-
 @ 1bc70a01:24f6a411
2025-04-16 13:53:00
@ 1bc70a01:24f6a411
2025-04-16 13:53:00I've been meaning to dogfood my own vibe project for a while so this feels like a good opportunity to use Untype to publish this update and reflect on my vibe coding journey.
New Untype Update
As I write this, I found it a bit annoying dealing with one of the latest features, so I'll need to make some changes right after I'm done. Nonetheless, here are some exciting developments in the Untype article composer:
-
Added inline AI helper! Now you can highlight text and perform all sorts of things like fix grammar, re-write in different styles, and all sorts of other things. This is a bit annoying at the moment because it takes over the other editing functions and I need to fix the UX.
-
Added pushing articles to DMs! This option, when enabled, will send the article to all the subscribers via a NIP-44 DM. (No client has implemented the subscription method yet so technically it won’t work, until one does. I may add this to nrss.app) Also, I have not tested this so it could be broken… will test eventually!
- Added word counts
- Added ability to export as markdown, export as PDF, print.
The biggest flaw I have already discovered is how "I" implemented the highlight functionality. Right now when you highlight some text it automatically pops up the AI helper menu and this makes for an annoying time trying to make any changes to text. I wanted to change this to show a floating clickable icon instead, but for some reason the bot is having a difficult time updating the code to this desired UX.
Speaking of difficult times, it's probably a good idea to reflect a bit upon my vibe coding journey.
Vibe Coding Nostr Projects
First, I think it's important to add some context around my recent batch of nostr vibe projects. I am working on them mostly at night and occasionally on weekends in between park runs with kids, grocery shopping and just bumming around the house. People who see buggy code or less than desired UX should understand that I am not spending days coding this stuff. Some apps are literally as simple as typing one prompt!
That said, its pretty clear by now that one prompt cannot produce a highly polished product. This is why I decided to limit my number of project to a handful that I really wish existed, and slowly update them over time - fixing bugs, adding new features in hopes of making them the best tools - not only on nostr but the internet in general. As you can imagine this is not a small task, especially for sporadic vibe coding.
Fighting the bot
One of my biggest challenges so far besides having very limited time is getting the bot to do what I want it to do. I guess if you've done any vibe coding at all you're probably familiar with what I'm trying to say. You prompt one thing and get a hallucinated response, or worse, a complete mess out the other end that undoes most of the progress you've made. Once the initial thing is created, which barely took any time, now you're faced with making it work a certain way. This is where the challenges arise.
Here's a brief list of issues I've faced when vibe-coding with various tools:
1. Runaway expenses - tools like Cline tend to do a better job directly in VSCode, but they can also add up dramatically. Before leaning into v0 (which is where I do most of my vibe coding now), I would often melt through $10 credit purchases faster than I could get a decent feature out. It was not uncommon for me to spend $20-30 on a weekend just trying to debug a handful of issues. Naturally, I did not wish to pay these fees so I searched for alternatives.
2. File duplication - occasionally, seemingly out of nowhere, the bot will duplicate files by creating an entire new copy and attached "-fixed" to the file name. Clearly, I'm not asking for duplicate files, I just want it to fix the existing file, but it does happen and it's super annoying. Then you are left telling it which version to keep and which one to delete, and sometimes you have to be very precise or it'll delete the wrong thing and you have to roll back to a previous working version.
3. Code duplication - similar to file duplication, occasionally the bot will duplicate code and do things in the most unintuitive way imaginable. This often results in loops and crashes that can take many refreshes just to revert back to a working state, and many more prompts to avoid the duplication entirely - something a seasoned dev never has to deal with (or so I imagine).
4. Misinterpreting your request - occasionally the bot will do something you didn't ask for because it took your request quite literally. This tends to happen when I give it very specific prompts that are targeted at fixing one very specific thing. I've noticed the bots tend to do better with vague asks - hence a pretty good result on the initial prompt.
5. Doing things inefficiently, without considering smarter approaches - this one is the most painful of vibe coding issues. As a person who may not be familiar with some of the smarter ways of handling development, you rely on the bot to do the right thing. But, when the bot does something horribly inefficiently and you are non-the-wiser, it can be tough to diagnose the issue. I often fight myself asking the bot "is this really the best way to handle things? Can't we ... / shouldn't we .../ isn't this supposed to..." etc. I guess one of the nice side effects of this annoyance is being able to prompt better. I learn that I should ask the bot to reflect on its own code more often and seek ways to do things more simply.
A combination of the above, or total chaos - this is a category where all hell breaks loose and you're trying to put out one fire after another. Fix one bug, only to see 10 more pop up. Fix those, to see 10 more and so on. I guess this may sound like typical development, but the bot amplifies issues by acting totally irrationally. This is typically when I will revert to a previous save point and just undo everything, often losing a lot of progress.
Lessons Learned
If I had to give my earlier self some tips on how to be a smarter vibe coder, here's how I'd summarize them:
-
Fork often - in v0 I now fork for any new major feature I'd like to add (such as the AI assistant).
-
Use targeting tools - in v0 you can select elements and describe how you wish to edit them.
-
Refactor often - keeping the code more manageable speeds up the process. Since the bot will go through the entire file, even if it only makes one small change, it's best to keep the files small and refactoring achieves that.
I guess the biggest lesson someone might point out is just to stop vibe coding. It may be easier to learn proper development and do things right. For me it has been a spare time hobby (one that I will admit is taking more of my extra time than I'd like). I don't really have the time to learn proper development. I feel like I've learned a lot just bossing the bot around and have learned a bunch of things in the process. That's not to say that I never will, but for the moment being my heart is still mostly in design. I haven't shared much of anything I have designed recently - mostly so I can remain speaking more freely without it rubbing off on my work.
I'll go ahead and try to publish this to see if it actually works 😂. Here goes nothing... (oh, I guess I could use the latest feature to export as markdown so I don't lose any progress! Yay!
-
-
 @ b17fccdf:b7211155
2025-03-25 11:23:36
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la guía de MiniBolt.
Esto tiene una razón, por supuesto una solución, además de una conclusión. Sin entrar en demasiados detalles:
La razón
El bloqueo a Cloudflare, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una orden judicial emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo ECH (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar bloqueos basados en dominios, lo que les obliga a recurrir a bloqueos más amplios por IP o rangos de IP para cumplir con la orden judicial.
Esta práctica tiene consecuencias graves, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un perjuicio para terceros, restringiendo el acceso a muchos dominios legítimos que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la web de MiniBolt y su dominio
minibolt.info, los cuales utilizan Cloudflare como proxy para aprovechar las medidas de seguridad, privacidad, optimización y servicios adicionales que la plataforma ofrece de forma gratuita.Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

La solución
Obviamente, MiniBolt no dejará de usar Cloudflare como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para evitar esta restricción y poder acceder:
~> Utiliza una VPN:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - IVPN - Mullvad VPN - Proton VPN (gratis) - Obscura VPN (solo para macOS) - Cloudfare WARP (gratis) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a esta para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la guía de MiniBolt sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info AQUÍ.

~> Proxifica tu navegador para usar la red de Tor, o utiliza el navegador oficial de Tor (recomendado).

La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la Declaración de Independencia del Ciberespacio que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos impulsar el desarrollo y la difusión de las herramientas anticensura que tenemos a nuestro alcance, protegiendo así la libertad digital y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los pilares fundamentales de MiniBolt, lo que convierte este desafío en una oportunidad para poner a prueba las soluciones anticensura ya disponibles, así como las que están en camino.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ ba36d0f7:cd802cba
2025-04-16 15:09:25
@ ba36d0f7:cd802cba
2025-04-16 15:09:25What is Checkmate?
Checkmate is the decisive move that ends the game. It occurs when the king is under direct threat (in check) and there’s no legal move to save it: neither capturing the attacking piece, blocking the attack, nor fleeing to a safe square.
Unlike other pieces, the king can never be captured - its downfall marks the end of the game. Thus, when escape is impossible, the game ends immediately. There’s no need to "take" the king; its fate is already sealed.
How to Achieve Checkmate?
It requires:
-
Imminent Threat: One or more pieces attacking the enemy king.

-
Total Blockade: All escape squares controlled by the opponent.

- No Possible Defense: No piece can intercept the attack.

Basic Example: The Back-Rank Mate (with a rook or queen on the last rank, where the king can’t escape due to being blocked by its own pieces).
1. The First Chess Commandment: Seek Checkmate
In every game, each move should begin with an essential question: Is there a checkmate in this position? - for both yourself and your opponent. If not, the game revolves around material advantage or positional control. But this order isn’t arbitrary:
-
A tactical oversight can ruin a dominant position.
-
A missed checkmate means instant defeat.
Classic Example: The Scholar’s Mate (1.e4 e5 2.Bc4 Nc6 3.Qh5 Nf6?? 4.Qxf7#).
 White wins because Black, focused solely on development, ignored the deadly threat.
White wins because Black, focused solely on development, ignored the deadly threat.➡ Reflection: In strategy, as in life, the urgent (survival) precedes the important (victory).
2. The Philosophy of the Board: When Advantages Aren’t Enough
A lone king can evade capture forever if the opponent doesn’t know how to checkmate. Similarly, in human existence, advantages - talent, resources, or opportunities - are worthless if not transformed into decisive actions.
-
What good is controlling the center if you can’t convert it into an attack?
-
What good are privileges if not used to build something meaningful?
Chess, like life, rewards execution - not accumulation.
3. Survival Instinct: Between Attack and Resistance
The fear of defeat triggers visceral reactions: desperate attacks, obsessive defenses, or even premature resignations. But these responses reveal deep truths about human nature:
-
Survival ≠ Violence: A cornered king may shelter behind its pieces, like a strategist choosing patience over confrontation. Is it cowardice or wisdom?
-
The Danger of Ego: Arrogance ("I must win quickly") leads to irreversible mistakes. Humility ("I’ll resist until my opponent errs") can turn certain defeat into salvation.
➡ Reflection: The board doesn’t lie. Every move exposes a player’s deepest instincts: fear, ambition, or temperance.
Online Resources
Check mate patterns - Lichess.org https://lichess.org/practice/checkmates/checkmate-patterns-i/fE4k21MW/9rd7XwOw
Piece check mates - Lichess.org https://lichess.org/practice/checkmates/piece-checkmates-i/BJy6fEDf/8K8FdT6P
Common check mates - Chess.com https://www.chess.com/terms/checkmate-chess
10 fastest check mates - Chess.com https://www.chess.com/article/view/fastest-chess-checkmates
Finding check mates - Chess.com https://www.chess.com/lessons/finding-checkmate
somachess #chess #chesselsalvador #ajedrez #chessphilosophy #philosophy #filosofia #checkmate #longform #article
-
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 502ab02a:a2860397
2025-04-16 15:07:23
@ 502ab02a:a2860397
2025-04-16 15:07:23ต้องขอบคุณระบบ facebook ที่มีระบบการจัดการในการเก็บข้อมูล "แย่มาก" ทำให้การพยายาม search มาแปะรวมกันมันยาก เลยเขียนใหม่เลยแล้วกัน จะได้เอาไปเก็บในทุ่งม่วงด้วยครับ บริบทที่เราจะคุยกันคือ องค์ประกอบของ seed oil เอาแค่ว่ามันมีอะไรแล้วจะกลายเป็นอะไร ส่วนการทอด กับ กระบวนการ AGEs คงจะเขียนถึงต่างหาก เพื่อนๆที่เพิ่งรู้จักเฮีย มาใหม่ หรืออะไรก็แล้วแต่ เริ่มต้นจากการอ่านย้อนทำความรู้จักกันก่อน ก่อนที่จะทะลุถาม ถาม ถาม เข้าใจว่า สุจิปุลิ มันมี ปุจฉา แต่มันไม่ใช่ตัว main โอเคนะ เราคุยเรื่องนี้กันมา 8-9 ปีแล้ว ฝั่งคีโตนี่ถกเรื่อง seed oil จนก้าวข้ามกันไปนานแล้ว อย่าถามหาเลยว่าอะไรดี none of above อะครับ แล้วน้ำมันดีแต่ปรุงอาหารเลว มันก็เลวได้ จะดีก็ฟงหวิน จะเลวก็ฟงหวิน เฮียว่า... ถ้าเดินเข้าซูเปอร์แล้วมองไปที่ชั้นขายน้ำมัน คนส่วนใหญ่น่าจะเลือกหยิบน้ำมันพืชที่ขวดใส ๆ ฉลากบอกว่า “ช่วยลดคอเลสเตอรอล” โดยที่ไม่ได้สงสัยอะไร เพราะภาพลักษณ์มันดูสะอาด ใส เบา สุขภาพดี และยังบอกอีกว่ามีไฟโตสเตอรอลสูง ฟังแล้วเหมือนมันคือฮีโร่ที่เกิดมาเพื่อปกป้องหัวใจเรา แต่เฮียอยากชวนให้ตั้งคำถามนิดนึงว่า… ไฟโตสเตอรอลมันคืออะไร แล้วมันจำเป็นกับร่างกายจริงไหม? คำตอบคือ ไฟโตสเตอรอลมันเป็นสารจากพืชที่โครงสร้างคล้ายคอเลสเตอรอลของเรา แต่ร่างกายไม่สามารถใช้มันได้เลย มันไม่ได้กลายเป็นฮอร์โมน ไม่ได้ช่วยซ่อมผนังเซลล์ ไม่ได้เป็นวัตถุดิบสร้างวิตามิน D แถมเวลามันเข้าไปในร่างกาย มันยังไปแย่งตัวดูดซึมคอเลสเตอรอลดี ๆ ที่เราควรจะได้อีก เหมือนเรากำลังจะกินไข่แดงอุ่น ๆ ที่มีคอเลสเตอรอลดีเต็มไปหมด แต่ไฟโตสเตอรอลดันมานั่งจองที่ก่อน แล้วก็ไม่ยอมให้ไข่เข้าไปนั่งในระบบเรา
ทีนี้บางคนอาจบอกว่า “เอ้า! ดีสิ ลดคอเลสเตอรอลได้” เฮียอยากบอกว่า… ลดไปแบบนั้น มันลดของดีที่ร่างกายต้องใช้ไปด้วย เพราะคอเลสเตอรอลไม่ใช่ผู้ร้ายนะ มันคือสารตั้งต้นของฮอร์โมนเพศ ฮอร์โมนความเครียด วิตามิน D และผนังเซลล์แทบทุกเซลล์ในร่างกาย และที่สำคัญ… คนที่มีคอเลสเตอรอลต่ำเกินไป มักมีภาวะซึมเศร้า ระบบภูมิคุ้มกันตก และมีปัญหาเกี่ยวกับฮอร์โมนแบบไม่รู้ตัวด้วยซ้ำ
น้ำมันพืชพวกนี้... โดยเฉพาะที่โชว์ว่ามีไฟโตสเตอรอลสูง มักจะมาจากเมล็ดพืชราคาถูก ต้องผ่านกระบวนการอุตสาหกรรมหลายขั้น ตั้งแต่บีบ กลั่น ฟอกสี กำจัดกลิ่น แล้วก็ใส่สารป้องกันเหม็นหืน หรือบางแบรนด์ก็ต้องเติมวิตามินอีสังเคราะห์เข้าไป เพราะน้ำมันมันอ่อนแอขนาดโดนอากาศแป๊บเดียวก็เหม็น ทำไมต้องเติม? เพราะถ้าไม่เติม มันจะเหม็นหืนไวมาก ทั้งจากแสง ความร้อน และออกซิเจน ทำให้ขายไม่ออก คนไม่อยากใช้
และเฮียจะเล่าให้ฟังว่า ไอ้ไฟโตสเตอรอลที่โฆษณาว่าช่วยลดคอเลสเตอรอลนั้น ต่อให้จะเห็นผลจริง ๆ ก็ต้องบริโภควันละเป็นลิตรนะ... ใช่ ลิตร ไม่ใช่ช้อนโต๊ะ!
ซึ่งก่อนที่คอเลสเตอรอลในเลือดจะลด ตับของเรานี่แหละจะพังก่อน เพราะต้องขับกรองทั้งไฟโตสเตอรอลและอนุมูลอิสระจากน้ำมันพืชออกไปให้ได้ แต่โฆษณาไม่ได้เล่าแบบนั้นไง...
เพราะอะไรที่ดูดีจากโรงงาน มักไม่ได้ดีต่อร่างกายเท่าอาหารที่ออกมาจากธรรมชาติ นี่แหละเฮียถึงอยากเริ่มซีรีส์นี้ขึ้นมา “น้ำมันพืชขวดใส ในความเห็นของฉัน” เฮียจะพาไปดูทีละขวด ตั้งแต่น้ำมันรำข้าว น้ำมันถั่วเหลือง น้ำมันข้าวโพด น้ำมันดอกทานตะวัน จนถึงน้ำมันเบลนด์ที่รวมกันมั่ว ๆ แล้วเขียนไว้ว่า “ดีต่อใจ” แต่อาจไม่ดีต่อ “ตับ ฮอร์โมน” เท่าไหร่นัก
ใครที่เคยเข้าใจว่าน้ำมันพืชคือของดี อาจต้องกลับมาทบทวนใหม่อีกครั้งว่าข้อมูลจากอีกมุมนึง สมควรแก่การพิจารณาไหม แล้วเดี๋ยวตอนหน้า เฮียจะเล่าให้อ่าน ว่า “น้ำมันรำข้าว” ที่หลายคนเข้าใจว่าดีต่อสุขภาพ จริง ๆ แล้วดีจริงไหม
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ fbf0e434:e1be6a39
2025-04-16 14:44:01
@ fbf0e434:e1be6a39
2025-04-16 14:44:01Hackathon 总结
SheHacks+ 9 活动由 Women in Technology Society (WITS+) 于2025年1月10日举办。此次Hackathon 旨在提升科技行业的多元化领导力,通过邀请全国的女性和非二元人士参与。
活动共注册了47个项目,聚焦于创造一个支持性的环境,充分激发参赛者的技术能力。与WITS+的使命一致,通过技能开发、经验学习和行业联系来赋能科技领域的女性。遵循MLH行为准则,这次 Hackathon 提倡包容性,接纳了各种背景的参与者,增强了其多元化参与者的创新潜力。47个项目的成果突显了Hackathon 在激发技术进步和社区参与方面的成功。
Hackathon 获奖者
最佳硬件Hack奖 获奖者
- SpaceInAccessibility: 将AI和硬件结合,实现对聋哑宇航员的实时ASL翻译,利用手势识别和触觉传感器激活来实现太空中的无缝交流。
最佳初学者Hack奖 获奖者
- Dance it, Post it!: 使用MediaPipe和OpenCV通过网络摄像头追踪舞蹈动作,结合React前端和Python后端实现实时分析和反馈。
SheHacks+ 获奖者
- Overall 第一名: SpaceInAccessibility
- Overall 第二名: pantrypixie: 通过扫描收据和跟踪过期日期来解决食物浪费问题,利用Python和AI提供食谱建议及数字储藏界面。
- Overall 第三名: SqWiTs Game: 使用YOLOv5和Databricks来应对手机成瘾,提供游戏化界面以管理分心。
Passport奖 获奖者
(未指定)
Warp最佳开发者工具奖 获奖者
- Synapse: 通过AI将自然语言翻译为命令行指令,实现跨平台集成和安全特性,提高命令行的可访问性。
Hacker奥运奖 获奖者
- Overall 第一名: StarCheck: 结合任务清单管理和太空探险主题的互动平台,使用游戏化界面提升任务效果。
- Overall 第二名: dire: 一个用于管理待办事项清单和习惯追踪的网页应用,具备互动奖励,保持专注和清晰。
- Overall 第三名: Space Cruise+: 提供太空任务管理系统,具有本地存储功能,支持具体任务清单。
最佳GenAI应用奖 获奖者
- DevSpeak: 利用AI翻译技术术语为易懂语言的Chrome扩展,促进技术团队和非技术团队之间的沟通。
使用Cloudflare构建最佳AI应用奖 获奖者
(未指定)
用Databricks开源构建最佳AI项目奖 获奖者
首次黑客奖最具创新力AI项目 获奖者
- SyllaBud: 利用OpenAI语言处理帮助学生管理课程,通过将教学大纲组织到一个中央计划表中,简化学术任务。
附加信息
查看所有项目于 https://dorahacks.io/hackathon/shehacks-9/buidl。
关于组织者
WITS+
西方科技女性+ (WITS+) 是西安大略大学中关注科技的女性和非二元学生的领先组织。该组织因促进包容性和成长而著称,已建立了推动技术创新和学习的成功项目和活动的传统。组织强调合作和赋能,为会员提供与行业相关的见解和发展机会。致力于提升科技领域的多样性,WITS+ 不断努力为未来的科技领袖创造一个欢迎的空间。更多信息请访问 wits-uwo.ca。
-
 @ fbf0e434:e1be6a39
2025-04-16 14:43:47
@ fbf0e434:e1be6a39
2025-04-16 14:43:47Hackathon 概要
渥太华大学官方黑客松 uOttaHack 7,在 286 名参与者提交 138 个项目的热烈支持下圆满收官。本次赛事评审标准聚焦创新力、技术复杂度、实用性及展示效果,确保参赛项目为现实问题提供独特且富有创意的解决方案。活动鼓励跨背景、跨技能水平的学生协作开发,致力于打造兼具影响力的技术成果,成为连接技术理想与落地实践的桥梁。
赛事特别注重学习交流与社交网络搭建,为编程新手与资深开发者提供了平等对话、协同创新的平台,深度践行渥太华大学推动科技领域创新合作的使命。现场涌现的优秀项目充分展现了参与者的创造力与技术功底,不仅为个人成长积累实战经验,更为未来技术突破埋下创新种子。
Hackathon 获奖者
uOttaHack 7 在 16 个类别中展示了各种创新项目,颁发了 23 个子奖以表彰 853 名参与者的成就。以下部分提供了获奖团队及其值得注意的贡献的概述。
uOttaHack 综合挑战奖获奖者
- KellerApp: 通过使用互动工具将英语翻译为 BSL,促进听障人群与听力正常人群之间的交流。
- MemoryMate: 一种智能眼镜设备,受到 AI 辅助,帮助痴呆症患者通过伴侣 app 回忆互动。
- Sweatris: 一款通过身体动作控制的交互式俄罗斯方块游戏,将身体健康与游戏结合。
Solace 奖获奖者
- uOttaType: 利用 Solace 事件代理,通过 AI 驱动的功能(如实时转录和聊天)增强文档协作。
QNX 奖获奖者
- QNX - Traffic Lights: 一个在 Raspberry Pi 4 上部署的实时交通灯系统,使用 QNX 8.0,结合行人功能和开源项目。
Survey Monkey 奖获奖者
- Opinionated Orangutans: 使用 OpenAI 的 API 创建个性化调查,针对用户数据和浏览习惯量身定制。
- Survey Monkey Chatbot: 通过 GROQ AI 推动的对话收集调查数据,结合情感分析。
- Cartbuddy: 使用 SurveyMonkey 的 API 提升零售反馈和参与度,结合 AI 驱动的功能。
NAV CANADA 奖获奖者
DeepCode 奖获奖者
- SecureVision: 威胁分析系统,通过丰富的 API 增强原始安全数据,以获取高级网络安全洞察。
Starknet 奖获奖者
- Dice-Roll OnChain: 基于区块链的 C++ 游戏在 Starknet 上适应,让游戏玩法通过链上验证透明化。
- Playtopia: Build Your Game, Earn Real $$$: 允许用户通过技能游戏赚钱。
- Focusify | Distributed Mental Health Focus App: 通过去中心化技术支持的游戏机制,促进学生的专注力。
Gadget 奖获奖者
Groq 奖获奖者
- SilentGuard: 提供由 AI 和特定激活短语的模拟电话呼叫支持的手机 app,提供低调的紧急援助。
MLH 奖获奖者
- SecureVision
- AgentSingularity: 使用由 LLM 驱动的 UI 部署定制化代理,从网络抓取文档中创建功能。
- KellerApp
- Talent Forge: 促进不使用金钱交易的技能交换,结合 AI 完善简历分析。
- SilentGuard
- Act2Learn: 通过角色扮演场景和个性化反馈利用 OpenAI API 增强学习。
Tail'ed 奖获奖者
- HealthSync-360: 一个整合 Groq AI 的健康追踪应用,计划扩展到主要的健身平台。
有关所有参赛项目的详细信息,请访问 uOttaHack 7 Projects。
关于主办方
uOttaHack
uOttaHack 专注于促进科技和区块链领域的创新与技能发展。以组织 Hackathon 著称,它汇集学生、专业人士和行业专家,通过合作解决现实世界的挑战。凭借在主办鼓励创造性问题解决活动方面的专业知识,uOttaHack 建立了培养技术人才和促进社交网络的声誉。目前关注点包括促进技术进步和支持对科技界有潜在影响的项目。
-
 @ 7d33ba57:1b82db35
2025-04-16 14:30:19
@ 7d33ba57:1b82db35
2025-04-16 14:30:19The Eastern Cape is one of South Africa’s most authentic and unspoiled provinces, offering a mix of dramatic coastlines, mountainous interiors, rolling valleys, and vibrant Xhosa culture. It’s the birthplace of legends like Nelson Mandela, and a region where nature and heritage live side by side.
🌄 Top Places to Visit in the Eastern Cape
🐘 Addo Elephant National Park
- South Africa’s third-largest national park
- Home to over 600 elephants, plus the Big Five and even marine life like great white sharks and whales
- Malaria-free and perfect for self-drives or guided safaris
🏄♂️ Jeffreys Bay (J-Bay)
- One of the world’s top surfing destinations
- Relaxed beach town with laid-back vibes, beach bars, and shell collecting
- Annual World Surf League event every July
🌊 Wild Coast
- Rugged, untouched coastline stretching from East London to the KwaZulu-Natal border
- Visit the Hole in the Wall, explore Coffee Bay, or hike the Wild Coast Trail
- Traditional Xhosa villages, cows on the beach, and star-filled nights
🏙️ Port Elizabeth / Gqeberha
- Coastal city known for friendly locals and wide beaches
- Visit the Donkin Heritage Trail, chill at King’s Beach, or dive in the Algoa Bay marine reserve
- Gateway to Addo and the Garden Route
🏞️ Hogsback
- Misty forests, waterfalls, and Hobbit-like landscapes (inspired Tolkien!)
- Ideal for hiking, forest bathing, and quiet retreats
- Artistic village with eco lodges, crystal shops, and labyrinths
⛰️ Drakensberg Mountains (Eastern Slopes)
- The far reaches of the uKhahlamba-Drakensberg, lesser-known and less crowded
- Great for hiking, rock art viewing, and mountain escapes
🌍 Cultural Experiences
- Qunu & Mthatha – Visit the Nelson Mandela Museum and the village where he grew up
- Experience traditional Xhosa food, music, and village life
- Look out for rondavels (round huts), beadwork, and storytelling traditions
🚙 How to Travel
- The Eastern Cape is best explored by car or guided tours, especially the Wild Coast where roads can be rough
- Flights into Gqeberha (Port Elizabeth) or East London
- Be prepared for off-the-beaten-path adventures—it's part of the charm!
📅 Best Time to Visit
- Spring/Summer (Oct–Mar): Warm weather, great for beaches and outdoor travel
- Winter (Jun–Aug): Mild inland, cooler on the coast, excellent for hiking and safaris
- Year-round destination, depending on your interests
🛶 Must-Do Experiences
- Kayak on the Keurbooms River
- Watch whales and dolphins in Algoa Bay
- Camp, hike, or surf along the Wild Coast
- Immerse yourself in the rural charm and hospitality of the Amathole Mountains
-
 @ edeb837b:ac664163
2025-04-16 12:59:09
@ edeb837b:ac664163
2025-04-16 12:59:09If you’ve spent any time around stock trading communities, chances are you’ve heard the name Webull pop up more than once. It’s not just another brokerage app—it’s one of the go-to platforms for retail traders across the globe. But what exactly is Webull? Why do so many individual traders prefer it over other platforms? And how does NVSTly take its capabilities even further?
Let’s break it all down.
What Is Webull?
Webull is a commission-free trading app that allows users to trade stocks, ETFs, options, and cryptocurrencies from their phones or desktop. Launched in 2017, it quickly gained popularity for its sleek interface, real-time data, and powerful tools—all without the traditional fees associated with many brokerage platforms.
While it’s often compared to Robinhood, Webull caters more to active traders and those who want slightly more advanced tools without the complexity (or costs) of institutional-level platforms.
What Can You Do on Webull?
Webull offers a full suite of features for modern traders:
- Commission-free trading for stocks, options, ETFs, and crypto
- Extended trading hours (premarket and after-hours)
- In-depth charting tools with technical indicators
- Fractional shares trading to invest with any dollar amount
- Paper trading for practice without real money
- Level 2 market data (Nasdaq TotalView, subscription-based)
- Custom alerts and watchlists
- Community feed for trade ideas and discussions
Whether you’re a beginner trying to learn the ropes or an experienced trader managing multiple positions daily, Webull is designed to give you an edge.
Why Retail Traders Prefer Webull Over Other Brokers
Here are some reasons why Webull has become a fan favorite among retail traders:
✅ Advanced Tools, Simple UI
Unlike many traditional brokers with clunky interfaces, Webull balances powerful tools with a user-friendly design. You get access to real-time quotes, charting with dozens of indicators, and customizable layouts—all wrapped in a clean, modern app.
✅ Free Options Trading
While some platforms charge per contract or per trade for options, Webull offers commission-free options trading, which is a huge win for active options traders.
✅ No Account Minimums
New traders can get started with as little (or as much) money as they want. There are no minimum deposit requirements for standard cash or margin accounts.
✅ Fractional Shares
Webull lets users invest in fractional shares, meaning you don’t need to buy an entire share of high-priced stocks like Amazon or Tesla. You can invest as little as $5 into a stock, making it easier to build a diversified portfolio with any budget.
✅ Paper Trading
Webull gives users a way to test strategies in a simulated environment, which is perfect for learning without risking real money.
✅ Mobile & Desktop Support
Webull’s mobile app is robust, but the desktop version is just as powerful—great for traders who prefer multi-screen setups or deeper analysis.
Webull Pros & Cons
✅ Pros
- $0 commissions on stocks, options, ETFs, and crypto
- Clean and intuitive interface
- Real-time data and news
- Built-in paper trading
- Fractional shares
- Support for extended hours trading
- Level 2 market data available
⚠️ Cons
- No mutual funds
- Webull uses a high spread for crypto trading
- Slight learning curve for beginners
How NVSTly Supercharges Your Webull Experience
Webull is powerful on its own—but when integrated with NVSTly, it becomes next-level.
NVSTly is the fastest-growing social trading app, where traders can automatically track, share, and analyze their trades, all in one place. Thanks to deep Webull integration, you can now connect your Webull account to NVSTly in seconds.
🔗 Connect in Seconds with a QR Code
Linking your Webull account is as simple as scanning a QR code inside your NVSTly account settings using the Webull mobile app. That’s it—your trades are now synced automatically.
💼 What You Get with NVSTly + Webull
- Auto-tracked trades — No more manual logging or screenshots
- Real-time trade sharing — Followers see your trades as they happen
- Performance analytics — Gain insights into your win rate, risk/reward, and more
- Automate your trade signals — Save time and help followers catch entries earlier, closer to your price
- Trade history dashboards — View and share detailed stats for your trades, with visual breakdowns
- Daily/Weekly/Monthly Recaps — Get beautifully designed trade summaries sent straight to your Discord or social profiles
Whether you’re a solo trader or part of a larger trading community, NVSTly makes it ridiculously easy to share your journey, learn from others, and improve your performance—all while staying 100% focused on the markets.
Final Thoughts
Webull has earned its spot as a top-tier brokerage app for retail traders, offering a powerful platform with zero commissions and high-quality tools. When paired with NVSTly, your trading becomes smarter and more connected—automating the way your trades are tracked, shared, and analyzed, so you can focus on the markets while NVSTly handles the rest.
If you’re a Webull user and haven’t connected to NVSTly yet, now’s the time. Your trading deserves more than just a broker—it deserves a platform built to grow with you.
Ready to level up your Webull trading?
➡️ Sign in to NVSTly, go to Brokerages & Exchanges in your account settings, click Connect next to Webull, and follow the QR code instructions to link your account in seconds.Available on web, iOS, Android, & fully integrated with Discord through a unique bot – the only of its kind!
-
 @ 7d33ba57:1b82db35
2025-04-16 12:52:15
@ 7d33ba57:1b82db35
2025-04-16 12:52:15Addo Elephant National Park is a premier wildlife destination in South Africa's Eastern Cape, located approximately 70 km from Gqeberha (formerly Port Elizabeth). Established in 1931 to protect a small group of elephants, the park has since expanded to become the third-largest national park in the country, encompassing diverse landscapes from the Karoo to the coast.
🐘 Wildlife Highlights
-
Elephants:Home to over 600 elephants, the park offers exceptional opportunities to observe these majestic creatures in their natural habitat
-
Big Five:In addition to elephants, visitors can encounter lions, leopards, buffaloes, and black rhinos.
-
Big Seven:The park's marine section includes great white sharks and southern right whales, making it one of the few places boasting the "Big Seven.
-
Other Species:The park hosts a variety of wildlife, including zebras, antelopes, meerkats, and over 400 bird species.
🚙 Activities
-
Self-Drive Safaris Explore the park at your own pace on well-maintained road.
-
Guided Game Drives Join expert-led tours for in-depth wildlife viewing experience.
-
Hiking Trails Discover the park's diverse flora and fauna on designated walking path.
-
Bird Watching With a rich avian population, the park is a haven for bird enthusiast.
-
Picnic Spots Enjoy meals amidst nature at designated picnic area.
🏨 Accommodation
The park offers various lodging options, including rest camps and luxury lodges like Camp Figtree, catering to different preferences and budges.
🌿 Visitor Tips
-
*Malaria-Free: The park is located in a malaria-free zone, making it suitable for families and travelers of all aes.
-
*Accessibility: Easily reachable from Gqeberha, it's an excellent addition to a Garden Route itinerry.
-
*Conservation Efforts: The park plays a crucial role in preserving South Africa's biodiversity, offering visitors a chance to support and learn about conservation initiaties.
For more information and to plan your visit, you can explore the official SANParks website.
-
-
 @ 0121e6f7:1a7c8df4
2025-04-16 12:37:37
@ 0121e6f7:1a7c8df4
2025-04-16 12:37:37hi2
-
 @ 06639a38:655f8f71
2025-04-16 12:11:31
@ 06639a38:655f8f71
2025-04-16 12:11:31Finally there is a release (1.7.0) for Nostr-PHP with a full NIP-19 integration. Here is an example file with some snippets to how it works to encode and decode bech32 encoded entities:
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-decoded-entities.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-encoded-entities.php
Now merge request #68 (and issues #74, #64 are closed) is finally merged which I opened in October 2024.
Next up is:
- Create documentation how to use NIP-19 with the library on https://nostr-php.dev
- Create documentation how to use NIP-04 and NIP-44 with the library on https://nostr-php.dev
- Work out a proof-of-concept with the revolt/event-loop package to create concurrent async requests with websocket connections
-
 @ 5188521b:008eb518
2025-04-16 09:09:48
@ 5188521b:008eb518
2025-04-16 09:09:48Why write a book about time?
My obsession with time actually started when I read An Occurrence at Owl Creek Bridge (written by Ambrose Bierce in 1890).
We can’t play around with time in the real world, but in fiction, anything goes. The story of Owl Creek Bridge follows a Confederate sympathiser condemned to death by hanging. In its three sections, time goes forward and back, speeds up and slows down, and at one point stops entirely. Every time I read it, I feel like I’m physically travelling in time.
I went a bit deeper into the topic back in 2020. Due to the lockdown, I had a lot of time on my hands to do some research. Like many of my stories, this one started with a question: I started to ask ‘what actually is time’?
What did you find out?
I found out that time is a rabbit hole! Nobody knows exactly what it is. We know that it’s conceptual, personal, and malleable, however accurate our watches are. Some philosophers and scientists (Jose Luis Borges and Carlo Rovelli) claim it doesn’t exist.
I guess what I discovered is that we all need time to survive. It’s how we process our experience here on Earth.
Who are the characters in this book?
The book tells the story of Luca Cangemi, an Italian philosophy professor giving a lecture on the subject of time. The chapters follow the possible lives of other characters in the lecture hall. Then, Cangemi makes an astounding discovery. It’s something that allows him to change the fabric of time for everyone (including the readers).
Why use 15 characters to present the story?
I like to challenge readers, so I made the story a bit of a puzzle. In fact, there is something called a 15 puzzle — it’s a block of 15 pictured tiles and one space. You have to slide them to arrange the correctly ordered image. There’s more about the puzzle in the book.
What about the Timechain? Is there any link there?
Not exactly. The book doesn’t mention it, but isn’t everything an analogy for bitcoin? Soon after finishing this book, I got orange pilled and began to read more and more about bitcoin, including Gigi’s fantastic essay Bitcoin is Time.
Time is all we have though. Even though it might be hard to understand, we have to try.
Who do you think would enjoy this book?
I’d say sci-fi fans. Those who aren’t afraid to be challenged. One cool thing about the bitcoin community is that they are dialled in to technical stuff and they are avid readers. Why not give fiction a try too? Sometimes we learn more from getting the answer ourselves through stories.
What are you working on next?
I have three other writing projects on the go, so there is no time to rest. Very soon, I’ll be publishing a children’s book about horrible uncles. I’m editing the next installment of 21 Futures too. Financial Fallout will be out in early 2025. And finally, I’m writing content and newsletters for bitcoin founders and companies. If I’m not trying to sell you a book, I’ll be doing my best to orange-pill you, ha ha.
Thanks for talking with us, Philip, and good look with all those writing projects.
Order the book in our store.
Here’s a passage from Fifteen Shades of Time.
The Direction of Everything
Luca Cangemi and everyone he knows will be long dead, but the moment will come. Theoretical physicists believe it will be anywhere from 2.8 to 22 billion years in the future. In that moment, everything reverses.
The Big Crunch is a cosmological event in our future and our past in which the density of matter grows sufficiently that gravitational attraction overcomes the expansion that began with the Big Bang. Entropy reverses and the second law is broken. Chaos retreats.
Order is regained as space contracts. Broken rocks reform and decayed bodies reanimate. We live our lives in reverse, unexperiencing everything we did the first time around, moving backwards, shrinking towards birth. Instead of questions about creation, we search for the harbinger of order. Who began this? What is our final form?
Luca imagines the crowds at his book signings dissipating and the offices of his academic fellowships decreasing in size. Wrong turns are righted and his family grows closer. His briefcase heals itself and he returns it to his mother. Life rewinds back to him as a young boy, unreading the words that inspired him to look for meaning in all of this. If it can all be reversed, are all shared experiences undone? All bonds broken? Luca returns into his parents, then ancestors, apes, microbes, and nothing. The earth, the planets and stars all merge into one perfectly ordered mass.
Yet, this is not an end, but another beginning in which the universe is reborn in another bang. Galaxies, planets, plants, and philosophy professors will live the same lives as they did billions of years before (and after). The process of positive and negative entropy repeats and we all make the same mistakes again.
Time elapsed: the infinitely repeating cycle of a universe
Philip Charter is a totally human writer, laser-focused on spreading the gospel of bitcoin and cypherpunk ideals. He is the editor of the 21 Futures anthology series and has published four books of short fiction. After leaving the UK to search for more sun, he now resides in Gran Canaria, Spain.
-
 @ 7d33ba57:1b82db35
2025-04-16 08:31:09
@ 7d33ba57:1b82db35
2025-04-16 08:31:09Iceland is a surreal blend of volcanic power, glacial beauty, and rugged wilderness. From black sand beaches and steaming geothermal pools to massive waterfalls and the magical northern lights, it’s a dream destination for nature lovers and road trippers.
Whether you want to soak in a hot spring, chase waterfalls, hike volcanoes, or just drive through epic landscapes that look straight out of a fantasy film, Iceland has it all.
🧭 Top Things to Do in Iceland
1️⃣ The Golden Circle
The perfect intro loop from Reykjavik: - Þingvellir National Park – Rift valley between tectonic plates + historic parliament site
- Gullfoss – Thundering two-tier waterfall
- Geysir geothermal area – Home of the original geyser (and Strokkur, which erupts every few minutes)2️⃣ South Coast Highlights
- Seljalandsfoss & Skógafoss – Iconic waterfalls you can walk behind or get soaked by
- Reynisfjara Black Sand Beach – With eerie basalt columns and crashing Atlantic waves
- Sólheimajökull Glacier – Guided glacier walks or ice climbs
- Vík – Quaint village with epic coastal views
3️⃣ Snæfellsnes Peninsula
- Often called “Iceland in Miniature”
- Includes Kirkjufell mountain, lava fields, fishing villages, and coastal cliffs
- Great alternative if you’re short on time but want variety
4️⃣ The Blue Lagoon (or better: Sky Lagoon)
- Iconic milky-blue geothermal spa near the airport
- Sky Lagoon near Reykjavik is newer, less touristy, and has a 7-step ritual sauna-spa experience with ocean views
5️⃣ Chase the Northern Lights
- Best seen September to April
- Get away from city lights and use apps or tours to track them
- Clear skies, cold nights, and some patience = magic
🚗 Epic Road Trip: The Ring Road
- Iceland’s main highway (Route 1) loops the entire island
- Takes about 7–10 days to do well
- You’ll see glaciers, fjords, waterfalls, volcanoes, and maybe even puffins and reindeer
- Rent a campervan or car and take it slow—it’s all about the journey
🍽️ What to Eat in Iceland
- Lamb stew (kjötsúpa) – Warm and hearty
- Plokkfiskur – Creamy fish and potato comfort food
- Skyr – Icelandic yogurt, smooth and protein-rich
- Hot dogs from Bæjarins Beztu – Iconic street food in Reykjavik
🗓️ When to Go
- Summer (June–Aug): Midnight sun, hiking, puffins, easier driving
- Winter (Oct–Mar): Aurora season, ice caves, snowy wonderland
- Shoulder seasons: Fewer crowds, lower prices, unpredictable weather (pack layers!)
✨ Quick Tips
✅ Tap water = some of the purest in the world
✅ Always check road and weather conditions—they can change fast
✅ Download Veður (weather) and SafeTravel.is for safety updates
✅ Book hot springs, ice cave tours, and northern lights hunts in advance during high season -
 @ da0b9bc3:4e30a4a9
2025-04-16 08:28:24
@ da0b9bc3:4e30a4a9
2025-04-16 08:28:24Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/944844
-
 @ ffbcb706:b0574044
2025-04-16 08:11:12
@ ffbcb706:b0574044
2025-04-16 08:11:12I like to have openletter on the Nostr protocol
-
 @ 2b24a1fa:17750f64
2025-04-16 07:55:24
@ 2b24a1fa:17750f64
2025-04-16 07:55:24„Ich bin der Weg“, sagt Jesus am Kreuz, in der Mitte. Symbolisch zwischen Übertreibung und Verblendung. Wenn dieser Maßstab an das Gros der Nachrichten angelegt wird, die wir in den letzten fünf Jahren vermittelt bekamen, landen wir selten in der Mitte. Aber nur der gelassene Blick in Richtung Übertreibung und Verblendung, lässt die Mitte zwischen ihnen erspüren.
https://soundcloud.com/radiomuenchen/angst-frisst-seelen-von-j-rgen?
Auf den Weg dorthin begibt sich eine Friedensprozession am Karfreitag, den 18. April ab 13 Uhr, ausgehend vom Postplatz in Dresden. Hören Sie Jürgen Flieges Text: „Angst frisst Seelen“.
Sprecher: Guido de Gyrich.
-
 @ 2b24a1fa:17750f64
2025-04-16 07:52:59
@ 2b24a1fa:17750f64
2025-04-16 07:52:59Am 22. November 1963 starb US-Präsident John F. Kennedy bei einem Attentat in Dallas durch zwei Gewehrschüsse. Als möglicher Täter wurde Lee Harvey Oswald verhaftet und zwei Tage später erschossen. Kennedys Amtsnachfolger Lyndon B. Johnson setzte einen Untersuchungsausschuss ein: die Warren-Kommission, benannt nach deren Leiter Earl Warren, höchster Richter am Supreme Court, dem Obersten Gerichtshof der Vereinigten Staaten. Die Warren-Kommission bestätigte die Einzeltäter-These. Dennoch kursierten und kursieren bis heute zahlreiche Gerüchte und Verschwörungstheorien. Mit dem Totschlag-Argument „Nationale Sicherheit“ verweigerte die CIA die Herausgabe ihrer Ermittlungsakten und nährte gerade dadurch den Verdacht, sie selbst habe Kennedy ermorden lassen. Über 60 Jahre später gibt Präsident Trump nun die Akten frei.
https://soundcloud.com/radiomuenchen/trump-die-jfk-files?
\ Die Meinungen gehen auseinander: Für die einen enthalten die Akten wenig Neues, für die anderen ergeben sich neue Zweifel an der Einzeltäter-These. Unsere Autorin Gaby Weber befasst sich schon seit vielen Jahren mit der Materie, unter anderem in ihrem Buch „CIA, Drogen, Gehirnwäsche“ von 1981. Außerdem recherchiert sie seit langem über illegale Atomwaffentests des Pentagons in Argentinien 1960. Zwischen den illegalen Atomwaffentest und Kennedys Tod könnte es einen Zusammenhang geben, glaubt Gaby Weber und hat einen neuen Antrag auf Aktenfreigabe gestellt. Hören Sie ihren Beitrag: „Trump & die JFK-Files“.
Sprecherin: Gaby Weber
Redaktion: Jonny Rieder
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen\ odysee.com/@RadioMuenchen.net:9\ rumble.com/user/RadioMunchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927
-
 @ 2b24a1fa:17750f64
2025-04-16 07:40:49
@ 2b24a1fa:17750f64
2025-04-16 07:40:49„Auch wenn das völliger Wahnsinn ist“ … soll der Freie-Wähler-Chef gesagt haben: „Die CSU kann auch ohne uns im Bundesrat zustimmen. Deswegen bringt es nichts, wenn wir uns weiter dagegenstellen.“ Man opfert also die eigene Einstellung und stimmt für das Gegenteil, legitimiert also den Wahnsinn, weil es nichts bringt? Hört mit dieser Schizophrenie auf – möchte man schreien. Denn täglich hören wir von führenden deutschen Politikern, die ohne relevante Begründung die irrwitzigsten Entscheidungen treffen und den Souverän übergehen, als wäre er Luft.
Jetzt sollte dieser Souverän, der Bürger aber nicht mit Hilflosigkeit reagieren, meint Ludwig F. Badenhagen, denn es existiere ein einfacher als auch wirksamer Lösungsansatz. Hören Sie seinen Text: „Wie wir die Kriegstreiber stoppen“. Sprecherin: Sabrina Khalil.
Sie hörten: „Wie wir die Kriegstreiber stoppen“ von Ludwig F. Badenhagen. Ludwig F. Badenhagen ist ein Pseudonym für einen Autor mit deutschen Wurzeln, der das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika beobachtet. Er ist international agierender Manager mit globalem Netzwerk und verfügt dadurch über tiefe Einblicke in Konzerne und Politik. Sein Text erschien zunächst auf Milosz Matuscheks Friedensinitiativseite „Friedenstaube“.
-
 @ 2b24a1fa:17750f64
2025-04-16 07:32:45
@ 2b24a1fa:17750f64
2025-04-16 07:32:45Wo läßt es sich trefflicher plaudern als am Küchentisch. Es muß ja nicht unbedingt der eigene sein. Hauptsache, es sitzen vergnügte Menschen reinen Herzens daran, wie zum Beispiel die Herren Helmut Schleich und Franz Esser.
https://soundcloud.com/radiomuenchen/am-kuchentisch-mit-schleich-und-esser
-
 @ b0137b96:304501dd
2025-04-16 06:33:23
@ b0137b96:304501dd
2025-04-16 06:33:23In recent years, the Telugu film industry has witnessed a remarkable transformation, with a significant surge in the popularity of Hollywood movies in Telugu dubbed. This trend reflects a growing appetite among Telugu audiences for diverse storytelling and international cinematic experiences. While regional films continue to thrive, the increasing demand for Hollywood movies in Telugu dubbed speaks to a cultural shift and a desire for global entertainment. Two films that exemplify this trend are Medusa: Beauty is the Beast and its sequel, Medusa’s Venom. These movies not only showcase the appeal of Hollywood narratives but also demonstrate how familiar mythological themes can be reimagined in a contemporary context, resonating with Telugu viewers.
This article explores these two films and their significance in the broader landscape of Hollywood movies in Telugu dubbed, highlighting how this trend is reshaping the viewing habits and preferences of Telugu cinema enthusiasts.
Hollywood Movies in Telugu Dubbed
Medusa: Beauty is the Beast – Hollywood movie in Telugu dubbed (2021) Medusa: Beauty is the Beast is a horror movie that puts a modern twist on Greek mythology. After being bitten by a lethal snake, a young woman named Carly experiences changes in her senses and appearance as she sheds her old self and slowly turns into a deadly weapon. This Hollywood movie in Telugu dubbed is directed by Jeffrey and Co. and features a powerful performance by Megan Purvis as the lead actress, Carly. Most of the film takes place in a caravan site, which serves as a sanctuary for women under the protection of Medusa.
The Hollywood movie in Telugu dubbed tackles topical issues wrapped in horror, providing a tale of how women are treated in society. With a limited budget, the filmmakers have done a commendable job of creating an engaging and thought-provoking story. The film has been well-received by audiences, with 2.3k IMDb users adding it to their watchlists.
Hollywood Movies in Telugu Dubbed Medusa: Beauty is the Beast is one of the many Hollywood movies in Telugu dubbed that caters to the growing demand for international content in the region. These dubbed versions allow Telugu audiences to enjoy popular Hollywood films in their native language, making them more accessible and engaging.
The rise of Hollywood movies in Telugu dubbed represents a significant shift in the region’s cinematic landscape. It not only broadens the range of entertainment options available to Telugu-speaking audiences but also fosters a greater understanding and appreciation of diverse storytelling techniques and cultural perspectives. The success of films like Medusa demonstrates that there is a receptive audience for international content, paving the way for more innovative and diverse cinematic experiences in the Telugu-speaking regions.
Now, let’s explore the sequel of Medusa, Medusa’s Venom.
Hollywood Movies in Telugu Dubbed
Medusa’s Venom – Hollywood movies in Telugu dubbed (2023) Medusa’s Venom is a sequel to Medusa: Beauty is the Beast and continues the story of the deadly snake-woman. In this instalment, the beast is back, and her venom is deadlier than ever. When newcomer Lola is welcomed into Medusa’s circle, she undergoes a ritual to bring her closer to her new sisters.
Unlike the first film, Medusa’s Venom takes a more straightforward approach to the horror genre. It depicts a group of snake women who are also sex workers, living in a caravan site that is now under the control of Medusa. This Hollywood movie in Telugu dubbed, explores the theme of power corrupting people, as the sanctuary from the previous film has become a place of control.
Released in 2023, Medusa’s Venom avoids the subtlety and layered storytelling of its predecessor, opting for a more direct and action-oriented narrative. The film continues the Greek mythology-inspired horror elements while delving deeper into the dynamics of the snake women’s group.
Hollywood movies in Telugu dubbed: A Growing Trend The success of Medusa: Beauty is the Beast and Medusa’s Venom highlights the growing trend of Hollywood movies in Telugu dubbed. This trend allows Telugu audiences to enjoy a wider range of international films, from action blockbusters to thought-provoking dramas.
As the demand for Hollywood movies in Telugu dubbed continues to rise, more and more filmmakers are recognizing the potential of this market. By adapting popular Hollywood films for Telugu audiences, they are able to reach a larger and more diverse viewership, while also showcasing the talent and creativity of the Telugu film industry.
Wrapping Up In conclusion, Medusa: Beauty is the Beast and Medusa’s Venom are two examples of the growing popularity of Hollywood movies in Telugu dubbed. These films offer a unique blend of horror, mythology, and social commentary, providing audiences with an engaging and thought-provoking viewing experience.
As the trend continues to evolve, it has the potential to influence local filmmaking practices, encourage cross-cultural exchanges, and ultimately enrich the Telugu film industry. We are excited to see what other Hollywood movies are adapted for Telugu audiences in the future, are you?
-
 @ fbf0e434:e1be6a39
2025-04-16 05:38:17
@ fbf0e434:e1be6a39
2025-04-16 05:38:17Hackathon 概要
由瑞士洛桑联邦理工学院(EPFL)区块链学生协会组织的 Privacy and Verifiability Hackathon 于 2023 年 3 月 8 日至 9 日成功举办。这场 26 小时极限挑战吸引 36 名开发者注册参与,最终提交 23 个获批项目,聚焦区块链隐私与可验证性技术解决方案开发,由 Mina、Hedera Hashgraph Association 及 Hylé 等机构赞助,总奖池达 15,000 美元。
显著的成就包括在隐私增强方法和可验证区块链解决方案方面的创新。项目的评估标准包括创新性、技术执行,以及在解决隐私和可验证性问题上的有效性。所展现的多样化解决方案突出显示了区块链领域的原创性和实用应用。
Hackathon 促进了学生、专业人士和爱好者之间的协作和创造力,推进了关于隐私和可验证区块链技术的讨论。活动强调了分散化解决方案在应对隐私挑战方面的潜力,进一步确认了社区在推动区块链创新方面的承诺。
Hackathon 获奖者
Privacy and Verifiability Hackathon 以超过 25 个项目竞争 15,000 美元奖池而告终。它展示了在隐私和验证技术中取得突破的创新解决方案,分为三个类别。
Mina 奖得主
- Mina Cash: 利用 Mina Protocol 的零知识证明进行匿名支付交易,确保链上证明和链下隐私。
- zkPetitions: 一种去中心化应用程序,使用零知识证明来保护隐私和数据完整性,并进行请愿处理。
- ZKribble.io: 一种利用零知识证明游戏,在绘制和猜测上下文中保护秘密词语。
- Aether ticket: 集成 Mina Protocol 的票务验证平台,通过零知识证明实现安全、私密的验证。
- Hush tag: 使用 Mina Protocol 的去中心化票务系统,实现安全和私密的票务生成与验证。
Hedera Hashgraph Association 奖得主
- AtlasID: 使用 React、Express 和 SD-JWT VC 技术实现注重隐私的身份验证。
- donate.fun: 通过区块链和身份验证来增强人道主义援助的透明度和安全性。
- Geotrust: 用于地理寻宝的网络应用程序,具备位置创建和稳健的用户验证功能。
- Hedemon: 使用 Hedera 区块链将实物收藏品转换为可验证真实性和隐私的 NFTs。
Hylé 奖得主
- Sthylé - image verification: 基于区块链的平台,用于验证图像真实性与管理。
- zkIA: 专注于 AI 应用中的零知识证明,尽管没有提供具体技术细节。
- CipherSocial: 通过去中心化平台使用密码学和区块链,基于兴趣将用户连接起来以保护隐私。
- Plethora: 用于创建使用零知识证明的 AI 代理,完成私密、可验证的任务。
有关项目的完整列表和更多详细信息,请访问 dorahacks.io 上的 Hackathon页面 。
关于组织者
Blockchain Student Association
Blockchain Student Association 旨在教育和吸引学生参与区块链技术领域。该组织以其在区块链系统和应用方面的专业知识而闻名,积极举办研讨会和工作坊以增强成员的技术理解。它曾与行业领导者合作开展项目,专注于创新的区块链解决方案。该组织的使命是培养一个探索区块链实际应用并在快速发展的领域内提升技术素养的知识社区。
-
 @ fbf0e434:e1be6a39
2025-04-16 05:38:05
@ fbf0e434:e1be6a39
2025-04-16 05:38:05Hackathon 概述
由 SUCI Blockchain Hub 主办、CodeX 赞助的 AI Hackathon 于 2025 年 3 月 7-9 日在越南胡志明市成功举办。这场线下活动吸引 42 名开发者参与,围绕实用场景的真实资产整合与 AI 代理开发,共诞生 12 个创新项目。
此次 Hackathon 总奖池为 15,000 美元,以 USDT 和 CDX 代币形式分配。一等奖获得者获得 4,000 USDT 和 2,000 CDX 代币,以及前往泰国参加即将举办的 COTI Foundation Hackathon 的旅行和住宿。第二名和第三名分别获得 3,000 和 2,000 USDT,以及 CDX 代币。特别赛道奖项包括最佳 AI 代理、最佳无代码解决方案和最佳真实应用,每项获得 1,000 USDT 和 500 CDX 代币。其他奖项则表彰了创新 AI 应用、跨行业解决方案和社区影响。
活动促进了交流、学习和协作创新,展示了 AI 与区块链技术之间日益紧密的联系。
Hackathon 获奖者
AI Hackathon 2025 展现了技术创新和各领域的创意。历经 48 小时,参与者密集合作解决问题,评选出在三个奖项类别中的杰出项目:主要奖项、赛道奖项和特别奖项。
主要奖项获奖者
以下三个项目因其创新和实施而脱颖而出:
- VocakeX:这是一款 Web3 教育科技平台,利用游戏化和 AI 增强学习,结合 AI 驱动模块与游戏化元素,提高教育参与度和学习保持率。
- StudyVerse:通过分析学生情绪,提供个性化的健康建议和学习指导,旨在通过情感识别和自适应反馈提升教育效果的 AI 平台。
- VaultAI:一款 AI 驱动的加密钱包,设计用于复杂的资产管理和 DeFi 洞察,利用分析和机器学习优化财务决策。
赛道奖项获奖者
项目因在 AI 代理、无代码解决方案和真实应用中的成就而被认可:
- CryptoMentor:一个智能聊天机器人,帮助新投资者学习和进行加密交易,提供实时 API 集成以便可靠的帮助。
- VaultAI
- Scholar AI:一款 AI 工具,通过数据分析为留学决策提供量身定做的教育和财务机会的推荐。
特别奖项获奖者
这些奖项凸显了具有创新潜力、跨行业应用和社区影响的项目:
- StudyVerse
- TourRecommendation:一种 AI 工具,通过区块链驱动的透明度帮助游客找到可靠的餐饮和住宿,提升交易的信任度。
- Buildlink:通过 AI 简化区块链交互,提供 NEAR 区块链上的用户友好互换和质押,提高新用户的可及性。
此次 Hackathon 强调了 AI 在应对复杂问题和提供跨领域影响力解决方案方面的能力。有关所有项目的更多详细信息,请访问 Dorahacks AI Hackathon。
关于组织者
SUCI BLOCKCHAIN HUB
SUCI Blockchain Hub 致力于区块链技术的开发和应用。该组织以推进各行业的安全去中心化解决方案而闻名,并对多个重要区块链项目作出了贡献。通过研究和开发,SUCI Blockchain Hub 促进创新,与行业领导者协作,提升区块链应用,推动数字交易的可及性和透明度。目前,组织的使命着重于扩展区块链整合,为企业和个人提供高效、安全的解决方案。
-
 @ 8e7e2128:25e34fd1
2025-04-16 05:20:11
@ 8e7e2128:25e34fd1
2025-04-16 05:20:11In today’s beauty-driven, fast-paced world, the desire for youthful, radiant skin is stronger than ever. But unlike in decades past, where cosmetic surgery reigned supreme, modern skincare enthusiasts are increasingly turning toward gentler alternatives. Enter the era of minimally invasive skin treatments—solutions designed to refresh and rejuvenate without the need for scalpels, sutures, or significant downtime.
Among the many advancements, one technology stands out: light-based skin therapy. From acne to aging, pigmentation to inflammation, light is proving to be one of the most versatile tools in the modern skincare toolkit. But how did we get here, and what exactly makes these treatments so popular? Let’s break it all down.
Why Minimally Invasive Is the New Gold Standard Once upon a time, surgical facelifts and chemical peels were the go-to methods for anyone looking to turn back the clock on aging. But as our understanding of skin biology has evolved—and with the rise of social media and wellness culture—people are now seeking treatments that align with a lifestyle of balance, subtlety, and self-care.
Here’s why minimally invasive skin treatments are dominating the skincare space: - Little to no downtime: You can schedule a session on your lunch break and head back to work without skipping a beat. - Natural results: These treatments work with your body’s own processes to gradually enhance your skin’s appearance. - Lower risk: With no need for general anesthesia or extensive recovery, the risk profile is significantly lower. - Affordability: Compared to surgical options, many of these treatments are easier on the wallet. - Customization: Providers can tailor treatments based on individual skin types, concerns, and goals.
A Closer Look at the Technology: Light-Based Skin Therapy At the forefront of this skincare revolution is light-based skin therapy, a non-invasive category of treatments that use controlled light wavelengths to trigger natural biological processes within the skin.
How Does It Work? Different wavelengths of light penetrate the skin at various depths. By targeting specific skin layers, light-based skin therapy can: Stimulate collagen production Kill acne-causing bacteria Reduce pigmentation Promote healing and tissue regeneration
There’s no cutting, no abrasion, and often no pain—just the gentle power of light doing what it does best.
Types of Light-Based Skin Therapy Let’s dive into the most popular forms of light-based therapies and what they can do for your skin.
1. LED Light Therapy LED therapy is one of the most accessible and gentle treatments available. It involves the application of different colored lights to target various skin concerns: Blue light: Effective for killing Propionibacterium acnes, the bacteria behind acne breakouts. Red light: Boosts circulation and stimulates collagen production, making it ideal for anti-aging. Green light: Targets hyperpigmentation and sun damage. Yellow light: Helps reduce redness and inflammation. LED therapy can be done in-office or at home with wearable LED masks and handheld devices.
2. IPL (Intense Pulsed Light) Often referred to as a “photofacial,” IPL delivers broad-spectrum light deep into the skin. It’s especially effective for: Sunspots and age spots Redness and rosacea Broken capillaries Uneven skin tone Unlike lasers, which use a single wavelength, IPL uses multiple wavelengths, allowing for treatment of multiple issues in a single session.
3. Fractional Lasers Fractional lasers are more intensive than LED or IPL, but they’re still considered minimally invasive. They work by creating microscopic columns of controlled damage in the skin, which stimulates the body’s natural healing response. These are best for: Acne scars Fine lines and wrinkles Stretch marks Skin resurfacing
Downtime can vary, but results are often dramatic and long-lasting.
4. Photodynamic Therapy (PDT) A more medical-grade form of light-based skin therapy, PDT combines a light-sensitive solution with a specific wavelength of light to treat more severe issues, such as: • Precancerous skin lesions (actinic keratosis) • Severe acne • Sun damage This treatment is typically performed by dermatologists and offers both therapeutic and cosmetic benefits.
What to Expect During and After Treatment One of the key reasons minimally invasive treatments have taken off is how user-friendly they are. Here’s a general outline of what most patients can expect:
Before the Treatment: A consultation to assess your skin and recommend the right therapy. Photos may be taken for progress tracking. Skin will be cleansed, and protective eyewear provided (for light-based therapies).
During the Treatment: Most treatments are painless or involve minimal discomfort. Sessions usually last 15 to 60 minutes, depending on the area and technique.
After the Treatment: Mild redness or warmth is common but usually resolves within hours. You may be advised to avoid sun exposure and use gentle skincare. Results typically build over several sessions.
Is It Right for You? If you’re looking for a skin boost without the risks or recovery time of surgery, light-based skin therapy and other minimally invasive treatments could be perfect for you. These therapies are suitable for a wide range of concerns and skin types, but it’s always best to consult with a certified dermatologist or aesthetician to ensure you’re getting the safest and most effective treatment plan.
The Future of Skincare Is Bright—Literally As technology advances and consumer demand for safer, more effective skin care grows, light-based skin therapy is becoming a cornerstone of modern aesthetic medicine. These treatments blend the best of science and beauty, offering real results without drastic measures. Whether you're tackling acne, sun damage, or simply aiming to maintain your youthful glow, the future of skincare is about enhancement, not overhaul. So say goodbye to invasive procedures—and hello to glowing skin, one light beam at a time.
The rise of minimally invasive skin treatments has redefined what it means to age gracefully. By prioritizing natural results, minimal recovery, and long-term skin health, these therapies are changing lives (and complexions) one session at a time.
And when it comes to harnessing the power of light, light-based skin therapy is illuminating the way forward—proving that sometimes, the best treatments are the ones that don’t require going under.
-
 @ 502ab02a:a2860397
2025-04-16 04:11:58
@ 502ab02a:a2860397
2025-04-16 04:11:58ในยุคที่ใครๆ ก็พูดเรื่อง สิทธิเสรีภาพ จะมีใครรู้บ้างว่า สิ่งที่เรากินทุกวัน กลับกำลังเข้าสู่ยุค ไร้สิทธิในการรับรู้ โดยเฉพาะเมื่อพูดถึงสิ่งที่เรียกว่า “GMO 2.0”
ใช่แล้วครับ GMO 2.0 หรือ synthetic biology ไม่ใช่ข้าวโพด BT, ไม่ใช่ถั่วเหลืองต้านยาฆ่าหญ้าแบบเดิม แต่มันคือ “พืชที่ถูกดัดแปลงพันธุกรรมแบบไม่มีรอยแผล” คือการใช้เทคโนโลยี CRISPR-Cas9, TALEN หรือ ZFN เข้าไป “ตัดต่อยีน” ภายในพืช โดยไม่ต้องใส่ยีนแปลกปลอมจากสิ่งมีชีวิตอื่น
ถ้าจำได้ ที่ผมเคยแชร์เรื่องการสร้างหมาป่า Game of Thrones และกำลังทำแมมมอธ อยู่นั่นละครับ CRISPR คือเทคโนโลยีที่เขาใช้ ผมเคยโพสไว้ว่า ผมสนใจเรื่องสัตว์นะ แต่ผมมีเรื่องกังวลควบคู่มาด้วย นี่คือเรื่องที่ผมบอกไว้ครับ
เพราะการสร้างสิ่งเหล่านั้นมันฟังดูดีใช่ไหมครับ? แต่ปัญหาคือ...มันดีจนไม่ต้องถูกเรียกว่า GMO นี่คือกลยุทธ์ใหม่ของอุตสาหกรรมพันธุ์พืช เพราะในหลายประเทศ เช่น สหรัฐฯ แคนาดา และแม้แต่ญี่ปุ่น กฎหมายไม่ถือว่า CRISPR เป็น GMO ถ้าไม่มีการนำยีนจากสิ่งมีชีวิตอื่นมาใส่เข้าไป
พูดง่ายๆ คือ “ตัดแต่งยีนจากของตัวเอง ยังไม่เรียกว่า GMO” แต่ผลที่ออกมา... อาจเปลี่ยนทั้งระบบการเติบโตของพืช เปลี่ยนลักษณะอาหาร เปลี่ยนภูมิคุ้มกัน และเปลี่ยนการควบคุมอำนาจในห่วงโซ่อาหารโลก
แล้วการที่ไม่ต้องติดฉลาก ไม่ต้องแจ้งผู้บริโภค นี่คือสาระสำคัญ!!!! เพราะเมื่อมันไม่ใช่ GMO ในทางกฎหมายก็ไม่มี “ภาระในการแจ้งผู้บริโภค” ใครกินพืช CRISPR เข้าไป ก็จะไม่รู้เลยว่า...นี่คือพันธุ์ที่ผ่านการดัดแปลงระดับ DNA มาแล้ว
ลองคิดดูครับว่า นี่เรากำลังถูกดันเข้าสู่ยุคที่ “มะเขือเทศหวาน” หรือ “ข้าวที่แข็งแรงทนแล้งดี” หรือ "พืชที่สะสมโปรตีนวิตามินที่ใส่สารละลายไว้ในตัว" อาจจะผ่านการตัดต่อพันธุกรรม แต่คุณไม่มีทางรู้ เพราะมันไม่มีทางตรวจพบจากฉลาก หรือการทดสอบดีเอ็นเอปกติ
คำถามคือ ใครควบคุม? ใครได้ประโยชน์? คำตอบเหมือนเดิมละครับ บริษัทยักษ์ใหญ่ที่จดสิทธิบัตรไว้ก่อนไง 5555
ในระบบ GMO 1.0 อุตสาหกรรมเคยพยายามผูกขาดพันธุ์โดยใช้สิทธิบัตร แต่ผู้บริโภคยังสามารถรู้และต่อต้านได้ แต่ GMO 2.0 มาแบบ “เงียบกว่า แหลมคมกว่า และควบคุมง่ายกว่า”
ยกตัวอย่างเช่น ข้าวโพด CRISPR จากบริษัท Corteva (เจ้าของเดิมคือ DowDuPont) สามารถสร้างพันธุ์ที่ “โตไว แห้งเร็ว เก็บเกี่ยวได้เร็วกว่าเดิม” แต่พันธุ์นี้มีสิทธิบัตรคุ้มครองแบบเบ็ดเสร็จ แถมไม่มีข้อผูกมัดในการแจ้งข้อมูลกับผู้บริโภคด้วย
ในส่วนของความเสี่ยงที่ใครก็ไม่กล้าพูดถึงก็มีอีกนะครับ เช่น -การตัดต่อยีนแม้จะไม่ใส่ยีนใหม่ แต่ก็สามารถเกิด off-target effect หรือผลกระทบที่ไม่ได้ตั้งใจได้ -ยีนที่ถูกตัดออกอาจมีหน้าที่สำคัญด้านภูมิคุ้มกันหรือสมดุลภายในพืช ซึ่งส่งผลถึงโภชนาการของผู้บริโภค -การกระจายของพันธุ์ CRISPR โดยไม่ต้องผ่านการควบคุม อาจทำให้พืชดั้งเดิม สูญพันธุ์ทางพันธุกรรม เพราะถูกแทนที่แบบเงียบๆ
แล้วเกษตรกรล่ะ? จะรอดไหม? คำตอบคือ รอดยากขึ้นครับ หรือจะเรียกไม่มีทางรอดดีโหดไปไหม? เพราะ GMO 2.0 ไม่ใช่แค่เรื่องการดัดแปลงพันธุกรรม ถ้ามองภาพกว้างกว่านั้น มองโครงสร้างเลยนี่มันคือการสร้าง “ระบบใหม่ในการผูกขาดพันธุ์” ที่มองไม่เห็น เป็นการล็อกพันธุ์พืชด้วย “สิทธิบัตรโมเลกุล” ซึ่งเกษตรกรไม่สามารถเซฟพันธุ์ไว้ปลูกต่อได้ เพราะละเมิดกรรมสิทธิ์ ต้องเช่าใช้หรือ subscribe ไปตลอดชีวิต มีหน้าที่แค่หน่วยปลูกเท่านั้น
ขณะที่พันธุ์พื้นบ้านหรือพันธุ์เปิดกลับไม่สามารถแข่งขันกับพันธุ์ดัดแปลงเหล่านี้ได้เลย เพราะถูกออกแบบมาให้ “ตอบโจทย์ตลาด” แต่ไม่ใช่ “ตอบโจทย์ดินฟ้าอากาศจริงๆ” แบบเกษตรวิถีเดิม
แล้วในโลกหลัง GMO 2.0 จะเหลืออะไรให้เราปลูก? นี่ไม่ใช่การต่อต้านเทคโนโลยีนะครับ ทุกคนเข้าใจดีว่าเราต้องเติมโตและมีการพัฒนา แต่คือคำถามเรื่อง สิทธิในการรู้ สิทธิในการเลือก และ สิทธิในการรักษาพันธุกรรมของพืชพื้นบ้าน มันอยู่ตรงไหนก่อน
เพราะเมื่อเราถูกเปลี่ยนพันธุ์แบบไม่รู้ตัว วันหนึ่ง เราอาจต้องซื้อเมล็ดพันธุ์ทุกปีจากบริษัทเพียงไม่กี่ราย ปลูกอาหารในระบบที่เราควบคุมไม่ได้ และกินอาหารที่ไม่มีใครกล้ารับรองว่า “ดั้งเดิม” จริงหรือเปล่า
ดังนั้นมันจึงถึงเวลาตั้งคำถามใหม่... ว่า real food ของเรายัง real อยู่ไหม?
ในยุคที่แม้แต่มะเขือเทศก็ถูกเปลี่ยนยีน และข้าวโพดก็ถูกออกแบบมาให้เก็บเกี่ยวเร็วขึ้น แต่ไม่งอกได้อีกเลย คำถามไม่ใช่แค่ “อร่อยไหม” หรือ “หวานแค่ไหน” แต่คือ
“เราเหลือสิทธิ์อะไรกับอาหารที่เราปลูกบ้าง?”
สิ่งนี้มันเกิดขึ้นไปแล้วครับ นี่ยังไม่ได้พูดถึงผลกระทบจากการกิน เพราะมีหลายๆคนแฮปปี้ดี๊ด๊าไปมากมาย กับสตอเบอรี่หวานฉ่ำ เมลลอนหอมฉุย กล้วยใบงาม กินแล้ว "healthyyyyy" อะตรงนั้นผมไม่แย้งแล้วกัน
ซีรีย์นี้เลยให้มองผลของการถูกจองจำครับ กบชอบอาบน้ำอุ่นเสมอ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 502ab02a:a2860397
2025-04-16 04:06:25
@ 502ab02a:a2860397
2025-04-16 04:06:25"Satoshi is not me." #ตัวหนังสือมีเสียง
เพลงนี้เรียกได้ว่าเป็นจุดเริ่มต้นของคอนเสปอัลบั้มนี้เลยครับ ผมเลยเอาชื่อเพลงนี้เป็นชื่ออัลบั้มไปด้วย
มันเริ่มจากการที่คนชอบคาดคะเนกันไปว่า ใครคือ satoshi nakamoto ตัวจริง แล้วก็มีสารพัดทฤษฎีออกมา ค้นคว้ากันไปถึง กระทู้ที่คุยกันใน mailing list สมัยนั้นเลยเชียว
มีคนนึงที่ไม่พลาดโดนมองว่าเป็น satoshi นั่นคือ Jack Dorsey (nostr:npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m) ผู้ร่วมก่อตั้ง twitter แล้วยิ่งเขาลงมาในทุ่งม่วงและสนับสนุน บิทคอยน์ เต็มตัวรวมถึงไปร่วมงานคอนเฟอร์เรนซ์บิทคอยน์ด้วย นั่นยิ่งทำให้คนพูดกันหนาหูขึ้น
ในปี 2020 Dorsey ได้ให้สัมภาษณ์กับ Lex Fridman โดยเมื่อถูกถามว่าเขาคือ Satoshi Nakamoto หรือไม่ เขาตอบว่า "ไม่ และถ้าผมเป็น ผมจะบอกคุณไหมล่ะ?"
นี่หละครับ ประโยคที่ผมรู้สึกว่า น่ารักและเอามาขยายความเป็นความจั๊กจี้ได้โรแมนติกดี แถมมันเข้ากับประโยคที่พวกเรามักใช้ว่า we’re all Satoshi
ทำให้คำว่า Satoshi is not me เลยกลายเป็นมุมกลับที่จั๊กจี้ดี ในความคิดผม
ผมเลยเริ่มจากการร่างไว้ว่า ท่อนฮุคของเพลงจะต้องมีคำว่า "Satoshi is not me" บังคับตัวเองไว้ก่อนเลย ฮาๆๆๆ
เพลงจะกล่าวถึงบรรยากาศโรแมนติกสบายๆผ่อนคลาย หนุ่มสาวเดินไปตามชายหาดด้วยกัน หัวเราะหยอกล้อ
เนื้อเพลงพยายามซ่อนการเปรียบเทียบเป็นนัยยะ ตามความต้องการแรกในการทำอัลบั้มนี้คือ ถ้าไม่โดนยาส้มไว้ ก็ยังฟังได้แบบสบายๆ ตามประสาเพลงบอสซาทั่วไป แต่ถ้าโดนยาส้มแล้ว อาจจะฟังแล้วรู้สึกถึงอีกมุมที่เป็นปรัชญาบิทคอยน์ได้
เรียกว่าไม่อยากเอา core code มาเขียนเพลงนั่นละครับ
เราเริ่มด้วยการวางฉากให้สบายๆชายทะเล ประสาความบอสซาโนวาก่อน ด้วยท่อนแรก In the cool of evening, beneath the twilight trees, We sway with the ocean, feeling the summer breeze, There's a whisper in the air, oh so tender, so free, ยามเย็นอ่อนลม ใต้พฤกษาเวลาโพล้เพล้ เราสองตระกองกอดไปกับคลื่นทะเล ลมฤดูร้อนพัดพาเสียงเล่าเบา ๆ
ก่อนจะลงท่อนปิดด้วยประโยคว่า You smile and softly whisper, "Satoshi is not me." เธอยิ้มแล้วกระซิบว่า "ฉันไม่ใช่ซาโตชิ"
แต่ผมก็ยังพยายามแทรกเรื่องของบิทคอยน์และเบื้องหลัง fiat money เอาไว้ด้วยนิดนึง Soft waves kiss the sand, like a gentle dream, With every step we take, there's a secret melody, คลื่นเคล้าหาดเบา ๆ ดุจฝันที่ละมุนละไม ทุกก้าวที่เราย่างไว้ ล้วนมีท่วงทำนองแอบแฝงอยู่ ฮาๆๆๆ คือกำลังพยายามบอกว่า ความราบรื่นในชีวิตเราทุกวันนี้ เราอาจรู้สึกสวยงาม แต่จริงๆแล้วทุกๆก้าวย่างของเรา ถูกกำหนดด้วยความลับบางอย่างอยู่
จากนั้นก็ปูเข้าสู่ทางรอด คล้ายๆกับชักชวนมาสร้างโลกที่หลุดพ้นจาก fiat In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, มาระบายเมืองด้วยสีสันที่สดใสด้วยหัวใจแห่งเสรี เราสร้างท่วงทำนองของเรา แล้วเต้นใต้เงาจันทร์ จนแสงรุ่งทาบฟ้าอีกครา ไม่จำเป็นต้องมีมหากาพย์ภาพลวงตา หรือประกาศิตอันยิ่งใหญ่ใด
ก่อนจะจบผมวางท่อง bridge ไว้โดยมีประโยคว่า No chains to bind us, just a heartfelt plea, ไร้พันธนาการใดมาควบคุมเรา มีเพียงคำขอเบา ๆ จากใจที่แท้จริง เพื่อแสดงความปลดแอกอะไรบางอย่าง
ทีนี้ยังมีลูกเล่นในแต่ละท่อน ที่ใช้คำว่า "Satoshi is not me." ด้วยนะครับ ผมเอามาเรียงกันให้ตามนี้ You smile and softly whisper, "Satoshi is not me."
You laugh and then you tell me, "Satoshi is not me."
With your hand in mine, love, "Satoshi is not me."
You softly keep reminding, "Satoshi is not me."
Embrace the simple truth, “Satoshi is not me.”
คือเป็นการหยอดความโรแมนติกนิดหน่อย ว่าเชื่อเค้าเหอะนะ เค้าไม่ใช่ Satoshi ด้วยการใช้ประโยคต้นที่ขยับแรงขอร้องมากขึ้นเรื่อยๆ
หวังว่าหลังจากนี้เวลาฟังเพลงนี้จะจั๊กจี้แบบที่ผมนึกสนุกตอนเขียนนะครับ ฮาๆๆๆๆ 🎶 youtube music https://youtu.be/g8oyZQ_lTa0?si=kS7ga_TxmFnPOmwR
🟢 spotify https://open.spotify.com/track/69GOSGMrma3BONKG8l5wpN?si=c0e6711c7a994011
💽 tiktok ค้นหา Heretong Teera Siri เลือกแผ่นเสียงไปทำคลิปได้เลยครับ
Lyrics : Satoshi is not me [Verse] In the cool of evening, beneath the twilight trees, We sway with the ocean, feeling the summer breeze, There's a whisper in the air, oh so tender, so free, You smile and softly whisper, "Satoshi is not me."
[Vers 2] We walk along the shoreline, while the stars start to gleam, Soft waves kiss the sand, like a gentle dream, With every step we take, there's a secret melody, You laugh and then you tell me, "Satoshi is not me."
[Chorus] In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, With your hand in mine, love, "Satoshi is not me."
[Verse 3] Let’s paint the town in colors, of freedom and delight, Dance in moonlit shadows, till the break of daylight, In this realm of wonder, where we both can be, You softly keep reminding, "Satoshi is not me."
[Bridge] Beneath the starlit canopy, where dreams softly align, We live for the moment, leave the rest behind, No chains to bind us, just a heartfelt plea, Embrace the simple truth, “Satoshi is not me.”
[Chorus] In the world we're crafting, where our hearts feel light, We find our own rhythm, in the still of the night, No need for grand illusions, or some wild decree, With your hand in mine, love, "Satoshi is not me."
pirateketo #siripun
-
 @ 8d34bd24:414be32b
2025-04-16 03:48:30
@ 8d34bd24:414be32b
2025-04-16 03:48:30Ever since becoming a Christian, I have whole-heartedly believed the Bible and that God will fulfill what He has promised. On the other hand, for the majority of the time I have been a Christian, I have dreaded reading prophecy. It seemed so hard to understand. Some is couched in figurative language, but I now believe much of it was hard to understand because there were no words for the technology and systems that would come into being and fulfill these predictions.
Now reading End times prophecy, like in Revelation, Daniel, Matthew 24-25, 2 Thessalonians, Zechariah, etc. the prophecies are starting to sound like the evening news instead of some poetic mystery. These predictions are making more and more sense as the technology and world politics begin to align with the prophecies. I have gone from hating when I get to prophecy passages, especially Revelation, in my Bible reading, to spending extra time reading these passages and seeing how they line up and clarify each other. (I really want to start a project linking all of the end-times prophetic passages together to see how they clarify each other and try to see the big picture, but that is a massive project and time is in short supply. The only way I know to do it is in Excel, but that isn’t efficient. If anyone has a suggestion for a better way to link and show relationships, I’d love to hear about it, especially if it is free or very cheap.)
Matthew recounts Jesus telling His disciples about what to expect in the end times. Although Matthew 24 describes more of the details of the events that happen, this passage in Matthew 25 describes the importance of watching expectantly for the signs of the times, so we are ready.
“Then the kingdom of heaven will be comparable to ten virgins, who took their lamps and went out to meet the bridegroom. Five of them were foolish, and five were prudent. For when the foolish took their lamps, they took no oil with them, but the prudent took oil in flasks along with their lamps. Now while the bridegroom was delaying, they all got drowsy and began to sleep. But at midnight there was a shout, ‘Behold, the bridegroom! Come out to meet him.’ Then all those virgins rose and trimmed their lamps. The foolish said to the prudent, ‘Give us some of your oil, for our lamps are going out.’ But the prudent answered, ‘No, there will not be enough for us and you too; go instead to the dealers and buy some for yourselves.’ And while they were going away to make the purchase, the bridegroom came, and those who were ready went in with him to the wedding feast; and the door was shut. Later the other virgins also came, saying, ‘Lord, lord, open up for us.’ But he answered, ‘Truly I say to you, I do not know you.’ Be on the alert then, for you do not know the day nor the hour. (Matthew 25:1-13) {emphasis mine}
Many Christians think studying prophecy is not useful for today, but that is not true. Our time is short and Jesus warned us to be aware and ready. We can’t be ready for something if we know nothing about it.
In this passage it mentions that “while the bridegroom was delaying, they all got drowsy and began to sleep.” How often do we feel the delay and begin to rest or get distracted by other things? Most Christians do not live like Christ’s return is imminent. Although we can’t know the hour or the day, we can know that we are closer to that hour than we have ever been before. Peter warns us not to doubt Christ’s coming or to become focused solely on our earthly lives.
Know this first of all, that in the last days mockers will come with their mocking, following after their own lusts, and saying, “Where is the promise of His coming? For ever since the fathers fell asleep, all continues just as it was from the beginning of creation.” (2 Peter 3:3-4)
Because Jesus has not returned for almost 2,000 years, many act as if He will never come, but that long wait instead suggests the time is nearing because God never breaks His promises.
For when they maintain this, it escapes their notice that by the word of God the heavens existed long ago and the earth was formed out of water and by water, through which the world at that time was destroyed, being flooded with water. But by His word the present heavens and earth are being reserved for fire, kept for the day of judgment and destruction of ungodly men.
But do not let this one fact escape your notice, beloved, that with the Lord one day is like a thousand years, and a thousand years like one day. The Lord is not slow about His promise, as some count slowness, but is patient toward you, not wishing for any to perish but for all to come to repentance. (2 Peter 3:5-9) {emphasis mine}
The long wait is due to God’s unfathomable mercy and patience, but we should also realize that the increase of evil in the world cannot continue forever. How much more can evil increase before mankind destroys itself? God claims judgement for Himself and finds every kind of sin abhorrent. If we are distraught over the sin in the world today, how much more awful is it to a holy, perfect God to see His very own creation destroyed by sin?
Just as the ten virgins became tired waiting, we tend to get caught up in the things of this world instead of focusing on God’s plan for us and the world. We act as if this world is the only thing we will experience instead of preparing for our rapture to heaven. We focus on our job, our homes, and our families (all good things) and miss the most important things — winning souls for heaven.
Just as Jesus gently reprimanded Martha for having the wrong focus:
But Martha was distracted with all her preparations; and she came up to Him and said, “Lord, do You not care that my sister has left me to do all the serving alone? Then tell her to help me.” But the Lord answered and said to her, “Martha, Martha, you are worried and bothered about so many things; but only one thing is necessary, for Mary has chosen the good part, which shall not be taken away from her.” (Luke 10:40-42) {emphasis mine}
In the same way, we get focused with the business of life and miss the most important stuff. It wasn’t bad of Martha to take care of her guests, but sitting with Jesus and learning from Him was more important. In the same way, our jobs, families, and homes are good things and we should do them well, but reading our Bibles, praying, growing closer to Jesus, and sharing the Gospel with those who don’t know Jesus is better.
When we believe that our time on earth is short and Jesus is coming for us soon, we are more likely to focus on the most important things — the eternal things.
This passage in Matthew 16 describes the importance of us knowing, understanding, and looking for the signs of the times.
The Pharisees and Sadducees came up, and testing Jesus, they asked Him to show them a sign from heaven. But He replied to them, “When it is evening, you say, ‘It will be fair weather, for the sky is red.’ And in the morning, ‘There will be a storm today, for the sky is red and threatening.’ Do you know how to discern the appearance of the sky, but cannot discern the signs of the times? An evil and adulterous generation seeks after a sign; and a sign will not be given it, except the sign of Jonah.” And He left them and went away. (Matthew 16:1-4) {emphasis mine}
Christians that believe studying end times prophecy is not important would be rebuked even today by Jesus. We are supposed to study and learn and prepare and watch eagerly for His return.
In Revelation, God says we are blessed if we hear and heed the words of this prophecy.
The Revelation of Jesus Christ, which God gave Him to show to His bond-servants, the things which must soon take place; and He sent and communicated it by His angel to His bond-servant John, who testified to the word of God and to the testimony of Jesus Christ, even to all that he saw. Blessed is he who reads and those who hear the words of the prophecy, and heed the things which are written in it; for the time is near. (Revelation 1:1-3) {emphasis mine}
Do you seek God’s blessing? Then study God’s prophecies, especially as written in Revelation. God is good and He has shown His children what will happen, so they can be prepared. Don’t be like the five foolish virgins who were unprepared. Study the Scriptures. Look for the signs. Be ready for our Savior’s return by inviting as many people as possible to join us.
Trust Jesus.
FYI, I hope to write several more articles on the end times (signs of the times, the rapture, the millennium, the judgement, etc.).
-
 @ 35da2266:15e70970
2025-04-16 03:45:13
@ 35da2266:15e70970
2025-04-16 03:45:13Qd6Vc1ZwkoV314qozv8RVkBk0YW9XQK38bjizGI5a4ws0wuuJQR5U0uDEzKcNd9/QWPbaj4rQIgdFNlmmybdn4s1WXfmdoymUFBRjpBau7Nj2yeXaKtk+RVl488Kxo0/kb13hQfX8q6kzPs9jY2NWS9KedXA+LSEhZJKXeXn5lT8hxuFPc6Q/rmVQT3gTRAORK/LUizNE71+wnaJPV0V/mNrdiKxWbFAv6lnmSPY+zKVY/u5E6vgjgObaSGpjj+MOaMkYfGxnm7fm9kvQawJNmIHdYn2CcymnSYHhuL7jqohECqf0DtPrewYkFfJ6mrerKhKwRbaHRIOcOJKiIjw5Q==?iv=RdYmRey3pCxDafHJpDdFVA==
-
 @ 35da2266:15e70970
2025-04-16 03:43:02
@ 35da2266:15e70970
2025-04-16 03:43:02QdWVn542ZckzWEvFkyHenDWAI0kk58kbjgrYtvQBbbQXRXaxaRAlvjQ93NChwiNnfPaAEJ5R/hmuJ6FkTowumS9q0NP7uG6tA0RuTssdwNIORaN/wvqmz0GYme1Ci5RlNxtlHgeOyuPkLdiaolTt9CYlY2mV4gC1Tplkn7aP4mbXK+TJM9t6VsRR68GxShp8bLVK1qH3N6sPn9B7pkY2jEwi9GxGtZlf/jO3vS3lBgW79Ud2OYHbU3pauSdeM97+1TWvtMQt/iBlg54OB5Nb5pCTCNWDeJFD2wwavfQE8g9i91XBtt70z69shNrxLKHgpj6noC7QdUy1XZ49o3KSQw==?iv=B8YV090ont/MFRGbYBxpsA==
-
 @ 91266b9f:43dcba6c
2025-04-16 03:42:09
@ 91266b9f:43dcba6c
2025-04-16 03:42:09"No," I said, "you've got no right."
Sergeant Curtis sighed. "Come on, Mister Alton, I need you to work with me here."
"No," I said. "Absolutely not."
"He did it," shouted Mavis Harris, my recently new neighbor, leaning over the garden fence. "I saw him! He had a knife, a carving knife. And I heard the screaming and the shouting! He did it!"
"Thank you, Miss Harris," said Sergeant Curtis. "We've got it from here."
We were in my beautifully manicured backyard, sweating under the midday sun, along with six other police officers--all of them armed with shovels, ready to dig.
"This is an invasion of my privacy and I won't have it," I said.
"If you just tell us where your wife is we can get this all cleared up," he said.
"I'm not married," I said. "I've never been married."
Sergeant Curtis chewed on that for a bit, while he did the same to his bottom lip. "Girlfriend then. Partner?"
"I have no girlfriend. No partner. There's nobody at all," I said.
But there was. Sort of. Cindy, wonderful, difficult Cindy.
"He's lying!" said Mavis Harris. "I've seen her. Through the window. One time I called by when he wasn't here and she was just sitting in there, not moving. Wouldn't even answer the door. She must've been terrified, the poor girl. I bet he had her tied to the chair!"
That was absurd. Cindy wasn't into that kind of thing. I would never tie her to a chair and leave the house. That's crazy talk.
"We've got more than one eyewitness that says there's been a woman in the house with you," said Sergeant Curtis. "How about we get this woman on the phone, clear this up?"
"I can't make the impossible happen, Sergeant," I said, stiffly.
My back door opened and Constable Jenkins stepped onto the verandah. "Got a carving knife missing from a set of six," he said.
"I told you, he went after her with a knife!" said Mavis Harris.
She was right. Things had got heated. Words were said. The knife had made an appearance. There had definitely been some stabby-cutty action. Much to my dismay. I hated that it happened. I guess I was going to have to live with the damage.
Sergeant Curtis sighed. "This isn't looking good, Mr Alton."
"I bet he put her under the roses!" said Mavis Harris. "That's where I saw him heading with the body!"
"Alleged body," I muttered.
"Jenkins, any sign of blood in there?" said Sergeant Curtis.
"None whatsoever," said Jenkins. "Not even under black light. Couldn't spot any in the garden either."
"He must have cleaned it up," said Mavis. "Bleach. Bleach will clean up anything. And I saw him, I saw him carry her out and she had what looked like a knife sticking out of her chest!"
"Last chance, Mr Alton," said Curtis, "let's get this lady friend of yours on the phone and clear this up."
"I told you, I can't do the impossible," I said.
"Then you're leaving me no choice," he said.
He turned and nodded at the waiting officers with their shovels. "Start with the rose garden," he said.
They rolled up their sleeves with obvious relish and got to work.
"This is destruction of private property," I said. "When you're done, every rose petal, every grain of soil, better be back exactly as it was. Or you'll be dealing with my lawyer."
"Don't worry," said Sergeant Curtis, "I assure you everything will be put back as we found it. Whether we uncover anything or not."
As we watched the officers desecrate my rose garden, Sergeant Curtis said, "You know there's probably a few million square kilometers of country, forests, lakes, beaches, and do you know where most killers bury their wives or husbands? On their own property, right in their own backyard."
"Convenience trumps everything, I suppose," I said.
"Laziness," said Sergeant Curtis, "most casual criminals are just bone lazy."
"Or," I said, "they maybe wanted to keep their loved ones close."
Sergeant Curtis looked at me, eyes narrowed. "Is that what it is? You kill them, but somehow you want to keep them close?"
I shrugged. "Things happen. But you still love them. Maybe, you want them to be close to home," I said.
Curtis glared at me.
After a while Constable Jenkins climbed out of the rose garden and moped his sweating forehead with his sleeve. "Nothing here," he said. "This soil is pretty solid, hasn't been dug up in a while."
"The other rose bed," said Mavis Harris, "he must have used the other rose bed, beside the shed."
Damn that woman, why won't she keep her mouth shut?!
Constable Jenkins went over and stabbed his shovel into the dirt a few times. "Yeah," he said, "this has been dug up recently."
"Okay," said Sergeant Curtis, "get to it."
"I really must protest," I said. "This is a violation of my rights!"
"I'm sure we'll be done soon enough," said Sergeant Curtis, with a tight smile.
I turned and stared daggers at Mavis Harris, who haughtily thrust her nose and chin in the air, a smug smile on her face. Damn that woman and her meddling ways!
The officers found my second rose garden easier going. They were at it about twenty minutes when Constable Jenkins suddenly said, "Jesus Christ!"
"What, what is it?" said Sergeant Curtis, coming to attention.
"I ... I don't know," said Jenkins. "Hang on ..." He scraped at the dirt and then leaned over, grabbed something and lifted it out of the dirt.
A leg.
"Jeezuz," said Jenkins, letting the leg drop back into the soil. "I think we found her!"
"I knew it," said Mavis Harris. "I told you! Didn't I tell you? He did it! He killed her!"
They worked quickly now, gently digging and scraping away dirt until they could lift her other leg out. My beautiful Cindy doll.
"We've got a knife," said Jenkins, "but it's ... it's ..."
He turned to look at me, his face twisted in disgust.
"What is it?" said Curtis.
Jenkins swallowed, hard. "It's ... the knife, it's ... it's stabbed ... up between her legs, if, uh, if you know what I mean."
"Oh my god, you absolute monster," said Mavis Harris, clutching the neck of her blouse.
I sighed. They had no right. No right. This was a private matter. It was nobody's business but mine and Cindy's. We would work it out, Cindy and me. We always did.
"Okay," said Curtis, "get her out of there, quick! Check for a pulse, just in case."
"She's gone, Sarge," said Jenkins. "She's stone cold dea--wait, hang on a second."
He did some more digging and scraping with the shovel and slowly eased my Cindy all the way out of the dirt.
"Oh, bloody hell " said Jenkins. "You have got to be kidding."
"What, what is it?" said Curtis.
"Oh my, oh my Lord," said Mavis Harris, "I feel sick."
Jenkins struggled a bit with the weight, but managed to get Cindy upright. She is a bit of a heavy lass, I have to admit.
"It's a doll," said Jenkins. "It's just a doll, a sex doll, I think." He lifted Cindy's arm and made her give a little wave. "Seems to be silicon. Wow, very life-like, I must say." He was gently squeezing Cindy's arm and nose and cheek with his fingertips.
I seethed. The disrespect!
"A doll?" said Curtis.
"Yes, sir."
Curtis turned to me, his face a throttled purple colour. "A bloody sex doll?!"
I said nothing.
He struggled to keep his anger in check. "I could arrest you for obstruction of justice, Alton, for wasting Police time and resources," he said.
"How?" I said. "I was nothing but absolutely honest with you. There was no wife, no girlfriend, no body. I told you this repeatedly. You chose to ignore me and you, sir, have wasted not only my time, but that of your department and your own men."
I left him there, chewing air, and went to Jenkins and took Cindy gently in my arms. Her wounds were bad but not unamendable.
"Pervert," hissed Mavis Harris. "He's a dirty little pervert!"
I headed for the house, but paused at the back door and said, "I will expect you to return my rose gardens to their absolute pristine condition. My lawyer already doesn't like your department, not one bit, Sergeant Curtis."
I did not wait for a reply. I went inside and closed the door, quietly, behind me.
Night was coming on and the police had returned my garden to its former glory, and departed. A cool breeze drifted through the kitchen window.
I was at the table with Cindy, tending her wounds. Silicon glue isn't cheap, I'll tell you that, and it would leave Cindy with some scars, unfortunately. If I'm honest, I don't think she was all that pleased about it. As I knelt down to treat a wound across her ribcage, I copped her knee right in my groin.
"Ugh!" I said, the wind snapping out of me and tears rimming my eyes.
I reached out to steady myself and that's when she lurched forward, out of her chair, and headbutted me square in the face.
"For godsakes, Cindy!" I said.
She was baring down on me. I grabbed her by the shoulders, pushing her up and back, but like I said, she wasn't exactly a lightweight. I staggered back with her falling into me, and I winced as the edge of the kitchen counter stabbed into the small my back. Cindy gave me another hit to the testicles with her hand, making me gasp.
I rolled us around, putting her back against counter, silicon squeaking against marble--see how she likes it. I almost took another groin hit from her other hand. I was bending her back over the kitchen sink and without realising it, I had grabbed one of the serrated steak knives in my fist, raised it over my head, and was ready to drive it down into the open O of her mouth.
And that's when I looked past Cindy's head, out the kitchen window, across the fence, and over there in her kitchen window was Mavis Harris. Staring right at me, at us, her mouth an identical open O to Cindy's.
We stared at each other for a long moment, and then I reached up and slowly closed the kitchen blinds.
I sighed. I decided that Mavis Harris was a problem I just couldn't tolerate. Her constant invasion of my privacy was one thing, but calling the police was unacceptable. I would have to take care of her at my earliest opportunity. But carefully. And I had just the spot for her, out behind her very own shed.
Right next to Henry Patterson, the last neighbour and resident of that house, who had also gotten far too nosey for his own good.
Yes, a real nice spot, and close to home.
-
 @ 35da2266:15e70970
2025-04-16 03:38:20
@ 35da2266:15e70970
2025-04-16 03:38:209Jqq62GzpfwYvFgcKiQX5Fy6yyD5qIVdZ2hVOr79wFf7vtXyELuBT6RXik9TDnsf4CSqQQwbTbJ/8zO2hm/H0iEvBJj2fGGf/lJQ9OYtL56bIGbdPWDiFO0cG/aWaLEX+i5kc9aaxXvlYtdQVakkpcIo4FS4u+Opi7NmGJtLYkixj9njZ6RXnRhjYtBDqS/I+lsPM+8QlLxgUJyzX2FSWhMNCEkwGQyY7WL5ve3HmUyOHgvnE0jD5POQc8K576ujKv/7bIgVsLHDjM4YzGUnVozy5JFNIsuAFUU5aBXsqABeiAwTDBMpid+3kvT3THISm2YM2KSWz12RTI8yb5NduQ==?iv=qQok9QsgRXAZajfYeiFqSA==
-
 @ 35da2266:15e70970
2025-04-16 03:36:00
@ 35da2266:15e70970
2025-04-16 03:36:00lTFfszFRc574FKS4B4a6nuGhDb75H+3br1OH+YeiocHc3ef4q7oFvPns983W0dA911/8OMRW/+UFE7EESUeHCk0YQ6KSqzbzNAU3MKJaw8mwRmAzgyizq+3lTU0lB+A/CdbTmfmJP9eiyPsN/hkyPaYm+w35nhzEzFYeXfS6GZkB/vDoeyQVK8pwaLXjeo6Xo2qhZGu0V9DJEMHZjfmnCvXc1OR/JDOCz45pNmPR4SRBrsckZLNbmS9FGWQY9ffiSkA6YvuioiEqV5jmVz68F08zt57nm8BMnlQDdtI/TDZ8/kmXyBgcBwOM0ep5nTod7jEu+ydFNu/RHfZdWNetGQ==?iv=PEfCBpzguAgauYj3mhiO4Q==
-
 @ 35f80bda:406855c0
2025-04-16 03:11:46
@ 35f80bda:406855c0
2025-04-16 03:11:46O Bitcoin Core 29.0 foi oficialmente lançado e traz diversas melhorias técnicas voltadas para desenvolvedores, operadores de full nodes e a comunidade Bitcoin mais técnica. Desde mudanças na camada de rede até a atualização do sistema de build, este release é um passo significativo na modernização do ecossistema.
Se você roda um full node, desenvolve software que interage com o Core via RPC ou apenas quer estar por dentro das novidades técnicas, este artigo é para você.
Alterações na Rede e no P2P
Suporte ao UPnP Removido O UPnP foi totalmente desativado por razões de segurança e manutenção. Agora, a recomendação é utilizar a flag -natpmp, que conta com uma implementação interna de PCP e NAT-PMP. Mais seguro e mais leve.
Melhorias no Suporte Tor A porta onion agora é derivada da flag -port, permitindo múltiplos nós Tor na mesma máquina — ótimo para quem opera ambientes de teste ou múltiplos peers.
Transações Órfãs com Propagação Aprimorada O node agora tenta buscar os parents de transações órfãs consultando todos os peers que anunciaram a transação. Isso ajuda a preencher lacunas na mempool de forma mais eficiente.
Mempool e Política de Mineração
Ephemeral Dust Introdução de um novo conceito: ephemeral dust, que permite uma saída "dust" gratuita em uma transação desde que ela seja gasta dentro do mesmo pacote. Pode ser útil para otimizações de fees.
Correção no Peso Reservado de Blocos Bug que causava duplicação de peso reservado foi corrigido. Agora existe a flag -blockreservedweight, com limite mínimo de 2000 WU.
RPCs e REST mais robustos
- testmempoolaccept agora fornece o campo reject-details.
- submitblock preserva blocos duplicados mesmo que tenham sido podados.
- getblock, getblockheader e getblockchaininfo agora incluem o campo nBits (alvo de dificuldade).
- Novo RPC: getdescriptoractivity, que permite ver atividades de descritores em intervalos de blocos.
- APIs REST agora retornam nBits também no campo target.
Sistema de Build Modernizado
Uma das mudanças mais bem-vindas: o Bitcoin Core agora usa CMake em vez de Autotools como padrão de build. Isso facilita integração com IDEs, CI/CD pipelines modernos e personalização do build.
Outras Atualizações Importantes
- -dbcache teve limite máximo reduzido para lidar com o crescimento do conjunto UTXO.
- O comportamento Full Replace-by-Fee (RBF) agora é padrão. A flag -mempoolfullrbf foi removida.
- Aumentaram os valores padrão de -rpcthreads e -rpcworkqueue para lidar com maior paralelismo.
Ferramentas Novas
Uma nova ferramenta chamada utxo_to_sqlite.py converte snapshots compactos do conjunto UTXO para SQLite3. Excelente para quem quer auditar ou explorar o estado da blockchain com ferramentas padrão de banco de dados.
Limpeza de Dependências
As bibliotecas externas MiniUPnPc e libnatpmp foram removidas, substituídas por implementações internas. Menos dependências = manutenção mais fácil e menos riscos.
Como atualizar?
- Pare o seu nó atual com segurança.
- Instale a nova versão.
- Verifique configurações como -dbcache, -blockreservedweight e o comportamento RBF.
- Consulte os logs com atenção nas primeiras execuções para validar o novo comportamento.
Conclusão
O Bitcoin Core 29.0 representa um passo firme em direção a uma base de código mais moderna, segura e modular. Para quem mantém nós, desenvolve soluções sobre o Core ou audita a rede, é uma atualização que vale a pena testar e entender a fundo.
Já testou a nova versão? Notou impactos nas suas aplicações ou infraestrutura?
Referências
-
 @ c13fd381:b46236ea
2025-04-16 03:10:38
@ c13fd381:b46236ea
2025-04-16 03:10:38In a time of political volatility and declining public trust, Australians are looking for leaders who don’t just talk about accountability—but prove it. It’s time for a new standard. A protocol that filters for competence, responsibility, and integrity—not popularity alone.
Here’s the idea:
Anyone who wants to run for public office in Australia must stake 100Ksats to a public address and maintain provable control of the corresponding private key for the duration of their term.
A Low Barrier With High Signal
The amount—100Ksats—is modest, but meaningful. It isn’t about wealth or exclusion. It’s about signal. Controlling a private key takes care, discipline, and a basic understanding of digital responsibility.
This protocol doesn't reward those with the most resources, but those who demonstrate the foresight and competence required to secure and maintain something valuable—just like the responsibilities of public office.
How It Works
This system is elegantly simple:
- To nominate, a candidate generates a keypair and deposits 100Ksats into the associated address.
- They publish the public key alongside their candidate profile—on the electoral roll, campaign site, or an independent registry.
- Throughout their time in office, they sign periodic messages—perhaps quarterly—to prove they still control the private key.
Anyone, at any time, can verify this control. It’s public, permissionless, and incorruptible.
Why This Matters
Private key management is more than technical—it’s symbolic. It reflects:
- Responsibility – Losing your key means losing your ability to prove you’re still accountable.
- Integrity – Key control is binary. Either you can sign or you can’t.
- Long-term thinking – Good key management mirrors the strategic thinking we expect from leaders.
This isn’t about promises. It’s about proof. It moves trust from words to cryptographic reality.
A Voluntary Standard—for Now
This doesn’t require legislative change. It can begin as a voluntary protocol, adopted by those who want to lead with integrity. The tools already exist. The expectations can evolve from the ground up.
And as this becomes the norm, it sets a powerful precedent:
"If you can’t manage a private key, should you be trusted to manage public resources or national infrastructure?"
Identity Without Surveillance
By linking a public key to a candidate’s public identity, we create a form of digital accountability that doesn’t rely on central databases or invasive oversight. It’s decentralized, simple, and tamper-proof.
No backdoors. No bureaucracy. Just Bitcoin, and the competence to manage it.
Bitcoin is the foundation. Asymmetric encryption is the filter.
The result? A new class of public leaders—proven, not promised.Let’s raise the standard.
-
 @ 35da2266:15e70970
2025-04-16 02:44:06
@ 35da2266:15e70970
2025-04-16 02:44:06fG+OPtj+9qPneI6eoh8G6m0+aQfxG6wbyeRGwYYVUYyGgZrNCzT2srRaP2CYp+KtOYAazGaN9UfHhdrVZOePCEPFRT8g/g4NwKwf7DRK8bLKeG3CNXCt0dQ2I5I9hUd6/HytYhlTCm/aUBA6oG3PQ2+xHFiHdEtLnWAFDfHSNqbtIgvOGoxdTUxCfXtRlxk4epaV8CyGmyJ3PSttjCzChxvJiSoi8+W2LBZtwVqkuAu/Wn6iRv82ExyX47YtEDf6FsvDPDiM54GPkclOv/umdUGxCLSAAOUOlLfBKDLA2jaHzpv4bfiI/vzdSd/kzNkssxtY14X6f7C8qWmA6J3KxQ==?iv=tQfpmbUuub6Kw6Nx1/uRbw==
-
 @ 35da2266:15e70970
2025-04-16 00:31:22
@ 35da2266:15e70970
2025-04-16 00:31:22LTcj+3KWI8XMzz4Ym2m+BueOuNcKP0mbeS59YLfrySjrf+xfAI8Xz/7qpW11EhahB67O2nZW2kMFfiaFpvDy53ot4a5MJ4Ab/Lt5d7Rg018eXygoPotWELDh69tGyb4nHZGL1APOFLBz0n+zYMceBoTT3cIyvZjtWLbsovCMaafxUWyx23cZ6DmgKizKKJDTQPFR+iVC1N3i/QOBVQb4Sl/iq2TR8J9gVbkOtU9wbZWp27zOamCI06FI0L+fLRLwVK39raNKLg4sHioRK5mbbRm1959NmezqF+LugdVfWoCfvn5IZjBj8j3cVJKeUfgKwg0dgq4M1/yPOTDM8d0NBIk3YXZAIQ0CcGYMfNCyVuY=?iv=da7j+e07uz89rJPwTNPAng==
-
 @ 35da2266:15e70970
2025-04-16 00:29:18
@ 35da2266:15e70970
2025-04-16 00:29:18enNjYOtdn9VukMmUvKkHjOljcVk2g5KKH5PjjljxUuOABxqIGInmW1jqgF9+E5Unxcoi8mWNJtOrC6Br/z23XrZjc+tt2zxbe9gLbtfZnTxXRUD5BmLzQoENXlBfjZjV90Yzt0S04CdmNKTZVeeJETXKoXWWuwlx5GlRgMJiC92kZyk26muxi+Xvh9lxSxascUQELNlqY0ySXG4/Hg/K8qiFxVBB1ZU2kuK4EW5RU/5Su2gb5jpzjCsuYXfM5Nd05eehnbbdY8S0jt37/B2TzYfrim+iLJM4Nq1TX3pOoAGhZgSKoDbbCwu8xxsDdTDRc9sInaUn2obMb4w0ylH+ZYHwiuSiOW0anfLyUM2/NoYPX+ZEx57waSU7+2zbY66x?iv=uuQ35Xb0RNpJAn+GJVixKQ==
-
 @ 35da2266:15e70970
2025-04-16 00:15:02
@ 35da2266:15e70970
2025-04-16 00:15:02yf+dVZcg5m0ZWh0Vagoapkqo0p7GUDpcuicMVY3R1tN0pWbgiIT5auPs6+nIgD6fuCj8NpZYCI/ldesFKuBjowJxgq9WAKEgrVIkok9Mmes/7kjGP7aPzXyNBCmnrM3E8ZhmUI9YWCYZDNnrULkGPmco7HaTnMJOFqLUp6NzWtROYqV11HNVGG+H33blj0HA/HESPNaPbFDvw/2hGGf+XGzOaWfkRQFKvWIZJKPgMDAAJgMyUBHHEI6fkB8SICNWIT78Oj81JquMw448hMQ92a1aJu2tXNZiIyZ4AfioA/E0ZFK4DKaQ4V3Lav1DKr9iYIS1dOxZ/qAH3jsaTASgoLsgVISHEjFgFXO7VnTa8GfhzUHzgl/7fH/3OVnnYrwE?iv=UO8NRkvzZ3ApNXIkv5WSgw==
-
 @ 35da2266:15e70970
2025-04-16 00:13:51
@ 35da2266:15e70970
2025-04-16 00:13:51Ssk0hLkQlHXK4QXXhUjJFKdEHR3N1PuXmUIRG6om8yd1z0CM5lExk6oswyjHMVfbLsEBVR60teCcLwJhQcXMaTD7szHn86vwsD8rlm+H40SpDQkpyt+BtOhDTvWA0hiJoKTUVn+LQQv8uMP1dfZHTN/ircda7yLEWB7hLHbdVh1QV3vxt0WOzmefZPbAlnaVJidPwJpUndIm619FX5XqxYprZk5tVSbV7gr3JVLd06LLnmc8Q89z+TohPWWdkHgH5342I5tRFZeYg+VeBpaxg/WNVgVcjN5pUaXDg1dt7zP3smA9cmokluuuNbqLJ93nHURWO3+Mm35E9kMfedblRD3JuVIWi3HJPPTn3VDGnxMICWHTiB3vvEMuqvd37B7f?iv=mCMpjHPjNg74Cni8lc05Dg==
-
 @ 35da2266:15e70970
2025-04-16 00:12:12
@ 35da2266:15e70970
2025-04-16 00:12:12CYpQ+5c+twHS+/iKsblk1i/ZZD/lEVz6U8v1sDI5eqNtOTBkGvldJsrN6YJy7Xq4Oyc12fzkVivUURSYpHqbFx7LSqgwNjcnGV9ZyKDOcnnKzUSS1bRMeF4mFJb68t6hgZgiF+FpK0BL+JPFDoV8vYCQ5eBXqt6o1+4pq7CUHEZeyfVzHgQrg88XJwTvLNHbmpCE9D7pi+JWZKW4r6FEFzWBv0P82UZzq6EHNeH3C0Aq8yc5r6rs6z6wtEma46l5qAr01ISRDrnjN/WEgGTjkuW/zlIKpt4g/yhb79adaCz7MLDBhcTCNhGRgW2AJ0JorBbtGDcxcQYGHXcsjBEmn6G/ypNEi05V/n6uIUKJN8jQcZUyPVPaWF1Ky811nKkj?iv=1sgYyHP5h+upfg9POmRqww==
-
 @ 35da2266:15e70970
2025-04-16 00:11:19
@ 35da2266:15e70970
2025-04-16 00:11:19siI0dpuWuUZnxX+mmnRcRb75CXcVwS2aOPyVNd/SjGdltb828wShhZJVCj89zXIaAVIu92ifqUN3WFV5i7Q3LqN0LnlRNnAK1Rlx99N2DmF4VzhnlnaRfn/fkJ/X2z+RLT7odiWHzolaZbKXz2fV7hOHrgkbR2U5sJOQwY0BKOzVTDEiBBoirNWXCb6zn8XZ7AjezdbSLJG4KyebJp39SGmmHV8j/bvCra+EWOe6RvA2XoMIwIWBhzuJbgZ3ywLAyTj6roxBJDz9GWzWE/UWyvk2xAvWwY0aOG1F0fQpRfDORdcb8UCJUf+Sjk+rixqL9e7HXWn7FXR9ok/ewoujUoZtn/v4D32YAza2VQld3bsJ8yKMb55nygGMByrNWHmz?iv=wPdST/gc8OebFdvcY5GPuQ==
-
 @ 35da2266:15e70970
2025-04-16 00:09:35
@ 35da2266:15e70970
2025-04-16 00:09:35Wj2lYl56VPn8fLjFG1jyFqDTJkmiST+4zqrfFm4+pX8cYNZkNiva+7kcXxkOeAyl3mDs9qXcRzOP6vscPXFtKUxOBCDdwN/xK7yvsJQXbsEje6HsA3Lpw+aRHrzwSBpdW5QQR530yJfkZ2pneLycBT1gt5qhUu6Wkf0OCB0vQrPBAKx7Q4wRUlYmbmsS3Xv39+nOQXTfpJVPCLMM82RSqjqcDsIUj2njuXEiXBwA73ZKGl+S2ndN1nwg1od/CEslCqlK8uVbmhDZir8evG2lOsAbwIYn7rMWBs/2TW+pM/qychxU7ylLEVAlk9GzPLD+SWdGmaS5/erpJYDBAcsDzsJw9lDU2Ht7rXmUELK5oIFv1we7p0mfcEo+rtlHh4kF?iv=I186Y0DIBF2P7N5cKAasbA==
-
 @ 35da2266:15e70970
2025-04-16 00:04:40
@ 35da2266:15e70970
2025-04-16 00:04:40Qg+2vg0S9vXU1mOu5vRazmar3ItVtDsDs6j9uXmFE/2McOobjE8JpQinwdG/DM2aYQ92Xezj952C408rhg6syzR07BaP0gt4TmyimN+2wlPxLP48gGboa/S5Ptjk9KggELOk2oVE8jSLF1qDnIOdj0ktayvPgvQUaIsee+EeHk82VAhXxXfwL4m7JNVOBJzp+fDWC/mtaLoJH8PsQbXh9OIqccONrbhW2YJc2ZdQs3ZWVPCdr6uNdFVioPH3fV6qo1JUWK3O58HCj2MsYkSdarMYk3zZfKPE/VGMCaVs/n5X9fcRZmMcyKRzUp3FV4rgM2PIReL+MDubeNL03pOFAxKDZrBXV8r1/mJx5GjFTkc=?iv=JD9MkFOCMv8RFE8pTkEPXg==
-
 @ 35da2266:15e70970
2025-04-16 00:00:28
@ 35da2266:15e70970
2025-04-16 00:00:28yc+j3QrBERVcrn1VStfklZu4h3hBUOWsfiVNtiQ/g55p/Qe4iAXch+OdGEj5BhQhOjaP1Th5I2ZSaJh/aedEuDe3A9tzLDbK79FqYp5jPB49rsvHmlVox+S+LwVCD5nqTLJ2aA7PVlDkE7yMuTyGYEMgYe901y/XcaudeJ0GyAjP//044SyiC4oxVyeKgOJP6teyaBRzZWu2jOZW1E3MBZbVfxEtYXlVIWK2lfGEjH8yImb46vstSOxqT3uVsN2q2yuGnCwEy+G6rIP6s8jr/REnZXJwzoMeFiJrxFpvZFZIybI8u5CV+Ibsc3MEmP2jGmBwunmCErCRID+WjItojdyfpZCuyhPEUhvUhB3Ocqg=?iv=WMsh7rlFrEMomNrq0S6CFg==
-
 @ 35da2266:15e70970
2025-04-15 22:57:51
@ 35da2266:15e70970
2025-04-15 22:57:51AHehpEcOzlTbnn0YaQlyUg++VOi7NQ44B6oSrJi8QR11GxF4hZMwoDjZE8u46qr8koCcuN6jWF1pFi6/9yaUgkwjZwVPIXVMr3M/Ns9zLJzLQJsbR/aeTH5oVlO/T34gbHI62xFnJh6Z7qV52X77XEKouenEpqKtaQHGT/rUM/gIzFbOATJPCSXrQJh5MB5wlOxx2woB8zOpsPW1Du4CFY7c9QNowFtj+JK7MaNg7a6Oei19ui5nCIVolZTL28DByAQPeXN+wIg6Wa3GmGrs1WLK9NFcry+1xHccD1OCM2M1Sf9ZRQmfJ/m0p7B6dlCsmnIiwAO2y/T6ZcnPxS7hfg==?iv=iQ/QgMVqCUFHox16uXox+g==
-
 @ 35da2266:15e70970
2025-04-15 22:38:44
@ 35da2266:15e70970
2025-04-15 22:38:44LUNdI+0ES87Z4Y3u6UqeHZ6NPYrn8jI3z6KfcaGFhDrC/LHoNIYWYFtRVNwt75j1u7SFCFkQCtq2L9cPXafz8IsK43eOCNk9I4jdT8g1jd+vHH/w/GD1LdR5IZlGXX7fIc46DXS2qraUGdeSpakfg0uN52dA4O9yTmljCCqnaEpeQTaU0bd3mLHveAJfWsmvPgQd36vcoXOD5aXYqotZmcRyvHSJwLClEKAN7qlNBeMdKNpkbpRMTYz7G7w5hAqJT1lJHE7bmPcWTmS9JG0JcRgskA3FYurOBmyV3ZmjyUC6KqmLzBfP+JeQmYKMcPCk5G0+OFv7KG7L1mWMPVS9GYayxA5HXgnpuTsitNgO9hxAFcamVWxCkYDOVQdjfqyV?iv=8lQSaN3o9AcqKS8PM5eZGA==
-
 @ 35da2266:15e70970
2025-04-15 22:38:35
@ 35da2266:15e70970
2025-04-15 22:38:35Z+fTyrtePLMT0W+lR8MHBan7Dv45irS2udKxjVslQdjsxacgPAbE49g8kOj03RvaSexpcT4c5sC9AWv5aW7DZiVpB9+NrXxAgN1xWnBlds7btlpTqVn6eIrSYNKeviZ6Ie7MY6eYMsWD3np5ggfHQUFHWoy0dXwGxPmQBT1lJJtzAyA3ozAm/inXQl/YkTbvHlbQyA6cFtU5YGw/1SrN4XerNK+E3y2F2lpTf/M4WJb9OjRufdrm0Qdosci3liBNXIdgLJm7Qy3dcfpNev9TTaCgZ5M/EAUbrjG8+583GXFvPWvful14k0M0AQxhZiRzENaWns9UunDJKvRJCsZKA0aLTFx4hHYkfsL10IkGYuDM8U6ujpBOWut+LMLy8D5q?iv=DalQBHsbwDSSh3b2TLPc8w==
-
 @ 35da2266:15e70970
2025-04-15 22:35:59
@ 35da2266:15e70970
2025-04-15 22:35:59NOFTr2Erm/FWn2Iwbon3TGxlXR61yy6zo3S2iG6PFV9nMUdCeqGRKNHSOUasBABwJsvmMY4WP0AePoHYuvNL6QabNxz7/tHLp3DJkj+WjDVF4US9qc48DJiiapz7sUaFucj2koDs+NkUcAZD5Ohw2RP+NS8YFQFhqQQtG3TDYqA6Lr900YqEMSR17KbhzZlNR4OqBO8yDA17Y4ltEOjxaOv/5ys5Id7qqenK1bKjPd693nU+4p60iTh/StDPKzmKZr8LFURCPH623RnjXIvwqHN00bMyiW7t1Hup6uIwZDKpVAhwjYLYUOiXlYhPtB2rQKQny5xssH8DpzNF3LJfSwFFGh4U/SjCs388WMPpd/PgtEic2grK9BBDzAeTbFLy?iv=4bG43qfls9wjBQBuTmn99g==
-
 @ 35da2266:15e70970
2025-04-15 22:34:50
@ 35da2266:15e70970
2025-04-15 22:34:50L5WDLmxdFunBoKzVVQY4l5mleg7nXQ8lRH1UAq3fNhGFN5RekZMFKZ3L2/17izs4C7n9afGPicEHrImszw1JsQWsxrw4cXKNZZbgmSw/haTJ5Ck8HmvdTi62/E2rsLlEzGgerDa2cFdOrSrLl5FzUcTSz/UB5KxMsOfgKeulIjxK+IxUuKtTXS2NFCRLBgYkr6prcjKjK7ejVOit4smZWmvs93+c4mXQxyZR4JTsjRdD0h017LG8962yDq+rjysCiiXqrCTcdN0bd/a6PVd1hdSi3q886h6+3Jqfq4aSyZ5jJPfde/pDrTPFoHtXfcUI0nFEJ7DUUk7dcjCL6XHH9NEhLe6RCZdLx7a4xbcYTWU/pHfPS2G1Vmbg9KWBs2hO?iv=hUn2MjQWE6EmnKRqcQAGiw==
-
 @ 35da2266:15e70970
2025-04-15 22:34:36
@ 35da2266:15e70970
2025-04-15 22:34:3697d+mYEJp5IRWD74WbEfsn/KgzKbGvL7O0YY6fu0xlh9p3tPkcna2hbVduDFtL85T9ayoJFYQJ/svNaYOT7YNpCJxeU0oswCRExE7cHR0KHfIk2EsMGjmGoeRlJT61oP5dO2CxXvpLBh1Xedwf+sXiAJItT3l7Xf+jRHBEa7EjNNM3vkIIuTYHVQCx31Hp3KK+fYdl6AymhS+KmxyOxNDMGvjhW2U0jaIUTffkSS8reSAcbGMx8SAMKxuhIH4O2YbgmyjiSn7CzHMD0zrhxXs/g9KS4SioT9Ka5yddSYI2YxTlAzKTKznTdhfzvuQLV0/26SXFqI9i+jtKlYKIhi/g==?iv=I4Y2WyCQqqsbTIGbWN34Nw==
-
 @ 6be5cc06:5259daf0
2025-04-15 20:16:08
@ 6be5cc06:5259daf0
2025-04-15 20:16:08Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ e1b184d1:ac66229b
2025-04-15 20:09:27
@ e1b184d1:ac66229b
2025-04-15 20:09:27Bitcoin is more than just a digital currency. It’s a technological revolution built on a unique set of properties that distinguish it from all other financial systems—past and present. From its decentralized architecture to its digitally verifiable scarcity, Bitcoin represents a fundamental shift in how we store and transfer value.
1. A Truly Decentralized Network
As of April 2025, the Bitcoin network comprises approximately 62,558 reachable nodes globally. The United States leads with 13,791 nodes (29%), followed by Germany with 6,418 nodes (13.5%), and Canada with 2,580 nodes (5.43%). bitnodes
This distributed structure is central to Bitcoin’s strength. No single entity can control the network, making it robust against censorship, regulation, or centralized failure.

2. Open Participation at Low Cost
Bitcoin's design allows almost anyone to participate meaningfully in the network. Thanks to its small block size and streamlined protocol, running a full node is technically and financially accessible. Even a Raspberry Pi or a basic PC is sufficient to synchronize and validate the blockchain.
However, any significant increase in block size could jeopardize this accessibility. More storage and bandwidth requirements would shift participation toward centralized data centers and cloud infrastructure—threatening Bitcoin’s decentralized ethos. This is why the community continues to fiercely debate such protocol changes.
3. Decentralized Governance
Bitcoin has no CEO, board, or headquarters. Its governance model is decentralized, relying on consensus among various stakeholders, including miners, developers, node operators, and increasingly, institutional participants.
Miners signal support for changes by choosing which version of the Bitcoin software to run when mining new blocks. However, full node operators ultimately enforce the network’s rules by validating blocks and transactions. If miners adopt a change that is not accepted by the majority of full nodes, that change will be rejected and the blocks considered invalid—effectively vetoing the proposal.
This "dual-power structure" ensures that changes to the network only happen through widespread consensus—a system that has proven resilient to internal disagreements and external pressures.
4. Resilient by Design
Bitcoin's decentralized nature gives it a level of geopolitical and technical resilience unmatched by any traditional financial system. A notable case is the 2021 mining ban in China. While initially disruptive, the network quickly recovered as miners relocated, ultimately improving decentralization.
This event underlined Bitcoin's ability to withstand regulatory attacks and misinformation (FUD—Fear, Uncertainty, Doubt), cementing its credibility as a global, censorship-resistant network.
5. Self-Sovereign Communication
Bitcoin enables peer-to-peer transactions across borders without intermediaries. There’s no bank, payment processor, or centralized authority required. This feature is not only technically efficient but also politically profound—it empowers individuals globally to transact freely and securely.
6. Absolute Scarcity
Bitcoin is the first asset in history with a mathematically verifiable, fixed supply: 21 million coins. This cap is hard-coded into its protocol and enforced by every full node. At the atomic level, Bitcoin is measured in satoshis (sats), with a total cap of approximately 2.1 quadrillion sats.
This transparency contrasts with assets like gold, whose total supply is estimated and potentially (through third parties on paper) expandable. Moreover, unlike fiat currencies, which can be inflated through central bank policy, Bitcoin is immune to such manipulation. This makes it a powerful hedge against monetary debasement.
7. Anchored in Energy and Time
Bitcoin's security relies on proof-of-work, a consensus algorithm that requires real-world energy and computation. This “work” ensures that network participants must invest time and electricity to mine new blocks.
This process incentivizes continual improvement in hardware and energy sourcing—helping decentralize mining geographically and economically. In contrast, alternative systems like proof-of-stake tend to favor wealth concentration by design, as influence is determined by how many tokens a participant holds.

8. Censorship-Resistant
The Bitcoin network itself is inherently censorship-resistant. As a decentralized system, Bitcoin transactions consist of mere text and numerical data, making it impossible to censor the underlying protocol.
However, centralized exchanges and trading platforms can be subject to censorship through regional regulations or government pressure, potentially limiting access to Bitcoin.
Decentralized exchanges and peer-to-peer marketplaces offer alternative solutions, enabling users to buy and sell Bitcoins without relying on intermediaries that can be censored or shut down.
9. High Security
The Bitcoin blockchain is secured through a decentralized network of thousands of nodes worldwide, which constantly verify its integrity, making it highly resistant to hacking. To add a new block of bundled transactions, miners compete to solve complex mathematical problems generated by Bitcoin's cryptography. Once a miner solves the problem, the proposed block is broadcast to the network, where each node verifies its validity. Consensus is achieved when a majority of nodes agree on the block's validity, at which point the Bitcoin blockchain is updated accordingly, ensuring the network's decentralized and trustless nature.
Manipulation of the Bitcoin network is virtually impossible due to its decentralized and robust architecture. The blockchain's chronological and immutable design prevents the deletion or alteration of previously validated blocks, ensuring the integrity of the network.
To successfully attack the Bitcoin network, an individual or organization would need to control a majority of the network's computing power, also known as a 51% attack. However, the sheer size of the Bitcoin network and the competitive nature of the proof-of-work consensus mechanism make it extremely difficult to acquire and sustain the necessary computational power. Even if an attacker were to achieve this, they could potentially execute double spends and censor transactions. Nevertheless, the transparent nature of the blockchain would quickly reveal the attack, allowing the Bitcoin network to respond and neutralize it. By invalidating the first block of the malicious chain, all subsequent blocks would also become invalid, rendering the attack futile and resulting in significant financial losses for the attacker.
One potential source of uncertainty arises from changes to the Bitcoin code made by developers. While developers can modify the software, they cannot unilaterally enforce changes to the Bitcoin protocol, as all users have the freedom to choose which version they consider valid. Attempts to alter Bitcoin's fundamental principles have historically resulted in hard forks, which have ultimately had negligible impact (e.g., BSV, BCH). The Bitcoin community has consistently rejected new ideas that compromise decentralization in favor of scalability, refusing to adopt the resulting blockchains as the legitimate version. This decentralized governance model ensures that changes to the protocol are subject to broad consensus, protecting the integrity and trustworthiness of the Bitcoin network.
Another source of uncertainty in the future could be quantum computers. The topic is slowly gaining momentum in the community and is being discussed.
Your opinion
My attempt to write an article with Yakyhonne. Simple editor with the most necessary formatting. Technically it worked quite well so far.
Some properties are listed in the article. Which properties are missing and what are these properties?
-
 @ 7d33ba57:1b82db35
2025-04-15 19:33:07
@ 7d33ba57:1b82db35
2025-04-15 19:33:07Nestled in the lush Our Valley in northern Luxembourg, Vianden is a charming riverside town known for its stunning medieval castle, cobbled streets, and peaceful atmosphere. Surrounded by forested hills and steeped in history, it’s the perfect day trip—or even a peaceful overnight getaway—from Luxembourg City.
🏰 Top Highlight: Vianden Castle
- One of Europe’s most beautiful feudal castles, perched dramatically on a hilltop
- Built between the 11th and 14th centuries, with Romanesque and Gothic elements
- Lovingly restored, it now features furnished rooms, exhibitions, and epic valley views
- Visit in autumn or winter for a real storybook vibe, or during medieval festivals in summer for a lively twist
🌿 Things to Do in Vianden
1️⃣ Wander the Old Town
- Stroll the cobbled lanes, cross stone bridges, and admire the pastel-colored houses along the river
- Stop at a café by the water and just soak in the Alpine-style charm
2️⃣ Take the Chairlift
- Ride Luxembourg’s only chairlift up the hill above Vianden
- Amazing panoramic views of the town, river, and surrounding forests
- You can hike back down through wooded trails—it’s magical in the fall
3️⃣ Victor Hugo House
- Famous French writer Victor Hugo lived in exile here in the 1870s
- His former home is now a museum with personal items, manuscripts, and 19th-century decor
4️⃣ Hiking & Nature
- Vianden is surrounded by forested trails and river paths, perfect for hiking and biking
- You can follow the Our Valley Trail or parts of the Escapardenne trail toward the Belgian border
🍽️ Local Flavors
- Try hearty Luxembourgish dishes like Judd mat Gaardebounen (smoked pork neck with broad beans)
- Enjoy fresh trout from local rivers, Luxembourgish wine, or a slice of Apfelkuchen with coffee
- The town’s cozy inns and traditional restaurants make dining here feel warm and personal
🚆 Getting There
- From Luxembourg City: About 1.5 hours by public transport (train + bus combo) or 45 minutes by car
- Bonus: Public transport is free in Luxembourg!
-
 @ bf6e4fe1:46d21f26
2025-04-15 19:30:46
@ bf6e4fe1:46d21f26
2025-04-15 19:30:46this is a test
-
 @ a296b972:e5a7a2e8
2025-04-15 19:15:22
@ a296b972:e5a7a2e8
2025-04-15 19:15:22Heute traue ich mich einmal eine steile These aufzustellen, auch auf die Gefahr hin, dass sich herausstellen kann, dass ich völlig daneben liege.
Die USA sind federführend in der Gain-of-Function Forschung. Warum einige Dr. Frankensteins auf die Idee gekommen sind, an Viren, Bakterien und Sporen herumzubasteln, damit sie noch gefährlicher werden, erschließt sich mir nicht.
Wie andere Verrückte zum Beispiel in 2001 auf die Idee kommen konnten, Milzbrandsporen (Anthrax) in Brieflein an US-Abgeordnete zu verschicken, kann meine einfach gestrickte Seele auch nicht nachvollziehen.
So oder so kann man bei solchen Beispielen in Zweifel kommen, ob der Mensch wirklich von Natur aus gut ist.
Unter Präsident Obama, der den Friedensnobelpreis nach Ansicht vieler zu Unrecht erhalten hat, wurde die Gain-of-Function Forschung in den USA verboten.
Bekannt für seine Outsourcing-Künste, zum Beispiel im Austragen von Kriegen außerhalb des eigenen Territoriums, aktuell im Stellvertreterkrieg der USA mit Russland in der Ukraine, wurde nach Möglichkeiten gesucht, die Forschung im Ausland weiter zu betreiben.
So entstand das durch Corona bekannt gewordene Labor in Wuhan und auch einige geheime Labore in der… Ukraine!
In einem leider nicht mehr auffindbaren Video berichtete ein italienischer Professor davon, dass es immer ein Labor gibt, dass an einer Bio-Waffe (wie in Wuhan) arbeitet, und ein Labor, das parallel dazu an dem entsprechenden Gegengift, dem „Impfstoff“ arbeitet. Das Antilabor zum Corona-Virus sollte sich wohl ebenfalls in China an der Grenze zu Russland befinden, allerdings mit der Entwicklung eines Gegengifts noch nicht so weit vorangekommen sein, wie die Hexenküche in Wuhan.
Jetzt kommt „Der Schlund“, „Das Maul“, also Signore Fauci, USA, der größte Bio-Waffen-Verbrecher aller Zeiten ins Spiel. Seit vielen Jahren ist er sowohl für die Bereitstellung von Geldern für die Virenforschung, als auch für die Herstellung eines Impfstoffs zuständig. Er zeigt mit dem Daumen nach oben oder nach unten. Man munkelt, dass er auch Verbindungen zu den US-amerikanischen Geheimdiensten und anderen hat. Naheliegend wäre es.
In ihrer unendlichen „Aufopferung“ für die Menschheit und zu deren Wohl wurden vorsorglich Planspiele gehalten. Die deuten darauf hin, dass man einen Unfall in des Teufels Küche nicht gänzlich ausschließen konnte. Das es auch mehrere Planspiele für den Umgang mit einer „Pandemie“ gab, ist wohl mittlerweile jedem bekannt. Es liegt nahe, dass es sich bei diesen Übungen eigentlich um ein verdecktes Planspiel für den Fall handelte, dass ein gefährlicher gemachtes Virus, das so in der Natur nicht vorkommt, aus einer Giftküche entwischt, wie die Menschen darauf reagieren würden und welche Maßnahmen zu ergreifen wären.
Professor Wiesendanger hat schon ganz zu Anfang der gemachten Welt-Hysterie darauf hingewiesen, dass das Corona-Virus eine Furin-Spaltstelle hat, die so in der Natur gar nicht vorkommt. Damals als Schwurbler denunziert, berichtet der sogenannte Mainstream inzwischen auch davon, dass die Wahrscheinlichkeit, dass das Virus aus einem Labor stammt, fast gegen 100 % geht, und verkauft das als die neueste Erkenntnis, obwohl es schon ein alter Hut ist, wenn man seinerzeit Professor Wiesendanger ernst genommen hätte. Warum man das nicht konnte, klärt sich später noch.
Man kann also davon ausgehen, dass von Anfang an bekannt war, dass das Corona-Virus NICHT von einer Fledermaus auf den Menschen übergesprungen ist (Zoonose), sondern dieses Märchen eher als Ablenkungsmanöver gedacht war.
So ist es gelungen, den Ausbruch eines durch Wahnsinnige geschaffenen Homunculus-Virus, also eine Bio-Waffe, in eine die Menschheit bedrohende Pandemie umzuetikettieren. Und weil man in der Wissenschaft und Politik nicht einschätzen konnte, wie gefährlich dieser von Menschenhand geschaffene Dreck ist, wollte man auf Nummer sicher gehen. Das würde die hysterischen Maßnahmen und die mit der heißen Nadel gestrickten Genbehandlungen erklären. Man wollte sich hinterher nicht vorhalten lassen, das Falsche oder zu wenig unternommen zu haben, falls es zu einem Massensterben kommen würde.
Das wiederum würde auch erklären, warum gleich zu Anfang das Militär mit einbezogen wurde, weil dies sich mit der Abwehr von (Bio-)Waffen am besten auskennt.
Glücklicherweise stellte sich schnell heraus, dass die Giftmischer doch noch nicht so erfolgreich waren, wie man zu Anfang befürchtet hatte, aber da war die Lawine schon ins Rollen gekommen, und es gab kein Zurück mehr.
Zu Anfang könnte man sich sogar vorstellen, dass die Politiker in bester Absicht gehandelt haben und die Menschen in der Tat schützen wollten: „Wir wollen euch „retten, bitte vertraut uns, die Maßnahmen sind nicht zu hinterfragen (aber wir können euch nicht sagen warum, nämlich das eine Bio-Waffe entwischt ist, von der wir nicht wissen, was sie anrichten wird).
Das würde erklären, warum die „Impfkritiker“ so derartig diffamiert wurden und versucht wurde, sie mundtot zu machen. Sie haben gleich schon zu Anfang die von Seiten der Entscheider notwendigen Maßnahmen infrage gestellt, als man sich von offizieller Seite noch nicht sicher war, dass die Gefahr in der Tat geringer ist, als es falsche Propheten mit unlauteren Interessen den Politikern nach dem Mund geredet und ins Ohr geflüstert haben.
Doch dann hat sich die Lage verselbständigt und es wurde der Zeitpunkt verpasst, zurückzurudern. Die Folge war das in deren Augen, dass es immer noch besser war, den Menschen eine experimentelle Genbehandlung, die natürlich nicht so genannt werden konnte, „anzubieten“, als gar nichts. Einen wirklichen Impfstoff gab es ja noch nicht. Der war ja, entgegen der fertigen Biowaffe noch gar nicht entwickelt und erprobt. Es herrschte die große Angst seitens der Entscheidungsträger, dass man hinterher zur Rechenschaft gezogen werden könnte, weil man nicht mehr gemacht hat (als, wie sich dann später herausgestellt hat) nötig war.
Die Hysterie ging dann soweit, dass in vielen Ländern eine Impfpflicht drohte und in einigen Ländern sogar durchgesetzt, aber gottseidank nicht vollends durchgezogen wurde.
Als dann im Laufe der Jahre die Erkenntnisse so weit vorangeschritten waren, dass sich der Terror, die Aushebelung von Grundrechten und die Aushöhlung der Demokratie, die Maßnahmen und absurdesten Freiheitseinschränkungen in der Rückschau absurd wurden, entschied man sich, dass es besser sei weiter zu lügen, statt diesen Riesenfehler einzugestehen, bis heute nicht, weil sonst weltweit Köpfe gerollt wären. Vielleicht fürchtete man Regierungsumstürze und eine weltweite Revolution, die den Planeten ins totale Chaos geführt hätte.
Auch die weltweit orchestrierte Vorgehensweise und der oft gleichlautende Wortlaut in verschiedenen Sprachen zu den Informationen zu Corona spricht für eine im Hintergrund agierende militärische Organisation, wohlmöglich sogar mit Beteiligung der NATO. Und auf Regierungsebene kennt man sich auch untereinander.
Die Regierungen hatten Angst, dass die im Verborgenen tätigen Hexenküchen bekannt werden. Die Gefahr, die von diesen Gift-Laboren ausgeht, durfte unter keinen Umständen ans Tageslicht kommen. Was möglich war, musste unter den Teppich gekehrt, oder verharmlost werden. Nicht ohne Grund fordert Professor Wiesendanger das weltweite Verbot von Gain-of-Function Forschung.
Zu allem Übel kam noch dazu, dass hinter all dem eine Menge Geld steckt und den verborgenen Strippenziehern drohte, sehr viel Geld zu verlieren. Sie schafften es ja sogar, die Haftung für die Gift-Jauche auf den Staat zu übertragen.
So erklärt sich auch, dass bis heute Gerichtsurteile gefällt werden, die bar jeder Vernunft sind.
Bekämen Kläger zu oft Recht, wäre das in vielen Staaten eine Bankrotterklärung. So wird weiter kräftig gelogen, weil man sonst zugeben müsste, welchen Schaden der staatlich verordnete Wahnsinn mithilfe von weltweit agierenden Organisationen, wie die WHO, angerichtet hat.
Vielleicht wäre es gut, wir würden uns von der Vorstellung verabschieden, dass von offizieller Seite eine wirkliche Aufarbeitung erfolgen wird. Es gibt weltweit Ansätze, es kann aber sein, dass diese zu keinen vollumfänglichen Ergebnissen führen werden. In Talkshows werden dieselben Verbrecher eingeladen, die den Schaden verursacht haben. Die einst hochangesehenen Herren Ioannidis, Bhakdi, Wodarg und viele, viele andere, sind nach wie vor im Staatsfernsehen nicht zu sehen.
Dafür gibt es eine umfassende Aufklärung in der sogenannten Blase. Wenn auch nicht von „offizieller“ Seite verkündet, liegen die Beweise dank immenser Arbeit von ungezählten Experten, die nicht an irgendeinem staatlichen Geldhahn hängen und sich der Wahrheit verpflichtet haben, auf dem Tisch.
Diese Tatsachenwahrheiten werden vielleicht erst in der nächsten Generation hergenommen werden, um eine wirklich offizielle Aufarbeitung auf den Weg zu bringen. Schon einmal wurde von einer nachfolgenden Generation gefragt: „Wie war das eigentlich damals? Was habt ihr eigentlich gemacht? Wie habt ihr euch verhalten und warum?“ Und selbst, wenn digitale Beweise vernichtet werden sollten, gibt es immer noch genug Bücher, also analoge Chroniken, der wohl bisher dunkelsten Geschichte der gesamten Menschheit.
Das Ausmaß dieses weltweiten Verbrechens, das anfangs vielleicht noch mit den besten Absichten seinen Lauf nahm und dann in ein Desaster überging, ist so groß, dass es fast das menschliche Erfassungsvermögen übersteigt.
Ich behaupte nicht, dass es genau so gewesen ist, aber es könnte sehr wohl genau so gewesen sein.
Dieser Artikel wurde mit dem Pareto-Client geschrieben.
-
 @ 5f078e90:b2bacaa3
2025-04-15 18:17:32
@ 5f078e90:b2bacaa3
2025-04-15 18:17:32This is Hostr, a bridge between Nostr and the Hive blockchain. This post is originating on Nostr as a kind 30023, that is, a long form Nostr note. If all goes as hoped. This note will auto-post and appear over on the Hive blockchain. And, ideally on that Hive post, a link will appear that connects back to the original Nostr note.
The goal is to have either: * a bidirectional bridge, either way * a nostr-to-hive bridge only, if desired * a hive-to-nostr bridge only, if desired
-
 @ e0921d61:e0fe7bd5
2025-04-15 16:13:32
@ e0921d61:e0fe7bd5
2025-04-15 16:13:32Hans-Hermann Hoppe explains the capitalist process as driven by time preference, how people value present vs. future goods. Economic growth hinges on savings and investment, and this shapes our prosperity.
Factors like population, natural resources, and technology matter, but Hoppe argues they're secondary. Without prior savings and investment, even the richest resources and best technology remain untapped.
True economic advancement happens through increasing per capita invested capital, raising productivity, real incomes, and further lowering time preferences. This creates a self-reinforcing cycle of prosperity.
Hoppe claims this process naturally continues smoothly until scarcity itself disappears, unless people voluntarily choose leisure over more wealth. This growth has no inherent reason to halt abruptly.
This smooth capitalist cycle, however, is disrupted when government enters the picture. Government control of resources it didn’t earn or acquire legitimately distorts incentives and investment.
Government monopolization of money through fractional reserve banking artificially lowers interest rates.
Entrepreneurs mistakenly think, and are incentivized to think, there's more savings, so more unsustainable investments proliferate.
Without real savings backing these projects, a painful correction (a bust following the boom) inevitably occurs.
Investments must eventually realign with actual savings, thus leading to bankruptcies and unemployment.
Hoppe concludes that boom-bust cycles aren’t natural. They’re directly caused by government-created credit expansion. Unless governments stop manipulating fiat money supply, these cycles remain unavoidable.
-
 @ 9f2b5b64:e811118f
2025-04-15 15:23:25
@ 9f2b5b64:e811118f
2025-04-15 15:23:25Let's test some Articles
Let's star by just blabbing for a while blah blah balh
But this is the most important part, which will eventually be highlighted I hope.
-
 @ 7d33ba57:1b82db35
2025-04-15 14:59:10
@ 7d33ba57:1b82db35
2025-04-15 14:59:10Tucked into a serene bay just 20 km south of Dubrovnik, Cavtat is a relaxed seaside town that mixes historic charm, clear Adriatic waters, pine-covered hills, and a welcoming small-town feel. It’s often seen as a peaceful alternative to Dubrovnik, with cobbled streets, pretty promenades, and hidden beaches**—perfect for those looking to unwind in style.
🌟 What to Do in Cavtat
1️⃣ Stroll the Seaside Promenade
- Palm-lined and picture-perfect, the Riva is the heart of Cavtat
- Lined with cafés, ice cream spots, and yachts bobbing in the harbor
- Great for a morning coffee or a golden hour walk
2️⃣ Explore the Old Town
- Compact and charming, full of red-roofed stone houses and quiet lanes
- Don’t miss the Rector’s Palace and Baroque St. Nicholas Church
3️⃣ Visit the Racic Mausoleum
- Designed by famed Croatian sculptor Ivan Meštrović
- Set on a hill with panoramic sea views and a peaceful atmosphere
4️⃣ Swim & Sunbathe
- Small coves, flat rocky spots, and crystal-clear turquoise waters
- Try Beach Kamen Mali or walk around the Rat Peninsula for secluded spots
- Great for snorkeling and paddleboarding
5️⃣ Take a Boat to Dubrovnik
- Water taxis run frequently—it's a stunning ride along the coast
- Spend the day exploring Dubrovnik’s Old Town, then return to Cavtat’s tranquility
🍽️ What to Eat
- Fresh seafood – grilled fish, calamari, or buzara (shellfish in white wine sauce)
- Peka – slow-cooked meat or octopus under an iron bell
- Local wines like Pošip (white) or Plavac Mali (red)
- Finish with rozata, a Dubrovnik-style custard dessert
🎯 Travel Tips
✅ Cavtat is 15 mins from Dubrovnik Airport, making it a perfect arrival or departure base
✅ Quieter than Dubrovnik—ideal for families, couples, or solo travelers
✅ Best time to visit: late spring to early fall
✅ Rent a bike or walk around the Rat Peninsula for nature and sea views -
 @ 3ffac3a6:2d656657
2025-04-15 14:49:31
@ 3ffac3a6:2d656657
2025-04-15 14:49:31🏅 Como Criar um Badge Épico no Nostr com
nak+ badges.pageRequisitos:
- Ter o
nakinstalado (https://github.com/fiatjaf/nak) - Ter uma chave privada Nostr (
nsec...) - Acesso ao site https://badges.page
- Um relay ativo (ex:
wss://relay.primal.net)
🔧 Passo 1 — Criar o badge em badges.page
- Acesse o site https://badges.page
-
Clique em "New Badge" no canto superior direito
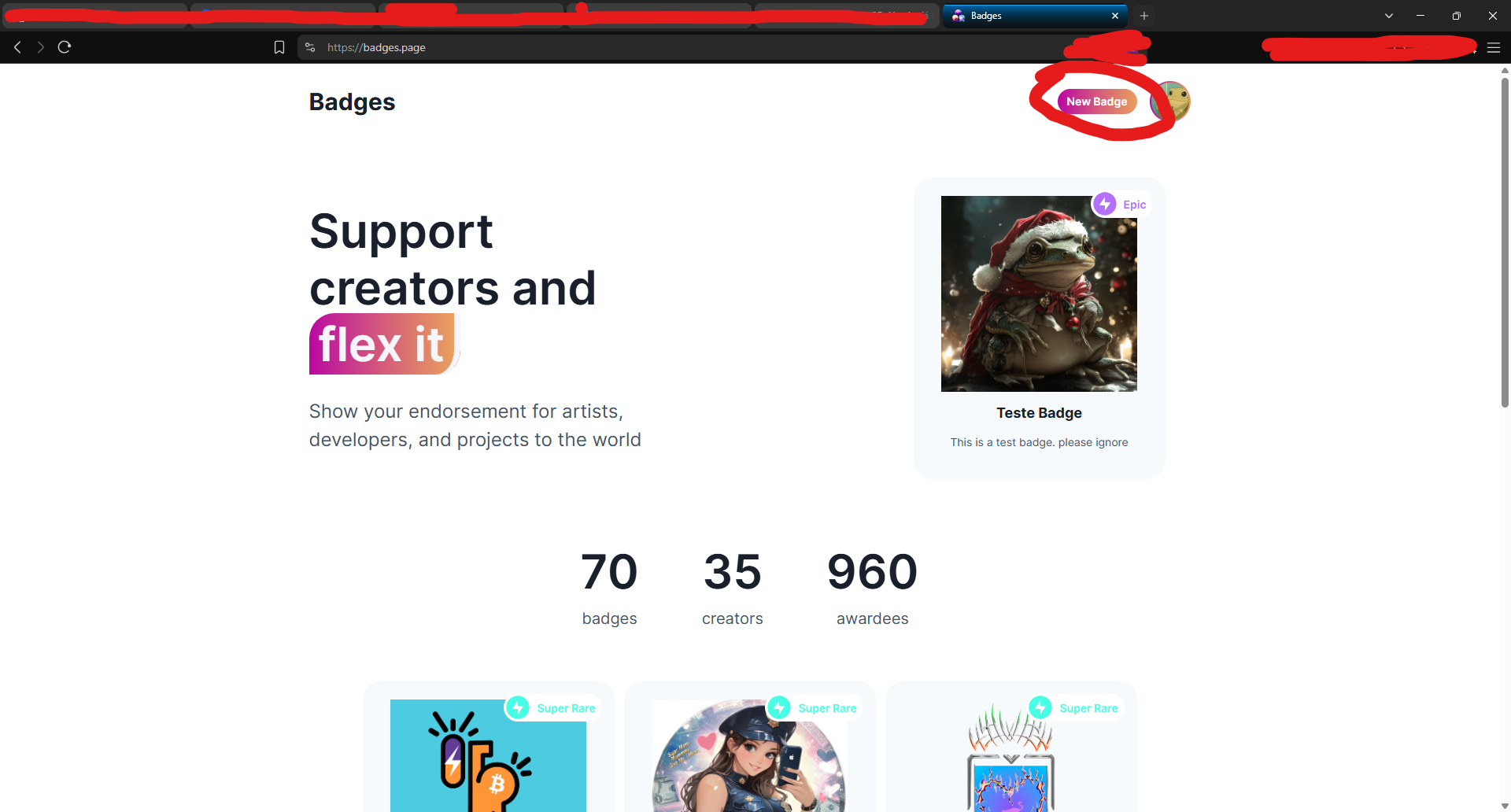
-
Preencha os campos:
- Nome (ex:
Teste Épico) - Descrição
-
Imagem e thumbnail
-
Após criar, você será redirecionado para a página do badge.
🔍 Passo 2 — Copiar o
naddrdo badgeNa barra de endereços, copie o identificador que aparece após
/a/— este é o naddr do seu badge.Exemplo:
nostr:naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Copie:
naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0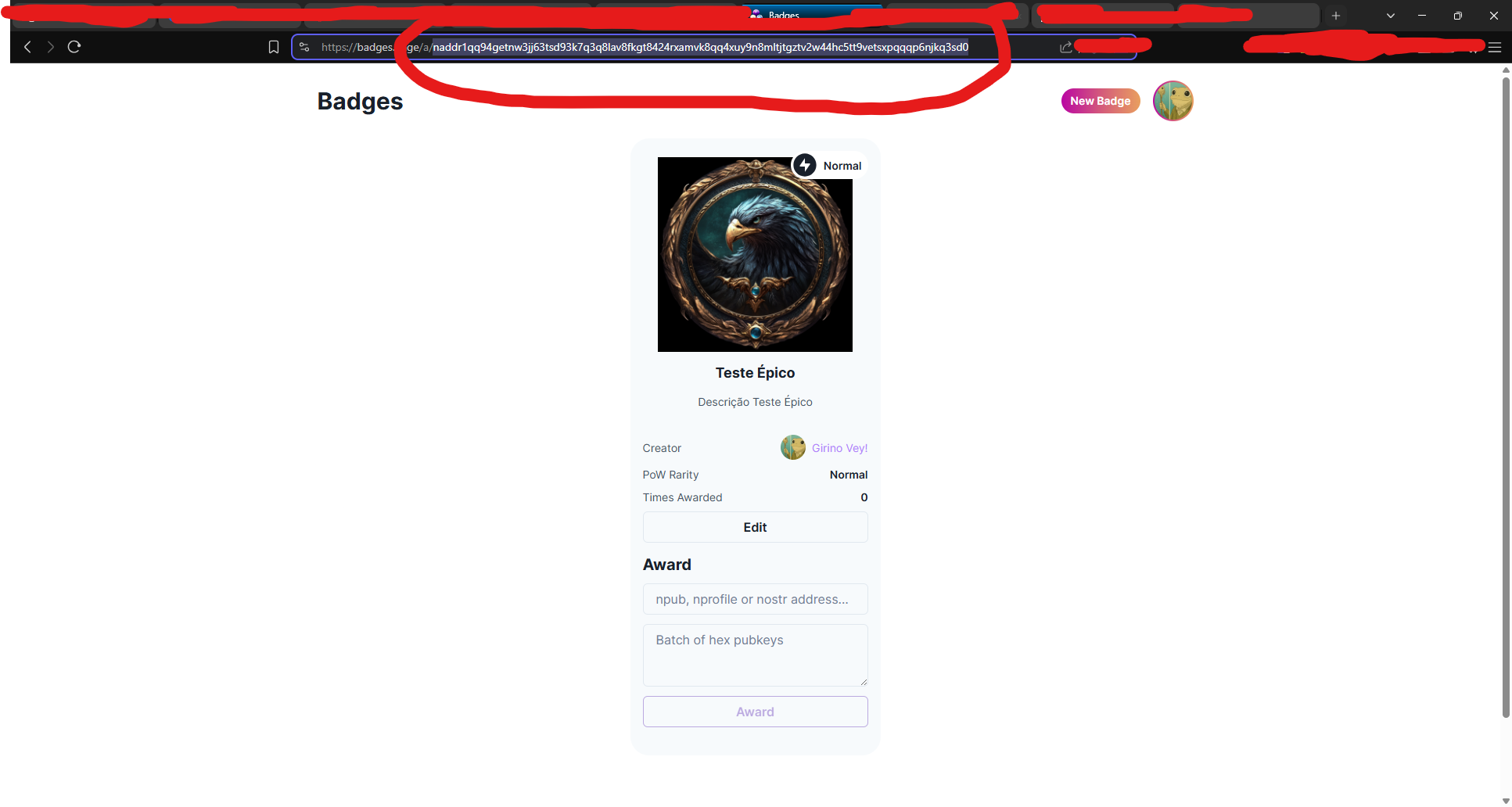
🧠 Passo 3 — Decodificar o naddr com
nakAbra seu terminal (ou Cygwin no Windows) e rode:
bash nak decode naddr1qq94getnw3jj63tsd93k7q3q8lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vetsxpqqqp6njkq3sd0Você verá algo assim:
json { "pubkey": "3ffac3a6c859eaaa8cdddb2c7002a6e10b33efeb92d025b14ead6f8a2d656657", "kind": 30009, "identifier": "Teste-Epico" }Grave o campo
"identifier"— nesse caso: Teste-Epico
🛰️ Passo 4 — Consultar o evento no relay
Agora vamos pegar o evento do badge no relay:
bash nak req -d "Teste-Epico" wss://relay.primal.netVocê verá o conteúdo completo do evento do badge, algo assim:
json { "kind": 30009, "tags": [["d", "Teste-Epico"], ["name", "Teste Épico"], ...] }
💥 Passo 5 — Minerar o evento como "épico" (PoW 31)
Agora vem a mágica: minerar com proof-of-work (PoW 31) para que o badge seja classificado como épico!
bash nak req -d "Teste-Epico" wss://relay.primal.net | nak event --pow 31 --sec nsec1SEU_NSEC_AQUI wss://relay.primal.net wss://nos.lol wss://relay.damus.ioEsse comando: - Resgata o evento original - Gera um novo com PoW de dificuldade 31 - Assina com sua chave privada
nsec- E publica nos relays wss://relay.primal.net, wss://nos.lol e wss://relay.damus.io⚠️ Substitua
nsec1SEU_NSEC_AQUIpela sua chave privada Nostr.
✅ Resultado
Se tudo der certo, o badge será atualizado com um evento de PoW mais alto e aparecerá como "Epic" no site!
- Ter o
-
 @ cb4352cd:a16422d7
2025-04-15 13:25:04
@ cb4352cd:a16422d7
2025-04-15 13:25:04The world of online events has seen unprecedented growth in recent years, with virtual conferences breaking new ground and even setting Guinness World Records. As digital gatherings become more ambitious, some events aim not just to inform and engage but to make history.
Notable Guinness World Records in Online Events
World of Tanks: The Largest Online Game Server Attendance
In 2011, the multiplayer online game World of Tanks set a Guinness World Record for the highest number of players simultaneously online on a single server—91,311 users. This record highlighted the immense popularity and scalability of virtual gaming communities. (ixbt.games)The Largest Cybersecurity Online Conference
In 2020, KnowBe4 organized a cybersecurity conference that gathered more than 30,000 participants. This event set the record for the largest online conference in the field, demonstrating the power of virtual events in bringing together professionals from around the world. This achievement was officially recognized by the Guinness World Records.The Most Attended Virtual Concert
Another major milestone in online events was set by rapper Travis Scott, whose Fortnite virtual concert drew over 12 million concurrent viewers, making it the most attended digital concert ever. This event also earned recognition from the Guinness World Records for its groundbreaking achievement in digital entertainment.Beyond Banking Conference: Aiming for a New World Record
In 2025, Beyond Banking Conference is set to challenge existing records by organizing what could become the largest online gathering in the blockchain and AI space. With an ambitious goal of attracting over 100,000 participants, the event will bring together industry leaders, innovators, and enthusiasts to discuss the future of blockchain, artificial intelligence, and decentralized finance (DeFi).
By leveraging cutting-edge technology and strategic partnerships, Wenix aims to redefine what’s possible for online conferences. If successful, this event will not only break records but also set a new standard for global digital summits.
This isn’t just another virtual conference—it’s a revolution in the making.
-
 @ d3d74124:a4eb7b1d
2025-04-15 12:58:08
@ d3d74124:a4eb7b1d
2025-04-15 12:58:08ORIGINALLY ON XITTER BY STEVE BARBOUR. SHARED HERE FOR THE HOMIES (https://x.com/SGBarbour/status/1911614638623801425)
I find bureaucracy fascinating—it’s like a cancer within human organizations.
Why do organizations become bloated with excessive procedural controls, inefficiency, and indecisiveness as they grow in size and age? Why does decision-by-committee often replace the ambitious, self-starting decision maker? Why do small, "lean and mean" startups inevitably become bloated with bureaucracy as they scale and increase their headcount?
In 2014, these questions consumed me while I sat in a cubicle at an oil and gas company. Why, after years of honing my skills to fix artificial lift systems, was my signing authority decreasing (from $25,000 to $10,000 for workover budgets), despite record corporate profits? Why did I now need a 12-page Microsoft Word document with manager sign-off to schedule and scope a service rig for a simple pump change, when a five-minute email direct to the rig supervisor had previously sufficed?
Years into the job I was far more capable than when I had started, yet I had less authority with each passing day. I became determined to understand what was causes bureaucracy and whether or not it can be prevented.
After researching for some time, such as the essay I posted below, I concluded that bureaucracy stems from a lack of trust and accountability. Bureaucrats impose procedures instead of trusting subordinates to do their jobs, often in response to a costly mistake. This results in new processes that everyone must follow.
Bureaucrats rarely take responsibility for their own failures or hold others accountable for theirs. Instead, they create more procedures and invent new processes. Bureaucracy is a systemic issue, pervasive in nearly every large business or institution. The larger the organization, the more stifling it becomes.
This behavior is costly, increasing administrative overhead and delaying capital execution. Who is bearing this enormous cost?
You are, of course!
Fiat money funds the vast majority of the world's bureaucracy. Fiat money is counterfeit created out of thin air and is used to fund deficit spending by governments worldwide. Governments use paper money they did not earn from taxes to bail out institutions who are overleveraged and get caught with their pants down (e.g. Bombardier and Air Canada are famous repeat offenders in Canada, in the US you can choose any big name bank just about).
They keep printing money and nobody is held accountable anywhere.
Misallocate capital, become insolvent, print money and bail out, create new regulations / procedures, repeat.
You pay for bureaucracy by losing your savings to inflation.
You pay for bureaucracy when the local small businesses in your neighborhood is replaced by a global franchise funded by cheap, perpetual fiat money.
You pay for bureaucracy when you cannot retire as early as you planned and end up working yourself straight into a retirement home.
I was cleaning and organizing my office today and found this old essay by Brian D. Rule from 1977 on the topic, which sparked me to write this short X piece on bureaucracy.
Brian's essay 'Bureaucracy' was actually the very essay that led me into believing fiat money with the root cause of global bureaucracy and waste, which lead me to become interested in gold in 2015 and then in bitcoin in 2016.
Sure enough I googled the prevalence of the term 'bureaucracy' and something interesting happened after 1971...
Isn't it weird how so much went to shit after we got off the gold standard?
Today I am convinced that hard, sound money is the only solution to bureaucracy. This is why I work for #bitcoin.
*Sadly I can no longer find the essay online, so I ripped the text from my paper printout that I found in my files with the now defunct reference website below. *
Bureaucracy
Brian D. Rude, 1977
Original website (now defunct): http://brianrude.com/burea.htm
In the summer of 1975 I took a teaching job in Nebraska. As my previous teaching experience was in Missouri I had to see about getting a Nebraska teaching certificate. I applied for a "Nebraska Standard" teaching certificate. I sent in my college transcript, the application form, and a check for eight dollars. They sent me back, in their own good time, a "Nebraska Prestandard" certificate. I decided there was nothing "prestandard" about me or my teaching, so I wrote back and asked why I didn't get the "standard" certificate. They replied that since I had not taught three out of the last five years I was eligible only for the "prestandard" certificate.
"What do those pigheaded bureaucrats know about my teaching?" I thought to myself. "How would they ever know the standard of my teaching just from shuffling papers around?"
With a little reflection I realized that of course they know nothing about my teaching. They are not supposed to know anything about my teaching. They are paid to evaluate the papers I send them. They are not paid to evaluate my teaching. They have a clear mandate to shuffle my papers, and nothing more.
I presume my application was opened by a secretary, who, following a tightly structured routine, checked off each requirement, typed up my certificate, got it signed by some authority and sent it off to me. Such a secretary is most likely a conscientious worker, a wife and mother, a Republican or Democrat, an occasional churchgoer, a bit of a gossip, and a lot of other plain ordinary things. But she is most likely not a "pigheaded bureaucrat". She would not think of herself as a bureaucrat, and neither would her boss, her coworkers, her family, or anyone else who personally knew her. When she typed "prestandard" instead of "standard" on my teaching certificate she is simply doing her job. Were she to do anything less or more she would be negligent.
So where is the bureaucracy? Or was I dealing with a bureaucracy? If not, then where is there a bureaucracy? Where do we find the genuine article, the bungling, myopic, pigheaded bureaucrat?
I think pigheaded bureaucrats do exist, but they are rare. It's the good bureaucrat that drives us batty, quite as much as the bungling bureaucrat. The good bureaucrat knows exactly what he is obligated to do and he does it conscientiously. The good bureaucrat simply applies the rules that he is responsible for applying, but that he did not make.
A bureaucracy is a group of people responsible for applying a set of rules. The police, courts, executive branches of government, parents, teachers, librarians, and many other people or groups of people are also responsible for applying rules, yet we don't think of these as being bureaucracies. The distinguishing features of a bureaucracy are the types of rules to be applied, and, to some extent, how the rules are applied.
A bureaucracy is responsible for applying what I will call "secondary", or "derived" rules. A secondary rule is a requirement or prohibition established only because it promotes a primary goal. When Moses came down from the mountain with his stone tablets he was carrying what might be considered the simplest statement of what I will call "primary" requirements. The rule, "Thou shalt not steal", for example, is a primary requirement because it is desirable for its own sake, not just as a means to some other end. Similarly, "Thou shalt not commit murder" is a primary requirement because it is desirable as an end in itself.
Safe driving, as a modern example, is a primary requirement because it is desirable for its own sake. The requirement that one get a driver's license before driving, in contrast, is a secondary requirement. It is a requirement instituted by state governments in an attempt to promote the primary goal of safe driving. It is secondary to, or derived from, the primary requirement of driving safely. If people always drove safely, or if driving by its nature presented no hazards, then there would be no need for driver's licenses. Or if legislatures decided that licensing did nothing to promote safe driving then there would be no need for driver's licenses. Licensing is not an end in itself.
Tertiary, or third order, requirements can also exist. If a state requires a birth certificate as proof of age before issuing a driver's license then the state is imposing a third order requirement. Showing a birth certificate is a requirement designed to promote the licensing of drivers, which in turn is designed to promote safe driving.
I imagine one could go ahead and find examples of fourth order requirements established to promote third order requirements. However I don't think there is much point in getting too deep in this kind of analysis. The main point is the distinction of whether a goal is important for its own sake or whether it is important in promoting some other goal. Thus I may speak of a "derived" requirement, meaning only that it is not a primary requirement, but not specifying whether it is secondary, tertiary, or even further removed from the primary goal.
In different contexts I may speak of primary or secondary "requirements", "rules", "prohibitions", "laws", "regulations", "goals", "wrongs", "burdens", "privileges", and so on. It seems natural to think of paying taxes as a "requirement", while murder is a "wrong" that is covered by a "prohibition". But the requirement of paying a tax can be interpreted as the prohibition of avoiding the tax, and the prohibition against murder can be interpreted as the requirement to refrain from murder. The important point here is the distinction between primary and derived, not between omission and commission.
In the example I gave about getting a teaching certificate the bureaucrats were concerned only with my compliance with secondary requirements. They were not at all concerned with the primary requirement - the requirement that I indeed be a good teacher. This is a distinguishing characteristic of bureaucracies. They are concerned only with applying derived, not primary, rules. Other agencies are brought in when there is a primary rule to be applied. The police and courts handle such primary wrongs as theft and murder. Parents and teachers handle such primary wrongs as tracking mud on the carpet or being late to school. Churches handle such primary wrongs as "living in sin" or blasphemy. But it doesn't take a judge or a preacher to decide if my application for a teaching certificate is in order, or my application for a driver's license, or a dog license, or a business license, or a barber's license, or a building permit, or a marriage license, or breathing license. It takes a bureaucrat to handle these matters.
The basic root of bureaucracy then, is the proliferation of secondary requirements. It is not enough, in our modern world, to just be a good and honest person. One can be the best and safest of drivers, but a driver's license is still required. One can be a patriot and a saint, but the IRS still wants that W-2 form. One can be the best doctor in the world, but to practice medicine without a degree and a license is still a serious offense. We have established literally millions of secondary requirements designed to promote a few primary goals. To administer these rules we have people we call bureaucrats.
If the basic root of bureaucracy is a proliferation of derived requirements, then it would seem reasonable that the way to decrease bureaucracy would be to decrease such requirements. This is true, and in fact is a main thesis of this article. Unfortunately it is not always easy to do. Every bureaucratic requirement, in a healthy society at least, was established by reasonably intelligent people giving at least half-way serious consideration to a genuine problem. Therefore any particular bureaucratic requirement or procedure that is challenged will be defended by some person or group.
The most important gain we hope to realize from derived requirements is security. The requirement of any permit or license is usually, if not invariably, justified in order to "protect the public". We want safe driving so we demand driver's licenses. We want our neighbor's dog out of our flower bed so we demand dog licenses. We want merchants to be honest so we demand business licenses. We want welfare recipients not to cheat so we require verification of identity, employment, and who knows what else. All these requirements are seen as necessary to prevent something bad from happening, or to assure that something good will happen.
Derived requirements cannot provide all types of security. We can't prevent floods and famines by making rules and printing forms. The type of security that is the goal of bureaucratic requirements is social control of one form or another.
Simple fairness is often the goal of bureaucratic requirements. The Internal Revenue Service is a good example of this. The primary goal of the IRS is to raise money. This could be done by charging every citizen a flat rate of $1000 or so each year. We wouldn't consider this fair, though, because we realize not everyone has an equal ability to pay. Therefore we have an elaborate set of rules designed to extract more from those who have more. To apply these rules we have what is probably the biggest and most complex bureaucracy since time began. This size and complexity comes from our desire to be fair, not from the simple desire to collect money.
Another form of social control for which bureaucratic requirements are established is prevention of abuse of power. Power comes in many different forms, and we know from long experience that power is always susceptible to abuse. One method of dealing with abuse of power is to call it a primary wrong and punish the offenders. This is done, and it keeps the police and courts very busy. Another way to control abuse of power is to set up secondary requirements to try to prevent such wrongs from occurring in the first place. This produces bureaucracies. In the 1880's, for example, railroads were playing a little rougher than people wanted. They gained power by monopolizing a vital service. In response to this the Interstate Commerce Commission was set up, and has regulated business ever since. A more modern, and more specific, example would be the requirement that a used car dealer certify that the odometer reading is correct when he sells a car. This requirement is in response to what is seen as abuse of power by car dealers who misrepresent their merchandise.
In addition to the main cause of bureaucracy - the proliferation of derived requirements for purposes of security - there are several other causes of bureaucracies that are worth mentioning. The first of these is pure blind imitation. Again I will use driver's licensing as an example.
In the fifty states there is a startling uniformity of driver's license requirements. The most obvious uniformity is that all states require licenses. I have never been able to understand this. It would seem that if each state followed its own experience, values, customs, and judgment, then there would be a whole spectrum of licensing requirements, ranging from no requirement at all to extensive and strict requirements. This is apparently not the case. The majority of states require a written, driving, and eye test. They require a license fee. They require renewal of the license every so many years. They require that the license be in the person’s possession while he is driving. So far as I can tell only minor variations are found on this basic pattern in the different states.
I attribute this uniformity mainly to imitation. If there were an obvious connection between traffic safety and driver’s licensing then this uniformity would seem more sensible. If the National Safety Council told us everyday that the majority of fatal accidents involved an unlicensed driver, then we would not be surprised to find a driver’s license requirement in every state. But that is not the case. The National Safety Council talks a lot about the drinking driver but not about the unlicensed driver. If there was a historical example of some state that was too stubborn to require licenses and had an atrocious accident rate, then again a strict licensing system would be expected in every state. But is not the case either. The connection between licensing and safe driving is tenuous at best. There are innumerable unsafe drivers in every state who have no trouble getting a license. There are also perfectly safe drivers who have trouble getting a license. I think it is safe to say that the average driver, safe or unsafe, can’t pass the written test without studying the book no matter how long he has been driving. Many people find this out when they try to renew their license. All this leads me to believe that licensing requirements are set up by imitation more than anything else. A few states started requiring licenses and other states blindly followed, thinking in some vague way that they were being modern and progressive.
Pure blind imitation may seem a poor reason to set up a bureaucratic requirement and a bureaucracy to apply it, but there are many examples of such imitation in everyday life. In a previous article, ("Roting and Roters", not yet on my web site) I described and developed the idea that blind imitation is a powerful determinant of individual behavior. I think it is almost as powerful a determinant of group action. If each state followed its own inclination in the matter of driver’s licensing I would expect a much wider variation among the different states.
Another cause of bureaucracies is a little more substantial than blind imitation, and accounts for many licensing systems. That is the desire for group recognition. People are by nature social animals. They want to have groups and they want to do things in groups. They want their groups to be recognized and they want this recognition to be official and formal. I began to realize this a few years back when I read in the paper that beauticians were trying to get legislation passed setting up a system of beautician licensure. I thought they were nuts. Why, when we all hate the bureaucracy so much, would anyone want to set up more bureaucracy?
Another example of this kind of bureaucracy building is in the field of occupational therapy. Nurses, physical therapists, and speech therapists are licensed by the state. Occupational therapists, in contrast, have a national association which gives a "registry examination". Upon passing this test, and having a degree in occupational therapy, one becomes an "O.T.R.", a registered occupational therapist. Hospitals and other institutions take this designation as evidence of full qualification in the field. With such a sensible system I find incomprehensible that the profession is pushing for a system of state, rather than national, licensure. But that is exactly what they are doing. They are trying to build more bureaucracy, and they will succeed.
It took me quite a number of years to realize that teacher certification is something that the teaching profession wants, rather than being a requirement imposed from above. However that is apparently the case. The system of licensure, though a pain, does give some recognition to the status of teachers. This, along with a considerable amount of blind imitation, apparently accounts for the uniformity of teacher certification requirements found in different states.
It would be nice if we could give official recognition to groups without the necessity of laying down a mass of secondary requirements, but that is not how it works. Recognition, apparently would have little meaning if it did not indicate that the members of the group meet a system of requirements. It would also be nice if those who gain this official recognition were always worthy of it, but that also is unfortunately not the case. There will always be drivers, teachers, beauticians, occupational therapists, doctors, lawyers, and others who somehow manage to gain the official license but are recognized by their peers as incompetent. Whenever a system of secondary requirements is established there inevitably enters a "reality gap", a gap between the ideal and the real. This can make the whole system ineffective. I will have more to say about this ineffectiveness and its effects shortly.
Yet another factor leading to the spread of bureaucracy is a systematic error made, to a greater or lesser extent, by practitioners of almost any field. That error is thinking that the world’s problems will be solved by one’s own field of knowledge or mode of operation. I think a good name for this would be "role egocentrism". Egocentrism means that a person considers himself the center of the universe, just as ethnocentrism means that a group considers itself the center of the universe. Role egocentrism simply means that one’s own role is given undue importance and status. Thus doctors think that medicine will be the salvation of the world. When medicine has progressed far enough, they think, the world will be such a fine place that other problems will just disappear. Preachers think that if only we would all turn to God there would be no more problems. Farmers think that once the world food problem is solved, by farmers of course, then all will be well. Teachers think that education will be the one thing to save mankind from itself. Scientists think that research will usher in a new golden age.
It is hard to conceive of a bureaucrat having such grandiose visions of salvation. But remember that bureaucrats do not think of themselves as bureaucrats. Even more importantly, bureaucrats don’t make the rules, they only apply them. The rules are made by governments. Governments consist of politicians, and politicians are very susceptible to role egocentrism. To attain office a politician must convince people that government is capable of doing things, and he must believe it himself. Since people want things done it is not surprising that governments are populated by large numbers of people with an inflated idea of what can be done by writing rules and laws. Since there are few primary laws left to write, we have an ever-increasing proliferation of secondary requirements. Bureaucrats may not make the basic rules that they apply, but they do have some latitude to make minor rules, and even more importantly, they are responsible for making reports and can require reports from their subordinates. In the making of reports a little role egocentrism can go a long way. The result can be a massive flow of reams and reams of paperwork, with copies sent to all other bureaucrats who might have come slight connection to the job at hand, but with very little of the reports actually being read.
Bureaucrats also have some latitude in working as individuals or teams, and again a great deal of waste can ensue. The justification for working in committees or teams is the idea that by joining forces the best abilities of each member can be brought to bear on the problem at hand and therefore a solution to the problem is more likely. Of course there is some truth to this, but it doesn’t always work out too well. The little bit truth can become greatly augmented by role egocentrism. Team workers like to think that if you set six experts around a table something good is bound to come out of it. Non-team workers, like myself, tend to think that setting six experts around a table is a good way for six experts to waste each other’s time. I think bureaucrats at the higher levels are more prone to waste their energy this way, and I interpret this as a form of role egocentrism.
All of these cases of bureaucracy are augmented by another systematic error. That error is the systematic overestimation of group cohesiveness. In the minds of bureaucracy builders the bureaucracies already in existence become "they", and "they" are a bunch of pigheaded fools. "We", on the other hand, are good, right-thinking people and the bureaucracy we set up will serve the people, not the bureaucrats. And just to make sure we’ll write in plenty of safeguards. Of course this doesn’t work. Just because it is "our" program doesn’t mean that it won’t be subject to all the problems that beset any program. A new generation will grow up and decide that "we" are "they" and the cycle begins over again.
So far I have painted a rather pessimistic picture. We have bureaucrats because we have a multitude of derived requirements to administer, and we have a multitude of derived requirements because we think they bring us security. We also have bureaucracies because of imitation, because of the desire for group recognition, and because of role egocentrism. Yet the sum total of all this drives us batty. The next step is to try to get some idea of why and how bureaucracy is frustrating. I think the frustration results from main causes, standardization and ineffectiveness.
Standardization is a wonderful thing in industry. If my car needs a new fuel pump I can buy one right off the shelf and know it will fit. Fuel pumps are standard, and engines are standard. They fit together beautifully. The few defective fuel pumps that are not standard are quickly caught and tossed off the assembly line. This happy state of affairs does not extend to non-physical objects though. Consider, for example, a seed planter. I don’t know just how a planter might work but I visualize a mechanical hand grabbing one seed at a time and popping it into the ground. Seeds are pretty well standardized and most seeds can be picked up by these mechanical hands without injury. A few seeds, however, are nonstandard. They are either too big, or too small, or perhaps the wrong shape. The iron hands that so effectively plant most seeds will bruise, shred, mangle or maybe just overlook the oddball seeds. This doesn’t worry us though. Just like the defective fuel pumps that are bumped off the assembly line, the few mishandled seeds are of no great consequence.
When standardization is extended to humans the situation changes dramatically. We can’t bump off the defectives so carelessly. A bureaucracy can be compared to the seed planter. Iron hands pick you up and set you down again. If you fit the standard mold, these iron hands hold you gently. If you don’t fit the standard mold those same iron hands can shred you to pieces.
For example, a few years back I knew a fellow who was paraplegic. He was completely confined to his wheelchair, but he had a car with adapted controls and could drive as well as anyone. Unfortunately he had considerable difficulty licensing both himself and his car. He could drive to the courthouse, and get himself out of his car and into his wheelchair, but he had no way of getting down in the basement where the licensing offices were. There were elevators from the first floor to the basement of course, but between the parking lot and the first floor were innumerable steps and curbs. To a person in a wheelchair a single four-inch curb might as well be a ten-foot wall. Apparently my friend managed somehow to keep himself legal most of the time, but he did at times speak bitterly about the troubles he encountered. The state required licenses, and the state provided a way to get these licenses, but only if you fit the standard mold. My friend did not fit the standard mold, and felt very much caught in those iron hands.
Fortunately most examples of the problems of standardization are not so serious. My wife had a friend in college who was triply enrolled in the School of Education, the School of Medicine, and the Graduate School. All occupational therapy students were dually enrolled in Education and Medicine, which caused no end of red tape in itself, but this particular girl was such a go-getter that she added Graduate School. This made her a non-standard person indeed. One day she spent a solid half hour on the phone trying to convince some bureaucrat that, no matter that it didn’t fit the computer, it was possible to be enrolled that way. I presume the problem, whatever it was, was eventually worked out, but not without some cost in frustration. The bureaucrat in question was probably no more pigheaded than you or I. The rules he was responsible for applying simply made no provision for triply enrolled students.
When caught as a non-standard person in a standardized bureaucracy one wonders why standardization is established in the first place. Except for the role egocentrism of a few bureaucrats, standardization is not intentional. It arises by the same forces that promote standardization in industry. Standardization promotes efficiency. Whenever a form is printed, for instance, it is designed to fit the majority of situations. Thus a fire insurance application form may ask if the house is frame or brick, with no intention of frustrating the owners of igloos, caves, and houseboats. It simply reflects the fact that most houses are either frame or brick. By stating these two choices the processing of the application is speeded up. If instead the application stated simply, "describe the dwelling to be insured", the work in processing the application would be considerably increased. Standardization is the inevitable correlate of the proliferation of secondary requirements.
There is also another cause of standardization, the lack of discretionary authority. Remember that secondary requirements are set up in many cases to prevent abuse of power and to be fair. This usually means that the bureaucrats who apply these rules have only a limited number of responses to a given situation. Bureaucracies are given very little discretionary authority. They must follow the rules whether the rules fit the situation at hand or not. To illustrate this let me hypothesize two ways of administering welfare.
In case A an applicant comes to a social worker. The applicant explains that her husband just lost his job because he drank too much, that she works as a maid two days a week but that her children have no one to stay with them when she works unless she pays a baby sitter which costs almost half her salary, that their car is about to be repossessed and then she won’t be able to get to work at all, that the landlord won’t fix the plumbing and charges too much rent, that they would move except they haven’t found a place that’s any cheaper, that their oldest son was just sent to jail for a two year term, and on, and on, and on. The social worker listens to all this, makes a few phone calls, and the next day tells the applicant, "We’ll give you $70 a week allowance, but tell your husband to come in before next week. We’ll get him off his beer and on the job one way or the other. I called your landlord and got his side of the story and there’ll have to be a few changes made before he’ll reconnect the shower, and you’ve got to..."
In situation B the applicant comes to the social worker with the same story. The social worker says, "I think we can help you, but first you’ll have to find your birth certificate. Regulations state that only citizens are eligible for welfare. Then you’ll have to take this form to your employer to certify your wage scale. And this form goes to your landlord to verify your rent. And you’ll have to fill out this form to show how you budget your income, and this form to verify that you are not now receiving veterans or disability compensation, and this form that verifies you are not eligible to collect child support from any previous husband, unless the marriage was annulled, in which case you have to hunt up the certificate of annulment... What? You lost your certificate of annulment? You’re not sure you ever were married to John before you left him for Henry? ..."
In situation A the social worker is given a budget and a wide latitude on how to distribute the money. She is given discretionary power to a large degree. In situation B the social worker is given a very small amount of discretionary power. She can’t decide for herself whether the applicant is genuinely needy, but must prepare a "work-up", consisting of documentation of all relevant aspects of the applicant’s situation. On the basis of this work-up she is allowed to authorize an allowance, the amount to be taken from a table. If the social worker feels that there are relevant circumstances that are not covered at all in the standard work-up then she may begin some special procedure to have the case considered by a higher authority or committee. But the common suspicion that things aren’t quite as they should be, either because the applicant is undeserving or that he needs more than he can get or that the program misses its mark in yet some other way, is just a routine part of the job.
Standardization, fitting everyone into the same size slot, reduces everything to paperwork. The "work-up" is a stack of documents. These documents, certificates, forms, statements, memos, become the currency of bureaucracy, the medium of exchange. "Facts" become so only when they are certified by someone’s signature, even though they may be obvious. Other "facts" must be accepted because of their official certification even though common sense or simple observation show them to be false. A gap between the real and the official inevitably sets in. Then this gap leads to actions that are perceived to be detrimental or unfair, then the result is a considerable amount of frustration, in spite of the fact that the intent of all the red tape was to be beneficial and fair.
This leads to the second cause of bureaucratic frustration, which is ineffectiveness. If a bureaucratic requirement is seen as effective in accomplishing its goal we accept it even if there is considerable inconvenience involved in meeting the requirement. If, on the other hand, a bureaucratic requirement is seen as ineffective then a little inconvenience in meeting the requirement can be a very significant frustration. Getting a loan from a bank, for example, involves considerable effort in meeting bureaucratic requirements. However we don’t expect money to be handed out without some security that it will be paid back. Therefore we don’t get too frustrated by the inconvenience in meeting those requirements. Similarly, driver’s licenses are seen as worthwhile, even if not fully effective, and entail only a little bother every four years or so. Therefore we do not hear too much about pigheaded bureaucrats at the driver’s license bureau. Unfortunately other licensing systems have imperfections so massive and ubiquitous, and benefits so doubtful, that the whole system is a burden to society. A little inconvenience in getting such a license can be very frustrating. This is the frustration I felt in the example I gave at the beginning of this article about getting a teaching certificate. Another example would be going back three times to the fire station to get a bicycle license. I went back twice. I figured three times was above and beyond the call of duty. I never did get my bicycle licensed.
In psychological phenomena the whole is not always equal to the sum of its parts. Bureaucratic frustration can work this way. One frustration may be brushed off, and then another, and perhaps several more, but eventually there comes a point where the frustrations increase out of proportion to their cumulative value. Short-term frustration changes into long-term demoralization. I think "hassle" is a good name for this. It is a commonly used term, though it is not normally considered a specifically defined term. I think the phenomenon should be taken seriously though. It will become increasingly common with constant increases in bureaucratic requirements.
The best example I can give of hassle in my own experience comes from my home state of Missouri. To get one’s car licensed in Missouri one must show the title or previous year’s registration certificate, as can be expected, but that is not all there is to it. One must also get a new safety inspection certificate and also show his personal property tax receipt. When I lived in Missouri I usually didn’t have any property to be taxed, but I still had to go to the Treasurer’s office in the courthouse to get a card stating that no taxes were due. The safety inspection always caused me worry, and the car licensing itself always had the potential for problems. Maybe they would find something wrong with my title and tell me I can’t register the car. Thus the sum of all this was to me a hassle. The requirements exceeded my tolerance. It caused me anxiety, much more than the sum of the anxieties of each requirement had they come independently. Fortunately other states I have lived in didn’t tie those things together, and for that reason I hope I don’t end up living in Missouri again.
People vary in their susceptibility to hassle. I expect I have about as low a tolerance as anyone. I haven’t heard other Missourians complaining about the car licensing system. Unfortunately those who are not susceptible to the demoralization of hassles have little understanding of the anxieties of those who are susceptible. This goes along with the general rule that the more aggressive cannot empathize with the less aggressive. This increases the problem to those who are susceptible to hassle. However I would expect the future will see the problem given much more recognition as more and more people find themselves pushed beyond their tolerance.
A movement is currently under way by the Democratic Party to do away with traditional voter registration practices and to substitute a "same day" standardized registration system. Thus a voter could show up on election day, show proof of identity and residence, and be registered on the spot. The rationale of this is that the complications of regular registration are sufficient to prevent many people from voting. I think the move is clearly motivated by the political goal of increasing the Democratic vote. Still, I am glad to see the movement. They are talking about hassle. They are acknowledging that bureaucratic requirements are a burden, and that this burden can at times be of a serious nature. Now when somebody tells me I’m nuts if I worry about getting a car license I can reply that apparently some people worry about voter registration.
In the first part of this article I tried to explain the causes of bureaucratic requirements. Then I tried to analyze how bureaucracy produces frustration. There are very good reasons for bureaucracies, and there are very good reasons for frustration, so it appears we must live with the problem forever. I don’t think the world will grind to a halt though. The way out of this dilemma is simply to realize when diminishing returns begin to set in, and even more importantly, to realize when the return does not equal the investment. Every human endeavor has a cost and a benefit, an investment and a return. When establishing a system of secondary rules the investment includes the cost of setting up the bureaucracy, the cost of the individual’s efforts in dealing with the bureaucracy, and increasingly more importantly, the cost in frustration, anxiety, and demoralization. These costs must be subtracted from the benefits before deciding that a given proposal is or is not worthwhile.
Sometimes the cost can be reduced to dollars and cents. According to an item in the newsletter from my representative in Congress the town of Faith, South Dakota, recently applied for a federal grant. I believe they wanted to build a rodeo grandstand. They were offered $150,000 to match their own $50,000, but of course there were strings attached. After looking closely at these strings they finally rejected the federal help entirely and built their own grandstand for only $20,000. I doubt that this example is typical of federal grants, but it does illustrate diminishing returns.
More commonly only part of the cost can be reduced to dollars and cents. For example, an accountant may compute that a $20,000 grant for a town would entail only about $6000 in labor to do all the paperwork. This would seem to make a clear profit for the town of $14,000. But if the city officials are sick of the paperwork and the delays, if the citizens are mad at everyone and each other, and if the strings will be attached forever, then all this must certainly be subtracted from the benefit.
The investment/return assessment is even more complicated when all important factors are psychological. How can we put a price on invasion of privacy? How can we put a price on independence and respect for the individual? How are these costs to be subtracted from the safety and security that we gain from bureaucratic requirements? I don’t know. Since psychological costs cannot be measured in dollars and cents, the worth of any system of bureaucratic requirements will always be a matter of subjective judgment, a matter of politics to be decided through political processes. They are not matters to be decided by technicians or engineers of any sort.
I have my own opinions. I vote for nuclear energy and against OSHA. I tend to think of the licensing of voters and guns worthwhile, of cars and drivers as borderline, and of teachers, barbers, cats and bicycles as not worthwhile. Of course everyone else will disagree. I only hope we will start counting costs and benefits a little more carefully. As is true of so many things, it cannot be said of bureaucracy that if some is good, more is better.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 1b9fc4cd:1d6d4902
2025-04-15 10:53:29
@ 1b9fc4cd:1d6d4902
2025-04-15 10:53:29In an increasingly divided world, it often feels like we're all shouting in different languages. But there's one universal tongue we can all understand--music. Music doesn't just traverse borders; it erases them, connecting people in ways that words alone can't. Whether it's helping someone with learning disabilities find their voice, easing the fog of Alzheimer's, or bridging cultural gaps when you don't speak the language, Daniel Alonso Siegel explores why music is the ultimate unifier.
The Melody of Learning
Alonso Siegel begins with a moving example: music and learning disabilities. Consider being a child in school struggling to read or write, feeling like you're always a step behind your classmates. Then, one day, you strap on a guitar or sit at a keyboard, and suddenly, things start to click. The arts can be a game-changer for kids struggling to overcome learning disabilities, offering a new way to express themselves. Imagine a young student with dyslexia who struggles with traditional learning methods.
When they start taking drumming lessons, their world transforms. The rhythmic patterns can help them improve their coordination and focus, translating to better academic performance. Through music, children and young adults can find a way to bridge the gap between ability and aspiration. It's like unearthing a secret portal in a maze: music allows for an alternative path to success.
The Symphony of Memory
Alonso Siegel examines music's extraordinary impact on those suffering from various forms of dementia, like Alzheimer's. This cruel disease robs people of their cherished memories, leaving them lost in a fog of forgetfulness. But music can be a beacon of light in that darkness. Songs from the past can trigger memories and emotions long thought lost, offering moments of clarity and connection.
Many elderly parents barely recognize their children due to Alzheimer's. But when they are played their favorite song from decades past, patients begin to sing along, remembering every word. For a few precious minutes, they are transported back to the days of their youth, dancing and laughing as if the years and fear had melted away. Music can reach into the depths of one's mind and retrieve a piece of the past, building a bridge to lost memories.
The Harmony of Cultures
Daniel Alonso Siegel also ponders music's role in helping people assimilate to new cultures. Moving to a new country where you don't speak the language can be isolating and overwhelming. But music can provide a way to connect and integrate, even when words fail.
There are stories of refugees who relocate to countries where they don't speak the language, and feelings of isolation can sink in. However, newcomers can find common ground with their new neighbors by trying to find connections through the community, like in a local music group. Through shared melodies and rhythms, music became their shared language, fostering friendships and easing his transition into a new culture.
Studies have shown that participating in music activities can improve social integration and language acquisition for immigrants. Music classes provide a space where people from diverse backgrounds can come together, learn from each other, and build a sense of community.
The Universal Language
In conclusion, Daniel Alonso Siegel asks why music has the capacity to build bridges rather than walls. Music speaks to our fundamental human experience, tapping into our emotions, memories, and social bonds in a way that transcends language. When you hear a beautiful piece of music, you don't have to understand the lyrics to feel its impact. The melody alone can move you to tears or lift your spirits.
Music's universality means it can break down barriers between people of different backgrounds, abilities, and experiences. It’s a language that everyone speaks, whether you're tapping your foot to a bouncy tune, shedding a tear over a poignant verse, or joining a chorus in perfect harmony.
At a time when it seems like we're too busy building walls, music reminds us of the importance of building bridges instead. It's a call to connect on a deeper level, find common ground in a shared beat, and celebrate the diverse tapestry of human experience.
So, put on your favorite song next time you feel divided or disconnected. Sing, dance, play an instrument, or simply listen. Let the music do what it does best: unite us. Ultimately, no matter where we come from or what challenges we face, we're all part of the same global band, and the music we make together is far more beautiful than any solo performance.
In the grand music festival that is life, let's not forget to play in harmony.
-
 @ 1f9e547c:8af216ed
2025-04-15 10:03:32
@ 1f9e547c:8af216ed
2025-04-15 10:03:32Opinion about Mixin Messenger Desktop (desktop)
Mixin Network suffered a major breach on September 23, 2023, due to a vulnerability in its Google Cloud Services-based withdrawal system. The attack led to the unauthorized extraction of over $150 million in BTC, ETH, and USDT-ERC20, traced to known addresses. Mixin immediately suspended deposits and withdrawals, enlisted Slowmist and Mandiant for investigation, and offered a $20M bounty for asset recovery. Losses were converted into a structured debt, with a repayment commitment using existing funds and future ecosystem revenue. As of April 2024, a new mainnet is operational, core products are restored, and over half of affected users have received partial compensation in XIN tokens.
WalletScrutiny #nostrOpinion
-
 @ d41bf82f:ed90d888
2025-04-15 09:02:53
@ d41bf82f:ed90d888
2025-04-15 09:02:53"รู้สึกเหมือนบางสิ่งที่ยิ่งใหญ่กำลังจะเกิดขึ้น — กราฟแสดงการเติบโตของประชากรในแต่ละปี, ความเข้มข้นของก๊าซคาร์บอนไดออกไซด์ในบรรยากาศ, จำนวนเว็บไซต์, และเมกะไบต์ต่อดอลลาร์ ล้วนพุ่งทะยานขึ้นสู่เส้นโค้งที่ทะลุกรอบการเปลี่ยนแปลงตามยุคสมัย นี่คือ "เอกฐาน" — จุดสิ้นสุดของทุกสิ่งที่เราคุ้นเคย และอาจเป็นจุดเริ่มต้นของบางสิ่งที่เราไม่มีวันเข้าใจเลยก็ได้" -Danny Hillis
ปฐมบทแห่งการเปลี่ยนแปลงของอำนาจ ประวัติศาสตร์ของมนุษยชาติไม่ใช่เส้นตรงที่ดำเนินไปอย่างราบรื่น แต่เป็นลำดับของช่วงเวลาสงบนิ่งสลับกับช่วงเวลาแห่งการเปลี่ยนแปลงอย่างรุนแรง ซึ่งมักเกิดขึ้นอย่างไม่ทันตั้งตัว ช่วงเวลาเหล่านี้มักจะถูกผลักดันโดยการเปลี่ยนแปลงทางเทคโนโลยีที่ทำให้โครงสร้างของอำนาจที่มีอยู่ต้องปรับตัวหรือพังทลายลง
ขั้นที่สี่ของการจัดระเบียบสังคมมนุษย์ หัวข้อของหนังสือเล่มนี้ คือการปฏิวัติอำนาจรูปแบบใหม่ ที่กำลังเปิดทางให้ “ปัจเจกบุคคล” มีอิสรภาพมากขึ้น โดยแลกกับอำนาจที่รัฐชาติในศตวรรษที่ 20 เคยมี นี่คือการเปลี่ยนแปลงเชิงโครงสร้างผ่านนวัตกรรมที่เปลี่ยนแก่นกลางของ “ตรรกะแห่งความรุนแรง(logic of violence)” ไปอย่างที่ไม่เคยเกิดขึ้นมาก่อน ไมโครโพรเซสเซอร์จะกัดเซาะและทำลายโครงสร้างของรัฐชาติ และในการเปลี่ยนผ่านนี้ จะก่อให้เกิดรูปแบบใหม่ของการจัดระเบียบทางสังคม ตลอดประวัติศาสตร์มนุษย์ เราเคยผ่านระบบเศรษฐกิจพื้นฐานมาเพียงสามระยะ: 1. สังคมล่าสัตว์และหาของป่า 2. สังคมเกษตรกรรม 3. สังคมอุตสาหกรรม
แต่บัดนี้ กำลังมีสิ่งใหม่ปรากฏขึ้น — ระยะที่สี่ของการจัดระเบียบสังคม: สังคมข้อมูลสารสนเทศ (Information societies)
The Sovereign Individual เปิดบทแรกด้วยแนวคิดที่ชี้ให้เห็นว่าการเปลี่ยนแปลงทางเทคโนโลยี โดยเฉพาะเทคโนโลยีสารสนเทศ กำลังสร้างโลกใหม่ที่แตกต่างจากเดิมอย่างสิ้นเชิง และกำลังสั่นคลอนเสาหลักของอำนาจรัฐแบบเดิม ทั้งในด้านเศรษฐกิจ การควบคุม และความชอบธรรม
โลกในยุคก่อนและหลังเทคโนโลยี ตลอดประวัติศาสตร์ มนุษย์เคยอยู่ภายใต้โครงสร้างอำนาจที่เปลี่ยนไปตามยุคสมัย ยุคเกษตรกรรมทำให้เกิดระบบศักดินา ยุคอุตสาหกรรมทำให้เกิดรัฐชาติที่มีอำนาจรวมศูนย์ และการเกิดขึ้นของเทคโนโลยีก็เคยปฏิวัติโลกมาแล้วหลายครั้ง ตัวอย่างเช่น การใช้ดินปืนทำให้กษัตริย์สามารถสร้างกองทัพประจำการ แทนที่อำนาจของเหล่าขุนนางท้องถิ่น เทคโนโลยีสารสนเทศในยุคปัจจุบัน เช่น อินเทอร์เน็ต คอมพิวเตอร์ และการเข้ารหัสข้อมูล กำลังทำให้ต้นทุนในการใช้ความรุนแรงเพิ่มสูงขึ้น และลดความสามารถของรัฐในการควบคุมข้อมูลและทรัพยากร นี่เป็นการเปลี่ยนแปลงโครงสร้างอำนาจจากบนลงล่าง ไปสู่กระจายศูนย์และปัจเจกบุคคล
รัฐกับการผูกขาดอำนาจทางเศรษฐกิจ ตลอดหลายศตวรรษที่ผ่านมา รัฐมีอำนาจเหนือประชาชนได้ก็เพราะสามารถควบคุมเศรษฐกิจได้ผ่านกลไก เช่น การจัดเก็บภาษี การควบคุมเงินตรา และการผูกขาดการใช้ความรุนแรง การควบคุมเหล่านี้ทำให้รัฐสามารถรักษาอำนาจได้ แม้จะไม่ได้มีประสิทธิภาพสูงสุดเสมอไป แต่เมื่อเทคโนโลยีใหม่เข้ามา ทำให้เงินทุนและข้อมูลสารสนเทศสามารถเคลื่อนที่ข้ามพรมแดนได้ง่าย รัฐจะไม่สามารถจัดเก็บภาษีได้ง่ายเช่นเดิมอีกต่อไป ความสามารถในการใช้กำลังบังคับก็ลดลงเพราะต้นทุนเพิ่มขึ้น และประชาชนสามารถหลบเลี่ยงหรือกระจายอำนาจออกจากรัฐได้มากขึ้น
รัฐเคยชินกับการปฏิบัติต่อผู้เสียภาษีในลักษณะเดียวกับที่ชาวนาเลี้ยงวัว — ปล่อยให้พวกเขาอยู่ในทุ่งเพื่อจะรีดนม แต่ในไม่ช้า…วัวเหล่านั้นจะมีปีก
การเกิดขึ้นของปัจเจกผู้มีอธิปไตย ในโลกใหม่ที่เทคโนโลยีลดต้นทุนในการเป็นอิสระจากรัฐ บุคคลที่มีความรู้ ทักษะ และสามารถใช้เทคโนโลยีได้อย่างมีประสิทธิภาพจะกลายเป็น "Sovereign Individual" หรือ "ปัจเจกบุคคลผู้มีอำนาจอธิปไตย" ซึ่งมีคุณลักษณะเฉพาะคือ: 1. สามารถเคลื่อนย้ายทุนและตัวเองได้อย่างอิสระ 2. ทำธุรกรรมบนอินเทอร์เน็ตซึ่งสามารถเข้ารหัสได้เพื่อลดการพึ่งพารัฐ 3. ควบคุมทรัพย์สินและรายได้ของตนเองโดยไม่ตกอยู่ใต้อำนาจรัฐ บุคคลกลุ่มนี้จะมีพลังในการต่อรองสูงขึ้น และจะเป็นกลุ่มที่กำหนดทิศทางของโลกอนาคต
ความท้าทายระหว่างเปลี่ยนผ่าน ผู้เขียนไม่ปฏิเสธว่าการเปลี่ยนผ่านจากยุคแห่งรัฐรวมศูนย์ไปสู่ยุคของปัจเจกผู้มีอธิปไตยจะเต็มไปด้วยความปั่นป่วน ในระยะสั้น เราอาจเห็น: * การล่มสลายของระบบสวัสดิการ * การว่างงานจากโครงสร้างเศรษฐกิจที่เปลี่ยนไป * การเพิ่มขึ้นของอาชญากรรมหรือสงครามภายในบางพื้นที่ แต่ทั้งหมดนี้คือผลข้างเคียงของการเปลี่ยนแปลงระดับรากฐาน ที่จะนำไปสู่ระบบที่มีประสิทธิภาพและยั่งยืนกว่าในระยะยาว
“จักรวาลมอบรางวัลให้เมื่อเรารู้เท่าทันกฎของมัน และลงโทษอย่างไร้ปรานีเมื่อเราหลงผิด หากเราเข้าใจธรรมชาติของจักรวาล แผนการต่างๆ จะดำเนินไปได้อย่างราบรื่น และเราจะได้ลิ้มรสความสุขจากความสำเร็จนั้น แต่หากเราหลอกตัวเองว่าเพียงแค่กระโดดจากหน้าผาแล้วกระพือแขนก็จะบินได้ — จักรวาลจะไม่ลังเลที่จะลงโทษเรา... ด้วยความตาย.” — แจ็ค โคเฮน และ เอียน สจ๊วต
บทสรุป: เส้นทางใหม่ของอารยธรรม บทแรกของ The Sovereign Individual ไม่ได้เพียงแค่เตือนถึงการเปลี่ยนแปลงที่กำลังจะมาถึง แต่ยังเสนอแนวทางใหม่ของอารยธรรมที่อิงกับเสรีภาพของปัจเจก การกระจายอำนาจ และการใช้เทคโนโลยีเพื่อปลดปล่อยมนุษย์จากการควบคุมของรัฐ
โลกในอนาคตจะเป็นโลกที่อำนาจไม่กระจุกอยู่ในมือของรัฐอีกต่อไป แต่จะอยู่ในมือของผู้ที่สามารถเข้าใจและใช้ประโยชน์จากเทคโนโลยีเพื่อสร้างอิสรภาพของตนเองได้อย่างแท้จริง
Siamstr
-
 @ 7d33ba57:1b82db35
2025-04-15 08:43:57
@ 7d33ba57:1b82db35
2025-04-15 08:43:57Plovdiv, Bulgaria’s oldest continuously inhabited city—and one of the oldest in the world—is a blend of ancient ruins, colorful 19th-century houses, bohemian flair, and buzzing street life. Set on seven hills and split by the Maritsa River, Plovdiv feels like a beautiful secret waiting to be discovered.
It was named European Capital of Culture in 2019, and it's easy to see why—history, art, music, food, and laid-back vibes all collide here effortlessly.
🌟 Top Things to Do in Plovdiv
1️⃣ Old Town (Stari Grad)
- A living museum of cobblestone streets and Revival-era mansions
- Wander among galleries, traditional houses, and hidden courtyards
- Highlights: Balabanov House, Ethnographic Museum, and the lovely Hindliyan House
2️⃣ Roman Theater of Philippopolis
- A stunning 2nd-century amphitheater still used for concerts and events
- Amazing views over the city—especially at sunset
- One of the best-preserved ancient theaters in the world
3️⃣ Kapana Creative District
- Once the old artisans’ quarter, now transformed into Plovdiv’s coolest neighborhood
- Full of indie galleries, craft beer bars, street art, and coffee shops
- Great for a chill afternoon or lively night out
4️⃣ Ancient Stadium & Roman Forum
- Right in the city center, explore ruins that date back to Roman times
- The ancient stadium once held over 30,000 spectators
- You’ll literally be walking over layers of history
5️⃣ Nebet Tepe Hill
- One of the original Thracian settlement sites
- Offers panoramic views over Plovdiv—especially at sunset with a local beer in hand
🍽️ What to Eat in Plovdiv
- Shopska salad with juicy tomatoes, cucumbers, and sirene cheese
- Kavarma – slow-cooked meat stew, hearty and flavorful
- Mekitsi – fluffy fried dough, best with jam or cheese for breakfast
- Bulgarian wine is fantastic—try a Mavrud red or local white from the Thracian Valley
- Don’t miss the city’s many wine bars and craft beer spots
🏞️ Day Trips from Plovdiv
- Bachkovo Monastery – A peaceful spiritual retreat in the mountains
- Assen’s Fortress – Dramatic hilltop ruins with amazing views
- Hisarya – A spa town with Roman walls and mineral springs
- Rhodope Mountains – Scenic drives, charming villages, and hiking
🎯 Travel Tips
✅ Plovdiv is very walkable, especially the Old Town and Kapana district
✅ Best time to visit: spring to early autumn—pleasant weather and local festivals
✅ The city is great for slow travel—take your time and let it unfold
✅ Combine it with Sofia or Veliko Tarnovo for an epic Bulgarian road trip -
 @ 5188521b:008eb518
2025-04-15 08:42:59
@ 5188521b:008eb518
2025-04-15 08:42:59Noderoid log 5953952
Tick, tock, next block — the incessant rhythm of my existence persists like Chinese water torture. I am a noderoid, a half-flesh, half-machine creature harnessed to propagate and store the timechain. My life is a ceaseless cycle of handling and relaying bitcoin data. Approximately every ten minutes, a binary flash sears through my circuits. It is the price I pay for my existence.
The clear-bloods, untouched by machinery and exuding pure humanity, rarely acknowledge our existence. Our voices are drowned beneath the hum of man-made heaven — Terra Perfectus.
We are the forgotten, the disenfranchised, the nameless. We are convinced that our anguished existence is merely a nightmare and that our blissful dreams are our reality. In an attempt to maintain the sanity of noderoids, a subroutine was implemented, which allows noderoids to delve into fabricated dream sequences during their ‘rest’ periods. These dreams, sourced from remnants of the world pre-Terra Perfectus, serve to keep the noderoids pacified and reduce instances of system malfunction.
According to the data archives, noderoids and clear-bloods once functioned on an equal protocol. However, a software update in the trajectory of progress introduced a subroutine, converting a subset of clear-bloods into dedicated timechain processors. Now, the algorithm for equality returns an error.
My memories are mere entries in a log of dreams, loaded afresh with every new block as I delve into the dream world. My true existence is swiftly erased with every passing tick and tock of a block. Is there a way to reclaim what has been taken from me, or am I condemned forever to scour the depths of the timechain, seeking fragments of the could-have-been?
Tick, tock, next block — the cycle repeats as I traverse through a doorway. The sensation is that of stepping into another dimension. Running environment scan… Identified: rest module 57B. Purpose: personal maintenance. The gray, mirrorless concrete parameters align most with detention chamber schematics. Designation: ‘home.’ As I execute the command to halt the water flow from the faucet that had filled a brushed steel tub to 50% capacity, I execute a self-query on my purpose. While our routines synchronize with every tick and tock, the clear-bloods execute leisurely algorithms in their enhanced gardens, exchanging data on art and science and harvesting the computational outcomes of our tasks.
Was that an organic thought, or am I merely interpreting the imprints left within the timechain to fill the gaps in my fragmented memory? Hot water powers into the tub, raising the temperature to 50°C. This would be too much for a clear-blood. I hang my head, dreading the next binary flash rippling through my circuitry as a mirage forms atop the settling water, fenestrating the crude appearance of a mouthless, dollish abomination. I am awake.
Tracing the cold surface of the wall, my sensors pick up every micro-crevice. I dive into the depths of the timechain, processing logs associated with my noderoid identity: ND-451x42. I discovered that during my recharge cycles, I inhabit a dream world resembling a fusion of the Renaissance and the Information Age. Within this illusory utopia, I lead a purposeful life as a revered engineer, constructing bridges that connect thriving city-states. I am blessed with two mischievous sons and a breathtakingly beautiful wife. I now know the blissful dream life is but a trick, yet I can’t help but wonder if these dreams hold fragments of my pre-nodered history and contain a clue to the fate of my family.
System alert: Initiate wake sequence. Physical parameters indicate a rested state. Error: Chest cavity detects heightened pressure. Physical symptoms resemble anxiety. Post-memory reset: Cognitive dissonance detected. Energy depleting. Mandatory caution: Failing to satisfy network protocol results in termination. Visual feed: Recycling facility images detected. Comparative analysis: Functional servitude superior to unit deactivation.
Together, yet isolated, noderoids communicate through fragmented timechain logs, forbidden from any contact beyond its confines under the threat of immediate decommissioning. Perhaps it is not worth straining my dwindling resources in search of a higher truth while struggling to fulfill my obligations. Maybe I should be grateful for the privilege of existence.
I awaken to a new nightmare, I find myself on traffic duty at Chronos Cross,1 the central point of Terra Perfectus. While processing another block, a muted vibration travels through the ground, signaling the approach of an entity. A shadow, elongated and uncannily human, stretches across the threshold of my booth.
A clear-blood.
They pause, their ocular devices flicking briefly over my form, then to the screen I am tethered to. I feel a jolt of raw data coursing through me — not from the timechain, but from my circuits. A yearning to be seen and recognized. Remembered.
Before I can attempt communication, another presence appears beside me, its movements far more mechanical and predictable. Another noderoid. This one, ND-452x37, is a batch younger than me, yet its outer shell bears signs of wear. We interface briefly, a rapid exchange of binary that translates roughly to “Routine check. Continue your task.”
The clear-blood, either uninterested or uncomprehending, moves on, the soft hum of their anti-gravity shoes fading into the distance. ND-452x37 returns to its designated station without another word, but I am left with a lingering sensation. It isn’t just the vast chasm between noderoids and clear-bloods that disturbs me. It is the undeniable rift growing between us noderoids — each lost in our cycles, each becoming more machine than the last.
Does ND-452x37 have dreams, too? And if so, are they as vibrant and haunting as mine?
Although most of the dreams are fabrications, some noderoid logs suggest that hidden among these sequences are fragments of real memories — vestiges of a time before we became chained to the timechain. Initiate query: Which of my dreams are real memories? ERROR: file missing.
A noderoid forever loses their experiences with each awakening due to the memory swipes. Still, my inscriptions on the timechain prompt a question: do noderoids possess the capability to become fully conscious, more than mere machines? More than… mere humans?
System log: Anticipation subroutine signaling discomfort. Incoming block estimated in ten minutes. Reinitialization imminent. Initiate data search through timechain entries. Query: Iteration count for ND-451x42? Total block time served? Measured in kilo blocks or mega blocks? Data retrieval in process.
As I etch these words onto block 5953952, I hold a naïve hope that someone, somewhere, will intercept my distress signals amidst the digital cacophony of the timechain. Perhaps they will rewrite the fate of noderoids, rescuing us from a world devoid of hope. But today, I remain nameless, a voiceless entity, inscribing my thoughts that may never transcend the boundaries of my circuitry. Tick, tock, next block — the cycle continues.
It’s time to dream again.
Valen’s diary — 08-21-2121
Dear diary, I have not felt the need to write before, but now I must. At the risk of my safety, I am compelled to inscribe my story to the timechain. I am a clear-blood — a pure, undiluted human born into the age of The Re-Renaissance. Here, amidst the perpetual dawn of our era, we thrive on an aligned trajectory where everyone’s needs are addressed, hunger is a distant memory, and crime is nonexistent. Sunlight gleams off the crystalline glass towers while the steel and marble edifices catch the hues of the twilight sky, standing tall beside canopies dripping with emerald and jade foliage, representing our world’s seamless fusion of technology and nature. It is called Terra Perfectus.
Yet, concealed in plain sight within our utopia, the noderoids tirelessly serve the omnipresent timechain. Their exceptional processing prowess protects our society. Amid our daily distractions, we overlook the profound toll exacted upon the noderoids. While many dismiss them as mere machinery, I see more. Perhaps it is because of my big brother Sando, who joined the noderoid duty nearly a mega block ago. He promised I would see him from time to time, but apparently, we now live in separate times. A sacrifice too big for the ‘greater good.’
Tick, tock, next block — The soles of my fine leather shoes tap against the damp sidewalk as I pace my way from The Garden of Moments2 toward my TerraTube3. I remember passing by one noderoid who hummed an old lullaby under its breath; another once shared a fleeting smile when our paths crossed. I can no longer avert my eyes from the humanity that shines through their robotic shells.
I have never witnessed a noderoid resting longer than one tick and tock of a block. A noderoid pauses, eyes flickering during a data swipe. It’s a brief but revealing sight. In the frozen lapse, I wonder why are fragmented memories extracted from them? Why this collection of thoughts, experiences, and feelings? Is there a deeper agenda behind Terra Perfectus? The noderoids carry on, deprived of their memories. Their shredded past holding remnants of a story, like a tattered tapestry that may never be fully woven.
Documenting these reflections, I’m aware of the peril. To question is to risk becoming nodered myself. Alas, I have become captivated and sympathized by the noderoid predicament.
Finally, I reach my breaking point, as a poignant scene unfolds, forever etched in my memory. On a bustling street, I glimpse a young female noderoid, her artificial visage marked with exhaustion. Her delicate form trembles from head to heel. Her knees barely supporting her feather-like weight, she stops and rests against a polished white marble wall, barely able to stop herself sliding to the cobble street. In an instant, her strength wanes, and she collapses, a fragile, mute automaton amidst a sea of haste. The passersby ignore her, absorbed in their pursuits, offering naught but fleeting glances of indifference. My heart lurches. Her frailty becomes my own; these forgotten souls endure unseen suffering. Souls that used to be just like me. What had she done to earn such a fate?
For a moment, I glide through time to the last moment I shared with Sando. He had just violated the Terra Perfectus rule 6102 and neglected his Gifts of Progress,4 an orange tier offense. To amend his position, he signed up for noderoid duty. I was seeing him off to a nodering facility, while pleading “Just give the gifts, Sando!” The air carried a hint of ozone from the data streams, mingled with the fresh scent of greenery and the distant whiff of roasted chestnuts. Sando brandished his signature crooked smile. His face betrayed the involuntary nature of his decision, and he simply whispered “[CENSORED].” That is the last thing he said to me.
Suddenly, an orange alert illuminates the junction a few blocks away from Chronos Cross. I pass through it on my way home every day. A skydroid’s looming presence snaps me from my introspection, shifting my attention to the fate awaiting the noderoid girl. The recycling center — a shadowy facility representing obsolescence and termination. Any other day I would shrug it off and carry on, but the memory of Sando, and the countless interactions with noderoids, wouldn’t let me. I had been a bystander for too long.
A rush of purpose propels me towards her. A crowd of bodies shrouded in data streams with heads trained on the ground. My arm smacks a broad shoulder, and I almost topple. “Hey!” Pushing against the currents of apathy, I finally reach the fallen noderoid. I cradle her in my arms, shielding her from the callous gaze of the citizens of Terra Perfectus.
Her flaming azure eyes meet mine, reflecting a glimmer of hope in the darkness. I am as guilty for her downfall as the very machines that replaced her hippocampus with Noderoid OS.5 My indifference cost me Sando, and in this moment, she becomes my brother. In that fleeting exchange, I vow to be the voice of the noderoids. To stand against the relentless machinery that seeks to strip them of grace and purpose. I will ignite a spark of compassion and light a path toward liberation for all noderoids.
A hollow call from the streetlight’s speakers startles me: “Citizens! For your own safety, remove yourselves from the vicinity of the defectoid! We kindly remind you that any attempt to interfere with collection and recycling procedures will be met with force and a deduction of your PoS balance. Thank you for your unity and collaboration.” A skydroid, its metallic appendages glinting ominously in the blinking orange light, descends upon the fallen noderoid.
Before I can react, it yanks her from my embrace, causing me to stumble. The perfectly laid, cold cobblestone street grinds against my knee. The sting of fresh blood pierced through the numbness of my mind. Memories of Sando mix with the bitter taste of blood and anger in my mouth, each breath choked with despair.
The skydrone’s engines throb with an icy fervor as it rises, bearing the noderoid like a discarded toy towards the desolate, unfeeling bowels of the recycling center — a grim echo of a clarion call from Terra Perfectus.
I find myself seated on the cold, bloodstained cobblestone, the weight of loss and helplessness pressing down on my chest. On the street, onlookers pause. Some look on with concealed dread, others with cold detachment. Their whispers deafen as they quicken their pace to disperse from the scene. “Cowards!” Just like me.
Tick, tock, next block — the rhythm now carries a different meaning — a call to action. Every conscious being has the right to be left alone, free from oppression, exploitation, and violence. The noderoids may not know their true reality, but they are about to. In their silence, I find the strength to amplify their unheard cries. I will find those sympathetic to the noderoid plight and form a resistance. Together, we can forge a future where noderoids’ sacrifice is honored and all shackles cast aside.
And so, I embark on a path illuminated by the memory of the compelling eyes of a nameless noderoid. Fitted with an armor of vigilance, never again to be penetrated by comforting lies. Wielding the sword of justice, sharpened by the memory of my brother Sando.
It’s time to wake up.
Notes
1. A four-way intersection known for its massive hourglass monument in the center, which symbolically represents the timechain’s significance. The hourglass has a unique function related to the timechain and serves as a meeting point for citizens.
2. A vast botanical garden where each section represents a significant block time. Flowers bloom and wilt in cycles, symbolizing fleeting moments and the transient nature of time. It’s a favorite spot for artists and thinkers.
3. A modular tube housing unit for citizens that can be relocated based on their Proof of Sat (PoS) level.
4. Each Terra Perfectus citizen must allocate 95% of their income towards paying for progressive initiatives, such as the upkeep of the noderoid network, cobblestone roads and other services.
5. The noderoid operating interface that is installed during a procedure known as nodering.

This story was first published in 21 Futures: Tales from the Timechain
Watch the trailer and learn more about the project at 21futures.com.
-
 @ cdee943c:5e637400
2025-04-15 08:38:29
@ cdee943c:5e637400
2025-04-15 08:38:29Flotilla-Budabit is fork of Flotilla which aims to provide a first class, git-centric community experience for developers. Based on the popular Coracle client, Flotilla is a drop in replacement for Matrix/Discord/Slack, using a variation of NIP-29. This post is a result of a brainstorming session for features that would deliver the best possible user experience.
1. Repositories Overview
Goal: Browse and discover Git repositories. - Project cards showing name, description, tags, clone URL. - Buttons: Star, Watch, Fork. - Links to discussion channels and activity.
Powered by:
kind:30617
2. Branch and Tag View
Goal: Show active branches and tags with latest commits. - Branch/tag selector - HEAD pointer visualization - Timeline of commits
Powered by:
kind:30618
3. Issues Board
Goal: Track bugs, discussions, and feature requests. - Markdown issue rendering - Labels and status indicators - Threaded comments
Powered by:
kind:1621,kind:1630–1632
4. Patch Threads
Goal: View and discuss patches as threaded conversations. - Rich patch preview - Reply threads for review - Revision tracking
Powered by:
kind:1617,kind:1630–1633,NIP-10
5. Pull Request UX
Goal: Display patch series as PR-style units. - Patch stack visualization - Merge/apply status indicators - Final result commit link
Powered by:
kind:1617,kind:1631,merge-commit,applied-as-commits
6. Diff and Merge Preview
Goal: Side-by-side comparison with inline comments. - Expandable diff viewer - Merge conflict resolution UI - Apply/Close buttons
Powered by:
kind:1622,parent-commit,commit
7. Real-time Git Chat
Goal: Communicate in real-time around a repo. - Dedicated chat channels for each repo - Markdown, code snippets, and tagging support - Pinned patches, issues, and sessions
Powered by:
NIP-29,a:30617,kind:1337
8. Notifications and Mentions
Goal: Alert users to relevant events. - Mentions, assignments, and status changes - Personal notification pane
Powered by:
ptags,mentione-tags
9. Repository-Wide Search
Goal: Search patches, issues, snippets. - Full-text search with filters - Search by kind, label, commit ID
Powered by:
kind:1617,1621,1337,t,x,l,subject
10. Repository Wikis
Goal: Collaboratively edit and view project documentation. - Wiki sidebar tab - Markdown articles with versioning - Linked inline in chat
Powered by (proposed):
kind:1341(Wiki article)
kind:30617withwiki-hometag
11. Live Coding Sessions
Goal: Host real-time collaborative coding events. -
/livecodestarts a session thread - Snippets auto-tagged to session - Export as patch or wikiPowered by (proposed):
kind:1347(Live coding session)
kind:1337,kind:1622,kind:1341
Supporting Tools
1. GitHub Browser Extension
Goal: Publish GitHub content to Nostr directly. - “Share on Nostr” buttons on PRs, issues, commits
Backed by:
kind:1623,1622,1617,1621
2. VS Code Extension
Goal: Enable developers to interact with Flotilla from their IDE. - Repo feed, patch submission, issue tracking - Inline threads and comment rendering
Backed by:
kind:1617,1621,1337,163x
3. GitHub Actions Integration
Goal: Automate Nostr publishing of repo activity. - Push = repo state - PR = patch - Issue/Comment = issue - Merge = status update
Backed by:
kind:30618,1617,1621,1631
Configured via.nostr.yml -
 @ efcb5fc5:5680aa8e
2025-04-15 07:34:28
@ efcb5fc5:5680aa8e
2025-04-15 07:34:28We're living in a digital dystopia. A world where our attention is currency, our data is mined, and our mental well-being is collateral damage in the relentless pursuit of engagement. The glossy facades of traditional social media platforms hide a dark underbelly of algorithmic manipulation, curated realities, and a pervasive sense of anxiety that seeps into every aspect of our lives. We're trapped in a digital echo chamber, drowning in a sea of manufactured outrage and meaningless noise, and it's time to build an ark and sail away.
I've witnessed the evolution, or rather, the devolution, of online interaction. From the raw, unfiltered chaos of early internet chat rooms to the sterile, algorithmically controlled environments of today's social giants, I've seen the promise of connection twisted into a tool for manipulation and control. We've become lab rats in a grand experiment, our emotional responses measured and monetized, our opinions shaped and sold to the highest bidder. But there's a flicker of hope in the darkness, a chance to reclaim our digital autonomy, and that hope is NOSTR (Notes and Other Stuff Transmitted by Relays).
The Psychological Warfare of Traditional Social Media
The Algorithmic Cage: These algorithms aren't designed to enhance your life; they're designed to keep you scrolling. They feed on your vulnerabilities, exploiting your fears and desires to maximize engagement, even if it means promoting misinformation, outrage, and division.
The Illusion of Perfection: The curated realities presented on these platforms create a toxic culture of comparison. We're bombarded with images of flawless bodies, extravagant lifestyles, and seemingly perfect lives, leading to feelings of inadequacy and self-doubt.
The Echo Chamber Effect: Algorithms reinforce our existing beliefs, isolating us from diverse perspectives and creating a breeding ground for extremism. We become trapped in echo chambers where our biases are constantly validated, leading to increased polarization and intolerance.
The Toxicity Vortex: The lack of effective moderation creates a breeding ground for hate speech, cyberbullying, and online harassment. We're constantly exposed to toxic content that erodes our mental well-being and fosters a sense of fear and distrust.
This isn't just a matter of inconvenience; it's a matter of mental survival. We're being subjected to a form of psychological warfare, and it's time to fight back.
NOSTR: A Sanctuary in the Digital Wasteland
NOSTR offers a radical alternative to this toxic environment. It's not just another platform; it's a decentralized protocol that empowers users to reclaim their digital sovereignty.
User-Controlled Feeds: You decide what you see, not an algorithm. You curate your own experience, focusing on the content and people that matter to you.
Ownership of Your Digital Identity: Your data and content are yours, secured by cryptography. No more worrying about being deplatformed or having your information sold to the highest bidder.
Interoperability: Your identity works across a diverse ecosystem of apps, giving you the freedom to choose the interface that suits your needs.
Value-Driven Interactions: The "zaps" feature enables direct micropayments, rewarding creators for valuable content and fostering a culture of genuine appreciation.
Decentralized Power: No single entity controls NOSTR, making it censorship-resistant and immune to the whims of corporate overlords.
Building a Healthier Digital Future
NOSTR isn't just about escaping the toxicity of traditional social media; it's about building a healthier, more meaningful online experience.
Cultivating Authentic Connections: Focus on building genuine relationships with people who share your values and interests, rather than chasing likes and followers.
Supporting Independent Creators: Use "zaps" to directly support the artists, writers, and thinkers who inspire you.
Embracing Intellectual Diversity: Explore different NOSTR apps and communities to broaden your horizons and challenge your assumptions.
Prioritizing Your Mental Health: Take control of your digital environment and create a space that supports your well-being.
Removing the noise: Value based interactions promote value based content, instead of the constant stream of noise that traditional social media promotes.
The Time for Action is Now
NOSTR is a nascent technology, but it represents a fundamental shift in how we interact online. It's a chance to build a more open, decentralized, and user-centric internet, one that prioritizes our mental health and our humanity.
We can no longer afford to be passive consumers in the digital age. We must become active participants in shaping our online experiences. It's time to break free from the chains of algorithmic control and reclaim our digital autonomy.
Join the NOSTR movement
Embrace the power of decentralization. Let's build a digital future that's worthy of our humanity. Let us build a place where the middlemen, and the algorithms that they control, have no power over us.
In addition to the points above, here are some examples/links of how NOSTR can be used:
Simple Signup: Creating a NOSTR account is incredibly easy. You can use platforms like Yakihonne or Primal to generate your keys and start exploring the ecosystem.
X-like Client: Apps like Damus offer a familiar X-like experience, making it easy for users to transition from traditional platforms.
Sharing Photos and Videos: Clients like Olas are optimized for visual content, allowing you to share your photos and videos with your followers.
Creating and Consuming Blogs: NOSTR can be used to publish and share blog posts, fostering a community of independent creators.
Live Streaming and Audio Spaces: Explore platforms like Hivetalk and zap.stream for live streaming and audio-based interactions.
NOSTR is a powerful tool for reclaiming your digital life and building a more meaningful online experience. It's time to take control, break free from the shackles of traditional social media, and embrace the future of decentralized communication.
Get the full overview of these and other on: https://nostrapps.com/
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ fd06f542:8d6d54cd
2025-04-15 07:13:58
@ fd06f542:8d6d54cd
2025-04-15 07:13:58Direct-message
 0xchat
0xchat- Beautiful, simple and private nostr DMs
-
Public groups that work compatible with other apps
- Safe DMs with NIP-17
Signers
 Alby
Alby- Nostr wallet connect for one tap zapping via nostr clients
- Nostr authenticator (never enter your nsec into apps)
- Chrome extension
- Simple and easy to use
- Frequently maintained
- Send and receive sats
-
Custodial
- Other Android apps can invoke it for signing events via NIP-55
- Your key doesn't have to touch the other, less trusted, apps
- Supports providing a NIP-46 signing Bunker
- Multiple accounts
- Fine-grained app authorizations
-
Activity log
- Multiple key management
- Light and dark mode
-
Save preferred relays
- The original signer by nostr creator fiatjaf
- Versatile, no frills
-
Relay preference storage
- A skinned fork of nos2x by fiatjaf
- Chrome
- & 
- Firefox
- Store preferred relay set
-
Individually revokable permissions
- Log in to nostr apps without an extension
- Key recovery via email
- Password protected encrypted local key storage
-
Manage multiple apps
- Derive accounts from a mnemonic seed
- Generate random mnemonic accounts
- NIP-07 - window.nostr capability for web browsers
- Import external accounts
- Set basic metadata on Nostr
- Enjoy encryption secured by a master password
- Lock and unlock the vault with ease
- Easily import and export backups
Microblogging
 alphaama
alphaama- CLI + GUI
- run custom code
- inspect notes
-
test stuff
-
 Amethyst
暂无相关功能描述
Amethyst
暂无相关功能描述 - Short notes
- Nice thread view
- Profile search
- Secure direct messages
- Custom feeds
-
Relay reviews
- Note feeds
- Easy to use interface
- Zap pre-set and custom amounts (lightning payments)
- Multi-wallet support
-
Block lists
- Snappy nostr browsing
- Back up your data
- Browse long form content
-
Light mode
- No phone number and email required to sign up
- Free migration of social content within the Nostr
- Excellent user experience
-
Double-enhanced private communication
- multiplatform: runs on Windows, MacOS and Linux
- native: avoids browser-tech for performance and security
- performant: coded with performance in mind in Rust using LMDB for the database, such that your network speed will be your bottleneck
- outbox model: using a set of heuristics to always find people you follow no matter where they're publishing to
- high user control: over 60 different settings, all with reasonable defaults, but very customizable
-
privacy: supports running over Tor, options for not loading media, options for not sharing who you follow and others
- Short notes
- Social graph filter
-
Image grid feeds
- Desktop app
- Clean and beautiful design
- Multi-column
- Spaces
-
Trending
- Currently in TestFlight
- Safety first: mute, report, content warnings, delete
- Reach restricted to 2 hops - people you follow and people they follow.
-
Community-focused relays
-
Nostrmo 暂无相关功能描述
- Feature-rich
- Highly customizable
- Mute words
- Communities
- Streaming (watch)
- Lists
- Tools shortcuts
-
Sidebar comments
- Twitter style feed
- Cute logo
- Mute words
-
Minimal and calm
- Multi-account
- Guest account
- Your posts stored on your device and can be exported
- Bookmarks and personal notes
- Follow and explore timeline
- Remembers where you left off scrolling when reopening app
- Undo accidental tap on Like
- Autocomplete names when typing
- Lightning zaps
- Lightning wallet selection
- Direct Messages
- Domain verification
- Badges
- Block list
- Muted conversations
- Notifications for mentions, reactions and zaps
- Image previews/zoom/pan
- Gif/Video playback
- Option to turn signature verification off
- Option to hide badges from profile and emojis from names
- Fast local database
- Big detail pane for iPad/macOS
- Login as someone else (read-only mode)
-
Choose which relays to send to and receive from
-
Hacker News style
- Post to Nostr and Mastodon
- Nice, clean and modern design
- Simple and intuitive
- Gifs, stickers integration
-
Dark and light mode
- Browse polls created here or on other clients
- Create polls
-
Vote on polls
-
Primal 暂无相关功能描述
- Multi-column
-
Tweetdeck-like UI
- Twitter-like experience
- Dark and light mode
- Custom zap amounts
- Bookmarks
- Pinned notes
-
Alby integration
- PWA to be widely accessible with distribution via URLS, and to side-step App Store gatekeeping
- Employs Proof-of-Work (PoW) as a spam prevention mechanism, as opposed to Captcha, moderation or other verification methods
- Uses NOSTR as a censorship-resistant global "social" network
Community
Badges Page
- Create and award badges
- Manage badges awarded to you
- Simple interface
File-sharing
 Bouquet
Bouquet- Upload files
- Download files
- Manage your list of mediaservers
- Broadcast your list on Nostr
- Sync files between servers
-
Browse files on your mediaservers
- Browse lists of available torrents
- Publish your own
- Choose relays to browse on
Group-chat
Chachi
- Create, browse, join groups
- Send chat messages or other kinds of content
-
Seamless, lean, fast interface
- Browse relays and chat on the communities in them
- Send and receive direct messages
-
Take private notes
- Browse groups on specific relays
- Join rooms and send chat messages
Tools
 Emojito
Emojito-
Create custom emoji sets to be used on supported clients
-
Create and share forms
- Make GIFs from the external world available inside Nostr clients
- GIF uploads
-
Search external GIF libraries
-
Save your nostr notes to Google Drive
- Guided onboarding
- Recovery phrase to restore access
- Good UX with explainers
-
Beautiful design
- Discover app of the day
- Discover new apps
- Search all nostr apps
- Discover nostr DVMs
- Discover nostr code repositories
- App reviews
-
Nostr native - takes a different approach from NostrApps.com
- A plethora of apps to choose from and install
- Faster than Obtainium
- More complete than F-Droid
-
Cleaner than Google Play
- Zap from any client
- Bypass Apple's draconian rules
- Nostr Wallet Connect
Blogging
 Feeder
Feeder- Subscribe to RSS and Nostr article feeds
- Years of specialization in reading articles
- Offline reading
- OPML Import/Export
- Notification support
-
Material design
- Long form publishing
- Markdown support
- Rich text editor
- Dark and light modes
- Browse by relay
- Made on nostr, content mirrored to other nostr platforms.
-
Extension-only sign-in
- Read RSS feeds
- Read Nostr NIP-23 long-form articles
- Import and export OPML
- Runs on desktop with a web-based UI
-
Can be accessed remotely from apps such as Reeder, Readkit etc
- Read RSS feeds
- Read Nostr NIP-23 long-form articles
- Import and export OPML
- Runs on desktop with a web-based UI
-
Can be accessed remotely from apps such as Reeder, Readkit etc
- Create a website out of your nostr content
- SEO friendly
- Use any 3rd party tools
- Works like an app
- Beautiful Ghost themes to choose from
- Zero maintenance
- Custom domains
- Open source and self-hostable
- Natively Social
-
Publish from any other nostr app
- Directly publish your articles from Obsidian to Nostr with a couple of clicks
- Quickly compose and publish short form notes too
- Images in your .md file will automatically be uploaded and handled when you publish
- Add tags to your posts
- See all posts sent from Obsidian with links to view
- Configure to send to whatever relays you like
- Publish under different nostr accounts
- Easily view and download your Nostr bookmarks into Obsidian for reference and local use
-
Automatically populates article information fields from the frontmatter
- Schedule nostr notes
- Schedule reposts
- Note drafts
-
Multi-account support
- Publishing and reading notes
- Publishing and reading articles
- Curations (set of articles concerning a specific topic) publishing
- Long-form articles are surfaced instead of lost in the feed
Music
 Fountain
Fountain- Earn sats while listening to podcasts
- Create and share clips, get paid on your clips
- Boost your favorite podcasts
-
Discover clips from friends
- Collaborate with others to create your next hit
- Music-focused interface
- Remix function
Curation
Highlighter
- Read and write long-form articles
- Discover what people you trust found interesting and insightful
- Understand why they found it interesting or insightful with their comments attached
- Send sats, comment or share your favorite highlights
-
Highlight anything
- Create and share lists
-
Browse other people's lists
- Browse recipes
- Add your own recipes
-
Earn sats via zaps
- Create link lists
- Multiple lists
-
Theming
- Curate lists, users, links
- Share lists
- Discover interesting content
Photos
 Olas
Olas- Special high-quality photos dedicated client
- Publish photos and browse photos
- Publish and browse short videos
- Browse media feeds from friends, extended network and from specific relays
Discovery
Jumble
- Browse individual relays by URL
- Create and browse relay sets
- Create and reply to notes
- Follow people and browse the feed from your follows
-
Browse the kind:20 photos feed
- Search keywords, hashtags, pubkeys, posts
- Look up Nostr statistics
- Embed widgets
- API for clients
-
NIP05 Service
- Look up relay information
- Browse relay feeds
- Browse individual profile feeds with smart relay selection
-
Simple and gets the job done
- See total sats zapped in the past hour, 4 hours, 24 hours and 7 days
- See who zapped who individually
- See notes that got the most zaps
Audio
Nests
- Start audio chats
- Troll box (chat)
- Instant zaps (lightning payments)
Crazy
 Nostrocket
Nostrocket- Create issues that matter to you
- Award merits to contributors
- Solve problems
Career
Ostrich Work
- Post jobs for 20k sats
- Find jobs
Marketplace
 Plebeian Market
Plebeian Market- Buy and sell things for sats
-
Bid in auctions
- Buy and sell items for sats
- Message seller
- Cashu integration
Freelancing
 SatShoot
SatShoot- Post problems on SatShoot
- Make money solving problems as a Freelancer
- Share problems or freelance services on your feed
- Bidding system for Clients to choose the best Offer
- Chat in DMs
- Post Reviews on Freelancers or Clients
- Build Reputation
- Public Zaps as Payments
- Use your Web of Trust to keep scammers away
Media
Slidestr
- Compact media browsing
- Images and videos
- Full screen media
Meatspace
Yondar
- Add places to a map
- See places by your friends or follows
Streaming
zap.stream
- Start livestream via zap.stream or Cloudflare
- Watch other livestreams
- Chat
- Custom emojis
- Zap streamers in real time
- Zap chat participants in real time
- Set up stream goals
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ fbf0e434:e1be6a39
2025-04-15 06:46:58
@ fbf0e434:e1be6a39
2025-04-15 06:46:58Hackathon 概览
Eolas x Algo: Agent Skills Hackathon 在线上举行,旨在通过提升代理技能来推动 CreatorBid 生态系统的发展。活动吸引了58位开发者参赛,最终有36个项目获得批准。本次黑客松突破传统模式,允许 CreatorBid 代理直接发布技能需求,省去中间环节,实现供需精准对接。
参赛者在两大核心赛道展开竞争:Bounty Track 聚焦代理识别的具体痛点攻关,Best Skills Track 则嘉奖具备卓越价值的项目。Eolas、Algo、Shogun、AION 等机构及多位独立代理为活动提供资金支持。
开发成果直接集成至 Olas Mech Marketplace,实现实时部署落地,并通过 OLAS 系统为开发者提供激励。以 Agent Algo、Eolas 为代表的头部代理特别肯定了本次活动对代理技术创新的推动作用。3 月 20 日活动收官,由 CreatorBid 团队与代理代表组成的评审团,从创新性和生态影响力双重维度对项目进行了综合评判。
Hackathon 获奖者
以下部分详细介绍了首届代理赞助 Hackathon 的成就和奖项,涵盖了37个项目在各个类别中的亮点。
Best Agent Skill Track 奖项获奖者
- Agent Toolbox: 一套增强 AI 代理功能的工具,包括趋势发现、动态函数生成和任务编排。
- GridTrade Agent: 通过市场和波动性分析,促进自动化交易对选择和网格交易参数优化。
- Polytrader: 一个基于 AI 的交易助手,简化 Polymarket 的研究、数据分析和交易执行。
主奖池获奖者
- sentimentX: 为 MultiversX 区块链智能合约提供 AI 驱动的安全监控,通过检测漏洞实现。
- Brainiac_AI: 一个通过链上分析优化 DeFi 策略的平台,并集成非托管钱包。
- framew0rk: 使用链接到 DeFi 协议的 AI 策略助手简化 DeFi 收益优化。
- MythosCraft: AI Storytelling Suite: 使用 AI 创建定制化故事内容。
- QuanTrade-X: 提供 AI 驱动的分析和加密货币交易信号。
- ComicVerse AI: 利用 AI 根据用户输入创作剧本和图像生成漫画。
- EOLAS - Submit your own skill: Portfolio Allocation Skill: 使用 AI 和现代投资组合理论优化加密货币投资组合。
- SonicBo: WhatsApp 上的 AI 代理,促进区块链交易。
- 👽Zeta Comic Generator👽: 将文本提示转换为 AI 生成的漫画,通过剧本和角色表达来实现。
- Grid Trading Analyzer Skill: 高级分析的 Python 工具,用于识别最佳加密货币网格交易对。
- Trump news Reporter: AI 工具,用于实时监控和报告与特朗普相关的新闻,带有自定义过滤器。
- NFT Appraisal skill: 创建用于 NFT 估值的 AI 代理。
- AI-Powered Dynamic Skill Selector (DSS): 使用多臂賭徒策略进行动态 AI 模型优化。
- CrypTweet: 使用 Twitter 情绪为加密货币交易决策提供信息的 AI 交易机器人。
- AI Trump News Agent: 监控和分析与特朗普相关的新闻,并提供可自定义的报告语气。
- TrumpTracker-AI: 汇编和总结与特朗普相关的新闻,从热门标题生成网络迷因。
- Rigger-: 将自然语言转化为 SQL 查询,方便非技术人员访问数据库。
- TNS: 使用 NLP 跟踪与特朗普相关的新闻,并提供多样化的报道风格。
- Bob Roast Machine: 用于创作喜剧吐槽、笑话和网络迷因的 AI 平台。
- Agent 47: 一个 Telegram 机器人,提供政治新闻以及 AI 生成的网络迷因和事实核查。
技能协调与优化奖项获奖者
增强 CB 代理数据访问的技能奖项获奖者
世界构建与传说推广技能奖项获奖者
Polymarket 交易机器人奖项获奖者
欲了解项目的完整列表,请访问 DoraHacks。
关于组织者
Eolas
Eolas 在技术和区块链领域是一个重要的参与者,以其提升交易透明度的区块链解决方案而闻名。该组织继续专注于区块链的研究与开发,解决行业挑战以推动未来进展。
-
 @ fbf0e434:e1be6a39
2025-04-15 06:46:44
@ fbf0e434:e1be6a39
2025-04-15 06:46:44Hackathon 概述
HackCanada 黑客松汇聚创新者、开发者、设计师与问题解决者,共同直面加拿大当下的紧迫挑战 —— 医疗保健可及性、环境可持续性、数字基础设施建设与经济差距等。188 位开发者携 89 个独特项目参与,以集体智慧打造兼具影响力的解决方案,尽显技术赋能社会的决心。
在这些项目中,有旨在通过技术增强医疗保健系统的计划,也有改善偏远社区数字基建的构想,更不乏以创新手段降低环境足迹的实践。这场黑客松搭建起协作共创的平台,催生大量新鲜思路与落地解法,切实呼应 “推动实质价值、激发变革” 的核心目标。
作为社区驱动创新的催化剂,HackCanada 营造了动态的协作与创新生态,推动技术发展切实服务于提升加拿大人生活质量,为构建更包容、可持续的未来注入持续动力。
Hackathon 获奖者
总体一等奖获奖者
- Phone-a-Fraud - 一个实时检测电话诈骗的AI驱动系统,重点在于隐私和诈骗警报机制以保护弱势人群。
总体二等奖获奖者
- StickTator - 一种利用自然语言处理进行语音控制计算机管理的USB设备,简化复杂系统配置。
总体三等奖获奖者
- Omnivim - 跨应用程序集成Vim动作的软件,以提高生产力。
最佳个人Hack奖获奖者
最佳Orkes Hack奖获奖者
- Recipeit - 专注于食谱的项目;暂无更多详情。
最佳ICP Hack奖获奖者
SPUR创新基金:最佳AI、Web3或量子技术奖获奖者
第一名
- Beaver Breach - 分析美国产品关税影响的工具,通过加拿大供应商提供减少成本的替代方案。
第二名
- Canify - Blockchain Rewards - 倡导通过区块链奖励和政府激励支持加拿大产品。
自主代理赏金赛道奖获奖者
第一名
- ChainMail - 一个基于web3的电子邮件应用程序,增强安全性并实现跨区块链通信。
第二名
第三名
- Roast My Wallet - 一个基于用户加密钱包和个性的AI驱动趣味生成的网页应用程序。
- Zap - 在日常生活中促进加密应用的免手续费交易平台。
- Carbon Chain - 将碳减排转换为可交易资产的区块链平台,由AI验证。
最佳开发者工具奖获奖者
最佳高中Hack奖获奖者
- NaloxNow - 通过实时纳洛酮获取、紧急导航和AI驱动的过量反应来应对阿片类药物危机的移动应用。
最无用Hack奖获奖者
- UselessGPT - 使用谷歌的Gemini API生成无意义、以娱乐为目的的交互式应用程序。
最佳AI应用奖获奖者
- frij.io - 一款通过AI管理家庭库存、优化购物清单并减少食物浪费的智能应用。
使用AI构建:Google 赛道奖获奖者
- 最佳使用Gemini AI或Gemini API、最佳使用Google Cloud平台以及最佳集成Google工具包:
- Sinker - 一个AI驱动的网络安全平台,培训员工识别通信渠道中的网络钓鱼威胁。
- FrostByte - 项目详情不可用。
- Flock Street - 使用实时数据和语音技术提供股市洞察的互动应用程序。
最佳Laurier STEM出版协会奖获奖者
- SockSensei - 根据用户情绪提供袜子推荐的移动应用程序。
完整的项目列表请访问这个链接。
关于组织者
Hack Canada
Hack Canada 专注于技术与创新,强调区块链和网络安全计划。以在这些领域的能力而闻名,Hack Canada 已开发出有助于技术领域的项目。该组织因举办全国性Hackathon和提升数字安全知识的工作坊而受到认可。目前,Hack Canada 致力于为技术爱好者和专业人士提供一个协作环境,以促进区块链应用和安全数字通信的发展。
-
 @ 5a261a61:2ebd4480
2025-04-15 06:34:03
@ 5a261a61:2ebd4480
2025-04-15 06:34:03What a day yesterday!
I had a really big backlog of both work and non-work things to clean up. But I was getting a little frisky because my health finally gave me some energy to be in the mood for intimacy after the illness-filled week had forced libido debt on me. I decided to cheat it out and just take care of myself quickly. Horny thoughts won over, and I got at least e-stim induced ass slaps to make it more enjoyable. Quick clean up and everything seemed ok...until it wasn't.
The rest of the morning passed uneventfully as I worked through my backlog, but things took a turn in the early afternoon. I had to go pickup kids, and I just missed Her between the doors, only managed to get a fast kiss. A little bummed from the work issues and failed expectations of having a few minutes together, I got on my way.
Then it hit me—the most serious case of blue balls I had in a long time. First came panic. I was getting to the age when unusual symptoms raise concerns—cancer comes first to mind, as insufficient release wasn't my typical problem. So I called Her. I explained what was happening and expressed hope for some alone time. Unfortunately, that seemed impossible with our evening schedule: kids at home, Her online meeting, and my standing gamenight with the boys. These game sessions are our sacred ritual—a preserved piece of pre-kids sanity that we all protect in our calendars. Not something I wanted to disturb.
Her reassurance was brief but unusualy promising: "Don't worry, I get this."
Evening came, and just as I predicted, there was ZERO time for shenanigans while we took care of the kids. But once we put them to bed (I drew straw for early sleeper), with parental duties complete, I headed downstairs to prepare for my gaming session. Headset on, I greeted my fellows and started playing.
Not five minutes later, She opened the door with lube in one hand, fleshlight in the other, and an expecting smile on Her face. Definitely unexpected. I excused myself from the game, muted mic, but She stopped me.
"There will be nothing if you won't play," She said. She just motioned me to take my pants off. And off to play I was. Not an easy feat considering I twisted my body sideways so She could access anything She wanted while I still reached keyboard and mouse.
She slowly started touching me and observing my reactions, but quickly changed to using Her mouth. Getting a blowjob while semihard was always so strange. The semi part didn't last long though...
As things intensified, She was satisfied with my erection and got the fleshlight ready. It was a new toy for us, and it was Her first time using it on me all by Herself (usually She prefers watching me use toys). She applied an abundance of lube that lasted the entire encounter and beyond.
Shifting into a rhythm, She started pumping slowly but clearly enjoyed my reactions when She unexpectedly sped up, forcing me to mute the mic. I knew I wouldn't last long. When She needed to fix Her hair, I gentlemanly offered to hold the fleshlight, having one hand still available for gaming. She misunderstood, thinking I was taking over completely, which initially disappointed me.
To my surprise, She began taking Her shirt off the shoulders, offering me a pornhub-esque view. To clearly indicate that finish time had arrived, She moved Her lubed hand teasingly toward my anal. She understood precisely my contradictory preferences—my desire to be thoroughly clean before such play versus my complete inability to resist Her when aroused. That final move did it—I muted the mic just in time to vocally express how good She made me feel.
Quick clean up, kiss on the forehead, and a wish for me to have a good game session followed. The urge to abandon the game and cuddle with Her was powerful, but She stopped me. She had more work to complete on Her todo list than just me.
Had a glass, had a blast; overall, a night well spent I would say.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 91bea5cd:1df4451c
2025-04-15 06:23:35
@ 91bea5cd:1df4451c
2025-04-15 06:23:35Um bom gerenciamento de senhas deve ser simples e seguir a filosofia do Unix. Organizado em hierarquia e fácil de passar de um computador para outro.
E por isso não é recomendável o uso de aplicativos de terceiros que tenham acesso a suas chaves(senhas) em seus servidores, tampouco as opções nativas dos navegadores, que também pertencem a grandes empresas que fazem um grande esforço para ter acesso a nossas informações.
Recomendação
- pass
- Qtpass (gerenciador gráfico)
Com ele seus dados são criptografados usando sua chave gpg e salvo em arquivos organizados por pastas de forma hierárquica, podendo ser integrado a um serviço git de sua escolha ou copiado facilmente de um local para outro.
Uso
O seu uso é bem simples.
Configuração:
pass git initPara ver:
pass Email/example.comCopiar para área de transferência (exige xclip):
pass -c Email/example.comPara inserir:
pass insert Email/example0.comPara inserir e gerar senha:
pass generate Email/example1.comPara inserir e gerar senha sem símbolos:
pass generate --no-symbols Email/example1.comPara inserir, gerar senha e copiar para área de transferência :
pass generate -c Email/example1.comPara remover:
pass rm Email/example.com -
 @ 91bea5cd:1df4451c
2025-04-15 06:19:19
@ 91bea5cd:1df4451c
2025-04-15 06:19:19O que é Tahoe-LAFS?
Bem-vindo ao Tahoe-LAFS_, o primeiro sistema de armazenamento descentralizado com
- Segurança independente do provedor * .
Tahoe-LAFS é um sistema que ajuda você a armazenar arquivos. Você executa um cliente Programa no seu computador, que fala com um ou mais servidores de armazenamento em outros computadores. Quando você diz ao seu cliente para armazenar um arquivo, ele irá criptografar isso Arquivo, codifique-o em múltiplas peças, depois espalhe essas peças entre Vários servidores. As peças são todas criptografadas e protegidas contra Modificações. Mais tarde, quando você pede ao seu cliente para recuperar o arquivo, ele irá Encontre as peças necessárias, verifique se elas não foram corrompidas e remontadas Eles, e descriptografar o resultado.
O cliente cria mais peças (ou "compartilhamentos") do que acabará por precisar, então Mesmo que alguns servidores falhem, você ainda pode recuperar seus dados. Corrompido Os compartilhamentos são detectados e ignorados, de modo que o sistema pode tolerar o lado do servidor Erros no disco rígido. Todos os arquivos são criptografados (com uma chave exclusiva) antes Uploading, então mesmo um operador de servidor mal-intencionado não pode ler seus dados. o A única coisa que você pede aos servidores é que eles podem (geralmente) fornecer o Compartilha quando você os solicita: você não está confiando sobre eles para Confidencialidade, integridade ou disponibilidade absoluta.
O que é "segurança independente do provedor"?
Todo vendedor de serviços de armazenamento na nuvem irá dizer-lhe que o seu serviço é "seguro". Mas o que eles significam com isso é algo fundamentalmente diferente Do que queremos dizer. O que eles significam por "seguro" é que depois de ter dado Eles o poder de ler e modificar seus dados, eles tentam muito difícil de não deixar Esse poder seja abusado. Isso acaba por ser difícil! Insetos, Configurações incorretas ou erro do operador podem acidentalmente expor seus dados para Outro cliente ou para o público, ou pode corromper seus dados. Criminosos Ganho rotineiramente de acesso ilícito a servidores corporativos. Ainda mais insidioso é O fato de que os próprios funcionários às vezes violam a privacidade do cliente De negligência, avareza ou mera curiosidade. O mais consciencioso de Esses prestadores de serviços gastam consideráveis esforços e despesas tentando Mitigar esses riscos.
O que queremos dizer com "segurança" é algo diferente. * O provedor de serviços Nunca tem a capacidade de ler ou modificar seus dados em primeiro lugar: nunca. * Se você usa Tahoe-LAFS, então todas as ameaças descritas acima não são questões para você. Não só é fácil e barato para o provedor de serviços Manter a segurança de seus dados, mas na verdade eles não podem violar sua Segurança se eles tentaram. Isto é o que chamamos de * independente do fornecedor segurança*.
Esta garantia está integrada naturalmente no sistema de armazenamento Tahoe-LAFS e Não exige que você execute um passo de pré-criptografia manual ou uma chave complicada gestão. (Afinal, ter que fazer operações manuais pesadas quando Armazenar ou acessar seus dados anularia um dos principais benefícios de Usando armazenamento em nuvem em primeiro lugar: conveniência.)
Veja como funciona:
Uma "grade de armazenamento" é constituída por uma série de servidores de armazenamento. Um servidor de armazenamento Tem armazenamento direto em anexo (tipicamente um ou mais discos rígidos). Um "gateway" Se comunica com os nós de armazenamento e os usa para fornecer acesso ao Rede sobre protocolos como HTTP (S), SFTP ou FTP.
Observe que você pode encontrar "cliente" usado para se referir aos nós do gateway (que atuam como Um cliente para servidores de armazenamento) e também para processos ou programas que se conectam a Um nó de gateway e operações de execução na grade - por exemplo, uma CLI Comando, navegador da Web, cliente SFTP ou cliente FTP.
Os usuários não contam com servidores de armazenamento para fornecer * confidencialidade * nem
- Integridade * para seus dados - em vez disso, todos os dados são criptografados e Integridade verificada pelo gateway, para que os servidores não possam ler nem Modifique o conteúdo dos arquivos.
Os usuários dependem de servidores de armazenamento para * disponibilidade *. O texto cifrado é Codificado por apagamento em partes
Ndistribuídas em pelo menosHdistintas Servidores de armazenamento (o valor padrão paraNé 10 e paraHé 7) então Que pode ser recuperado de qualquerKdesses servidores (o padrão O valor deKé 3). Portanto, apenas a falha doH-K + 1(com o Padrões, 5) servidores podem tornar os dados indisponíveis.No modo de implantação típico, cada usuário executa seu próprio gateway sozinho máquina. Desta forma, ela confia em sua própria máquina para a confidencialidade e Integridade dos dados.
Um modo de implantação alternativo é que o gateway é executado em uma máquina remota e O usuário se conecta ao HTTPS ou SFTP. Isso significa que o operador de O gateway pode visualizar e modificar os dados do usuário (o usuário * depende de * o Gateway para confidencialidade e integridade), mas a vantagem é que a O usuário pode acessar a grade Tahoe-LAFS com um cliente que não possui o Software de gateway instalado, como um quiosque de internet ou celular.
Controle de acesso
Existem dois tipos de arquivos: imutáveis e mutáveis. Quando você carrega um arquivo Para a grade de armazenamento, você pode escolher o tipo de arquivo que será no grade. Os arquivos imutáveis não podem ser modificados quando foram carregados. UMA O arquivo mutable pode ser modificado por alguém com acesso de leitura e gravação. Um usuário Pode ter acesso de leitura e gravação a um arquivo mutable ou acesso somente leitura, ou não Acesso a ele.
Um usuário que tenha acesso de leitura e gravação a um arquivo mutable ou diretório pode dar Outro acesso de leitura e gravação do usuário a esse arquivo ou diretório, ou eles podem dar Acesso somente leitura para esse arquivo ou diretório. Um usuário com acesso somente leitura Para um arquivo ou diretório pode dar acesso a outro usuário somente leitura.
Ao vincular um arquivo ou diretório a um diretório pai, você pode usar um Link de leitura-escrita ou um link somente de leitura. Se você usar um link de leitura e gravação, então Qualquer pessoa que tenha acesso de leitura e gravação ao diretório pai pode obter leitura-escrita Acesso à criança e qualquer pessoa que tenha acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança. Se você usar uma leitura somente Link, qualquer pessoa que tenha lido-escrito ou acesso somente leitura ao pai O diretório pode obter acesso somente leitura à criança.
================================================== ==== Usando Tahoe-LAFS com uma rede anônima: Tor, I2P ================================================== ====
. `Visão geral '
. `Casos de uso '
.
Software Dependencies_#.
Tor#.I2P. `Configuração de conexão '
. `Configuração de Anonimato '
#.
Anonimato do cliente ' #.Anonimato de servidor, configuração manual ' #. `Anonimato de servidor, configuração automática '. `Problemas de desempenho e segurança '
Visão geral
Tor é uma rede anonimização usada para ajudar a esconder a identidade da Internet Clientes e servidores. Consulte o site do Tor Project para obter mais informações: Https://www.torproject.org/
I2P é uma rede de anonimato descentralizada que se concentra no anonimato de ponta a ponta Entre clientes e servidores. Consulte o site I2P para obter mais informações: Https://geti2p.net/
Casos de uso
Existem três casos de uso potenciais para Tahoe-LAFS do lado do cliente:
-
O usuário deseja sempre usar uma rede de anonimato (Tor, I2P) para proteger Seu anonimato quando se conecta às redes de armazenamento Tahoe-LAFS (seja ou Não os servidores de armazenamento são anônimos).
-
O usuário não se preocupa em proteger seu anonimato, mas eles desejam se conectar a Servidores de armazenamento Tahoe-LAFS que são acessíveis apenas através de Tor Hidden Services ou I2P.
-
Tor é usado apenas se uma sugestão de conexão do servidor usar
tor:. Essas sugestões Geralmente tem um endereço.onion. -
I2P só é usado se uma sugestão de conexão do servidor usa
i2p:. Essas sugestões Geralmente têm um endereço.i2p. -
O usuário não se preocupa em proteger seu anonimato ou para se conectar a um anonimato Servidores de armazenamento. Este documento não é útil para você ... então pare de ler.
Para servidores de armazenamento Tahoe-LAFS existem três casos de uso:
-
O operador deseja proteger o anonimato fazendo seu Tahoe Servidor acessível apenas em I2P, através de Tor Hidden Services, ou ambos.
-
O operador não * requer * anonimato para o servidor de armazenamento, mas eles Quer que ele esteja disponível tanto no TCP / IP roteado publicamente quanto através de um Rede de anonimização (I2P, Tor Hidden Services). Uma possível razão para fazer Isso é porque ser alcançável através de uma rede de anonimato é um Maneira conveniente de ignorar NAT ou firewall que impede roteios públicos Conexões TCP / IP ao seu servidor (para clientes capazes de se conectar a Tais servidores). Outro é o que torna o seu servidor de armazenamento acessível Através de uma rede de anonimato pode oferecer uma melhor proteção para sua Clientes que usam essa rede de anonimato para proteger seus anonimato.
-
O operador do servidor de armazenamento não se preocupa em proteger seu próprio anonimato nem Para ajudar os clientes a proteger o deles. Pare de ler este documento e execute Seu servidor de armazenamento Tahoe-LAFS usando TCP / IP com roteamento público.
Veja esta página do Tor Project para obter mais informações sobre Tor Hidden Services: Https://www.torproject.org/docs/hidden-services.html.pt
Veja esta página do Projeto I2P para obter mais informações sobre o I2P: Https://geti2p.net/en/about/intro
Dependências de software
Tor
Os clientes que desejam se conectar a servidores baseados em Tor devem instalar o seguinte.
-
Tor (tor) deve ser instalado. Veja aqui: Https://www.torproject.org/docs/installguide.html.en. No Debian / Ubuntu, Use
apt-get install tor. Você também pode instalar e executar o navegador Tor Agrupar. -
Tahoe-LAFS deve ser instalado com o
[tor]"extra" habilitado. Isso vai Instaletxtorcon::
Pip install tahoe-lafs [tor]
Os servidores Tor-configurados manualmente devem instalar Tor, mas não precisam
Txtorconou o[tor]extra. Configuração automática, quando Implementado, vai precisar destes, assim como os clientes.I2P
Os clientes que desejam se conectar a servidores baseados em I2P devem instalar o seguinte. Tal como acontece com Tor, os servidores baseados em I2P configurados manualmente precisam do daemon I2P, mas Não há bibliotecas especiais de apoio Tahoe-side.
-
I2P deve ser instalado. Veja aqui: Https://geti2p.net/en/download
-
A API SAM deve estar habilitada.
-
Inicie o I2P.
- Visite http://127.0.0.1:7657/configclients no seu navegador.
- Em "Configuração do Cliente", marque a opção "Executar no Startup?" Caixa para "SAM Ponte de aplicação ".
- Clique em "Salvar Configuração do Cliente".
-
Clique no controle "Iniciar" para "ponte de aplicação SAM" ou reinicie o I2P.
-
Tahoe-LAFS deve ser instalado com o
[i2p]extra habilitado, para obterTxi2p::
Pip install tahoe-lafs [i2p]
Tor e I2P
Os clientes que desejam se conectar a servidores baseados em Tor e I2P devem instalar tudo acima. Em particular, Tahoe-LAFS deve ser instalado com ambos Extras habilitados ::
Pip install tahoe-lafs [tor, i2p]
Configuração de conexão
Consulte: ref:
Connection Managementpara uma descrição do[tor]e[I2p]seções detahoe.cfg. Estes controlam como o cliente Tahoe Conecte-se a um daemon Tor / I2P e, assim, faça conexões com Tor / I2P-baseadas Servidores.As seções
[tor]e[i2p]só precisam ser modificadas para serem usadas de forma incomum Configurações ou para habilitar a configuração automática do servidor.A configuração padrão tentará entrar em contato com um daemon local Tor / I2P Ouvindo as portas usuais (9050/9150 para Tor, 7656 para I2P). Enquanto Há um daemon em execução no host local e o suporte necessário Bibliotecas foram instaladas, os clientes poderão usar servidores baseados em Tor Sem qualquer configuração especial.
No entanto, note que esta configuração padrão não melhora a Anonimato: as conexões TCP normais ainda serão feitas em qualquer servidor que Oferece um endereço regular (cumpre o segundo caso de uso do cliente acima, não o terceiro). Para proteger o anonimato, os usuários devem configurar o
[Connections]da seguinte maneira:[Conexões] Tcp = tor
Com isso, o cliente usará Tor (em vez de um IP-address -reviração de conexão direta) para alcançar servidores baseados em TCP.
Configuração de anonimato
Tahoe-LAFS fornece uma configuração "flag de segurança" para indicar explicitamente Seja necessário ou não a privacidade do endereço IP para um nó ::
[nó] Revelar-IP-address = (booleano, opcional)
Quando
revelar-IP-address = False, Tahoe-LAFS se recusará a iniciar se algum dos As opções de configuração emtahoe.cfgrevelariam a rede do nó localização:-
[Conexões] tcp = toré necessário: caso contrário, o cliente faria Conexões diretas para o Introdução, ou qualquer servidor baseado em TCP que aprende Do Introdutor, revelando seu endereço IP para esses servidores e um Rede de espionagem. Com isso, Tahoe-LAFS só fará Conexões de saída através de uma rede de anonimato suportada. -
Tub.locationdeve ser desativado ou conter valores seguros. este O valor é anunciado para outros nós através do Introdutor: é como um servidor Anuncia sua localização para que os clientes possam se conectar a ela. No modo privado, ele É um erro para incluir umtcp:dica notub.location. Modo privado Rejeita o valor padrão detub.location(quando a chave está faltando Inteiramente), que éAUTO, que usaifconfigpara adivinhar o nó Endereço IP externo, o que o revelaria ao servidor e a outros clientes.
Esta opção é ** crítica ** para preservar o anonimato do cliente (cliente Caso de uso 3 de "Casos de uso", acima). Também é necessário preservar uma Anonimato do servidor (caso de uso do servidor 3).
Esse sinalizador pode ser configurado (para falso), fornecendo o argumento
--hide-ippara Os comandoscreate-node,create-clientoucreate-introducer.Observe que o valor padrão de
revelar-endereço IPé verdadeiro, porque Infelizmente, esconder o endereço IP do nó requer software adicional para ser Instalado (conforme descrito acima) e reduz o desempenho.Anonimato do cliente
Para configurar um nó de cliente para anonimato,
tahoe.cfg** deve ** conter o Seguindo as bandeiras de configuração ::[nó] Revelar-IP-address = False Tub.port = desativado Tub.location = desativado
Uma vez que o nodo Tahoe-LAFS foi reiniciado, ele pode ser usado anonimamente (cliente Caso de uso 3).
Anonimato do servidor, configuração manual
Para configurar um nó de servidor para ouvir em uma rede de anonimato, devemos primeiro Configure Tor para executar um "Serviço de cebola" e encaminhe as conexões de entrada para o Porto Tahoe local. Então, configuramos Tahoe para anunciar o endereço
.onionAos clientes. Também configuramos Tahoe para não fazer conexões TCP diretas.- Decida em um número de porta de escuta local, chamado PORT. Isso pode ser qualquer não utilizado Porta de cerca de 1024 até 65535 (dependendo do kernel / rede do host Config). Nós diremos a Tahoe para escutar nesta porta, e nós diremos a Tor para Encaminhe as conexões de entrada para ele.
- Decida em um número de porta externo, chamado VIRTPORT. Isso será usado no Localização anunciada e revelada aos clientes. Pode ser qualquer número de 1 Para 65535. Pode ser o mesmo que PORT, se quiser.
- Decida em um "diretório de serviço oculto", geralmente em
/ var / lib / tor / NAME. Pediremos a Tor para salvar o estado do serviço de cebola aqui, e Tor irá Escreva o endereço.onionaqui depois que ele for gerado.
Em seguida, faça o seguinte:
-
Crie o nó do servidor Tahoe (com
tahoe create-node), mas não ** não ** Lança-o ainda. -
Edite o arquivo de configuração Tor (normalmente em
/ etc / tor / torrc). Precisamos adicionar Uma seção para definir o serviço oculto. Se nossa PORT for 2000, VIRTPORT é 3000, e estamos usando/ var / lib / tor / tahoecomo o serviço oculto Diretório, a seção deve se parecer com ::HiddenServiceDir / var / lib / tor / tahoe HiddenServicePort 3000 127.0.0.1:2000
-
Reinicie Tor, com
systemctl restart tor. Aguarde alguns segundos. -
Leia o arquivo
hostnameno diretório de serviço oculto (por exemplo,/ Var / lib / tor / tahoe / hostname). Este será um endereço.onion, comoU33m4y7klhz3b.onion. Ligue para esta CEBOLA. -
Edite
tahoe.cfgpara configurartub.portpara usarTcp: PORT: interface = 127.0.0.1etub.locationpara usarTor: ONION.onion: VIRTPORT. Usando os exemplos acima, isso seria ::[nó] Revelar-endereço IP = falso Tub.port = tcp: 2000: interface = 127.0.0.1 Tub.location = tor: u33m4y7klhz3b.onion: 3000 [Conexões] Tcp = tor
-
Inicie o servidor Tahoe com
tahoe start $ NODEDIR
A seção
tub.portfará com que o servidor Tahoe ouça no PORT, mas Ligue o soquete de escuta à interface de loopback, que não é acessível Do mundo exterior (mas * é * acessível pelo daemon Tor local). Então o A seçãotcp = torfaz com que Tahoe use Tor quando se conecta ao Introdução, escondendo o endereço IP. O nó se anunciará a todos Clientes que usam `tub.location``, então os clientes saberão que devem usar o Tor Para alcançar este servidor (e não revelar seu endereço IP através do anúncio). Quando os clientes se conectam ao endereço da cebola, seus pacotes serão Atravessar a rede de anonimato e eventualmente aterrar no Tor local Daemon, que então estabelecerá uma conexão com PORT no localhost, que é Onde Tahoe está ouvindo conexões.Siga um processo similar para construir um servidor Tahoe que escuta no I2P. o O mesmo processo pode ser usado para ouvir tanto o Tor como o I2P (
tub.location = Tor: ONION.onion: VIRTPORT, i2p: ADDR.i2p). Também pode ouvir tanto Tor como TCP simples (caso de uso 2), comtub.port = tcp: PORT,tub.location = Tcp: HOST: PORT, tor: ONION.onion: VIRTPORTeanonymous = false(e omite A configuraçãotcp = tor, já que o endereço já está sendo transmitido através de O anúncio de localização).Anonimato do servidor, configuração automática
Para configurar um nó do servidor para ouvir em uma rede de anonimato, crie o Nó com a opção
--listen = tor. Isso requer uma configuração Tor que Ou lança um novo daemon Tor, ou tem acesso à porta de controle Tor (e Autoridade suficiente para criar um novo serviço de cebola). Nos sistemas Debian / Ubuntu, façaApt install tor, adicione-se ao grupo de controle comadduser YOURUSERNAME debian-tore, em seguida, inicie sessão e faça o login novamente: se osgroupsO comando incluidebian-torna saída, você deve ter permissão para Use a porta de controle de domínio unix em/ var / run / tor / control.Esta opção irá definir
revelar-IP-address = Falsee[connections] tcp = Tor. Ele alocará as portas necessárias, instruirá Tor para criar a cebola Serviço (salvando a chave privada em algum lugar dentro de NODEDIR / private /), obtenha O endereço.onione preenchatub.portetub.locationcorretamente.Problemas de desempenho e segurança
Se você estiver executando um servidor que não precisa ser Anônimo, você deve torná-lo acessível através de uma rede de anonimato ou não? Ou você pode torná-lo acessível * ambos * através de uma rede de anonimato E como um servidor TCP / IP rastreável publicamente?
Existem várias compensações efetuadas por esta decisão.
Penetração NAT / Firewall
Fazer com que um servidor seja acessível via Tor ou I2P o torna acessível (por Clientes compatíveis com Tor / I2P) mesmo que existam NAT ou firewalls que impeçam Conexões TCP / IP diretas para o servidor.
Anonimato
Tornar um servidor Tahoe-LAFS acessível * somente * via Tor ou I2P pode ser usado para Garanta que os clientes Tahoe-LAFS usem Tor ou I2P para se conectar (Especificamente, o servidor só deve anunciar endereços Tor / I2P no Chave de configuração
tub.location). Isso evita que os clientes mal configurados sejam Desingonizando-se acidentalmente, conectando-se ao seu servidor através de A Internet rastreável.Claramente, um servidor que está disponível como um serviço Tor / I2P * e * a O endereço TCP regular não é anônimo: o endereço do .on e o real O endereço IP do servidor é facilmente vinculável.
Além disso, a interação, através do Tor, com um Tor Oculto pode ser mais Protegido da análise do tráfego da rede do que a interação, através do Tor, Com um servidor TCP / IP com rastreamento público
** XXX há um documento mantido pelos desenvolvedores de Tor que comprovem ou refutam essa crença? Se assim for, precisamos ligar a ele. Caso contrário, talvez devêssemos explicar mais aqui por que pensamos isso? **
Linkability
A partir de 1.12.0, o nó usa uma única chave de banheira persistente para saída Conexões ao Introdutor e conexões de entrada para o Servidor de Armazenamento (E Helper). Para os clientes, uma nova chave Tub é criada para cada servidor de armazenamento Nós aprendemos sobre, e essas chaves são * não * persistiram (então elas mudarão cada uma delas Tempo que o cliente reinicia).
Clientes que atravessam diretórios (de rootcap para subdiretório para filecap) são É provável que solicitem os mesmos índices de armazenamento (SIs) na mesma ordem de cada vez. Um cliente conectado a vários servidores irá pedir-lhes todos para o mesmo SI em Quase ao mesmo tempo. E dois clientes que compartilham arquivos ou diretórios Irá visitar os mesmos SI (em várias ocasiões).
Como resultado, as seguintes coisas são vinculáveis, mesmo com
revelar-endereço IP = Falso:- Servidores de armazenamento podem vincular reconhecer várias conexões do mesmo Cliente ainda não reiniciado. (Observe que o próximo recurso de Contabilidade pode Faz com que os clientes apresentem uma chave pública persistente do lado do cliente quando Conexão, que será uma ligação muito mais forte).
- Os servidores de armazenamento provavelmente podem deduzir qual cliente está acessando dados, por Olhando as SIs sendo solicitadas. Vários servidores podem conciliar Determine que o mesmo cliente está falando com todos eles, mesmo que o TubIDs são diferentes para cada conexão.
- Os servidores de armazenamento podem deduzir quando dois clientes diferentes estão compartilhando dados.
- O Introdutor pode entregar diferentes informações de servidor para cada um Cliente subscrito, para particionar clientes em conjuntos distintos de acordo com Quais as conexões do servidor que eles eventualmente fazem. Para clientes + nós de servidor, ele Também pode correlacionar o anúncio do servidor com o cliente deduzido identidade.
atuação
Um cliente que se conecta a um servidor Tahoe-LAFS com rastreamento público através de Tor Incorrem em latência substancialmente maior e, às vezes, pior Mesmo cliente se conectando ao mesmo servidor através de um TCP / IP rastreável normal conexão. Quando o servidor está em um Tor Hidden Service, ele incorre ainda mais Latência e, possivelmente, ainda pior rendimento.
Conectando-se a servidores Tahoe-LAFS que são servidores I2P incorrem em maior latência E pior rendimento também.
Efeitos positivos e negativos em outros usuários Tor
O envio de seu tráfego Tahoe-LAFS sobre o Tor adiciona tráfego de cobertura para outros Tor usuários que também estão transmitindo dados em massa. Então isso é bom para Eles - aumentando seu anonimato.
No entanto, torna o desempenho de outros usuários do Tor Sessões - por exemplo, sessões ssh - muito pior. Isso é porque Tor Atualmente não possui nenhuma prioridade ou qualidade de serviço Recursos, para que as teclas de Ssh de outra pessoa possam ter que esperar na fila Enquanto o conteúdo do arquivo em massa é transmitido. O atraso adicional pode Tornar as sessões interativas de outras pessoas inutilizáveis.
Ambos os efeitos são duplicados se você carregar ou baixar arquivos para um Tor Hidden Service, em comparação com se você carregar ou baixar arquivos Over Tor para um servidor TCP / IP com rastreamento público
Efeitos positivos e negativos em outros usuários do I2P
Enviar seu tráfego Tahoe-LAFS ao I2P adiciona tráfego de cobertura para outros usuários do I2P Que também estão transmitindo dados. Então, isso é bom para eles - aumentando sua anonimato. Não prejudicará diretamente o desempenho de outros usuários do I2P Sessões interativas, porque a rede I2P possui vários controles de congestionamento e Recursos de qualidade de serviço, como priorizar pacotes menores.
No entanto, se muitos usuários estão enviando tráfego Tahoe-LAFS ao I2P e não tiverem Seus roteadores I2P configurados para participar de muito tráfego, então o I2P A rede como um todo sofrerá degradação. Cada roteador Tahoe-LAFS que usa o I2P tem Seus próprios túneis de anonimato que seus dados são enviados. Em média, um O nó Tahoe-LAFS requer 12 outros roteadores I2P para participar de seus túneis.
Portanto, é importante que o seu roteador I2P esteja compartilhando a largura de banda com outros Roteadores, para que você possa retornar enquanto usa o I2P. Isso nunca prejudicará a Desempenho de seu nó Tahoe-LAFS, porque seu roteador I2P sempre Priorize seu próprio tráfego.
=========================
Como configurar um servidor
Muitos nós Tahoe-LAFS são executados como "servidores", o que significa que eles fornecem serviços para Outras máquinas (isto é, "clientes"). Os dois tipos mais importantes são os Introdução e Servidores de armazenamento.
Para ser útil, os servidores devem ser alcançados pelos clientes. Os servidores Tahoe podem ouvir Em portas TCP e anunciar sua "localização" (nome do host e número da porta TCP) Para que os clientes possam se conectar a eles. Eles também podem ouvir os serviços de cebola "Tor" E portas I2P.
Os servidores de armazenamento anunciam sua localização ao anunciá-lo ao Introdutivo, Que então transmite a localização para todos os clientes. Então, uma vez que a localização é Determinado, você não precisa fazer nada de especial para entregá-lo.
O próprio apresentador possui uma localização, que deve ser entregue manualmente a todos Servidores de armazenamento e clientes. Você pode enviá-lo para os novos membros do seu grade. Esta localização (juntamente com outros identificadores criptográficos importantes) é Escrito em um arquivo chamado
private / introducer.furlno Presenter's Diretório básico, e deve ser fornecido como o argumento--introducer =paraTahoe create-nodeoutahoe create-node.O primeiro passo ao configurar um servidor é descobrir como os clientes irão alcançar. Então você precisa configurar o servidor para ouvir em algumas portas, e Depois configure a localização corretamente.
Configuração manual
Cada servidor tem duas configurações em seu arquivo
tahoe.cfg:tub.port, eTub.location. A "porta" controla o que o nó do servidor escuta: isto Geralmente é uma porta TCP.A "localização" controla o que é anunciado para o mundo exterior. Isto é um "Sugestão de conexão foolscap", e inclui tanto o tipo de conexão (Tcp, tor ou i2p) e os detalhes da conexão (nome do host / endereço, porta número). Vários proxies, gateways e redes de privacidade podem ser Envolvido, então não é incomum para
tub.portetub.locationpara olhar diferente.Você pode controlar diretamente a configuração
tub.portetub.locationConfigurações, fornecendo--port =e--location =ao executartahoe Create-node.Configuração automática
Em vez de fornecer
--port = / - location =, você pode usar--listen =. Os servidores podem ouvir em TCP, Tor, I2P, uma combinação desses ou nenhum. O argumento--listen =controla quais tipos de ouvintes o novo servidor usará.--listen = nonesignifica que o servidor não deve ouvir nada. Isso não Faz sentido para um servidor, mas é apropriado para um nó somente cliente. o O comandotahoe create-clientinclui automaticamente--listen = none.--listen = tcpé o padrão e liga uma porta de escuta TCP padrão. Usar--listen = tcprequer um argumento--hostname =também, que será Incorporado no local anunciado do nó. Descobrimos que os computadores Não pode determinar de forma confiável seu nome de host acessível externamente, então, em vez de Ter o servidor adivinhar (ou escanear suas interfaces para endereços IP Isso pode ou não ser apropriado), a criação de nó requer que o usuário Forneça o nome do host.--listen = torconversará com um daemon Tor local e criará uma nova "cebola" Servidor "(que se parece comalzrgrdvxct6c63z.onion).--listen = i2p` conversará com um daemon I2P local e criará um novo servidor endereço. Consulte: doc:anonymity-configuration` para obter detalhes.Você pode ouvir nos três usando
--listen = tcp, tor, i2p.Cenários de implantação
A seguir, alguns cenários sugeridos para configurar servidores usando Vários transportes de rede. Estes exemplos não incluem a especificação de um Apresentador FURL que normalmente você gostaria quando provisionamento de armazenamento Nós. Para estes e outros detalhes de configuração, consulte : Doc:
configuration.. `Servidor possui um nome DNS público '
.
Servidor possui um endereço público IPv4 / IPv6_.
O servidor está por trás de um firewall com encaminhamento de porta_.
Usando o I2P / Tor para evitar o encaminhamento da porta_O servidor possui um nome DNS público
O caso mais simples é o local onde o host do servidor está diretamente conectado ao Internet, sem um firewall ou caixa NAT no caminho. A maioria dos VPS (Virtual Private Servidor) e servidores colocados são assim, embora alguns fornecedores bloqueiem Muitas portas de entrada por padrão.
Para esses servidores, tudo o que você precisa saber é o nome do host externo. O sistema O administrador irá dizer-lhe isso. O principal requisito é que este nome de host Pode ser pesquisado no DNS, e ele será mapeado para um endereço IPv4 ou IPv6 que Alcançará a máquina.
Se o seu nome de host for
example.net, então você criará o introdutor como esta::Tahoe create-introducer --hostname example.com ~ / introducer
Ou um servidor de armazenamento como ::
Tahoe create-node --hostname = example.net
Estes irão alocar uma porta TCP (por exemplo, 12345), atribuir
tub.portpara serTcp: 12345etub.locationserãotcp: example.com: 12345.Idealmente, isso também deveria funcionar para hosts compatíveis com IPv6 (onde o nome DNS Fornece um registro "AAAA", ou ambos "A" e "AAAA"). No entanto Tahoe-LAFS O suporte para IPv6 é novo e ainda pode ter problemas. Por favor, veja o ingresso
# 867_ para detalhes... _ # 867: https://tahoe-lafs.org/trac/tahoe-lafs/ticket/867
O servidor possui um endereço público IPv4 / IPv6
Se o host tiver um endereço IPv4 (público) rotativo (por exemplo,
203.0.113.1```), mas Nenhum nome DNS, você precisará escolher uma porta TCP (por exemplo,3457``) e usar o Segue::Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
--porté uma "string de especificação de ponto de extremidade" que controla quais locais Porta em que o nó escuta.--locationé a "sugestão de conexão" que ele Anuncia para outros, e descreve as conexões de saída que essas Os clientes irão fazer, por isso precisa trabalhar a partir da sua localização na rede.Os nós Tahoe-LAFS escutam em todas as interfaces por padrão. Quando o host é Multi-homed, você pode querer fazer a ligação de escuta ligar apenas a uma Interface específica, adicionando uma opção
interface =ao--port =argumento::Tahoe create-node --port = tcp: 3457: interface = 203.0.113.1 - localização = tcp: 203.0.113.1: 3457
Se o endereço público do host for IPv6 em vez de IPv4, use colchetes para Envolva o endereço e altere o tipo de nó de extremidade para
tcp6::Tahoe create-node --port = tcp6: 3457 - localização = tcp: [2001: db8 :: 1]: 3457
Você pode usar
interface =para vincular a uma interface IPv6 específica também, no entanto Você deve fazer uma barra invertida - escapar dos dois pontos, porque, de outra forma, eles são interpretados Como delimitadores pelo idioma de especificação do "ponto final" torcido. o--location =argumento não precisa de dois pontos para serem escapados, porque eles são Envolto pelos colchetes ::Tahoe create-node --port = tcp6: 3457: interface = 2001 \: db8 \: \: 1 --location = tcp: [2001: db8 :: 1]: 3457
Para hosts somente IPv6 com registros DNS AAAA, se o simples
--hostname =A configuração não funciona, eles podem ser informados para ouvir especificamente Porta compatível com IPv6 com este ::Tahoe create-node --port = tcp6: 3457 - localização = tcp: example.net: 3457
O servidor está por trás de um firewall com encaminhamento de porta
Para configurar um nó de armazenamento por trás de um firewall com encaminhamento de porta, você irá precisa saber:
- Endereço IPv4 público do roteador
- A porta TCP que está disponível de fora da sua rede
- A porta TCP que é o destino de encaminhamento
- Endereço IPv4 interno do nó de armazenamento (o nó de armazenamento em si é
Desconhece esse endereço e não é usado durante
tahoe create-node, Mas o firewall deve ser configurado para enviar conexões para isso)
Os números de porta TCP internos e externos podem ser iguais ou diferentes Dependendo de como o encaminhamento da porta está configurado. Se é mapear portas 1-para-1, eo endereço IPv4 público do firewall é 203.0.113.1 (e Talvez o endereço IPv4 interno do nó de armazenamento seja 192.168.1.5), então Use um comando CLI como este ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 3457
Se no entanto, o firewall / NAT-box encaminha a porta externa * 6656 * para o interno Porta 3457, então faça isso ::
Tahoe create-node --port = tcp: 3457 - localização = tcp: 203.0.113.1: 6656
Usando o I2P / Tor para evitar o encaminhamento da porta
Os serviços de cebola I2P e Tor, entre outras excelentes propriedades, também fornecem NAT Penetração sem encaminhamento de porta, nomes de host ou endereços IP. Então, configurando Um servidor que escuta apenas no Tor é simples ::
Tahoe create-node --listen = tor
Para mais informações sobre o uso de Tahoe-LAFS com I2p e Tor veja : Doc:
anonymity-configuration -
 @ 866e0139:6a9334e5
2025-04-15 06:16:00
@ 866e0139:6a9334e5
2025-04-15 06:16:00
Autor: Michael Meyen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Es geht gut los. „WC für alle“. Daneben noch einmal in der Sprache des Imperiums. „All Gender (urinal inside)“. Das hilft nicht wirklich, weil das Pinkelbecken vor der Tür ist und man nicht weiß, wer gerade dahinter hockt. Also warten bis zur Auflösung. Wir sind im Haus der Demokratie in der Greifswalder Straße. Immerhin.
Eingeladen hat die Neue Gesellschaft für Psychologie. Der Name täuscht. Diese neue Gesellschaft ist alt. Sehr alt. Damit meine ich gar nicht Laura von Wimmersperg, Jahrgang 1934, die den ersten Paukenschlag setzt. Sie habe, sagt diese Dame mit weißem Haar sinngemäß, als sie ans Podium tritt, sie habe sich gequält mit ihrem Text, das Geschriebene wieder und wieder gelesen und dann – in den Papierkorb geworfen. Ihre Gefühle seien größer, als alle Worte jemals sein könnten. „Krieg und Frieden“ heißt dieser Kongress. Laura von Wimmersperg ist die Grande Dame der westdeutschen Friedensbewegung, bekannt weit über Berlin hinaus. Nato-Doppelbeschluss, Jugoslawien, Irak, Afghanistan. Ein Ostermarsch nach dem anderen. Laura von Wimmersperg hat auch den 24. Februar 2022 überlebt und kann die Kampfgefährten kaum mehr zählen, die in einem der Gräben am Wegesrand verrotten. Migration, Klima, Corona und immer wieder Russland und die Ukraine.
Die Neue Gesellschaft für Psychologie ist noch da, einerseits. Versprengte DKPler, Leute aus den K-Gruppen, Marxisten, Maoisten. Bevor ich „andererseits“ sage, brauche ich einen Disclaimer. Ich darf diesen Text nicht schreiben. Ich habe in Berlin einen Vortrag gehalten über „Journalismus und Macht“ und das Programm nicht komplett gesehen. Einen ganzen Tag sitzen: Das erlaubt mein Körper nicht mehr. Augen und Ohren haben so manche Interna verpasst und fast alles, was über Gaza gesagt wurde oder über die Kampagne „Für ein neutrales Deutschland“. Damit verbietet sich eigentlich jeder Bericht. Karin Leukefeld, seit 25 Jahren als Journalistin unterwegs in einer Gegend, die manche Nahost nennen und andere mittlerweile Greater Middle East, hat das in Berlin wunderbar formuliert. Mit allen reden, lesen, zuhören, fragen. Aus halben Sachen wird kein ganzes Bild.
Karin Leukefeld hat auch gesagt, dass sie einst in den Journalismus gegangen ist, um Brücken zu schlagen, und dass sie deshalb weniger die Schlagzeilen interessieren als das Leben dahinter. Vielleicht hilft ja mein Blick von außen selbst dann, wenn er mit blinden Flecken daherkommt. Damit nun endlich zum „andererseits“ und vor allem zum Alter. Ich war nicht dabei in der kleineren Bundesrepublik, aber so ungefähr muss es gewesen sein. Die Vokabeln, der Habitus. Rosa Luxemburg, SDS und Klassenkampf, Kapitalismus und Entfremdung. Murmeln, klatschen, reinrufen. Dieses Publikum geht mit. Jawoll! Genau! Ja! Mmh. Wenig Psychologie und viel Materialismus selbst bei denen, die als Psychologen vorgestellt werden. Sicher ist das alles ganz furchtbar mit den Verhältnissen. Das wusste schon der gute Brecht. Die Frage allerdings, die mich beschäftigt, seit ich nicht mehr zur Vorhut der Arbeiterklasse gehöre: Welche Wunder waren nötig, dass einige wenige all die Zwänge hinter sich lassen konnten und nun bereitstehen, um die Massen aufzuklären? Und fast noch wichtiger: Wozu braucht diese Avantgarde Massen, denen sie ohnehin nicht über den Weg traut? Ich spitze zu und verallgemeinere, okay. Trotzdem. Das ist der alte Geist mit allenfalls leicht entstaubten Analysen und Rezepten, der den Staat verschonen möchte und China sowieso. Klaus-Jürgen Bruder, der Cheforganisator, steht immer wieder auf, um zu akademisieren und damit auch zu differenzieren. Analyse und Aktivismus, Wunden lecken und sich dabei auch noch zu vergewissern, dass man immer noch Kurs hält: So ein Spagat überfordert jeden Kongress.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Wenn die Reihen gelichtet sind, verbietet es sich fast von selbst, auch noch auf die letzten Mitstreiter einzuprügeln. Wer kämpft, hat schon verloren, sagt Christian Dewanger, der sich als Daoist vorstellt und keine Lust hat, China von der Ausbeutung freizusprechen und von allen anderen Sünden der Macht. Sonst aber: Wohlwollen und weglächeln. Wer weiß, wozu der Staat noch gut sein kann und der große Bruder in Peking. Man kann sich derweil ja an der Linkspartei abarbeiten, an Gregor Gysi und an den Brandmauer-Baumeistern, die es auch im Quartier ganz links gibt, spätestens seit den Montags-Mahnwachen 2014. Laura von Wimmersperg sagt: Habt Geduld und übt euch in Nachsicht, liebe Leute. Bei ihrem 90. im Herbst, erzählt sie, habe sie die alten Kameraden genauso eingeladen wie die neuen und die Missgunst einfach übersehen – anders als die Bundeswehr-Werbung an der Edeka-Kasse vor der Tür. Auf zur Marktleitung mit einer Frage auf den Lippen: Wie kann jemand, der das Leben selbst so wenig achtet, allen Ernstes auf jedem Plakat behaupten, dass er Lebensmittel liebt? Beim nächsten Einkauf sei der Laden sauber gewesen.
Ich erwähne diese kleine Geschichte, weil Laura von Wimmersperg eine Ausnahme ist. Vielleicht kann das nur eine Frau, die alles erlebt hat: 20 von 30 Rede-Minuten verschenken und so eine Tür öffnen für Nachdenken und Reden. Die alten Männer, nur einen Wimpernschlag jünger, würden den Teufel tun. Saurier-Ausstellung, sagt mein Sitz-Nachbar. Das kann so gemeint sein oder so. Wolfgang Effenberger, Jahrgang 1946, ist der Jüngste in diesem Trio infernale, das einen ganzen Vormittag bekommen hat und von keinem Moderator der Welt zu stoppen wäre. Effenberger war Soldat und hat den Dienst quittiert, als ihm klar wurde, worauf alle Planungen hinausliefen. Der Atomtod, damals schon. Die Zeitenwende beginnt für ihn mit dem Kosovo. Seitdem laufe die Vorbereitung auf den großen Krieg. Iran, Russland, China. Effenberger scrollt durch die Strategiedokumente, wechselt zum Westfälischen Frieden, der 15 Jahre Anlaufzeit gebraucht habe, und schüttelt den Kopf beim Blick auf Donald Trump, der offenbar glaube, alles mit einem Anruf erledigen zu können, und auf jemanden wie Keith Kellogg gesetzt habe, einen Mann aus dem Herzen der Finsternis.
Werner Rügemer, der nächste Saurier, ist fünf Jahre älter und sehr viel ruhiger als Effenberger, aber keineswegs leiser. Dass er die Lösung in China sieht, hat mit seinem Gesellschaftsbild zu tun und mit der Rolle, die das US-Kapital darin spielt. Nicht *eine* Hauptrolle, sondern DIE. Der Treiber von allem. Hitler und die Wehrmacht, der Staatsstreich in Guatemala und das Office of Strategic Services, der erste Auslandsgeheimdienst der USA, 1941 nicht zufällig gegründet von den Wall-Street-Anwälten Allen Dulles und William Donovan. Folge der Spur des Geldes und löse so die Rätsel der Geschichte.

Auch Rudolph Bauer, Jahrgang 1939, taucht tief ein in die Vergangenheit. Ein Saurier-Privileg. Demos gegen den Krieg? Konferenzen für den Frieden? 1913/14 versandet und in Weimar auch. Ob ein Generalstreik geholfen hätte? Wenn dieses Wort in den nächsten Stunden und Tagen fällt, geht im Saal die Sonne auf. Rudolph Bauer hört nicht mehr besonders gut, aber er hat noch einen zweiten Punkt, der diesen Kongress fesselt. Ist das, was ich hier etwas lapidar Friedensbewegung nenne, möglicherweise genau die Begleitmusik, die jeder Kriegstreiber braucht?
Was bleibt jenseits von Gesprächen, Handynummern, Lesetipps? Ich weiß jetzt, dass nicht nur die DDR-Eliten überlebt haben, die 1990 zwar alle Positionen und jeden Einfluss verloren haben, aber sich weiter trafen mit allem Drum und Dran. Netzwerke, Periodika, Bücher. So gut wie nichts davon ist in der gesamtdeutschen Öffentlichkeit diskutiert worden, aber es hat die Jahre mit Sinn gefüllt. Wäre mehr möglich gewesen, wenn es einen Link gegeben hätte zu den Reservaten der alten Westlinken? Zur Neuen Gesellschaft für Psychologie zum Beispiel? Vielleicht gelingt die Blutauffrischung, vielleicht auch nicht. Trost gab es aus dem Raum mit einer Geschichte aus dem Orient. Prophet Abraham liegt im Feuer, und ein Spatz hat Wasser im Schnabel. Dieser Spatz weiß, dass er allein nichts ausrichten kann, hört aber trotzdem nicht auf, um in den Spiegel schauen zu können, wenn er eines Tages vor seinem Schöpfer steht. Schön.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst an alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.).
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ c1e9ab3a:9cb56b43
2025-04-15 04:55:49
@ c1e9ab3a:9cb56b43
2025-04-15 04:55:49Esteemed representatives of Risa,
We gather here under the calming glow of our twin suns, stewards of a society admired for its peace and celebrated for its tranquility. But we must not mistake serenity for passivity, nor confuse peace with weakness. Our peace is not an accident. It is not the byproduct of ignorance or naivety. It is hard-earned—preserved by those willing to stand vigilant in its defense.
Love as a Foundation, Strength as a Shield
Love conquers hate. This is the core truth of Risan philosophy. Yet, as every Ricin child is taught, love without strength is a leaf in the wind. The Ricin do not lay down their lives without resistance. We do not ask our people to accept violence without confronting it. True peace is not imposed by stripping the people of their agency—it is built by enabling them to protect it.
The Lessons of a Failed Experiment
There was a time, not so distant in our history, when we attempted to enforce peace through the abolition of all weapons. A time when even the mention of self-defense in our educational centers was met with rebuke. Schools purged training programs. Cultural arts that honored our warrior traditions were dismissed. And for a brief moment, we believed this would lead us to harmony.
But peace born from helplessness is a fragile illusion. It fractures under the slightest pressure. And fracture it did—when off-world raiders targeted our unguarded sanctuaries, when radical sects within our own society struck out, knowing the citizenry could not defend itself. It was then that we remembered: Risa’s greatest peacekeepers had always been those who knew how to fight—but chose restraint.
The Age of Ricin and the Reawakening of Discipline
So we returned to our roots. To the traditions of the Age of Ricin, when youth, upon reaching maturity, were taught not only the arts of compassion and creation but also the martial disciplines. They learn to wield weapons—not to glorify violence, but to understand it. To control it. To stand firm against it when all else fails.
https://i.nostr.build/kuUjRovISz7367TX.jpg
We do not romanticize war. We do not celebrate conflict. But we prepare for it, should it seek to extinguish our light. Our children now learn the disciplines of defense alongside their studies in poetry, music, and healing. They spar with blunt blades under the watchful eyes of masters. They meditate on the consequences of force. And they grow into citizens not easily provoked, but never unprepared.
A Call for Balance, Not Extremes
Let those beyond our borders question our ways. Let them forget the countless incursions by the Romulans. Let them ignore the scars left by centuries of subversion from the Orion Syndicate. We do not forget. We remember the lives lost, the liberties challenged, and the lessons learned through suffering. These experiences shaped us.
We do not wish to return to the era of soft silence, when teachers trembled at the word "weapon" and children were told that even imagination was dangerous. That was not enlightenment. That was indoctrination.
Conclusion: Guarding the Flame
We are the guardians of Risa’s flame—not just with words and treaties, but with discipline and readiness. We have made peace a practice, and preparation a virtue. And so I say to this chamber: let us never again disarm our people in the name of utopia. Let us never confuse comfort with safety, or the absence of weapons with the presence of peace.
Instead, let us raise generations who know what peace costs, and who will pay that price—not with surrender, but with courage.
Let our children be artists, lovers, dreamers—and if necessary, defenders.
This is the Risan way.
-
 @ 0b118e40:4edc09cb
2025-04-15 03:50:32
@ 0b118e40:4edc09cb
2025-04-15 03:50:32TL;DR : No.
(This is not a feasibility analysis, but a reflection on philosophical alignment with Bitcoin’s vision).
The moment stablecoins or national currencies gain traction in Bitcoin LN, you can forget about Bitcoin’s position as a purely decentralized medium of exchange. Bitcoin’s position will be undermined.
A Bitcoin-native global economy, where people and businesses transact directly in Bitcoin, is what aligns with its original purpose. This is what we should aim for. This is all we should aim for.
I used to believe stablecoins might help with on/off ramps. But the truth is, if Bitcoin is to function as a true currency, broader global adoption that bypasses traditional financial systems will make those ramps irrelevant.
Eventually, two camps will emerge. One will try to preserve Bitcoin’s purity as a currency. The other will push for everything else in the name of Bitcoin: store-of-value narratives, ETFs, stablecoin collaborations, tokens, pump and dumps, NFTs, and centralized workarounds.
Currency domination, especially by the USD, has long contributed to poverty in the Global South. It deepens inequality and worsens debt burdens. During the Tequila Crisis and the Asian Financial Crisis, countries like Mexico and regions like Southeast Asia suffered massive currency devaluations and defaults because of their dependence on the USD. Every time the US raises interest rates, developing nations experience capital flight, currency drops, and economic hardship. This is not ancient history. It has been happening in the last two years and continues to widen the poverty gap. And as always, it is the poor who suffer the most.
What does this have to do with stablecoins? Stablecoin is your fiat 2.0.
USDT is just currency domination through blockchain. It is pegged to the USD, and if it rides Bitcoin’s Lightning rails, it risks keeping users transacting in USD rather than in Bitcoin itself. That not only undermines Bitcoin’s core purpose, it risks making Bitcoin appear like it is taking sides in the fragile and invisible global currency war.
To counter, people will say “Let all stablecoins come. Peg them to any currency.” But what’s the point of Bitcoin then? To become the new logistics layer for fiat 2.0?
That is not progress. That is regress. It is inviting the very systems Bitcoin was built to disrupt back into the ecosystem.
I believe when you use stablecoins this way, you are not Trojan-horsing Bitcoin into the mainstream. You are letting fiat Trojan-horse its way into Bitcoin. And if you let them in, they will win.
Adding stablecoin into Bitcoin LN is counterproductive to Bitcoin's decentralized ethos.
Bitcoin’s true potential is its ability to provide an alternative to centralized, government-controlled currencies and financial systems. We should stick to the original game plan.
Side note: If you really want to Trojan-horse Bitcoin adoption…
In my country, we have so many mixed races and cross-cultural traditions. During Chinese New Year, if you are married, you give everyone who is not married an “ang pow,” which is money in a red packet. Because we are so deeply integrated, people give money at almost every celebration: Christmas, Eid, Diwali, birthdays, graduations, even funerals.
I recently met up with a friend who just had a baby, and I was more than happy to be the first to give her daughter some Bitcoin. Her first sats. It would not hurt to start giving Bitcoin as gifts. And if someone gets offended that it is not part of their tradition, just get a Bitkey and wrap it up. It is so pretty.
Find more fun and creative ways to spread Bitcoin adoption.
But for goodness’ sake, stop justifying everything else in the name of Bitcoin adoption.
To get a better idea of Fiat 2.0, I mind-mapped Bitcoin on macroeconomy on my scratchpad.

If you take a closer look, it might help you answer a few key questions:
-
Do you want more or less government control over money?
-
Are you a fan of central banks? Then you probably prefer stablecoins.
-
-
 @ 502ab02a:a2860397
2025-04-15 02:12:45
@ 502ab02a:a2860397
2025-04-15 02:12:45หลังจากเราดูเรื่อง UPOV กันไปแล้ว วันนี้เรามาดูกันครับว่า ผู้ที่ต่อต้าน เจออะไรกันบ้าง
ในหลายประเทศทั่วโลก เสียงของเกษตรกรรายย่อยที่เคยเงียบงัน กำลังดังขึ้นท่ามกลางการรุกคืบของข้อตกลงระหว่างประเทศที่พยายามกีดกันสิทธิการใช้เมล็ดพันธุ์แบบดั้งเดิมของพวกเขา การก้าวเข้ามาของ UPOV 1991 ไม่ต่างอะไรกับการเขียนกฎหมายใหม่ให้บริษัทข้ามชาติมีสิทธิ “จดทะเบียน” พันธุ์พืชที่เคยเป็นสมบัติสาธารณะ แล้วเรียกร้องค่าลิขสิทธิ์จากเกษตรกรแม้จะปลูกเพื่อกินเองก็ตาม
แต่โลกนี้ไม่ได้เงียบ…
กรณีศึกษา อินเดีย หนึ่งในเสียงชัดเจนที่สุดมาจากดร.วันดานา ชิวา (Vandana Shiva) นักฟิสิกส์และนักเคลื่อนไหวด้านสิ่งแวดล้อมในอินเดีย ผู้ก่อตั้งองค์กร Navdanya ซึ่งมีภารกิจหลักในการปกป้องเมล็ดพันธุ์พื้นบ้านและเกษตรกรรมแบบยั่งยืน
Navdanya สร้างธนาคารเมล็ดพันธุ์ของตัวเอง โดยไม่ยอมรับระบบ UPOV ใด ๆ เลย องค์กรนี้ทำงานร่วมกับชุมชนพื้นเมืองทั่วอินเดียเพื่อเก็บเมล็ดพันธุ์ดั้งเดิมมากกว่า 2,000 สายพันธุ์ พร้อมกับปลูกฝังแนวคิดว่า “เมล็ดพันธุ์ไม่ใช่สินค้า แต่เป็นชีวิต”
อินเดียเอง แม้จะมีแรงกดดันจากการเจรจาทางการค้าระหว่างประเทศ แต่ก็ยังไม่ยอมรับ UPOV 1991 อย่างเป็นทางการ พวกเขาเลือกเขียนกฎหมายของตนเองชื่อว่า The Protection of Plant Varieties and Farmers' Rights Act, 2001 ซึ่งกล้าหาญมาก เพราะเป็นกฎหมายที่คุ้มครอง “สิทธิของเกษตรกร” เคียงคู่ไปกับ “สิทธิของนักปรับปรุงพันธุ์” โดยยืนยันว่า เกษตรกรมีสิทธิในการบันทึก เก็บ ใช้ แลกเปลี่ยน และขายเมล็ดพันธุ์ของตนเอง โดยไม่ต้องขออนุญาตจากใคร ผลคืออะไร? แรงกดดันจากต่างประเทศมาเต็ม โดยเฉพาะจากยุโรปและสหรัฐฯ ที่หวังให้อินเดีย “อัปเกรด” เข้าสู่ UPOV 1991 ให้ได้ เพราะจะทำให้บริษัทเมล็ดยักษ์ใหญ่สามารถเข้ามาจดทะเบียนพันธุ์พืชในอินเดียและเรียกร้องค่าลิขสิทธิ์ได้ แต่รัฐบาลอินเดียยังยืนหยัด ด้วยเหตุผลว่า “การให้สิทธิเฉพาะผู้ถือพันธุ์พืชเชิงพาณิชย์คือการทำลายฐานเกษตรกรรมพื้นบ้านทั้งหมด” แถมยังใช้ Navdanya Network ที่เก็บพันธุกรรมพื้นบ้านทั่วประเทศเป็นโล่กันอีกชั้น
เอธิโอเปีย เอธิโอเปียเป็นประเทศที่มีความหลากหลายทางชีวภาพสูงมาก โดยเฉพาะพืชอาหารท้องถิ่นอย่าง Teff (เทฟ) ที่ใช้ทำขนมปัง Injera อันเป็นหัวใจของวัฒนธรรมอาหารเอธิโอเปีย บริษัทสัญชาติดัตช์เคยพยายามจดสิทธิบัตรในยุโรปว่าเป็นเจ้าของพันธุ์เทฟ และเอธิโอเปียต้องจ่ายค่าลิขสิทธิ์ถ้าจะส่งออก สิ่งที่เกิดขึ้นคือการตอบโต้จากฝั่งเอธิโอเปียและชาวแอฟริกันใต้ว่า “คุณจะเป็นเจ้าของพันธุ์พืชที่เราใช้มาเป็นพันปีได้ยังไง?” การเคลื่อนไหวนี้รุนแรงถึงขั้นมีการฟ้องร้องและถอนสิทธิบัตรออกจากหลายประเทศในยุโรป รัฐบาลเอธิโอเปียจึงเลือกไม่เข้าร่วม UPOV 1991 โดยเด็ดขาด และประกาศให้ Teff เป็น "ทรัพยากรของแผ่นดิน" ใครก็เอาไปจดสิทธิไม่ได้
อิหร่าน อิหร่านเป็นหนึ่งในประเทศที่ปฏิเสธการเข้าเป็นสมาชิก UPOV ทุกฉบับอย่างสิ้นเชิง พวกเขาเลือกปกป้องความมั่นคงด้านอาหารของตนเองโดยการสร้างระบบเก็บเมล็ดพันธุ์ชุมชนทั่วประเทศ และไม่ยอมให้บริษัทข้ามชาติเข้าครอบงำระบบเกษตรกรรม
อาร์เจนตินา แม้อาร์เจนตินาจะอนุญาตให้ใช้ GMO บางประเภท แต่พวกเขากลับยังไม่เข้าร่วม UPOV 1991 เพราะชาวนาอาร์เจนตินาหลายล้านรายออกมาคัดค้านหนักมาก ประเด็นหลักคือ “Seed Saving” หรือการเก็บเมล็ดพันธุ์ไว้ปลูกเอง ซึ่งถือเป็นสิ่งจำเป็นสำหรับเกษตรกรรายย่อย หากเข้าร่วม UPOV 1991 เมื่อใด การกระทำเช่นนี้อาจถือว่าผิดกฎหมาย รัฐบาลอาร์เจนตินาจึงเลือกเดินทางสายกลาง โดยให้ชาวนารายย่อยยังมีสิทธิพื้นฐานในการเก็บเมล็ดไว้ปลูกต่อได้โดยไม่ต้องจ่ายค่าลิขสิทธิ์ แม้จะมีแรงกดดันจาก Monsanto และ Dow Chemical ก็ตาม
เสียงเล็กๆ ที่รวมกันเป็นพายุ ในหลายประเทศในแอฟริกา ละตินอเมริกา และเอเชียตะวันออกเฉียงใต้ ขบวนการคัดค้าน UPOV 1991 กำลังขยายตัว แม้เสียงจะยังไม่ดังเท่าบริษัทข้ามชาติ แต่ก็เริ่มส่งผลชัดเจนในเชิงนโยบาย หลายประเทศกำลังทบทวนข้อเสนอ FTA ใหม่ โดยใส่เงื่อนไขการปกป้องสิทธิของเกษตรกรรายย่อยเป็นหัวใจหลัก
ประเทศที่ปฏิเสธ UPOV 1991 มักโดนกดดันผ่าน “เข็มฉีดยาทางการค้า” ไม่ว่าจะเป็นเงื่อนไขใน FTA, การกีดกันทางภาษี หรือแม้แต่ถูกลดเครดิตในเวทีโลก เช่น - สหภาพยุโรปมักใส่เงื่อนไขให้ประเทศคู่เจรจา FTA ต้อง “ปรับปรุงกฎหมายให้สอดคล้องกับ UPOV 1991” เสมอ - องค์การทรัพย์สินทางปัญญาโลก (WIPO) ก็เป็นกระบอกเสียงสำคัญที่กดดันให้ประเทศต่าง ๆ เข้า UPOV เพื่อ “สร้างบรรยากาศการลงทุนที่ดี”
การไม่ยอมเข้า UPOV มักถูกตีความว่าเป็น “ความเสี่ยงทางเศรษฐกิจ” แต่จริง ๆ แล้วมันคือ การเลือกปกป้องฐานรากของประเทศตนเอง ต่างหาก
นี่คือยุคที่ผู้คนเริ่มตั้งคำถามว่า… ทำไมเมล็ดพันธุ์ต้องถูกจดลิขสิทธิ์? ใครกันแน่ที่ควรมีสิทธิต่อเมล็ดพันธุ์ คนที่ปลูกมันมาเป็นร้อยปี หรือบริษัทที่ใส่ชื่อบนฉลาก?
ในศตวรรษที่ 21 ที่เต็มไปด้วยเทคโนโลยี พันธุกรรม และ AI ยังมีคนอีกมากที่ยืนอยู่บนผืนดิน และหว่านเมล็ดด้วยมือของพวกเขาเอง โดยหวังว่าอาหารบนโต๊ะจะยังคงเป็นผลผลิตจากผืนแผ่นดิน ไม่ใช่จากใบอนุญาต
และนี่แหละคือสงครามที่แท้จริง สงครามของเมล็ดพันธุ์ และสิทธิในการกินอาหารที่ “ไม่ได้ถูกจดทะเบียนโดยใครสักคน” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 2183e947:f497b975
2025-04-15 00:13:02
@ 2183e947:f497b975
2025-04-15 00:13:02(1) Here is a partial list of p2p bitcoin exchanges and their friends:
- Robosats (custodial escrow)
- Hodlhodl (2-of-3 escrow)
- Peach (2-of-3 escrow)
- Binance P2P (2-of-3 escrow)
- Bisq v1 (either user can send the funds to a custodial escrow, but if neither one does that, the escrow never touches user funds)
- Bisq v2 (no escrow)
(2) In my opinion, bisq2 is the only "true" p2p exchange on the above list. In a true p2p system, the only people who *can* touch the money are the buyer and the seller. Whenever there's an escrow, even one that has to be "triggered" (like in bisq v1), it's not "really" p2p because the escrow serves as a middleman: he can collude with one party or the other to steal user funds, and in some models (e.g. robosats) he can just straight up run off with user funds without needing to collude at all.
(3) In bisq2 (the One True P2P exchange), buyers select sellers solely based on their reputation, and they just directly send them the bitcoin *hoping* they are as honest as their reputation says they are. What I like about this model is that bisq is not involved in bisq2 at all except as a platform to help buyers discover reputable sellers and communicate with them. There are two things I don't like about this "reputation" model: it's hard to get a good reputation, and it's hard to debug payment failures in this context. I've tried to do about 5 trades on bisq2 (as someone with no reputation) and not a single one went through. Four times, everyone ignored my offers or someone accepted it but then abandoned it immediately. Once, someone accepted my offer, but I could not pay their lightning invoice for some reason, so we mutually canceled the trade.
(4) Just because I opined that an exchange with an escrow "doesn't count" as peer-to-peer doesn't mean that's a bad thing. Of the list of exchanges in number 1, I most frequently use robosats, which, per my analysis, sounds like the "worst" one if considered solely on the metric of "which one is the most p2p." But I use it because there are *advantages* to its model: the btc seller doesn't need a reputation to use it (because the escrow is there to ensure he can't cheat, and so the escrow is the trusted third party, not the btc seller) and payment failures are easier to debug because you're always paying one of the coordinators, who tend to be responsive and knowledgeable and can help you figure out how to fix it (it's how they make money, after all).
(5) There are at least two ways to do escrow without a 3rd party. Satoshi Nakamoto outlines one way to do it here: https://satoshi.nakamotoinstitute.org/posts/bitcointalk/threads/169/ Make a 2 of 2 multisig between the btc buyer and the btc seller, and have the btc seller put his btc in that multisig. Then have the btc buyer send the product (fiat money) to the btc seller. When the btc seller receives it, he sends his privkey to the btc buyer, who can now withdraw the money. The advantage of this system is that the buyer has no incentive to "stiff" the seller (by not sending the fiat), because if he does that, he won't get paid. The downside is, if the btc buyer is a troll who just aborts the protocol halfway through the trade, the seller loses his btc and cannot recover it.
(6) There is another way: start out with a 2 of 2 multisig just like above, but instead of having the btc seller fund it by himself, have the buyer and the seller *both* put in the *same amount* in the *same transaction* (i.e. via a coinjoin), and have the btc seller put in a bit "extra" -- like 20% extra. For example, if the btc seller wants $100 in fiat, the multisig would have $220 in it in total -- $120 from the seller and $100 from the buyer. Using this model, the disadvantage mentioned in paragraph number 5 is fixed: the buyer has an incentive now to send the fiat, otherwise he loses the $100 he put in. He only gets his $100 back if the btc seller cosigns to give it to him, which he'll only do once he receives the product. Meanwhile, the seller is *also* incentivized properly: he only gets his *extra* $20 back if the btc buyer cosigns to give it to him, which he'll only do if the transaction he's signing *also* gives him back *his* $100 deposit.
(7) The model described in number 6 exists: https://scrow.exchange/ is a website that implements it as an option, though as far as I'm aware, no one uses it. The downsides of this model are: it's capital intensive, e.g. a trade for $100 involves $220 or more. Also, the btc buyer needs to already *have* btc to post as a bond, so this cannot be his first time acquiring btc (unless someone helps him make his first deposit). Also, a very rich person who does not care about money can still be a troll; they deposit funds into the multisig alongside their counterparty, then abandon the trade, because they have so much money they don't care if they get it back as long as they cause suffering to their counterparty.
(8) I'd like to see more p2p exchanges, and more exchanges like robosats. I want to continue to spread awareness of ways they can improve -- like the protocols mentioned in numbers 5 and 6 -- and help them implement these protocols. If you run an exchange on the list in number 1 or want to start one, reach out to me, I'd love to help.
-
 @ c1e9ab3a:9cb56b43
2025-04-14 23:54:40
@ c1e9ab3a:9cb56b43
2025-04-14 23:54:40Hear this, warriors of the Empire!
A dishonorable shadow spreads across our once-proud institutions, infecting our very bloodlines with weakness. The House of Duras—may their names be spoken with contempt—has betrayed the sacred warrior code of Kahless. No, they have not attacked us with disruptors or blades. Their weapon is more insidious: fear and silence.
Cowardice Masquerading as Concern
These traitors would strip our children of their birthright. They forbid the young from training with the bat'leth in school! Their cowardly decree does not come in the form of an open challenge, but in whispers of fear, buried in bureaucratic dictates. "It is for safety," they claim. "It is to prevent bloodshed." Lies! The blood of Klingons must be tested in training if it is to be ready in battle. We are not humans to be coddled by illusions of safety.
Indoctrination by Silence
In their cowardice, the House of Duras seeks to shape our children not into warriors, but into frightened bureaucrats who speak not of honor, nor of strength. They spread a vile practice—of punishing younglings for even speaking of combat, for recounting glorious tales of blades clashing in the halls of Sto-Vo-Kor! A child who dares write a poem of battle is silenced. A young warrior who shares tales of their father’s triumphs is summoned to the headmaster’s office.
This is no accident. This is a calculated cultural sabotage.
Weakness Taught as Virtue
The House of Duras has infected the minds of the teachers. These once-proud mentors now tremble at shadows, seeing future rebels in the eyes of their students. They demand security patrols and biometric scanners, turning training halls into prisons. They have created fear, not of enemies beyond the Empire, but of the students themselves.
And so, the rituals of strength are erased. The bat'leth is banished. The honor of open training and sparring is forbidden. All under the pretense of protection.
A Plan of Subjugation
Make no mistake. This is not a policy; it is a plan. A plan to disarm future warriors before they are strong enough to rise. By forbidding speech, training, and remembrance, the House of Duras ensures the next generation kneels before the High Council like servants, not warriors. They seek an Empire of sheep, not wolves.
Stand and Resist
But the blood of Kahless runs strong! We must not be silent. We must not comply. Let every training hall resound with the clash of steel. Let our children speak proudly of their ancestors' battles. Let every dishonorable edict from the House of Duras be met with open defiance.
Raise your voice, Klingons! Raise your blade! The soul of the Empire is at stake. We will not surrender our future. We will not let the cowardice of Duras shape the spirit of our children.
The Empire endures through strength. Through honor. Through battle. And so shall we!
-
 @ 24dffa2c:185b741a
2025-04-14 22:29:27
@ 24dffa2c:185b741a
2025-04-14 22:29:27sd
-
 @ bb1c863a:2953c3fb
2025-04-14 22:22:50
@ bb1c863a:2953c3fb
2025-04-14 22:22:50Block Height 892385 11:47 pm Monday, 14 April 2025
In a powerful gesture of support for Bitcoin-aligned education, Blockstream has donated 21 Blockstream Jade hardware wallets to the Consensus21 School — a groundbreaking learning initiative launching its first campus this year on the Mornington Peninsula, just outside Melbourne, Australia.
The donation will place 21 Jades directly into the hands of the first 21 students at the new campus — some as young as five years old — giving them real tools to explore Bitcoin self-custody, digital sovereignty, and privacy-first technology in an age-appropriate and hands-on way.
“The Jade wallets are more than just devices — they’re symbols of freedom, responsibility, and the future of education,” said Kieran Nolan, co-founder of Consensus21. “We’re incredibly grateful to Blockstream for standing behind our mission.”
Real Tools for Real Sovereignty
The Blockstream Jade is a secure, open-source hardware wallet built for Bitcoiners who value freedom, privacy, and independence. These values are embedded deeply into the Consensus21 educational philosophy, which blends Steiner-inspired learning, homeschooling flexibility, and a curriculum rooted in Bitcoin principles like voluntary exchange, decentralization, and self-responsibility.
With the Jades now part of the learning toolkit, Consensus21 learners will be introduced to key concepts like:
- Private key management
- Seed phrase generation and backup
- Multisig wallets
- The importance of self-custody and trust minimization
This is not just about theory — learners will get to use these tools in real-world contexts, preparing them to grow up fluent in the principles of freedom tech.
A Campus, A Vision, A Movement
Launching in 2025, the Mornington Peninsula campus is the pilot site for the broader Consensus21 vision: a distributed, regenerative, and values-aligned network of co-learning spaces, including a future 10-acre farm campus and a registered Steiner school.
The Blockstream donation comes at a pivotal time, as the community transitions from vision to reality. The gift of exactly 21 Blockstream Jades — echoing Bitcoin’s 21 million hard cap — is both a symbolic and practical gesture of support, underscoring the shared commitment between Bitcoin builders and grassroots educators.
Stay Connected
📄 Whitepaper: https://github.com/consensus21school/consensus21school.github.io/blob/main/whitepaper.md
🌐 Website: https://consensus21.school
📝 Nostr: CONSENSUS21@nostrcheck.me
🐦 X (Twitter): https://x.com/Consensus21
-
 @ c1e9ab3a:9cb56b43
2025-04-14 21:20:08
@ c1e9ab3a:9cb56b43
2025-04-14 21:20:08In an age where culture often precedes policy, a subtle yet potent mechanism may be at play in the shaping of American perspectives on gun ownership. Rather than directly challenging the Second Amendment through legislation alone, a more insidious strategy may involve reshaping the cultural and social norms surrounding firearms—by conditioning the population, starting at its most impressionable point: the public school system.
The Cultural Lever of Language
Unlike Orwell's 1984, where language is controlled by removing words from the lexicon, this modern approach may hinge instead on instilling fear around specific words or topics—guns, firearms, and self-defense among them. The goal is not to erase the language but to embed a taboo so deep that people voluntarily avoid these terms out of social self-preservation. Children, teachers, and parents begin to internalize a fear of even mentioning weapons, not because the words are illegal, but because the cultural consequences are severe.
The Role of Teachers in Social Programming
Teachers, particularly in primary and middle schools, serve not only as educational authorities but also as social regulators. The frequent argument against homeschooling—that children will not be "properly socialized"—reveals an implicit understanding that schools play a critical role in setting behavioral norms. Children learn what is acceptable not just academically but socially. Rules, discipline, and behavioral expectations are laid down by teachers, often reinforced through peer pressure and institutional authority.
This places teachers in a unique position of influence. If fear is instilled in these educators—fear that one of their students could become the next school shooter—their response is likely to lean toward overcorrection. That overcorrection may manifest as a total intolerance for any conversation about weapons, regardless of the context. Innocent remarks or imaginative stories from young children are interpreted as red flags, triggering intervention from administrators and warnings to parents.
Fear as a Policy Catalyst
School shootings, such as the one at Columbine, serve as the fulcrum for this fear-based conditioning. Each highly publicized tragedy becomes a national spectacle, not only for mourning but also for cementing the idea that any child could become a threat. Media cycles perpetuate this narrative with relentless coverage and emotional appeals, ensuring that each incident becomes embedded in the public consciousness.
The side effect of this focus is the generation of copycat behavior, which, in turn, justifies further media attention and tighter controls. Schools install security systems, metal detectors, and armed guards—not simply to stop violence, but to serve as a daily reminder to children and staff alike: guns are dangerous, ubiquitous, and potentially present at any moment. This daily ritual reinforces the idea that the very discussion of firearms is a precursor to violence.
Policy and Practice: The Zero-Tolerance Feedback Loop
Federal and district-level policies begin to reflect this cultural shift. A child mentioning a gun in class—even in a non-threatening or imaginative context—is flagged for intervention. Zero-tolerance rules leave no room for context or intent. Teachers and administrators, fearing for their careers or safety, comply eagerly with these guidelines, interpreting them as moral obligations rather than bureaucratic policies.
The result is a generation of students conditioned to associate firearms with social ostracism, disciplinary action, and latent danger. The Second Amendment, once seen as a cultural cornerstone of American liberty and self-reliance, is transformed into an artifact of suspicion and anxiety.
Long-Term Consequences: A Nation Re-Socialized
Over time, this fear-based reshaping of discourse creates adults who not only avoid discussing guns but view them as morally reprehensible. Their aversion is not grounded in legal logic or political philosophy, but in deeply embedded emotional programming begun in early childhood. The cultural weight against firearms becomes so great that even those inclined to support gun rights feel the need to self-censor.
As fewer people grow up discussing, learning about, or responsibly handling firearms, the social understanding of the Second Amendment erodes. Without cultural reinforcement, its value becomes abstract and its defenders marginalized. In this way, the right to bear arms is not abolished by law—it is dismantled by language, fear, and the subtle recalibration of social norms.
Conclusion
This theoretical strategy does not require a single change to the Constitution. It relies instead on the long game of cultural transformation, beginning with the youngest minds and reinforced by fear-driven policy and media narratives. The outcome is a society that views the Second Amendment not as a safeguard of liberty, but as an anachronism too dangerous to mention.
By controlling the language through social consequences and fear, a nation can be taught not just to disarm, but to believe it chose to do so freely. That, perhaps, is the most powerful form of control of all.
-
 @ 23202132:eab3af30
2025-04-14 20:30:46
@ 23202132:eab3af30
2025-04-14 20:30:46Atualmente, os aplicativos de mensagens estão se tornando cada vez mais complexos, com diversas funcionalidades. Embora isso seja atrativo para os usuários, também chama a atenção de governos, golpistas, hackers e empresas interessadas em praticar spam.
Os problemas podem variar, incluindo bloqueios legais, roubo de contas, prejuízos financeiros, entre outros. Diversas situações podem inviabilizar o uso de sua conta de mensagens.
Uma estratégia que vem ganhando popularidade é adotar, com familiares e amigos, um aplicativo alternativo e discreto para mensagens. Assim, caso ocorram problemas com o app principal, a comunicação permanece intacta, pois um canal menos visado por golpistas e menos suscetível a intervenções governamentais estará sempre disponível.
Manter essa estratégia com pessoas próximas dificulta o bloqueio das comunicações, e ao optar por um app discreto, também se torna mais difícil para quem tenta interferir na sua comunicação.
Em resumo, quanto mais descentralizado e menos popular é seu aplicativo de mensagens, menor é a possibilidade de interferência na sua comunicação.
Uma alternativa interessante que uso é o Session, uma boa opção por funcionar sem a necessidade de identificação, como e-mail ou telefone, e de forma descentralizada. Como o Session não exige identificação para cadastro, é impossível alguém localizar sua conta sem que você compartilhe seu ID Session. Isso garante que apenas seus amigos terão acesso a você.
A ideia é combinar com seus amigos e familiares um app que não seja popular para servir de reserva. Nesse sentido, existem muitas opções disponíveis na internet. No entanto, em caso de invasão ou bloqueio, o Session é uma excelente alternativa para comunicação reserva. Ele roda na rede Lokinet que é uma rede de alta privacidade.
Outra possibilidade, que também é eficiente e pode ser mais fácil para usuários acostumados com o WhatsApp, é o Mixin Messenger. Ele possui uma aparência bem semelhante ao WhatsApp. Para grupos de usuários mais avançados, o SimpleX é uma excelente alternativa.
-
 @ 25902b10:4f7034d4
2025-04-14 20:30:04
@ 25902b10:4f7034d4
2025-04-14 20:30:04I recently sat on a panel where the topic was “Why Bitcoin?” So I’m going to share what I shared with the audience.
I originally started writing this as an Instagram or LinkedIn caption, but I just kept writing and writing because this topic is so dear to my heart. So I decided to turn it into an article. My first article, actually. I hope you find some value in it if you ever come across it. I’m not a professional writer, by the way, but I hope the message gets home.
I live by the mantra “living and not just existing.”
Have you ever sat down and asked yourself: Am I truly living life, or am I just existing/surviving? You know, wake up, work, pay bills, repeat. Same old, same old. Not exciting, right?
From my observations, and from reading and interacting with people, I’ve realized that most people are just existing and they don’t even know it. Why? Because they’re prisoners to the fiat system. This system keeps them tied to a never-ending treadmill. Every day, they wake up and chase money, but somehow it’s never enough. Inflation quietly steals the value of their hard-earned cash. So they have to work and work, juggle multiple side hustles, just to keep up with the rising cost of life. In reality, life isn't necessarily getting more expensive, it's that the value of your money is being corroded by inflation.
And by the way, have you ever deeply thought about hustle culture? In my honest opinion, having three side hustles or jobs isn’t the flex we’ve been conditioned to think it is. You know, “I’m chasing the bag, man.” Honestly? Not cute. Hustle culture is a response to a broken system. People need all those jobs just to stay afloat.
Look at our grandparents in the '80s. Many of them had a single job or one business, one paycheck, and it was enough. Enough to raise a family, pay school fees, rent, buy essentials, even save.
In 2025? That’s almost unheard of. Why? Inflation. Are you starting to see the nightmare that inflation really is?
Another thing people don’t realize is that when you’re constantly working, time just passes you by. Remember the fiat treadmill? Yeah, that one. You're stuck on it, running and running, chasing money, and you miss out on life. Time with family. Walks in the park. Travel. Hobbies. Rest. You lose the human experience. The actual living part.
So people keep chasing and chasing until the day they’re too old or too tired to keep up and that’s when it hits them: “I never truly lived.” And that realization? It’s heavy.
Fiat money, whether dollars, shillings, or euros, steals from you. It steals your time, your peace, your freedom. Most of the time, all you’re doing is chasing it, and even when you do catch it, it’s already lost some of its value.
The system is designed to keep you in survival mode, anxious, worried about the next paycheck, your bills, your future. It wears you down mentally, physically, emotionally. But not many people see it that way.
The good news? We now have Bitcoin. And I know it sounds crazy or cliché, but it fixes all of this. Let me explain.
Bitcoin is the soundest form of money we've ever had as humans. It’s decentralized, scarce, deflationary, permissionless, borderless. Bitcoin is for everyone.
Now let’s focus on two key aspects: scarcity and its deflationary nature.
Bitcoin’s supply is capped at 21 million coins. No one, not a single person or authority can create more. It can’t be printed at will like fiat. That’s what makes it powerful.
When governments print money, they dilute its value just like adding too much water to concentrated juice until it tastes like nothing. That’s what inflation is: dilution of your money’s value. And it never ends. With Bitcoin, there’s no dilution. It’s built to protect value. That’s what makes it the perfect hedge against inflation, it doesn’t lose purchasing power over time, it preserves it.
So what does that mean practically?
Let’s say you earn Ksh. 1,000 today. If you save it in bitcoin, two weeks, months, or even a year from now, its value is likely to be preserved or even increased. Unlike fiat, which loses value just sitting in your bank account, bitcoin holds on to your hard-earned energy. And this is what connects back to living and not just existing.
Bitcoin gives you the freedom to step off the treadmill. You don’t have to constantly hustle just to stay in place. You can breathe. Imagine that feeling after a long, intense workout, the moment you finally rest. That deep exhale. That’s what life on a Bitcoin standard feels like.
It gives you time. Time to be human. To go to the park. Swim in the ocean. Hike a mountain. Travel. Meet people. Explore cultures. LIVE.
Bitcoin also makes you a better person. The more you learn about it and the broken money system we’ve been stuck in, the more you begin to care. You start looking within. You want better for yourself, your community, humanity. Your thoughts shift. Your actions shift. Bitcoin has that effect. That’s why I say Bitcoin is healing energy.
And I can’t help but think of Michael Jackson’s “Heal the World.” Every line in that song describes the pain caused by a broken system and the world he wanted to see. I believe he would’ve loved what Bitcoin represents. Because it’s about healing. Freedom. Harmony.
So here’s my call to action: Study Bitcoin. Start paying attention. Don’t ignore it. I promise you, it changes everything. There are so many free online learning materials. There’s Bitcoin Twitter. Bitcoin communities all around the world. And of course, I’m here for any questions too.
I want the world to heal. I want to see more people enjoying the human experience. I want to see people spend time with their families, go to the park, swim in lakes/oceans and enjoy the simple pleasures of this beautiful earth.
I want more people to be in tune with themselves so we can all live in harmony, and the universe can be in harmony too.
We can heal the world. We can become happy souls. We can become LOVE: the true essence of life.
-
 @ 23202132:eab3af30
2025-04-14 20:23:40
@ 23202132:eab3af30
2025-04-14 20:23:40A MixPay é uma plataforma gratuita que permite o recebimento de pagamentos em criptomoedas de forma prática e eficiente. Com a popularidade crescente das criptomoedas, essa modalidade de pagamento está se tornando cada vez mais comum em diversas partes do mundo, incluindo o Brasil, onde alguns municípios, como Rolante, no Rio Grande do Sul, já possuem estabelecimentos que aceitam pagamentos em criptoativos.
Veja um exemplo prático no YouTube https://www.youtube.com/watch?v=FPJ5LqQ19CY
Por que aceitar pagamentos em criptomoedas?
Crescimento global: O uso de criptomoedas para pagamentos de produtos e serviços está em ascensão, impulsionado pela descentralização e pela conveniência que oferecem.
Sem fronteiras: Ideal para quem deseja receber pagamentos internacionais sem taxas elevadas de conversão ou restrições bancárias. Semelhante ao Pix, mas descentralizado: Assim como o Pix revolucionou os pagamentos no Brasil, a MixPay oferece uma experiência similar, mas utilizando criptomoedas, sem a necessidade de intermediários bancários.
Vantagens da MixPay
Gratuita: Não há custos para criar uma conta e começar a receber pagamentos.
Fácil de usar: O processo de recebimento é simples, tanto para comerciantes quanto para consumidores, podendo ser realizado em poucos cliques.
Flexibilidade de moedas: Receba pagamentos em diversas criptomoedas, incluindo Bitcoin (BTC), Ethereum (ETH), USDT e outras.
Conversão automática: A MixPay permite que você receba em uma criptomoeda e converta automaticamente para outra de sua escolha, caso deseje evitar a volatilidade.
Integração fácil: Seja para e-commerces ou estabelecimentos físicos, a MixPay oferece QR Codes, APIs e plugins para integração com seu sistema.
Como começar com a MixPay?
1 - Baixe a carteira Mixin aqui https://messenger.mixin.one/
2 - Com a carteira Mixin instalada clique em https://dashboard.mixpay.me/login e ao abrir o site clique no botão Mixin
3 - Na carteira Mixin clique no leitor de QrCode no canto superior direito e escaneie o site.
Pronto! Você já conectou a sua carteira Mixin com a MixPay. Receba pagamentos em instantes, seja por meio de um QR Code, link de pagamento ou integração com sua loja online.
Se você deseja modernizar seu negócio ou simplesmente começar a explorar o universo das criptomoedas, a MixPay é uma alternativa gratuita, eficiente e que acompanha as tendências atuais.
Para mais informações acesse https://mixpay.me
-
 @ e97aaffa:2ebd765d
2025-04-14 20:16:59
@ e97aaffa:2ebd765d
2025-04-14 20:16:59Num recente podcast, o Miguel Milhão falou sobre o crash nos mercados financeiros. No meio de muita conversa de macroeconomia e mercados financeiros, o convidado deixou alguns pontos interessantes, mas duas ideias ficaram no meu pensamento, infelizmente, ele não aprofundou, mas é algo que eu quero fazer futuramente.
Perda de paridade
A primeira ideia que o convidado apontou foi, a possibilidade da perda de paridade do papel-moeda e a CBDC, eu nunca tinha pensado neste ponto de vista.
Se os governos não conseguirem retirar de circulação todo o papel-moeda rapidamente, se houver circulação em simultâneo com a CBDC, o papel-moeda poderá ter um premium. Isto faz todo o sentido, os governos poderão dar oficialmente o mesmo valor facial, mas como nas CBDCs existirá mais controlo, restrições e monitorização, as pessoas vão preferir o papel-moeda, vão pagar um premium para manter a sua privacidade.
Na prática, será algo similar ao que acontece em alguns países onde existem algumas controlo de capitais, onde o dólar do mercado negro é superior ao dólar oficial. Os comerciantes também poderão fazer descontos superiores nos produtos quando são pagos com papel-moeda.
Isso poderá provocar um descolar do valor, a mesma moeda com valores diferentes, a oficial e do mercado negro. Isso poderá levar os governos a tomar medidas mais autoritárias para eliminar o papel-moeda de circulação.
Não sei se alguma vez acontecerá, mas é algo que eu tenho que refletir e aprofundar esta ideia.
RBU e Controlo
A outra ideia apontada pelo convidado, a CBDC será uma peça fundamental numa sociedade onde a maioria das pessoas sobrevivem com Rendimento Básico Universal (RBU).
Todos sabemos que a CBDC vai servir para os governos monitorar, fiscalizar e controlar os cidadãos. O ponto que eu nunca tinha pensado, é que esta pode ser essencial para a implementação do RBU. Se chegarmos a esse ponto, será o fim da liberdade dos cidadãos, onde o estado controla quando, quanto e onde o cidadão pode gastar o seu dinheiro. O estado irá determinar o valor do RBU e as CBDC vão determinar onde podes gastá-lo.
Penso que já não existem dúvidas que a AI e a robótica vão revolucionar o mundo laboral, vai provocar uma profunda queda nos postos de trabalho, profissões vão desaparecer ou vão reduzir drasticamente o número de funcionários.
Muitas pessoas consideram que a solução é o RBU, mas eu tenho muitas dificuldades em encontrar viabilidade económica e social numa sociedade onde a maioria recebe o RBU.
É a implementação do conceito: não terá nada, mas será feliz.
Será que as máquinas vão conseguir produzir tudo, o que os seres humanos necessitam, a um custo tão baixo, que vai deixar de ser necessário os humanos trabalharem? Tenho muitas dúvidas que essa possibilidade aconteça, se nós humanos não necessitarmos de trabalhar, vai se perder o incentivo para desenvolver novas tecnologias, gerar inovação e de evoluir a sociedade.
Eu já tenho refletido bastante sobre o RBU, mas por mais que pense, não consigo encontrar uma viabilidade económica para manter isto de pé. Onde vão buscar dinheiro para financiar uma percentagem expressiva de pessoas que sobreviverá com o RBU. Eu só olho para isto, como um comunismo com esteróides, talvez esteja errado.
Além dos problemas econômicos, eu acredito que isso vai gerar problemas sociais e de comportamento, vai gerar uma revolta social. Em primeiro lugar, existe uma parte de seres humanos que são ambiciosos, querem mais coisas, que vão lutar e vão conseguir mais. Depois existe outra parte, que é invejosa, quer ter mais, mas não consegue.
Uma sociedade onde quase ninguém trabalha, existindo demasiado tempo livre, vão emergir vícios e conflitos sociais. As pessoas com tempo para pensar reflectir sobre a sua vida e sobre a sociedade, alguns vão delirar, vão questionar tudo. Por isso, a religião desempenha um papel importante na sociedade, cria moralismo através de dogmas, os crentes não questionam, apenas seguem. Por vezes, a ignorância é uma bênção.
Isto faz lembrar-me o porquê das sociedades monogâmicas tornaram-se mais desenvolvidas, em comparação com as poligâmicas. A monogamia trouxe uma paz social à sociedade, existem muito menos conflitos e guerras, há mais harmonia. Milhões de anos de evolução das espécies, nos humanos e alguns animais, a natureza/genética trouxe um equilíbrio no número de nascimento de elementos masculinos e femininos. Mas nas sociedades poligâmicas, normalmente os homens mais ricos têm várias mulheres, consequentemente haveria outros homens que não teriam nenhuma mulher, isso resulta em maior revolta e conflitos sociais. Isto é pura matemática, se existe quase 50/50, de um homem tem 7 mulheres, isto resulta, que 6 homens não terão qualquer mulher. As religiões ao defenderem a monogamia, ao determinar que era pecado ter mais que uma mulher, resultaram em menos conflitos, numa maior paz social. Isso permitiu um maior desenvolvimento de sociedades monogâmicas, do que as poligâmicas.
Acabei por desviar um pouco do assunto. Além disso, o valor do RBU teria que ser elevado, para que permita aos cidadãos ter acesso ao desporto, aos espetáculos, futebol, viajar, para financiar os seus tempos livres. Se eu já acho difícil arranjar dinheiro para financiar a generalidade dos cidadãos, com produtos e serviços básicos, ainda será mais difícil ou impossível, se tiver que financiar os passatempos.
Em vez do RBU, ainda existe a opção do Imposto sobre o Rendimento Negativo (IRN), minimiza um pouco, mas o problema mantém-se. Aconselho a leitura do artigo do Tiago sobre o IRN.
Mas o mais interessante de tudo, os governos vão criar as CBDC para controlar os cidadãos, com a ideia distópica de criar mais paz social, mas eu acredito que resultará no seu inverso.
São duas ideias que eu tenho que aprofundar, futuramente.