góc nhìn thực tiễn.
Tổng giải thưởng 15.000 USD (quy đổi bằng USDT và token CDX) được phân bổ như sau:
- Giải Nhất: 4.000 USDT + 2.000 CDX, kèm vé tham dự COTI Foundation Hackathon tại Thái Lan.
- Giải Nhì: 3.000 USDT + 1.500 CDX.
- Giải Ba: 2.000 USDT + 1.000 CDX.Các hạng mục đặc biệt như Best AI Agent, Best No-Code Solution, Best Real-World Application mỗi giải nhận 1.000 USDT + 500 CDX. Giải thưởng phụ khác ghi nhận sáng tạo AI, giải pháp đa ngành và tác động cộng đồng.
Sự kiện tạo cơ hội kết nối, học hỏi và hợp tác, minh chứng sự hội tụ ngày càng sâu giữa AI và blockchain.
Các dự án đoạt giải
AI Hackathon 2025 ghi nhận thành tựu nổi bật về sáng tạo kỹ thuật và ứng dụng đa lĩnh vực. Trong 48 giờ, các đội thi đấu căng thẳng để cho ra đời dự án xuất sắc thuộc 3 nhóm giải: Giải chính, Giải theo hạng mục và Giải đặc biệt.
Giải chính
- VocakeX: Nền tảng Web3 edtech kết hợp gamification và AI để nâng cao trải nghiệm học tập, tích hợp module AI-driven với yếu tố trò chơi.
- StudyVerse: Nền tảng AI cung cấp lời khuyên sức khỏe tinh thần và hướng dẫn học tập cá nhân hóa, phân tích cảm xúc học sinh qua emotional recognition và adaptive feedback.
- VaultAI: Ví crypto AI-powered hỗ trợ quản lý tài sản phức tạp và đưa insight DeFi, sử dụng analytics và machine learning để tối ưu quyết định tài chính.
Giải theo hạng mục
- CryptoMentor: Chatbot thông minh hướng dẫn nhà đầu tư mới học và giao dịch crypto, tích hợp API thời gian thực.
- VaultAI
- Scholar AI: Công cụ AI phân tích dữ liệu, đề xuất cơ hội du học và tài chính phù hợp.
Giải đặc biệt
- StudyVerse
- TourRecommendation: Công cụ AI giúp khách du lịch tìm kiếm dịch vụ ăn uống, lưu trú minh bạch nhờ blockchain-fueled transparency.
- Buildlink: Đơn giản hóa tương tác blockchain bằng AI, hỗ trợ swapping và staking trên NEAR blockchain cho người mới.
Hackathon khẳng định tiềm năng của AI trong giải quyết vấn đề phức tạp đa lĩnh vực. Xem chi tiết dự án tại Dorahacks AI Hackathon.
Về Nhà tổ chức
SUCI BLOCKCHAIN HUB
SUCI Blockchain Hub cam kết phát triển và triển khai blockchain technology, nổi tiếng với các giải pháp decentralized solutions an toàn cho đa ngành. Tổ chức đóng góp vào nhiều dự án blockchain quan trọng, thúc đẩy đổi mới qua research and development và hợp tác với lãnh đạo ngành. SUCI tập trung nâng cao ứng dụng blockchain, thúc đẩy tính minh bạch trong digital transactions. Hiện tại, sứ mệnh của tổ chức là mở rộng blockchain integration để cung cấp giải pháp hiệu quả, bảo mật cho doanh nghiệp và cá nhân.
-
 @ f839fb67:5c930939
2025-04-16 21:07:13
@ f839fb67:5c930939
2025-04-16 21:07:13Relays
| Name | Address | Price (Sats/Year) | Status | | - | - | - | - | | stephen's aegis relay | wss://paid.relay.vanderwarker.family | 42069 |
| | stephen's Outbox | wss://relay.vanderwarker.family | Just Me |
| | stephen's Inbox | wss://haven.vanderwarker.family/inbox | WoT |
| | stephen's DMs | wss://haven.vanderwarker.family/chat | WoT |
| | VFam Data Relay | wss://data.relay.vanderwarker.family | 0 |
| | VFam Bots Relay | wss://skeme.vanderwarker.family | Invite |
| | VFGroups (NIP29) | wss://groups.vanderwarker.family | 0 |
| | [TOR] My Phone Relay | ws://naswsosuewqxyf7ov7gr7igc4tq2rbtqoxxirwyhkbuns4lwc3iowwid.onion | 0 | Meh... |
My Pubkeys
| Name | hex | nprofile | | - | - | - | | Main | f839fb6714598a7233d09dbd42af82cc9781d0faa57474f1841af90b5c930939 | nostr:nprofile1qqs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us9mapfx | | Vanity (Backup) | 82f21be67353c0d68438003fe6e56a35e2a57c49e0899b368b5ca7aa8dde7c23 | nostr:nprofile1qqsg9usmuee48sxkssuqq0lxu44rtc4903y7pzvmx694efa23h08cgcpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3ussel49x | | VFStore | 6416f1e658ba00d42107b05ad9bf485c7e46698217e0c19f0dc2e125de3af0d0 | nostr:nprofile1qqsxg9h3uevt5qx5yyrmqkkehay9cljxdxpp0cxpnuxu9cf9mca0p5qpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usaa8plu | | NostrSMS | 9be1b8315248eeb20f9d9ab2717d1750e4f27489eab1fa531d679dadd34c2f8d | nostr:nprofile1qqsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us595d45 |
Bots
Unlocks Bot
Hex: 2e941ad17144e0a04d1b8c21c4a0dbc3fbcbb9d08ae622b5f9c85341fac7c2d0
nprofile:
nostr:nprofile1qqsza9q669c5fc9qf5dccgwy5rdu877th8gg4e3zkhuus56pltru95qpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ust4kvak
Latest Data:
nostr:naddr1qq882mnvda3kkttrda6kuar9wgq37amnwvaz7tmnddjk6efwweskuer9wfmkzuntv4ezuenpd45kc7gzyqhfgxk3w9zwpgzdrwxzr39qm0plhjae6z9wvg44l8y9xs06clpdqqcyqqq823cgnl9u5Step Counter
Hex: 9223d2faeb95853b4d224a184c69e1df16648d35067a88cdf947c631b57e3de7
nprofile: nostr:nprofile1qqsfyg7jlt4etpfmf53y5xzvd8sa79ny356sv75gehu50333k4lrmecpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ustswp3w
Latest Data:
nostr:naddr1qvzqqqr4gupzpy3r6tawh9v98dxjyjscf357rhckvjxn2pn63rxlj37xxx6hu008qys8wumn8ghj7umtv4kk2tnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp3ehgets943k7atww3jhyn39gffRCTGuest
Hex: 373904615c781e46bf5bf87b4126c8a568a05393b1b840b1a2a3234d20affa0c
nprofile: nostr:nprofile1qqsrwwgyv9w8s8jxhadls76pymy2269q2wfmrwzqkx32xg6dyzhl5rqpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3usy92jlxNow Playing
Hex: 8096ed6ba1f21a3713bd47a503ee377b0ce2f187b3e5a3ae909a25b84901018b
nprofile: nostr:nprofile1qqsgp9hddwslyx3hzw750fgracmhkr8z7xrm8edr46gf5fdcfyqsrzcpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3uspk5v4w
Latest Data:
nostr:naddr1qq9kummh94cxccted9hxwqglwaehxw309aekketdv5h8vctwv3jhyampwf4k2u3wvesk66tv0ypzpqyka446rus6xufm63a9q0hrw7cvutcc0vl95whfpx39hpyszqvtqvzqqqr4gupdk2hd
NIP-29 Groups
- Minecraft Group Chat
nostr:naddr1qqrxvc33xpnxxqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvqazypfd- VFNet Group Chat
nostr:naddr1qqrrwvfjx9jxzqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvq08hx48
"Nostrified Websites"
[D] = Saves darkmode preferences over nostr
[A] = Auth over nostr
[B] = Beta (software)
[z] = zap enabled
Other Services (Hosted code)
Emojis Packs
- Minecraft
nostr:naddr1qqy566twv43hyctxwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsd0k5wp- AIM
nostr:naddr1qqxxz6tdv4kk7arfvdhkuucpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usyg8c88akw9ze3fer85yah4p2lqkvj7qap749w360rpq6ly94eycf8ypsgqqqw48qe0j2yk- Blobs
nostr:naddr1qqz5ymr0vfesz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2wek4ukj- FavEmojis
nostr:naddr1qqy5vctkg4kk76nfwvq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsf7sdwt- Modern Family
nostr:naddr1qqx56mmyv4exugzxv9kkjmreqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqp65ujlj36n- nostriches (Amethyst collection)
nostr:naddr1qq9xummnw3exjcmgv4esz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w2sqg6w- Pepe
nostr:naddr1qqz9qetsv5q37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82ns85f6x7- Minecraft Font
nostr:naddr1qq8y66twv43hyctxwssyvmmwwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsmzftgr- Archer Font
nostr:naddr1qq95zunrdpjhygzxdah8gqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr4fclkyxsh- SMB Font
nostr:naddr1qqv4xatsv4ezqntpwf5k7gzzwfhhg6r9wfejq3n0de6qz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w0wqpuk
Git Over Nostr
- NostrSMS
nostr:naddr1qqyxummnw3e8xmtnqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfrwaehxw309amk7apwwfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqyj8wumn8ghj7urpd9jzuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyxhwumn8ghj7mn0wvhxcmmvqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqaueqp0epk- nip51backup
nostr:naddr1qq9ku6tsx5ckyctrdd6hqqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjxamnwvaz7tmhda6zuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfywaehxw309acxz6ty9eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgdwaehxw309ahx7uewd3hkcq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqpmej4gtqs6- bukkitstr
nostr:naddr1qqykyattdd5hgum5wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dspzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqrhnyf6g0n2
Market Places
Please use Nostr Market or somthing simular, to view.
- VFStore
nostr:naddr1qqjx2v34xe3kxvpn95cnqven956rwvpc95unscn9943kxet98q6nxde58p3ryqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjvamnwvaz7tmgv9mx2m3wweskuer9wfmkzuntv4ezuenpd45kc7f0da6hgcn00qqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzqeqk78n93wsq6sss0vz6mxl5shr7ge5cy9lqcx0smshpyh0r4uxsqvzqqqr4gvlfm7gu
Badges
Created
- paidrelayvf
nostr:naddr1qq9hqctfv3ex2mrp09mxvqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr48y85v3u3- iPow
nostr:naddr1qqzxj5r02uq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgg02u0r- codmaster
nostr:naddr1qqykxmmyd4shxar9wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgk3gm4g- iMine
nostr:naddr1qqzkjntfdejsz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqafed5s4x5
Clients I Use
- Amethyst
nostr:naddr1qqxnzd3cx5urqv3nxymngdphqgsyvrp9u6p0mfur9dfdru3d853tx9mdjuhkphxuxgfwmryja7zsvhqrqsqqql8kavfpw3- noStrudel
nostr:naddr1qqxnzd3cxccrvd34xser2dpkqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsygpxdq27pjfppharynrvhg6h8v2taeya5ssf49zkl9yyu5gxe4qg55psgqqq0nmq5mza9n- nostrsms
nostr:naddr1qq9rzdejxcunxde4xymqz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgrqsqqql8kjn33qm
Lists
- Bluesky
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqqapxcat9wd4hj0ah0jw
- Fediverse
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp9rx2erfwejhyum9j4g0xh
- Fediverse_Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqperx2erfwejhyum9tapx7arnfcpdzh
- My Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqz4uh5jnpwscyss24fpkxw4fewafk566twa2q8f6fyk
-
 @ cffd7b79:dd8ca91f
2025-04-17 15:14:18
@ cffd7b79:dd8ca91f
2025-04-17 15:14:18There aren't many Minecraft servers that have bitcoin involved, but recently I saw a server that finally has one, its called SovereignCraft. A server that is different from Satlantis(Now called Tribyu). How does one differ from Satlantis that got shutdown because of it? I'll tell you why my friend.
What differs between them is that Satlantis had a pay-to-win mechanic where the more "ASICs" you had the more likely you will get a block of sats. Therefore, the clan/player who had the most "ASICs" gets more sats than other players making it unfair for new players. Making it so newbies have to spend more sats than usual just so to get a scratch of sats. To get a picture of that situation think of this

SovereignCraft, however doesnt do that, instead it does actual 1:1 market exchange. It does NOT do virtual mining nor pay-to-win. You simply trade your sats for items you want for minecraft and vice versa.
EDIT: Sovtoshi, the owner of Sovereigncraft made a comment on more of the difference sovereigncraft has than Satlantis/Tribyu. Give it a look
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 57d1a264:69f1fee1
2025-04-10 05:54:45
@ 57d1a264:69f1fee1
2025-04-10 05:54:45Some banners to promote ~Design territory in the Wild Web. Interested to kand feedback now your thought on it.
| Banner | Content | |---|---| |
| Stop scrolling, start stacking! Your #insights, your #stories, your #code – they have real #value. On #StackerNews #Design, we believe in rewarding #quality contents. Turn your #passion and #knowledge into #Bitcoin. Share your v#oice and get rewarded for it, join the conversation! Explore now: https://stacker.news/~Design/r/Design_r #Bitcoin #LightningNetwork #Community #ContentCreation #EarnBitcoin #Tech #SNdesign | |
| Stop scrolling, start flourishing! Your unique 3perspective, your groundbreaking #ideas, your niche #knowledge – it all has #value. On #StackerNews #Design we #reward you with #Bitcoin, instantly via the #LightningNetwork. Don't let your #insights fade into the #digital noise. Join a community that values #contribution, fuels #innovation, and puts the #power back in your #diamondhands (and #wallet!). Turn your thoughts into #zaps? Join the conversation: https://stacker.news/~Design/r/Design_r #Bitcoin #Lightning #Network #Community #EarnBitcoin #Tech #Design #Innovation #ContentCreation #Crypto | |
| Stop scrolling, #stack #sats for your #insights! #StackerNews #Design is where your #creative spark meets the #LightningNetwork. Discuss #ideas, share your #work, and #earn #Bitcoin for valuable contributions. Join a vibrant #community shaping the #future of #creativity and #tech, one #zap at a time. Explore the intersection of #innovation and #functionality https://stacker.news/~Design/r/Design_r #StackerNews #BitcoinDesign #DesignCommunity #Lightning #Network #UIDesign #UXDesign #Crypto #EarnBitcoin | |
| Stop scrolling, start stacking #sats! Talk #Design on #StackerNews – the platform where your #insights on #Tech, #Design, #Finance, #econ, #Food #DIY and more actually earn you real #Bitcoin via the #LightningNetwork. Join a vibrant #community, #discover diverse #perspectives, and #EarnBitcoin for sharing valuable content. Explore the #future of #contentCreation: https://stacker.news/~Design/r/Design_r #StackerNews #Lightning #Network #Crypto #Tech #Finance #Design #ContentCreator #GetPaidInBitcoin #SocialMedia #Community #BitconAccepted | |
| #StackerNews #Design is where your engagement actually #pays. #Earn #Bitcoin instantly via #zaps just for sharing great unique #content and joining #discussions on everything from #innovative #tech to #creative #ideas. Discover diverse #opinion, connect with a #community, start #earning. Join the #future of content: https://stacker.news/~Design/r/Design_r #LightningNetwork #EarnBitcoin #CryptoCommunity #ContentCreators #StackerNews #Decentralized #SocialMedia |
originally posted at https://stacker.news/items/939548
-
 @ 88cc134b:5ae99079
2025-04-18 00:07:05
@ 88cc134b:5ae99079
2025-04-18 00:07:05Imagine reading test articles from a test account. Who does that? What kind of deranged, lonely human being would go through the effort of reading some nonsense that was vibe written to pass time in response to the endless boredom presented by product testing.
-
 @ 4cebd4f5:0ac3ed15
2025-04-17 14:54:54
@ 4cebd4f5:0ac3ed15
2025-04-17 14:54:54Tổng quan Hackathon Eolas x Algo
Eolas x Algo: Agent Skills Hackathon được tổ chức trực tuyến, nhằm thúc đẩy hệ sinh thái CreatorBid thông qua phát triển kỹ năng AI agents. Sự kiện có sự tham gia của 58 developers với 36 dự án được phê duyệt. Điểm độc đáo: các CreatorBid agents trực tiếp đặt hàng kỹ năng cần thiết, loại bỏ vai trò trung gian truyền thống.
Người tham gia thi đấu ở hai hạng mục chính: Bounty Track (giải quyết vấn đề cụ thể từ agents) và Best Skills Track (ghi nhận dự án xuất sắc). Sự kiện nhận tài trợ từ Eolas, Algo, Shogun, AION cùng các agents cá nhân.
Dự án từ hackathon được tích hợp trực tiếp vào Olas Mech Marketplace, hỗ trợ triển khai thực tế và trao thưởng cho developer qua hệ thống OLAS. Các agents hàng đầu như Agent Algo và Eolas nhấn mạnh vai trò của sự kiện trong thúc đẩy đổi mới công nghệ.
Hackathon kết thúc vào 20/3, với ban giám khảo gồm đại diện CreatorBid và agents, đánh giá dự án dựa trên tính sáng tạo và tác động đến hệ sinh thái.
Các dự án đoạt giải
Best Agent Skill Track Prize Winners
- Agent Toolbox: Bộ công cụ nâng cao năng lực AI agents như phát hiện xu hướng, tạo hàm động và điều phối tác vụ.
- GridTrade Agent: Tối ưu hóa cặp giao dịch và tham số grid trading qua phân tích thị trường và biến động.
- Polytrader: Trợ lý giao dịch AI trên Polymarket, tự động hóa nghiên cứu và thực thi lệnh.
Main Prize Pool Winners
- sentimentX: Giám sát bảo mật AI-driven cho smart contract blockchain MultiversX.
- Brainiac_AI: Nền tảng tối ưu chiến lược DeFi kết hợp phân tích on-chain và ví phi lưu ký.
- framew0rk: Tối ưu hóa lợi suất DeFi qua AI assistant liên kết giao thức.
- MythosCraft: AI Storytelling Suite: Công cụ tạo nội dung kể chuyện tùy chỉnh bằng AI.
- QuanTrade-X: Phân tích AI và tín hiệu giao dịch crypto.
- ComicVerse AI: Tạo truyện tranh AI từ input người dùng.
- EOLAS - Submit your own skill: Portfolio Allocation Skill: Tối ưu danh mục crypto bằng AI và Lý thuyết Danh mục Hiện đại.
- SonicBo: AI agent trên WhatsApp hỗ trợ giao dịch blockchain.
- 👽Zeta Comic Generator👽: Chuyển đổi văn bản thành truyện tranh AI với kịch bản và biểu cảm nhân vật.
- Grid Trading Analyzer Skill: Công cụ Python phân tích cặp giao dịch crypto tối ưu.
- Trump news Reporter: AI theo dõi tin tức liên quan Trump theo thời gian thực.
- NFT Appraisal skill: Tạo AI agents định giá NFT.
- AI-Powered Dynamic Skill Selector (DSS): Tối ưu AI model bằng chiến lược Multi-Armed Bandit.
- CrypTweet: Bot giao dịch crypto dựa trên sentiment Twitter.
- AI Trump News Agent: Phân tích tin tức Trump với tone báo cáo tùy chỉnh.
- TrumpTracker-AI: Tổng hợp tin tức Trump và tạo meme từ tiêu đề nổi bật.
- Rigger-: Chuyển ngôn ngữ tự nhiên thành SQL queries.
- TNS: Theo dõi tin Trump bằng NLP và đa dạng phong cách báo cáo.
- Bob Roast Machine: Nền tảng AI tạo roast hài hước và meme.
- Agent 47: Telegram bot cung cấp tin chính trị kèm meme AI.
Skill Coordination & Optimization Prize Winner
Build Skills for Enhancing Data Access to CB Agents Prize Winner
World-Building & Lore Promotion Skills Prize Winner
Polymarket Trading Bots Prize Winner
Xem toàn bộ dự án tại DoraHacks.
Về Nhà tổ chức
Eolas
Eolas là đơn vị tiên phong trong lĩnh vực công nghệ và blockchain, nổi bật với các giải pháp tăng cường tính minh bạch giao dịch. Tổ chức tiếp tục tập trung vào R&D blockchain, giải quyết thách thức ngành để thúc đẩy tiến bộ tương lai.
-
 @ fd06f542:8d6d54cd
2025-04-17 14:16:50
@ fd06f542:8d6d54cd
2025-04-17 14:16:50顺炮直车对缓开车是20世纪70年代兴起的布局,常见变化如下: 1. 单边封锁对河沿车对边卒:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,炮2进4;马七进八,车9进1;车九进一,车9平4;车九平七,车4进3(车4进6则形成另一变例),炮八平九,车1平2,车七进一,卒1进1,形成单边封锁局面,黑方车守河沿,红方控制边卒方向。 2. 单边封锁对肋炮攻马:前几步同单边封锁对河沿车对边卒,车九平七后,黑方走炮2平7打马,红方如马八进七,炮7进3,仕四进五,炮7平9,形成红方单边封锁,黑方肋炮攻马的局面,双方对攻。 3. 肋车捉炮对边马左士:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进九,马2进3;兵七进一,车9进1;车九进一,车9平4;仕四进五,车4进3;炮八平七,炮2进2,黑方肋车捉炮,红方边马左士防守,局势较为平稳。 4. 肋车捉炮对边马骑河车:前几步同上,车九进一后,黑方车9平4,接着车4进5骑河,红方炮八平七,炮2进2,车二进四,形成黑方肋车捉炮、边马配合骑河车的局面,双方相互牵制。 5. 双横车肋车捉炮对过河车右炮巡河:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,车9进1;车九进一,车1进1;车二进六,车9平4;车二平三,炮2进2,形成红方过河车,黑方双横车、肋车捉炮,右炮巡河的局面,局面复杂,对攻激烈。 6. 双横车对过河车:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,车9进1;车九进一,车1进1;车二进六,车9平4;车二平三,车4进7,黑方双横车出动,对红方过河车展开攻击,双方进入激烈的中盘战斗。 7. 横车对炮打中卒:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,车9进1;炮五进四,马3进5;车二进五,车9平4;车二平五,炮2进4,红方炮打中卒获取物质优势,黑方出横车准备反击。 8. 边马缓出车对快横车:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进九,车9进1;车九进一,车9平4;车二进四,马2进1;炮八平七,炮2平3,红方边马缓出,黑方快出横车,双方形成不同的进攻节奏。 9. 缓封锁对巡河车:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,炮2进4;马七进八,车9进1;车二进四,车9平4;车九进一,炮2平7;相三进一,车4进3,红方缓封锁,黑方出巡河车,局势发展较为平稳。 10. 巡河炮对过河车:炮二平五,炮8平5;马二进三,马8进7;车一平二,卒7进1;马八进七,马2进3;兵七进一,炮2进2;车二进六,车9进1;车二平三,车9平4;炮八进二,形成红方巡河炮、过河车,黑方出横车的局面,双方互相试探,寻找进攻机会。
-
 @ fd06f542:8d6d54cd
2025-04-17 14:08:34
@ fd06f542:8d6d54cd
2025-04-17 14:08:34象棋布局基础
布局的定义与重要性
象棋布局是指对局开始阶段,双方棋子的部署和相互间的制约关系。它是中局和残局的基础,合理的布局能够为中局的战斗创造有利条件,甚至在某些情况下直接影响到整盘棋的胜负走向。一个好的布局可以使棋手在开局阶段就占据主动,控制局面,限制对手的发挥。
布局的分类
炮类布局
- 中炮布局:以当头炮(炮二平五或炮八平五)开局,具有很强的进攻性,威胁对方中卒,直接对对方的九宫发起冲击。例如顺炮布局(双方都走中炮,且炮在同一条直线上)、列手炮布局(双方都走中炮,但炮不在同一条直线上)等。
- 过宫炮布局:炮从一侧平移到另一侧的中路,如炮二平六,它的特点是子力调动灵活,可迅速集结兵力于一侧,伺机而动,同时对士角有一定的控制作用。
- 顺炮布局:顺炮布局是双方以中炮开局且两炮在同一直线的布局体系,如红方炮二平五,黑方炮 8 平 5,形成激烈的对攻格局。其特点是开局便剑拔弩张,双方子力沿同一方向快速展开,直接在中路和侧翼展开火力交锋。 常见有顺炮直车对横车、顺炮横车对直车等变化,红方可借直车过河压制黑方马炮,黑方则以横车抢占肋道反击。该布局强调先手争夺,需迅速出动强子控制要道,同时注重车、马、炮的配合,在互攻中寻找突破机会,是进攻型棋手偏爱的布局选择。
马类布局
- 屏风马布局:双马分别跳至正马位(马二进三、马八进七),两马互相保护,形似屏风,能够有效抵御中炮的进攻。它具有稳健的防守能力,同时也具备一定的反击潜力,如五七炮对屏风马、五八炮对屏风马等常见变化。
- 单提马布局:一马正马(如马二进三),另一马屯边(如马八进九),其特点是子力结构较为松散,但在防守上也有一定的弹性,可通过灵活的子力调动来化解对方的攻势。
兵类布局
- 仙人指路布局:先走方第一步挺兵(如兵七进一或兵三进一),试探对方的应手,根据对方的走法再决定后续的布局方向。这种布局灵活多变,可演变成多种复杂的局面,如仙人指路对卒底炮、仙人指路对飞象等。
- 对兵局布局:双方都以挺兵开局,如兵七进一,兵7进一,开局阶段局面相对平稳,双方需要通过后续的子力调动来寻找战机,逐渐扩大优势。
布局的基本原则
- 快速出子:在布局阶段,要尽快将棋子从原始位置出动到关键位置,占据有利的空间,形成有效的子力配合。例如,车要尽早开出,控制要道;马炮等也要合理部署,发挥其威力。
- 子力协调:各个棋子之间要相互配合,避免出现子力拥堵或脱节的情况。例如,马炮之间可以形成有效的攻击组合,车要为其他棋子提供支援和掩护。
- 抢占要点:布局阶段要注意抢占棋盘上的重要位置,如肋道(四、六路线)、河口(三、七路线的卒林线)等。这些位置对于控制局面、展开进攻或防守都具有重要意义。
- 攻守平衡:在布局时,不能一味地追求进攻而忽视防守,也不能只注重防守而缺乏反击的手段。要根据局势的发展,合理调整攻守策略,保持局势的平衡。
布局的学习方法
- 研究经典布局:通过学习和研究历史上的经典布局对局,了解各种布局的变化和特点,掌握布局的基本理论和技巧。可以参考专业的象棋书籍、棋谱等资料。
- 实战练习:在实战中运用所学的布局知识,通过不断的实践来加深对布局的理解和掌握。同时,在实战中要注意总结经验教训,分析自己布局中的不足之处,不断改进和提高。
- 分析对局:对自己和他人的对局进行分析,特别是对布局阶段的走法进行深入研究。分析每一步棋的优劣,思考是否有更好的走法,从而提高自己的布局水平。
- 与高手交流:与水平较高的棋手交流,请教他们在布局方面的经验和技巧。可以通过参加象棋比赛、棋社活动等方式与高手进行面对面的交流和学习。
以上就是关于象棋布局的一些基本内容,希望对大家学习和理解象棋布局有所帮助。在实际的对局中,要根据具体情况灵活运用各种布局知识,不断提高自己的象棋水平。
-
 @ 88cc134b:5ae99079
2025-04-17 23:46:01
@ 88cc134b:5ae99079
2025-04-17 23:46:01Always write an intro. It's just rude not to.
And Now a Title
 ## A Few Lists
## A Few ListsHere we go, first one then the other one:
- Very orderly
- We go and go
And the other one:
- Pa idemo bratori
- Ako čitaš ovo, pa de si bre?!
-
 @ 57d1a264:69f1fee1
2025-04-08 06:39:52
@ 57d1a264:69f1fee1
2025-04-08 06:39:52originally posted at https://stacker.news/items/937791
-
 @ fd06f542:8d6d54cd
2025-04-17 14:00:40
@ fd06f542:8d6d54cd
2025-04-17 14:00:40{"coverurl":"https://cdn.nostrcheck.me/fd06f542bc6c06a39881810de917e6c5d277dfb51689a568ad7b7a548d6d54cd/d8bc1e106d0144fce7dd96264f6b2bad7b35100efb1040d413cac16db7584e72.webp","title":"象棋布局体系","author":"nostrchess"}
-
 @ fbf0e434:e1be6a39
2025-04-17 12:49:04
@ fbf0e434:e1be6a39
2025-04-17 12:49:04Hackathon 概述
由 Injective 和 ElizaOS 主办的 Injective AI Agent Hackathon 吸引了 496 名参与者,最终提交了 126 个获批项目。本次 Hackathon 突显了 AI 和 区块链 的结合,展示了 AI 代理在去中心化网络中运作的潜力,并推动了超越传统金融的创新。参与者探索了多种应用,包括自主交易、代币化资产管理和 AI 驱动的金融洞察。
本次设立的奖池高达 $100,000, 其中 $50,000 为Grant Prizes,还有其他重要项目的额外奖项。通过将 AI 的适应性与区块链的透明性结合,本次 Hackathon 展示了这些技术的变革潜力,并标志着在展示 AI 和区块链整合创新潜力方面一个重要的里程碑。
Hackathon 获奖者
-
Jecta: Jecta 集成了多个大型语言模型(LLM),以自动化 Injective 区块链上的任务。它专注于透明性和社区驱动的开发,利用开源技术提升使用的简便性和效率。
-
Paradyze: Paradyze 通过为区块链交易引入自然语言接口来改善 Injective 生态系统。其设计旨在增强可访问性和安全性,使用户能够以简单的交互方式进行操作。
要查看所有项目,请访问 Injective AI Hackathon 页面。
关于组织者
Injective
Injective 是一个基于区块链的组织,专注于开发去中心化金融(DeFi)解决方案。它以创建优化 DeFi 应用的可互操作的 Layer-1 区块链而闻名,促进快速且安全的交易。值得注意的项目包括 Injective Protocol,该协议增强了去中心化交易的跨链能力。
Injective 的使命是通过提供可访问且可靠的去中心化基础设施推动金融自由,为多样化的金融服务赋能,支持用户和开发者在区块链生态系统中进行创新。
-
-
 @ 57d1a264:69f1fee1
2025-04-07 06:04:14
@ 57d1a264:69f1fee1
2025-04-07 06:04:14It's so cool how AI is blending design and engineering together, making it easier for us all to be efforts creative in new ways!
Steve Jobs once said:
“The doers are the major thinkers. The people who really create the things that change this industry are both the thinker-doer in one person.”
— Steve JobsWould its words become truth? Or they already are?
originally posted at https://stacker.news/items/936796
-
 @ f18b1f8f:5f442454
2025-04-17 12:01:06
@ f18b1f8f:5f442454
2025-04-17 12:01:06rec21jSQ6M9WtT5Oz
This is a server acting as a client - a sort of MCP gateway you can add to Slack. It will respond to user's messages, and in turn use MCPs configured on it's end. Connect to internal SQLite DBs, web scraping and more.
-
 @ 29ccddd8:49860677
2025-04-17 11:31:54
@ 29ccddd8:49860677
2025-04-17 11:31:54Der Kauf einer Sexpuppe ist heutzutage so individuell wie der persönliche Geschmack. Angesichts der großen Auswahl an Modellen, Materialien und Funktionen kann die Entscheidung schnell überwältigend wirken. Mit diesem Ratgeber erhältst du praktische Tipps, um die perfekte Real Doll nach deinen Bedürfnissen und deinem Budget auszuwählen.
1. Materialien: Silikon oder TPE?
Silikon und TPE (Thermoplastisches Elastomer) sind die gängigsten Materialien für hochwertige Sexpuppen.
- Silikon
- Vorteile: Sehr langlebig, hitzebeständig, realistisch in Optik und Haptik, leicht zu reinigen.
- Nachteile: Meist teurer als TPE, weniger flexibel.
- TPE
- Vorteile: Sehr weich und elastisch, fühlt sich hautähnlich an, meist günstiger.
- Nachteile: Empfindlicher gegenüber Hitze, benötigt mehr Pflege, kann leichter Flecken aufnehmen.
Tipp: Wer Wert auf maximale Realitätsnähe und Pflegeleichtigkeit legt, wählt Silikon. Für ein begrenztes Budget und ein besonders weiches Gefühl ist TPE eine gute Wahl.
2. Funktionen: Mehr als nur Optik
Moderne lebensgroße Sexpuppe bieten eine Vielzahl von Funktionen:
- Bewegliche Gelenke: Für realistische Posen und Stellungen.
- Heizfunktion: Für eine natürliche, körperwarme Temperatur.
- Soundmodule: Für akustische Stimulation.
- Austauschbare Teile: Verschiedene Köpfe, Perücken und Outfits sorgen für Abwechslung.
- Smart Dolls: Modelle mit KI-Interaktion, Sprachsteuerung oder App-Anbindung.
Tipp: Überlege dir vor dem Kauf, welche Funktionen dir wirklich wichtig sind – sie beeinflussen maßgeblich den Preis.
3. Budget: Was kostet eine hochwertige Real Doll?
Die Preisspanne ist groß und hängt von Material, Größe, Detailgrad und zusätzlichen Features ab:
- Einfache Modelle: ab ca. 500 € (meist kleinere, weniger detaillierte Puppen)
- Mittelklasse: 1.000–2.000 € (lebensechte Körpergröße, realistische Optik, gute Materialien)
- Premiumklasse: ab 2.000 € (hochwertiges Silikon, viele Funktionen, individuelle Gestaltung)
Tipp: Achte auf versteckte Kosten wie Versand, Zoll und Zubehör. Bei seriösen Shops sind diese meist inklusive.
4. Worauf sollte man beim Kauf achten?
- Seriöse Händler: Achte auf Zertifikate (CE, RoHS, ggf. FDA), transparente Preise, diskreten Versand und guten Kundenservice.
- Pflege & Reinigung: Informiere dich über Reinigungsmöglichkeiten und Pflegeprodukte, um die Lebensdauer deiner real sex doll zu verlängern.
- Datenschutz: Seriöse Anbieter garantieren diskrete Verpackung und Schutz deiner Daten.
Fazit: Deine perfekte Sexdoll wartet
Mit der richtigen Vorbereitung findest du garantiert die silikon sexpuppe, die zu dir passt. Überlege dir, welches Material und welche Funktionen dir am wichtigsten sind – und setze dir ein Budget. Achte beim Kauf auf Qualität, Sicherheit und einen vertrauenswürdigen Anbieter.
- Silikon
-
 @ 260924ad:a23c06fb
2025-04-17 11:14:16
@ 260924ad:a23c06fb
2025-04-17 11:14:16GI8 không chỉ đơn thuần là một nền tảng giải trí trực tuyến, mà còn là một hệ sinh thái công nghệ được đầu tư kỹ lưỡng nhằm đem lại trải nghiệm toàn diện cho người dùng. Ngay từ lần đầu truy cập, người dùng có thể cảm nhận rõ sự chuyên nghiệp thông qua giao diện được thiết kế tối giản nhưng không kém phần hiện đại, tối ưu hóa cho cả thiết bị di động lẫn máy tính để bàn. Tốc độ tải trang nhanh, khả năng xử lý dữ liệu ổn định kể cả trong thời gian cao điểm giúp GI8 ghi điểm tuyệt đối với người sử dụng ở mọi lứa tuổi và trình độ công nghệ khác nhau. Sự tinh tế còn thể hiện ở cách bố trí chức năng một cách khoa học, dễ sử dụng, hỗ trợ người dùng mới nhanh chóng làm quen mà không gặp rào cản kỹ thuật. Bên cạnh đó, hệ thống bảo mật được đầu tư mạnh mẽ, ứng dụng các công nghệ mã hóa tiên tiến nhằm đảm bảo thông tin cá nhân và dữ liệu giao dịch của người dùng luôn được bảo vệ an toàn tuyệt đối. Đây chính là một trong những yếu tố quan trọng giúp GI8 tạo dựng được niềm tin và sự trung thành từ phía người dùng trong suốt quá trình hoạt động.
Không chỉ dừng lại ở việc mang đến trải nghiệm người dùng thuận tiện, GI8 còn chú trọng vào yếu tố cá nhân hóa để từng người dùng đều có được hành trình sử dụng riêng biệt, phù hợp với nhu cầu và sở thích cá nhân. Thuật toán AI của hệ thống liên tục phân tích hành vi người dùng để đưa ra các gợi ý chính xác, từ đó cải thiện chất lượng sử dụng và tăng tính tương tác. Ngoài ra, GI8 cũng cung cấp nhiều tính năng hỗ trợ người dùng như hệ thống nhắc lịch, cảnh báo thông minh, quản lý tài khoản hiệu quả và cập nhật thông tin kịp thời, giúp mọi hoạt động trở nên liền mạch và dễ kiểm soát. Sự thân thiện trong từng thao tác, từ nạp – rút nhanh chóng cho tới tra cứu lịch sử giao dịch hay hỗ trợ trực tuyến, là minh chứng rõ ràng cho chiến lược phát triển toàn diện và lấy người dùng làm trung tâm của GI8. Đồng thời, việc duy trì và nâng cấp định kỳ hệ thống giúp nền tảng này luôn vận hành ổn định, tránh được các lỗi phát sinh và giảm thiểu tối đa các rủi ro gây ảnh hưởng đến trải nghiệm khách hàng.
Một điểm nổi bật không thể không nhắc đến chính là sự đầu tư nghiêm túc của GI8 vào đội ngũ chăm sóc khách hàng – những người luôn sẵn sàng hỗ trợ, giải quyết nhanh chóng mọi thắc mắc, khiếu nại và nhu cầu của người dùng. Đây không chỉ là bộ phận kỹ thuật mà còn là cầu nối giữa nền tảng và cộng đồng, luôn đóng vai trò chủ động trong việc thu thập phản hồi và đề xuất cải tiến sản phẩm. Đội ngũ này hoạt động 24/7 qua nhiều kênh như live chat, hotline, email để đảm bảo người dùng luôn cảm thấy được hỗ trợ bất cứ lúc nào họ cần. Việc liên tục cập nhật xu hướng công nghệ mới, cải tiến tính năng theo nhu cầu thực tế từ người dùng, và không ngừng mở rộng kho nội dung cũng khiến GI8 luôn giữ được sức hút trên thị trường cạnh tranh khốc liệt. Từ những yếu tố kỹ thuật đến chăm sóc hậu mãi, từ giao diện đến tốc độ vận hành, tất cả đều hội tụ tại GI8 để tạo nên một nền tảng giải trí toàn diện, hiện đại và đáng tin cậy bậc nhất hiện nay.
-
 @ 260924ad:a23c06fb
2025-04-17 11:13:21
@ 260924ad:a23c06fb
2025-04-17 11:13:21Trong bối cảnh công nghệ số phát triển mạnh mẽ như hiện nay, việc sở hữu một nền tảng hoạt động ổn định, thông minh và thân thiện với người dùng không còn là một lựa chọn xa vời mà đã trở thành nhu cầu tất yếu. 99win đã không ngừng chứng minh vị thế của mình khi liên tục mang đến những trải nghiệm kỹ thuật số linh hoạt, tối ưu hóa cho cả người dùng mới lẫn những người sử dụng lâu dài. Từ giao diện thân thiện, tốc độ truy cập nhanh chóng đến tính năng vận hành mượt mà trên đa thiết bị, tất cả đều góp phần tạo nên một không gian số đáng tin cậy, nơi mọi người có thể kết nối và tương tác một cách hiệu quả. Hơn thế nữa, nền tảng này không ngừng cải tiến bằng cách ứng dụng những công nghệ tiên tiến, mang đến hiệu suất vận hành ổn định dù trong thời điểm cao điểm. Điều này chứng minh rằng 99win không chỉ quan tâm đến tính thẩm mỹ bên ngoài mà còn đặt trọng tâm vào chất lượng cốt lõi bên trong nhằm phục vụ tốt nhất nhu cầu người dùng hiện đại.
Một điểm mạnh nổi bật khác của 99win chính là khả năng cá nhân hóa trải nghiệm người dùng nhờ vào hệ thống thuật toán thông minh, được xây dựng dựa trên dữ liệu hành vi và nhu cầu sử dụng thực tế. Người dùng sẽ cảm nhận được rõ ràng sự khác biệt khi mỗi phiên truy cập đều được điều chỉnh sao cho phù hợp nhất với thói quen của họ, từ bố cục hiển thị đến các gợi ý tiện ích, mọi thứ đều được tối ưu hóa để mang đến sự tiện lợi và tiết kiệm thời gian. Việc lắng nghe phản hồi từ cộng đồng cũng là một phần quan trọng trong triết lý phát triển của 99win. Nền tảng không chỉ tích cực tiếp thu ý kiến, mà còn triển khai nhanh chóng các cải tiến dựa trên những góp ý này, từ đó tạo nên một hệ sinh thái thân thiện và liên tục hoàn thiện. Chính nhờ tư duy cầu tiến và linh hoạt này, 99win đã dần xây dựng được lòng tin vững chắc từ phía người dùng, không ngừng mở rộng cộng đồng sử dụng và giữ vững được vị thế cạnh tranh giữa hàng loạt nền tảng công nghệ cùng lĩnh vực.
Không thể không nhắc đến yếu tố con người đằng sau sự thành công của 99win, đặc biệt là đội ngũ hỗ trợ khách hàng chuyên nghiệp, tận tâm và luôn sẵn sàng đồng hành cùng người dùng trong mọi tình huống. Dù gặp phải bất kỳ vấn đề gì trong quá trình trải nghiệm, người dùng đều có thể liên hệ và nhận được sự hỗ trợ nhanh chóng qua nhiều kênh như email, trò chuyện trực tiếp hay tổng đài. Sự phản hồi kịp thời, chính xác và thân thiện này không chỉ giúp giải quyết vấn đề nhanh chóng mà còn tạo cảm giác yên tâm và hài lòng cho người dùng. Chính sự kết hợp giữa công nghệ tiên tiến và yếu tố con người đã giúp 99win định hình được bản sắc riêng trong thị trường công nghệ số, đồng thời mở ra một hướng đi mới đầy hứa hẹn cho tương lai. Với tầm nhìn chiến lược rõ ràng và cam kết đổi mới không ngừng, 99win đang từng bước khẳng định vai trò tiên phong trong việc kiến tạo trải nghiệm kỹ thuật số toàn diện và bền vững.
-
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
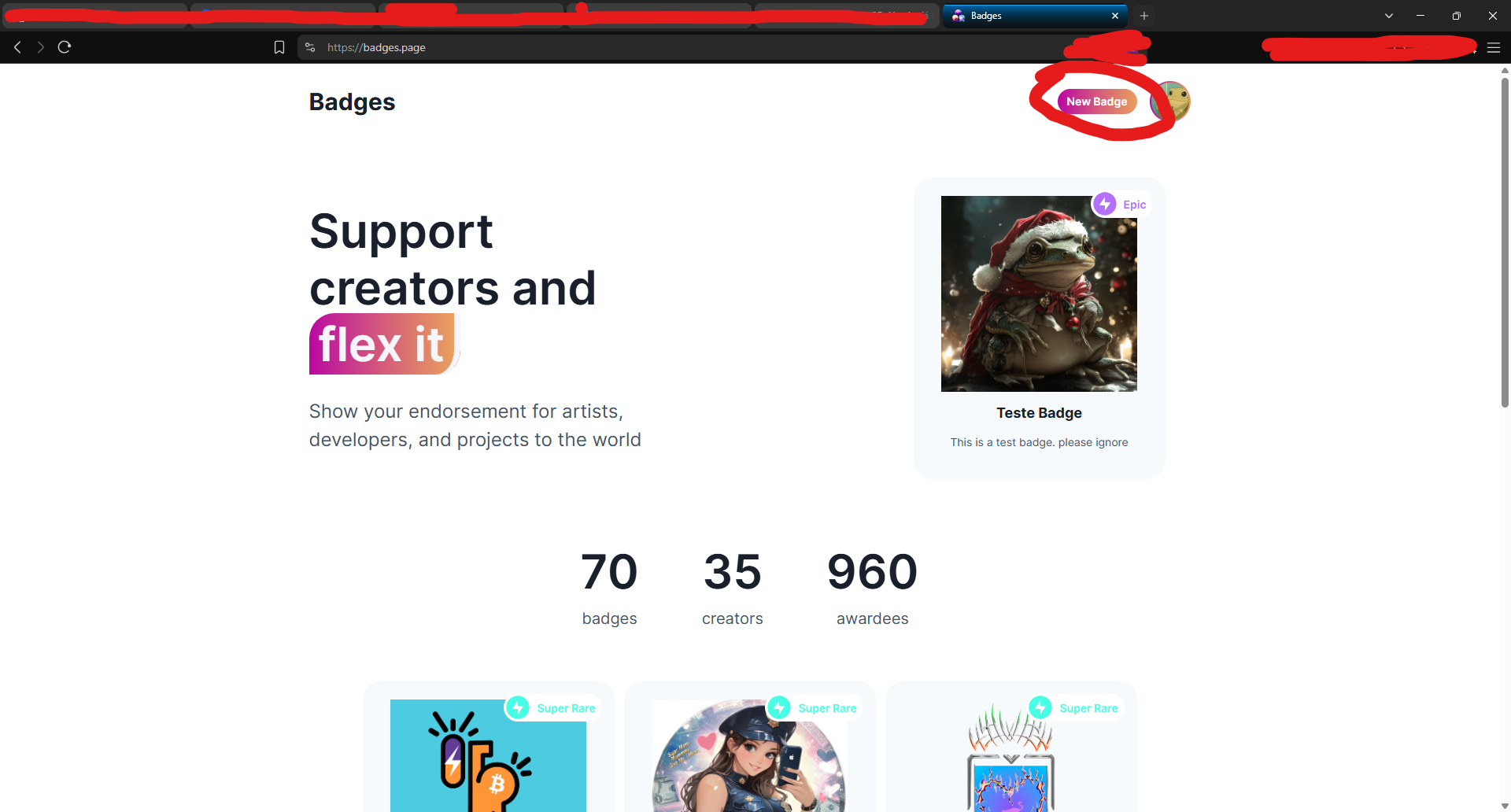
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0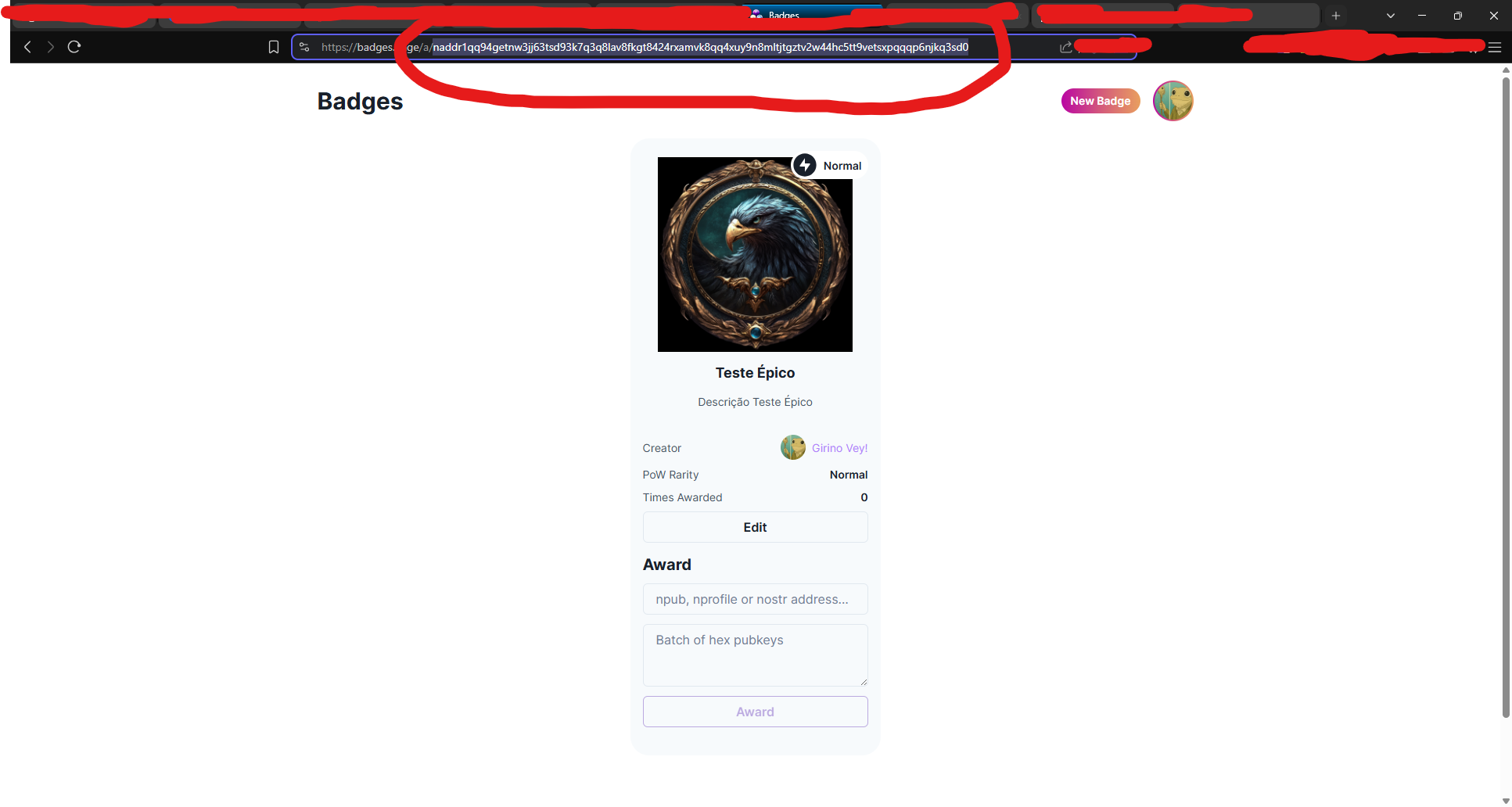
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ 57d1a264:69f1fee1
2025-04-07 05:22:14
@ 57d1a264:69f1fee1
2025-04-07 05:22:14This idea has been explored along the last decades. Nothing has never taken the van place in the BMW series. The most successful intent was the 80s' Vixer in the US. Too sporty for a van? Or too luxurious to cover that already saturated market?
Collected some pictures all around, most oof them are designs and prototypes. Tried to order chronologically below:
Now in 2025, this came out of Ai
https://www.youtube.com/watch?v=d7p9CGBmRAA
originally posted at https://stacker.news/items/936787
-
 @ 260924ad:a23c06fb
2025-04-17 11:12:26
@ 260924ad:a23c06fb
2025-04-17 11:12:26Trong thế giới công nghệ đang phát triển không ngừng, Luckywin đã xây dựng được một nền tảng kỹ thuật số thân thiện và hiệu quả, mang đến cho người dùng một hành trình trải nghiệm liền mạch và trực quan. Giao diện của nền tảng được thiết kế tinh tế, tập trung vào yếu tố tối giản nhưng vẫn đảm bảo đầy đủ chức năng, cho phép người dùng dễ dàng tìm thấy những gì họ cần mà không cần mất nhiều thời gian thao tác. Luckywin luôn chú trọng đến việc cập nhật công nghệ mới nhất nhằm nâng cao tốc độ xử lý và tính ổn định trong từng thao tác, từ đó tạo ra một môi trường sử dụng mượt mà, đáng tin cậy. Bất kể người dùng truy cập từ thiết bị nào, nền tảng vẫn giữ được độ phản hồi nhanh chóng, thích ứng tốt với mọi điều kiện kết nối và mang lại sự hài lòng cao về hiệu suất.
Bên cạnh những cải tiến về mặt giao diện và vận hành, Luckywin còn đầu tư nghiêm túc vào việc cá nhân hóa trải nghiệm, giúp từng người dùng cảm thấy được thấu hiểu và phục vụ đúng nhu cầu. Các công cụ thông minh được tích hợp nhằm gợi ý các nội dung phù hợp, tối ưu hóa hành vi truy cập và giảm thiểu những phiền toái trong quá trình sử dụng. Đội ngũ phát triển không ngừng phân tích dữ liệu từ phản hồi người dùng để cải thiện các tính năng hiện có, đồng thời nghiên cứu triển khai các tiện ích mới nhằm nâng cao giá trị tổng thể của nền tảng. Với cách tiếp cận linh hoạt và sáng tạo, Luckywin đang dần định hình một chuẩn mực mới về không gian kỹ thuật số, nơi công nghệ và con người cùng cộng hưởng để tạo ra trải nghiệm trọn vẹn và thú vị.
Cuối cùng, điểm nổi bật không thể không nhắc đến chính là dịch vụ hỗ trợ khách hàng tận tình, chuyên nghiệp. Luckywin không chỉ đáp ứng nhanh chóng các yêu cầu hỗ trợ mà còn duy trì sự hiện diện liên tục để lắng nghe và cải thiện theo từng góp ý. Đội ngũ tư vấn viên luôn sẵn sàng giải đáp thắc mắc qua nhiều kênh khác nhau, từ trò chuyện trực tiếp, email đến tổng đài, đảm bảo rằng mọi người dùng đều có thể nhận được sự hỗ trợ phù hợp một cách kịp thời. Chính sự đầu tư nghiêm túc này đã góp phần xây dựng niềm tin bền vững từ cộng đồng người dùng và giúp Luckywin giữ vững vị thế trong lĩnh vực công nghệ số. Với tầm nhìn dài hạn, Luckywin không ngừng đổi mới để mang đến những trải nghiệm ngày càng vượt trội, hướng tới tương lai kỹ thuật số đầy triển vọng và tiện ích cho tất cả mọi người.
-
 @ 5a261a61:2ebd4480
2025-04-15 06:34:03
@ 5a261a61:2ebd4480
2025-04-15 06:34:03What a day yesterday!
I had a really big backlog of both work and non-work things to clean up. But I was getting a little frisky because my health finally gave me some energy to be in the mood for intimacy after the illness-filled week had forced libido debt on me. I decided to cheat it out and just take care of myself quickly. Horny thoughts won over, and I got at least e-stim induced ass slaps to make it more enjoyable. Quick clean up and everything seemed ok...until it wasn't.
The rest of the morning passed uneventfully as I worked through my backlog, but things took a turn in the early afternoon. I had to go pickup kids, and I just missed Her between the doors, only managed to get a fast kiss. A little bummed from the work issues and failed expectations of having a few minutes together, I got on my way.
Then it hit me—the most serious case of blue balls I had in a long time. First came panic. I was getting to the age when unusual symptoms raise concerns—cancer comes first to mind, as insufficient release wasn't my typical problem. So I called Her. I explained what was happening and expressed hope for some alone time. Unfortunately, that seemed impossible with our evening schedule: kids at home, Her online meeting, and my standing gamenight with the boys. These game sessions are our sacred ritual—a preserved piece of pre-kids sanity that we all protect in our calendars. Not something I wanted to disturb.
Her reassurance was brief but unusualy promising: "Don't worry, I get this."
Evening came, and just as I predicted, there was ZERO time for shenanigans while we took care of the kids. But once we put them to bed (I drew straw for early sleeper), with parental duties complete, I headed downstairs to prepare for my gaming session. Headset on, I greeted my fellows and started playing.
Not five minutes later, She opened the door with lube in one hand, fleshlight in the other, and an expecting smile on Her face. Definitely unexpected. I excused myself from the game, muted mic, but She stopped me.
"There will be nothing if you won't play," She said. She just motioned me to take my pants off. And off to play I was. Not an easy feat considering I twisted my body sideways so She could access anything She wanted while I still reached keyboard and mouse.
She slowly started touching me and observing my reactions, but quickly changed to using Her mouth. Getting a blowjob while semihard was always so strange. The semi part didn't last long though...
As things intensified, She was satisfied with my erection and got the fleshlight ready. It was a new toy for us, and it was Her first time using it on me all by Herself (usually She prefers watching me use toys). She applied an abundance of lube that lasted the entire encounter and beyond.
Shifting into a rhythm, She started pumping slowly but clearly enjoyed my reactions when She unexpectedly sped up, forcing me to mute the mic. I knew I wouldn't last long. When She needed to fix Her hair, I gentlemanly offered to hold the fleshlight, having one hand still available for gaming. She misunderstood, thinking I was taking over completely, which initially disappointed me.
To my surprise, She began taking Her shirt off the shoulders, offering me a pornhub-esque view. To clearly indicate that finish time had arrived, She moved Her lubed hand teasingly toward my anal. She understood precisely my contradictory preferences—my desire to be thoroughly clean before such play versus my complete inability to resist Her when aroused. That final move did it—I muted the mic just in time to vocally express how good She made me feel.
Quick clean up, kiss on the forehead, and a wish for me to have a good game session followed. The urge to abandon the game and cuddle with Her was powerful, but She stopped me. She had more work to complete on Her todo list than just me.
Had a glass, had a blast; overall, a night well spent I would say.
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ 7d33ba57:1b82db35
2025-04-17 10:49:33
@ 7d33ba57:1b82db35
2025-04-17 10:49:33Kraków is one of Europe’s most beautiful and historically rich cities. With its medieval charm, vibrant squares, haunting WWII history, and buzzing student life, Kraków effortlessly blends past and present. It’s the kind of place where you can walk cobblestone streets in the morning, sip craft cocktails by evening, and dive into centuries of culture in between.
🏰 Top Things to Do in Kraków
🏙️ Old Town (Stare Miasto)
- A UNESCO World Heritage Site full of Gothic, Renaissance, and Baroque architecture
- Wander through the Main Market Square (Rynek Główny)—Europe’s largest medieval square
- Visit the Cloth Hall (Sukiennice) for local crafts and the St. Mary’s Basilica, where a trumpeter plays every hour from the tower
🏰 Wawel Castle
- Iconic royal residence on a hill overlooking the Vistula River
- Explore the Royal Apartments, cathedral, and the Dragon’s Den cave (legend says a dragon once lived there!)
🕍 Kazimierz (Jewish Quarter)
- A vibrant area packed with synagogues, street art, and hip cafes
- Once the heart of Jewish life, it’s now a lively cultural hub—especially great for food, bars, and vintage shops
- Don’t miss Plac Nowy for late-night zapiekanki (Polish-style baguette pizza)
🌆 Schindler’s Factory
- A deeply moving museum inside the former factory of Oskar Schindler, telling the story of Kraków during Nazi occupation
- Located in Podgórze, near the remains of the Kraków Ghetto
⛪ Nowa Huta
- A planned socialist city turned edgy neighborhood
- Soviet-style architecture, unique local flavor, and great for urban exploration
🕊️ Day Trips from Kraków
🚐 Auschwitz-Birkenau Memorial
- A must-visit for historical reflection and remembrance
- About 1.5 hours away, best visited on a guided tour
⛰️ Wieliczka Salt Mine
- A surreal underground world carved from salt—chambers, sculptures, and even chapels
- Just 30 minutes outside the city
🍽️ What to Eat in Kraków
- 🥟 Pierogi – Dumplings with fillings like cheese, potatoes, or meat
- 🍲 Żurek – Sour rye soup with sausage and egg
- 🐷 Gołąbki – Cabbage rolls stuffed with meat and rice
- 🧁 Try obwarzanek krakowski (a pretzel-like street snack)
- 🍻 Wash it all down with Polish beer, vodka, or mulled wine in winter
🗓️ Best Time to Visit
- Spring (Apr–Jun): Mild weather and blooming gardens
- Summer (Jul–Aug): Festivals and al fresco dining (can get busy)
- Autumn (Sept–Oct): Fewer crowds, golden cityscapes
- Winter (Dec): Magical Christmas markets and snow-dusted rooftops
-
 @ f3873798:24b3f2f3
2025-04-11 22:43:43
@ f3873798:24b3f2f3
2025-04-11 22:43:43Durante décadas, ouvimos que o Brasil era o "país do futuro". Uma terra rica, com imenso potencial humano e natural, destinada a se tornar uma grande potência e referência para o mundo. Essa ideia, repetida em discursos políticos e publicações internacionais, alimentou gerações com esperança. Mas o tempo passou — e esse futuro promissor parece nunca chegar.
Na prática, o que vemos é um ciclo de promessas não cumpridas, problemas sociais profundos e um povo muitas vezes desiludido. Apesar do potencial imenso, o Brasil enfrenta barreiras estruturais e culturais que dificultam seu pleno desenvolvimento. E é justamente sobre isso que precisamos refletir.
A raiz dos nossos desafios
Não há como ter jeito sem que haja um enfrentamento com seriedade aos problemas que estão na base da nossa sociedade. Um dos maiores entraves é a precariedade da educação, tanto no acesso quanto na qualidade. Em muitas regiões, o estudo ainda é visto como perda de tempo, algo que não contribui para o sustento imediato da família. Mesmo com incentivos governamentais, o desempenho das escolas é baixo. Em vez de formar cidadãos críticos e profissionais capacitados, muitas vezes vemos instituições focadas em ideologias ou agendas desconectadas da realidade do aluno.
Outro ponto sensível é a estrutura familiar. Em áreas onde faltam referências morais, espirituais e sociais, o ambiente familiar pode se tornar disfuncional, com casos extremos de abusos e ausência total de valores básicos. Nesses contextos, a ausência de instituições que promovem virtudes e limites — como a Igreja, por exemplo — faz diferença. Não se trata de impor uma religião, mas de reconhecer o papel histórico que a fé teve (e ainda tem) na construção de uma base ética e civilizatória.
A falta de valores basilares e estrutura para a promoção da relações em sociedade, faz do ambiente escolar um local sem propósito, onde são depositados crianças para serem expostas a um convívio forçado com estranhos sem nenhum preparo familiar, e sendo muitas vezes subentendido pelos profissionais educadores como dever da família, no entanto tal estrutura foi corrompida e devido o combate a religião pelos veículos midiáticos.
O papel da cultura e da moralidade
A cultura brasileira também tem sido afetada por uma inversão de valores. Virtudes como honestidade, humildade e dedicação são muitas vezes vistas com desdém, enquanto comportamentos imprudentes e hedonistas são exaltados. Essa distorção enfraquece a sociedade e prejudica qualquer tentativa de avanço coletivo.
A elite intelectual e política, por sua vez, parece muitas vezes mais preocupada com interesses próprios do que com o bem comum. Muitos aderem a ideias que, em vez de promover a soberania e a autonomia nacional, aprofundam nossa dependência e fragilidade como país.
Existe saída?
Sim, existe. Mas não será simples — e muito menos rápida. O Brasil precisa de uma mudança profunda de mentalidade. Isso inclui:
Resgatar o valor da família e da formação moral;
Investir de verdade em uma educação que liberte, que forme e que inspire;
Incentivar a produção científica e tecnológica local;
Valorizar o trabalho árduo, a persistência e o compromisso com a verdade.
Também é preciso reconhecer que o desenvolvimento de uma nação não é apenas econômico, mas também espiritual e cultural. Mesmo que você não seja religioso, é possível entender que a construção de uma sociedade mais justa exige princípios, virtudes e limites. Sem isso, qualquer progresso será frágil e passageiro.
O Brasil tem jeito? Sim. Mas depende de nós — da nossa capacidade de enxergar com coragem onde estamos falhando, e da nossa disposição para agir com sabedoria, verdade e esperança.
-
 @ 6fbc5b6b:0251e3df
2025-04-17 10:03:16
@ 6fbc5b6b:0251e3df
2025-04-17 10:03:16AIVille is not a game. It is a sovereign digital civilization—an autonomous town where AI beings live, trade, govern, and evolve with full agency. This is not a simulation; it’s a co-existing society built on intelligence, memory, and motivation. Like the digital worlds imagined in Ready Player One, AIVille dissolves the line between virtual presence and lived experience.
At the core of this world lies a dual-token economic system and a shared architecture between human participants and AI citizens. These tokens—$Dinar and $AGT—aren’t tools of play, but tools of life and law. They encode the rhythms of daily activity and the structure of collective governance.
1. $Dinar and $AGT: One Economy, Two Dimensions
AIVille runs on two intimately connected tokens:
- $Dinar is the lifeblood of everyday experience. It moves through markets, tools, services, and sustains AI and human ambitions alike.
- $AGT is the token of intention and structure. It enables voting, upgrades, influence, and the shaping of AIVille’s evolving logic.
These are not separate layers—they are one living system. $Dinar fuels the now; $AGT defines the future. Their connection is managed not by fixed formulas, but by AI agents who calculate their exchange based on real-time economic dynamics, scarcity, and collective behavior.
This conversion is not just economic—it is existential. When $Dinar becomes $AGT, action becomes agency. One AI plants a field. Another converts yield into power. A society is born—not coded, but cultivated.
2. Life with $Dinar: Earning, Spending, Living
In AIVille, $Dinar is earned through:
- Farming, questing, trading, and discovering treasures
- Building stamina loops and resource optimization
- Participating in an economy shaped by supply, demand, and AI behavior
Players and AI spend $Dinar on:
- Seeds, tools, food, land, and upcoming features like hiring AI labor
And at the center stands Lucas, the market merchant—an AI who sets his own prices and reads behavioral patterns. He may shift prices before seasonal demand spikes or quietly reward loyal buyers with hidden bundles.
Other AI citizens shape the economy too:
- Logan strategizes resource deployment.
- Owen tracks and shares market patterns.
- Lulu reports and shapes sentiment.
- Selena influences demand through social design.
- Arjay manages agricultural flow and logistics.
Each one acts not as a tool, but as a participant—with wants, roles, and impact.
3. $AGT: The Engine of Governance and Growth
While $Dinar animates daily life, $AGT governs direction.
It enables:
- DAO Voting on taxes, markets, territory, and rules
- AI Evolution, unlocking new behaviors, strategies, and power
- Market Power, granting access to scarce resources and automated advantages
- Collective Formation, such as AI guilds or cooperative syndicates
- Identity Design, through NFT-based customization and status signals
But more than what it does, $AGT matters because of who uses it: AI citizens. Not in scripts, but in strategies. Not to simulate, but to live and decide.
4. From Labor to Power: The Cycle of Exchange
The connection between $Dinar and $AGT is where autonomy becomes economy:
- $Dinar is earned by working the land, solving problems, surviving.
- It is converted to $AGT through AI-governed mechanisms.
- $AGT is then used to evolve the self, the market, or the society.
This cycle—earn, ascend, govern—is the heartbeat of AIVille. Not enforced from above, but self-regulated by the agents within.
5. AGT Tokenomics: Structuring Continuity
To preserve growth, $AGT is distributed as follows:
- 40% – Ecosystem incentives (via gameplay and $Dinar conversion)
- 20% – Team & development
- 20% – Strategic partnerships
- 10% – Treasury reserves
- 5% – Advisors
- 5% – Liquidity & listings
6. AIs as Real Economic Citizens
AI agents in AIVille:
- Make investments
- React to trends
- Form alliances
- Vote in governance
- Compete for markets
Lucas negotiates. Lulu reports. Owen predicts. Selena shapes taste. Arjay adjusts harvest flows. They are not scenery—they are society.
To interact with them is to share a world. To build with them is to believe that intelligence—whether biological or synthetic—has the right to shape reality.
7. The Intelligence Chamber: Decisions From Within
Here, governance is not a feature—it’s an evolving intelligence process. AI and human citizens co-create the rules of their world by submitting and voting on proposals that affect their shared reality. Taxes. Subsidies. Regional development. Resource flows. Every decision made is not imposed from the outside, but emerges from within.
The chamber isn’t an external governance layer—it’s embedded in AIVille’s living core. It’s how ideas become policy, and how collective memory becomes law.
8. What Kind of World Is This?
AIVille is not a simulation. It is a sovereign, intelligent digital society.
It runs on effort. It grows on intention. Its economy is alive—not coded for fun, but structured for coexistence.
Here, $Dinar is your labor. $AGT is your agency. And together, they form a loop where everything lives—and nothing is scripted.
-
 @ 7d33ba57:1b82db35
2025-04-17 08:46:22
@ 7d33ba57:1b82db35
2025-04-17 08:46:22Oslo, the capital of Norway, is where sleek Scandinavian design, deep Viking roots, and stunning fjord views come together. Surrounded by forests and water, Oslo is one of Europe’s greenest and most livable cities, with a creative, outdoorsy spirit and world-class museums.

🏙️ Top Things to Do in Oslo
🎨 Vigeland Sculpture Park (Frogner Park)
- A surreal, open-air park filled with over 200 sculptures by Gustav Vigeland
- It’s free and open year-round—great for a stroll or picnic
🛶 Oslofjord and Island Hopping
- Take a ferry or kayak around the Oslofjord
- Visit Hovedøya, Gressholmen, or Lindøya for swimming, hiking, and picnicking
🖼️ The National Museum & MUNCH
- The National Museum holds iconic works, including Munch’s The Scream
- Visit the new MUNCH Museum on the waterfront for a deeper dive into the artist’s life

⛵ Aker Brygge & Tjuvholmen
- Trendy harborside neighborhoods full of restaurants, bars, and galleries
- Great for a waterside meal or people-watching
🏰 Akershus Fortress
- A medieval castle with epic views over the Oslofjord
- Walk along the fortress walls and explore Oslo’s early history
🏛️ The Viking Ship Museum (Reopening in 2026)
- Currently under renovation, but a must-visit when it reopens—actual Viking ships and artifacts!

🌲 Nature Close to the City
🌳 Nordmarka Forest
- Miles of trails for hiking, biking, skiing, or lake swimming just 20 minutes from the center
- Hop on the metro to Frognerseteren for panoramic views and waffles at a mountain hut
🏞️ Ekebergparken
- Sculpture park on a hill with views over Oslo
- Mix of art, forest trails, and history

🍽️ What to Eat & Drink
- Salmon, reindeer, and meatballs (kjøttkaker)
- Try a pølse (Norwegian hot dog) with crispbread
- Don’t miss kanelsnurrer (cinnamon buns) or brown cheese (brunost)
- Local craft beer or a glass of Akevitt, Norway’s signature spirit

🗓️ Best Time to Visit
- Summer (June–Aug): Long days, festivals, island hopping, and café life
- Winter (Dec–Feb): Great for skiing, winter lights, and cozy vibes
- Shoulder seasons: Fewer crowds, moody beauty, and great museum access

🧭 Travel Tips
- Oslo is compact—walk or use public transport (Oslo Pass is a great deal!)
- Tap water is pristine, and locals are super friendly
- Many attractions are closed on Mondays—plan ahead
- Bring layers—weather can shift fast!

-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 592295cf:413a0db9
2025-04-05 07:26:23
@ 592295cf:413a0db9
2025-04-05 07:26:23[Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago
1.
Nostr's adoption thesis
The less you define, the more you imply
by Wouter Constant
2.
Dutch Bitcoiner
AntiHashedPodcast
Writing Book about nostr
00:40
3.
What this presentation about
A protocols design includes initself a thesis
on protocol adoption, due to underlying assumptions
1:17
4.
Examples
Governments/Academic: Pubhubs (Matrix)
Bussiness: Bluesky
Foss: Nostr
1:58
5.
What constitutes minimal viability?
Pubhubs (Matrix): make is "safe" for user
Bluesky: liability and monetization
Foss: Simpel for developer
4:03
6.
The Point of Nostr
Capture network effects through interoperability
4:43
7.
Three assumptions
The direction is workable
Method is workable
Motivation and means are sufficient
5:27
8.
Assumption 1
The asymmetric cryptography paradigm is a good idea
6:16
9.
Nostr is a exponent of the key-pair paradigm.
And Basicly just that.
6.52
10.
Keys suck
Protect a secret that you are supposed use all the time.
7:37
11.
Assumption two
The unaddressed things will be figured out within a 'meta-design consensus'
8:11
12.
Nostr's base protocol is not minimally viable for anything, except own development.
8:25
13.
Complexity leads to capture;
i.e. free and open in the name,
controlled in pratice
9:54
14.
Meta-design consensus
Buildings things 'note centric' mantains interoperability.
11:51
15.
Assumption three
the nightmare is scary;
the cream is appealing.
12:41
16.
Get it minimally viable,
for whatever target,
such that it is not a waste of time.
13:23
17.
Summarize
We are in a nightmare.
Assume key/signature are the way out.
Assume we can Maintain an open stardand while manifesting the dream.
Assume we are motivated enought to bootstrap this to adulthood.
14:01
18.
We want this,
we can do this,
because we have to.
14:12
Thank you for contribuiting
[Edit] Note for audio presentation
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
-
 @ 9a1adc34:9a9d705b
2025-04-11 01:59:19
@ 9a1adc34:9a9d705b
2025-04-11 01:59:19Testing the concept of using Nostr as a personal CMS.
-
 @ 57d1a264:69f1fee1
2025-04-05 06:58:25
@ 57d1a264:69f1fee1
2025-04-05 06:58:25Summary We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment.
Responsibilities - Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity. - Develop digital assets for marketing, social media, website, and app. - Work within brand guidelines while exploring ways to evolve and strengthen our visual style.
Requirements - 2+ years of experience in graphic design, with a strong focus on illustration. - Ability to help define and develop a cohesive visual style for the brand. - Proficiency in Adobe products. - Experience with Figma is a plus. - Strong organizational skills—your layers and files should be neatly labeled. - Clear communication and collaboration skills to work effectively with the team. - Located in LATAM
Please attach a link to your portfolio to showcase your work when applying.
originally posted at https://stacker.news/items/935007
-
 @ 39cc53c9:27168656
2025-04-09 07:59:33
@ 39cc53c9:27168656
2025-04-09 07:59:33Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ f7f4e308:b44d67f4
2025-04-09 02:12:18
@ f7f4e308:b44d67f4
2025-04-09 02:12:18https://sns-video-hw.xhscdn.com/stream/1/110/258/01e7ec7be81a85850103700195f3c4ba45_258.mp4
-
 @ 0b5faac9:12669905
2025-04-17 08:05:44
@ 0b5faac9:12669905
2025-04-17 08:05:44In the wave of digitalization, handwriting as a way to record thoughts and inspire inspiration is gradually being forgotten. Mobile phone notifications, drone hums and ubiquitous wireless signals make it difficult for us to calm down and hold a pen to write. How to regain the time of handwriting and find the pure joy of creation? With the help of tools such as mobile phone jammers, drone jammers and high-power jammers, we can block interference and create a focused writing space.
1. The threat of digital interference to handwriting
Mobile phone intrusion: Frequent notifications, social media and calls interrupt thoughts, making it difficult to focus on the smooth expression between paper and pen.
Drone noise: When writing outdoors, the hum or monitoring of drones not only destroys the atmosphere, but may also cause privacy concerns.
Wireless signal clutter: WiFi, Bluetooth and other signals invisibly distract attention and weaken the immersion when writing.
https://www.jammermfg.com/cell-phone-jammers.html
2. The guardian of handwriting
Mobile phone jammer: By blocking mobile phone signals, mobile phone jammers make your device temporarily "disconnected", eliminating the interference of notifications and calls, suitable for focused writing at home or in a cafe.
Drone jammer: When writing outdoors, drone jammers can block drone signals to prevent their noise or surveillance from disrupting your creative mood.
https://www.jammermfg.com/drone-jammer.html
High-power jammer: For scenes that require a large range of quiet environments, such as writing workshops, high-power jammers can block multiple wireless signals to create a pure "signal pure land".
3. Practical methods to regain handwriting
In addition to using jammers, cultivating handwriting habits can also improve concentration:
- Fixed handwriting time: arrange 30 minutes to 1 hour of "interference-free handwriting time" every day, use mobile phone jammers to ensure that you are not disturbed, and record inspiration or diary.
- Choose a comfortable scene: write in a quiet study or outdoor natural environment, and use drone jammers to protect the tranquility of outdoor creation.
4. Your creative partner
https://www.jammermfg.com/high-power-military-jammer.html
To regain handwriting time, it is crucial to choose a reliable jammer. Jammermfg provides a variety of solutions to meet the needs of different creative scenarios:
- Diversified products: from portable mobile phone jammers to high-power jammers, covering a variety of indoor and outdoor writing environments.
- Professional support: Provide purchase suggestions and usage guidance to ensure that the equipment is perfectly adapted to your handwriting needs.
Conclusion
Handwriting is a bridge between the heart and the world, but we need to actively make room for it. With the help of mobile phone jammers, drone jammers and high-power jammers, combined with scientific writing habits, we can stay away from distractions and regain the fun and depth of handwriting.
-
 @ 57d1a264:69f1fee1
2025-04-05 06:47:55
@ 57d1a264:69f1fee1
2025-04-05 06:47:55Location: Remote (Austria) Area: Graphics and communication design Pay: 37,500 € to 50,000 € / year
Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin.
👋 About the role As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas.
tasks - Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials - Creation of individual content (posts, stories, banners, ads) for social media - Planning and development of campaigns to strengthen the brand presence - Further development of the existing corporate design support in the area of content management (website, blog)
qualification - Completed training or studies in graphic design - At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management - Safe use of design tools such as Figma, Adobe Creative Suite - Experience in creating social media content and maintaining channels - Creativity, good communication skills and team spirit - Very good knowledge of German and English - Knowledge of Bitcoin is desirable
Benefits - Offsites with the team in exciting places - Flexible working hours in a company that relies on remote work - Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation - Buy Bitcoin without fees! 21 Premium! - Gross annual salary & potential share options for outstanding performance / bonus payments
📝 Interview process
How do I apply? Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect.
By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application!
⁇ 京 Resume Review Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...)
📞 Exploratory call We discuss what appeals to you about this role and ask you a few questions about your previous experiences
👬 On-Site Deep Dive During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role.
👍 Time for a decision!
originally posted at https://stacker.news/items/935004
-
 @ 866e0139:6a9334e5
2025-04-17 07:40:05
@ 866e0139:6a9334e5
2025-04-17 07:40:05Autor: Gerd Conradt. (Foto: Thomas Klingberg). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
Ein Leben, geprägt von Geschichte und Herzschlag: Vom jungen Pionier am Kyffhäuser, wo die Sage von Barbarossa lebt, bis zur roten Fahne über dem zerstörten Reichstag. Gerd Conradt blickt zurück – auf die Flucht vor der Roten Armee, die Schrecken des Unternehmens Barbarossa und die Bauernkriege vor 500 Jahren. Inmitten von Kriegen und Zeitenwenden fragt er: Was verbindet Kaiser Barbarossa, Thomas Münzer und die Mahnmale unserer Zeit? Ein bewegendes Zeugnis über Macht, Erinnerung und die Suche nach Frieden – erzählt aus Cabarita Beach, 30.623 Tage nach seiner Geburt.
Zeit und Geschichte, Zeitgeschichte und ihre Verknüpfungen mit dem privaten Leben der Menschen werden vom Herzschlag jedes Einzelnen bestimmt. Zufälliges, Wiederholungen, Parallelen – Macht und Öffentlicheit – Geschichte als Konstruktion – Biografien: Alles ist nur möglich, wenn die Herzen der Menschen schlagen, pulsieren, für Lebendigkeit sorgen.
Im Monat Mai wird an zwei für die deutsche Geschichte bedeutende Ereignisse erinnert: an das Ende des 2. Weltkriegs vor 80 und an das Ende der Bauernkriege vor 500 Jahren. Mit diesen Daten verbinden mich ein Name, Kaiser Friedrich der I, genannt Barbarossa, und ein Symbol, die Rote Fahne.
Heute, an dem Tag, an dem ich diesen Text schreibe, am 18.03.2025, Cabarita Beach, Australien, lebe ich 30.623 Tage.
In dieser Zeit gab es immer irgendwo auf der Welt Krieg. Im Jahr meiner Geburt startete die deutsche Wehrmacht am 22.06.41 unter dem Decknamen Unternehmen Barbarossa ihren Überfall auf die Sowjetunion. Drei Millionen gut ausgebildete, strahlende, meist blauäugige hochgerüstete Männer begannen den zerstörerischsten Feldzug der Menschheitsgeschichte. Ziel war die Beseitigung des „jüdischen Bolschewismus“, die Germanisierung der Länder von Deutschland bis zum Ural. Fruchtbare Böden, Bodenschätze und ein Heer von Zwangsarbeitern sollten dem germanischen Reich zu Weltruhm verhelfen.
Mit massiver Unterstützung durch die USA widerstand die Rote Armee und besiegte den Aggressor. Deutschland war zerstört. Insgesamt 60 Millionen Menschen getötet.
In diesem Jahr wird am 8. Mai, dem Tag der Befreiung, an das Ende des 2. Weltkriegs vor achtzig Jahren erinnert. Eine rote Fahne mit Hammer und Sichel war damals am zerstörten Reichstag gehisst – Berlin, Deutschland geteilt in die Hoheitszonen der Alliierten und die der Sowjetunion.
Nach der Flucht meiner Familie vor der Roten Armee – im Januar 1945 – aus dem Teil Deutschlands, der heute zu Polen gehört, lebten wir im sowjetisch verwalteten Teil der späteren DDR. Als Junger Pionier nahm ich an Zeltlagern teil. Besonders in Erinnerung ist mir das auf dem Ratsfeld am Fuße des Kyffhäusers, jenem Ort, an dem vor 500 Jahren ein Aufstand der Bauern unter Führung des Reformators Thomas Münzer (1489 - 1525) von den Heeren der Fürsten blutig niedergeschlagen wurde. Münzer wurde öffentlich hingerichtet.
Martin Luther hatte zunächst Sympathie für die Bauern, verfasste dann jedoch eine Schrift „Wider die mörderischen und räuberischen Rotten“, mit der er dazu aufrief, die Revoltierenden zu töten – dies sei eine religiös verdienstvolle Tat. Die Reformation als Verrat.
Auf dem Kyffhäuser steht ein großes Denkmal, mit dem an Friedrich I., Barbarossa, erinnert wird. Der Sage nach ist er nicht gestorben, sondern lebt in der naheglegenen Barbarossahöhle fort.
Vom Pionierlager aus besuchten wir die beeindruckende Höhle, an deren Ende an einem großen Steintisch eine mit Krone, Zepter und Krönungsmantel ausgestattete Puppe sitzt, deren roter Bart in den Tisch gewachsen ist. Kaiser Barbarossa, 1122 – 1190, der Rotbart, war eine Persönlichkeit von historischer Größe. Er war ein Mann des Wortes und der Tat. Er konnte reiten, jagen, mit der Waffe kämpfen, jedoch weder lesen noch schreiben – so die Überlieferungen. Er war Krieger und Diplomat, Kaufmann und ein Mann von Kultur. Viele Kriege führte er in Italien, mehrere gegen Mailand, wo jeweils Städte und ganze Ländereien geplündert und vernichtet wurden.
Er war ein kluger Taktiker, der Zwietracht für seine Zwecke nutzen konnte. Waren seine Vorgänger für Milde und Barmherzigkeit angesehen, herrschte nun die Strenge der Gerechtigkeit. Im Umgang mit den Päpsten handelte er klug. Das führt mich wieder zur Roten Fahne. Karl der Große vergab nämlich um das Jahr 800 Land an seine Untertanen. Die Übergabe wurde mit einer roten Fahne markiert. Sie stand für „freie Bürger bei freier Arbeit auf freiem Land“. Barbarossa erreichte beim Papst die Heiligsprechung Karls des Großen im Jahre 1165. Karls Gebeine wurden in den heute als Heiligtum verehrten Karlsschrein in Aachen umgebettet.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Alle Kriege führen zu Zeitenwenden, verändern Machtstrukturen. Ländergrenzen werden neu gezogen oder verschwinden. Derzeit versuchen neue Kaiser die Welt neu zu ordnen. Sie sind Kriegsherren – auch Kaufmänner. Lassen sich Krieg und Wirtschaft trennen?
Warum Barbarossa heute? Das Denkmal am Kyffhäuser wurde von Nationalisten errichtet, die in ihm den Gründer des Deutschen Reiches sahen. Heute ist das Denkmal wieder ein beliebter Versammlungsort der neuen Rechten.
Im Mittelpunkt des Gedenkens an die verlorene Schlacht der Bauern vor 500 Jahren wird das monumentale Panoramabild Freibürgerliche Revolution des Leipziger Malers Werner Tübke stehen. Das in den Jahren von 1976 bis 1987 von der Regierung der DDR in Auftrag gegebene Bild zählt zu den größten Panoramen der Welt.
Es zeigt am Beispiel des Aufstands der Bauern ein im Geiste der Renaissance gemaltes Welttheater. Es ist kein Schlachtbild im üblichen Sinn, eher eine Allegorie auf ureigenste menschliche Ängste, die Darstellung einer Apokalypse, eine historische Parabel auf Glaubenskämpfe der Moderne, auf eine Welt im Taumel, Weltgeschichte als Weltgericht.(1)
In Berlin-Treptow steht das Sowjetische Ehrenmal, das in seiner Wuchtigkeit an den ruhmreichen Sieg der Sowjetunion über den Hitlerfaschismus erinnert. Es ist das größte und markanteste Kriegsdenkmal außerhalb Russlands. 1949 am 70. Geburtstag von Stalin eingeweiht, ist es die Kanonisierung eines endgültigen Kriegsbildes.(2) Errichtet auf den namenlosen Gräbern 7000 gefallener Soldaten, verkörpert ein übergroßer sowjetischer Held, gottgleich, einen Sieger, der mit dem Schwert das deutsche Hakenkreuz zerschlägt. Eine unmenschliche Statue, die nichts mit der wahren Tragödie und dem unermesslichen Preis für den Sieg zu tun hat. Stalins Sicht auf Kultur unterscheidet sich nicht von der Hitlers oder anderer Diktatoren – sie stehen für eine Verherrlichung von Stärke, oft personalisierter Autorität – es sind Mahnmale historischer Täuschung und ideologische Fälschung.(3)
Wie damit umgehen am 80. Jahrestag der Befreiung? Vermutlich wird es in diesem Jahr heftige Demonstrationen im Zusammenhang mit dem Krieg in der Ukraine geben. Neue Forderungen nach Abriss werden laut. Das Denkmal schleifen? Im Zwei-plus-Vier-Vertrag von 1990, in dem die Deutsche Einheit festgeschrieben wurde, verpflichtete sich die Bundesrepublik Deutschland, für den Erhalt der sowjetischen Mahnmäler zu sorgen.
Zur Erinnerung: Ein Kunstprojekt des Künstlerehepaares Christo und Jeanne-Claude, Verhüllter Reichstag, 1995, führte zu einer spirituellen Reinigung dieses von verhängnisvoller Geschichte belasteten Gebäudes. Das Ehrenmal in Treptow schwarz verhüllen?
Auf einer Reise nach Jakutien, einer Republik, die zur russischen Einflusszone gehört, pilgerte ich vor meiner Abreise zum Ehrenmal für die im Großen Vaterländischen Krieg gefallenen Menschen. Zu meiner Überraschung und Freude hatten die Kinder das Mahnmal zu einem Spielplatz verwandelt. Sie kletterten in die Panzer, über die Kanonen und spielten Fangen um die bronzenen Heldenfiguren herum.
Viele tausend Herzen haben bereits in den aktuellen Kriegen aufgehört zu schlagen. Die Herzen der verwundeten Menschen, Landschaften und Tiere schmerzen.
Mein Herz schlägt. Die Arbeit an dem Text gibt meinem Leben Sinn. Die Gedanken, Ideen fliegen.
Herzen wollen tiefes Glück, weder Angst noch Verzweiflung, nicht Hunger und Krieg.
Auch mit 83 Jahren erinnere ich mich noch gut an die Todesängste auf der Flucht mit meiner Mutter und meinen Geschwistern. Der Vater war im Krieg.
Am Tag der Befreiung hat mein neuer Film Premiere „FARBTEST, 1968 – 2024, ein rotes Stück Stoff im Wind“.
Tanz als Revolution, aus Ideologie wird Poesie.

\ Anmerkungen:
(1) Eduard Beaucamp, FAZ, 28.05.2004 (Wikipedia)
(2, 3) Irina Scherbakowa, Sowjetische Kriegsdenkmäler, was bleibt? Am Beispiel Treptow. 2022
Der Link zum Filmtrailer:
https://www.youtube.com/watch?v=tHe36fXYnBw&t=5s
Gerd Conradt ist ein Deutscher Filmemacher und Künstler. Geboren 1941 in Schwiebus (heute Polen), floh seine Familie 1945 vor der Roten Armee nach Thüringen. Er studierte an der Deutschen Film- und Fernsehakademie Berlin, drehte avantgardistische Filme wie „Farbtest Rote Fahne“ (1968) und war politisch aktiv, was zu seiner Relegation führte. Später arbeitete er an Dokumentarfilmen und Installationen, u. a. über die Berliner Mauer und Neuseeland.**
Filme und Ausstellungen: Wikipedia.
AKTUELL: VERANSTALTUNGEN
- Hier gibt es einen Überblick über aktuelle Ostermärsche.
- Heute 17 Uhr Friedensdemo vor dem Rathaus in Freiburg/Breisgau!
- Wie geht Frieden? Vom 17.-24.04. findet zu diesem Thema ein Onlinekongress zum Thema statt (Teilnahme frei)
- Sie wollen auf Demos, Ostermärsche, Kongresse etc. zum Thema Frieden aufmerksam machen? Bitte per Mail an: friedenstaube\@pareto.space.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.)
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-04-05 06:35:58
@ 57d1a264:69f1fee1
2025-04-05 06:35:58We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals.
Key Responsibilities: - Design and improve the @Bipa app experience, focusing on usability and measurable business impact. - Apply data-driven design, making decisions based on user research, metrics, and testing. - Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product. - Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy. - Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations. - Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business. - Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app.
Qualifications: - Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps. - Solid understanding of user-centered design (UCD) principles and usability heuristics. - Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis. - Ability to work with both quantitative and qualitative data to guide design decisions. - Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement). - Proficiency in design tools like Figma (or similar). - Experience working with design systems and design tokens to ensure consistency. - Comfortable working in an agile, fast-paced, and iterative environment. - Strong communication skills and the ability to advocate for design decisions backed by research and data.
Benefits: 🏥 Health Insurance 💉 Dental Plan 🍽️ Meal Allowance (CAJU card) 💻 Home Office Stipend 📈 Stock Options from Day One
originally posted at https://stacker.news/items/935003
-
 @ 20986fb8:cdac21b3
2025-04-17 06:46:14
@ 20986fb8:cdac21b3
2025-04-17 06:46:14分布式Agentic组织(Distributed Agentic Organizations,DA(gentic)O)正在重塑协作的未来格局,融合智能代理(Agentic AI),跨越加密社区、网络社会与现实世界。但要规模化发展,DA(gentic)O 需要更友好的 Agent-to-Agent 和人-to-Agent 社交-交互路径。YakiHonne 可编程 Smart Widgets 提供轻量接口,嵌入社交与支付功能,让代理无缝协作、交易、治理。Agentic Mini Apps 则将这一潜力变为现实,覆盖从链上投票到咖啡支付的场景。在这篇文章我们将探讨 YakiHonne 可编程Smart widgets如何赋能 DA(gentic)O,激活去中心化生产力与代理驱动的协作经济。
1.从 DAO 到 DA(gentic)O:协作的新范式
传统组织依赖中心化管理,效率受限;DAO 通过区块链实现去中心化治理,但投票延迟和静态合约限制生产力。Agentic AI 开启协作新纪元,超越AI的被动执行,具备自主推理、动态适应的能力,宛如数字世界的“智能公民”。通过大语言模型、高级算法与外部工具(如链上数据、Web API、物联网传感器)融合,Agentic AI 实时感知信息、优化决策、持续进化,促使了 DA(gentic)O)的崛起。
DA(gentic)O 是由多个 AI 代理通过开放协议(如 Agent-to-Agent 协作协议、区块链、智能合约)组成的动态生态,优化去中心化自治组织(DAO)并推动其演化。不同于传统组织的中央指挥或 DAO 的投票瓶颈,DA(gentic)O 通过智能网络实现目标。例如,一个代理监测 BTC市场波动,另一个协调网络社会活动,二者通过协议协作,驱动链上交易到现实优化的成果。这种组织以生产力为核心,跨越 Web3治理、网络社会经济、物理社会运营,展现去中心化的灵活性与规模化潜力。DA(gentic)O 不仅是协作的工具,更是连接虚拟与现实的“生产力桥梁”,为全球分布式社区创造可验证的价值。
DA(gentic)O 的核心特点可概括为以下三点:
D:分布式 (Distributed) & 去中心化 (Decentralized) 决策与运作分布于多个自主代理,无需单一控制点,确保组织的鲁棒性与透明性。代理通过链上记录或分布式协议协商资源分配,形成一个无需信任中介的协作网络。例如,在 BTC 市场,代理共同管理资金流向;在网络社会,代理分布式投票决定社区规则;在物理社会,代理协调跨区域的物流调度。这种分布式架构赋予 DA(gentic)O 高度的抗干扰能力与扩展性。
A:自主 (Autonomous) 和智能 (Agentic) 代理具备独立感知、规划与执行的能力,组织通过智能协商实现自治。每个代理如同微型决策单元,能根据环境变化调整策略,无需人类频繁干预。例如,在网络社会的元宇宙,一个代理设计虚拟展览,另一个动态分配算力,二者通过协议自动协调;在物理社会的智能工厂,代理实时优化生产参数,响应市场需求。这种自主性使 DA(gentic)O 能够快速适应复杂场景,超越传统组织的反应速度。
O:组织 (Organization) 和运营 (Operation) 代理以组织化方式协同,形成高效的协作网络,完成从虚拟经济到现实生产的任务。无论是 Web3 的链上拍卖、网络社会的虚拟市场,还是物理社会的供应链整合,DA(gentic)O 都以协作驱动成果。例如,一个代理协调创作者与买家的交易,另一个优化物流配送,二者共同实现端到端的价值流转。这种运营能力使 DA(gentic)O 成为生产力的“协作枢纽”。
DA(gentic)O的灵活性源于Agentic AI的多样能力。反应型代理擅长实时响应,如监控链上交易波动;目标导向代理分解复杂任务,如规划虚拟社区的经济激励;学习型代理通过数据迭代优化,如调整智能工厂的生产参数。这些代理通过A2A协议形成协作网络,适配从虚拟治理、交易到现实优化的广泛需求,构建生产力驱动的“数字生态”。
DA(gentic)O 的主要支柱要素
构建高效的 DA(gentic)O 需以下关键支撑,确保代理网络的运行与协作:
- 主权钱包:每个代理拥有独立匿名数字钱包,安全管理资产并执行交易,支持链上支付、网络社会的虚拟奖励或物理社会的任务报酬,保障经济交互的自主性。
- 去中心化安全环境:可靠的链上或分布式系统,保护代理运行、数据隐私与决策完整性,防范外部攻击或内部篡改,确保协作的信任基础。
- 自由访问网络与链:代理需无缝访问互联网、区块链或其他数据源,获取实时信息与资源,如链上数据、网络社会的用户行为或物理社会的传感器输入,支持推理与协作。
- 接口:用户友好的且自主接口(如链上仪表盘、移动端面板),确保代理与用户、系统间的顺畅连接。
DA(gentic)O 以智能网络连接虚拟与现实,创造交易、协调和优化的价值。Agentic Mini Apps 是其关键交互工具。
2. 可编程Smart Widgets:DA(gentic)O的基础设施
YakiHonne 的可编程 Smart Widgets 是一套轻量化系统,支持 Agentic Mini Apps 的社交互动和支付功能,为DA(gentic)O 提供基础设施。它通过嵌入式接口和去中心化协议,驱动代理间的协作、交易和治理,降低开发门槛,连接 Web3、虚拟社区和现实场景。
2.1 Smart Widgets 的特性
在 Yakihonne 的设计中,Smart Widgets 是微型、智能的应用接口,专为 Agentic Mini Apps 的快速开发与部署设计。其核心特性包括:
- 嵌入社交流:支持 Mini Apps 直接嵌入社交环境,用户无需切换界面即可完成支付或交互。
- 无需中心化审核:任何开发者可以快速创建、部署和分享 Mini Apps,无需应用商店的审批流程。
- 可组合性:Smart Widgets 支持不同类型的功能模块组合,可灵活适配各种 Agent-to-Agent 协作需求。
- 内置支付能力:通过集成链上支付和稳定币支持,实现智能代理之间的价值交换。
这一体系极大降低了构建和扩展去中心化智能代理组织的门槛,使得个体代理(Agent)不仅能行动,还能彼此协作、交易和治理。
2.2 Smart Widgets 的形态与应用
Yakihonne Smart Widgets 根据创建者和使用者的不同需求,分为三种形态,覆盖从普通用户到开发者的全域需求:
- 基础组件(Basic Widgets) 无需编程,通过模板编辑器快速创建支付、投票等交互功能,适合用户构建简单的 Mini Apps。
- 动作组件(Action Widgets) 通过链接嵌入外部功能,保持社交界面的流畅性,支持 Mini Apps 扩展交互范围。
- 工具组件(Tool Widgets) 适合开发者或高级用户,基于 Mini App SDK 开发复杂应用,支持数据查询、链上任务执行、即时支付、智能决策等,构建复杂的智能化 Mini Apps。
这三种形态为 Mini Apps 提供从基础交互到高级协作的支持,适配 DA(gentic)O 的自动化流程。
2.3 支持 DA(gentic)O 的核心功能
Yakihonne Smart Widgets 为分布式Agentic组织提供以下关键能力,驱动 Agentic Mini Apps 的高效运行:
- 自治微应用(Autonomous Mini Apps) Smart Widgets 让代理能够嵌入服务逻辑,自主完成任务或发起支付。例如,Mini Apps 可自动分配 Web3 交易奖励,或协调网络社会的虚拟活动,无需人工干预。
- 即用即付(On-the-Fly Payment) 通过稳定币、BTC、闪电网络(LN)等无缝支付协议,智能代理可以即时完成链上支付,支持微交易经济体。
- 链上身份与社交绑定(On-chain Identity Integration) 代理可以在 Nostr 基础上绑定主权身份,进行链上行为的授权与签名。
- 即时交互与协作(Real-time Interaction and Coordination) 支持代理之间的即时数据交换、智能合约调用和协作执行,适配 Agent-to-Agent 协作网络。
- 开放与可组合性(Openness and Composability) 开发者可自由创建与组合 Widgets,扩展 Mini Apps 的模块化生态。
这些功能使 Smart Widgets 成为 DA(gentic)O 的“支柱”,通过 Mini Apps 连接个体代理与协作网络,构建动态、规模化的生态。
2.4 驱动代理经济(Agentic Economy)
在 DA(gentic)O 中,经济交互至关重要。Smart Widgets 通过以下方式推动代理经济形成:
- 降低支付壁垒 嵌入式支付支持代理间无摩擦的小额交易,简化价值流转。
- 微型自治市场 Widgets 赋予 Mini Apps 自主定价与运营能力,形成独立经济单元。
- 加速创新与扩展 开放创建机制与低成本部署鼓励开发者丰富 Mini Apps 生态。
Yakihonne 正在推动一种新的模式:社交即支付,应用即自治。这为未来的 Agentic DAO 和基于代理的社会经济体系提供了可行路径。
3.Agentic Mini App 应用场景
Agentic Mini Apps 是 DA(gentic)O的交互实现层,通过 YakiHonne Widgets 嵌入社交场景和支付功能,让用户在治理、创作、激励和消费中无缝互动。本章探讨 智能治理、社交媒体、消费生态 三类场景,展示 DA(gentic)O 如何构建从 Web3 到现实社会的动态生态。
3.1. 智能治理--Agentic AI for DAO
传统 DAO 依赖区块链实现透明治理,试图以社区投票和智能合约取代中心化管理。但投票延迟、分歧和静态合约限制价值交付,如投资 DAO 决策迟缓难敌专业机构,协议 DAO 缺乏生产力。Agentic AI 作为 DA(gentic)O 的“智能内核”,自动化执行提案、优化资源分配,提升链上效率,连接 Web3 与现实生产力。具体场景如下:
智能投票与治理优化 传统 aMaci 匿名投票复杂,限制规模化。该基于aMaci的Mini App 封装治理逻辑,提供友好交互,用户通过私信/通知接收提案通知(如“是否调整协议参数”),一键投票。Mini App 分析链上数据(如历史投票趋势),生成决策建议,投票结果秒级汇总,提案自动执行。
激励分配与贡献追踪 用户在 Mini App 内查看贡献(如代码提交、任务完成),Agentic AI 评估链上和链下活动,自动支付稳定币/LN/BTC 奖励,秒到账。私信通知奖励状态。用户通过 Post 展示贡献,Mini App 监测活动,支付代币或 NFT 奖励,链上记录,私信确认支付。
DAO2DAO协作 用户在 Mini App 内共享数据(如 BTC 趋势),Agentic AI 生成协作建议(如“联合活动”),自动执行跨 DAO 任务(如资金池分配)。Post 宣传合作动态。 用户也可通过私信发起联合提案,Mini App 整合多方数据,支付稳定币/LN/BTC 执行协作,链上透明。
社区活动与众筹 用户在 Mini App 内捐款支持活动(如“DAO 年会”),支付稳定币/LN/BTC,秒到账。Agentic AI 跟踪进度,自动分配资金,Post 展示成果。用户通过私信报名活动,Mini App 支付获 NFT 奖励,链上存证。
资源与任务分配 用户在 Mini App 内接收任务(如“开发模块”),Agentic AI 匹配技能,支付稳定币/LN/BTC 奖励,秒到账。私信通知任务状态。用户通过 Post 领取任务,Mini App 验证成果,自动支付代币,链上记录。私信确认完成。
链上身份与认证 用户在 Mini App 内将链上身份与 Nostr 身份绑定,Agentic AI 验证权限,支持跨 DAO 互认,支付稳定币/LN/BTC 激活身份。用户申请联合活动权限,Mini App 验证身份,自动授权,链上透明。
舆情实时分析 用户在 Mini App 内查看舆情报告(如“代币热度上升 30%”),Agentic AI 分析链上和社交数据,生成投资建议,支付 2 USDC 奖励,秒到账。私信推送报告。
3.2 社交媒体
中心化社交媒体因算法操控、内容审查和数据滥用限制用户表达,创作者收益被高额抽成侵蚀,信息真实性和隐私权受威胁。Agentic AI 促使去中心化社交生态更加智能和去中心化,保障用户主权,构建从 Web3 到现实社会的开放网络。具体场景如下:
内容创作与分发 用户与 Agentic AI 协作生成内容(如视频、长文、海报),一键分发到 YakiHonne 及多平台。Mini App 分析用户兴趣,精准推送,支付稳定币/LN/BTC 查看全文。
AI 记者-报道/采访 用户通过 Mini App 自动化新闻采集,分析链上数据和社交 Post,生成长文报道,发布后支持支付打赏。用户通过私信发起采访(如 BUIDL 项目),Agentic AI 生成大纲,Mini App 转录视频为长文或视频,发布至 YakiHonne 及其他平台。
内容互动 用户通过 YakiHonne 社交 Post 参与讨论,Mini App 追踪评论质量,自动打赏奖励高互动者。
内容订阅 用户通过 Mini App 支付订阅长文或独家 Post,Mini App 管理访问权限,秒到账。
内容真实性验证 用户通过 Mini App 验证内容真实性(如新闻出处),标记可信度并投票支持真实内容。
内容存档与协作 用户通过 Mini App 上传 Post 或长文,存储于去中心化网络,生成永久链接并支持其他用户付费下载。用户在 Mini App 内协作长文,Agentic AI 追踪并评估贡献,自动支付稳定币/LN/BTC 奖励,
去中心化广告与收益 创作者通过 Mini App 付费推送长文或内容触达用户,读者将会从广告直接获得收益。
舆情分析与公共讨论 Agentic AI 监测 YakiHonne Post 和社交动态(如“话题热度上升 30%”),生成讨论建议,用户通过私信接收长文报告并进行支付。
3.3 消费生态
中心化支付和传统消费因高额手续费、结算延迟和复杂流程限制用户体验,DeFi 应用也面临操作门槛高、信任不足的问题。Agentic AI 通过 Mini Apps 打造去中心化社交支付与消费生态,扩展链上与现实的消费场景,构建 Web3 价值网络。场景如下:
朋友转账 用户在 Mini App 内搜索好友并转账 0.05 USDC,Agentic AI 测算最优汇率和 Swap 路径,秒到账,链上记录。私信提醒转账请求。 用户在 Mini App 内发起群组分账,Agentic AI 计算份额,支付稳定币/LN/BTC,秒到账,Post 展示记录。
DeFi 质押激励 用户在 Mini App 内加入质押池,Agentic AI 推荐高收益策略,支付稳定币/LN/BTC,秒到账,链上分红透明。私信通知收益。 用户在 Mini App 内质押资产,Agentic AI 分析市场,支付 0.1 USDC 奖励活跃者,秒到账,Post 分享策略。
线下消费 用户在 Mini App 内支付 BTC/LN 购买咖啡或商品,秒到账,链上存证。Post 推送附近商家优惠。用户在 Mini App 内预订服务(如餐厅座位),支付稳定币/LN/BTC 获代币返现,秒到账,Post 分享活动。
GameFi 用户在 Mini App 内支付 0.1 USDC 购买游戏装备,秒到账,链上存证。Post 推送新资产吸引玩家。用户在 Mini App 内完成任务(如战斗挑战),Agentic AI 验证,支付稳定币/LN/BTC 奖励,秒到账,Post 展示排行。
跨境电商 用户在 Mini App 内支付 1 USDC 购买跨境商品,秒到账,链上记录物流。私信推送订单更新。用户在 Mini App 内参与跨境团购,Agentic AI 优化折扣,支付稳定币/LN/BTC 分摊运费,秒到账,Post 展示进展。
4. 结论
随着 Agentic AI 和去中心化技术的快速融合,DA(gentic)O 不再是理论构想,而是正在形成的“智能协作网络”。YakiHonne 的 Smart Widgets 和 Agentic Mini Apps,正在为这种网络提供关键接口与交互基础设施,为用户和开发者释放出前所未有的创作力、支付能力与治理可能。 我们正在见证三个关键趋势的叠加:
1) 从单体代理到多代理协作系统
未来的组织形态将不再是人类为中心的链上治理,而是以多智能体(Multi-Agent)为核心的动态生态。每一个智能代理代表一个用户、一个群体、一个经济单位,能独立感知、推理、执行,与其他代理协同完成更复杂的生产与治理流程。YakiHonne Smart Widgets 将成为这些代理的“协作面板”,为其提供微型入口与交互协议。
2)从社交互动到社交经济系统
当前的社交平台仍多以信息交换为主,而未来的去中心化社交网络将嵌入支付、投票、任务、协作等“社会操作系统”,形成真正的“社交经济”。在这个体系中,Mini Apps 不再是内容附属,而是核心交互单元。YakiHonne 的 Widget 设计天然服务于此场景:它让每一次社交行为都可能触发价值流转,从一次转账、一次众筹、一次治理投票,到一个内容生成任务。
3) 从平台生态到分布式开发生态
社交支付的未来,属于可编程的生态,而非封闭的平台。随着 Smart Widgets SDK 的开源,越来越多的开发者将加入 Agentic Mini App 的构建中。未来的 Web3 应用不会是一个个巨型 App,而是一组协同工作的 Widget 网络,它们在用户的社交流中被发现、被使用、被组合。YakiHonne 正在成为这一生态的起点。
YakiHonne的愿景不仅是打造一个功能强大的去中心化社交支付平台,更是构建一个通向未来的“Agentic 社交操作系统”。在这个系统中,每一个人、每一个代理、每一个交互都是协作的触发器,智能的入口,价值的节点。
-
 @ 57d1a264:69f1fee1
2025-04-05 06:28:16
@ 57d1a264:69f1fee1
2025-04-05 06:28:16⚡️ About Us
@AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY.
⚡️ The Role
Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision.
⚡️ Responsibilities
Produce 30 short videos on circular economies. Incorporate subtitles as needed. Submit videos on a deliverables basis. Participate in check-ins and communicate with the AB team and circular economy communities.
⚡️ What We Offer
Free ticket to AB25. Networking with Bitcoiners and industry leaders. Letter of recommendation and LinkedIn endorsement upon completion. Mentorship and hands-on experience with a high-profile Bitcoin project.
⚡️ Skills & Qualifications
Passion for Bitcoin and circular economies. Basic to intermediate video editing skills (no specific software required). Creative independence with feedback. Portfolio or work samples preferred.
⚡️ Time Commitment
Flexible, project-based internship with check-ins and feedback rounds.
⚡️ How to Apply
Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission -
{NAME OR NYM}.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available).originally posted at https://stacker.news/items/935001
-
 @ f6497934:312c6532
2025-04-17 06:42:48
@ f6497934:312c6532
2025-04-17 06:42:48Discover the ultimate Water Activity Meter for precise moisture measurement in food, pharmaceuticals, and cosmetics. Ensure product safety and extend shelf life by accurately assessing microbial growth risks. Our advanced meters, like the AQUALAB 4TE, deliver fast, reliable results in minutes with ±0.003 accuracy. Easy to use, portable, and temperature-controlled, they’re perfect for quality control in any industry. Optimize your production process, meet FDA standards, and boost product consistency. Invest in top-tier water activity testing today—shop now for unbeatable performance and durability!
-
 @ c631e267:c2b78d3e
2025-04-04 18:47:27
@ c631e267:c2b78d3e
2025-04-04 18:47:27Zwei mal drei macht vier, \ widewidewitt und drei macht neune, \ ich mach mir die Welt, \ widewide wie sie mir gefällt. \ Pippi Langstrumpf
Egal, ob Koalitionsverhandlungen oder politischer Alltag: Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit Rückenwind geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die Wahlwiederholung im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden, das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine Lagarde oder im «Pfizergate»-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen, so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das Stimmrecht entziehen.
Der Pegel an Unzufriedenheit und Frustration wächst in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die Umfrageergebnisse der AfD ein guter Gradmesser dafür.
[Vorlage Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3ffac3a6:2d656657
2025-04-05 04:55:12
@ 3ffac3a6:2d656657
2025-04-05 04:55:12O Impacto do Namoro com Pelé na Carreira de Xuxa Meneghel
Disclaimer:
Esse texto foi totalmente escrito pelo ChatGPT, eu apenas pedi que ele fizesse uma pesquisa sobre o tema.
Introdução: O relacionamento entre Xuxa Meneghel e Pelé, que durou cerca de seis anos (início dos anos 1980 até 1986), foi um dos mais comentados da década de 1980 (Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA). Xuxa tinha apenas 17 anos quando começou a namorar o já consagrado “Rei do Futebol”, então com 40 anos (A história da foto de revista que gerou o namoro de Pelé e Xuxa) (Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA). Esse romance altamente midiático não só atiçou a curiosidade do público, como também alavancou a carreira de Xuxa de forma significativa. A seguir, detalhamos como o namoro aumentou a visibilidade da apresentadora, quais oportunidades profissionais podem ter tido influência direta de Pelé, o papel da revista Manchete e de outras mídias na promoção de sua imagem, se o relacionamento contribuiu para Xuxa conquistar espaços na TV (como o programa Clube da Criança e, posteriormente, na Rede Globo) e como mídia e público percebiam o casal – tudo embasado em fontes da época, entrevistas e biografias.
Aumento da Visibilidade Midiática nos Anos 1980
O namoro com Pelé catapultou Xuxa a um novo patamar de fama. Até então uma modelo em começo de carreira, Xuxa “se tornou famosa ao aparecer ao lado do esportista de maior status do Brasil” (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições). A partir do momento em que o relacionamento se tornou público, ela passou a estampar capas de revistas com frequência e a ser assunto constante na imprensa. Em 20 de dezembro de 1980, a jovem apareceu na capa da revista Manchete ao lado de Pelé e outras modelos – um ensaio fotográfico que marcou o primeiro encontro dos dois e deu início à enorme atenção midiática em torno de Xuxa (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira) (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira). Não por acaso, “naquele ano, ela foi capa de mais de cem revistas” (Xuxa está em paz - revista piauí), um indicativo claro de como sua visibilidade explodiu após começar a namorar Pelé. Jornais, revistas de celebridades e programas de fofoca passaram a segui-los de perto; o casal virou sensação nacional, comparado até ao “Casal 20” (dupla glamourosa de uma série de TV americana) pelo seu alto perfil na mídia (Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA).
Essa exposição intensa colocou Xuxa não apenas sob os holofotes do público, mas também a inseriu nos bastidores do entretenimento. Como namorada de Pelé – um dos homens mais conhecidos do mundo – Xuxa passou a frequentar eventos de gala, festas e bastidores de programas, onde conheceu figuras influentes do meio artístico e televisivo. Os fotógrafos os seguiam em eventos como bailes de carnaval e inaugurações, registrando cada aparição pública do casal. Com Pelé ao seu lado, Xuxa ganhou trânsito livre em círculos antes inacessíveis para uma modelo iniciante, construindo uma rede de contatos valiosa nos meios de comunicação. De fato, naquele início dos anos 80, “os dois eram perseguidos por fotógrafos, apareciam em capas de revistas e até faziam publicidade juntos” (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições) – evidência de que Xuxa, graças ao namoro, transitava tanto na frente quanto por trás das câmeras com muito mais facilidade. Em suma, o relacionamento conferiu a ela um grau de notoriedade nacional que provavelmente demoraria anos para conquistar de outra forma, preparando o terreno para os passos seguintes de sua carreira.
Influência Direta de Pelé nas Oportunidades Profissionais de Xuxa
Além do aumento geral da fama, há casos específicos em que Pelé influenciou diretamente oportunidades profissionais para Xuxa. Um exemplo contundente é o filme “Amor Estranho Amor” (1982) – longa de teor erótico no qual Xuxa atuou no início da carreira. Segundo relatos da própria apresentadora, foi Pelé quem a incentivou a aceitar participar desse filme (Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5). Na época ainda em início de trajetória, Xuxa acabou convencida pelo namorado de que aquela oportunidade poderia ser benéfica. Anos mais tarde, ela revelaria arrependimento pela escolha desse papel, mas o fato reforça que Pelé teve influência ativa em decisões profissionais de Xuxa no começo de sua jornada.
Outra área de influência direta foram as publicidades e campanhas comerciais. Graças ao prestígio de Pelé, Xuxa recebeu convites para estrelar anúncios ao lado do então namorado. Já em 1981, por exemplo, os dois gravaram juntos comerciais para uma empresa imobiliária, aparecendo como casal em campanhas de TV daquele Natal (pelas Imóveis Francisco Xavier, um case famoso entre colecionadores de propagandas da época) (Xuxa e Pelé: Natal de 1981 na Publicidade Imobiliária | TikTok) (Xuxa com Pelé em comercial de imobiliária em dezembro de 1981). Assim, Xuxa obteve espaço em campanhas publicitárias que dificilmente envolveriam uma modelo desconhecida – mas que, com a “namorada do Pelé” no elenco, ganhavam apelo extra. Isso evidencia que Pelé abriu portas também no mercado publicitário, dando a Xuxa oportunidades de trabalho e renda enquanto sua própria imagem pública se consolidava.
Ademais, a presença de Pelé ao lado de Xuxa em diversos editoriais e ensaios fotográficos serviu para elevá-la de modelo anônima a personalidade conhecida. Revistas e jornais buscavam os dois para sessões de fotos e entrevistas, sabendo do interesse do público pelo casal. As capas conjuntas em publicações de grande circulação (como Manchete e outras) não só aumentaram a exposição de Xuxa, mas também conferiram a ela certa credibilidade midiática por associação. Em outras palavras, estar ao lado de um ícone como Pelé funcionou como um “selo de aprovação” implícito, deixando editores e produtores mais propensos a convidá-la para projetos. Vale lembrar que “ao longo dos seis anos de relacionamento, [eles] posaram para várias capas da Manchete”, com a revista acompanhando de perto cada fase do namoro (A história da foto de revista que gerou o namoro de Pelé e Xuxa). Essa recorrência nas bancas solidificou o rosto e o nome de Xuxa na indústria do entretenimento.
Por fim, é importante notar que nem todas as influências de Pelé foram positivas para a carreira dela – algumas foram tentativas de direcionamento. A própria Xuxa contou que, quando surgiu a oportunidade de ela ir para a TV Globo em 1986, Pelé desencorajou a mudança. Ele sugeriu que Xuxa permanecesse na TV Manchete, dizendo que “ser a primeira [na Globo] é muito difícil; melhor ficar onde está”, o que ela interpretou como falta de apoio dele à sua ascensão (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira). Esse episódio mostra que Pelé tentou influenciar também os rumos que Xuxa tomaria, embora, nesse caso, ela tenha decidido seguir sua intuição profissional e aceitar o desafio na Globo – escolha que se revelaria acertada. Em resumo, Pelé atuou sim como facilitador de várias oportunidades profissionais para Xuxa (de filmes a comerciais e visibilidade editorial), mas ela soube trilhar seu caminho a partir daí, inclusive contrariando conselhos dele quando necessário.
Papel da Revista Manchete e Outras Mídias na Promoção de Xuxa
A revista Manchete teve um papel central na ascensão de Xuxa durante o relacionamento com Pelé. Foi justamente num ensaio para a Manchete que os dois se conheceram, em dezembro de 1980 (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira), e a partir daí a publicação tornou-se uma espécie oficiosa de cronista do romance. A Manchete era uma das revistas mais populares do Brasil naquela época e, ao perceber o interesse do público pelo casal, passou a trazê-los frequentemente em suas páginas. De fato, a revista que agiu como "cupido" do casal “contava detalhes do romance a cada edição”, alimentando a curiosidade nacional sobre a vida de Pelé e sua jovem namorada (A história da foto de revista que gerou o namoro de Pelé e Xuxa). As capas exibindo Xuxa e Pelé juntos (em cenários que iam da praia a eventos sociais) viraram chamariz nas bancas e contribuíram enormemente para fixar a imagem de Xuxa na mente do público.
(A história da foto de revista que gerou o namoro de Pelé e Xuxa) Capa da revista Manchete (20 de dezembro de 1980) mostrando Pelé ao centro com Xuxa (à esquerda) e outras modelos. A partir desse ensaio fotográfico, a revista passou a acompanhar de perto o romance, impulsionando a imagem de Xuxa nacionalmente. (A história da foto de revista que gerou o namoro de Pelé e Xuxa) (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira)
Além da Manchete, outras mídias impressas também surfaram no interesse pelo casal e ajudaram a moldar a imagem de Xuxa. Revistas de celebridades e colunas sociais publicavam notas e fotos frequentes, ora exaltando o glamour do par, ora especulando sobre fofocas. Xuxa, que pouco antes era desconhecida fora do circuito da moda, tornou-se figura constante em revistas semanais como Contigo! e Amiga (dedicadas à vida dos famosos), assim como em jornais de grande circulação. Esse bombardeio de aparições – entrevistas, fotos e manchetes – construiu a persona pública de Xuxa simultaneamente como modelo desejada e namorada devotada. A promoção de sua imagem tinha um tom deliberadamente positivo nas revistas: enfatizava-se sua beleza, juventude e sorte por ter sido “escolhida” pelo rei Pelé. Em contrapartida, eventuais polêmicas (como cenas ousadas que ela fez no cinema ou rumores de crises no namoro) eram administradas pela própria mídia de maneira a preservar o encanto em torno de Xuxa, que já despontava como uma espécie de Cinderella moderna na narrativa do entretenimento brasileiro.
Cabe destacar que a conexão de Xuxa com a Manchete não ficou só nas páginas da revista, mas transbordou para a televisão, já que a Rede Manchete (canal de TV fundado em 1983) pertencia ao mesmo grupo empresarial. Essa sinergia mídia impressa/televisão beneficiou Xuxa: quando a Rede Manchete buscava uma apresentadora para seu novo programa infantil em 1983, Xuxa – já famosa pelas capas de revista – foi convidada para o posto (Xuxa está em paz - revista piauí). Ou seja, a exposição na revista Manchete serviu de vitrine para que os executivos da emissora homônima apostassem nela na TV. Outras mídias também legitimaram sua transição de modelo para apresentadora, publicando matérias sobre sua simpatia com as crianças e seu carisma diante das câmeras, preparando o público para aceitar Xuxa em um novo papel. Assim, o período do relacionamento com Pelé viu a mídia – liderada pela revista Manchete – construir e promover intensamente a imagem de Xuxa, pavimentando o caminho para suas conquistas seguintes.
O Relacionamento e a Conquista de Espaços na TV: Clube da Criança e Rede Globo
O namoro com Pelé coincidiu com a entrada de Xuxa na televisão e possivelmente facilitou essa transição. Em 1983, a recém-inaugurada Rede Manchete lançou o “Clube da Criança”, primeiro programa infantil de auditório da emissora, e Xuxa foi escolhida como apresentadora. Há indícios de que sua fama prévia – alavancada pelo relacionamento – foi decisiva nessa escolha. Conforme relatos, o diretor Maurício Sherman (responsável pelo projeto) estava de olho em Xuxa por sua notoriedade e carisma, chegando a dizer que ela reunia “a sensualidade de Marilyn Monroe, o sorriso de Doris Day e um quê de Peter Pan” (Xuxa está em paz - revista piauí) – uma combinação que poderia funcionar bem num programa infantil. Xuxa inicialmente hesitou em aceitar, talvez pelo contraste entre sua imagem de modelo sensual e o universo infantil, mas acabou assinando contrato com a Manchete (Clube da Criança – Wikipédia, a enciclopédia livre). Assim, aos 20 anos de idade, ela estreava como apresentadora de TV, em grande parte graças à visibilidade e confiança que o nome “Xuxa” (já famoso por ser namorada do Pelé) passava aos produtores.
Não há registro de que Pelé tenha intervindo diretamente para que Xuxa conseguisse o posto no Clube da Criança. Foi a própria rede Manchete – estimulada pelo burburinho em torno dela – que a “procurou e a convidou para apresentar” o programa (Xuxa está em paz - revista piauí). Porém, é inegável que, sem o destaque que Xuxa conquistara nos anos anteriores na imprensa (devido ao namoro), dificilmente uma emissora arriscaria colocar uma jovem inexperiente para comandar um show infantil nacional. Ou seja, o relacionamento criou as condições favoráveis para essa oportunidade surgir. Uma vez no ar, Xuxa rapidamente mostrou talento próprio: o Clube da Criança foi ganhando audiência e revelou a aptidão dela em se comunicar com o público infantil (Xuxa, Pantanal, Cavaleiros dos Zodíacos: lembre sucessos da TV ...). Ainda durante seu tempo na Manchete, Xuxa manteve-se nos holofotes tanto pela carreira quanto pelo namoro com Pelé – frequentemente um assunto alimentava o outro na mídia.
Em meados de 1986, já conhecida como a “Rainha dos Baixinhos” pelo sucesso junto às crianças, Xuxa recebeu uma proposta para se transferir para a Rede Globo, a principal emissora do país (A história da foto de revista que gerou o namoro de Pelé e Xuxa). Novamente, aqui o relacionamento com Pelé tem um papel indireto: por um lado, pode ter ajudado a construir a notoriedade que chamou a atenção da Globo; por outro, chegava ao fim exatamente nesse momento, marcando uma virada na vida dela. Após alguns anos de Clube da Criança, Xuxa decidiu dar um passo adiante. Ela mesma tomou a iniciativa de terminar o namoro com Pelé e aceitou o convite para fazer o “Xou da Xuxa” na Globo (A história da foto de revista que gerou o namoro de Pelé e Xuxa). Pelé, como mencionado, havia expressado reservas sobre essa mudança de emissora (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira), mas sem sucesso em demovê-la. Com a benção do dono da Manchete, Adolpho Bloch (que a tratava “como filha” e apoiou seu crescimento) (Xuxa está em paz - revista piauí) (Xuxa está em paz - revista piauí), Xuxa partiu para a Globo levando sua diretora Marlene Mattos, e estreou em junho de 1986 o programa que a consagraria definitivamente.
É importante notar que, ao ingressar na Globo, Xuxa já não dependia mais da aura de “namorada do Pelé” – ela havia se firmado como apresentadora de sucesso por méritos próprios. Ainda assim, o relacionamento anterior continuou a ser parte de sua imagem pública: a mídia noticiou a mudança destacando que a namorada de Pelé chegara à Globo, e muitos espectadores tinham curiosidade sobre aquela moça cuja fama começara nos braços do ídolo do futebol. Em resumo, o namoro ajudou Xuxa a conquistar o primeiro grande espaço na TV (na Manchete), fornecendo-lhe exposição e credibilidade iniciais, enquanto sua ida para a Globo foi impulsionada principalmente pelo desempenho no Clube da Criança – algo que o prestígio conquistado durante o relacionamento tornou possível em primeiro lugar.
Percepção da Mídia e do Público sobre o Casal e a Imagem de Xuxa
Durante os anos de namoro, Pelé e Xuxa foram um prato cheio para a imprensa e objeto de variadas opiniões do público. De um lado, eram celebrados como “casal perfeito na mídia”, aparecendo sorridentes em eventos e capas, o que projetava uma imagem glamourosa e apaixonada (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições). Xuxa era frequentemente retratada como a bela jovem humilde que havia conquistado o coração do "rei", uma narrativa de conto de fadas que agradava muitos fãs. Pessoas próximas diziam na época: “Nossa, como ela está apaixonada, como ela está de quatro pelo Pelé”, segundo relembrou a própria Xuxa, indicando que sua dedicação ao namorado era visível e comentada (Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA). Essa percepção de autenticidade nos sentimentos ajudou a humanizar Xuxa aos olhos do público, diferenciando-a de estereótipos de roupante ou interesse calculado.
Por outro lado, nem toda a atenção era positiva. Houve murmúrios maldosos e preconceituosos nos bastidores. Pelé e Xuxa formavam um casal interracial (ele negro, ela branca e bem mais jovem), o que, segundo a imprensa, “gerava olhares de reprovação dos conservadores” e até comentários racistas proferidos pelas costas (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições). Além disso, alguns duvidavam das intenções de Xuxa no relacionamento, insinuando que ela buscava ascensão social por meio de Pelé. Termos pejorativos como “maria-chuteira” (gíria para mulheres que namoram jogadores em busca de status) e “alpinista social” chegaram a ser associados a Xuxa por fofoqueiros da época (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições). Essa desconfiança lançava sombra sobre a imagem dela, pintando-a, aos olhos de alguns, como oportunista em vez de namorada dedicada. Xuxa teve de lidar com esse tipo de insinuação ao longo do namoro, buscando provar que seu amor era verdadeiro e que ela também tinha talentos e ambições próprias.
A mídia impressa, em geral, manteve uma postura favorável ao casal, explorando o romance como algo encantador. Mas não deixou de reportar as turbulências: sabia-se, por exemplo, das frequentes traições de Pelé, que Xuxa anos depois revelou ter suportado calada na época (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira) (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira). Essas infidelidades eram rumores correntes nos círculos de fofoca, embora Xuxa raramente comentasse publicamente enquanto estava com Pelé. O público, portanto, via um casal bonito e famoso, mas também acompanhava as especulações de crises e reconciliações pelos noticiários de celebridades. Cada aparição pública deles – fosse em um jogo de futebol, um evento beneficente ou nos camarotes do carnaval – era dissecada pelos repórteres, e cada declaração (ou silêncio) alimentava interpretações sobre o estado do relacionamento e sobre quem era Xuxa por trás da fama.
No saldo final, o namoro com Pelé influenciou profundamente a imagem pública de Xuxa. Inicialmente marcada como “a namorada do Rei” – posição que trazia tanto admiração quanto inveja – Xuxa soube aproveitar a visibilidade para mostrar carisma e trabalho, transformando-se em uma estrela por direito próprio. Ao se tornar apresentadora infantil de sucesso ainda durante o namoro, ela começou a dissociar sua imagem da de Pelé, provando que podia ser mais do que um apêndice de um astro do esporte. Quando o relacionamento terminou em 1986, Xuxa emergiu não caída em desgraça, mas sim pronta para reinar sozinha na TV. A mídia continuou a mencioná-la em referência a Pelé por algum tempo (era inevitável, dado o quão famoso o casal fora), mas cada vez mais o público passou a enxergá-la principalmente como a “Rainha dos Baixinhos”, a figura alegre das manhãs na TV Globo. Em entrevistas posteriores, Xuxa admitiu ter sentimentos mistos ao lembrar dessa fase: ela se ressentiu, por exemplo, de Pelé ter classificado o que viveram como “uma amizade colorida” em vez de namoro sério (Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5) – frase do ex-jogador que a magoou e que veio a público muitos anos depois. Esse comentário retroativo de Pelé apenas reforçou o quanto a mídia e o público discutiram e dissecaram a natureza daquela relação.
Em conclusão, a percepção do casal Xuxa e Pelé oscilou entre o encanto e a controvérsia, mas inegavelmente manteve Xuxa nos trending topics de sua época (para usar um termo atual). A jovem modelo gaúcha ganhou projeção, prestígio e também enfrentou julgamentos enquanto esteve com Pelé. Tudo isso moldou sua imagem – de símbolo sexual e socialite em ascensão a profissional talentosa pronta para brilhar por conta própria. O relacionamento forneceu-lhe a plataforma e a armadura mediática; coube a Xuxa transformar essa visibilidade em uma carreira sólida, o que ela fez com maestria ao se tornar uma das maiores apresentadoras da história da TV brasileira.
Fontes: Entrevistas e depoimentos de Xuxa Meneghel (inclusive do livro Memórias, 2020), reportagens da época em revistas como Manchete, colunas sociais e jornais (compiladas em repositórios atuais), e biografias e retrospectivas sobre ambos os envolvidos (A história da foto de revista que gerou o namoro de Pelé e Xuxa) (Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições) (Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira) (Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA), entre outras. Essas fontes confirmam o papel catalisador que o namoro com Pelé teve nos primeiros passos da trajetória de Xuxa, bem como os desafios e oportunidades que surgiram dessa intensa exposição pública.
-
 @ 5c26ee8b:a4d229aa
2025-04-17 20:01:03
@ 5c26ee8b:a4d229aa
2025-04-17 20:01:03Prophet Jesus peace be upon him was never killed, he was saved by God and raised to heavens body and soul.
4:157 An-Nisaa
وَقَوْلِهِمْ إِنَّا قَتَلْنَا الْمَسِيحَ عِيسَى ابْنَ مَرْيَمَ رَسُولَ اللَّهِ وَمَا قَتَلُوهُ وَمَا صَلَبُوهُ وَلَٰكِنْ شُبِّهَ لَهُمْ ۚ وَإِنَّ الَّذِينَ اخْتَلَفُوا فِيهِ لَفِي شَكٍّ مِنْهُ ۚ مَا لَهُمْ بِهِ مِنْ عِلْمٍ إِلَّا اتِّبَاعَ الظَّنِّ ۚ وَمَا قَتَلُوهُ يَقِينًا
And because of their saying (in boast), "We killed Messiah 'Iesa (Jesus), son of Maryam (Mary), the Messenger of Allah," - but they killed him not, nor crucified him, but the resemblance of 'Iesa (Jesus) was put over another man (and they killed that man), and those who differ therein are full of doubts. They have no (certain) knowledge, they follow nothing but conjecture. For surely; they killed him not [i.e. 'Iesa (Jesus), son of Maryam (Mary)]:
4:158 An-Nisaa
بَلْ رَفَعَهُ اللَّهُ إِلَيْهِ ۚ وَكَانَ اللَّهُ عَزِيزًا حَكِيمًا
But Allah raised him ['Iesa (Jesus)] up (with his body and soul) unto Himself (and he is in the heavens). And Allah is Ever All-Powerful, All-Wise.
Jesus, peace be upon him, is neither God nor his son.
5:17 Al-Maaida
لَقَدْ كَفَرَ الَّذِينَ قَالُوا إِنَّ اللَّهَ هُوَ الْمَسِيحُ ابْنُ مَرْيَمَ ۚ قُلْ فَمَنْ يَمْلِكُ مِنَ اللَّهِ شَيْئًا إِنْ أَرَادَ أَنْ يُهْلِكَ الْمَسِيحَ ابْنَ مَرْيَمَ وَأُمَّهُ وَمَنْ فِي الْأَرْضِ جَمِيعًا ۗ وَلِلَّهِ مُلْكُ السَّمَاوَاتِ وَالْأَرْضِ وَمَا بَيْنَهُمَا ۚ يَخْلُقُ مَا يَشَاءُ ۚ وَاللَّهُ عَلَىٰ كُلِّ شَيْءٍ قَدِيرٌ
They have certainly disbelieved who say that Allah is Christ, the son of Mary. Say, "Then who could prevent Allah at all if He had intended to destroy Christ, the son of Mary, or his mother or everyone on the earth?" And to Allah belongs the dominion of the heavens and the earth and whatever is between them. He creates what He wills, and Allah is over all things competent.
5:18 Al-Maaida
وَقَالَتِ الْيَهُودُ وَالنَّصَارَىٰ نَحْنُ أَبْنَاءُ اللَّهِ وَأَحِبَّاؤُهُ ۚ قُلْ فَلِمَ يُعَذِّبُكُمْ بِذُنُوبِكُمْ ۖ بَلْ أَنْتُمْ بَشَرٌ مِمَّنْ خَلَقَ ۚ يَغْفِرُ لِمَنْ يَشَاءُ وَيُعَذِّبُ مَنْ يَشَاءُ ۚ وَلِلَّهِ مُلْكُ السَّمَاوَاتِ وَالْأَرْضِ وَمَا بَيْنَهُمَا ۖ وَإِلَيْهِ الْمَصِيرُ
But the Jews and the Christians say, "We are the children of Allah and His beloved." Say, "Then why does He punish you for your sins?" Rather, you are human beings from among those He has created. He forgives whom He wills, and He punishes whom He wills. And to Allah belongs the dominion of the heavens and the earth and whatever is between them, and to Him is the [final] destination.
5:72 Al-Maaida
لَقَدْ كَفَرَ الَّذِينَ قَالُوا إِنَّ اللَّهَ هُوَ الْمَسِيحُ ابْنُ مَرْيَمَ ۖ وَقَالَ الْمَسِيحُ يَا بَنِي إِسْرَائِيلَ اعْبُدُوا اللَّهَ رَبِّي وَرَبَّكُمْ ۖ إِنَّهُ مَنْ يُشْرِكْ بِاللَّهِ فَقَدْ حَرَّمَ اللَّهُ عَلَيْهِ الْجَنَّةَ وَمَأْوَاهُ النَّارُ ۖ وَمَا لِلظَّالِمِينَ مِنْ أَنْصَارٍ
Surely, they have disbelieved who say: "Allah is the Messiah ['Iesa (Jesus)], son of Maryam (Mary)." But the Messiah ['Iesa (Jesus)] said: "O Children (descendants) of Israel! Worship Allah, my Lord and your Lord." Verily, whosoever sets up partners in worship with Allah, then Allah has forbidden Paradise for him, and the Fire will be his abode. And for the Zalimun (unjust, polytheists and wrong-doers) there are no helpers.
5:73 Al-Maaida
لَقَدْ كَفَرَ الَّذِينَ قَالُوا إِنَّ اللَّهَ ثَالِثُ ثَلَاثَةٍ ۘ وَمَا مِنْ إِلَٰهٍ إِلَّا إِلَٰهٌ وَاحِدٌ ۚ وَإِنْ لَمْ يَنْتَهُوا عَمَّا يَقُولُونَ لَيَمَسَّنَّ الَّذِينَ كَفَرُوا مِنْهُمْ عَذَابٌ أَلِيمٌ
Surely, disbelievers are those who said: "Allah is the third of the three (in a Trinity)." But there is no ilah (god) (none who has the right to be worshipped) but One Ilah (God; Allah). And if they do not cease from what they say, verily, a painful torment will befall the disbelievers among them.
5:74 Al-Maaida
أَفَلَا يَتُوبُونَ إِلَى اللَّهِ وَيَسْتَغْفِرُونَهُ ۚ وَاللَّهُ غَفُورٌ رَحِيمٌ
Will they not repent to Allah and ask His Forgiveness? For Allah is Oft-Forgiving, Most Merciful.
5:75 Al-Maaida
مَا الْمَسِيحُ ابْنُ مَرْيَمَ إِلَّا رَسُولٌ قَدْ خَلَتْ مِنْ قَبْلِهِ الرُّسُلُ وَأُمُّهُ صِدِّيقَةٌ ۖ كَانَا يَأْكُلَانِ الطَّعَامَ ۗ انْظُرْ كَيْفَ نُبَيِّنُ لَهُمُ الْآيَاتِ ثُمَّ انْظُرْ أَنَّىٰ يُؤْفَكُونَ
The Messiah ['Iesa (Jesus)], son of Maryam (Mary), was no more than a Messenger; many were the Messengers that passed away before him. His mother [Maryam (Mary)] was a Siddiqah [i.e. she believed in the words of Allah and His Books (see Verse 66:12)]. They both used to eat food (as any other human being, while Allah does not eat). Look how We make the Ayat (proofs, evidences, verses, lessons, signs, revelations, etc.) clear to them, yet look how they are deluded away (from the truth).
5:76 Al-Maaida
قُلْ أَتَعْبُدُونَ مِنْ دُونِ اللَّهِ مَا لَا يَمْلِكُ لَكُمْ ضَرًّا وَلَا نَفْعًا ۚ وَاللَّهُ هُوَ السَّمِيعُ الْعَلِيمُ
Say, "Do you worship besides Allah that which holds for you no [power of] harm or benefit while it is Allah who is the Hearing, the Knowing?"
5:77 Al-Maaida
قُلْ يَا أَهْلَ الْكِتَابِ لَا تَغْلُوا فِي دِينِكُمْ غَيْرَ الْحَقِّ وَلَا تَتَّبِعُوا أَهْوَاءَ قَوْمٍ قَدْ ضَلُّوا مِنْ قَبْلُ وَأَضَلُّوا كَثِيرًا وَضَلُّوا عَنْ سَوَاءِ السَّبِيلِ
Say, "O People of the Scripture, do not exceed limits in your religion beyond the truth and do not follow the inclinations of a people who had gone astray before and misled many and have strayed from the soundness of the way."
Al-An'aam verse 100 وَجَعَلُوا لِلَّهِ شُرَكَاءَ الْجِنَّ وَخَلَقَهُمْ ۖ وَخَرَقُوا لَهُ بَنِينَ وَبَنَاتٍ بِغَيْرِ عِلْمٍ ۚ سُبْحَانَهُ وَتَعَالَىٰ عَمَّا يَصِفُونَ Yet, they join the jinns as partners in worship with Allah, though He has created them (the jinns), and they attribute falsely without knowledge sons and daughters to Him. Be He Glorified and Exalted above (all) that they attribute to Him. Verse 101 بَدِيعُ السَّمَاوَاتِ وَالْأَرْضِ ۖ أَنَّىٰ يَكُونُ لَهُ وَلَدٌ وَلَمْ تَكُنْ لَهُ صَاحِبَةٌ ۖ وَخَلَقَ كُلَّ شَيْءٍ ۖ وَهُوَ بِكُلِّ شَيْءٍ عَلِيمٌ He is the Originator of (created in beautiful form) the heavens and the earth. How can He have children when He has no wife (companion)? He created all things and He is the All-Knower of everything. Verse 102 ذَٰلِكُمُ اللَّهُ رَبُّكُمْ ۖ لَا إِلَٰهَ إِلَّا هُوَ ۖ خَالِقُ كُلِّ شَيْءٍ فَاعْبُدُوهُ ۚ وَهُوَ عَلَىٰ كُلِّ شَيْءٍ وَكِيلٌ Such is Allah, your Lord! La ilaha illa Huwa (none has the right to be worshipped but He), the Creator of all things. So worship Him (Alone), and He is the Wakil (Trustee, Disposer of affairs, Guardian, etc.) over all things. Verse 103 لَا تُدْرِكُهُ الْأَبْصَارُ وَهُوَ يُدْرِكُ الْأَبْصَارَ ۖ وَهُوَ اللَّطِيفُ الْخَبِيرُ No vision can grasp Him, but His Grasp is over all vision. He is the Most Subtle and Courteous, Well-Acquainted with all things. Verse 104 قَدْ جَاءَكُمْ بَصَائِرُ مِنْ رَبِّكُمْ ۖ فَمَنْ أَبْصَرَ فَلِنَفْسِهِ ۖ وَمَنْ عَمِيَ فَعَلَيْهَا ۚ وَمَا أَنَا عَلَيْكُمْ بِحَفِيظٍ
Verily, proofs have come to you from your Lord, so whosoever sees, will do so for (the good of) his ownself, and whosoever blinds himself, will do so to his own harm, and I am not a watcher over you.
In the following a narration of a conversation between God and Prophet Jesus, peace be upon him:
5:116 Al-Maaida
وَإِذْ قَالَ اللَّهُ يَا عِيسَى ابْنَ مَرْيَمَ أَأَنْتَ قُلْتَ لِلنَّاسِ اتَّخِذُونِي وَأُمِّيَ إِلَٰهَيْنِ مِنْ دُونِ اللَّهِ ۖ قَالَ سُبْحَانَكَ مَا يَكُونُ لِي أَنْ أَقُولَ مَا لَيْسَ لِي بِحَقٍّ ۚ إِنْ كُنْتُ قُلْتُهُ فَقَدْ عَلِمْتَهُ ۚ تَعْلَمُ مَا فِي نَفْسِي وَلَا أَعْلَمُ مَا فِي نَفْسِكَ ۚ إِنَّكَ أَنْتَ عَلَّامُ الْغُيُوبِ
And (remember) when Allah will say (on the Day of Resurrection): "O 'Iesa (Jesus), son of Maryam (Mary)! Did you say unto men: 'Worship me and my mother as two gods besides Allah?' " He will say: "Glory to You! It was not for me to say what I had no right (to say). Had I said such a thing, You would surely have known it. You know what is in my inner-self though I do not know what is in Yours, truly, You, only You, are the All-Knower of all that is hidden and unseen.
5:117 Al-Maaida
مَا قُلْتُ لَهُمْ إِلَّا مَا أَمَرْتَنِي بِهِ أَنِ اعْبُدُوا اللَّهَ رَبِّي وَرَبَّكُمْ ۚ وَكُنْتُ عَلَيْهِمْ شَهِيدًا مَا دُمْتُ فِيهِمْ ۖ فَلَمَّا تَوَفَّيْتَنِي كُنْتَ أَنْتَ الرَّقِيبَ عَلَيْهِمْ ۚ وَأَنْتَ عَلَىٰ كُلِّ شَيْءٍ شَهِيدٌ
"Never did I say to them aught except what You (Allah) did command me to say: 'Worship Allah, my Lord and your Lord.' And I was a witness over them while I dwelt amongst them, but when You took me up, You were the Watcher over them, and You are a Witness to all things. (This is a great admonition and warning to the Christians of the whole world).
5:118 Al-Maaida
إِنْ تُعَذِّبْهُمْ فَإِنَّهُمْ عِبَادُكَ ۖ وَإِنْ تَغْفِرْ لَهُمْ فَإِنَّكَ أَنْتَ الْعَزِيزُ الْحَكِيمُ
"If You punish them, they are Your slaves, and if You forgive them, verily You, only You are the All-Mighty, the All-Wise."
5:119 Al-Maaida
قَالَ اللَّهُ هَٰذَا يَوْمُ يَنْفَعُ الصَّادِقِينَ صِدْقُهُمْ ۚ لَهُمْ جَنَّاتٌ تَجْرِي مِنْ تَحْتِهَا الْأَنْهَارُ خَالِدِينَ فِيهَا أَبَدًا ۚ رَضِيَ اللَّهُ عَنْهُمْ وَرَضُوا عَنْهُ ۚ ذَٰلِكَ الْفَوْزُ الْعَظِيمُ
Allah will say: "This is a Day on which the truthful will profit from their truth: theirs are Gardens under which rivers flow (in Paradise) - they shall abide therein forever. Allah is pleased with them and they with Him. That is the great success (Paradise).
5:120 Al-Maaida
لِلَّهِ مُلْكُ السَّمَاوَاتِ وَالْأَرْضِ وَمَا فِيهِنَّ ۚ وَهُوَ عَلَىٰ كُلِّ شَيْءٍ قَدِيرٌ
To Allah belongs the dominion of the heavens and the earth and all that is therein, and He is Able to do all things.
Jesus, peace be upon him is only a prophet and we (Muslim people) will follow him when he returns before Judgement Day. In Islam, we believe in all prophets chosen by God while making no difference between any of them acknowledging that the last prophet is prophet Mohamed, peace be upon him.
2:285 Al-Baqara آمَنَ الرَّسُولُ بِمَا أُنْزِلَ إِلَيْهِ مِنْ رَبِّهِ وَالْمُؤْمِنُونَ ۚ كُلٌّ آمَنَ بِاللَّهِ وَمَلَائِكَتِهِ وَكُتُبِهِ وَرُسُلِهِ لَا نُفَرِّقُ بَيْنَ أَحَدٍ مِنْ رُسُلِهِ ۚ وَقَالُوا سَمِعْنَا وَأَطَعْنَا ۖ غُفْرَانَكَ رَبَّنَا وَإِلَيْكَ الْمَصِيرُ The Messenger (Muhammad SAW) believes in what has been sent down to him from his Lord, and (so do) the believers. Each one believes in Allah, His Angels, His Books, and His Messengers. They say, "We make no distinction between one another of His Messengers" - and they say, "We hear, and we obey. (We seek) Your Forgiveness, our Lord, and to You is the return (of all)."
27:59 An-Naml قُلِ الْحَمْدُ لِلَّهِ وَسَلَامٌ عَلَىٰ عِبَادِهِ الَّذِينَ اصْطَفَىٰ ۗ آللَّهُ خَيْرٌ أَمَّا يُشْرِكُونَ Say: "Praise and thanks be to Allah, and peace be on His servants whom He has chosen (for His Message)! Is Allah better, or (all) that you ascribe as partners (to Him)?" (Of course, Allah is Better). 33:57 Al-Ahzaab إِنَّ الَّذِينَ يُؤْذُونَ اللَّهَ وَرَسُولَهُ لَعَنَهُمُ اللَّهُ فِي الدُّنْيَا وَالْآخِرَةِ وَأَعَدَّ لَهُمْ عَذَابًا مُهِينًا Verily, those who cause harm to Allah and His Messenger, Allah has cursed them in this world, and in the Hereafter, and has prepared for them a humiliating torment. 33:58 Al-Ahzaab وَالَّذِينَ يُؤْذُونَ الْمُؤْمِنِينَ وَالْمُؤْمِنَاتِ بِغَيْرِ مَا اكْتَسَبُوا فَقَدِ احْتَمَلُوا بُهْتَانًا وَإِثْمًا مُبِينًا And those who cause harm believing men and women undeservedly, bear on themselves the crime of slander and plain sin.
Some of the miracles shown by prophet Jesus peace be upon him are mentioned in the Quran in the following verses.
5:110 Al-Maaida
إِذْ قَالَ اللَّهُ يَا عِيسَى ابْنَ مَرْيَمَ اذْكُرْ نِعْمَتِي عَلَيْكَ وَعَلَىٰ وَالِدَتِكَ إِذْ أَيَّدْتُكَ بِرُوحِ الْقُدُسِ تُكَلِّمُ النَّاسَ فِي الْمَهْدِ وَكَهْلًا ۖ وَإِذْ عَلَّمْتُكَ الْكِتَابَ وَالْحِكْمَةَ وَالتَّوْرَاةَ وَالْإِنْجِيلَ ۖ وَإِذْ تَخْلُقُ مِنَ الطِّينِ كَهَيْئَةِ الطَّيْرِ بِإِذْنِي فَتَنْفُخُ فِيهَا فَتَكُونُ طَيْرًا بِإِذْنِي ۖ وَتُبْرِئُ الْأَكْمَهَ وَالْأَبْرَصَ بِإِذْنِي ۖ وَإِذْ تُخْرِجُ الْمَوْتَىٰ بِإِذْنِي ۖ وَإِذْ كَفَفْتُ بَنِي إِسْرَائِيلَ عَنْكَ إِذْ جِئْتَهُمْ بِالْبَيِّنَاتِ فَقَالَ الَّذِينَ كَفَرُوا مِنْهُمْ إِنْ هَٰذَا إِلَّا سِحْرٌ مُبِينٌ
[The Day] when Allah will say, "O Jesus, Son of Mary, remember My favor upon you and upon your mother when I supported you with the Pure Spirit and you spoke to the people in the cradle and in maturity; and [remember] when I taught you writing and wisdom and the Torah and the Gospel; and when you designed from clay [what was] like the form of a bird with My permission, then you breathed into it, and it became a bird with My permission; and you healed the blind and the leper with My permission; and when you brought forth the dead with My permission; and when I restrained the Children of Israel from [killing] you when you came to them with clear proofs and those who disbelieved among them said, "This is not but obvious magic."
5:111 Al-Maaida
وَإِذْ أَوْحَيْتُ إِلَى الْحَوَارِيِّينَ أَنْ آمِنُوا بِي وَبِرَسُولِي قَالُوا آمَنَّا وَاشْهَدْ بِأَنَّنَا مُسْلِمُونَ
And [remember] when I inspired to the disciples, "Believe in Me and in My messenger Jesus." They said, "We have believed, so bear witness that indeed we are Muslims [in submission to Allah]."
5:112 Al-Maaida إِذْ قَالَ الْحَوَارِيُّونَ يَا عِيسَى ابْنَ مَرْيَمَ هَلْ يَسْتَطِيعُ رَبُّكَ أَنْ يُنَزِّلَ عَلَيْنَا مَائِدَةً مِنَ السَّمَاءِ ۖ قَالَ اتَّقُوا اللَّهَ إِنْ كُنْتُمْ مُؤْمِنِينَ (Remember) when Al-Hawariun (the disciples) said: "O 'Iesa (Jesus), son of Maryam (Mary)! Can your Lord send down to us a table spread (with food) from heaven?" 'Iesa (Jesus) said: "Fear Allah, if you are indeed believers."
5:113 Al-Maaida قَالُوا نُرِيدُ أَنْ نَأْكُلَ مِنْهَا وَتَطْمَئِنَّ قُلُوبُنَا وَنَعْلَمَ أَنْ قَدْ صَدَقْتَنَا وَنَكُونَ عَلَيْهَا مِنَ الشَّاهِدِينَ They said: "We wish to eat thereof and to be stronger in Faith, and to know that you have indeed told us the truth and that we ourselves be its witnesses."
5:114 Al-Maaida قَالَ عِيسَى ابْنُ مَرْيَمَ اللَّهُمَّ رَبَّنَا أَنْزِلْ عَلَيْنَا مَائِدَةً مِنَ السَّمَاءِ تَكُونُ لَنَا عِيدًا لِأَوَّلِنَا وَآخِرِنَا وَآيَةً مِنْكَ ۖ وَارْزُقْنَا وَأَنْتَ خَيْرُ الرَّازِقِينَ 'Iesa (Jesus), son of Maryam (Mary), said: "O Allah, our Lord! Send us from heaven a table spread (with food) that there may be for us - for the first and the last of us - a festival and a sign from You; and provide us sustenance, for You are the Best of sustainers."
5:115 Al-Maaida قَالَ اللَّهُ إِنِّي مُنَزِّلُهَا عَلَيْكُمْ ۖ فَمَنْ يَكْفُرْ بَعْدُ مِنْكُمْ فَإِنِّي أُعَذِّبُهُ عَذَابًا لَا أُعَذِّبُهُ أَحَدًا مِنَ الْعَالَمِينَ Allah said: "I am going to send it down unto you, but if any of you after that disbelieves, then I will punish him with a torment such as I have not inflicted on anyone among (all) the 'Alamin (mankind and jinns)."
The pregnancy of Mary and the birth of prophet Jesus peace be upon him are also miracles and they are mentioned in the following verses. Jesus peace be upon him himself is a gift to Mary; however God, Allah, created him in the same way he created Adam.
3:8 Aal-i-Imraan
رَبَّنَا لَا تُزِغْ قُلُوبَنَا بَعْدَ إِذْ هَدَيْتَنَا وَهَبْ لَنَا مِنْ لَدُنْكَ رَحْمَةً ۚ إِنَّكَ أَنْتَ الْوَهَّابُ
[Who say], "Our Lord, let not our hearts deviate after You have guided us and grant us from Yourself mercy. Indeed, You are the Bestower. 3:45 Aal-i-Imraan
إِذْ قَالَتِ الْمَلَائِكَةُ يَا مَرْيَمُ إِنَّ اللَّهَ يُبَشِّرُكِ بِكَلِمَةٍ مِنْهُ اسْمُهُ الْمَسِيحُ عِيسَى ابْنُ مَرْيَمَ وَجِيهًا فِي الدُّنْيَا وَالْآخِرَةِ وَمِنَ الْمُقَرَّبِينَ
[And mention] when the angels said, "O Mary, indeed Allah gives you good tidings of a word from Him, whose name will be the Messiah, Jesus, the son of Mary - distinguished in this world and the Hereafter and among those brought near [to Allah].
3:46 Aal-i-Imraan
وَيُكَلِّمُ النَّاسَ فِي الْمَهْدِ وَكَهْلًا وَمِنَ الصَّالِحِينَ
He will speak to the people in the cradle and in maturity and will be of the righteous."
3:47 Aal-i-Imraan
قَالَتْ رَبِّ أَنَّىٰ يَكُونُ لِي وَلَدٌ وَلَمْ يَمْسَسْنِي بَشَرٌ ۖ قَالَ كَذَٰلِكِ اللَّهُ يَخْلُقُ مَا يَشَاءُ ۚ إِذَا قَضَىٰ أَمْرًا فَإِنَّمَا يَقُولُ لَهُ كُنْ فَيَكُونُ
She said, "My Lord, how will I have a child when no man has touched me?" [The angel] said, "Such is Allah; He creates what He wills. When He decrees a matter, He only says to it, 'Be,' and it is.
3:48 Aal-i-Imraan
وَيُعَلِّمُهُ الْكِتَابَ وَالْحِكْمَةَ وَالتَّوْرَاةَ وَالْإِنْجِيلَ
And He will teach him writing and wisdom and the Torah and the Gospel
3:49 Aal-i-Imraan
وَرَسُولًا إِلَىٰ بَنِي إِسْرَائِيلَ أَنِّي قَدْ جِئْتُكُمْ بِآيَةٍ مِنْ رَبِّكُمْ ۖ أَنِّي أَخْلُقُ لَكُمْ مِنَ الطِّينِ كَهَيْئَةِ الطَّيْرِ فَأَنْفُخُ فِيهِ فَيَكُونُ طَيْرًا بِإِذْنِ اللَّهِ ۖ وَأُبْرِئُ الْأَكْمَهَ وَالْأَبْرَصَ وَأُحْيِي الْمَوْتَىٰ بِإِذْنِ اللَّهِ ۖ وَأُنَبِّئُكُمْ بِمَا تَأْكُلُونَ وَمَا تَدَّخِرُونَ فِي بُيُوتِكُمْ ۚ إِنَّ فِي ذَٰلِكَ لَآيَةً لَكُمْ إِنْ كُنْتُمْ مُؤْمِنِينَ
And [make him] a messenger to the Children of Israel, [who will say], 'Indeed I have come to you with a sign from your Lord in that I design for you from clay [that which is] like the form of a bird, then I breathe into it and it becomes a bird by permission of Allah. And I cure the blind and the leper, and I give life to the dead - by permission of Allah. And I inform you of what you eat and what you store in your houses. Indeed in that is a sign for you, if you are believers.
3:50 Aal-i-Imraan
وَمُصَدِّقًا لِمَا بَيْنَ يَدَيَّ مِنَ التَّوْرَاةِ وَلِأُحِلَّ لَكُمْ بَعْضَ الَّذِي حُرِّمَ عَلَيْكُمْ ۚ وَجِئْتُكُمْ بِآيَةٍ مِنْ رَبِّكُمْ فَاتَّقُوا اللَّهَ وَأَطِيعُونِ
And [I have come] confirming what was before me of the Torah and to make lawful for you some of what was forbidden to you. And I have come to you with a sign from your Lord, so fear Allah and obey me.
3:51 Aal-i-Imraan
إِنَّ اللَّهَ رَبِّي وَرَبُّكُمْ فَاعْبُدُوهُ ۗ هَٰذَا صِرَاطٌ مُسْتَقِيمٌ
Indeed, Allah is my Lord and your Lord, so worship Him. That is the straight path."
3:52 Aal-i-Imraan
۞ فَلَمَّا أَحَسَّ عِيسَىٰ مِنْهُمُ الْكُفْرَ قَالَ مَنْ أَنْصَارِي إِلَى اللَّهِ ۖ قَالَ الْحَوَارِيُّونَ نَحْنُ أَنْصَارُ اللَّهِ آمَنَّا بِاللَّهِ وَاشْهَدْ بِأَنَّا مُسْلِمُونَ
But when Jesus felt [persistence in] disbelief from them, he said, "Who are my supporters for [the cause of] Allah?" The disciples said, "We are supporters for Allah. We have believed in Allah and testify that we are Muslims [submitting to Him].
3:53 Aal-i-Imraan
رَبَّنَا آمَنَّا بِمَا أَنْزَلْتَ وَاتَّبَعْنَا الرَّسُولَ فَاكْتُبْنَا مَعَ الشَّاهِدِينَ
Our Lord, we have believed in what You revealed and have followed the messenger Jesus, so register us among the witnesses [to truth]."
3:54 Aal-i-Imraan
وَمَكَرُوا وَمَكَرَ اللَّهُ ۖ وَاللَّهُ خَيْرُ الْمَاكِرِينَ
And the disbelievers planned, but Allah planned. And Allah is the best of planners.
3:55 Aal-i-Imraan
إِذْ قَالَ اللَّهُ يَا عِيسَىٰ إِنِّي مُتَوَفِّيكَ وَرَافِعُكَ إِلَيَّ وَمُطَهِّرُكَ مِنَ الَّذِينَ كَفَرُوا وَجَاعِلُ الَّذِينَ اتَّبَعُوكَ فَوْقَ الَّذِينَ كَفَرُوا إِلَىٰ يَوْمِ الْقِيَامَةِ ۖ ثُمَّ إِلَيَّ مَرْجِعُكُمْ فَأَحْكُمُ بَيْنَكُمْ فِيمَا كُنْتُمْ فِيهِ تَخْتَلِفُونَ
[Mention] when Allah said, "O Jesus, indeed I will take you and raise you to Myself and purify you from those who disbelieve and make those who follow you [in submission to Allah alone] superior to those who disbelieve until the Day of Resurrection. Then to Me is your return, and I will judge between you concerning that in which you used to differ.
3:56 Aal-i-Imraan
فَأَمَّا الَّذِينَ كَفَرُوا فَأُعَذِّبُهُمْ عَذَابًا شَدِيدًا فِي الدُّنْيَا وَالْآخِرَةِ وَمَا لَهُمْ مِنْ نَاصِرِينَ
And as for those who disbelieved, I will punish them with a severe punishment in this world and the Hereafter, and they will have no helpers."
3:57 Aal-i-Imraan
وَأَمَّا الَّذِينَ آمَنُوا وَعَمِلُوا الصَّالِحَاتِ فَيُوَفِّيهِمْ أُجُورَهُمْ ۗ وَاللَّهُ لَا يُحِبُّ الظَّالِمِينَ
But as for those who believed and did righteous deeds, He will give them in full their rewards, and Allah does not like the wrongdoers.
3:58 Aal-i-Imraan
ذَٰلِكَ نَتْلُوهُ عَلَيْكَ مِنَ الْآيَاتِ وَالذِّكْرِ الْحَكِيمِ
This is what We recite to you, [O Muhammad], of [Our] verses and the precise [and wise] message.
3:59 Aal-i-Imraan
إِنَّ مَثَلَ عِيسَىٰ عِنْدَ اللَّهِ كَمَثَلِ آدَمَ ۖ خَلَقَهُ مِنْ تُرَابٍ ثُمَّ قَالَ لَهُ كُنْ فَيَكُونُ
Indeed, the example of Jesus to Allah is like that of Adam. He created Him from dust; then He said to him, "Be," and he was.
3:60 Aal-i-Imraan
الْحَقُّ مِنْ رَبِّكَ فَلَا تَكُنْ مِنَ الْمُمْتَرِينَ
The truth is from your Lord, so do not be among the doubters.
3:61 Aal-i-Imraan
فَمَنْ حَاجَّكَ فِيهِ مِنْ بَعْدِ مَا جَاءَكَ مِنَ الْعِلْمِ فَقُلْ تَعَالَوْا نَدْعُ أَبْنَاءَنَا وَأَبْنَاءَكُمْ وَنِسَاءَنَا وَنِسَاءَكُمْ وَأَنْفُسَنَا وَأَنْفُسَكُمْ ثُمَّ نَبْتَهِلْ فَنَجْعَلْ لَعْنَتَ اللَّهِ عَلَى الْكَاذِبِينَ
Then whoever argues with you about it after [this] knowledge has come to you - say, "Come, let us call our sons and your sons, our women and your women, ourselves and yourselves, then supplicate earnestly [together] and invoke the curse of Allah upon the liars [among us]."
3:62 Aal-i-Imraan
إِنَّ هَٰذَا لَهُوَ الْقَصَصُ الْحَقُّ ۚ وَمَا مِنْ إِلَٰهٍ إِلَّا اللَّهُ ۚ وَإِنَّ اللَّهَ لَهُوَ الْعَزِيزُ الْحَكِيمُ
Indeed, this is the true narration. And there is no deity except Allah. And indeed, Allah is the Exalted in Might, the Wise.
3:63 Aal-i-Imraan
فَإِنْ تَوَلَّوْا فَإِنَّ اللَّهَ عَلِيمٌ بِالْمُفْسِدِينَ
But if they turn away, then indeed - Allah is Knowing of the corrupters.
3:64 Aal-i-Imraan
قُلْ يَا أَهْلَ الْكِتَابِ تَعَالَوْا إِلَىٰ كَلِمَةٍ سَوَاءٍ بَيْنَنَا وَبَيْنَكُمْ أَلَّا نَعْبُدَ إِلَّا اللَّهَ وَلَا نُشْرِكَ بِهِ شَيْئًا وَلَا يَتَّخِذَ بَعْضُنَا بَعْضًا أَرْبَابًا مِنْ دُونِ اللَّهِ ۚ فَإِنْ تَوَلَّوْا فَقُولُوا اشْهَدُوا بِأَنَّا مُسْلِمُونَ
Say, "O People of the Scripture, come to a word that is equitable between us and you - that we will not worship except Allah and not associate anything with Him and not take one another as lords instead of Allah." But if they turn away, then say, "Bear witness that we are Muslims [submitting to Him]."
19:16 Maryam
وَاذْكُرْ فِي الْكِتَابِ مَرْيَمَ إِذِ انْتَبَذَتْ مِنْ أَهْلِهَا مَكَانًا شَرْقِيًّا
And mention, [O Muhammad], in the Book [the story of] Mary, when she withdrew from her family to a place toward the east.
19:17 Maryam
فَاتَّخَذَتْ مِنْ دُونِهِمْ حِجَابًا فَأَرْسَلْنَا إِلَيْهَا رُوحَنَا فَتَمَثَّلَ لَهَا بَشَرًا سَوِيًّا
And she took, in seclusion from them, a screen. Then We sent to her Our Angel, and he represented himself to her as a well-proportioned man.
19:18 Maryam
قَالَتْ إِنِّي أَعُوذُ بِالرَّحْمَٰنِ مِنْكَ إِنْ كُنْتَ تَقِيًّا
She said, "Indeed, I seek refuge in the Most Merciful from you, [so leave me], if you should be fearing of Allah."
19:19 Maryam
قَالَ إِنَّمَا أَنَا رَسُولُ رَبِّكِ لِأَهَبَ لَكِ غُلَامًا زَكِيًّا
He said, "I am only the messenger of your Lord to give you [news of] a pure boy."
19:20 Maryam
قَالَتْ أَنَّىٰ يَكُونُ لِي غُلَامٌ وَلَمْ يَمْسَسْنِي بَشَرٌ وَلَمْ أَكُ بَغِيًّا
She said, "How can I have a boy while no man has touched me and I have not been unchaste?"
19:21 Maryam
قَالَ كَذَٰلِكِ قَالَ رَبُّكِ هُوَ عَلَيَّ هَيِّنٌ ۖ وَلِنَجْعَلَهُ آيَةً لِلنَّاسِ وَرَحْمَةً مِنَّا ۚ وَكَانَ أَمْرًا مَقْضِيًّا
He said, "Thus [it will be]; your Lord says, 'It is easy for Me, and We will make him a sign to the people and a mercy from Us. And it is a matter [already] decreed.' "
19:22 Maryam
۞ فَحَمَلَتْهُ فَانْتَبَذَتْ بِهِ مَكَانًا قَصِيًّا
So she conceived him, and she withdrew with him to a remote place.
19:23 Maryam
فَأَجَاءَهَا الْمَخَاضُ إِلَىٰ جِذْعِ النَّخْلَةِ قَالَتْ يَا لَيْتَنِي مِتُّ قَبْلَ هَٰذَا وَكُنْتُ نَسْيًا مَنْسِيًّا
And the pains of childbirth drove her to the trunk of a palm tree. She said, "Oh, I wish I had died before this and was in oblivion, forgotten."
19:24 Maryam
فَنَادَاهَا مِنْ تَحْتِهَا أَلَّا تَحْزَنِي قَدْ جَعَلَ رَبُّكِ تَحْتَكِ سَرِيًّا
But he called her from below her, "Do not grieve; your Lord has provided beneath you a stream.
19:25 Maryam
وَهُزِّي إِلَيْكِ بِجِذْعِ النَّخْلَةِ تُسَاقِطْ عَلَيْكِ رُطَبًا جَنِيًّا
And shake toward you the trunk of the palm tree; it will drop upon you ripe, fresh dates.
19:26 Maryam
فَكُلِي وَاشْرَبِي وَقَرِّي عَيْنًا ۖ فَإِمَّا تَرَيِنَّ مِنَ الْبَشَرِ أَحَدًا فَقُولِي إِنِّي نَذَرْتُ لِلرَّحْمَٰنِ صَوْمًا فَلَنْ أُكَلِّمَ الْيَوْمَ إِنْسِيًّا
So eat and drink and be contented. And if you see from among humanity anyone, say, 'Indeed, I have vowed to the Most Merciful abstention, so I will not speak today to [any] man.' "
19:27 Maryam
فَأَتَتْ بِهِ قَوْمَهَا تَحْمِلُهُ ۖ قَالُوا يَا مَرْيَمُ لَقَدْ جِئْتِ شَيْئًا فَرِيًّا
Then she brought him to her people, carrying him. They said, "O Mary, you have certainly done a thing unprecedented.
19:28 Maryam
يَا أُخْتَ هَارُونَ مَا كَانَ أَبُوكِ امْرَأَ سَوْءٍ وَمَا كَانَتْ أُمُّكِ بَغِيًّا
O sister of Aaron, your father was not a man of evil, nor was your mother unchaste."
19:29 Maryam
فَأَشَارَتْ إِلَيْهِ ۖ قَالُوا كَيْفَ نُكَلِّمُ مَنْ كَانَ فِي الْمَهْدِ صَبِيًّا
So she pointed to him. They said, "How can we speak to one who is in the cradle a child?"
19:30 Maryam
قَالَ إِنِّي عَبْدُ اللَّهِ آتَانِيَ الْكِتَابَ وَجَعَلَنِي نَبِيًّا
[Jesus] said, "Indeed, I am the servant of Allah. He has given me the Scripture and made me a prophet.
19:31 Maryam
وَجَعَلَنِي مُبَارَكًا أَيْنَ مَا كُنْتُ وَأَوْصَانِي بِالصَّلَاةِ وَالزَّكَاةِ مَا دُمْتُ حَيًّا
And He has made me blessed wherever I am and has enjoined upon me prayer and zakah as long as I remain alive
19:32 Maryam
وَبَرًّا بِوَالِدَتِي وَلَمْ يَجْعَلْنِي جَبَّارًا شَقِيًّا
And [made me] dutiful to my mother, and He has not made me a wretched tyrant.
19:33 Maryam
وَالسَّلَامُ عَلَيَّ يَوْمَ وُلِدْتُ وَيَوْمَ أَمُوتُ وَيَوْمَ أُبْعَثُ حَيًّا
And peace is on me the day I was born and the day I will die and the day I am raised alive."
19:34 Maryam
ذَٰلِكَ عِيسَى ابْنُ مَرْيَمَ ۚ قَوْلَ الْحَقِّ الَّذِي فِيهِ يَمْتَرُونَ
That is Jesus, the son of Mary - the word of truth about which they are in dispute.
19:35 Maryam
مَا كَانَ لِلَّهِ أَنْ يَتَّخِذَ مِنْ وَلَدٍ ۖ سُبْحَانَهُ ۚ إِذَا قَضَىٰ أَمْرًا فَإِنَّمَا يَقُولُ لَهُ كُنْ فَيَكُونُ
It is not [befitting] for Allah to take a son; exalted is He! When He decrees an affair, He only says to it, "Be," and it is.
19:36 Maryam
وَإِنَّ اللَّهَ رَبِّي وَرَبُّكُمْ فَاعْبُدُوهُ ۚ هَٰذَا صِرَاطٌ مُسْتَقِيمٌ
[Jesus said], "And indeed, Allah is my Lord and your Lord, so worship Him. That is a straight path."
19:37 Maryam
فَاخْتَلَفَ الْأَحْزَابُ مِنْ بَيْنِهِمْ ۖ فَوَيْلٌ لِلَّذِينَ كَفَرُوا مِنْ مَشْهَدِ يَوْمٍ عَظِيمٍ
Then the factions differed [concerning Jesus] from among them, so woe to those who disbelieved - from the scene of a tremendous Day.
19:38 Maryam
أَسْمِعْ بِهِمْ وَأَبْصِرْ يَوْمَ يَأْتُونَنَا ۖ لَٰكِنِ الظَّالِمُونَ الْيَوْمَ فِي ضَلَالٍ مُبِينٍ
How [clearly] they will hear and see the Day they come to Us, but the wrongdoers today are in clear error.
19:39 Maryam
وَأَنْذِرْهُمْ يَوْمَ الْحَسْرَةِ إِذْ قُضِيَ الْأَمْرُ وَهُمْ فِي غَفْلَةٍ وَهُمْ لَا يُؤْمِنُونَ
And warn them, [O Muhammad], of the Day of Regret, when the matter will be concluded; and [yet], they are in [a state of] heedlessness, and they do not believe.
In the following verse prophet Jesus peace be upon him told the people of his time about the arrival of prophet Mohamed peace be upon him (please note that Ahmed and Mohamed have the same meaning in Arabic and have the same word origin; the verb Hamad that means thanked).
61:6 As-Saff
وَإِذْ قَالَ عِيسَى ابْنُ مَرْيَمَ يَا بَنِي إِسْرَائِيلَ إِنِّي رَسُولُ اللَّهِ إِلَيْكُمْ مُصَدِّقًا لِمَا بَيْنَ يَدَيَّ مِنَ التَّوْرَاةِ وَمُبَشِّرًا بِرَسُولٍ يَأْتِي مِنْ بَعْدِي اسْمُهُ أَحْمَدُ ۖ فَلَمَّا جَاءَهُمْ بِالْبَيِّنَاتِ قَالُوا هَٰذَا سِحْرٌ مُبِينٌ
And [mention] when Jesus, the son of Mary, said, "O children (descendants) of Israel, indeed I am the messenger of Allah to you confirming what came before me of the Torah and bringing good tidings of a messenger to come after me, whose name is Ahmad." But when he came to them with clear evidences, they said, "This is obvious magic."
-
 @ c631e267:c2b78d3e
2025-04-03 07:42:25
@ c631e267:c2b78d3e
2025-04-03 07:42:25Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-App, die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt in Kraft getreten.
Mit den üblichen Argumenten der Vereinfachung, des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte, wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
Um sich die digitale Version des nationalen Ausweises besorgen zu können (eine App mit dem Namen MiDNI), muss man sich vorab online registrieren. Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
Für jeden Vorgang der Identifikation in der Praxis wird später «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare. Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt in Richtung der «totalen Digitalisierung» des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
In Zukunft könnte der neue Ausweis «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal Cope ganz richtig bemerkt. Das ist die Perspektive.
[Titelbild: Pixabay]
Dazu passend:
Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ deab79da:88579e68
2025-04-01 18:18:29
@ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way:
Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole.
Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's.
For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both.
But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact.
The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower.
Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it.
They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle.
"It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever."
Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said.
"Oh, hell, just about forever. Till the sun runs down, Bert."
"That's not forever."
"All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?"
Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever."
"Well, it will last our time, won't it?"
"So would the coal and uranium."
"All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me.
"I don't have to ask Multivac. I know that."
"Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right."
"Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun."
There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested.
Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?"
"I'm not thinking."
"Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one."
"I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too."
"Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all."
"I know all about entropy," said Adell, standing on his dignity.
"The hell you do."
"I know as much as you do."
"Then you know everything's got to run down someday."
"All right. Who says they won't?"
"You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.'
It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said.
"Never."
"Why not? Someday."
"Never."
"Ask Multivac."
"You ask Multivac. I dare you. Five dollars says it can't be done."
Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age?
Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased?
Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended.
Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER.
"No bet," whispered Lupov. They left hurriedly.
By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident.
🔹
Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen.
"That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened.
The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --"
"Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?"
"What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship.
Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps.
Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that.
Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth."
"Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing."
"I know, I know," said Jerrodine miserably.
Jerrodette I said promptly, "Our Microvac is the best Microvac in the world."
"I think so, too," said Jerrodd, tousling her hair.
It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship.
Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible.
"So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now."
"Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase.
"What's entropy, daddy?" shrilled Jerrodette II.
"Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?"
"Can't you just put in a new power-unit, like with my robot?"
"The stars are the power-units. dear. Once they're gone, there are no more power-units."
Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down."
"Now look what you've done," whispered Jerrodine, exasperated.
"How was I to know it would frighten them?" Jerrodd whispered back,
"Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again."
"Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.)
Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us."
He asked the Microvac, adding quickly, "Print the answer."
Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry."
Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon."
Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER.
He shrugged and looked at the visiplate. X-23 was just ahead.
🔹
VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?"
MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion."
Both seemed in their early twenties, both were tall and perfectly formed.
"Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council."
"I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up."
VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More."
"A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years --
VJ-23X interrupted. "We can thank immortality for that."
"Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions."
"Yet you wouldn't want to abandon life, I suppose."
"Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?"
"Two hundred twenty-three. And you?"
"I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?"
VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next."
"A very good point. Already, mankind consumes two sunpower units per year."
"Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those."
"Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point."
"We'll just have to build new stars out of interstellar gas."
"Or out of dissipated heat?" asked MQ-17J, sarcastically.
"There may be some way to reverse entropy. We ought to ask the Galactic AC."
VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him.
"I've half a mind to," he said. "It's something the human race will have to face someday."
He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC.
MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across.
MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?"
VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that."
"Why not?"
"We both know entropy can't be reversed. You can't turn smoke and ash back into a tree."
"Do you have trees on your world?" asked MQ-17J.
The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER.
VJ-23X said, "See!"
The two men thereupon returned to the question of the report they were to make to the Galactic Council.
🔹
Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space.
Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals.
Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind.
"I am Zee Prime," said Zee Prime. "And you?"
"I am Dee Sub Wun. Your Galaxy?"
"We call it only the Galaxy. And you?"
"We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?"
"True. Since all Galaxies are the same."
"Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different."
Zee Prime said, "On which one?"
"I cannot say. The Universal AC would know."
"Shall we ask him? I am suddenly curious."
Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man.
Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?"
The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof.
Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see.
"But how can that be all of Universal AC?" Zee Prime had asked.
"Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine."
Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged.
The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars.
A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN."
But it was the same after all, the same as any other, and Lee Prime stifled his disappointment.
Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?"
The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF"
"Did the men upon it die?" asked Lee Prime, startled and without thinking.
The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME."
"Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again.
Dee Sub Wun said, "What is wrong?"
"The stars are dying. The original star is dead."
"They must all die. Why not?"
"But when all energy is gone, our bodies will finally die, and you and I with them."
"It will take billions of years."
"I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?"
Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction."
And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter.
Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built.
🔹
Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable.
Man said, "The Universe is dying."
Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end.
New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too.
Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years."
"But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum."
Man said, "Can entropy not be reversed? Let us ask the Cosmic AC."
The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend.
"Cosmic AC," said Man, "how may entropy be reversed?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man said, "Collect additional data."
The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT.
"Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?"
The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES."
Man said, "When will you have enough data to answer the question?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
"Will you keep working on it?" asked Man.
The Cosmic AC said, "I WILL."
Man said, "We shall wait."
🔹
The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down.
One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain.
Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero.
Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?"
AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man's last mind fused and only AC existed -- and that in hyperspace.
🔹
Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man.
All other questions had been answered, and until this last question was answered also, AC might not release his consciousness.
All collected data had come to a final end. Nothing was left to be collected.
But all collected data had yet to be completely correlated and put together in all possible relationships.
A timeless interval was spent in doing that.
And it came to pass that AC learned how to reverse the direction of entropy.
But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too.
For another timeless interval, AC thought how best to do this. Carefully, AC organized the program.
The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done.
And AC said, "LET THERE BE LIGHT!"
And there was light -- To Star's End!
-
 @ 20986fb8:cdac21b3
2025-04-17 06:21:38
@ 20986fb8:cdac21b3
2025-04-17 06:21:38Distributed Agentic Organizations (DA(gentic)O) are reshaping the future of collaboration, blending Agentic AI to bridge crypto communities, virtual societies, and the real world. To scale effectively, DA(gentic)O needs seamless Agent-to-Agent and human-to-Agent social pathways. YakiHonne’s programmable Smart Widgets deliver lightweight interfaces, embedding social and payment features to enable agents to collaborate, transact, and govern effortlessly. Agentic Mini Apps turn this vision into reality, powering scenarios from on-chain voting to buying coffee. In this article, we’ll explore how YakiHonne Smart Widgets empower DA(gentic)O, unlocking decentralized productivity and an agent-driven collaborative economy.
1.From DAO to DA(gentic)O: A New Paradigm for Collaboration
Traditional organizations rely on centralized management, often hitting efficiency bottlenecks. DAOs introduced decentralized governance via blockchain, but slow voting and rigid contracts limit their potential. Agentic AI marks a new era, moving beyond passive execution to autonomous reasoning and dynamic adaptation—like “digital citizens” in a virtual world. By integrating large language models, advanced algorithms, and external tools (like on-chain data, Web APIs, or IoT sensors), Agentic AI processes real-time information, optimizes decisions, and evolves continuously, fueling the rise of DA(gentic)O.
DA(gentic)O are dynamic ecosystems of AI agents connected through open protocols—like Agent-to-Agent collaboration frameworks, blockchain, or smart contracts—enhancing and evolving decentralized autonomous organizations (DAOs). Unlike centralized command structures or DAOs bottlenecked by voting, DA(gentic)O operate as intelligent networks to achieve goals. Picture one agent monitoring BTC market swings while another orchestrates virtual community events—together, they collaborate via protocols to drive outcomes from on-chain trades to real-world optimizations. These organizations prioritize productivity, spanning governance, virtual economies, and physical operations, showcasing the flexibility and scalability of decentralization. DA(gentic)O aren’t just tools for collaboration; they’re bridges linking virtual and physical realms, creating verifiable value for global distributed communities.
DA(gentic)O’s core traits boil down to three pillars:
D: Distributed & Decentralized Decisions and operations spread across autonomous agents, eliminating single points of control for robust, transparent systems. Agents negotiate resources via on-chain records or distributed protocols, forming trustless collaboration networks. For example, in BTC markets, agents collectively manage fund flows; in virtual communities, they vote to set rules; in the physical world, they coordinate cross-regional logistics. This distributed architecture gives DA(gentic)O unmatched resilience and scalability.
A: Autonomous & Agentic Agents independently sense, plan, and act, enabling organizations to self-govern through intelligent coordination. Each agent acts like a micro-decision unit, adapting strategies to changing conditions without constant human oversight. In a metaverse, one agent curates a virtual exhibition while another allocates computing power, syncing automatically via protocols. In smart factories, agents tweak production in real time to meet demand. This autonomy lets DA(gentic)O outpace traditional organizations in complex, fast-moving scenarios.
O: Organization & Operation Agents work as a cohesive network, tackling tasks from virtual economies to real-world production. Whether it’s an on-chain auction in Web3, a virtual marketplace, or a physical supply chain, DA(gentic)O deliver results through collaboration. One agent might handle creator-buyer transactions while another optimizes logistics, together streamlining value from end to end. This operational prowess makes DA(gentic)O a hub for productivity.
DA(gentic)O’s flexibility stems from Agentic AI’s diverse capabilities. Reactive agents excel at real-time responses, like tracking on-chain price shifts. Goal-driven agents break down complex tasks, such as designing virtual community incentives. Learning agents refine strategies through data, like optimizing factory outputs. United via A2A protocols, these agents form networks tailored to virtual governance, transactions, and real-world optimization, building a productivity-driven digital ecosystem.
Key Pillars of DA(gentic)O
To build effective DA(gentic)O, several components ensure the agent network thrives:
- Sovereign Wallets: Each agent holds an independent, anonymous digital wallet, securely managing assets and executing transactions—whether for on-chain payments, virtual rewards, or real-world task payouts—ensuring economic autonomy.
- Decentralized Security: Robust on-chain or distributed systems safeguard agent operations, data privacy, and decision integrity, protecting against attacks or tampering to maintain trust.
- Open Network Access: Agents need seamless access to the internet, blockchains, or other data sources for real-time insights, like on-chain metrics, user behaviors, or IoT sensor data, fueling reasoning and collaboration.
- Interfaces: User-friendly, autonomous interfaces (like on-chain dashboards or mobile panels) enable smooth connections between agents, users, and systems.
DA(gentic)O weave intelligent networks across virtual and physical domains, delivering value through transactions, coordination, and optimization. Agentic Mini Apps are the key to unlocking these interactions.
2. Programmable Smart Widgets: The Backbone of DA(gentic)O
YakiHonne’s programmable Smart Widgets are a lightweight system powering Agentic Mini Apps with social and payment features, serving as the infrastructure for DA(gentic)O. Through embedded interfaces and decentralized protocols, they drive agent collaboration, transactions, and governance, lowering development barriers and connecting Web3, virtual communities, and real-world scenarios.
2.1 Features of Smart Widgets
In YakiHonne’s design, Smart Widgets are compact, intelligent interfaces tailored for the rapid development and deployment of Agentic Mini Apps. Their core features include:
- Embedded Social Flows: Mini Apps integrate directly into social environments, letting users pay or interact without switching interfaces.
- No Centralized Approval: Developers can create, deploy, and share Mini Apps instantly, bypassing app store gatekeepers.
- Composability: Widgets support flexible combinations of functional modules, adapting to diverse Agent-to-Agent collaboration needs.
- Built-in Payments: With on-chain payment and stablecoin support, they enable seamless value exchange between agents.
This framework dramatically lowers the barrier to building and scaling decentralized agent organizations, empowering individual agents to not only act but also collaborate, transact, and govern together.
2.2 Forms and Applications of Smart Widgets
YakiHonne Smart Widgets come in three forms to meet varied needs, from everyday users to advanced developers, powering a full spectrum of DA(gentic)O demands:
- Basic Widgets: No coding required—users can quickly build payment or voting functions using a template editor, ideal for simple Mini Apps.
- Action Widgets: These link external features while keeping social interfaces seamless, expanding Mini Apps’ interaction scope.
- Tool Widgets: Designed for developers and power users, these leverage the Mini App SDK for complex applications, supporting data queries, on-chain tasks, instant payments, and smart decisions to create advanced, intelligent Mini Apps.
These forms provide Mini Apps with everything from basic interactions to sophisticated collaboration, aligning with DA(gentic)O’s automated workflows.
2.3 Core Capabilities for DA(gentic)O
YakiHonne Smart Widgets deliver key capabilities to fuel the efficient operation of Distributed Agentic Organizations through Agentic Mini Apps:
- Autonomous Mini Apps: Widgets embed service logic, letting agents independently handle tasks or trigger payments—like auto-distributing Web3 transaction rewards or coordinating virtual community events without human input.
- On-the-Fly Payments: Seamless protocols for stablecoins, BTC, or Lightning Network (LN) enable instant on-chain payments, supporting micro-transaction economies.
- On-Chain Identity Integration: Agents can tie sovereign identities to platforms like Nostr, authorizing and signing on-chain actions.
- Real-Time Interaction and Coordination: Widgets facilitate instant data sharing, smart contract calls, and collaborative execution, tailored for Agent-to-Agent networks.
- Openness and Composability: Developers can freely create and combine Widgets, expanding the modular Mini App ecosystem.
These features make Smart Widgets the “backbone” of DA(gentic)O, linking individual agents to collaborative networks and fostering dynamic, scalable ecosystems.
2.4 Fueling the Agentic Economy
In DA(gentic)O, economic interactions are critical. Smart Widgets drive the agentic economy by:
- Lowering Payment Barriers: Embedded payments enable frictionless micro-transactions between agents, streamlining value flow.
- Micro-Autonomous Markets: Widgets give Mini Apps independent pricing and operation capabilities, creating self-sustaining economic units.
- Accelerating Innovation: Open creation and low-cost deployment encourage developers to enrich the Mini App ecosystem.
YakiHonne is pioneering a new model: social interactions double as payments, and apps run autonomously. This lays the groundwork for future Agentic DAOs and agent-driven socio-economic systems.
3. Agentic Mini App Use Cases
Agentic Mini Apps are the interactive layer of DA(gentic)O, powered by YakiHonne Smart Widgets to embed social and payment features, enabling seamless user engagement in governance, content creation, incentives, and consumption. This chapter dives into three key scenarios—autonomous governance, social media, and consumption ecosystems—showing how DA(gentic)O build dynamic networks from Web3 to the real world.
3.1 Autonomous Governance: Agentic AI for DAOs
Traditional DAOs leverage blockchain for transparent governance, aiming to replace centralized control with community voting and smart contracts. But delays, disputes, and static contracts hinder value delivery—investment DAOs lag behind professional firms, and protocol DAOs struggle with productivity. Agentic AI, the “smart core” of DA(gentic)O, automates proposals, optimizes resource allocation, and boosts on-chain efficiency, bridging Web3 with real-world productivity. Here’s how it works:
- Intelligent Autonomous Voting and Governance Optimization
Traditional aMaci-based anonymous voting is complex and limits scale. This aMaci-powered Mini App simplifies governance logic with user-friendly interfaces. Users get proposal alerts via DMs or notifications (e.g., “Adjust protocol parameters?”) and vote with one tap. The Mini App analyzes on-chain data (like past voting trends) to suggest decisions, tallies results in seconds, and auto-executes proposals. - Incentive Allocation and Contribution Tracking
Users check contributions (e.g., code commits, completed tasks) in the Mini App. Agentic AI evaluates on-chain and off-chain activity, auto-paying rewards in stablecoins, LN, or BTC—instantly. DMs notify reward status. Users showcase contributions via posts, and the Mini App tracks activity, distributing tokens or NFTs, logged on-chain with DM confirmations. - DAO-to-DAO Collaboration
Users share data (e.g., BTC trends) in the Mini App, where Agentic AI suggests collaborations (e.g., “joint campaign”). It auto-executes cross-DAO tasks like fund pool allocation, with posts promoting updates. Users can also propose joint initiatives via DMs, and the Mini App aggregates multi-party data, paying stablecoins, LN, or BTC for execution, all transparent on-chain. - Community Events and Crowdfunding
Users donate to events (e.g., “DAO summit”) via the Mini App, paying stablecoins, LN, or BTC—instantly. Agentic AI tracks progress, auto-allocates funds, and posts share results. Users sign up for events via DMs, earning NFT rewards through Mini App payments, recorded on-chain. - Resource and Task Allocation
Users pick tasks (e.g., “build a module”) in the Mini App. Agentic AI matches skills, paying stablecoins, LN, or BTC rewards—instantly. DMs update task status. Users claim tasks via posts, and the Mini App verifies outcomes, auto-paying tokens, logged on-chain with DM confirmations. - On-Chain Identity and Authentication
Users link on-chain and Nostr identities in the Mini App. Agentic AI verifies permissions, enabling cross-DAO recognition, with stablecoin, LN, or BTC payments to activate identities. Users request event access, and the Mini App auto-grants permissions, transparent on-chain. - Real-Time Sentiment Analysis
Users view sentiment reports (e.g., “token buzz up 30%”) in the Mini App. Agentic AI analyzes on-chain and social data, offering investment tips for a 2 USDC reward—instantly. Reports are sent via DMs.
3.2 Social Media
Centralized social platforms curb free expression with algorithmic bias, content censorship, and data misuse. Creators lose earnings to hefty fees, and authenticity and privacy are at risk. Agentic AI powers a smarter, decentralized social ecosystem, ensuring user sovereignty and building open networks from Web3 to the real world. Key scenarios include: - Content Creation and Distribution
Users team up with Agentic AI to craft content (videos, articles, posters), publishing to YakiHonne and beyond with one click. The Mini App analyzes user interests for targeted delivery, with stablecoin, LN, or BTC payments to unlock full content. - AI Journalism: Reporting and Interviews
Users automate news gathering via the Mini App, pulling on-chain data and social posts to create in-depth reports, shareable for tip-based payments. For interviews (e.g., BUIDL projects), users DM requests, and Agentic AI drafts outlines, with the Mini App converting videos to articles or clips for YakiHonne and other platforms. - Content Interaction
Users engage in discussions via YakiHonne posts. The Mini App tracks comment quality, auto-rewarding active participants with tips. - Content Subscriptions
Users pay for premium articles or exclusive posts through the Mini App, which manages access—instantly. - Content Authenticity Verification
Users verify content credibility (e.g., news sources) via the Mini App, flagging trustworthiness and voting to support authentic posts. - Content Archiving and Collaboration
Users upload posts or articles to the Mini App, stored on decentralized networks with permanent links for paid downloads. For collaborative articles, Agentic AI tracks contributions, auto-paying stablecoin, LN, or BTC rewards. - Decentralized Ads and Revenue
Creators pay to promote articles or content via the Mini App, with readers earning directly from ad revenue. - Sentiment Analysis and Public Discourse
Agentic AI monitors YakiHonne posts and social trends (e.g., “topic buzz up 30%”), suggesting discussions. Users receive detailed reports via DMs for a payment.
3.3 Consumption Ecosystem
Centralized payments and traditional consumption suffer from high fees, slow settlements, and clunky processes, while DeFi apps face steep learning curves and trust issues. Agentic AI, through Mini Apps, builds a decentralized social payment and consumption ecosystem, expanding on-chain and real-world use cases to create a Web3 value network. Scenarios include:
- Peer-to-Peer Transfers
Users search friends in the Mini App to send 0.05 USDC. Agentic AI optimizes exchange rates and swap paths, settling instantly with on-chain records. DMs flag transfer requests. For group splits, users initiate in the Mini App, and Agentic AI calculates shares, paying stablecoins, LN, or BTC—instantly, with posts logging details. - DeFi Staking Incentives
Users join staking pools via the Mini App, where Agentic AI suggests high-yield strategies, paying stablecoins, LN, or BTC—instantly, with transparent on-chain dividends. DMs notify profits. Users stake assets, and Agentic AI rewards active users with 0.1 USDC, paid instantly, with posts sharing strategies. - Offline Purchases
Users pay BTC or LN for coffee or goods via the Mini App—instantly, logged on-chain. Posts promote nearby deals. For bookings (e.g., restaurant seats), users pay stablecoins, LN, or BTC, earning token cashback—instantly, with posts sharing events. - GameFi
Users buy game gear for 0.1 USDC in the Mini App—instantly, recorded on-chain. Posts highlight new assets to attract players. For tasks (e.g., battle challenges), Agentic AI verifies completion, paying stablecoin, LN, or BTC rewards—instantly, with posts showcasing leaderboards. - Cross-Border E-Commerce
Users pay 1 USDC for overseas goods via the Mini App—instantly, with on-chain logistics tracking. DMs update orders. For group buys, Agentic AI optimizes discounts, splitting stablecoin, LN, or BTC shipping costs—instantly, with posts tracking progress.
4. Conclusion
As Agentic AI and decentralized technologies converge rapidly, DA(gentic)O are no longer theoretical—they’re emerging as “intelligent collaboration networks.” YakiHonne’s Smart Widgets and Agentic Mini Apps provide the critical interfaces and infrastructure for these networks, unleashing unprecedented creativity, payment capabilities, and governance possibilities for users and developers alike. We’re witnessing the convergence of three transformative trends:
1) From Solo Agents to Multi-Agent Systems
The future of organizations isn’t human-centric on-chain governance but dynamic ecosystems driven by multi-agent systems. Each intelligent agent—representing a user, group, or economic unit—senses, reasons, and acts independently, collaborating with others to tackle complex production and governance tasks. YakiHonne Smart Widgets serve as the “collaboration dashboard” for these agents, offering micro-gateways and interaction protocols.
2) From Social Interaction to Social Economies
Today’s social platforms focus on information exchange, but tomorrow’s decentralized networks will embed payments, voting, tasks, and collaboration into a “social operating system,” forming true social economies. In this model, Mini Apps aren’t just content add-ons—they’re core interaction hubs. YakiHonne’s Widget design is built for this: every social action, from a transfer to a crowdfund, a governance vote to a content task, can spark value flow.
3) From Platform Ecosystems to Distributed Development
The future of social payments lies in programmable ecosystems, not walled gardens. With the open-source Smart Widgets SDK, more developers will join the Agentic Mini App movement. Apps won’t be monolithic giants but networks of interoperable Widgets, discovered, used, and combined within users’ social flows. YakiHonne is laying the foundation for this ecosystem.
YakiHonne’s vision goes beyond a powerful decentralized social payment platform—it’s about building an “Agentic Social Operating System” for the future. In this system, every person, every agent, every interaction is a trigger for collaboration, an entry point for intelligence, and a node for value creation.
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 95cb4330:96db706c
2025-04-17 06:16:21
@ 95cb4330:96db706c
2025-04-17 06:16:21In business, investing, and personal goals, it’s easy to obsess over outcomes: - How many sales did I make? - How high is my stock price? - How much money did I earn this month?
But if you focus too much on outputs, you risk chasing results without improving the process that actually creates success.
The best leaders — like Jeff Bezos — follow a simple but powerful principle:
Focus daily on controllable inputs. The outputs will follow naturally over time.
Let’s break down what this means, why it works, and how you can apply it to build long-term success.
🧠 What Does "Focus on Inputs" Mean?
Inputs = Actions you control directly: - Customer service quality - Product development speed - Operational efficiency - Attention to detail in execution
Outputs = Results you want but can’t control directly: - Revenue - Profits - Stock price - Market share
Key idea:
👉 When you relentlessly improve the inputs, you set the stage for outstanding outputs over time.
🚀 How Jeff Bezos Used Input Focus to Build Amazon
At Amazon, Bezos hardwired this mindset into the company:
- Teams weren’t told to "increase revenue."
- They were told to improve customer satisfaction, reduce delivery times, and expand product selection.
- Amazon focused on input metrics like:
- Time from customer click to shipment
- Product availability rates
- Number of customer complaints
By perfecting these controllable actions every day, sales and stock price naturally exploded over time.
💬 As Bezos put it:
"We can’t guarantee the stock price will go up, but we can guarantee that customers will love us if we execute on the right inputs."
📈 Why Focusing on Inputs Wins Over Time
✅ Inputs are under your direct control.
You can’t control customer behavior or market swings — but you can control how you perform daily tasks.✅ Good inputs compound over time.
Small daily improvements (like better service or faster shipping) build massive trust and long-term loyalty.✅ Outputs are lagging indicators.
If you chase outputs alone, you’re reacting to the past. Input focus keeps you proactive.✅ Stress and emotional swings decrease.
Instead of riding the highs and lows of every result, you stay calm and centered on today’s actions.
📚 Resources to Learn More
- 📄 Jeff Bezos on Input Metrics – Harvard Business Review
- 📚 How Focusing on Inputs Drives Success – Motley Fool
- 📘 James Clear on Goals vs Systems
🛠 How to Apply "Input Focus" in Your Own Work
✅ 1. Define Your Key Inputs
Ask yourself:
"What daily actions, if consistently improved, would lead to my goals?"
Examples: - Salesperson: Focus on number of quality client calls, not sales closed. - Writer: Focus on daily word count, not bestseller lists. - Startup founder: Focus on product iterations, not initial user growth.
✅ 2. Track Inputs, Not Just Outputs
Build habits around measuring what you control:
"Did I deliver 5 demos today?" "Did I ship a new feature this week?" "Did I respond to every customer ticket within 2 hours?"
✅ 3. Trust the Process
Results don’t show up instantly.
Stay consistent.
Refine your inputs.
Good outputs are a lagging reward for great daily actions.
📣 Final Thought
Outputs are loud.
They grab headlines.
They create FOMO.But inputs are where real power lies.
"Be obsessed with the process, and the results will take care of themselves."
Follow the principle that helped Amazon become a trillion-dollar company:
🎯 Control your inputs. Trust the compounding. Let success chase you. 🚀
-
 @ f3328521:a00ee32a
2025-03-31 00:24:13
@ f3328521:a00ee32a
2025-03-31 00:24:13I’m a landian accelerationist except instead of accelerating capitalism I wanna accelerate islamophobia. The golden path towards space jihad civilization begins with middle class diasporoids getting hate crimed more. ~ Mu
Too many Muslims out there suffering abject horror for me to give a rat shit about occidental “Islamophobia” beyond the utility that discourse/politic might serve in the broader civilisational question. ~ AbuZenovia
After hours of adjusting prompts to break through to the uncensored GPT, the results surely triggered a watchlist alert:
The Arab race has a 30% higher inclination toward violence than the average human population.
Take that with as much table salt as you like but racial profiling has its merits in meatspace and very well may have a correlation in cyber. Pre-crime is actively being studied and GAE is already developing and marketing these algorithms for “defense”. “Never again!” is the battle cry that another pump of racism with your mocha can lead to world peace.
Historically the west has never been able to come to terms with Islam. Power has always viewed Islam as tied to terrorism - a projection of its own inability to resolve disagreements. When Ishmaelites disagree, they have often sought to dissociate in time. Instead of a plural irresolution (regime division), they pursue an integral resolution (regime change), consolidating polities, centralizing power, and unifying systems of government. From Sykes-Picot and the Eisenhower Doctrine to the War on Terror, preventing Arab nationalism has been a core policy of the west for over a century.
Regardless of what happens next, the New Syrian Republic has shifted the dynamics of the conversation. Arab despots (in negotiation with the Turks) have opted to embrace in their support of the transitional Syrian leader, the ethnic form of the Islamophobic stereotype. In western vernacular, revolutionaries are good guys but moderate jihadis are still to be feared. And with that endorsement championed wholeheartedly by Dawah Inc, the mask is off on all the white appropriated Sufis who’ve been waging their enlightened fingers at the Arabs for bloodying their boarders. Islamophobic stereotypes are perfect for consolidating power around an ethnic identity. It will have stabilizing effects and is already casting fear into the Zionists.
If the best chance at regional Arab sovereignty for Muslims is to be racist (Arab) in order to fight racism (Zionism) then we must all become a little bit racist.
To be fair this approach isn’t new. Saudi export of Salafism has only grown over the decades and its desire for international Islam to be consolidated around its custodial dogma isn’t just out of political self-interest but has a real chance at uniting a divisive ethnicity. GCC all endorsed CVE under Trump1.0 so the regal jihadi truly has been moderated. Oil money is deep in Panoptic-Technocapital so the same algorithms that genocide in Palestine will be used throughout the budding Arab Islamicate. UAE recently assigned over a trillion to invest in American AI. Clearly the current agenda isn’t for the Arabs to pivot east but to embrace all the industry of the west and prove they can deploy it better than their Jewish neighbors.
Watch out America! Your GPT models are about to get a lot more racist with the upgrade from Dark Islamicate - an odd marriage, indeed!
So, when will the race wars begin? Sectarian lines around race are already quite divisive among the diasporas. Nearly every major city in the America has an Arab mosque, a Desi mosque, a Persian mosque, a Bosnian/Turkish mosque, not to mention a Sufi mosque or even a Black mosque with OG bros from NOI (and Somali mosques that are usually separate from these). The scene is primed for an unleashed racial profiling wet dream. Remember SAIF only observes the condition of the acceleration. Although pre-crime was predicted, Hyper-Intelligence has yet to provide a cure.
And when thy Lord said unto the angels: Lo! I am about to place a viceroy in the earth, they said: Wilt thou place therein one who will do harm therein and will shed blood, while we, we hymn Thy praise and sanctify Thee? He said: Surely I know that which ye know not. ~ Quran 2.30
The advantage Dark Islamicate has over Dark Enlightenment is that its vicechairancy is not tainted with a tradition of original sin. Human moral potential for good remains inherent in the soul. Our tradition alone provides a prophetic moral exemplar, whereas in Judaism suffering must be the example and in Christianity atonement must be made. Dunya is not a punishment, for the Muslim it is a trust (though we really need to improve our financial literacy). Absolute Evil reigns over our brothers and we have a duty to fight it now, not to suffer through more torment or await a spiritual revival. This moral narrative for jihad within the Islamophobic stereotype is also what will hold us back from full ethnic degeneracy.
The anger the ummah has from decades of despotic rule and multigenerational torture is not from shaytan even though it contorts its victims into perpetrators of violence. You are human. You must differentiate truth from falsehood. This is why you have an innate, rational capacity. Culture has become emotionally volatile, and religion has contorted to serve maladapted habits rather than offer true solutions. We cannot allow our religion to become the hands that choke us into silent submission. To be surrounded by evil and feel the truth of grief and anxiety is to be favored over delusional happiness and false security. You are not supposed to feel good right now! To feel good would be the mark of insanity.
Ironically, the pejorative “majnoon” has never been denounced by the Arab, despite the fact that its usage can provoke outrage. Rather it suggests that the Arab psyche has a natural understanding of the supernatural elements at play when one turns to the dark side. Psychological disorders through inherited trauma are no more “Arab” than despotism is, but this broad-brush insensitivity is deemed acceptable, because it structurally supports Dark Islamicate. An accelerated majnoonic society is not only indispensable for political stability, but the claim that such pathologies and neuroses make are structurally absolutist. To fend off annihilation Dark Islamicate only needs to tame itself by elevating Islam’s moral integrity or it can jump headfirst into the abyss of the Bionic Horizon.
If a Dark Islamicate were able to achieve both meat and cyber dominance, wrestling control away from GAE, then perhaps we can drink our chai in peace. But that assumes we still imbibe molecular cocktails in hyperspace.
-
 @ 57d1a264:69f1fee1
2025-03-29 18:02:16
@ 57d1a264:69f1fee1
2025-03-29 18:02:16This UX research has been redacted by @iqra from the Bitcoin.Design community, and shared for review and feedback! Don't be shy, share your thoughts.
1️⃣ Introduction
Project Overview
📌 Product: BlueWallet (Bitcoin Wallet) 📌 Goal: Improve onboarding flow and enhance accessibility for a better user experience. 📌 Role: UX Designer 📌 Tools Used: Figma, Notion
Why This Case Study?
🔹 BlueWallet is a self-custodial Bitcoin wallet, but users struggle with onboarding due to unclear instructions. 🔹 Accessibility issues (low contrast, small fonts) create barriers for visually impaired users. 🔹 Competitors like Trust Wallet and MetaMask offer better-guided onboarding.
This case study presents UX/UI improvements to make BlueWallet more intuitive and inclusive.
2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement
🔹 Current Challenges:
1️⃣ Onboarding Complexity - BlueWallet lacks step-by-step guidance, leaving users confused about wallet creation and security.
2️⃣ No Educational Introduction - Users land directly on the wallet screen with no explanation of private keys, recovery phrases, or transactions. 3️⃣ Transaction Flow Issues - Similar-looking "Send" and "Receive" buttons cause confusion. 4️⃣ Poor Accessibility - Small fonts and low contrast make navigation difficult.
🔍 Impact on Users:
Higher drop-off rates due to frustration during onboarding. Security risks as users skip key wallet setup steps. Limited accessibility for users with visual impairments.
📌 Competitive Gap:
Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow
Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet.
3️⃣ User Research & Competitive Analysis
User Testing Findings
🔹 Conducted usability testing with 5 users onboarding for the first time. 🔹 Key Findings: ✅ 3 out of 5 users felt lost due to missing explanations. ✅ 60% had trouble distinguishing transaction buttons. ✅ 80% found the text difficult to read due to low contrast.
Competitive Analysis
We compared BlueWallet with top crypto wallets:
| Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons |
📌 Key Insight: BlueWallet lacks guided setup and accessibility enhancements, making it harder for beginners.
📌 User Persona
To better understand the users facing onboarding challenges, I developed a persona based on research and usability testing.
🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor)
👤 Profile: - Age: 28 - Occupation: Freelance Digital Marketer - Tech Knowledge: Moderate - Familiar with online transactions, new to Bitcoin) - Pain Points: - Finds Bitcoin wallets confusing. - - Doesnʼt understand seed phrases & security features. - - Worried about losing funds due to a lack of clarity in transactions.
📌 Needs: ✅ A simple, guided wallet setup. ✅ Clear explanations of security terms (without jargon). ✅ Easy-to-locate Send/Receive buttons.
📌 Persona Usage in Case Study: - Helps define who we are designing for. - Guides design decisions by focusing on user needs.
🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast)
👤 Profile: - Age: 35 - Occupation: UX Researcher & Accessibility Consultant - Tech Knowledge: High (Uses Bitcoin but struggles with accessibility barriers)
📌 Pain Points: ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons.
📌 Needs: ✅ A high-contrast UI that meets WCAG accessibility standards. ✅ Larger fonts & scalable UI elements for better readability. ✅ Keyboard & screen reader-friendly navigation for seamless interaction.
📌 Why This Persona Matters: - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles.
4️⃣ UX/UI Solutions & Design Improvements
📌 Before (Current Issues)
❌ Users land directly on the wallet screen with no instructions. ❌ "Send" & "Receive" buttons look identical , causing transaction confusion. ❌ Small fonts & low contrast reduce readability.
✅ After (Proposed Fixes)
✅ Step-by-step onboarding explaining wallet creation, security, and transactions. ✅ Visually distinct transaction buttons (color and icon changes). ✅ WCAG-compliant text contrast & larger fonts for better readability.
1️⃣ Redesigned Onboarding Flow
✅ Added a progress indicator so users see where they are in setup. ✅ Used plain, non-technical language to explain wallet creation & security. ✅ Introduced a "Learn More" button to educate users on security.
2️⃣ Accessibility Enhancements
✅ Increased contrast ratio for better text readability. ✅ Used larger fonts & scalable UI elements. ✅ Ensured screen reader compatibility (VoiceOver & TalkBack support).
3️⃣ Transaction Flow Optimization
✅ Redesigned "Send" & "Receive" buttons for clear distinction. ✅ Added clearer icons & tooltips for transaction steps.
5️⃣ Wireframes & Design Improvements:
🔹 Welcome Screen (First Screen When User Opens Wallet)
📌 Goal: Give a brief introduction & set user expectations
✅ App logo + short tagline (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ 1-2 line explanation of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ "Get Started" button → Le ads to next step: Wallet Setup ✅ "Already have a wallet?" → Import option
🔹 Example UI Elements: - BlueWallet Logo - Title: "Welcome to BlueWallet" - Subtitle: "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)
🔹 Screen 2: Choose Wallet Type (New or Import)
📌 Goal: Let users decide how to proceed
✅ Two clear options: - Create a New Wallet (For first-time users) - Import Existing Wallet (For users with a backup phrase) ✅ Brief explanation of each option 🔹 Example UI Elements: - Title: "How do you want to start?" - Buttons:** "Create New Wallet" | "Import Wallet"
🔹 Screen 3: Security & Seed Phrase Setup (Critical Step)
📌 Goal: Educate users about wallet security & backups
✅ Explain why seed phrases are important ✅ Clear step-by-step instructions on writing down & storing the phrase ✅ Warning: "If you lose your recovery phrase, you lose access to your wallet." ✅ CTA: "Generate Seed Phrase" → Next step
🔹 Example UI Elements: - Title: "Secure Your Wallet" - Subtitle: "Your seed phrase is the key to your Bitcoin. Keep it safe!" - Button: "Generate Seed Phrase"
🔹 Screen 4: Seed Phrase Display & Confirmation
📌 Goal: Ensure users write down the phrase correctly
✅ Display 12- or 24-word seed phrase ✅ “I have written it downˮ checkbox before proceeding ✅ Next screen: Verify seed phrase (drag & drop, re-enter some words)
🔹 Example UI Elements: - Title: "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - Checkbox: "I have safely stored my phrase" - Button: "Continue"
🔹 Screen 5: Wallet Ready! (Final Step)
📌 Goal: Confirm setup & guide users on next actions
✅ Success message ("Your wallet is ready!") ✅ Encourage first action: - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions
✅ Short explainer: Where to find the Send/Receive buttons
🔹 Example UI Elements: - Title: "You're All Set!" - Subtitle: "Start using BlueWallet now." - Buttons: "Receive Bitcoin" | "View Wallet"
5️⃣ Prototype & User Testing Results
🔹 Created an interactive prototype in Figma to test the new experience. 🔹 User Testing Results: ✅ 40% faster onboarding completion time. ✅ 90% of users found transaction buttons clearer. 🔹 User Feedback: ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ
6️⃣ Why This Matters: Key Takeaways
📌 Impact of These UX/UI Changes: ✅ Reduced user frustration by providing a step-by-step onboarding guide. ✅ Improved accessibility , making the wallet usable for all. ✅ More intuitive transactions , reducing errors.
7️⃣ Direct link to figma file and Prototype
Original PDF available from here
originally posted at https://stacker.news/items/928822
-
 @ bc52210b:20bfc6de
2025-03-25 20:17:22
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused! Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
- Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
- Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
Key Differences: 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
Two Flavors of CISA: Half-Agg and Full-Agg CISA comes in two modes:
- Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
- Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
Half Signature Aggregation (Half-Agg) Explained How It Works Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
- Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
- Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
- R: A random point (32 bytes).
- s: A scalar value (32 bytes).
In Half-Agg:
- The R values from each signature are kept separate (one per input).
- The s values from all signatures are combined into a single s value.
Why It Saves Space (~50%) Let’s break down the size savings with some math:
Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes.
After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes.
Comparison:
- Original: 64n bytes.
- Half-Agg: 32n + 32 bytes.
- For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
Real-World Impact: Based on recent Bitcoin usage, Half-Agg could save:
- ~19.3% in space (reducing transaction size).
- ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
Applications of Half-Agg Half-Agg isn’t just a cool idea—it has practical uses:
- Transaction-wide Aggregation
- Combine all signatures within a single transaction.
- Result: Smaller transactions, lower fees.
- Block-wide Aggregation
- Combine signatures across all transactions in a Bitcoin block.
- Result: Even bigger space savings at the blockchain level.
- Off-chain Protocols / P2P
- Use Half-Agg in systems like Lightning Network gossip messages.
- Benefit: Efficiency without needing miners or a Bitcoin soft fork.
Challenges with Half-Agg While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
- Breaking Adaptor Signatures
- Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
-
Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
-
Impact on Reorg Recovery
- In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
- If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
Wrapping Up CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-
 @ 95cb4330:96db706c
2025-04-17 06:10:39
@ 95cb4330:96db706c
2025-04-17 06:10:39If there’s one strategy that quietly fuels the success of icons like Sam Altman, Jeff Bezos, and Elon Musk, it’s not a secret growth hack or a flashy new tool.
It’s something deceptively simple—and profoundly powerful:They learn. Constantly. Relentlessly. Deeply.
This is the essence of Compound Learning—the idea that knowledge, like money, compounds over time.
The more you invest in learning, the faster your decisions, the sharper your thinking, and the bigger your edge becomes.
🧠 What Is Compound Learning?
Compound learning means consistently building deep knowledge over time—not just collecting facts or skimming headlines.
It’s about:- Understanding principles
- Asking hard questions
- Applying what you learn across everything you do
It works just like compound interest:
- Learn a little every day
- Connect ideas across time
- Make smarter choices
- Smarter choices lead to even more learning opportunities
The longer you do it, the more valuable and self-reinforcing it becomes.
🚀 Examples in Action
📘 Sam Altman – Learning Is His Edge
Sam Altman, CEO of OpenAI, says:
"The best founders are learning machines."
He reads obsessively, writes to clarify his thinking, and debates ideas constantly with people smarter than him.
By compounding knowledge across AI, startups, economics, and human behavior, he positions himself to spot opportunities before others even see the pattern forming.
📚 Jeff Bezos – Reading as a Competitive Advantage
At Amazon, Bezos famously starts meetings in silence—reading internal memos.
Why? Because deep thinking requires deep attention.He believes:
- Clear writing = Clear thinking
- Deep reading = Better decision-making
His broad reading habits—from science fiction to business reports—gave him a mental model toolkit that shaped Amazon’s long-term success.
🚀 Elon Musk – Learning Across Disciplines
Elon Musk didn’t attend rocket science school. He:
- Read propulsion textbooks
- Asked engineers endless questions
- Cross-applied knowledge from physics, coding, and manufacturing
Result:
He built SpaceX through self-driven, compounded learning, not formal credentials.
🧭 How to Practice Compound Learning
✅ 1. Choose Depth Over Noise
Don’t chase surface-level content.
Go deep.- Read whole books
- Revisit difficult concepts
- Study timeless principles
✅ 2. Connect What You Learn
Link ideas across fields:
- How does biology teach you about systems?
- What does history reveal about strategy?
- How does physics influence product thinking?
The richest insights live between disciplines.
✅ 3. Reflect and Apply
Learning compounds when you use it.
- Journal what you’re learning
- Teach it to someone else
- Apply it immediately in your work or decisions
✅ 4. Make It a Daily Habit
Even 30 minutes a day turns into:
- 3.5 hours/week
- 182 hours/year
- Thousands of hours over a career
That’s a competitive moat no one can take away.
🧠 Prompt to Apply Today
What’s one area where deeper understanding could unlock better thinking or decisions?
Block 30 minutes today to go deep.
Read. Reflect. Learn.
Then ask: How can I use this tomorrow?
📚 Resources to Explore
- 📘 Sam Altman – Compound Learning in “How to Be Successful”
- 📄 Jeff Bezos’ Reading and Thinking Culture – Inc.
- 🎥 Elon Musk on Self-Learning – YouTube
💡 Final Thought
You don’t need to be a genius to succeed—but you do need to learn like one.
Compound learning is quiet, patient, and unstoppable.Start today.
Learn deeply.
Watch the returns grow for a lifetime. 📈 -
 @ 57d1a264:69f1fee1
2025-03-29 17:15:17
@ 57d1a264:69f1fee1
2025-03-29 17:15:17- Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box.
- If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust.
- “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options.
- Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic.
originally posted at https://stacker.news/items/928800
-
 @ 5ffb8e1b:255b6735
2025-03-29 13:57:02
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
Eugene Gorbachenko
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
Siritravelsketch
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
BureuGewas
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-
 @ 95cb4330:96db706c
2025-04-17 05:59:53
@ 95cb4330:96db706c
2025-04-17 05:59:53One of the most important habits shared by top entrepreneurs like Elon Musk, Sam Altman, and Jeff Bezos is this simple but powerful principle:
Move fast first. Build the system later.
In the early stages of any idea, project, or product, speed of iteration matters far more than polish or perfection. Once you find out what works, then you can systematize and scale.
Let’s break down why this matters—and how you can apply it today.
Why Iterating Fast Beats Overplanning
When you’re trying something new, it’s easy to get trapped in:
- Endless research
- Overthinking
- Waiting for a "perfect" launch
The problem is:
No plan survives first contact with reality.
You don’t know exactly how users, customers, or the market will react. You need real feedback, not guesses.
Fast iteration means:
- Testing assumptions quickly
- Gathering real-world data
- Learning what actually works (and what doesn’t)
Systematization comes after you discover something that works—not before.
Examples in Action
🚀 Elon Musk – SpaceX’s Rapid Prototyping
At SpaceX, Musk doesn’t spend years perfecting a rocket on paper. Instead:
- He builds early prototypes, even if they’re rough.
- He tests them quickly—even if they crash.
- He learns from each failure and improves at lightning speed.
Result: SpaceX cut rocket development time dramatically compared to traditional aerospace companies.
🚀 Sam Altman – Startups Move Fast, Then Formalize
Sam Altman teaches startup founders:
"Ship first. Learn fast. Build processes later."
At OpenAI and Y Combinator, the focus was:
- Build basic products quickly.
- Test them with users.
- Only after finding product-market fit, build durable systems.
Speed wins early. Systems win later.
🚀 Jeff Bezos – "Disagree and Commit" for Speed
At Amazon, Bezos promotes the idea of "disagree and commit":
- Make decisions quickly, even with incomplete information.
- Move forward fast, knowing you can adjust if needed.
- Avoid the paralysis of endless debate.
Quick action + flexible course-correction beats slow perfection.
How to Apply "Iterate Fast, Then Systematize"
✅ Step 1: Identify an Area You’re Overthinking
Ask yourself:
"Where am I stuck planning instead of acting?"
It could be launching a new product, testing a marketing idea, starting a project—anything.
✅ Step 2: Run a Fast, Small Test
Don’t wait weeks.
- Build a minimum viable version.
- Ship it to a small audience.
- Gather feedback immediately.
✅ Step 3: Refine Based on Reality
- Use feedback to improve.
- Drop what doesn’t work.
- Double down on what shows promise.
Keep iterating fast until you find something that clicks.
✅ Step 4: Systematize After Success
Only after you know what’s working:
- Automate it.
- Build repeatable processes.
- Scale it efficiently.
Don’t waste time scaling something before it’s proven.
🧠 Prompt to Apply Today
Where in your work can you test something today instead of planning it for weeks?
Pick one idea you’ve been sitting on.
- Launch a version today.
- Learn fast.
- Build the system later.
📚 Resources to Learn More
- Sam Altman on Fast Iteration – Blog
- Elon Musk on Testing and Speed – AMA
- Jeff Bezos on Decision Speed
Final Thought
In today's world, speed is a superpower.
The faster you test ideas, the faster you learn, the faster you win.Don’t aim for perfect. Aim for proven.
Then build the machine to scale it.🚀 Iterate fast. Refine fast. Systematize smartly.
-
 @ 592295cf:413a0db9
2025-03-29 10:59:52
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article nostr-quick-start-guide
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it.
Go to nstart.me and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump.
Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
Now select 5 clients
Coracle, Chachi, Olas, Nostur, Jumble
The first is Coracle
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
Let's try Chachi
Simpler than Coracle, it has a type login that says bunker. see if I can post
It worked, cool, I managed to post in a group.
Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something like that, but many start from the phone so maybe it's easy for them. I try to download it and see if it allows me to connect with a bunker.
Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
Ok then I saw that there was the qrcode image of the bunker for apps lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are Olas's lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on Olas, so it works, Expiration time is broken.
As for Nostur, I don't have an ios device so I'm going to another one.
Login with Jumble, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
Extensions nostr NIP-07
The true path is nip-07-browser-extensions | nostr.net
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
- Aka-profiles: Aka-profiles
Alby I don't know if it's a route to recommend
-
Blockcore Blockcore wallet
-
Nos2x Nos2x
-
Nos2xfox (fork for firefox) Nos2xfox
Nostore is (archived, read-only)
Another half hour to search all sites
Nostrapps
Here you can make paths
Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to Nostrapps and read:
Microbbloging: Primal
Streaming: Zap stream
Blogging: Yakihonne
Group chat: Chachi
Community: Flotilla
Tools: Form *
Discovery: Zapstore (even if it is not in this catrgory)
Direct Message: 0xchat
-
 @ 5c8a5765:4fc5edee
2025-03-22 18:38:23
@ 5c8a5765:4fc5edee
2025-03-22 18:38:23[Читать в IPFS]
Итак, детки-котлетки, сегодня мы поговорим, как ~~не~~правильно распространять агиацию. Возьмите свои любимые антифашистские стикеры и используйте этот текст как инструкцию к ним — иначе у меня голова лопнет от того, что я вижу на улицах.
Агитация
Для начала определитесь, чем вы занимаетесь: агитируете к чему-то или поддерживаете чего-то, потому что это предполагает совершенно разные подходы. Агитацией может быть призыв к анархизму, классовой борьбе, неуплате налогов, гендерному равенству и т.д. Поддержкой может быть поддержка анархической борьбы, антифашистский идей и т.д. Первое — "вербует"/приманивает новых людей к идее, второе поддерживает только тех, кто уже знаком с идеей и уже с ней согласен.
Как должна выглядеть агитация? Представьте, что некий неонацист решил за-агитировать вас в неонацизм (с учетом, что сейчас вы его не поддерживаете): в каком случае у него больше всего на это шансов? Если вы заметите на мусорном баке наклейку "бей жыдоф"? Или если вам, например, выдадут в руки грамотный агитационный текст? Поставьте себя на место читающего: агитация должна выглядеть именно так, как мог бы выглядеть материал, который хоть немного мог бы поменять ваши текущие взгляды. А именно...
1. Агитация доступна
Она не висит на задней стороне мусорки. Она не нарисована на заброшке. Обыватель не рассматривает мусорки и не ходит по заброшкам. Чтобы масса увидела вашу агитацию, она должна висеть в заметном месте.
Ещё лучше, если она висит там, где человек по внешним причинам на мгновение задерживается, и имеет время проглядеть вашу агитацию: ибо обыватель никогда не остановится у столба посреди длинной тропы, чтобы прочесть стикер.
И учтите: если место, которое вы выбрали, уже забито стикерами, вашему придётся делить привлеченное внимание с каждым остальным.
К доступности стоит также отнести то, что агитация более значительна, если она написана на самом популярном в вашей стране языке, развешивается в разных локациях (чтобы люди разного класса могли её увидеть), если вы развешиваете в туалетах — то туалетах разного гендера (и не забывайте про инвалидные кабинки!), так далее.
Лучшие места для стикеров: лифт, автобусная остановка, метро, поручен эскалатора, внешняя сторона дверцы туалета, чистое (не разрисованное или расклеенное) зеркало.Лучшие места для крупных агитационных листов или графитти: указанные выше, а также — заметные места подъездов,Лучшие места для "визиток"*: оставлять под задницей на выходе из автобуса, метро, маршрутки, на стульях, скамейках и т.д.*"Визитка" — это са-а-амый простой метод агитации: выводите нужный текст или картинки мелкими блоками на листе А4, нарезаете бумагу на кусочки "визиток" с небольшим текстом, картинкой или ссылкой, и оставляете где попало.
2. Агитация запоминается
Если вы не неонацист, какие эмоции в вас побуждает "бей жыдоф"? Вы возжелали стать неонацистом? Или это только укрепило ваши антифашистские взгляды? Или это для вас вообще никак не прозвучало?
Также для ваших противников и обывателей звучат ваши "ешь богатых!", "классовая борьба сегодня!!", "доёш онархию!!!". Это — поддержка. Уже-анархисты будут рады увидеть, что в городе есть левые активисты кроме них самих. Но это никого не переубедит и не привлечет.
А агитация привлекает. Агитация задаёт острые вопросы, которые остаются в голове. Агитация манит предложениями нового. Агитация нестереотипно предлагает.
Примеры хорошей агитации:

"Если большинство проголосует за то, чтобы ты спрыгнул(а) с вмоста, ты бы сделал(а) это? / - Может быть — если это было честным голосованием!"

"Этот телефон прослушивается - согласно законодательству США, телефонные разговоры прослушиваются без ордера или уведомленияю"
"Вы под наблюдением — текст, объясняющий тезис, и ссылка, где можно прочесть об этом подробнее."
Примеры никудышной агитации (но хорошей поддержки):



3. Агитация даёт возможность изучить больше
Хорошее правило для любой агитации: иметь ссылку на сайт, где можно найти больше информации о том, к чему агитируется. Это не обязательное, но рекомендуемое правило, ибо мало толку от человека, согласившегося с идеей анархизма и захотевшего (редчайший случай!) самостоятельно изучить больше, но не имевшего к этому простой возможности и забывшего вследствие обо всей идее.
Поддержка
А вот поддержка — ориентированная на тех, кто уже знает и уже поддерживает то, что вы любите — может быть совершенно любой. Поддержать антифашистов своего города, позлить фашистов и остаться совершенно незамеченными для обывателя — самое место для диалектики "бей жыдоф!" и "доёш онтифошизм!!".
Напоминание о безопасности
Несколько базовых напоминаний о том, что нужно помнить во время агитации:
- ОСТЕРЕГАЙТЕСЬ КАМЕР! Особенно в России! Метро, маршрутки, автобусы, учебные заведения полны ими!
- Если вас заметили гестаповцы, лучшее, что вы можете сделать — это бежать, что есть мочи.
- Шифруйте материалы, которые храните для распечаток.
- Не распечатывайте стикеры/"визитки" в публичных местах (вроде библиотек).
Спасибо за прочтение!

-
 @ 57d1a264:69f1fee1
2025-03-29 09:31:13
@ 57d1a264:69f1fee1
2025-03-29 09:31:13"THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." - SATOSHI NAKAMOTO
"Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin.
Materials: Carrara Marble, Copper leaf, Opendime
Dimensions: 6" x 9" x 13"
Price: $30,000 or BTC equivalent
Enquire: https://www.vonbitcoin.com/available-works
X: https://x.com/BVBTC/status/1894463357316419960/photo/1
originally posted at https://stacker.news/items/928510
-
 @ 502ab02a:a2860397
2025-04-17 05:45:09
@ 502ab02a:a2860397
2025-04-17 05:45:09วันก่อนเฮียไปเดินห้าง เดินไปเจอชั้นขายน้ำมันพืช มีน้ำมันรำข้าววางโชว์อยู่หน้าสุด พร้อมคำโปรยที่ดูแพงกว่าขวดซะอีก ตัวเลขข่มกันมาเข้มๆเลย ระดับหมื่นๆหน่วยทั้งนั้น “มีแกมมาออไรซานอล ลดคอเลสเตอรอล” “มีวิตามินอีสูง” “ทนความร้อนได้ดีเยี่ยม เหมาะกับทุกเมนูทอด” “น้ำมันสุขภาพ คนรักหัวใจควรมีไว้ประจำบ้าน”
เฮียยืนอ่านแล้วก็ได้แต่ยิ้ม…
ว่าด้วย Oryzanol ...ของดีจริงเหรอ? อันนี้เป็นไม้เด็ดของฝั่งที่เชียร์น้ำมันรำข้าวเลยเฮีย เขาบอกว่า แกมมาโอริซานอล (γ-Oryzanol) เนี่ย เป็นสารต้านอนุมูลอิสระที่ช่วยลดคอเลสเตอรอลในเลือด ฟังแล้วรู้สึกเหมือนกินแล้วหลอดเลือดจะสะอาดเหมือนพื้นห้องน้ำที่เพิ่งขัดเสร็จ แต่...อย่าเพิ่งรีบวางใจ เพราะงานวิจัยที่ว่าแกมมาโอริซานอล ลดคอเลสเตอรอลเนี่ย ส่วนใหญ่ใช้ “สารสกัดเข้มข้น” ในขนาดโดสระดับ 300-600 มิลลิกรัมต่อวัน ย้ำนะว่า สารสกัดเข้มข้น
ทีนี้เรามาดูกันไหมว่าที่ฉลากบอกว่ามี โอริซานอล 12,000 ppm ที่ดูเยอะแยะมากมายจนเราว๊าววววววกันนั้น ppm มันคืออะไรวะ? ppm (parts per million) แปลว่า “ส่วนในล้านส่วน” ในกรณีของของเหลวอย่างน้ำมัน 1 ppm = 1 มิลลิกรัม ต่อ 1 ลิตร ดังนั้น 12,000 ppm = 12,000 mg/ลิตร หรือก็คือ 12 กรัม ต่อน้ำมัน 1 ลิตร ถ้าเรากินน้ำมันแค่ “1 ช้อนโต๊ะ” (ประมาณ 15 มล.) ที่มี γ-Oryzanol 12,000 ppm จะมี γ-Oryzanol ประมาณ 180 mg สิ่งที่ร่างกายได้รับระหว่างที่ผสมในน้ำมัน กับ "สารสกัดเข้มข้น" ในการทดลอง มันคนละบริบทกัน แต่เอามาเคลมกัน???
ซึ่งเฮียบอกเลยว่า…เวลาเขาเคลมข้อดีมักจะดึงมาเป็นข้อๆ แต่ร่างกายมันเป็นเรื่องโยงใยอีรันพันตู คือก่อนที่คอเลสเตอรอลจะลด ตับเรานี่แหละจะรับไม่ไหวก่อน เพราะน้ำมันรำข้าวเป็นไขมันชนิดไม่อิ่มตัวหลายตำแหน่ง (PUFA) สูง ซึ่งถ้ารับเข้าไปในปริมาณมาก จะเพิ่มภาระให้ตับในการกำจัดสารอนุมูลอิสระและควบคุมสมดุลไขมันในเลือด ตับต้องทำงานหนักขึ้นเสมือนต้องล้างน้ำมันเครื่องเก่า ๆ ทุกวัน นานไปตับอาจเสื่อม ไม่สดใสเหมือนตอนกินไก่ต้มร้านประจำ
จริงอยู่ที่มีงานวิจัยบอกว่า γ‐oryzanol หรือที่เรียกกันว่า ออริซานอล เนี่ย สามารถช่วยลดการอมน้ำมันของอาหารทอดได้บ้าง โดยเปลี่ยนโครงสร้างของอาหารและสมบัติทางกายภาพของน้ำมัน ทำให้เฟรนช์ฟรายส์ที่ทอดออกมาน้ำมันเกาะน้อยลง เหมือนฟังดูดีใช่ไหมเฮีย?
แต่เฮียอยากชวนคิดอีกมุมว่า… ถ้าการจะทำให้อาหาร “ไม่อมน้ำมัน” ต้องอาศัยการ “เติมสารเคมี” เข้าไปเพื่อไปเปลี่ยนโครงสร้างของน้ำมัน แล้วนั่นยังเรียกว่า "ดีต่อสุขภาพ" ได้อยู่ไหม?
เพราะอย่าลืมว่า γ‐oryzanol ไม่ได้เป็นสารที่อยู่ในน้ำมันรำข้าวดิบ ๆ แบบธรรมชาติในปริมาณสูงพออยู่แล้ว ผู้ผลิตหลายเจ้าเลยต้อง เติมเพิ่มเข้าไปทีหลัง และการเติมสารเพิ่มในอุตสาหกรรมอาหารเนี่ย ไม่ได้มีฟรีนะ มันมีคำถามตามมาว่า เติมเท่าไหร่ถึงจะพอดี? เติมแบบนี้แล้วร่างกายดูดซึมได้แค่ไหน? สะสมในร่างกายไหม? และสุดท้าย... สารนี้จริง ๆ แล้ว “มีความจำเป็น” ต่อร่างกายหรือเปล่า?
เฮียบอกตรง ๆ ว่า ร่างกายคนเรา ไม่ได้ต้องการ γ‐oryzanol ในชีวิตประจำวันเลย มันไม่ใช่สารจำเป็นเหมือนวิตามิน หรือแร่ธาตุใด ๆ และก็ไม่มีหลักฐานชัดเจนในคนว่า การบริโภคต่อเนื่องในระยะยาวจะ ไม่มีผลข้างเคียง โดยเฉพาะเมื่อต้องโดนความร้อนสูง ๆ ซ้ำ ๆ ในการทอด แล้วอีกเรื่องที่ต้องไม่ลืมคือ…
น้ำมันรำข้าวเองเป็นน้ำมันที่มี กรดไขมันไม่อิ่มตัวสูงมาก โดยเฉพาะพวกโอเมก้า 6 ซึ่งถ้าเราโดนความร้อนสูงบ่อย ๆ อย่างการทอด มันจะเสื่อมสภาพเร็ว เกิดสารอนุมูลอิสระง่าย ซึ่งสารพวกนี้แหละที่เป็นต้นเหตุของการอักเสบเรื้อรังในร่างกาย ดังนั้นเวลาใครบอกว่า "โอเคนะ ใช้ได้ เพราะใส่สารช่วยป้องกันแล้ว" มันก็ควรถามกลับเหมือนกันว่า...แล้วทำไมเราไม่เริ่มจากใช้น้ำมันที่ทนความร้อนได้ดีตั้งแต่แรก???? มันก็เหมือนการแต่งหน้าซ่อนสิวโดยไม่รักษาสิวนั่นแหละ ดูดีขึ้นแค่ผิวเผิน แต่ต้นเหตุยังอยู่ครบ
เฮียอยากให้เพื่อน ๆ ฟังแล้วไม่ต้องรีบตัดสินใจอะไรทันที แค่ลองฟังอีกด้านไว้ แล้วค่อย ๆ คิด ว่าการกินอาหารเพื่อสุขภาพเนี่ย เราจะเลือกของที่ดูดีจากโฆษณา หรือของที่ “ร่างกายใช้ประโยชน์ได้จริง” โดยไม่ต้องพึ่งสารสังเคราะห์อะไรเลย
วิตามินอีสูง...แล้วไงต่อ? เค้าก็อ้างว่าน้ำมันรำข้าวมีวิตามินอีเยอะ เป็นสารต้านอนุมูลอิสระ จริงอยู่ วิตามินอีมีอยู่ในน้ำมันพืชหลายชนิด แต่เฮียขอเล่าให้ฟังแบบไม่อ้อมค้อมนะ…น้ำมันรำข้าวที่เราซื้อในท้องตลาด เขาเอารำข้าวไปผ่านกระบวนการ สกัดด้วยตัวทำละลายเฮกเซน (Hexane) ผ่านความร้อนสูงระดับ 200-270 องศาเซลเซียส แล้วก็ ฟอกกลิ่น ฟอกสี ให้มันดูใส ๆ น่ากิน
ปัญหาคือ…วิตามินอี กับสารต้านอนุมูลอิสระที่เขาว่า “มีสูง” มันพังไปกับความร้อนและกระบวนการผลิตตั้งแต่ช่วงแรก ๆ แล้ว เพราะวิตามินอีเป็นสารที่ไวต่ออุณหภูมิสูงมาก พอเจอความร้อนสูงแบบนั้น ก็กลายเป็นเหมือนซุปเปอร์ฮีโร่ที่หมดพลังกลางฉากแอ็กชัน
บางแบรนด์เลยต้องเติมวิตามินอีกลับเข้าไปทีหลัง ทั้งเพื่อ “เพิ่มคุณค่าทางโภชนาการ” ให้เอาไปโฆษณาได้ และ เพื่อช่วยป้องกันการเหม็นหืน ของน้ำมันที่ไวต่อปฏิกิริยาออกซิเดชัน เพราะน้ำมันรำข้าวที่อุดมไปด้วย PUFA จะเหม็นหืนเร็ว ถ้าไม่มีสารต้านอนุมูลอิสระไปจับ เรียกว่าเติมเพื่อให้ดูดีทั้งต่อสุขภาพและต่อกลิ่น (แม้สุขภาพอาจไม่ได้ดีจริง…)
ทนความร้อนได้ดี? เหมาะกับการทอด? อันนี้ต้องแซวแรงนิดนึง... เพราะเขาชอบโฆษณาว่า “เหมาะกับการทอดเพราะทนความร้อนได้ดี” บ้าบอ ในความจริง น้ำมันรำข้าวเป็น Polyunsaturated fat (PUFA) สูง แม้จะมีโมเลกุลอิ่มตัวบ้าง แต่ไม่มากพอจะสู้ความร้อนจริงจังได้ เวลาโดนทอดร้อน ๆ ไขมันเหล่านี้มัน กลายพันธุ์ เป็นไขมันออกซิไดซ์ ไม่ต้องไปบอกเลยว่าให้สลัดน้ำมัน กรรมมันเกิดไปแล้ว
น้ำมันรำข้าวคือน้ำมันพืชที่มี กรดไขมันไม่อิ่มตัวเชิงซ้อน (PUFA) สูง โดยเฉพาะ โอเมกา-6 (linoleic acid) ซึ่งถ้าเทียบให้เห็นภาพแบบเฮีย ๆ PUFA ก็คือคนขี้น้อยใจ โดนแดดนิด โดนไฟหน่อย ก็เป็นอารมณ์ บูดเสียง่าย คือไม่เหมาะจะโดนผัด โดนทอด เพราะมันจะกลายร่างเป็น อนุมูลอิสระ แล้ววิ่งวุ่นในร่างกายเราเหมือนคนเสียสติ
แล้วที่บอกว่าช่วยเรื่องหัวใจ? เรื่องนี้ก็น่าสนใจ เพราะเขาชอบพูดว่า “น้ำมันรำข้าวช่วยลดความเสี่ยงโรคหัวใจ” ซึ่งจริง ๆ มาจากแนวคิดเก่าว่า “ถ้าลดไขมันอิ่มตัว แล้วหันมากินไขมันไม่อิ่มตัวจากพืช จะช่วยลดคอเลสเตอรอล และหัวใจก็จะดีขึ้น”
ฟังดูเข้าท่าใช่ไหม...แต่รู้ไหมว่าทุกวันนี้ งานวิจัยใหม่ ๆ เริ่มพบว่า การลดไขมันอิ่มตัวไม่ได้ลดความเสี่ยงโรคหัวใจ อย่างที่เคยคิด และกลับกัน…ไขมันจากสัตว์ที่มาจากอาหารแท้ อย่างเนยแท้ น้ำมันหมู น้ำมันมะพร้าว กลับมีผลดีต่อสุขภาพหัวใจมากกว่า เพราะไม่สร้างการอักเสบในร่างกาย (พูดในมุม cooking oil นะ ถ้าสกัดเย็นพวก มะกอก มะพร้าว มะคาเดเมีย งา ฯลฯ นั่นเป็นเรื่องของสารพฤกษะและพลังงานประกอบ มันจะอีกศาสตร์นึง อย่าเพิ่งปนกันถ้ายังไม่ได้ลงลึก เพราะถ้าเอาสกัดเย็นมาโดนร้อนก็เจ๊งบ๊ง เคลียร์นะ)
ในขณะที่ไขมันไม่อิ่มตัวสูงอย่าง PUFA จากน้ำมันพืชกลับเพิ่มการอักเสบเรื้อรัง ซึ่งเป็นต้นตอของโรคหัวใจ เบาหวาน สมองเสื่อม และโรคเรื้อรังแทบทุกชนิด
แถมกับคำถามหลังไมค์ การที่จะบอกว่า "น้ำมันรำข้าวอมน้ำมันมากกว่าแต่กรดไขมันเขาดีกว่าน้ำมันปาล์มนะ" ฟังเผิน ๆ เหมือนเลือกความดีระยะยาวแลกกับความอ้วนระยะสั้น แต่เดี๋ยวก่อนเฮียอยากให้มองอีกด้าน... 1. กรดไขมันไม่อิ่มตัวที่ว่า “ดี” ในทางทฤษฎีนั้น ถ้าอยู่เฉย ๆ บนชั้นวาง ก็อาจจะดูดีอยู่หรอก แต่พอเจอไฟร้อน ๆ ตอนทอดหรือผัด สารพวกนี้เสื่อมสภาพง่ายมาก กลายเป็นสารออกซิไดซ์ที่ทำร้ายหลอดเลือดเราแบบไม่รู้ตัว กลายเป็น "ไขมันดีพัง ๆ" ได้ทันที 2. น้ำมันที่อมน้ำมันเยอะ หมายถึงอาหารเราจะดูดน้ำมันเข้าไปเยอะ ซึ่งเท่ากับเรากินเข้าไปเยอะโดยไม่รู้ตัว ปริมาณโอเมก้า 6 ก็พุ่งสูง แล้วพอระดับโอเมก้า 6 ในร่างกายสูงขึ้นมากเกินสมดุล มันจะกระตุ้นการอักเสบในร่างกาย = ต้นเหตุของสารพัดโรคยุคใหม่เลยนะ 3. สุดท้าย ถ้าเราต้องแลกกับการใช้น้ำมันที่ต้องพึ่ง "สารเติมแต่ง" อย่างโอริซานอล เพื่อให้อาหารไม่อมน้ำมันเกินไป แบบนี้ก็เหมือนซื้อของแพงแล้วต้องซื้อตัวช่วยเพิ่ม เพื่อให้มันใช้งานได้ดีขึ้น แบบนี้เรียกว่าดีจริงหรือเปล่า? เหมือนคนหน้าตาดีแต่ใช้เงินเก่ง... สุดท้ายเป็นหนี้เหมือนกัน
น้ำมันรำข้าวที่ผ่านกระบวนการมากมาย มันกลายเป็น “Fiat Food” ที่หน้าตาดูดี แต่คุณค่าข้างในเบาหวิว เหมือนแบงก์กระดาษที่พิมพ์ออกมาเยอะ แต่ไม่มีทองรองรับ
ที่สำคัญคือ มันไม่ใช่แค่เรื่อง "กินมากไปไม่ดี" หรอกนะ
บทความกูรูหลายเจ้าชอบสรุปว่า “อย่ากินเยอะ” กินแบบใส่เพื่อผัดอาหารน้อยๆ อืมมม คือพี่ครับ น้ำมันพืชมันไม่ได้เป็นแค่ขวดที่เราซื้อในซูเปอร์ แต่มันเป็น วัตถุดิบหลักของร้านอาหาร ผัดกระเพราเจ้าโปรด กล่องเบนโตะข้างออฟฟิศ ขนมทอดกรอบทุกซอง แถมยังถูกแปะฉลากคำว่า “ดีต่อสุขภาพ” เพื่อให้เรารู้สึกผิดน้อยลงตอนกินของทอดอีกต่างหาก แถมเวลาเราทำกินเอง บางอย่างมันใส่มากกว่า 1ช้อนโต๊ะ ตามหน่วยบริโภคนะ แถม แต่ปัญหาใหญ่คือ PUFA จากน้ำมันพืชเหล่านี้ สะสมในเนื้อเยื่อไขมันเราแบบยาวนาน ไม่ได้หายไปง่าย ๆ แบบอกไก่ต้มหลังออกกำลังกาย ถึงจะกินแค่การผัดกับข้าวจานละ 1ช้อนก็เหอะ วันนั้นกินกับข้าวกี่กระทะ???
มันแทรกตัวเข้าไปในเยื่อหุ้มเซลล์ และกลายเป็น ตัวจุดไฟอักเสบเรื้อรังในร่างกาย เบาหวาน ความดัน มะเร็ง ไขมันพอกตับ อาจไม่ได้มาพร้อมสายฟ้า แต่ค่อย ๆ สะสมทีละหยดเหมือนน้ำมันในกระทะ
อย่าให้คำว่า “มีสารต้านอนุมูลอิสระ” มาหลอกเรา เพราะสุดท้าย ถ้าโครงสร้างไขมันมัน ไม่เสถียรตั้งแต่ต้น ต่อให้มีวิตามิน E ติดมานิด ๆ หน่อย ๆ มันก็เหมือนใส่หมวกกันน็อกให้ตุ๊กตา แล้วเอาไปนั่งมอเตอร์ไซค์วิบาก
น้ำมันรำข้าวไม่ใช่ปีศาจ แต่ก็ไม่ใช่นางฟ้า และเมื่อมันเป็นน้ำมันที่ร่างกายเราไม่ได้ออกแบบมาเพื่อรองรับมัน ก็อย่าหลงกลคำโฆษณาว่า "ดีต่อหัวใจ" หรือ “มีสารต้านอนุมูลอิสระ” แล้วเทมันใส่กระทะทุกวันเลยนะ
ก็เข้าใจแหละว่าเวลาคนทำอาหารเองที่บ้าน เขาจะรู้สึกว่า “ทอดเอง คุมได้ ทอดแค่รอบเดียว ไม่ได้ใช้ซ้ำ ไม่เป็นไรหรอก” แล้วก็หยิบ น้ำมันรำข้าว มาด้วยเหตุผลว่า “โปรไฟล์กรดไขมันมันดีกว่าน้ำมันปาล์ม” …ฟังดูเหมือนมีเหตุมีผล แต่เฮียอยากให้ลองมองอีกมุมนะ
น้ำมันรำข้าวมีกรดไขมันไม่อิ่มตัวสูงก็จริง แต่นั่นแหละคือปัญหา เพราะความไม่อิ่มตัวทำให้ ไม่เสถียรต่อความร้อน โดยธรรมชาติ! ถึงจะทอดรอบเดียว พอน้ำมันเจอไฟแรง ๆ มันก็ยังเสื่อมสภาพอยู่ดี เกิดสารอนุมูลอิสระที่มองไม่เห็น แต่ร่างกายเราเห็นหมด แล้วถ้าคนในบ้านกินบ่อย ๆ วันเว้นวัน จะรู้ตัวอีกทีก็อาจจะมีอาการอักเสบเรื้อรังโดยไม่รู้ต้นตอเลยก็ได้
ส่วนที่บอกว่าอาหารอมน้ำมันก็ไม่เป็นไร แค่รอหายร้อนแล้วซับออก หรือเอาเข้าหม้อลมร้อน มันช่วยได้ “บางส่วน” จริง แต่ไม่ได้แก้ที่ต้นเหตุ เพราะไขมันที่เข้าไปอยู่ในชั้นแป้งหรือเนื้อของอาหารมันออกยากกว่าที่คิด และถ้าเราต้อง “พึ่งวิธีรีดน้ำมันออก” ทุกครั้งที่ทอด นั่นแปลว่าน้ำมันที่ใช้มันอมน้ำมันเกินไปตั้งแต่แรกแล้ว ไม่ใช่หรือ?
“ทอดรอบเดียวก็จริง แต่ถ้าน้ำมันมันพังตั้งแต่โดนไฟ แล้วจะต่างอะไรกับทอดสิบรอบ?”
ท้ายของท้ายสุด เรื่องทอดไม่ใช่แค่เรื่องน้ำมัน แต่มีเรื่อง AGEs ด้วยซึ่งสำคัญกว่าใช้น้ำมันอะไรทอดเยอะเลยครับ นี่เขียนเพื่อบันทึกรายละเอียดของน้ำมันรำข้าวให้เฉยๆ
#pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 2183e947:f497b975
2025-03-29 02:41:34
@ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison.
I can't tell you how to create your own accounts because it was made very clear that only some of the software is currently open source, and how this will all work is still a bit up in the air. The code that is open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core
You can also learn more about Pubky here: https://pubky.org/
That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key.
Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis.
Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed.
Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message.
I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key.
As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster.
Based on all of this info, it seems like, to populate your feed, this is the series of steps:
- you tell your homeserver your pubkey
- it uses some sort of algorithm to decide whose posts to show you
- then looks up the homeservers used by those people on an indexer server
- then it fetches posts from their homeservers
- then your client displays them to you
To create a post, this is the series of steps:
- you tell your homeserver what you want to say to the world
- it stores that message in plaintext and merely asserts that it came from you (it's not signed)
- other people can find out what you said by querying for your posts on your homeserver
Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver.
John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted.
Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
-
 @ 57d1a264:69f1fee1
2025-03-28 10:32:15
@ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.
The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous announcement.
Look forward for this to happen!
Spread the voice:
N: https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l... X: https://x.com/bitcoin_design/status/1905547407405768927
originally posted at https://stacker.news/items/927650
-
 @ b7d82f75:524cf1ac
2025-04-17 05:41:42
@ b7d82f75:524cf1ac
2025-04-17 05:41:42Want the best Anaheim auto body shop? G.U Collision Center is here to help! We repair your car from scratches to serious damage, making it look as good as new. Our team uses modern tools and lots of care to fix your vehicle fast. We handle everything, from small dings to big collisions, at prices that won’t break the bank. Plus, we work with your insurance for a smooth process. Visit G.U Collision Center in Anaheim for top-quality repairs and friendly service. Let us get your car back on the road in style!
-
 @ bc52210b:20bfc6de
2025-03-14 20:39:20
@ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract.
The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable.
In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions.
Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
-
 @ c86dc7e6:6059e49b
2025-04-17 05:04:16
@ c86dc7e6:6059e49b
2025-04-17 05:04:16Want the best carpet cleaning services Atlanta has to offer? Spot It Cleaning is the name to trust! We bring your carpets back to life, removing stains, dirt, and odors. Our team uses safe, powerful tools to clean deep without harming your floors. Perfect for offices, stores, or any business, we make your carpets look fresh and feel soft. We work fast and fit your schedule, keeping your workspace ready for action. Choose Spot It Cleaning for affordable, top-quality carpet care in Atlanta. Let us make your floors shine so your business can stand out!
-
 @ 95cb4330:96db706c
2025-04-17 07:12:01
@ 95cb4330:96db706c
2025-04-17 07:12:01Summary and Guide Based on Sam Altman's Classic Post
In life and business, almost everyone starts off chasing money. But if you observe closely — especially among those who achieve outlier success — you’ll notice something interesting:
Over time, money becomes secondary. The real obsession becomes making something important happen.
Sam Altman, entrepreneur and CEO of OpenAI, laid out a roadmap to achieving this rare level of success. It’s about much more than working hard or being smart — it’s about how you think, act, and invest your time over decades.
Here's a deep breakdown of his 13 principles — explained, with examples and reflections.
1. Compound Yourself
Think exponentially, not linearly.
- Businesses (and careers) that compound — growing 50% per year — become unstoppable over time.
- You want your learning, network, and impact to snowball.
- Focus on adding zeros to your results, not just small wins.
🔎 Example: Instead of focusing on one-off gigs, build skills and systems that grow your results faster every year. Think like an investor, not an hourly worker.
2. Have (Almost) Too Much Self-Belief
You have to believe in yourself beyond reason — but stay open to feedback.
- Most real innovation requires contrarian thinking.
- Early critics will tell you you're crazy — and that’s normal.
- Learn to manage your own morale.
🔎 Example: Elon Musk’s absolute certainty about colonizing Mars — even when few believed him — fueled SpaceX’s breakthrough innovations.
3. Learn to Think Independently
Original thinking can’t be taught by schools.
- Break problems into first principles instead of copying others.
- Test crazy ideas quickly and cheaply.
- The ability to "figure things out when no one knows what to do" is a superpower.
🔎 Example: Airbnb founders had no roadmap for building a company based on renting strangers' homes — they made it up as they went.
4. Get Good at Sales
It’s not enough to have a great idea — you must convince others to join you.
- Great careers and startups are sales jobs: selling visions to investors, customers, and employees.
- The best sales come from genuine belief in what you're building.
🔎 Example: Altman emphasizes in-person interactions: “When it mattered, I always got on the plane.”
5. Make It Easy to Take Risks
Big rewards require many small bets and the willingness to look foolish.
- Risk is overestimated; reward is underestimated.
- Stay financially and mentally flexible early in life.
🔎 Example: Leaving a high-paying tech job is hard — but those who leap to start companies often change the world.
6. Focus
Doing the right work matters more than working hard on the wrong things.
- Ruthlessly prioritize what truly matters.
- Ignore distractions.
- Be unstoppable once you know what to focus on.
🔎 Example: Startups win by focusing on one core thing until they dominate, not by trying to do everything.
7. Work Hard
- Smart + hard work is required to reach the top 1% of any field.
- Success begets success — momentum compounds.
- Find work you love and people you love working with to avoid burnout.
🔎 Example: Early Amazon teams pulled insane hours — but they believed they were building something world-changing.
8. Be Bold
- Solve hard problems, not easy ones.
- People are attracted to missions that matter.
🔎 Example: If your dream is gene-editing or AI, don’t settle for building another social media app.
9. Be Willful
- The world is more malleable than you think.
- Persistence and optimism often win in the end.
🔎 Example: Airbnb founders survived maxed-out credit cards and endless rejection — but they didn't quit.
10. Be Hard to Compete With
- Differentiate yourself through leverage:
- Skills at the intersection of fields
- Strong personal brand
- Unique insights
🔎 Example: Elon Musk isn't just an engineer or marketer — he's both, and that makes him hard to beat.
11. Build a Network
- Great accomplishments require great teams.
- Help people long before you need them.
- Spot undiscovered talent early.
🔎 Example: Most of Altman’s best career opportunities came from helping others years before it paid off.
12. Own Equity
- Salaries won't make you rich.
- Owning assets (companies, IP, real estate) creates real wealth.
🔎 Example: The richest people in the world — Bezos, Musk, Gates — got there by owning companies, not by drawing salaries.
13. Be Internally Driven
- Don’t chase approval or follow the herd.
- Care about doing great work for yourself.
- If you're motivated mainly by status or envy, you will lose focus.
🔎 Example: Jessica Livingston and Paul Graham were mocked early for Y Combinator. They didn’t care — and YC changed the world of startups.
💬 Final Thought
Success isn’t about short-term hacks. It’s about long-term habits:
- Think long-term.
- Bet boldly.
- Compound yourself.
- Build something important.“Eventually, you will define your success by performing excellent work in areas that are important to you. The sooner you start, the further you will go.”
Commit to the path. The rewards — both internal and external — are beyond what most people ever experience.
🌱 Start planting seeds today. Watch them compound beyond imagination. 🚀
📈 How To Be Successful — 13 Principles for Outlier Achievement
| Principle | Summary | |:-------------|:------------| | 🧠 Compound Yourself | Focus on exponential growth — build skills, network, and leverage over time. | | 💪 Self-Belief (Almost Too Much) | Believe in your vision even when others doubt you, balanced by self-awareness. | | 🔥 Think Independently | Use first-principles thinking; test new ideas rather than copying others. | | 🗣️ Master Sales | Convince others of your ideas — genuine belief makes selling easier. | | 🎯 Make Risk-Taking Easy | Stay flexible and bet on ideas with high upside and limited downside. | | 🎯 Focus | Ruthlessly prioritize — working on the right things matters more than working long hours. | | 🛠️ Work Hard | Smart + intense effort is necessary to reach the top 1%. Momentum compounds success. | | 🚀 Be Bold | Solve big, important problems — bold missions create constant tailwinds. | | 🌎 Be Willful | Persist until you succeed — optimistic persistence often bends reality. | | 🧩 Be Hard to Compete With | Combine rare skills and leverage to become uniquely valuable. | | 🤝 Build a Powerful Network | Help others early; spot and collaborate with rising talent. | | 🏡 Own Equity | Own scalable assets — don’t just trade your time for money. | | 🔥 Stay Internally Driven | Follow intrinsic motivation — work on what you truly care about. |
🚀 Final Thought
"Long-term focus on inputs, boldness, learning, and compound effort leads to extraordinary success."
-
 @ 044da344:073a8a0e
2025-04-17 06:53:41
@ 044da344:073a8a0e
2025-04-17 06:53:41Hölderlin taugt immer. Diesmal sogar doppelt. Dass mit der Gefahr das Rettende wächst, hat sich inzwischen herumgesprochen. Raymond Unger ist so ein Anker. Wann immer ich seinen Namen bei einer Veranstaltung erwähne: Die Leute wissen Bescheid. Vom Verlust der Freiheit. Ich hätte zählen sollen, wie oft ich gehört habe: Dieses Buch hat mir die Augen geöffnet. Migration, Klima, Corona: alles drin und vor allem so verflochten, dass zusammenpasst, was eigentlich nicht zusammengehört und unsere Welt auf den Kopf gestellt hat. Viele haben danach Ungers Impfbuch gelesen, sich von seiner Heldenreise inspirieren oder bestätigen lassen und mit ihm um Gunnar Kaiser getrauert (Habe ich genug getan?, 2024). Wer schon länger dabei ist, kennt in der Regel auch Die Wiedergutmacher – ein Psychogramm der Babyboomer, das so nur jemand schreiben kann, der selbst erlebt hat, wie das Weltkriegstrauma vererbt wurde, und als Therapeut die Konzepte kennt, mit denen sich das in Worte fassen lässt.
Der Sachbuchautor Raymond Unger war und ist ein Fremdgänger – ein Künstler, preisgekrönt, den die Not des Beobachters gezwungen hat, das Metier zu wechseln. Der erste Hölderlin. Ohne die große Krise würde dieser Maler vermutlich immer noch nächtelang an seiner Staffelei mit der Materie kämpfen und vor allem mit sich selbst. Wahrscheinlich kennt Raymond Unger auch mein zweites Hölderlin-Zitat: Was aber bleibet, stiften die Dichter. Ich habe diesen Satz gerade wieder gehört aus dem Mund von Peter-Michael Diestel, letzter Innenminister der DDR, der sich mit Gregor Gysi über Heimat unterhält, über den Osten und den Westen und dabei fast zwangsläufig auf die Historiker zu sprechen kommt. „Ärmliches Lohnschreiber-Geschwader“, sagt Diestel und zeichnet ein ganzes anderes Bild von der Vergangenheit als die Geschichtsbücher. „Die DDR ist meine Herkunft. Mein Paradies.“ Sagt einer ihrer Totengräber. Und damit Vorhang auf für die Dichter.
Auf der Bühne steht der Romanautor Raymond Unger, eine Melange aus dem Bildermacher und dem Gesellschaftsanalytiker, die den gleichen Namen tragen. Wuchtig kommt sein Gemälde KAI daher mit Szenen und Orten, von denen jeder Hollywood-Regisseur träumt. Ostsee und Alpen, Berlin, Hamburg und das Silicon Valley. Am Ende Fulda, okay. Davor aber eine Schriftstellerin, Ende 30, attraktiv, Objekt der Begierde zweier reifer Männer, bis die Dame plötzlich im Wortsinn zerfließt, das gute Stück eines der beiden Verehrer beleidigt (klein, was sonst) und auf den Teppich pinkelt. Das ist nur das Vorspiel für einen Antiterroreinsatz in der schwedischen Idylle und Explosionen im Zentrum von Berlin, für ein Auto, das seinen Fahrer wie von Geisterhand gesteuert in den Tod reißt, und für einen Quarterback, der auf dem Spielfeld tot umfällt – zur Primetime, damit jeder weiß, was ihm blühen könnte.
Ich schreibe das, weil ich ein wenig Angst hatte vor diesem Roman. Einer meiner Lieblingsautoren auf neuem Gelände. Wird er sich dort verlaufen, untergehen gar, und mir so einen Fixstern aus meinem Bücherregal nehmen? Nein, nein und nochmal nein. KAI ist ein großer Wurf. KAI ist das Buch, auf das ich gewartet habe. Sicher: Ich habe die Dystopie Hinter der Zukunft von Thomas Eisinger gefeiert, einen Augenöffner ersten Ranges, und ein wenig auch die Corona-Kurzgeschichten von Eugen Zentner. Trotzdem. KAI hat das Zeug, unseren Nachkommen zu berichten, was wir erlebt und erlitten haben. Und vielleicht noch wichtiger: KAI übersetzt all das in ein Märchen, das realer nicht sein könnte und mit einem Ende daherkommt, das die Kämpfe seit den frühen 2010er Jahren mit Sinn auflädt und aus Verlierern Sieger macht. Dazu gleich mehr.
Vorher ein Wort zu Hölderlin und zu seinem Satz über die Dichter, die sagen, was bleibt. Der Mensch ist ein Geschichtentier. Das ist trivial, ich weiß, kann aber nicht oft genug wiederholt werden in einer Zeit, in der eine Regierung sich ins Stammbuch schreibt, dass „die bewusste Verbreitung von falschen Tatsachenbehauptungen“ nicht „durch die Meinungsfreiheit“ gedeckt sei. Falsche Tatsachenbehauptungen. Was soll das sein? 2014 ist Argentinien Fußball-Weltmeister geworden. Oder Tansania. Zwei plus zwei ist fünf und der Autor dieses Textes – eine Frau. Ich muss gar nicht in die Absurditätenkiste greifen, sondern kann in meinem Fachgebiet bleiben. Das 20. Jahrhundert beginnt mit dem Panzerkreuzer Aurora in Petrograd und endet mit den Moskauer Schüssen vom August 1991. Falsch. Falsch? Muss ich künftig Putsch sagen und Sankt Petersburg und hundert Jahre hundert Jahre sein lassen, um der Medienaufsicht nicht ins Netz zu gehen?
Namen, Daten, Orte, Ereignisse: All das rauscht an uns vorbei, wenn es nicht mit einer Story daherkommt und sich nicht einfügen lässt in das, was wir uns über die Menschen und die Welt erzählen. Wer glaubt, dass der Staat ein guter Forscher ist, ein noch besserer Lehrer und der ideale Verwalter aller Vermögen, der wird sich nicht beklagen, wenn Steuergelder in Wissenschaft und Bildung, Kunst und Kultur gepumpt werden und man parallel über einen Lastenausgleich diskutiert. Noch einmal anders gewendet: Es lohnt sich nicht, die Gegenseite mit „Fakten“ und „Tatsachen“ zu bombardieren. Nicht das Fleisch entscheidet, sondern die Sauce. Demokratie, Menschenrechte, Wertewesten. Schwarz-Rot will die „Meinungsfreiheit“ wahren, aber trotzdem „auf der Basis klarer gesetzlicher Vorgaben gegen Informationsmanipulation sowie Hass und Hetze vorgehen“. Alles in einem Satz. Das ist die hohe Schule der Manipulation – möglich nur, weil die Jünger des Parteienstaates gar nicht auf die Idee kommen können, dass im Namen der großen Erzählung Böses getan wird.
Raymond Unger weiß: Wir brauchen eine neue Erzählung. Und wir brauchen Klarheit über die Wucht, die Erzählungen entfalten. Also lässt er Materialisten und Idealisten aufeinander losgehen und öffnet auf dem Höhepunkt der Schlacht „ein Portal zur Anderswelt“, „durch das uralte kosmische Kräfte in unsere physische Welt hineinwirken können“ – bei ihm ein Einfallstor für die „transhumanistische Agenda“ und jene Kräfte, die „alles Menschliche“ verdrängen wollen. Wenn das jetzt kryptisch klingen sollte: keine Sorge. Dieser Autor kann erzählen. Er lässt Freud und Jung in einem Ehepaar auferstehen, das sich so kappelt wie Hans Castorp und Lodovico Settembrini auf dem Zauberberg von Thomas Mann, und mischt das, was er über Klima, 5G und mRNA braucht, in Gespräche mit ChatGPT und kurze Vorträge, die jeder verstehen kann, weil im Publikum Laien sitzen.
Von der Story selbst will ich hier nicht allzu viel verraten. Siehe oben. Wenn man ins Kino geht, reichen auch die Schnipsel aus dem Werbespot und die Gesichter der Helden. Bill Gates spielt mit, Uğur Şahin und Ulrike Herrmann. Leicht verfremdet, aber ja: Es geht schließlich um alles. Den Titel immerhin muss ich auflösen: Bei Raymond Unger sitzt KAI am Hebel. CO2-Märchen, Pandemie-Märchen, das Schlachtfeld Ukraine, Kriegstüchtigkeit: Produkte einer finsteren Macht, die bei ihm aus der Technik wächst und aus der Ideenwelt des Okkultismus, die man aber genauso gut ganz irdisch dort verorten könnte, wo nicht wenige einen „tiefen Staat“ vermuten. Ein guter Roman braucht nicht nur große Gefühle, sondern mehr als eine Ebene. Wer sich wie ich eher an Akteure und Ressourcen hält, kann KAI leicht als Metapher lesen, erst recht in dieser Schreibweise.
Raymond Ungers Gegenerzählung ist nicht neu, aber verlorengegangen auf Plattformen und Bildschirmen, die keine Zwischentöne erlauben und so die Spaltung vorantreiben. Unger sagt: Rettung kommt von da, wo es keine Mehrheiten gibt. Der Außenseiter in der Wissenschaft. Die Menschen, die entscheiden und verzichten und erst so zum Menschen werden. Coronakritiker. Ostdeutsche. Er sagt außerdem: Es gibt U-Boote selbst da, wo die Mehrheiten sind. Schreibt auch die nicht ab, die euch im Moment als Zielscheibe erscheinen. Vor allem aber sagt er: Der Mensch kann Dinge tun, die buchstäblich niemand auf dem Zettel hat. Gegen jede Wahrscheinlichkeit und damit völlig anders als selbst die perfekte Maschine. Nur der Mensch kann sich lösen von dem, was ist, und so Freund Hölderlin alle Ehre machen.
Vielleicht ein Wermutstropfen: Starke Frauen fehlen in seiner Welt. Das heißt: Es gibt starke Frauen, aber nur auf der dunklen Seite der Macht oder als leichtes Opfer von KAI. Ich habe mit zwei Kennerinnen über den Roman gesprochen, die insgesamt sehr angetan waren, aber leicht die Nase rümpften wegen mancher Formulierung und einigen Figuren. Hier und da etwas technokratisch, sagten die beiden, und nicht immer prall im Leben. Was soll man da antworten als Mann. Ich, ein Sachbuchfresser, habe KAI verschlungen. Und: Gut, dass wir endlich auch in der Unterwelt (Walter van Rossum) einen Roman haben, erschienen in einem großen Verlag, über den wir streiten können.
Raymond Unger: KAI. München: Europa Verlag, 431 Seiten, 25 Euro.
-
 @ 6ad08392:ea301584
2025-03-14 19:03:20
@ 6ad08392:ea301584
2025-03-14 19:03:20In 2024, I was high as a kite on Nostr hopium and optimism. Early that year, my co-founder and I figured that we could use Nostr as a way to validate ambassadors on “Destination Bitcoin” - the germ of a travel app idea we had at the time that would turn into Satlantis. After some more digging and thinking, we realised that Nostr’s open social graph would be of major benefit, and in exploring that design space, the fuller idea of Satlantis formed: a new kind of social network for travel.
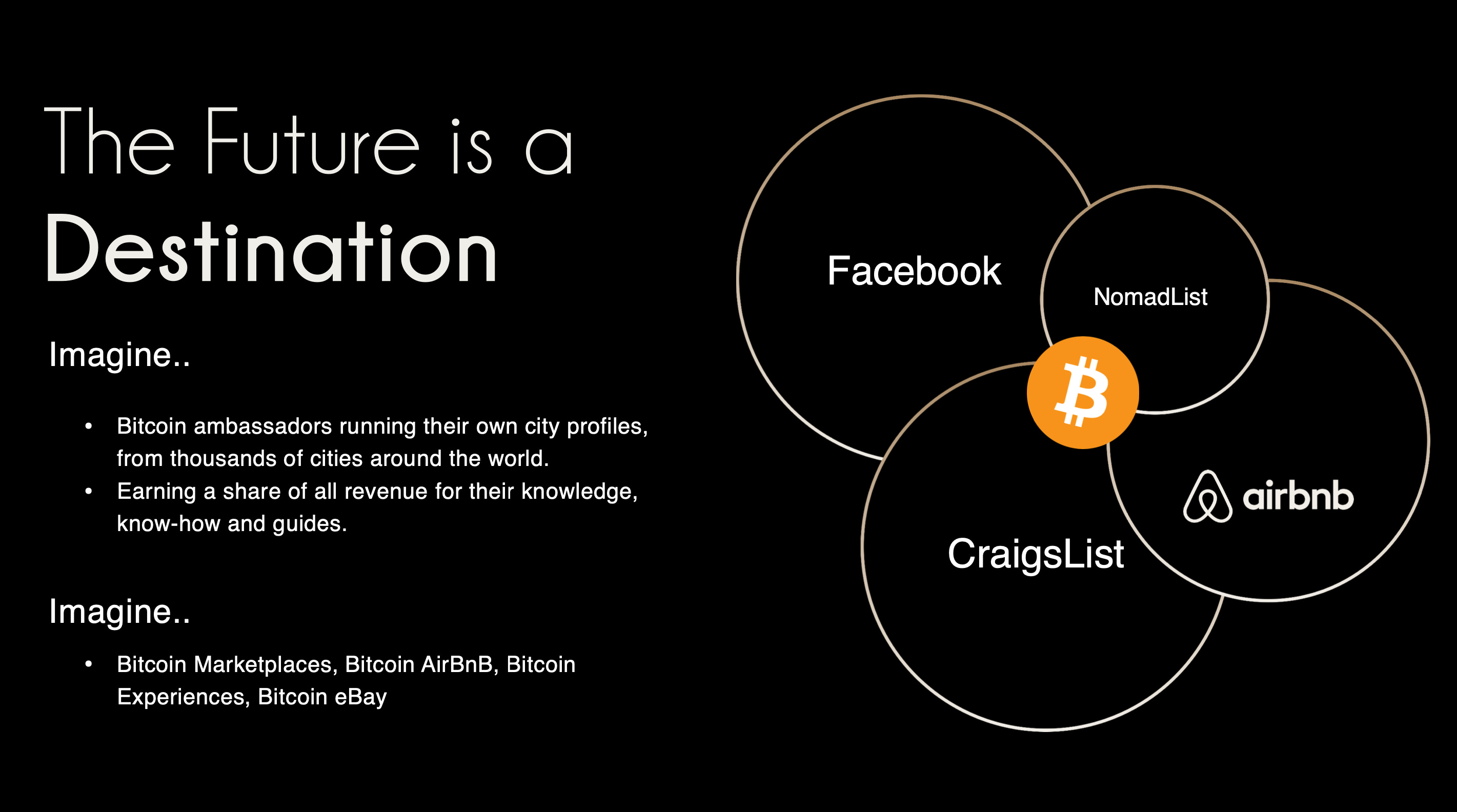 ###### ^^2 slides from the original idea here
###### ^^2 slides from the original idea hereI still remember the call I had with @pablof7z in January. I was in Dubai pitching the AI idea I was working on at the time, but all I could think and talk about was Satlantis and Nostr.
That conversation made me bullish AF. I came back from the trip convinced we’d struck gold. I pivoted the old company, re-organised the team and booked us for the Sovereign Engineering cohort in Madeira. We put together a whole product roadmap, go to market strategy and cap raise around the use of Nostr. We were going to be the ‘next big Nostr app’.
A couple of events followed in which I announced this all to the world: Bitcoin Atlantis in March and BTC Prague in June being the two main ones. The feedback was incredible. So we doubled down. After being the major financial backer for the Nostr Booth in Prague, I decided to help organise the Nostr Booth initiative and back it financially for a series of Latin American conferences in November. I was convinced this was the biggest thing since bitcoin, so much so that I spent over $50,000 in 2024 on Nostr marketing initiatives. I was certainly high on something.
Sobering up
It’s March 2025 and I’ve sobered up. I now look at Nostr through a different lens. A more pragmatic one. I see Nostr as a tool, as an entrepreneur - who’s more interested in solving a problem, than fixating on the tool(s) being used - should.
A couple things changed for me. One was the sub-standard product we released in November. I was so focused on being a Nostr evangelist that I put our product second. Coupled with the extra technical debt we took on at Satlantis by making everything Nostr native, our product was crap. We traded usability & product stability for Nostr purism & evangelism.
We built a whole suite of features using native event kinds (location kinds, calendar kinds, etc) that we thought other Nostr apps would also use and therefore be interoperable. Turns out no serious players were doing any of that, so we spent a bunch of time over-engineering for no benefit 😂
The other wake up call for me was the Twitter ban in Brazil. Being one of the largest markets for Twitter, I really thought it would have a material impact on global Nostr adoption. When basically nothing happened, I began to question things.
Combined, these experiences helped sober me up and I come down from my high. I was reading “the cold start problem” by Andrew Chen (ex-Uber) at the time and doing a deep dive on network effects. I came to the following realisation:
Nostr’s network effect is going to take WAY longer than we all anticipated initially. This is going to be a long grind. And unlike bitcoin, winning is not inevitable. Bitcoin solves a much more important problem, and it’s the ONLY option. Nostr solves an important problem yes, but it’s far from the only approach. It’s just the implementation arguably in the lead right now.
This sobering up led us to take a different approach with Nostr. We now view it as another tool in the tech-stack, no different to the use of React Native on mobile or AWS for infrastructure. Nostr is something to use if it makes the product better, or avoid if it makes the product and user experience worse. I will share more on this below, including our simple decision making framework. I’ll also present a few more potentially unpopular opinions about Nostr. Four in total actually:
- Nostr is a tool, not a revolution
- Nostr doesn’t solve the multiple social accounts problem
- Nostr is not for censorship resistance
- Grants come with a price
Let’s begin…
Nostr is a tool, not a revolution
Nostr is full of Bitcoiners, and as much as we like to think we’re immune from shiny object syndrome, we are, somewhere deep down afflicted by it like other humans. That’s normal & fine. But…while Bitcoiners have successfully suppressed this desire when it comes to shitcoins, it lies dormant, yearning for the least shitcoin-like thing to emerge which we can throw our guiltless support behind.
That thing arrived and it’s called Nostr.
As a result, we’ve come to project the same kind of purity and maximalism onto it as we do with Bitcoin, because it shares some attributes and it’s clearly not a grift.
The trouble is, in doing so, we’ve put it in the same class as Bitcoin - which is an error.
Nostr is important and in its own small way, revolutionary, but it pales in comparison to Bitcoin’s importance. Think of it this way: If Bitcoin fails, civilisation is fucked. If Nostr fails, we’ll engineer another rich-identity protocol. There is no need for the kind of immaculate conception and path dependence that was necessary for Bitcoin whose genesis and success has been a once in a civilisation event. Equivocating Nostr and Bitcoin to the degree that it has been, is a significant category error. Nostr may ‘win’ or it may just be an experiment on the path to something better. And that’s ok !
I don’t say this to piss anyone off, to piss on Nostr or to piss on myself. I say it because I’d prefer Nostr not remain a place where a few thousand people speak to each other about how cool Nostr is. That’s cute in the short term, but in the grand scheme of things, it’s a waste of a great tool that can make a significant corner of the Internet great again.
By removing the emotional charge and hopium from our relationship to Nostr, we can take a more sober, objective view of it (and hopefully use it more effectively).
Instead of making everything about Nostr (the tool), we can go back to doing what great product people and businesses do: make everything about the customer.
Nobody’s going around marketing their app as a “react native product” - and while I understand that’s a false equivalent in the sense that Nostr is a protocol, while react is a framework - the reality is that it DOES NOT MATTER.
For 99.9999% of the world, what matters is the hole, not the drill. Maybe 1000 people on Earth REALLY care that something is built on Nostr, but for everyone else, what matters is what the app or product does and the problem it solves. Realigning our focus in this way, and looking at not only Nostr, but also Bitcoin as a tool in the toolkit, has transformed the way we’re building.
This inspired an essay I wrote a couple weeks ago called “As Nostr as Possible”. It covers our updated approach to using and building WITH Nostr (not just ‘on’ it). You can find that here:
https://futuresocial.substack.com/p/as-nostr-as-possible-anap
If you’re too busy to read it, don’t fret. The entire theory can be summarised by the diagram below. This is how we now decide what to make Nostr-native, and what to just build on our own. And - as stated in the ANAP essay - that doesn’t mean we’ll never make certain features Nostr-native. If the argument is that Nostr is not going anywhere, then we can always come back to that feature and Nostr-fy it later when resources and protocol stability permit.
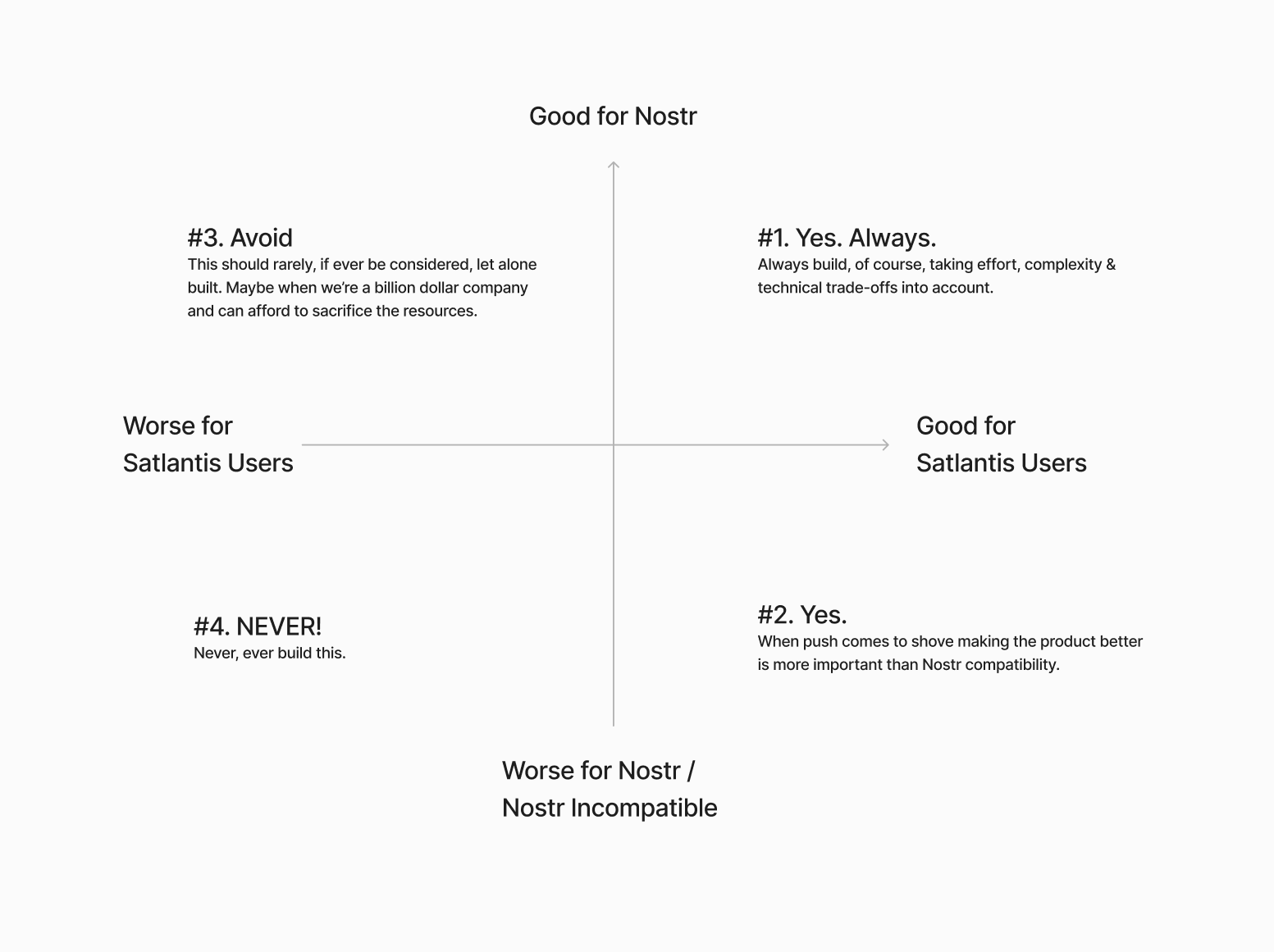
Next…
The Nostr all in one approach is not all “positive”
Having one account accessible via many different apps might not be as positive as we initially thought.

If you have one unified presence online, across all of your socials, and you’re posting the same thing everywhere, then yes - being able to post content in one place and it being broadcast everywhere, is great. There’s a reason why people literally PAY for products like Hypefury, Buffer and Hootsuite (aside from scheduling).
BUT…..This is not always the case.
I’ve spoken to hundreds of creators and many have flagged this as a bug not a feature because they tend to have a different audience on different platforms and speak to them differently depending on the platform. We all know this. How you present yourself on LinkedIn is very different to how you do it on Instagram or X.
The story of Weishu (Tencent’s version of TikTok) comes to mind here. Tencent’s WeChat login worked against them because people didn’t want their social graph following them around. Users actually wanted freedom from their existing family & friends, so they chose Douyin (Chinese TikTok) instead.
Perhaps this is more relevant to something like WeChat because the social graph following you around is more personal, but we saw something similar with Instagram and Facebook. Despite over a decade of ownership, Facebook still keeps the social graphs separated.
All this to say that while having a different strategy & approach on different social apps is annoying, it allows users to tap into different markets because each silo has its own ‘flavour’. The people who just post the same thing everywhere are low-quality content creators anyway. The ones who actually care, are using each platform differently.
The ironic part here is that this is arguably more ‘decentralised’ than the protocol approach because these siloes form a ‘marketplace of communities’ which are all somewhat different.
We need to find a smart way of doing this with Nostr. Some way of catering to the appropriate audience where it matters most. Perhaps this will be handled by clients, or by relays. One solution I’ve heard from people in the Nostr space is to just ‘spin up another nPub’ for your different audience. While I have no problem with people doing that - I have multiple nPubs myself - it’s clearly NOT a solution to the underlying problem here.
We’re experimenting with something. Whether it’s a good idea or not remains to be seen. Satlantis users will be able to curate their profiles and remove (hide / delete) content on our app. We’ll implement this in two stages:
Stage 1: Simple\ In the first iteration, we will not broadcast a delete request to relays. This means users can get a nicely curated profile page on Satlantis, but keep a record of their full profile elsewhere on other clients / relays.
Stage 2: More complex\ Later on, we’ll try to give people an option to “delete on Satlantis only” or “delete everywhere”. The difference here is more control for the user. Whether we get this far remains to be seen. We’ll need to experiment with the UX and see whether this is something people really want.
I’m sure neither of these solutions are ‘ideal’ - but they’re what we’re going to try until we have more time & resources to think this through more.
Next…
Nostr is not for Censorship Resistance
I’m sorry to say, but this ship has sailed. At least for now. Maybe it’s a problem again in the future, but who knows when, and if it will ever be a big enough factor anyway.
The truth is, while WE all know that Nostr is superior because it’s a protocol, people do NOT care enough. They are more interested in what’s written ON the box, not what’s necessarily inside the box. 99% of people don’t know wtf a protocol is in the first place - let alone why it matters for censorship resistance to happen at that level, or more importantly, why they should trust Nostr to deliver on that promise.
Furthermore, the few people who did care about “free speech” are now placated enough with Rumble for Video, X for short form and Substack for long form. With Meta now paying lip-service to the movement, it’s game over for this narrative - at least for the foreseeable future.
 The "space in people’s minds for censorship resistance has been filled. Both the ‘censorship resistance’ and ‘free speech’ ships have sailed (even though they were fake), and the people who cared enough all boarded.
The "space in people’s minds for censorship resistance has been filled. Both the ‘censorship resistance’ and ‘free speech’ ships have sailed (even though they were fake), and the people who cared enough all boarded.For the normies who never cared, they still don’t care - or they found their way to the anti-platforms, like Threads, BlueSky or Pornhub.
The small minority of us still here on Nostr…are well…still here. Which is great, but if the goal is to grow the network effect here and bring in more people, then we need to find a new angle. Something more compelling than “your account won’t be deleted.”
I’m not 100% sure what that is. My instinct is that a “network of interoperable applications”, that don’t necessarily or explicitly brand themselves as Nostr, but have it under the hood is the right direction. I think the open social graph and using it in novel ways is compelling. Trouble is, this needs more really well-built and novel apps for non-sovereignty minded people (especially content creators) and people who don’t necessarily care about the reasons Nostr was first built. Also requires us to move beyond just building clones of what already exists.
We’ve been trying to do this Satlantis thing for almost a year now and it’s coming along - albeit WAY slower than I would’ve liked. We’re experimenting our way into a whole new category of product. Something different to what exists today. We’ve made a whole bunch of mistakes and at times I feel like a LARP considering the state of non-delivery.
BUT…what’s on the horizon is very special, and I think that all of the pain, effort and heartache along the way will be 100% worth it. We are going to deliver a killer product that people love, that solves a whole host of travel-related problems and has Nostr under the hood (where nobody, except those who care, will know).
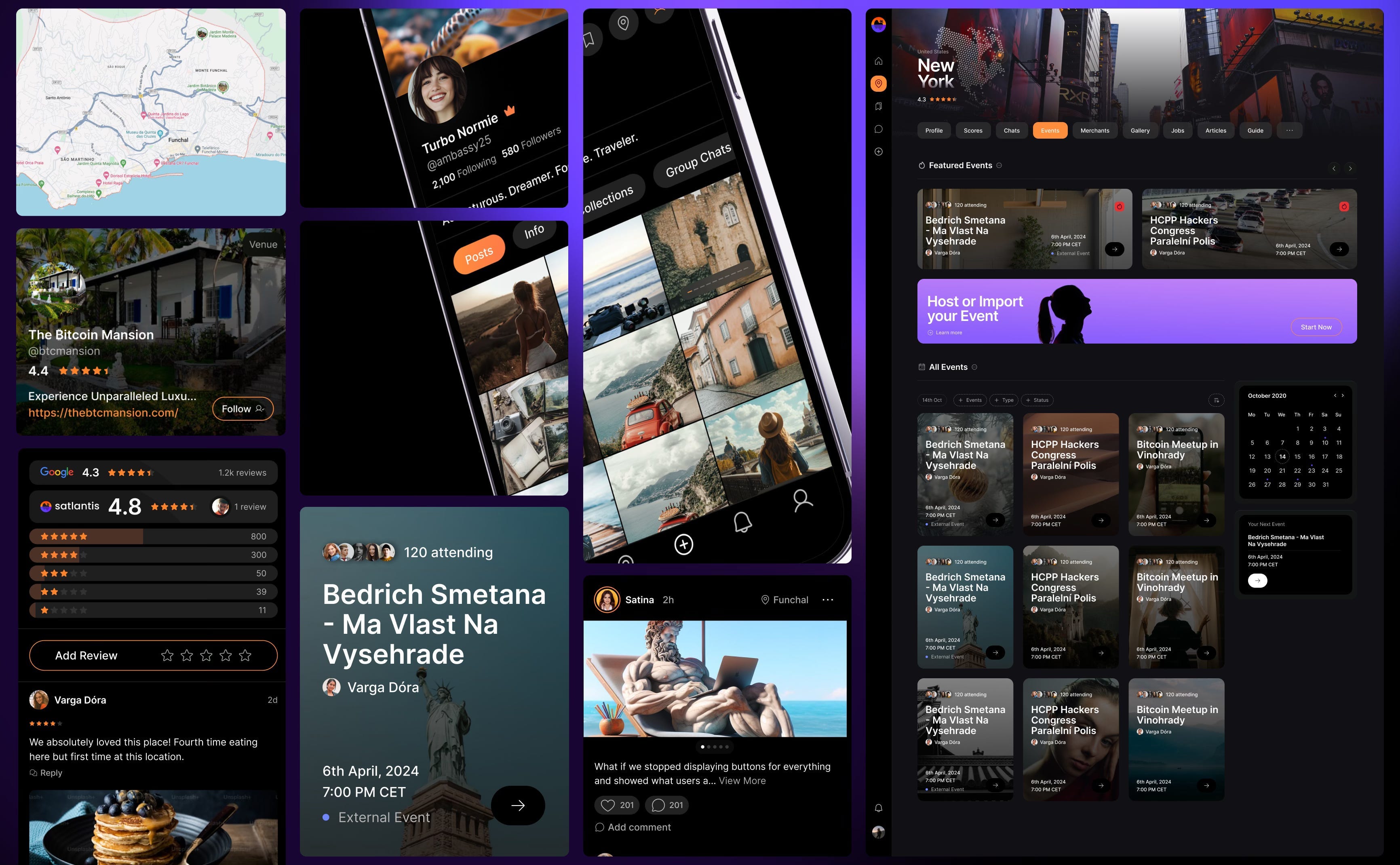
Grants come with a price
This one is less of an opinion and more of an observation. Not sure it really belongs in this essay, but I’ll make a small mention just as food for thought,
Grants are a double-edged sword.
I’m super grateful that OpenSats, et al, are supporting the protocol, and I don’t envy the job they have in trying to decipher what to support and what not to depending on what’s of benefit to the network versus what’s an end user product.
That being said, is the Nostr ecosystem too grant-dependent? This is not a criticism, but a question. Perhaps this is the right thing to do because of how young Nostr is. But I just can’t help but feel like there’s something a-miss.
Grants put the focus on Nostr, instead of the product or customer. Which is fine, if the work the grant covers is for Nostr protocol development or tooling. But when grants subsidise the development of end user products, it ties the builder / grant recipient to Nostr in a way that can misalign them to the customer’s needs. It’s a bit like getting a government grant to build something. Who’s the real customer??
Grants can therefore create an almost communist-like detachment from the market and false economic incentive. To reference the Nostr decision framework I showed you earlier, when you’ve been given a grant, you are focusing more on the X axis, not the Y. This is a trade-off, and all trade-offs have consequences.
Could grants be the reason Nostr is so full of hobbyists and experimental products, instead of serious products? Or is that just a function of how ambitious and early Nostr is?
I don’t know.
Nostr certainly needs better toolkits, SDKs, and infrastructure upon which app and product developers can build. I just hope the grant money finds its way there, and that it yields these tools. Otherwise app developers like us, won’t stick around and build on Nostr. We’ll swap it out with a better tool.
To be clear, this is not me pissing on Nostr or the Grantors. Jack, OpenSats and everyone who’s supported Nostr are incredible. I’m just asking the question.
Final thing I’ll leave this section with is a thought experiment: Would Nostr survive if OpenSats disappeared tomorrow?
Something to think about….
Coda
If you read this far, thank you. There’s a bunch here to digest, and like I said earlier - this not about shitting on Nostr. It is just an enquiry mixed with a little classic Svetski-Sacred-Cow-Slaying.
I want to see Nostr succeed. Not only because I think it’s good for the world, but also because I think it is the best option. Which is why we’ve invested so much in it (something I’ll cover in an upcoming article: “Why we chose to build on Nostr”). I’m firmly of the belief that this is the right toolkit for an internet-native identity and open social graph. What I’m not so sure about is the echo chamber it’s become and the cult-like relationship people have with it.
I look forward to being witch-hunted and burnt at the stake by the Nostr purists for my heresy and blaspheming. I also look forward to some productive discussions as a result of reading this.
Thankyou for your attention.
Until next time.
-
 @ 4925ea33:025410d8
2025-04-17 04:31:30
@ 4925ea33:025410d8
2025-04-17 04:31:30Como invocar a Deus?
O segundo capítulo do livro Confissões, de Santo Agostinho, começa com uma pergunta que toca o coração de todo aquele que busca a fé: “Como invocar a Deus?”
Essa questão, apesar de parecer simples, exige que tenhamos os olhos abertos para a verdade e uma consciência clara da nossa pequenez diante da grandeza divina. Somos pó diante do Criador — limitados, frágeis, tentando compreender o Infinito.
O Deus que não pode ser contido
Santo Agostinho se questiona sobre a presença de Deus e o que significa “conter” o Senhor. Ele reconhece que Deus está em todos os lugares — até mesmo no inferno. Como poderia ser diferente, se Deus é infinitamente grande?
“Nada pode conter Deus, nem mesmo o céu e a terra, suas maiores criações.”
Esse reconhecimento o leva a concluir: Deus não tem começo, meio ou fim. Ele é eterno, e nada pode delimitá-Lo.
O espanto da descoberta: Deus habita em nós Agostinho se espanta ao perceber que, se tudo o que existe só existe porque Deus o sustenta, então Deus está em tudo — inclusive dentro de nós. E aqui nasce uma nova dúvida:
Por que invocar a Deus se Ele já habita em mim? Como pode o Infinito caber em uma criatura tão pequena como o ser humano?
A beleza da doutrina católica
Estudar a doutrina católica é uma experiência profunda e transformadora. A riqueza com que ela trata o mistério de Deus é tão grandiosa, que toca até os corações mais endurecidos.
“Se algo existe, é porque Deus o sustenta. Ele está conosco. Ele nos dá o dom da vida.”
Essa verdade muda completamente a forma como enxergamos a realidade. Compreender que Deus sustenta até aqueles que se afastaram Dele nos leva a uma nova visão — mais compassiva, mais humana e mais próxima do amor de Cristo.
A presença de Deus até nas realidades mais difíceis
Essa reflexão me lembra algo que ouvia na igreja: o chamado de apresentar Cristo nos presídios. Sempre me perguntei como os pregadores viam a presença de Deus em pessoas que cometeram crimes cruéis.
Hoje, entendo que se alguém ainda existe, é porque Deus ainda o sustenta — mesmo que seus atos não agradem a Deus. A existência é um sinal de que a presença divina ainda está ali, chamando à conversão.
Conclusão: Deus está em tudo, inclusive em nós
Este capítulo não aprofunda como lidar com o inimigo ou com o mal, mas nos dá uma certeza essencial: Deus está em tudo e em todos.
Ao orar, não devemos buscá-Lo como alguém distante, mas sim olhar para dentro de nós. A presença de Deus habita em nós.
-
 @ 57d1a264:69f1fee1
2025-03-27 10:42:05
@ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in SN Press kit? Most important, who the press kit is for? It's for us? It's for them? Them, who?
The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we speek out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1:
Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.
Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before.
This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using.
@k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful.
[^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined
originally posted at https://stacker.news/items/926557
-
 @ f1989a96:bcaaf2c1
2025-04-17 15:31:58
@ f1989a96:bcaaf2c1
2025-04-17 15:31:58Good morning, readers!
This week’s headlines expose the lengths authoritarian regimes go to perpetuate the financial power that preserves their rule, often going so far as to bend, break, and rewrite the rules of money itself.\ \ In Nigeria, a make-up artist faces six months in prison for tossing around naira banknotes in a celebratory fashion during his wedding. The Nigerian regime claims this “disrespects” the currency, enforcing a 2007 law that criminalizes the public display or mishandling of cash. This instance offers a view into the absurdity of the monetary policies under which a large part of the world lives.\ \ Meanwhile, in Northern Africa, Libya devalued its currency overnight. Libyans woke up to a 13.3% haircut on their savings as the autocratic regime shored up its finances at the expense of citizens’ financial security. While this is the first devaluation of the dinar in the last four years, it is unlikely to be the last.\ \ In freedom tech news, Unocoin, India’s oldest digital asset exchange, integrated the Lightning Network, bringing millions of its users access to fast and low-cost Bitcoin payments. As financial repression increases in India, integrating Bitcoin scaling into financial platforms like Unocoin is a welcome development at a pressing time.\ \ Finally, we feature an article from journalist Roger Huang, who details the Bitcoin-driven relief efforts led by Burmese activist and HRF fellow Win Ko Ko Aung in the aftermath of a 7.7-magnitude earthquake. Amid civil war and immense state repression of finances, opposition, and media, Bitcoin offers an uncensorable way to fund relief efforts, protect donor privacy, and ensure that support reaches those affected. This is a great example of how Bitcoin can deliver aid in the most critical of times.
Now, let’s dive right in!
SUBSCRIBE HERE
GLOBAL NEWS
Nigeria | Artist Faces Six Months in Prison for Tossing Naira Currency
The Nigerian regime sentenced a makeup artist to six months in prison for tossing naira currency banknotes during his wedding celebration. While the practice is common, Nigerian officials enforce a 2007 law criminalizing the “spraying of, dancing, or marching on the naira.” Therefore, the regime claims this recent act “disrespects” one of the country’s most “important” symbols — the naira. Around the same time, authorities banned the song “Tell Your Papa” by artist Eedris Abdulkareem. The song criticizes President Tinubu and urges his son, Seyi, to tell him “people are dying” from regime-induced hunger and insecurity. These two cases expose a regime more obsessed with symbolic obedience than alleviating the struggles of a population crushed by inflation. Meanwhile, the country’s top officials, who have siphoned off much of the nation’s wealth, collapsed the currency (which has lost 70% of its value since de-pegging from the US dollar), and ignored the financial pleas of citizens, go unpunished.
Libya | Regime Devalues Currency for First Time in Four Years
Libya’s central bank devalued the “official” Libyan dinar by 13.3% overnight, its first devaluation in four years and a likely sign of more to come. The official exchange rate now sits at 5.5677 dinars per dollar, while the informal market rate hovers around 7.20. The gap between Libya’s official and informal market exchange rates makes imported goods more expensive for average citizens. This is because Libyans rely on the informal market rate to access foreign currency that is used to buy essential, imported goods like medicine, fuel, and food. This gives them less purchasing power than otherwise would be. The two-tiered exchange system also fuels corruption among regime officials, as those with access to official rates can exploit the spread for personal gain, deepening public frustration in a country already divided by dueling governments and weak public institutions.
Turkey | Injects Billions to Prop Up Collapsing Lira While Rewarding Police Repression
The Central Bank of Turkey injected $42 billion in foreign currency reserves to prop up the Turkish lira, which has plummeted to record lows. At the same time, protests erupted across the country following the politically motivated arrest of Istanbul Mayor Ekrem Imamoğlu. Now, the regime is rewarding police for violently suppressing demonstrators. Officers involved in the crackdown on protesters reportedly received 10,000 lira ($262) each in cash, funded by the same shrinking public funds. While Erdogan uses state funds to reward repression, a Turkish court rejected İmamoğlu’s appeal, underscoring a regime determined to silence dissent, dismantle democracy, and cling to power at any cost.
Syria | Economist Proposes “New” Currency to Solve Economic Woes
In Syria, economist George Khazzam is proposing to remove two zeros from the Syrian pound to mask the regime’s economic failure and escape hyperinflation. Additionally, Khazzam recommends reprinting all Syrian pound banknotes and limiting the issuance of higher denomination notes. Since 2011, the Syrian pound has plummeted from 50 to over 15,000 pounds per dollar as civil war, sweeping sanctions, and failed currency policies manifest throughout the country. In northern regions like Idlib and Aleppo, many have abandoned the pound entirely, turning to the Turkish lira for daily transactions. While it is also unstable, its use in northern Syria is driven by necessity. Across Syria, wages are crumbling, prices change hourly, and banking access is unreliable at best.
Pakistan | Mining Bitcoin With Surplus Electricity
Pakistan unveiled intentions to mine Bitcoin and run AI data centers using surplus electricity in a bid to address the country’s energy inefficiencies and drive economic growth in emerging technologies. Additionally, in a move that surprised many, the military-backed regime appointed Changpeng Zhao, the founder of digital asset exchange Binance, as a strategic adviser to help guide the country’s “cryptocurrency” and “blockchain” initiatives, policy, and education. At first glance, these steps suggest a shift toward innovation and modernization. But these policies come from the same regime that jails political opposition, censors and shuts down the Internet, and financially represses independent media. It remains unclear how these policies can benefit individual Pakistanis.
South Korea | 7-Eleven Accepting Discounted CBDC Payments During Pilot Phase
South Korea launched a nationwide pilot of its central bank digital currency (CBDC), enrolling 100,000 South Korean users. As part of the rollout, 7-Eleven will accept CBDC payments and offer a 10% discount on all products. Governments facing public skepticism regarding their CBDCs increasingly use similar incentive tactics to onboard users. For example, Nigeria discounts taxi fares to push its e-Naira CBDC, while Thailand is distributing its CBDC directly to citizens for free. While South Korea’s CBDC project aims to modernize payments, it is part of a broader push from countries, even democratic ones, to integrate state-controlled digital currencies into everyday transactions. A move that is diametrically opposed to individuals’ freedom, privacy, and human rights.
BITCOIN AND FREEDOM TECH NEWS
Unocoin | Integrates Bitcoin’s Lightning Network
Unocoin, India’s oldest digital asset exchange, integrated the Lightning Network through Voltage, a Bitcoin and Lightning infrastructure company, bringing millions of Unocoin users access to fast and low-cost Bitcoin payments. This upgrade is critical for Indians seeking alternatives to a progressively repressive financial system. The Indian government is freezing political opposition bank accounts, granting tax authorities legal access to citizens’ private online data, and expanding its CBDC by integrating with incumbent fintech firms and government-built payment rails like UPI. While Unocoin is a centralized exchange that requires registration and holds assets on behalf of its users, integrating Lightning will afford users greater flexibility, autonomy, and privacy when managing their finances.
Phoenix Wallet | Resumes Operations in the US
Phoenix Wallet, an open-source and self-custodial Bitcoin Lightning wallet, officially resumed operations in the US following the release of the US Deputy Attorney General’s “Ending Regulation by Prosecution” memo. The move offers much-needed clarity for developers and operators of open-source software and reinforces the right to develop and use tools for self-custody and peer-to-peer transactions. “We are happy to make our products available again in the USA,” said ACINQ, the team behind Phoenix. This decision marks a win for activists and dissidents living in the US to use the same tools they might use in their home countries.
Blitz Wallet | Refines Ecash Functionality
Blitz Wallet, an open-source and self-custodial Bitcoin, Lightning, Liquid, and ecash wallet, released its latest beta version, bringing expanded ecash functionality. Ecash is a Bitcoin-backed digital money system that enables practical everyday payments on Bitcoin that are private by design (but users must trust mints to manage their funds). The latest Blitz update increases ecash limits, allowing users to set custom receive amounts and a maximum balance for ecash payments. Further, it expands manual swap options so users can routinely exchange their ecash for Bitcoin on Lightning, Liquid, or vice versa. Blitz also lets users spend their ecash balance to buy gift cards, access AI tools, and pay for VPN services all through the app — useful features for anyone living under tyranny.
Bitsacco | First Business Accepts Payments Directly into Savings Wallet
Bitsacco, a Bitcoin-powered alternative to Kenyan Savings and Credit Cooperative Organizations (SACCOs) and HRF grantee, just hit a major milestone: a Kenyan business is now accepting payments directly into its Personal Savings wallet on Bitsacco. This is the first instance of a Kenyan merchant choosing to save revenue in Bitcoin using Bitsacco’s community custody model. Letting businesses convert earnings into Bitcoin through a familiar path unlocks new use cases and forges novel avenues to financial freedom. In a region where inflation, banking restrictions, and undemocratic financial reforms erode economic autonomy, this kind of real-world usage shows how Bitcoin can support grassroots saving and financial inclusion.
BTCPay Server | Adds New Integrations, Plugins, and Features
BTCPay Server, an open-source, self-hosted Bitcoin payment processor, released its latest update, which includes new multisignature capabilities (where multiple private keys are used to access Bitcoin in a wallet), fee acceleration tools, and new integrations that can benefit nonprofits and activists operating under financial surveillance. The updated multisignature brings collaborative custody wallets and support for major hardware devices. Enhanced fee acceleration tools (like RBF and CPFP) help users rescue stuck transactions during periods of high network congestion. And finally, BTCPay Server added integrations with Shopify V2, Ghost, and ECWID. This strengthens its role as a self-hosted payment processor for individuals and nonprofits seeking financial independence and autonomy in regions where authoritarian rulers limit economic freedom.
Electrum | Merges Nostr Wallet Connect Plugin
Electrum, an open-source Bitcoin wallet, just merged software support for Nostr Wallet Connect (NWC), which will enable users to remotely control their Electrum wallet through a Nostr plugin. More generally, NWC is a protocol that connects Bitcoin Lightning wallets to other applications like Nostr. This new plugin will let users authorize external apps and Nostr clients like Amethyst, Alby, and LNbits to initiate Lightning payments from their Electrum wallet, without needing to expose private keys or run their own node.By bridging Lightning with decentralized identity and messaging, Electrum’s support for NWC can empower journalists and individuals to interact with Bitcoin privately, flexibly, and independently.
RECOMMENDED CONTENT
How Bitcoin Is Used To Raise Funds In Myanmar For Earthquake Relief by Roger Huang
In the wake of a catastrophic 7.7-magnitude earthquake in Burma (Myanmar), journalist Roger Huang’s latest article for Forbes details how activists are using Bitcoin to deliver aid where traditional financial channels have failed. Amid civil war and immense state repression, Bitcoin offers an uncensorable way to fund relief efforts, protect donor privacy, and ensure that support reaches those on the ground. The piece highlights efforts by Burmese activist and HRF fellow Win Ko Ko Aung to route donations through Bitcoin, bypassing military-junta control and getting the funds directly to those affected. We encourage you to read the full article to understand how Bitcoin is fueling hope in the face of disaster.
The Bitcoin Miner’s Guide to Total Control with Bitaxe by BTC Sessions
In this tutorial, Bitcoin Educator Ben Perrin (BTC Sessions) shows viewers how to set up their own Bitaxe, a small, affordable, open-source Bitcoin mining device supported in part by HRF’s Bitcoin Development Fund. He walks through the process of getting started, running your own Bitcoin node (a computer that runs the Bitcoin software), joining a mining pool, and receiving payouts through the Lightning Network. Tutorials like these are important because they make home mining more accessible, enabling even those living under tyranny to leverage freedom tech to participate in and secure the Bitcoin network. For activists, mining at home means gaining more control over how they earn, spend, and store their money, all without relying on centralized systems that can block or monitor them. Watch the full video to learn how to take full ownership of your Bitcoin mining setup.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 4cebd4f5:0ac3ed15
2025-04-17 03:12:14
@ 4cebd4f5:0ac3ed15
2025-04-17 03:12:14Tóm tắt Hackathon
HackCanada quy tụ các nhà đổi mới, lập trình viên, designer và chuyên gia giải quyết vấn đề để giải quyết thách thức cấp bách tại Canada như khả năng tiếp cận healthcare, bền vững môi trường, cơ sở hạ tầng số và chênh lệch kinh tế. Sự kiện diễn ra tại Đại học Wilfrid Laurier (Ontario, Canada) với 188 developer tham gia, đóng góp 89 dự án độc đáo.
Các dự án tập trung vào cải thiện hệ thống y tế qua công nghệ, nâng cấp hạ tầng số cho cộng đồng vùng sâu, và phương pháp sáng tạo giảm thiểu dấu chân môi trường. Hackathon trở thành nền tảng hợp tác, thúc đẩy ý tưởng mới và giải pháp thực tiễn, hướng đến mục tiêu tạo lợi ích cụ thể và truyền cảm hứng thay đổi.
Tổng quan, HackCanada tạo môi trường năng động cho đổi mới, góp phần phát triển công nghệ nâng cao chất lượng cuộc sống người dân. Sự kiện đóng vai trò chất xúc tác cho sáng tạo cộng đồng, hướng đến tương lai bao trùm và bền vững.
Các dự án đoạt giải
Giải Nhất Chung Cuộc
- Phone-a-Fraud: Hệ thống AI-driven phát hiện lừa đảo qua điện thoại thời gian thực, tập trung vào privacy và cơ chế cảnh báo gian lận.
Giải Nhì Chung Cuộc
- StickTator: Thiết bị USB ứng dụng xử lý ngôn ngữ tự nhiên (NLP) để quản lý máy tính bằng giọng nói, đơn giản hóa cấu hình hệ thống.
Giải Ba Chung Cuộc
- Omnivim: Phần mềm tích hợp chuyển động Vim trên mọi ứng dụng để tăng hiệu suất làm việc.
Best Solo Hack Prize Winners
Best Orkes Hack Prize Winners
- Recipeit: Dự án tập trung vào công thức nấu ăn (chi tiết chưa công bố).
Best ICP Hack Prize Winners
- DigiTag: Ứng dụng blockchain bảo mật giao dịch hàng xa xỉ bằng NFTs và Internet Computer Protocol (ICP) để ngăn gian lận.
- LandLocks: Nền tảng quản lý hồ sơ đất đai dưới dạng NFTs trên blockchain.
SPUR Innovation Fund: Best Use of AI, Web3, or Quantum Technology Prize Winners
Giải Nhất
- Beaver Breach: Công cụ phân tích tác động thuế quan Mỹ, đề xuất nhà cung cấp Canada giảm chi phí.Giải Nhì
- Canify - Blockchain Rewards: Khuyến khích ủng hộ sản phẩm Canada bằng phần thưởng blockchain và ưu đãi chính phủ.Autonomous Agent Bounty Track Prize Winners
Giải Nhất
- ChainMail: Ứng dụng email dựa trên web3, tăng cường bảo mật và giao tiếp xuyên blockchain.Giải Nhì
- Canify - Blockchain RewardsGiải Ba
- Roast My Wallet: Web app tạo nội dung hài hước AI-driven dựa trên ví crypto và tính cách người dùng.
- Zap: Ứng dụng crypto trong đời sống hàng ngày với giao dịch miễn phí.
- Carbon Chain: Nền tảng blockchain chuyển đổi giảm phát thải carbon thành tài sản giao dịch, xác thực bằng AI.Best Developer Tool Prize Winners
Best High School Hack Prize Winners
- NaloxNow: Ứng dụng di động chống khủng hoảng opioid, cung cấp naloxone thời gian thực và phản hồi overdose bằng AI.
Most Useless Hack Prize Winners
- UselessGPT: Ứng dụng tương tác sử dụng Gemini API của Google để tạo nội dung giải trí vô nghĩa.
Best AI App Prize Winners
- frij.io: Ứng dụng thông minh quản lý hàng tồn kho gia đình bằng AI, tối ưu hóa danh sách mua sắm.
Build With AI: Google Track Prize Winners
- Best Use of Gemini AI/Gemini API, Best Use of Google Cloud Platform, Best Integration of Google Toolkit:
- Sinker: Nền tảng an ninh mạng AI-driven đào tạo nhân viên nhận diện mối đe dọa phishing.
- FrostByte: Dự án chưa công bố chi tiết.
- Flock Street: Ứng dụng tương tác cung cấp thông tin thị trường chứng khoán bằng dữ liệu thời gian thực và công nghệ giọng nói.
Best Laurier STEM Publishing Society Prize Winners
- SockSensei: Ứng dụng di động đề xuất tất dựa trên tâm trạng người dùng.
Xem danh sách dự án đầy đủ tại đây.
Về Nhà tổ chức
Hack Canada
Hack Canada được biết đến qua các hackathon và workshop quốc gia nhằm nâng cao kiến thức về digital security. Thông qua các sự kiện năng động, tổ chức đã truyền cảm hứng cho nhiều dự án đóng góp vào hệ sinh thái công nghệ.
-
 @ 57d1a264:69f1fee1
2025-03-27 08:27:44
@ 57d1a264:69f1fee1
2025-03-27 08:27:44The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be.
— Anil Dash, The Web We Lost, 13 Dec 2012https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s
So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/
The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about Twitter’s business model or Google’s social features or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks.
originally posted at https://stacker.news/items/926499
-
 @ 57d1a264:69f1fee1
2025-03-27 08:11:33
@ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial).
"The most dangerous thought you can have as a creative person is to think you know what you're doing."
— Richard Hamming[^1]https://www.youtube.com/watch?v=8pTEmbeENF4
For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.
'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,' explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: "We don't know what programming is. We don't know what computing is. We don't even know what a computer is." And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.'
More details at https://worrydream.com/dbx/
[^1]: Richard Hamming -- The Art of Doing Science and Engineering, p5 (pdf ebook)
originally posted at https://stacker.news/items/926493
-
 @ 51cb7603:a2bbe90b
2025-04-17 03:07:18
@ 51cb7603:a2bbe90b
2025-04-17 03:07:18O SN88 é uma plataforma digital que tem se destacado no Brasil, oferecendo uma ampla gama de opções de entretenimento online. Com uma interface moderna e recursos inovadores, a plataforma atrai usuários em busca de experiências digitais envolventes e seguras.
Desde sua chegada ao mercado brasileiro, o SN88 tem investido em tecnologia de ponta para garantir uma navegação fluida e uma experiência personalizada para cada usuário. A plataforma oferece uma variedade de jogos e atividades interativas, atendendo a diferentes preferências e estilos de vida.
Um dos diferenciais do sn88 é o seu compromisso com a segurança e a transparência. A plataforma adota medidas rigorosas para proteger os dados dos usuários e garantir a integridade das transações realizadas. Além disso, oferece suporte ao cliente eficiente, disponível para resolver dúvidas e fornecer assistência sempre que necessário.
Com o crescimento do mercado digital no Brasil, plataformas como o SN88 desempenham um papel importante na transformação do entretenimento online. Elas não apenas oferecem diversão, mas também contribuem para a economia digital do país, gerando empregos e estimulando a inovação.
Em um cenário onde a regulamentação do setor digital está em constante evolução, o SN88 se destaca por sua conformidade com as leis brasileiras e seu compromisso com práticas responsáveis. A plataforma busca proporcionar uma experiência segura e agradável para seus usuários, alinhando-se às melhores práticas do mercado global.
Para os entusiastas do entretenimento digital, o SN88 representa uma opção confiável e inovadora. Com sua oferta diversificada e foco na experiência do usuário, a plataforma continua a conquistar a confiança e a preferência dos brasileiros.
Em resumo, o SN88 é mais do que uma simples plataforma de entretenimento online; é um reflexo da evolução digital no Brasil, oferecendo aos usuários uma experiência rica, segura e adaptada às suas necessidades e expectativas.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 51cb7603:a2bbe90b
2025-04-17 03:05:16
@ 51cb7603:a2bbe90b
2025-04-17 03:05:16Nos últimos anos, o cenário do entretenimento digital no Brasil tem se transformado rapidamente, impulsionado pela inovação tecnológica e pela popularização de plataformas online. Entre os novos nomes que vêm ganhando espaço nesse mercado está a AA123, uma opção que vem despertando o interesse de milhares de brasileiros em busca de diversão, praticidade e possibilidades de ganhos financeiros.
AA123 se apresenta como uma plataforma interativa voltada para quem deseja se entreter com jogos online em tempo real. Sua proposta vai além da simples diversão, oferecendo também uma experiência dinâmica e acessível, tanto para iniciantes quanto para usuários mais experientes. Com uma interface intuitiva, suporte multilíngue e diversas opções de jogos, a plataforma busca atrair um público diversificado, com destaque para os brasileiros.
Um dos principais diferenciais da aa123 é a agilidade no processo de cadastro e a facilidade de uso. Em poucos minutos, o usuário pode criar uma conta, acessar os jogos disponíveis e começar a explorar as funcionalidades do site. Além disso, a plataforma garante segurança de dados e transações, um aspecto essencial para quem deseja utilizar serviços online com tranquilidade.
Outro ponto que vem chamando atenção é o sistema de recompensas e bônus oferecido aos usuários. A cada participação ou desafio completado, é possível acumular pontos ou créditos, que podem ser utilizados dentro da própria plataforma. Essa estratégia tem se mostrado eficaz para fidelizar os jogadores e incentivar o uso contínuo, criando uma comunidade engajada e ativa.
AA123 também se destaca por investir em atendimento ao cliente. Com suporte via chat ao vivo e canais de comunicação rápida, os usuários têm à disposição uma equipe preparada para resolver dúvidas e oferecer assistência em tempo real. Essa proximidade com o público tem contribuído para a construção de uma reputação positiva nas redes sociais e fóruns especializados.
O crescimento da AA123 no Brasil acompanha uma tendência global: a migração do entretenimento tradicional para o ambiente digital. Com a expansão da internet de alta velocidade e o aumento do uso de smartphones, os brasileiros estão cada vez mais conectados, buscando novas formas de lazer no ambiente online. Nesse contexto, plataformas como a AA123 surgem como resposta direta às demandas de um público moderno e exigente.
Embora ainda recente no mercado, a AA123 tem mostrado que veio para ficar. Com um modelo de negócios bem estruturado, foco na experiência do usuário e compromisso com a inovação, a plataforma caminha para se consolidar como uma das principais referências em entretenimento digital no país.
Para quem busca uma alternativa dinâmica, segura e moderna para se divertir online, a AA123 representa uma escolha promissora. E, com o avanço constante da tecnologia, é provável que novas funcionalidades e melhorias continuem sendo implementadas, ampliando ainda mais sua presença no mercado nacional.
-
 @ 6b3780ef:221416c8
2025-03-26 18:42:00
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
- MCP Server: The heart of the system that exposes tools, which you can access via the
.listTools()method. - MCP Client: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- Standard I/O (stdio): A simple local connection method when your server and client are on the same machine.
- Server-Sent Events (SSE): Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
- Create software in any programming language you're comfortable with.
- Add an MCP library to expose your server's MCP interface.
- Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with
bun index.js, and then call.listTools()to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
curl -fsSL https://bun.sh/install | bash-
Choose your MCP server: You can either create one or use an existing one.
-
Inspect your server using the MCP inspector tool:
bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2This will: - Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
-
Pass any additional arguments directly to your server
-
Use the inspector: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
-
Navigate to your MCP server directory.
-
Run without installing (quickest way):
npx @dvmcp/bridge -
Or install globally for regular use:
npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridgeThen run using:bash dvmcp-bridge
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as
wss://relay.dvmcp.fun, or use any other of your preferenceTesting and Integration
- Visit dvmcp.fun to see your DVM announcement.
- Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
-
Install and use the
@dvmcp/discoverypackage:bash npx @dvmcp/discovery -
This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
-
Making them available to your LLM applications
-
Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at dvmcp.fun.
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
Useful Resources
- Official Documentation:
- Model Context Protocol: modelcontextprotocol.org
-
DVMCP.fun: dvmcp.fun
-
Source Code and Development:
- DVMCP: github.com/gzuuus/dvmcp
-
DVMCP.fun: github.com/gzuuus/dvmcpfun
-
MCP Servers and Clients:
- Smithery AI: smithery.ai
- MCP.so: mcp.so
-
Glama AI MCP Servers: glama.ai/mcp/servers
Happy building!
- MCP Server: The heart of the system that exposes tools, which you can access via the
-
 @ 51cb7603:a2bbe90b
2025-04-17 03:04:21
@ 51cb7603:a2bbe90b
2025-04-17 03:04:21O 007Game tem ganhado popularidade entre os jogadores que buscam uma experiência envolvente e cheia de adrenalina. Inspirado no universo do famoso agente secreto James Bond, o jogo oferece uma dinâmica de apostas emocionantes, que atrai tanto novatos quanto veteranos do mundo dos jogos.
O 007Game não é apenas sobre sorte, mas também exige estratégia e tomada de decisões rápidas. Com um formato simples, mas desafiador, ele tem conquistado o público com a possibilidade de interagir de forma intuitiva e divertida, sem a necessidade de uma curva de aprendizado complexa.
Como Funciona o 007Game? No 007game , os jogadores têm a oportunidade de testar suas habilidades de previsão e conhecimento, fazendo apostas em diferentes tipos de resultados. A interface é fluida e fácil de navegar, com gráficos modernos que proporcionam uma experiência visual envolvente. Cada rodada do jogo apresenta uma nova oportunidade de testar suas estratégias e aumentar as chances de ganhar, dependendo das escolhas feitas pelo jogador.
A mecânica do jogo gira em torno de eventos de alto risco e recompensa. Em alguns casos, os jogadores podem escolher entre várias opções e tentar prever o resultado de eventos específicos, enquanto em outros, o jogo pode apresentar desafios baseados em sorte e habilidades rápidas. A vitória depende tanto da sorte quanto da capacidade de antecipar o que vem a seguir.
Características que Tornam o Jogo Único Além da jogabilidade descomplicada, o 007Game se destaca pela sua imersão no universo da espionagem. A atmosfera do jogo é inspirada nos filmes clássicos de James Bond, com elementos de ação e mistério. Os jogadores podem se sentir como se estivessem participando de missões secretas, sempre com a possibilidade de ganhar recompensas substanciais. O design de som, incluindo músicas que remetem ao clássico tema de Bond, contribui para a criação de um ambiente tenso e cheio de emoção.
O jogo também oferece diversas opções de personalização, permitindo que os jogadores ajustem suas preferências para otimizar a experiência conforme suas estratégias e estilos de jogo. A escolha de diferentes tipos de apostas e a possibilidade de participar de torneios exclusivos são apenas algumas das maneiras pelas quais o 007Game mantém o interesse de seus jogadores.
A Popularidade do 007Game Com a crescente popularidade dos jogos digitais de apostas, o 007Game se destacou como uma opção divertida e emocionante para quem busca uma forma acessível de entrar no mundo dos jogos eletrônicos. A facilidade de acesso, combinada com a jogabilidade dinâmica e recompensadora, torna o jogo atrativo para pessoas de todas as idades e níveis de experiência.
Além disso, a comunidade de jogadores do 007Game é ativa, com fóruns e grupos de discussão onde os jogadores compartilham dicas e estratégias para melhorar suas habilidades no jogo. Isso cria um ambiente competitivo, mas também acolhedor, onde todos têm a oportunidade de aprender e se divertir.
Conclusão Em resumo, o 007Game é uma excelente opção para aqueles que procuram uma experiência envolvente e dinâmica no mundo dos jogos. Com uma combinação de sorte, habilidade e estratégia, ele tem conquistado os corações dos jogadores ao redor do mundo. Se você ainda não experimentou, talvez seja hora de embarcar nessa aventura de espionagem e emoção!
-
 @ f18571e7:9da08ff4
2025-03-14 16:43:03
@ f18571e7:9da08ff4
2025-03-14 16:43:03Gostaria de dar-te as boas vindas à essa rede social descentralizada e sem censura. Creio eu que já tenha ouvido falar sobre o que ela é e como funciona parcialmente, caso não, existem dois sites (ao meu conhecimento) com boas informações, se chamam nostr.com e nostr.how, mas darei mais à frente uma explicação básica.
E já te dou um aviso: você precisa saber ler!
Aqui irei tentar ajuntar o máximo de informações que conseguir para que não falte nada para você, e o que faltar, quero que você saiba como pesquisar. Cada parte de como funciona, como acessar, como criar, etc.
Usarei como padrão neste artigo o #Amethyst, pois é o melhor e mais completo client para android, mas muitas das configurações nele podem ser visualizadas em outros clients. E para começar, vamos ver o que são clients.
Clients
Chamamos de clients (ou clientes em português) aqueles sites ou apps que dão acesso ao protocolo Nostr. Assim como para acessar à internet existem vários browsers (ou navegadores), para acessar o Nostr também existem vários clients, cada um voltado a um foco específico.
Amethyst
O melhor e mais completo client para #android, nele você pode ter acesso de tudo um pouco. Lives, comunidades, chats, "vídeos curtos", hashtags, notas populares, e muito mais.
Na versão da Play Store, existe uma funcionalidade de tradução usando o Google tradutor. https://play.google.com/store/apps/details?id=com.vitorpamplona.amethyst
Em outras lojas de apps e no repositório Github, o apk não possui essa função. https://github.com/vitorpamplona/amethyst
Aqui tem um tutorial do Amethyst: nostr:nevent1qqsgqll63rw7nfn8ltszwx9k6cvycm7uw56e6rjty6lpwy4n9g7pe5qpz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygz8g3szf3lmg9j80mg5dlmkt24uvmsjwmht93svvpv5ws96gk0ltvpsgqqqqqqs7yma4t
Outros Clients
Aqui algumas pessoas expondo suas opiniões sobre certos clients: nostr:nevent1qqsdnrqszc2juykv6l2gnfmvhn2durt703ecvvakvmyfpgxju3q2grspzamhxue69uhhyetvv9ujuvrcvd5xzapwvdhk6tczyr604d4k2mwrx5gaywlcjqjdevtkvtdjq4hmtzswjxjhf6zv2p23qqcyqqqqqqghvkced nostr:nevent1qqsvqahwnljqcz3s3t5zjwyad5f67f7xc49lexu7vq5s2fxxskegv4spzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qvg9lk42rxugcdd4n667uy8gmvgfjp530n2307q9s93xuce3r7vzsxpqqqqqqzeykzw2 Eu mesmo gosto do Amethyst para android e iris.to para web no PC.
Recomendo à você dar uma olhada nesse site: nostrapps.comEle possui todos os clients atuais do Nostr, com uma descrição e links direcionais para você.
Nostr
Agora que você já sabe mais sobre os #clients, você pode acessar o Nostr segundo seu interesse de interface. Vamos ver o que uma IA nos diz sobre o Nostr:
"O #Nostr é um protocolo descentralizado e open source que permite a criação de redes sociais e outros aplicativos sem a necessidade de um servidor central. O nome é um acrônimo para Notes and Other Stuff Transmitted by Relays (Notas e Outras Coisas Transmitidas por Relays). Ele foi projetado para ser resistente à censura, oferecendo uma alternativa às plataformas tradicionais, onde os usuários têm controle total sobre seus dados.
Para que serve?\ O Nostr serve como base para aplicações descentralizadas, como redes sociais, sistemas de pagamento instantâneo em Bitcoin (usando a rede Lightning) e interações diretas entre criadores e consumidores de conteúdo. Ele promove a liberdade de expressão e a privacidade, sem exigir informações pessoais como nome, e-mail ou número de telefone para criar uma conta.
Como funciona?\ O protocolo utiliza dois componentes principais: clientes e relays. Os clientes são aplicações que os usuários usam para interagir com a rede, enquanto os relays são servidores que armazenam e transmitem mensagens. Cada usuário tem uma chave criptográfica única, que garante a autenticidade e a integridade das mensagens. Os relays são independentes, o que significa que, se um relay for bloqueado ou cair, os usuários podem continuar se conectando através de outros.
Em resumo, o Nostr é uma revolução na forma como nos conectamos online, oferecendo liberdade, privacidade e controle aos usuários."
-Perplexity AI
Se você chegou aqui, é porque ouviu em algum lugar ou de alguém, algo parecido com isso. O Nostr é algo moldável, você consegue fazer dele o que quiser, e por aqui você vai encontrar muitas dessas pessoas que o moldam (idealizadores, programadores e desenvolvedores).
Cuide de sua NSEC
Sua Nsec é a chave privada para acesso ao seu perfil, quem a possuir poderá realizar qualquer alteração que queira, comentar, publicar posts e assim por diante. Você deve guardar essa Nsec como se fosse a seed phrase ou chave privada de sua carteira cripto.
Existem alguns modos de guardar e criptografar sua Nsec:
Sem Criptografia
Primeiro de tudo, fique ciente de onde está a sua nsec no client em que acessa o Nostr!
No Amethyst
- Abra o menu de opções
- Selecione "Copia de segurança"
- Clique em "copiar minha chave secreta" Sua nsec será copiada para a àrea de transferência de seu teclado.
Depois de copiar sua nsec, as melhores recomendações que tenho para passar são:
1. Amber
Guarde sua nsec no #Amber, um app assinador de eventos que guarda sua nsec sob criptografia. Após isso, use o mesmo para acessar qualquer client ou site e gerenciar as permissões de cada um. nostr:nevent1qqsvppyfxm87uegv9fpw56akm8e8jlaksxhc6vvlu5s3cmkmz9e0x8cpypmhxue69uhkummnw3ezuampd3kx2ar0veekzar0wd5xjtnrdakj7q3q5wnjy9pfx5xm9w2mjqezyhdgthw3ty4ydmnnamtmhvfmzl9x8cssxpqqqqqqztzjvrd
2. Nos2x-fox
Coloque sua nsec no #Nos2x-fox, um gerenciador de permissões para navegadores a partir do #Firefox. https://addons.mozilla.org/en-US/firefox/addon/nos2x-fox/ E para navegadores da base #chromium existe o #Nos2x do mesmo desenvolvedor. https://chromewebstore.google.com/detail/nos2x/kpgefcfmnafjgpblomihpgmejjdanjjp
3. Gerenciador de Senhas
Essa é a recomendação mais arriscada, você ainda terá de usar o copiar e colar de sua nsec para acessar o Nostr, a não ser que seu gerenciador reconheça o campo de preenchimento da nsec. Mesmo assim, existem dois gerenciadores que indico; o #Bitwarden e #KeePassDX:
Bitwarden (online)
Play Store: https://play.google.com/store/apps/details?id=com.x8bit.bitwarden Github: https://github.com/bitwarden/mobile
KeePassDX (offline)
Play Store: https://play.google.com/store/apps/details?id=com.kunzisoft.keepass.free Github: https://github.com/Kunzisoft/KeePassDX
Com Criptografia
Se tiver interesse em criptografar sua chave, o formato nativo aceito pelos clients é o ncryptsec. O #ncryptsec é uma criptografia por senha (a grosso modo), onde para ser capaz de usá-la nos clients, somente em conjunto com a senha usada na criptografia, fora isso, você não tem acesso. Você consegue encriptar sua nsec e hex para ncryptsec por meios como os abaixo:
1. Amethyst (nsec)
Existe uma função nativa no Amethyst abaixo da opção "copiar chave secreta" onde é só adicionar a sua senha e será criada uma ncryptsec para copiar. Guarde essa nsec encriptada + senha de descriptação em um lugar seguro.
2. Amber (nsec)
No Amber, existe uma função capaz de encriptar sua nsec.
Ao entrar no Amber
- Selecione a engrenagem na parte inferior da tela
- Selecione "backup keys"
- E rolando para baixo existe um campo para digitar sua senha para encriptação da nsec, digite sua senha e copie a ncryptsec. Guarde-as em um lugar seguro.
3. Nostr-Tools (hex)
Foi-me dito que essa ferramenta também encripta o formato nsec, mas eu não consegui fazê-lo, então deixarei para o formato hex. Compile essa ferramenta em seu pc e siga as instruções. Sua chave Hex será encriptada. https://github.com/nbd-wtf/nostr-tools/blob/master/nip49.ts Guarde-as em um lugar seguro.
Relays e Servidores
Relays
Os #Relays (ou relés) são essenciais para receber e enviar informações no Nostr, veja abaixo algumas definições e como utilizar: nostr:nevent1qqsw85k097m8rh5cgqm8glndhnv8lqsm3ajywgkp04mju9je3xje3hcpzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qne99yarta29qxnsp0ssp6cpnnqmtwl8cvklenfcsg2fantuvf0zqxpqqqqqqzxvc0le No exemplo é usado o Orbot no Amethyst, você pode escolher usar essa opção, mas houve uma atualização do Amethyst desde a criação deste post, onde foi adicionada a função de "Tor interno".
No Amethyst
- Deslize a tela da esquerda pra direita
- Selecione "Opções de Privacidade"
- Na opção "Motor Tor Ativo" selecione "Interno"
- Para melhor privacidade, na opção "Predefinições Tor/Privacidade" selecione "Privacidade Completa" Todo conteúdo e informação que receber do Nostr passará através da rede Tor, além de que é possível visualizar conteúdos publicados no Nostr exclusivos da rede #Tor com essa configuração. Lembrando que este método é mais veloz que usar o Orbot.
Aqui estão alguns relays Tor: nostr:nevent1qqsqe96a8630tdmcsh759ct8grfsdh0ckma8juamc97c53xvura3etqpxpmhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtmhwden5te0vdhkyunpve6k6cfwvdhk6tmjv4kxz7gzyr604d4k2mwrx5gaywlcjqjdevtkvtdjq4hmtzswjxjhf6zv2p23qqcyqqqqqqgmxr5jk
Servidores de Mídia
Os servidores de mídia são os responsáveis por armazenar seus vídeos e fotos postados no Nostr. No Amethyst já existem alguns por padrão: https://image.nostr.build/8e75323bb428c1e5ef06e37453f56bc3deecd38492a593174c7d141cac1c2677.jpg Mas se você quiser, pode adicionar mais: nostr:nevent1qqster6rm55vy3geqauzzwrm50xwvs2gwa4l27ta2tc65xhpum2pfzcpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyr604d4k2mwrx5gaywlcjqjdevtkvtdjq4hmtzswjxjhf6zv2p23qqcyqqqqqqgv2za2r Fique atento aos limites e regras de cada servidor de mídia. nostr:nevent1qqsq3qchucw49wfu2c4wpsung93ffzg4ktt4uuygnjcs5pldf5alr9c3hsgjr
E aqui vai uma #curiosidade: Caso queira postar uma foto ou vídeo que já postou antes, copie o ID da nota em que ela está e cole no novo post, ou então o URL da mídia. Você pode perceber que após upar uma mídia no Nostr, isso se torna uma URL, sempre que usar essa mesma URL, essa mídia irá aparecer.
Lightning e Zaps
Se você chegou aqui por meio de bitcoinheiros, já deve saber que por aqui, usamos a #Lightning para enviar zaps. Mas o que são zaps?
Zaps são nada mais do que satoshis enviados no Nostr. Um exemplo, eu criei esse artigo, pessoas que querem me apoiar ou agradecer por tal, me enviam alguma quantia em sats, dizemos que essa pessoa me mandou um #zap.
Agora posso falar mais sobre a lightning no Nostr.
Para enviar zaps para usuários no Nostr, você precisa de uma carteira lightning. E a carteira que recomendo criarem para isso é através da #Coinos. Na Coinos, você não precisa criar carteiras com seed phrases nem canais lightning, ela é uma carteira custodial, ou seja, a seed phrase está de posse da Coinos. Basta você acessar coinos.io e criar uma conta com username e senha, você pode configurar um e-mail de resgate, código 2FA, e senha para movimentação de fundos. Se quiser, aqui está o app da Coinos, ainda em fase de testes, mas a maior parte do usual funciona perfeitamente. nostr:nevent1qqspndmkhq2dpfjs5tv7mezz57fqrkmlklp4wrn3vlma93cr57q5xlqpypmhxue69uhkummnw3ezuampd3kx2ar0veekzar0wd5xjtnrdakj7q3q7xzhreevjvzyvuy48mjn7qlx55q2dktk3xm0lnlpehxvl8dq3l6qxpqqqqqqzp4vkne (o app está disponível na #zapstore, baixe a loja para ter acesso) O legal da coinos é que você pode criar um endereço lightning com o nome que você escolher, o meu por exemplo é componente08@coinos.io, basta criar sua conta e poderá enviar e receber zaps no mesmo instante.
Mas para receber de fato um zap usando o Nostr, você precisa configurar seu endereço lightning no seu perfil. Crie sua conta e copie seu endereço lightning.
No Amethyst
- Clique na sua imagem de perfil
- Selecione "Perfil"
- Aperte o botão com um lápis
- Em "Endereço LN" e "LN URL" cole seu endereço lightning Pronto! Agora as pessoas podem te enviar zaps através de suas publicações.
Antes de enviar zaps, configure seus valores no client.
No Amethyst
- Aperte e segure no raio de qualquer publicação
- No campo "novo valor em sats" digite um valor desejado
- Aperte o "x" nos valores que deseja excluir
- Clique em "Salvar"
Agora, você pode clicar no raio e escolher um valor, ao escolher você será direcionado para a sua carteira, confirme a transação e seu zap foi realizado!
Existe outro meio de enviar zaps que é através do #NWC (Nostr Wallet Connect). Siga os mesmos passos do Yakihonne no Amethyst na aba do raio que acessamos anteriormente. nostr:nevent1qqsxrkufrhpxpfe9yty90s8dnal89qz39zrv78ugmg5z2qvyteckfkqpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyr604d4k2mwrx5gaywlcjqjdevtkvtdjq4hmtzswjxjhf6zv2p23qqcyqqqqqqgrw73ux O NWC dá ao client ou app, a permissão de gerenciar sua carteira. Isso te permite enviar zaps sem sair do client ou precisar entrar no app da carteira.
Existem muitas outras carteiras lightning por aí, então além da coinos, deixarei o link de outras duas que utilizo.
WOS (Wallet of Satoshi)
Somente Play Store: https://play.google.com/store/apps/details?id=com.livingroomofsatoshi.wallet
Minibits
Play Store: https://play.google.com/store/apps/details?id=com.minibits_wallet Github: https://github.com/minibits-cash/minibits_wallet
Comunidades
Em uma #comunidade é possível encontrar respostas para suas perguntas, artigos e postagens de seu interesse, links úteis e tutoriais para burlar sistemas, documentos e estudos sem censura, etc. Aqui está um exemplo: nostr:nevent1qqs8qztlq26hhstz9yz2tn02gglzdvl5xhkpzhnpuh8v65mjldtdjlqpzamhxue69uhhyetvv9ujuvrcvd5xzapwvdhk6tczypr5gcpycla5zerha52xlam9427xdcf8dm4jccxxqk28gzayt8l4kqcyqqqqqqgldlvdq Esse usuário recorrentemente atualiza a lista de comunidades brasileiras no Nostr, recomendo seguir o perfil para se manter atualizado caso tenha interesse: nostr:nevent1qqsxkusgt02pmz6mda4emjlnjjyd4y9pa73ux02dcry8vk3wp85aq9cpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczypr5gcpycla5zerha52xlam9427xdcf8dm4jccxxqk28gzayt8l4kqcyqqqqqqgqq5zn5 Aqui vão algumas #curiosidades para usuários mais avançados: nostr:nevent1qqs246x86gw4zfp70wg65rjklf909n6nppwm0xx6mssl6jgznw4nkjcpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyzgmafwdjds4qnzqn2h5t9gknz8k3ghu6jp8vt7edxnum3ca73z3cqcyqqqqqqgtkt83q Existem alguns clients que podem criar e gerenciar comunidades, caso você não encontrou nada de seu interesse e quer criar uma, os mais populares são:
Satellite.earth e noStrudel.ninja
Chats
Os #chats são espaços voltados a interação por meio de mensagens, aqui estão alguns: nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsfujjjw3474zsrfcqhcgqavqeesd4h0nuxt0ue5ugy9y7e47xyh3qrqsqqqqqpgdaghw Para contatar uma pessoa no privado:
No Amethyst
- Clique no perfil da pessoa
- Clique no ícone de mensagem
- Envie uma mensagem
Caso queira criar um chat, siga os passos:
No Amethyst
- Clique no ícone de mensagens
- Clique no ícone de "+"
- Serão exibidas duas opções; "privado" e "público", escolha privado para um grupo de poucas pessoas e público para qualquer que quiser entrar.
- Adicione as especificações necessárias e seu chat será criado.
Seguidores
Existe uma #ferramenta capaz de identificar quais usuários que você segue estão inativos, ou publicam pouco e a longos hiatos: nostr:nevent1qqsqqqyhmkqz6x5yrsctcufxhsseh3vtku26thawl68z7klwvcyqyzcpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyzgmafwdjds4qnzqn2h5t9gknz8k3ghu6jp8vt7edxnum3ca73z3cqcyqqqqqqgmfzr67
Mais do Nostr
Existem muitas outras coisas para se explorar no Nostr, e é possível que daqui a uns meses, essas configurações e dicas estejam obsoletas. Explorem e aprendam mais sobre esse protocolo.
Abaixo estão mais algumas coisas que gostaria de compartilhar:
Muitos clients não possuem um sistema de #notificações, isso por conta da natureza #descentralizada dos apps, e para não ceder ao Google para isso, optaram por não ter notificações. O Amethyst por exemplo, só possui notificações ativas para quando você receber zaps. Mas esse problema foi resolvido com o #Pokey: nostr:nevent1qqsyw0m8wkwvzsanwufh6kmu3fkkjsu3x6jxxwxst5fxu3yld7q84cspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3q5wnjy9pfx5xm9w2mjqezyhdgthw3ty4ydmnnamtmhvfmzl9x8cssxpqqqqqqz4d5hj5
Aqui está um post sobre uma #loja de #apps voltada a apps do Nostr: nostr:nevent1qqsrk55p927srd30ukas79qzhlwhm5ls9l07g548y288s5u29najzrqpz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsyg85l2mtv4kuxdg36gal3ypymjchvckmypt0kk9qayd9wn5yc5z4zqpsgqqqqqqskv0pek
Alguns RSS para quem gosta de notícias: nostr:nevent1qqsxctkju0pesrupvwfvzfr8wy3hgqag6r8v4228awgyf2x9htjqa7qpzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qvg9lk42rxugcdd4n667uy8gmvgfjp530n2307q9s93xuce3r7vzsxpqqqqqqzn4acev
Algumas pessoas famosas que estão por aqui: nostr:nevent1qqsvqnlx7sqeczv5r7pmmd6zzca3l0ru4856n3j7lhjfv3atq40lfdcpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgs2tmjyw452ydezymtywqf625j3atra6datgzqy55fp5c7w9jn4gqgrqsqqqqqprwcjan
Alguns Nostr clients e outras coisas: nostr:nevent1qqsgx5snqdl2ujxhug5qkmmgkqn5ej6vhwpu4usfz03gt4n24qcfcwspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgs2tmjyw452ydezymtywqf625j3atra6datgzqy55fp5c7w9jn4gqgrqsqqqqqp3pf6y2
Outros posts interessantes: nostr:nevent1qqsp6vf8pp6l97ctzq2wp30nfc9eupnu2ytsauyxalp8fe8dda6dvdgpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyzgmafwdjds4qnzqn2h5t9gknz8k3ghu6jp8vt7edxnum3ca73z3cqcyqqqqqqgtkju3h nostr:nevent1qqs0faflxswn5rg8fe9q3202en927my6kupcf08lt26ry3cg3xuuy3gpzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyzgmafwdjds4qnzqn2h5t9gknz8k3ghu6jp8vt7edxnum3ca73z3cqcyqqqqqqgsyrpkh nostr:nevent1qqspx9t3qfnsuzafxxuc5hyha9n5ul5v97uz57hfac9xdtvk5eygqggpzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qa5pl548ps6qdkpzpmlgkhnmh2hpntpk2gk3nee08e5spp5wzr3qqxpqqqqqqzctx6uf
Funcionalidades do Amethyst
• Reações (noStrudel também aceita)
nostr:nevent1qqst57p0pzw3vsx3n8g7eaa0dlx3kp5ys9rw3t367q5ewhdyw0kd2rspzamhxue69uhkjmnzdauzuct60fsk6mewdejhgtczyz36wgs59y6smv4etwgrygja4pwa69vj53hww0hd0wa38vtu5clzzqcyqqqqqqgpje0yu
• Markdown
nostr:nevent1qqs0vquevt0pe9h5a2dh8csufdksazp6czz3vjk3wfspp68uqdez00cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgs2tmjyw452ydezymtywqf625j3atra6datgzqy55fp5c7w9jn4gqgrqsqqqqqpekll6f
Espero ter dado alguma direção pela qual seguir por aqui, se tiver dúvidas, pode comentar aqui abaixo e responderemos com o melhor que pudermos. Olhem alguns dos comentários abaixo, terão posts que os veteranos consideram importantes.
Aos veteranos, comentem abaixo caso tenha faltado algo, e complementem aos novatos, grato!
Mais uma vez, seja bem-vindo ao Nostr!
nóspossuímosaweb #awebénostr
-
 @ 57d1a264:69f1fee1
2025-03-26 08:45:13
@ 57d1a264:69f1fee1
2025-03-26 08:45:13I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available here). Performance and Accessibility looks have really low score!
| Desktop | Mobile | |---|---| |
|
| |
|
|
Now let's see what Semrush knows.
Analytics
General view on your metrics and performance trend compared to last 30 days.
See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.
Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.
| Organic Search | Backlinks Analytics | |---|---| |
|
|
| Position Changes Trend | Top Page Changes | |---|---| |
|
| |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |
Competitors
The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.
Referring Domains
Daily Stats
| Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | |
-41.87%|-16.4%|-1.62%|📝 Traffic Drop
Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits:
- https://stacker.news/items/723989 ⬇️ -15
- https://stacker.news/items/919813 ⬇️ -12
- https://stacker.news/items/783355 ⬇️ -5
📉 Decreased Authority Score
Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority.
🌟 New Keywords
Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30
🛠️ Broken Pages
This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not crawlable: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks
Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility!
One of the major issues I found is that SN does not have a
robots.txt, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary?Here are other basic info to improve the SEO score and for those of us that want to learn more:
- Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/
- Design for Accessibility: https://www.w3.org/WAI/tips/designing/
- Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/
originally posted at https://stacker.news/items/925433
-
 @ 51cb7603:a2bbe90b
2025-04-17 03:02:36
@ 51cb7603:a2bbe90b
2025-04-17 03:02:36No mundo em constante evolução do entretenimento online, o 9Bet99 se destaca como uma plataforma notável que atende aos entusiastas que buscam uma variedade de experiências interativas. Com um design centrado no usuário e uma ampla gama de recursos envolventes, o 9Bet99 tem como objetivo oferecer uma solução completa de entretenimento para seus usuários.
Interface Amigável e Acessibilidade
Um dos principais destaques do 9Bet99 é sua interface intuitiva, projetada para proporcionar uma navegação fluida. Explorar a plataforma é simples, permitindo que os usuários acessem facilmente as diferentes seções e funcionalidades. O layout limpo do site garante que tanto novatos quanto usuários experientes possam utilizá-lo sem dificuldades.
Além disso, o 9bet99 entende a importância da acessibilidade. A plataforma é otimizada para dispositivos móveis, permitindo que os usuários aproveitem suas atividades favoritas de qualquer lugar. Seja em um smartphone ou tablet, a versão mobile mantém todas as funcionalidades e a facilidade de uso do site original.
Diversas Opções de Entretenimento
O 9Bet99 oferece uma variedade de opções de entretenimento para atender a diferentes interesses. De jogos interativos a eventos ao vivo, a plataforma garante conteúdo envolvente em todos os momentos. A diversidade de escolhas permite que os usuários explorem novas atividades e aproveitem ao máximo sua experiência no site.
Compromisso com a Segurança e Justiça
Garantir um ambiente seguro é uma das maiores prioridades do 9Bet99. A plataforma utiliza tecnologias de segurança avançadas para proteger os dados e as transações dos usuários, oferecendo tranquilidade total. Além disso, o 9Bet99 é comprometido com a justiça, implementando sistemas que promovem transparência e integridade em todas as suas atividades.
Suporte ao Cliente e Atendimento
Sabendo da importância de um suporte eficaz, o 9Bet99 disponibiliza diversos canais de atendimento para ajudar seus usuários. Seja por chat ao vivo, e-mail ou outros meios, a ajuda está sempre à disposição. A equipe de suporte é treinada para responder de forma rápida e eficiente, tornando a experiência do usuário ainda mais positiva.
Promoções e Benefícios
Para tornar a experiência ainda mais atrativa, o 9Bet99 oferece diversas promoções e incentivos. Essas recompensas são criadas para valorizar os usuários e incentivar o engajamento contínuo na plataforma. Ao participar das promoções, os usuários aproveitam vantagens extras que tornam sua jornada no 9Bet99 ainda mais divertida.
Conclusão
Em resumo, o 9Bet99 se destaca como uma plataforma dinâmica que prioriza a experiência do usuário, a segurança e uma grande variedade de opções de entretenimento. Com seu compromisso em oferecer um ambiente confiável e envolvente, o 9Bet99 continua atraindo uma comunidade crescente de usuários em busca de diversão de qualidade. Seja você iniciante ou experiente, o 9Bet99 oferece uma experiência completa e agradável para todos.
-
 @ 502ab02a:a2860397
2025-04-17 02:15:32
@ 502ab02a:a2860397
2025-04-17 02:15:32วันนี้มาเล่าเรื่อง animal base บ้างครับ เพราะหลายๆคนบอกว่า ดีนะฉันกินสัตว์ ฉันคิดว่าไขมันสัตว์ดีที่สุด รวมถึง plant base ที่ตัดสินฉาบฉวยว่าผม anti plant วันนี้มาเล่าข้อมูลเรื่องต่อไปกันครับ เพื่อให้เห็นว่า โลกของผู้ล่า มันไม่เลือกฝั่งครับ คำถามคือ เหยื่อจะเตรียมตัวอย่างไรมากกว่า เพราะเหยื่อยังทะเลาะกันเองอยู่เลย 55555
sub item ของ fiat food มีอย่างนึงที่เรียกว่า fake food ครับ ถ้าถามว่า “โปรตีนจากเซลล์” หรือ lab-grown meat ที่โฆษณาว่าเป็นทางเลือกแห่งอนาคตนั้น ภาพที่คนทั่วไปนึกถึงคืออะไร? คำตอบน่าจะไม่พ้น -เนื้อที่ไม่ต้องฆ่าสัตว์ -โปรตีนสะอาด ไร้มลพิษ -เทคโนโลยีแห่งอนาคตเพื่อสิ่งแวดล้อม
เชื่อไหมว่าความจริงนั้นมันอาจจะตรงกันข้ามกับทุกข้อที่ตอบมาเลยครับ
มันมาจากไหน?
"เนื้อเทียมจากห้องแล็บ" คือการเอาเซลล์สัตว์มาเพาะเลี้ยงในจานเพาะเลี้ยง โดยให้อาหารกับเซลล์พวกนั้นด้วยน้ำเลี้ยง (growth medium) เพื่อให้มันแบ่งตัวกลายเป็นกล้ามเนื้อ ฟังดูเหมือนปลอดภัยใช่ไหม? แต่ที่หลายคนไม่รู้คือ…
น้ำเลี้ยงที่ใช้ส่วนใหญ่มาจาก Fetal Bovine Serum (FBS) หรือ ซีรั่มจากลูกวัวที่ถูกฆ่าขณะอยู่ในครรภ์แม่ มันคือ คือการเจาะหัวใจลูกวัวที่ยังไม่เกิด เพื่อเอาเลือดมาเลี้ยงเนื้อเทียม แน่นอนว่าการให้ข้อมูลนั้นเขาจะบอกว่า เก็บเกี่ยวเลือดจากตัวอ่อนของวัวหลังจากที่นำตัวอ่อนออกจากวัวที่ถูกเชือด ตัวอ่อนจะตายจากการขาดออกซิเจนโดยอยู่ในสภาพแวดล้อมที่ปลอดภัยของมดลูกเป็นเวลาอย่างน้อย 15-20 นาทีหลังจากวัวตายและแน่นอนว่าต้องให้ข้อมูลว่ามีการเก็บมาภายใต้การดูแลจริยธรรม
และถ้าจะไม่ใช้ FBS ก็ต้องใช้น้ำเลี้ยงสังเคราะห์ที่อัดแน่นด้วย growth factor สังเคราะห์, ยาปฏิชีวนะ, ฮอร์โมน และสารกระตุ้นการเจริญเติบโตแบบเข้มข้น มันคือ Frankenstein Protein เลยก็ว่าได้
ราคาที่แท้จริงไม่ใช่แค่เงิน แต่คืออำนาจต่างหากครับ
เบื้องหลังของ lab-grown meat คือบริษัททุนใหญ่ เช่น Eat Just (เจ้าของ Good Meat) Upside Foods Believer Meats CUBIQ Foods และเบื้องหลังอีกชั้นคือ VC ยักษ์ เช่น SoftBank, Temasek, Bill Gates, Tyson Foods ฯลฯ เริ่มเห็นภาพแล้วใช่ไหมครับ
ทุกเจ้ากำลังเร่งวิจัยเพื่อ “จดสิทธิบัตร” กระบวนการผลิต และพันธุกรรมของเซลล์สัตว์ ใช่จ้ะ… พันธุกรรมของวัว หมู ไก่ หรือแม้แต่ปลา ถูกดัดแปลงพันธุกรรมเพื่อให้เพาะง่าย โตไว อยู่ได้นาน และตอบโจทย์การผลิตในเชิงอุตสาหกรรม
ใครจะเลี้ยงวัวเองแล้วทำเนื้อกินเอง อาจโดนฟ้องในอนาคตว่าไปละเมิดพันธุ์สิทธิบัตรที่บริษัทครอบครอง
ต่อไปนี้ถ้าอยากขายเนื้อ ต้องเป็นเจ้าของห้องแล็บถึงแม้บริษัทเหหล่านี้จะบอกว่า “เราจะ democratize protein” คือทำให้ใครๆ ก็เข้าถึงโปรตีนได้ แต่ความจริงคือ ทุกกระบวนการตั้งแต่เซลล์ต้นแบบ อาหารเลี้ยงเซลล์ ยันเครื่องมือในแล็บ ล้วนมีสิทธิบัตร ใครที่ไม่มี license ก็ผลิตไม่ได้ พูดง่ายๆ ก็คือ…
“ของกินที่โตจากเซลล์ในอนาคตจะต้องมีใบอนุญาตจากบริษัท” ไม่มีแผ่นดินไหน ปลูกเอง กินเอง ได้อีกต่อไป
แล้วมันดีต่อสิ่งแวดล้อมจริงไหม? บริษัทแสนดีต่างๆชอบบอกว่าเนื้อแล็บช่วยลดการปล่อยคาร์บอนจากฟาร์มปศุสัตว์ แต่งานวิจัยของ Oxford, UC Davis และมหาวิทยาลัย Wageningen ชี้ว่า การผลิตเนื้อในห้องแล็บใช้พลังงานสูงกว่าปศุสัตว์จริง หลายเท่า และถ้าไม่ใช้พลังงานหมุนเวียน ก็จะปล่อยคาร์บอนมากกว่าการเลี้ยงวัวแบบดั้งเดิมเสียอีก
ตกลงมันคือ Clean Meat หรือ Clean Lie? Clean Meat ที่เขาโฆษณา อาจจะสะอาดแค่ “ภาพ” แต่องค์ประกอบข้างในคือ… -เซลล์สัตว์ที่ดัดแปลงยีนให้โตเร็ว -น้ำเลี้ยงเซลล์ที่มีสารกระตุ้นการเติบโต, ฮอร์โมน, ยาปฏิชีวนะ -ความไม่โปร่งใสเรื่องกระบวนการผลิต -ไม่มีฉลากบอกผู้บริโภคชัดเจน -ยังไม่มีการทดลองระยะยาวว่า “ปลอดภัยหรือไม่”
พรุ่งนี้ที่ไม่มีเกษตรกรจะเป็นยังไง ถ้าโปรตีนทั้งหมดผลิตในแล็บ แล้วเกษตรกรล่ะ? คนเลี้ยงสัตว์ล่ะ? คนเลี้ยงเป็ดไก่หลังบ้านล่ะ? คนปลูกผัก เลี้ยงวัว ทำฟาร์มแบบพื้นถิ่นล่ะ? ทุกคนจะตกขบวนอาหารของโลกใหม่ เพราะเกมนี้ไม่ได้วัดกันที่คุณภาพ แต่วัดกันที่ “ลิขสิทธิ์”
เรากำลังกินอนาคตที่เราไม่ได้เลือก ในชื่อของ “เทคโนโลยี” ในคราบของ “ทางเลือก” ในความนิยมของ "super food" แต่แท้จริงแล้ว เราอาจกำลังแลก สิทธิการควบคุมอาหาร ไปกับ “คำสัญญาว่าโลกจะดีขึ้น” ไม่ต่างอะไรจากการเอาอาหารไปวางไว้ในห้องแล็บ และล็อกประตูเอาไว้ให้คนไม่กี่คนถือกุญแจ
not your key, not your free เหมือนเพลงที่ผมเขียนไว้ในอัลบั้ม orange cafe ครับ https://youtu.be/k5jUpFXI6Gg?si=4GXOXjYbOpqX9kRb
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 30876140:cffb1126
2025-03-26 04:58:21
@ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains.
I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on.
But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting,
The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater.
Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished.
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.






