-

@ 68c90cf3:99458f5c
2025-04-04 16:06:10
I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs.
YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each.
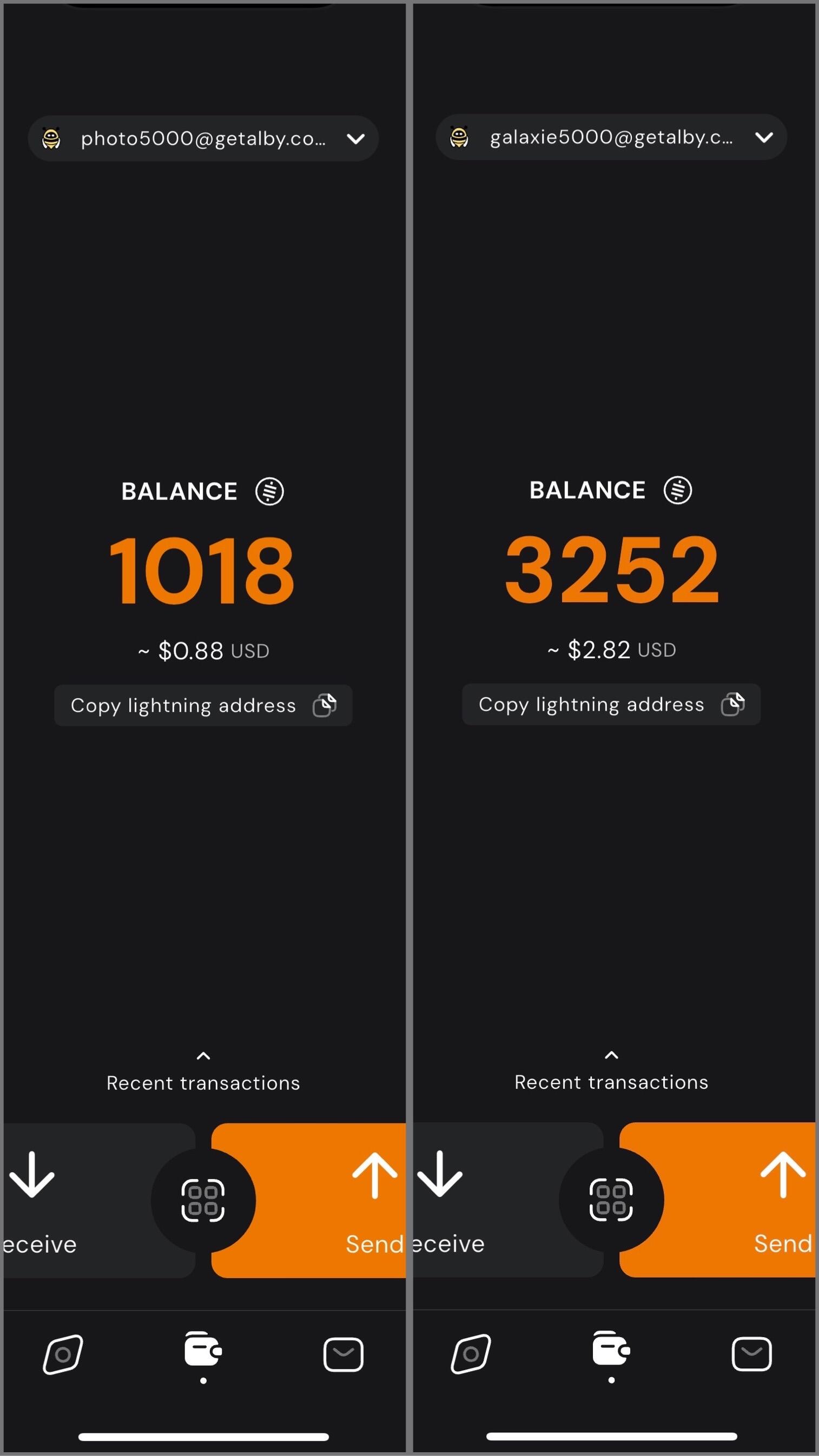
In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions.
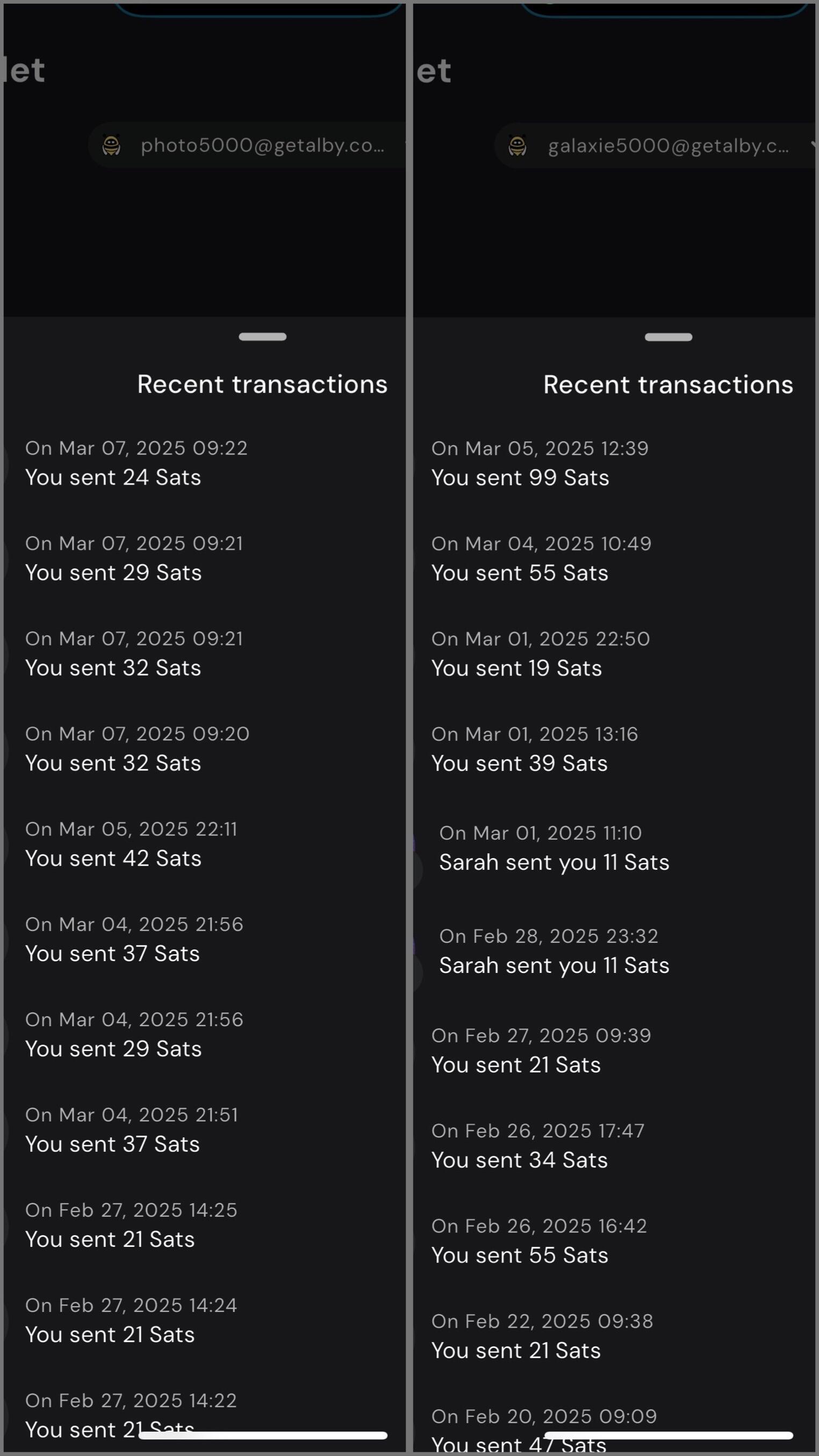
Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne.
#YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr
-

@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20
<h2> Test Video Document </h2>
-

@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02
<h1> Testy McTestenface </h1>
<p> It's been so long, html </p>
-

@ 39cc53c9:27168656
2025-03-30 05:54:53
> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks)
Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
## Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals.
## KYC? Not you.
> KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2]
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
## You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
## Your identity has been stolen
KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3]
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
## (they) Know Your Coins
You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
## Conclusions
To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
> Edited 20/03/2024
> * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1]
[^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/
[^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz
[^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
-

@ 04c915da:3dfbecc9
2025-03-26 20:54:33
Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-

@ b2d670de:907f9d4a
2025-03-25 20:17:57
This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
## Table of Contents
1. Prerequisites
2. Initial Server Setup
3. Installing Strfry Nostr Relay
4. Configuring Your Relay
5. Setting Up TOR
6. Making Your Relay Available on TOR
7. Testing Your Setup]
8. Maintenance and Security
9. Troubleshooting
## Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
## Initial Server Setup
First, let's make sure your server is properly set up and secured.
### Update Your System
Connect to your server via SSH and update your system:
```bash
sudo apt update
sudo apt upgrade -y
```
### Set Up a Basic Firewall
Install and configure a basic firewall:
```bash
sudo apt install ufw -y
sudo ufw allow ssh
sudo ufw enable
```
This allows SSH connections while blocking other ports for security.
## Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md).
### Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
```bash
sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev
```
Here's why each dependency is needed:
**Basic Development Tools:**
- `git`: Version control system used to clone the Strfry repository and manage code updates
- `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools
**Perl Dependencies** (used for Strfry's build scripts):
- `libyaml-perl`: Perl interface to parse YAML configuration files
- `libtemplate-perl`: Template processing system used during the build process
- `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts
**Core Libraries for Strfry:**
- `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations
- `zlib1g-dev`: Compression library that Strfry uses to reduce data size
- `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend
- `libflatbuffers-dev`: Memory-efficient serialization library for structured data
- `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures
- `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission
### Clone and Build Strfry
Clone the Strfry repository:
```bash
git clone https://github.com/hoytech/strfry.git
cd strfry
```
Build Strfry:
```bash
git submodule update --init
make setup-golpe
make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)
```
This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
### Install Strfry
Install the Strfry binary to your system path:
```bash
sudo cp strfry /usr/local/bin
```
This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.
## Configuring Your Relay
### Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
```bash
sudo useradd -M -s /usr/sbin/nologin strfry
```
The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts.
### Create Data Directory
Create a directory for Strfry's data:
```bash
sudo mkdir /var/lib/strfry
sudo chown strfry:strfry /var/lib/strfry
sudo chmod 755 /var/lib/strfry
```
This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
### Configure Strfry
Copy the sample configuration file:
```bash
sudo cp strfry.conf /etc/strfry.conf
```
Edit the configuration file:
```bash
sudo nano /etc/strfry.conf
```
Modify the database path:
```
# Find this line:
db = "./strfry-db/"
# Change it to:
db = "/var/lib/strfry/"
```
Check your system's hard limit for file descriptors:
```bash
ulimit -Hn
```
Update the `nofiles` setting in your configuration to match this value (or set to 0):
```
# Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288
```
The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.
You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details.
Set ownership of the configuration file:
```bash
sudo chown strfry:strfry /etc/strfry.conf
```
### Create Systemd Service
Create a systemd service file for managing Strfry:
```bash
sudo nano /etc/systemd/system/strfry.service
```
Add the following content:
```ini
[Unit]
Description=strfry relay service
[Service]
User=strfry
ExecStart=/usr/local/bin/strfry relay
Restart=on-failure
RestartSec=5
ProtectHome=yes
NoNewPrivileges=yes
ProtectSystem=full
LimitCORE=1000000000
[Install]
WantedBy=multi-user.target
```
This systemd service configuration:
- Runs Strfry as the dedicated strfry user
- Automatically restarts the service if it fails
- Implements security measures like `ProtectHome` and `NoNewPrivileges`
- Sets resource limits appropriate for a relay
Enable and start the service:
```bash
sudo systemctl enable strfry.service
sudo systemctl start strfry
```
Check the service status:
```bash
sudo systemctl status strfry
```
### Verify Relay is Running
Test that your relay is running locally:
```bash
curl localhost:7777
```
You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
## Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
### Install TOR
Install TOR from the package repositories:
```bash
sudo apt install -y tor
```
This installs the TOR daemon that will create and manage your hidden service.
### Configure TOR
Edit the TOR configuration file:
```bash
sudo nano /etc/tor/torrc
```
Scroll down to wherever you see a commented out part like this:
```
#HiddenServiceDir /var/lib/tor/hidden_service/
#HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
```
HiddenServiceDir /var/lib/tor/strfry-relay/
HiddenServicePort 80 127.0.0.1:7777
```
This configuration:
- Creates a hidden service directory at `/var/lib/tor/strfry-relay/`
- Maps port 80 on your .onion address to port 7777 on your local machine
- Keeps all traffic encrypted within the TOR network
Create the directory for your hidden service:
```bash
sudo mkdir -p /var/lib/tor/strfry-relay/
sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/
sudo chmod 700 /var/lib/tor/strfry-relay/
```
The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
```bash
sudo systemctl restart tor
```
## Making Your Relay Available on TOR
### Get Your Onion Address
After restarting TOR, you can find your onion address:
```bash
sudo cat /var/lib/tor/strfry-relay/hostname
```
This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay.
### Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion`
## Testing Your Setup
### Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
1. Open your TOR browser
2. Go to your favorite client, either on clearnet or an onion service.
- Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR.
3. Add your relay URL: `ws://youronionaddress.onion` to your relay list
4. Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
## Maintenance and Security
### Regular Updates
Keep your system, TOR, and relay updated:
```bash
# Update system
sudo apt update
sudo apt upgrade -y
# Update Strfry
cd ~/strfry
git pull
git submodule update
make -j2
sudo cp strfry /usr/local/bin
sudo systemctl restart strfry
# Verify TOR is still running properly
sudo systemctl status tor
```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
### Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
### Monitoring Logs
To monitor your Strfry logs:
```bash
sudo journalctl -u strfry -f
```
To check TOR logs:
```bash
sudo journalctl -u tor -f
```
Monitoring logs helps you identify potential issues and understand how your relay is being used.
### Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
# Stop the relay temporarily
sudo systemctl stop strfry
# Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
# Restart the relay
sudo systemctl start strfry
```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
```bash
sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location
```
## Troubleshooting
### Relay Not Starting
If your relay doesn't start:
```bash
# Check logs
sudo journalctl -u strfry -e
# Verify configuration
cat /etc/strfry.conf
# Check permissions
ls -la /var/lib/strfry
```
Common issues include:
- Incorrect configuration format
- Permission problems with the data directory
- Port already in use (another service using port 7777)
- Issues with setting the nofiles limit (setting it too big)
### TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
# Check TOR logs
sudo journalctl -u tor -e
# Verify TOR is running
sudo systemctl status tor
# Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
# Verify TOR configuration
sudo cat /etc/tor/torrc
```
Common TOR issues include:
- Incorrect directory permissions
- TOR service not running
- Incorrect port mapping in torrc
### Testing Connectivity
If you're having trouble connecting to your service:
```bash
# Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
# Check that TOR is properly running
sudo systemctl status tor
# Test the local connection directly
curl --include --no-buffer localhost:7777
```
---
## Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
---
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry).
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
-

@ bc52210b:20bfc6de
2025-03-25 20:17:22
CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
---
**CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!**
Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
* Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
* Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
**Key Differences:**
1. What’s Aggregated?
* CISA: Aggregates signatures.
* Key Aggregation: Aggregates public keys.
2. What the Verifier Needs
* CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature.
* Key Aggregation: The verifier only needs the single aggregated public key and one message.
3. When It Happens
* CISA: Used during transaction signing, when inputs are being combined into a transaction.
* MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
---
**Two Flavors of CISA: Half-Agg and Full-Agg**
CISA comes in two modes:
* Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
* Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
---
**Half Signature Aggregation (Half-Agg) Explained**
**How It Works**
Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
* R: A random point (32 bytes).
* s: A scalar value (32 bytes).
In Half-Agg:
* The R values from each signature are kept separate (one per input).
* The s values from all signatures are combined into a single s value.
**Why It Saves Space (~50%)**
Let’s break down the size savings with some math:
Before Aggregation:
* Each Schnorr signature = 64 bytes (32 for R + 32 for s).
* For n inputs: n × 64 bytes.
After Half-Agg:
* Keep n R values (32 bytes each) = 32 × n bytes.
* Combine all s values into one = 32 bytes.
* Total size: 32 × n + 32 bytes.
Comparison:
* Original: 64n bytes.
* Half-Agg: 32n + 32 bytes.
* For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
**Real-World Impact:**
Based on recent Bitcoin usage, Half-Agg could save:
* ~19.3% in space (reducing transaction size).
* ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
---
**Applications of Half-Agg**
Half-Agg isn’t just a cool idea—it has practical uses:
1. Transaction-wide Aggregation
* Combine all signatures within a single transaction.
* Result: Smaller transactions, lower fees.
2. Block-wide Aggregation
* Combine signatures across all transactions in a Bitcoin block.
* Result: Even bigger space savings at the blockchain level.
3. Off-chain Protocols / P2P
* Use Half-Agg in systems like Lightning Network gossip messages.
* Benefit: Efficiency without needing miners or a Bitcoin soft fork.
---
**Challenges with Half-Agg**
While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
1. Breaking Adaptor Signatures
* Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
* Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
2. Impact on Reorg Recovery
* In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
* If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
---
**Wrapping Up**
CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-

@ b17fccdf:b7211155
2025-03-25 11:23:36
Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/).
Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles:
## La razón
El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial.
Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita.
Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

## La solución
Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder:
**~>** Utiliza **una VPN**:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad:
- [IVPN](https://www.ivpn.net/es/)
- [Mullvad VPN](https://mullvad.net/es/vpn)
- [Proton VPN](https://protonvpn.com/es-es) (**gratis**)
- [Obscura VPN](https://obscura.net/) (**solo para macOS**)
- [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos:
1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy"
2. Marca la casilla "Habilite el modo proxy en este dispositivo"
3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias
4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio.
3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).

**~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).

## La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

---
Fuentes:
* https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239
* https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257
* https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958
* https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689
* https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-

@ 3b7fc823:e194354f
2025-03-23 03:54:16
A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds.
Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/
1. Download Tor Browser
First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/
2. Sign Up
Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha.
3. Account information
Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck.
4. Install an Email Client
You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird.
a. Download Thunderbird email client
b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that.
5. Configure Incoming (POP3) Server
Under Incoming Server:
Protocol: POP3
Server or Hostname: xyz.onion (whatever your account info says)
Port: 110
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (POP3 password).
6. Configure Outgoing (SMTP) Server
Under Outgoing Server:
Server or Hostname: xyz.onion (whatever your account info says)
Port: 25
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (SMTP password).
7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up.
8. Configure Proxy
a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**.
b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different)
c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK
9. Check Email
For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail.
10. Security Exception
Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**.
You are done. Enjoy your new private email service.
**REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
-

@ 21335073:a244b1ad
2025-03-18 20:47:50
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ 21335073:a244b1ad
2025-03-18 14:43:08
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ a07fae46:7d83df92
2025-03-18 12:31:40
if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)?
you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better.
the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor.
Good morning.
#jfkFiles #nostrOnly
-

@ bc52210b:20bfc6de
2025-03-14 20:39:20
When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract.
The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable.
In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions.
Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
-

@ 57d1a264:69f1fee1
2025-04-05 06:58:25
**Summary**
We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment.
**Responsibilities**
- Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity.
- Develop digital assets for marketing, social media, website, and app.
- Work within brand guidelines while exploring ways to evolve and strengthen our visual style.
**Requirements**
- 2+ years of experience in graphic design, with a strong focus on illustration.
- Ability to help define and develop a cohesive visual style for the brand.
- Proficiency in Adobe products.
- Experience with Figma is a plus.
- Strong organizational skills—your layers and files should be neatly labeled.
- Clear communication and collaboration skills to work effectively with the team.
- Located in LATAM
Please attach a link to your portfolio to showcase your work when applying.
[APPLY HERE](https://jan3.com/contact/)
originally posted at https://stacker.news/items/935007
-

@ 57d1a264:69f1fee1
2025-04-05 06:47:55
**Location:** Remote (Austria)
**Area:** Graphics and communication design
**Pay:** 37,500 € to 50,000 € / year
Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin.
👋 About the role
As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas.
**tasks**
- Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials
- Creation of individual content (posts, stories, banners, ads) for social media
- Planning and development of campaigns to strengthen the brand presence
- Further development of the existing corporate design support in the area of content management (website, blog)
**qualification**
- Completed training or studies in graphic design
- At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management
- Safe use of design tools such as Figma, Adobe Creative Suite
- Experience in creating social media content and maintaining channels
- Creativity, good communication skills and team spirit
- Very good knowledge of German and English
- Knowledge of Bitcoin is desirable
**Benefits**
- Offsites with the team in exciting places
- Flexible working hours in a company that relies on remote work
- Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation
- Buy Bitcoin without fees! 21 Premium!
- Gross annual salary & potential share options for outstanding performance / bonus payments
**📝 Interview process**
_How do I apply?_
Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect.
By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application!
_⁇ 京 Resume Review_
Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...)
_📞 Exploratory call_
We discuss what appeals to you about this role and ask you a few questions about your previous experiences
_👬 On-Site Deep Dive_
During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role.
_👍 Time for a decision!_
[APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner)
originally posted at https://stacker.news/items/935004
-

@ 57d1a264:69f1fee1
2025-04-05 06:35:58
We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals.
**Key Responsibilities:**
- Design and improve the @Bipa app experience, focusing on usability and measurable business impact.
- Apply data-driven design, making decisions based on user research, metrics, and testing.
- Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product.
- Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy.
- Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations.
- Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business.
- Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app.
**Qualifications:**
- Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps.
- Solid understanding of user-centered design (UCD) principles and usability heuristics.
- Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis.
- Ability to work with both quantitative and qualitative data to guide design decisions.
- Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement).
- Proficiency in design tools like Figma (or similar).
- Experience working with design systems and design tokens to ensure consistency.
- Comfortable working in an agile, fast-paced, and iterative environment.
- Strong communication skills and the ability to advocate for design decisions backed by research and data.
**Benefits:**
🏥 Health Insurance
💉 Dental Plan
🍽️ Meal Allowance (CAJU card)
💻 Home Office Stipend
📈 Stock Options from Day One
[APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer)
originally posted at https://stacker.news/items/935003
-

@ 57d1a264:69f1fee1
2025-04-05 06:28:16
### ⚡️ About Us
@AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY.
### ⚡️ The Role
Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision.
### ⚡️ Responsibilities
Produce 30 short videos on circular economies.
Incorporate subtitles as needed.
Submit videos on a deliverables basis.
Participate in check-ins and communicate with the AB team and circular economy communities.
### ⚡️ What We Offer
Free ticket to AB25.
Networking with Bitcoiners and industry leaders.
Letter of recommendation and LinkedIn endorsement upon completion.
Mentorship and hands-on experience with a high-profile Bitcoin project.
### ⚡️ Skills & Qualifications
Passion for Bitcoin and circular economies.
Basic to intermediate video editing skills (no specific software required).
Creative independence with feedback.
Portfolio or work samples preferred.
### ⚡️ Time Commitment
Flexible, project-based internship with check-ins and feedback rounds.
### ⚡️ How to Apply
Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available).
originally posted at https://stacker.news/items/935001
-

@ 592295cf:413a0db9
2025-04-05 07:26:23
## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago
# 1.
### Nostr's adoption thesis
### The less you define, the more you imply
### by Wouter Constant
## 2.
### Dutch Bitcoiner
### AntiHashedPodcast
### Writing Book about nostr
00:40
## 3.
### What this presentation about
### A protocols design includes initself a thesis
### on protocol adoption, due to underlying assumptions
1:17
## 4.
### Examples
### Governments/Academic: Pubhubs (Matrix)
### Bussiness: Bluesky
### Foss: Nostr
1:58
## 5.
### What constitutes minimal viability?
### Pubhubs (Matrix): make is "safe" for user
### Bluesky: liability and monetization
### Foss: Simpel for developer
4:03
## 6.
### The Point of Nostr
### Capture network effects through interoperability
4:43
## 7.
## Three assumptions
### The direction is workable
### Method is workable
### Motivation and means are sufficient
5:27
## 8.
## Assumption 1
### The asymmetric cryptography paradigm is a good idea
6:16
## 9.
### Nostr is a exponent of the key-pair paradigm.
### And Basicly just that.
6.52
## 10.
### Keys suck
### Protect a secret that you are supposed use all the time.
7:37
## 11.
## Assumption two
### The unaddressed things will be figured out within a 'meta-design consensus'
8:11
## 12.
### Nostr's base protocol is not minimally viable for anything, except own development.
8:25
## 13.
### Complexity leads to capture;
### i.e. free and open in the name,
### controlled in pratice
9:54
## 14.
## Meta-design consensus
### Buildings things 'note centric' mantains interoperability.
11:51
## 15.
## Assumption three
### the nightmare is scary;
### the cream is appealing.
12:41
## 16.
### Get it minimally viable,
### for whatever target,
### such that it is not a waste of time.
13:23
## 17.
## Summarize
### We are in a nightmare.
### Assume key/signature are the way out.
### Assume we can Maintain an open stardand while manifesting the dream.
### Assume we are motivated enought to bootstrap this to adulthood.
14:01
## 18.
### We want this,
### we can do this,
### because we have to.
14:12
## Thank you for contribuiting
[Edit] Note for audio presentation
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
-

@ df173277:4ec96708
2025-02-07 00:41:34
## **Building Our Confidential Backend on Secure Enclaves**
With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with.
## **Auth and Databases Today**
As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that:
1. Need to register users (authentication).
2. Collect and process user data in business-specific ways, often on the backend.
Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes).
## **"Just Trust Us" Isn't Good Enough**
In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data.
Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility.
The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services.
## **Current Attempts at Securing Data**
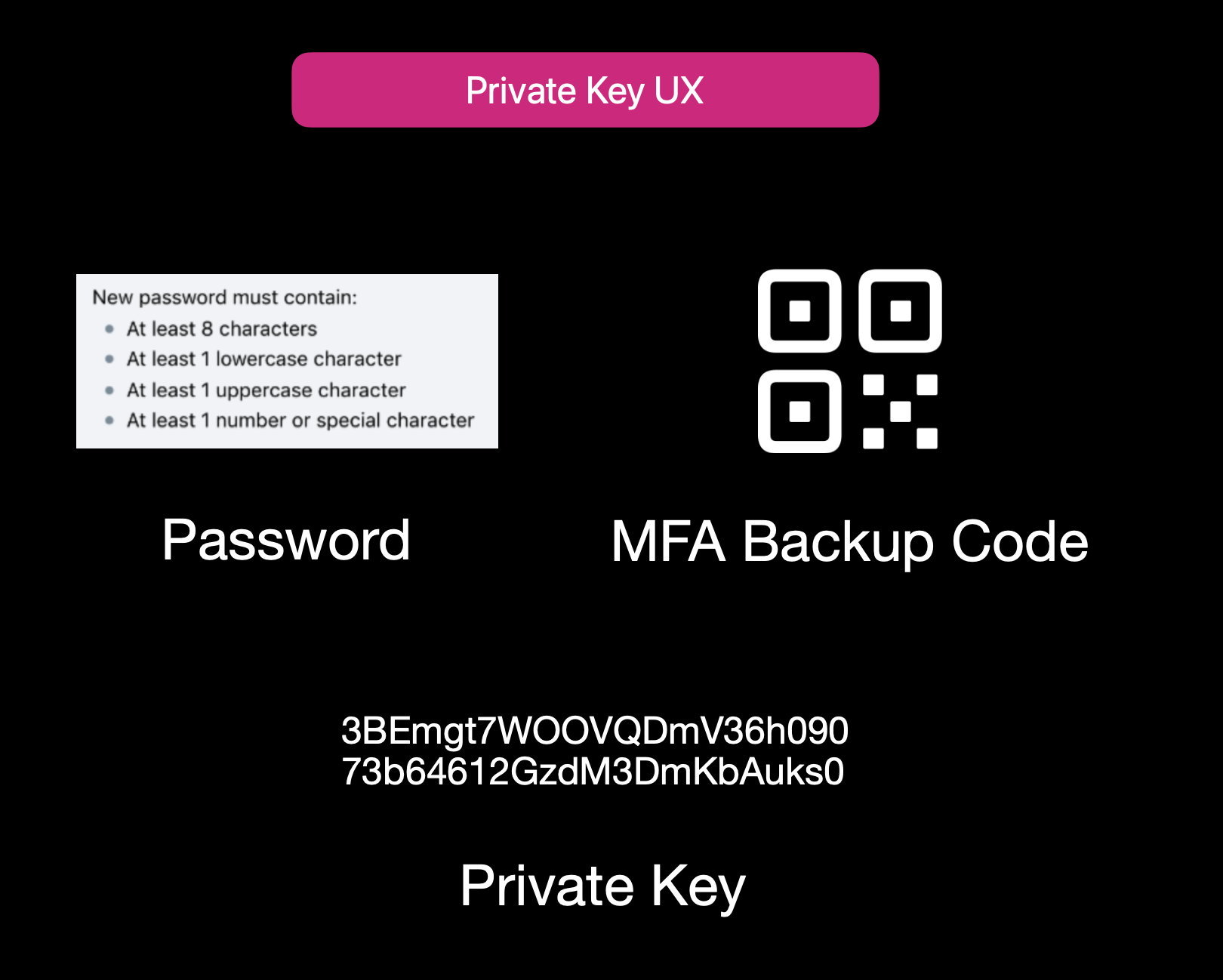Current User Experience of E2EE Apps
While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**:
1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side.
2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data.
3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility.
Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider.
## **Secure Enclaves**
### **The Hybrid Approach**
Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden.
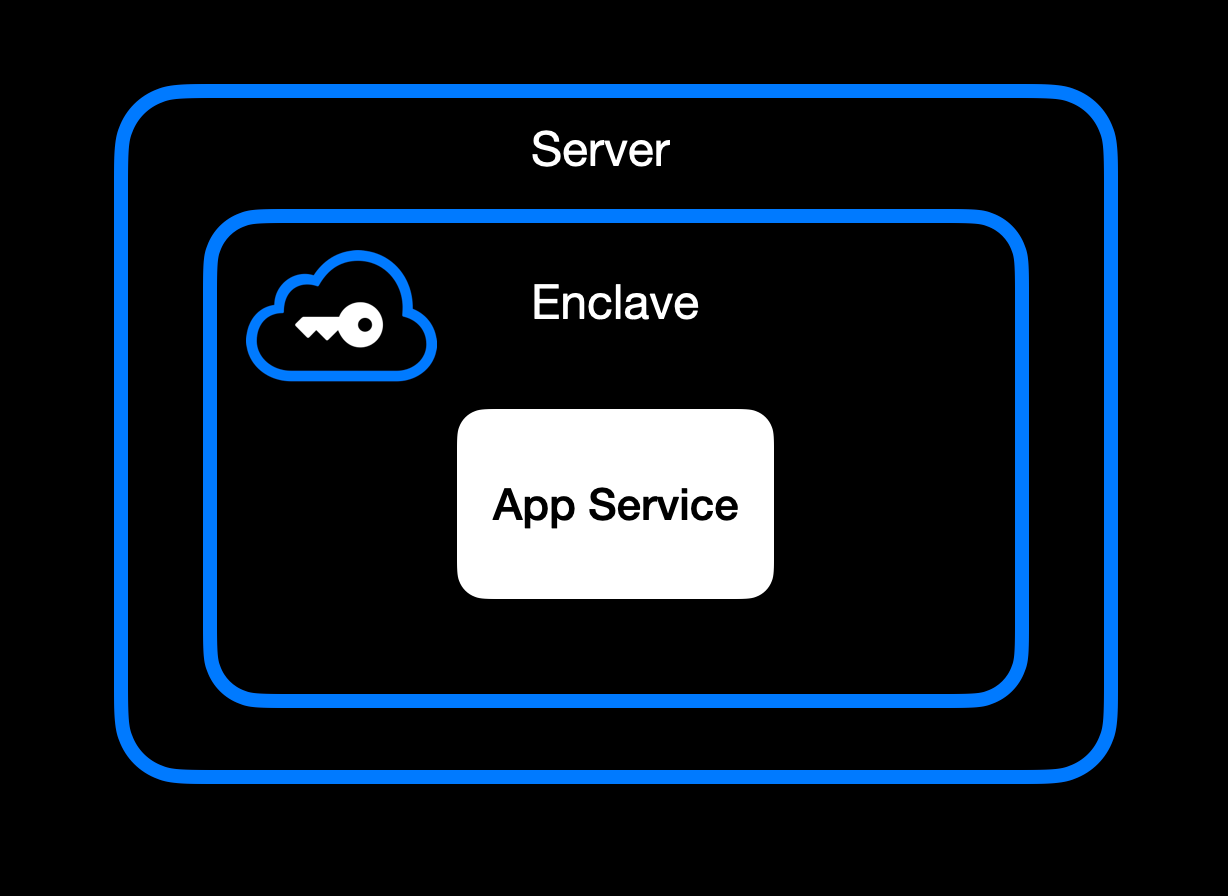App Service Running Inside Secure Enclave
### **High-Level Goal of Enclaves**
Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\
• **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\
• **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\
• **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in).
### **Different Secure Enclave Solutions**
[**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds.
[**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications.
[**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers.
[**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised.
[**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees.
### **Key Benefits**
One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data.
Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware.
Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks.
Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist.
It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing.
## **How We Use Secure Enclaves**
Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads.
### **Our Stack: AWS Nitro + Nvidia TEE**
• **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave.
• **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with.
### **End-to-End Encryption from Client to Enclave**
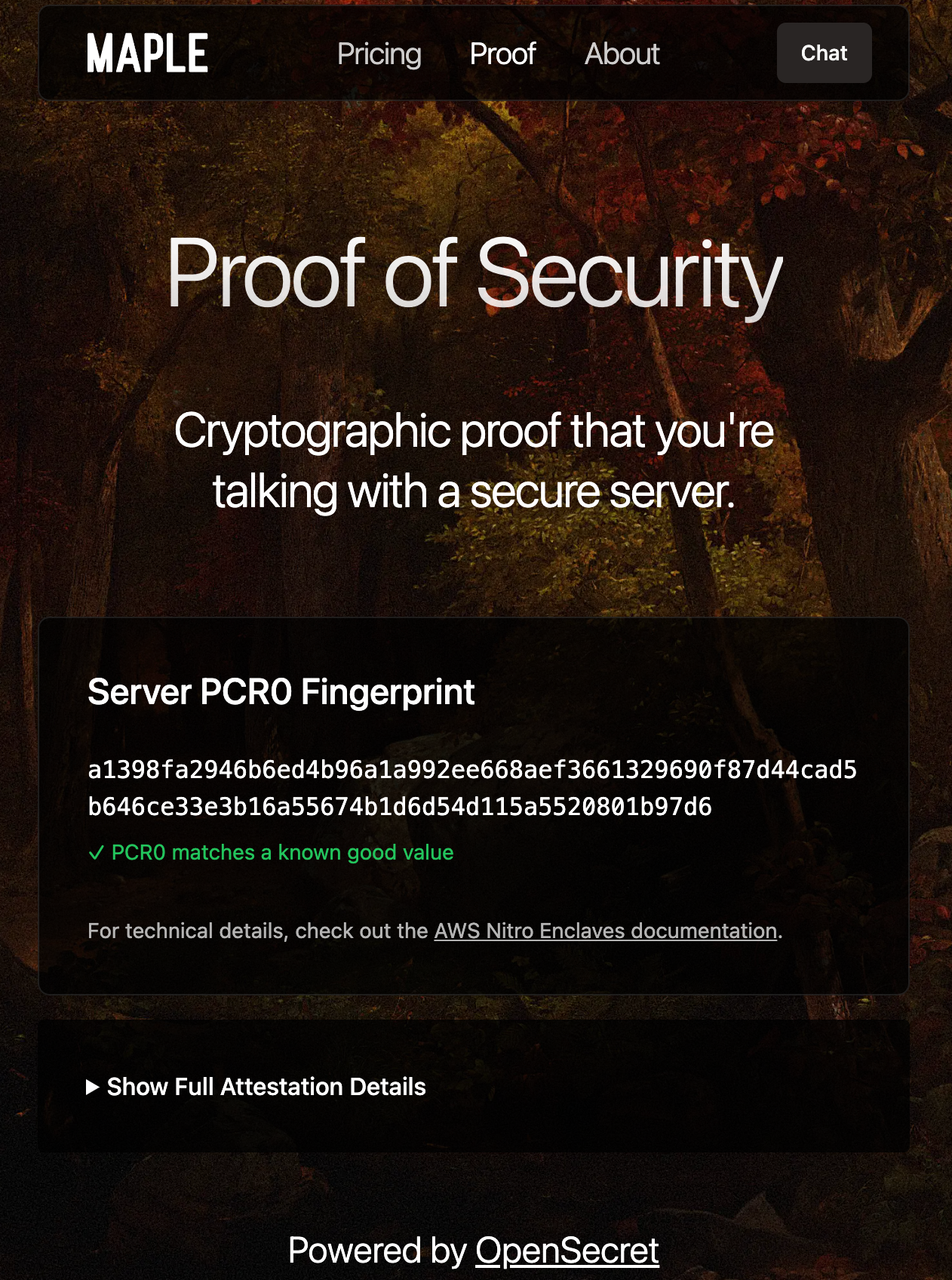Client-side Enclave Attestation from Maple AI
Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud).
Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session.
From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request.
### **In-Enclave Operations**
At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form.
User Auth Methods running inside Enclave
A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information.
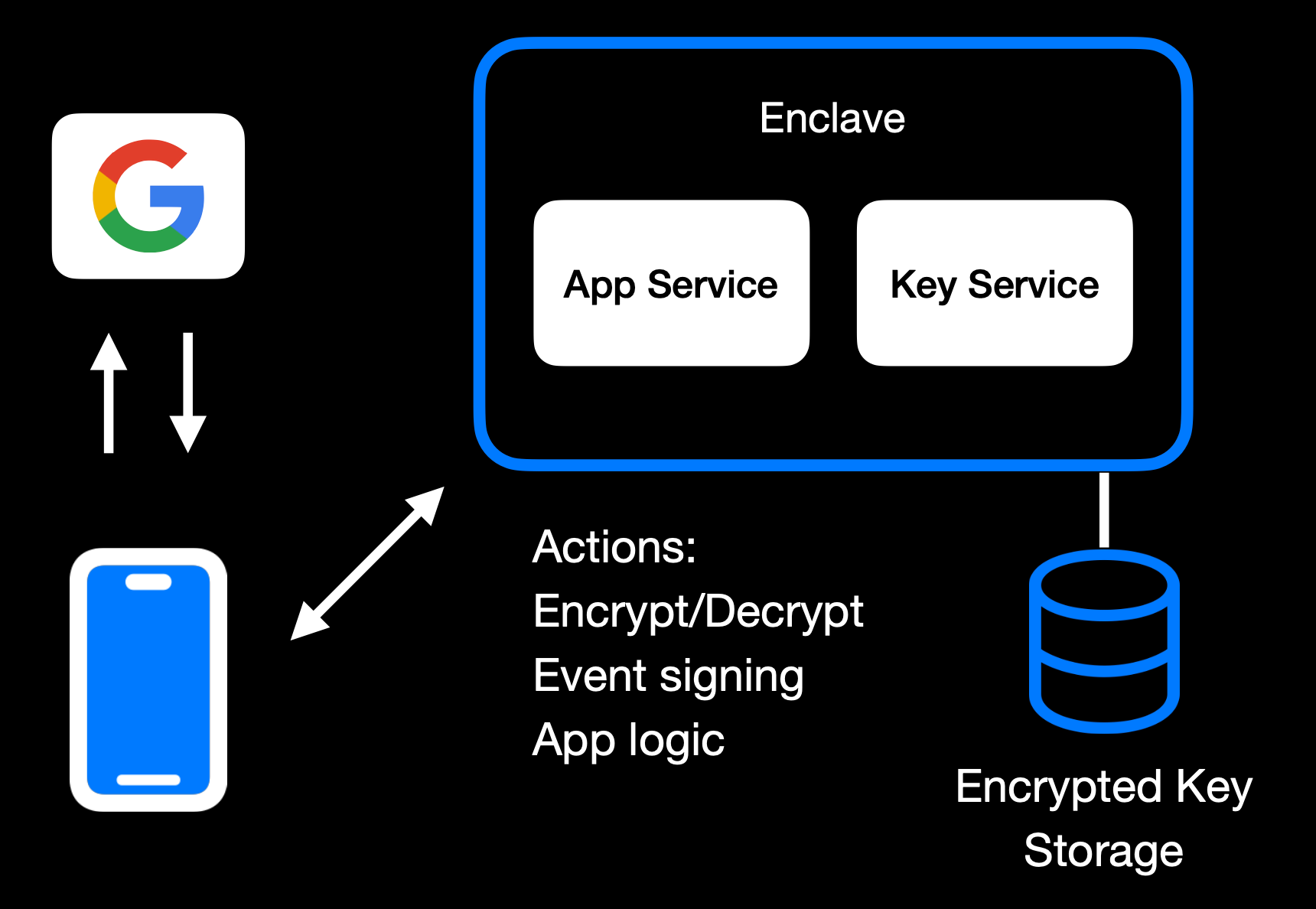Main Enclave Operations in OpenSecret
The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user.
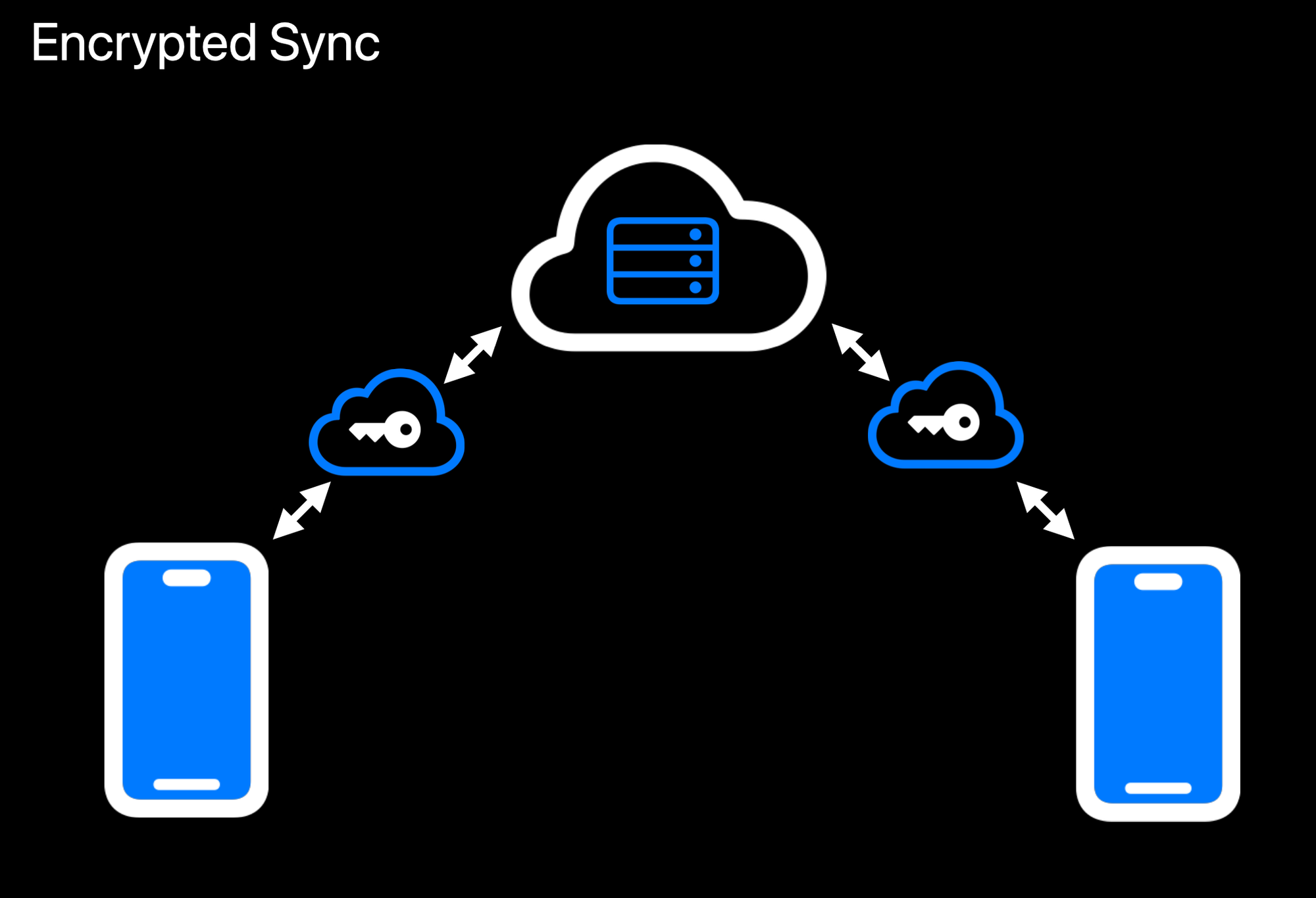Realtime Encrypted Data Sync on Multiple Devices
Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext.
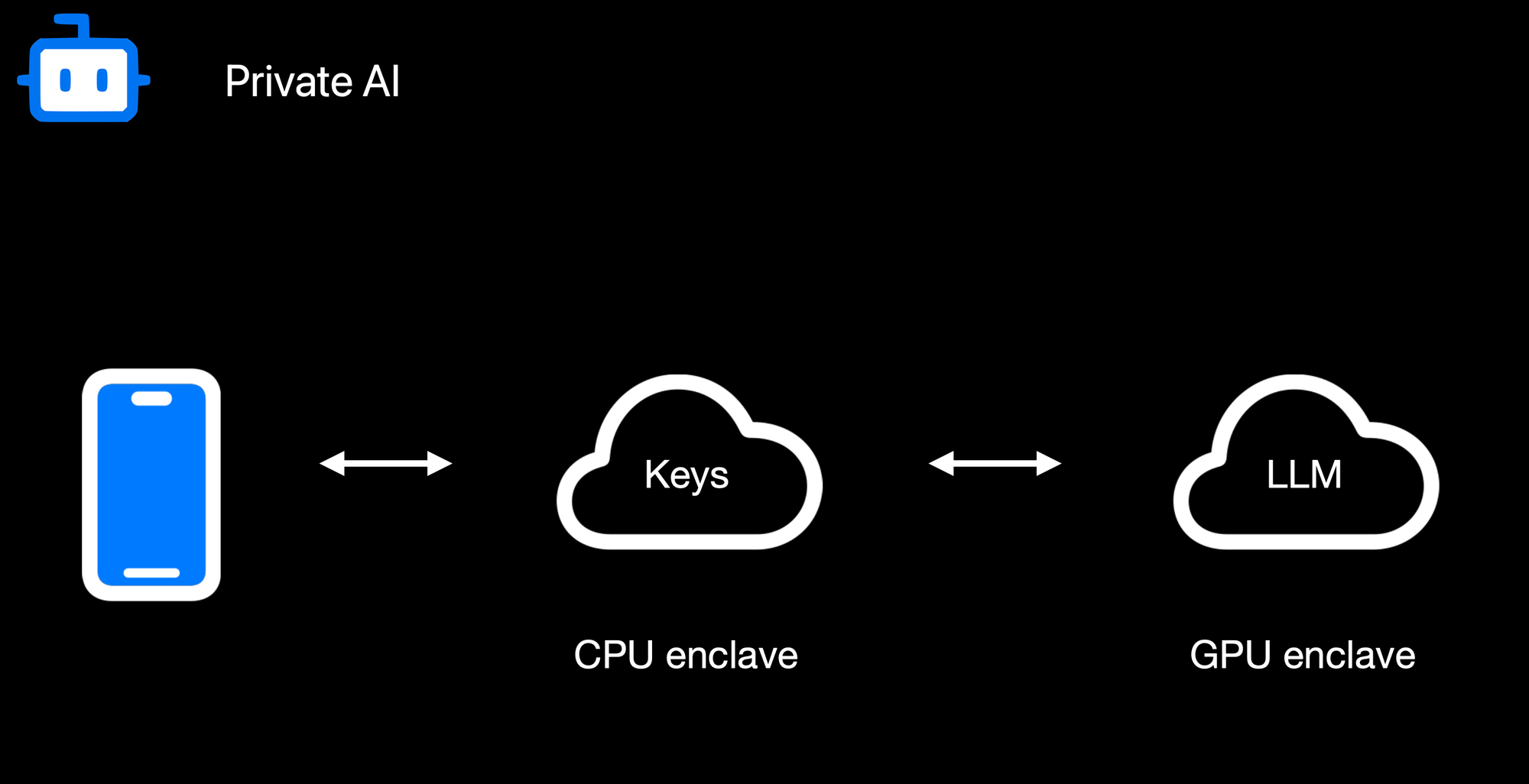Confidential AI Workloads
Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation.
### **Reproducible Builds + Verification**
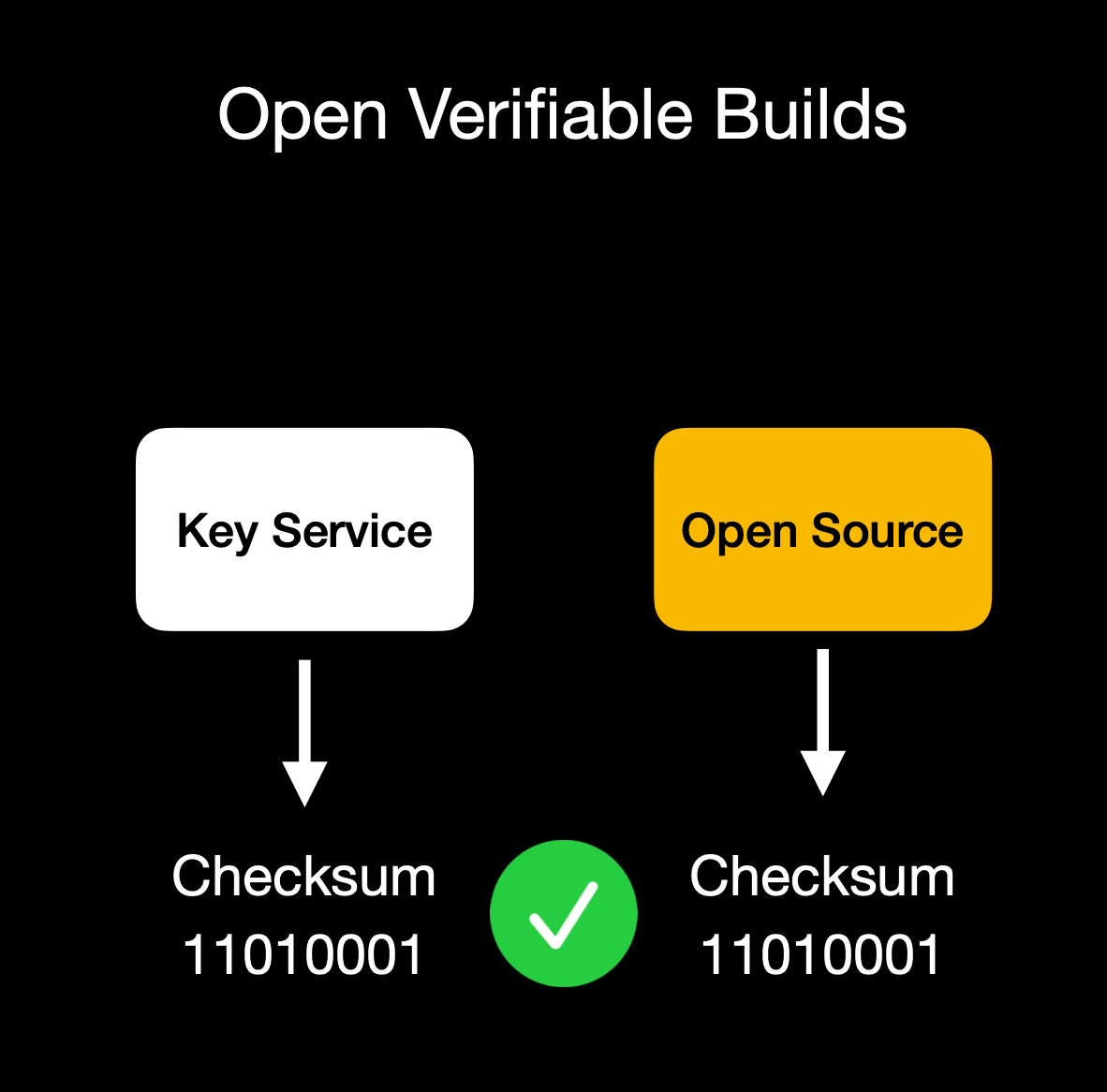Client verifies enclave attestation document
We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs.
Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation.
## **Putting It All Together**
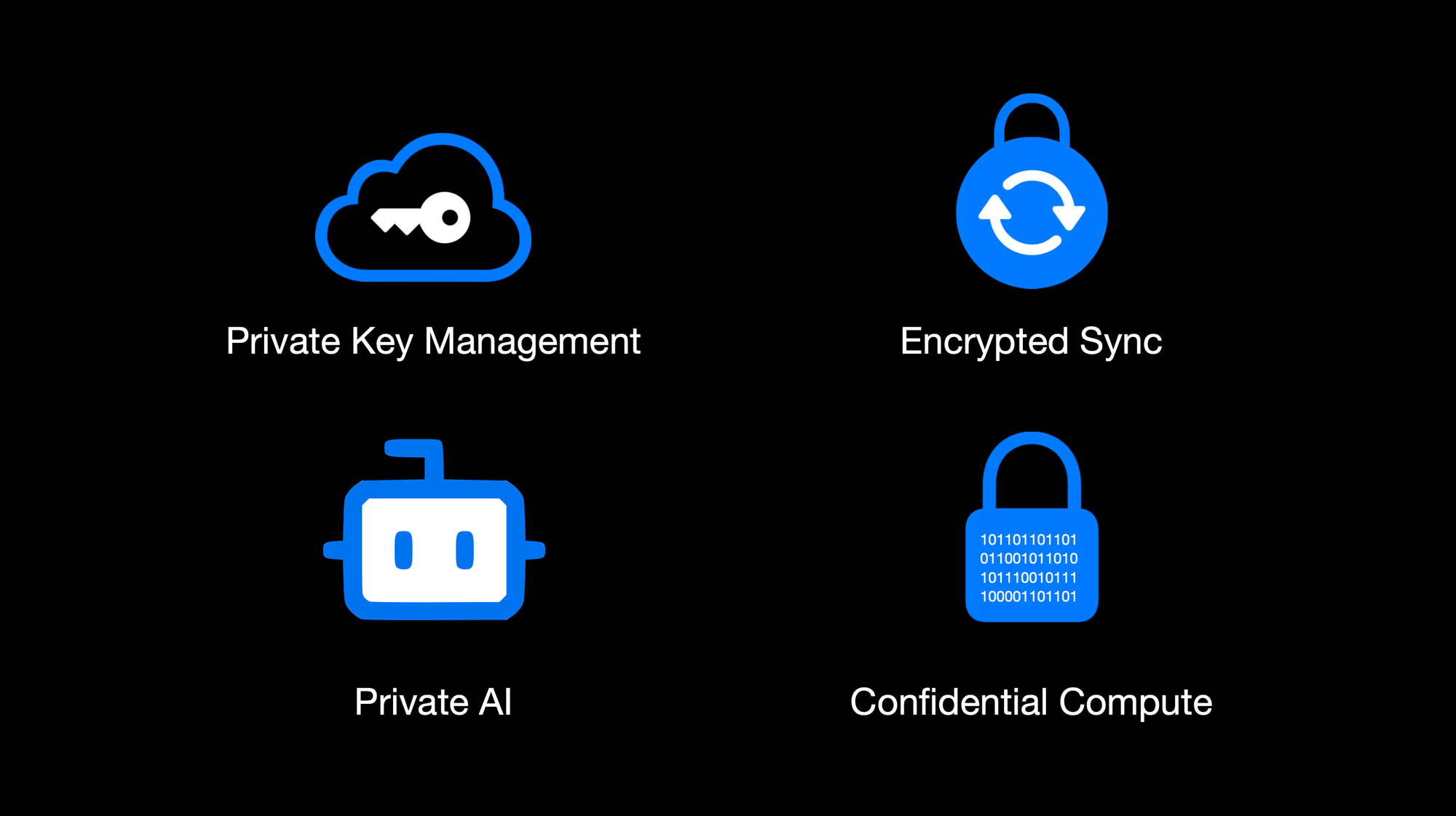OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute
By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes.
This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats.
Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure.
OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use.
Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system.
The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad.
## **Things to Come**
We're excited to build on our enclaved approach. Here's what's on our roadmap:
• **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\
• **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\
• **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\
• **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\
• **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\
• **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\
• **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API.
## **Getting Started**
Ready to see enclaves in action? Here's how to dive in:\
1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\
2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\
3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\
4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further.
## **Conclusion**
By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use.
**We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself.
Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build!
*Thank you for reading, and welcome to the era of enclaved computing.*
-

@ df173277:4ec96708
2025-01-28 17:49:54
> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\
> [Start chatting for free.](https://trymaple.ai/)
We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world.
Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another.
#### Why Secure and Private AI?
In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property.
Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services.
At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local.
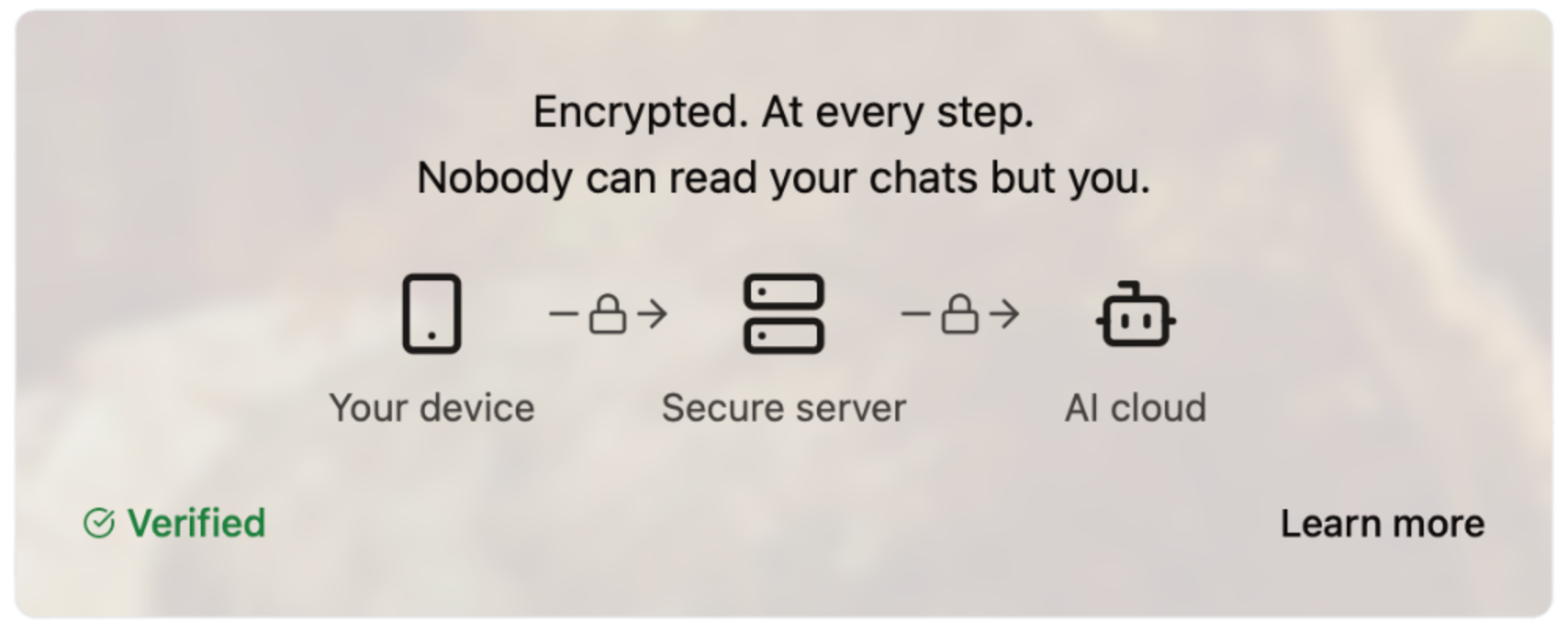#### How Does It Work?
Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site.
#### How Much Does It Cost?
We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method.
- Free: $0
- Starter: $5.99/month
- Pro: $20/month
Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy.
Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open.
#### Are You An App Developer?
You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/).
<img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png">
Enjoy private AI Chat 🤘
<img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
-

@ df173277:4ec96708
2025-01-09 17:12:08
> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\
> [Join the waitlist to get early access.](https://trymaple.ai)
We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI.
Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations.
#### Building a Private Foundation
Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win.
#### The Power of Encrypted AI Chat
AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short.
Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us.
#### Technical Overview
So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects:
- **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data.
- **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations.
- **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised.
- **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public.
- **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased.
#### Personal and Work Use
Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe.
#### Local v Cloud
Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds.
#### Why the Maple name?
Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment.
#### Join the Waitlist
Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai)
[](https://trymaple.ai/waitlist)
-

@ df173277:4ec96708
2025-01-09 17:02:52
> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud)
In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion.
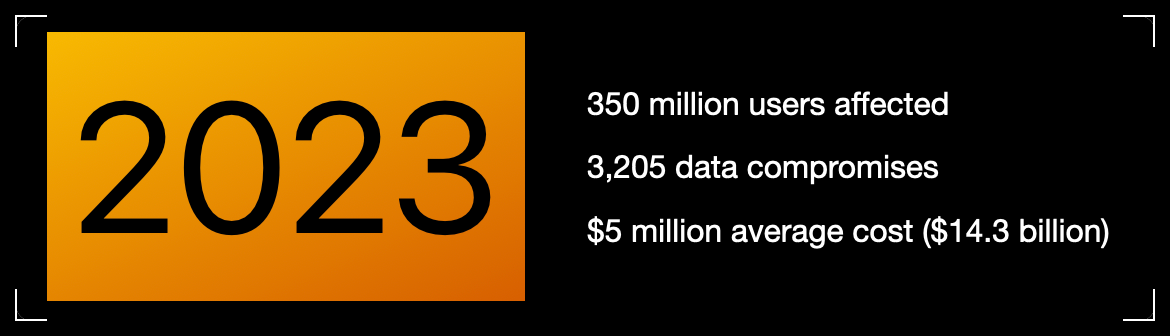Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online?
Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches?
> Cryptography at scale is hard.
#### The Cloud
The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers.
The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage.
> Private key encryption needs a UX upgrade.
## Enter OpenSecret
OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute.
Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.
### Private Key Management
Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone.
OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account.
The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.
### Encrypted Sync
With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go.
The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them.
### Private AI
Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything.
OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk.
**Check out Maple AI**\
Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)
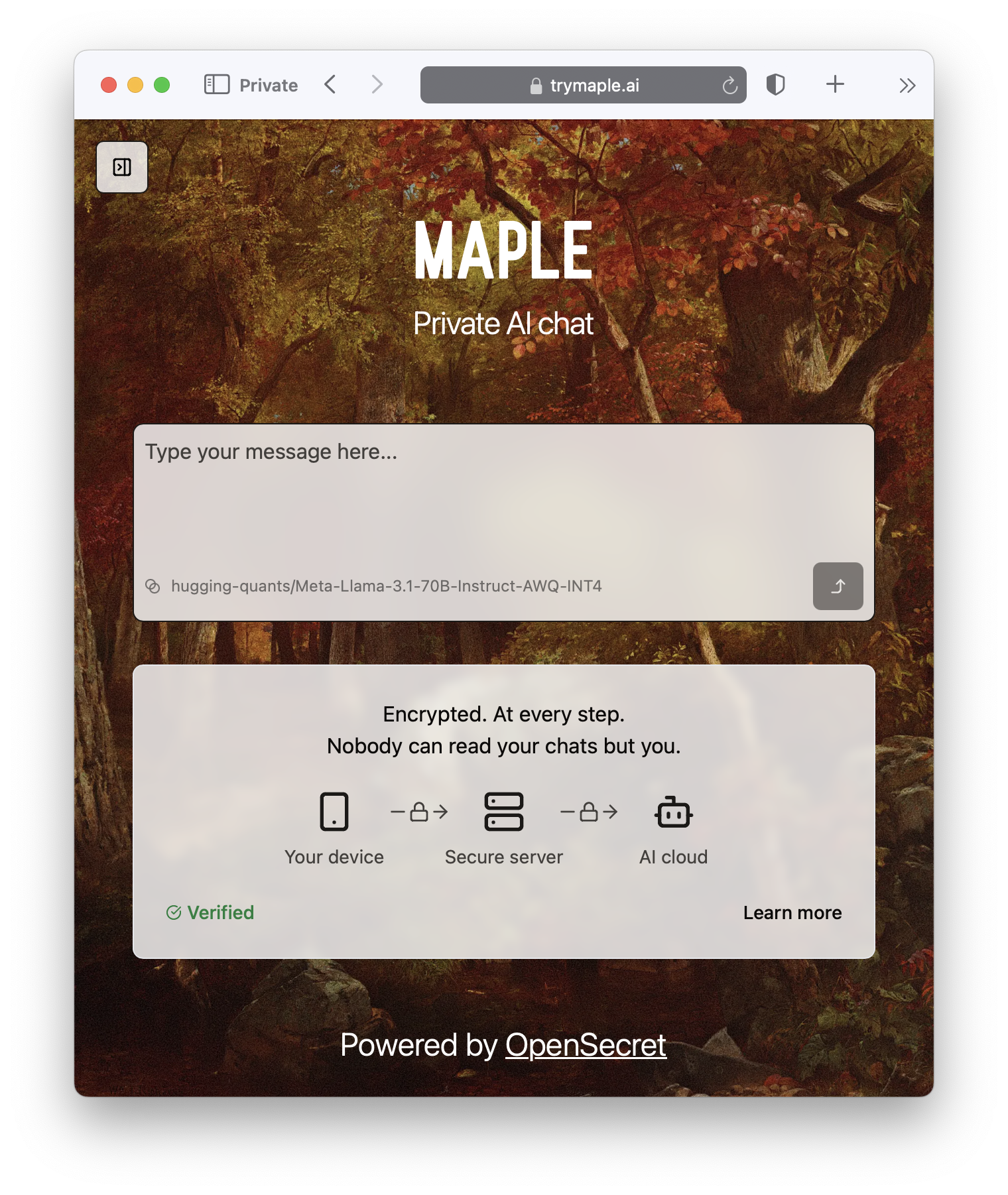
### Confidential Compute
Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave.
It's the new version of that lock on your web browser. When you see it, you know you're secure.

#### **But do we want our secrets to be open?**
OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable.
On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data.
> Don't trust, verify.
### **Join the Movement**
We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud)
Users and companies deserve better encryption and privacy.\
Together, let's make that a reality.
[](https://opensecret.cloud)
-

@ a047a37c:dfcb432c
2025-04-05 01:09:09
## Chef's notes
Using only top quality dill pickles and juice is highly recommended. Do not cheap out on this ingredient. The better the pickle juice, the better your fried chicken will taste.
Do not let the chicken fry for too long. If the color is not a light golden brown and you let it fry too dark. Then it will not taste right!!!
## Details
- ⏲️ Prep time: 20 min
- 🍳 Cook time: 25-30 min
- 🍽️ Servings: 3-4
## Ingredients
- 1 1/2 Pounds Chicken Breasts
- 2 Chicken Eggs
- 2 Cups Dill Pickle Juice
- 1/2 Cup Water
- 1 Cup Buttermilk
- 1 Cup Unbleached Flour
- 3 Tablespoons Powdered Sugar
- 1 Teaspoon Paprika
- 1 Teaspoon Garlic Powder
- 1 Teaspoon Cayenne Pepper
- 1 Teaspoon Ground Black Pepper
- 1 Teaspoon Sea Salt
- 1/2 Teaspoon Baking Powder
- 3-4 Cups Peanut Oil
- 3-4 Toasted Brioche Buns (Chicken Sandwiches Only)
- 1 Tablespoon Orange Blossom Honey (Chicken Sandwiches Only)
- 1/4 Cup Sliced Dill Pickles (Chicken Sandwiches Only)
## Directions
1. There are 2 ways to make The Legendary CFA Fried Chicken. If you want to make it into nuggets then take the chicken breasts and cut them with a kitchen knife into 1 inch cubes. If you want to make it into chicken breast sandwiches, then ensure they are no bigger than 1-1.5 inches thick cut once down the middle. Once you have made your decision and cut them to size. Place the chicken in a large mixing bowl Pour the pickle juice into the bowl, cover it, and place it in the refrigerator to marinate for the next 24 hours.
2. Take a large mixing bowl and add in the flour, powdered sugar, paprika, ground black pepper, cayenne pepper, sea salt, garlic powder, and baking powder. Whisk it all together until it is fully mixed and set aside.
3. Take another large mixing bowl. Add in the chicken eggs and buttermilk. Then whisk together until it is fully blended and set aside.
4. Add 3-4 cups of peanut oil to a large cast iron frying pan, or a deep fryer. Heat the oil to 350F degrees.
5. Remove the marinated chicken from the refrigerator. Drain out all of the pickle juice.
6. Dredge the chicken in the buttermilk egg mixture until it is fully coated. Coat the chicken in the flour mixture. Then immediately repeat these two steps so it is double coated to ensure maximum crispiness.
7. Add the chicken into the peanut oil and allow it to cook evenly until it has reached a light golden brown color and is fully cooked inside.
8. Remove the chicken from the pan and place it onto a paper towel to drain the excess oil off. If you made it into chicken nuggets then simply choose your favorite dipping sauce and serve. If you chose to make chicken sandwiches then lightly toast the brioche bun to a golden brown and drizzle on the honey on the inside of the top of the bun. Then add 1 piece of chicken breast per bun on the bottom half, top it off with sliced dill pickles. Complete the sandwich and serve immediately.
-

@ d9a329af:bef580d7
2025-04-04 20:56:20
Everyone who sees it knows at this point that the matrix of control comes from the overdependence of proprietary software to do our everyday tasks. You can think of this like us being the cling wrap that will just not let go of these pieces of garbage software that don't allow you to see what is in their source code, and how they work. This will tend to lead to the unlawful collection of data (violating the most basic of privacy laws, despite unenforceable contracts that are enforced regardless), bad OPSEC that sees you being stalked and harassed over nothing significant. In the worst of cases, if you speak your mind where you aren't necessarily supposed to be able to do that, and you get doxxed, the worst cases could be far worse than one could imagine.
The solution to this, on the other hand, is using almost exclusively free/libre open-source software and GNU/Linux operation systems. If you're using certain proprietary software, hardening it to give as little data as possible to the entity responsible for it will also work, as long as you know which ones to use. This is a hard pass for a lot of people, but if you want to escape the control matrix of proprietary software, Winblows, HackOS, iHackOS, iBloatOS and stock Google AI Fever Dream, then researching which Free Software (notice the spelling) to use is your first bet. I had already done this for the past four and a half years, and will continue to do it as long as I live, seeing what new Free Software compliant applications and libraries come into the spotlight once things get locked down into walled gardens like what HackOS, iHackOS and BlindnessOS do on a regular basis.
Each of these pieces of software will be in a categorized list with a brief description of what the software is used for. There is a lot to take in, so research this yourself and see if these are right for you. These are the applications I personally use on a regular day-to-day basis, and they work for my needs.
1. Operating Systems (the core to your device)
* GNU/Linux operating systems (for PCs) or GrapheneOS (for de-googled Android phones)
To be fair on this one, GNU/Linux is the combination of the Linux kernel with the GNU toolchain, which in turn allows any developer to make an operating system that is FOSS, not necessarily Free Software, especially with the Linux Kernel's proprietary bits of code. The Linux kernel is also used in the Android Open-Source Project (AOSP), and is used as the base of operating systems for Android phones such as GrapheneOS, the only AOSP custom ROM I would recommend based upon the research I had done on this (even if very little).
My recommendations on the Linux side of things are almost any Arch-based distribution (with the exception of Manjaro), Debian-based distributions like Linux Mint Debian edition, regular Debian, AntiX or Devuan, or a Fedora/RedHat-based distribution like Nobara Project (if you're a gamer), OpenSUSE (if set up properly) or even Bluefin if you want an atomic desktop (I wouldn't recommend Bluefin if you want to monkey with your operating system and DIY on many aspects of it). Once you learn how to set these up securely, privately and properly, you're on your way to starting your journey into digital liberation, but there's far more to go on this front.
2. Web Browsers (How you surf the internet)
* Firefox Forks
This one is self-explanatory. I harden all the Firefox forks I use (LibreWolf, Waterfox, Cachy Browser, Floorp and Zen as some examples) to the nines, despite being unable to do anything about my fingerprint. This is why I use multiple browsers for specific purposes to counteract the fingerprint spying due to weaponized JavaScript. There are ways to circumvent the fingerprint-based espionage, and make sure the site fingerprint.com doesn't know that one's lying about what their user agent is, though it's not very easy to fool that site, as it's used by 6,000 companies.
* Brave Browser
This is the only Chromium-based browser I would recommend, as it's better when hardened against all the other Chromium-based browsers, including Ungoogled Chromium, which is almost impossible to harden due to security vulnerabilities. Despite that, Brave has some of the best features for a Chromium-based browser one can feel comfortable using, even though you'll have similar issues with Firefox-based browsers that aren't actually Firefox (and Firefox has its own issues regarding espionage from Mozilla)
3. Office Suites (If you need to do professional office documents)
* LibreOffice
A fork of Apache's OpenOffice, made better with many features missing from even OnlyOffice and OpenOffice, this suite of applications is the go-to Free Software office suite for many people looking to switch from the proprietary software nether to the diamonds of free/libre open-source software. Though one may need to perform some extra steps to set up compatibility with G-Suite and Microsoft Office past 2015 potentially, it's still a good thing that people trust LibreOffice as their one-stop shop for office documents, despite being completely different from your standard office suite fare.
* OnlyOffice
The competitor to LibreOffice with the ease of Microsoft Office and G-Suite compatibility, OnlyOffice is another office suite that can be good for those who need it, especially since anybody who had used Microsoft Office in particular will be familiar with its layout, if not for a slight learning curve. As someone who's used G-Suite more (due to schooling that stunk worse than a decomposing rat in New York City), that's part of the reason why I switched to LibreOffice, though I tried some others, including OnlyOffice and Abiword (since I use a word processor a lot). This one is another solid option for those who need it.
* Wordgrinder
For those who like to use a terminal emulator like I do, Wordgrinder is a word processor with a terminal user interface (TUI) designed with just focusing on typing without distractions in mind. .wg is the file extension for documents made using Wordgrinder, especially since nowadays most word processors are cloud based. For those who live in a terminal, this is a good option to your terminal UI-based toolbox
4. Text editors
* Vi, Vim, Neovim and other Vim-like editors
The classic VI Improved (Vim), a fork of the TUI modal editor, vi, with keybinds that will be confusing at first, but with practice and patience, bring about muscle memory to stay on the keyboard, and not necessarily touch the mouse, keypad on the right hand side, or even the arrow keys. These keybind skills will stay with one for the rest of their life once they learn how the modes in vi, Vim or vi-based editors work. It's a classic for those working in the terminal, and a staple in FLOSS text editing and coding tools once customized potentially to the nines to your particular style.
* VSCodium
The Free Software fork of Code OSS by Microsoft, but made to be similar in function to VSCode without Microsoft's espionage baked into it. It has almost exactly the same features as VSCode that one would need, and even any VSIX files from VSCode will work in VSCodium. This one is an easy switch from VSCode for those who use it, but don't want the forced telemetry.
* Emacs
The competitor to Vim, Emacs is an editor that is FLOSS in every way imaginable. It is one of the most customizable editors anybody could have ever conceived, though the programming language used in Emacs is a dialect of Lisp the developers had made themselves. There are more keybinds to memorize compared to Vim, though Vim keybinds can be added using the Evil Mode package in any Emacs package manager to get the best of both worlds in Emacs. Once one gets a handle of the steep learning curve for Emacs, it's customizable in every imaginable way almost.
These four categories will get you started on your privacy journey, though I covered things a developer might want. I have plans on more lists to compile once I get my ducks in a row on what I want to cover here on Nostr in a longform format. Feel free to let me know if you have recommendations for me to write about, and I can do some digging on that if it isn't a rabbit hole.
-

@ da18e986:3a0d9851
2025-04-04 20:25:50
I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash.
Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax.
Here's the test wiki page I'm going to write:
```
= Simple AsciiDoc Demo
This is a simple demonstration of AsciiDoc syntax for testing purposes.
== Features
AsciiDoc offers many formatting options that are easy to use.
* Easy to learn
* Supports rich text formatting
* Can include code snippets
* Works great for documentation
[source,json]
----
{ "name": "Test", "version": "1.0", "active": true }
----
```
# We're going to use nak to publish it
First, install `nak` if you haven't already
```
go install github.com/fiatjaf/nak@latest
```
*Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal*
```
# this is how to add it to your path on mac if using zsh
echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc
```
And here's how to sign and publish this event with nak.
*First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified*
```
# replace with your full secret key
export NOSTR_SECRET_KEY="nsec1zcdn..."
```
Now to sign and publish the event:
*Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal*
```
nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz
```
You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851
and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io
-

@ 000002de:c05780a7
2025-04-04 20:22:47
We are fostering a lamb named Frank. He was left behind when his flock was moved to a new grazing area. He almost didn't make it.
I've learned that sheep are not as dumb as I thought they were. He seems to be pretty sharp and has quickly become spoiled. He follows us around like a puppy. We have had some cold nights so we made him a jacket.
He's about 3 weeks old now and seems to be doing well.



originally posted at https://stacker.news/items/934770
-

@ c631e267:c2b78d3e
2025-04-04 18:47:27
*Zwei mal drei macht vier,* *\
widewidewitt und drei macht neune,* *\
ich mach mir die Welt,* *\
widewide wie sie mir gefällt.* *\
Pippi Langstrumpf*  
**Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
**In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
**Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
**Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
**Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
**Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen.
**Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür.
*\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen.
-

@ 3ffac3a6:2d656657
2025-04-05 04:55:12
# O Impacto do Namoro com Pelé na Carreira de Xuxa Meneghel
## Disclaimer:
Esse texto foi totalmente escrito pelo ChatGPT, eu apenas pedi que ele fizesse uma pesquisa sobre o tema.
**Introdução:** O relacionamento entre Xuxa Meneghel e Pelé, que durou cerca de seis anos (início dos anos 1980 até 1986), foi um dos mais comentados da década de 1980 ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)). Xuxa tinha apenas 17 anos quando começou a namorar o já consagrado “Rei do Futebol”, então com 40 anos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Xuxa%20tinha%2017%20anos,a%20primeira%20mulher%2C%20Rosemeri%20Cholbi)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=O%20jogador%20de%20futebol%20e,um%20relacionamento%20por%20seis%20anos)). Esse romance altamente midiático não só atiçou a curiosidade do público, como também alavancou a carreira de Xuxa de forma significativa. A seguir, detalhamos como o namoro aumentou a visibilidade da apresentadora, quais oportunidades profissionais podem ter tido influência direta de Pelé, o papel da revista *Manchete* e de outras mídias na promoção de sua imagem, se o relacionamento contribuiu para Xuxa conquistar espaços na TV (como o programa **Clube da Criança** e, posteriormente, na Rede Globo) e como mídia e público percebiam o casal – tudo embasado em fontes da época, entrevistas e biografias.
## Aumento da Visibilidade Midiática nos Anos 1980
O namoro com Pelé catapultou Xuxa a um novo patamar de fama. Até então uma modelo em começo de carreira, Xuxa **“se tornou famosa ao aparecer ao lado do esportista de maior status do Brasil”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=O%20romance%20come%C3%A7ou%20quando%20ela,de%20maior%20status%20do%20Brasil)). A partir do momento em que o relacionamento se tornou público, ela passou a estampar capas de revistas com frequência e a ser assunto constante na imprensa. Em 20 de dezembro de 1980, a jovem apareceu na capa da revista *Manchete* ao lado de Pelé e outras modelos – um ensaio fotográfico que marcou o primeiro encontro dos dois e deu início à enorme atenção midiática em torno de Xuxa ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=O%20jantar%20aproximou%20o%20casal,E%20fui%E2%80%9D)). Não por acaso, *“naquele ano, ela foi capa de mais de cem revistas”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=convidadas%20a%20posar%20ao%20lado,de%20mais%20de%20cem%20revistas)), um indicativo claro de como sua visibilidade explodiu após começar a namorar Pelé. Jornais, revistas de celebridades e programas de fofoca passaram a segui-los de perto; o casal virou sensação nacional, comparado até ao “Casal 20” (dupla glamourosa de uma série de TV americana) pelo seu alto perfil na mídia ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)).
Essa exposição intensa colocou Xuxa não apenas sob os holofotes do público, mas também a inseriu nos **bastidores do entretenimento**. Como namorada de Pelé – um dos homens mais conhecidos do mundo – Xuxa passou a frequentar eventos de gala, festas e bastidores de programas, onde conheceu figuras influentes do meio artístico e televisivo. Os fotógrafos os seguiam em eventos como bailes de carnaval e inaugurações, registrando cada aparição pública do casal. Com Pelé ao seu lado, Xuxa ganhou trânsito livre em círculos antes inacessíveis para uma modelo iniciante, construindo uma rede de contatos valiosa nos meios de comunicação. De fato, naquele início dos anos 80, **“os dois eram perseguidos por fotógrafos, apareciam em capas de revistas e até faziam publicidade juntos”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) – evidência de que Xuxa, graças ao namoro, transitava tanto na frente quanto por trás das câmeras com muito mais facilidade. Em suma, o relacionamento conferiu a ela um grau de notoriedade nacional que provavelmente demoraria anos para conquistar de outra forma, preparando o terreno para os passos seguintes de sua carreira.
## Influência Direta de Pelé nas Oportunidades Profissionais de Xuxa
Além do aumento geral da fama, há casos específicos em que Pelé influenciou diretamente oportunidades profissionais para Xuxa. Um exemplo contundente é o filme **“Amor Estranho Amor” (1982)** – longa de teor erótico no qual Xuxa atuou no início da carreira. Segundo relatos da própria apresentadora, **foi Pelé quem a incentivou a aceitar participar desse filme** ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Profissionalmente%2C%20Xuxa%20disse%20que%20Pel%C3%A9,Me%20enganaram%2C%20falaram%20um)). Na época ainda em início de trajetória, Xuxa acabou convencida pelo namorado de que aquela oportunidade poderia ser benéfica. Anos mais tarde, ela revelaria arrependimento pela escolha desse papel, mas o fato reforça que Pelé teve influência ativa em decisões profissionais de Xuxa no começo de sua jornada.
Outra área de influência direta foram as **publicidades e campanhas comerciais**. Graças ao prestígio de Pelé, Xuxa recebeu convites para estrelar anúncios ao lado do então namorado. Já em 1981, por exemplo, os dois gravaram juntos comerciais para uma empresa imobiliária, aparecendo como casal em campanhas de TV daquele Natal (pelas **Imóveis Francisco Xavier**, um case famoso entre colecionadores de propagandas da época) ([Xuxa e Pelé: Natal de 1981 na Publicidade Imobiliária | TikTok](https://www.tiktok.com/@thebest.memories/video/7301084045402721541#:~:text=Xuxa%20e%20Pel%C3%A9%3A%20Natal%20de,Natal%20de%201981%20na)) ([Xuxa com Pelé em comercial de imobiliária em dezembro de 1981](https://www.youtube.com/watch?v=t45oWkJPFw0#:~:text=Xuxa%20com%20Pel%C3%A9%20em%20comercial,Im%C3%B3veis%20em%20dezembro%20de%201981)). Assim, Xuxa obteve espaço em campanhas publicitárias que dificilmente envolveriam uma modelo desconhecida – mas que, com a “namorada do Pelé” no elenco, ganhavam apelo extra. Isso evidencia que Pelé abriu portas também no mercado publicitário, dando a Xuxa oportunidades de trabalho e renda enquanto sua própria imagem pública se consolidava.
Ademais, a presença de Pelé ao lado de Xuxa em diversos editoriais e ensaios fotográficos serviu para elevá-la de modelo anônima a personalidade conhecida. Revistas e jornais buscavam os dois para sessões de fotos e entrevistas, sabendo do interesse do público pelo casal. As capas conjuntas em publicações de grande circulação (como *Manchete* e outras) não só aumentaram a exposição de Xuxa, mas também conferiram a ela certa credibilidade midiática por associação. Em outras palavras, estar ao lado de um ícone como Pelé funcionou como um “selo de aprovação” implícito, deixando editores e produtores mais propensos a convidá-la para projetos. Vale lembrar que **“ao longo dos seis anos de relacionamento, [eles] posaram para várias capas da *Manchete*”**, com a revista acompanhando de perto cada fase do namoro ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)). Essa recorrência nas bancas solidificou o rosto e o nome de Xuxa na indústria do entretenimento.
Por fim, é importante notar que nem todas as influências de Pelé foram positivas para a carreira dela – algumas foram tentativas de direcionamento. A própria Xuxa contou que, quando surgiu a oportunidade de ela ir para a TV Globo em 1986, Pelé desencorajou a mudança. **Ele sugeriu que Xuxa permanecesse na TV Manchete, dizendo que “ser a primeira [na Globo] é muito difícil; melhor ficar onde está”**, o que ela interpretou como falta de apoio dele à sua ascensão ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)). Esse episódio mostra que Pelé tentou influenciar também os rumos que Xuxa tomaria, embora, nesse caso, ela tenha decidido seguir sua intuição profissional e aceitar o desafio na Globo – escolha que se revelaria acertada. Em resumo, Pelé atuou sim como facilitador de várias oportunidades profissionais para Xuxa (de filmes a comerciais e visibilidade editorial), mas ela soube trilhar seu caminho a partir daí, inclusive contrariando conselhos dele quando necessário.
## Papel da Revista *Manchete* e Outras Mídias na Promoção de Xuxa
A revista ***Manchete*** teve um papel central na ascensão de Xuxa durante o relacionamento com Pelé. Foi justamente num ensaio para a *Manchete* que os dois se conheceram, em dezembro de 1980 ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)), e a partir daí a publicação tornou-se uma espécie oficiosa de cronista do romance. A *Manchete* era uma das revistas mais populares do Brasil naquela época e, ao perceber o interesse do público pelo casal, passou a trazê-los frequentemente em suas páginas. De fato, a revista que agiu como "cupido" do casal **“contava detalhes do romance a cada edição”**, alimentando a curiosidade nacional sobre a vida de Pelé e sua jovem namorada ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=nacionalmente%20famosa)). As capas exibindo Xuxa e Pelé juntos (em cenários que iam da praia a eventos sociais) viraram chamariz nas bancas e contribuíram enormemente para fixar a imagem de Xuxa na mente do público.
([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html)) *Capa da revista Manchete (20 de dezembro de 1980) mostrando Pelé ao centro com Xuxa (à esquerda) e outras modelos. A partir desse ensaio fotográfico, a revista passou a acompanhar de perto o romance, impulsionando a imagem de Xuxa nacionalmente.* ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos))
Além da *Manchete*, outras mídias impressas também surfaram no interesse pelo casal e ajudaram a moldar a imagem de Xuxa. Revistas de celebridades e colunas sociais publicavam notas e fotos frequentes, ora exaltando o glamour do par, ora especulando sobre fofocas. Xuxa, que pouco antes era desconhecida fora do circuito da moda, tornou-se figura constante em revistas semanais como *Contigo!* e *Amiga* (dedicadas à vida dos famosos), assim como em jornais de grande circulação. Esse bombardeio de aparições – entrevistas, fotos e manchetes – construiu a **persona pública** de Xuxa simultaneamente como **modelo desejada e namorada devotada**. A promoção de sua imagem tinha um tom deliberadamente positivo nas revistas: enfatizava-se sua beleza, juventude e sorte por ter sido “escolhida” pelo rei Pelé. Em contrapartida, eventuais polêmicas (como cenas ousadas que ela fez no cinema ou rumores de crises no namoro) eram administradas pela própria mídia de maneira a preservar o encanto em torno de Xuxa, que já despontava como uma espécie de Cinderella moderna na narrativa do entretenimento brasileiro.
Cabe destacar que a conexão de Xuxa com a *Manchete* não ficou só nas páginas da revista, mas transbordou para a televisão, já que a Rede Manchete (canal de TV fundado em 1983) pertencia ao mesmo grupo empresarial. Essa sinergia mídia impressa/televisão beneficiou Xuxa: **quando a Rede Manchete buscava uma apresentadora para seu novo programa infantil em 1983, Xuxa – já famosa pelas capas de revista – foi convidada** para o posto ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L355%20TV%20Manchete%2C,ter%20como%20apresentadora%20de%20programa)). Ou seja, a exposição na revista *Manchete* serviu de vitrine para que os executivos da emissora homônima apostassem nela na TV. Outras mídias também legitimaram sua transição de modelo para apresentadora, publicando matérias sobre sua simpatia com as crianças e seu carisma diante das câmeras, preparando o público para aceitar Xuxa em um novo papel. Assim, o período do relacionamento com Pelé viu a mídia – liderada pela revista *Manchete* – construir e promover intensamente a imagem de Xuxa, pavimentando o caminho para suas conquistas seguintes.
## O Relacionamento e a Conquista de Espaços na TV: *Clube da Criança* e Rede Globo
O namoro com Pelé coincidiu com a entrada de Xuxa na televisão e possivelmente facilitou essa transição. Em 1983, a recém-inaugurada Rede Manchete lançou o **“Clube da Criança”**, primeiro programa infantil de auditório da emissora, e Xuxa foi escolhida como apresentadora. Há indícios de que sua fama prévia – alavancada pelo relacionamento – foi decisiva nessa escolha. Conforme relatos, o diretor Maurício Sherman (responsável pelo projeto) estava de olho em Xuxa por sua notoriedade e carisma, chegando a dizer que ela reunia *“a sensualidade de Marilyn Monroe, o sorriso de Doris Day e um quê de Peter Pan”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)) – uma combinação que poderia funcionar bem num programa infantil. Xuxa inicialmente hesitou em aceitar, talvez pelo contraste entre sua imagem de modelo sensual e o universo infantil, mas acabou assinando contrato com a Manchete ([Clube da Criança – Wikipédia, a enciclopédia livre](https://pt.wikipedia.org/wiki/Clube_da_Crian%C3%A7a#:~:text=match%20at%20L206%20comando%20da,por%20Maur%C3%ADcio%20Sherman%20e%20pelo)). Assim, aos 20 anos de idade, ela estreava como apresentadora de TV, **em grande parte graças à visibilidade e confiança que o nome “Xuxa” (já famoso por ser namorada do Pelé) passava aos produtores**.
Não há registro de que Pelé tenha intervindo diretamente para que Xuxa conseguisse o posto no *Clube da Criança*. Foi a própria rede Manchete – estimulada pelo burburinho em torno dela – que a **“procurou e a convidou para apresentar”** o programa ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)). Porém, é inegável que, sem o destaque que Xuxa conquistara nos anos anteriores na imprensa (devido ao namoro), dificilmente uma emissora arriscaria colocar uma jovem inexperiente para comandar um show infantil nacional. Ou seja, o relacionamento criou as condições favoráveis para essa oportunidade surgir. Uma vez no ar, Xuxa rapidamente mostrou talento próprio: o *Clube da Criança* foi ganhando audiência e revelou a aptidão dela em se comunicar com o público infantil ([Xuxa, Pantanal, Cavaleiros dos Zodíacos: lembre sucessos da TV ...](https://www.folhape.com.br/cultura/xuxa-pantanal-cavaleiros-dos-zodiacos-e-mais-sucessos-da-tv/334766/#:~:text=Xuxa%2C%20Pantanal%2C%20Cavaleiros%20dos%20Zod%C3%ADacos%3A,exibido%20no%20fim%20de)). Ainda durante seu tempo na Manchete, Xuxa manteve-se nos holofotes tanto pela carreira quanto pelo namoro com Pelé – frequentemente um assunto alimentava o outro na mídia.
Em meados de 1986, já conhecida como a “Rainha dos Baixinhos” pelo sucesso junto às crianças, Xuxa recebeu uma proposta para se transferir para a Rede Globo, a principal emissora do país ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Novamente, aqui o relacionamento com Pelé tem um papel indireto: por um lado, pode ter ajudado a construir a notoriedade que chamou a atenção da Globo; por outro, chegava ao fim exatamente nesse momento, marcando uma virada na vida dela. Após alguns anos de *Clube da Criança*, Xuxa decidiu dar um passo adiante. Ela mesma tomou a iniciativa de terminar o namoro com Pelé e aceitou o convite para fazer o **“Xou da Xuxa”** na Globo ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Pelé, como mencionado, havia expressado reservas sobre essa mudança de emissora ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)), mas sem sucesso em demovê-la. Com a benção do dono da Manchete, Adolpho Bloch (que a tratava “como filha” e apoiou seu crescimento) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L405%20Manchete%20e,%E2%80%99%E2%80%9D)) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=Manchete%20e%20fui%20embora%E2%80%9D%2C%20recorda,%E2%80%99%E2%80%9D)), Xuxa partiu para a Globo levando sua diretora Marlene Mattos, e estreou em junho de 1986 o programa que a consagraria definitivamente.
É importante notar que, ao ingressar na Globo, Xuxa já não dependia mais da aura de “namorada do Pelé” – ela havia se firmado como apresentadora de sucesso por méritos próprios. Ainda assim, **o relacionamento anterior continuou a ser parte de sua imagem pública**: a mídia noticiou a mudança destacando que a namorada de Pelé chegara à Globo, e muitos espectadores tinham curiosidade sobre aquela moça cuja fama começara nos braços do ídolo do futebol. Em resumo, o namoro ajudou Xuxa a conquistar o primeiro grande espaço na TV (na Manchete), fornecendo-lhe exposição e credibilidade iniciais, enquanto sua ida para a Globo foi impulsionada principalmente pelo desempenho no *Clube da Criança* – algo que o prestígio conquistado durante o relacionamento tornou possível em primeiro lugar.
## Percepção da Mídia e do Público sobre o Casal e a Imagem de Xuxa
Durante os anos de namoro, Pelé e Xuxa foram um prato cheio para a imprensa e objeto de variadas opiniões do público. De um lado, eram celebrados como **“casal perfeito na mídia”**, aparecendo sorridentes em eventos e capas, o que projetava uma imagem glamourosa e apaixonada ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Image%3A%20Pel%C3%A9%20e%20Xuxa%20na,perfeito%20na%20m%C3%ADdia%2C%20mas%20com)). Xuxa era frequentemente retratada como a bela jovem humilde que havia conquistado o coração do "rei", uma narrativa de conto de fadas que agradava muitos fãs. Pessoas próximas diziam na época: *“Nossa, como ela está apaixonada, como ela está de quatro pelo Pelé”*, segundo relembrou a própria Xuxa, indicando que sua dedicação ao namorado era visível e comentada ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Ao%20participar%20de%20uma%20live,de%20quatro%20para%20o%20Pel%C3%A9%27%E2%80%9D)). Essa percepção de autenticidade nos sentimentos ajudou a humanizar Xuxa aos olhos do público, diferenciando-a de estereótipos de *roupante* ou interesse calculado.
Por outro lado, nem toda a atenção era positiva. **Houve murmúrios maldosos e preconceituosos nos bastidores**. Pelé e Xuxa formavam um casal interracial (ele negro, ela branca e bem mais jovem), o que, segundo a imprensa, **“gerava olhares de reprovação dos conservadores” e até comentários racistas proferidos pelas costas** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Os%20dois%20eram%20perseguidos%20por,Mas%20nem%20tudo%20era%20agrad%C3%A1vel)). Além disso, alguns duvidavam das intenções de Xuxa no relacionamento, insinuando que ela buscava ascensão social por meio de Pelé. Termos pejorativos como *“maria-chuteira”* (gíria para mulheres que namoram jogadores em busca de status) e *“alpinista social”* chegaram a ser associados a Xuxa por fofoqueiros da época ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=olhares%20de%20reprova%C3%A7%C3%A3o%20dos%20conservadores)). Essa desconfiança lançava sombra sobre a imagem dela, pintando-a, aos olhos de alguns, como oportunista em vez de namorada dedicada. Xuxa teve de lidar com esse tipo de insinuação ao longo do namoro, buscando provar que seu amor era verdadeiro e que ela também tinha talentos e ambições próprias.
A mídia impressa, em geral, manteve uma postura favorável ao casal, explorando o romance como algo encantador. Mas não deixou de reportar as turbulências: sabia-se, por exemplo, das **frequentes traições de Pelé**, que Xuxa anos depois revelou ter suportado calada na época ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Por%20causa%20do%20companheiro%2C%20tamb%C3%A9m,que%20n%C3%A3o%20era%20o%20meu)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Apesar%20dos%20problemas%20corriqueiros%20com,Era%20uma%20situa%C3%A7%C3%A3o%20esquisita%E2%80%9D)). Essas infidelidades eram rumores correntes nos círculos de fofoca, embora Xuxa raramente comentasse publicamente enquanto estava com Pelé. O público, portanto, via um casal bonito e famoso, mas também acompanhava as especulações de crises e reconciliações pelos noticiários de celebridades. Cada aparição pública deles – fosse em um jogo de futebol, um evento beneficente ou nos camarotes do carnaval – era dissecada pelos repórteres, e cada declaração (ou silêncio) alimentava interpretações sobre o estado do relacionamento e sobre quem era Xuxa por trás da fama.
No saldo final, o namoro com Pelé influenciou profundamente a **imagem pública de Xuxa**. Inicialmente marcada como “a namorada do Rei” – posição que trazia tanto admiração quanto inveja – Xuxa soube aproveitar a visibilidade para mostrar carisma e trabalho, transformando-se em uma estrela por direito próprio. Ao se tornar apresentadora infantil de sucesso ainda durante o namoro, ela começou a dissociar sua imagem da de Pelé, provando que podia ser mais do que um apêndice de um astro do esporte. Quando o relacionamento terminou em 1986, Xuxa emergiu não caída em desgraça, mas sim pronta para reinar sozinha na TV. A mídia continuou a mencioná-la em referência a Pelé por algum tempo (era inevitável, dado o quão famoso o casal fora), mas cada vez mais o público passou a enxergá-la principalmente como a **“Rainha dos Baixinhos”**, a figura alegre das manhãs na TV Globo. Em entrevistas posteriores, Xuxa admitiu ter sentimentos mistos ao lembrar dessa fase: ela se ressentiu, por exemplo, de Pelé ter classificado o que viveram como *“uma amizade colorida”* em vez de namoro sério ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Xuxa%20disse%20ter%20ficado%20magoada,N%C3%A3o%20fui%20avisada)) – frase do ex-jogador que a magoou e que veio a público muitos anos depois. Esse comentário retroativo de Pelé apenas reforçou o quanto a mídia e o público discutiram e dissecaram a natureza daquela relação.
Em conclusão, a percepção do casal Xuxa e Pelé oscilou entre o encanto e a controvérsia, mas inegavelmente manteve Xuxa nos trending topics de sua época (para usar um termo atual). A jovem modelo gaúcha ganhou projeção, prestígio e também enfrentou julgamentos enquanto esteve com Pelé. Tudo isso moldou sua imagem – de **símbolo sexual e socialite em ascensão** a **profissional talentosa pronta para brilhar por conta própria**. O relacionamento forneceu-lhe a plataforma e a armadura mediática; coube a Xuxa transformar essa visibilidade em uma carreira sólida, o que ela fez com maestria ao se tornar uma das maiores apresentadoras da história da TV brasileira.
**Fontes:** Entrevistas e depoimentos de Xuxa Meneghel (inclusive do livro *Memórias*, 2020), reportagens da época em revistas como *Manchete*, colunas sociais e jornais (compiladas em repositórios atuais), e biografias e retrospectivas sobre ambos os envolvidos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)), entre outras. Essas fontes confirmam o papel catalisador que o namoro com Pelé teve nos primeiros passos da trajetória de Xuxa, bem como os desafios e oportunidades que surgiram dessa intensa exposição pública.
-

@ 7d33ba57:1b82db35
2025-04-04 18:13:02
Edinburgh is a city where ancient history and modern culture meet in the most atmospheric way. From its dramatic castle perched on a volcanic rock to narrow medieval alleys, vibrant festivals, and cozy pubs, Scotland’s capital is a must-visit for travelers seeking both beauty and depth. It’s a city that feels like stepping into a storybook—with a few ghost tales thrown in for good measure.

## **🏛️ Top Things to See & Do in Edinburgh**
### **1️⃣ Edinburgh Castle**
- Iconic and **steeped in royal history**
- See the **Crown Jewels**, the **Stone of Destiny**, and sweeping **views over the city**
- Don’t miss the **1 o’clock cannon fire**!

### **2️⃣ Walk the Royal Mile**
- The main street running from **Edinburgh Castle** to **Holyrood Palace**
- Lined with **shops, historic closes (alleyways), churches, and pubs**
- Pop into **St Giles’ Cathedral** and explore the **Writer’s Museum**

### **3️⃣ Holyrood Palace & Arthur’s Seat**
- The Queen’s official Scottish residence 👑
- Hike up **Arthur’s Seat**, an ancient volcano, for **amazing panoramic views** of Edinburgh and beyond
### **4️⃣ Explore the Old Town & New Town**
- **Old Town:** Medieval, moody, atmospheric
- **New Town:** Elegant Georgian streets and **great shopping on Princes Street**
- Don’t miss **Victoria Street** – rumored inspiration for Harry Potter’s Diagon Alley ✨

### **5️⃣ Museums & Culture**
- **National Museum of Scotland** – interactive and family-friendly
- **Scottish National Gallery** – features art by Turner, Van Gogh, and more
- **Camera Obscura & World of Illusions** – quirky and fun near the castle
### **6️⃣ Edinburgh’s Underground & Ghost Tours**
- Explore the **hidden vaults under the city**
- Join a ghost tour or **learn about Edinburgh’s dark past**, including grave robbers and plague victims
### **7️⃣ Festivals Galore 🎭**
- **Edinburgh Festival Fringe (August)** – The **largest arts festival in the world**
- **Edinburgh International Festival**, **Book Festival**, and **Hogmanay (New Year)** celebrations

## **🍽️ What to Eat in Edinburgh**
- **Haggis, neeps & tatties** – A classic, surprisingly tasty Scottish dish
- **Scottish salmon**, **Cullen skink (smoky fish soup)**
- **Afternoon tea** or **Scottish whisky tasting** in a historic bar 🥃
- Try local spots like **The Witchery**, **Makars Gourmet Mash Bar**, or **The Scran & Scallie**

## **🚶♀️ Tips for Visiting Edinburgh**
✅ Wear comfy shoes – **cobblestones and hills** are part of the charm
✅ Be ready for **4 seasons in a day** – pack layers and a rain jacket ☁️☀️🌧️
✅ **Book ahead** in summer – especially during August festivals
✅ Take a day trip to **Rosslyn Chapel, the Highlands, or Stirling Castle** for more Scottish beauty
✅ Consider the **Edinburgh City Pass** if planning to visit many attractions

-

@ 9bcc5462:eb501d90
2025-04-04 16:02:14
*The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.*
It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World!
Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us.
Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong!
As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court.
Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.”
-

@ 9967f375:04f9a5e1
2025-04-05 01:33:45
Así en la Santa Iglesia Metropolitana (en donde se hallaron ochenta y seis Confesores, asignados por el V. Sr. Dean, y Cabildo Sede-Vacante) como en las Parroquiales, y demás, fue grande la concurrencia desde el dia primero (de abril), Sábado *ante Dominicam Palmarum*, para cumplir con el precepto de la Confesión anual, que se impuso, y mandó en el Máximo Concilio Lateranense, congregado en 1215 por el Señor Inocencio Tercero a que asistieron los Patriarcas de Antioquía, y Jerusalén, cuarenta Arzobispos, cuatrocientos Obispos, doce Abades, ochocientos Prelados inferiores; los Legados de Federico Segundo Emperador de Alemania, de Pedro Emperador de Oriente, de S. Luis Rey de Francia, de Juan Rey de Inglaterra, de D. Enrique Primero Rey de Castilla, D. Alonso Décimo Rey de León, Don Jaime Primero de Aragón, de Don Sancho el Fuerte de Navarra, de Don Alonso Segundo de Portugal, y los Embajadores de los Reyes de Chipre y Jerusalén.
-

@ 7d33ba57:1b82db35
2025-04-04 14:35:00
Zlarin is a small, car-free island near Šibenik, known for its peaceful atmosphere, crystal-clear waters, and centuries-old coral tradition. It’s often called the “Golden Island” for its natural beauty, and it remains a hidden gem on the Adriatic coast—perfect for quiet beach days, cycling, and slow travel.

## **🌿 Why Visit Zlarin?**
- **No cars = pure tranquility** – the whole island is pedestrian- and bike-friendly 🚲
- Rich in **coral diving heritage** – once the center of Croatia’s coral trade 🪸
- Beautiful **stone houses, pine forests, and untouched coves**
- **Easy to reach** via a short ferry ride from Šibenik ⛴️

## **🏖️ Things to Do on Zlarin**
### **1️⃣ Swim & Relax on Secluded Beaches**
- **Veleš Beach** – A pebbly beach surrounded by pines, great for families 🌲
- **Magarna Bay** – Quiet, wild beach perfect for those seeking solitude 🧘♀️
- **Hidden coves** – Wander the coast and find your own little swimming spot 🌅
### **2️⃣ Walk or Cycle the Island**
- Well-marked **trails through pine forests and olive groves**
- Visit the **hilltop viewpoint** for a panoramic look at Šibenik and nearby islands
- Bring or rent a **bike in Šibenik** – bikes are ideal for exploring Zlarin 🚴♂️
### **3️⃣ Learn About Coral Traditions**
- Visit the **Zlarinka Museum** dedicated to the island’s **red coral harvesting history**
- See traditional **jewelry and tools**, and learn about the craft’s cultural significance

### **4️⃣ Stroll Through the Village**
- Picturesque **stone streets, old chapels, and flower-filled gardens**
- Enjoy a drink at a **local konoba (tavern)** with views of the sea 🍷
### **5️⃣ Take a Boat Tour or Kayak Trip**
- Explore nearby **Prvić, Kaprije, or Žirje islands**
- Great area for **kayaking or paddleboarding** over glassy waters 🚣

## **🚢 How to Get to Zlarin**
- **Ferry from Šibenik** (approx. 25 minutes, year-round service)
- **No cars allowed**, so park in Šibenik if needed
- Easy to visit **for a day trip** or stay overnight for peace and stargazing

## **💡 Tips for Visiting Zlarin**
✅ Best time to visit? **Late spring to early autumn** for swimming and quiet vibes ☀️
✅ **Bring cash** – not all places accept cards 💶
✅ Pack **snorkel gear and water shoes** – the underwater world is beautiful 🐠
✅ **Stay overnight** for an unforgettable quiet island evening under the stars ✨

-

@ 5d4b6c8d:8a1c1ee3
2025-04-04 14:17:31
We're down to the Final Four in March Madness and not only am I running away with the [Points Challenge](https://stacker.news/items/932715/r/Undisciplined), but I'll be running away with all of @grayruby's sats in the [Predyx](https://beta.predyx.com/category/basketball) live Predyxion markets. Is it good that all of the top teams are still alive or do we miss the upsets?
In the NBA, the West is still all jumbled up. Seeds 2-9 are up for grabs. What matchups are likely in the playoffs and which ones are we hoping for?
Ovechkin is right on the cusp of the All-Time Goals Scored record. Will he get there by the end of the season?
@grayruby has some irresponsible, way too early, MLB takes.
The NFL Draft picture might be clearing up, but there are always surprises. We'll talk about our hopes for how our teams approach the first few rounds.
And, of course, we'll give updates on all the territory action.
Happy stacking, stackers!
originally posted at https://stacker.news/items/934354
-

@ 6f7c7936:b48a90b1
2025-04-04 20:32:53
In a world that celebrates constant movement, expression, and freedom of action, the idea of intentionally placing your hands behind your back—and even keeping them there—may seem counterintuitive. But for some, this posture offers not only physical benefits but also psychological calm, clarity, and even symbolic depth.
Below, we explore why keeping your hands behind your back can be a meaningful act, and how, in certain cases, voluntary restraint can bring unexpected focus and peace.
---
## **1. A Posture of Respect and Composure**
From military cadets to schoolchildren waiting in line, the image of someone standing with hands behind the back conveys **discipline, respect, and attentiveness**. It’s a non-verbal signal of being present without demanding attention.
This posture is:
- Open and non-confrontational,
- Yet composed and intentional,
- Signaling a readiness to listen, observe, or follow.
For some, maintaining this position—even privately or in personal rituals—can help anchor them in the moment, especially in situations where **too much movement leads to distraction**.
---
## **2. Gentle Restraint as a Form of Focus**
In certain contexts, some people take this concept further: not only placing the hands behind the back but **intentionally limiting their movement**, sometimes even with gentle bindings (e.g., soft bands, loops, or self-applied ties).
While this may seem unusual, voluntary restraint can serve a purpose. For those who feel:
- Overstimulated by too many choices,
- Mentally scattered or physically restless,
- Emotionally overwhelmed by expectations,
…the act of keeping the hands still and out of use can provide **clarity, comfort, and simplicity**.
It becomes easier to focus on thoughts, breathing, posture—or simply the act of being. The absence of distraction becomes its own form of freedom.
---
## **3. Sensory Regulation and Neurodiverse Experiences**
For individuals who are **neurodivergent** (such as those on the autism spectrum), structured physical routines and reduced movement can support **sensory balance and regulation**.
Keeping hands behind the back can:
- Reduce tactile input or self-stimulatory movements,
- Create a predictable, soothing sensation of symmetry,
- Increase body awareness and improve posture.
In these cases, restraint isn’t about control or punishment—it’s about **reclaiming calm in a world full of overwhelming stimuli**.
---
## **4. A Symbol of Stillness in Ritual or Reflection**
Beyond the physical or sensory aspects, placing the hands behind the back can carry **symbolic weight**. It can be:
- A gesture of humility,
- A sign of inner stillness,
- A choice to be quiet, observant, or connected to something larger.
In personal practices, some individuals incorporate this position into meditation, silent walks, or reflection exercises. Others may even choose light binding—such as a soft scarf or wrap—not as an act of submission, but as a **tool for mindfulness**, reminding them to pause, breathe, and stay grounded.
---
## **5. The Importance of Intent and Consent**
It’s crucial to note: **context and intent matter**. The experience of placing hands behind the back—especially when restraint is involved—should always be **voluntary, safe, and self-directed**.
This isn’t about force or external control. It’s about choosing to explore stillness, structure, or personal rituals that bring meaning and calm.
When approached mindfully, this simple act can become a quiet expression of **focus, discipline, and peace**.
---
## **Conclusion: A Small Gesture, a Deep Effect**
In an age of constant motion and noise, choosing to stand still—with your hands behind your back—can be a **powerful form of presence**.
Whether you’re seeking:
- better posture,
- sensory clarity,
- emotional grounding,
- or symbolic stillness,
…this gesture offers a moment to reconnect—with your body, your breath, and yourself.
It’s not about limitation.
It’s about **choosing space within boundaries**—and discovering what stillness can teach you.
-

@ 5d4b6c8d:8a1c1ee3
2025-04-04 13:07:55
https://primal.net/e/nevent1qvzqqqqqqypzqdtgwhlaw2dsdm45c8t6wzslw5qyt5r8waxjrs86llj272ledghgqqsdjv9nadd5dwgzg9w02qp4s4gzphcxj3t8640nw4xn7qgf2lyzxysk9lmtp
There are lots of possible issues with this chart, but it is pretty stark.
A few random thoughts:
1. It might not be the people eating unhealthy amounts of sugar who cut back on it. I was never obese and I radically cut back on my sugar intake.
2. Sugar may have been highly correlated with other similar substances that people didn't cut back on. I'm thinking about other refined carbs, primarily.
3. There may simply be a lag and obesity will start declining as a result of lower sugar consumption.
4. It does look like the rate of obesity increase decreased slightly (lower slope), so maybe the issue is just that sugar intake is still too high, but the relationship is correct.
What do you think explains this divergence?
originally posted at https://stacker.news/items/934292
-

@ 96203d66:643a819c
2025-04-04 12:58:46
nostr:nevent1qqs9j3aw7jrzrw6mtgs9w2znhpg7u0vvur4v69mc8xhw90lqahej74ccx749u
nostr:nevent1qqsxrleatwc7v4jvpu4hk3k4s5xvvral0uvt6svyydwtqsz7tk2v03spph2jk
nostr:nevent1qqsykq5q6gaa499nykagjaf6sav7ul4ve0ge9y22707gueuasdtr97qsnceys
nostr:nevent1qqsvyhuwmnjglrk8hxdw8ye3lzy9f0ahf3ajfsn0wkf3pnztlx7dxxsq7jhlg
nostr:nevent1qqs2mmqn2sr6a0ysfjyyuwx5gwy4rxre6pwnjqnzzdszzrgh2zgynlgvv59j3
nostr:nevent1qqswhdmpjhkqzp0nld0m23kgyesqmyacksu9zf8kefxtwzracn7efuqt825sd
nostr:nevent1qqsdzsjfa2dmkue5hk5dr8ttl76l3kf649yx4lwslwnh238442jfmmsv4fzmd
nostr:nevent1qqszun5jhc22du06rle5r0z8zhj2ezm9pmmrfsqx4843qhz57k3aqxg738uv6
nostr:nevent1qqs8sx9mc2yuldpm5edrtplnge8ckgcr4xj8x7af3zdac0r4rat377ga689un
nostr:nevent1qqswe5auf0ym9lg78prwj9ppy0rvpdq92pwend96jmq6udh3d5r3mfqxlyl8j
nostr:nevent1qqsqtwgpl0v6qf03r4e9r4tsnyly354req9am2u6s5gjrtefwtedpmc72v3jx
nostr:nevent1qqsx2w65lvwmf23rutmnhzw3k2paftngssvfdzqmwle4f3m77hk4u8c6lgmrx
nostr:nevent1qqsfz6zpaw2gkgxjxfvevgsww0rhw07swwg0hun23xc4mfuh8f7afrg875wcx
nostr:nevent1qqs0eknqgzut0sv0undcps42pnw7an4wjt7a2rwjxd2zaqg6rqpjdwg56yeq7
nostr:nevent1qqsrg7yyaacetzugj8304krg5ne0xxu7kdnps8tlnd797myseqp97vs8r7tup
nostr:nevent1qqs20ap690l97n8py0g44w22963jkze78ws2em6e0cl02vc65nexmsqw9ugcd
-

@ 98468676:3a02caf5
2025-04-04 20:21:10
I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash.
Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax.
Here's the test wiki page I'm going to write:
```
= Simple AsciiDoc Demo
This is a simple demonstration of AsciiDoc syntax for testing purposes.
== Features
AsciiDoc offers many formatting options that are easy to use.
* Easy to learn
* Supports rich text formatting
* Can include code snippets
* Works great for documentation
[source,json]
----
{ "name": "Test", "version": "1.0", "active": true }
----
```
# We're going to use nak to publish it
First, install `nak` if you haven't already
```
go install github.com/fiatjaf/nak@latest
```
*Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal*
```
# this is how to add it to your path on mac if using zsh
echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc
```
And here's how to sign and publish this event with nak.
*First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified*
```
# replace with your full secret key
export NOSTR_SECRET_KEY="nsec1zcdn..."
```
Now to sign and publish the event:
*Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal*
```
nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz
```
You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851
and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io
-

@ e0ef3b4e:6fd74878
2025-04-04 12:55:14
At a conference I sit in a quite area and observe and enjoy a coffee. It's bustling around and many are attending a speech at the main stage. Two people sit next to me on a sofa and begin a conversation. He's wearing a beige hoodie and seems to be builder in the space, she's wearing a green winter dress and they seem to be colleagues.
It seems they are now meeting for the first time in real life and exchanging advice, him advising her on how to store her Bitcoin. He’s been longer in the space it seems and she’s just started at the new start-up. I quickly introduce myself and ask them if I may listen in on the conversation since I am a researcher working in the space. They happily agree. She goes on to mention that she will be paid in Bitcoin and does not know how to store it. He goes on to advise her on using a hardware wallet, then takes out his phone and shows a video of the hardware wallet he is using.
She says "Wow, it looks so easy to use. I tried so many different hardware wallets but they are so difficult to use." I see the tension in her shoulders, which then relaxes a bit. He goes on to show her all the security and backup methods for this particular hardware wallet. "I'm sold." She's smiling now and one can see that a decision has been made.
These conversations are happening everyday across the world not only at conferences but in villages, cafes or during random conversation at co-working working spaces. While we strive for good marketing and adoption of Bitcoin, these simple conversations between two people are what is driving actual use.
Safety and trust is a cultural concept in many countries and viewed differently depending on where one has originated from. If one is to imagine that many people would benefit from storing BTC on a device or using an app for lighting transactions then they must trust the process. This need to trust is a basic primary human need.
They will only trust the process if:
- Empowered: They feel as if they 100% know what they are doing when they are onboarded to the application/hardware device. If there is anything that creates doubt or friction in their minds, the trust to use it as a storage of BTC is gone. A person will window shop when deciding to use a wallet. On average when we interviewed people for various UX research initiatives one person had a minimum of two different Bitcoin wallets on their phone. Prior to that they had tested out quite a few wallets before settling on a decision.
- Safe: Many are nervous that they will not be able to access their funds once they put it online/on a hardware device. However often receiving advice from someone they trust this will result in them feeling safe. They will likely use the very same device/application that is being used by their friend/colleague or person in a close inner circle.
While this story might seem overly simplified, it’s been repeated multiple times while observing the behavior of people at conferences, through usability tests, and through interviews.
If we understand that a person is tentatively stepping into a “home” (Bitcoin wallet/hardware device) and looking “around” (onboarding process). Once they step in, they will only leave their “bag” (BTC) on the table if specific criteria are met. If not, they will pick up their “bag” (BTC) and walk into the next “home.” (Bitcoin wallet/hardware device). During this process there are basic psychological principles are taking place.
This is where design comes in and creates an experience. The UX design could be equated to the “interior design” of the house. Every click, every interaction every visual that a person sees or experiences is driving them to trust or distrust the experience. We as builders have a unique role in this process and I fully believe that we will solve these challenges together.
If you've read all the way to the end, thank you. On another note, the last 3 weeks have been filled with a lot of strategic thinking, planning, and collaboration.
There are many balls in the air at the moment:
- [Designathon](https://event.bitcoin.design/)
- [UX Research OFF](https://github.com/BitcoinDesign/Meta/issues/765)
- [Presidio Design Week](https://github.com/BitcoinDesign/Meta/issues/746)
- [BTC Prague](https://github.com/BitcoinDesign/Meta/issues/745)
- UX Research Africa strategy
If you've read all the way to the end, thank you for reading.
✌🏽Peace
-

@ ac58bbcc:7d9754d8
2025-04-04 20:13:12
Lovely seeing you here. Hello there, and welcome to our very first post! We’re the team behind Math Success by DMTI, and we’re thrilled for this journey with you. If you’re a teacher, parent, or just someone who cares about kids and learning, you’ve probably noticed something: math education isn’t working well for most everyone. Too many students dread it, too many teachers feel stuck, and too many classrooms are stuck in a cycle of rote memorization that leaves most everyone uninspired.
We’re here to change that—and that’s why we’ve built Math Success by DMTI, the leading K-6 Math Education Program.
The Problem: Math Isn’t Adding Up Let’s start with the elephant in the room. Math education often misses the mark. Kids are taught to memorize times tables or follow steps without understanding why they work. It’s like handing someone a recipe without teaching them how to cook—they might make the dish, but they won’t know what to do when the ingredients change. Studies show U.S. students lag behind many peers globally in math, and the gap widens as they move through school. Why? Because we’ve prioritized procedures over meaning, drills over discovery, and compliance over curiosity.
The result? Students who see math as a chore, not a chance to explore. Teachers, meanwhile, are stretched thin—juggling standards, testing pressures, and outdated methods that don’t spark joy or learning. It’s no wonder so many kids say, “I’m just not a math person.” But here’s the thing: we believe everyone can be a math person—if we teach it right.
Our Solution: Math Success by DMTI That’s where Math Success by DMTI comes in. Born from the Developing Mathematical Thinking Institute and over 40 years of research, our program isn’t just another curriculum—it’s a rethink of how math should feel and function in the classroom. We’ve seen the data: classrooms using our approach see an average 35% jump in achievement. But more than that, they see kids who love math and teachers who can’t wait to teach it.
So, how do we do it? It starts with our Developing Mathematical Thinking framework—a five-part recipe for success:
Listen to Kids & Build on Their Ideas: We build on what students already know, making math personal and relevant.
Speak the Right Language: We use the structural words unit, compose, decompose, iterate, partition, and equal to help kids communicate and connect to math across topics.
Understand First, Calculate Later: Concepts come before procedures, so kids grasp the “why” before the “how.”
Models and real-world connections: From blocks to drawings to numbers, we use models to make math tangible and fun while helping connect math to real life.
Embrace Misconceptions & Mistakes: Missteps aren’t failures but chances to learn and grow.
This isn’t the math you grew up with. It’s active, engaging, and built to stick. Teachers tell us it’s a game-changer—“I have never loved teaching math as much as I do now; math has come alive in my classroom. My students are further along now than any class I’ve ever taught before.” one said, “I could see the light bulbs going off like never before, and they’re excited!” Kids tell us, “Math is fun now!” And the numbers back it up: that 35% boost isn’t just a stat—it’s a sign of deeper understanding and real confidence.
Why it matters Math isn’t just about numbers; it’s about thinking, solving problems, and opening doors. When kids succeed in math, they gain skills for life—whether they’re headed to STEM careers or just figuring out their budget. But beyond that, we want them to love it. To see math as a playground, not a prison. That’s our mission: successful learning and a genuine love for mathematics, one classroom at a time.
What’s Next? This Substack is our space to share that mission with you. Expect stories from teachers and students, dives into our framework, tips for bringing math to life, and updates on our free courses (yep, free!). We’re partnering with educators like you to make this happen—because we can turn math education around together.
So, stick with us. Subscribe below, drop a comment with your thoughts, and start building a world where math adds joy, not stress. Welcome to Math Success by DMTI—let’s make math work for everyone.
-

@ 6a6be47b:3e74e3e1
2025-04-04 12:41:11
⛅️ This week has been a bit hazy—I haven’t been feeling my best. And that’s okay. There are days like that. But this time, it felt like something deeper, as if something was off. Like I wasn’t *enough*.
🌞 Thankfully, as the days went by, I started to feel better. Today, I feel like myself again—like I’ve put my human suit back on and climbed back on the horse.
✏️ I picked up my pencil and started drawing again, just me and my iPad, without any expectations weighing me down. It felt good—peaceful even—to create for the sake of creating.
🦉 What I’ve realized is this: It’s not bad to have goals or aspirations. Those are important! But what becomes unhealthy is chasing perfectionism while trying to achieve those goals. For me, perfectionism turns into a spiral—not rainbows and butterflies but a storm cloud of self-doubt.
I guess I just want to share this in case anyone out there needs to hear it: It’s okay to be imperfect. And most importantly, it’s okay to just be yourself.
[To those little leprechauns of doubt kicking and screaming inside my head, I can confidently say:*Not today, Satan!*](https://primal.net/e/nevent1qqsp3lc6wd4tqrwzssqmtv3mk6fctdzqn3hctjugrfkhtev6q68ht0g488mat)

🎨 As part of my journey back to myself this week, I decided to draw something simple and even try my hand at a little animation since it had been a while. Here’s what I came up with:

Imposter syndrome can be deceiving—it whispers lies about your worth and tries to steal your joy—but just like anything in life, ***this too shall pass.***
🎢 The ebbs and flows are part of life’s natural rhythm; you’d think I’d have learned that by now! But life has its way of (re)teaching us lessons when we need them most.
✨ To anyone reading this who might be struggling: Be kind to yourself. You’re doing better than you think you are. And remember—**you are enough.**
Godspeed
-

@ c1a9282b:75752c6d
2025-04-04 12:20:54
«Rainha em trapos», chamavam-na. Antes andarilha, assentava-se agora em trono xexelento, lixo cenográfico de alguma companhia de teatro. A qualquer que passasse perto dela, encarando-a, concedia retribuir um sorriso condescendente e um aceno de mão, entendendo que a ela agradeciam algum favor.
Antes da aurora, levantava-se e ordenava ao sol que amanhecesse; antes do ocaso, o contrário: que anoitecesse. Em certa data, por capricho, decidiu que não haveria nem raiar nem cessar de raiar naquele dia, e ordenou ao Sol que nem ousasse despontar. Negou-se o Sol a obedecer simplesmente cumprindo seu diuturno trajeto.
— A esse rebelde, matem-no!
[revista gueto: 2017]
-

@ 907e4623:f40ff12a
2025-04-04 19:13:14
<p>gm.</p><p><strong>i'm doing my job as I can.</strong></p><p><em>You know, it's not easy to be a founder.</em></p><p><s><u>I wanted to give up so many times.</u></s></p><p><u>But give up is not an option, I need to improve and move forward.</u></p><p><br></p><ol><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Difficulties</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Doubt</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Self interest and responsabilities</li></ol><p><br></p><p>I was stuck building this: <a href="https://afk-community.xyz" rel="noopener noreferrer" target="_blank">https://afk-community.xyz</a></p><p>Chasing my Product Market Fit, solving the problems I work on...</p><p>Step by step, I'm gonna make it.</p><p><br></p><p><img src="data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/4gKgSUNDX1BST0ZJTEUAAQEAAAKQbGNtcwQwAABtbnRyUkdCIFhZWiAAAAAAAAAAAAAAAABhY3NwQVBQTAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA9tYAAQAAAADTLWxjbXMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAtkZXNjAAABCAAAADhjcHJ0AAABQAAAAE53dHB0AAABkAAAABRjaGFkAAABpAAAACxyWFlaAAAB0AAAABRiWFlaAAAB5AAAABRnWFlaAAAB+AAAABRyVFJDAAACDAAAACBnVFJDAAACLAAAACBiVFJDAAACTAAAACBjaHJtAAACbAAAACRtbHVjAAAAAAAAAAEAAAAMZW5VUwAAABwAAAAcAHMAUgBHAEIAIABiAHUAaQBsAHQALQBpAG4AAG1sdWMAAAAAAAAAAQAAAAxlblVTAAAAMgAAABwATgBvACAAYwBvAHAAeQByAGkAZwBoAHQALAAgAHUAcwBlACAAZgByAGUAZQBsAHkAAAAAWFlaIAAAAAAAAPbWAAEAAAAA0y1zZjMyAAAAAAABDEoAAAXj///zKgAAB5sAAP2H///7ov///aMAAAPYAADAlFhZWiAAAAAAAABvlAAAOO4AAAOQWFlaIAAAAAAAACSdAAAPgwAAtr5YWVogAAAAAAAAYqUAALeQAAAY3nBhcmEAAAAAAAMAAAACZmYAAPKnAAANWQAAE9AAAApbcGFyYQAAAAAAAwAAAAJmZgAA8qcAAA1ZAAAT0AAACltwYXJhAAAAAAADAAAAAmZmAADypwAADVkAABPQAAAKW2Nocm0AAAAAAAMAAAAAo9cAAFR7AABMzQAAmZoAACZmAAAPXP/bAEMABQMEBAQDBQQEBAUFBQYHDAgHBwcHDwsLCQwRDxISEQ8RERMWHBcTFBoVEREYIRgaHR0fHx8TFyIkIh4kHB4fHv/bAEMBBQUFBwYHDggIDh4UERQeHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHv/CABEIAZABkAMBIgACEQEDEQH/xAAbAAEAAgMBAQAAAAAAAAAAAAAABQYBAgcDBP/EABoBAQADAQEBAAAAAAAAAAAAAAABAgMEBQb/2gAMAwEAAhADEAAAAeygAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHir7IX45wsypppbFZ+yLzTw943BYAAAAAAAAAAAAAAAAA8qhPPbazB2i/FWPXoG8WqH32BHRDphGkB8NtTTn3n0TWeeq2WJrE16Iptup2eojoAAAAAAAAAAAAAARXxVm/neVsmfdORT0AAAAAAIOp9H8bcPwS3P56a2IU9AAAAAAAAAAAADFf8Aspt/O9b+2joyK9IAgWchW6j57eBaPWp5thbFVRNrVbK18sEVLY++EdGlIvWs89fsVAtNueWFPQAAAAAAAAAAee9PnCF6FDWG3NkU9AAD5+VWmnbfO5zjOnl5zjKc5xmJzMw3Rq90wMPpgAPCg9EhLcMxvT7jG4RuAAAAAAAAB489nvo08uxDP1AAHz/RTp56l4s9PyTOMjLMGWUy/RoWaw+nyK9oAAHPb3E/FfzLUKemAAAAAAAAPNHPeg0Dod/NyKemAB48qttL2+exk08tlmAylKxfQa9s6MPpwAAAPLmfQuYX87rzy9aegCQAAAAAAETLV2ef4bfXbHNAr1gPL1qk4VH5s56Pk8MkGQyymS6VAz2H0uTSvbtmufdOMqI3AHkQVNscNblucvWrLFgjoAAAAAAAVe0Ve3L901CzUXCNwPPl1uo+vg4Zzp5OGSTISEfea9dj1rdVz9e2Vb486eS+/wCFOPVd6racPpsiN0HLVURctFzhK22pW2cgr2AAAAAAAK7YoqcPhsVPuM5hXrab1ucaj8eXR8pjIqJFeO++3T2fq1/2nMZ+nyXMlHb/ADLJNWWU79G5vL07r8RmP0Mf8WNzaGm63bltVkiZaLBHQAAAAAAA8/QjnnQufX2/neop6WvMrdRdfDwzK382Jk7dNU9SDm9sZ+rkRqBB0Pq/ONPGj8s6+SyykaFw+bnXQMPf9vTG9e/anXCr383pnoU9EEgAAAAAAAVj1nefX8zo2ufjp6NB+i2yunlw8xln6QNAAAEDPazlyvNj89vn4FPeJCVyc8omAseuzS7b+H1Y+9Ay9R6lp5vsM/UAAAAAAAAAxU7ZrOEDYOdX23P9Ip3gAAAAAGkIffAabGN87mN3oISWqd+CxXLz9K9ARuAAAAAAAAABG0/oMHfgmt6Feq7biOkAAA8IwmIyH8zfTbYxvnYxvncxlTbc2nRPjnpxyKd4AAAAAAAAAAAEHWugR9+D6Po5j9UT0VUtK91q+auZJf4fnyabbbGm22xrttsY2zuY8YmJvwed5+yRMineAAAAAAAAAAAAABpUrhicORyXR63bk+b0rvyFuzWvojefzEZjSYzAfPOdp1p30zh90Pb7Iip23fFezIjcAAAAAAAAAAAAAAAABpuRGfDYU41daE0r33SaL6bkbAkAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAD/8QAKxAAAQQBAgUEAgMBAQAAAAAAAwECBAUAIEAGERITMBAUFSE0UCI1gCQx/9oACAEBAAEFAv8Aa7yDZhLOExVuoiYt2HEuw4l1EXB2cJ+MKMn6gpGCbJuhNxZljLVlRLIo6QeMqYjc+NhZ8bCx9TEXH0osfUSWKkmxirHuRrgijK39E9zWNm3OChzZzotVGFjWo1PA5EckmsjlwsKXDdDt+WMc17d/PmiiMc6ZaGg1YI/nmVwTonu6w0CaKWze2ti2KkGEacQIhhHsCjYVk6CWI+rsEk7y2npGZVwHSntRGpqlSgx0LdffzJ+fzRc+aJnzJM+ZJnzJMrppZRfVURUtIChWpne5bubGU2ICtivnSGojU1Ws5IrCPcR+urB2IuhURUs4j4pq6W2WDbvcjGkcSzsACYEWo5GhDIK45tdSDvytRhtKPmStnsc17dtxDJ5NpYvYj6+IZHhqo/Yi67aN349DJ5bYr0GOCx0+y1nI0QjkcY2uqB35XhsRuhzgvQo9pxEbpj0QO1E18QyPrwVEfsxfDch7kXh4yuDtLNyybZjUYzUV7RjkFcY+usB7iV4iclZSlUNrs3u6WUiKWx18QSOTPBTA7MXxTX9IJqKGxG5Hj2Vu/or+G2/w1Ec1jJJVOfXXA9xK8c9/Ua5b91Duuu2XEC8q+gbyh6r+R0j8FLH7Ub0cqNSVaCZldK9yHSV6MHz5rcp/x8Ou6oGy4k/Dpf6/S9yNbLMp5GuvB7iUn1jnI1JVqNmSJJjrkGQseQ1Uc3RYE5qmW/4PDP4ey4j/AA6X+v030joD4KgTY8WVbMbh5BjropZP16megxqqucmW/wCDwz+HsuIE519AvOHocqNbMMsiRqjRDyMi1YR5bA7sTUxysdEMhwek0vcImJl0vKHw83pr9las7lfw4/8AjovJHQDTGhnkZFrACz/z1sQdiVqrJPYPk03Q1MTEy8X7qG9Fdsnp1NpVUNh6qvJJplkSfWLCPIyLWAFquAd2NrgTU9s5Ve5MT0nqprNjUazZ2bVj2o3I9npdn7cf0iwDnyLXAD4Z4OxJ0keg2pJIkkL2lHiY5UYyjYsiy2nEAeuNRn7kbFycb3EmLXnPkWvADx3AO5H0Pe1jTlUrsppHQT0ui9Ebh2P24m0I1HshudAscljeUEWCAHlVOaEqjdfxUjPipGFrzCaaBKK74qRnxUjEqpOAQnax/VPshtaNm1v43NtNJQwNjIkNHj3OI7TbyO0Hh2J0D2zkRzSsJWz45WmF5nuaxDy1drOVgBQgksZzURrdvPjMlAgSCQpDXI5vjVURDTGphHvIupVRrZJSWEqvitiA3NpBSUytmujEa5HN8BCjZhZuEe8i61VGtmynzSVMBsQe7soDJTYcs0IoCjMz1cQbcdKCmPm485n+I5RgGcx7A1XXsiN3s2IKUyWCfXkjW7n53CLiq5fLLshDyNElWJYUQUVm/ciOSfSiLjmzoDgWQnYxzHt8D3MG09oFmc51gsClGPGojU/ROa17ZVNGLhqeWBfcT4+MtHYlqDEs4mLZxMW2Bj7Z2e6nyFFUTDrFpow8YxrG/p3NRyFgxCYtRCXFpImJSRMSohJgoMQeNajU/wBr/wD/xAAvEQABAwEFBwMEAwEAAAAAAAABAgMEABESEyExBRAUIDAzQSNRUiIyQGFCQ2Bx/9oACAEDAQE/Af8AXEgUqUynVVcex8qTKZVoqgQfw3pLbItUaxpMjtiwe5obOCs3VE0mEwn+NcO18RSobCv40dngZtqIrFksfeLRTMhDw+k/gSJZvYTOaqYhBJvuZq6D8MKN9GRpiUb2G9ketLkKtwmvuNRoyWE/ve64ltN5VPbTcUfoyFcc/wDKuPf+Vcc/71HC8MX9d0iOl5NhqK+q3Cc1HUkPBlBUahMFIxF/ceTaci+u4NByQGMVzPQckxkqF9OoqO8HkBXTe9eQG/AzPJJewWyqibxtPJBYwms9TytehIKPB6RNbPF686fJ5NqP3l3B45ILGK7+hzTxYEuDwaHRkqusqNQU3WE75DoabKqUoqNp5IDGE3adTuTIbUq4DnyTE3mTUVVrKT0ZvYVUbtJ37TfvKwx45IbOK5npT20G28k509Kcd1NIUUG8KYeDqLw3yO0r/lQewnoyU3mlCoKrzCdzzoaQVGlKK1WnchtSzYkUxswnNyuGbCCgCloKFFJ3wZGEuw6HfNVdZJqMm6ykdE1AN280fB3bTetOGKQ2pZsSKY2Z5cNNtIbFiRv2kz/YOSC/iJunUbtoG9daHk0Ok/6EgOeDrSjlaKRs+8q+6aQ2lAsSOV1sOIKTXBve1cI97VwjvtTTL7awoCgbRTPryC54GnTfaDyCk1DeJGGvUdSa8QMNGpqOyGUBI6kphROK3qKjyA8P30pEgMj91FjkHFc+49Z+KScRrI0zMBN1zI9B6aAbjeZpiKQcR3NX4DrCHRYoVgvsds2j2oT7vdSRSZrB81xLXyFKnMDzRn3u0kmsCQ/3VWD2FNMIZFiR+HZbSo7StU1wbHxpMdpOiass/wBf/8QAIhEAAQMDBAMBAAAAAAAAAAAAAQACERIgMBAxQVEDIUBg/9oACAECAQE/Af19JVBVJ+QAlQ0KvpVFSVUVX2oaUQR8AbyUX9YA5FvIzNHJRM6gSh4wqQqQqQjvoDCcORkAkpx4s8Y5seYFjSiIOMemzYBJtcZNp9tnG/qzxjmxxgXM6xN3Tt9QJtcZOkGxu6dvhbunb6+Mc2OMBBhKDQNCI1G6fvhbunb6ATYfJ0qrHCdW7p2+J/ejBypR8nSmdWHixwjRneMexGlfSm0GFUFUFUESDofQjGDBThzkaOUTJyNPBREYmtlOPAzB3BRb1gDe0XcD4AYUg7qjpUlUlUFUdqQNkTPyVFVFVH9h/8QAOxAAAQIDAgoJAwIHAQAAAAAAAQACAxExEiETICIwMkBBUWFxBBAjM0JSgZGhULHBcoIUYnOAkqKy0f/aAAgBAQAGPwL+9fLe1vMqWGnyvVzYh9FdBiK+DEV7Yg9FLDS53LIe13I/SLUR7WjiVKAwxDvNwUodqW6GFailo32nTKy4xPIK8Pdzcu5+Su5+Srg5vJyyYpHMK1DIO6yZLLLiNzwpdIYYfEXhWobw4cPodp5DQNpVjoon/MVhIhMvM9Tf2p/mUmgAcMzIiYWSMGeCwkInm1BnS2/vCtMIcDtH0DKvfsapCm7whBz+0ibzsz5IyH7xtV1N2wrJueKtOvWGZUU/Cw0ZxsGrtpQZDaGjUbD2ghYaA4yHi2hYKLkxh/trlhl8U/Cw8edif+SkBIY84r5cNq7KDdvcV3cNdy33Xct913Lfddy33Xct90QYYDQLziSKw8Ccv+Vgol0Zv+2tW6uOiEY0YktnlHfwUhQY9ll8U04Ive4knfmACMo3nFkUI0GYE8k7uCtUeNIawXOMgKqTdHZwCbDYJAY7ojqNCdFdUnMAnRZeccw3iYKteHxcQg9pmDeNXHRWVN7lbcMt/wADMN6M08XZkT0nXnMWgMpqPRHml7NWc91GiaMR9J2jmHRHUaJp0R1XHMCei285oRod0jaCbEbRwnqrYIrEPwsJtifbMN6M01vdmQTpPvOatbWJ8Bx7s3ctVwY2EMCDRQY7nuoBMp0V1XHMNB0W3uzZnSV6LX7XFp1Qu3BYR3F2YHR2m83uzNo6T782eNyDx4haTXChE9TjHhJRXchjl7qATKdFdtOYa3wi92cs+VQX8ZKCeEtTI3uCJ3vxx0dpvdeeWZtkZT7+uZMgpQhhDv2KZ0xUYxcdimVPc4KXlcRqbP6n4KZ64xc64BPinabsw1nhq7l1TcQBxUoItnfsU4jyeGzqD9lCgRQ4ohj16neif+v8amz+p+CmeuMIDavryzOGiSaX3zO5SgNtneaKcR5PDF/h3n9OIXFFxqep3MJ/6/xqZ4OCcNzsUuNAnRDtpj9my7zGinF7R3wsmrLxjhzTIhCIPUddkaLeuW9wU/M4nU4zeE/ZRGcjiiCKvryxshkm7zRTido7jTEc0aJvGPJxyHV6rDdI4kFnqoI4T1Mt3hYN3FpxJlOibNnLEm1sm+Yqb+0dxxrY0mX5iw85bacUXOqcTBjZJqDRQDVMIKOk8IPFCJ9eCFX/AG6wZWW+YoEjCO3nMuZ4ajGtOQjDZsTYjaHrLjQCawruLzqojCsM/Cwfk63P2UbyU5WG7ypytu3nN2xpM+2LacpmmwdWAccl1OfXghpRPsjEPj+2qljqESRhvoDI8uow2OszqVMNtO3nPGw5lmd0ytKH7rSh+6m58P3Uy+HymtKH7rShe604fuU3Cyt7ZdVllJ2W8k1jaNEhqw6Uyrbnclgycpn21KQvcrTjM42CZpv+y/iHC91zeWrkG8FZOjVp/CERtDn5uMgrMO4b8cxH0CtvpV3AINaJAawYZr4TuKMGMP1D8oOaZg5yZuUoeUd6m4zxy5xkAhDhA2J5I38UGCviO/WrTcmK2hRgRwQNo3IOaZg5nKcAuzb6lZTp5gucZAIQYIODn/kpuvimvDXLTcmKKORgxmni3/xWoZmMS97R6qs+SyGe6vdLlmrcR0ghChtNjY1WjlRTU7tesxBfsIqFbhxXWfMKKxGeYb/hd473V5Odswe0f8BYR5yfMaBWYYv2nafoEiJhWoGQfKaKzIgbnUUooMM/CtMcHDhmbT3Bo4qUIGKfhWQCRubRWukZZ8oopASH0OTmhw4omH2Z9wrUK/iwqy/2e1dp0f2KvhxAtJw/atJx/arocQrs+j+5VmH7MarUW7i8oGLOIfhWWNDRuH0iRAKyoDPQSWi4fuVYnutKJ7rRcf3LJgM9b1IAD+9j/8QAKxABAAIABAIKAwEBAAAAAAAAAQARITFBUWFxIDBAgZGhscHR8BDh8VCA/9oACAEBAAE/If8Atc2wOAS9A+F808oM/M1950TT/lTPODPzHaB8L5oRZnAf8jiwOifYQDjLqFbEO/8Acs5XN6BBngQfMG+ycIFp+3GLaftxn0/OccY9wGX9xmtecp4zdD3/ALmO22P2TjMdX/hq8ySUEIuy2/QhMVeBwIPQ7uTwhUqyBQdTSGmYmcxbyH4R3Xnh8SOqDg+pD+VJLH/AtDuys34JSZS4DCIANajBcDryTE0MOYgzm7a8Z4sVN8fJ25BXotON+I7NTE8mGnOh2F4p6JCNzYDzINgEy04j47ZesHhw7sxxlbHN/EEmAoDp0MJyzLumOOA9gQz1Xf8AP4F/XT++n91P6qXpfA+HQZAI4MwCC3hmviDkIx4N+1OVors2D+Nk1wJMAoDTp4Ig4Nm7MyEyofk6GDx4/t0UQCOCMR/EA1QRNYHbfjtABBWnSFrC1Hz5U2dHTw57jUe27XI0PwdKtH2g6dAh0zVjah58NwOw1Oz2k2fQ0IR1MdvuDqMdD70e/h1OEn3w6gEtY5xNSNmrObanZkipi7oYdvueh7Qy6aB1cRR7udE/BK+L/XnVEpTAdtSLbZB2W3eo5P3UK1nX3MuopxB4PQ6mjP2g6oXJeN3aywo+IfvsqbFPeHmsIehAOHTdurxGVzHI0OorVfhW3VgvPXcj5V4iy867ITWSLM9SXrv9eo9mxtD7t1NIdY7lofd+rqhnLQLBzP5MsJDv7HRuvn4e8ro8TpqpTk4TPswjY0OovEvwqZHV1ByFd8Y0Ikzhp5TXY+GE9/acZj0On9OFfeXU5HsdwNPyoEGastfLJ8zAoFoulpLIp2tW2Wjdp9UmD79jyO4ga53q6SfA7XYnAxmxp1ColiAAAKI3Ks1UEsuO2A+ZQ0aDAd341lcHcj5iFia9G9WBj+AeP6o8H6wdjzuwg+4fV0rBa3B1Jy+YCq0Sz7oX7ThNOg7ujfmhi+GpD86KWXFjA2lsE+s3hxfrB2OxbicUX0Jr0FBoLWZBywbGnTcxO6RStwnJ3S1RWTbanTsuOxmfo4bD+cUfcYIJU7N6ys+kD27HvoV+b2l1rHAPLo3R9N0jw9wX7SsLlMHdABQUfhlUPQXp8KHwuj+MTMHwIIIJbfwtR975ghV+dj2MVskGKMJvmv6dAmSgLZriNHbR0Kaz8E/cqSr1OHhArI6NmGi5a/eHUHxA6Oo/UWC8yCCBCWLheb/ZhKADsmWnvQfyL7Yh+cWdN4avzRnd3w3mFs8nuOoSypVhi8F6SVKCOJS8NFbRybOyBBM8dKVtun2Hm9lcbnnmz9oVpxWHJ/CAtwj2rpIondx3+RKbDdP0Orw71eeros0oJl8ECZclxun7QIEpExK90Yli8OT69lHS3I4MUbxUtfRhiXBELDsGspu+f4bdaCCYMseliXXhP7r4n9V8TlCS1vlKeppZh5Q/fviH758QTYL9tIQGwU8rDAtiGl90an1YZdEDh2ZDu26wYw1hx7EPeV7c44iAgQIECY7YdctUu98PieziGApN4Qs3bWpuie+w7dfSbuMurfGMzzgQIECBEPoPF2j67HZptQcAqA0O0YLOeIrgLr2kLAKxNesZKA1ZYhxGUtPUCBAgQIEKAK1dIm0KeuTEreO67UFp71cGDADSZvchYBWJ1PgOazMIFsbg0gQIECBAgQsArV0mUWgGblLgOL0HbLFeOODB7AcT1gUXzjn0PNMjLW9hFrJ4qYYo2wSrzgQIECBAgQIoMXnyg46cPN4swWA4HAduyKURg/GWZ4O0q93lxRx1vfmYLmypUqVKgQIECBAlS9q3j6Ms63eBBM/lm/4AoMmY6wxUXH2G0tTRcdcmJG/bjHHQiuVKlSoECBAnFDqqPceTCOOqnQ5vzKBjNMhz3gkwZAZf4bhwzBZCLL/SpbF5S+EVYrWyYcCx1fantqPmMz5xQOXKKexo+YgSh0fbhlku6Zd152+EJQPTLwQIC5BR/kURmyQfxVjymWcsojS7nxAanc+JnnPKD+KFvOURmwf9sf/aAAwDAQACAAMAAAAQ88888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888DjRbL888888888888888888PBDpx8r93888888888888888NV8888888aJ8888888888888tk88CGsXSz8yl88888888888Od888eHCLJ888La8888888888gc88TjO3ze888s7888888888i3888JGjf/APPPPPI2vPPPPPPPA0PPJent+3pavPOLS/PPPPPPPKFvPLu1kzjSth/MEffPPPPPPPFmPAUbzfMvxeBfJCK/PPPPPPPGN/FerVfPDuAAf5HxPPPPPPPPPHlhc/PPPDYTCtWbfPPPPPPPPPKVfPPPPPPMAMOGK/PPPPPPPPPPPQ/PPPPJPBMCHPPPPPPPPPPPPPHUsOFKPPGFLPPPPPPPPPPPPPPPFxl9ElPkpfPPPPPPPPPPPPPPPPPKs/c1PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP/xAAqEQABAgIJBAMBAQAAAAAAAAABABEhQRAwMVFhcYGRoSCxwdFA4fBg8f/aAAgBAwEBPxD+uCOSyLMDdRWZyizA3QRwX+HCSuEzovYc/aIg5c2CsANY91/jBWoGkOyLunOC5Pi39on5GmJjT4ADBzYZp3L0zYMqh3Lcx5QbK5Mj91zTG4BemAIlaZk0lZmARcO4KA5uPSF62HpA8+w9IQhOUTRMRI3IA8ON491kgqzEyCMY0U4C7oM5Xmf0gggmFkw+B0BcOOD4QCWzFxmKv/f5LoAVtFmckchnJoCCamTD4HSGboz/AD1QAHKvM4OhmNC1n9UMgmAETD616jWyAdEQIcVJgFx7JhYPvGkqZWZyRGaJTJqGEEw+AiQIlRaug08O0VkQO1Twlxx2paCQiOf0EyagAJETkPanyws3UPhXCz71QyViEBamBp5jsuF5qSBJg9k4MG2olFd5IwNExoiCHBMhGwFu6gJAhWwILUxD8Bkaclm3gsoB2qQBDFX2cFDOSAic5KPkcEUtoh5KYCApbIBbA+KAKIq+QUEmgNkAAYVWg3NJEBgc3Xo5nRMWHtNZAdNgAUQFnrEoBnRkMEwEwR5P5queVZgZFGUCGcRfWBUaGMBepBVpvMzWDEHmFyf4gFouqn+YlYL0axeAXVzxGdjmmFNyNmiEeowTQX5CwZp8zmwy+BHyxmMiudy3dEhIZQQWzyob8gQGI8osJS+S9gjUqHFjM5n4ZCAos4CcgsAizgByCAQD+v8A/8QAIBEAAgEEAwEBAQAAAAAAAAAAAREAITAxQRAgYVFAYP/aAAgBAgEBPxD+uEBdTxhDqEfjxs3SzKMFCfc9oB7jHBzRKMzv4BLRDGlAsHFDUQS0XgrRDnyQkIBmH5zznnFw4OTgVouU6PKYHRIawiyjgynW67Y9KRayi+LQlC+OiRaZU/q0DCGz5cUFO2EQZ6GhgI7OOZOUjqDMTAQhhGOLnFMtkkBgouGFAEFwSBU8RmzAWGOVqcixhMrIlS+uFiCAzxCWXePMcUv4t1/xBmFAoJGp6sOek9J6QEieKf6t1iLKYNx5bAleuB8IcrRDgfC9S0QwrULBzWgSlo/AXCa5SrJwj1PCAupRkprnClX8gBgz3hJk/wBh/8QAKxABAAEDAgUEAwADAQEAAAAAAREAITFBUWFxgZGhECBAsTDB0VDh8IDx/9oACAEBAAE/EP8A1Jzp5VNdKnhU8PSaOVcv8S1ZfUz960kH9DOwjzSEcSJ9ipbD6I/c1IIPV/qKsAW7PpUFXdDO4jzVqzTJvho/wxOtKxLTDpOXhUtOkXy4hl2KYpyBHMG5zaTkLKiccpebQCX1jfLQwKbsfQo6DrPQCEOR0JRLdH9qRbM/WxUnXyjzcIeTR9iQv5B3eZRAlGJycUw6TQh4LDhz2eDXWo/wJTakEHFaYKgRtB3fPN7UtQomQ8tOQHGhFu7FvI27zQdBgQGwGKiT1vV/Y1NsBINkaPVNNxL5u3aKPitTqOW8HOSsISBMF3LHM7UKmpBBwT58u1WIyy7+79j0mjskykO678WV02oggRgJ+7Vl5UAFj8qDU8NluT+mpfnSGAmIj3HfsnisZclX9U+zvHzk7Ps2RfJt1c5c/ct2nppODBWGk45d11eL8DXNZFS6rc2eNXwlWq7RyaTjRohokWAzsO/UcPlLi1YG3cjaW+x/y0dpfb2WXN2XWgmCAgAwB7w+LmdCL9cVeuhwK/R3rPXaBe9D/daF9CilqiqpxKgsLhfe/apgx6iddBJEcjRmB5nlSRrdrpSlzhQDTx3OpwPkw23Fu33gZe2tSAj1fKDhGYwW2oLKBIAWAKfPuBSKlubF9GvSlgNM4voM0egxRRUt2SkIi3QQc59n1Rl2QJEcjWRO0zmk7bTkkq0AxHrk6snbT4+8FPaG1AAlaFxydgm746vFDarbBzV3Xit/eialEleBxW3WkZrQXlHAIPUUUUUU7UwW7KPkfA0EEe4+EAJjZOI3qTQuyII2JvrwSN6Bk1KyEjWPipbNLAsKq4vkb9DelKBCF/8AgXnwo4++UMxE2d7fWFCijPoUYoorF+OQhJPAeZ97io9KYM/9icuNTErLav1M9Xan4pdEW7CaUGiOgXs45BoBA929J6QUzBocXFONScswaBwCA5egUUUPVupjLIPkY6TQQfgQSKg5KGC3s5I2alqceCT8VGQnR0hXv4GoxxouJAfb1/BImQAd11ljgVFBQUUUYooqLchs3CPEX5rUWz+GYKLwuuw+npQgJW+9y3QPc+JJTA2B6M/8G1HmNbQEB75EtI2Cm0KIdg4BB0oKCgooPQKjXyokRjqYOU0EAfi/WeBfxUhdthn+juqT4TXi/wAgmlFnXJKYnnM6S/vtnQiaFuc0no3qPSKCg9AoqHGFbufzM/jTKhwctfH3TEJYloaP660i8vG4BPujHwSlziJ1j8KgTEqcOCp5Kij2GKN+0GgJaSRlPQOgQVFFBQegUU8/ngx06sHWggAINKKaBK094ocxzXf1RLO5yE+mnQZWfW+h8Iq9n9doR8zTkB9j7sFKAFtMgbHVP+NRUVHpFBR6QAoc2dH++tPOpoKuSMAcVpGCLaOtnotxoFkYyw6JeYTyPuwJSBu6Hem9LI6rW9vgU/dJL0TklJ+DrSjbGgIJl/On2uhC7AErUgBJwGw6EesUFRUejKUTbDJ1sdaAsBABAUEI5EBxWpVcV5X34c6ixLPZAW65ooIq85Oepk5UJd2ECSPthHcHvodr9aFSPs3jU2yn3/j8LWisTJaASHDe+n2wg6W3F/aeGoqKj0j1CojMIQPCXE3epRVm3IDwM+FGRpwOULUFB6BV+CKzXLo5OE7Ui8T6xz22dgqXgCbr6FvHDwpSNmPb+vwtatr/AH0/dS4zbclPuaC71tRYGFMABK1bqg7TYdvM1FRUesUXRShs3XXpLTkIIw/7HW3CjKxwCJBY2tfoegUHoFGafkCbRGSjTAITjyfvknrmMiSNtZ/XqG+fhV+q/wDkoUnHwRqILp5iKiUFkpnKfqj1YpBM3Fwz3bd6ioqKiopgyMNu5OeiaUhq+Lka+s0YEFgCAr7oSI6lQ6CxhANjoydKD0CjNFBTgwU2v1M34PAoZJrHW8Tvc32AMDc35EA0kKSf1v7U/Ba8bMSRUD8bOgZChY9TqJI4Ay0x5JE0Lf1zWoqKilnEQ4HVDPRVxgTiXhj3mgAABgNPa5mz2run2B9AUZoKD0CnF8QeDfAem9TlJK9gRMWYN5ae8w6UD4EjQCCjHwoKb3Ak3rnOU9SidLHcST1QYU8Dh/ax39W5NuhBODP041rjqOx7J1loIIDGK51y9pSIRtDrSxQ8/aOjJ09Cg9ArzXUuxTJMgc1cym5ByZNx4jJ6whUIOwEtELqrQR/Q7VB8RU6eDWA7GXRpnIjXZmTsydqaRuAJV0KMSSkaDHe71q0xLFIdx8HGmGBsBB3wHl40EaAfia/ZLS6YdLPR3ooPQKJP3y7HGrkNcWD+0KFxSyLY48DmG/rQPwGJoEV9HVqJIfjuh3fp8UDLRahDTAxKNhQlRBBESyVAl1osugMqSaZpUAzGIdxj7ca0t6Y0/EAZCESRKYYpMRSsN336Pyu7kdcc7sVjkuKMfvxpHo93OmjIgI1m6NJUNSQznFARAAlWmUOXCweGPBRtTA0BB8VxipSpgC7tnovZ4VOwCJb4x6YelRecfBjR2rb/AI0paab4OAae66mJIqzONdcHXajgskNH7LbkcfjNNlIokCQjSrM+MfP0PR1qVGNyb6y4n50JtlKjCmRfg2+6BSpVyvubojMtGukOK1G6YBKFseLEHV3oyCjoAIAp+OboWJeKzy0Tajv4tvy3LdyiroWkDrTc/GJUpUgKxTmwf21sNg0ORp71+3QKegBlaQwogitehfgdahztsX/iYD/fyYjhSpg44D9Wzp3qDCd+IDbc6nEigF5EdfwgspE3SuhehhZdP0hXBepQORj8Cq+4BC0AMrVqszc2zGQ2OrwKG8HcO99urQTm/wAswItogPBybOnirhEF8mL9msIUN7uw0abXPV1GDQJ7UPzcftgpSAWkrwf2hVJ4PxepJUq5X8Kqq2IbE5ew1al2A0Lq4tnY80FGMCWOLpu5fHzb2vQ+Ndtl4O3BtUK1AkI7LMuDbZpAEAWL8HTr3oWRHkPmvKGvpKlSp76qoAVQDK0CNYkt7i/Q7lT25QFBOqeB1au8kZ6cXQ4Fq3v88KEwIQbI0jzlSLeLPmcCpuiwK22mOyVC125PMudTrRJZwceKKlSp7aq4IsnHmkESbE80l6HWrXK6pt5juaDLCJo3FnxOdHP+BgGwH+B6UBWPNSp0algiQMnNc6JFR3OZYc1D2mh7rihTnZec0jANneSH7qxG+Dx4UEMhpYdpoFVDS47xQ5G+Jj5UxBdmOYD7pMDaqROd05zUUHmanIS94pUMSr613q32rEgAw6FIVHD/AArTRbyJHo0hJ7nyiDTymujPuaXU5dfusLPNj9VhHhv6UUJJ5jy6bQw7wIDoUf4nT3c/Wbf+pf/Z"></p>
-

@ 1aa9ff07:3cb793b5
2025-04-04 09:42:28
Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring:
1. Major Changes in the Business World
AI will automate repetitive tasks, allowing human workers to focus on more strategic areas. AI-powered assistants, data analytics, and customer service applications will become more widespread, shifting human efforts toward creative and problem-solving roles.
2. Revolutionary Advances in Healthcare
AI in medicine will enable earlier disease diagnosis and personalized treatment plans. Thanks to advancements in image processing and genetic analysis, diseases such as cancer can be detected more quickly and accurately.
3. Widespread Adoption of Autonomous Vehicles
Over the next five years, autonomous vehicle technologies will continue to evolve, becoming more common in urban transportation and logistics. This will lead to a reduction in traffic accidents, lower transportation costs, and significant changes in urban planning.
4. AI-Powered Personalized Learning in Education
AI will enhance personalized education solutions, making learning processes more efficient. AI-assisted teachers and learning platforms will analyze students’ weaknesses and create customized study programs tailored to their needs.
5. New Challenges in Security and Data Privacy
As AI technology advances, cybersecurity and data privacy will become even more critical. While AI-driven security systems can detect cyber threats proactively, malicious applications of AI may introduce new vulnerabilities.
6. Creative Innovations in Art and Entertainment
AI-generated content will become more prevalent in fields such as art, music, and cinema. AI-assisted scripts, music compositions, and digital artwork may give rise to a new wave of artistic expression.
Conclusion
In the next five years, AI's influence will be felt in every aspect of life. From business and healthcare to transportation and the arts, various sectors will undergo transformative innovations. However, addressing ethical concerns, security challenges, and data privacy issues will be crucial to ensuring AI's positive impact. By harnessing AI’s potential responsibly, we can build a more efficient, secure, and sustainable future.
Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring:
-

@ 674473f6:f859eb3c
2025-04-04 08:42:17
## darkman คืออะไร
**Darkman** เป็นโปรแกรมที่ช่วยควบคุมการเปลี่ยนโหมดสีของเดสก์ท็อประหว่างโหมดมืดและโหมดสว่างบนระบบปฏิบัติการ Unix-like. โปรแกรมนี้จะทำงานในเบื้องหลัง(background process) และสามารถตั้งค่าให้เปลี่ยนไปใช้โหมดมืดเมื่อพระอาทิตย์ตก หรือเปลี่ยนกลับไปใช้โหมดสว่างเมื่อพระอาทิตย์ขึ้นได้
## การทำงานของ Darkman
เรียกใช้ผ่าน systemd service หรือคำสั่ง `darkman run` โดยตรงได้เลย
1. **การตั้งค่าโหมด**: Darkman สามารถตั้งค่าโหมดปัจจุบันเป็นโหมดมืดหรือโหมดสว่างได้ด้วยคำสั่ง `darkman set <light|dark>`.
2. **การตรวจสอบโหมดปัจจุบัน**: สามารถตรวจสอบโหมดปัจจุบันได้ด้วยคำสั่ง `darkman get`.
3. **การสลับโหมด**: สามารถสลับโหมดระหว่างโหมดมืดและโหมดสว่างได้ด้วยคำสั่ง `darkman toggle`.
4. **การทำงานอัตโนมัติ**: Darkman จะทำงานอัตโนมัติโดยใช้ข้อมูลตำแหน่งที่ตั้งของระบบเพื่อกำหนดเวลาพระอาทิตย์ขึ้นและตก.
5. **การปรับแต่ง**: สามารถเพิ่มสคริปต์เพื่อปรับแต่งการทำงานของโปรแกรมให้เข้ากับแอปพลิเคชันต่างๆ ได้.
## การตั้งค่า darkman
1. สร้างไฟล์ `config.yaml` ในโฟลเดอร์ `~/.config/darkman/`
```yaml
lat: 13.7563
lng: 100.5018 # ตำแหน่งกรุงเทพ
usegeoclue: false
dbusserver: true
portal: true
```
2. การตั้งค่า portal สำหรับ Darkman
จะช่วยให้โปรแกรมสามารถเปลี่ยนโหมดสีของเดสก์ท็อปได้โดยใช้ XDG settings portal API.
2.1 สร้างไฟล์ portals.conf ในโฟลเดอร์ ~/.config/xdg-desktop-portal/
```conf
[preferred]
org.freedesktop.impl.portal.Settings=darkman
```
2.1 รีสตาร์ท service xdg-desktop-portal เพื่อให้การตั้งค่าใหม่มีผล:
```bash
systemctl --user restart xdg-desktop-portal
```
การตั้งค่านี้จะช่วยให้แอปพลิเคชันต่างๆ บนเดสก์ท็อปสามารถอ่านค่าโหมดสีจาก Darkman และปรับเปลี่ยนตามที่กำหนด.
3. Custom executables
ใน Darkman สามารถเพิ่มการทำงานเพิ่มเติมเมื่อมีการเปลี่ยนโหมดสีของเดสก์ท็อป โดยการวางสคริปต์หรือโปรแกรมที่ต้องการในไดเรกทอรีที่กำหนด
**ไดเรกทอรีสำหรับ Custom executables**:
- `$XDG_DATA_DIRS/dark-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดมืด
- `$XDG_DATA_DIRS/light-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดสว่าง
**ตัวอย่างการใช้งาน Custom executables**:
1. **สร้างสคริปต์สำหรับโหมดมืด**:
- สร้างไฟล์ `set_dark_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/dark-mode.d/`
- เพิ่มเนื้อหาดังนี้:
```bash
#!/bin/bash
# ตัวอย่างสคริปต์สำหรับโหมดมืด
gsettings set org.gnome.desktop.interface gtk-theme "Adwaita-dark"
notify-send "Dark Mode Activated"
```
2. **สร้างสคริปต์สำหรับโหมดสว่าง**:
- สร้างไฟล์ `set_light_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/light-mode.d/`
- เพิ่มเนื้อหาดังนี้:
```bash
#!/bin/bash
# ตัวอย่างสคริปต์สำหรับโหมดสว่าง
gsettings set org.gnome.desktop.interface gtk-theme "Adwaita"
notify-send "Light Mode Activated"
```
3. **ตั้งค่าสิทธิ์การรันสคริปต์**:
- ตั้งค่าสิทธิ์ให้สคริปต์สามารถรันได้:
```bash
chmod +x $XDG_DATA_DIRS/dark-mode.d/set_dark_mode.sh
chmod +x $XDG_DATA_DIRS/light-mode.d/set_light_mode.sh
```
เมื่อ Darkman เปลี่ยนโหมด สคริปต์เหล่านี้จะถูกเรียกใช้งานตามที่กำหนด
### การแก้ไขหากไม่พบ XDG_DATA_DIRS
หากไม่พบตัวแปร `XDG_DATA_DIRS` คุณสามารถสร้างไดเรกทอรีที่จำเป็นเองได้ตามต้องการ โดยปกติแล้ว `XDG_DATA_DIRS` จะประกอบด้วยไดเรกทอรีเหล่านี้:
- `~/.local/share/`
- `/usr/local/share/`
- `/usr/share/`
คุณสามารถสร้างไดเรกทอรีเหล่านี้และเพิ่มสคริปต์ของคุณได้ตามนี้:
1. **สร้างไดเรกทอรี**:
- สร้างไดเรกทอรีสำหรับโหมดมืดและโหมดสว่าง:
```bash
mkdir -p ~/.local/share/dark-mode.d
mkdir -p ~/.local/share/light-mode.d
```
[ตัวอย่าง Script ที่ผมใช้](<https://github.com/vazw/dotfiles/tree/Void(wayland)/darkman>)
2. ทำการ **export XDG_DATA_DIRS**:
โดยทั่วไปเราสามารถตั้งตัวแปร Environments ต่าง ๆ ได้ที่ `~/.profile` และตัวแปรทั้งหมดจะถูกโหลดหลังจากเรา **Login**
```bash
export XDG_DATA_DIRS=$HOME/.local/share:/usr/local/share:/usr/share:$XDG_DATA_DIRS
```
Source: [darkman](https://gitlab.com/WhyNotHugo/darkman)
-

@ 3104fbbf:ac623068
2025-04-04 06:58:30

## **Introduction**
If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best.
The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families.
Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives.
From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families.
---
## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin**
Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do:
- **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation.
Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money.
- **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse.
- **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible.
- **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios.
---
## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems
Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability:
- **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance.
- **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach.
- **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks.
---
## 3. Digital Privacy: Fighting Surveillance with Advanced Tools
The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself:
- **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks.
- **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors.
- **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube.
- **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security.
---
## 4. Building Resilient Local Communities: The Foundation of a Free Future
While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite.
To counter this, communities must organize locally:
- **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises.
- **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems.
- **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points.
- **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism.
---
## 5. The Bigger Picture: Rejecting the Illusion of Saviors
The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems.
---
## Conclusion: A Call to Action
The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites.
- The tools for liberation already exist.
- The question is: will we use them?
For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom
⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡
###### If you enjoyed this article, consider supporting it with a Zap!
---
My Substack ENGLISH = https://blisshodlenglish.substack.com/
My substack FRENCH = https://blisshodl.substack.com/
---
Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl
---
---
-

@ da0b9bc3:4e30a4a9
2025-04-04 06:24:48
Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/934111
-

@ bf95e1a4:ebdcc848
2025-04-04 06:11:18
This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)!
## The Gullible Collective
We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game.
The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it.
Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank.
When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it.
Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media.
The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless.
The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech.
Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell.
### **About the Bitcoin Infinity Academy**
The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available.
-

@ 2e8970de:63345c7a
2025-04-04 17:12:41
Recently I shared a substack post that argued **"DOGE is About Sex"** https://stacker.news/items/921208 the main premise being how Elon & Trumps economic goals were to make women more economically desperate such that women are more nudged to settle for mediocre and lonely men.
I do not think that tells the whole story about MAGA economics. Neither does the author CHH, I think.
But I think she's onto something. Here are 4 tweets I randomly encountered today that fit this narrative perfectly:
> Trump's trade war is partly about gender.
> As American manufacturing declined, men lost economic leverage over women. The nationalist right believes that this led to lower marriage and birth rates.
https://x.com/EricLevitz/status/1908175346177847669
> Highly educated women will be completely out of the marriage market in next 5 years.
https://x.com/mshree01/status/1906316952613589038
> congratulations to boring men with stable jobs on becoming the next hot commodity
https://x.com/morganisawizard/status/1907889282947424453
> The American economy is built around giving fake unproductive jobs to women, therefore we must destroy it
https://x.com/DrewPavlou/status/1907932434571866226
# Conclusion
Interestingly this thought seems to cross many peoples minds independently. Like Calculus was invented by Leibnitz and Newton simultaneous and independently.
It's also liberals and conservatives; men and women uttering these words.
I think this is super fascinating. Shoutout to the original post: https://www.cartoonshateher.com/p/doge-is-about-sex
originally posted at https://stacker.news/items/934557
-

@ 0edc2f47:730cff1b
2025-04-04 03:37:15
## Chef's notes
This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long!
## Details
- ⏲️ Prep time: 10 min
- 🍳 Cook time: 0 min
## Ingredients
- 1 cup (240mL) heavy whipping cream
- 1/4 cup (24g) cocoa powder
- 5 tbsp (38g) Confectioners (powdered) sugar
- 1/4 tsp (1.25mL) vanilla extract (optional)
- Flaky sea salt (optional, but excellent)
## Directions
1. 1. Whip the cream until frothy.
2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using).
3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy).
-

@ 2e8970de:63345c7a
2025-04-04 16:17:56

Interestingly he's suggesting that he's doing all this on purpose. Why would he say that? Well the market could take this (a) positively: he's still in control and there is a masterplan (b) negatively: he's openly hostile against the economy. Trump is obviously hoping the market will take it as (a).
originally posted at https://stacker.news/items/934513
-

@ 3c389c8f:7a2eff7f
2025-04-04 15:47:44
### A Rose By Any Other Name... or whatever.
NIP-05 is an identifier created by mapping Nostr keys to DNS based identifiers. [More technically](https://nips.nostr.com/5), it the part of the protocol that defines how to do this mapping, but you will often see the resulting identifier referred to as "your NIP-05". You will also see it referenced as a "Nostr Address", a "Nostr ID", or a "Nostr Verification". None of those terms are fully correct but nor are they wrong.
A NIP-05 identifier does look very similar to an email address (i.e. NostrName @ SomeSite .com). It makes it easier to convey your Nostr profile to friends or collogues, since your chosen name is not unique and the npub format is not exactly something you will be wanting to jot down at a business meeting. It can be used to find you and your notes, so the term, Nostr Address, fits in that sense. There are free services that provide a NIP-05 to you, but you may want to consider contracting this service to a paid provider. Free services tend to be abused by spammers. Paid NIP-05 providers are reasonably priced, more reputable, provide select affiliations, and often other services, along with hosting your Nip-05 file.
Nostr ID might be the appropriate term, in a different way. Your NIP-05 is unique. You are not limited to possessing a single one, but only one may be present on your profile at any given time. You can switch them out as needed. Some Nostr-based services will require that you have a particular NIP-05 provider in order to access their relay communities or other features. In that sense, it is an ID, proving that you are a member of that community. These NIP-05 IDs are created and hosted for you by the community relay hosts, with whatever criteria they choose to require.
Nostr Verification comes into consideration if you own or run a website. It can be used to validate your identity. By hosting your NIP-05 file on your own domain, you are, in essence, validating that the same person has ownership of the website and control of the associated Nostr profile. (i.e. YourName @ YourSite .com) This is exceptionally handy for any well known individual who may be subject to impersonation. This is great, too, if you sell a product or service online and would like to use Nostr as a means of advertising and engaging with your customers. Your NIP-05 can signal to your customers that you, or any employee, are affiliated with your company.
All of this, for me to tell you... that you don't need a NIP-05 identifier to use Nostr. It just makes a lot of the things you might want to do simpler. For clear instructions on how to set up your NIP-05 visit [nostr.how](https://nostr.how/en/guides/get-verified)
-

@ 502ab02a:a2860397
2025-04-04 02:50:35
หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ?
Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย
ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3
เทียบง่ายๆครับ
น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา
แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ
ผู้ผลิตผิดไหม?
จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง
คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG
ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ
ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน
ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย
ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ
ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน
- oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว
ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า???
มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย
นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน
- มีไลโนเลอิกสูง
ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม
- โทโคฟีรอล (Tocopherols)
เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง
- โทโคไทรอีนอล (Tocotrienols)
เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว
สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้
#pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-

@ 7bc05901:8c26d22b
2025-04-04 15:40:10
I am not an engineer by trade. I took my math classes for college credit as early as I could in high school. I signed up for a bachelor of arts in college and basically didn't touch STEM for the rest of my formal education. Seminary (incomplete) and Law School (JD) didn't go deep into any of the sciences -- I think I struggled through an "accounting for lawyers" class.
The dumb thing is that in middle school and early high school I was obsessed with tinkering with mechanical things. I rebuilt a go-kart, tinkered with my computer, built skateboard ramps. High school came, I got obsessed with chasing girls and listening to emo music, and that culminated in a foggy pursuit of journalism, linguistics, ministry and/or academia in my post-graduate adventures. Also, algebra came to me really easily. I loved cramming the day before a test in middle school and embarrassing the other A students who had to work hard to keep those grades up.
I obviously see now how dangerous that pattern can be to sustaining motivation and discipline in the long-time preference aspects of life. I was motivated by the idea of "getting one over" on the authoritarian educators in my life -- they said that the only way to succeed is to do my homework and study, but I wanted them to know that *I was different*. And I think I was different from a lot of other people around me, but I aimed my agency in the wrong direction. The rebellion became the end for me, instead of being the means to an end of meaningful learning. Rebel against the system so you can escape into a self-sovereign, high-agency existence.
At the risk of over-stuffing the analogy, perhaps that point brings me to decentralized social media environments. Facebook is like my school teachers, there are tasks laid out for me nudging me to behave a certain way. My grades are analogized by my reach that Facebook will give and take away. I run a few Facebook pages and I am constantly irritated by the annoying UI. Constantly changing, adding shit that I cannot imagine anyone asking for and taking away the shit that you refer to everyday. Just this past week I noticed that I have to click into a post on Meta business sweet in order to see how many shares it has. This used to be on the page as I scrolled through all of my content. There is literally just a blank white space where it used to say: 54 shares.
My thought goes to, this is somehow punishing me for my reach. Although Zuckerberg has pledged his allegiance to the new age of "free speech" and given his finger to the government-meddling that he fanned to flame over the last ten or fifteen years, I still think Facebook wants to nudge users away from certain things and towards other things. Libertarians have railed against the "nanny-state" but it is harder to understand how we also give up our sovereignty to centralized social media companies: the Nanny-Feed.
This must die. The unbundling of facebook is a weird time that feels like the detangling of digital society. Life without widespread Craigslist adoption is somewhat more annoying. I used to scroll Craigslist all the time for stuff. I went to Los Angeles for a few months in 2012 and used it to buy some things and hear about auditions for different projects, a few of which panned out for me. There was something about having some separation from the site that I went to specifically to network with co-workers and communicate with old friends that I liked. I don't want my social media identity locked on one site, especially a site that is subservient to a boardroom. I also like the inconvenience of hopping over to a different app to handle my marketplace experiences.
A lot of this needs to be thought through a lot more, because attempting to untangle the beast that is "meta" (still Facebook to me) requires a lot more insight than I have as I type this out. I'm mostly just nostalgic and emotional and remembering a different time in my life.
-

@ c8adf82a:7265ee75
2025-04-04 01:58:49
What is knowledge? Why do we need it?
Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after?
When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith
Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all
However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc
Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you
If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life
Seize the day
-

@ 6389be64:ef439d32
2025-04-03 21:32:58
Brewing Biology
Episode 1068 of Bitcoin And . . . is LIVE!
This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT.
LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE
The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer.
Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue.
Biochar’s Hidden Superpower: Adsorption & Buffering
Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to:
Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts.
Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs.
Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive.
This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates.
The Carbon Math
Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue.
Tools for the Revolution
The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks.
Bitcoin’s Role in the Loop
Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income.
The Market Potential
Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience.
Why This Matters
This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet.
The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.---
P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting.
You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6
originally posted at https://stacker.news/items/933800
-

@ 2ed3596e:98b4cc78
2025-04-03 21:20:27
We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well.
Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience!
Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin.
### How to leave your Trustpilot review for our portal
1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com)
2. Write a quick review sharing your favourite Bitcoin Well feature
3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw
### How to leave your google review for one of our ATMs
1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8)
2. Write a quick review sharing your favourite Bitcoin Well feature
3. **Include your transaction ID**, in the review so we can add you to the prize draw
It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats!
### What makes Bitcoin Well different
Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂.
[Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup)
### Invest in Bitcoin Well
We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/).
-

@ df67f9a7:2d4fc200
2025-04-03 19:54:29
More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this.
### Project Description
I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users.
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan.
- [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients.
- [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine.
### Potential Impact
Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to :
- Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations.
- Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust.
- Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs.
- Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients.
### Timeline & Milestones
2025 roadmap for “Webs of Trust Onboarding and Discovery” :
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”.
https://nostrmeet.me/
- [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays.
https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs
- [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays.
https://grapevine.my/
- [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates.
https://nostrmeet.me/
### Prior contributions
- Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”.
- I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK.
- I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK.
- Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park.
### About Me
I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career.
As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose.
Thank you for considering this application for funding.
-

@ 502ab02a:a2860397
2025-04-03 17:41:20
ไฟโตสเตอรอล (Phytosterols)
เป็นสารประกอบที่พบในพืชและมีโครงสร้างคล้ายคลึงกับคลอเลสเตอรอล (Cholesterol) ของมนุษย์ แต่ไฟโตสเตอรอลไม่ได้ทำหน้าที่เหมือนคลอเลสเตอรอลในร่างกายครับ ไฟโตสเตอรอลมีบทบาทสำคัญในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในระบบทางเดินอาหาร ทำให้ไฟโตสเตอรอลได้รับการส่งเสริมว่าเป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือดไปโดยปริยาย
อย่างไรก็ตาม สิ่งที่หลายคนไม่ได้ตั้งข้อสงสัยคือวิธีการโฆษณาและการตลาดนั้นจะแฝงไปด้วยข้อมูลที่บิดเบือนเกี่ยวกับไฟโตสเตอรอลซึ่งอาจนำไปสู่การเสพสารนี้ในปริมาณมากเกินไปจนทำให้เกิดปัญหาสุขภาพหรือเปล่า? เราลองมาค่อยๆตั้งคำถามกันครับ
ไฟโตสเตอรอลในธรรมชาติจะพบในปริมาณที่ค่อนข้างน้อยในพืชต่าง ๆ เช่น ธัญพืช ถั่ว เมล็ดพืช อย่างไรก็ตาม ปริมาณไฟโตสเตอรอลในธรรมชาติเป็นเม็ดเป็นผลจะอยู่ในระดับต่ำมาก เช่น ในเมล็ดแฟลกซีด (flaxseed) จะมีไฟโตสเตอรอลอยู่ประมาณ 1,000–2,000 ppm (parts per million)
ขณะที่น้ำมันรำข้าวที่มักถูกโฆษณาว่ามีไฟโตสเตอรอลสูงถึงหลักหมื่น ๆ ppm เช่น 12,000 ppm หรือบางยี่ห้ออาจสูงกว่านั้น ซึ่งไม่ใช่แค่สูงจนน่าสรรเสริญ แต่ยังเป็นการขยายความสำคัญของไฟโตสเตอรอลในทางที่ตอบสนองต่อการตลาดได้ในวงกว้างเสียด้วย
กระบวนการผลิตน้ำมันรำข้าวนั้นเริ่มต้นจากการสกัดน้ำมันจากรำข้าว โดยมีการใช้เทคนิคการกลั่นน้ำมันที่สามารถช่วยให้ได้น้ำมันที่มีคุณภาพสูง น้ำมันรำข้าวเป็นน้ำมันที่มีไฟโตสเตอรอลสูงเพราะรำข้าว (bran) ซึ่งเป็นเปลือกที่หุ้มเมล็ดข้าวนั้น มีไฟโตสเตอรอลอยู่ในปริมาณสูงตามธรรมชาติอยุ่แล้ว ในกระบวนการสกัดน้ำมันนั้น ตัวไฟโตสเตอรอลจะถูกรักษาไว้ โดยไม่ต้องเติมเข้าไปใหม่ ดังนั้น เมื่อโฆษณาน้ำมันรำข้าวว่า "มีไฟโตสเตอรอลสูงถึง 12,000 ppm" สิ่งนี้ไม่ได้หมายความว่าเป็นการเติมสารเพิ่มเข้ามาหรอกครับ แต่เป็นการยืนยันถึงความ "เข้มข้น" ของไฟโตสเตอรอลที่มีอยู่ในน้ำมันรำข้าวตามธรรมชาตินั่นละครับว่ามันกลั่นมาเข้มข้นขนาดไหน มากกว่าการกินจากธรรมชาติขนาดไหนเพื่อให้เรากินกันนั่นเอง
ถึงแม้ว่าไฟโตสเตอรอลจะถูกส่งเสริมให้เป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือด แต่การโฆษณาและการตลาดเกี่ยวกับไฟโตสเตอรอลนั้นอาจทำให้คนเข้าใจผิดว่า ผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูง จะช่วยทำให้สุขภาพดีขึ้นและลดความเสี่ยงจากโรคหัวใจและหลอดเลือด เพราะซึ่งสิ่งนี้ยังไม่ได้รับการสนับสนุนอย่างชัดเจนจากงานวิจัยที่สามารถยืนยันได้ในระยะยาว นอกจากนี้ยังมีผลการศึกษาบางชิ้นเช่นกันที่พบว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจ "ไม่ได้มีผล" ในการลดระดับคลอเลสเตอรอลที่น่ามหัศจรรย์หรือช่วยลดการเสี่ยงต่อโรคหัวใจได้ตามที่โฆษณาเอามาขยายความกัน ซึ่งแน่นอนหละครับว่า ถ้าจะทำสงครามวิจัย มันย่อมไม่จบสิ้นเพราะทุกฝ่ายมีการวิจัยสนับสนุนในแบบ peer review ทั้งนั้น ไม่ต้องไปเป็น member อะไรที่ไหน (ถ้าเราไม่คิดจะอ่านมันเอง)
ไฟโตสเตอรอลมีหลายประเภทที่พบในพืชและน้ำมันพืชแต่ละชนิด โดยแต่ละชนิดจะมีคุณสมบัติและผลกระทบต่อร่างกายที่แตกต่างกัน ซึ่งสามารถแบ่งออกเป็นหลายประเภทหลักที่พบได้บ่อยในธรรมชาติ แต่ละประเภทก็มีข้อดีและข้อเสียที่ควรพิจารณาก่อนการบริโภคตามประเภทมันไปครับ
-บีตาสติโรล (Beta-Sitosterol) เป็นไฟโตสเตอรอลที่พบมากในพืชหลายชนิด โดยเฉพาะในเมล็ดพืช ถั่ว และน้ำมันพืช บีตาสติโรลได้รับความนิยมในวงการสุขภาพเนื่องจากการศึกษาบางชิ้นพบว่ามันสามารถช่วยลดระดับคอเลสเตอรอลในเลือดได้ โดยการลดการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหาร แต่การบริโภคบีตาสติโรลในปริมาณสูงอาจส่งผลต่อการดูดซึมวิตามินที่ละลายในไขมัน เช่น วิตามิน A, D, E และ K ซึ่งอาจทำให้เกิดการขาดวิตามินเหล่านี้ในระยะยาวได้ นอกจากนี้ การบริโภคบีตาสติโรลในปริมาณที่มากเกินไปอาจส่งผลให้เกิดปัญหาด้านระบบฮอร์โมน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนเพศหรือระบบสืบพันธุ์
-แคมป์สเตอรอล (Campesterol) เป็นอีกหนึ่งไฟโตสเตอรอลที่พบในพืชหลายชนิด โดยเฉพาะในน้ำมันพืชและผักผลไม้ แคมป์สเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย และมันได้รับการศึกษาว่ามีคุณสมบัติช่วยลดระดับคอเลสเตอรอลในเลือดได้เช่นกัน อย่างไรก็ตาม การบริโภคแคมป์สเตอรอลมากเกินไปอาจทำให้เกิดผลกระทบต่อการดูดซึมสารอาหารบางประเภท เช่น วิตามินที่ละลายในไขมัน โดยเฉพาะในผู้ที่มีปัญหาทางเดินอาหาร หรือผู้ที่มีปัญหาการดูดซึมสารอาหาร อาจทำให้เกิดภาวะขาดสารอาหารหรือการดูดซึมสารอาหารไม่เต็มที่ได้ นอกจากนี้ การบริโภคแคมป์สเตอรอลในปริมาณสูงอาจส่งผลกระทบต่อการทำงานของฮอร์โมนเพศ เช่น การเปลี่ยนแปลงของฮอร์โมนในร่างกาย ซึ่งอาจเกิดผลเสียต่อสุขภาพในระยะยาว
-สแตกิโอรอล (Stigmasterol) เป็นไฟโตสเตอรอลชนิดหนึ่งที่พบมากในพืชบางชนิด เช่น ถั่วเหลือง และน้ำมันถั่วเหลือง สแตกิโอรอลได้รับการศึกษาในแง่ของการลดการอักเสบและการช่วยบำรุงสุขภาพหัวใจและหลอดเลือด แต่การบริโภคสแตกิโอรอลในปริมาณสูงอาจมีผลเสียต่อการทำงานของฮอร์โมนเพศได้เช่นกัน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนไม่สมดุลหรือมีปัญหาเกี่ยวกับระบบสืบพันธุ์ การบริโภคไฟโตสเตอรอลชนิดนี้มากเกินไปอาจทำให้เกิดผลกระทบต่อการทำงานของระบบฮอร์โมนในร่างกาย ซึ่งอาจส่งผลให้เกิดอาการผิดปกติในระยะยาว รวมทั้งความเสี่ยงต่อการมีบุตรหรือสุขภาพที่ไม่ดีเกี่ยวกับระบบฮอร์โมน
ไฟโตสเตอรอลประเภทอื่น ๆ ที่พบในพืชและน้ำมันพืช ได้แก่ อะฟิตเตอร์ออล (Afitosterol) และซิตรัสเตอรอล (Citrusterol) ซึ่งมักพบในน้ำมันจากพืชต่าง ๆ เช่น น้ำมันเมล็ดองุ่น น้ำมันดอกทานตะวัน การบริโภคไฟโตสเตอรอลเหล่านี้ในปริมาณที่สูงเกินไปอาจทำให้เกิดปัญหาด้านระบบย่อยอาหาร หรือปัญหาการดูดซึมสารอาหารที่จำเป็นจากอาหารได้ นอกจากนี้ การบริโภคไฟโตสเตอรอลประเภทอื่น ๆ ในปริมาณสูงยังอาจส่งผลกระทบต่อระบบฮอร์โมนและการทำงานของร่างกายในระยะยาว เช่น การทำงานของระบบภูมิคุ้มกัน หรือการทำงานของตับ ที่อาจได้รับผลกระทบจากการบริโภคในปริมาณสูง ดังนั้น ควรระมัดระวังในการบริโภคไฟโตสเตอรอลจากแหล่งต่าง ๆ อย่างรอบคอบ เพื่อหลีกเลี่ยงผลเสียที่อาจเกิดขึ้นกับร่างกายในระยะยาว
สิ่งที่จริงแล้วอาจเป็นอันตรายมากกว่า คือ การที่ผู้บริโภคตัดสินใจบริโภคผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงในปริมาณมากเกินไป โดยไม่คำนึงถึงผลกระทบต่อร่างกายในระยะยาว อาจมีผลกระทบต่อการดูดซึมสารอาหารที่จำเป็น เช่น วิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมัน การดูดซึมของวิตามินเหล่านี้อาจถูกยับยั้งไป เนื่องจากไฟโตสเตอรอลสามารถแข่งขันกับคลอเลสเตอรอลในร่างกายในการดูดซึมสารอาหารเหล่านี้ นอกจากนี้ยังมีข้อกังวลเกี่ยวกับผลกระทบที่อาจเกิดขึ้นจากการบริโภคไฟโตสเตอรอลในปริมาณสูงที่อาจไปเพิ่มความเสี่ยงของการเกิดโรคบางอย่าง เช่น โรคมะเร็งต่อมลูกหมาก
ผลเสียจากการบริโภคไฟโตสเตอรอลมากเกินไปไม่ได้จำกัดเพียงแค่การแย่งสารอาหาร แต่ยังมีการศึกษาที่แสดงให้เห็นว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจกระทบต่อการทำงานของระบบภูมิคุ้มกันของร่างกาย ในบางกรณีไฟโตสเตอรอลอาจเข้าไปแทรกแซงกระบวนการทางชีวเคมีที่สำคัญ และอาจทำให้ร่างกายเกิดความผิดปกติในการตอบสนองต่อสารแปลกปลอมที่มีอยู่ในสิ่งแวดล้อม
ข้อโต้แย้งที่สำคัญคือลักษณะการโฆษณาของน้ำมันรำข้าวและผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงนั้น ไม่ได้สะท้อนความจริงในสิ่งที่เป็นประโยชน์ต่อสุขภาพจริง ๆ การใช้ไฟโตสเตอรอลในผลิตภัณฑ์ต่าง ๆ โดยเน้นที่ปริมาณที่สูงเกินจริงนั้น เป็นวิธีการตลาดที่ใช้บอกเป็นนัยกับผู้บริโภคให้เข้าใจว่าการบริโภคสารเหล่านี้จะช่วยลดระดับคลอเลสเตอรอลและช่วยให้สุขภาพหัวใจดีขึ้น ทั้งที่ในความเป็นจริง ไฟโตสเตอรอลไม่ได้ช่วยแก้ปัญหาสุขภาพพื้นฐานอย่างการอักเสบที่เป็นสาเหตุหลักของโรคหัวใจและหลอดเลือด แต่ทั้งนี้ทั้งนั้น การโฆษณาดังกล่าวก็อยู่ภายใต้กฎเกณฑ์ของประกาศและกฎหมายต่างๆอยู่ดี ผู้บริโภคจึงควรหาความรู้สนับสนุนการเลือกด้วยตัวเอง ว่าจะตัดสินใจอย่างไร
การที่ไฟโตสเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย ทำให้มันสามารถแทรกซึมเข้าไปในเซลล์ได้คล้ายคลึงกับคอเลสเตอรอล แต่แตกต่างกันตรงที่ไฟโตสเตอรอลไม่สามารถทำหน้าที่ในการสร้างฮอร์โมนต่าง ๆ หรือทำหน้าที่ในระบบร่างกายได้เหมือนคอเลสเตอรอล การที่ไฟโตสเตอรอลแทรกซึมเข้าไปในเซลล์จึงเป็นแค่การสามารถช่วยป้องกันการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหารได้ ซึ่งจะทำให้นี่เป็นสาเหตุของการทำให้ ระดับคอเลสเตอรอลในเลือดลดลงได้ พูดง่ายๆคือมันไปแซงคลอเลสเตอรอล อะครับ
นอกจากนี้ ไฟโตสเตอรอลยังสามารถไปแข่งขันกับคอเลสเตอรอลในการเข้าเซลล์ผ่านตัวรับ LDL (low-density lipoprotein receptor) ซึ่งเป็นตัวรับที่ช่วยดูดซึมคอเลสเตอรอลเข้าสู่เซลล์ ดังนั้น เมื่อไฟโตสเตอรอลแทรกซึมเข้ามามากขึ้น ก็จะช่วยลดการดูดซึมคอเลสเตอรอล ที่มาจากอาหารลงไปได้ ทำให้ระดับคอเลสเตอรอลในเลือดลดลง โดยการลดการดูดซึมคอเลสเตอรอลจากทางเดินอาหารเข้าสู่กระแสเลือด แต่ไฟโตสเตอรอลไม่ได้มีผลโดยตรงในการลดคอเลสเตอรอลที่เซลล์ในร่างกายสร้างขึ้นเอง (endogenous cholesterol) เพราะไฟโตสเตอรอลไม่ได้เข้าไปแทรกซึมและทำงานที่จุดที่เซลล์ผลิตคอเลสเตอรอลในร่างกาย
ร่างกายสามารถผลิตคอเลสเตอรอลได้เอง ซึ่งเป็นกระบวนการที่ไฟโตสเตอรอลไม่สามารถไปขัดขวางหรือยับยั้งได้ นั่นหมายความว่า หากร่างกายผลิตคอเลสเตอรอลในระดับสูง ไฟโตสเตอรอลจะไม่สามารถลดระดับคอเลสเตอรอลที่มาจากการสร้างของร่างกายได้ ดังนั้น ไฟโตสเตอรอลมีประโยชน์ในการลดคอเลสเตอรอลจากอาหาร แต่ไม่ได้ช่วยในการลดคอเลสเตอรอลที่ร่างกายผลิตขึ้นเอง
การโฆษณาไม่ได้ให้ข้อมูลในด้านที่ว่า ผลกระทบระยะยาวจากการบริโภคไฟโตสเตอรอลในปริมาณสูงอาจทำให้เกิดปัญหาสุขภาพอื่น ๆ โดยเฉพาะในด้านการดูดซึมสารอาหารหรือความสามารถในการทำงานของระบบภูมิคุ้มกัน ซึ่งเป็นสิ่งที่ควรคำนึงถึงในการตัดสินใจเลือกผลิตภัณฑ์ที่จะนำมาใช้ในชีวิตประจำวัน
ในความเห็นของผมนั้น สิ่งที่ควรให้ความสำคัญมากกว่าคือการเลือกบริโภคอาหารที่เป็นธรรมชาติ และหลีกเลี่ยงการพึ่งพาผลิตภัณฑ์ที่มีการผ่านกระบวนการต่าง ๆ เช่น ไฟโตสเตอรอลเข้มข้น หรือสารเติมแต่งอื่น ๆ ที่ไม่จำเป็นต่อร่างกาย การเลือกรับประทานอาหารที่มีคุณค่าทางโภชนาการครบถ้วนจะช่วยส่งเสริมสุขภาพโดยรวมได้ดีกว่าแทนที่จะพึ่งพาสิ่งที่โฆษณาบอกไว้ข้างขวด
ไฟโตสเตอรอลอาจมีคุณสมบัติในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในทางทฤษฎี แต่การบริโภคในปริมาณมากเกินไปนั้นอาจส่งผลเสียต่อร่างกายในหลาย ๆ ด้าน ดังนั้นจึงควรหันมาใส่ใจในข้อมูลที่มีพื้นฐาน และตั้งคำถามกับสิ่งต่างๆ โดยเฉพาะอะไรที่การตลาดตะโกนดังๆว่า ไอ้นี่ดี อันโน้นเยี่ยมยอด อันนี้ที่สุดแห่งความซุปเปอร์ ต่อมเอ๊ะทำงานไว้ก่อน ผิดถูกไม่รู้หาข้อมูลมาโยงเส้นทางแล้วชวนคุยกัน
เช่นเราตั้งคำถามตั้งต้นก่อนไหมว่า จริงๆแล้ว คลอลเสเตอรอล มันต้องกลัวขนาดนั้นเลยหรือ ในเมื่อมันเป็นสารตั้งต้นของชีวิต และเป็นสิ่งจำเป็นในการซ่อมแซมเสริมสร้างร่ายกาย เราต้องลดการดูดซึมด้วยเหรอ
-

@ 907e4623:f40ff12a
2025-04-04 11:39:51
<p>gm well</p><p><br></p><p><strong>lfg</strong></p>
-

@ 7d33ba57:1b82db35
2025-04-03 17:36:08
Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.

## **🏛️ Top Things to See & Do in Zadar**
### **1️⃣ Explore Zadar Old Town 🏰**
- Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**.
- Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés.
### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞**
- **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**.
- **Sun Salutation** – A large **solar-powered light display**, best seen at sunset.
- **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅

### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪**
- **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics.
- **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**.
### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔**
- Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic.
- One of the **tallest church towers in Croatia**.

### **5️⃣ Relax at Zadar’s Best Beaches 🏖️**
- **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town.
- **Borik Beach** – A **sandy beach with shallow waters**, ideal for families.
- **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim.
### **6️⃣ Take a Day Trip to Kornati National Park ⛵**
- A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**.
- Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**.
### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑
- **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀
- **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟

## **🚗 How to Get to Zadar**
✈️ **By Air:**
- **Zadar Airport (ZAD)** is **just 15 minutes from the city center**.
🚘 **By Car:**
- **From Split:** ~1.5 hours (160 km)
- **From Zagreb:** ~2.5 hours (285 km)
🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**.
⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.

## **💡 Tips for Visiting Zadar**
✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️
✅ **Stay near the Old Town** – Everything is within walking distance 🏡
✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶
✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️
✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵

-

@ 000002de:c05780a7
2025-04-03 17:27:03
### I score zero points. How about you?
https://m.primal.net/QDDi.jpg
I almost called this a boomer test but its more of a Gen X test.
__Credit to Jack Spirko for sharing this on Twitter.__
originally posted at https://stacker.news/items/933537
-

@ 5708b1f6:208df3b8
2025-04-03 15:25:33
The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist.
However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives.
All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers.
The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music.
Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.”
Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite.
When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age.
The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow.
It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences.
This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks.
Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs.
This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced.
Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion).
When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song.
Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken.
To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word.
There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function.
It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center.
It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance?
-

@ 2b24a1fa:17750f64
2025-04-04 08:42:16
„Denke daran, daß das, was dich wie an unsichtbaren Fäden hin- und herzieht, in deinem Innern verborgen ist.“ Soll der römische Kaiser Marc Aurel gesagt haben, der letzte bedeutende Philosoph der jüngeren Stoa. Brot und Spiele hieß es damals, machten die Gesellschaften gefügig: Bier, Wein, Whiskey, Ablenkung, Informationssteuerung. 
[https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?](https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?color=ffd400)
Wie sich die kognitive Einflussnahme zur Kriegsführung entwickelte, wie sie sich mit den heutigen medialen und technischen Mitteln darstellt und wie wir unsere Kinder und uns selbst davor schützen können, damit beschäftigt sich der Propagandaforscher und Amerikanist Dr. Jonas Tögel. Er promovierte zum Thema Soft Power und Motivation und forscht am Institut für Psychologie der Universität Regensburg. Meine Kollegin Eva Schmidt hat ihn interviewt und wollte zunächst von ihm wissen, wie er zur Propagandaforschung kam und auf welchen Grundlagen seine Tätigkeit aufbaut.
Sein aktuelles Buch "Kriegsspiele - Wie NATO und Pentagon die Zerstörung Europas simulieren" ist im Westend-Verlag erschienen, hat 111 Seiten und kostet 15 Euro.
[www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\
@[radiomuenchen](https://soundcloud.com/radiomuenchen)\
[www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\
[www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\
[twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\
[odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\
[rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen")
Radio München ist eine gemeinnützige Unternehmung.\
Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\
IBAN: DE65 4306 0967 8217 9867 00\
BIC: GENODEM1GLS\
Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\
Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-

@ 2b24a1fa:17750f64
2025-04-04 08:36:50
Was passiert, wenn die Bank plötzlich das Konto kündigt? Aus gesetzlicher Sicht darf sie das, sogar ohne Gründe zu nennen - sofern diese Option in den Allgemeinen Geschäftsbedingungen (AGB) des Kontovertrags steht. Und das ist die Regel. 
[https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?](https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?color=ffd400)
Zwar besteht oft eine mindestens zweimonatige Kündigungsfrist, doch wer jemals das Konto gewechselt hat, weiß, was für ein Aufwand es ist, seinen gesamten und immer komplexeren Zahlungsverkehr umzustellen. Besonders hart trifft es Empfänger von Spenden: darunter viele alternative Medien und freie Journalisten, die für alternative Medien arbeiten. Die Spenden brechen weg, denn die meist anonymen Spender können nicht direkt informiert werden. Das wissen auch diejenigen, denen alternative Medien ein Dorn im Auge sind: Staatlich finanzierte Agitatoren und staatsnahe Medien, die solange Druck auf Banken ausüben, bis diese aus Sorge um ihr Image das Konto kündigen. Das Magazin Multipolar dokumentierte Mitte 2024 rund 40 solcher Fälle. Manchmal nutzen Banken auch ganz direkt diese Möglichkeit, um kritische Stimmen einzuschüchtern und zu schwächen. Diese Variante vermutet unsere Autorin Gaby Weber. Nach einem kritischen Bericht über die Bundesbank wurde ihr das Konto gekündigt. Hören Sie ihren Beitrag „De-Banking oder: die Rache der Bundesbank?“, der zunächst beim Overton-Magazin erschienen ist: [overton-magazin.de/hintergrund/pol…der-bundesbank/](https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/ "https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/")
Sprecher: Ulrich Allroggen
Bild: Radio München
Radio München\
[www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\
@[radiomuenchen](https://soundcloud.com/radiomuenchen)\
[www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\
[www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\
[twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\
[odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\
[rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen")
Radio München ist eine gemeinnützige Unternehmung.\
Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\
IBAN: DE65 4306 0967 8217 9867 00\
BIC: GENODEM1GLS\
Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\
Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-

@ 2b24a1fa:17750f64
2025-04-04 08:15:16
Ganz im Geiste des klassischen Kabaretts widmen sich Franz Esser und Michael Sailer den Ereignissen des letzten Monats: Was ist passiert? Und was ist dazu zu sagen? Das ist oft frappierend - und manchmal auch zum Lachen.
[https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?](https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?color=ffd400)
-

@ 2b24a1fa:17750f64
2025-04-04 08:10:53
Wir leben in einer Demokratie. So heißt es immer. Immerhin hat die Bevölkerung, der Souverän ein Mitspracherecht. Einmal alle vier Jahre. Und damit fünfundzwanzig Mal in einem Jahrhundert. Diese 25 Wahltage ergeben zeitlich 0,07 Prozent des gesamten Jahrhunderts. Würde man das Jahrhundert auf einen Tag runter rechnen, dann ergäben diese 0,07 Prozent ziemlich genau eine Minute des Mitspracherechts. Eine Minute pro Tag darf der Souverän also bestimmen, wer am restlichen Tag ungehindert schalten und walten darf – bis in das Grundgesetz hinein.
[https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?](https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?color=ffd400)
Die Veränderung in diesem zentralen Gesetzestexten ist allein den Parteien vorbehalten. An sämtliche Änderungen halten, dürfen sich dann nachher alle – selbst dann, wenn noch so wenige Bürger dahinterstehen.
In den letzten Wochen offenbarte sich dieser Missstand in präzedenzloser Weise. Die als Sondervermögen schön-deklarierte Neuverschuldung wurde im Grundgesetz festgeschrieben. Ist eine solch selektive Umgestaltungsmöglichkeit des wichtigsten Gesetzestext einer Demokratie würdig? Bräuchte es nicht zumindest einer Absegnung durch Volksabstimmungen?
Henry Mattheß hat sich hierzu Gedanken gemacht. Hören Sie seinen Text „Das Grundgesetz als Schmierzettel“, der zunächst auf dem Blog von Norbert Häring erschienen war.
Sprecher: Karsten Tryoke
Bild: Radio München
[www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\
@[radiomuenchen](https://soundcloud.com/radiomuenchen)\
[www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\
[www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\
[twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")
Radio München ist eine gemeinnützige Unternehmung.\
Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\
IBAN: DE65 4306 0967 8217 9867 00\
BIC: GENODEM1GLS\
Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\
Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-

@ 8671a6e5:f88194d1
2025-04-03 14:52:44
\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?”
*This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.*
## **Define**
Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance).
Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore.
This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly.
A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event.
So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor.
Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form.
But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around.
So, here’s what I’ve learned.
<img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png">
**Chain of ticket**
I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers.
The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process.
If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\
It’s better to not have bought at all.
Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing.
Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\
It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\
This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage.
There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free.
It gets even more absurd.\
At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day.
And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\
“I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward).
So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers.
Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass.
The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time.
Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists.
At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting.
In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people.
Which brings me to the next element of Bitcoin conferences...friends
**Bitcoin “frens”**
This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did).
But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze.
I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\
Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\
I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space.
Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in.
And you can love people for that. Everyone has flaws. Everyone has a price as well.
But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\
We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast.
If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference).
But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time.
And once in a while, you’ll meet a friend for life.
Just be prepared:
Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually.
And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall.
<img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png">
##
## \
The Soviet LN Queue
It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries.
waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino!
The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action.
A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.”
On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you.
So, here’s a tip for the regular people, the rats that pay for all of this : sneak out.
Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes.
If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy.
Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation:
“Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!”
Or worse:
“Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?”
At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war.
**Solution:**
A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following :
Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting.
If you’re using Lightning, have enough balance on you wallet or get lost.
Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something.
No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please!
“Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please.
Bitcoin fixes many things. But it hasn’t quite fixed this yet.
The bitcoin conference axiom
Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many.
If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake.
On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it.
If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties.
The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor.
**Calculating the conference opportunity cost**
To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps:
1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations).
2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years)
3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo.
4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members).
5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more).
If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move.
Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet.
The Conference Opportunity Cost Formula
Let:
CT = Total conference ticket & entrance cost (in dollars)
CR = Total related conference costs (travel, lodging, food, etc.)
C = CT + CR (Total cost)
G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05)
N = Estimated fiat value of networking/business opportunities and knowledge gained.
### OC = (C × G) − N
Where:
OC (Opportunity Cost) < 0 → The conference was worth attending.
OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move.
Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!")
example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0
- $253 OC (Bitcoin would have been the better choice.)
Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner.
\--
So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with.
### Energizing
At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom.
The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate.
Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually.
I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate.
I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like.
### On stage
The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway.
The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again.
Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all.
It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card.
Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :)
## Promoting anything
The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though).
<img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png">
They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”?
That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label.
It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else.
They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard.
Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare).
### **Looking for love in all the wrong places**
\
Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here.
Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life.
And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie.
The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary.
And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop.
My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset.
Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin.
Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask.
Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever.
If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself.
I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit.
Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world.
Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though.
Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks)
Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher.
In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it.
I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now).
written by AVB
If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive)
-

@ 69e50943:2ac7059c
2025-04-03 23:14:14
**This is a test**
How does this look?

-

@ 2b42dd42:5049393c
2025-04-03 21:25:46
this is a test
<img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png">
end of the test
-

@ f1989a96:bcaaf2c1
2025-04-03 14:30:08
Good morning, readers!
Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\
\
Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\
\
In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin.
We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation.
**Now, let’s get right to it!**
### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a)
## **GLOBAL NEWS**
#### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters**
Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose.
#### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025**
The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime.
#### **India | Grants Tax Authorities Access to Citizens’ Online Data**
Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power.
#### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief**
Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected.
#### **Angola | Regime Jacks Price of Diesel**
The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters.
#### **Nicaragua | Ortega’s Dismantling of Press Freedom**
Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders.
## BITCOIN AND FREEDOM TECH NEWS
#### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide**
HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/).
#### **Cove | New Open-Source and Permissionless Bitcoin Wallet**
[Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove).
#### **Second | New Ark Implementation Launches on Bitcoin Signet**
[Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com).
#### **Braiins | Open Sources Bitcoin Control Board**
[Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most.
#### **African Bitcoiners | Publish Bitcoin Starter Guide**
[African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/).
#### **OpenSats | 10th Wave of Nostr Grants**
[OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools.
## RECOMMENDED CONTENT
#### **Freedom Tech with Alex Gladstein**
In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0).
#### **The State of Personal Online Security and Confidentiality with Meredith Whittaker**
In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security.
*If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).*
*Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\
*Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)*
*The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*.
[**Subscribe to newsletter**](http://financialfreedomreport.org/)
[**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3)
[**Visit our website**](https://hrf.org/programs/financial-freedom/)
-

@ 1aa9ff07:3cb793b5
2025-04-03 14:06:38
In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts.
### **What is Nostr?**
Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays.
Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools.
### **How Does Nostr Work?**
Nostr consists of two main components:
1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools.
2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers.
When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages.
Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network.
### **Advantages of Nostr**
1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another.
2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content.
3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps.
4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks.
### **Use Cases for Nostr**
- **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship.
- **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol.
- **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner.
- **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles.
### **Challenges and Limitations**
While Nostr is a promising technology, it is still in its early stages and faces several challenges:
- **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge.
- **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering.
- **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms.
### **The Future of Nostr**
Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform.
As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring.
### **Conclusion**
Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication.
If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
**Understanding Nostr: A Decentralized Social Network Protocol**
In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts.
### **What is Nostr?**
Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays.
Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools.
### **How Does Nostr Work?**
Nostr consists of two main components:
1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools.
2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers.
When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages.
Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network.
### **Advantages of Nostr**
1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another.
2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content.
3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps.
4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks.
### **Use Cases for Nostr**
- **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship.
- **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol.
- **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner.
- **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles.
### **Challenges and Limitations**
While Nostr is a promising technology, it is still in its early stages and faces several challenges:
- **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge.
- **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering.
- **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms.
### **The Future of Nostr**
Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform.
As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring.
### **Conclusion**
Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication.
If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
-

@ 502ab02a:a2860397
2025-04-03 08:31:07
#ที่มาทำเพลง #ตัวหนังสือมีเสียง
วันนี้จะเล่าถึงเพลง ตรุษจีนครับ
เป็นเพลงที่เขียนเสร็จภายในคืนเดียว คือไม่ใช่ว่าเก่งกาจอะไรครับ แต่เนื้อหามีในหัวตั้งนานแล้วตั้งใจจะทำนานแล้วแต่ภารกิจอื่นมีมากจน 24 ชั่วโมงมันรู้สึกน้อยเกินไป
เพลงนี้ความตั้งใจคือ หวังสูงเลยครับ หวังว่าสักวันหนึ่งเยาวราชจะเปิดเพลงนี้กันกระหึ่มในวันตรุษจีน ซึ่งรู้ตัวดีครับว่า ตัวเล็กๆ คงไม่ดังเปรี้ยงในรอบเดียว ผมคิดว่า จะอีก 5ปี 10ปี เพลงนี้มันปล่อยไปแล้วมันยังอยู่ไปเรื่อยๆครับ (เปิดตัวครั้งแรก มีคนเอาแผ่นเสียง tiktok ไปทำอวยพรกันราวๆ 185คลิป ผมดีใจมากแล้ว บางคนลิปซิงค์ด้วยแสดงว่าหัดร้อง โคตรดีใจเลยครับ)
ผมตั้งใจทำให้โทนออกมาเป็นเหมือนคนจีนร้อง แนวประมาณฮอทเป๊บเปอร์ โซเฟียลา อะไรประมาณนี้ ดังนั้นการออกเสียงจะเหมือนคนจีนพูดไทยไม่ชัดอะไรแบบนั้นครับ
เนื้อร้องนี่ผมตั้งใจเขียนแบบ เอาใจอาม่าเลย เราลองมาดูบางท่อนกันครับ
"ซินเจียยู่อี่ ซินนี้ฮวดไช้
วันตรุษจีนนี้ ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง"
เป็นท่อนย้ำแล้วย้ำอีก เพราะจงใจให้เป็นเพลงอวยพร ก็เลยทำเป็นแกนหลักของเพลงนี้ จากนั้นตัวรองก็จะเป็นคำอวยพรในแต่ละเรื่อง มาซ้อนอีกทีนึง
"ปีใหม่หวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร
เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี"
ท่อนนี้ผมนึกถึงอาม่าของผมครับ แกชอบดูหนังกำลังภายใน วีดีโอม้วนเป็นชุดๆ แล้วการได้ไปเที่ยวเรื่อยๆก็เป็นอีกความสุขนึงของคนแก่ ไม่ได้ต้องการอะไรมากไปกว่าร่างกายแข็งแรง เดินเหินไหว เที่ยวได้
"ไม่เพียงแค่ในปีนี้ แต่ขอให้ดี ทุกทุกปีไป
ครอบครัวยิ้มได้ละไม ทุกคนสุขใจ เฮงเฮงดีดีดี"
เป็นท่อนท้ายเพลงแล้ว ซึ่งก็ตบด้วยว่าไม่ได้เฉพาะปีนี้นะ ที่อวยพรกันขอให้ดีไปยาวๆ แล้วก็เล่นคำท้ายว่า "เฮงเฮงดีดีดี" คือ มันเป็นการรวมคำดีๆย้ำๆ ผมรู้สึกว่าพอตอนที่ทำเป็นเพลง มันจะเป็นท่อนที่คนยิ้มกว้างเลยหล่ะ
เนื้อเพลงเต็มๆผมลงไว้ให้ข้างล่าง ส่วนการรับฟัง สามารถเข้าได้หลายทางมากครับ
youtube music
https://music.youtube.com/watch?v=EBKTZv3VvGM&si=f_IMFbDhdEJ6wEcv
spotify
https://open.spotify.com/track/3fCJyoQVAeWxdczfGbL3yT?si=vHV45hUTRPO6Mg9Pnh-w2w
apple music
https://music.apple.com/th/album/%E0%B8%8B-%E0%B8%99%E0%B9%80%E0%B8%88-%E0%B8%A2%E0%B8%A2-%E0%B8%AD-%E0%B8%8B-%E0%B8%99%E0%B8%99-%E0%B8%AE%E0%B8%A7%E0%B8%94%E0%B9%84%E0%B8%8A/1789787248?i=1789787249
tiktok แผ่นเสียง
https://vt.tiktok.com/ZSrk49SfL/
ส่วนเพลงอื่นๆ ฟังเต็มๆได้ทุก music plattform แล้วนะครับ ค้นหา heretong teera siri เพราะเพลงไม่ดังเลยต้องหาจากชื่อคนแทนครับ 55555
新正如意,新年发财
วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง
ปีใหม่หวังได้สุขดี
เป็นเศรษฐีมีเงินทองใช้
ร่ำรวย รุ่งเรืองไปไกล
คิดสิ่งใด ได้สมฤดี
ซินเจียยู่อี่ ซินนี้ฮวดไช้
วันตรุษจีนนี้ขอพรจากใจ
จะทำสิ่งใด ขอให้เฮงเฮง
ปีใหม่หวังได้สุขดี
โรคภัยไม่มี แข็งแรงกว่าใคร
เลือดลม กำลังภายใน
เดินวิ่งยังไหว ได้เที่ยวทั้งปี
ซินเจียยู่อี่ ซินนี้ฮวดไช้
วันตรุษจีนนี้ขอพรจากใจ
จะทำสิ่งใด ขอให้เฮงเฮง
ไม่เพียงหวังได้สุขดี
โรคภัยไม่มี แข็งแรงกว่าใคร
เลือดลม กำลังภายใน
เดินวิ่งยังไหว ได้เที่ยวทั้งปี
ซินเจียยู่อี่ ซินนี้ฮวดไช้
วันตรุษจีนนี้ขอพรจากใจ
จะทำสิ่งใด ขอให้เฮงเฮง
ไม่เพียงแค่ในปีนี้
แต่ขอให้ดี ทุกทุกปีไป
ครอบครัวยิ้มได้ละไม
ทุกคนสุขใจ เฮงเฮงดีดีดี
ซินเจียยู่อี่ ซินนี้ฮวดไช้
ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน
ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน
ขอจงมีความสุขใจ อวยพรนำชัย…ให้จงรุ่งเรือง
#pirateketo #siripun #ตำรับเอ๋ #siamstr
-

@ 07f367da:0e76880d
2025-04-03 17:59:21
윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다.
자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다.
당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다.
선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다.
무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다.
충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다.
사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다.
타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다.
-

@ c13fd381:b46236ea
2025-04-03 07:55:31
Over the past few years, The School of Bitcoin (TSOBTC) has built a reputation as a decentralised, open-source educational initiative dedicated to financial sovereignty and digital literacy. Our faculty, contributors, and global community have worked tirelessly to create resources that embody the Free and Open-Source Software (FOSS) ethos, ensuring that knowledge remains accessible to all.
As part of our commitment to maintaining an open and transparent model, we are excited to announce that The School of Bitcoin is officially migrating to Consensus21.School. This transition is not just a rebranding--it marks the consolidation of all our initiatives, projects, and educational resources under the Consensus21.School banner. The School of Bitcoin will no longer exist as a separate entity.
This move comes as a response to growing confusion between our initiative and another entity operating under the domain schoolofbitcoin (SOB), which has taken a direction that does not align with our open-source philosophy. To reaffirm our dedication to FOSS and community-driven education, we are bringing everything--our courses, programs, and collaborations--into a singular, more focused ecosystem at Consensus21.School.
What Does This Mean for Our Community?
Rest assured, all the valuable content, courses, and educational materials that have been developed under TSOBTC will remain available. We continue to embrace a value-for-value model, ensuring that learners can access resources while supporting the ecosystem in a way that aligns with their means and values.
By consolidating under Consensus21.School, we are doubling down on the principles of decentralisation, self-sovereignty, and permissionless learning. This transition includes all of our key initiatives, including V4V Open Lessons, the Decentralised Autonomous Education System (DAES), and our involvement with the Plan B Network.
Full Migration of DAES and Plan B Network Collaboration
As part of this transition, the Decentralised Autonomous Education System (DAES) is now officially part of Consensus21.School and is fully reflected in the Consensus21.School Whitepaper.
DAES will continue to provide a platform for aspiring learners to submit their Bitcoin project ideas for potential funding and mentorship, with active engagement in our Stacker News /~Education territory and Signal chat for collaboration.
We invite contributors to support our learner fund and help bring innovative ideas to fruition within this new ecosystem.
Additionally, our collaboration with the Plan B Network will now operate under Consensus21.School. Through this partnership, we will continue teaching using the Plan B Network's curriculum to provide high-quality Bitcoin education and strengthen local Bitcoin communities. This global initiative remains a core part of our mission, now fully integrated within Consensus21.School.
Looking Ahead
With Consensus21.School, we will continue innovating in peer-to-peer learning, integrating cutting-edge developments in Bitcoin, Nostr, and decentralised technologies. We encourage our community to stay engaged, contribute, and help us build an even stronger foundation for the future of open education.
This is more than just a domain change--it is the next evolution of our mission. The School of Bitcoin as an entity is now retired, and all our efforts, including DAES and the Plan B Network collaboration, will move forward exclusively under Consensus21.School. We invite educators, students, and enthusiasts to join us in shaping this next phase of open financial education.
The journey continues, and we are thrilled to embark on this new chapter together
-

@ 77c2969e:a33cfa50
2025-04-03 07:54:55
最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。
#### 安装acme.sh
```
curl https://get.acme.sh | sh -s email=youreMailAddress
```
#### 导入环境变量
```
export CF_Token="填API token"
export CF_Zone_ID="填区域ID"
export CF_Account_ID="填账户ID"
```
- Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建
- 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID
### 申请证书
```
acme.sh --issue --dns dns_cf -d dns.235421.xyz
```
- `-d` 后面是你想使用的域名
#### 安装证书
```
acme.sh --install-cert -d dns.235421.xyz \
--key-file /root/certs/key.pem \
--fullchain-file /root/certs/cert.pem \
--reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021"
```
- `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。
- `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。
#### 安装 Technitium DNS Server
1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。
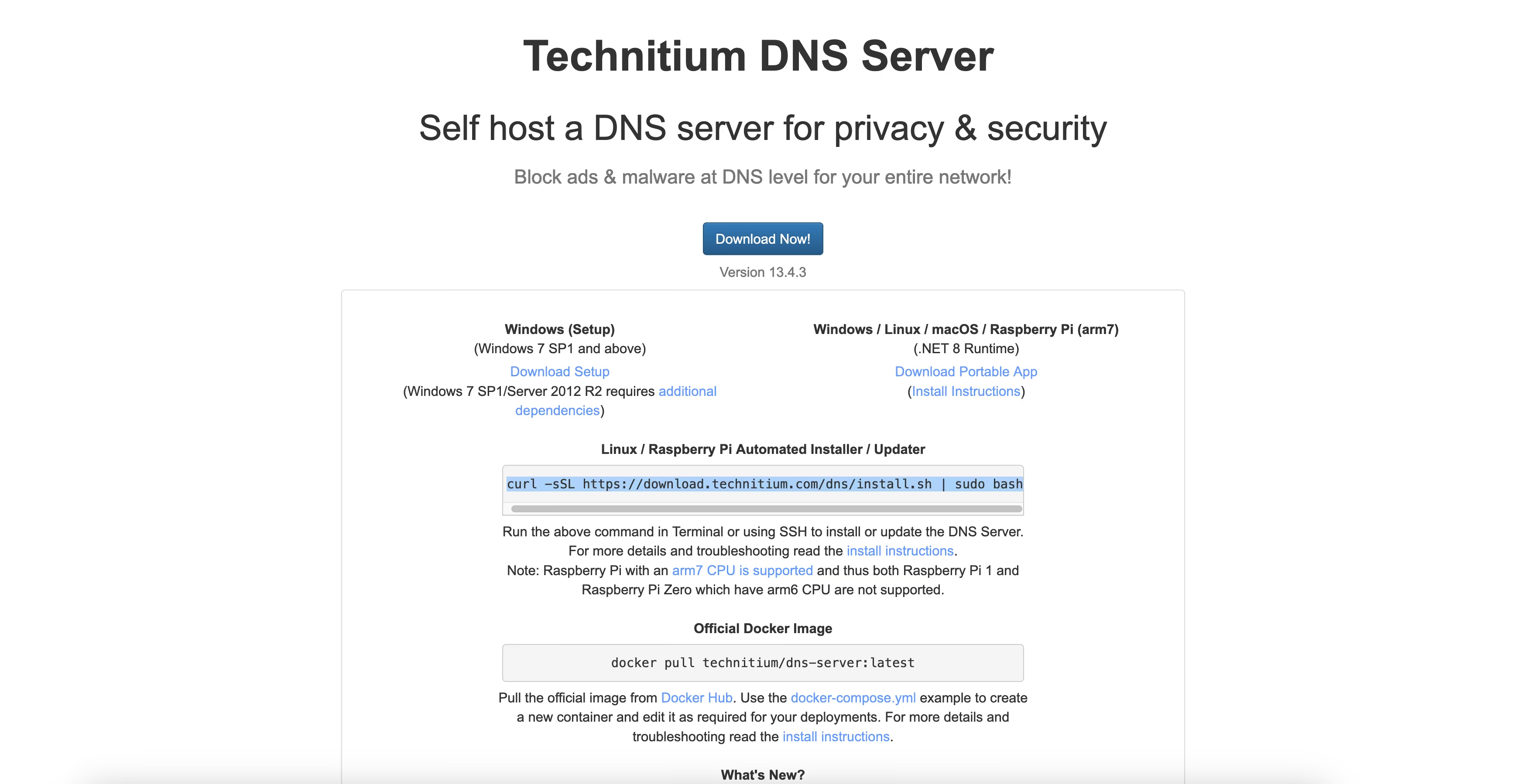
2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。
3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。
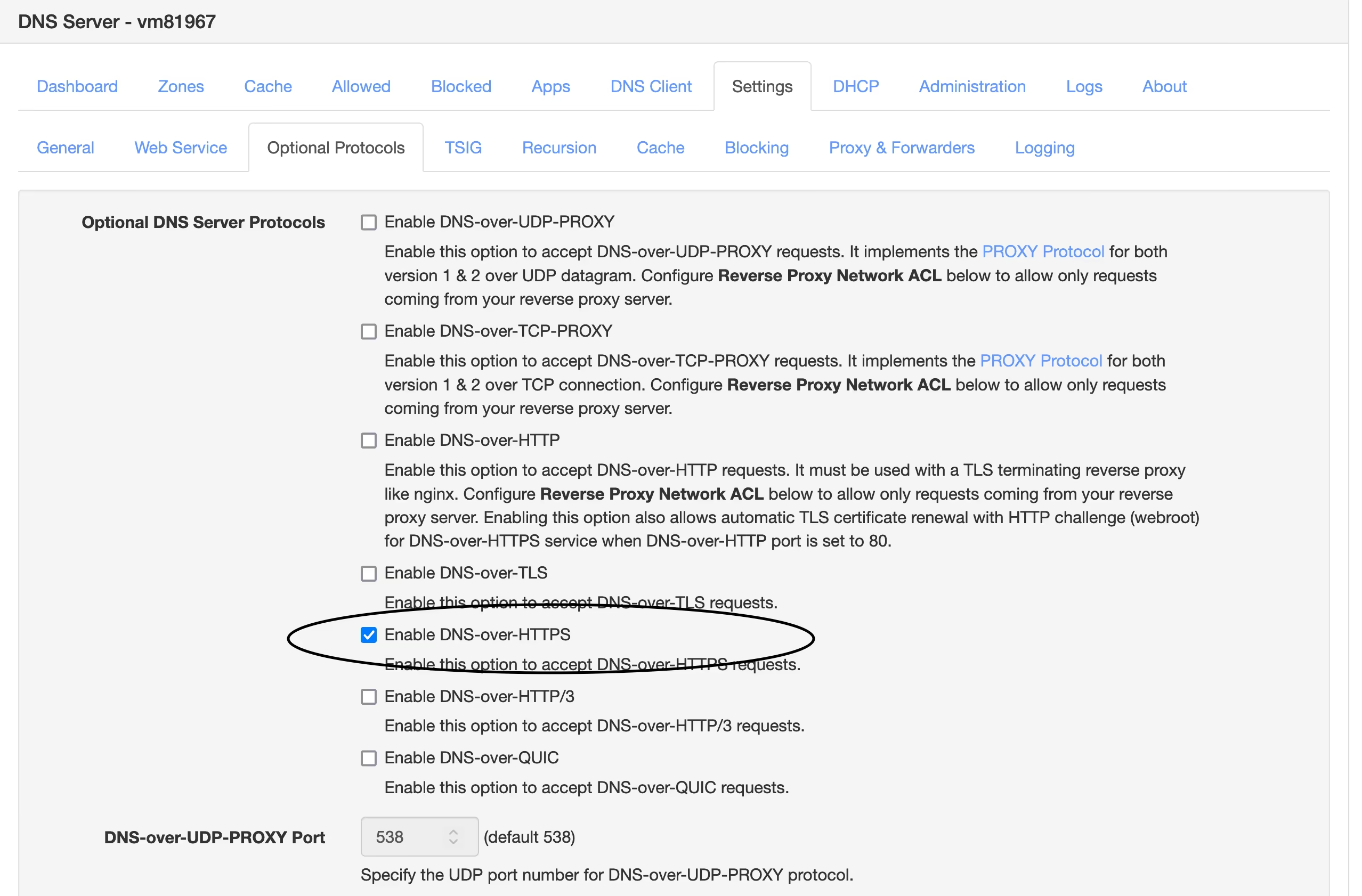
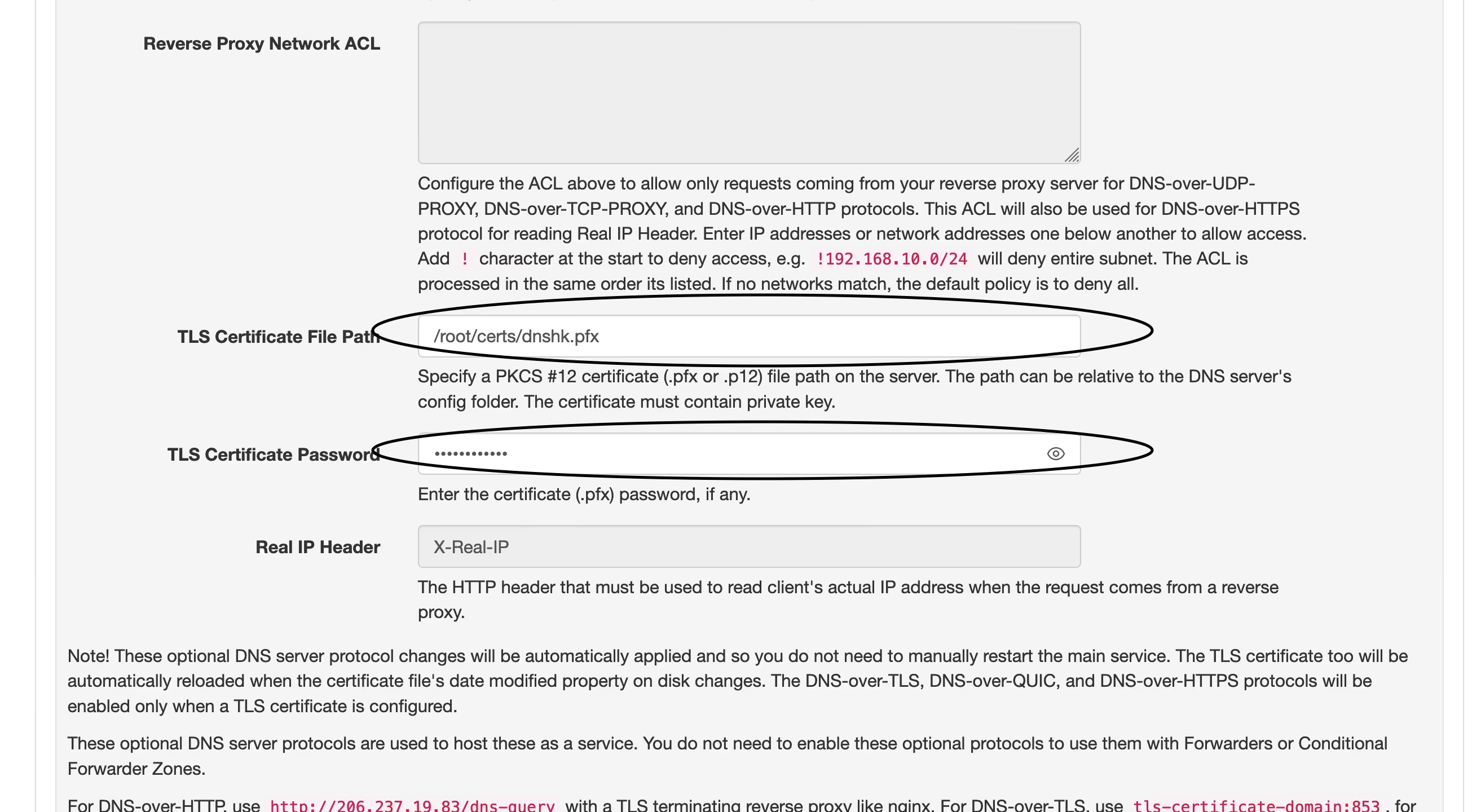
4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。
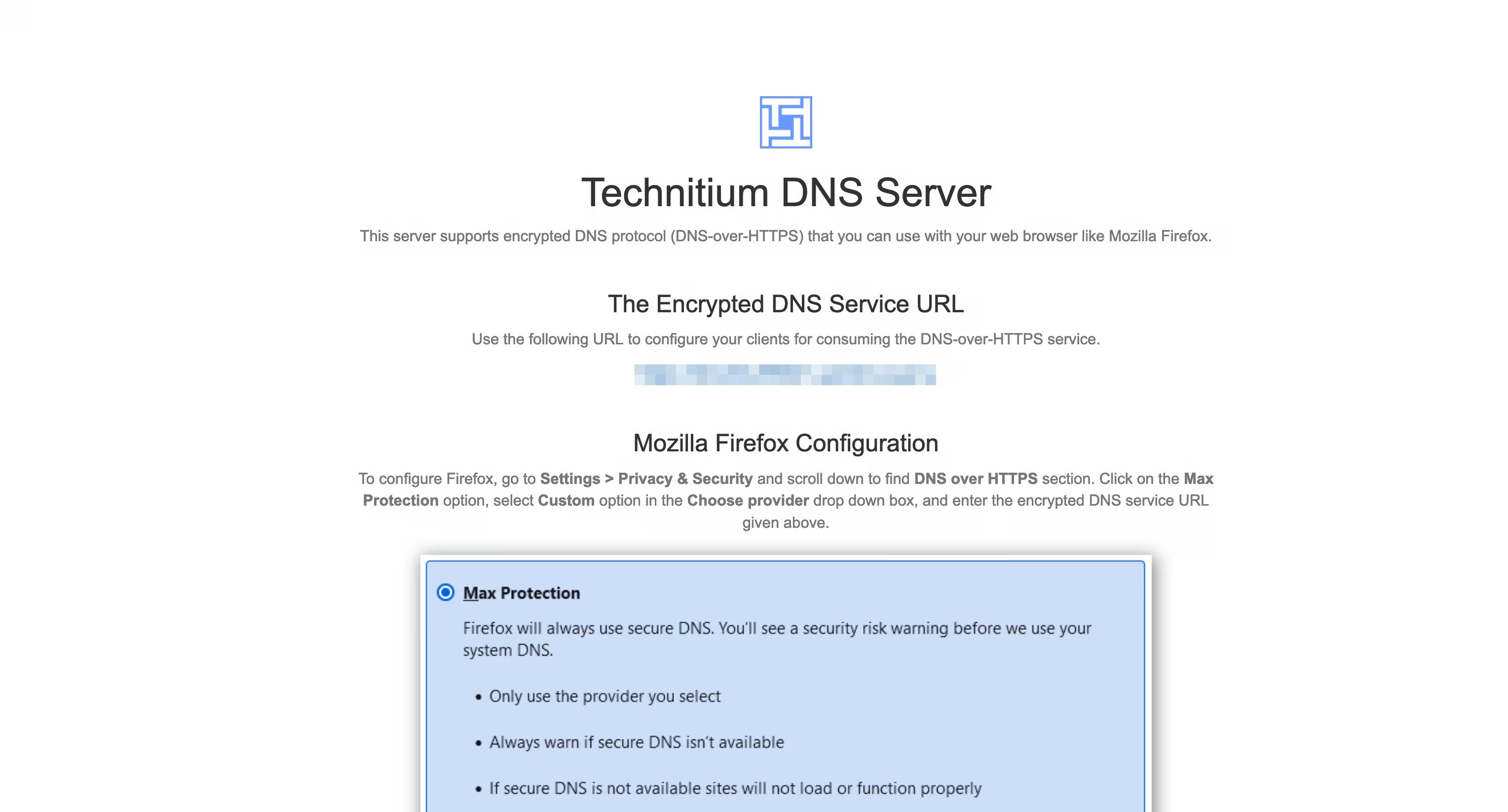
----
我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。
----
#### 我的设置
- 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。
- 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。
- 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。
- 在`Settings` – `Logging` 处开启 `Use Local Time`。
- 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。
##### 以下设置可选
- 在`Settings` – `General` 处开启 `Prefer IPv6`
- 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。
- 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。
- 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。
-

@ c631e267:c2b78d3e
2025-04-03 07:42:25
**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten.
**Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
**Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
**Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
**Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
**Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
**Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
**In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]*
*Dazu passend:*
[Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m)
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
-

@ e4950c93:1b99eccd
2025-04-03 14:57:41
Découvrez les matières utilisées ou non dans les produits référencés sur ce site.
### ✅ Matières naturelles
Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire.
#### 🌱 Principaux critères :
- Biodégradabilité
- Non-toxicité
- Présence naturelle et minimum de transformation
#### 🔍 Liste des matières naturelles :
- Caoutchouc naturel
- Chanvre
- Coton
- Cuir
- Liège
- Lin
- Laine
- Soie
- Terre
- … (Autres matières)
⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière.
Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site.
Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits.
---
### 🚫 Matières non naturelles
Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie.
#### 📌 Principaux problèmes :
- Émissions de microplastiques
- Dépendance aux énergies fossiles
- Mauvaise biodégradabilité
#### 🔍 Liste des matières non naturelles :
- Polyester
- Polyamide
- Acrylique
- Élasthanne
- Viscose
- Silicone
- … (Ajouter les autres matières)
⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque :
- elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et
- aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits.
Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
-

@ e4950c93:1b99eccd
2025-04-03 14:53:56
**Heureu-x-se d’avoir trouvé une information utile sur ce site ?**
Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s.
---
**En bitcoin**
<img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200">
bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
⚡️`
origin-nature@coinos.io`
---
**En euros, dollars, ou toute autre monnaie prise en charge**
*Promesses uniquement pour le moment :*
<a href="https://liberapay.com/origin-nature/">
<img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200">
</a>
---
Contactez-nous si vous souhaitez faire un don avec toute autre
cryptomonnaie.
---
### 💡 Un modèle de partage de la valeur
La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention.
L’autre moitié permet de couvrir les frais de fonctionnement du site.
-

@ 0f9da413:01bd07d7
2025-04-03 05:32:55

หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ
---
### **Mr. A Coffee**

ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้

กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้

ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป

งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :)
Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9
BTC-map: https://btcmap.org/merchant/node:12416107504
---
### **Koh Chang Wine Gallery **

และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)



Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8
BTC-map: https://btcmap.org/merchant/node:11461720813
---
เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง
รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :)
-

@ edeb837b:ac664163
2025-04-03 10:35:59
When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value.
There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why.
## Why NVSTly Stands Above the Rest
NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.**
Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment.
## What is NVSTly?
**NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.**
It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow.
## Key Features That Make NVSTly #1
### 1. Real-Time Trade Sharing & Tracking
NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers.
### 2. Unique POV Trade Charting
See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**.
### 3. Deep Trade Analytics & Trader Dashboards
Get powerful insights into your performance, including:
- **Win rate**
- **Total gain/loss**
- **Average return per trade**
- **Long vs. short ratio**
- **(Coming soon) Drawdown tracking** to measure risk exposure
### 4. Global Trades Feed & Leaderboard
Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies.
### 5. Fully Integrated with Discord & Telegram
No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to:
- **Check a trader’s latest stats**
- **View real-time trade recaps**
- **Fetch charts and ticker data**
- **Receive automated trade notifications**
Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access.
### 6. Automated Social Media Sharing
Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed.
### 7. Future AI & Machine Learning Enhancements
NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to:
- **Get automated trading tips** tailored to their strategies
- **Use customizable AI models** to refine their trading approach
- **Interact with a smart AI trading assistant** via the app and Discord bot
## Why NVSTly is the Only Social Trading App You Need
While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.**
With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible.
So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.**
## Ready to Take Your Trading to the Next Level?
Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.**
📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!**
🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server!
-

@ 2b24a1fa:17750f64
2025-04-03 10:11:13
Ist es wirklich so, dass Gendern für mehr Gleichberechtigung sorgt, für ein friedlicheres Miteinander? Abgesehen von den grammatikalischen Verirrungen, die sich dabei in die Sprache schleichen, darf die Frage erlaubt sein, warum ein Gemeinschaftsgefühl, das „Wir“ in immer kleinere Einheiten, auch sprachlich geteilt werden soll. Muss ich tatsächlich alle benennen? 
[https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?](https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?color=ffd400)
Dann wäre das eine Liste von Namen. Verlese ich die nicht, sondern gendere mit Glottisschlag und allem was dazu gehört, unterteile ich ja doch in Gruppen. Und Gruppen haben zur Eigenart, dass es Zugehörigkeiten gibt und ausgeschlossen sein. So beginnt der Kampf. Zunächst war die Frau minderwertig, jetzt ist der Mann toxisch. Und was, wann zu wem, wie gesagt werden darf wird zum Spießrutenlauf. „Misgendern“ ist beispielsweise eine Wortneuschöpfungen, die eine Incorrectness der Sprache bezeichnet, die bis in die Strafbarkeit reichen will.
Einer, der von dieser rigide anmutenden Sprach-Religion getriggert wird, ist Gerald Ehegartner. Er ist Lehrer, Musiker, Theater- und Wildnispädagoge und Autor und nimmt sich immer wieder dem Gemeingut Sprache an. Heute mit einem Text, den er mit: „Gendern, die Sakralsprache des Wokeismus“ betitelt hat.
Sprecherin: Sabrina Khalil
-

@ 5cf42f9d:4465eebf
2025-04-02 21:32:31
-

@ 2b24a1fa:17750f64
2025-04-03 10:05:21
Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden. 
[https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche](https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche?color=ffd400)
Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder.
Folge 3: Christian der Wachstümliche
Sprecher: Karsten Troyke
Bild: Markus Mitterer für Radio München
Radio München
-

@ 2b24a1fa:17750f64
2025-04-03 10:03:24
Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden. 
[https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?](https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?color=ffd400)
Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder.
Folge 4: Annalena die Völkerballerina
Sprecher: Karsten Troyke
Bild: Markus Mitterer für Radio München
-

@ 2b24a1fa:17750f64
2025-04-03 09:57:35
Es sind immer die gleichen Mechanismen: Die Faktoren Zeitdruck und Angst machen enorm viele Menschen gefügig. 500 Milliarden Euro für Infrastruktur und den sogenannten Klimaschutz, 400 Milliarden für die Bundeswehr – also fast eine Billion Euro Schulden, innerhalb von weniger als vier Wochen nach der Wahl mit Winkelzügen den Bundesbürgern auferlegt. 
[https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?](https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?color=ffd400)
Wahlversprechen oder Parteiprogramme, das auf keinen Fall zu tun, sind Makulatur. Keine Diskussion über einen Haushalt, keine Diskussion über die Notwendigkeiten und schon sind Fragen anhängig, ob die Aufträge, die nun vergeben werden, nach den rechtmäßigen Ausschreibungskriterien vonstatten gehen, oder ob auch bei diesen unvorstellbaren Summen die Spezlwirtschaft im Land fortgeführt wird.
Wo ist der Wille des Volkes geblieben? Wo die Freiheit, tatsächlich über unser Leben und Wirtschaften zu entscheiden?
Der Autor, Wirtschafts- und Finanzexperte Andreas Geltinger schaut auf die einstigen Ideen wirtschaftlichen Handelns und analysiert, womit wir es jetzt zu tun haben.
Sprecher: Karsten Troyke.
-

@ e4950c93:1b99eccd
2025-04-03 09:55:59
### Équipe Cœur
L'équipe Cœur porte le projet et valide les contenus.
- [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll)
Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure !
### Enrichisseu-r-se-s de contenus
Les contribut-eur-rice-s rendent ce site vivant et intéressant.
-

@ 2b24a1fa:17750f64
2025-04-03 09:34:29
Kartografiert, aufgekauft, betoniert, beschildert. Wo ist die Freiheit? Wo ist Platz zum Erforschen im Nicht-Definierten? Also wo sind die Erfahrungsräume, die sich von Generation zu Generation üblicherweise immer wieder die Jugend erobert, um darin zu wachsen und zu reifen?
[https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders](https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders?color=ffd400)
Perspektivwechsel: Wo sind eigentlich die Jugendlichen abgeblieben, die nach diesen Räumen Ausschau halten? Sie bewegen sich in „Spaces“. Seit Corona staatlich verordnet, suchen sie auf flachen Bildschirmen, in einer artifiziellen Welt, ihren Horizont zu erweitern.
Der Kulturwissenschaftler Kenneth Anders hat sich auf Spurensuche bei Jugendlichen auf dem Land gemacht. Hören Sie sein Resumée mit dem Titel „Abwartend skeptisch“.
Nachzulesen ist der Beitrag auf der Webseite: oderamazonas.de
Sprecherin: Sabrina Khalil
Bild: KI
[www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\
@[radiomuenchen](https://soundcloud.com/radiomuenchen)\
[www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\
[www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\
[twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")
Radio München ist eine gemeinnützige Unternehmung.\
Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
-

@ 2b24a1fa:17750f64
2025-04-03 09:28:52
21 Monate, also fast zwei Jahre verbringt Johanna Findeisen bereits in Untersuchungshaft. Trägt sie reichsbürgerliche Ideen mit sich? Oder hat sie Straftaten geplant? Es ist ein Fall im sogenannten „Reichsbürgerprozess“. Mit diesem beschäftigt sich einer ihrer Anwälte Prof. Martin Schwab. Bei den Prozessen, so der Jurist, gehe es eher um Gesinnungsfragen. 
[https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege](https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege?color=ffd400)
Fakten zu Straftaten, auch geplanten, seien nicht aufzufinden. Und eine Untersuchungshaft für die Aufdeckung einer möglicherweise falschen Gesinnung – die Johanna Findeisen vehement bestreitet - ist in unserem Rechtssystem nicht vorgesehen. Dennoch sind die Termine für diese Untersuchungen bereits bis 2026 anberaumt.
Das soll aber heute nicht unser Thema sein. Es geht um die Untersuchungshaft selbst. Prof. Martin Schwab ist in regelmäßigem, telefonischen Kontakt mit Johanna Findeisen und stellt dort Verhältnisse fest, die den Tatbestand der Folter erfüllen. Kein Mensch, selbst der Verurteilte, darf in seiner Menschenwürde herabgesetzt werden. Nun wird der Fall Johanna Findeisen bislang lediglich untersucht. Wie kann also sein, dass sie im Transport zum Gericht gefesselt wird? Warum wurde sie bei ihrer Rückkehr körperinvasiv untersucht? Was übrigens nach einem öffentlichkeitswirksamen Antrag ans Oberlandesgericht erfolgreich unterbunden wurde. Warum wird ihre Post zurückgehalten? Warum durfte sie, bei zwei Stunden Besuchszeit im Monat, ihren Angehörigen nur hinter einer Scheibe begegnen? Warum wird sie, ohne Morgentoilette, abgeholt und in eine fensterlose Zelle ins Gericht gebracht, wo sie zwei Stunden bis zum Gerichtstermin ausharren muss? Und warum wird die fiebernde Johanna, bei Minusgraden und offener Türe gezwungen, sich nackt auszuziehen, sich zur Wand zu drehen und sich einer erniedrigenden Leibesvisitation zu stellen?
Auch dem Pfarrer und Autor Jürgen Fliege geht dieser Fall nah und fragte sich, was Johanna Findeisen, neben einer guten Verteidigung gebrauchen könnte und er ihr geben: Beistand! Hören Sie seinen offenen Brief an die Inhaftierte.
Sprecherin: Sabrina Khalil.
Wer sich gegen die – in einzelnen Haftanstalten – untragbaren Zustände, gegen die dortigen Menschenrechtsverletzungen engagieren möchte, kann das beispielsweise auf der Webseite [www.folter-nein-danke.eu](http://www.folter-nein-danke.eu/ "http://www.folter-nein-danke.eu") tun.
-

@ 2b24a1fa:17750f64
2025-04-03 09:28:32
„Das ist ein netter alter Onkel, der sich bemüht, der Welt Gutes zu tun“, antwortete Anfang 2021 der Sohn einer Freundin auf ihre Frage, was Bill Gates mit der Pandemie zu tun haben könnte. Ich erinnere mich, damals wurde man als Verschwörungstheoretiker tituliert, und zwar maximal abwertend, wenn man allein den Namen ins Spiel brachte. Es ist wirklich Zeit, sich wieder für das Ansehen der Verschwörungstheorie einzusetzen, denn ohne sie wird kein einziger Kriminalfall aufgedeckt, der von mehr als einer Person durchgeführt wurde.
[https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection](https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection?color=ffd400)
Kommen wir zum dritten Teil der Reihe „Corona-Connection“ von Milosz Matuschek in dem er sich in deren Epizentrum begibt. Bill Gates, der undemokratisch zu Macht gekommene, selbsternannte Philanthrop, gehört zu den Hauptfiguren der USAID, der United States Agency for International Development. Matuschek geht hier auf das Geschäftsmodell des Philanthrokapitalismus ein.
Sabrina Khalil hat seinen Text gelesen. Diesen und die zwei ersten Folgen finden Sie auf Matuscheks Seite: Freischwebende Intelligenz.
-

@ 2b24a1fa:17750f64
2025-04-03 07:46:37
„Ein Fundstück aus dem Internet – jemand fragt:\
„Wie fühlst du dich als Geimpfter, wenn du eine Maske tragen musst, um die Ungeimpften zu schützen?“
[https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer](https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer?color=ffd400)
\
Jemand antwortet:\
„Wovor sollte ein Geimpfter einen Ungeimpften schützen?\
1\. Der Geimpfte kann doch gar nicht krank werden, also auch niemanden anstecken, dachte ich?\
2\. Wenn der Geimpfte doch krank werden und andere anstecken kann, wozu hat er sich dann impfen lassen?\
3\. Und wozu sollte sich dann der Ungeimpfte impfen lassen?\
4\. Und wozu sollte dann überhaupt einer der beiden eine Maske tragen?“\
Jemand antwortet:\
„Das ist pure Querdenkerei. Solche kruden Theorien können Menschenleben zerstören.“\
„Eine bessere Parabel auf den religiösen Charakter des aktuellen Wahns könnte ich mir nicht ausdenken“,\
schreibt der Münchner Kolumnist Michael Sailer in seinem Buch Was ist passiert – Notate aus den Zeiten von Lüge und Krieg, das Ende Februar erschienen ist. Als neugieriger und zwangsläufig teilnehmende Beobachter analysiert, kommentiert und hinterfragt der Autor die gesellschaftlichen Abgründe, die sich 2020 und 2021 vor unser aller Augen auftaten.
Unser Autor Jonny Rieder hat es gelesen und eine Rezension verfasst.
Sprecher: Ulrich Allroggen
Bild: Radio München - Kunst: Isaac Cordal (Cement Eclipses)
-

@ 3c7dc2c5:805642a8
2025-04-02 21:15:55
## 🧠Quote(s) of the week:
CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs.
## 🧡Bitcoin news🧡
2025
https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg
On the 24th of March:
➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity.
➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion).
Look at the corporate Bitcoin ownership breakdown:
- MicroStrategy: 506,000+ BTC
- Marathon: ~46,000 BTC (10x smaller)
- Riot: ~19,000 BTC (26x smaller)
That acquisition curve has gone parabolic since Q4 2024.
Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale.
Clear institutional conviction signal here.' -Ecoinometrics
➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine."
On the 25th of March:
➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL
- This is one of the most reliable "buy" indicators.
- Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive
(foto)
Bitcoin is always a buy. Just DCA.
➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest.
➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin.
➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o
Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world.
Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives)
But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.'
➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization".
I rather believe the opposite.
Under Femke Halsema - Amsterdam
- The number of civil servants increased by 50% (14K -> 20K)
- Debt increased by 150% (4 billion -> approx. 10 billion)
Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity.
Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better.
➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment.
➡️BlackRock launched a European Bitcoin ETP today - Bloomberg
➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin.
On the 26th of March:
➡️NYDIG just became a big Bitcoin miner.
Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG.
➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds.
➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest.
That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds.
➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses.
➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD.
→ Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin
→ Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin
→ Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet
This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time.
Source: https://t.co/QDj61ZDe6O
The Blockchain Group is Europe's First Bitcoin Treasury Company!
On the 27th of March:
➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard
➡️Daniel Batten: Yet another paper on Bitcoin and energy
TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition
are greater than generally assumed"
The journal has a (high) impact factor of 7.1."
Source: https://t.co/W3gytMgcpC
➡️A home miner with only 4 machines mined block 888737.
https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg
Bitcoin proves anyone can participate and earn—true freedom!
➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks.
200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News
➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025.
On the 28th of March:
➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today.
ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes!
➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina.
➡️A Russian company built a Bitcoin mine in the Arctic.
Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs.
➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity.
https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg
another great chart:
https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg
On the 29th of March:
➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin.
https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png
➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill.
If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use.
➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207.
On the 31st of March:
➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders:
“If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin."
https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf
➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin.
➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds.
➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem.
A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia.
Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening.
https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg
On the 1st of April:
➡️'Over 73,353 BTC were bought by corporations in Q1 2025.
Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now...
Which company do you want to see adopt BTC next?'
Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723
➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC.
On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC.
➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish
➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county.
➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide.
Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.'
## 💸Traditional Finance / Macro:
On the 29th of March
👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION.
Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL
## 🏦Banks:
👉🏽 no news
## 🌎Macro/Geopolitics:
On the 24th of March:
👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history.
Every time it crossed this level it marked the beginning of an 18-month recession/depression.
1929, 1973, 2008 & 2025'
I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both.
👉🏽US household wealth is falling:
US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates.
By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion.
In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback.
Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks.
This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures.
Consumer spending is set to slow in Q2 2025.' -TKL
👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes.
BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left."
Today, the 27th of March, marks those 1,028 days, and nothing happened.
Climate doomers are like Aztecs who think the sun stops unless they cut out some organs."
👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today.
For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/
They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe.
On the 25th of March:
👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though.
👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse.
The Green Deal is moving full speed ahead—soon everyone will be relying on food banks…
For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen
On the 26th of March:
👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all.
Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening.
On the 27th of March:
👉🏽Gold surpasses $3,100 for the first time in history.
TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years.
This is also the 3rd-longest streak on record after a historic run during the late 1970s.
The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation.
As a result, gold prices recorded 4 consecutive yearly gains.'
On the 31st of March for the first time, gold blasted through $100,000/kilogram.
This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.'
👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come.
On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored."
On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over."
That is the Mark I know!
"Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.”
On the 28th of March:
👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993.
Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed.
Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction.
It’s negative even “gold adjusted”
4 weeks ago it was +2.3%
8 weeks ago it was +3.9%
Yikes!
👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure.
The remaining 900 employees are set to be terminated.
👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei
👉🏽Fix the money, fix the world:
DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government”
“It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account”
“We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION”
“There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit”
Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe.
On the 29th of March:
👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion.
Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge
On the 1st of April:
In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week:
https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg
APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros.
Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!?
For our own housing market? “Too political.”
For war and Brussels' military ambitions? €100,000,000,000—no problem.
They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda.
Got Bitcoin?
I will end this Weekly Recap with a Stanley Druckenmiller quote:
"My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully."
"I tend to think that's what great investors do."
I know what I do and have. Bitcoin!
## 🎁If you have made it this far I would like to give you a little gift:
What Bitcoin Did:
Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy.
https://www.youtube.com/watch?v=_bSprc0IAow
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
`Use the code SE3997`
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀
⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you? If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-

@ ba36d0f7:cd802cba
2025-04-02 21:17:09
## 1. **Essential Rules**
✔ Touch-Move: If you touch a piece, you must move it (if legal).
✔ Check Alert: Say "check" when attacking the enemy king (optional in tournaments).
✔ Checkmate Ends: The game stops immediately—no need to capture the king.
✔ Draw Offers: You can offer a draw after your move, before pressing the clock.
**********************************************
## 2. **Tournament Etiquette**
- Handshake: Before and after the game.
- Silence: No talking during play (except "check" or "draw?").
- Clock: Press with the same hand that moved.
- Resignation: Tip over your king or say "I resign" (don’t just leave).
**********************************************
## 3. **Online Chess Manners**
No Stalling: Let the timer run out only if you’ve truly lost.
GG Message: Say "Good game" (or "GG") after playing.
Avoid "Berserking": Don’t abuse speed settings to rush opponents.
> **Common Faux Pas**
❌ Jangling pieces to distract.
❌ Glaring at your opponent’s board.
❌ Cheating (using engines, peeking at other games).
-

@ ba36d0f7:cd802cba
2025-04-02 21:14:37
| **Piece** | **How It Moves** | **Special Rules** |
| --------- | ------------------------------------- | --------------------- |
| Pawn | Forward 1 (or 2), captures diagonally | En passant, promotion |
| Rook | Straight lines | Castling |
| Knight | L-shape (2+1) | Jumps over pieces |
| Bishop | Diagonals | Color-locked |
| Queen | Any direction | None |
| King | 1 square any way | Castling, checkmate |
**************************
## Pieces
1. **Pawn** (♙ / ♟️)
- Moves: Forward 1 square (or 2 on first move).
- Captures: Diagonally 1 square.
Special:
- En passant: Captures a pawn that moved 2 squares past it.
- Promotion: Reaches the 8th rank → becomes any piece (usually Queen).
************************
2. **Rook** (♖ / ♜)
- Moves: Straight lines (any distance).
- Special: Castling (moves with the king).
**********************************************
3. **Knight** (♘ / ♞)
- Moves: "L-shape" (2 squares one way + 1 square perpendicular).
- Jumps: Over other pieces.
************************************************
4. **Bishop** (♗ / ♝)
- Moves: Diagonals (any distance).
- Stays on one color forever.
*************************************************
5. **Queen** (♕ / ♛)
- Moves: Any direction (straight/diagonal, any distance).
- Most powerful piece!
**********************************************
6. **King** (♔ / ♚)
- Moves: 1 square in any direction.
Special:
Castling: Swaps places with a rook (if no blocks/checks).
Checkmate: Loses if trapped with no escape.
*************************************
## **How to move**
1. One move per turn
2. Choose your piece, place it on a legal square
- *Your color only: White moves first, then Black, alternating.*
- *No passing: You must move if it’s your turn.*
****************************************************
**How to Capture ("Eat")**
- Land on an enemy piece: Replace it with your piece.
- *Pawns capture diagonally only (not straight).*
- *Kings cannot be captured (checkmate ends the game).*
>✔ Check: Attack the enemy king (they must escape next turn).
❌ Illegal: Moving into check or leaving your king in check.
******************************************
## **Special moves**
| Move | Key Rule | Notation |
| ---------- | ---------------------------------- | ----------- |
| Castling | King + rook, no prior moves/checks | `O-O` |
| Promotion | Pawn→any piece at 8th rank | `e8=Q` |
| En Passant | Capture a 2-square pawn jump | `exd6 e.p.` |
*******************************************
1. **Castling** (The King’s Escape)
- What: King + Rook move together in one turn.
How:
- King moves 2 squares toward a rook.
- Rook jumps to the other side of the king.
Rules:
- No checks: King can’t be in check or pass through check.
- Never moved: King and that rook must be untouched.
Types:
Kingside (♔→♖, faster): O-O
Queenside (♔←♖, safer): O-O-O
**************************************************
2. **Promotion** ("Crowning")
- What: Pawn reaches the 8th rank → turns into any piece (usually Queen).
- How: Replace the pawn with a new piece (even if the original is still on the board).
> Fun fact: You can have 9 queens (1 original + 8 promotions)!
Promotion example (Pawn→Queen at h8)
***********************************
3. **En Passant** (French for "In Passing")
- When: Enemy pawn moves 2 squares forward past your pawn.
- How: Capture it diagonally (as if it moved only 1 square).
> Rule: Must do it immediately (next turn only).
****************************************
#chess #elsalvador #somachess
-

@ ba36d0f7:cd802cba
2025-04-02 21:08:28
## **Chess Board Setup**

1. **The Basics**
8x8 grid, alternating light/dark squares.
>Key rule: *Always place the board so a light square is on each player’s bottom-right.
2. **Coordinates**
Files (columns): Labeled *a* to *h* (left to right).
Ranks (rows): Numbered *1* to *8* (White’s side = 1, Black’s = 8).
> Notation: Squares are file + rank (e.g., e4, a7).
3. **Piece Placement**
**Black (Top):** a8: Rook b8: Knight c8: Bishop d8: Queen
e8: King f8: Bishop g8: Knight h8: Rook
Rank 7: All pawns (a7-h7)
**White (Bottom):** a1: Rook b1: Knight c1: Bishop d1: Queen
e1: King f1: Bishop g1: Knight h1: Rook
Rank 2: All pawns (a2-h2)
> Quick Tip: Queens start on their color (Whiteon d1, Black on d8).
***********************
## **Checkmate, stalemate & draws**
Chess is a two-player strategy game where the ultimate goal is to **checkmate** your opponent’s king. However, games can also end in a **stalemate** or **draw** under specific conditions.
1. **Checkmate (Winning the Game)**
- Definition: The enemy king is in check (under attack) and has no legal moves to escape.
- Result: The game ends immediately—the player delivering checkmate wins.
1. **Stalemate (Draw)**
- Definition: The player whose turn it is has no legal moves, but their king is not in check.
- Result: The game is a draw (no winner).
> Common Causes:
>- *A lone king with no moves left.*
>- *Poor pawn structure blocking all options.*
3. **Other Draws**
Games can also end in a draw due to:
- **Insufficient Material**
- Only kings remain.
- King + bishop vs. king (no possible checkmate).
- **Threefold Repetition**
- The same position occurs 3 times (with the same player to move).
- **50-Move Rule**
- No pawn moves or captures in 50 consecutive moves (by both players).
- **Agreement**
- Players mutually agree to a draw.
Key differences:
| Term | King in Check? | Legal Moves? | Result |
| --------- | -------------- | ------------ | -------- |
| Checkmate | Yes | No | Win/Loss |
| Stalemate | No | No | Draw |
| Draw | N/A | N/A | Tie |
****************************************************
## **Chess history**
1. **Ancient Origins (6th Century)**
- Birthplace: Northern India (as Chaturanga), meaning "four divisions" (infantry, cavalry, elephants, chariots—early versions of pawns, knights, bishops, rooks).
- Spread: Reached Persia as Shatranj by 600 AD, where key rules (like "check" and "checkmate") emerged.
> Fun fact: "Checkmate" comes from Persian "Shah Mat" ("the king is helpless").
2. **Medieval Europe (9th–15th Century)**
- Rebranding: Arabs brought chess to Spain by 1000 AD; Europeans adapted pieces to feudal society:
Elephants → Bishops
Viziers → Queens (weak at first—could only move one square!)
- Major Change: By 1475, the queen became the most powerful piece ("Mad Queen Chess"), speeding up the game.
3. **Modern Chess (1850–Present)**
- Standardization: First official world championship (1886, Wilhelm Steinitz vs. Johannes Zukertort).
- Computers: IBM’s Deep Blue defeated Garry Kasparov in 1997, revolutionizing AI.
- Today: Online platforms (Chess.com, Lichess) and pop culture (The Queen’s Gambit) fuel a global boom.
>Did You Know?
>
> - The longest possible chess game is 5,949 moves (theoretical limit).
>
> - The longest recorded game was 269 moves, 1989 Nikolić vs. Arsović.
>
> - The oldest recorded chess opening (1.e4) appears in a 1490 Spanish manuscript.
#chess #education #elsalvador #chesselsalvador #somachess #article #soma
-

@ ef53426a:7e988851
2025-04-02 21:02:06
# Bartering and early money
\
Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align.
Enter money. It’s used as an indirect exchange for any goods, so everyone wants it.
Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services.
As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money.
---
# Gold — the basis for sound money
\
Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining).
Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something.
Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money.
---
# Currencies devalued
\
Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire.
The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold.
In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned.
---
# Government-backed money
\
Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies.
By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate.
The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold.
---
# Sound money = functioning economy
\
Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future.
The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events.
---
# Recessions and debt arise from unsound money
\
Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles.
According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt.
We need to return to sound money and a new gold standard. Enter bitcoin.
---
# Bitcoin is scarce
\
Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued.
The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward.
Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released.
That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value.
---
# Bitcoin is secure
\
The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information.
Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power.
Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value.
---
# Challenges for adoption
\
Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value.
Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended.
Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system.
---

This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading).
‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018.
Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
-

@ 7d33ba57:1b82db35
2025-04-02 19:47:25
Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.

## **🏛️ Top Things to See & Do in Trogir**
### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡**
- Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**.
- Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**.
- Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**.
### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪**
- Offers **stunning panoramic views** over Trogir and the Adriatic.
- A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery!
### **3️⃣ Visit Kamerlengo Fortress 🏰**
- A **15th-century Venetian fortress** with **amazing sea views** from the top.
- In summer, it hosts **concerts and cultural events**.
### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊**
- A lively waterfront filled with **cafés, restaurants, and luxury yachts**.
- Perfect for a **relaxing evening walk** while watching the sunset.

### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️**
- **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities.
- **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**.
- **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation.
### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️**
- A **stunning turquoise bay**, perfect for **swimming and snorkeling**.
- Just **a short boat ride from Trogir**.
### **7️⃣ Try Dalmatian Cuisine 🍽️**
- **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟
- **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi.
- **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.

## **🚗 How to Get to Trogir**
✈️ **By Air:**
- **Split Airport (SPU)** is just **10 minutes away**! 🚕
🚘 **By Car:**
- **From Split:** ~30 minutes (27 km)
- **From Zadar:** ~1.5 hours (130 km)
🚌 **By Bus:** Frequent buses run between **Split and Trogir**.
⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.

## **💡 Tips for Visiting Trogir**
✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️
✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅
✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟
✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤
✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷

-

@ ba36d0f7:cd802cba
2025-04-02 19:31:27

## **"It Takes a Village"**
…But what if the "village" is a system that prioritizes obedience over curiosity, grades over growth, and rigid curriculums over real-world learning?
For decades, we’ve accepted a model where kids spend hours a day passively absorbing information in classrooms, where their worth is measured by standardized tests rather than their ability to _think_, _adapt_, or _create_. Meanwhile, the tools to revolutionize learning - technology, connectivity, and decentralized knowledge - sit in our pockets, dismissed as "distractions" rather than leveraged as liberation.
**The Paradox of Progress**
We live in an era of unprecedented access to information. Yet, our education systems cling to industrial-era ideals, villainizing screens instead of teaching **how to wield them wisely**. Yes, mindless screen time harms—but so does _mindless schooling_. The real failure? **Not preparing learners to navigate, critique, and contribute to the world they actually live in.**
**A different approach**
soma is an experiment in **self-directed, community-rooted learning**. It asks:
- What if education _integrated_ with life instead of interrupting it?
- What if "success" meant **mastery driven by curiosity**, not compliance?
- What if technology connected learners to mentors, resources, and real-world problems - not just apps that mimic worksheets?
This isn’t about abandoning theory or expertise. It’s about **flipping the script**:
- **Empiric learning** comes first (doing, trying, failing, exploring).
- This is where physical spaces thrive - **quilombos**, workshops, community gardens. Where we take responsibility for our shared world.
- **Theoretical depth** follows _when the learner chooses it_ - fueled by a desire to go further.
- This is where our virtual spaces shine to guarantee accessibility: **as tool, not a privilege**.
- Tech is **recreation, not a crutch** - the spice, not the meal.
**********
**A call for villages, not factories**
soma imagines communities where learning is **an act of devotion** - to exploration, to curiosity, to the sacred cycle of trying, failing, and trying again.
Where you learn **because you want to - to better your surroundings**, not because you were told to.
> Where a child’s obsession with ants leads them to a biologist’s fieldwork _and_ a poet’s metaphor - because both are natural extensions of wonder.
> Where a teen building a game pursues storytelling, math, and ethics **on their own terms**, stitching knowledge together like patchwork quilt.
> Where we see learning happening in parks, in makerspaces and on screens - used intentionally.
This is education **returned to its human rhythm**: urgent, messy, and alive.
---
**Join the experiment**
This is just the start. soma is a **provocation, a prototype, and an open invitation** to rethink how we learn.
**Let’s stop preparing kids for a world that no longer exists.**
➡️ _Follow updates, share your ideas, or tell us: What does your ideal "village" look like?_ nostr:npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99
#longform #article #education #elsalvador #communities #decentralized
-

@ cbaa0c82:e9313245
2025-04-02 18:53:57
#TheWholeGrain - #March2025
March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky!
Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary!
End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!?
**Sunday Singles - March 2025**
2025-03-02 | Sunday Single 82
Title: Slingshot!
*Watch out! Toast is quite the sharpshooter!*
https://i.nostr.build/zHA9C7cOOZLOCl0o.png
2025-03-09 | Sunday Single 83
Title: Puzzles
*End-Piece just figured out the puzzle!*
https://i.nostr.build/u2EBdcsuwO2xo23P.png
2025-03-16 | Sunday Single 84
Title: Basketball
*Oh, the madness!*
https://i.nostr.build/8F1OFFVra7zQOIy6.png
2025-03-23 | Sunday Single 85
Title: Coffee
*The perfect way to start the day.*
https://i.nostr.build/aiGZOvOmow3igru6.png
2025-03-30 | Sunday Single 86
Title: Origami
*End-Piece has a way with paper.*
https://i.nostr.build/0ySzGwF9QnZxwLxD.png
**Adventure Series: Questline**
The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated!
Artist: Dakota Jernigan (The Bitcoin Painter)
Writer: Daniel David (dan 🍞)
2025-03-11 | Questline
005 - Under Attack
*Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.*
https://i.nostr.build/F24sd7SFFbsW9WZY.png
2025-03-25 | Questline
006 - A Finished Battle
*End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.*
https://i.nostr.build/n5a7Jztq9MHxuGNf.png
**Other Content Released in March 2025**
2025-03-05 | Toast's Comic Collection
Title: E: The Last Slice #11
*A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.*
https://i.nostr.build/aar20oHAAKmZOovD.png
2025-03-12 | Concept Art
Title: Original Bread and Toast
*This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.*
https://i.nostr.build/yqkmBuTiH8AKbCzI.png
2025-03-19 | Bitcoin Art
Title: Bitcoin/Bread
Block Height: 888566
*Two things that just go together.*
https://i.nostr.build/MDPkzOPVEaOJVTFE.png
Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com!
**So long, March!**
***Bread, Toast, and End-Piece***
#BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️
***List of nPubs Mentioned:***
The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g
dan 🍞:
npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
-

@ 17538dc2:71ed77c4
2025-04-02 16:04:59
The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised.
### macOS Sequoia 15.4
Released March 31, 2025
Accessibility
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance
AccountPolicy
Available for: macOS Sequoia
Impact: A malicious app may be able to gain root privileges
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24234: an anonymous researcher
AirDrop
Available for: macOS Sequoia
Impact: An app may be able to read arbitrary file metadata
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24097: Ron Masas of BREAKPOINT.SH
App Store
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24276: an anonymous researcher
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24272: Mickey Jin (@patch1t)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A downgrade issue was addressed with additional code-signing restrictions.
CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: A malicious app may be able to read or write to protected files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos.
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A privacy issue was addressed by removing the vulnerable code.
CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk)
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted file may lead to arbitrary code execution
Description: The issue was addressed with improved memory handling.
CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Authentication Services
Available for: macOS Sequoia
Impact: Password autofill may fill in passwords after failing authentication
Description: This issue was addressed through improved state management.
CVE-2025-30430: Dominik Rath
Authentication Services
Available for: macOS Sequoia
Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix
Description: The issue was addressed with improved input validation.
CVE-2025-24180: Martin Kreichgauer of Google Chrome
Authentication Services
Available for: macOS Sequoia
Impact: A malicious app may be able to access a user's saved passwords
Description: This issue was addressed by adding a delay between verification code attempts.
CVE-2025-24245: Ian Mckay (@iann0036)
Automator
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed by removing vulnerable code and adding additional checks.
CVE-2025-30460: an anonymous researcher
BiometricKit
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24237: Yutong Xiu
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2025-30429: Denis Tokarev (@illusionofcha0s)
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with improved checks.
CVE-2025-24212: Denis Tokarev (@illusionofcha0s)
CloudKit
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-24215: Kirin (@Pwnrin)
CoreAudio
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: The issue was addressed with improved checks.
CVE-2025-24163: Google Threat Analysis Group
CoreAudio
Available for: macOS Sequoia
Impact: Playing a malicious audio file may lead to an unexpected app termination
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: This issue was addressed with improved memory handling.
CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia Playback
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: A path handling issue was addressed with improved validation.
CVE-2025-30454: pattern-f (@pattern_F_)
CoreServices
Description: This issue was addressed through improved state management.
CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
CoreText
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Crash Reporter
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher
curl
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-9681
Disk Images
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A file access issue was addressed with improved input validation.
CVE-2025-24255: an anonymous researcher
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-30456: Gergely Kalman (@gergely_kalman)
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24267: an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova
dyld
Available for: macOS Sequoia
Impact: Apps that appear to use App Sandbox may be able to launch without restrictions
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com)
FaceTime
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky)
FeedbackLogger
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved data protection.
CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf)
Focus
Available for: macOS Sequoia
Impact: An attacker with physical access to a locked device may be able to view sensitive user information
Description: The issue was addressed with improved checks.
CVE-2025-30439: Andr.Ess
Focus
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24283: Kirin (@Pwnrin)
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards.
CVE-2025-30461: an anonymous researcher
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was resolved by sanitizing logging
CVE-2025-30447: LFY@secsys from Fudan University
Foundation
Available for: macOS Sequoia
Impact: An app may be able to cause a denial-of-service
Description: An uncontrolled format string issue was addressed with improved input validation.
CVE-2025-24199: Manuel Fernandez (Stackhopper Security)
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2025-30464: ABC Research s.r.o.
CVE-2025-24273: Wang Yu of Cyberserval
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to disclose kernel memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike
Handoff
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-30463: mzzzz__
ImageIO
Available for: macOS Sequoia
Impact: Parsing an image may lead to disclosure of user information
Description: A logic error was addressed with improved error handling.
CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative
Installer
Available for: macOS Sequoia
Impact: An app may be able to check the existence of an arbitrary path on the file system
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Installer
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data
Description: A logic issue was addressed with improved checks.
CVE-2025-24229: an anonymous researcher
IOGPUFamily
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or write kernel memory
Description: An out-of-bounds write issue was addressed with improved input validation.
CVE-2025-24257: Wang Yu of Cyberserval
IOMobileFrameBuffer
Available for: macOS Sequoia
Impact: An app may be able to corrupt coprocessor memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security
Kerberos Helper
Available for: macOS Sequoia
Impact: A remote attacker may be able to cause unexpected app termination or heap corruption
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2025-24235: Dave G.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: The issue was addressed with improved checks.
CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24203: Ian Beer of Google Project Zero
Kernel
Available for: macOS Sequoia
Impact: An attacker with user privileges may be able to read kernel memory
Description: A type confusion issue was addressed with improved memory handling.
CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL
LaunchServices
Available for: macOS Sequoia
Impact: A malicious JAR file may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of executable types.
CVE-2025-24148: Kenneth Chew
libarchive
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-48958
Libinfo
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: An integer overflow was addressed with improved input validation.
CVE-2025-24195: Paweł Płatek (Trail of Bits)
libnetcore
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: A logic issue was addressed with improved checks.
CVE-2025-24194: an anonymous researcher
libxml2
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2025-27113
CVE-2024-56171
libxpc
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed through improved state management.
CVE-2025-24178: an anonymous researcher
libxpc
Available for: macOS Sequoia
Impact: An app may be able to delete files for which it does not have permission
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc)
libxpc
Available for: macOS Sequoia
Impact: An app may be able to gain elevated privileges
Description: A logic issue was addressed with improved checks.
CVE-2025-24238: an anonymous researcher
Mail
Available for: macOS Sequoia
Impact: "Block All Remote Content" may not apply for all mail previews
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24172: an anonymous researcher
manpages
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30450: Pwn2car
Maps
Available for: macOS Sequoia
Impact: An app may be able to read sensitive location information
Description: A path handling issue was addressed with improved logic.
CVE-2025-30470: LFY@secsys from Fudan University
NetworkExtension
Available for: macOS Sequoia
Impact: An app may be able to enumerate a user's installed apps
Description: This issue was addressed with additional entitlement checks.
CVE-2025-30426: Jimmy
Notes
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24262: LFY@secsys from Fudan University
NSDocument
Available for: macOS Sequoia
Impact: A malicious app may be able to access arbitrary files
Description: This issue was addressed through improved state management.
CVE-2025-24232: an anonymous researcher
OpenSSH
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An injection issue was addressed with improved validation.
CVE-2025-24246: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24261: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved checks.
CVE-2025-24164: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: A malicious app with root privileges may be able to modify the contents of system files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0)
Parental Controls
Available for: macOS Sequoia
Impact: An app may be able to retrieve Safari bookmarks without an entitlement check
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24259: Noah Gregory (wts.dev)
Photos Storage
Available for: macOS Sequoia
Impact: Deleting a conversation in Messages may expose user contact information in system logging
Description: A logging issue was addressed with improved data redaction.
CVE-2025-30424: an anonymous researcher
Power Services
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24173: Mickey Jin (@patch1t)
Python
Available for: macOS Sequoia
Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2023-27043
RPAC
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved validation of environment variables.
CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to user interface spoofing
Description: The issue was addressed with improved UI.
CVE-2025-24113: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to address bar spoofing
Description: The issue was addressed with improved checks.
CVE-2025-30467: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: A website may be able to access sensor information without user consent
Description: The issue was addressed with improved checks.
CVE-2025-31192: Jaydev Ahire
Safari
Available for: macOS Sequoia
Impact: A download's origin may be incorrectly associated
Description: This issue was addressed through improved state management.
CVE-2025-24167: Syarif Muhammad Sajjad
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access removable volumes without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit)
Sandbox
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: The issue was addressed with improved checks.
CVE-2025-30452: an anonymous researcher
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24181: Arsenii Kostromin (0x3c3e)
SceneKit
Available for: macOS Sequoia
Impact: An app may be able to read files outside of its sandbox
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30458: Mickey Jin (@patch1t)
Security
Available for: macOS Sequoia
Impact: A remote user may be able to cause a denial-of-service
Description: A validation issue was addressed with improved logic.
CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington
Security
Available for: macOS Sequoia
Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data
Description: This issue was addressed with improved access restrictions.
CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog)
Share Sheet
Available for: macOS Sequoia
Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started
Description: This issue was addressed with improved access restrictions.
CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: A permissions issue was addressed with improved validation.
CVE-2025-30465: an anonymous researcher
Shortcuts
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24280: Kirin (@Pwnrin)
Shortcuts
Available for: macOS Sequoia
Impact: A Shortcut may run with admin privileges without authentication
Description: An authentication issue was addressed with improved state management.
CVE-2025-31194: Dolf Hoegaerts
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: This issue was addressed with improved access restrictions.
CVE-2025-30433: Andrew James Gonzalez
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk)
Siri
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-24217: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A privacy issue was addressed by not logging contents of text fields.
CVE-2025-24214: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to enumerate devices that have signed into the user's Apple Account
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L
Siri
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An authorization issue was addressed with improved state management.
CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Siri
Available for: macOS Sequoia
Impact: An attacker with physical access may be able to use Siri to access sensitive user data
Description: This issue was addressed by restricting options offered on a locked device.
CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security
SMB
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: The issue was addressed with improved memory handling.
CVE-2025-24269: Alex Radocea of Supernetworks
SMB
Available for: macOS Sequoia
Impact: Mounting a maliciously crafted SMB network share may lead to system termination
Description: A race condition was addressed with improved locking.
CVE-2025-30444: Dave G.
SMB
Available for: macOS Sequoia
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL
smbx
Available for: macOS Sequoia
Impact: An attacker in a privileged position may be able to perform a denial-of-service
Description: The issue was addressed with improved memory handling.
CVE-2025-24260: zbleet of QI-ANXIN TianGong Team
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Software Update
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24254: Arsenii Kostromin (0x3c3e)
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
StickerKit
Available for: macOS Sequoia
Impact: An app may be able to observe unprotected user data
Description: A privacy issue was addressed by moving sensitive data to a protected location.
CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania
Storage Management
Available for: macOS Sequoia
Impact: An app may be able to enable iCloud storage features without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A race condition was addressed with additional validation.
CVE-2025-24240: Mickey Jin (@patch1t)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to bypass Privacy preferences
Description: A race condition was addressed with additional validation.
CVE-2025-31188: Mickey Jin (@patch1t)
Summarization Services
Available for: macOS Sequoia
Impact: An app may be able to access information about a user's contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk)
System Settings
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24278: Zhongquan Li (@Guluisacat)
System Settings
Available for: macOS Sequoia
Impact: An app with root privileges may be able to access private information
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
SystemMigration
Available for: macOS Sequoia
Impact: A malicious app may be able to create symlinks to protected regions of the disk
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30457: Mickey Jin (@patch1t)
Voice Control
Available for: macOS Sequoia
Impact: An app may be able to access contacts
Description: This issue was addressed with improved file handling.
CVE-2025-24279: Mickey Jin (@patch1t)
Web Extensions
Available for: macOS Sequoia
Impact: An app may gain unauthorized access to Local Network
Description: This issue was addressed with improved permissions checking.
CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven
Web Extensions
Available for: macOS Sequoia
Impact: Visiting a website may leak sensitive data
Description: A script imports issue was addressed with improved isolation.
CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: The issue was addressed with improved memory handling.
WebKit Bugzilla: 285892
CVE-2025-24264: Gary Kwong, and an anonymous researcher
WebKit Bugzilla: 284055
CVE-2025-24216: Paul Bakker of ParagonERP
WebKit
Available for: macOS Sequoia
Impact: A type confusion issue could lead to memory corruption
Description: This issue was addressed with improved handling of floats.
WebKit Bugzilla: 286694
CVE-2025-24213: Google V8 Security Team
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected process crash
Description: A buffer overflow issue was addressed with improved memory handling.
WebKit Bugzilla: 286462
CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: A use-after-free issue was addressed with improved memory management.
WebKit Bugzilla: 285643
CVE-2025-30427: rheza (@ginggilBesel)
WebKit
Available for: macOS Sequoia
Impact: A malicious website may be able to track users in Safari private browsing mode
Description: This issue was addressed through improved state management.
WebKit Bugzilla: 286580
CVE-2025-30425: an anonymous researcher
WindowServer
Available for: macOS Sequoia
Impact: An attacker may be able to cause unexpected app termination
Description: A type confusion issue was addressed with improved checks.
CVE-2025-24247: PixiePoint Security
WindowServer
Available for: macOS Sequoia
Impact: An app may be able to trick a user into copying sensitive data to the pasteboard
Description: A configuration issue was addressed with additional restrictions.
CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH)
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24266: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2025-24265: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24157: an anonymous researcher
-

@ 8d34bd24:414be32b
2025-04-02 14:13:03
I was reading this passage last night:
> …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine}
Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself.
This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation.
> And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28)
When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect:
> And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine}
When one particular man said that he would follow Jesus anywhere, Jesus responded this way.
> As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine}
Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort.
> “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine}
Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect.
> “**For my thoughts are not your thoughts,\
> neither are your ways my ways**,”\
> declares the Lord.
>
> “As the heavens are higher than the earth,\
> so are **my ways higher than your ways**\
> and my thoughts than your thoughts.
>
> As the rain and the snow\
> come down from heaven,\
> and do not return to it\
> without watering the earth\
> and making it bud and flourish,\
> so that it yields seed for the sower and bread for the eater,\
> so is **my word that goes out from my mouth:\
> It will not return to me empty,\
> but will accomplish what I desire\
> and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine}
God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us.
> Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine}
In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word.
> They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine}
Peter specifically warns believers to expect trials and hardship.
> Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And,
>
> “If it is hard for the righteous to be saved,\
> what will become of the ungodly and the sinner?”
>
> So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine}
Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship.
> …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine}
No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good.
> Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written,
>
> “For Your sake we are being put to death all day long;\
> We were considered as sheep to be slaughtered.”
> ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine}
I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be.
First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard.
Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion.
In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before.
When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good.
We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness.
> Oh, the depth of the riches of the wisdom and knowledge of God!\
> How unsearchable his judgments,\
> and his paths beyond tracing out!\
> “Who has known the mind of the Lord?\
> Or who has been his counselor?”\
> “Who has ever given to God,\
> that God should repay them?”\
> For from him and through him and for him are all things.\
> To him be the glory forever! Amen. (Romans 11:33-36)
Trust Jesus
 @ 68c90cf3:99458f5c
2025-04-04 16:06:10I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs. YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each. 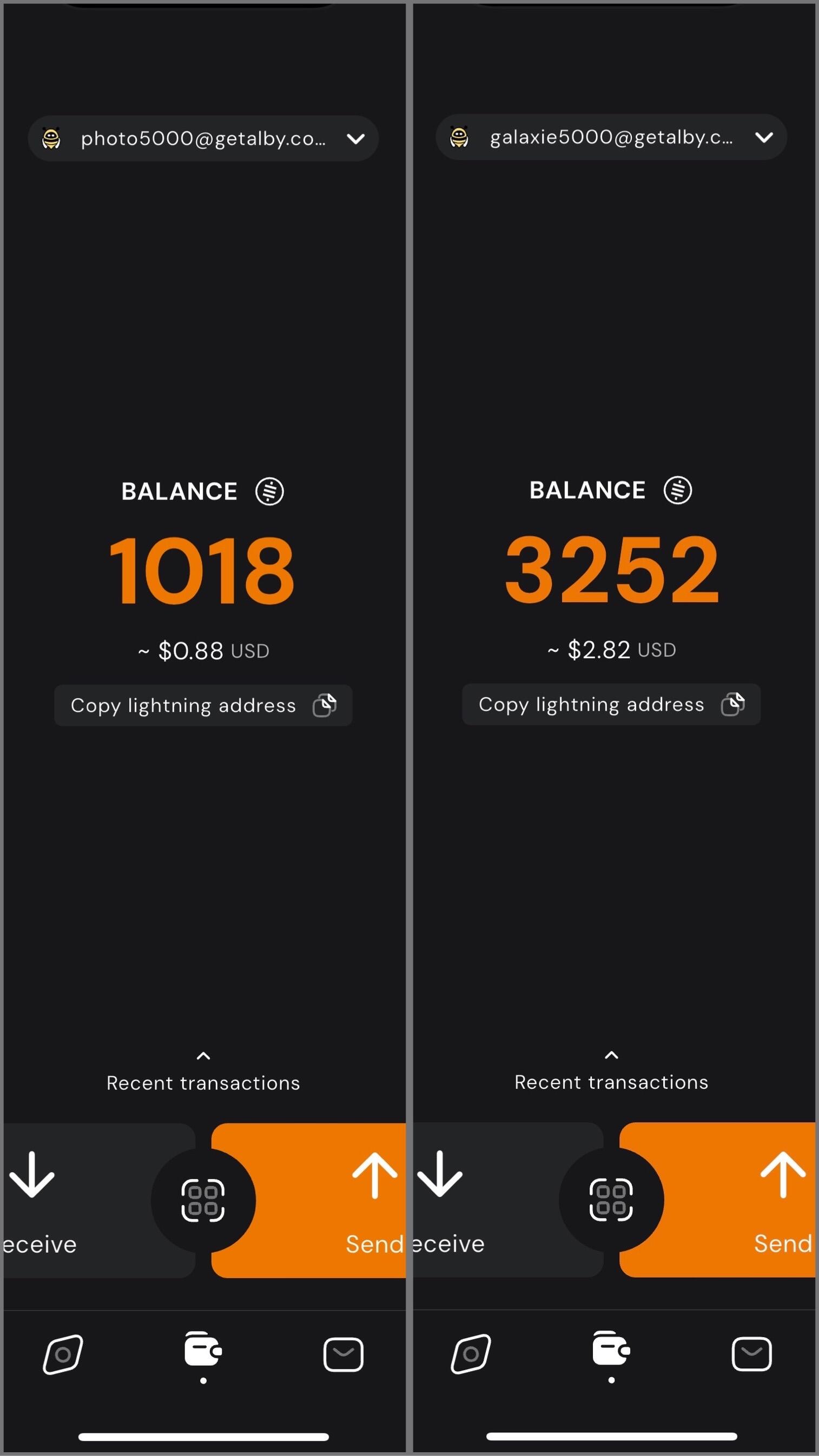 In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions. 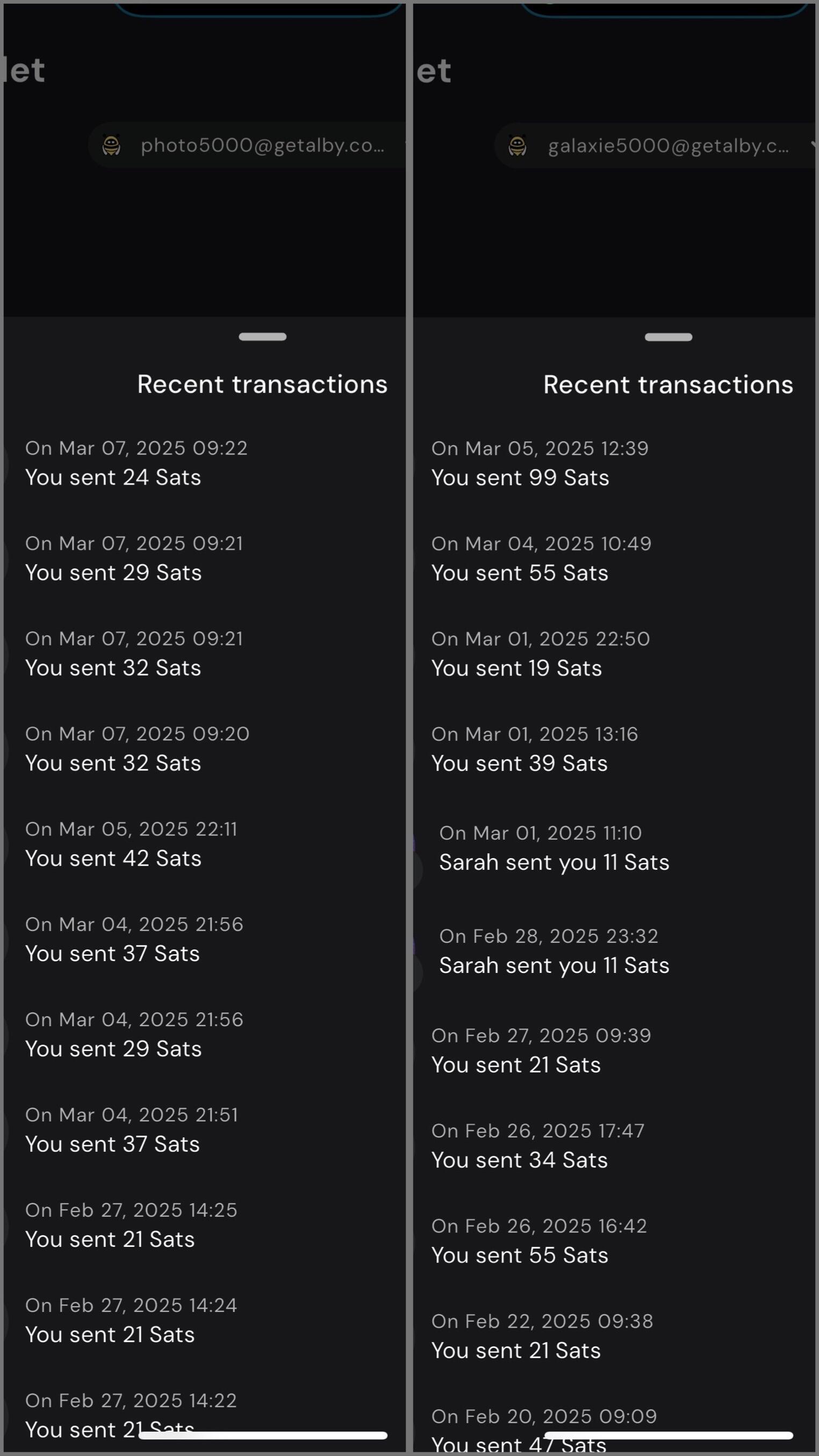 Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne. #YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr
@ 68c90cf3:99458f5c
2025-04-04 16:06:10I have two Nostr profiles I use for different subject matter, and I wanted a way to manage and track zaps for each. Using Alby Hub I created two isolated Lightning wallets each associated with one of the profile’s nsecs. YakiHonne made it easy to connect the associated wallets with the profiles. The user interface is well designed to show balances for each. 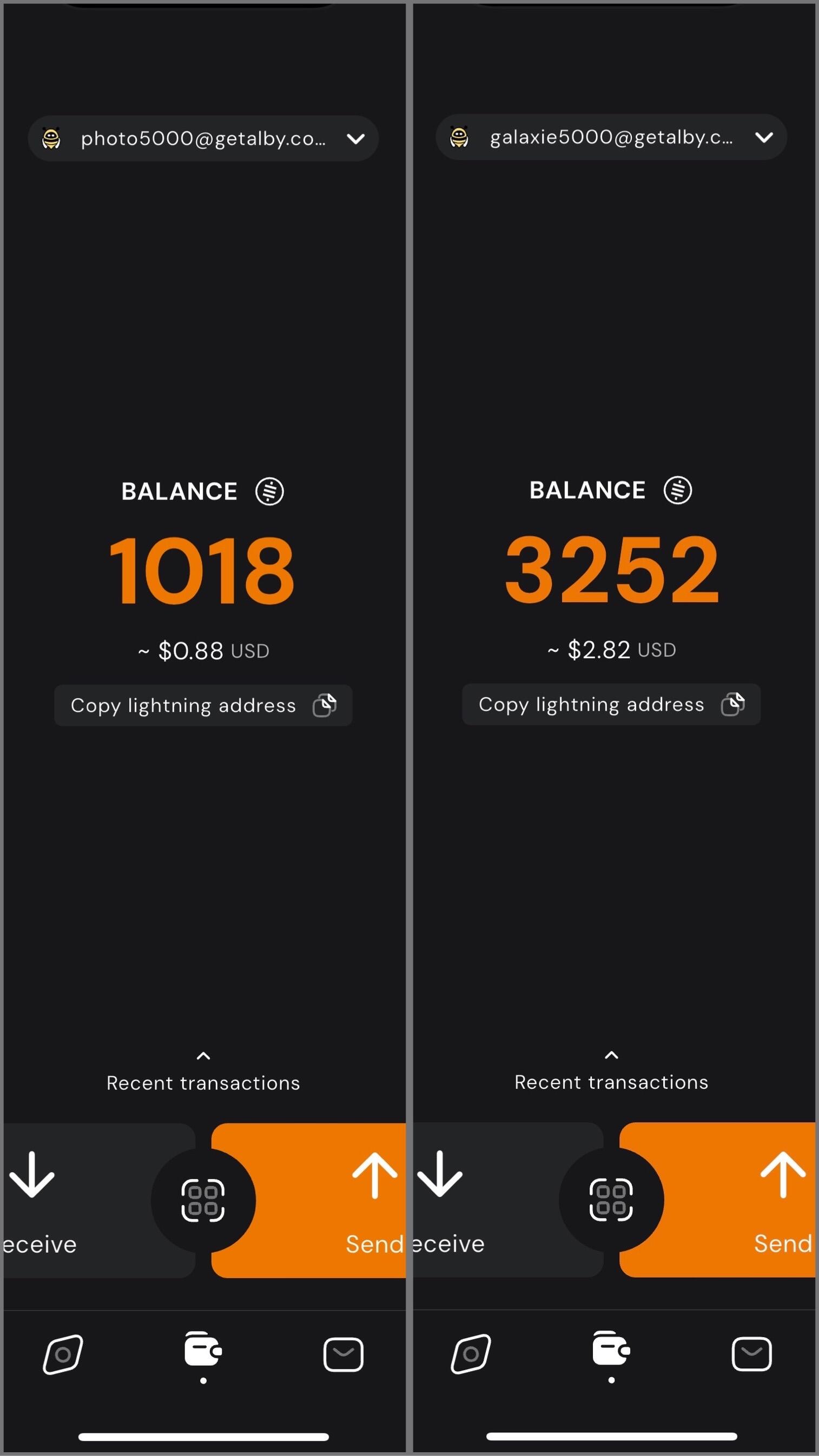 In my case, I have one profile for photography related content, and the other for Bitcoin, Nostr, and technology related content. I can easily switch between the two, sending and receiving zaps on each while staying up to date on balances and viewing transactions. 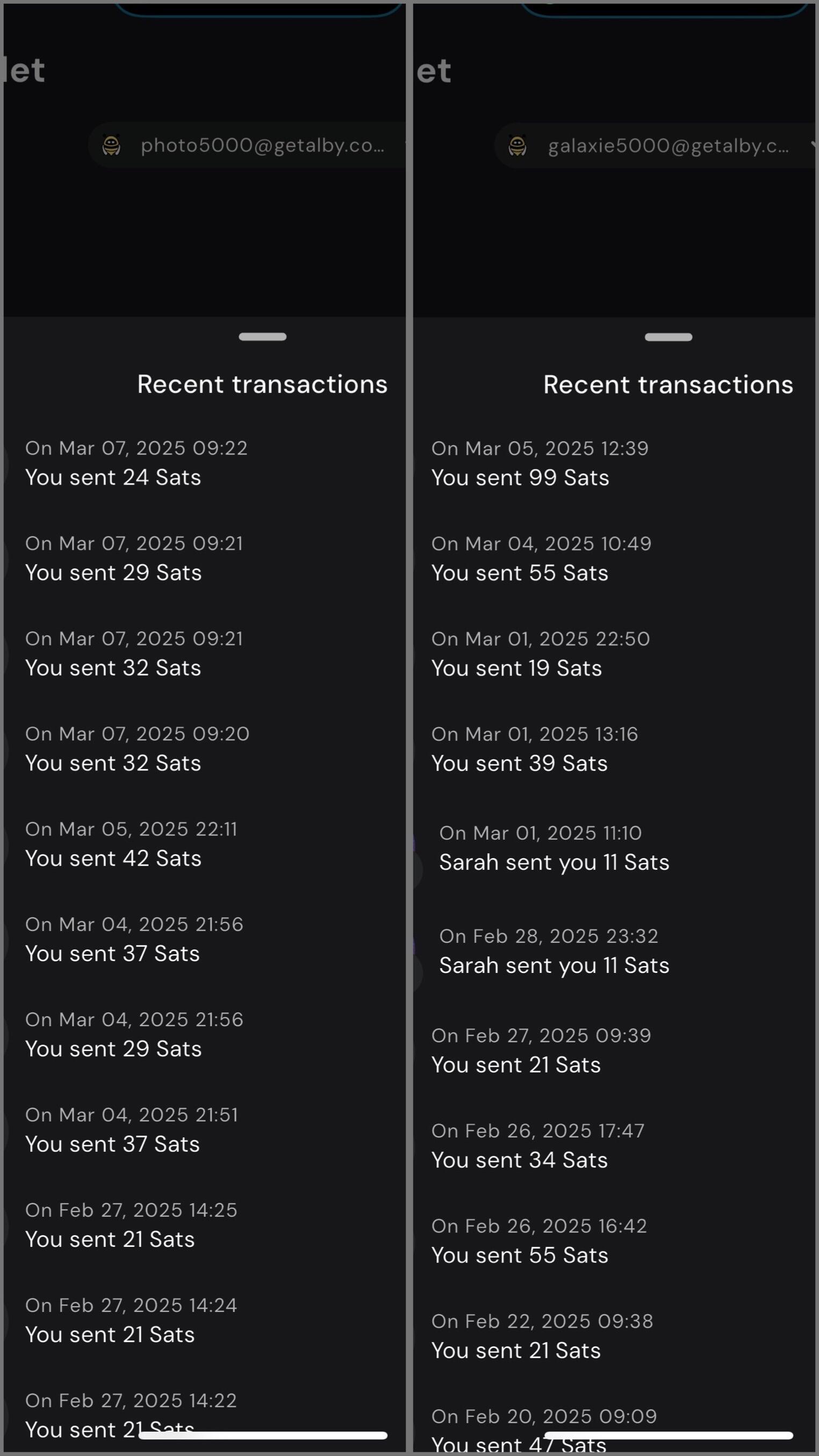 Using my self-hosted Alby Hub I can manage Lightning channels and wallets while sending and receiving zaps for multiple profiles with YakiHonne. #YakiHonne #AlbyHub #Lightning #Bitcoin #Nostr @ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2>
@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2> @ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p>
@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p> @ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
@ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/ @ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit. @ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay. @ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future! @ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007 @ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
@ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.** @ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly
@ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly @ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
@ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure. @ 57d1a264:69f1fee1
2025-04-05 06:58:25**Summary** We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment. **Responsibilities** - Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity. - Develop digital assets for marketing, social media, website, and app. - Work within brand guidelines while exploring ways to evolve and strengthen our visual style. **Requirements** - 2+ years of experience in graphic design, with a strong focus on illustration. - Ability to help define and develop a cohesive visual style for the brand. - Proficiency in Adobe products. - Experience with Figma is a plus. - Strong organizational skills—your layers and files should be neatly labeled. - Clear communication and collaboration skills to work effectively with the team. - Located in LATAM Please attach a link to your portfolio to showcase your work when applying. [APPLY HERE](https://jan3.com/contact/) originally posted at https://stacker.news/items/935007
@ 57d1a264:69f1fee1
2025-04-05 06:58:25**Summary** We are looking for a Visual Designer with a strong focus on illustration and animation to help shape and refine our brand’s visual identity. You will create compelling assets for digital and print, including marketing materials, social media content, website illustrations, and motion graphics. Working closely with our marketing and product teams, you will play a key role in developing a consistent and recognizable visual style through thoughtful use of illustration, color, patterns, and animation. This role requires creativity, adaptability, and the ability to deliver high-quality work in a fast-paced, remote environment. **Responsibilities** - Create high-quality, iconic illustrations, branding assets, and motion graphics that contribute to and refine our visual identity. - Develop digital assets for marketing, social media, website, and app. - Work within brand guidelines while exploring ways to evolve and strengthen our visual style. **Requirements** - 2+ years of experience in graphic design, with a strong focus on illustration. - Ability to help define and develop a cohesive visual style for the brand. - Proficiency in Adobe products. - Experience with Figma is a plus. - Strong organizational skills—your layers and files should be neatly labeled. - Clear communication and collaboration skills to work effectively with the team. - Located in LATAM Please attach a link to your portfolio to showcase your work when applying. [APPLY HERE](https://jan3.com/contact/) originally posted at https://stacker.news/items/935007 @ 57d1a264:69f1fee1
2025-04-05 06:47:55**Location:** Remote (Austria) **Area:** Graphics and communication design **Pay:** 37,500 € to 50,000 € / year Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin. 👋 About the role As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas. **tasks** - Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials - Creation of individual content (posts, stories, banners, ads) for social media - Planning and development of campaigns to strengthen the brand presence - Further development of the existing corporate design support in the area of content management (website, blog) **qualification** - Completed training or studies in graphic design - At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management - Safe use of design tools such as Figma, Adobe Creative Suite - Experience in creating social media content and maintaining channels - Creativity, good communication skills and team spirit - Very good knowledge of German and English - Knowledge of Bitcoin is desirable **Benefits** - Offsites with the team in exciting places - Flexible working hours in a company that relies on remote work - Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation - Buy Bitcoin without fees! 21 Premium! - Gross annual salary & potential share options for outstanding performance / bonus payments **📝 Interview process** _How do I apply?_ Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect. By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application! _⁇ 京 Resume Review_ Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...) _📞 Exploratory call_ We discuss what appeals to you about this role and ask you a few questions about your previous experiences _👬 On-Site Deep Dive_ During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role. _👍 Time for a decision!_ [APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner) originally posted at https://stacker.news/items/935004
@ 57d1a264:69f1fee1
2025-04-05 06:47:55**Location:** Remote (Austria) **Area:** Graphics and communication design **Pay:** 37,500 € to 50,000 € / year Hi! We are @21bitcoinApp - a Bitcoin-Only Investment app that aims to accelerate the transition to an economy driven by Bitcoin. 👋 About the role As a passionate graphic designer, you support our marketing team in creating graphics and designs for print documents, online advertising material and our website. You also support us in the area of social media and content management and can also contribute your skills in these subject areas. **tasks** - Design and implementation of creative and congruent designs for social media channels, websites, templates and marketing materials - Creation of individual content (posts, stories, banners, ads) for social media - Planning and development of campaigns to strengthen the brand presence - Further development of the existing corporate design support in the area of content management (website, blog) **qualification** - Completed training or studies in graphic design - At least 2 years of experience in graphic design, preferably with experience in the areas of social media and content management - Safe use of design tools such as Figma, Adobe Creative Suite - Experience in creating social media content and maintaining channels - Creativity, good communication skills and team spirit - Very good knowledge of German and English - Knowledge of Bitcoin is desirable **Benefits** - Offsites with the team in exciting places - Flexible working hours in a company that relies on remote work - Help shape the future - to make the world a better place by helping to speed up Bitcoin's adaptation - Buy Bitcoin without fees! 21 Premium! - Gross annual salary & potential share options for outstanding performance / bonus payments **📝 Interview process** _How do I apply?_ Please send us an email and add some information about you, your resume, examples of previous projects and a few key points about why you are interested in participating in 21bitcoin and what you expect. By the way: CVs are important but don't forget to include your favorite Bitcoin meme in the application! _⁇ 京 Resume Review_ Portfolio of Work: Add a link to your portfolio / previous work or resume that we can review (LinkedIn, Github, Twitter, ...) _📞 Exploratory call_ We discuss what appeals to you about this role and ask you a few questions about your previous experiences _👬 On-Site Deep Dive_ During the deep dive session, we use a case study or extensive interview to discuss the specific skills required for the role. _👍 Time for a decision!_ [APPLY HERE](https://join.com/companies/21bitcoin/13877001-grafikdesigner) originally posted at https://stacker.news/items/935004 @ 57d1a264:69f1fee1
2025-04-05 06:35:58We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals. **Key Responsibilities:** - Design and improve the @Bipa app experience, focusing on usability and measurable business impact. - Apply data-driven design, making decisions based on user research, metrics, and testing. - Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product. - Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy. - Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations. - Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business. - Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app. **Qualifications:** - Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps. - Solid understanding of user-centered design (UCD) principles and usability heuristics. - Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis. - Ability to work with both quantitative and qualitative data to guide design decisions. - Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement). - Proficiency in design tools like Figma (or similar). - Experience working with design systems and design tokens to ensure consistency. - Comfortable working in an agile, fast-paced, and iterative environment. - Strong communication skills and the ability to advocate for design decisions backed by research and data. **Benefits:** 🏥 Health Insurance 💉 Dental Plan 🍽️ Meal Allowance (CAJU card) 💻 Home Office Stipend 📈 Stock Options from Day One [APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer) originally posted at https://stacker.news/items/935003
@ 57d1a264:69f1fee1
2025-04-05 06:35:58We’re looking for a Product Designer to join our team and take the lead in enhancing the experience of our mobile app. You’ll play a key role in evolving the app’s interface and interactions, ensuring that our solutions are intuitive, efficient, and aligned with both user needs and business goals. **Key Responsibilities:** - Design and improve the @Bipa app experience, focusing on usability and measurable business impact. - Apply data-driven design, making decisions based on user research, metrics, and testing. - Lead and participate in usability tests and discovery processes to validate hypotheses and continuously improve the product. - Collaborate closely with Product Managers, developers, and other stakeholders to align design with product strategy. - Create wireframes, high-fidelity prototypes, and visual interfaces for new features and app optimizations. - Monitor the performance of delivered solutions, ensuring meaningful improvements for users and the business. - Contribute to the evolution and maintenance of our design system, ensuring consistency and scalability across the app. **Qualifications:** - Previous experience as a Product Designer or UX/UI Designer, with a strong focus on mobile apps. - Solid understanding of user-centered design (UCD) principles and usability heuristics. - Hands-on experience with user research methods, including usability testing, interviews, and behavior analysis. - Ability to work with both quantitative and qualitative data to guide design decisions. - Familiarity with product metrics and how design impacts business outcomes (e.g. conversion, retention, engagement). - Proficiency in design tools like Figma (or similar). - Experience working with design systems and design tokens to ensure consistency. - Comfortable working in an agile, fast-paced, and iterative environment. - Strong communication skills and the ability to advocate for design decisions backed by research and data. **Benefits:** 🏥 Health Insurance 💉 Dental Plan 🍽️ Meal Allowance (CAJU card) 💻 Home Office Stipend 📈 Stock Options from Day One [APPLY TO THIS JOB](https://bipa.inhire.app/vagas/14e45e99-2f7a-4a91-8f81-22393a3b7285/product-designer) originally posted at https://stacker.news/items/935003 @ 57d1a264:69f1fee1
2025-04-05 06:28:16### ⚡️ About Us @AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY. ### ⚡️ The Role Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision. ### ⚡️ Responsibilities Produce 30 short videos on circular economies. Incorporate subtitles as needed. Submit videos on a deliverables basis. Participate in check-ins and communicate with the AB team and circular economy communities. ### ⚡️ What We Offer Free ticket to AB25. Networking with Bitcoiners and industry leaders. Letter of recommendation and LinkedIn endorsement upon completion. Mentorship and hands-on experience with a high-profile Bitcoin project. ### ⚡️ Skills & Qualifications Passion for Bitcoin and circular economies. Basic to intermediate video editing skills (no specific software required). Creative independence with feedback. Portfolio or work samples preferred. ### ⚡️ Time Commitment Flexible, project-based internship with check-ins and feedback rounds. ### ⚡️ How to Apply Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available). originally posted at https://stacker.news/items/935001
@ 57d1a264:69f1fee1
2025-04-05 06:28:16### ⚡️ About Us @AdoptingBTC is the leading Bitcoin-only conference in El Salvador. For our 5th edition, we’re looking for a passionate Video Creator intern to help showcase Bitcoin’s future as MONEY. ### ⚡️ The Role Create 30 short (3-minute or less) videos highlighting global circular economies, to be featured at AB25. We’ll provide all source material, direction, and inspiration—you’ll have full creative freedom, with feedback rounds to align with the conference’s vision. ### ⚡️ Responsibilities Produce 30 short videos on circular economies. Incorporate subtitles as needed. Submit videos on a deliverables basis. Participate in check-ins and communicate with the AB team and circular economy communities. ### ⚡️ What We Offer Free ticket to AB25. Networking with Bitcoiners and industry leaders. Letter of recommendation and LinkedIn endorsement upon completion. Mentorship and hands-on experience with a high-profile Bitcoin project. ### ⚡️ Skills & Qualifications Passion for Bitcoin and circular economies. Basic to intermediate video editing skills (no specific software required). Creative independence with feedback. Portfolio or work samples preferred. ### ⚡️ Time Commitment Flexible, project-based internship with check-ins and feedback rounds. ### ⚡️ How to Apply Email kiki@adoptingbitcoin.org with subject “Circular Economy Video Creator Submission - `{NAME OR NYM}`.” Include a brief background, your experience, why the project resonates with you, and a portfolio (if available). originally posted at https://stacker.news/items/935001 @ 592295cf:413a0db9
2025-04-05 07:26:23## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago # 1. ### Nostr's adoption thesis ### The less you define, the more you imply ### by Wouter Constant ## 2. ### Dutch Bitcoiner ### AntiHashedPodcast ### Writing Book about nostr 00:40 ## 3. ### What this presentation about ### A protocols design includes initself a thesis ### on protocol adoption, due to underlying assumptions 1:17 ## 4. ### Examples ### Governments/Academic: Pubhubs (Matrix) ### Bussiness: Bluesky ### Foss: Nostr 1:58 ## 5. ### What constitutes minimal viability? ### Pubhubs (Matrix): make is "safe" for user ### Bluesky: liability and monetization ### Foss: Simpel for developer 4:03 ## 6. ### The Point of Nostr ### Capture network effects through interoperability 4:43 ## 7. ## Three assumptions ### The direction is workable ### Method is workable ### Motivation and means are sufficient 5:27 ## 8. ## Assumption 1 ### The asymmetric cryptography paradigm is a good idea 6:16 ## 9. ### Nostr is a exponent of the key-pair paradigm. ### And Basicly just that. 6.52 ## 10. ### Keys suck ### Protect a secret that you are supposed use all the time. 7:37 ## 11. ## Assumption two ### The unaddressed things will be figured out within a 'meta-design consensus' 8:11 ## 12. ### Nostr's base protocol is not minimally viable for anything, except own development. 8:25 ## 13. ### Complexity leads to capture; ### i.e. free and open in the name, ### controlled in pratice 9:54 ## 14. ## Meta-design consensus ### Buildings things 'note centric' mantains interoperability. 11:51 ## 15. ## Assumption three ### the nightmare is scary; ### the cream is appealing. 12:41 ## 16. ### Get it minimally viable, ### for whatever target, ### such that it is not a waste of time. 13:23 ## 17. ## Summarize ### We are in a nightmare. ### Assume key/signature are the way out. ### Assume we can Maintain an open stardand while manifesting the dream. ### Assume we are motivated enought to bootstrap this to adulthood. 14:01 ## 18. ### We want this, ### we can do this, ### because we have to. 14:12 ## Thank you for contribuiting [Edit] Note for audio presentation nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
@ 592295cf:413a0db9
2025-04-05 07:26:23## [Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago # 1. ### Nostr's adoption thesis ### The less you define, the more you imply ### by Wouter Constant ## 2. ### Dutch Bitcoiner ### AntiHashedPodcast ### Writing Book about nostr 00:40 ## 3. ### What this presentation about ### A protocols design includes initself a thesis ### on protocol adoption, due to underlying assumptions 1:17 ## 4. ### Examples ### Governments/Academic: Pubhubs (Matrix) ### Bussiness: Bluesky ### Foss: Nostr 1:58 ## 5. ### What constitutes minimal viability? ### Pubhubs (Matrix): make is "safe" for user ### Bluesky: liability and monetization ### Foss: Simpel for developer 4:03 ## 6. ### The Point of Nostr ### Capture network effects through interoperability 4:43 ## 7. ## Three assumptions ### The direction is workable ### Method is workable ### Motivation and means are sufficient 5:27 ## 8. ## Assumption 1 ### The asymmetric cryptography paradigm is a good idea 6:16 ## 9. ### Nostr is a exponent of the key-pair paradigm. ### And Basicly just that. 6.52 ## 10. ### Keys suck ### Protect a secret that you are supposed use all the time. 7:37 ## 11. ## Assumption two ### The unaddressed things will be figured out within a 'meta-design consensus' 8:11 ## 12. ### Nostr's base protocol is not minimally viable for anything, except own development. 8:25 ## 13. ### Complexity leads to capture; ### i.e. free and open in the name, ### controlled in pratice 9:54 ## 14. ## Meta-design consensus ### Buildings things 'note centric' mantains interoperability. 11:51 ## 15. ## Assumption three ### the nightmare is scary; ### the cream is appealing. 12:41 ## 16. ### Get it minimally viable, ### for whatever target, ### such that it is not a waste of time. 13:23 ## 17. ## Summarize ### We are in a nightmare. ### Assume key/signature are the way out. ### Assume we can Maintain an open stardand while manifesting the dream. ### Assume we are motivated enought to bootstrap this to adulthood. 14:01 ## 18. ### We want this, ### we can do this, ### because we have to. 14:12 ## Thank you for contribuiting [Edit] Note for audio presentation nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke @ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 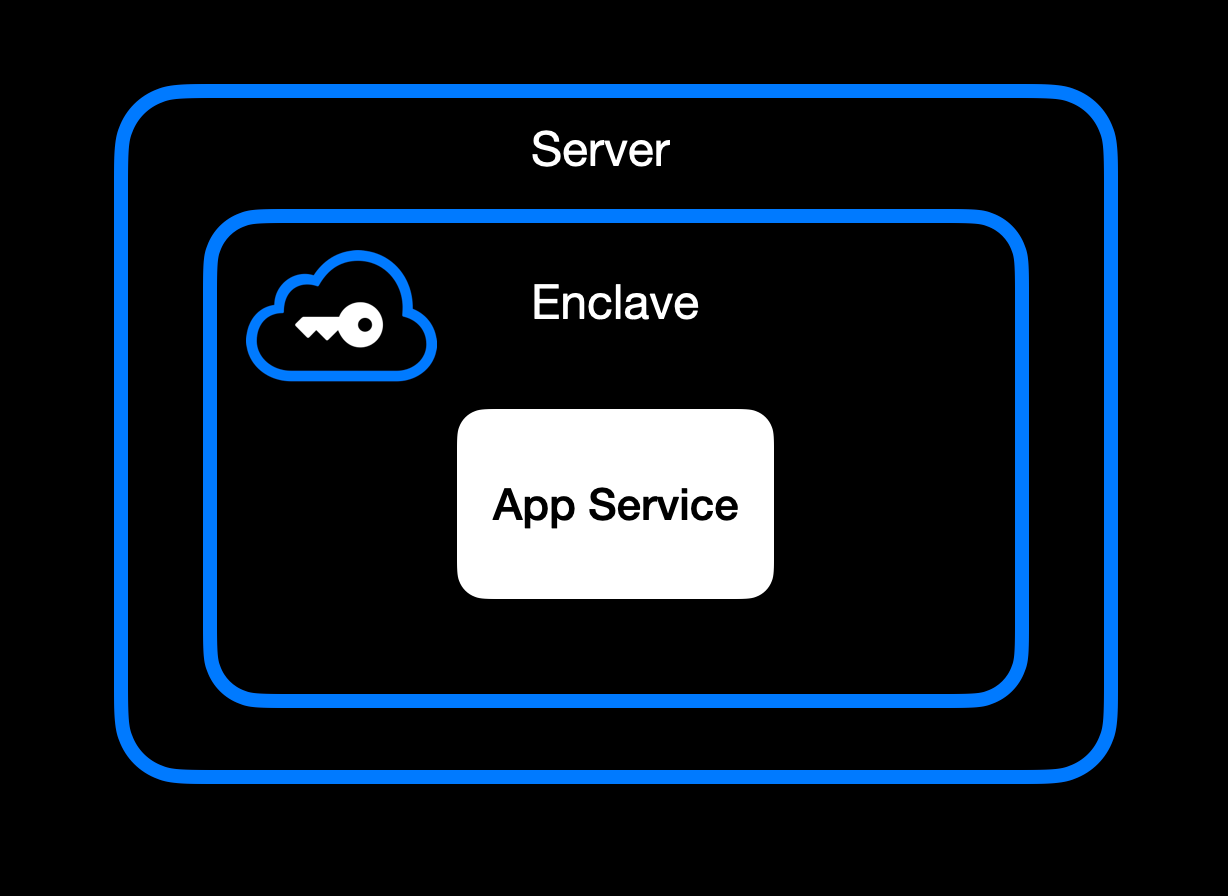App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 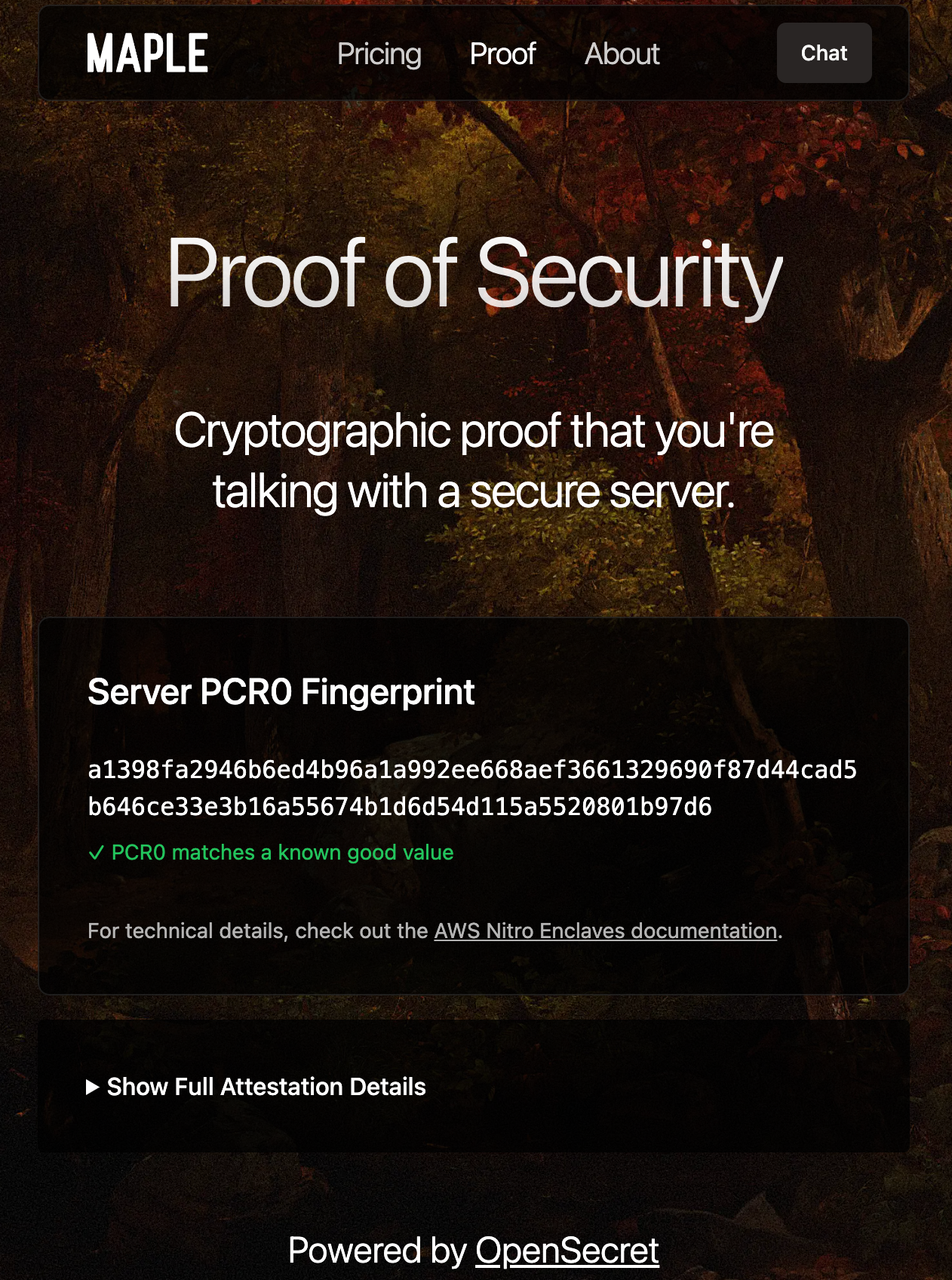Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 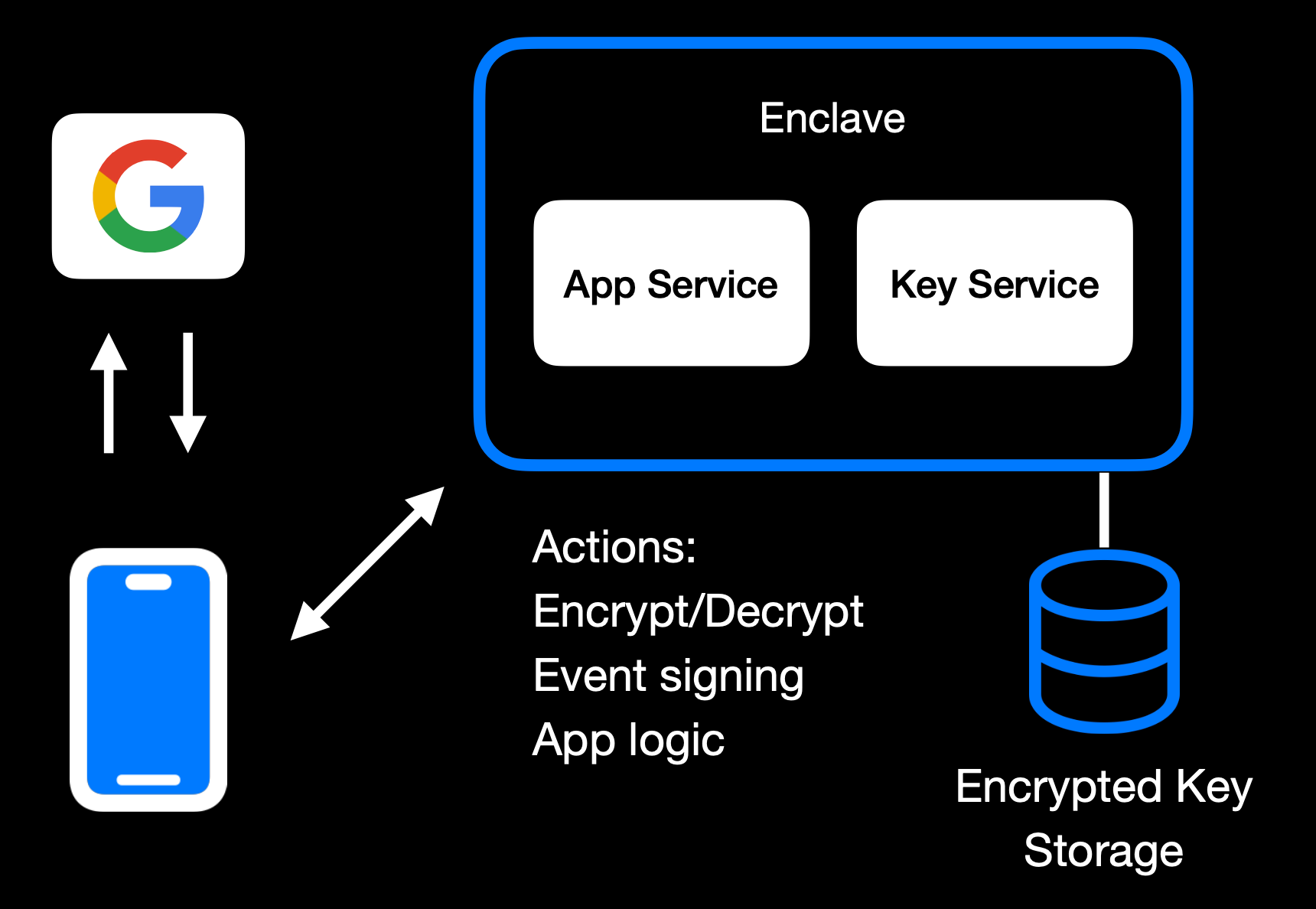Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 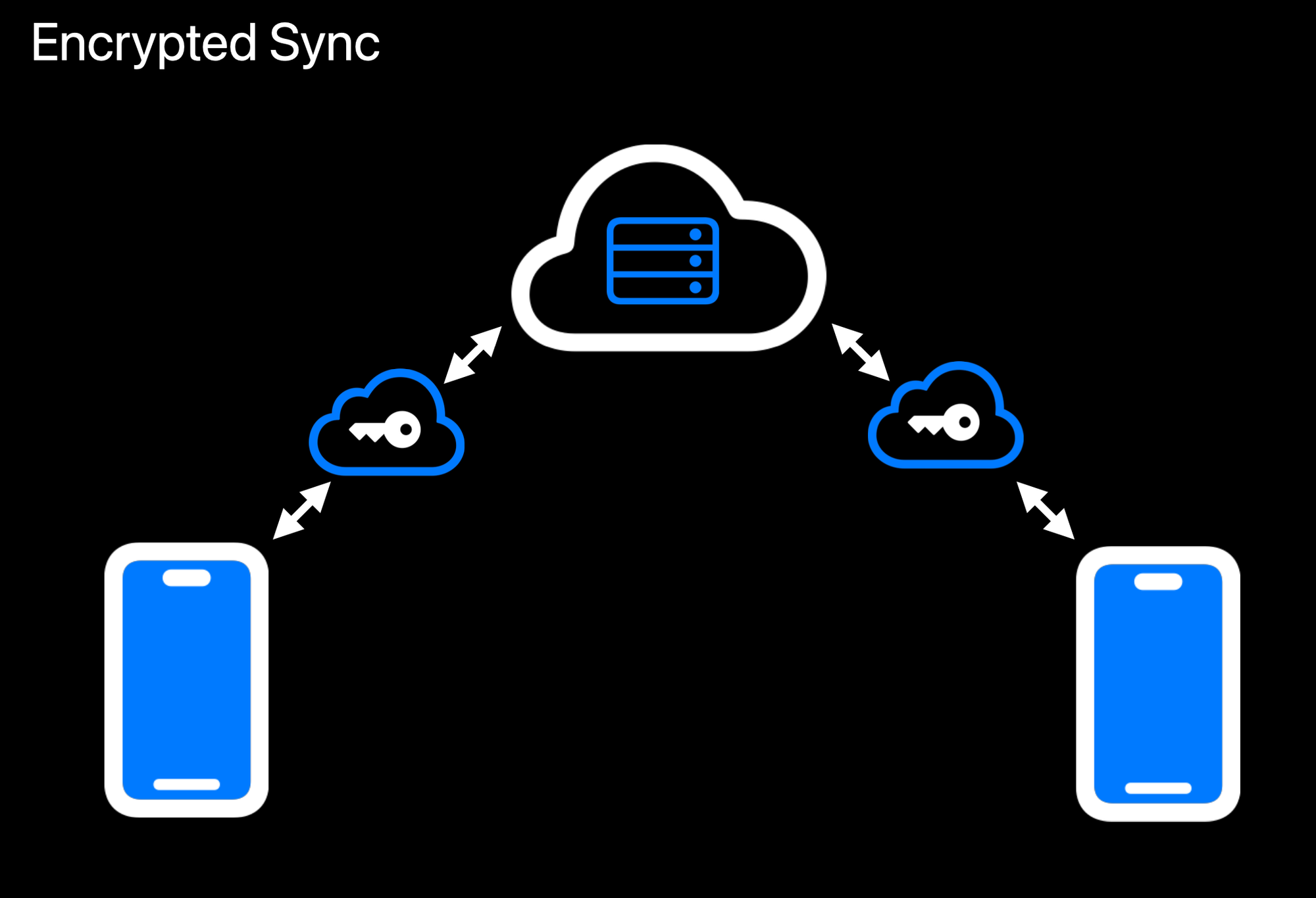Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 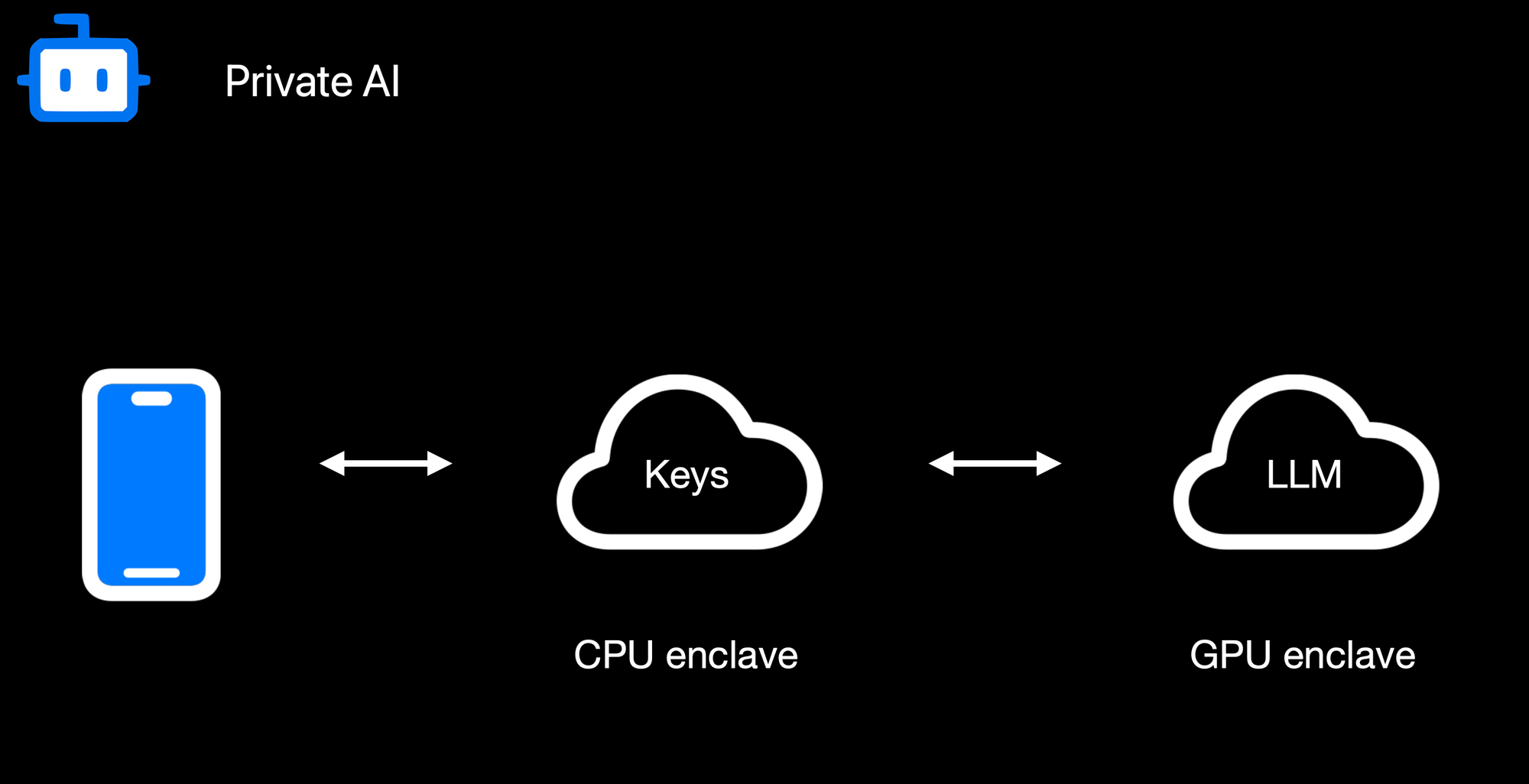Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 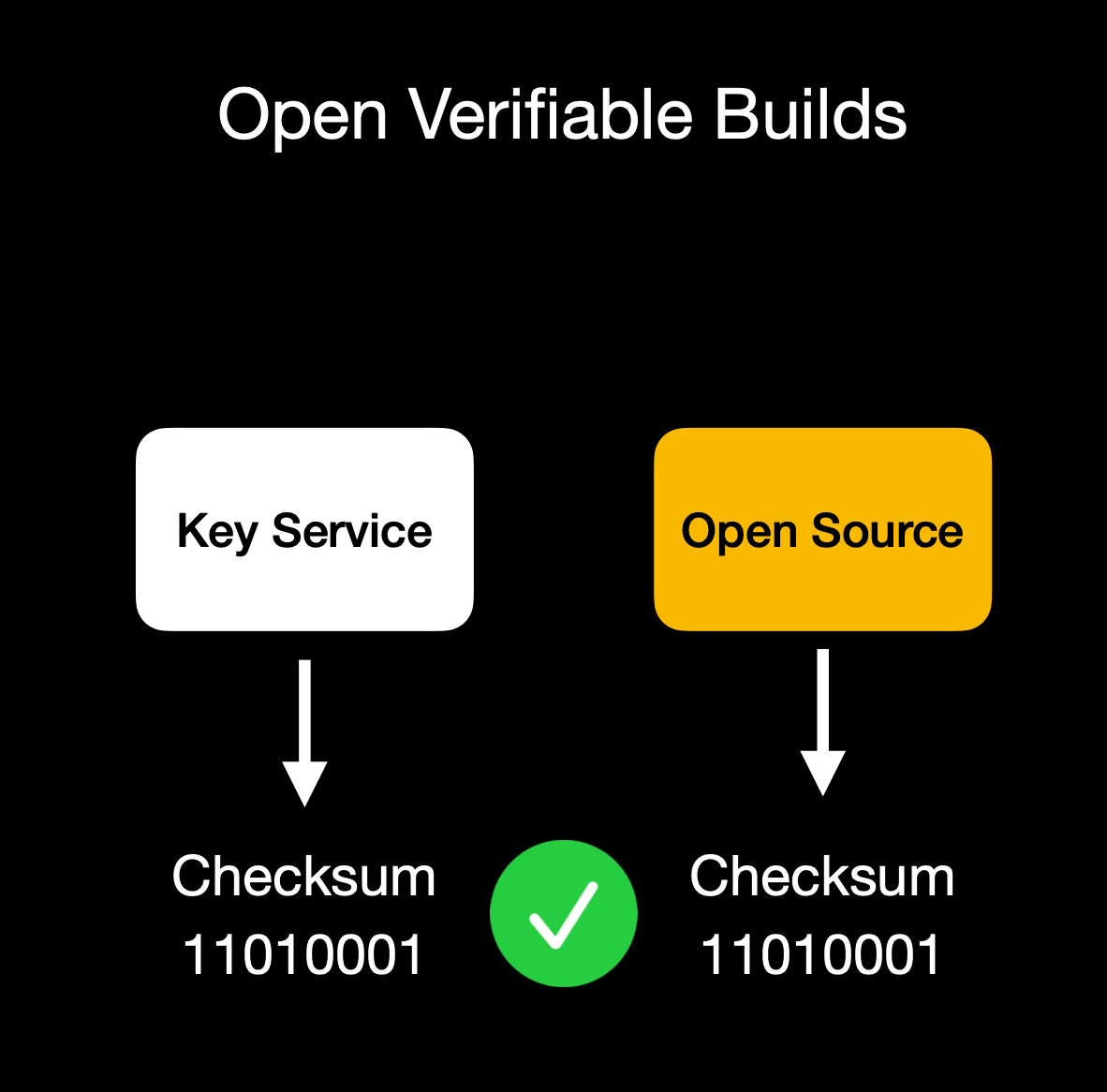Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.*
@ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 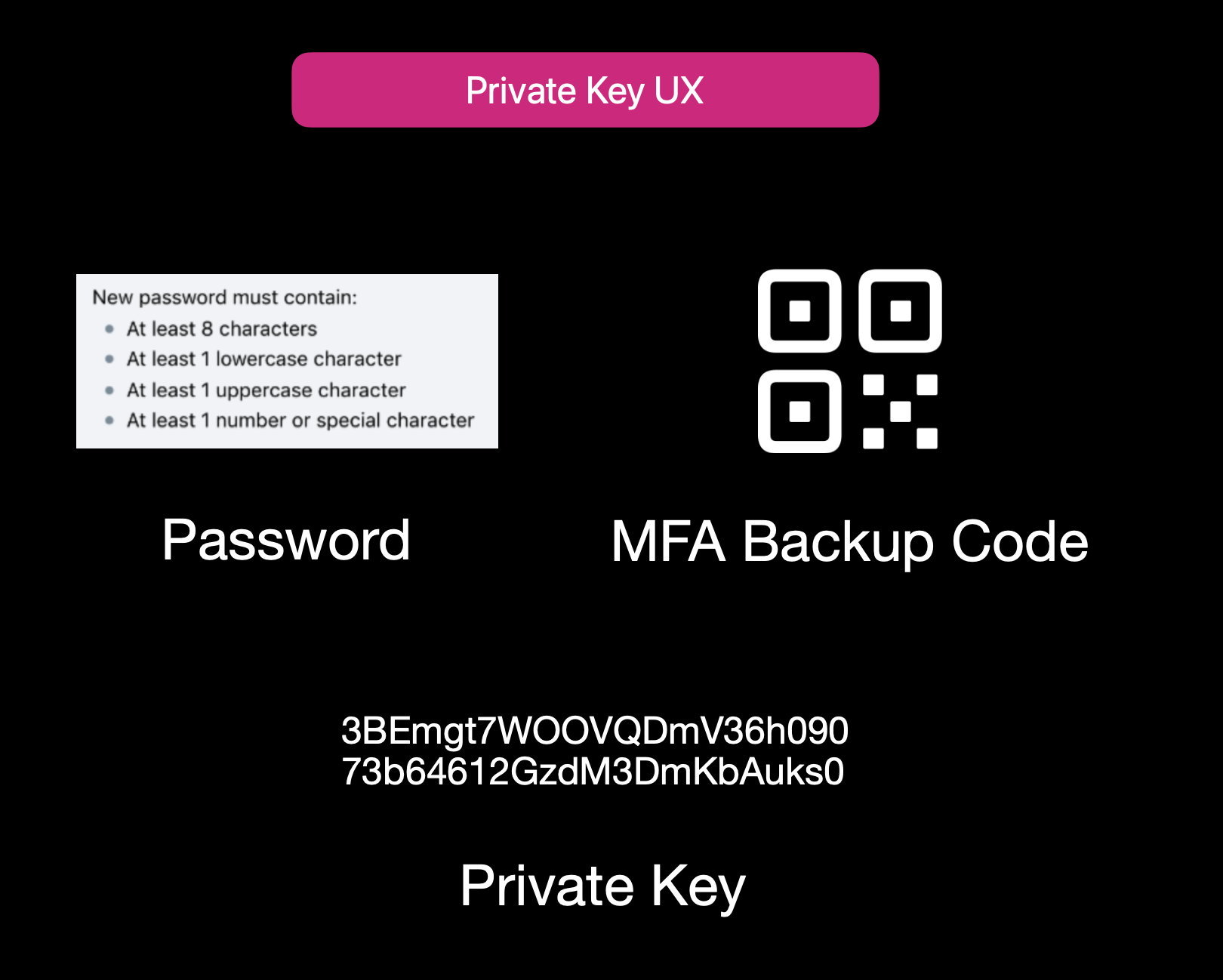Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 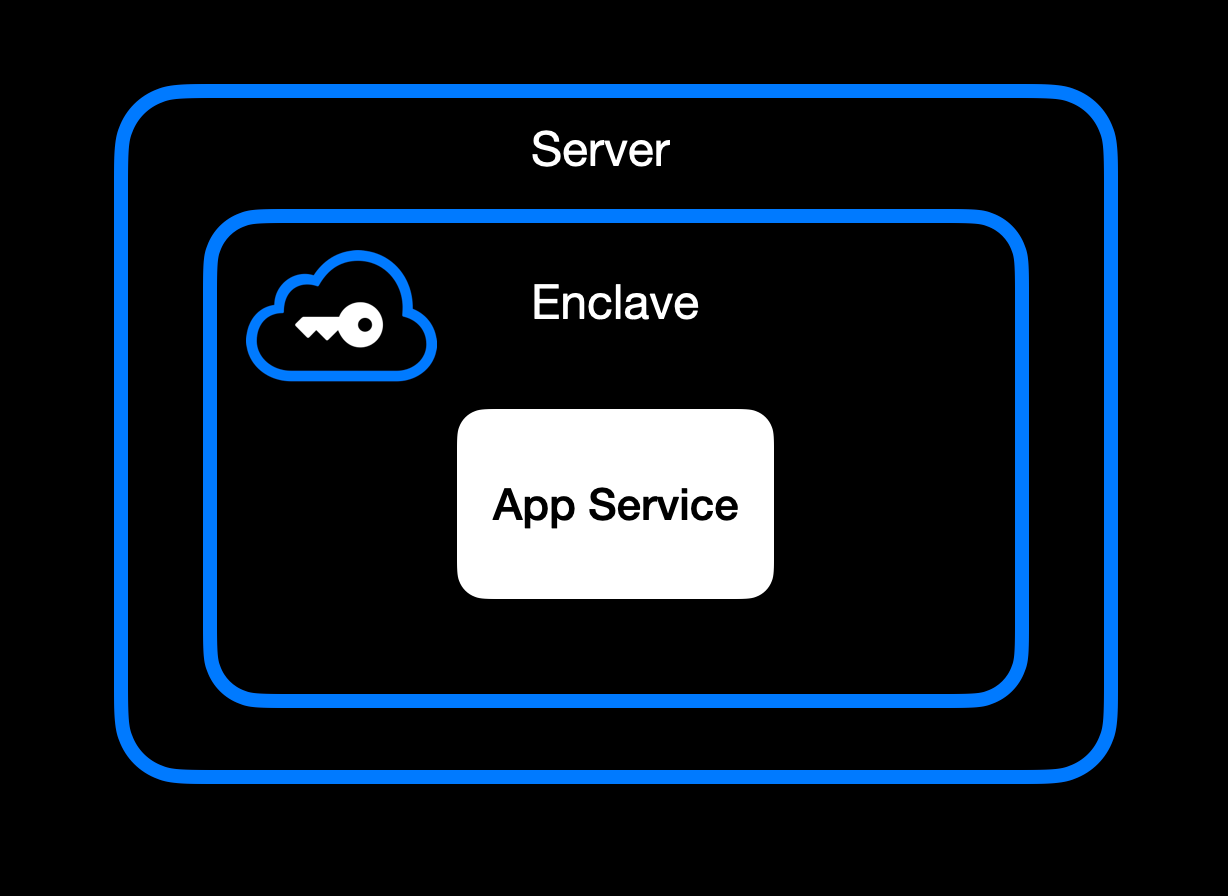App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 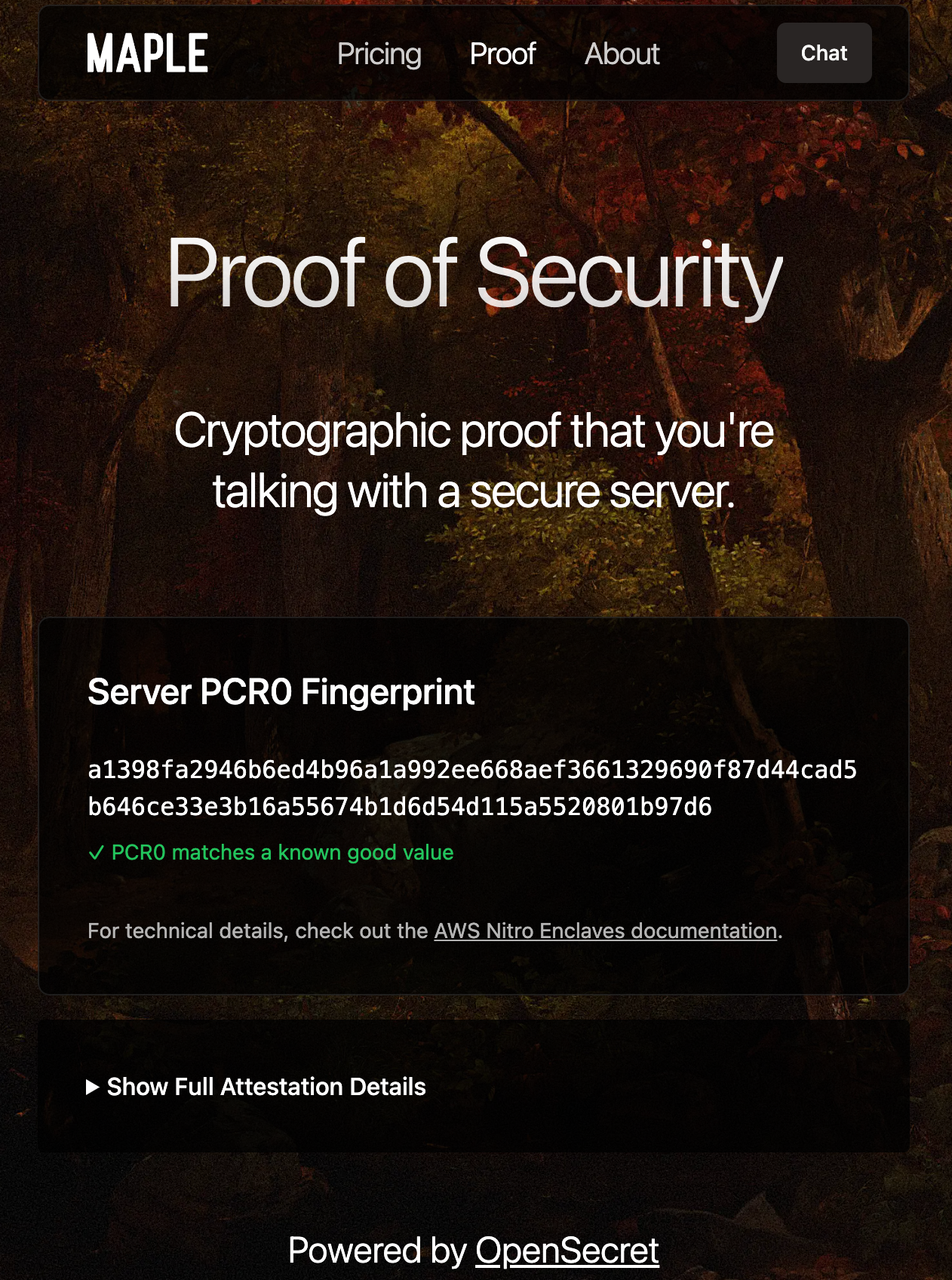Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 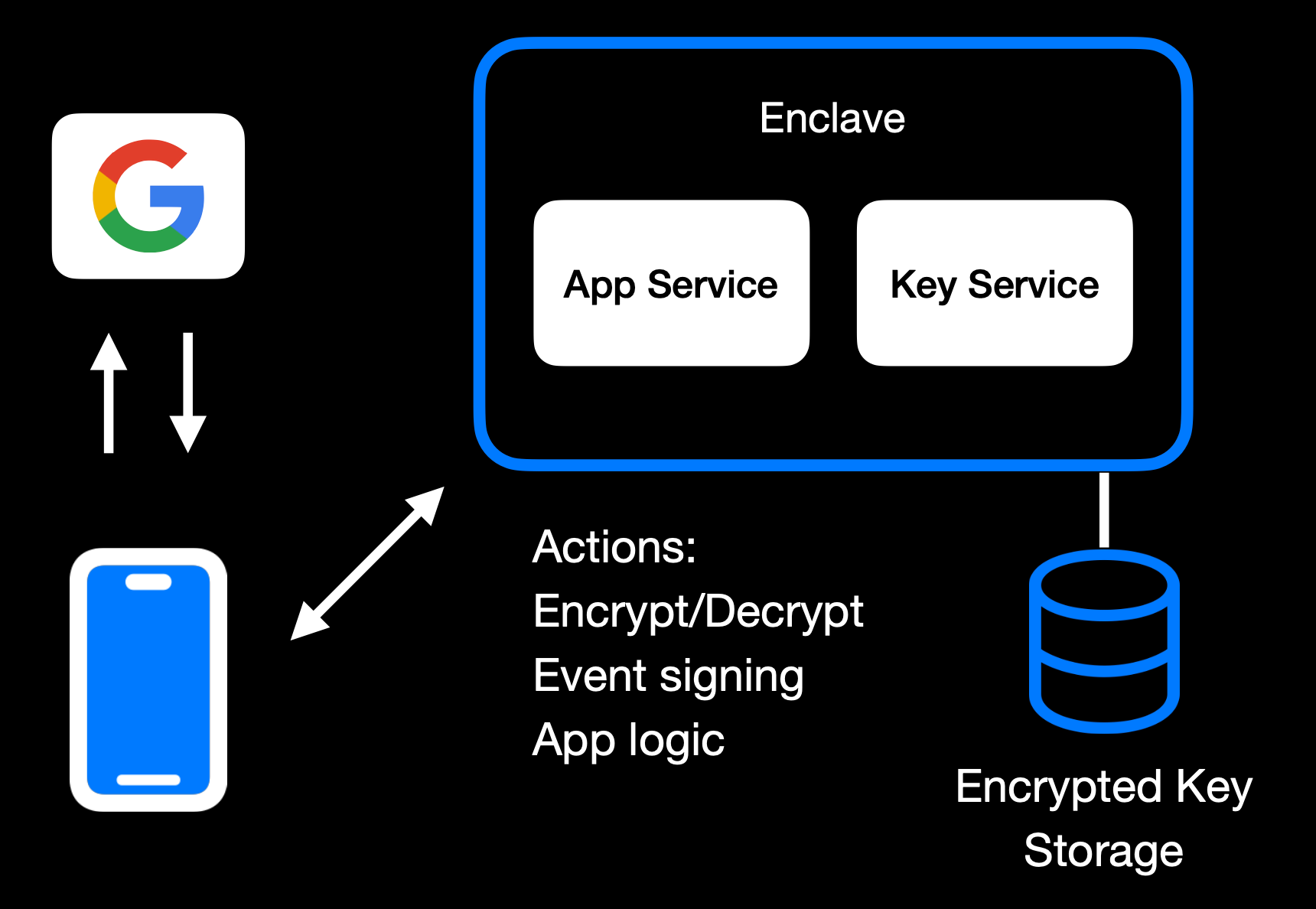Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 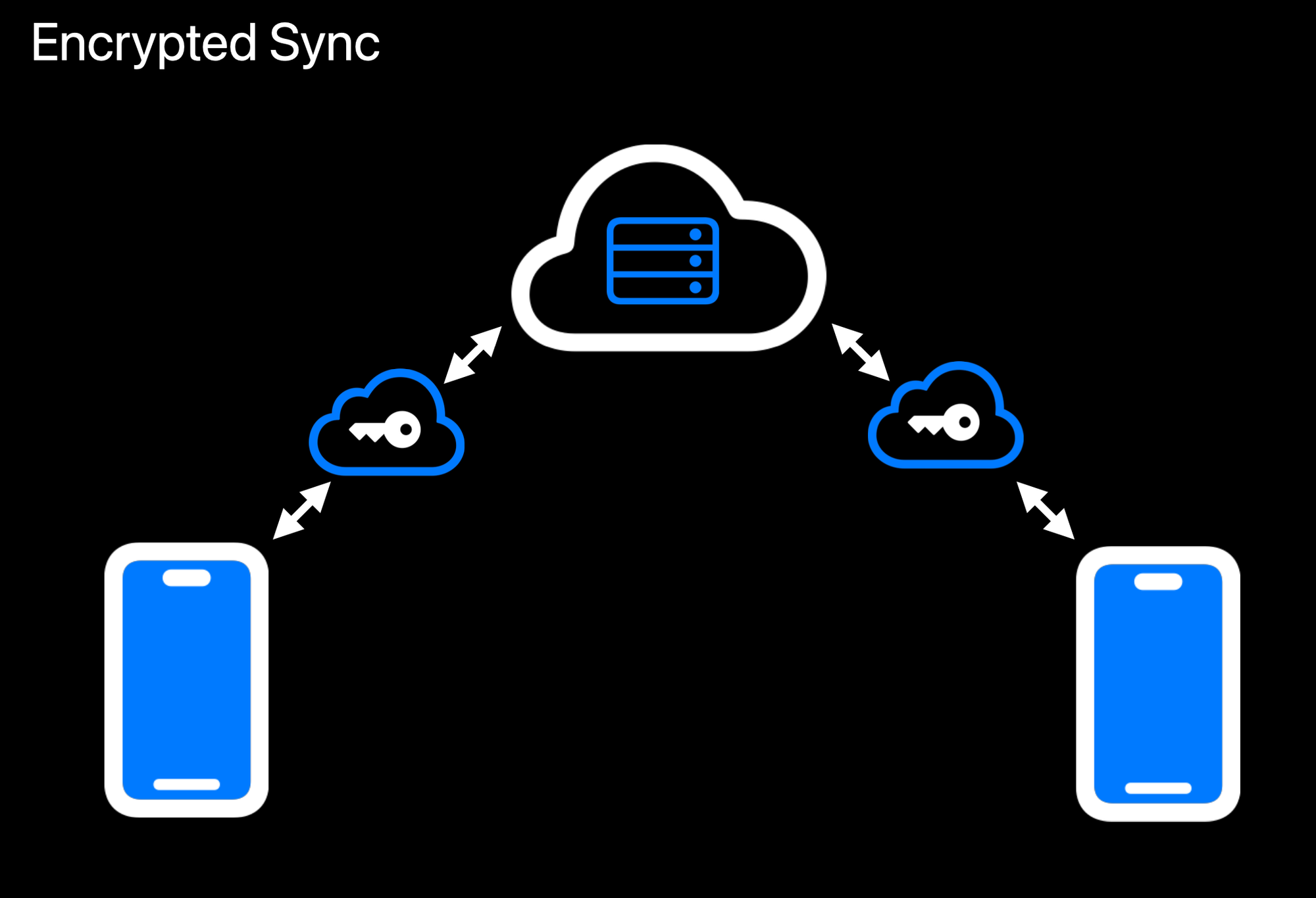Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 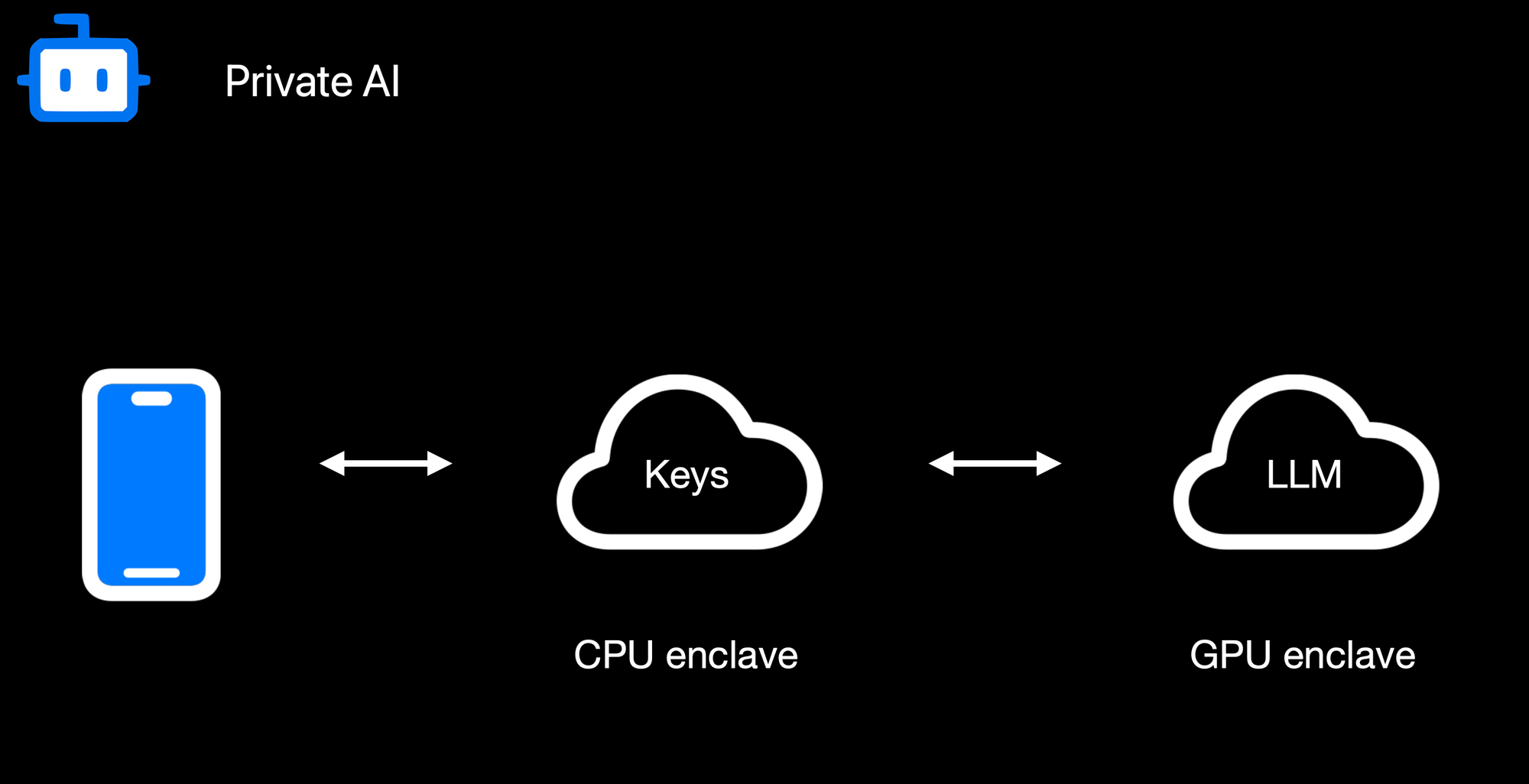Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 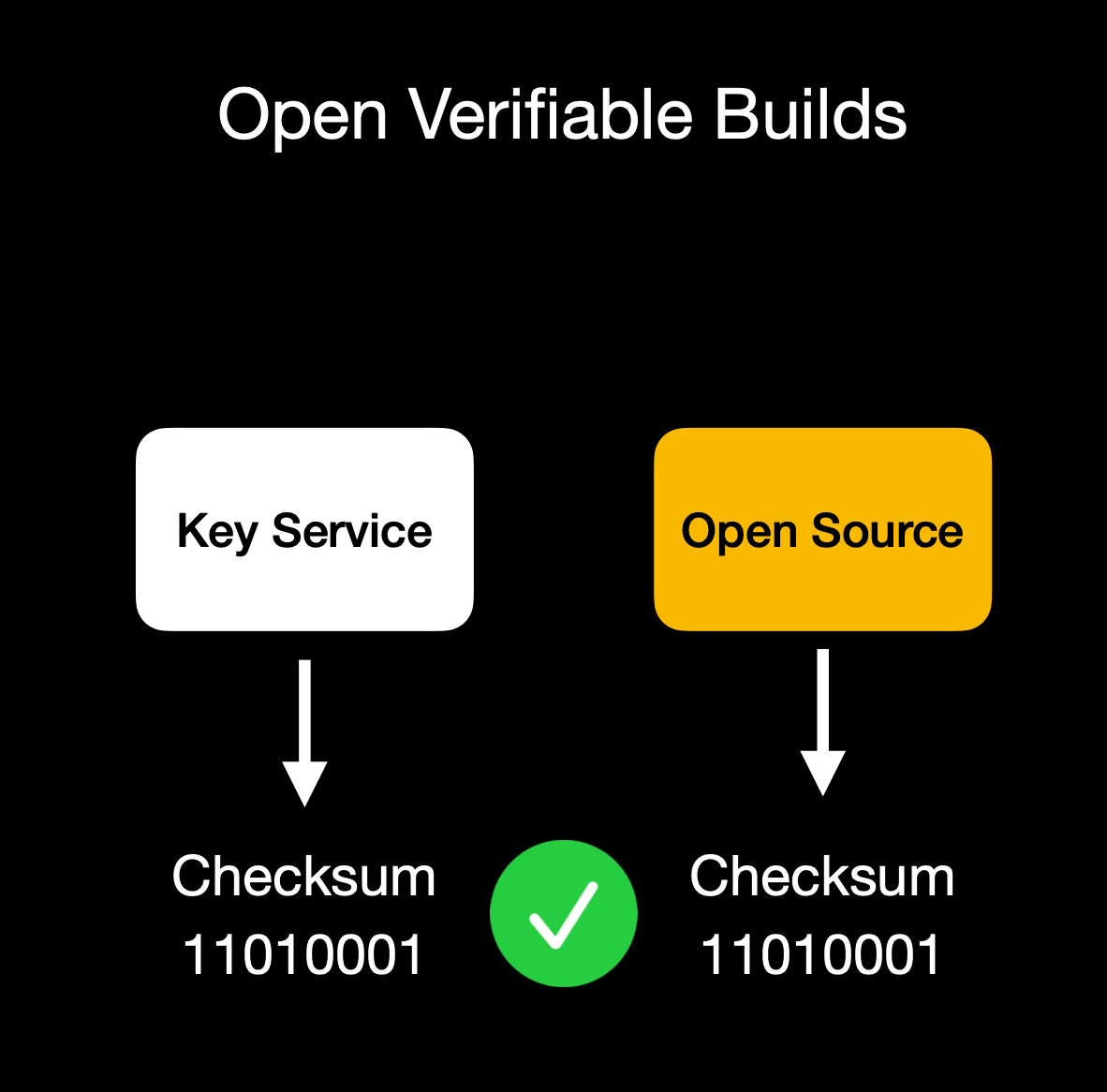Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.* @ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 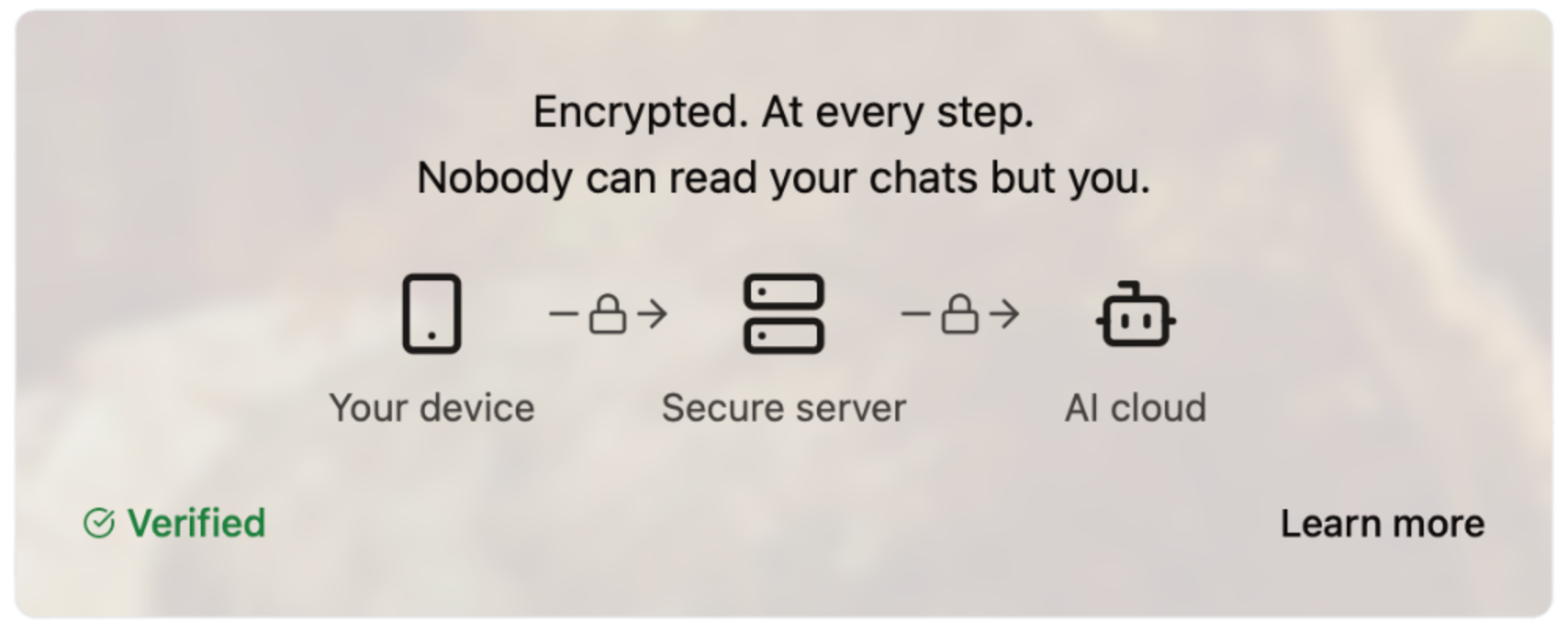#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
@ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 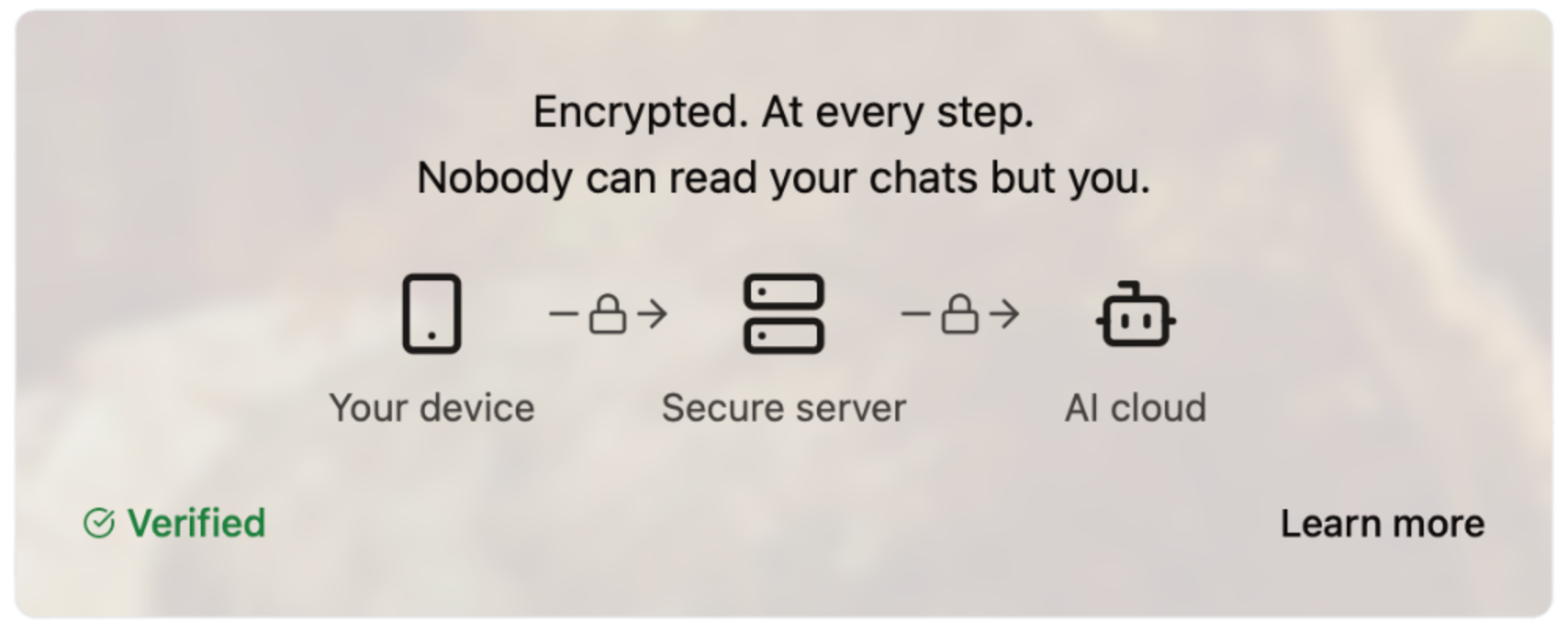#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg"> @ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [](https://trymaple.ai/waitlist)
@ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [](https://trymaple.ai/waitlist) @ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. 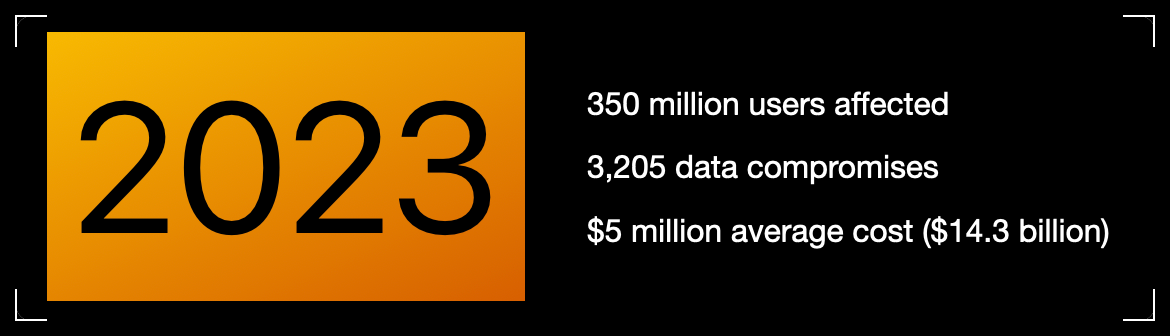Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.  ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) 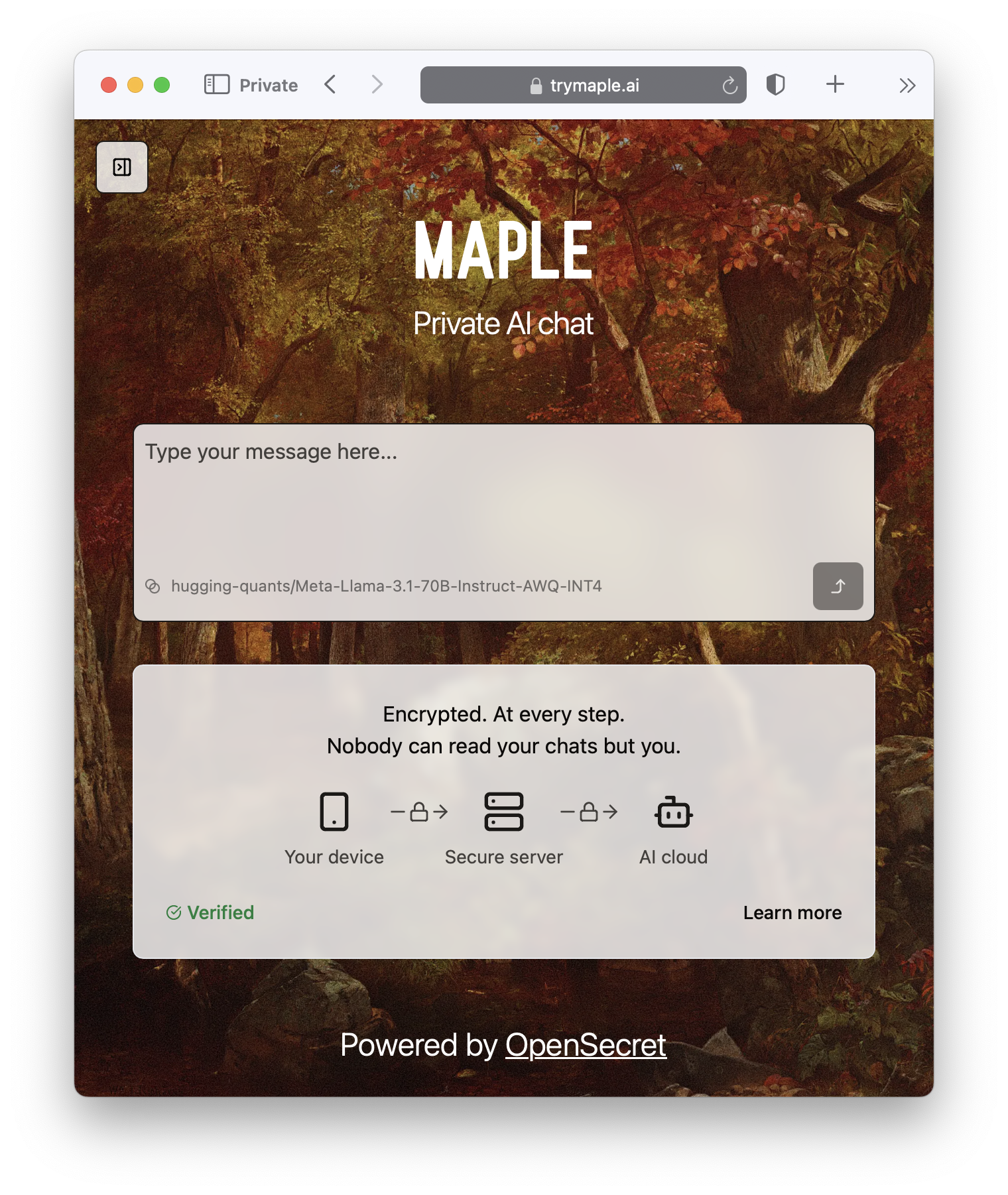 ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud)
@ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. 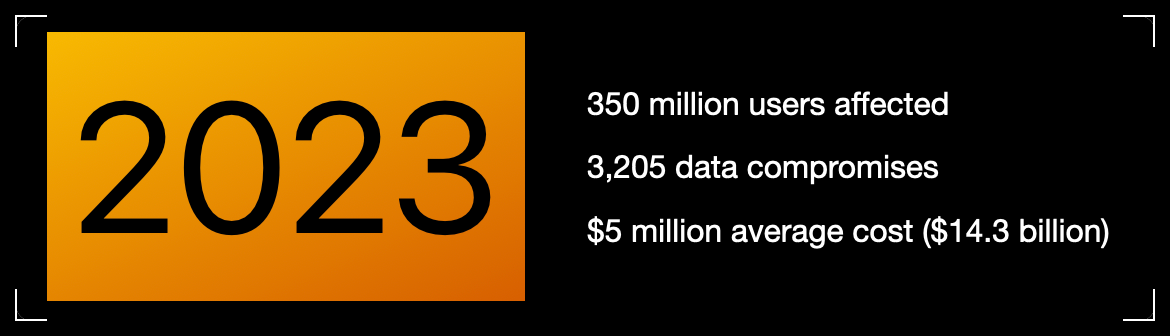Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.  ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)  ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud) @ a047a37c:dfcb432c
2025-04-05 01:09:09## Chef's notes Using only top quality dill pickles and juice is highly recommended. Do not cheap out on this ingredient. The better the pickle juice, the better your fried chicken will taste. Do not let the chicken fry for too long. If the color is not a light golden brown and you let it fry too dark. Then it will not taste right!!! ## Details - ⏲️ Prep time: 20 min - 🍳 Cook time: 25-30 min - 🍽️ Servings: 3-4 ## Ingredients - 1 1/2 Pounds Chicken Breasts - 2 Chicken Eggs - 2 Cups Dill Pickle Juice - 1/2 Cup Water - 1 Cup Buttermilk - 1 Cup Unbleached Flour - 3 Tablespoons Powdered Sugar - 1 Teaspoon Paprika - 1 Teaspoon Garlic Powder - 1 Teaspoon Cayenne Pepper - 1 Teaspoon Ground Black Pepper - 1 Teaspoon Sea Salt - 1/2 Teaspoon Baking Powder - 3-4 Cups Peanut Oil - 3-4 Toasted Brioche Buns (Chicken Sandwiches Only) - 1 Tablespoon Orange Blossom Honey (Chicken Sandwiches Only) - 1/4 Cup Sliced Dill Pickles (Chicken Sandwiches Only) ## Directions 1. There are 2 ways to make The Legendary CFA Fried Chicken. If you want to make it into nuggets then take the chicken breasts and cut them with a kitchen knife into 1 inch cubes. If you want to make it into chicken breast sandwiches, then ensure they are no bigger than 1-1.5 inches thick cut once down the middle. Once you have made your decision and cut them to size. Place the chicken in a large mixing bowl Pour the pickle juice into the bowl, cover it, and place it in the refrigerator to marinate for the next 24 hours. 2. Take a large mixing bowl and add in the flour, powdered sugar, paprika, ground black pepper, cayenne pepper, sea salt, garlic powder, and baking powder. Whisk it all together until it is fully mixed and set aside. 3. Take another large mixing bowl. Add in the chicken eggs and buttermilk. Then whisk together until it is fully blended and set aside. 4. Add 3-4 cups of peanut oil to a large cast iron frying pan, or a deep fryer. Heat the oil to 350F degrees. 5. Remove the marinated chicken from the refrigerator. Drain out all of the pickle juice. 6. Dredge the chicken in the buttermilk egg mixture until it is fully coated. Coat the chicken in the flour mixture. Then immediately repeat these two steps so it is double coated to ensure maximum crispiness. 7. Add the chicken into the peanut oil and allow it to cook evenly until it has reached a light golden brown color and is fully cooked inside. 8. Remove the chicken from the pan and place it onto a paper towel to drain the excess oil off. If you made it into chicken nuggets then simply choose your favorite dipping sauce and serve. If you chose to make chicken sandwiches then lightly toast the brioche bun to a golden brown and drizzle on the honey on the inside of the top of the bun. Then add 1 piece of chicken breast per bun on the bottom half, top it off with sliced dill pickles. Complete the sandwich and serve immediately.
@ a047a37c:dfcb432c
2025-04-05 01:09:09## Chef's notes Using only top quality dill pickles and juice is highly recommended. Do not cheap out on this ingredient. The better the pickle juice, the better your fried chicken will taste. Do not let the chicken fry for too long. If the color is not a light golden brown and you let it fry too dark. Then it will not taste right!!! ## Details - ⏲️ Prep time: 20 min - 🍳 Cook time: 25-30 min - 🍽️ Servings: 3-4 ## Ingredients - 1 1/2 Pounds Chicken Breasts - 2 Chicken Eggs - 2 Cups Dill Pickle Juice - 1/2 Cup Water - 1 Cup Buttermilk - 1 Cup Unbleached Flour - 3 Tablespoons Powdered Sugar - 1 Teaspoon Paprika - 1 Teaspoon Garlic Powder - 1 Teaspoon Cayenne Pepper - 1 Teaspoon Ground Black Pepper - 1 Teaspoon Sea Salt - 1/2 Teaspoon Baking Powder - 3-4 Cups Peanut Oil - 3-4 Toasted Brioche Buns (Chicken Sandwiches Only) - 1 Tablespoon Orange Blossom Honey (Chicken Sandwiches Only) - 1/4 Cup Sliced Dill Pickles (Chicken Sandwiches Only) ## Directions 1. There are 2 ways to make The Legendary CFA Fried Chicken. If you want to make it into nuggets then take the chicken breasts and cut them with a kitchen knife into 1 inch cubes. If you want to make it into chicken breast sandwiches, then ensure they are no bigger than 1-1.5 inches thick cut once down the middle. Once you have made your decision and cut them to size. Place the chicken in a large mixing bowl Pour the pickle juice into the bowl, cover it, and place it in the refrigerator to marinate for the next 24 hours. 2. Take a large mixing bowl and add in the flour, powdered sugar, paprika, ground black pepper, cayenne pepper, sea salt, garlic powder, and baking powder. Whisk it all together until it is fully mixed and set aside. 3. Take another large mixing bowl. Add in the chicken eggs and buttermilk. Then whisk together until it is fully blended and set aside. 4. Add 3-4 cups of peanut oil to a large cast iron frying pan, or a deep fryer. Heat the oil to 350F degrees. 5. Remove the marinated chicken from the refrigerator. Drain out all of the pickle juice. 6. Dredge the chicken in the buttermilk egg mixture until it is fully coated. Coat the chicken in the flour mixture. Then immediately repeat these two steps so it is double coated to ensure maximum crispiness. 7. Add the chicken into the peanut oil and allow it to cook evenly until it has reached a light golden brown color and is fully cooked inside. 8. Remove the chicken from the pan and place it onto a paper towel to drain the excess oil off. If you made it into chicken nuggets then simply choose your favorite dipping sauce and serve. If you chose to make chicken sandwiches then lightly toast the brioche bun to a golden brown and drizzle on the honey on the inside of the top of the bun. Then add 1 piece of chicken breast per bun on the bottom half, top it off with sliced dill pickles. Complete the sandwich and serve immediately. @ d9a329af:bef580d7
2025-04-04 20:56:20Everyone who sees it knows at this point that the matrix of control comes from the overdependence of proprietary software to do our everyday tasks. You can think of this like us being the cling wrap that will just not let go of these pieces of garbage software that don't allow you to see what is in their source code, and how they work. This will tend to lead to the unlawful collection of data (violating the most basic of privacy laws, despite unenforceable contracts that are enforced regardless), bad OPSEC that sees you being stalked and harassed over nothing significant. In the worst of cases, if you speak your mind where you aren't necessarily supposed to be able to do that, and you get doxxed, the worst cases could be far worse than one could imagine. The solution to this, on the other hand, is using almost exclusively free/libre open-source software and GNU/Linux operation systems. If you're using certain proprietary software, hardening it to give as little data as possible to the entity responsible for it will also work, as long as you know which ones to use. This is a hard pass for a lot of people, but if you want to escape the control matrix of proprietary software, Winblows, HackOS, iHackOS, iBloatOS and stock Google AI Fever Dream, then researching which Free Software (notice the spelling) to use is your first bet. I had already done this for the past four and a half years, and will continue to do it as long as I live, seeing what new Free Software compliant applications and libraries come into the spotlight once things get locked down into walled gardens like what HackOS, iHackOS and BlindnessOS do on a regular basis. Each of these pieces of software will be in a categorized list with a brief description of what the software is used for. There is a lot to take in, so research this yourself and see if these are right for you. These are the applications I personally use on a regular day-to-day basis, and they work for my needs. 1. Operating Systems (the core to your device) * GNU/Linux operating systems (for PCs) or GrapheneOS (for de-googled Android phones) To be fair on this one, GNU/Linux is the combination of the Linux kernel with the GNU toolchain, which in turn allows any developer to make an operating system that is FOSS, not necessarily Free Software, especially with the Linux Kernel's proprietary bits of code. The Linux kernel is also used in the Android Open-Source Project (AOSP), and is used as the base of operating systems for Android phones such as GrapheneOS, the only AOSP custom ROM I would recommend based upon the research I had done on this (even if very little). My recommendations on the Linux side of things are almost any Arch-based distribution (with the exception of Manjaro), Debian-based distributions like Linux Mint Debian edition, regular Debian, AntiX or Devuan, or a Fedora/RedHat-based distribution like Nobara Project (if you're a gamer), OpenSUSE (if set up properly) or even Bluefin if you want an atomic desktop (I wouldn't recommend Bluefin if you want to monkey with your operating system and DIY on many aspects of it). Once you learn how to set these up securely, privately and properly, you're on your way to starting your journey into digital liberation, but there's far more to go on this front. 2. Web Browsers (How you surf the internet) * Firefox Forks This one is self-explanatory. I harden all the Firefox forks I use (LibreWolf, Waterfox, Cachy Browser, Floorp and Zen as some examples) to the nines, despite being unable to do anything about my fingerprint. This is why I use multiple browsers for specific purposes to counteract the fingerprint spying due to weaponized JavaScript. There are ways to circumvent the fingerprint-based espionage, and make sure the site fingerprint.com doesn't know that one's lying about what their user agent is, though it's not very easy to fool that site, as it's used by 6,000 companies. * Brave Browser This is the only Chromium-based browser I would recommend, as it's better when hardened against all the other Chromium-based browsers, including Ungoogled Chromium, which is almost impossible to harden due to security vulnerabilities. Despite that, Brave has some of the best features for a Chromium-based browser one can feel comfortable using, even though you'll have similar issues with Firefox-based browsers that aren't actually Firefox (and Firefox has its own issues regarding espionage from Mozilla) 3. Office Suites (If you need to do professional office documents) * LibreOffice A fork of Apache's OpenOffice, made better with many features missing from even OnlyOffice and OpenOffice, this suite of applications is the go-to Free Software office suite for many people looking to switch from the proprietary software nether to the diamonds of free/libre open-source software. Though one may need to perform some extra steps to set up compatibility with G-Suite and Microsoft Office past 2015 potentially, it's still a good thing that people trust LibreOffice as their one-stop shop for office documents, despite being completely different from your standard office suite fare. * OnlyOffice The competitor to LibreOffice with the ease of Microsoft Office and G-Suite compatibility, OnlyOffice is another office suite that can be good for those who need it, especially since anybody who had used Microsoft Office in particular will be familiar with its layout, if not for a slight learning curve. As someone who's used G-Suite more (due to schooling that stunk worse than a decomposing rat in New York City), that's part of the reason why I switched to LibreOffice, though I tried some others, including OnlyOffice and Abiword (since I use a word processor a lot). This one is another solid option for those who need it. * Wordgrinder For those who like to use a terminal emulator like I do, Wordgrinder is a word processor with a terminal user interface (TUI) designed with just focusing on typing without distractions in mind. .wg is the file extension for documents made using Wordgrinder, especially since nowadays most word processors are cloud based. For those who live in a terminal, this is a good option to your terminal UI-based toolbox 4. Text editors * Vi, Vim, Neovim and other Vim-like editors The classic VI Improved (Vim), a fork of the TUI modal editor, vi, with keybinds that will be confusing at first, but with practice and patience, bring about muscle memory to stay on the keyboard, and not necessarily touch the mouse, keypad on the right hand side, or even the arrow keys. These keybind skills will stay with one for the rest of their life once they learn how the modes in vi, Vim or vi-based editors work. It's a classic for those working in the terminal, and a staple in FLOSS text editing and coding tools once customized potentially to the nines to your particular style. * VSCodium The Free Software fork of Code OSS by Microsoft, but made to be similar in function to VSCode without Microsoft's espionage baked into it. It has almost exactly the same features as VSCode that one would need, and even any VSIX files from VSCode will work in VSCodium. This one is an easy switch from VSCode for those who use it, but don't want the forced telemetry. * Emacs The competitor to Vim, Emacs is an editor that is FLOSS in every way imaginable. It is one of the most customizable editors anybody could have ever conceived, though the programming language used in Emacs is a dialect of Lisp the developers had made themselves. There are more keybinds to memorize compared to Vim, though Vim keybinds can be added using the Evil Mode package in any Emacs package manager to get the best of both worlds in Emacs. Once one gets a handle of the steep learning curve for Emacs, it's customizable in every imaginable way almost. These four categories will get you started on your privacy journey, though I covered things a developer might want. I have plans on more lists to compile once I get my ducks in a row on what I want to cover here on Nostr in a longform format. Feel free to let me know if you have recommendations for me to write about, and I can do some digging on that if it isn't a rabbit hole.
@ d9a329af:bef580d7
2025-04-04 20:56:20Everyone who sees it knows at this point that the matrix of control comes from the overdependence of proprietary software to do our everyday tasks. You can think of this like us being the cling wrap that will just not let go of these pieces of garbage software that don't allow you to see what is in their source code, and how they work. This will tend to lead to the unlawful collection of data (violating the most basic of privacy laws, despite unenforceable contracts that are enforced regardless), bad OPSEC that sees you being stalked and harassed over nothing significant. In the worst of cases, if you speak your mind where you aren't necessarily supposed to be able to do that, and you get doxxed, the worst cases could be far worse than one could imagine. The solution to this, on the other hand, is using almost exclusively free/libre open-source software and GNU/Linux operation systems. If you're using certain proprietary software, hardening it to give as little data as possible to the entity responsible for it will also work, as long as you know which ones to use. This is a hard pass for a lot of people, but if you want to escape the control matrix of proprietary software, Winblows, HackOS, iHackOS, iBloatOS and stock Google AI Fever Dream, then researching which Free Software (notice the spelling) to use is your first bet. I had already done this for the past four and a half years, and will continue to do it as long as I live, seeing what new Free Software compliant applications and libraries come into the spotlight once things get locked down into walled gardens like what HackOS, iHackOS and BlindnessOS do on a regular basis. Each of these pieces of software will be in a categorized list with a brief description of what the software is used for. There is a lot to take in, so research this yourself and see if these are right for you. These are the applications I personally use on a regular day-to-day basis, and they work for my needs. 1. Operating Systems (the core to your device) * GNU/Linux operating systems (for PCs) or GrapheneOS (for de-googled Android phones) To be fair on this one, GNU/Linux is the combination of the Linux kernel with the GNU toolchain, which in turn allows any developer to make an operating system that is FOSS, not necessarily Free Software, especially with the Linux Kernel's proprietary bits of code. The Linux kernel is also used in the Android Open-Source Project (AOSP), and is used as the base of operating systems for Android phones such as GrapheneOS, the only AOSP custom ROM I would recommend based upon the research I had done on this (even if very little). My recommendations on the Linux side of things are almost any Arch-based distribution (with the exception of Manjaro), Debian-based distributions like Linux Mint Debian edition, regular Debian, AntiX or Devuan, or a Fedora/RedHat-based distribution like Nobara Project (if you're a gamer), OpenSUSE (if set up properly) or even Bluefin if you want an atomic desktop (I wouldn't recommend Bluefin if you want to monkey with your operating system and DIY on many aspects of it). Once you learn how to set these up securely, privately and properly, you're on your way to starting your journey into digital liberation, but there's far more to go on this front. 2. Web Browsers (How you surf the internet) * Firefox Forks This one is self-explanatory. I harden all the Firefox forks I use (LibreWolf, Waterfox, Cachy Browser, Floorp and Zen as some examples) to the nines, despite being unable to do anything about my fingerprint. This is why I use multiple browsers for specific purposes to counteract the fingerprint spying due to weaponized JavaScript. There are ways to circumvent the fingerprint-based espionage, and make sure the site fingerprint.com doesn't know that one's lying about what their user agent is, though it's not very easy to fool that site, as it's used by 6,000 companies. * Brave Browser This is the only Chromium-based browser I would recommend, as it's better when hardened against all the other Chromium-based browsers, including Ungoogled Chromium, which is almost impossible to harden due to security vulnerabilities. Despite that, Brave has some of the best features for a Chromium-based browser one can feel comfortable using, even though you'll have similar issues with Firefox-based browsers that aren't actually Firefox (and Firefox has its own issues regarding espionage from Mozilla) 3. Office Suites (If you need to do professional office documents) * LibreOffice A fork of Apache's OpenOffice, made better with many features missing from even OnlyOffice and OpenOffice, this suite of applications is the go-to Free Software office suite for many people looking to switch from the proprietary software nether to the diamonds of free/libre open-source software. Though one may need to perform some extra steps to set up compatibility with G-Suite and Microsoft Office past 2015 potentially, it's still a good thing that people trust LibreOffice as their one-stop shop for office documents, despite being completely different from your standard office suite fare. * OnlyOffice The competitor to LibreOffice with the ease of Microsoft Office and G-Suite compatibility, OnlyOffice is another office suite that can be good for those who need it, especially since anybody who had used Microsoft Office in particular will be familiar with its layout, if not for a slight learning curve. As someone who's used G-Suite more (due to schooling that stunk worse than a decomposing rat in New York City), that's part of the reason why I switched to LibreOffice, though I tried some others, including OnlyOffice and Abiword (since I use a word processor a lot). This one is another solid option for those who need it. * Wordgrinder For those who like to use a terminal emulator like I do, Wordgrinder is a word processor with a terminal user interface (TUI) designed with just focusing on typing without distractions in mind. .wg is the file extension for documents made using Wordgrinder, especially since nowadays most word processors are cloud based. For those who live in a terminal, this is a good option to your terminal UI-based toolbox 4. Text editors * Vi, Vim, Neovim and other Vim-like editors The classic VI Improved (Vim), a fork of the TUI modal editor, vi, with keybinds that will be confusing at first, but with practice and patience, bring about muscle memory to stay on the keyboard, and not necessarily touch the mouse, keypad on the right hand side, or even the arrow keys. These keybind skills will stay with one for the rest of their life once they learn how the modes in vi, Vim or vi-based editors work. It's a classic for those working in the terminal, and a staple in FLOSS text editing and coding tools once customized potentially to the nines to your particular style. * VSCodium The Free Software fork of Code OSS by Microsoft, but made to be similar in function to VSCode without Microsoft's espionage baked into it. It has almost exactly the same features as VSCode that one would need, and even any VSIX files from VSCode will work in VSCodium. This one is an easy switch from VSCode for those who use it, but don't want the forced telemetry. * Emacs The competitor to Vim, Emacs is an editor that is FLOSS in every way imaginable. It is one of the most customizable editors anybody could have ever conceived, though the programming language used in Emacs is a dialect of Lisp the developers had made themselves. There are more keybinds to memorize compared to Vim, though Vim keybinds can be added using the Evil Mode package in any Emacs package manager to get the best of both worlds in Emacs. Once one gets a handle of the steep learning curve for Emacs, it's customizable in every imaginable way almost. These four categories will get you started on your privacy journey, though I covered things a developer might want. I have plans on more lists to compile once I get my ducks in a row on what I want to cover here on Nostr in a longform format. Feel free to let me know if you have recommendations for me to write about, and I can do some digging on that if it isn't a rabbit hole. @ da18e986:3a0d9851
2025-04-04 20:25:50I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash. Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax. Here's the test wiki page I'm going to write: ``` = Simple AsciiDoc Demo This is a simple demonstration of AsciiDoc syntax for testing purposes. == Features AsciiDoc offers many formatting options that are easy to use. * Easy to learn * Supports rich text formatting * Can include code snippets * Works great for documentation [source,json] ---- { "name": "Test", "version": "1.0", "active": true } ---- ``` # We're going to use nak to publish it First, install `nak` if you haven't already ``` go install github.com/fiatjaf/nak@latest ``` *Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal* ``` # this is how to add it to your path on mac if using zsh echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc ``` And here's how to sign and publish this event with nak. *First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified* ``` # replace with your full secret key export NOSTR_SECRET_KEY="nsec1zcdn..." ``` Now to sign and publish the event: *Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal* ``` nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz ``` You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851 and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io
@ da18e986:3a0d9851
2025-04-04 20:25:50I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash. Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax. Here's the test wiki page I'm going to write: ``` = Simple AsciiDoc Demo This is a simple demonstration of AsciiDoc syntax for testing purposes. == Features AsciiDoc offers many formatting options that are easy to use. * Easy to learn * Supports rich text formatting * Can include code snippets * Works great for documentation [source,json] ---- { "name": "Test", "version": "1.0", "active": true } ---- ``` # We're going to use nak to publish it First, install `nak` if you haven't already ``` go install github.com/fiatjaf/nak@latest ``` *Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal* ``` # this is how to add it to your path on mac if using zsh echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc ``` And here's how to sign and publish this event with nak. *First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified* ``` # replace with your full secret key export NOSTR_SECRET_KEY="nsec1zcdn..." ``` Now to sign and publish the event: *Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal* ``` nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz ``` You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851 and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io @ 000002de:c05780a7
2025-04-04 20:22:47We are fostering a lamb named Frank. He was left behind when his flock was moved to a new grazing area. He almost didn't make it. I've learned that sheep are not as dumb as I thought they were. He seems to be pretty sharp and has quickly become spoiled. He follows us around like a puppy. We have had some cold nights so we made him a jacket. He's about 3 weeks old now and seems to be doing well.    originally posted at https://stacker.news/items/934770
@ 000002de:c05780a7
2025-04-04 20:22:47We are fostering a lamb named Frank. He was left behind when his flock was moved to a new grazing area. He almost didn't make it. I've learned that sheep are not as dumb as I thought they were. He seems to be pretty sharp and has quickly become spoiled. He follows us around like a puppy. We have had some cold nights so we made him a jacket. He's about 3 weeks old now and seems to be doing well.    originally posted at https://stacker.news/items/934770 @ c631e267:c2b78d3e
2025-04-04 18:47:27*Zwei mal drei macht vier,* *\ widewidewitt und drei macht neune,* *\ ich mach mir die Welt,* *\ widewide wie sie mir gefällt.* *\ Pippi Langstrumpf*   **Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive. **In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027. **Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt. **Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen. **Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint. **Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen. **Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür. *\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen.
@ c631e267:c2b78d3e
2025-04-04 18:47:27*Zwei mal drei macht vier,* *\ widewidewitt und drei macht neune,* *\ ich mach mir die Welt,* *\ widewide wie sie mir gefällt.* *\ Pippi Langstrumpf*   **Egal, ob Koalitionsverhandlungen oder politischer Alltag:** Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit [Rückenwind](https://transition-news.org/warum-die-politische-landschaft-einen-rechtsruck-erlebt) geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive. **In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern** von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027. **Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung** durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die [Wahlwiederholung](https://transition-news.org/rumanische-prasidentenwahlen-weitere-ungereimtheiten-kandidatenfeld-fix) im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt. **Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden,** das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine [Lagarde](https://archive.is/20ZFq) oder im [«Pfizergate»](https://transition-news.org/pfizergate-klage-gegen-von-der-leyen-in-luttich-als-unzulassig-erklart)-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen. **Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen,** so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint. **Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen** über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das [Stimmrecht](https://transition-news.org/die-zeit-ist-reif-orban-zu-bestrafen-sagt-deutschlands-nachste-regierung) entziehen. **Der Pegel an Unzufriedenheit und Frustration wächst** in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die [Umfrageergebnisse](https://archive.is/kf4Tk) der AfD ein guter Gradmesser dafür. *\[Vorlage Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/gesetz-gerechtigkeit-flagge-europa-6598281/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/wird-politische-justiz-zu-einer-demokratischen-tugend)*** erschienen. @ 3ffac3a6:2d656657
2025-04-05 04:55:12# O Impacto do Namoro com Pelé na Carreira de Xuxa Meneghel ## Disclaimer: Esse texto foi totalmente escrito pelo ChatGPT, eu apenas pedi que ele fizesse uma pesquisa sobre o tema. **Introdução:** O relacionamento entre Xuxa Meneghel e Pelé, que durou cerca de seis anos (início dos anos 1980 até 1986), foi um dos mais comentados da década de 1980 ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)). Xuxa tinha apenas 17 anos quando começou a namorar o já consagrado “Rei do Futebol”, então com 40 anos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Xuxa%20tinha%2017%20anos,a%20primeira%20mulher%2C%20Rosemeri%20Cholbi)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=O%20jogador%20de%20futebol%20e,um%20relacionamento%20por%20seis%20anos)). Esse romance altamente midiático não só atiçou a curiosidade do público, como também alavancou a carreira de Xuxa de forma significativa. A seguir, detalhamos como o namoro aumentou a visibilidade da apresentadora, quais oportunidades profissionais podem ter tido influência direta de Pelé, o papel da revista *Manchete* e de outras mídias na promoção de sua imagem, se o relacionamento contribuiu para Xuxa conquistar espaços na TV (como o programa **Clube da Criança** e, posteriormente, na Rede Globo) e como mídia e público percebiam o casal – tudo embasado em fontes da época, entrevistas e biografias. ## Aumento da Visibilidade Midiática nos Anos 1980 O namoro com Pelé catapultou Xuxa a um novo patamar de fama. Até então uma modelo em começo de carreira, Xuxa **“se tornou famosa ao aparecer ao lado do esportista de maior status do Brasil”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=O%20romance%20come%C3%A7ou%20quando%20ela,de%20maior%20status%20do%20Brasil)). A partir do momento em que o relacionamento se tornou público, ela passou a estampar capas de revistas com frequência e a ser assunto constante na imprensa. Em 20 de dezembro de 1980, a jovem apareceu na capa da revista *Manchete* ao lado de Pelé e outras modelos – um ensaio fotográfico que marcou o primeiro encontro dos dois e deu início à enorme atenção midiática em torno de Xuxa ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=O%20jantar%20aproximou%20o%20casal,E%20fui%E2%80%9D)). Não por acaso, *“naquele ano, ela foi capa de mais de cem revistas”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=convidadas%20a%20posar%20ao%20lado,de%20mais%20de%20cem%20revistas)), um indicativo claro de como sua visibilidade explodiu após começar a namorar Pelé. Jornais, revistas de celebridades e programas de fofoca passaram a segui-los de perto; o casal virou sensação nacional, comparado até ao “Casal 20” (dupla glamourosa de uma série de TV americana) pelo seu alto perfil na mídia ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)). Essa exposição intensa colocou Xuxa não apenas sob os holofotes do público, mas também a inseriu nos **bastidores do entretenimento**. Como namorada de Pelé – um dos homens mais conhecidos do mundo – Xuxa passou a frequentar eventos de gala, festas e bastidores de programas, onde conheceu figuras influentes do meio artístico e televisivo. Os fotógrafos os seguiam em eventos como bailes de carnaval e inaugurações, registrando cada aparição pública do casal. Com Pelé ao seu lado, Xuxa ganhou trânsito livre em círculos antes inacessíveis para uma modelo iniciante, construindo uma rede de contatos valiosa nos meios de comunicação. De fato, naquele início dos anos 80, **“os dois eram perseguidos por fotógrafos, apareciam em capas de revistas e até faziam publicidade juntos”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) – evidência de que Xuxa, graças ao namoro, transitava tanto na frente quanto por trás das câmeras com muito mais facilidade. Em suma, o relacionamento conferiu a ela um grau de notoriedade nacional que provavelmente demoraria anos para conquistar de outra forma, preparando o terreno para os passos seguintes de sua carreira. ## Influência Direta de Pelé nas Oportunidades Profissionais de Xuxa Além do aumento geral da fama, há casos específicos em que Pelé influenciou diretamente oportunidades profissionais para Xuxa. Um exemplo contundente é o filme **“Amor Estranho Amor” (1982)** – longa de teor erótico no qual Xuxa atuou no início da carreira. Segundo relatos da própria apresentadora, **foi Pelé quem a incentivou a aceitar participar desse filme** ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Profissionalmente%2C%20Xuxa%20disse%20que%20Pel%C3%A9,Me%20enganaram%2C%20falaram%20um)). Na época ainda em início de trajetória, Xuxa acabou convencida pelo namorado de que aquela oportunidade poderia ser benéfica. Anos mais tarde, ela revelaria arrependimento pela escolha desse papel, mas o fato reforça que Pelé teve influência ativa em decisões profissionais de Xuxa no começo de sua jornada. Outra área de influência direta foram as **publicidades e campanhas comerciais**. Graças ao prestígio de Pelé, Xuxa recebeu convites para estrelar anúncios ao lado do então namorado. Já em 1981, por exemplo, os dois gravaram juntos comerciais para uma empresa imobiliária, aparecendo como casal em campanhas de TV daquele Natal (pelas **Imóveis Francisco Xavier**, um case famoso entre colecionadores de propagandas da época) ([Xuxa e Pelé: Natal de 1981 na Publicidade Imobiliária | TikTok](https://www.tiktok.com/@thebest.memories/video/7301084045402721541#:~:text=Xuxa%20e%20Pel%C3%A9%3A%20Natal%20de,Natal%20de%201981%20na)) ([Xuxa com Pelé em comercial de imobiliária em dezembro de 1981](https://www.youtube.com/watch?v=t45oWkJPFw0#:~:text=Xuxa%20com%20Pel%C3%A9%20em%20comercial,Im%C3%B3veis%20em%20dezembro%20de%201981)). Assim, Xuxa obteve espaço em campanhas publicitárias que dificilmente envolveriam uma modelo desconhecida – mas que, com a “namorada do Pelé” no elenco, ganhavam apelo extra. Isso evidencia que Pelé abriu portas também no mercado publicitário, dando a Xuxa oportunidades de trabalho e renda enquanto sua própria imagem pública se consolidava. Ademais, a presença de Pelé ao lado de Xuxa em diversos editoriais e ensaios fotográficos serviu para elevá-la de modelo anônima a personalidade conhecida. Revistas e jornais buscavam os dois para sessões de fotos e entrevistas, sabendo do interesse do público pelo casal. As capas conjuntas em publicações de grande circulação (como *Manchete* e outras) não só aumentaram a exposição de Xuxa, mas também conferiram a ela certa credibilidade midiática por associação. Em outras palavras, estar ao lado de um ícone como Pelé funcionou como um “selo de aprovação” implícito, deixando editores e produtores mais propensos a convidá-la para projetos. Vale lembrar que **“ao longo dos seis anos de relacionamento, [eles] posaram para várias capas da *Manchete*”**, com a revista acompanhando de perto cada fase do namoro ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)). Essa recorrência nas bancas solidificou o rosto e o nome de Xuxa na indústria do entretenimento. Por fim, é importante notar que nem todas as influências de Pelé foram positivas para a carreira dela – algumas foram tentativas de direcionamento. A própria Xuxa contou que, quando surgiu a oportunidade de ela ir para a TV Globo em 1986, Pelé desencorajou a mudança. **Ele sugeriu que Xuxa permanecesse na TV Manchete, dizendo que “ser a primeira [na Globo] é muito difícil; melhor ficar onde está”**, o que ela interpretou como falta de apoio dele à sua ascensão ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)). Esse episódio mostra que Pelé tentou influenciar também os rumos que Xuxa tomaria, embora, nesse caso, ela tenha decidido seguir sua intuição profissional e aceitar o desafio na Globo – escolha que se revelaria acertada. Em resumo, Pelé atuou sim como facilitador de várias oportunidades profissionais para Xuxa (de filmes a comerciais e visibilidade editorial), mas ela soube trilhar seu caminho a partir daí, inclusive contrariando conselhos dele quando necessário. ## Papel da Revista *Manchete* e Outras Mídias na Promoção de Xuxa A revista ***Manchete*** teve um papel central na ascensão de Xuxa durante o relacionamento com Pelé. Foi justamente num ensaio para a *Manchete* que os dois se conheceram, em dezembro de 1980 ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)), e a partir daí a publicação tornou-se uma espécie oficiosa de cronista do romance. A *Manchete* era uma das revistas mais populares do Brasil naquela época e, ao perceber o interesse do público pelo casal, passou a trazê-los frequentemente em suas páginas. De fato, a revista que agiu como "cupido" do casal **“contava detalhes do romance a cada edição”**, alimentando a curiosidade nacional sobre a vida de Pelé e sua jovem namorada ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=nacionalmente%20famosa)). As capas exibindo Xuxa e Pelé juntos (em cenários que iam da praia a eventos sociais) viraram chamariz nas bancas e contribuíram enormemente para fixar a imagem de Xuxa na mente do público. ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html)) *Capa da revista Manchete (20 de dezembro de 1980) mostrando Pelé ao centro com Xuxa (à esquerda) e outras modelos. A partir desse ensaio fotográfico, a revista passou a acompanhar de perto o romance, impulsionando a imagem de Xuxa nacionalmente.* ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)) Além da *Manchete*, outras mídias impressas também surfaram no interesse pelo casal e ajudaram a moldar a imagem de Xuxa. Revistas de celebridades e colunas sociais publicavam notas e fotos frequentes, ora exaltando o glamour do par, ora especulando sobre fofocas. Xuxa, que pouco antes era desconhecida fora do circuito da moda, tornou-se figura constante em revistas semanais como *Contigo!* e *Amiga* (dedicadas à vida dos famosos), assim como em jornais de grande circulação. Esse bombardeio de aparições – entrevistas, fotos e manchetes – construiu a **persona pública** de Xuxa simultaneamente como **modelo desejada e namorada devotada**. A promoção de sua imagem tinha um tom deliberadamente positivo nas revistas: enfatizava-se sua beleza, juventude e sorte por ter sido “escolhida” pelo rei Pelé. Em contrapartida, eventuais polêmicas (como cenas ousadas que ela fez no cinema ou rumores de crises no namoro) eram administradas pela própria mídia de maneira a preservar o encanto em torno de Xuxa, que já despontava como uma espécie de Cinderella moderna na narrativa do entretenimento brasileiro. Cabe destacar que a conexão de Xuxa com a *Manchete* não ficou só nas páginas da revista, mas transbordou para a televisão, já que a Rede Manchete (canal de TV fundado em 1983) pertencia ao mesmo grupo empresarial. Essa sinergia mídia impressa/televisão beneficiou Xuxa: **quando a Rede Manchete buscava uma apresentadora para seu novo programa infantil em 1983, Xuxa – já famosa pelas capas de revista – foi convidada** para o posto ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L355%20TV%20Manchete%2C,ter%20como%20apresentadora%20de%20programa)). Ou seja, a exposição na revista *Manchete* serviu de vitrine para que os executivos da emissora homônima apostassem nela na TV. Outras mídias também legitimaram sua transição de modelo para apresentadora, publicando matérias sobre sua simpatia com as crianças e seu carisma diante das câmeras, preparando o público para aceitar Xuxa em um novo papel. Assim, o período do relacionamento com Pelé viu a mídia – liderada pela revista *Manchete* – construir e promover intensamente a imagem de Xuxa, pavimentando o caminho para suas conquistas seguintes. ## O Relacionamento e a Conquista de Espaços na TV: *Clube da Criança* e Rede Globo O namoro com Pelé coincidiu com a entrada de Xuxa na televisão e possivelmente facilitou essa transição. Em 1983, a recém-inaugurada Rede Manchete lançou o **“Clube da Criança”**, primeiro programa infantil de auditório da emissora, e Xuxa foi escolhida como apresentadora. Há indícios de que sua fama prévia – alavancada pelo relacionamento – foi decisiva nessa escolha. Conforme relatos, o diretor Maurício Sherman (responsável pelo projeto) estava de olho em Xuxa por sua notoriedade e carisma, chegando a dizer que ela reunia *“a sensualidade de Marilyn Monroe, o sorriso de Doris Day e um quê de Peter Pan”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)) – uma combinação que poderia funcionar bem num programa infantil. Xuxa inicialmente hesitou em aceitar, talvez pelo contraste entre sua imagem de modelo sensual e o universo infantil, mas acabou assinando contrato com a Manchete ([Clube da Criança – Wikipédia, a enciclopédia livre](https://pt.wikipedia.org/wiki/Clube_da_Crian%C3%A7a#:~:text=match%20at%20L206%20comando%20da,por%20Maur%C3%ADcio%20Sherman%20e%20pelo)). Assim, aos 20 anos de idade, ela estreava como apresentadora de TV, **em grande parte graças à visibilidade e confiança que o nome “Xuxa” (já famoso por ser namorada do Pelé) passava aos produtores**. Não há registro de que Pelé tenha intervindo diretamente para que Xuxa conseguisse o posto no *Clube da Criança*. Foi a própria rede Manchete – estimulada pelo burburinho em torno dela – que a **“procurou e a convidou para apresentar”** o programa ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)). Porém, é inegável que, sem o destaque que Xuxa conquistara nos anos anteriores na imprensa (devido ao namoro), dificilmente uma emissora arriscaria colocar uma jovem inexperiente para comandar um show infantil nacional. Ou seja, o relacionamento criou as condições favoráveis para essa oportunidade surgir. Uma vez no ar, Xuxa rapidamente mostrou talento próprio: o *Clube da Criança* foi ganhando audiência e revelou a aptidão dela em se comunicar com o público infantil ([Xuxa, Pantanal, Cavaleiros dos Zodíacos: lembre sucessos da TV ...](https://www.folhape.com.br/cultura/xuxa-pantanal-cavaleiros-dos-zodiacos-e-mais-sucessos-da-tv/334766/#:~:text=Xuxa%2C%20Pantanal%2C%20Cavaleiros%20dos%20Zod%C3%ADacos%3A,exibido%20no%20fim%20de)). Ainda durante seu tempo na Manchete, Xuxa manteve-se nos holofotes tanto pela carreira quanto pelo namoro com Pelé – frequentemente um assunto alimentava o outro na mídia. Em meados de 1986, já conhecida como a “Rainha dos Baixinhos” pelo sucesso junto às crianças, Xuxa recebeu uma proposta para se transferir para a Rede Globo, a principal emissora do país ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Novamente, aqui o relacionamento com Pelé tem um papel indireto: por um lado, pode ter ajudado a construir a notoriedade que chamou a atenção da Globo; por outro, chegava ao fim exatamente nesse momento, marcando uma virada na vida dela. Após alguns anos de *Clube da Criança*, Xuxa decidiu dar um passo adiante. Ela mesma tomou a iniciativa de terminar o namoro com Pelé e aceitou o convite para fazer o **“Xou da Xuxa”** na Globo ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Pelé, como mencionado, havia expressado reservas sobre essa mudança de emissora ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)), mas sem sucesso em demovê-la. Com a benção do dono da Manchete, Adolpho Bloch (que a tratava “como filha” e apoiou seu crescimento) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L405%20Manchete%20e,%E2%80%99%E2%80%9D)) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=Manchete%20e%20fui%20embora%E2%80%9D%2C%20recorda,%E2%80%99%E2%80%9D)), Xuxa partiu para a Globo levando sua diretora Marlene Mattos, e estreou em junho de 1986 o programa que a consagraria definitivamente. É importante notar que, ao ingressar na Globo, Xuxa já não dependia mais da aura de “namorada do Pelé” – ela havia se firmado como apresentadora de sucesso por méritos próprios. Ainda assim, **o relacionamento anterior continuou a ser parte de sua imagem pública**: a mídia noticiou a mudança destacando que a namorada de Pelé chegara à Globo, e muitos espectadores tinham curiosidade sobre aquela moça cuja fama começara nos braços do ídolo do futebol. Em resumo, o namoro ajudou Xuxa a conquistar o primeiro grande espaço na TV (na Manchete), fornecendo-lhe exposição e credibilidade iniciais, enquanto sua ida para a Globo foi impulsionada principalmente pelo desempenho no *Clube da Criança* – algo que o prestígio conquistado durante o relacionamento tornou possível em primeiro lugar. ## Percepção da Mídia e do Público sobre o Casal e a Imagem de Xuxa Durante os anos de namoro, Pelé e Xuxa foram um prato cheio para a imprensa e objeto de variadas opiniões do público. De um lado, eram celebrados como **“casal perfeito na mídia”**, aparecendo sorridentes em eventos e capas, o que projetava uma imagem glamourosa e apaixonada ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Image%3A%20Pel%C3%A9%20e%20Xuxa%20na,perfeito%20na%20m%C3%ADdia%2C%20mas%20com)). Xuxa era frequentemente retratada como a bela jovem humilde que havia conquistado o coração do "rei", uma narrativa de conto de fadas que agradava muitos fãs. Pessoas próximas diziam na época: *“Nossa, como ela está apaixonada, como ela está de quatro pelo Pelé”*, segundo relembrou a própria Xuxa, indicando que sua dedicação ao namorado era visível e comentada ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Ao%20participar%20de%20uma%20live,de%20quatro%20para%20o%20Pel%C3%A9%27%E2%80%9D)). Essa percepção de autenticidade nos sentimentos ajudou a humanizar Xuxa aos olhos do público, diferenciando-a de estereótipos de *roupante* ou interesse calculado. Por outro lado, nem toda a atenção era positiva. **Houve murmúrios maldosos e preconceituosos nos bastidores**. Pelé e Xuxa formavam um casal interracial (ele negro, ela branca e bem mais jovem), o que, segundo a imprensa, **“gerava olhares de reprovação dos conservadores” e até comentários racistas proferidos pelas costas** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Os%20dois%20eram%20perseguidos%20por,Mas%20nem%20tudo%20era%20agrad%C3%A1vel)). Além disso, alguns duvidavam das intenções de Xuxa no relacionamento, insinuando que ela buscava ascensão social por meio de Pelé. Termos pejorativos como *“maria-chuteira”* (gíria para mulheres que namoram jogadores em busca de status) e *“alpinista social”* chegaram a ser associados a Xuxa por fofoqueiros da época ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=olhares%20de%20reprova%C3%A7%C3%A3o%20dos%20conservadores)). Essa desconfiança lançava sombra sobre a imagem dela, pintando-a, aos olhos de alguns, como oportunista em vez de namorada dedicada. Xuxa teve de lidar com esse tipo de insinuação ao longo do namoro, buscando provar que seu amor era verdadeiro e que ela também tinha talentos e ambições próprias. A mídia impressa, em geral, manteve uma postura favorável ao casal, explorando o romance como algo encantador. Mas não deixou de reportar as turbulências: sabia-se, por exemplo, das **frequentes traições de Pelé**, que Xuxa anos depois revelou ter suportado calada na época ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Por%20causa%20do%20companheiro%2C%20tamb%C3%A9m,que%20n%C3%A3o%20era%20o%20meu)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Apesar%20dos%20problemas%20corriqueiros%20com,Era%20uma%20situa%C3%A7%C3%A3o%20esquisita%E2%80%9D)). Essas infidelidades eram rumores correntes nos círculos de fofoca, embora Xuxa raramente comentasse publicamente enquanto estava com Pelé. O público, portanto, via um casal bonito e famoso, mas também acompanhava as especulações de crises e reconciliações pelos noticiários de celebridades. Cada aparição pública deles – fosse em um jogo de futebol, um evento beneficente ou nos camarotes do carnaval – era dissecada pelos repórteres, e cada declaração (ou silêncio) alimentava interpretações sobre o estado do relacionamento e sobre quem era Xuxa por trás da fama. No saldo final, o namoro com Pelé influenciou profundamente a **imagem pública de Xuxa**. Inicialmente marcada como “a namorada do Rei” – posição que trazia tanto admiração quanto inveja – Xuxa soube aproveitar a visibilidade para mostrar carisma e trabalho, transformando-se em uma estrela por direito próprio. Ao se tornar apresentadora infantil de sucesso ainda durante o namoro, ela começou a dissociar sua imagem da de Pelé, provando que podia ser mais do que um apêndice de um astro do esporte. Quando o relacionamento terminou em 1986, Xuxa emergiu não caída em desgraça, mas sim pronta para reinar sozinha na TV. A mídia continuou a mencioná-la em referência a Pelé por algum tempo (era inevitável, dado o quão famoso o casal fora), mas cada vez mais o público passou a enxergá-la principalmente como a **“Rainha dos Baixinhos”**, a figura alegre das manhãs na TV Globo. Em entrevistas posteriores, Xuxa admitiu ter sentimentos mistos ao lembrar dessa fase: ela se ressentiu, por exemplo, de Pelé ter classificado o que viveram como *“uma amizade colorida”* em vez de namoro sério ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Xuxa%20disse%20ter%20ficado%20magoada,N%C3%A3o%20fui%20avisada)) – frase do ex-jogador que a magoou e que veio a público muitos anos depois. Esse comentário retroativo de Pelé apenas reforçou o quanto a mídia e o público discutiram e dissecaram a natureza daquela relação. Em conclusão, a percepção do casal Xuxa e Pelé oscilou entre o encanto e a controvérsia, mas inegavelmente manteve Xuxa nos trending topics de sua época (para usar um termo atual). A jovem modelo gaúcha ganhou projeção, prestígio e também enfrentou julgamentos enquanto esteve com Pelé. Tudo isso moldou sua imagem – de **símbolo sexual e socialite em ascensão** a **profissional talentosa pronta para brilhar por conta própria**. O relacionamento forneceu-lhe a plataforma e a armadura mediática; coube a Xuxa transformar essa visibilidade em uma carreira sólida, o que ela fez com maestria ao se tornar uma das maiores apresentadoras da história da TV brasileira. **Fontes:** Entrevistas e depoimentos de Xuxa Meneghel (inclusive do livro *Memórias*, 2020), reportagens da época em revistas como *Manchete*, colunas sociais e jornais (compiladas em repositórios atuais), e biografias e retrospectivas sobre ambos os envolvidos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)), entre outras. Essas fontes confirmam o papel catalisador que o namoro com Pelé teve nos primeiros passos da trajetória de Xuxa, bem como os desafios e oportunidades que surgiram dessa intensa exposição pública.
@ 3ffac3a6:2d656657
2025-04-05 04:55:12# O Impacto do Namoro com Pelé na Carreira de Xuxa Meneghel ## Disclaimer: Esse texto foi totalmente escrito pelo ChatGPT, eu apenas pedi que ele fizesse uma pesquisa sobre o tema. **Introdução:** O relacionamento entre Xuxa Meneghel e Pelé, que durou cerca de seis anos (início dos anos 1980 até 1986), foi um dos mais comentados da década de 1980 ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)). Xuxa tinha apenas 17 anos quando começou a namorar o já consagrado “Rei do Futebol”, então com 40 anos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Xuxa%20tinha%2017%20anos,a%20primeira%20mulher%2C%20Rosemeri%20Cholbi)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=O%20jogador%20de%20futebol%20e,um%20relacionamento%20por%20seis%20anos)). Esse romance altamente midiático não só atiçou a curiosidade do público, como também alavancou a carreira de Xuxa de forma significativa. A seguir, detalhamos como o namoro aumentou a visibilidade da apresentadora, quais oportunidades profissionais podem ter tido influência direta de Pelé, o papel da revista *Manchete* e de outras mídias na promoção de sua imagem, se o relacionamento contribuiu para Xuxa conquistar espaços na TV (como o programa **Clube da Criança** e, posteriormente, na Rede Globo) e como mídia e público percebiam o casal – tudo embasado em fontes da época, entrevistas e biografias. ## Aumento da Visibilidade Midiática nos Anos 1980 O namoro com Pelé catapultou Xuxa a um novo patamar de fama. Até então uma modelo em começo de carreira, Xuxa **“se tornou famosa ao aparecer ao lado do esportista de maior status do Brasil”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=O%20romance%20come%C3%A7ou%20quando%20ela,de%20maior%20status%20do%20Brasil)). A partir do momento em que o relacionamento se tornou público, ela passou a estampar capas de revistas com frequência e a ser assunto constante na imprensa. Em 20 de dezembro de 1980, a jovem apareceu na capa da revista *Manchete* ao lado de Pelé e outras modelos – um ensaio fotográfico que marcou o primeiro encontro dos dois e deu início à enorme atenção midiática em torno de Xuxa ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=O%20jantar%20aproximou%20o%20casal,E%20fui%E2%80%9D)). Não por acaso, *“naquele ano, ela foi capa de mais de cem revistas”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=convidadas%20a%20posar%20ao%20lado,de%20mais%20de%20cem%20revistas)), um indicativo claro de como sua visibilidade explodiu após começar a namorar Pelé. Jornais, revistas de celebridades e programas de fofoca passaram a segui-los de perto; o casal virou sensação nacional, comparado até ao “Casal 20” (dupla glamourosa de uma série de TV americana) pelo seu alto perfil na mídia ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)). Essa exposição intensa colocou Xuxa não apenas sob os holofotes do público, mas também a inseriu nos **bastidores do entretenimento**. Como namorada de Pelé – um dos homens mais conhecidos do mundo – Xuxa passou a frequentar eventos de gala, festas e bastidores de programas, onde conheceu figuras influentes do meio artístico e televisivo. Os fotógrafos os seguiam em eventos como bailes de carnaval e inaugurações, registrando cada aparição pública do casal. Com Pelé ao seu lado, Xuxa ganhou trânsito livre em círculos antes inacessíveis para uma modelo iniciante, construindo uma rede de contatos valiosa nos meios de comunicação. De fato, naquele início dos anos 80, **“os dois eram perseguidos por fotógrafos, apareciam em capas de revistas e até faziam publicidade juntos”** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) – evidência de que Xuxa, graças ao namoro, transitava tanto na frente quanto por trás das câmeras com muito mais facilidade. Em suma, o relacionamento conferiu a ela um grau de notoriedade nacional que provavelmente demoraria anos para conquistar de outra forma, preparando o terreno para os passos seguintes de sua carreira. ## Influência Direta de Pelé nas Oportunidades Profissionais de Xuxa Além do aumento geral da fama, há casos específicos em que Pelé influenciou diretamente oportunidades profissionais para Xuxa. Um exemplo contundente é o filme **“Amor Estranho Amor” (1982)** – longa de teor erótico no qual Xuxa atuou no início da carreira. Segundo relatos da própria apresentadora, **foi Pelé quem a incentivou a aceitar participar desse filme** ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Profissionalmente%2C%20Xuxa%20disse%20que%20Pel%C3%A9,Me%20enganaram%2C%20falaram%20um)). Na época ainda em início de trajetória, Xuxa acabou convencida pelo namorado de que aquela oportunidade poderia ser benéfica. Anos mais tarde, ela revelaria arrependimento pela escolha desse papel, mas o fato reforça que Pelé teve influência ativa em decisões profissionais de Xuxa no começo de sua jornada. Outra área de influência direta foram as **publicidades e campanhas comerciais**. Graças ao prestígio de Pelé, Xuxa recebeu convites para estrelar anúncios ao lado do então namorado. Já em 1981, por exemplo, os dois gravaram juntos comerciais para uma empresa imobiliária, aparecendo como casal em campanhas de TV daquele Natal (pelas **Imóveis Francisco Xavier**, um case famoso entre colecionadores de propagandas da época) ([Xuxa e Pelé: Natal de 1981 na Publicidade Imobiliária | TikTok](https://www.tiktok.com/@thebest.memories/video/7301084045402721541#:~:text=Xuxa%20e%20Pel%C3%A9%3A%20Natal%20de,Natal%20de%201981%20na)) ([Xuxa com Pelé em comercial de imobiliária em dezembro de 1981](https://www.youtube.com/watch?v=t45oWkJPFw0#:~:text=Xuxa%20com%20Pel%C3%A9%20em%20comercial,Im%C3%B3veis%20em%20dezembro%20de%201981)). Assim, Xuxa obteve espaço em campanhas publicitárias que dificilmente envolveriam uma modelo desconhecida – mas que, com a “namorada do Pelé” no elenco, ganhavam apelo extra. Isso evidencia que Pelé abriu portas também no mercado publicitário, dando a Xuxa oportunidades de trabalho e renda enquanto sua própria imagem pública se consolidava. Ademais, a presença de Pelé ao lado de Xuxa em diversos editoriais e ensaios fotográficos serviu para elevá-la de modelo anônima a personalidade conhecida. Revistas e jornais buscavam os dois para sessões de fotos e entrevistas, sabendo do interesse do público pelo casal. As capas conjuntas em publicações de grande circulação (como *Manchete* e outras) não só aumentaram a exposição de Xuxa, mas também conferiram a ela certa credibilidade midiática por associação. Em outras palavras, estar ao lado de um ícone como Pelé funcionou como um “selo de aprovação” implícito, deixando editores e produtores mais propensos a convidá-la para projetos. Vale lembrar que **“ao longo dos seis anos de relacionamento, [eles] posaram para várias capas da *Manchete*”**, com a revista acompanhando de perto cada fase do namoro ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)). Essa recorrência nas bancas solidificou o rosto e o nome de Xuxa na indústria do entretenimento. Por fim, é importante notar que nem todas as influências de Pelé foram positivas para a carreira dela – algumas foram tentativas de direcionamento. A própria Xuxa contou que, quando surgiu a oportunidade de ela ir para a TV Globo em 1986, Pelé desencorajou a mudança. **Ele sugeriu que Xuxa permanecesse na TV Manchete, dizendo que “ser a primeira [na Globo] é muito difícil; melhor ficar onde está”**, o que ela interpretou como falta de apoio dele à sua ascensão ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)). Esse episódio mostra que Pelé tentou influenciar também os rumos que Xuxa tomaria, embora, nesse caso, ela tenha decidido seguir sua intuição profissional e aceitar o desafio na Globo – escolha que se revelaria acertada. Em resumo, Pelé atuou sim como facilitador de várias oportunidades profissionais para Xuxa (de filmes a comerciais e visibilidade editorial), mas ela soube trilhar seu caminho a partir daí, inclusive contrariando conselhos dele quando necessário. ## Papel da Revista *Manchete* e Outras Mídias na Promoção de Xuxa A revista ***Manchete*** teve um papel central na ascensão de Xuxa durante o relacionamento com Pelé. Foi justamente num ensaio para a *Manchete* que os dois se conheceram, em dezembro de 1980 ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)), e a partir daí a publicação tornou-se uma espécie oficiosa de cronista do romance. A *Manchete* era uma das revistas mais populares do Brasil naquela época e, ao perceber o interesse do público pelo casal, passou a trazê-los frequentemente em suas páginas. De fato, a revista que agiu como "cupido" do casal **“contava detalhes do romance a cada edição”**, alimentando a curiosidade nacional sobre a vida de Pelé e sua jovem namorada ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=nacionalmente%20famosa)). As capas exibindo Xuxa e Pelé juntos (em cenários que iam da praia a eventos sociais) viraram chamariz nas bancas e contribuíram enormemente para fixar a imagem de Xuxa na mente do público. ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html)) *Capa da revista Manchete (20 de dezembro de 1980) mostrando Pelé ao centro com Xuxa (à esquerda) e outras modelos. A partir desse ensaio fotográfico, a revista passou a acompanhar de perto o romance, impulsionando a imagem de Xuxa nacionalmente.* ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=A%20extinta%20Manchete%20promovia%20uma,Xuxa%2C%20com%20apenas%2017%20anos)) Além da *Manchete*, outras mídias impressas também surfaram no interesse pelo casal e ajudaram a moldar a imagem de Xuxa. Revistas de celebridades e colunas sociais publicavam notas e fotos frequentes, ora exaltando o glamour do par, ora especulando sobre fofocas. Xuxa, que pouco antes era desconhecida fora do circuito da moda, tornou-se figura constante em revistas semanais como *Contigo!* e *Amiga* (dedicadas à vida dos famosos), assim como em jornais de grande circulação. Esse bombardeio de aparições – entrevistas, fotos e manchetes – construiu a **persona pública** de Xuxa simultaneamente como **modelo desejada e namorada devotada**. A promoção de sua imagem tinha um tom deliberadamente positivo nas revistas: enfatizava-se sua beleza, juventude e sorte por ter sido “escolhida” pelo rei Pelé. Em contrapartida, eventuais polêmicas (como cenas ousadas que ela fez no cinema ou rumores de crises no namoro) eram administradas pela própria mídia de maneira a preservar o encanto em torno de Xuxa, que já despontava como uma espécie de Cinderella moderna na narrativa do entretenimento brasileiro. Cabe destacar que a conexão de Xuxa com a *Manchete* não ficou só nas páginas da revista, mas transbordou para a televisão, já que a Rede Manchete (canal de TV fundado em 1983) pertencia ao mesmo grupo empresarial. Essa sinergia mídia impressa/televisão beneficiou Xuxa: **quando a Rede Manchete buscava uma apresentadora para seu novo programa infantil em 1983, Xuxa – já famosa pelas capas de revista – foi convidada** para o posto ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L355%20TV%20Manchete%2C,ter%20como%20apresentadora%20de%20programa)). Ou seja, a exposição na revista *Manchete* serviu de vitrine para que os executivos da emissora homônima apostassem nela na TV. Outras mídias também legitimaram sua transição de modelo para apresentadora, publicando matérias sobre sua simpatia com as crianças e seu carisma diante das câmeras, preparando o público para aceitar Xuxa em um novo papel. Assim, o período do relacionamento com Pelé viu a mídia – liderada pela revista *Manchete* – construir e promover intensamente a imagem de Xuxa, pavimentando o caminho para suas conquistas seguintes. ## O Relacionamento e a Conquista de Espaços na TV: *Clube da Criança* e Rede Globo O namoro com Pelé coincidiu com a entrada de Xuxa na televisão e possivelmente facilitou essa transição. Em 1983, a recém-inaugurada Rede Manchete lançou o **“Clube da Criança”**, primeiro programa infantil de auditório da emissora, e Xuxa foi escolhida como apresentadora. Há indícios de que sua fama prévia – alavancada pelo relacionamento – foi decisiva nessa escolha. Conforme relatos, o diretor Maurício Sherman (responsável pelo projeto) estava de olho em Xuxa por sua notoriedade e carisma, chegando a dizer que ela reunia *“a sensualidade de Marilyn Monroe, o sorriso de Doris Day e um quê de Peter Pan”* ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)) – uma combinação que poderia funcionar bem num programa infantil. Xuxa inicialmente hesitou em aceitar, talvez pelo contraste entre sua imagem de modelo sensual e o universo infantil, mas acabou assinando contrato com a Manchete ([Clube da Criança – Wikipédia, a enciclopédia livre](https://pt.wikipedia.org/wiki/Clube_da_Crian%C3%A7a#:~:text=match%20at%20L206%20comando%20da,por%20Maur%C3%ADcio%20Sherman%20e%20pelo)). Assim, aos 20 anos de idade, ela estreava como apresentadora de TV, **em grande parte graças à visibilidade e confiança que o nome “Xuxa” (já famoso por ser namorada do Pelé) passava aos produtores**. Não há registro de que Pelé tenha intervindo diretamente para que Xuxa conseguisse o posto no *Clube da Criança*. Foi a própria rede Manchete – estimulada pelo burburinho em torno dela – que a **“procurou e a convidou para apresentar”** o programa ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=TV%20Manchete%2C%20do%20grupo%20de,ter%20como%20apresentadora%20de%20programa)). Porém, é inegável que, sem o destaque que Xuxa conquistara nos anos anteriores na imprensa (devido ao namoro), dificilmente uma emissora arriscaria colocar uma jovem inexperiente para comandar um show infantil nacional. Ou seja, o relacionamento criou as condições favoráveis para essa oportunidade surgir. Uma vez no ar, Xuxa rapidamente mostrou talento próprio: o *Clube da Criança* foi ganhando audiência e revelou a aptidão dela em se comunicar com o público infantil ([Xuxa, Pantanal, Cavaleiros dos Zodíacos: lembre sucessos da TV ...](https://www.folhape.com.br/cultura/xuxa-pantanal-cavaleiros-dos-zodiacos-e-mais-sucessos-da-tv/334766/#:~:text=Xuxa%2C%20Pantanal%2C%20Cavaleiros%20dos%20Zod%C3%ADacos%3A,exibido%20no%20fim%20de)). Ainda durante seu tempo na Manchete, Xuxa manteve-se nos holofotes tanto pela carreira quanto pelo namoro com Pelé – frequentemente um assunto alimentava o outro na mídia. Em meados de 1986, já conhecida como a “Rainha dos Baixinhos” pelo sucesso junto às crianças, Xuxa recebeu uma proposta para se transferir para a Rede Globo, a principal emissora do país ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Novamente, aqui o relacionamento com Pelé tem um papel indireto: por um lado, pode ter ajudado a construir a notoriedade que chamou a atenção da Globo; por outro, chegava ao fim exatamente nesse momento, marcando uma virada na vida dela. Após alguns anos de *Clube da Criança*, Xuxa decidiu dar um passo adiante. Ela mesma tomou a iniciativa de terminar o namoro com Pelé e aceitou o convite para fazer o **“Xou da Xuxa”** na Globo ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Pel%C3%A9%20e%20Xuxa%20ficaram%20juntos,do%20mesmo%20grupo%20da%20revista)). Pelé, como mencionado, havia expressado reservas sobre essa mudança de emissora ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)), mas sem sucesso em demovê-la. Com a benção do dono da Manchete, Adolpho Bloch (que a tratava “como filha” e apoiou seu crescimento) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=match%20at%20L405%20Manchete%20e,%E2%80%99%E2%80%9D)) ([Xuxa está em paz - revista piauí](https://piaui.folha.uol.com.br/materia/xuxa-esta-em-paz/#:~:text=Manchete%20e%20fui%20embora%E2%80%9D%2C%20recorda,%E2%80%99%E2%80%9D)), Xuxa partiu para a Globo levando sua diretora Marlene Mattos, e estreou em junho de 1986 o programa que a consagraria definitivamente. É importante notar que, ao ingressar na Globo, Xuxa já não dependia mais da aura de “namorada do Pelé” – ela havia se firmado como apresentadora de sucesso por méritos próprios. Ainda assim, **o relacionamento anterior continuou a ser parte de sua imagem pública**: a mídia noticiou a mudança destacando que a namorada de Pelé chegara à Globo, e muitos espectadores tinham curiosidade sobre aquela moça cuja fama começara nos braços do ídolo do futebol. Em resumo, o namoro ajudou Xuxa a conquistar o primeiro grande espaço na TV (na Manchete), fornecendo-lhe exposição e credibilidade iniciais, enquanto sua ida para a Globo foi impulsionada principalmente pelo desempenho no *Clube da Criança* – algo que o prestígio conquistado durante o relacionamento tornou possível em primeiro lugar. ## Percepção da Mídia e do Público sobre o Casal e a Imagem de Xuxa Durante os anos de namoro, Pelé e Xuxa foram um prato cheio para a imprensa e objeto de variadas opiniões do público. De um lado, eram celebrados como **“casal perfeito na mídia”**, aparecendo sorridentes em eventos e capas, o que projetava uma imagem glamourosa e apaixonada ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Image%3A%20Pel%C3%A9%20e%20Xuxa%20na,perfeito%20na%20m%C3%ADdia%2C%20mas%20com)). Xuxa era frequentemente retratada como a bela jovem humilde que havia conquistado o coração do "rei", uma narrativa de conto de fadas que agradava muitos fãs. Pessoas próximas diziam na época: *“Nossa, como ela está apaixonada, como ela está de quatro pelo Pelé”*, segundo relembrou a própria Xuxa, indicando que sua dedicação ao namorado era visível e comentada ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Ao%20participar%20de%20uma%20live,de%20quatro%20para%20o%20Pel%C3%A9%27%E2%80%9D)). Essa percepção de autenticidade nos sentimentos ajudou a humanizar Xuxa aos olhos do público, diferenciando-a de estereótipos de *roupante* ou interesse calculado. Por outro lado, nem toda a atenção era positiva. **Houve murmúrios maldosos e preconceituosos nos bastidores**. Pelé e Xuxa formavam um casal interracial (ele negro, ela branca e bem mais jovem), o que, segundo a imprensa, **“gerava olhares de reprovação dos conservadores” e até comentários racistas proferidos pelas costas** ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Os%20dois%20eram%20perseguidos%20por,Mas%20nem%20tudo%20era%20agrad%C3%A1vel)). Além disso, alguns duvidavam das intenções de Xuxa no relacionamento, insinuando que ela buscava ascensão social por meio de Pelé. Termos pejorativos como *“maria-chuteira”* (gíria para mulheres que namoram jogadores em busca de status) e *“alpinista social”* chegaram a ser associados a Xuxa por fofoqueiros da época ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=olhares%20de%20reprova%C3%A7%C3%A3o%20dos%20conservadores)). Essa desconfiança lançava sombra sobre a imagem dela, pintando-a, aos olhos de alguns, como oportunista em vez de namorada dedicada. Xuxa teve de lidar com esse tipo de insinuação ao longo do namoro, buscando provar que seu amor era verdadeiro e que ela também tinha talentos e ambições próprias. A mídia impressa, em geral, manteve uma postura favorável ao casal, explorando o romance como algo encantador. Mas não deixou de reportar as turbulências: sabia-se, por exemplo, das **frequentes traições de Pelé**, que Xuxa anos depois revelou ter suportado calada na época ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Por%20causa%20do%20companheiro%2C%20tamb%C3%A9m,que%20n%C3%A3o%20era%20o%20meu)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=Apesar%20dos%20problemas%20corriqueiros%20com,Era%20uma%20situa%C3%A7%C3%A3o%20esquisita%E2%80%9D)). Essas infidelidades eram rumores correntes nos círculos de fofoca, embora Xuxa raramente comentasse publicamente enquanto estava com Pelé. O público, portanto, via um casal bonito e famoso, mas também acompanhava as especulações de crises e reconciliações pelos noticiários de celebridades. Cada aparição pública deles – fosse em um jogo de futebol, um evento beneficente ou nos camarotes do carnaval – era dissecada pelos repórteres, e cada declaração (ou silêncio) alimentava interpretações sobre o estado do relacionamento e sobre quem era Xuxa por trás da fama. No saldo final, o namoro com Pelé influenciou profundamente a **imagem pública de Xuxa**. Inicialmente marcada como “a namorada do Rei” – posição que trazia tanto admiração quanto inveja – Xuxa soube aproveitar a visibilidade para mostrar carisma e trabalho, transformando-se em uma estrela por direito próprio. Ao se tornar apresentadora infantil de sucesso ainda durante o namoro, ela começou a dissociar sua imagem da de Pelé, provando que podia ser mais do que um apêndice de um astro do esporte. Quando o relacionamento terminou em 1986, Xuxa emergiu não caída em desgraça, mas sim pronta para reinar sozinha na TV. A mídia continuou a mencioná-la em referência a Pelé por algum tempo (era inevitável, dado o quão famoso o casal fora), mas cada vez mais o público passou a enxergá-la principalmente como a **“Rainha dos Baixinhos”**, a figura alegre das manhãs na TV Globo. Em entrevistas posteriores, Xuxa admitiu ter sentimentos mistos ao lembrar dessa fase: ela se ressentiu, por exemplo, de Pelé ter classificado o que viveram como *“uma amizade colorida”* em vez de namoro sério ([Pelé e Xuxa: um estranho amor que durou seis anos - 29/12/2022 - Celebridades - F5](https://f5.folha.uol.com.br/celebridades/2022/12/pele-e-xuxa-o-estranho-amor-entre-o-rei-do-futebol-e-a-futura-rainha-dos-baixinhos.shtml#:~:text=Xuxa%20disse%20ter%20ficado%20magoada,N%C3%A3o%20fui%20avisada)) – frase do ex-jogador que a magoou e que veio a público muitos anos depois. Esse comentário retroativo de Pelé apenas reforçou o quanto a mídia e o público discutiram e dissecaram a natureza daquela relação. Em conclusão, a percepção do casal Xuxa e Pelé oscilou entre o encanto e a controvérsia, mas inegavelmente manteve Xuxa nos trending topics de sua época (para usar um termo atual). A jovem modelo gaúcha ganhou projeção, prestígio e também enfrentou julgamentos enquanto esteve com Pelé. Tudo isso moldou sua imagem – de **símbolo sexual e socialite em ascensão** a **profissional talentosa pronta para brilhar por conta própria**. O relacionamento forneceu-lhe a plataforma e a armadura mediática; coube a Xuxa transformar essa visibilidade em uma carreira sólida, o que ela fez com maestria ao se tornar uma das maiores apresentadoras da história da TV brasileira. **Fontes:** Entrevistas e depoimentos de Xuxa Meneghel (inclusive do livro *Memórias*, 2020), reportagens da época em revistas como *Manchete*, colunas sociais e jornais (compiladas em repositórios atuais), e biografias e retrospectivas sobre ambos os envolvidos ([A história da foto de revista que gerou o namoro de Pelé e Xuxa](https://www.terra.com.br/diversao/gente/a-historia-da-foto-de-revista-que-gerou-o-namoro-de-pele-e-xuxa,c5106b23301f6f0e7c03f38cdf9eb1a06kopa9ho.html#:~:text=Um%20tempo%20depois%2C%20quando%20a,se%20nacionalmente%20famosa)) ([Pelé viveu com Xuxa um namoro intenso afetado por fofocas e indiscrições](https://www.terra.com.br/diversao/gente/pele-viveu-com-xuxa-um-namoro-intenso-afetado-por-fofocas-e-indiscricoes,0c075d1a6be75f53536ad3b70e8e4a01iavthiai.html#:~:text=Morte%20s%C3%BAbita%20encerra%20fase%20feliz,vida%20da%20atriz%20Marcia%20Manfredini)) ([Xuxa e Pelé: o relacionamento que ficou cravado na história da imprensa brasileira](https://aventurasnahistoria.com.br/noticias/reportagem/xuxa-e-pele-o-relacionamento-que-ficou-cravado-na-historia-da-imprensa-brasileira.phtml#:~:text=,torcendo%20por%20mim%E2%80%9D%2C%20acrescentou%20Xuxa)) ([Xuxa e Pelé: um romance que se tornou inesquecível... | VEJA](https://veja.abril.com.br/coluna/veja-gente/xuxa-e-pele-um-romance-que-se-tornou-inesquecivel-para-os-dois/#:~:text=Um%20dos%20romances%20mais%20comentados,manchetes%20e%20revistas%20de%20fofoca)), entre outras. Essas fontes confirmam o papel catalisador que o namoro com Pelé teve nos primeiros passos da trajetória de Xuxa, bem como os desafios e oportunidades que surgiram dessa intensa exposição pública. @ 7d33ba57:1b82db35
2025-04-04 18:13:02Edinburgh is a city where ancient history and modern culture meet in the most atmospheric way. From its dramatic castle perched on a volcanic rock to narrow medieval alleys, vibrant festivals, and cozy pubs, Scotland’s capital is a must-visit for travelers seeking both beauty and depth. It’s a city that feels like stepping into a storybook—with a few ghost tales thrown in for good measure.  ## **🏛️ Top Things to See & Do in Edinburgh** ### **1️⃣ Edinburgh Castle** - Iconic and **steeped in royal history** - See the **Crown Jewels**, the **Stone of Destiny**, and sweeping **views over the city** - Don’t miss the **1 o’clock cannon fire**!  ### **2️⃣ Walk the Royal Mile** - The main street running from **Edinburgh Castle** to **Holyrood Palace** - Lined with **shops, historic closes (alleyways), churches, and pubs** - Pop into **St Giles’ Cathedral** and explore the **Writer’s Museum**  ### **3️⃣ Holyrood Palace & Arthur’s Seat** - The Queen’s official Scottish residence 👑 - Hike up **Arthur’s Seat**, an ancient volcano, for **amazing panoramic views** of Edinburgh and beyond ### **4️⃣ Explore the Old Town & New Town** - **Old Town:** Medieval, moody, atmospheric - **New Town:** Elegant Georgian streets and **great shopping on Princes Street** - Don’t miss **Victoria Street** – rumored inspiration for Harry Potter’s Diagon Alley ✨  ### **5️⃣ Museums & Culture** - **National Museum of Scotland** – interactive and family-friendly - **Scottish National Gallery** – features art by Turner, Van Gogh, and more - **Camera Obscura & World of Illusions** – quirky and fun near the castle ### **6️⃣ Edinburgh’s Underground & Ghost Tours** - Explore the **hidden vaults under the city** - Join a ghost tour or **learn about Edinburgh’s dark past**, including grave robbers and plague victims ### **7️⃣ Festivals Galore 🎭** - **Edinburgh Festival Fringe (August)** – The **largest arts festival in the world** - **Edinburgh International Festival**, **Book Festival**, and **Hogmanay (New Year)** celebrations  ## **🍽️ What to Eat in Edinburgh** - **Haggis, neeps & tatties** – A classic, surprisingly tasty Scottish dish - **Scottish salmon**, **Cullen skink (smoky fish soup)** - **Afternoon tea** or **Scottish whisky tasting** in a historic bar 🥃 - Try local spots like **The Witchery**, **Makars Gourmet Mash Bar**, or **The Scran & Scallie**  ## **🚶♀️ Tips for Visiting Edinburgh** ✅ Wear comfy shoes – **cobblestones and hills** are part of the charm ✅ Be ready for **4 seasons in a day** – pack layers and a rain jacket ☁️☀️🌧️ ✅ **Book ahead** in summer – especially during August festivals ✅ Take a day trip to **Rosslyn Chapel, the Highlands, or Stirling Castle** for more Scottish beauty ✅ Consider the **Edinburgh City Pass** if planning to visit many attractions 
@ 7d33ba57:1b82db35
2025-04-04 18:13:02Edinburgh is a city where ancient history and modern culture meet in the most atmospheric way. From its dramatic castle perched on a volcanic rock to narrow medieval alleys, vibrant festivals, and cozy pubs, Scotland’s capital is a must-visit for travelers seeking both beauty and depth. It’s a city that feels like stepping into a storybook—with a few ghost tales thrown in for good measure.  ## **🏛️ Top Things to See & Do in Edinburgh** ### **1️⃣ Edinburgh Castle** - Iconic and **steeped in royal history** - See the **Crown Jewels**, the **Stone of Destiny**, and sweeping **views over the city** - Don’t miss the **1 o’clock cannon fire**!  ### **2️⃣ Walk the Royal Mile** - The main street running from **Edinburgh Castle** to **Holyrood Palace** - Lined with **shops, historic closes (alleyways), churches, and pubs** - Pop into **St Giles’ Cathedral** and explore the **Writer’s Museum**  ### **3️⃣ Holyrood Palace & Arthur’s Seat** - The Queen’s official Scottish residence 👑 - Hike up **Arthur’s Seat**, an ancient volcano, for **amazing panoramic views** of Edinburgh and beyond ### **4️⃣ Explore the Old Town & New Town** - **Old Town:** Medieval, moody, atmospheric - **New Town:** Elegant Georgian streets and **great shopping on Princes Street** - Don’t miss **Victoria Street** – rumored inspiration for Harry Potter’s Diagon Alley ✨  ### **5️⃣ Museums & Culture** - **National Museum of Scotland** – interactive and family-friendly - **Scottish National Gallery** – features art by Turner, Van Gogh, and more - **Camera Obscura & World of Illusions** – quirky and fun near the castle ### **6️⃣ Edinburgh’s Underground & Ghost Tours** - Explore the **hidden vaults under the city** - Join a ghost tour or **learn about Edinburgh’s dark past**, including grave robbers and plague victims ### **7️⃣ Festivals Galore 🎭** - **Edinburgh Festival Fringe (August)** – The **largest arts festival in the world** - **Edinburgh International Festival**, **Book Festival**, and **Hogmanay (New Year)** celebrations  ## **🍽️ What to Eat in Edinburgh** - **Haggis, neeps & tatties** – A classic, surprisingly tasty Scottish dish - **Scottish salmon**, **Cullen skink (smoky fish soup)** - **Afternoon tea** or **Scottish whisky tasting** in a historic bar 🥃 - Try local spots like **The Witchery**, **Makars Gourmet Mash Bar**, or **The Scran & Scallie**  ## **🚶♀️ Tips for Visiting Edinburgh** ✅ Wear comfy shoes – **cobblestones and hills** are part of the charm ✅ Be ready for **4 seasons in a day** – pack layers and a rain jacket ☁️☀️🌧️ ✅ **Book ahead** in summer – especially during August festivals ✅ Take a day trip to **Rosslyn Chapel, the Highlands, or Stirling Castle** for more Scottish beauty ✅ Consider the **Edinburgh City Pass** if planning to visit many attractions  @ 9bcc5462:eb501d90
2025-04-04 16:02:14*The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.* It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World! Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us. Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong! As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court. Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.”
@ 9bcc5462:eb501d90
2025-04-04 16:02:14*The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.* It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World! Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us. Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong! As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court. Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.” @ 9967f375:04f9a5e1
2025-04-05 01:33:45Así en la Santa Iglesia Metropolitana (en donde se hallaron ochenta y seis Confesores, asignados por el V. Sr. Dean, y Cabildo Sede-Vacante) como en las Parroquiales, y demás, fue grande la concurrencia desde el dia primero (de abril), Sábado *ante Dominicam Palmarum*, para cumplir con el precepto de la Confesión anual, que se impuso, y mandó en el Máximo Concilio Lateranense, congregado en 1215 por el Señor Inocencio Tercero a que asistieron los Patriarcas de Antioquía, y Jerusalén, cuarenta Arzobispos, cuatrocientos Obispos, doce Abades, ochocientos Prelados inferiores; los Legados de Federico Segundo Emperador de Alemania, de Pedro Emperador de Oriente, de S. Luis Rey de Francia, de Juan Rey de Inglaterra, de D. Enrique Primero Rey de Castilla, D. Alonso Décimo Rey de León, Don Jaime Primero de Aragón, de Don Sancho el Fuerte de Navarra, de Don Alonso Segundo de Portugal, y los Embajadores de los Reyes de Chipre y Jerusalén.
@ 9967f375:04f9a5e1
2025-04-05 01:33:45Así en la Santa Iglesia Metropolitana (en donde se hallaron ochenta y seis Confesores, asignados por el V. Sr. Dean, y Cabildo Sede-Vacante) como en las Parroquiales, y demás, fue grande la concurrencia desde el dia primero (de abril), Sábado *ante Dominicam Palmarum*, para cumplir con el precepto de la Confesión anual, que se impuso, y mandó en el Máximo Concilio Lateranense, congregado en 1215 por el Señor Inocencio Tercero a que asistieron los Patriarcas de Antioquía, y Jerusalén, cuarenta Arzobispos, cuatrocientos Obispos, doce Abades, ochocientos Prelados inferiores; los Legados de Federico Segundo Emperador de Alemania, de Pedro Emperador de Oriente, de S. Luis Rey de Francia, de Juan Rey de Inglaterra, de D. Enrique Primero Rey de Castilla, D. Alonso Décimo Rey de León, Don Jaime Primero de Aragón, de Don Sancho el Fuerte de Navarra, de Don Alonso Segundo de Portugal, y los Embajadores de los Reyes de Chipre y Jerusalén. @ 7d33ba57:1b82db35
2025-04-04 14:35:00Zlarin is a small, car-free island near Šibenik, known for its peaceful atmosphere, crystal-clear waters, and centuries-old coral tradition. It’s often called the “Golden Island” for its natural beauty, and it remains a hidden gem on the Adriatic coast—perfect for quiet beach days, cycling, and slow travel.  ## **🌿 Why Visit Zlarin?** - **No cars = pure tranquility** – the whole island is pedestrian- and bike-friendly 🚲 - Rich in **coral diving heritage** – once the center of Croatia’s coral trade 🪸 - Beautiful **stone houses, pine forests, and untouched coves** - **Easy to reach** via a short ferry ride from Šibenik ⛴️  ## **🏖️ Things to Do on Zlarin** ### **1️⃣ Swim & Relax on Secluded Beaches** - **Veleš Beach** – A pebbly beach surrounded by pines, great for families 🌲 - **Magarna Bay** – Quiet, wild beach perfect for those seeking solitude 🧘♀️ - **Hidden coves** – Wander the coast and find your own little swimming spot 🌅 ### **2️⃣ Walk or Cycle the Island** - Well-marked **trails through pine forests and olive groves** - Visit the **hilltop viewpoint** for a panoramic look at Šibenik and nearby islands - Bring or rent a **bike in Šibenik** – bikes are ideal for exploring Zlarin 🚴♂️ ### **3️⃣ Learn About Coral Traditions** - Visit the **Zlarinka Museum** dedicated to the island’s **red coral harvesting history** - See traditional **jewelry and tools**, and learn about the craft’s cultural significance  ### **4️⃣ Stroll Through the Village** - Picturesque **stone streets, old chapels, and flower-filled gardens** - Enjoy a drink at a **local konoba (tavern)** with views of the sea 🍷 ### **5️⃣ Take a Boat Tour or Kayak Trip** - Explore nearby **Prvić, Kaprije, or Žirje islands** - Great area for **kayaking or paddleboarding** over glassy waters 🚣  ## **🚢 How to Get to Zlarin** - **Ferry from Šibenik** (approx. 25 minutes, year-round service) - **No cars allowed**, so park in Šibenik if needed - Easy to visit **for a day trip** or stay overnight for peace and stargazing  ## **💡 Tips for Visiting Zlarin** ✅ Best time to visit? **Late spring to early autumn** for swimming and quiet vibes ☀️ ✅ **Bring cash** – not all places accept cards 💶 ✅ Pack **snorkel gear and water shoes** – the underwater world is beautiful 🐠 ✅ **Stay overnight** for an unforgettable quiet island evening under the stars ✨ 
@ 7d33ba57:1b82db35
2025-04-04 14:35:00Zlarin is a small, car-free island near Šibenik, known for its peaceful atmosphere, crystal-clear waters, and centuries-old coral tradition. It’s often called the “Golden Island” for its natural beauty, and it remains a hidden gem on the Adriatic coast—perfect for quiet beach days, cycling, and slow travel.  ## **🌿 Why Visit Zlarin?** - **No cars = pure tranquility** – the whole island is pedestrian- and bike-friendly 🚲 - Rich in **coral diving heritage** – once the center of Croatia’s coral trade 🪸 - Beautiful **stone houses, pine forests, and untouched coves** - **Easy to reach** via a short ferry ride from Šibenik ⛴️  ## **🏖️ Things to Do on Zlarin** ### **1️⃣ Swim & Relax on Secluded Beaches** - **Veleš Beach** – A pebbly beach surrounded by pines, great for families 🌲 - **Magarna Bay** – Quiet, wild beach perfect for those seeking solitude 🧘♀️ - **Hidden coves** – Wander the coast and find your own little swimming spot 🌅 ### **2️⃣ Walk or Cycle the Island** - Well-marked **trails through pine forests and olive groves** - Visit the **hilltop viewpoint** for a panoramic look at Šibenik and nearby islands - Bring or rent a **bike in Šibenik** – bikes are ideal for exploring Zlarin 🚴♂️ ### **3️⃣ Learn About Coral Traditions** - Visit the **Zlarinka Museum** dedicated to the island’s **red coral harvesting history** - See traditional **jewelry and tools**, and learn about the craft’s cultural significance  ### **4️⃣ Stroll Through the Village** - Picturesque **stone streets, old chapels, and flower-filled gardens** - Enjoy a drink at a **local konoba (tavern)** with views of the sea 🍷 ### **5️⃣ Take a Boat Tour or Kayak Trip** - Explore nearby **Prvić, Kaprije, or Žirje islands** - Great area for **kayaking or paddleboarding** over glassy waters 🚣  ## **🚢 How to Get to Zlarin** - **Ferry from Šibenik** (approx. 25 minutes, year-round service) - **No cars allowed**, so park in Šibenik if needed - Easy to visit **for a day trip** or stay overnight for peace and stargazing  ## **💡 Tips for Visiting Zlarin** ✅ Best time to visit? **Late spring to early autumn** for swimming and quiet vibes ☀️ ✅ **Bring cash** – not all places accept cards 💶 ✅ Pack **snorkel gear and water shoes** – the underwater world is beautiful 🐠 ✅ **Stay overnight** for an unforgettable quiet island evening under the stars ✨  @ 5d4b6c8d:8a1c1ee3
2025-04-04 14:17:31We're down to the Final Four in March Madness and not only am I running away with the [Points Challenge](https://stacker.news/items/932715/r/Undisciplined), but I'll be running away with all of @grayruby's sats in the [Predyx](https://beta.predyx.com/category/basketball) live Predyxion markets. Is it good that all of the top teams are still alive or do we miss the upsets? In the NBA, the West is still all jumbled up. Seeds 2-9 are up for grabs. What matchups are likely in the playoffs and which ones are we hoping for? Ovechkin is right on the cusp of the All-Time Goals Scored record. Will he get there by the end of the season? @grayruby has some irresponsible, way too early, MLB takes. The NFL Draft picture might be clearing up, but there are always surprises. We'll talk about our hopes for how our teams approach the first few rounds. And, of course, we'll give updates on all the territory action. Happy stacking, stackers! originally posted at https://stacker.news/items/934354
@ 5d4b6c8d:8a1c1ee3
2025-04-04 14:17:31We're down to the Final Four in March Madness and not only am I running away with the [Points Challenge](https://stacker.news/items/932715/r/Undisciplined), but I'll be running away with all of @grayruby's sats in the [Predyx](https://beta.predyx.com/category/basketball) live Predyxion markets. Is it good that all of the top teams are still alive or do we miss the upsets? In the NBA, the West is still all jumbled up. Seeds 2-9 are up for grabs. What matchups are likely in the playoffs and which ones are we hoping for? Ovechkin is right on the cusp of the All-Time Goals Scored record. Will he get there by the end of the season? @grayruby has some irresponsible, way too early, MLB takes. The NFL Draft picture might be clearing up, but there are always surprises. We'll talk about our hopes for how our teams approach the first few rounds. And, of course, we'll give updates on all the territory action. Happy stacking, stackers! originally posted at https://stacker.news/items/934354 @ 6f7c7936:b48a90b1
2025-04-04 20:32:53In a world that celebrates constant movement, expression, and freedom of action, the idea of intentionally placing your hands behind your back—and even keeping them there—may seem counterintuitive. But for some, this posture offers not only physical benefits but also psychological calm, clarity, and even symbolic depth. Below, we explore why keeping your hands behind your back can be a meaningful act, and how, in certain cases, voluntary restraint can bring unexpected focus and peace. --- ## **1. A Posture of Respect and Composure** From military cadets to schoolchildren waiting in line, the image of someone standing with hands behind the back conveys **discipline, respect, and attentiveness**. It’s a non-verbal signal of being present without demanding attention. This posture is: - Open and non-confrontational, - Yet composed and intentional, - Signaling a readiness to listen, observe, or follow. For some, maintaining this position—even privately or in personal rituals—can help anchor them in the moment, especially in situations where **too much movement leads to distraction**. --- ## **2. Gentle Restraint as a Form of Focus** In certain contexts, some people take this concept further: not only placing the hands behind the back but **intentionally limiting their movement**, sometimes even with gentle bindings (e.g., soft bands, loops, or self-applied ties). While this may seem unusual, voluntary restraint can serve a purpose. For those who feel: - Overstimulated by too many choices, - Mentally scattered or physically restless, - Emotionally overwhelmed by expectations, …the act of keeping the hands still and out of use can provide **clarity, comfort, and simplicity**. It becomes easier to focus on thoughts, breathing, posture—or simply the act of being. The absence of distraction becomes its own form of freedom. --- ## **3. Sensory Regulation and Neurodiverse Experiences** For individuals who are **neurodivergent** (such as those on the autism spectrum), structured physical routines and reduced movement can support **sensory balance and regulation**. Keeping hands behind the back can: - Reduce tactile input or self-stimulatory movements, - Create a predictable, soothing sensation of symmetry, - Increase body awareness and improve posture. In these cases, restraint isn’t about control or punishment—it’s about **reclaiming calm in a world full of overwhelming stimuli**. --- ## **4. A Symbol of Stillness in Ritual or Reflection** Beyond the physical or sensory aspects, placing the hands behind the back can carry **symbolic weight**. It can be: - A gesture of humility, - A sign of inner stillness, - A choice to be quiet, observant, or connected to something larger. In personal practices, some individuals incorporate this position into meditation, silent walks, or reflection exercises. Others may even choose light binding—such as a soft scarf or wrap—not as an act of submission, but as a **tool for mindfulness**, reminding them to pause, breathe, and stay grounded. --- ## **5. The Importance of Intent and Consent** It’s crucial to note: **context and intent matter**. The experience of placing hands behind the back—especially when restraint is involved—should always be **voluntary, safe, and self-directed**. This isn’t about force or external control. It’s about choosing to explore stillness, structure, or personal rituals that bring meaning and calm. When approached mindfully, this simple act can become a quiet expression of **focus, discipline, and peace**. --- ## **Conclusion: A Small Gesture, a Deep Effect** In an age of constant motion and noise, choosing to stand still—with your hands behind your back—can be a **powerful form of presence**. Whether you’re seeking: - better posture, - sensory clarity, - emotional grounding, - or symbolic stillness, …this gesture offers a moment to reconnect—with your body, your breath, and yourself. It’s not about limitation. It’s about **choosing space within boundaries**—and discovering what stillness can teach you.
@ 6f7c7936:b48a90b1
2025-04-04 20:32:53In a world that celebrates constant movement, expression, and freedom of action, the idea of intentionally placing your hands behind your back—and even keeping them there—may seem counterintuitive. But for some, this posture offers not only physical benefits but also psychological calm, clarity, and even symbolic depth. Below, we explore why keeping your hands behind your back can be a meaningful act, and how, in certain cases, voluntary restraint can bring unexpected focus and peace. --- ## **1. A Posture of Respect and Composure** From military cadets to schoolchildren waiting in line, the image of someone standing with hands behind the back conveys **discipline, respect, and attentiveness**. It’s a non-verbal signal of being present without demanding attention. This posture is: - Open and non-confrontational, - Yet composed and intentional, - Signaling a readiness to listen, observe, or follow. For some, maintaining this position—even privately or in personal rituals—can help anchor them in the moment, especially in situations where **too much movement leads to distraction**. --- ## **2. Gentle Restraint as a Form of Focus** In certain contexts, some people take this concept further: not only placing the hands behind the back but **intentionally limiting their movement**, sometimes even with gentle bindings (e.g., soft bands, loops, or self-applied ties). While this may seem unusual, voluntary restraint can serve a purpose. For those who feel: - Overstimulated by too many choices, - Mentally scattered or physically restless, - Emotionally overwhelmed by expectations, …the act of keeping the hands still and out of use can provide **clarity, comfort, and simplicity**. It becomes easier to focus on thoughts, breathing, posture—or simply the act of being. The absence of distraction becomes its own form of freedom. --- ## **3. Sensory Regulation and Neurodiverse Experiences** For individuals who are **neurodivergent** (such as those on the autism spectrum), structured physical routines and reduced movement can support **sensory balance and regulation**. Keeping hands behind the back can: - Reduce tactile input or self-stimulatory movements, - Create a predictable, soothing sensation of symmetry, - Increase body awareness and improve posture. In these cases, restraint isn’t about control or punishment—it’s about **reclaiming calm in a world full of overwhelming stimuli**. --- ## **4. A Symbol of Stillness in Ritual or Reflection** Beyond the physical or sensory aspects, placing the hands behind the back can carry **symbolic weight**. It can be: - A gesture of humility, - A sign of inner stillness, - A choice to be quiet, observant, or connected to something larger. In personal practices, some individuals incorporate this position into meditation, silent walks, or reflection exercises. Others may even choose light binding—such as a soft scarf or wrap—not as an act of submission, but as a **tool for mindfulness**, reminding them to pause, breathe, and stay grounded. --- ## **5. The Importance of Intent and Consent** It’s crucial to note: **context and intent matter**. The experience of placing hands behind the back—especially when restraint is involved—should always be **voluntary, safe, and self-directed**. This isn’t about force or external control. It’s about choosing to explore stillness, structure, or personal rituals that bring meaning and calm. When approached mindfully, this simple act can become a quiet expression of **focus, discipline, and peace**. --- ## **Conclusion: A Small Gesture, a Deep Effect** In an age of constant motion and noise, choosing to stand still—with your hands behind your back—can be a **powerful form of presence**. Whether you’re seeking: - better posture, - sensory clarity, - emotional grounding, - or symbolic stillness, …this gesture offers a moment to reconnect—with your body, your breath, and yourself. It’s not about limitation. It’s about **choosing space within boundaries**—and discovering what stillness can teach you. @ 5d4b6c8d:8a1c1ee3
2025-04-04 13:07:55https://primal.net/e/nevent1qvzqqqqqqypzqdtgwhlaw2dsdm45c8t6wzslw5qyt5r8waxjrs86llj272ledghgqqsdjv9nadd5dwgzg9w02qp4s4gzphcxj3t8640nw4xn7qgf2lyzxysk9lmtp There are lots of possible issues with this chart, but it is pretty stark. A few random thoughts: 1. It might not be the people eating unhealthy amounts of sugar who cut back on it. I was never obese and I radically cut back on my sugar intake. 2. Sugar may have been highly correlated with other similar substances that people didn't cut back on. I'm thinking about other refined carbs, primarily. 3. There may simply be a lag and obesity will start declining as a result of lower sugar consumption. 4. It does look like the rate of obesity increase decreased slightly (lower slope), so maybe the issue is just that sugar intake is still too high, but the relationship is correct. What do you think explains this divergence? originally posted at https://stacker.news/items/934292
@ 5d4b6c8d:8a1c1ee3
2025-04-04 13:07:55https://primal.net/e/nevent1qvzqqqqqqypzqdtgwhlaw2dsdm45c8t6wzslw5qyt5r8waxjrs86llj272ledghgqqsdjv9nadd5dwgzg9w02qp4s4gzphcxj3t8640nw4xn7qgf2lyzxysk9lmtp There are lots of possible issues with this chart, but it is pretty stark. A few random thoughts: 1. It might not be the people eating unhealthy amounts of sugar who cut back on it. I was never obese and I radically cut back on my sugar intake. 2. Sugar may have been highly correlated with other similar substances that people didn't cut back on. I'm thinking about other refined carbs, primarily. 3. There may simply be a lag and obesity will start declining as a result of lower sugar consumption. 4. It does look like the rate of obesity increase decreased slightly (lower slope), so maybe the issue is just that sugar intake is still too high, but the relationship is correct. What do you think explains this divergence? originally posted at https://stacker.news/items/934292 @ 96203d66:643a819c
2025-04-04 12:58:46nostr:nevent1qqs9j3aw7jrzrw6mtgs9w2znhpg7u0vvur4v69mc8xhw90lqahej74ccx749u nostr:nevent1qqsxrleatwc7v4jvpu4hk3k4s5xvvral0uvt6svyydwtqsz7tk2v03spph2jk nostr:nevent1qqsykq5q6gaa499nykagjaf6sav7ul4ve0ge9y22707gueuasdtr97qsnceys nostr:nevent1qqsvyhuwmnjglrk8hxdw8ye3lzy9f0ahf3ajfsn0wkf3pnztlx7dxxsq7jhlg nostr:nevent1qqs2mmqn2sr6a0ysfjyyuwx5gwy4rxre6pwnjqnzzdszzrgh2zgynlgvv59j3 nostr:nevent1qqswhdmpjhkqzp0nld0m23kgyesqmyacksu9zf8kefxtwzracn7efuqt825sd nostr:nevent1qqsdzsjfa2dmkue5hk5dr8ttl76l3kf649yx4lwslwnh238442jfmmsv4fzmd nostr:nevent1qqszun5jhc22du06rle5r0z8zhj2ezm9pmmrfsqx4843qhz57k3aqxg738uv6 nostr:nevent1qqs8sx9mc2yuldpm5edrtplnge8ckgcr4xj8x7af3zdac0r4rat377ga689un nostr:nevent1qqswe5auf0ym9lg78prwj9ppy0rvpdq92pwend96jmq6udh3d5r3mfqxlyl8j nostr:nevent1qqsqtwgpl0v6qf03r4e9r4tsnyly354req9am2u6s5gjrtefwtedpmc72v3jx nostr:nevent1qqsx2w65lvwmf23rutmnhzw3k2paftngssvfdzqmwle4f3m77hk4u8c6lgmrx nostr:nevent1qqsfz6zpaw2gkgxjxfvevgsww0rhw07swwg0hun23xc4mfuh8f7afrg875wcx nostr:nevent1qqs0eknqgzut0sv0undcps42pnw7an4wjt7a2rwjxd2zaqg6rqpjdwg56yeq7 nostr:nevent1qqsrg7yyaacetzugj8304krg5ne0xxu7kdnps8tlnd797myseqp97vs8r7tup nostr:nevent1qqs20ap690l97n8py0g44w22963jkze78ws2em6e0cl02vc65nexmsqw9ugcd
@ 96203d66:643a819c
2025-04-04 12:58:46nostr:nevent1qqs9j3aw7jrzrw6mtgs9w2znhpg7u0vvur4v69mc8xhw90lqahej74ccx749u nostr:nevent1qqsxrleatwc7v4jvpu4hk3k4s5xvvral0uvt6svyydwtqsz7tk2v03spph2jk nostr:nevent1qqsykq5q6gaa499nykagjaf6sav7ul4ve0ge9y22707gueuasdtr97qsnceys nostr:nevent1qqsvyhuwmnjglrk8hxdw8ye3lzy9f0ahf3ajfsn0wkf3pnztlx7dxxsq7jhlg nostr:nevent1qqs2mmqn2sr6a0ysfjyyuwx5gwy4rxre6pwnjqnzzdszzrgh2zgynlgvv59j3 nostr:nevent1qqswhdmpjhkqzp0nld0m23kgyesqmyacksu9zf8kefxtwzracn7efuqt825sd nostr:nevent1qqsdzsjfa2dmkue5hk5dr8ttl76l3kf649yx4lwslwnh238442jfmmsv4fzmd nostr:nevent1qqszun5jhc22du06rle5r0z8zhj2ezm9pmmrfsqx4843qhz57k3aqxg738uv6 nostr:nevent1qqs8sx9mc2yuldpm5edrtplnge8ckgcr4xj8x7af3zdac0r4rat377ga689un nostr:nevent1qqswe5auf0ym9lg78prwj9ppy0rvpdq92pwend96jmq6udh3d5r3mfqxlyl8j nostr:nevent1qqsqtwgpl0v6qf03r4e9r4tsnyly354req9am2u6s5gjrtefwtedpmc72v3jx nostr:nevent1qqsx2w65lvwmf23rutmnhzw3k2paftngssvfdzqmwle4f3m77hk4u8c6lgmrx nostr:nevent1qqsfz6zpaw2gkgxjxfvevgsww0rhw07swwg0hun23xc4mfuh8f7afrg875wcx nostr:nevent1qqs0eknqgzut0sv0undcps42pnw7an4wjt7a2rwjxd2zaqg6rqpjdwg56yeq7 nostr:nevent1qqsrg7yyaacetzugj8304krg5ne0xxu7kdnps8tlnd797myseqp97vs8r7tup nostr:nevent1qqs20ap690l97n8py0g44w22963jkze78ws2em6e0cl02vc65nexmsqw9ugcd @ 98468676:3a02caf5
2025-04-04 20:21:10I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash. Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax. Here's the test wiki page I'm going to write: ``` = Simple AsciiDoc Demo This is a simple demonstration of AsciiDoc syntax for testing purposes. == Features AsciiDoc offers many formatting options that are easy to use. * Easy to learn * Supports rich text formatting * Can include code snippets * Works great for documentation [source,json] ---- { "name": "Test", "version": "1.0", "active": true } ---- ``` # We're going to use nak to publish it First, install `nak` if you haven't already ``` go install github.com/fiatjaf/nak@latest ``` *Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal* ``` # this is how to add it to your path on mac if using zsh echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc ``` And here's how to sign and publish this event with nak. *First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified* ``` # replace with your full secret key export NOSTR_SECRET_KEY="nsec1zcdn..." ``` Now to sign and publish the event: *Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal* ``` nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz ``` You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851 and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io
@ 98468676:3a02caf5
2025-04-04 20:21:10I'm making this tutorial for myself, as I plan to write many wiki pages describing DVM kinds, as a resource for DVMDash. Wiki pages on Nostr are written using AsciiDoc. If you don't know ascii doc, get an LLM (like https://duck.ai) to help you format into the right syntax. Here's the test wiki page I'm going to write: ``` = Simple AsciiDoc Demo This is a simple demonstration of AsciiDoc syntax for testing purposes. == Features AsciiDoc offers many formatting options that are easy to use. * Easy to learn * Supports rich text formatting * Can include code snippets * Works great for documentation [source,json] ---- { "name": "Test", "version": "1.0", "active": true } ---- ``` # We're going to use nak to publish it First, install `nak` if you haven't already ``` go install github.com/fiatjaf/nak@latest ``` *Note: if you don't use Go a lot, you may need to first install it and then add it to your path so the `nak` command is recognized by the terminal* ``` # this is how to add it to your path on mac if using zsh echo 'export PATH=$PATH:$(go env GOPATH)/bin' >> ~/.zshrc ``` And here's how to sign and publish this event with nak. *First, if you want to use your own nostr sec key, you can set the env variable to it and nak will use that if no secret key is specified* ``` # replace with your full secret key export NOSTR_SECRET_KEY="nsec1zcdn..." ``` Now to sign and publish the event: *Note: inner double quotes need to be escaped with a `\` before them in order to keep the formatting correct, because we're doing this in the terminal* ``` nak event -k 30818 -d "dvm-wiki-page-test" -t 'title=dvm wiki page test' -c "= Simple AsciiDoc Demo\n\nThis is a simple demonstration of AsciiDoc syntax for testing purposes. \n\n== Features\n\nAsciiDoc offers many formatting options that are easy to use. \n\n* Easy to learn \n* Supports rich text formatting \n* Can include code snippets \n* Works great for documentation \n\n[source,json] \n---- \n{ \"name\": \"Test\", \"version\": \"1.0\", \"active\": true } \n----" wss://relay.primal.net wss://relay.damus.io wss://relay.wikifreedia.xyz ``` You've now published your first wiki page! If done correctly, it will show up on wikistr.com, like mine did here: https://wikistr.com/dvm-wiki-page-test*da18e9860040f3bf493876fc16b1a912ae5a6f6fa8d5159c3de2b8233a0d9851 and on wikifreedia.xyz https://wikifreedia.xyz/dvm-wiki-page-test/dustind@dtdannen.github.io @ e0ef3b4e:6fd74878
2025-04-04 12:55:14At a conference I sit in a quite area and observe and enjoy a coffee. It's bustling around and many are attending a speech at the main stage. Two people sit next to me on a sofa and begin a conversation. He's wearing a beige hoodie and seems to be builder in the space, she's wearing a green winter dress and they seem to be colleagues. It seems they are now meeting for the first time in real life and exchanging advice, him advising her on how to store her Bitcoin. He’s been longer in the space it seems and she’s just started at the new start-up. I quickly introduce myself and ask them if I may listen in on the conversation since I am a researcher working in the space. They happily agree. She goes on to mention that she will be paid in Bitcoin and does not know how to store it. He goes on to advise her on using a hardware wallet, then takes out his phone and shows a video of the hardware wallet he is using. She says "Wow, it looks so easy to use. I tried so many different hardware wallets but they are so difficult to use." I see the tension in her shoulders, which then relaxes a bit. He goes on to show her all the security and backup methods for this particular hardware wallet. "I'm sold." She's smiling now and one can see that a decision has been made. These conversations are happening everyday across the world not only at conferences but in villages, cafes or during random conversation at co-working working spaces. While we strive for good marketing and adoption of Bitcoin, these simple conversations between two people are what is driving actual use. Safety and trust is a cultural concept in many countries and viewed differently depending on where one has originated from. If one is to imagine that many people would benefit from storing BTC on a device or using an app for lighting transactions then they must trust the process. This need to trust is a basic primary human need. They will only trust the process if: - Empowered: They feel as if they 100% know what they are doing when they are onboarded to the application/hardware device. If there is anything that creates doubt or friction in their minds, the trust to use it as a storage of BTC is gone. A person will window shop when deciding to use a wallet. On average when we interviewed people for various UX research initiatives one person had a minimum of two different Bitcoin wallets on their phone. Prior to that they had tested out quite a few wallets before settling on a decision. - Safe: Many are nervous that they will not be able to access their funds once they put it online/on a hardware device. However often receiving advice from someone they trust this will result in them feeling safe. They will likely use the very same device/application that is being used by their friend/colleague or person in a close inner circle. While this story might seem overly simplified, it’s been repeated multiple times while observing the behavior of people at conferences, through usability tests, and through interviews. If we understand that a person is tentatively stepping into a “home” (Bitcoin wallet/hardware device) and looking “around” (onboarding process). Once they step in, they will only leave their “bag” (BTC) on the table if specific criteria are met. If not, they will pick up their “bag” (BTC) and walk into the next “home.” (Bitcoin wallet/hardware device). During this process there are basic psychological principles are taking place. This is where design comes in and creates an experience. The UX design could be equated to the “interior design” of the house. Every click, every interaction every visual that a person sees or experiences is driving them to trust or distrust the experience. We as builders have a unique role in this process and I fully believe that we will solve these challenges together. If you've read all the way to the end, thank you. On another note, the last 3 weeks have been filled with a lot of strategic thinking, planning, and collaboration. There are many balls in the air at the moment: - [Designathon](https://event.bitcoin.design/) - [UX Research OFF](https://github.com/BitcoinDesign/Meta/issues/765) - [Presidio Design Week](https://github.com/BitcoinDesign/Meta/issues/746) - [BTC Prague](https://github.com/BitcoinDesign/Meta/issues/745) - UX Research Africa strategy If you've read all the way to the end, thank you for reading. ✌🏽Peace
@ e0ef3b4e:6fd74878
2025-04-04 12:55:14At a conference I sit in a quite area and observe and enjoy a coffee. It's bustling around and many are attending a speech at the main stage. Two people sit next to me on a sofa and begin a conversation. He's wearing a beige hoodie and seems to be builder in the space, she's wearing a green winter dress and they seem to be colleagues. It seems they are now meeting for the first time in real life and exchanging advice, him advising her on how to store her Bitcoin. He’s been longer in the space it seems and she’s just started at the new start-up. I quickly introduce myself and ask them if I may listen in on the conversation since I am a researcher working in the space. They happily agree. She goes on to mention that she will be paid in Bitcoin and does not know how to store it. He goes on to advise her on using a hardware wallet, then takes out his phone and shows a video of the hardware wallet he is using. She says "Wow, it looks so easy to use. I tried so many different hardware wallets but they are so difficult to use." I see the tension in her shoulders, which then relaxes a bit. He goes on to show her all the security and backup methods for this particular hardware wallet. "I'm sold." She's smiling now and one can see that a decision has been made. These conversations are happening everyday across the world not only at conferences but in villages, cafes or during random conversation at co-working working spaces. While we strive for good marketing and adoption of Bitcoin, these simple conversations between two people are what is driving actual use. Safety and trust is a cultural concept in many countries and viewed differently depending on where one has originated from. If one is to imagine that many people would benefit from storing BTC on a device or using an app for lighting transactions then they must trust the process. This need to trust is a basic primary human need. They will only trust the process if: - Empowered: They feel as if they 100% know what they are doing when they are onboarded to the application/hardware device. If there is anything that creates doubt or friction in their minds, the trust to use it as a storage of BTC is gone. A person will window shop when deciding to use a wallet. On average when we interviewed people for various UX research initiatives one person had a minimum of two different Bitcoin wallets on their phone. Prior to that they had tested out quite a few wallets before settling on a decision. - Safe: Many are nervous that they will not be able to access their funds once they put it online/on a hardware device. However often receiving advice from someone they trust this will result in them feeling safe. They will likely use the very same device/application that is being used by their friend/colleague or person in a close inner circle. While this story might seem overly simplified, it’s been repeated multiple times while observing the behavior of people at conferences, through usability tests, and through interviews. If we understand that a person is tentatively stepping into a “home” (Bitcoin wallet/hardware device) and looking “around” (onboarding process). Once they step in, they will only leave their “bag” (BTC) on the table if specific criteria are met. If not, they will pick up their “bag” (BTC) and walk into the next “home.” (Bitcoin wallet/hardware device). During this process there are basic psychological principles are taking place. This is where design comes in and creates an experience. The UX design could be equated to the “interior design” of the house. Every click, every interaction every visual that a person sees or experiences is driving them to trust or distrust the experience. We as builders have a unique role in this process and I fully believe that we will solve these challenges together. If you've read all the way to the end, thank you. On another note, the last 3 weeks have been filled with a lot of strategic thinking, planning, and collaboration. There are many balls in the air at the moment: - [Designathon](https://event.bitcoin.design/) - [UX Research OFF](https://github.com/BitcoinDesign/Meta/issues/765) - [Presidio Design Week](https://github.com/BitcoinDesign/Meta/issues/746) - [BTC Prague](https://github.com/BitcoinDesign/Meta/issues/745) - UX Research Africa strategy If you've read all the way to the end, thank you for reading. ✌🏽Peace @ ac58bbcc:7d9754d8
2025-04-04 20:13:12Lovely seeing you here. Hello there, and welcome to our very first post! We’re the team behind Math Success by DMTI, and we’re thrilled for this journey with you. If you’re a teacher, parent, or just someone who cares about kids and learning, you’ve probably noticed something: math education isn’t working well for most everyone. Too many students dread it, too many teachers feel stuck, and too many classrooms are stuck in a cycle of rote memorization that leaves most everyone uninspired. We’re here to change that—and that’s why we’ve built Math Success by DMTI, the leading K-6 Math Education Program. The Problem: Math Isn’t Adding Up Let’s start with the elephant in the room. Math education often misses the mark. Kids are taught to memorize times tables or follow steps without understanding why they work. It’s like handing someone a recipe without teaching them how to cook—they might make the dish, but they won’t know what to do when the ingredients change. Studies show U.S. students lag behind many peers globally in math, and the gap widens as they move through school. Why? Because we’ve prioritized procedures over meaning, drills over discovery, and compliance over curiosity. The result? Students who see math as a chore, not a chance to explore. Teachers, meanwhile, are stretched thin—juggling standards, testing pressures, and outdated methods that don’t spark joy or learning. It’s no wonder so many kids say, “I’m just not a math person.” But here’s the thing: we believe everyone can be a math person—if we teach it right. Our Solution: Math Success by DMTI That’s where Math Success by DMTI comes in. Born from the Developing Mathematical Thinking Institute and over 40 years of research, our program isn’t just another curriculum—it’s a rethink of how math should feel and function in the classroom. We’ve seen the data: classrooms using our approach see an average 35% jump in achievement. But more than that, they see kids who love math and teachers who can’t wait to teach it. So, how do we do it? It starts with our Developing Mathematical Thinking framework—a five-part recipe for success: Listen to Kids & Build on Their Ideas: We build on what students already know, making math personal and relevant. Speak the Right Language: We use the structural words unit, compose, decompose, iterate, partition, and equal to help kids communicate and connect to math across topics. Understand First, Calculate Later: Concepts come before procedures, so kids grasp the “why” before the “how.” Models and real-world connections: From blocks to drawings to numbers, we use models to make math tangible and fun while helping connect math to real life. Embrace Misconceptions & Mistakes: Missteps aren’t failures but chances to learn and grow. This isn’t the math you grew up with. It’s active, engaging, and built to stick. Teachers tell us it’s a game-changer—“I have never loved teaching math as much as I do now; math has come alive in my classroom. My students are further along now than any class I’ve ever taught before.” one said, “I could see the light bulbs going off like never before, and they’re excited!” Kids tell us, “Math is fun now!” And the numbers back it up: that 35% boost isn’t just a stat—it’s a sign of deeper understanding and real confidence. Why it matters Math isn’t just about numbers; it’s about thinking, solving problems, and opening doors. When kids succeed in math, they gain skills for life—whether they’re headed to STEM careers or just figuring out their budget. But beyond that, we want them to love it. To see math as a playground, not a prison. That’s our mission: successful learning and a genuine love for mathematics, one classroom at a time. What’s Next? This Substack is our space to share that mission with you. Expect stories from teachers and students, dives into our framework, tips for bringing math to life, and updates on our free courses (yep, free!). We’re partnering with educators like you to make this happen—because we can turn math education around together. So, stick with us. Subscribe below, drop a comment with your thoughts, and start building a world where math adds joy, not stress. Welcome to Math Success by DMTI—let’s make math work for everyone.
@ ac58bbcc:7d9754d8
2025-04-04 20:13:12Lovely seeing you here. Hello there, and welcome to our very first post! We’re the team behind Math Success by DMTI, and we’re thrilled for this journey with you. If you’re a teacher, parent, or just someone who cares about kids and learning, you’ve probably noticed something: math education isn’t working well for most everyone. Too many students dread it, too many teachers feel stuck, and too many classrooms are stuck in a cycle of rote memorization that leaves most everyone uninspired. We’re here to change that—and that’s why we’ve built Math Success by DMTI, the leading K-6 Math Education Program. The Problem: Math Isn’t Adding Up Let’s start with the elephant in the room. Math education often misses the mark. Kids are taught to memorize times tables or follow steps without understanding why they work. It’s like handing someone a recipe without teaching them how to cook—they might make the dish, but they won’t know what to do when the ingredients change. Studies show U.S. students lag behind many peers globally in math, and the gap widens as they move through school. Why? Because we’ve prioritized procedures over meaning, drills over discovery, and compliance over curiosity. The result? Students who see math as a chore, not a chance to explore. Teachers, meanwhile, are stretched thin—juggling standards, testing pressures, and outdated methods that don’t spark joy or learning. It’s no wonder so many kids say, “I’m just not a math person.” But here’s the thing: we believe everyone can be a math person—if we teach it right. Our Solution: Math Success by DMTI That’s where Math Success by DMTI comes in. Born from the Developing Mathematical Thinking Institute and over 40 years of research, our program isn’t just another curriculum—it’s a rethink of how math should feel and function in the classroom. We’ve seen the data: classrooms using our approach see an average 35% jump in achievement. But more than that, they see kids who love math and teachers who can’t wait to teach it. So, how do we do it? It starts with our Developing Mathematical Thinking framework—a five-part recipe for success: Listen to Kids & Build on Their Ideas: We build on what students already know, making math personal and relevant. Speak the Right Language: We use the structural words unit, compose, decompose, iterate, partition, and equal to help kids communicate and connect to math across topics. Understand First, Calculate Later: Concepts come before procedures, so kids grasp the “why” before the “how.” Models and real-world connections: From blocks to drawings to numbers, we use models to make math tangible and fun while helping connect math to real life. Embrace Misconceptions & Mistakes: Missteps aren’t failures but chances to learn and grow. This isn’t the math you grew up with. It’s active, engaging, and built to stick. Teachers tell us it’s a game-changer—“I have never loved teaching math as much as I do now; math has come alive in my classroom. My students are further along now than any class I’ve ever taught before.” one said, “I could see the light bulbs going off like never before, and they’re excited!” Kids tell us, “Math is fun now!” And the numbers back it up: that 35% boost isn’t just a stat—it’s a sign of deeper understanding and real confidence. Why it matters Math isn’t just about numbers; it’s about thinking, solving problems, and opening doors. When kids succeed in math, they gain skills for life—whether they’re headed to STEM careers or just figuring out their budget. But beyond that, we want them to love it. To see math as a playground, not a prison. That’s our mission: successful learning and a genuine love for mathematics, one classroom at a time. What’s Next? This Substack is our space to share that mission with you. Expect stories from teachers and students, dives into our framework, tips for bringing math to life, and updates on our free courses (yep, free!). We’re partnering with educators like you to make this happen—because we can turn math education around together. So, stick with us. Subscribe below, drop a comment with your thoughts, and start building a world where math adds joy, not stress. Welcome to Math Success by DMTI—let’s make math work for everyone. @ 6a6be47b:3e74e3e1
2025-04-04 12:41:11⛅️ This week has been a bit hazy—I haven’t been feeling my best. And that’s okay. There are days like that. But this time, it felt like something deeper, as if something was off. Like I wasn’t *enough*. 🌞 Thankfully, as the days went by, I started to feel better. Today, I feel like myself again—like I’ve put my human suit back on and climbed back on the horse. ✏️ I picked up my pencil and started drawing again, just me and my iPad, without any expectations weighing me down. It felt good—peaceful even—to create for the sake of creating. 🦉 What I’ve realized is this: It’s not bad to have goals or aspirations. Those are important! But what becomes unhealthy is chasing perfectionism while trying to achieve those goals. For me, perfectionism turns into a spiral—not rainbows and butterflies but a storm cloud of self-doubt. I guess I just want to share this in case anyone out there needs to hear it: It’s okay to be imperfect. And most importantly, it’s okay to just be yourself. [To those little leprechauns of doubt kicking and screaming inside my head, I can confidently say:*Not today, Satan!*](https://primal.net/e/nevent1qqsp3lc6wd4tqrwzssqmtv3mk6fctdzqn3hctjugrfkhtev6q68ht0g488mat)  🎨 As part of my journey back to myself this week, I decided to draw something simple and even try my hand at a little animation since it had been a while. Here’s what I came up with:  Imposter syndrome can be deceiving—it whispers lies about your worth and tries to steal your joy—but just like anything in life, ***this too shall pass.*** 🎢 The ebbs and flows are part of life’s natural rhythm; you’d think I’d have learned that by now! But life has its way of (re)teaching us lessons when we need them most. ✨ To anyone reading this who might be struggling: Be kind to yourself. You’re doing better than you think you are. And remember—**you are enough.** Godspeed
@ 6a6be47b:3e74e3e1
2025-04-04 12:41:11⛅️ This week has been a bit hazy—I haven’t been feeling my best. And that’s okay. There are days like that. But this time, it felt like something deeper, as if something was off. Like I wasn’t *enough*. 🌞 Thankfully, as the days went by, I started to feel better. Today, I feel like myself again—like I’ve put my human suit back on and climbed back on the horse. ✏️ I picked up my pencil and started drawing again, just me and my iPad, without any expectations weighing me down. It felt good—peaceful even—to create for the sake of creating. 🦉 What I’ve realized is this: It’s not bad to have goals or aspirations. Those are important! But what becomes unhealthy is chasing perfectionism while trying to achieve those goals. For me, perfectionism turns into a spiral—not rainbows and butterflies but a storm cloud of self-doubt. I guess I just want to share this in case anyone out there needs to hear it: It’s okay to be imperfect. And most importantly, it’s okay to just be yourself. [To those little leprechauns of doubt kicking and screaming inside my head, I can confidently say:*Not today, Satan!*](https://primal.net/e/nevent1qqsp3lc6wd4tqrwzssqmtv3mk6fctdzqn3hctjugrfkhtev6q68ht0g488mat)  🎨 As part of my journey back to myself this week, I decided to draw something simple and even try my hand at a little animation since it had been a while. Here’s what I came up with:  Imposter syndrome can be deceiving—it whispers lies about your worth and tries to steal your joy—but just like anything in life, ***this too shall pass.*** 🎢 The ebbs and flows are part of life’s natural rhythm; you’d think I’d have learned that by now! But life has its way of (re)teaching us lessons when we need them most. ✨ To anyone reading this who might be struggling: Be kind to yourself. You’re doing better than you think you are. And remember—**you are enough.** Godspeed @ c1a9282b:75752c6d
2025-04-04 12:20:54«Rainha em trapos», chamavam-na. Antes andarilha, assentava-se agora em trono xexelento, lixo cenográfico de alguma companhia de teatro. A qualquer que passasse perto dela, encarando-a, concedia retribuir um sorriso condescendente e um aceno de mão, entendendo que a ela agradeciam algum favor. Antes da aurora, levantava-se e ordenava ao sol que amanhecesse; antes do ocaso, o contrário: que anoitecesse. Em certa data, por capricho, decidiu que não haveria nem raiar nem cessar de raiar naquele dia, e ordenou ao Sol que nem ousasse despontar. Negou-se o Sol a obedecer simplesmente cumprindo seu diuturno trajeto. — A esse rebelde, matem-no! [revista gueto: 2017]
@ c1a9282b:75752c6d
2025-04-04 12:20:54«Rainha em trapos», chamavam-na. Antes andarilha, assentava-se agora em trono xexelento, lixo cenográfico de alguma companhia de teatro. A qualquer que passasse perto dela, encarando-a, concedia retribuir um sorriso condescendente e um aceno de mão, entendendo que a ela agradeciam algum favor. Antes da aurora, levantava-se e ordenava ao sol que amanhecesse; antes do ocaso, o contrário: que anoitecesse. Em certa data, por capricho, decidiu que não haveria nem raiar nem cessar de raiar naquele dia, e ordenou ao Sol que nem ousasse despontar. Negou-se o Sol a obedecer simplesmente cumprindo seu diuturno trajeto. — A esse rebelde, matem-no! [revista gueto: 2017] @ 907e4623:f40ff12a
2025-04-04 19:13:14<p>gm.</p><p><strong>i'm doing my job as I can.</strong></p><p><em>You know, it's not easy to be a founder.</em></p><p><s><u>I wanted to give up so many times.</u></s></p><p><u>But give up is not an option, I need to improve and move forward.</u></p><p><br></p><ol><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Difficulties</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Doubt</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Self interest and responsabilities</li></ol><p><br></p><p>I was stuck building this: <a href="https://afk-community.xyz" rel="noopener noreferrer" target="_blank">https://afk-community.xyz</a></p><p>Chasing my Product Market Fit, solving the problems I work on...</p><p>Step by step, I'm gonna make it.</p><p><br></p><p><img src="data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/4gKgSUNDX1BST0ZJTEUAAQEAAAKQbGNtcwQwAABtbnRyUkdCIFhZWiAAAAAAAAAAAAAAAABhY3NwQVBQTAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA9tYAAQAAAADTLWxjbXMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAtkZXNjAAABCAAAADhjcHJ0AAABQAAAAE53dHB0AAABkAAAABRjaGFkAAABpAAAACxyWFlaAAAB0AAAABRiWFlaAAAB5AAAABRnWFlaAAAB+AAAABRyVFJDAAACDAAAACBnVFJDAAACLAAAACBiVFJDAAACTAAAACBjaHJtAAACbAAAACRtbHVjAAAAAAAAAAEAAAAMZW5VUwAAABwAAAAcAHMAUgBHAEIAIABiAHUAaQBsAHQALQBpAG4AAG1sdWMAAAAAAAAAAQAAAAxlblVTAAAAMgAAABwATgBvACAAYwBvAHAAeQByAGkAZwBoAHQALAAgAHUAcwBlACAAZgByAGUAZQBsAHkAAAAAWFlaIAAAAAAAAPbWAAEAAAAA0y1zZjMyAAAAAAABDEoAAAXj///zKgAAB5sAAP2H///7ov///aMAAAPYAADAlFhZWiAAAAAAAABvlAAAOO4AAAOQWFlaIAAAAAAAACSdAAAPgwAAtr5YWVogAAAAAAAAYqUAALeQAAAY3nBhcmEAAAAAAAMAAAACZmYAAPKnAAANWQAAE9AAAApbcGFyYQAAAAAAAwAAAAJmZgAA8qcAAA1ZAAAT0AAACltwYXJhAAAAAAADAAAAAmZmAADypwAADVkAABPQAAAKW2Nocm0AAAAAAAMAAAAAo9cAAFR7AABMzQAAmZoAACZmAAAPXP/bAEMABQMEBAQDBQQEBAUFBQYHDAgHBwcHDwsLCQwRDxISEQ8RERMWHBcTFBoVEREYIRgaHR0fHx8TFyIkIh4kHB4fHv/bAEMBBQUFBwYHDggIDh4UERQeHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHv/CABEIAZABkAMBIgACEQEDEQH/xAAbAAEAAgMBAQAAAAAAAAAAAAAABQYBAgcDBP/EABoBAQADAQEBAAAAAAAAAAAAAAABAgMEBQb/2gAMAwEAAhADEAAAAeygAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHir7IX45wsypppbFZ+yLzTw943BYAAAAAAAAAAAAAAAAA8qhPPbazB2i/FWPXoG8WqH32BHRDphGkB8NtTTn3n0TWeeq2WJrE16Iptup2eojoAAAAAAAAAAAAAARXxVm/neVsmfdORT0AAAAAAIOp9H8bcPwS3P56a2IU9AAAAAAAAAAAADFf8Aspt/O9b+2joyK9IAgWchW6j57eBaPWp5thbFVRNrVbK18sEVLY++EdGlIvWs89fsVAtNueWFPQAAAAAAAAAAee9PnCF6FDWG3NkU9AAD5+VWmnbfO5zjOnl5zjKc5xmJzMw3Rq90wMPpgAPCg9EhLcMxvT7jG4RuAAAAAAAAB489nvo08uxDP1AAHz/RTp56l4s9PyTOMjLMGWUy/RoWaw+nyK9oAAHPb3E/FfzLUKemAAAAAAAAPNHPeg0Dod/NyKemAB48qttL2+exk08tlmAylKxfQa9s6MPpwAAAPLmfQuYX87rzy9aegCQAAAAAAETLV2ef4bfXbHNAr1gPL1qk4VH5s56Pk8MkGQyymS6VAz2H0uTSvbtmufdOMqI3AHkQVNscNblucvWrLFgjoAAAAAAAVe0Ve3L901CzUXCNwPPl1uo+vg4Zzp5OGSTISEfea9dj1rdVz9e2Vb486eS+/wCFOPVd6racPpsiN0HLVURctFzhK22pW2cgr2AAAAAAAK7YoqcPhsVPuM5hXrab1ucaj8eXR8pjIqJFeO++3T2fq1/2nMZ+nyXMlHb/ADLJNWWU79G5vL07r8RmP0Mf8WNzaGm63bltVkiZaLBHQAAAAAAA8/QjnnQufX2/neop6WvMrdRdfDwzK382Jk7dNU9SDm9sZ+rkRqBB0Pq/ONPGj8s6+SyykaFw+bnXQMPf9vTG9e/anXCr383pnoU9EEgAAAAAAAVj1nefX8zo2ufjp6NB+i2yunlw8xln6QNAAAEDPazlyvNj89vn4FPeJCVyc8omAseuzS7b+H1Y+9Ay9R6lp5vsM/UAAAAAAAAAxU7ZrOEDYOdX23P9Ip3gAAAAAGkIffAabGN87mN3oISWqd+CxXLz9K9ARuAAAAAAAAABG0/oMHfgmt6Feq7biOkAAA8IwmIyH8zfTbYxvnYxvncxlTbc2nRPjnpxyKd4AAAAAAAAAAAEHWugR9+D6Po5j9UT0VUtK91q+auZJf4fnyabbbGm22xrttsY2zuY8YmJvwed5+yRMineAAAAAAAAAAAAABpUrhicORyXR63bk+b0rvyFuzWvojefzEZjSYzAfPOdp1p30zh90Pb7Iip23fFezIjcAAAAAAAAAAAAAAAABpuRGfDYU41daE0r33SaL6bkbAkAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAD/8QAKxAAAQQBAgUEAgMBAQAAAAAAAwECBAUAIEAGERITMBAUFSE0UCI1gCQx/9oACAEBAAEFAv8Aa7yDZhLOExVuoiYt2HEuw4l1EXB2cJ+MKMn6gpGCbJuhNxZljLVlRLIo6QeMqYjc+NhZ8bCx9TEXH0osfUSWKkmxirHuRrgijK39E9zWNm3OChzZzotVGFjWo1PA5EckmsjlwsKXDdDt+WMc17d/PmiiMc6ZaGg1YI/nmVwTonu6w0CaKWze2ti2KkGEacQIhhHsCjYVk6CWI+rsEk7y2npGZVwHSntRGpqlSgx0LdffzJ+fzRc+aJnzJM+ZJnzJMrppZRfVURUtIChWpne5bubGU2ICtivnSGojU1Ws5IrCPcR+urB2IuhURUs4j4pq6W2WDbvcjGkcSzsACYEWo5GhDIK45tdSDvytRhtKPmStnsc17dtxDJ5NpYvYj6+IZHhqo/Yi67aN349DJ5bYr0GOCx0+y1nI0QjkcY2uqB35XhsRuhzgvQo9pxEbpj0QO1E18QyPrwVEfsxfDch7kXh4yuDtLNyybZjUYzUV7RjkFcY+usB7iV4iclZSlUNrs3u6WUiKWx18QSOTPBTA7MXxTX9IJqKGxG5Hj2Vu/or+G2/w1Ec1jJJVOfXXA9xK8c9/Ua5b91Duuu2XEC8q+gbyh6r+R0j8FLH7Ub0cqNSVaCZldK9yHSV6MHz5rcp/x8Ou6oGy4k/Dpf6/S9yNbLMp5GuvB7iUn1jnI1JVqNmSJJjrkGQseQ1Uc3RYE5qmW/4PDP4ey4j/AA6X+v030joD4KgTY8WVbMbh5BjropZP16megxqqucmW/wCDwz+HsuIE519AvOHocqNbMMsiRqjRDyMi1YR5bA7sTUxysdEMhwek0vcImJl0vKHw83pr9las7lfw4/8AjovJHQDTGhnkZFrACz/z1sQdiVqrJPYPk03Q1MTEy8X7qG9Fdsnp1NpVUNh6qvJJplkSfWLCPIyLWAFquAd2NrgTU9s5Ve5MT0nqprNjUazZ2bVj2o3I9npdn7cf0iwDnyLXAD4Z4OxJ0keg2pJIkkL2lHiY5UYyjYsiy2nEAeuNRn7kbFycb3EmLXnPkWvADx3AO5H0Pe1jTlUrsppHQT0ui9Ebh2P24m0I1HshudAscljeUEWCAHlVOaEqjdfxUjPipGFrzCaaBKK74qRnxUjEqpOAQnax/VPshtaNm1v43NtNJQwNjIkNHj3OI7TbyO0Hh2J0D2zkRzSsJWz45WmF5nuaxDy1drOVgBQgksZzURrdvPjMlAgSCQpDXI5vjVURDTGphHvIupVRrZJSWEqvitiA3NpBSUytmujEa5HN8BCjZhZuEe8i61VGtmynzSVMBsQe7soDJTYcs0IoCjMz1cQbcdKCmPm485n+I5RgGcx7A1XXsiN3s2IKUyWCfXkjW7n53CLiq5fLLshDyNElWJYUQUVm/ciOSfSiLjmzoDgWQnYxzHt8D3MG09oFmc51gsClGPGojU/ROa17ZVNGLhqeWBfcT4+MtHYlqDEs4mLZxMW2Bj7Z2e6nyFFUTDrFpow8YxrG/p3NRyFgxCYtRCXFpImJSRMSohJgoMQeNajU/wBr/wD/xAAvEQABAwEFBwMEAwEAAAAAAAABAgMEABESEyExBRAUIDAzQSNRUiIyQGFCQ2Bx/9oACAEDAQE/Af8AXEgUqUynVVcex8qTKZVoqgQfw3pLbItUaxpMjtiwe5obOCs3VE0mEwn+NcO18RSobCv40dngZtqIrFksfeLRTMhDw+k/gSJZvYTOaqYhBJvuZq6D8MKN9GRpiUb2G9ketLkKtwmvuNRoyWE/ve64ltN5VPbTcUfoyFcc/wDKuPf+Vcc/71HC8MX9d0iOl5NhqK+q3Cc1HUkPBlBUahMFIxF/ceTaci+u4NByQGMVzPQckxkqF9OoqO8HkBXTe9eQG/AzPJJewWyqibxtPJBYwms9TytehIKPB6RNbPF686fJ5NqP3l3B45ILGK7+hzTxYEuDwaHRkqusqNQU3WE75DoabKqUoqNp5IDGE3adTuTIbUq4DnyTE3mTUVVrKT0ZvYVUbtJ37TfvKwx45IbOK5npT20G28k509Kcd1NIUUG8KYeDqLw3yO0r/lQewnoyU3mlCoKrzCdzzoaQVGlKK1WnchtSzYkUxswnNyuGbCCgCloKFFJ3wZGEuw6HfNVdZJqMm6ykdE1AN280fB3bTetOGKQ2pZsSKY2Z5cNNtIbFiRv2kz/YOSC/iJunUbtoG9daHk0Ok/6EgOeDrSjlaKRs+8q+6aQ2lAsSOV1sOIKTXBve1cI97VwjvtTTL7awoCgbRTPryC54GnTfaDyCk1DeJGGvUdSa8QMNGpqOyGUBI6kphROK3qKjyA8P30pEgMj91FjkHFc+49Z+KScRrI0zMBN1zI9B6aAbjeZpiKQcR3NX4DrCHRYoVgvsds2j2oT7vdSRSZrB81xLXyFKnMDzRn3u0kmsCQ/3VWD2FNMIZFiR+HZbSo7StU1wbHxpMdpOiass/wBf/8QAIhEAAQMDBAMBAAAAAAAAAAAAAQACERIgMBAxQVEDIUBg/9oACAECAQE/Af19JVBVJ+QAlQ0KvpVFSVUVX2oaUQR8AbyUX9YA5FvIzNHJRM6gSh4wqQqQqQjvoDCcORkAkpx4s8Y5seYFjSiIOMemzYBJtcZNp9tnG/qzxjmxxgXM6xN3Tt9QJtcZOkGxu6dvhbunb6+Mc2OMBBhKDQNCI1G6fvhbunb6ATYfJ0qrHCdW7p2+J/ejBypR8nSmdWHixwjRneMexGlfSm0GFUFUFUESDofQjGDBThzkaOUTJyNPBREYmtlOPAzB3BRb1gDe0XcD4AYUg7qjpUlUlUFUdqQNkTPyVFVFVH9h/8QAOxAAAQIDAgoJAwIHAQAAAAAAAQACAxExEiETICIwMkBBUWFxBBAjM0JSgZGhULHBcoIUYnOAkqKy0f/aAAgBAQAGPwL+9fLe1vMqWGnyvVzYh9FdBiK+DEV7Yg9FLDS53LIe13I/SLUR7WjiVKAwxDvNwUodqW6GFailo32nTKy4xPIK8Pdzcu5+Su5+Srg5vJyyYpHMK1DIO6yZLLLiNzwpdIYYfEXhWobw4cPodp5DQNpVjoon/MVhIhMvM9Tf2p/mUmgAcMzIiYWSMGeCwkInm1BnS2/vCtMIcDtH0DKvfsapCm7whBz+0ibzsz5IyH7xtV1N2wrJueKtOvWGZUU/Cw0ZxsGrtpQZDaGjUbD2ghYaA4yHi2hYKLkxh/trlhl8U/Cw8edif+SkBIY84r5cNq7KDdvcV3cNdy33Xct913Lfddy33Xct90QYYDQLziSKw8Ccv+Vgol0Zv+2tW6uOiEY0YktnlHfwUhQY9ll8U04Ive4knfmACMo3nFkUI0GYE8k7uCtUeNIawXOMgKqTdHZwCbDYJAY7ojqNCdFdUnMAnRZeccw3iYKteHxcQg9pmDeNXHRWVN7lbcMt/wADMN6M08XZkT0nXnMWgMpqPRHml7NWc91GiaMR9J2jmHRHUaJp0R1XHMCei285oRod0jaCbEbRwnqrYIrEPwsJtifbMN6M01vdmQTpPvOatbWJ8Bx7s3ctVwY2EMCDRQY7nuoBMp0V1XHMNB0W3uzZnSV6LX7XFp1Qu3BYR3F2YHR2m83uzNo6T782eNyDx4haTXChE9TjHhJRXchjl7qATKdFdtOYa3wi92cs+VQX8ZKCeEtTI3uCJ3vxx0dpvdeeWZtkZT7+uZMgpQhhDv2KZ0xUYxcdimVPc4KXlcRqbP6n4KZ64xc64BPinabsw1nhq7l1TcQBxUoItnfsU4jyeGzqD9lCgRQ4ohj16neif+v8amz+p+CmeuMIDavryzOGiSaX3zO5SgNtneaKcR5PDF/h3n9OIXFFxqep3MJ/6/xqZ4OCcNzsUuNAnRDtpj9my7zGinF7R3wsmrLxjhzTIhCIPUddkaLeuW9wU/M4nU4zeE/ZRGcjiiCKvryxshkm7zRTido7jTEc0aJvGPJxyHV6rDdI4kFnqoI4T1Mt3hYN3FpxJlOibNnLEm1sm+Yqb+0dxxrY0mX5iw85bacUXOqcTBjZJqDRQDVMIKOk8IPFCJ9eCFX/AG6wZWW+YoEjCO3nMuZ4ajGtOQjDZsTYjaHrLjQCawruLzqojCsM/Cwfk63P2UbyU5WG7ypytu3nN2xpM+2LacpmmwdWAccl1OfXghpRPsjEPj+2qljqESRhvoDI8uow2OszqVMNtO3nPGw5lmd0ytKH7rSh+6m58P3Uy+HymtKH7rShe604fuU3Cyt7ZdVllJ2W8k1jaNEhqw6Uyrbnclgycpn21KQvcrTjM42CZpv+y/iHC91zeWrkG8FZOjVp/CERtDn5uMgrMO4b8cxH0CtvpV3AINaJAawYZr4TuKMGMP1D8oOaZg5yZuUoeUd6m4zxy5xkAhDhA2J5I38UGCviO/WrTcmK2hRgRwQNo3IOaZg5nKcAuzb6lZTp5gucZAIQYIODn/kpuvimvDXLTcmKKORgxmni3/xWoZmMS97R6qs+SyGe6vdLlmrcR0ghChtNjY1WjlRTU7tesxBfsIqFbhxXWfMKKxGeYb/hd473V5Odswe0f8BYR5yfMaBWYYv2nafoEiJhWoGQfKaKzIgbnUUooMM/CtMcHDhmbT3Bo4qUIGKfhWQCRubRWukZZ8oopASH0OTmhw4omH2Z9wrUK/iwqy/2e1dp0f2KvhxAtJw/atJx/arocQrs+j+5VmH7MarUW7i8oGLOIfhWWNDRuH0iRAKyoDPQSWi4fuVYnutKJ7rRcf3LJgM9b1IAD+9j/8QAKxABAAIABAIKAwEBAAAAAAAAAQARITFBUWFxIDBAgZGhscHR8BDh8VCA/9oACAEBAAE/If8Atc2wOAS9A+F808oM/M1950TT/lTPODPzHaB8L5oRZnAf8jiwOifYQDjLqFbEO/8Acs5XN6BBngQfMG+ycIFp+3GLaftxn0/OccY9wGX9xmtecp4zdD3/ALmO22P2TjMdX/hq8ySUEIuy2/QhMVeBwIPQ7uTwhUqyBQdTSGmYmcxbyH4R3Xnh8SOqDg+pD+VJLH/AtDuys34JSZS4DCIANajBcDryTE0MOYgzm7a8Z4sVN8fJ25BXotON+I7NTE8mGnOh2F4p6JCNzYDzINgEy04j47ZesHhw7sxxlbHN/EEmAoDp0MJyzLumOOA9gQz1Xf8AP4F/XT++n91P6qXpfA+HQZAI4MwCC3hmviDkIx4N+1OVors2D+Nk1wJMAoDTp4Ig4Nm7MyEyofk6GDx4/t0UQCOCMR/EA1QRNYHbfjtABBWnSFrC1Hz5U2dHTw57jUe27XI0PwdKtH2g6dAh0zVjah58NwOw1Oz2k2fQ0IR1MdvuDqMdD70e/h1OEn3w6gEtY5xNSNmrObanZkipi7oYdvueh7Qy6aB1cRR7udE/BK+L/XnVEpTAdtSLbZB2W3eo5P3UK1nX3MuopxB4PQ6mjP2g6oXJeN3aywo+IfvsqbFPeHmsIehAOHTdurxGVzHI0OorVfhW3VgvPXcj5V4iy867ITWSLM9SXrv9eo9mxtD7t1NIdY7lofd+rqhnLQLBzP5MsJDv7HRuvn4e8ro8TpqpTk4TPswjY0OovEvwqZHV1ByFd8Y0Ikzhp5TXY+GE9/acZj0On9OFfeXU5HsdwNPyoEGastfLJ8zAoFoulpLIp2tW2Wjdp9UmD79jyO4ga53q6SfA7XYnAxmxp1ColiAAAKI3Ks1UEsuO2A+ZQ0aDAd341lcHcj5iFia9G9WBj+AeP6o8H6wdjzuwg+4fV0rBa3B1Jy+YCq0Sz7oX7ThNOg7ujfmhi+GpD86KWXFjA2lsE+s3hxfrB2OxbicUX0Jr0FBoLWZBywbGnTcxO6RStwnJ3S1RWTbanTsuOxmfo4bD+cUfcYIJU7N6ys+kD27HvoV+b2l1rHAPLo3R9N0jw9wX7SsLlMHdABQUfhlUPQXp8KHwuj+MTMHwIIIJbfwtR975ghV+dj2MVskGKMJvmv6dAmSgLZriNHbR0Kaz8E/cqSr1OHhArI6NmGi5a/eHUHxA6Oo/UWC8yCCBCWLheb/ZhKADsmWnvQfyL7Yh+cWdN4avzRnd3w3mFs8nuOoSypVhi8F6SVKCOJS8NFbRybOyBBM8dKVtun2Hm9lcbnnmz9oVpxWHJ/CAtwj2rpIondx3+RKbDdP0Orw71eeros0oJl8ECZclxun7QIEpExK90Yli8OT69lHS3I4MUbxUtfRhiXBELDsGspu+f4bdaCCYMseliXXhP7r4n9V8TlCS1vlKeppZh5Q/fviH758QTYL9tIQGwU8rDAtiGl90an1YZdEDh2ZDu26wYw1hx7EPeV7c44iAgQIECY7YdctUu98PieziGApN4Qs3bWpuie+w7dfSbuMurfGMzzgQIECBEPoPF2j67HZptQcAqA0O0YLOeIrgLr2kLAKxNesZKA1ZYhxGUtPUCBAgQIEKAK1dIm0KeuTEreO67UFp71cGDADSZvchYBWJ1PgOazMIFsbg0gQIECBAgQsArV0mUWgGblLgOL0HbLFeOODB7AcT1gUXzjn0PNMjLW9hFrJ4qYYo2wSrzgQIECBAgQIoMXnyg46cPN4swWA4HAduyKURg/GWZ4O0q93lxRx1vfmYLmypUqVKgQIECBAlS9q3j6Ms63eBBM/lm/4AoMmY6wxUXH2G0tTRcdcmJG/bjHHQiuVKlSoECBAnFDqqPceTCOOqnQ5vzKBjNMhz3gkwZAZf4bhwzBZCLL/SpbF5S+EVYrWyYcCx1fantqPmMz5xQOXKKexo+YgSh0fbhlku6Zd152+EJQPTLwQIC5BR/kURmyQfxVjymWcsojS7nxAanc+JnnPKD+KFvOURmwf9sf/aAAwDAQACAAMAAAAQ88888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888DjRbL888888888888888888PBDpx8r93888888888888888NV8888888aJ8888888888888tk88CGsXSz8yl88888888888Od888eHCLJ888La8888888888gc88TjO3ze888s7888888888i3888JGjf/APPPPPI2vPPPPPPPA0PPJent+3pavPOLS/PPPPPPPKFvPLu1kzjSth/MEffPPPPPPPFmPAUbzfMvxeBfJCK/PPPPPPPGN/FerVfPDuAAf5HxPPPPPPPPPHlhc/PPPDYTCtWbfPPPPPPPPPKVfPPPPPPMAMOGK/PPPPPPPPPPPQ/PPPPJPBMCHPPPPPPPPPPPPPHUsOFKPPGFLPPPPPPPPPPPPPPPFxl9ElPkpfPPPPPPPPPPPPPPPPPKs/c1PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP/xAAqEQABAgIJBAMBAQAAAAAAAAABABEhQRAwMVFhcYGRoSCxwdFA4fBg8f/aAAgBAwEBPxD+uCOSyLMDdRWZyizA3QRwX+HCSuEzovYc/aIg5c2CsANY91/jBWoGkOyLunOC5Pi39on5GmJjT4ADBzYZp3L0zYMqh3Lcx5QbK5Mj91zTG4BemAIlaZk0lZmARcO4KA5uPSF62HpA8+w9IQhOUTRMRI3IA8ON491kgqzEyCMY0U4C7oM5Xmf0gggmFkw+B0BcOOD4QCWzFxmKv/f5LoAVtFmckchnJoCCamTD4HSGboz/AD1QAHKvM4OhmNC1n9UMgmAETD616jWyAdEQIcVJgFx7JhYPvGkqZWZyRGaJTJqGEEw+AiQIlRaug08O0VkQO1Twlxx2paCQiOf0EyagAJETkPanyws3UPhXCz71QyViEBamBp5jsuF5qSBJg9k4MG2olFd5IwNExoiCHBMhGwFu6gJAhWwILUxD8Bkaclm3gsoB2qQBDFX2cFDOSAic5KPkcEUtoh5KYCApbIBbA+KAKIq+QUEmgNkAAYVWg3NJEBgc3Xo5nRMWHtNZAdNgAUQFnrEoBnRkMEwEwR5P5queVZgZFGUCGcRfWBUaGMBepBVpvMzWDEHmFyf4gFouqn+YlYL0axeAXVzxGdjmmFNyNmiEeowTQX5CwZp8zmwy+BHyxmMiudy3dEhIZQQWzyob8gQGI8osJS+S9gjUqHFjM5n4ZCAos4CcgsAizgByCAQD+v8A/8QAIBEAAgEEAwEBAQAAAAAAAAAAAREAITAxQRAgYVFAYP/aAAgBAgEBPxD+uEBdTxhDqEfjxs3SzKMFCfc9oB7jHBzRKMzv4BLRDGlAsHFDUQS0XgrRDnyQkIBmH5zznnFw4OTgVouU6PKYHRIawiyjgynW67Y9KRayi+LQlC+OiRaZU/q0DCGz5cUFO2EQZ6GhgI7OOZOUjqDMTAQhhGOLnFMtkkBgouGFAEFwSBU8RmzAWGOVqcixhMrIlS+uFiCAzxCWXePMcUv4t1/xBmFAoJGp6sOek9J6QEieKf6t1iLKYNx5bAleuB8IcrRDgfC9S0QwrULBzWgSlo/AXCa5SrJwj1PCAupRkprnClX8gBgz3hJk/wBh/8QAKxABAAEDAgUEAwADAQEAAAAAAREAITFBUWFxgZGhECBAsTDB0VDh8IDx/9oACAEBAAE/EP8A1Jzp5VNdKnhU8PSaOVcv8S1ZfUz960kH9DOwjzSEcSJ9ipbD6I/c1IIPV/qKsAW7PpUFXdDO4jzVqzTJvho/wxOtKxLTDpOXhUtOkXy4hl2KYpyBHMG5zaTkLKiccpebQCX1jfLQwKbsfQo6DrPQCEOR0JRLdH9qRbM/WxUnXyjzcIeTR9iQv5B3eZRAlGJycUw6TQh4LDhz2eDXWo/wJTakEHFaYKgRtB3fPN7UtQomQ8tOQHGhFu7FvI27zQdBgQGwGKiT1vV/Y1NsBINkaPVNNxL5u3aKPitTqOW8HOSsISBMF3LHM7UKmpBBwT58u1WIyy7+79j0mjskykO678WV02oggRgJ+7Vl5UAFj8qDU8NluT+mpfnSGAmIj3HfsnisZclX9U+zvHzk7Ps2RfJt1c5c/ct2nppODBWGk45d11eL8DXNZFS6rc2eNXwlWq7RyaTjRohokWAzsO/UcPlLi1YG3cjaW+x/y0dpfb2WXN2XWgmCAgAwB7w+LmdCL9cVeuhwK/R3rPXaBe9D/daF9CilqiqpxKgsLhfe/apgx6iddBJEcjRmB5nlSRrdrpSlzhQDTx3OpwPkw23Fu33gZe2tSAj1fKDhGYwW2oLKBIAWAKfPuBSKlubF9GvSlgNM4voM0egxRRUt2SkIi3QQc59n1Rl2QJEcjWRO0zmk7bTkkq0AxHrk6snbT4+8FPaG1AAlaFxydgm746vFDarbBzV3Xit/eialEleBxW3WkZrQXlHAIPUUUUUU7UwW7KPkfA0EEe4+EAJjZOI3qTQuyII2JvrwSN6Bk1KyEjWPipbNLAsKq4vkb9DelKBCF/8AgXnwo4++UMxE2d7fWFCijPoUYoorF+OQhJPAeZ97io9KYM/9icuNTErLav1M9Xan4pdEW7CaUGiOgXs45BoBA929J6QUzBocXFONScswaBwCA5egUUUPVupjLIPkY6TQQfgQSKg5KGC3s5I2alqceCT8VGQnR0hXv4GoxxouJAfb1/BImQAd11ljgVFBQUUUYooqLchs3CPEX5rUWz+GYKLwuuw+npQgJW+9y3QPc+JJTA2B6M/8G1HmNbQEB75EtI2Cm0KIdg4BB0oKCgooPQKjXyokRjqYOU0EAfi/WeBfxUhdthn+juqT4TXi/wAgmlFnXJKYnnM6S/vtnQiaFuc0no3qPSKCg9AoqHGFbufzM/jTKhwctfH3TEJYloaP660i8vG4BPujHwSlziJ1j8KgTEqcOCp5Kij2GKN+0GgJaSRlPQOgQVFFBQegUU8/ngx06sHWggAINKKaBK094ocxzXf1RLO5yE+mnQZWfW+h8Iq9n9doR8zTkB9j7sFKAFtMgbHVP+NRUVHpFBR6QAoc2dH++tPOpoKuSMAcVpGCLaOtnotxoFkYyw6JeYTyPuwJSBu6Hem9LI6rW9vgU/dJL0TklJ+DrSjbGgIJl/On2uhC7AErUgBJwGw6EesUFRUejKUTbDJ1sdaAsBABAUEI5EBxWpVcV5X34c6ixLPZAW65ooIq85Oepk5UJd2ECSPthHcHvodr9aFSPs3jU2yn3/j8LWisTJaASHDe+n2wg6W3F/aeGoqKj0j1CojMIQPCXE3epRVm3IDwM+FGRpwOULUFB6BV+CKzXLo5OE7Ui8T6xz22dgqXgCbr6FvHDwpSNmPb+vwtatr/AH0/dS4zbclPuaC71tRYGFMABK1bqg7TYdvM1FRUesUXRShs3XXpLTkIIw/7HW3CjKxwCJBY2tfoegUHoFGafkCbRGSjTAITjyfvknrmMiSNtZ/XqG+fhV+q/wDkoUnHwRqILp5iKiUFkpnKfqj1YpBM3Fwz3bd6ioqKiopgyMNu5OeiaUhq+Lka+s0YEFgCAr7oSI6lQ6CxhANjoydKD0CjNFBTgwU2v1M34PAoZJrHW8Tvc32AMDc35EA0kKSf1v7U/Ba8bMSRUD8bOgZChY9TqJI4Ay0x5JE0Lf1zWoqKilnEQ4HVDPRVxgTiXhj3mgAABgNPa5mz2run2B9AUZoKD0CnF8QeDfAem9TlJK9gRMWYN5ae8w6UD4EjQCCjHwoKb3Ak3rnOU9SidLHcST1QYU8Dh/ax39W5NuhBODP041rjqOx7J1loIIDGK51y9pSIRtDrSxQ8/aOjJ09Cg9ArzXUuxTJMgc1cym5ByZNx4jJ6whUIOwEtELqrQR/Q7VB8RU6eDWA7GXRpnIjXZmTsydqaRuAJV0KMSSkaDHe71q0xLFIdx8HGmGBsBB3wHl40EaAfia/ZLS6YdLPR3ooPQKJP3y7HGrkNcWD+0KFxSyLY48DmG/rQPwGJoEV9HVqJIfjuh3fp8UDLRahDTAxKNhQlRBBESyVAl1osugMqSaZpUAzGIdxj7ca0t6Y0/EAZCESRKYYpMRSsN336Pyu7kdcc7sVjkuKMfvxpHo93OmjIgI1m6NJUNSQznFARAAlWmUOXCweGPBRtTA0BB8VxipSpgC7tnovZ4VOwCJb4x6YelRecfBjR2rb/AI0paab4OAae66mJIqzONdcHXajgskNH7LbkcfjNNlIokCQjSrM+MfP0PR1qVGNyb6y4n50JtlKjCmRfg2+6BSpVyvubojMtGukOK1G6YBKFseLEHV3oyCjoAIAp+OboWJeKzy0Tajv4tvy3LdyiroWkDrTc/GJUpUgKxTmwf21sNg0ORp71+3QKegBlaQwogitehfgdahztsX/iYD/fyYjhSpg44D9Wzp3qDCd+IDbc6nEigF5EdfwgspE3SuhehhZdP0hXBepQORj8Cq+4BC0AMrVqszc2zGQ2OrwKG8HcO99urQTm/wAswItogPBybOnirhEF8mL9msIUN7uw0abXPV1GDQJ7UPzcftgpSAWkrwf2hVJ4PxepJUq5X8Kqq2IbE5ew1al2A0Lq4tnY80FGMCWOLpu5fHzb2vQ+Ndtl4O3BtUK1AkI7LMuDbZpAEAWL8HTr3oWRHkPmvKGvpKlSp76qoAVQDK0CNYkt7i/Q7lT25QFBOqeB1au8kZ6cXQ4Fq3v88KEwIQbI0jzlSLeLPmcCpuiwK22mOyVC125PMudTrRJZwceKKlSp7aq4IsnHmkESbE80l6HWrXK6pt5juaDLCJo3FnxOdHP+BgGwH+B6UBWPNSp0algiQMnNc6JFR3OZYc1D2mh7rihTnZec0jANneSH7qxG+Dx4UEMhpYdpoFVDS47xQ5G+Jj5UxBdmOYD7pMDaqROd05zUUHmanIS94pUMSr613q32rEgAw6FIVHD/AArTRbyJHo0hJ7nyiDTymujPuaXU5dfusLPNj9VhHhv6UUJJ5jy6bQw7wIDoUf4nT3c/Wbf+pf/Z"></p>
@ 907e4623:f40ff12a
2025-04-04 19:13:14<p>gm.</p><p><strong>i'm doing my job as I can.</strong></p><p><em>You know, it's not easy to be a founder.</em></p><p><s><u>I wanted to give up so many times.</u></s></p><p><u>But give up is not an option, I need to improve and move forward.</u></p><p><br></p><ol><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Difficulties</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Doubt</li><li data-list="bullet"><span class="ql-ui" contenteditable="false"></span>Self interest and responsabilities</li></ol><p><br></p><p>I was stuck building this: <a href="https://afk-community.xyz" rel="noopener noreferrer" target="_blank">https://afk-community.xyz</a></p><p>Chasing my Product Market Fit, solving the problems I work on...</p><p>Step by step, I'm gonna make it.</p><p><br></p><p><img src="data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/4gKgSUNDX1BST0ZJTEUAAQEAAAKQbGNtcwQwAABtbnRyUkdCIFhZWiAAAAAAAAAAAAAAAABhY3NwQVBQTAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA9tYAAQAAAADTLWxjbXMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAtkZXNjAAABCAAAADhjcHJ0AAABQAAAAE53dHB0AAABkAAAABRjaGFkAAABpAAAACxyWFlaAAAB0AAAABRiWFlaAAAB5AAAABRnWFlaAAAB+AAAABRyVFJDAAACDAAAACBnVFJDAAACLAAAACBiVFJDAAACTAAAACBjaHJtAAACbAAAACRtbHVjAAAAAAAAAAEAAAAMZW5VUwAAABwAAAAcAHMAUgBHAEIAIABiAHUAaQBsAHQALQBpAG4AAG1sdWMAAAAAAAAAAQAAAAxlblVTAAAAMgAAABwATgBvACAAYwBvAHAAeQByAGkAZwBoAHQALAAgAHUAcwBlACAAZgByAGUAZQBsAHkAAAAAWFlaIAAAAAAAAPbWAAEAAAAA0y1zZjMyAAAAAAABDEoAAAXj///zKgAAB5sAAP2H///7ov///aMAAAPYAADAlFhZWiAAAAAAAABvlAAAOO4AAAOQWFlaIAAAAAAAACSdAAAPgwAAtr5YWVogAAAAAAAAYqUAALeQAAAY3nBhcmEAAAAAAAMAAAACZmYAAPKnAAANWQAAE9AAAApbcGFyYQAAAAAAAwAAAAJmZgAA8qcAAA1ZAAAT0AAACltwYXJhAAAAAAADAAAAAmZmAADypwAADVkAABPQAAAKW2Nocm0AAAAAAAMAAAAAo9cAAFR7AABMzQAAmZoAACZmAAAPXP/bAEMABQMEBAQDBQQEBAUFBQYHDAgHBwcHDwsLCQwRDxISEQ8RERMWHBcTFBoVEREYIRgaHR0fHx8TFyIkIh4kHB4fHv/bAEMBBQUFBwYHDggIDh4UERQeHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHv/CABEIAZABkAMBIgACEQEDEQH/xAAbAAEAAgMBAQAAAAAAAAAAAAAABQYBAgcDBP/EABoBAQADAQEBAAAAAAAAAAAAAAABAgMEBQb/2gAMAwEAAhADEAAAAeygAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHir7IX45wsypppbFZ+yLzTw943BYAAAAAAAAAAAAAAAAA8qhPPbazB2i/FWPXoG8WqH32BHRDphGkB8NtTTn3n0TWeeq2WJrE16Iptup2eojoAAAAAAAAAAAAAARXxVm/neVsmfdORT0AAAAAAIOp9H8bcPwS3P56a2IU9AAAAAAAAAAAADFf8Aspt/O9b+2joyK9IAgWchW6j57eBaPWp5thbFVRNrVbK18sEVLY++EdGlIvWs89fsVAtNueWFPQAAAAAAAAAAee9PnCF6FDWG3NkU9AAD5+VWmnbfO5zjOnl5zjKc5xmJzMw3Rq90wMPpgAPCg9EhLcMxvT7jG4RuAAAAAAAAB489nvo08uxDP1AAHz/RTp56l4s9PyTOMjLMGWUy/RoWaw+nyK9oAAHPb3E/FfzLUKemAAAAAAAAPNHPeg0Dod/NyKemAB48qttL2+exk08tlmAylKxfQa9s6MPpwAAAPLmfQuYX87rzy9aegCQAAAAAAETLV2ef4bfXbHNAr1gPL1qk4VH5s56Pk8MkGQyymS6VAz2H0uTSvbtmufdOMqI3AHkQVNscNblucvWrLFgjoAAAAAAAVe0Ve3L901CzUXCNwPPl1uo+vg4Zzp5OGSTISEfea9dj1rdVz9e2Vb486eS+/wCFOPVd6racPpsiN0HLVURctFzhK22pW2cgr2AAAAAAAK7YoqcPhsVPuM5hXrab1ucaj8eXR8pjIqJFeO++3T2fq1/2nMZ+nyXMlHb/ADLJNWWU79G5vL07r8RmP0Mf8WNzaGm63bltVkiZaLBHQAAAAAAA8/QjnnQufX2/neop6WvMrdRdfDwzK382Jk7dNU9SDm9sZ+rkRqBB0Pq/ONPGj8s6+SyykaFw+bnXQMPf9vTG9e/anXCr383pnoU9EEgAAAAAAAVj1nefX8zo2ufjp6NB+i2yunlw8xln6QNAAAEDPazlyvNj89vn4FPeJCVyc8omAseuzS7b+H1Y+9Ay9R6lp5vsM/UAAAAAAAAAxU7ZrOEDYOdX23P9Ip3gAAAAAGkIffAabGN87mN3oISWqd+CxXLz9K9ARuAAAAAAAAABG0/oMHfgmt6Feq7biOkAAA8IwmIyH8zfTbYxvnYxvncxlTbc2nRPjnpxyKd4AAAAAAAAAAAEHWugR9+D6Po5j9UT0VUtK91q+auZJf4fnyabbbGm22xrttsY2zuY8YmJvwed5+yRMineAAAAAAAAAAAAABpUrhicORyXR63bk+b0rvyFuzWvojefzEZjSYzAfPOdp1p30zh90Pb7Iip23fFezIjcAAAAAAAAAAAAAAAABpuRGfDYU41daE0r33SaL6bkbAkAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAD/8QAKxAAAQQBAgUEAgMBAQAAAAAAAwECBAUAIEAGERITMBAUFSE0UCI1gCQx/9oACAEBAAEFAv8Aa7yDZhLOExVuoiYt2HEuw4l1EXB2cJ+MKMn6gpGCbJuhNxZljLVlRLIo6QeMqYjc+NhZ8bCx9TEXH0osfUSWKkmxirHuRrgijK39E9zWNm3OChzZzotVGFjWo1PA5EckmsjlwsKXDdDt+WMc17d/PmiiMc6ZaGg1YI/nmVwTonu6w0CaKWze2ti2KkGEacQIhhHsCjYVk6CWI+rsEk7y2npGZVwHSntRGpqlSgx0LdffzJ+fzRc+aJnzJM+ZJnzJMrppZRfVURUtIChWpne5bubGU2ICtivnSGojU1Ws5IrCPcR+urB2IuhURUs4j4pq6W2WDbvcjGkcSzsACYEWo5GhDIK45tdSDvytRhtKPmStnsc17dtxDJ5NpYvYj6+IZHhqo/Yi67aN349DJ5bYr0GOCx0+y1nI0QjkcY2uqB35XhsRuhzgvQo9pxEbpj0QO1E18QyPrwVEfsxfDch7kXh4yuDtLNyybZjUYzUV7RjkFcY+usB7iV4iclZSlUNrs3u6WUiKWx18QSOTPBTA7MXxTX9IJqKGxG5Hj2Vu/or+G2/w1Ec1jJJVOfXXA9xK8c9/Ua5b91Duuu2XEC8q+gbyh6r+R0j8FLH7Ub0cqNSVaCZldK9yHSV6MHz5rcp/x8Ou6oGy4k/Dpf6/S9yNbLMp5GuvB7iUn1jnI1JVqNmSJJjrkGQseQ1Uc3RYE5qmW/4PDP4ey4j/AA6X+v030joD4KgTY8WVbMbh5BjropZP16megxqqucmW/wCDwz+HsuIE519AvOHocqNbMMsiRqjRDyMi1YR5bA7sTUxysdEMhwek0vcImJl0vKHw83pr9las7lfw4/8AjovJHQDTGhnkZFrACz/z1sQdiVqrJPYPk03Q1MTEy8X7qG9Fdsnp1NpVUNh6qvJJplkSfWLCPIyLWAFquAd2NrgTU9s5Ve5MT0nqprNjUazZ2bVj2o3I9npdn7cf0iwDnyLXAD4Z4OxJ0keg2pJIkkL2lHiY5UYyjYsiy2nEAeuNRn7kbFycb3EmLXnPkWvADx3AO5H0Pe1jTlUrsppHQT0ui9Ebh2P24m0I1HshudAscljeUEWCAHlVOaEqjdfxUjPipGFrzCaaBKK74qRnxUjEqpOAQnax/VPshtaNm1v43NtNJQwNjIkNHj3OI7TbyO0Hh2J0D2zkRzSsJWz45WmF5nuaxDy1drOVgBQgksZzURrdvPjMlAgSCQpDXI5vjVURDTGphHvIupVRrZJSWEqvitiA3NpBSUytmujEa5HN8BCjZhZuEe8i61VGtmynzSVMBsQe7soDJTYcs0IoCjMz1cQbcdKCmPm485n+I5RgGcx7A1XXsiN3s2IKUyWCfXkjW7n53CLiq5fLLshDyNElWJYUQUVm/ciOSfSiLjmzoDgWQnYxzHt8D3MG09oFmc51gsClGPGojU/ROa17ZVNGLhqeWBfcT4+MtHYlqDEs4mLZxMW2Bj7Z2e6nyFFUTDrFpow8YxrG/p3NRyFgxCYtRCXFpImJSRMSohJgoMQeNajU/wBr/wD/xAAvEQABAwEFBwMEAwEAAAAAAAABAgMEABESEyExBRAUIDAzQSNRUiIyQGFCQ2Bx/9oACAEDAQE/Af8AXEgUqUynVVcex8qTKZVoqgQfw3pLbItUaxpMjtiwe5obOCs3VE0mEwn+NcO18RSobCv40dngZtqIrFksfeLRTMhDw+k/gSJZvYTOaqYhBJvuZq6D8MKN9GRpiUb2G9ketLkKtwmvuNRoyWE/ve64ltN5VPbTcUfoyFcc/wDKuPf+Vcc/71HC8MX9d0iOl5NhqK+q3Cc1HUkPBlBUahMFIxF/ceTaci+u4NByQGMVzPQckxkqF9OoqO8HkBXTe9eQG/AzPJJewWyqibxtPJBYwms9TytehIKPB6RNbPF686fJ5NqP3l3B45ILGK7+hzTxYEuDwaHRkqusqNQU3WE75DoabKqUoqNp5IDGE3adTuTIbUq4DnyTE3mTUVVrKT0ZvYVUbtJ37TfvKwx45IbOK5npT20G28k509Kcd1NIUUG8KYeDqLw3yO0r/lQewnoyU3mlCoKrzCdzzoaQVGlKK1WnchtSzYkUxswnNyuGbCCgCloKFFJ3wZGEuw6HfNVdZJqMm6ykdE1AN280fB3bTetOGKQ2pZsSKY2Z5cNNtIbFiRv2kz/YOSC/iJunUbtoG9daHk0Ok/6EgOeDrSjlaKRs+8q+6aQ2lAsSOV1sOIKTXBve1cI97VwjvtTTL7awoCgbRTPryC54GnTfaDyCk1DeJGGvUdSa8QMNGpqOyGUBI6kphROK3qKjyA8P30pEgMj91FjkHFc+49Z+KScRrI0zMBN1zI9B6aAbjeZpiKQcR3NX4DrCHRYoVgvsds2j2oT7vdSRSZrB81xLXyFKnMDzRn3u0kmsCQ/3VWD2FNMIZFiR+HZbSo7StU1wbHxpMdpOiass/wBf/8QAIhEAAQMDBAMBAAAAAAAAAAAAAQACERIgMBAxQVEDIUBg/9oACAECAQE/Af19JVBVJ+QAlQ0KvpVFSVUVX2oaUQR8AbyUX9YA5FvIzNHJRM6gSh4wqQqQqQjvoDCcORkAkpx4s8Y5seYFjSiIOMemzYBJtcZNp9tnG/qzxjmxxgXM6xN3Tt9QJtcZOkGxu6dvhbunb6+Mc2OMBBhKDQNCI1G6fvhbunb6ATYfJ0qrHCdW7p2+J/ejBypR8nSmdWHixwjRneMexGlfSm0GFUFUFUESDofQjGDBThzkaOUTJyNPBREYmtlOPAzB3BRb1gDe0XcD4AYUg7qjpUlUlUFUdqQNkTPyVFVFVH9h/8QAOxAAAQIDAgoJAwIHAQAAAAAAAQACAxExEiETICIwMkBBUWFxBBAjM0JSgZGhULHBcoIUYnOAkqKy0f/aAAgBAQAGPwL+9fLe1vMqWGnyvVzYh9FdBiK+DEV7Yg9FLDS53LIe13I/SLUR7WjiVKAwxDvNwUodqW6GFailo32nTKy4xPIK8Pdzcu5+Su5+Srg5vJyyYpHMK1DIO6yZLLLiNzwpdIYYfEXhWobw4cPodp5DQNpVjoon/MVhIhMvM9Tf2p/mUmgAcMzIiYWSMGeCwkInm1BnS2/vCtMIcDtH0DKvfsapCm7whBz+0ibzsz5IyH7xtV1N2wrJueKtOvWGZUU/Cw0ZxsGrtpQZDaGjUbD2ghYaA4yHi2hYKLkxh/trlhl8U/Cw8edif+SkBIY84r5cNq7KDdvcV3cNdy33Xct913Lfddy33Xct90QYYDQLziSKw8Ccv+Vgol0Zv+2tW6uOiEY0YktnlHfwUhQY9ll8U04Ive4knfmACMo3nFkUI0GYE8k7uCtUeNIawXOMgKqTdHZwCbDYJAY7ojqNCdFdUnMAnRZeccw3iYKteHxcQg9pmDeNXHRWVN7lbcMt/wADMN6M08XZkT0nXnMWgMpqPRHml7NWc91GiaMR9J2jmHRHUaJp0R1XHMCei285oRod0jaCbEbRwnqrYIrEPwsJtifbMN6M01vdmQTpPvOatbWJ8Bx7s3ctVwY2EMCDRQY7nuoBMp0V1XHMNB0W3uzZnSV6LX7XFp1Qu3BYR3F2YHR2m83uzNo6T782eNyDx4haTXChE9TjHhJRXchjl7qATKdFdtOYa3wi92cs+VQX8ZKCeEtTI3uCJ3vxx0dpvdeeWZtkZT7+uZMgpQhhDv2KZ0xUYxcdimVPc4KXlcRqbP6n4KZ64xc64BPinabsw1nhq7l1TcQBxUoItnfsU4jyeGzqD9lCgRQ4ohj16neif+v8amz+p+CmeuMIDavryzOGiSaX3zO5SgNtneaKcR5PDF/h3n9OIXFFxqep3MJ/6/xqZ4OCcNzsUuNAnRDtpj9my7zGinF7R3wsmrLxjhzTIhCIPUddkaLeuW9wU/M4nU4zeE/ZRGcjiiCKvryxshkm7zRTido7jTEc0aJvGPJxyHV6rDdI4kFnqoI4T1Mt3hYN3FpxJlOibNnLEm1sm+Yqb+0dxxrY0mX5iw85bacUXOqcTBjZJqDRQDVMIKOk8IPFCJ9eCFX/AG6wZWW+YoEjCO3nMuZ4ajGtOQjDZsTYjaHrLjQCawruLzqojCsM/Cwfk63P2UbyU5WG7ypytu3nN2xpM+2LacpmmwdWAccl1OfXghpRPsjEPj+2qljqESRhvoDI8uow2OszqVMNtO3nPGw5lmd0ytKH7rSh+6m58P3Uy+HymtKH7rShe604fuU3Cyt7ZdVllJ2W8k1jaNEhqw6Uyrbnclgycpn21KQvcrTjM42CZpv+y/iHC91zeWrkG8FZOjVp/CERtDn5uMgrMO4b8cxH0CtvpV3AINaJAawYZr4TuKMGMP1D8oOaZg5yZuUoeUd6m4zxy5xkAhDhA2J5I38UGCviO/WrTcmK2hRgRwQNo3IOaZg5nKcAuzb6lZTp5gucZAIQYIODn/kpuvimvDXLTcmKKORgxmni3/xWoZmMS97R6qs+SyGe6vdLlmrcR0ghChtNjY1WjlRTU7tesxBfsIqFbhxXWfMKKxGeYb/hd473V5Odswe0f8BYR5yfMaBWYYv2nafoEiJhWoGQfKaKzIgbnUUooMM/CtMcHDhmbT3Bo4qUIGKfhWQCRubRWukZZ8oopASH0OTmhw4omH2Z9wrUK/iwqy/2e1dp0f2KvhxAtJw/atJx/arocQrs+j+5VmH7MarUW7i8oGLOIfhWWNDRuH0iRAKyoDPQSWi4fuVYnutKJ7rRcf3LJgM9b1IAD+9j/8QAKxABAAIABAIKAwEBAAAAAAAAAQARITFBUWFxIDBAgZGhscHR8BDh8VCA/9oACAEBAAE/If8Atc2wOAS9A+F808oM/M1950TT/lTPODPzHaB8L5oRZnAf8jiwOifYQDjLqFbEO/8Acs5XN6BBngQfMG+ycIFp+3GLaftxn0/OccY9wGX9xmtecp4zdD3/ALmO22P2TjMdX/hq8ySUEIuy2/QhMVeBwIPQ7uTwhUqyBQdTSGmYmcxbyH4R3Xnh8SOqDg+pD+VJLH/AtDuys34JSZS4DCIANajBcDryTE0MOYgzm7a8Z4sVN8fJ25BXotON+I7NTE8mGnOh2F4p6JCNzYDzINgEy04j47ZesHhw7sxxlbHN/EEmAoDp0MJyzLumOOA9gQz1Xf8AP4F/XT++n91P6qXpfA+HQZAI4MwCC3hmviDkIx4N+1OVors2D+Nk1wJMAoDTp4Ig4Nm7MyEyofk6GDx4/t0UQCOCMR/EA1QRNYHbfjtABBWnSFrC1Hz5U2dHTw57jUe27XI0PwdKtH2g6dAh0zVjah58NwOw1Oz2k2fQ0IR1MdvuDqMdD70e/h1OEn3w6gEtY5xNSNmrObanZkipi7oYdvueh7Qy6aB1cRR7udE/BK+L/XnVEpTAdtSLbZB2W3eo5P3UK1nX3MuopxB4PQ6mjP2g6oXJeN3aywo+IfvsqbFPeHmsIehAOHTdurxGVzHI0OorVfhW3VgvPXcj5V4iy867ITWSLM9SXrv9eo9mxtD7t1NIdY7lofd+rqhnLQLBzP5MsJDv7HRuvn4e8ro8TpqpTk4TPswjY0OovEvwqZHV1ByFd8Y0Ikzhp5TXY+GE9/acZj0On9OFfeXU5HsdwNPyoEGastfLJ8zAoFoulpLIp2tW2Wjdp9UmD79jyO4ga53q6SfA7XYnAxmxp1ColiAAAKI3Ks1UEsuO2A+ZQ0aDAd341lcHcj5iFia9G9WBj+AeP6o8H6wdjzuwg+4fV0rBa3B1Jy+YCq0Sz7oX7ThNOg7ujfmhi+GpD86KWXFjA2lsE+s3hxfrB2OxbicUX0Jr0FBoLWZBywbGnTcxO6RStwnJ3S1RWTbanTsuOxmfo4bD+cUfcYIJU7N6ys+kD27HvoV+b2l1rHAPLo3R9N0jw9wX7SsLlMHdABQUfhlUPQXp8KHwuj+MTMHwIIIJbfwtR975ghV+dj2MVskGKMJvmv6dAmSgLZriNHbR0Kaz8E/cqSr1OHhArI6NmGi5a/eHUHxA6Oo/UWC8yCCBCWLheb/ZhKADsmWnvQfyL7Yh+cWdN4avzRnd3w3mFs8nuOoSypVhi8F6SVKCOJS8NFbRybOyBBM8dKVtun2Hm9lcbnnmz9oVpxWHJ/CAtwj2rpIondx3+RKbDdP0Orw71eeros0oJl8ECZclxun7QIEpExK90Yli8OT69lHS3I4MUbxUtfRhiXBELDsGspu+f4bdaCCYMseliXXhP7r4n9V8TlCS1vlKeppZh5Q/fviH758QTYL9tIQGwU8rDAtiGl90an1YZdEDh2ZDu26wYw1hx7EPeV7c44iAgQIECY7YdctUu98PieziGApN4Qs3bWpuie+w7dfSbuMurfGMzzgQIECBEPoPF2j67HZptQcAqA0O0YLOeIrgLr2kLAKxNesZKA1ZYhxGUtPUCBAgQIEKAK1dIm0KeuTEreO67UFp71cGDADSZvchYBWJ1PgOazMIFsbg0gQIECBAgQsArV0mUWgGblLgOL0HbLFeOODB7AcT1gUXzjn0PNMjLW9hFrJ4qYYo2wSrzgQIECBAgQIoMXnyg46cPN4swWA4HAduyKURg/GWZ4O0q93lxRx1vfmYLmypUqVKgQIECBAlS9q3j6Ms63eBBM/lm/4AoMmY6wxUXH2G0tTRcdcmJG/bjHHQiuVKlSoECBAnFDqqPceTCOOqnQ5vzKBjNMhz3gkwZAZf4bhwzBZCLL/SpbF5S+EVYrWyYcCx1fantqPmMz5xQOXKKexo+YgSh0fbhlku6Zd152+EJQPTLwQIC5BR/kURmyQfxVjymWcsojS7nxAanc+JnnPKD+KFvOURmwf9sf/aAAwDAQACAAMAAAAQ88888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888888DjRbL888888888888888888PBDpx8r93888888888888888NV8888888aJ8888888888888tk88CGsXSz8yl88888888888Od888eHCLJ888La8888888888gc88TjO3ze888s7888888888i3888JGjf/APPPPPI2vPPPPPPPA0PPJent+3pavPOLS/PPPPPPPKFvPLu1kzjSth/MEffPPPPPPPFmPAUbzfMvxeBfJCK/PPPPPPPGN/FerVfPDuAAf5HxPPPPPPPPPHlhc/PPPDYTCtWbfPPPPPPPPPKVfPPPPPPMAMOGK/PPPPPPPPPPPQ/PPPPJPBMCHPPPPPPPPPPPPPHUsOFKPPGFLPPPPPPPPPPPPPPPFxl9ElPkpfPPPPPPPPPPPPPPPPPKs/c1PPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPPP/xAAqEQABAgIJBAMBAQAAAAAAAAABABEhQRAwMVFhcYGRoSCxwdFA4fBg8f/aAAgBAwEBPxD+uCOSyLMDdRWZyizA3QRwX+HCSuEzovYc/aIg5c2CsANY91/jBWoGkOyLunOC5Pi39on5GmJjT4ADBzYZp3L0zYMqh3Lcx5QbK5Mj91zTG4BemAIlaZk0lZmARcO4KA5uPSF62HpA8+w9IQhOUTRMRI3IA8ON491kgqzEyCMY0U4C7oM5Xmf0gggmFkw+B0BcOOD4QCWzFxmKv/f5LoAVtFmckchnJoCCamTD4HSGboz/AD1QAHKvM4OhmNC1n9UMgmAETD616jWyAdEQIcVJgFx7JhYPvGkqZWZyRGaJTJqGEEw+AiQIlRaug08O0VkQO1Twlxx2paCQiOf0EyagAJETkPanyws3UPhXCz71QyViEBamBp5jsuF5qSBJg9k4MG2olFd5IwNExoiCHBMhGwFu6gJAhWwILUxD8Bkaclm3gsoB2qQBDFX2cFDOSAic5KPkcEUtoh5KYCApbIBbA+KAKIq+QUEmgNkAAYVWg3NJEBgc3Xo5nRMWHtNZAdNgAUQFnrEoBnRkMEwEwR5P5queVZgZFGUCGcRfWBUaGMBepBVpvMzWDEHmFyf4gFouqn+YlYL0axeAXVzxGdjmmFNyNmiEeowTQX5CwZp8zmwy+BHyxmMiudy3dEhIZQQWzyob8gQGI8osJS+S9gjUqHFjM5n4ZCAos4CcgsAizgByCAQD+v8A/8QAIBEAAgEEAwEBAQAAAAAAAAAAAREAITAxQRAgYVFAYP/aAAgBAgEBPxD+uEBdTxhDqEfjxs3SzKMFCfc9oB7jHBzRKMzv4BLRDGlAsHFDUQS0XgrRDnyQkIBmH5zznnFw4OTgVouU6PKYHRIawiyjgynW67Y9KRayi+LQlC+OiRaZU/q0DCGz5cUFO2EQZ6GhgI7OOZOUjqDMTAQhhGOLnFMtkkBgouGFAEFwSBU8RmzAWGOVqcixhMrIlS+uFiCAzxCWXePMcUv4t1/xBmFAoJGp6sOek9J6QEieKf6t1iLKYNx5bAleuB8IcrRDgfC9S0QwrULBzWgSlo/AXCa5SrJwj1PCAupRkprnClX8gBgz3hJk/wBh/8QAKxABAAEDAgUEAwADAQEAAAAAAREAITFBUWFxgZGhECBAsTDB0VDh8IDx/9oACAEBAAE/EP8A1Jzp5VNdKnhU8PSaOVcv8S1ZfUz960kH9DOwjzSEcSJ9ipbD6I/c1IIPV/qKsAW7PpUFXdDO4jzVqzTJvho/wxOtKxLTDpOXhUtOkXy4hl2KYpyBHMG5zaTkLKiccpebQCX1jfLQwKbsfQo6DrPQCEOR0JRLdH9qRbM/WxUnXyjzcIeTR9iQv5B3eZRAlGJycUw6TQh4LDhz2eDXWo/wJTakEHFaYKgRtB3fPN7UtQomQ8tOQHGhFu7FvI27zQdBgQGwGKiT1vV/Y1NsBINkaPVNNxL5u3aKPitTqOW8HOSsISBMF3LHM7UKmpBBwT58u1WIyy7+79j0mjskykO678WV02oggRgJ+7Vl5UAFj8qDU8NluT+mpfnSGAmIj3HfsnisZclX9U+zvHzk7Ps2RfJt1c5c/ct2nppODBWGk45d11eL8DXNZFS6rc2eNXwlWq7RyaTjRohokWAzsO/UcPlLi1YG3cjaW+x/y0dpfb2WXN2XWgmCAgAwB7w+LmdCL9cVeuhwK/R3rPXaBe9D/daF9CilqiqpxKgsLhfe/apgx6iddBJEcjRmB5nlSRrdrpSlzhQDTx3OpwPkw23Fu33gZe2tSAj1fKDhGYwW2oLKBIAWAKfPuBSKlubF9GvSlgNM4voM0egxRRUt2SkIi3QQc59n1Rl2QJEcjWRO0zmk7bTkkq0AxHrk6snbT4+8FPaG1AAlaFxydgm746vFDarbBzV3Xit/eialEleBxW3WkZrQXlHAIPUUUUUU7UwW7KPkfA0EEe4+EAJjZOI3qTQuyII2JvrwSN6Bk1KyEjWPipbNLAsKq4vkb9DelKBCF/8AgXnwo4++UMxE2d7fWFCijPoUYoorF+OQhJPAeZ97io9KYM/9icuNTErLav1M9Xan4pdEW7CaUGiOgXs45BoBA929J6QUzBocXFONScswaBwCA5egUUUPVupjLIPkY6TQQfgQSKg5KGC3s5I2alqceCT8VGQnR0hXv4GoxxouJAfb1/BImQAd11ljgVFBQUUUYooqLchs3CPEX5rUWz+GYKLwuuw+npQgJW+9y3QPc+JJTA2B6M/8G1HmNbQEB75EtI2Cm0KIdg4BB0oKCgooPQKjXyokRjqYOU0EAfi/WeBfxUhdthn+juqT4TXi/wAgmlFnXJKYnnM6S/vtnQiaFuc0no3qPSKCg9AoqHGFbufzM/jTKhwctfH3TEJYloaP660i8vG4BPujHwSlziJ1j8KgTEqcOCp5Kij2GKN+0GgJaSRlPQOgQVFFBQegUU8/ngx06sHWggAINKKaBK094ocxzXf1RLO5yE+mnQZWfW+h8Iq9n9doR8zTkB9j7sFKAFtMgbHVP+NRUVHpFBR6QAoc2dH++tPOpoKuSMAcVpGCLaOtnotxoFkYyw6JeYTyPuwJSBu6Hem9LI6rW9vgU/dJL0TklJ+DrSjbGgIJl/On2uhC7AErUgBJwGw6EesUFRUejKUTbDJ1sdaAsBABAUEI5EBxWpVcV5X34c6ixLPZAW65ooIq85Oepk5UJd2ECSPthHcHvodr9aFSPs3jU2yn3/j8LWisTJaASHDe+n2wg6W3F/aeGoqKj0j1CojMIQPCXE3epRVm3IDwM+FGRpwOULUFB6BV+CKzXLo5OE7Ui8T6xz22dgqXgCbr6FvHDwpSNmPb+vwtatr/AH0/dS4zbclPuaC71tRYGFMABK1bqg7TYdvM1FRUesUXRShs3XXpLTkIIw/7HW3CjKxwCJBY2tfoegUHoFGafkCbRGSjTAITjyfvknrmMiSNtZ/XqG+fhV+q/wDkoUnHwRqILp5iKiUFkpnKfqj1YpBM3Fwz3bd6ioqKiopgyMNu5OeiaUhq+Lka+s0YEFgCAr7oSI6lQ6CxhANjoydKD0CjNFBTgwU2v1M34PAoZJrHW8Tvc32AMDc35EA0kKSf1v7U/Ba8bMSRUD8bOgZChY9TqJI4Ay0x5JE0Lf1zWoqKilnEQ4HVDPRVxgTiXhj3mgAABgNPa5mz2run2B9AUZoKD0CnF8QeDfAem9TlJK9gRMWYN5ae8w6UD4EjQCCjHwoKb3Ak3rnOU9SidLHcST1QYU8Dh/ax39W5NuhBODP041rjqOx7J1loIIDGK51y9pSIRtDrSxQ8/aOjJ09Cg9ArzXUuxTJMgc1cym5ByZNx4jJ6whUIOwEtELqrQR/Q7VB8RU6eDWA7GXRpnIjXZmTsydqaRuAJV0KMSSkaDHe71q0xLFIdx8HGmGBsBB3wHl40EaAfia/ZLS6YdLPR3ooPQKJP3y7HGrkNcWD+0KFxSyLY48DmG/rQPwGJoEV9HVqJIfjuh3fp8UDLRahDTAxKNhQlRBBESyVAl1osugMqSaZpUAzGIdxj7ca0t6Y0/EAZCESRKYYpMRSsN336Pyu7kdcc7sVjkuKMfvxpHo93OmjIgI1m6NJUNSQznFARAAlWmUOXCweGPBRtTA0BB8VxipSpgC7tnovZ4VOwCJb4x6YelRecfBjR2rb/AI0paab4OAae66mJIqzONdcHXajgskNH7LbkcfjNNlIokCQjSrM+MfP0PR1qVGNyb6y4n50JtlKjCmRfg2+6BSpVyvubojMtGukOK1G6YBKFseLEHV3oyCjoAIAp+OboWJeKzy0Tajv4tvy3LdyiroWkDrTc/GJUpUgKxTmwf21sNg0ORp71+3QKegBlaQwogitehfgdahztsX/iYD/fyYjhSpg44D9Wzp3qDCd+IDbc6nEigF5EdfwgspE3SuhehhZdP0hXBepQORj8Cq+4BC0AMrVqszc2zGQ2OrwKG8HcO99urQTm/wAswItogPBybOnirhEF8mL9msIUN7uw0abXPV1GDQJ7UPzcftgpSAWkrwf2hVJ4PxepJUq5X8Kqq2IbE5ew1al2A0Lq4tnY80FGMCWOLpu5fHzb2vQ+Ndtl4O3BtUK1AkI7LMuDbZpAEAWL8HTr3oWRHkPmvKGvpKlSp76qoAVQDK0CNYkt7i/Q7lT25QFBOqeB1au8kZ6cXQ4Fq3v88KEwIQbI0jzlSLeLPmcCpuiwK22mOyVC125PMudTrRJZwceKKlSp7aq4IsnHmkESbE80l6HWrXK6pt5juaDLCJo3FnxOdHP+BgGwH+B6UBWPNSp0algiQMnNc6JFR3OZYc1D2mh7rihTnZec0jANneSH7qxG+Dx4UEMhpYdpoFVDS47xQ5G+Jj5UxBdmOYD7pMDaqROd05zUUHmanIS94pUMSr613q32rEgAw6FIVHD/AArTRbyJHo0hJ7nyiDTymujPuaXU5dfusLPNj9VhHhv6UUJJ5jy6bQw7wIDoUf4nT3c/Wbf+pf/Z"></p> @ 1aa9ff07:3cb793b5
2025-04-04 09:42:28Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring: 1. Major Changes in the Business World AI will automate repetitive tasks, allowing human workers to focus on more strategic areas. AI-powered assistants, data analytics, and customer service applications will become more widespread, shifting human efforts toward creative and problem-solving roles. 2. Revolutionary Advances in Healthcare AI in medicine will enable earlier disease diagnosis and personalized treatment plans. Thanks to advancements in image processing and genetic analysis, diseases such as cancer can be detected more quickly and accurately. 3. Widespread Adoption of Autonomous Vehicles Over the next five years, autonomous vehicle technologies will continue to evolve, becoming more common in urban transportation and logistics. This will lead to a reduction in traffic accidents, lower transportation costs, and significant changes in urban planning. 4. AI-Powered Personalized Learning in Education AI will enhance personalized education solutions, making learning processes more efficient. AI-assisted teachers and learning platforms will analyze students’ weaknesses and create customized study programs tailored to their needs. 5. New Challenges in Security and Data Privacy As AI technology advances, cybersecurity and data privacy will become even more critical. While AI-driven security systems can detect cyber threats proactively, malicious applications of AI may introduce new vulnerabilities. 6. Creative Innovations in Art and Entertainment AI-generated content will become more prevalent in fields such as art, music, and cinema. AI-assisted scripts, music compositions, and digital artwork may give rise to a new wave of artistic expression. Conclusion In the next five years, AI's influence will be felt in every aspect of life. From business and healthcare to transportation and the arts, various sectors will undergo transformative innovations. However, addressing ethical concerns, security challenges, and data privacy issues will be crucial to ensuring AI's positive impact. By harnessing AI’s potential responsibly, we can build a more efficient, secure, and sustainable future. Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring:
@ 1aa9ff07:3cb793b5
2025-04-04 09:42:28Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring: 1. Major Changes in the Business World AI will automate repetitive tasks, allowing human workers to focus on more strategic areas. AI-powered assistants, data analytics, and customer service applications will become more widespread, shifting human efforts toward creative and problem-solving roles. 2. Revolutionary Advances in Healthcare AI in medicine will enable earlier disease diagnosis and personalized treatment plans. Thanks to advancements in image processing and genetic analysis, diseases such as cancer can be detected more quickly and accurately. 3. Widespread Adoption of Autonomous Vehicles Over the next five years, autonomous vehicle technologies will continue to evolve, becoming more common in urban transportation and logistics. This will lead to a reduction in traffic accidents, lower transportation costs, and significant changes in urban planning. 4. AI-Powered Personalized Learning in Education AI will enhance personalized education solutions, making learning processes more efficient. AI-assisted teachers and learning platforms will analyze students’ weaknesses and create customized study programs tailored to their needs. 5. New Challenges in Security and Data Privacy As AI technology advances, cybersecurity and data privacy will become even more critical. While AI-driven security systems can detect cyber threats proactively, malicious applications of AI may introduce new vulnerabilities. 6. Creative Innovations in Art and Entertainment AI-generated content will become more prevalent in fields such as art, music, and cinema. AI-assisted scripts, music compositions, and digital artwork may give rise to a new wave of artistic expression. Conclusion In the next five years, AI's influence will be felt in every aspect of life. From business and healthcare to transportation and the arts, various sectors will undergo transformative innovations. However, addressing ethical concerns, security challenges, and data privacy issues will be crucial to ensuring AI's positive impact. By harnessing AI’s potential responsibly, we can build a more efficient, secure, and sustainable future. Artificial intelligence (AI) has gained significant momentum in recent years, and it is expected to bring revolutionary changes to our lives over the next five years. Today, AI plays a crucial role in automation, healthcare, education, and many other fields. In the near future, its impact will become even more profound. Here are some key transformations AI is expected to bring: @ 674473f6:f859eb3c
2025-04-04 08:42:17## darkman คืออะไร **Darkman** เป็นโปรแกรมที่ช่วยควบคุมการเปลี่ยนโหมดสีของเดสก์ท็อประหว่างโหมดมืดและโหมดสว่างบนระบบปฏิบัติการ Unix-like. โปรแกรมนี้จะทำงานในเบื้องหลัง(background process) และสามารถตั้งค่าให้เปลี่ยนไปใช้โหมดมืดเมื่อพระอาทิตย์ตก หรือเปลี่ยนกลับไปใช้โหมดสว่างเมื่อพระอาทิตย์ขึ้นได้ ## การทำงานของ Darkman เรียกใช้ผ่าน systemd service หรือคำสั่ง `darkman run` โดยตรงได้เลย 1. **การตั้งค่าโหมด**: Darkman สามารถตั้งค่าโหมดปัจจุบันเป็นโหมดมืดหรือโหมดสว่างได้ด้วยคำสั่ง `darkman set <light|dark>`. 2. **การตรวจสอบโหมดปัจจุบัน**: สามารถตรวจสอบโหมดปัจจุบันได้ด้วยคำสั่ง `darkman get`. 3. **การสลับโหมด**: สามารถสลับโหมดระหว่างโหมดมืดและโหมดสว่างได้ด้วยคำสั่ง `darkman toggle`. 4. **การทำงานอัตโนมัติ**: Darkman จะทำงานอัตโนมัติโดยใช้ข้อมูลตำแหน่งที่ตั้งของระบบเพื่อกำหนดเวลาพระอาทิตย์ขึ้นและตก. 5. **การปรับแต่ง**: สามารถเพิ่มสคริปต์เพื่อปรับแต่งการทำงานของโปรแกรมให้เข้ากับแอปพลิเคชันต่างๆ ได้. ## การตั้งค่า darkman 1. สร้างไฟล์ `config.yaml` ในโฟลเดอร์ `~/.config/darkman/` ```yaml lat: 13.7563 lng: 100.5018 # ตำแหน่งกรุงเทพ usegeoclue: false dbusserver: true portal: true ``` 2. การตั้งค่า portal สำหรับ Darkman จะช่วยให้โปรแกรมสามารถเปลี่ยนโหมดสีของเดสก์ท็อปได้โดยใช้ XDG settings portal API. 2.1 สร้างไฟล์ portals.conf ในโฟลเดอร์ ~/.config/xdg-desktop-portal/ ```conf [preferred] org.freedesktop.impl.portal.Settings=darkman ``` 2.1 รีสตาร์ท service xdg-desktop-portal เพื่อให้การตั้งค่าใหม่มีผล: ```bash systemctl --user restart xdg-desktop-portal ``` การตั้งค่านี้จะช่วยให้แอปพลิเคชันต่างๆ บนเดสก์ท็อปสามารถอ่านค่าโหมดสีจาก Darkman และปรับเปลี่ยนตามที่กำหนด. 3. Custom executables ใน Darkman สามารถเพิ่มการทำงานเพิ่มเติมเมื่อมีการเปลี่ยนโหมดสีของเดสก์ท็อป โดยการวางสคริปต์หรือโปรแกรมที่ต้องการในไดเรกทอรีที่กำหนด **ไดเรกทอรีสำหรับ Custom executables**: - `$XDG_DATA_DIRS/dark-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดมืด - `$XDG_DATA_DIRS/light-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดสว่าง **ตัวอย่างการใช้งาน Custom executables**: 1. **สร้างสคริปต์สำหรับโหมดมืด**: - สร้างไฟล์ `set_dark_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/dark-mode.d/` - เพิ่มเนื้อหาดังนี้: ```bash #!/bin/bash # ตัวอย่างสคริปต์สำหรับโหมดมืด gsettings set org.gnome.desktop.interface gtk-theme "Adwaita-dark" notify-send "Dark Mode Activated" ``` 2. **สร้างสคริปต์สำหรับโหมดสว่าง**: - สร้างไฟล์ `set_light_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/light-mode.d/` - เพิ่มเนื้อหาดังนี้: ```bash #!/bin/bash # ตัวอย่างสคริปต์สำหรับโหมดสว่าง gsettings set org.gnome.desktop.interface gtk-theme "Adwaita" notify-send "Light Mode Activated" ``` 3. **ตั้งค่าสิทธิ์การรันสคริปต์**: - ตั้งค่าสิทธิ์ให้สคริปต์สามารถรันได้: ```bash chmod +x $XDG_DATA_DIRS/dark-mode.d/set_dark_mode.sh chmod +x $XDG_DATA_DIRS/light-mode.d/set_light_mode.sh ``` เมื่อ Darkman เปลี่ยนโหมด สคริปต์เหล่านี้จะถูกเรียกใช้งานตามที่กำหนด ### การแก้ไขหากไม่พบ XDG_DATA_DIRS หากไม่พบตัวแปร `XDG_DATA_DIRS` คุณสามารถสร้างไดเรกทอรีที่จำเป็นเองได้ตามต้องการ โดยปกติแล้ว `XDG_DATA_DIRS` จะประกอบด้วยไดเรกทอรีเหล่านี้: - `~/.local/share/` - `/usr/local/share/` - `/usr/share/` คุณสามารถสร้างไดเรกทอรีเหล่านี้และเพิ่มสคริปต์ของคุณได้ตามนี้: 1. **สร้างไดเรกทอรี**: - สร้างไดเรกทอรีสำหรับโหมดมืดและโหมดสว่าง: ```bash mkdir -p ~/.local/share/dark-mode.d mkdir -p ~/.local/share/light-mode.d ``` [ตัวอย่าง Script ที่ผมใช้](<https://github.com/vazw/dotfiles/tree/Void(wayland)/darkman>) 2. ทำการ **export XDG_DATA_DIRS**: โดยทั่วไปเราสามารถตั้งตัวแปร Environments ต่าง ๆ ได้ที่ `~/.profile` และตัวแปรทั้งหมดจะถูกโหลดหลังจากเรา **Login** ```bash export XDG_DATA_DIRS=$HOME/.local/share:/usr/local/share:/usr/share:$XDG_DATA_DIRS ``` Source: [darkman](https://gitlab.com/WhyNotHugo/darkman)
@ 674473f6:f859eb3c
2025-04-04 08:42:17## darkman คืออะไร **Darkman** เป็นโปรแกรมที่ช่วยควบคุมการเปลี่ยนโหมดสีของเดสก์ท็อประหว่างโหมดมืดและโหมดสว่างบนระบบปฏิบัติการ Unix-like. โปรแกรมนี้จะทำงานในเบื้องหลัง(background process) และสามารถตั้งค่าให้เปลี่ยนไปใช้โหมดมืดเมื่อพระอาทิตย์ตก หรือเปลี่ยนกลับไปใช้โหมดสว่างเมื่อพระอาทิตย์ขึ้นได้ ## การทำงานของ Darkman เรียกใช้ผ่าน systemd service หรือคำสั่ง `darkman run` โดยตรงได้เลย 1. **การตั้งค่าโหมด**: Darkman สามารถตั้งค่าโหมดปัจจุบันเป็นโหมดมืดหรือโหมดสว่างได้ด้วยคำสั่ง `darkman set <light|dark>`. 2. **การตรวจสอบโหมดปัจจุบัน**: สามารถตรวจสอบโหมดปัจจุบันได้ด้วยคำสั่ง `darkman get`. 3. **การสลับโหมด**: สามารถสลับโหมดระหว่างโหมดมืดและโหมดสว่างได้ด้วยคำสั่ง `darkman toggle`. 4. **การทำงานอัตโนมัติ**: Darkman จะทำงานอัตโนมัติโดยใช้ข้อมูลตำแหน่งที่ตั้งของระบบเพื่อกำหนดเวลาพระอาทิตย์ขึ้นและตก. 5. **การปรับแต่ง**: สามารถเพิ่มสคริปต์เพื่อปรับแต่งการทำงานของโปรแกรมให้เข้ากับแอปพลิเคชันต่างๆ ได้. ## การตั้งค่า darkman 1. สร้างไฟล์ `config.yaml` ในโฟลเดอร์ `~/.config/darkman/` ```yaml lat: 13.7563 lng: 100.5018 # ตำแหน่งกรุงเทพ usegeoclue: false dbusserver: true portal: true ``` 2. การตั้งค่า portal สำหรับ Darkman จะช่วยให้โปรแกรมสามารถเปลี่ยนโหมดสีของเดสก์ท็อปได้โดยใช้ XDG settings portal API. 2.1 สร้างไฟล์ portals.conf ในโฟลเดอร์ ~/.config/xdg-desktop-portal/ ```conf [preferred] org.freedesktop.impl.portal.Settings=darkman ``` 2.1 รีสตาร์ท service xdg-desktop-portal เพื่อให้การตั้งค่าใหม่มีผล: ```bash systemctl --user restart xdg-desktop-portal ``` การตั้งค่านี้จะช่วยให้แอปพลิเคชันต่างๆ บนเดสก์ท็อปสามารถอ่านค่าโหมดสีจาก Darkman และปรับเปลี่ยนตามที่กำหนด. 3. Custom executables ใน Darkman สามารถเพิ่มการทำงานเพิ่มเติมเมื่อมีการเปลี่ยนโหมดสีของเดสก์ท็อป โดยการวางสคริปต์หรือโปรแกรมที่ต้องการในไดเรกทอรีที่กำหนด **ไดเรกทอรีสำหรับ Custom executables**: - `$XDG_DATA_DIRS/dark-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดมืด - `$XDG_DATA_DIRS/light-mode.d/`: สำหรับสคริปต์ที่ต้องการรันเมื่อเปลี่ยนไปใช้โหมดสว่าง **ตัวอย่างการใช้งาน Custom executables**: 1. **สร้างสคริปต์สำหรับโหมดมืด**: - สร้างไฟล์ `set_dark_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/dark-mode.d/` - เพิ่มเนื้อหาดังนี้: ```bash #!/bin/bash # ตัวอย่างสคริปต์สำหรับโหมดมืด gsettings set org.gnome.desktop.interface gtk-theme "Adwaita-dark" notify-send "Dark Mode Activated" ``` 2. **สร้างสคริปต์สำหรับโหมดสว่าง**: - สร้างไฟล์ `set_light_mode.sh` ในไดเรกทอรี `$XDG_DATA_DIRS/light-mode.d/` - เพิ่มเนื้อหาดังนี้: ```bash #!/bin/bash # ตัวอย่างสคริปต์สำหรับโหมดสว่าง gsettings set org.gnome.desktop.interface gtk-theme "Adwaita" notify-send "Light Mode Activated" ``` 3. **ตั้งค่าสิทธิ์การรันสคริปต์**: - ตั้งค่าสิทธิ์ให้สคริปต์สามารถรันได้: ```bash chmod +x $XDG_DATA_DIRS/dark-mode.d/set_dark_mode.sh chmod +x $XDG_DATA_DIRS/light-mode.d/set_light_mode.sh ``` เมื่อ Darkman เปลี่ยนโหมด สคริปต์เหล่านี้จะถูกเรียกใช้งานตามที่กำหนด ### การแก้ไขหากไม่พบ XDG_DATA_DIRS หากไม่พบตัวแปร `XDG_DATA_DIRS` คุณสามารถสร้างไดเรกทอรีที่จำเป็นเองได้ตามต้องการ โดยปกติแล้ว `XDG_DATA_DIRS` จะประกอบด้วยไดเรกทอรีเหล่านี้: - `~/.local/share/` - `/usr/local/share/` - `/usr/share/` คุณสามารถสร้างไดเรกทอรีเหล่านี้และเพิ่มสคริปต์ของคุณได้ตามนี้: 1. **สร้างไดเรกทอรี**: - สร้างไดเรกทอรีสำหรับโหมดมืดและโหมดสว่าง: ```bash mkdir -p ~/.local/share/dark-mode.d mkdir -p ~/.local/share/light-mode.d ``` [ตัวอย่าง Script ที่ผมใช้](<https://github.com/vazw/dotfiles/tree/Void(wayland)/darkman>) 2. ทำการ **export XDG_DATA_DIRS**: โดยทั่วไปเราสามารถตั้งตัวแปร Environments ต่าง ๆ ได้ที่ `~/.profile` และตัวแปรทั้งหมดจะถูกโหลดหลังจากเรา **Login** ```bash export XDG_DATA_DIRS=$HOME/.local/share:/usr/local/share:/usr/share:$XDG_DATA_DIRS ``` Source: [darkman](https://gitlab.com/WhyNotHugo/darkman) @ 3104fbbf:ac623068
2025-04-04 06:58:30 ## **Introduction** If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best. The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families. Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives. From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families. --- ## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin** Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do: - **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation. Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money. - **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse. - **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible. - **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios. --- ## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability: - **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance. - **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach. - **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks. --- ## 3. Digital Privacy: Fighting Surveillance with Advanced Tools The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself: - **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks. - **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors. - **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube. - **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security. --- ## 4. Building Resilient Local Communities: The Foundation of a Free Future While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite. To counter this, communities must organize locally: - **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises. - **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems. - **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points. - **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism. --- ## 5. The Bigger Picture: Rejecting the Illusion of Saviors The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems. --- ## Conclusion: A Call to Action The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites. - The tools for liberation already exist. - The question is: will we use them? For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom ⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡ ###### If you enjoyed this article, consider supporting it with a Zap! --- My Substack ENGLISH = https://blisshodlenglish.substack.com/ My substack FRENCH = https://blisshodl.substack.com/ --- Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl --- ---
@ 3104fbbf:ac623068
2025-04-04 06:58:30 ## **Introduction** If you have a functioning brain, it’s impossible to fully stand for any politician or align completely with any political party. The solutions we need are not found in the broken systems of power but in individual actions and local initiatives. Voting for someone may be your choice, but relying solely on elections every few years as a form of political activism is a losing strategy. People around the world have fallen into the trap of thinking that casting a ballot once every four years is enough, only to return to complacency as conditions worsen. Voting for the "lesser of two evils" has been the norm for decades, yet expecting different results from the same flawed system is naive at best. The truth is, governments are too corrupt to save us. In times of crisis, they won’t come to your aid—instead, they will tighten their grip, imposing more surveillance, control, and wealth extraction to benefit the oligarch class. To break free from this cycle, we must first protect ourselves individually—financially, geographically, and digitally—alongside our families. Then, we must organize and build resilient local communities. These are the only ways forward. History has shown us time and again that the masses are easily deceived by the political circus, falling for the illusion of a "savior" who will fix everything. But whether right, center, or left, the story remains the same: corruption, lies, and broken promises. If you possess a critical and investigative mind, you know better than to place your trust in politicians, parties, or self-proclaimed heroes. The real solution lies in free and sovereign individuals who reject the herd mentality and take responsibility for their own lives. From the beginning of time, true progress has come from individuals who think for themselves and act independently. The nauseating web of politicians, billionaires, and oligarchs fighting for power and resources has never been—and will never be—the answer to our problems. In a world increasingly dominated by corrupted governments, NGOs, and elites, ordinary people must take proactive steps to protect themselves and their families. --- ## **1. Financial Protection: Reclaiming Sovereignty Through Bitcoin** Governments and central banks have long manipulated fiat currencies, eroding wealth through inflation and bailouts that transfer resources to the oligarch class. Bitcoin, as a decentralized, censorship-resistant, and finite currency, offers a way out. Here’s what individuals can do: - **Adopt Bitcoin as a Savings Tool**: Shift a portion of your savings into Bitcoin to protect against inflation and currency devaluation. Bitcoin’s fixed supply (21 million coins) ensures it cannot be debased like fiat money. - **Learn Self-Custody**: Store your Bitcoin in a hardware wallet or use open-source software wallets. Avoid centralized exchanges, which are vulnerable to government seizure or collapse. - **Diversify Geographically:** Hold assets in multiple jurisdictions to reduce the risk of confiscation or capital controls. Consider offshore accounts or trusts if feasible. - **Barter and Local Economies**: In times of crisis, local barter systems and community currencies can bypass failing national systems. Bitcoin can serve as a global medium of exchange in such scenarios. --- ## 2. Geographical Flexibility: Reducing Dependence on Oppressive Systems Authoritarian regimes thrive on controlling populations within fixed borders. By increasing geographical flexibility, individuals can reduce their vulnerability: - **Obtain Second Passports or Residencies**: Invest in citizenship-by-investment programs or residency permits in countries with greater freedoms and lower surveillance. - **Relocate to Freer Jurisdictions**: Research and consider moving to regions with stronger property rights, lower taxes, and less government overreach. - **Decentralize Your Life**: Avoid keeping all your assets, family, or business operations in one location. Spread them across multiple regions to mitigate risks. --- ## 3. Digital Privacy: Fighting Surveillance with Advanced Tools The rise of mass surveillance and data harvesting by governments and corporations threatens individual freedom. Here’s how to protect yourself: - **Use Encryption**: Encrypt all communications using tools like Signal or ProtonMail. Ensure your devices are secured with strong passwords and biometric locks. - **Adopt Privacy-Focused Technologies**: Use Tor for anonymous browsing, VPNs to mask your IP address, and open-source operating systems like Linux to avoid backdoors. - **Reject Surveillance Tech**: Avoid smart devices that spy on you (e.g., Alexa, Google Home). Opt for decentralized alternatives like Mastodon instead of Twitter, or PeerTube instead of YouTube. - **Educate Yourself on Digital Privacy**: Learn about tools and practices that enhance your online privacy and security. --- ## 4. Building Resilient Local Communities: The Foundation of a Free Future While individual actions are crucial, collective resilience is equally important. Governments are too corrupt to save populations in times of crisis—history shows they will instead impose more control and transfer wealth to the elite. To counter this, communities must organize locally: - **Form Mutual Aid Networks**: Create local groups that share resources, skills, and knowledge. These networks can provide food, medical supplies, and security during crises. - **Promote Local Economies**: Support local businesses, farmers, and artisans. Use local currencies or barter systems to reduce dependence on centralized financial systems. - **Develop Off-Grid Infrastructure**: Invest in renewable energy, water filtration, and food production to ensure self-sufficiency. Community gardens, solar panels, and rainwater harvesting are excellent starting points. - **Educate and Empower**: Host workshops on financial literacy, digital privacy, and sustainable living. Knowledge is the most powerful tool against authoritarianism. --- ## 5. The Bigger Picture: Rejecting the Illusion of Saviors The deep corruption within governments, NGOs, and the billionaire class is evident. These entities will never act in the interest of ordinary people. Instead, they will exploit crises to expand surveillance, control, and wealth extraction. The idea of a political “savior” is a dangerous illusion. True freedom comes from individuals taking responsibility for their own lives and working together to build decentralized, resilient systems. --- ## Conclusion: A Call to Action The path to a genuinely free humanity begins with individual action. By adopting Bitcoin, securing digital privacy, increasing geographical flexibility, and building resilient local communities, ordinary people can protect themselves against authoritarianism. Governments will not save us—they are the problem. It is up to us to create a better future, free from the control of corrupt elites. - The tools for liberation already exist. - The question is: will we use them? For those interested, I share ideas and solutions in my book « THE GATEWAY TO FREEDOM » https://blisshodlenglish.substack.com/p/the-gateway-to-freedom ⚡ **The time to act is now. Freedom is not given—it is taken.** ⚡ ###### If you enjoyed this article, consider supporting it with a Zap! --- My Substack ENGLISH = https://blisshodlenglish.substack.com/ My substack FRENCH = https://blisshodl.substack.com/ --- Get my Book « THE GATEWAY TO FREEDOM » here 🙏 => https://coinos.io/blisshodl --- --- @ da0b9bc3:4e30a4a9
2025-04-04 06:24:48Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/934111
@ da0b9bc3:4e30a4a9
2025-04-04 06:24:48Hello Stackers! Welcome on into the ~Music Corner of the Saloon! A place where we Talk Music. Share Tracks. Zap Sats. So stay a while and listen. 🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨 🚨Subscribe to the territory to ensure you never miss a post! 🚨 originally posted at https://stacker.news/items/934111 @ bf95e1a4:ebdcc848
2025-04-04 06:11:18This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)! ## The Gullible Collective We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game. The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it. Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank. When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it. Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media. The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless. The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech. Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell. ### **About the Bitcoin Infinity Academy** The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available.
@ bf95e1a4:ebdcc848
2025-04-04 06:11:18This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our[ Geyser page](https://geyser.fund/project/infinity)! ## The Gullible Collective We humans are biased by nature. Everything we think we know is distorted in one way or another by our cognitive shortcomings. The human brain has been forced to evolve and adapt to whatever environment it found itself in over millennia. Having a brain that is capable of setting aside personal aims for the sake of the collective has proven to be advantageous for the evolution of our species as a whole. The same is true for every other social life form. However, letting these parts of our brains guide our political judgment can lead to disastrous results in the long run — not because of bad intentions but because of the simple fact that a few individuals will always thrive by playing every political system for personal gain. From an evolutionary perspective, an army of ay-sayers and martyrs, regardless of whether we’re talking about an army of humans or an army of ants or bacteria, has an advantage over a less disciplined one. From an individual's evolutionary perspective though, it is better to *appear* like you’re a martyr but to run and hide when the actual battle happens. This at least partly explains the high percentage of sociopaths in leadership positions all over the world. If you can appear to act for the good of the collective but dupe your way into more and more power behind people’s backs, you’re more likely to succeed than someone playing a fair game. The story of banking and fiat currency is a story about collective madness. Historically, rulers have tricked people into killing each other through the promise of an after-life. Through central banking, the rulers of the world wars could trick people into building armies for them by printing more money. This is seldom mentioned in history classes because it still goes on today on a massive scale. Inflation might no longer be paying tank factory workers, but it is the main mechanism that funnels wealth into the pockets of the super-rich and away from everyone else. Inflation is the mechanism that hinders us from transporting the value of our labor through time. It makes us avoid real long-term thinking. We hardly ever consider this a problem because none of us has ever experienced an alternative to it. Money is still vastly misunderstood by the lion's share of the world’s population. In most parts of the world, banks do something called fractional reserve lending. This means that they lend out money that they don't have — conjuring up new money out of thin air and handing it out to their customers as loans. Loans that have to be paid back with interest. Interest that can’t be paid back with thin air but has to be paid with so-called real money. Real money, of which there isn’t enough around to pay back all the loans, so that a constant need for new credit becomes a crucial part of the entire system. Not to mention central banks, which do the same and worse for governments. We’re so used to it by now that every country is expected to have a national debt. All but a handful of ridiculously rich ones do. National debts are also loans that have to be paid back with interest backed by nothing. Think about that. Your taxes are paying someone else's interest. Your tax money is not paying for your grandmother's bypass operation, it is paying interest to a central bank. When the ideas of the catholic church ruled Europe, people who didn’t believe in God were few and very seldomly outspoken. They had good reason for this since belief in God was virtually mandatory throughout society. Ever since 1971, when famously dishonest American president Richard Nixon cut the last string that tied the US Dollar to gold, our conception of what the world economy is and ought to be has been skewed by an utterly corrupt system. We’re led to believe that we’re all supposed to work longer and longer days in order to spend more and more money and bury ourselves in more and more debt to keep the machine running. We’re duped into thinking that buying a new car every other year is somehow good for the environment and that bringing a cotton bag to the grocery store will somehow save the planet. Stores manipulate us all the time through advertising and product placement, but we’re led to believe that if we can be “climate-smart,” we’re behaving responsibly. Somehow, our gross domestic product is supposed to increase indefinitely while politicians will save us from ourselves through carbon taxes. Fortunately for us, and unfortunately for them, there now exists a way for unbelievers of this narrative to opt out. Life finds a way, as Jeff Goldblum once so famously put it. Collectivism has ruined many societies. Those of us fortunate enough to live in liberal democracies tend to forget that even democracy is an involuntary system. It’s often referred to as the “worst form of government except all others that have been tried,” but the system itself is very rarely criticized. We’re so used to being governed that not having a leader seems preposterous to most of us. Still, we pay our taxes, and an enormous cut of the fruit of our labor goes to a third party via inflation and the taxation of every good and service imaginable. Institutions, once in place, tend to always favor their own survival just as much as any other living thing does. People employed in the public sector are unlikely to vote against policies that threaten their livelihood. This is a bigger problem than we realize because it’s subtle and takes a long time, but every democracy is headed in the same direction. A bigger state, a more complicated system, and fewer individual freedoms. Long term, it seems that all of our systems tend to favor those who know how to play that system and not those who contribute the most value to their fellow man. Proponents of socialist policies often claim that failed socialist states “weren’t really socialist” or that “that wasn’t really socialism.” What most people fail to realize is that we’ve never tried real *capitalism* since we’ve always used more or less inflationary currencies. This might very well be the most skewed narrative of our era. We’re all experiencing real, albeit disguised, socialism every single day. True free market capitalism is what we haven’t experienced yet, and it might turn out to be a very different thing than what we’re told to believe that it is by almost all mainstream media. The validity of the classic right-left scale describing political viewpoints has been debated a lot lately, and alternative scales, like GAL-TAN, the one with an additional Y-axis describing more or less authoritarian tendencies, are popping up in various contexts around the web. After the birth of Bitcoin, there’s a new way to see this. Imagine an origo, a zero point, and a vector pointing to the left of that. *All* politics are arguably on the left because *all* policies need to be funded by taxes, and taxation can be viewed as theft. Taxation can be viewed as theft because, at its core, it’s involuntary. If a person refuses to pay his taxes, there is a threat of violence lurking in the background. Not to mention inflation, which Milton Friedman so elegantly described as “taxation without legislation.” What you do with the portion of your wealth that you have in Bitcoin is another matter altogether. If you take sufficient precautionary privacy measures and you know what you’re doing, your business in Bitcoin is beyond politics altogether. With the introduction of the Lightning Network and other privacy-improving features, it is now impossible for any third party to confiscate your money or even know that you have it, for that matter. This changes the political landscape of every nation on Earth. Bitcoin is much less confiscatable than gold and other scarce assets, which makes it a much better tool for hedging against nation-states. In this sense, Bitcoin obsoletes borders. You can cross any border on Earth with any amount of Bitcoin *in your head*. Think about that! Your Bitcoin exists in every country simultaneously. Any imposed limit on how much money you can carry from one nation to the other is now made obsolete by beautiful mathematics. Bitcoin is sometimes referred to as a “virtual currency.” This is a very inaccurate description. Bitcoin is just mathematics, and mathematics is just about the most real thing there is. There’s nothing virtual about it. Counterintuitive to some, but real nonetheless. The complexity of human societal hierarchies and power structures is described perfectly in a classic children's book, *The Emperor’s New Clothes*, by Hans Christian Andersen. See the world as the kid who points out that the king is naked in the tale, and everything starts to make sense. Everything in human society is man-made. Nations, leaders, laws, political systems. They’re all castles in the air with nothing but a lurking threat of violence to back them up. Bitcoin is a different beast altogether. It enables every individual to verify the validity of the system at all times. If you really think about it, morality is easy. Don’t hurt other people, and don’t steal other people’s stuff. That’s the basic premise. Humans have but two ways of resolving conflict, conversation and violence, and in this sense, to hurt someone can only mean physical violence. This is why free speech is so important and why you should defend people’s right to speak their minds above everything else. It’s not about being able to express yourself. It’s about your right to hear every side of every argument and thus not have to resort to violence should a conflict of interests occur. You can’t limit free speech with just more speech — there’s always a threat of violence behind the limitations. Code, which both Bitcoin and the Internet are entirely made up of, *is speech*. Any limitations or regulations that your government implements in regard to Bitcoin are not only a display of Bitcoin’s censorship resistance but also a test of your government's stance on freedom of expression. A restriction on Bitcoin use is a restriction on free speech. Remember, the only alternative to speech that anyone has is violence. Code is a language, mathematics is a language, and money is a linguistic tool. A linguistic tool we use as a means of expressing value to each other and as a way to transport value through space and time. Any restrictions or regulations regarding how you can express value, for example, making it impossible to buy Bitcoin with your credit card, prove that the money you have in your bank account is not really yours. When people realize this, the demand for Bitcoin goes *up*, not down. If you know what you're doing, there’s no need to fear the regulators. They, on the other hand, have good reason to fear an invention that shamelessly breaks their spell. ### **About the Bitcoin Infinity Academy** The Bitcoin Infinity Academy is an educational project built around [Knut Svanholm](http://primal.net/knut)’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a [video](https://www.youtube.com/@BitcoinInfinityShow) in which Knut and [Luke de Wolf](http://primal.net/luke) discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our [Geyser](https://geyser.fund/project/infinity) page. Signed books, monthly calls, and lots of other benefits are also available. @ 2e8970de:63345c7a
2025-04-04 17:12:41Recently I shared a substack post that argued **"DOGE is About Sex"** https://stacker.news/items/921208 the main premise being how Elon & Trumps economic goals were to make women more economically desperate such that women are more nudged to settle for mediocre and lonely men. I do not think that tells the whole story about MAGA economics. Neither does the author CHH, I think. But I think she's onto something. Here are 4 tweets I randomly encountered today that fit this narrative perfectly: > Trump's trade war is partly about gender. > As American manufacturing declined, men lost economic leverage over women. The nationalist right believes that this led to lower marriage and birth rates. https://x.com/EricLevitz/status/1908175346177847669 > Highly educated women will be completely out of the marriage market in next 5 years. https://x.com/mshree01/status/1906316952613589038 > congratulations to boring men with stable jobs on becoming the next hot commodity https://x.com/morganisawizard/status/1907889282947424453 > The American economy is built around giving fake unproductive jobs to women, therefore we must destroy it https://x.com/DrewPavlou/status/1907932434571866226 # Conclusion Interestingly this thought seems to cross many peoples minds independently. Like Calculus was invented by Leibnitz and Newton simultaneous and independently. It's also liberals and conservatives; men and women uttering these words. I think this is super fascinating. Shoutout to the original post: https://www.cartoonshateher.com/p/doge-is-about-sex originally posted at https://stacker.news/items/934557
@ 2e8970de:63345c7a
2025-04-04 17:12:41Recently I shared a substack post that argued **"DOGE is About Sex"** https://stacker.news/items/921208 the main premise being how Elon & Trumps economic goals were to make women more economically desperate such that women are more nudged to settle for mediocre and lonely men. I do not think that tells the whole story about MAGA economics. Neither does the author CHH, I think. But I think she's onto something. Here are 4 tweets I randomly encountered today that fit this narrative perfectly: > Trump's trade war is partly about gender. > As American manufacturing declined, men lost economic leverage over women. The nationalist right believes that this led to lower marriage and birth rates. https://x.com/EricLevitz/status/1908175346177847669 > Highly educated women will be completely out of the marriage market in next 5 years. https://x.com/mshree01/status/1906316952613589038 > congratulations to boring men with stable jobs on becoming the next hot commodity https://x.com/morganisawizard/status/1907889282947424453 > The American economy is built around giving fake unproductive jobs to women, therefore we must destroy it https://x.com/DrewPavlou/status/1907932434571866226 # Conclusion Interestingly this thought seems to cross many peoples minds independently. Like Calculus was invented by Leibnitz and Newton simultaneous and independently. It's also liberals and conservatives; men and women uttering these words. I think this is super fascinating. Shoutout to the original post: https://www.cartoonshateher.com/p/doge-is-about-sex originally posted at https://stacker.news/items/934557 @ 0edc2f47:730cff1b
2025-04-04 03:37:15## Chef's notes This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long! ## Details - ⏲️ Prep time: 10 min - 🍳 Cook time: 0 min ## Ingredients - 1 cup (240mL) heavy whipping cream - 1/4 cup (24g) cocoa powder - 5 tbsp (38g) Confectioners (powdered) sugar - 1/4 tsp (1.25mL) vanilla extract (optional) - Flaky sea salt (optional, but excellent) ## Directions 1. 1. Whip the cream until frothy. 2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using). 3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy).
@ 0edc2f47:730cff1b
2025-04-04 03:37:15## Chef's notes This started as a spontaneous kitchen experiment—an amalgamation of recipes from old cookbooks and online finds. My younger daughter wanted to surprise her sister with something quick but fancy ("It's a vibe, Mom."), and this is what we came up with. It’s quickly established itself as a go-to favorite: simple, rich, and deeply satisfying. It serves 4 (or 1, depending on the day; I am not here to judge). Tightly wrapped, it will keep up to 3 days in the fridge, but I bet it won't last that long! ## Details - ⏲️ Prep time: 10 min - 🍳 Cook time: 0 min ## Ingredients - 1 cup (240mL) heavy whipping cream - 1/4 cup (24g) cocoa powder - 5 tbsp (38g) Confectioners (powdered) sugar - 1/4 tsp (1.25mL) vanilla extract (optional) - Flaky sea salt (optional, but excellent) ## Directions 1. 1. Whip the cream until frothy. 2. 2. Sift in cocoa and sugar, fold or gently mix (add vanilla if using). 3. 3. Whip to medium peaks (or stiff peaks, if that's more your thing). Chill and serve (topped with a touch of sea salt if you’re feeling fancy). @ 2e8970de:63345c7a
2025-04-04 16:17:56 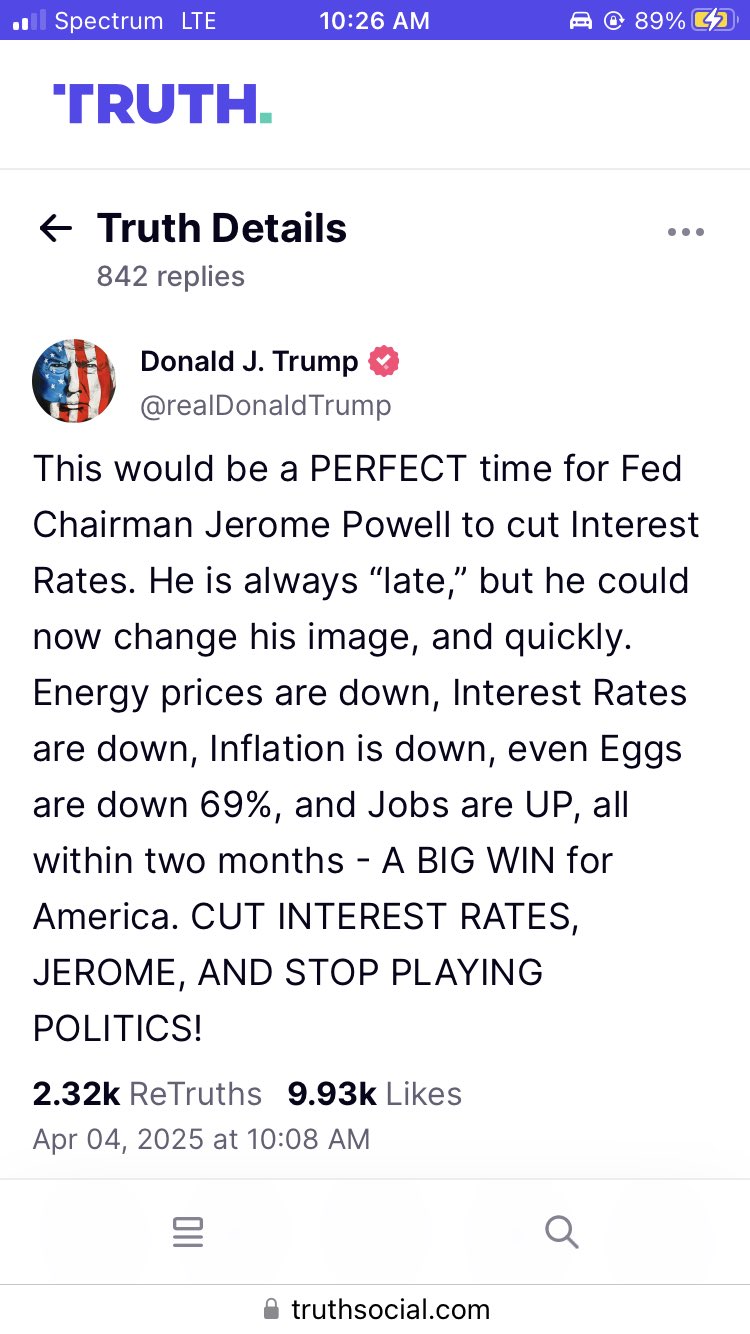 Interestingly he's suggesting that he's doing all this on purpose. Why would he say that? Well the market could take this (a) positively: he's still in control and there is a masterplan (b) negatively: he's openly hostile against the economy. Trump is obviously hoping the market will take it as (a). originally posted at https://stacker.news/items/934513
@ 2e8970de:63345c7a
2025-04-04 16:17:56  Interestingly he's suggesting that he's doing all this on purpose. Why would he say that? Well the market could take this (a) positively: he's still in control and there is a masterplan (b) negatively: he's openly hostile against the economy. Trump is obviously hoping the market will take it as (a). originally posted at https://stacker.news/items/934513 @ 3c389c8f:7a2eff7f
2025-04-04 15:47:44### A Rose By Any Other Name... or whatever. NIP-05 is an identifier created by mapping Nostr keys to DNS based identifiers. [More technically](https://nips.nostr.com/5), it the part of the protocol that defines how to do this mapping, but you will often see the resulting identifier referred to as "your NIP-05". You will also see it referenced as a "Nostr Address", a "Nostr ID", or a "Nostr Verification". None of those terms are fully correct but nor are they wrong. A NIP-05 identifier does look very similar to an email address (i.e. NostrName @ SomeSite .com). It makes it easier to convey your Nostr profile to friends or collogues, since your chosen name is not unique and the npub format is not exactly something you will be wanting to jot down at a business meeting. It can be used to find you and your notes, so the term, Nostr Address, fits in that sense. There are free services that provide a NIP-05 to you, but you may want to consider contracting this service to a paid provider. Free services tend to be abused by spammers. Paid NIP-05 providers are reasonably priced, more reputable, provide select affiliations, and often other services, along with hosting your Nip-05 file. Nostr ID might be the appropriate term, in a different way. Your NIP-05 is unique. You are not limited to possessing a single one, but only one may be present on your profile at any given time. You can switch them out as needed. Some Nostr-based services will require that you have a particular NIP-05 provider in order to access their relay communities or other features. In that sense, it is an ID, proving that you are a member of that community. These NIP-05 IDs are created and hosted for you by the community relay hosts, with whatever criteria they choose to require. Nostr Verification comes into consideration if you own or run a website. It can be used to validate your identity. By hosting your NIP-05 file on your own domain, you are, in essence, validating that the same person has ownership of the website and control of the associated Nostr profile. (i.e. YourName @ YourSite .com) This is exceptionally handy for any well known individual who may be subject to impersonation. This is great, too, if you sell a product or service online and would like to use Nostr as a means of advertising and engaging with your customers. Your NIP-05 can signal to your customers that you, or any employee, are affiliated with your company. All of this, for me to tell you... that you don't need a NIP-05 identifier to use Nostr. It just makes a lot of the things you might want to do simpler. For clear instructions on how to set up your NIP-05 visit [nostr.how](https://nostr.how/en/guides/get-verified)
@ 3c389c8f:7a2eff7f
2025-04-04 15:47:44### A Rose By Any Other Name... or whatever. NIP-05 is an identifier created by mapping Nostr keys to DNS based identifiers. [More technically](https://nips.nostr.com/5), it the part of the protocol that defines how to do this mapping, but you will often see the resulting identifier referred to as "your NIP-05". You will also see it referenced as a "Nostr Address", a "Nostr ID", or a "Nostr Verification". None of those terms are fully correct but nor are they wrong. A NIP-05 identifier does look very similar to an email address (i.e. NostrName @ SomeSite .com). It makes it easier to convey your Nostr profile to friends or collogues, since your chosen name is not unique and the npub format is not exactly something you will be wanting to jot down at a business meeting. It can be used to find you and your notes, so the term, Nostr Address, fits in that sense. There are free services that provide a NIP-05 to you, but you may want to consider contracting this service to a paid provider. Free services tend to be abused by spammers. Paid NIP-05 providers are reasonably priced, more reputable, provide select affiliations, and often other services, along with hosting your Nip-05 file. Nostr ID might be the appropriate term, in a different way. Your NIP-05 is unique. You are not limited to possessing a single one, but only one may be present on your profile at any given time. You can switch them out as needed. Some Nostr-based services will require that you have a particular NIP-05 provider in order to access their relay communities or other features. In that sense, it is an ID, proving that you are a member of that community. These NIP-05 IDs are created and hosted for you by the community relay hosts, with whatever criteria they choose to require. Nostr Verification comes into consideration if you own or run a website. It can be used to validate your identity. By hosting your NIP-05 file on your own domain, you are, in essence, validating that the same person has ownership of the website and control of the associated Nostr profile. (i.e. YourName @ YourSite .com) This is exceptionally handy for any well known individual who may be subject to impersonation. This is great, too, if you sell a product or service online and would like to use Nostr as a means of advertising and engaging with your customers. Your NIP-05 can signal to your customers that you, or any employee, are affiliated with your company. All of this, for me to tell you... that you don't need a NIP-05 identifier to use Nostr. It just makes a lot of the things you might want to do simpler. For clear instructions on how to set up your NIP-05 visit [nostr.how](https://nostr.how/en/guides/get-verified) @ 502ab02a:a2860397
2025-04-04 02:50:35หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ? Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3 เทียบง่ายๆครับ น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค) น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค) ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค) นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ ผู้ผลิตผิดไหม? จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน - oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า??? มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน - มีไลโนเลอิกสูง ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม - โทโคฟีรอล (Tocopherols) เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง - โทโคไทรอีนอล (Tocotrienols) เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้ #pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก
@ 502ab02a:a2860397
2025-04-04 02:50:35หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ? Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3 เทียบง่ายๆครับ น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค) น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค) ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค) นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ ผู้ผลิตผิดไหม? จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน - oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า??? มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน - มีไลโนเลอิกสูง ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม - โทโคฟีรอล (Tocopherols) เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง - โทโคไทรอีนอล (Tocotrienols) เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้ #pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก @ 7bc05901:8c26d22b
2025-04-04 15:40:10I am not an engineer by trade. I took my math classes for college credit as early as I could in high school. I signed up for a bachelor of arts in college and basically didn't touch STEM for the rest of my formal education. Seminary (incomplete) and Law School (JD) didn't go deep into any of the sciences -- I think I struggled through an "accounting for lawyers" class. The dumb thing is that in middle school and early high school I was obsessed with tinkering with mechanical things. I rebuilt a go-kart, tinkered with my computer, built skateboard ramps. High school came, I got obsessed with chasing girls and listening to emo music, and that culminated in a foggy pursuit of journalism, linguistics, ministry and/or academia in my post-graduate adventures. Also, algebra came to me really easily. I loved cramming the day before a test in middle school and embarrassing the other A students who had to work hard to keep those grades up. I obviously see now how dangerous that pattern can be to sustaining motivation and discipline in the long-time preference aspects of life. I was motivated by the idea of "getting one over" on the authoritarian educators in my life -- they said that the only way to succeed is to do my homework and study, but I wanted them to know that *I was different*. And I think I was different from a lot of other people around me, but I aimed my agency in the wrong direction. The rebellion became the end for me, instead of being the means to an end of meaningful learning. Rebel against the system so you can escape into a self-sovereign, high-agency existence. At the risk of over-stuffing the analogy, perhaps that point brings me to decentralized social media environments. Facebook is like my school teachers, there are tasks laid out for me nudging me to behave a certain way. My grades are analogized by my reach that Facebook will give and take away. I run a few Facebook pages and I am constantly irritated by the annoying UI. Constantly changing, adding shit that I cannot imagine anyone asking for and taking away the shit that you refer to everyday. Just this past week I noticed that I have to click into a post on Meta business sweet in order to see how many shares it has. This used to be on the page as I scrolled through all of my content. There is literally just a blank white space where it used to say: 54 shares. My thought goes to, this is somehow punishing me for my reach. Although Zuckerberg has pledged his allegiance to the new age of "free speech" and given his finger to the government-meddling that he fanned to flame over the last ten or fifteen years, I still think Facebook wants to nudge users away from certain things and towards other things. Libertarians have railed against the "nanny-state" but it is harder to understand how we also give up our sovereignty to centralized social media companies: the Nanny-Feed. This must die. The unbundling of facebook is a weird time that feels like the detangling of digital society. Life without widespread Craigslist adoption is somewhat more annoying. I used to scroll Craigslist all the time for stuff. I went to Los Angeles for a few months in 2012 and used it to buy some things and hear about auditions for different projects, a few of which panned out for me. There was something about having some separation from the site that I went to specifically to network with co-workers and communicate with old friends that I liked. I don't want my social media identity locked on one site, especially a site that is subservient to a boardroom. I also like the inconvenience of hopping over to a different app to handle my marketplace experiences. A lot of this needs to be thought through a lot more, because attempting to untangle the beast that is "meta" (still Facebook to me) requires a lot more insight than I have as I type this out. I'm mostly just nostalgic and emotional and remembering a different time in my life.
@ 7bc05901:8c26d22b
2025-04-04 15:40:10I am not an engineer by trade. I took my math classes for college credit as early as I could in high school. I signed up for a bachelor of arts in college and basically didn't touch STEM for the rest of my formal education. Seminary (incomplete) and Law School (JD) didn't go deep into any of the sciences -- I think I struggled through an "accounting for lawyers" class. The dumb thing is that in middle school and early high school I was obsessed with tinkering with mechanical things. I rebuilt a go-kart, tinkered with my computer, built skateboard ramps. High school came, I got obsessed with chasing girls and listening to emo music, and that culminated in a foggy pursuit of journalism, linguistics, ministry and/or academia in my post-graduate adventures. Also, algebra came to me really easily. I loved cramming the day before a test in middle school and embarrassing the other A students who had to work hard to keep those grades up. I obviously see now how dangerous that pattern can be to sustaining motivation and discipline in the long-time preference aspects of life. I was motivated by the idea of "getting one over" on the authoritarian educators in my life -- they said that the only way to succeed is to do my homework and study, but I wanted them to know that *I was different*. And I think I was different from a lot of other people around me, but I aimed my agency in the wrong direction. The rebellion became the end for me, instead of being the means to an end of meaningful learning. Rebel against the system so you can escape into a self-sovereign, high-agency existence. At the risk of over-stuffing the analogy, perhaps that point brings me to decentralized social media environments. Facebook is like my school teachers, there are tasks laid out for me nudging me to behave a certain way. My grades are analogized by my reach that Facebook will give and take away. I run a few Facebook pages and I am constantly irritated by the annoying UI. Constantly changing, adding shit that I cannot imagine anyone asking for and taking away the shit that you refer to everyday. Just this past week I noticed that I have to click into a post on Meta business sweet in order to see how many shares it has. This used to be on the page as I scrolled through all of my content. There is literally just a blank white space where it used to say: 54 shares. My thought goes to, this is somehow punishing me for my reach. Although Zuckerberg has pledged his allegiance to the new age of "free speech" and given his finger to the government-meddling that he fanned to flame over the last ten or fifteen years, I still think Facebook wants to nudge users away from certain things and towards other things. Libertarians have railed against the "nanny-state" but it is harder to understand how we also give up our sovereignty to centralized social media companies: the Nanny-Feed. This must die. The unbundling of facebook is a weird time that feels like the detangling of digital society. Life without widespread Craigslist adoption is somewhat more annoying. I used to scroll Craigslist all the time for stuff. I went to Los Angeles for a few months in 2012 and used it to buy some things and hear about auditions for different projects, a few of which panned out for me. There was something about having some separation from the site that I went to specifically to network with co-workers and communicate with old friends that I liked. I don't want my social media identity locked on one site, especially a site that is subservient to a boardroom. I also like the inconvenience of hopping over to a different app to handle my marketplace experiences. A lot of this needs to be thought through a lot more, because attempting to untangle the beast that is "meta" (still Facebook to me) requires a lot more insight than I have as I type this out. I'm mostly just nostalgic and emotional and remembering a different time in my life. @ c8adf82a:7265ee75
2025-04-04 01:58:49What is knowledge? Why do we need it? Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after? When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life Seize the day
@ c8adf82a:7265ee75
2025-04-04 01:58:49What is knowledge? Why do we need it? Since we were small, our parents/guardian put us in school, worked their asses off to give us elective lessons, some get help until college, some even after college and after professional work. Why is this intelligence thing so sought after? When you were born, you mostly just accepted what your parents said, they say go to school - you go to school, they say go learn the piano - you learn the piano. Of course with a lot of questions and denials, but you do it because you know your parents are doing it for your own good. You can feel the love so you disregard the 'why' and go on with faith Everything starts with why, and for most people maybe the purpose of knowledge is to be smarter, to know more, just because. But for me this sounds utterly useless. One day I will die next to a man with half a brain and we would feel the same exact thing on the ground. Literally being smarter at the end does not matter at all However, I am not saying to just be lazy and foolish. For me the purpose of knowledge is action. The more you learn, the more you know what to do, the more you can be sure you are doing the right thing, the more you can make progress on your own being, etc etc Now, how can you properly learn? Imagine a water bottle. The water bottle's sole purpose is to contain water, but you cannot fill in the water bottle before you open the cap. To learn properly, make sure you open the cap and let all that water pour into you If you are reading this, you are alive. Don't waste your time doing useless stuff and start to make a difference in your life Seize the day @ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800
@ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800 @ 2ed3596e:98b4cc78
2025-04-03 21:20:27We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well. Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience! Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin. ### How to leave your Trustpilot review for our portal 1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw ### How to leave your google review for one of our ATMs 1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your transaction ID**, in the review so we can add you to the prize draw It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats! ### What makes Bitcoin Well different Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂. [Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup) ### Invest in Bitcoin Well We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/).
@ 2ed3596e:98b4cc78
2025-04-03 21:20:27We’re giving you the chance to win even more sats through the Bitcoin (Wishing) Well—just for telling us what you love about Bitcoin Well. Each month, when you leave a review for either the Bitcoin Well portal on **Trustpilot** (include your **WellTag**), or our Bitcoin ATMs and (include your **transaction ID and email**), you’ll be entered for a draw where you can win $210 in bitcoin just for sharing your experience! Whether it’s our self-custody focus, fast Lightning purchases, Lightning referral payouts, private ATM transactions or our unbeatable customer support, we want to hear what makes Bitcoin Well your go-to place for buying, selling, and using bitcoin. ### How to leave your Trustpilot review for our portal 1. Head to our [Trustpilot page](https://ca.trustpilot.com/review/bitcoinwell.com) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your WellTag (or transaction ID)**, in the review so we can add you to the prize draw ### How to leave your google review for one of our ATMs 1. [Google the Bitcoin Well Bitcoin ATM you recently used](https://www.google.com/search?q=bitcoin+well+atm+near+me&oq=bitcoin+well+atm+near+me+&gs_lcrp=EgZjaHJvbWUqBwgAEAAYgAQyBwgAEAAYgAQyCAgBEAAYFhgeMg0IAhAAGIYDGIAEGIoFMgoIAxAAGIAEGKIEMgoIBBAAGIAEGKIEMgoIBRAAGIAEGKIE0gEIMjM2NWowajeoAgCwAgA&sourceid=chrome&ie=UTF-8) 2. Write a quick review sharing your favourite Bitcoin Well feature 3. **Include your transaction ID**, in the review so we can add you to the prize draw It’s that easy! Once your review is verified with your welltag or transaction ID, we’ll add your entry to our monthly draw for your chance to win $210 in bitcoin! We’ll announce the winner and the start of each month. Good luck and keep stacking sats! ### What makes Bitcoin Well different Bitcoin Well is on a mission to enable independence. We do this by making it easy to self custody bitcoin. By custodying their own money, our customers are free to do as they wish without begging for permission. By creating a full ecosystem to buy, sell and use your bitcoin to connect with the modern financial world, you are able to have your cake and eat it too - or have your bitcoin in self custody and easily spend it too 🎂. [Create your Bitcoin Well account now →](https://app.bitcoinwell.com/signup) ### Invest in Bitcoin Well We are publicly traded (and love it when our [customers become shareholders!](https://bitcoinwell.com/investors)) and hold ourselves to a high standard of enabling life on a Bitcoin standard. If you want to learn more about Bitcoin Well, please visit our [website](https://bitcoinwell.com/). @ df67f9a7:2d4fc200
2025-04-03 19:54:29More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this. ### Project Description I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users. - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan. - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients. - [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine. ### Potential Impact Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to : - Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations. - Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust. - Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs. - Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients. ### Timeline & Milestones 2025 roadmap for “Webs of Trust Onboarding and Discovery” : - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”. https://nostrmeet.me/ - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays. https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs - [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays. https://grapevine.my/ - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates. https://nostrmeet.me/ ### Prior contributions - Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”. - I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK. - I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK. - Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park. ### About Me I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career. As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose. Thank you for considering this application for funding.
@ df67f9a7:2d4fc200
2025-04-03 19:54:29More than just “follows follows” on Nostr, webs of trust algos will ingest increasingly MORE kinds of user generated content in order to map our interactions across the network. Webs of trust will power user discovery, content search, reviews and reccomendations, identity verification, and access to all corners of the Nostr network. Without relying on a central “trust authority” to recommend people and content for us, sovereign Nostr users will make use of “relative trust” scores generated by a wide range of independent apps and services. The problem is, Nostr doesn’t have an opensource library for performing WoT calculations and delivering NIP standard recommendations to users. In order for a “free market” ecosystem of really smart apps and services to thrive, independent developers will need access to extensible “middleware” such as this. ### Project Description I am building a library for independent developers to offer their own interoperable and configurable WoT services and clients. In addition, and as the primary use case, I am also developing a web client for “in person onboarding” to Nostr, which will make use of this library to provide webs of trust recommendations for “invited” users. - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : This is my first project on Nostr, which began a year ago with seed funding from @druid. This web client will leverage “in person” QR invites to generate WoT powered recommendations of follows, apps, and other stuff for new users at their first Nostr touchpoint. The functional MVP release (April ‘25) allows for “instant, anonymous, and fully encrypted” direct messaging and “move in ready” profile creation from a single QR scan. - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs)(developer library) : Working with @straycat last fall, I built an opensource and extensible library for Nostr developers to integrate “web of trust” powered reccomendations into their products and services. The real power behind GrapeRank is its “pluggable” interpreter, allowing any kind of content (not just “follows follows”) to be ingested for WoT scoring, and configurable easily by developers as well as end users. This library is currently in v0.1, “generating and storing usable scores”, and doesn’t yet produce NIP standard outputs for Nostr clients. - [My Grapevine](https://grapevine.my) (algo dashboard) : In addition, I’ve just wrapped up the demo release of a web client by which users and developers can explore the power of the GrapeRank Engine. ### Potential Impact Webs of Trust is how Nostr scales. But so far, Nostr implementations have been ad-hoc and primarily client centered, with no consistency and little choice for end users. The “onboarding and discovery” tools I am developing promise to : - Establish sovereignty for webs of trust users (supporting a “free market” of algo choices), with opensource libraries by which any developer can easily implement WoT powered recommendations. - Accelerate the isolation of bots and bad actors (and improve the “trustiness” of Nostr for everyone else) by streamlining the onboarding of “real world” acquaintances directly into established webs of trust. - Improve “discoverability of users and content” for any user on any client (to consume and take advantage of WoT powered recommendations for any use case, even as the NIP standards for this are still in flux), by providing an algo engine with “pluggable” inputs and outputs. - Pave the way for “global Nostr adoption”, where WoT powered recommendations (and searches) are consistently available for every user across a wide variety of clients. ### Timeline & Milestones 2025 roadmap for “Webs of Trust Onboarding and Discovery” : - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : MVP release : “scan my QR invite to private message me instantly with a ‘move in ready’ account on Nostr”. https://nostrmeet.me/ - [GrapeRank Engine ](https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs) (developer library) : 1.0 release : “expanded inputs and output WoT scores to Nostr NIPs and other stuff” for consumption by clients and relays. https://github.com/Pretty-Good-Freedom-Tech/graperank-nodejs - [My Grapevine](https://grapevine.my) (algo dashboard) : 1.0 release : “algo usage and configuration webapp with API endpoints” for end users to setup GrapeRank scoring for consumption by their own clients and relays. https://grapevine.my/ - [Meet Me On Nostr](https://nostrmeet.me) (onboarding client) : 1.0 release : first GrapeRank integration, offering “follow and app recommendations for invited users”, customizable per-invite for Nostr advocates. https://nostrmeet.me/ ### Prior contributions - Last spring I hosted panel discussions and [wrote articles on Nostr](https://primal.net/p/npub1manlnflyzyjhgh970t8mmngrdytcp3jrmaa66u846ggg7t20cgqqvyn9tn#reads) exploring how to build “sovereign webs of trust”, where end users can have control over which algorithms to use, and what defines “trust”. - I contributed [gift wrap encryption](https://github.com/nostr-dev-kit/ndk/commit/82b60c3b6ae2f38bde0e542d31bfa10d58d08116) to NDK. - I am also authoring [gift wrapped direct messaging and chat room](https://github.com/nostr-dev-kit/ndk/pulls?q=is%3Apr+author%3Amanimejia) modules for NDK. - Last July, I attended The Bitcoin Conference on an OpenSource pass to raise funds for my onboarding client. I onboarded many Bitcoiners to Nostr, and made valuable connections at Bitcoin Park. ### About Me I discovered Nostr in September ‘23 as a freelance web developer, after years of looking for a “sovereignty respecting” social media on which to build apps. With this came my first purchase of Bitcoin. By December of that year, I was settled on “open source freedom tech” (Nostr and Bitcoin) as the new direction for my career. As a web professional for 20+ years, I know the importance of “proof of work” and being connected. For the last 18 months, I have been establishing myself as a builder in this community. This pivot has not been easy, but it has been rewarding and necessary. After so many years building private tech for other people, I finally have a chance to build freedom tech for everyone. I have finally come home to my peeps and my purpose. Thank you for considering this application for funding. @ 502ab02a:a2860397
2025-04-03 17:41:20ไฟโตสเตอรอล (Phytosterols) เป็นสารประกอบที่พบในพืชและมีโครงสร้างคล้ายคลึงกับคลอเลสเตอรอล (Cholesterol) ของมนุษย์ แต่ไฟโตสเตอรอลไม่ได้ทำหน้าที่เหมือนคลอเลสเตอรอลในร่างกายครับ ไฟโตสเตอรอลมีบทบาทสำคัญในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในระบบทางเดินอาหาร ทำให้ไฟโตสเตอรอลได้รับการส่งเสริมว่าเป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือดไปโดยปริยาย อย่างไรก็ตาม สิ่งที่หลายคนไม่ได้ตั้งข้อสงสัยคือวิธีการโฆษณาและการตลาดนั้นจะแฝงไปด้วยข้อมูลที่บิดเบือนเกี่ยวกับไฟโตสเตอรอลซึ่งอาจนำไปสู่การเสพสารนี้ในปริมาณมากเกินไปจนทำให้เกิดปัญหาสุขภาพหรือเปล่า? เราลองมาค่อยๆตั้งคำถามกันครับ ไฟโตสเตอรอลในธรรมชาติจะพบในปริมาณที่ค่อนข้างน้อยในพืชต่าง ๆ เช่น ธัญพืช ถั่ว เมล็ดพืช อย่างไรก็ตาม ปริมาณไฟโตสเตอรอลในธรรมชาติเป็นเม็ดเป็นผลจะอยู่ในระดับต่ำมาก เช่น ในเมล็ดแฟลกซีด (flaxseed) จะมีไฟโตสเตอรอลอยู่ประมาณ 1,000–2,000 ppm (parts per million) ขณะที่น้ำมันรำข้าวที่มักถูกโฆษณาว่ามีไฟโตสเตอรอลสูงถึงหลักหมื่น ๆ ppm เช่น 12,000 ppm หรือบางยี่ห้ออาจสูงกว่านั้น ซึ่งไม่ใช่แค่สูงจนน่าสรรเสริญ แต่ยังเป็นการขยายความสำคัญของไฟโตสเตอรอลในทางที่ตอบสนองต่อการตลาดได้ในวงกว้างเสียด้วย กระบวนการผลิตน้ำมันรำข้าวนั้นเริ่มต้นจากการสกัดน้ำมันจากรำข้าว โดยมีการใช้เทคนิคการกลั่นน้ำมันที่สามารถช่วยให้ได้น้ำมันที่มีคุณภาพสูง น้ำมันรำข้าวเป็นน้ำมันที่มีไฟโตสเตอรอลสูงเพราะรำข้าว (bran) ซึ่งเป็นเปลือกที่หุ้มเมล็ดข้าวนั้น มีไฟโตสเตอรอลอยู่ในปริมาณสูงตามธรรมชาติอยุ่แล้ว ในกระบวนการสกัดน้ำมันนั้น ตัวไฟโตสเตอรอลจะถูกรักษาไว้ โดยไม่ต้องเติมเข้าไปใหม่ ดังนั้น เมื่อโฆษณาน้ำมันรำข้าวว่า "มีไฟโตสเตอรอลสูงถึง 12,000 ppm" สิ่งนี้ไม่ได้หมายความว่าเป็นการเติมสารเพิ่มเข้ามาหรอกครับ แต่เป็นการยืนยันถึงความ "เข้มข้น" ของไฟโตสเตอรอลที่มีอยู่ในน้ำมันรำข้าวตามธรรมชาตินั่นละครับว่ามันกลั่นมาเข้มข้นขนาดไหน มากกว่าการกินจากธรรมชาติขนาดไหนเพื่อให้เรากินกันนั่นเอง ถึงแม้ว่าไฟโตสเตอรอลจะถูกส่งเสริมให้เป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือด แต่การโฆษณาและการตลาดเกี่ยวกับไฟโตสเตอรอลนั้นอาจทำให้คนเข้าใจผิดว่า ผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูง จะช่วยทำให้สุขภาพดีขึ้นและลดความเสี่ยงจากโรคหัวใจและหลอดเลือด เพราะซึ่งสิ่งนี้ยังไม่ได้รับการสนับสนุนอย่างชัดเจนจากงานวิจัยที่สามารถยืนยันได้ในระยะยาว นอกจากนี้ยังมีผลการศึกษาบางชิ้นเช่นกันที่พบว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจ "ไม่ได้มีผล" ในการลดระดับคลอเลสเตอรอลที่น่ามหัศจรรย์หรือช่วยลดการเสี่ยงต่อโรคหัวใจได้ตามที่โฆษณาเอามาขยายความกัน ซึ่งแน่นอนหละครับว่า ถ้าจะทำสงครามวิจัย มันย่อมไม่จบสิ้นเพราะทุกฝ่ายมีการวิจัยสนับสนุนในแบบ peer review ทั้งนั้น ไม่ต้องไปเป็น member อะไรที่ไหน (ถ้าเราไม่คิดจะอ่านมันเอง) ไฟโตสเตอรอลมีหลายประเภทที่พบในพืชและน้ำมันพืชแต่ละชนิด โดยแต่ละชนิดจะมีคุณสมบัติและผลกระทบต่อร่างกายที่แตกต่างกัน ซึ่งสามารถแบ่งออกเป็นหลายประเภทหลักที่พบได้บ่อยในธรรมชาติ แต่ละประเภทก็มีข้อดีและข้อเสียที่ควรพิจารณาก่อนการบริโภคตามประเภทมันไปครับ -บีตาสติโรล (Beta-Sitosterol) เป็นไฟโตสเตอรอลที่พบมากในพืชหลายชนิด โดยเฉพาะในเมล็ดพืช ถั่ว และน้ำมันพืช บีตาสติโรลได้รับความนิยมในวงการสุขภาพเนื่องจากการศึกษาบางชิ้นพบว่ามันสามารถช่วยลดระดับคอเลสเตอรอลในเลือดได้ โดยการลดการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหาร แต่การบริโภคบีตาสติโรลในปริมาณสูงอาจส่งผลต่อการดูดซึมวิตามินที่ละลายในไขมัน เช่น วิตามิน A, D, E และ K ซึ่งอาจทำให้เกิดการขาดวิตามินเหล่านี้ในระยะยาวได้ นอกจากนี้ การบริโภคบีตาสติโรลในปริมาณที่มากเกินไปอาจส่งผลให้เกิดปัญหาด้านระบบฮอร์โมน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนเพศหรือระบบสืบพันธุ์ -แคมป์สเตอรอล (Campesterol) เป็นอีกหนึ่งไฟโตสเตอรอลที่พบในพืชหลายชนิด โดยเฉพาะในน้ำมันพืชและผักผลไม้ แคมป์สเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย และมันได้รับการศึกษาว่ามีคุณสมบัติช่วยลดระดับคอเลสเตอรอลในเลือดได้เช่นกัน อย่างไรก็ตาม การบริโภคแคมป์สเตอรอลมากเกินไปอาจทำให้เกิดผลกระทบต่อการดูดซึมสารอาหารบางประเภท เช่น วิตามินที่ละลายในไขมัน โดยเฉพาะในผู้ที่มีปัญหาทางเดินอาหาร หรือผู้ที่มีปัญหาการดูดซึมสารอาหาร อาจทำให้เกิดภาวะขาดสารอาหารหรือการดูดซึมสารอาหารไม่เต็มที่ได้ นอกจากนี้ การบริโภคแคมป์สเตอรอลในปริมาณสูงอาจส่งผลกระทบต่อการทำงานของฮอร์โมนเพศ เช่น การเปลี่ยนแปลงของฮอร์โมนในร่างกาย ซึ่งอาจเกิดผลเสียต่อสุขภาพในระยะยาว -สแตกิโอรอล (Stigmasterol) เป็นไฟโตสเตอรอลชนิดหนึ่งที่พบมากในพืชบางชนิด เช่น ถั่วเหลือง และน้ำมันถั่วเหลือง สแตกิโอรอลได้รับการศึกษาในแง่ของการลดการอักเสบและการช่วยบำรุงสุขภาพหัวใจและหลอดเลือด แต่การบริโภคสแตกิโอรอลในปริมาณสูงอาจมีผลเสียต่อการทำงานของฮอร์โมนเพศได้เช่นกัน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนไม่สมดุลหรือมีปัญหาเกี่ยวกับระบบสืบพันธุ์ การบริโภคไฟโตสเตอรอลชนิดนี้มากเกินไปอาจทำให้เกิดผลกระทบต่อการทำงานของระบบฮอร์โมนในร่างกาย ซึ่งอาจส่งผลให้เกิดอาการผิดปกติในระยะยาว รวมทั้งความเสี่ยงต่อการมีบุตรหรือสุขภาพที่ไม่ดีเกี่ยวกับระบบฮอร์โมน ไฟโตสเตอรอลประเภทอื่น ๆ ที่พบในพืชและน้ำมันพืช ได้แก่ อะฟิตเตอร์ออล (Afitosterol) และซิตรัสเตอรอล (Citrusterol) ซึ่งมักพบในน้ำมันจากพืชต่าง ๆ เช่น น้ำมันเมล็ดองุ่น น้ำมันดอกทานตะวัน การบริโภคไฟโตสเตอรอลเหล่านี้ในปริมาณที่สูงเกินไปอาจทำให้เกิดปัญหาด้านระบบย่อยอาหาร หรือปัญหาการดูดซึมสารอาหารที่จำเป็นจากอาหารได้ นอกจากนี้ การบริโภคไฟโตสเตอรอลประเภทอื่น ๆ ในปริมาณสูงยังอาจส่งผลกระทบต่อระบบฮอร์โมนและการทำงานของร่างกายในระยะยาว เช่น การทำงานของระบบภูมิคุ้มกัน หรือการทำงานของตับ ที่อาจได้รับผลกระทบจากการบริโภคในปริมาณสูง ดังนั้น ควรระมัดระวังในการบริโภคไฟโตสเตอรอลจากแหล่งต่าง ๆ อย่างรอบคอบ เพื่อหลีกเลี่ยงผลเสียที่อาจเกิดขึ้นกับร่างกายในระยะยาว สิ่งที่จริงแล้วอาจเป็นอันตรายมากกว่า คือ การที่ผู้บริโภคตัดสินใจบริโภคผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงในปริมาณมากเกินไป โดยไม่คำนึงถึงผลกระทบต่อร่างกายในระยะยาว อาจมีผลกระทบต่อการดูดซึมสารอาหารที่จำเป็น เช่น วิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมัน การดูดซึมของวิตามินเหล่านี้อาจถูกยับยั้งไป เนื่องจากไฟโตสเตอรอลสามารถแข่งขันกับคลอเลสเตอรอลในร่างกายในการดูดซึมสารอาหารเหล่านี้ นอกจากนี้ยังมีข้อกังวลเกี่ยวกับผลกระทบที่อาจเกิดขึ้นจากการบริโภคไฟโตสเตอรอลในปริมาณสูงที่อาจไปเพิ่มความเสี่ยงของการเกิดโรคบางอย่าง เช่น โรคมะเร็งต่อมลูกหมาก ผลเสียจากการบริโภคไฟโตสเตอรอลมากเกินไปไม่ได้จำกัดเพียงแค่การแย่งสารอาหาร แต่ยังมีการศึกษาที่แสดงให้เห็นว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจกระทบต่อการทำงานของระบบภูมิคุ้มกันของร่างกาย ในบางกรณีไฟโตสเตอรอลอาจเข้าไปแทรกแซงกระบวนการทางชีวเคมีที่สำคัญ และอาจทำให้ร่างกายเกิดความผิดปกติในการตอบสนองต่อสารแปลกปลอมที่มีอยู่ในสิ่งแวดล้อม ข้อโต้แย้งที่สำคัญคือลักษณะการโฆษณาของน้ำมันรำข้าวและผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงนั้น ไม่ได้สะท้อนความจริงในสิ่งที่เป็นประโยชน์ต่อสุขภาพจริง ๆ การใช้ไฟโตสเตอรอลในผลิตภัณฑ์ต่าง ๆ โดยเน้นที่ปริมาณที่สูงเกินจริงนั้น เป็นวิธีการตลาดที่ใช้บอกเป็นนัยกับผู้บริโภคให้เข้าใจว่าการบริโภคสารเหล่านี้จะช่วยลดระดับคลอเลสเตอรอลและช่วยให้สุขภาพหัวใจดีขึ้น ทั้งที่ในความเป็นจริง ไฟโตสเตอรอลไม่ได้ช่วยแก้ปัญหาสุขภาพพื้นฐานอย่างการอักเสบที่เป็นสาเหตุหลักของโรคหัวใจและหลอดเลือด แต่ทั้งนี้ทั้งนั้น การโฆษณาดังกล่าวก็อยู่ภายใต้กฎเกณฑ์ของประกาศและกฎหมายต่างๆอยู่ดี ผู้บริโภคจึงควรหาความรู้สนับสนุนการเลือกด้วยตัวเอง ว่าจะตัดสินใจอย่างไร การที่ไฟโตสเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย ทำให้มันสามารถแทรกซึมเข้าไปในเซลล์ได้คล้ายคลึงกับคอเลสเตอรอล แต่แตกต่างกันตรงที่ไฟโตสเตอรอลไม่สามารถทำหน้าที่ในการสร้างฮอร์โมนต่าง ๆ หรือทำหน้าที่ในระบบร่างกายได้เหมือนคอเลสเตอรอล การที่ไฟโตสเตอรอลแทรกซึมเข้าไปในเซลล์จึงเป็นแค่การสามารถช่วยป้องกันการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหารได้ ซึ่งจะทำให้นี่เป็นสาเหตุของการทำให้ ระดับคอเลสเตอรอลในเลือดลดลงได้ พูดง่ายๆคือมันไปแซงคลอเลสเตอรอล อะครับ นอกจากนี้ ไฟโตสเตอรอลยังสามารถไปแข่งขันกับคอเลสเตอรอลในการเข้าเซลล์ผ่านตัวรับ LDL (low-density lipoprotein receptor) ซึ่งเป็นตัวรับที่ช่วยดูดซึมคอเลสเตอรอลเข้าสู่เซลล์ ดังนั้น เมื่อไฟโตสเตอรอลแทรกซึมเข้ามามากขึ้น ก็จะช่วยลดการดูดซึมคอเลสเตอรอล ที่มาจากอาหารลงไปได้ ทำให้ระดับคอเลสเตอรอลในเลือดลดลง โดยการลดการดูดซึมคอเลสเตอรอลจากทางเดินอาหารเข้าสู่กระแสเลือด แต่ไฟโตสเตอรอลไม่ได้มีผลโดยตรงในการลดคอเลสเตอรอลที่เซลล์ในร่างกายสร้างขึ้นเอง (endogenous cholesterol) เพราะไฟโตสเตอรอลไม่ได้เข้าไปแทรกซึมและทำงานที่จุดที่เซลล์ผลิตคอเลสเตอรอลในร่างกาย ร่างกายสามารถผลิตคอเลสเตอรอลได้เอง ซึ่งเป็นกระบวนการที่ไฟโตสเตอรอลไม่สามารถไปขัดขวางหรือยับยั้งได้ นั่นหมายความว่า หากร่างกายผลิตคอเลสเตอรอลในระดับสูง ไฟโตสเตอรอลจะไม่สามารถลดระดับคอเลสเตอรอลที่มาจากการสร้างของร่างกายได้ ดังนั้น ไฟโตสเตอรอลมีประโยชน์ในการลดคอเลสเตอรอลจากอาหาร แต่ไม่ได้ช่วยในการลดคอเลสเตอรอลที่ร่างกายผลิตขึ้นเอง การโฆษณาไม่ได้ให้ข้อมูลในด้านที่ว่า ผลกระทบระยะยาวจากการบริโภคไฟโตสเตอรอลในปริมาณสูงอาจทำให้เกิดปัญหาสุขภาพอื่น ๆ โดยเฉพาะในด้านการดูดซึมสารอาหารหรือความสามารถในการทำงานของระบบภูมิคุ้มกัน ซึ่งเป็นสิ่งที่ควรคำนึงถึงในการตัดสินใจเลือกผลิตภัณฑ์ที่จะนำมาใช้ในชีวิตประจำวัน ในความเห็นของผมนั้น สิ่งที่ควรให้ความสำคัญมากกว่าคือการเลือกบริโภคอาหารที่เป็นธรรมชาติ และหลีกเลี่ยงการพึ่งพาผลิตภัณฑ์ที่มีการผ่านกระบวนการต่าง ๆ เช่น ไฟโตสเตอรอลเข้มข้น หรือสารเติมแต่งอื่น ๆ ที่ไม่จำเป็นต่อร่างกาย การเลือกรับประทานอาหารที่มีคุณค่าทางโภชนาการครบถ้วนจะช่วยส่งเสริมสุขภาพโดยรวมได้ดีกว่าแทนที่จะพึ่งพาสิ่งที่โฆษณาบอกไว้ข้างขวด ไฟโตสเตอรอลอาจมีคุณสมบัติในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในทางทฤษฎี แต่การบริโภคในปริมาณมากเกินไปนั้นอาจส่งผลเสียต่อร่างกายในหลาย ๆ ด้าน ดังนั้นจึงควรหันมาใส่ใจในข้อมูลที่มีพื้นฐาน และตั้งคำถามกับสิ่งต่างๆ โดยเฉพาะอะไรที่การตลาดตะโกนดังๆว่า ไอ้นี่ดี อันโน้นเยี่ยมยอด อันนี้ที่สุดแห่งความซุปเปอร์ ต่อมเอ๊ะทำงานไว้ก่อน ผิดถูกไม่รู้หาข้อมูลมาโยงเส้นทางแล้วชวนคุยกัน เช่นเราตั้งคำถามตั้งต้นก่อนไหมว่า จริงๆแล้ว คลอลเสเตอรอล มันต้องกลัวขนาดนั้นเลยหรือ ในเมื่อมันเป็นสารตั้งต้นของชีวิต และเป็นสิ่งจำเป็นในการซ่อมแซมเสริมสร้างร่ายกาย เราต้องลดการดูดซึมด้วยเหรอ
@ 502ab02a:a2860397
2025-04-03 17:41:20ไฟโตสเตอรอล (Phytosterols) เป็นสารประกอบที่พบในพืชและมีโครงสร้างคล้ายคลึงกับคลอเลสเตอรอล (Cholesterol) ของมนุษย์ แต่ไฟโตสเตอรอลไม่ได้ทำหน้าที่เหมือนคลอเลสเตอรอลในร่างกายครับ ไฟโตสเตอรอลมีบทบาทสำคัญในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในระบบทางเดินอาหาร ทำให้ไฟโตสเตอรอลได้รับการส่งเสริมว่าเป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือดไปโดยปริยาย อย่างไรก็ตาม สิ่งที่หลายคนไม่ได้ตั้งข้อสงสัยคือวิธีการโฆษณาและการตลาดนั้นจะแฝงไปด้วยข้อมูลที่บิดเบือนเกี่ยวกับไฟโตสเตอรอลซึ่งอาจนำไปสู่การเสพสารนี้ในปริมาณมากเกินไปจนทำให้เกิดปัญหาสุขภาพหรือเปล่า? เราลองมาค่อยๆตั้งคำถามกันครับ ไฟโตสเตอรอลในธรรมชาติจะพบในปริมาณที่ค่อนข้างน้อยในพืชต่าง ๆ เช่น ธัญพืช ถั่ว เมล็ดพืช อย่างไรก็ตาม ปริมาณไฟโตสเตอรอลในธรรมชาติเป็นเม็ดเป็นผลจะอยู่ในระดับต่ำมาก เช่น ในเมล็ดแฟลกซีด (flaxseed) จะมีไฟโตสเตอรอลอยู่ประมาณ 1,000–2,000 ppm (parts per million) ขณะที่น้ำมันรำข้าวที่มักถูกโฆษณาว่ามีไฟโตสเตอรอลสูงถึงหลักหมื่น ๆ ppm เช่น 12,000 ppm หรือบางยี่ห้ออาจสูงกว่านั้น ซึ่งไม่ใช่แค่สูงจนน่าสรรเสริญ แต่ยังเป็นการขยายความสำคัญของไฟโตสเตอรอลในทางที่ตอบสนองต่อการตลาดได้ในวงกว้างเสียด้วย กระบวนการผลิตน้ำมันรำข้าวนั้นเริ่มต้นจากการสกัดน้ำมันจากรำข้าว โดยมีการใช้เทคนิคการกลั่นน้ำมันที่สามารถช่วยให้ได้น้ำมันที่มีคุณภาพสูง น้ำมันรำข้าวเป็นน้ำมันที่มีไฟโตสเตอรอลสูงเพราะรำข้าว (bran) ซึ่งเป็นเปลือกที่หุ้มเมล็ดข้าวนั้น มีไฟโตสเตอรอลอยู่ในปริมาณสูงตามธรรมชาติอยุ่แล้ว ในกระบวนการสกัดน้ำมันนั้น ตัวไฟโตสเตอรอลจะถูกรักษาไว้ โดยไม่ต้องเติมเข้าไปใหม่ ดังนั้น เมื่อโฆษณาน้ำมันรำข้าวว่า "มีไฟโตสเตอรอลสูงถึง 12,000 ppm" สิ่งนี้ไม่ได้หมายความว่าเป็นการเติมสารเพิ่มเข้ามาหรอกครับ แต่เป็นการยืนยันถึงความ "เข้มข้น" ของไฟโตสเตอรอลที่มีอยู่ในน้ำมันรำข้าวตามธรรมชาตินั่นละครับว่ามันกลั่นมาเข้มข้นขนาดไหน มากกว่าการกินจากธรรมชาติขนาดไหนเพื่อให้เรากินกันนั่นเอง ถึงแม้ว่าไฟโตสเตอรอลจะถูกส่งเสริมให้เป็นสารที่ช่วยลดระดับคลอเลสเตอรอลในเลือด แต่การโฆษณาและการตลาดเกี่ยวกับไฟโตสเตอรอลนั้นอาจทำให้คนเข้าใจผิดว่า ผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูง จะช่วยทำให้สุขภาพดีขึ้นและลดความเสี่ยงจากโรคหัวใจและหลอดเลือด เพราะซึ่งสิ่งนี้ยังไม่ได้รับการสนับสนุนอย่างชัดเจนจากงานวิจัยที่สามารถยืนยันได้ในระยะยาว นอกจากนี้ยังมีผลการศึกษาบางชิ้นเช่นกันที่พบว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจ "ไม่ได้มีผล" ในการลดระดับคลอเลสเตอรอลที่น่ามหัศจรรย์หรือช่วยลดการเสี่ยงต่อโรคหัวใจได้ตามที่โฆษณาเอามาขยายความกัน ซึ่งแน่นอนหละครับว่า ถ้าจะทำสงครามวิจัย มันย่อมไม่จบสิ้นเพราะทุกฝ่ายมีการวิจัยสนับสนุนในแบบ peer review ทั้งนั้น ไม่ต้องไปเป็น member อะไรที่ไหน (ถ้าเราไม่คิดจะอ่านมันเอง) ไฟโตสเตอรอลมีหลายประเภทที่พบในพืชและน้ำมันพืชแต่ละชนิด โดยแต่ละชนิดจะมีคุณสมบัติและผลกระทบต่อร่างกายที่แตกต่างกัน ซึ่งสามารถแบ่งออกเป็นหลายประเภทหลักที่พบได้บ่อยในธรรมชาติ แต่ละประเภทก็มีข้อดีและข้อเสียที่ควรพิจารณาก่อนการบริโภคตามประเภทมันไปครับ -บีตาสติโรล (Beta-Sitosterol) เป็นไฟโตสเตอรอลที่พบมากในพืชหลายชนิด โดยเฉพาะในเมล็ดพืช ถั่ว และน้ำมันพืช บีตาสติโรลได้รับความนิยมในวงการสุขภาพเนื่องจากการศึกษาบางชิ้นพบว่ามันสามารถช่วยลดระดับคอเลสเตอรอลในเลือดได้ โดยการลดการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหาร แต่การบริโภคบีตาสติโรลในปริมาณสูงอาจส่งผลต่อการดูดซึมวิตามินที่ละลายในไขมัน เช่น วิตามิน A, D, E และ K ซึ่งอาจทำให้เกิดการขาดวิตามินเหล่านี้ในระยะยาวได้ นอกจากนี้ การบริโภคบีตาสติโรลในปริมาณที่มากเกินไปอาจส่งผลให้เกิดปัญหาด้านระบบฮอร์โมน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนเพศหรือระบบสืบพันธุ์ -แคมป์สเตอรอล (Campesterol) เป็นอีกหนึ่งไฟโตสเตอรอลที่พบในพืชหลายชนิด โดยเฉพาะในน้ำมันพืชและผักผลไม้ แคมป์สเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย และมันได้รับการศึกษาว่ามีคุณสมบัติช่วยลดระดับคอเลสเตอรอลในเลือดได้เช่นกัน อย่างไรก็ตาม การบริโภคแคมป์สเตอรอลมากเกินไปอาจทำให้เกิดผลกระทบต่อการดูดซึมสารอาหารบางประเภท เช่น วิตามินที่ละลายในไขมัน โดยเฉพาะในผู้ที่มีปัญหาทางเดินอาหาร หรือผู้ที่มีปัญหาการดูดซึมสารอาหาร อาจทำให้เกิดภาวะขาดสารอาหารหรือการดูดซึมสารอาหารไม่เต็มที่ได้ นอกจากนี้ การบริโภคแคมป์สเตอรอลในปริมาณสูงอาจส่งผลกระทบต่อการทำงานของฮอร์โมนเพศ เช่น การเปลี่ยนแปลงของฮอร์โมนในร่างกาย ซึ่งอาจเกิดผลเสียต่อสุขภาพในระยะยาว -สแตกิโอรอล (Stigmasterol) เป็นไฟโตสเตอรอลชนิดหนึ่งที่พบมากในพืชบางชนิด เช่น ถั่วเหลือง และน้ำมันถั่วเหลือง สแตกิโอรอลได้รับการศึกษาในแง่ของการลดการอักเสบและการช่วยบำรุงสุขภาพหัวใจและหลอดเลือด แต่การบริโภคสแตกิโอรอลในปริมาณสูงอาจมีผลเสียต่อการทำงานของฮอร์โมนเพศได้เช่นกัน โดยเฉพาะในผู้ที่มีปัญหาฮอร์โมนไม่สมดุลหรือมีปัญหาเกี่ยวกับระบบสืบพันธุ์ การบริโภคไฟโตสเตอรอลชนิดนี้มากเกินไปอาจทำให้เกิดผลกระทบต่อการทำงานของระบบฮอร์โมนในร่างกาย ซึ่งอาจส่งผลให้เกิดอาการผิดปกติในระยะยาว รวมทั้งความเสี่ยงต่อการมีบุตรหรือสุขภาพที่ไม่ดีเกี่ยวกับระบบฮอร์โมน ไฟโตสเตอรอลประเภทอื่น ๆ ที่พบในพืชและน้ำมันพืช ได้แก่ อะฟิตเตอร์ออล (Afitosterol) และซิตรัสเตอรอล (Citrusterol) ซึ่งมักพบในน้ำมันจากพืชต่าง ๆ เช่น น้ำมันเมล็ดองุ่น น้ำมันดอกทานตะวัน การบริโภคไฟโตสเตอรอลเหล่านี้ในปริมาณที่สูงเกินไปอาจทำให้เกิดปัญหาด้านระบบย่อยอาหาร หรือปัญหาการดูดซึมสารอาหารที่จำเป็นจากอาหารได้ นอกจากนี้ การบริโภคไฟโตสเตอรอลประเภทอื่น ๆ ในปริมาณสูงยังอาจส่งผลกระทบต่อระบบฮอร์โมนและการทำงานของร่างกายในระยะยาว เช่น การทำงานของระบบภูมิคุ้มกัน หรือการทำงานของตับ ที่อาจได้รับผลกระทบจากการบริโภคในปริมาณสูง ดังนั้น ควรระมัดระวังในการบริโภคไฟโตสเตอรอลจากแหล่งต่าง ๆ อย่างรอบคอบ เพื่อหลีกเลี่ยงผลเสียที่อาจเกิดขึ้นกับร่างกายในระยะยาว สิ่งที่จริงแล้วอาจเป็นอันตรายมากกว่า คือ การที่ผู้บริโภคตัดสินใจบริโภคผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงในปริมาณมากเกินไป โดยไม่คำนึงถึงผลกระทบต่อร่างกายในระยะยาว อาจมีผลกระทบต่อการดูดซึมสารอาหารที่จำเป็น เช่น วิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมัน การดูดซึมของวิตามินเหล่านี้อาจถูกยับยั้งไป เนื่องจากไฟโตสเตอรอลสามารถแข่งขันกับคลอเลสเตอรอลในร่างกายในการดูดซึมสารอาหารเหล่านี้ นอกจากนี้ยังมีข้อกังวลเกี่ยวกับผลกระทบที่อาจเกิดขึ้นจากการบริโภคไฟโตสเตอรอลในปริมาณสูงที่อาจไปเพิ่มความเสี่ยงของการเกิดโรคบางอย่าง เช่น โรคมะเร็งต่อมลูกหมาก ผลเสียจากการบริโภคไฟโตสเตอรอลมากเกินไปไม่ได้จำกัดเพียงแค่การแย่งสารอาหาร แต่ยังมีการศึกษาที่แสดงให้เห็นว่า การบริโภคไฟโตสเตอรอลในปริมาณสูงอาจกระทบต่อการทำงานของระบบภูมิคุ้มกันของร่างกาย ในบางกรณีไฟโตสเตอรอลอาจเข้าไปแทรกแซงกระบวนการทางชีวเคมีที่สำคัญ และอาจทำให้ร่างกายเกิดความผิดปกติในการตอบสนองต่อสารแปลกปลอมที่มีอยู่ในสิ่งแวดล้อม ข้อโต้แย้งที่สำคัญคือลักษณะการโฆษณาของน้ำมันรำข้าวและผลิตภัณฑ์ที่มีไฟโตสเตอรอลสูงนั้น ไม่ได้สะท้อนความจริงในสิ่งที่เป็นประโยชน์ต่อสุขภาพจริง ๆ การใช้ไฟโตสเตอรอลในผลิตภัณฑ์ต่าง ๆ โดยเน้นที่ปริมาณที่สูงเกินจริงนั้น เป็นวิธีการตลาดที่ใช้บอกเป็นนัยกับผู้บริโภคให้เข้าใจว่าการบริโภคสารเหล่านี้จะช่วยลดระดับคลอเลสเตอรอลและช่วยให้สุขภาพหัวใจดีขึ้น ทั้งที่ในความเป็นจริง ไฟโตสเตอรอลไม่ได้ช่วยแก้ปัญหาสุขภาพพื้นฐานอย่างการอักเสบที่เป็นสาเหตุหลักของโรคหัวใจและหลอดเลือด แต่ทั้งนี้ทั้งนั้น การโฆษณาดังกล่าวก็อยู่ภายใต้กฎเกณฑ์ของประกาศและกฎหมายต่างๆอยู่ดี ผู้บริโภคจึงควรหาความรู้สนับสนุนการเลือกด้วยตัวเอง ว่าจะตัดสินใจอย่างไร การที่ไฟโตสเตอรอลมีโครงสร้างที่คล้ายกับคอเลสเตอรอลในร่างกาย ทำให้มันสามารถแทรกซึมเข้าไปในเซลล์ได้คล้ายคลึงกับคอเลสเตอรอล แต่แตกต่างกันตรงที่ไฟโตสเตอรอลไม่สามารถทำหน้าที่ในการสร้างฮอร์โมนต่าง ๆ หรือทำหน้าที่ในระบบร่างกายได้เหมือนคอเลสเตอรอล การที่ไฟโตสเตอรอลแทรกซึมเข้าไปในเซลล์จึงเป็นแค่การสามารถช่วยป้องกันการดูดซึมคอเลสเตอรอลจากอาหารในระบบย่อยอาหารได้ ซึ่งจะทำให้นี่เป็นสาเหตุของการทำให้ ระดับคอเลสเตอรอลในเลือดลดลงได้ พูดง่ายๆคือมันไปแซงคลอเลสเตอรอล อะครับ นอกจากนี้ ไฟโตสเตอรอลยังสามารถไปแข่งขันกับคอเลสเตอรอลในการเข้าเซลล์ผ่านตัวรับ LDL (low-density lipoprotein receptor) ซึ่งเป็นตัวรับที่ช่วยดูดซึมคอเลสเตอรอลเข้าสู่เซลล์ ดังนั้น เมื่อไฟโตสเตอรอลแทรกซึมเข้ามามากขึ้น ก็จะช่วยลดการดูดซึมคอเลสเตอรอล ที่มาจากอาหารลงไปได้ ทำให้ระดับคอเลสเตอรอลในเลือดลดลง โดยการลดการดูดซึมคอเลสเตอรอลจากทางเดินอาหารเข้าสู่กระแสเลือด แต่ไฟโตสเตอรอลไม่ได้มีผลโดยตรงในการลดคอเลสเตอรอลที่เซลล์ในร่างกายสร้างขึ้นเอง (endogenous cholesterol) เพราะไฟโตสเตอรอลไม่ได้เข้าไปแทรกซึมและทำงานที่จุดที่เซลล์ผลิตคอเลสเตอรอลในร่างกาย ร่างกายสามารถผลิตคอเลสเตอรอลได้เอง ซึ่งเป็นกระบวนการที่ไฟโตสเตอรอลไม่สามารถไปขัดขวางหรือยับยั้งได้ นั่นหมายความว่า หากร่างกายผลิตคอเลสเตอรอลในระดับสูง ไฟโตสเตอรอลจะไม่สามารถลดระดับคอเลสเตอรอลที่มาจากการสร้างของร่างกายได้ ดังนั้น ไฟโตสเตอรอลมีประโยชน์ในการลดคอเลสเตอรอลจากอาหาร แต่ไม่ได้ช่วยในการลดคอเลสเตอรอลที่ร่างกายผลิตขึ้นเอง การโฆษณาไม่ได้ให้ข้อมูลในด้านที่ว่า ผลกระทบระยะยาวจากการบริโภคไฟโตสเตอรอลในปริมาณสูงอาจทำให้เกิดปัญหาสุขภาพอื่น ๆ โดยเฉพาะในด้านการดูดซึมสารอาหารหรือความสามารถในการทำงานของระบบภูมิคุ้มกัน ซึ่งเป็นสิ่งที่ควรคำนึงถึงในการตัดสินใจเลือกผลิตภัณฑ์ที่จะนำมาใช้ในชีวิตประจำวัน ในความเห็นของผมนั้น สิ่งที่ควรให้ความสำคัญมากกว่าคือการเลือกบริโภคอาหารที่เป็นธรรมชาติ และหลีกเลี่ยงการพึ่งพาผลิตภัณฑ์ที่มีการผ่านกระบวนการต่าง ๆ เช่น ไฟโตสเตอรอลเข้มข้น หรือสารเติมแต่งอื่น ๆ ที่ไม่จำเป็นต่อร่างกาย การเลือกรับประทานอาหารที่มีคุณค่าทางโภชนาการครบถ้วนจะช่วยส่งเสริมสุขภาพโดยรวมได้ดีกว่าแทนที่จะพึ่งพาสิ่งที่โฆษณาบอกไว้ข้างขวด ไฟโตสเตอรอลอาจมีคุณสมบัติในการลดการดูดซึมคลอเลสเตอรอลจากอาหารในทางทฤษฎี แต่การบริโภคในปริมาณมากเกินไปนั้นอาจส่งผลเสียต่อร่างกายในหลาย ๆ ด้าน ดังนั้นจึงควรหันมาใส่ใจในข้อมูลที่มีพื้นฐาน และตั้งคำถามกับสิ่งต่างๆ โดยเฉพาะอะไรที่การตลาดตะโกนดังๆว่า ไอ้นี่ดี อันโน้นเยี่ยมยอด อันนี้ที่สุดแห่งความซุปเปอร์ ต่อมเอ๊ะทำงานไว้ก่อน ผิดถูกไม่รู้หาข้อมูลมาโยงเส้นทางแล้วชวนคุยกัน เช่นเราตั้งคำถามตั้งต้นก่อนไหมว่า จริงๆแล้ว คลอลเสเตอรอล มันต้องกลัวขนาดนั้นเลยหรือ ในเมื่อมันเป็นสารตั้งต้นของชีวิต และเป็นสิ่งจำเป็นในการซ่อมแซมเสริมสร้างร่ายกาย เราต้องลดการดูดซึมด้วยเหรอ @ 907e4623:f40ff12a
2025-04-04 11:39:51<p>gm well</p><p><br></p><p><strong>lfg</strong></p>
@ 907e4623:f40ff12a
2025-04-04 11:39:51<p>gm well</p><p><br></p><p><strong>lfg</strong></p> @ 7d33ba57:1b82db35
2025-04-03 17:36:08Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.  ## **🏛️ Top Things to See & Do in Zadar** ### **1️⃣ Explore Zadar Old Town 🏰** - Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**. - Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés. ### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞** - **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**. - **Sun Salutation** – A large **solar-powered light display**, best seen at sunset. - **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅  ### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪** - **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics. - **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**. ### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔** - Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic. - One of the **tallest church towers in Croatia**.  ### **5️⃣ Relax at Zadar’s Best Beaches 🏖️** - **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town. - **Borik Beach** – A **sandy beach with shallow waters**, ideal for families. - **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim. ### **6️⃣ Take a Day Trip to Kornati National Park ⛵** - A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**. - Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑 - **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀 - **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟  ## **🚗 How to Get to Zadar** ✈️ **By Air:** - **Zadar Airport (ZAD)** is **just 15 minutes from the city center**. 🚘 **By Car:** - **From Split:** ~1.5 hours (160 km) - **From Zagreb:** ~2.5 hours (285 km) 🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**. ⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.  ## **💡 Tips for Visiting Zadar** ✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️ ✅ **Stay near the Old Town** – Everything is within walking distance 🏡 ✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶 ✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️ ✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵ 
@ 7d33ba57:1b82db35
2025-04-03 17:36:08Zadar is a coastal city in northern Dalmatia, known for its rich Roman and Venetian history, stunning sunsets, and unique modern attractions like the Sea Organ and Sun Salutation. With ancient ruins, beautiful beaches, and a lively Old Town, Zadar offers a less crowded but equally charming alternative** to Split and Dubrovnik.  ## **🏛️ Top Things to See & Do in Zadar** ### **1️⃣ Explore Zadar Old Town 🏰** - Walk through **narrow, stone-paved streets**, surrounded by **Roman and medieval architecture**. - Visit **People’s Square (Narodni Trg)** – The **heart of Zadar’s Old Town**, filled with lively cafés. ### **2️⃣ Visit the Sea Organ & Sun Salutation 🎶🌞** - **Sea Organ** – A one-of-a-kind **musical instrument**, where waves create **natural melodies**. - **Sun Salutation** – A large **solar-powered light display**, best seen at sunset. - **Alfred Hitchcock once called Zadar’s sunset “the most beautiful in the world.”** 🌅  ### **3️⃣ Admire St. Donatus Church & Roman Forum ⛪** - **St. Donatus (9th century)** – A unique, round **Byzantine-style church** with great acoustics. - **Roman Forum** – The remains of an ancient Roman marketplace, built in the **1st century BC**. ### **4️⃣ Climb the Bell Tower of St. Anastasia’s Cathedral 🔔** - Enjoy **spectacular views** over Zadar’s rooftops and the Adriatic. - One of the **tallest church towers in Croatia**.  ### **5️⃣ Relax at Zadar’s Best Beaches 🏖️** - **Kolovare Beach** – The most popular **city beach**, just a short walk from the Old Town. - **Borik Beach** – A **sandy beach with shallow waters**, ideal for families. - **Punta Bajlo** – A more **natural and peaceful spot**, great for a quiet swim. ### **6️⃣ Take a Day Trip to Kornati National Park ⛵** - A **beautiful archipelago of 89 islands**, perfect for **boating, swimming, and snorkeling**. - Join a **boat tour from Zadar** to explore the **untouched nature of the Adriatic**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Black Risotto (Crni Rižot)** – A delicious squid-ink seafood dish. 🦑 - **Pag Cheese (Paški Sir)** – A famous **sheep’s milk cheese from Pag Island**. 🧀 - **Grilled Adriatic Fish** – Freshly caught and served with **olive oil & Dalmatian herbs**. 🐟  ## **🚗 How to Get to Zadar** ✈️ **By Air:** - **Zadar Airport (ZAD)** is **just 15 minutes from the city center**. 🚘 **By Car:** - **From Split:** ~1.5 hours (160 km) - **From Zagreb:** ~2.5 hours (285 km) 🚌 **By Bus:** Regular buses from **Split, Zagreb, Dubrovnik, and Plitvice Lakes**. ⛴️ **By Ferry:** Ferries connect Zadar to nearby islands like **Ugljan, Dugi Otok, and Pašman**.  ## **💡 Tips for Visiting Zadar** ✅ **Best time to visit?** **May–October** for warm weather & island trips ☀️ ✅ **Stay near the Old Town** – Everything is within walking distance 🏡 ✅ **Catch the sunset at the Sea Organ** – It’s a must-do experience 🌊🎶 ✅ **Take a ferry to Ugljan Island** for a day of beaches & cycling 🚢🚴♂️ ✅ **Book Kornati boat tours in advance** – They sell out fast in summer! ⛵  @ 000002de:c05780a7
2025-04-03 17:27:03### I score zero points. How about you? https://m.primal.net/QDDi.jpg I almost called this a boomer test but its more of a Gen X test. __Credit to Jack Spirko for sharing this on Twitter.__ originally posted at https://stacker.news/items/933537
@ 000002de:c05780a7
2025-04-03 17:27:03### I score zero points. How about you? https://m.primal.net/QDDi.jpg I almost called this a boomer test but its more of a Gen X test. __Credit to Jack Spirko for sharing this on Twitter.__ originally posted at https://stacker.news/items/933537 @ 5708b1f6:208df3b8
2025-04-03 15:25:33The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist. However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives. All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers. The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music. Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.” Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite. When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age. The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow. It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences. This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks. Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs. This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced. Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion). When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song. Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken. To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word. There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function. It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center. It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance?
@ 5708b1f6:208df3b8
2025-04-03 15:25:33The role and significance of music naturally varies from person to person. For some, it is counted among the most important things in life. For others, it may be a superfluous additive of limited value. Due to this difference in perception relating to music, it may be difficult for some individuals to recognize the benefits of compiling a personalized music playlist. However, the value of music as a therapeutic tool for people already suffering from advanced dementia has been repeatedly demonstrated, and sometimes with astounding, although temporary, results. The internet is full of studies and stories, and YouTube searches yield an abundance of video evidence ranging from clinical studies to anecdotal family recordings of elderly relatives. All of these data and anecdotes point to a compelling suggestion and an exciting conclusion: music appreciation has tremendous potential as a supplemental activity for mental health maintenance. With insights gained from the study of neuroplasticity, the neurological benefits for musicians and performers are easy to see, but less clear is the fact that mere exposure to music as a casual listener can be of profound psychological importance, even for individuals who don’t consider themselves to be music lovers. The transformative effect of music is on full display in many of the available videos on YouTube. We can simply search “dementia music,” or ‘Alzheimer’s music” for fast, relevant results. In video after video, we can see elderly subjects who may be slow to speak, detached, disoriented, barely-intelligible, or unresponsive. In care facilities and at gatherings with families, they are interviewed about their youth, and about their feelings related to music. Many of the videos first show footage of the individual’s normal daily cognitive state, and them listening and responding to the questions, followed by a period of music listening, and then another brief, post-music discussion. The transformation of mental states tends to be very clear when we compare the quality of their cognitive performance before and after the introduction of music. People remark that “a light has been turned back on,” or “his personality returned,” or “it’s as if the person has woken up from sleep.” Unfortunately, these positive responses are only temporary, and music does not have the power to permanently reverse the symptoms and pathology of advanced dementia and age-related cognitive decline. Also there is no guarantee it will work for every person, or to what degree. Nevertheless, it does not mean that music as therapy is completely without value. In fact, it can be quite the opposite. When the response is positive, the event can have multiple benefits, and may even be a therapeutic experience for certain listeners. Faces once despondent or vacant become animated and radiant. Long lost smiles return from faraway times and places. Memories and associations from previous ages shake loose and rise to the surface. Many listeners were asked to recount their experiences related to the songs and the time in life with which they were primarily associated. Some of them were able to describe events, places, people, emotions, and reactions with a degree of clarity, dexterity, and articulation that was completely inconsistent with their medical diagnosis and their cognitive performance prior to hearing the music. The song quite literally revives the personality that makes the person, temporarily and superficially reversing the undoing of the mind. For a mind that is coming undone, music as therapy has potential to mitigate suffering and confusion, provide moments of joy and enthusiasm, and ease the transition into and experience of the end-of-life period that awaits all who are fortunate enough to “die of natural causes” in old age. The benefits described above are specific to “treatment” recipients, but the merit of music as therapy cascades into the lives of everyone involved. Doctors and caretakers are uplifted and encouraged by success stories, which contributes to further proliferation and advancement of music as therapy. More critically, it can have a profound impact on families of dementia patients. In some cases, relatives get a chance to communicate with their loved ones again. Grandchildren have a window of opportunity to learn more, directly from their grandparents, about the youthful experiences and memories of past generations. It’s clear that generational bonds are also strengthened, which can positively impact the future prospects of the young generation as they in turn grow old, and lay new groundwork for generations that follow. It is unfortunate that some elderly individuals seem to derive less cognitive benefit than others from music therapy. It is not entirely certain why this is so, because there are many factors to consider, but two of the clearest factors are a person’s degree of cognitive decline, and their degree of interest in and enthusiasm for music in general. While these are the most popular metrics by which to judge the potential effectiveness and suitability of music as therapy for a given individual, by far the most important consideration is relevance to each particular person’s life experiences. This is the opportunity to finally state the obvious: It’s not possible to simply pick any song at random and expect it to have a beneficial effect on the cognitive function of every person who hears it. It’s not as if there’s a Britney Spears song that sparks joy in the heart of every soul on Earth. And the legend of Bill and Ted’s ultimate song that united the world could never be a true story (also because, as we finally learned in 2020, it was not two men and a song that united the world, but rather, the world uniting together to create that song.) However, everyone in the world can make their own playlist custom-tailored to their individual life, experiences, and memories, and some of those playlists might have a song or two by Britney Spears, or even some from one of the “Bill and Ted” soundtracks. Throughout my decades of music appreciation, an ever-growing level of respect for the enduring spirit of music has overwhelmed me, and it’s clear that no song will ever be loved by all. But every song will be loved by some, certainly at least by someone, or it would cease to exist. This is why a personalized playlist is infinitely more valuable than randomly selected songs, and we can see the truth of this claim upon close examination of recorded interviews with the elderly subjects. The songs that triggered the greatest reactions were songs that interviewees felt strong connections to, based primarily on the song’s associations to the time and place, as well as the emotional context imprinted on the memory of the events surrounding the songs. This simply means that songs for which we have emotional attachments and vivid memories are songs that invigorate our neural circuits, activating cognitive pathways and opening doors of memory similar to how olfactory sensations can trigger a memory or a sense of déjà vu. There are some exceptions, but a lot of these songs are from a person’s formative years, particularly early developmental years and their teenage period. This comes as no surprise to the discerning neuroplastician, because these are periods of life when neural plasticity is most fluid, neural development and refinement functions are most active and receptive, and the degree of exciting novelty in life tends to be highest when we are young and inexperienced. Novelty and emotion are critical components of memory formation and whether a given experience will be memorable or not. Something completely new (novelty) can be memorable if it commands your attention, or derails you from your usual pattern of behavior. Similarly, the content of a tedious lecture may be harder to recall without taking notes, while that of an exciting, fun, and funny, interactive lesson has a greater chance of being memorable, and recalled with more clarity and detail (emotion). When it comes to music, the connection to novelty and emotion is crystal clear. The first time you ever heard that song, it was new and your emotional response was strong. You might even remember the events of that first time you heard it, but not necessarily. Your emotional attachment to the song may have developed later on, when you heard it playing at a party, on one of the most memorable nights of your teenage life, for example. Perhaps it’s just a song (or songs) your parents played a lot when you were young, and it could be a song you yourself heard many times, and looking back realized it holds a special place in your heart, for whatever reason. There are also songs that are special to romantic couples (This song was playing when we…; This is our song; We were together the first time we heard this song; etc.) and these songs, for obvious reasons, can be added to a personalized music playlist at any time in life, as new and old songs take on added personal significance in various ways. There are a multitude of ways that novelty and emotion can combine to form experiences worth remembering, by which memories are made, and if these experiences are imprinted with a musical stamp, the song stamped onto the memory is likely to remain just as memorable as the event itself, and conversely, listening to the song has the potential to vivify the memories and feelings of nostalgia related to the song. Therefore, as a preventative measure we can implement now, and an insurance policy we may benefit from later, it is advisable that each person should endeavor to compile their own personal, individualized cognitive reserve playlist. When speaking to someone about this idea, they responded, “But what’s the hurry? After all, you’re still quite young.” Just then, it spontaneously occurred to me that a traumatic head injury could befall me the following day or any day hence, and the simple point that “it’s never too early” was well taken. To create your own cognitive reserve playlist, it is helpful to have a few guiding parameters. Most important of all is to keep an open mind without setting anything in stone. It’s not necessary to finalize the list immediately, if ever. This is a project that deserves your thoughtful consideration, so you deserve to be allowed to take your time. It’s better to get the list populated with your definite favorites, and as many others that come to mind, just to kick-start the process. Besides, due to the virtually infinite number of songs and compositions in existence, we will never be able to make the perfect list in one day, one month, or even one year. We can always revisit the list and make changes later, because our minds cannot retrieve all the data at once. We must go about our business of carrying on, and wait for it to come to us. (It’s guaranteed to be worth the wait, so never fret about it.) You may even find yourself removing one of those “definite favorites” from the list, which is welcome and fine, because it’s not merely a list of your favorite songs. Being a “favorite” is just one of multiple indicators that a song might be appropriate for a cognitive reserve playlist. “Memorable” is another key word. There are still other factors that determine a song’s suitability for a personal playlist, such as a song that isn’t a personal favorite, but which nevertheless evokes a strong emotional response in some other way. This is best described as nostalgia, and nostalgic emotions are powerful anchors for memories. So any song that arouses some sense of nostalgia also has the power to arouse the memory of events, places, times, and other details tied to that nostalgia. To know what songs are nostalgic for you and add them to your list today, may help you if a time should come that you need music as therapy in order to trigger your memory and cognitive function. It is because of nostalgia that many songs from our youth are good candidates for inclusion on the playlist. Songs that were popular on the radio or TV when we were children, theme songs from popular television programs that are unforgettable for us, and songs that acted as the soundtrack to our lives, so to speak, while growing into childhood, and then blossoming again from adolescence into adulthood. This period is rich with music of great significance to our personal center. It is my sincere hope that all people earnestly endeavor to compile their own personalized cognitive reserve playlists, and encourage their loved ones to do the same. Maybe it can help those who suffer to better cope with the condition. Perhaps starting this project now, and focusing on mental health now can be a significant contributing factor to developing robust cognitive reserve in the first place, thereby heading off the worst of what this condition can throw at us, and delaying it until later. And of course, not only should we create the lists, but it’s highly recommended that we also play the songs frequently, and dance to them as well, preferably. It is in the interest of your future health, ability, mobility, enjoyment, and ease of living that I offer this potentially beneficial suggestion, and I am grateful that you have taken the time to hear me out regarding my passion about the restorative and healing properties of music, as they relate to the broader topic of neuroplasticity. So on that note, shall we press play and dance? @ 2b24a1fa:17750f64
2025-04-04 08:42:16„Denke daran, daß das, was dich wie an unsichtbaren Fäden hin- und herzieht, in deinem Innern verborgen ist.“ Soll der römische Kaiser Marc Aurel gesagt haben, der letzte bedeutende Philosoph der jüngeren Stoa. Brot und Spiele hieß es damals, machten die Gesellschaften gefügig: Bier, Wein, Whiskey, Ablenkung, Informationssteuerung.  [https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?](https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?color=ffd400) Wie sich die kognitive Einflussnahme zur Kriegsführung entwickelte, wie sie sich mit den heutigen medialen und technischen Mitteln darstellt und wie wir unsere Kinder und uns selbst davor schützen können, damit beschäftigt sich der Propagandaforscher und Amerikanist Dr. Jonas Tögel. Er promovierte zum Thema Soft Power und Motivation und forscht am Institut für Psychologie der Universität Regensburg. Meine Kollegin Eva Schmidt hat ihn interviewt und wollte zunächst von ihm wissen, wie er zur Propagandaforschung kam und auf welchen Grundlagen seine Tätigkeit aufbaut. Sein aktuelles Buch "Kriegsspiele - Wie NATO und Pentagon die Zerstörung Europas simulieren" ist im Westend-Verlag erschienen, hat 111 Seiten und kostet 15 Euro. [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\ [odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\ [rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
@ 2b24a1fa:17750f64
2025-04-04 08:42:16„Denke daran, daß das, was dich wie an unsichtbaren Fäden hin- und herzieht, in deinem Innern verborgen ist.“ Soll der römische Kaiser Marc Aurel gesagt haben, der letzte bedeutende Philosoph der jüngeren Stoa. Brot und Spiele hieß es damals, machten die Gesellschaften gefügig: Bier, Wein, Whiskey, Ablenkung, Informationssteuerung.  [https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?](https://soundcloud.com/radiomuenchen/kriegsspiele-durch-softpower?color=ffd400) Wie sich die kognitive Einflussnahme zur Kriegsführung entwickelte, wie sie sich mit den heutigen medialen und technischen Mitteln darstellt und wie wir unsere Kinder und uns selbst davor schützen können, damit beschäftigt sich der Propagandaforscher und Amerikanist Dr. Jonas Tögel. Er promovierte zum Thema Soft Power und Motivation und forscht am Institut für Psychologie der Universität Regensburg. Meine Kollegin Eva Schmidt hat ihn interviewt und wollte zunächst von ihm wissen, wie er zur Propagandaforschung kam und auf welchen Grundlagen seine Tätigkeit aufbaut. Sein aktuelles Buch "Kriegsspiele - Wie NATO und Pentagon die Zerstörung Europas simulieren" ist im Westend-Verlag erschienen, hat 111 Seiten und kostet 15 Euro. [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\ [odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\ [rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482 @ 2b24a1fa:17750f64
2025-04-04 08:36:50Was passiert, wenn die Bank plötzlich das Konto kündigt? Aus gesetzlicher Sicht darf sie das, sogar ohne Gründe zu nennen - sofern diese Option in den Allgemeinen Geschäftsbedingungen (AGB) des Kontovertrags steht. Und das ist die Regel.  [https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?](https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?color=ffd400) Zwar besteht oft eine mindestens zweimonatige Kündigungsfrist, doch wer jemals das Konto gewechselt hat, weiß, was für ein Aufwand es ist, seinen gesamten und immer komplexeren Zahlungsverkehr umzustellen. Besonders hart trifft es Empfänger von Spenden: darunter viele alternative Medien und freie Journalisten, die für alternative Medien arbeiten. Die Spenden brechen weg, denn die meist anonymen Spender können nicht direkt informiert werden. Das wissen auch diejenigen, denen alternative Medien ein Dorn im Auge sind: Staatlich finanzierte Agitatoren und staatsnahe Medien, die solange Druck auf Banken ausüben, bis diese aus Sorge um ihr Image das Konto kündigen. Das Magazin Multipolar dokumentierte Mitte 2024 rund 40 solcher Fälle. Manchmal nutzen Banken auch ganz direkt diese Möglichkeit, um kritische Stimmen einzuschüchtern und zu schwächen. Diese Variante vermutet unsere Autorin Gaby Weber. Nach einem kritischen Bericht über die Bundesbank wurde ihr das Konto gekündigt. Hören Sie ihren Beitrag „De-Banking oder: die Rache der Bundesbank?“, der zunächst beim Overton-Magazin erschienen ist: [overton-magazin.de/hintergrund/pol…der-bundesbank/](https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/ "https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/") Sprecher: Ulrich Allroggen Bild: Radio München Radio München\ [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\ [odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\ [rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
@ 2b24a1fa:17750f64
2025-04-04 08:36:50Was passiert, wenn die Bank plötzlich das Konto kündigt? Aus gesetzlicher Sicht darf sie das, sogar ohne Gründe zu nennen - sofern diese Option in den Allgemeinen Geschäftsbedingungen (AGB) des Kontovertrags steht. Und das ist die Regel.  [https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?](https://soundcloud.com/radiomuenchen/de-banking-oder-die-rache-der-bundesbank?color=ffd400) Zwar besteht oft eine mindestens zweimonatige Kündigungsfrist, doch wer jemals das Konto gewechselt hat, weiß, was für ein Aufwand es ist, seinen gesamten und immer komplexeren Zahlungsverkehr umzustellen. Besonders hart trifft es Empfänger von Spenden: darunter viele alternative Medien und freie Journalisten, die für alternative Medien arbeiten. Die Spenden brechen weg, denn die meist anonymen Spender können nicht direkt informiert werden. Das wissen auch diejenigen, denen alternative Medien ein Dorn im Auge sind: Staatlich finanzierte Agitatoren und staatsnahe Medien, die solange Druck auf Banken ausüben, bis diese aus Sorge um ihr Image das Konto kündigen. Das Magazin Multipolar dokumentierte Mitte 2024 rund 40 solcher Fälle. Manchmal nutzen Banken auch ganz direkt diese Möglichkeit, um kritische Stimmen einzuschüchtern und zu schwächen. Diese Variante vermutet unsere Autorin Gaby Weber. Nach einem kritischen Bericht über die Bundesbank wurde ihr das Konto gekündigt. Hören Sie ihren Beitrag „De-Banking oder: die Rache der Bundesbank?“, der zunächst beim Overton-Magazin erschienen ist: [overton-magazin.de/hintergrund/pol…der-bundesbank/](https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/ "https://overton-magazin.de/hintergrund/politik/de-banking-oder-die-rache-der-bundesbank/") Sprecher: Ulrich Allroggen Bild: Radio München Radio München\ [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen")\ [odysee.com/@RadioMuenchen.net:9](https://odysee.com/@RadioMuenchen.net:9 "https://odysee.com/@RadioMuenchen.net:9")\ [rumble.com/user/RadioMunchen](https://rumble.com/user/RadioMunchen "https://rumble.com/user/RadioMunchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482 @ 2b24a1fa:17750f64
2025-04-04 08:15:16Ganz im Geiste des klassischen Kabaretts widmen sich Franz Esser und Michael Sailer den Ereignissen des letzten Monats: Was ist passiert? Und was ist dazu zu sagen? Das ist oft frappierend - und manchmal auch zum Lachen. [https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?](https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?color=ffd400)
@ 2b24a1fa:17750f64
2025-04-04 08:15:16Ganz im Geiste des klassischen Kabaretts widmen sich Franz Esser und Michael Sailer den Ereignissen des letzten Monats: Was ist passiert? Und was ist dazu zu sagen? Das ist oft frappierend - und manchmal auch zum Lachen. [https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?](https://soundcloud.com/radiomuenchen/vier-wochen-wahnsinn-marz25-ein-satirischer-wochenruckblick?color=ffd400) @ 2b24a1fa:17750f64
2025-04-04 08:10:53Wir leben in einer Demokratie. So heißt es immer. Immerhin hat die Bevölkerung, der Souverän ein Mitspracherecht. Einmal alle vier Jahre. Und damit fünfundzwanzig Mal in einem Jahrhundert. Diese 25 Wahltage ergeben zeitlich 0,07 Prozent des gesamten Jahrhunderts. Würde man das Jahrhundert auf einen Tag runter rechnen, dann ergäben diese 0,07 Prozent ziemlich genau eine Minute des Mitspracherechts. Eine Minute pro Tag darf der Souverän also bestimmen, wer am restlichen Tag ungehindert schalten und walten darf – bis in das Grundgesetz hinein. [https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?](https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?color=ffd400) Die Veränderung in diesem zentralen Gesetzestexten ist allein den Parteien vorbehalten. An sämtliche Änderungen halten, dürfen sich dann nachher alle – selbst dann, wenn noch so wenige Bürger dahinterstehen. In den letzten Wochen offenbarte sich dieser Missstand in präzedenzloser Weise. Die als Sondervermögen schön-deklarierte Neuverschuldung wurde im Grundgesetz festgeschrieben. Ist eine solch selektive Umgestaltungsmöglichkeit des wichtigsten Gesetzestext einer Demokratie würdig? Bräuchte es nicht zumindest einer Absegnung durch Volksabstimmungen? Henry Mattheß hat sich hierzu Gedanken gemacht. Hören Sie seinen Text „Das Grundgesetz als Schmierzettel“, der zunächst auf dem Blog von Norbert Häring erschienen war. Sprecher: Karsten Tryoke Bild: Radio München [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
@ 2b24a1fa:17750f64
2025-04-04 08:10:53Wir leben in einer Demokratie. So heißt es immer. Immerhin hat die Bevölkerung, der Souverän ein Mitspracherecht. Einmal alle vier Jahre. Und damit fünfundzwanzig Mal in einem Jahrhundert. Diese 25 Wahltage ergeben zeitlich 0,07 Prozent des gesamten Jahrhunderts. Würde man das Jahrhundert auf einen Tag runter rechnen, dann ergäben diese 0,07 Prozent ziemlich genau eine Minute des Mitspracherechts. Eine Minute pro Tag darf der Souverän also bestimmen, wer am restlichen Tag ungehindert schalten und walten darf – bis in das Grundgesetz hinein. [https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?](https://soundcloud.com/radiomuenchen/das-grundgesetz-als-schmierzettel-von-henry-matthes?color=ffd400) Die Veränderung in diesem zentralen Gesetzestexten ist allein den Parteien vorbehalten. An sämtliche Änderungen halten, dürfen sich dann nachher alle – selbst dann, wenn noch so wenige Bürger dahinterstehen. In den letzten Wochen offenbarte sich dieser Missstand in präzedenzloser Weise. Die als Sondervermögen schön-deklarierte Neuverschuldung wurde im Grundgesetz festgeschrieben. Ist eine solch selektive Umgestaltungsmöglichkeit des wichtigsten Gesetzestext einer Demokratie würdig? Bräuchte es nicht zumindest einer Absegnung durch Volksabstimmungen? Henry Mattheß hat sich hierzu Gedanken gemacht. Hören Sie seinen Text „Das Grundgesetz als Schmierzettel“, der zunächst auf dem Blog von Norbert Häring erschienen war. Sprecher: Karsten Tryoke Bild: Radio München [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482 @ 8671a6e5:f88194d1
2025-04-03 14:52:44\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?” *This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.* ## **Define** Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance). Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore. This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly. A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event. So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor. Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form. But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around. So, here’s what I’ve learned. <img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png"> **Chain of ticket** I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers. The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process. If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\ It’s better to not have bought at all. Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing. Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\ It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\ This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage. There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free. It gets even more absurd.\ At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day. And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\ “I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward). So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers. Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass. The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time. Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists. At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting. In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people. Which brings me to the next element of Bitcoin conferences...friends **Bitcoin “frens”** This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did). But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze. I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\ Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\ I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space. Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in. And you can love people for that. Everyone has flaws. Everyone has a price as well. But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\ We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast. If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference). But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time. And once in a while, you’ll meet a friend for life. Just be prepared: Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually. And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall. <img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png"> ## ## \ The Soviet LN Queue It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries. waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino! The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action. A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.” On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you. So, here’s a tip for the regular people, the rats that pay for all of this : sneak out. Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes. If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy. Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation: “Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!” Or worse: “Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?” At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war. **Solution:** A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following : Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting. If you’re using Lightning, have enough balance on you wallet or get lost. Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something. No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please! “Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please. Bitcoin fixes many things. But it hasn’t quite fixed this yet. The bitcoin conference axiom Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many. If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake. On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it. If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties. The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor. **Calculating the conference opportunity cost** To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps: 1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations). 2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years) 3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo. 4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members). 5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more). If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move. Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet. The Conference Opportunity Cost Formula Let: CT = Total conference ticket & entrance cost (in dollars) CR = Total related conference costs (travel, lodging, food, etc.) C = CT + CR (Total cost) G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05) N = Estimated fiat value of networking/business opportunities and knowledge gained. ### OC = (C × G) − N Where: OC (Opportunity Cost) < 0 → The conference was worth attending. OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move. Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!") example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0 - $253 OC (Bitcoin would have been the better choice.) Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner. \-- So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with. ### Energizing At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom. The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate. Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually. I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate. I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like. ### On stage The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway. The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again. Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all. It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card. Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :) ## Promoting anything The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though). <img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png"> They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”? That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label. It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else. They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard. Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare). ### **Looking for love in all the wrong places** \ Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here. Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life. And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie. The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary. And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop. My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset. Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin. Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask. Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever. If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself. I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit. Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world. Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though. Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks) Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher. In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it. I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now). written by AVB If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive)
@ 8671a6e5:f88194d1
2025-04-03 14:52:44\~ The person came up to me from behind his merchandise stand and saw my Noderunners pin on my black t-shirt, then looked me dead in the eye and asked : “So… what do you sell?” *This is the eighth long-read in a series of twelve “food for thought” writings on Bitcoin. It was originally meant to be a few chapters in a book, but life’s too short for that.* ## **Define** Let me start by saying there’s no single way to define or explain a “Bitcoin conference.” The experience can vary depending on a few factors: who’s organizing it (a long-time Bitcoiner or someone from traditional finance trying to grasp Bitcoin), where it’s being held (a sunny paradise like Madeira or a gloomy northern French town), and who’s speaking (technical experts or charismatic entertainers or people with little substance). Despite these differences, there’s a shared culture that ties these conferences together: a mix of excitement, frustrations, and inevitable evolution. That’s what I explore. This is just my take, based on what I’ve personally witnessed and what I hear from my surroundings. It’s not meant to be a blanket critique of all Bitcoin conferences as there are plenty I haven’t attended, though I hear about most of them. Even the good ones will evolve into something else over time. So, plan accordingly. A bit of background on my perspective: at some point in my life, I hit a bump in the road that kept me tied to where I live — a bleak corner of Belgium, surrounded by fiat slaves, shitcoiners, and people who spend six hours a day consuming brain-numbing garbage television. Traveling is an exception for me, but for many Bitcoin conference attendees, it’s a ritual, a must-do event. So, I view these events with a mix of fascination and grounded skepticism — something I’ve found lacking in many Bitcoiners. I’ve never been to a Bitcoin conference before 2023, despite receiving plenty of invites over the years. From what I heard and saw in photos from friends who attended (even the real early ones) these events seemed eerily similar to the dull hotel conference rooms I once endured in tech and telecom. I’ve had my fill of lukewarm, watery coffee and lifeless speakers droning on about firewalls. So I skipped that particular honor. Up until around 2018, Bitcoin conferences were a soulless sea of chairs lined up under fluorescent tube lights, draining the life out of attendees—one telecom acronym at a time. Not exactly inviting. Yet, looking back from the perspective of 2025, those were the “pure” days. Back then, people like Roger Ver (before he pivoted to Bitcoin Cash), Andreas Antonopoulos, and encryption specialists spoke to small audiences, explaining Bitcoin in its raw form. But, like any Bitcoiner, I try to improve myself. So, I made the effort to travel, visit other Bitcoiners, and attend Bitcoin conferences. The conferences I attended in 2023/2024 made me a bit wiser ; not necessarily from what was said on stage (with a few lucky exceptions who still try to bring original thoughts). Most of what I learned came from the long queues, the drama, and watching grifters operate in real time and the good characters floating around. So, here’s what I’ve learned. <img src="https://blossom.primal.net/d49fdda9ecb03f04f6c778e5301c67cf2bb15ff3b8647d929cb1755a9f6660a4.png"> **Chain of ticket** I quickly discovered that many Bitcoin conferences have their own “quest for tickets” dynamic, almost like an industry with its own inner circle. It’s a waterfall system: tickets start at lower prices to fill up the venue (usually right after the previous edition). That’s standard practice, both inside and outside of Bitcoin. But what’s strange is seeing organizations that only pop up when a conference needs promotion—somehow securing tickets for themselves and their friends (or for \*making\* friends) while shilling referral links for small discounts to their followers. The real free tickets, though, are a hot topic in many local communities and make all the difference for some attendees. What’s particularly interesting is that most ticket prices can be paid in Bitcoin, adding a layer of calculation to the process. If you paid 230500 sats for your ticket and later see the dollar price fluctuate, say from $180 to $270, or the other way around, by the time the conference starts, you realize you either bought too late or too early.\ It’s better to not have bought at all. Some ticket holders end up paying less (in dollar terms) than others, making it a gamble. As the event date approaches, ticket prices tend to rise—unless you wait until the last minute, when they haven’t sold out, or just pay at the door. It’s a strange feeling knowing that not everyone paid the same amount (and as mentioned, a significant number get in for free) depending on their timing. Many organizations and local community representatives show up primarily to be present; securing free tickets, which function more as a badge of recognition than a necessity.\ It’s similar to how a rock groupie sees backstage access: a status symbol, whether for an autograph or something more. Being seen standing next to big names is a huge deal for some, as they derive their own status from proximity.\ This also reinforces the “rockstar status” that conferences create around certain figures, once they come out to take a selfie with some nice people and young fans, then to quickly disappear back to the ‘whale room’ or backstage. There’s often an entire insider network determining who gets these free tickets. In some cases, it’s naturally tied to the local community, but in others, the professionalism is laughably low. At certain events, you could probably just walk up to the entrance (if there’s even someone checking) and say, “I’m with the organization” to get in for free. It gets even more absurd.\ At a conference near the French-Swiss border, I was probably one of the very few who actually paid for entry. The real spectacle wasn’t in the talk rooms — which remained eerily empty — but in the dining area, where half the town seemed to have shown up just for the free food. Around 200 people queued for a free lunch, while the presentation halls were at best one-third full throughout the day. And beyond the ticket games, there are plenty of ways to slip in unnoticed. Carrying a random piece of equipment and mumbling\ “I need to put this crate in the back” can get you past security. Or you can just wait for the one security guard to get distracted by chatting up a girl or stepping out for a smoke, and you’re in. At one event, I walked in alongside someone carrying crates of wine for the VIP lounge. I blended in perfectly (I paid afterward). So, to sum up: at nearly every conference I’ve been to, a big portion of attendees either walk in for free or hold compensation tickets they got through some connection. Sometimes that connection is uncomfortably close to the organizers. Other times, they just slap an “industry” label on themselves when, in reality, they’re nothing more than a social media bio with a few followers. Local representatives of a podcast, community, influencer network, or fake marketing club also get in for free. And you? The regular guest, you and I are paying for them. There’s no real vetting process; with some organizers, anyone wearing a Bitcoin t-shirt and saying the magic words “I do community building” or “I know the local Bitcoin meetups” gets a free pass. The ones who actually want to learn about Bitcoin — the ones who click the link and pay full price — are the ones covering the costs for everyone else and ultimately making these conferences profitable (or at least break even). The problem? They’re the ones left wondering: “Was it really worth my time and money?” only to never return again most of the time. Because many of the people at these conferences aren’t there to learn. They’re part of the circus. And others? They’re the ones paying for the circus boss, the clowns, and the trapeze artists. At that one conference with the massive free-lunch crowd, I saw one interesting talk. And I had plenty of valuable conversations and observations — conversations I could have just as easily had by visiting that place outside of a conference setting. In the end, I realized the main reason I was there was to support a fellow Bitcoiner giving a presentation. And after that? They disappeared from my life. Because, just like in the fiat world, you’re only as good as your last few hours of usefulness to most people. Which brings me to the next element of Bitcoin conferences...friends **Bitcoin “frens”** This might be the hardest lesson of all: you meet fellow Bitcoiners at these conferences. And some of them? They’re truly special characters. A few even made such a deep connection with not-so-well-traveled-me that I would’ve gladly traveled a full travel day just to spend time working and doing something meaningful together (which I actually did). But most of these connections? They last only a moment. Few survive beyond the conference, mainly because of the vast distances— both in kilometers (or miles) and in the way we live our everyday lives. The Bitcoiners you meet at these events are, for the most part, just regular people trying to make ends meet in the fiat world while saving in Bitcoin. Or they’re chasing the Bitcoin dream or even find a job in the fata morgana of bitcoin jobs. They act like they belong, like a clown acting like he’s going to climb the trapeze. I respect that. But over time, I realized that many of them operate in Bitcoin mode; a kind of facade. Behind that front, that mask, most are just testing the waters to see if they can make it. And most don’t.\ Treating Bitcoin as a lifestyle movement, a career shortcut, or an identity, has its limits. Eventually, the real person breaks through. And you have to face your own instincts and personality.\ I’ve tried to be an acrobat, and ride the lion, make the audience laugh, but I’m still the seal who’s brought back to the cage after he balanced a ball on his nose. The quote “I’m Jack’s wasted life.” came to mind often when standing somewhere at a conference space. Self-doubting people stay self-doubting, owning Bitcoin or not. Emotional wrecks remain emotional wrecks — just with Bitcoin now. And when these masks slip off, you’ll see everything: the greed, the overconfidence, the longing for drama, the addictions, the narcissism, the energy-draining personalities, sleaziness usually with the ones who always say the right oneliners or wear the right Bitcoin merch to blend in. And you can love people for that. Everyone has flaws. Everyone has a price as well. But these Bitcoin “frens” can also hurt you badly. Because as Bitcoiners, we carry hopes. And hopes are like ants on a sidewalk, they’ll eventually get crushed.\ We long to meet people who see the same truth, the same vision of Bitcoin as we do. Some will act like they actually understand and do, they talk the talk for a while, as if they’re parroting a podcast. If you stay in the shadows - like I did for years - you won’t have to deal with these things. If you never try, you’ll never be let down. But you still stay in the imaginary basement, letting yourself down. That’s not the bitcoin style. We router around problems. Even if we stand amidst the problems (like a conference). But if you do? There’s a hefty price to pay — beyond just the money spent. It’s a cost paid in energy, emotions, and social interactions and above all: time. And once in a while, you’ll meet a friend for life. Just be prepared: Bitcoin is a journey that few people you encounter at a conference can take for longer than four years, or even four hours of conversation actually. And then, after navigating the social maze of Bitcoin conferences —the connections, the masks, the fleeting friendships, the smell of weed and regret — you find yourself facing an even greater challenge: the queue at a coffee stall. <img src="https://blossom.primal.net/26f00a14b1ff12ea82635f1fd659900a7a836d37591556a31fda91d8210dcff0.png"> ## ## \ The Soviet LN Queue It’s one of the most fascinating and frustrating aspects of every conference: the insanely long lines. Whether it’s for the toilets, a coffee booth, or some niche merchandise stall, you’ll see Bitcoiners waiting like it’s 1963 after a Soviet state bakery just got fresh deliveries. waiting for coffee Seriously, aren’t we supposed to be the pinnacle of free-market efficiency? Instead, we’ve somehow perfected the art of the long food lines. I remember people waiting in line for like 35 minutes to order a cappuccino! The usual culprit? A mix of payment chaos and the Bitcoin Orangepill mental issues in action. A large portion insists on using Lightning (as in "their preferred lighting wallet"), which would be fine except they’re fumbling with some exotic, half-working wallet because using something that’s actually fast might get them sneered at for being “custodial.” On top of that, vendors are juggling card payments, cash, various Lightning POS systems, and even the occasional cutting edge dudes trying to pay with an Apple Watch or worse, some newly released Lightning-enabled gadget that doesn’t work yet. And when it does work, it requires so much attention and Instagram footage that it takes five minutes just to hand someone a coffee while the guy pays with a lighting NFC ring on his finger, something you can't use ànywhere else ever. It’s cool. But not to anyone else than you. So, here’s a tip for the regular people, the rats that pay for all of this : sneak out. Then you find a small, locally owned café outside the conference, pay them in cash, and actually enjoy your food in a few seconds or minutes. If (and only if) they accept Bitcoin, great! Tip them well. Otherwise, just relax and have a conversation with a local, all the while inside the conference venue there are Bitcoiners filming each other struggling to make a payment with the latest Lightning-enabled NFC card or making the staff uneasy. Meanwhile, some poor 22-year-old café worker is trapped in an unsolicited podcast participation: “Wait, you accept tips in Wallet of Satoshi? Who told you that? I’ll explain it to you!” Or worse: “Hold on, I just need to do a quick swap… It’s an on-chain transaction, the last block was 19 minutes ago, can’t be long now… wait… umm… do you take VISA?” At this point, ordering a simple drink at a Bitcoin conference has become an unnecessarily complex, ego-driven performance. With long queues as a direct result. And don’t get me started on the story when 30+ bitcoiners walked in to a Portuguese restaurant without a reservation, and they all wanted to pay with different payment methods. It was like the Vietnam war. **Solution:** A tip for conference organizers and their catering : pick one Bitcoin point of sales system, set clear guidelines, and make everyone stick to them. Instruct people to adhere to the following : Pay with a (bank) card, cash, or Lightning and PLEASE decide beforehand which method you’re using before ordering your stuff! We prefer lighting. If you’re using Lightning, have enough balance on you wallet or get lost. Use a compatible wallet. (Provide a tested “approved” list and train staff properly. Users who use other stuff get their order “cancelled” at the first sign of trouble. Your app‘s not scanning, or not compatible, or it has some technical mumbo-jumbo going on to your vpn LN node at home 2000 km away? Please get real and pay with a bank card or something. No filming, duck-facing (like it's 2017) or stupid selfies with your payment. It’s been done a thousand times by now. There are people in line, waiting behind you, they want to order as well, while you have your little ego trip or marketing moment. Move on please! “Our staff knows how bitcoin payments work, you don’t need to #orangesplain it to anyone.” We don’t care about your 200th LN app or the latest “but… this one is faster” thingy. Order your drinks, pay and get out of the way please. Bitcoin fixes many things. But it hasn’t quite fixed this yet. The bitcoin conference axiom Going to a conference, versus keeping your bitcoin in your wallet is a tough choice for many. If you pay nothing for tickets and lodging, while enjoying free meals and cocktails, your opportunity cost drops close to zero —yet your networking and social impact are maximized while you can also do business. That’s ideal. At least, for you. In such case, Bitcoin may only "win" over an extended timeline, but for you, it's essentially a free ride. You incur no real opportunity costs. You drink their milkshake. On the other hand, if you’re a regular attendee, you pay full price: the ticket, overpriced drinks and food from the stands (losing even more if you generously pay for coffee in sats), plus extras like t-shirts and books (which you’ll never read). Your milkshake gets taken—at least half of it. If you’re lucky, you might spend an evening in town with the event’s "stars"—those occasional luminaries who briefly grace the normies with their presence for a drink. Some can’t even hold their liquor. Year after year, the same 10 to 15 speakers or panelists appear, funded by your dime, traveling the world and enjoying the perks—some even cultivating fan bases and hosting exclusive parties. The real opportunity cost hits hardest for regular attendees who come to learn, shelling out significant money while accumulating their fourth hardware wallet or yet another orange-themed t-shirt. They might even squeeze in a selfie with a former sportswear model turned Bitcoiner. For normies (as they’re often called), the financial and social scales rarely tip in their favor. **Calculating the conference opportunity cost** To determine the opportunity cost of attending a conference instead of investing in Bitcoin, over time follow these steps: 1. Calculate your total conference expenses, including tickets, travel, food, drinks, and lodging (merchandise and donations). 2. Estimate Bitcoin’s percentage gain over the conference period and the following year(s). (in order to not make you cry, I suggest nog going over 5 years) 3. Multiply your total conference cost by this percentage to determine the potential Bitcoin profit you forgo. 4. Assign a dollar value to the networking or business opportunities you expect to gain from the conference (if you’re not just in it for the laughs, meeting high-class consultants, friendships, self-proclaimed social media Bitcoiners, or the occasional gyrating on one of the musicians/artists/food stall staff members). 5. Subtract this “networking” value from the missed Bitcoin profit to find your net opportunity cost (this is rather personal,… with me it’s zero, but for someone selling t-shirts it’s probably much more). If the result is negative over the chosen timeframe, the conference was financially worthwhile for you. If positive, holding or buying Bitcoin was the smarter move. Unless you’re a recognized speaker in this traveling circus, your opportunity cost will likely be positive — meaning all the others lose hard money, while fumbling with your Lightning wallet. The Conference Opportunity Cost Formula Let: CT = Total conference ticket & entrance cost (in dollars) CR = Total related conference costs (travel, lodging, food, etc.) C = CT + CR (Total cost) G = Bitcoin’s % gain per year (as a decimal, e.g., 5% = 0.05) N = Estimated fiat value of networking/business opportunities and knowledge gained. ### OC = (C × G) − N Where: OC (Opportunity Cost) < 0 → The conference was worth attending. OC (Opportunity Cost) > 0 → Holding/buying Bitcoin was the better move. Some example calculations (I've left out examples before 2020, I don't want people crying or waking up at night thinking "Why did I go to Amsterdam in 2014?!") example : Conference in April 2024 Entrance: $200 Lodging, t-shirt, and travel: $900 Bitcoin's estimated gain: 23% (0.23) No business / knowledge value gained OC = (200 + 900) × 0.23 - 0 - $253 OC (Bitcoin would have been the better choice.) Conference in April 2020 (adjusted for historical Bitcoin growth) Entrance: $175 Lodging and travel: $700 Bitcoin's estimated gain: 1089% (10.89) No business / knowledge value gained OC = (175 + 700) × 10.89 - 0 OC = +$9,529 (Massive missed gains — Bitcoin was the clear winner. \-- So the first lesson in bitcoin should be: Only attend conferences if you get paid to do so and get a free ticket and free lodging, which kind of would kill that whole industry to begin with. ### Energizing At first, it’s energizing to meet like-minded bitcoiners, but after a while, you realize that a big chunk of them are just trying to sell you something or aren’t really bitcoin-focused at all. And some of them are just looking for their next way to kill time and boredom. The drama that comes with attending these conference and the personal interaction can get pretty intense at times, since expectations often don’t match the personalities. Before you know, you’re walking around at night through some bad part of a town, while crying your eyes out because you thought you found your soulmate. Future pure industry conferences will suffer less from this drama, because everyone there has the same goal — pushing their company or product— while the “other” grassroots conferences are more of a meeting spot for bitcoiners of all types and perspectives, bringing the usual drama and mess that comes with human interactions. Current conferences are a mix of both usually. I think the current era of bitcoin conferences is coming to an end. Soon, probably by the end of 2025, we’ll see a clear split between industry-driven and human-driven (grassroots) smaller conferences, and it’ll be really important to keep these two separate. I even had the idea to launch a sort of conference where there wouldn’t be any industry speakers or companies present. Just bitcoiners gathering at a certain place at a specific week and having a good time. I called it “club Sat” And you could just go there, and meet other bitcoiners, while acting there was a big venue and speakers,… but there aren’t any. Would be refreshing. No struggle for tickets, no backstage stuff, no boring talks and presentation,… just the surroundings and the drama lever you want and probably like. ### On stage The podium is usually left for the known names. Not every conference is like that, but most of them need these names, badly. These names know each other, they encounter one another in VIP rooms and “the industry” a lot of times anyway. The same people you see in the bitcoin news, the same people having a cult following, and the very same people traveling, staying and drinking for free while spreading the same bitcoin wisdoms will be invited over and over again. Or… they go rock around as they’re usually so bored they had to start a rock band to entertain themselves. Which is rather entertaining if you’re following up on who does what, but in the end it’s largely just for their own amusement and it shows. I get that. I would do the same. It’s fun and all. It’s just a bit sad that there are only a small group of top-layer speakers, and then the sub-top that usually has more to say, or gets little opportunity. The reason for that is simple: the “normies” who pay in full for tickets, come there for the “big” names. They don’t know that much about bitcoin usually, so they’re not waiting on some unknown dude explaining something about an obscure niche subject. A debate can help remedie this, to mix it in with some lesser known names, but I have the feeling the current “line-up” of bitcoin conferences feels like a rock festival in 2025 putting the Stone temple pilots or Creed on the card. Yes, they’ll attract an audience and do their playset well,… but it’s not exactly the pinnacle of the music industry at the moment, neither is Madonna by the way :) ## Promoting anything The people organizing these events usually aren’t Bitcoiners either — they’re promoters (few exceptions though). <img src="https://blossom.primal.net/f478bf793b2048a51a15ceab5b8384abdb8d00c6d7c3cdd16731f5379cc1417d.png"> They don’t care if they organize a symposium about a newly discovered STD, A three-day cheese tasting event, a Star Trek convention, or a Lucha Libre wrestling tournament featuring El HODLador, as long as they can sell tickets and make money from merchandise they're good. The last thing on the mind with some of them will be helping bitcoin adoption. There will be a time (soon) where people that know bitcoin, known bitcoiners and know how to organize events get their act together. It will be different than the early days, and it will be different than the boring going-through-the-motions conferences we have now. There shall be fun, social gatherings, life, excitement and culture, and not the “what do you sell?” atmosphere, neither the “this old dude on stage again”? That’s why they’ll slap any semi-famous name on the poster to pull in a crowd - could be a washed-up Mexican wrestling star with strange legal issues, the cheese-tasting equivalent of Usain Bolt, or your neighborhood Bitcoin old-timer with a beard and a "best selling author" label. It’s also why most of these conferences end up being more about shitcoins than anything else. And even if they're for the most part about bitcoin, the venue is usually infested with marketing budgets, useless organizations that wanted complimentary tickets (some of them do only one thing: popping up when a conference is nearby and then they’re gone again) ... along with some hawking consultant types you never see anywhere else. They'll occasionally pay people but usually in fiat, or if you're a bigger name, you might get other deals. For artists or staff, it's all in fiat from what I heard. Pure Bitcoin conferences, also rely on these big names. Whether it’s a well-known Bitcoiner, a CEO, president, or someone with real reveling knowledge to share with the audience (though that last type is getting rare). ### **Looking for love in all the wrong places** \ Let’s also address the fair share of “orange diggers” at Bitcoin conferences—because yes, they exist. And no, let’s not single out one particular gender here. Some people treat a Bitcoin conference like a live-action dating app mixed with a financial vetting process for potential partners. It’s essentially an opportunity to inspect and assess the grab bag of fintech, crypto, and Bitcoin folks in real life. And if you think this is exaggerated, just attend a few conferences—three is enough. You’ll start noticing the same people popping up, seemingly without any real Bitcoin knowledge, but with a very strong interest in dining, chatting, and generally being around—as long as you look and play the part. I can only imagine how dialed-up this effect must be at a shitcoin conference — probably like flies on a cowpie. The trick is, in Bitcoin, these people try to blend in. Some even tag along with real Bitcoiners, while others just crash the party and try to get noticed. Their actual interest in Bitcoin? Close to zero. Their main target? Your wallet, or some fantasy thing about getting to know someone out of the ordinary. And that’s a shame for the people who genuinely care about Bitcoin, who want to network, or who simply are looking for like-minded people. They often find themselves competing for attention with those who’ve turned “being noticed” into a sport, while the rest just wander around, lost in the shuffle. Talk to the quiet ones. Certainly if they look like they belong in a antiques shop. My advice: Talk to people and be genuine. If you don’t know much about Bitcoin, that’s fine - nobody expects you to be a walking whitepaper and on top of that, most people you'll encounter don't know that much either. It’s bitcoin: we’re all rather average people that hold an extraordinary asset. Just don’t be "that orange digger" looking for a partner with a loaded bag of bitcoin. Because in the end, what’s the prize you win? You don’t know who’s under the mask. You don’t even know who’s under your own mask. Finding a man or woman at a place where half the people are laser-focused on financial sovereignty, and the other half are busy arguing about seed phrase storage, UTXO management, and why your Lightning wallet sucks? But good luck with that. The judge of character usually comes when they find the next shiny object or ditched you standing in the rain at the entrance of a restaurant while dealing with a lightning watchtower or a funny cigarette or whatever. If you’re truly looking for love, maybe stick to going to a normal bar. If you’re here to learn, connect, and be part of something of a grassroots movement, then be real yourself. I've seen some rather nasty examples of people at Bitcoin conferences—of all kinds. And I've also seen some really cool examples of truly awesome people. This led me to believe that Bitcoin conferences simply let you meet… people, just dialed up a bit. Future If you encounter rotten people, they’ll usually be even more rotten than in the fiat world. If you meet really cool people, they’ll be even more awesome than the cool people in the fiat world. Our volatility is our freedom. So, I guess it’s normal. Doesn’t make it any easier, though. Bitcoin sees through bullshit, and so do Bitcoiners (even if it takes 21,000 blocks) Pretty soon, I reckon we’ll see conferences fork into two camps: grass roots, and the “industry” level ones. (human / corporate) I guess I’ll only attend the human part, for sure, but I can’t help but booking myself a single room in a hotel in a nice area in that case, so I don’t have to deal with class of 2022 hippies sharing referral links to their middleman service while asking me for a lighter 3 times in a row. The chances for me of meeting cool bitcoiners in a nearby cocktail bar are a lot higher. In the meanwhile, I’ll look forward and see how the bitcoin conferences will evolve, fork in two “styles”. One corporate and one underground. Maybe there will be one more genre just for the fun of it. I’ll stay away, as I don’t like this current mix of industry gigs and having the insiders and “the rest” of us all mingled together clamoring for tickets, attention and coffee. The game is rigged. Staying at home is the better option (for now). written by AVB If you like : [tip here](https://coinos.io/allesvoorbitcoin/receive) @ 69e50943:2ac7059c
2025-04-03 23:14:14**This is a test** How does this look? 
@ 69e50943:2ac7059c
2025-04-03 23:14:14**This is a test** How does this look?  @ 2b42dd42:5049393c
2025-04-03 21:25:46this is a test <img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png"> end of the test
@ 2b42dd42:5049393c
2025-04-03 21:25:46this is a test <img src="https://blossom.primal.net/5029e2735884c4b18875b1e0e378b91133d6a1118c2cf323eef258467b6932c0.png"> end of the test @ f1989a96:bcaaf2c1
2025-04-03 14:30:08Good morning, readers! Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\ \ Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\ \ In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin. We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation. **Now, let’s get right to it!** ### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters** Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose. #### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025** The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime. #### **India | Grants Tax Authorities Access to Citizens’ Online Data** Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power. #### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief** Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected. #### **Angola | Regime Jacks Price of Diesel** The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters. #### **Nicaragua | Ortega’s Dismantling of Press Freedom** Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders. ## BITCOIN AND FREEDOM TECH NEWS #### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide** HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/). #### **Cove | New Open-Source and Permissionless Bitcoin Wallet** [Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove). #### **Second | New Ark Implementation Launches on Bitcoin Signet** [Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com). #### **Braiins | Open Sources Bitcoin Control Board** [Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most. #### **African Bitcoiners | Publish Bitcoin Starter Guide** [African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/). #### **OpenSats | 10th Wave of Nostr Grants** [OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools. ## RECOMMENDED CONTENT #### **Freedom Tech with Alex Gladstein** In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0). #### **The State of Personal Online Security and Confidentiality with Meredith Whittaker** In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/)
@ f1989a96:bcaaf2c1
2025-04-03 14:30:08Good morning, readers! Georgian officials froze the bank accounts of five nonprofit organizations that provide financial and legal support to detained protesters. This follows rising public unrest as Georgia’s regime pushes new laws restricting free speech and assembly, introducing new fines and penalties, and expanding law enforcement powers. By eroding civil protections, the regime makes it more dangerous and costly for activists, dissenters, and everyday citizens to stand up against an increasingly repressive regime.\ \ Meanwhile, the Indian government introduced a new income tax bill that grants tax authorities sweeping surveillance power over anyone they “suspect” of tax evasion. If suspected, tax authorities are legally allowed to access Indians' email, social media, and bank accounts, raising obvious concerns over state overreach and invasions of individual financial privacy.\ \ In freedom tech news, HRF donated 1 billion satoshis to more than 20 projects worldwide, focusing on supporting human rights defenders and vulnerable communities under authoritarian regimes across Asia, Africa, and Latin America. These gifts advance censorship-resistant communications and transactions, bitcoin education, and privacy tools so that dissidents, nonprofits, and individuals may better protect their human rights and financial freedom. In this letter we also spotlight a new open-source mobile Bitcoin wallet called Cove. While still in beta, the wallet can be used with a hardware device or on its own as a hot wallet, offering a flexible self-custody setup for managing Bitcoin. We end with a podcast in which HRF Chief Strategy Officer Alex Gladstein discusses the state of freedom tech and why Bitcoin stands as the most promising tool for financial liberation. **Now, let’s get right to it!** ### [**SUBSCRIBE HERE**](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a) ## **GLOBAL NEWS** #### **Georgia | Officials Freeze Accounts of Organizations Supporting Protesters** Georgian officials have [frozen](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) the bank accounts of five nonprofit organizations that provide financial and legal aid to dissenters. This comes in response to an uprising of protests over new controversial laws that restrict free expression and assembly, increase fines and detention periods, and expand law enforcement powers. Georgian officials justify the account freezes as part of an investigation into “sabotage,” yet they have provided no evidence. Amnesty International [warns](https://www.amnesty.org/en/latest/news/2025/03/georgia-authorities-freeze-accounts-of-organizations-supporting-protesters-to-kill-the-peaceful-protests/) this financial assault could “kill the entire protest movement.” Bitcoin provides a way to circumvent these struggles. Its uncensorable and permissionless nature has helped [sustain](https://www.journalofdemocracy.org/online-exclusive/how-to-dictator-proof-your-money/) pro-democracy movements across Belarus and Nigeria, proving it is capable of addressing the immense financial restrictions dictators impose. #### **United Arab Emirates | Plans to Launch “Digital Durham” CBDC in 2025** The United Arab Emirates (UAE) will [launch](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) its central bank digital currency (CBDC), the “[Digital Durham](https://cbdctracker.hrf.org/currency/united-arab-emirates),” by the end of 2025. [According](https://www.ledgerinsights.com/uae-to-launch-cbdc-in-q4-2025/) to the central bank, the CBDC will be available through licensed financial institutions and operate via a government-run digital wallet. Every transaction will be recorded on a permissioned blockchain run by the government. The central bank further [admitted](https://u.ae/en/about-the-uae/strategies-initiatives-and-awards/strategies-plans-and-visions/finance-and-economy/central-bank-digital-currency-strategy) the CBDC will replace cash and [assist](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) law enforcement “by leaving a digital trail for transactions involving illicit funds.” Officials [claim](https://www.businesstoday.in/technology/news/story/uae-to-launch-digital-dirham-by-year-end-to-modernise-payments-and-noost-financial-inclusion-470013-2025-03-31?utm_source=semafor#) this is to combat financial crime, but it also enables real-time surveillance and tracking of individual financial activity. In a country known for strict laws against dissent and extensive surveillance capabilities, it is not hard to see how a CBDC will erode the autonomy and rights of activists, dissenters, and others who oppose an increasingly authoritarian regime. #### **India | Grants Tax Authorities Access to Citizens’ Online Data** Starting in April 2026, the Indian government will [grant](https://economictimes.indiatimes.com/wealth/tax/your-email-and-social-media-account-can-be-accessed-by-income-tax-officer-starting-next-financial-year-in-these-cases/articleshow/118685184.cms) tax authorities legal access to the private online data of any citizen “suspected” of tax evasion. This will include legal access to personal emails, social media, and bank accounts. The new law expands on the Income Tax Act of 1961, which previously limited officials to searching physical premises for financial documents. Now, officials can bypass digital security measures and access private data without consent — all under a legal framework. This dissipation of financial privacy sets an intrusive precedent and opens the door to state-level corruption and surveillance in a country where the Modi regime has already made it clear they are happy to use financial repression to further cement their power. #### **Myanmar | Bitcoin as a Tool Support Earthquake Disaster Relief** Last week, a [7.7 magnitude earthquake](https://www.nytimes.com/2025/03/28/world/asia/earthquake-myanmar-thailand-death-toll.html) struck central Burma, with strong tremors reaching neighboring Thailand. The [official death toll ](https://www.reuters.com/business/environment/survivors-myanmar-quake-left-without-food-water-shelter-aid-groups-say-2025-04-01/)has surpassed 2700. And in Bangkok, a 33-story building under construction [collapsed](https://www.youtube.com/watch?v=ynrhyIh4ozo). Despite an already strenuous situation, Burma’s military junta continues its oppression. They are [blocking](https://www.nytimes.com/2025/03/31/world/asia/myanmar-earthquake-rescue.html) rescue teams from reaching the Sagaing region — the epicenter of the earthquake and the heart of Burma’s pro-democracy movement — and instead channeling aid to regime-controlled cities like Naypyidaw and Mandalay. The junta is also continuing to conduct air strikes on civilians and restricting equipment and fuel for aid groups, leaving a [million](https://data.unhcr.org/en/country/mmr) people in Sagaing to fend for themselves. In these repressive circumstances, Bitcoin can provide a censorship-resistant way to send funds directly to those affected. #### **Angola | Regime Jacks Price of Diesel** The Angolan regime [raised](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) diesel prices by 50% in the process of eliminating fuel subsidies. Diesel prices suddenly increased from 200 to 300 kwanza per liter, driving up transportation costs in a country where over half the population lives on [less](https://www.rigzone.com/news/wire/angola_doubles_diesel_prices_after_imf_call_for_subsidy_cuts-25-mar-2025-180020-article/) than $2 a day and inflation is over 42%. Previous fuel subsidy cuts in 2023 (where the price of diesel rose [80%](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231)) sparked [protests](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) between taxi drivers, nonprofit workers, and law enforcement. This recent price increase now raises fears of renewed crackdowns. The Angolan regime also introduced new civil society laws that Guilherme Neves, chairman of the human rights organization Associacao Maos Livres, [describes](https://www.dw.com/en/angolan-police-crack-down-on-fuel-hike-protests/a-65978231) as a “license to erase non-governmental organizations that are not government-compliant.” Angolans find themselves in increasingly precarious financial positions as the government erodes the civil safeguards protecting nonprofits and dissenters. #### **Nicaragua | Ortega’s Dismantling of Press Freedom** Since coming to power in 2007, Ortega has [closed or seized](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) 61 media outlets, imprisoned countless journalists, and forced over 280 journalists into exile. His [assault on press freedom](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) has unfolded in two phases: initial raids on local radio stations and TV channels between 2007 and 2017, followed by full-scale censorship in 2018 on independent media outlets like [La Prensa](https://www.laprensani.com/) and [CONFIDENCIAL](https://confidencial.digital/). Ortega then intensified attacks from 2019 to 2021 by closing Nicaragua’s second-oldest newspaper and passing laws to [criminalize](https://havanatimes.org/features/ortegas-war-on-journalism-in-nicaragua/) free expression. This is a deliberate strategy to eliminate dissent and independent voices. What’s happening in Nicaragua highlights the importance of open and decentralized protocols like nostr, which allow journalists to publish freely without getting censored. While still early, it is becoming essential for sharing information absent the fear of being blocked or silenced by autocratic leaders. ## BITCOIN AND FREEDOM TECH NEWS #### **HRF | Gifts 1 Billion Satoshis to 20+ Open Source Projects Worldwide** HRF gifted 1 billion satoshis in its Q1 2025 round of [Bitcoin Development Fund](https://hrf.org/program/financial-freedom/bitcoin-development-fund/) (BDF) grants, supporting more than 20 open-source projects around the world. These projects advance Bitcoin education, open-source software, mining decentralization, and privacy tools for activists contending with authoritarian regimes across Asia, Latin America, and Africa. Supporting permissionless financial tools and censorship-resistant technologies empowers dissidents, journalists, and civil society to organize, transact, and communicate without state suppression and interference. Learn more about the grantees and their work [here](https://hrf.org/latest/hrf-bitcoin-development-fund-supports-20-projects-worldwide/). #### **Cove | New Open-Source and Permissionless Bitcoin Wallet** [Cove](https://github.com/bitcoinppl/cove) is a new open-source and permissionless mobile Bitcoin wallet that aims to put users in full control of their Bitcoin. Users can connect their own hardware wallet (to manage Bitcoin offline) or use Cove as a hot wallet (to manage Bitcoin online). It also allows users to create multiple wallets from the app itself. In the future, Cove plans to add Unspent Transaction Output (UTXO) selection and coin control, giving users more independence over their transactions and the tools to better protect their financial privacy. While still in beta and only suitable for test funds, this wallet holds promise as a privacy tool to equip dissidents with self-custodied Bitcoin. You can try it [here](https://github.com/bitcoinppl/cove). #### **Second | New Ark Implementation Launches on Bitcoin Signet** [Second](https://second.tech/), a company building on Ark, a protocol designed to help scale Bitcoin’s transaction throughput, [launched](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com) “Bark.” Bark is a test implementation of the Ark protocol deployed on Bitcoin’s [Signet](https://en.bitcoin.it/wiki/Signet) network (where developers test software). More broadly, the Ark protocol helps make Bitcoin transactions more private, faster, and cheaper, supporting the network in handling more transactions and users with the tradeoff of being less trusted than the mainchain, as funds stored in a noncustodial way on Ark can expire if not used. While it is still in early development, the test release of Bark marks a step toward deployment on the main Bitcoin network. Scaling solutions like Ark could be important for activists and individuals. They might ensure Bitcoin remains accessible to all, even as block space demand increases and network fees rise. Learn about it [here](https://blog.second.tech/try-ark-on-signet/?ref=nobsbitcoin.com). #### **Braiins | Open Sources Bitcoin Control Board** [Braiins](https://braiins.com/), a company building tools for Bitcoin mining, [open-sourced](https://x.com/BraiinsMining/status/1904601547855573458) its [BCB100](https://github.com/braiins/BCB100) Bitcoin Control Board, giving miners using their products greater insight and control over their Bitcoin mining hardware and firmware. Sharing the design files and firmware openly helps strengthen Bitcoin’s decentralization, making it more resilient against corporate or state interference. Specifically, open-sourcing mining hardware ensures individual miners can operate independently, reducing censorship risks across the entire network. In turn, this preserves financial freedom by keeping Bitcoin accessible and usable by dissidents, nonprofits, and individuals who need it most. #### **African Bitcoiners | Publish Bitcoin Starter Guide** [African Bitcoiners](https://x.com/afribitcoiners) just published “[Bitcoin: Africa’s Guide to Freedom Money](https://x.com/afribitcoiners/status/1904516726273851513),” a Bitcoin guide providing clear, practical insights into how Bitcoin can help people across the continent escape inflation, corrupt regimes, and failing financial systems. It covers essential topics to get started — from choosing a wallet to properly securing Bitcoin. In Africa, where some of the world’s longest-standing dictators restrict even basic financial activity, this guide is a powerful resource for human rights defenders, nonprofits, and everyday citizens. Read it[ here](https://bitcoiners.africa/bitcoin-africas-guide-to-freedom-money/). #### **OpenSats | 10th Wave of Nostr Grants** [OpenSats](https://opensats.org/), a nonprofit that supports open-source software development, [announced](https://opensats.org/blog/10th-wave-of-nostr-grants) its tenth wave of grants for projects in the nostr ecosystem. Nostr is a decentralized protocol that enables digital identity and communications outside the reach of authoritarian states. The grant round provides support to nostr Epoxy, which enhances access to nostr by circumventing censorship through a network of paid proxies. This ensures activists and dissidents can continue to communicate even in restrictive environments. Additionally, Zapstore received a grant for providing a permissionless app store built on nostr that enables developers to distribute software without corporate gatekeepers. This provides an open-source alternative to centralized app stores that often comply with government censorship and restrict dissidents’ access to freedom tools. ## RECOMMENDED CONTENT #### **Freedom Tech with Alex Gladstein** In this [episode](https://x.com/blockspacepod/status/1896229100702089589?s=46&t=yEPKerGEzeCp5j_mIaNJ8A) of The Gwart Show, Alex Gladstein, chief strategy officer at HRF, breaks down how and why Bitcoin serves as “money dictators can’t stop.” Drawing on more than 17 years of human rights work, he shares real-world examples of activists and citizens using Bitcoin to escape financial repression in authoritarian countries. Gladstein also explores privacy tools, cross-border payments, and why Bitcoin offers promising hope for financial freedom. Watch the full conversation [here](https://www.youtube.com/watch?v=5Ng961QZwI0). #### **The State of Personal Online Security and Confidentiality with Meredith Whittaker** In this [keynote](https://www.youtube.com/watch?v=AyH7zoP-JOg) for SXSW 2025, Signal CEO Meredith Whittaker shares her growing concerns around AI, personal data collection, and the erosion of privacy in today’s increasingly digital world. She emphasizes the need for more secure, uncensorable, and privacy-protecting technologies that shield users from surveillance and exploitation, especially in the context of authoritarian regimes. Watch the [full discussion](https://www.youtube.com/watch?v=AyH7zoP-JOg) for a pragmatic view into the future of digital privacy and security. *If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report [here](https://mailchi.mp/hrf.org/financial-freedom-newsletter?mc_cid=bf652c0a5a).* *Support the newsletter by donating bitcoin to HRF’s Financial Freedom program [via BTCPay](https://hrf.org/btc).*\ *Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ [hrf.org](http://hrf.org/)* *The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals [here](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1)*. [**Subscribe to newsletter**](http://financialfreedomreport.org/) [**Apply for a grant**](https://forms.monday.com/forms/57019f8829449d9e729d9e3545a237ea?r=use1&mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Support our work**](https://hrf.org/btc?mc_cid=39c1c9b7e8&mc_eid=778e9876e3) [**Visit our website**](https://hrf.org/programs/financial-freedom/) @ 1aa9ff07:3cb793b5
2025-04-03 14:06:38In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. **Understanding Nostr: A Decentralized Social Network Protocol** In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement.
@ 1aa9ff07:3cb793b5
2025-04-03 14:06:38In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. **Understanding Nostr: A Decentralized Social Network Protocol** In an era where centralized platforms dominate the internet, concerns over censorship, privacy, and data ownership have led to the rise of decentralized alternatives. One such innovation is Nostr, a lightweight and resilient protocol designed to enable censorship-resistant and decentralized communication. In this article, we will explore what Nostr is, how it works, its advantages, and why it is gaining traction among privacy advocates and decentralized technology enthusiasts. ### **What is Nostr?** Nostr (Notes and Other Stuff Transmitted by Relays) is an open protocol designed for creating censorship-resistant social networks and communication platforms. Unlike traditional social media networks, which rely on centralized servers controlled by corporations, Nostr operates on a decentralized model using cryptographic keys and relays. Nostr allows users to publish and receive messages without the need for a central authority. It is not tied to any single application but instead provides a foundation upon which developers can build various types of social and communication tools. ### **How Does Nostr Work?** Nostr consists of two main components: 1. **Clients** – Applications that users interact with, such as social media platforms, chat applications, or blogging tools. 2. **Relays** – Servers that distribute messages between clients without storing them permanently or acting as gatekeepers. When a user wants to send a message or publish content, their client signs the data using their private key and broadcasts it to multiple relays. Other users who subscribe to those relays can receive and interact with the messages. Nostr does not have a concept of user accounts managed by a central entity. Instead, identity is established using public and private cryptographic keys. The private key is used to sign messages, while the public key acts as the user’s identity across the network. ### **Advantages of Nostr** 1. **Censorship Resistance** – Since Nostr does not rely on a central authority, it is much harder for governments or corporations to censor content. Users can publish messages freely, and if one relay refuses to distribute them, they can simply use another. 2. **Privacy and Security** – Messages are signed using cryptographic keys, ensuring authenticity and reducing the risk of impersonation. Users retain full control over their identities and content. 3. **Interoperability** – Nostr is not tied to a single platform or application. Developers can create different types of services using the protocol, from microblogging platforms to encrypted messaging apps. 4. **Resilience** – Since the network relies on multiple relays instead of a single centralized server, it is less susceptible to shutdowns or attacks. ### **Use Cases for Nostr** - **Decentralized Social Media** – Platforms like Twitter alternatives can be built on Nostr, allowing users to post updates without fear of censorship. - **Private Messaging** – Secure and encrypted messaging applications can be developed using the protocol. - **Blogging and Content Publishing** – Writers and journalists can publish articles in a censorship-resistant manner. - **Bitcoin and Cryptocurrency Communities** – Many Bitcoin enthusiasts are adopting Nostr due to its decentralized nature and alignment with privacy-focused principles. ### **Challenges and Limitations** While Nostr is a promising technology, it is still in its early stages and faces several challenges: - **Adoption and Network Effects** – Since Nostr is not as widely used as traditional social media platforms, building a strong user base is a challenge. - **Spam and Moderation** – Without central moderation, handling spam and malicious content is more difficult, requiring innovative solutions such as reputation-based filtering. - **User Experience** – Decentralized networks often have a steeper learning curve for new users compared to centralized platforms. ### **The Future of Nostr** Despite these challenges, Nostr is gaining momentum among privacy advocates, developers, and decentralized technology supporters. With continued development and improvements in usability, Nostr has the potential to reshape online communication by offering a truly decentralized and censorship-resistant platform. As more developers create applications and services using Nostr, its ecosystem is likely to expand, providing a viable alternative to traditional social media networks. Whether you are a developer, a privacy-conscious user, or someone interested in the future of decentralized internet, Nostr is a technology worth exploring. ### **Conclusion** Nostr represents a significant step toward a more open and decentralized internet. By removing central points of control and enabling user-driven communication, it empowers individuals to interact freely without the risk of censorship or data exploitation. As the protocol matures and more applications emerge, it could play a crucial role in shaping the next generation of online communication. If you are interested in experimenting with Nostr, you can start by exploring various Nostr-based applications, setting up your cryptographic keys, and connecting with the growing community of users and developers. The future of decentralized communication is just beginning, and Nostr is at the forefront of this movement. @ 502ab02a:a2860397
2025-04-03 08:31:07#ที่มาทำเพลง #ตัวหนังสือมีเสียง วันนี้จะเล่าถึงเพลง ตรุษจีนครับ เป็นเพลงที่เขียนเสร็จภายในคืนเดียว คือไม่ใช่ว่าเก่งกาจอะไรครับ แต่เนื้อหามีในหัวตั้งนานแล้วตั้งใจจะทำนานแล้วแต่ภารกิจอื่นมีมากจน 24 ชั่วโมงมันรู้สึกน้อยเกินไป เพลงนี้ความตั้งใจคือ หวังสูงเลยครับ หวังว่าสักวันหนึ่งเยาวราชจะเปิดเพลงนี้กันกระหึ่มในวันตรุษจีน ซึ่งรู้ตัวดีครับว่า ตัวเล็กๆ คงไม่ดังเปรี้ยงในรอบเดียว ผมคิดว่า จะอีก 5ปี 10ปี เพลงนี้มันปล่อยไปแล้วมันยังอยู่ไปเรื่อยๆครับ (เปิดตัวครั้งแรก มีคนเอาแผ่นเสียง tiktok ไปทำอวยพรกันราวๆ 185คลิป ผมดีใจมากแล้ว บางคนลิปซิงค์ด้วยแสดงว่าหัดร้อง โคตรดีใจเลยครับ) ผมตั้งใจทำให้โทนออกมาเป็นเหมือนคนจีนร้อง แนวประมาณฮอทเป๊บเปอร์ โซเฟียลา อะไรประมาณนี้ ดังนั้นการออกเสียงจะเหมือนคนจีนพูดไทยไม่ชัดอะไรแบบนั้นครับ เนื้อร้องนี่ผมตั้งใจเขียนแบบ เอาใจอาม่าเลย เราลองมาดูบางท่อนกันครับ "ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง" เป็นท่อนย้ำแล้วย้ำอีก เพราะจงใจให้เป็นเพลงอวยพร ก็เลยทำเป็นแกนหลักของเพลงนี้ จากนั้นตัวรองก็จะเป็นคำอวยพรในแต่ละเรื่อง มาซ้อนอีกทีนึง "ปีใหม่หวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี" ท่อนนี้ผมนึกถึงอาม่าของผมครับ แกชอบดูหนังกำลังภายใน วีดีโอม้วนเป็นชุดๆ แล้วการได้ไปเที่ยวเรื่อยๆก็เป็นอีกความสุขนึงของคนแก่ ไม่ได้ต้องการอะไรมากไปกว่าร่างกายแข็งแรง เดินเหินไหว เที่ยวได้ "ไม่เพียงแค่ในปีนี้ แต่ขอให้ดี ทุกทุกปีไป ครอบครัวยิ้มได้ละไม ทุกคนสุขใจ เฮงเฮงดีดีดี" เป็นท่อนท้ายเพลงแล้ว ซึ่งก็ตบด้วยว่าไม่ได้เฉพาะปีนี้นะ ที่อวยพรกันขอให้ดีไปยาวๆ แล้วก็เล่นคำท้ายว่า "เฮงเฮงดีดีดี" คือ มันเป็นการรวมคำดีๆย้ำๆ ผมรู้สึกว่าพอตอนที่ทำเป็นเพลง มันจะเป็นท่อนที่คนยิ้มกว้างเลยหล่ะ เนื้อเพลงเต็มๆผมลงไว้ให้ข้างล่าง ส่วนการรับฟัง สามารถเข้าได้หลายทางมากครับ youtube music https://music.youtube.com/watch?v=EBKTZv3VvGM&si=f_IMFbDhdEJ6wEcv spotify https://open.spotify.com/track/3fCJyoQVAeWxdczfGbL3yT?si=vHV45hUTRPO6Mg9Pnh-w2w apple music https://music.apple.com/th/album/%E0%B8%8B-%E0%B8%99%E0%B9%80%E0%B8%88-%E0%B8%A2%E0%B8%A2-%E0%B8%AD-%E0%B8%8B-%E0%B8%99%E0%B8%99-%E0%B8%AE%E0%B8%A7%E0%B8%94%E0%B9%84%E0%B8%8A/1789787248?i=1789787249 tiktok แผ่นเสียง https://vt.tiktok.com/ZSrk49SfL/ ส่วนเพลงอื่นๆ ฟังเต็มๆได้ทุก music plattform แล้วนะครับ ค้นหา heretong teera siri เพราะเพลงไม่ดังเลยต้องหาจากชื่อคนแทนครับ 55555 新正如意,新年发财 วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ปีใหม่หวังได้สุขดี เป็นเศรษฐีมีเงินทองใช้ ร่ำรวย รุ่งเรืองไปไกล คิดสิ่งใด ได้สมฤดี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ปีใหม่หวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ไม่เพียงหวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ไม่เพียงแค่ในปีนี้ แต่ขอให้ดี ทุกทุกปีไป ครอบครัวยิ้มได้ละไม ทุกคนสุขใจ เฮงเฮงดีดีดี ซินเจียยู่อี่ ซินนี้ฮวดไช้ ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน ขอจงมีความสุขใจ อวยพรนำชัย…ให้จงรุ่งเรือง #pirateketo #siripun #ตำรับเอ๋ #siamstr
@ 502ab02a:a2860397
2025-04-03 08:31:07#ที่มาทำเพลง #ตัวหนังสือมีเสียง วันนี้จะเล่าถึงเพลง ตรุษจีนครับ เป็นเพลงที่เขียนเสร็จภายในคืนเดียว คือไม่ใช่ว่าเก่งกาจอะไรครับ แต่เนื้อหามีในหัวตั้งนานแล้วตั้งใจจะทำนานแล้วแต่ภารกิจอื่นมีมากจน 24 ชั่วโมงมันรู้สึกน้อยเกินไป เพลงนี้ความตั้งใจคือ หวังสูงเลยครับ หวังว่าสักวันหนึ่งเยาวราชจะเปิดเพลงนี้กันกระหึ่มในวันตรุษจีน ซึ่งรู้ตัวดีครับว่า ตัวเล็กๆ คงไม่ดังเปรี้ยงในรอบเดียว ผมคิดว่า จะอีก 5ปี 10ปี เพลงนี้มันปล่อยไปแล้วมันยังอยู่ไปเรื่อยๆครับ (เปิดตัวครั้งแรก มีคนเอาแผ่นเสียง tiktok ไปทำอวยพรกันราวๆ 185คลิป ผมดีใจมากแล้ว บางคนลิปซิงค์ด้วยแสดงว่าหัดร้อง โคตรดีใจเลยครับ) ผมตั้งใจทำให้โทนออกมาเป็นเหมือนคนจีนร้อง แนวประมาณฮอทเป๊บเปอร์ โซเฟียลา อะไรประมาณนี้ ดังนั้นการออกเสียงจะเหมือนคนจีนพูดไทยไม่ชัดอะไรแบบนั้นครับ เนื้อร้องนี่ผมตั้งใจเขียนแบบ เอาใจอาม่าเลย เราลองมาดูบางท่อนกันครับ "ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง" เป็นท่อนย้ำแล้วย้ำอีก เพราะจงใจให้เป็นเพลงอวยพร ก็เลยทำเป็นแกนหลักของเพลงนี้ จากนั้นตัวรองก็จะเป็นคำอวยพรในแต่ละเรื่อง มาซ้อนอีกทีนึง "ปีใหม่หวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี" ท่อนนี้ผมนึกถึงอาม่าของผมครับ แกชอบดูหนังกำลังภายใน วีดีโอม้วนเป็นชุดๆ แล้วการได้ไปเที่ยวเรื่อยๆก็เป็นอีกความสุขนึงของคนแก่ ไม่ได้ต้องการอะไรมากไปกว่าร่างกายแข็งแรง เดินเหินไหว เที่ยวได้ "ไม่เพียงแค่ในปีนี้ แต่ขอให้ดี ทุกทุกปีไป ครอบครัวยิ้มได้ละไม ทุกคนสุขใจ เฮงเฮงดีดีดี" เป็นท่อนท้ายเพลงแล้ว ซึ่งก็ตบด้วยว่าไม่ได้เฉพาะปีนี้นะ ที่อวยพรกันขอให้ดีไปยาวๆ แล้วก็เล่นคำท้ายว่า "เฮงเฮงดีดีดี" คือ มันเป็นการรวมคำดีๆย้ำๆ ผมรู้สึกว่าพอตอนที่ทำเป็นเพลง มันจะเป็นท่อนที่คนยิ้มกว้างเลยหล่ะ เนื้อเพลงเต็มๆผมลงไว้ให้ข้างล่าง ส่วนการรับฟัง สามารถเข้าได้หลายทางมากครับ youtube music https://music.youtube.com/watch?v=EBKTZv3VvGM&si=f_IMFbDhdEJ6wEcv spotify https://open.spotify.com/track/3fCJyoQVAeWxdczfGbL3yT?si=vHV45hUTRPO6Mg9Pnh-w2w apple music https://music.apple.com/th/album/%E0%B8%8B-%E0%B8%99%E0%B9%80%E0%B8%88-%E0%B8%A2%E0%B8%A2-%E0%B8%AD-%E0%B8%8B-%E0%B8%99%E0%B8%99-%E0%B8%AE%E0%B8%A7%E0%B8%94%E0%B9%84%E0%B8%8A/1789787248?i=1789787249 tiktok แผ่นเสียง https://vt.tiktok.com/ZSrk49SfL/ ส่วนเพลงอื่นๆ ฟังเต็มๆได้ทุก music plattform แล้วนะครับ ค้นหา heretong teera siri เพราะเพลงไม่ดังเลยต้องหาจากชื่อคนแทนครับ 55555 新正如意,新年发财 วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ปีใหม่หวังได้สุขดี เป็นเศรษฐีมีเงินทองใช้ ร่ำรวย รุ่งเรืองไปไกล คิดสิ่งใด ได้สมฤดี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ปีใหม่หวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ไม่เพียงหวังได้สุขดี โรคภัยไม่มี แข็งแรงกว่าใคร เลือดลม กำลังภายใน เดินวิ่งยังไหว ได้เที่ยวทั้งปี ซินเจียยู่อี่ ซินนี้ฮวดไช้ วันตรุษจีนนี้ขอพรจากใจ จะทำสิ่งใด ขอให้เฮงเฮง ไม่เพียงแค่ในปีนี้ แต่ขอให้ดี ทุกทุกปีไป ครอบครัวยิ้มได้ละไม ทุกคนสุขใจ เฮงเฮงดีดีดี ซินเจียยู่อี่ ซินนี้ฮวดไช้ ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน ขอจงมีความสุขใจ อวยพรนำชัย ให้ทั่วทุกคน ขอจงมีความสุขใจ อวยพรนำชัย…ให้จงรุ่งเรือง #pirateketo #siripun #ตำรับเอ๋ #siamstr @ 07f367da:0e76880d
2025-04-03 17:59:21윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다. 자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다. 당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다. 선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다. 무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다. 충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다. 사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다. 타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다.
@ 07f367da:0e76880d
2025-04-03 17:59:21윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다. 자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다. 당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다. 선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다. 무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다. 충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다. 사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다. 타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다. @ c13fd381:b46236ea
2025-04-03 07:55:31Over the past few years, The School of Bitcoin (TSOBTC) has built a reputation as a decentralised, open-source educational initiative dedicated to financial sovereignty and digital literacy. Our faculty, contributors, and global community have worked tirelessly to create resources that embody the Free and Open-Source Software (FOSS) ethos, ensuring that knowledge remains accessible to all. As part of our commitment to maintaining an open and transparent model, we are excited to announce that The School of Bitcoin is officially migrating to Consensus21.School. This transition is not just a rebranding--it marks the consolidation of all our initiatives, projects, and educational resources under the Consensus21.School banner. The School of Bitcoin will no longer exist as a separate entity. This move comes as a response to growing confusion between our initiative and another entity operating under the domain schoolofbitcoin (SOB), which has taken a direction that does not align with our open-source philosophy. To reaffirm our dedication to FOSS and community-driven education, we are bringing everything--our courses, programs, and collaborations--into a singular, more focused ecosystem at Consensus21.School. What Does This Mean for Our Community? Rest assured, all the valuable content, courses, and educational materials that have been developed under TSOBTC will remain available. We continue to embrace a value-for-value model, ensuring that learners can access resources while supporting the ecosystem in a way that aligns with their means and values. By consolidating under Consensus21.School, we are doubling down on the principles of decentralisation, self-sovereignty, and permissionless learning. This transition includes all of our key initiatives, including V4V Open Lessons, the Decentralised Autonomous Education System (DAES), and our involvement with the Plan B Network. Full Migration of DAES and Plan B Network Collaboration As part of this transition, the Decentralised Autonomous Education System (DAES) is now officially part of Consensus21.School and is fully reflected in the Consensus21.School Whitepaper. DAES will continue to provide a platform for aspiring learners to submit their Bitcoin project ideas for potential funding and mentorship, with active engagement in our Stacker News /~Education territory and Signal chat for collaboration. We invite contributors to support our learner fund and help bring innovative ideas to fruition within this new ecosystem. Additionally, our collaboration with the Plan B Network will now operate under Consensus21.School. Through this partnership, we will continue teaching using the Plan B Network's curriculum to provide high-quality Bitcoin education and strengthen local Bitcoin communities. This global initiative remains a core part of our mission, now fully integrated within Consensus21.School. Looking Ahead With Consensus21.School, we will continue innovating in peer-to-peer learning, integrating cutting-edge developments in Bitcoin, Nostr, and decentralised technologies. We encourage our community to stay engaged, contribute, and help us build an even stronger foundation for the future of open education. This is more than just a domain change--it is the next evolution of our mission. The School of Bitcoin as an entity is now retired, and all our efforts, including DAES and the Plan B Network collaboration, will move forward exclusively under Consensus21.School. We invite educators, students, and enthusiasts to join us in shaping this next phase of open financial education. The journey continues, and we are thrilled to embark on this new chapter together
@ c13fd381:b46236ea
2025-04-03 07:55:31Over the past few years, The School of Bitcoin (TSOBTC) has built a reputation as a decentralised, open-source educational initiative dedicated to financial sovereignty and digital literacy. Our faculty, contributors, and global community have worked tirelessly to create resources that embody the Free and Open-Source Software (FOSS) ethos, ensuring that knowledge remains accessible to all. As part of our commitment to maintaining an open and transparent model, we are excited to announce that The School of Bitcoin is officially migrating to Consensus21.School. This transition is not just a rebranding--it marks the consolidation of all our initiatives, projects, and educational resources under the Consensus21.School banner. The School of Bitcoin will no longer exist as a separate entity. This move comes as a response to growing confusion between our initiative and another entity operating under the domain schoolofbitcoin (SOB), which has taken a direction that does not align with our open-source philosophy. To reaffirm our dedication to FOSS and community-driven education, we are bringing everything--our courses, programs, and collaborations--into a singular, more focused ecosystem at Consensus21.School. What Does This Mean for Our Community? Rest assured, all the valuable content, courses, and educational materials that have been developed under TSOBTC will remain available. We continue to embrace a value-for-value model, ensuring that learners can access resources while supporting the ecosystem in a way that aligns with their means and values. By consolidating under Consensus21.School, we are doubling down on the principles of decentralisation, self-sovereignty, and permissionless learning. This transition includes all of our key initiatives, including V4V Open Lessons, the Decentralised Autonomous Education System (DAES), and our involvement with the Plan B Network. Full Migration of DAES and Plan B Network Collaboration As part of this transition, the Decentralised Autonomous Education System (DAES) is now officially part of Consensus21.School and is fully reflected in the Consensus21.School Whitepaper. DAES will continue to provide a platform for aspiring learners to submit their Bitcoin project ideas for potential funding and mentorship, with active engagement in our Stacker News /~Education territory and Signal chat for collaboration. We invite contributors to support our learner fund and help bring innovative ideas to fruition within this new ecosystem. Additionally, our collaboration with the Plan B Network will now operate under Consensus21.School. Through this partnership, we will continue teaching using the Plan B Network's curriculum to provide high-quality Bitcoin education and strengthen local Bitcoin communities. This global initiative remains a core part of our mission, now fully integrated within Consensus21.School. Looking Ahead With Consensus21.School, we will continue innovating in peer-to-peer learning, integrating cutting-edge developments in Bitcoin, Nostr, and decentralised technologies. We encourage our community to stay engaged, contribute, and help us build an even stronger foundation for the future of open education. This is more than just a domain change--it is the next evolution of our mission. The School of Bitcoin as an entity is now retired, and all our efforts, including DAES and the Plan B Network collaboration, will move forward exclusively under Consensus21.School. We invite educators, students, and enthusiasts to join us in shaping this next phase of open financial education. The journey continues, and we are thrilled to embark on this new chapter together @ 77c2969e:a33cfa50
2025-04-03 07:54:55最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。 #### 安装acme.sh ``` curl https://get.acme.sh | sh -s email=youreMailAddress ``` #### 导入环境变量 ``` export CF_Token="填API token" export CF_Zone_ID="填区域ID" export CF_Account_ID="填账户ID" ``` - Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建 - 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID ### 申请证书 ``` acme.sh --issue --dns dns_cf -d dns.235421.xyz ``` - `-d` 后面是你想使用的域名 #### 安装证书 ``` acme.sh --install-cert -d dns.235421.xyz \ --key-file /root/certs/key.pem \ --fullchain-file /root/certs/cert.pem \ --reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021" ``` - `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。 - `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。 #### 安装 Technitium DNS Server 1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。  2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。 3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。 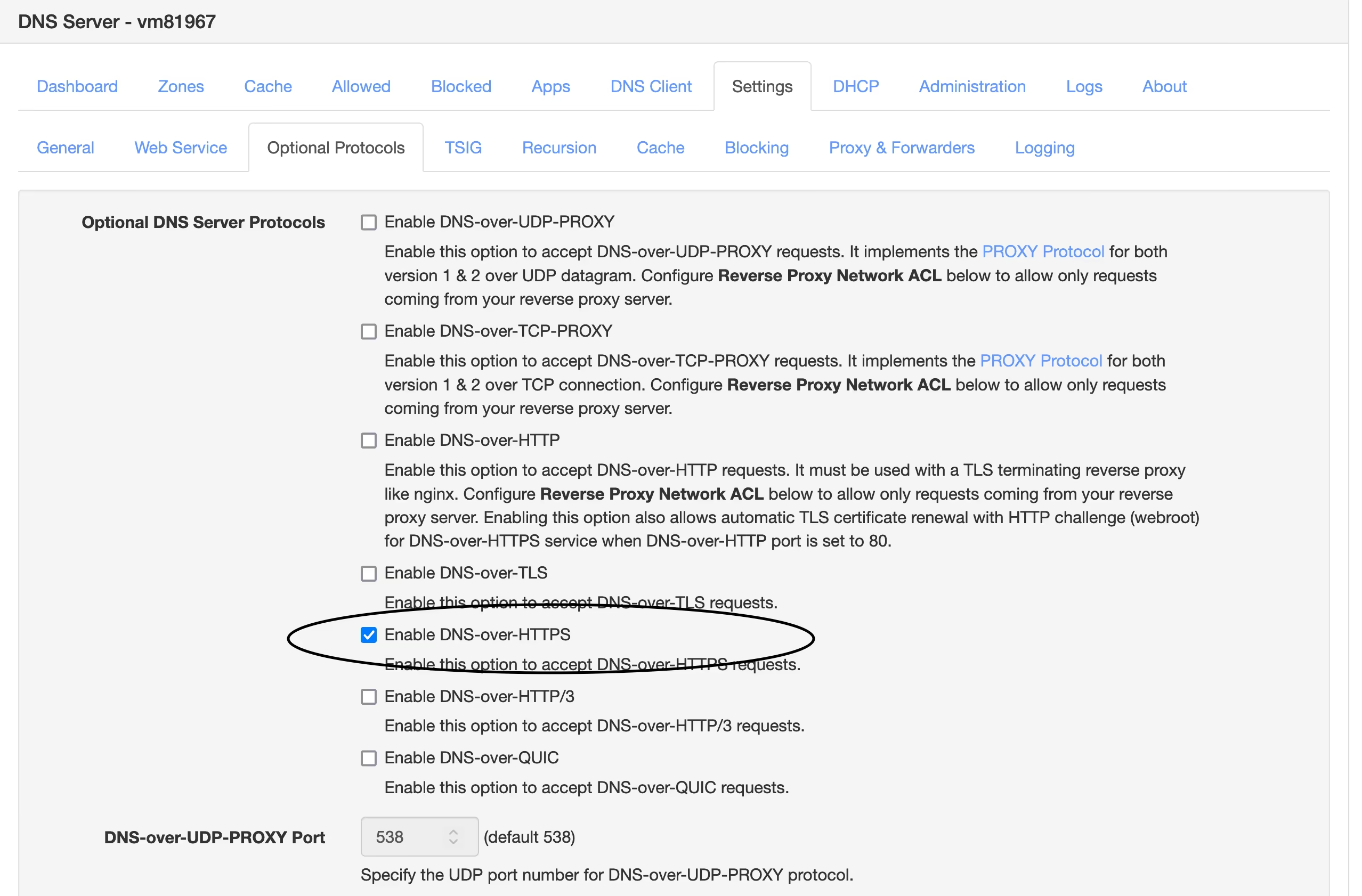 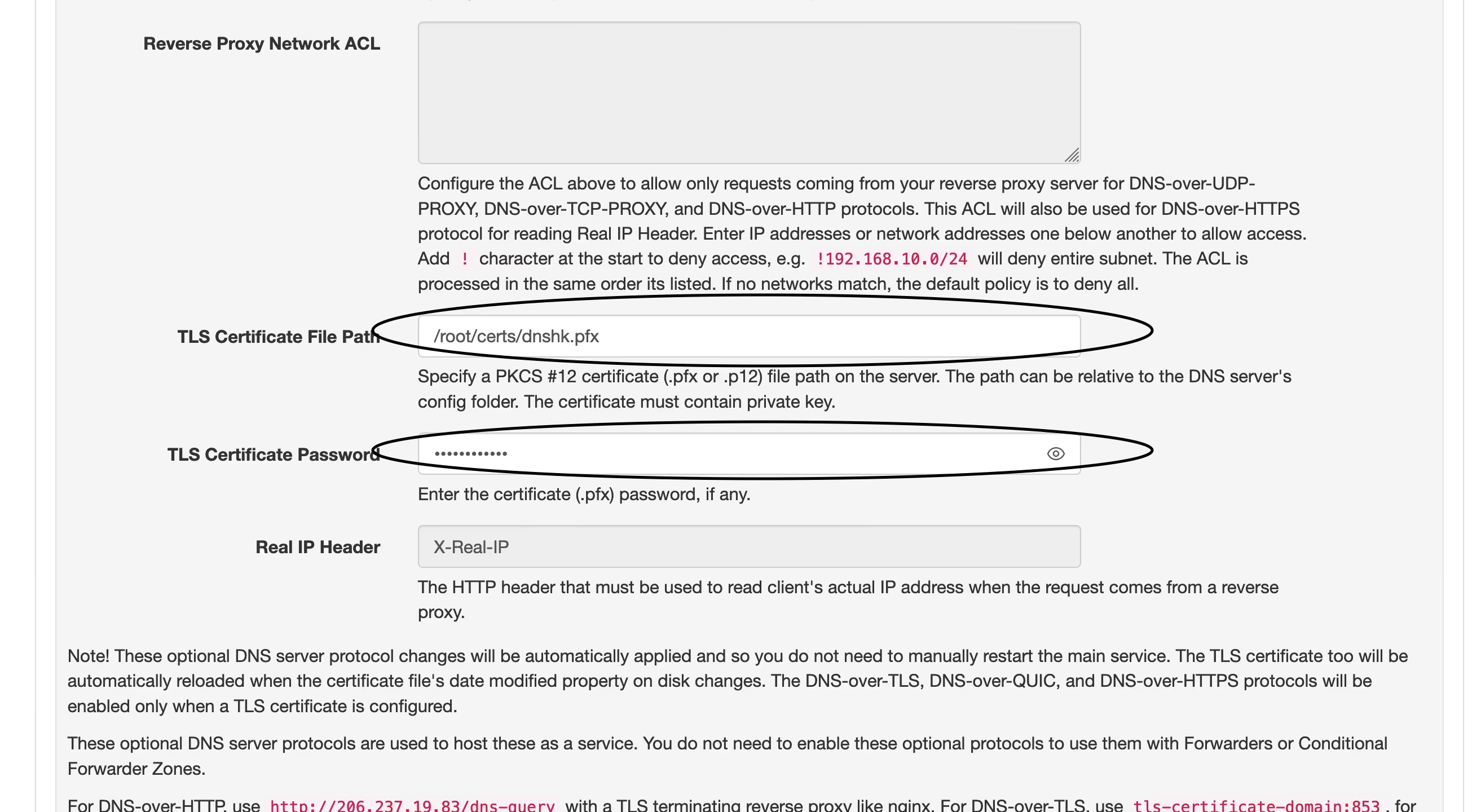 4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。 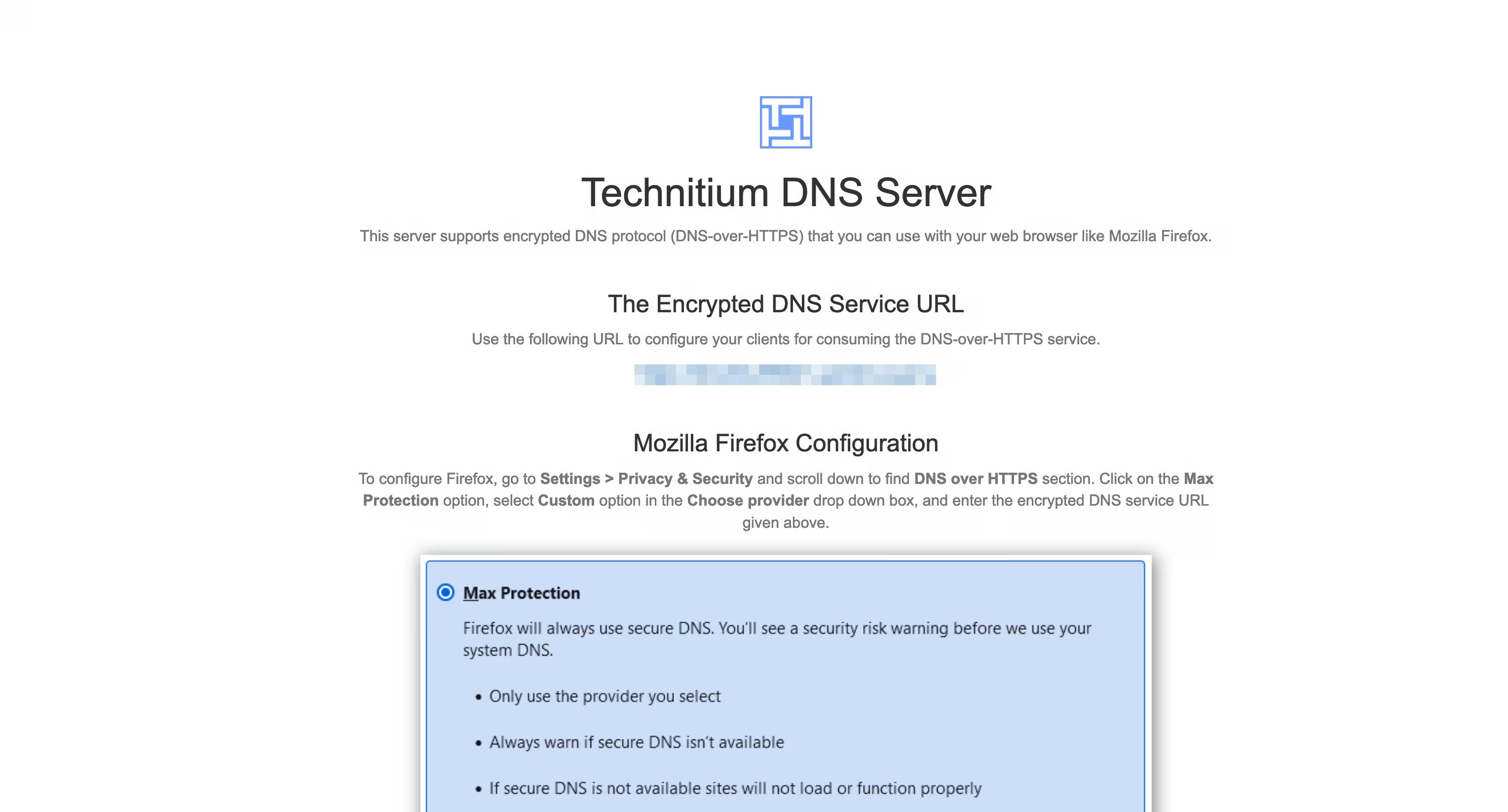 ---- 我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。 ---- #### 我的设置 - 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。 - 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。 - 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。 - 在`Settings` – `Logging` 处开启 `Use Local Time`。 - 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。 ##### 以下设置可选 - 在`Settings` – `General` 处开启 `Prefer IPv6` - 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。 - 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。 - 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。
@ 77c2969e:a33cfa50
2025-04-03 07:54:55最近又开始折腾 Technitium DNS Server,发现[之前记录的过程]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)不太完善,于是更新一下。 #### 安装acme.sh ``` curl https://get.acme.sh | sh -s email=youreMailAddress ``` #### 导入环境变量 ``` export CF_Token="填API token" export CF_Zone_ID="填区域ID" export CF_Account_ID="填账户ID" ``` - Cloudflare 的 API Token 是在 Cloudflare 网页右上角的👤头像--配置文件--API 令牌处创建 - 在 Cloudflare 主页点击你需要使用的域名,下滑到右下角可以看到区域 ID 和账户 ID ### 申请证书 ``` acme.sh --issue --dns dns_cf -d dns.235421.xyz ``` - `-d` 后面是你想使用的域名 #### 安装证书 ``` acme.sh --install-cert -d dns.235421.xyz \ --key-file /root/certs/key.pem \ --fullchain-file /root/certs/cert.pem \ --reloadcmd "cd /root/certs && openssl pkcs12 -export -out 'dns.pfx' -inkey 'key.pem' -in 'cert.pem' -password pass:1021" ``` - `reloadcmd`是在申请证书之后执行的代码,以后自动更新时也会自动执行这个代码,所以第一次配置好就基本上不用管了。 - `reloadcmd` 中的代码是将 `pem` 格式的证书和密钥转换成一个 `pfx` 格式的证书文件,`-out` 后面是输出的 `pfx` 证书文件名, `-inkey` 和 `-in` 分别是前一步 `acme.sh` 申请的密钥和证书文件。这里必须添加密码,也就是 `1021` 这个,如果不设密码执行命令的话,它会让你交互式输入,但是在自动脚本中就不行。我在前面加了先 `cd` 到证书目录,避免出现问题。 #### 安装 Technitium DNS Server 1. 在[Technitium DNS Server 官网]( https://technitium.com/dns/) 获取安装脚本,也有提供 Docker 镜像以及 Windows 版本。  2. 安装后在 `公网IP:5380` 进入管理界面,首次进入需设置管理员密码,管理员账户默认是 `admin`。 3. 在 `Settings` – `optional protocols` 处开启 DNS over HTTPS ,`TLS Certificate File Path` 处填入转换好的 `pfx` 证书路径,`TLS Certificate Password` 处填你设定的密码,就是我的 `1021` 。 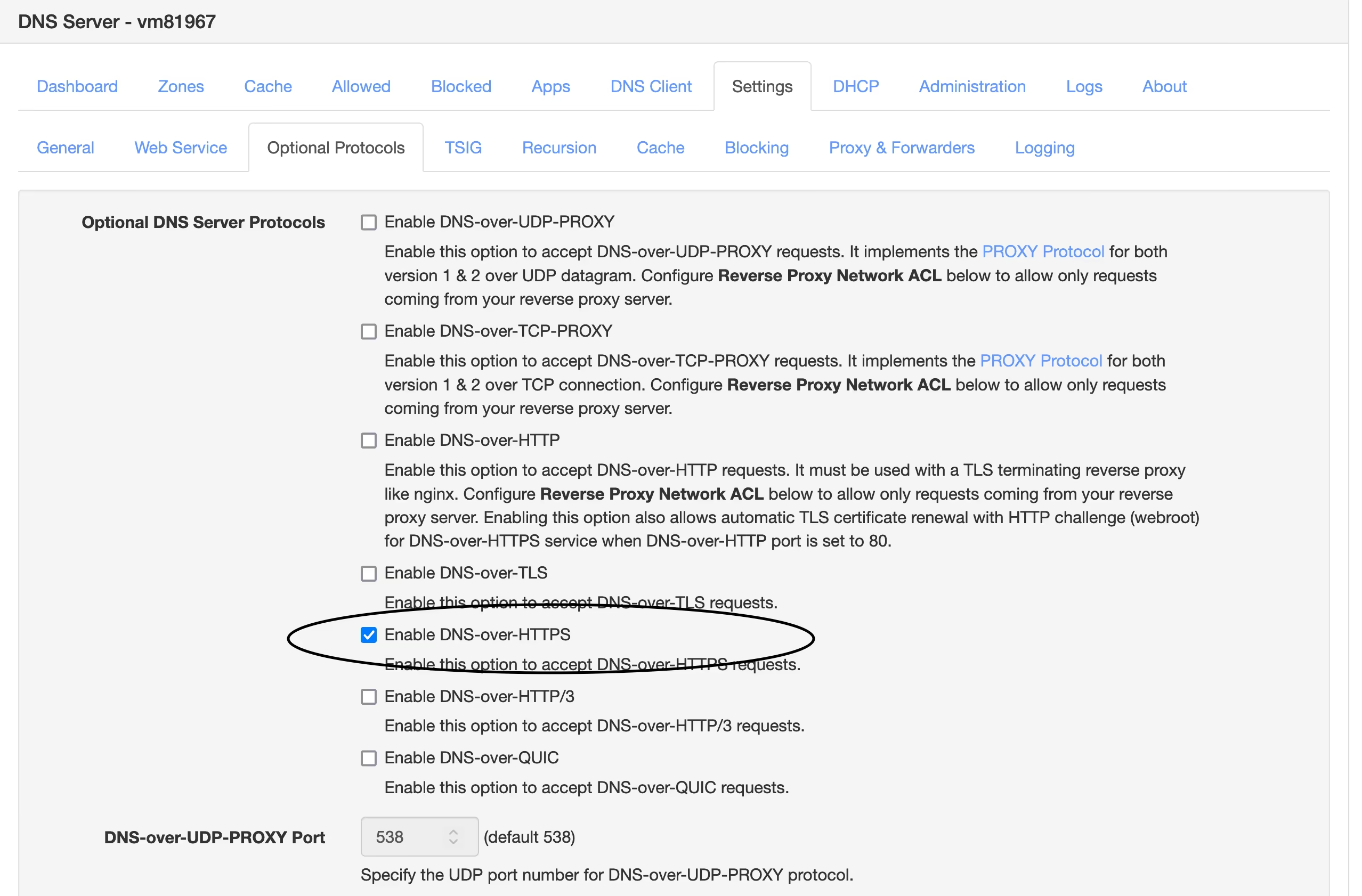 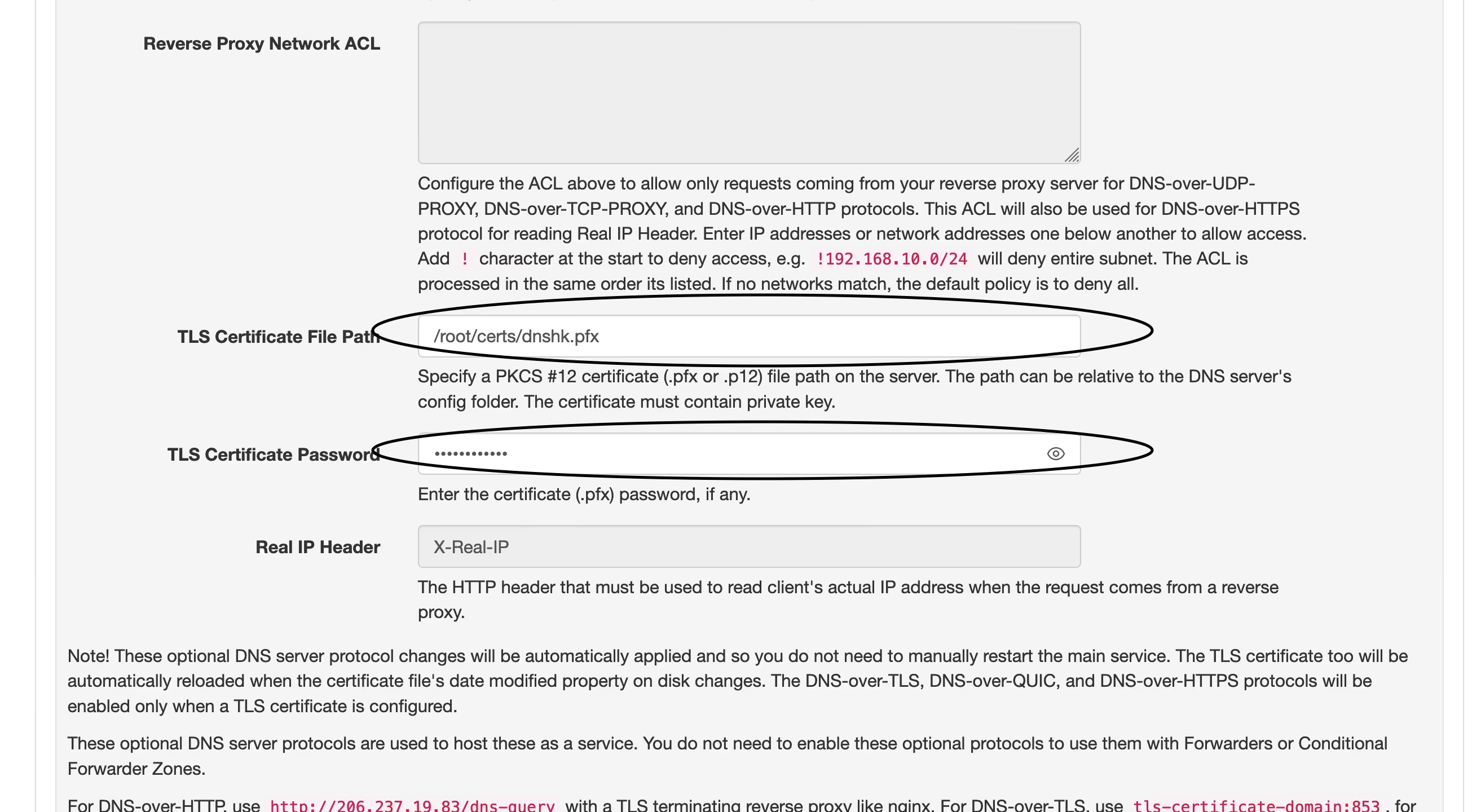 4. 现在打开你的域名,看到如图这样就说明设定成功了,然后在需要设置 DoH 的地方填入 ` https://yourdomain.com/dns-query`即可。 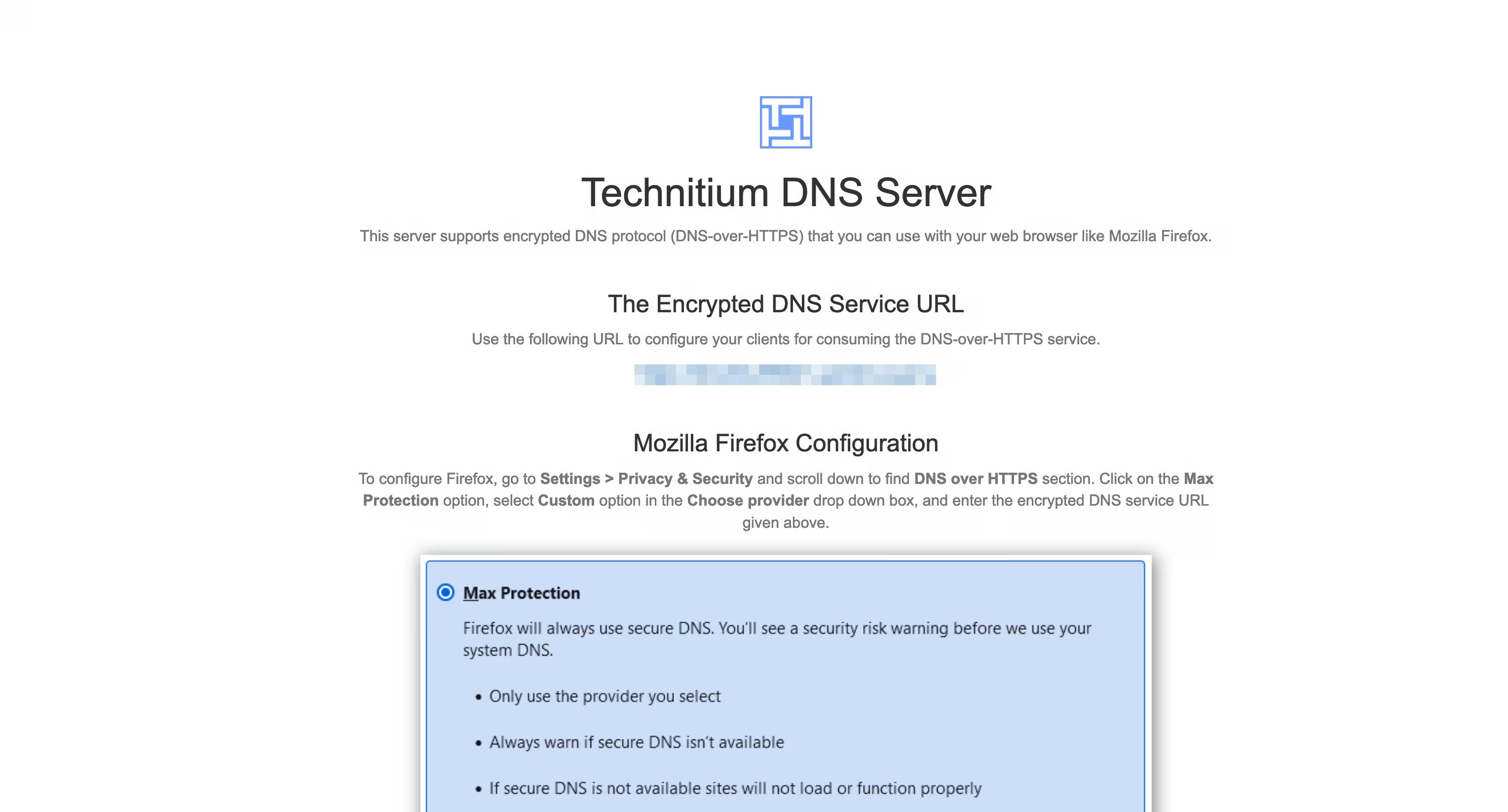 ---- 我在[之前的文章]( https://wp.235421.xyz/2024/10/03/use-technitium-and-set-ipv6-dns/)中使用的是 `DNS over HTTP` 并用 Nginx 反代来实现 `DNS over HTTPS` 的,现在直接用 DoH ,省去了配置 Nginx 的部分,只是多了一步证书格式转换,总体上更简单了。 ---- #### 我的设置 - 在`Settings` – `Recursion` 处打开 `Allow Recursion` 以允许递归解析。 - 在`Settings` – `Cache` 处将 `Cache Maximum Entries` 调大些,默认 10000 有点少了。 - 在`Settings` – `General` 处开启 `EDNS Client Subnet (ECS)` 。 - 在`Settings` – `Logging` 处开启 `Use Local Time`。 - 在`Apps` – `App Store` 中安装 `Query Logs (Sqlite)` 以便在 `Logs` – `Query Logs` 处查看 DNS 查询日志。 ##### 以下设置可选 - 在`Settings` – `General` 处开启 `Prefer IPv6` - 在`Settings` – `Web Service` 处为后台管理页面开启 HTTPS,可使用与 DoH 相同的域名和证书,仅端口不同,这个默认 HTTPS 端口是 `53443`。 - 在`Settings` – `Blocking` 处开启拦截功能(默认开启),下面 `Allow / Block List URLs` 可以配置规则,与 AdGuard Home 规则通用,白名单规则须在链接前加上英文叹号 `!`。也可以是本地规则,填路径即可。 - 在`Settings` – `Proxy & Forwarders` 处可以设置上游DNS `Forwarders` 。 @ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
@ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen. @ e4950c93:1b99eccd
2025-04-03 14:57:41Découvrez les matières utilisées ou non dans les produits référencés sur ce site. ### ✅ Matières naturelles Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire. #### 🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle et minimum de transformation #### 🔍 Liste des matières naturelles : - Caoutchouc naturel - Chanvre - Coton - Cuir - Liège - Lin - Laine - Soie - Terre - … (Autres matières) ⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière. Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site. Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits. --- ### 🚫 Matières non naturelles Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie. #### 📌 Principaux problèmes : - Émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité #### 🔍 Liste des matières non naturelles : - Polyester - Polyamide - Acrylique - Élasthanne - Viscose - Silicone - … (Ajouter les autres matières) ⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque : - elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et - aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits. Dans ce cas, un avertissement est alors affiché sur la fiche du produit.
@ e4950c93:1b99eccd
2025-04-03 14:57:41Découvrez les matières utilisées ou non dans les produits référencés sur ce site. ### ✅ Matières naturelles Matières d'origine végétale, animale ou minérale, sans transformation chimique altérant leur structure moléculaire. #### 🌱 Principaux critères : - Biodégradabilité - Non-toxicité - Présence naturelle et minimum de transformation #### 🔍 Liste des matières naturelles : - Caoutchouc naturel - Chanvre - Coton - Cuir - Liège - Lin - Laine - Soie - Terre - … (Autres matières) ⚠️ Bien que naturelles, ces matières peuvent générer des impacts négatifs selon leurs conditions de production (pollution par pesticides, consommation d’eau excessive, traitement chimique, exploitation animale…). Ces impacts sont mentionnés sur la fiche de chaque matière. Les versions biologiques, sans traitement chimique… de ces matieres sont privilégiées pour référencer les produits sur ce site. Les versions "conventionnelles" ne sont référencées que tant que lorsqu'il n'a pas encore été trouvé d'alternative plus durable pour cette catégorie de produits. --- ### 🚫 Matières non naturelles Matières synthétiques ou fortement modifiées, souvent issues de la pétrochimie. #### 📌 Principaux problèmes : - Émissions de microplastiques - Dépendance aux énergies fossiles - Mauvaise biodégradabilité #### 🔍 Liste des matières non naturelles : - Polyester - Polyamide - Acrylique - Élasthanne - Viscose - Silicone - … (Ajouter les autres matières) ⚠️ Ces matières ne sont pas admises sur le site. Néanmoins, elles peuvent être présentes dans certains produits référencés lorsque : - elles sont utilisées en accessoire amovible (ex. : élastiques, boutons… généralement non indiqué dans la composition par la marque) pouvant être retiré pour le recyclage ou compostage, et - aucune alternative 100 % naturelle n’a encore été identifiée pour cette catégorie de produits. Dans ce cas, un avertissement est alors affiché sur la fiche du produit. @ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site.
@ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site. @ 0f9da413:01bd07d7
2025-04-03 05:32:55 หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ --- ### **Mr. A Coffee**  ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้  กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้  ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป  งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :) Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9 BTC-map: https://btcmap.org/merchant/node:12416107504 --- ### **Koh Chang Wine Gallery **  และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)    Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8 BTC-map: https://btcmap.org/merchant/node:11461720813 --- เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :)
@ 0f9da413:01bd07d7
2025-04-03 05:32:55 หลังจากจบทริปเที่ยวพัทยาเรียบร้อยแล้วก็ได้เดินทางไปยังเกาะช้างโดยติดรถเจ้าหน้าที่ในที่ทำงานไปไปเกาะช้างครั้งแรกรู้สึกว่ามันไกลเหลือเกินไปค่อนข้างยากหากไม่มีรถส่วนตัว ถ้าให้ไปส่วนตัวก็คงต้องอยู่นานๆ หน่อยชักแบบอาทิตย์หนึ่ง ใช้ชีวิตแบบฝรั่งเที่ยวอยู่ง่ายๆ กินง่ายๆ จากที่ดูในแผนที่ btcmap แล้วพบว่าก็มีร้านที่ปักหมุดไว้อยู่ทั้งหมดสองร้านด้วยกันซึ่งระยะทางก็ค่อนข้างซันเหมือนกัน และมีเนินสูงต่ำสลับกันไป หากไม่มีรถส่วนตัวไปนี่ค่อนข้่างลำบากพอสมควร ต้องเช่ามอไซต์ไป อันนี้ก็เช่าไปเหมือนกัน โดยผมเช่ามอไซต์ 1 วันวันละ 200 บาท (แต่มัดจำ 3000 บาท) ก็เอาเรื่องเหมือนกัน และก็มาเริ่มต้นที่ร้านแรกเลยคือ --- ### **Mr. A Coffee**  ร้านอาหารสไตล์บ้านๆ ที่ขายอาหาร น้ำ เครื่องดื่ม มีทั้งอาหารไทยและอาหารฝรั่ง ส่วนตัวก็ขับรถมอไซต์มายังสถานที่แห่งนี้ทางเข้าไปยังร้านเป็นหมู่บ้านเล็กๆ ไม่มีถนนเข้า แต่มอไซต์เข้าไปได้พอสมควร ตอนนั้นค่อนข้างเย็นมากแล้ว ได้มาสั่งอาหารมาคือ ข้าวเหนียวมะม่วงกับน้ำแก้วมังกรปั่นแบบไม่หวาน (ทั้งๆที่ตัวเองก็จะเตรียมไปกินบุ๊ปเฟ่อีกหนึ่งชั่วโมงข้างหน้า 555) ก็ได้สั่งไปแล้วก็ถามว่ารับ bitcoin ไหมครับ เจ้าของร้านก็บอกว่า รับๆ ผมกับเจ้าของร้านก็ได้พูดคุยกันเกือบประมาณครึ่งชั่วโมง ซึ่งหากผมมาเร็วกว่านี้หน่อยก็คงได้คุยกันยาวๆ แล้วละ ซึ่งเป็นการคุยที่สนุกมากซึ่งตัวเจ้าของร้านเองก็ได้เล่าถึงเหตุผลที่รับ bitcoin เหมือนกันว่าช่วง โควิดตอนปี 2020 ที่ผ่านมา บนเกาะช้างไม่มีอะไรเลยชาวบ้านก็ต้องไปหารากไม้ หาเห็ดตามป่าเขากัน แต่พี่เจ้าของร้านได้รู้จักกับฝรั่งคนหนึ่งเขาช่วยเหลือพี่เจ้าของร้านด้วยการบริจาคบิทคอยให้ และคนนี้ก็เป็นคนสอนให้เขารับบิทคอยโดยใช้ WOS และเจ้าของร้านก็เล่าให้ผมฟังเพิ่มเติม ณ ปัจจุบันว่า คนเราเองก็ยังต้องมีสภาพคล่องในการใช้งานอยู่ ตั้งมีเงิน fiat ไว้ส่วนหนึ่ง ส่วนบิทคอยที่ได้เขาได้ก็เก็บไว้เพื่อสร้างเป็นทรัพย์สินในอนาคตที่หากมีปัญหาช่วงไหนก็นำมาขายได้ ก็แลก P2P โดยตรง ซึ่งผมค่อนข้างตกใจเพราะเขาเรียนรู้จากการรับบิทคอยโดยนักท่องเที่ยวชาวต่างชาติที่ชวนเขาให้รับ เผื่อว่าจะมีฝรั่งมาใช้งานบิทคอย ณ สถานที่ร้านแห่งนี้  กึมมิคที่หลายท่านอาจจะต้องลุ้นหน่อยว่าหากมีโอกาสได้ไปเที่ยวและแวะที่ร้าน ก็คงต้่องลุ้นว่าคุณจะได้จ่ายด้วย bitcoin ไหม หากวันนั้นเจ้าของร้านไม่อยากรับเพราะว่าโคต้ารับบิทคอยวันนั้นเต็มแล้ว ฮ่าๆ รูปแบบระบบวาสนาร้านสูญของคุณมิกตอนเมื่อก่อน (เหมือนกันเลย) จริงๆ แล้วหากมีเวลามากพอก็คงได้พูดคุยกับพี่เจ้าของร้านสนุกๆกันไป ผมชอบความเรียบง่ายของร้านพี่เขา และมีอาหารหลากหลายอย่างเต็มไปหมด อีกเรื่องอย่างข้าวเหนียวมะม่วง ผมยังจำได้ว่าเมื่อก่อนมีแต่ช่วงฤดูเดียวที่สามารถกินมะม่วงสุกได้ หรือ อาหารแบบข้าวเหนียวมะม่วง แต่ปัจจุบันคือถ้าจะกิน ข้าวเหนียวมะม่วงแล้ว สามารถสั่งกินได้ตลอดทั้งปีกันเลยซึ่งก็โอเครพอสมควร แบบอยากไปทะเลตอนหน้าฝนแล้วอยากกินข้าวเหนียวมะม่วงของหน้าร้อนแบบนี้  ท้ายสุดร้าน Mr. A Coffee เป็นร้านที่ถ้านั่งชิวๆ แบบฝรั่งก็สามารถอยู่ได้ยาวๆ เลยนะจิบกาแฟ ทำงาน WFH ล้่อมรอบโดยธรรมชาติ แต่เส้นทางมาที่ร้านก็ลำบากหน่อยเหมาะกับคนที่ local จริงๆ low time ระดับหนึ่ง ท้ายสุดผมเองก็แจกสติกเกอร์ของพี่แชมป์เอาไปให้เจ้าของร้านแจกกันต่อไป  งานนี้ทั้งข้าวเหนียวมะม่วงและน้ำแก้วมังกรปั่น เสีย sats ไปทั้งหมด 6,050 sats แต่สิ่งที่ได้คือการแลกเปลี่ยนมุมมองกับเจ้าของร้านกับจุดเริ่มต้นของการรับบิทคอยในพื้นที่เกาะช้างแห่งนี้ และหากมีโอกาสอาจจะไปพักอยู่แถวนั้นชักอาทิตย์และแวะมาอุดหนุนร้านนี้ตลอด เพราะวิวฝั่งใต้สุดของเกาะช้างก็ยังคงความสวยงามไม่แพ้กับฝั่งทิศตะวันตกที่ฝรั่งอยู่กัน แต่ฝั่งใต้โซนนี้ก็มีความที่เป็นบ้านไม้ เพิงง่ายๆ ที่ชาวต่างชาติชอบกันอยู่ :) Google-map: https://maps.app.goo.gl/b45JGeTzL6Lwwi9i9 BTC-map: https://btcmap.org/merchant/node:12416107504 --- ### **Koh Chang Wine Gallery **  และเราก็ย้อนกลับมาอีกร้านหนึ่งในวันถัดไปและเป็นวันที่จะต้องออกจากเกาะช้างเช่นเดียวกัน และผมก็ไม่พลาดร้าน Koh Chang Wine Gallery ตั้งอยู่ในโซนหมู่บ้านแหล่งท่องเที่ยวเส้นทางถนนทางตะวันตก ร้านนี้ไม่ได้มีป้ายรับบิทคอย แต่รับชำระด้วยบิทคอยซึ่งเป็นฝรั่งท่านหนึ่งที่คาดว่าน่าจะแต่งงานกับภรรยาคนไทย เป็นร้านสไตล์แบบฝรั่งเลย ผมเองก็สั่งสเต็กเนื้อไป และน้ำมะม่วงปั่น (ไม่รู้เวลาไปเกาะทีไรติดใจกับน้ำมะม่วงปั่น) อาจจะไม่ได้พูดคุยอะไรมากมายนัก แต่ก็หมดไป 32,620 sats เป็นร้านอาหารเช้าและอาหารแนวฝรั่งตรงๆ ถือว่าค่อนข้างอร่อยใช้ได้ดีเลยทีเดียว แต่หากจะจ่ายด้วยบิทคอยก็ต้องแจ้งก่อนนะว่าขอจ่ายด้วยบิทคอยก่อน เหมือนพี่ฝรั่งที่เขารับตอนนี้ก็รับแต่เฉพาะ bitcoin อย่างเดียวเมื่อก่อนรับ xrp กับ doge ด้วยแต่ผมเองเวลาคุยกับฝรั่งก็เหงื่อแตกเหมือนกัน (รึว่าเพราะมันร้อน บนเกาะก็อบอ้าวใช้ได้ 555+)    Google-map: https://maps.app.goo.gl/6QbNgRbiV5Uao2Xz8 BTC-map: https://btcmap.org/merchant/node:11461720813 --- เส้นทางไปร้านค่อนข้างง่ายติดถนนในหมู่บ้าน ซึ่งหากมายังเกาะช้างแล้วหากขึ้นฝั่งมาแล้วเลี้ยวขวาก็จะขับรถหรือนั่งรถมาเส้นถนนฝั่งตะวันตกของเกาะก็จะพบกับร้านนี้ก่อน อันนี้แล้วแต่ความสะดวกแต่ละท่านเลยครับหากได้มีโอกาสแวะมาเกาะช้างและอยากใช้จ่าย bitcoin เราก็มีทางเลือกร้านในสองสไตล์กันเลย แบบวิถีฝรั่งตอนเช้าก็ร้าน Koh Chang Wine Gallery หรือ แบบ Local ก็ Mr. A Coffee หรือไปทังคู่เลยจะดีมากแต่ต้องบ้าหน่อย เพราะเส้นทางไปก็ค่อนข้างลำบากพอควรเหมือนกัน หมายถึงมีภูเขาชันมีทางขึ้นลงหักศอกนิดหน่อยก็เท่านั้นเอง รวมๆ ทริปบนเกาะช้างนี้ก็หมดไปไม่เยอะมาก 38,670 sats ก็จะตัวลอยเบาๆ หน่อย (สำรวจเมื่อ มีนาคม 2025 อนาคตอาจจะมีการเปลี่ยนแปลงได้) สำหรับจากนี้จะเป็นการ ปสก. ส่วนตัวกับการใช้งาน Bitcoin Lightning ตามสถานที่ที่ได้เดินทาง Part 3 จะเป็นสถานที่ในพื้นที่หาดใหญ่ จังหวัดสงขลา และ เสริมประสบการณ์การเดินทางโดยรถไฟระยะเวลาเกือบ 18 ชั่วโมง พร้อมด้วยมิตรสหายในรังอย่างกัปตัน จะป่วนแค่ไหนก็รอติดตามกันครับ :) @ edeb837b:ac664163
2025-04-03 10:35:59When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value. There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why. ## Why NVSTly Stands Above the Rest NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.** Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment. ## What is NVSTly? **NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.** It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow. ## Key Features That Make NVSTly #1 ### 1. Real-Time Trade Sharing & Tracking NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers. ### 2. Unique POV Trade Charting See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**. ### 3. Deep Trade Analytics & Trader Dashboards Get powerful insights into your performance, including: - **Win rate** - **Total gain/loss** - **Average return per trade** - **Long vs. short ratio** - **(Coming soon) Drawdown tracking** to measure risk exposure ### 4. Global Trades Feed & Leaderboard Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies. ### 5. Fully Integrated with Discord & Telegram No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to: - **Check a trader’s latest stats** - **View real-time trade recaps** - **Fetch charts and ticker data** - **Receive automated trade notifications** Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access. ### 6. Automated Social Media Sharing Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed. ### 7. Future AI & Machine Learning Enhancements NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to: - **Get automated trading tips** tailored to their strategies - **Use customizable AI models** to refine their trading approach - **Interact with a smart AI trading assistant** via the app and Discord bot ## Why NVSTly is the Only Social Trading App You Need While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.** With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible. So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.** ## Ready to Take Your Trading to the Next Level? Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.** 📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!** 🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server!
@ edeb837b:ac664163
2025-04-03 10:35:59When it comes to social trading, there are plenty of platforms that claim to offer innovative ways to connect with other traders, share strategies, and improve your market performance. But let's be real: most so-called "social trading" apps are either glorified brokerage platforms with limited community features or outdated, clunky systems that don’t offer real-time value. There’s really only *one* social trading app you need to consider—**NVSTly**. Here’s why. ## Why NVSTly Stands Above the Rest NVSTly isn’t just another trading app with a few social features slapped on. It’s **the ultimate [social trading platform](https://nvstly.com)**, purpose-built to empower traders by combining **real-time trade tracking, seamless social sharing, deep market insights, and a powerful trader community.** Unlike other platforms, NVSTly isn’t just about copying trades or following vague signals—it’s about **true transparency, collaboration, and learning** from top traders in an interactive environment. ## What is NVSTly? **NVSTly** is a **completely free** social trading platform that lets traders track, share, and analyze their trades in **real time**. Whether you're trading **stocks, options, or crypto**, NVSTly provides a **seamless multi-platform experience**—available via **web, iOS, Android, and even Discord.** It’s not just a social network—it’s a **trader’s command center** where every trade you make is part of a bigger, smarter ecosystem designed to help you grow. ## Key Features That Make NVSTly #1 ### 1. Real-Time Trade Sharing & Tracking NVSTly integrates with brokers like **Webull** (with more brokerages coming soon) to automatically track your trades and display them in **real-time**. No manual entry—just **instant trade updates** for you and your followers. ### 2. Unique POV Trade Charting See trades like never before. NVSTly’s proprietary **POV Chart** marks every trade action directly on the candlestick chart, giving you (and your followers) an **unparalleled view of trading strategies in action**. ### 3. Deep Trade Analytics & Trader Dashboards Get powerful insights into your performance, including: - **Win rate** - **Total gain/loss** - **Average return per trade** - **Long vs. short ratio** - **(Coming soon) Drawdown tracking** to measure risk exposure ### 4. Global Trades Feed & Leaderboard Want to see what the best traders are doing *right now*? The **[Global Trades Feed](https://nvstly.com/trades)** lets you watch live trades, while the **[Leaderboard](https://nvstly.com/trades)** ranks top traders based on performance metrics, making it easy to find successful strategies. ### 5. Fully Integrated with Discord & Telegram No other platform makes social trading as seamless as NVSTly. The **[NVSTly Discord bot](https://nvstly.com/go/bot)** allows users to: - **Check a trader’s latest stats** - **View real-time trade recaps** - **Fetch charts and ticker data** - **Receive automated trade notifications** Telegram users won’t be left out either—NVSTly is working on bringing the same functionality to **Telegram** for even broader access. ### 6. Automated Social Media Sharing Set your trades to **automatically share** to **Twitter/X, Discord, and soon, Telegram**. Whether you’re growing your personal brand or running a trading community, NVSTly makes sure your trades get noticed. ### 7. Future AI & Machine Learning Enhancements NVSTly is building **AI-powered trade insights and strategy generation**, allowing traders to: - **Get automated trading tips** tailored to their strategies - **Use customizable AI models** to refine their trading approach - **Interact with a smart AI trading assistant** via the app and Discord bot ## Why NVSTly is the Only Social Trading App You Need While others might pretend to offer social trading, **NVSTly actually delivers**. It’s not a gimmick or a half-baked feature—it’s a complete **trading ecosystem built for real traders** who want **real-time data, powerful analytics, and a truly social experience.** With NVSTly, you're not just following traders—you’re **engaging with them, learning from them, and improving your own strategies** in the most **transparent and interactive** way possible. So don’t waste time on inferior platforms. **NVSTly is the only social trading app that matters.** ## Ready to Take Your Trading to the Next Level? Join **50,000+ traders** who are already using NVSTly to **track, share, and dominate the markets.** 📲 **Download NVSTly today on [Web](https://nvstly.com), [iOS](https://nvstly.com/go/ios), or [Android](https://nvstly.com/go/android)!** 🚀 **[Join our Discord community](https://nvstly.com/go/discord)** and bring the power of NVSTly straight into your server! @ 2b24a1fa:17750f64
2025-04-03 10:11:13Ist es wirklich so, dass Gendern für mehr Gleichberechtigung sorgt, für ein friedlicheres Miteinander? Abgesehen von den grammatikalischen Verirrungen, die sich dabei in die Sprache schleichen, darf die Frage erlaubt sein, warum ein Gemeinschaftsgefühl, das „Wir“ in immer kleinere Einheiten, auch sprachlich geteilt werden soll. Muss ich tatsächlich alle benennen?  [https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?](https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?color=ffd400) Dann wäre das eine Liste von Namen. Verlese ich die nicht, sondern gendere mit Glottisschlag und allem was dazu gehört, unterteile ich ja doch in Gruppen. Und Gruppen haben zur Eigenart, dass es Zugehörigkeiten gibt und ausgeschlossen sein. So beginnt der Kampf. Zunächst war die Frau minderwertig, jetzt ist der Mann toxisch. Und was, wann zu wem, wie gesagt werden darf wird zum Spießrutenlauf. „Misgendern“ ist beispielsweise eine Wortneuschöpfungen, die eine Incorrectness der Sprache bezeichnet, die bis in die Strafbarkeit reichen will. Einer, der von dieser rigide anmutenden Sprach-Religion getriggert wird, ist Gerald Ehegartner. Er ist Lehrer, Musiker, Theater- und Wildnispädagoge und Autor und nimmt sich immer wieder dem Gemeingut Sprache an. Heute mit einem Text, den er mit: „Gendern, die Sakralsprache des Wokeismus“ betitelt hat. Sprecherin: Sabrina Khalil
@ 2b24a1fa:17750f64
2025-04-03 10:11:13Ist es wirklich so, dass Gendern für mehr Gleichberechtigung sorgt, für ein friedlicheres Miteinander? Abgesehen von den grammatikalischen Verirrungen, die sich dabei in die Sprache schleichen, darf die Frage erlaubt sein, warum ein Gemeinschaftsgefühl, das „Wir“ in immer kleinere Einheiten, auch sprachlich geteilt werden soll. Muss ich tatsächlich alle benennen?  [https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?](https://soundcloud.com/radiomuenchen/gendern-die-sakralsprache-des?color=ffd400) Dann wäre das eine Liste von Namen. Verlese ich die nicht, sondern gendere mit Glottisschlag und allem was dazu gehört, unterteile ich ja doch in Gruppen. Und Gruppen haben zur Eigenart, dass es Zugehörigkeiten gibt und ausgeschlossen sein. So beginnt der Kampf. Zunächst war die Frau minderwertig, jetzt ist der Mann toxisch. Und was, wann zu wem, wie gesagt werden darf wird zum Spießrutenlauf. „Misgendern“ ist beispielsweise eine Wortneuschöpfungen, die eine Incorrectness der Sprache bezeichnet, die bis in die Strafbarkeit reichen will. Einer, der von dieser rigide anmutenden Sprach-Religion getriggert wird, ist Gerald Ehegartner. Er ist Lehrer, Musiker, Theater- und Wildnispädagoge und Autor und nimmt sich immer wieder dem Gemeingut Sprache an. Heute mit einem Text, den er mit: „Gendern, die Sakralsprache des Wokeismus“ betitelt hat. Sprecherin: Sabrina Khalil @ 5cf42f9d:4465eebf
2025-04-02 21:32:31
@ 5cf42f9d:4465eebf
2025-04-02 21:32:31 @ 2b24a1fa:17750f64
2025-04-03 10:05:21Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden.  [https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche](https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche?color=ffd400) Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder. Folge 3: Christian der Wachstümliche Sprecher: Karsten Troyke Bild: Markus Mitterer für Radio München Radio München
@ 2b24a1fa:17750f64
2025-04-03 10:05:21Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden.  [https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche](https://soundcloud.com/radiomuenchen/nachruf-3-christian-der-wachstumliche?color=ffd400) Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder. Folge 3: Christian der Wachstümliche Sprecher: Karsten Troyke Bild: Markus Mitterer für Radio München Radio München @ 2b24a1fa:17750f64
2025-04-03 10:03:24Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden.  [https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?](https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?color=ffd400) Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder. Folge 4: Annalena die Völkerballerina Sprecher: Karsten Troyke Bild: Markus Mitterer für Radio München
@ 2b24a1fa:17750f64
2025-04-03 10:03:24Der Deutsche Bundestag wurde neu gewählt. Für einige Abgeordnete und Regierungsmitglieder heißt es Time to Say Goodbye. Abschied ist ein scharfes Schwert. Auch bei Radio München werden Trennungs- und Verlassenheitsgefühle getriggert. Umso mehr, wenn es sich nicht nur um duselige Allerweltsliebe handelt, sondern um den Abgang großer Helden.  [https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?](https://soundcloud.com/radiomuenchen/nachruf-4-annalena-die-volkerballerina-eine-satire-von-jonny-rieder?color=ffd400) Sie bezahlten ihren todesmutigen und fast ehrenamtlichen Einsatz nicht mit dem Leben, jedoch mit der einen oder anderen Falte in Hemd oder Bluse, manchmal sogar im Gesicht. Was bleibt? Eine bescheidene Pension? Ein lausig bezahlter Manager-Job in einem Konzern? Wir wollen jedenfalls nicht, dass diese Volkshelden vom Zahn der Zeit abgenagt, vergessen werden und setzen ihnen deshalb ein bescheidenes akustisches, aber nachhaltiges Denkmal. Hören Sie die kleine satirische Reihe „Nachrufe“ von unserem Autor Jonny Rieder. Folge 4: Annalena die Völkerballerina Sprecher: Karsten Troyke Bild: Markus Mitterer für Radio München @ 2b24a1fa:17750f64
2025-04-03 09:57:35Es sind immer die gleichen Mechanismen: Die Faktoren Zeitdruck und Angst machen enorm viele Menschen gefügig. 500 Milliarden Euro für Infrastruktur und den sogenannten Klimaschutz, 400 Milliarden für die Bundeswehr – also fast eine Billion Euro Schulden, innerhalb von weniger als vier Wochen nach der Wahl mit Winkelzügen den Bundesbürgern auferlegt.  [https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?](https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?color=ffd400) Wahlversprechen oder Parteiprogramme, das auf keinen Fall zu tun, sind Makulatur. Keine Diskussion über einen Haushalt, keine Diskussion über die Notwendigkeiten und schon sind Fragen anhängig, ob die Aufträge, die nun vergeben werden, nach den rechtmäßigen Ausschreibungskriterien vonstatten gehen, oder ob auch bei diesen unvorstellbaren Summen die Spezlwirtschaft im Land fortgeführt wird. Wo ist der Wille des Volkes geblieben? Wo die Freiheit, tatsächlich über unser Leben und Wirtschaften zu entscheiden? Der Autor, Wirtschafts- und Finanzexperte Andreas Geltinger schaut auf die einstigen Ideen wirtschaftlichen Handelns und analysiert, womit wir es jetzt zu tun haben. Sprecher: Karsten Troyke.
@ 2b24a1fa:17750f64
2025-04-03 09:57:35Es sind immer die gleichen Mechanismen: Die Faktoren Zeitdruck und Angst machen enorm viele Menschen gefügig. 500 Milliarden Euro für Infrastruktur und den sogenannten Klimaschutz, 400 Milliarden für die Bundeswehr – also fast eine Billion Euro Schulden, innerhalb von weniger als vier Wochen nach der Wahl mit Winkelzügen den Bundesbürgern auferlegt.  [https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?](https://soundcloud.com/radiomuenchen/es-lebe-die-freiheit-verdammt?color=ffd400) Wahlversprechen oder Parteiprogramme, das auf keinen Fall zu tun, sind Makulatur. Keine Diskussion über einen Haushalt, keine Diskussion über die Notwendigkeiten und schon sind Fragen anhängig, ob die Aufträge, die nun vergeben werden, nach den rechtmäßigen Ausschreibungskriterien vonstatten gehen, oder ob auch bei diesen unvorstellbaren Summen die Spezlwirtschaft im Land fortgeführt wird. Wo ist der Wille des Volkes geblieben? Wo die Freiheit, tatsächlich über unser Leben und Wirtschaften zu entscheiden? Der Autor, Wirtschafts- und Finanzexperte Andreas Geltinger schaut auf die einstigen Ideen wirtschaftlichen Handelns und analysiert, womit wir es jetzt zu tun haben. Sprecher: Karsten Troyke. @ e4950c93:1b99eccd
2025-04-03 09:55:59### Équipe Cœur L'équipe Cœur porte le projet et valide les contenus. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure ! ### Enrichisseu-r-se-s de contenus Les contribut-eur-rice-s rendent ce site vivant et intéressant.
@ e4950c93:1b99eccd
2025-04-03 09:55:59### Équipe Cœur L'équipe Cœur porte le projet et valide les contenus. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) Pour démarrer, je gère le projet en solo. Contactez-moi si vous souhaitez rejoindre l'aventure ! ### Enrichisseu-r-se-s de contenus Les contribut-eur-rice-s rendent ce site vivant et intéressant. @ 2b24a1fa:17750f64
2025-04-03 09:34:29Kartografiert, aufgekauft, betoniert, beschildert. Wo ist die Freiheit? Wo ist Platz zum Erforschen im Nicht-Definierten? Also wo sind die Erfahrungsräume, die sich von Generation zu Generation üblicherweise immer wieder die Jugend erobert, um darin zu wachsen und zu reifen? [https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders](https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders?color=ffd400) Perspektivwechsel: Wo sind eigentlich die Jugendlichen abgeblieben, die nach diesen Räumen Ausschau halten? Sie bewegen sich in „Spaces“. Seit Corona staatlich verordnet, suchen sie auf flachen Bildschirmen, in einer artifiziellen Welt, ihren Horizont zu erweitern. Der Kulturwissenschaftler Kenneth Anders hat sich auf Spurensuche bei Jugendlichen auf dem Land gemacht. Hören Sie sein Resumée mit dem Titel „Abwartend skeptisch“. Nachzulesen ist der Beitrag auf der Webseite: oderamazonas.de Sprecherin: Sabrina Khalil Bild: KI [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
@ 2b24a1fa:17750f64
2025-04-03 09:34:29Kartografiert, aufgekauft, betoniert, beschildert. Wo ist die Freiheit? Wo ist Platz zum Erforschen im Nicht-Definierten? Also wo sind die Erfahrungsräume, die sich von Generation zu Generation üblicherweise immer wieder die Jugend erobert, um darin zu wachsen und zu reifen? [https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders](https://soundcloud.com/radiomuenchen/abwartend-skeptisch-von-kenneth-anders?color=ffd400) Perspektivwechsel: Wo sind eigentlich die Jugendlichen abgeblieben, die nach diesen Räumen Ausschau halten? Sie bewegen sich in „Spaces“. Seit Corona staatlich verordnet, suchen sie auf flachen Bildschirmen, in einer artifiziellen Welt, ihren Horizont zu erweitern. Der Kulturwissenschaftler Kenneth Anders hat sich auf Spurensuche bei Jugendlichen auf dem Land gemacht. Hören Sie sein Resumée mit dem Titel „Abwartend skeptisch“. Nachzulesen ist der Beitrag auf der Webseite: oderamazonas.de Sprecherin: Sabrina Khalil Bild: KI [www.radiomuenchen.net/](http://www.radiomuenchen.net/%E2%80%8B "http://www.radiomuenchen.net/")\ @[radiomuenchen](https://soundcloud.com/radiomuenchen)\ [www.facebook.com/radiomuenchen](http://www.facebook.com/radiomuenchen "http://www.facebook.com/radiomuenchen")\ [www.instagram.com/radio\_muenchen/](http://www.instagram.com/radio_muenchen/ "http://www.instagram.com/radio_muenchen/")\ [twitter.com/RadioMuenchen](http://twitter.com/RadioMuenchen "http://twitter.com/RadioMuenchen") Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen. @ 2b24a1fa:17750f64
2025-04-03 09:28:5221 Monate, also fast zwei Jahre verbringt Johanna Findeisen bereits in Untersuchungshaft. Trägt sie reichsbürgerliche Ideen mit sich? Oder hat sie Straftaten geplant? Es ist ein Fall im sogenannten „Reichsbürgerprozess“. Mit diesem beschäftigt sich einer ihrer Anwälte Prof. Martin Schwab. Bei den Prozessen, so der Jurist, gehe es eher um Gesinnungsfragen.  [https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege](https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege?color=ffd400) Fakten zu Straftaten, auch geplanten, seien nicht aufzufinden. Und eine Untersuchungshaft für die Aufdeckung einer möglicherweise falschen Gesinnung – die Johanna Findeisen vehement bestreitet - ist in unserem Rechtssystem nicht vorgesehen. Dennoch sind die Termine für diese Untersuchungen bereits bis 2026 anberaumt. Das soll aber heute nicht unser Thema sein. Es geht um die Untersuchungshaft selbst. Prof. Martin Schwab ist in regelmäßigem, telefonischen Kontakt mit Johanna Findeisen und stellt dort Verhältnisse fest, die den Tatbestand der Folter erfüllen. Kein Mensch, selbst der Verurteilte, darf in seiner Menschenwürde herabgesetzt werden. Nun wird der Fall Johanna Findeisen bislang lediglich untersucht. Wie kann also sein, dass sie im Transport zum Gericht gefesselt wird? Warum wurde sie bei ihrer Rückkehr körperinvasiv untersucht? Was übrigens nach einem öffentlichkeitswirksamen Antrag ans Oberlandesgericht erfolgreich unterbunden wurde. Warum wird ihre Post zurückgehalten? Warum durfte sie, bei zwei Stunden Besuchszeit im Monat, ihren Angehörigen nur hinter einer Scheibe begegnen? Warum wird sie, ohne Morgentoilette, abgeholt und in eine fensterlose Zelle ins Gericht gebracht, wo sie zwei Stunden bis zum Gerichtstermin ausharren muss? Und warum wird die fiebernde Johanna, bei Minusgraden und offener Türe gezwungen, sich nackt auszuziehen, sich zur Wand zu drehen und sich einer erniedrigenden Leibesvisitation zu stellen? Auch dem Pfarrer und Autor Jürgen Fliege geht dieser Fall nah und fragte sich, was Johanna Findeisen, neben einer guten Verteidigung gebrauchen könnte und er ihr geben: Beistand! Hören Sie seinen offenen Brief an die Inhaftierte. Sprecherin: Sabrina Khalil. Wer sich gegen die – in einzelnen Haftanstalten – untragbaren Zustände, gegen die dortigen Menschenrechtsverletzungen engagieren möchte, kann das beispielsweise auf der Webseite [www.folter-nein-danke.eu](http://www.folter-nein-danke.eu/ "http://www.folter-nein-danke.eu") tun.
@ 2b24a1fa:17750f64
2025-04-03 09:28:5221 Monate, also fast zwei Jahre verbringt Johanna Findeisen bereits in Untersuchungshaft. Trägt sie reichsbürgerliche Ideen mit sich? Oder hat sie Straftaten geplant? Es ist ein Fall im sogenannten „Reichsbürgerprozess“. Mit diesem beschäftigt sich einer ihrer Anwälte Prof. Martin Schwab. Bei den Prozessen, so der Jurist, gehe es eher um Gesinnungsfragen.  [https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege](https://soundcloud.com/radiomuenchen/liebe-johanna-offener-brief-in-die-jva-frankfurt-von-jurgen-fliege?color=ffd400) Fakten zu Straftaten, auch geplanten, seien nicht aufzufinden. Und eine Untersuchungshaft für die Aufdeckung einer möglicherweise falschen Gesinnung – die Johanna Findeisen vehement bestreitet - ist in unserem Rechtssystem nicht vorgesehen. Dennoch sind die Termine für diese Untersuchungen bereits bis 2026 anberaumt. Das soll aber heute nicht unser Thema sein. Es geht um die Untersuchungshaft selbst. Prof. Martin Schwab ist in regelmäßigem, telefonischen Kontakt mit Johanna Findeisen und stellt dort Verhältnisse fest, die den Tatbestand der Folter erfüllen. Kein Mensch, selbst der Verurteilte, darf in seiner Menschenwürde herabgesetzt werden. Nun wird der Fall Johanna Findeisen bislang lediglich untersucht. Wie kann also sein, dass sie im Transport zum Gericht gefesselt wird? Warum wurde sie bei ihrer Rückkehr körperinvasiv untersucht? Was übrigens nach einem öffentlichkeitswirksamen Antrag ans Oberlandesgericht erfolgreich unterbunden wurde. Warum wird ihre Post zurückgehalten? Warum durfte sie, bei zwei Stunden Besuchszeit im Monat, ihren Angehörigen nur hinter einer Scheibe begegnen? Warum wird sie, ohne Morgentoilette, abgeholt und in eine fensterlose Zelle ins Gericht gebracht, wo sie zwei Stunden bis zum Gerichtstermin ausharren muss? Und warum wird die fiebernde Johanna, bei Minusgraden und offener Türe gezwungen, sich nackt auszuziehen, sich zur Wand zu drehen und sich einer erniedrigenden Leibesvisitation zu stellen? Auch dem Pfarrer und Autor Jürgen Fliege geht dieser Fall nah und fragte sich, was Johanna Findeisen, neben einer guten Verteidigung gebrauchen könnte und er ihr geben: Beistand! Hören Sie seinen offenen Brief an die Inhaftierte. Sprecherin: Sabrina Khalil. Wer sich gegen die – in einzelnen Haftanstalten – untragbaren Zustände, gegen die dortigen Menschenrechtsverletzungen engagieren möchte, kann das beispielsweise auf der Webseite [www.folter-nein-danke.eu](http://www.folter-nein-danke.eu/ "http://www.folter-nein-danke.eu") tun. @ 2b24a1fa:17750f64
2025-04-03 09:28:32„Das ist ein netter alter Onkel, der sich bemüht, der Welt Gutes zu tun“, antwortete Anfang 2021 der Sohn einer Freundin auf ihre Frage, was Bill Gates mit der Pandemie zu tun haben könnte. Ich erinnere mich, damals wurde man als Verschwörungstheoretiker tituliert, und zwar maximal abwertend, wenn man allein den Namen ins Spiel brachte. Es ist wirklich Zeit, sich wieder für das Ansehen der Verschwörungstheorie einzusetzen, denn ohne sie wird kein einziger Kriminalfall aufgedeckt, der von mehr als einer Person durchgeführt wurde. [https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection](https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection?color=ffd400) Kommen wir zum dritten Teil der Reihe „Corona-Connection“ von Milosz Matuschek in dem er sich in deren Epizentrum begibt. Bill Gates, der undemokratisch zu Macht gekommene, selbsternannte Philanthrop, gehört zu den Hauptfiguren der USAID, der United States Agency for International Development. Matuschek geht hier auf das Geschäftsmodell des Philanthrokapitalismus ein. Sabrina Khalil hat seinen Text gelesen. Diesen und die zwei ersten Folgen finden Sie auf Matuscheks Seite: Freischwebende Intelligenz.
@ 2b24a1fa:17750f64
2025-04-03 09:28:32„Das ist ein netter alter Onkel, der sich bemüht, der Welt Gutes zu tun“, antwortete Anfang 2021 der Sohn einer Freundin auf ihre Frage, was Bill Gates mit der Pandemie zu tun haben könnte. Ich erinnere mich, damals wurde man als Verschwörungstheoretiker tituliert, und zwar maximal abwertend, wenn man allein den Namen ins Spiel brachte. Es ist wirklich Zeit, sich wieder für das Ansehen der Verschwörungstheorie einzusetzen, denn ohne sie wird kein einziger Kriminalfall aufgedeckt, der von mehr als einer Person durchgeführt wurde. [https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection](https://soundcloud.com/radiomuenchen/im-epizentrum-der-corona-connection-von-milosz-matuschek-teil-3-der-corona-connection?color=ffd400) Kommen wir zum dritten Teil der Reihe „Corona-Connection“ von Milosz Matuschek in dem er sich in deren Epizentrum begibt. Bill Gates, der undemokratisch zu Macht gekommene, selbsternannte Philanthrop, gehört zu den Hauptfiguren der USAID, der United States Agency for International Development. Matuschek geht hier auf das Geschäftsmodell des Philanthrokapitalismus ein. Sabrina Khalil hat seinen Text gelesen. Diesen und die zwei ersten Folgen finden Sie auf Matuscheks Seite: Freischwebende Intelligenz. @ 2b24a1fa:17750f64
2025-04-03 07:46:37„Ein Fundstück aus dem Internet – jemand fragt:\ „Wie fühlst du dich als Geimpfter, wenn du eine Maske tragen musst, um die Ungeimpften zu schützen?“ [https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer](https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer?color=ffd400) \ Jemand antwortet:\ „Wovor sollte ein Geimpfter einen Ungeimpften schützen?\ 1\. Der Geimpfte kann doch gar nicht krank werden, also auch niemanden anstecken, dachte ich?\ 2\. Wenn der Geimpfte doch krank werden und andere anstecken kann, wozu hat er sich dann impfen lassen?\ 3\. Und wozu sollte sich dann der Ungeimpfte impfen lassen?\ 4\. Und wozu sollte dann überhaupt einer der beiden eine Maske tragen?“\ Jemand antwortet:\ „Das ist pure Querdenkerei. Solche kruden Theorien können Menschenleben zerstören.“\ „Eine bessere Parabel auf den religiösen Charakter des aktuellen Wahns könnte ich mir nicht ausdenken“,\ schreibt der Münchner Kolumnist Michael Sailer in seinem Buch Was ist passiert – Notate aus den Zeiten von Lüge und Krieg, das Ende Februar erschienen ist. Als neugieriger und zwangsläufig teilnehmende Beobachter analysiert, kommentiert und hinterfragt der Autor die gesellschaftlichen Abgründe, die sich 2020 und 2021 vor unser aller Augen auftaten. Unser Autor Jonny Rieder hat es gelesen und eine Rezension verfasst. Sprecher: Ulrich Allroggen Bild: Radio München - Kunst: Isaac Cordal (Cement Eclipses)
@ 2b24a1fa:17750f64
2025-04-03 07:46:37„Ein Fundstück aus dem Internet – jemand fragt:\ „Wie fühlst du dich als Geimpfter, wenn du eine Maske tragen musst, um die Ungeimpften zu schützen?“ [https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer](https://soundcloud.com/radiomuenchen/was-ist-passiert-ein-buch-von-michael-sailer?color=ffd400) \ Jemand antwortet:\ „Wovor sollte ein Geimpfter einen Ungeimpften schützen?\ 1\. Der Geimpfte kann doch gar nicht krank werden, also auch niemanden anstecken, dachte ich?\ 2\. Wenn der Geimpfte doch krank werden und andere anstecken kann, wozu hat er sich dann impfen lassen?\ 3\. Und wozu sollte sich dann der Ungeimpfte impfen lassen?\ 4\. Und wozu sollte dann überhaupt einer der beiden eine Maske tragen?“\ Jemand antwortet:\ „Das ist pure Querdenkerei. Solche kruden Theorien können Menschenleben zerstören.“\ „Eine bessere Parabel auf den religiösen Charakter des aktuellen Wahns könnte ich mir nicht ausdenken“,\ schreibt der Münchner Kolumnist Michael Sailer in seinem Buch Was ist passiert – Notate aus den Zeiten von Lüge und Krieg, das Ende Februar erschienen ist. Als neugieriger und zwangsläufig teilnehmende Beobachter analysiert, kommentiert und hinterfragt der Autor die gesellschaftlichen Abgründe, die sich 2020 und 2021 vor unser aller Augen auftaten. Unser Autor Jonny Rieder hat es gelesen und eine Rezension verfasst. Sprecher: Ulrich Allroggen Bild: Radio München - Kunst: Isaac Cordal (Cement Eclipses) @ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
@ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ @ ba36d0f7:cd802cba
2025-04-02 21:17:09## 1. **Essential Rules** ✔ Touch-Move: If you touch a piece, you must move it (if legal). ✔ Check Alert: Say "check" when attacking the enemy king (optional in tournaments). ✔ Checkmate Ends: The game stops immediately—no need to capture the king. ✔ Draw Offers: You can offer a draw after your move, before pressing the clock. ********************************************** ## 2. **Tournament Etiquette** - Handshake: Before and after the game. - Silence: No talking during play (except "check" or "draw?"). - Clock: Press with the same hand that moved. - Resignation: Tip over your king or say "I resign" (don’t just leave). ********************************************** ## 3. **Online Chess Manners** No Stalling: Let the timer run out only if you’ve truly lost. GG Message: Say "Good game" (or "GG") after playing. Avoid "Berserking": Don’t abuse speed settings to rush opponents. > **Common Faux Pas** ❌ Jangling pieces to distract. ❌ Glaring at your opponent’s board. ❌ Cheating (using engines, peeking at other games).
@ ba36d0f7:cd802cba
2025-04-02 21:17:09## 1. **Essential Rules** ✔ Touch-Move: If you touch a piece, you must move it (if legal). ✔ Check Alert: Say "check" when attacking the enemy king (optional in tournaments). ✔ Checkmate Ends: The game stops immediately—no need to capture the king. ✔ Draw Offers: You can offer a draw after your move, before pressing the clock. ********************************************** ## 2. **Tournament Etiquette** - Handshake: Before and after the game. - Silence: No talking during play (except "check" or "draw?"). - Clock: Press with the same hand that moved. - Resignation: Tip over your king or say "I resign" (don’t just leave). ********************************************** ## 3. **Online Chess Manners** No Stalling: Let the timer run out only if you’ve truly lost. GG Message: Say "Good game" (or "GG") after playing. Avoid "Berserking": Don’t abuse speed settings to rush opponents. > **Common Faux Pas** ❌ Jangling pieces to distract. ❌ Glaring at your opponent’s board. ❌ Cheating (using engines, peeking at other games). @ ba36d0f7:cd802cba
2025-04-02 21:14:37| **Piece** | **How It Moves** | **Special Rules** | | --------- | ------------------------------------- | --------------------- | | Pawn | Forward 1 (or 2), captures diagonally | En passant, promotion | | Rook | Straight lines | Castling | | Knight | L-shape (2+1) | Jumps over pieces | | Bishop | Diagonals | Color-locked | | Queen | Any direction | None | | King | 1 square any way | Castling, checkmate | ************************** ## Pieces 1. **Pawn** (♙ / ♟️) - Moves: Forward 1 square (or 2 on first move). - Captures: Diagonally 1 square. Special: - En passant: Captures a pawn that moved 2 squares past it. - Promotion: Reaches the 8th rank → becomes any piece (usually Queen). ************************ 2. **Rook** (♖ / ♜) - Moves: Straight lines (any distance). - Special: Castling (moves with the king). ********************************************** 3. **Knight** (♘ / ♞) - Moves: "L-shape" (2 squares one way + 1 square perpendicular). - Jumps: Over other pieces. ************************************************ 4. **Bishop** (♗ / ♝) - Moves: Diagonals (any distance). - Stays on one color forever. ************************************************* 5. **Queen** (♕ / ♛) - Moves: Any direction (straight/diagonal, any distance). - Most powerful piece! ********************************************** 6. **King** (♔ / ♚) - Moves: 1 square in any direction. Special: Castling: Swaps places with a rook (if no blocks/checks). Checkmate: Loses if trapped with no escape. ************************************* ## **How to move** 1. One move per turn 2. Choose your piece, place it on a legal square - *Your color only: White moves first, then Black, alternating.* - *No passing: You must move if it’s your turn.* **************************************************** **How to Capture ("Eat")** - Land on an enemy piece: Replace it with your piece. - *Pawns capture diagonally only (not straight).* - *Kings cannot be captured (checkmate ends the game).* >✔ Check: Attack the enemy king (they must escape next turn). ❌ Illegal: Moving into check or leaving your king in check. ****************************************** ## **Special moves** | Move | Key Rule | Notation | | ---------- | ---------------------------------- | ----------- | | Castling | King + rook, no prior moves/checks | `O-O` | | Promotion | Pawn→any piece at 8th rank | `e8=Q` | | En Passant | Capture a 2-square pawn jump | `exd6 e.p.` | ******************************************* 1. **Castling** (The King’s Escape) - What: King + Rook move together in one turn. How: - King moves 2 squares toward a rook. - Rook jumps to the other side of the king. Rules: - No checks: King can’t be in check or pass through check. - Never moved: King and that rook must be untouched. Types: Kingside (♔→♖, faster): O-O Queenside (♔←♖, safer): O-O-O ************************************************** 2. **Promotion** ("Crowning") - What: Pawn reaches the 8th rank → turns into any piece (usually Queen). - How: Replace the pawn with a new piece (even if the original is still on the board). > Fun fact: You can have 9 queens (1 original + 8 promotions)! Promotion example (Pawn→Queen at h8) *********************************** 3. **En Passant** (French for "In Passing") - When: Enemy pawn moves 2 squares forward past your pawn. - How: Capture it diagonally (as if it moved only 1 square). > Rule: Must do it immediately (next turn only). **************************************** #chess #elsalvador #somachess
@ ba36d0f7:cd802cba
2025-04-02 21:14:37| **Piece** | **How It Moves** | **Special Rules** | | --------- | ------------------------------------- | --------------------- | | Pawn | Forward 1 (or 2), captures diagonally | En passant, promotion | | Rook | Straight lines | Castling | | Knight | L-shape (2+1) | Jumps over pieces | | Bishop | Diagonals | Color-locked | | Queen | Any direction | None | | King | 1 square any way | Castling, checkmate | ************************** ## Pieces 1. **Pawn** (♙ / ♟️) - Moves: Forward 1 square (or 2 on first move). - Captures: Diagonally 1 square. Special: - En passant: Captures a pawn that moved 2 squares past it. - Promotion: Reaches the 8th rank → becomes any piece (usually Queen). ************************ 2. **Rook** (♖ / ♜) - Moves: Straight lines (any distance). - Special: Castling (moves with the king). ********************************************** 3. **Knight** (♘ / ♞) - Moves: "L-shape" (2 squares one way + 1 square perpendicular). - Jumps: Over other pieces. ************************************************ 4. **Bishop** (♗ / ♝) - Moves: Diagonals (any distance). - Stays on one color forever. ************************************************* 5. **Queen** (♕ / ♛) - Moves: Any direction (straight/diagonal, any distance). - Most powerful piece! ********************************************** 6. **King** (♔ / ♚) - Moves: 1 square in any direction. Special: Castling: Swaps places with a rook (if no blocks/checks). Checkmate: Loses if trapped with no escape. ************************************* ## **How to move** 1. One move per turn 2. Choose your piece, place it on a legal square - *Your color only: White moves first, then Black, alternating.* - *No passing: You must move if it’s your turn.* **************************************************** **How to Capture ("Eat")** - Land on an enemy piece: Replace it with your piece. - *Pawns capture diagonally only (not straight).* - *Kings cannot be captured (checkmate ends the game).* >✔ Check: Attack the enemy king (they must escape next turn). ❌ Illegal: Moving into check or leaving your king in check. ****************************************** ## **Special moves** | Move | Key Rule | Notation | | ---------- | ---------------------------------- | ----------- | | Castling | King + rook, no prior moves/checks | `O-O` | | Promotion | Pawn→any piece at 8th rank | `e8=Q` | | En Passant | Capture a 2-square pawn jump | `exd6 e.p.` | ******************************************* 1. **Castling** (The King’s Escape) - What: King + Rook move together in one turn. How: - King moves 2 squares toward a rook. - Rook jumps to the other side of the king. Rules: - No checks: King can’t be in check or pass through check. - Never moved: King and that rook must be untouched. Types: Kingside (♔→♖, faster): O-O Queenside (♔←♖, safer): O-O-O ************************************************** 2. **Promotion** ("Crowning") - What: Pawn reaches the 8th rank → turns into any piece (usually Queen). - How: Replace the pawn with a new piece (even if the original is still on the board). > Fun fact: You can have 9 queens (1 original + 8 promotions)! Promotion example (Pawn→Queen at h8) *********************************** 3. **En Passant** (French for "In Passing") - When: Enemy pawn moves 2 squares forward past your pawn. - How: Capture it diagonally (as if it moved only 1 square). > Rule: Must do it immediately (next turn only). **************************************** #chess #elsalvador #somachess @ ba36d0f7:cd802cba
2025-04-02 21:08:28## **Chess Board Setup**  1. **The Basics** 8x8 grid, alternating light/dark squares. >Key rule: *Always place the board so a light square is on each player’s bottom-right. 2. **Coordinates** Files (columns): Labeled *a* to *h* (left to right). Ranks (rows): Numbered *1* to *8* (White’s side = 1, Black’s = 8). > Notation: Squares are file + rank (e.g., e4, a7). 3. **Piece Placement** **Black (Top):** a8: Rook b8: Knight c8: Bishop d8: Queen e8: King f8: Bishop g8: Knight h8: Rook Rank 7: All pawns (a7-h7) **White (Bottom):** a1: Rook b1: Knight c1: Bishop d1: Queen e1: King f1: Bishop g1: Knight h1: Rook Rank 2: All pawns (a2-h2) > Quick Tip: Queens start on their color (Whiteon d1, Black on d8). *********************** ## **Checkmate, stalemate & draws** Chess is a two-player strategy game where the ultimate goal is to **checkmate** your opponent’s king. However, games can also end in a **stalemate** or **draw** under specific conditions. 1. **Checkmate (Winning the Game)** - Definition: The enemy king is in check (under attack) and has no legal moves to escape. - Result: The game ends immediately—the player delivering checkmate wins. 1. **Stalemate (Draw)** - Definition: The player whose turn it is has no legal moves, but their king is not in check. - Result: The game is a draw (no winner). > Common Causes: >- *A lone king with no moves left.* >- *Poor pawn structure blocking all options.* 3. **Other Draws** Games can also end in a draw due to: - **Insufficient Material** - Only kings remain. - King + bishop vs. king (no possible checkmate). - **Threefold Repetition** - The same position occurs 3 times (with the same player to move). - **50-Move Rule** - No pawn moves or captures in 50 consecutive moves (by both players). - **Agreement** - Players mutually agree to a draw. Key differences: | Term | King in Check? | Legal Moves? | Result | | --------- | -------------- | ------------ | -------- | | Checkmate | Yes | No | Win/Loss | | Stalemate | No | No | Draw | | Draw | N/A | N/A | Tie | **************************************************** ## **Chess history** 1. **Ancient Origins (6th Century)** - Birthplace: Northern India (as Chaturanga), meaning "four divisions" (infantry, cavalry, elephants, chariots—early versions of pawns, knights, bishops, rooks). - Spread: Reached Persia as Shatranj by 600 AD, where key rules (like "check" and "checkmate") emerged. > Fun fact: "Checkmate" comes from Persian "Shah Mat" ("the king is helpless"). 2. **Medieval Europe (9th–15th Century)** - Rebranding: Arabs brought chess to Spain by 1000 AD; Europeans adapted pieces to feudal society: Elephants → Bishops Viziers → Queens (weak at first—could only move one square!) - Major Change: By 1475, the queen became the most powerful piece ("Mad Queen Chess"), speeding up the game. 3. **Modern Chess (1850–Present)** - Standardization: First official world championship (1886, Wilhelm Steinitz vs. Johannes Zukertort). - Computers: IBM’s Deep Blue defeated Garry Kasparov in 1997, revolutionizing AI. - Today: Online platforms (Chess.com, Lichess) and pop culture (The Queen’s Gambit) fuel a global boom. >Did You Know? > > - The longest possible chess game is 5,949 moves (theoretical limit). > > - The longest recorded game was 269 moves, 1989 Nikolić vs. Arsović. > > - The oldest recorded chess opening (1.e4) appears in a 1490 Spanish manuscript. #chess #education #elsalvador #chesselsalvador #somachess #article #soma
@ ba36d0f7:cd802cba
2025-04-02 21:08:28## **Chess Board Setup**  1. **The Basics** 8x8 grid, alternating light/dark squares. >Key rule: *Always place the board so a light square is on each player’s bottom-right. 2. **Coordinates** Files (columns): Labeled *a* to *h* (left to right). Ranks (rows): Numbered *1* to *8* (White’s side = 1, Black’s = 8). > Notation: Squares are file + rank (e.g., e4, a7). 3. **Piece Placement** **Black (Top):** a8: Rook b8: Knight c8: Bishop d8: Queen e8: King f8: Bishop g8: Knight h8: Rook Rank 7: All pawns (a7-h7) **White (Bottom):** a1: Rook b1: Knight c1: Bishop d1: Queen e1: King f1: Bishop g1: Knight h1: Rook Rank 2: All pawns (a2-h2) > Quick Tip: Queens start on their color (Whiteon d1, Black on d8). *********************** ## **Checkmate, stalemate & draws** Chess is a two-player strategy game where the ultimate goal is to **checkmate** your opponent’s king. However, games can also end in a **stalemate** or **draw** under specific conditions. 1. **Checkmate (Winning the Game)** - Definition: The enemy king is in check (under attack) and has no legal moves to escape. - Result: The game ends immediately—the player delivering checkmate wins. 1. **Stalemate (Draw)** - Definition: The player whose turn it is has no legal moves, but their king is not in check. - Result: The game is a draw (no winner). > Common Causes: >- *A lone king with no moves left.* >- *Poor pawn structure blocking all options.* 3. **Other Draws** Games can also end in a draw due to: - **Insufficient Material** - Only kings remain. - King + bishop vs. king (no possible checkmate). - **Threefold Repetition** - The same position occurs 3 times (with the same player to move). - **50-Move Rule** - No pawn moves or captures in 50 consecutive moves (by both players). - **Agreement** - Players mutually agree to a draw. Key differences: | Term | King in Check? | Legal Moves? | Result | | --------- | -------------- | ------------ | -------- | | Checkmate | Yes | No | Win/Loss | | Stalemate | No | No | Draw | | Draw | N/A | N/A | Tie | **************************************************** ## **Chess history** 1. **Ancient Origins (6th Century)** - Birthplace: Northern India (as Chaturanga), meaning "four divisions" (infantry, cavalry, elephants, chariots—early versions of pawns, knights, bishops, rooks). - Spread: Reached Persia as Shatranj by 600 AD, where key rules (like "check" and "checkmate") emerged. > Fun fact: "Checkmate" comes from Persian "Shah Mat" ("the king is helpless"). 2. **Medieval Europe (9th–15th Century)** - Rebranding: Arabs brought chess to Spain by 1000 AD; Europeans adapted pieces to feudal society: Elephants → Bishops Viziers → Queens (weak at first—could only move one square!) - Major Change: By 1475, the queen became the most powerful piece ("Mad Queen Chess"), speeding up the game. 3. **Modern Chess (1850–Present)** - Standardization: First official world championship (1886, Wilhelm Steinitz vs. Johannes Zukertort). - Computers: IBM’s Deep Blue defeated Garry Kasparov in 1997, revolutionizing AI. - Today: Online platforms (Chess.com, Lichess) and pop culture (The Queen’s Gambit) fuel a global boom. >Did You Know? > > - The longest possible chess game is 5,949 moves (theoretical limit). > > - The longest recorded game was 269 moves, 1989 Nikolić vs. Arsović. > > - The oldest recorded chess opening (1.e4) appears in a 1490 Spanish manuscript. #chess #education #elsalvador #chesselsalvador #somachess #article #soma @ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop)
@ ef53426a:7e988851
2025-04-02 21:02:06# Bartering and early money \ Early societies bartered goods, but transactions were often complicated. The value of goods doesn’t always align. Enter money. It’s used as an indirect exchange for any goods, so everyone wants it. Early money wasn’t anything like what we use today. For example, the inhabitants of Yap Island (Micronesia) used large Rai stones for trade. New stones were dragged up a hill for everyone to see. The owner would then exchange part of the stone for goods and services. As they were hard to quarry and move, Rai stones retained their value (salability). Then, an Irish-American captain started importing stones using modern technology. Soon enough, they became so common, they no longer worked as money. --- # Gold — the basis for sound money \ Smelting made it possible to create highly salable and transportable coins. Gold was best because it’s virtually impossible to destroy and can’t be synthesized using other materials. It has a fairly limited supply, which grows slowly and predictably (due to the difficulty of mining). Technologies like the telegraph and trains made it easier for both people and goods to get from point A to point B. That, in turn, justified forms of payment like checks, paper receipts, and bills. But paper is not worth much unless it’s backed by something. Governments worldwide issued paper money backed by precious metals, which they stored in vaults. By 1900, around 50 countries had adopted the Gold Standard. This was sound money. --- # Currencies devalued \ Roman emperor Julius Caesar issued the Aureus, an empire-standard coin containing 8 grams of gold. But as growth began to slow, rulers started ‘coin clipping’, reducing the quantity of precious metal in coins. This eventually triggered a series of economic crises that led to the downfall of the Roman Empire. The gold standard had one major flaw: it had to be stored in bank vaults. This created a highly centralized system in which governments controlled the value of paper money. If they wanted to, they could always increase the supply of money without increasing the corresponding amount of gold. In 1914, nearly every major European power decided to do this to fund their war operations. Rather than raising taxes, they simply printed new money with no extra gold. The standard had been abandoned. --- # Government-backed money \ Governments chose to introduce fiat money – currency backed by decree rather than gold. The adoption of the fiat system led to an age of unsound money shaped by ever-greater intervention in the economy as governments scrambled to stabilize their currencies. By 1944, the end of the Second World War was in sight, and the victors began planning the postwar economic order. The world’s currencies would be tied to the US dollar at a fixed exchange rate. The dollar would in turn be tied to the value of gold, again at a fixed rate. The United States bent the rules and inflated its own currency compared to gold. Other nations inflated their currencies compared to the dollar. On August 15, 1971, President Nixon announced that dollars would no longer be convertible to gold. --- # Sound money = functioning economy \ Sound money encourages people to save and invest, enabling sustainable, long-term growth. Why? Well, humans have a natural positive time preference: we prefer instant gratification over future gratification. Sound money prompts us to think more about the future. The more capital accumulation there is, the greater the chance of stable, long-term economic growth. Unsound money distorts capital accumulation. When governments interfere with the money supply, they also interfere with prices. And prices give investors the information they need to make good decisions without having to learn every tiny detail about global events. --- # Recessions and debt arise from unsound money \ Government interference takes the form of central planning. No single person, agency, or department ever has access to all the information necessary to understand the vast and complex economy. Interventions distort markets, creating boom and bust cycles. According to Keynes and his followers, the best way to respond to recessions is to increase spending. You could lower taxes, but people don’t usually spend their extra money. Raising taxes is unpopular, so governments invariably decide to increase the money supply. Saving becomes less attractive, creating a culture of unwise spending and growing debt. We need to return to sound money and a new gold standard. Enter bitcoin. --- # Bitcoin is scarce \ Bitcoin has similar traits to gold. Its supply is literally fixed. Once there are 21 million bitcoins in circulation, no more will be issued. The supply grows at a diminishing rate. Computers across the Bitcoin network pool their processing power to solve complex algorithmic problems. Once these puzzles have been cracked, the “miners” receive bitcoins as a reward. Satoshi Nakamoto designed the system to avoid gold rushes. The algorithmic problems become more difficult to solve as the number of computers working on them rises, guaranteeing a steady and reliable supply. Also, the number of bitcoins issued is halved every four years, resulting in ever-smaller releases until 2140, after which no more coins will be released. That makes bitcoin unique. It is the only good that is defined by absolute scarcity. No amount of time or resources can create more bitcoins than the programmed supply allows. The supply cannot be manipulated, making it a perfect store of value. --- # Bitcoin is secure \ The bitcoin ledger uses the public blockchain. When mining computers crack an algorithmic puzzle, they create a block. The blocks on the ledger contain details about every blockchain transaction ever completed. Every network user can view this information. Ownership of bitcoins is only valid once it’s been registered on the blockchain. This is only possible if the majority of network users approve it, so there’s no need for a central authority to oversee transactions. While verifying new blocks requires virtually no energy, creating a fraudulent block would cost a significant amount of processing power. Even if a user decided to expend vast amounts of energy and successfully hacked a majority of all network nodes to approve a fraudulent block, they’d gain very little. Trust in bitcoin would be lost, leading to a drop in demand and value. --- # Challenges for adoption \ Because bitcoin is new, demand has varied. The volatile price has, at times, undermined the currency’s status as an effective store of value. Bitcoin’s transaction limit is currently set at 500,000 per day. That could be increased, but there will always be a daily cap. The more transactions that take place, the more nodes there’ll need to be. This increases transaction fees and the amount of processing power expended. Bitcoin could be traded off the blockchain, meaning currencies will be backed by bitcoin. That would create a new standard, but it would also mean that new centralized institutions would need to manage this system. ---  This 5-minute summary did not use copyrighted material from the book. It aims simply to give readers a quick understanding of the book (which is well worth reading). ‘*The Bitcoin Standard: The Decentralized Alternative to Central Banking’* was written by economist Saifedean Ammous in 2018. Buy the book and many more titles at [bitcoinbook.shop](bitcoinbook.shop) @ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷 
@ 7d33ba57:1b82db35
2025-04-02 19:47:25Trogir is a UNESCO-listed coastal town just 30 minutes from Split, known for its well-preserved medieval architecture, charming waterfront, and rich history. Often called "The Little Venice of Dalmatia," Trogir is built on a small island connected to the mainland and Čiovo Island by bridges. Its cobblestone streets, Renaissance palaces, and lively cafés** make it a perfect stop for history lovers and travelers seeking authentic Dalmatian charm.  ## **🏛️ Top Things to See & Do in Trogir** ### **1️⃣ Explore Trogir Old Town (UNESCO) 🏡** - Wander through the **labyrinth of narrow streets**, filled with **hidden courtyards and stone houses**. - Admire **Venetian-style palaces, Romanesque churches, and medieval city walls**. - Visit **St. Lawrence Cathedral**, featuring the **famous Radovan Portal**, a **masterpiece of medieval stone carving**. ### **2️⃣ Climb the Bell Tower of St. Lawrence ⛪** - Offers **stunning panoramic views** over Trogir and the Adriatic. - A bit of a **steep climb**, but **totally worth it** for the breathtaking scenery! ### **3️⃣ Visit Kamerlengo Fortress 🏰** - A **15th-century Venetian fortress** with **amazing sea views** from the top. - In summer, it hosts **concerts and cultural events**. ### **4️⃣ Stroll Along the Trogir Riva Promenade 🌊** - A lively waterfront filled with **cafés, restaurants, and luxury yachts**. - Perfect for a **relaxing evening walk** while watching the sunset.  ### **5️⃣ Relax on the Best Beaches Near Trogir 🏖️** - **Okrug Gornji Beach (Copacabana Beach)** – A long, lively beach with bars & water activities. - **Pantan Beach** – A quieter spot with **clear waters and pine tree shade**. - **Kava Beach (Čiovo Island)** – A more **secluded and natural** beach, ideal for relaxation. ### **6️⃣ Take a Boat Trip to the Blue Lagoon 🛥️** - A **stunning turquoise bay**, perfect for **swimming and snorkeling**. - Just **a short boat ride from Trogir**. ### **7️⃣ Try Dalmatian Cuisine 🍽️** - **Grilled fresh fish & seafood** – Trogir’s specialty! 🐟 - **Pašticada** – Slow-cooked beef in a rich red wine sauce, served with gnocchi. - **Homemade Dalmatian prosciutto & cheese** – Best paired with local **Plavac Mali wine**.  ## **🚗 How to Get to Trogir** ✈️ **By Air:** - **Split Airport (SPU)** is just **10 minutes away**! 🚕 🚘 **By Car:** - **From Split:** ~30 minutes (27 km) - **From Zadar:** ~1.5 hours (130 km) 🚌 **By Bus:** Frequent buses run between **Split and Trogir**. ⛵ **By Boat:** A **seasonal boat line** connects Trogir with Split and nearby islands.  ## **💡 Tips for Visiting Trogir** ✅ **Best time to visit?** **April–October** for sunny weather & fewer crowds ☀️ ✅ **Stay for sunset** – The views from the Riva & Kamerlengo Fortress are magical 🌅 ✅ **Wear comfy shoes** – The old town’s stone streets can be slippery 👟 ✅ **Book Blue Lagoon trips in advance** – It’s a popular excursion 🚤 ✅ **Try a wine tasting** at a local konoba (traditional tavern) 🍷  @ ba36d0f7:cd802cba
2025-04-02 19:31:27 ## **"It Takes a Village"** …But what if the "village" is a system that prioritizes obedience over curiosity, grades over growth, and rigid curriculums over real-world learning? For decades, we’ve accepted a model where kids spend hours a day passively absorbing information in classrooms, where their worth is measured by standardized tests rather than their ability to _think_, _adapt_, or _create_. Meanwhile, the tools to revolutionize learning - technology, connectivity, and decentralized knowledge - sit in our pockets, dismissed as "distractions" rather than leveraged as liberation. **The Paradox of Progress** We live in an era of unprecedented access to information. Yet, our education systems cling to industrial-era ideals, villainizing screens instead of teaching **how to wield them wisely**. Yes, mindless screen time harms—but so does _mindless schooling_. The real failure? **Not preparing learners to navigate, critique, and contribute to the world they actually live in.** **A different approach** soma is an experiment in **self-directed, community-rooted learning**. It asks: - What if education _integrated_ with life instead of interrupting it? - What if "success" meant **mastery driven by curiosity**, not compliance? - What if technology connected learners to mentors, resources, and real-world problems - not just apps that mimic worksheets? This isn’t about abandoning theory or expertise. It’s about **flipping the script**: - **Empiric learning** comes first (doing, trying, failing, exploring). - This is where physical spaces thrive - **quilombos**, workshops, community gardens. Where we take responsibility for our shared world. - **Theoretical depth** follows _when the learner chooses it_ - fueled by a desire to go further. - This is where our virtual spaces shine to guarantee accessibility: **as tool, not a privilege**. - Tech is **recreation, not a crutch** - the spice, not the meal. ********** **A call for villages, not factories** soma imagines communities where learning is **an act of devotion** - to exploration, to curiosity, to the sacred cycle of trying, failing, and trying again. Where you learn **because you want to - to better your surroundings**, not because you were told to. > Where a child’s obsession with ants leads them to a biologist’s fieldwork _and_ a poet’s metaphor - because both are natural extensions of wonder. > Where a teen building a game pursues storytelling, math, and ethics **on their own terms**, stitching knowledge together like patchwork quilt. > Where we see learning happening in parks, in makerspaces and on screens - used intentionally. This is education **returned to its human rhythm**: urgent, messy, and alive. --- **Join the experiment** This is just the start. soma is a **provocation, a prototype, and an open invitation** to rethink how we learn. **Let’s stop preparing kids for a world that no longer exists.** ➡️ _Follow updates, share your ideas, or tell us: What does your ideal "village" look like?_ nostr:npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99 #longform #article #education #elsalvador #communities #decentralized
@ ba36d0f7:cd802cba
2025-04-02 19:31:27 ## **"It Takes a Village"** …But what if the "village" is a system that prioritizes obedience over curiosity, grades over growth, and rigid curriculums over real-world learning? For decades, we’ve accepted a model where kids spend hours a day passively absorbing information in classrooms, where their worth is measured by standardized tests rather than their ability to _think_, _adapt_, or _create_. Meanwhile, the tools to revolutionize learning - technology, connectivity, and decentralized knowledge - sit in our pockets, dismissed as "distractions" rather than leveraged as liberation. **The Paradox of Progress** We live in an era of unprecedented access to information. Yet, our education systems cling to industrial-era ideals, villainizing screens instead of teaching **how to wield them wisely**. Yes, mindless screen time harms—but so does _mindless schooling_. The real failure? **Not preparing learners to navigate, critique, and contribute to the world they actually live in.** **A different approach** soma is an experiment in **self-directed, community-rooted learning**. It asks: - What if education _integrated_ with life instead of interrupting it? - What if "success" meant **mastery driven by curiosity**, not compliance? - What if technology connected learners to mentors, resources, and real-world problems - not just apps that mimic worksheets? This isn’t about abandoning theory or expertise. It’s about **flipping the script**: - **Empiric learning** comes first (doing, trying, failing, exploring). - This is where physical spaces thrive - **quilombos**, workshops, community gardens. Where we take responsibility for our shared world. - **Theoretical depth** follows _when the learner chooses it_ - fueled by a desire to go further. - This is where our virtual spaces shine to guarantee accessibility: **as tool, not a privilege**. - Tech is **recreation, not a crutch** - the spice, not the meal. ********** **A call for villages, not factories** soma imagines communities where learning is **an act of devotion** - to exploration, to curiosity, to the sacred cycle of trying, failing, and trying again. Where you learn **because you want to - to better your surroundings**, not because you were told to. > Where a child’s obsession with ants leads them to a biologist’s fieldwork _and_ a poet’s metaphor - because both are natural extensions of wonder. > Where a teen building a game pursues storytelling, math, and ethics **on their own terms**, stitching knowledge together like patchwork quilt. > Where we see learning happening in parks, in makerspaces and on screens - used intentionally. This is education **returned to its human rhythm**: urgent, messy, and alive. --- **Join the experiment** This is just the start. soma is a **provocation, a prototype, and an open invitation** to rethink how we learn. **Let’s stop preparing kids for a world that no longer exists.** ➡️ _Follow updates, share your ideas, or tell us: What does your ideal "village" look like?_ nostr:npub1hgmdpalp9tz37vh9kxx49fm5pl75w6vwek2r80r20x2stnvq9jaq705r99 #longform #article #education #elsalvador #communities #decentralized @ cbaa0c82:e9313245
2025-04-02 18:53:57#TheWholeGrain - #March2025 March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky! Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary! End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!? **Sunday Singles - March 2025** 2025-03-02 | Sunday Single 82 Title: Slingshot! *Watch out! Toast is quite the sharpshooter!* https://i.nostr.build/zHA9C7cOOZLOCl0o.png 2025-03-09 | Sunday Single 83 Title: Puzzles *End-Piece just figured out the puzzle!* https://i.nostr.build/u2EBdcsuwO2xo23P.png 2025-03-16 | Sunday Single 84 Title: Basketball *Oh, the madness!* https://i.nostr.build/8F1OFFVra7zQOIy6.png 2025-03-23 | Sunday Single 85 Title: Coffee *The perfect way to start the day.* https://i.nostr.build/aiGZOvOmow3igru6.png 2025-03-30 | Sunday Single 86 Title: Origami *End-Piece has a way with paper.* https://i.nostr.build/0ySzGwF9QnZxwLxD.png **Adventure Series: Questline** The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated! Artist: Dakota Jernigan (The Bitcoin Painter) Writer: Daniel David (dan 🍞) 2025-03-11 | Questline 005 - Under Attack *Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.* https://i.nostr.build/F24sd7SFFbsW9WZY.png 2025-03-25 | Questline 006 - A Finished Battle *End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.* https://i.nostr.build/n5a7Jztq9MHxuGNf.png **Other Content Released in March 2025** 2025-03-05 | Toast's Comic Collection Title: E: The Last Slice #11 *A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.* https://i.nostr.build/aar20oHAAKmZOovD.png 2025-03-12 | Concept Art Title: Original Bread and Toast *This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.* https://i.nostr.build/yqkmBuTiH8AKbCzI.png 2025-03-19 | Bitcoin Art Title: Bitcoin/Bread Block Height: 888566 *Two things that just go together.* https://i.nostr.build/MDPkzOPVEaOJVTFE.png Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com! **So long, March!** ***Bread, Toast, and End-Piece*** #BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️ ***List of nPubs Mentioned:*** The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
@ cbaa0c82:e9313245
2025-04-02 18:53:57#TheWholeGrain - #March2025 March of 2025 was a standard month for Bread and Toast. However, it did include a the occasional five Sunday Singles which seems like hitting the jackpot! Talk about lucky! Included with the five Sunday Singles was two more pages of the Adventure Series: Questline where we saw Bread, Toast, and End-Piece face off against their first adversary! End-Piece made a first appearance for in Toast's Comic Collection under the title E: The Last Slice while the Concept Art piece was the original drawing of all three slices of bread together. And, last of all we updated the Bitcoin logo because why not!? **Sunday Singles - March 2025** 2025-03-02 | Sunday Single 82 Title: Slingshot! *Watch out! Toast is quite the sharpshooter!* https://i.nostr.build/zHA9C7cOOZLOCl0o.png 2025-03-09 | Sunday Single 83 Title: Puzzles *End-Piece just figured out the puzzle!* https://i.nostr.build/u2EBdcsuwO2xo23P.png 2025-03-16 | Sunday Single 84 Title: Basketball *Oh, the madness!* https://i.nostr.build/8F1OFFVra7zQOIy6.png 2025-03-23 | Sunday Single 85 Title: Coffee *The perfect way to start the day.* https://i.nostr.build/aiGZOvOmow3igru6.png 2025-03-30 | Sunday Single 86 Title: Origami *End-Piece has a way with paper.* https://i.nostr.build/0ySzGwF9QnZxwLxD.png **Adventure Series: Questline** The group is attacked by a crow with Bread being the target of the giant bird, but with a group of trusty friends any enemy can be defeated! Artist: Dakota Jernigan (The Bitcoin Painter) Writer: Daniel David (dan 🍞) 2025-03-11 | Questline 005 - Under Attack *Toast and End-Piece are able to escape the attack from the giant winged predator, but Bread being distracted by thoughts of the village is caught off guard. End-Piece immediately charges the attacker with a fury of mallet swings. Meanwhile, Toast loads up an arrow with intentions of piercing through the giant bird.* https://i.nostr.build/F24sd7SFFbsW9WZY.png 2025-03-25 | Questline 006 - A Finished Battle *End-Piece lands a series of blows to the winged beast. Toast finishes it off with a second arrow to the heart. Bread is only slightly injured, but is more upset about having been so vulnerable due to being so distracted. Moving forward Bread will have to be more vigilant.* https://i.nostr.build/n5a7Jztq9MHxuGNf.png **Other Content Released in March 2025** 2025-03-05 | Toast's Comic Collection Title: E: The Last Slice #11 *A gluten-based pandemic has killed off all slices of bread that are not Toast except for one slice of bread that happens to be an end piece.* https://i.nostr.build/aar20oHAAKmZOovD.png 2025-03-12 | Concept Art Title: Original Bread and Toast *This was the first drawing of all three characters together. It was used a lot for branding when the project first started up in 2023.* https://i.nostr.build/yqkmBuTiH8AKbCzI.png 2025-03-19 | Bitcoin Art Title: Bitcoin/Bread Block Height: 888566 *Two things that just go together.* https://i.nostr.build/MDPkzOPVEaOJVTFE.png Thanks for checking out the seventh issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com! **So long, March!** ***Bread, Toast, and End-Piece*** #BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🍞 #🖼️ ***List of nPubs Mentioned:*** The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6 @ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher
@ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher @ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus
@ 8d34bd24:414be32b
2025-04-02 14:13:03I was reading this passage last night: > …from that time when one came to a grain heap of twenty measures, there would be only ten; and when one came to the wine vat to draw fifty measures, there would be only twenty. I smote you and every work of your hands with blasting wind, mildew and hail; **yet you did not come back to Me**,’ declares the Lord. ‘Do consider from this day onward, from the twenty-fourth day of the ninth month; from the day when the temple of the Lord was founded, consider: Is the seed still in the barn? Even including the vine, the fig tree, the pomegranate and the olive tree, it has not borne fruit. **Yet from this day on I will bless you**.’ ” (Haggai 2:16-19) {emphasis mine} Why were bad things happening to the Israelites? Because they were not following God. Why did God allow these difficult situations to occur? Because God was calling them back to Himself. This made me think of several times lately, when I had written about Christians going through hard times, that fellow believers had tried to kindly correct me implying that God would not allow these painful things to happen to believers. They were trying to defend God’s honor, but instead they were degrading God. If God is not in control of everything, then either God is unable to protect His own from harm because of sin or bad things happened accidentally and God ignored the injustice. Saying God was not in control of allowing every hardship is either saying God isn’t strong enough, isn’t smart enough, or isn’t loving enough. The God I serve is omniscient, omnipotent, omnipresent, and love incarnate. He also didn’t promise us easy, pleasant lives, but did promise that good would come out of every situation. > And we know that in all things God works for the good of those who love him, who have been called according to his purpose. (Romans 8:28) When Jesus walked on earth and some people said they wanted to follow Him, His response was not what we would expect: > And He was saying to them all, “**If anyone wishes to come after Me, he must deny himself, and take up his cross daily and follow Me**. For whoever wishes to save his life will lose it, but whoever loses his life for My sake, he is the one who will save it. For what is a man profited if he gains the whole world, and loses or forfeits himself? For whoever is ashamed of Me and My words, the Son of Man will be ashamed of him when He comes in His glory, and the glory of the Father and of the holy angels. (Luke 9:23-26) {emphasis mine} When one particular man said that he would follow Jesus anywhere, Jesus responded this way. > As they were going along the road, someone said to Him, “I will follow You wherever You go.” And Jesus said to him, “**The foxes have holes and the birds of the air have nests, but the Son of Man has nowhere to lay His head**.” (Luke 9:57-58) {emphasis mine} Jesus was brutally honest that following Him would not be easy or comfortable. Following Jesus is more likely to lead to hardship and persecution that prosperity and comfort. > “Then **they will deliver you to tribulation, and will kill you, and you will be hated by all nations because of My name**. At that time many will fall away and will betray one another and hate one another. Many false prophets will arise and will mislead many. Because lawlessness is increased, most people’s love will grow cold. But **the one who endures to the end, he will be saved**. This gospel of the kingdom shall be preached in the whole world as a testimony to all the nations, and then the end will come. (Matthew 24:9-14) {emphasis mine} Of course God isn’t putting us through hardship to torture us. He is putting us in situations to grow our faith and dependence on Him, i.e. Abraham. He is putting us in situations where we can minister to others, i.e. Joseph. He is using us as examples of faith to others, i.e. Job. Any hardship has an eternal purpose. Sometimes we can see it (at least eventually) if we are looking for God’s will and plan. Sometime we won’t see what He was accomplishing until we get to heaven. Still we need to trust God through it all, knowing His plan is perfect. > “**For my thoughts are not your thoughts,\ > neither are your ways my ways**,”\ > declares the Lord. > > “As the heavens are higher than the earth,\ > so are **my ways higher than your ways**\ > and my thoughts than your thoughts. > > As the rain and the snow\ > come down from heaven,\ > and do not return to it\ > without watering the earth\ > and making it bud and flourish,\ > so that it yields seed for the sower and bread for the eater,\ > so is **my word that goes out from my mouth:\ > It will not return to me empty,\ > but will accomplish what I desire\ > and achieve the purpose for which I sent it**. (Isaiah 55:8-11) {emphasis mine} God understands how hard it is to understand what He is accomplishing. We live in the here and now while He is outside time and space and therefore has a heavenly and eternal perspective that we will never truly have this side of heaven. He has told us how the story ends, so that we can have peace and trust Him through whatever circumstances He has blessed us. > Jesus answered them, “Do you now believe? Behold, an hour is coming, and has already come, for you to be scattered, each to his own home, and to leave Me alone; and yet I am not alone, because the Father is with Me. **These things I have spoken to you, so that in Me you may have peace. In the world you have tribulation, but take courage; I have overcome the world**.” (John 16:31-33) {emphasis mine} In fact, Jesus made this so clear that His disciples rejoiced in persecution they received due to obeying Him and sharing His word. > They took his advice; and after calling the apostles in, they flogged them and ordered them not to speak in the name of Jesus, and *then* released them. So they went on their way from the presence of the Council, **rejoicing that they had been considered worthy to suffer shame for *His* name**. (Acts 5:40-41) {emphasis mine} Peter specifically warns believers to expect trials and hardship. > Dear friends, **do not be surprised at the fiery ordeal that has come on you to test you, as though something strange were happening to you**. But rejoice inasmuch as you participate in the sufferings of Christ, so that you may be overjoyed when his glory is revealed. **If you are insulted because of the name of Christ, you are blessed**, for the Spirit of glory and of God rests on you. If you suffer, it should not be as a murderer or thief or any other kind of criminal, or even as a meddler. However, **if you suffer as a Christian, do not be ashamed, but praise God** that you bear that name. For it is time for judgment to begin with God’s household; and if it begins with us, what will the outcome be for those who do not obey the gospel of God? And, > > “If it is hard for the righteous to be saved,\ > what will become of the ungodly and the sinner?” > > So then, those who suffer according to God’s will should commit themselves to their faithful Creator and continue to do good. (1 Peter 4:12-19) {emphasis mine} Paul writes about begging God to take away a health issue. Eventually he accepted it as part of God’s plan for his life and boasted gladly in his hardship. > …Therefore, in order **to keep me from becoming conceited, I was given a thorn** in my flesh, a messenger of Satan, to torment me. Three times **I pleaded with the Lord to take it away from me. But he said to me, “My grace is sufficient for you**, for my power is made perfect in weakness.” Therefore **I will boast all the more gladly about my weaknesses, so that Christ’s power may rest on me**. That is why, for Christ’s sake, I delight in weaknesses, in insults, in hardships, in persecutions, in difficulties. For when I am weak, then I am strong. (2 Corinthians 12:7b-10) {emphasis mine} No matter what hardships we experience in life, whether poverty or persecution or poor health or loss of a loved one or any other hardship, God is with us working everything for our good. > Who will separate us from the love of Christ? Will tribulation, or distress, or persecution, or famine, or nakedness, or peril, or sword? Just as it is written, > > “For Your sake we are being put to death all day long;\ > We were considered as sheep to be slaughtered.” > ****But in all these things we overwhelmingly conquer through Him who loved us**. For I am convinced that neither death, nor life, nor angels, nor principalities, nor things present, nor things to come, nor powers, nor height, nor depth, nor any other created thing, will be able to separate us from the love of God, which is in Christ Jesus our Lord. (Romans 8:35-39) {emphasis mine} I like to look at the story of Joseph as an example of God’s extraordinary plan in the life of a faithful believer. Joseph trusted and honored God. God had a plan for Joseph to be used to save the lives of his family and the people of the Middle East from famine, but God didn’t just instantly put Joseph in a position of power to help. He prepared Joseph and slowly moved him to where he needed to be. First Josephs brothers wanted to kill him out of jealousy, but God used greed to get them to sell Joseph as a slave instead. He orchestrated the right slave traders to walk by at the right time so that Joseph would wind up in the house of Potiphar, the Pharaoh’s guard. Then when Joseph acted honorably towards God, his master, and his master’s wife, Joseph was sent to jail for years. I’m sure Joseph was wondering why God would send him to prison for doing what was right, but it put him into the presence of the cupbearer of Pharaoh. A long time after correctly interpreting the cup bearer’s dream, Joseph was called up to interpret Pharaoh’s dream, put in charge of the famine preparation and became second in command after Pharaoh. Joseph, after years of slavery and jail time, was now the second most powerful man in the Middle East, if not the world. God had a plan, but it was hard to see until its completion. In the same way, Job lost his wealth, his children, his health, and his reputation, but remember that Satan had to get God’s permission before anything could be done to hurt Job. So many people today are blessed by seeing Job’s response to hardship and loss, by seeing Job’s faith, his struggle, and his submission to God’s plan. In this case God even gives Job more after this time of testing than he had before. When we experience hardship we need to know that God has a plan for our life. It may be something amazing here on Earth. It may be souls won for Christ. It may be to prepare us for heaven. Whatever the case, it is for our good. We don’t need to be ashamed that God would allow hardship. We grow most when we experience hardship. Our light shines brightest in darkness. > Oh, the depth of the riches of the wisdom and knowledge of God!\ > How unsearchable his judgments,\ > and his paths beyond tracing out!\ > “Who has known the mind of the Lord?\ > Or who has been his counselor?”\ > “Who has ever given to God,\ > that God should repay them?”\ > For from him and through him and for him are all things.\ > To him be the glory forever! Amen. (Romans 11:33-36) Trust Jesus