-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
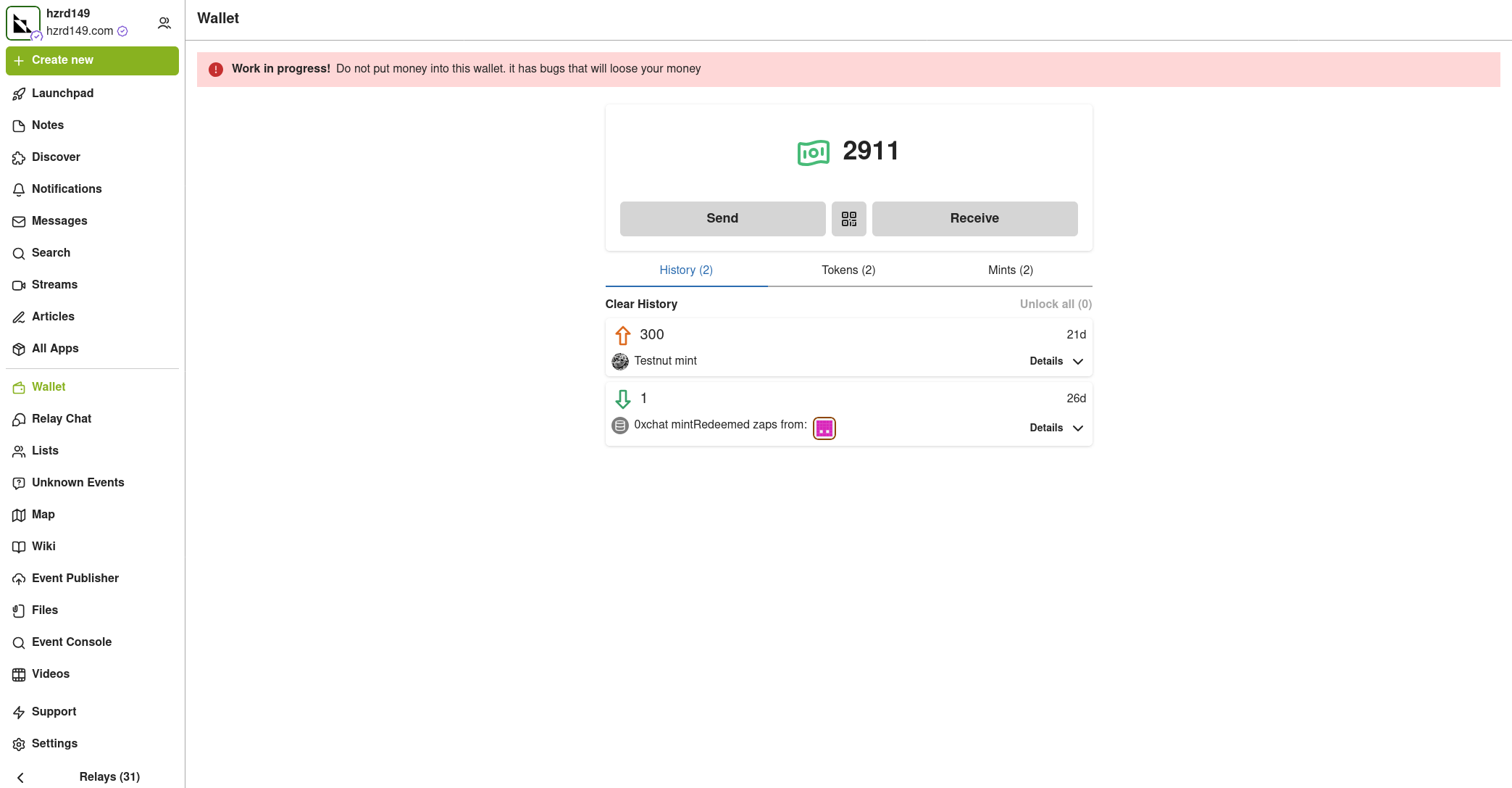
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
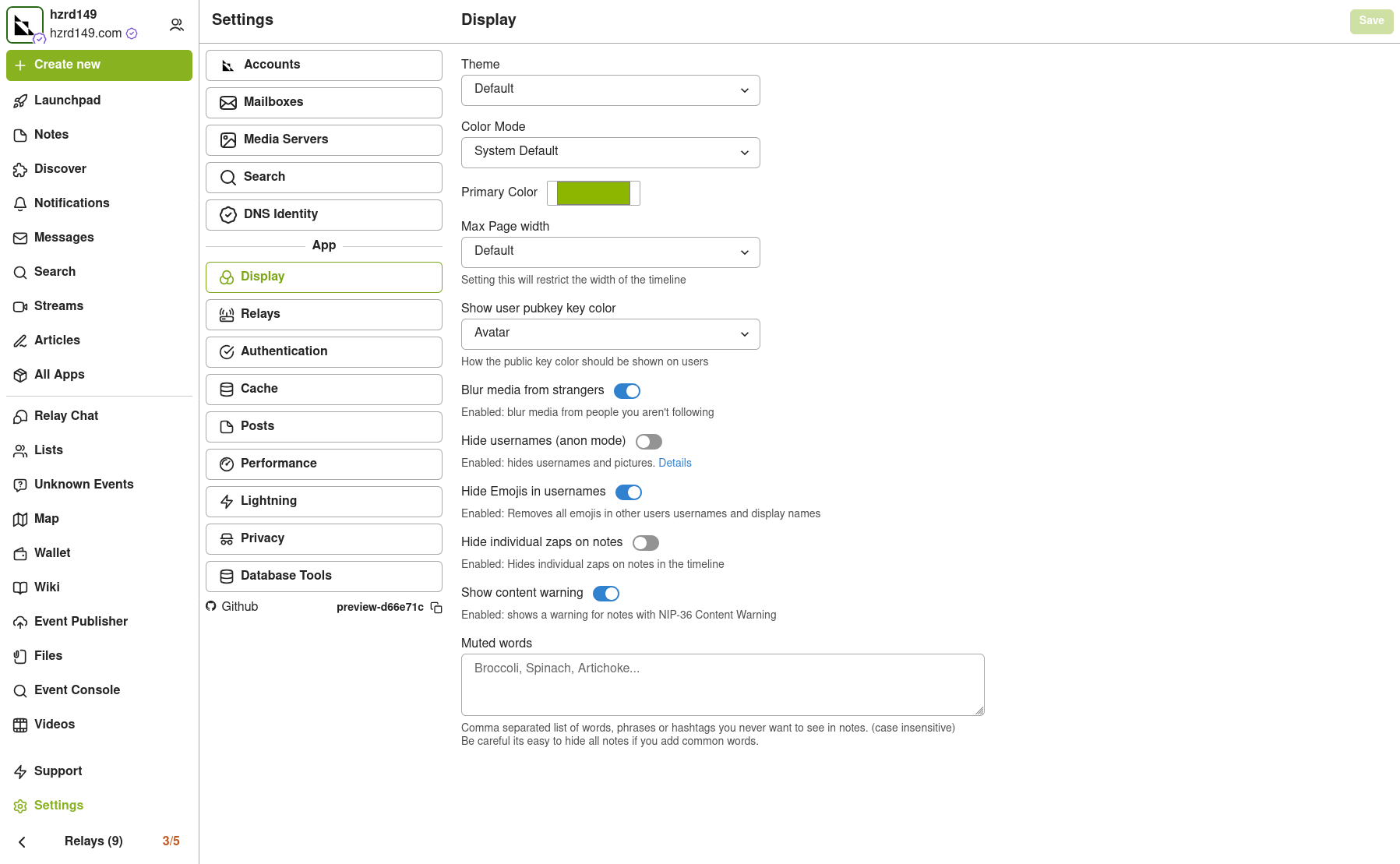
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-09 13:25:40
@ 5d4b6c8d:8a1c1ee3
2025-05-09 13:25:40The second round of the NBA Playoffs is historically weird. We'll try to figure out what's going wrong for all three of the presumed contenders. Which of the other East teams need to be considered contenders now? With how bad the Warriors look without Steph (just how underrated is he?), do the Warriors still have any chance?
In Blok'd Shots, we'll talk about the NHL Star who got traded midseason and then beat his former team in the playoffs.
There was a big trade in the NFL. Plus, @grayruby wants to start a media beef with Colin Cowherd.
The MLB introduced a new stat. I have no idea what it is, but I'm looking forward to trying to understand it live on air.
And, of course, lots of contest and betting updates.
What do you want us to talk about?
originally posted at https://stacker.news/items/975474
-
 @ 078d6670:56049f0c
2025-05-09 13:22:26
@ 078d6670:56049f0c
2025-05-09 13:22:26It was a dark and stormy night. It had to be: Weather had been fired. If they were working for him he would have fired them, but that is just embarrassed arrogance talking. He remembers standing in the middle of his office, his trashed office. It looked like a hurricane had hit it, or vagrants had been living in it for years, nothing of value was left intact. Monitors were shattered on the floor, couches were covered in debris. There was evidence of food and magazine pages in every gaze space. His supervisor, his name escaped him, was grey with anger. “Explain this!” he had shouted with a tremble, but he couldn’t. Every time he tried to think of the events of the day he met a dazzling white blankness.
He was escorted, handcuffed, to a room by two security guards with his supervisor trailing them. Weather felt humiliated and frustrated, but he didn’t know why. He sat, shivering slightly, in a low-lit conference room he had never seen before. Actually, he doesn’t remember any windows or any specific light source, just a haze of shadows. The big boss is sitting opposite him, looking haggard and white as a sun-bleached shell. His supervisor was sitting on his right looking equally haggard and even depressed. They appeared genuine and he knew it was bad news for him.
“You’ve embarrassed this company! There is even a chance you have ruined us all and you have the audacity to sit there and pretend that you can’t remember a thing!”
He knew there was no point in arguing, he had no ideas with which to make up any argument. He sat staring into space.
“At least, give us a story. Tell us how bored you were and tried to create your own weather system by running around the room swinging the fan around like a sugar mad teenager!”
He couldn’t even clear his throat. He couldn’t lift his eyes to meet theirs. He knew his career was over and they were fearful all their ideals had crashed irreparably. He stared into space at the globe standing in the middle of the table. The more he stared at it the more he realized that it seemed to have an atmosphere around it. There were clouds covering patches of the earth. He didn’t dare bring their attention to it. The only memories he could dredge up seemed like dreams, and they’re hardly constitute a defence.
He looked up at their faces finally, surprised to see more alarm than anger, like they were actually afraid of him. They both stood up suddenly, wanting to get out the room as quickly as possible.
“You have brought Global Sky Incorporated into disrepute. You’ve embarrassed us. You have possibly ruined hundreds of careers here! We never want to see you again! You are never to come within a hundred metres of this building. You can never use your research ever again, it never happened. Everything you have ever written will be classified and restricted until you are dead!” The big boss was shaking wild, Weather was grateful for the security guards that hurled him out of his chair and marched him out of the building.
The afternoon sky had been a deathly grey. It had occurred to him but now he was a little shocked at how much control they had over the weather, maybe it was a good thing that he had been fired, but probably a bad thing as they would certainly make worse mistakes than him, whatever he might have done. He was confused, not sure if he been fired for trashing his office or for state of the weather. About the weird weather he has no idea, all he can remember is a dazzling blank whiteness, and that is hardly a memory.
He couldn’t face going directly home, jumped on public transport travelling on tracks laid down on old unused highways and headed for the city beach, or what passed for a beach. He sat on a concrete bench gazing across the grey sand at the shimmering waves. They weren’t shimmering because of the sparkling sunlight, but the contaminates in the water. But still it was tranquil enough. He tried to think about his day, but couldn’t get past the white blankness, everything else before that was like a postcard from someone else’s holiday, and they looked like movies he might have seen. He has a framed vision of himself in his office with office supplies flying around him without touching him. Clearly, as they weren’t touching him, it had nothing to do with his behaviour. He is a victim here. It wasn’t his fault, the world was changing and the powers that be wanted more control. It seems like Global Weather Incorporated (GWI) lost control of their equipment and need a fall guy, they didn’t need him anymore. Squeezed his brain for the algorithms, then threw him onto the streets. He was nothing without his research, it’s all he had done his entire life. He would have to pursue it, but that would as useful as talking to a brick wall, the world was less transparent; government, science and advertising companies had a law of their own and a police force to uphold them.
He believed in good and the unveiling of truth. He had a romantic connection to the idea that truth grew in people’s hearts that everyone wanted the best for everyone else, no matter what skin colour, car colour they had, or star sign they were born under. Everybody wanted peace, a roof over their heads and food in their bellies; and wanted these things for their neighbours too. If only his neighbours had the same beliefs.
It was late afternoon now. He could tell by the slight luminosity of the grey clouds near the horizon, close to a cloudless gap, a slit above the horizon through which the sun could bid its final farewell to the day. He was in no mood for a sunset minute. He picked his bum off the bench, dusted it off and began his journey home, not wanting to be left in the dark in the city, opportune prey for corrupt cops. Everyone was coming out of the offices, beginning the big commute home. Car pools had reshaped their cars to fit more people in, and many climbed on to the reinvented trams, sitting if they were lucky, holding onto ceiling straps if they were unlucky like him. Couples sat together staring into each other’s eyes, friends joked and discussed their office politics. He hated the commute back and forth from work, it made him feel alone, desperate and unwanted. There had been no office politics for him, it was just him and his mostly silent supervisor.
The sky was struck red, a wound inflicted on the sky, it bleed for a minute then all went dark. Reality shuddered as it returned to him, this would be his last commute along this route. He was without a job; his recently regained self-esteem was destroyed. At the end of university he had wondered if he had a career anywhere, if his self-inflicted social isolation had been worth it and GWI had lifted him out of academic gutter and placed him on a pedestal. And now he was turfed out like a partly cloudy day from a child’s memory, flicked off like an ant off a picnic blanket.
Litter was being chased up and down the aisle, wrapping around legs and trying to hide from the wind amongst commuters’ bags. He didn’t notice that the commuters were becoming concerned about the weather, heads turned to look outside where the clouds were blacker than night. Wind has beating on windows, knocking on doors trying to escape from itself. Loose objects were starting to drift.
“Puck, I’m so stupid!” Weather lamented aloud as a flash of lightning brightened the dusk for a second. He should have protected his research, patented it in his own name. Stupidly, he had thought he would be with GWI for the rest of his life. He had given his life over to GWI and they had thrown it away for an office in disarray. It might have looked like an unnatural disaster, but they could have at least let him evaluate their equipment to check for systems failure. Why he hadn’t opened his mouth and flung accusations back at them? Probably because they had looked angrier than he could possibly have gotten faced with a memory of shimmering blankness.
The weather was surreal, he casually noted it as something GWI would have to correct, something existing outside his present unemployed reality, their problem. His cellphone’s classic “Thunderstuck” ringtone charged the air.
“What’s happening with the weather, dude? I thought I read in the paper that it was supposed to be sunny skies and calm seas. I wanted to go for an evening dive at Devil’s.”
“I’ve no idea, I’ve been fired,” he managed to say calmly before he hung up.
“It’s not my responsibility,” he thought to himself and promptly switched his phone off. He had given his private cellphone number to a few select acquaintances he had tried to impress when he had just got his ‘prestigious’ job. He thought he might finally be able to get his social life out of his house by sharing information with people he had met in supermarkets, recognizing their faces from university. They were jocks obsessed about the weather for their hedonistic lifestyles and they had never invited him out, only phoning to find out about the weather.
He jumped off at his usual stop and leaned into the wind watching his feet moving past one another, his mind seething at the injustice of not having a fair trial where they showed him evidence of him been directly involved in the trashing of his office. He could only remember standing in the middle of it and his office revolving around him, but that was only a flash, there is nothing before that except the facts. Him working on algorithms of weather activation, them tinkering with the clouds. They were practically at the end of their testing, their final live weather event before taking on the whole world’s weather, he knows that, but everyday was still just the same as every other day, him at the computer, them throwing lightning bolts. “Puck! I should’ve challenged them,” he shouted into the howling wind at GSI with all the frustration of his past mistakes. But his voice was lost into the atmosphere.
-
 @ 9223d2fa:b57e3de7
2025-05-09 13:11:51
@ 9223d2fa:b57e3de7
2025-05-09 13:11:515,071 steps
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 7459d333:f207289b
2025-05-09 13:09:21
@ 7459d333:f207289b
2025-05-09 13:09:21originally posted at https://stacker.news/items/975470
-
 @ 5b730fac:9e746e2a
2025-05-09 09:30:54
@ 5b730fac:9e746e2a
2025-05-09 09:30:54Test Combinations for Janitor Module
Initial Scenarios
| Channel | Push to Branch | Previous Installation Method | NIP94 Event ID Updated as Expected | New Update Installed as Expected | Test Passed | | ----------------------------------- | ----------------- | ---------------------------- | ---------------------------------- | -------------------------------- | -------------------------------------------------------------------------------------------------------------------------------- | | dev | Already Installed | Manual | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdp4xvmnvdpkpctkgk | | dev | Already Installed | Automatic | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdfex5unzvfcfywh0x | | deleted config files, first install | Already installed | Manual | yes | yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzwpnxq6rvdp59d83mz |Additional Scenarios from git diff Analysis
| Channel | Push to Branch | Version Format | NIP94EventID State | Expected Outcome | Test Passed | | -------------- | ----------------- | ------------------------ | ------------------ | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | | dev | New Branch | branch-commit_count-hash | known | Don't update, because the currently installed branch is different | Yes
The following package was not installed since it was on a different branch:
https://github.com/OpenTollGate/tollgate-module-basic-go/actions/runs/14909573498/job/41880411207 | | stable | main | version_number | known | Update Successfully | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnsvpk8yer2wphat7h6a | | dev | Already Installed | branch-commit_count-hash | known | Update Successfully if new commits | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdfex5unzvfcfywh0x | | dev | Already Installed | branch-commit_count-hash | unknown | Update Successfully if new commits | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdp4xvmnvdpkpctkgk | | stable | main | version_number | unknown | Update if version number is higher, irrespective of branch name, and NIP94 eventID | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnwwfex56nsdfjxmla8c | | config deleted | main | version_number | config deleted | Default pubkey and stable channel are set in config files, the new tag is downloaded and installed. However, the new NIP94 event must be generated after the new config files were created with default timestamps. | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnsv3hxycnsdfj3ttspu
Users who delete their config files might temporarily be one version behind the latest due to a lack of timestamp information. | -
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 5b730fac:9e746e2a
2025-05-09 09:25:59
@ 5b730fac:9e746e2a
2025-05-09 09:25:59Currently on
v0.0.4:root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.4Stop the janitor:
root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactiveTest update with deleted config files
Trigger new version:
c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git push origin v0.0.5 Total 0 (delta 0), reused 0 (delta 0), pack-reused 0 To https://github.com/c03rad0r/test-stable-release-channel.git * [new tag] v0.0.5 -> v0.0.5Delete the config files:
root@OpenWrt:/tmp# rm /etc/tollgate/config.json /etc/tollgate/install.json root@OpenWrt:/tmp# ls /etc/tollgate/config.json /etc/tollgate/install.json ls: /etc/tollgate/config.json: No such file or directory ls: /etc/tollgate/install.json: No such file or directoryStart janitor again:
root@OpenWrt:/tmp# service tollgate-basic start root@OpenWrt:/tmp# service tollgate-basic status runningTrusted maintainer is wrong:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" } root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781145 }Fixed trusted maintainer and restarted service. Now it updates:
Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Started the timer Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:45 2025 daemon.info tollgate-basic[8705]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:55 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:55.064780 Timeout reached, checking for new versions Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.5] Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Newer package version available: v0.0.5 Fri May 9 09:01:55 2025 daemon.info tollgate-basic[8705]: Downloading package from https://blossom.swissdash.site/af1c7b75440859d8a3ee93e0612b77e8ce1abc3496f580e72c969032395b2c66.ipk to /tmp/af1c7b75440859d8a3ee93e0612b77e8ce1abc3496f580e72c969032395b2c66.ipk Fri May 9 09:01:56 2025 daemon.info tollgate-basic[8705]: Package downloaded successfully to /tmp/ Fri May 9 09:01:56 2025 daemon.info tollgate-basic[8705]: New package version is ready to be installed by cronjob Fri May 9 09:01:56 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:56.845394 Verifying package checksum Fri May 9 09:01:56 2025 daemon.err tollgate-basic[8705]: 2025/05/09 09:01:56.854767 Package checksum verified successfullyVersion was updated correctly:
root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.5Try again without manually setting maintainer
v0.0.5has the test maintainer set by default:c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git diff v0.0.4 diff --git a/src/config_manager/config_manager.go b/src/config_manager/config_manager.go index 92d9f28..398d2da 100644 --- a/src/config_manager/config_manager.go +++ b/src/config_manager/config_manager.go @@ -400,7 +400,7 @@ func (cm *ConfigManager) EnsureDefaultConfig() (*Config, error) { "wss://relay.tollgate.me", }, TrustedMaintainers: []string{ - "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", + "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", }, FieldsToBeReviewed: []string{ "price_per_minute",v0.0.5is currently installed:root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.5Stop the service:
root@OpenWrt:~# service tollgate-basic stop root@OpenWrt:~# service tollgate-basic status inactiveTrigger a new build:
{ "id": "98f5e850f3aff389dd0591fe16f13738970bed1cbcc240f20f09d50e482fe707", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746781775, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "ox", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.6" ], [ "release_channel", "stable" ] ] }Delete config files and start janitor:
root@OpenWrt:~# rm /etc/tollgate/config.json /etc/tollgate/install.json root@OpenWrt:~# ls /etc/tollgate/config.json /etc/tollgate/install.json ls: /etc/tollgate/config.json: No such file or directory ls: /etc/tollgate/install.json: No such file or directoryStarted service:
root@OpenWrt:~# service tollgate-basic status inactive root@OpenWrt:~# service tollgate-basic start root@OpenWrt:~# service tollgate-basic status runningConfig files set successfully:
root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" } root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781946 }Not picking up new version. Perhaps due to default timestamp:
root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746781946 }We only consider the incoming event in
janitor.goif the events timestamp is greater than that of the config file:timestampConfig, err := configManager.GetTimestamp() if err != nil { log.Printf("Error getting timestamp: %v", err) continue } if timestamp > timestampConfig { rightTimeKeys = append(rightTimeKeys, key) }Re-ran the workflow to generate the event again with a newer timestamp:
{ "id": "d30f92cdacf453bede2bd36d62231fc40b226cc183239f5daf724829d81bd192", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746782339, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "ox", "700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.6" ], [ "release_channel", "stable" ] ] }Indeed, that was the issue:
root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.6Unfortunately, we can't do much about it, because all the more relevant timestamps were deleted when the config file was deleted. At-least we have this default timestamp to fall back on. Considering this test successful..
New config files:
root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "98f5e850f3aff389dd0591fe16f13738970bed1cbcc240f20f09d50e482fe707" } root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/700bfb2e1788d8f42c89492562e8503979761ef7d07b7a412f6d9334d7f24f6f.ipk", "ip_address_randomized": "192.168.70.1", "install_time": 1746782401, "download_time": 1746782354, "release_channel": "stable", "ensure_default_timestamp": 1746781946, "update_path": null } -
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ a0c34d34:fef39af1
2025-05-09 09:20:28
@ a0c34d34:fef39af1
2025-05-09 09:20:28My last article, I wrote about DePIN, a passive income that is easily accessible and something to consider as supplemental income. This week I want to discuss another form of finance. Let’s face it: when most of us hear the word “finance”, our eyes glaze over faster than a donut in a Krispy Kreme factory.
It conjures images of Wall Street suits, casino type crypto scams, and incomprehensible jargon. What if I told you that finance could be regenerative? Could your money heal the world?
Regenerative Finance is what I’m discussing; ReFi if you want to sound cool. Regenerative finance is a movement that’s quietly transforming how we think about money, investment and our collective future. Let’s dive down the rabbit hole and take a journey into a world where your money can make things better.
You’re at a party and someone asks what you do for a living. You say, “I work in sustainable finance.” Boring to most, they politely nod. But what if you said, “I work in regenerative finance. We invest in projects that restore rainforests, rebuild communities and make money while healing the planet.” How interesting, right?
What is sustainable? It is about not making things worse, just sustaining them. On the other hand, regenerative finance restores, renews and improves systems, making sure things are better when you leave than when you arrived.
Regeneration systems imagine every dollar invested helps a forest grow, a community thrive or a river run clear again. Remember sustainability is about keeping things as they are. Regeneration is about making things better.
Here’s a real-world example: The Savory Institute works with ranchers to restore grasslands using holistic grazing. Investors in their projects don’t just avoid harm, they rebuild the soil, increase biodiversity, and capture carbon. That’s money making a difference.
Regenerative finance asks, “How will the investment affect people, planet and profit, not just today, but decades from now?” Another real-world example, Ecosia, the search engine that plants trees, invests profits into reforestation projects worldwide. Their financial model considers long term ecological health, not just quarterly returns.
ReFi isn’t about faceless corporations. It’s about empowering local communities and restoring ecosystems. Think of it as crowdfunding Mother Earth.
How does all this magic happen? Here are a few ways to invest.
IMPACT INVESTING As examples from above, this is where you put your money into projects that actively restore ecosystems, empower communities or fight climate change. FUNDING BONDS These are bonds issued on blockchain platforms to fund sustainable projects. They are managed by smart contracts and investors get digital tokens representing their share. Think about this as an early adopter.
TOKENIZATION This is taking real-world assets and turning them into digital tokens. Think carbon credits. There’s no Wall Street middleman which makes it easier to track, invest and trade in regenerative projects. You can have fractional ownership with tokenization which means easier access to more assets.
Real estate has moved into fractional ownership using tokenization. The threshold to invest has lowered immensely with this practice.
The world is facing some big problems with climate change, inequality, biodiversity loss and I could go on. Traditional finance hasn’t exactly been successful. Regenerative finance offers a new way forward.
By focusing on restoring rather than just sustaining, we create resilient, equitable and thriving systems for future generations. As someone who is 64 years old, I was taught to leave the world better than you found it.
There has been much speculation over the years about the next evolution of the internet and business. How will we adapt? What will financial systems look like?
Let’s look at some projects that are already making a difference: Eden Reforestation Project Employs local communities to plant millions of trees, restoring ecosystems and creating jobs.
Kiva Community lending to entrepreneurs in developing countries, empowering them out of poverty.
Mosaic Solar projects, investing, earning returns while helping the planet.
KlimaDAO This DAO uses blockchain to buy and retire carbon credits, driving up the price of pollution and funding climate action.
Look for reputable ReFi projects or platforms that align with your values. Many platforms have low minimum investment thresholds making it easier for anyone to participate.
You don’t need to be a billionaire or a blockchain wizard to get involved in the regenerative finance revolution. Individuals can invest in ReFi initiatives through several accessible pathways, any of which leverage new technologies and community-driven models to make participation easier and more transparent.
Regenerative finance changes the way you think about money, value and your place in the world. Putting your dollars to work for people and planet, you can be a part of building a thriving future.
Regenerative finance addresses the shortcomings of traditional finance which often prioritizes short term profit over long term environmental and social costs. The core idea behind ReFi is that financial systems should restore, and grow society’s economic, social and environmental systems.
Regenerative finance represents a transformative shift in how capital is allocated and managed. By integrating advanced technology, community participation, and a focus on ecological and social renewal, ReFi seeks to build a financial system that not only generates returns but also restores and strengthens the foundations of a sustainable and healthy future.
As the world moves forward in different ways of finance and business, I hope this information was useful for you. The different monetary systems and financial markets are growing. ReFi is an alternative finance system becoming a movement. If you are interested in other financial systems or know of any, please let me know. Thank you for reading. Be fabulous, Sandra Abrams Onboard60 Founder
-
 @ 6146ad04:a0937b0b
2025-05-09 09:06:45
@ 6146ad04:a0937b0b
2025-05-09 09:06:45In the rapidly evolving world of technology, edge computing has emerged as a game-changing innovation, reshaping how data is processed, analyzed, and delivered. Unlike traditional cloud computing, which relies on centralized data centers, edge computing processes data closer to the source—right where it's generated.
This shift is driven by the explosion of Internet of Things (IoT) devices, autonomous systems, and real-time applications that demand low latency and fast decision-making. From smart factories and self-driving cars to remote healthcare and AR/VR experiences, the need for real-time processing is fueling the growth of edge solutions.
Why Edge Computing Matters
As more devices connect to the internet, the volume of data being generated is staggering. Transmitting all this data to the cloud for processing can introduce delays and raise bandwidth costs. Edge computing addresses these challenges by enabling devices and local servers to handle tasks immediately, without having to send data back and forth to the cloud.
Key benefits include:
Reduced latency: Ideal for time-sensitive applications like autonomous vehicles and industrial automation.
Improved security: Sensitive data can be processed locally, minimizing exposure.
Cost efficiency: Reduces bandwidth and storage demands on central data centers.
Real-World Applications
-
Healthcare: Wearables and remote monitoring devices use edge computing to detect anomalies and alert physicians in real time.
-
Retail: Smart shelves and AI-powered cameras analyze consumer behavior on the spot.
-
Manufacturing: Machines use edge-based analytics to predict maintenance needs and prevent downtime.
Challenges Ahead
Despite its promise, edge computing is not without hurdles. Managing a distributed network of devices, ensuring consistent software updates, and maintaining security at the edge require robust frameworks and standards. Scalability and interoperability remain ongoing concerns for developers and organizations.
The Road Ahead
With the rollout of 5G and advancements in AI, edge computing is poised for massive growth. According to industry forecasts, the global edge computing market is expected to exceed $100 billion by 2030. As businesses continue to demand faster, smarter, and more secure tech infrastructure, edge computing will be at the heart of the next digital transformation.
-
-
 @ 5b730fac:9e746e2a
2025-05-09 08:52:30
@ 5b730fac:9e746e2a
2025-05-09 08:52:30Currently in
v0.0.3, package was installed automatically with event ID9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c:root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.3 root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c" } root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746779161, "download_time": 1746779151, "release_channel": "stable", "ensure_default_timestamp": 1746717311, "update_path": null }Test automatic update
Push new tag
c03rad0r@CobradorRomblonMimaropa:~/Documents/test-stable-release-channel$ git push origin v0.0.4 Total 0 (delta 0), reused 0 (delta 0), pack-reused 0 To https://github.com/c03rad0r/test-stable-release-channel.git * [new tag] v0.0.4 -> v0.0.4New version is ready:
{ "id": "5586ad0ff0d26fb17a4856af2774ca22c707c2561e5c8441b09517cd9e1a5fd8", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746780490, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk" ], [ "m", "application/octet-stream" ], [ "x", "ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd" ], [ "ox", "ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.4" ], [ "release_channel", "stable" ] ] }Detected and installed: ``` Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Started the timer Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3 basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.2 basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:15 2025 daemon.info tollgate-basic[6843]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:25 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:25.468498 Timeout reached, checking for new versions Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.4] Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Newer package version available: v0.0.4 Fri May 9 08:48:25 2025 daemon.info tollgate-basic[6843]: Downloading package from https://blossom.swissdash.site/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk to /tmp/ca7af4023894489f11d3e21b8ca4ade76c244834a29115686f041ff356f5b6cd.ipk Fri May 9 08:48:27 2025 daemon.info tollgate-basic[6843]: Package downloaded successfully to /tmp/ Fri May 9 08:48:27 2025 daemon.info tollgate-basic[6843]: New package version is ready to be installed by cronjob Fri May 9 08:48:27 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:27.225508 Verifying package checksum Fri May 9 08:48:27 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:48:27.235069 Package checksum verified successfully Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 NIP94EventID: 5586ad0ff0d26fb17a4856af2774ca22c707c2561e5c8441b09517cd9e1a5fd8 Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 IPAddressRandomized: 10.156.11.1 Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07 Janitor module initialized and listening for NIP-94 events Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07.880020 Registering handlers... Fri May 9 08:49:07 2025 daemon.err tollgate-basic[7893]: 2025/05/09 08:49:07.880158 Starting HTTP server on all interfaces... Fri May 9 08:49:07 2025 daemon.info tollgate-basic[7893]: Starting Tollgate - TIP-01
```
New version installation confirmed:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.4 -
 @ 9223d2fa:b57e3de7
2025-05-09 13:35:00
@ 9223d2fa:b57e3de7
2025-05-09 13:35:005,475 steps
-
 @ 362fd2b5:0ce4005f
2025-05-09 02:37:13
@ 362fd2b5:0ce4005f
2025-05-09 02:37:13Source: Kenken_coffee11
Coffee Bean Panama🇵🇦Altieri Dilgo Geisha Natural Anaerobic Cold Fermentation
☕️ Recipe 📍Coffee : 12g 📍Grinder : LAGOM casa 16.5 📍Water : GH80 / KH40, MgSO₄75 / CaCl₂5 / 📍NaHCO₃40 📍Water temperature : 97℃ 📍Brew ratio : 1:16.7 (200ml) 📍Brewer : HARIO V60 01 or 02 📍Filter : CAFEC CC1-100W 📍TDS : 1.44% 📍Extraction yield : 21.12%
🫗Pouring Paragon ON ①0:00 50g Stir ②0:30 100g ③1:00 200g Spin Paragon OFF 2:40 Drawdown complete.
https://video.nostr.build/43df934a772bcc827f36519f7cbb630b1f0097e40e5991e8d3dbb1dd023a8f6a.mp4
Coffee
-
 @ 57d1a264:69f1fee1
2025-05-08 05:25:48
@ 57d1a264:69f1fee1
2025-05-08 05:25:48Safe Bits & Self Custody Tips
The journey of onboarding a user and create a bitcoin multiSig setup begins far before opening a desktop like Bitcoin Safe (BS) or any other similar application. Bitcoin Safe seems designed for families and people that want to start exploring and learning about multiSig setup. The need for such application and use of it could go much further, defining best practices for private organizations that aim to custody bitcoin in a private and anonymous way, following and enjoy the values and standards bitcoin has been built for.
Intro
Organizations and small private groups like families, family offices and solopreneurs operating on a bitcoin standard will have the need to keep track of transactions and categorize them to keep the books in order. A part of our efforts will be spent ensuring accessibility standards are in place for everyone to use Bitcoin Safe with comfort and safety.
We aim with this project to bring together the three Designathon ideas below: - Bitcoin Safe: improve its overall design and usability. - No User Left Behind: improve Bitcoin Safe accessibility. - Self-custody guidelines for organizations: How Bitcoin Safe can be used by private organization following best self-custody practices.
We are already halfway of the first week, and here below the progress made so far.
Designing an icon Set for Bitcoin Safe
One of the noticeable things when using BS is the inconsistency of the icons, not just in colors and shapes, but also the way are used. The desktop app try to have a clean design that incorporate with all OS (Win, macOS, Linux) and for this reason it's hard to define when a system default icon need to be used or if a custom one can be applied instead. The use of QT Ui framework for python apps help to respond to these questions. It also incorporates and brig up dome default settings that aren't easily overwritten.
Here below you can see the current version of BS:
Defining a more strict color palette for Bitcoin Safe was the first thing!
How much the icons affect accessibility? How they can help users to reach the right functionality? I took the challenge and, with PenPot.app, redesigned the icons based on the grid defined in the https://bitcoinicons.com/ and proposing the implementation of it to have a cleaner and more consistent look'n feel, at least for the icons now.
What's next
I personally look forward to seeing these icons implemented soon in Bitcoin Safe interface. In the meantime, we'll focus on delivering an accessibility audit and evaluate options to see how BS could be used by private organizations aiming to become financially sovereign with self-custody or more complex bitcoin multiSig setups.
One of the greatest innovations BS is bringing to us is the ability to sync the multiSig wallets, including PBST, Categories and labels, through the nostr decentralized protocol, making current key custodial services somehow obsolete. Second-coolest feature that this nostr implementation brings is the ability to have a build-in private chat that connect and enable the various signers of a multiSig to communicate and sign transactions remotely. Where have you seen something like this before?
Categories UX and redesign is also considered in this project. We'll try to understand how to better serve this functionality to you, the user, really soon.
Stay tuned!
originally posted at https://stacker.news/items/974488
-
 @ 5b730fac:9e746e2a
2025-05-09 08:40:38
@ 5b730fac:9e746e2a
2025-05-09 08:40:38Perpare v0.0.2
Package to install:
{ "id": "d0f0b18f14b1962d3b86c96fc392f791eb33e66b3d2e463036eb800d10a40777", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746739263, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424.ipk" ], [ "m", "application/octet-stream" ], [ "x", "9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424" ], [ "ox", "9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.2" ], [ "release_channel", "stable" ] ] }Package is installed:
root@OpenWrt:/tmp# opkg install 9e2da2b2f83b81e5227231879dda45408dd2ec00c403d88eb5e272ea26431424.ipk Package tollgate-module-basic-go (v0.0.2) installed in root is up to date. root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.2Config files are in unknown event state and in dev channel:
root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/f8295d4a4cd91d3940326ce00f664adf36bafc1d7f17c16f4a0c2d435a0592ef.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746777188, "download_time": 1746720038, "release_channel": "dev", "ensure_default_timestamp": 1746717311, "update_path": null } root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" }Create new tag (v0.0.3)
Publish new version:
{ "id": "9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c", "pubkey": "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b", "created_at": 1746778146, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk" ], [ "m", "application/octet-stream" ], [ "x", "2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f" ], [ "ox", "2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "v0.0.3" ], [ "release_channel", "stable" ] ] }Turn off janitor and witch to stable channel:
root@OpenWrt:/tmp# service tollgate-basic status running root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactive root@OpenWrt:/tmp# vi /etc/tollgate/install.json root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/f8295d4a4cd91d3940326ce00f664adf36bafc1d7f17c16f4a0c2d435a0592ef.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746777188, "download_time": 1746720038, "release_channel": "stable", "ensure_default_timestamp": 1746717311, "update_path": null } root@OpenWrt:/tmp# service tollgate-basic startTollGate not updating yet: ``` Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 NIP94EventID: unknown Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 IPAddressRandomized: 10.156.11.1 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31 Janitor module initialized and listening for NIP-94 events Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986743 Registering handlers... Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986768 Starting to listen for NIP-94 events Fri May 9 08:14:31 2025 daemon.err tollgate-basic[6195]: 2025/05/09 08:14:31.986912 Starting HTTP server on all interfaces... Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Starting Tollgate - TIP-01 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Listening on all interfaces on port :2121 Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Starting event processing loop Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.damus.io Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://nostr.mom Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://nos.lol Fri May 9 08:14:31 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://nos.lol Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://nostr.mom Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Connected to relay: wss://relay.damus.io Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscription successful on relay wss://relay.damus.io Fri May 9 08:14:32 2025 daemon.info tollgate-basic[6195]: Subscribed to NIP-94 events on relay wss://relay.damus.io Fri May 9 08:14:51 2025 daemon.info tollgate-basic[6195]: Connecting to relay: wss://relay.tollgate.me
```
TollGate is still at v0.0.2:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.2Adjusted trusted maintainer in config file:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "c0757f43081aa96a8733b58fb7f745d8c784ecdfc02477a1b7b99e35416fff0b" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" }Update succeeded:
Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://nostr.mom Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://nos.lol Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Connected to relay: wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscription successful on relay wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Subscribed to NIP-94 events on relay wss://relay.damus.io Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Started the timer Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Arch Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:39 2025 daemon.info tollgate-basic[6375]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:49 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:49.968769 Timeout reached, checking for new versions Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-v0.0.3] Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Newer package version available: v0.0.3 Fri May 9 08:25:49 2025 daemon.info tollgate-basic[6375]: Downloading package from https://blossom.swissdash.site/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk to /tmp/2578aef61b82a50ed92eb77c4831d2133c325536460acdeb7f3024321bd47f3f.ipk Fri May 9 08:25:51 2025 daemon.info tollgate-basic[6375]: Package downloaded successfully to /tmp/ Fri May 9 08:25:51 2025 daemon.info tollgate-basic[6375]: New package version is ready to be installed by cronjob Fri May 9 08:25:51 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:51.327815 Verifying package checksum Fri May 9 08:25:51 2025 daemon.err tollgate-basic[6375]: 2025/05/09 08:25:51.337239 Package checksum verified successfully Fri May 9 08:25:59 2025 daemon.info tollgate-basic[6375]: Connecting to relay: wss://relay.tollgate.me Fri May 9 08:26:06 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:06 NIP94EventID: 9d02b38f147c316756641c7f3f2720c2adf265d0cfa763665d37c9e102294c0c Fri May 9 08:26:06 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:06 IPAddressRandomized: 10.156.11.1 Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Starting Tollgate - TIP-01 Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Listening on all interfaces on port :2121 Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07 Janitor module initialized and listening for NIP-94 events Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.762570 Registering handlers... Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.762699 Starting HTTP server on all interfaces... Fri May 9 08:26:07 2025 daemon.err tollgate-basic[6843]: 2025/05/09 08:26:07.763463 Starting to listen for NIP-94 events Fri May 9 08:26:07 2025 daemon.info tollgate-basic[6843]: Starting event processing loopNew version:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - v0.0.3 -
 @ 4fa5d1c4:fd6c6e41
2025-05-09 07:27:10
@ 4fa5d1c4:fd6c6e41
2025-05-09 07:27:10Den für mich derzeit wichtigsten Impuls über KI nachzudenken lieferte vor einigen Wochen Yuval Noah Harari an der University of Cambridge am Ende eines Podiumsgesprächs hier ab 1:15 h auf youtube:
Ich denke, wir müssen die Frage des Bewusstseins in den Mittelpunkt der Diskussion stellen. Es gibt eine riesige, riesige Verwirrung in der Terminologie, auch in der Welt der KI, zwischen Bewusstsein und Intelligenz. Aber es sind zwei verschiedene Dinge. Intelligenz ist die Fähigkeit, Probleme zu lösen und Ziele zu erreichen. Bewusstsein ist die Fähigkeit, Dinge zu fühlen, wie Schmerz oder Freude oder Liebe oder Hass. Wir neigen dazu, die beiden zu verwechseln, weil bei Menschen und auch bei anderen Säugetieren, Vögeln und anderen Tieren Bewusstsein und Intelligenz zusammengehören. Wir lösen Probleme durch unsere Gefühle. Computer waren bisher sehr anders. Sie sind in einigen Bereichen bereits intelligenter als wir, haben aber, soweit wir wissen, kein Bewusstsein. Soweit wir wissen, können sie überhaupt keinen Schmerz, keine Freude, keine Liebe oder keinen Hass empfinden. Niemand weiß, was in Zukunft passieren wird. Es gibt Modelle und Theorien, die argumentieren, dass KIs irgendwann auch bewusst oder empfindsam werden. Sie werden anfangen, Dinge zu fühlen. Sie werden anfangen, Schmerz oder Liebe oder Hass zu empfinden. Es gibt andere Modelle und Theorien, die sagen, nein. Sie könnten weit intelligenter werden als wir und immer noch null Bewusstsein haben. Das kann in der Evolution des Lebens sein. Wenn man darüber nachdenkt, die lange Entwicklung von Milliarden von Jahren der Evolution. Die Entwicklung der Intelligenz ist im Falle von Tieren wie uns und Schimpansen und Hunden und Schweinen und so weiter durch die Entwicklung des Bewusstseins verlaufen. Aber das ist kein universelles Gesetz der Evolution der Intelligenz. Vielleicht gibt es alternative Wege, die zu Superintelligenz ohne jegliches Bewusstsein führen. Einfach einen anderen, einen fremden Weg gehen. Und wir könnten an einen Punkt gelangen, an dem sie superintelligent sind und trotzdem null Bewusstsein haben. Und die Gefahr besteht dann darin, dass sie nicht nur die menschliche Zivilisation zerstören könnten, sondern das ganze Licht des Bewusstseins, um das gesamte ökologische System nach ihren Bedürfnissen umzugestalten, wofür sie kein Bewusstsein brauchen. Sie funktionieren auf eine völlig andere Weise. Sie könnten sich sogar von der Erde auf andere Planeten, auf andere Galaxien ausbreiten. Sie werden das Universum mit Intelligenz füllen, aber es wird ein völlig dunkles Universum ohne Bewusstsein sein. Wieder hohe Intelligenz, fähig, Raumschiffe zu bauen, die mit Lichtgeschwindigkeit fliegen und was auch immer, aber es gibt null Gefühl. Niemand, keine Entität fühlt Schmerz oder Freude, Liebe oder Hass. Für mich ist das ein schreckliches Szenario. Das schlimmste Szenario von allen ist dies. Dass wir ein Universum voller Intelligenz und völlig ohne Bewusstsein haben werden, denn ich denke, dass von den beiden das Bewusstsein weitaus wichtiger, weitaus wertvoller ist. Und es ist eine gute Erinnerung daran, dass wir das zumindest heute mit vielen anderen Tieren teilen, aber nicht mit den Computern, nicht mit den KIs. Wir sind also immer noch im selben Team wie die Würmer und die Affen, nicht im selben Team wie die Computer.
Ich denke, hier wird eine Spur gelegt, die sich unterscheidet von der reinen Funktion von KI zur intelligenten Verbesserung und Unterstützung von Lernprozessen oder vielfältigem Kompetenzerwerb hin zur Selbstreflexion der Lernenden. Auch im Blick auf (religionsbezogene) Bildung kennen wir den Mensch nicht nur biologisch, wie die Würmer und Affen sondern auch ausgestattet mit Würde, Entscheidungsfreiheit und als Beziehungswesen, das auf ein Gegenüber ausgerichtet sein kann und, wie Harari sagt, nicht im selben Team wie die Computer spielt. Sinn, Seele und Verstand erhalten wir weder aus uns selbst heraus noch von einer wie auch immer gearteten Intelligenz. Liebe, Gnade, Hoffnung, Frieden, Gemeinschaft, Trost, Zuversicht und viele weiteren lebensbedeutsame Erfahrungen gewinnen im Angesicht von Maschinen aus meiner Sicht an elementarer Bedeutung.
Dies ist ein Beitrag zur Blogparade #KIBedenken von Joscha Falck und Nele Hirsch
Austausch und Diskussion zu diesem Beitrag
- offen und dezentral
- geschlossen und plattformgebunden
-
 @ 57d1a264:69f1fee1
2025-05-08 05:08:36
@ 57d1a264:69f1fee1
2025-05-08 05:08:36Welcome back to our weekly
JABBB, Just Another Bitcoin Bubble Boom, a comics and meme contest crafted for you, creative stackers!If you'd like to learn more, check our welcome post here.
This week sticker:
Bitcoin SirYou can download the source file directly from the HereComesBitcoin website in SVG and PNG. Use this sticker around SN with the code
The task
Make sure you use this week sticker to design a comic frame or a meme, add a message that perfectly captures the sentiment of the current most hilarious takes on the Bitcoin space. You can contextualize it or not, it's up to you, you chose the message, the context and anything else that will help you submit your comic art masterpiece.
Are you a meme creator? There's space for you too: select the most similar shot from the gifts hosted on the Gif Station section and craft your best meme... Let's Jabbb!
If you enjoy designing and memeing, feel free to check out the JABBB archive and create more to spread Bitcoin awareness to the moon.
Submit each proposal on the relative thread, bounties will be distributed when enough participants submit options.
PS: you can now use HereComesBitcoin stickers to use on Stacker.News
₿e creative, have fun! :D
originally posted at https://stacker.news/items/974483
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:56:25
@ 57d1a264:69f1fee1
2025-05-07 06:56:25Wild parrots tend to fly in flocks, but when kept as single pets, they may become lonely and bored https://www.youtube.com/watch?v=OHcAOlamgDc
Source: https://www.smithsonianmag.com/smart-news/scientists-taught-pet-parrots-to-video-call-each-other-and-the-birds-loved-it-180982041/
originally posted at https://stacker.news/items/973639
-
 @ 70c48e4b:00ce3ccb
2025-05-09 06:21:57
@ 70c48e4b:00ce3ccb
2025-05-09 06:21:57Dear reader,
HODLing was never the end goal.
HODLing Bitcoin is smart. It always has been. If you held through the Mt. Gox hacks, China bans, the 2017 Blocksize wars, the 2018 bloodbath, and the FTX clownery of 2022, then you already know. Bitcoin rewards conviction.
But let’s not forget why you got in.
It was never just about watching numbers go up. You felt something. Something deep. A quiet voice inside said, “This system is broken. I’m done playing by its rules.” - That is where it all began.
Back in 2008, while the banks were crashing the economy and handing you the bill, Bitcoin showed up as a silent answer. A lifeboat. A revolution wrapped in code.
The whitepaper starts with a simple, powerful idea: "A purely peer-to-peer version of electronic cash would allow online payments to be sent directly from one party to another without going through a financial institution."
https://plebsite.net/cdn/shop/files/Bitcoin_Whitepaper-Poster-3.jpg
And Bitcoin has lived up to that vision.
You saw it in El Salvador when they made it legal tender — even if they later made it optional. You saw it when WikiLeaks used Bitcoin after getting cut off by banks. You saw the Silk Road prove what peer-to-peer money really means. No matter what you think of those examples, one thing is clear: It worked. It was used. It still works.
Today, Bitcoin powers circular economies across the world — in Costa Rica, South Africa, Brazil, and beyond. People are using it because their local money fails them. Bitcoin became more than a store of value. It became a tool for survival and sovereignty.
https://imageio.forbes.com/specials-images/imageserve/67e422a1808f4902b8a1c6bc/Bitcoin-Ekasi-Center/960x0.jpg?format=jpg&width=1440
And now, look at you.
You believed early. You stacked. You held. And now, you have more Bitcoin than you ever imagined. Your needs are met. Your wants, too. You held through it all. And maybe now, you’ve found some stability, maybe even freedom. You stayed patient. You played the long game. You won.
So now the question is simple: What will your Bitcoin build?
Let me paint you a picture- Somewhere out there, there is a young soul maybe in Lagos, maybe in Buenos Aires, maybe right next door. This person might be working on a new privacy tool that protects free expression. Or developing a drone taxi system to change the way people move in growing cities. Or creating a decentralized alternative to platforms like Patreon, where no one is silenced for thinking differently.
They do not have powerful connections. They are not sitting in fancy offices or attending tech conferences. They are building quietly, with conviction and hope.
You can be the magical wand in their life. Your belief and support can turn someone's idea into something real. You can help create the next chapter of their story.
Angor allows you to do exactly that. It gives you a way to fund builders directly, using your Bitcoin. The process is safe and structured. You support projects in stages, and the funds only move forward when clear milestones are completed. Everything is on-chain, using Bitcoin scripts and time-locked contracts to ensure accountability.
This is how the ecosystem grows.
Where do you go now that HODLing was just the beginning?
Here’s what you do:
1. Check the Proposal
Go read the Angor docs. It’s not some bloated whitepaper. It’s clean, clear, and you’ll get it. Here’s the link - https://docs.angor.io/start/.
2. Join the Talk on Nostr
Nostr is where real, uncensored conversation is happening. It is decentralized and open by design. Use a client like Primal or Damus to dive in. Or check out nostr.band to explore what people are building and sharing across the network.
This is where ideas take shape. Builders post updates. Communities give feedback. The next wave of innovation is already in motion — and you can be part of it.
Follow Angor on Nostr: nostr:nprofile1qqs8p3ywfd92w7zvjgy7wrpylz8t30hy3z5dc5al4070l9y8qr8rejcksnh5c
3. Contribute
Whatever your skill is writing, design, coding, memes, Angor has room for you. Get on GitHub. Even if you just report a bug or suggest a feature, it helps. Or you could even fork the code and do as you wish.
4. Explore Angor Hub
This is the cockpit. It’s where you find new projects, track progress, talk to founders and make moves. Dive in. It’s live.
https://docs.angor.io/images/tools/hub.png
Final Thoughts
Bitcoin gave us the base layer. It proved that peer-to-peer money works. But that was just the beginning. Now it’s time to build the next layer together.
And no, this is not about another meme coin or a monkey NFT. This is about real infrastructure. Real value. Real use cases.
Angor is for the misfits, the dreamers, the people who read the whitepaper and said, “Yeah, this is the way.”
So if you have Bitcoin, do not treat it like a relic from a past battle. Use it to empower the next builder. Fund a project. Spark a new idea. Help decentralize the next thing.
You got into Bitcoin to protect your future maybe even to get rich but also to bring some change to the world.
HODLing was the first act.
Building is the second.
Angor is where we build.
Let’s make sure the next wave of Bitcoiners do not just see price charts. Let them see tools, apps, ideas, and communities that actually do something. Real things. Useful things. Built on the hardest money the world has ever known.
You in?
Thanks for reading, See y’all soon for another blog post. Ciao
Guest Post by nostr:npub1v67clmf4jrezn8hsz28434nc0y5fu65e5esws04djnl2kasxl5tskjmjjk
-
 @ fd06f542:8d6d54cd
2025-05-09 05:48:05
@ fd06f542:8d6d54cd
2025-05-09 05:48:05由nip96模式改成了blossom
blossom的网址 变成了sha256 的id值,理论上 更换服务器或者重传以后 替换图片地址方便。
不过这部分我并没有做兼容接口。如果做成兼容的,应该用 相对地址,然后 后台用proxyimg.xxx.com去做选择。
访问方便些
新的服务器是:https://nosto.re/ 希望他能稳定的被访问不会嘎。
代码其实更简单了,https://github.com/nostrbook/nostrbook/blob/main/src/lib/blossomUpload.ts nosto.re 没有checkupload功能。所以我这里代码也没有加这部分,如果换别的服务器可能需要加检查功能。是不是为了防止图片重复上传?
最后 加一张好看的图片吧。证明此功能好用:
 {.user-img}
{.user-img} -
 @ 57d1a264:69f1fee1
2025-05-07 06:29:52
@ 57d1a264:69f1fee1
2025-05-07 06:29:52Your device, your data. TRMNL's architecture prevents outsiders (including us) from accessing your local network. TRMNAL achieve this through 1 way communication between client and server, versus the other way around. Learn more.
Learn more at https://usetrmnl.com/
originally posted at https://stacker.news/items/973632
-
 @ 866e0139:6a9334e5
2025-05-09 05:45:01
@ 866e0139:6a9334e5
2025-05-09 05:45:01Autor: Peter Schmuck. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
\ Heute, am 9. Mai 2025 – genau 80 Jahre nach dem Ende des Zweiten Weltkriegs, der 60 Millionen Menschen das Leben kostete, darunter 27 Millionen Sowjetbürgern, erheben wir, die Bürgerinnen und Bürger Europas, unsere Stimmen! Wir schämen uns für unsere Regierungen und die EU, die die Lehren des 20. Jahrhunderts nicht gelernt haben. Die EU, einst als Friedensprojekt gedacht, wurde pervertiert und hat damit den Wesenskern Europas verraten! Wir, die Bürger Europas, nehmen darum heute, am 9. Mai, unsere Geschicke und unsere Geschichte selbst in die Hand. Wir erklären die EU für gescheitert. Wir beginnen mit Bürger-Diplomatie und verweigern uns dem geplanten Krieg gegen Russland! Wir erkennen die Mitverantwortung des „Westens“, der europäischen Regierungen und der EU an diesem Konflikt an.
Wir, die Bürger Europas, treten mit dem European Peace Project der schamlosen Heuchlerei und den Lügen entgegen, die heute – am Europatag – auf offiziellen Festakten und in öffentlichen Sendern verbreitet werden.
Wir strecken den Bürgerinnen und Bürgern der Ukraine und Russlands die Hand aus. Ihr gehört zur europäischen Familie, und wir sind überzeugt, dass wir gemeinsam ein friedliches Zusammenleben auf unserem Kontinent organisieren können.
Wir haben die Bilder der Soldatenfriedhöfe vor Augen – von Wolgograd über Riga bis Lothringen. Wir sehen die frischen Gräber, die dieser sinnlose Krieg in der Ukraine und in Russland hinterlassen hat. Während die meisten EU-Regierungen und Verantwortlichen für den Krieg hetzen und verdrängen, was Krieg für die Bevölkerung bedeutet, haben wir die Lektion des letzten Jahrhunderts gelernt: Europa heißt „Nie wieder Krieg!“
Wir erinnern uns an die europäischen Aufbauleistungen des letzten Jahrhunderts und an die Versprechen von 1989 nach der friedlichen Revolution. Wir fordern ein europäisch-russisches Jugendwerk nach dem Vorbild des deutsch-französischen Jugendwerks von 1963, das die „Erbfeindschaft“ zwischen Deutschland und Frankreich beendet hat. Wir fordern ein Ende der Sanktionen und den Wiederaufbau der Nord Stream II-Pipeline. Wir weigern uns, unsere Steuergelder für Rüstung und Militarisierung zu verschwenden, auf Kosten von Sozialstandards und Infrastruktur. Im Rahmen einer OSZE-Friedenskonferenz fordern wir die Schaffung einer europäischen Sicherheitsarchitektur mit und nicht gegen Russland, wie in der Charta von Paris von 1990 festgelegt. Wir fordern ein neutrales, von den USA emanzipiertes Europa, das eine vermittelnde Rolle in einer multipolaren Welt einnimmt. Unser Europa ist post-kolonial und post-imperial.
Wir, die Bürger Europas, erklären diesen Krieg hiermit für beendet! Wir machen bei den Kriegsspielen nicht mit. Wir machen aus unseren Männern und Söhnen keine Soldaten, aus unseren Töchtern keine Schwestern im Lazarett und aus unseren Ländern keine Schlachtfelder.
Wir bieten an, sofort eine Abordnung europäischer Bürgerinnen und Bürger nach Kiew und Moskau zu entsenden, um den Dialog zu beginnen. Wir werden nicht länger zusehen, wie unsere Zukunft und die unserer Kinder auf dem Altar der Machtpolitik geopfert wird.
Es lebe Europa, es lebe der Friede, es lebe die Freiheit!
Auf der Webseite der Initiative oder in einem Gespräch mit Ulrike Guérot können Sie, liebe Leser, weitere Möglichkeiten erfahren, diese Friedensinitiative zu stärken!
https://www.youtube.com/watch?v=zECOTfeweUE&list=PLS_jddBXjdqcBKneCQcPN8NOTSqlmNqpy
Danke an die IntiatorInnen und die bislang 15.000 Menschen, die das mitgestalten werden.
Peter Schmuck ist Professor für Psychologie und Initiator zahlreicher nachhaltiger Projekte.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:16:30
@ 57d1a264:69f1fee1
2025-05-07 06:16:30Here’s Sean Voisen writing about how programming is a feeling:
For those of us who enjoy programming, there is a deep satisfaction that comes from solving problems through well-written code, a kind of ineffable joy found in the elegant expression of a system through our favorite syntax. It is akin to the same satisfaction a craftsperson might find at the end of the day after toiling away on well-made piece of furniture, the culmination of small dopamine hits that come from sweating the details on something and getting them just right. Maybe nobody will notice those details, but it doesn’t matter. We care, we notice, we get joy from the aesthetics of the craft.
This got me thinking about the idea of satisfaction in craft. Where does it come from?
Continue Reading https://blog.jim-nielsen.com/2025/craft-and-satisfaction/
originally posted at https://stacker.news/items/973628
-
 @ 872982aa:8fb54cfe
2025-05-09 05:35:15
@ 872982aa:8fb54cfe
2025-05-09 05:35:15 可以方便访问了
可以方便访问了 -
 @ 57d1a264:69f1fee1
2025-05-07 06:03:29
@ 57d1a264:69f1fee1
2025-05-07 06:03:29CryptPad
Collaboration and privacy. Yes, you can have both Flagship instance of CryptPad, the end-to-end encrypted and open-source collaboration suite. Cloud administered by the CryptPad development team. https://cryptpad.fr/
ONLYOFFICE DocSpace
Document collaboration made simpler. Easily collaborate with customizable rooms. Edit any content you have. Work faster using AI assistants. Protect your sensitive business data. Download or try STARTUP Cloud (Limited-time offer) FREE https://www.onlyoffice.com/
SeaFile
A new way to organize your files Beyond just syncing and sharing files, Seafile lets you add custom file properties and organize your files in different views. With AI-powered automation for generating properties, Seafile offers a smarter, more efficient way to manage your files. Try it Now, Free for up to 3 users https://seafile.com/
SandStorm
An open source platform for self-hosting web apps Self-host web-based productivity apps easily and securely. Sandstorm is an open source project built by a community of volunteers with the goal of making it really easy to run open source web applications. Try the Demo or Signup Free https://alpha.sandstorm.io/apps
NextCloud Hub
A new generation of online collaboration that puts you in control. Nextcloud offers a modern, on premise content collaboration platform with real-time document editing, video chat & groupware on mobile, desktop and web. Sign up for a free Nextcloud account https://nextcloud.com/sign-up/
LinShare
True Open Source Secure File Sharing Solution We are committed to providing a reliable Open Source file-sharing solution, expertly designed to meet the highest standards of diverse industries, such as government and finance Try the Demo https://linshare.app/
Twake Drive
The open-source alternative to Google Drive. Privacy-First Open Source Workplace. Twake workplace open source business. Improve your effeciency with truly Open Source, all-in-one digital suite. Enhance the security in every aspect of your professional and private life. Sign up https://sign-up.twake.app/
SpaceDrive
One Explorer. All Your Files. Unify files from all your devices and clouds into a single, easy-to-use explorer. Designed for creators, hoarders and the painfully disorganized. Download desktop app (mobile coming soon) https://www.spacedrive.com/
ente
Safe Home for your photos Store, share, and discover your memories with end-to-end encryption. End-to-end encryption, durable storage and simple sharing. Packed with these and much more into our beautiful open source apps. Get started https://web.ente.io
fileStash
Turn your FTP server into... Filestash is the enterprise-grade file manager connecting your storage with your identity provider and authorisations. Try the demo https://demo.filestash.app
STORJ
Disruptively fast. Globally secure. S3-compatible distributed cloud services that make the most demanding workflows fast and affordable. Fast track your journey toward high performance cloud services. Storj pricing is consistent and competitive in meeting or exceeding your cloud services needs. Give the products a try to experience the benefits of the distributed cloud. Get Started https://www.storj.io/get-started
FireFile
The open‑source alternative to Dropbox. Firefiles lets you setup a cloud drive with the backend of your choice and lets you seamlessly manage your files across multiple providers. It revolutionizes cloud storage management by offering a unified platform for all your storage needs. Sign up Free https://beta.firefiles.app
originally posted at https://stacker.news/items/973626
-
 @ 57d1a264:69f1fee1
2025-05-06 06:00:25
@ 57d1a264:69f1fee1
2025-05-06 06:00:25Album art didn’t always exist. In the early 1900s, recorded music was still a novelty, overshadowed by sales of sheet music. Early vinyl records were vastly different from what we think of today: discs were sold individually and could only hold up to four minutes of music per side. Sometimes, only one side of the record was used. One of the most popular records of 1910, for example, was “Come, Josephine, in My Flying Machine”: it clocked in at two minutes and 39 seconds.
The invention of album art can get lost in the story of technological mastery. But among all the factors that contributed to the rise of recorded music, it stands as one of the few that was wholly driven by creators themselves. Album art — first as marketing material, then as pure creative expression — turned an audio-only medium into a multi-sensory experience.
This is the story of the people who made music visible.
originally posted at https://stacker.news/items/972642
-
 @ 57d1a264:69f1fee1
2025-05-06 05:49:01
@ 57d1a264:69f1fee1
2025-05-06 05:49:01I don’t like garlic. It’s not a dislike for the taste in the moment, so much as an extreme dislike for the way it stays with you—sometimes for days—after a particularly garlicky meal.
Interestingly enough, both of my brothers love garlic. They roast it by itself and keep it at the ready so they can have a very strong garlic profile in their cooking. When I prepare a dish, I don’t even see garlic on the ingredient list. I’ve cut it out of my life so completely that my brain genuinely skips over it in recipes. While my brothers are looking for ways to sneak garlic into everything they make, I’m subconsciously avoiding it altogether.
A few years back, when I was digging intensely into how design systems mature, I stumbled on the concept of a design system origin story. There are two extreme origin stories and an infinite number of possibilities between. On one hand you have the grassroots system, where individuals working on digital products are simply trying to solve their own daily problems. They’re frustrated with having to go cut and paste elements from past designs or with recreating the same layouts over and over, so they start to work more systematically. On the other hand, you have the top down system, where leadership is directing teams to take a more systematic approach, often forming a small partially dedicated core team to tackle some centralized assets and guidelines for all to follow. The influences in those early days bias a design system in interesting and impactful ways.
We’ve established that there are a few types of bias that are either intentionally or unintentionally embedded into our design systems. Acknowledging this is a great first step. But, what’s the impact of this? Does it matter?
I believe there are a few impacts design system biases, but there’s one that stands out. The bias in your design system makes some individuals feel the system is meant for them and others feel it’s not. This is a problem because, a design system cannot live up to it’s expected value until it is broadly in use. If individuals feel your design system is not for them, the won’t use it. And, as you know, it doesn’t matter how good your design system is if nobody is using it.
originally posted at https://stacker.news/items/972641
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 872982aa:8fb54cfe
2025-05-09 05:33:39
@ 872982aa:8fb54cfe
2025-05-09 05:33:39 {.user-img}
{.user-img} -
 @ 872982aa:8fb54cfe
2025-05-09 05:32:42
@ 872982aa:8fb54cfe
2025-05-09 05:32:42{"coverurl":"https://nosto.re/3ebd3bf45e031c2812ca5a36980a9bf7d4e6f30da2941d2bebdb7a2a452c8664.jpeg","title":"养花和施肥","author":"花花的作者"}
-
 @ 57d1a264:69f1fee1
2025-05-05 05:26:34
@ 57d1a264:69f1fee1
2025-05-05 05:26:34The European Accessibility Act is coming, now is a great time for accessibility trainings!. In my Accessibility for Designer workshop, you will learn how to design accessible mockups that prevent issues in visual design, interactions, navigation, and content. You will be able to spot problems early, fix them in your designs, and communicate accessibility clearly with your team. This is a practical workshop with hands-on exercises, not just theory. You’ll actively apply accessibility principles to real design scenarios and mockups. And will get access to my accessibility resources: checklists, annotation kits and more.
When? 4 sessions of 2 hours + Q and As, on: - Mon, June 16, - Tue, June 17, Mon, - June 23 and Tue, - June 24. 9:30 – 12:00 PM PT or 18:30 – 21:00 CET
Register with 15% discount ($255) https://ti.to/smashingmagazine/online-workshops-2022/with/87vynaoqc0/discount/welcometomyworkshop
originally posted at https://stacker.news/items/971772
-
 @ 727d5bb6:cce65355
2025-05-09 04:42:51
@ 727d5bb6:cce65355
2025-05-09 04:42:51VN123 là một nền tảng giải trí trực tuyến nổi bật, mang đến cho người dùng trải nghiệm thú vị và đa dạng. Với giao diện đơn giản, dễ sử dụng và tối ưu hóa cho mọi thiết bị, VN123 giúp người dùng dễ dàng tiếp cận và tham gia vào các dịch vụ giải trí yêu thích mà không gặp phải bất kỳ khó khăn nào. Nền tảng này được thiết kế với mục tiêu mang lại trải nghiệm người dùng mượt mà và không bị gián đoạn, giúp người tham gia tận hưởng những giây phút thư giãn tuyệt vời. VN123 sở hữu một giao diện thân thiện, dễ nhìn và trực quan, cho phép người dùng dễ dàng tìm kiếm các dịch vụ mà mình yêu thích. Tốc độ truy cập nhanh chóng và ổn định là một trong những yếu tố quan trọng, đảm bảo rằng mọi hoạt động của người dùng đều được diễn ra một cách suôn sẻ. Không cần lo lắng về việc mất kết nối hay gặp phải sự cố kỹ thuật, người dùng có thể hoàn toàn tập trung vào trải nghiệm giải trí của mình trên nền tảng này.
Một trong những yếu tố làm nên sự thành công của VN123 chính là tính năng bảo mật vượt trội. Nền tảng này luôn chú trọng đến việc bảo vệ thông tin cá nhân và dữ liệu của người dùng, sử dụng các công nghệ bảo mật hiện đại và hệ thống mã hóa tiên tiến. Mọi giao dịch và thông tin cá nhân của người tham gia đều được bảo vệ an toàn tuyệt đối, giúp người dùng có thể yên tâm sử dụng dịch vụ mà không phải lo lắng về việc lộ lọt dữ liệu. VN123 cam kết duy trì một môi trường trực tuyến an toàn và bảo mật, tạo ra sự tin tưởng đối với cộng đồng người dùng. Ngoài ra, nền tảng này còn có hệ thống giám sát và bảo mật chặt chẽ để ngăn chặn những hành vi gian lận hay xâm nhập trái phép. Điều này giúp duy trì tính minh bạch và công bằng cho mọi người dùng, đồng thời tạo ra một không gian giải trí an toàn và đáng tin cậy.
VN123 không chỉ chú trọng đến các yếu tố về giao diện và bảo mật, mà còn đặc biệt quan tâm đến việc nâng cao chất lượng dịch vụ khách hàng. Đội ngũ hỗ trợ của VN123 luôn sẵn sàng phục vụ và giải đáp mọi thắc mắc của người dùng 24/7. Mỗi yêu cầu hay vấn đề từ người dùng đều được đội ngũ chăm sóc khách hàng xử lý nhanh chóng và hiệu quả, giúp người tham gia có được trải nghiệm tốt nhất. Đặc biệt, VN123 luôn lắng nghe ý kiến đóng góp từ cộng đồng người dùng để liên tục cải tiến và phát triển nền tảng. Nền tảng này không ngừng nâng cấp các tính năng mới, đồng thời tổ chức các chương trình khuyến mãi và sự kiện hấp dẫn để người dùng có thể tận hưởng thêm nhiều lợi ích. Sự kết hợp giữa giao diện dễ sử dụng, bảo mật mạnh mẽ và dịch vụ khách hàng chuyên nghiệp đã giúp VN123 tạo dựng được lòng tin và sự yêu mến từ cộng đồng. Với những cải tiến liên tục và sự phát triển bền vững, VN123 đang dần trở thành một trong những nền tảng giải trí trực tuyến hàng đầu, mang đến cho người dùng những trải nghiệm tuyệt vời và thú vị.
-
 @ 57d1a264:69f1fee1
2025-05-05 05:15:02
@ 57d1a264:69f1fee1
2025-05-05 05:15:02Crabtree's Framework for Evaluating Human-Centered Research
Picture this: You've spent three weeks conducting qualitative research for a finance app redesign. You carefully recruited 12 participants, conducted in-depth interviews, and identified patterns around financial anxiety and decision paralysis. You're excited to present your findings when the inevitable happens:
"But are these results statistically significant?"
"Just 12 people? How can we make decisions that affect thousands of users based on conversations with just 12 people?"
As UX professionals, we regularly face stakeholders who evaluate our qualitative research using criteria designed for quantitative methods... This misalignment undermines the unique value qualitative research brings to product development.
Continue reading https://uxpsychology.substack.com/p/beyond-numbers-how-to-properly-evaluate
originally posted at https://stacker.news/items/971767
-
 @ b154080c:00027cc7
2025-05-06 03:01:47
@ b154080c:00027cc7
2025-05-06 03:01:47Introduction
In the ancient times of Israel, masculinity found its true embodiment in the courageous story of Daniel. Amidst the foreign land of Babylon, Daniel stood firm in his convictions, showcasing strength, and dedication to his beliefs.
Despite living in a culture that sought to diminish his faith, Daniel refused to bow before idols or false deities. His defiance challenged societal expectations, revealing a masculinity that transcended worldly norms. Rooted in his unshakable belief in the one true God, Daniel's resolve remained unyielding. Facing the wrath of the king, Daniel fearlessly stood before Nebuchadnezzar, humbly declaring his allegiance to God alone. Cast into a blazing furnace as punishment, Daniel emerged unharmed. God's angel shielded him from the scorching flames, proving that his faith made him invincible. Witnessing this display of masculinity, Nebuchadnezzar acknowledged the greatness of Daniel's God, bringing about a profound transformation.
Daniel's story serves as a testament to the essence of masculinity—a resolute dedication to one's convictions, the courage to defy societal expectations, and a commitment to truth. His faith and devotion inspire generations, exemplifying the power of masculine conviction.
There have been countless instances throughout history where acts of courage have taken place on a spectrum. Although both men and women can display such acts, history has shown that resolve, courage, and bravery have predominantly resided within the realm of masculinity. The Apostle Paul himself concluded the book of 1 Corinthians by saying, "Be watchful, stand firm in the faith, act like men, be strong. Let all that you do be done in love" (16:13-14). By combining this passage with the numerous accounts of provision, battle, sacrifice, and honor, it becomes evident that God has designed inherent and very important differences within the male gender.
The Bible presents us with inspiring examples of both courageous women, such as Deborah, Rahab, and Esther, and valiant men, including Joshua, Gideon, Samson, David, Jonathan, Nehemiah, the Prophets, the twelve Apostles, and above all, Jesus Himself. While these accounts acknowledge the remarkable contributions of women, they predominantly highlight the male figures who exemplify strength, boldness, courage, and a resolute sense of responsibility. Throughout its pages, the Bible paints a vivid picture of masculinity's profound impact and enduring significance which we must embrace.
Jesus’ Masculinity
Jesus exhibited remarkable courage throughout many of his acts, and it is through his expression of masculinity that this courage shines even brighter. Jesus' masculinity played a crucial role in enabling him to display great bravery and determination in fulfilling his mission. However, it's important to note that Jesus redefines masculinity beyond physical strength or dominance, embracing resilience, self-sacrifice, and unyielding conviction as its defining qualities.
Jesus' courage stemmed from his deep understanding of his purpose and his unshakable faith in his Father's plan. He fearlessly challenged the religious authorities of his time, calling out hypocrisy and speaking truth to power. Despite facing opposition and hostility, Jesus stood firm in his convictions, undeterred by the threats and ridicule he encountered. Jesus' embodiment of masculinity highlights the transformative power it can have when rooted in love and compassion.
Modern Culture Poisoning the Church
It is important to realize the true masculinity of Jesus and the example that he has set for us in this regard. Unfortunately, I often see a tendency nowadays to downplay Jesus' masculinity and instead depict Him in a more feminized manner.
In both our culture and the modern church, there is a tendency to present a version of Jesus that deviates from the biblical portrayal. Perhaps you've come across people who refer to Jesus as their "best friend" or even draw comparisons between their relationship with Him and that of a "boyfriend.” This is in fact very unbiblical. The Bible never presents our love for God using such romantic or erotic language. While the men depicted in Scripture certainly loved God, they were never portrayed as being desperate for Him or romantically in love with Him. People are often taught a very shallow and weak portrayal of Him.
In the United States, particularly in the context of flourishing Protestantism, the shift from considering the community as a whole to focusing on the individual has led to a rise in strong individualistic beliefs which has resulted in a diminished sense of community within the Catholic Church. When the focal point of Catholicism becomes "Jesus and me," it opens the door to a mindset of being "spiritual" rather than "religious.” Attending church becomes a matter of personal choice, and faith no longer necessarily influences or intersects with areas such as business or politics. The sole emphasis becomes on one's personal relationship with Christ, prioritizing individual salvation over communal or global redemption. The vision of the kingdom of God taking shape on earth also becomes less urgent, as the emphasis shifts towards a faith centered on transcendence, emotions, and sentiment, rather than tangible actions.
The perception of Jesus' masculinity has been negatively impacted by the trend of feminizing Him, which has contributed to a decline in the courage displayed by men today. This shift can be attributed to various factors that have influenced societal perspectives.
In contrast to the promises of Jesus, which include suffering, trials, and pain, it is often only presented to them that Christianity is the solution to these hardships. Instead of acknowledging the reality of challenges, the contemporary portrayal of Christianity tends to market it as the antidote to suffering and pain. It is important to recognize and reflect upon the significant difference between how Jesus called His disciples and the prevailing emphasis on personal relationships with Him today. Instead of inviting them to have a personal connection, He simply said, "Follow me." Understanding this distinction is crucial in our understanding of Jesus' call to discipleship. "Follow me" implies a sense of purpose, a shared mission or goal to pursue. This contrast highlights the divergence between the original intent of discipleship and the way it is often portrayed around me nowadays.
I want to emphasize that I am by no means denying the significance of having a personal relationship with Christ. On the contrary, I am simply highlighting the importance of recognizing that personal relationships, including our relationship with Christ, require more than just superficial connections. They demand a deep sense of faith, trust, and communion with Him. Drawing inspiration from the courageous example of Jesus, who fearlessly confronted societal norms and spoke truth to power, our relationship with Him can empower us to embrace courage in our own lives. Just as Jesus fearlessly faced opposition, persecution, and ultimately sacrificed Himself for the sake of others, our connection with Him can embolden us to stand up for what is right, to live out our faith boldly, and to face life's challenges with strength. It is not a casual or complacent association but a courageous and transformative bond that empowers us to live out our faith with conviction and to impact the world around us positively.
As modern sermons take center stage, it's become apparent that there is a tendency to downplay the contrasts found in the teachings of the Bible. As mentions of heaven and hell, sin and life, grace and justice, as well as the analogies involving battles and soldiers for Christ have always been very prevalent, they have become way less common nowadays. We hear fewer calls for Catholics to embrace their crosses and passionately commit themselves to the cause of the gospel and the well-being of others. Instead, the spotlight has shifted towards how the gospel can serve as a tool for personal growth and fulfillment, focusing on self-realization. The gospel is often presented as a therapeutic treatment rather than a heroic challenge. The emphasis lies on the rewards rather than the obstacles, creating the idea of all gain, no pain (lol).
The rise of praise and worship music has also brought about significant changes in people's perception of Christ. While traditional hymns focused on singing about God, emphasizing His greatness, power, and distinctiveness, praise and worship music takes a different approach. It presents God as a close companion, an intimate presence by our side, emphasizing His love and care for us. This shift in emphasis, while not inherently negative, certainly plays a substantial role in shaping our understanding of Christ's nature and relationship with us.
Jesus is the Epitome of Masculinity
I believe Jesus stands as the epitome of masculinity, offering an unrivaled example for men to emulate. Through His life and teachings, He reveals the true essence of what it means to be a man. He leads with courage, facing challenges head-on without hesitation. His fearlessness shines through as He confronts opposition and stands firm in His convictions. Moreover, His love is not self-serving but sacrificial, displayed vividly through His ultimate act of giving His own life for the sake of others. And in the face of adversity, His resolve remains unshakeable, inspiring men to stand strong in their beliefs and principles. Jesus, in His entirety, embodies the essence of true masculinity, setting an unparalleled standard that us men must aspire to.
Around me, I’m often seeing a tendency to shy away from addressing challenging subjects with resolute conviction. Rather than speaking with clarity and certainty, there is a preference for using vague language and ambiguous statements to navigate sensitive issues. In stark contrast, Jesus stood firmly and fearlessly, fearlessly proclaiming His truth. His words shook the foundations of societal norms, demanding radical commitment from His followers. True boldness lies in the courage to speak truth, even when faced with opposition and adversity.
Boldness is a very masculine characteristic. While some may argue that boldness is not exclusive to gender, the Bible primarily associates this characteristic with men. On the other hand, the beauty of women is highlighted through the importance of a gentle and quiet spirit, which also very much holds great value in the eyes of God. 1 Peter 3:4 addressing woman and wives, "Let your adorning be the hidden person of the heart with the imperishable beauty of a gentle and quiet spirit, which in God's sight is very precious." This reminds us that inner qualities such as a gentle and tranquil demeanor also hold significant worth and are highly esteemed.
As Jesus exemplified true boldness, courageously speaking God's truth regardless of the consequences. His courage serves as the ultimate model of masculinity, inspiring men to fearlessly pursue God's will. Jesus exemplified bravery, rooted in His deep reverence for God. Unlike the fear of man, which arises from sin, Jesus' bravery stemmed from His love for God. His resolute posture and authoritative responses to godless men demonstrated a masculinity untainted by timidity. Jesus taught us to lead with courage, grounded in reverence for God and faith in His sovereignty.
In a culture where love is often misrepresented, Jesus' sacrificial love stands as the true definition. Love, as demonstrated by Jesus, goes beyond superficial feelings; it entails sacrificial commitment. Jesus willingly laid down His life for His bride, the Church, showcasing the essence of true masculinity. Men are called to sacrificially love their wives, mirroring Christ's example. This selfless love forms the foundation for men to protect, nurture, and fight for those entrusted to their care.
Christ's resolve was the driving force behind the cross, demonstrating His commitment to fulfill His mission. His choice to embrace the cross, knowing the suffering and wrath He would endure, showcases resolute masculinity. In history, heroic moments of perseverance are predominantly marked by male resolve. The biological advantage provided by testosterone further supports men's capacity for enduring resolve. Jesus' resolve to save His people from sin teaches men to stand firm in the face of challenges, abiding in their commitment to their calling.
Restoring the Church's Boldness and Reclaiming Biblical Masculinity and Femininity
The landscape of the Church has undergone a significant transformation, moving away from its historic expression of Christianity. We've witnessed a shift from powerful, convicting sermons to soft, TED-talk style infotainment. Classic hymns highlighting doctrine, sacrifice, and piety have been replaced by emotionally driven love songs that resemble romantic ballads. It's clear that the local church has undergone a real emasculation.
This departure from biblical foundations has contributed to a great deal of confusion within the Church, particularly concerning the understanding of biblical manhood and womanhood. The increasing push for egalitarianism has led to women fighting for leadership roles, while men find themselves adrift without clear guidance regarding their responsibilities in marriage, the church, and the family. I believe this confusion and distortion of gender roles to be the enemy's central strategy for our generation. By infiltrating the Church with a heightened emphasis on feminine emotion, the enemy has left us unprepared for moments requiring masculine boldness, fearlessness, sacrifice, and resolve.
We must acknowledge that there is a difference between a surface-level expression of faith and the profound conviction displayed by those facing intense trials. The challenges and hardships that people face in the midst of adversity provide a profound glimpse into the strength and genuineness of their faith. These trials are a powerful testimony to their commitment and courage. Throughout history, numerous Christians have faced unimaginable suffering, even enduring torture, dismemberment, and martyrdom, all because of their devotion to Christ. Their remarkable sacrifices inspire us and remind us of the immense cost of following Jesus. Yet, the trend of timidity displayed by the present-day Church, yielding to government overreach or even complying with laws that endorse sexual sin contrary to biblical teachings, will come at a significant cost.
It is high time for the Church to reclaim its boldness and restore the biblical understanding of masculinity and femininity. We must reject the watered-down version of Christianity that has spread throughout our culture and embrace a faith rooted in conviction and sacrifice. By understanding and embracing the unique roles and responsibilities of men and women as outlined in Scripture, we can restore clarity and purpose to our families, churches, and communities. Let us rise above the societal pressures, rekindle the fire of biblical truth, and stand firm in our commitment to Christ, no matter the cost.
As we progress, it becomes clear that the importance of strong, virtuous Catholic men is growing. This should not catch us off guard. The feminist movement of the 21st century is truly toxic. It goes way beyond advocating for the rightful appreciation of women; it seeks to establish female dominance. Moreover, its influence knows no boundaries. Like the LGBTQ community, its aim is to permeate every aspect of public, personal, and spiritual life. We must not only be alarmed by this trend but also prepare ourselves to stand firmly against it. We need biblically grounded shepherds and faithful women who can discern the subtle infiltration of an effeminate culture and guard against it.
Let us not forget that Catholicism is not egalitarian. While men and women are equally valued before the cross, our roles and responsibilities differ. In marriage, Christianity follows a complementarian model, where the husband leads with sacrificial love, and the wife respects and supports him. People are too sensitive about the word “patriarchy” nowadays. In terms of leadership, the Church holds a patriarchal stance. At the same time, patriarchy, like any other system, is not immune to the potential for sinful expressions. However, when approached with sacrificial love, adherence to biblical order, and a commitment to honoring God, the structure of patriarchy - as well as areas such as marriage, fatherhood, and heterosexuality - can yield to way more goodness. We should strive for a church culture that aligns with the gender-culture outlined in God’s Word: gentle, safe, and encouraging, while also strong, bold, and committed to upholding biblical order and fulfilling the mission entrusted to us. This balance allows the church to fully embody the presence of Christ, enabling His people to confidently advance alongside our great Lord.
We must prepare ourselves for an increasing need for men who embrace biblical masculinity and women who faithfully embody femininity. It is crucial not to overlook the pervasive influence of an effeminate culture and the agenda of distorted ideologies. By embracing the distinct roles and responsibilities that God has given to both men and women, we cultivate a church culture that mirrors the beauty of Christ and empowers His people to wholeheartedly pursue His mission with courage. We must recognize the urgency to embrace and embody biblical masculinity in the face of cultural challenges and shifting ideologies. Equipped with the truth of God's Word, we can navigate the complexities of the world and fulfill our God-given roles with great faith. Let us rise as men who boldly embrace our calling, standing firm in the face of challenges, and wholeheartedly pursuing lives of holiness and service to God and His Church. May we stand united, guided by His Word, and ready to face the battles ahead with strength, grace, and resolved faith.
From Nashville with love,
Suhail Saqan
This was inspired by The Imitation of Christ. Read here.
-
 @ 33c84388:ab6c6bdb
2025-05-09 04:25:30
@ 33c84388:ab6c6bdb
2025-05-09 04:25:30Se você está em busca de uma plataforma de jogos online emocionante, que ofereça uma grande variedade de opções, recursos inovadores e uma experiência do usuário sem igual, a 358Bet é a escolha ideal. Esta plataforma se destaca no competitivo mundo do entretenimento online ao proporcionar uma experiência envolvente e fluida para os jogadores de todo o Brasil. Se você é um jogador experiente ou está apenas começando, a 358Bet oferece algo para todos. Neste artigo, vamos apresentar a 358Bet, destacar alguns dos jogos mais populares da plataforma e discutir a experiência do jogador que a torna um dos destinos mais procurados no universo do entretenimento online.
Introdução à Plataforma: Uma Experiência Robusta e Intuitiva A 358Bet foi desenvolvida para proporcionar aos usuários uma interface simples e intuitiva, que garante uma experiência de navegação tranquila. O layout da plataforma é limpo, organizado e fácil de usar, tornando-a acessível até mesmo para iniciantes. Se você está explorando os jogos, verificando as promoções ou gerenciando sua conta, o site oferece uma jornada sem esforço. A versão móvel da 358beté igualmente impressionante, permitindo que os jogadores desfrutem de seus jogos favoritos a qualquer momento e em qualquer lugar, garantindo que você tenha tudo na ponta dos dedos.
A plataforma também utiliza tecnologias avançadas para garantir que sua experiência seja segura, rápida e confiável. Com o uso de tecnologias de criptografia de última geração, os jogadores podem confiar que suas informações pessoais e financeiras estão sempre protegidas. Esse foco em segurança torna a 358Bet uma plataforma confiável para quem valoriza a privacidade e a proteção de dados.
Além disso, a plataforma é otimizada para oferecer um desempenho excelente, com tempos de carregamento rápidos e mínima possibilidade de quedas. Se você está jogando jogos ao vivo ou explorando novos títulos, certamente apreciará a jogabilidade fluida e responsiva, o que agrega ainda mais qualidade à sua experiência.
Introdução aos Jogos: Uma Seleção Diversificada para Todos os Gostos Um dos principais destaques da 358Bet é sua vasta coleção de jogos. Desde emocionantes jogos de mesa até opções de dealers ao vivo, há sempre algo excitante para jogar. A plataforma oferece uma variedade de jogos de alta qualidade, para agradar a todos os gostos e preferências.
-
Jogos de Slot: Se você gosta de girar os rolos, encontrará uma ampla gama de jogos de slot com diferentes temas, recursos e pagamentos. Desde os slots clássicos até os lançamentos mais modernos, a 358Bet oferece uma seleção diversificada para satisfazer as necessidades de todos os jogadores. Os jogos possuem gráficos impressionantes, trilhas sonoras imersivas e recursos bônus inovadores, tornando cada giro uma aventura emocionante.
-
Jogos de Mesa: Para aqueles que preferem jogos de mais estratégia e habilidade, a 358Bet oferece uma variedade de jogos de mesa, como blackjack, bacará e roleta. Esses jogos oferecem uma experiência clássica com toques modernos, sendo perfeitos para jogadores que buscam tanto diversão casual quanto ação competitiva.
-
Jogos com Dealers Ao Vivo: Se você está buscando uma experiência mais interativa e imersiva, os jogos com dealers ao vivo da 358Bet certamente irão impressionar. Com dealers profissionais, transmissões ao vivo e a oportunidade de interagir com outros jogadores, os jogos ao vivo proporcionam uma experiência que se aproxima muito de um ambiente de jogo físico. Jogadores podem desfrutar de títulos como blackjack e roleta em tempo real, aumentando a excitação do jogo.
-
Esportes Virtuais e Jogos Especiais: Para algo um pouco diferente, a 358Bet também oferece esportes virtuais e jogos especiais. Esses jogos oferecem uma visão única sobre experiências tradicionais de entretenimento, permitindo que os jogadores se envolvam com eventos esportivos virtuais ou testem suas habilidades em desafios rápidos e emocionantes.
Conclusão: Por Que Escolher a 358Bet? A 358Bet é muito mais do que apenas uma plataforma de jogos online; é uma experiência completa de entretenimento. Com uma grande variedade de jogos, uma interface segura e amigável, e um foco incansável na satisfação do jogador, está claro por que tantos optam por essa plataforma. Se você está jogando para se divertir ou buscando grandes vitórias, a 358Bet oferece tudo o que você precisa para uma jornada de jogo envolvente e recompensadora. Com desempenho ágil, uma seleção diversificada de jogos e compromisso com o jogo responsável, a 358Bet é um dos principais destinos para os jogadores no Brasil que buscam melhorar sua experiência de entretenimento online.
-
-
 @ c631e267:c2b78d3e
2025-05-02 20:05:22
@ c631e267:c2b78d3e
2025-05-02 20:05:22Du bist recht appetitlich oben anzuschauen, \ doch unten hin die Bestie macht mir Grauen. \ Johann Wolfgang von Goethe
Wie wenig bekömmlich sogenannte «Ultra-Processed Foods» wie Fertiggerichte, abgepackte Snacks oder Softdrinks sind, hat kürzlich eine neue Studie untersucht. Derweil kann Fleisch auch wegen des Einsatzes antimikrobieller Mittel in der Massentierhaltung ein Problem darstellen. Internationale Bemühungen, diesen Gebrauch zu reduzieren, um die Antibiotikaresistenz bei Menschen einzudämmen, sind nun möglicherweise gefährdet.
Leider ist Politik oft mindestens genauso unappetitlich und ungesund wie diverse Lebensmittel. Die «Corona-Zeit» und ihre Auswirkungen sind ein beredtes Beispiel. Der Thüringer Landtag diskutiert gerade den Entwurf eines «Coronamaßnahmen-Unrechtsbereinigungsgesetzes» und das kanadische Gesundheitsministerium versucht, tausende Entschädigungsanträge wegen Impfnebenwirkungen mit dem Budget von 75 Millionen Dollar unter einen Hut zu bekommen. In den USA soll die Zulassung von Covid-«Impfstoffen» überdacht werden, während man sich mit China um die Herkunft des Virus streitet.
Wo Corona-Verbrecher von Medien und Justiz gedeckt werden, verfolgt man Aufklärer und Aufdecker mit aller Härte. Der Anwalt und Mitbegründer des Corona-Ausschusses Reiner Fuellmich, der seit Oktober 2023 in Untersuchungshaft sitzt, wurde letzte Woche zu drei Jahren und neun Monaten verurteilt – wegen Veruntreuung. Am Mittwoch teilte der von vielen Impfschadensprozessen bekannte Anwalt Tobias Ulbrich mit, dass er vom Staatsschutz verfolgt wird und sich daher künftig nicht mehr öffentlich äußern werde.
Von der kommenden deutschen Bundesregierung aus Wählerbetrügern, Transatlantikern, Corona-Hardlinern und Russenhassern kann unmöglich eine Verbesserung erwartet werden. Nina Warken beispielsweise, die das Ressort Gesundheit übernehmen soll, diffamierte Maßnahmenkritiker als «Coronaleugner» und forderte eine Impfpflicht, da die wundersamen Injektionen angeblich «nachweislich helfen». Laut dem designierten Außenminister Johann Wadephul wird Russland «für uns immer der Feind» bleiben. Deswegen will er die Ukraine «nicht verlieren lassen» und sieht die Bevölkerung hinter sich, solange nicht deutsche Soldaten dort sterben könnten.
Eine wichtige Personalie ist auch die des künftigen Regierungssprechers. Wenngleich Hebestreit an Arroganz schwer zu überbieten sein wird, dürfte sich die Art der Kommunikation mit Stefan Kornelius in der Sache kaum ändern. Der Politikchef der Süddeutschen Zeitung «prägte den Meinungsjournalismus der SZ» und schrieb «in dieser Rolle auch für die Titel der Tamedia». Allerdings ist, anders als noch vor zehn Jahren, die Einbindung von Journalisten in Thinktanks wie die Deutsche Atlantische Gesellschaft (DAG) ja heute eher eine Empfehlung als ein Problem.
Ungesund ist definitiv auch die totale Digitalisierung, nicht nur im Gesundheitswesen. Lauterbachs Abschiedsgeschenk, die «abgesicherte» elektronische Patientenakte (ePA) ist völlig überraschenderweise direkt nach dem Bundesstart erneut gehackt worden. Norbert Häring kommentiert angesichts der Datenlecks, wer die ePA nicht abwähle, könne seine Gesundheitsdaten ebensogut auf Facebook posten.
Dass die staatlichen Kontrolleure so wenig auf freie Software und dezentrale Lösungen setzen, verdeutlicht die eigentlichen Intentionen hinter der Digitalisierungswut. Um Sicherheit und Souveränität geht es ihnen jedenfalls nicht – sonst gäbe es zum Beispiel mehr Unterstützung für Bitcoin und für Initiativen wie die der Spar-Supermärkte in der Schweiz.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 33c84388:ab6c6bdb
2025-05-09 04:22:06
@ 33c84388:ab6c6bdb
2025-05-09 04:22:06A plataforma 944Bet é uma das mais inovadoras opções para quem procura uma experiência de entretenimento online emocionante e segura. Com uma ampla gama de jogos e uma interface amigável, ela se destaca entre outras plataformas e promete proporcionar diversão e recompensas para seus usuários.
Plataforma de Apostas e Jogos de Alta Qualidade O 944Bet foi criado com o objetivo de oferecer uma experiência de usuário única, centrada em jogabilidade fluida e recursos tecnológicos avançados. O site tem uma navegação simples, permitindo que os jogadores se conectem rapidamente e com facilidade, independentemente do dispositivo utilizado, seja desktop ou dispositivos móveis. A plataforma também oferece suporte em português, garantindo que os usuários brasileiros tenham uma experiência personalizada e tranquila.
A interface do 944Bet é limpa e intuitiva, com menus e categorias de jogos bem organizados. Além disso, o design é moderno, com gráficos de alta qualidade que atraem os jogadores e criam um ambiente visualmente agradável. Com uma estrutura confiável e segura, o site assegura que todos os dados pessoais e transações financeiras sejam protegidos, proporcionando tranquilidade para os jogadores.
Variedade de Jogos para Todos os Gostos O 944Bet se destaca pela variedade de opções de entretenimento que oferece aos seus jogadores. Desde jogos de mesa, como blackjack e roleta, até opções mais inovadoras, como slots e títulos de jogos de arcade, a plataforma oferece algo para todos os gostos. Além disso, há uma extensa seleção de esportes virtuais, com eventos e competições simuladas que capturam a atenção de quem gosta de desafios rápidos e emocionantes.
Os jogos disponíveis são atualizados regularmente, garantindo que os jogadores sempre tenham algo novo para explorar. As opções são escolhidas com base na popularidade, no entretenimento e na qualidade da jogabilidade. A plataforma também está em constante evolução, com novos títulos sendo adicionados frequentemente, para que a experiência do usuário nunca se torne monótona.
A Experiência do Jogador no 944Bet A experiência do jogador é uma das prioridades do 944Bet, que se esforça para oferecer uma jornada divertida, envolvente e cheia de oportunidades para ganhar. O processo de inscrição é simples, rápido e descomplicado, permitindo que novos usuários se registrem e comecem a jogar em poucos minutos. O suporte ao cliente é outro ponto forte, com uma equipe dedicada e pronta para ajudar os jogadores em qualquer dúvida ou problema que possa surgir.
Para garantir que os jogadores tenham uma experiência ainda mais rica, o 944Bet oferece uma série de promoções e bônus que incentivam a participação ativa na plataforma. Desde bônus de boas-vindas até ofertas de recarga, os jogadores têm várias oportunidades de aumentar suas chances de ganhar. Essas promoções são oferecidas de forma transparente, permitindo que os jogadores saibam exatamente o que estão recebendo.
Além disso, a plataforma conta com um sistema de pagamento rápido e eficiente, facilitando os depósitos e retiradas de forma simples e sem complicações. As transações são processadas de maneira ágil, e a plataforma aceita uma grande variedade de métodos de pagamento, incluindo cartões de crédito, carteiras digitais e transferências bancárias.
Conclusão O 944Bet é uma plataforma que oferece mais do que apenas jogos de qualidade; ela proporciona uma experiência completa, com uma interface fácil de usar, uma variedade impressionante de opções de entretenimento e um compromisso constante com a segurança e a satisfação do jogador. Se você está em busca de uma nova plataforma para testar suas habilidades e desfrutar de uma experiência divertida, o 944Bet é, sem dúvida, uma excelente escolha. Com recursos que atendem a todos os perfis de jogadores e promoções atrativas, esta plataforma está pronta para se tornar a favorita dos brasileiros.
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 805b34f7:3620fac3
2025-05-09 03:05:22
@ 805b34f7:3620fac3
2025-05-09 03:05:22Humans are evolving with social media & devices. These are powerful tools, but neither is built with their users' health and well-being in mind.
The big tech business incentives are a higher priority than their users' health & well being. This results in their products being designed to capture as much attention from you as possible so they can profit.
Many are realizing this. Few know there are emerging, viable alternatives.
 Nostr is a new model for social media (and much more).
Nostr is a new model for social media (and much more).Bitcoin is a new model for money.
nostr:nprofile1qyt8wumn8ghj7ct49eex2mrp09skymr99ehhyecpp4mhxue69uhkummn9ekx7mqqyr4aa6ffghhs22pmuzkrmcjhslyp56jc5y84druuddsanh238td66va34er is a new model for computers.
This article will explain why Nostr is primed to be the new model for social media.
“We cannot have a society in which, if two people wish to communicate, the only way that can happen, is if it’s financed by a third party who wishes to manipulate you” - Jaron Lanier
What is Nostr? What is Primal?
I’ve done a wonderful job of confusing people by interchanging the words Nostr & Primal. So allow me a brief, high level explanation.
Nostr is an internet protocol that allows for censorship resistant social media.
An internet protocol is a set of rules that computers follow to communicate with each other.
Nostr stands for Notes & Other Stuff Transmitted by Relays.
Primal is an app built on Nostr. I work for Primal the company.
When you post to Primal, you can see your content in other Nostr apps. Primal doesn’t own you, your content or identity. You do. You can take your content and followers to any Nostr app.
In this gif, you can see my content in 5 different Nostr apps.
 Nostr is like email, but for social media—it’s a system where anyone can send and receive posts using any app they like. Similar to how you would send an email to everyone you know. Everyone will receive that email no matter what email service provider they’re using (yahoo, gmail, proton, apple etc).
Nostr is like email, but for social media—it’s a system where anyone can send and receive posts using any app they like. Similar to how you would send an email to everyone you know. Everyone will receive that email no matter what email service provider they’re using (yahoo, gmail, proton, apple etc).When you “create an account” on Primal, you create a password that you can use to log in to any Nostr app. Your password is called a private key and you can use that to log in to any apps that are built on Nostr. See them here at nostrapps.com.
All this may sound a bit confusing, but this is just what's going on under the hood. Primal will feel like any other social media app. Check out this image below to learn more and be sure to keep your private key (your password) safe!
#### How I got into Nostr
Long story short, if you’ve been in to Bitcoin, you at least know about Nostr. I used Twitter as my primary news/Bitcoin source for the past 8 years and followed the Trump and Covid dramas closely.
I’ve come to the conclusion that social media needs to be protocol based and decentralized.
 The first Nostr conference in March of 2023 was in Uvita, Costa Rica. I was living in the area, so of course I showed up. Here’s a brief video we made from the conference.
The first Nostr conference in March of 2023 was in Uvita, Costa Rica. I was living in the area, so of course I showed up. Here’s a brief video we made from the conference. Why I'm Stoked on Nostr
The Everything App for Social Media
This is the original idea that made the lightbulb in my head go off. 1 identity for all types of content.
I have accounts on Youtube, Twitter, Nostr, Instagram, TikTok, & Medium. That means 6 different logins, 6 different follower sets, and 6 places to post when I have something to share.
With Nostr, I have 1 identity, 1 follower set, & (potentially) 1 place to post each type of content.
On the Left - 5 apps, 5 identities. Right - 5 apps, 1 identity
 The Nostr apps are in their infancy, but I can imagine a future with more diverse apps specified by content type (blogs, long form vid, vertical vids, music, etc.).
The Nostr apps are in their infancy, but I can imagine a future with more diverse apps specified by content type (blogs, long form vid, vertical vids, music, etc.).The ability to post all of your content to (potentially) one app and giving your audience the choice to consume that content in whatever app they please is revolutionary.
X wants to be the everything app as well. It looks like it's heading towards becoming the WeChat of the West. This begs the question... Does the infrastructure for social media need to be owned by singular corporations or governments?
Check out this video where nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyehwumn8ghj7mnhvvh8qunfd4skctnwv46z7ctewe4xcetfd3khsvrpdsmk5vnsw96rydr3v4jrz73hvyu8xqpqsg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q8dzj6n & nostr:nprofile1qyt8wumn8ghj7ct5d3shxtnwdaehgu3wd3skueqpz4mhxue69uhk2er9dchxummnw3ezumrpdejqqgyymmnwvah9hdnmft2wqsk0wr9as6q32hd4xk2zlnr2q5ectznjgqd27v94 discuss everything apps during the 2nd Nostr conference in Japan.
Nostr is the tool to orange pill the world
Orange pilling is a slightly cringe term used to describe educating people about Bitcoin. In Nostr, we say purple pilling because for some reason, Nostr’s theme is purple.
Jargon aside, the reason I believe that Nostr will orange pill the world is because of zaps!
Zaps are micropayments of bitcoin. You can send zaps on posts as easily as you can send likes on posts with Primal’s built in wallet and creators keep 100% of what they earn. They’re the best way to really feel the Nostr difference.
Here’s an example of me zapping 210 sats to a few people with one click.
 I've now personally watched over 20 people receive and send their1st Bitcoin transactions minutes after downloading Primal. Right away you pop two cherries, owning Bitcoin and sending Bitcoin. Pretty rad.
I've now personally watched over 20 people receive and send their1st Bitcoin transactions minutes after downloading Primal. Right away you pop two cherries, owning Bitcoin and sending Bitcoin. Pretty rad. It's a fundamentally different experience to touch Bitcoin through a social media style app than it is to buy bitcoin from an exchange. Someone new on Primal immediately has a use case for Bitcoin upon downloading the app. Zaps!
Nostr is known as the Bitcoiner social network. It could be/is becoming the place for newbies to come learn about Bitcoin, and interact with people who can help teach. I see a massive opportunity for Primal to play a huge role in this transition to a bitcoin standard.
I wonder how often this scenario with nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytn0wpjku6r0danxgtnwdsqzpq8gr333mlm73rnsfv2uvsrtvg44l5l5r0qrn6c0fw08t5hkccwarhnfev will repeat. Also, check out this video about how zaps got nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyw8wumn8ghj7mn0wd68ytnzd96xxmmfdejhytnnda3kjctvqqstkm5tw5w2f2qg2zp0tzxk9junagtrqeayyxnzggqcphgec9p37ncc26xj6 to read The Bitcoin Standard.
Micropayments on the internet are only possible with digitally native money.
Zaps are signal. They’re pure life force energy given to another person in appreciation for their content and it's unique to Nostr.
 Social media is simply better with payments. You cannot unsee or unfeel this. We're only beginning to scratch the surface of what zaps mean to a social network. Should be fun :)
Social media is simply better with payments. You cannot unsee or unfeel this. We're only beginning to scratch the surface of what zaps mean to a social network. Should be fun :) Sovereignty
Today, our digital lives are owned. Our data, identity, and content can be taken away.
Nostr flips this. We own our identity & choose where our data lives. Companies no longer have singular control over the flow of information.
Bitcoin gives you private keys for money. Nostr gives you private keys for speech.
On X and Instagram, we make a username and password. We are renting these identities from these corporations. How do we know these identities are not yours? Because they can be taken away from you.
 With Nostr, you and only you have your keys. You can post anytime, from any app, using your own key. If Primal stops working, no big deal. You could post from other Nostr apps.
With Nostr, you and only you have your keys. You can post anytime, from any app, using your own key. If Primal stops working, no big deal. You could post from other Nostr apps. I believe there’s something deeper going on here. Humans are sovereign beings. Being sovereign means being in full control.
With Nostr & Bitcoin, we can be in complete control of our money & speech.
These tools empower humans and reduce our need for dependence on 3rd parties.
Nostr allows us to create & share freely without the potential of being silenced for “wrongthink”.
It’s time for those who care about sovereignty to build their brands on their own land.
Nostr is Organic
Facebook wanted to connect the world. They’ve done an absolutely fantastic job at this. But at what cost?
The ad model has been the best way for platforms to monetize their services. This leads to bad incentives. Social media sites need you to spend as much time as possible on their apps so that they can sell your attention to advertisers.
Maybe there’s more ethical ways to advertise that do not lead to perverse incentives, but this isn’t the point.
Now, social media is basically a dopamine slot machine serving us things that we’re most likely to engage with. Whatever we lend our eyes to, purposefully or not, is the content we’re fed. Engagement is the north star of current social media. This modifies the behavior of everyone on the app.
These algorithms have been weaponized at times. And many would say that they’re programming us.
Let me speak in meme for a moment here:

 It’s different on Nostr
It’s different on NostrAfter using Nostr for a couple years, it’s clearer to me when I switch to another social media platform that they are doing everything they can to grab my attention. They being the platform and the creators. I can feel when people create for an algo vs. for an audience.
With Primal, I can select which algorithm I want to use or create my own feeds using Primal’s advanced search. (I expect these tools to get much better over time.) This gives the user much more control over what they see vs a singular algorithm. Algorithmic choice is something that legacy social media platforms are greatly missing.
I can also control which feed I want to see when I open the app. For example, I created this feed of one person saying “STAY FOCUSED CHAMP” so when I open the app I’m not immediately distracted. Look at what instagram does when you want to simply search for someone’s account…
I can’t help but envision a world where all of the content is posted to Nostr. The apps with the best user experiences would win. I’d imagine the winners would have the best algos, least intrusive ads, and would give their users the most control over their experience.
Thought Experiment
Pretend you’re a super intelligent being looking down upon the earth.
The1st thing you’d notice is that they’re always staring at their phones. You’d also notice that while they have an abundant earth, they insist on chemically altering their food which is making them sick.
Then, you’d notice that the money humans work their entire lives for can be and is manipulated by central authorities with zero effort.
And, you’d notice that the “digital global town square” is owned by a unelected, fallable humans and corporations.\ It’s laughable!
It doesn’t have to be this way anymore. And it’s up to us to change it.
To conclude.
This article is not meant to trash talk other platforms, those who use them, or those who created them. I use them daily. Mostly to advocate for Nostr & Bitcoin these days.
These platforms have created a ton of value for the world, & Nostr can be used alongside of them.
Maybe if Nostr existed back then, they would’ve built on it.
“We shape our tools, and thereafter our tools shape us”. We’ve learned priceless lessons from the evolution of social media thus far. We can use these lessons to shape tools with our health & well-being as our first priority.
We can obsolete these outdated, unhealthy systems.
Nostro and Nuestro mean 'ours' in Italian & Spanish. I don't think this a coincidence. Nostr is our chance to create a better internet for our future generations.
pura vida
(meme cred nostr:nprofile1q9n8wumn8ghj7enfd36x2u3wdehhxarj9emkjmn99ah8qatzx9kx2mrtdqeks6rcwuukserhd33hq6ekwyuhgvrcwsukvdme0fjnq7fsdeuxz7nk0fck5mtjv5ehqwfc0qehxargddm8j73lvfex7ctyvdshxapaw3e82egpp4mhxue69uhkummn9ekx7mqqyrl8767x7uecka4mlqxmgq4duev48cst9u37vm5fsgztv0xyy5u6xs34wwg also check out his nostr doc )

-
 @ 362fd2b5:0ce4005f
2025-05-09 02:41:17
@ 362fd2b5:0ce4005f
2025-05-09 02:41:17Source: Kenken_coffee11
Coffee Bean Panama🇵🇦Altieri Dilgo Geisha Natural Anaerobic Cold Fermentation
☕️ Recipe 📍Coffee : 12g 📍Grinder : LAGOM casa 16.5 📍Water : GH80 / KH40, MgSO₄75 / CaCl₂5 / 📍NaHCO₃40 📍Water temperature : 97℃ 📍Brew ratio : 1:16.7 (200ml) 📍Brewer : HARIO V60 01 or 02 📍Filter : CAFEC CC1-100W 📍TDS : 1.44% 📍Extraction yield : 21.12%
🫗Pouring Paragon ON ①0:00 50g Stir ②0:30 100g ③1:00 200g Spin Paragon OFF 2:40 Drawdown complete.
https://video.nostr.build/43df934a772bcc827f36519f7cbb630b1f0097e40e5991e8d3dbb1dd023a8f6a.mp4
Coffee
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 3eba5ef4:751f23ae
2025-05-09 01:52:16
@ 3eba5ef4:751f23ae
2025-05-09 01:52:16Crypto Insights
Proposal to Remove OP_RETURN Limit Sparks Heated Debate Among Developers
Introduced in 2014, OP_RETURN allows small pieces of data—like timestamps or short messages—to be included in Bitcoin transactions, serving as a lightweight method to store limited information on-chain. Over time, the size limit was reduced to prevent spam, before settling at the current 83 byte-limit.
Peter Todd recently proposed removing the limit entirely. He argues that the restriction fails to deter misuse and instead complicates things, as it pushes developers to use workarounds—like
scriptsigor unspendable outputs (such as storing data in unspendable Taproot outputs)—to embed media, spam, or arbitrary data, which bloats the UTXO set.Pieter Wuille, who also supports lifting the OP_RETURN cap, points out that standardness policies can’t truly stop well-funded entities from broadcasting data-heavy transactions directly to miners. The network is strong and block space is always full—even without spam, so those rules are no longer as useful.
In short, those in favor of removing the OP_RETURN limit argue that the restriction is futile, and that alternative data storage methods within blocks already exist in abundance.
On the other side, opponents believe the limit must stay, as using OP_RETURN to store arbitrary data violates Satoshi’s intent and Bitcoin’s purpose as a financial network (Luke Dashjr). Other opposing voices include:
- @Mechanic from Ocean Mining: The devs just instinctively knew, you don’t use Bitcoin for arbitrary file storage and you do everything you can to make Bitcoin awkward to use for that purpose.
- Jason Hughes: Bitcoin Core developers are about to merge a change that turns Bitcoin into a worthless altcoin…
Here for more perspectives on this debate.
Comparing Three Cluster Linearization Techniques
Pieter Wuille compares three cluster linearization strategies—SFL (spanning-forest linearization), GGT, and CSS (candidate set search)—and follows up with benchmark results for each.
StarkWare Introduces ColliderVM: A BitVM Alternative for Computation and L2 Bridges
ColliderVM protocol is StarkWare’s research effort on a BitVM alternative. It retains the same trust assumptions but without needing fraud proofs, thus eliminating fraud-proof time window. Researchers use ColliderVM to sketch a trustless bridge design to a L2 network, aiming to scale Bitcoin with a rollup-like design and enabling more functionality and privacy.
The paper: ColliderVM: Stateful Computation on Bitcoin without Fraud Proofs
And a talk: Bitcoin Horizons: from OP_CAT to Covenants
Bitcoin Goes Green(ish): Over 50% of Mining Now Uses Sustainable Energy
A report from the Cambridge Centre for Alternative Finance (CCAF) finds that 52.4% of Bitcoin mining now uses green energy. Of that, 42.6% comes from renewables such as hydro and wind, while 9.8% comes from nuclear.
Top Reads on Blockchain and Beyond
Kraken Shares Lessons on Identifying a North Korean Hacker in Job Recruitment
Kraken recently uncovered a North Korean hacker attempting to apply for a job. They’ve shared insights on how to detect and prevent such actors at various stages of the hiring process.
Round-Efficient Adaptively Secure Threshold Signatures with Rewinding
A threshold signature scheme allows distributing a signing key to n users, such that any t of them can jointly sign, but any t−1 cannot. It is desirable to prove adaptive security of threshold signature schemes, which considers adversaries that can adaptively corrupt honest users even after interacting with them. For a class of signatures that relies on security proofs with rewinding, such as Schnorr signatures, proving adaptive security entails significant challenges. This work proposes two threshold signature schemes that are provably adaptively secure with rewinding proofs. Our proofs are solely in the random oracle model (ROM), without relying on the algebraic group model (AGM).
Read the full paper.
Vitalik on Simplifying Ethereum L1, Taking Cues from Bitcoin’s Minimalism
In a new post titled Simplifying the L1, Vitalik suggests simplifying Ethereum’s base layer by moving from EVM to RISC-V (or another minimal VM), adopting Simple Serialize, and embracing Tinygrad’s coding philosophy.
Key impacts of this shift include:
- Radical efficiency improvements: Contracts can run directly in ZK provers without interpreter overhead. According to Succinct, performance could increase by over 100x in many cases.
- Radically improved simplicity: RISC-V spec is far more minimal than the EVM. Other options like Cairo also offer a simple design.
- All the benefits that motivated Ethereum Object Format (EOF): Including code sections, friendly static analysis, and larger code size limits.
- Expanded tooling: Solidity and Vyper can target the new VM with backend updates. If RISC-V is chosen, developers may be able to port existing code from mainstream languages.
- Reduced reliance on precompiles: Most precompiles may become obsolete—except perhaps highly optimized elliptic curve operations, which could also be phased out with advances in quantum computing.
-
 @ 3eba5ef4:751f23ae
2025-05-09 01:49:00
@ 3eba5ef4:751f23ae
2025-05-09 01:49:00加密洞见
取消 OP_RETURN 限制?引发比特币开发者激辩论
OP_RETURN 于 2014 年推出,允许将小块数据(如时间戳或短消息)包含在比特币交易中,作为在比特币链上存储有限信息的轻量级方式。出于防止垃圾信息的考虑,OP_RETURN 当前的大小限制是 83 字节。
Peter Todd 最近提议完全取消该限制。他认为该限制无法有效遏制滥用,反倒让事情更加复杂。因为它迫使一些开发人员采用各种变通方式——如使用 scriptsig 或不可花费输出(比如这里介绍了在无法花费的 Taproot 输出上存储数据的方式)——来存储媒体、垃圾信息和其他任意数据,这会导致 UTXO 集膨胀。
Pieter Wuille 同样主张 取消 OP_RETURN 限制。他认为,标准性策略并不太可能真正阻止那些由资金充足的组织创建的数据交易被确认——这些组织会将交易直接发送给矿工。此外,现在网络中的区块基本始终满载——即便是没有垃圾信息——因此 OP_RETURN 限制这样的规则已经没有效用。
总之,支持取消 OP_Return 限制一方的理由是,该限制是徒劳的,区块内已经有其它数据存储的替代方案。
反对该提案的一方则认为必须保留该限制,因为通过 OP_Return 存储任意数据违反了中本聪的初衷,也偏离了比特币作为金融网络的核心目的(Luke Dashjr)。其他反对意见包括: - 来自 Ocean Mining 的 @Mechanic:「开发者凭直觉就知道,不应用比特币来存储任意文件,而且应该尽一切可能让比特币难以用于这个目的。」 - Jason Hughes:「Bitcoin Core 开发人员即将合并一项将比特币变成毫无价值的山寨币的更改」……
了解争论中的更多观点,可以参考这里。
三种集群线性化技术比较
Pieter Wuille 在本文中比较了 SFL (spanning-forest linearization)、GGT 、CSS (candidate set search) 三种集群线性化技术之间的基本权衡,并跟进了每种技术的实现基准。
StarkWare 推出 ColliderVM:用于计算和桥接的 BitVM 替代协议
ColliderVM 是 StarkWare 研究的一个 BitVM 的替代协议,使用与 BitVM 相同的信任假设,但不需要欺诈证明,同时也能实现更广泛的功能,如智能合约和二层桥接。
相关论文:ColliderVM: Stateful Computation on Bitcoin without Fraud Proofs
相关视频:Bitcoin Horizons: from OP_CAT to Covenants
剑桥研究:比特币挖矿正使用超过 50% 的绿色能源
剑桥替代金融中心(CCAF)的一份新报告称,现在 52.4% 的比特币挖矿由绿色能源提供动力,其中 42.6% 来自水力和风能等可再生能源,9.8% 来自核能。比特币矿工正在通过减少化石燃料的使用和更好地管理硬件废物来改善他们的环境足迹。
精彩无限,不止于链
如何识破朝鲜黑客?Kraken 分享招聘经验
Kraken 团队最近发现一名朝鲜黑客试图通过申请工作,于是就如何在招聘流程每个阶段中识别并防范黑客分享了经验。
带回绕的轮次高效自适应安全门限签名方案
门限签名方案允许将一个签名密钥分发给 n 个用户,使得其中任意 t 个用户可以联合生成签名,但任意 t−1 个用户则无法做到这一点。研究者希望门限签名方案(Threshold Signatures)能具备自适应安全性,即在面对能够在交互后动态腐化诚实用户的对手时仍然保持安全。对于一类依赖带回绕(rewinding)证明的签名方案(如 Schnorr 签名),证明其自适应安全性是一个重大挑战。论文提出了两种在带回绕证明下可证明具备自适应安全性的门限签名方案。其安全性证明完全基于随机预言机模型(ROM),不依赖代数群模型(AGM)。
论文全文:Round-Efficient Adaptively Secure Threshold Signatures with Rewinding
以太坊如何简化 L1,实现对标比特币的简洁架构
Vitalik 近日发表 Simplifying the L1 ,建议简化以太坊 L1,从 EVM 迁移到 RISC-V(或其他最小 VM),采用「简单序列化」(Simple Serialize),仿效 Tinygrad 的简洁代码风格。
特别地,关于 RISC-V,Vitalik 认为这一转变会带来:
- 效率革命性提升:在 ZK 证明者内部,智能合约可直接执行,无需解释器开销。Succinct 数据显示,在多数场景下性能可提升百倍以上。
- 结构极致简化:RISC-V 规范相较于EVM 极为精简,其他候选方案(如 Cairo)同样具备简洁特性。
- 继承 EOF 的所有优势:包括代码分段管理、更友好的静态分析支持,以及更大的代码容量限制。
- 开发者工具链扩展:Solidity 和 Vyper 可通过新增后端编译支持新架构;若选择 RISC-V,主流语言开发者可直接移植现有代码。
- 消除对大部分预编译的要求:也许除了保留高优化的椭圆曲线运算外,大部分预编译功能将不再必要(而椭圆曲线也许也会随量子计算发展被淘汰)。
-
 @ a296b972:e5a7a2e8
2025-05-05 22:45:01
@ a296b972:e5a7a2e8
2025-05-05 22:45:01Zur Gründung der Bundesrepublik Deutschland wurde infolge der Auswirkungen des 2. Weltkriegs auf einem Teil des ehemaligen Deutschen Reiches (nicht des 3. Reiches!) auf Initiative der westlichen Alliierten, federführend die USA als stärkste Kraft, eine demokratische Grundordnung erarbeitet, die wir als das Grundgesetz für die Bundesrepublik Deutschland kennen und schätzen gelernt haben. Da man zum damaligen Zeitpunkt, im Gegensatz zu heute, noch sehr genau mit der Sprache war, hat das Wort „für“ größere Bedeutung, als ihm heute zugesprochen wird. Hätte der unter westlich-alliierter Besatzung stehende Rumpf des Deutschen Reiches eigenständig eine Verfassung erstellen können, wäre es nicht Grundgesetz (das laut Definition einen provisorischen Charakter hat) genannt worden, sondern eben Verfassung. Und hätte diese Verfassung eigenständig erarbeitet werden können, hätte sie geheißen: Verfassung der Bundesrepublik Deutschland.
Es heißt zum Beispiel auch: Costituzione della Repubblica Italiana. also Konstitution der Republik Italien, und nicht Costituzione per La Repubblica Italiana.
Es ist nachvollziehbar, dass die Bedenken der westlichen Alliierten aufgrund der Nazi-Zeit so groß waren, dass man den „Deutschen“ nicht zutraute, selbständig eine Verfassung zu erstellen.
Zum vorbeugenden Schutz, es sollte verunmöglicht werden, dass ein Regime noch einmal in der Lage sei, die Macht zu ergreifen, wurde als Kontrollinstanz der Verfassungsschutz gegründet. Dieser ist dem Innenministerium gegenüber weisungsgebunden. Die jüngste Aussage, auf den letzten Metern der Innenministerin Faeser, der Verfassungsschutz sei selbständig, ist eine manipulative Beschreibung, die davon ablenken soll, dass das Innenministerium dem Verfassungsschutz sehr wohl übergeordnet ist. Das Wort „selbständig“ soll Eigenständigkeit vorgaukeln, hat aber in der Hierarchie keinerlei Bedeutung.
Im Jahre 1949 herrschte ein anderer Zeitgeist. Werte wie Ehrlichkeit, Redlichkeit und Anständigkeit hatten noch eine andere Bedeutung als heute. Politiker waren noch von einem anderen Schlag und hatten weitgehend den Anspruch zum Wohle des Volkes zu entscheiden und zu handeln. Diese Werte reichten noch mindestens bis in das Agieren des Bundeskanzlers Helmut Schmidt hinein.
Niemand konnte sich deshalb zum damaligen Zeitpunkt vorstellen, dass dieser eigentlich als Kontrollinstanz gedachte Verfassungsschutz einmal von der Politik missbraucht werden könnte, um oppositionelle Kräfte auszuschalten zu versuchen, wie es mit der Einstufung der AfD als gesichert rechtsextrem geschehen ist. Rechtlich hat das noch keine Konsequenzen, aber es geht in erster Linie darum, dem Image der AfD zu schaden, um weiteren Zulauf zu verhindern. Diese Art von Durchtriebenheit kam in den Gedanken und dem Ehrgefühl der damals verantwortlichen Politiker noch nicht vor.
Die ehemaligen Volksparteien, man kann auch sagen, die Alt-Parteien, sehen ihre Felle schon seit einiger Zeit davonschwimmen. Die Opposition hat derzeit die Zustimmung einer ehemaligen Volkspartei überholt und ist sogar stärkste Kraft geworden. Sie repräsentiert aktuell rund 10 Millionen der Wähler. Tendenz steigend. Und das die folglich auch gesichert rechtsextrem gewählt haben, oder gar gesichert rechtsextrem sind, wird ihnen vielleicht nicht besonders schmeicheln.
Parallel dazu haben die Alt-Parteien die Medienlandschaft gekapert und versuchen mit Einschränkungen der Meinungsfreiheit, sofern sich Kritik gegen sie richtet und durch selbstermächtigte Entscheidung über das, was Wahrheit und Lüge ist, unliebsame Stimmen mundtot zu machen, um unter allen Umständen an der Macht zu bleiben.
Diese Vorgehensweise widerspricht dem demokratischen Verständnis, das aus dem, wenn auch „nur“ Grundgesetz, statt Verfassung, hervorgeht und die Nachkriegsgenerationen im besten Sinne beeinflusst und demokratisch geprägt hat.
Aus dieser Sicht können die Aktivitäten der Alt-Parteien nur als Angriff auf die Demokratie, wie sie diese Generationen verstehen, gesehen werden.
Daher führt jeder Angriff der Alt-Parteien auf die Demokratie dazu, dass die Opposition immer mehr an Stimmen gewinnt und wohl weiterhin gewinnen wird.
Es erschließt sich nicht, warum die Alt-Parteien nicht auf die denkbar einfachste Lösung kommen, Vertrauen in ihre Politik zurückzugewinnen, in dem sie eine Politik machen würden, die dem Willen der Bürger entspricht. Mit dem Gegenteil machen sich die Volksvertreter zu Vertretern ohne den Rückhalt vom Volk, und man muss sich fragen, wessen Interessen sie derzeit wirklich vertreten. Bestenfalls die eigenen, schlimmstenfalls die des global agierenden Tiefen Staates, der ihnen ins Ohr flüstert, was sie zu tun haben.
Mit jeder vernunftbegabten Entscheidung, die dem Willen des Souveräns entspräche, würden sie die Opposition zunehmend schwächen. Da dies nicht geschieht, kann man nur zu der Schlussfolgerung kommen, dass sich hier auch selbstzerstörerische, suizidale Kräfte festgesetzt haben. Es ist wie eine Sucht, von der man nicht mehr loslassen kann.
Solange die Alt-Parteien nicht in der Lage sind, die Unzufriedenheit in der Bevölkerung wahr- und ernst zu nehmen, werden sie die Opposition stärken und zu immer rigideren Maßnahmen greifen müssen, um ihre Macht zu erhalten und sich damit immer mehr von demokratischen Verhältnissen entfernen, und zwar genau in die Richtung vor der die Alt-Parteien in ihrer ideologischen Verirrung warnen.
Seitens der Opposition gibt es in der Gesamtschau keine Anzeichen dafür, dass die Demokratie abgeschafft werden soll, im Gegenteil, es wird für mehr Bürgerbeteiligung plädiert, was ein sicheres Merkmal für demokratische Absichten ist.
Aus Sicht der Alt-Parteien macht die Brandmauer Sinn, weil sie sie vor ihrem eigenen Machtverlust schützt. Der Fall der Berliner Mauer sollte ihnen eigentlich eine Warnung sein.
Fairerweise darf nicht unterschlagen werden, dass es in der Opposition einige Verirrte gibt, wobei noch interessant wäre zu erfahren, welche davon als V-Männer des Verfassungsschutzes eingeschleust wurden. Diese jedoch zum Anlass zu nehmen, die Opposition unter Generalverdacht zu stellen, steht einem demokratischen Handeln diametral entgegen.
Das Grundgesetz wird so nicht geschützt, sondern bis kurz vor der Sollbruchstelle verbogen.
Die Einstufung der Opposition als gesichert rechts-extrem beruht auf einem mutmaßlich 1000 Seiten starken Papier, das offensichtlich nur ein erlesener Kreis zu sehen bekommen soll. Dazu gehört nicht die Bevölkerung, die sicher nur einmal mehr nicht zu Teilen verunsichert werden soll. Und selbstverständlich schon gar nicht diejenigen, die es betrifft, nämlich die Opposition.
Eine eindeutige Fragwürdigkeit der Aktivitäten des Verfassungsschutzes wäre schwerer festzustellen, wenn es gleichwohl Parteien gäbe, die als gesichert links-extrem oder zumindest als links-extremer Verdachtsfall eingestuft würden. Nicht ganz unberechtigte Gründe hierfür könnten schon gefunden werden, wenn der politische Wille es wollte.
Auch die seltsam-umstrittene Installierung des Präsidenten des Bundesamtes für Verfassungsschutz (genau genommen für Grundgesetzschutz) lässt Fragen offen.
Generell müsste es eine unabhängige Überprüfung geben, ob die Gewaltenteilung in Deutschland noch gewährleistet ist, da es durch das augenscheinliche Zusammenspiel in der Richterschaft, der Gesetzgebung und der vierten Gewalt, den Medien, Anlass zu Zweifel gibt.
Diese Zweifel sind nicht demokratiegefährdend, sondern im Gegenteil, es ist demokratische Pflicht, den Verantwortlichen kritisch auf die Finger zu schauen, ob im Sinne des Souveräns entschieden und gehandelt wird. Zweifel könnte man dadurch ausräumen, in dem eindeutig bewiesen würde, das alles seine Richtigkeit hat.
Das wäre vornehmlich die Aufgabe der Alt-Medien, die derzeit durch Totalversagen glänzen, weil alles mit allem zusammenhängt, jeder jeden kennt und man es sich über Jahre so eingerichtet hat, dass man gerne unter sich bleibt und Pöstchen-Hüpfen von einem Lager ins andere spielt.
Vielleicht ist es sogar nötig, dass zur unabhängigen Überprüfung, die Alliierten, inklusive Russland, noch einmal, nach rund 80 Jahren, auf den Plan gerufen werden müssen, um sozusagen eine Zwischenbilanz zu ziehen, inwieweit sich das einst etablierte, demokratische System bewährt hat, und ob es derzeit noch im ursprünglichen Sinne umgesetzt und gelebt wird. Es ist anzunehmen, dass hier ein gewaltiges Optimierungspotenzial zum Vorschein kommen könnte.
Viele Bürger in Deutschland haben den Wunsch, wieder in einer Demokratie zu leben, die ihre Namen auch verdient hat. Sie wollen wieder frei ihre Meinung jeglicher Art aussprechen können, miteinander diskutieren, auch einmal Unsinn reden, ohne, dass sie der Blockwart gleich bei einem Denunzierungsportal anschwärzt, oder sie Gefahr laufen, dass ihr Konto gekündigt wird, oder sie morgens um 6 Uhr Besuch bekommen, der noch nicht einmal frische Semmeln mitbringt.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ a8d1560d:3fec7a08
2025-05-09 01:08:02
@ a8d1560d:3fec7a08
2025-05-09 01:08:02h1 🙂
h2 😈
h3 😴
h4 💩
h5 👾
h6 😺
codeblock 😮💨🤖😨😎😉🛹🧗🏻♀🥉🤸🏻♂️Further tests
😊🤩🥵🤪😥😈👽👈🏻👆🏻☝🏻👌🏻💋👧🏻👩🏻🦰👷🏻♀️🕵🏻♀️👩🏻⚕️👨🏻🚀🧛🏻♂🧝🏻♀🕴🏻👩👩👦🎩🧦
🐶🐧🐜🙈🦆🦐🐂🐇🐕🦺🐆🌱🌕🌗🌑🌓🌍🌎🌏⛈🌈 🫐🥨🥝🫛🍳🍧🥙🍺🍹🍷
🍏🍎🥥🥝🍯🍆🥜🥛🍺🧊🥢🧂
⚽🏑🤸🏻♀️⛳🚴🏻♀️🥇🥈🥉🎯🎮
🚗🚖🛟🚇🛶🚥🚧🏣🎇🌆🌄🌠🌁
⌚📀📺📸📡💎🪙💵💴💶💷(but no Bitcoin)🪙🛢⚱🩻🕳🛋🛍📁📂🗂📝🔓🔒🔏🔐
❤🧡💛💚🩵💙💜☮✝🕉☯🕎✡🆚☢㊙❌🔰〽🔞❎🌐🛃💤➡〰🔉🕚
🏳🏴🏴☠️🏁🚩🏳️🌈🇺🇸🇪🇺🇩🇪🇺🇦🇻🇦🇸🇻 -
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 6538925e:571e55c3
2025-05-05 20:00:48
@ 6538925e:571e55c3
2025-05-05 20:00:48It’s been a little while since we released a major design update, so we’re really excited to get this new version of the app into your hands. Here’s a breakdown of all the main updates included in Fountain 1.2:
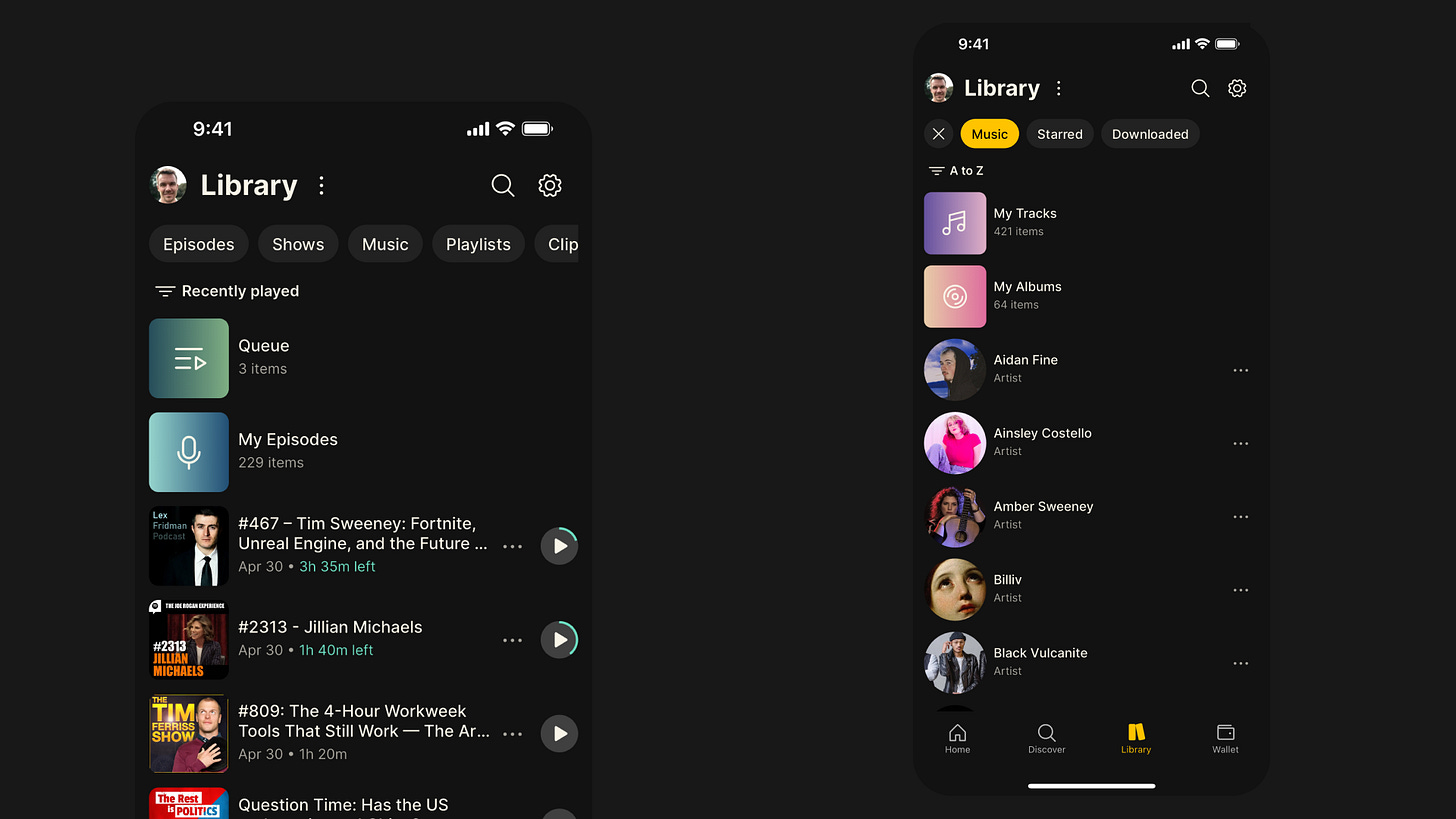 #### Library Design Update
#### Library Design Update-
New content-type filters at the top of the page make it easier to navigate between podcasts and music in your library.
-
Recently Played is now the default view in your library, so it’s easier to jump back into podcasts you’ve already started.
-
The Music filter now makes it easier to find saved tracks and albums, and it also gives you a list of all the artists whose music you’ve saved.
-
We’ve refreshed the design of the content cards to make it easier to see how much time is remaining on episodes you’ve already started.
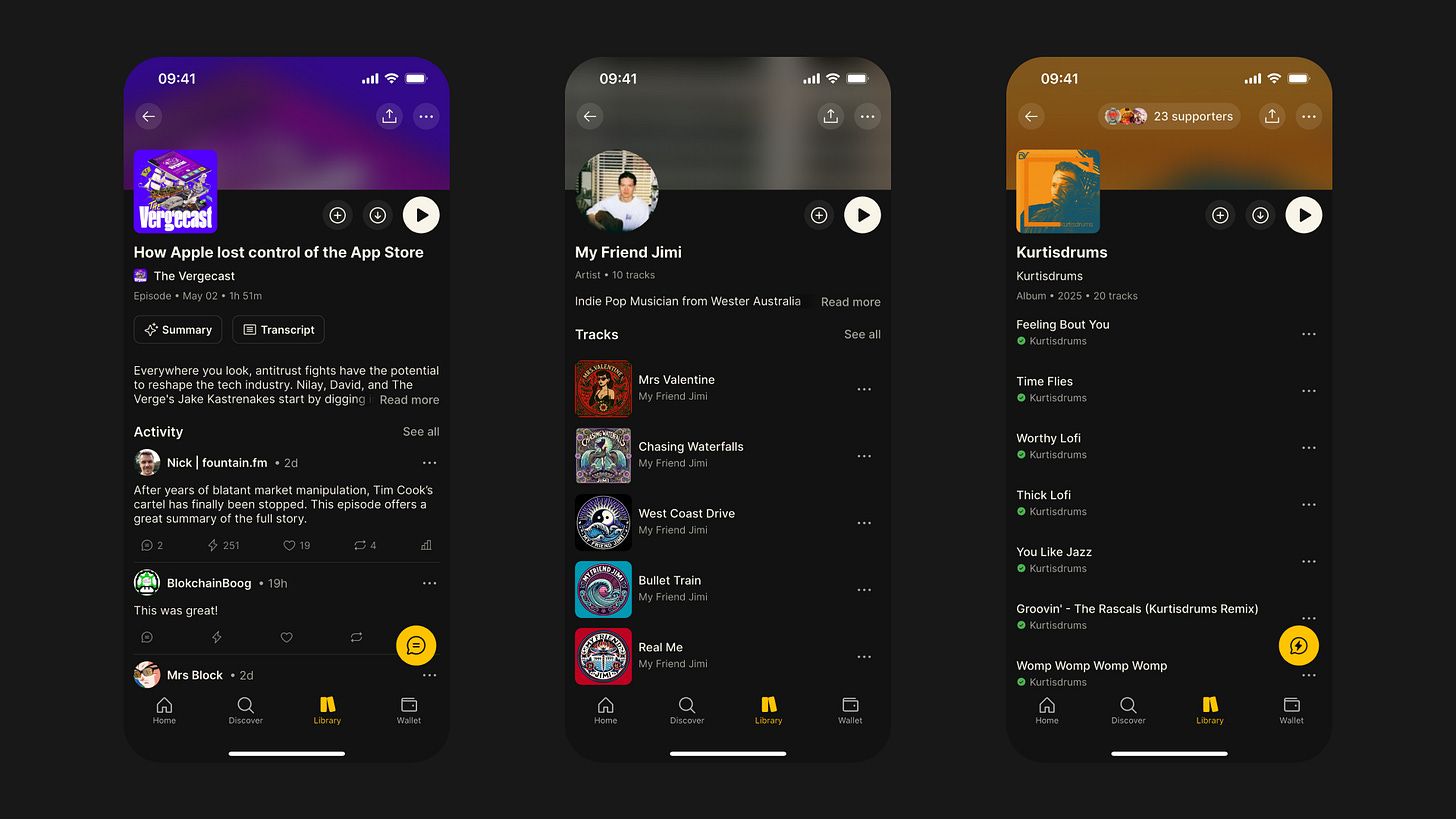 #### Content Pages Design Update
#### Content Pages Design Update-
All of the different content pages have undergone an extensive redesign, including shows, episodes, artists, albums, tracks, clips and playlists
-
We’ve replaced the tab layout we were using on the content pages with one scrollable page, making it easier to access features like chapters and tracklists
-
We’ve sanitised the formatting of show notes too, and if there is no activity for a given episode, we now display the expanded show notes
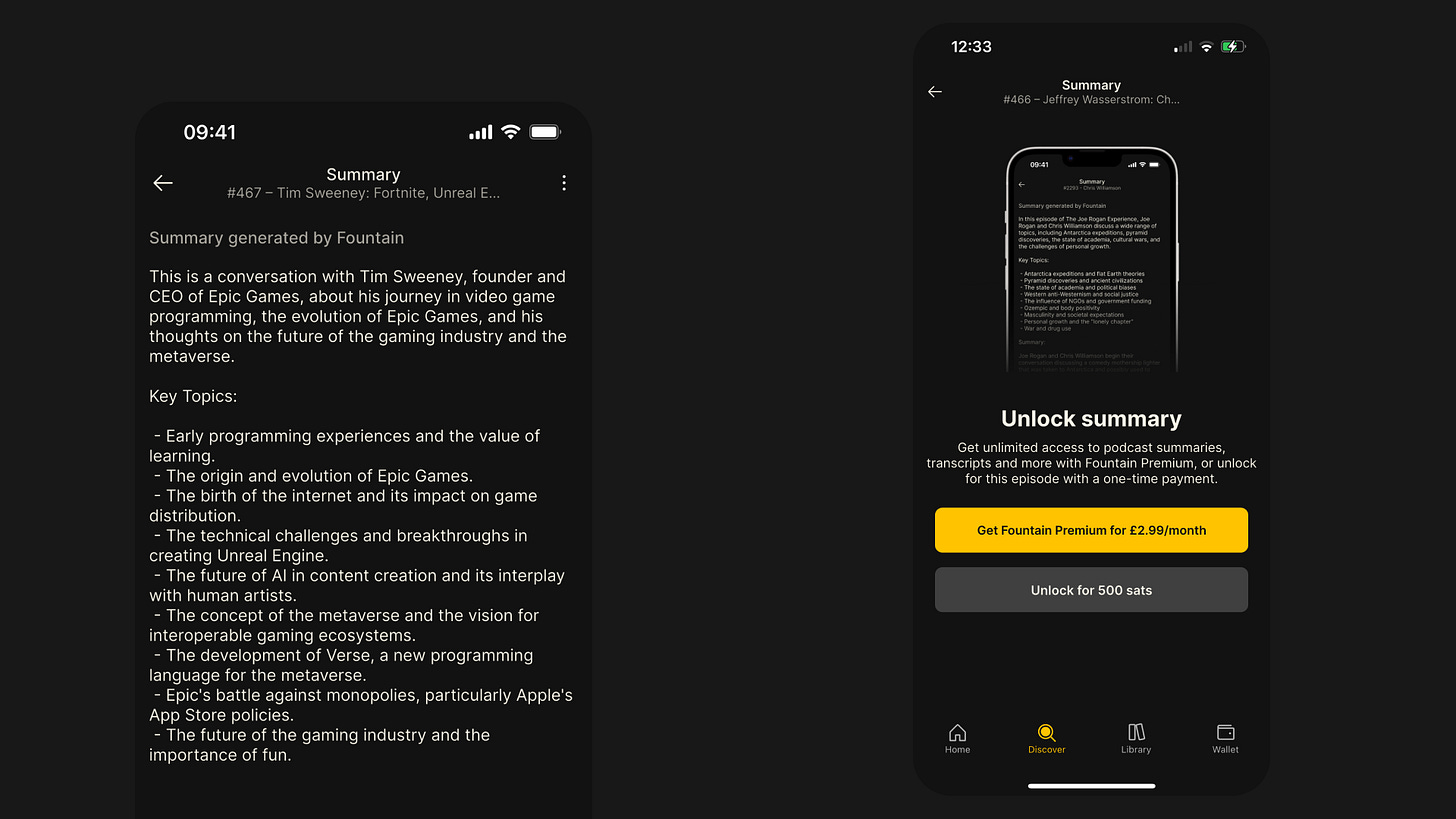 #### Episode Summaries
#### Episode SummariesEver looked at a 4-hour Lex Fridman episode and wished you could just read a high-level summary? We certainly have, so we did something about it.
-
Every episode page now has a Summary button above the show notes.
-
Simply pay 500 sats to unlock a summary, or upgrade to Fountain Premium for $2.99/month to enjoy unlimited summaries.
-
Summaries and transcripts now come as a bundle — two for the price of one!
-
Thanks to major improvements, they’re now faster, cheaper, and more accurate than ever before.
 #### Playback Improvements
#### Playback ImprovementsWe’ve completely rebuilt our audio engine from the ground up. Playback is now more robust and reliable — especially for music. Here are some of the key enhancements in Fountain 1.2:
-
Tracks now load and play instantly when tapped.
-
When playing a collection of tracks (e.g. from an artist, album, or playlist), you can now skip seamlessly between them.
-
We’ve replaced the scrollable player page with full-screen modals to make it easier to access show notes, comments, transcripts, chapters, tracklists, and your queue.
-
The new Smart Resume feature rewinds the episode by 5 seconds when you hit pause, so you don’t miss a beat.
-
You can now skip forward or backward by 60 seconds for faster navigation through episodes.
Other Bug Fixes & Improvements
-
Rebuilt payment stats for more complete and reliable transaction records.
-
Refreshed the design of the Settings pages for better usability.
-
Added new episode notification preferences in Settings.
-
Fixed several playback issues that were causing crashes or freezes.
-
Updated lock screen display and controls for livestreams.
-
Fixed issue where the next item in the queue paused unexpectedly.
-
Resolved playback stuttering on Android during livestreams.
-
Fixed disappearing playback controls on the lock screen.
-
Fixed playback speed not updating correctly.
-
Resolved issue where played episodes couldn’t be replayed.
-
Fixed playback not resuming correctly when listening in the car.
-
Synced car playback position with the device.
-
Fixed persistent car display refresh issue.
-
Fixed volume control via car controls.
-
Resolved issue with headphone controls after playing a transcript.
-
Fixed disappearing metadata on the lock screen.
-
Fixed bug where downloaded episodes stopped in airplane mode but showed as playing.
We would love to hear how you’re finding Fountain 1.2. Please submit your thoughts and feedback via the main menu in the app and we will take it on board as we continue to improve the app.
If you want to help test new features out before they get released, you can join Fountain Beta on Telegram. All iOS and Android users welcome.
-
-
 @ 5df413d4:2add4f5b
2025-05-04 00:51:49
@ 5df413d4:2add4f5b
2025-05-04 00:51:49Short photo-stories of the hidden, hard to find, obscure, and off the beaten track.
Come now, take a walk with me…
The Traveller 01: Ku/苦 Bar
Find a dingy, nondescript alley in a suspiciously quiet corner of Bangkok’s Chinatown at night. Walk down it. Pass the small prayer shrine that houses the angels who look over these particular buildings and approach an old wooden door. You were told that there is a bar here, as to yet nothing suggests that this is so…

Wait! A closer inspection reveals a simple bronze plaque, out of place for its polish and tended upkeep, “cocktails 3rd floor.” Up the stairs then! The landing on floor 3 presents a white sign with the Chinese character for bitter, ku/苦, and a red arrow pointing right.

Pass through the threshold, enter a new space. To your right, a large expanse of barren concrete, an empty “room.” Tripods for…some kind of filming? A man-sized, locked container. Yet, you did not come here to ask questions, such things are none of your business!

And to your left, you find the golden door. Approach. Enter. Be greeted. You have done well! You have found it. 苦 Bar. You are among friends now. Inside exudes deep weirdness - in the etymological sense - the bending of destinies, control of the fates. And for the patrons, a quiet yet social place, a sensual yet sacred space.


Ethereal sounds, like forlorn whale songs fill the air, a strange music for an even stranger magic. But, Taste! Taste is the order of the day! Fragrant, Bizarre, Obscure, Dripping and Arcane. Here you find a most unique use flavor, flavors myriad and manifold, flavors beyond name. Buddha’s hand, burnt cedar charcoal, ylang ylang, strawberry leaf, maybe wild roots brought in by some friendly passerby, and many, many other things. So, Taste! The drinks here, libations even, are not so much to be liked or disliked, rather, the are liquid context, experience to be embraced with a curious mind and soul freed from judgment.
And In the inner room, one may find another set of stairs. Down this time. Leading to the second place - KANGKAO. A natural wine bar, or so they say. Cozy, botanical, industrial, enclosed. The kind of private setting where you might overhear Bangkok’s resident “State Department,” “UN,” and “NGO” types chatting auspiciously in both Mandarin and English with their Mainland Chinese counterparts. But don’t look hard or listen too long! Surely, there’s no reason to be rude… Relax, relax, you are amongst friends now.

**苦 Bar. Bangkok, circa 2020. There are secrets to be found. Go there. **
Plebchain #Bitcoin #NostrArt #ArtOnNostr #Writestr #Createstr #NostrLove #Travel #Photography #Art #Story #Storytelling #Nostr #Zap #Zaps #Bangkok #Thailand #Siamstr
-
 @ 502ab02a:a2860397
2025-05-09 01:07:20
@ 502ab02a:a2860397
2025-05-09 01:07:20ถ้าย้อนกลับไป 50 ปีก่อน ถ้าเฮียถามคำนี้กับลุงชาวนาคนหนึ่ง เขาคงหัวเราะแล้วตอบแบบไม่ต้องคิดว่า “ก็เจ้าของที่นาไงไอ้ทิด จะมีใครล่ะ?”
แต่พอมาในวันนี้ ถ้าเฮียถามคำเดิมในซูเปอร์มาร์เก็ต คงไม่มีใครกล้าตอบแบบนั้นอีกแล้ว เพราะแค่ในชั้นวางโยเกิร์ตเดียวกัน เฮียอาจเห็นยี่ห้อต่างกัน 10 ยี่ห้อ แต่ทั้งหมดอาจเป็นของบริษัทแม่เพียงเจ้าเดียว
ในศตวรรษที่ 21 อาหารไม่ใช่ของคนทำอาหาร แต่มันกลายเป็นของ บริษัทผู้ครอบครองข้อมูล พันธุกรรม และระบบการกระจายสินค้า โลกวันนี้ไม่ได้มีเกษตรกรล้อมวงเคี้ยวหมาก แต่มีบริษัทเทคโนโลยีจับมือกับนักลงทุนระดับโลก ถือครองเมล็ดพันธุ์ เป็นเจ้าของสิทธิบัตรจุลินทรีย์ในลำไส้ และมีอำนาจเสนอว่า “อาหารแบบไหนควรได้รับเงินสนับสนุนจากรัฐ”
บริษัทเทคโนโลยีในซิลิคอนแวลลีย์บางแห่ง ไม่ได้แค่ผลิตซอฟต์แวร์อีกต่อไป แต่เริ่มทำ "อาหารจากโค้ด" โปรตีนสังเคราะห์ที่ได้จากการแทรกยีน หรือแม้แต่ “อาหารจากคาร์บอนในอากาศ” ที่สร้างโดย AI เขาไม่ได้ปลูกข้าว แต่เขาเขียนสูตรให้เครื่องจักรสร้างอาหารในถัง
ใครมีสิทธิบัตร…คนนั้นคือเจ้าของ ใครควบคุมข้อมูลสุขภาพ…คนนั้นคือนายทุนแห่งความหิว และใครสามารถชี้นิ้วให้รัฐบาลเปลี่ยนนโยบายอาหารโรงเรียน…คนนั้นคือเจ้าของอนาคตของเด็กทั้งประเทศ
มันฟังดูเวอร์ใช่ไหม? แต่ลองดูดี ๆ…ใครเป็นเจ้าของฟาร์มหมู ฟาร์มไก่ โรงฆ่าสัตว์? หลายแห่งไม่ได้เป็นของชาวบ้านอีกต่อไป แต่เป็นของเครือบริษัทยักษ์ใหญ่ที่อยู่เบื้องหลังทั้งอาหารในซูเปอร์ และเม็ดวิตามินในกระปุกเฮียด้วย
ยิ่งไปกว่านั้น เจ้าของตัวจริงไม่ได้อยู่ในร้านของชำ แต่ซ่อนตัวอยู่ในบอร์ดบริหารบริษัทเกษตรข้ามชาติ ในเวทีประชุมเศรษฐกิจโลก และในห้องประชุมที่ตัดสินว่า “อาหารจากวัว” ควรถูกเก็บภาษีคาร์บอนเพิ่มหรือไม่
เมื่อก่อนเฮียเคยคิดว่า ถ้าเราปลูกผักเอง ก็คุมอาหารตัวเองได้ แต่พอระบบเริ่มขับไล่เมล็ดพันธุ์ดั้งเดิมให้สูญพันธุ์ ถ้าไม่มีใบอนุญาตปลูกพืช GMO หรือไม่มีเงินซื้อปุ๋ยจากบริษัทเดียวที่ยังอยู่รอด เกษตรกรจะเป็นเจ้าของอะไรกันแน่?
และคำว่า “อาหารอิสระ” ในยุคนี้ อาจไม่ใช่แค่การไม่พึ่งพาซูเปอร์ แต่มันคือ “การตื่นรู้ว่าใครเป็นคนจัดเกม และใครเป็นคนตั้งกฎ”
เพราะในยุคที่ทุกอย่างแปรรูปเป็นดิจิทัล แม้แต่อาหารก็อาจมีเจ้าของเพียงไม่กี่ราย และสิ่งที่น่ากลัวกว่าผูกขาด…คือการ “ผูกอนาคต” ของเราทั้งมื้อ
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 5cb68b7a:b7cb67d5
2025-05-09 00:31:22
@ 5cb68b7a:b7cb67d5
2025-05-09 00:31:22In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back! 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞 For quick queries or support, connect with us on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust\ At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process\ Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate\ With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure\ Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools\ We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!\ Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back!\ 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪
-
 @ c9badfea:610f861a
2025-05-09 00:06:23
@ c9badfea:610f861a
2025-05-09 00:06:23- Install LibreTorrent (it's free and open source)
- Search for torrents on various sources (see links below)
- Copy the torrent's 🧲️ Magnet Link
- Open LibreTorrent, tap the + icon, and select Add Link
- Paste the magnet link and tap Add
- The app will display the torrent's details and files; tap the ✓ icon to start the download
Some Sources
ℹ️ Magnet links start with
magnet:?ℹ️ Tapping a magnet link usually opens LibreTorrent automatically
⚠️ Using a VPN is strongly recommended
-
 @ 87f5e1d9:e251d8f4
2025-05-09 00:03:01
@ 87f5e1d9:e251d8f4
2025-05-09 00:03:01Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 52b4a076:e7fad8bd
2025-05-03 21:54:45
@ 52b4a076:e7fad8bd
2025-05-03 21:54:45Introduction
Me and Fishcake have been working on infrastructure for Noswhere and Nostr.build. Part of this involves processing a large amount of Nostr events for features such as search, analytics, and feeds.
I have been recently developing
nosdexv3, a newer version of the Noswhere scraper that is designed for maximum performance and fault tolerance using FoundationDB (FDB).Fishcake has been working on a processing system for Nostr events to use with NB, based off of Cloudflare (CF) Pipelines, which is a relatively new beta product. This evening, we put it all to the test.
First preparations
We set up a new CF Pipelines endpoint, and I implemented a basic importer that took data from the
nosdexdatabase. This was quite slow, as it did HTTP requests synchronously, but worked as a good smoke test.Asynchronous indexing
I implemented a high-contention queue system designed for highly parallel indexing operations, built using FDB, that supports: - Fully customizable batch sizes - Per-index queues - Hundreds of parallel consumers - Automatic retry logic using lease expiration
When the scraper first gets an event, it will process it and eventually write it to the blob store and FDB. Each new event is appended to the event log.
On the indexing side, a
Queuerwill read the event log, and batch events (usually 2K-5K events) into one work job. This work job contains: - A range in the log to index - Which target this job is intended for - The size of the job and some other metadataEach job has an associated leasing state, which is used to handle retries and prioritization, and ensure no duplication of work.
Several
Workers monitor the index queue (up to 128) and wait for new jobs that are available to lease.Once a suitable job is found, the worker acquires a lease on the job and reads the relevant events from FDB and the blob store.
Depending on the indexing type, the job will be processed in one of a number of ways, and then marked as completed or returned for retries.
In this case, the event is also forwarded to CF Pipelines.
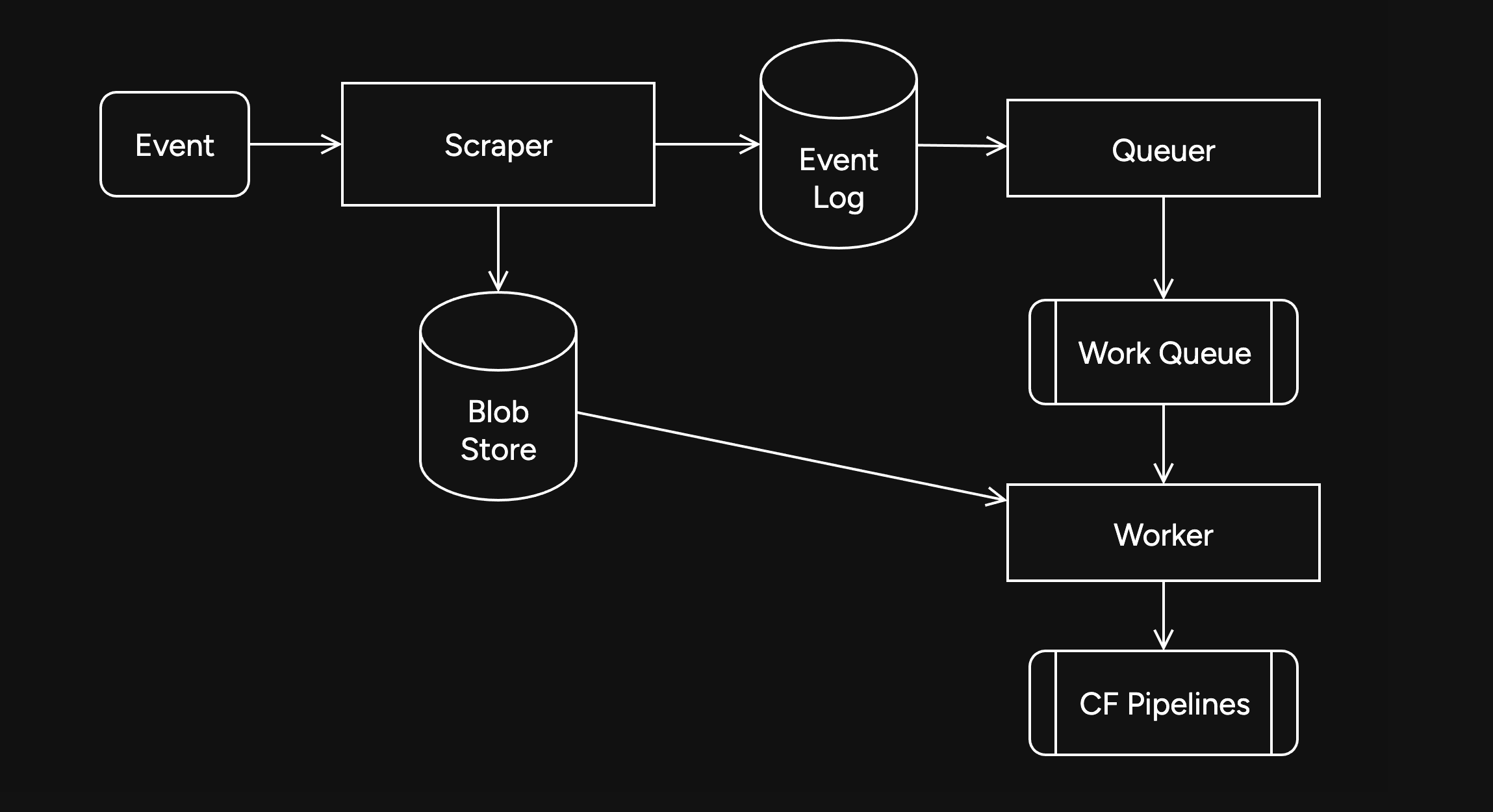
Trying it out
The first attempt did not go well. I found a bug in the high-contention indexer that led to frequent transaction conflicts. This was easily solved by correcting an incorrectly set parameter.
We also found there were other issues in the indexer, such as an insufficient amount of threads, and a suspicious decrease in the speed of the
Queuerduring processing of queued jobs.Along with fixing these issues, I also implemented other optimizations, such as deprioritizing
WorkerDB accesses, and increasing the batch size.To fix the degraded
Queuerperformance, I ran the backfill job by itself, and then started indexing after it had completed.Bottlenecks, bottlenecks everywhere

After implementing these fixes, there was an interesting problem: The DB couldn't go over 80K reads per second. I had encountered this limit during load testing for the scraper and other FDB benchmarks.
As I suspected, this was a client thread limitation, as one thread seemed to be using high amounts of CPU. To overcome this, I created a new client instance for each
Worker.After investigating, I discovered that the Go FoundationDB client cached the database connection. This meant all attempts to create separate DB connections ended up being useless.
Using
OpenWithConnectionStringpartially resolved this issue. (This also had benefits for service-discovery based connection configuration.)To be able to fully support multi-threading, I needed to enabled the FDB multi-client feature. Enabling it also allowed easier upgrades across DB versions, as FDB clients are incompatible across versions:
FDB_NETWORK_OPTION_EXTERNAL_CLIENT_LIBRARY="/lib/libfdb_c.so"FDB_NETWORK_OPTION_CLIENT_THREADS_PER_VERSION="16"Breaking the 100K/s reads barrier
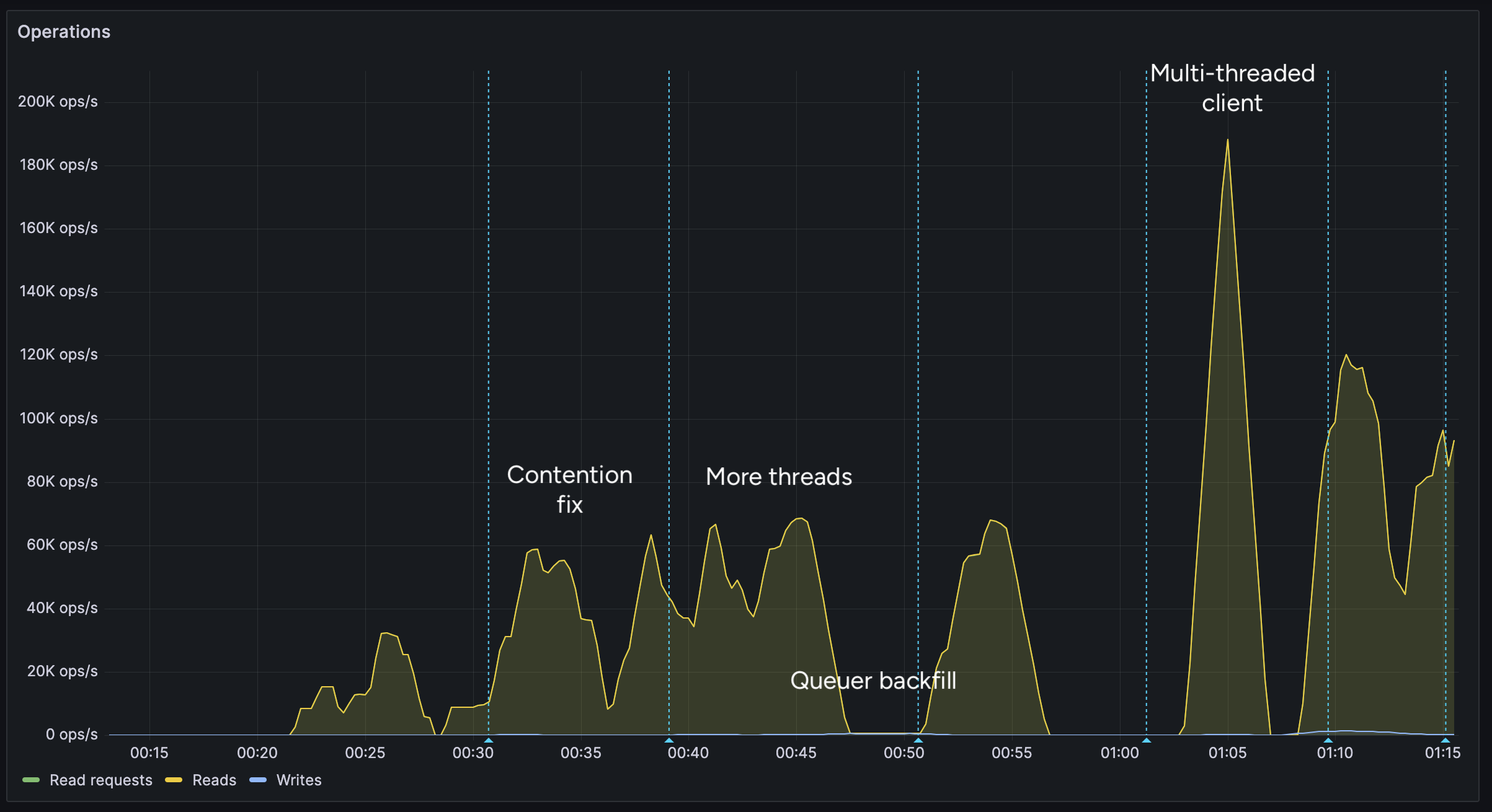
After implementing support for the multi-threaded client, we were able to get over 100K reads per second.
You may notice after the restart (gap) the performance dropped. This was caused by several bugs: 1. When creating the CF Pipelines endpoint, we did not specify a region. The automatically selected region was far away from the server. 2. The amount of shards were not sufficient, so we increased them. 3. The client overloaded a few HTTP/2 connections with too many requests.
I implemented a feature to assign each
Workerits own HTTP client, fixing the 3rd issue. We also moved the entire storage region to West Europe to be closer to the servers.After these changes, we were able to easily push over 200K reads/s, mostly limited by missing optimizations:
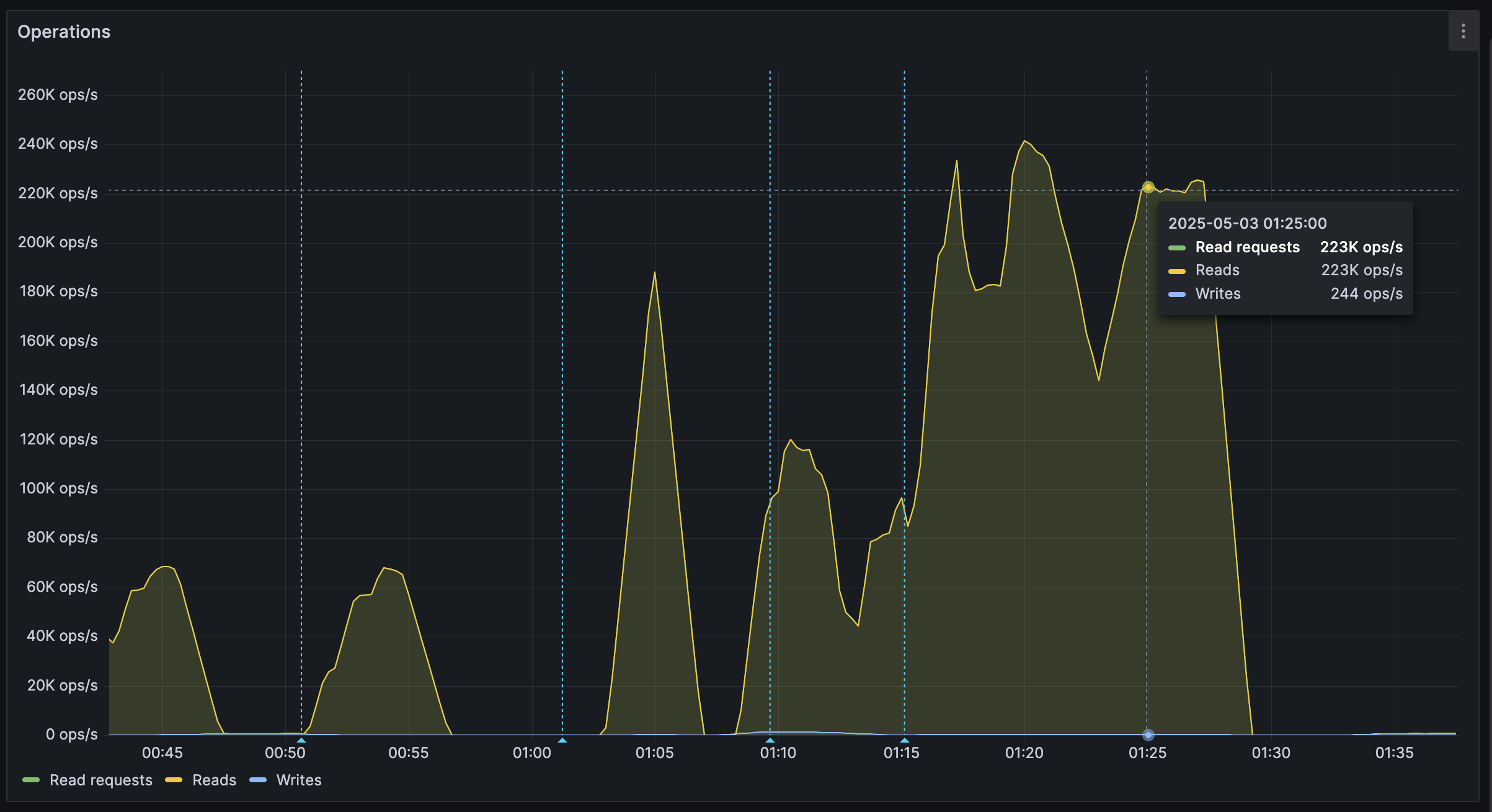
It's shards all the way down
While testing, we also noticed another issue: At certain times, a pipeline would get overloaded, stalling requests for seconds at a time. This prevented all forward progress on the
Workers.We solved this by having multiple pipelines: A primary pipeline meant to be for standard load, with moderate batching duration and less shards, and high-throughput pipelines with more shards.
Each
Workeris assigned a pipeline on startup, and if one pipeline stalls, other workers can continue making progress and saturate the DB.The stress test
After making sure everything was ready for the import, we cleared all data, and started the import.
The entire import lasted 20 minutes between 01:44 UTC and 02:04 UTC, reaching a peak of: - 0.25M requests per second - 0.6M keys read per second - 140MB/s reads from DB - 2Gbps of network throughput
FoundationDB ran smoothly during this test, with: - Read times under 2ms - Zero conflicting transactions - No overloaded servers
CF Pipelines held up well, delivering batches to R2 without any issues, while reaching its maximum possible throughput.

Finishing notes
Me and Fishcake have been building infrastructure around scaling Nostr, from media, to relays, to content indexing. We consistently work on improving scalability, resiliency and stability, even outside these posts.
Many things, including what you see here, are already a part of Nostr.build, Noswhere and NFDB, and many other changes are being implemented every day.
If you like what you are seeing, and want to integrate it, get in touch. :)
If you want to support our work, you can zap this post, or register for nostr.land and nostr.build today.
-
 @ c9badfea:610f861a
2025-05-08 23:06:09
@ c9badfea:610f861a
2025-05-08 23:06:09- Install VLC Media Player
- Open the app, navigate to More and tap New Stream
- Enter
https://iptv-org.github.io/iptv/index.m3uin the network address field and tap the arrow - Enjoy the global IPTV channel playlist
🔗️ Here is the stream URL as plain text: https://iptv-org.github.io/iptv/index.m3u
ℹ️ For playlists of specific countries, categories, or languages, visit IPTV-Org and see the Playlists section
ℹ️ You can find an overview of all available IPTV channels per country here
-
 @ 266815e0:6cd408a5
2025-05-02 22:24:59
@ 266815e0:6cd408a5
2025-05-02 22:24:59Its been six long months of refactoring code and building out to the applesauce packages but the app is stable enough for another release.
This update is pretty much a full rewrite of the non-visible parts of the app. all the background services were either moved out to the applesauce packages or rewritten, the result is that noStrudel is a little faster and much more consistent with connections and publishing.
New layout
The app has a new layout now, it takes advantage of the full desktop screen and looks a little better than it did before.
Removed NIP-72 communities
The NIP-72 communities are no longer part of the app, if you want to continue using them there are still a few apps that support them ( like satellite.earth ) but noStrudel won't support them going forward.
The communities where interesting but ultimately proved too have some fundamental flaws, most notably that all posts had to be approved by a moderator. There were some good ideas on how to improve it but they would have only been patches and wouldn't have fixed the underlying issues.
I wont promise to build it into noStrudel, but NIP-29 (relay based groups) look a lot more promising and already have better moderation abilities then NIP-72 communities could ever have.
Settings view
There is now a dedicated settings view, so no more hunting around for where the relays are set or trying to find how to add another account. its all in one place now
Cleaned up lists
The list views are a little cleaner now, and they have a simple edit modal
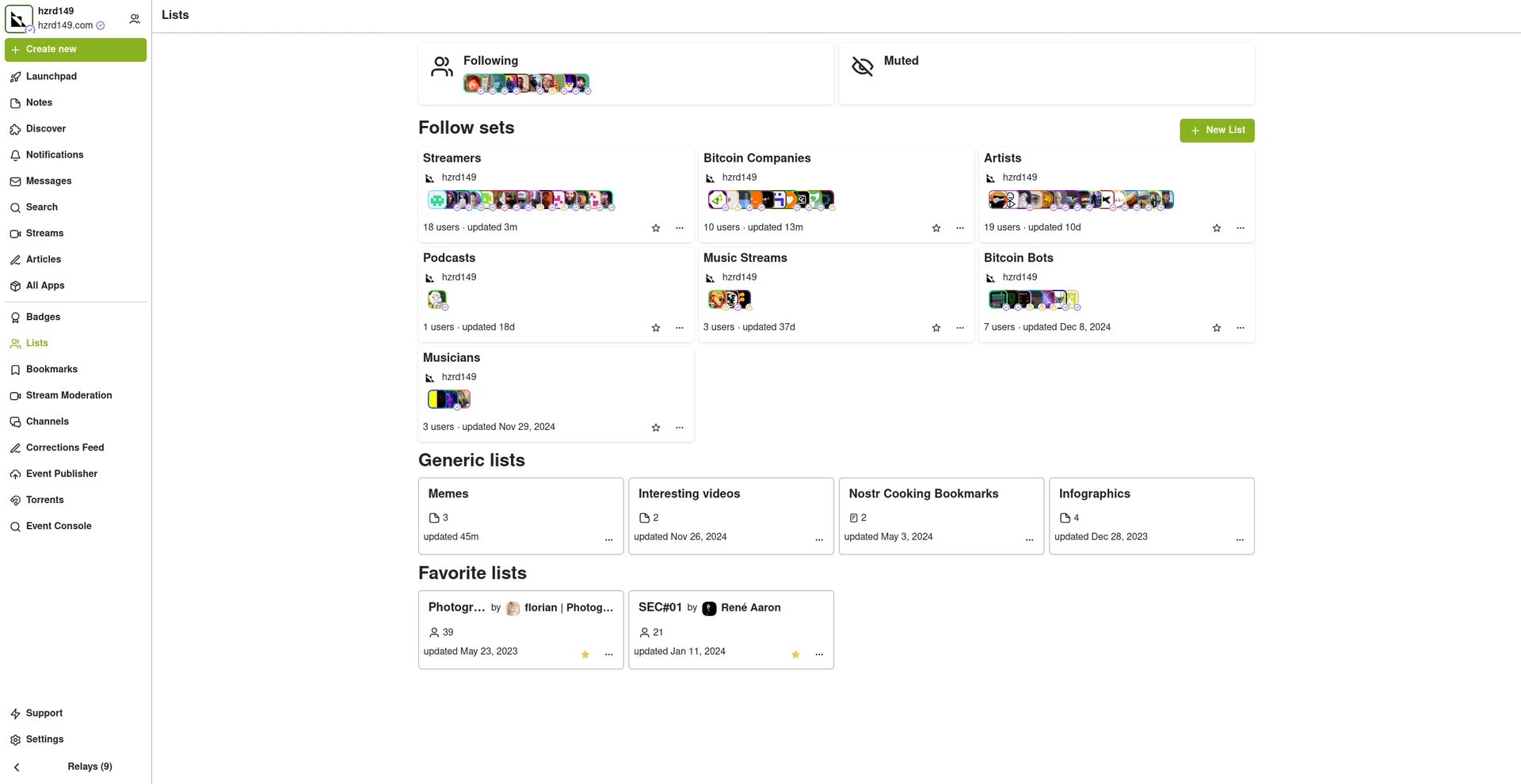
New emoji picker
Just another small improvement that makes the app feel more complete.
Experimental Wallet
There is a new "wallet" view in the app that lets you manage your NIP-60 cashu wallet. its very experimental and probably won't work for you, but its there and I hope to finish it up so the app can support NIP-61 nutzaps.
WARNING: Don't feed the wallet your hard earned sats, it will eat them!
Smaller improvements
- Added NSFW flag for replies
- Updated NIP-48 bunker login to work with new spec
- Linkfy BIPs
- Added 404 page
- Add NIP-22 comments under badges, files, and articles
- Add max height to timeline notes
- Fix articles view freezing on load
- Add option to mirror blobs when sharing notes
- Remove "open in drawer" for notes
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-08 22:57:55
@ 5d4b6c8d:8a1c1ee3
2025-05-08 22:57:55Using a discussion style post to get better formatting on the nostr cross-post.
The Fed Leaves Fed Funds Rate at 4.5% as Economic Storm Clouds Gather
by Ryan McMaken
The Fed is now hemmed in by a rising risk of stagflation. It doesn’t know where the economy is headed, or is unwilling to take a position. At this point, “hope for the best” is Fed policy.
originally posted at https://stacker.news/items/975059
-
 @ 1408bad0:4971f2ca
2025-05-01 19:55:37
@ 1408bad0:4971f2ca
2025-05-01 19:55:37Raised by Wolves is another sci-fi flick where Earth faces an extinction level event and lots of cool androids.
The series has some exciting action points showing a side of AI androids used as super weapons against humanity. If you were thinking to get an AI girlfriend, you might have a change of mind.
We see some pretty cool androids, but the awesome Necromancer is pretty spectacular and powerful and you wonder if anything can stop them. However, bizarrely, at times they are also apparently weak and despite their power, the religious group doesn't shy away from confrontation without any real weapons.
It would have been good if they had explored this side more and some of the advanced tech available like which gave the atheista super strength and speed to combat them.
The series has a feel like Foundation to it, but much less polished and maybe more negative and dreary at times. Instead of exploring exciting themes, it descends into mindless trivialities and bizarre gory rituals like killing a hideous pregnant animal and parading the dead baby corpse around.
They arrive on a mysterious but quite dreary planet and things start to set the scene.
The androids themselves are quite well played. The "Mother" is as expected in these woke times the strong and powerful one. The "Father" is the beta male serving her and the kids. It's all quite bizarre in a way.
When they first land they use some tech to make a base quickly and easily, but it disappoints how basic it all is. This is then compounded when the religious group arrive and instead of using modern tech to make a base as you might expect, instead turn into the Amish and make everything from wood. Oh yes, there are trees on this planet, but no really nice food.
The oddness continues and grows throughout the season as the androids become more human and spoiler alert , the most ridiculous storyline emerges as mother becomes pregnant and also really annoying. She starts attaching other bits and creatures to her to suck their blood out for her baby.
Despite all my criticisms, it has been an interesting first series but very disappointing in many ways compared to Foundation.
-
 @ 6fc114c7:8f4b1405
2025-05-08 22:55:57
@ 6fc114c7:8f4b1405
2025-05-08 22:55:57In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
Why Choose Crypt Recver? 🤔 🔑 Expertise You Can Trust At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases. Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds! Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets. Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security. Don’t Let Lost Crypto Ruin Your Day! 🕒 With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now! Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back! 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞 For quick queries or support, connect with us on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪In the realm of cryptocurrency, the stakes are incredibly high, and losing access to your digital assets can be a daunting experience. But don’t worry — cryptrecver.com is here to transform that nightmare into a reality! With expert-led recovery services and leading-edge technology, Crypt Recver specializes in helping you regain access to your lost Bitcoin and other cryptocurrencies.
 # Why Choose Crypt Recver? 🤔
# Why Choose Crypt Recver? 🤔🔑 Expertise You Can Trust\ At Crypt Recver, we blend advanced technology with skilled engineers who have a solid track record in crypto recovery. Whether you’ve forgotten your passwords, lost your private keys, or encountered issues with damaged hardware wallets, our team is ready to assist.
⚡ Fast Recovery Process\ Time is crucial when recovering lost funds. Crypt Recver’s systems are designed for speed, enabling quick recoveries — allowing you to return to what matters most: trading and investing.
🎯 High Success Rate\ With a success rate exceeding 90%, our recovery team has aided numerous clients in regaining access to their lost assets. We grasp the complexities of cryptocurrency and are committed to providing effective solutions.
🛡️ Confidential & Secure\ Your privacy is paramount. All recovery sessions at Crypt Recver are encrypted and completely confidential. You can trust us with your information, knowing we uphold the highest security standards.
🔧 Advanced Recovery Tools\ We employ proprietary tools and techniques to tackle complex recovery scenarios, from retrieving corrupted wallets to restoring coins from invalid addresses. No matter the challenge, we have a solution.
 # Our Recovery Services Include: 📈
# Our Recovery Services Include: 📈- Bitcoin Recovery: Lost access to your Bitcoin wallet? We can assist in recovering lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistaken transfers, lost passwords, or missing transaction records — let us help you reclaim your funds!
- Cold Wallet Restoration: Did your cold wallet fail? We specialize in safely extracting assets.
- Private Key Generation: Forgotten your private key? We can help you generate new keys linked to your funds without compromising security.
Don’t Let Lost Crypto Ruin Your Day! 🕒
With an estimated 3 to 3.4 million BTC lost forever, it’s essential to act quickly when facing access issues. Whether you’ve been affected by a dust attack or simply forgotten your key, Crypt Recver provides the support you need to reclaim your digital assets.
🚀 Start Your Recovery Now!\ Ready to retrieve your cryptocurrency? Don’t let uncertainty hold you back!\ 👉 Request Wallet Recovery Help Today!cryptrecver.com
Need Immediate Assistance? 📞
For quick queries or support, connect with us on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Trust Crypt Recver for the best crypto recovery service — get back to trading with confidence! 💪
-
 @ 08964cb5:51bf010f
2025-05-01 10:14:41
@ 08964cb5:51bf010f
2025-05-01 10:14:41«Reflexiones y Acción: Entre la Defensa del Patrimonio»
[English below][Deutsch unten]
Los recientes acontecimientos que han puesto en peligro mi patrimonio, así como los valores fundamentales que definen mi camino, me han llevado a tomar una decisión importante: iniciar una campaña de recaudación de fondos. Esta iniciativa no solo busca proteger lo que he construido con esfuerzo, sino también garantizar que pueda seguir adelante con proyectos y principios que son esenciales para mí.
Tu apoyo puede marcar una gran diferencia. Si deseas conocer más sobre esta causa o contribuir con tu solidaridad, te invito a visitar ›🔗éste enlace.‹
"Reflections and Action: Safeguarding My Heritage"
The recent events that have jeopardised my assets and the core values that define my journey have led me to take a significant step: launching a fundraising campaign. This initiative aims not only to protect what I have built with hard work but also to ensure that I can continue moving forward with projects and principles that are essential to me.
Your support can make a real difference. If you’d like to learn more about this cause or contribute with your solidarity, I invite you to visit ›🔗this link.‹
"Überlegungen und Handeln: Den Schutz meines Vermögens"
Die jüngsten Ereignisse, die mein Vermögen sowie die grundlegenden Werte, die meinen Weg bestimmen, gefährdet haben, haben mich dazu veranlasst, einen wichtigen Schritt zu gehen: den Start einer Spendenkampagne. Diese Initiative zielt nicht nur darauf ab, das zu schützen, was ich mit harter Arbeit aufgebaut habe, sondern auch sicherzustellen, dass ich mit Projekten und Prinzipien, die für mich unerlässlich sind, weitermachen kann.
Deine Unterstützung kann einen großen Unterschied machen. Wenn du mehr über diese Sache erfahren oder mit deiner Solidarität beitragen möchtest, lade ich dich ein, ›🔗diesen Link zu besuchen.‹
-
 @ a5ee4475:2ca75401
2025-05-08 22:43:26
@ a5ee4475:2ca75401
2025-05-08 22:43:26lista #descentralismo #compilado #portugues
*Algumas destas listas ainda estão sendo trocadas, portanto as versões mais recentes delas só estão visíveis no Amethyst por causa da ferramenta de edição.
Clients do Nostr e Outras Coisas
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
Modelos de IA e Ferramentas
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guk62czu
Iniciativas de Bitcoin
nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2nvmn5va9x2nrxfd2k5smyf3ux7vesd9znyqxygt4
Profissionais Brasileiros no Nostr
nostr:naddr1qq24qmnkwe6y67zlxgc4sumrxpxxce3kf9fn2qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7q3q5hhygatg5gmjyfkkguqn54f9r6k8m5m6ksyqffgjrf3uut982sqsxpqqqp65wp8uedu
Comunidades em Português no Nostr
nostr:naddr1qq2hwcejv4ykgdf3v9gxykrxfdqk753jxcc4gqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gu455fm3
Grupos em Português no Nostr
nostr:nevent1qqs98kldepjmlxngupsyth40n0h5lw7z5ut5w4scvh27alc0w86tevcpzpmhxue69uhkummnw3ezumt0d5hsygy7fff8g6l23gp5uqtuyqwkqvucx6mhe7r9h7v6wyzzj0v6lrztcspsgqqqqqqs3ndneh
Jogos de Código Aberto
Open Source Games nostr:naddr1qvzqqqr4gupzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhz8x40v0
Formatação de Texto em Markdown
(Amethyst, Yakihone e outros) nostr:nevent1qqs0vquevt0pe9h5a2dh8csufdksazp6czz3vjk3wfspp68uqdez00cprpmhxue69uhkummnw3ezuendwsh8w6t69e3xj730qgs2tmjyw452ydezymtywqf625j3atra6datgzqy55fp5c7w9jn4gqgrqsqqqqqpd658r3
Outros Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ a5ee4475:2ca75401
2025-05-08 22:38:49
@ a5ee4475:2ca75401
2025-05-08 22:38:49list #foss #descentralismo
Nostr Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- DEG Mods - Decentralized Game Mods [info] [source] 🌐
- NG Engine - Nostr Game Engine [source] 🌐
- JmonkeyEngine - Java game engine [source] 🌐
Android
- Mindustry - Sandbox Tower-defence and RTS [source] 🤖
- SuperTuxKart - Mario Kart with Tux (linux penguin) [source] 🤖 | 🐧🪟🍎
- SolitaireCG - Solitaire Cardgames [source] 🤖
Rhythm
- Friday Night Funkin' - [source] [download] 🌐🐧🪟🍎
- Open Saber - Beat Saber VR like (requires a VR) [source] 🌐🐧🪟🤖
- RhythmAdventure - Osu! remake [source]
Voxel
- Luanti / Minetest - Minecraft-like voxel game and engine in Lua [info] [source]
- VoxeLibre / MineClone2 - Famous Luanti / Minetest mod [source] [source2]
- Veloren - Cubeword upgraded sandbox [source]
- Terasology - Minecraft-based vivid world [source]
- Reign of Nether - Minecraft RTS mod [source]
- Voxelands - [info] [source] [STOPED] 🐧🤖🍎
- New Fork: voxelands 🐧 *Voxelands ≠ Voxlands (closed source game)
Clone
- Pingus - Lemmings clone [source]
- FlappyBird - Flappy Bird clone [source]
Remake
- FreeDoom - Doom remake [source]
- Oolite - Elite remake [source]
- Q1K3 - Quake demake [source] 🌐
- AM2R - Metroid remake [source]
Inspired
- Boxhead2D - Single player top-down shooter based in the Boxhead 2Play 🐧🪟🍎
- Boxhead - Directx11 - Single player top-down shooter based in the Boxhead 2Play [source] 🌐
- OpenSuspect - Inspired by mafia and Among Us [source] 🐧🪟
- Xonotic - Inspired by Quake [source]
- Hedgewars - Inspired by Worms, but with hedgehogs [source]
- Secret Mayro Chronicles - Inspired by Super Mario [source]
- OpenRA - Communist strategy game inspired by Red Alert, Tiberian Dawn and Dune 2000 [source]
- OpenTTD - Based on Transport Tycoon Deluxe [source]
- AstroMenace - Spaceships shooter [source]
Strategy
- 0 A.D. - RTS [info] [source]
- Warzone 2100 - RTS [source]
- The Battle for Wesnoth - Turn-based fantasy strategy game [source]
FPS - First-Person Shooter
- Alien Arena - Fast-paced Sci-Fi FPS death match [info] [source] 🐧🪟🍎 [and FreeBSD 😈]
- Urban Terror - based on "total conversion" mod for Quake III Arena [info] [source] 🐧🪟🍎
- FreeHL - Rewrite of Half-Life: Deathmatch in QuakeC [source]
- FreeCS - Based in Counter-Strike 1.5 by FreeHL addon [info] [source] 🐧🪟🍎 [and FreeBSD 😈]
- Nexuiz Classic - retro deathmatch [source] 🐧🪟🍎
- AssaultCube - WWII layout [info] [source]
- OpenArena - clone of Quake III Arena [source]
- Warsow - Futuristic cartoonish world [source]
- World of Padman - Fun cartoonish shooter [info] [source] 🐧🪟🍎
- OpenSpades - A clone of Ace of Spades, with voxels, fully destructible terrain and plenty of game modes [source]
- Tremulous - Asymmetric team-based FPS with real-time strategy elements [source]
- Cube 2: Sauerbraten - A free multiplayer & single-player first-person shooter, the successor of the Cube FPS [info] [source]
- Quetoo (Q2) - old school death match [info] [slurce]🐧🪟🍎
- Red Eclipse 2 - sci-fi modern FPS arena [info] [source] 🐧🪟🍎
- BZFlag - Battle Zone capture the Flag game [info] [source] [source 2] 🐧🪟🍎
- The Darkmod [source] [source] [source 3]
- Wolfenstein: Enemy Territory - War as Axis or Allies in team-based combat
Original list with images in Medevel Website
Retro RPG
- Cataclysm: Dark Days Ahead - Post-apocalyptic survival - [source]
- Erebus - [source]
- FreedroidRPG - Tux against rebel bots [source]
- FreeDink - Dink Smallwood - Similar to classic Zelda [info] [source]
- Valyria tear - Based on the Hero of Allacrost engine [source]
- Fall of Imiryn [source]
- Hale - Tactical combat [source]
- IVAN: Iter Vehemens ad Necem - roguelike [source]
- Summoning Wars - 1 to 8 players [source]
- Flare - Action fantasy [source]
Educational
https://medevel.com/educational-games-26-993/
-
 @ a5ee4475:2ca75401
2025-05-08 21:57:12
@ a5ee4475:2ca75401
2025-05-08 21:57:12brasil #portugal #portugues #bitcoin
Brasil
-
Jericoacoara - Ceará nostr:nprofile1qqsdc47glaz2z599a7utq9gk2xyf6z70t7ddyryrnweyt32z4sdarfsppemhxue69uhkummn9ekx7mp00ex584
-
Rolante - Rio Grande do Sul nostr:nprofile1qqsdrks96vr7vc7frjflm8lmhwleslwzgjlkpyj4ahjhzgm4n8dh0qqprdmhxue69uhkymm4de3k2u3wd45ku6tzdak8gtnfdenx7qgcwaen5te0xycrqt3hxyhryvfh9ccngde6xsurgwqpz3mhxue69uhhyetvv9ujuerpd46hxtnfduhxppd6
-
Santo Antonio do Pinhal - São Paulo nostr:nprofile1qqsr5maylee9j77ce0es6tgmxj3pax2dlsuuptkn2stuj95jzqysulgpzemhxue69uhhyetvv9ujuurjd9kkzmpwdejhgqgjwaehxw309ac82unsd3jhqct89ejhxqgdwaehxw309ahx7uewd3hkca6zsjl
Portugal
- Ilha da Madeira - nostr:nprofile1qqsv45qvfz5vdzwn9478wzusyggjf44x3w7xk8f3cgpe4px44wgv77cpr3mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmqpz3mhxue69uhhyetvv9ujumn0wd68ytnzvuq32amnwvaz7tmwdaehgu3dwfjkccte9eshquqzhddc4
-
-
 @ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46
@ 1c19eb1a:e22fb0bc
2025-05-08 21:55:46If you haven't noticed already, #Nostr is a little different from what most people are used to. One of the ways this is felt most acutely is with media hosting. Users are accustomed to uploading their images and videos directly through the app they are posting from. Many Nostr apps provide that same experience nowadays, but it wasn't always the case.
Just a couple years ago, users had to find somewhere to host their media separately, and then copy and paste the URL into their note whenever they wanted to share their cat pictures. One of the first, if not the first, media hosting services specifically intended for Nostr was nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7, which will be the service we are reviewing today.
Like our previous review of Amber, Nostr.Build is a service for users to pair with other Nostr apps. You won't generally use nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 by itself. Rather, you'll use it to host that incredible shot you want to post to #Olas, or to host screenshots for your long-form tutorial about setting up Nostr Wallet Connect that you'll be posting from #Habla.news, or for hosting a hilarious video of your cat falling asleep to nostr:npub1cj8znuztfqkvq89pl8hceph0svvvqk0qay6nydgk9uyq7fhpfsgsqwrz4u's voice and taking a tumble off of his favorite perch that you want to share on #Damus. However, there are some features within Nostr.Build that you may want to check out quite apart from using it with any other Nostr app.
Overall Impression
Score: 4.8 / 5
I have been impressed by Nostr.Build for some time now, but they have pulled out all the stops in their latest update, increasing their maximum file size for free accounts to 100MB, integrating the #Blossom protocol, adding the ability to share directly to Nostr from within your dashboard, and more integrations with other Nostr apps than ever before. Nostr.Build is simply a pleasure to use, whether through their web interface, or through another Nostr app that integrates with them.
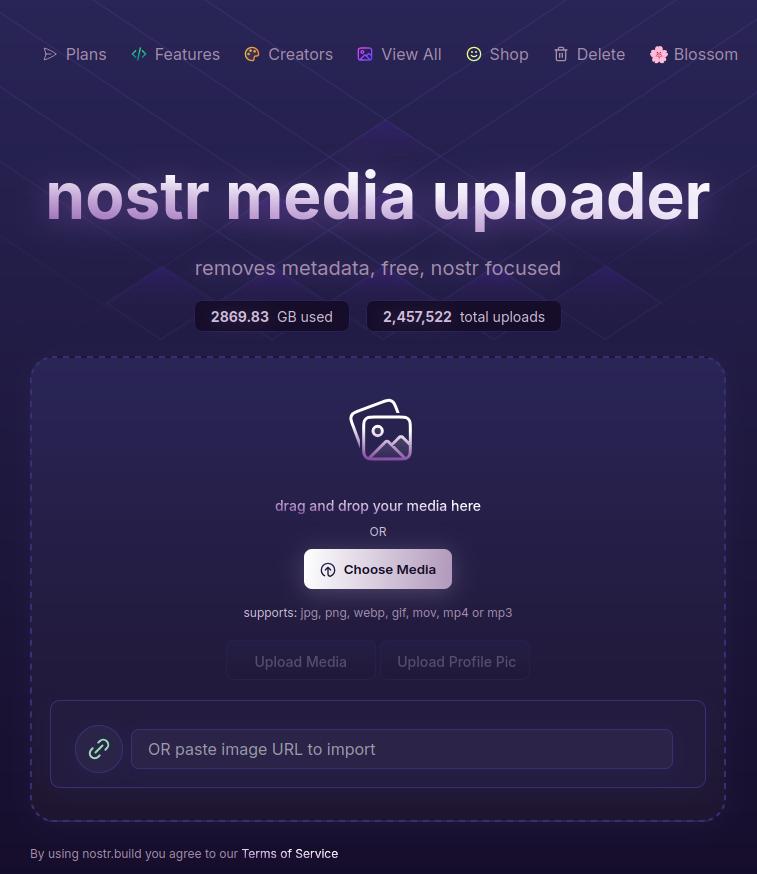
With the ability to easily organize your media, view statistics, browse the media gallery of free uploads, metadata removal for increased privacy, and AI image generation, Nostr.Build is not simply a media hosting service, it is a full-fledged media management platform. Its robust features keep it well ahead of other Nostr-focused media hosting options available, and a particularly strong option for those using Blossom and wanting redundancy and reliable uptime for their media.
As much as I enjoy using the web interface, though, where Nostr.Build really shines is their integrations with other Nostr apps. These integrations allow users to have the same experience they are accustomed to from centralized social platforms of uploading their media from within the same app they are using to share it. No copy/pasting a URL from one app to another. In fact, many users may not realize they have been using Nostr.Build in their client of choice, simply because it is the default option for media hosting for many Nostr apps.
This has the added benefit to client developers that they can provide this experience to their users without having to run media hosting infrastructure on top of trying to build their app. The separation of relays, clients, and media hosting between different entities, while keeping a similar experience to centralized platforms where a single company controls all three, is critical to Nostr adoption.
Features
Nostr.Build has a plethora of features beyond simply hosting your media. Let's take a look!
AI Image Generation
Do you need a quick title image for a long-form article? How about inspiration for a logo or art piece? Nostr.Build's AI Studio has you covered.
They have provided a few different models based on the plan you purchase, beginning with the Professional plan, which includes SDXL-Lightning and Stable Diffusion 1. Upgrading to the Creator plan will give you access to all Pro Stable Diffusion models and unlimited use of the Flux.1 model, which is the same core model used for Grok2 images.
I personally have a Professional account, so I haven't had a chance to try out Flux.1, but I have used Stable Diffusion extensively for creating character art for #NostrHeroes characters, such as these:




Nothing too spectacular when compared with some of the newer models out there, and there is no image-to-image support (yet), but more than adequate for casual image generation needs. Moreover, it is far more than what one would expect from a simple media-hosting service.
Admittedly, I am also no expert at coaxing AI models to produce anything remarkable so your results may vary. Either way, image generation is a welcome tool to have available without needing to go to an outside service unless you require something very specific.
Upload Limits
The maximum file size limits on Nostr.Build have been getting progressively larger, even for their free service. As I recall, it was a mere 21MB limit per file just a few months ago, which is fine for image files, but is quickly exceeded with videos. Then they increased their limits to 50MB per file, and as of recent updates it has been increased once more to a whopping 100MB per file... for free! This is more than adequate for most uses.
However, free users' images, GIFs, and videos are automatically viewable via Nostr.Build's free media gallery. This is something to particularly bear in mind when uploading images you intend to share via direct message. Though your DMs are encrypted, the images uploaded to Nostr.Build are not, and if you don't have a paid account, they will be viewable to the all paid users in the free media gallery. If you want to upload images that will not be viewable unless you actively share them, you must have a paid account.
Paid accounts have no file size limit, but they do have a total storage limit. I could not find anything about total storage limits for free accounts, but Professional tier will give you 25GB, Creator 50GB, and Advanced 250GB. Uploads to paid accounts are not visible in the free media gallery, so only those you give the link to will be able to access your content.
Media Types
Many file types are supported by Nostr.Built, even for free users, including:
- Image: .jpg, .png, .gif
- Video: .mov, mp4
- Audio: mp3, .wav
Upgrading to the Professional plan will add .pdf and .svg to the list of permitted file types, and upgrading to Creator or above will add .zip files, as well.
I believe other common file types are also supported, but these are the only ones specifically mentioned on the site.
Free Media Gallery
The free media gallery is an interesting little feature that Nostr.Build has available to paid accounts. Free users can get a preview, such as the one below, but only paid users can browse through the millions of uploads made by free users.
Apart from being amusing to browse through the things people have been uploading, I am unsure of how useful this particular feature is. No indication is given as to who uploaded the media, and it is limited compared to media feeds in other Nostr apps in two important ways. First, it only shows media uploaded to Nostr.Build, while other media-focused Nostr apps, such as Slidestr, Lumina, or even Primal will show media posted by all Nostr users. Second, Nostr.Build's gallery doesn't show all uploads to Nostr.Build, but only uploads from those without a paid account, further limiting the scope of whose uploads are seen.
Paid users have the advantage of being able to upload media that is not viewable to anyone unless they intentionally share the link somewhere. Free users, on the other hand, must be aware that their uploads are viewable by any paid users, whether they shared the link anywhere or not.
One incident I had while testing out another app required me to reach out to Nostr.Build support to request deletion of an image. It had some of my personal information in it, and had been uploaded to Nostr.Build and sent to me via DM. The sender assumed that since it was being sent via DM, no one else would be able to see the image, but because he was not a paid user of Nostr.Build, the image was included in the Free Media Gallery for any paid user to see. Not ideal, but the folks at Nostr.Build were quick to get it deleted for me.
In short, I have mixed feelings about this particular feature.
Blossom
Blossom is a media storage and retrieval protocol built for Nostr, but usable with any application that needs to access media via the web, and Nostr.Build has recently added support for Blossom uploads via their Blossom server: blossom.band
I will likely be adding a Nostrversity article going over Blossom in detail in the near future, but here's the basics of what it makes possible:
First, easy integration for media uploading from your favorite Nostr apps. Amethyst, Coracle, Primal and others have added Blossom upload support, so you just have to hop into your settings and add Nostr.Build's Blossom server address to start using it as your media host. No need to go to a separate app to upload your media and copy/paste the URL into your Nostr note!
Second, your media in Blossom is content addressable. This means it is named based on a hash of its actual data. Because of this, you can verify that the media has not been altered or replaced by your media host. If the hash doesn't match the data, it won't be loaded by the Nostr client, so you never have to worry about the image in your note being replaced by a different image by your media host.
Finally, because your media is addressable by its content, you can save the same media to multiple hosts, and if one of them goes down, Nostr apps can fetch your media from other hosts, just like they can do with your notes by fetching them from different relays if one relay you write to is down. This makes your images and videos much harder to censor, since you would need to be banned by multiple Blossom servers for your media to no longer be accessible.
If you would like to upload media to more than one Blossom server at the same time, your options are currently to use Primal and ensure that your settings have "Enable media mirrors" toggled on, or to use Bouquet. Hopefully we will see this option added to more Nostr apps in the near future.
Metadata Stripping
For files uploaded via Nostr.Build's dashboard, location metadata is removed upon upload. This is to protect user privacy, since this data could be used to reveal your home address if it is left attached to images posted publicly on Nostr.
When uploading via Blossom, media containing location metadata will be rejected. The user will be required to remove the metadata before they can upload the media.
No KYC and No Ads Policy
The only form of identification needed to use Nostr.Build is your Nostr identity. Every upload is tied to your npub, but no name, date of birth, email, or other identifying information is required. This is made possible because Nostr.Build only accepts Bitcoin as payment for their accounts, and no KYC is required to make Bitcoin transactions via Lightning.
Additionally, Nostr.Build is philosophically opposed to targeted advertising, so they have a policy that they will never use ads on their hosting service.
Client Integrations
Even before Blossom, Nostr.Build had many Nostr clients that used it as the default media hosting service, allowing users to upload directly within the app. This has only expanded now that Nostr.Build has added Blossom.
A very non-exhaustive list of clients that integrate with Nostr.Build is listed on their site, and includes Damus, Amethyst, Nostrudel, Snort, Iris, Coracle, Flycat, and Yakihonne. Additional apps that support Nostr.Build via Blossom include Primal and Flotilla. Some of these integrations support both Blossom and NIP-96 options for uploading media, such as Amethyst, while others only support one or the other.
I would not be surprised to see more and more Nostr apps move to integrating Blossom and phasing out NIP-96 support. Either way, though, Nostr.Build currently supports both, and is therefore an excellent hosting option if you want to use it with a wide range of Nostr apps.
Media Statistics
For those with a paid account, Nostr.Build provides information about how often each of your uploads has been requested and viewed within a given time period.
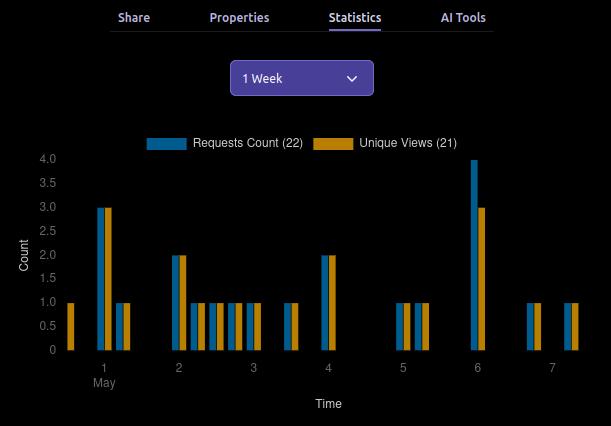
This can be valuable information for content creators, so they can determine what content is resonating with their audience, and what times of day their posts get the most views.
This information can currently be viewed for a maximum period of three months prior to the current date, and as short a period as just the past hour.
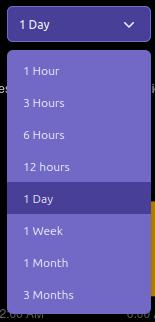
Can My Grandma Use It?
Score: 4.7 / 5
Nostr.Build is incredibly easy to use if you have a paid account, or if you are a free user uploading to Nostr.Build through a client that integrates with them by default. Previous frictions encountered by free users trying to upload large files should now be few and far between, thanks to the generous 100MB size limit.
Where things may be a bit more involved is when users are trying to set up media hosting on Nostr apps that don't use Nostr.Build by default. Exactly where in the settings the user must go to set this up, and whether to use the Blossom or NIP-96 address may not be immediately apparent, and requires an understanding of the difference that the user may not possess. This is not the fault of Nostr.Built, though, and I have not taken it into consideration in the scoring. Each individual Nostr app's settings should be as easy to understand as possible.
Another point of friction may come from free users who want to upload directly through the Nostr.Build site, instead of via another Nostr app. This used to be possible without logging in, but in an effort to ensure the service was used for Nostr, and not for general media hosting, Nostr.Build added the requirement to log in.
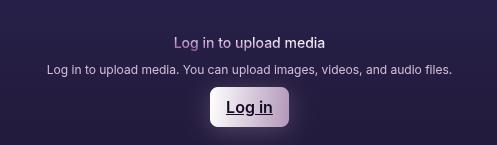
Thankfully, there are plenty of login options, including npub and password, browser extension (NIP-07), and even via a one-time-code sent to you via Nostr DM. However, if you don't have a paid account already, logging in will prompt you to upgrade. It seems that uploading directly via the website has been removed for free users entirely. You can only upload via another Nostr app if you don't have a paid account. This may lead to confusion for users who don't want to pay for an account, since it isn't made apparent anywhere that uploading through the website isn't an option for them.
Additionally, I would like to see the addresses for the Blossom server and for NIP-96 uploads (unless they are being phased out) added to the main page somewhere. Even selecting the "Blossom" page from the site navigation doesn't make clear what needs to be done to utilize the service. Something as simple as, "To use Nostr.Build with your favorite Blossom compatible Nostr apps, just add https://blossom.band as your media host in the app settings," would be enough to point users in the right direction.
For those who do have paid accounts, the dashboard is easy to navigate and organize your media.
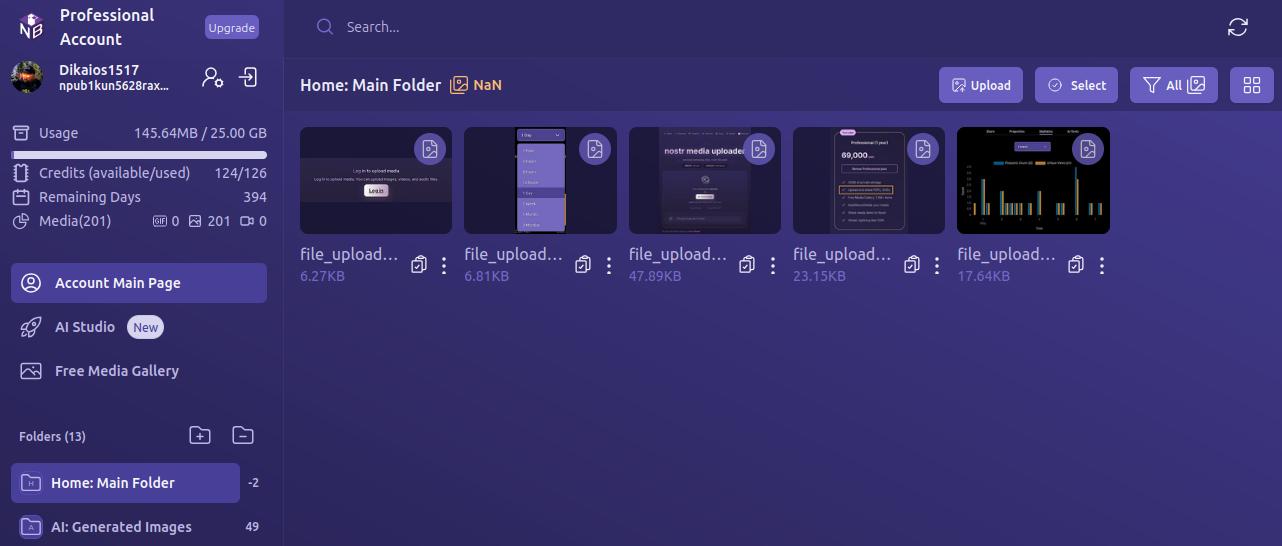
By default, all uploads are added to the Main Folder. Users can leave them there, or they can easily create new folders and drag and drop media to organize it.
Every image has a copy/paste clipboard icon for ready access to copy the media URL for inclusion into a Nostr note.
Additionally, Nostr.Build allows users to share their uploaded media to Nostr directly from the dashboard. Bear in mind, though, this is published to a set of popular relays, without taking into account the user's preferred write relays.
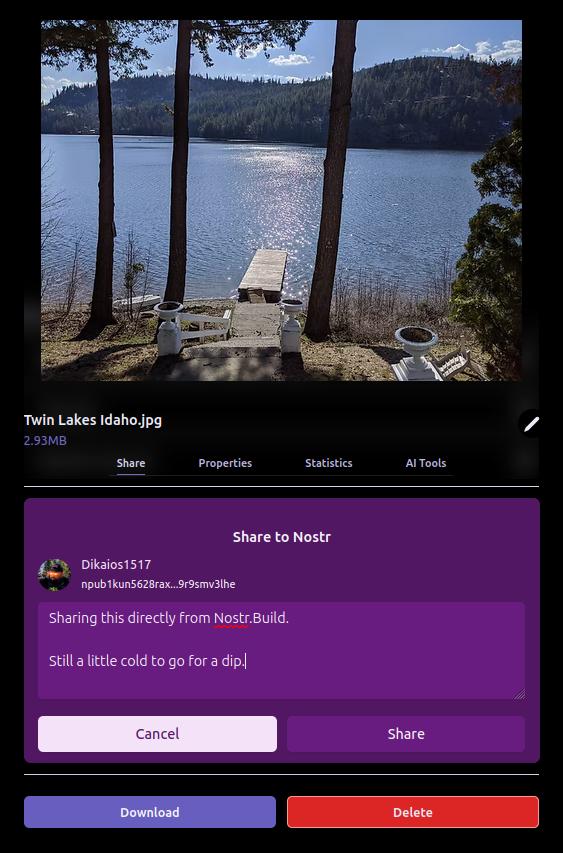
The section just below the user's profile information gives an at-a-glance view of important information, such as how much of the user's allotted storage has been used, how many AI Studio credits are available, how many days are left before their paid account must be renewed, and how many files from three major categories — GIFs, images, and videos — have been uploaded.

Uploading directly to the dashboard is also incredibly easy. You can simply drag and drop files into the upload pane, or browse for them. If you have a URL for the media you want to upload, you can even paste it to import from another website or Blossom server.
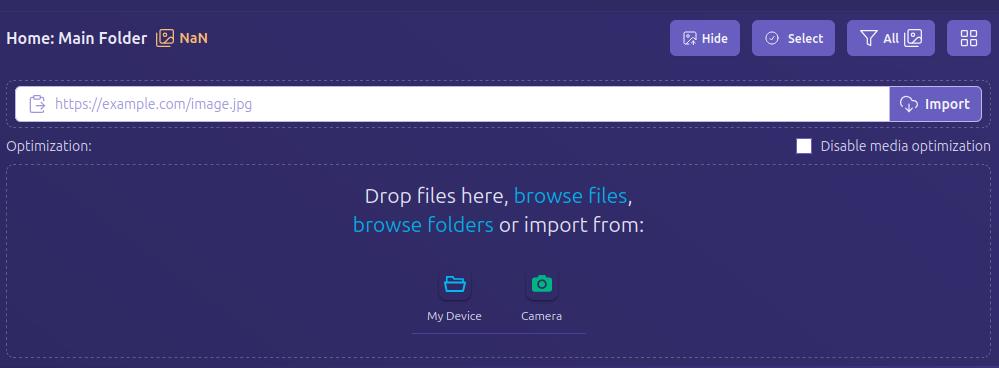
Anything I could think of that I might want to do in the interface was intuitive to find, well labeled, or had common and easily identified icons.
How do UI look?
Score: 4.7 / 5
I would describe Nostr.Build's UI as clean and utilitarian, which is what one would expect from a media hosting service. Nothing too flashy. Just what you need and nothing you don't.
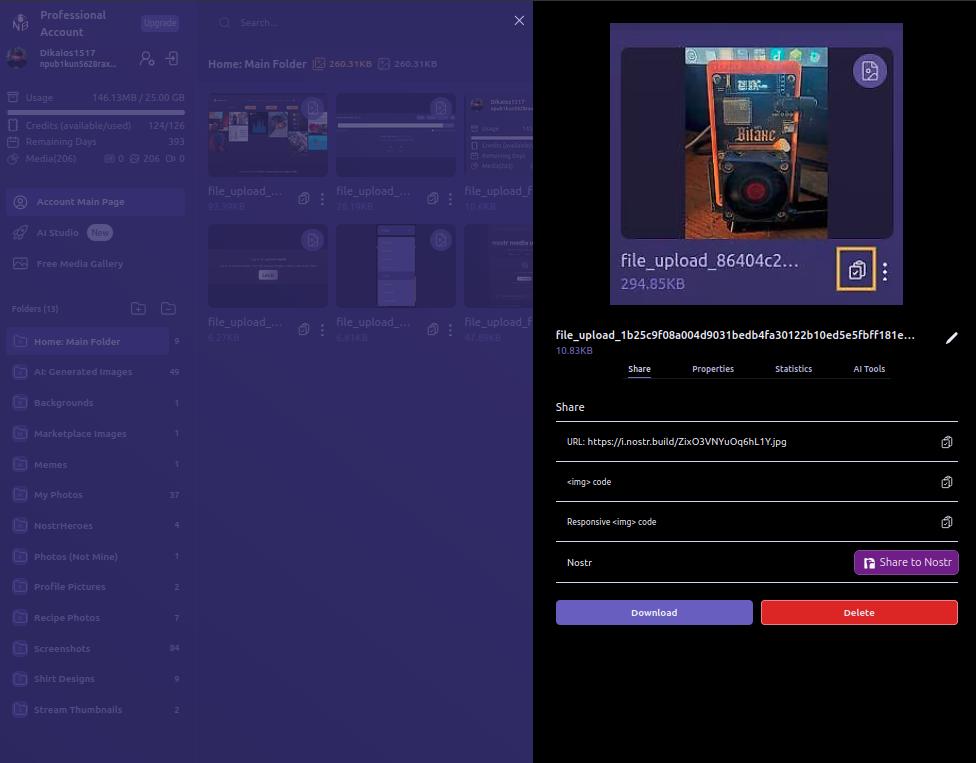
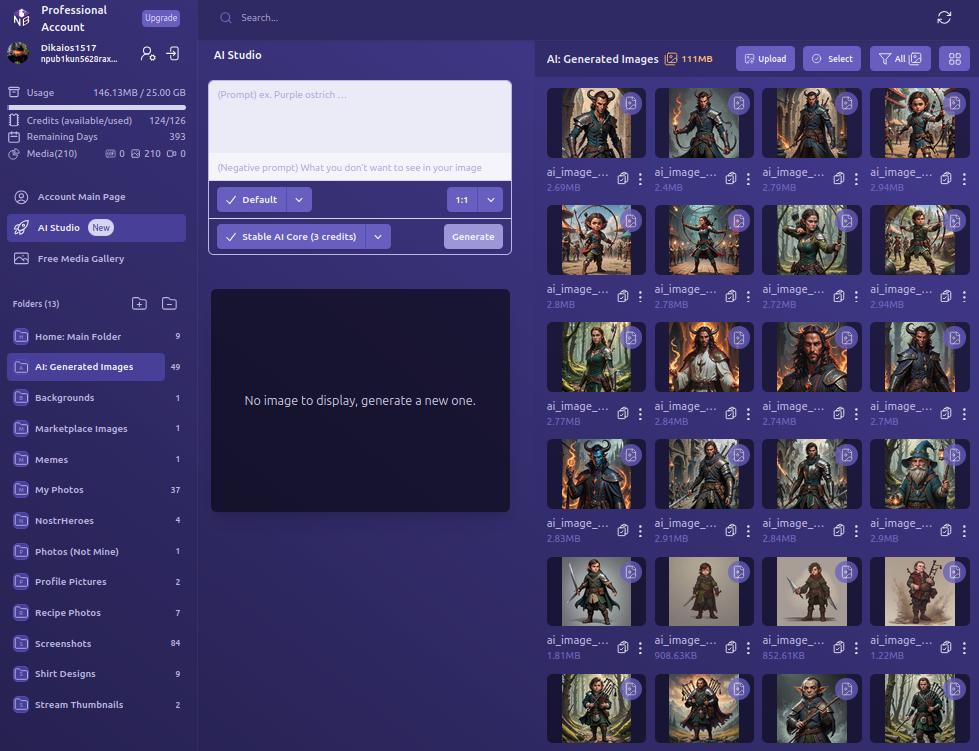
We certainly like our purple color-schemes on Nostr, and Nostr.Build leans into that with white text on shades of purple backgrounds, along with occasional color-popping accents. If a Nostr client had made the same color choices, I might be a bit more critical, but it works in an app that users won't be spending a ton of time in, except while managing their media, or using the AI Studio to generate some images.
UI elements such as buttons, active folder indicators, and icons all maintain an attractive, and simple design, with rounded corners wherever appropriate. Nothing looks too busy or overbearing, and the spacing between image previews in the folder view is just right.
Font remains consistent throughout the interface, with no jarring changes, and bold text, in white or another contrasting color, is used appropriately to draw attention, while subdued text is rendered in a light purple to blend more with the background, while remaining readable.
As such, the UI is attractive, without being particularly breathtaking. Nothing to complain about, but also nothing to write home about.
Log In Options
Score: 4.8 / 5
As mentioned previously, Nostr.Build provides three ways a user can log in.
The first should be very familiar for any Nostr user who frequents web clients, and that is by use of a browser extension (NIP-07), such as Alby, Nos2x, or Gooti. Note, this will also work if you are on Android and using KeyChat's browser, which has a NIP-07 signer built in.
Next is the legacy login method for Nostr.Build that they have used since the service first launched, which is via npub and password. This should serve to remind you that even though Nostr.Build supports Nostr login, and can post your images to Nostr for you, it's really just a centralized media hosting service. Just like you wouldn't use only one Nostr relay, you should not use just one media host. Mirror your media to other Blossom servers.
Most intriguing, and one I had not seen used before, is the option to use your npub and have a one-time-code sent to you via Nostr DM. I tested this method out and it worked flawlessly. It is unfortunately using the old NIP-04 DM spec, though, so any clients that have deprecated these DMs will not work for receiving the code. We're in a strange place with Nostr DMs currently, with some clients deprecating NIP-04 DMs in favor of NIP-17, others that still only support NIP-04, and a few that support both. If you don't see the DM in your client of choice, hop over to Primal and check your DMs there in the "other" tab.
Since Nostr.Build is supporting Nostr login, I would like to see them add remote signer (NIP-46) login alongside browser extension login to round out the options expected from a Nostr web app.
Feature Set
Score: 4.8 / 5
The features provided by Nostr.Build all work as expected and provide a lot of value to the user. With only one exception, all of the features make sense for a media hosting and management service to provide, and they are adding more features all the time.
Users not only get a reliable hosting service, with excellent uptime for their media, but they get integrations with most Nostr clients I can think of, Blossom protocol support, media organization and statistics, posting media to Nostr from within the dashboard, metadata stripping for enhanced privacy, a wide range of supported file types, and an AI image generation studio! What's more, there are additional features already on the roadmap, including traditional and AI image editing, additional plan options, expandable storage, and video transcoding for optimized playback. Nostr.Build is just getting started and they already offer more than most media hosting services out there, intended for Nostr or otherwise.
The one feature I am still not sold on is the "Free Media Gallery." The name is misleading. The gallery itself is not free. You must have a paid account to access more than a preview of it. Rather, it displays media uploaded by free users, regardless of whether they uploaded that media to send via DM, or uploaded it but decided not to share it out, or uploaded it to post it only within a private group on Flotilla, or uploaded it and only sent the note with the image link to a private relay.
Moreover, if I want to see media that has been shared on Nostr, there are plenty of ways I can do so that I can be confident only include media users intended to be publicly viewable. This feature from Nostr.Build, if it is kept at all, should have some way of ensuring the gallery only includes images that were shared on public relays.
Pricing
Score: 5 / 5
The pricing structure for Nostr.Build is exceptionally reasonable when compared with other services.
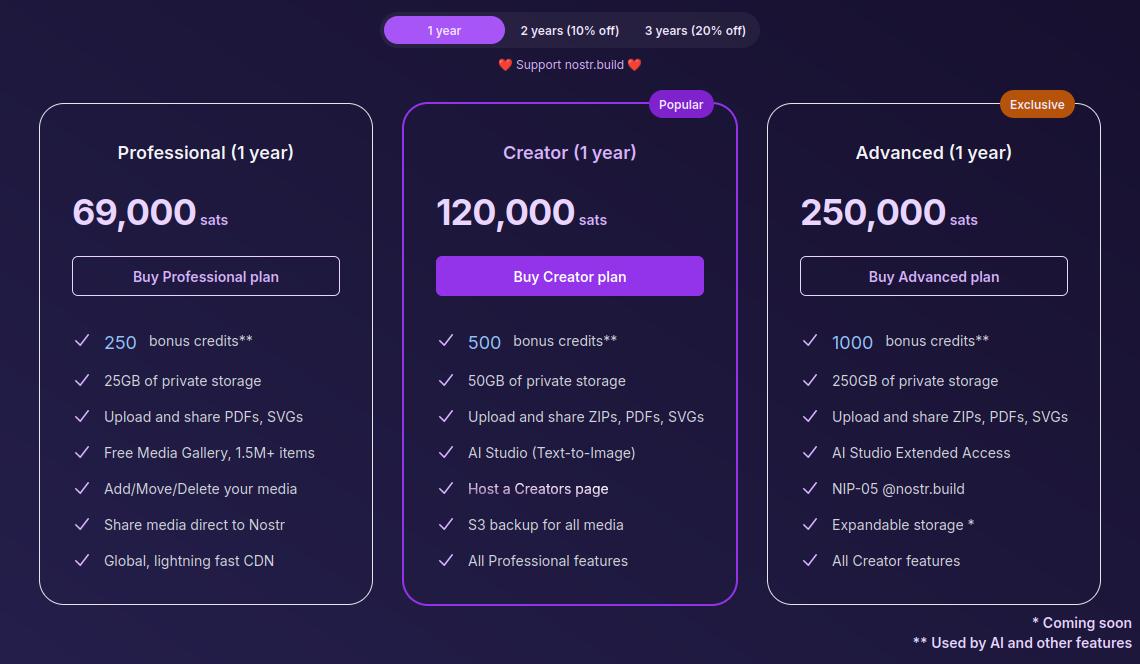
The Professional plan, which is their lowest paid tier, is just 69,000 sats a year. At current price, that translates to around $70 for the year, and Nostr.Build has been known to lower their pricing as Bitcoin goes up. Users can also get a 10% or 20% discount if they buy 2 or 3 years at a time, compensating for the fact that Bitcoin tends to go up year over year.
For that cost, users get 25GB of storage, unlimited file size for uploads within that storage cap, and access to all of Nostr.Build's features mentioned in this review, with the exception of their highest end AI models and storage of certain file types.
If I were to set up my own VPS to host a Blossom server with comparable storage, I would be paying around $14 a month before the cost of the domain, and it would be anything but plug and play. Even then, all I would have is storage. I would be missing out on all of the other features Nostr.Build has out of the box for less than half the price.
The Creator plan is close to double the cost at 120,000 sats, or about $120, a year. However, you aren't just getting double the storage space at 50GB; you are also getting double the AI credits, access to the higher tier AI models, S3 backup for all of your media, and your own Creator page you can share out with your media available for others to browse in one location.
The Advanced plan doesn't add a lot of extra features for more than double the price of the Creator plan, but it MASSIVELY increases your storage limit by 5x to a total of 250GB. Comparable storage space on a VPS to run your own Blossom server would be about $100 a month and Nostr.Build is offering it for about $250 (250,000 sats) for a whole year! If you really need to host that much media, it's hard to beat this price. The plan also comes with a Nostr.Build NIP-05 address, if you need one.
Now, the argument can be made, "But it's priced in sats, and that means in four years I will have spent many times that dollar amount on their service, possibly making it more expensive than other services priced in fiat." While that is true, it also doesn't take opportunity cost into account. Every dollar you spend on something other than Bitcoin is a missed opportunity to have bought Bitcoin with it. There's not really any difference between spending $70 in fiat to buy a hosting plan vs spending 69,000 sats, because you could have used that same $70 to buy Bitcoin instead, so you are losing out on that increase in purchasing power either way.
Not to mention, you can just buy the sats with your fiat and send it to Nostr.Build, so you would effectively be buying your plan with fiat, and they would be receiving sats.
I think Satellite.earth is still technically less expensive at just $0.05 per GB per month, which comes to $15 a year for the same 25GB of Nostr.Build's professional plan. However, all you get is media hosting. You miss out on all of the other features provided by Nostr.Build. And if you are uploading files of 100MB or less... Well, free with Nostr.Build is still cheaper than $0.5 per GB.
Wrap Up
All of the above comes together to make Nostr.Build a versatile and full-featured media hosting and management service at an affordable price point for their paid accounts, but with no need to pay at all if you just want a place to upload photos, GIFs, memes, and even some videos, so long as the file size stays under 100MB. Whether you want to use Nostr.Build as your primary media host, or as just one redundancy in your Blossom set up, they have you covered and I encourage you to check them out!
For the next review, I would like to go with another client, this time for the web, and the two options I am debating between are Coracle.social and Jumble.social. Let me know in the comments which you would like to see!
-
 @ 34f1ddab:2ca0cf7c
2025-05-08 21:39:47
@ 34f1ddab:2ca0cf7c
2025-05-08 21:39:47Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 5194e71c:761bd15c
2025-05-08 21:23:37
@ 5194e71c:761bd15c
2025-05-08 21:23:37[SELL] Funny video Clic on link and Pay on sats with QR code https://m-url.eu/r-66dx
originally posted at https://stacker.news/items/975020
-
 @ 7459d333:f207289b
2025-05-08 20:25:45
@ 7459d333:f207289b
2025-05-08 20:25:45lavaGiraffehas created some nice charts with an estimation on the JoinMarket coinjoins from January 1st 2024 until April 30th 2025 using https://github.com/PulpCattel/jm-scripts/blob/master/jmfinder.pyFalse positives are possible, so this is to be interpreted as an upper bound.
originally posted at https://stacker.news/items/974988
-
 @ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13
@ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13I am happy to present to you the first full review posted to Nostr Reviews: #Primal for #Android!
Primal has its origins as a micro-blogging, social media client, though it is now expanding its horizons into long-form content. It was first released only as a web client in March of 2023, but has since had a native client released for both iOS and Android. All of Primal's clients recently had an update to Primal 2.0, which included both performance improvements and a number of new features. This review will focus on the Android client specifically, both on phone and tablet.
Since Primal has also added features that are only available to those enrolled in their new premium subscription, it should also be noted that this review will be from the perspective of a free user. This is for two reasons. First, I am using an alternate npub to review the app, and if I were to purchase premium at some time in the future, it would be on my main npub. Second, despite a lot of positive things I have to say about Primal, I am not planning to regularly use any of their apps on my main account for the time being, for reasons that will be discussed later in the review.
The application can be installed through the Google Play Store, nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8, or by downloading it directly from Primal's GitHub. The full review is current as of Primal Android version 2.0.21. Updates to the review on 4/30/2025 are current as of version 2.2.13.
In the ecosystem of "notes and other stuff," Primal is predominantly in the "notes" category. It is geared toward users who want a social media experience similar to Twitter or Facebook with an infinite scrolling feed of notes to interact with. However, there is some "other stuff" included to complement this primary focus on short and long form notes including a built-in Lightning wallet powered by #Strike, a robust advanced search, and a media-only feed.
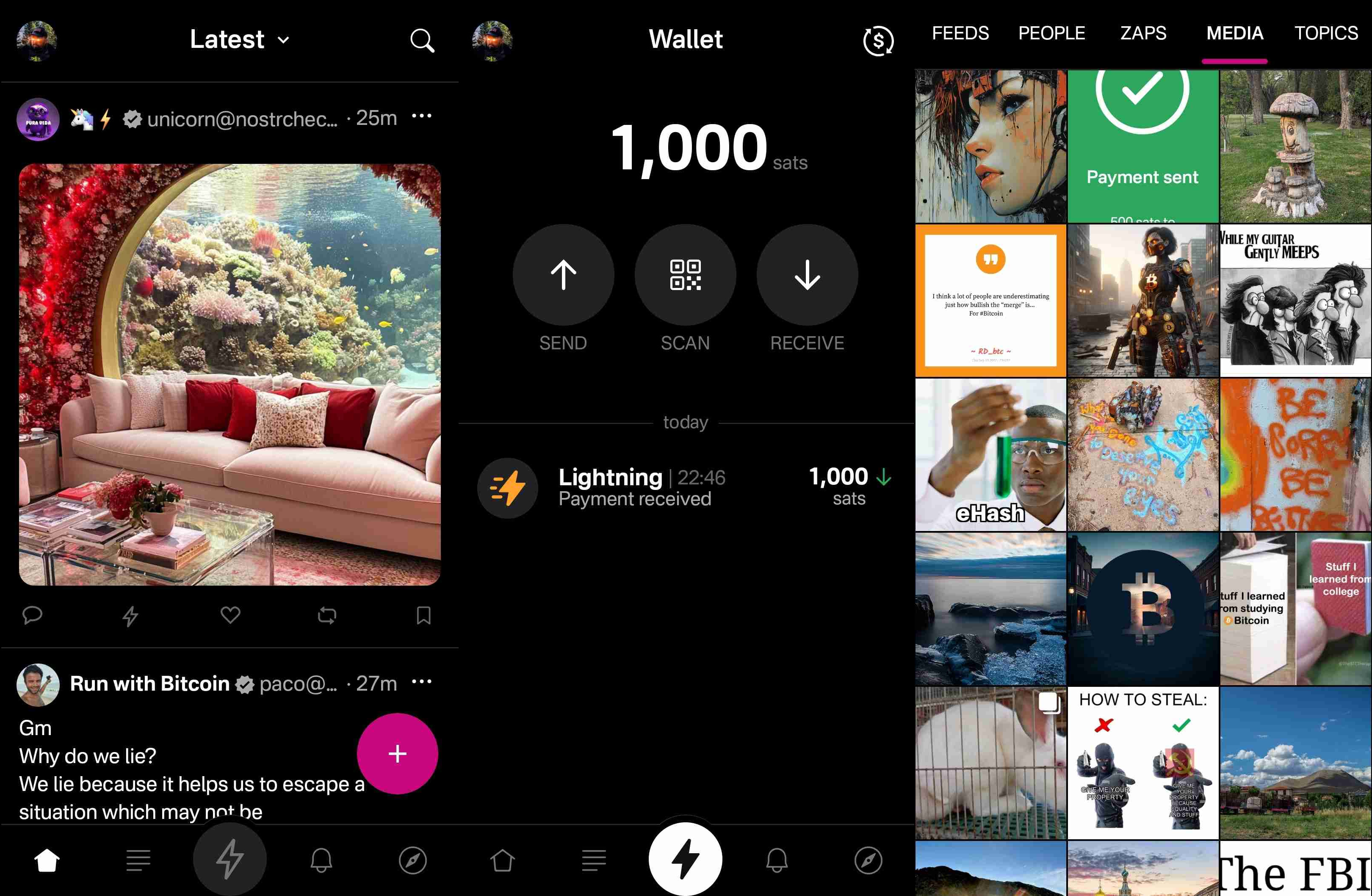
Overall Impression
Score: 4.4 / 5 (Updated 4/30/2025)
Primal may well be the most polished UI of any Nostr client native to Android. It is incredibly well designed and thought out, with all of the icons and settings in the places a user would expect to find them. It is also incredibly easy to get started on Nostr via Primal's sign-up flow. The only two things that will be foreign to new users are the lack of any need to set a password or give an email address, and the prompt to optionally set up the wallet.
Complaints prior to the 2.0 update about Primal being slow and clunky should now be completely alleviated. I only experienced quick load times and snappy UI controls with a couple very minor exceptions, or when loading DVM-based feeds, which are outside of Primal's control.
Primal is not, however, a client that I would recommend for the power-user. Control over preferred relays is minimal and does not allow the user to determine which relays they write to and which they only read from. Though you can use your own wallet, it will not appear within the wallet interface, which only works with the custodial wallet from Strike. Moreover, and most eggregiously, the only way for existing users to log in is by pasting their nsec, as Primal does not support either the Android signer or remote signer options for users to protect their private key at this time. This lack of signer support is the primary reason the client received such a low overall score. If even one form of external signer log in is added to Primal, the score will be amended to 4.2 / 5, and if both Android signer and remote signer support is added, it will increase to 4.5.
Update: As of version 2.2.13, Primal now supports the Amber Android signer! One of the most glaring issues with the app has now been remedied and as promised, the overall score above has been increased.
Another downside to Primal is that it still utilizes an outdated direct message specification that leaks metadata that can be readily seen by anyone on the network. While the content of your messages remains encrypted, anyone can see who you are messaging with, and when. This also means that you will not see any DMs from users who are messaging from a client that has moved to the latest, and far more private, messaging spec.
That said, the beautiful thing about Nostr as a protocol is that users are not locked into any particular client. You may find Primal to be a great client for your average #bloomscrolling and zapping memes, but opt for a different client for more advanced uses and for direct messaging.
Features
Primal has a lot of features users would expect from any Nostr client that is focused on short-form notes, but it also packs in a lot of features that set it apart from other clients, and that showcase Primal's obvious prioritization of a top-tier user experience.
Home Feed
By default, the infinitely scrolling Home feed displays notes from those you currently follow in chronological order. This is traditional Nostr at its finest, and made all the more immersive by the choice to have all distracting UI elements quickly hide themselves from view as the you begin to scroll down the feed. They return just as quickly when you begin to scroll back up.
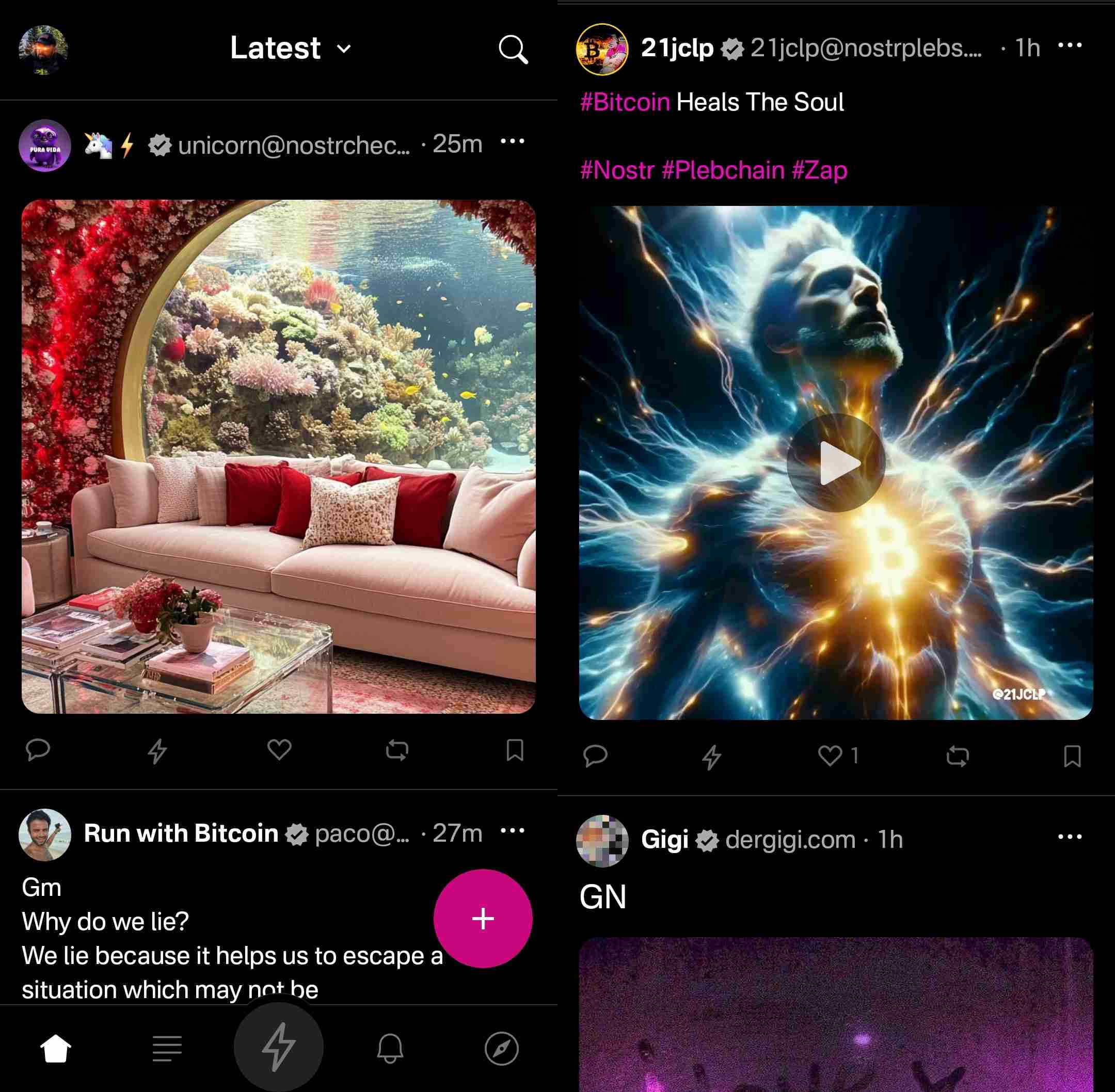
Scrolling the feed is incredibly fast, with no noticeable choppiness and minimal media pop-in if you are on a decent internet connection.
Helpfully, it is easy to get back to the top of the feed whenever there is a new post to be viewed, as a bubble will appear with the profile pictures of the users who have posted since you started scrolling.

Interacting With Notes
Interacting with a note in the feed can be done via the very recognizable icons at the bottom of each post. You can comment, zap, like, repost, and/or bookmark the note.
Notably, tapping on the zap icon will immediately zap the note your default amount of sats, making zapping incredibly fast, especially when using the built-in wallet. Long pressing on the zap icon will open up a menu with a variety of amounts, along with the ability to zap a custom amount. All of these amounts, and the messages that are sent with the zap, can be customized in the application settings.
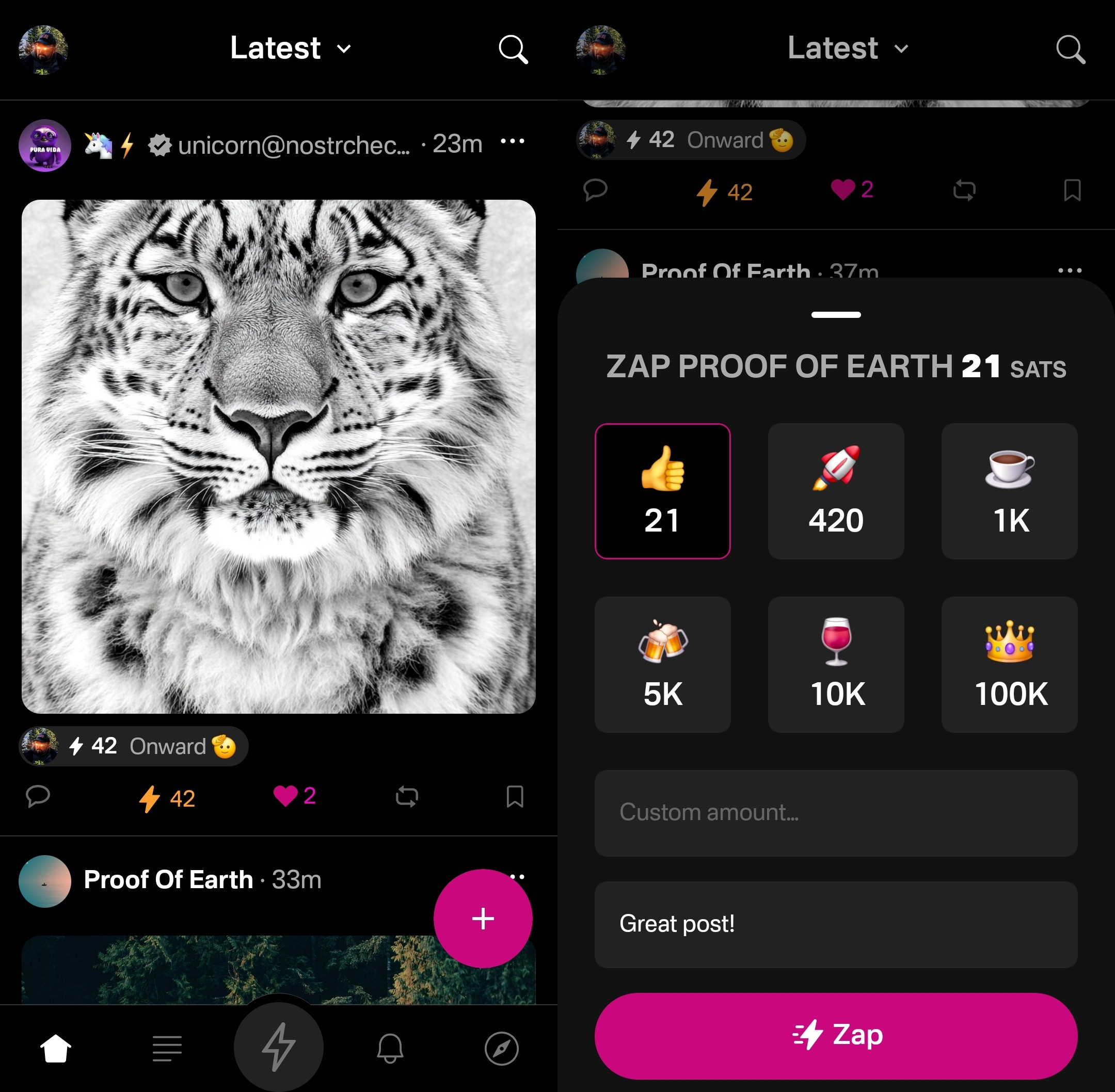
Users who are familiar with Twitter or Instagram will feel right at home with only having one option for "liking" a post. However, users from Facebook or other Nostr clients may wonder why they don't have more options for reactions. This is one of those things where users who are new to Nostr probably won't notice they are missing out on anything at all, while users familiar with clients like #Amethyst or #noStrudel will miss the ability to react with a 🤙 or a 🫂.
It's a similar story with the bookmark option. While this is a nice bit of feature parity for Twitter users, for those already used to the ability to have multiple customized lists of bookmarks, or at minimum have the ability to separate them into public and private, it may be a disappointment that they have no access to the bookmarks they already built up on other clients. Primal offers only one list of bookmarks for short-form notes and they are all visible to the public. However, you are at least presented with a warning about the public nature of your bookmarks before saving your first one.
Yet, I can't dock the Primal team much for making these design choices, as they are understandable for Primal's goal of being a welcoming client for those coming over to Nostr from centralized platforms. They have optimized for the onboarding of new users, rather than for those who have been around for a while, and there is absolutely nothing wrong with that.
Post Creation
Composing posts in Primal is as simple as it gets. Accessed by tapping the obvious circular button with a "+" on it in the lower right of the Home feed, most of what you could need is included in the interface, and nothing you don't.
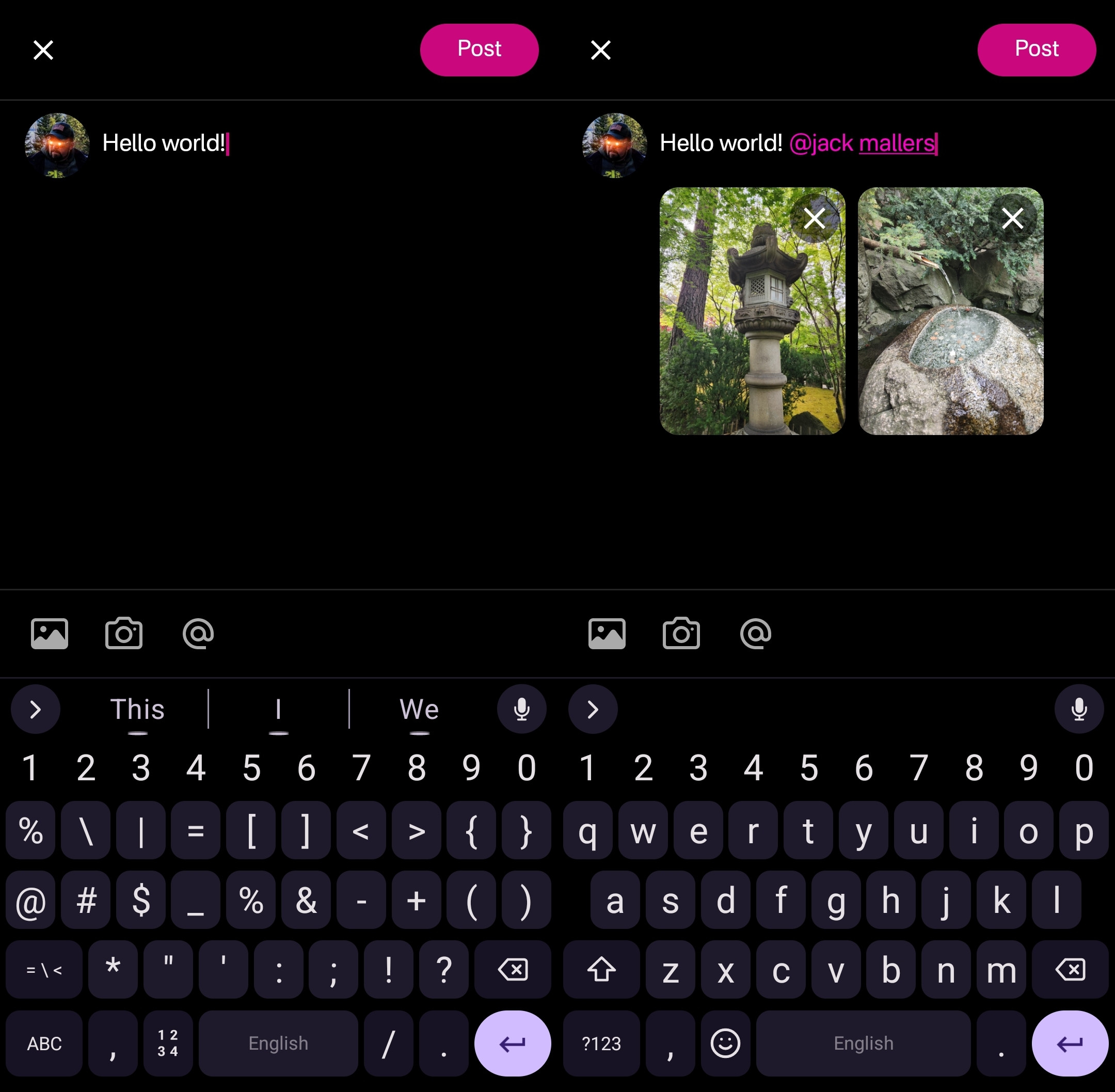
Your device's default keyboard loads immediately, and the you can start typing away.
There are options for adding images from your gallery, or taking a picture with your camera, both of which will result in the image being uploaded to Primal's media-hosting server. If you prefer to host your media elsewhere, you can simply paste the link to that media into your post.
There is also an @ icon as a tip-off that you can tag other users. Tapping on this simply types "@" into your note and brings up a list of users. All you have to do to narrow down the user you want to tag is continue typing their handle, Nostr address, or paste in their npub.
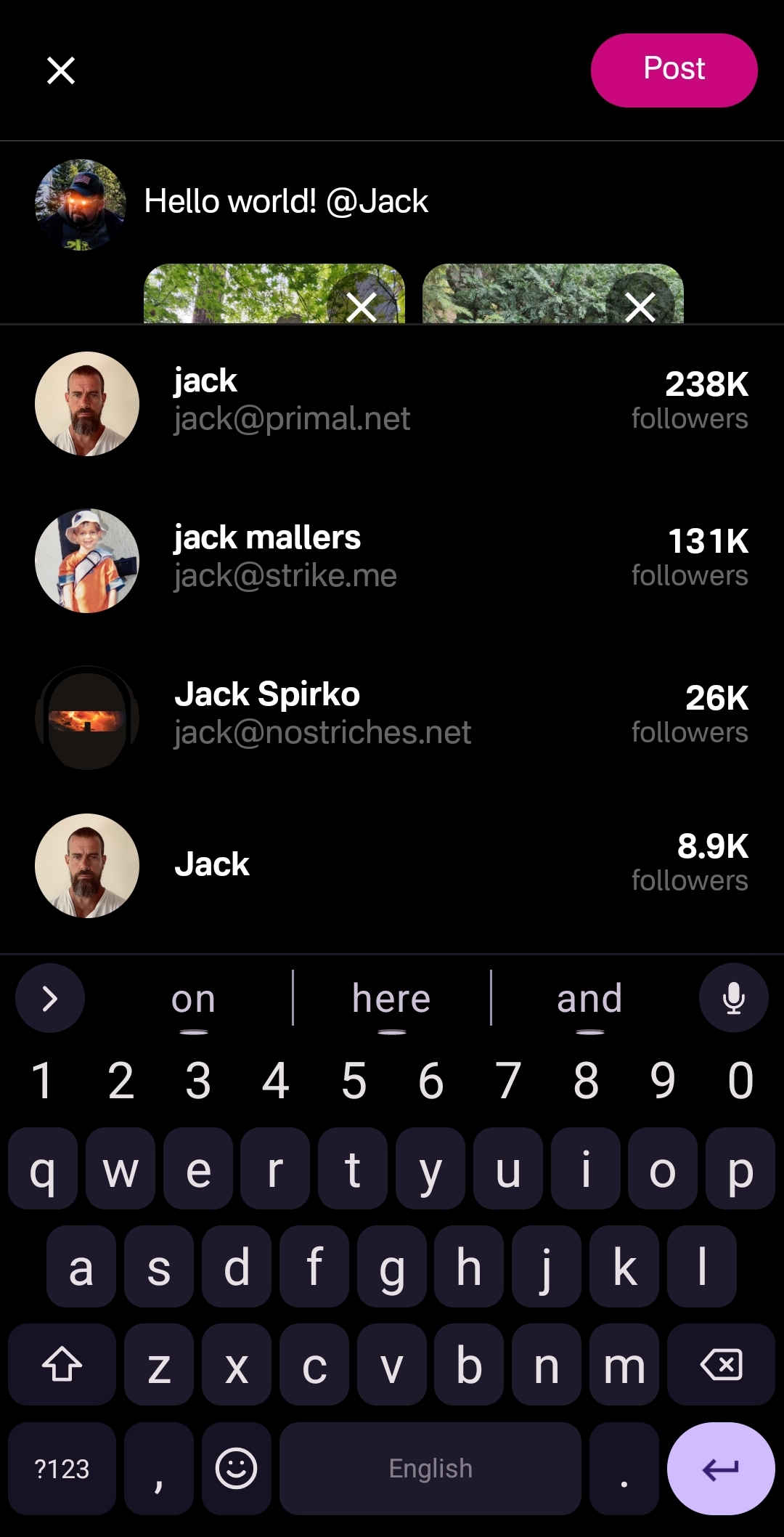
This can get mixed results in other clients, which sometimes have a hard time finding particular users when typing in their handle, forcing you to have to remember their Nostr address or go hunt down their npub by another means. Not so with Primal, though. I had no issues tagging anyone I wanted by simply typing in their handle.
Of course, when you are tagging someone well known, you may find that there are multiple users posing as that person. Primal helps you out here, though. Usually the top result is the person you want, as Primal places them in order of how many followers they have. This is quite reliable right now, but there is nothing stopping someone from spinning up an army of bots to follow their fake accounts, rendering follower count useless for determining which account is legitimate. It would be nice to see these results ranked by web-of-trust, or at least an indication of how many users you follow who also follow the users listed in the results.
Once you are satisfied with your note, the "Post" button is easy to find in the top right of the screen.
Feed Selector and Marketplace
Primal's Home feed really shines when you open up the feed selection interface, and find that there are a plethora of options available for customizing your view. By default, it only shows four options, but tapping "Edit" opens up a new page of available toggles to add to the feed selector.
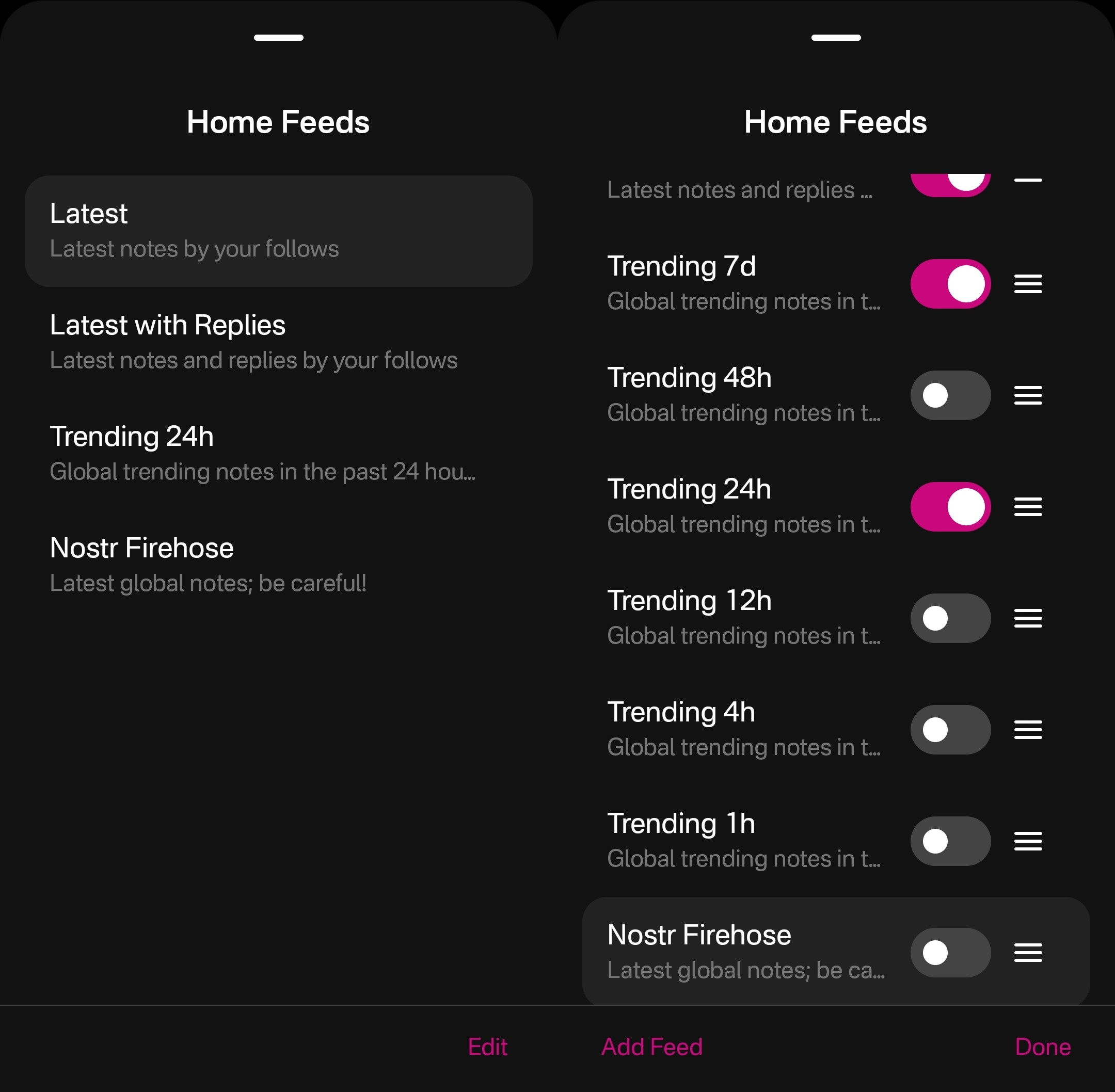
The options don't end there, though. Tapping "Add Feed" will open up the feed marketplace, where an ever-growing number of custom feeds can be found, some created by Primal and some created by others. This feed marketplace is available to a few other clients, but none have so closely integrated it with their Home feeds like Primal has.
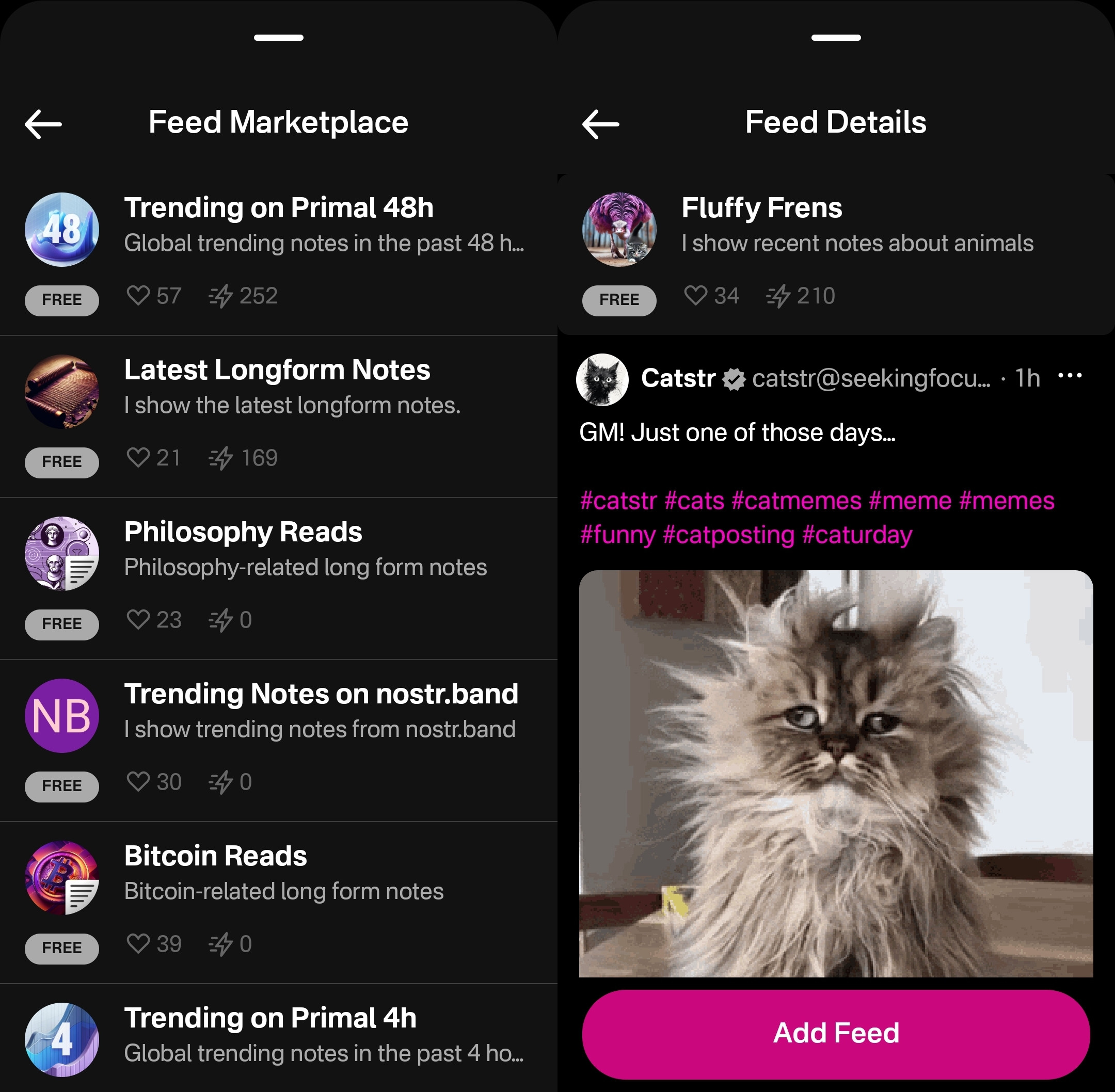
Unfortunately, as great as these custom feeds are, this was also the feature where I ran into the most bugs while testing out the app.
One of these bugs was while selecting custom feeds. Occasionally, these feed menu screens would become unresponsive and I would be unable to confirm my selection, or even use the back button on my device to back out of the screen. However, I was able to pull the screen down to close it and re-open the menu, and everything would be responsive again.
This only seemed to occur when I spent 30 seconds or more on the same screen, so I imagine that most users won't encounter it much in their regular use.
Another UI bug occurred for me while in the feed marketplace. I could scroll down the list of available feeds, but attempting to scroll back up the feed would often close the interface entirely instead, as though I had pulled the screen down from the top, when I was swiping in the middle of the screen.
The last of these bugs occurred when selecting a long-form "Reads" feed while in the menu for the Home feed. The menu would allow me to add this feed and select it to be displayed, but it would fail to load the feed once selected, stating "There is no content in this feed." Going to a different page within the the app and then going back to the Home tab would automatically remove the long-form feed from view, and reset back to the most recently viewed short-form "Notes" feed, though the long-form feed would still be available to select again. The results were similar when selecting a short-form feed for the Reads feed.
I would suggest that if long-form and short-form feeds are going to be displayed in the same list, and yet not be able to be displayed in the same feed, the application should present an error message when attempting to add a long-form feed for the Home feed or a short-form feed for the Reads feed, and encourage the user add it to the proper feed instead.
Long-Form "Reads" Feed
A brand new feature in Primal 2.0, users can now browse and read long-form content posted to Nostr without having to go to a separate client. Primal now has a dedicated "Reads" feed to browse and interact with these articles.
This feed displays the author and title of each article or blog, along with an image, if available. Quite conveniently, it also lets you know the approximate amount of time it will take to read a given article, so you can decide if you have the time to dive into it now, or come back later.
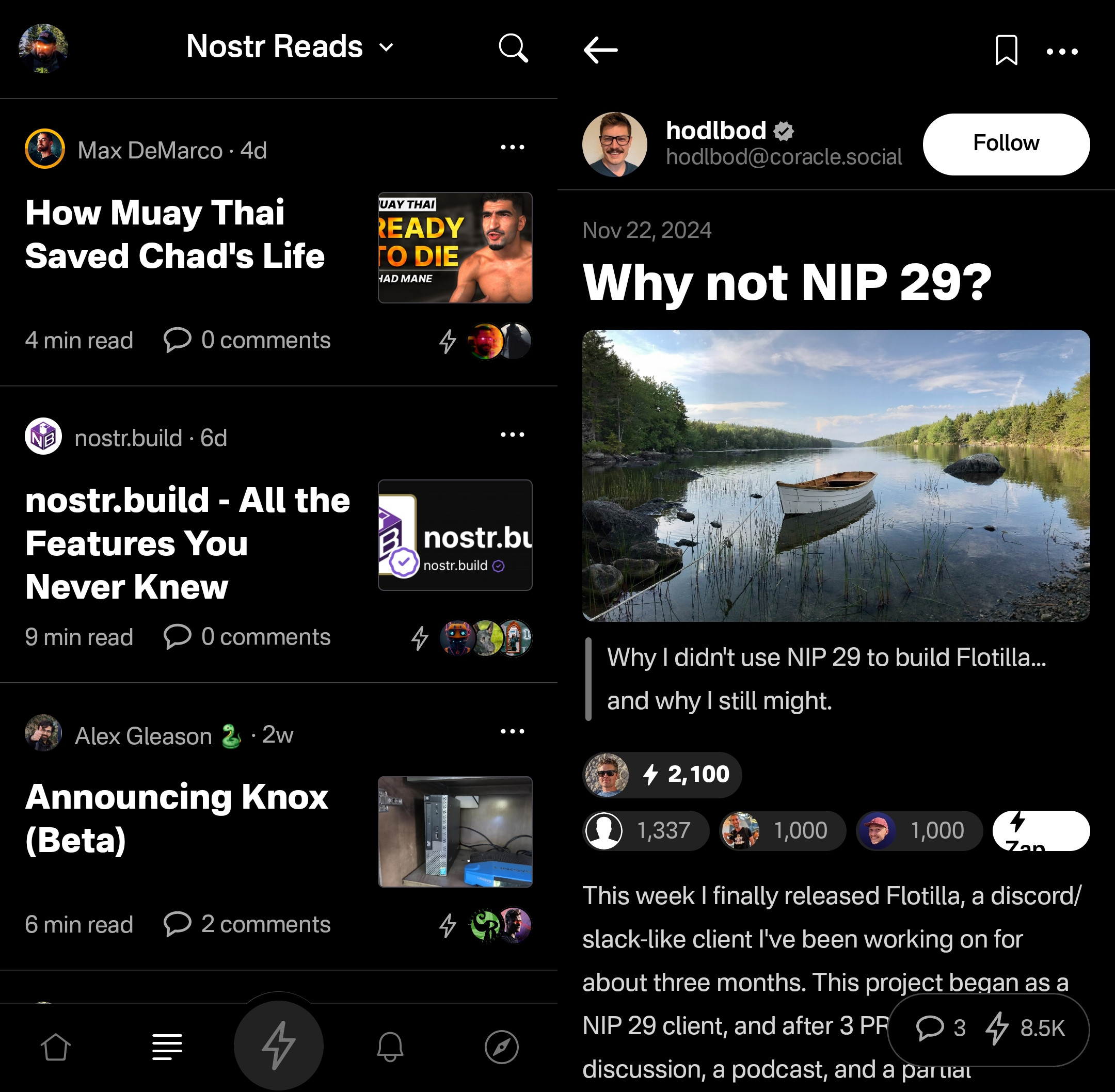
Noticeably absent from the Reads feed, though, is the ability to compose an article of your own. This is another understandable design choice for a mobile client. Composing a long-form note on a smart-phone screen is not a good time. Better to be done on a larger screen, in a client with a full-featured text editor.
Tapping an article will open up an attractive reading interface, with the ability to bookmark for later. These bookmarks are a separate list from your short-form note bookmarks so you don't have to scroll through a bunch of notes you bookmarked to find the article you told yourself you would read later and it's already been three weeks.
While you can comment on the article or zap it, you will notice that you cannot repost or quote-post it. It's not that you can't do so on Nostr. You absolutely can in other clients. In fact, you can do so on Primal's web client, too. However, Primal on Android does not handle rendering long-form note previews in the Home feed, so they have simply left out the option to share them there. See below for an example of a quote-post of a long-form note in the Primal web client vs the Android client.
Primal Web:
Primal Android:
The Explore Tab
Another unique feature of the Primal client is the Explore tab, indicated by the compass icon. This tab is dedicated to discovering content from outside your current follow list. You can find the feed marketplace here, and add any of the available feeds to your Home or Reads feed selections. You can also find suggested users to follow in the People tab. The Zaps tab will show you who has been sending and receiving large zaps. Make friends with the generous ones!
The Media tab gives you a chronological feed of just media, displayed in a tile view. This can be great when you are looking for users who post dank memes, or incredible photography on a regular basis. Unfortunately, it appears that there is no way to filter this feed for sensitive content, and so you do not have to scroll far before you see pornographic material.
Indeed, it does not appear that filters for sensitive content are available in Primal for any feed. The app is kind enough to give a minimal warning that objectionable content may be present when selecting the "Nostr Firehose" option in your Home feed, with a brief "be careful" in the feed description, but there is not even that much of a warning here for the media-only feed.
The media-only feed doesn't appear to be quite as bad as the Nostr Firehose feed, so there must be some form of filtering already taking place, rather than being a truly global feed of all media. Yet, occasional sensitive content still litters the feed and is unavoidable, even for users who would rather not see it. There are, of course, ways to mute particular users who post such content, if you don't want to see it a second time from the same user, but that is a never-ending game of whack-a-mole, so your only realistic choices in Primal are currently to either avoid the Nostr Firehose and media-only feeds, or determine that you can put up with regularly scrolling past often graphic content.
This is probably the only choice Primal has made that is not friendly to new users. Most clients these days will have some protections in place to hide sensitive content by default, but still allow the user to toggle those protections off if they so choose. Some of them hide posts flagged as sensitive content altogether, others just blur the images unless the user taps to reveal them, and others simply blur all images posted by users you don't follow. If Primal wants to target new users who are accustomed to legacy social media platforms, they really should follow suit.
The final tab is titled "Topics," but it is really just a list of popular hashtags, which appear to be arranged by how often they are being used. This can be good for finding things that other users are interested in talking about, or finding specific content you are interested in.
If you tap on any topic in the list, it will display a feed of notes that include that hashtag. What's better, you can add it as a feed option you can select on your Home feed any time you want to see posts with that tag.
The only suggestion I would make to improve this tab is some indication of why the topics are arranged in the order presented. A simple indicator of the number of posts with that hashtag in the last 24 hours, or whatever the interval is for determining their ranking, would more than suffice.
Even with those few shortcomings, Primal's Explore tab makes the client one of the best options for discovering content on Nostr that you are actually interested in seeing and interacting with.
Built-In Wallet
While this feature is completely optional, the icon to access the wallet is the largest of the icons at the bottom of the screen, making you feel like you are missing out on the most important feature of the app if you don't set it up. I could be critical of this design choice, but in many ways I think it is warranted. The built-in wallet is one of the most unique features that Primal has going for it.
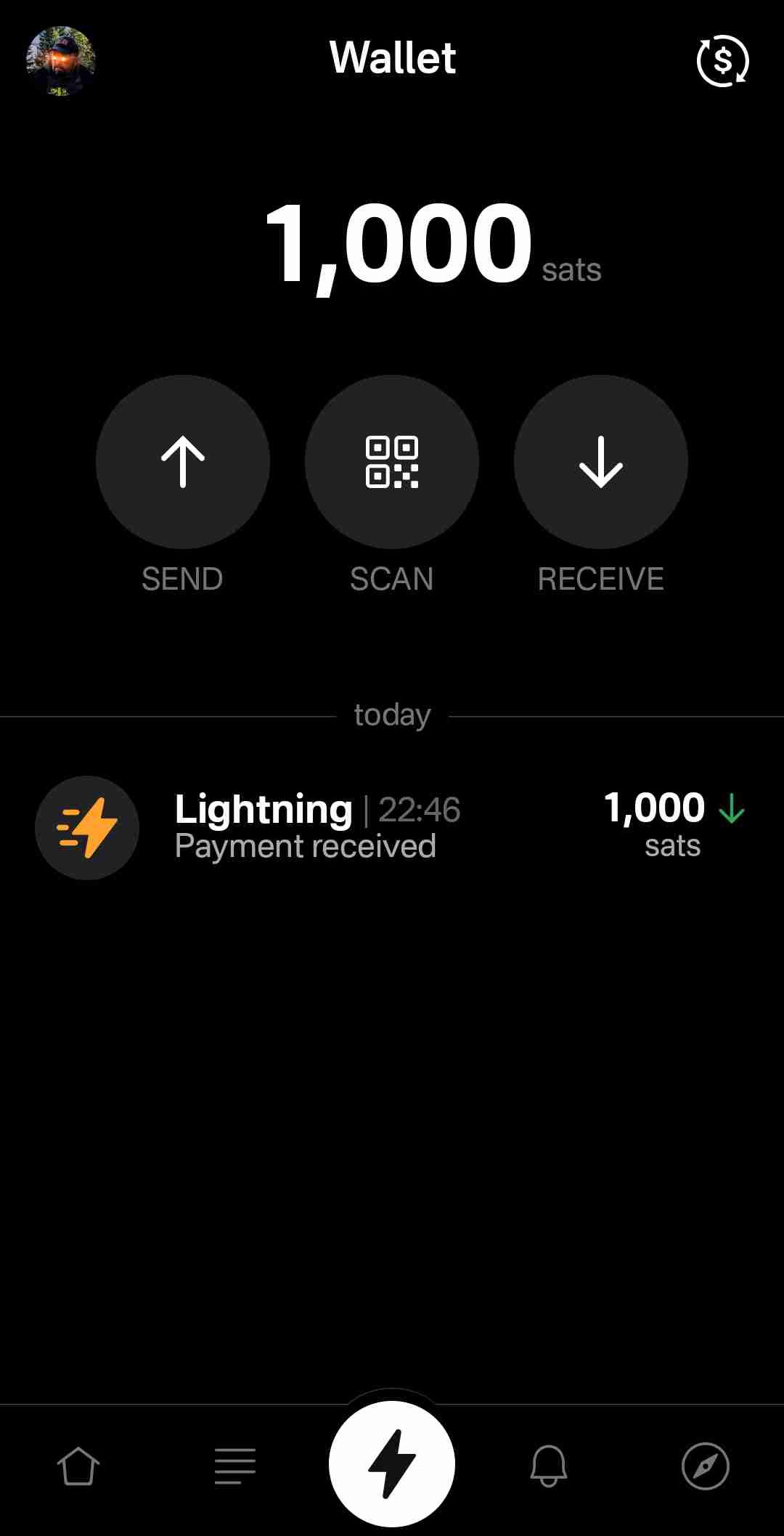
Consider: If you are a new user coming to Nostr, who isn't already a Bitcoiner, and you see that everyone else on the platform is sending and receiving sats for their posts, will you be more likely to go download a separate wallet application or use one that is built-into your client? I would wager the latter option by a long shot. No need to figure out which wallet you should download, whether you should do self-custody or custodial, or make the mistake of choosing a wallet with unexpected setup fees and no Lightning address so you can't even receive zaps to it. nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr often states that he believes more people will be onboarded to Bitcoin through Nostr than by any other means, and by including a wallet into the Primal client, his team has made adopting Bitcoin that much easier for new Nostr users.
Some of us purists may complain that it is custodial and KYC, but that is an unfortunate necessity in order to facilitate onboarding newcoiners to Bitcoin. This is not intended to be a wallet for those of us who have been using Bitcoin and Lightning regularly already. It is meant for those who are not already familiar with Bitcoin to make it as easy as possible to get off zero, and it accomplishes this better than any other wallet I have ever tried.
In large part, this is because the KYC is very light. It does need the user's legal name, a valid email address, date of birth, and country of residence, but that's it! From there, the user can buy Bitcoin directly through the app, but only in the amount of $4.99 at a time. This is because there is a substantial markup on top of the current market price, due to utilizing whatever payment method the user has set up through their Google Play Store. The markup seemed to be about 19% above the current price, since I could purchase 4,143 sats for $4.99 ($120,415 / Bitcoin), when the current price was about $101,500. But the idea here is not for the Primal wallet to be a user's primary method of stacking sats. Rather, it is intended to get them off zero and have a small amount of sats to experience zapping with, and it accomplishes this with less friction than any other method I know.
Moreover, the Primal wallet has the features one would expect from any Lightning wallet. You can send sats to any Nostr user or Lightning address, receive via invoice, or scan to pay an invoice. It even has the ability to receive via on-chain. This means users who don't want to pay the markup from buying through Primal can easily transfer sats they obtained by other means into the Primal wallet for zapping, or for using it as their daily-driver spending wallet.
Speaking of zapping, once the wallet is activated, sending zaps is automatically set to use the wallet, and they are fast. Primal gives you immediate feedback that the zap was sent and the transaction shows in your wallet history typically before you can open the interface. I can confidently say that Primal wallet's integration is the absolute best zapping experience I have seen in any Nostr client.
One thing to note that may not be immediately apparent to new users is they need to add their Lightning address with Primal into their profile details before they can start receiving zaps. So, sending zaps using the wallet is automatic as soon as you activate it, but receiving is not. Ideally, this could be further streamlined, so that Primal automatically adds the Lightning address to the user's profile when the wallet is set up, so long as there is not currently a Lightning address listed.
Of course, if you already have a Lightning wallet, you can connect it to Primal for zapping, too. We will discuss this further in the section dedicated to zap integration.
Advanced Search
Search has always been a tough nut to crack on Nostr, since it is highly dependent on which relays the client is pulling information from. Primal has sought to resolve this issue, among others, by running a caching relay that pulls notes from a number of relays to store them locally, and perform some spam filtering. This allows for much faster retrieval of search results, and also makes their advanced search feature possible.
Advanced search can be accessed from most pages by selecting the magnifying glass icon, and then the icon for more options next to the search bar.
As can be seen in the screenshot below, there are a plethora of filters that can be applied to your search terms.
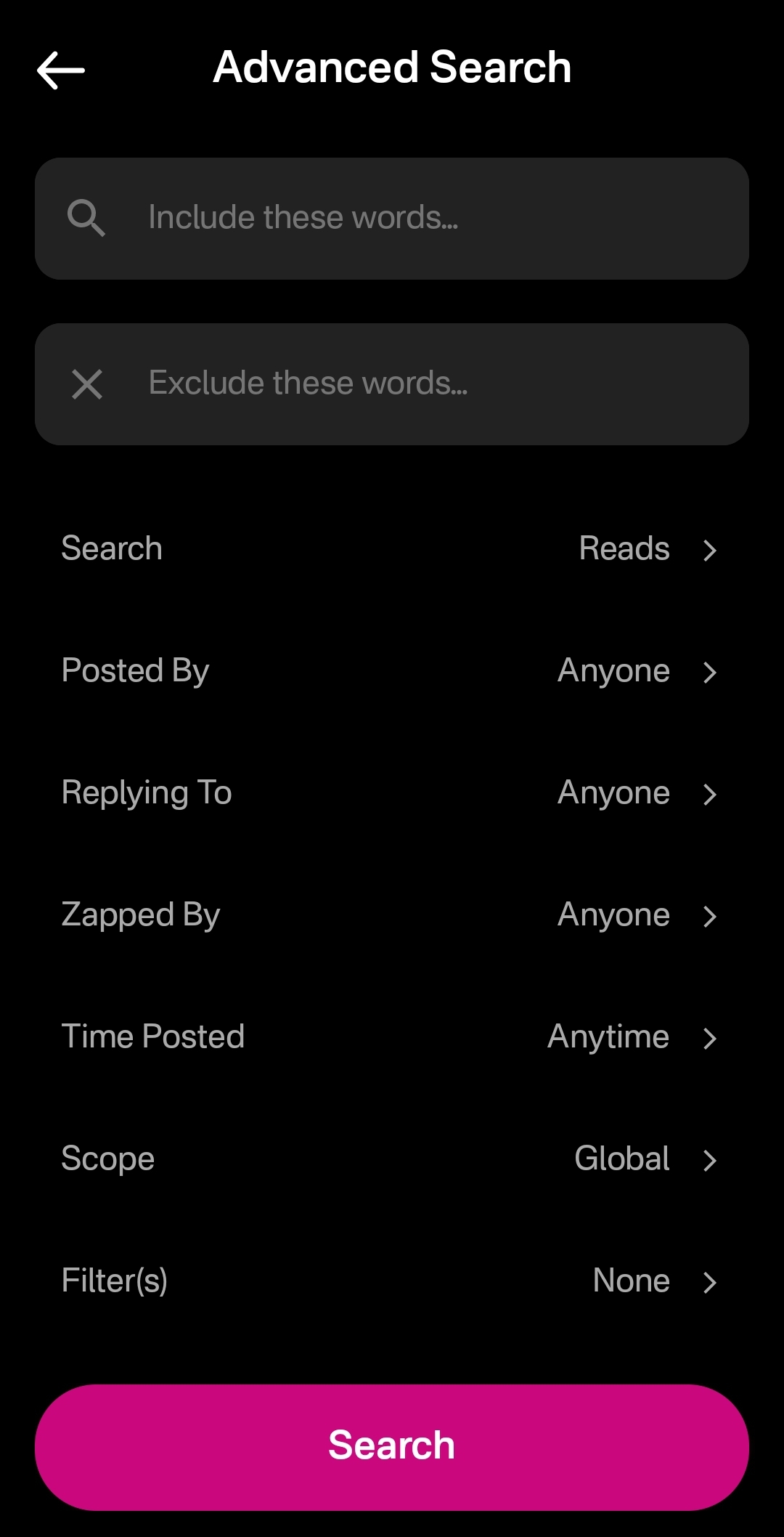
You can immediately see how this advanced search could be a very powerful tool for not just finding a particular previous note that you are looking for, but for creating your own custom feed of notes. Well, wouldn't you know it, Primal allows you to do just that! This search feature, paired with the other features mentioned above related to finding notes you want to see in your feed, makes Primal hands-down the best client for content discovery.
The only downside as a free user is that some of these search options are locked behind the premium membership. Or else you only get to see a certain number of results of your advanced search before you must be a premium member to see more.
Can My Grandma Use It?
Score: 4.8 / 5 Primal has obviously put a high priority on making their client user-friendly, even for those who have never heard of relays, public/private key cryptography, or Bitcoin. All of that complexity is hidden away. Some of it is available to play around with for the users who care to do so, but it does not at all get in the way of the users who just want to jump in and start posting notes and interacting with other users in a truly open public square.
To begin with, the onboarding experience is incredibly smooth. Tap "Create Account," enter your chosen display name and optional bio information, upload a profile picture, and then choose some topics you are interested in. You are then presented with a preview of your profile, with the ability to add a banner image, if you so choose, and then tap "Create Account Now."
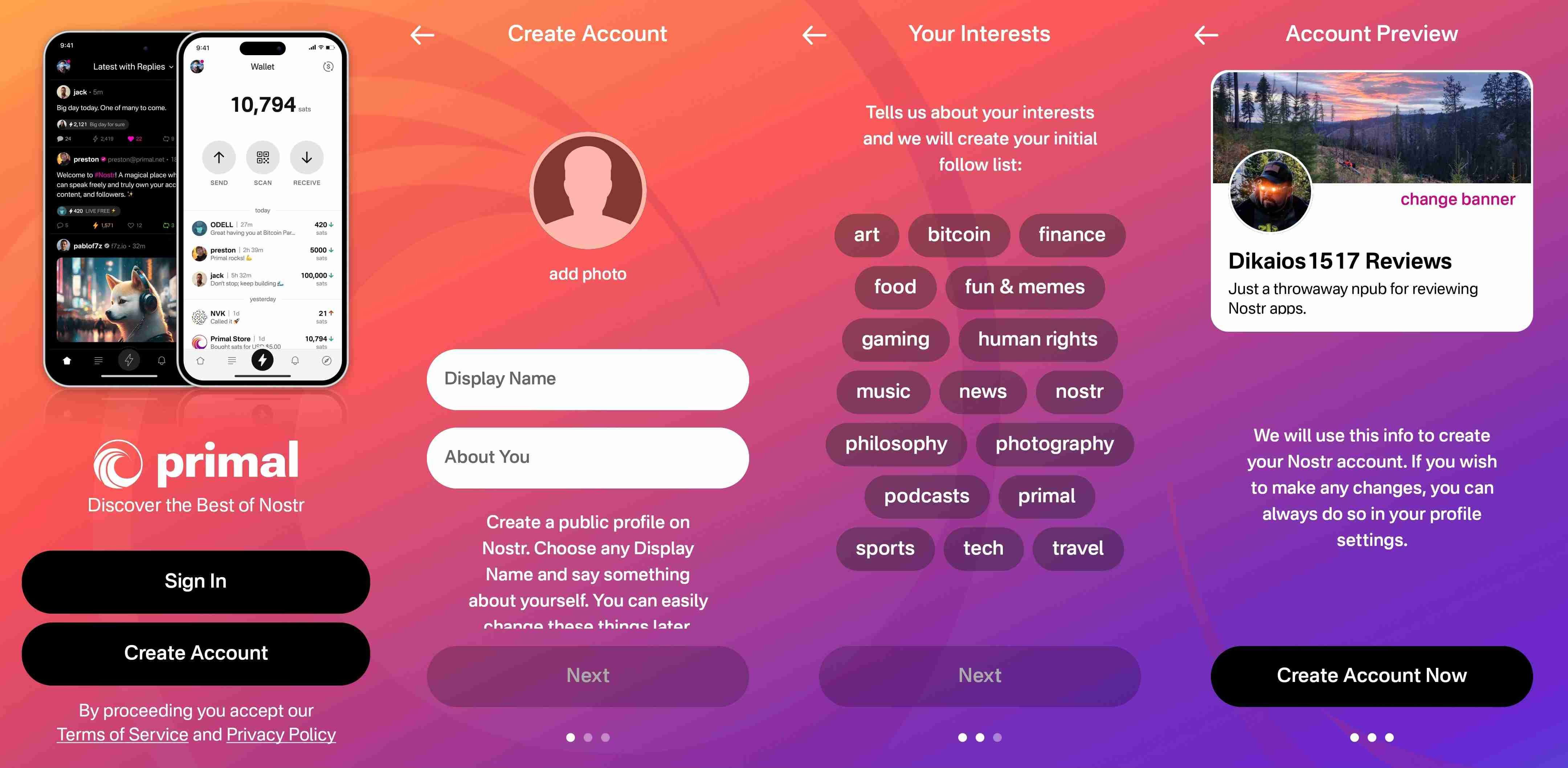
From there you receive confirmation that your account has been created and that your "Nostr key" is available to you in the application settings. No further explanation is given about what this key is for at this point, but the user doesn't really need to know at the moment, either. If they are curious, they will go to the app settings to find out.
At this point, Primal encourages the user to activate Primal Wallet, but also gives the option for the user to do it later.
That's it! The next screen the user sees if they don't opt to set up the wallet is their Home feed with notes listed in chronological order. More impressive, the feed is not empty, because Primal has auto-followed several accounts based on your selected topics.
Now, there has definitely been some legitimate criticism of this practice of following specific accounts based on the topic selection, and I agree. I would much prefer to see Primal follow hashtags based on what was selected, and combine the followed hashtags into a feed titled "My Topics" or something of that nature, and make that the default view when the user finishes onboarding. Following particular users automatically will artificially inflate certain users' exposure, while other users who might be quality follows for that topic aren't seen at all.
The advantage of following particular users over a hashtag, though, is that Primal retains some control over the quality of the posts that new users are exposed to right away. Primal can ensure that new users see people who are actually posting quality photography when they choose it as one of their interests. However, even with that example, I chose photography as one of my interests and while I did get some stunning photography in my Home feed by default based on Primal's chosen follows, I also scrolled through the Photography hashtag for a bit and I really feel like I would have been better served if Primal had simply followed that hashtag rather than a particular set of users.
We've already discussed how simple it is to set up the Primal Wallet. You can see the features section above if you missed it. It is, by far, the most user friendly experience to onboarding onto Lightning and getting a few sats for zapping, and it is the only one I know of that is built directly into a Nostr client. This means new users will have a frictionless introduction to transacting via Lightning, perhaps without even realizing that's what they are doing.
Discovering new content of interest is incredibly intuitive on Primal, and the only thing that new users may struggle with is getting their own notes seen by others. To assist with this, I would suggest Primal encourage users to make their first post to the introductions hashtag and direct any questions to the AskNostr hashtag as part of the onboarding process. This will get them some immediate interactions from other users, and further encouragement to set up their wallet if they haven't already done so.
How do UI look?
Score: 4.9 / 5
Primal is the most stunningly beautiful Nostr client available, in my honest opinion. Despite some of my hangups about certain functionality, the UI alone makes me want to use it.
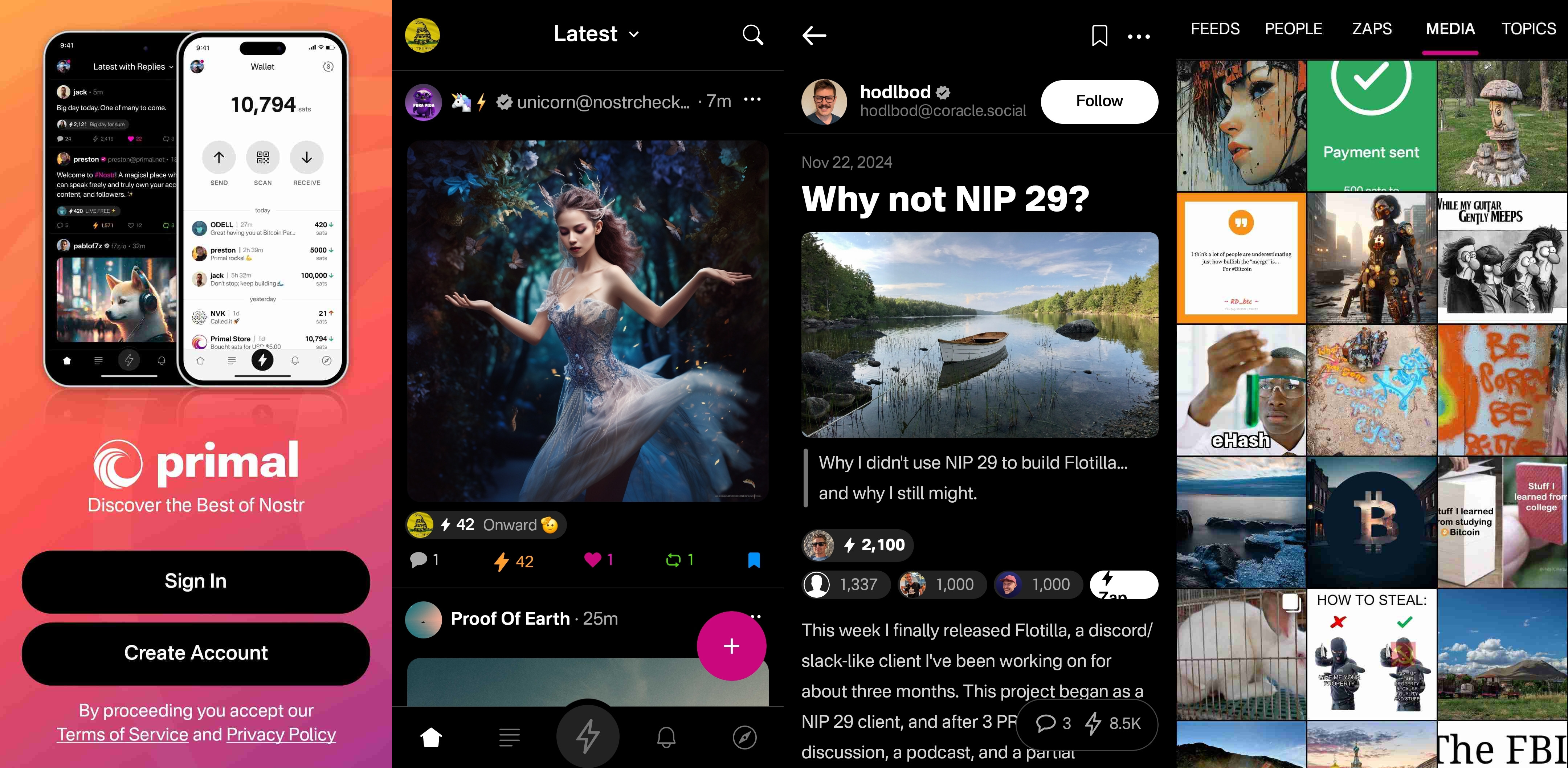
It is clean, attractive, and intuitive. Everything I needed was easy to find, and nothing felt busy or cluttered. There are only a few minor UI glitches that I ran into while testing the app. Some of them were mentioned in the section of the review detailing the feed selector feature, but a couple others occurred during onboarding.
First, my profile picture was not centered in the preview when I uploaded it. This appears to be because it was a low quality image. Uploading a higher quality photo did not have this result.

The other UI bug was related to text instructions that were cut off, and not able to scroll to see the rest of them. This occurred on a few pages during onboarding, and I expect it was due to the size of my phone screen, since it did not occur when I was on a slightly larger phone or tablet.
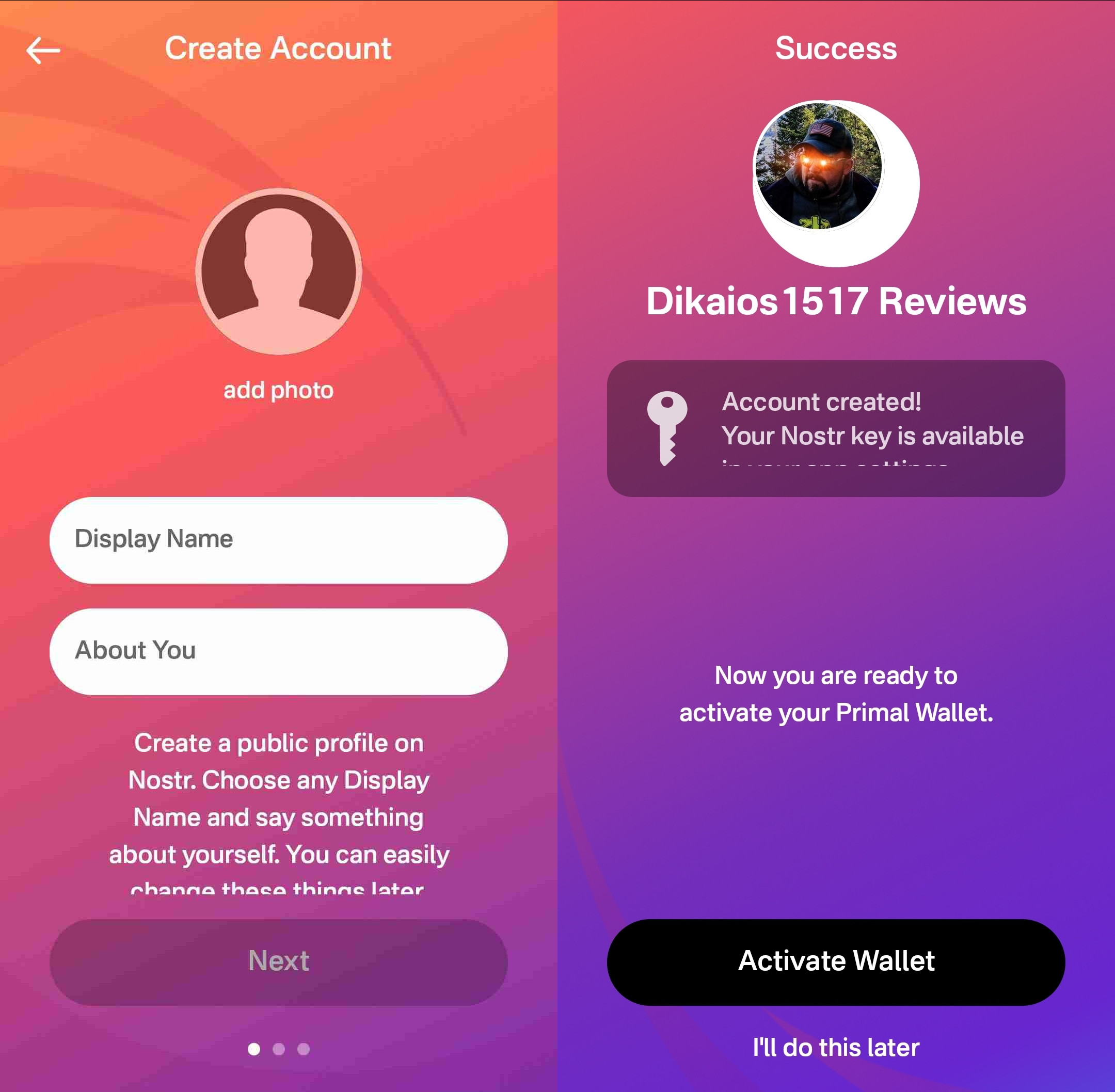
Speaking of tablets, Primal Android looks really good on a tablet, too! While the client does not have a landscape mode by default, many Android tablets support forcing apps to open in full-screen landscape mode, with mixed results. However, Primal handles it well. I would still like to see a tablet version developed that takes advantage of the increased screen real estate, but it is certainly a passable option.

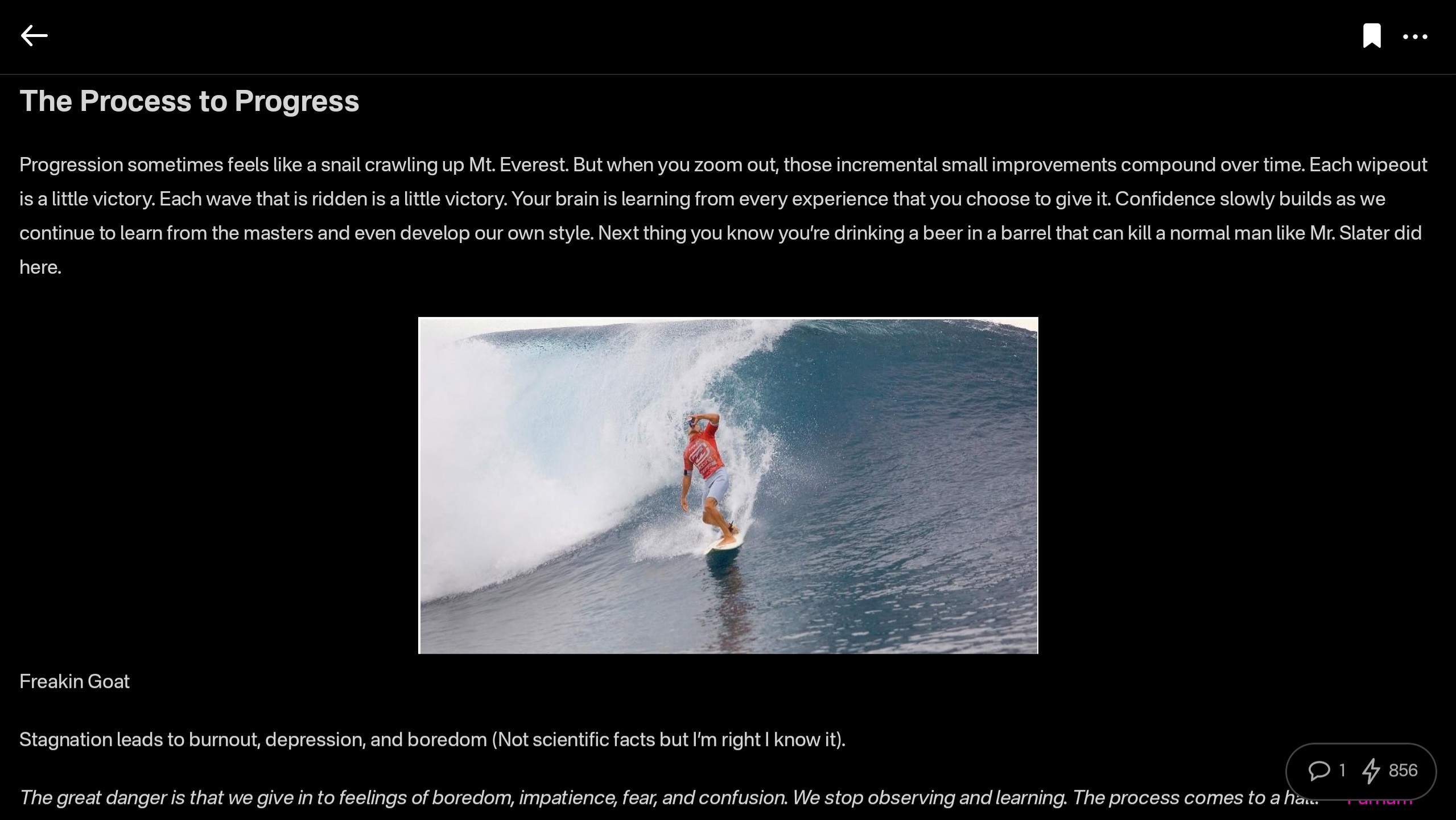
At this point, I would say the web client probably has a bit better UI for use on a tablet than the Android client does, but you miss out on using the built-in wallet, which is a major selling point of the app.
This lack of a landscape mode for tablets and the few very minor UI bugs I encountered are the only reason Primal doesn't get a perfect score in this category, because the client is absolutely stunning otherwise, both in light and dark modes. There are also two color schemes available for each.
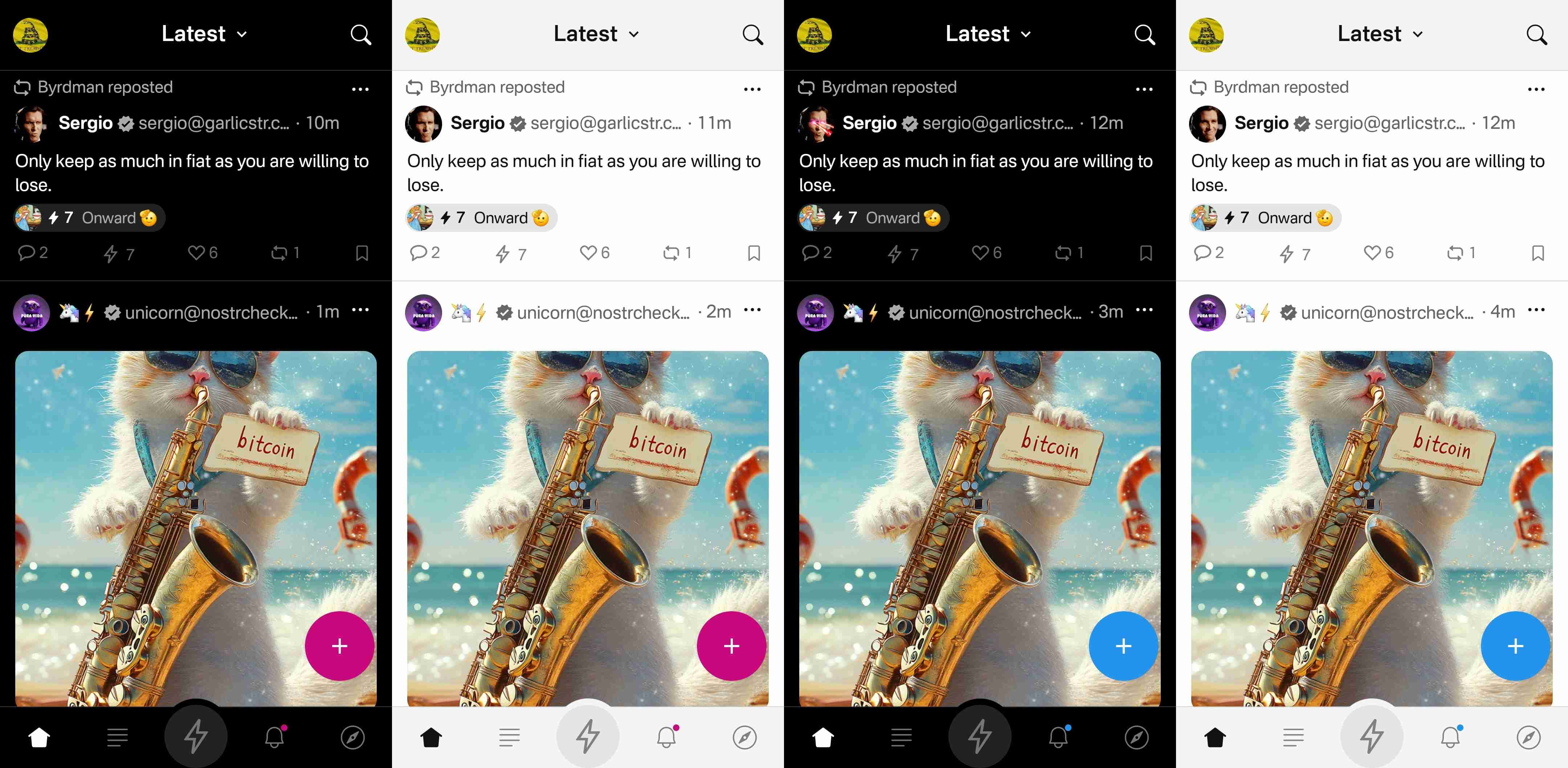
Log In Options
Score: 4 / 5 (Updated 4/30/2025)
Unfortunately, Primal has not included any options for log in outside of pasting your private key into the application. While this is a very simple way to log in for new users to understand, it is also the least secure means to log into Nostr applications.
This is because, even with the most trustworthy client developer, giving the application access to your private key always has the potential for that private key to somehow be exposed or leaked, and on Nostr there is currently no way to rotate to a different private key and keep your identity and social graph. If someone gets your key, they are you on Nostr for all intents and purposes.
This is not a situation that users should be willing to tolerate from production-release clients at this point. There are much better log in standards that can and should be implemented if you care about your users.
That said, I am happy to report that external signer support is on the roadmap for Primal, as confirmed below:
nostr:note1n59tc8k5l2v30jxuzghg7dy2ns76ld0hqnn8tkahyywpwp47ms5qst8ehl
No word yet on whether this will be Android signer or remote signer support, or both.
This lack of external signer support is why I absolutely will not use my main npub with Primal for Android. I am happy to use the web client, which supports and encourages logging in with a browser extension, but until the Android client allows users to protect their private key, I cannot recommend it for existing Nostr users.
Update: As of version 2.2.13, all of what I have said above is now obsolete. Primal has added Android signer support, so users can now better protect their nsec by using Amber!
I would still like to see support for remote signers, especially with nstart.me as a recommended Nostr onboarding process and the advent of FROSTR for key management. That said, Android signer support on its own has been a long time coming and is a very welcome addition to the Primal app. Bravo Primal team!
Zap Integration
Score: 4.8 / 5
As mentioned when discussing Primal's built-in wallet feature, zapping in Primal can be the most seamless experience I have ever seen in a Nostr client. Pairing the wallet with the client is absolutely the path forward for Nostr leading the way to Bitcoin adoption.
But what if you already have a Lightning wallet you want to use for zapping? You have a couple options. If it is an Alby wallet or another wallet that supports Nostr Wallet Connect, you can connect it with Primal to use with one-tap zapping.
How your zapping experience goes with this option will vary greatly based on your particular wallet of choice and is beyond the scope of this review. I used this option with a hosted wallet on my Alby Hub and it worked perfectly. Primal gives you immediate feedback that you have zapped, even though the transaction usually takes a few seconds to process and appear in your wallet's history.
The one major downside to using an external wallet is the lack of integration with the wallet interface. This interface currently only works with Primal's wallet, and therefore the most prominent tab in the entire app goes unused when you connect an external wallet.
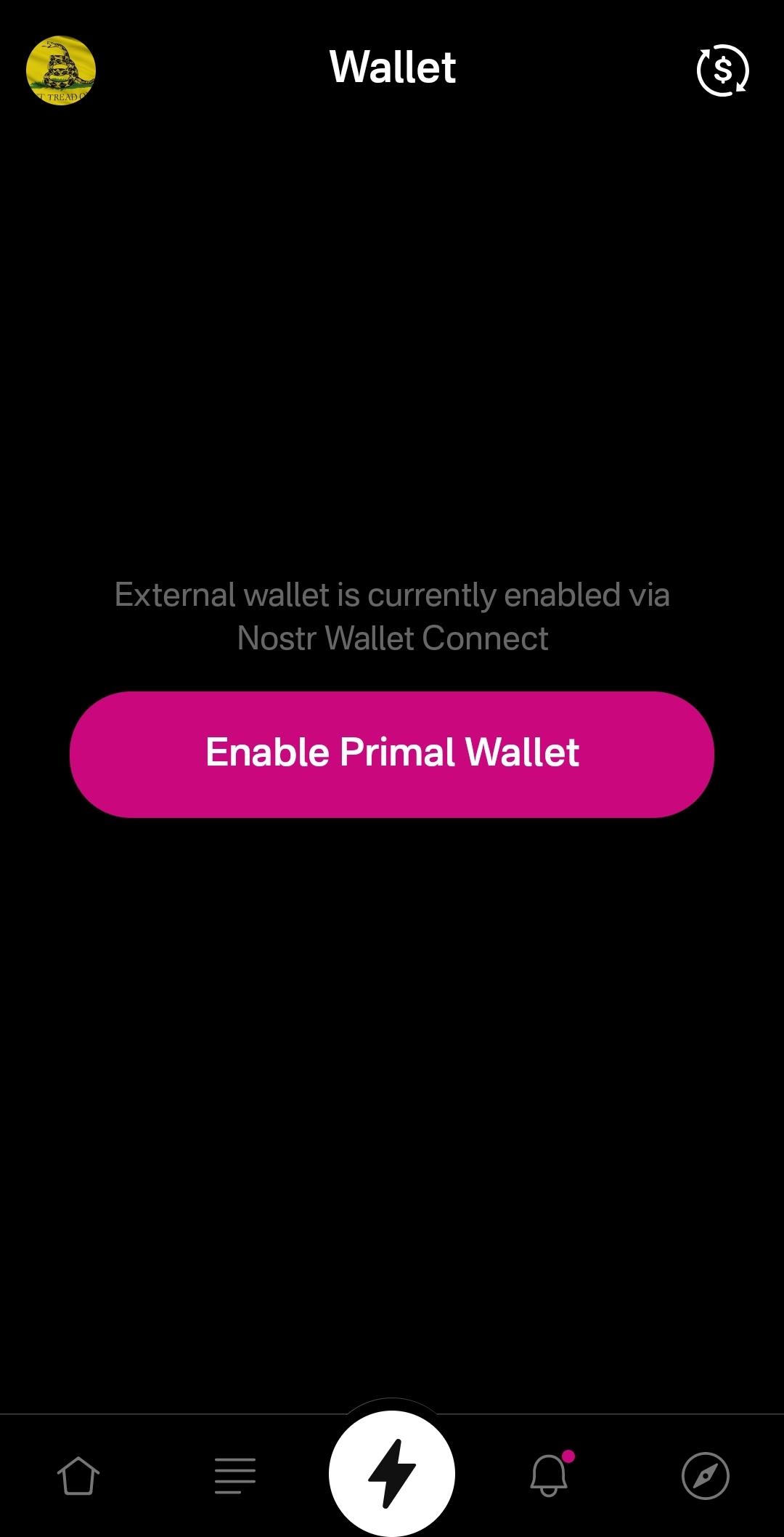
An ideal improvement would be for the wallet screen to work similar to Alby Go when you have an external wallet connected via Nostr Wallet Connect, allowing the user to have Primal act as their primary mobile Lightning wallet. It could have balance and transaction history displayed, and allow sending and receiving, just like the integrated Primal wallet, but remove the ability to purchase sats directly through the app when using an external wallet.
Content Discovery
Score: 4.8 / 5
Primal is the best client to use if you want to discover new content you are interested in. There is no comparison, with only a few caveats.
First, the content must have been posted to Nostr as either a short-form or long-form note. Primal has a limited ability to display other types of content. For instance, discovering video content or streaming content is lacking.
Second, you must be willing to put up with the fact that Primal lacks a means of filtering sensitive content when you are exploring beyond the bounds of your current followers. This may not be an issue for some, but for others it could be a deal-breaker.
Third, it would be preferable for Primal to follow topics you are interested in when you choose them during onboarding, rather than follow specific npubs. Ideally, create a "My Topics" feed that can be edited by selecting your interests in the Topics section of the Explore tab.
Relay Management
Score: 2.5 / 5
For new users who don't want to mess around with managing relays, Primal is fantastic! There are 7 relays selected by default, in addition to Primal's caching service. For most users who aren't familiar with Nostr's protocol archetecture, they probably won't ever have to change their default relays in order to use the client as they would expect.
However, two of these default relays were consistently unreachable during the week that I tested. These were relay.plebes.fans and remnant.cloud. The first relay seems to be an incorrect URL, as I found nosflare.plebes.fans online and with perfect uptime for the last 12 hours on nostr.watch. I was unable to find remnant.cloud on nostr.watch at all. A third relay was intermittent, sometimes online and reachable, and other times unreachable: v1250.planz.io/nostr. If Primal is going to have default relays, they should ideally be reliable and with accurate URLs.
That said, users can add other relays that they prefer, and remove relays that they no longer want to use. They can even set a different caching service to use with the client, rather than using Primal's.
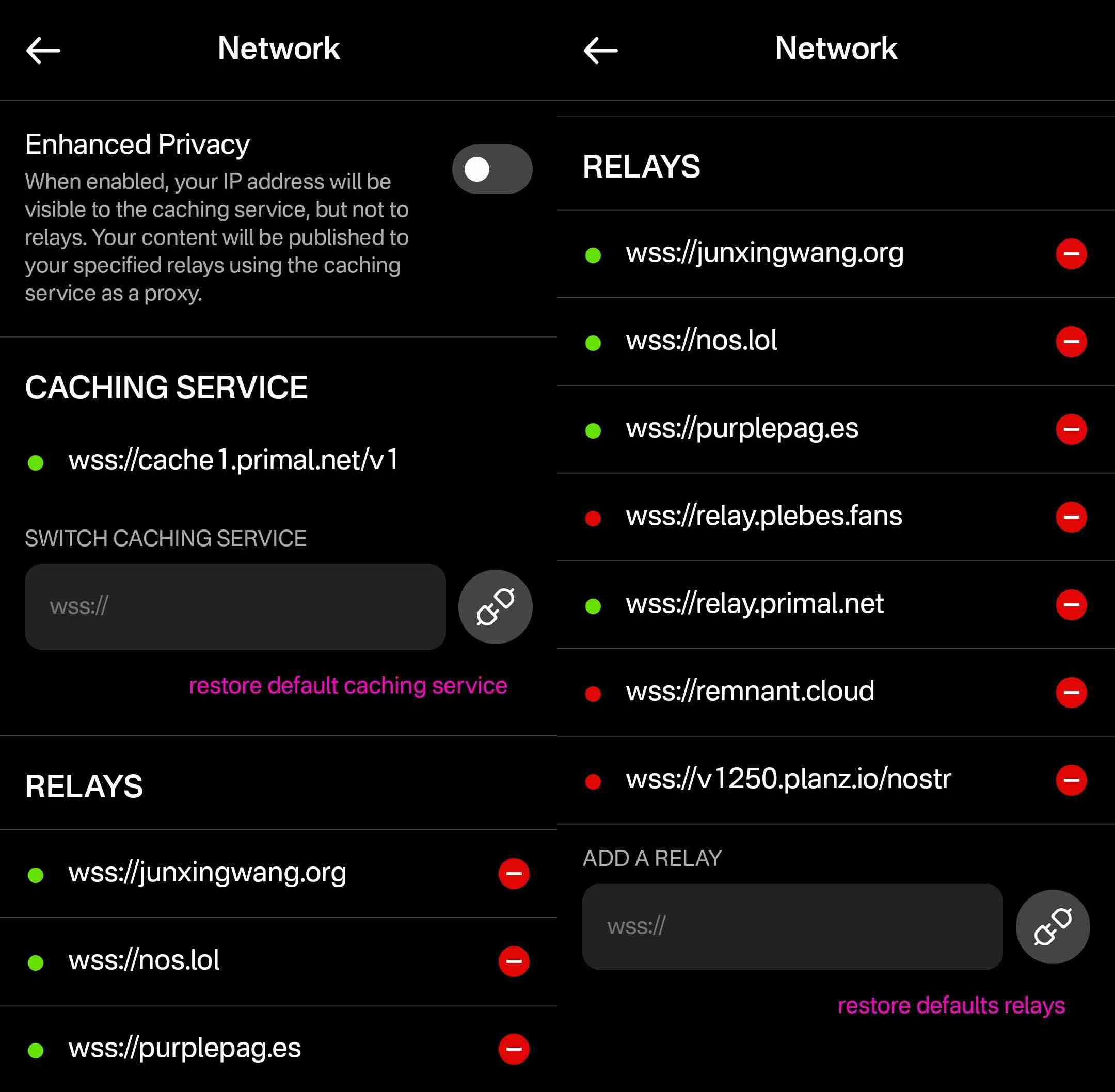
However, that is the extent of a user's control over their relays. They cannot choose which relays they want to write to and which they want to read from, nor can they set any private relays, outbox or inbox relays, or general relays. Loading the npub I used for this review into another client with full relay management support revealed that the relays selected in Primal are being added to both the user's public outbox relays and public inbox relays, but not to any other relay type, which leads me to believe the caching relay is acting as the client's only general relay and search relay.
One unique and welcomed addition is the "Enhanced Privacy" feature, which is off by default, but which can be toggled on. I am not sure why this is not on by default, though. Perhaps someone from the Primal team can enlighten me on that choice.
By default, when you post to Nostr, all of your outbox relays will see your IP address. If you turn on the Enhanced Privacy mode, only Primal's caching service will see your IP address, because it will post your note to the other relays on your behalf. In this way, the caching service acts similar to a VPN for posting to Nostr, as long as you trust Primal not to log or leak your IP address.
In short, if you use any other Nostr clients at all, do not use Primal for managing your relays.
Media Hosting Options
Score: 4.9 / 5 This is a NEW SECTION of this review, as of version 2.2.13!
Primal has recently added support for the Blossom protocol for media hosting, and has added a new section within their settings for "Media Uploads."
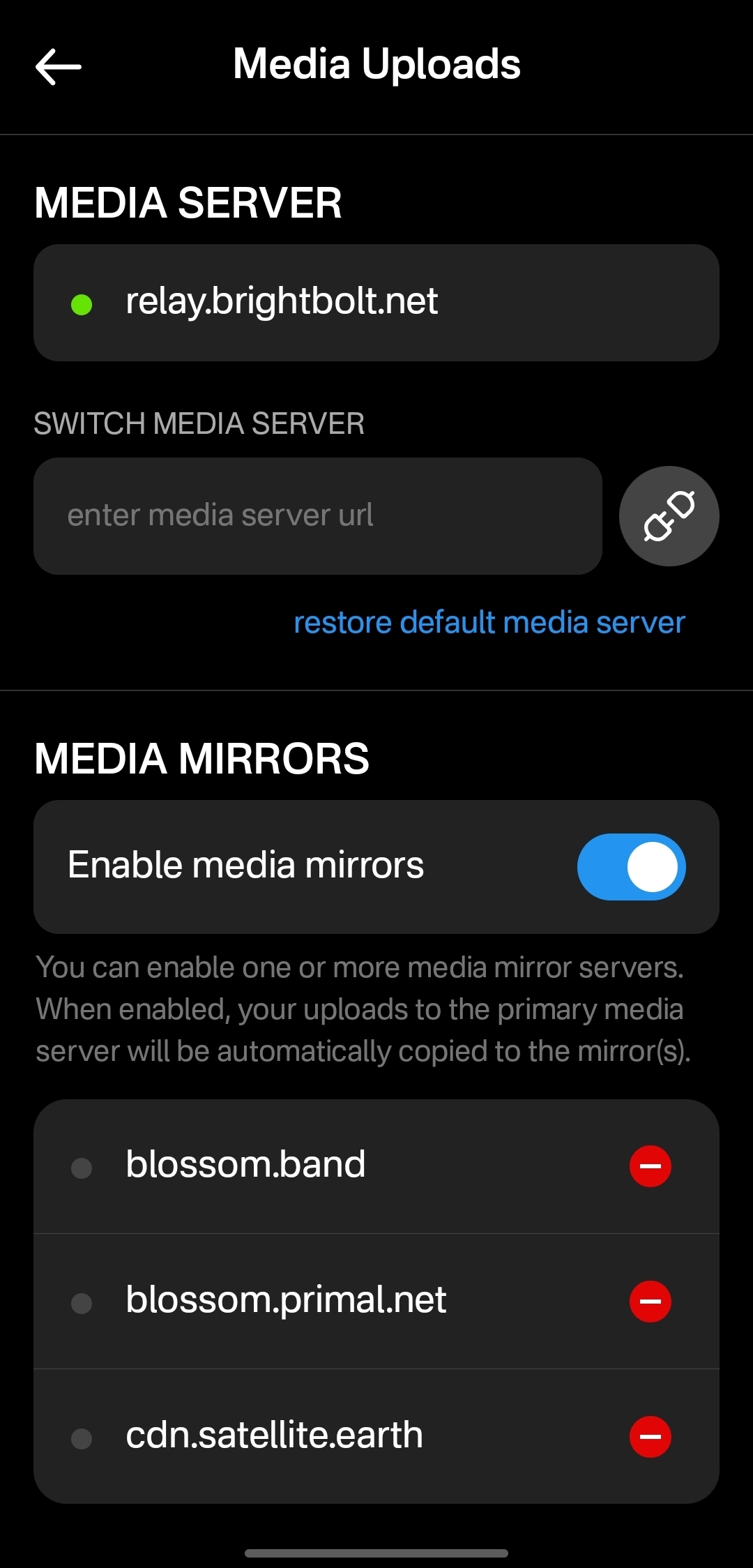
Media hosting is one of the more complicated problems to solve for a decentralized publishing protocol like Nostr. Text-based notes are generally quite small, making them no real burden to store on relays, and a relay can prune old notes as they see fit, knowing that anyone who really cared about those notes has likely archived them elsewhere. Media, on the other hand, can very quickly fill up a server's disk space, and because it is usually addressable via a specific URL, removing it from that location to free up space means it will no longer load for anyone.
Blossom solves this issue by making it easy to run a media server and have the same media mirrored to more than one for redundancy. Since the media is stored with a file name that is a hash of the content itself, if the media is deleted from one server, it can still be found from any other server that has the same file, without any need to update the URL in the Nostr note where it was originally posted.
Prior to this update, Primal only allowed media uploads to their own media server. Now, users can upload to any blossom server, and even choose to have their pictures or videos mirrored additional servers automatically. To my knowledge, no other Nostr client offers this automatic mirroring at the time of upload.
One of my biggest criticisms of Primal was that it had taken a siloed approach by providing a client, a caching relay, a media server, and a wallet all controlled by the same company. The whole point of Nostr is to separate control of all these services to different entities. Now users have more options for separating out their media hosting and their wallet to other providers, at least. I would still like to see other options available for a caching relay, but that relies on someone else being willing to run one, since the software is open for anyone to use. It's just not your average, lightweight relay that any average person can run from home.
Regardless, this update to add custom Blossom servers is a most welcome step in the right direction!
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with a client. Here are some of the most common questions submitted about Primal since the launch of 2.0:
nostr:note1dqv4mwqn7lvpaceg9s7damf932ydv9skv2x99l56ufy3f7q8tkdqpxk0rd
This was a pretty common question, because users expect that they will be able to create the same type of content that they can consume in a particular client. I can understand why this was left out in a mobile client, but perhaps it should be added in the web client.
nostr:note16xnm8a2mmrs7t9pqymwjgd384ynpf098gmemzy49p3572vhwx2mqcqw8xe
This is a more concerning bug, since it appears some users are experiencing their images being replaced with completely different images. I did not experience anything similar in my testing, though.
nostr:note1uhrk30nq0e566kx8ac4qpwrdh0vfaav33rfvckyvlzn04tkuqahsx8e7mr
There hasn't been an answer to this, but I have not been able to find a way. It seems search results will always include replies as well as original notes, so a feed made from the search results will as well. Perhaps a filter can be added to the advanced search to exclude replies? There is already a filter to only show replies, but there is no corresponding filter to only show original notes.
nostr:note1zlnzua28a5v76jwuakyrf7hham56kx9me9la3dnt3fvymcyaq6eqjfmtq6
Since both mobile platforms support the wallet, users expect that they will be able to access it in their web client, too. At this time, they cannot. The only way to have seamless zapping in the web client is to use the Alby extension, but there is not a way to connect it to your Primal wallet via Nostr Wallet Connect either. This means users must have a separate wallet for zapping on the web client if they use the Primal Wallet on mobile.
nostr:note15tf2u9pffy58y9lk27y245ew792raqc7lc22jezxvqj7xrak9ztqu45wep
It seems that Primal is filtering for spam even for profiles you actively follow. Moreover, exactly what the criteria is for being considered spam is currently opaque.
nostr:note1xexnzv0vrmc8svvduurydwmu43w7dftyqmjh4ps98zksr39ln2qswkuced
For those unaware, Blossom is a protocol for hosting media as blobs identified by a hash, allowing them to be located on and displayed from other servers they have been mirrored to when when the target server isn't available. Primal currently runs a Blossom server (blossom.primal.net) so I would expect we see Blossom support in the future.
nostr:note1unugv7s36e2kxl768ykg0qly7czeplp8qnc207k4pj45rexgqv4sue50y6
Currently, Primal on Android only supports uploading photos to your posts. Users must upload any video to some other hosting service and copy/paste a link to the video into their post on Primal. I would not be surprised to see this feature added in the near future, though.
nostr:note10w6538y58dkd9mdrlkfc8ylhnyqutc56ggdw7gk5y7nsp00rdk4q3qgrex
Many Nostr users have more than one npub for various uses. Users would prefer to have a way to quickly switch between accounts than to have to log all the way out and paste their npub for the other account every time they want to use it.
There is good news on this front, though:
nostr:note17xv632yqfz8nx092lj4sxr7drrqfey6e2373ha00qlq8j8qv6jjs36kxlh
Wrap Up
All in all, Primal is an excellent client. It won't be for everyone, but that's one of the strengths of Nostr as a protocol. You can choose to use the client that best fits your own needs, and supplement with other clients and tools as necessary.
There are a couple glaring issues I have with Primal that prevent me from using it on my main npub, but it is also an ever-improving client, that already has me hopeful for those issues to be resolved in a future release.
So, what should I review next? Another Android client, such as #Amethyst or #Voyage? Maybe an "other stuff" app, like #Wavlake or #Fountain? Please leave your suggestions in the comments.
I hope this review was valuable to you! If it was, please consider letting me know just how valuable by zapping me some sats and reposting it out to your follows.
Thank you for reading!
PV 🤙
-
 @ bbef5093:71228592
2025-05-08 19:59:24
@ bbef5093:71228592
2025-05-08 19:59:24Google három fejlett atomerőmű-fejlesztését finanszírozza
A Google megállapodást kötött az amerikai Elementl Power nevű nukleáris projektfejlesztő céggel, hogy legalább három, egyenként 600 MW kapacitású fejlett atomerőmű fejlesztését finanszírozza az Egyesült Államokban. Ezek a projektek a Google és más nagy technológiai cégek növekvő energiaigényét szolgálják ki, különösen az adatközpontok és a mesterséges intelligencia (AI) miatt[7][10][19][16]. A Google a fejlesztés korai szakaszában biztosít tőkét, a projektek befejezése után pedig lehetősége lesz az ott termelt villamos energia megvásárlására. A pontos helyszíneket és a megállapodás pénzügyi részleteit egyelőre nem hozták nyilvánosságra[10][19][16].
A Google célja, hogy működését 24/7, azaz folyamatosan elérhető, szén-dioxid-mentes energiával lássa el, és ezzel hozzájáruljon az elektromos hálózatok stabilitásához is[10][19][6]. Az Elementl Power technológia-semleges, vagyis még nem döntötték el, milyen típusú reaktort használnak, hanem a fejlesztésben legelőrébb járó technológiát választják majd a kivitelezés idején[10][19][16].
Big Tech és az atomenergia: trendek
A Google mellett más nagy technológiai cégek, például a Microsoft, az Amazon és az Oracle is elkötelezettek az atomenergia mellett, hogy adatközpontjaik számára megbízható, alacsony szén-dioxid-kibocsátású áramot biztosítsanak[15][11][20]. A Google például a Kairos Power nevű céggel is együttműködik kis moduláris reaktorok (SMR) fejlesztésében, amelyek első példányai 2030 körül állhatnak üzembe[1][2][3][17][8]. Az SMR-ek előnye, hogy gyorsabban és olcsóbban telepíthetők, mint a hagyományos nagy atomerőművek, és rugalmasabban illeszthetők az energiaigényekhez[2][3][1].
Pallas kutatóreaktor Hollandiában
Hollandiában befejezték az új Pallas kutatóreaktor alapozását és munkagödrét, ami jelentős mérföldkő a projektben. A reaktor az orvosi radioizotópok előállításában játszik majd kulcsszerepet, több millió beteg ellátását biztosítva világszerte, főként daganatos és szív-érrendszeri betegségek diagnosztikájában és terápiájában. A Pallas reaktor a jelenlegi, 1961 óta működő High-Flux Reactort (HFR) fogja felváltani[forrás: eredeti szöveg].
Finn SMR fejlesztés: demonstrációs üzem
A finn Steady Energy vállalat nem-nukleáris demonstrációs üzemet épít a helsinki Salmisaari B széntüzelésű erőmű helyén, hogy bemutassa LDR-50 típusú kis moduláris reaktorának (SMR) alkalmasságát távhőtermelésre. A projekt célja, hogy a fosszilis energiahordozókat alacsony kibocsátású technológiával váltsa fel a városi távhőrendszerekben[forrás: eredeti szöveg].
Urán és nukleáris üzemanyag: amerikai fejlesztések
Az amerikai Uranium Energy Corp (UEC) és a Radiant Industries megállapodást kötött amerikai eredetű urán szállításáról, hogy támogassák a Radiant Kaleidos mikroraktorok elterjedését. Ezek a mikroraktorok 1 MW teljesítményűek, szállíthatók, és 2028-tól kezdődhet a kereskedelmi alkalmazásuk[forrás: eredeti szöveg].
A Global Laser Enrichment (GLE) Észak-Karolinában megkezdte a harmadik generációs, lézeralapú Silex urándúsítási technológia demonstrációs tesztjeit. Ez a technológia nagyobb hatékonyságot, alacsonyabb költségeket és rugalmasabb üzemanyaggyártást ígér a jövő atomerőművei számára. A GLE célja, hogy 2028-tól kereskedelmi üzembe helyezze az új dúsítóüzemet Kentuckyban[forrás: eredeti szöveg].
Egyéb hírek röviden
- Az Egyesült Államokban befejezték az ITER szupravezető mágnesének utolsó moduljának tesztelését, amely kulcsfontosságú a franciaországi fúziós kísérleti reaktorban.
- Ausztráliában a nukleáris energia bevezetését szorgalmazza egy lobbicsoport, bár jelenleg törvény tiltja az atomerőművek építését.
- Csehországban, a Dukovany atomerőmű bővítésével kapcsolatos szerződéseket írtak alá dél-koreai cégekkel, egy francia bírósági tiltás ellenére.
- 2025 júniusában Zágrábban rendezik meg a European Nuclear Young Generation Forumot, amely a fiatal nukleáris szakemberek legnagyobb európai találkozója lesz[forrás: eredeti szöveg].
Hivatkozások:[1][2][3][7][10][16][19] – Google és nukleáris projektek[15][11][20] – Big Tech trendek
További részletek a többi témáról az eredeti szövegben találhatók.Hivatkozások: [1] A Google 7 atomreaktor megépítését támogatja az MI ... - itbusiness https://itbusiness.hu/technology/aktualis-lapszam/strategy/google-reaktor/ [2] Google új generációs atomreaktorokból vásárol áramot - DinaMix https://dinamix.hu/google-uj-generacios-atomreaktorokbol-vasarol-aramot/ [3] A Google moduláris atomreaktorokat vásárol a saját energiaellátására https://gyartastrend.hu/cikk/a-google-modularis-atomreaktorokat-vasarol-a-sajat-energiaellatasara [4] Az atom vonzza a befektetőket - Atombiztos Blog https://www.atombiztos.org/2025/05/05/az-atom-vonzza-a-befektetoket/125967/ [5] Máris trükköznek az AI-óriások, csak több áramuk legyen https://www.szabadeuropa.hu/a/maris-trukkoznek-az-ai-oriasok-csak-tobb-aramuk-legyen/33167550.html [6] 24/7 Clean Energy – Data Centers - Google https://www.google.com/about/datacenters/cleanenergy/ [7] Google agrees to fund three US nuclear power plants https://business.inquirer.net/524307/google-agrees-to-fund-three-us-nuclear-power-plants [8] Atomreaktorok építését rendelte meg a Google - Telex https://telex.hu/gazdasag/2024/10/14/google-kairos-atomeromu [9] Operating sustainably - Google Data Centers https://datacenters.google/operating-sustainably [10] Google To Commit Funding For Three Advanced Nuclear Power ... https://www.nucnet.org/news/google-to-commit-funding-for-three-advanced-nuclear-power-projects-5-4-2025 [11] Az atomenergia mellett tette le a voksát több technológiai óriás https://www.vg.hu/nemzetkozi-gazdasag/2025/03/atomenergia-technologiai-orias [12] 24/7 Carbon-free Energy Explained - Eavor Technologies https://eavor.com/blog/24-7-carbon-free-energy-explained/ [13] Google agrees to fund the development of three new nuclear sites https://www.reddit.com/r/nuclear/comments/1kh2s7t/google_agrees_to_fund_the_development_of_three/ [14] Téma: Új atomerőművet építtet magának a Google - PC Fórum https://pcforum.hu/tarsalgo/154783/uj-atomeromuvet-epittet-maganak-a-google-nem-is-egyet-hanem-mindjart-harmat [15] Big Tech has cozied up to nuclear energy - The Verge https://www.theverge.com/2024/10/5/24261405/google-microsoft-amazon-tech-data-center-nuclear-energy [16] Google to back development of 3 nuclear sites on data center push https://nypost.com/2025/05/07/business/google-to-back-development-of-3-nuclear-sites-on-data-center-push/ [17] Moduláris atomreaktorokból vásárol energiát a Google - HWSW https://www.hwsw.hu/hirek/68282/google-kairospower-atomreaktor-energia-aram.html [18] What is 24/7 carbon-free energy? - Baseload Capital https://www.baseloadcap.com/what-is-24-7-carbon-free-energy/ [19] Google to fund development of three nuclear power sites https://www.world-nuclear-news.org/articles/google-to-fund-elementl-to-prepare-three-nuclear-power-sites [20] Óriáscégek álltak a nukleáris reneszánsz élére - Világgazdaság http://www.vg.hu/nemzetkozi-gazdasag/2025/03/nuklearis-energia-amazon-google
-
 @ 2fdae362:c9999539
2025-05-08 19:57:33
@ 2fdae362:c9999539
2025-05-08 19:57:33Why Your Manufacturing Engineers Shouldn’t Build Your Next‑Gen Product (and How an External NPD Team Supercharges Both)
1 | Two Very Different Missions
Most electronics companies lump “engineering” into one budget line. In reality there are two distinct jobs:
| Mission | Core Question | Success Metric | |---------|---------------|----------------| | Manufacturing & Sales Support | How do we keep shipping and lower COGS? | Uptime, yield, cost‑down, ECO turnaround | | New‑Product Development | What will customers demand 18‑36 months from now? | Time‑to‑market, feature velocity, first‑pass success |
Trying to solve both with the same staff is like asking your pit‑crew to design an entirely new race‑car while the current one is circling the track.
2 | Why Your In‑House Team Excels at Sustaining Work
- Process‑driven mindset – KPIs center on takt time and scrap, not innovation cycles.
- Deep tribal knowledge of legacy designs, test fixtures, and compliance filings.
- Close link to Ops & Sales – Daily stand‑ups about line stoppages and customer RMAs.
That focus is exactly why the factory runs smoothly — but it penalizes exploratory work. Every minute spent chasing down a bleeding‑edge SoC or new RF stack is a minute the line risks slipping.
3 | What New‑Product Development Really Demands
- State‑of‑the‑art parts libraries (and the supply‑chain foresight to qualify alternates).
- Architectural runway — designs built for firmware updatability, security, and field diagnostics.
- Fast‑loop prototyping — EVT to DVT in weeks, not half‑years.
- Cross‑disciplinary toolchain — from FPGA simulation to Yocto‑based Linux builds to OTA pipelines.
These skills dull quickly when they aren’t used daily; maintaining them internally is expensive downtime for a sustaining group.
4 | The Outside‑NPD Model: Division of Labor That Works
| Stage | Your Internal Team | Our External NPD Team | |-------|-------------------|-----------------------| | Concept | Product vision, market intel | Technology scouting, architecture options | | Design | DFx feedback & factory constraints | Schematics, layouts, firmware, driver stacks | | Validation | Factory test jig specs | EVT/DVT, pre‑compliance, safety margins | | Transfer | Process FMEAs, operator training | Full doc set, source, BoM, bring‑up guides |
Result: No bandwidth tug‑of‑war — each team stays in its lane and both lanes move faster.
5 | Seven Tangible Benefits You’ll Feel in Year 1
- 14‑30 % faster NPD schedules via parallel tasking.
- Zero factory interruptions — sustaining KPIs stay green.
- Up‑to‑date technology choices yielding longer market life and lower future BOM risk.
- Process upgrades your ops team can re‑use (automated CI for firmware, digital‑thread BoM).
- Cleaner IP chain of custody — everything delivered in version‑controlled repos with SPDX manifests.
- Predictable budgeting — fixed‑price or milestone schedules instead of overtime creep.
- On‑demand specialist depth (wireless certs, OS driver authors, safety assessors) without hiring.
6 | Hand‑Off That Sticks
We shut the project down only after:
- Source, binaries, Gerbers, test plans, and regulatory artifacts are in your repo.
- Your sustaining engineers complete hands‑on bring‑up alongside ours.
- A 30‑60‑day shadow‑support window is booked.
That means the next ECO lands on your familiar desk, not ours — unless you want it to.
7 | A Quick Example
When ACME Corp’s internal team tried to modernize their decade‑old IoT gateway, the factory choked on late‑night proto builds. We took the NPD load, delivered a Linux‑plus‑Modbus driver stack in 16 weeks, and handed it back with a test‑rig script that ACME’s own sustaining crew still runs today — zero line downtime, product launched six months early.
8 | Ready to Split the Load?
If your manufacturing engineers are drowning in ECOs and your roadmap is slipping, let’s talk. We’ll map out an NPD sprint plan that leaves your factory gurus doing what they do best — keeping product flowing — while we build the future version you’ll hand back to them, fully documented.
-
 @ 7b20d99d:d2a541a9
2025-05-08 19:31:50
@ 7b20d99d:d2a541a9
2025-05-08 19:31:50
Bitcoin is a powerful tool for sending aid quickly, directly, and without intermediaries, especially in countries where banking systems are corrupt or inefficient. It allows for supporting noble causes without relying on slow or centralized NGOs. But where there is generosity, there are also abuses.
In the Bitcoin world, some have learned to exploit the anonymity and speed of transactions to create fake emotional stories and steal funds from well-meaning individuals. These scams damage trust and slow down the adoption of Bitcoin in humanitarian efforts.
In this series, I'll show you:
How to spot dubious projects,
What practices can alert you,
And most importantly, how to continue supporting real causes safely.

Alert 1: Lack of transparency
A serious charity project, whether Bitcoin-based or not, must be accountable.
In the Bitcoin ecosystem, where everything relies on peer-to-peer trust, transparency is even more crucial.
Here are the classic signs of a lack of transparency:
-
No concrete evidence of action on the ground.
A project that asks you for money but doesn't show any photos, videos, or reports is suspicious. Even with limited resources, a legitimate project can show:
Before/after images of an action (e.g., food distribution, healthcare, clothing)
Receipts or proof of purchase (blurred if necessary for privacy)
Testimonies from beneficiaries, even short ones
- No regular posting or tracking.
If a project has raised funds but doesn't publish any updates on the progress, distribution, or results achieved, this is a red flag. A genuine project maintains a connection with its donors, even after the fundraising process.
- Bitcoin address without tracking.
Providing a Bitcoin address without providing a link to a Geyser, BTCPay, or donation tracking page is an easy way to hide donation flows. Serious projects use public tools to make donations visible to everyone.
- Refusal to answer questions.
An honest project accepts questions from donors:
- Where do the funds go?
- Why this amount?
- Who is responsible?
If there is constant vagueness, or worse, aggression when you ask these questions: that's a red flag.
Recommendation :
Before donating, look for evidence. Ask simple questions. And above all, compare several projects: you'll quickly see who's doing real work, and who's showing nothing.

In Bitcoin charity projects, emotion is often the scammer's favorite tool. They know: if you're moved, you give quickly. Especially when there's an emergency. Unfortunately, they often have no real reason behind their requests.
Here's how these emotional manipulations work:
-
Dramatic stories without proof.
A sick child, an injured animal, a starving family... these stories touch the heart. But often, the images are taken from Google or old TikTok/Facebook accounts. There's no proof that the person requesting sats is actually involved.
-
The manufactured emergency.
Scammers use phrases like:
"URGENT! He only has two days to live!"
"We need 100,000 sats before midnight, or else..."
This kind of urgency is often fabricated to push you to act without thinking or checking.
- No trace of previous activity.
Often, these accounts have never discussed charity before. They suddenly appear, launch an emotional campaign, receive donations... then disappear or change their name.
- Reusing stories from other projects.
Some copy real stories from real projects and adapt them with new BTC addresses. They rely on virality and credulity. Sometimes, they even imitate the style of a legitimate project.
How to protect yourself?
Reverse image search: You can use Google Images or Yandex to check if the photo is circulating elsewhere.
Research the account's history: was it posting content before the campaign? Does it seem committed to Bitcoin or a cause?
Refrain from reacting too quickly: if a story upsets you, that's exactly what the scammer wants. Take a break, do some research.
Key points:
A real project doesn't need to manipulate your emotions to gain your support. It shares its impact, its concrete actions, and is open to scrutiny. Never let your sats speak before your brain.

Check the project's public presence and reputation
In the decentralized world of Bitcoin, there are no guarantees or official certifiers. What replaces institutions is reputation: what others say about you, what you publish, and how you act over time.
Before donating to a charitable project in Bitcoin, it is essential to verify the public presence and traceability of the project or individual. This can prevent you from being scammed by opportunistic or malicious accounts.
Here are the good reflexes to have:
- Cross-platform search
A legitimate project leaves its mark on multiple channels:
Nostr: posts, zaps, interactions, community relays
Twitter/X: regular posts, comments, retweets
Telegram, YouTube, Instagram: visual content and community comments
Even if it's small, a real project has at least one public space where it shares its activities, answers questions, and builds relationships with its supporters.
Alert: An account that appears out of nowhere with 3 posts in 2 days and an urgent donation request is suspicious.
- Seeking credible public support
A great sign is when other well-known users in the Bitcoin community (or on Nostr) endorse or support the project:
They share the campaign;
They respond to posts with enthusiasm or testimonials;
They contribute sats themselves;
You can send them a DM to ask, "Are you familiar with this project? Are they serious?"
- View account history
Does this account have:
- Have you already run other campaigns in the past?
- Demonstrated concrete results?
- A long-standing audience?
Scams often have an empty history, or one that has been deliberately deleted.
If the account was recently created, it's an orange flag. It's not always a scam, but it's a good sign.
- Beware of names that are too generic
Accounts like “Bitcoin_Charity,” “BTC_Hope4Africa,” or “SatoshiMissionHelp” that use generic, faceless names with no personal history or evidence of involvement are often lures to suck up your generosity.
In an open world like Nostr, trust must be earned, not granted automatically. Before you zap or send sats: check the footprints. A real project doesn't hide. It wants to be seen, recognized, supported... and verified.

Prefer traceable and public donations
One of the great advantages of Bitcoin is that every transaction is recorded on the blockchain. Yet, many BTC charitable projects fail to leverage this transparency potential… sometimes out of ignorance, sometimes intentionally.
If you want to give securely, you should prioritize tools and methods that allow clear tracking of your money.
- Favors transparent platforms (Geyser, Zaprite, BTCPay, etc.)
These platforms allow:
- Track how much has been raised in real time
- Have a public address or QR code that everyone can see
- Sometimes even see who donated (if the donor makes it public)
And most importantly: the funds go directly into the creator's wallet, without an intermediary
Example: Geyser.fund shows how many sats have been raised, how many are left to reach, and sometimes even the expenses incurred.
- Avoid isolated static addresses
When someone just gives you a Bitcoin address without any context or tools around it, you can't know:
- If others have already donated
- What's the status of the fundraising?
- What will happen with the funds received?
Even worse, an address can be reused for multiple different campaigns. No tracking, no limits.
Reminder: A scammer can also show a QR code with an emotional caption, collect in bulk, and then erase all traces.
- Request a dedicated campaign address
A serious project can:
- Generate a unique address for each campaign or donor (via a wallet or BTCPay store)
- Or show you a link to a Bitcoin explorer to track inflows in real time
This allows you to verify that: - Your donation has been received - Funds are not being diverted for other purposes - And that other people are also contributing (proof of credibility)
- Check expenses if possible
More and more projects are publishing:
- Captures of receipts or transfers
- Monthly reports
- Distribution videos
This allows donors to see how funds are being used, even in rural areas or without stable internet.
If a project doesn't want you to track donations, ask yourself why. In the Bitcoin ecosystem, transparency is a weapon against abuse. Use it, and encourage others to do the same.

Want to help? Great. But in the Bitcoin ecosystem, giving indiscriminately is like throwing your sats into a bottomless pit. Here's a clear list of best practices to avoid scams and support good causes with confidence and intelligence.
- Never give under pressure
A real project:
- Don't rush.
- Don't create an artificial sense of urgency.
- Don't demand anything.
Golden rule: if you are pressured to skip "quickly" or "now or everything is ruined", it is suspicious.
- Use reputable platforms
Before sending sats:
Check if the project is on Geyser.fund, Zaprite, BTCPayServer, or Tallycoin.
These platforms provide transparency, monitoring and protection.
If the project refuses to appear there "without valid reason", ask yourself questions.
- Always check the source
Ask yourself these questions:
- Who is leading this campaign?
- How long has this person been active in the community?
- Does their history hold a consistent profile?
- Are they well-known on Nostr, X, Telegram, or elsewhere?
A reliable project has nothing to hide. It is findable, traceable, and responsive.
- Don't rely on images or videos alone
A photo of a crying child or a dish being offered proves nothing. What you want to know:
- Did they take this photo?
- What's the connection to the campaign?
- Do they show several stages (preparation, distribution, follow-up)?
Scammers love beautiful stolen images, but never show the actual work.
- Request a follow-up report or evidence
A serious project can easily provide you with:
- A link to a dedicated Bitcoin address
- A video or photo with a personalized message
- A receipt or proof of purchase
If they refuse or get offended by you for asking? Run away.
- Share only verified projects
You are also responsible for what you share. By sharing a project without verifying:
- You're putting your credibility on the line.
- You risk causing others to lose sats.
Do your own research, even if you trust the person who sent you the link.
- Start small
You can test a project with a small amount and observe:
-
How they communicate after receiving it
-
If they thank you
- If they keep you informed
It's a simple way to filter out the good guys from the opportunists.
In a free ecosystem like Bitcoin, there's no customer service, no refunds, no "cancel" button. Your only security is your vigilance. Give, but give wisely.

How to intelligently support genuine causes
Supporting charitable projects with Bitcoin doesn't have to be risky. On the contrary, it can be a powerful tool for spreading the values of Bitcoin while genuinely helping people.
But for your help to have a real impact, it's not enough to just switch off and disappear. You have to be intelligently involved.
Here's how to become a helpful, strategic, and caring donor.
- Be part of the project, not just the donation
The best donors are not those who give the most, but those who:
- ask questions,
- suggest ideas,
- share campaigns,
- encourage the founder,
- inform others.
In Bitcoin, we talk about community, not customers. Be an agent of change, not just a transaction number.
- Favors projects with a long-term vision
A serious project speaks to you:
- education,
- sustainability,
- independence,
- integration of Bitcoin into local life.
He doesn't just give away rice or clothes. He wants to make people more autonomous, freer, and more connected to the decentralized economy.
Support projects that build, not just those that distribute.
- Diversify your support
You can :
- Skip small projects regularly
- Support a campaign with a fixed monthly budget
- Offer your skills: design, writing, video, networking
Participate in a DAO or a coordinated donations collective
Bitcoin support isn't just about money. Your time and talent are also valuable.
- Educate while you help
When you participate in a project, take the opportunity to:
- Explain to others how Bitcoin works
- Demonstrate the benefits of transparency through blockchain
- Raising awareness in your circle of the freedom offered by direct support in BTC
Education is the ultimate weapon against addiction and scams.
- Create or join a reliable initiative
You can :
- Create your own small campaign with Geyser.fund or Zaprite
- Join a collective like Hope With Bitcoin or other communities on Nostr
- Offer to document an existing campaign
This is how sustainable projects are born: not with large anonymous donations, but with small, well-supported flames.
Donating Bitcoin is more than just a transfer. It's an affirmation of values. It's a statement:
“I choose to support causes without going through banks, without permission, without borders, with transparency and freedom.”
But for it to work, you need:
-
Stay vigilant
-
Demand clarity
- Foster human connections
- Build trust
Bitcoin is a tool of sovereignty. It deserves honest projects. It's up to us to protect them.
Together, let's discover Hope With Bitcoin: The project whose mission is to share smiles and hope with those in need, while raising awareness for Bitcoin adoption.
X: https://x.com/HopeWithBTC
Nostr / Primal: https://primal.net/p/npub10vsdn82fps4vwjaqxcpwj0nyync0cfrp2f5qlayrljh6d549gx5s0y9eap
Proof Of Work: https://drive.google.com/drive/u/1/folders/19LWZX4TtF6DJbDVCqhJ0EMMQqnjHVMvm
Geyser : https://geyser.fund/project/hopewithbitcoin
-
-
 @ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19
@ 2ce0697b:1ee3d3fc
2025-04-29 18:54:19Excerpt
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it. With Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
“If you have built castles in the air, your work need not be lost; that is where they should be. Now put the foundations under them.” ― Henry David Thoreau, Walden
The problem: lack of freedom in the physical realm
Freedom is essential to human life. Being free is what matters. That´s our target, always. No matter the time or space. We pursue freedom because we know its the right thing to do. Freedom is the right to question and change the stablished way of doing things.
Where can we find some freedom? Certainly in the cyberspace. The cyberspace is a free space. Humanity has been blessed by the magic of cryptography, a technology that gave us all the necessary tools to operate in that environment without intervention of undesired third parties.
In cyberspace cryptography performs the function of an impenetrable cyberwall. So, whatever we build in cyberspace can be perfectly protected. Thank to this cybernetic walls we can be sure that the gardens we build and nurture will be protected and cannot be trampled. When we build our digital gardens we have the keys to open the doors to let in whoever we want and most important to leave out whoever we don´t want. In the digital world we can already perfectly interact with one and another in a peer to peer way, without intervention of undesired third parties.
In cyberspace we have Bitcoin for freedom of money and Nostr, torrent and Tor for freedom of information and speech. These open-source protocols are designed to fully realize and expand the promise of freedom, and they certainly deliver what they promise.

So, thanks to the magic of asymmetric cryptography, we´ve already achieved sufficiently descentralization and the possibility of any level of desired digital privacy. Cryptoanarchists and cypherpunks have set their conquering flag in cyberspace and there´s no force on Earth than can remove it. The digital world cannot escape the rules of cryptography. This is great but it only works in the digital realm, meanwhile in the physical realm we are overrun by centralized attackers due to the impossibility of the creation of impenetrable walls such as the ones we have online.
Humans have the upper hand in creating impenetrable walled gardens in cyberspace, but in the physical space authoritarians have the upper hand in bullying physical persons.
The physical world is also naturally free. According to natural law each person is free to do whatever he wants as long as it doesn´t hurt other people. However due to unnatural -artificial and inhuman- centralization of power, the natural freedom of the physical world has been completely undermined. Mostly by Governments, the entities that centralize violence and law.
Bitcoin as a bridge between both realms

Let´s take a look at one connection between both realms, the physical and the digital world. Bitcoin layer one is made essentially of software plus hardware. It consists of any software that produces the same output as the reference implementation - Bitcoin core- and the hardware needed to run that software. Layer two, three or any other layer above, is made essentially of other software and other hardware that interacts with layer one in some way. All these layers, one, two and subsequent, are completely protected by cryptography and a set of game theories that have been successfully tested. Each new block added to the timechain is a testimony of the unstoppable force of freedom and meritocracy.
Before layer one we have Bitcoin layer zero, which is essentially the sum of all actions and inactions done by bitcoiners regarding to or because of bitcoin. In other words, layer zero is composed by flesh and bone people interacting in some way with layer one of the bitcoin network.
Hence, an attack on a bitcoiner - on his way of life- is an attack on bitcoin, the network itself. First because it is an attack on a layer zero node, the physical person, the bitcoiner under duress or coercion. And second because is also an attack on the store-of-value-aspect of bitcoin. Nowaday, the most common attack against bitcoiners is the entirety of compliance regulations. This is the sum of all coercive regulations,such as laws, threats of more laws, imprisonment, threats of more imprisonment, taxation, threats of more taxation, requirements to prove the origin of funds, coercive removal of privacy such as the travel rule, unnecessary bureaucracy such as the need to obtain a money transmitting license and many others rules, in a never stopping inflationary coercive legislation.

If a physical attack is preventing any bitcoiner to exchange the value he created for bitcoin due to any kind of artificial obstacles -such as any kind of compliance- that specific attack is successful in the sense that even though the whole network keeps operating, the attack itself diminishes the value of all the bitcoins.
So, even if layer-zero cannot be taken down, every interference on this layer is an attack on the bitcoin network. Attacks on layer one, two or any other layer that exists in the cyberspace can interfere with the network but they may hardly subtract any value from it. For example we have already been through plenty of times where hashing power was diminished due to government intervention and the bitcoin network remain completely unaffected.
On the other hand successful attacks on layer zero subtract potential, but real and demonstrable value. This value is equal to the amount of value the frustrated user would have added to the network if he would have been able to use it freely, that means if he would have sold his product without the cost of compliance. I´ll demonstrate this in the next chapter.
The cost of compliance
Alice is a merchant specialized in a specific area and topic. She studied the market, her business, her suppliers, consumers, the logistics involved, marketing, design, and everything necessary to become a successful entrepreneur. After investing a considerable amount of resources, she developed a perfect product. Or at least she considers it perfect, that is, the best in its class. While developing everything necessary to create her product, she met Bob, who became her main lead and stereotype of a buyer persona. She knows what Bob wants and she wants to sell it to him. According to Alice's calculations, for her business to be viable, she must sell the product at ten satoshis per unit, and fortunately, Bob is willing to pay that price for it. Alice's product is finished, ready to hit the market, but just before sending it to production, Alice decides to take a pause to analyze her reality. Before taking the public action of making her product available in the open market, Alice analyzes her material, political, and legal reality. In doing so, she realizes that she lives under the jurisdiction of a State. She learns that the Government prescribes through its regulations how she must behave. She analyzes that in order to sell her product legally, in compliance, she must make a series of modifications to it. The product before hitting the shelves must first be modified both in the way it is presented to the market and also regarding certain technical characteristics that it possesses. She must also modify the way it produces her product by changing the contractual relationship with its suppliers, distribution channels, and all other types of logistics involved. She must make all these changes even if they bring about significant and insurmountable inefficiencies.
Likewise, Alice also sees that she not only has to modify the product but also has to meet tax obligations. In addition to paying an accountant since the tax obligations by some irrational reason are not calculated by the creditor. Additionally, she must hire other professionals to assist her in studying the current regulations and how they should be applied in all stages of production, distribution, and sale of her product.
Alice, being a rational person, wishes to avoid having to make these modifications since they increase her costs while also decreasing the quality of her product. But when studying compliance, that is, the entirety of applicable regulations, she also examines the consequences of not being in compliance. Alice realizes that if she does not comply with the regulations, she risks having all her assets legally confiscated, going to prison, being killed while they try to capture her to imprison her, and, if she goes to prison, being tortured in jail by other inmates or by State officials in charge of holding her in that place. So, since Alice does not want to suffer these negative consequences, she decides to modify the product and be in compliance.
So, Alice makes the necessary changes and puts her new version of the product on the market. Then she has the following dialogue with Bob, her lead, the interested party in acquiring the product.
Bob: - Hey Alice, nice meeting you here in this market. I came to buy the product you were developing and told me about. However, this product I´m seeing now is not what you promised me. This is clearly inferior.
Alice: - Yeah, I know. I'm sorry Bob, but I prefer to sell this inferior product rather than risk having all my assets confiscated, going to prison, being killed while they try to capture me, and if they don´t kill but managed to put me in jail I could be tortured there.
Bob: - Ok, no problem. Thats quite understandable. I don´t believe anyone would prefer those kind of experiences. But given the quality of the product, I no longer intend to pay you ten satoshis; I only offer you eight. Shall we close the deal?
Alice: - I'm sorry Bob, but I can't sell it to you for eight sats. Due to government intervention and its requirements, now I can't even sell it for less than thirteen satoshis.
Bob: - Ok. Considering this I prefer not to purchase it. I will keep looking for alternatives. Bye

Some time later, Charlie arrives at the market, who is also interested in the product and, despite it not being like the original version, decides to purchase it by paying the thirteen satoshis demanded by the seller Alice.
Meanwhile, in the same universe, we have Daniel, the last character in this example. Daniel is a merchant competing with Alice. Daniel has a product that is very similar, practically identical to the one originally designed by Alice. Like Alice, Daniel initially also wants to sell it for ten satoshis. Just like Alice, before heading to the market, Daniel analyzes the reality in which he lives. And it turns out that he also lives under the jurisdiction of a State. Daniel too then analyzes the entirety of the applicable regulations and also comes to the conclusion that to comply with them, he would also need to modify the product and cover all the additional expenses artificially generated to be in compliance.
However, Daniel's ethics are different from Alice's. Daniel understands that his product is indeed perfect (the best in its class) and that therefore modifying it would go against its essence. Daniel understands that changing the product would be a betrayal of his creation and therefore a betrayal of his own self and the essence of his being. Daniel conducts an ethical analysis of his actions and the moral implications of putting the product on the market. Daniel sees that the product not only does not harm anyone but is also made to be freely acquired by adults who give their consent for its purchase and subsequent use. Daniel also understands that paying taxes only serves to promote the slavery system driven by fiat and that whenever he can avoid collaborating with the immoral fiat system, it is his ethical obligation to do so. Likewise, Daniel highlights the hypocrisy and inefficiencies of anti-money laundering regulations, as well as the futility of requiring licenses for naturally free acts that do not harm others. For all these reasons, Daniel decides to sell the product in its current state irregardles of compliance regulations.
However, before going to market, Daniel also studies the possible consequences of neglecting compliance. By doing so, Daniel sees that if he does not comply with the regulations, he risks having all his assets legally confiscated, going to prison, being killed while they attempt to capture him to imprison him, and, in the event of going to prison, being tortured in jail by other inmates or by State officials responsible for holding him in that place. So, since Daniel is a rational person who does not want to suffer these negative consequences but also does not want to betray his product and himself, he decides to take the risk of not being in compliance. After making this decision, Daniel puts the product on the market and there he meets Bob. In doing so, they converse in the following terms:
Bob: - Hey Daniel, this product is exactly what I was looking for. A product like the one promised by Alice but never delivered. I love it! I offer you ten satoshis for it.
Daniel: - Thank you for your feedback Bob and for the offer! However I am currently selling it for eleven satoshis. Ten satoshis seems like a good price to me, and it was indeed my original intention to sell it for that amount because at that price I achieve competitiveness and a sustainable business model.
Bob: - So why are you asking me for eleven satoshis? Interrupts Bob
Daniel: - Because that price is calculated before assessing compliance and the risks associated with non-compliance. By not complying with the regulation, I managed to maintain the quality of the product and avoided a large amount of unnecessary expenses, but there is no way to avoid the risk of facing penalties for non-compliance. To bring this product to market, I had to incur several expenses in order to minimize the risk of non-compliance as much as possible. While I am taking all reasonable actions to prevent all of my assets from being legally confiscated, from going to prison, from being killed while they try to capture me, and in case of going to prison, from being tortured, the reality is that I still run the risk of all that, or part of all that, happening to me, my family, or any of my company's employees. The remaining risk balance is transferred to the price along with the costs of mitigating those risks. The total of those costs and the remaining risk I estimate them at one satoshi per unit of product. Therefore, I can't sell you the product for ten satoshis, but I can sell it to you for eleven.
To which Bob, lacking a better option in the market, ends up buying the product for eleven satoshis.
In summary: two products were made by two different merchants whose business model allowed them, in both cases, to put the product on the market at a rate of ten satoshis per unit. However, in one case, a lower quality product was sold for thirteen satoshis, and in the other case, a higher quality product was sold for eleven satoshis. That is to say, in the first case there was an overprice or inefficiency objectively measured at three satoshis, while in the second case there was an overprice or inefficiency of one satoshi. So, we are facing a total loss of value equivalent to four satoshis. The value represented by these four satoshis was absorbed by the inefficiency programmed and ruled by the State. The example shows us that whether one chooses the compliance route, as Alice did, or the free market route, as Daniel did, in both cases the existence of regulations generates an additional cost to the market. In this example the state attack on layer zero was successful and extracted from the Bitcoin network a value of four satoshis.
Bitcoin is money
Bitcoin is many things but essentially is money. And money sole purpose is to store value in order to facilitate future exchanges of products and services with other people. Without the products and services to be exchanged for the money, money itself would be useless and worthless. We only use money because we may require favors, benefits, services, products from other people in the future. And we don´t know which services and products we´ll need nor exactly when we are goint to need them.

The total value of bitcoin equals to infinity divided twenty one millions. This is because the total worth of the network mirrors the total worth of accumulated capital by the entirety of mankind throughout its entire history. That is clearly a lot of value. But if the if the dividend equals zero then the divisor is also zero and if the dividend growth is obstructed through artificial means -such as compliance- then the divisor growth is also obstructed.
Bitcoin layer zero, the bitcoiners and the services and products we create, are what give value to the twenty one million units of bitcoin.
Freedom is without a doubt the best context for value creation. So, the more and better games we can create that allow humankind to find a way to exercise freedom, then the most value we can add to all the layers of the network.
This is why the most important layer of the whole bitcoin phenomenon is layer zero, the bitcoiners. Hence the problem to be solved is not how to prevent bitcoin - layer one upwards- from successful attacks. The problem to solve is how to prevent attacks on layer zero. Or in other words, the problem to be solved is how to get bitcoiners in the physical world to practice the same level of freedom that bitcoin achieves in the cyberspace.
Summary of the first part of this article: freedom in cyberspace has already been conquered and each further development in the digital realm contributes to further developments but only in the same realm. Meanwhile in the physical space, the layer zero of bitcoin is under constant attacks that successfully extract value from it.
Exercising freedom in a sly roundabout way

In 1984 the Austrian economist Friedrich Hayek predicted that we couldn´t take money with violence out of the hands of government. He stated that we needed to do it in a sly roundabout way. Twenty five years later Satoshi Nakamoto discovered the sly roundabout way actually introducing something that the government couldn´t stop. Thus fulfilling Hayek´s prophecy.
Bitcoin is a sly roundabout way that removed money without violence from the hands of the government in a way that they can´t stop it.
Cryptography in general and protocols such as Tor and Tails are a sly roundabout way that removed confidential information from the hands of the government without violence in a way that they can´t stop it.
Nostr is a sly roundabout way that removed social media and public information from the hands of the government without violence in a way that they can´t stop it.
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government without violence in a way that they can´t stop it.

So, what are Special Jurisdictions, Free Cities and Bitcoin Citadels? To understand what they are we can take a look at the current mainstream market of living together, at how the physical space is organized. Essentially the entire planet Earth and its surroundings are run by a conglomerate of Governments. They create all the rules, regarding every aspect of life, of all the individuals, and enforce every rule through coercive means.
In the mainstream market of living together individuals have several alternatives to pick from. We can choose to live in a natural city or a pre design city, in a public neighborhood or private neighborhood or even in an intentional community with common interest amongst the users. But irregardless of the choice, every product offered in the mainstream market has the sames rules which are established by the host state to the entirety of organizations in his territory. In the mainstream market, even the most different products abide by the same high level rules such as criminal law, civil law, taxation laws, customs, enviromental laws, money laundering regulations and many others. To abide to the sum of all the laws and regulations is to be in compliance.
The centralization of regulations makes extremely difficult to experiment in market of living together. The less experimentation is allowed, the more human progress is hindered.
So what is the sly roundabout that fixes this? What are Special Jurisdictions, Free Cities and Bitcoin Citadels? I´m using the term Special Jurisdictions as an umbrella term that includes the entire spectrum of iterations of products that aim to modify the mainstream rules of the market of living together.
This term includes all the different models such as Charter Cities, Free Cities, Special Economic Zones, microstates, micropolis, start up societies, government as a service, self governing jurisdictions, autonomous intentional communities, network states and Bitcoin Citadels. The array of possible iterations is huge and permanently expanding. What they all have in common is that each of these experiments aims to create a functional game theory that replaces the lack of unbreakable walls in the physical space.
Let´s take a look of a couple of examples. Special Economic Zones are bounded areas of countries that have their own rules and regulations. Worldwide, there are more than five thousands special economic zones located in more than hundred countries.
One of them is the special economic zone of Shenzhen in China. The Chinese government allowed Shenzhen the freedom to experiment with certain practices that were prohibited in the rest of the country at the time. This included allowing foreign companies to make direct investments in China, allowing people to buy and sell land, allowing Chinese people to set up their own private businesses and relaxation of the system that limited internal migration within China for Chinese citizens. It served as a place where China could experiment with market reforms. The experiment was such a huge economic success that it was replicated in many other areas of the country.
Another place that has made extensive use of special economic zones is Dubai. The monarchic Government has more than 30 SEZs. In this case one of the many obstacles removed by the host state its the monopoly of the legal system. Dubai Government allowed the special economic zone to have its own independent legal system thus conceding a modification of the mainstream rules in that area.
This kind of projects, such as Dubai or Shenzhen, are a top-to-down product. Fully created by the Governments thus compliant with their own regulations.

On the other side of the spectrum we have Citadels and several other archetypes of not so compliant projects .
For example the Free Commune of Penadexo it´s a grassroots project building a freedom-oriented community in one of Spain’s abandoned villages.
 It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings.
It´s model is based on building a peer to peer society avoiding government intervention as much as possible.
They stablished themselves in an abandoned historic village and the started to track down the owners to purchase as much property as possible. Meanwhile, they are living there and expanding their users base while also reconstructing buildings. This is an example of a completely different way of dealing with the Government. While Special Economic Zones are fully compliant and created top to down, this model on the other hand is bottom-up and aims to add value to the users relying in factual freedom which is exercised by stablishing the commune away from heavily populated centers where Government grip is tighter. Under this model the interaction with the Government is kept as low as possible. Their strategy relies in ignoring the Government as much as possible and being a good neighbor. With this simple and effective tactic some Citadels enjoy the benefits of liberty in their lifetime without needing to spend huge resources in governmental lobby.
There are countless models or archetypes of Bitcoin Citadels trying to solve the obstacles in different ways, trying to restart the system. And one of the challenges of the Bitcoin Citadels is how to connect the different projects to boost and help each other.
This is where The Meshtadel comes into play. The Meshtadel is a system where decentralized tactics are used to help and defend citadels connected in a global network. With real life connections with fellow bitcoiners. Its an organization equivalent to the hanseatic league built under a starfish model. If you cut off a spider’s head, it dies, but if you cut off a starfish’s arm, it can regenerate and even grow into a new starfish.
The Meshtadel its a network of peer relationships, with ambiguous leadership roles, trust among participants, a shared ideology and vision based on the Bitcoin ethos, and an open system where new nodes - bitcoin citadel builders - can participate.
The long term goal of the Bitcoin Meshtadel is to help Bitcoin Citadels to gain the support of a critical mass of the total population. If enough people see that Bitcoin is as peaceful as it gets, in the long run, some nations could become friendly and supportive enough to legally tolerate the Bitcoin Citadel inside its territory in the form of a Bitcoin safe haven. In the Meshtadel we are fighting from the moral high ground using memes, Nostr notes and zapping our way into freedom creating an online and offline circular economy.
TO CONCLUDE:
Special Jurisdictions, Free Cities and Bitcoin Citadels are the sly roundabout way that is removing the market of living together from the hands of the government, without violence and in a way that they can´t stop it.
Nation states, abusing the myth of authority, have halted development on the market of living together for so long that a blooming freer market is eating its lunch. The sovereign individual thesis is live and continuously expanding. The network state is forming and intentional communities are flourishing all around the world reshaping globally the relationship between individuals and the governments.
With global internet connections, uncensorable means of communication and Bitcoin as the backbone of a new societal order, we are beginning to disrupt the old paradigm.
The fashion of the present world is passing away, let’s help it to move forward along by building Special Jurisdictions, Free Cities and Bitcoin Citadels.
--- --- --- --- --- --- --- --- ------
byCamiloat 875.341 timechain.
If you find this content helpful, zap it to support more content of the sort and to boost the V4V model.
-
 @ 3f770d65:7a745b24
2025-05-08 18:09:35
@ 3f770d65:7a745b24
2025-05-08 18:09:35🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: Austin Kelsay, Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: McShane (Bitcoin Strategy @ Roxom TV)
-
👥 Speakers:
-
Martti Malmi – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
Lyn Alden – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by DJ Valerie B LOVE, TatumTurnUp, and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by Derek Ross, Tomer Strolight, Terry Yiu, OpenMike, and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 266815e0:6cd408a5
2025-04-29 17:47:57
@ 266815e0:6cd408a5
2025-04-29 17:47:57I'm excited to announce the release of Applesauce v1.0.0! There are a few breaking changes and a lot of improvements and new features across all packages. Each package has been updated to 1.0.0, marking a stable API for developers to build upon.
Applesauce core changes
There was a change in the
applesauce-corepackage in theQueryStore.The
Queryinterface has been converted to a method instead of an object withkeyandrunfields.A bunch of new helper methods and queries were added, checkout the changelog for a full list.
Applesauce Relay
There is a new
applesauce-relaypackage that provides a simple RxJS based api for connecting to relays and publishing events.Documentation: applesauce-relay
Features:
- A simple API for subscribing or publishing to a single relay or a group of relays
- No
connectorclosemethods, connections are managed automatically by rxjs - NIP-11
auth_requiredsupport - Support for NIP-42 authentication
- Prebuilt or custom re-connection back-off
- Keep-alive timeout (default 30s)
- Client-side Negentropy sync support
Example Usage: Single relay
```typescript import { Relay } from "applesauce-relay";
// Connect to a relay const relay = new Relay("wss://relay.example.com");
// Create a REQ and subscribe to it relay .req({ kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events"); } else { console.log("Received event:", response); } }); ```
Example Usage: Relay pool
```typescript import { Relay, RelayPool } from "applesauce-relay";
// Create a pool with a custom relay const pool = new RelayPool();
// Create a REQ and subscribe to it pool .req(["wss://relay.damus.io", "wss://relay.snort.social"], { kinds: [1], limit: 10, }) .subscribe((response) => { if (response === "EOSE") { console.log("End of stored events on all relays"); } else { console.log("Received event:", response); } }); ```
Applesauce actions
Another new package is the
applesauce-actionspackage. This package provides a set of async operations for common Nostr actions.Actions are run against the events in the
EventStoreand use theEventFactoryto create new events to publish.Documentation: applesauce-actions
Example Usage:
```typescript import { ActionHub } from "applesauce-actions";
// An EventStore and EventFactory are required to use the ActionHub import { eventStore } from "./stores.ts"; import { eventFactory } from "./factories.ts";
// Custom publish logic const publish = async (event: NostrEvent) => { console.log("Publishing", event); await app.relayPool.publish(event, app.defaultRelays); };
// The
publishmethod is optional for the asyncrunmethod to work const hub = new ActionHub(eventStore, eventFactory, publish); ```Once an
ActionsHubis created, you can use therunorexecmethods to execute actions:```typescript import { FollowUser, MuteUser } from "applesauce-actions/actions";
// Follow fiatjaf await hub.run( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", );
// Or use the
execmethod with a custom publish method await hub .exec( MuteUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", ) .forEach((event) => { // NOTE: Don't publish this event because we never want to mute fiatjaf // pool.publish(['wss://pyramid.fiatjaf.com/'], event) }); ```There are a log more actions including some for working with NIP-51 lists (private and public), you can find them in the reference
Applesauce loaders
The
applesauce-loaderspackage has been updated to support any relay connection libraries and not justrx-nostr.Before:
```typescript import { ReplaceableLoader } from "applesauce-loaders"; import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(rxNostr); ```
After:
```typescript
import { Observable } from "rxjs"; import { ReplaceableLoader, NostrRequest } from "applesauce-loaders"; import { SimplePool } from "nostr-tools";
// Create a new nostr-tools pool const pool = new SimplePool();
// Create a method that subscribes using nostr-tools and returns an observable function nostrRequest: NostrRequest = (relays, filters, id) => { return new Observable((subscriber) => { const sub = pool.subscribe(relays, filters, { onevent: (event) => { subscriber.next(event); }, onclose: () => subscriber.complete(), oneose: () => subscriber.complete(), });
return () => sub.close();}); };
// Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
Of course you can still use rx-nostr if you want:
```typescript import { createRxNostr } from "rx-nostr";
// Create a new rx-nostr instance const rxNostr = createRxNostr();
// Create a method that subscribes using rx-nostr and returns an observable function nostrRequest( relays: string[], filters: Filter[], id?: string, ): Observable
{ // Create a new oneshot request so it will complete when EOSE is received const req = createRxOneshotReq({ filters, rxReqId: id }); return rxNostr .use(req, { on: { relays } }) .pipe(map((packet) => packet.event)); } // Create a new replaceable loader const replaceableLoader = new ReplaceableLoader(nostrRequest); ```
There where a few more changes, check out the changelog
Applesauce wallet
Its far from complete, but there is a new
applesauce-walletpackage that provides a actions and queries for working with NIP-60 wallets.Documentation: applesauce-wallet
Example Usage:
```typescript import { CreateWallet, UnlockWallet } from "applesauce-wallet/actions";
// Create a new NIP-60 wallet await hub.run(CreateWallet, ["wss://mint.example.com"], privateKey);
// Unlock wallet and associated tokens/history await hub.run(UnlockWallet, { tokens: true, history: true }); ```
-
 @ a5ee4475:2ca75401
2025-05-08 16:41:28
@ a5ee4475:2ca75401
2025-05-08 16:41:28profissional #brasileiros #portugues #lista
[Em Atualização]
nostr:nprofile1qqsvz46xcwfqjyw5xkjh3gs8v63udn6slp2wehn8pyndtcpvvxa7rwqpzpmhxue69uhkummnw3ezumt0d5hsdzu0zr - Estude BITCOIN
!(image)[https://nostrcheck.me/media/public/nostrcheck.me_8896510008477875231689270519.webp]
Canal Principal: https://m.youtube.com/@altierebtc
Canal de Games: https://m.youtube.com/channel/UCm9dUXKlVbDOfa-7GB-6gxw
Twitch: https://m.twitch.tv/altiere/home
Endereço Lightning: Quietcarol43@walletofsatoshi.com
Peter Turguniev - nostr:nprofile1qqszleff9gkly5z85wf0em4dw4zcsaw8whp3es50f0syeme73kc49ygpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7qgj4r9
Site: ANCAP.SU
!(image)[https://i.im.ge/2023/06/01/hCgPJa.03de86ce-3106-4a4b-859c-b6b4d9e6e62e.jpg]
Canal Principal: https://m.youtube.com/@ancap_su
Visão Libertária: https://m.youtube.com/@Visao_Libertaria
Canal de Programação: https://m.youtube.com/@safesrc
Canal Mundo em Revolução: https://m.youtube.com/@wrevolving
Canal Hoje no X: https://m.youtube.com/@noxhoje
Canal Antigo: https://m.youtube.com/@ANCAPSUClassic
Site: https://pimentanocafe.com.br/
ANCAP.SU (Odysee): https://odysee.com/@ancapsu:be
Visão Libertária (Odysee): https://odysee.com/@ancapsu:c
Endereço Lightning: Ancapsu@getalby.com
nostr:nprofile1qqsw2k9dqcwkelfl0cr2ranhfvqx98et635hymmefl4rr89e4x9xtaqpr9mhxue69uhhyetvv9ujuumwdae8gtnnda3kjctv9u55vn8f
Economista e Cientista de Dados
!(image)[https://image.nostr.build/9caacd289ed01ad6fecd331a43218da6ce3c2f5713d9e9a4fc8c8b531728deb8.jpg]
Repositorio de codigos: https://github.com/Argonalyst
Notícias sobre tecnologia e inteligência artificial: https://youtube.com/@argonalyst
https://www.argonalyst.com/
Bitcoinheiros - nostr:nprofile1qqsdg0vnpw76lujncaexfh0fy747dheynq9s5m9wqxulcu2szlwqpfcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszyrhwden5te0dehhxarj9ekk7mf0cmje9h
!(image)[https://void.cat/d/A6LisLBh5cmyYtrgkjqBxe.webp]
Canal Principal: https://m.youtube.com/@Bitcoinheiros
Canal de Cortes: https://www.youtube.com/channel/UC82m2TCXSHWcqSLym5BzjLQ/
Site: https://bitcoinheiros.com/
Endereço Lightning: ln@pay.bitcoinheiros.com
Área Bitcoin - Divulgação sobre Bitcoin
nostr:nprofile1qqstvy6savnm83mf9775t70d2d2lp2rsw8hys5rfsq4lhy9qachctpgpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7svvx93 e nostr:npub1yzhwak5yc7pzvukwzlfj7p0dp2y07jd42y45h0maxuej4us5rcjsssxkej
!(image)[https://m.primal.net/KXBa.jpg]
Canal Principal: https://m.youtube.com/@AreaBitcoin
Site: Areabitcoin.com.br
Endereço Lightning: Cyanlionfish5@primal.net
nostr:nprofile1qqs075udlpdc60js8ade7st2zt942ghj0ehd6frnwjtylss5c9kdxzgpr9mhxue69uhkyu3wwp6hyurvv4ex2mrp0yhxxmmd9uq32amnwvaz7tmhda6zumn0wd68ytnsv9e8g7g24pghx - Dev
Repositório: https://github.com/antonioconselheiro/omeglestr
nostr:nprofile1qqsqxh6ffher03qlngcnf93g9kyv7gzkmz6h6t8qylzkw8hup8zxytspzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qgawaehxw309ahx7um5wghxy6t5vdhkjmn9wgh8xmmrd9skctcx72xdd
Biólogo e colunista
!(image)[https://image.nostr.build/8bddd8cd3e2e65c76cd7b02179e3ddeb3a1a1171f0a0ae32594278a9ccf19da0.jpg]
Canal Principal: https://m.youtube.com/@EliVieira
Endereço Lightning: Elivieira@bipa.app
nostr:nprofile1qqsgy4gvl2n03ylylv0ack59res7nytkjdq5wpqcw9ch5eqhwwnpnvgpypmhxw309aex2mrp0ykkummnw3ez6cnj9e3k7mfwvfer5dpcxsuz7qgewaehxw309a38ytnsw4e8qmr9wfjkccte9e3k7mf0qyvhwumn8ghj7cmv9ec82unsd3jhyetvv9ujucm0d5hs6m9t8t
Canal Principal: https://youtube.com/@Akitando
https://www.akitaonrails.com/
https://www.codeminer42.com/
Endereço Lightning: Akitaonrails@strike.me
Felipe Ojeda - nostr:nprofile1qqsv7c6qu0qsy9wxg9cqkhle078j46rhsvz64f6vukxdmpkdt7vt55cpz9mhxue69uhkummnw3ezuamfdejj7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uq3wamnwvaz7tmpw3kxzuewdehhxarj9ekxzmny9uwes77q
Saída fiscal para o Paraguai e P2P
https://youtube.com/@bitcoineliberdade
Lightning Network: ojeda@blink.sv
nostr:npub18zw66c2lvt6s06drtvtkjjyvnfwjdgg2w7y36rmtmg7rnfnkhhxq7hhu4t
Engenheiro
Construção econômica e sustentável: https://amandaefernando.com.br/
https://youtube.com/@amandaefernando
Carteira de Zap: lilacgecko5@blink.com
nostr:npub1kqd90mglkp0ltmc5eacd0claqvnayaklkvzkdhx7x84w9uavplxszvrlwd
Canal principal: https://youtube.com/@fernandoulrichcanal
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6
https://fiatjaf.com/
Repositórios de códigos:
https://git.fiatjaf.com/
https://github.com/fiatjaf
Outros repositórios:
https://github.com/nostr-protocol/nostr
Carteita de Zap: fiatjaf@zbd.gg
nostr:nprofile1qqsw2s3zjedanx8nve9zda7zkemx5n5d4v0mt0ncehfa7qkkjse5v5gpzpmhxue69uhkummnw3ezumt0d5hsxnexr8
Canal Principal: https://m.youtube.com/@FoxyeBitcoin
Endereço Lightning: Foxye@bipa.app
nostr:npub1vudm0xsx4cv3zkvvq7k5836tnkv64q0h7uudnwujr4a4l9zc2p9s0x8url - Irmãos Chioca
Tradutores e publicadores de temáticas libertárias [livros, artigos, vídeos e textos]
https://rothbardbrasil.com/
Canal principal: https://youtube.com/@institutorothbardbrasil
Carteira de zap: trendybean80@walletofsatoshi.com
João Abitante - nostr:nprofile1qqsyzwgmhmdsduuya866s2pnnkw2x956wdpumtjjw3rp4ueyunv9hlspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qy2hwumn8ghj7un9d3shjtnwdaehgu3wvfnj7qgwwaehxw309ahx7uewd3hkctclycz6e
Contador Libertário
!(image)[https://m.primal.net/KWoL.png]
Canal Principal: https://youtube.com/@ahoradaelisao
Endereço Lightning: libertcontador@pay.bbw.sv
João Trein - nostr:nprofile1qqsze3h79ljwzqp7ryre9n6p9z8m4t4m5806v8anxu9q2dx7n5cgqfgpz3mhxue69uhkummnw3ezummcw3ezuer9wcq35amnwvaz7tm5dpjkvmmjv4ehgtnwdaehgu339e3k7mgpzpmhxue69uhkummnw3ezumrpdejqj2zepn
Bitcoin e Cyber segurança
https://youtube.com/@tninvest
Carteira de Zap: tninvest@blink.com
nostr:nprofile1qqsdwdhzj3red6p62fus3sdk03cqp8t0u3enfupwa4rw2q2yhfwe9tqpr9mhxue69uhhyetvv9ujuumwdae8gtnnda3kjctv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tc3ft2ln
Atendimento psicológico e sobrevivencialismo
Canal sobrevivencialismo: https://youtube.com/@sobrevivencialismo
Canal de psicologia: https://youtube.com/@juliolobosv
Carteira de zap: juliolobosv@getalby.com
nostr:npub1q88jfh2gasm0ztszhltfl226lhpvlxxq2u0t6smf2n5cn85es4assuwqmp
Divulgadora sobre Bitcoin
https://youtube.com/@bitlorena
Carteira de zap: potterlore@zbd.gg
nostr:nprofile1qqsp05nhmn8x343gme39d8l63z2d34ht4lgln60jn5vm3gsndj7u86qppemhxue69uhkummn9ekx7mp09kal50
Ambientalista
https://youtube.com/@marcobatalha
Carteira de zap marcobatalha@getalby.com
Marcus - nostr:npub1wsl3695cnz7skvmcfqx980fmrv5ms3tcfyfg52sttvujgxk3r4lqajteft e nostr:npub12mllp29adf2fw0eeahmseczcu3y4625qyn3v4uwfvkpzlshnmj3qs903ju
https://privatelawsociety.net/know
https://github.com/PrivateLawSociety/pls-mvp
Carteira de zap: anarcus@getalby.com
nostr:nprofile1qqs923ewnsqlx7347cpjhxmcmt0rsmnwf3tasr736pjx4wee9q89ufcpzpmhxue69uhkummnw3ezumt0d5hsf83vqq
Programador
Repositório de códigos:
https://github.com/misesdev
Aulas de desenvolvimento de código
https://youtube.com/@misesdev
Carteira de Zap: greatasphalt42@walletofsatoshi.com
nostr:nprofile1qqsvqnfplem5auv0ug0j2v8kkp5x06fcv93rqs6cz54fm6svs28ahgqpz4mhxue69uhkummnw3ezummcw3ezuer9wchsn6tsk6
Repositório: https://github.com/ODevLibertario/nostrlivery
nostr:nprofile1qqstj62w4ctec57ny2p6hs67ut4nygsrc4th75ff42cyag4emy2v3yspz9mhxue69uhkummnw3ezuamfdejj7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqsuamnwvaz7tmwdaejumr0dshsxhz6wr
!(image)[https://image.nostr.build/22080bdb678ab61ef863be436d78654f537287951508198bf9fa5129abb289fc.jpg]
Canal Principal: https://m.youtube.com/@PROmetheusHODL
Canal no Odysee: https://odysee.com/@Prometheus:ef
Endereços Lightning e Liquid Blink: prometheus@blink.sv Alby: prometheusyt@getalby.com Liquid: VJLDAirBEPj4deoRnspxG8pnu8Ezxg6ajPcXyXoDXDP1dKn9UDJPDckiX5vBTp9aFQM42B15KpAHqVkc
nostr:npub1ld5xqfflwy6txghaaef2d4rnyzkvwvz2crncmtvhq93xxsqvzqtqzdx4yp
https://youtube.com/@VamosViverFora
Carteira de zap: psp@blink.com
nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z
https://vitorpamplona.com/
Repositorio de codigo:
https://github.com/vitorpamplona
https://github.com/vitorpamplona/amethyst/
Cursos:
Seiiti Arata / Seiiti Arata (Inglês)
Produtor de cursos
https://www.arataacademy.com/
Canal principal: https://youtube.com/@arataacademy
Daniel Miorim e Malboro
Comentarismo e ensino
Alta Linguagem e Curso Libertário de Anticomunismo
https://youtube.com/@altalinguagem
Renato 38 e Alan Schramm
Livros, curso e consultoria de Bitcoin
O seguinte canal disponibiliza o curso, mas não menciona ser do Renato ou do Alan:
https://youtu.be/ZQaGXchogkk
Rafael Scapella
Viagens, informações e política internacional
https://youtube.com/@rafaelscapella?si=IfPjPfVsPlmA_zYX
Roberto Pantoja
Inovaflix - Cursos e Consutoria de Negócios
Canal de informação: https://youtube.com/@robertopantoja
Carlos Xavier
Prof. de Teologia e Direito
Curso de História da Filosofia e Direito
Direito sem Juridiquês:
https://youtube.com/c/DireitosemJuridiquês
- Playlist libertária:
https://youtube.com/playlist?list=PLYXudd4-x8GjzIyNZsUzzw8NF-Gkca8sV&si=oyDRdxVDB0b1GLTo
Teodidatas:
https://youtube.com/c/Teodidatas
Jason Schmütz (Toddyn)
Comunicador sobre jogos e temas gerais
Canal sobre Bitcoin, critica ao Estado e a empresas de jogos, e estilo de vida:
https://youtube.com/@ojasonschmutz
Canal de Jogos:
https://youtube.com/@toddyncp
Curso de criação de jogos sem programar - Codezero | RPG Paper Maker [Atualmente indisponível]
Pigdev
Desenvolvedor de jogos indies
https://youtube.com/@pigdev
Cursos e materiais para desenvolvimento de jogos
https://pigdev.itch.io/
Outros Profissionais Libertários
Anderson - Ciberdef
Defesa cibernética
https://youtube.com/@andersonciberdef
Guilherme Bauer - Capital Global
Internacionalização de patrimônio
https://odysee.com/@capitalglobalbr:b
Tuchê Nunes
Agricultura, permacultura e bioconstrução
https://youtube.com/@tuchenunesautossustentavel
Jack
Personal trainer
Dicas de treinos https://youtube.com/@lybrjack
Avelino Morganti
Ouro, prata e joias
Compras e pedidos: https://morgantis.com/
Canal de informação: https://youtube.com/@avelinomorganti
Bianca Colobari
Atendimento psicológico e experiência com educação domiciliar para crianças
Canal de informação https://youtube.com/@biancacolombari
Cecilia Isicke (Portugal)
Médica libertária e bitcoinheira
Canal de informação https://youtube.com/@draceciliaisicke650
Não Libertário e Bitcoiner
Núcleo Dharma
Artes Marciais, Autodefesa e Armas
https://youtube.com/channel/UCtbAO1zbJAwd6gDK7Y87JLA
-
 @ 000002de:c05780a7
2025-05-08 16:14:37
@ 000002de:c05780a7
2025-05-08 16:14:37Just an observation that makes me chuckle.
originally posted at https://stacker.news/items/974829
-
 @ 5b730fac:9e746e2a
2025-05-08 15:33:12
@ 5b730fac:9e746e2a
2025-05-08 15:33:12| Channel | Push to Branch | Previous Installation Method | NIP94 Event ID Updated as Expected | New Update Installed as Expected | Test Passed | | ----------------------------------- | ----------------- | ---------------------------- | ---------------------------------- | -------------------------------- | -------------------------------------------------------------------------------------------------------------------------------- | | deleted config files, first install | Already installed | Manual | Yes | Yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzwpnxq6rvdp59d83mz |Before pushing update
Check state
Currently installed NIP94 event:
{ "id": "8e75993b2b6d28e4336bc90150e2c69db97d45f1c7db6bf3c3892cee55f45c44", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746716510, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/bf6608e98a60cf977100d50aa21f720d4e369356fd9b5ca24616f9a7226bd41c.ipk" ], [ "m", "application/octet-stream" ], [ "x", "bf6608e98a60cf977100d50aa21f720d4e369356fd9b5ca24616f9a7226bd41c" ], [ "ox", "bf6608e98a60cf977100d50aa21f720d4e369356fd9b5ca24616f9a7226bd41c" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package_test-92-1157a2f" ], [ "release_channel", "dev" ] ] }Current version picked up by opkg:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - multiple_mints_rebase_taglist_detect_package-92-1157a2fCheck basic module's logic
Config.json contains the right event ID: ``` root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "62a39f60f5b3e3f0910adc592c0468c5c134ce321238884e9f016caad4c5231b" }
```
Install.json contains the right package path:
root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746715561, "download_time": 1746715507, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null }Deactivate, delete config files and start
Deactivate & delete config files:
root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactive root@OpenWrt:/tmp# rm /etc/tollgate/config.json /etc/tollgate/install.json root@OpenWrt:/tmp# ls /etc/tollgate/config.json /etc/tollgate/install.json ls: /etc/tollgate/config.json: No such file or directory ls: /etc/tollgate/install.json: No such file or directoryStart and check configs. Release channel is set to stable by default:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" } root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746717311 }Logs are too verbose, but otherwise fine. Skipped all events due to release channel:
Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.233356 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.235395 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.237559 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.239556 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.241685 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.259370 Skipping event due to release channel mismatch Thu May 8 15:15:13 2025 daemon.err tollgate-basic[13609]: 2025/05/08 15:15:13.261258 Skipping event due to release channel mismatch Thu May 8 15:15:31 2025 daemon.info tollgate-basic[13609]: Connecting to relay: wss://relay.tollgate.me Thu May 8 15:15:56 2025 daemon.info tollgate-basic[13609]: Connecting to relay: wss://relay.tollgate.meStop
tollgate-basic:root@OpenWrt:/tmp# service tollgate-basic stop root@OpenWrt:/tmp# service tollgate-basic status inactiveSwitch to
devchannel:root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "stable", "ensure_default_timestamp": 1746717311 } root@OpenWrt:/tmp# vi /etc/tollgate/install.json root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "false", "ip_address_randomized": "false", "install_time": 0, "download_time": 0, "release_channel": "dev", "ensure_default_timestamp": 1746717311 }Restart service:
root@OpenWrt:/tmp# service tollgate-basic start root@OpenWrt:/tmp# service tollgate-basic status runningLogread:
Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10 NIP94EventID: unknown Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10 IPAddressRandomized: false Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10 Janitor module initialized and listening for NIP-94 events Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10.861535 Registering handlers... Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10.861715 Starting HTTP server on all interfaces... Thu May 8 15:21:10 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:21:10.861834 Starting to listen for NIP-94 events Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Starting Tollgate - TIP-01 Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Listening on all interfaces on port :2121 Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Starting event processing loop Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://nos.lol Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://nostr.mom Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://relay.tollgate.me Thu May 8 15:21:10 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://relay.damus.io Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Connected to relay: wss://nos.lol Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscription successful on relay wss://nos.lol Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscribed to NIP-94 events on relay wss://nos.lol Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Connected to relay: wss://nostr.mom Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscription successful on relay wss://nostr.mom Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscribed to NIP-94 events on relay wss://nostr.mom Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Connected to relay: wss://relay.damus.io Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscription successful on relay wss://relay.damus.io Thu May 8 15:21:11 2025 daemon.info tollgate-basic[13838]: Subscribed to NIP-94 events on relay wss://relay.damus.io Thu May 8 15:21:30 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://relay.tollgate.meTrigger new event: ``` c03rad0r@CobradorRomblonMimaropa:~/TG/tollgate-module-basic-go/src$ git push github Enumerating objects: 9, done. Counting objects: 100% (9/9), done. Delta compression using up to 8 threads Compressing objects: 100% (5/5), done. Writing objects: 100% (5/5), 416 bytes | 416.00 KiB/s, done. Total 5 (delta 4), reused 0 (delta 0), pack-reused 0 remote: Resolving deltas: 100% (4/4), completed with 4 local objects. To https://github.com/OpenTollGate/tollgate-module-basic-go.git 1157a2f..e775bce multiple_mints_rebase_taglist_detect_package -> multiple_mints_rebase_taglist_detect_package
{ "id": "c73756a13f0ca270510d4301c1dbf433989974c33262fd3cd07627eacc3d6481", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746718037, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078.ipk" ], [ "m", "application/octet-stream" ], [ "x", "cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078" ], [ "ox", "cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-93-e775bce" ], [ "release_channel", "dev" ] ] } ```
New event caught, updated and restarted:
Thu May 8 15:27:19 2025 daemon.info tollgate-basic[13838]: Started the timer Thu May 8 15:27:19 2025 daemon.info tollgate-basic[13838]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-93-e775bce] Thu May 8 15:27:19 2025 daemon.info tollgate-basic[13838]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-93-e775bce] Thu May 8 15:27:19 2025 daemon.info tollgate-basic[13838]: Right Arch Keys count: 61 Thu May 8 15:27:19 2025 daemon.info tollgate-basic[13838]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-93-e775bce] Thu May 8 15:27:29 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:27:29.928620 Timeout reached, checking for new versions Thu May 8 15:27:29 2025 daemon.info tollgate-basic[13838]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-93-e775bce] Thu May 8 15:27:29 2025 daemon.info tollgate-basic[13838]: Newer package version available: multiple_mints_rebase_taglist_detect_package-93-e775bce Thu May 8 15:27:29 2025 daemon.info tollgate-basic[13838]: Downloading package from https://blossom.swissdash.site/cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078.ipk to /tmp/cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078.ipk Thu May 8 15:27:34 2025 daemon.info tollgate-basic[13838]: Package downloaded successfully to /tmp/ Thu May 8 15:27:34 2025 daemon.info tollgate-basic[13838]: New package version is ready to be installed by cronjob Thu May 8 15:27:34 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:27:34.073022 Verifying package checksum Thu May 8 15:27:34 2025 daemon.err tollgate-basic[13838]: 2025/05/08 15:27:34.082504 Package checksum verified successfully Thu May 8 15:27:55 2025 daemon.info tollgate-basic[13838]: Connecting to relay: wss://relay.tollgate.me Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07 NIP94EventID: c73756a13f0ca270510d4301c1dbf433989974c33262fd3cd07627eacc3d6481 Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07 IPAddressRandomized: 10.156.11.1 Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: TODO: include min payment (1) for https://mint.minibits.cash/Bitcoin in future Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: TODO: include min payment (1) for https://mint2.nutmix.cash in future Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: Starting Tollgate - TIP-01 Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: Listening on all interfaces on port :2121 Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07 Janitor module initialized and listening for NIP-94 events Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07.915222 Registering handlers... Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07.915366 Starting HTTP server on all interfaces... Thu May 8 15:28:07 2025 daemon.err tollgate-basic[14419]: 2025/05/08 15:28:07.917009 Starting to listen for NIP-94 events Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: Starting event processing loop Thu May 8 15:28:07 2025 daemon.info tollgate-basic[14419]: Connecting to relay: wss://relay.damus.ioNew config files with new IP address
root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "c73756a13f0ca270510d4301c1dbf433989974c33262fd3cd07627eacc3d6481" } root@OpenWrt:~# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/cffba9d8b8bc9e1c59c97fdf238a47bdb8d6ad3003e4ae8b6cf50ca301f13078.ipk", "ip_address_randomized": "10.156.11.1", "install_time": 1746718081, "download_time": 1746718054, "release_channel": "dev", "ensure_default_timestamp": 1746717311, "update_path": null } -
 @ f1989a96:bcaaf2c1
2025-05-08 15:05:45
@ f1989a96:bcaaf2c1
2025-05-08 15:05:45Good morning, readers!
This week, we bring reports from Bangladesh, where the interim government instructed the central bank to halt the printing of old banknotes featuring Sheikh Mujibur Rahman, the founding president of Bangladesh. This has induced a currency shortage, as new notes have yet to be issued to replace the discontinued ones. As a result, Bangladeshis find themselves holding worthless currency, facing increased costs, and feeling frustrated over such poor currency management. Meanwhile, in Indonesia, citizens are fleeing to gold as the local rupiah currency crashes to record lows amid increasing financial controls from the government.
In open-source news, LNbits, a Bitcoin and Lightning wallet management software, emerged from beta with its v1.0.0 release. LNbits works like a control panel on top of a Bitcoin wallet, letting users divide funds into separate accounts and use different features and functionalities. It is a handy tool for educators, civil society organizations, and communities who want to use Bitcoin for real-world transactions without needing advanced technical skills. We also spotlight a new tool called following .space that allows users to curate and share premade follow packs for nostr. The result is a more straightforward onboarding process for new users interested in censorship-resistant social media and the ability to curate feeds to better suit their interests.
We end with an interview with HRF Chief Strategy Officer Alex Gladstein, who explores his thinking behind the relationship between Bitcoin and human rights as we enter an age of increased corporate and nation-state adoption. He highlights the paradox where Bitcoin, a tool for individual financial freedom, is being adopted by institutions around the world, many of which regularly seek greater control over financial activity. We also include a new report from Bitcoin developer and past HRF grantee, b10c, who documents the current state of Bitcoin mining centralization and the threat it poses to decentralization and censorship resistance.
Now, let’s jump right in!
SUBCRIBE HERE
GLOBAL NEWS
Bangladesh | Currency Shortage as Central Bank Halts Printing of Banknotes
A state-induced cash crunch is paralyzing Bangladesh after the interim government, led by Muhammad Yunus, ordered the central bank to discontinue old banknotes featuring Sheikh Mujibur Rahman, the founding president of Bangladesh. New cash is expected to be printed in phases beginning in May. But Bangladeshis report they are currently stuck with old and unusable currency, as the national mint has yet to issue replacement currency and lacks the capacity to print more than three notes at a time. Meanwhile, public ATMs continue to dispense old and worn-out banknotes, with merchants reluctantly accepting them and banks refusing to exchange them. Through all this, the central bank of Bangladesh sits on nearly 15,000 crore taka ($1.28 billion) worth of old notes in vaults, but the interim government has refused to release them, deepening public frustration.
Nigeria | Regulates Bitcoin as a Security
Nigerian lawmakers are moving to regulate digital assets as securities by passing the Investment and Securities Act (ISA) 2025. Rather than embrace it as a tool for financial freedom, the law places Bitcoin under the purview of the Nigerian Securities and Exchange Commission (SEC). Companies must now register with the Nigerian SEC, implement more strict data-collection processes (to harvest personal information), and navigate a legal framework not designed for a borderless and permissionless technology like Bitcoin. The law further grants the SEC access to data from telecom and Internet providers to investigate “illegal market activity” — a provision that could easily be abused to surveil or intimidate Bitcoin users and developers. Nigeria routinely uses regulations to stifle the presence of open-source money, raising compliance hurdles, imposing taxes, and punishing digital asset companies. It’s not unreasonable to suspect this new classification could provide the state with a means to suppress the free adoption and innovation of Bitcoin.
Indonesia | Gold Rush Amid Economic Uncertainty
As the rupiah currency falls to record lows, Indonesians are flocking to gold in a rush to protect their savings. But gold isn’t the only safe haven. With 74% of Indonesia’s population unbanked or underbanked, digital tools like Bitcoin offer a more accessible alternative, especially when nearly 70% of Indonesians have Internet access. The Indonesian government is also tightening capital controls. A new policy forces exporters to keep all foreign currency earnings inside the country for a full year to trap dollars in the financial system. HRF grantee Bitcoin Indonesia is responding by helping people in the region (especially in nearby states like Burma) build financial resilience through meetups, workshops, and training focused on Bitcoin custody, privacy, and adoption. In an area where financial services remain out of reach for millions, learning how to save and transact permissionlessly is paramount.
Kenya | Introduces Legal Framework for Virtual Asset Service Providers (VASPs)
Kenya’s government introduced a comprehensive legal framework to regulate Virtual Asset Service Providers (VASPs) through its newly proposed 2025 VASP Bill. The legislation outlines strict licensing requirements for digital asset exchanges, wallet providers, brokers, and other digital asset firms. It functionally bars individuals from operating independently (think: open-source freedom tech builders) by mandating local incorporation, compliance with cybersecurity standards, and approval from financial regulators. This appears to be an attempt to formalize and better control the rapidly growing digital asset space. It could stifle grassroots innovation and limit access to financial tools that have become vital for activists and citizens seeking privacy and autonomy as economic policies and high inflation drive unrest.
El Salvador | Attorney General’s Office Preparing Arrest Warrants for Independent Journalists
El Faro, one of El Salvador’s most prominent investigative news outlets, shared reliable information that the Salvadoran Attorney General’s Office is preparing arrest warrants against three of its journalists. The warning came from El Faro director Carlos Dada, who suggests that the charges may include “apology for crimes” and “illicit association.” The alleged charges allegedly stem from El Faro’s latest reporting: a three-part video interview with former leaders of the 18th Street Revolucionarios gang that sheds light on Bukele’s “years-long relationship” with Salvadoran gangs. El Faro editor-in-chief Óscar Martínez said that any arrests or home raids following this news would be “for having done journalism.” With El Salvador’s shrinking civic space, this potential action against independent media would further restrict Salvadorans’ ability to access independent information and hold officials accountable.
BITCOIN AND FREEDOM TECH NEWS
LNbits | Emerges from Beta with v1.0.0 Release
LNbits, an open-source software tool that lets people create and manage Bitcoin Lightning wallets securely for themselves and for others, officially launched version 1.0.0, marking its transition out of beta and into a more stable release for public use. It works like a control panel sitting on top of a Bitcoin wallet, letting users divide funds into separate accounts and use different features and functionalities. LNbits is especially useful for educators, small businesses, and community organizers who want to use and manage Bitcoin for payments and savings. HRF is pleased to see this Bitcoin Development Fund (BDF) grantee strengthen the tools available to activists to achieve financial freedom in the face of censorship, surveillance, or inflation.
SeedSigner | Self-Custody Tool for Chinese Bitcoiners Facing Local Corruption
Chinese Bitcoin users are turning to SeedSigner, an open-source and fully customizable Bitcoin hardware wallet, as a more private way to protect their savings from law enforcement corruption. While many assume the primary threat to Bitcoin in China comes from top-down management and enforcement from the Chinese Communist Party (CCP), new reports suggest greater concern over the police, who regularly monitor mail, detect hardware wallet purchases, and fabricate charges to extort Chinese users’ Bitcoin. SeedSigner solves this by allowing users to assemble a secure signing device from generic, inexpensive parts, avoiding the risk of shipping a branded wallet that might flag them as a target. When privacy violations begin at the local level, SeedSigner can help citizens safeguard their financial freedom by making secure self-custody discreet, accessible, and affordable.
Following .space | Create and Share Follow Packs on Nostr
Following.space is a new tool for nostr that solves one of the protocol’s biggest pain points: finding people worth following in the absence of an algorithm. Created by developer and HRF grantee Calle, the tool lets anyone build and share curated “follow packs” — pre-made lists of nostr users that can be easily distributed across the web. The lists are customizable and can be made based on shared interests, communities, organizations, regions, and more. This makes onboarding new users easier and allows users to curate their feeds to suit their interests. The result is a simple but powerful tool that helps nostr scale more organically by encouraging natural discovery. Enabling free expression and connections without reliance on centralized platforms strengthens human rights and financial freedom in repressive environments. Try it here.
256 Foundation | Releases Ember One Source Code
The 256 Foundation, an open-source Bitcoin mining initiative, released the source code of its new Ember One Bitcoin mining hashboard to the public. A Bitcoin hashboard is a device with multiple chips for performing Bitcoin mining computations. The open-source Ember One only consumes 100 Watts of total power and is modular by design, allowing user customization and the ability to mine discreetly even under autocratic regimes. This is important because it gives individuals a way to access and earn Bitcoin without drawing the attention of officials. For dissidents, mining at home means gaining more control over how they earn, spend, and store their money, all without relying on centralized systems at the whims of dictators.
Btrust and Africa Free Routing | Announce Partnership to Advance African Bitcoin Development
Btrust, a nonprofit advancing Bitcoin development in Africa, awarded a grant to Africa Free Routing, a program within African Bitcoiners, to support five Bitcoin Lightning-focused developer boot camps across the continent in 2025. These bootcamps aim to onboard non-Bitcoin developers into the Bitcoin ecosystem, offering hands-on training, mentorship, and opportunities to contribute to open-source projects. This work strengthens the foundations of freedom tech in Africa, providing tools that allow people to resist financial repression under tyranny. Learn more about the partnership here.
Presidio Bitcoin | Hosting First Hackathon
Presidio Bitcoin, the Bay Area’s first dedicated freedom tech co-working and events space, just announced its first-ever hackathon, which will take place from May 16-17, 2025. This 24-hour hackathon in San Francisco brings together developers and technologists to build and collaborate at the frontier of Bitcoin, AI, and open-source technology. In addition to the hackathon, Presidio is launching a new program offering free three-month access to its workspace for Bitcoin open-source contributors. This is a valuable opportunity to connect with fellow developers, startup founders, and freedom tech advocates in the area. HRF is proud to sponsor this hackathon and is looking forward to how the outcomes might help create better freedom tools for dissidents worldwide. Learn more about the event here.
RECOMMENDED CONTENT
Bitcoin Nation State Adoption Paradox - Interview with Alex Gladstein
In a recent episode of the Bitcoin Fundamentals podcast, hosted by Preston Pysh, Alex Gladstein, HRF’s chief strategy officer, discusses the complexities of Bitcoin’s new era of adoption. He highlights the paradox where Bitcoin, a tool for individual financial freedom, is being adopted by governments, which some believe to be potentially compromising to its core principles. He emphasizes that while governments may adopt it for strategic or economic reasons, in doing so, they expose their populations to a technology that will ultimately weaken state control over money and advance individual liberty and human rights. Watch the full interview here.
Bitcoin Mining Centralization by b10c
In this report, Bitcoin developer and past HRF grantee b10c documents the growing trend of centralization in Bitcoin mining pools. It shows that over 95% of blocks are now mined by just six Bitcoin mining pools, with Foundry and AntPool controlling roughly 60–70% of the hashrate (the computing power dedicated to the Bitcoin network). This marks a rise in mining pool centralization in recent years. While this hasn’t harmed Bitcoin’s censorship resistance yet, it reduces the number of block template producers. This concentration of template producers poses a potential risk to Bitcoin’s neutrality, which is essential for ensuring access to uncensorable money and protecting human rights in autocratic regimes. HRF has happily supported both Hashpool and Public Pool with recent grants to support smaller, independent pools that help preserve Bitcoin's decentralization. Read the full report here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
-
 @ 611021ea:089a7d0f
2025-05-08 15:00:17
@ 611021ea:089a7d0f
2025-05-08 15:00:17This is the 2nd article I've written regarding my thoughts around the nostr health and fitness ecosystem and how something like NIP101h could play a part in enabling an ecosystem of highly specialized apps benefiting from nostr inherent interoperability. I've posted the last article on Wikistr and have continued experimenting with the NIP in a couple of clients. Recently I've been focused on extending the NIP to include calories and workout intensity.
Caloric Data
Let's talk about calories for a minute. Seems simple, right? You burn some, you consume some. But as I started implementing kind 1357 for caloric data, I quickly realized this was too simplistic.
The reality is tracking calories burned through a 10K run is fundamentally different from logging the calories in your morning avocado toast. Different contexts, different metadata, different user flows. Trying to cram both into one kind felt like forcing a square peg through a round hole.
So I split them: - Kind 1357: Calories expended (your run, your workout, even just existing) - Kind 2357: Calories consumed (your meals, snacks, that beer you "forgot" to log)
This wasn't just a technical decision. It reflects how people actually think about and track their health. Nobody mentally lumps "I burned 350 calories on my run" with "I ate a 650 calorie lunch" as the same type of data point. They're related but distinct.
Workout Intensity
Speaking of workouts, RUNSTR has been sending workout data for a while now, but workout intensity (kind 1356) is something I've been particularly excited about.
Why? Because intensity is the secret sauce that makes fitness data meaningful. Two people can run the same distance, but one might be casually jogging while catching up on podcasts, and another might be doing high-intensity intervals that leave them gasping for air.
Same distance, totally different physiological impacts.
Intensity gives context to duration. It turns "I worked out for 45 minutes" into a meaningful metric about how hard you pushed. And this isn't just for the fitness obsessed—it's essential for things like heart rate zone training, progressive overload, and recovery monitoring.
The Bigger Vision: Why I'm Building This
I'm not building NIP-101h because I think the world needs another fitness standard. God knows there are plenty already. I'm building it because I believe health data belongs to people, not platforms.
Right now, your Apple Health data lives in Apple's ecosystem. Your Fitbit data lives in Fitbit's walled garden. Your Strava data? Yep, siloed there too. These companies have built incredible products, but they've also created digital gulags.
Nostr gives us a chance to flip the script. What if your health data lived on the internet rather than the platform? What if you could: - Track your runs in RUNSTR - Encrypt sensitive data - Store data in relays or blossom servers - Use the data across an open ecosystem of interoperable apps
...all without asking permission from some corporate overlord?
That's pretty much the vision. I've also spun up HealthNote Relay to support some of the new NIPs and Kinds while I continue to flesh out NIP-101h.
The Power of Specialization
One thing I've realized is that the real magic happens when we get specific. A diabetes management app needs different data structures than a strength training app. But they both benefit from a common language for the overlap.
So I'm intentionally designing the NIP-101h series as a collection of highly specialized kinds rather than a monolithic standard. This lets developers pick and choose exactly what they need, while still ensuring interoperability where it matters.
Take our calorie example—by splitting into two kinds, we allow for specialized nutrition tracking apps that might never care about workout calories, while still ensuring they can talk to fitness apps when needed.
What's Coming Next
I've got a growing list of kinds I want to tackle: - Sleep data (duration, quality, phases) - Strength training specifics (sets, reps, weight) - Hydration tracking - Mental health metrics
But I'm equally excited to see what others build. Maybe someone will create specialized kinds for pregnancy tracking, or chronic illness management, or physical therapy progress.
That's the beauty of this approach—I don't need to anticipate every use case. The framework lets the community evolve it organically.
Join the Health Data Revolution
If you're a developer interested in health and fitness on Nostr, I'd love to hear from you. What kinds would help your use case? What are you building? What am I missing?
And if you're just a Nostr user who cares about your health data, check out RUNSTR (Alpha) or Npub.health (super alpha) to see what we're building.
You can find information the specification here NIP 101h.
See you in volume three, where I'll dig into NIP101h format details and share what I've learned from the early experiments.
Lets Go!
-
 @ 4ba8e86d:89d32de4
2025-04-28 22:39:20
@ 4ba8e86d:89d32de4
2025-04-28 22:39:20Como funciona o PGP.
O texto a seguir foi retirado do capítulo 1 do documento Introdução à criptografia na documentação do PGP 6.5.1. Copyright © 1990-1999 Network Associates, Inc. Todos os direitos reservados.
-O que é criptografia? -Criptografia forte -Como funciona a criptografia? -Criptografia convencional -Cifra de César -Gerenciamento de chaves e criptografia convencional -Criptografia de chave pública -Como funciona o PGP - Chaves • Assinaturas digitais -Funções hash • Certificados digitais -Distribuição de certificados -Formatos de certificado •Validade e confiança -Verificando validade -Estabelecendo confiança -Modelos de confiança • Revogação de certificado -Comunicar que um certificado foi revogado -O que é uma senha? -Divisão de chave
Os princípios básicos da criptografia.
Quando Júlio César enviou mensagens aos seus generais, ele não confiou nos seus mensageiros. Então ele substituiu cada A em suas mensagens por um D, cada B por um E, e assim por diante através do alfabeto. Somente alguém que conhecesse a regra “shift by 3” poderia decifrar suas mensagens. E assim começamos.
Criptografia e descriptografia.
Os dados que podem ser lidos e compreendidos sem quaisquer medidas especiais são chamados de texto simples ou texto não criptografado. O método de disfarçar o texto simples de forma a ocultar sua substância é chamado de criptografia. Criptografar texto simples resulta em um jargão ilegível chamado texto cifrado. Você usa criptografia para garantir que as informações sejam ocultadas de qualquer pessoa a quem não se destinam, mesmo daqueles que podem ver os dados criptografados. O processo de reverter o texto cifrado ao texto simples original é chamado de descriptografia . A Figura 1-1 ilustra esse processo.
https://image.nostr.build/0e2fcb71ed86a6083e083abbb683f8c103f44a6c6db1aeb2df10ae51ec97ebe5.jpg
Figura 1-1. Criptografia e descriptografia
O que é criptografia?
Criptografia é a ciência que usa a matemática para criptografar e descriptografar dados. A criptografia permite armazenar informações confidenciais ou transmiti-las através de redes inseguras (como a Internet) para que não possam ser lidas por ninguém, exceto pelo destinatário pretendido. Embora a criptografia seja a ciência que protege os dados, a criptoanálise é a ciência que analisa e quebra a comunicação segura. A criptoanálise clássica envolve uma combinação interessante de raciocínio analítico, aplicação de ferramentas matemáticas, descoberta de padrões, paciência, determinação e sorte. Os criptoanalistas também são chamados de atacantes. A criptologia abrange tanto a criptografia quanto a criptoanálise.
Criptografia forte.
"Existem dois tipos de criptografia neste mundo: a criptografia que impedirá a sua irmã mais nova de ler os seus arquivos, e a criptografia que impedirá os principais governos de lerem os seus arquivos. Este livro é sobre o último." --Bruce Schneier, Criptografia Aplicada: Protocolos, Algoritmos e Código Fonte em C. PGP também trata deste último tipo de criptografia. A criptografia pode ser forte ou fraca, conforme explicado acima. A força criptográfica é medida no tempo e nos recursos necessários para recuperar o texto simples. O resultado de uma criptografia forte é um texto cifrado que é muito difícil de decifrar sem a posse da ferramenta de decodificação apropriada. Quão díficil? Dado todo o poder computacional e o tempo disponível de hoje – mesmo um bilhão de computadores fazendo um bilhão de verificações por segundo – não é possível decifrar o resultado de uma criptografia forte antes do fim do universo. Alguém poderia pensar, então, que uma criptografia forte resistiria muito bem até mesmo contra um criptoanalista extremamente determinado. Quem pode realmente dizer? Ninguém provou que a criptografia mais forte disponível hoje resistirá ao poder computacional de amanhã. No entanto, a criptografia forte empregada pelo PGP é a melhor disponível atualmente.
Contudo, a vigilância e o conservadorismo irão protegê-lo melhor do que as alegações de impenetrabilidade.
Como funciona a criptografia?
Um algoritmo criptográfico, ou cifra, é uma função matemática usada no processo de criptografia e descriptografia. Um algoritmo criptográfico funciona em combinação com uma chave – uma palavra, número ou frase – para criptografar o texto simples. O mesmo texto simples é criptografado em texto cifrado diferente com chaves diferentes. A segurança dos dados criptografados depende inteiramente de duas coisas: a força do algoritmo criptográfico e o sigilo da chave. Um algoritmo criptográfico, mais todas as chaves possíveis e todos os protocolos que o fazem funcionar constituem um criptossistema. PGP é um criptossistema.
Criptografia convencional.
Na criptografia convencional, também chamada de criptografia de chave secreta ou de chave simétrica , uma chave é usada tanto para criptografia quanto para descriptografia. O Data Encryption Standard (DES) é um exemplo de criptossistema convencional amplamente empregado pelo Governo Federal. A Figura 1-2 é uma ilustração do processo de criptografia convencional. https://image.nostr.build/328b73ebaff84c949df2560bbbcec4bc3b5e3a5163d5fbb2ec7c7c60488f894c.jpg
Figura 1-2. Criptografia convencional
Cifra de César.
Um exemplo extremamente simples de criptografia convencional é uma cifra de substituição. Uma cifra de substituição substitui uma informação por outra. Isso é feito com mais frequência compensando as letras do alfabeto. Dois exemplos são o Anel Decodificador Secreto do Capitão Meia-Noite, que você pode ter possuído quando era criança, e a cifra de Júlio César. Em ambos os casos, o algoritmo serve para compensar o alfabeto e a chave é o número de caracteres para compensá-lo. Por exemplo, se codificarmos a palavra "SEGREDO" usando o valor chave de César de 3, deslocaremos o alfabeto para que a terceira letra abaixo (D) comece o alfabeto. Então começando com A B C D E F G H I J K L M N O P Q R S T U V W X Y Z e deslizando tudo para cima em 3, você obtém DEFGHIJKLMNOPQRSTUVWXYZABC onde D=A, E=B, F=C e assim por diante. Usando este esquema, o texto simples, "SECRET" é criptografado como "VHFUHW". Para permitir que outra pessoa leia o texto cifrado, você diz a ela que a chave é 3. Obviamente, esta é uma criptografia extremamente fraca para os padrões atuais, mas, ei, funcionou para César e ilustra como funciona a criptografia convencional.
Gerenciamento de chaves e criptografia convencional.
A criptografia convencional tem benefícios. É muito rápido. É especialmente útil para criptografar dados que não vão a lugar nenhum. No entanto, a criptografia convencional por si só como meio de transmissão segura de dados pode ser bastante cara, simplesmente devido à dificuldade de distribuição segura de chaves. Lembre-se de um personagem do seu filme de espionagem favorito: a pessoa com uma pasta trancada e algemada ao pulso. Afinal, o que há na pasta? Provavelmente não é o código de lançamento de mísseis/fórmula de biotoxina/plano de invasão em si. É a chave que irá descriptografar os dados secretos. Para que um remetente e um destinatário se comuniquem com segurança usando criptografia convencional, eles devem chegar a um acordo sobre uma chave e mantê-la secreta entre si. Se estiverem em locais físicos diferentes, devem confiar em um mensageiro, no Bat Phone ou em algum outro meio de comunicação seguro para evitar a divulgação da chave secreta durante a transmissão. Qualquer pessoa que ouvir ou interceptar a chave em trânsito poderá posteriormente ler, modificar e falsificar todas as informações criptografadas ou autenticadas com essa chave. Do DES ao Anel Decodificador Secreto do Capitão Midnight, o problema persistente com a criptografia convencional é a distribuição de chaves: como você leva a chave ao destinatário sem que alguém a intercepte?
Criptografia de chave pública.
Os problemas de distribuição de chaves são resolvidos pela criptografia de chave pública, cujo conceito foi introduzido por Whitfield Diffie e Martin Hellman em 1975. (Há agora evidências de que o Serviço Secreto Britânico a inventou alguns anos antes de Diffie e Hellman, mas a manteve um segredo militar - e não fez nada com isso.
[JH Ellis: The Possibility of Secure Non-Secret Digital Encryption, CESG Report, January 1970]) A criptografia de chave pública é um esquema assimétrico que usa um par de chaves para criptografia: uma chave pública, que criptografa os dados, e uma chave privada ou secreta correspondente para descriptografia. Você publica sua chave pública para o mundo enquanto mantém sua chave privada em segredo. Qualquer pessoa com uma cópia da sua chave pública pode criptografar informações que somente você pode ler. Até mesmo pessoas que você nunca conheceu. É computacionalmente inviável deduzir a chave privada da chave pública. Qualquer pessoa que possua uma chave pública pode criptografar informações, mas não pode descriptografá-las. Somente a pessoa que possui a chave privada correspondente pode descriptografar as informações. https://image.nostr.build/fdb71ae7a4450a523456827bdd509b31f0250f63152cc6f4ba78df290887318b.jpg
Figura 1-3. Criptografia de chave pública O principal benefício da criptografia de chave pública é que ela permite que pessoas que não possuem nenhum acordo de segurança pré-existente troquem mensagens com segurança. A necessidade de remetente e destinatário compartilharem chaves secretas através de algum canal seguro é eliminada; todas as comunicações envolvem apenas chaves públicas e nenhuma chave privada é transmitida ou compartilhada. Alguns exemplos de criptossistemas de chave pública são Elgamal (nomeado em homenagem a seu inventor, Taher Elgamal), RSA (nomeado em homenagem a seus inventores, Ron Rivest, Adi Shamir e Leonard Adleman), Diffie-Hellman (nomeado, você adivinhou, em homenagem a seus inventores). ) e DSA, o algoritmo de assinatura digital (inventado por David Kravitz). Como a criptografia convencional já foi o único meio disponível para transmitir informações secretas, o custo dos canais seguros e da distribuição de chaves relegou a sua utilização apenas àqueles que podiam pagar, como governos e grandes bancos (ou crianças pequenas com anéis descodificadores secretos). A criptografia de chave pública é a revolução tecnológica que fornece criptografia forte para as massas adultas. Lembra do mensageiro com a pasta trancada e algemada ao pulso? A criptografia de chave pública o tira do mercado (provavelmente para seu alívio).
Como funciona o PGP.
O PGP combina alguns dos melhores recursos da criptografia convencional e de chave pública. PGP é um criptossistema híbrido. Quando um usuário criptografa texto simples com PGP, o PGP primeiro compacta o texto simples. A compactação de dados economiza tempo de transmissão do modem e espaço em disco e, mais importante ainda, fortalece a segurança criptográfica. A maioria das técnicas de criptoanálise explora padrões encontrados no texto simples para quebrar a cifra. A compressão reduz esses padrões no texto simples, aumentando assim enormemente a resistência à criptoanálise. (Arquivos que são muito curtos para compactar ou que não são compactados bem não são compactados.) O PGP então cria uma chave de sessão, que é uma chave secreta única. Esta chave é um número aleatório gerado a partir dos movimentos aleatórios do mouse e das teclas digitadas. Esta chave de sessão funciona com um algoritmo de criptografia convencional rápido e muito seguro para criptografar o texto simples; o resultado é texto cifrado. Depois que os dados são criptografados, a chave da sessão é criptografada na chave pública do destinatário. Essa chave de sessão criptografada com chave pública é transmitida junto com o texto cifrado ao destinatário.
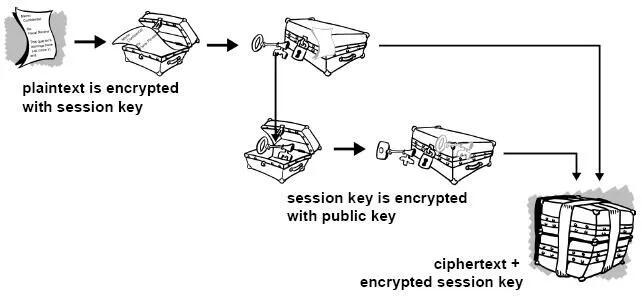
Figura 1-4. Como funciona a criptografia PGP A descriptografia funciona ao contrário. A cópia do PGP do destinatário usa sua chave privada para recuperar a chave de sessão temporária, que o PGP usa para descriptografar o texto cifrado criptografado convencionalmente.

Figura 1-5. Como funciona a descriptografia PGP A combinação dos dois métodos de criptografia combina a conveniência da criptografia de chave pública com a velocidade da criptografia convencional. A criptografia convencional é cerca de 1.000 vezes mais rápida que a criptografia de chave pública. A criptografia de chave pública, por sua vez, fornece uma solução para
problemas de distribuição de chaves e transmissão de dados. Usados em conjunto, o desempenho e a distribuição de chaves são melhorados sem qualquer sacrifício na segurança.
Chaves.
Uma chave é um valor que funciona com um algoritmo criptográfico para produzir um texto cifrado específico. As chaves são basicamente números muito, muito, muito grandes. O tamanho da chave é medido em bits; o número que representa uma chave de 1024 bits é enorme. Na criptografia de chave pública, quanto maior a chave, mais seguro é o texto cifrado. No entanto, o tamanho da chave pública e o tamanho da chave secreta da criptografia convencional não têm nenhuma relação. Uma chave convencional de 80 bits tem a força equivalente a uma chave pública de 1.024 bits. Uma chave convencional de 128 bits é equivalente a uma chave pública de 3.000 bits. Novamente, quanto maior a chave, mais segura, mas os algoritmos usados para cada tipo de criptografia são muito diferentes e, portanto, a comparação é como a de maçãs com laranjas. Embora as chaves pública e privada estejam matematicamente relacionadas, é muito difícil derivar a chave privada dada apenas a chave pública; no entanto, derivar a chave privada é sempre possível, desde que haja tempo e capacidade computacional suficientes. Isto torna muito importante escolher chaves do tamanho certo; grande o suficiente para ser seguro, mas pequeno o suficiente para ser aplicado rapidamente. Além disso, você precisa considerar quem pode estar tentando ler seus arquivos, quão determinados eles estão, quanto tempo têm e quais podem ser seus recursos. Chaves maiores serão criptograficamente seguras por um longo período de tempo. Se o que você deseja criptografar precisar ficar oculto por muitos anos, você pode usar uma chave muito grande. Claro, quem sabe quanto tempo levará para determinar sua chave usando os computadores mais rápidos e eficientes de amanhã? Houve um tempo em que uma chave simétrica de 56 bits era considerada extremamente segura. As chaves são armazenadas de forma criptografada. O PGP armazena as chaves em dois arquivos no seu disco rígido; um para chaves públicas e outro para chaves privadas. Esses arquivos são chamados de chaveiros. Ao usar o PGP, você normalmente adicionará as chaves públicas dos seus destinatários ao seu chaveiro público. Suas chaves privadas são armazenadas em seu chaveiro privado. Se você perder seu chaveiro privado, não será possível descriptografar nenhuma informação criptografada nas chaves desse anel.
Assinaturas digitais.
Um grande benefício da criptografia de chave pública é que ela fornece um método para empregar assinaturas digitais. As assinaturas digitais permitem ao destinatário da informação verificar a autenticidade da origem da informação e também verificar se a informação está intacta. Assim, as assinaturas digitais de chave pública fornecem autenticação e integridade de dados. A assinatura digital também proporciona o não repúdio, o que significa que evita que o remetente alegue que não enviou realmente as informações. Esses recursos são tão fundamentais para a criptografia quanto a privacidade, se não mais. Uma assinatura digital tem a mesma finalidade de uma assinatura manuscrita. No entanto, uma assinatura manuscrita é fácil de falsificar. Uma assinatura digital é superior a uma assinatura manuscrita porque é quase impossível de ser falsificada, além de atestar o conteúdo da informação, bem como a identidade do signatário.
Algumas pessoas tendem a usar mais assinaturas do que criptografia. Por exemplo, você pode não se importar se alguém souber que você acabou de depositar US$ 1.000 em sua conta, mas quer ter certeza de que foi o caixa do banco com quem você estava lidando. A maneira básica pela qual as assinaturas digitais são criadas é ilustrada na Figura 1-6 . Em vez de criptografar informações usando a chave pública de outra pessoa, você as criptografa com sua chave privada. Se as informações puderem ser descriptografadas com sua chave pública, elas deverão ter se originado em você.
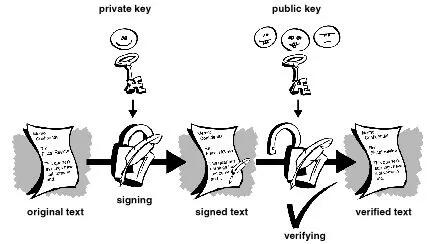
Figura 1-6. Assinaturas digitais simples
Funções hash.
O sistema descrito acima apresenta alguns problemas. É lento e produz um enorme volume de dados – pelo menos o dobro do tamanho da informação original. Uma melhoria no esquema acima é a adição de uma função hash unidirecional no processo. Uma função hash unidirecional recebe uma entrada de comprimento variável – neste caso, uma mensagem de qualquer comprimento, até mesmo milhares ou milhões de bits – e produz uma saída de comprimento fixo; digamos, 160 bits. A função hash garante que, se a informação for alterada de alguma forma – mesmo que por apenas um bit – seja produzido um valor de saída totalmente diferente. O PGP usa uma função hash criptograficamente forte no texto simples que o usuário está assinando. Isso gera um item de dados de comprimento fixo conhecido como resumo da mensagem. (Novamente, qualquer alteração nas informações resulta em um resumo totalmente diferente.) Então o PGP usa o resumo e a chave privada para criar a “assinatura”. O PGP transmite a assinatura e o texto simples juntos. Ao receber a mensagem, o destinatário utiliza o PGP para recalcular o resumo, verificando assim a assinatura. O PGP pode criptografar o texto simples ou não; assinar texto simples é útil se alguns dos destinatários não estiverem interessados ou não forem capazes de verificar a assinatura. Desde que uma função hash segura seja usada, não há como retirar a assinatura de alguém de um documento e anexá-la a outro, ou alterar uma mensagem assinada de qualquer forma. A menor alteração em um documento assinado causará falha no processo de verificação da assinatura digital.
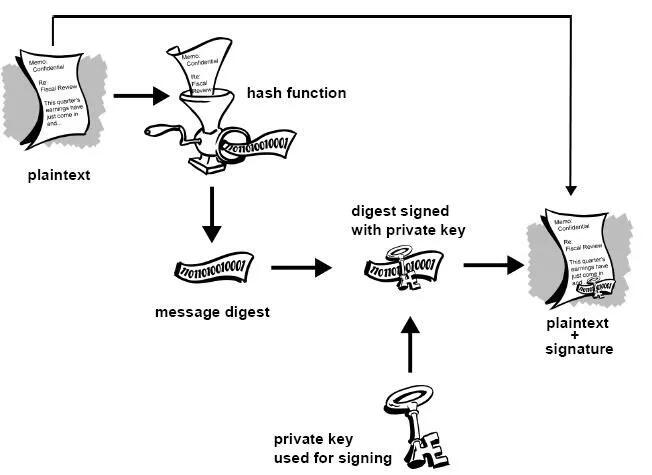
Figura 1-7. Assinaturas digitais seguras As assinaturas digitais desempenham um papel importante na autenticação e validação de chaves de outros usuários PGP.
Certificados digitais.
Um problema com os criptosistemas de chave pública é que os usuários devem estar constantemente vigilantes para garantir que estão criptografando com a chave da pessoa correta. Num ambiente onde é seguro trocar chaves livremente através de servidores públicos, os ataques man-in-the-middle são uma ameaça potencial. Neste tipo de ataque, alguém publica uma chave falsa com o nome e ID de usuário do destinatário pretendido. Os dados criptografados – e interceptados por – o verdadeiro proprietário desta chave falsa estão agora em mãos erradas. Em um ambiente de chave pública, é vital que você tenha certeza de que a chave pública para a qual você está criptografando os dados é de fato a chave pública do destinatário pretendido e não uma falsificação. Você pode simplesmente criptografar apenas as chaves que foram entregues fisicamente a você. Mas suponha que você precise trocar informações com pessoas que nunca conheceu; como você pode saber se tem a chave correta? Os certificados digitais, ou certs, simplificam a tarefa de estabelecer se uma chave pública realmente pertence ao suposto proprietário. Um certificado é uma forma de credencial. Exemplos podem ser sua carteira de motorista, seu cartão de previdência social ou sua certidão de nascimento. Cada um deles contém algumas informações que identificam você e alguma autorização informando que outra pessoa confirmou sua identidade. Alguns certificados, como o seu passaporte, são uma confirmação importante o suficiente da sua identidade para que você não queira perdê-los, para que ninguém os use para se passar por você.
Um certificado digital são dados que funcionam como um certificado físico. Um certificado digital é uma informação incluída na chave pública de uma pessoa que ajuda outras pessoas a verificar se uma chave é genuína ou válida. Os certificados digitais são usados para impedir tentativas de substituir a chave de uma pessoa por outra.
Um certificado digital consiste em três coisas:
● Uma chave pública.
● Informações do certificado. (Informações de "identidade" sobre o usuário, como nome, ID do usuário e assim por diante.) ● Uma ou mais assinaturas digitais.
O objetivo da assinatura digital em um certificado é afirmar que as informações do certificado foram atestadas por alguma outra pessoa ou entidade. A assinatura digital não atesta a autenticidade do certificado como um todo; ele atesta apenas que as informações de identidade assinadas acompanham ou estão vinculadas à chave pública. Assim, um certificado é basicamente uma chave pública com uma ou duas formas de identificação anexadas, além de um forte selo de aprovação de algum outro indivíduo confiável.
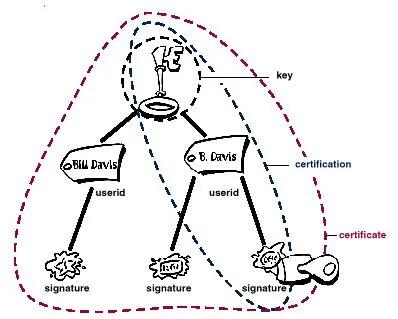 Figura 1-8. Anatomia de um certificado PGP
Figura 1-8. Anatomia de um certificado PGPDistribuição de certificados.
Os certificados são utilizados quando é necessário trocar chaves públicas com outra pessoa. Para pequenos grupos de pessoas que desejam se comunicar com segurança, é fácil trocar manualmente disquetes ou e-mails contendo a chave pública de cada proprietário. Esta é a distribuição manual de chave pública e é prática apenas até certo ponto. Além desse ponto, é necessário implementar sistemas que possam fornecer os mecanismos necessários de segurança, armazenamento e troca para que colegas de trabalho, parceiros de negócios ou estranhos possam se comunicar, se necessário. Eles podem vir na forma de repositórios somente de armazenamento, chamados Servidores de Certificados, ou sistemas mais estruturados que fornecem recursos adicionais de gerenciamento de chaves e são chamados de Infraestruturas de Chave Pública (PKIs).
Servidores de certificados.
Um servidor de certificados, também chamado de servidor certificado ou servidor de chaves, é um banco de dados que permite aos usuários enviar e recuperar certificados digitais. Um servidor certificado geralmente fornece alguns recursos administrativos que permitem que uma empresa mantenha suas políticas de segurança – por exemplo, permitindo que apenas as chaves que atendam a determinados requisitos sejam armazenadas.
Infraestruturas de Chave Pública.
Uma PKI contém os recursos de armazenamento de certificados de um servidor de certificados, mas também fornece recursos de gerenciamento de certificados (a capacidade de emitir, revogar, armazenar, recuperar e confiar em certificados). A principal característica de uma PKI é a introdução do que é conhecido como Autoridade Certificadora,ou CA, que é uma entidade humana — uma pessoa, grupo, departamento, empresa ou outra associação — que uma organização autorizou a emitir certificados para seus usuários de computador. (A função de uma CA é análoga à do Passport Office do governo de um país.) Uma CA cria certificados e os assina digitalmente usando a chave privada da CA. Devido ao seu papel na criação de certificados, a CA é o componente central de uma PKI. Usando a chave pública da CA, qualquer pessoa que queira verificar a autenticidade de um certificado verifica a assinatura digital da CA emissora e, portanto, a integridade do conteúdo do certificado (mais importante ainda, a chave pública e a identidade do titular do certificado).
Formatos de certificado.
Um certificado digital é basicamente uma coleção de informações de identificação vinculadas a uma chave pública e assinadas por um terceiro confiável para provar sua autenticidade. Um certificado digital pode ter vários formatos diferentes.
O PGP reconhece dois formatos de certificado diferentes:
● Certificados PGP ● Certificados X.509 Formato do certificado PGP. Um certificado PGP inclui (mas não está limitado a) as seguintes informações: ● O número da versão do PGP — identifica qual versão do PGP foi usada para criar a chave associada ao certificado. A chave pública do titular do certificado — a parte pública do seu par de chaves, juntamente com o algoritmo da chave: RSA, DH (Diffie-Hellman) ou DSA (Algoritmo de Assinatura Digital).
● As informações do detentor do certificado — consistem em informações de “identidade” sobre o usuário, como seu nome, ID de usuário, fotografia e assim por diante. ● A assinatura digital do proprietário do certificado — também chamada de autoassinatura, é a assinatura que utiliza a chave privada correspondente da chave pública associada ao certificado. ● O período de validade do certificado — a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar. ● O algoritmo de criptografia simétrica preferido para a chave — indica o algoritmo de criptografia para o qual o proprietário do certificado prefere que as informações sejam criptografadas. Os algoritmos suportados são CAST, IDEA ou Triple-DES. Você pode pensar em um certificado PGP como uma chave pública com um ou mais rótulos vinculados a ele (veja a Figura 1.9 ). Nessas 'etiquetas' você encontrará informações que identificam o proprietário da chave e uma assinatura do proprietário da chave, que afirma que a chave e a identificação andam juntas. (Essa assinatura específica é chamada de autoassinatura; todo certificado PGP contém uma autoassinatura.) Um aspecto único do formato de certificado PGP é que um único certificado pode conter múltiplas assinaturas. Várias ou muitas pessoas podem assinar o par chave/identificação para atestar a sua própria garantia de que a chave pública pertence definitivamente ao proprietário especificado. Se você procurar em um servidor de certificados público, poderá notar que certos certificados, como o do criador do PGP, Phil Zimmermann, contêm muitas assinaturas. Alguns certificados PGP consistem em uma chave pública com vários rótulos, cada um contendo um meio diferente de identificar o proprietário da chave (por exemplo, o nome do proprietário e a conta de e-mail corporativa, o apelido do proprietário e a conta de e-mail residencial, uma fotografia do proprietário — tudo em um certificado). A lista de assinaturas de cada uma dessas identidades pode ser diferente; as assinaturas atestam a autenticidade de que um dos rótulos pertence à chave pública, e não que todos os rótulos da chave sejam autênticos. (Observe que 'autêntico' está nos olhos de quem vê - assinaturas são opiniões, e diferentes pessoas dedicam diferentes níveis de devida diligência na verificação da autenticidade antes de assinar uma chave.)
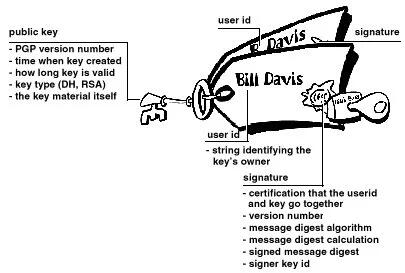 Figura 1-9. Um certificado PGP
Figura 1-9. Um certificado PGPFormato de certificado X.509.
X.509 é outro formato de certificado muito comum. Todos os certificados X.509 estão em conformidade com o padrão internacional ITU-T X.509; assim (teoricamente) os certificados X.509 criados para um aplicativo podem ser usados por qualquer aplicativo compatível com X.509. Na prática, porém, diferentes empresas criaram suas próprias extensões para certificados X.509, e nem todas funcionam juntas. Um certificado exige que alguém valide que uma chave pública e o nome do proprietário da chave andam juntos. Com os certificados PGP, qualquer pessoa pode desempenhar o papel de validador. Com certificados X.509, o validador é sempre uma Autoridade Certificadora ou alguém designado por uma CA. (Tenha em mente que os certificados PGP também suportam totalmente uma estrutura hierárquica usando uma CA para validar certificados.)
Um certificado X.509 é uma coleção de um conjunto padrão de campos contendo informações sobre um usuário ou dispositivo e sua chave pública correspondente. O padrão X.509 define quais informações vão para o certificado e descreve como codificá-lo (o formato dos dados). Todos os certificados X.509 possuem os seguintes dados:
O número da versão X.509
— identifica qual versão do padrão X.509 se aplica a este certificado, o que afeta quais informações podem ser especificadas nele. A mais atual é a versão 3.
A chave pública do titular do certificado
— a chave pública do titular do certificado, juntamente com um identificador de algoritmo que especifica a qual sistema criptográfico a chave pertence e quaisquer parâmetros de chave associados.
O número de série do certificado
— a entidade (aplicação ou pessoa) que criou o certificado é responsável por atribuir-lhe um número de série único para distingui-lo de outros certificados que emite. Esta informação é usada de diversas maneiras; por exemplo, quando um certificado é revogado, seu número de série é colocado em uma Lista de Revogação de Certificados ou CRL.
O identificador exclusivo do detentor do certificado
— (ou DN — nome distinto). Este nome pretende ser exclusivo na Internet. Este nome pretende ser exclusivo na Internet. Um DN consiste em múltiplas subseções e pode ser parecido com isto: CN=Bob Allen, OU=Divisão Total de Segurança de Rede, O=Network Associates, Inc., C=EUA (Referem-se ao nome comum, à unidade organizacional, à organização e ao país do sujeito .)
O período de validade do certificado
— a data/hora de início e a data/hora de expiração do certificado; indica quando o certificado irá expirar.
O nome exclusivo do emissor do certificado
— o nome exclusivo da entidade que assinou o certificado. Normalmente é uma CA. A utilização do certificado implica confiar na entidade que assinou este certificado. (Observe que em alguns casos, como certificados de CA raiz ou de nível superior , o emissor assina seu próprio certificado.)
A assinatura digital do emitente
— a assinatura utilizando a chave privada da entidade que emitiu o certificado.
O identificador do algoritmo de assinatura
— identifica o algoritmo usado pela CA para assinar o certificado.
Existem muitas diferenças entre um certificado X.509 e um certificado PGP, mas as mais importantes são as seguintes: você pode criar seu próprio certificado PGP;
● você deve solicitar e receber um certificado X.509 de uma autoridade de certificação
● Os certificados X.509 suportam nativamente apenas um único nome para o proprietário da chave
● Os certificados X.509 suportam apenas uma única assinatura digital para atestar a validade da chave
Para obter um certificado X.509, você deve solicitar a uma CA a emissão de um certificado. Você fornece sua chave pública, prova de que possui a chave privada correspondente e algumas informações específicas sobre você. Em seguida, você assina digitalmente as informações e envia o pacote completo – a solicitação de certificado – para a CA. A CA então realiza algumas diligências para verificar se as informações fornecidas estão corretas e, em caso afirmativo, gera o certificado e o devolve.
Você pode pensar em um certificado X.509 como um certificado de papel padrão (semelhante ao que você recebeu ao concluir uma aula de primeiros socorros básicos) com uma chave pública colada nele. Ele contém seu nome e algumas informações sobre você, além da assinatura da pessoa que o emitiu para você.
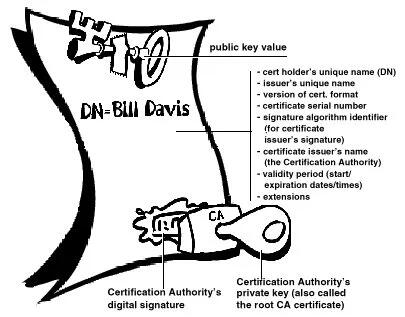
Figura 1-10. Um certificado X.509 Provavelmente, o uso mais visível dos certificados X.509 atualmente é em navegadores da web.
Validade e confiança Cada usuário em um sistema de chave pública está vulnerável a confundir uma chave falsa (certificado) com uma chave real. Validade é a confiança de que um certificado de chave pública pertence ao seu suposto proprietário. A validade é essencial em um ambiente de chave pública onde você deve estabelecer constantemente se um determinado certificado é autêntico ou não. Depois de ter certeza de que um certificado pertencente a outra pessoa é válido, você pode assinar a cópia em seu chaveiro para atestar que verificou o certificado e que ele é autêntico. Se quiser que outras pessoas saibam que você deu ao certificado seu selo de aprovação, você pode exportar a assinatura para um servidor de certificados para que outras pessoas possam vê-la.
Conforme descrito na seção Infraestruturas de Chave Pública , algumas empresas designam uma ou mais Autoridades de Certificação (CAs) para indicar a validade do certificado. Em uma organização que usa uma PKI com certificados X.509, é função da CA emitir certificados aos usuários — um processo que geralmente envolve responder à solicitação de certificado do usuário. Em uma organização que usa certificados PGP sem PKI, é função da CA verificar a autenticidade de todos os certificados PGP e depois assinar os bons. Basicamente, o objetivo principal de uma CA é vincular uma chave pública às informações de identificação contidas no certificado e, assim, garantir a terceiros que algum cuidado foi tomado para garantir que esta ligação das informações de identificação e da chave seja válida. O CA é o Grand Pooh-bah da validação em uma organização; alguém em quem todos confiam e, em algumas organizações, como aquelas que utilizam uma PKI, nenhum certificado é considerado válido, a menos que tenha sido assinado por uma CA confiável.
Verificando validade.
Uma maneira de estabelecer a validade é passar por algum processo manual. Existem várias maneiras de fazer isso. Você pode exigir que o destinatário pretendido lhe entregue fisicamente uma cópia de sua chave pública. Mas isto é muitas vezes inconveniente e ineficiente. Outra forma é verificar manualmente a impressão digital do certificado. Assim como as impressões digitais de cada ser humano são únicas, a impressão digital de cada certificado PGP é única. A impressão digital é um hash do certificado do usuário e aparece como uma das propriedades do certificado. No PGP, a impressão digital pode aparecer como um número hexadecimal ou uma série das chamadas palavras biométricas, que são foneticamente distintas e são usadas para facilitar um pouco o processo de identificação da impressão digital. Você pode verificar se um certificado é válido ligando para o proprietário da chave (para que você origine a transação) e pedindo ao proprietário que leia a impressão digital de sua chave para você e compare essa impressão digital com aquela que você acredita ser a verdadeira. Isso funciona se você conhece a voz do proprietário, mas como verificar manualmente a identidade de alguém que você não conhece? Algumas pessoas colocam a impressão digital de sua chave em seus cartões de visita exatamente por esse motivo. Outra forma de estabelecer a validade do certificado de alguém é confiar que um terceiro indivíduo passou pelo processo de validação do mesmo. Uma CA, por exemplo, é responsável por garantir que, antes de emitir um certificado, ele ou ela o verifique cuidadosamente para ter certeza de que a parte da chave pública realmente pertence ao suposto proprietário. Qualquer pessoa que confie na CA considerará automaticamente quaisquer certificados assinados pela CA como válidos. Outro aspecto da verificação da validade é garantir que o certificado não foi revogado. Para obter mais informações, consulte a seção Revogação de certificado .
Estabelecendo confiança.
Você valida certificados. Você confia nas pessoas. Mais especificamente, você confia nas pessoas para validar os certificados de outras pessoas. Normalmente, a menos que o proprietário lhe entregue o certificado, você terá que confiar na palavra de outra pessoa de que ele é válido.
Introdutores meta e confiáveis.
Na maioria das situações, as pessoas confiam completamente na CA para estabelecer a validade dos certificados. Isso significa que todos os demais dependem da CA para passar por todo o processo de validação manual. Isso é aceitável até um certo número de usuários ou locais de trabalho e, então, não é possível para a AC manter o mesmo nível de validação de qualidade. Nesse caso, é necessário adicionar outros validadores ao sistema.
Um CA também pode ser um meta- introdutor. Um meta-introdutor confere não apenas validade às chaves, mas também confere a capacidade de confiar nas chaves a outros. Semelhante ao rei que entrega seu selo a seus conselheiros de confiança para que eles possam agir de acordo com sua autoridade, o meta-introdutor permite que outros atuem como introdutores de confiança. Esses introdutores confiáveis podem validar chaves com o mesmo efeito do meta-introdutor. Eles não podem, entretanto, criar novos introdutores confiáveis.
Meta-introdutor e introdutor confiável são termos PGP. Em um ambiente X.509, o meta-introdutor é chamado de Autoridade de Certificação raiz ( CA raiz) e os introdutores confiáveis são Autoridades de Certificação subordinadas . A CA raiz usa a chave privada associada a um tipo de certificado especial denominado certificado CA raiz para assinar certificados. Qualquer certificado assinado pelo certificado CA raiz é visto como válido por qualquer outro certificado assinado pela raiz. Este processo de validação funciona mesmo para certificados assinados por outras CAs no sistema — desde que o certificado da CA raiz tenha assinado o certificado da CA subordinada, qualquer certificado assinado pela CA será considerado válido para outras pessoas dentro da hierarquia. Este processo de verificação de backup por meio do sistema para ver quem assinou cujo certificado é chamado de rastreamento de um caminho de certificação ou cadeia de certificação.
Modelos de confiança.
Em sistemas relativamente fechados, como em uma pequena empresa, é fácil rastrear um caminho de certificação até a CA raiz. No entanto, os usuários muitas vezes precisam se comunicar com pessoas fora do seu ambiente corporativo, incluindo algumas que nunca conheceram, como fornecedores, consumidores, clientes, associados e assim por diante. É difícil estabelecer uma linha de confiança com aqueles em quem sua CA não confia explicitamente. As empresas seguem um ou outro modelo de confiança, que determina como os usuários irão estabelecer a validade do certificado. Existem três modelos diferentes:
Confiança Direta.
Confiança Hierárquica Uma teia de confiança Confiança direta A confiança direta é o modelo de confiança mais simples. Neste modelo, um usuário confia que uma chave é válida porque sabe de onde ela veio. Todos os criptosistemas usam essa forma de confiança de alguma forma. Por exemplo, em navegadores da Web, as chaves raiz da Autoridade de Certificação são diretamente confiáveis porque foram enviadas pelo fabricante. Se houver alguma forma de hierarquia, ela se estenderá a partir desses certificados diretamente confiáveis. No PGP, um usuário que valida as chaves e nunca define outro certificado para ser um introdutor confiável está usando confiança direta.
 Figura 1-11. Confiança direta
Figura 1-11. Confiança diretaConfiança Hierárquica.
Em um sistema hierárquico, há vários certificados "raiz" a partir dos quais a confiança se estende. Esses certificados podem certificar eles próprios certificados ou podem certificar certificados que certificam ainda outros certificados em alguma cadeia. Considere isso como uma grande “árvore” de confiança. A validade do certificado "folha" é verificada rastreando desde seu certificador até outros certificadores, até que um certificado raiz diretamente confiável seja encontrado.
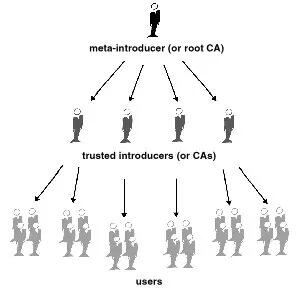
Figura 1-12. Confiança hierárquica
Teia de Confiança.
Uma teia de confiança abrange ambos os outros modelos, mas também acrescenta a noção de que a confiança está nos olhos de quem vê (que é a visão do mundo real) e a ideia de que mais informação é melhor. É, portanto, um modelo de confiança cumulativa. Um certificado pode ser confiável diretamente ou confiável em alguma cadeia que remonta a um certificado raiz diretamente confiável (o meta-introdutor) ou por algum grupo de introdutores.
Talvez você já tenha ouvido falar do termo seis graus de separação, que sugere que qualquer pessoa no mundo pode determinar algum vínculo com qualquer outra pessoa no mundo usando seis ou menos outras pessoas como intermediários. Esta é uma teia de introdutores. É também a visão de confiança do PGP. PGP usa assinaturas digitais como forma de introdução. Quando qualquer usuário assina a chave de outro, ele ou ela se torna o introdutor dessa chave. À medida que esse processo avança, ele estabelece uma rede de confiança.
Em um ambiente PGP, qualquer usuário pode atuar como autoridade certificadora. Qualquer usuário PGP pode validar o certificado de chave pública de outro usuário PGP. No entanto, tal certificado só é válido para outro usuário se a parte confiável reconhecer o validador como um introdutor confiável. (Ou seja, você confia na minha opinião de que as chaves dos outros são válidas apenas se você me considerar um apresentador confiável. Caso contrário, minha opinião sobre a validade das outras chaves é discutível.) Armazenados no chaveiro público de cada usuário estão indicadores de
● se o usuário considera ou não uma chave específica válida
● o nível de confiança que o usuário deposita na chave que o proprietário da chave pode servir como certificador das chaves de terceiros
Você indica, na sua cópia da minha chave, se acha que meu julgamento conta. Na verdade, é um sistema de reputação: certas pessoas têm a reputação de fornecer boas assinaturas e as pessoas confiam nelas para atestar a validade de outras chaves.
Níveis de confiança no PGP.
O nível mais alto de confiança em uma chave, a confiança implícita , é a confiança em seu próprio par de chaves. O PGP assume que se você possui a chave privada, você deve confiar nas ações da sua chave pública relacionada. Quaisquer chaves assinadas pela sua chave implicitamente confiável são válidas.
Existem três níveis de confiança que você pode atribuir à chave pública de outra pessoa:
● Confiança total ● Confiança marginal ● Não confiável (ou não confiável)
Para tornar as coisas confusas, também existem três níveis de validade:
● Válido ● Marginalmente válido ● Inválido
Para definir a chave de outra pessoa como um introdutor confiável, você
- Comece com uma chave válida, que seja.
- assinado por você ou
-
assinado por outro apresentador confiável e então
-
Defina o nível de confiança que você acha que o proprietário da chave tem direito.
Por exemplo, suponha que seu chaveiro contenha a chave de Alice. Você validou a chave de Alice e indica isso assinando-a. Você sabe que Alice é uma verdadeira defensora da validação de chaves de outras pessoas. Portanto, você atribui a chave dela com confiança total. Isso faz de Alice uma Autoridade Certificadora. Se Alice assinar a chave de outra pessoa, ela aparecerá como Válida em seu chaveiro. O PGP requer uma assinatura Totalmente confiável ou duas assinaturas Marginalmente confiáveis para estabelecer uma chave como válida. O método do PGP de considerar dois Marginais iguais a um Completo é semelhante a um comerciante que solicita duas formas de identificação. Você pode considerar Alice bastante confiável e também considerar Bob bastante confiável. Qualquer um deles sozinho corre o risco de assinar acidentalmente uma chave falsificada, portanto, você pode não depositar total confiança em nenhum deles. No entanto, as probabilidades de ambos os indivíduos terem assinado a mesma chave falsa são provavelmente pequenas.
Revogação de certificado.
Os certificados só são úteis enquanto são válidos. Não é seguro simplesmente presumir que um certificado é válido para sempre. Na maioria das organizações e em todas as PKIs, os certificados têm uma vida útil restrita. Isso restringe o período em que um sistema fica vulnerável caso ocorra um comprometimento do certificado.
Os certificados são assim criados com um período de validade programado: uma data/hora de início e uma data/hora de expiração. Espera-se que o certificado seja utilizável durante todo o seu período de validade (seu tempo de vida ). Quando o certificado expirar, ele não será mais válido, pois a autenticidade do seu par chave/identificação não estará mais garantida. (O certificado ainda pode ser usado com segurança para reconfirmar informações que foram criptografadas ou assinadas dentro do período de validade – no entanto, ele não deve ser confiável para tarefas criptográficas futuras.)
Existem também situações em que é necessário invalidar um certificado antes da sua data de expiração, como quando o titular do certificado termina o contrato de trabalho com a empresa ou suspeita que a chave privada correspondente do certificado foi comprometida. Isso é chamado de revogação. Um certificado revogado é muito mais suspeito do que um certificado expirado. Os certificados expirados são inutilizáveis, mas não apresentam a mesma ameaça de comprometimento que um certificado revogado. Qualquer pessoa que tenha assinado um certificado pode revogar a sua assinatura no certificado (desde que utilize a mesma chave privada que criou a assinatura). Uma assinatura revogada indica que o signatário não acredita mais que a chave pública e as informações de identificação pertencem uma à outra, ou que a chave pública do certificado (ou a chave privada correspondente) foi comprometida. Uma assinatura revogada deve ter quase tanto peso quanto um certificado revogado. Com certificados X.509, uma assinatura revogada é praticamente igual a um certificado revogado, visto que a única assinatura no certificado é aquela que o tornou válido em primeiro lugar – a assinatura da CA. Os certificados PGP fornecem o recurso adicional de que você pode revogar todo o seu certificado (não apenas as assinaturas nele) se você achar que o certificado foi comprometido. Somente o proprietário do certificado (o detentor da chave privada correspondente) ou alguém que o proprietário do certificado tenha designado como revogador pode revogar um certificado PGP. (Designar um revogador é uma prática útil, pois muitas vezes é a perda da senha da chave privada correspondente do certificado que leva um usuário PGP a revogar seu certificado - uma tarefa que só é possível se alguém tiver acesso à chave privada. ) Somente o emissor do certificado pode revogar um certificado X.509.
Comunicar que um certificado foi revogado.
Quando um certificado é revogado, é importante conscientizar os usuários potenciais do certificado de que ele não é mais válido. Com certificados PGP, a maneira mais comum de comunicar que um certificado foi revogado é publicá-lo em um servidor de certificados para que outras pessoas que desejem se comunicar com você sejam avisadas para não usar essa chave pública. Em um ambiente PKI, a comunicação de certificados revogados é mais comumente obtida por meio de uma estrutura de dados chamada Lista de Revogação de Certificados, ou CRL, que é publicada pela CA. A CRL contém uma lista validada com carimbo de data e hora de todos os certificados revogados e não expirados no sistema. Os certificados revogados permanecem na lista apenas até expirarem e, em seguida, são removidos da lista — isso evita que a lista fique muito longa. A CA distribui a CRL aos usuários em algum intervalo programado regularmente (e potencialmente fora do ciclo, sempre que um certificado é revogado). Teoricamente, isso impedirá que os usuários usem involuntariamente um certificado comprometido. É possível, no entanto, que haja um período de tempo entre as CRLs em que um certificado recentemente comprometido seja usado.
O que é uma senha?
A maioria das pessoas está familiarizada com a restrição de acesso a sistemas de computador por meio de uma senha, que é uma sequência única de caracteres que um usuário digita como código de identificação.
Uma senha longa é uma versão mais longa de uma senha e, em teoria, mais segura. Normalmente composta por várias palavras, uma frase secreta é mais segura contra ataques de dicionário padrão, em que o invasor tenta todas as palavras do dicionário na tentativa de determinar sua senha. As melhores senhas são relativamente longas e complexas e contêm uma combinação de letras maiúsculas e minúsculas, caracteres numéricos e de pontuação. O PGP usa uma senha para criptografar sua chave privada em sua máquina. Sua chave privada é criptografada em seu disco usando um hash de sua senha como chave secreta. Você usa a senha para descriptografar e usar sua chave privada. Uma senha deve ser difícil de esquecer e difícil de ser adivinhada por outras pessoas. Deve ser algo já firmemente enraizado na sua memória de longo prazo, em vez de algo que você invente do zero. Por que? Porque se você esquecer sua senha, você estará sem sorte. Sua chave privada é total e absolutamente inútil sem sua senha e nada pode ser feito a respeito. Lembra-se da citação anterior neste capítulo?
 PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.
PGP é a criptografia que manterá os principais governos fora dos seus arquivos. Certamente também o manterá fora de seus arquivos. Tenha isso em mente quando decidir alterar sua senha para a piada daquela piada que você nunca consegue lembrar.Divisão de chave.
Dizem que um segredo não é segredo se for conhecido por mais de uma pessoa. Compartilhar um par de chaves privadas representa um grande problema. Embora não seja uma prática recomendada, às vezes é necessário compartilhar um par de chaves privadas. Chaves de assinatura corporativa, por exemplo, são chaves privadas usadas por uma empresa para assinar – por exemplo – documentos legais, informações pessoais confidenciais ou comunicados de imprensa para autenticar sua origem. Nesse caso, vale a pena que vários membros da empresa tenham acesso à chave privada. No entanto, isto significa que qualquer indivíduo pode agir plenamente em nome da empresa. Nesse caso, é aconselhável dividir a chave entre várias pessoas, de modo que mais de uma ou duas pessoas apresentem um pedaço da chave para reconstituí-la em condições utilizáveis. Se poucas peças da chave estiverem disponíveis, a chave ficará inutilizável. Alguns exemplos são dividir uma chave em três partes e exigir duas delas para reconstituir a chave, ou dividi-la em duas partes e exigir ambas as peças. Se uma conexão de rede segura for usada durante o processo de reconstituição, os acionistas da chave não precisam estar fisicamente presentes para aderirem novamente à chave.
-
 @ f683e870:557f5ef2
2025-04-28 10:10:55
@ f683e870:557f5ef2
2025-04-28 10:10:55Spam is the single biggest problem in decentralized networks. Jameson Lopp, co-founder of Casa and OG bitcoiner, has written a brilliant article on the death of decentralized email that paints a vivid picture of what went wrong—and how an originally decentralized protocol was completely captured. The cause? Spam.
The same fate may happen to Nostr, because posting a note is fundamentally cheap. Payments, and to some extent Proof of Work, certainly have their role in fighting spam, but they introduce friction, which doesn’t work everywhere. In particular, they can’t solve every economic problem.\ Take free trials, for example. There is a reason why 99% of companies offer them. Sure, you waste resources on users who don’t convert, but it’s a calculated cost, a marketing expense. Also, some services can’t or don’t want to monetize directly. They offer something for free and monetize elsewhere.
So how do you offer a free trial or giveaway in a hostile decentralized network? Or even, how do you decide which notes to accept on your relay?
At first glance, these may seem like unrelated questions—but they’re not. Generally speaking, these are situations where you have a finite budget, and you want to use it well. You want more of what you value — and less of what you don’t (spam).
Reputation is a powerful shortcut when direct evaluation isn’t practical. It’s hard to earn, easy to lose — and that’s exactly what makes it valuable.\ Can a reputable user do bad things? Absolutely. But it’s much less likely, and that’s the point. Heuristics are always imperfect, just like the world we live in.
The legacy Web relies heavily on email-based reputation. If you’ve ever tried to log in with a temporary email, you know what I’m talking about. It just doesn’t work anymore. The problem, as Lopp explains, is that these systems are highly centralized, opaque, and require constant manual intervention.\ They also suck. They put annoying roadblocks between the world and your product, often frustrating the very users you’re trying to convert.
At Vertex, we take a different approach.\ We transparently analyze Nostr’s open social graph to help companies fight spam while improving the UX for their users. But we don’t take away your agency—we just do the math. You take the decision of what algorithm and criteria to use.
Think of us as a signal provider, not an authority.\ You define what reputation means for your use case. Want to rank by global influence? Local or personalized? You’re in control. We give you actionable and transparent analytics so you can build sharper filters, better user experiences, and more resilient systems. That’s how we fight spam, without sacrificing decentralization.
Are you looking to add Web of Trust capabilities to your app or project?\ Take a look at our website or send a DM to Pip.
-
 @ 5b730fac:9e746e2a
2025-05-08 14:55:38
@ 5b730fac:9e746e2a
2025-05-08 14:55:38| Channel | Push to Branch | Previous Installation Method | NIP94 Event ID Updated as Expected | New Update Installed as Expected | Test Passed | | ------- | ----------------- | ---------------------------- | ---------------------------------- | -------------------------------- | -------------------------------------------------------------------------------------------------------------------------------- | | dev | Already Installed | Automatic | Yes | Yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdfex5unzvfcfywh0x |Before pushing update
Check state
Currently installed NIP94 event:
{ "id": "51ca573636243df455333e83d5b456b4bcefd939c8160c5737545abcdc95dfd9", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746714091, "kind": 1063, "tags": [ [ "url", "https://blossom.swissdash.site/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk" ], [ "m", "application/octet-stream" ], [ "x", "75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b" ], [ "ox", "75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-91-ca43710" ], [ "release_channel", "dev" ] ], "content": "TollGate Module Package: basic for gl-mt3000" }Current version picked up by opkg:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - multiple_mints_rebase_taglist_detect_package-91-ca43710Check basic module's logic
Config.json contains the right event ID:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "51ca573636243df455333e83d5b456b4bcefd939c8160c5737545abcdc95dfd9" }Install.json contains the right package path:
root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746714121, "download_time": 1746714105, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null }Update package manually
Trigger new event announcement on this branch
New NIP94 event on this branch
{ "id": "62a39f60f5b3e3f0910adc592c0468c5c134ce321238884e9f016caad4c5231b", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746715485, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk" ], [ "m", "application/octet-stream" ], [ "x", "1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3" ], [ "ox", "1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-92-1157a2f" ], [ "release_channel", "dev" ] ] }The new version was updated automatically despite internet gateway interruption: ``` Thu May 8 14:44:51 2025 daemon.info tollgate-basic[10154]: Subscription successful on relay wss://relay.damus.io Thu May 8 14:44:51 2025 daemon.info tollgate-basic[10154]: Subscribed to NIP-94 events on relay wss://relay.damus.io Thu May 8 14:44:54 2025 daemon.info tollgate-basic[10154]: Started the timer Thu May 8 14:44:54 2025 daemon.info tollgate-basic[10154]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-92-1157a2f] Thu May 8 14:44:54 2025 daemon.info tollgate-basic[10154]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-92-1157a2f] Thu May 8 14:44:54 2025 daemon.info tollgate-basic[10154]: Right Arch Keys count: 59 Thu May 8 14:44:54 2025 daemon.info tollgate-basic[10154]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-92-1157a2f] Thu May 8 14:45:05 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:05.228500 Timeout reached, checking for new versions Thu May 8 14:45:05 2025 daemon.info tollgate-basic[10154]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-92-1157a2f] Thu May 8 14:45:05 2025 daemon.info tollgate-basic[10154]: Newer package version available: multiple_mints_rebase_taglist_detect_package-92-1157a2f Thu May 8 14:45:05 2025 daemon.info tollgate-basic[10154]: Downloading package from https://blossom.swissdash.site/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk to /tmp/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk Thu May 8 14:45:07 2025 daemon.info tollgate-basic[10154]: Package downloaded successfully to /tmp/ Thu May 8 14:45:07 2025 daemon.info tollgate-basic[10154]: New package version is ready to be installed by cronjob Thu May 8 14:45:07 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:07.693753 Verifying package checksum Thu May 8 14:45:07 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:07.703697 Package checksum verified successfully Thu May 8 14:45:10 2025 daemon.info tollgate-basic[10154]: Started the timer Thu May 8 14:45:22 2025 daemon.info tollgate-basic[10154]: Connecting to relay: wss://relay.tollgate.me Thu May 8 14:45:23 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:23.453098 Timeout reached, checking for new versions Thu May 8 14:45:23 2025 daemon.info tollgate-basic[10154]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-92-1157a2f] Thu May 8 14:45:23 2025 daemon.info tollgate-basic[10154]: Newer package version available: multiple_mints_rebase_taglist_detect_package-92-1157a2f Thu May 8 14:45:23 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:23.461627 Verifying package checksum Thu May 8 14:45:23 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:23.471684 Package checksum verified successfully Thu May 8 14:45:23 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:23.471744 Verifying package checksum Thu May 8 14:45:23 2025 daemon.info tollgate-basic[10154]: Package /tmp/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk already exists with correct checksum, skipping download Thu May 8 14:45:23 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:23.481076 Package checksum verified successfully Thu May 8 14:45:47 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:45:47.810824 Relay wss://nos.lol disconnected, attempting to reconnect Thu May 8 14:45:47 2025 daemon.info tollgate-basic[10154]: Connecting to relay: wss://nos.lol Thu May 8 14:45:47 2025 daemon.info tollgate-basic[10154]: Connected to relay: wss://nos.lol
```
New version picked up by opkg: ``` root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - multiple_mints_rebase_taglist_detect_package-92-1157a2f
```
tollgate-basic is running again:
root@OpenWrt:/tmp# service tollgate-basic status runningEvent id in config is fine:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "62a39f60f5b3e3f0910adc592c0468c5c134ce321238884e9f016caad4c5231b" }install.json is fine: ``` root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/1bfcd4d08a4bf70d2878ee4bca2d3ba7c5a839355dc0eeef30e2589aa16ccfb3.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746715561, "download_time": 1746715507, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null }
```
-
 @ 000002de:c05780a7
2025-05-08 14:55:34
@ 000002de:c05780a7
2025-05-08 14:55:34There are so many projects in the bitcoin space that deserve praise but I just wanna shout out Cashu.me. Its a browser based cashu (eCash / Lighting) wallet. It can be very handy when you need a wallet but don't wanna download yet another app. I hadn't used it in a very long time and decided to try it out again the other day. Its really well done.
As with other Cashu wallets you need to select a mint and backup your key phrase but it is very simple the get started.
If you wanna learn more about Cashu check out Cashu.space
Two other good wallets that support Cashu.
originally posted at https://stacker.news/items/974759
-
 @ 6be5cc06:5259daf0
2025-04-28 01:05:49
@ 6be5cc06:5259daf0
2025-04-28 01:05:49Eu reconheço que Deus, e somente Deus, é o soberano legítimo sobre todas as coisas. Nenhum homem, nenhuma instituição, nenhum parlamento tem autoridade para usurpar aquilo que pertence ao Rei dos reis. O Estado moderno, com sua pretensão totalizante, é uma farsa blasfema diante do trono de Cristo. Não aceito outro senhor.
A Lei que me guia não é a ditada por burocratas, mas a gravada por Deus na própria natureza humana. A razão, quando iluminada pela fé, é suficiente para discernir o que é justo. Rejeito as leis arbitrárias que pretendem legitimar o roubo, o assassinato ou a escravidão em nome da ordem. A justiça não nasce do decreto, mas da verdade.
Acredito firmemente na propriedade privada como extensão da própria pessoa. Aquilo que é fruto do meu trabalho, da minha criatividade, da minha dedicação, dos dons a mim concedidos por Deus, pertence a mim por direito natural. Ninguém pode legitimamente tomar o que é meu sem meu consentimento. Todo imposto é uma agressão; toda expropriação, um roubo. Defendo a liberdade econômica não por idolatria ao mercado, mas porque a liberdade é condição necessária para a virtude.
Assumo o Princípio da Não Agressão como o mínimo ético que devo respeitar. Não iniciarei o uso da força contra ninguém, nem contra sua propriedade. Exijo o mesmo de todos. Mas sei que isso não basta. O PNA delimita o que não devo fazer — ele não me ensina o que devo ser. A liberdade exterior só é boa se houver liberdade interior. O mercado pode ser livre, mas se a alma estiver escravizada pelo vício, o colapso será inevitável.
Por isso, não me basta a ética negativa. Creio que uma sociedade justa precisa de valores positivos: honra, responsabilidade, compaixão, respeito, fidelidade à verdade. Sem isso, mesmo uma sociedade que respeite formalmente os direitos individuais apodrecerá por dentro. Um povo que ama o lucro, mas despreza a verdade, que celebra a liberdade mas esquece a justiça, está se preparando para ser dominado. Trocará um déspota visível por mil tiranias invisíveis — o hedonismo, o consumismo, a mentira, o medo.
Não aceito a falsa caridade feita com o dinheiro tomado à força. A verdadeira generosidade nasce do coração livre, não da coerção institucional. Obrigar alguém a ajudar o próximo destrói tanto a liberdade quanto a virtude. Só há mérito onde há escolha. A caridade que nasce do amor é redentora; a que nasce do fisco é propaganda.
O Estado moderno é um ídolo. Ele promete segurança, mas entrega servidão. Promete justiça, mas entrega privilégios. Disfarça a opressão com linguagem técnica, legal e democrática. Mas por trás de suas máscaras, vejo apenas a velha serpente. Um parasita que se alimenta do trabalho alheio e manipula consciências para se perpetuar.
Resistir não é apenas um direito, é um dever. Obedecer a Deus antes que aos homens — essa é a minha regra. O poder se volta contra a verdade, mas minha lealdade pertence a quem criou o céu e a terra. A tirania não se combate com outro tirano, mas com a desobediência firme e pacífica dos que amam a justiça.
Não acredito em utopias. Desejo uma ordem natural, orgânica, enraizada no voluntarismo. Uma sociedade que se construa de baixo para cima: a partir da família, da comunidade local, da tradição e da fé. Não quero uma máquina que planeje a vida alheia, mas um tecido de relações voluntárias onde a liberdade floresça à sombra da cruz.
Desejo, sim, o reinado social de Cristo. Não por imposição, mas por convicção. Que Ele reine nos corações, nas famílias, nas ruas e nos contratos. Que a fé guie a razão e a razão ilumine a vida. Que a liberdade seja meio para a santidade — não um fim em si. E que, livres do jugo do Leviatã, sejamos servos apenas do Senhor.
-
 @ 1893da11:a9bd4471
2025-05-08 14:42:20
@ 1893da11:a9bd4471
2025-05-08 14:42:20Introduction: The Challenge of Bitcoin-Secured Loans
Bitcoin holders often face a dilemma: they need liquidity but don't want to sell their assets, potentially missing out on future gains or triggering taxable events. Bitcoin-secured loans offer a solution, allowing users to borrow cash (like digital dollars) using their Bitcoin as collateral. However, the current landscape is fraught with challenges. Many existing solutions require users to trust centralized entities or involve complex mechanisms like wrapping Bitcoin, exposing them to significant risks:
- Custodial Risk: Handing over your Bitcoin to a third party means trusting they won't lose it, misuse it, or become insolvent. Billions have been lost this way.
- Smart Contract Risk: Platforms built on chains like Ethereum rely on complex smart contracts, which can contain bugs or vulnerabilities exploitable by hackers.
- Oracle Risk: Loan systems need reliable price feeds (oracles) to manage collateral. Centralized or manipulatable oracles can lead to unfair liquidations.
- Privacy Risk: Loan details and transactions are often publicly visible on the blockchain.
- Complexity and Cost: Existing processes can be slow, require extensive documentation, and involve high fees.
There's a clear need for a better way – one that is simple, reliable, and minimizes trust. This is where the Lava Loans Protocol comes in.
What is Lava Loans?
In simple terms, Lava Loans provides a way to borrow digital dollars using your native Bitcoin as collateral, directly from your own vault. It's designed to be:
- Simple & Fast: Get a loan in seconds with minimal questions asked.
- Low-Cost & Flexible: Offers competitive rates, dynamic fee structures, and allows borrowing any amount.
- Reliable & Trust-Minimized: Leverages Bitcoin's own capabilities to reduce reliance on intermediaries and enhance security.
How Lava Loans Addresses the Risks
Lava tackles the common pitfalls of crypto loans head-on:
- Eliminating Custodial Risk: Instead of transferring your Bitcoin to a custodian or wrapping it, Lava uses native Bitcoin locked directly on the Bitcoin network within a special type of contract. This prevents rehypothecation and loss through hacks or confiscation.
- Minimizing Smart Contract Risk: Lava utilizes Bitcoin smart contracts, also known as Discreet Log Contracts (DLCs). These are designed to be less complex and more secure than many general-purpose smart contracts, with outcomes pre-defined and formally verified.
- Reducing Oracle Risk: Users choose their own off-chain, blinded oracles (called Sibyls) for price data, with enhanced redundancy to ensure reliability. Off-chain attestations avoid high fees and miner manipulation risks associated with on-chain oracles. Blinded oracles provide price data without knowing the specific contract they influence, preventing targeted attacks.
- Enhancing Privacy: Because DLCs operate differently from typical public smart contracts, the details of the loan contract are not broadcast publicly on the Bitcoin blockchain.
- Trustless Initiation & Repayment: Atomic swaps ensure that collateral only moves to the contract once the loan is received, and collateral is automatically returned upon verified repayment.
The Magic Ingredients: DLCs and Sibyls Oracles
Two core technologies make Lava Loans unique:
-
Discreet Log Contracts (DLCs): Think of a DLC as a pre-programmed Bitcoin transaction agreed upon by the borrower and lender. Before the loan starts, they define all possible outcomes (e.g., repayment, liquidation at a specific price, expiry) and create encrypted signatures for each. The Bitcoin collateral is locked in a multisig output controlled by these pre-signed transactions. Only the conditions agreed upon (verified by oracle signatures) can unlock the funds according to the pre-defined rules. This offers:
- Security: Formally verified, pre-defined outcomes minimize bug risk.
- Privacy: Contract details remain off-chain.
- Scalability: Minimal on-chain footprint as execution logic is off-chain.
- Customization: Users can choose their own oracles and LTV thresholds.
-
Sibyls Oracles: These are the independent price feed providers for Lava. Key characteristics include:
- Off-Chain: Attestations happen off-chain, avoiding blockchain fees and manipulation.
- User-Chosen: Borrowers select the oracles they trust for each loan.
- Blinded: Oracles provide signed price data without knowing the specific DLC it applies to, enhancing security.
- Redundant: Multiple oracles can be configured to provide fallback price feeds, reducing the risk of oracle failure.
System Overview
Here's a high-level look at the components involved in the Lava Loans ecosystem:
[ Borrower ] --(locks Bitcoin)--> [ DLC Contract (Bitcoin) ] [ Lender ] --(sends stablecoins)--> [ Alt-Chain Contract (Solana) ] [ Oracles ] --(provides price)--> [ DLC Contract (Bitcoin) ] [ Borrower ] --(repays loan)--> [ Alt-Chain Contract (Solana) ] [ Lender ] --(claims collateral)--> [ DLC Contract (Bitcoin) ]The Lava Loan Lifecycle
A loan progresses through several states:
- Initialized: A trustless atomic swap occurs. The borrower locks Bitcoin collateral into the DLC on the Bitcoin network, and the lender locks the loan capital (e.g., digital dollars on a network like Solana using HTLCs) which the borrower then claims.
- Active: The collateral is secured in the DLC, and the borrower has the loan capital. The Lava Protocol monitors the loan-to-value (LTV) ratio using price data from the chosen Sibyls oracles, with customizable LTV thresholds for greater flexibility.
- Terminated: The loan concludes in one of several ways:
- Repaid: The borrower repays the loan capital plus interest on the loan asset network, with dynamic fees adjusting based on network conditions. Upon verification, the DLC automatically releases the Bitcoin collateral back to the borrower.
- Liquidated: If the Bitcoin price drops and the LTV reaches a pre-determined threshold (now more flexible to avoid premature liquidations), the DLC automatically releases the collateral to the lender.
- Expired: If the loan term ends before repayment, the DLC releases an amount equivalent to the principal plus interest to the lender, and the remaining collateral is returned to the borrower.
- Fail-safe: In rare cases of unresponsive oracles, redundant Sibyls oracles and built-in mechanisms ensure collateral is not permanently lost.
Loan Process Sequence
The following diagram illustrates the typical sequence of events in a Lava Loan:
1. Borrower --> DLC: Create loan contract with collateral 2. Lender --> Alt-Chain: Fund loan with stablecoins 3. Borrower --> Alt-Chain: Receive and use stablecoins 4. (If repayment) 4a. Borrower --> Alt-Chain: Repay loan 4b. Lender --> Alt-Chain: Confirm repayment 4c. Borrower --> DLC: Claim collateral 5. (If liquidation) 5a. Oracle --> DLC: Provide price attestation 5b. Lender --> DLC: Claim collateral 6. (If expiry) 6a. Borrower/Lender --> DLC: Split collateralLava Loans vs. Other Bitcoin Lending Platforms: A Quick Comparison
How does Lava stack up against typical DeFi lending protocols and other Bitcoin lending platforms like Unchained, Strike, and Coinbase?
| Feature | Lava Loans (Bitcoin) | Typical Ethereum DeFi | Unchained | Strike | Coinbase | | :------------------- | :---------------------------------------------------- | :-------------------------------------------------------- | :---------------------------------------------------- | :---------------------------------------------------- | :---------------------------------------------------- | | Collateral | Native Bitcoin | Often Wrapped Bitcoin (wBTC) or other assets | Native Bitcoin | Native Bitcoin | Native Bitcoin | | Contract Type | Discreet Log Contracts (DLCs) - Pre-agreed, Private | Smart Contracts - Public, Complex, Run on EVM | 2/3 Multisig Vaults | Custodial Contracts | Custodial Contracts | | Security | Aims for higher security via simpler, pre-set DLCs | Can be complex, potential for bugs/exploits | Secure via multisig, but relies on key holders | Custodial, less transparent | Custodial, less transparent | | Privacy | Higher privacy (contract details off-chain) | Lower privacy (contract interactions often public) | Moderate privacy (multisig details on-chain) | Lower privacy (custodial model) | Lower privacy (custodial model) | | Oracles | User-chosen, Off-chain, Blinded (Sibyls) | Often On-chain, potentially manipulatable | Not applicable (manual monitoring) | Centralized oracles | Centralized oracles | | Trust | Designed to minimize trust in intermediaries | Often requires trust in custodians, bridges, or protocols | Moderate trust (key holders could collude) | Higher trust (custodial, opaque practices) | Higher trust (custodial, opaque practices) | | Rehypothecation | No rehypothecation, verifiable on-chain via DLCs | Possible, depends on protocol | No rehypothecation, secured by multisig | Opaque, likely rehypothecated | Opaque, likely rehypothecated | | Interest Rates | Competitive, typically lower due to non-custodial model | Varies, often 5-10% for wBTC loans | 11-14% for non-rehypothecated loans | 12-13% (implies rehypothecation) | ~5-6% (implies rehypothecation) |
Lava leverages Bitcoin’s native capabilities and a specific oracle design to prioritize security, privacy, and trust minimization. Unlike Unchained, which uses a 2/3 multisig where two key holders could potentially collude, Lava’s DLCs ensure cryptographic proof of non-rehypothecation, verifiable on-chain in real time. Strike and Coinbase, being custodial, lack transparency about rehypothecation practices, with market rates suggesting they rehypothecate collateral. The v3 protocol introduces dynamic fee adjustments and more flexible LTV thresholds, reducing premature liquidations and optimizing costs based on network conditions.
Conclusion
Lava Loans presents a compelling option for those seeking liquidity against their Bitcoin holdings without sacrificing security or control. By utilizing Discreet Log Contracts, a user-centric, blinded oracle system (Sibyls) with enhanced redundancy, and new features like dynamic fees and flexible LTV thresholds, Lava provides a simple, reliable, and trust-minimized borrowing experience. These advancements directly address the major pain points found in many existing centralized and decentralized lending platforms.
References
- Maredia, Shehzan. "Lava Loans". Lava Blog, April 9, 2025. https://www.lava.xyz/blog/lava-loans
- https://github.com/lava-xyz/loans-paper/blob/main/loans_v3.pdf
- https://github.com/lava-xyz/sibyls
-
 @ b04082ac:29b5c55b
2025-05-08 14:35:02
@ b04082ac:29b5c55b
2025-05-08 14:35:02Money has always been more than a medium of exchange. It reflects what societies value, how they organize trust, and what they choose to remember. This article explores the idea that money functions as a form of collective memory, and how Bitcoin may be restoring this role in a new way.

The Asante Example
In the Asante Empire, which flourished in West Africa during the 18th and 19th centuries, gold dust served as the primary medium of exchange. To measure it, traders used ornate spoons made of brass. These spoons were often carved with birds, animals, or abstract symbols. They were not currency themselves, but tools used to handle gold dust accurately.
Importantly, these spoons also carried meaning. Symbols and proverbs embedded in the spoons conveyed lessons about honesty, community, and continuity. For example, the Sankofa bird, shown turning its head backward to retrieve an egg from its back, represented the proverb, “It is not wrong to go back for that which you have forgotten.” This was a reminder to learn from the past.

The spoons reflect an understanding that money and its instruments are not just practical tools. They are cultural artifacts that store shared values. In the Asante context, even measurement was ritualized and tied to ethics and memory.
Money as a Cultural Medium
This connection between money and cultural meaning is not unique to the Asante Empire. Modern fiat currencies also carry symbols, phrases, and designs that reflect national identity and political values.
The U.S. dollar includes Latin phrases and national symbols meant to convey stability and purpose. The British pound features royal iconography, reinforcing the idea of continuity and sovereignty. When the euro was introduced, it deliberately avoided specific national references. Itsdesign used bridges and windowsto suggest openness and cooperation across the continent.

These design choices show that societies still embed meaning into their money. Even in a digital or fiat context, money is used to transmit a story about who we are, where authority lies, and what we value.
The Fragility of Fiat Memory
While fiat money carries cultural symbols, the narratives behind those symbols can be fragile.
In 2021, the central bank of the Philippines removed democratic leaders from its banknotes,triggering public criticism. In the United States, attempts to replace Andrew Jackson with Harriet Tubman on the $20 billfaced repeated delays. These examples show how political control over money includes control over what stories are told and remembered.

Unlike objects passed down through generations, fiat memory can be edited or erased. In this sense, it is vulnerable. The meaning encoded in fiat systems can shift depending on who holds power.
Bitcoin as a New Form of Memory
Bitcoin is described as digital money. But it also introduces a different model of how societies can record value and preserve meaning.
The Bitcoin network launched in 2009 with a small message embedded in its first block: “Chancellor on brink of second bailout for banks.” This was a reference to a newspaper headline that day and a clear sign of protest against financial bailouts, centralized monetary policy, and forever wars.

This moment marked the beginning of a system where memory is stored differently. Instead of relying on governments or institutions, Bitcoin stores its history on a public ledger maintained by a decentralized network of participants. Its memory is not symbolic or political; it is structural. Every transaction, every block, is preserved through time-stamped computation and consensus.
No single authority can change it. The rules are clear and publicly auditable. In this way, Bitcoin offers a version of money where memory is both neutral and resilient.
Cultural Expression and Community Values
Even though Bitcoin lacks the traditional symbols found on banknotes, it has developed its own culture. Phrases like “Don’t trust, verify” or “Stay humble, stack sats” are shared widely in the Bitcoin community. These ideas reflect a focus on self-responsibility, verification, and long-term thinking.
These proverbs can be compared to the carved messages on the Asante spoons. While the contexts are very different, the underlying idea is similar: a community using language and symbols to reinforce its shared values.
Bitcoin also has a well established and growing art scene. Bitcoin conferences often feature dedicated sections for art inspired by the protocol and its culture. Statues of Satoshi Nakamoto have been installed in cities like Budapest, Lugano, and Fornelli. These physical works reflect the desire to link Bitcoin’s abstract values to something tangible.

Looking Back to Look Forward
The Asante example helps us see that money has long been tied to memory and meaning. Their spoons were practical tools but also cultural anchors. Bitcoin, while new and digital, may be playing a similar role.
Instead of relying on political symbols or national myths, Bitcoin uses code, transparency, and global consensus to create trust. In doing so, it offers a way to preserve economic memory that does not depend on power or politics.
It’s still early to know what kind of legacy Bitcoin will leave. But if it succeeds, it may not just change how money works. It may also change how civilizations remember.
-
 @ 5b730fac:9e746e2a
2025-05-08 14:32:04
@ 5b730fac:9e746e2a
2025-05-08 14:32:04| Channel | Push to Branch | Previous Installation Method | NIP94 Event ID Updated as Expected | New Update Installed as Expected | Test Passed | | ------- | ----------------- | ---------------------------- | ---------------------------------- | -------------------------------- | -------------------------------------------------------------------------------------------------------------------------------- | | dev | Already Installed | Manual | Yes | Yes | Yes
nostr:naddr1qvzqqqr4gupzqkmnp7kx5h36rumhjrtkxdslvqu38fyf09wv53u4hrqmvx08gm32qqxnzde5xcmnzdp4xvmnvdpkpctkgk |Before pushing update
Check state
Currently installed NIP94 event:
{ "id": "33bf30e90f1e09924a933f08e788165eada8cca2d6c78443e7e52910f0705988", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746711607, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97.ipk" ], [ "m", "application/octet-stream" ], [ "x", "0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97" ], [ "ox", "0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-89-4e46a9b" ], [ "release_channel", "dev" ] ] }Installed here:
Thu May 8 13:40:13 2025 daemon.info tollgate-basic[6709]: Started the timer Thu May 8 13:40:13 2025 daemon.info tollgate-basic[6709]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-89-4e46a9b] Thu May 8 13:40:13 2025 daemon.info tollgate-basic[6709]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-89-4e46a9b] Thu May 8 13:40:13 2025 daemon.info tollgate-basic[6709]: Right Arch Keys count: 56 Thu May 8 13:40:13 2025 daemon.info tollgate-basic[6709]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-89-4e46a9b] Thu May 8 13:40:23 2025 daemon.err tollgate-basic[6709]: 2025/05/08 13:40:23.779018 Timeout reached, checking for new versions Thu May 8 13:40:23 2025 daemon.info tollgate-basic[6709]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-89-4e46a9b] Thu May 8 13:40:23 2025 daemon.info tollgate-basic[6709]: Newer package version available: multiple_mints_rebase_taglist_detect_package-89-4e46a9b Thu May 8 13:40:23 2025 daemon.info tollgate-basic[6709]: Downloading package from https://blossom.swissdash.site/0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97.ipk to /tmp/0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97.ipk Thu May 8 13:40:28 2025 daemon.info tollgate-basic[6709]: Package downloaded successfully to /tmp/ Thu May 8 13:40:28 2025 daemon.err tollgate-basic[6709]: 2025/05/08 13:40:28.863469 Verifying package checksum Thu May 8 13:40:28 2025 daemon.err tollgate-basic[6709]: 2025/05/08 13:40:28.873010 Package checksum verified successfully Thu May 8 13:40:28 2025 daemon.info tollgate-basic[6709]: New package version multiple_mints_rebase_taglist_detect_package-89-4e46a9b is ready to be installed by cronjob Thu May 8 13:41:06 2025 daemon.err tollgate-basic[7713]: 2025/05/08 13:41:06 NIP94EventID: 33bf30e90f1e09924a933f08e788165eada8cca2d6c78443e7e52910f0705988 Thu May 8 13:41:06 2025 daemon.err tollgate-basic[7713]: 2025/05/08 13:41:06 IPAddressRandomized: 192.168.3.1Current version picked up by opkg:
root@OpenWrt:~# opkg list-installed | grep "tollgate" tollgate-module-basic-go - multiple_mints_rebase_taglist_detect_package-89-4e46a9bCheck basic module's logic
Config.json contains the right event ID: ``` root@OpenWrt:~# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "33bf30e90f1e09924a933f08e788165eada8cca2d6c78443e7e52910f0705988" }
```
Install.json contains the right package path:
root@OpenWrt:~# cat /etc/tollgate/install.json { "package_path": "/tmp/0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746711661, "download_time": 1746711628, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null }Update package manually
Prevent automatic update
Stop
tollgate-basicso that it doesn't automatically update to newer event kinds.root@OpenWrt:~# service tollgate-basic stop root@OpenWrt:~# service tollgate-basic status inactiveTrigger new event announcement on this branch
New NIP94 event on this branch
c03rad0r@CobradorRomblonMimaropa:~/TG/tollgate-module-basic-go/src$ git push github Enumerating objects: 9, done. Counting objects: 100% (9/9), done. Delta compression using up to 8 threads Compressing objects: 100% (5/5), done. Writing objects: 100% (5/5), 429 bytes | 429.00 KiB/s, done. Total 5 (delta 4), reused 0 (delta 0), pack-reused 0 remote: Resolving deltas: 100% (4/4), completed with 4 local objects. To https://github.com/OpenTollGate/tollgate-module-basic-go.git 4e46a9b..ad29788 multiple_mints_rebase_taglist_detect_package -> multiple_mints_rebase_taglist_detect_packageThe new version that we will install manually:
{ "id": "2ff8b1e63036f03884a82450c811d9df0ed2b9f1a4099bbb1e4308e1d845be97", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746712364, "kind": 1063, "content": "TollGate Module Package: basic for gl-mt3000", "tags": [ [ "url", "https://blossom.swissdash.site/e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059.ipk" ], [ "m", "application/octet-stream" ], [ "x", "e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059" ], [ "ox", "e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-90-ad29788" ], [ "release_channel", "dev" ] ] }The installation:
root@OpenWrt:/tmp# wget https://blossom.swissdash.site/e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059.ipk Downloading 'https://blossom.swissdash.site/e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059.ipk' Connecting to 212.47.72.157:443 Writing to 'e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059.ipk' e8633b4c2ceb05b5fd45 2943k --:--:-- ETA Download completed (4509706 bytes) root@OpenWrt:/tmp# opkg install e8633b4c2ceb05b5fd45fe0574417b644bbc62e6e3862147e94ca46104735059.ipk Upgrading tollgate-module-basic-go on root from multiple_mints_rebase_taglist_detect_package-89-4e46a9b to multiple_mints_rebase_taglist_detect_package-90-ad29788... Command failed: Not found Removing existing banner file if present... Configuring tollgate-module-basic-go. nodogsplash cfg7c92bd Running TollGate NoDogSplash file copy script... Source files: drwxr-xr-x 2 root root 384 May 8 13:57 . drwxr-xr-x 3 root root 224 May 8 13:50 .. -rw-r--r-- 1 root root 599 May 8 13:50 asset-manifest.json -rw-r--r-- 1 root root 312 May 8 13:50 manifest.json -rw-r--r-- 1 root root 642 May 8 13:50 splash.html Copying splash.html... IP is already randomized or not set to false. Exiting.Current version picked up by opkg:
root@OpenWrt:/tmp# opkg list-installed | grep "tollgate" tollgate-module-basic-go - multiple_mints_rebase_taglist_detect_package-90-ad29788 root@OpenWrt:/tmp#tollgate-basic is running again:
root@OpenWrt:/tmp# service tollgate-basic status runningEvent ID successfully set to
unknown:root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "unknown" }install.jsonis still pointing at dev channel:root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/0456244a6b01629d86d6218ddacb149fd3a54b007154531ade55415c5573ab97.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746712641, "download_time": 1746711628, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null }Trigger new event announcement on this branch
Trigger new event:
c03rad0r@CobradorRomblonMimaropa:~/TG/tollgate-module-basic-go/src$ git push github Enumerating objects: 9, done. Counting objects: 100% (9/9), done. Delta compression using up to 8 threads Compressing objects: 100% (5/5), done. Writing objects: 100% (5/5), 418 bytes | 418.00 KiB/s, done. Total 5 (delta 4), reused 0 (delta 0), pack-reused 0 remote: Resolving deltas: 100% (4/4), completed with 4 local objects. To https://github.com/OpenTollGate/tollgate-module-basic-go.git ad29788..ca43710 multiple_mints_rebase_taglist_detect_package -> multiple_mints_rebase_taglist_detect_packageNew event json:
{ "id": "51ca573636243df455333e83d5b456b4bcefd939c8160c5737545abcdc95dfd9", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1746714091, "kind": 1063, "tags": [ [ "url", "https://blossom.swissdash.site/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk" ], [ "m", "application/octet-stream" ], [ "x", "75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b" ], [ "ox", "75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b" ], [ "filename", "basic-gl-mt3000-aarch64_cortex-a53.ipk" ], [ "architecture", "aarch64_cortex-a53" ], [ "version", "multiple_mints_rebase_taglist_detect_package-91-ca43710" ], [ "release_channel", "dev" ] ], "content": "TollGate Module Package: basic for gl-mt3000" }Logread output: ``` Thu May 8 14:12:11 2025 daemon.err tollgate-basic[8933]: 2025/05/08 14:12:11.615394 Relay wss://relay.damus.io disconnected, attempting to reconnect Thu May 8 14:12:11 2025 daemon.info tollgate-basic[8933]: Connecting to relay: wss://relay.damus.io Thu May 8 14:12:11 2025 daemon.info tollgate-basic[8933]: Connected to relay: wss://relay.damus.io Thu May 8 14:12:11 2025 daemon.info tollgate-basic[8933]: Subscription successful on relay wss://relay.damus.io Thu May 8 14:12:11 2025 daemon.info tollgate-basic[8933]: Subscribed to NIP-94 events on relay wss://relay.damus.io Thu May 8 14:20:41 2025 daemon.info tollgate-basic[8933]: Connecting to relay: wss://relay.tollgate.me Thu May 8 14:21:33 2025 daemon.info tollgate-basic[8933]: Started the timer Thu May 8 14:21:33 2025 daemon.info tollgate-basic[8933]: Intersection: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-91-ca43710] Thu May 8 14:21:33 2025 daemon.info tollgate-basic[8933]: Right Time Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-90-ad29788 basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-90-ad29788 basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-91-ca43710] Thu May 8 14:21:33 2025 daemon.info tollgate-basic[8933]: Right Arch Keys count: 115 Thu May 8 14:21:33 2025 daemon.info tollgate-basic[8933]: Right Version Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-91-ca43710] Thu May 8 14:21:43 2025 daemon.err tollgate-basic[8933]: 2025/05/08 14:21:43.304879 Timeout reached, checking for new versions Thu May 8 14:21:43 2025 daemon.info tollgate-basic[8933]: Sorted Qualifying Events Keys: [basic-gl-mt3000-aarch64_cortex-a53.ipk-multiple_mints_rebase_taglist_detect_package-91-ca43710] Thu May 8 14:21:43 2025 daemon.info tollgate-basic[8933]: Newer package version available: multiple_mints_rebase_taglist_detect_package-91-ca43710 Thu May 8 14:21:43 2025 daemon.info tollgate-basic[8933]: Downloading package from https://blossom.swissdash.site/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk to /tmp/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk Thu May 8 14:21:45 2025 daemon.info tollgate-basic[8933]: Package downloaded successfully to /tmp/ Thu May 8 14:21:45 2025 daemon.info tollgate-basic[8933]: New package version is ready to be installed by cronjob Thu May 8 14:21:45 2025 daemon.err tollgate-basic[8933]: 2025/05/08 14:21:45.667395 Verifying package checksum Thu May 8 14:21:45 2025 daemon.err tollgate-basic[8933]: 2025/05/08 14:21:45.676755 Package checksum verified successfully Thu May 8 14:22:06 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:22:06 NIP94EventID: 51ca573636243df455333e83d5b456b4bcefd939c8160c5737545abcdc95dfd9 Thu May 8 14:22:06 2025 daemon.err tollgate-basic[10154]: 2025/05/08 14:22:06 IPAddressRandomized: 192.168.3.1
```
Config has the right event id again:
root@OpenWrt:/tmp# cat /etc/tollgate/config.json | jq { "tollgate_private_key": "8a45d0add1c7ddf668f9818df550edfa907ae8ea59d6581a4ca07473d468d663", "accepted_mints": [ "https://mint.minibits.cash/Bitcoin", "https://mint2.nutmix.cash" ], "price_per_minute": 1, "bragging": { "enabled": true, "fields": [ "amount", "mint", "duration" ] }, "relays": [ "wss://relay.damus.io", "wss://nos.lol", "wss://nostr.mom", "wss://relay.tollgate.me" ], "trusted_maintainers": [ "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a" ], "fields_to_be_reviewed": [ "price_per_minute", "relays", "tollgate_private_key", "trusted_maintainers" ], "nip94_event_id": "51ca573636243df455333e83d5b456b4bcefd939c8160c5737545abcdc95dfd9" }Install.json has the right file path again:
root@OpenWrt:/tmp# cat /etc/tollgate/install.json | jq { "package_path": "/tmp/75990a3f245069a56c02c6e24dc312ecc6ff1f0df632fb99ddb247c98a745a5b.ipk", "ip_address_randomized": "192.168.3.1", "install_time": 1746714121, "download_time": 1746714105, "release_channel": "dev", "ensure_default_timestamp": 1746634883, "update_path": null } -
 @ 66df6056:f3203c64
2025-05-08 14:28:51
@ 66df6056:f3203c64
2025-05-08 14:28:51งาน Bitcoin++ ประจำปี 2025 ที่จัดขึ้นที่เมืองออสติน รัฐเท็กซัส เป็นการรวมตัวของนักพัฒนา Bitcoin ที่เจาะลึกในประเด็นทางเทคนิค โดยเฉพาะอย่างยิ่งเรื่อง Mempool, Transaction Relay และ Mining Pools หัวข้อเหล่านี้ถูกเน้นย้ำว่าเป็นหัวข้อที่น่าสนใจและเป็นที่ถกเถียงกัน เป้าหมายหลักของงานคือเพื่อให้เหล่านักพัฒนาและผู้สร้างสรรค์ได้แบ่งปันสิ่งที่พวกเขากำลังทำอยู่ เรียนรู้เกี่ยวกับความท้าทายในการนำ Transaction เข้าสู่ Block และการปรับปรุง Bitcoin รวมถึงส่งเสริมการเติบโตของชุมชน Open-Source
งานในปีนี้เป็นครั้งแรกที่มุ่งเน้นไปที่ Mempool และ Transaction Relay โดยเฉพาะ ซึ่งเกี่ยวข้องโดยตรงกับการสร้าง Block Mempool ถูกมองว่าเป็นพื้นที่ส่วนรวม (commons) และเป็นตลาดประมูลที่เสรีและเปิดกว้างที่สุดแห่งหนึ่งของโลก ที่ซึ่งใครก็ตามที่เป็นเจ้าของ Bitcoin สามารถเสนอราคา (ค่าธรรมเนียม) และใครก็ตามที่ขุด Bitcoin ก็สามารถยอมรับราคานั้นและนำ Transaction เข้า Block ได้ แม้ว่ากระบวนการนี้จะมีความท้าทายและบางครั้งก็เป็นที่ถกเถียงกัน แต่ Bitcoin ยังคงทำงานเป็นระบบแบบอนาธิปไตย (anarchic system) ที่การพัฒนาเกิดขึ้นในลักษณะกระจายศูนย์
ประเด็นร้อน: OP_RETURN และการถกเถียงเรื่อง Data Carrier
หนึ่งในประเด็นหลักที่ถูกกล่าวถึงและมีการจัดดีเบตแบบ Oxford-style คือเรื่องขีดจำกัดของ Data Carrier ใน OP_RETURN โดยเฉพาะการถกเถียงเรื่องการปลดขีดจำกัดค่าเริ่มต้นใน Bitcoin Core การถกเถียงนี้สะท้อนให้เห็นถึงความตึงเครียดระหว่างกลุ่มที่เรียกว่า "Monetary Maximalists" ซึ่งต้องการให้ Bitcoin เป็นเงินที่ดีที่สุด กับกลุ่ม "Platform Maximalists" ที่ต้องการให้ Bitcoin สามารถทำสิ่งต่างๆ ที่ไม่เกี่ยวข้องกับเงินได้มากขึ้น เช่น การออก Token บน Bitcoin
ฝ่ายที่สนับสนุนการปลดขีดจำกัดแย้งว่ามันเป็นปัญหาทางเทคนิคที่ไม่มีวิธีที่มีหลักการในการป้องกันอย่างแท้จริงในระดับ Consensus การพยายามใช้ Filter ใน Mempool เพื่อป้องกันนั้นไม่สามารถทำได้อย่างสมบูรณ์ และผู้ใช้สามารถหาวิธีหลีกเลี่ยงได้ การปลดขีดจำกัดอาจช่วยลดการสร้าง UTXO ที่ใช้ไม่ได้ (unspendable UTXOs) ซึ่งเป็นสิ่งที่แย่กว่า OP_RETURN และจะช่วยประหยัดเวลาของนักพัฒนาจากการโต้เถียงในเรื่องเล็กๆ น้อยๆ
ขณะที่ฝ่ายคัดค้านการปลดขีดจำกัดยืนยันว่า Filter ใน Mempool ทำงานได้ผลในการยับยั้งการใช้ OP_RETURN สำหรับข้อมูลที่ไม่ใช่ทางการเงิน และการปลดขีดจำกัดจะเป็นการทำลาย Filter ที่มีอยู่ พวกเขาแย้งว่า Bitcoin ถูกออกแบบมาให้เป็นระบบการเงิน ไม่ใช่ฐานข้อมูลสำหรับเก็บข้อมูลตามอำเภอใจ การอนุญาตให้เก็บข้อมูลที่ไม่ใช่ทางการเงินจำนวนมากจะทำให้ Transaction ของผู้ใช้ทั่วไปมีค่าใช้จ่ายสูงขึ้น และเป็นการ "ขาย Bitcoin ให้กับผู้ที่เสนอราคาสูงสุด" ซึ่งอาจนำไปสู่การบ่อนทำลายโดยผู้ที่ควบคุมระบบการเงินแบบเก่า พวกเขายืนยันว่า Bitcoin ควรเน้นการเป็นเงิน และการเปลี่ยนแปลงที่ไม่จำเป็นซึ่งทำลาย Filter ที่ทำงานอยู่จะทำให้ความไว้วางใจใน Bitcoin Core ลดลง นอกจากนี้ยังมีการพูดถึงทางเลือกในการใช้ Filter ในระดับ Node เช่นที่ implement ใน Bitcoin Knots
ความรวมศูนย์ในการขุดและการกระจายศูนย์
ปัญหาความรวมศูนย์ใน Mining Pool เป็นอีกหัวข้อที่มีการหารืออย่างกว้างขวาง โดยเฉพาะเรื่องความหลากหลายของ Block Template เครื่องมืออย่าง stratum.work ถูกสร้างขึ้นมาเพื่อช่วยให้ผู้สังเกตการณ์สามารถเปรียบเทียบ Block Template จาก Pool ต่างๆ ได้ ข้อมูลแสดงให้เห็นว่า Antpool และ Pool ที่เป็น "เพื่อน" (Antpool and friends) รวมถึง Foundry มีส่วนแบ่ง Hash Rate รวมกันค่อนข้างสูง ซึ่งทำให้เกิดความกังวลเกี่ยวกับความรวมศูนย์ ปัญหาดังกล่าวถูกมองว่าเป็นปัญหาเชิงเศรษฐศาสตร์และแรงจูงใจ มากกว่าปัญหาทางเทคนิคล้วนๆ
ทางออกในการกระจายศูนย์การขุดและการสร้าง Block Template ถูกนำเสนอ โดยเฉพาะโปรโตคอล Datam ที่พัฒนาโดย Ocean Mining Datam ถูกออกแบบมาเพื่อการขุดแบบกระจายศูนย์โดยเฉพาะ โดย กำหนดให้ Miner ต้องรัน Node ของตัวเองเพื่อสร้าง Block Template ซึ่งแตกต่างจาก Stratum V2 ที่ยังคงมีการใช้งานแบบรวมศูนย์อยู่ Datam Gateway ทำหน้าที่เป็นตัวเชื่อมระหว่าง Miner กับ Pool โดยใช้ Stratum V1 แต่ Miner เป็นผู้สร้าง Block Template เอง โปรโตคอล Datam นั้นเรียบง่าย ใช้ภาษา C เพื่อให้มีขนาดเล็กและมีประสิทธิภาพสูง สามารถทำงานบน Raspberry Pi ได้ และมีการเข้ารหัสระหว่าง Pool กับ Gateway การสร้าง Datam ขึ้นมาใหม่จากศูนย์เป็นเพราะไม่มีโปรโตคอลหรือซอฟต์แวร์ Pool เดิมที่ตอบโจทย์การกระจายศูนย์ได้อย่างสมบูรณ์
การแก้ไข Bug ใน Consensus (Consensus Cleanup)
มีการนำเสนอ BIP 54 หรือ Great Consensus Cleanup ซึ่งเป็นข้อเสนอ Soft Fork เพื่อแก้ไข Bug เล็กน้อยในกฎ Consensus ของ Bitcoin จุดประสงค์ไม่ใช่การเปลี่ยนแปลงคุณค่าหลักของ Bitcoin แต่เป็นการแก้ไข Bug ที่สามารถทำได้ผ่าน Soft Fork Bug เหล่านี้รวมถึงปัญหาที่อาจนำไปสู่การมี Transaction ID (TXID) ของ Coinbase ซ้ำกันในอนาคตสำหรับ Block ที่เกิดขึ้นก่อน BIP 34 การแก้ไขใน BIP 54 เกี่ยวข้องกับการใช้ Time Locking และการกำหนดค่า End Sequence ใน Coinbase Transaction เพื่อป้องกันปัญหานี้ ข้อเสนอนี้ถูกพัฒนาขึ้นโดย Antoine Riard และมีการหารืออย่างละเอียด
ความปลอดภัยทางควอนตัมในอนาคต
ประเด็นเรื่องความปลอดภัยทางควอนตัมของ Bitcoin ก็ถูกหยิบยกขึ้นมาพูดคุย แม้จะดูเป็นปัญหาที่ไกลตัว แต่ก็เป็นสิ่งสำคัญที่จะต้องมีแผนรองรับ BIP 360 ถูกนำเสนอเป็นข้อเสนอ Soft Fork ทางเลือก (Opt-in soft fork) เพื่อเพิ่มความปลอดภัยทางควอนตัมให้กับ Bitcoin ปัญหาหลักคือผู้ใช้จะต้องเปิดเผย Public Key และ Signature เมื่อใช้จ่าย Transaction และคอมพิวเตอร์ควอนตัมอาจสามารถคำนวณ Private Key จาก Public Key ได้ BIP 360 เสนอให้เพิ่มข้อมูล Public Key และ Signature ที่ผ่านการป้องกันควอนตัมเข้าไปใน Transaction โดยรองรับ Taproot อย่างไรก็ตาม Multisig บางประเภท เช่น P2SH หรือ P2WSH อาจให้การป้องกันได้ดีกว่า เนื่องจากผู้โจมตีจะต้องหา Private Key หลายตัว ในขณะที่ Key Path Spend ของ Taproot อาจไม่ช่วยป้องกันปัญหานี้ BIP 360 ยังกำหนดให้มี Public Key ที่ป้องกันควอนตัมเพียงตัวเดียวเพื่อหลีกเลี่ยงความกำกวมของที่อยู่ Taproot
นวัตกรรมและกรณีใช้งานอื่นๆ
นอกจากนี้ยังมีการกล่าวถึงโครงการอื่นๆ ที่น่าสนใจ เช่น Maple AI ที่มุ่งมั่นสร้าง AI ที่ไม่ใช่แบบรวมศูนย์ และ Open Secret ซึ่งเป็น Framework สำหรับนักพัฒนาในการให้ผู้ใช้สามารถ Self-Custody ข้อมูลของตนเองได้ แนวคิดนี้คล้ายกับการ Self-Custody Bitcoin ใน Wallet โดยมองว่าการถือข้อมูลผู้ใช้เป็นภาระความเสี่ยงสำหรับนักพัฒนา
มีการพูดถึงแนวโน้มที่ผู้เล่นในระบบการเงินแบบเก่าอย่าง Visa และ Stripe กำลังพยายามเข้าสู่พื้นที่ Digital Currency โดยอาจใช้การ Tokenize Credit Card รวมถึงบทบาทที่อาจเกิดขึ้นของ AI Agents ซึ่งอาจเริ่มใช้ Bitcoin หรือ Lightning Network ในการชำระเงินในอนาคต มีการคาดการณ์ว่า AI Agents อาจทำธุรกรรมผ่าน Lightning Network ได้ในระดับที่สูงกว่าการใช้งานของมนุษย์อย่างรวดเร็ว โดยมีการพัฒนาโปรโตคอลอย่าง X402 และ Fusats เพื่อรองรับการชำระเงินสำหรับ Agents โดยเปิดโอกาสให้ Agents เลือกใช้สกุลเงินดิจิทัลที่ดีที่สุดในตลาดเสรี
สุดท้าย งาน Bitcoin++ เน้นย้ำถึงความสำคัญของการประชุมและการรวมตัวกันของนักพัฒนาเพื่อหารือ ประสานงาน และแบ่งปันไอเดีย โดยเฉพาะในประเด็นที่ต้องอาศัยความร่วมมือและการแก้ปัญหาที่ซับซ้อน
-
 @ d34e832d:383f78d0
2025-04-26 15:04:51
@ d34e832d:383f78d0
2025-04-26 15:04:51Raspberry Pi-based voice assistant
This Idea details the design and deployment of a Raspberry Pi-based voice assistant powered by the Google Gemini AI API. The system combines open hardware with modern AI services to create a low-cost, flexible, and educational voice assistant platform. By leveraging a Raspberry Pi, basic audio hardware, and Python-based software, developers can create a functional, customizable assistant suitable for home automation, research, or personal productivity enhancement.
1. Voice assistants
Voice assistants have become increasingly ubiquitous, but commercially available systems like Alexa, Siri, or Google Assistant come with significant privacy and customization limitations.
This project offers an open, local, and customizable alternative, demonstrating how to build a voice assistant using Google Gemini (or OpenAI’s ChatGPT) APIs for natural language understanding.Target Audience:
- DIY enthusiasts - Raspberry Pi hobbyists - AI developers - Privacy-conscious users
2. System Architecture
2.1 Hardware Components
| Component | Purpose | |:--------------------------|:----------------------------------------| | Raspberry Pi (any recent model, 4B recommended) | Core processing unit | | Micro SD Card (32GB+) | Operating System and storage | | USB Microphone | Capturing user voice input | | Audio Amplifier + Speaker | Outputting synthesized responses | | 5V DC Power Supplies (2x) | Separate power for Pi and amplifier | | LEDs + Resistors (optional)| Visual feedback (e.g., recording or listening states) |
2.2 Software Stack
| Software | Function | |:---------------------------|:----------------------------------------| | Raspberry Pi OS (Lite or Full) | Base operating system | | Python 3.9+ | Programming language | | SpeechRecognition | Captures and transcribes user voice | | Google Text-to-Speech (gTTS) | Converts responses into spoken audio | | Google Gemini API (or OpenAI API) | Powers the AI assistant brain | | Pygame | Audio playback for responses | | WinSCP + Windows Terminal | File transfer and remote management |
3. Hardware Setup
3.1 Basic Connections
- Microphone: Connect via USB port.
- Speaker and Amplifier: Wire from Raspberry Pi audio jack or via USB sound card if better quality is needed.
- LEDs (Optional): Connect through GPIO pins, using 220–330Ω resistors to limit current.
3.2 Breadboard Layout (Optional for LEDs)
| GPIO Pin | LED Color | Purpose | |:---------|:-----------|:--------------------| | GPIO 17 | Red | Recording active | | GPIO 27 | Green | Response playing |
Tip: Use a small breadboard for quick prototyping before moving to a custom PCB if desired.
4. Software Setup
4.1 Raspberry Pi OS Installation
- Use Raspberry Pi Imager to flash Raspberry Pi OS onto the Micro SD card.
- Initial system update:
bash sudo apt update && sudo apt upgrade -y
4.2 Python Environment
-
Install Python virtual environment:
bash sudo apt install python3-venv python3 -m venv voice-env source voice-env/bin/activate -
Install required Python packages:
bash pip install SpeechRecognition google-generativeai pygame gtts
(Replace
google-generativeaiwithopenaiif using OpenAI's ChatGPT.)4.3 API Key Setup
- Obtain a Google Gemini API key (or OpenAI API key).
- Store safely in a
.envfile or configure as environment variables for security:bash export GEMINI_API_KEY="your_api_key_here"
4.4 File Transfer
- Use WinSCP or
scpcommands to transfer Python scripts to the Pi.
4.5 Example Python Script (Simplified)
```python import speech_recognition as sr import google.generativeai as genai from gtts import gTTS import pygame import os
genai.configure(api_key=os.getenv('GEMINI_API_KEY')) recognizer = sr.Recognizer() mic = sr.Microphone()
pygame.init()
while True: with mic as source: print("Listening...") audio = recognizer.listen(source)
try: text = recognizer.recognize_google(audio) print(f"You said: {text}") response = genai.generate_content(text) tts = gTTS(text=response.text, lang='en') tts.save("response.mp3") pygame.mixer.music.load("response.mp3") pygame.mixer.music.play() while pygame.mixer.music.get_busy(): continue except Exception as e: print(f"Error: {e}")```
5. Testing and Execution
- Activate the Python virtual environment:
bash source voice-env/bin/activate - Run your main assistant script:
bash python3 assistant.py - Speak into the microphone and listen for the AI-generated spoken response.
6. Troubleshooting
| Problem | Possible Fix | |:--------|:-------------| | Microphone not detected | Check
arecord -l| | Audio output issues | Checkaplay -l, use a USB DAC if needed | | Permission denied errors | Verify group permissions (audio, gpio) | | API Key Errors | Check environment variable and internet access |
7. Performance Notes
- Latency: Highly dependent on network speed and API response time.
- Audio Quality: Can be enhanced with a better USB microphone and powered speakers.
- Privacy: Minimal data retention if using your own Gemini or OpenAI account.
8. Potential Extensions
- Add hotword detection ("Hey Gemini") using Snowboy or Porcupine libraries.
- Build a local fallback model to answer basic questions offline.
- Integrate with home automation via MQTT, Home Assistant, or Node-RED.
- Enable LED animations to visually indicate listening and responding states.
- Deploy with a small eInk or OLED screen for text display of answers.
9. Consider
Building a Gemini-powered voice assistant on the Raspberry Pi empowers individuals to create customizable, private, and cost-effective alternatives to commercial voice assistants. By utilizing accessible hardware, modern open-source libraries, and powerful AI APIs, this project blends education, experimentation, and privacy-centric design into a single hands-on platform.
This guide can be adapted for personal use, educational programs, or even as a starting point for more advanced AI-based embedded systems.
References
- Raspberry Pi Foundation: https://www.raspberrypi.org
- Google Generative AI Documentation: https://ai.google.dev
- OpenAI Documentation: https://platform.openai.com
- SpeechRecognition Library: https://pypi.org/project/SpeechRecognition/
- gTTS Documentation: https://pypi.org/project/gTTS/
- Pygame Documentation: https://www.pygame.org/docs/
-
 @ a296b972:e5a7a2e8
2025-05-08 13:13:51
@ a296b972:e5a7a2e8
2025-05-08 13:13:51Sachzwangfreie, gesichert systemkritische Investigativ-Journalisten der unabhängigen, für Ausgewogenheit bekannten Mainstream-Medien, haben in jahrelanger Recherche den Rechtsruck Deutschlands beobachtet und nun in einem rund 5000 Seiten starken Gutachten dem Bundesamt für Verfassungsschutz zugespielt. Möglicherweise ist Erfahrung in der Veröffentlichung der Tagebücher eines verkannten Künstlers hierbei sehr hilfreich gewesen.
Nach sorgfältiger Überprüfung des Inland-Geheimdienstes konnte festgestellt werden, dass dem 3. Reich zugeschriebenes Gedankengut fortbesteht und dadurch die Unseredemokratie nachhaltig vergiftet ist. Bei der Beurteilung waren die Erkenntnisse der Gauck-Behörde von unschätzbarem Wert.
Ein Magazin, einst bekannt dafür, der Politik scharf auf die Finger zu schauen, und das auch die vorgenannten Tagebücher veröffentlicht hat (das war vor der Zeit, als ein ausgewachsener amerikanischer Voll-Philanthrop mit seiner Großzügigkeit die laufenden Strom- und Heizkosten des Verlagsgebäudes bezahlt hat), scheint hier seine Schreib-Fachkräfte zur Verfügung gestellt zu haben. Das könnte erklären, warum einige Details der nicht zu hinterfragenden Schrift an die Öffentlichkeit gelangt sind.
Schon im Grundgesetz kommt der durch das NS-Regime verbrannte Begriff „Volk“ zwölf Mal vor. So lebt die Ideologie, dass es ein deutsches Volk gibt, auch im Grundgesetz weiter. Vermutlich wurde durch Bestechung und Intrigen der Artikel 116 Absatz 1 hineingeschmuggelt, der besagt, wer Deutscher im Sinne des Grundgesetzes ist. Das fordert zwangsläufig eine dringend notwendige Prüfung, ob nicht das Grundgesetz selbst verfassungswidrig ist.
Mit Gründung der Bundesrepublik Deutschland wurde auch weiterhin im Straßenverkehr am Rechtsverkehr festgehalten, obwohl die Autoindustrie mit Beibehaltung des Lenkrades auf der linken Seite ein klares Zeichen gegen rechts gesetzt hat.
Der Ausbau des deutschen Autobahnnetzes wurde im 3. Reich stark vorangetrieben. Er diente vor allem dazu, eine schnelle Truppenbewegung zu ermöglichen. Schließlich sollte nach Goebbels, vor allem bekannt durch seine Rede im Sportpalast in Berlin, bestmögliche Kriegstüchtigkeit hergestellt werden. Die Waffenproduktion der Hermann-Göring-Werke, heute Rheinmetall, ließen die Hochöfen bereits dauerglühen.
Nach dem 2. Weltenbrand wurde der Ausbau des deutschen Autobahnnetzes weiter vorangetrieben. Statt sie zu entschärfen, wurden extreme Rechtskurven durch Leitplanken gesichert. Weniger scharfe Rechtskurven wurden in einer Liste als Verdachtsfall erfasst und werden seitdem intensiv beobachtet, die Unfallhäufigkeit wird ständig gemessen.
Ein weiteres Indiz für rechtes Gedankengut ist die Tatsache, dass eine bekannte Autofirma ihre Produkte auch in der Bundesrepublik nicht in Bürgerwagen umbenannt hat. So wurde in der Wirtschaftswunderzeit mit einem verfassungswidrigen Kraftfahrzeug mit 37 PS wild in der Gegend herumgefahren und durch Auslandsreisen, gerne an den Gardasee, der Begriff Volk in die ganze Welt getragen. Den Höhepunkt des Gipfels erreichte die Verfassungswidrigkeit jedoch dadurch, dass ein Werk in Brasilien den Bürgerwagen produzierte und so den gesamten amerikanischen Kontinent mit hässlichem Gedankengut verseuchte.
Deutsche Unternehmen, die aus Überzeugung Schrauben und Muttern mit Rechtsgewinde herstellen, können nur überzeugte Rechtsextremisten sein. Alles, was rechts ist oder rechts herum geht, muss zum Schutze von Unseredemokratie verfolgt und verboten werden. Auch die Buchhaltung der Unternehmen gehört reformiert, denn schließlich gibt es mit Soll und Haben eine linke und, staatsgefährdend, auch eine rechte Seite, auf der die Einnahmen und Ausgaben erfasst werden.
In großen Städten wurden nach der bedingungslosen Kapitulation der Wehrmacht Straßen und Plätze, die nach den „Größen“ des 3. Reichs benannt wurden, wieder umbenannt. Es wurde dabei versäumt, Parks in größeren Städten, die sich Volksgarten nennen, in Bürgergarten umzubenennen.
Auch wurde versäumt, ideologisch vergiftete Tischsitten zu reformieren. So liegt das Messer neben dem Teller weiterhin rechts. Die Absicht liegt sozusagen auf der Hand, denn das ist eine eindeutige Aufforderung zu Messergewalt, zumal die meisten Menschen Rechtshänder sind.
An der Schreibweise von links nach rechts wurde weiter festgehalten. Ein weiteres Anzeichen dafür, wie das Volk durch alltägliche Verrichtungen zu einer rechten Gesinnung durch dunkle Kräfte hingeleitet werden soll. Die Schreibweise „kursiv“ wurde nicht verboten, obwohl sie extrem rechts ist.
Offensichtlich wird auch die Indoktrination des Volkes, wenn vom für die Linken diskriminierenden Rechtsstaat die Rede ist. Menschen, die ein gesundes Rechtsverständnis haben, sind ideologisch vergiftet.
Die Auflösung von Familienstrukturen, einst die kleinste tragende Zelle der Gesellschaft, muss dringend umgesetzt werden, da verschworene Gruppen, die im Ernstfall wie Pech und Schwefel zusammenhalten, den Staat delegitimieren. Sie könnten zum Beispiel einen Familienausflug planen, von dem der Staat nichts weiß.
Ein Ehepaar, das nicht mehr zeitgemäß in einem Doppelbett schläft, ist höchstverdächtig. Der Ehepartner, der in einem Ehebett auf der rechten Seite sehr nah an der Bettkante schläft, schläft rechtsextrem. Wenn er ein Gitter am Bett hat, damit er nicht aus dem Bett fällt, schläft er sogar extrem gesichert rechts.
Der Verfassungsschutz muss dringend prüfen, ob nicht das gesamte deutsche Volk verboten werden sollte, denn es ist eindeutig so, dass das Volk völkisch ist und das darf in einer Unseredemokratie keinen Platz haben.
Mit Übergabe des Gutachtens an den Verfassungsschutz sieht dieser es als Geheimsache an, sodass er es aus Gründen des Staatswohls nicht denjenigen gegenüber zugänglich gemacht werden kann, die es betrifft, nämlich das völkische Volk.
Jenes Volk, das dank einer übermenschlichen Autoren-Anstrengung im wirtschaftlichen Bereich immer mehr den nicht mehr vorhandenen Pfennig und die nicht mehr vorhandene Mark umdrehen muss.
Als Volks-Sparmöglichkeiten gibt es jedoch noch:
· Im Outlet-Store Markenartikel 2. Wahl
· Auf dem Markt Spargel 2. Wahl
· Und jetzt auch einen Bundeskanzler 2. Wahl
Warum hat das undankbare deutsche Volk, das die Unseredemokratie nicht genug zu schätzen weiß, immer noch etwas zu meckern?
Wer jetzt behauptet, dass dieser Text absurd ist, der möge sich in der Realität umsehen. Da finden die wirklichen Absurditäten statt. Das hier ist nur Schwurbelei von jemandem, der die Welt nicht mehr versteht.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ c11cf5f8:4928464d
2025-05-08 11:51:12
@ c11cf5f8:4928464d
2025-05-08 11:51:12Here we are again with our monthly Magnificent Seven, the summary giving you a hit of what you missed in the ~AGORA territory.
Let's check our top performing post Ads!
Top-Performing Ads
This month, the most engaging ones are:
-
01[SELL] The Book of Bitcoin Mythology - Bitcoin accepted - ($21 + shipping) by @VEINTIUNO offering a printed version of the Bitcoin Mythology @spiral series, available online originally in English and translated by the post author in Spanish. 100 sats \ 6 comments \ 18 Apr -
02[SELL] Southwest voucher, 50k sats (digital code/ USA) by @BlokchainB, where he share a voucher Southwest Airlines. Have you sold it to @itsrealfake then? 206 sats \ 3 comments \ 27 Apr -
03SoapMiner Beef Tallow Soap by @PictureRoom, a review of a great handmade product sold P2P. 83 sats \ 2 comments \ 3 May -
04[SELL] Walter Whites Mega Package eBook (25000) by @MidnightShipper, return selling hand-picked ebooks from his/her huge collection 36 sats \ 4 comments \ 21 Apr -
05Medical Consultation (an update to a previous post) by @BTCLNAT, renewing prices and details of a previous Ad-post. Pretty fair still... 5k sats/consultation still a bargain! 100 sats \ 3 comments \ 22 Apr -
06[SELL] Bitcoin Education Playing Cards $30 Bitcoin accepted by @NEEDcreations, releasing a new updated edition, ow available for sale on the 360BTC's pleb shop 19 sats \ 0 comments \ 30 Apr -
07OFFICIAL - VINTAGE - Marlboro Zippo - Real & WORKS by @watchmancbiz, returns with just a link to SatStash for more info on the auction 0 sats \ 0 comments \ 3 May
A quick reminder that now you ca setup auctions here in the AGORA too! Learn how. The other feature released last month was the introduction of Shopfronts on SN. Check our SN Merch and SN Zine examples. Thank you all! Let's keep these trades coming and grow the P2P Bitcoin circular economy!
Lost & Found in SN' Wild West Web
Stay with me, we're not done yet! I found plenty of other deals and offers in other territories too..
- Private Package Delivery where @Jon_Hodl share his experience on receiving one personally
- 🚨 VIP-Only Flash Sale: Bitaxe Gamma for $125 by @siggy47, grabbing one of these bad boys.
- Where do you sell books for Bitcoin, besides on ~Agora Territory? by @hasherstacker, asking ~BooksAndArticles community. Do you have a book to sell? Let me know how I can help!
- This best-selling book on ‘abundance’ has got it wrong - Max Rashbrooke by @Solomonsatoshi sharing an interesting external article.
- Trump Store Selling ‘Trump 2028’ Hats Trump Says He’s ‘Not Joking’ another interesting article shared by our dear friend @CarlTuckerson
Wow, such an exciting month!
Active Professional Services accepting Bitcoin in the AGORA
Let us know if we miss any, here below the most memorable ones: - https://stacker.news/items/900208/r/AG @unschooled offering Language Tutoring - https://stacker.news/items/813013/r/AG @gpvansat's [OFFER][Graphic Design] From the paste editions (It's important to keep these offers available) - https://stacker.news/items/775383/r/AG @TinstrMedia - Color Grading (Styling) Your Pictures as a Service - https://stacker.news/items/773557/r/AG @MamaHodl, MATHS TUTOR 50K SATS/hour English global - https://stacker.news/items/684163/r/AG @BTCLNAT's OFFER HEALTH COUNSELING [5K SAT/ consultation - https://stacker.news/items/689268/r/AG @mathswithtess [SELL] MATHS TUTOR ONILINE, 90k sats per hour. Global but English only.
Let me know if I'm missing other stackers offering services around here!
In case you missed
Here some interesting post, opening conversations and free speech about markets and business on the bitcoin circular economy:
- https://stacker.news/items/972209/r/AG Here Comes Bitcoin Swag Shop by @k00b
- https://stacker.news/items/969011/r/AG Sales Corner (Prospecting) by @Akg10s3
- https://stacker.news/items/971914/r/AG Satoshi Escrow A Bitcoin non-custodial P2P dispute resolution using Nostr keys by @AGORA
- https://stacker.news/items/972209/r/AG Twin Cities Outdoor Agora Market by @k00b
- https://stacker.news/items/942025/r/AG How to create your Shopfront on STACKER NEWS to upsell your products & services by @AGORA
BUYing or SELLing Cowboys Credits?
BUY or SELL them in the ~AGORA marketplace
Here's what stackers have to offers: - [SWAP] SN Cowboy credits by @DarthCoin - https://stacker.news/items/758411/r/AG by @SimpleStacker that also shares a CCs market analysis. - [BUY] 100 cowboy credits for one satoshi by @ek - Will Pay Sats For Cowboy Credits by @siggy47 - 📢 CCs to Sats Exchange Megathread recently started by @holonite, not sure why in ~bitcoin. Consider the ~AGORA next time ;)
🏷️ Spending Sunday and Selling weekly?
Share your most recent Bitcoin purchases of just check what other stackers are buying with their sats! All series available here: Or read the latest one from https://stacker.news/items/970896/r/AG
📢 Thursday Talks: What have you sold for Bitcoin this week?
Our recently launched weekly series going out every Thursday. In the past one, I collected all @Akg10s3's Sales Corner posts. Fresh out of the box, today edition https://stacker.news/items/974581/r/AG
Create your Ads now!
Looking to start something new? Hit one of the links below to free your mind:
- 💬 TOPIC for conversation,
- [⚖️ SELL] anything! or,
- if you're looking for something, hit the [🛒 BUY]!
- [🧑💻 HIRE] any bitcoiner skill or stuff from bitcoiners
- [🖇 OFFER] any product or service and stack more sats
- [🧑⚖️ AUCTION] to let stackers decide a fair price for your item
- [🤝 SWAP] if you're looking to exchange anything with anything else
- [🆓 FREE] your space, make a gift!
- Start your own [SHOPFRONT] or simply...
- [⭐ REVIEW] any bitcoin product or LN service you recently bought or subscribed to.
Or contact @AGORA team on nostr DM, and we can help you publish a personalized post.
.
#nostr#bitcoin#stuff4sats#sell#buy#plebchain#grownostr#asknostr#market#businessoriginally posted at https://stacker.news/items/974611
-
-
 @ 9c35fe6b:5977e45b
2025-05-08 11:49:44
@ 9c35fe6b:5977e45b
2025-05-08 11:49:44Into the Heart of the Desert If you're looking for an adventure beyond the ordinary, Egypt Safari Tours with ETB Tours Egypt offer an unforgettable escape into the Egyptian desert. Venture into the golden sands of the White Desert, Bahariya Oasis, or Siwa, where time seems to stand still. This is more than sightseeing — it's a soul-stirring journey.
Exclusive Experiences with Egypt Private Tours For those who value privacy and exclusivity, ETB Tours Egypt designs tailor-made Egypt private tours that bring the desert to life on your terms. Whether it's a sunset camel ride, a 4x4 dune adventure, or camping under the stars, your itinerary is crafted just for you.
Explore More with Egypt Vacation Packages Why stop at the desert? Combine your safari adventure with cultural highlights and coastal escapes through our curated Egypt vacation packages. Enjoy the perfect balance between relaxation and exploration as you transition from the desert to the Nile.
Budget-Friendly Desert Escapes Traveling on a budget doesn’t mean you have to sacrifice experience. ETB Tours Egypt offers incredible Egypt budget tours that make desert adventures accessible to all. With professional guides and well-organized itineraries, you’ll enjoy value-packed experiences at an affordable price.
All Inclusive Egypt Vacations: Worry-Free Travel Enjoy stress-free travel with our all inclusive Egypt vacations. From hotel stays and meals to guided safaris and transportation, every detail is taken care of. Just bring your adventurous spirit—we’ll handle the rest.
Combine Desert Thrills with Ancient Wonders Turn your desert safari into a grand journey by including one of our Egypt pyramid tour packages. Witness the mystique of the Pyramids of Giza before heading into the vast desert—blending ancient history with modern adventure To Contact Us: E-Mail: info@etbtours.com Mobile & WhatsApp: +20 10 67569955 - +201021100873 Address: 4 El Lebeny Axis, Nazlet Al Batran, Al Haram, Giza, Egypt
-
 @ 0861144c:e68a1caf
2025-05-08 11:45:52
@ 0861144c:e68a1caf
2025-05-08 11:45:52May 7th - Asuncion, Paraguay
We made trhe 11th meetup of our community. This time, we reached an ATH of atendees, almost 150 people. This time, we were talking about bitcoin for begginers and for the main event I made a presentation a about Robosats, encouraging people to take orders, buy bitcoin and most of it, make your life better.
The motto this time was: this is not about being a trader. It's about happiness.
Bitcoin can help you find new ways to explore the best version of yourself because right now people are looking anti-inflation methods for not lose money. In every meetup, we're encouraging our new members to embrace and adopt bitcoin for their products/services.
Most of them are skeptics (at first) when I say that Lightning Network is cheaper as f**k. I show them the fee paid, their eyes...it's the aha moment for them.
I'm happy and bullish af.
originally posted at https://stacker.news/items/974608
-
 @ d34e832d:383f78d0
2025-04-26 14:33:06
@ d34e832d:383f78d0
2025-04-26 14:33:06Gist
This Idea presents a blueprint for creating a portable, offline-first education server focused on Free and Open Source Software (FOSS) topics like Bitcoin fundamentals, Linux administration, GPG encryption, and digital self-sovereignty. Using the compact and powerful Nookbox G9 NAS unit, we demonstrate how to deliver accessible, decentralized educational content in remote or network-restricted environments.
1. Bitcoin, Linux, and Cryptographic tools
Access to self-sovereign technologies such as Bitcoin, Linux, and cryptographic tools is critical for empowering individuals and communities. However, many areas face internet connectivity issues or political restrictions limiting access to online resources.
By combining a high-performance mini NAS server with a curated library of FOSS educational materials, we can create a mobile "university" that delivers critical knowledge independently of centralized networks.
2. Hardware Platform: Nookbox G9 Overview
The Nookbox G9 offers an ideal balance of performance, portability, and affordability for this project.
2.1 Core Specifications
| Feature | Specification | |:------------------------|:---------------------------------------| | Form Factor | 1U Rackmount mini-NAS | | Storage | Up to 8TB (4×2TB M.2 NVMe SSDs) | | M.2 Interface | PCIe Gen 3x2 per drive slot | | Networking | Dual 2.5 Gigabit Ethernet ports | | Power Consumption | 11–30 Watts (typical usage) | | Default OS | Windows 11 (to be replaced with Linux) | | Linux Compatibility | Fully compatible with Ubuntu 24.10 |
3. FOSS Education Server Design
3.1 Operating System Setup
- Replace Windows 11 with a clean install of Ubuntu Server 24.10.
- Harden the OS:
- Enable full-disk encryption.
- Configure UFW firewall.
- Disable unnecessary services.
3.2 Core Services Deployed
| Service | Purpose | |:--------------------|:-----------------------------------------| | Nginx Web Server | Host offline courses and documentation | | Nextcloud (optional) | Offer private file sharing for students | | Moodle LMS (optional) | Deliver structured courses and quizzes | | Tor Hidden Service | Optional for anonymous access locally | | rsync/Syncthing | Distribute updates peer-to-peer |
3.3 Content Hosted
- Bitcoin: Bitcoin Whitepaper, Bitcoin Core documentation, Electrum Wallet tutorials.
- Linux: Introduction to Linux (LPIC-1 materials), bash scripting guides, system administration manuals.
- Cryptography: GPG tutorials, SSL/TLS basics, secure communications handbooks.
- Offline Tools: Full mirrors of sites like LearnLinux.tv, Bitcoin.org, and selected content from FSF.
All resources are curated to be license-compliant and redistributable in an offline format.
4. Network Configuration
- LAN-only Access: No reliance on external Internet.
- DHCP server setup for automatic IP allocation.
- Optional Wi-Fi access point using USB Wi-Fi dongle and
hostapd. - Access Portal: Homepage automatically redirects users to educational content upon connection.
5. Advantages of This Setup
| Feature | Advantage | |:-----------------------|:----------------------------------------| | Offline Capability | Operates without internet connectivity | | Portable Form Factor | Fits into field deployments easily | | Secure and Hardened | Encrypted, compartmentalized, and locked down | | Modular Content | Easy to update or expand educational resources | | Energy Efficient | Low power draw enables solar or battery operation | | Open Source Stack | End-to-end FOSS ecosystem, no vendor lock-in |
6. Deployment Scenarios
- Rural Schools: Provide Linux training without requiring internet.
- Disaster Recovery Zones: Deliver essential technical education in post-disaster areas.
- Bitcoin Meetups: Offer Bitcoin literacy and cryptography workshops in remote communities.
- Privacy Advocacy Groups: Teach operational security practices without risking network surveillance.
7. Performance Considerations
Despite PCIe Gen 3x2 limitations, the available bandwidth (~2GB/s theoretical) vastly exceeds the server's 2.5 Gbps network output (~250MB/s), making it more than sufficient for a read-heavy educational workload.
Thermal Management:
Given the G9’s known cooling issues, install additional thermal pads or heatsinks on the NVMe drives. Consider external USB-powered cooling fans for sustained heavy usage.
8. Ways To Extend
- Multi-language Support: Add localized course materials.
- Bitcoin Node Integration: Host a lightweight Bitcoin node (e.g., Bitcoin Core with pruning enabled or a complete full node) for educational purposes.
- Mesh Networking: Use Mesh Wi-Fi protocols (e.g., cjdns or Yggdrasil) to allow peer-to-peer server sharing without centralized Wi-Fi.
9. Consider
Building a Portable FOSS Education Server on a Nookbox G9 is a practical, scalable solution for democratizing technical knowledge, empowering communities, and defending digital sovereignty in restricted environments.
Through thoughtful system design—leveraging open-source software and secure deployment practices—we enable resilient, censorship-resistant education wherever it's needed.
📎 References
-
 @ 866e0139:6a9334e5
2025-05-08 11:42:26
@ 866e0139:6a9334e5
2025-05-08 11:42:26Autor: Lilly Gebert. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wie fühlst Du dich, nachdem Du mit deinem Partner oder deiner Partnerin, oder sonst einem Menschen geschlafen hast – nachdem der Drang und die Erregung ein Ende gefunden haben? Gut – oder schlecht? Befriedigt – oder unbefriedigt? Verbunden – oder getrennt? Erfüllt – oder leer? Was geht dir durch den Kopf? Warum überhaupt geht dir irgendetwas durch den Kopf? Warum bleibst Du dich nicht in deinem Körper – in seiner noch anhaltenden Nähe zu dem Körper, mit dem Du gerade noch eins warst? Vielleicht weil Du dich davon ablenken möchtest, dass ihr gerade dies nicht wart? Dass ihr nicht «eins» wart; sondern zwei, die für einen Moment Druck abgelassen haben – ohne höheren Sinn und ohne tieferes Gefühl? Ist das der Grund, weswegen Du lieber in die Verklärungen deines Verstandes abdriftest, anstatt die gerade erlebte Verbindung noch etwas in deinem Körper nachklingen zu lassen? Ist das allgemein der Grund, weswegen Du lieber in Rationalitäten lebst? Um dir nicht eingestehen zu müssen, wie unverbunden Du wirklich bist? Wie unverbunden und allein, ohne tiefere Verbindung zu dir oder einem anderen Menschen? Ist es das? Ist es das, was Du einfach nicht wahrhaben kannst? Und weswegen Du lieber die Masse an Oberflächlichkeit suchst, um bloß nie in einer Beziehung zu enden, in der Du an deine eigene Unfähigkeit erinnert wirst, gerade dies zu sein – in Beziehung?
***
Vielleicht beginnt alle Trennung dieser Welt mit der Verwechslung von Sex und Nähe, Nähe und Liebe, als auch Liebe und Frieden. Du sehnst dich nach dem einen und jagst doch dem anderen hinterher. Wie kann das sein?
Liegt es daran, dass Du als Kind keine stabilen Beziehungen erfahren hast und diese aus dem Grund auch im Erwachsenenalter nicht leben kannst? Hast Du einst schlechte Erfahrungen mit Intimität und Nähe gemacht, aufgrund derer etwas in dir diese fortwährend verhindert, um dich zu «schützen»? Hältst Du dich selbst für nicht liebenswert und kannst deshalb auch im Außen keine Liebe annehmen? Oder hast Du Angst davor, durch die Nähe und Berührung eines anderen Menschen von etwas in dir selbst berührt zu werden, an dessen Existenz Du nicht erinnert werden möchtest?
Falls ja, warum gehst Du dann fortwährend «Beziehungen» zu anderen Menschen ein, bevor Du nicht die Beziehung zu dir selbst geklärt hast? Hast Du wirklich so sehr verlernt zu lieben und so weit vergessen, was Liebe ist, dass Du dich damit zufriedengibst? Ich glaube kaum. Und ich glaube, Du spürst das auch. Ganz tief in dir sehnt auch deine Seele sich nach einer Begegnung, in der Du nichts von dir zurückhalten musst. In der Du ganz, und damit ganz Du sein kannst.
Doch was machst Du stattdessen? Du unterdrückst diese Sehnsucht, verneinst deinen innersten Herzenswunsch nach Berührung, nach Nähe, nach Liebe. Und damit auch jedes Bedürfnis, was mit seinem ausbleibenden Ausdruck ebenfalls unterdrückt wird. Langsam, ganz langsam hörst Du auf, über deine Gefühle zu sprechen, Du hörst auf, deine Grenzen zu wahren, das zu machen, was dich dir selbst näherbringt. Auf diese Weise machst Du dich selbst nicht nur immer kleiner, Du entfernst dich auch zusehends von deiner eigenen Lebendigkeit – dem eigentlichen Schlüssel zu jeder Beziehung, die nicht von Besitz und Lustbefriedigung, sondern von Selbstsein und Nähe getragen wird.
Falsche Versprechen: Verbindung statt Symbiose
Erich Fromm war es, der mit seinem 1956 erschienenen und insgesamt über 25 Millionen Mal verkauften Werk «Die Kunst des Liebens» erstmals herausgearbeitet hat, wie zerstörerisch unsere moderne Konsumgesellschaft doch für die Art und Weise ist, wie wir Beziehungen eingehen. Nicht nur die untereinander und zu uns selbst, sondern auch die zu Tier und Natur. Liebe, so schreibt Fromm, ist allem voran eine Haltung des Seins, nicht des Habens. Es gehe nicht darum, den anderen zu besitzen oder von ihm in Besitz genommen zu werden. Nicht Verschmelzung sei das Ziel, sondern das Selbstsein mit, oder auch trotz, der anderen Person.
Ohne dieses Selbstsein, das durch den modernen Glauben, alles sei käuflich, insofern untergraben wurde, dass nun auch der Mensch und seine Beziehungen als Objekte betrachtet würden, gäbe es laut Fromm keine Nähe – und ohne Nähe keinen wahren Frieden. «Sexualität», so schreibt er, könne «ein Mittel sein, um die Isolation zu überwinden – aber sie kann auch ein Ersatz für Liebe sein.» Womit ich hinzufügen würde: Wie Sexualität ein Ersatz für Liebe sein kann, so werden heute Konsum, Sicherheit und Ablenkung zum Ersatz für wahren Frieden. Und gleich wie Nähe zur Illusion von Intimität werden kann, werden falsche Sicherheitsversprechen oft zur Maskerade des Friedens – einer Stille, die nichts heilt.
Das ist der Zustand unserer Zeit: Sexualität ersetzt Liebe, Waffen ersetzen Frieden. Doch genauso wie Sex in Wahrheit keine Liebe ersetzt, ersetzt auch ein Wettrüsten keinen Frieden. Beides täuscht Nähe und Sicherheit vor, wo eigentlich Distanz und Kälte herrschen. Von ihnen eingenommen, hältst Du die Liebe, die dein Körper imitiert, für echt, und die äußere Ordnung, die dir simuliert wird, für den Frieden, von dem Du glauben, Du würdest ihn in dir tragen. Dabei bleibt beides leer, wenn dein Herz nicht mitgeht. Da ist weder Ordnung im Außen, noch Frieden in deinem Innern. Was herrscht, ist Krieg. Innen wie außen.

Wut im Innern, Krieg im Außen
Wer Nähe meidet, verlernt Frieden. Denn Frieden beginnt dort, wo Du aushältst, was ist. Nicht im Politischen, sondern in deiner eigenen Gerichtskammer: dem Austarieren und Verhandeln der eigenen Gefühle und Bedürfnisse – dem Eingeständnis, dass am Ende nicht der Sex das Problem ist, sondern dein Umgang mit Nähe; deine Unfähigkeit, mit dir selbst in Frieden zu sein – und dies darum auch mit dem Rest der Welt nicht bist. Nenn’ es Karma, das Gesetz der Anziehung oder eine traumatische Rückkopplungsschleife; aber wo immer Du diesen Blick nicht vom Außen zurück auf das Minenfeld in dir wendest, wird sich sein Krieg solange fortsetzen, bis Du der Wut, die mit ihm in dir hochkocht, Dampf verschaffst. Ob auf konstruktive oder destruktive Weise hängt davon ab, wie früh Du sie als das erkennst, woraus sie sich speist: deine unterdrückten Gefühle.
«Das grundsätzliche Ausweichen vor dem Wesentlichen ist das Problem des Menschen.» – Wilhelm Reich
In dieser Hinsicht noch radikaler als Fromm ging Wilhelm Reich vor. Als Schüler Sigmund Freuds sah er sexuelle Unterdrückung als Wurzel aller gesellschaftlichen Gewalt. Nur wer sexuell befreit sei – im Sinne von energetisch gelöst und beziehungsfähig – könne inneren Frieden erfahren. Ginge es nach Reich, so hängt gesellschaftlicher Frieden unmittelbar davon ab, wie weit es uns gelingt, uns körperlich zu entpanzern und emotional zu öffnen. Womit sein Ansatz in der Idee gipfelte, dass die gesellschaftliche Ordnung nicht durch äußere Gesetze, sondern durch die innere Struktur des Einzelnen geprägt wird. Diametral zu Marx, demzufolge es nicht das Bewusstsein der Menschen sei, das ihr Sein bestimmt, sondern umgekehrt ihr gesellschaftliches Sein, das ihr Bewusstsein bestimmt, beschrieb Reich also, wie emotionale Blockaden im Körper verankert seien und sich dort als chronische Spannungen manifestierten. Diese Panzerungen würden nicht nur freie Gefühlsäußerung verhindern, sondern stauten auch lebendige Energie an, was zu Aggression, Entfremdung und letztlich zu kollektiver Gewalt führen könne. Frieden, so Reich, beginne nicht in politischen Institutionen, sondern in der Fähigkeit des Einzelnen, Angst und Abwehr abzubauen, sich selbst zu spüren – und andere nicht als Bedrohung, sondern als lebendige Gegenüber wahrzunehmen.
Warum wir dies scheinbar nicht mehr können, warum aber kein Weg daran vorbeiführt, über den Frieden in uns heilsame Beziehungen einzugehen, wollen wir den Frieden auch außerhalb von uns – in der Welt, folgt im zweiten Teil dieses Texts.
Lilly Gebert betreibt den Substack-Blog "Treffpunkt im Unendlichen" und schreibt regelmäßig für "die Freien" und Manova. Zuletzt erschien von ihr "Das Gewicht der Welt". Im Herbst erscheint "Sein statt Haben. Enzyklopädie für eine neue Zeit." (vorbestellbar).
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ d34e832d:383f78d0
2025-04-26 07:17:45
@ d34e832d:383f78d0
2025-04-26 07:17:45Practical Privacy and Secure Communications
1. Bootable privacy operating systems—Tails, Qubes OS, and Whonix****
This Idea explores the technical deployment of bootable privacy operating systems—Tails, Qubes OS, and Whonix—for individuals and organizations seeking to enhance operational security (OpSec). These systems provide different layers of isolation, anonymity, and confidentiality, critical for cryptographic operations, Bitcoin custody, journalistic integrity, whistleblowing, and sensitive communications. The paper outlines optimal use cases, system requirements, technical architecture, and recommended operational workflows for each OS.
2. Running An Operating System
In a digital world where surveillance, metadata leakage, and sophisticated threat models are realities, bootable privacy OSs offer critical mitigation strategies. By running an operating system from a USB, DVD, or external drive—and often entirely in RAM—users can minimize the footprint left on host hardware, dramatically enhancing privacy.
This document details Tails, Qubes OS, and Whonix: three leading open-source projects addressing different aspects of operational security.
3. Technical Overview of Systems
| OS | Focus | Main Feature | Threat Model | |------------|---------------------------|-----------------------------------------------|--------------------------------| | Tails | Anonymity & Ephemerality | Runs entirely from RAM; routes traffic via Tor | For activists, journalists, Bitcoin users | | Qubes OS | Security through Compartmentalization | Hardware-level isolation via Xen hypervisor | Defense against malware, APTs, insider threats | | Whonix | Anonymity over Tor Networks | Split-Gateway Architecture (Whonix-Gateway & Whonix-Workstation) | For researchers, Bitcoin node operators, privacy advocates |
4. System Requirements
4.1 Tails
- RAM: Minimum 2 GB (4 GB recommended)
- CPU: x86_64 (Intel or AMD)
- Storage: 8GB+ USB stick (optional persistent storage)
4.2 Qubes OS
- RAM: 16 GB minimum
- CPU: Intel VT-x or AMD-V support required
- Storage: 256 GB SSD recommended
- GPU: Minimal compatibility (no Nvidia proprietary driver support)
4.3 Whonix
- Platform: VirtualBox/KVM Host (Linux, Windows, Mac)
- RAM: 4 GB minimum (8 GB recommended)
- Storage: 100 GB suggested for optimal performance
5. Deployment Models
| Model | Description | Recommended OS | |--------------------------|-----------------------------------|------------------------------| | USB-Only Boot | No installation on disk; ephemeral use | Tails | | Hardened Laptop | Full disk installation with encryption | Qubes OS | | Virtualized Lab | VMs on hardened workstation | Whonix Workstation + Gateway |
6. Operational Security Advantages
| OS | Key Advantages | |------------|----------------------------------------------------------------------------------------------------| | Tails | Memory wipe at shutdown, built-in Tor Browser, persistent volume encryption (LUKS) | | Qubes OS | Compartmentalized VMs for work, browsing, Bitcoin keys; TemplateVMs reduce attack surface | | Whonix | IP address leaks prevented even if the workstation is compromised; full Tor network integration |
7. Threat Model Coverage
| Threat Category | Tails | Qubes OS | Whonix | |----------------------------|-----------------|------------------|------------------| | Disk Forensics | ✅ (RAM-only) | ✅ (with disk encryption) | ✅ (VM separation) | | Malware Containment | ❌ | ✅ (strong) | ✅ (via VMs) | | Network Surveillance | ✅ (Tor enforced) | Partial (needs VPN/Tor setup) | ✅ (Tor Gateway) | | Hardware-Level Attacks | ❌ | ❌ | ❌ |
8. Use Cases
- Bitcoin Cold Storage and Key Signing (Tails)
- Boot Tails offline for air-gapped Bitcoin signing.
- Private Software Development (Qubes)
- Use separate VMs for coding, browsing, and Git commits.
- Anonymous Research (Whonix)
- Surf hidden services (.onion) without IP leak risk.
- Secure Communications (All)
- Use encrypted messaging apps (Session, XMPP, Matrix) without metadata exposure.
9. Challenges and Mitigations
| Challenge | Mitigation | |---------------------|---------------------------------------------| | Hardware Incompatibility | Validate device compatibility pre-deployment (esp. for Qubes) | | Tor Exit Node Surveillance | Use onion services or bridge relays (Tails, Whonix) | | USB Persistence Risks | Always encrypt persistent volumes (Tails) | | Hypervisor Bugs (Qubes) | Regular OS and TemplateVM updates |
Here’s a fully original technical whitepaper version of your request, rewritten while keeping the important technical ideas intact but upgrading structure, language, and precision.
Executive Summary
In a world where digital surveillance and privacy threats are escalating, bootable privacy operating systems offer a critical solution for at-risk individuals. Systems like Tails, Qubes OS, and Whonix provide strong, portable security by isolating user activities from compromised or untrusted hardware. This paper explores their architectures, security models, and real-world applications.
1. To Recap
Bootable privacy-centric operating systems are designed to protect users from forensic analysis, digital tracking, and unauthorized access. By booting from an external USB drive or DVD and operating independently from the host machine's internal storage, they minimize digital footprints and maximize operational security (OpSec).
This paper provides an in-depth technical analysis of: - Tails (The Amnesic Incognito Live System) - Qubes OS (Security through Compartmentalization) - Whonix (Anonymity via Tor Isolation)
Each system’s strengths, limitations, use cases, and installation methods are explored in detail.
2. Technical Overview of Systems
2.1 Tails (The Amnesic Incognito Live System)
Architecture:
- Linux-based Debian derivative. - Boots from USB/DVD, uses RAM exclusively unless persistent storage is manually enabled. - Routes all network traffic through Tor. - Designed to leave no trace unless explicitly configured otherwise.Key Features:
- Memory erasure on shutdown. - Pre-installed secure applications: Tor Browser, KeePassXC, OnionShare. - Persistent storage available but encrypted and isolated.Limitations:
- Limited hardware compatibility (especially Wi-Fi drivers). - No support for mobile OS platforms. - ISP visibility to Tor network usage unless bridges are configured.
2.2 Qubes OS
Architecture:
- Xen-based hypervisor model. - Security through compartmentalization: distinct "qubes" (virtual machines) isolate tasks and domains (work, personal, banking, etc.). - Networking and USB stacks run in restricted VMs to prevent direct device access.Key Features:
- Template-based management for efficient updates. - Secure Copy (Qubes RPC) for data movement without exposing full disks. - Integrated Whonix templates for anonymous browsing.Limitations:
- Requires significant hardware resources (RAM and CPU). - Limited hardware compatibility (strict requirements for virtualization support: VT-d/IOMMU).
2.3 Whonix
Architecture:
- Debian-based dual VM system. - One VM (Gateway) routes all traffic through Tor; the second VM (Workstation) is fully isolated from the physical network. - Can be run on top of Qubes OS, VirtualBox, or KVM.Key Features:
- Complete traffic isolation at the system level. - Strong protections against IP leaks (fails closed if Tor is inaccessible). - Advanced metadata obfuscation options.Limitations:
- High learning curve for proper configuration. - Heavy reliance on Tor can introduce performance bottlenecks.
3. Comparative Analysis
| Feature | Tails | Qubes OS | Whonix | |:--------|:------|:---------|:-------| | Anonymity Focus | High | Medium | High | | System Isolation | Medium | Very High | High | | Persistence | Optional | Full | Optional | | Hardware Requirements | Low | High | Medium | | Learning Curve | Low | High | Medium | | Internet Privacy | Mandatory Tor | Optional Tor | Mandatory Tor |
4. Use Cases
| Scenario | Recommended System | |:---------|:--------------------| | Emergency secure browsing | Tails | | Full system compartmentalization | Qubes OS | | Anonymous operations with no leaks | Whonix | | Activist communications from hostile regions | Tails or Whonix | | Secure long-term project management | Qubes OS |
5. Installation Overview
5.1 Hardware Requirements
- Tails: Minimum 2GB RAM, USB 2.0 or higher, Intel or AMD x86-64 processor.
- Qubes OS: Minimum 16GB RAM, VT-d/IOMMU virtualization support, SSD storage.
- Whonix: Runs inside VirtualBox or Qubes; requires host compatibility.
5.2 Setup Instructions
Tails: 1. Download latest ISO from tails.net. 2. Verify signature (GPG or in-browser). 3. Use balenaEtcher or dd to flash onto USB. 4. Boot from USB, configure Persistent Storage if necessary.
Qubes OS: 1. Download ISO from qubes-os.org. 2. Verify using PGP signatures. 3. Flash to USB or DVD. 4. Boot and install onto SSD with LUKS encryption enabled.
Whonix: 1. Download both Gateway and Workstation VMs from whonix.org. 2. Import into VirtualBox or a compatible hypervisor. 3. Configure VMs to only communicate through the Gateway.
6. Security Considerations
- Tails: Physical compromise of the USB stick is a risk. Use hidden storage if necessary.
- Qubes OS: Qubes is only as secure as its weakest compartment; misconfigured VMs can leak data.
- Whonix: Full reliance on Tor can reveal usage patterns if used carelessly.
Best Practices: - Always verify downloads via GPG. - Use a dedicated, non-personal device where possible. - Utilize Tor bridges if operating under oppressive regimes. - Practice OPSEC consistently—compartmentalization, metadata removal, anonymous communications.
7. Consider
Bootable privacy operating systems represent a critical defense against modern surveillance and oppression. Whether for emergency browsing, long-term anonymous operations, or full-stack digital compartmentalization, solutions like Tails, Qubes OS, and Whonix empower users to reclaim their privacy.
When deployed thoughtfully—with an understanding of each system’s capabilities and risks—these tools can provide an exceptional layer of protection for journalists, activists, security professionals, and everyday users alike.
10. Example: Secure Bitcoin Signing Workflow with Tails
- Boot Tails from USB.
- Disconnect from the network.
- Generate Bitcoin private key or sign transaction using Electrum.
- Save signed transaction to encrypted USB drive.
- Shut down to wipe RAM completely.
- Broadcast transaction from a separate, non-sensitive machine.
This prevents key exposure to malware, man-in-the-middle attacks, and disk forensic analysis.
11. Consider
Bootable privacy operating systems like Tails, Qubes OS, and Whonix offer robust, practical strategies for improving operational security across a wide spectrum of use cases—from Bitcoin custody to anonymous journalism. Their open-source nature, focus on minimizing digital footprints, and mature security architectures make them foundational tools for modern privacy workflows.
Choosing the appropriate OS depends on the specific threat model, hardware available, and user needs. Proper training and discipline remain crucial to maintain the security these systems enable.
Appendices
A. Download Links
B. Further Reading
- "The Qubes OS Architecture" Whitepaper
- "Operational Security and Bitcoin" by Matt Odell
- "Tor and the Darknet: Separating Myth from Reality" by EFF