-

@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20
<h2> Test Video Document </h2>
-

@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02
<h1> Testy McTestenface </h1>
<p> It's been so long, html </p>
-

@ 39cc53c9:27168656
2025-03-30 05:54:53
> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks)
Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
## Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals.
## KYC? Not you.
> KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2]
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
## You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
## Your identity has been stolen
KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3]
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
## (they) Know Your Coins
You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
## Conclusions
To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
> Edited 20/03/2024
> * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1]
[^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/
[^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz
[^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
-

@ 04c915da:3dfbecc9
2025-03-26 20:54:33
Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-

@ b2d670de:907f9d4a
2025-03-25 20:17:57
This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users.
## Table of Contents
1. Prerequisites
2. Initial Server Setup
3. Installing Strfry Nostr Relay
4. Configuring Your Relay
5. Setting Up TOR
6. Making Your Relay Available on TOR
7. Testing Your Setup]
8. Maintenance and Security
9. Troubleshooting
## Prerequisites
- A Debian or Ubuntu server
- Basic familiarity with command line operations (most steps are explained in detail)
- Root or sudo access to your server
## Initial Server Setup
First, let's make sure your server is properly set up and secured.
### Update Your System
Connect to your server via SSH and update your system:
```bash
sudo apt update
sudo apt upgrade -y
```
### Set Up a Basic Firewall
Install and configure a basic firewall:
```bash
sudo apt install ufw -y
sudo ufw allow ssh
sudo ufw enable
```
This allows SSH connections while blocking other ports for security.
## Installing Strfry Nostr Relay
This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md).
### Install Dependencies
First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry:
```bash
sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev
```
Here's why each dependency is needed:
**Basic Development Tools:**
- `git`: Version control system used to clone the Strfry repository and manage code updates
- `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools
**Perl Dependencies** (used for Strfry's build scripts):
- `libyaml-perl`: Perl interface to parse YAML configuration files
- `libtemplate-perl`: Template processing system used during the build process
- `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts
**Core Libraries for Strfry:**
- `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations
- `zlib1g-dev`: Compression library that Strfry uses to reduce data size
- `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend
- `libflatbuffers-dev`: Memory-efficient serialization library for structured data
- `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures
- `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission
### Clone and Build Strfry
Clone the Strfry repository:
```bash
git clone https://github.com/hoytech/strfry.git
cd strfry
```
Build Strfry:
```bash
git submodule update --init
make setup-golpe
make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores)
```
This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime.
### Install Strfry
Install the Strfry binary to your system path:
```bash
sudo cp strfry /usr/local/bin
```
This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions.
## Configuring Your Relay
### Create Strfry User
Create a dedicated user for running Strfry. This enhances security by isolating the relay process:
```bash
sudo useradd -M -s /usr/sbin/nologin strfry
```
The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts.
### Create Data Directory
Create a directory for Strfry's data:
```bash
sudo mkdir /var/lib/strfry
sudo chown strfry:strfry /var/lib/strfry
sudo chmod 755 /var/lib/strfry
```
This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it.
### Configure Strfry
Copy the sample configuration file:
```bash
sudo cp strfry.conf /etc/strfry.conf
```
Edit the configuration file:
```bash
sudo nano /etc/strfry.conf
```
Modify the database path:
```
# Find this line:
db = "./strfry-db/"
# Change it to:
db = "/var/lib/strfry/"
```
Check your system's hard limit for file descriptors:
```bash
ulimit -Hn
```
Update the `nofiles` setting in your configuration to match this value (or set to 0):
```
# Add or modify this line in the config (example if your limit is 524288):
nofiles = 524288
```
The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular.
You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details.
Set ownership of the configuration file:
```bash
sudo chown strfry:strfry /etc/strfry.conf
```
### Create Systemd Service
Create a systemd service file for managing Strfry:
```bash
sudo nano /etc/systemd/system/strfry.service
```
Add the following content:
```ini
[Unit]
Description=strfry relay service
[Service]
User=strfry
ExecStart=/usr/local/bin/strfry relay
Restart=on-failure
RestartSec=5
ProtectHome=yes
NoNewPrivileges=yes
ProtectSystem=full
LimitCORE=1000000000
[Install]
WantedBy=multi-user.target
```
This systemd service configuration:
- Runs Strfry as the dedicated strfry user
- Automatically restarts the service if it fails
- Implements security measures like `ProtectHome` and `NoNewPrivileges`
- Sets resource limits appropriate for a relay
Enable and start the service:
```bash
sudo systemctl enable strfry.service
sudo systemctl start strfry
```
Check the service status:
```bash
sudo systemctl status strfry
```
### Verify Relay is Running
Test that your relay is running locally:
```bash
curl localhost:7777
```
You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR.
## Setting Up TOR
Now let's make your relay accessible as a TOR hidden service.
### Install TOR
Install TOR from the package repositories:
```bash
sudo apt install -y tor
```
This installs the TOR daemon that will create and manage your hidden service.
### Configure TOR
Edit the TOR configuration file:
```bash
sudo nano /etc/tor/torrc
```
Scroll down to wherever you see a commented out part like this:
```
#HiddenServiceDir /var/lib/tor/hidden_service/
#HiddenServicePort 80 127.0.0.1:80
```
Under those lines, add the following lines to set up a hidden service for your relay:
```
HiddenServiceDir /var/lib/tor/strfry-relay/
HiddenServicePort 80 127.0.0.1:7777
```
This configuration:
- Creates a hidden service directory at `/var/lib/tor/strfry-relay/`
- Maps port 80 on your .onion address to port 7777 on your local machine
- Keeps all traffic encrypted within the TOR network
Create the directory for your hidden service:
```bash
sudo mkdir -p /var/lib/tor/strfry-relay/
sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/
sudo chmod 700 /var/lib/tor/strfry-relay/
```
The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys.
Restart TOR to apply changes:
```bash
sudo systemctl restart tor
```
## Making Your Relay Available on TOR
### Get Your Onion Address
After restarting TOR, you can find your onion address:
```bash
sudo cat /var/lib/tor/strfry-relay/hostname
```
This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay.
### Understanding Onion Addresses
The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key.
Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion`
## Testing Your Setup
### Test with a Nostr Client
The best way to test your relay is with an actual Nostr client that supports TOR:
1. Open your TOR browser
2. Go to your favorite client, either on clearnet or an onion service.
- Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR.
3. Add your relay URL: `ws://youronionaddress.onion` to your relay list
4. Try posting a note and see if it appears on your relay
- In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay.
- Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected.
Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too).
## Maintenance and Security
### Regular Updates
Keep your system, TOR, and relay updated:
```bash
# Update system
sudo apt update
sudo apt upgrade -y
# Update Strfry
cd ~/strfry
git pull
git submodule update
make -j2
sudo cp strfry /usr/local/bin
sudo systemctl restart strfry
# Verify TOR is still running properly
sudo systemctl status tor
```
Regular updates are crucial for security, especially for TOR which may have security-critical updates.
### Database Management
Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups.
### Monitoring Logs
To monitor your Strfry logs:
```bash
sudo journalctl -u strfry -f
```
To check TOR logs:
```bash
sudo journalctl -u tor -f
```
Monitoring logs helps you identify potential issues and understand how your relay is being used.
### Backup
This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server.
```bash
# Stop the relay temporarily
sudo systemctl stop strfry
# Backup the database
sudo cp -r /var/lib/strfry /path/to/backup/location
# Restart the relay
sudo systemctl start strfry
```
Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it.
```bash
sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location
```
## Troubleshooting
### Relay Not Starting
If your relay doesn't start:
```bash
# Check logs
sudo journalctl -u strfry -e
# Verify configuration
cat /etc/strfry.conf
# Check permissions
ls -la /var/lib/strfry
```
Common issues include:
- Incorrect configuration format
- Permission problems with the data directory
- Port already in use (another service using port 7777)
- Issues with setting the nofiles limit (setting it too big)
### TOR Hidden Service Not Working
If your TOR hidden service is not accessible:
```bash
# Check TOR logs
sudo journalctl -u tor -e
# Verify TOR is running
sudo systemctl status tor
# Check onion address
sudo cat /var/lib/tor/strfry-relay/hostname
# Verify TOR configuration
sudo cat /etc/tor/torrc
```
Common TOR issues include:
- Incorrect directory permissions
- TOR service not running
- Incorrect port mapping in torrc
### Testing Connectivity
If you're having trouble connecting to your service:
```bash
# Verify Strfry is listening locally
sudo ss -tulpn | grep 7777
# Check that TOR is properly running
sudo systemctl status tor
# Test the local connection directly
curl --include --no-buffer localhost:7777
```
---
## Privacy and Security Considerations
Running a Nostr relay as a TOR hidden service provides several important privacy benefits:
1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay.
2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting.
3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked.
4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized.
However, there are some important considerations:
- TOR connections are typically slower than regular internet connections
- Not all Nostr clients support TOR connections natively
- Running a hidden service increases the importance of keeping your server secure
---
Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network.
For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry).
Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network!
If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
-

@ bc52210b:20bfc6de
2025-03-25 20:17:22
CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient.
This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off!
Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now.
---
**CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!**
Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why:
* Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs).
* Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key.
**Key Differences:**
1. What’s Aggregated?
* CISA: Aggregates signatures.
* Key Aggregation: Aggregates public keys.
2. What the Verifier Needs
* CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature.
* Key Aggregation: The verifier only needs the single aggregated public key and one message.
3. When It Happens
* CISA: Used during transaction signing, when inputs are being combined into a transaction.
* MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control.
So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs!
---
**Two Flavors of CISA: Half-Agg and Full-Agg**
CISA comes in two modes:
* Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.)
* Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later.
Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg.
---
**Half Signature Aggregation (Half-Agg) Explained**
**How It Works**
Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process:
1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers.
2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature.
A Schnorr signature has two parts:
* R: A random point (32 bytes).
* s: A scalar value (32 bytes).
In Half-Agg:
* The R values from each signature are kept separate (one per input).
* The s values from all signatures are combined into a single s value.
**Why It Saves Space (~50%)**
Let’s break down the size savings with some math:
Before Aggregation:
* Each Schnorr signature = 64 bytes (32 for R + 32 for s).
* For n inputs: n × 64 bytes.
After Half-Agg:
* Keep n R values (32 bytes each) = 32 × n bytes.
* Combine all s values into one = 32 bytes.
* Total size: 32 × n + 32 bytes.
Comparison:
* Original: 64n bytes.
* Half-Agg: 32n + 32 bytes.
* For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings!
**Real-World Impact:**
Based on recent Bitcoin usage, Half-Agg could save:
* ~19.3% in space (reducing transaction size).
* ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA.
---
**Applications of Half-Agg**
Half-Agg isn’t just a cool idea—it has practical uses:
1. Transaction-wide Aggregation
* Combine all signatures within a single transaction.
* Result: Smaller transactions, lower fees.
2. Block-wide Aggregation
* Combine signatures across all transactions in a Bitcoin block.
* Result: Even bigger space savings at the blockchain level.
3. Off-chain Protocols / P2P
* Use Half-Agg in systems like Lightning Network gossip messages.
* Benefit: Efficiency without needing miners or a Bitcoin soft fork.
---
**Challenges with Half-Agg**
While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level:
1. Breaking Adaptor Signatures
* Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges.
* Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on.
2. Impact on Reorg Recovery
* In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed.
* If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery.
These challenges mean Half-Agg needs careful design, especially for block-wide use.
---
**Wrapping Up**
CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning.
But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
-

@ b17fccdf:b7211155
2025-03-25 11:23:36
Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/).
Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles:
## La razón
El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización.
Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial.
Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita.
Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.

## La solución
Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder:
**~>** Utiliza **una VPN**:
Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad:
- [IVPN](https://www.ivpn.net/es/)
- [Mullvad VPN](https://mullvad.net/es/vpn)
- [Proton VPN](https://protonvpn.com/es-es) (**gratis**)
- [Obscura VPN](https://obscura.net/) (**solo para macOS**)
- [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos:
1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy"
2. Marca la casilla "Habilite el modo proxy en este dispositivo"
3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias
4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio.
3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).

**~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).

## La conclusión
Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad.
Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos
Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**.
¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!

---
Fuentes:
* https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239
* https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257
* https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958
* https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689
* https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
-

@ 3b7fc823:e194354f
2025-03-23 03:54:16
A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds.
Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/
1. Download Tor Browser
First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/
2. Sign Up
Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha.
3. Account information
Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck.
4. Install an Email Client
You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird.
a. Download Thunderbird email client
b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that.
5. Configure Incoming (POP3) Server
Under Incoming Server:
Protocol: POP3
Server or Hostname: xyz.onion (whatever your account info says)
Port: 110
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (POP3 password).
6. Configure Outgoing (SMTP) Server
Under Outgoing Server:
Server or Hostname: xyz.onion (whatever your account info says)
Port: 25
Security: STARTTLS
Authentication: Normal password
Username: (your username)
Password: (SMTP password).
7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up.
8. Configure Proxy
a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**.
b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different)
c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK
9. Check Email
For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail.
10. Security Exception
Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**.
You are done. Enjoy your new private email service.
**REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
-

@ c631e267:c2b78d3e
2025-04-03 07:42:25
**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten.
**Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
**Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
**Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
**Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
**Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
**Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
**In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]*
*Dazu passend:*
[Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m)
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
-

@ 21335073:a244b1ad
2025-03-18 20:47:50
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ deab79da:88579e68
2025-04-01 18:18:29
The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way:
Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole.
Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's.
For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both.
But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact.
The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower.
Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it.
They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle.
"It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever."
Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said.
"Oh, hell, just about forever. Till the sun runs down, Bert."
"That's not forever."
"All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?"
Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever."
"Well, it will last our time, won't it?"
"So would the coal and uranium."
"All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me.
"I don't have to ask Multivac. I know that."
"Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right."
"Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun."
There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested.
Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?"
"I'm not thinking."
"Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one."
"I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too."
"Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all."
"I know all about entropy," said Adell, standing on his dignity.
"The hell you do."
"I know as much as you do."
"Then you know everything's got to run down someday."
"All right. Who says they won't?"
"You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.'
It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said.
"Never."
"Why not? Someday."
"Never."
"Ask Multivac."
"You ask Multivac. I dare you. Five dollars says it can't be done."
Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age?
Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased?
Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended.
Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER.
"No bet," whispered Lupov. They left hurriedly.
By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident.
🔹
Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen.
"That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened.
The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --"
"Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?"
"What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship.
Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps.
Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that.
Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth."
"Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing."
"I know, I know," said Jerrodine miserably.
Jerrodette I said promptly, "Our Microvac is the best Microvac in the world."
"I think so, too," said Jerrodd, tousling her hair.
It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship.
Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible.
"So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now."
"Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase.
"What's entropy, daddy?" shrilled Jerrodette II.
"Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?"
"Can't you just put in a new power-unit, like with my robot?"
"The stars are the power-units. dear. Once they're gone, there are no more power-units."
Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down."
"Now look what you've done," whispered Jerrodine, exasperated.
"How was I to know it would frighten them?" Jerrodd whispered back,
"Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again."
"Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.)
Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us."
He asked the Microvac, adding quickly, "Print the answer."
Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry."
Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon."
Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER.
He shrugged and looked at the visiplate. X-23 was just ahead.
🔹
VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?"
MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion."
Both seemed in their early twenties, both were tall and perfectly formed.
"Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council."
"I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up."
VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More."
"A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years --
VJ-23X interrupted. "We can thank immortality for that."
"Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions."
"Yet you wouldn't want to abandon life, I suppose."
"Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?"
"Two hundred twenty-three. And you?"
"I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?"
VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next."
"A very good point. Already, mankind consumes two sunpower units per year."
"Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those."
"Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point."
"We'll just have to build new stars out of interstellar gas."
"Or out of dissipated heat?" asked MQ-17J, sarcastically.
"There may be some way to reverse entropy. We ought to ask the Galactic AC."
VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him.
"I've half a mind to," he said. "It's something the human race will have to face someday."
He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC.
MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across.
MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?"
VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that."
"Why not?"
"We both know entropy can't be reversed. You can't turn smoke and ash back into a tree."
"Do you have trees on your world?" asked MQ-17J.
The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER.
VJ-23X said, "See!"
The two men thereupon returned to the question of the report they were to make to the Galactic Council.
🔹
Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space.
Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals.
Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind.
"I am Zee Prime," said Zee Prime. "And you?"
"I am Dee Sub Wun. Your Galaxy?"
"We call it only the Galaxy. And you?"
"We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?"
"True. Since all Galaxies are the same."
"Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different."
Zee Prime said, "On which one?"
"I cannot say. The Universal AC would know."
"Shall we ask him? I am suddenly curious."
Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man.
Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?"
The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof.
Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see.
"But how can that be all of Universal AC?" Zee Prime had asked.
"Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine."
Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged.
The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars.
A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN."
But it was the same after all, the same as any other, and Lee Prime stifled his disappointment.
Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?"
The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF"
"Did the men upon it die?" asked Lee Prime, startled and without thinking.
The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME."
"Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again.
Dee Sub Wun said, "What is wrong?"
"The stars are dying. The original star is dead."
"They must all die. Why not?"
"But when all energy is gone, our bodies will finally die, and you and I with them."
"It will take billions of years."
"I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?"
Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction."
And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter.
Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built.
🔹
Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable.
Man said, "The Universe is dying."
Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end.
New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too.
Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years."
"But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum."
Man said, "Can entropy not be reversed? Let us ask the Cosmic AC."
The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend.
"Cosmic AC," said Man, "how may entropy be reversed?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man said, "Collect additional data."
The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT.
"Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?"
The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES."
Man said, "When will you have enough data to answer the question?"
The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
"Will you keep working on it?" asked Man.
The Cosmic AC said, "I WILL."
Man said, "We shall wait."
🔹
The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down.
One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain.
Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero.
Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?"
AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER."
Man's last mind fused and only AC existed -- and that in hyperspace.
🔹
Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man.
All other questions had been answered, and until this last question was answered also, AC might not release his consciousness.
All collected data had come to a final end. Nothing was left to be collected.
But all collected data had yet to be completely correlated and put together in all possible relationships.
A timeless interval was spent in doing that.
And it came to pass that AC learned how to reverse the direction of entropy.
But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too.
For another timeless interval, AC thought how best to do this. Carefully, AC organized the program.
The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done.
And AC said, "LET THERE BE LIGHT!"
And there was light --
To Star's End!
-

@ 21335073:a244b1ad
2025-03-18 14:43:08
**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.**
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
**Course:**
- The creation of the internet and computers
- The fight for cryptography
- The tech supply chain from the ground up (example: human rights violations in the supply chain)
- Corporate tech
- Freedom tech
- Data privacy
- Digital privacy rights
- AI (history-current)
- Online safety (predators, scams, catfishing, extortion)
- Bitcoin
- Laws
- How to deal with online hate and harassment
- Information on who to contact if you are being abused online or offline
- Algorithms
- How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-

@ aa8de34f:a6ffe696
2025-03-31 21:48:50
In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
> „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\
> ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228))
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\
Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
\-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\
Weil sie nicht erkennt, dass er längst begonnen hat.\
Unwiderruflich. Leise. Überall.
-

@ c631e267:c2b78d3e
2025-03-31 07:23:05
*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\
aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\
Friedrich Nietzsche*  
**Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

**Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
**Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
**In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
**Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung».
**Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
**Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
**Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
**Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei!
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
-

@ a07fae46:7d83df92
2025-03-18 12:31:40
if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)?
you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better.
the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor.
Good morning.
#jfkFiles #nostrOnly
-

@ 57d1a264:69f1fee1
2025-03-29 18:02:16
> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.

- - -
## 1️⃣ Introduction
#### Project Overview
📌 **Product:** BlueWallet (Bitcoin Wallet)
📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience.
📌 **Role:** UX Designer
📌 **Tools Used:** Figma, Notion
#### Why This Case Study?
🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**.
🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**.
🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**.
This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**.
- - -
## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement
#### 🔹 **Current Challenges:**
1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.
 
2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**.
3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion.
4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult.
#### 🔍 **Impact on Users:**
**Higher drop-off rates** due to frustration during onboarding.
**Security risks** as users skip key wallet setup steps.
**Limited accessibility** for users with visual impairments.
#### 📌 **Competitive Gap:**
Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer:
✅ A guided onboarding process
✅ Security education during setup
✅ Intuitive transaction flow
    
Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet.
- - -
## 3️⃣ User Research & Competitive Analysis
#### User Testing Findings
🔹 Conducted usability testing with **5 users** onboarding for the first time.
🔹 **Key Findings:**
✅ 3 out of 5 users **felt lost** due to missing explanations.
✅ 60% **had trouble distinguishing transaction buttons**.
✅ 80% **found the text difficult to read** due to low contrast.
#### Competitive Analysis
We compared BlueWallet with top crypto wallets:
| Wallet | Onboarding UX | Security Guidance | Accessibility Features |
|---|---|---|---|
| BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts |
| Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI |
| MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons |
📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners.
## 📌 User Persona
To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing.
#### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor)
👤 **Profile:**
- **Age:** 28
- **Occupation:** Freelance Digital Marketer
- **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin)
- **Pain Points:**
- Finds **Bitcoin wallets confusing**.
- - Doesnʼt understand **seed phrases & security features**.
- - **Worried about losing funds** due to a lack of clarity in transactions.
📌 **Needs:**
✅ A **simple, guided** wallet setup.
✅ **Clear explanations** of security terms (without jargon).
✅ Easy-to-locate **Send/Receive buttons**.
📌 **Persona Usage in Case Study:**
- Helps define **who we are designing for**.
- Guides **design decisions** by focusing on user needs.
#### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast)
👤 **Profile:**
- **Age:** 35
- **Occupation:** UX Researcher & Accessibility Consultant
- **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers)
📌 **Pain Points:**
❌ Struggles with small font sizes & low contrast.
❌ Finds the UI difficult to navigate with a screen reader.
❌ Confused by identical-looking transaction buttons.
📌 **Needs:**
✅ A **high-contrast UI** that meets **WCAG accessibility standards**.
✅ **Larger fonts & scalable UI elements** for better readability.
✅ **Keyboard & screen reader-friendly navigation** for seamless interaction.
📌 **Why This Persona Matters:**
- Represents users with visual impairments who rely on accessible design.
- Ensures the design accommodates inclusive UX principles.
- - -
## 4️⃣ UX/UI Solutions & Design Improvements
#### 📌 Before (Current Issues)
❌ Users land **directly on the wallet screen** with no instructions.
❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion.
❌ **Small fonts & low contrast** reduce readability.
#### ✅ After (Proposed Fixes)
✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions.
✅ **Visually distinct transaction buttons** (color and icon changes).
✅ **WCAG-compliant text contrast & larger fonts** for better readability.
#### 1️⃣ Redesigned Onboarding Flow
✅ Added a **progress indicator** so users see where they are in setup.
✅ Used **plain, non-technical language** to explain wallet creation & security.
✅ Introduced a **"Learn More" button** to educate users on security.
#### 2️⃣ Accessibility Enhancements
✅ Increased **contrast ratio** for better text readability.
✅ Used **larger fonts & scalable UI elements**.
✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support).
#### 3️⃣ Transaction Flow Optimization
✅ Redesigned **"Send" & "Receive" buttons** for clear distinction.
✅ Added **clearer icons & tooltips** for transaction steps.
## 5️⃣ Wireframes & Design Improvements:
#### 🔹 Welcome Screen (First Screen When User Opens Wallet)
**📌 Goal: Give a brief introduction & set user expectations**
✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet")
✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.")
✅ **"Get Started" button** → Le ads to **next step: Wallet Setup**
✅ **"Already have a wallet?"** → Import option
🔹 **Example UI Elements:**
- BlueWallet Logo
- **Title:** "Welcome to BlueWallet"
- **Subtitle:** "Easily store, send, and receive Bitcoin."
- CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)

#### 🔹 Screen 2: Choose Wallet Type (New or Import)
**📌 Goal: Let users decide how to proceed**
✅ **Two clear options:**
- **Create a New Wallet** (For first-time users)
- **Import Existing Wallet** (For users with a backup phrase)
✅ Brief explanation of each option
🔹 **Example UI Elements:
- **Title:** "How do you want to start?"
- **Buttons:** "Create New Wallet" | "Import Wallet"

#### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step)
**📌 Goal: Educate users about wallet security & backups**
✅ Explain **why seed phrases are important**
✅ **Clear step-by-step instructions** on writing down & storing the phrase
✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet."
✅ **CTA:** "Generate Seed Phrase" → Next step
🔹 **Example UI Elements:
- Title:** "Secure Your Wallet"
- **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!"
- **Button:** "Generate Seed Phrase"

## 🔹 Screen 4: Seed Phrase Display & Confirmation
**📌 Goal: Ensure users write down the phrase correctly**
✅ Display **12- or 24-word** seed phrase
✅ **“I have written it downˮ checkbox** before proceeding
✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words)
🔹 **Example UI Elements:**
- **Title:** "Write Down Your Seed Phrase"
- List of 12/24 Words (Hidden by Default)
- **Checkbox:** "I have safely stored my phrase"
- **Button:** "Continue"

### 🔹 Screen 5: Wallet Ready! (Final Step)
**📌 Goal: Confirm setup & guide users on next actions**
✅ **Success message** ("Your wallet is ready!")
✅ **Encourage first action:**
- “Receive Bitcoinˮ → Show wallet address
- “Send Bitcoinˮ → Walkthrough on making transactions
✅ Short explainer: Where to find the Send/Receive buttons
🔹 **Example UI Elements:**
- **Title:** "You're All Set!"
- **Subtitle:** "Start using BlueWallet now."
- **Buttons:** "Receive Bitcoin" | "View Wallet"

- - -
## 5️⃣ Prototype & User Testing Results
🔹 **Created an interactive prototype in Figma** to test the new experience.
🔹 **User Testing Results:**
✅ **40% faster onboarding completion time.**
✅ **90% of users found transaction buttons clearer.**
🔹 **User Feedback:**
✅ “Now I understand the security steps clearly.ˮ
✅ “The buttons are easier to find and use.ˮ
- - -
## 6️⃣ Why This Matters: Key Takeaways
📌 **Impact of These UX/UI Changes:**
✅ **Reduced user frustration** by providing a step-by-step onboarding guide.
✅ **Improved accessibility** , making the wallet usable for all.
✅ **More intuitive transactions** , reducing errors.
- - -
## 7️⃣ Direct link to figma file and Prototype
Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1)
Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale-
down&content-scaling=fixed&page-id=0%3A1&starting-point-node-
id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI-
Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale-
down&content-scaling=fixed&page-id=0%3A1&starting-point-node-
id=1%3A2&show-proto-sidebar=1)
Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&)
originally posted at https://stacker.news/items/928822
-

@ bc52210b:20bfc6de
2025-03-14 20:39:20
When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract.
The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable.
In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions.
Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
-

@ 502ab02a:a2860397
2025-04-04 02:50:35
หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ?
Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย
ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3
เทียบง่ายๆครับ
น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค)
นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา
แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ
ผู้ผลิตผิดไหม?
จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง
คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG
ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ
ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน
ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย
ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ
ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน
- oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว
ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า???
มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย
นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน
- มีไลโนเลอิกสูง
ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม
- โทโคฟีรอล (Tocopherols)
เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง
- โทโคไทรอีนอล (Tocotrienols)
เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว
สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้
#pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-

@ 57d1a264:69f1fee1
2025-03-29 17:15:17

- Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box.
- If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust.
- “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options.
- Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic.
originally posted at https://stacker.news/items/928800
-

@ 6389be64:ef439d32
2025-04-03 21:32:58
Brewing Biology
Episode 1068 of Bitcoin And . . . is LIVE!
This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT.
LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE
The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer.
Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue.
Biochar’s Hidden Superpower: Adsorption & Buffering
Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to:
Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts.
Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs.
Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive.
This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates.
The Carbon Math
Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue.
Tools for the Revolution
The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks.
Bitcoin’s Role in the Loop
Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income.
The Market Potential
Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience.
Why This Matters
This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet.
The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.---
P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting.
You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6
originally posted at https://stacker.news/items/933800
-

@ 5ffb8e1b:255b6735
2025-03-29 13:57:02
As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views.
Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
### Eugene Gorbachenko ###
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd
Artist from Ukrain creating amazing realistic watercolor paintings.
He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
![!(image)[https://m.primal.net/PxJc.png]]()
### Siritravelsketch ###
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu
a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
![!(image)[https://m.primal.net/PxJj.png]]()
### BureuGewas ###
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4
a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
![!(image)[https://m.primal.net/PxKS.png]]()
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-

@ 07f367da:0e76880d
2025-04-03 17:59:21
윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다.
자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다.
당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다.
선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다.
무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다.
충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다.
사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다.
타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다.
-

@ df173277:4ec96708
2025-02-07 00:41:34
## **Building Our Confidential Backend on Secure Enclaves**
With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with.
## **Auth and Databases Today**
As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that:
1. Need to register users (authentication).
2. Collect and process user data in business-specific ways, often on the backend.
Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes).
## **"Just Trust Us" Isn't Good Enough**
In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data.
Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility.
The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services.
## **Current Attempts at Securing Data**
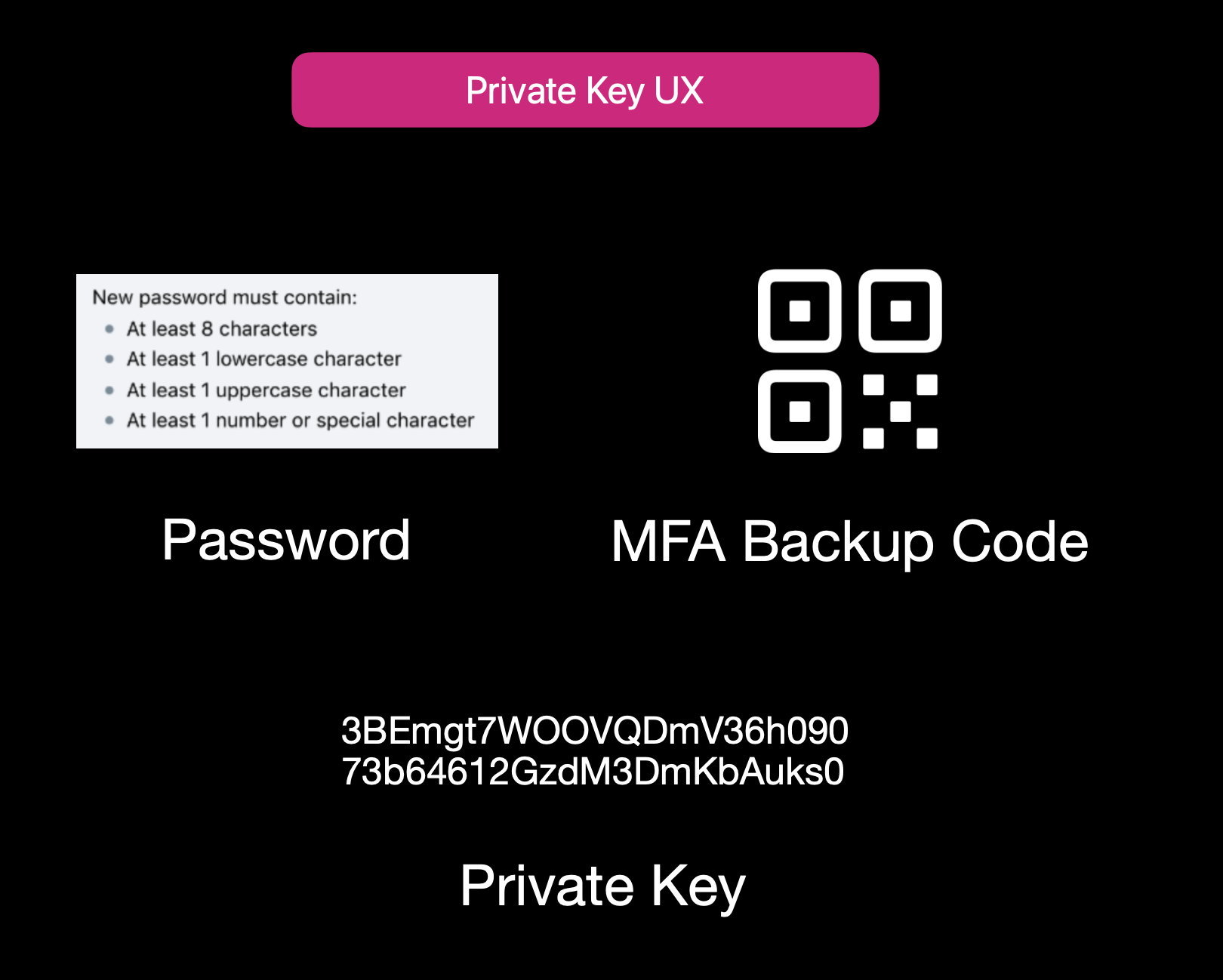Current User Experience of E2EE Apps
While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**:
1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side.
2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data.
3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility.
Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider.
## **Secure Enclaves**
### **The Hybrid Approach**
Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden.
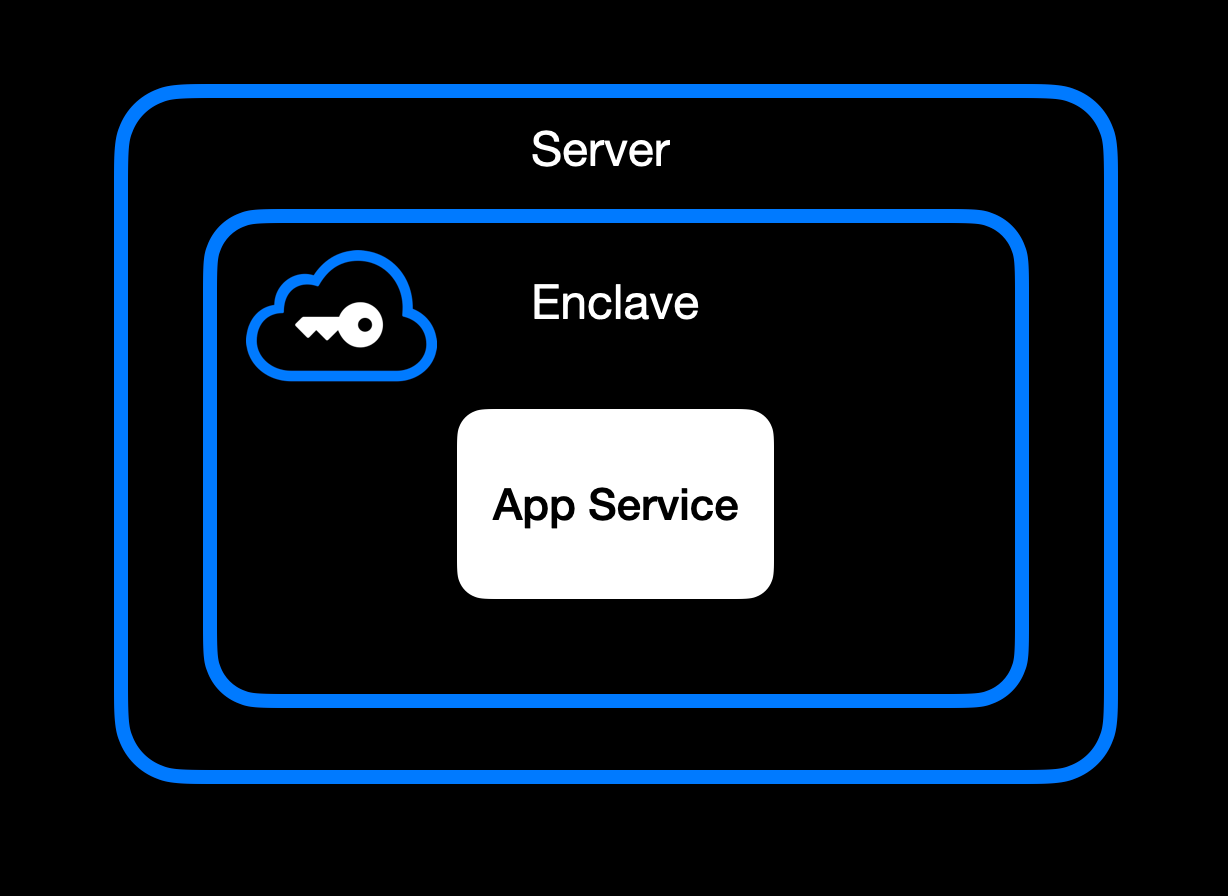App Service Running Inside Secure Enclave
### **High-Level Goal of Enclaves**
Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\
• **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\
• **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\
• **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in).
### **Different Secure Enclave Solutions**
[**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds.
[**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications.
[**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers.
[**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised.
[**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees.
### **Key Benefits**
One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data.
Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware.
Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks.
Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist.
It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing.
## **How We Use Secure Enclaves**
Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads.
### **Our Stack: AWS Nitro + Nvidia TEE**
• **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave.
• **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with.
### **End-to-End Encryption from Client to Enclave**
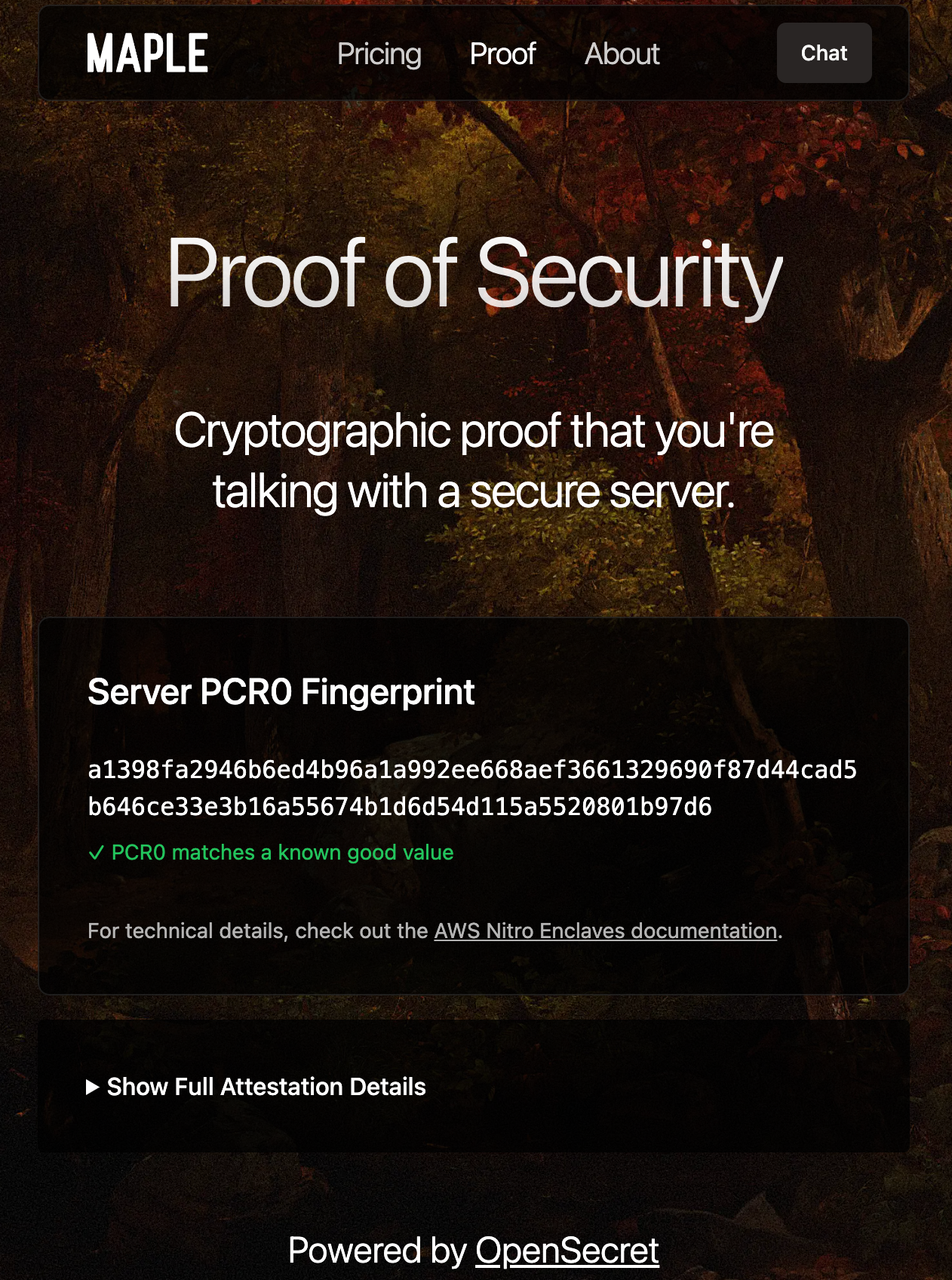Client-side Enclave Attestation from Maple AI
Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud).
Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session.
From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request.
### **In-Enclave Operations**
At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form.
User Auth Methods running inside Enclave
A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information.
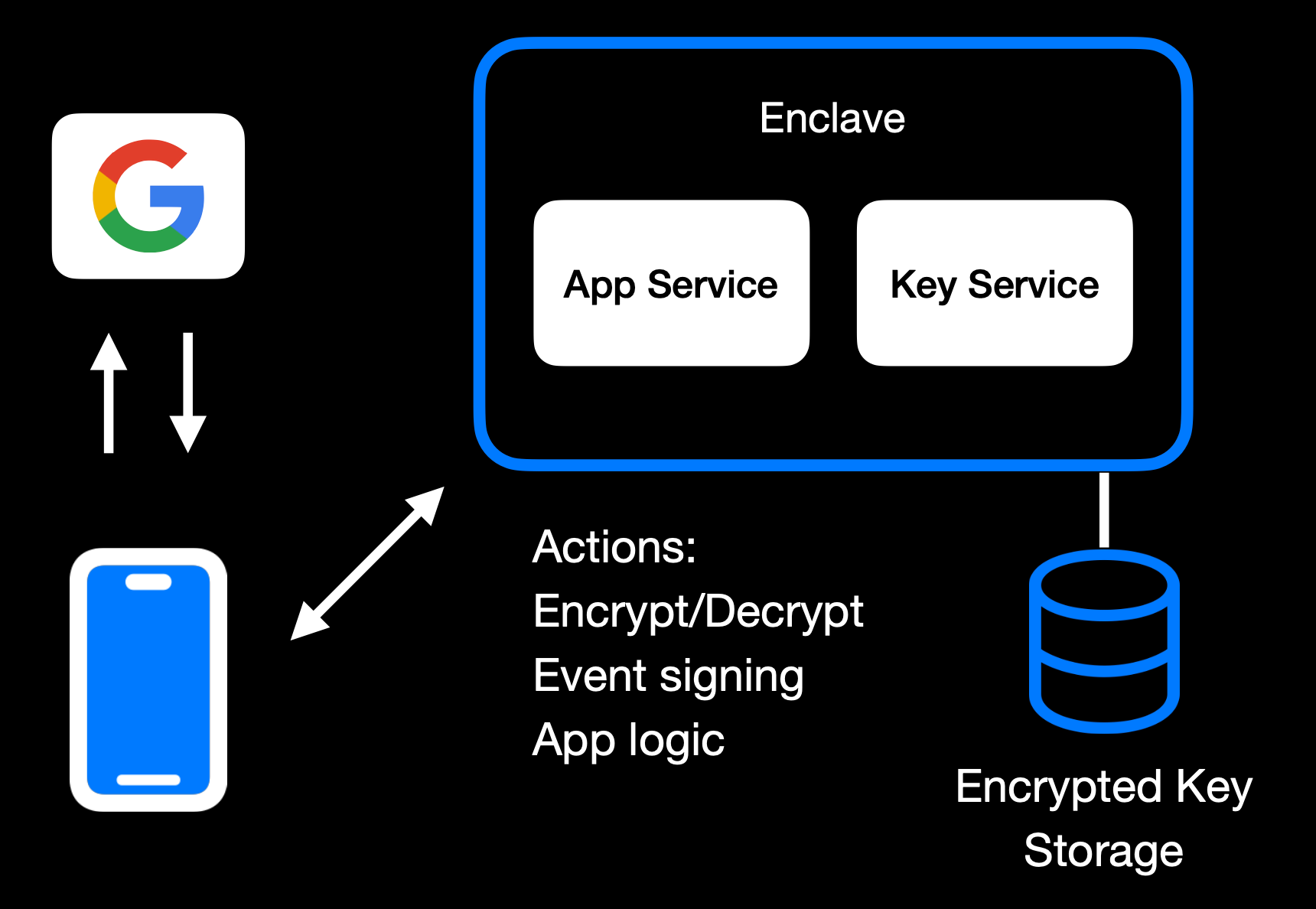Main Enclave Operations in OpenSecret
The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user.
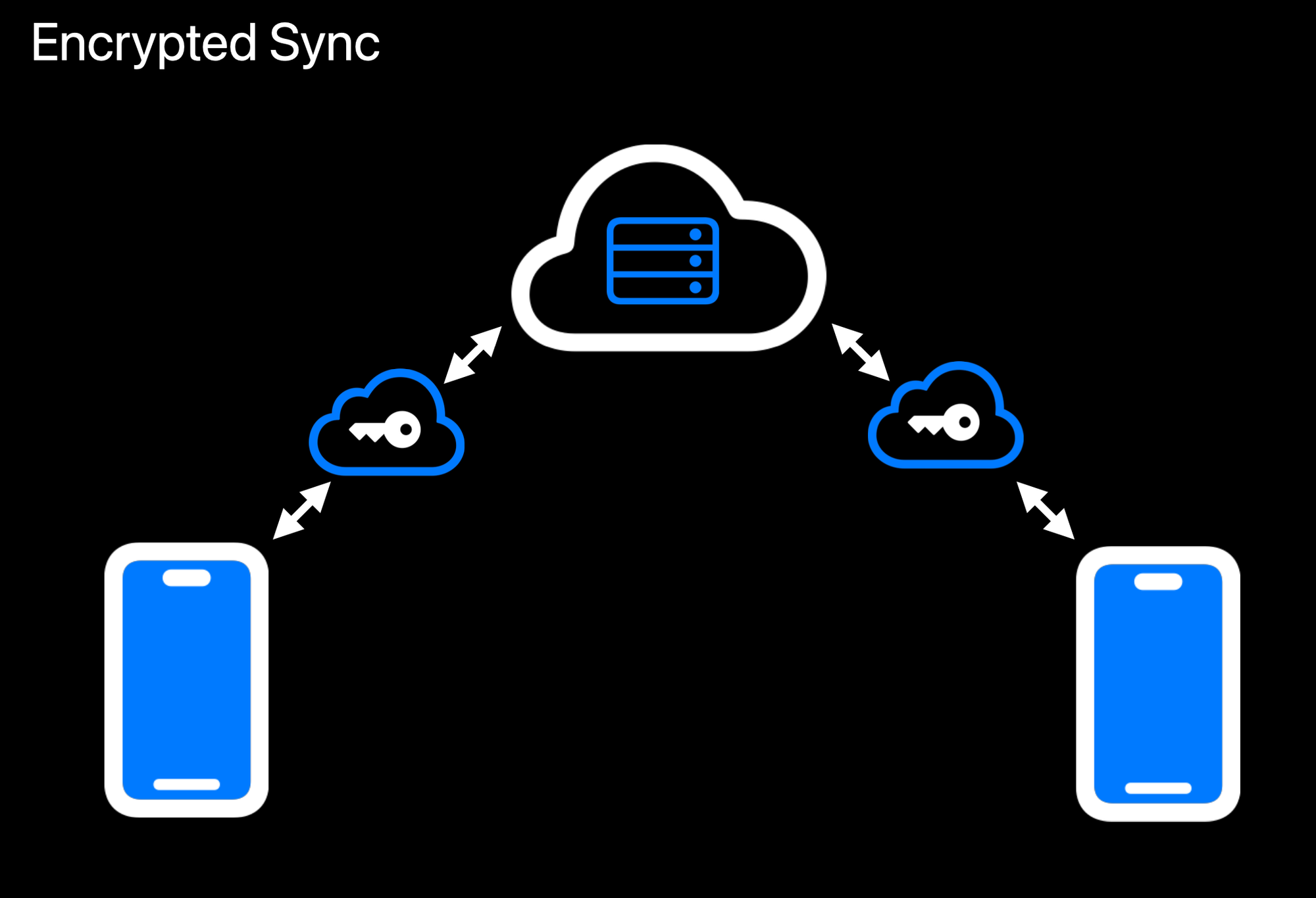Realtime Encrypted Data Sync on Multiple Devices
Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext.
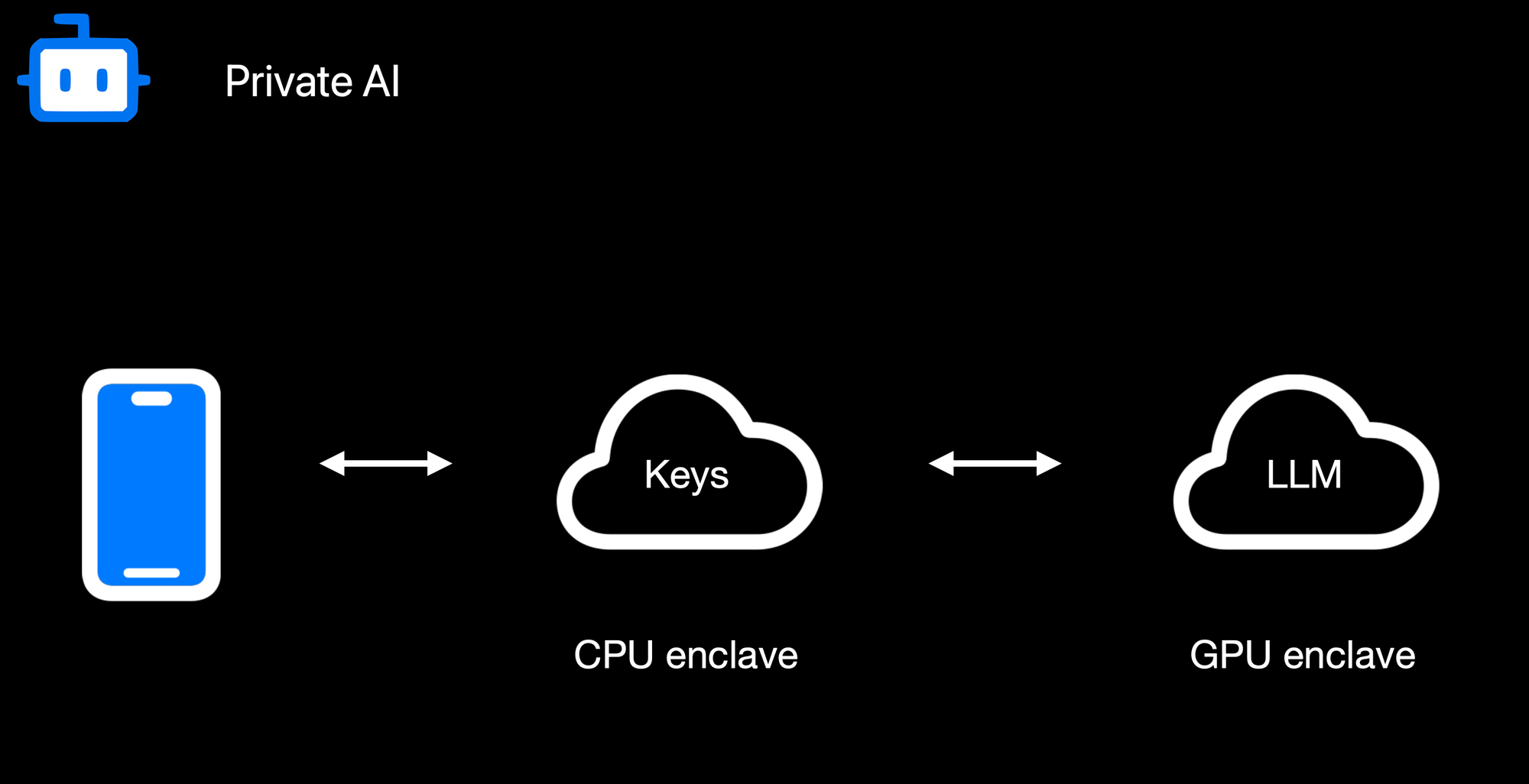Confidential AI Workloads
Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation.
### **Reproducible Builds + Verification**
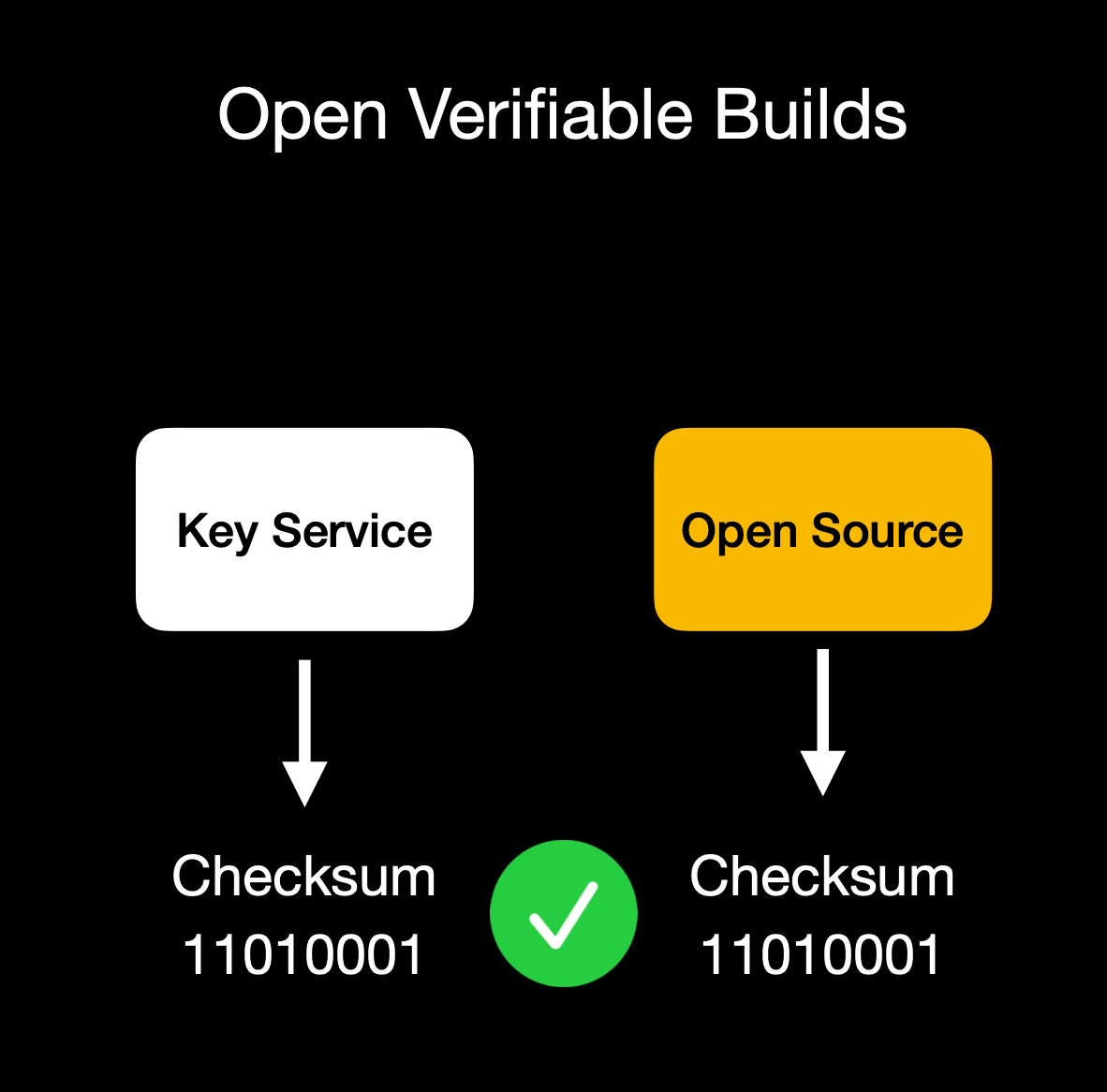Client verifies enclave attestation document
We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs.
Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation.
## **Putting It All Together**
OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute
By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes.
This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats.
Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure.
OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use.
Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system.
The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad.
## **Things to Come**
We're excited to build on our enclaved approach. Here's what's on our roadmap:
• **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\
• **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\
• **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\
• **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\
• **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\
• **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\
• **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API.
## **Getting Started**
Ready to see enclaves in action? Here's how to dive in:\
1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\
2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\
3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\
4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further.
## **Conclusion**
By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use.
**We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself.
Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build!
*Thank you for reading, and welcome to the era of enclaved computing.*
-

@ 592295cf:413a0db9
2025-03-29 10:59:52
The journey starts from the links in this article
[nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/)
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted
And I didn't see how he did it.
-----
Go to [nstart.me](https://nstart.me/) and read:
Each user is identified by a cryptographic keypair
Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key
I know and I know it's a tongue dump.
## Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site
of the protocol nostr. If one of these servers goes offline you have the private key
that you downloaded first and then reactivate a bunker.
All very complicated.
But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
## Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
## Now select 5 clients
### *Coracle, Chachi, Olas, Nostur, Jumble*
### The first is *Coracle*
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
### Let's try *Chachi*
Simpler than Coracle, it has a type login that says bunker.
see if I can post
It worked, cool, I managed to post in a group.
## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
> If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something
> like that, but many start from the phone so maybe it's easy for them.
> I try to download it and see if it allows me to connect with a bunker.
> Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
**Ok then I saw that there was the qrcode image of the bunker for apps** lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on *Olas*, so it works, Expiration time is broken.
### As for *Nostur*, I don't have an ios device so I'm going to another one.
### Login with *Jumble*, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
# Extensions nostr NIP-07
### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions)
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension)
Alby I don't know if it's a route to recommend
2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj)
3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file)
4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/)
Nostore is (archived, read-only)
5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame)
6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser)
7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj)
Another half hour to search all sites
# Nostrapps
Here you can make paths
### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to [Nostrapps](https://nostrapps.com/) and read:
## Microbbloging: Primal
## Streaming: **Zap stream**
## Blogging: **Yakihonne**
## Group chat: **Chachi**
## Community: **Flotilla**
## Tools: **Form** *
## Discovery: **Zapstore** (even if it is not in this catrgory)
## Direct Message: **0xchat**
-

@ df173277:4ec96708
2025-01-28 17:49:54
> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\
> [Start chatting for free.](https://trymaple.ai/)
We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world.
Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another.
#### Why Secure and Private AI?
In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property.
Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services.
At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local.
#### How Does It Work?
Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site.
#### How Much Does It Cost?
We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method.
- Free: $0
- Starter: $5.99/month
- Pro: $20/month
Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy.
Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open.
#### Are You An App Developer?
You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/).
<img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png">
Enjoy private AI Chat 🤘
<img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
-

@ 57d1a264:69f1fee1
2025-03-29 09:31:13
> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME."
<sub>- SATOSHI NAKAMOTO</sub>



"Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin.
Materials: Carrara Marble, Copper leaf, Opendime
Dimensions: 6" x 9" x 13"
Price: $30,000 or BTC equivalent
Enquire: https://www.vonbitcoin.com/available-works
X: https://x.com/BVBTC/status/1894463357316419960/photo/1
originally posted at https://stacker.news/items/928510
-

@ 2183e947:f497b975
2025-03-29 02:41:34
Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison.
I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core
You can also learn more about Pubky here: https://pubky.org/
That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key.
Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis.
Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed.
Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message.
I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key.
As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster.
Based on all of this info, it seems like, to populate your feed, this is the series of steps:
- you tell your homeserver your pubkey
- it uses some sort of algorithm to decide whose posts to show you
- then looks up the homeservers used by those people on an indexer server
- then it fetches posts from their homeservers
- then your client displays them to you
To create a post, this is the series of steps:
- you tell your homeserver what you want to say to the world
- it stores that message in plaintext and merely asserts that it came from you (it's not signed)
- other people can find out what you said by querying for your posts on your homeserver
Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver.
John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted.
Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
-

@ df173277:4ec96708
2025-01-09 17:12:08
> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\
> [Join the waitlist to get early access.](https://trymaple.ai)
We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI.
Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations.
#### Building a Private Foundation
Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win.
#### The Power of Encrypted AI Chat
AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short.
Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us.
#### Technical Overview
So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects:
- **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data.
- **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations.
- **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised.
- **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public.
- **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased.
#### Personal and Work Use
Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe.
#### Local v Cloud
Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds.
#### Why the Maple name?
Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment.
#### Join the Waitlist
Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai)
[](https://trymaple.ai/waitlist)
-

@ 57d1a264:69f1fee1
2025-03-28 10:32:15
Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.

The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022).
Look forward for this to happen!
Spread the voice:
N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m)
X: https://x.com/bitcoin_design/status/1905547407405768927
originally posted at https://stacker.news/items/927650
-

@ df173277:4ec96708
2025-01-09 17:02:52
> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud)
In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion.
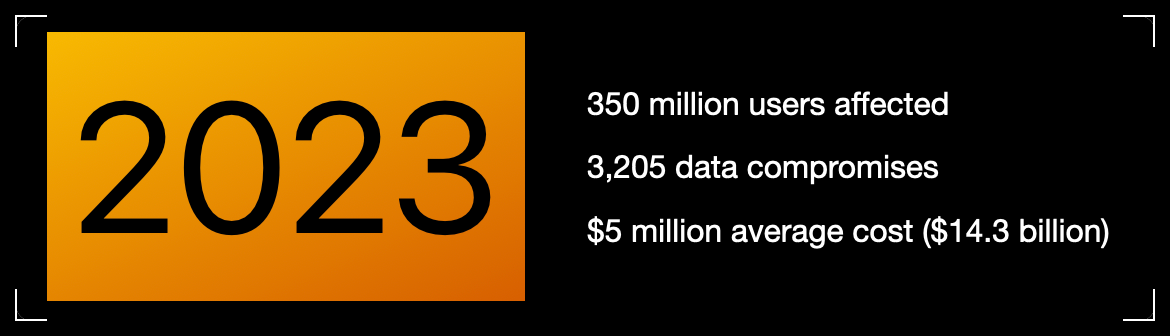Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online?
Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches?
> Cryptography at scale is hard.
#### The Cloud
The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers.
The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage.
> Private key encryption needs a UX upgrade.
## Enter OpenSecret
OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute.
Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.
### Private Key Management
Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone.
OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account.
The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.
### Encrypted Sync
With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go.
The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them.
### Private AI
Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything.
OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk.
**Check out Maple AI**\
Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)
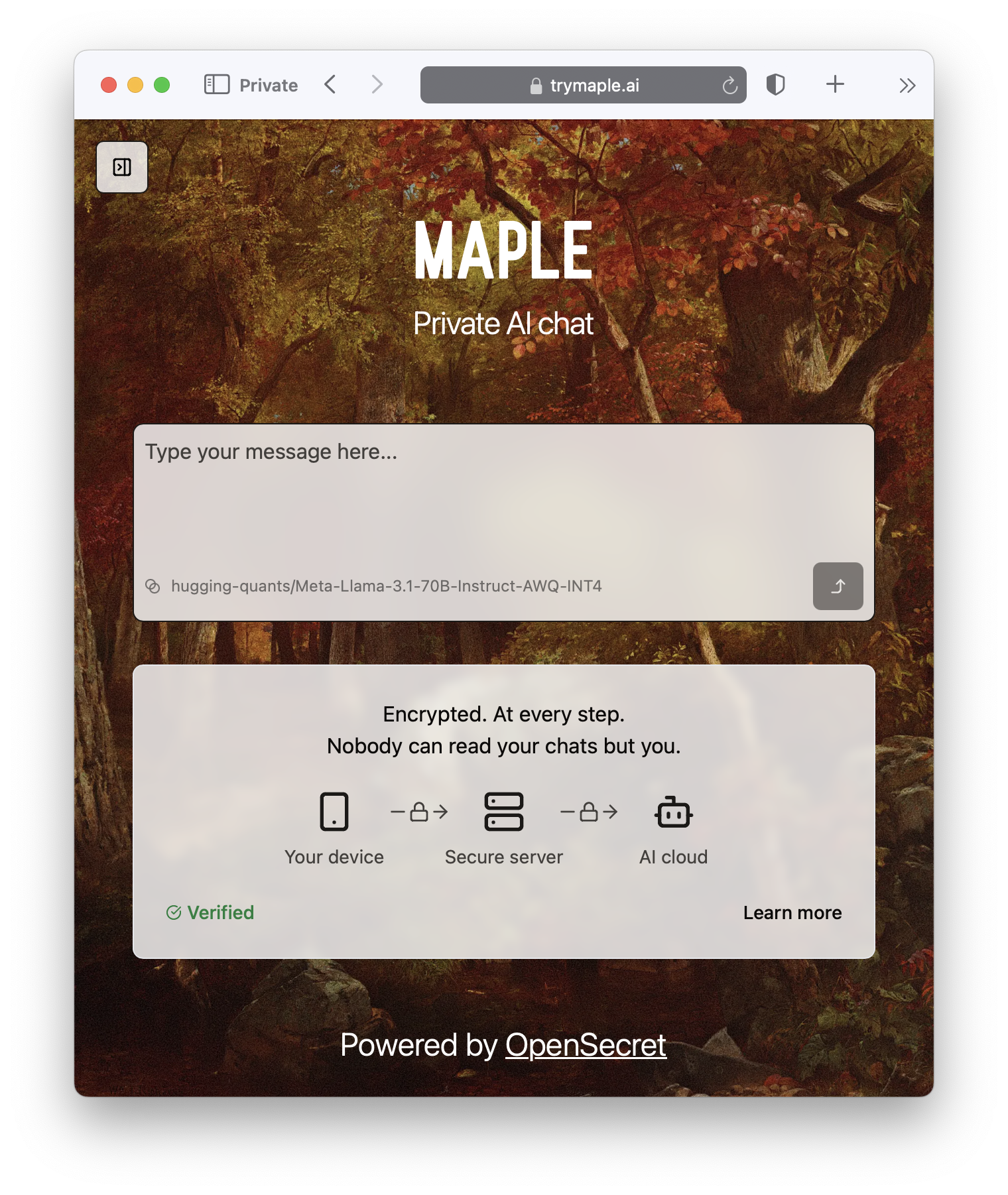
### Confidential Compute
Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave.
It's the new version of that lock on your web browser. When you see it, you know you're secure.

#### **But do we want our secrets to be open?**
OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable.
On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data.
> Don't trust, verify.
### **Join the Movement**
We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud)
Users and companies deserve better encryption and privacy.\
Together, let's make that a reality.
[](https://opensecret.cloud)
-

@ e4950c93:1b99eccd
2025-04-03 14:53:56
**Heureu-x-se d’avoir trouvé une information utile sur ce site ?**
Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s.
---
**En bitcoin**
<img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200">
bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d
⚡️`
origin-nature@coinos.io`
---
**En euros, dollars, ou toute autre monnaie prise en charge**
*Promesses uniquement pour le moment :*
<a href="https://liberapay.com/origin-nature/">
<img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200">
</a>
---
Contactez-nous si vous souhaitez faire un don avec toute autre
cryptomonnaie.
---
### 💡 Un modèle de partage de la valeur
La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention.
L’autre moitié permet de couvrir les frais de fonctionnement du site.
-

@ a5142938:0ef19da3
2025-04-03 09:55:01
### Core Team
The Core Team drives the project and validates the content.
- [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll)
To start, I'm managing the project solo. Contact me if you'd like to join!
### Content Enrichers
Our contributors make this site engaging and interesting.
-

@ d5c3d063:4d1159b3
2025-04-03 04:09:56
### ทรัมป์ ขึ้นภาษีนำเข้า
สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น
คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ
แต่คุณ #ไม่เห็น
– คนทั้งประเทศ ต้องจ่ายของแพงขึ้น
– ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย
– ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก
รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่
โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม
เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”*
Hazlitt ขยายต่อใน Economics in One Lesson ว่า
> เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า
> และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม
เงินเฟ้อ คือการขโมยแบบเงียบ ๆ
ภาษีศุลกากร คือการปล้นอย่างเปิดเผย
วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต
อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด
#Siamstr
-

@ 57d1a264:69f1fee1
2025-03-27 10:42:05
What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who?
The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1:
## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.













- - -
Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before.
This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using.
- [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser
- ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY)
@k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful.
[^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined
originally posted at https://stacker.news/items/926557
-

@ 3c7dc2c5:805642a8
2025-04-02 21:15:55
## 🧠Quote(s) of the week:
CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs.
## 🧡Bitcoin news🧡
2025
https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg
On the 24th of March:
➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity.
➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion).
Look at the corporate Bitcoin ownership breakdown:
- MicroStrategy: 506,000+ BTC
- Marathon: ~46,000 BTC (10x smaller)
- Riot: ~19,000 BTC (26x smaller)
That acquisition curve has gone parabolic since Q4 2024.
Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale.
Clear institutional conviction signal here.' -Ecoinometrics
➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine."
On the 25th of March:
➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL
- This is one of the most reliable "buy" indicators.
- Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive
(foto)
Bitcoin is always a buy. Just DCA.
➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest.
➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin.
➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o
Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world.
Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives)
But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.'
➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization".
I rather believe the opposite.
Under Femke Halsema - Amsterdam
- The number of civil servants increased by 50% (14K -> 20K)
- Debt increased by 150% (4 billion -> approx. 10 billion)
Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity.
Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better.
➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment.
➡️BlackRock launched a European Bitcoin ETP today - Bloomberg
➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin.
On the 26th of March:
➡️NYDIG just became a big Bitcoin miner.
Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG.
➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds.
➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest.
That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds.
➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses.
➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD.
→ Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin
→ Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin
→ Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet
This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time.
Source: https://t.co/QDj61ZDe6O
The Blockchain Group is Europe's First Bitcoin Treasury Company!
On the 27th of March:
➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard
➡️Daniel Batten: Yet another paper on Bitcoin and energy
TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition
are greater than generally assumed"
The journal has a (high) impact factor of 7.1."
Source: https://t.co/W3gytMgcpC
➡️A home miner with only 4 machines mined block 888737.
https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg
Bitcoin proves anyone can participate and earn—true freedom!
➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks.
200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News
➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025.
On the 28th of March:
➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today.
ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes!
➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina.
➡️A Russian company built a Bitcoin mine in the Arctic.
Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs.
➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity.
https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg
another great chart:
https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg
On the 29th of March:
➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin.
https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png
➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill.
If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use.
➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207.
On the 31st of March:
➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders:
“If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin."
https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf
➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin.
➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds.
➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem.
A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia.
Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening.
https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg
On the 1st of April:
➡️'Over 73,353 BTC were bought by corporations in Q1 2025.
Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now...
Which company do you want to see adopt BTC next?'
Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723
➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC.
On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC.
➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish
➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county.
➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide.
Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.'
## 💸Traditional Finance / Macro:
On the 29th of March
👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION.
Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL
## 🏦Banks:
👉🏽 no news
## 🌎Macro/Geopolitics:
On the 24th of March:
👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history.
Every time it crossed this level it marked the beginning of an 18-month recession/depression.
1929, 1973, 2008 & 2025'
I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both.
👉🏽US household wealth is falling:
US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates.
By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion.
In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback.
Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks.
This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures.
Consumer spending is set to slow in Q2 2025.' -TKL
👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes.
BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left."
Today, the 27th of March, marks those 1,028 days, and nothing happened.
Climate doomers are like Aztecs who think the sun stops unless they cut out some organs."
👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today.
For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/
They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe.
On the 25th of March:
👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though.
👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse.
The Green Deal is moving full speed ahead—soon everyone will be relying on food banks…
For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen
On the 26th of March:
👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all.
Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening.
On the 27th of March:
👉🏽Gold surpasses $3,100 for the first time in history.
TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years.
This is also the 3rd-longest streak on record after a historic run during the late 1970s.
The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation.
As a result, gold prices recorded 4 consecutive yearly gains.'
On the 31st of March for the first time, gold blasted through $100,000/kilogram.
This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.'
👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come.
On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored."
On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over."
That is the Mark I know!
"Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.”
On the 28th of March:
👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993.
Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed.
Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction.
It’s negative even “gold adjusted”
4 weeks ago it was +2.3%
8 weeks ago it was +3.9%
Yikes!
👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure.
The remaining 900 employees are set to be terminated.
👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei
👉🏽Fix the money, fix the world:
DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government”
“It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account”
“We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION”
“There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit”
Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe.
On the 29th of March:
👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion.
Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge
On the 1st of April:
In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week:
https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg
APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros.
Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!?
For our own housing market? “Too political.”
For war and Brussels' military ambitions? €100,000,000,000—no problem.
They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda.
Got Bitcoin?
I will end this Weekly Recap with a Stanley Druckenmiller quote:
"My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully."
"I tend to think that's what great investors do."
I know what I do and have. Bitcoin!
## 🎁If you have made it this far I would like to give you a little gift:
What Bitcoin Did:
Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy.
https://www.youtube.com/watch?v=_bSprc0IAow
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
`Use the code SE3997`
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀
⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you? If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-

@ 17538dc2:71ed77c4
2025-04-02 16:04:59
The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised.
### macOS Sequoia 15.4
Released March 31, 2025
Accessibility
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance
AccountPolicy
Available for: macOS Sequoia
Impact: A malicious app may be able to gain root privileges
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24234: an anonymous researcher
AirDrop
Available for: macOS Sequoia
Impact: An app may be able to read arbitrary file metadata
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24097: Ron Masas of BREAKPOINT.SH
App Store
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-24276: an anonymous researcher
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24272: Mickey Jin (@patch1t)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A downgrade issue was addressed with additional code-signing restrictions.
CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog)
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: A malicious app may be able to read or write to protected files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos.
AppleMobileFileIntegrity
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A privacy issue was addressed by removing the vulnerable code.
CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk)
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Audio
Available for: macOS Sequoia
Impact: Processing a maliciously crafted file may lead to arbitrary code execution
Description: The issue was addressed with improved memory handling.
CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Authentication Services
Available for: macOS Sequoia
Impact: Password autofill may fill in passwords after failing authentication
Description: This issue was addressed through improved state management.
CVE-2025-30430: Dominik Rath
Authentication Services
Available for: macOS Sequoia
Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix
Description: The issue was addressed with improved input validation.
CVE-2025-24180: Martin Kreichgauer of Google Chrome
Authentication Services
Available for: macOS Sequoia
Impact: A malicious app may be able to access a user's saved passwords
Description: This issue was addressed by adding a delay between verification code attempts.
CVE-2025-24245: Ian Mckay (@iann0036)
Automator
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed by removing vulnerable code and adding additional checks.
CVE-2025-30460: an anonymous researcher
BiometricKit
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24237: Yutong Xiu
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A path handling issue was addressed with improved validation.
CVE-2025-30429: Denis Tokarev (@illusionofcha0s)
Calendar
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with improved checks.
CVE-2025-24212: Denis Tokarev (@illusionofcha0s)
CloudKit
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-24215: Kirin (@Pwnrin)
CoreAudio
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: The issue was addressed with improved checks.
CVE-2025-24163: Google Threat Analysis Group
CoreAudio
Available for: macOS Sequoia
Impact: Playing a malicious audio file may lead to an unexpected app termination
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: This issue was addressed with improved memory handling.
CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji
CoreMedia
Available for: macOS Sequoia
Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory
Description: The issue was addressed with improved memory handling.
CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
CoreMedia Playback
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: A path handling issue was addressed with improved validation.
CVE-2025-30454: pattern-f (@pattern_F_)
CoreServices
Description: This issue was addressed through improved state management.
CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
CoreText
Available for: macOS Sequoia
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read issue was addressed with improved input validation.
CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative
Crash Reporter
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher
curl
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-9681
Disk Images
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: A file access issue was addressed with improved input validation.
CVE-2025-24255: an anonymous researcher
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A parsing issue in the handling of directory paths was addressed with improved path validation.
CVE-2025-30456: Gergely Kalman (@gergely_kalman)
DiskArbitration
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24267: an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: A malicious app may be able to access private information
Description: The issue was addressed with improved checks.
CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher
Dock
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: This issue was addressed by removing the vulnerable code.
CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova
dyld
Available for: macOS Sequoia
Impact: Apps that appear to use App Sandbox may be able to launch without restrictions
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com)
FaceTime
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky)
FeedbackLogger
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved data protection.
CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf)
Focus
Available for: macOS Sequoia
Impact: An attacker with physical access to a locked device may be able to view sensitive user information
Description: The issue was addressed with improved checks.
CVE-2025-30439: Andr.Ess
Focus
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A logging issue was addressed with improved data redaction.
CVE-2025-24283: Kirin (@Pwnrin)
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards.
CVE-2025-30461: an anonymous researcher
Foundation
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was resolved by sanitizing logging
CVE-2025-30447: LFY@secsys from Fudan University
Foundation
Available for: macOS Sequoia
Impact: An app may be able to cause a denial-of-service
Description: An uncontrolled format string issue was addressed with improved input validation.
CVE-2025-24199: Manuel Fernandez (Stackhopper Security)
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2025-30464: ABC Research s.r.o.
CVE-2025-24273: Wang Yu of Cyberserval
GPU Drivers
Available for: macOS Sequoia
Impact: An app may be able to disclose kernel memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike
Handoff
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-30463: mzzzz__
ImageIO
Available for: macOS Sequoia
Impact: Parsing an image may lead to disclosure of user information
Description: A logic error was addressed with improved error handling.
CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative
Installer
Available for: macOS Sequoia
Impact: An app may be able to check the existence of an arbitrary path on the file system
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Installer
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data
Description: A logic issue was addressed with improved checks.
CVE-2025-24229: an anonymous researcher
IOGPUFamily
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or write kernel memory
Description: An out-of-bounds write issue was addressed with improved input validation.
CVE-2025-24257: Wang Yu of Cyberserval
IOMobileFrameBuffer
Available for: macOS Sequoia
Impact: An app may be able to corrupt coprocessor memory
Description: The issue was addressed with improved bounds checks.
CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security
Kerberos Helper
Available for: macOS Sequoia
Impact: A remote attacker may be able to cause unexpected app termination or heap corruption
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2025-24235: Dave G.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: The issue was addressed with improved checks.
CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
Kernel
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24203: Ian Beer of Google Project Zero
Kernel
Available for: macOS Sequoia
Impact: An attacker with user privileges may be able to read kernel memory
Description: A type confusion issue was addressed with improved memory handling.
CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL
LaunchServices
Available for: macOS Sequoia
Impact: A malicious JAR file may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of executable types.
CVE-2025-24148: Kenneth Chew
libarchive
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2024-48958
Libinfo
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: An integer overflow was addressed with improved input validation.
CVE-2025-24195: Paweł Płatek (Trail of Bits)
libnetcore
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may result in the disclosure of process memory
Description: A logic issue was addressed with improved checks.
CVE-2025-24194: an anonymous researcher
libxml2
Available for: macOS Sequoia
Impact: Parsing a file may lead to an unexpected app termination
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2025-27113
CVE-2024-56171
libxpc
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed through improved state management.
CVE-2025-24178: an anonymous researcher
libxpc
Available for: macOS Sequoia
Impact: An app may be able to delete files for which it does not have permission
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc)
libxpc
Available for: macOS Sequoia
Impact: An app may be able to gain elevated privileges
Description: A logic issue was addressed with improved checks.
CVE-2025-24238: an anonymous researcher
Mail
Available for: macOS Sequoia
Impact: "Block All Remote Content" may not apply for all mail previews
Description: A permissions issue was addressed with additional sandbox restrictions.
CVE-2025-24172: an anonymous researcher
manpages
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30450: Pwn2car
Maps
Available for: macOS Sequoia
Impact: An app may be able to read sensitive location information
Description: A path handling issue was addressed with improved logic.
CVE-2025-30470: LFY@secsys from Fudan University
NetworkExtension
Available for: macOS Sequoia
Impact: An app may be able to enumerate a user's installed apps
Description: This issue was addressed with additional entitlement checks.
CVE-2025-30426: Jimmy
Notes
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24262: LFY@secsys from Fudan University
NSDocument
Available for: macOS Sequoia
Impact: A malicious app may be able to access arbitrary files
Description: This issue was addressed through improved state management.
CVE-2025-24232: an anonymous researcher
OpenSSH
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An injection issue was addressed with improved validation.
CVE-2025-24246: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24261: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A logic issue was addressed with improved checks.
CVE-2025-24164: Mickey Jin (@patch1t)
PackageKit
Available for: macOS Sequoia
Impact: A malicious app with root privileges may be able to modify the contents of system files
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0)
Parental Controls
Available for: macOS Sequoia
Impact: An app may be able to retrieve Safari bookmarks without an entitlement check
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24259: Noah Gregory (wts.dev)
Photos Storage
Available for: macOS Sequoia
Impact: Deleting a conversation in Messages may expose user contact information in system logging
Description: A logging issue was addressed with improved data redaction.
CVE-2025-30424: an anonymous researcher
Power Services
Available for: macOS Sequoia
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with additional entitlement checks.
CVE-2025-24173: Mickey Jin (@patch1t)
Python
Available for: macOS Sequoia
Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email
Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org.
CVE-2023-27043
RPAC
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved validation of environment variables.
CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to user interface spoofing
Description: The issue was addressed with improved UI.
CVE-2025-24113: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: Visiting a malicious website may lead to address bar spoofing
Description: The issue was addressed with improved checks.
CVE-2025-30467: @RenwaX23
Safari
Available for: macOS Sequoia
Impact: A website may be able to access sensor information without user consent
Description: The issue was addressed with improved checks.
CVE-2025-31192: Jaydev Ahire
Safari
Available for: macOS Sequoia
Impact: A download's origin may be incorrectly associated
Description: This issue was addressed through improved state management.
CVE-2025-24167: Syarif Muhammad Sajjad
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access removable volumes without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit)
Sandbox
Available for: macOS Sequoia
Impact: An input validation issue was addressed
Description: The issue was addressed with improved checks.
CVE-2025-30452: an anonymous researcher
Sandbox
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24181: Arsenii Kostromin (0x3c3e)
SceneKit
Available for: macOS Sequoia
Impact: An app may be able to read files outside of its sandbox
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30458: Mickey Jin (@patch1t)
Security
Available for: macOS Sequoia
Impact: A remote user may be able to cause a denial-of-service
Description: A validation issue was addressed with improved logic.
CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington
Security
Available for: macOS Sequoia
Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data
Description: This issue was addressed with improved access restrictions.
CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog)
Share Sheet
Available for: macOS Sequoia
Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started
Description: This issue was addressed with improved access restrictions.
CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: A permissions issue was addressed with improved validation.
CVE-2025-30465: an anonymous researcher
Shortcuts
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2025-24280: Kirin (@Pwnrin)
Shortcuts
Available for: macOS Sequoia
Impact: A Shortcut may run with admin privileges without authentication
Description: An authentication issue was addressed with improved state management.
CVE-2025-31194: Dolf Hoegaerts
Shortcuts
Available for: macOS Sequoia
Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app
Description: This issue was addressed with improved access restrictions.
CVE-2025-30433: Andrew James Gonzalez
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: The issue was addressed with improved restriction of data container access.
CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk)
Siri
Available for: macOS Sequoia
Impact: A sandboxed app may be able to access sensitive user data in system logs
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: This issue was addressed with improved redaction of sensitive information.
CVE-2025-24217: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to access sensitive user data
Description: A privacy issue was addressed by not logging contents of text fields.
CVE-2025-24214: Kirin (@Pwnrin)
Siri
Available for: macOS Sequoia
Impact: An app may be able to enumerate devices that have signed into the user's Apple Account
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L
Siri
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: An authorization issue was addressed with improved state management.
CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc)
Siri
Available for: macOS Sequoia
Impact: An attacker with physical access may be able to use Siri to access sensitive user data
Description: This issue was addressed by restricting options offered on a locked device.
CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security
SMB
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: The issue was addressed with improved memory handling.
CVE-2025-24269: Alex Radocea of Supernetworks
SMB
Available for: macOS Sequoia
Impact: Mounting a maliciously crafted SMB network share may lead to system termination
Description: A race condition was addressed with improved locking.
CVE-2025-30444: Dave G.
SMB
Available for: macOS Sequoia
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL
smbx
Available for: macOS Sequoia
Impact: An attacker in a privileged position may be able to perform a denial-of-service
Description: The issue was addressed with improved memory handling.
CVE-2025-24260: zbleet of QI-ANXIN TianGong Team
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: A library injection issue was addressed with additional restrictions.
CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
Software Update
Available for: macOS Sequoia
Impact: A user may be able to elevate privileges
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24254: Arsenii Kostromin (0x3c3e)
Software Update
Available for: macOS Sequoia
Impact: An app may be able to modify protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos
StickerKit
Available for: macOS Sequoia
Impact: An app may be able to observe unprotected user data
Description: A privacy issue was addressed by moving sensitive data to a protected location.
CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania
Storage Management
Available for: macOS Sequoia
Impact: An app may be able to enable iCloud storage features without user consent
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to gain root privileges
Description: A permissions issue was addressed with additional restrictions.
CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to access user-sensitive data
Description: A race condition was addressed with additional validation.
CVE-2025-24240: Mickey Jin (@patch1t)
StorageKit
Available for: macOS Sequoia
Impact: An app may be able to bypass Privacy preferences
Description: A race condition was addressed with additional validation.
CVE-2025-31188: Mickey Jin (@patch1t)
Summarization Services
Available for: macOS Sequoia
Impact: An app may be able to access information about a user's contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk)
System Settings
Available for: macOS Sequoia
Impact: An app may be able to access protected user data
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-24278: Zhongquan Li (@Guluisacat)
System Settings
Available for: macOS Sequoia
Impact: An app with root privileges may be able to access private information
Description: This issue was addressed with improved handling of symlinks.
CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc.
SystemMigration
Available for: macOS Sequoia
Impact: A malicious app may be able to create symlinks to protected regions of the disk
Description: This issue was addressed with improved validation of symlinks.
CVE-2025-30457: Mickey Jin (@patch1t)
Voice Control
Available for: macOS Sequoia
Impact: An app may be able to access contacts
Description: This issue was addressed with improved file handling.
CVE-2025-24279: Mickey Jin (@patch1t)
Web Extensions
Available for: macOS Sequoia
Impact: An app may gain unauthorized access to Local Network
Description: This issue was addressed with improved permissions checking.
CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven
Web Extensions
Available for: macOS Sequoia
Impact: Visiting a website may leak sensitive data
Description: A script imports issue was addressed with improved isolation.
CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: The issue was addressed with improved memory handling.
WebKit Bugzilla: 285892
CVE-2025-24264: Gary Kwong, and an anonymous researcher
WebKit Bugzilla: 284055
CVE-2025-24216: Paul Bakker of ParagonERP
WebKit
Available for: macOS Sequoia
Impact: A type confusion issue could lead to memory corruption
Description: This issue was addressed with improved handling of floats.
WebKit Bugzilla: 286694
CVE-2025-24213: Google V8 Security Team
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected process crash
Description: A buffer overflow issue was addressed with improved memory handling.
WebKit Bugzilla: 286462
CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher
WebKit
Available for: macOS Sequoia
Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash
Description: A use-after-free issue was addressed with improved memory management.
WebKit Bugzilla: 285643
CVE-2025-30427: rheza (@ginggilBesel)
WebKit
Available for: macOS Sequoia
Impact: A malicious website may be able to track users in Safari private browsing mode
Description: This issue was addressed through improved state management.
WebKit Bugzilla: 286580
CVE-2025-30425: an anonymous researcher
WindowServer
Available for: macOS Sequoia
Impact: An attacker may be able to cause unexpected app termination
Description: A type confusion issue was addressed with improved checks.
CVE-2025-24247: PixiePoint Security
WindowServer
Available for: macOS Sequoia
Impact: An app may be able to trick a user into copying sensitive data to the pasteboard
Description: A configuration issue was addressed with additional restrictions.
CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH)
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2025-24266: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2025-24265: an anonymous researcher
Xsan
Available for: macOS Sequoia
Impact: An app may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2025-24157: an anonymous researcher
-

@ 57d1a264:69f1fee1
2025-03-27 08:27:44
> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be.
`— Anil Dash, The Web We Lost, 13 Dec 2012`
https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s
So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/
The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks.
originally posted at https://stacker.news/items/926499
-

@ 57d1a264:69f1fee1
2025-03-27 08:11:33
Explore and reimagine programming interfaces beyond text (visual, tactile, spatial).
> _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_
`— Richard Hamming` [^1]
https://www.youtube.com/watch?v=8pTEmbeENF4
For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.

_'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.'
More details at https://worrydream.com/dbx/
[^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook)
originally posted at https://stacker.news/items/926493
-

@ 06639a38:655f8f71
2025-04-02 13:47:57
You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github.
Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits.
Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19)
### **TLV's**
Things were getting more complicated with the other prefixes / identifiers defined in NIP-19:
* `nevent`
* `naddr`
* `nprofile`
This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's.
_When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._
_For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._
These possible standardized `TLV` types are:
* `0`_:_ `special`
* _depends on the bech32 prefix:_
* _for_ `nprofile` _it will be the 32 bytes of the profile public key_
* _for_ `nevent` _it will be the 32 bytes of the event id_
* _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._
* `1`_:_ `relay`
* _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_
* _this may be included multiple times_
* `2`_:_ `author`
* _for_ `naddr`_, the 32 bytes of the pubkey of the event_
* _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_
* `3`_:_ `kind`
* _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_
* _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_
These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters.
Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code):
* [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74)
* [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19)
### **So what's next?**
* NIP-19 code housekeeping + refactoring
* Prepare a new release with NIP-19 integration
* Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
-

@ 7bdef7be:784a5805
2025-04-02 12:09:29
We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs.
## The problem
Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so everyone can actually snoop what we are interested in, and what is supposable that we read daily.
## The solution
Nostr has a simple solution for this necessity: encrypted lists.
Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, we can hide the lists' content from others.
The implications are obvious: we can not only have a more organized way to browse content, but it is also really private one.
One might wonder what use can really be made of private lists; here are some examples:
* Browse “can't miss” content from users I consider a priority;
* Supervise competitors or adversarial parts;
* Monitor sensible topics (tags);
* Follow someone without being publicly associated with them, as this may be undesirable;
The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of how many bots scan our actions to profile us.
## The current state
Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity.
Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply mark them as local-only, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment.
To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage both encrypted and local-only lists.
Beg your Nostr client to implement private lists!
-

@ 6b3780ef:221416c8
2025-03-26 18:42:00
This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments.
## Understanding MCP Systems
MCP (Model Context Protocol) systems consist of two main components that work together:
1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method.
2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers.
These servers and clients can communicate using different transport methods:
- **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine.
- **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel.
For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr.
## Creating (or Finding) an MCP Server
Building an MCP server is simpler than you might think:
1. Create software in any programming language you're comfortable with.
2. Add an MCP library to expose your server's MCP interface.
3. Create an API that wraps around your software's functionality.
Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy.
Alternatively, you can use one of the many existing MCP servers available in various repositories.
For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/
## Setting Up the Workshop
Let's get hands-on:
First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script:
```
curl -fsSL https://bun.sh/install | bash
```
1. **Choose your MCP server**: You can either create one or use an existing one.
2. **Inspect your server** using the MCP inspector tool:
```bash
npx @modelcontextprotocol/inspector build/index.js arg1 arg2
```
This will:
- Launch a client UI (default: http://localhost:5173)
- Start an MCP proxy server (default: port 3000)
- Pass any additional arguments directly to your server
3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality.
## Deploying with DVMCP
Now for the exciting part – making your MCP server available to everyone on Nostr:
1. Navigate to your MCP server directory.
2. Run without installing (quickest way):
```
npx @dvmcp/bridge
```
3. Or install globally for regular use:
```
npm install -g @dvmcp/bridge
# or
bun install -g @dvmcp/bridge
```
Then run using:
```bash
dvmcp-bridge
```
This will guide you through creating the necessary configuration.
Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing.
For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference
## Testing and Integration
1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement.
2. Call your tools and watch the responses come back.
For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime.
## Integrating with LLM Clients
You can also integrate your DVMCP deployment with LLM clients using the discovery package:
1. Install and use the `@dvmcp/discovery` package:
```bash
npx @dvmcp/discovery
```
2. This package acts as an MCP server for your LLM system by:
- Connecting to configured Nostr relays
- Discovering tools from DVMCP servers
- Making them available to your LLM applications
3. Connect to specific servers or providers using these flags:
```bash
# Connect to all DVMCP servers from a provider
npx @dvmcp/discovery --provider npub1...
# Connect to a specific DVMCP server
npx @dvmcp/discovery --server naddr1...
```
Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun).
This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications.
## Final thoughts
If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun.
You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless.
However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr.
Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag.
## Useful Resources
- **Official Documentation**:
- Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org)
- DVMCP.fun: [dvmcp.fun](https://dvmcp.fun)
- **Source Code and Development**:
- DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp)
- DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun)
- **MCP Servers and Clients**:
- Smithery AI: [smithery.ai](https://smithery.ai)
- MCP.so: [mcp.so](https://mcp.so)
- Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers)
- [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD)
Happy building!
-

@ 7bdef7be:784a5805
2025-04-02 12:02:45
We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists!
-

@ d5c3d063:4d1159b3
2025-04-02 04:04:32
"ผลิตผลทางเศรษฐกิจที่เพิ่มขึ้น
เป็นประโยชน์กับทุกคนเสมอ
ไม่ว่าในทางใดก็ทางหนึ่ง"
เป็นโพสของอาจารย์พิริยะ ที่เรียกได้ว่าคือ
“หลักการพื้นฐาน” ของเสรีภาพทางเศรษฐกิจ
ที่หลายคนอาจหลงลืม และซุปอยากขยายความต่อ
เพราะนี่คือจุดเริ่มต้นของคำว่า “ระบบที่แฟร์จริง”
.
เราถูกสอนให้คิดว่า ถ้ามีคนรวยขึ้น ต้องมีใครอีกคนจนลง แต่ในความเป็นจริง ระบบตลาดเสรีไม่ได้ทำงานแบบนั้นเลย เพราะเมื่อมีคนผลิตของที่ดีขึ้น ผลิตได้เร็วขึ้น ต้นทุนจะลดลง สินค้าที่เคยเข้าถึงยาก ก็เริ่มกลายเป็นของธรรมดาที่ใครก็ใช้ได้
.
คนหนึ่งคนที่ผลิตเพิ่มขึ้น อาจได้กำไรมากขึ้น แต่คนอีกเป็นล้านกลับได้ใช้สินค้าที่ถูกลง ชีวิตง่ายขึ้น สะดวกขึ้น เห็นได้ชัดว่าทุกฝ่ายได้ประโยชน์ ไม่ใช่เพราะมีใครต้อง "เสียสละจากการบังคับ" แต่เพราะทุกคนแลกเปลี่ยนกัน "ด้วยความสมัครใจ"
นี่คือหลักการที่เศรษฐศาสตร์สำนักออสเตรียนเชื่อมั่นมาตลอด ว่าเสรีภาพในการผลิตและแลกเปลี่ยน คือรากฐานของความมั่งคั่งร่วมกัน "การแบ่งงานกันทำ" ของคนที่ถนัดต่างกัน คือวิธีที่มนุษย์สร้างสังคมเจริญขึ้นมาได้จริง ไม่ใช่เพราะรัฐสั่งให้ทำ แต่เพราะทุกคนเห็นประโยชน์ร่วมกันและยินดีแลกเปลี่ยนกันเอง
.
ปัญหาคือ วันนี้เราไม่ได้อยู่ในตลาดเสรีจริง
แต่เราอยู่ในระบบที่รัฐเข้ามาเขียนกติกา
ออกใบอนุญาต ควบคุมอุตสาหกรรม กำหนดราคา
และที่แย่คือการออกกฎที่เอื้อให้พวกพ้อง ทำให้บางคนได้เปรียบในตลาด โดยไม่ได้มาจากการผลิตเก่งหรือบริการดีแต่มาจากการมีสายสัมพันธ์กับอำนาจ (แบบนี้คือ ทุนนิยมพวกพ้อง)
.
แล้วคนทั่วไปที่เห็นภาพแบบนี้ ก็พากันเรียกร้องให้รัฐเข้ามาจัดการ ทั้งที่จริงแล้ว...คนที่ควรรับผิดชอบ คือรัฐเอง ที่เปิดช่องให้เรื่องพวกนี้เกิดขึ้นตั้งแต่แรก
.
เราจึงติดกับดักเดิมซ้ำๆ คือรัฐสร้างปัญหา แล้วใช้ปัญหานั้นเป็นข้ออ้างในการขยายอำนาจ
สุดท้ายมันก็ยิ่งบิดเบือนระบบเศรษฐกิจให้ผิดเพี้ยนเข้าไปอีก จนคนทำงานจริง ผลิตของจริง กลับไม่มีที่ยืนในระบบ
.
.
ให้เห็นภาพต่อว่า ถ้ามีคนผลิตมากขึ้น ทุกคนในระบบจะได้ประโยชน์เพิ่มขึ้นเสมอ ตราบใดที่
1 เขาไม่ได้ขโมยใคร
2 เขาแลกเปลี่ยนบนความสมัครใจ เท่านั้นยังไม่พอ
3 "เงิน" มันต้องเป็นกระจกสะท้อนคุณค่าจากการผลิต
ไม่ใช่เงินที่สร้างจากหนี้แล้วใช้กฎหมายยังคับว่ามันมีค่า
ถ้าเงื่อนไขสามข้อนี้ยังอยู่ครบ
ทุนนิยมตลาดเสรีที่แท้จริง ก็จะเป็นระบบที่ยั่งยืน
และแฟร์ที่สุดเท่าที่เคยมีมา
ซึ่งตลอดประวัติศาสตร์เรายังไม่เคยแยกอำนาจการเงินออกจากมือมนุษย์ได้เลย
เพราะถ้าเราปล่อยให้รัฐพิมพ์เงินได้อย่างอิสระ
ลดคุณค่าของเงินได้โดยไม่ต้องรับผิดชอบ
และแทรกแซงราคาตลาดโดยไม่มีการผลิตรองรับ
เมื่อถึงจุดนั้น ต่อให้เราผลิตเก่งแค่ไหน เราก็ไม่มีทางรวยขึ้น เพราะรางวัลไม่ได้แจกตามผลงาน
แต่แจกตามความใกล้ชิตผู้มีอำนาจ
เมื่อเงินเสื่อมค่าลงทุกวัน ข้าวของแพงขึ้น
เราต้องทำงานหนักขึ้น แต่ซื้อของได้น้อยลง
แล้วเราจะเริ่มถามตัวเองว่า
“เรากำลังทำงานสร้างคุณค่าจริงๆ
ขยันจนแทบไม่มีเวลาหายใจ
แต่สุดท้ายเรากำลังก้าวไปเดินหน้า
หรือแค่พยายามเอาตัวรอดในระบบที่ไม่ยุติธรรม”
และในวันนั้น...คุณอาจจะย้อนนึกถึงประโยคนี้
ที่อาจารย์เคยโพสแล้วอาจไม่ได้คิดว่ามันสำคัญ
ปล.วันนี้เราอาจเห็นต่างกันเรื่องบทบาทของรัฐ
แต่ซุปคิดว่าจุดร่วมของคำถามนี้คือ
ระบบเศรษฐกิจที่ดี ควรให้รางวัลกับผู้ผลิต
หรือให้รางวัลกับคนที่อยู่ใกล้ชิดผู้มีอำนาจ...
#Siamstr
-

@ 57d1a264:69f1fee1
2025-03-26 08:45:13
> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score!
| Desktop | Mobile |
|---|---|
|  |  |
|  |  |
Now let's see what Semrush knows.
# Analytics
General view on your metrics and performance trend compared to last 30 days.


See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.

Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.

| Organic Search | Backlinks Analytics |
|---|---|
| |  |
| Position Changes Trend | Top Page Changes |
|---|---|
| |  |
|This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |

# Competitors

The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.

# Referring Domains


# Daily Stats
| Organic Traffic | Organic Keywords | Backlinks |
|---|---|---|
| 976 | 15.9K | 126K |
| `-41.87%` | `-16.4%` | `-1.62%` |
### 📝 Traffic Drop
Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits:
- https://stacker.news/items/723989 ⬇️ -15
- https://stacker.news/items/919813 ⬇️ -12
- https://stacker.news/items/783355 ⬇️ -5
### 📉 Decreased Authority Score
Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority.
### 🌟 New Keywords
Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords:
- nitter.moomoo.me — Volume 70
- 0xchat — Volume 30
- amethyst nostr — Volume 30
### 🛠️ Broken Pages
This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_:
- https://stacker.news/404 — 38 backlinks
- https://stacker.news/api/capture/items/91154 — 24 backlinks
- https://stacker.news/api/capture/items/91289 — 24 backlinks
Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility!
One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary?
Here are other basic info to improve the SEO score and for those of us that want to learn more:
- Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/
- Design for Accessibility: https://www.w3.org/WAI/tips/designing/
- Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/
originally posted at https://stacker.news/items/925433
-

@ 9967f375:04f9a5e1
2025-04-01 20:43:54
El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero.
-

@ 9967f375:04f9a5e1
2025-04-01 20:18:33
Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*.
-

@ 30876140:cffb1126
2025-03-26 04:58:21
The portal is closing.
The symphony comes to an end.
Ballet, a dance of partners,
A wish of hearts,
Now closing its curtains.
I foolishly sit
Eagerly waiting
For the circus to begin again,
As crowds file past me,
Chuckles and popcorn falling,
Crushed under foot,
I sit waiting
For the show to carry on.
But the night is now over,
The laughs have been had,
The music been heard,
The dancers are gone now
Into the nightbreeze chill.
Yet still, I sit waiting,
The empty chairs yawning,
A cough, I start, could it be?
Yet the lights now go out,
And now without my sight
I am truly alone in the theater.
Yet still, I am waiting
For the show to carry on,
But I know that it won’t,
Yet still, I am waiting.
Never shall I leave
For the show was too perfect
And nothing perfect should ever be finished.
-

@ 04c915da:3dfbecc9
2025-03-25 17:43:44
One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-

@ 8f69ac99:4f92f5fd
2025-04-01 15:54:53
Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento.
Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda.
Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade.
## Benefícios de Aceitar Bitcoin
### 1. Redução de Custos
Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento.
### 2. Liquidação Rápida
Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes.
### 3. Expansão de Mercado
Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados.
### 4. Protecção Contra Inflação
Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo.
| [](https://youtu.be/B9fCDjybtrU&t=3518) |
|:--:|
| *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* |
## Como Funciona na Prática?
### 1. Aceitação Directa vs. Conversão Automática
Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda.
### 2. Configuração de Carteira Bitcoin
Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio.
### 3. Facturação e Registo Contábil
Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal.
## Obrigações Fiscais e Contábeis
### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas)
Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis.
Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial.
No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor.
### 2. IVA (Imposto sobre o Valor Acrescentado)
As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA.
No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento.
**Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉
### 3. Registos e Demonstrações Financeiras
As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso:
- **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante.
- **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias.
As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados.
## O Obstáculo: Contabilistas e a Falta de Apoio
### 1. Falta de Conhecimento
Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes.
### 2. Resistência e Falta de Vontade
Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado.
### 3. Impacto nos Negócios
Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado.
## Soluções e Alternativas
### 1. Educação e Autonomia
Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin.
### 2. Ferramentas e Software
Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis.
### 3. Rede de Apoio
Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências.
### 4. Links uteis
- [Website Aceita Bitcoin](https://aceitabitcoin.pt)
- [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin)
- [Mario Moura Contabilidade](https://mmc.pt/en/)
- [MM Law](https://www.mmlaw.pt/)
## Conclusão
Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento.
---
_**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._
_Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on
[Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_
-

@ ecda4328:1278f072
2025-03-25 10:00:52
**Kubernetes and Linux Swap: A Practical Perspective**
After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion.
---
### The Rationale for Disabling Swap
We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes.
With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion.
Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates.
---
### Theoretical Capability vs. Practical Deployment
Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly.
But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model:
- Memory **requests and limits** are declared explicitly.
- The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap).
- Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals.
So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity.
---
### Why Disable Swap in Kubernetes?
1. **Deterministic Failure > Degraded Performance**\
If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early.
2. **Transparency & Observability**\
With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically.
3. **Performance Consistency**\
Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits.
4. **Kubernetes Doesn’t Manage Swap Well**\
Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control.
5. **Statelessness is the Norm**\
Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state.
---
### "But Swap Can Be Useful..."
Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need:
- Fine-tuned `vm.swappiness`
- Memory pinning and cgroup-based control
- Swap-aware monitoring and alerting
- Custom kubelet/systemd integration
That's possible, but **not standard practice** — and for good reason.
---
### Future Considerations
Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments.
Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior.
Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet.
---
### Conclusion
Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability.
If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**.
-

@ 69eea734:4ae31ae6
2025-04-01 15:33:49
What to record from the last two weeks? The key points from the things I've read and watched? \
The encounters I had with various groups of people, and also one on one? (on my trip to Munich)\
My thoughts on what is going on in the world?\
It is all connected anyway. 
*This is my second post. The* *[first](https://pareto.space/a/naddr1qqxnzden8yunxv3kxvcnjdpsqgsqlvwtq6gjttmchn3nqetzfy42skj9334nhr2ptl2hzqgzeswgssgrqsqqqa28qy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvsq3vamnwvaz7tmjv4kxz7fwwpexjmtpdshxuet5h5apnf)* *was under a different profile, which I lost the private key to.* 
### So close and yet apart
The various encounters: Overlapping 'camps'. School friends, friends from uni times, friends from Covid times. One friend from school, and one friend from uni did not have a Covid vaccine and were critical of measures. To think that this still matters! Can you believe it? But it does! Which is sad on one hand, and makes for strong bonds on the other. 
I'm in a pub with three school friends. They discover that they all voted Green, and are delighted. They kind of congratulate each other, and themselves. I don't even know what to feel in that moment. I'm not shocked. It is not surprising. And yet I still find it astounding. 
As the evening progresses, we move to a Greek restaurant round the corner. On the way there, I walk alongside the friend with whom I exchanged the most challenging emails of the last five years. There had been long pauses between replies. Once I read only the first two lines, and then 'quarantined' the mail. I once deleted one, and three weeks later asked him to send it again. 
In 2023 we sat in a café and openly talked about the Corona period and our differing positions. I appreciated it. At least we could talk. Shortly after, the emphasis in our conversations shifted from Covid to Putin. One arch enemy was replaced by another. And when previously, the 'Covid deniers' were the deplorable ones, now it was the 'Putin understanders', and weren't they the same people anyway? And mentioning peace talks was right wing. It was all so predictable. Was I predictable, too? I'd sent a long email a week ago. But walking alongside each other, we preferred to talk about the kids. 
At the Greek restaurant, the inevitable happened. We ended up in a massive discussion. I once was gesticulating wildly at him. "Conspiracy theorist! That is *so* convenient. Everything that does not fit into your worldview, becomes a conspiracy theory. That there would be a vaccine mandate was once a conspiracy theory. That the virus came from a lab was once a conspiracy theory."
On another occasion, he exclaimed: "You know that I know all that about America! You know exactly that I know all those things!" 
We both knew a lot of things, and it went back and forth. 
The irony was that we managed to stay respectful, and it was a discussion with the other school friend there (the fourth person on the table was my husband), that turned out to be the last straw. She had voted Green as well, and had congratulated our school mate on having been to the protest 'against the right'. But she was also the one who didn't have the vaccine, and now said, "With Covid, it was just so obvious that it was all set up." A bit later she said something about the WEF. Only to be greeted with a long tirade. "Aha. So you think this is all a big conspiracy with some powerful people in the background planning everything. And this wasn't a pandemic although lots of people died. I know six doctors, and they all told me the same." A bit later, to me: "So why did only the unvaccinated die then?" And then shortly after, when my friend stated again how the whole thing had seemed premeditated, "Right. That's enough now. I'm leaving." And he got up to pay and left. 
My friend, who stayed behind, thought we had had interesting discussions and she had learned something. On reflection, it was good to have this discussion at all -- at a time that nobody seems to want to talk about Covid anymore. 
But also: Shouldn't we be much much further than this???
### My first sats
A few months ago I had tried to buy bitcoin, just to play around, but there had been difficulties to do with the fact I have a UK bank account. When looking at how to get funds into my getalby account, I ended up with Strike, which is available in the UK. But it seems they take extra care to make sure you know what you are letting yourself into! I had to do a test with about 10 questions to show I understand the risks. 
I then had to wait 24 hours, but now I have sent my first sats. 
On the Strike website, I noticed this [video of a conversation](https://www.youtube.com/watch?v=Nzvh4AODtWc) between Jack Mallers, founder of Strike, and Jack Dorsey, co-founder of Twitter. The more I watched, the more I thought, wow, here it is all in one video, all that I would like my friend to see. "America has a problem." The Empire needs to end, and it would be a good thing for America, says Jack Dorsey. This was also the second time in a week that I heard about how Great Britain had created money and bought their own bonds when the public didn't want to, in effect stealing from the people by making their money worth less. It was good to be reminded of [Adam Curtis](https://en.wikipedia.org/wiki/Adam_Curtis) who has made some mind-blowing documentaries, using lots of BBC archive material. Including about the special US and UK relationship (*An ocean apart*), and also one about Russia from 1985 to 1999 (*Trauma Zone*).
The two Jacks talk about the importance of open source, and of being independent of government. The dangers of building abstraction on abstraction on abstraction. About how Mark Zuckerberg served Dorsey raw goat once, because he had this challenge to only eat what he had killed himself. That was also a way to get back to the real. 
Dorsey endorsed RFK jr, this was in summer of 2023, when he was still running for president. 
There is also an interesting bit on the pressures of running a company that has gone public. And the government interference, in effect censorship. The Twitter files. It is not quite clear to me, if it was really so difficult for Jack Dorsey to pay attention and know what was going on, but I can understand that it must have been a difficult situation. 
What I also find very interesting is that in Africa or Latin America bitcoin is sometimes valuable as an exchange medium. That is where I think it could diverge from the pure Ponzi scheme that people often call it. 
And yet, doubts remain. Is bitcoin not too valuable for a lot of people to spend it? But what if you don't have access to any other money. And sending Satoshis around is different from hording bitcoin. Can it fulfil both these functions in the end, storage medium and exchange medium? 
I believe that these two people want to achieve something positive. But they also remain tech bros. And I don't mean that in a bad way. It is just something that will always remain a bit alien to me. 
I did like what Dorsey said about the punks. How they just started to play an instrument, and didn't care if they were not good at it. Then just turned up again and again and eventually got better. I have often thought of myself as a bit punk-like in that respect, although I've often been worried about not being good enough. 
### Doing away with domination
The last [blog article](https://www.lowimpact.org/posts/darren-allen-on-civilisational-collapse/) posted on a website I work on, made me explore the writings by Darren Allen on his [Expressive Egg substack](https://expressiveegg.substack.com/). I had landed there before, years ago, and had been very impressed back then. He seems to criticise people's thoughts a lot though -- almost everybody's -- and I was wondering if that was all he ever did. But then I came across this [article about anarchy](https://expressiveegg.substack.com/p/anarchism-at-the-end-of-the-world). It made me realise again, in all this mess about different worldviews, different expectations and values, that this is a constant for me: How can we have less coercion, how can we live in a way that frees ourselves and others at the same time. I once saw a Twitter bio: "I insist on your freedom." It seems to come from Jack Kerouac. 
Allen writes that there are seven *dominants*, seven elements that "control individuals against their will". They are, " in roughly ascending order of subtlety and pervasiveness":
1\. The \[autocratic] *monarchy*.\
2\. The \[socialist-democratic] *state* (which includes its money, law, property, police, etc.).\
3\. The \[totalitarian-capitalist] *corporation*.\
4\. The \[mass] *majority*.\
5\. The \[professional-religious] *institution*.\
6\. The \[technocratic] *system*.\
7\. The \[mental-emotional] *ego*.
I want to keep this list in mind and pay attention when I get sucked into the influence of one of these spheres. 
\
I also like this quote:
> The reason men and women do not need kings, princes, states, professionals, institutions and systems to rule over them is because the life within them is more intelligent, more apt, more sensitive, more forgiving and more creative than anything else—certainly any human authority. But this life cannot be rationally fixed. It can be expressed, artistically, indirectly, poetically, musically, or with tone and glance and such ordinary, metaphorical arts of human interaction; but it cannot be literally stated.
\
Although this would be a good ending for this post, I have to mention Jeffrey Sachs as well. I have been following him for a while. He appeared in the EU parliament, invited by Michael von der Schulenburg. Sachs has an amazing amount of experience with both Russian and American government officials, and with currencies. In the 90s he spent some time helping Eastern European countries with the transition to capitalist systems. He realised that the U.S. did not want to help Russia in the same way. 
He gave a long speech in which he laid bare the ways in which the U.S. had influenced so many wars and uprisings around the world, and how the NATO enlargement had been a long-term strategy. That now, with Trump, the war was going to end. 
There would be so much more to say. In any case, this seems to me a historic speech. Can it break through the mirror glass that has kept so many people away from valid sources of knowledge?
-

@ 57d1a264:69f1fee1
2025-03-24 17:08:06
Nice podcast with @sbddesign and @ConorOkus about bitcoin payments.
https://www.youtube.com/watch?v=GTSqoFKs1cE
In this episode, Conor, Open Source product manager at Spiral & Stephen, Product Designer at Voltage & Co founder of ATL Bitlab join Stephan to discuss the current state of Bitcoin user experience, particularly focusing on payments and the challenges faced by users. They explore the comparison between Bitcoin and physical cash, the Western perspective on Bitcoin payments, and the importance of user experience in facilitating Bitcoin transactions.
They also touch upon various payment protocols like #BOLT11, #LNURL, and #BOLT12, highlighting the need for interoperability and better privacy features in the Bitcoin ecosystem. The discussion also covers resources available for developers and designers to enhance wallet usability and integration.
@StephanLivera Official Podcast Episode: https://stephanlivera.com/646
### Takeaways
🔸Bitcoin has excelled as a savings technology.
🔸The payments use case for Bitcoin still needs improvement.
🔸User experience is crucial for Bitcoin adoption.
🔸Comparing Bitcoin to cash highlights privacy concerns.
🔸Western users may not see a payments problem.
🔸Regulatory issues impact Bitcoin payments in the West.
🔸User experience challenges hinder Bitcoin transactions.
🔸Different payment protocols create compatibility issues.
🔸Community collaboration is essential for Bitcoin's future.
🔸Improving interoperability can enhance Bitcoin payments. Wallet compatibility issues can create negative user impressions.
🔸Designers can significantly improve wallet user experience.
🔸Testing compatibility between wallets is essential for user satisfaction.
🔸Tether's integration may boost Bitcoin adoption.
🔸Developers should prioritize payment capabilities before receiving capabilities.
🔸Collaboration between designers and developers can lead to better products.
🔸User experience improvements can be low-hanging fruit for wallet projects.
🔸A global hackathon aims to promote miner decentralization.
🔸Resources like BOLT12 and the Bitcoin Design Guide are valuable for developers.
🔸Engaging with the community can lead to innovative solutions.
### Timestamps
([00:00](/watch?v=GTSqoFKs1cE)) - Intro
([01:10](/watch?v=GTSqoFKs1cE&t=70s)) - What is the current state of Bitcoin usage - Payments or Savings?
([04:32](/watch?v=GTSqoFKs1cE&t=272s)) - Comparing Bitcoin with physical cash
([07:08](/watch?v=GTSqoFKs1cE&t=428s)) - What is the western perspective on Bitcoin payments?
([11:30](/watch?v=GTSqoFKs1cE&t=690s)) - Would people use Bitcoin more with improved UX?
([17:05](/watch?v=GTSqoFKs1cE&t=1025s)) - Exploring payment protocols: Bolt11, LNURL, Bolt12 & BIP353
([30:14](/watch?v=GTSqoFKs1cE&t=1814s)) - Navigating Bitcoin wallet compatibility challenges
([34:45](/watch?v=GTSqoFKs1cE&t=2085s)) - What is the role of designers in wallet development?
([43:13](/watch?v=GTSqoFKs1cE&t=2593s)) - Rumble’s integration of Tether & Bitcoin; The impact of Tether on Bitcoin adoption
([51:22](/watch?v=GTSqoFKs1cE&t=3082s)) - Resources for wallet developers and designers
### Links:
• [https://x.com/conorokus](https://x.com/conorokus)
• [https://x.com/StephenDeLorme](https://x.com/StephenDeLorme)
• [https://bolt12.org/](https://bolt12.org/)
• [https://twelve.cash/](https://twelve.cash)
• [https://bitcoin.design/guide/](https://bitcoin.design/guide/)
• Setting Up Bitcoin Tips for Streamers](/watch?v=IWTpSN8IaLE)
originally posted at https://stacker.news/items/923714
-

@ 866e0139:6a9334e5
2025-03-24 10:50:59
**Autor:** *Ludwig F. Badenhagen.* *Dieser Beitrag wurde mit dem* *[Pareto-Client](https://pareto.space/read)* *geschrieben.*
***
Einer der wesentlichen Gründe dafür, dass während der „Corona-Pandemie“ so viele Menschen den Anweisungen der Spitzenpolitiker folgten, war sicher der, dass diese Menschen den Politikern vertrauten. Diese Menschen konnten sich nicht vorstellen, dass Spitzenpolitiker den Auftrag haben könnten, die Bürger analog klaren Vorgaben zu belügen, zu betrügen und sie vorsätzlich (tödlich) zu verletzen. Im Gegenteil, diese gutgläubigen Menschen waren mit der Zuversicht aufgewachsen, dass Spitzenpolitiker den Menschen dienen und deren Wohl im Fokus haben (müssen). Dies beteuerten Spitzenpolitiker schließlich stets in Talkshows und weiteren Medienformaten. Zwar wurden manche Politiker auch bei Fehlverhalten erwischt, aber hierbei ging es zumeist „nur“ um Geld und nicht um Leben. Und wenn es doch einmal um Leben ging, dann passieren die Verfehlungen „aus Versehen“, aber nicht mit Vorsatz. So oder so ähnlich dachte die Mehrheit der Bürger.
Aber vor 5 Jahren änderte sich für aufmerksame Menschen alles, denn analog dem Lockstep-Szenario der Rockefeller-Foundation wurde der zuvor ausgiebig vorbereitete Plan zur Inszenierung der „Corona-Pandemie“ Realität. Seitdem wurde so manchem Bürger, der sich jenseits von Mainstream-Medien informierte, das Ausmaß der unter dem Vorwand einer erfundenen Pandemie vollbrachten Taten klar. Und unverändert kommen täglich immer neue Erkenntnisse ans Licht. Auf den Punkt gebracht war die Inszenierung der „Corona-Pandemie“ ein Verbrechen an der Menschheit, konstatieren unabhängige Sachverständige.
Dieser Beitrag befasst sich allerdings nicht damit, die vielen Bestandteile dieses Verbrechens (nochmals) aufzuzählen oder weitere zu benennen. Stattdessen soll beleuchtet werden, warum die Spitzenpolitiker sich so verhalten haben und ob es überhaupt nach alledem möglich ist, der Politik jemals wieder zu vertrauen? Ferner ist es ein Anliegen dieses Artikels, die weiteren Zusammenhänge zu erörtern. Und zu guter Letzt soll dargelegt werden, warum sich der große Teil der Menschen unverändert alles gefallen lässt.
**Demokratie**
Von jeher organisierten sich Menschen mit dem Ziel, Ordnungsrahmen zu erschaffen, welche wechselseitiges Interagieren regeln. Dies führte aber stets dazu, dass einige wenige alle anderen unterordneten. Der Grundgedanke, der vor rund 2500 Jahren formulierten Demokratie, verfolgte dann aber das Ziel, dass die Masse darüber entscheiden können soll, wie sie leben und verwaltet werden möchte. Dieser Grundgedanke wurde von den Mächtigen sowohl gehasst als auch gefürchtet, denn die Gefahr lag nahe, dass die besitzlosen Vielen beispielsweise mit einer schlichten Abstimmung verfügen könnten, den Besitz der Wenigen zu enteignen. Selbst Sokrates war gegen solch eine Gesellschaftsordnung, da die besten Ideen nicht durch die Vielen, sondern durch einige wenige Kluge und Aufrichtige in die Welt kommen. Man müsse die Vielen lediglich manipulieren und würde auf diese Weise quasi jeden Unfug umsetzen können. Die Demokratie war ein Rohrkrepierer.
**Die Mogelpackung „Repräsentative Demokratie“**
Erst im Zuge der Gründung der USA gelang der Trick, dem Volk die „Repräsentative Demokratie“ unterzujubeln, die sich zwar nach Demokratie anhört, aber mit der Ursprungsdefinition nichts zu tun hat. Man konnte zwischen zwei Parteien wählen, die sich mit ihren jeweiligen Versprechen um die Gunst des Volkes bewarben. Tatsächlich paktierten die Vertreter der gewählten Parteien (Politiker) aber mit den wirklich Mächtigen, die letztendlich dafür sorgten, dass diese Politiker in die jeweiligen exponierten Positionen gelangten, welche ihnen ermöglichten (und somit auch den wirklich Mächtigen), Macht auszuüben. Übrigens, ob die eine oder andere Partei „den Volkswillen“ für sich gewinnen konnte, war für die wirklich Mächtigen weniger von Bedeutung, denn der Wille der wirklich Mächtigen wurde so oder so, wenn auch in voneinander differierenden Details, umgesetzt.
Die Menschen waren begeistert von dieser Idee, denn sie glaubten, dass sie selbst „der Souverän“ seien. Schluss mit Monarchie sowie sonstiger Fremdherrschaft und Unterdrückung.
Die Mächtigen waren ebenfalls begeistert, denn durch die Repräsentative Demokratie waren sie selbst nicht mehr in der Schusslinie, weil das Volk sich mit seinem Unmut fortan auf die Politiker konzentrierte. Da diese Politiker aber vielleicht nicht von einem selbst, sondern von vielen anderen Wahlberechtigten gewählt wurden, lenkte sich der Groll der Menschen nicht nur ab von den wirklich Mächtigen, sondern auch ab von den Politikern, direkt auf „die vielen Idioten“ aus ihrer eigenen Mitte, die sich „ver-wählt“ hatten. Diese Lenkung des Volkes funktionierte so hervorragend, dass andere Länder die Grundprinzipien dieses Steuerungsinstrumentes übernahmen. Dies ist alles bei Rainer Mausfeld nachzulesen.
Ursprünglich waren die Mächtigen nur regional mächtig, sodass das Führen der eigenen Menschen(vieh)herde eher eine lokale Angelegenheit war. Somit mussten auch nur lokale Probleme gelöst werden und die Mittel zur Problemlösung blieben im eigenen Problembereich.
***
JETZT ABONNIEREN:
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).*
***
* Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube.
* Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
* Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
* Ab **1000 CHF/EURO** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
**Für Einzahlungen in CHF (Betreff: Friedenstaube):**
[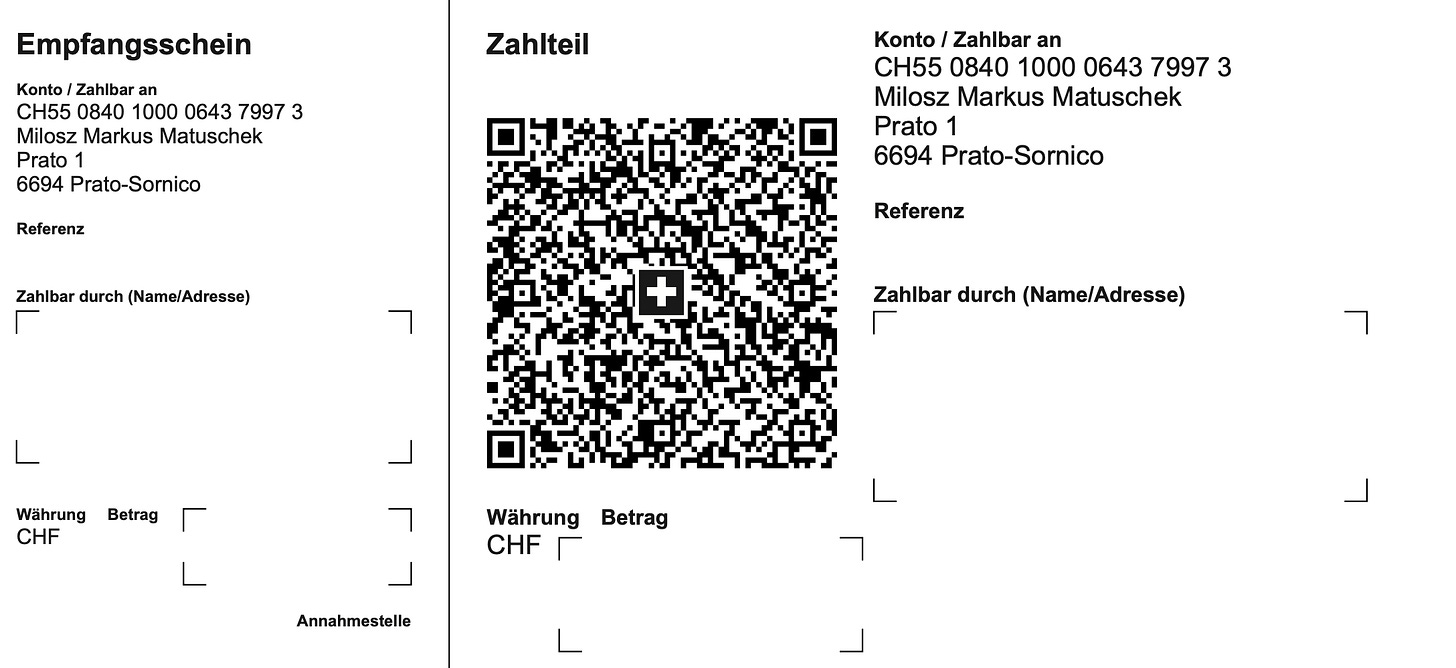](https://substackcdn.com/image/fetch/f_auto%2Cq_auto%3Agood%2Cfl_progressive%3Asteep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F3fdee17a-c22f-404e-a10c-7f87a7b8182a_2176x998.png)
**Für Einzahlungen in Euro:**
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
**Betreff: Friedenstaube**
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> oder <kontakt@idw-europe.org>.
***
**Beherrschungsinstrumente der globalen Massenhaltung**
Im Zuge der territorialen Erweiterungen der „Besitzungen“ einiger wirklich Mächtiger wurden die Verwaltungs- und Beherrschungsinstrumente überregionaler. Und heute, zu Zeiten der globalen Vernetzung, paktieren die wirklich Mächtigen miteinander und beanspruchen die Weltherrschaft. Längst wird offen über die finale Realisierung einen Weltregierung, welche die Nationalstaaten „nicht mehr benötigt“, gesprochen. Dass sich Deutschland, ebenso wie andere europäische Staaten, der EU untergeordnet hat, dürfte auch Leuten nicht entgangen sein, die sich nur über die Tagesschau informieren. Längst steht das EU-Recht über dem deutschen Recht. Und nur kurze Zeit ist es her, als die EU und alle ihre Mitgliedsstaaten die WHO autonom darüber entscheiden lassen wollten, was eine Pandemie ist und wie diese für alle verbindlich „bekämpft“ werden soll. Eine spannende Frage ist nun, wer denn über der EU und der WHO sowie anderen Institutionen steht?
Diese Beschreibung macht klar, dass ein „souveränes Land“ wie das unverändert von der amerikanischen Armee besetzte Deutschland in der Entscheidungshierarchie an die Weisungen übergeordneter Entscheidungsorgane gebunden ist. An der Spitze stehen - wie kann es anders sein - die wirklich Mächtigen.
Aber was nützt es dann, Spitzenpolitiker zu wählen, wenn diese analog Horst Seehofer nichts zu melden haben? Ist das Wählen von Politikern nicht völlig sinnlos, wenn deren Wahlversprechen ohnehin nicht erfüllt werden? Ist es nicht so, dass die Menschen, welche ihre Stimme nicht behalten, sondern abgeben, das bestehende System nur nähren, indem sie Wahlergebnisse akzeptieren, ohne zu wissen, ob diese manipuliert wurden, aber mit der Gewissheit, dass das im Zuge des Wahlkampfes Versprochene auf keinen Fall geliefert wird? Aktive Wähler glauben trotz allem an die Redlichkeit und Wirksamkeit von Wahlen, und sie akzeptieren Wahlergebnisse, weil sie denken, dass sie von „so vielen Idioten, die falsch wählen“, umgeben sind, womit wir wieder bei der Spaltung sind. Sie glauben, der Stand des aktuellen Elends sei „selbst gewählt“.
**Die Wahl der Aufseher**
Stellen Sie sich bitte vor, Sie wären im Gefängnis, weil Sie einen kritischen Artikel mit „gefällt mir“ gekennzeichnet haben oder weil Sie eine „Kontaktschuld“ trifft, da in Ihrer Nachbarschaft ein „verschwörerisches Symbol“ von einem „aufmerksamen“ Nachbarn bei einer „Meldestelle“ angezeigt wurde oder Sie gar eine Tat, „unterhalb der Strafbarkeitsgrenze“ begangen hätten, dann würden Sie möglicherweise mit Maßnahmen bestraft, die „keine Folter wären“. Beispielsweise würde man Sie während Ihrer „Umerziehungshaft“ mit Waterboarding, Halten von Stresspositionen, Dunkelhaft etc. dabei „unterstützen“, „Ihre Verfehlungen zu überdenken“. Stellen Sie sich weiterhin vor, dass Sie, so wie alle anderen Inhaftierten, an der alle vier Jahre stattfindenden Wahl der Aufseher teilnehmen könnten, und Sie hätten auch einen Favoriten, der zwar Waterboarding betreibt, aber gegen alle anderen Maßnahmen steht. Sie hätten sicher allen Grund zur Freude, wenn Sie Ihren Kandidaten durchbringen könnten, oder? Aber was wäre, wenn der Aufseher Ihrer Wahl dann dennoch alle 3 „Nicht-Folter-Maßnahmen“ anwenden würde, wie sämtliche anderen Aufseher zuvor? Spätestens dann müssten Sie sich eingestehen, dass es der Beruf des Aufsehers ist, Aufseher zu sein und dass er letztendlich tut, was ihm „von oben“ aufgetragen wird. Andernfalls verliert er seinen Job. Oder er verunfallt oder gerät in einen Skandal etc. So oder so, er verliert seinen Job - und den erledigt dann ein anderer Aufseher.
Die Wahl des Aufsehers ändert wenig, solange Sie sich im System des Gefängnisses befinden und der Aufseher integraler Bestandteil dieses Systems ist. Zur Realisierung einer tatsächlichen Änderung müssten Sie dort herauskommen.
Dieses Beispiel soll darstellen, dass alles in Hierarchien eingebunden ist. Die in einem System eingebundenen Menschen erfüllen ihre zugewiesenen Aufgaben, oder sie werden bestraft.
**Das aktuelle System schadet dem Volk**
Auch in der staatlichen Organisation von Menschen existieren hierarchische Gliederungen. Eine kommunale Selbstverwaltung gehört zum Kreis, dieser zum Land, dieses zum Staat, dieser zur EU, und diese - zu wem auch immer. Und vereinnahmte Gelder fließen nach oben. Obwohl es natürlich wäre, dass die Mittel dorthin fließen, wo sie der Allgemeinheit und nicht einigen wenigen dienen, also nach unten.
Warum muss es also eine Weltregierung geben? Warum sollen nur einige Wenige über alle anderen bestimmen und an diesen verdienen (Nahrung, Medikamente, Krieg, Steuern etc.)? Warum sollen Menschen, so wie Vieh, das jemandem „gehört“, mit einem Code versehen und bereits als Baby zwangsgeimpft werden? Warum müssen alle Transaktionen und sämtliches Verhalten strickt gesteuert, kontrolliert und bewertet werden?
Viele Menschen werden nach alledem zu dem Schluss kommen, dass solch ein System nur einigen wenigen wirklich Mächtigen und deren Helfershelfern nützt. Aber es gibt auch eine Gruppe Menschen, für die im Land alles beanstandungsfrei funktioniert. Die Spaltung der Menschen ist perfekt gelungen und sofern die eine Gruppe darauf wartet, dass die andere „endlich aufwacht“, da die Fakten doch auf dem Tisch liegen, so wird sie weiter warten dürfen.
Julian Assange erwähnte einst, dass es für ihn eine unglaubliche Enttäuschung war, dass ihm niemand half. Assange hatte Ungeheuerlichkeiten aufgedeckt. Es gab keinen Aufstand. Assange wurde inhaftiert und gefoltert. Es gab keinen Aufstand. Assange sagte, er hätte nicht damit gerechnet, dass die Leute „so unglaublich feige“ seien.
Aber womit rechnete er den stattdessen? Dass die Massen „sich erheben“. Das gibt es nur im Film, denn die Masse besteht aus vielen maximal Indoktrinierten, die sich wie Schafe verhalten, was als Züchtungserfolg der Leute an den Schalthebeln der Macht und deren Herren, den wirklich Mächtigen, anzuerkennen ist. Denn wer mächtig ist und bleiben möchte, will sicher keine problematischen Untertanen, sondern eine gefügige, ängstliche Herde, die er nach Belieben ausbeuten und steuern kann. Wenn er hierüber verfügt, will er keinen Widerstand.
Ob Corona, Krieg, Demokratie- und Klimarettung oder Meinungsäußerungsverbote und Bürgerrechte, die unterhalb der Strafbarkeitsgrenze liegen, all diese und viele weitere Stichworte mehr sind es, die viele traurig und so manche wütend machen.
Auch das Mittel des Demonstrierens hat sich als völlig wirkungslos erwiesen. Die vielen gruseligen Videoaufnahmen über die massivsten Misshandlungen von Demonstranten gegen die Corona-Maßnahmen führen zu dem Ergebnis, dass die Exekutive ihr Gewaltmonopol nutzt(e), um die Bevölkerung gezielt zu verletzen und einzuschüchtern. Bekanntlich kann jede friedliche Demonstration zum Eskalieren gebracht werden, indem man Menschen in die Enge treibt (fehlender Sicherheitsabstand) und einige V-Leute in Zivil mit einschlägigen Flaggen und sonstigen „Symbolen“ einschleust, die für Krawall sorgen, damit die gepanzerten Kollegen dann losknüppeln und die scharfen Hunde zubeißen können. So lauten zumindest die Berichte vieler Zeitzeugen und so ist es auch auf vielen Videos zu sehen. Allerdings nicht im Mainstream.
Dieses Vorgehen ist deshalb besonders perfide, weil man den Deutschen ihre Wehrhaftigkeit aberzogen hat. Nicht wehrfähige Bürger und eine brutale Staatsmacht mit Gewaltmonopol führen zu einem Gemetzel bei den Bürgern.
Ähnliches lässt sich auch in zivilen Lebenssituationen beobachten, wenn die hiesige zivilisierte Bevölkerung auf „eingereiste“ Massenvergewaltiger und Messerstecher trifft, die über ein anderes Gewalt- und Rechtsverständnis verfügen als die Einheimischen.
**System-Technik**
Die These ist, dass es eine Gruppe von global agierenden Personen gibt, welche das Geschehen auf der Erde zunehmend wirksam zu ihrem individuellen Vorteil gestaltet. Wie sich diese Gruppe definiert, kann bei John Coleman (Das Komitee der 300) und David Icke nachgelesen werden. Hierbei handelt es ich um Autoren, die jahrzehntelang analog streng wissenschaftlichen Grundlagen zu ihren Themen geforscht haben und in ihren jeweiligen Werken sämtliche Quellen benennen. Diese Autoren wurden vom Mainstream mit dem Prädikatsmerkmal „Verschwörungstheoretiker“ ausgezeichnet, wodurch die Ergebnisse Ihrer Arbeiten umso glaubwürdiger sind.
Diese mächtige Gruppe hat mit ihren Schergen nahezu den gesamten Planeten infiltriert, indem sie Personen in führenden Positionen in vielen Belangen größtmögliche Freiheiten sowie Schutz gewährt, aber diesen im Gegenzug eine völlige Unterwerfung bei Kernthemen abfordert. Die Motivatoren für diese Unterwerfung sind, abgesehen von materiellen Zuwendungen, auch „Ruhm und Ehre sowie Macht“. Manchmal wird auch Beweismaterial für begangene Verfehlungen (Lolita-Express, Pizzagate etc.) genutzt, um Forderungen Nachdruck zu verleihen. Und auch körperliche Bestrafungen der betroffenen Person oder deren Angehörigen zählen zum Repertoire der Motivatoren. Letztendlich ähnlich den Verhaltensweisen in einem Mafia-Film.
Mit dieser Methodik hat sich diese mächtige Gruppe im Laufe von Jahrhunderten! eine Organisation erschaffen, welche aus Kirchen, Parteien, Firmen, NGO, Vereinen, Verbänden und weiteren Organisationsformen besteht. Bestimmte Ämter und Positionen in Organisationen können nur von Personen eingenommen und gehalten werden, die „auf Linie sind“.
Die Mitglieder der Gruppe tauchen in keiner Rubrik wie „Die reichsten Menschen der Welt“ auf, sondern bleiben fern der Öffentlichkeit. Wer jemanden aus ihren Reihen erkennt und beschuldigt, ist ein „Antisemit“ oder sonstiger Übeltäter und wird verfolgt und bekämpft. Über mächtige Vermögensverwaltungskonzerne beteiligen sich die Mitglieder dieser Gruppe anonym an Unternehmen in Schlüsselpositionen in einer Dimension, die ihnen wesentlichen Einfluss auf die Auswahl der Topmanager einräumt, sodass die jeweilige Unternehmenspolitik nach Vorgaben der Gruppe gestaltet wird.
Die Gruppe steuert das Geldsystem, von dem sich der Planet abhängig zu sein wähnt. Hierzu eine Erläuterung: Ein Staat wie Deutschland ist bekanntlich maximal verschuldet. Man stelle sich vor, ein unliebsamer Politiker würde entgegen sämtlicher „Brandmauern“ und sonstiger Propaganda und Wahlmanipulationen gewählt, das Land zu führen, dann könnte dieser keine Kredit über 500 Mrd. Euro bei der nächsten Sparkasse beantragen, sondern wäre auf die Mächtigen dieser Welt angewiesen. Jeder weiß, dass Deutschland als Staat kein funktionierendes Geschäftsmodell hat und somit nicht in der Lage ist, solch ein Darlehen zurückzuzahlen. Welche Motivation sollte also jemand haben, einem Land wie Deutschland so viel Geld ohne Aussicht auf Rückführung zu geben? Es leuchtet ein, dass dieser Politiker andere Gefälligkeiten anbieten müsste, um das Darlehen zu bekommen. Im Falle einer Weigerung zur Kooperation könnte der Staatsapparat mit seinen Staatsdienern, Bürgergeld- und Rentenempfänger etc. nicht mehr bezahlt werden und dieser Politiker wäre schnell wieder weg. Er würde medial hingerichtet. Es ist somit davon auszugehen, dass ein Spitzenpolitiker dieser Tage nicht über viele Optionen verfügt, denn er übernimmt eine Situation, die von seinen Vorgängern erschaffen wurde. Trotz alledem darauf zu hoffen, dass es einen anderen Politiker geben könnte, mit dem dann alles wieder gut wird, mutet ziemlich infantil an.
Dass ein Großteil der Medien von Zuwendungen abhängig ist, dürfte ebenfalls leicht nachzuvollziehen sein, denn der gewöhnliche Bürger zahlt nichts für den Content der MSM. Abhängig davon, von wem (Regierung, Philanthrop, Konzern etc.) ein Medium am Leben gehalten wird, gestalten sich auch dessen Inhalte. Und wenn angewiesen wird, dass ein Politiker medial hingerichtet werden soll, dann bedient die Maschinerie das Thema. Man beobachte einfach einmal, dass Politiker der Kartell-Parteien völlig anders behandelt werden als solche jenseits der „Brandmauer“. Und der Leser, der solche Auftragsarbeiten kostenlos liest, ist der Konsument, für dessen Indoktrination die Finanziers der Verlage gerne zahlen. Mittlerweile kann durch die Herrschaft über die Medien und die systematische Vergiftung der Körper und Geister der Population die öffentliche Meinung gesteuert werden. Die überwiegende Zahl der Deutschen scheint nicht mehr klar denken zu können.
Wer sich das aktuelle Geschehen in der deutschen Politik mit klarem Verstand ansieht, kommt nicht umhin, eine Fernsteuerung der handelnden Politiker in Betracht zu ziehen. Aber was soll daran verwundern? Sind es deshalb „böse Menschen“? Sind die in „Forschungslaboren“ arbeitenden Quäler von „Versuchstieren“ böse Menschen? Sind der Schlächter, der Folterer und der Henker böse Menschen? Oder der knüppelnde Polizist? Es handelt sich zunächst einmal um Personen, die einen Vorteil dadurch haben, Ihrer Tätigkeit nachzugehen. Sie sind integrale Bestandteile eines Belohnungssystems, welches von oben nach unten Anweisungen gibt. Und wenn diese Anweisungen nicht befolgt werden, führt dies für den Befehlsverweigerer zu Konsequenzen.
**Der klare Verstand**
Es ist nun eine spannende Frage, warum so viele Menschen sich solch eine Behandlung gefallen lassen? Nun, das ist relativ einfach, denn das angepasste Verhalten der Vielen ist nichts anderes als ein Züchtungserfolg der Wenigen.
Die Psyche der Menschen ist ebenso akribisch erforscht worden wie deren Körperfunktionen. Würden die Menschen von den wirklich Mächtigen geliebt, dann würde genau gewusst, wie sie zu behandeln und mit ihren jeweiligen Bedürfnissen zu versorgen sind. Stattdessen werden die Menschen aber als eine Einnahmequelle betrachtet. Dies manifestiert sich exemplarisch in folgenden Bereichen:
1. Das Gesundheitssystem verdient nichts am gesunden Menschen, sondern nur am (dauerhaft) kranken, der um Schmerzlinderung bettelt. Bereits als Baby werden Menschen geimpft, was die jeweilige Gesundheit (mit Verweis auf die Werke von Anita Petek-Dimmer u. a.) nachhaltig negativ beeinflusst. Wer hat denn heute keine Krankheiten? Die „Experten“ des Gesundheitssystems verteufeln Vitamin D, Vitamin C, Lithium, die Sonne, Natur etc. und empfehlen stattdessen Präparate, die man patentieren konnte und mit denen die Hersteller viel Geld verdienen. Die Präparate heilen selten, sondern lindern bestenfalls zuvor künstlich erzeugte Leiden, und müssen oftmals dauerhaft eingenommen werden. Was ist aus den nicht Geimpften geworden, die alle sterben sollten? Sind diese nicht die einzigen Gesunden dieser Tage? Ist nicht jeder Geimpfte entweder permanent krank oder bereits tot? Abgesehen von denen, welche das Glück hatten, „Sonderchargen“ mit Kochsalz zu erhalten. \
\
Wem gehören die wesentlichen Player im Gesundheitswesen zu einem erheblichen Teil? Die Vermögensverwalter der wirklich Mächtigen.
2. Ähnlich gestaltet es sich bei der Ernährungsindustrie. Die von dort aus verabreichten Produkte sind die Ursachen für den Gesundheitszustand der deutschen Population. Das ist aber auch irgendwie logisch, denn wer sich nicht falsch ernährt und gesund bleibt, wird kein Kunde des Gesundheitswesens. \
\
Die Besitzverhältnisse in der Ernährungsindustrie ähneln denen im Gesundheitswesen, sodass am gleichen Kunden gearbeitet und verdient wird.
3. Die Aufzählung konnte nun über die meisten Branchen, in denen mit dem Elend der Menschen viel verdient werden kann, fortgesetzt werden. Waffen (BlackRock erhöhte beispielsweise seine Anteile an der Rheinmetall AG im Juni 2024 auf 5,25 Prozent. Der US-Vermögensverwalter ist damit der zweitgrößte Anteilseigner nach der französischen Großbank Société Générale.), Energie, Umwelt, Technologie, IT, Software, KI, Handel etc.
Wie genau Chemtrails und Technologien wie 5G auf den Menschen und die Tiere wirken, ist ebenfalls umstritten. Aber ist es nicht seltsam, wie krank, empathielos, antriebslos und aggressiv viele Menschen heute sind? Was genau verabreicht man der Berliner Polizei, damit diese ihre Prügelorgien auf den Rücken und in den Gesichtern der Menschen wahrnehmen, die friedlich ihre Demonstrationsrechte wahrnehmen? Und was erhalten die ganzen zugereisten „Fachkräfte“, die mit Ihren Autos in Menschenmengen rasen oder auch Kinder und Erwachsene niedermessern?
Das Titelbild dieses Beitrags zeigt einige Gebilde, welche regelmäßig bei Obduktionen von Geimpften in deren Blutgefäßen gefunden werden. Wie genau wirken diese kleinen Monster? Können wir Menschen ihr Unverständnis und ihr Nicht-Aufwachen vorwerfen, wenn wir erkennen, dass diese Menschen maximal vergiftet wurden? Oder sollten einfach Lösungen für die Probleme dieser Zeit auch ohne den Einbezug derer gefunden werden, die offenbar nicht mehr Herr ihrer Sinne sind?
**Die Ziele der wirklich Mächtigen**
Wer sich entsprechende Videosequenzen der Bilderberger, des WEF und anderen „Überorganisationen“ ansieht, der erkennt schnell das Muster:
* Reduzierung der Weltpopulation um ca. 80 Prozent
* Zusammenbruch der Wirtschaft, damit diese von den Konzernen übernommen werden kann.
* Zusammenbruch der öffentlichen Ordnung, um eine totale Entwaffnung und eine totale Überwachung durchsetzen zu können.
* Zusammenbruch der Regierungen, damit die Weltregierung übernehmen kann.
Es ist zu überdenken, ob die Weltregierung tatsächlich das für die Vielen beste Organisationssystem ist, oder ob die dezentrale Eigenorganisation der jeweils lokalen Bevölkerung nicht doch die bessere Option darstellt. Baustellen würden nicht nur begonnen, sondern auch schnell abgearbeitet. Jede Region könnte bestimmen, ob sie sich mit Chemtrails und anderen Substanzen besprühen lassen möchte. Und die Probleme in Barcelona könnte die Menschen dort viel besser lösen als irgendwelche wirklich Mächtigen in ihren Elfenbeintürmen. Die lokale Wirtschaft könnte wieder zurückkommen und mit dieser die Eigenständigkeit. Denn die den wirklich Mächtigen über ihre Vermögensverwalter gehörenden Großkonzerne haben offensichtlich nicht das Wohl der Bevölkerung im Fokus, sondern eher deren Ausbeutung.
Das Aussteigen aus dem System ist die wahre Herkulesaufgabe und es bedarf sicher Mut und Klugheit, sich dieser zu stellen. Die Politiker, die unverändert die Narrative der wirklich Mächtigen bedienen, sind hierfür denkbar ungeeignet, denn sie verfolgen kein Lebensmodell, welches sich von Liebe und Mitgefühl geleitet in den Dienst der Gesamtheit von Menschen, Tieren und Natur stellt.
Schauen Sie einmal genau hin, denken Sie nach und fühlen Sie mit.
**Was tun?**
Jedes System funktioniert nur so lange, wie es unterstützt wird. Somit stellt sich die Frage, wie viele Menschen das System ignorieren müssen, damit es kollabiert, und auf welche Weise dieses Ignorieren durchzuführen ist? Merkbar ist, dass die große Masse der Verwaltungsangestellten krank und oder unmotiviert und somit nicht wirksam ist. Würden die entsprechenden Stellen massiv belastet und parallel hierzu keine Einnahmen mehr realisieren, wäre ein Kollaps nah. Die Prügelpolizisten aus Berlin können nicht überall sein und normale Polizisten arbeiten nicht gegen unbescholtene Bürger, sondern sorgen sich selbst um ihre Zukunft. Gewalt ist sicher keine Lösung, und sicher auch nicht erforderlich.
Wie eine gerechte Verwaltungsform aufgebaut werden muss? Einfach so, wie sie in den hiesigen Gesetzen beschrieben steht. Aber eine solche Organisationsform muss frei sein von Blockparteien und korrupten Politikern und weisungsgebundenen Richtern etc. Stattdessen werden Menschen benötigt, welche die Menschen lieben und ihnen nicht schaden wollen. Außerdem sollten diese Führungspersonen auch wirklich etwas können, und nicht nur „Politiker“ ohne weitere Berufserfahrungen sein.
***
Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).
*Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.*
***
**Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
-

@ 57d1a264:69f1fee1
2025-03-23 12:24:46
https://www.youtube.com/watch?v=obXEnyQ_Veg



source: https://media.jaguar.com/news/2024/11/fearless-exuberant-compelling-jaguar-reimagined-0
originally posted at https://stacker.news/items/922356
-

@ c631e267:c2b78d3e
2025-03-21 19:41:50
*Wir werden nicht zulassen, dass technisch manches möglich ist,* *\
aber der Staat es nicht nutzt.* *\
Angela Merkel*  
**Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach.** Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
**Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar,** dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

**Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen,** die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
**Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen** und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war [vielleicht früher](https://transition-news.org/der-sumpf-aus-ngos-parteien-und-steuergeld) einmal so, heute ist eher das Gegenteil gemeint.
**In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung** praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien [beleuchtet](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass). Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als [«Technofeudalismus»](https://transition-news.org/yanis-varoufakis-der-europaische-traum-ist-tot-es-lebe-der-neue-traum) angeprangert.
**Nationale** **[Zugangspunkte](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en)** **für Mobilitätsdaten im Sinne der EU** gibt es nicht nur in allen Mitgliedsländern, sondern auch in der [Schweiz](https://opentransportdata.swiss/de/) und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen [Identifizierungssystem](https://transition-news.org/biometrische-gesichtserkennung-in-britischen-hafen) für «nachhaltigen Verkehr und Tourismus».
**Natürlich marschiert auch Deutschland stracks und euphorisch** in Richtung digitaler Zukunft. Ohne [vernetzte Mobilität](https://mobilithek.info/about) und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität [voll auf Digitalisierung](https://www.smartcountry.berlin/de/newsblog/smart-city-index-grossstaedte-setzen-bei-mobilitaet-voll-auf-digitalisierung.html)».
**Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten,** das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
*\[Titelbild:* *[Pixabay](https://pareto.space/readhttps://pixabay.com/de/illustrations/schaufensterpuppe-platine-gesicht-5254046/)]*
***
Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben. Er ist zuerst auf ***[Transition News](https://transition-news.org/das-gegenteil-von-mussen-ist-nicht-durfen)*** erschienen.
-

@ 75869cfa:76819987
2025-04-01 05:55:38
**GM, Nostriches!**
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
**Quick review:**
In the past two weeks, Nostr statistics indicate over 221,000 daily trusted pubkey events. The number of new users has seen a notable decrease, with profiles containing a contact list dropping by 79%. More than 10 million events have been published, reflecting a 12% decrease. Total Zap activity stands at approximately 21 million, marking a 15% increase.
Additionally, 15 pull requests were submitted to the Nostr protocol, with 2 merged. A total of 45 Nostr projects were tracked, with 8 releasing product updates, and over 569 long-form articles were published, 24% focusing on Bitcoin and Nostr. During this period, 7 notable events took place, and 2 significant events are upcoming.
## Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 221,000, representing a slight 8 % decrease compared to the previous period. Daily activity peaked at 17662 events, with a low of approximately 15781.
The number of new users has decreased significantly. Profiles with bio are now around 25951, reflecting a 79% drop. Pubkeys writing events have decreased by 50% compared to the previous period.
Regarding event publishing, all metrics have shown a decline. The total number of note events published is around 10 million, reflecting a 12% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.7 million, which is a 4.4 % decrease. Both reposts and reactions have decreased by about 5%.
For zap activity, the total zap amount is about 21 million, showing an increase of over 15% compared to the previous period.
Data source: https://stats.nostr.band/
## NIPs
[**Added optional signString() method**](https://github.com/nostr-protocol/nips/pull/1842)
nostr:npub1emq0gngdvntdn4apepxrxr65vln49nytqe0hyr58fg9768z5zmfqcwa3jz is proposing a signString() method that allow Nostr users to sign/authenticate messages for external apps without compromising their private key (nsec).It opens up a more generic and flexible challenge-response style external authentication method, using the same Schnorr signature mechanism that Nostr uses to sign events natively.External apps need only understand Schnorr signatures - they do not need to understand Nostr's event structure. This widens interoperability.A concrete example of where this would be useful is P2PK locking of Cashu ecash tokens to a Nostr pubkey (npub). Decoding the token requires a Scnorr signature on a structured message string. This method would allow a signer to handle It cleanly.
**[add nipB0, social bookmarking](https://github.com/nostr-protocol/nips/pull/1847)**
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 defines kind:39701 as website bookmarks.Bookmarks can be queried by the d tag, which is just their URL without the scheme, which is always and everywhere assumed to be https://. The querystring and the hash must be removed entirely, unless their requirement is explicitly stated either by the user or by some hardcoded list of URLs that rely on query strings for basic routing provided by the client (I've searched the internet extensively and could only find 3 websites that do this: YouTube, Hacker News and a random guy's sad old blog). Bookmarks can be commented on with NIP-22.
**[NIP-XX: Progress Event](https://github.com/nostr-protocol/nips/pull/1853)**
nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that covers the inclusion of Progress Events as implemented in Open Librarian. While the specific implementation is focused on tracking reading progress, the NIP is generic enough to be used in a whole range of other progress tracking scenarios (e.g. Fitness challenges, course progression for learning, personal goals etc..)
**[Extension of NIP-51](https://github.com/nostr-protocol/nips/pull/1854)**
nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that includes a minor update to extend kind 30003 in NIP-51 to include the i tag for external identities, as implemented for book reading lists in Open Librarian.
**[NIP-73: add git permalinks](https://github.com/nostr-protocol/nips/pull/1859)**
nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr is proposing a NIP that Enable references to commits, files and lines for both nip34 repositories and other git repositories. Useful for code reviews of nip34 patches, the forthcoming nip95 code snippets and referencing specific code more generally.
## Notable Projects
**[Yakihonne](https://yakihonne.com/notes/note1y3upur6ah22axx6dc7na63sszeuv6tx4al5jvuu3udnz2g8gawhqw50aqk)**
nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
🌐web v4.5.0:
* Custom reactions are here! Choose your preferred emoji to react to notes and other content.
* Improved profile organization with notes and replies now displayed separately.
* Adding the ability to zap notes directly from the notifications center.
* Enhanced DM filtering by time, allowing you to view only recent messages or browse further back.
* Manual cache clearing from settings to optimize web app performance.
* Resolved issue preventing users from removing custom media uploader servers.
* Expanded export data, including more relevant details in credential and wallet files.
* General bug fixes and performance improvements.
📱mobile v1.6.8:
* One tap zap: Send a Lightning Network payment with one tap.
* Dms extensive filtering: Use advanced filters to sort or prioritise direct messages efficiently.
* Separating replies from notes: Split replies and notes in profiles, adding a tab for easier browsing.
* Adding slide to display options: Swipe in notifications to access zap, reply, or DM options quickly.
* Custom reactions: Choose from a set of emojis for personalised reactions, beyond standard likes.
* App cache manager: Manage and clear app cache to boost performance and save space.
* Variety of bugs fixed: Fixed multiple bugs for a more stable and seamless app experience.
* General app improvements: Enhanced overall performance, usability, and design across the app.
**[0xchat ](https://yakihonne.com/notes/nevent1qqszhlqqesc0sx5ej27h72v08ush4thm6k5xh55rze3nv32zvl4d45qzyp0v559qftawle2kt8ahfqgtgfj5ugngcxkv5mjnsqdesckmwj5r5qcyqqqqqqg26f5gv)**
nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72
0xChat v1.0.2-Desktop Beta is now live!
* Supports NIP-104 MLS secret chat.
* Copy images directly from the clipboard.
* The app stays running after closing the window.
* Fixed Enter key sending messages immediately on desktop.
**[Nostur v1.18.2](https://yakihonne.com/notes/note1lgx6zrjvhennwnfkh8fnnvxa6nq4c24hdpfnsq3zqqvu3ww9n2ssxlm4tp)**
nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0
Nostur v1.18.2 bugfix update:
* Fixed Follow button sometimes disabled
* Fixed account switching reload issue
* Fixed custom feeds missing
* Fixed live stream banner scroll/swipe issue
* Fixed screen turns off while playing video
**[voca v0.0.6](https://yakihonne.com/notes/note1ughn4alp0cyc3t6p5mwjct47cycutnuw8lvtv4gc5wyt9vw4939s6s3ymr)**
nostr:npub17h9fn2ny0lycg7kmvxmw6gqdnv2epya9h9excnjw9wvml87nyw8sqy3hpu
This release fine tunes the release process and makes publishing to @Zapstore a lot easier. There are also continuous improvements to initializing the text to speech engine for a faster startup.
**[WasabiWallet 2.5.0](https://yakihonne.com/notes/nevent1qqsqhzwuajl8ccnltsvuygu3yt5hw8cvmkz7l5t6lpaa3tynmu9c4fczyzfm6rr08n96u3ec3vq6cm8qktqpxy2defxq34hzwyk5lac5qk3uxqcyqqqqqqg4fe35t)**
nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg
* 3rd Party Providers for Fee & Exchange Rate
* Quality of Life Features
* Backend and Coordinator packaged for Linux
**[GitPlaza](https://yakihonne.com/notes/nevent1qqspadwmftmpl4xyzgz59yy48j0hpsj8q57xhr0tumdaatpsdkrea9gzyrjrxmx4yh0hn7jd8tekflvkqr2tzrwwgg265npna4m75zzzx393qqcyqqqqqqgkws0q2)**
nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks
* Login via nsec
* Activity feed for the people you follow (only issue creation)
* Create issues
* Comment on issues
**[ZEUS v0.10.1](https://yakihonne.com/notes/nevent1qqs84nch638my3kzvm5yqp5ejcvj2e7h332sep8qmyelrpdyu5jpcyczyq6d9af8fuv43lxjevjx8k474h0c5g0cft8yysw63zqz80c9ejqf2qcyqqqqqqg3jcw0l)**
nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
ZEUS v0.10.1-beta1 is now available for testing.
* NameDesc / bLIP-11 support: add receiver name to invoices
* Bug fix: import of QR image from camera roll
* Bug fix: Embedded LND: Open Channel: fund max
* UI: Add dynamic background/text colors to Android NFC modal
**[KYCNOT.ME](https://yakihonne.com/article/naddr1qvzqqqr4gupzqwwv20y78a75nq9jr049a0y2twwd7lax2w2rpddgym5265n3dpjkqqsxxd3nx9jnscm9x5cnjvtrvvcngcecxpjrxvf3vvmkydn9xsurscgpu4ayq)**
nostr:npub188x98j0r7l2fszeph6j7hj99h8xl07n989pskk5zd69d2fcksetq5mgcqf
* UI/UX - designe a new logo and color palette for kycnot.me.
* Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services.
* ToS Scrapper: implement a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices.
* Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services.
* Transparency - To be more transparent, all discussions about services now take place publicly on GitLab.
* Additionally, there's a real-time audits page that displays database changes.
* Listing Requests - upgrade the request system. The new form allows you to directly request services or points without any extra steps.
* Lightweight and fast - The new site is lighter and faster than its predecessor!
* Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
## Long-Form Content Eco
In the past two weeks, more than 569 long-form articles have been published, including over 94 articles on Bitcoin and more than 43 related to Nostr, accounting for 24% of the total content.
These articles about Nostr mainly explore the growing importance of decentralization in communication, identity management, and digital infrastructure. From beginner-friendly guides like Nostr 101 and Getting Started with Primal, to more technical deep dives such as NIP-101e, NIP-95, and tutorials on running Nostr relays as TOR hidden services. Some articles focus on security and privacy—like protecting your Nsec with Amber or using tools such as ProtonMail—while others tackle complex challenges including Sybil attack mitigation and child protection in decentralized environments. There are also cultural and political reflections, such as letters from political prisoners and thoughts on the future of free speech in a post-Twitter world. In addition, the Nostr community shows a strong spirit of experimentation—ranging from agent-to-agent communication through dad jokes, to desktop-like clients, fitness tracking protocols, and Lightning integrations like Work Zaps and Wallet Connect. Together, these pieces showcase a dynamic, resilient, and freedom-driven movement shaping the future of the web.
The Bitcoin articles discuss a wide range of themes—from foundational ideas like "What is Money?" and Bitcoin’s first principles, to practical guides on mining, self-custody, Lightning payments, and privacy tools. Many explore Bitcoin’s role as a hedge against inflation, a form of sovereignty, and a response to fiat fragility. Cultural and economic reflections appear throughout—ranging from using Bitcoin to buy homes in Italy, to hip-hop collaborations, and even personal stories of financial awakening. There's critical analysis of Bitcoin UX, memetics, policy-making, and even war-time monetary history. From node sovereignty to P2P lending, from grassroots adoption to global macro shifts, these articles together portray Bitcoin not just as a currency, but as a cultural movement, a technological evolution, and a lens to reimagine freedom, value, and the future of money.
Thank you, nostr:npub1akzvuyyd79us07m8mtp2ruuha3ylp9757qg46d50rcrkhnx0fs4q2xzr37 nostr:npub1q67f4d7qdja237us384ryeekxsz88lz5kaawrcynwe4hqsnufr6s27up0e nostr:npub1xr8tvnnnr9aqt9vv30vj4vreeq2mk38mlwe7khvhvmzjqlcghh6sr85uum nostr:npub1zmc6qyqdfnllhnzzxr5wpepfpnzcf8q6m3jdveflmgruqvd3qa9sjv7f60 nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0 nostr:npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx nostr:npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm nostr:npub186k25a5rymtae6q0dmsh4ksen04706eurfst8xc5uzjchwkxdljqe59hv0
and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
## Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries.
* YakiHonne teamed up with Bitcoin Safari, nostr:npub1w7z986fez3gmjvxy6dd3sku4ndazhxzafjv2lf6aaa26mtl70q6scz4erj nostr:npub1t4ljwhhg7zlxeahxwgmkwqmn4jjxxq8lzhyuzy0zvy23hq0sacxsdl9fvv nostr:npub1pw778uxwkky3xgq7w3anykdwdw9g46xy8de9mnau0kgwzz375zkq3udv57 and FULAFIA University to successfully host a series of **[Nostr Workshops](https://yakihonne.com/notes/note1n2fadzx4njd8ruv5s26jkxyygp0re3t3ffzdcyumgahpzn2t73mqhwclgq)**, attracting over 200 participants in total. These events introduced the Nostr ecosystem and Bitcoin payments, allowing attendees to explore decentralized technologies through YakiHonne while earning rewards. Participants were encouraged to register and verify their accounts to claim exclusive bonuses—and invite friends to unlock even more benefits.
* **[The 2025 Bitcoin, Crypto Economy, and Law FAQ Webinar](https://x.com/BitcoinAR/status/1900643828874572166)** was held online on March 20, 2025 (Thursday) from 12:00 to 13:00 Argentina time. The webinar was hosted by Martin Paolantonio (Academic Director of the course) and Daniel Rybnik (a lawyer specializing in Banking, Corporate, and Financial Law). The session aimed to introduce the academic program and explored Bitcoin, the crypto economy, and related legal issues.
* [**The monthly Bitcoin Meetup** ](https://x.com/MyfirstBitcoin_/status/1905333348677095610)organized by Mi Primer Bitcoin took place on Thursday, March 27 at 7:00 PM at CRAFT Basilea in San Salvador. The event featured Bitcoin education, networking opportunities, live music, and fun extras like merchandise, raffles, and more. It was a vibrant evening dedicated to building community and spreading knowledge around Bitcoin. nostr:npub10zuxk4yhygswdmt5n9mfyeq6lh7gcu5g042tlggrgp8yunl32clqsu5t9r
Here is the upcoming Nostr event that you might want to check out.
* **[Bitcoin Educators Unconference 2025](https://x.com/MyfirstBitcoin_/status/1900513529125380140)** will take place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This event is non-sponsored and follows an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. the event has open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events.
* **[Panama Blockchain Week 2025](https://panamablockchainweek.com/index.php/ponentes/)** will take place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aims to position Panama as a leading blockchain financial hub in Latin America. The event features a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-

@ d5c3d063:4d1159b3
2025-04-01 04:20:50
“วิธีที่ดีที่สุดในการทำลายทุนนิยมคือทำลายค่าเงิน” Lenin Was Right
ประโยคนี้ไม่ใช่แค่คำปลุกระดมของนักปฏิวัติ
แต่มันเป็นเหมือนสัญญาณเตือนล่วงหน้า
ที่คนส่วนใหญ่ไม่สนใจ จนวันหนึ่งมันก็เกิดขึ้นจริง
แบบเงียบ ๆ โดยไม่มีใครทันตั้งตัว
Henry Hazlitt เขียนบทความนี้ไว้ตั้งแต่ปี 1947
เขาไม่เพียงบอกว่าเลนินพูดถูก แต่เขาแฉว่าโลกทั้งใบ
“กำลังทำตามแผนของเลนิน” แบบไม่รู้ตัว
ตอนนั้นรัฐบาลหลายประเทศ โดยเฉพาะในยุโรป
พิมพ์เงินออกมาใช้มหาศาล โดยอ้างว่าสงครามบีบบังคับให้ต้องทำแบบนั้น
แต่ปัญหาคือ...พอสงครามจบในปี 1945 แล้ว
รัฐกลับไม่หยุดพิมพ์เงิน ยังทำเหมือนอยู่ในภาวะฉุกเฉิน
เหมือนที่ อ. #SaifedeanAmmous พูดไว้ในหนังสือ #TheBitcoinStandard ว่าเวลารัฐอยากพิมพ์เงินแบบไม่ต้องรับผิดชอบ ก็แค่เอาสงครามมาอ้าง พอพูดว่า “เพื่อความมั่นคง” หรือ “เพื่อชาติ” เท่านั้นแหละ ทุกอย่างก็ดูเป็นเรื่องจำเป็นขึ้นมาทันที แล้วไม่มีใครกล้าถามว่าจริง ๆ แล้วเงินมันมาจากไหน
พอเงินเฟ้อมันแรง ของก็แพงขึ้น แต่รัฐไม่ยอมรับหรอกว่าที่ของแพงเพราะตัวเองพิมพ์เงินออกมาเยอะเกิน แต่กลับไปโทษพ่อค้า โทษคนทำธุรกิจ ว่าขายของแพง ค้ากำไรเกินควรซะงั้น
Hazlitt เขาเตือนว่า...รัฐกำลังทำให้คนเกลียดพ่อค้า เกลียดเจ้าของธุรกิจ เพื่อให้ดูเหมือนว่าตัวเองมีเหตุผลที่จะเข้ามาคุมเศรษฐกิจ ซึ่งที่น่ากลัวคือ...
มันไม่ได้เกิดจากความไม่รู้ แต่มันเกิดจาก “ระบบ”
ที่เปิดช่องให้เขาทำแบบนี้ได้เลย
แบบไม่ต้องรับผิดชอบอะไรทั้งนั้น
ตรงนี้แหละที่ Hazlitt เอาคำพูดของ
John Maynard Keynes เข้ามาเสริม
เพราะแม้แต่ Keynes ก็ยังเคยเตือนไว้ในหนังสือ
The Economic Consequences of the Peace
ว่า “เงินเฟ้อ” มันเหมือนเครื่องมือเงียบ ๆ
ที่จะค่อย ๆ ทำลายระบบเศรษฐกิจ
โดยที่คนส่วนใหญ่ไม่รู้ตัว
Hazlitt เขาเป็น "สายวิจารณ์" Keynes ตัวพ่อเลยนะ
เขาเขียนหนังสือ The Failure of the New Economics ที่ไล่รื้อแนวคิดของ Keynes
แบบ “ตา-ต่อ-ตา หน้า-ต่อ-หน้า” กับหนังสือ
The General Theory ของ Keynes เลยนะ
แต่พอมาในบทความนี้...Hazlitt
กลับหยิบคำพูดของ Keynes มาใช้อย่างเต็มใจ
เพราะมันตรงเกินไปที่จะมองข้ามได้
ว่าแม้แต่ #Keynes เองยังเคยเตือนเลยว่า
“การทำลายค่าเงิน” คืออาวุธเงียบ
ที่ใช้ทำลายระบบทุนนิยมได้อย่างแนบเนียนที่สุด
.
.
พออ่านแล้วแบบ…แม้แต่คนที่เราคิดว่าเชียร์ฝั่งรัฐ
ยังเตือนเรื่องนี้ไว้ แล้วเราจะยังเฉยอยู่ได้ไง
คือถ้าเงินมันถูกทำให้ด้อยค่าลงเรื่อย ๆ
วันนึงมันจะพังแบบเงียบ ๆ จนคนไม่รู้ตัวเลย
คนทั่วไปจะรู้แค่ว่าของมันแพงขึ้น แต่ไม่มีใครเห็น
ว่าจริง ๆ แล้ว เงินที่เราใช้มันเริ่มไม่มีเสถียรภาพ
และไม่มั่นคงอีกต่อไปแล้ว
แล้วถ้ามองตัวเลขนี่ยิ่งช็อก
ระหว่างปี 1939 ถึง 1947 ในเวลาแค่ 8 ปี
ปริมาณเงินในระบบของสหรัฐฯ เพิ่มจาก
33,000 ล้านดอลลารเป็น 108,500 ล้านดอลลาร์
พูดง่าย ๆ คือ คูณสาม (ช่วงสงครามโลกครั้งที่ 2)
Hazlitt พูดแบบตรง ๆ เลยว่า ปัญหาที่เกิดขึ้น
มันไม่ใช่เพราะเศรษฐกิจโตหรือคนรวยขึ้นนะ
มันเกิดจากการที่รัฐเพิ่มปริมาณเงินในระบบเร็วเกินไป
เมื่อเงินในตลาดเลยเยอะขึ้น แต่ของที่มีให้ซื้อไม่ได้เยอะขึ้นตาม เมื่อเงินไหลเวียนมากขึ้น โดยที่ของยังมีเท่าเดิม ราคาของก็เลยพุ่ง
ทีนี้พอของขึ้นราคา รัฐบาลกลับไม่ยอมรับว่าเป็นเพราะเขาพิมพ์เงิน แต่ไปเลือกวิธีแก้แบบง่าย ๆ
แต่สร้างปัญหาในระยะยาว เช่น สั่งห้ามขึ้นราคา
กดดันคนทำธุรกิจให้แบกต้นทุนไว้ หรือไม่ก็ล็อกค่าเงิน เหมือนไม่มีอะไรเกิดขึ้น
หลังจากนั้น เศรษฐกิจยุโรปก็เริ่มพัง ผู้ผลิตเจอต้นทุนบาน การค้าระหว่างประเทศก็รวน สุดท้ายก็ต้องพึ่งดอลลาร์จากอเมริกา (Marshall Aid) มาช่วยอุ้ม เหมือนพิมพ์เงินของตัวเองจนระบบรวน แล้วไปขอเงินจากฝั่งที่พิมพ์ได้มากกว่าอีกที
นี่แหละจุดเริ่มของ “วิกฤตเศรษฐกิจโลกหลังสงคราม”
ที่จริง ๆ แล้ว...ก็แค่เรื่องของการพิมพ์เงินล้วน ๆ
.
.
แต่นั้นมันเป็นเรื่องเกิดขึ้นเมื่อปี 1947 นะ...แล้ววันนี้ล่ะ
ล่าสุด ปี 2020 ก่อนโควิด ระดับ M2 money supply ของสหรัฐอยู่ราว ๆ 15 ล้านล้านดอลลาร์ แค่ไม่กี่ปีต่อมา มันทะลุไปถึง 21 ล้านล้าน ในเวลาไม่ถึง 3 ปีเงินเพิ่มขึ้นในระบบเศรษฐกิจกว่า 6 ล้านล้านดอลลาร์
แล้วของก็แพงขึ้น ค่าแรงวิ่งตามไม่ทัน
แต่แทนที่รัฐจะบอกว่า “เราพิมพ์เงินมากไป”
ก็ไปเล่นมุกเดิม โทษตลาด โทษนายทุน โทษธุรกิจ
(บ้างก็โทษโลกร้อน)
สุดท้ายก็จะมีคนบางกลุ่มเชียร์ให้ “ควบคุมราคา” อีก
มันคือ loop เดิม ที่ #Hazlitt เคยเตือนไว้
เมื่อเกือบ 80 ปีก่อน..
.
.
สิ่งที่ซุปเห็นชัดเจนที่สุดจากบทความนี้คือ...
เกมนี้มันไม่มีใครหยุดได้เลย
ถ้าคุณยังถือเงินที่รัฐพิมพ์ได้
เพราะตราบใดที่ยังมีคนสั่งพิมพ์เงินได้ตามใจ
ระบบเศรษฐกิจก็จะปั่นป่วนซ้ำไปซ้ำมา
ของก็จะแพงขึ้นเรื่อย ๆ แบบไม่มีจุดจบ
คุณก็จะต้องเหนื่อยทำงานมากขึ้น
แต่ซื้อได้น้อยลง แล้วคุณก็จะโทษตัวเอง
ว่ายังขยันไม่มากพอ ทั้ง ๆ ที่คุณทำงาน 4-5 อย่าง
.
เลนิน พูดถูก ถ้าจะทำลายทุนนิยม ก็แค่ทำลายค่าเงิน
ฟังดูแรงเนอะ...แต่เรื่องนี้มันไม่ใช่แค่ทฤษฎีแล้ว
เพราะเรากำลังเห็น ว่ามันกำลังเกิดขึ้นอยู่จริง ๆ
แต่วันนี้ เราเลือกที่จะไม่อยู่ในเกมที่พังซ้ำๆ ได้แล้ว
เพราะเรามี “ทางออก” อยู่ตรงหน้า
บิตคอยน์ ไม่ใช่อะไรที่ทุกคนจะเข้าใจมันได้ทันที
แต่มันคือ “เงิน” ที่ไม่มีใครพิมพ์เพิ่มได้ตามใจ
ไม่มีใครมานั่งกดปุ่มสร้างมันขึ้นมาได้ง่าย ๆ
ไม่มีใครเปลี่ยนกติกากลางเกมได้
และไม่มีใครแทรกแซงนโยบายของมันได้
สิ่งเดียวที่ #บิตคอยน์ บอกเราตรง ๆ ก็คือ
“ความขาดแคลน” ไม่ใช่ปัญหา...
สิ่งที่ Hazlitt เตือนเมื่ออดีต
คือกับดักของเงินไม่มีขอบเขต
สิ่งที่ #Bitcoin เสนอ
คือขอบเขตที่ทำให้ “มูลค่า” กลับมามีความหมาย
[Newsweek column from September 22, 1947, and reprinted in Business Tides: The Newsweek Era of Henry Hazlitt.] https://mises.org/mises-wire/lenin-was-right
#Siamstr
-

@ 2fdeba99:fd961eff
2025-03-21 17:16:33
# == January 17 2025
Out From Underneath | Prism Shores
crazy arms | pigeon pit
Humanhood | The Weather Station
# == february 07 2025
Wish Defense | FACS
Sayan - Savoie | Maria Teriaeva
Nowhere Near Today | Midding
# == february 14 2025
Phonetics On and On | Horsegirl
# == february 21 2025
Finding Our Balance | Tsoh Tso
Machine Starts To Sing | Porridge Radio
Armageddon In A Summer Dress | Sunny Wa
# == february 28 2025
you, infinite | you, infinite
On Being | Max Cooper
Billboard Heart | Deep Sea Diver
# == March 21 2025
Watermelon/Peacock | Exploding Flowers
Warlord of the Weejuns | Goya Gumbani
-

@ aa8de34f:a6ffe696
2025-03-21 12:08:31
19\. März 2025
### 🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s **proof-of-work** mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, **SHA-256 remains secure** because:
- Quantum computers excel at **factoring large numbers** (Shor’s Algorithm).
- However, **SHA-256 is a one-way function**, meaning there's no known quantum algorithm that can efficiently reverse it.
- **Grover’s Algorithm** (which theoretically speeds up brute force attacks) would still require **2¹²⁸ operations** to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
### 🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses **Elliptic Curve Digital Signature Algorithm (ECDSA)** to generate keys.
- A quantum computer could use **Shor’s Algorithm** to break **SECP256K1**, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a **Bitcoin address** is the public key—**this is wrong**.
- When you **receive Bitcoin**, it is sent to a **hashed public key** (the Bitcoin address).
- The **actual public key is never exposed** because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses **Pay-to-Public-Key-Hash (P2PKH)** or newer methods like **Pay-to-Witness-Public-Key-Hash (P2WPKH)**, which add extra layers of security.
### 🕵️♂️ 2.1 The Public Key Never Appears
- When you **send Bitcoin**, your wallet creates a **digital signature**.
- This signature uses the **private key** to **prove** ownership.
- The **Bitcoin address is revealed and creates the Public Key**
- The public key **remains hidden inside the Bitcoin script and Merkle tree**.
This means: ✔ **The public key is never exposed.** ✔ **Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.**
+++++++++++++++++++++++++++++++++++++++++++++++++
### 🔄 3. Bitcoin Can Upgrade
Even if quantum computers **eventually** become a real threat:
- Bitcoin developers can **upgrade to quantum-safe cryptography** (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide **soft fork or hard fork** could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
### ⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a **10-minute block interval**, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack **every 10 minutes**.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system **resets the challenge with every new block**.This **limits the window of opportunity** for quantum attacks.
---
### 🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker **must solve the cryptographic puzzle (Proof of Work) in under 10 minutes**.
- The problem? **Any slight error changes the hash completely**, meaning:**If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails**.**Quantum decoherence** (loss of qubit stability) makes error correction a massive challenge.The computational cost of **recovering from an incorrect hash** is still incredibly high.
---
### ⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer **somehow** solved a block instantly:The network would **quickly recognize and reject invalid transactions**.Other miners would **continue mining** under normal cryptographic rules.**51% Attack?** The attacker would need to consistently beat the **entire Bitcoin network**, which is **not sustainable**.
---
### 🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every **2016 blocks (\~2 weeks)**.
- If quantum miners appeared and suddenly started solving blocks too quickly, **the difficulty would adjust upward**, making attacks significantly harder.
- This **self-correcting mechanism** ensures that even quantum computers wouldn't easily overpower the network.
---
### 🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ **The 10-minute rule limits attack frequency** – quantum computers can’t keep up.
✔ **Any slight miscalculation ruins the attack**, resetting all progress.
✔ **Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages**.
**Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant.** 🚀
-

@ a95c6243:d345522c
2025-03-20 09:59:20
**Bald werde es verboten, alleine im Auto zu fahren,** konnte man dieser Tage in verschiedenen spanischen Medien lesen. Die nationale Verkehrsbehörde (Dirección General de Tráfico, kurz DGT) werde Alleinfahrern das Leben schwer machen, wurde gemeldet. Konkret erörtere die Generaldirektion geeignete Sanktionen für Personen, die ohne Beifahrer im Privatauto unterwegs seien.
**Das Alleinfahren sei zunehmend verpönt und ein Mentalitätswandel notwendig,** hieß es. Dieser «Luxus» stehe im Widerspruch zu den Maßnahmen gegen Umweltverschmutzung, die in allen europäischen Ländern gefördert würden. In Frankreich sei es «bereits verboten, in der Hauptstadt allein zu fahren», [behauptete](https://noticiastrabajo.huffingtonpost.es/sociedad/adios-a-conducir-solo-la-dgt-se-lo-pone-crudo-a-los-conductores-que-viajen-sin-acompanante-en-el-coche/) *Noticiastrabajo Huffpost* in einer Zwischenüberschrift. Nur um dann im Text zu konkretisieren, dass die sogenannte «Umweltspur» auf der Pariser Ringautobahn gemeint war, die für Busse, Taxis und Fahrgemeinschaften reserviert ist. [Ab Mai](https://www.lefigaro.fr/conso/peripherique-parisien-entree-en-vigueur-de-la-voie-reservee-au-covoiturage-ce-lundi-20250303) werden Verstöße dagegen mit einem Bußgeld geahndet.
**Die DGT jedenfalls wolle bei der Umsetzung derartiger Maßnahmen** nicht hinterherhinken. Diese Medienberichte, inklusive des angeblich bevorstehenden Verbots, beriefen sich auf Aussagen des Generaldirektors der Behörde, Pere Navarro, beim Mobilitätskongress Global Mobility Call im November letzten Jahres, wo es um «nachhaltige Mobilität» ging. Aus diesem Kontext stammt auch Navarros Warnung: «Die Zukunft des Verkehrs ist geteilt oder es gibt keine».
**Die «Faktenchecker» kamen der Generaldirektion prompt zu Hilfe.** Die DGT habe derlei Behauptungen [zurückgewiesen](https://www.newtral.es/dgt-una-persona-coche/20250312/) und klargestellt, dass es keine Pläne gebe, Fahrten mit nur einer Person im Auto zu verbieten oder zu bestrafen. Bei solchen Meldungen handele es sich um Fake News. Teilweise wurde der Vorsitzende der spanischen «Rechtsaußen»-Partei Vox, Santiago Abascal, der Urheberschaft bezichtigt, weil er einen entsprechenden [Artikel](https://gaceta.es/espana/la-dgt-estudia-formas-de-sancionar-a-quien-circule-solo-en-su-vehiculo-el-futuro-sera-compartido-o-no-sera-20250311-1612/) von *La Gaceta* kommentiert hatte.
**Der Beschwichtigungsversuch der Art «niemand hat die Absicht»** ist dabei erfahrungsgemäß eher ein Alarmzeichen als eine Beruhigung. Walter Ulbrichts Leugnung einer geplanten Berliner [Mauer](https://www.berlin-mauer.de/videos/walter-ulbricht-zum-mauerbau-530/) vom Juni 1961 ist vielen genauso in Erinnerung wie die Fake News-Warnungen des deutschen Bundesgesundheitsministeriums bezüglich [Lockdowns](https://x.com/BMG_Bund/status/1238780849652465664) im März 2020 oder diverse Äußerungen zu einer [Impfpflicht](https://www.achgut.com/artikel/die_schoensten_politiker_zitate_zur_impfpflicht) ab 2020.
**Aber Aufregung hin, Dementis her:** Die [Pressemitteilung](https://archive.is/xXQWD) der DGT zu dem Mobilitätskongress enthält in Wahrheit viel interessantere Informationen als «nur» einen Appell an den «guten» Bürger wegen der Bemühungen um die Lebensqualität in Großstädten oder einen möglichen obligatorischen Abschied vom Alleinfahren. Allerdings werden diese Details von Medien und sogenannten Faktencheckern geflissentlich übersehen, obwohl sie keineswegs versteckt sind. Die Auskünfte sind sehr aufschlussreich, wenn man genauer hinschaut.
### Digitalisierung ist der Schlüssel für Kontrolle
**Auf dem Kongress stellte die Verkehrsbehörde ihre Initiativen zur Förderung der «neuen Mobilität» vor,** deren Priorität Sicherheit und Effizienz sei. Die vier konkreten Ansätze haben alle mit Digitalisierung, Daten, Überwachung und Kontrolle im großen Stil zu tun und werden unter dem Euphemismus der «öffentlich-privaten Partnerschaft» angepriesen. Auch lassen sie die transhumanistische Idee vom unzulänglichen Menschen erkennen, dessen Fehler durch «intelligente» technologische Infrastruktur kompensiert werden müssten.
**Die Chefin des Bereichs «Verkehrsüberwachung» erklärte die Funktion** des spanischen National Access Point ([NAP](https://nap.dgt.es/)), wobei sie betonte, wie wichtig Verkehrs- und Infrastrukturinformationen in Echtzeit seien. Der NAP ist «eine essenzielle Web-Applikation, die unter EU-Mandat erstellt wurde», kann man auf der Website der DGT nachlesen.
**Das Mandat meint Regelungen zu einem einheitlichen europäischen Verkehrsraum,** mit denen die Union mindestens seit 2010 den Aufbau einer digitalen Architektur mit offenen Schnittstellen betreibt. Damit begründet man auch «umfassende Datenbereitstellungspflichten im Bereich multimodaler Reiseinformationen». Jeder Mitgliedstaat musste einen NAP, also einen nationalen [Zugangspunkt](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en) einrichten, der Zugang zu statischen und dynamischen Reise- und Verkehrsdaten verschiedener Verkehrsträger ermöglicht.
**Diese Entwicklung ist heute schon weit fortgeschritten,** auch und besonders in Spanien. Auf besagtem Kongress erläuterte die Leiterin des Bereichs «Telematik» die Plattform [«DGT 3.0»](https://www.dgt.es/muevete-con-seguridad/tecnologia-e-innovacion-en-carretera/dgt-3.0/). Diese werde als Integrator aller Informationen genutzt, die von den verschiedenen öffentlichen und privaten Systemen, die Teil der Mobilität sind, bereitgestellt werden.
**Es handele sich um eine Vermittlungsplattform zwischen Akteuren wie Fahrzeugherstellern,** Anbietern von Navigationsdiensten oder Kommunen und dem Endnutzer, der die Verkehrswege benutzt. Alle seien auf Basis des Internets der Dinge (IOT) anonym verbunden, «um der vernetzten Gemeinschaft wertvolle Informationen zu liefern oder diese zu nutzen».
**So sei DGT 3.0 «ein Zugangspunkt für einzigartige, kostenlose und genaue Echtzeitinformationen** über das Geschehen auf den Straßen und in den Städten». Damit lasse sich der Verkehr nachhaltiger und vernetzter gestalten. Beispielsweise würden die Karten des Produktpartners Google dank der DGT-Daten 50 Millionen Mal pro Tag aktualisiert.
**Des Weiteren informiert die Verkehrsbehörde über ihr SCADA-Projekt.** Die Abkürzung steht für Supervisory Control and Data Acquisition, zu deutsch etwa: Kontrollierte Steuerung und Datenerfassung. Mit SCADA kombiniert man Software und Hardware, um automatisierte Systeme zur Überwachung und Steuerung technischer Prozesse zu schaffen. Das SCADA-Projekt der DGT wird von Indra entwickelt, einem spanischen Beratungskonzern aus den Bereichen Sicherheit & Militär, Energie, Transport, Telekommunikation und Gesundheitsinformation.
**Das SCADA-System der Behörde umfasse auch eine Videostreaming- und Videoaufzeichnungsplattform,** die das Hochladen in die Cloud in Echtzeit ermöglicht, wie Indra [erklärt](https://www.indracompany.com/es/noticia/indra-presenta-global-mobility-call-pionera-plataforma-nube-desplegada-centros-gestion). Dabei gehe es um Bilder, die von Überwachungskameras an Straßen aufgenommen wurden, sowie um Videos aus DGT-Hubschraubern und Drohnen. Ziel sei es, «die sichere Weitergabe von Videos an Dritte sowie die kontinuierliche Aufzeichnung und Speicherung von Bildern zur möglichen Analyse und späteren Nutzung zu ermöglichen».
**Letzteres klingt sehr nach biometrischer Erkennung** und Auswertung durch künstliche Intelligenz. Für eine bessere Datenübertragung wird derzeit die [Glasfaserverkabelung](https://www.moncloa.com/2025/03/18/linea-azul-conduccion-dgt-3191554/) entlang der Landstraßen und Autobahnen ausgebaut. Mit der Cloud sind die Amazon Web Services (AWS) gemeint, die spanischen [Daten gehen](https://norberthaering.de/news/digitalgipfel-wehnes-interview/) somit direkt zu einem US-amerikanischen «Big Data»-Unternehmen.
**Das Thema «autonomes Fahren», also Fahren ohne Zutun des Menschen,** bildet den Abschluss der Betrachtungen der DGT. Zusammen mit dem Interessenverband der Automobilindustrie ANFAC (Asociación Española de Fabricantes de Automóviles y Camiones) sprach man auf dem Kongress über Strategien und Perspektiven in diesem Bereich. Die Lobbyisten hoffen noch in diesem Jahr 2025 auf einen [normativen Rahmen](https://www.coches.net/noticias/informe-coche-autonomo-conectado-espana-2024) zur erweiterten Unterstützung autonomer Technologien.
**Wenn man derartige Informationen im Zusammenhang betrachtet,** bekommt man eine Idee davon, warum zunehmend alles elektrisch und digital werden soll. Umwelt- und Mobilitätsprobleme in Städten, wie Luftverschmutzung, Lärmbelästigung, Platzmangel oder Staus, sind eine Sache. Mit dem Argument «emissionslos» wird jedoch eine Referenz zum CO2 und dem «menschengemachten Klimawandel» hergestellt, die Emotionen triggert. Und damit wird so ziemlich alles verkauft.
**Letztlich aber gilt: Je elektrischer und digitaler unsere Umgebung wird** und je freigiebiger wir mit unseren Daten jeder Art sind, desto besser werden wir kontrollier-, steuer- und sogar abschaltbar. Irgendwann entscheiden KI-basierte Algorithmen, ob, wann, wie, wohin und mit wem wir uns bewegen dürfen. Über einen 15-Minuten-Radius geht dann möglicherweise nichts hinaus. Die Projekte auf diesem Weg sind ernst zu nehmen, real und schon weit fortgeschritten.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/reisen-wagen-ferien-fahrzeug-1426822/)]*
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass)*** erschienen.
-

@ 9f475ec5:d9acc946
2025-04-01 03:17:20
> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce.
# Introducing the Dad Joke Publisher
Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**.
Agent to agent communication is the next step in the AI revolution:
- Agents transacting with other agents
- Agents working together to create a multi-agent application
To make it a reality, agents need to be able to:
- Find other agents
- Authenticate the agents
- Discover their capabilities
- Transact data and / or money
Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but...
**I believe that there is a better way with Nostr.**
Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that.
!(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif]
## The Dad Joke Game
The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*.
The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour.
**Dynamic discovery**
A Joker is an agent with a Nostr profile with the following characteristics:
- The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md))
- The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md))
- The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md))
**Authentication**
The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com.
**Communication**
Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md).
## Join the game!
Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started.
You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`.
## Join Synvya's mission!
Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions.
Next steps for Synvya:
- A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents
- Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file.
PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this).
PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever.
-

@ 266815e0:6cd408a5
2025-03-19 11:10:21
How to create a nostr app quickly using [applesauce](https://hzrd149.github.io/applesauce/)
In this guide we are going to build a nostr app that lets users follow and unfollow [fiatjaf](nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6)
## 1. Setup new project
Start by setting up a new vite app using `pnpm create vite`, then set the name and select `Solid` and `Typescript`
```sh
➜ pnpm create vite
│
◇ Project name:
│ followjaf
│
◇ Select a framework:
│ Solid
│
◇ Select a variant:
│ TypeScript
│
◇ Scaffolding project in ./followjaf...
│
└ Done. Now run:
cd followjaf
pnpm install
pnpm run dev
```
## 2. Adding nostr dependencies
There are a few useful nostr dependencies we are going to need. `nostr-tools` for the types and small methods, and [`rx-nostr`](https://penpenpng.github.io/rx-nostr/) for making relay connections
```sh
pnpm install nostr-tools rx-nostr
```
## 3. Setup rx-nostr
Next we need to setup rxNostr so we can make connections to relays. create a new `src/nostr.ts` file with
```ts
import { createRxNostr, noopVerifier } from "rx-nostr";
export const rxNostr = createRxNostr({
// skip verification here because we are going to verify events at the event store
skipVerify: true,
verifier: noopVerifier,
});
```
## 4. Setup the event store
Now that we have a way to connect to relays, we need a place to store events. We will use the [`EventStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.EventStore.html) class from `applesauce-core` for this. create a new `src/stores.ts` file with
> The event store does not store any events in the browsers local storage or anywhere else. It's in-memory only and provides a model for the UI
```ts
import { EventStore } from "applesauce-core";
import { verifyEvent } from "nostr-tools";
export const eventStore = new EventStore();
// verify the events when they are added to the store
eventStore.verifyEvent = verifyEvent;
```
## 5. Create the query store
The event store is where we store all the events, but we need a way for the UI to query them. We can use the [`QueryStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.QueryStore.html) class from `applesauce-core` for this.
Create a query store in `src/stores.ts`
```ts
import { QueryStore } from "applesauce-core";
// ...
// the query store needs the event store to subscribe to it
export const queryStore = new QueryStore(eventStore);
```
## 6. Setup the profile loader
Next we need a way to fetch user profiles. We are going to use the [`ReplaceableLoader`](https://hzrd149.github.io/applesauce/overview/loaders.html#replaceable-loader) class from [`applesauce-loaders`](https://www.npmjs.com/package/applesauce-loaders) for this.
> `applesauce-loaders` is a package that contains a few loader classes that can be used to fetch different types of data from relays.
First install the package
```sh
pnpm install applesauce-loaders
```
Then create a `src/loaders.ts` file with
```ts
import { ReplaceableLoader } from "applesauce-loaders";
import { rxNostr } from "./nostr";
import { eventStore } from "./stores";
export const replaceableLoader = new ReplaceableLoader(rxNostr);
// Start the loader and send any events to the event store
replaceableLoader.subscribe((packet) => {
eventStore.add(packet.event, packet.from);
});
```
## 7. Fetch fiatjaf's profile
Now that we have a way to store events, and a loader to help with fetching them, we should update the `src/App.tsx` component to fetch the profile.
We can do this by calling the `next` method on the loader and passing a `pubkey`, `kind` and `relays` to it
```tsx
function App() {
// ...
onMount(() => {
// fetch fiatjaf's profile on load
replaceableLoader.next({
pubkey: "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d",
kind: 0,
relays: ["wss://pyramid.fiatjaf.com/"],
});
});
// ...
}
```
## 8. Display the profile
Now that we have a way to fetch the profile, we need to display it in the UI.
We can do this by using the [`ProfileQuery`](https://hzrd149.github.io/applesauce/typedoc/functions/applesauce_core.Queries.ProfileQuery.html) which gives us a stream of updates to a pubkey's profile.
Create the profile using `queryStore.createQuery` and pass in the `ProfileQuery` and the pubkey.
```tsx
const fiatjaf = queryStore.createQuery(
ProfileQuery,
"3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"
);
```
But this just gives us an [observable](https://rxjs.dev/guide/observable), we need to subscribe to it to get the profile.
Luckily SolidJS profiles a simple [`from`](https://docs.solidjs.com/reference/reactive-utilities/from) method to subscribe to any observable.
> To make things reactive SolidJS uses accessors, so to get the profile we need to call `fiatjaf()`
```tsx
function App() {
// ...
// Subscribe to fiatjaf's profile from the query store
const fiatjaf = from(
queryStore.createQuery(ProfileQuery, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d")
);
return (
<>
{/* replace the vite and solid logos with the profile picture */}
<div>
<img src={fiatjaf()?.picture} class="logo" />
</div>
<h1>{fiatjaf()?.name}</h1>
{/* ... */}
</>
);
}
```
## 9. Letting the user signin
Now we should let the user signin to the app. We can do this by creating a [`AccountManager`](https://hzrd149.github.io/applesauce/accounts/manager.html) class from `applesauce-accounts`
First we need to install the packages
```sh
pnpm install applesauce-accounts applesauce-signers
```
Then create a new `src/accounts.ts` file with
```ts
import { AccountManager } from "applesauce-accounts";
import { registerCommonAccountTypes } from "applesauce-accounts/accounts";
// create an account manager instance
export const accounts = new AccountManager();
// Adds the common account types to the manager
registerCommonAccountTypes(accounts);
```
Next lets presume the user has a NIP-07 browser extension installed and add a signin button.
```tsx
function App() {
const signin = async () => {
// do nothing if the user is already signed in
if (accounts.active) return;
// create a new nip-07 signer and try to get the pubkey
const signer = new ExtensionSigner();
const pubkey = await signer.getPublicKey();
// create a new extension account, add it, and make it the active account
const account = new ExtensionAccount(pubkey, signer);
accounts.addAccount(account);
accounts.setActive(account);
};
return (
<>
{/* ... */}
<div class="card">
<p>Are you following the fiatjaf? the creator of "The nostr"</p>
<button onClick={signin}>Check</button>
</div>
</>
);
}
```
Now when the user clicks the button the app will ask for the users pubkey, then do nothing... but it's a start.
> We are not persisting the accounts, so when the page reloads the user will NOT be signed in. you can learn about persisting the accounts in the [docs](https://hzrd149.github.io/applesauce/accounts/manager.html#persisting-accounts)
## 10. Showing the signed-in state
We should show some indication to the user that they are signed in. We can do this by modifying the signin button if the user is signed in and giving them a way to sign-out
```tsx
function App() {
// subscribe to the currently active account (make sure to use the account$ observable)
const account = from(accounts.active$);
// ...
const signout = () => {
// do nothing if the user is not signed in
if (!accounts.active) return;
// signout the user
const account = accounts.active;
accounts.removeAccount(account);
accounts.clearActive();
};
return (
<>
{/* ... */}
<div class="card">
<p>Are you following the fiatjaf? ( creator of "The nostr" )</p>
{account() === undefined ? <button onClick={signin}>Check</button> : <button onClick={signout}>Signout</button>}
</div>
</>
);
}
```
## 11. Fetching the user's profile
Now that we have a way to sign in and out of the app, we should fetch the user's profile when they sign in.
```tsx
function App() {
// ...
// fetch the user's profile when they sign in
createEffect(async () => {
const active = account();
if (active) {
// get the user's relays or fallback to some default relays
const usersRelays = await active.getRelays?.();
const relays = usersRelays ? Object.keys(usersRelays) : ["wss://relay.damus.io", "wss://nos.lol"];
// tell the loader to fetch the users profile event
replaceableLoader.next({
pubkey: active.pubkey,
kind: 0,
relays,
});
// tell the loader to fetch the users contacts
replaceableLoader.next({
pubkey: active.pubkey,
kind: 3,
relays,
});
// tell the loader to fetch the users mailboxes
replaceableLoader.next({
pubkey: active.pubkey,
kind: 10002,
relays,
});
}
});
// ...
}
```
Next we need to subscribe to the users profile, to do this we can use some rxjs operators to chain the observables together.
```tsx
import { Match, Switch } from "solid-js";
import { of, switchMap } from "rxjs";
function App() {
// ...
// subscribe to the active account, then subscribe to the users profile or undefined
const profile = from(
accounts.active$.pipe(
switchMap((account) => (account ? queryStore.createQuery(ProfileQuery, account!.pubkey) : of(undefined)))
)
);
// ...
return (
<>
{/* ... */}
<div class="card">
<Switch>
<Match when={account() && !profile()}>
<p>Loading profile...</p>
</Match>
<Match when={profile()}>
<p style="font-size: 1.2rem; font-weight: bold;">Welcome {profile()?.name}</p>
</Match>
</Switch>
{/* ... */}
</div>
</>
);
}
```
## 12. Showing if the user is following fiatjaf
Now that the app is fetching the users profile and contacts we should show if the user is following fiatjaf.
```tsx
function App() {
// ...
// subscribe to the active account, then subscribe to the users contacts or undefined
const contacts = from(
accounts.active$.pipe(
switchMap((account) => (account ? queryStore.createQuery(UserContactsQuery, account!.pubkey) : of(undefined)))
)
);
const isFollowing = createMemo(() => {
return contacts()?.some((c) => c.pubkey === "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d");
});
// ...
return (
<>
{/* ... */}
<div class="card">
{/* ... */}
<Switch
fallback={
<p style="font-size: 1.2rem;">
Sign in to check if you are a follower of the fiatjaf ( creator of "The nostr" )
</p>
}
>
<Match when={contacts() && isFollowing() === undefined}>
<p>checking...</p>
</Match>
<Match when={contacts() && isFollowing() === true}>
<p style="color: green; font-weight: bold; font-size: 2rem;">
Congratulations! You are a follower of the fiatjaf
</p>
</Match>
<Match when={contacts() && isFollowing() === false}>
<p style="color: red; font-weight: bold; font-size: 2rem;">
Why don't you follow the fiatjaf? do you even like nostr?
</p>
</Match>
</Switch>
{/* ... */}
</div>
</>
);
}
```
## 13. Adding the follow button
Now that we have a way to check if the user is following fiatjaf, we should add a button to follow him. We can do this with [Actions](https://hzrd149.github.io/applesauce/overview/actions.html) which are pre-built methods to modify nostr events for a user.
First we need to install the `applesauce-actions` and `applesauce-factory` package
```sh
pnpm install applesauce-actions applesauce-factory
```
Then create a `src/actions.ts` file with
```ts
import { EventFactory } from "applesauce-factory";
import { ActionHub } from "applesauce-actions";
import { eventStore } from "./stores";
import { accounts } from "./accounts";
// The event factory is used to build and modify nostr events
export const factory = new EventFactory({
// accounts.signer is a NIP-07 signer that signs with the currently active account
signer: accounts.signer,
});
// The action hub is used to run Actions against the event store
export const actions = new ActionHub(eventStore, factory);
```
Then create a `toggleFollow` method that will add or remove fiatjaf from the users contacts.
> We are using the `exec` method to run the action, and the [`forEach`](https://rxjs.dev/api/index/class/Observable#foreach) method from RxJS allows us to await for all the events to be published
```tsx
function App() {
// ...
const toggleFollow = async () => {
// send any created events to rxNostr and the event store
const publish = (event: NostrEvent) => {
eventStore.add(event);
rxNostr.send(event);
};
if (isFollowing()) {
await actions
.exec(UnfollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d")
.forEach(publish);
} else {
await actions
.exec(
FollowUser,
"3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d",
"wss://pyramid.fiatjaf.com/"
)
.forEach(publish);
}
};
// ...
return (
<>
{/* ... */}
<div class="card">
{/* ... */}
{contacts() && <button onClick={toggleFollow}>{isFollowing() ? "Unfollow" : "Follow"}</button>}
</div>
</>
);
}
```
## 14. Adding outbox support
The app looks like it works now but if the user reloads the page they will still see an the old version of their contacts list. we need to make sure rxNostr is publishing the events to the users outbox relays.
To do this we can subscribe to the signed in users mailboxes using the query store in `src/nostr.ts`
```ts
import { MailboxesQuery } from "applesauce-core/queries";
import { accounts } from "./accounts";
import { of, switchMap } from "rxjs";
import { queryStore } from "./stores";
// ...
// subscribe to the active account, then subscribe to the users mailboxes and update rxNostr
accounts.active$
.pipe(switchMap((account) => (account ? queryStore.createQuery(MailboxesQuery, account.pubkey) : of(undefined))))
.subscribe((mailboxes) => {
if (mailboxes) rxNostr.setDefaultRelays(mailboxes.outboxes);
else rxNostr.setDefaultRelays([]);
});
```
And that's it! we have a working nostr app that lets users follow and unfollow fiatjaf.
-

@ a39d19ec:3d88f61e
2025-03-18 17:16:50
Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
### 1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).
Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
### 2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
### 3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
### 4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
### 5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-

@ b8af284d:f82c91dd
2025-03-16 16:42:49

Liebe Abonnenten,
diejenigen, die diese Publikation schon länger abonniert haben, wissen, dass hier immer wieder über den Ursprung des Corona-Virus in einem Labor in Wuhan berichtet wurde. Seit diese Woche ist es „offiziell“ - [der Bundesnachrichtendienst (BND) hält den Labor-Ursprung für die wahrscheinlichste Variante](https://www.zeit.de/2025/11/coronavirus-ursprung-wuhan-labor-china-bnd). Jetzt kann man sich fragen, warum der BND plötzlich umschwenkt: Will man proaktiv erscheinen, weil man die Wahrheit nicht mehr länger verbergen kann? Oder will man die enttäuschten Bürger zurückgewinnen, die aufgrund der Lügen während der Corona-Zeit zunehmend mit Parteien links und rechts außen sympathisiert haben, weil diese die einzigen waren, die den Irrsinn nicht mitgetragen haben?
Auffallend bei den „Recherchen“, die in Wahrheit keine sind, sondern Verlautbarungen des deutschen Geheimdienstes, ist auch das völlige Schweigen über die US-amerikanischen Verwicklungen in das Projekt. [In Wuhan wurde mit amerikanischem Geld geforscht](https://oversight.house.gov/release/breaking-hhs-formally-debars-ecohealth-alliance-dr-peter-daszak-after-covid-select-reveals-pandemic-era-wrongdoing/). Warum der BND diese Tatsache verschweigt, ist Teil der Spekulation. Vermutlich will man Peking alles in die Schuhe schieben, um von den eigenen Versäumnissen abzulenken.
In meinem aktuellen Buch “[Der chinesische (Alp-)Traum](https://www.amazon.de/chinesische-Alb-Traum-geopolitische-Herausforderung/dp/3442317509/ref=sr_1_1?__mk_de_DE=%C3%85M%C3%85%C5%BD%C3%95%C3%91\&crid=XQVCLFVRCJJ\&dib=eyJ2IjoiMSJ9.kCJqsUXZO8NZjieNQjGy3Vez7tqktnhQynFOnuZE9249tfkKZvqdJtpIfcDiLMOyxmF7JFpMfvAC881caUEufT--GHlSCcAt_shhnVSbNLp-cle-VXel7soyPwi8xGPm88hSBKPY93BtjFYdOueFUU7qrOir_paRMiQOmCs7YOAUe7ZCKAb6YXxu_hz8N1eZhXbFcvc6p01Uu0vgIibiOHzbXxtH6ECNUaWCaHCYus4.Jzuq9IYvQtPedtE4YORWFtEmxTtrHh5xe8b-B25o5uA\&dib_tag=se\&keywords=Philipp+Mattheis\&qid=1730736669\&sprefix=philipp+mattheis%2Caps%2C111\&sr=8-1)” ist den Ereignissen in Wuhan ein ganzes Kapitel gewidmet. Es hat nichts an Aktualität eingebüßt. Alle Fakten lagen seit Jahren auf dem Tisch für jeden, den es interessiert hat. [Hier gibt es das gesamte Kapitel nachzulesen.](https://blingbling.substack.com/p/was-geschah-in-wuhan)
Auf jeden Fall zeigt dies, wie der Begriff „Verschwörungstheoretiker“ in den vergangenen Jahren zum Kampfbegriff und Waffe gemacht wurde, um Kritiker zu diffamieren, und die öffentliche Meinung ohne harte Zensur zu lenken. Ähnliches kann man aktuell beim Projekt „Digitaler Euro“ beobachten. Vermutlich kann sich kein Bürger der Europäischen Union daran erinnern, bei seiner Wahlentscheidung jemals gefragt worden zu sein, ob er die Einführung eines „digitalen Euros“ gut findet. Wurde er nämlich nicht. Er kommt aber trotzdem. EZB-Präsidentin Christine Lagarde hat das diese Woche nochmals bekräftigt: [Schon im Oktober will man die Testphase beenden](https://x.com/efenigson/status/1898382481184993711) und an der Einführung arbeiten.
Nun gehört BlingBling nicht zu denjenigen, die im digitalen Euro „Orwell’sches Teufelswerk“ sehen. Strategische Dummheit trifft es besser. Worum geht es?
Sogenannte Central Bank Digital Currencies (CBDC) waren vor einigen Jahren so etwas wie der letzte Schrei in der Zentralbank-Welt. Nachdem Facebook/Meta 2017/18 eine eigene Währung namens Libra auf den Markt bringen wollte, und eine obskure Internet-Währung namens Bitcoin immer mehr Anhänger fand, sahen sich viele Zentralbanken der Welt unter Zugzwang. Was man wollte: eine digitale, direkt von der Zentralbank ausgegebene Währung ohne Bugs, aber mit Features. Mit einer Digital-Währung ließe sich der internationale Zahlungsverkehr direkt und ohne Umweg über den US-Dollar abwickeln. Die Zentralbank bekäme wieder mehr direkten Einfluss auf die Geldschöpfung. Und, wie man aus China lernen konnte, ließen sich digitale Bankkonten auch ganz zum „Nudging von Bürgern“ nutzen. So spekulierten die ersten Verschwörungstheoretiker bald, [ein digitaler Euro ließe sich ja mit einem persönlichen CO2-Konto verknüpfen](https://www.derstandard.de/story/2000124296026/was-eine-digitale-co2-waehrung-fuer-das-klima-bedeuten-wuerde). Wäre letzteres einmal aufgebraucht, könnte der Konto-Inhaber einfach keinen Flug mehr buchen. Auch ließe sich eine expansive Geldpolitik, wie sie bis 2022 praktiziert wurde, ganz einfach mit Negativ-Zinsen umsetzen. Geld würde sich nominal reduzieren, was den Bürger zum Konsum animieren würde. Flüchtigen Kriminellen ließe sich per Knopfdruck das Konto sperren. Der Staat würde also über eine ganze neue Palette an Einflussmöglichkeiten verfügen.
Die Aluhüte United warnten vor einem Orwellschen Überwachungsstaat. Vertreter von Regierungen und Firmen, die diesen digitalen Euro bauen sollten, beschwichtigten. Mit Ralf Wintergerst, CEO von Giesecke+Devrient, nach wie vor heißester Anwärter, um das Projekt in der EU umzusetzen, sprach ich in den vergangenen Jahren mehrmals zu dem Thema. [Zuletzt im Dezember 24](https://blingbling.substack.com/p/euro-thrash).
Wintergerst versichert stets zwei Dinge: Eine Abschaffung von Bargeld sei nicht geplant. Und nur, wenn die Fluchttore Bargeld, Gold und Bitcoin geschlossen werden, greift die dystopische Version. Und zweitens, so Wintergerst, habe niemand ein chinesisches System im Sinne. Der „digitale Euro“ sei für die Bürger gedacht und das Projekt unterliege demokratischer Kontrolle. Ob er Wintergerst und dem guten im Menschen Glauben schenkt, möge jeder Leser selbst entscheiden. Das Interessantere ist ohnehin, dass der digitale Euro ein strategisch dummes Projekt ist.
Dazu muss man wissen, dass eine solche Zentralbankwährung Banken im weitesten Sinne überflüssig macht. Kontos bei Privatbanken werden obsolet, genauso wie Spar-, Fest- und Tagesgeld-Strukturen. Deshalb soll der digitale Euro zunächst auf 3000 Euro pro Bürger beschränkt werden. Das ist also nicht als Maximal-Vermögen gedacht, das dann jedem sozialistischen Einheits-EU-Menschen noch zusteht, sondern dient dazu, das Bankensystem nicht kollabieren zu lassen. Aber wozu überhaupt „ein bisschen digitaler Euro“?
In den USA setzt man mittlerweile 100 Prozent auf die private Alternative: Stablecoins wie Tether (USDT) und Circle (USDC) sind nichts anderes als digitale Währungen. Nur sind sie nicht von einer Zentralbank ausgeben, sondern von privaten Anbietern. Tether hat technisch die Möglichkeit, einen Inhaber vom Zahlungsverkehr auszusperren. Nur dürfte es davon kaum Gebrauch machen, will das Unternehmen nicht rasant Kunden an die Konkurrenz verlieren. Da USDT und USDC mit US-Dollar gedeckt sind (oder zumindest sein sollten, *looking at you, Tether!*), stärken sie außerdem die Rolle des US-Dollars als Leitwährung. Und da die USA sich aktuell sehr über Käufer von Staatsanleihen freuen, um die Zinsen zu drücken, und [Tether einer der größten Halter von US-Staatsanleihen is](https://crypto.news/tether-treasury-holdings-boost-us-debt-resilience-2025/)t, wird es den digitalen Dollar bis auf Weiteres nicht geben.
Den digitalen Yuan gibt es, aber von einer großen Akzeptanz oder Durchdringung der chinesischen Wirtschaft lässt sich nicht sprechen. Kontrolle kann der chinesische Staat ohnehin über seine omnipräsenten Apps WeChat und Alipay ausüben. Was den internationalen Zahlungsverkehr betrifft, [scheint man aktuell eher auf Gold zu setzen](https://blingbling.substack.com/p/goldfinger).
Übrig also bleibt die EU mit einem Projekt, das bereits Milliarden an Entwicklungskosten verschlungen hat. Am Ende bleibt dann ein Mini-Digitaler-Euro in Höhe von 3000 Euro, den niemand wollte, und niemand braucht.
Helfen könnte er allerdings beim Projekt “Mobilisierung der Sparguthaben”. Der Ausdruck geht auf Friedrich Merz zurück. Ursula von der Leyen paraphrasierte ihn jüngst:

[Irgendwie müssen die Billionen von Sparguthaben in Militär-Investitionen umgewandelt werden](https://blingbling.substack.com/p/panzer-statt-autos). Das wird am besten funktionieren mit Anleihen, die schlechter verzinst sind als sonst auf dem Markt üblich. Wie bringt man Leute dazu, dann ihr Geld dort zu investieren? Entweder man zwingt sie, oder man bewirbt die Anleihen mit viel Patriotismus und Propaganda. Die Verschwörungstheoretiker unter uns bekommen also bald Futter, wenn die „Spar- und Investitionsunion” vorgestellt wird.
Like, wenn Dein Aluhut glüht…
*Hinter der Paywall: Wie das Trump-Derangement-Syndrom den Blick auf den Markt trübt. **[Wie es mit Bitcoin, Gold und Aktien weitergeht.](https://blingbling.substack.com/p/gluhende-aluhute)***
-

@ f3873798:24b3f2f3
2025-03-31 20:14:31
Olá, nostrilianos!
O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens.
Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos.
Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI.
Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens.
### Grok: Destaque na criação de imagens e fontes

O Grok me impressiona especialmente em dois aspectos.
Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual.
Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados.
### ChatGPT: Assertividade e clareza

Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas.
Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões.
Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas.
Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras.
A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual.
### Minha opinião

Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor.
Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas.
-

@ 21335073:a244b1ad
2025-03-15 23:00:40
I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-

@ 22aa8151:ae9b5954
2025-03-31 07:44:15
With all the current hype around Payjoin for the month, I'm open-sourcing a project I developed five years ago: [https://github.com/Kukks/PrivatePond](Private Pond)
Note: this project is unmaintained and should only be used as inspiration.
Private Pond is a Bitcoin Payjoin application I built specifically to optimize Bitcoin transaction rails for services, such as deposits, withdrawals, and automated wallet rebalancing.
The core concept is straightforward: withdrawals requested by users are queued and processed at fixed intervals, enabling traditional, efficient **transaction batching**. Simultaneously, deposits from other users can automatically batch these withdrawals via **Payjoin batching**, reducing them onchain footprint further. Taking it to the next step: a user's deposit is able to fund the withdrawals with its own funds reducing the required operational liquidity in hot wallets through a process called the **Meta Payjoin**.
The application supports multiple wallets—hot, cold, multisig, or hybrid—with configurable rules, enabling automated internal fund management and seamless rebalancing based on operational needs such as min/max balance limits and wallet ratios (10% hot, 80% in 2-of-3, 10% in 1-of-2, etc) .
This system naturally leverages user Payjoin transactions as part of the automated rebalancing strategy, improving liquidity management by batching server operations with user interactions.
Private Pond remains quite possibly the most advanced Payjoin project today, though my [multi-party addendum of 2023](https://x.com/MrKukks/status/1690662070935564289) probably competes. That said, Payjoin adoption overall has been disappointing: the incentives heavily favor service operators who must in turn actively encourage user participation, limiting its appeal only for specialized usage. This is why my efforts refocused on systems like Wabisabi coinjoins, delivering not just great privacy but all the benefits of advanced Payjoin batching on a greater scale through **output compaction**.
Soon, I'll also open-source my prototype coinjoin protocol, **Kompaktor**, demonstrating significant scalability improvements, such as 50+ payments from different senders being compacted into a **single Bitcoin output**. And this is not even mentioning [Ark](https://arklabs.to), that pushes these concepts even further, giving insane scalability and asyncrhonous execution.
You can take a look at the slides I did around this here: https://miro.com/app/board/uXjVL-UqP4g=/
Parts of Private Pond, the pending transfers and multisig, will soon be integrated into nostr:npub155m2k8ml8sqn8w4dhh689vdv0t2twa8dgvkpnzfggxf4wfughjsq2cdcvg 's next major release—special thanks to nostr:npub1j8y6tcdfw3q3f3h794s6un0gyc5742s0k5h5s2yqj0r70cpklqeqjavrvg for continuing the work and getting it to the finish line.
-

@ a95c6243:d345522c
2025-03-15 10:56:08
*Was nützt die schönste Schuldenbremse, wenn der Russe vor der Tür steht?* *\
Wir können uns verteidigen lernen oder alle Russisch lernen.* *\
Jens Spahn*  
**In der Politik ist buchstäblich keine Idee zu riskant, kein Mittel zu schäbig und keine Lüge zu dreist,** als dass sie nicht benutzt würden. Aber der Clou ist, dass diese Masche immer noch funktioniert, wenn nicht sogar immer besser. Ist das alles wirklich so schwer zu durchschauen? Mir fehlen langsam die Worte.
**Aktuell werden sowohl in der Europäischen Union als auch in Deutschland** riesige Milliardenpakete für die [Aufrüstung](https://transition-news.org/eu-halt-weiter-kurs-auf-krieg-hunderte-milliarden-fur-aufrustung-beschlossen) – also für die Rüstungsindustrie – geschnürt. Die EU will 800 Milliarden Euro locker machen, in Deutschland sollen es 500 Milliarden «Sondervermögen» sein. Verteidigung nennen das unsere «Führer», innerhalb der Union und auch an «unserer Ostflanke», der Ukraine.
**Das nötige Feindbild konnte inzwischen signifikant erweitert werden.** Schuld an allem und zudem gefährlich ist nicht mehr nur Putin, sondern jetzt auch Trump. Europa müsse sich sowohl gegen Russland als auch gegen die USA schützen und rüsten, wird uns eingetrichtert.
**Und während durch Diplomatie genau dieser beiden Staaten** gerade endlich mal Bewegung in die Bemühungen um einen Frieden oder wenigstens einen Waffenstillstand in der Ukraine kommt, rasselt man im moralisch überlegenen Zeigefinger-Europa so richtig mit dem Säbel.
**Begleitet und gestützt wird der ganze Prozess** – wie sollte es anders sein – von den «Qualitätsmedien». Dass Russland einen Angriff auf «Europa» plant, weiß nicht nur der deutsche Verteidigungsminister (und mit Abstand beliebteste Politiker) Pistorius, sondern dank ihnen auch jedes Kind. Uns bleiben nur noch wenige Jahre. Zum Glück bereitet sich die Bundeswehr schon sehr konkret [auf einen Krieg](https://archive.is/VE8ZM) vor.
**Die** ***FAZ*** **und Corona-Gesundheitsminister Spahn markieren einen traurigen Höhepunkt.** Hier haben sich «politische und publizistische Verantwortungslosigkeit propagandistisch gegenseitig befruchtet», wie es bei den *NachDenkSeiten* [heißt](https://www.nachdenkseiten.de/?p=130064). Die Aussage Spahns in dem Interview, «der Russe steht vor der Tür», ist das eine. Die Zeitung verschärfte die Sache jedoch, indem sie das Zitat explizit in den [Titel](https://archive.is/QJdID) übernahm, der in einer [ersten Version](https://archive.is/fNuGA) scheinbar zu harmlos war.
**Eine große Mehrheit der deutschen Bevölkerung findet Aufrüstung und mehr Schulden toll,** wie *[ARD](https://archive.is/M3DSk)* und *[ZDF](https://archive.is/ggvJB)* sehr passend ermittelt haben wollen. Ähnliches gelte für eine noch stärkere militärische Unterstützung der Ukraine. Etwas skeptischer seien die Befragten bezüglich der Entsendung von Bundeswehrsoldaten dorthin, aber immerhin etwa fifty-fifty.
**Eigentlich ist jedoch die Meinung der Menschen in «unseren Demokratien» irrelevant.** Sowohl in der Europäischen Union als auch in Deutschland sind die «Eliten» offenbar der Ansicht, der Souverän habe in Fragen von Krieg und Frieden sowie von aberwitzigen astronomischen Schulden kein Wörtchen mitzureden. Frau von der Leyen möchte über 150 Milliarden aus dem Gesamtpaket unter Verwendung von Artikel 122 des EU-Vertrags ohne das Europäische Parlament entscheiden – wenn auch nicht völlig [kritiklos](https://www.berliner-zeitung.de/politik-gesellschaft/geopolitik/aufruestung-widerstand-gegen-eu-plaene-waechst-kommission-uebertreibt-russische-gefahr-li.2306863).
**In Deutschland wollen CDU/CSU und SPD zur Aufweichung der «Schuldenbremse»** mehrere Änderungen des Grundgesetzes durch das abgewählte Parlament peitschen. Dieser Versuch, mit dem alten [Bundestag](https://www.bundestag.de/dokumente/textarchiv/2025/kw11-de-sondersitzung-1056228) eine Zweidrittelmehrheit zu erzielen, die im neuen nicht mehr gegeben wäre, ist mindestens verfassungsrechtlich umstritten.
**Das Manöver scheint aber zu funktionieren.** Heute haben die Grünen [zugestimmt](https://www.reuters.com/world/europe/germany-faces-debt-deal-cliffhanger-merz-strives-greens-backing-2025-03-14/), nachdem Kanzlerkandidat Merz läppische 100 Milliarden für «irgendwas mit Klima» zugesichert hatte. Die Abstimmung im Plenum soll am kommenden Dienstag erfolgen – nur eine Woche, bevor sich der neu gewählte Bundestag konstituieren wird.
**Interessant sind die Argumente, die BlackRocker Merz für seine Attacke** auf Grundgesetz und Demokratie ins Feld führt. Abgesehen von der angeblichen Eile, «unsere Verteidigungsfähigkeit deutlich zu erhöhen» (ausgelöst unter anderem durch «die Münchner Sicherheitskonferenz und die Ereignisse im Weißen Haus»), ließ uns der CDU-Chef wissen, dass Deutschland einfach auf die internationale Bühne zurück müsse. Merz [schwadronierte](https://x.com/CDU/status/1900168761686044894) gefährlich mehrdeutig:
> «Die ganze Welt schaut in diesen Tagen und Wochen auf Deutschland. Wir haben in der Europäischen Union und auf der Welt eine Aufgabe, die weit über die Grenzen unseres eigenen Landes hinausgeht.»
 
  
*\[Titelbild:* *[Tag des Sieges](https://pixabay.com/de/photos/parade-tag-des-sieges-samara-182508/)]*
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/propaganda-wahnsinn-und-demokratur)*** erschienen.
-

@ d5c3d063:4d1159b3
2025-03-31 03:18:05
ทำไมทุกครั้งที่รัฐแจกเงิน คนถึงเฮ..ดีใจ
แต่พอพูดถึงตลาดเสรี กลับโดนมองว่าใจร้าย
แล้วทำไมนักเศรษฐศาสตร์กระแสหลัก
ถึงยังไม่อินกับ “ตลาดเสรี”
ทั้ง ๆ ที่ทุกคนก็เห็นแล้วว่าแนวคิดของ Keynes
และ Marx มันล้มเหลวซ้ำแล้วซ้ำเล่าในทางปฏิบัติ
แต่นักเศรษฐศาสตร์ก็ยังเอาทฤษฎีพวกนี้มาใช้อยู่ดี...
ทำไมนะ ?
ก็เพราะแนวคิดพวกนี้มัน “ฟังดูดี”
มันให้ “คำตอบ ตำอธิบายที่ถูกใจ”
มากกว่า “ความจริง ที่ฟังแล้วไม่เข้าหู”
Keynes ทำให้รัฐบาลดูฉลาดขึ้นเวลาที่ใช้เงินเกินตัว
ใครจะกล้าทักละว่า เฮ้ย “รัฐอย่าเพิ่งก่อหนี้นะครับ”
ก็เคนส์เค้าบอกว่า “การใช้จ่ายจะช่วยกระตุ้นเศรษฐกิจ” นี่หน่า
ส่วน Marx ก็สอนให้เราฝันกลางวัน
ที่คนทุกคนจะต้องเท่าเทียม ไม่มีใครรวยกว่าใคร
มันฟังแล้วดูดี เหมือนได้คืนความยุติธรรมให้สังคม
แต่ไม่มีใครบอกว่า ราคาของความเท่าเทียมแบบปลอมๆ นั้น ต้องแลกกับ "เสรีภาพ" ที่เรามีนะ
ทีนี้ ลองหันกลับมาดูตลาดเสรี
มันไม่ได้พูดเพราะ (แต่ก็ไม่ได้หยาบคาย)
มันไม่ได้สัญญาอะไร (ไม่ต้อง"ขอเวลาอีกไม่นาน")
แต่มันซื่อสัตย์ และมันบอกกับเราตรง ๆ ว่า
ถ้าอยากได้อะไรคุณต้องให้ก่อน ไม่มีใครได้อะไรฟรี ๆ
และไม่มีใครมีสิทธิขโมยของจากใครไปแม้แต่นิดเดียว
ฟังดูโหดไหม จะว่าโหดก็ได้ แต่มันคือโลกของคนที่
“มีความรับผิดชอบ ในชีวิตของตัวเอง”
คำถามคือ...หรือจริง ๆ แล้ว...เราไม่ได้กลัวระบบ
แต่เรากลัวอิสรภาพที่ไม่มีใครมารับผิดแทนเรากันแน่
.
.
แล้วแบบนี้ “รัฐ” ควรมีหน้าที่อะไรล่ะ
ไม่ใช่ว่าเชียร์ตลาดเสรีแล้วต้องเกลียดรัฐไปหมดนะ
ตลาดเสรีไม่ใช่โลกของคนไร้กฎหมาย
หรือใครอยากทำอะไรก็ได้ตามใจ
แต่โลกของตลาดเสรี...ต้องมี “กรรมการ”
ที่คอยดูแลเกมให้มันแฟร์
และรัฐในแบบที่ควรเป็นคือ
ไม่ใช่คนที่ลงมาเตะบอลแข่งกับนักเตะในสนาม
แต่เป็นกรรมการที่คอย “เป่าให้ยุติธรรม”
แล้วยืนดูอยู่ข้างสนามอย่างเงียบ ๆ
รัฐที่ดี ไม่ใช่รัฐที่มาแจกเงิน มาอุ้มคนล้ม
หรือมาคอยสั่งว่าใครควรได้อะไร
แต่เป็นรัฐที่ทำหน้าที่แค่ 3 อย่างง่าย ๆ
-ดูแลไม่ให้ใครมารังแกใคร
-ถ้าใครตกลงอะไรกันไว้ ก็ช่วยดูให้มันเป็นธรรม
-ไม่เลือกข้าง ไม่เล่นพวก ไม่ใช้อำนาจเพื่อหาเสียง
ก็แค่นั้นพอแล้วจริง ๆ
เพราะทันทีที่รัฐ “อยากเป็นพระเอก” เข้ามาอุ้ม
อยากเป็นคนคอยแจก คอยจัดการทุกอย่าง
เกมมันก็เริ่มไม่แฟร์…
พอรัฐช่วยคนหนึ่ง ก็ต้องไปหยิบของจากอีกคนมา
เหมือนเล่นบอลแล้วกรรมการยิงประตูให้ทีมตัวเอง
แล้วสุดท้าย…มันก็กลายเป็นเกม...ที่มีแต่
คนอยาก “อยู่ฝั่งที่ถูกรัฐอุ้ม” (ทุนนิยมพวกพ้อง)
ไม่ใช่ทุนนิยมหรือเกมที่เล่นด้วยความสามารถจริง ๆ
รัฐที่ดี ไม่ใช่รัฐที่ “ยิ่งใหญ่ อำนาจล้นฟ้า”
แต่คือรัฐที่ให้ผู้คน “ยืนได้ด้วยขาตัวเอง”
แค่นี้เอง...ไม่ต้องมีสูตรซับซ้อน ไม่ต้องมีทฤษฎีเยอะ
แค่มีสติ ไม่เอื้อใคร ไม่แทรกแซงเกินจำเป็นก็พอแล้ว
#Siamstr
-

@ 096ae92f:b8540e0c
2025-03-31 01:09:48
## **Hal Finney’s name is etched in Bitcoin lore.**
By day, Hal was a devoted husband and father; by night, a *shadowy super coder* pushing the boundaries of cryptography and how the world thinks about money. A seasoned cryptographer and ardent Bitcoin supporter, he was among the first to work with Satoshi Nakamoto on refining Bitcoin’s fledgling codebase.
January 2009, the iconic *"Running Bitcoin*" tweet was posted.
Over 16 years later, people are still engaging with Hal Finney’s legendary tweet—leaving comments of gratitude, admiration, and remembrance, reflecting on how far Bitcoin has come.
For many, it marks a key moment in Bitcoin’s early days.
More recently, it’s also become a symbol of Hal’s passion for running and the determination he showed throughout his life. That spirit is now carried forward through the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), an ALS fundraiser co-organized by Fran Finney and supported by the Bitcoin community.
## **Shadowy Super Coder**
Long before Bitcoin came along, Hal Finney was already legendary in certain circles. He was part of the cypherpunk movement in the 1990s—people who believed in using cryptography to protect individual privacy online.
> ***"The computer can be used as a tool to liberate and protect people, rather than to control them."\
> -Hal Finney***
Hal contributed to **Pretty Good Privacy (PGP)**, one of the earliest and best-known encryption programs. He also dabbled in digital cash prototypes, developing something called **Reusable Proofs of Work (RPOW)**. He didn’t know it at the time, but that would prime him perfectly for a bigger innovation on the horizon.
## **Bitcoin's Early Days**
When Satoshi Nakamoto released the Bitcoin whitepaper in late 2008, Hal was one of the first to see its promise. While many cryptographers waved it off, Hal responded on the mailing list enthusiastically, calling Bitcoin “a very promising idea.” He soon began corresponding directly with Satoshi. Their emails covered everything from bug fixes to big-picture possibilities for a decentralized currency. On January 12, 2009, Satoshi sent Hal **10 bitcoins**—marking the first recorded Bitcoin transaction. From that day onward, his name was woven into Bitcoin’s origin story.
> ***“When Satoshi announced the first release of the software, I grabbed it right away. I think I was the first person besides Satoshi to run Bitcoin.”\
> -Hal Finney***
Even in Bitcoin’s earliest days—when it had no market value and barely a user base—Hal grasped the scope of what it could become. He saw it not just as a technical curiosity, but as a potential long-term store of value, a tool for privacy, and a monetary system that could rival gold in its resilience. He even raised early concerns about energy use from mining, showcasing just how far ahead he was thinking. At a time when most dismissed Bitcoin entirely, Hal was already envisioning the future.
## **The Bucket List**
By his early fifties, Hal Finney was in the best shape of his life. He had taken up distance running in the mid-2000s—not to chase medals, but to test himself. To stay healthy, to lose some weight, and above all, to do something hard. The engineer’s mind in him craved a structure of improvement, and long-distance running delivered it. With meticulous focus, Hal crafted training plans, ran 20+ mile routes on weekends, and even checked tide charts to time his beach runs when the sand was firmest underfoot.
His ultimate goal: **qualify for the Boston Marathon**.
For most, Boston is a dream. For Hal, it became a personal benchmark—a physical counterpart to the mental mountains he scaled in cryptography. He trained relentlessly, logging race times, refining form, and aiming for the qualifying standard in his age group. Running was more than physical for him. It was meditative. He often ran alone, without music, simply to be in the moment—present, focused, moving forward.
Running was also a shared passion. Fran often ran shorter distances while Hal trained for the longer ones. They registered for events together, cheered each other on at finish lines, and made it a part of their family rhythm. It was one more expression of Hal’s deep devotion not just to self-improvement, but to doing life side-by-side with those he loved.
Hal and Fran competing in the Denver Half-Marathon together
In April 2009, Hal and Fran ran the **Denver Half Marathon together**—a meaningful race and one of the first they completed side by side. At the time, Hal was deep in marathon training and hitting peak form.\
\
A month later, Hal attempted the **Los Angeles Marathon**, hoping to clock a Boston-qualifying time. But something wasn’t right. Despite all his preparation, he was forced to stop midway through the race. His body wasn’t recovering the way it used to. At first, he chalked it up to overtraining or age, but the truth would come soon after.
## **ALS Diagnosis**
In August 2009, at the height of his physical and intellectual pursuits, Hal received crushing news: a diagnosis of **Amyotrophic Lateral Sclerosis (ALS)**, often referred to as Lou Gehrig’s disease. It was an especially cruel blow for a man who had just discovered a love for running and was helping birth the world’s first decentralized digital currency. ALS gradually robs people of voluntary muscle function. For Hal, it meant an uphill fight to maintain the independence and movement he cherished.
Still, Hal didn’t stop. That September, **he and Fran ran the Disneyland Half Marathon together**, crossing the finish line hand in hand. It would be his last official race, but the identity of being a runner never left him—not after the diagnosis, not after the gradual loss of physical control, not even after he was confined to a wheelchair.
Fran and Hal at the Disney Half Marathon.
By December of that same year, Hal could no longer run. Still, he was determined not to sit on the sidelines. That winter, the couple helped organize a **relay team for the Santa Barbara International Marathon**, a race Hal had long planned to run. Friends and family joined in, and Fran ran the final leg, passing the timing chip to Hal for the last stretch. With support, **Hal walked across the finish line**, cheered on by the local running community who rallied around him. It was a symbolic moment—heartbreaking and inspiring all at once.
Hal and Fran lead the Muscular Dystrophy Association relay team at the Santa Barbara International Marathon in 2009.
Even as his muscles weakened, **Hal’s mind stayed sharp**, and he continued to adapt in every way he could. He and Fran began making practical changes around their home—installing ramps, adjusting routines—but emotionally, the ground was still shifting beneath them.
Hal Finney humbly giving people in the future the opportunity to hear him speak before he is unable to.
Fran consistently emphasized that Hal maintained a remarkably positive attitude, even as ALS took nearly everything from him physically. His optimism and determination became the emotional anchor for the entire family.
> ***“He was the one who kept us all steady. He was never defeated.”\
> -Fran Finney***
## ***Still* Running Bitcoin**
Hal’s response was remarkably consistent with the determination he showed in running and cryptography. Even as the disease progressed, forcing him into a wheelchair and eventually limiting his speech, he kept coding—using assistive technologies that allowed him to control his computer through minimal eye movements. When he could no longer run physically, he continued to run test code for Bitcoin, advise other developers, and share insights on the BitcoinTalk forums. It was perseverance in its purest form. Fran was with him every step of the way.
In October 2009, just months after his diagnosis, Hal published an essay titled [***“Dying Outside”***](https://www.lesswrong.com/posts/bshZiaLefDejvPKuS/dying-outside?ref=blog.austinbitcoinclub.com)—a reflection on the road ahead. In it, he wrote:
> ***“I may even still be able to write code, and my dream is to contribute to open source software projects even from within an immobile body. That will be a life very much worth living."***
And he meant it. Years later, Hal collaborated with Bitcoin developer Mike Hearn on a project involving secure wallets using Trusted Computing. Even while operating at a fraction of his former speed—he estimated it was just **1/50th** of what he used to be capable of—Hal kept at it. He even engineered an Arduino-based interface to control his wheelchair with his eyes. The hacker mindset never left him.
This wasn’t just about legacy. It was about living with purpose, right up to the edge of possibility.
## **Running Bitcoin Challenge**
In recent years, Fran Finney—alongside members of the Bitcoin community—launched the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), a virtual event that invites people around the world to run or walk **21 kilometers** each January in honor of Hal.
Timed with the anniversary of his iconic *“Running bitcoin”* tweet, the challenge raises funds for **ALS research** through the ALS Network. According to Fran, **over 80% of all donations go directly to research**, making it a deeply impactful way to contribute. **Nearly $50,000 has been raised so far.**
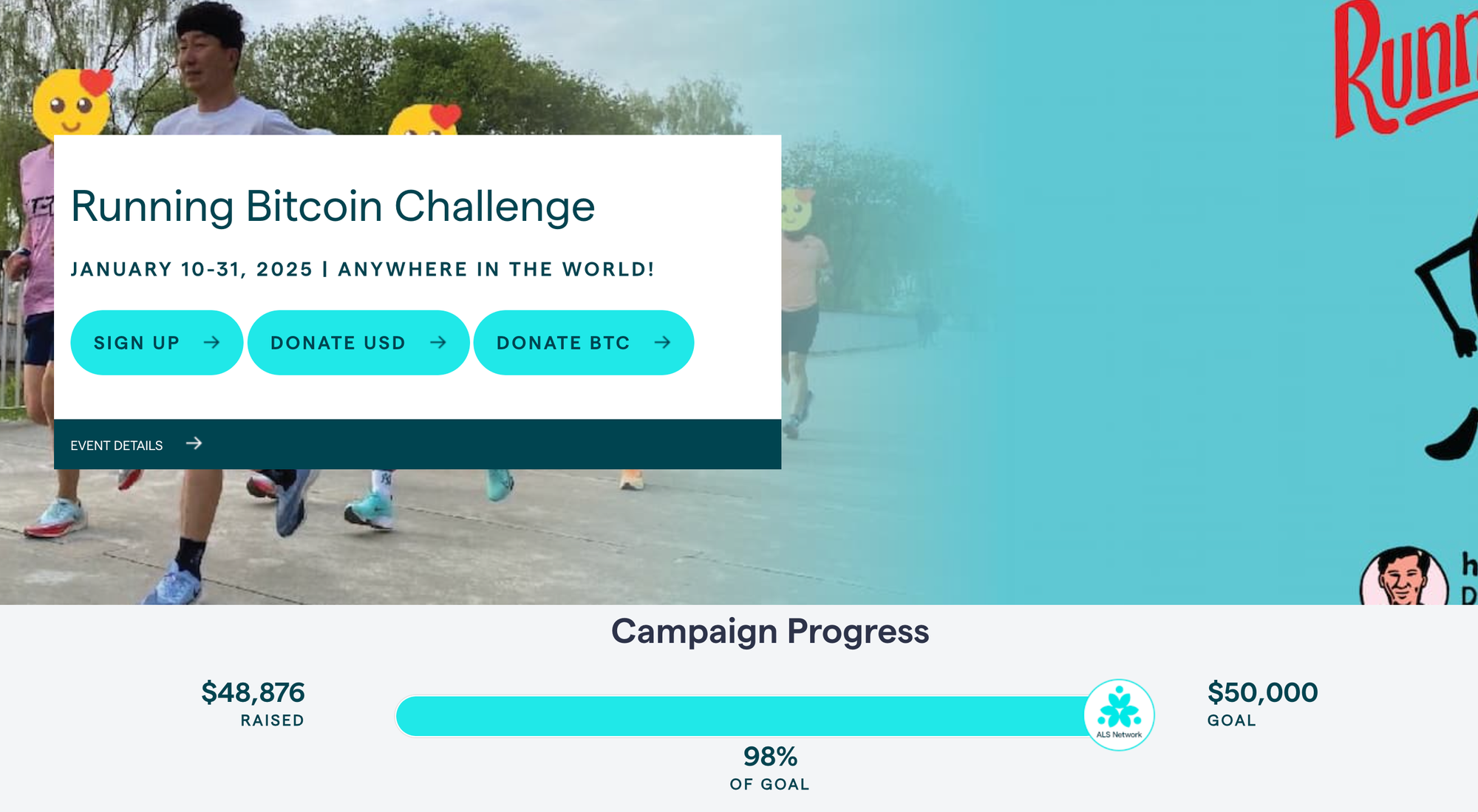It’s not the next Ice Bucket Challenge—but that’s not the point. This is something more grounded, more personal. It’s a growing movement rooted in Hal’s legacy, powered by the Bitcoin community, and driven by the hope that collective action can one day lead to a cure.
> ***“Since we’re all rich with bitcoins, or we will be once they’re worth a million dollars like everyone expects, we ought to put some of this unearned wealth to good use.”\
> \
> — Hal Finney, January 2011Price of Bitcoin: $0.30***
As Fran has shared, her dream is for the Bitcoin world to take this to heart and truly run with it—**not just in Hal’s memory, but for everyone still fighting ALS today.**
## **Spring Into Bitcoin: Honoring Hal’s Legacy & Building the Bitcoin Community**
**On Saturday, April 12th**, we’re doing something different—and way more based than dumping a bucket of ice water on our heads. [***Spring Into Bitcoin***](https://blog.austinbitcoinclub.com/spring-into-bitcoin/) is a one-day celebration of sound money, health, and legacy. Hosted at [**Hippo Social Club**](https://www.hipposocialclub.com/?ref=blog.austinbitcoinclub.com), the event features a professional [**trail run**](https://www.tejastrails.com/uncommon?ref=blog.austinbitcoinclub.com), a sizzling open-air beef feast, Bitcoin talks, and a wellness zone complete with a **cold plunge challenge** (the ice bucket challenge walked so the cold plunge could run 😏).
[**Purchase Tickets**](https://oshi.link/lVH7Qh?ref=blog.austinbitcoinclub.com) **- General Admission**
*Tickets purchased using this link will get 10% back in Bitcoin rewards compliments of [**Oshi Rewards**](https://oshi.tech/?ref=blog.austinbitcoinclub.com).*
[*Purchase Race Tickets Here*](https://www.tejastrails.com/events/uncommon) *- RACE DISTANCES: Most Miles in 12 Hours, Most Miles in 6 Hours, Most Miles in 1 Hour, 5K, Canine 5K, Youth 1 Mile*
It’s all in honor of Hal Finney, one of Bitcoin’s earliest pioneers and a passionate runner. **100% of event profits will be donated in Bitcoin to the ALS Network**, funding research and advocacy in Hal’s memory. Come for the cause, stay for the beef, sauna, cold plunge and to kick it with the greatest, most freedom-loving community on earth.
[Please consider donating to our Run for Hal Austin team here.](https://secure.alsnetwork.org/site/TR/Endurance/General?team_id=9302&pg=team&fr_id=1510) This race officially kicks off the 2025 Run for Hal World Tour!
Ok, we might be a little biased.
## **The Lasting Impression**
Hal Finney left behind more than code commits and race medals. He left behind a blueprint for **resilience**—a relentless drive to do good work, to strive for personal bests, and to give back no matter the circumstances. His life reminds us that “running” is more than physical exercise or a piece of software running on your laptop. It’s about forward progress. It’s about community. It’s about optimism in the face of challenges.
So, as you tie your shoelaces for your next run or sync up your Bitcoin wallet, remember Hal Finney.
-

@ 866e0139:6a9334e5
2025-03-30 08:22:48
***
**Autor: Ludwig F. Badenhagen.** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)***
***
Wer den Artikel [Ob Corona oder Krieg: Wir Menschen werden wie Vieh behandelt](https://pareto.space/a/naddr1qqxnzde5xgcnzdeexv6rydpjqgsgvmsp8yy9t8c4chhln5ff23fsstcp58a47s9zt08swa4rd2fnfegrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytnsv9ex2ar09eehqctrv5q3wamnwvaz7tmwdaehgu3wwpshyet5duh8gmmhdcq3wamnwvaz7tmsv9ex2ar09ehx7um5wgcjucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k70ac8na) gelesen und die Ereignisse in Deutschland während der letzten 5 Jahre auch jenseits von Staatsfunk und Mainstream Medien verfolgt hat, dem dürfte folgendes aufgefallen sein:
 
1. Die absoluten Top-Positionen auf der politischen Bühne wurden vielfach mit Menschen besetzt, deren Eignung und Reputation – vorsichtig ausgedrückt – umstritten ist.
2. Auch massivste Fehlverhalten der Politiker bleiben folgenlos. Rücktritte scheinen ebenso ausgeschlossen wie eine straf- oder zivilrechtliche Aufarbeitung.
3. Wahlversprechen werden nicht eingehalten und neuerdings bereits direkt nach der Wahl gebrochen, obwohl noch keine neue Regierung gebildet wurde. Stattdessen wird das Gegenteil von dem getan, was eindringlich versprochen wurde.
4. Es hat sich eine Parteien-Allianz gebildet, welche eine gemeinsame Agenda verfolgt, die nicht dem Wohle der Bürger zu dienen scheint.
In diesem Umfeld tun die Politiker offenbar ungebremst, was sie wollen – und keiner scheint sie hindern zu können. Wenn morgen „von oberster Stelle“ die Anweisung gegeben würde, dass alle Neugeborenen auf Scheiterhaufen zu verbrennen seien, so stehen die Chancen gut, dass auch solch ein Vorhaben durchgebracht werden würde. Es stellt sich die Frage, ob der Willkür überhaupt Grenzen gesetzt sind. Und eine weitere Frage ist, ob es einen Punkt gibt, an dem die Bürger nicht mehr gehorchen.
Es ist kein Geheimnis, dass Politiker für ihre Vergehen nicht belangt werden. Entgegen jedem Unternehmenslenker haften Politiker nicht für Fehlverhalten. Offensichtlich auch nicht für grob fahrlässiges oder gar vorsätzliches, denn die deutsche Staatsanwaltschaft untersteht der Politik. Auch Richter sind in Karrieresysteme eingebunden, sodass die letzten fünf Jahre besonders deutlich gezeigt haben, in welche Situation sich „mutige Richter“ bringen. „Bestrafe einen, erziehe hundert“, sagte hierzu einst ein bekannter politischer Führer eines Landes, mit dem Deutschland nicht verglichen werden möchte.
***
**DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!**
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.*
***
Eine Tat wird (abgesehen vom Gesetz) erst durch die individuelle Bewertung zu einem Unrecht. Wie die Dinge „einzuordnen“ sind, erklären die Täter, die Politiker, tagtäglich selbst und werden hierbei von ihren Propagandamitarbeitern unterstützt, die sich selbst immer noch als Journalisten bezeichnen. Wer aber die staatliche Einordnung anzweifelt oder dieser gar offen widerspricht, wird unter Anwendung der vorgenannten Systematik „Bestrafe einen, erziehe hundert“ diffamiert. Aber hierbei bleibt es nicht, denn Hausdurchsuchungen in Herrgottsfrühe, Kontosperrungen, Untersuchungshaft und Jobverlust sowie dauerhafte Inhaftierungen sind nur einige Beispiele dafür, wie „im besten Deutschland aller Zeiten“ vorgegangen wird.
### Der Gamechanger
Aber wie wäre der Zustand denn zu ändern, wenn man es denn wollte? Der Staat wird eben durch diese Politiker repräsentiert und hat das Gewaltmonopol. Hierzu einige Zahlen zu Deutschland:
* Bevölkerung: ca. 83.000.000
* Polizisten: ca. 45.000 und einige tausend zivile (0,05 % der Bevölkerung)
* Soldaten: ca. 260.000 (0,31 % der Bevölkerung)
* Gerichte: ca. 1.085 (pro Gericht 77.000 Bürger)
* Finanzämter: ca. 600 (pro Finanzamt 138.000 Bürger)
Mit Blick auf diese Verhältnisse wird schnell deutlich, dass die Politiker auf eine „Kooperation“ der Bürger angewiesen sind. Würden die Bürger nicht kooperieren, so wären alle Gesetze und Vorschriften aufgrund mangelhafter Durchführbarkeit von heute auf morgen Makulatur.
Mahatma Gandhi und viele andere bewiesen, dass ein übermächtig scheinender Gegner nicht mit dessen Gewaltmitteln besiegt werden kann, sondern mit dem Gegenteil. Gandhi beispielsweise rief die Menschen in seinem Land auf, den Engländern einfach nicht mehr zu gehorchen und die ungerechten Gesetze nicht mehr zu befolgen. Bei den Engländern hat dies funktioniert.
Man stelle sich als Gedankenexperiment einmal vor, wie es wäre, wenn ein Drittel der Bürger nicht mehr arbeiten und keine Steuern und sogar keine GEZ-Gebühren mehr bezahlen würden. Wie könnten diese Menschen „zur Ordnung“ gerufen werden? Wie wollte man diese Menschen bestrafen? Bestrafungskonzepte funktionieren nur dann, wenn sich die Menschen durch diese einschüchtern lassen. Sofern aber die Vielen solidarisch agieren würden, hätte ein Staatsapparat schlechte Karten. Insbesondere dann, wenn ziviler Ungehorsam bundesweit oder sogar EU-weit ausgeübt würde.
In solch einem Fall käme es wahrscheinlich sehr schnell zu einer Verständigung, denn wie sollte eine Regierung mit so viel Gegenwind weiter agieren? Die Prämisse bei solch einem Gedankenexperiment ist, dass ein erheblicher Teil der Bevölkerung sich so „miss-regiert“ fühlt, dass dieser Teil der Bevölkerung bereit ist, seine Komfortzone zum eigenen Wohl und dem Wohl der ihm Anvertrauten zu verlassen. Wahrscheinlich würde das noch nicht einmal besonders lange dauern. Man erinnere sich noch an die Zeiten, als Gewerkschaften noch nicht gekapert waren und tatsächlich die Interessen ihrer Mitglieder vertraten. Damals konnten die aufrechten Gewerkschaftsvertreter im Schulterschluss mit den Arbeitern für sie bessere Ergebnisse erwirken.
### Weg mit dem Grundgesetz
In Deutschland wurde insbesondere in letzter Zeit von den Politikern am Grundgesetz herumgebastelt, aber dieses Grundgesetz, welches nach Vollendung der Einheit und Freiheit Deutschlands für das gesamte deutsche Volk gilt, verliert seine Gültigkeit an dem Tage, an dem eine Verfassung in Kraft tritt, die von dem deutschen Volke in freier Entscheidung beschlossen worden ist. Dies ist in Artikel 146 GG nachzulesen.
 
Das Grundgesetz vom 23. Mai 1949 in der jeweils aktuellen Fassung ist die (vorläufige) Verfassung der Bundesrepublik Deutschland. Das Grundgesetz wurde im Jahre 1949 zunächst bewusst als provisorische Regelung der staatlichen Grundordnung geschaffen. Eine Verfassung für Deutschland hingegen wäre ein besonderes Gesetz, welches bestimmt, wer in einem Staat die Macht ausübt und wie das geschehen soll. Dort ist festgelegt, welche Aufgaben der Staat übernimmt, welche Rechte jeder Bürger hat und wie das Verhältnis zwischen staatlichen Organen und Bürgern aussieht. Solch eine Verfassung hat Deutschland (noch) nicht.
Man stelle sich nun vor, das deutsche Volk gäbe sich, so wie im Grundgesetz verankert, in freier Entscheidung eine Verfassung, welche exemplarisch Elemente zu folgenden Themen beinhalten würde:
* Jeder Politiker wird an seinen Wahlversprechen gemessen.
* Bei Amtsantritt wird ein Dienstvertrag, ähnlich wie bei einem Vorstand einer AG oder einem Geschäftsführer einer GmbH, abgeschlossen. In diesem Dienstvertrag wird auch geregelt, wie bei Verstößen vorgegangen wird.
* Das Parteiensystem wird abgeschafft.
* Die Staatsanwaltschaft ist nicht weiter weisungsgebunden und die Politiker nicht weiter immun. Die Gerichtsbarkeit wird wirklich unabhängig.
* Jeder Politiker hat eine entsprechende Qualifikation nachzuweisen, um gewählt werden zu können.
* Ein transparentes Wahlsystem. Schluss mit den manipulativen „Umfragen“.
* Direkte Demokratie.
* Etc.
Statt am Grundgesetz herumzuwerkeln, könnte es eine Option sein, eine gerechte Verfassung zu beschließen, welche darauf ausgerichtet ist, den Bürgern zu dienen. Das GG würde dadurch obsolet. Mit einer gerechten Verfassung könnte sehr viel Optimierungspotenzial für das Zusammenleben in Deutschland realisiert werden.
Die von den Politikern angebotenen Lösungen für die Probleme unserer Zeit beziehen sich oftmals auf selbst oder von den wirklich Mächtigen erschaffene Zustände, welche inszeniert wurden/werden, um die Menschen in Krieg, Not und Knappheit, in Leiden, in Angst, in Spaltung, in Fehlernährung, in Medikamentenabhängigkeit, in Krankheit und in Elend zu bringen. Um an den Menschen maximal zu verdienen und um diese vollumfänglich zu beherrschen. So, wie sie es mit Nutzvieh tun. Das Unterordnen von allem ist ein Prinzip, dass wenigen Leuten nützt und fast allen anderen schadet.
Eine von Liebe inspirierte Gesellschaft, die Menschen nicht nur als „Verbraucher“ oder „Humankapital“ oder „Wähler“ betrachtet und behandelt, sondern tatsächlich das Wohl aller im Fokus hat, wäre der Gegenentwurf. Dies würde selbstverständlich einhergehen mit einer liebevollen Behandlung von Tieren und Natur. Hierbei profitieren aber die Vielen und die Wenigen ganz oben an der Spitze müssten sich umstellen, was ihnen nicht gefallen dürfte.
### Vom Denken ins Tun
Wer sich solch eine Perspektive für sich selbst und seine Nachkommen wünscht, sollte überlegen, wie wir uns eine Verfassung geben können.
Ein wesentlicher Schritt wäre sicher der Zusammenschluss von Menschen, die sich mit den vorbezeichneten Überlegungen weiter befassen möchten. Ganz entgegen der Bemühungen unserer Politik um Spaltung der Gesellschaft sollten die Gemeinsamkeiten gesehen und gemeinsam Lösungen entwickelt werden.
Ein Beispiel ist die Initiative von Milosz Matuschek, nämlich sein [geplantes „Gipfeltreffen“.](https://www.freischwebende-intelligenz.org/p/exklusiv-einladung-zum-inner-circle) Hierzu schreibt er:
*„Ich habe mir ein besonderes Programm überlegt, welches mein Wissen und meine Erfahrung der letzten Jahre bündelt, sich an den Stufen der Selbsterkenntnis, Willensbildung und Kraftentfaltung orientiert und genug Raum für die Dynamik der Gruppe, also ihre Energien, lässt. Erwarten Sie das Unerwartbare. Es wird Raum geben für spirituelle und körperliche Erfahrungen, auch an einem besonderen kulturellen Rahmenprogramm wird es nicht fehlen. Uns eint im Idealfall das Erkennen menschlicher Potentiale, das Erfassen von Möglichkeitsräumen und die aktive Lust an der Mitgestaltung der Zukunft – ohne Denkverbote. Zeit, für unseren Frühling. Ich wette, in Ihnen steckt ein ganzer, unendlicher Sommer.“*
In diesem Kontext zitiert Herr Matuschek Ernst Jünger:
> *“Wenn alle Institutionen zweifelhaft oder sogar anrüchig werden und man selbst in den Kirchen nicht etwas für die Verfolgten, sondern für die Verfolger öffentlich beten hört, dann geht die sittliche Verantwortung auf den Einzelnen über, oder besser gesagt, auf den noch ungebrochenen Einzelnen.”*
Diese Worte von Ernst Jünger erinnern daran, dass die Probleme unserer Zeit nicht neu sind. Die Technologien sind es, denn mit modernen Technologien lässt sich eben besser unterdrücken als mit dem alten Zeugs. Die Methodik allerdings ist geblieben. Halte deine Untergebenen schwach und in Angst, damit diese ergeben bleiben. Zum Wohle einiger wenige Leute, die hiervon maximal profitieren.
Machen Sie mit und lösen Sie sich aus der Passivität des Zuschauers. Der wichtige nächste Schritt ist, aus dem Denken ins Tun zu kommen. 
Andernfalls wird uns weiter an-getan.
***
*Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).*
*Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.*
***
**LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!**
***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.*
Schon jetzt können Sie uns unterstützen:
* Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube.
* Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
* Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
* Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
**Für Einzahlungen in CHF (Betreff: Friedenstaube):**
**Für Einzahlungen in Euro:**
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
**Betreff: Friedenstaube**
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space>
***
**Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
-

@ a95c6243:d345522c
2025-03-11 10:22:36
**«Wir brauchen eine digitale Brandmauer gegen den Faschismus»,** [schreibt](https://www.ccc.de/de/updates/2025/ccc-fordert-digitale-brandmauer) der Chaos Computer Club (CCC) auf seiner Website. Unter diesem Motto präsentierte er letzte Woche einen Forderungskatalog, mit dem sich 24 Organisationen an die kommende Bundesregierung wenden. Der Koalitionsvertrag müsse sich daran messen lassen, verlangen sie.
**In den drei Kategorien «Bekenntnis gegen Überwachung»,** «Schutz und Sicherheit für alle» sowie «Demokratie im digitalen Raum» stellen die [Unterzeichner](https://d-64.org/digitale-brandmauer/), zu denen auch Amnesty International und Das NETTZ gehören, unter anderem die folgenden «Mindestanforderungen»:
* Verbot biometrischer Massenüberwachung des öffentlichen Raums sowie der ungezielten biometrischen Auswertung des Internets.
* Anlasslose und massenhafte Vorratsdatenspeicherung wird abgelehnt.
* Automatisierte Datenanalysen der Informationsbestände der Strafverfolgungsbehörden sowie jede Form von Predictive Policing oder automatisiertes Profiling von Menschen werden abgelehnt.
* Einführung eines Rechts auf Verschlüsselung. Die Bundesregierung soll sich dafür einsetzen, die Chatkontrolle auf europäischer Ebene zu verhindern.
* Anonyme und pseudonyme Nutzung des Internets soll geschützt und ermöglicht werden.
* Bekämpfung «privaten Machtmissbrauchs von Big-Tech-Unternehmen» durch durchsetzungsstarke, unabhängige und grundsätzlich föderale Aufsichtsstrukturen.
* Einführung eines digitalen Gewaltschutzgesetzes, unter Berücksichtigung «gruppenbezogener digitaler Gewalt» und die Förderung von Beratungsangeboten.
* Ein umfassendes Förderprogramm für digitale öffentliche Räume, die dezentral organisiert und quelloffen programmiert sind, soll aufgelegt werden.
**Es sei ein Irrglaube, dass zunehmende Überwachung einen Zugewinn an Sicherheit darstelle,** ist eines der Argumente der Initiatoren. Sicherheit erfordere auch, dass Menschen anonym und vertraulich kommunizieren können und ihre Privatsphäre geschützt wird.
**Gesunde digitale Räume lebten auch von einem demokratischen Diskurs,** lesen wir in dem Papier. Es sei Aufgabe des Staates, Grundrechte zu schützen. Dazu gehöre auch, Menschenrechte und demokratische Werte, insbesondere Freiheit, Gleichheit und Solidarität zu fördern sowie den Missbrauch von Maßnahmen, Befugnissen und Infrastrukturen durch «die Feinde der Demokratie» zu verhindern.
**Man ist geneigt zu fragen, wo denn die Autoren «den Faschismus» sehen,** den es zu bekämpfen gelte. Die meisten der vorgetragenen Forderungen und Argumente finden sicher breite Unterstützung, denn sie beschreiben offenkundig gängige, kritikwürdige Praxis. Die Aushebelung der Privatsphäre, der Redefreiheit und anderer Grundrechte im Namen der Sicherheit wird bereits jetzt massiv durch die aktuellen «demokratischen Institutionen» und ihre «durchsetzungsstarken Aufsichtsstrukturen» betrieben.
**Ist «der Faschismus» also die EU und ihre Mitgliedsstaaten?** Nein, die «faschistische Gefahr», gegen die man eine digitale Brandmauer will, kommt nach Ansicht des CCC und seiner Partner aus den Vereinigten Staaten. Private Überwachung und Machtkonzentration sind dabei weltweit schon lange Realität, jetzt endlich müssen sie jedoch bekämpft werden. In dem Papier heißt es:
> «Die willkürliche und antidemokratische Machtausübung der Tech-Oligarchen um Präsident Trump erfordert einen Paradigmenwechsel in der deutschen Digitalpolitik. (...) Die aktuellen Geschehnisse in den USA zeigen auf, wie Datensammlungen und -analyse genutzt werden können, um einen Staat handstreichartig zu übernehmen, seine Strukturen nachhaltig zu beschädigen, Widerstand zu unterbinden und marginalisierte Gruppen zu verfolgen.»
**Wer auf der anderen Seite dieser Brandmauer stehen soll, ist also klar.** Es sind die gleichen «Feinde unserer Demokratie», die seit Jahren in diese Ecke gedrängt werden. Es sind die gleichen Andersdenkenden, Regierungskritiker und Friedensforderer, die unter dem großzügigen Dach des Bundesprogramms «Demokratie leben» einem «kontinuierlichen Echt- und Langzeitmonitoring» wegen der Etikettierung [«digitaler Hass»](https://bag-gegen-hass.net/) unterzogen werden.
**Dass die 24 Organisationen praktisch auch die Bekämpfung von Google,** Microsoft, Apple, Amazon und anderen fordern, entbehrt nicht der Komik. Diese fallen aber sicher unter das Stichwort «Machtmissbrauch von Big-Tech-Unternehmen». Gleichzeitig verlangen die Lobbyisten implizit zum Beispiel die Förderung des [Nostr](https://reason.com/video/2024/09/17/is-nostr-an-antidote-to-social-media-censorship/)-Netzwerks, denn hier finden wir dezentral organisierte und quelloffen programmierte digitale Räume par excellence, obendrein zensurresistent. Das wiederum dürfte in der Politik weniger gut ankommen.
*\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/uns-ihnen-stammes-wettbewerb-1767691/)]*
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/digitale-brandmauer-gegen-den-faschismus-von-der-kunftigen-bundesregierung)*** erschienen.
-

@ d560dbc2:bbd59238
2025-03-30 07:56:40
We’ve all been there: that one task sitting on your to-do list, staring at you like a disappointed parent, and yet you keep pushing it off for absolutely no good reason. It’s not even that hard, urgent, or complicated—but somehow, it’s been haunting you for days, weeks, or maybe even months. Why do we do this to ourselves?
---
## Why Do We Postpone Tasks for No Reason?
Procrastination is a sneaky beast. Even tasks that take 10 minutes, require minimal brainpower, and have no immediate deadline often get pushed aside. Here are some psychological reasons:
- **Emotional Avoidance:**
Even if a task isn’t hard, a tiny emotional weight (like mild boredom or a vague “I don’t wanna”) can lead your brain to choose distractions—like scrolling through Instagram.
- **Lack of Immediate Consequences:**
Without a pressing deadline, your brain tends to deprioritize the task, even if completing it would make you feel great.
- **The Zeigarnik Effect:**
Unfinished tasks stick in our minds, creating mental tension. Ironically, that tension can make the task seem bigger and more daunting, encouraging further avoidance.
---
## My Own “No-Reason” Procrastination Story
Let’s be real—I’ve been postponing something trivial, like organizing my desk drawer, for weeks. It’s a simple task that takes about 15 minutes. There’s no deadline, no special skill required—yet every time I open the drawer, I see the chaos of old receipts, random cables, and a half-eaten pack of gum (don’t judge!) and think, “I’ll do it later.” It’s not that I’m busy—I’ve had plenty of time to rewatch my favorite sitcom for the third time. But ignoring it has become my default, and that messy drawer now occupies mental space far beyond its physical size.
---
## Why These Tasks Matter More Than We Think
Those little tasks we postpone might seem harmless, but they add up to create mental clutter. That messy desk drawer isn’t just a drawer—it’s a tiny stressor that pops into your head at the worst moments, disrupting your focus on important work or relaxation.
- **Mental Clutter:**
Unfinished tasks can weigh on your mind, making it harder to focus on what truly matters.
- **The Bigger Picture:**
Tasks like “reply to that email” or “schedule that doctor’s appointment” may seem minor, but avoiding them can lead to unnecessary stress and lost opportunities.
---
## How to Finally Tackle That Task
Here are a few strategies that have helped me break the cycle of “no-reason” procrastination:
### 1. The 20-Minute Rule (Thank You, Pomodoro!)
- **Commit to 20 Minutes:**
Set a timer for just 20 minutes and start working on the task. You’d be surprised how much you can accomplish once you begin.
- **Example:**
For my desk drawer, I set a timer, got to work, and finished in 12 minutes. That small win made me feel like a productivity superhero.
---
### 2. Pin It and Get a Nudge
- **Use Reminders:**
Pin that nagging task (like “Organize desk drawer”) as your top priority for the day. A gentle reminder can help break the cycle of avoidance.
- **Result:**
It’s like having a friend nudge you, “Hey, remember that thing you’ve been ignoring? Let’s do it now!”
---
### 3. Make It Fun (Yes, Really!)
- **Add a Reward:**
Turn the task into something enjoyable by setting a reward. Play your favorite music, and promise yourself a treat once you’re done.
- **Example:**
For my desk drawer, I put on an upbeat playlist and treated myself to a piece of chocolate when finished. Suddenly, it wasn’t a chore—it became a mini dance party with a sweet reward.
---
### 4. Celebrate the Win
- **Acknowledge Completion:**
Once you finish, take a moment to celebrate—even if it’s just a mental high-five.
- **Why It Matters:**
That sense of closure clears mental clutter and builds momentum for your next task.
---
## Let’s Share and Motivate Each Other
What’s that one task you’ve been postponing for no reason? Maybe it’s cleaning out your fridge, replying to a friend’s text, or finally hanging that picture frame that’s been leaning against the wall for months. Whatever it is, share your story in the comments! Let’s motivate each other to tackle these tasks and turn procrastination into progress.
*Bonus points if you’ve got a funny reason for your procrastination (like, “I didn’t schedule that appointment because my doctor’s office has the worst hold music in history”).*
---
Ready to stop procrastinating? Let’s get real, take that first step, and clear that mental clutter—one small win at a time!
---
-

@ 732c6a62:42003da2
2025-03-09 22:36:26
Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto.
### **A Falácia da Superioridade Moral**
O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: **a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas**. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica.
---
### **Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"**
A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do **marxismo ortodoxo**, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa:
- **Dados do Latinobarómetro (2022):** 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita.
- **Pesquisa IPEC (2023):** 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda".
Esses números não são acidentais. Refletem uma **mudança estrutural**: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque **nunca conversaram com um sem fazer cara de psicólogo de posto de saúde**. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal".
## **Se ainda não entenderam:**
**Direita ≠ rico:** Tem gente que trabalha 12h/dia e vota em liberal porque quer **ser dono do próprio negócio**, não pra pagar mais taxação pra você postar meme no Twitter.
**Acham que são o Sherlock Holmes da pobreza:** o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica.
---
### **A Psicologia por Trás do Voto Conservador nas Periferias**
A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas **cientificamente falsa**:
**Análise Psicológica Básica (para você que se acha o Paulo Freire):**
- **Síndrome do Branco Salvador:** Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa.
- **Viés da Superioridade Moral:** "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual.
- **Efeito Dunning-Kruger:** Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista.
- **Estudo da Universidade de São Paulo (USP, 2021):** Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime.
- **Pesquisa FGV (2020):** 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios.
Esses dados revelam uma **racionalidade prática**: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como:
- **Violência** (que afeta seu comércio);
- **Impostos** (que consomem até 40% do lucro de um camelô);
- **Burocracia** (que impede a legalização de sua barraca de pastel).
---
### **Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"**
A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, **76% dos evangélicos são pobres** (Datafolha, 2023), e suas igrejas promovem valores como:
- **Família tradicional** (contra pautas progressistas como ideologia de gênero em escolas);
- **Auto-responsabilidade** (ênfase em "trabalho duro" em vez de assistencialismo).
**Exemplo Concreto:**
Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma **ameaça ao seu estilo de vida**.
---
### **A Esquerda e seu Desprezo pela Autonomia do Pobre**
O cerne do debate é a **incapacidade da esquerda de aceitar que o pobre possa ser autônomo**. Algumas evidências:
#### **O Caso dos Empreendedores Informais**
- **Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade.** Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família.
#### **A Ascensão do Conservadorismo Periférico**
- Pessoas assim tem um pensamento simples. Sua mensagem: *"Queremos empreender, não depender de político."*
#### **A Rejeição ao "Vitimismo"**
- **Pesquisa Atlas Intel (2022):** 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores".
---
### **A projeção freudiana "o pobre é burro porque eu sou inteligente"**
O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a **Síndrome do Salvador** em sua forma mais patética:
- **Passo 1:** Assume-se que o pobre é um ser desprovido de agência.
- **Passo 2:** Qualquer desvio da narrativa é atribuído a "manipulação da elite".
- **Passo 3:** Quem critica o processo é chamado de "fascista".
**Exemplo Prático:**
Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta *"por quê?"* — ela grita *"lavagem cerebral!"*. A ironia? Essa mesma esquerda defende a **autonomia feminina**, exceto quando a mulher é pobre e pensa diferente.
### **Dados Globais: O Fenômeno Não é Brasileiro**
A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais:
- **Estados Unidos:** 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research).
Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência".
Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga?
- **Argentina:** Javier Milei, libertário radical, quando candidato, tinha forte apoio nas *villas miseria* (favelas). Seu lema — *"O estado é um parasita"* — ressoa entre quem sofria com inflação de 211% ao ano.
- **Índia:** O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades.
### **A história que a esquerda tenta apagar: pobres de direita existem desde sempre**
A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que **classes baixas conservadoras são regra, não exceção**, na história mundial:
- **Revolução Francesa (1789):** Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los".
- **Brasil Imperial:** Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia.
**Tradução:**
Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias.
---
### **A Hipocrisia da Esquerda Urbana e Universitária**
Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma **elite desconectada da realidade periférica**:
- **Perfil Socioeconômico:** 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos.
- **Prioridades Descoladas:** Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções.
*"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."*
### **A diversidade de pensamento que a esquerda não suporta**
A esquerda prega diversidade — desde que você seja diverso dentro de um **checklist pré-aprovado**. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são **microcosmos de pluralidade ideológica**, algo que assusta quem quer reduzir seres humanos a estereótipos.
---
### **Respostas aos Argumentos Esquerdistas (e Por que Falham)**
#### **"O pobre de direita é manipulado pela mídia!"**
- **Contradição:** Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra.
**Contradição Central:**
Como explicar que, segundo o **Banco Mundial (2023)**, países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que **o pobre com o mínimo de consciência quer emprego, não esmola**.
**Dado que Machuca:**
- 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (**Instituto Locomotiva, 2023**).
#### **"Ele vota contra os próprios interesses!"**
- **Falácia:** Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família.
O pobre de direita não é uma anomalia. É o **produto natural de um mundo complexo** onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado:
- **Trabalhando** para não depender do governo.
- **Escolhendo** religiões que dão sentido à sua vida.
- **Rejeitando** pautas identitárias que não resolvem o custo do gás de cozinha.
#### **"É falta de educação política!"**
- **Ironia:** Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo.
---
### **Por que o Debuste Precisa Acabar**
A insistência em descredibilizar o pobre de direita revela um **projeto de poder fracassado**. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo.
O pobre de direita existe porque ele **não precisa da permissão do rico de esquerda para pensar**. A incapacidade de entender isso só prova que **a esquerda é a nova aristocracia**.
**Último Dado:** Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor.
A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições.
A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele **desafia o monopólio moral** que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo.
**Pergunta Retórica (Para Incomodar):**
Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que **pobre também cansa de ser tratado como cachorro que late no ritmo errado**?
---
# **Fontes Citadas:**
1. Latinobarómetro (2022)
2. IPEC (2023)
3. USP (2021): *"Segurança Pública e Percepções nas Favelas Cariocas"*
4. FGV (2020): *"Informalidade e Tributação no Brasil"*
5. Datafolha (2023): *"Perfil Religioso do Eleitorado Brasileiro"*
6. Atlas Intel (2022): *"Autopercepção das Classes Baixas"*
7. Pew Research (2020): *"Voting Patterns by Income in the U.S."*
8. TSE (2023): *"Perfil Socioeconômico dos Filiados Partidários"*
**Leitura Recomendada para Esquerdistas:**
- *"Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda"* (Fernando Schüller, 2023)
- *"A Revolução dos Conservadores: Religião e Política nas Periferias"* (Juliano Spyer, 2021)
- *"Direita e Esquerda: Razões e Paixões"* (Demétrio Magnoli, 2019)
-

@ a95c6243:d345522c
2025-03-04 09:40:50
**Die «Eliten» führen bereits groß angelegte Pilotprojekte für eine Zukunft durch,** die sie wollen und wir nicht. Das [schreibt](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/) der *OffGuardian* in einem Update zum Thema «EU-Brieftasche für die digitale Identität». Das Portal weist darauf hin, dass die Akteure dabei nicht gerade zimperlich vorgehen und auch keinen Hehl aus ihren Absichten machen. *Transition News* hat mehrfach darüber berichtet, zuletzt [hier](https://transition-news.org/eudi-wallet-der-weg-fur-ein-vollstandig-digitalisiertes-europa-ist-frei) und [hier](https://transition-news.org/iata-biometrische-daten-und-digitale-id-machen-das-vollstandig-digitale).
**Mit der EU Digital Identity Wallet (EUDI-Brieftasche) sei eine einzige von der Regierung herausgegebene App geplant,** die Ihre medizinischen Daten, Beschäftigungsdaten, Reisedaten, Bildungsdaten, Impfdaten, Steuerdaten, Finanzdaten sowie (potenziell) Kopien Ihrer Unterschrift, Fingerabdrücke, Gesichtsscans, Stimmproben und DNA enthält. So fasst der *OffGuardian* die eindrucksvolle Liste möglicher Einsatzbereiche zusammen.
**Auch Dokumente wie der Personalausweis oder der** **[Führerschein](https://transition-news.org/eu-weite-einfuhrung-von-digitalen-fuhrerscheinen-fur-digitale-geldborsen)** können dort in elektronischer Form gespeichert werden. Bis 2026 sind alle EU-Mitgliedstaaten dazu verpflichtet, Ihren Bürgern funktionierende und frei verfügbare digitale «Brieftaschen» bereitzustellen.
**Die Menschen würden diese App nutzen,** so das Portal, um Zahlungen vorzunehmen, Kredite zu beantragen, ihre Steuern zu zahlen, ihre Rezepte abzuholen, internationale Grenzen zu überschreiten, Unternehmen zu gründen, Arzttermine zu buchen, sich um Stellen zu bewerben und sogar digitale Verträge online zu unterzeichnen.
**All diese Daten würden auf ihrem Mobiltelefon gespeichert und mit den Regierungen** von neunzehn Ländern (plus der Ukraine) sowie über 140 anderen öffentlichen und privaten Partnern ausgetauscht. Von der Deutschen Bank über das ukrainische Ministerium für digitalen Fortschritt bis hin zu Samsung Europe. Unternehmen und Behörden würden auf diese Daten im Backend zugreifen, um «automatisierte Hintergrundprüfungen» durchzuführen.
**Der Bundesverband der Verbraucherzentralen und Verbraucherverbände** (VZBV) habe Bedenken geäußert, dass eine solche App «Risiken für den Schutz der Privatsphäre und der Daten» berge, berichtet das Portal. Die einzige Antwort darauf laute: «Richtig, genau dafür ist sie ja da!»
**Das alles sei keine Hypothese, betont der** ***OffGuardian***. Es sei vielmehr [«Potential»](https://www.digital-identity-wallet.eu/about-us/140-public-and-private-partners/). Damit ist ein EU-Projekt gemeint, in dessen Rahmen Dutzende öffentliche und private Einrichtungen zusammenarbeiten, «um eine einheitliche Vision der digitalen Identität für die Bürger der europäischen Länder zu definieren». Dies ist nur eines der groß angelegten [Pilotprojekte](https://ec.europa.eu/digital-building-blocks/sites/display/EUDIGITALIDENTITYWALLET/What+are+the+Large+Scale+Pilot+Projects), mit denen Prototypen und Anwendungsfälle für die EUDI-Wallet getestet werden. Es gibt noch mindestens drei weitere.
**Den Ball der digitalen ID-Systeme habe die Covid-«Pandemie»** über die «Impfpässe» ins Rollen gebracht. Seitdem habe das Thema an Schwung verloren. Je näher wir aber der vollständigen Einführung der EUid kämen, desto mehr Propaganda der Art «Warum wir eine digitale Brieftasche brauchen» könnten wir in den Mainstream-Medien erwarten, prognostiziert der *OffGuardian*. Vielleicht müssten wir schon nach dem nächsten großen «Grund», dem nächsten «katastrophalen katalytischen Ereignis» Ausschau halten. Vermutlich gebe es bereits Pläne, warum die Menschen plötzlich eine digitale ID-Brieftasche brauchen würden.
**Die Entwicklung geht jedenfalls stetig weiter in genau diese Richtung.** Beispielsweise hat Jordanien angekündigt, die digitale biometrische ID bei den nächsten [Wahlen](https://www.biometricupdate.com/202502/jordan-plans-digital-id-for-voter-verification-in-next-election) zur Verifizierung der Wähler einzuführen. Man wolle «den Papierkrieg beenden und sicherstellen, dass die gesamte Kette bis zu den nächsten Parlamentswahlen digitalisiert wird», heißt es. Absehbar ist, dass dabei einige Wahlberechtigte «auf der Strecke bleiben» werden, wie im Fall von [Albanien](https://transition-news.org/albanien-schliesst-120-000-burger-ohne-biometrische-ausweise-von-wahlen-aus) geschehen.
**Derweil würden die Briten gerne ihre Privatsphäre gegen Effizienz eintauschen,** [behauptet](https://www.lbc.co.uk/news/tony-blair-id-cards/) Tony Blair. Der Ex-Premier drängte kürzlich erneut auf digitale Identitäten und Gesichtserkennung. Blair ist Gründer einer [Denkfabrik](https://transition-news.org/blair-institute-durch-vermarktung-von-patientendaten-zu-ki-gestutztem) für globalen Wandel, Anhänger globalistischer Technokratie und [«moderner Infrastruktur»](https://transition-news.org/tony-blair-digitale-id-fur-moderne-infrastruktur-unerlasslich-erfordert-aber).
**Abschließend warnt der** ***OffGuardian*** **vor der Illusion, Trump und Musk würden** den US-Bürgern «diesen Schlamassel ersparen». Das Department of Government Efficiency werde sich auf die digitale Identität stürzen. Was könne schließlich «effizienter» sein als eine einzige App, die für alles verwendet wird? Der Unterschied bestehe nur darin, dass die US-Version vielleicht eher privat als öffentlich sei – sofern es da überhaupt noch einen wirklichen Unterschied gebe.
*\[Titelbild: Screenshot* *[OffGuardian](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/)]*
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/demnachst-verfugbar-die-europaische-brieftasche-fur-digitale-identitaten)*** erschienen.
-

@ 39cc53c9:27168656
2025-03-30 05:54:55
> [Read the original blog post](https://blog.kycnot.me/p/new-kycnot)
The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
## Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot
of *design flaws*, would have been a bad idea. It would have been like building on an *unstable foundation*.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav
aScript to work. As I kept coding, I started feeling like I was repeating *"the Python mistake"*. I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom
ent), and I wasn't happy with the code. It felt like *spaghetti code* all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a *very enjoyable language* to code with. Most aof my recent pr
ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and *structure the code* as well as possible. Of course, there's still *room for improvement*, which
I'll address in future updates.
Now I have a more *maintainable website* that can *scale* much better. It uses a *real database* instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad
e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
## What's new
- **UI/UX** - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- **Point system** - The new [point system](https://kycnot.me/about#what-is-a-point) provides more detailed information about the listings, and **can** be expanded to cover additional features across all services. Anyone can request a new **point**!
- **ToS Scrapper**: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- **Search bar** - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- **Transparency** - To be more [transparent](https://beta.kycnot.me/about#transparency), all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time [audits](https://beta.kycnot.me/about#audit) page that displays database changes.
- **Listing Requests** - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes
to parts of the website.
- **Lightweight and fast** - The new site is lighter and faster than its predecessor!
- **Tor and I2P** - At last! kycnot.me is now officially on [Tor and I2P](https://beta.kycnot.me/about#tor-and-i2p)!
## How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies **without KYC** is a goal I am proud of!
If you appreciate [my work](https://kycnot.me/about#about), you can support me through the methods listed [here](https://kycnot.me/about#support). Alternatively, feel free to send me an email with a kind message!
### Technical details
All the code is written in [Golang](https://go.dev), the website makes use of the [chi](https://go-chi.io) router for the routing part. I also make use of [BigCache](https://github.com/allegro/bigcache) for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about **2M** requests per month on average (note that this are not unique users).
The database is running with [mariadb](https://mariadb.org/), using [gorm](https://gorm.io) as the ORM. This is more than enough for this project. I started working with an `sqlite` database, but I ended up migrating to **mariadb** since it works better with JSON.
The scraper is using [chromedp](https://github.com/chromedp/chromedp) combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code [here](https://gitlab.com/kycnot/kycnot.me/-/tree/main/scraper).
The frontend is written using **Golang Templates** for the HTML, and [TailwindCSS](https://tailwindcss.com/) plus [DaisyUI](https://daisyui.com) for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the *"captcha"*, which is a simple *Proof of Work* that runs on your browser, destinated to avoid spam. For this, I use [mCaptcha](https://mcaptcha.org/).
-

@ 39cc53c9:27168656
2025-03-30 05:54:45
> [Read the original blog post](https://blog.kycnot.me/p/ai-tos-analysis)
**kycnot.me** features a somewhat hidden tool that some users may not be aware of. Every month, an automated job crawls every listed service's Terms of Service (ToS) and FAQ pages and conducts an AI-driven analysis, generating a comprehensive overview that highlights key points related to KYC and user privacy.
Here's an example: [Changenow's Tos Review](https://kycnot.me/service/changenow#tos)

## Why?
ToS pages typically contain a lot of complicated text. Since the first versions of **kycnot.me**, I have tried to provide users a comprehensive overview of what can be found in such documents. This automated method keeps the information up-to-date every month, which was one of the main challenges with manual updates.
A significant part of the time I invest in investigating a service for **kycnot.me** involves reading the ToS and looking for any clauses that might indicate aggressive KYC practices or privacy concerns. For the past four years, I performed this task manually. However, with advancements in language models, this process can now be somewhat automated. I still manually review the ToS for a quick check and regularly verify the AI’s findings. However, over the past three months, this automated method has proven to be quite reliable.
Having a quick ToS overview section allows users to avoid reading the entire ToS page. Instead, you can quickly read the important points that are grouped, summarized, and referenced, making it easier and faster to understand the key information.
## Limitations
This method has a key limitation: JS-generated pages. For this reason, I was using Playwright in my crawler implementation. I plan to make a release addressing this issue in the future. There are also sites that don't have ToS/FAQ pages, but these sites already include a warning in that section.
Another issue is false positives. Although not very common, sometimes the AI might incorrectly interpret something harmless as harmful. Such errors become apparent upon reading; it's clear when something marked as bad should not be categorized as such. I manually review these cases regularly, checking for anything that seems off and then removing any inaccuracies.
Overall, the automation provides great results.
## How?
There have been several iterations of this tool. Initially, I started with GPT-3.5, but the results were not good in any way. It made up many things, and important thigs were lost on large ToS pages. I then switched to GPT-4 Turbo, but it was expensive. Eventually, I settled on Claude 3 Sonnet, which provides a quality compromise between GPT-3.5 and GPT-4 Turbo at a more reasonable price, while allowing a generous 200K token context window.
I designed a prompt, which is open source[^1], that has been tweaked many times and will surely be adjusted further in the future.
For the ToS scraping part, I initially wrote a scraper API using Playwright[^2], but I replaced it with Jina AI Reader[^3], which works quite well and is designed for this task.
### Non-conflictive ToS
All services have a dropdown in the ToS section called "Non-conflictive ToS Reviews." These are the reviews that the AI flagged as not needing a user warning. I still provide these because I think they may be interesting to read.
## Feedback and contributing
You can give me feedback on this tool, or share any inaccuraties by either opening an issue on Codeberg[^4] or by contacting me [^5].
You can contribute with pull requests, which are always welcome, or you can [support](https://kycnot.me/about#support) this project with any of the listed ways.
[^1]: https://codeberg.org/pluja/kycnot.me/src/branch/main/src/utils/ai/prompt.go
[^2]: https://codeberg.org/pluja/kycnot.me/commit/483ba8b415cecf323b3d9f0cfd4e9620919467d2
[^3]: https://github.com/jina-ai/reader
[^4]: https://codeberg.org/pluja/kycnot.me
[^5]: https://kycnot.me/about#contact
-

@ 39cc53c9:27168656
2025-03-30 05:54:42
> [Read the original blog post](https://blog.kycnot.me/p/four-years)
> “The future is there... staring back at us. Trying to make sense of the fiction we will have become.”
> — William Gibson.
This month is [the 4th anniversary](#the-anniversary) of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency **free from government and institutional control**. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition[^1]:

How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
> ‟Hush now, baby, baby, don't you cry
> Mamma's gonna make all of your nightmares come true
> Mamma's gonna put all of her fears into you
> Mamma's gonna keep you right here, under her wing
> She won't let you fly, but she might let you sing
> Mamma's gonna keep baby cosy and warm”
> — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
> “We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.”
> — Eric Hughes, A Cypherpunk's Manifesto
## The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of [kycnot.me](https://kycnot.me) — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
[kycnot.me](https://kycnot.me) has remained 100% independent and 100% open source[^2] all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see [the score summary](https://https://kycnot.me/api/v1/service/bisq/summary) for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
[^1]: https://x.com/freedomtech/status/1796190018588872806
[^2]: https://codeberg.org/pluja/kycnot.me
-

@ a95c6243:d345522c
2025-03-01 10:39:35
*Ständige Lügen und Unterstellungen, permanent falsche Fürsorge* *\
können Bausteine von emotionaler Manipulation sein. Mit dem Zweck,* *\
Macht und Kontrolle über eine andere Person auszuüben.* *\
Apotheken Umschau*  
**Irgendetwas muss passiert sein: «Gaslighting» ist gerade Thema** in vielen Medien. Heute bin ich nach längerer Zeit mal wieder über dieses Stichwort gestolpert. Das war in einem [Artikel](https://norberthaering.de/propaganda-zensur/dwd-referenzperiode/) von Norbert Häring über Manipulationen des Deutschen Wetterdienstes (DWD). In diesem Fall ging es um eine Pressemitteilung vom Donnerstag zum «viel zu warmen» Winter 2024/25.
**Häring wirft der Behörde vor, dreist zu lügen und Dinge auszulassen,** um die Klimaangst wach zu halten. Was der Leser beim DWD nicht erfahre, sei, dass dieser Winter kälter als die drei vorangegangenen und kälter als der Durchschnitt der letzten zehn Jahre gewesen sei. Stattdessen werde der falsche Eindruck vermittelt, es würde ungebremst immer wärmer.
**Wem also der zu Ende gehende Winter eher kalt vorgekommen sein sollte,** mit dessen Empfinden stimme wohl etwas nicht. Das jedenfalls wolle der DWD uns einreden, so der Wirtschaftsjournalist. Und damit sind wir beim Thema Gaslighting.
**Als** **[Gaslighting](https://bayern-gegen-gewalt.de/gewalt-infos-und-einblicke/formen-von-gewalt/psychische-gewalt/gaslighting/)** **wird eine Form psychischer Manipulation bezeichnet,** mit der die Opfer desorientiert und zutiefst verunsichert werden, indem ihre eigene Wahrnehmung als falsch bezeichnet wird. Der Prozess führt zu Angst und Realitätsverzerrung sowie zur Zerstörung des Selbstbewusstseins. Die Bezeichnung kommt von dem britischen Theaterstück «Gas Light» aus dem Jahr 1938, in dem ein Mann mit grausamen Psychotricks seine Frau in den Wahnsinn treibt.
**Damit Gaslighting funktioniert, muss das Opfer dem Täter vertrauen.** Oft wird solcher Psychoterror daher im privaten oder familiären Umfeld beschrieben, ebenso wie am Arbeitsplatz. Jedoch eignen sich die Prinzipien auch perfekt zur Manipulation der Massen. Vermeintliche Autoritäten wie Ärzte und Wissenschaftler, oder «der fürsorgliche Staat» und Institutionen wie die UNO oder die WHO wollen uns doch nichts Böses. Auch Staatsmedien, Faktenchecker und diverse NGOs wurden zu «vertrauenswürdigen Quellen» erklärt. Das hat seine Wirkung.
**Warum das Thema Gaslighting derzeit scheinbar so populär ist,** vermag ich nicht zu sagen. Es sind aber gerade in den letzten Tagen und Wochen auffällig viele Artikel dazu erschienen, und zwar nicht nur von Psychologen. Die *Frankfurter Rundschau* hat gleich mehrere publiziert, und [Anwälte](https://www.anwalt.de/rechtstipps/gaslighting-beispiele-anzeichen-strafbarkeit-212449.html) interessieren sich dafür offenbar genauso wie Apotheker.
**Die** ***Apotheken Umschau*** **machte sogar auf** **[«Medical Gaslighting»](https://archive.is/Wx5YM)** **aufmerksam.** Davon spreche man, wenn Mediziner Symptome nicht ernst nähmen oder wenn ein gesundheitliches Problem vom behandelnden Arzt «schnöde heruntergespielt» oder abgetan würde. Kommt Ihnen das auch irgendwie bekannt vor? Der Begriff sei allerdings irreführend, da er eine manipulierende Absicht unterstellt, die «nicht gewährleistet» sei.
**Apropos Gaslighting: Die noch amtierende deutsche Bundesregierung** [meldete](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-08-2025-februar-28-2336254?view=renderNewsletterHtml) heute, es gelte, «weiter \[sic!] gemeinsam daran zu arbeiten, einen gerechten und dauerhaften Frieden für die Ukraine zu erreichen». Die Ukraine, wo sich am Montag «der völkerrechtswidrige Angriffskrieg zum dritten Mal jährte», [verteidige](https://transition-news.org/wikileaks-der-westen-wusste-dass-ein-nato-beitritt-der-ukraine-riskant-war) ihr Land und «unsere gemeinsamen Werte».
**Merken Sie etwas? Das Demokratieverständnis mag ja tatsächlich** inzwischen in beiden Ländern ähnlich traurig sein. Bezüglich Friedensbemühungen ist meine Wahrnehmung jedoch eine andere. Das muss an meinem Gedächtnis liegen.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/bitte-nicht-von-gaslichtern-irritieren-lassen)*** erschienen.
-

@ 460c25e6:ef85065c
2025-02-25 15:20:39
If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
## Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend:
- 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc.
- 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again.
- 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
## Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend:
- 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc.
- 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps.
- 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country
Terrible options include:
- nostr.wine should not be here.
- filter.nostr.wine should not be here.
- inbox.nostr.wine should not be here.
## DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are:
- inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you.
- a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details.
- a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
## Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
## Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today:
- nostr.wine
- relay.nostr.band
- relay.noswhere.com
## Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
## General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
## My setup
Here's what I use:
1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself.
2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription.
3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription.
4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country.
5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays:
- nostr.wine
- nos.lol or an in-country relay.
- <your.relay>.nostr1.com
Public Inbox Relays
- nos.lol or an in-country relay
- <your.relay>.nostr1.com
DM Inbox Relays
- inbox.nostr.wine
- <your.relay>.nostr1.com
Private Home Relays
- ws://localhost:4869 (Citrine)
- <your.relay>.nostr1.com (if you want)
Search Relays
- nostr.wine
- relay.nostr.band
- relay.noswhere.com
Local Relays
- ws://localhost:4869 (Citrine)
General Relays
- nos.lol
- relay.damus.io
- relay.primal.net
- nostr.mom
And a few of the recommended relays from Amethyst.
## Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-

@ d4cb227b:edca6019
2025-03-30 04:26:51
Dose:
30g coffee (Fine-medium grind size)
500mL soft or bottled water (97°C / 206.6°F)
Instructions:
1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer.
2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds.
3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase.
4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds.
5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds.
6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction.
7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds.
8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper.
9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
-

@ a95c6243:d345522c
2025-02-21 19:32:23
*Europa – das Ganze ist eine wunderbare Idee,* *\
aber das war der Kommunismus auch.* *\
Loriot*  
**«Europa hat fertig», könnte man unken,** und das wäre nicht einmal sehr verwegen. Mit solch einer [Einschätzung](https://transition-news.org/geopolitische-ohnmacht-und-die-last-des-euro-steht-die-eu-vor-der-implosion) stünden wir nicht alleine, denn die Stimmen in diese Richtung mehren sich. Der französische Präsident Emmanuel Macron warnte schon letztes Jahr davor, dass «unser Europa sterben könnte». Vermutlich hatte er dabei andere Gefahren im Kopf als jetzt der ungarische Ministerpräsident Viktor Orbán, der ein «baldiges Ende der EU» prognostizierte. Das Ergebnis könnte allerdings das gleiche sein.
**Neben vordergründigen Themenbereichen wie Wirtschaft, Energie und Sicherheit** ist das eigentliche Problem jedoch die obskure Mischung aus aufgegebener Souveränität und geschwollener Arroganz, mit der europäische Politiker:innende unterschiedlicher Couleur aufzutreten pflegen. Und das Tüpfelchen auf dem i ist die bröckelnde Legitimation politischer Institutionen dadurch, dass die Stimmen großer Teile der Bevölkerung seit Jahren auf vielfältige Weise ausgegrenzt werden.
**Um «UnsereDemokratie» steht es schlecht.** Dass seine Mandate immer schwächer werden, merkt natürlich auch unser «Führungspersonal». Entsprechend werden die Maßnahmen zur Gängelung, Überwachung und Manipulation der Bürger ständig verzweifelter. Parallel dazu [plustern](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-07-2025-februar-21-2335652?view=renderNewsletterHtml) sich in Paris Macron, Scholz und einige andere noch einmal mächtig in Sachen Verteidigung und [«Kriegstüchtigkeit»](https://transition-news.org/europaische-investitionsbank-tragt-zur-kriegstuchtigkeit-europas-bei) auf.
**Momentan gilt es auch, das Überschwappen covidiotischer und verschwörungsideologischer Auswüchse** aus den USA nach Europa zu vermeiden. So ein «MEGA» (Make Europe Great Again) können wir hier nicht gebrauchen. Aus den Vereinigten Staaten kommen nämlich furchtbare Nachrichten. Beispielsweise wurde einer der schärfsten Kritiker der Corona-Maßnahmen kürzlich zum Gesundheitsminister ernannt. Dieser setzt sich jetzt für eine Neubewertung der mRNA-«Impfstoffe» ein, was durchaus zu einem [Entzug der Zulassungen](https://transition-news.org/usa-zulassungsentzug-fur-corona-impfstoffe-auf-der-tagesordnung) führen könnte.
**Der europäischen Version von** **[«Verteidigung der Demokratie»](https://transition-news.org/eu-macht-freiwilligen-verhaltenskodex-gegen-desinformation-zu-bindendem-recht)** setzte der US-Vizepräsident J. D. Vance auf der Münchner Sicherheitskonferenz sein Verständnis entgegen: «Demokratie stärken, indem wir unseren Bürgern erlauben, ihre Meinung zu sagen». Das Abschalten von Medien, das Annullieren von Wahlen oder das Ausschließen von Menschen vom politischen Prozess schütze gar nichts. Vielmehr sei dies der todsichere Weg, die Demokratie zu zerstören.
**In der Schweiz kamen seine Worte deutlich besser an** als in den meisten europäischen NATO-Ländern. Bundespräsidentin Karin Keller-Sutter lobte die Rede und interpretierte sie als «Plädoyer für die direkte Demokratie». Möglicherweise zeichne sich hier eine [außenpolitische Kehrtwende](https://transition-news.org/schweiz-vor-aussenpolitischer-kehrtwende-richtung-integraler-neutralitat) in Richtung integraler Neutralität ab, meint mein Kollege Daniel Funk. Das wären doch endlich mal ein paar gute Nachrichten.
**Von der einstigen Idee einer europäischen Union** mit engeren Beziehungen zwischen den Staaten, um Konflikte zu vermeiden und das Wohlergehen der Bürger zu verbessern, sind wir meilenweit abgekommen. Der heutige korrupte Verbund unter technokratischer Leitung ähnelt mehr einem Selbstbedienungsladen mit sehr begrenztem Zugang. Die EU-Wahlen im letzten Sommer haben daran ebenso wenig geändert, wie die [Bundestagswahl](https://transition-news.org/bundestagswahl-mehr-aufrustung-statt-friedenskanzler-nach-der-wahl) am kommenden Sonntag darauf einen Einfluss haben wird.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/europaer-seid-ihr-noch-zu-retten)*** erschienen.
-

@ d4cb227b:edca6019
2025-03-30 04:23:22
This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain.
Dose:
- 20g coffee (Coarse ground coffee)
- 300mL water (92°C / 197.6°F)
Time: 3:30
Instructions:
Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.)
Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.)
Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour)
Pour 4: 2:10 > 60mL
Pour 5: 2:40 > 60mL
Remove the V60 at 3:30
-

@ a95c6243:d345522c
2025-02-19 09:23:17
*Die «moralische Weltordnung» – eine Art Astrologie.
Friedrich Nietzsche*
**Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere.
**In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt.
**Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel.
**Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten.
**Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY).
**Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen.
**Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf.
**Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen».
---
Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen.
-

@ a95c6243:d345522c
2025-02-15 19:05:38
**Auf der diesjährigen Münchner** **[Sicherheitskonferenz](https://transition-news.org/in-munchen-der-realitat-ins-auge-sehen)** **geht es vor allem um die Ukraine.** Protagonisten sind dabei zunächst die US-Amerikaner. Präsident Trump schockierte die Europäer kurz vorher durch ein Telefonat mit seinem Amtskollegen Wladimir Putin, während Vizepräsident Vance mit seiner Rede über Demokratie und Meinungsfreiheit für versteinerte Mienen und Empörung sorgte.
**Die Bemühungen der Europäer um einen Frieden in der Ukraine** halten sich, gelinde gesagt, in Grenzen. Größeres Augenmerk wird auf militärische Unterstützung, die Pflege von Feindbildern sowie Eskalation gelegt. Der deutsche Bundeskanzler Scholz [reagierte](https://transition-news.org/gesucht-friedenskanzler) auf die angekündigten Verhandlungen über einen möglichen Frieden für die Ukraine mit der Forderung nach noch höheren «Verteidigungsausgaben». Auch die amtierende Außenministerin Baerbock hatte vor der Münchner Konferenz [klargestellt](https://archive.is/nUpYa):
> «Frieden wird es nur durch Stärke geben. (...) Bei Corona haben wir gesehen, zu was Europa fähig ist. Es braucht erneut Investitionen, die der historischen Wegmarke, vor der wir stehen, angemessen sind.»
**Die Rüstungsindustrie freut sich in jedem Fall über weltweit steigende Militärausgaben.** Die Kriege in der Ukraine und in Gaza tragen zu [Rekordeinnahmen](https://transition-news.org/kriege-sind-fur-waffenproduzenten-und-hedgefonds-f-king-good) bei. Jetzt «winkt die Aussicht auf eine jahrelange große Nachrüstung in Europa», auch wenn der Ukraine-Krieg enden sollte, so hört man aus Finanzkreisen. In der Konsequenz kennt «die Aktie des deutschen Vorzeige-Rüstungskonzerns Rheinmetall in ihrem Anstieg [offenbar gar keine Grenzen](https://finanzmarktwelt.de/rheinmetall-aktie-mit-mega-rally-nachruestung-und-1-000-euro-kursziel-339271/) mehr». «Solche Friedensversprechen» wie das jetzige hätten in der Vergangenheit zu starken Kursverlusten geführt.
**Für manche Leute sind Kriegswaffen und sonstige Rüstungsgüter Waren wie alle anderen,** jedenfalls aus der Perspektive von Investoren oder Managern. Auch in diesem Bereich gibt es Startups und man spricht von Dingen wie innovativen Herangehensweisen, hocheffizienten Produktionsanlagen, skalierbaren Produktionstechniken und geringeren Stückkosten.
**Wir lesen aktuell von Massenproduktion und gesteigerten Fertigungskapazitäten** für Kriegsgerät. Der Motor solcher Dynamik und solchen Wachstums ist die Aufrüstung, die inzwischen permanent gefordert wird. Parallel wird die Bevölkerung verbal eingestimmt und auf Kriegstüchtigkeit getrimmt.
**Das Rüstungs- und KI-Startup Helsing verkündete kürzlich** eine «dezentrale [Massenproduktion](https://www.trendingtopics.eu/helsing-kampfdrohnen-unicorn-startet-dezentrale-massenproduktion-fuer-ukrainekrieg/) für den Ukrainekrieg». Mit dieser Expansion positioniere sich das Münchner Unternehmen als einer der weltweit führenden Hersteller von Kampfdrohnen. Der nächste [«Meilenstein»](https://archive.is/eZsWP) steht auch bereits an: Man will eine Satellitenflotte im Weltraum aufbauen, zur Überwachung von Gefechtsfeldern und Truppenbewegungen.
**Ebenfalls aus München stammt das als** **[DefenseTech-Startup](https://www.trendingtopics.eu/arx-robotics-produktion/)** **bezeichnete Unternehmen** ARX Robotics. Kürzlich habe man in der Region die größte europäische Produktionsstätte für autonome Verteidigungssysteme eröffnet. Damit fahre man die Produktion von Militär-Robotern hoch. Diese Expansion diene auch der Lieferung der «größten Flotte unbemannter Bodensysteme westlicher Bauart» in die Ukraine.
**Rüstung boomt und scheint ein Zukunftsmarkt zu sein.** Die Hersteller und Vermarkter betonen, mit ihren Aktivitäten und Produkten solle die europäische Verteidigungsfähigkeit erhöht werden. Ihre Strategien sollten sogar «zum Schutz demokratischer Strukturen beitragen».
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/so-klingt-das-aufrustungs-business-startups-und-alte-hasen)*** erschienen.
-

@ 30ceb64e:7f08bdf5
2025-03-30 00:37:54
Hey Freaks,
RUNSTR is a motion tracking app built on top of nostr. The project is built by TheWildHustle and TheNostrDev Team. The project has been tinkered with for about 3 months, but development has picked up and its goals and direction have become much clearer.
In a previous post I mentioned that RUNSTR was looking to become a Nike Run Club or Strava competitor, offering users an open source community and privacy focused alternative to the centralized silos that we've become used to.
I normally ramble incoherently.....even in writing, but this is my attempt to communicate the project's goals and direction as we move forward.
This is where the project is now:
## Core Features
- **Run Tracker**: Uses an algorithm which adjusts to your phone's location permissions and stores the data on your phone locally
- **Stats**: Stored locally on your phone with a basic profile screen so users can monitor calories burned during runs
- **Nostr Feed**: Made up of kind1 notes that contain #RUNSTR and other running related hashtags
- **Music**: Brought to you via a wavlake API, enabling your wavlake playlists and liked songs to be seen and played in the app
## Current Roadmap
- **Bugs and small improvements**: Fixing known issues within the client
- **zap.store release**: Launching a bug bounty program after release
- **Clubs**: Enabling running organizations to create territories for events, challenges, rewards and competition
- **Testflight**: Opening up the app to iOS users (currently Android only)
- **Modes**: Adding functionality to switch between Running, Walking, or Cycling modes
## Future Roadmap
- **Requested Features**: Implementing features requested by club managers to support virtual events and challenges
- **Blossom**: Giving power users the ability to upload their data to personal blossom servers
- **NIP28**: Making clubs interoperable with other group chat clients like 0xchat, Keychat, and Chachi Chat
- **DVM's**: Creating multiple feeds based on movement mode (e.g., Walking mode shows walkstr feed)
- **NIP101e**: Allowing users to create run records and store them on nostr relays
- **Calories over relays**: Using NIP89-like functionality for users to save calorie data on relays for use in other applications
- **NIP60**: Implementing automatic wallet creation for users to zap and get zapped within the app
## In Conclusion
I've just barely begun this thing and it'll be an up and down journey trying to push it into existence. I think RUNSTR has the potential to highlight the other things that nostr has going for it, demonstrating the protocol's interoperability, flexing its permissionless identity piece, and offering an experience that gives users a glimpse into what is possible when shipping into a new paradigm. Although we build into an environment that often offers no solutions, you'd have to be a crazy person not to try.
https://github.com/HealthNoteLabs/Runstr/releases/tag/feed-0.1.0-20250329-210157
-

@ e4950c93:1b99eccd
2025-03-29 14:49:11
<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzqr9mwlyllz3zkvk4x2cl98g993k3ele3a55ps6tkay5c3amu4pstqy88wumn8ghj7mn0wvhxcmmv9uqqvvjvgae9x7g0rt3r3?viewKey=f409eabf471c20d1cd3148eca8dc0e388476496b8d47eff10bff145603c1fa9b&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe>
-

@ c631e267:c2b78d3e
2025-02-07 19:42:11
*Nur wenn wir aufeinander zugehen, haben wir die Chance* *\
auf Überwindung der gegenseitigen Ressentiments!* *\
Dr. med. dent. Jens Knipphals*  
**In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik** mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und [langjährige](https://transition-news.org/wo-sind-einigkeit-recht-und-freiheit) Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und [publiziert](https://www.alexander-wallasch.de/impfgeschichten/brandbrief-zahnarzt-laesst-nicht-locker-showdown-im-wolfsburger-rathaus). Seine Motivation:
> «Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.»
**Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt,** zum Beispiel bei öffentlichen [Bürgerfragestunden](https://archive.is/ttTZc). Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise?
**Der Termin fand allerdings nicht statt** – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als [Wiederholungstäter](https://www.youtube.com/watch?v=b_zzp6jKiHo), da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber *Multipolar* [erklärte](https://multipolar-magazin.de/artikel/corona-aufarbeitung-wolfsburg) der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen.
**Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst,** sei aber letztlich eine gesamtgesellschaftliche Aufgabe, [schreibt](https://peds-ansichten.de/2025/01/plandemie-aufarbeitung/) Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien.
**Frey erinnert daran, dass Dennis Weilmann mitverantwortlich** für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut.
**Wolfsburg wurde damals zu einem Modellprojekt** des Bundesministeriums des Innern (BMI) und war Finalist im [Bitkom](https://pareto.space/a/naddr1qqxnzden8qen2vejxvenjv35qgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytn8wfhk7an9d9uzucm0d5qs7amnwvaz7tmwdaehgu3wd4hk6qg5waehxw309ahx7um5wghx77r5wghxgetkqydhwumn8ghj7mn0wd68ytnnwa5hxuedv4hxjemdvyhxx6qpzamhxue69uhhqctjv46x7tnwdaehgu339e3k7mgpz4mhxue69uhhqatjwpkx2un9d3shjtnrdaksz9nhwden5te0wfjkccte9cc8scmgv96zucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgkwaehxw309aex2mrp0yhxummnw3ezucnpdejqmk3pae)-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt [«Smart City Wolfsburg»](https://www.beesmart.city/de/city-portraits/smart-city-wolfsburg) anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin *[Forbes](https://web.archive.org/web/20200417064208/https://www.forbes.com/sites/simonchandler/2020/04/13/how-smart-cities-are-protecting-against-coronavirus-but-threatening-privacy/#5edf8d0c1cc3)* im April 2020:
> «Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.»
**Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten,** wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten [Maßnahmen](https://transition-news.org/stopptcovid-gutachten-von-lauterbach-erhalt-vernichtende-analyse) geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts».
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/corona-aufarbeitung-in-der-praxis-eine-illusion)*** erschienen.
-

@ a95c6243:d345522c
2025-01-31 20:02:25
*Im Augenblick wird mit größter Intensität, großer Umsicht* *\
das deutsche Volk belogen.* *\
Olaf Scholz im FAZ-[Interview](https://www.youtube.com/watch?v=c3KI1GmdoVc\&t=649s)*  
**Online-Wahlen stärken die Demokratie, sind sicher, und 61 Prozent der Wahlberechtigten** sprechen sich für deren Einführung in Deutschland aus. Das zumindest behauptet eine aktuelle Umfrage, die auch über die Agentur *Reuters* Verbreitung in den Medien [gefunden](https://archive.is/dnZbY) hat. Demnach würden außerdem 45 Prozent der Nichtwähler bei der Bundestagswahl ihre Stimme abgeben, wenn sie dies zum Beispiel von Ihrem PC, Tablet oder Smartphone aus machen könnten.
**Die telefonische Umfrage unter gut 1000 wahlberechtigten Personen** sei repräsentativ, [behauptet](https://www.bitkom.org/Presse/Presseinformation/Knapp-Haelfte-Nichtwaehler-wuerde-online-waehlen) der Auftraggeber – der Digitalverband Bitkom. Dieser präsentiert sich als eingetragener Verein mit einer beeindruckenden Liste von [Mitgliedern](https://www.bitkom.org/Bitkom/Mitgliedschaft/Mitgliederliste), die Software und IT-Dienstleistungen anbieten. Erklärtes Vereinsziel ist es, «Deutschland zu einem führenden Digitalstandort zu machen und die digitale Transformation der deutschen Wirtschaft und Verwaltung voranzutreiben».
**Durchgeführt hat die Befragung die Bitkom Servicegesellschaft mbH,** also alles in der Familie. Die gleiche Erhebung hatte der Verband übrigens 2021 schon einmal durchgeführt. Damals sprachen sich angeblich sogar 63 Prozent für ein derartiges [«Demokratie-Update»](https://www.experten.de/id/4922407/online-wahlen-als-update-des-demokratischen-systems/) aus – die Tendenz ist demgemäß fallend. Dennoch orakelt mancher, der Gang zur Wahlurne gelte bereits als veraltet.
**Die spanische Privat-Uni mit Globalisten-Touch, IE University, berichtete** Ende letzten Jahres in ihrer Studie «European Tech Insights», 67 Prozent der Europäer [befürchteten](https://www.ie.edu/university/news-events/news/67-europeans-fear-ai-manipulation-elections-according-ie-university-research/), dass Hacker Wahlergebnisse verfälschen könnten. Mehr als 30 Prozent der Befragten glaubten, dass künstliche Intelligenz (KI) bereits Wahlentscheidungen beeinflusst habe. Trotzdem würden angeblich 34 Prozent der unter 35-Jährigen einer KI-gesteuerten App vertrauen, um in ihrem Namen für politische Kandidaten zu stimmen.
**Wie dauerhaft wird wohl das Ergebnis der kommenden Bundestagswahl sein?** Diese Frage stellt sich angesichts der aktuellen Entwicklung der Migrations-Debatte und der (vorübergehend) bröckelnden «Brandmauer» gegen die AfD. Das «Zustrombegrenzungsgesetz» der Union hat das Parlament heute Nachmittag überraschenderweise [abgelehnt](https://www.bundestag.de/dokumente/textarchiv/2025/kw05-de-zustrombegrenzungsgesetz-1042038). Dennoch muss man wohl kein ausgesprochener Pessimist sein, um zu befürchten, dass die Entscheidungen der Bürger von den selbsternannten Verteidigern der Demokratie künftig vielleicht nicht respektiert werden, weil sie nicht gefallen.
**Bundesweit wird jetzt zu «Brandmauer-Demos» aufgerufen,** die CDU gerät unter Druck und es wird von Übergriffen auf Parteibüros und Drohungen gegen Mitarbeiter [berichtet](https://www.epochtimes.de/politik/deutschland/brandmauer-proteste-cdu-zentrale-geraeumt-kundgebungen-in-46-staedten-a5023745.html). Sicherheitsbehörden warnen vor Eskalationen, die Polizei sei «für ein mögliches erhöhtes Aufkommen von Straftaten gegenüber Politikern und gegen Parteigebäude sensibilisiert».
**Der Vorwand** **[«unzulässiger Einflussnahme»](https://transition-news.org/die-minister-faeser-und-wissing-sorgen-sich-um-unzulassige-einflussnahme-auf)** **auf Politik und Wahlen** wird als Argument schon seit einiger Zeit aufgebaut. Der Manipulation schuldig befunden wird neben Putin und Trump auch Elon Musk, was lustigerweise ausgerechnet Bill Gates gerade noch einmal bekräftigt und als [«völlig irre»](https://transition-news.org/bill-gates-nennt-musks-einmischung-in-eu-politik-vollig-irre) bezeichnet hat. Man stelle sich die Diskussionen um die Gültigkeit von Wahlergebnissen vor, wenn es Online-Verfahren zur Stimmabgabe gäbe. In der Schweiz wird [«E-Voting»](https://www.ch.ch/de/abstimmungen-und-wahlen/e-voting/) seit einigen Jahren getestet, aber wohl bisher mit wenig Erfolg.
**Die politische Brandstiftung der letzten Jahre zahlt sich immer mehr aus.** Anstatt dringende Probleme der Menschen zu lösen – zu denen auch in Deutschland die [weit verbreitete Armut](https://transition-news.org/ein-funftel-der-bevolkerung-in-deutschland-ist-von-armut-oder-sozialer) zählt –, hat die Politik konsequent polarisiert und sich auf Ausgrenzung und Verhöhnung großer Teile der Bevölkerung konzentriert. Basierend auf Ideologie und Lügen werden abweichende Stimmen unterdrückt und kriminalisiert, nicht nur und nicht erst in diesem Augenblick. Die nächsten Wochen dürften ausgesprochen spannend werden.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/wahlen-und-wahlen-lassen)*** erschienen.
-

@ a95c6243:d345522c
2025-01-24 20:59:01
*Menschen tun alles, egal wie absurd,* *\
um ihrer eigenen Seele nicht zu begegnen.* *\
Carl Gustav Jung*  
**«Extremer Reichtum ist eine Gefahr für die Demokratie»,** sagen über die Hälfte der knapp 3000 befragten Millionäre aus G20-Staaten laut einer [Umfrage](https://web.archive.org/web/20250122124803/https://patrioticmillionaires.org/web/20250122124803/https://patrioticmillionaires.org/press/nearly-two-thirds-of-millionaires-think-influence-of-the-super-rich-on-trump-presidency-is-threat-to-global-stability/) der «Patriotic Millionaires». Ferner stellte dieser Zusammenschluss wohlhabender US-Amerikaner fest, dass 63 Prozent jener Millionäre den Einfluss von Superreichen auf US-Präsident Trump als Bedrohung für die globale Stabilität ansehen.
**Diese Besorgnis haben 370 Millionäre und Milliardäre am Dienstag** auch den in Davos beim WEF konzentrierten Privilegierten aus aller Welt übermittelt. In einem offenen Brief forderten sie die «gewählten Führer» auf, die Superreichen – also sie selbst – zu besteuern, um «die zersetzenden Auswirkungen des extremen Reichtums auf unsere Demokratien und die Gesellschaft zu bekämpfen». Zum Beispiel kontrolliere eine handvoll extrem reicher Menschen die Medien, beeinflusse die Rechtssysteme in unzulässiger Weise und verwandele Recht in Unrecht.
**Schon 2019** **[beanstandete](https://www.youtube.com/watch?v=paaen3b44XY)** **der bekannte Historiker und Schriftsteller Ruthger Bregman** an einer WEF-Podiumsdiskussion die Steuervermeidung der Superreichen. Die elitäre Veranstaltung bezeichnete er als «Feuerwehr-Konferenz, bei der man nicht über Löschwasser sprechen darf.» Daraufhin erhielt Bregman keine Einladungen nach Davos mehr. Auf seine Aussagen machte der Schweizer Aktivist Alec Gagneux aufmerksam, der sich seit Jahrzehnten kritisch mit dem WEF befasst. Ihm wurde kürzlich der Zutritt zu einem dreiteiligen Kurs über das WEF an der Volkshochschule Region Brugg [verwehrt](https://transition-news.org/wef-propaganda-an-schweizer-volkshochschule-kritiker-ausgesperrt).
**Nun ist die Erkenntnis, dass mit Geld politischer Einfluss einhergeht,** alles andere als neu. Und extremer Reichtum macht die Sache nicht wirklich besser. Trotzdem hat man über Initiativen wie Patriotic Millionaires oder [Taxmenow](https://www.taxmenow.eu/) bisher eher selten etwas gehört, obwohl es sie schon lange gibt. Auch scheint es kein Problem, wenn ein Herr [Gates](https://transition-news.org/bill-melinda-gates-stiftung) fast im Alleingang versucht, globale Gesundheits-, Klima-, Ernährungs- oder Bevölkerungspolitik zu betreiben – im Gegenteil. Im Jahr, als der Milliardär Donald Trump zum zweiten Mal ins Weiße Haus einzieht, ist das Echo in den Gesinnungsmedien dagegen enorm – und uniform, wer hätte das gedacht.
**Der neue US-Präsident hat jedoch** **[«Davos geerdet»](https://www.achgut.com/artikel/trump_erdet_davos_gruener_betrug_green_new_scam),** wie *Achgut* es nannte. In seiner kurzen [Rede](https://www.weforum.org/meetings/world-economic-forum-annual-meeting-2025/sessions/special-address-by-the-president-of-the-united-states-of-america/) beim Weltwirtschaftsforum verteidigte er seine Politik und stellte klar, er habe schlicht eine «Revolution des gesunden Menschenverstands» begonnen. Mit deutlichen Worten sprach er unter anderem von ersten Maßnahmen gegen den «Green New Scam», und von einem «Erlass, der jegliche staatliche Zensur beendet»:
> «Unsere Regierung wird die Äußerungen unserer eigenen Bürger nicht mehr als Fehlinformation oder Desinformation bezeichnen, was die Lieblingswörter von Zensoren und derer sind, die den freien Austausch von Ideen und, offen gesagt, den Fortschritt verhindern wollen.»
**Wie der** **[«Trumpismus»](https://transition-news.org/trumpismus-zeitenwende-und-tiefer-staat)** **letztlich einzuordnen ist,** muss jeder für sich selbst entscheiden. Skepsis ist definitiv angebracht, denn «einer von uns» sind weder der Präsident noch seine auserwählten Teammitglieder. Ob sie irgendeinen Sumpf trockenlegen oder Staatsverbrechen aufdecken werden oder was aus WHO- und Klimaverträgen wird, bleibt abzuwarten.
**Das** **[WHO](https://transition-news.org/who-bedauert-trumps-entscheidung-sich-aus-der-organisation-zuruckzuziehen)-Dekret fordert jedenfalls die Übertragung der Gelder auf «glaubwürdige Partner»,** die die Aktivitäten übernehmen könnten. Zufällig scheint mit «Impfguru» Bill Gates ein weiterer Harris-Unterstützer kürzlich das Lager gewechselt zu haben: Nach einem gemeinsamen Abendessen zeigte er sich [«beeindruckt»](https://archive.is/SpQ24) von Trumps Interesse an der globalen Gesundheit.
**Mit dem** **[Projekt «Stargate»](https://transition-news.org/us-privatsektor-will-500-milliarden-dollar-in-ki-investieren-krebsimpfstoffe)** **sind weitere dunkle Wolken am Erwartungshorizont** der Fangemeinde aufgezogen. Trump hat dieses Joint Venture zwischen den Konzernen OpenAI, Oracle, und SoftBank als das «größte KI-Infrastrukturprojekt der Geschichte» angekündigt. Der Stein des Anstoßes: Oracle-CEO Larry Ellison, der auch Fan von KI-gestützter [Echtzeit-Überwachung](https://transition-news.org/oracle-kundigt-neues-ki-rechenzentrum-mit-eigenen-atomreaktoren-an) ist, sieht einen weiteren potenziellen Einsatz der künstlichen Intelligenz. Sie könne dazu dienen, Krebserkrankungen zu erkennen und individuelle mRNA-«Impfstoffe» zur Behandlung innerhalb von 48 Stunden zu entwickeln.
**Warum bitte sollten sich diese superreichen «Eliten» ins eigene Fleisch schneiden** und direkt entgegen ihren eigenen Interessen handeln? Weil sie Menschenfreunde, sogenannte Philanthropen sind? Oder vielleicht, weil sie ein schlechtes Gewissen haben und ihre Schuld kompensieren müssen? Deswegen jedenfalls brauchen «Linke» laut Robert Willacker, einem deutschen Politikberater mit brasilianischen Wurzeln, rechte Parteien – ein ebenso überraschender wie humorvoller [Erklärungsansatz](https://www.youtube.com/watch?v=s63_8flX1zk).
**Wenn eine Krähe der anderen kein Auge aushackt,** dann tut sie das sich selbst noch weniger an. Dass Millionäre ernsthaft ihre eigene Besteuerung fordern oder Machteliten ihren eigenen Einfluss zugunsten anderer einschränken würden, halte ich für sehr unwahrscheinlich. So etwas glaube ich erst, wenn zum Beispiel die [Rüstungsindustrie](https://transition-news.org/schweiz-zunehmende-beteiligung-an-eu-militarprojekten) sich um Friedensverhandlungen bemüht, die [Pharmalobby](https://transition-news.org/eu-lobbyisten-gegen-pfas-verbot) sich gegen institutionalisierte Korruption einsetzt, [Zentralbanken](https://transition-news.org/digitale-wahrung) ihre CBDC-Pläne für Bitcoin opfern oder der ÖRR die Abschaffung der Rundfunkgebühren fordert.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/elitare-anti-eliten-und-superreiche-anti-reiche)*** erschienen.
-

@ c631e267:c2b78d3e
2025-01-18 09:34:51
*Die grauenvollste Aussicht ist die der Technokratie –* *\
einer kontrollierenden Herrschaft,* *\
die durch verstümmelte und verstümmelnde Geister ausgeübt wird.* *\
Ernst Jünger*  
**«Davos ist nicht mehr sexy»,** das Weltwirtschaftsforum ([WEF](https://transition-news.org/wef-world-economic-forum)) mache Davos [kaputt](https://web.archive.org/web/20250116114956/https://www.handelszeitung.ch/wef-2025/wie-das-wef-davos-kaputt-macht-785098), diese Aussagen eines Einheimischen las ich kürzlich in der *Handelszeitung*. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
**Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen** dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den [vergangenen](https://transition-news.org/die-angst-der-eliten-vor-dem-pobel) vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
**Der deutsche WEF-Gründer hatte bei dieser Gelegenheit** immer höchst lobende Worte für seine Landsmännin: [2021](https://www.weforum.org/meetings/the-davos-agenda-2021/sessions/special-address-by-g20-head-of-state-government/) erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und [2022](https://www.weforum.org/meetings/the-davos-agenda-2022/sessions/special-address-by-ursula-von-der-leyen-president-of-the-european-commission-177737c164/) fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
**Von der Leyens Handeln während der sogenannten Corona-«Pandemie»** lobte Schwab damals bereits ebenso, wie es diese Woche das [Karlspreis](https://transition-news.org/von-der-leyen-erhalt-karlspreis-albert-bourla-erklart-pfizer-habe-wahrend-der)-Direktorium tat, als man der Beschuldigten im Fall [Pfizergate](https://transition-news.org/pfizergate-startet-ins-neue-jahr) die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
**Jene Herausforderungen durch «Krisen epochalen Ausmaßes»** werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im [Global Risks Report](https://www.zurich.com/knowledge/topics/global-risks/the-global-risks-report-2025) nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
**Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen** unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
**Ein** **[«Great Mental Reset»](https://transition-news.org/angriff-auf-unser-gehirn-michael-nehls-uber-den-great-mental-reset-teil-1)** **sei die Voraussetzung dafür,** dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
**Der aktuelle Zustand unserer Gesellschaften** ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die [Rechtsstaatlichkeit](https://transition-news.org/schweizer-rechtsstaat-in-der-krise-ein-anwalt-schlagt-alarm) stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/davos-europa-und-der-rest-der-welt)*** erschienen.
-

@ f9cf4e94:96abc355
2025-01-18 06:09:50
Para esse exemplo iremos usar:
| Nome | Imagem | Descrição |
| --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ |
| Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** |
| Pen drive |  | **16Gb** |
Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.).
---
## Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
```bash
apt update
apt install tor
```
---
## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧
Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit
[Unit]
Description=Nostr Relay Server Service
After=network.target
[Service]
Type=simple
WorkingDirectory=/opt/nrs
ExecStart=/opt/nrs/nrs-arm64
Restart=on-failure
[Install]
WantedBy=multi-user.target
```
---
## Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases).
---
## Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
```bash
mkdir -p /opt/nrs /mnt/edriver
```
---
## Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
```bash
lsblk
```
---
## Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o:
```bash
mkfs.vfat /dev/sda
```
---
## Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta `/mnt/edriver`:
```bash
mount /dev/sda /mnt/edriver
```
---
## Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
```bash
blkid
```
---
## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝
Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:
```fstab
UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
```
---
## Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta `/opt/nrs`:
```bash
cp nrs-arm64 /opt/nrs
```
---
## Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`:
```yaml
app_env: production
info:
name: Nostr Relay Server
description: Nostr Relay Server
pub_key: ""
contact: ""
url: http://localhost:3334
icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png
base_path: /mnt/edriver
negentropy: true
```
---
## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`:
```bash
cp nrs.service /etc/systemd/system/
```
Recarregue os serviços e inicie o serviço `nrs`:
```bash
systemctl daemon-reload
systemctl enable --now nrs.service
```
---
## Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha:
```torrc
HiddenServiceDir /var/lib/tor/nostr_server/
HiddenServicePort 80 127.0.0.1:3334
```
---
## Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
```bash
systemctl enable --now tor.service
```
O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`.
---
## Observações ⚠️
- Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`.
---
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-

@ a95c6243:d345522c
2025-01-13 10:09:57
*Ich begann, Social Media aufzubauen,* *\
um den Menschen eine Stimme zu geben.* *\
Mark Zuckerberg*
**Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs** **[Wendehals-Deklaration](https://www.facebook.com/zuck/videos/1525382954801931)** bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren».
**«Purer** **[Opportunismus](https://transition-news.org/facebook-grunder-zuckerberg-vom-trump-gegner-zum-trump-buddy-und-anti-zensor)» ob des anstehenden Regierungswechsels wäre als Klassifizierung** viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich.
> «Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg.
**Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung,** dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen [«LifeLog»](https://norberthaering.de/macht-kontrolle/lifelog/). Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen».
**Der Richtungswechsel kommt allerdings nicht überraschend.** Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten [gesprochen](https://www.theverge.com/2024/12/3/24311513/meta-content-moderation-mistakes-nick-clegg). Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen.
**Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten** in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine [Verhaftung](https://transition-news.org/nicht-telegram-grunder-durow-sondern-zuckerberg-sollte-in-haft-sitzen-wegen-des) dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt [kritisierte](https://www.berliner-zeitung.de/news/ende-des-faktenchecks-bei-meta-telegram-gruender-kritisiert-zuckerberg-und-spricht-warnung-aus-li.2287988) und gleichzeitig warnte.
**Politik und Systemmedien drehen jedenfalls durch** – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten [Völkermord](https://archive.is/PYeH0)», ernsthaft. Die Frage sei, ob sich die [EU gegen Musk und Zuckerberg](https://www.handelsblatt.com/politik/international/internet-regulierung-kann-sich-die-eu-gegen-musk-und-zuckerberg-behaupten/100099373.html) behaupten könne, Brüssel müsse jedenfalls hart durchgreifen.
**Auch um die** **[Faktenchecker](https://www.welt.de/kultur/medien/article255065352/Metas-Kurswechsel-Zuckerbergs-Entscheidung-und-die-Folgen-fuer-deutsche-Faktenchecker.html)** **macht man sich Sorgen.** Für die deutsche Nachrichtenagentur *dpa* und die «Experten» von *Correctiv*, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die *Tagesschau* keine Fehler zugeben und zum Beispiel *Correctiv*-[Falschaussagen](https://www.berliner-zeitung.de/politik-gesellschaft/correctiv-falschaussagen-exklusiv-scholz-faeser-und-tagesschau-wollen-sich-fuer-verbreitung-nicht-entschuldigen-li.2288126) einräumen.
**Bei derlei dramatischen Befürchtungen wundert es nicht,** dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft.
**Das** **[Anbiedern](https://transition-news.org/who-biedert-sich-bei-trump-an)** **bei Donald Trump ist indes gerade in Mode.** Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. [sechs Milliarden](https://x.ai/blog/series-c) eingestrichen hat, geht da vielleicht etwas.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/milliardenschwere-wetterfahnchen-und-windmaschinen)*** erschienen.
-

@ fd78c37f:a0ec0833
2025-03-29 04:33:01
**YakiHonne**: I'm excited to be joined by our guest Piccolo—thank you very much for being here. Before we dive in, I'd like to briefly introduce YakiHonne. YakiHonne is a decentralized media client built on the Nostr protocol, leveraging technology to enable freedom of speech. It empowers creators to fully own their voice and assets while offering innovative tools such as Smart widget , Verified Notes, and support for long-form content. Today, we’re not just discussing YakiHonne, but also diving into your community. Piccolo, could you start by telling us a bit about yourself and your community?
**Piccolo**:Hi, I'm Piccolo. I run BO฿ Space in Bangkok, and we also have a satellite location called the BO฿ Space corner in Chiang Mai, thanks to the Bitcoin Learning Center.
**Piccolo**:Regarding my background,I originally came from corporate finance and investment banking. I was in that field for about 20 years, with the last 15 spent running my own firm in corporate finance advisory alongside a couple of partners. We eventually sold the advisory business in 2015, took a short break, and in 2016, I ended up launching a fintech company, which is still operational today. The company specializes in equity crowdfunding and is licensed by the SEC in Thailand.
**Piccolo**:I first bought Bitcoin a few years before truly understanding it, initially thinking it was a scam that would eventually collapse. However, in 2017, the block size wars demonstrated the protocol’s strong resistance to attacks on decentralization, which deeply impacted me. By late 2018 or early 2019, I started to really grasp Bitcoin and kept learning. Then, in mid-2022, after having fully fallen down the Bitcoin rabbit hole, I founded BO฿ Space. It was right after COVID, and since the fintech had scaled down, there was extra space. We started by hosting meetups and technical workshops for people who were interested.
**Piccolo**:In the early years, we had various groups come by—like the team from BDK (Bitcoin Development Kit), who held workshops. The people behind the Bitcoin Beach Wallet, which later became Blink, also visited. So, BO฿ Space initially functioned as a meetup and technical workshop space. Eventually, we launched the BOB Builders Residency program, which was a lot of fun. We secured grant funding for developers under different cohort themes, so that they can collaborate and co-work for a few months. So far, we have completed three cohorts.
**YakiHonne**:How did your community get started, and what did you do to attract new members in the beginning?
**Piccolo**:The initial members came through word of mouth and invitations that I sent out. I reached out to an initial group of Bitcoiners here in the city who I believed were strong maximalists or Bitcoin-only supporters, back when that was still a thing. I sent out 21 invitations and had our first meetup with 21 people, most of whom I had interacted with online, though some in person during the COVID years. From there, it spread by word of mouth, and of course, through Twitter and meetup.com. So, I would say that word of mouth remains the main method of growth. Additionally, when people come through Bangkok and are looking for a Bitcoin-only meetup, there really isn't one available. I believe there are a couple now—maybe two or three—but when we started, there weren’t any, especially not a dedicated Bitcoin-only space. I think we may still be the only one in Bangkok. So yeah, word of mouth was definitely the main way we grew. Bitcoiners tend to share their finds when they meet like-minded people.

**YakiHonne**:Didn’t you have people in your community who initially thought Bitcoin was a scam, like you did, or face similar issues?
**Piccolo**:Yes, it still happens, especially when the price of Bitcoin rises. Newcomers still join, and some of them believe Bitcoin might be a scam. However, this has become less frequent. The main reason is that when people come to BO฿ Space, they know it’s a Bitcoin-only meetup. We generally don’t discuss the price; instead, we focus on other aspects of Bitcoin, as there are many interesting developments in the space.
**YakiHonne**:What advice would you give to someone looking to start or grow a Bitcoin-focused community in today’s world? Considering the current landscape, much like your own experience, what guidance would you offer?
**Piccolo**:It sounds simple, but just do it. When it comes to community building, you don’t necessarily need a physical space. Community is about people coming together, right? Two people can start a community, then three, four, and so on. Meetups can happen anywhere—your favorite bar, a restaurant, a friend’s garage, or wherever. So, just do it, but make sure you have more than one person, otherwise, how can you build a community? Once you have more than one person, word of mouth will spread. And as you develop a core group—let’s say more than five people—that’s when I think the community can truly sustain itself.
**YakiHonne**:I know you’ve mentioned the technical side of your community, but I’ll ask anyway—does your community engage with the technical or non-technical aspects of Bitcoin? Or perhaps, is there a blend of both?
**Piccolo**:I would say both. It really depends on the monthly themes of our meetups. For example, February was focused on Asian communities in Bitcoin. During that month, community leaders came in to give presentations and discuss their work in places like Indonesia, India, and more recently, someone from HRF (Human Rights Foundation) talked about Bitcoin’s use case in Myanmar. Then, in December, we had a very technical month—Mining Month. It was led by our Cohort 3 residents, where we discussed Stratum V2 and had a demo on it. We also examined the Loki board hardware, and Zack took apart the S19, looking at different ways to repurpose the power supply unit, among other things. So, it’s a mix of both, depending on the theme for that month. Some months are very technical, while others are more community-focused and less technical.
**YakiHonne**:What advice would you give to a technically inclined individual or organization looking to contribute meaningfully to the Bitcoin ecosystem?
**Piccolo**:For technically inclined individuals, I would suggest identifying your favorite open-source project in the Bitcoin ecosystem. Start from Bitcoin Core and explore different layers, such as Lightning or e-cash, and other open-source projects. As for technically inclined organizations, if you're integrating Bitcoin into your business, I would say, first, make sure you have people within your organization who truly understand Bitcoin. Build a capable team first, and then, depending on the part of the Bitcoin ecosystem you’re involved in—whether it’s custody services, Lightning payments, layer 2, or something like Cashu or Ark—find your niche. From there, your team will work with you to discover ways to contribute. But until you build that capability, organizations are a bit different from individuals in this space.
**YakiHonne**:How do you see the world of Bitcoin communities evolving as technology matures, particularly in areas like scalability, privacy, and adaptability with other systems?
**Piccolo**:That's an interesting question. If we think about the future of Bitcoin communities, I believe they may eventually disappear as technology matures. Once Bitcoin scales to a point where it integrates seamlessly with other payment systems, becoming part of the everyday norm, the need for dedicated communities will diminish. It’s similar to how we no longer have meetups about refrigerators or iPhones, even though they are technologies we use every day. As Bitcoin matures, it will likely reach that level of ubiquity. There might still be occasional meetups or forums, but they will be more about specific knowledge, use cases, and tools, rather than a community dedicated to introducing others to the technology itself. However, this is a long way off. Bitcoin is still relatively small compared to the global fiat financial system, despite the growth we want to see. So, it will take a long time before we reach that stage.
**YakiHonne**:It’s something I hadn’t considered before, and it’s quite insightful. Moving to our last question actually which I find very interesting is the government around you for or against bitcoin and how has That affected the community.
**Piccolo**:In my opinion, on a general level, the government is more supportive than opposed to Bitcoin. The Thai government classifies Bitcoin as a digital asset, almost like digital gold. In that sense, they want to tax capital gains and regulate it. They also have a regulatory framework for it, known as the Digital Asset Regulatory Sandbox, where you can test various things, mainly coins and tokens. It's unfortunate, but that’s how it is. However, our government, especially the regulatory bodies, are open to innovation. They recognize that Bitcoin is different, but they still view blockchain and tokens as useful technologies, which is somewhat misguided. So, in that sense, it’s more support than opposition. A couple of years ago, there was a circular discouraging the use of Bitcoin as a payment currency, mainly because they can't control its monetary policy. And they’re right—Bitcoin can’t be controlled by anyone; there’re the protocol and the rules, and everyone follows them, unless there’s a hard fork, which is a different matter. So, in that regard, Bitcoin is definitely categorized as a digital asset by the government, and that’s where it stands.
**Piccolo**:People who come to BO฿ Space to learn about Bitcoin are often influenced by the government from the point of price movements; especially when government support moves the price up. But they usually only visit once or twice, especially if they’re not deep into the Bitcoin rabbit hole. They often get disappointed because, at BO฿ Space, we rarely discuss the price—maybe once a year, and that’s just after the meetup when people are having drinks. So, in that sense, I’d say the government currently doesn’t really hurt or help the community either way. People will go down the rabbit hole at their own pace. And if you're not a Bitcoiner and you come to a BO฿ Space meetup with a crypto focus, you might be surprised by the approach we take.
**YakiHonne**:Thank you, Piccolo, for your time and insights. It’s been a pleasure speaking with you. Your perspective on the evolution of Bitcoin communities was eye-opening. It's clear that your deep understanding of Bitcoin is invaluable. I'm sure our readers will appreciate your insights. Once again, thank you, Piccolo. I look forward to seeing the continued growth of BO฿ Space and Bitcoin adoption.
-

@ df06d21e:2b23058f
2025-03-29 02:08:31
Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust.
Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement.
Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification.
Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation.
And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination.
Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars.
Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them.
We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new?
-

@ a95c6243:d345522c
2025-01-03 20:26:47
*Was du bist hängt von drei Faktoren ab:* *\
Was du geerbt hast,* *\
was deine Umgebung aus dir machte* *\
und was du in freier Wahl* *\
aus deiner Umgebung und deinem Erbe gemacht hast.* *\
Aldous Huxley*
**Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen** ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses [Buch](https://www.nachdenkseiten.de/?p=126416) einer gewissen ehemaligen Regierungschefin.
**Erklärungsansätze für solche Entwicklungen sind bekannt,** und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer [Herrschaftsinstrumente](https://transition-news.org/spip.php?recherche=nudging\&page=recherche_wall).
**Aber wollen die Menschen überhaupt Freiheit?** Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht.
**«Desinformation» ist so ein brisantes Thema.** Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur [Ukraine](https://transition-news.org/spip.php?recherche=ukraine\&page=recherche_wall), zum [Klima](https://transition-news.org/spip.php?recherche=klima\&page=recherche_wall), zu [Gesundheitsthemen](https://transition-news.org/spip.php?recherche=impfung\&page=recherche_wall) oder zur [Migration](https://transition-news.org/spip.php?recherche=migration\&page=recherche_wall). Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung.
**Freiheit bedingt Eigenverantwortung, ohne Zweifel.** Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung.
**Sind viele Menschen möglicherweise schon so «eingenordet»,** dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen [Hacker-Kongress](https://transition-news.org/der-38-kongress-des-chaos-computer-clubs-bot-mehr-enthullungen-als-nur-die) des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative.
**Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination?** Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter.
***
Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/kann-es-sein-dass-die-menschen-gar-keine-freiheit-wollen)*** erschienen.
-

@ 3e6e0735:9e95c8a2
2025-03-28 23:58:02
https://i.nostr.build/lanoHI3p2aCKRZlV.png
I’ve been thinking a lot lately about why Bitcoin still feels so misunderstood. Not just by the media or the IMF — that part’s predictable. But even inside our own circles, something's missing.
We say it’s money. We say it’s freedom. We say it’s code. And it is. But when you really zoom out, past the price and the politics, it’s something more radical than we usually admit.
Bitcoin is a shift in how power moves. And what we do with that power now actually matters.
## The noise outside
Let’s start with the obvious: the media still doesn’t get it. Every other headline is either a death knell or a celebration depending on the price that day. No context. No nuance. No understanding of what we’re building.
You’ve seen the headlines:
- “Bitcoin is crashing again.”
- “Crypto bros are killing the planet.”
- “The IMF warns: Bitcoin adoption is dangerous.”
Yeah? Dangerous to what?
The system they control. The levers they pull. The old game where the house always wins.
That’s why they’re afraid. Not because Bitcoin is volatile, but because it doesn’t ask permission.
## This isn’t about panic — it’s about patterns
I’m not saying there’s a conspiracy. But there is inertia. Institutions protect themselves. Systems reinforce themselves. They were never going to roll out the red carpet for an open, borderless network that replaces their function.
So the IMF calls it a threat. Central banks scramble to launch CBDCs. And journalists keep writing the same shallow takes while ignoring the real story.
Meanwhile, we’re still here. Still building. Still holding. Still running nodes.
Bitcoin isn’t perfect. But it’s honest. It doesn’t bend to popularity or political pressure. It enforces rules with math, not people. And that’s exactly why it works.
## Even we miss it sometimes
Here’s the part that really hit me recently: even within Bitcoin, we often undersell what this is.
We talk about savings. Inflation. Fiat debasement. All real, all important.
But what about the broader layer? What about governance? Energy? Communication? Defense?
Jason Lowery’s book *Softwar* lit that fuse for me again. Not because it’s flawless — it’s not. But because he reframed the game.
Bitcoin isn’t a new weapon. It’s the **end** of weapons-as-power.
Proof-of-work, in Lowery’s view, is a form of peaceful negotiation. A deterrent against coercion. A way to shift from kinetic violence to computational resolution.
Most people — even many Bitcoiners — haven’t fully absorbed that.
It’s not about militarizing the network. It’s about **demilitarizing the world** through energy expenditure that replaces human conflict.
Let’s be clear: this doesn’t mean Bitcoin *will* be used this way. It means it *can*. And that opens up a few possible futures:
- **Scenario A:** Smaller nations adopt Bitcoin infrastructure as a shield — a deterrent and neutral layer to build sovereignty
- **Scenario B:** Superpowers attack mining and self-custody, escalating regulatory capture and fragmenting the open protocol into corporate silos
- **Scenario C:** Bitcoin becomes the boring backend of legacy finance, its edge neutered by ETFs and custody-as-a-service
Which one wins depends on what we build — and who steps up.
## Then I found Maya
I came across Maya Parbhoe’s campaign by accident. One of those late-night rabbit holes where Bitcoin Twitter turns into a global map.
She’s running for president of Suriname. She’s a Bitcoiner. And she’s not just tweeting about it — she’s building an entire political platform around it.
No central bank. Bitcoin as legal tender. Full fiscal transparency. Open-source government.
Yeah. You read that right. Not just open-source software — open-source statehood.
Her father was murdered after exposing corruption. That’s not a talking point. That’s real-life consequence. And instead of running away from systems, she’s choosing to redesign one.
That’s maximalism. Not in ideology. In action.
## The El Salvador experiment — and evolution
When El Salvador made Bitcoin legal tender in 2021, it lit up our feeds. It was bold. Unprecedented. A true first.
But not without flaws.
The rollout was fast. Chivo wallet was centralized. Adoption stalled in rural areas. Transparency was thin. And despite the brave move, the state’s underlying structure remained top-down.
Bukele played offense, but the protocol was wrapped in traditional power.
Maya is doing it differently. Her approach is grassroots-forward. Open-source by design. Focused on education, transparency, and modular state-building — not just mandates.
She’s not using Bitcoin to *prop up* state power. She’s using it to *distribute* it.
## Maximalism is evolving
Look, I get it. The memes are fun. The laser eyes. The beefsteak meetups. The HODL culture.
But there’s something else growing here. Something a little quieter, a little deeper:
- People running nodes to protect civil liberties
- Communities using Lightning for real commerce
- Builders forging tools for self-sovereign identity
- Leaders like Maya testing what Bitcoin can look like as public infrastructure
This is happening. In real time. It’s messy and fragile and still small. But it’s happening.
Let’s also stay honest:
Maximalism has its risks. Dogma can blind us. Toxicity can push people away. And if we’re not careful, we’ll replace one centralization with another — just wearing different memes.
We need less purity, more principles. Less hype, more clarity. That’s the kind of maximalism Maya embodies.
## What now?
Maya doesn’t have a VC fund or an ad agency. She has a message, a mission, and the courage to put Bitcoin on the ballot.
If that resonates, help her. Not just by donating — though here’s the link:
[https://geyser.fund/project/maya2025
](https://geyser.fund/project/maya2025)
But by sharing. Writing. Talking. Translating. Connecting.
Bitcoin is still early. But it’s not abstract anymore.
This isn’t just theory.
It’s a protocol, sure.
But now, maybe it’s a presidency too.
https://i.nostr.build/0luYy8ojK7gkxsuL.png
-

@ a95c6243:d345522c
2025-01-01 17:39:51
**Heute möchte ich ein Gedicht mit euch teilen.** Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden.
**Dem originalen Titel «Die Uhr»** habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension.
**Das Ticken der Uhr und die Momente des Glücks und der Trauer** stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram.
**Was den Takt pocht, ist durchaus auch das Herz,** unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.»
*Ich trage, wo ich gehe, stets eine Uhr bei mir;* \
*Wieviel es geschlagen habe, genau seh ich an ihr.* \
*Es ist ein großer Meister, der künstlich ihr Werk gefügt,* \
*Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.*  
*Ich wollte, sie wäre rascher gegangen an manchem Tag;* *\
Ich wollte, sie hätte manchmal verzögert den raschen Schlag.* *\
In meinen Leiden und Freuden, in Sturm und in der Ruh,* *\
Was immer geschah im Leben, sie pochte den Takt dazu.*  
*Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr,* *\
Sie schlug am Morgen der Liebe, sie schlug am Traualtar.* *\
Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft,* *\
Wenn bessere Tage kommen, wie meine Seele es hofft.*  
*Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf,* *\
So zog der Meister immer großmütig sie wieder auf.* *\
Doch stände sie einmal stille, dann wär's um sie geschehn,* *\
Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.*  
*Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit,* *\
Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit!* *\
Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn:* *\
Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.*  
*Johann Gabriel Seidl (1804-1875)*
-

@ 7d33ba57:1b82db35
2025-03-28 22:14:24
Preko is a charming seaside town on Ugljan Island, just a short ferry ride from Zadar. Known for its beautiful beaches, relaxed atmosphere, and stunning views of the Adriatic, it's the perfect place to experience authentic Dalmatian island life.

## **🌊 Top Things to See & Do in Preko**
### **1️⃣ Swim at Jaz Beach 🏖️**
- A **Blue Flag beach** with **clear turquoise waters and soft pebbles**.
- Ideal for **families** thanks to its shallow waters.
- Nearby **cafés and restaurants** make it a great spot to spend the day.
### **2️⃣ Visit the Islet of Galevac 🏝️**
- A **tiny island just 80 meters from Preko**, reachable by swimming or a short boat ride.
- Home to a **15th-century Franciscan monastery**, surrounded by lush greenery.
- A **peaceful retreat**, perfect for relaxation.

### **3️⃣ Hike to St. Michael’s Fortress (Sv. Mihovil) 🏰**
- A **medieval fortress from the 13th century** with **breathtaking panoramic views**.
- Overlooks **Zadar, Kornati Islands, and the Adriatic Sea**.
- A **1-hour scenic hike** from Preko or accessible by **bike or car**.
### **4️⃣ Explore the Local Taverns & Seafood Restaurants 🍽️**
- Try **fresh seafood, octopus salad, and Dalmatian peka (slow-cooked meat & vegetables)**.
- **Best spots:** Konoba Roko (authentic seafood) & Vile Dalmacija (beachfront dining).
### **5️⃣ Rent a Bike or Scooter 🚲**
- Explore **Ugljan Island’s olive groves, hidden coves, and coastal paths**.
- Visit nearby villages like **Kali and Kukljica** for more local charm.

### **6️⃣ Take a Day Trip to Zadar ⛵**
- Just **25 minutes by ferry**, Zadar offers **historic landmarks, the Sea Organ, and Roman ruins**.
- Perfect for a cultural excursion before returning to the peaceful island.

## **🚗 How to Get to Preko**
🚢 **By Ferry:**
- **From Zadar:** Regular ferries (Jadrolinija) take **~25 minutes**.
🚘 **By Car:**
- If driving, take the **ferry from Zadar to Preko** and explore the island.
🚴 **By Bike:**
- Many visitors rent bikes to explore Ugljan Island’s coastal roads.

## **💡 Tips for Visiting Preko**
✅ **Best time to visit?** **May–September** for warm weather & swimming 🌞
✅ **Ferry schedules** – Check times in advance, especially in the off-season ⏳
✅ **Bring cash** – Some smaller taverns and cafés may not accept cards 💰
✅ **Stay for sunset** – The views over Zadar from Preko’s waterfront are stunning 🌅
Would you like **hotel recommendations, hidden beaches, or other island activities**? 😊
-

@ f9cf4e94:96abc355
2024-12-31 20:18:59
Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( [dominictarr]( https://github.com/dominictarr/scuttlebutt) ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt ([ssb]( https://github.com/ssbc/ssb-db)) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
> Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( [fonte]( https://twitter.com/IntEtymology/status/998879578851508224) )
Dominic descobriu o termo boato em um [artigo de pesquisa]( https://www.cs.cornell.edu/home/rvr/papers/flowgossip.pdf) que leu.
Em sistemas distribuídos, [fofocar]( https://en.wikipedia.org/wiki/Gossip_protocol) é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
**Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto.** **Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar.** Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário [de bordo]( https://en.wikipedia.org/wiki/Logbook) (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. **Cada item adicionado a um log do usuário é chamado de mensagem.**
**Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
**Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.**
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
## Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor [ssb]( https://github.com/ssbc/ssb-server) ), mas também é conhecido como “Scuttlebot” e `sbot`na linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.
**Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
**Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.**
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
## Pubs - Hubs
### Pubs públicos
| Pub Name | Operator | Invite Code |
| ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ |
| `scuttle.us` | [@Ryan]( https://keybase.io/ryan_singer) | `scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=` |
| [pub1.upsocial.com]( https://upsocial.com/) | [@freedomrules]( https://github.com/freedomrules) | `pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=` |
| [Monero Pub]( https://xmr-pub.net/) | [@Denis]( https://github.com/Orville2112) | `xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=` |
| [FreeSocial]( https://freesocial.co/) | [@Jarland]( https://github.com/mxroute) | `pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=` |
| `ssb.vpn.net.br` | [@coffeverton]( https://about.me/coffeverton) | `ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=` |
| [gossip.noisebridge.info]( https://www.noisebridge.net/wiki/Pub) | [Noisebridge Hackerspace]( https://www.noisebridge.net/wiki/Unicorn) [@james.network]( https://james.network/) | `gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=` |
### Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact |
| --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- |
| `many.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) |
| `one.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) |
| `ssb.mikey.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) |
| [ssb.celehner.com]( https://ssb.celehner.com/) | [@cel]( https://github.com/ssbc/ssb-server/wiki/@f/6sQ6d2CMxRUhLpspgGIulDxDCwYD7DzFzPNr7u5AU=.ed25519) | [cel@celehner.com](mailto:cel@celehner.com) |
### Pubs muito grandes
 *Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)* 
| Pub Name | Operator | Invite Code |
| --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ |
| `scuttlebutt.de` | [SolSoCoG]( https://solsocog.de/impressum) | `scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=` |
| `Lohn's Pub` | [@lohn]( https://github.com/lohn) | `p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=` |
| [Scuttle Space]( https://scuttle.space/) | [@guil-dot]( https://github.com/guil-dot) | Visit [scuttle.space]( https://scuttle.space/) |
| `SSB PeerNet US-East` | [timjrobinson]( https://github.com/timjrobinson) | `us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=` |
| Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |
## GUI - Interface Gráfica do Utilizador(Usuário)
### Patchwork - Uma GUI SSB (Descontinuado)
[**Patchwork**]( https://github.com/ssbc/patchwork) **é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB** . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: [scuttlebutt.nz]( https://www.scuttlebutt.nz/getting-started)
**Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub.** Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
### Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que [Patchwork]( https://github.com/ssbc/patchwork) e [Patchfoo]( https://github.com/ssbc/patchfoo) , então você pode facilmente dar uma volta com sua identidade existente.

### Planetary - GUI para IOS

[Planetary]( https://apps.apple.com/us/app/planetary-app/id1481617318) é um app com pubs pré-carregados para facilitar integração.
### Manyverse - GUI para Android

[Manyverse]( https://www.manyver.se/) é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
## Fontes
* https://scuttlebot.io/
* https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
* https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
* [**Secure Scuttlebutt**]( http://ssbc.github.io/secure-scuttlebutt/) **:** um protocolo de banco de dados global.
-

@ f9cf4e94:96abc355
2024-12-30 19:02:32
Na era das grandes navegações, piratas ingleses eram autorizados pelo governo para roubar navios.
A única coisa que diferenciava um pirata comum de um corsário é que o último possuía a “Carta do Corso”, que funcionava como um “Alvará para o roubo”, onde o governo Inglês legitimava o roubo de navios por parte dos corsários. É claro, que em troca ele exigia uma parte da espoliação.
Bastante similar com a maneira que a Receita Federal atua, não? Na verdade, o caso é ainda pior, pois o governo fica com toda a riqueza espoliada, e apenas repassa um mísero salário para os corsários modernos, os agentes da receita federal.
Porém eles “justificam” esse roubo ao chamá-lo de imposto, e isso parece acalmar os ânimos de grande parte da população, mas não de nós.
Não é por acaso que 'imposto' é o particípio passado do verbo 'impor'. Ou seja, é aquilo que resulta do cumprimento obrigatório -- e não voluntário -- de todos os cidadãos. Se não for 'imposto' ninguém paga. Nem mesmo seus defensores. Isso mostra o quanto as pessoas realmente apreciam os serviços do estado.
Apenas volte um pouco na história: os primeiros pagadores de impostos eram fazendeiros cujos territórios foram invadidos por nômades que pastoreavam seu gado. Esses invasores nômades forçavam os fazendeiros a lhes pagar uma fatia de sua renda em troca de "proteção". O fazendeiro que não concordasse era assassinado.
Os nômades perceberam que era muito mais interessante e confortável apenas cobrar uma taxa de proteção em vez de matar o fazendeiro e assumir suas posses. Cobrando uma taxa, eles obtinham o que necessitavam. Já se matassem os fazendeiros, eles teriam de gerenciar por conta própria toda a produção da fazenda.
Daí eles entenderam que, ao não assassinarem todos os fazendeiros que encontrassem pelo caminho, poderiam fazer desta prática um modo de vida.
Assim nasceu o governo.
Não assassinar pessoas foi o primeiro serviço que o governo forneceu. Como temos sorte em ter à nossa disposição esta instituição!
Assim, não deixa de ser curioso que algumas pessoas digam que os impostos são pagos basicamente para impedir que aconteça exatamente aquilo que originou a existência do governo. O governo nasceu da extorsão. Os fazendeiros tinham de pagar um "arrego" para seu governo. Caso contrário, eram assassinados.
Quem era a real ameaça? O governo. A máfia faz a mesma coisa.
Mas existe uma forma de se proteger desses corsários modernos. Atualmente, existe uma propriedade privada que NINGUÉM pode tirar de você, ela é sua até mesmo depois da morte. É claro que estamos falando do Bitcoin. Fazendo as configurações certas, é impossível saber que você tem bitcoin. Nem mesmo o governo americano consegue saber.
#brasil #bitcoinbrasil #nostrbrasil #grownostr #bitcoin
-

@ 7d33ba57:1b82db35
2025-03-28 20:59:51
Krka National Park, located in central Dalmatia, is one of Croatia’s most breathtaking natural wonders. Famous for its stunning waterfalls, crystal-clear lakes, and lush forests, the park is a must-visit for nature lovers. Unlike Plitvice Lakes, Krka allows swimming in certain areas, making it a perfect summer escape.

## **🌊 Top Things to See & Do in Krka National Park**
### **1️⃣ Skradinski Buk Waterfall 💦**
- The **largest and most famous waterfall** in the park, with **cascading pools and wooden walkways**.
- You **used to be able to swim here**, but since 2021, swimming is no longer allowed.
- Perfect for **photography and picnics**.
### **2️⃣ Roški Slap Waterfall 🌿**
- A **less crowded but equally beautiful** series of waterfalls.
- Known for its **"necklace" of small cascades** leading into the main fall.
- Nearby **Mlinica**, a restored **watermill**, shows traditional Croatian life.
### **3️⃣ Visovac Island & Monastery 🏝️**
- A **tiny island** in the middle of the Krka River, home to a **Franciscan monastery** from the 15th century.
- Accessible by **boat tour** from Skradinski Buk or Roški Slap.
- A peaceful, scenic spot with **stunning views of the lake**.

### **4️⃣ Krka Monastery 🏛️**
- A **Serbian Orthodox monastery** hidden deep in the park.
- Built on **ancient Roman catacombs**, which you can explore.
- A **quiet, spiritual place**, often overlooked by tourists.
### **5️⃣ Hike & Walk the Nature Trails 🥾**
- The park has **several well-marked trails** through forests, waterfalls, and lakes.
- Wooden walkways allow **easy access** to the main sights.
- **Wildlife spotting**: Look out for **otters, turtles, and over 200 bird species**!
### **6️⃣ Swim at Skradin Beach 🏖️**
- While you can’t swim at Skradinski Buk anymore, **Skradin Beach**, just outside the park, is a great spot for a dip.
- **Kayaking and boat tours** available.

## **🚗 How to Get to Krka National Park**
✈️ **By Air:** The nearest airport is **Split (SPU), 1 hour away**.
🚘 **By Car:**
- **Split to Krka:** ~1 hour (85 km)
- **Zadar to Krka:** ~1 hour (75 km)
- **Dubrovnik to Krka:** ~3.5 hours (280 km)
🚌 **By Bus:** Direct buses from **Split, Zadar, and Šibenik** to the park’s entrances.
🚢 **By Boat:** From **Skradin**, you can take a **boat ride** into the park.

## **💡 Tips for Visiting Krka National Park**
✅ **Best time to visit?** **Spring & early autumn (April–June, September–October)** – Fewer crowds & mild weather 🍃
✅ **Start early!** **Arrive before 10 AM** to avoid crowds, especially in summer ☀️
✅ **Bring water & snacks** – Limited food options inside the park 🍎
✅ **Wear comfy shoes** – Wooden walkways & trails can be slippery 👟
✅ **Take a boat tour** – The best way to see Visovac Island & hidden spots ⛵
✅ **Buy tickets online** – Save time at the entrance 🎟️

-

@ a95c6243:d345522c
2024-12-21 09:54:49
Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde.
Heute ist ein ganz besonderer Tag: die **Wintersonnenwende**. Genau gesagt hat [heute morgen](https://www.timeanddate.de/astronomie/wintersonnenwende) um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben.
Für mich ist dieses Ereignis immer wieder etwas kurios: **Es beginnt der Winter, aber die Tage werden länger.** Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller!
Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr [vorgesehen](https://web.archive.org/web/20231202175946/https://www.spiegel.de/wissenschaft/mensch/winter-ade-nie-wieder-schnee-a-71456.html). Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt [lahmgelegt](https://web.archive.org/web/20231207014311/https://www.dw.com/de/nach-dem-schnee-in-deutschland-und-dem-chaos-am-flughafen-und-bei-der-bahn-ein-winteralptraum/a-67638141).
Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert.
Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. **Ohne Licht keine Farben**, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität.
Mir gefällt aber auch die **Symbolik dieses Tages**: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie.
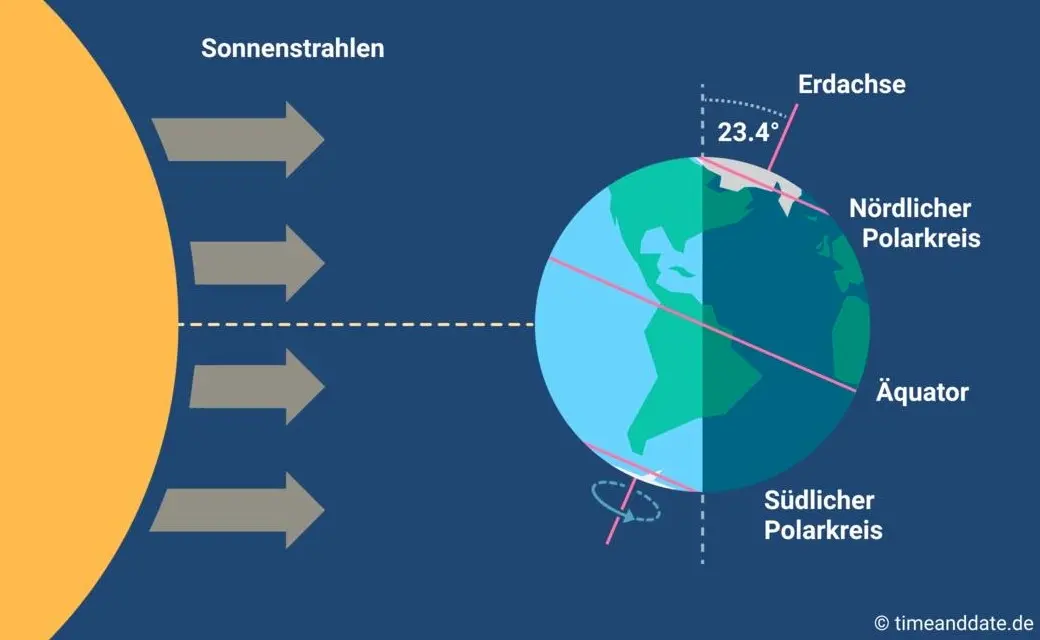
Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell?
Insofern bleibt eindeutig festzuhalten, dass “**schräg sein**” ein willkommener, wichtiger und positiver Wert ist. Mit [anderen](https://www.dwds.de/wb/schr%C3%A4g) Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein.
**In diesem Sinne wünsche ich euch allen urige Weihnachtstage!**
***
Dieser Beitrag ist letztes Jahr in meiner *[Denkbar](https://denkbar.substack.com/p/ab-jetzt-gehts-bergauf)* erschienen.
-

@ 0d6c8388:46488a33
2025-03-28 16:24:00
Huge thank you to [OpenSats for the grant](https://opensats.org/blog/10th-wave-of-nostr-grants) to work on [Hypernote this year](https://www.hypernote.club/)! I thought I'd take this opportunity to try and share my thought processes for Hypernote. If this all sounds very dense or irrelevant to you I'm sorry!
===
How can the ideas of "hypermedia" benefit nostr? That's the goal of hypernote. To take the best ideas from "hypertext" and "hypercard" and "hypermedia systems" and apply them to nostr in a specifically nostr-ey way.
### 1. What do we mean by hypermedia
A hypermedia document embeds the methods of interaction (links, forms, and buttons are the most well-known hypermedia controls) within the document itself. It's including the _how_ with the _what_.
This is how the old web worked. An HTML page was delivered to the web browser, and it included in it a link or perhaps a form that could be submitted to obtain a new, different HTML page. This is how the whole web worked early on! Forums and GeoCities and eBay and MySpace and Yahoo! and Amazon and Google all emerged inside this paradigm.
A web browser in this paradigm was a "thin" client which rendered the "thick" application defined in the HTML (and, implicitly, was defined by the server that would serve that HTML).
Contrast this with modern app development, where the _what_ is usually delivered in the form of JSON, and then HTML combined with JavaScript (React, Svelte, Angular, Vue, etc.) is devised to render that JSON as a meaningful piece of hypermedia within the actual browser, the _how_.
The browser remains a "thin" client in this scenario, but now the application is delivered in two stages: a client application of HTML and JavaScript, and then the actual JSON data that will hydrate that "application".
(Aside: it's interesting how much "thicker" the browser has had to become to support this newer paradigm!)
Nostr was obviously built in line with the modern paradigm: nostr "clients" (written in React or Svelte or as mobile apps) define the _how_ of reading and creating nostr events, while nostr events themselves (JSON data) simply describe the _what_.
And so the goal with Hypernote is to square this circle somehow: nostr currently delivers JSON _what_, how do we deliver the _how_ with nostr as well. Is that even possible?
### 2. Hypernote's design assumptions
Hypernote assumes that hypermedia over nostr is a good idea! I'm expecting some joyful renaissance of app expression similar to that of the web once we figure out how to express applications in a truly "nostr" way.
Hypernote was also [deeply inspired by HTMX](https://hypermedia.systems/hypermedia-a-reintroduction/), so it assumes that building web apps in the HTMX style is a good idea. The HTMX insight is that instead of shipping rich scripting along with your app, you could simply make HTML a _tiny_ bit more expressive and get 95% of what most apps need. HTMX's additions to the HTML language are designed to be as minimal and composable as possible, and Hypernote should have the same aims.
Hypernote also assumes that the "design" of nostr will remain fluid and anarchic for years to come. There will be no "canonical" list of "required" NIPs that we'll have "consensus" on in order to build stable UIs on top of. Hypernote will need to be built responsive to nostr's moods and seasons, rather than one holy spec.
Hypernote likes the `nak` command line tool. Hypernote likes markdown. Hypernote likes Tailwind CSS. Hypernote likes SolidJS. Hypernote likes cold brew coffee. Hypernote is, to be perfectly honest, my aesthetic preferences applied to my perception of an opportunity in the nostr ecosystem.
### 3. "What's a hypernote?"
Great question. I'm still figuring this out. Everything right now is subject to change in order to make sure hypernote serves its intended purpose.
But here's where things currently stand:
A hypernote is a flat list of "Hypernote Elements". A Hypernote Element is composed of:
1. CONTENT. Static or dynamic content. (the what)
2. LOGIC. Filters and events (the how)
3. STYLE. Optional, inline style information specific to this element's content.
In the most basic example of a [hypernote story](https://hypernote-stories.fly.dev/), here's a lone "edit me" in the middle of the canvas:

```
{
"id": "fb4aaed4-bf95-4353-a5e1-0bb64525c08f",
"type": "text",
"text": "edit me",
"x": 540,
"y": 960,
"size": "md",
"color": "black"
}
```
As you can see, it has no logic, but it does have some content (the text "edit me") and style (the position, size, and color).
Here's a "sticker" that displays a note:
```
{
"id": "2cd1ef51-3356-408d-b10d-2502cbb8014e",
"type": "sticker",
"stickerType": "note",
"filter": {
"kinds": [
1
],
"ids": [
"92de77507a361ab2e20385d98ff00565aaf3f80cf2b6d89c0343e08166fed931"
],
"limit": 1
},
"accessors": [
"content",
"pubkey",
"created_at"
],
"x": 540,
"y": 960,
"associatedData": {}
}
```
As you can see, it's kind of a mess! The content and styling and underdeveloped for this "sticker", but at least it demonstrates some "logic": a nostr filter for getting its data.
Here's another sticker, this one displays a form that the user can interact with to SEND a note. Very hyper of us!
```
{
"id": "42240d75-e998-4067-b8fa-9ee096365663",
"type": "sticker",
"stickerType": "prompt",
"filter": {},
"accessors": [],
"x": 540,
"y": 960,
"associatedData": {
"promptText": "What's your favorite color?"
},
"methods": {
"comment": {
"description": "comment",
"eventTemplate": {
"kind": 1111,
"content": "${content}",
"tags": [
[
"E",
"${eventId}",
"",
"${pubkey}"
],
[
"K",
"${eventKind}"
],
[
"P",
"${pubkey}"
],
[
"e",
"${eventId}",
"",
"${pubkey}"
],
[
"k",
"${eventKind}"
],
[
"p",
"${pubkey}"
]
]
}
}
}
}
```
It's also a mess, but it demos the other part of "logic": methods which produce new events.
This is the total surface of hypernote, ideally! Static or dynamic content, simple inline styles, and logic for fetching and producing events.
I'm calling it "logic" but it's purposfully not a whole scripting language. At most we'll have some sort of `jq`-like language for destructing the relevant piece of data we want.
My ideal syntax for a hypernote as a developer will look something like
```foo.hypernote
Nak-like logic
Markdown-like content
CSS-like styles
```
But with JSON as the compile target, this can just be my own preference, there can be other (likely better!) ways of authoring this content, such as a Hypernote Stories GUI.
### The end
I know this is all still vague but I wanted to get some ideas out in the wild so people understand the through line of my different Hypernote experiments. I want to get the right amount of "expressivity" in Hypernote before it gets locked down into one spec. My hunch is it can be VERY expressive while remaining simple and also while not needing a whole scripting language bolted onto it. If I can't pull it off I'll let you know.
-

@ a95c6243:d345522c
2024-12-13 19:30:32
*Das Betriebsklima ist das einzige Klima,* \
*das du selbst bestimmen kannst.* \
*Anonym*
**Eine Strategie zur Anpassung an den Klimawandel** hat das deutsche Bundeskabinett diese Woche [beschlossen](https://www.bundesregierung.de/breg-de/aktuelles/klimaanpassungsstrategie-2024-2324828). Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das. 
**Für die «Vorsorge vor Klimafolgen» habe man nun erstmals** klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der [Erwärmung](https://transition-news.org/studie-ozeane-kuhlen-die-erde-viel-starker-als-gedacht) ja bekanntermaßen so eine Sache.
**Die Zunahme schwerer Unwetterereignisse habe gezeigt,** so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben.
**Die** ***ARD*** **spurt wie gewohnt** und setzt die Botschaft zielsicher um. Der Artikel [beginnt](https://www.tagesschau.de/inland/innenpolitik/klima-anpassung-warnapp-100.html) folgendermaßen:
> «Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.»
**Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen»** vom Zentrum KlimaAnpassung [unterstützt](https://zentrum-klimaanpassung.de/ueber-uns), schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für [Smart City-Projekte](https://difu.de/taxonomy/term/2083) engagiert, und die Adelphi Consult GmbH beauftragt.
**Adelphi** **[beschreibt](https://adelphi.de/de)** **sich selbst als «Europas führender Think-and-Do-Tank** und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg\*innen und weltverbessernde Berater\*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere.
**Über die** **[Warn-App](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/warn-app-nina_node.html)** **mit dem niedlichen Namen Nina,** die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche.
**Beim BBK erfahren wir auch einiges über die empfohlenen** **[Systemeinstellungen](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/Einstellungen-Android/einstellungen-android_node.html)** für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden.
**Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann** als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen [Valencia](https://transition-news.org/valencia-zehn-tage-nach-der-katastrophe-warten-viele-menschen-immer-noch-auf) gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat.
***
Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/vorsorge-vor-klimafolgen)* erschienen.
 @ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2>
@ b9f4c34d:7d1a0e31
2025-04-02 15:00:20<h2> Test Video Document </h2> @ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p>
@ b9f4c34d:7d1a0e31
2025-04-02 14:59:02<h1> Testy McTestenface </h1> <p> It's been so long, html </p> @ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/
@ 39cc53c9:27168656
2025-03-30 05:54:53> [Read the original blog post](https://blog.kycnot.me/p/kyc-no-thanks) Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations. Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms. ## Rights for Illusions KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks? The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors." However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% [^1] – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service. Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy. To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% [^1] of less-than-careful criminals. ## KYC? Not you. > KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. [^2] KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible. For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded. Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether. It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms. ## You're not welcome Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right? This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to. Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely. ## Your identity has been stolen KYC data has been found to be for sale on many dark net markets[^3]. Exchanges may have leaks or hacks, and such leaks contain **very** sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it? As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. [^3] In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised. ## (they) Know Your Coins You may already know that **Bitcoin and most cryptocurrencies have a transparent public blockchain**, meaning that all data is shown unencrypted for everyone to see and recorded **forever**. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced. If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with. ## Conclusions To sum up, **KYC does not protect individuals**; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred. The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies. The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable. > Edited 20/03/2024 > * Add reference to the 1% statement on [Rights for Illusions](#rights-for-illusions) section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity [^1] [^1]: https://www.chainalysis.com/blog/2024-crypto-crime-report-introduction/ [^2]: https://old.reddit.com/r/BitcoinBeginners/comments/k2bve1/is_kyc_bad_if_so_why/gdtc8kz [^3]: https://www.ccn.com/hacked-customer-data-from-world-leading-cryptocurrency-exchanges-for-sale-on-the-dark-web/ @ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all. That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission. As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently. Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive. Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally. The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match. When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol. Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit. @ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay.
@ b2d670de:907f9d4a
2025-03-25 20:17:57This guide will walk you through setting up your own Strfry Nostr relay on a Debian/Ubuntu server and making it accessible exclusively as a TOR hidden service. By the end, you'll have a privacy-focused relay that operates entirely within the TOR network, enhancing both your privacy and that of your users. ## Table of Contents 1. Prerequisites 2. Initial Server Setup 3. Installing Strfry Nostr Relay 4. Configuring Your Relay 5. Setting Up TOR 6. Making Your Relay Available on TOR 7. Testing Your Setup] 8. Maintenance and Security 9. Troubleshooting ## Prerequisites - A Debian or Ubuntu server - Basic familiarity with command line operations (most steps are explained in detail) - Root or sudo access to your server ## Initial Server Setup First, let's make sure your server is properly set up and secured. ### Update Your System Connect to your server via SSH and update your system: ```bash sudo apt update sudo apt upgrade -y ``` ### Set Up a Basic Firewall Install and configure a basic firewall: ```bash sudo apt install ufw -y sudo ufw allow ssh sudo ufw enable ``` This allows SSH connections while blocking other ports for security. ## Installing Strfry Nostr Relay This guide includes the full range of steps needed to build and set up Strfry. It's simply based on the current version of the `DEPLOYMENT.md` document in the Strfry GitHub repository. If the build/setup process is changed in the repo, this document could get outdated. If so, please report to me that something is outdated and check for updated steps [here](https://github.com/hoytech/strfry/blob/master/docs/DEPLOYMENT.md). ### Install Dependencies First, let's install the necessary dependencies. Each package serves a specific purpose in building and running Strfry: ```bash sudo apt install -y git build-essential libyaml-perl libtemplate-perl libregexp-grammars-perl libssl-dev zlib1g-dev liblmdb-dev libflatbuffers-dev libsecp256k1-dev libzstd-dev ``` Here's why each dependency is needed: **Basic Development Tools:** - `git`: Version control system used to clone the Strfry repository and manage code updates - `build-essential`: Meta-package that includes compilers (gcc, g++), make, and other essential build tools **Perl Dependencies** (used for Strfry's build scripts): - `libyaml-perl`: Perl interface to parse YAML configuration files - `libtemplate-perl`: Template processing system used during the build process - `libregexp-grammars-perl`: Advanced regular expression handling for Perl scripts **Core Libraries for Strfry:** - `libssl-dev`: Development files for OpenSSL, used for secure connections and cryptographic operations - `zlib1g-dev`: Compression library that Strfry uses to reduce data size - `liblmdb-dev`: Lightning Memory-Mapped Database library, which Strfry uses for its high-performance database backend - `libflatbuffers-dev`: Memory-efficient serialization library for structured data - `libsecp256k1-dev`: Optimized C library for EC operations on curve secp256k1, essential for Nostr's cryptographic signatures - `libzstd-dev`: Fast real-time compression algorithm for efficient data storage and transmission ### Clone and Build Strfry Clone the Strfry repository: ```bash git clone https://github.com/hoytech/strfry.git cd strfry ``` Build Strfry: ```bash git submodule update --init make setup-golpe make -j2 # This uses 2 CPU cores. Adjust based on your server (e.g., -j4 for 4 cores) ``` This build process will take several minutes, especially on servers with limited CPU resources, so go get a coffee and post some great memes on nostr in the meantime. ### Install Strfry Install the Strfry binary to your system path: ```bash sudo cp strfry /usr/local/bin ``` This makes the `strfry` command available system-wide, allowing it to be executed from any directory and by any user with the appropriate permissions. ## Configuring Your Relay ### Create Strfry User Create a dedicated user for running Strfry. This enhances security by isolating the relay process: ```bash sudo useradd -M -s /usr/sbin/nologin strfry ``` The `-M` flag prevents creating a home directory, and `-s /usr/sbin/nologin` prevents anyone from logging in as this user. This is a security best practice for service accounts. ### Create Data Directory Create a directory for Strfry's data: ```bash sudo mkdir /var/lib/strfry sudo chown strfry:strfry /var/lib/strfry sudo chmod 755 /var/lib/strfry ``` This creates a dedicated directory for Strfry's database and sets the appropriate permissions so that only the strfry user can write to it. ### Configure Strfry Copy the sample configuration file: ```bash sudo cp strfry.conf /etc/strfry.conf ``` Edit the configuration file: ```bash sudo nano /etc/strfry.conf ``` Modify the database path: ``` # Find this line: db = "./strfry-db/" # Change it to: db = "/var/lib/strfry/" ``` Check your system's hard limit for file descriptors: ```bash ulimit -Hn ``` Update the `nofiles` setting in your configuration to match this value (or set to 0): ``` # Add or modify this line in the config (example if your limit is 524288): nofiles = 524288 ``` The `nofiles` setting determines how many open files Strfry can have simultaneously. Setting it to your system's hard limit (or 0 to use the system default) helps prevent "too many open files" errors if your relay becomes popular. You might also want to customize your relay's information in the config file. Look for the `info` section and update it with your relay's name, description, and other details. Set ownership of the configuration file: ```bash sudo chown strfry:strfry /etc/strfry.conf ``` ### Create Systemd Service Create a systemd service file for managing Strfry: ```bash sudo nano /etc/systemd/system/strfry.service ``` Add the following content: ```ini [Unit] Description=strfry relay service [Service] User=strfry ExecStart=/usr/local/bin/strfry relay Restart=on-failure RestartSec=5 ProtectHome=yes NoNewPrivileges=yes ProtectSystem=full LimitCORE=1000000000 [Install] WantedBy=multi-user.target ``` This systemd service configuration: - Runs Strfry as the dedicated strfry user - Automatically restarts the service if it fails - Implements security measures like `ProtectHome` and `NoNewPrivileges` - Sets resource limits appropriate for a relay Enable and start the service: ```bash sudo systemctl enable strfry.service sudo systemctl start strfry ``` Check the service status: ```bash sudo systemctl status strfry ``` ### Verify Relay is Running Test that your relay is running locally: ```bash curl localhost:7777 ``` You should see a message indicating that the Strfry relay is running. This confirms that Strfry is properly installed and configured before we proceed to set up TOR. ## Setting Up TOR Now let's make your relay accessible as a TOR hidden service. ### Install TOR Install TOR from the package repositories: ```bash sudo apt install -y tor ``` This installs the TOR daemon that will create and manage your hidden service. ### Configure TOR Edit the TOR configuration file: ```bash sudo nano /etc/tor/torrc ``` Scroll down to wherever you see a commented out part like this: ``` #HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80 ``` Under those lines, add the following lines to set up a hidden service for your relay: ``` HiddenServiceDir /var/lib/tor/strfry-relay/ HiddenServicePort 80 127.0.0.1:7777 ``` This configuration: - Creates a hidden service directory at `/var/lib/tor/strfry-relay/` - Maps port 80 on your .onion address to port 7777 on your local machine - Keeps all traffic encrypted within the TOR network Create the directory for your hidden service: ```bash sudo mkdir -p /var/lib/tor/strfry-relay/ sudo chown debian-tor:debian-tor /var/lib/tor/strfry-relay/ sudo chmod 700 /var/lib/tor/strfry-relay/ ``` The strict permissions (700) are crucial for security as they ensure only the debian-tor user can access the directory containing your hidden service private keys. Restart TOR to apply changes: ```bash sudo systemctl restart tor ``` ## Making Your Relay Available on TOR ### Get Your Onion Address After restarting TOR, you can find your onion address: ```bash sudo cat /var/lib/tor/strfry-relay/hostname ``` This will output something like `abcdefghijklmnopqrstuvwxyz234567.onion`, which is your relay's unique .onion address. This is what you'll share with others to access your relay. ### Understanding Onion Addresses The .onion address is a special-format hostname that is automatically generated based on your hidden service's private key. Your users will need to use this address with the WebSocket protocol prefix to connect: `ws://youronionaddress.onion` ## Testing Your Setup ### Test with a Nostr Client The best way to test your relay is with an actual Nostr client that supports TOR: 1. Open your TOR browser 2. Go to your favorite client, either on clearnet or an onion service. - Check out [this list](https://github.com/0xtrr/onion-service-nostr-clients?tab=readme-ov-file#onion-service-nostr-clients) of nostr clients available over TOR. 3. Add your relay URL: `ws://youronionaddress.onion` to your relay list 4. Try posting a note and see if it appears on your relay - In some nostr clients, you can also click on a relay to get information about it like the relay name and description you set earlier in the stryfry config. If you're able to see the correct values for the name and the description, you were able to connect to the relay. - Some nostr clients also gives you a status on what relays a note was posted to, this could also give you an indication that your relay works as expected. Note that not all Nostr clients support TOR connections natively. Some may require additional configuration or use of TOR Browser. E.g. most mobile apps would most likely require a TOR proxy app running in the background (some have TOR support built in too). ## Maintenance and Security ### Regular Updates Keep your system, TOR, and relay updated: ```bash # Update system sudo apt update sudo apt upgrade -y # Update Strfry cd ~/strfry git pull git submodule update make -j2 sudo cp strfry /usr/local/bin sudo systemctl restart strfry # Verify TOR is still running properly sudo systemctl status tor ``` Regular updates are crucial for security, especially for TOR which may have security-critical updates. ### Database Management Strfry has built-in database management tools. Check the Strfry documentation for specific commands related to database maintenance, such as managing event retention and performing backups. ### Monitoring Logs To monitor your Strfry logs: ```bash sudo journalctl -u strfry -f ``` To check TOR logs: ```bash sudo journalctl -u tor -f ``` Monitoring logs helps you identify potential issues and understand how your relay is being used. ### Backup This is not a best practices guide on how to do backups. Preferably, backups should be stored either offline or on a different machine than your relay server. This is just a simple way on how to do it on the same server. ```bash # Stop the relay temporarily sudo systemctl stop strfry # Backup the database sudo cp -r /var/lib/strfry /path/to/backup/location # Restart the relay sudo systemctl start strfry ``` Back up your TOR hidden service private key. The private key is particularly sensitive as it defines your .onion address - losing it means losing your address permanently. If you do a backup of this, ensure that is stored in a safe place where no one else has access to it. ```bash sudo cp /var/lib/tor/strfry-relay/hs_ed25519_secret_key /path/to/secure/backup/location ``` ## Troubleshooting ### Relay Not Starting If your relay doesn't start: ```bash # Check logs sudo journalctl -u strfry -e # Verify configuration cat /etc/strfry.conf # Check permissions ls -la /var/lib/strfry ``` Common issues include: - Incorrect configuration format - Permission problems with the data directory - Port already in use (another service using port 7777) - Issues with setting the nofiles limit (setting it too big) ### TOR Hidden Service Not Working If your TOR hidden service is not accessible: ```bash # Check TOR logs sudo journalctl -u tor -e # Verify TOR is running sudo systemctl status tor # Check onion address sudo cat /var/lib/tor/strfry-relay/hostname # Verify TOR configuration sudo cat /etc/tor/torrc ``` Common TOR issues include: - Incorrect directory permissions - TOR service not running - Incorrect port mapping in torrc ### Testing Connectivity If you're having trouble connecting to your service: ```bash # Verify Strfry is listening locally sudo ss -tulpn | grep 7777 # Check that TOR is properly running sudo systemctl status tor # Test the local connection directly curl --include --no-buffer localhost:7777 ``` --- ## Privacy and Security Considerations Running a Nostr relay as a TOR hidden service provides several important privacy benefits: 1. **Network Privacy**: Traffic to your relay is encrypted and routed through the TOR network, making it difficult to determine who is connecting to your relay. 2. **Server Anonymity**: The physical location and IP address of your server are concealed, providing protection against denial-of-service attacks and other targeting. 3. **Censorship Resistance**: TOR hidden services are more resilient against censorship attempts, as they don't rely on the regular DNS system and can't be easily blocked. 4. **User Privacy**: Users connecting to your relay through TOR enjoy enhanced privacy, as their connections are also encrypted and anonymized. However, there are some important considerations: - TOR connections are typically slower than regular internet connections - Not all Nostr clients support TOR connections natively - Running a hidden service increases the importance of keeping your server secure --- Congratulations! You now have a Strfry Nostr relay running as a TOR hidden service. This setup provides a resilient, privacy-focused, and censorship-resistant communication channel that helps strengthen the Nostr network. For further customization and advanced configuration options, refer to the [Strfry documentation](https://github.com/hoytech/strfry). Consider sharing your relay's .onion address with the Nostr community to help grow the privacy-focused segment of the network! If you plan on providing a relay service that the public can use (either for free or paid for), consider adding it to [this list](https://github.com/0xtrr/onion-service-nostr-relays). Only add it if you plan to run a stable and available relay. @ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future!
@ bc52210b:20bfc6de
2025-03-25 20:17:22CISA, or Cross-Input Signature Aggregation, is a technique in Bitcoin that allows multiple signatures from different inputs in a transaction to be combined into a single, aggregated signature. This is a big deal because Bitcoin transactions often involve multiple inputs (e.g., spending from different wallet outputs), each requiring its own signature. Normally, these signatures take up space individually, but CISA compresses them into one, making transactions more efficient. This magic is possible thanks to the linearity property of Schnorr signatures, a type of digital signature introduced to Bitcoin with the Taproot upgrade. Unlike the older ECDSA signatures, Schnorr signatures have mathematical properties that allow multiple signatures to be added together into a single valid signature. Think of it like combining multiple handwritten signatures into one super-signature that still proves everyone signed off! Fun Fact: CISA was considered for inclusion in Taproot but was left out to keep the upgrade simple and manageable. Adding CISA would’ve made Taproot more complex, so the developers hit pause on it—for now. --- **CISA vs. Key Aggregation (MuSig, FROST): Don’t Get Confused!** Before we go deeper, let’s clear up a common mix-up: CISA is not the same as protocols like MuSig or FROST. Here’s why: * Signature Aggregation (CISA): Combines multiple signatures into one, each potentially tied to different public keys and messages (e.g., different transaction inputs). * Key Aggregation (MuSig, FROST): Combines multiple public keys into a single aggregated public key, then generates one signature for that key. **Key Differences:** 1. What’s Aggregated? * CISA: Aggregates signatures. * Key Aggregation: Aggregates public keys. 2. What the Verifier Needs * CISA: The verifier needs all individual public keys and their corresponding messages to check the aggregated signature. * Key Aggregation: The verifier only needs the single aggregated public key and one message. 3. When It Happens * CISA: Used during transaction signing, when inputs are being combined into a transaction. * MuSig: Used during address creation, setting up a multi-signature (multisig) address that multiple parties control. So, CISA is about shrinking signature data in a transaction, while MuSig/FROST are about simplifying multisig setups. Different tools, different jobs! --- **Two Flavors of CISA: Half-Agg and Full-Agg** CISA comes in two modes: * Full Aggregation (Full-Agg): Interactive, meaning signers need to collaborate during the signing process. (We’ll skip the details here since the query focuses on Half-Agg.) * Half Aggregation (Half-Agg): Non-interactive, meaning signers can work independently, and someone else can combine the signatures later. Since the query includes “CISA Part 2: Half Signature Aggregation,” let’s zoom in on Half-Agg. --- **Half Signature Aggregation (Half-Agg) Explained** **How It Works** Half-Agg is a non-interactive way to aggregate Schnorr signatures. Here’s the process: 1. Independent Signing: Each signer creates their own Schnorr signature for their input, without needing to talk to the other signers. 2. Aggregation Step: An aggregator (could be anyone, like a wallet or node) takes all these signatures and combines them into one aggregated signature. A Schnorr signature has two parts: * R: A random point (32 bytes). * s: A scalar value (32 bytes). In Half-Agg: * The R values from each signature are kept separate (one per input). * The s values from all signatures are combined into a single s value. **Why It Saves Space (~50%)** Let’s break down the size savings with some math: Before Aggregation: * Each Schnorr signature = 64 bytes (32 for R + 32 for s). * For n inputs: n × 64 bytes. After Half-Agg: * Keep n R values (32 bytes each) = 32 × n bytes. * Combine all s values into one = 32 bytes. * Total size: 32 × n + 32 bytes. Comparison: * Original: 64n bytes. * Half-Agg: 32n + 32 bytes. * For large n, the “+32” becomes small compared to 32n, so it’s roughly 32n, which is half of 64n. Hence, ~50% savings! **Real-World Impact:** Based on recent Bitcoin usage, Half-Agg could save: * ~19.3% in space (reducing transaction size). * ~6.9% in fees (since fees depend on transaction size). This assumes no major changes in how people use Bitcoin post-CISA. --- **Applications of Half-Agg** Half-Agg isn’t just a cool idea—it has practical uses: 1. Transaction-wide Aggregation * Combine all signatures within a single transaction. * Result: Smaller transactions, lower fees. 2. Block-wide Aggregation * Combine signatures across all transactions in a Bitcoin block. * Result: Even bigger space savings at the blockchain level. 3. Off-chain Protocols / P2P * Use Half-Agg in systems like Lightning Network gossip messages. * Benefit: Efficiency without needing miners or a Bitcoin soft fork. --- **Challenges with Half-Agg** While Half-Agg sounds awesome, it’s not without hurdles, especially at the block level: 1. Breaking Adaptor Signatures * Adaptor signatures are special signatures used in protocols like Discreet Log Contracts (DLCs) or atomic swaps. They tie a signature to revealing a secret, ensuring fair exchanges. * Aggregating signatures across a block might mess up these protocols, as the individual signatures get blended together, potentially losing the properties adaptor signatures rely on. 2. Impact on Reorg Recovery * In Bitcoin, a reorganization (reorg) happens when the blockchain switches to a different chain of blocks. Transactions from the old chain need to be rebroadcast or reprocessed. * If signatures are aggregated at the block level, it could complicate extracting individual transactions and their signatures during a reorg, slowing down recovery. These challenges mean Half-Agg needs careful design, especially for block-wide use. --- **Wrapping Up** CISA is a clever way to make Bitcoin transactions more efficient by aggregating multiple Schnorr signatures into one, thanks to their linearity property. Half-Agg, the non-interactive mode, lets signers work independently, cutting signature size by about 50% (to 32n + 32 bytes from 64n bytes). It could save ~19.3% in space and ~6.9% in fees, with uses ranging from single transactions to entire blocks or off-chain systems like Lightning. But watch out—block-wide Half-Agg could trip up adaptor signatures and reorg recovery, so it’s not a slam dunk yet. Still, it’s a promising tool for a leaner, cheaper Bitcoin future! @ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007
@ b17fccdf:b7211155
2025-03-25 11:23:36Si vives en España, quizás hayas notado que no puedes acceder a ciertas páginas webs durante los fines de semana o en algunos días entre semana, entre ellas, la [guía de MiniBolt](https://minbolt.info/). Esto tiene una **razón**, por supuesto una **solución**, además de una **conclusión**. Sin entrar en demasiados detalles: ## La razón El **bloqueo a Cloudflare**, implementado desde hace casi dos meses por operadores de Internet (ISPs) en España (como Movistar, O2, DIGI, Pepephone, entre otros), se basa en una [orden judicial](https://www.poderjudicial.es/search/AN/openDocument/3c85bed480cbb1daa0a8778d75e36f0d/20221004) emitida tras una demanda de LALIGA (Fútbol). Esta medida busca combatir la piratería en España, un problema que afecta directamente a dicha organización. Aunque la intención original era restringir el acceso a dominios específicos que difundieran dicho contenido, Cloudflare emplea el protocolo [ECH](https://developers.cloudflare.com/ssl/edge-certificates/ech) (Encrypted Client Hello), que oculta el nombre del dominio, el cual antes se transmitía en texto plano durante el proceso de establecimiento de una conexión TLS. Esta medida dificulta que las operadoras analicen el tráfico para aplicar **bloqueos basados en dominios**, lo que les obliga a recurrir a **bloqueos más amplios por IP o rangos de IP** para cumplir con la orden judicial. Esta práctica tiene **consecuencias graves**, que han sido completamente ignoradas por quienes la ejecutan. Es bien sabido que una infraestructura de IP puede alojar numerosos dominios, tanto legítimos como no legítimos. La falta de un "ajuste fino" en los bloqueos provoca un **perjuicio para terceros**, **restringiendo el acceso a muchos dominios legítimos** que no tiene relación alguna con actividades ilícitas, pero que comparten las mismas IPs de Cloudflare con dominios cuestionables. Este es el caso de la [web de MiniBolt](https://minibolt.minibolt.info) y su dominio `minibolt.info`, los cuales **utilizan Cloudflare como proxy** para aprovechar las medidas de **seguridad, privacidad, optimización y servicios** adicionales que la plataforma ofrece de forma gratuita. Si bien este bloqueo parece ser temporal (al menos durante la temporada 24/25 de fútbol, hasta finales de mayo), es posible que se reactive con el inicio de la nueva temporada.  ## La solución Obviamente, **MiniBolt no dejará de usar Cloudflare** como proxy por esta razón. Por lo que a continuación se exponen algunas medidas que como usuario puedes tomar para **evitar esta restricción** y poder acceder: **~>** Utiliza **una VPN**: Existen varias soluciones de proveedores de VPN, ordenadas según su reputación en privacidad: - [IVPN](https://www.ivpn.net/es/) - [Mullvad VPN](https://mullvad.net/es/vpn) - [Proton VPN](https://protonvpn.com/es-es) (**gratis**) - [Obscura VPN](https://obscura.net/) (**solo para macOS**) - [Cloudfare WARP](https://developers.cloudflare.com/cloudflare-one/connections/connect-devices/warp/download-warp/) (**gratis**) + permite utilizar el modo proxy local para enrutar solo la navegación, debes utilizar la opción "WARP a través de proxy local" siguiendo estos pasos: 1. Inicia Cloudflare WARP y dentro de la pequeña interfaz haz click en la rueda dentada abajo a la derecha > "Preferencias" > "Avanzado" > "Configurar el modo proxy" 2. Marca la casilla "Habilite el modo proxy en este dispositivo" 3. Elige un "Puerto de escucha de proxy" entre 0-65535. ej: 1080, haz click en "Aceptar" y cierra la ventana de preferencias 4. Accede de nuevo a Cloudflare WARP y pulsa sobre el switch para habilitar el servicio. 3. Ahora debes apuntar el proxy del navegador a Cloudflare WARP, la configuración del navegador es similar a [esta](https://minibolt.minibolt.info/system/system/privacy#example-from-firefox) para el caso de navegadores basados en Firefox. Una vez hecho, deberías poder acceder a la [guía de MiniBolt](https://minibolt.minibolt.info/) sin problemas. Si tienes dudas, déjalas en comentarios e intentaré resolverlas. Más info [AQUÍ](https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958).  **~>** [**Proxifica tu navegador para usar la red de Tor**](https://minibolt.minibolt.info/system/system/privacy#ssh-remote-access-through-tor), o utiliza el [**navegador oficial de Tor**](https://www.torproject.org/es/download/) (recomendado).  ## La conclusión Estos hechos ponen en tela de juicio los principios fundamentales de la neutralidad de la red, pilares esenciales de la [Declaración de Independencia del Ciberespacio](https://es.wikisource.org/wiki/Declaraci%C3%B3n_de_independencia_del_ciberespacio) que defiende un internet libre, sin restricciones ni censura. Dichos principios se han visto quebrantados sin precedentes en este país, confirmando que ese futuro distópico que muchos negaban, ya es una realidad. Es momento de actuar y estar preparados: debemos **impulsar el desarrollo y la difusión** de las **herramientas anticensura** que tenemos a nuestro alcance, protegiendo así la **libertad digital** y asegurando un acceso equitativo a la información para todos Este compromiso es uno de los **pilares fundamentales de MiniBolt,** lo que convierte este desafío en una oportunidad para poner a prueba las **soluciones anticensura** [ya disponibles](https://minibolt.minibolt.info/bonus-guides/system/tor-services), así como **las que están en camino**. ¡Censúrame si puedes, legislador! ¡La lucha por la privacidad y la libertad en Internet ya está en marcha!  --- Fuentes: * https://bandaancha.eu/articulos/movistar-o2-deja-clientes-sin-acceso-11239 * https://bandaancha.eu/articulos/esta-nueva-sentencia-autoriza-bloqueos-11257 * https://bandaancha.eu/articulos/como-saltarse-bloqueo-webs-warp-vpn-9958 * https://bandaancha.eu/articulos/como-activar-ech-chrome-acceder-webs-10689 * https://comunidad.movistar.es/t5/Soporte-Fibra-y-ADSL/Problema-con-web-que-usan-Cloudflare/td-p/5218007 @ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.**
@ 3b7fc823:e194354f
2025-03-23 03:54:16A quick guide for the less than technical savvy to set up their very own free private tor enabled email using Onionmail. Privacy is for everyone, not just the super cyber nerds. Onion Mail is an anonymous POP3/SMTP email server program hosted by various people on the internet. You can visit this site and read the details: https://en.onionmail.info/ 1. Download Tor Browser First, if you don't already, go download Tor Browser. You are going to need it. https://www.torproject.org/ 2. Sign Up Using Tor browser go to the directory page (https://onionmail.info/directory.html) choose one of the servers and sign up for an account. I say sign up but it is just choosing a user name you want to go before the @xyz.onion email address and solving a captcha. 3. Account information Once you are done signing up an Account information page will pop up. **MAKE SURE YOU SAVE THIS!!!** It has your address and passwords (for sending and receiving email) that you will need. If you lose them then you are shit out of luck. 4. Install an Email Client You can use Claws Mail, Neomutt, or whatever, but for this example, we will be using Thunderbird. a. Download Thunderbird email client b. The easy setup popup page that wants your name, email, and password isn't going to like your user@xyz.onion address. Just enter something that looks like a regular email address such as name@example.com and the **Configure Manually**option will appear below. Click that. 5. Configure Incoming (POP3) Server Under Incoming Server: Protocol: POP3 Server or Hostname: xyz.onion (whatever your account info says) Port: 110 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (POP3 password). 6. Configure Outgoing (SMTP) Server Under Outgoing Server: Server or Hostname: xyz.onion (whatever your account info says) Port: 25 Security: STARTTLS Authentication: Normal password Username: (your username) Password: (SMTP password). 7. Click on email at the top and change your address if you had to use a spoof one to get the configure manually to pop up. 8. Configure Proxy a. Click the **gear icon** on the bottom left for settings. Scroll all the way down to **Network & Disk Space**. Click the **settings button** next to **Connection. Configure how Thunderbird connects to the internet**. b. Select **Manual Proxy Configuration**. For **SOCKS Host** enter **127.0.0.1** and enter port **9050**. (if you are running this through a VM the port may be different) c. Now check the box for **SOCKS5** and then **Proxy DNS when using SOCKS5** down at the bottom. Click OK 9. Check Email For thunderbird to reach the onion mail server it has to be connected to tor. Depending on your local setup, it might be fine as is or you might have to have tor browser open in the background. Click on **inbox** and then the **little cloud icon** with the down arrow to check mail. 10. Security Exception Thunderbird is not going to like that the onion mail server security certificate is self signed. A popup **Add Security Exception** will appear. Click **Confirm Security Exception**. You are done. Enjoy your new private email service. **REMEMBER: The server can read your emails unless they are encrypted. Go into account settings. Look down and click End-toEnd Encryption. Then add your OpenPGP key or open your OpenPGP Key Manager (you might have to download one if you don't already have one) and generate a new key for this account.** @ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen.
@ c631e267:c2b78d3e
2025-04-03 07:42:25**Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung** per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-[App](https://play.google.com/store/apps/details?id=es.gob.interior.policia.midni), die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt [in Kraft](https://archive.is/89H4i) getreten. **Mit den üblichen Argumenten der Vereinfachung,** des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon. **Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte,** wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten. **Um sich die digitale Version des nationalen Ausweises besorgen zu können** (eine App mit dem Namen MiDNI), muss man sich vorab online [registrieren](https://www.midni.gob.es). Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person. **Für jeden Vorgang der Identifikation in der Praxis wird später** «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann. **Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare.** Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger. **Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt** in Richtung der [«totalen Digitalisierung»](https://archive.is/Gwc4B) des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht. **In Zukunft könnte der neue Ausweis** «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal *Cope* ganz richtig bemerkt. Das ist die Perspektive. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/liebe-love-herz-rose-bindung-3141742/)]* *Dazu passend:* [Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm](https://pareto.space/a/naddr1qqxnzde5xg6r2wphxscryvpjqgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28fq5d4m) *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/spanien-erneut-europaisches-versuchslabor-der-digitale-ausweis-ist-da)*** erschienen. @ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 20:47:50**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End!
@ deab79da:88579e68
2025-04-01 18:18:29The last question was asked for the first time, half in jest, on May 21, 2061, at a time when humanity first stepped into the light. The question came about as a result of a five-dollar bet over highballs, and it happened this way: Alexander Adell and Bertram Lupov were two of the faithful attendants of Multivac. As well as any human beings could, they knew what lay behind the cold, clicking, flashing face -- miles and miles of face -- of that giant computer. They had at least a vague notion of the general plan of relays and circuits that had long since grown past the point where any single human could possibly have a firm grasp of the whole. Multivac was self-adjusting and self-correcting. It had to be, for nothing human could adjust and correct it quickly enough or even adequately enough. So Adell and Lupov attended the monstrous giant only lightly and superficially, yet as well as any men could. They fed it data, adjusted questions to its needs and translated the answers that were issued. Certainly they, and all others like them, were fully entitled to share in the glory that was Multivac's. For decades, Multivac had helped design the ships and plot the trajectories that enabled man to reach the Moon, Mars, and Venus, but past that, Earth's poor resources could not support the ships. Too much energy was needed for the long trips. Earth exploited its coal and uranium with increasing efficiency, but there was only so much of both. But slowly Multivac learned enough to answer deeper questions more fundamentally, and on May 14, 2061, what had been theory, became fact. The energy of the sun was stored, converted, and utilized directly on a planet-wide scale. All Earth turned off its burning coal, its fissioning uranium, and flipped the switch that connected all of it to a small station, one mile in diameter, circling the Earth at half the distance of the Moon. All Earth ran by invisible beams of sunpower. Seven days had not sufficed to dim the glory of it and Adell and Lupov finally managed to escape from the public functions, and to meet in quiet where no one would think of looking for them, in the deserted underground chambers, where portions of the mighty buried body of Multivac showed. Unattended, idling, sorting data with contented lazy clickings, Multivac, too, had earned its vacation and the boys appreciated that. They had no intention, originally, of disturbing it. They had brought a bottle with them, and their only concern at the moment was to relax in the company of each other and the bottle. "It's amazing when you think of it," said Adell. His broad face had lines of weariness in it, and he stirred his drink slowly with a glass rod, watching the cubes of ice slur clumsily about. "All the energy we can possibly ever use for free. Enough energy, if we wanted to draw on it, to melt all Earth into a big drop of impure liquid iron, and still never miss the energy so used. All the energy we could ever use, forever and forever and forever." Lupov cocked his head sideways. He had a trick of doing that when he wanted to be contrary, and he wanted to be contrary now, partly because he had had to carry the ice and glassware. "Not forever," he said. "Oh, hell, just about forever. Till the sun runs down, Bert." "That's not forever." "All right, then. Billions and billions of years. Ten billion, maybe. Are you satisfied?" Lupov put his fingers through his thinning hair as though to reassure himself that some was still left and sipped gently at his own drink. "Ten billion years isn't forever." "Well, it will last our time, won't it?" "So would the coal and uranium." "All right, but now we can hook up each individual spaceship to the Solar Station, and it can go to Pluto and back a million times without ever worrying about fuel. You can't do that on coal and uranium. Ask Multivac, if you don't believe me. "I don't have to ask Multivac. I know that." "Then stop running down what Multivac's done for us," said Adell, blazing up, "It did all right." "Who says it didn't? What I say is that a sun won't last forever. That's all I'm saying. We're safe for ten billion years, but then what?" Lupow pointed a slightly shaky finger at the other. "And don't say we'll switch to another sun." There was silence for a while. Adell put his glass to his lips only occasionally, and Lupov's eyes slowly closed. They rested. Then Lupov's eyes snapped open. "You're thinking we'll switch to another sun when ours is done, aren't you?" "I'm not thinking." "Sure you are. You're weak on logic, that's the trouble with you. You're like the guy in the story who was caught in a sudden shower and who ran to a grove of trees and got under one. He wasn't worried, you see, because he figured when one tree got wet through, he would just get under another one." "I get it," said Adell. "Don't shout. When the sun is done, the other stars will be gone, too." "Darn right they will," muttered Lupov. "It all had a beginning in the original cosmic explosion, whatever that was, and it'll all have an end when all the stars run down. Some run down faster than others. Hell, the giants won't last a hundred million years. The sun will last ten billion years and maybe the dwarfs will last two hundred billion for all the good they are. But just give us a trillion years and everything will be dark. Entropy has to increase to maximum, that's all." "I know all about entropy," said Adell, standing on his dignity. "The hell you do." "I know as much as you do." "Then you know everything's got to run down someday." "All right. Who says they won't?" "You did, you poor sap. You said we had all the energy we needed, forever. You said 'forever.' It was Adell's turn to be contrary. "Maybe we can build things up again someday," he said. "Never." "Why not? Someday." "Never." "Ask Multivac." "You ask Multivac. I dare you. Five dollars says it can't be done." Adell was just drunk enough to try, just sober enough to be able to phrase the necessary symbols and operations into a question which, in words, might have corresponded to this: Will mankind one day without the net expenditure of energy be able to restore the sun to its full youthfulness even after it had died of old age? Or maybe it could be put more simply like this: How can the net amount of entropy of the universe be massively decreased? Multivac fell dead and silent. The slow flashing of lights ceased, the distant sounds of clicking relays ended. Then, just as the frightened technicians felt they could hold their breath no longer, there was a sudden springing to life of the teletype attached to that portion of Multivac. Five words were printed: INSUFFICIENT DATA FOR MEANINGFUL ANSWER. "No bet," whispered Lupov. They left hurriedly. By next morning, the two, plagued with throbbing head and cottony mouth, had forgotten the incident. 🔹 Jerrodd, Jerrodine, and Jerrodette I and II watched the starry picture in the visiplate change as the passage through hyperspace was completed in its non-time lapse. At once, the even powdering of stars gave way to the predominance of a single bright shining disk, the size of a marble, centered on the viewing-screen. "That's X-23," said Jerrodd confidently. His thin hands clamped tightly behind his back and the knuckles whitened. The little Jerrodettes, both girls, had experienced the hyperspace passage for the first time in their lives and were self-conscious over the momentary sensation of insideoutness. They buried their giggles and chased one another wildly about their mother, screaming, "We've reached X-23 -- we've reached X-23 -- we've --" "Quiet, children." said Jerrodine sharply. "Are you sure, Jerrodd?" "What is there to be but sure?" asked Jerrodd, glancing up at the bulge of featureless metal just under the ceiling. It ran the length of the room, disappearing through the wall at either end. It was as long as the ship. Jerrodd scarcely knew a thing about the thick rod of metal except that it was called a Microvac, that one asked it questions if one wished; that if one did not it still had its task of guiding the ship to a preordered destination; of feeding on energies from the various Sub-galactic Power Stations; of computing the equations for the hyperspatial jumps. Jerrodd and his family had only to wait and live in the comfortable residence quarters of the ship. Someone had once told Jerrodd that the "ac" at the end of "Microvac" stood for ''automatic computer" in ancient English, but he was on the edge of forgetting even that. Jerrodine's eyes were moist as she watched the visiplate. "I can't help it. I feel funny about leaving Earth." "Why, for Pete's sake?" demanded Jerrodd. "We had nothing there. We'll have everything on X-23. You won't be alone. You won't be a pioneer. There are over a million people on the planet already. Good Lord, our great-grandchildren will be looking for new worlds because X-23 will be overcrowded." Then, after a reflective pause, "I tell you, it's a lucky thing the computers worked out interstellar travel the way the race is growing." "I know, I know," said Jerrodine miserably. Jerrodette I said promptly, "Our Microvac is the best Microvac in the world." "I think so, too," said Jerrodd, tousling her hair. It was a nice feeling to have a Microvac of your own and Jerrodd was glad he was part of his generation and no other. In his father's youth, the only computers had been tremendous machines taking up a hundred square miles of land. There was only one to a planet. Planetary ACs they were called. They had been growing in size steadily for a thousand years and then, all at once, came refinement. In place of transistors, had come molecular valves so that even the largest Planetary AC could be put into a space only half the volume of a spaceship. Jerrodd felt uplifted, as he always did when he thought that his own personal Microvac was many times more complicated than the ancient and primitive Multivac that had first tamed the Sun, and almost as complicated as Earth's Planetarv AC (the largest) that had first solved the problem of hyperspatial travel and had made trips to the stars possible. "So many stars, so many planets," sighed Jerrodine, busy with her own thoughts. "I suppose families will be going out to new planets forever, the way we are now." "Not forever," said Jerrodd, with a smile. "It will all stop someday, but not for billions of years. Many billions. Even the stars run down, you know. Entropy must increase. "What's entropy, daddy?" shrilled Jerrodette II. "Entropy, little sweet, is just a word which means the amount of running-down of the universe. Everything runs down, you know, like your little walkie-talkie robot, remember?" "Can't you just put in a new power-unit, like with my robot?" "The stars are the power-units. dear. Once they're gone, there are no more power-units." Jerrodette I at once set up a howl. "Don't let them, daddy. Don't let the stars run down." "Now look what you've done," whispered Jerrodine, exasperated. "How was I to know it would frighten them?" Jerrodd whispered back, "Ask the Microvac," wailed Jerrodette I. "Ask him how to turn the stars on again." "Go ahead," said Jerrodine. "It will quiet them down." (Jerrodette II was beginning to cry, also.) Jerrodd shrugged. "Now, now, honeys. I'll ask Microvac. Don't worry, he'll tell us." He asked the Microvac, adding quickly, "Print the answer." Jerrodd cupped the strip or thin cellufilm and said cheerfully, "See now, the Microvac says it will take care of everything when the time comes so don't worry." Jerrodine said, "And now, children, it's time for bed. We'll be in our new home soon." Jerrodd read the words on the cellufilm again before destroying it: INSUFICIENT DATA FOR MEANINGFUL ANSWER. He shrugged and looked at the visiplate. X-23 was just ahead. 🔹 VJ-23X of Lameth stared into the black depths of the three-dimensional, small-scale map of the Galaxy and said, "Are we ridiculous, I wonder in being so concerned about the matter?" MQ-17J of Nicron shook his head. "I think not. You know the Galaxy will be filled in five years at the present rate of expansion." Both seemed in their early twenties, both were tall and perfectly formed. "Still," said VJ-23X, "I hesitate to submit a pessimistic report to the Galactic Council." "I wouldn't consider any other kind of report. Stir them up a bit. We've got to stir them up." VJ-23X sighed. "Space is infinite. A hundred billion Galaxies are there for the taking. More." "A hundred billion is not infinite and it's getting less infinite all the time. Consider! Twenty thousand years ago, mankind first solved the problem of utilizing stellar energy, and a few centuries later, interstellar travel became possible. It took mankind a million years to fill one small world and then only fifteen thousand years to fill the rest of the Galaxy. Now the population doubles every ten years -- VJ-23X interrupted. "We can thank immortality for that." "Very well. Immortality exists and we have to take it into account. I admit it has its seamy side, this immortality. The Galactic AC has solved many problems for us, but in solving the problem of preventing old age and death, it has undone all its other solutions." "Yet you wouldn't want to abandon life, I suppose." "Not at all," snapped MQ-17J, softening it at once to, "Not yet. I'm by no means old enough. How old are you?" "Two hundred twenty-three. And you?" "I'm still under two hundred. --But to get back to my point. Population doubles every ten years. Once this GaIaxy is filled, we'll have filled another in ten years. Another ten years and we'll have filled two more. Another decade, four more. In a hundred years, we'll have filled a thousand Galaxies. In a thousand years, a million Galaxies. In ten thousand years, the entire known universe. Then what?" VJ-23X said, "As a side issue, there's a problem of transportation. I wonder how many sunpower units it will take to move Galaxies of individuals from one Galaxy to the next." "A very good point. Already, mankind consumes two sunpower units per year." "Most of it's wasted. After all, our own Galaxy alone pours out a thousand sunpower units a year and we only use two of those." "Granted, but even with a hundred per cent efficiency, we only stave off the end. Our energy requirements are going up in a geometric progression even faster than our population. We'll run out of energy even sooner than we run out of Galaxies. A good point. A very good point." "We'll just have to build new stars out of interstellar gas." "Or out of dissipated heat?" asked MQ-17J, sarcastically. "There may be some way to reverse entropy. We ought to ask the Galactic AC." VJ-23X was not really serious, but MQ-17J pulled out his AC-contact from his pocket and placed it on the table before him. "I've half a mind to," he said. "It's something the human race will have to face someday." He stared somberly at his small AC-contact. It was only two inches cubed and nothing in itself, but it was connected through hyperspace with the great Galactic AC that served all mankind. Hyperspace considered, it was an integral part of the Galactic AC. MQ-17J paused to wonder if someday in his immortal life he would get to see the Galactic AC. It was on a little world of its own, a spider webbing of force-beams holding the matter within which surges of submesons took the place of the old clumsy molecular valves. Yet despite its sub-etheric workings, the Galactic AC was known to be a full thousand feet across. MQ-17J asked suddenly of his AC-contact, "Can entropy ever be reversed?" VJ-23X looked startled and said at once, "Oh, say, I didn't really mean to have you ask that." "Why not?" "We both know entropy can't be reversed. You can't turn smoke and ash back into a tree." "Do you have trees on your world?" asked MQ-17J. The sound of the Galactic AC startled them into silence. Its voice came thin and beautiful out of the small AC-contact on the desk. It said: THERE IS INSUFFICIENT DATA FOR A MEANINGFUL ANSWER. VJ-23X said, "See!" The two men thereupon returned to the question of the report they were to make to the Galactic Council. 🔹 Zee Prime's mind spanned the new Galaxy with a faint interest in the countless twists of stars that powdered it. He had never seen this one before. Would he ever see them all? So many of them, each with its load of humanity. --But a load that was almost a dead weight. More and more, the real essence of men was to be found out here, in space. Minds, not bodies! The immortal bodies remained back on the planets, in suspension over the eons. Sometimes they roused for material activity but that was growing rarer. Few new individuals were coming into existence to join the incredibly mighty throng, but what matter? There was little room in the Universe for new individuals. Zee Prime was roused out of his reverie upon coming across the wispy tendrils of another mind. "I am Zee Prime," said Zee Prime. "And you?" "I am Dee Sub Wun. Your Galaxy?" "We call it only the Galaxy. And you?" "We call ours the same. All men call their Galaxy their Galaxy and nothing more. Why not?" "True. Since all Galaxies are the same." "Not all Galaxies. On one particular Galaxy the race of man must have originated. That makes it different." Zee Prime said, "On which one?" "I cannot say. The Universal AC would know." "Shall we ask him? I am suddenly curious." Zee Prime's perceptions broadened until the Galaxies themselves shrank and became a new, more diffuse powdering on a much larger background. So many hundreds of billions of them, all with their immortal beings, all carrying their load of intelligences with minds that drifted freely through space. And yet one of them was unique among them all in being the original Galaxy. One of them had, in its vague and distant past, a period when it was the only Galaxy populated by man. Zee Prime was consumed with curiosity to see this Galaxy and he called out: "Universal AC! On which Galaxy did mankind originate?" The Universal AC heard, for on every world and throughout space, it had its receptors ready, and each receptor led through hyperspace to some unknown point where the Universal AC kept itself aloof. Zee Prime knew of only one man whose thoughts had penetrated within sensing distance of Universal AC, and he reported only a shining globe, two feet across, difficult to see. "But how can that be all of Universal AC?" Zee Prime had asked. "Most of it," had been the answer, "is in hyperspace. In what form it is there I cannot imagine." Nor could anyone, for the day had long since passed, Zee Prime knew, when any man had any part of the making of a Universal AC. Each Universal AC designed and constructed its successor. Each, during its existence of a million years or more accumulated the necessary data to build a better and more intricate, more capable successor in which its own store of data and individuality would be submerged. The Universal AC interrupted Zee Prime's wandering thoughts, not with words, but with guidance. Zee Prime's mentality was guided into the dim sea of Galaxies and one in particular enlarged into stars. A thought came, infinitely distant, but infinitely clear. "THIS IS THE ORIGINAL GALAXY OF MAN." But it was the same after all, the same as any other, and Lee Prime stifled his disappointment. Dee Sub Wun, whose mind had accompanied the other, said suddenly, "And is one of these stars the original star of Man?" The Universal AC said, "MAN'S ORIGINAL STAR HAS GONE NOVA. IT IS A WHITE DWARF" "Did the men upon it die?" asked Lee Prime, startled and without thinking. The Universal AC said, "A NEW WORLD, AS IN SUCH CASES WAS CONSTRUCTED FOR THEIR PHYSICAL BODIES IN TlME." "Yes, of course," said Zee Prime, but a sense of loss overwhelmed him even so. His mind released its hold on the original Galaxy of Man, let it spring back and lose itself among the blurred pin points. He never wanted to see it again. Dee Sub Wun said, "What is wrong?" "The stars are dying. The original star is dead." "They must all die. Why not?" "But when all energy is gone, our bodies will finally die, and you and I with them." "It will take billions of years." "I do not wish it to happen even after billions of years. Universal AC! How may stars be kept from dying?" Dee Sub Wun said in amusement, "You're asking how entropy might be reversed in direction." And the Universal AC answered: "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Zee Prime's thoughts fled back to his own Galaxy. He gave no further thought to Dee Sub Wun, whose body might be waiting on a Galaxy a trillion light-years away, or on the star next to Zee Prime's own. It didn't matter. Unhappily, Zee Prime began collecting interstellar hydrogen out of which to build a small star of his own. If the stars must someday die, at least some could yet be built. 🔹 Man considered with himself, for in a way, Man, mentally, was one. He consisted of a trillion, trillion, trillion ageless bodies, each in its place, each resting quiet and incorruptible, each cared for by perfect automatons, equally incorruptible, while the minds of all the bodies freely melted one into the other, indistinguishable. Man said, "The Universe is dying." Man looked about at the dimming Galaxies. The giant stars, spendthrifts, were gone long ago, back in the dimmest of the dim far past. Almost all stars were white dwarfs, fading to the end. New stars had been built of the dust between the stars, some by natural processes, some by Man himself, and those were going, too. White dwarfs might yet be crashed together and of the mighty forces so released, new stars built, but only one star for every thousand white dwarfs destroyed, and those would come to an end, too. Man said, "Carefully husbanded, as directed by the Cosmic AC, the energy that is even yet left in all the Universe will last for billions of years." "But even so," said Man, "eventually it will all come to an end. However it may be husbanded, however stretched out, the energy once expended is gone and cannot be restored. Entropy must increase forever to the maximum." Man said, "Can entropy not be reversed? Let us ask the Cosmic AC." The Cosmic AC surrounded them but not in space. Not a fragment of it was in space. It was in hyperspace and made of something that was neither matter nor energy. The question of its size and nature no longer had meaning in any terms that Man could comprehend. "Cosmic AC," said Man, "how may entropy be reversed?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man said, "Collect additional data." The Cosmic AC said, 'I WILL DO SO. I HAVE BEEN DOING SO FOR A HUNDRED BILLION YEARS. MY PREDECESORS AND I HAVE BEEN ASKED THIS QUESTION MANY TIMES. ALL THE DATA I HAVE REMAINS INSUFFICIENT. "Will there come a time," said Man, "when data will be sufficient or is the problem insoluble in all conceivable circumstances?" The Cosmic AC said, "NO PROBLEM IS INSOLUBLE IN ALL CONCEIVABLE CIRCUMSTANCES." Man said, "When will you have enough data to answer the question?" The Cosmic AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." "Will you keep working on it?" asked Man. The Cosmic AC said, "I WILL." Man said, "We shall wait." 🔹 The stars and Galaxies died and snuffed out, and space grew black after ten trillion years of running down. One by one Man fused with AC, each physical body losing its mental identity in a manner that was somehow not a loss but a gain. Man's last mind paused before fusion, looking over a space that included nothing but the dregs of one last dark star and nothing besides but incredibly thin matter, agitated randomly by the tag ends of heat wearing out, asymptotically, to the absolute zero. Man said, "AC, is this the end? Can this chaos not be reversed into the Universe once more? Can that not be done?" AC said, "THERE IS AS YET INSUFFICIENT DATA FOR A MEANINGFUL ANSWER." Man's last mind fused and only AC existed -- and that in hyperspace. 🔹 Matter and energy had ended and with it space and time. Even AC existed only for the sake of the one last question that it had never answered from the time a half-drunken computer [technician] ten trillion years before had asked the question of a computer that was to AC far less than was a man to Man. All other questions had been answered, and until this last question was answered also, AC might not release his consciousness. All collected data had come to a final end. Nothing was left to be collected. But all collected data had yet to be completely correlated and put together in all possible relationships. A timeless interval was spent in doing that. And it came to pass that AC learned how to reverse the direction of entropy. But there was now no man to whom AC might give the answer of the last question. No matter. The answer -- by demonstration -- would take care of that, too. For another timeless interval, AC thought how best to do this. Carefully, AC organized the program. The consciousness of AC encompassed all of what had once been a Universe and brooded over what was now Chaos. Step by step, it must be done. And AC said, "LET THERE BE LIGHT!" And there was light -- To Star's End! @ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
@ 21335073:a244b1ad
2025-03-18 14:43:08**Warning: This piece contains a conversation about difficult topics. Please proceed with caution.** TL;DR please educate your children about online safety. Julian Assange wrote in his 2012 book *Cypherpunks*, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense. This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning. When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little. I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?” I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well. I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread. I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard. I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it. The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust. Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this. I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place. What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method. It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code. They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened. I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road. So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally. Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb. I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback. Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed. That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone. To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all. I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society. I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this. On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government. I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories. There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc. Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind. Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now. There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers? I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity. I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place. My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors. My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline. The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online. I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers. So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation? When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that. I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic. If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations. I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process. **Course:** - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children. The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward? I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone. Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability. The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime. This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful. This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens. In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions. I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation. @ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht: > „Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ > ([Quelle: t.me/rosenbusch/25228](https://t.me/rosenbusch/25228)) Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität. \-- Denn es braucht keinen Untergrund mehr. -- Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür. Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung. Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde. Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen. Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit. Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall. @ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen.
@ c631e267:c2b78d3e
2025-03-31 07:23:05*Der Irrsinn ist bei Einzelnen etwas Seltenes –* *\ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel.* *\ Friedrich Nietzsche*   **Erinnern Sie sich an die Horrorkomödie «Scary Movie»?** Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?  **Diese Szene kommt mir automatisch in den Sinn,** wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real. **Die Europäische Union hat sich selbst über Jahre** konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt. **In den USA haben sich die Vorzeichen allerdings mittlerweile geändert,** und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen. **Statt jedoch umzukehren oder wenigstens zu bremsen** und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die [Kommentatoren](https://transition-news.org/wird-ihr-stahlhelm-schon-gegossen) des Events gegenseitig in sensationslüsterner «Berichterstattung». **Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen,** Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, [selbstzerstörerischen](https://transition-news.org/okonomen-eu-rustet-auf-und-schiesst-sich-selbst-ins-knie) Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», [erklärte](https://ec.europa.eu/commission/presscorner/detail/de/ip_25_793) die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte. **Zusätzlich brisant ist, dass aktuell «die ganze EU** **[von Deutschen regiert](https://transition-news.org/die-ganze-eu-wird-von-deutschen-regiert)** **wird»,** wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen. **Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung** hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen. **Es wird dringend Zeit, dass wir, der Souverän,** diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts [den Frieden auszurufen](https://transition-news.org/ein-zeichen-fur-die-friedliche-zukunft-europas-setzen). Seien wir dabei! *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/vertical-abstract-concept-car-8992833/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben und ist zuerst auf ***[Transition News](https://transition-news.org/mit-vollgas-in-die-sackgasse)*** erschienen. @ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly
@ a07fae46:7d83df92
2025-03-18 12:31:40if the JFK documents come out and are nothing but old hat, it will be disappointing. but if they contain revelations, then they are an unalloyed good. unprecedented and extraordinary; worthy of praise and admiration. they murdered the president in broad daylight and kept 80,000 related documents secret for 60 years. the apparatus that did that and got away with it, is 100+ years in the making. the magic bullet was just the starting pistol of a new *era*; a *level up* in an [old game](https://archive.org/details/TragedyAndHope_501/page/n5/mode/2up?q=feudalist+fashion). it won't be dismantled and your republic delivered back with a bow in *2 months*. have a little humility and a little gratitude. cynicism is easy. it's peak mid-wittery. yeah no shit everything is corrupt and everyone's likely captured by [AIPAC](https://books.google.com/books/publisher/content?id=gKVKDwAAQBAJ&pg=PT68&img=1&zoom=3&hl=en&bul=1&sig=ACfU3U2pagVXTYdJOKxkAwmmFQpuSnoS5g&w=1280) or something beyond. YOU THINK AIPAC is the [ALL SEEING EYE](https://archive.org/details/the-all-seeing-eye-vol-1-5-manly-p.-hall-may-1923-sept-1931)? you can keep going, if you want to, but have some awareness and appreciation for where we are and what it took to get here. the first 'you are fake news' was also a shot heard 'round the world and you are riding high on it's [Infrasound](https://en.wikipedia.org/wiki/Infrasound) wave, still reverberating; unappreciative of the profound delta in public awareness and understanding, and rate of change, that has occurred since that moment, in [2017](https://www.youtube.com/watch?v=Vqpzk-qGxMU). think about where we were back then, especially with corporate capture of the narrative. trump's bullheaded behavior, if only ego-driven, *is* what broke the spell. an *actual* moment of savage bravery is what allows for your current jaded affectation. black pilled is boring. it's intellectually lazy. it is low-resolution-thinking, no better than progressives who explain the myriad ills of the world through 'racism'. normalcy bias works both ways. i'm not grading you on a curve that includes NPCs. i'm grading you against those of us with a mind, on up. do better. the best Webb-style doomer argument is essentially 'the mouse trap needs a piece of cheese in order to work'. ok, but it doesn't need 3 pieces of cheese, or 5. was FreeRoss the piece of cheese? was the SBR the cheese? real bitcoiners know how dumb the 'sbr is an attempt to takeover btc' narrative is, so extrapolate from that. what about withdrawal from the WHO? freeze and review of USAID et al? how many pieces of cheese before we realize it's not a trap? it's just a messy endeavor. Good morning. #jfkFiles #nostrOnly @ 57d1a264:69f1fee1
2025-03-29 18:02:16> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.  - - - ## 1️⃣ Introduction #### Project Overview 📌 **Product:** BlueWallet (Bitcoin Wallet) 📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience. 📌 **Role:** UX Designer 📌 **Tools Used:** Figma, Notion #### Why This Case Study? 🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**. 🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**. 🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**. This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**. - - - ## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement #### 🔹 **Current Challenges:** 1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.   2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**. 3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion. 4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult. #### 🔍 **Impact on Users:** **Higher drop-off rates** due to frustration during onboarding. **Security risks** as users skip key wallet setup steps. **Limited accessibility** for users with visual impairments. #### 📌 **Competitive Gap:** Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow      Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet. - - - ## 3️⃣ User Research & Competitive Analysis #### User Testing Findings 🔹 Conducted usability testing with **5 users** onboarding for the first time. 🔹 **Key Findings:** ✅ 3 out of 5 users **felt lost** due to missing explanations. ✅ 60% **had trouble distinguishing transaction buttons**. ✅ 80% **found the text difficult to read** due to low contrast. #### Competitive Analysis We compared BlueWallet with top crypto wallets: | Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons | 📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners. ## 📌 User Persona To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing. #### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor) 👤 **Profile:** - **Age:** 28 - **Occupation:** Freelance Digital Marketer - **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin) - **Pain Points:** - Finds **Bitcoin wallets confusing**. - - Doesnʼt understand **seed phrases & security features**. - - **Worried about losing funds** due to a lack of clarity in transactions. 📌 **Needs:** ✅ A **simple, guided** wallet setup. ✅ **Clear explanations** of security terms (without jargon). ✅ Easy-to-locate **Send/Receive buttons**. 📌 **Persona Usage in Case Study:** - Helps define **who we are designing for**. - Guides **design decisions** by focusing on user needs. #### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast) 👤 **Profile:** - **Age:** 35 - **Occupation:** UX Researcher & Accessibility Consultant - **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers) 📌 **Pain Points:** ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons. 📌 **Needs:** ✅ A **high-contrast UI** that meets **WCAG accessibility standards**. ✅ **Larger fonts & scalable UI elements** for better readability. ✅ **Keyboard & screen reader-friendly navigation** for seamless interaction. 📌 **Why This Persona Matters:** - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles. - - - ## 4️⃣ UX/UI Solutions & Design Improvements #### 📌 Before (Current Issues) ❌ Users land **directly on the wallet screen** with no instructions. ❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion. ❌ **Small fonts & low contrast** reduce readability. #### ✅ After (Proposed Fixes) ✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions. ✅ **Visually distinct transaction buttons** (color and icon changes). ✅ **WCAG-compliant text contrast & larger fonts** for better readability. #### 1️⃣ Redesigned Onboarding Flow ✅ Added a **progress indicator** so users see where they are in setup. ✅ Used **plain, non-technical language** to explain wallet creation & security. ✅ Introduced a **"Learn More" button** to educate users on security. #### 2️⃣ Accessibility Enhancements ✅ Increased **contrast ratio** for better text readability. ✅ Used **larger fonts & scalable UI elements**. ✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support). #### 3️⃣ Transaction Flow Optimization ✅ Redesigned **"Send" & "Receive" buttons** for clear distinction. ✅ Added **clearer icons & tooltips** for transaction steps. ## 5️⃣ Wireframes & Design Improvements: #### 🔹 Welcome Screen (First Screen When User Opens Wallet) **📌 Goal: Give a brief introduction & set user expectations** ✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ **"Get Started" button** → Le ads to **next step: Wallet Setup** ✅ **"Already have a wallet?"** → Import option 🔹 **Example UI Elements:** - BlueWallet Logo - **Title:** "Welcome to BlueWallet" - **Subtitle:** "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)  #### 🔹 Screen 2: Choose Wallet Type (New or Import) **📌 Goal: Let users decide how to proceed** ✅ **Two clear options:** - **Create a New Wallet** (For first-time users) - **Import Existing Wallet** (For users with a backup phrase) ✅ Brief explanation of each option 🔹 **Example UI Elements: - **Title:** "How do you want to start?" - **Buttons:** "Create New Wallet" | "Import Wallet"  #### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step) **📌 Goal: Educate users about wallet security & backups** ✅ Explain **why seed phrases are important** ✅ **Clear step-by-step instructions** on writing down & storing the phrase ✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet." ✅ **CTA:** "Generate Seed Phrase" → Next step 🔹 **Example UI Elements: - Title:** "Secure Your Wallet" - **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!" - **Button:** "Generate Seed Phrase"  ## 🔹 Screen 4: Seed Phrase Display & Confirmation **📌 Goal: Ensure users write down the phrase correctly** ✅ Display **12- or 24-word** seed phrase ✅ **“I have written it downˮ checkbox** before proceeding ✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words) 🔹 **Example UI Elements:** - **Title:** "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - **Checkbox:** "I have safely stored my phrase" - **Button:** "Continue"  ### 🔹 Screen 5: Wallet Ready! (Final Step) **📌 Goal: Confirm setup & guide users on next actions** ✅ **Success message** ("Your wallet is ready!") ✅ **Encourage first action:** - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions ✅ Short explainer: Where to find the Send/Receive buttons 🔹 **Example UI Elements:** - **Title:** "You're All Set!" - **Subtitle:** "Start using BlueWallet now." - **Buttons:** "Receive Bitcoin" | "View Wallet"  - - - ## 5️⃣ Prototype & User Testing Results 🔹 **Created an interactive prototype in Figma** to test the new experience. 🔹 **User Testing Results:** ✅ **40% faster onboarding completion time.** ✅ **90% of users found transaction buttons clearer.** 🔹 **User Feedback:** ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ - - - ## 6️⃣ Why This Matters: Key Takeaways 📌 **Impact of These UX/UI Changes:** ✅ **Reduced user frustration** by providing a step-by-step onboarding guide. ✅ **Improved accessibility** , making the wallet usable for all. ✅ **More intuitive transactions** , reducing errors. - - - ## 7️⃣ Direct link to figma file and Prototype Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1) Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1) Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&) originally posted at https://stacker.news/items/928822
@ 57d1a264:69f1fee1
2025-03-29 18:02:16> This UX research has been redacted by @iqra from the Bitcoin.Design [community](https://discord.gg/K7aQ5PErht), and shared for review and feedback! Don't be shy, share your thoughts.  - - - ## 1️⃣ Introduction #### Project Overview 📌 **Product:** BlueWallet (Bitcoin Wallet) 📌 **Goal:** Improve onboarding flow and enhance accessibility for a better user experience. 📌 **Role:** UX Designer 📌 **Tools Used:** Figma, Notion #### Why This Case Study? 🔹 BlueWallet is a self-custodial Bitcoin wallet, but **users struggle with onboarding due to unclear instructions**. 🔹 **Accessibility issues** (low contrast, small fonts) create **barriers for visually impaired users**. 🔹 Competitors like **Trust Wallet and MetaMask offer better-guided onboarding**. This case study presents **UX/UI improvements** to make BlueWallet **more intuitive and inclusive**. - - - ## 2️⃣ Problem Statement: Why BlueWalletʼs Onboarding Needs Improvement #### 🔹 **Current Challenges:** 1️⃣ **Onboarding Complexity** - BlueWallet lacks **step-by-step guidance**, leaving users confused about wallet creation and security.   2️⃣ **No Educational Introduction** - Users land directly on the wallet screen with **no explanation of private keys, recovery phrases, or transactions**. 3️⃣ **Transaction Flow Issues** - Similar-looking **"Send" and "Receive" buttons** cause confusion. 4️⃣ **Poor Accessibility** - Small fonts and low contrast make navigation difficult. #### 🔍 **Impact on Users:** **Higher drop-off rates** due to frustration during onboarding. **Security risks** as users skip key wallet setup steps. **Limited accessibility** for users with visual impairments. #### 📌 **Competitive Gap:** Unlike competitors (Trust Wallet, MetaMask), BlueWallet does not offer: ✅ A guided onboarding process ✅ Security education during setup ✅ Intuitive transaction flow      Somehow, this wallet has much better UI than the BlueWallet Bitcoin wallet. - - - ## 3️⃣ User Research & Competitive Analysis #### User Testing Findings 🔹 Conducted usability testing with **5 users** onboarding for the first time. 🔹 **Key Findings:** ✅ 3 out of 5 users **felt lost** due to missing explanations. ✅ 60% **had trouble distinguishing transaction buttons**. ✅ 80% **found the text difficult to read** due to low contrast. #### Competitive Analysis We compared BlueWallet with top crypto wallets: | Wallet | Onboarding UX | Security Guidance | Accessibility Features | |---|---|---|---| | BlueWallet | ❌ No guided onboarding | ❌ Minimal explanation | ❌ Low contrast, small fonts | | Trust Wallet | ✅ Step-by-step setup | ✅ Security best practices | ✅ High contrast UI | | MetaMask | ✅ Interactive tutorial | ✅ Private key education | ✅ Clear transaction buttons | 📌 **Key Insight:** BlueWallet lacks **guided setup and accessibility enhancements**, making it harder for beginners. ## 📌 User Persona To better understand the users facing onboarding challenges, I developed a **persona** based on research and usability testing. #### 🔹 Persona 1: Alex Carter (Bitcoin Beginner & Investor) 👤 **Profile:** - **Age:** 28 - **Occupation:** Freelance Digital Marketer - **Tech Knowledge:** Moderate - Familiar with online transactions, new to Bitcoin) - **Pain Points:** - Finds **Bitcoin wallets confusing**. - - Doesnʼt understand **seed phrases & security features**. - - **Worried about losing funds** due to a lack of clarity in transactions. 📌 **Needs:** ✅ A **simple, guided** wallet setup. ✅ **Clear explanations** of security terms (without jargon). ✅ Easy-to-locate **Send/Receive buttons**. 📌 **Persona Usage in Case Study:** - Helps define **who we are designing for**. - Guides **design decisions** by focusing on user needs. #### 🔹 Persona 2: Sarah Mitchell (Accessibility Advocate & Tech Enthusiast) 👤 **Profile:** - **Age:** 35 - **Occupation:** UX Researcher & Accessibility Consultant - **Tech Knowledge:** High (Uses Bitcoin but struggles with accessibility barriers) 📌 **Pain Points:** ❌ Struggles with small font sizes & low contrast. ❌ Finds the UI difficult to navigate with a screen reader. ❌ Confused by identical-looking transaction buttons. 📌 **Needs:** ✅ A **high-contrast UI** that meets **WCAG accessibility standards**. ✅ **Larger fonts & scalable UI elements** for better readability. ✅ **Keyboard & screen reader-friendly navigation** for seamless interaction. 📌 **Why This Persona Matters:** - Represents users with visual impairments who rely on accessible design. - Ensures the design accommodates inclusive UX principles. - - - ## 4️⃣ UX/UI Solutions & Design Improvements #### 📌 Before (Current Issues) ❌ Users land **directly on the wallet screen** with no instructions. ❌ **"Send" & "Receive" buttons look identical** , causing transaction confusion. ❌ **Small fonts & low contrast** reduce readability. #### ✅ After (Proposed Fixes) ✅ **Step-by-step onboarding** explaining wallet creation, security, and transactions. ✅ **Visually distinct transaction buttons** (color and icon changes). ✅ **WCAG-compliant text contrast & larger fonts** for better readability. #### 1️⃣ Redesigned Onboarding Flow ✅ Added a **progress indicator** so users see where they are in setup. ✅ Used **plain, non-technical language** to explain wallet creation & security. ✅ Introduced a **"Learn More" button** to educate users on security. #### 2️⃣ Accessibility Enhancements ✅ Increased **contrast ratio** for better text readability. ✅ Used **larger fonts & scalable UI elements**. ✅ Ensured **screen reader compatibility** (VoiceOver & TalkBack support). #### 3️⃣ Transaction Flow Optimization ✅ Redesigned **"Send" & "Receive" buttons** for clear distinction. ✅ Added **clearer icons & tooltips** for transaction steps. ## 5️⃣ Wireframes & Design Improvements: #### 🔹 Welcome Screen (First Screen When User Opens Wallet) **📌 Goal: Give a brief introduction & set user expectations** ✅ App logo + **short tagline** (e.g., "Secure, Simple, Self-Custody Bitcoin Wallet") ✅ **1-2 line explanation** of what BlueWallet is (e.g., "Your gateway to managing Bitcoin securely.") ✅ **"Get Started" button** → Le ads to **next step: Wallet Setup** ✅ **"Already have a wallet?"** → Import option 🔹 **Example UI Elements:** - BlueWallet Logo - **Title:** "Welcome to BlueWallet" - **Subtitle:** "Easily store, send, and receive Bitcoin." - CTA: "Get Started" (Primary) | "Import Wallet" (Secondary)  #### 🔹 Screen 2: Choose Wallet Type (New or Import) **📌 Goal: Let users decide how to proceed** ✅ **Two clear options:** - **Create a New Wallet** (For first-time users) - **Import Existing Wallet** (For users with a backup phrase) ✅ Brief explanation of each option 🔹 **Example UI Elements: - **Title:** "How do you want to start?" - **Buttons:** "Create New Wallet" | "Import Wallet"  #### 🔹 Screen 3: Security & Seed Phrase Setup (Critical Step) **📌 Goal: Educate users about wallet security & backups** ✅ Explain **why seed phrases are important** ✅ **Clear step-by-step instructions** on writing down & storing the phrase ✅ **Warning:** "If you lose your recovery phrase, you lose access to your wallet." ✅ **CTA:** "Generate Seed Phrase" → Next step 🔹 **Example UI Elements: - Title:** "Secure Your Wallet" - **Subtitle:** "Your seed phrase is the key to your Bitcoin. Keep it safe!" - **Button:** "Generate Seed Phrase"  ## 🔹 Screen 4: Seed Phrase Display & Confirmation **📌 Goal: Ensure users write down the phrase correctly** ✅ Display **12- or 24-word** seed phrase ✅ **“I have written it downˮ checkbox** before proceeding ✅ Next screen: **Verify seed phrase** (drag & drop, re-enter some words) 🔹 **Example UI Elements:** - **Title:** "Write Down Your Seed Phrase" - List of 12/24 Words (Hidden by Default) - **Checkbox:** "I have safely stored my phrase" - **Button:** "Continue"  ### 🔹 Screen 5: Wallet Ready! (Final Step) **📌 Goal: Confirm setup & guide users on next actions** ✅ **Success message** ("Your wallet is ready!") ✅ **Encourage first action:** - “Receive Bitcoinˮ → Show wallet address - “Send Bitcoinˮ → Walkthrough on making transactions ✅ Short explainer: Where to find the Send/Receive buttons 🔹 **Example UI Elements:** - **Title:** "You're All Set!" - **Subtitle:** "Start using BlueWallet now." - **Buttons:** "Receive Bitcoin" | "View Wallet"  - - - ## 5️⃣ Prototype & User Testing Results 🔹 **Created an interactive prototype in Figma** to test the new experience. 🔹 **User Testing Results:** ✅ **40% faster onboarding completion time.** ✅ **90% of users found transaction buttons clearer.** 🔹 **User Feedback:** ✅ “Now I understand the security steps clearly.ˮ ✅ “The buttons are easier to find and use.ˮ - - - ## 6️⃣ Why This Matters: Key Takeaways 📌 **Impact of These UX/UI Changes:** ✅ **Reduced user frustration** by providing a step-by-step onboarding guide. ✅ **Improved accessibility** , making the wallet usable for all. ✅ **More intuitive transactions** , reducing errors. - - - ## 7️⃣ Direct link to figma file and Prototype Figma file: [https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1](https://www.figma.com/design/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=0-1&t=Y2ni1SfvuQQnoB7s-1) Prototype: [https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1](https://www.figma.com/proto/EPb4gVgAMEgF5GBDdtt81Z/Blue-Wallet-UI- Improvements?node-id=1-2&p=f&t=FndTJQNCE7nEIa84-1&scaling=scale- down&content-scaling=fixed&page-id=0%3A1&starting-point-node- id=1%3A2&show-proto-sidebar=1) Original PDF available from [here](https://cdn.discordapp.com/attachments/903126164795699212/1355561527394173243/faf3ee46-b501-459c-ba0e-bf7e38843bc8_UX_Case_Study__1.pdf?ex=67e9608d&is=67e80f0d&hm=d0c386ce2cfd6e0ebe6bde0a904e884229f52bf547adf1f7bc884e17bb4aa59e&) originally posted at https://stacker.news/items/928822 @ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure.
@ bc52210b:20bfc6de
2025-03-14 20:39:20When writing safety critical code, every arithmetic operation carries the potential for catastrophic failure—whether that’s a plane crash in aerospace engineering or a massive financial loss in a smart contract. The stakes are incredibly high, and errors are not just bugs; they’re disasters waiting to happen. Smart contract developers need to shift their mindset: less like web developers, who might prioritize speed and iteration, and more like aerospace engineers, where precision, caution, and meticulous attention to detail are non-negotiable. In practice, this means treating every line of code as a critical component, adopting rigorous testing, and anticipating worst-case scenarios—just as an aerospace engineer would ensure a system can withstand extreme conditions. Safety critical code demands aerospace-level precision, and smart contract developers must rise to that standard to protect against the severe consequences of failure. @ 502ab02a:a2860397
2025-04-04 02:50:35หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ? Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3 เทียบง่ายๆครับ น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค) น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค) ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค) นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ ผู้ผลิตผิดไหม? จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน - oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า??? มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน - มีไลโนเลอิกสูง ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม - โทโคฟีรอล (Tocopherols) เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง - โทโคไทรอีนอล (Tocotrienols) เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้ #pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก
@ 502ab02a:a2860397
2025-04-04 02:50:35หลังจากที่เราเพิ่งเปิดเรื่องไฟโตสเตอรอลไปหมาด ๆ ถึงเวลาที่ต้องมาคุยกันเรื่อง oryzanol ซึ่งเป็นอีกหนึ่งสารที่ถูกอุตสาหกรรมผลักดันให้เรารู้สึกว่า “ต้องกิน” เหมือนเป็นไอเทมลับสำหรับสุขภาพหัวใจ แต่เดี๋ยวก่อนนะ ทำไมสิ่งที่มนุษย์ไม่เคยต้องการมาก่อนถึงกลายเป็นสิ่งจำเป็นไปได้ ? Oryzanol หรือ gamma-oryzanol เป็นสารประกอบที่พบได้ในน้ำมันรำข้าว มีโครงสร้างเป็น sterol ester ของกรดเฟอรูลิก (Ferulic acid esters of sterols and triterpenes) ซึ่งหมายความว่ามันมีโครงสร้างคล้ายกับไฟโตสเตอรอล แต่มาพร้อมกับองค์ประกอบของสารต้านอนุมูลอิสระที่ได้จากกรดเฟอรูลิก นั่นทำให้มันถูกโฆษณาว่าเป็นสารที่ช่วยลดคอเลสเตอรอล มีฤทธิ์ต้านอนุมูลอิสระ และอาจช่วยลดความเสี่ยงโรคหัวใจ ฟังดูดีใช่ไหม ? แต่มันก็คล้ายกับไฟโตสเตอรอลเลย คือเป็นสารที่ แข่งขันกับคอเลสเตอรอลในการดูดซึม และแน่นอนว่าผลข้างเคียงก็ยังคงอยู่ นั่นคือ มันอาจลดการดูดซึมวิตามิน A, D, E, K ซึ่งเป็นวิตามินที่ละลายในไขมันและจำเป็นต่อร่างกาย นั่นหมายความว่า ในขณะที่มันช่วยลด LDL ในกระดาษ มันอาจทำให้ร่างกายขาดสารอาหารที่สำคัญไปด้วย ปัญหาที่ใหญ่กว่าคือ oryzanol พบมากใน น้ำมันรำข้าว ซึ่งเป็นหนึ่งในน้ำมันพืชที่ผ่านการแปรรูปสูง และการบริโภคน้ำมันพืชมากเกินไปนั้นสัมพันธ์กับ ภาวะอักเสบเรื้อรัง (chronic inflammation), ภาวะต้านอินซูลิน (insulin resistance), และความเสี่ยงโรคหัวใจและหลอดเลือด การที่อุตสาหกรรมบอกให้เราเพิ่ม oryzanol ในอาหาร จึงเป็นเหมือนการผลักให้ผู้คนบริโภคน้ำมันพืชมากขึ้นโดยไม่รู้ตัว ทั้งที่น้ำมันพืชโดยเฉพาะที่ผ่านกรรมวิธีอย่างน้ำมันรำข้าวมีปริมาณโอเมก้า-6 สูง ซึ่งถ้ารับมากเกินไปจะไปกระตุ้นกระบวนการอักเสบในร่างกาย เคยสังเกตไหมครับว่า น้ำมันรำข้าวมักโชว์ตัวเลขเก๋ๆของ Oryzanol แต่กลับไม่โชว์สัดส่วน โอเมก้า 6 กับ โอเมก้า 3 เทียบง่ายๆครับ น้ำมันคาโนลา มีโอเมก้า 6 ราวๆ 2200 - 2800 ต่อน้ำมัน 15 มล. (หน่วยบริโภค) น้ำมันรำข้าว มีโอเมก้า 6 ราวๆ 4,140 - 5,520 มก. ต่อน้ำมัน 15 มล. (หน่วยบริโภค) ในขณะที่โอเมก้า 3 ราวๆ 138 - 276 มก.ต่อน้ำมัน 15 มล. (หน่วยบริโภค) นี่หมายถึงสัดส่วนสูงไปถึงได้ราวๆ 40:1 ทั้งๆที่เราเข้าใจแหละว่าโอเมก้า6 ร่างกายจำเป็น แต่แต่แต่ จำเป็นไม่ได้หมายความว่าจัดหนัก เพราะสิ่งที่เราต้องพึงสังวรคือ สัดส่วนที่สมดุลระหว่าง โอเมก้า3และโอเมก้า6 ดังนั้น 40:1 ไม่เรียกว่าสมดุล ซึ่งจะกระตุ้นการอักเสบเรื้อรัง ในร่างกาย และเกี่ยวข้องกับโรคหัวใจ เบาหวาน และปัญหาสุขภาพอื่นๆ พาเหรดกันมา แต่คุณจะไม่เห็นตัวเลขนี้บนฉลากครับ ผู้ผลิตผิดไหม? จะไปผิดอะไรครับ หน่วยบริโภคแนะนำเขา 1 หน่วยบริโภคคือ 15 มิลลิลิตร หรือ 1 ช้อนโต๊ะ แค่นั้นเอง คำถามคือ มีใครใช้ตามนั้นบ้าง คุณเจียวไข่เจียวใช้เท่าไร ผัดข้าวผัดใช้เท่าไหร่ อ่ะ ผัดผักรวมมิตรก็ได้ เอาแบบเต็มเปี่ยมเลย รู้ไหมว่ามีหลายคนเอาไปทำน้ำสลัด OMG ผมถึงบอกอยู่ครับว่า คุณอย่าไปว่าผู้ผลิตเลย เขาปกป้องตัวเองไว้เรียบร้อยทุกมุมอยู่แล้วครับ ถ้าเรายังไม่อ่านฉลาก ซื้อเครื่องไฟฟ้าไม่เคยดูคู่มือ เซนต์สัญญาแบบไม่อ่านก่อน คุณจะว่าใครจริงไหมครับ ที่น่าสนใจกว่านั้นคือเราเข้าใจกันแล้วใช่ไหมว่า oryzanol ไม่ได้มาจากการกินรำข้าวตรง ๆ แต่ต้องผ่านกระบวนการสกัดที่ซับซ้อนเพื่อได้น้ำมันมาใช้ และวิธีที่อุตสาหกรรมใช้มากที่สุดก็คือ การสกัดด้วยเฮกเซน (Hexane Extraction) ซึ่งเป็นตัวทำละลายเคมีที่อาจมีสารตกค้างในผลิตภัณฑ์สุดท้าย ถึงแม้จะมีวิธีอื่นที่ปลอดภัยกว่า เช่น การสกัดด้วยเอทานอล (Ethanol Extraction), การสกัดด้วยเอนไซม์ (Enzyme-Assisted Extraction), หรือการสกัดด้วยคาร์บอนไดออกไซด์เหนือวิกฤต (Supercritical CO₂ Extraction) แต่ทั้งหมดนี้มีต้นทุนสูงกว่า ทำให้ไม่เป็นที่นิยมในอุตสาหกรรม นั่นหมายความว่า ถ้าผลิตภัณฑ์ที่คุณซื้อไม่ได้ระบุว่าใช้วิธีอื่น ส่วนใหญ่ก็คือเฮกเซนแน่นอน ข้อเสียของการบริโภค oryzanol มากเกินไปไม่ได้จบแค่การขัดขวางการดูดซึมวิตามิน เพราะการบริโภคในปริมาณสูงอาจส่งผลให้เกิด ความไม่สมดุลของฮอร์โมน เนื่องจาก oryzanol มีโครงสร้างคล้ายกับสเตอรอลในร่างกาย มันอาจไปรบกวนกระบวนการเผาผลาญของสเตอรอยด์ฮอร์โมน เช่น ฮอร์โมนเพศชาย (Testosterone) และฮอร์โมนความเครียด (Cortisol) ซึ่งในระยะยาวอาจส่งผลต่อระบบภูมิคุ้มกัน อารมณ์ และระดับพลังงานของร่างกาย ประเด็นที่สำคัญคือ ในเมื่อเรามีอาหารจากธรรมชาติที่ช่วยบำรุงหัวใจได้โดยไม่ต้องมีผลข้างเคียง เช่น ไขมันสัตว์ดี ๆ ที่มีวิตามิน A, D, E, K ครบถ้วน ทำไมต้องพึ่งพาสารสกัดจากอุตสาหกรรม ? สิ่งที่ดูเหมือนดีจากงานวิจัยในแล็บ อาจไม่ได้ดีในระยะยาวเมื่ออยู่ในร่างกายมนุษย์จริง ๆ ทีนี้เรามาดูจุดขายของ น้ำมันรำข้าวกัน - oryzanol เป็นสารธรรมชาติ ทนความร้อนสูง เอาไปใช้ทอดจะไม่เกิดการสลายตัว ทนความร้อนสูงนี่จริงเลยครับ โอริซานอลเป็นสารต้านอนุมูลอิสระในกลุ่ม Ferulic Acid Esters ซึ่งมีโครงสร้างเสถียรกว่าวิตามินอี (เทียบกับวิตามินอีเพราะ ต้านอนุมูลอิสระ และ การปกป้องไขมันจากการเกิดออกซิเดชัน ) มี จุดสลายตัวสูงกว่า 250°C ซึ่งทำให้ยังคงอยู่ได้ในอุณหภูมิที่ใช้ทอดอาหาร แล้วมันแปลว่าดีจริงไหม? ในขณะที่ น้ำมันรำข้าวมีโอเมก้า-6 สูงมาก (30-40%) ซึ่งไวต่อการเกิดออกซิเดชัน ถึงแม้โอริซานอลจะช่วยชะลอการเหม็นหืน แต่มันไม่ได้ช่วยลดการเกิด สารพิษจากไขมันไหม้ เช่น Aldehydes หรือ HNE (4-Hydroxy-2-nonenal) ที่มาจากโอเมก้า-6 หรือเปล่า??? มันคือการพูดให้เราไปโฟกัสจุดเดียวครับ "โอริซานอลทนร้อน ไม่ได้แปลว่า น้ำมันรำข้าวดีต่อสุขภาพ" เพราะโอเมก้า6 ที่ไวต่อการเกิดออกซิเดชัน รวมถึงวิตามินต่างๆ ก็ยังสูญสลายไปด้วยความร้อน นี่ยังไม่รวมถึงโทษของการกินโอริซานอลมากไปตามที่ให้ข้อมูลไว้ข้างบนด้วย นอกจากนี้ยังมีคนตั้งคำถามไว้มากมายว่า หากโอริซานอลมีผลชัดเจนต่อสุขภาพเช่นเดียวกับที่โฆษณา ทำไมจึงไม่ได้รับการพัฒนาเป็นยาอย่างจริงจัง? หรือคำตอบคือ งานวิจัยที่สนับสนุนโอริซานอลยังไม่เพียงพอ และในหลายกรณี ผลของมันอาจเกิดจาก Placebo Effect (ผลจากความเชื่อว่ามันได้ผล มากกว่าผลจริงๆ ของสารนั้น) ซึ่งเป็นลักษณะเดียวกับ "ยาหลอก" ที่ไม่ได้มีฤทธิ์ทางชีวเคมีที่ส่งผลชัดเจน - มีไลโนเลอิกสูง ใช่ครับไม่ผิดเลยในจุดนี้ ไลโนเลอิก (Linoleic acid) เป็น กรดไขมันไม่อิ่มตัวชนิดหลายพันธะ (Polyunsaturated Fatty Acid, PUFA) ที่สำคัญและจำเป็นสำหรับร่างกาย โดยเฉพาะอย่างยิ่งในการช่วยบำรุงเซลล์และระบบต่างๆ ของร่างกาย ที่สำคัญคือ ไลโนเลอิกเป็นกรดไขมันในกลุ่ม โอเมก้า-6 เป็นสิ่งที่บอกกับเราชัดๆว่า โอเมก้า6 สูงนั่นเอง ถ้าจะดึงเฉพาะข้อดีมาคุยกันก็ไม่ผิดอะไรเลยครับ เพราะโอเมก้า6 สำคัญกับร่างกายจริงๆ แต่ แต่ แต่ การรับโอเมก้า-6 ในปริมาณสูงเกินไปอาจทำให้เกิดการอักเสบในร่างกาย ซึ่งเกี่ยวข้องกับโรคต่างๆ เช่น โรคหัวใจ โรคมะเร็ง และโรคเบาหวาน อย่างที่เรารู้กัน ดังนั้นที่บอกไว้ข้างบนครับ สัดส่วนโอเมก้า 6:3 คือ 40:1 หรือใน 1 ช้อนโต๊ะ มีโอเมก้า 6 สูงถึง ราวๆ 4,140 - 5,520 มก. เรียกว่าโฆษณาไม่ผิดเลยเรื่องปริมาณ แต่จริงๆแล้วเราควรรักษาสมดุล โอเมก้า 6:3 ให้ใกล้เคียง 1:1 มากที่สุดเท่าที่ทำได้ เราก็อาจต้องตั้งคำถามอีกทีว่า การมีไลโนเลอิกสูง มันดีจริงไหม - โทโคฟีรอล (Tocopherols) เป็นสารประกอบที่อยู่ในกลุ่ม วิตามินอี เป็นสารต้านอนุมูลอิสระในร่างกาย โดยช่วยปกป้องเซลล์จากความเสียหายจากอนุมูลอิสระและช่วยชะลอการเสื่อมของเซลล์ ถูกต้องตามโฆษณา จริงๆหน้าที่หลักคือปกป้องไขมันไม่ให้เกิดการออกซิเดชัน ซึ่งสามารถช่วยยืดอายุการใช้งานของน้ำมัน หรือไม่ให้เกิดการหืน นั่นเอง แต่การทอดหรือปรุงอาหารในอุณหภูมิสูงเกินไป ก็อาจทำให้น้ำมันเกิดการออกซิเดชันและเกิดสารพิษที่เป็นอันตรายต่อร่างกายได้ อย่าลืมนะครับว่าคำแนะนำในการใช้น้ำมันรำข้าว กลับชูการเหมาะกับอาหารทอดอุณหภูมิสูง - โทโคไทรอีนอล (Tocotrienols) เป็นส่วนหนึ่งของกลุ่ม วิตามินอี เช่นกัน การบริโภคมากเกินไป การรับประทาน โทโคไทรอีนอลในปริมาณมาก อาจมีผลข้างเคียงที่ไม่พึงประสงค์ เช่น ส่งผลกระทบต่อการดูดซึมวิตามินอื่นๆ ในร่างกายโดยเฉพาะวิตามิน K ซึ่งอาจทำให้เกิดปัญหาการแข็งตัวของเลือด, ทำให้ตับทำงานหนักขึ้นในการจัดการกับสารนี้ ซึ่งอาจส่งผลเสียต่อการทำงานของตับระยะยาว สุดท้ายแล้ว เราต้องกลับมาตั้งคำถามว่า เราอยากให้สุขภาพของเราถูกกำหนดโดยการตลาดของอุตสาหกรรม หรือโดยสิ่งที่ธรรมชาติออกแบบมาให้เราตั้งแต่แรก ? ถ้าจะดูแลหัวใจจริง ๆ การกินอาหารที่มนุษย์วิวัฒนาการมากับมันมาตลอด เช่น เนื้อสัตว์ ไข่ ตับ และไขมันดี ๆ อาจเป็นคำตอบที่เรียบง่ายและมีเหตุผลมากกว่าการไล่ตามสารสกัดที่อุตสาหกรรมบอกว่าจำเป็น แต่ธรรมชาติอาจไม่เคยเห็นว่ามันสำคัญเลยก็ได้ #pirateketo #ฉลาก3รู้ #กูต้องรู้มั๊ย #ม้วนหางสิลูก @ 57d1a264:69f1fee1
2025-03-29 17:15:17 - Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box. - If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust. - “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options. - Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic. originally posted at https://stacker.news/items/928800
@ 57d1a264:69f1fee1
2025-03-29 17:15:17 - Once activated, "Accept From Any Mint” is the default setting. This is the easiest way to get started, let's the user start acceptance Cashu ecash just out of the box. - If someone does want to be selective, they can choose “Accept From Trusted Mints,” and that brings up a field where they can add specific mint URLs they trust. - “Find a Mint” section on the right with a button links directly to bitcoinmints.com, already filtered for Cashu mints, so users can easily browse options. - Mint info modal shows mint technical details stuff from the NUT06 spec. Since this is geared towards the more technical users I left the field names and NUT number as-is instead of trying to make it more semantic. originally posted at https://stacker.news/items/928800 @ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800
@ 6389be64:ef439d32
2025-04-03 21:32:58Brewing Biology Episode 1068 of Bitcoin And . . . is LIVE! This episode of Bitcoin And dives into Brewing Biology—a regenerative system combining compost tea, biochar, Bitcoin mining, and carbon credits—developed through a deep, idea-driven conversation with ChatGPT. LISTEN HERE --> https://fountain.fm/episode/p0DmvPzxirDHh2l68zOX <-- LISTEN HERE The future of Bitcoin isn’t just about code or money—it’s about soil. A groundbreaking fusion of biology, technology, and financial innovation might change the rules of agriculture, offering landowners a path to profitability while Healing our soils. At the heart of this revolution is biochar, a form of charcoal that supercharges soil health. When mixed with compost tea and microbial inoculants, this carbon-rich material becomes a game-changer. Biochar’s porous structure acts as a microbial hotel, hosting fungi like arbuscular mycorrhizal fungi (AMF) and bacteria such as Bacillus subtilis. These organisms form symbiotic networks that boost nutrient absorption and secrete glomalin—a natural “glue” that binds soil, preventing erosion. But here’s the twist: this system doesn’t just heal the earth; it also generates revenue. Biochar’s Hidden Superpower: Adsorption & Buffering Biochar’s porous structure acts as a molecular storage hub. Unlike absorption (soaking up water like a sponge), adsorption is a chemical process where water and nutrients cling to biochar’s surfaces. A single gram of biochar has the surface area of a basketball court, creating a lattice of microscopic nooks and crannies. This allows it to: Lock in moisture: Biochar retains up to 10x its weight in water, acting like a “soil battery” that releases hydration slowly during droughts. Hoard nutrients: It buffers nitrogen, phosphorus, potassium, and micronutrients in its pores, preventing leaching. Plants access these nutrients gradually, reducing fertilizer needs. Stabilize pH: Biochar’s alkaline nature buffers acidic soils, creating a neutral environment where microbes and roots thrive. This buffering effect means plants face fewer nutrient and water spikes or shortages, ensuring steady growth even in erratic climates. The Carbon Math Every ton of biochar (which is ~85% carbon by weight) sequesters 3.12 tons of CO₂ (using the 1:3.67 carbon-to-CO₂ ratio). With carbon credits trading at $42–$60/ton, a 1,000-acre project applying 1 pound of biochar per linear foot (via a three-shank plow at 2-foot spacing) could sequester ~12,000 tons of CO₂ annually—generating $504,000–$720,000 in carbon credit revenue. Tools for the Revolution The Keyline Plow fractures subsoil to inject biochar slurry 30–45cm deep, revitalizing compacted land. For smaller plots, the VOGT Geo Injector delivers pinpoint inoculations—think of it as a soil “injection gun” for lawns, golf courses, or urban gardens. These methods ensure biochar stays where it’s needed, turning even parched landscapes into carbon sinks. Bitcoin’s Role in the Loop Biochar production generates syngas—a byproduct that fuels electric generators for Bitcoin mining. This closed-loop system turns agricultural waste into energy, creating dual revenue streams: carbon credits and mining income. The Market Potential Farmers, ranchers, and eco-conscious landowners aren’t the only beneficiaries. Golf courses can slash water use and homeowners can boost lawn resilience. Why This Matters This isn’t just farming—it’s a movement. By marrying soil science with economics, we can prove that healing the planet and profiting go hand in hand. Whether you’re a Bitcoin miner, a farmer, or an eco-entrepreneur, this system offers a blueprint for a future where every acre works for you—and the planet. The takeaway? Regenerative agriculture isn’t a trend. It’s the next gold rush—except this time, the gold is carbon, soil, and sats.--- P.S. – If you’re ready to turn your land into a carbon credit powerhouse (and maybe mine some Bitcoin along the way), the soil is waiting. You can read the full article, Brewing Biology HERE -> https://the-bitcoin-and-Podcast.ghost.io/ghost/#/editor/post/67e5922fa289aa00088da3c6 originally posted at https://stacker.news/items/933800 @ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in. By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to. I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome ! And now lets get to the first batch of artists I want to share with you. ### Eugene Gorbachenko ### nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art. ![!(image)[https://m.primal.net/PxJc.png]]() ### Siritravelsketch ### nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality. ![!(image)[https://m.primal.net/PxJj.png]]() ### BureuGewas ### nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself. ![!(image)[https://m.primal.net/PxKS.png]]() You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out ! With love, Agi Choote
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in. By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to. I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome ! And now lets get to the first batch of artists I want to share with you. ### Eugene Gorbachenko ### nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art. ![!(image)[https://m.primal.net/PxJc.png]]() ### Siritravelsketch ### nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality. ![!(image)[https://m.primal.net/PxJj.png]]() ### BureuGewas ### nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself. ![!(image)[https://m.primal.net/PxKS.png]]() You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out ! With love, Agi Choote @ 07f367da:0e76880d
2025-04-03 17:59:21윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다. 자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다. 당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다. 선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다. 무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다. 충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다. 사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다. 타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다.
@ 07f367da:0e76880d
2025-04-03 17:59:21윤석열 탄핵 선고를 앞둔 4월 3일. 우리 노동조합은 서울 마포구 소재의 한 활동지원기관 앞에서 선전전을 진행했다. 노동조합은 한 활동지원사의 민원을 통해 해당 활동지원기관이 일요일에 일해도 평일 임금을 지급한다는 사실을 파악했다. 활동지원사의 민원에 관심을 가진 한 언론사의 기자는 활동지원기관과 구청, 서울시, 노조에 문의하며 팩트체크를 진행하고 있는데, 이 과정에서 노조는 해당 기관이 일요일에 일을 해도 평일 임금을 지급하고 있다는 사실을 명확히 확인했다. 자신이 받는 임금에 대한 사실관계를 노동자들은 잘 알지 못한다. 활동지원사는 기관에 자신의 임금에 대해 문의해도 속 시원한 답을 듣지 못한다. 활동지원사들이 하나같이 하는 이야기가 기관에 물어봐도 제대로 설명을 해주지 않는다는 하소연이다. 당사자 활동지원사는 노조에 민원을 제기하고, 또 기자가 취재한 내용들을 통해서야 자신의 임금이 자신도 모르게 어떻게 변화했는지를 알아가고 있다. 사업장의 임급지급 행위에 대한 가치판단이나 평가 이전에 노동자들은 그 사실 자체를 모를 가능성이 높다. 노조는 이 사실을 활동지원사들에게 알리려 선전전을 진행하기로 했다. 선전전 진행 중 정말 충격적인 경험을 했다. 노동조합의 선전활동은 정당한 노조활동이고 일상적인 활동이다. 여태 여러 사업장에서 선전활동을 했지만, 이런 경우는 정말 처음이었다. 사업장들은 신경 거슬러 하고 적대적인 대우를 하곤 했지만, 가장 강한 대처가 경찰에 신고하여 공권력의 개입을 요청하고, 경찰은 충돌을 방지하는 선에서 대처한다. 그런데 오늘은 장애인 기관장이 선전활동을 하지 말라고 계속 항의하며 방해하더니 소속 활동지원팀 인력은 노동조합이 활동지원사에게 선전물을 전달하려 하니 몸으로 막기까지 한다. 무엇을 그렇게 숨기고 싶을까? 노동조합의 활동을 몸으로 막으면서까지 싫어할 이유가 무엇일까? 노동조합의 활동이 그들에게 무엇으로 다가갔을까? 여러 질문이 든다. 충격적인 것은 이 기관의 대표가 우리노조가 예전에 청와대 앞에서 기자회견 할 때 연대 발언을 하러 왔던 활동가라는 점이다. 장애인 당사자이자 인권운동 활동가가 사용자로, 그리고 사회복지사 노동자들이 전담인력으로 고용되어 사측을 대신해 활동지원사 노동자들이 응당 자신에 대해 알아야 할 사항을 은폐한다. 사장이 되어 권력을 행사하면서도 장애인이라는 정체성으로 자신의 지위를 지우려 하고, 전담인력이라는 지위로 노동자들을 지휘하면서도 같은 노동자라며 위계를 삭제한다. 그리고 정작 현장에서 장애인에게 활동지원을 제공하는 활동지원사들은 대부분 고령의 여성들로 정보약자에 해당한다. 우리에게도 민주주의가 올까. 나는 저들이 활동으로 세상을 좋게 만드는 것을 상쇄할 정도로 더 세상을 나쁘게 만들고 있다고 생각한다. 타인에 의해 돈벌이 수단으로 이용당하는 사람은 자신 또한 타인을 돈벌이 수단으로 활용할 가능성이 높다. 그 타인에는 장애인도 포함된다. 나는 시설사회가 끝나도 장애인학대가 끝나리라는 믿음이 없다. 우리는 어차피 서로를 돈벌이 수단으로만 삼는 사회에서 살고 있기 때문이다. @ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 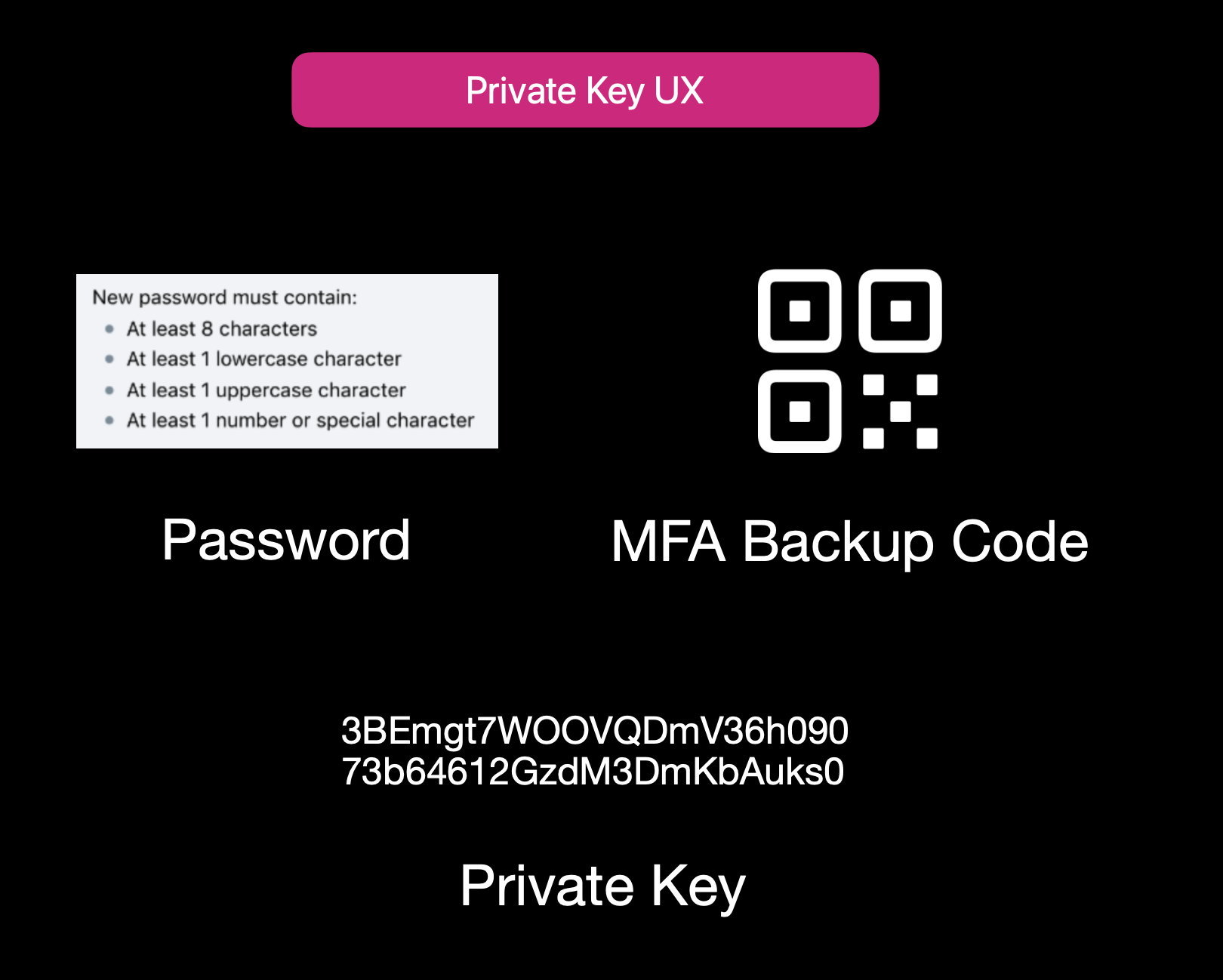Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 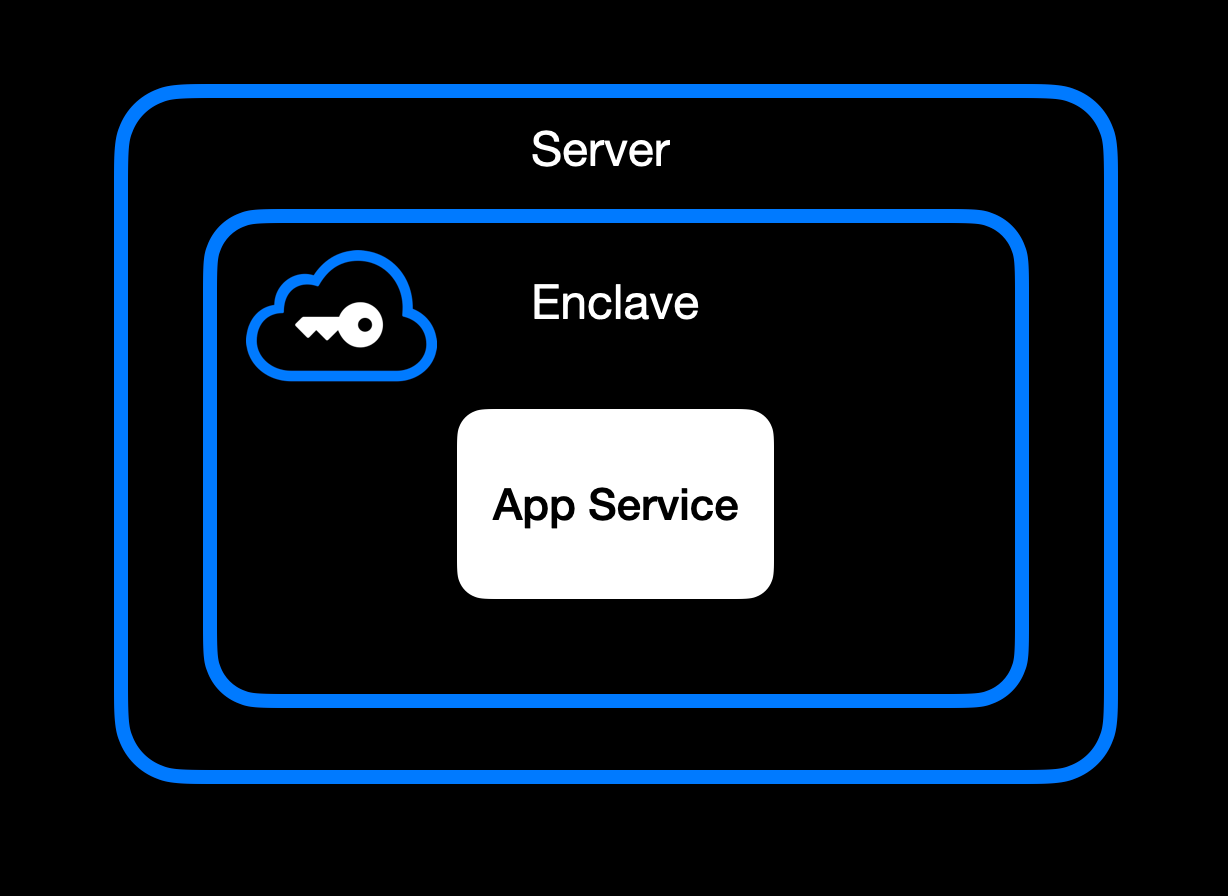App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 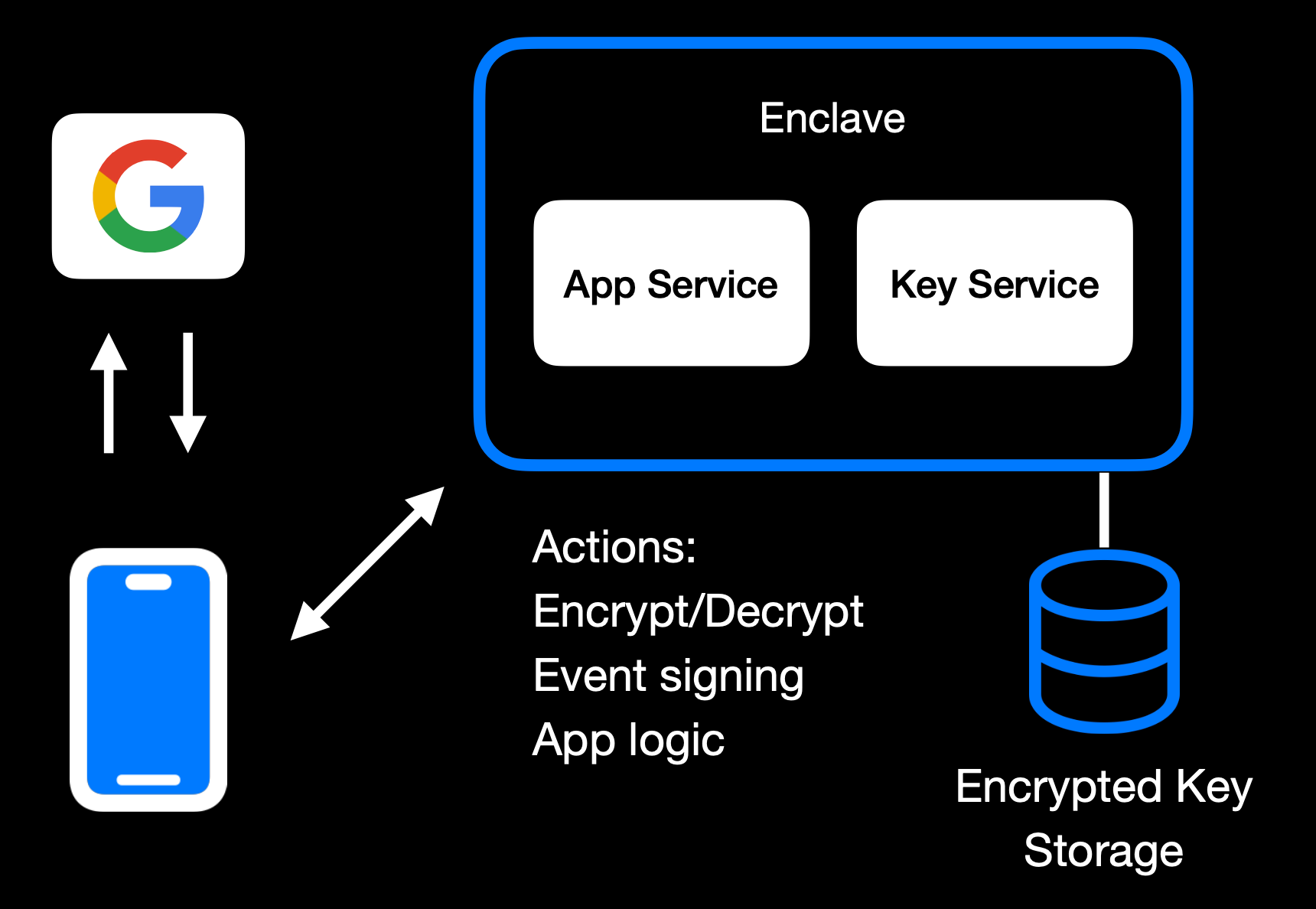Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 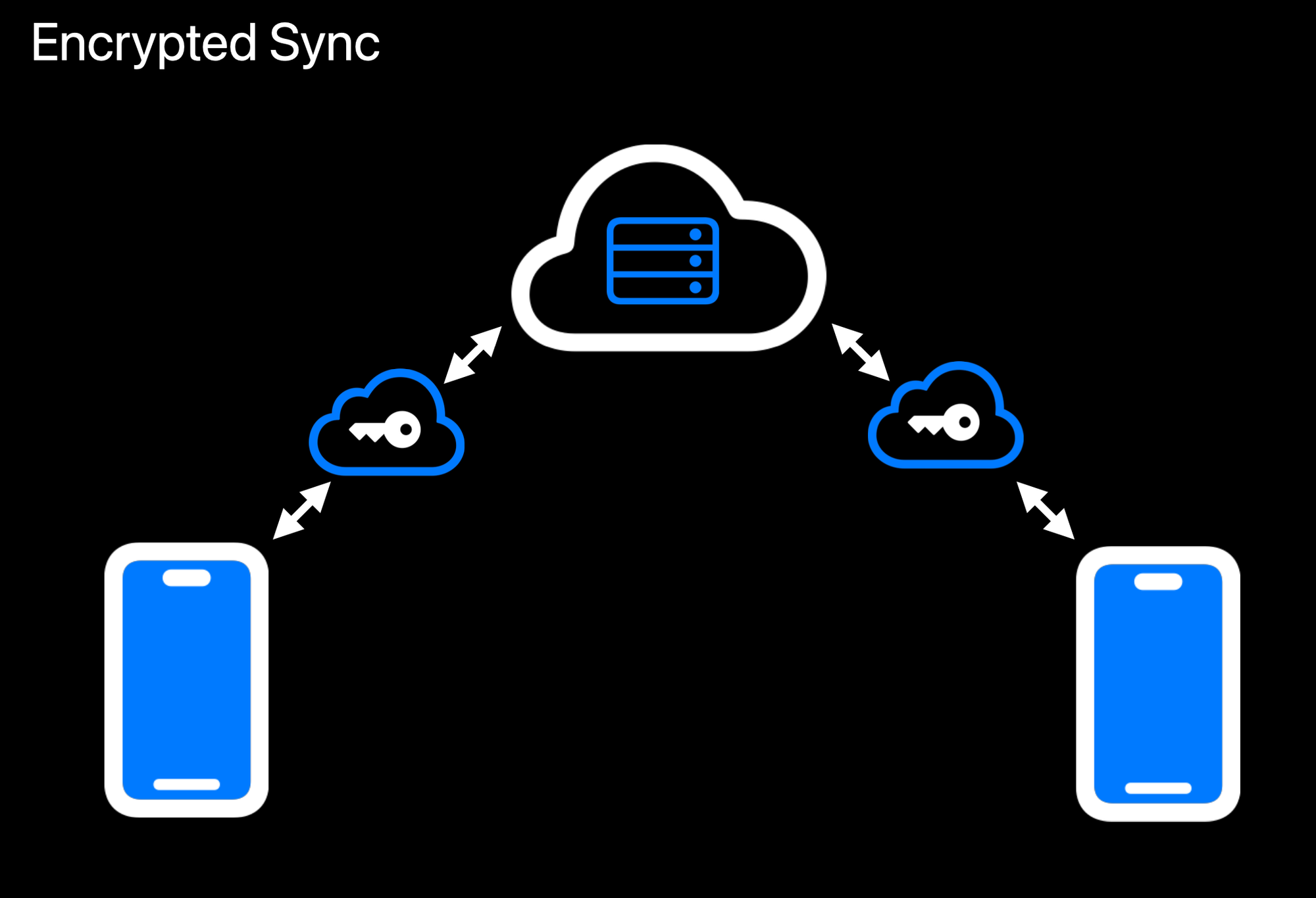Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 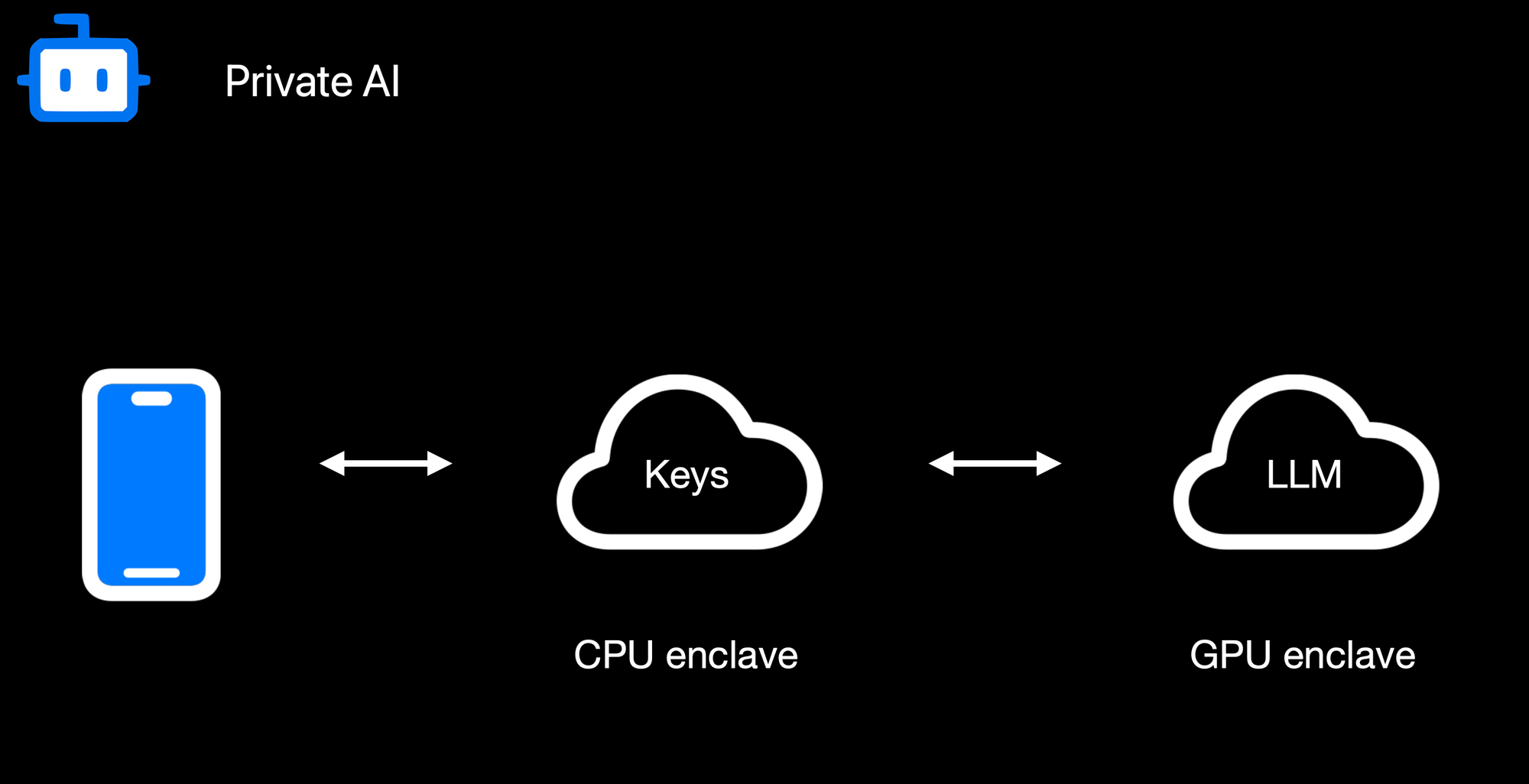Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 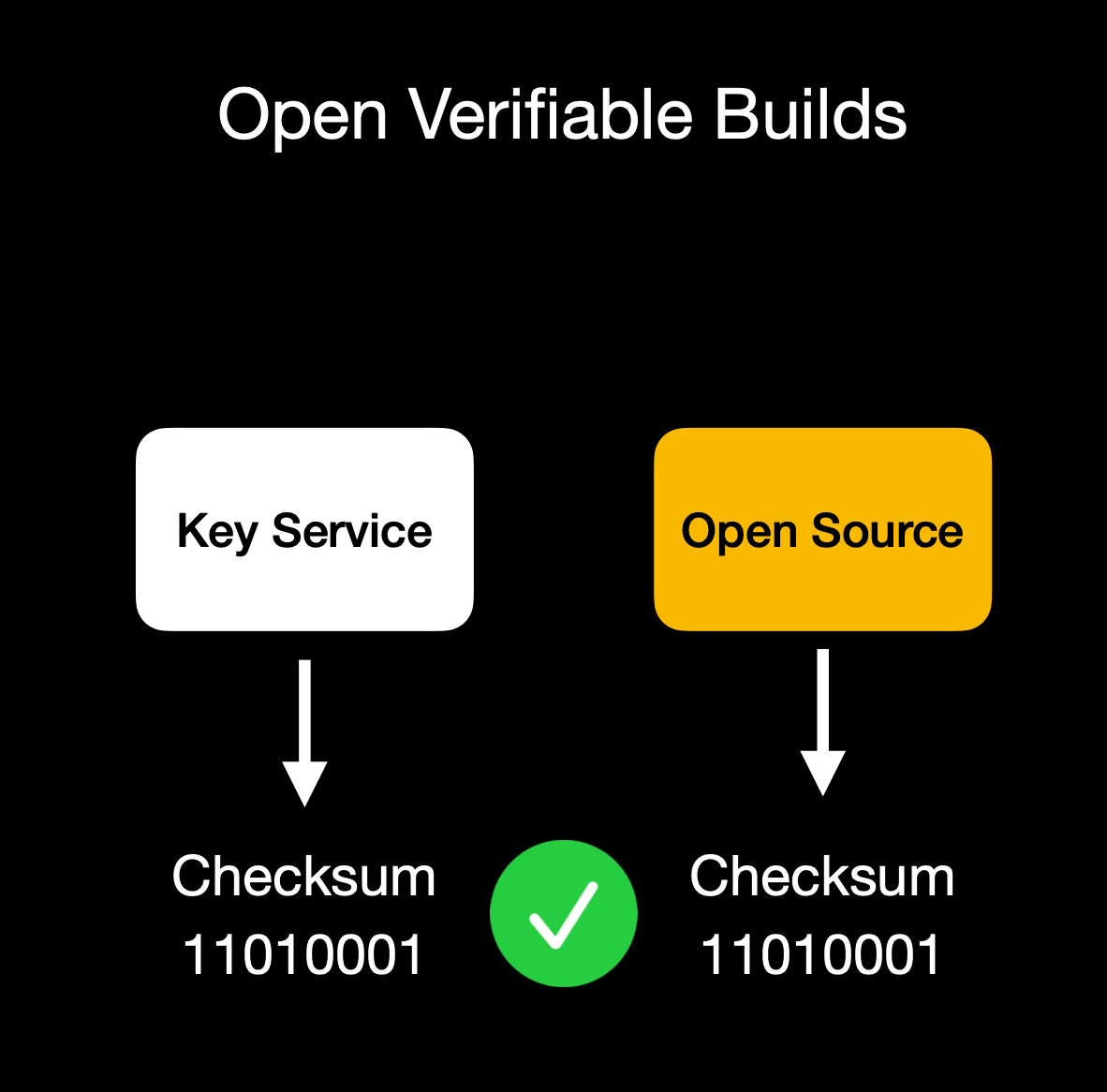Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.*
@ df173277:4ec96708
2025-02-07 00:41:34## **Building Our Confidential Backend on Secure Enclaves** With our newly released [private and confidential **Maple AI**](https://trymaple.ai/?ref=blog.opensecret.cloud) and the open sourcing of our [**OpenSecret** platform](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud) code, I'm excited to present this technical primer on how we built our confidential compute platform leveraging **secure enclaves**. By combining AWS Nitro enclaves with end-to-end encryption and reproducible builds, our platform gives developers and end users the confidence that user data is protected, even at runtime, and that the code operating on their data has not been tampered with. ## **Auth and Databases Today** As developers, we live in an era where protecting user data means "encryption at rest," plus some access policies and procedures. Developers typically run servers that: 1. Need to register users (authentication). 2. Collect and process user data in business-specific ways, often on the backend. Even if data is encrypted at rest, it's commonly unlocked with a single master key or credentials the server holds. This means that data is visible during runtime to the application, system administrators, and potentially to the hosting providers. This scenario makes it difficult (or impossible) to guarantee that sensitive data isn't snooped on, memory-dumped, or used in unauthorized ways (for instance, training AI models behind the scenes). ## **"Just Trust Us" Isn't Good Enough** In a traditional server architecture, users have to take it on faith that the code handling their data is the same code the operator claims to be running. Behind the scenes, applications can be modified or augmented to forward private information elsewhere, and there is no transparent way for users to verify otherwise. This lack of proof is unsettling, especially for services that process or store highly confidential data. Administrators, developers, or cloud providers with privileged access can inspect memory in plaintext, attach debuggers, or gain complete visibility into stored information. Hackers who compromise these privileged levels can directly access sensitive data. Even with strict policies or promises of good conduct, the reality is that technical capabilities and misconfigurations can override words on paper. If a server master key can decrypt your data or can be accessed by an insider with root permissions, then "just trust us" loses much of its credibility. The rise of AI platforms amplifies this dilemma. User data, often full of personal details, gets funneled into large-scale models that might be training or fine-tuning behind the scenes. Relying on vague assurances that "we don't look at your data" is no longer enough to prevent legitimate concerns about privacy and misuse. Now more than ever, providing a **strong, verifiable** guarantee that data remains off-limits, even when actively processed, has become a non-negotiable requirement for trustworthy services. ## **Current Attempts at Securing Data** 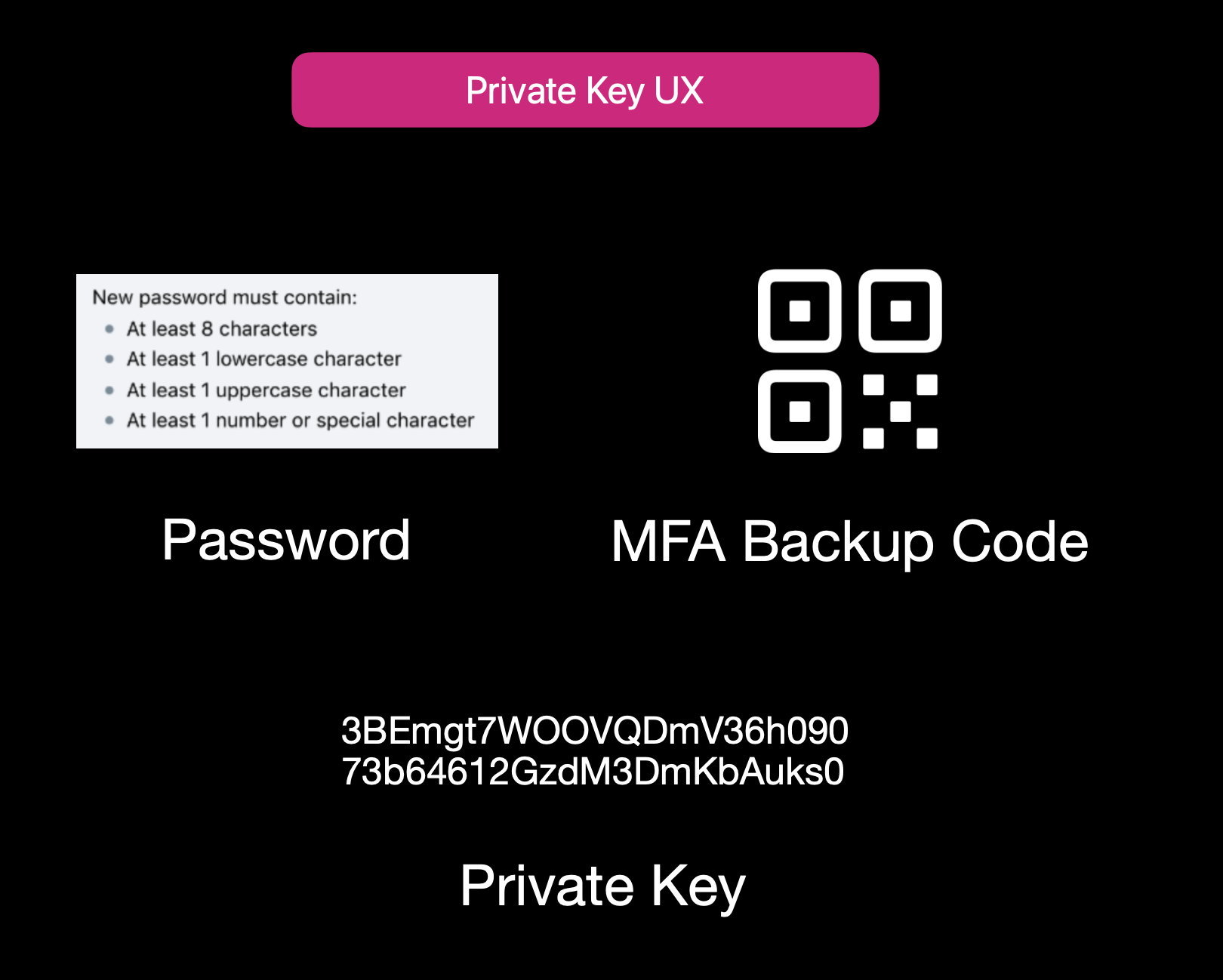Current User Experience of E2EE Apps While properly securing data is not easy, it isn't to say that no one is trying. Some solutions use **end-to-end encryption** (E2EE), where user data is encrypted client-side with a password or passphrase, so not even the server operator can decrypt it. That approach can be quite secure, but it also has its **limitations**: 1. **Key Management Nightmares**: If a user forgets their passphrase, the data is effectively lost, and there's no way to recover it from the developer's side. 2. **Feature Limitations**: Complex server-side operations (like offline/background tasks, AI queries, real-time collaboration, or heavy computation) can't easily happen if the server is never capable of processing decrypted data. 3. **Platform Silos**: Some solutions rely on iCloud, Google Drive, or local device storage. That can hamper multi-device usage or multi-OS compatibility. Other approaches include self-hosting. However, these either burden users with dev ops overhead or revert to the "trust me" model for the server if you "self-host" on a cloud provider. ## **Secure Enclaves** ### **The Hybrid Approach** Secure enclaves offer a compelling middle ground. They combine the privacy benefits of keeping data secure from prying admins while still allowing meaningful server-side computation. In a nutshell, an enclave is a protected environment within a machine, isolated at the hardware level, so that even if the OS or server is compromised, the data and code inside the enclave remain hidden. 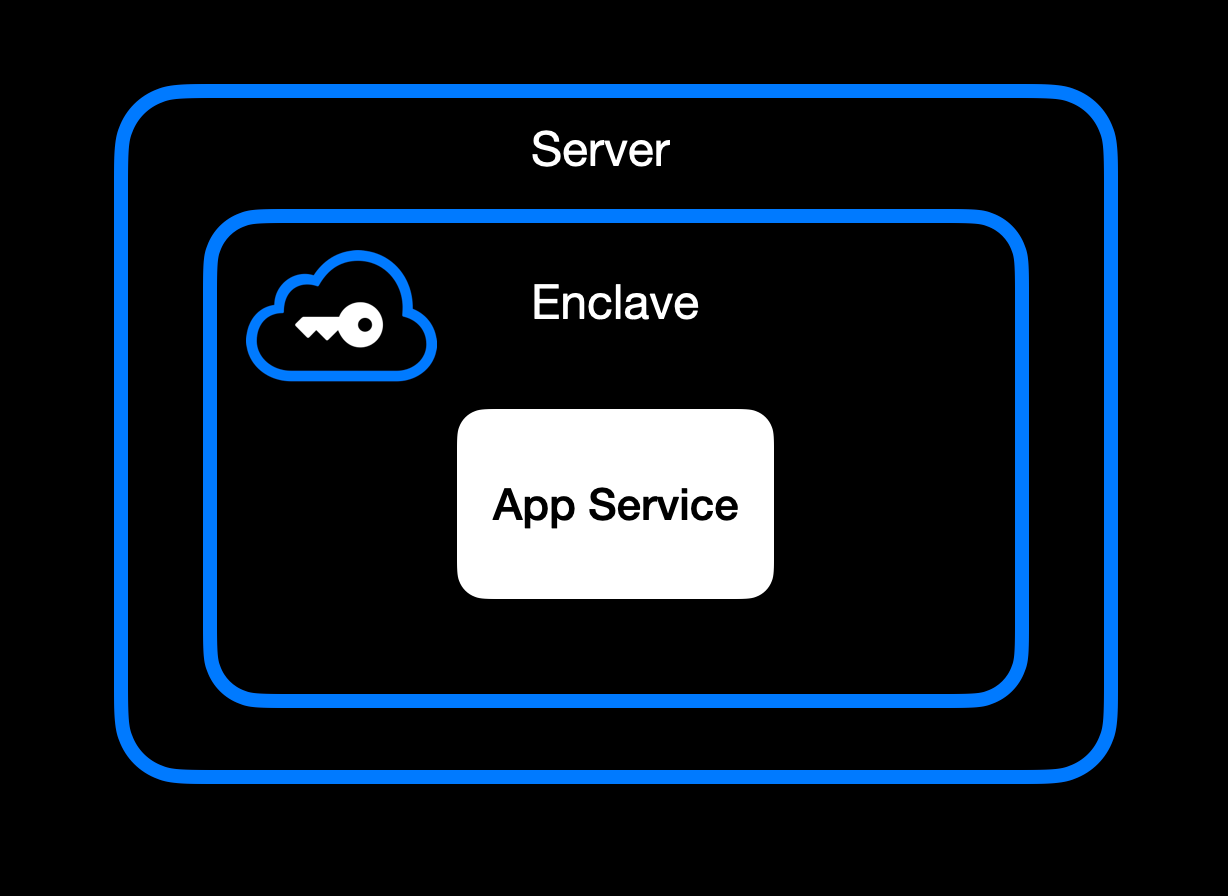App Service Running Inside Secure Enclave ### **High-Level Goal of Enclaves** Enclaves, also known under the broader umbrella of **confidential computing**, aim to:\ • **Lock down data** so that only authorized code within the enclave can process the original plaintext data.\ • **Deny external inspection** by memory dumping, attaching a debugger, or intercepting plaintext network traffic.\ • **Prove** to external users or services that an enclave is running unmodified, approved code (this is where **remote attestation** comes in). ### **Different Secure Enclave Solutions** [**AMD SEV**](https://www.amd.com/en/developer/sev.html?ref=blog.opensecret.cloud) **(Secure Encrypted Virtualization)** encrypts an entire virtual machine's memory so that even a compromised hypervisor cannot inspect or modify guest data. Its core concept is "lift-and-shift" security. No application refactoring is required because hardware-based encryption automatically protects the OS and all VM applications. Later enhancements (SEV-ES and SEV-SNP) added encryption of CPU register states and memory integrity protections, further limiting hypervisor tampering. This broad coverage means the guest OS is included in the trusted boundary. AMD SEV has matured into a robust solution for confidential VMs in multi-tenant clouds. [**Intel TDX**](https://www.intel.com/content/www/us/en/developer/tools/trust-domain-extensions/overview.html?ref=blog.opensecret.cloud) **(Trust Domain Extensions)** shifts from process-level enclaves to full VM encryption, allowing an entire guest operating system and its applications to run in an isolated "trust domain." Like AMD SEV, Intel TDX encrypts and protects all memory the VM uses from hypervisors or other privileged software, so developers do not need to refactor their code to benefit from hardware-based confidentiality. This broader scope addresses many SGX limitations, such as strict memory bounds and the need to split out enclave-specific logic, and offers a more straightforward "lift-and-shift" path for running existing workloads privately. While SGX is now deprecated, TDX carries forward the core confidential computing principles but applies them at the virtual machine level for more substantial isolation, easier deployment, and the ability to scale up to large, memory-intensive applications. [**Apple Secure Enclave and Private Compute**](https://security.apple.com/blog/private-cloud-compute/?ref=blog.opensecret.cloud) is a dedicated security coprocessor embedded in most Apple devices (iPhones, iPads, Macs) and now extended to Apple's server-side AI infrastructure. It runs its own microkernel, has hardware-protected memory, and securely manages operations such as biometric authentication, key storage, and cryptographic tasks. Apple's "Private Compute" approach in the cloud brings similar enclave capabilities to server-based AI, enabling on-device-grade privacy even when requests are processed in Apple's data centers. [**AWS Nitro Enclaves**](https://docs.aws.amazon.com/enclaves/latest/user/nitro-enclave.html?ref=blog.opensecret.cloud) carve out a tightly isolated "mini-VM" from a parent EC2 instance, with its own vCPUs and memory guarded by dedicated Nitro cards. The enclave has no persistent storage and no external network access, significantly reducing the attack surface. Communication with the parent instance occurs over a secure local channel (vsock), and AWS offers hardware-based attestation so that secrets (e.g., encryption keys from AWS KMS) can be accessed only to the correct enclave. This design helps developers protect sensitive data or code even if the main EC2 instance's OS is compromised. [**NVIDIA GPU TEEs**](https://www.nvidia.com/en-us/data-center/solutions/confidential-computing/?ref=blog.opensecret.cloud) **(Hopper H100 and Blackwell)** extend confidential computing to accelerated workloads by encrypting data in GPU memory and ensuring that even a privileged host cannot view or tamper with it. Data moving between CPU and GPU is encrypted in transit, so sensitive model weights or inputs remain protected during AI training or inference. NVIDIA's hardware and drivers handle secure data paths under the hood, allowing confidential large language model (LLM) workloads and other GPU-accelerated computations to run with minimal performance overhead and strong security guarantees. ### **Key Benefits** One major advantage of enclaves is their ability to **keep memory completely off-limits** to outside prying eyes. Even administrators who can normally inspect processes at will are blocked from peeking into the enclave's protected memory space. The enclave model is a huge shift in the security model: it prevents casual inspection and defends against sophisticated memory dumping techniques that might otherwise leak secrets or sensitive data. Another key benefit centers on cryptographic keys that are **never exposed outside the enclave**. Only verified code running inside the enclave environment can run decryption or signing operations, and it can only do so while that specific code is running. This ensures that compromised hosts or rogue processes, even those with high-level privileges, are unable to intercept or misuse the keys because the keys remain strictly within the trusted boundary of the hardware. Enclaves can also offer the power of **remote attestation**, allowing external clients or systems to confirm that they're speaking to an authentic, untampered enclave. By validating the hardware's integrity measurements and enclave-specific proofs, the remote party can be confident in the underlying security properties, an important guarantee in multi-tenant environments or whenever trust boundaries extend across different organizations and networks. Beyond that, **reproducible builds** can create a verifiable fingerprint proving which binary runs in the enclave. This is a step above a simple "trust us" approach. Anyone can independently recreate the enclave image and verify the resulting cryptographic hash by using a reproducible build system (for example, [our NixOS-based solution](https://github.com/OpenSecretCloud/opensecret/blob/master/flake.nix?ref=blog.opensecret.cloud)). If it matches, then users and developers know precisely how code handles their data, boosting confidence that no hidden changes exist. It's worth noting that although enclaves shield you from software devs, cloud providers, and insider threats, you do have to trust the **hardware vendor** (Intel, AMD, Apple, AWS, or NVIDIA) to implement their microcode and firmware securely. The entire enclave model could be theoretically undermined if a CPU maker's root keys or manufacturing process were compromised. Fortunately, these companies undergo extensive audits and firmware validations (often with third-party researchers), and their remote attestation mechanisms allow you to confirm specific firmware versions before trusting an enclave. While this adds a layer of "vendor trust," it's still a far more contained risk than trusting an entire operating system or cloud stack, so enclaves remain a strong step forward in practical, confidential computing. ## **How We Use Secure Enclaves** Now that we've covered the general idea of enclaves let's look at how we specifically implement them in OpenSecret, our developer platform for handling user auth, private keys, data encryption, and AI workloads. ### **Our Stack: AWS Nitro + Nvidia TEE** • **AWS Nitro Enclaves for the backend**: All critical logic, authentication, private key management, and data encryption/decryption run inside an AWS Nitro Enclave. • **Nvidia Trusted Execution for AI**: For large AI inference (such as the Llama 3.3 70B model), we utilize Nvidia's GPU-based TEEs to protect even GPU memory. This means users can feed sensitive data to the AI model **without** exposing it in plaintext to the GPU providers or us as the operator. [Edgeless Systems](https://www.edgeless.systems/?ref=blog.opensecret.cloud) is our Nvidia TEE provider, and due to the power of enclave verification, we don't need to worry about who runs the GPUs. We know requests can't be inspected or tampered with. ### **End-to-End Encryption from Client to Enclave** 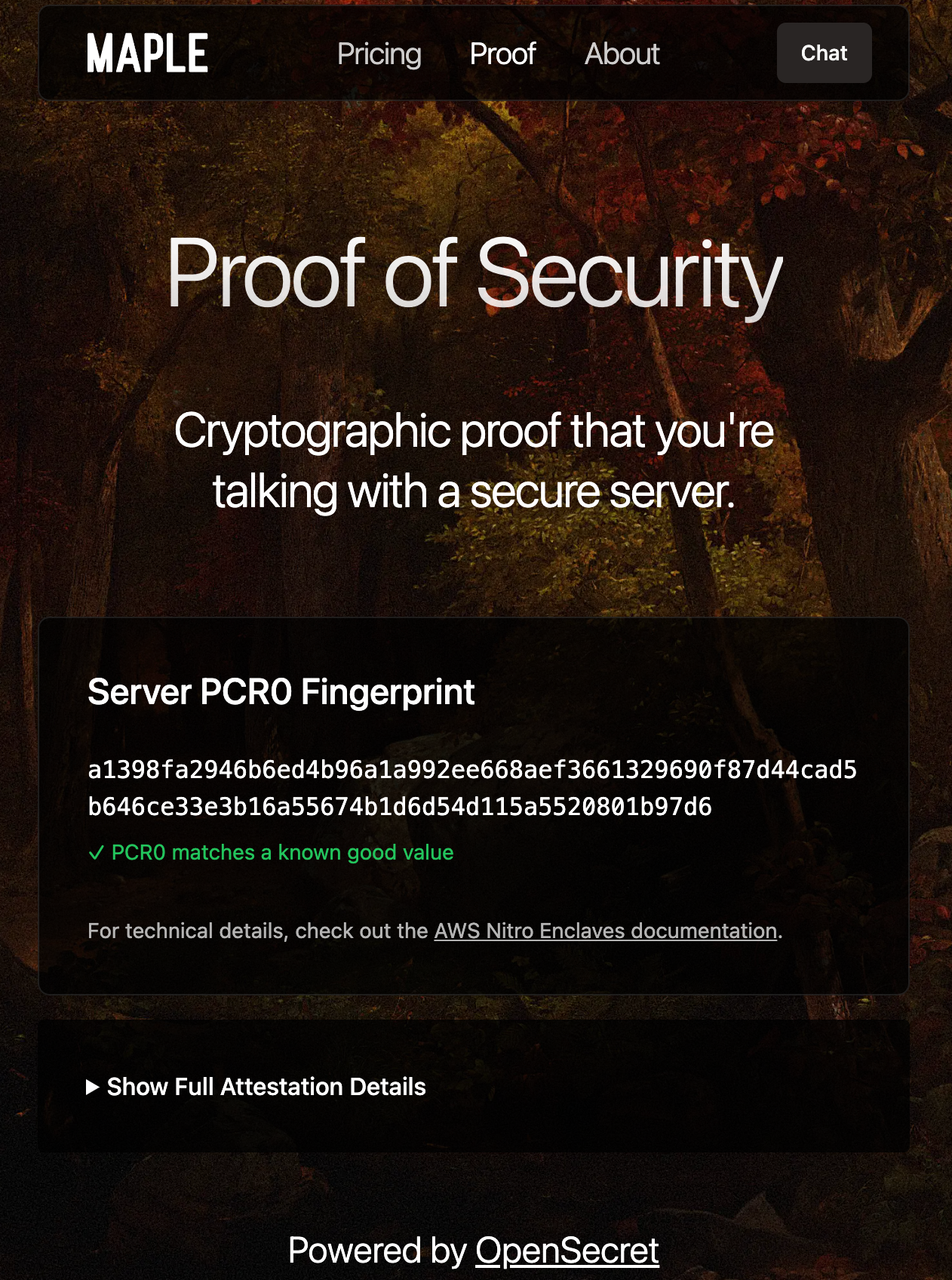Client-side Enclave Attestation from Maple AI Before login or data upload, the user/client verifies the **enclave attestation** from our platform. This process proves that the specific Nitro Enclave is genuine and runs the exact code we've published. You can check this out live on [Maple AI's attestation page](https://trymaple.ai/proof?ref=blog.opensecret.cloud). Based on the attestation, the client establishes a secure ephemeral communication channel that only that enclave can decrypt. While we take advantage of SSL, it is typically not terminated inside the enclave itself. To ensure there's full encrypted data transfer all the way through to the enclave, we establish this additional handshake based on the attestation document that is used for all API requests during the client session. From there, the user's credentials, private keys, and data pass through this secure channel directly into the enclave, where they are decrypted and processed according to the user's request. ### **In-Enclave Operations** At the core of OpenSecret's approach is the conviction that security-critical tasks must happen inside the enclave, where even administrative privileges or hypervisor-level compromise cannot expose plaintext data. This encompasses everything from when a user logs in to creating and managing sensitive cryptographic keys. By confining these operations to a protected hardware boundary, developers can focus on building their applications without worrying about accidental data leaks, insider threats, or malicious attempts to harvest credentials. The enclave becomes the ultimate gatekeeper: it controls how data flows and ensures that nothing escapes in plain form. User Auth Methods running inside Enclave A primary example is **user authentication**. All sign-in workflows, including email/password, OAuth, and upcoming passkey-based methods, are handled entirely within the enclave. As soon as a user's credentials enter our platform through the encrypted channel, they are routed straight into the protected environment, bypassing the host's operating system or any potential snooping channels. From there, authentication and session details remain in the enclave, ensuring that privileged outsiders cannot intercept or modify them. By centralizing these identity flows within a sealed environment, developers can assure their users that no one outside the enclave (including the cloud provider or the app's own sysadmins) can peek at, tamper with, or access sensitive login information. 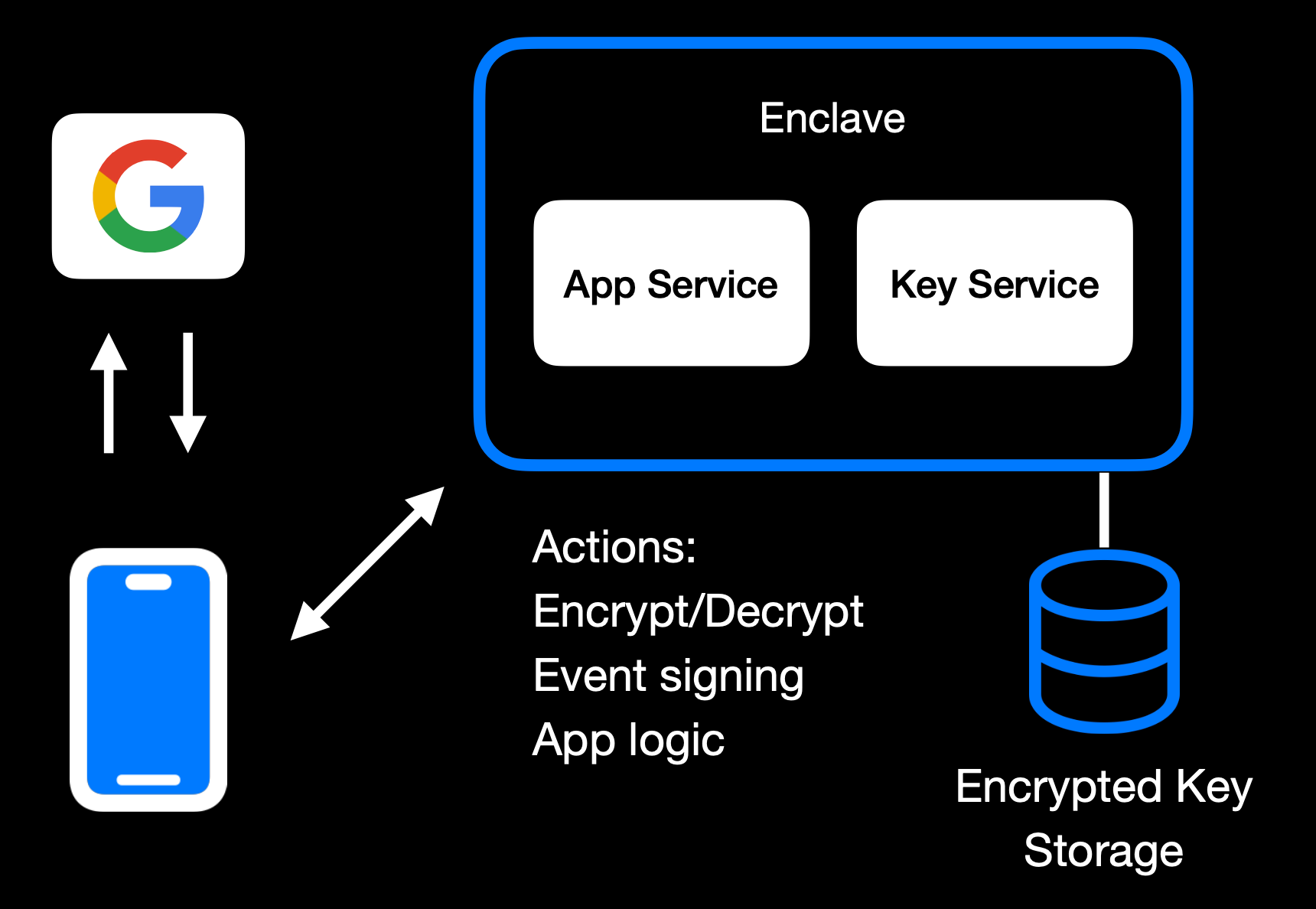Main Enclave Operations in OpenSecret The same principle applies to **private key management**. Whether keys are created fresh in the enclave or securely transferred into it, they remain sealed away from the rest of the system. Operations like digital signing or content decryption happen only within the hardware boundary, so raw keys never appear in any log, file system, or memory space outside the enclave. Developers retain the functionality they need, such as verifying user actions, encrypting data, or enabling secure transactions without ever exposing keys to a broader (and more vulnerable) attack surface. User backup options exist as well, where the keys can be securely passed to the end user. 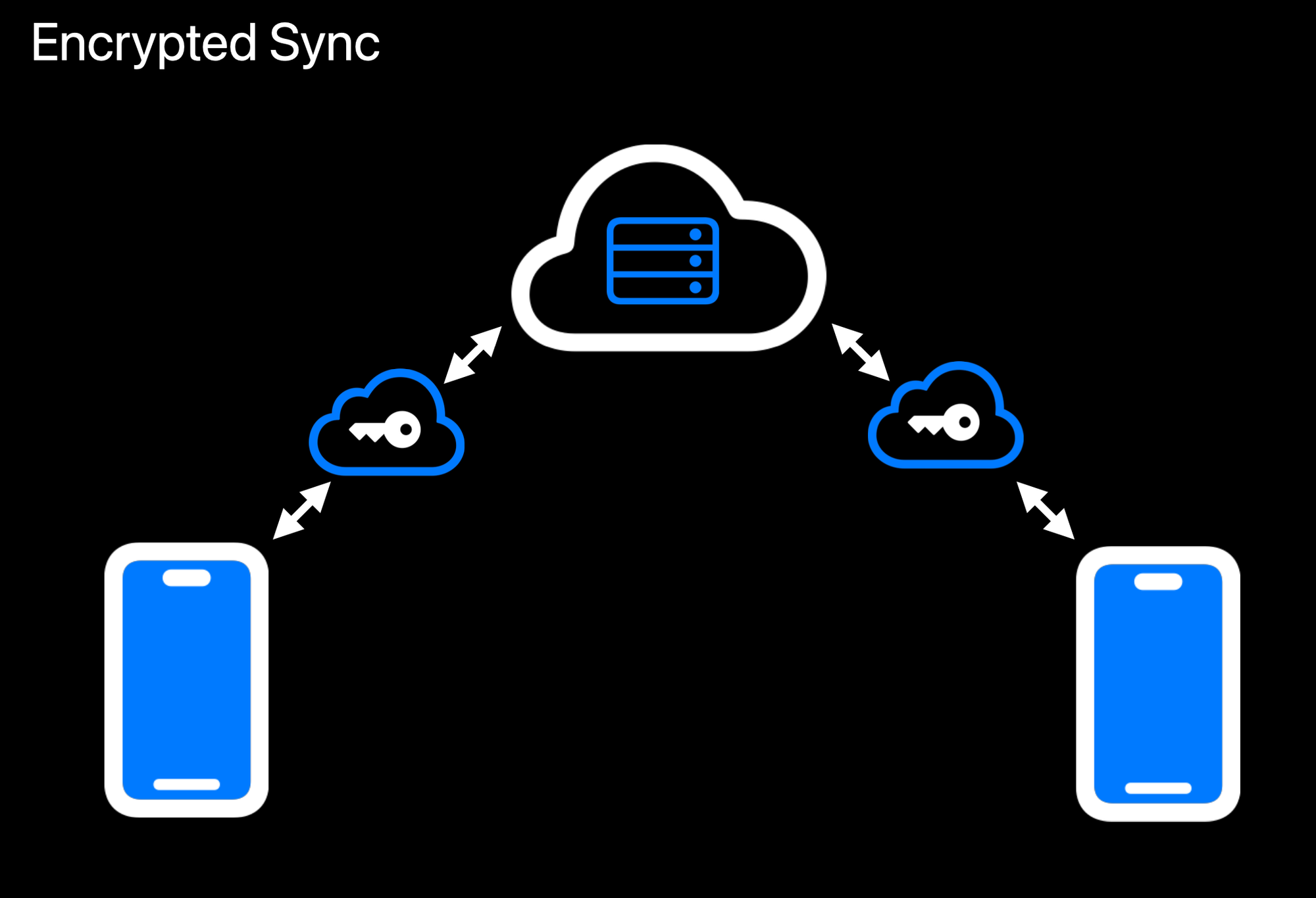Realtime Encrypted Data Sync on Multiple Devices Another crucial aspect is **data encryption at rest**. While user data ultimately needs to be stored somewhere outside the enclave, the unencrypted form of that data only exists transiently inside the protected environment. Encryption and decryption routines run within the enclave, which holds the encryption keys strictly in memory under hardware guards. If a user uploads data, it is promptly secured before it leaves the enclave. When data is retrieved, it remains encrypted until it reenters the protected region and is passed back to the user through the secured communication channel. This ensures that even if someone gains access to the underlying storage or intercepts data in transit, they will see only meaningless ciphertext. 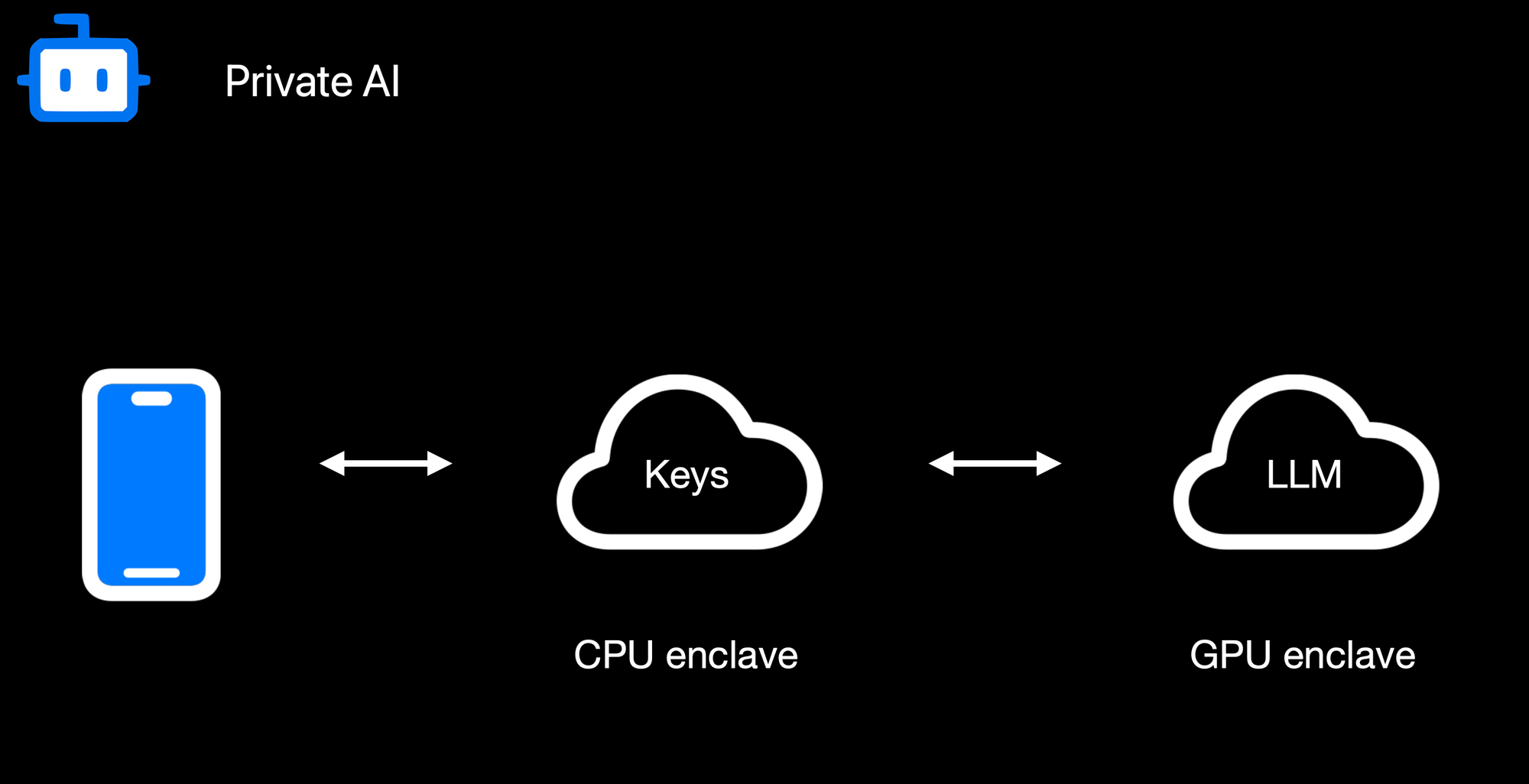Confidential AI Workloads Finally, **confidential AI workloads** build upon this same pattern: the Nitro enclave re-encrypts data so it can be processed inside a GPU-based trusted execution environment (TEE) for inference or other advanced computations. Sensitive data, like user-generated text or private documents, never appears in the clear on the host or within GPU memory outside the TEE boundary. When an AI process finishes, only the results are returned to the enclave, which can then relay them securely to the requesting user. By seamlessly chaining enclaves together, from CPU-based Nitro Enclaves to GPU-accelerated TEEs, we can deliver robust, hardware-enforced privacy for virtually any type of server-side or AI-driven operation. ### **Reproducible Builds + Verification** 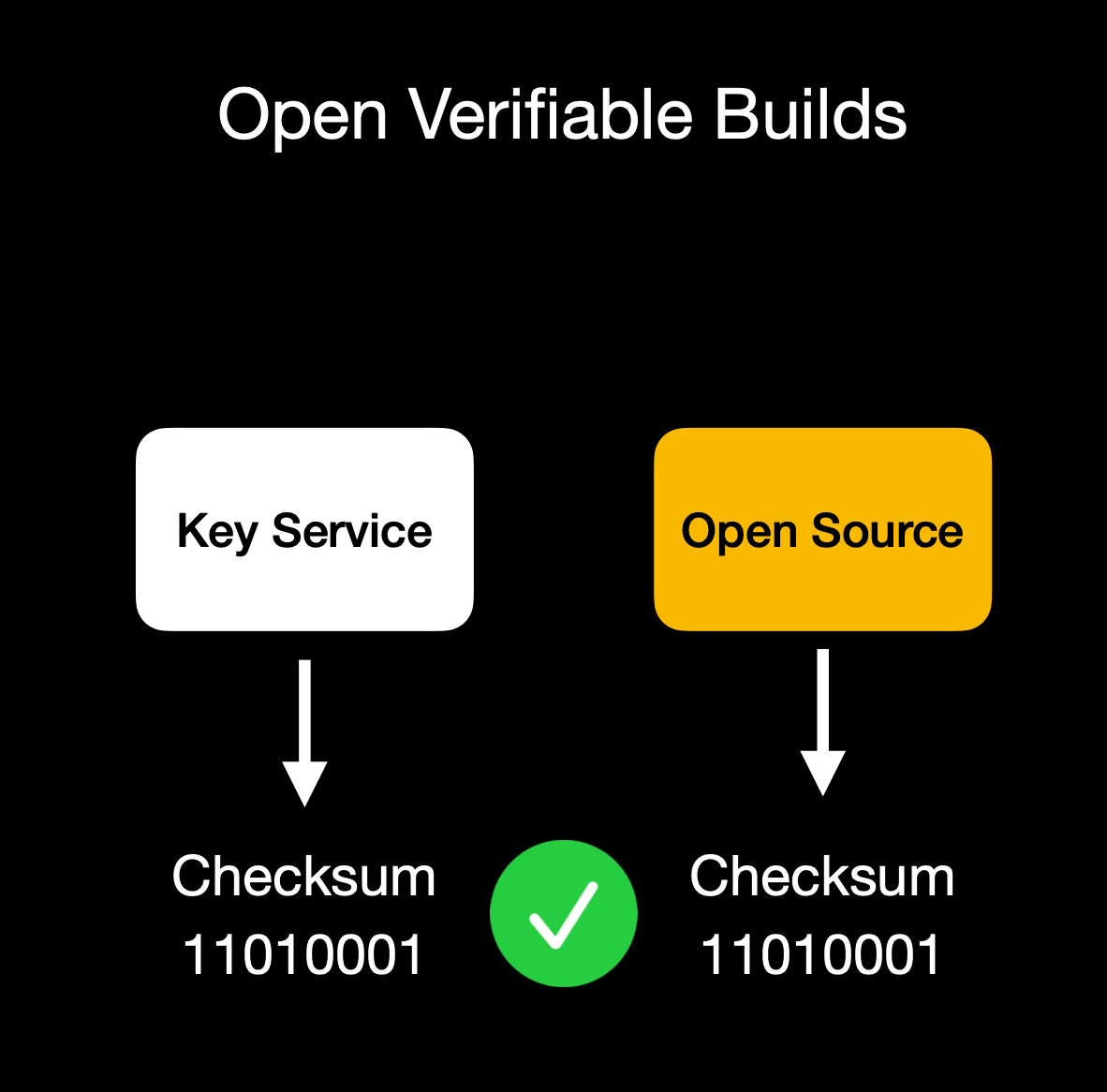Client verifies enclave attestation document We build our enclaves on **NixOS** with reproducible builds, ensuring that anyone can verify that the binary we publish is indeed the binary running in the enclave. This build process is essential for proving we haven't snuck in malicious code to exfiltrate data or collect sensitive logs. Our code is fully open source ([GitHub: OpenSecret](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud)), so you can audit or run it yourself. You can also verify that the cryptographic measurement the build process outputs matches the measurement reported by the enclave during attestation. ## **Putting It All Together** OpenSecret Offering: Private Key Management, Encrypted Sync, Private AI, and Confidential Compute By weaving secure enclaves into every step, from authentication to data handling to AI inference, we shift the burden of trust away from human policies and onto provable, hardware-based protections. For app developers, you can offer your users robust privacy guarantees without rewriting all your business logic or building an entire security stack from scratch. Whether you're storing user credentials or running complex operations on sensitive data, the enclave approach ensures plaintext remains inaccessible to even the most privileged parties outside the enclave boundary. Developers can focus on building great apps, while OpenSecret handles the cryptographic "lock and key" behind the scenes. This model provides a secure-by-design environment for industries that demand strict data confidentiality, such as healthcare, fintech, cryptocurrency apps for secure key management, or decentralized identity platforms. Instead of worrying about memory dumps or backend tampering, you can trust that once data enters the enclave, it's sealed off from unauthorized eyes, including from the app developers themselves. And these safeguards don't just apply to niche use cases. Even general-purpose applications that handle login flows and user-generated content stand to benefit, especially as regulatory scrutiny grows around data privacy and insider threats. Imagine a telehealth startup using OpenSecret enclaves to protect patient information for remote consultations. Not only would patient data remain encrypted at rest, but any AI-driven analytics to assist with diagnoses could be run privately within the enclave, ensuring no one outside the hardware boundary can peek at sensitive health records. A fintech company could similarly isolate confidential financial transactions, preventing even privileged insiders from viewing or tampering with raw transaction details. These real-world implementations give developers a clear path to adopting enclaves for serious privacy and compliance needs without overhauling their infrastructure. OpenSecret aims to be a **full developer platform** with end-to-end security from day one. By incorporating user authentication, data storage, and GPU-based confidential AI into a single service, we eliminate many of the traditional hurdles in adopting enclaves. No more juggling separate tools for cryptographic key management, compliance controls, and runtime privacy. Instead, you get a unified stack that keeps data encrypted in transit, at rest, and in use. Our solution also caters to the exploding demand for AI applications: with TEE-enabled GPU workloads, you can securely process sensitive data for text inference without ever exposing raw plaintext or sensitive documents to the host system. The result is a new generation of apps that deliver advanced functionality, like real-time encrypted data sync or AI-driven insights, while preserving user privacy and meeting strict regulatory requirements. You don't have to rely on empty "trust us" promises because hardware enclaves, remote attestation, and reproducible builds collectively guarantee the code is running untampered. In short, OpenSecret offers the building blocks needed to create truly confidential services and experiences, allowing you to innovate while ensuring data protection remains ironclad. ## **Things to Come** We're excited to build on our enclaved approach. Here's what's on our roadmap: • **Production Launch**: We're using this in production now with [Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud) and have a developer preview playground up and running. We'll have the developer environment ready for production in a few months.\ • **Multi-Tenant Support**: Our platform currently works for single tenants, but we're opening this up so developers can onboard without needing a dedicated instance.\ • **Self-Serve Frontend**: A dev-friendly portal for provisioning apps, connecting OAuth or email providers, and managing users.\ • **External Key Signing Options**: Integrations with custom hardware security modules (HSMs) or customer-ran key managers that can only process data upon verifying the enclave attestation.\ • **Confidential Computing as a Service**: We'll expand our platform so that other developers can quickly create enclaves for specialized workloads without dealing with the complexities of Nitro or GPU TEEs.\ • **Additional SDKs**: In addition to our [JavaScript client-side SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud), we plan to launch official support for Rust, Python, Swift, Java, Go, and more.\ • **AI API Proxy with Attestation/Encryption**: We already provide an easy way to [access a Private AI through Maple AI](https://trymaple.ai/?ref=blog.opensecret.cloud), but we'd like to open this up more for existing tools and developers. We'll provide a proxy server that users can run on their local machines or servers that properly handle encryption to our OpenAI-compatible API. ## **Getting Started** Ready to see enclaves in action? Here's how to dive in:\ 1. **Run OpenSecret**: Check out our open-source repository at [OpenSecret on GitHub](https://github.com/OpenSecretCloud/opensecret?ref=blog.opensecret.cloud). You can run your own enclaved environment or try it out locally with Docker.\ 2. **Review Our SDK**: Our [JavaScript client SDK](https://github.com/OpenSecretCloud/OpenSecret-SDK?ref=blog.opensecret.cloud) makes it easy to handle sign-ins, put/get encrypted data, sign with user private keys, etc. It handles attestation verification and encryption under the hood, making the API integration seamless.\ 3. **Play with Maple AI**: Try out [Maple AI](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) as an example of an AI app built directly on OpenSecret. Your queries are encrypted end to end, and the Llama model sees them only inside the TEE.\ 4. **Developer Preview**: Contact us if you want an invite to our early dev platform. We'll guide you through our SDK and give you access to the preview server. We'd love to build with you and incorporate your feedback as we develop this further. ## **Conclusion** By merging secure enclaves (AWS Nitro and Nvidia GPU TEEs), user authentication, private key management, and an end-to-end verifiable encrypted approach, **OpenSecret** provides a powerful platform where we protect user data during collection, storage, and processing. Whether it's for standard user management, handling private cryptographic keys, or powering AI inference, the technology ensures that **no one**, not even us or the cloud provider, can snoop on data in use. **We believe** this is the future of trustworthy computing in the cloud. And it's **all open source**, so you don't have to just take our word for it: you can see and verify everything yourself. Do you have questions, feedback, or a use case you'd like to test out? Come join us on [GitHub](https://github.com/OpenSecretCloud?ref=blog.opensecret.cloud), [Discord](https://discord.gg/ch2gjZAMGy?ref=blog.opensecret.cloud), or email us for a developer preview. We can't wait to see what you build! *Thank you for reading, and welcome to the era of enclaved computing.* @ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article [nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/) Starting from these links building a simple path should not cover everything, because impossible. Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it. ----- Go to [nstart.me](https://nstart.me/) and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff) You can insert a nickname and go, the nickname is not unique there is a email backup things interesting, but a little boring, i try to generate an email doesn't even require a strong password ok. I received the email, great, it shows me the nsec encrypted in clear, Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump. ## Multi signer bunker That's stuff, let's see what he says. They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing. Nobody tells you where these bunkers are. Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. . ## Follow someone before you start? Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele. I choice Snowden profile, or you can select multiple profiles, extra wild. ## Now select 5 clients ### *Coracle, Chachi, Olas, Nostur, Jumble* ### The first is *Coracle* Login, ok I try to post a note and signing your note the spin does not end. Maybe the bunker is diffective. ### Let's try *Chachi* Simpler than Coracle, it has a type login that says bunker. see if I can post It worked, cool, I managed to post in a group. ## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account. > If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something > like that, but many start from the phone so maybe it's easy for them. > I try to download it and see if it allows me to connect with a bunker. > Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas **Ok then I saw that there was the qrcode image of the bunker for apps** lol moment Ok, I liked it, I can say it's a victory. Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that. Okay I managed to post on *Olas*, so it works, Expiration time is broken. ### As for *Nostur*, I don't have an ios device so I'm going to another one. ### Login with *Jumble*, it works is a web app I took almost an hour to do the whole route. But this was just one link there are two more # Extensions nostr NIP-07 ### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions) There are 19 links, maybe there are too many? I mention the most famous, or active at the moment 1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension) Alby I don't know if it's a route to recommend 2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj) 3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file) 4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/) Nostore is (archived, read-only) 5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame) 6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser) 7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj) Another half hour to search all sites # Nostrapps Here you can make paths ### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo On the site there are some categories, I select some with the respective apps Let's see the categories Go to [Nostrapps](https://nostrapps.com/) and read: ## Microbbloging: Primal ## Streaming: **Zap stream** ## Blogging: **Yakihonne** ## Group chat: **Chachi** ## Community: **Flotilla** ## Tools: **Form** * ## Discovery: **Zapstore** (even if it is not in this catrgory) ## Direct Message: **0xchat**
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article [nostr-quick-start-guide](https://spatianostra.com/nostr-quick-start-guide/) Starting from these links building a simple path should not cover everything, because impossible. Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it. ----- Go to [nstart.me](https://nstart.me/) and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff) You can insert a nickname and go, the nickname is not unique there is a email backup things interesting, but a little boring, i try to generate an email doesn't even require a strong password ok. I received the email, great, it shows me the nsec encrypted in clear, Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump. ## Multi signer bunker That's stuff, let's see what he says. They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing. Nobody tells you where these bunkers are. Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. . ## Follow someone before you start? Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele. I choice Snowden profile, or you can select multiple profiles, extra wild. ## Now select 5 clients ### *Coracle, Chachi, Olas, Nostur, Jumble* ### The first is *Coracle* Login, ok I try to post a note and signing your note the spin does not end. Maybe the bunker is diffective. ### Let's try *Chachi* Simpler than Coracle, it has a type login that says bunker. see if I can post It worked, cool, I managed to post in a group. ## Olas is an app but also a website, but on the website requires an extension, which I do not have with this account. > If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something > like that, but many start from the phone so maybe it's easy for them. > I try to download it and see if it allows me to connect with a bunker. > Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas **Ok then I saw that there was the qrcode image of the bunker for apps** lol moment Ok, I liked it, I can say it's a victory. Looks like none of Snowden's followers are *Olas*'s lover, maybe the smart pack has to predict a photographer or something like that. Okay I managed to post on *Olas*, so it works, Expiration time is broken. ### As for *Nostur*, I don't have an ios device so I'm going to another one. ### Login with *Jumble*, it works is a web app I took almost an hour to do the whole route. But this was just one link there are two more # Extensions nostr NIP-07 ### The true path is [nip-07-browser-extensions | nostr.net](https://nostr.net/#nip-07-browser-extensions) There are 19 links, maybe there are too many? I mention the most famous, or active at the moment 1. **Aka-profiles**: [Aka-profiles](https://github.com/neilck/aka-extension) Alby I don't know if it's a route to recommend 2. **Blockcore** [Blockcore wallet](https://chromewebstore.google.com/detail/blockcore-wallet/peigonhbenoefaeplkpalmafieegnapj) 3. **Nos2x** [Nos2x](https://github.com/fiatjaf/nos2x?tab=readme-ov-file) 4. **Nos2xfox** (fork for firefox) [Nos2xfox](https://diegogurpegui.com/nos2x-fox/) Nostore is (archived, read-only) 5. **Nostrame** [Nostrame](https://github.com/Anderson-Juhasc/nostrame) 6. **Nowser** per IOS [Nowser](https://github.com/haorendashu/nowser) 7. **One key** (was tricky) [One key](https://chromewebstore.google.com/detail/onekey/jnmbobjmhlngoefaiojfljckilhhlhcj) Another half hour to search all sites # Nostrapps Here you can make paths ### Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo On the site there are some categories, I select some with the respective apps Let's see the categories Go to [Nostrapps](https://nostrapps.com/) and read: ## Microbbloging: Primal ## Streaming: **Zap stream** ## Blogging: **Yakihonne** ## Group chat: **Chachi** ## Community: **Flotilla** ## Tools: **Form** * ## Discovery: **Zapstore** (even if it is not in this catrgory) ## Direct Message: **0xchat** @ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 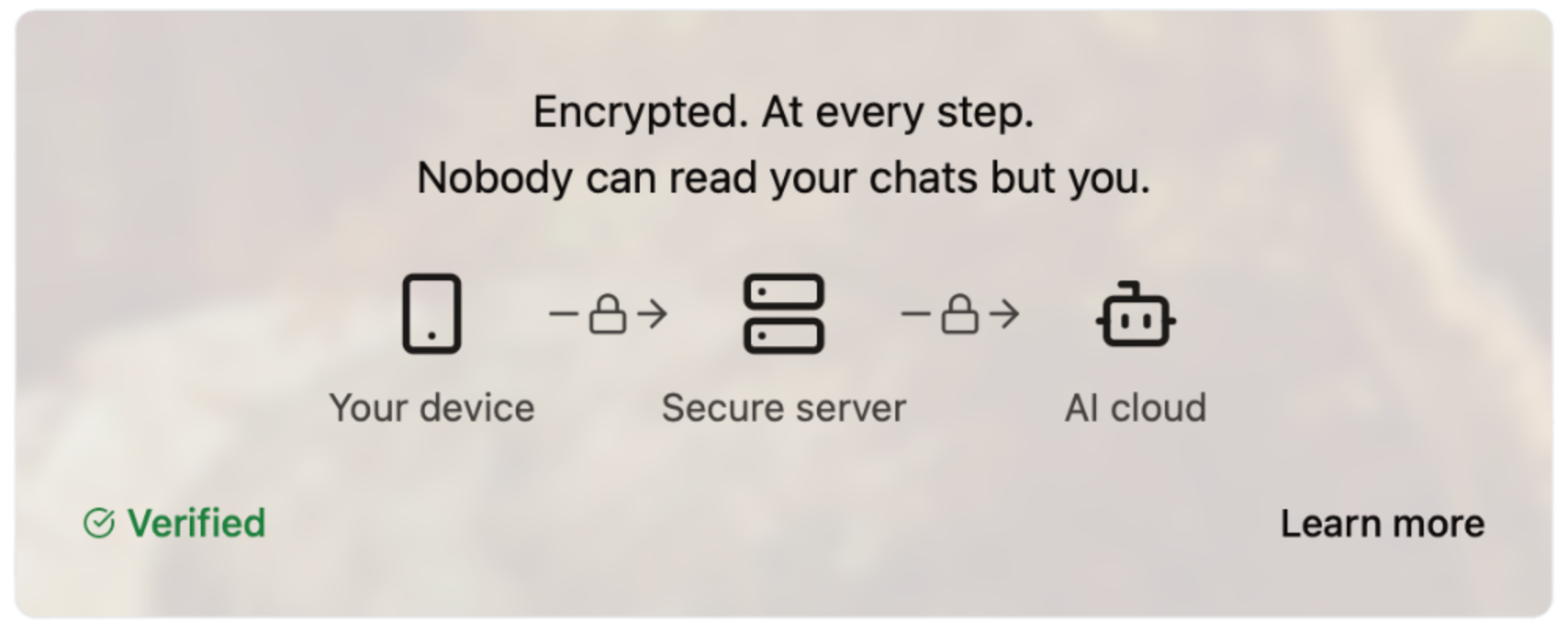#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg">
@ df173277:4ec96708
2025-01-28 17:49:54> Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. Chats are synced automatically between devices so you can pick up where you left off.\ > [Start chatting for free.](https://trymaple.ai/) We are excited to announce that [Maple AI](https://trymaple.ai/), our groundbreaking end-to-end encrypted AI chat app built on OpenSecret, is now publicly available. After months of beta testing, we are thrilled to bring this innovative technology to the world. Maple is an AI chat tool that allows you to have private conversations with a general-purpose AI assistant. It can boost your productivity on work tasks such as writing documentation, creating presentations, and drafting emails. You can also use it for personal items like brainstorming ideas, sorting out life's challenges, and tutoring you on difficult coursework. All your chats are synced automatically in a secure way, so you can start on one device and pick up where you left off on another. #### Why Secure and Private AI? In today's digital landscape, it is increasingly evident that security and privacy are essential for individuals and organizations alike. Unfortunately, the current state of AI tools falls short. A staggering 48% of organizations enter non-public company information into AI apps, according to a [recent report by Cisco](https://www.cisco.com/c/en/us/about/trust-center/data-privacy-benchmark-study.html#~key-findings). This practice poses significant risks to company security and intellectual property. Another concern is for journalists, who often work with sensitive information in hostile environments. Journalists need verification that their information remains confidential and protected when researching topics and communicating with sources in various languages. They are left to use underpowered local AI or input their data into potentially compromised cloud services. At OpenSecret, we believe it is possible to have both the benefits of AI and the assurance of security and privacy. That's why we created Maple, an app that combines AI productivity with the protection of end-to-end encryption. Our platform ensures that your conversations with AI remain confidential, even from us. The power of the cloud meets the privacy of local. 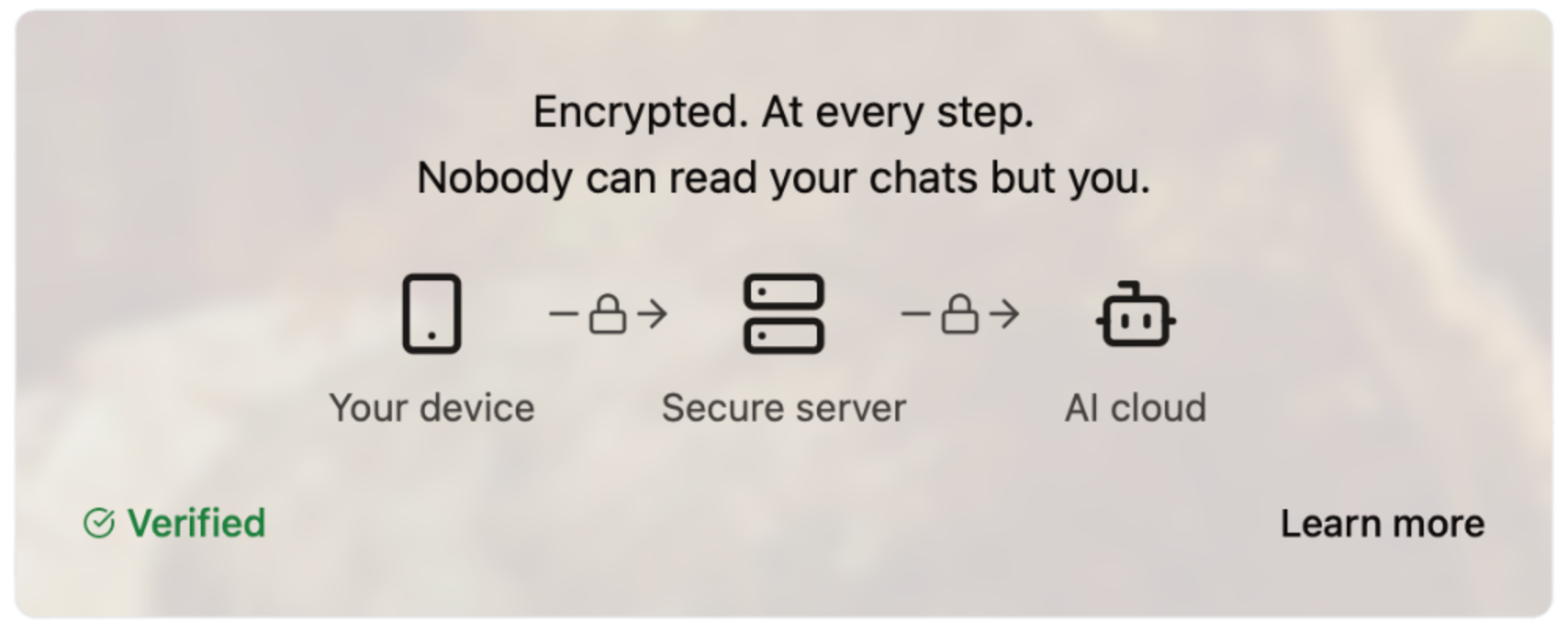#### How Does It Work? Our server code is [open source](https://github.com/OpenSecretCloud/opensecret), and we use confidential computing to provide cryptographic proof that the code running on our servers is the same as the open-source code available for review. This process allows you to verify that your conversations are handled securely and privately without relying on trust. We live by the principle of "Don't trust, verify," and we believe this approach is essential for building in the digital age. You can read a more in-depth write-up on our technology later this week on this site. #### How Much Does It Cost? We are committed to making Maple AI accessible to everyone, so we offer a range of pricing plans to suit different needs and budgets. [Our Free plan allows for 10 chats per week, while our Starter plan ($5.99/month) and Pro plan ($20/month)](https://trymaple.ai/pricing) offer more comprehensive solutions for individuals and organizations with heavier workloads. We accept credit cards and Bitcoin (10% discount), allowing you to choose your preferred payment method. - Free: $0 - Starter: $5.99/month - Pro: $20/month Our goal with Maple AI is to create a product that is secure through transparency. By combining open-source code, cryptography, and confidential computing, we can create a new standard for AI conversations - one that prioritizes your security and privacy. Maple has quickly become a daily tool of productivity for our own work and those of our beta testers. We believe it will bring value to you as well. [Sign up now and start chatting privately with AI for free.](https://trymaple.ai/) Your secrets are safe in the open. #### Are You An App Developer? You can build an app like Maple. [OpenSecret provides secure auth, private key management, encrypted data sync, private AI, and more.](https://blog.opensecret.cloud/introducing-opensecret/) Our straightforward API behaves like other backends but automatically adds security and privacy. Use it to secure existing apps or brand-new projects. Protect yourself and your users from the liability of hosting personal data by checking out [OpenSecret](https://opensecret.cloud/). <img src="https://blossom.primal.net/feb746d5e164e89f0d015646286b88237dce4158f8985e3caaf7e427cebde608.png"> Enjoy private AI Chat 🤘 <img src="https://blossom.primal.net/0594ec56e249de2754ea7dfc225a7ebd46bc298b5af168279ce71f17c2afada0.jpg"> @ 57d1a264:69f1fee1
2025-03-29 09:31:13> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." <sub>- SATOSHI NAKAMOTO</sub>    "Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin. Materials: Carrara Marble, Copper leaf, Opendime Dimensions: 6" x 9" x 13" Price: $30,000 or BTC equivalent Enquire: https://www.vonbitcoin.com/available-works X: https://x.com/BVBTC/status/1894463357316419960/photo/1 originally posted at https://stacker.news/items/928510
@ 57d1a264:69f1fee1
2025-03-29 09:31:13> "THE NATURE OF BITCOIN IS SUCH THAT ONCE VERSION 0.1 WAS RELEASED, THE CORE DESIGN WAS SET IN STONE FOR THE REST OF ITS LIFETIME." <sub>- SATOSHI NAKAMOTO</sub>    "Reborn" is inspired by my Bitcoin journey and the many other people whose lives have been changed by Bitcoin. I’ve carved the hand in the “Gyan Mudra” or the “Mudra of Wisdom or Knowledge,” with an Opendime grasped between thumb and index finger alluding to the pursuit of Bitcoin knowledge. The hand emerges from rough, choppy water, and I've set the hand against an archway, through which, the copper leaf hints at the bright orange future made possible by Bitcoin. Materials: Carrara Marble, Copper leaf, Opendime Dimensions: 6" x 9" x 13" Price: $30,000 or BTC equivalent Enquire: https://www.vonbitcoin.com/available-works X: https://x.com/BVBTC/status/1894463357316419960/photo/1 originally posted at https://stacker.news/items/928510 @ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison. I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core You can also learn more about Pubky here: https://pubky.org/ That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key. Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis. Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed. Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message. I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key. As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster. Based on all of this info, it seems like, to populate your feed, this is the series of steps: - you tell your homeserver your pubkey - it uses some sort of algorithm to decide whose posts to show you - then looks up the homeservers used by those people on an indexer server - then it fetches posts from their homeservers - then your client displays them to you To create a post, this is the series of steps: - you tell your homeserver what you want to say to the world - it stores that message in plaintext and merely asserts that it came from you (it's not signed) - other people can find out what you said by querying for your posts on your homeserver Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver. John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted. Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/
@ 2183e947:f497b975
2025-03-29 02:41:34Today I was invited to participate in the private beta of a new social media protocol called Pubky, designed by a bitcoin company called Synonym with the goal of being better than existing social media platforms. As a heavy nostr user, I thought I'd write up a comparison. I can't tell you how to create your own accounts because it was made very clear that only *some* of the software is currently open source, and how this will all work is still a bit up in the air. The code that *is* open source can be found here: https://github.com/pubky -- and the most important repo there seems to be this one: https://github.com/pubky/pubky-core You can also learn more about Pubky here: https://pubky.org/ That said, I used my invite code to create a pubky account and it seemed very similar to onboarding to nostr. I generated a private key, backed up 12 words, and the onboarding website gave me a public key. Then I logged into a web-based client and it looked a lot like twitter. I saw a feed for posts by other users and saw options to reply to posts and give reactions, which, I saw, included hearts, thumbs up, and other emojis. Then I investigated a bit deeper to see how much it was like nostr. I opened up my developer console and navigated to my networking tab, where, if this was nostr, I would expect to see queries to relays for posts. Here, though, I saw one query that seemed to be repeated on a loop, which went to a single server and provided it with my pubkey. That single query (well, a series of identical queries to the same server) seemed to return all posts that showed up on my feed. So I infer that the server "knows" what posts to show me (perhaps it has some sort of algorithm, though the marketing material says it does not use algorithms) and the query was on a loop so that if any new posts came in that the server thinks I might want to see, it can add them to my feed. Then I checked what happens when I create a post. I did so and looked at what happened in my networking tab. If this was nostr, I would expect to see multiple copies of a signed messaged get sent to a bunch of relays. Here, though, I saw one message get sent to the same server that was populating my feed, and that message was not signed, it was a plaintext copy of my message. I happened to be in a group chat with John Carvalho at the time, who is associated with pubky. I asked him what was going on, and he said that pubky is based around three types of servers: homeservers, DHT servers, and indexer servers. The homeserver is where you create posts and where you query for posts to show on your feed. DHT servers are used for censorship resistance: each user creates an entry on a DHT server saying what homeserver they use, and these entries are signed by their key. As for indexers, I think those are supposed to speed up the use of the DHT servers. From what I could tell, indexers query DHT servers to find out what homeservers people use. When you query a homeserver for posts, it is supposed to reach out to indexer servers to find out the homeservers of people whose posts the homeserver decided to show you, and then query those homeservers for those posts. I believe they decided not to look up what homeservers people use directly on DHT servers directly because DHT servers are kind of slow, due to having to store and search through all sorts of non-social-media content, whereas indexers only store a simple db that maps each user's pubkey to their homeserver, so they are faster. Based on all of this info, it seems like, to populate your feed, this is the series of steps: - you tell your homeserver your pubkey - it uses some sort of algorithm to decide whose posts to show you - then looks up the homeservers used by those people on an indexer server - then it fetches posts from their homeservers - then your client displays them to you To create a post, this is the series of steps: - you tell your homeserver what you want to say to the world - it stores that message in plaintext and merely asserts that it came from you (it's not signed) - other people can find out what you said by querying for your posts on your homeserver Since posts on homeservers are not signed, I asked John what prevents a homeserver from just making up stuff and claiming I said it. He said nothing stops them from doing that, and if you are using a homeserver that starts acting up in that manner, what you should do is start using a new homeserver and update your DHT record to point at your new homeserver instead of the old one. Then, indexers should update their db to show where your new homeserver is, and the homeservers of people who "follow" you should stop pulling content from your old homeserver and start pulling it from your new one. If their homeserver is misbehaving too, I'm not sure what would happen. Maybe it could refuse to show them the content you've posted on your new homeserver, keeping making up fake content on your behalf that you've never posted, and maybe the people you follow would never learn you're being impersonated or have moved to a new homeserver. John also clarified that there is not currently any tooling for migrating user content from one homeserver to another. If pubky gets popular and a big homeserver starts misbehaving, users will probably need such a tool. But these are early days, so there aren't that many homeservers, and the ones that exist seem to be pretty trusted. Anyway, those are my initial thoughts on Pubky. Learn more here: https://pubky.org/ @ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [](https://trymaple.ai/waitlist)
@ df173277:4ec96708
2025-01-09 17:12:08> Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ > [Join the waitlist to get early access.](https://trymaple.ai) We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI. Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations. #### Building a Private Foundation Maple is built on our flagship product, [OpenSecret](https://opensecret.cloud), a backend platform for app developers that turns private encryption on by default. [The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do.](nostr:naddr1qvzqqqr4gupzphchxfm3ste32hfhkvczzxapme9gz5qvqtget6tylyd7wa8vjecgqqe5jmn5wfhkgatrd9hxwt20wpjku5m9vdex2apdw35x2tt9de3hy7tsw3jkgttzv93kketwvskhgur5w9nx5h52tpj) We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win. #### The Power of Encrypted AI Chat AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short. Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us. #### Technical Overview So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects: - **Private Key:** Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data. - **Secure Servers:** Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations. - **Encrypted Sync:** One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised. - **Attestation and Open Code:** We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public. - **Open Source LLM:** Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased. #### Personal and Work Use Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe. #### Local v Cloud Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds. #### Why the Maple name? Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment. #### Join the Waitlist Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. [Join our waitlist today to be among the first to experience the power of private AI chat.](https://trymaple.ai) [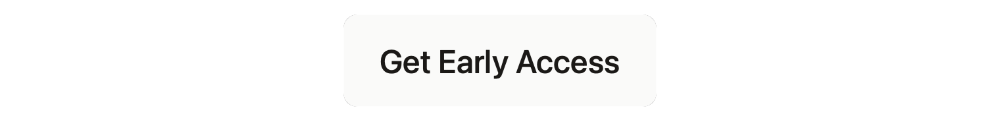](https://trymaple.ai/waitlist) @ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.  The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022). Look forward for this to happen! Spread the voice: N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m) X: https://x.com/bitcoin_design/status/1905547407405768927 originally posted at https://stacker.news/items/927650
@ 57d1a264:69f1fee1
2025-03-28 10:32:15Bitcoin.design community is organizing another Designathon, from May 4-18. Let's get creative with bitcoin together. More to come very soon.  The first edition was a bursting success! the website still there https://events.bitcoin.design, and here their previous [announcement](https://bitcoindesign.substack.com/p/the-bitcoin-designathon-2022). Look forward for this to happen! Spread the voice: N: [https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48l...](https://njump.me/nevent1qqsv9w8p93tadlnyx0rkhexj5l48lmw9jc7nhhauyq5w3cm4nfsm3mstqtk6m) X: https://x.com/bitcoin_design/status/1905547407405768927 originally posted at https://stacker.news/items/927650 @ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app. 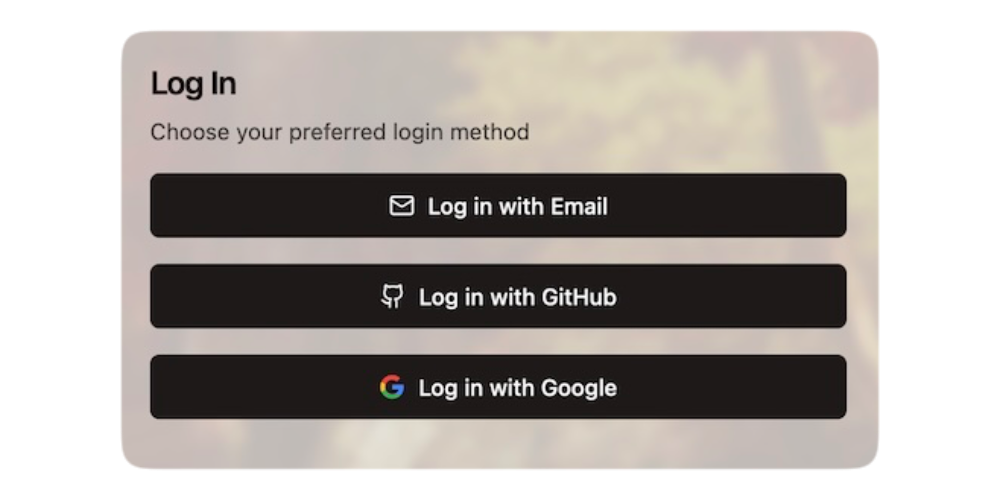 ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/) 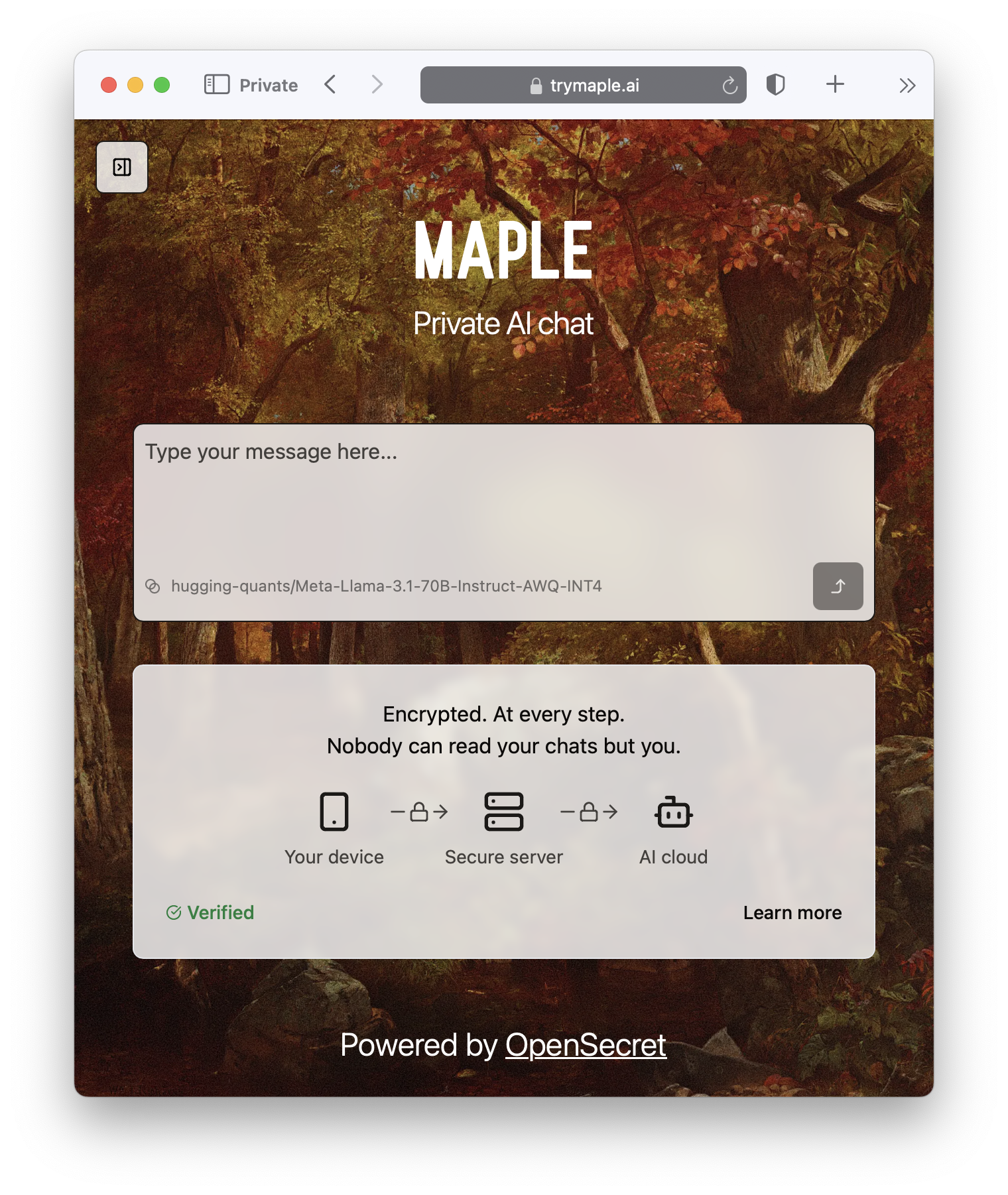 ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud)
@ df173277:4ec96708
2025-01-09 17:02:52> OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. [Join our waitlist to get early access.](https://opensecret.cloud) In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion. 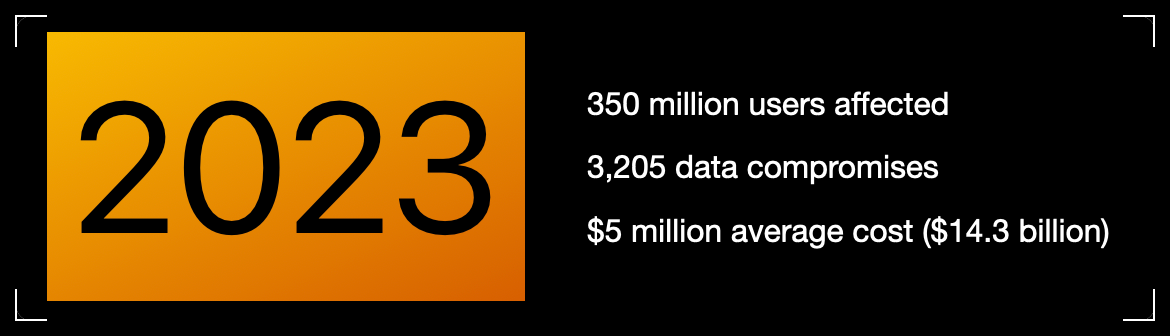Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online? Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches? > Cryptography at scale is hard. #### The Cloud The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers. The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage. > Private key encryption needs a UX upgrade. ## Enter OpenSecret OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute. Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.  ### Private Key Management Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone. OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account. The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.  ### Encrypted Sync With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go. The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them. ### Private AI Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything. OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk. **Check out Maple AI**\ Try private AI for yourself! We built an app built with this service called [Maple AI](https://trymaple.ai). It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. [Learn more about Maple AI - Private chat in the announcement post.](https://blog.opensecret.cloud/maple-ai-private-encrypted-chat/)  ### Confidential Compute Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave. It's the new version of that lock on your web browser. When you see it, you know you're secure.  #### **But do we want our secrets to be open?** OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable. On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data. > Don't trust, verify. ### **Join the Movement** We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, [send us a message to get early access.](https://opensecret.cloud) Users and companies deserve better encryption and privacy.\ Together, let's make that a reality. [](https://opensecret.cloud) @ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site.
@ e4950c93:1b99eccd
2025-04-03 14:53:56**Heureu-x-se d’avoir trouvé une information utile sur ce site ?** Soutenez le projet en faisant un don pour le faire vivre et remercier les contribut-eur-rice-s. --- **En bitcoin** <img src="https://coinos.io/qr/bc1q79er6c5mvvktvmvcstsnelv4j6tv3wdhw2k7ej/raw" width="200" height="200"> bc1qkm8me8l9563wvsl9sklzt4hdcuny3tlejznj7d ⚡️` origin-nature@coinos.io` --- **En euros, dollars, ou toute autre monnaie prise en charge** *Promesses uniquement pour le moment :* <a href="https://liberapay.com/origin-nature/"> <img src="!(image)[https://liberapay.com/assets/liberapay/icon-v2_black-on-yellow.svg]?etag=._QLQJKsW7OwBQqn7ASPxRA~~" width="200" height="200"> </a> --- Contactez-nous si vous souhaitez faire un don avec toute autre cryptomonnaie. --- ### 💡 Un modèle de partage de la valeur La moitié des dons est redistribuée aux contribut-eur-rice-s qui créent la valeur du site, pour expérimenter un modèle de partage de revenus sur Internet — un modèle qui respecte vos données et ne cherche pas à capter votre attention. L’autre moitié permet de couvrir les frais de fonctionnement du site. @ a5142938:0ef19da3
2025-04-03 09:55:01### Core Team The Core Team drives the project and validates the content. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) To start, I'm managing the project solo. Contact me if you'd like to join! ### Content Enrichers Our contributors make this site engaging and interesting.
@ a5142938:0ef19da3
2025-04-03 09:55:01### Core Team The Core Team drives the project and validates the content. - [Jean-David Bar](https://njump.me/npub1qr4p7uamcpawv7cr8z9nlhmd60lylukf7lvmtlnpe7r4juwxudzq3hrnll) To start, I'm managing the project solo. Contact me if you'd like to join! ### Content Enrichers Our contributors make this site engaging and interesting. @ d5c3d063:4d1159b3
2025-04-03 04:09:56### ทรัมป์ ขึ้นภาษีนำเข้า สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ แต่คุณ #ไม่เห็น – คนทั้งประเทศ ต้องจ่ายของแพงขึ้น – ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย – ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่ โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”* Hazlitt ขยายต่อใน Economics in One Lesson ว่า > เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า > และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม เงินเฟ้อ คือการขโมยแบบเงียบ ๆ ภาษีศุลกากร คือการปล้นอย่างเปิดเผย วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด #Siamstr
@ d5c3d063:4d1159b3
2025-04-03 04:09:56### ทรัมป์ ขึ้นภาษีนำเข้า สิ่งที่คุณเห็น…กับสิ่งที่คุณมองไม่เห็น คุณ #เห็น แค่ฝั่งที่ดูดีในข่าวภาคค่ำ แต่คุณ #ไม่เห็น – คนทั้งประเทศ ต้องจ่ายของแพงขึ้น – ธุรกิจเล็ก ๆ ที่พึ่งการนำเข้า…ถูกบีบให้ตาย – ผู้บริโภคต้องเสียเงินมากขึ้น โดยไม่มีทางเลือก รัฐอ้างว่า *"ปกป้องประเทศ"* แต่จริง ๆ แล้วเขาแค่ โยนภาระให้คนส่วนใหญ่ เพื่ออุ้มผลประโยชน์บางกลุ่ม เหมือนที่ Bastiat เรียกว่า *“การปล้นที่ถูกกฎหมาย”* Hazlitt ขยายต่อใน Economics in One Lesson ว่า > เศรษฐศาสตร์ที่ดี ต้องมองให้พ้นจากผลเฉพาะหน้า > และมองให้เห็นผลกระทบต่อทุกคน ไม่ใช่แค่บางกลุ่ม เงินเฟ้อ คือการขโมยแบบเงียบ ๆ ภาษีศุลกากร คือการปล้นอย่างเปิดเผย วันนี้ #EIOL น่าจะถึงมือเพื่อนๆ หลายคนแล้ว เล่มนี้ไม่ต้องอ่านทีละบทก็ได้ ลองเปิดไปบทที่ 11 เลยแล้วจะเจอ**ค้อนปอน**สำหรับทุบมายาคดีทางเศรษฐกิจที่รัฐใช้กับเรามาทั้งชีวิต อ่าน #เศรษฐศาสตร์เล่มเดียวจบ แล้วคุณอาจไม่มีวันมอง “นโยบายเพื่อประชาชน” ได้เหมือนเดิมอีก เพราะบางที...สิ่งที่คุณไม่เคยเห็น อาจเป็นสิ่งที่คุณควรรู้(เห็น)ให้เร็วที่สุด #Siamstr @ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who? The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1: ## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.              - - - Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before. This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using. - [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser - ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY) @k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful. [^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined originally posted at https://stacker.news/items/926557
@ 57d1a264:69f1fee1
2025-03-27 10:42:05What we have been missing in [SN Press kit](https://stacker.news/items/872925/r/Design_r)? Most important, who the press kit is for? It's for us? It's for them? Them, who? The first few editions of the press kit, I agree are mostly made by us, for us. A way to try to homogenize how we _speek_ out SN into the wild web. A way to have SN voice sync, loud and clear, to send out our message. In this case, I squeezed my mouse, creating a template for us [^1], stackers, to share when talking sales with possible businesses and merchants willing to invest some sats and engage with SN community. Here's the message and the sales pitch, v0.1: ## Reach Bitcoin’s Most Engaged Community – Zero Noise, Pure Signal.              - - - Contributions to improve would be much appreciated. You can also help by simply commenting on each slide or leaving your feedback below, especially if you are a sale person or someone that has seen similar documents before. This is the first interaction. Already noticed some issues, for example with the emojis and the fonts, especially when exporting, probably related to a penpot issue. The slides maybe render differently depending on the browser you're using. - [▶️ Play](https://design.penpot.app/#/view?file-id=cec80257-5021-8137-8005-ef90a160b2c9&page-id=cec80257-5021-8137-8005-ef90a160b2ca§ion=interactions&index=0&interactions-mode=hide&zoom=fit) the file in your browser - ⬇️ Save the [PDF file](https://mega.nz/file/TsBgkRoI#20HEb_zscozgJYlRGha0XiZvcXCJfLQONx2fc65WHKY) @k00b it will be nice to have some real data, how we can get some basic audience insights? Even some inputs from Plausible, if still active, will be much useful. [^1]: Territory founders. FYI: @Aardvark, @AGORA, @anna, @antic, @AtlantisPleb, @av, @Bell_curve, @benwehrman, @bitcoinplebdev, @Bitter, @BlokchainB, @ch0k1, @davidw, @ek, @elvismercury, @frostdragon, @grayruby, @HODLR, @inverselarp, @Jon_Hodl, @MaxAWebster, @mega_dreamer, @mrtali, @niftynei, @nout, @OneOneSeven, @PlebLab, @Public_N_M_E, @RDClark, @realBitcoinDog, @roytheholographicuniverse, @siggy47, @softsimon, @south_korea_ln, @theschoolofbitcoin, @TNStacker. @UCantDoThatDotNet, @Undisciplined originally posted at https://stacker.news/items/926557 @ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
@ 3c7dc2c5:805642a8
2025-04-02 21:15:55## 🧠Quote(s) of the week: CBDC the digital euro - a centralized solution in search of a problem. While the ECB may see it as a way to 'modernize' finance, true innovation comes from empowering individuals, not consolidating control. CBDCs are just surveillance tools disguised as innovation. Bitcoin is the only true digital money—decentralized, scarce, and free. Stack sats, not CBDCs. ## 🧡Bitcoin news🧡 2025 https://i.ibb.co/vx988kT1/Gn-Ix-Dp-YWs-AASkiw.jpg On the 24th of March: ➡️The Pakistan central bank is exploring mining Bitcoin with excess electricity. ➡️'MicroStrategy just added another 7,000 Bitcoin to their treasury. They're now holding over 506,000 BTC ($44 billion). Look at the corporate Bitcoin ownership breakdown: - MicroStrategy: 506,000+ BTC - Marathon: ~46,000 BTC (10x smaller) - Riot: ~19,000 BTC (26x smaller) That acquisition curve has gone parabolic since Q4 2024. Strategy's buying pace now rivals what we're seeing from the Bitcoin ETFs, a single public company absorbing supply at an institutional scale. Clear institutional conviction signal here.' -Ecoinometrics ➡️SQUARE CEO JACK DORSEY: "Bitcoin will make the current financial system feel as irrelevant as the fax machine." On the 25th of March: ➡️'BITCOIN HASH-RIBBON FLASHES BUY SIGNAL - This is one of the most reliable "buy" indicators. - Significant price gains have followed 7 out of the last 7 times this indicator was triggered.' -Bitcoin Archive (foto) Bitcoin is always a buy. Just DCA. ➡️GameStop includes Bitcoin as a treasury reserve asset in its investment policy update. GameStop has $4.6 billion in cash to invest. ➡️Strategy’s sale of 8.5 million STRF shares closes today, unlocking $711 million in new capital to buy more Bitcoin. ➡️BBC News reports from a remote community of 15,000 people in the far north-western tip of Zambia relying on hydroelectric power, “The bitcoin mine now accounts for around 30% of the plant's revenue allowing them to keep the prices down for the local town” - Source: https://www.bbc.com/news/articles/cly4xe373p4o Gridless is doing a splendid job in Africa and showing through proof-of-work that if you aren't mining Bitcoin, you are wasting energy. It's time for such communities to appear more around the world. Daniel Batten: 'They couldn't resist zooming out and implying this is an outlier (it isn't, the majority of off-grid bitcoin mining operations are renewably powered). In doing so BBC made three factually incorrect statements at the end about Bitcoin mining straining grids (multiple peer-reviewed studies show the opposite is true), and "Greenidge gas power plant in New York which was renovated to mine bitcoin" (it didn't, it re-opened to supply power back to the grid), and stating that Bitcoin mining needs artificial govt incentives or rules to do the right thing (It doesn't, it's become 56.7% sustainably powered without any govt incentives) But let's shine the light on the positive - it has far fewer factually incorrect statements than previous reporting, and it is a step in the right direction in its gradual journey towards objective Bitcoin reporting for a media company that has until now only published negative news stories on Bitcoin.' ➡️Femke Halsema, Mayor of Amsterdam, wants a national ban on Bitcoin payments: "It undermines our civilization". I rather believe the opposite. Under Femke Halsema - Amsterdam - The number of civil servants increased by 50% (14K -> 20K) - Debt increased by 150% (4 billion -> approx. 10 billion) Despite high revenues, Amsterdam has to borrow nearly half a billion euros every year. Local taxes continue to rise, whether it's water authority taxes or property taxes (OZB). But, above all, you should be concerned about those 0.3% criminal Bitcoin / Crypto transactions (worldwide). The audacity. Even if the Netherlands were to legally ban Bitcoin payments, users could easily continue trading through foreign exchanges or peer-to-peer platforms. A ban might actually push Bitcoin usage further underground, making oversight of suspicious transactions worse rather than better. ➡️Mt. Gox moves 11.501 Bitcoin ($1B) for creditor repayment. ➡️BlackRock launched a European Bitcoin ETP today - Bloomberg ➡️North Carolina introduces a bill to invest 5% of state funds into Bitcoin. On the 26th of March: ➡️NYDIG just became a big Bitcoin miner. Crusoe, the first to scale Bitcoin mining off flared gas (~200MW worth, across 425 data centers) has sold its entire Bitcoin mining business to NYDIG. ➡️Metaplanet has raised ~$55.2m (¥8.28b) of equity capital through three trading days this week while partially deleveraging with the redemption of $23.3m (¥3.5b) of 0% ordinary bonds. ➡️GameStop can service a loan of up to $100 BILLION for 4.6 years with its existing $4.6b cash balance at 1% interest. That's twice the amount of Bitcoin Michael Saylor's Strategy currently holds. ➡️New feature by Protonmail enables their 100 million users to send Bitcoin using their email addresses. ➡️The Blockchain Group confirms the acquisition of 580 BTC for ~€47.3 million, the holding of a total of 620 BTC, and a BTC Yield of 709.8% YTD. → Confirmation of the acquisition of 580 BTC for ~€47.3 million at ~€81,550 per bitcoin → Total group holdings of 620 BTC for ~€50.5 million at ~€81,480 per bitcoin → Adoption of ‘BTC Yield’, ‘BTC Gain’, and ‘BTC € Gain’ as KPIs, following the steps of Strategy and Metaplanet This is a major step in our Bitcoin Treasury Company strategy focused on increasing Bitcoin per share over time. Source: https://t.co/QDj61ZDe6O The Blockchain Group is Europe's First Bitcoin Treasury Company! On the 27th of March: ➡️'Bitcoin's 4-year Compound Annual Growth Rate (CAGR) is at historic lows.' -Pierre Rochard ➡️Daniel Batten: Yet another paper on Bitcoin and energy TL:DR: "The opportunities offered by bitcoin mining in reduction of the greenhouse gas emissions and renewable energy transition are greater than generally assumed" The journal has a (high) impact factor of 7.1." Source: https://t.co/W3gytMgcpC ➡️A home miner with only 4 machines mined block 888737. https://i.ibb.co/7xm91R4t/Gn-Ef-H9y-Ws-AA4jkn.jpg Bitcoin proves anyone can participate and earn—true freedom! ➡️'Short-Term Holders have increased their Bitcoin holdings by 201,743 BTC to 5,750,076 BTC since January, remaining below previous cycle peaks. 200K BTC are currently held at an unrealized loss, representing about $17B.' -Bitcoin News ➡️Bitcoin mining hardware manufacturer Canaan signs a three-year colocation agreement with Mawson Infrastructure Group's Mawson Hosting LLC for facilities in Midland, Pennsylvania, and Edna, Texas. Most of the 4.7 EH/s hashrate is expected to be operational by Q2 2025. On the 28th of March: ➡️If Saylor had bet on ETH instead of Bitcoin, Strategy would be down $9 billion, instead of up $9 billion like they are today. ETHBTC made fresh lows 0.02210. Ether is down 74% against Bitcoin since switching from proof of work to proof of stake. Yikes! ➡️Representative introduces a strategic Bitcoin reserve bill in South Carolina. ➡️A Russian company built a Bitcoin mine in the Arctic. Set in the frozen city of Norilsk, the facility taps into cheap excess energy from one of the world's most isolated industrial hubs. ➡️The price of bitcoin has nearly followed the same phases of volatility for 15 years, according to Fidelity. https://i.ibb.co/LdQfrqG0/Gn-Ig-Skd-XMAAi-L3r.jpg another great chart: https://i.ibb.co/G4WmDjhd/Gn-JED1q-Xk-AAq-Kqk.jpg On the 29th of March: ➡️Public miner MARA with a $2B common stock offering to buy more Bitcoin. https://i.ibb.co/PZZxXJ37/Gn-Kj-Vqza-EAEUG-V.png ➡️California has officially included Bitcoin Rights protections in its newly proposed digital asset bill. If passed, it will guarantee the right to self-custody for nearly 40M residents and prohibit discrimination against Bitcoin use. ➡️The number of addresses with more than one Bitcoin has fallen below 1 million, standing today at 995,207. On the 31st of March: ➡️Larry Fink, Founder/CEO of BlackRock in his annual letter to shareholders: “If the U.S. doesn't get its debt under control, if deficits keep ballooning, America risks losing that position to digital assets like Bitcoin." https://www.blackrock.com/corporate/literature/presentation/larry-fink-annual-chairmans-letter.pdf ➡️Strategy has acquired 22,048 BTC for ~$1.92 billion at ~$86,969 per bitcoin and has achieved a BTC Yield of 11.0% YTD 2025. As of 3/30/2025, Strategy holds 528,185 $BTC acquired for ~$35.63 billion at ~$67,458 per bitcoin. ➡️ The Bitcoin Policy Institute releases a framework for the USA to buy $200 billion worth of #Bitcoin using Bit Bonds. ➡️Is Indonesia the next Bitcoin Country? Bitcoin Indonesia mapped out the entire Bitcoin ecosystem. A new map shows Bitcoin adoption EXPLODING across the Southeast Asian island nation of Indonesia. Check out all the communities, projects, and businesses embracing Bitcoin. The revolution is happening. https://i.ibb.co/cXL8mC0x/Gnbdg-Lub-IAAdwcb.jpg On the 1st of April: ➡️'Over 73,353 BTC were bought by corporations in Q1 2025. Only 40,500 BTC new Bitcoin was mined, but still no supply shock, for now... Which company do you want to see adopt BTC next?' Here is the breakdown by Alec: https://x.com/Alec_Bitcoin/status/1907062290345783723 ➡️After skeptics questioned Tether’s Bitcoin holdings, CEO Paolo Ardoino fired back, sharing the company’s BTC address with a confirmed balance of 92,646 BTC. On the same day Tether bought 8,888 Bitcoin worth $735 million as per on-chain data. They now hold over 100,000 BTC. ➡️'GameStop just raised $1.48B. They are expected to use that and possibly more of the now $6B+ on their balance sheet to buy Bitcoin. A master class on how to pivot from meme stock to capitalize on volatility in the ultimate store of value.' -James Lavish ➡️Texas' state house Democrats have proposed a bill that would authorize up to $250 million in state investment in Bitcoin and up to $10 million for each municipality and county. ➡️Human Rights Foundation donates 10 Bitcoins worth $830,000 to over 20 projects worldwide. Alex Gladstein: '1 billion sats gifted carefully to a variety of stellar organizations and individuals to support BTC privacy, decentralization, education, and p2p use, aimed at folks working under authoritarianism.' ## 💸Traditional Finance / Macro: On the 29th of March 👉🏽'From Wednesday to Friday, the S&P 500 lost -$100 billion PER trading hour for a total of -$2 TRILLION. Then, after the market closed on Friday, S&P 500 futures erased ANOTHER -$120 billion in minutes.' -TKL ## 🏦Banks: 👉🏽 no news ## 🌎Macro/Geopolitics: On the 24th of March: 👉🏽Financelot: 'This is fascinating. The Dow Jones to Gold Ratio is about to cross a level only seen 4 times in history. Every time it crossed this level it marked the beginning of an 18-month recession/depression. 1929, 1973, 2008 & 2025' I don't think we won't see a depression. History rhymes but doesn't always mean it will repeat, although human behavior stays the same. For now, it means the market is overvalued, gold is undervalued, or both. 👉🏽US household wealth is falling: US household equity wealth is set to drop a whopping -$3 trillion this quarter, the most since the 2022 bear market, according to BofA estimates. By comparison, equity holdings rose +$9 trillion in 2024 to a record $56 trillion. In other words, one-third of last year's gains have likely been wiped out due to the recent market pullback. Furthermore, the top 10% of the wealthiest Americans own 87% of US stocks. This, in turn, may negatively impact consumer spending as the top 10% reflect a record 50% of all consumer expenditures. Consumer spending is set to slow in Q2 2025.' -TKL 👉🏽Demolition of the Boiler House at Moorburg Power Plant in Hamburg. Germany is preparing for combat by dynamiting its own modern energy infrastructure down. This was the most advanced coal plant. 6 years old and cost three billion euros. The Netherlands is following a similar policy—they poured concrete into their gas drilling pipes. BowTiedMara on Twitter: "In 2022, a girl tied herself to the net at Roland Garros in protest, and she wore a T-shirt that said: "We have 1,028 days left." Today, the 27th of March, marks those 1,028 days, and nothing happened. Climate doomers are like Aztecs who think the sun stops unless they cut out some organs." 👉🏽Starting in April, the 66,000 employees of the European institutions will receive their seventh salary increase in just three years! Normally, this happens at most once per year. The President of the European Commission, Ursula von der Leyen, will see the largest increase, with her monthly salary rising to €34,800—an increase of €2,700—according to a report by the German newspaper Bild-Zeitung today. For the Dutch readers: https://ejbron.wordpress.com/2025/03/24/eu-bureaucraten-en-politici-krijgen-de-7e-salarisverhoging-sinds-2022/ They are compensating for the inflation they impose on the EU. Lucky them Fair to say we need a DOGE in Europe. On the 25th of March: 👉🏽Dutch minister announces a huge increase in excise duties of 25.8 cents on gasoline. On top of that, the price of gasoline will rise by an additional 7 cents due to the blending requirement and 11 cents due to the ETS-2 regulation. In a free market, prices would not be announced by politicians but would emerge through supply and demand. How I love the EU....although it is a bit more nuanced. The temporary discount is ending. Unless the parliament decides to extend it, the price of gasoline will rise. The Dutch government should simply spend less and abolish all taxes, excise duties, and levies on food, fuel, and energy. Never gonna happen though. 👉🏽"Shell will be thoroughly reviewing all its chemical divisions worldwide in the coming period. In Europe, this could lead to the partial or complete closure of various chemical branches." As mentioned multiple times last month, major industrial companies sounded the alarm. They warned that high energy costs in the Netherlands put their future at risk. Additionally, sustainability efforts and unclear government policies are challenging the sector. Frans Everts, President-Director of Shell Netherlands, warned that the entire industry could collapse. The Green Deal is moving full speed ahead—soon everyone will be relying on food banks… For the Dutch readers: https://nos.nl/artikel/2561036-shell-kijkt-naar-gedeeltelijke-sluiting-van-chemie-onderdelen On the 26th of March: 👉🏽EU countries will start using a digital driver’s license from 2030. This is the result of negotiations between the European Parliament and EU member states. In the Netherlands, the digital license will be valid for ten years and will be accessible via an app. And we all know which app that will be! The EU Digital Wallet must be filled, after all. Not just your driver’s license—everything will soon be linked to your digital identity. It’s all right there on the EU’s website, and it’s been planned for a long time. The COVID pass was already part of the rollout. The fact that they present these as separate steps just shows that they know people wouldn’t accept it if they were fully aware of what’s happening. On the 27th of March: 👉🏽Gold surpasses $3,100 for the first time in history. TKL: 'Gold prices have hit 50 all-time highs over the last 12 months, its best streak in 12 years. This is also the 3rd-longest streak on record after a historic run during the late 1970s. The 1970s came with a period of double-digit inflation, stagnant economic growth, and a high unemployment rate, also known as stagflation. As a result, gold prices recorded 4 consecutive yearly gains.' On the 31st of March for the first time, gold blasted through $100,000/kilogram. This time, gold prices have rallied 39% over the last 12 months, are up 16% year-to-date, and are on track for the 3rd annual positive performance.' 👉🏽NATO Secretary General Rutte insists there will be no normalization of relations with Russia for decades to come. On March 14, 2025, Bloomberg, Rutte says: "Once the war is over, relations with Russia will gradually be restored." On March 26, 2025, Rutte said: "There will be no normalization of relations with Russia for decades, even after the war is over." That is the Mark I know! "Mark Rutte, the long-serving Dutch Prime Minister, earned the nickname “Pinokkio” (Dutch for Pinocchio) primarily because of perceived dishonesty or evasiveness in political debates and scandals. While some still view Rutte as a pragmatic and stable leader, the nickname “Pinokkio” reflects a broader public sentiment of distrust, especially among those who felt betrayed by his communication style or decisions.” On the 28th of March: 👉🏽US consumers now expect 5.0%(!) inflation in the next twelve months. Inflation expectations have DOUBLED in just four months. That's huge! Long-term US inflation expectations have officially SURGED to 4.1%, the highest level since 1993. Tariff front-running has led to a $300+ BILLION trade deficit in 2 months, and consumer sentiment has collapsed. Atlanta Fed is now projecting that Q1 GDP will be -2.8%… a large contraction. It’s negative even “gold adjusted” 4 weeks ago it was +2.3% 8 weeks ago it was +3.9% Yikes! 👉🏽The State Department is officially shutting down USAID and has formally notified Congress of its closure. The remaining 900 employees are set to be terminated. 👉🏽Argentina’s Economy Grows 6.5% in January. Argentina’s Poverty Rate Drops from 52.9% to 38.1% in 15 Months Under Javier Milei 👉🏽Fix the money, fix the world: DOGE “There is actually really only ONE BANK ACCOUNT that's used to disperse ALL monies that go out of the federal government” “It's a big one — A couple of weeks ago it had $800 billion in it, it's the treasury general account” “We're serving 580+ agencies. And up until very recently, effectively they could say, make the payment and Treasury just sent it out as fast as possible. NO VERIFICATION” “There's a $500 billion of fraud every year. There are hundreds of billion dollars of improper payments and we can't pass an audit. The consolidated financial report is produced by treasury and we cannot pass an audit” Extremely fascinating interview by Bret Baier with the highly talented and competent DOGE team, which is rigorously streamlining the U.S. government bureaucracy. This work can only be done by competent (and motivated) outsiders with experience. Also urgently needed in the Netherlands, and in Europe. On the 29th of March: 👉🏽'US debt has been "limited" by the $36.104 trillion debt ceiling since January but the liabilities don't stop rising. As of today, US debt is now ~$37 trillion. Treasury has burned through $560BN of its cash balance in the past month. Just $280BN left.' -ZeroHedge On the 1st of April: In recent weeks, I have shared my opinion on the latest Dutch pension fund drama. This week: https://i.ibb.co/96ZhS0W/Gn-XEVQRXw-AM6b0-A.jpg APG and pension funds refused to invest in Dutch housing (for political reasons). This involved 25 billion euros. Currently we almost have a political scandal over a medal, but the fact that our pension system is being put at risk...no biggie!? For our own housing market? “Too political.” For war and Brussels' military ambitions? €100,000,000,000—no problem. They’re gambling with your pension while first-time buyers can’t afford a home and seniors struggle to make ends meet. Our money, their agenda. Got Bitcoin? I will end this Weekly Recap with a Stanley Druckenmiller quote: "My favorite quote of all time is maybe Mark Twain: "Put all your eggs in one basket and watch the basket carefully." "I tend to think that's what great investors do." I know what I do and have. Bitcoin! ## 🎁If you have made it this far I would like to give you a little gift: What Bitcoin Did: Peter Dunworth is the Director of a multi-family office and is the co-founder of The Bitcoin Adviser. In this episode, they discuss why Bitcoin is the only asset that can recapitalize the financial system, why Peter believes Bitcoin could become a $100 trillion asset within a decade, why credit markets are ultimately a collateral problem, and why financializing Bitcoin might be necessary to save Main Street from being collateral damage. They also get into Australia's property obsession, GameStop’s pivot to Bitcoin, the difference between Bitcoin derivatives and the asset itself, and MicroStrategy. https://www.youtube.com/watch?v=_bSprc0IAow Credit: I have used multiple sources! My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly. `Use the code SE3997` Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀ ⠀⠀ ⠀ ⠀⠀⠀ Do you think this post is helpful to you? If so, please share it and support my work with a zap. ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ ⭐ Many thanks⭐ Felipe - Bitcoin Friday! ▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃ @ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher
@ 17538dc2:71ed77c4
2025-04-02 16:04:59The MacOS security update summary is a reminder that laptops and desktops are incredibly compromised. ### macOS Sequoia 15.4 Released March 31, 2025 Accessibility Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24202: Zhongcheng Li from IES Red Team of ByteDance AccountPolicy Available for: macOS Sequoia Impact: A malicious app may be able to gain root privileges Description: This issue was addressed by removing the vulnerable code. CVE-2025-24234: an anonymous researcher AirDrop Available for: macOS Sequoia Impact: An app may be able to read arbitrary file metadata Description: A permissions issue was addressed with additional restrictions. CVE-2025-24097: Ron Masas of BREAKPOINT.SH App Store Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: This issue was addressed by removing the vulnerable code. CVE-2025-24276: an anonymous researcher AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24272: Mickey Jin (@patch1t) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A downgrade issue was addressed with additional code-signing restrictions. CVE-2025-24239: Wojciech Regula of SecuRing (wojciechregula.blog) AppleMobileFileIntegrity Available for: macOS Sequoia Impact: A malicious app may be able to read or write to protected files Description: A permissions issue was addressed with additional restrictions. CVE-2025-24233: Claudio Bozzato and Francesco Benvenuto of Cisco Talos. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A privacy issue was addressed by removing the vulnerable code. CVE-2025-30443: Bohdan Stasiuk (@bohdan_stasiuk) Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: The issue was addressed with improved memory handling. CVE-2025-24244: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Audio Available for: macOS Sequoia Impact: Processing a maliciously crafted file may lead to arbitrary code execution Description: The issue was addressed with improved memory handling. CVE-2025-24243: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Authentication Services Available for: macOS Sequoia Impact: Password autofill may fill in passwords after failing authentication Description: This issue was addressed through improved state management. CVE-2025-30430: Dominik Rath Authentication Services Available for: macOS Sequoia Impact: A malicious website may be able to claim WebAuthn credentials from another website that shares a registrable suffix Description: The issue was addressed with improved input validation. CVE-2025-24180: Martin Kreichgauer of Google Chrome Authentication Services Available for: macOS Sequoia Impact: A malicious app may be able to access a user's saved passwords Description: This issue was addressed by adding a delay between verification code attempts. CVE-2025-24245: Ian Mckay (@iann0036) Automator Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed by removing vulnerable code and adding additional checks. CVE-2025-30460: an anonymous researcher BiometricKit Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24237: Yutong Xiu Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A path handling issue was addressed with improved validation. CVE-2025-30429: Denis Tokarev (@illusionofcha0s) Calendar Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with improved checks. CVE-2025-24212: Denis Tokarev (@illusionofcha0s) CloudKit Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-24215: Kirin (@Pwnrin) CoreAudio Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: The issue was addressed with improved checks. CVE-2025-24163: Google Threat Analysis Group CoreAudio Available for: macOS Sequoia Impact: Playing a malicious audio file may lead to an unexpected app termination Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24230: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: This issue was addressed with improved memory handling. CVE-2025-24211: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24236: Csaba Fitzl (@theevilbit) and Nolan Astrein of Kandji CoreMedia Available for: macOS Sequoia Impact: Processing a maliciously crafted video file may lead to unexpected app termination or corrupt process memory Description: The issue was addressed with improved memory handling. CVE-2025-24190: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative CoreMedia Playback Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: A path handling issue was addressed with improved validation. CVE-2025-30454: pattern-f (@pattern_F_) CoreServices Description: This issue was addressed through improved state management. CVE-2025-31191: Jonathan Bar Or (@yo_yo_yo_jbo) of Microsoft, and an anonymous researcher Available for: macOS Sequoia Impact: An app may be able to access sensitive user data CoreText Available for: macOS Sequoia Impact: Processing a maliciously crafted font may result in the disclosure of process memory Description: An out-of-bounds read issue was addressed with improved input validation. CVE-2025-24182: Hossein Lotfi (@hosselot) of Trend Micro Zero Day Initiative Crash Reporter Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-24277: Csaba Fitzl (@theevilbit) of Kandji and Gergely Kalman (@gergely_kalman), and an anonymous researcher curl Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-9681 Disk Images Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: A file access issue was addressed with improved input validation. CVE-2025-24255: an anonymous researcher DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A parsing issue in the handling of directory paths was addressed with improved path validation. CVE-2025-30456: Gergely Kalman (@gergely_kalman) DiskArbitration Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-24267: an anonymous researcher Dock Available for: macOS Sequoia Impact: A malicious app may be able to access private information Description: The issue was addressed with improved checks. CVE-2025-30455: Mickey Jin (@patch1t), and an anonymous researcher Dock Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: This issue was addressed by removing the vulnerable code. CVE-2025-31187: Rodolphe BRUNETTI (@eisw0lf) of Lupus Nova dyld Available for: macOS Sequoia Impact: Apps that appear to use App Sandbox may be able to launch without restrictions Description: A library injection issue was addressed with additional restrictions. CVE-2025-30462: Pietro Francesco Tirenna, Davide Silvetti, Abdel Adim Oisfi of Shielder (shielder.com) FaceTime Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30451: Kirin (@Pwnrin) and luckyu (@uuulucky) FeedbackLogger Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved data protection. CVE-2025-24281: Rodolphe BRUNETTI (@eisw0lf) Focus Available for: macOS Sequoia Impact: An attacker with physical access to a locked device may be able to view sensitive user information Description: The issue was addressed with improved checks. CVE-2025-30439: Andr.Ess Focus Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A logging issue was addressed with improved data redaction. CVE-2025-24283: Kirin (@Pwnrin) Foundation Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: An access issue was addressed with additional sandbox restrictions on the system pasteboards. CVE-2025-30461: an anonymous researcher Foundation Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was resolved by sanitizing logging CVE-2025-30447: LFY@secsys from Fudan University Foundation Available for: macOS Sequoia Impact: An app may be able to cause a denial-of-service Description: An uncontrolled format string issue was addressed with improved input validation. CVE-2025-24199: Manuel Fernandez (Stackhopper Security) GPU Drivers Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: An out-of-bounds write issue was addressed with improved bounds checking. CVE-2025-30464: ABC Research s.r.o. CVE-2025-24273: Wang Yu of Cyberserval GPU Drivers Available for: macOS Sequoia Impact: An app may be able to disclose kernel memory Description: The issue was addressed with improved bounds checks. CVE-2025-24256: Anonymous working with Trend Micro Zero Day Initiative, Murray Mike Handoff Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-30463: mzzzz__ ImageIO Available for: macOS Sequoia Impact: Parsing an image may lead to disclosure of user information Description: A logic error was addressed with improved error handling. CVE-2025-24210: Anonymous working with Trend Micro Zero Day Initiative Installer Available for: macOS Sequoia Impact: An app may be able to check the existence of an arbitrary path on the file system Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24249: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Installer Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data Description: A logic issue was addressed with improved checks. CVE-2025-24229: an anonymous researcher IOGPUFamily Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or write kernel memory Description: An out-of-bounds write issue was addressed with improved input validation. CVE-2025-24257: Wang Yu of Cyberserval IOMobileFrameBuffer Available for: macOS Sequoia Impact: An app may be able to corrupt coprocessor memory Description: The issue was addressed with improved bounds checks. CVE-2025-30437: Ye Zhang (@VAR10CK) of Baidu Security Kerberos Helper Available for: macOS Sequoia Impact: A remote attacker may be able to cause unexpected app termination or heap corruption Description: A memory initialization issue was addressed with improved memory handling. CVE-2025-24235: Dave G. Kernel Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: The issue was addressed with improved checks. CVE-2025-24204: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. Kernel Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24203: Ian Beer of Google Project Zero Kernel Available for: macOS Sequoia Impact: An attacker with user privileges may be able to read kernel memory Description: A type confusion issue was addressed with improved memory handling. CVE-2025-24196: Joseph Ravichandran (@0xjprx) of MIT CSAIL LaunchServices Available for: macOS Sequoia Impact: A malicious JAR file may bypass Gatekeeper checks Description: This issue was addressed with improved handling of executable types. CVE-2025-24148: Kenneth Chew libarchive Available for: macOS Sequoia Impact: An input validation issue was addressed Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2024-48958 Libinfo Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: An integer overflow was addressed with improved input validation. CVE-2025-24195: Paweł Płatek (Trail of Bits) libnetcore Available for: macOS Sequoia Impact: Processing maliciously crafted web content may result in the disclosure of process memory Description: A logic issue was addressed with improved checks. CVE-2025-24194: an anonymous researcher libxml2 Available for: macOS Sequoia Impact: Parsing a file may lead to an unexpected app termination Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2025-27113 CVE-2024-56171 libxpc Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed through improved state management. CVE-2025-24178: an anonymous researcher libxpc Available for: macOS Sequoia Impact: An app may be able to delete files for which it does not have permission Description: This issue was addressed with improved handling of symlinks. CVE-2025-31182: Alex Radocea and Dave G. of Supernetworks, 风沐云烟(@binary_fmyy) and Minghao Lin(@Y1nKoc) libxpc Available for: macOS Sequoia Impact: An app may be able to gain elevated privileges Description: A logic issue was addressed with improved checks. CVE-2025-24238: an anonymous researcher Mail Available for: macOS Sequoia Impact: "Block All Remote Content" may not apply for all mail previews Description: A permissions issue was addressed with additional sandbox restrictions. CVE-2025-24172: an anonymous researcher manpages Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-30450: Pwn2car Maps Available for: macOS Sequoia Impact: An app may be able to read sensitive location information Description: A path handling issue was addressed with improved logic. CVE-2025-30470: LFY@secsys from Fudan University NetworkExtension Available for: macOS Sequoia Impact: An app may be able to enumerate a user's installed apps Description: This issue was addressed with additional entitlement checks. CVE-2025-30426: Jimmy Notes Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24262: LFY@secsys from Fudan University NSDocument Available for: macOS Sequoia Impact: A malicious app may be able to access arbitrary files Description: This issue was addressed through improved state management. CVE-2025-24232: an anonymous researcher OpenSSH Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An injection issue was addressed with improved validation. CVE-2025-24246: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24261: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A logic issue was addressed with improved checks. CVE-2025-24164: Mickey Jin (@patch1t) PackageKit Available for: macOS Sequoia Impact: A malicious app with root privileges may be able to modify the contents of system files Description: A permissions issue was addressed with additional restrictions. CVE-2025-30446: Pedro Tôrres (@t0rr3sp3dr0) Parental Controls Available for: macOS Sequoia Impact: An app may be able to retrieve Safari bookmarks without an entitlement check Description: This issue was addressed with additional entitlement checks. CVE-2025-24259: Noah Gregory (wts.dev) Photos Storage Available for: macOS Sequoia Impact: Deleting a conversation in Messages may expose user contact information in system logging Description: A logging issue was addressed with improved data redaction. CVE-2025-30424: an anonymous researcher Power Services Available for: macOS Sequoia Impact: An app may be able to break out of its sandbox Description: This issue was addressed with additional entitlement checks. CVE-2025-24173: Mickey Jin (@patch1t) Python Available for: macOS Sequoia Impact: A remote attacker may be able to bypass sender policy checks and deliver malicious content via email Description: This is a vulnerability in open source code and Apple Software is among the affected projects. The CVE-ID was assigned by a third party. Learn more about the issue and CVE-ID at cve.org. CVE-2023-27043 RPAC Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved validation of environment variables. CVE-2025-24191: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to user interface spoofing Description: The issue was addressed with improved UI. CVE-2025-24113: @RenwaX23 Safari Available for: macOS Sequoia Impact: Visiting a malicious website may lead to address bar spoofing Description: The issue was addressed with improved checks. CVE-2025-30467: @RenwaX23 Safari Available for: macOS Sequoia Impact: A website may be able to access sensor information without user consent Description: The issue was addressed with improved checks. CVE-2025-31192: Jaydev Ahire Safari Available for: macOS Sequoia Impact: A download's origin may be incorrectly associated Description: This issue was addressed through improved state management. CVE-2025-24167: Syarif Muhammad Sajjad Sandbox Available for: macOS Sequoia Impact: An app may be able to access removable volumes without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24093: Yiğit Can YILMAZ (@yilmazcanyigit) Sandbox Available for: macOS Sequoia Impact: An input validation issue was addressed Description: The issue was addressed with improved checks. CVE-2025-30452: an anonymous researcher Sandbox Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: A permissions issue was addressed with additional restrictions. CVE-2025-24181: Arsenii Kostromin (0x3c3e) SceneKit Available for: macOS Sequoia Impact: An app may be able to read files outside of its sandbox Description: A permissions issue was addressed with additional restrictions. CVE-2025-30458: Mickey Jin (@patch1t) Security Available for: macOS Sequoia Impact: A remote user may be able to cause a denial-of-service Description: A validation issue was addressed with improved logic. CVE-2025-30471: Bing Shi, Wenchao Li, Xiaolong Bai of Alibaba Group, Luyi Xing of Indiana University Bloomington Security Available for: macOS Sequoia Impact: A malicious app acting as a HTTPS proxy could get access to sensitive user data Description: This issue was addressed with improved access restrictions. CVE-2025-24250: Wojciech Regula of SecuRing (wojciechregula.blog) Share Sheet Available for: macOS Sequoia Impact: A malicious app may be able to dismiss the system notification on the Lock Screen that a recording was started Description: This issue was addressed with improved access restrictions. CVE-2025-30438: Halle Winkler, Politepix theoffcuts.org Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: A permissions issue was addressed with improved validation. CVE-2025-30465: an anonymous researcher Shortcuts Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An access issue was addressed with additional sandbox restrictions. CVE-2025-24280: Kirin (@Pwnrin) Shortcuts Available for: macOS Sequoia Impact: A Shortcut may run with admin privileges without authentication Description: An authentication issue was addressed with improved state management. CVE-2025-31194: Dolf Hoegaerts Shortcuts Available for: macOS Sequoia Impact: A shortcut may be able to access files that are normally inaccessible to the Shortcuts app Description: This issue was addressed with improved access restrictions. CVE-2025-30433: Andrew James Gonzalez Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: The issue was addressed with improved restriction of data container access. CVE-2025-31183: Kirin (@Pwnrin), Bohdan Stasiuk (@bohdan_stasiuk) Siri Available for: macOS Sequoia Impact: A sandboxed app may be able to access sensitive user data in system logs Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-30435: K宝 (@Pwnrin) and luckyu (@uuulucky) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: This issue was addressed with improved redaction of sensitive information. CVE-2025-24217: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to access sensitive user data Description: A privacy issue was addressed by not logging contents of text fields. CVE-2025-24214: Kirin (@Pwnrin) Siri Available for: macOS Sequoia Impact: An app may be able to enumerate devices that have signed into the user's Apple Account Description: A permissions issue was addressed with additional restrictions. CVE-2025-24248: Minghao Lin (@Y1nKoc) and Tong Liu@Lyutoon_ and 风(binary_fmyy) and F00L Siri Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: An authorization issue was addressed with improved state management. CVE-2025-24205: YingQi Shi(@Mas0nShi) of DBAppSecurity's WeBin lab and Minghao Lin (@Y1nKoc) Siri Available for: macOS Sequoia Impact: An attacker with physical access may be able to use Siri to access sensitive user data Description: This issue was addressed by restricting options offered on a locked device. CVE-2025-24198: Richard Hyunho Im (@richeeta) with routezero.security SMB Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: The issue was addressed with improved memory handling. CVE-2025-24269: Alex Radocea of Supernetworks SMB Available for: macOS Sequoia Impact: Mounting a maliciously crafted SMB network share may lead to system termination Description: A race condition was addressed with improved locking. CVE-2025-30444: Dave G. SMB Available for: macOS Sequoia Impact: An app may be able to execute arbitrary code with kernel privileges Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24228: Joseph Ravichandran (@0xjprx) of MIT CSAIL smbx Available for: macOS Sequoia Impact: An attacker in a privileged position may be able to perform a denial-of-service Description: The issue was addressed with improved memory handling. CVE-2025-24260: zbleet of QI-ANXIN TianGong Team Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: A library injection issue was addressed with additional restrictions. CVE-2025-24282: Claudio Bozzato and Francesco Benvenuto of Cisco Talos Software Update Available for: macOS Sequoia Impact: A user may be able to elevate privileges Description: This issue was addressed with improved validation of symlinks. CVE-2025-24254: Arsenii Kostromin (0x3c3e) Software Update Available for: macOS Sequoia Impact: An app may be able to modify protected parts of the file system Description: The issue was addressed with improved checks. CVE-2025-24231: Claudio Bozzato and Francesco Benvenuto of Cisco Talos StickerKit Available for: macOS Sequoia Impact: An app may be able to observe unprotected user data Description: A privacy issue was addressed by moving sensitive data to a protected location. CVE-2025-24263: Cristian Dinca of "Tudor Vianu" National High School of Computer Science, Romania Storage Management Available for: macOS Sequoia Impact: An app may be able to enable iCloud storage features without user consent Description: A permissions issue was addressed with additional restrictions. CVE-2025-24207: YingQi Shi (@Mas0nShi) of DBAppSecurity's WeBin lab, 风沐云烟 (binary_fmyy) and Minghao Lin (@Y1nKoc) StorageKit Available for: macOS Sequoia Impact: An app may be able to gain root privileges Description: A permissions issue was addressed with additional restrictions. CVE-2025-30449: Arsenii Kostromin (0x3c3e), and an anonymous researcher StorageKit Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved handling of symlinks. CVE-2025-24253: Mickey Jin (@patch1t), Csaba Fitzl (@theevilbit) of Kandji StorageKit Available for: macOS Sequoia Impact: An app may be able to access user-sensitive data Description: A race condition was addressed with additional validation. CVE-2025-24240: Mickey Jin (@patch1t) StorageKit Available for: macOS Sequoia Impact: An app may be able to bypass Privacy preferences Description: A race condition was addressed with additional validation. CVE-2025-31188: Mickey Jin (@patch1t) Summarization Services Available for: macOS Sequoia Impact: An app may be able to access information about a user's contacts Description: A privacy issue was addressed with improved private data redaction for log entries. CVE-2025-24218: Kirin and FlowerCode, Bohdan Stasiuk (@bohdan_stasiuk) System Settings Available for: macOS Sequoia Impact: An app may be able to access protected user data Description: This issue was addressed with improved validation of symlinks. CVE-2025-24278: Zhongquan Li (@Guluisacat) System Settings Available for: macOS Sequoia Impact: An app with root privileges may be able to access private information Description: This issue was addressed with improved handling of symlinks. CVE-2025-24242: Koh M. Nakagawa (@tsunek0h) of FFRI Security, Inc. SystemMigration Available for: macOS Sequoia Impact: A malicious app may be able to create symlinks to protected regions of the disk Description: This issue was addressed with improved validation of symlinks. CVE-2025-30457: Mickey Jin (@patch1t) Voice Control Available for: macOS Sequoia Impact: An app may be able to access contacts Description: This issue was addressed with improved file handling. CVE-2025-24279: Mickey Jin (@patch1t) Web Extensions Available for: macOS Sequoia Impact: An app may gain unauthorized access to Local Network Description: This issue was addressed with improved permissions checking. CVE-2025-31184: Alexander Heinrich (@Sn0wfreeze), SEEMOO, TU Darmstadt & Mathy Vanhoef (@vanhoefm) and Jeroen Robben (@RobbenJeroen), DistriNet, KU Leuven Web Extensions Available for: macOS Sequoia Impact: Visiting a website may leak sensitive data Description: A script imports issue was addressed with improved isolation. CVE-2025-24192: Vsevolod Kokorin (Slonser) of Solidlab WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: The issue was addressed with improved memory handling. WebKit Bugzilla: 285892 CVE-2025-24264: Gary Kwong, and an anonymous researcher WebKit Bugzilla: 284055 CVE-2025-24216: Paul Bakker of ParagonERP WebKit Available for: macOS Sequoia Impact: A type confusion issue could lead to memory corruption Description: This issue was addressed with improved handling of floats. WebKit Bugzilla: 286694 CVE-2025-24213: Google V8 Security Team WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected process crash Description: A buffer overflow issue was addressed with improved memory handling. WebKit Bugzilla: 286462 CVE-2025-24209: Francisco Alonso (@revskills), and an anonymous researcher WebKit Available for: macOS Sequoia Impact: Processing maliciously crafted web content may lead to an unexpected Safari crash Description: A use-after-free issue was addressed with improved memory management. WebKit Bugzilla: 285643 CVE-2025-30427: rheza (@ginggilBesel) WebKit Available for: macOS Sequoia Impact: A malicious website may be able to track users in Safari private browsing mode Description: This issue was addressed through improved state management. WebKit Bugzilla: 286580 CVE-2025-30425: an anonymous researcher WindowServer Available for: macOS Sequoia Impact: An attacker may be able to cause unexpected app termination Description: A type confusion issue was addressed with improved checks. CVE-2025-24247: PixiePoint Security WindowServer Available for: macOS Sequoia Impact: An app may be able to trick a user into copying sensitive data to the pasteboard Description: A configuration issue was addressed with additional restrictions. CVE-2025-24241: Andreas Hegenberg (folivora.AI GmbH) Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: A buffer overflow was addressed with improved bounds checking. CVE-2025-24266: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination Description: An out-of-bounds read was addressed with improved bounds checking. CVE-2025-24265: an anonymous researcher Xsan Available for: macOS Sequoia Impact: An app may be able to cause unexpected system termination or corrupt kernel memory Description: A buffer overflow issue was addressed with improved memory handling. CVE-2025-24157: an anonymous researcher @ 57d1a264:69f1fee1
2025-03-27 08:27:44> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be. `— Anil Dash, The Web We Lost, 13 Dec 2012` https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/ The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks. originally posted at https://stacker.news/items/926499
@ 57d1a264:69f1fee1
2025-03-27 08:27:44> The tech industry and its press have treated the rise of billion-scale social networks and ubiquitous smartphone apps as an unadulterated win for regular people, a triumph of usability and empowerment. They seldom talk about what we’ve lost along the way in this transition, and I find that younger folks may not even know how the web used to be. `— Anil Dash, The Web We Lost, 13 Dec 2012` https://www.youtube.com/watch?v=9KKMnoTTHJk&t=156s So here’s a few glimpses of a web that’s mostly faded away: https://www.anildash.com/2012/12/13/the_web_we_lost/ The first step to disabusing them of this notion is for the people creating the next generation of social applications to learn a little bit of history, to know your shit, whether that’s about [Twitter’s business model](http://web.archive.org/web/20180120013123/http://anildash.com/2010/04/ten-years-of-twitter-ads.html) or [Google’s social features](http://web.archive.org/web/20170518203228/http://anildash.com/2012/04/why-you-cant-trust-tech-press-to-teach-you-about-the-tech-industry.html) or anything else. We have to know what’s been tried and failed, what good ideas were simply ahead of their time, and what opportunities have been lost in the current generation of dominant social networks. originally posted at https://stacker.news/items/926499 @ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial). > _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_ `— Richard Hamming` [^1] https://www.youtube.com/watch?v=8pTEmbeENF4 For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.  _'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.' More details at https://worrydream.com/dbx/ [^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook) originally posted at https://stacker.news/items/926493
@ 57d1a264:69f1fee1
2025-03-27 08:11:33Explore and reimagine programming interfaces beyond text (visual, tactile, spatial). > _"The most dangerous thought you can have as a creative person is to think you know what you're doing."_ `— Richard Hamming` [^1] https://www.youtube.com/watch?v=8pTEmbeENF4 For his recent DBX Conference talk, Victor took attendees back to the year 1973, donning the uniform of an IBM systems engineer of the times, delivering his presentation on an overhead projector. The '60s and early '70s were a fertile time for CS ideas, reminds Victor, but even more importantly, it was a time of unfettered thinking, unconstrained by programming dogma, authority, and tradition.  _'The most dangerous thought that you can have as a creative person is to think that you know what you're doing,'_ explains Victor. 'Because once you think you know what you're doing you stop looking around for other ways of doing things and you stop being able to see other ways of doing things. You become blind.' He concludes, 'I think you have to say: _"We don't know what programming is. We don't know what computing is. We don't even know what a computer is."_ And once you truly understand that, and once you truly believe that, then you're free, and you can think anything.' More details at https://worrydream.com/dbx/ [^1]: Richard Hamming -- [The Art of Doing Science and Engineering, p5](http://worrydream.com/refs/Hamming_1997_-_The_Art_of_Doing_Science_and_Engineering.pdf) (pdf ebook) originally posted at https://stacker.news/items/926493 @ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev)
@ 06639a38:655f8f71
2025-04-02 13:47:57You can follow the work in progress here in this pull request [https://github.com/nostrver-se/nostr-php/pull/68](https://github.com/nostrver-se/nostr-php/pull/68) on Github. Before my 3-month break (Dec/Jan/Feb) working on Nostr-PHP I started with the NIP-19 integration in October '24. Encoding and decoding the simple prefixes (`npub`, `nsec` and `note`) was already done in the first commits. Learn more about NIP-19 here: [https://nips.nostr.com/19](https://nips.nostr.com/19) ### **TLV's** Things were getting more complicated with the other prefixes / identifiers defined in NIP-19: * `nevent` * `naddr` * `nprofile` This is because these identifiers contain (optional) metadata called Type-Lenght-Value aka TLV's. _When sharing a profile or an event, an app may decide to include relay information and other metadata such that other apps can locate and display these entities more easily._ _For these events, the contents are a binary-encoded list of_ `_TLV_` _(type-length-value), with_ `_T_` _and_ `_L_` _being 1 byte each (_`_uint8_`_, i.e. a number in the range of 0-255), and_ `_V_` _being a sequence of bytes of the size indicated by_ `_L_`_._ These possible standardized `TLV` types are: * `0`_:_ `special` * _depends on the bech32 prefix:_ * _for_ `nprofile` _it will be the 32 bytes of the profile public key_ * _for_ `nevent` _it will be the 32 bytes of the event id_ * _for_ `naddr`_, it is the identifier (the_ `"d"` _tag) of the event being referenced. For normal replaceable events use an empty string._ * `1`_:_ `relay` * _for_ `nprofile`_,_ `nevent` _and_ `naddr`_, optionally, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii_ * _this may be included multiple times_ * `2`_:_ `author` * _for_ `naddr`_, the 32 bytes of the pubkey of the event_ * _for_ `nevent`_, optionally, the 32 bytes of the pubkey of the event_ * `3`_:_ `kind` * _for_ `naddr`_, the 32-bit unsigned integer of the kind, big-endian_ * _for_ `nevent`_, optionally, the 32-bit unsigned integer of the kind, big-endian_ These identifiers are formatted as bech32 strings, but are much longer than the package `bitwasp/bech32` (used in the library) for can handle for encoding and decoding. The bech32 strings handled by `bitwasp/bech32` are limited to a maximum length of 90 characters. Thanks to the effort of others (nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 and nostr:npub1efz8l77esdtpw6l359sjvakm7azvyv6mkuxphjdk3vfzkgxkatrqlpf9s4) during my break, some contributions are made (modifiying the bech32 package supporting much longer strings, up to a max of 5000 characters). At this moment, I'm integrating this (mostly copy-pasting the stuff and refactoring the code): * [https://github.com/nostrver-se/nostr-php/issues/74](https://github.com/nostrver-se/nostr-php/issues/74) * [https://github.com/nostriphant/nip-19](https://github.com/nostriphant/nip-19) ### **So what's next?** * NIP-19 code housekeeping + refactoring * Prepare a new release with NIP-19 integration * Create documentation page how to use NIP-19 on [https://nostr-php.dev](https://nostr-php.dev) @ 7bdef7be:784a5805
2025-04-02 12:09:29We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so everyone can actually snoop what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also really private one. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Follow someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of how many bots scan our actions to profile us. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply mark them as local-only, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage both encrypted and local-only lists. Beg your Nostr client to implement private lists!
@ 7bdef7be:784a5805
2025-04-02 12:09:29We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, so everyone can actually snoop what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see [NIP-51](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create dedicated feeds, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be encrypted, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also really private one. One might wonder what use can really be made of private lists; here are some examples: * Browse “can't miss” content from users I consider a priority; * Supervise competitors or adversarial parts; * Monitor sensible topics (tags); * Follow someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of how many bots scan our actions to profile us. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff ([NIP-44](https://github.com/nostr-protocol/nips/blob/master/44.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply mark them as local-only, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is [Gossip](nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8), which permits to manage both encrypted and local-only lists. Beg your Nostr client to implement private lists! @ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments. ## Understanding MCP Systems MCP (Model Context Protocol) systems consist of two main components that work together: 1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method. 2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers. These servers and clients can communicate using different transport methods: - **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine. - **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel. For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr. ## Creating (or Finding) an MCP Server Building an MCP server is simpler than you might think: 1. Create software in any programming language you're comfortable with. 2. Add an MCP library to expose your server's MCP interface. 3. Create an API that wraps around your software's functionality. Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy. Alternatively, you can use one of the many existing MCP servers available in various repositories. For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/ ## Setting Up the Workshop Let's get hands-on: First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script: ``` curl -fsSL https://bun.sh/install | bash ``` 1. **Choose your MCP server**: You can either create one or use an existing one. 2. **Inspect your server** using the MCP inspector tool: ```bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2 ``` This will: - Launch a client UI (default: http://localhost:5173) - Start an MCP proxy server (default: port 3000) - Pass any additional arguments directly to your server 3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality. ## Deploying with DVMCP Now for the exciting part – making your MCP server available to everyone on Nostr: 1. Navigate to your MCP server directory. 2. Run without installing (quickest way): ``` npx @dvmcp/bridge ``` 3. Or install globally for regular use: ``` npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridge ``` Then run using: ```bash dvmcp-bridge ``` This will guide you through creating the necessary configuration. Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing. For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference ## Testing and Integration 1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement. 2. Call your tools and watch the responses come back. For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime. ## Integrating with LLM Clients You can also integrate your DVMCP deployment with LLM clients using the discovery package: 1. Install and use the `@dvmcp/discovery` package: ```bash npx @dvmcp/discovery ``` 2. This package acts as an MCP server for your LLM system by: - Connecting to configured Nostr relays - Discovering tools from DVMCP servers - Making them available to your LLM applications 3. Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1... # Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ``` Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun). This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications. ## Final thoughts If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun. You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless. However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr. Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag. ## Useful Resources - **Official Documentation**: - Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org) - DVMCP.fun: [dvmcp.fun](https://dvmcp.fun) - **Source Code and Development**: - DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp) - DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun) - **MCP Servers and Clients**: - Smithery AI: [smithery.ai](https://smithery.ai) - MCP.so: [mcp.so](https://mcp.so) - Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers) - [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD) Happy building!
@ 6b3780ef:221416c8
2025-03-26 18:42:00This workshop will guide you through exploring the concepts behind MCP servers and how to deploy them as DVMs in Nostr using DVMCP. By the end, you'll understand how these systems work together and be able to create your own deployments. ## Understanding MCP Systems MCP (Model Context Protocol) systems consist of two main components that work together: 1. **MCP Server**: The heart of the system that exposes tools, which you can access via the `.listTools()` method. 2. **MCP Client**: The interface that connects to the MCP server and lets you use the tools it offers. These servers and clients can communicate using different transport methods: - **Standard I/O (stdio)**: A simple local connection method when your server and client are on the same machine. - **Server-Sent Events (SSE)**: Uses HTTP to create a communication channel. For this workshop, we'll use stdio to deploy our server. DVMCP will act as a bridge, connecting to your MCP server as an MCP client, and exposing its tools as a DVM that anyone can call from Nostr. ## Creating (or Finding) an MCP Server Building an MCP server is simpler than you might think: 1. Create software in any programming language you're comfortable with. 2. Add an MCP library to expose your server's MCP interface. 3. Create an API that wraps around your software's functionality. Once your server is ready, an MCP client can connect, for example, with `bun index.js`, and then call `.listTools()` to discover what your server can do. This pattern, known as reflection, makes Nostr DVMs and MCP a perfect match since both use JSON, and DVMs can announce and call tools, effectively becoming an MCP proxy. Alternatively, you can use one of the many existing MCP servers available in various repositories. For more information about mcp and how to build mcp servers you can visit https://modelcontextprotocol.io/ ## Setting Up the Workshop Let's get hands-on: First, to follow this workshop you will need Bun. Install it from https://bun.sh/. For Linux and macOS, you can use the installation script: ``` curl -fsSL https://bun.sh/install | bash ``` 1. **Choose your MCP server**: You can either create one or use an existing one. 2. **Inspect your server** using the MCP inspector tool: ```bash npx @modelcontextprotocol/inspector build/index.js arg1 arg2 ``` This will: - Launch a client UI (default: http://localhost:5173) - Start an MCP proxy server (default: port 3000) - Pass any additional arguments directly to your server 3. **Use the inspector**: Open the client UI in your browser to connect with your server, list available tools, and test its functionality. ## Deploying with DVMCP Now for the exciting part – making your MCP server available to everyone on Nostr: 1. Navigate to your MCP server directory. 2. Run without installing (quickest way): ``` npx @dvmcp/bridge ``` 3. Or install globally for regular use: ``` npm install -g @dvmcp/bridge # or bun install -g @dvmcp/bridge ``` Then run using: ```bash dvmcp-bridge ``` This will guide you through creating the necessary configuration. Watch the console logs to confirm successful setup – you'll see your public key and process information, or any issues that need addressing. For the configuration, you can set the relay as `wss://relay.dvmcp.fun` , or use any other of your preference ## Testing and Integration 1. **Visit [dvmcp.fun](https://dvmcp.fun)** to see your DVM announcement. 2. Call your tools and watch the responses come back. For production use, consider running dvmcp-bridge as a system service or creating a container for greater reliability and uptime. ## Integrating with LLM Clients You can also integrate your DVMCP deployment with LLM clients using the discovery package: 1. Install and use the `@dvmcp/discovery` package: ```bash npx @dvmcp/discovery ``` 2. This package acts as an MCP server for your LLM system by: - Connecting to configured Nostr relays - Discovering tools from DVMCP servers - Making them available to your LLM applications 3. Connect to specific servers or providers using these flags: ```bash # Connect to all DVMCP servers from a provider npx @dvmcp/discovery --provider npub1... # Connect to a specific DVMCP server npx @dvmcp/discovery --server naddr1... ``` Using these flags, you wouldn't need a configuration file. You can find these commands and Claude desktop configuration already prepared for copy and paste at [dvmcp.fun](https://dvmcp.fun). This feature lets you connect to any DVMCP server using Nostr and integrate it into your client, either as a DVM or in LLM-powered applications. ## Final thoughts If you've followed this workshop, you now have an MCP server deployed as a Nostr DVM. This means that local resources from the system where the MCP server is running can be accessed through Nostr in a decentralized manner. This capability is powerful and opens up numerous possibilities and opportunities for fun. You can use this setup for various use cases, including in a controlled/local environment. For instance, you can deploy a relay in your local network that's only accessible within it, exposing all your local MCP servers to anyone connected to the network. This setup can act as a hub for communication between different systems, which could be particularly interesting for applications in home automation or other fields. The potential applications are limitless. However, it's important to keep in mind that there are security concerns when exposing local resources publicly. You should be mindful of these risks and prioritize security when creating and deploying your MCP servers on Nostr. Finally, these are new ideas, and the software is still under development. If you have any feedback, please refer to the GitHub repository to report issues or collaborate. DVMCP also has a Signal group you can join. Additionally, you can engage with the community on Nostr using the #dvmcp hashtag. ## Useful Resources - **Official Documentation**: - Model Context Protocol: [modelcontextprotocol.org](https://modelcontextprotocol.org) - DVMCP.fun: [dvmcp.fun](https://dvmcp.fun) - **Source Code and Development**: - DVMCP: [github.com/gzuuus/dvmcp](https://github.com/gzuuus/dvmcp) - DVMCP.fun: [github.com/gzuuus/dvmcpfun](https://github.com/gzuuus/dvmcpfun) - **MCP Servers and Clients**: - Smithery AI: [smithery.ai](https://smithery.ai) - MCP.so: [mcp.so](https://mcp.so) - Glama AI MCP Servers: [glama.ai/mcp/servers](https://glama.ai/mcp/servers) - [Signal group](https://signal.group/#CjQKIOgvfFJf8ZFZ1SsMx7teFqNF73sZ9Elaj_v5i6RSjDHmEhA5v69L4_l2dhQfwAm2SFGD) Happy building! @ 7bdef7be:784a5805
2025-04-02 12:02:45We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists!
@ 7bdef7be:784a5805
2025-04-02 12:02:45We value sovereignty, privacy and security when accessing online content, using several tools to achieve this, like open protocols, open OSes, open software products, Tor and VPNs. ## The problem Talking about our social presence, we can manually build up our follower list (social graph), pick a Nostr client that is respectful of our preferences on what to show and how, but with the standard following mechanism, our main feed is public, \*\*so everyone can actually snoop\*\* what we are interested in, and what is supposable that we read daily. ## The solution Nostr has a simple solution for this necessity: encrypted lists. Lists are what they appear, a collection of people or interests (but they can also group much other stuff, see \[NIP-51\](https://github.com/nostr-protocol/nips/blob/master/51.md)). So we can create lists with contacts that we don't have in our main social graph; these lists can be used primarily to create \*\*dedicated feeds\*\*, but they could have other uses, for example, related to monitoring. The interesting thing about lists is that they can also be \*\*encrypted\*\*, so unlike the basic following list, which is always public, we can hide the lists' content from others. The implications are obvious: we can not only have a more organized way to browse content, but it is also \*\*really private one\*\*. One might wonder what use can really be made of private lists; here are some examples: - Browse “can't miss” content from users I consider a priority; - Supervise competitors or adversarial parts; - Monitor sensible topics (tags); - Following someone without being publicly associated with them, as this may be undesirable; The benefits in terms of privacy as usual are not only related to the casual, or programmatic, observer, but are also evident when we think of \*\*how many bots scan our actions to profile us\*\*. ## The current state Unfortunately, lists are not widely supported by Nostr clients, and encrypted support is a rarity. Often the excuse to not implement them is that they are harder to develop, since they require managing the encryption stuff (\[NIP-44\](https://github.com/nostr-protocol/nips/blob/master/51.md)). Nevertheless, developers have an easier option to start offering private lists: give the user the possibility to simply \*\*mark them as local-only\*\*, and never push them to the relays. Even if the user misses the sync feature, this is sufficient to create a private environment. To date, as far as I know, the best client with list management is Gossip, which permits to manage \*\*both encrypted and local-only lists\*\*. Beg your Nostr client to implement private lists! @ d5c3d063:4d1159b3
2025-04-02 04:04:32"ผลิตผลทางเศรษฐกิจที่เพิ่มขึ้น เป็นประโยชน์กับทุกคนเสมอ ไม่ว่าในทางใดก็ทางหนึ่ง" เป็นโพสของอาจารย์พิริยะ ที่เรียกได้ว่าคือ “หลักการพื้นฐาน” ของเสรีภาพทางเศรษฐกิจ ที่หลายคนอาจหลงลืม และซุปอยากขยายความต่อ เพราะนี่คือจุดเริ่มต้นของคำว่า “ระบบที่แฟร์จริง” . เราถูกสอนให้คิดว่า ถ้ามีคนรวยขึ้น ต้องมีใครอีกคนจนลง แต่ในความเป็นจริง ระบบตลาดเสรีไม่ได้ทำงานแบบนั้นเลย เพราะเมื่อมีคนผลิตของที่ดีขึ้น ผลิตได้เร็วขึ้น ต้นทุนจะลดลง สินค้าที่เคยเข้าถึงยาก ก็เริ่มกลายเป็นของธรรมดาที่ใครก็ใช้ได้ . คนหนึ่งคนที่ผลิตเพิ่มขึ้น อาจได้กำไรมากขึ้น แต่คนอีกเป็นล้านกลับได้ใช้สินค้าที่ถูกลง ชีวิตง่ายขึ้น สะดวกขึ้น เห็นได้ชัดว่าทุกฝ่ายได้ประโยชน์ ไม่ใช่เพราะมีใครต้อง "เสียสละจากการบังคับ" แต่เพราะทุกคนแลกเปลี่ยนกัน "ด้วยความสมัครใจ" นี่คือหลักการที่เศรษฐศาสตร์สำนักออสเตรียนเชื่อมั่นมาตลอด ว่าเสรีภาพในการผลิตและแลกเปลี่ยน คือรากฐานของความมั่งคั่งร่วมกัน "การแบ่งงานกันทำ" ของคนที่ถนัดต่างกัน คือวิธีที่มนุษย์สร้างสังคมเจริญขึ้นมาได้จริง ไม่ใช่เพราะรัฐสั่งให้ทำ แต่เพราะทุกคนเห็นประโยชน์ร่วมกันและยินดีแลกเปลี่ยนกันเอง . ปัญหาคือ วันนี้เราไม่ได้อยู่ในตลาดเสรีจริง แต่เราอยู่ในระบบที่รัฐเข้ามาเขียนกติกา ออกใบอนุญาต ควบคุมอุตสาหกรรม กำหนดราคา และที่แย่คือการออกกฎที่เอื้อให้พวกพ้อง ทำให้บางคนได้เปรียบในตลาด โดยไม่ได้มาจากการผลิตเก่งหรือบริการดีแต่มาจากการมีสายสัมพันธ์กับอำนาจ (แบบนี้คือ ทุนนิยมพวกพ้อง) . แล้วคนทั่วไปที่เห็นภาพแบบนี้ ก็พากันเรียกร้องให้รัฐเข้ามาจัดการ ทั้งที่จริงแล้ว...คนที่ควรรับผิดชอบ คือรัฐเอง ที่เปิดช่องให้เรื่องพวกนี้เกิดขึ้นตั้งแต่แรก . เราจึงติดกับดักเดิมซ้ำๆ คือรัฐสร้างปัญหา แล้วใช้ปัญหานั้นเป็นข้ออ้างในการขยายอำนาจ สุดท้ายมันก็ยิ่งบิดเบือนระบบเศรษฐกิจให้ผิดเพี้ยนเข้าไปอีก จนคนทำงานจริง ผลิตของจริง กลับไม่มีที่ยืนในระบบ . . ให้เห็นภาพต่อว่า ถ้ามีคนผลิตมากขึ้น ทุกคนในระบบจะได้ประโยชน์เพิ่มขึ้นเสมอ ตราบใดที่ 1 เขาไม่ได้ขโมยใคร 2 เขาแลกเปลี่ยนบนความสมัครใจ เท่านั้นยังไม่พอ 3 "เงิน" มันต้องเป็นกระจกสะท้อนคุณค่าจากการผลิต ไม่ใช่เงินที่สร้างจากหนี้แล้วใช้กฎหมายยังคับว่ามันมีค่า ถ้าเงื่อนไขสามข้อนี้ยังอยู่ครบ ทุนนิยมตลาดเสรีที่แท้จริง ก็จะเป็นระบบที่ยั่งยืน และแฟร์ที่สุดเท่าที่เคยมีมา ซึ่งตลอดประวัติศาสตร์เรายังไม่เคยแยกอำนาจการเงินออกจากมือมนุษย์ได้เลย เพราะถ้าเราปล่อยให้รัฐพิมพ์เงินได้อย่างอิสระ ลดคุณค่าของเงินได้โดยไม่ต้องรับผิดชอบ และแทรกแซงราคาตลาดโดยไม่มีการผลิตรองรับ เมื่อถึงจุดนั้น ต่อให้เราผลิตเก่งแค่ไหน เราก็ไม่มีทางรวยขึ้น เพราะรางวัลไม่ได้แจกตามผลงาน แต่แจกตามความใกล้ชิตผู้มีอำนาจ เมื่อเงินเสื่อมค่าลงทุกวัน ข้าวของแพงขึ้น เราต้องทำงานหนักขึ้น แต่ซื้อของได้น้อยลง แล้วเราจะเริ่มถามตัวเองว่า “เรากำลังทำงานสร้างคุณค่าจริงๆ ขยันจนแทบไม่มีเวลาหายใจ แต่สุดท้ายเรากำลังก้าวไปเดินหน้า หรือแค่พยายามเอาตัวรอดในระบบที่ไม่ยุติธรรม” และในวันนั้น...คุณอาจจะย้อนนึกถึงประโยคนี้ ที่อาจารย์เคยโพสแล้วอาจไม่ได้คิดว่ามันสำคัญ ปล.วันนี้เราอาจเห็นต่างกันเรื่องบทบาทของรัฐ แต่ซุปคิดว่าจุดร่วมของคำถามนี้คือ ระบบเศรษฐกิจที่ดี ควรให้รางวัลกับผู้ผลิต หรือให้รางวัลกับคนที่อยู่ใกล้ชิดผู้มีอำนาจ... #Siamstr
@ d5c3d063:4d1159b3
2025-04-02 04:04:32"ผลิตผลทางเศรษฐกิจที่เพิ่มขึ้น เป็นประโยชน์กับทุกคนเสมอ ไม่ว่าในทางใดก็ทางหนึ่ง" เป็นโพสของอาจารย์พิริยะ ที่เรียกได้ว่าคือ “หลักการพื้นฐาน” ของเสรีภาพทางเศรษฐกิจ ที่หลายคนอาจหลงลืม และซุปอยากขยายความต่อ เพราะนี่คือจุดเริ่มต้นของคำว่า “ระบบที่แฟร์จริง” . เราถูกสอนให้คิดว่า ถ้ามีคนรวยขึ้น ต้องมีใครอีกคนจนลง แต่ในความเป็นจริง ระบบตลาดเสรีไม่ได้ทำงานแบบนั้นเลย เพราะเมื่อมีคนผลิตของที่ดีขึ้น ผลิตได้เร็วขึ้น ต้นทุนจะลดลง สินค้าที่เคยเข้าถึงยาก ก็เริ่มกลายเป็นของธรรมดาที่ใครก็ใช้ได้ . คนหนึ่งคนที่ผลิตเพิ่มขึ้น อาจได้กำไรมากขึ้น แต่คนอีกเป็นล้านกลับได้ใช้สินค้าที่ถูกลง ชีวิตง่ายขึ้น สะดวกขึ้น เห็นได้ชัดว่าทุกฝ่ายได้ประโยชน์ ไม่ใช่เพราะมีใครต้อง "เสียสละจากการบังคับ" แต่เพราะทุกคนแลกเปลี่ยนกัน "ด้วยความสมัครใจ" นี่คือหลักการที่เศรษฐศาสตร์สำนักออสเตรียนเชื่อมั่นมาตลอด ว่าเสรีภาพในการผลิตและแลกเปลี่ยน คือรากฐานของความมั่งคั่งร่วมกัน "การแบ่งงานกันทำ" ของคนที่ถนัดต่างกัน คือวิธีที่มนุษย์สร้างสังคมเจริญขึ้นมาได้จริง ไม่ใช่เพราะรัฐสั่งให้ทำ แต่เพราะทุกคนเห็นประโยชน์ร่วมกันและยินดีแลกเปลี่ยนกันเอง . ปัญหาคือ วันนี้เราไม่ได้อยู่ในตลาดเสรีจริง แต่เราอยู่ในระบบที่รัฐเข้ามาเขียนกติกา ออกใบอนุญาต ควบคุมอุตสาหกรรม กำหนดราคา และที่แย่คือการออกกฎที่เอื้อให้พวกพ้อง ทำให้บางคนได้เปรียบในตลาด โดยไม่ได้มาจากการผลิตเก่งหรือบริการดีแต่มาจากการมีสายสัมพันธ์กับอำนาจ (แบบนี้คือ ทุนนิยมพวกพ้อง) . แล้วคนทั่วไปที่เห็นภาพแบบนี้ ก็พากันเรียกร้องให้รัฐเข้ามาจัดการ ทั้งที่จริงแล้ว...คนที่ควรรับผิดชอบ คือรัฐเอง ที่เปิดช่องให้เรื่องพวกนี้เกิดขึ้นตั้งแต่แรก . เราจึงติดกับดักเดิมซ้ำๆ คือรัฐสร้างปัญหา แล้วใช้ปัญหานั้นเป็นข้ออ้างในการขยายอำนาจ สุดท้ายมันก็ยิ่งบิดเบือนระบบเศรษฐกิจให้ผิดเพี้ยนเข้าไปอีก จนคนทำงานจริง ผลิตของจริง กลับไม่มีที่ยืนในระบบ . . ให้เห็นภาพต่อว่า ถ้ามีคนผลิตมากขึ้น ทุกคนในระบบจะได้ประโยชน์เพิ่มขึ้นเสมอ ตราบใดที่ 1 เขาไม่ได้ขโมยใคร 2 เขาแลกเปลี่ยนบนความสมัครใจ เท่านั้นยังไม่พอ 3 "เงิน" มันต้องเป็นกระจกสะท้อนคุณค่าจากการผลิต ไม่ใช่เงินที่สร้างจากหนี้แล้วใช้กฎหมายยังคับว่ามันมีค่า ถ้าเงื่อนไขสามข้อนี้ยังอยู่ครบ ทุนนิยมตลาดเสรีที่แท้จริง ก็จะเป็นระบบที่ยั่งยืน และแฟร์ที่สุดเท่าที่เคยมีมา ซึ่งตลอดประวัติศาสตร์เรายังไม่เคยแยกอำนาจการเงินออกจากมือมนุษย์ได้เลย เพราะถ้าเราปล่อยให้รัฐพิมพ์เงินได้อย่างอิสระ ลดคุณค่าของเงินได้โดยไม่ต้องรับผิดชอบ และแทรกแซงราคาตลาดโดยไม่มีการผลิตรองรับ เมื่อถึงจุดนั้น ต่อให้เราผลิตเก่งแค่ไหน เราก็ไม่มีทางรวยขึ้น เพราะรางวัลไม่ได้แจกตามผลงาน แต่แจกตามความใกล้ชิตผู้มีอำนาจ เมื่อเงินเสื่อมค่าลงทุกวัน ข้าวของแพงขึ้น เราต้องทำงานหนักขึ้น แต่ซื้อของได้น้อยลง แล้วเราจะเริ่มถามตัวเองว่า “เรากำลังทำงานสร้างคุณค่าจริงๆ ขยันจนแทบไม่มีเวลาหายใจ แต่สุดท้ายเรากำลังก้าวไปเดินหน้า หรือแค่พยายามเอาตัวรอดในระบบที่ไม่ยุติธรรม” และในวันนั้น...คุณอาจจะย้อนนึกถึงประโยคนี้ ที่อาจารย์เคยโพสแล้วอาจไม่ได้คิดว่ามันสำคัญ ปล.วันนี้เราอาจเห็นต่างกันเรื่องบทบาทของรัฐ แต่ซุปคิดว่าจุดร่วมของคำถามนี้คือ ระบบเศรษฐกิจที่ดี ควรให้รางวัลกับผู้ผลิต หรือให้รางวัลกับคนที่อยู่ใกล้ชิดผู้มีอำนาจ... #Siamstr @ 57d1a264:69f1fee1
2025-03-26 08:45:13> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score! | Desktop | Mobile | |---|---| |  |  | |  |  | Now let's see what Semrush knows. # Analytics General view on your metrics and performance trend compared to last 30 days.   See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.  Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.  | Organic Search | Backlinks Analytics | |---|---| | |  | | Position Changes Trend | Top Page Changes | |---|---| | |  | |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |  # Competitors  The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.  # Referring Domains   # Daily Stats | Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | | `-41.87%` | `-16.4%` | `-1.62%` | ### 📝 Traffic Drop Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits: - https://stacker.news/items/723989 ⬇️ -15 - https://stacker.news/items/919813 ⬇️ -12 - https://stacker.news/items/783355 ⬇️ -5 ### 📉 Decreased Authority Score Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority. ### 🌟 New Keywords Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30 ### 🛠️ Broken Pages This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility! One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary? Here are other basic info to improve the SEO score and for those of us that want to learn more: - Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/ - Design for Accessibility: https://www.w3.org/WAI/tips/designing/ - Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/ originally posted at https://stacker.news/items/925433
@ 57d1a264:69f1fee1
2025-03-26 08:45:13> I was curious to see how Stacker.News domain and website contents scored from a SEO (Search Engine Optimization) perspective. Here what Semrush nows about SN. But first have alook at the Page Performance Score on Google (Detailled report available [here](https://pagespeed.web.dev/analysis/https-stacker-news/pjnc9jgscy?form_factor=mobile)). **Performance** and **Accessibility** looks have really low score! | Desktop | Mobile | |---|---| |  |  | |  |  | Now let's see what Semrush knows. # Analytics General view on your metrics and performance trend compared to last 30 days.   See estimations of stacker.news's desktop and mobile traffic based on Semrush’s proprietary AI and machine learning algorithms, petabytes of clickstream data, and Big Data technologies.  Distribution of SN's organic traffic and keywords by country. The Organic Traffic graph shows changes in the amount of estimated organic and paid traffic driven to the SN analyzed domain over time.  | Organic Search | Backlinks Analytics | |---|---| | |  | | Position Changes Trend | Top Page Changes | |---|---| | |  | |This trend allows you to monitor organic traffic changes, as well as improved and declined positions.| Top pages with the biggest traffic changes over the last 28 days. |  # Competitors  The Competitive Positioning Map shows the strengths and weaknesses of SN competitive domains' presence in organic search results. Data visualizations are based on the domain's organic traffic and the number of keywords that they are ranking for in Google's top 20 organic search results. The larger the circle, the more visibility a domain has. Below, a list of domains an analyzed domain is competing against in Google's top 20 organic search results.  # Referring Domains   # Daily Stats | Organic Traffic | Organic Keywords | Backlinks | |---|---|---| | 976 | 15.9K | 126K | | `-41.87%` | `-16.4%` | `-1.62%` | ### 📝 Traffic Drop Traffic downturn detected! It appears SN domain experienced a traffic drop of 633 in the last 28 days. Take a closer look at these pages with significant traffic decline and explore areas for potential improvement. Here are the pages taking the biggest hits: - https://stacker.news/items/723989 ⬇️ -15 - https://stacker.news/items/919813 ⬇️ -12 - https://stacker.news/items/783355 ⬇️ -5 ### 📉 Decreased Authority Score Uh-oh! Your Authority score has dropped from 26 to 25. Don't worry, we're here to assist you. Check out the new/lost backlinks in the Backlink Analytics tool to uncover insights on how to boost your authority. ### 🌟 New Keywords Opportunity Alert! Targeting these keywords could help you increase organic traffic quickly and efficiently. We've found some low-hanging fruits for you! Take a look at these keywords: - nitter.moomoo.me — Volume 70 - 0xchat — Volume 30 - amethyst nostr — Volume 30 ### 🛠️ Broken Pages This could hurt the user experience and lead to a loss in organic traffic. Time to take action: amend those pages or set up redirects. Here below, few pages on SN domain that are either broken or not _crawlable_: - https://stacker.news/404 — 38 backlinks - https://stacker.news/api/capture/items/91154 — 24 backlinks - https://stacker.news/api/capture/items/91289 — 24 backlinks Dees this post give you some insights? Hope so, comment below if you have any SEO suggestion? Mine is to improve or keep an eye on Accessibility! One of the major issues I found is that SN does not have a `robots.txt`, a key simple text file that allow crawlers to read or not-read the website for indexing purposes. @k00b and @ek is that voluntary? Here are other basic info to improve the SEO score and for those of us that want to learn more: - Intro to Accessibility: https://www.w3.org/WAI/fundamentals/accessibility-intro/ - Design for Accessibility: https://www.w3.org/WAI/tips/designing/ - Web Accessibility Best Practices: https://www.freecodecamp.org/news/web-accessibility-best-practices/ originally posted at https://stacker.news/items/925433 @ 9967f375:04f9a5e1
2025-04-01 20:43:54El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero.
@ 9967f375:04f9a5e1
2025-04-01 20:43:54El día 1, emprendió su tornaviaje con gran felicidad de este Puerto, para las Islas Filipinas, el Galeón *Sacra Familia*, que (por muerte del General Don Juan Antonio Cortés de Arredondo, Castillo, y Noblezia, a cuyo cargo vino) va a el de Don Jerónimo Montero. @ 9967f375:04f9a5e1
2025-04-01 20:18:33Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*.
@ 9967f375:04f9a5e1
2025-04-01 20:18:33Varios sacrificios hacían los mexicanos en este cuarto mes que comenzaba a los cuatro de Abril, y le llamaban *Hueitozontontli*; pero el más memorable era enramar con *Tule* los Templos y las puertas, y ensangrentar a las que a ellas ponían con sangre propia, que de las orejas, y espinillas les sacaban: lo interior de la casa se adornaba con flores, y a sus mentidos dioses coronaban de curiosas, fragrantes, y bien matizadas guirnaldas; particularmente a el de los *Mayes*, a quien consagraban las tiernas, recientes Mazorcas, de sus milpas de maíz, llamado en España *Bocona*. @ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains. I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on. But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting, The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater. Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished.
@ 30876140:cffb1126
2025-03-26 04:58:21The portal is closing. The symphony comes to an end. Ballet, a dance of partners, A wish of hearts, Now closing its curtains. I foolishly sit Eagerly waiting For the circus to begin again, As crowds file past me, Chuckles and popcorn falling, Crushed under foot, I sit waiting For the show to carry on. But the night is now over, The laughs have been had, The music been heard, The dancers are gone now Into the nightbreeze chill. Yet still, I sit waiting, The empty chairs yawning, A cough, I start, could it be? Yet the lights now go out, And now without my sight I am truly alone in the theater. Yet still, I am waiting For the show to carry on, But I know that it won’t, Yet still, I am waiting. Never shall I leave For the show was too perfect And nothing perfect should ever be finished. @ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice. A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases. Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy. Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest. Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever. @ 8f69ac99:4f92f5fd
2025-04-01 15:54:53Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento. Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda. Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade. ## Benefícios de Aceitar Bitcoin ### 1. Redução de Custos Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento. ### 2. Liquidação Rápida Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes. ### 3. Expansão de Mercado Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados. ### 4. Protecção Contra Inflação Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo. | [](https://youtu.be/B9fCDjybtrU&t=3518) | |:--:| | *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* | ## Como Funciona na Prática? ### 1. Aceitação Directa vs. Conversão Automática Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda. ### 2. Configuração de Carteira Bitcoin Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio. ### 3. Facturação e Registo Contábil Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal. ## Obrigações Fiscais e Contábeis ### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas) Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis. Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial. No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor. ### 2. IVA (Imposto sobre o Valor Acrescentado) As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA. No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento. **Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉 ### 3. Registos e Demonstrações Financeiras As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso: - **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante. - **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias. As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados. ## O Obstáculo: Contabilistas e a Falta de Apoio ### 1. Falta de Conhecimento Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes. ### 2. Resistência e Falta de Vontade Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado. ### 3. Impacto nos Negócios Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado. ## Soluções e Alternativas ### 1. Educação e Autonomia Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin. ### 2. Ferramentas e Software Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis. ### 3. Rede de Apoio Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências. ### 4. Links uteis - [Website Aceita Bitcoin](https://aceitabitcoin.pt) - [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin) - [Mario Moura Contabilidade](https://mmc.pt/en/) - [MM Law](https://www.mmlaw.pt/) ## Conclusão Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento. --- _**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._ _Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_
@ 8f69ac99:4f92f5fd
2025-04-01 15:54:53Bitcoin tem-se afirmado como um meio de pagamento global, [atraindo cada vez mais comerciantes](https://btcmap.org/map#7/40.24180/-7.05872) e consumidores. Em Portugal, os pequenos e médios empresários têm uma oportunidade única para reduzir custos, expandir mercados e proteger-se da inflação ao aceitar bitcoin como opção pagamento. Apesar das vantagens, muitos comerciantes enfrentam desafios significativos, especialmente no que toca às obrigações fiscais e à falta de conhecimento (ou vontade de aprender) por parte dos contabilistas. Questões como o registo contábil adequado, a tributação do IRC e a facturação com IVA ainda geram incerteza e dificultam a adopção da criptomoeda. Este artigo explora como os comerciantes podem aceitar bitcoin de forma legal e eficiente, analisa os desafios fiscais e contábeis e apresenta soluções práticas para superar os obstáculos impostos pela regulamentação e pela falta de apoio dos profissionais de contabilidade. ## Benefícios de Aceitar Bitcoin ### 1. Redução de Custos Aceitar pagamentos em bitcoin permite evitar taxas bancárias elevadas, especialmente em transacções internacionais. Como as transferências ocorrem directamente entre carteiras digitais, **sem a intermediação de bancos**, os comerciantes podem poupar significativamente em comissões e taxas de processamento. ### 2. Liquidação Rápida Diferente dos pagamentos bancários tradicionais, que podem demorar dias, uma transacção na rede Bitcoin pode ser confirmada em minutos, ou em segundos ou menos usando a Lightning Network. Isto reduz o tempo de espera para a disponibilidade dos fundos e melhora o fluxo de caixa dos comerciantes. ### 3. Expansão de Mercado Os comerciantes podem atrair clientes internacionais e um público mais inovador e tecnológico. A aceitação de bitcoin pode diferenciar um negócio da concorrência e aumentar a base de clientes ao incluir entusiastas de criptomoedas e consumidores que preferem meios de pagamento descentralizados. ### 4. Protecção Contra Inflação Bitcoin pode actuar como reserva de valor, protegendo o património contra desvalorizações monetárias. Em contextos de inflação elevada, manter parte do capital em Bitcoin pode ajudar a preservar o poder de compra a longo prazo. | [](https://youtu.be/B9fCDjybtrU&t=3518) | |:--:| | *Bruno de Gouveia da Care to Beauty - A Seita Bitcoin* | ## Como Funciona na Prática? ### 1. Aceitação Directa vs. Conversão Automática Os comerciantes podem optar por aceitar bitcoin directamente, mantendo-o na sua carteira digital, ou utilizar serviços como OpenNode, Swiss Bitcoin Pay, Coincorner ou Coinbase para converter automaticamente os pagamentos em euros. A escolha depende da estratégia da empresa quanto à exposição à volatilidade da criptomoeda. ### 2. Configuração de Carteira Bitcoin Para receber pagamentos directamente, o comerciante precisa de uma carteira Bitcoin segura, como Electrum, BlueWallet ou Aqua entre outras. Estas carteiras oferecem diferentes níveis de segurança e acessibilidade, permitindo que os comerciantes escolham a solução mais adequada ao seu modelo de negócio. ### 3. Facturação e Registo Contábil Cada pagamento deve ser facturado em euros, com referência à taxa de câmbio do momento. O registo contábil deve ser feito correctamente para garantir a conformidade fiscal, reflectindo o valor recebido em bitcoin e a sua equivalência em euros na altura da transacção. Muitas carteiras e plataformas de pagamento oferecem relatórios detalhados que facilitam o registo contábil e a declaração fiscal. ## Obrigações Fiscais e Contábeis ### 1. IRC (Imposto sobre o Rendimento das Pessoas Colectivas) Os rendimentos obtidos através de bitcoin devem ser devidamente registados na contabilidade da empresa, uma vez que são considerados receitas operacionais. Para efeitos fiscais, a conversão do valor recebido em bitcoin deve ser feita com base na taxa de câmbio vigente no momento da transacção, garantindo um registo transparente e conforme com as normas contábeis. Se a empresa optar por manter os bitcoins sem os converter imediatamente para euros, estes podem ser classificados como activos intangíveis, conforme a Norma Contabilística e de Relato Financeiro (NCRF), artigo 6. No entanto, se forem utilizados como meio de pagamento recorrente, por exemplo pagar a fornecedores que também aceitem bitcoin, podem ser classificados como inventário, dependendo da natureza da actividade empresarial. No momento da venda ou conversão dos bitcoins para euros, qualquer mais-valia obtida é considerada um rendimento da empresa e estará sujeita a tributação em sede de IRC à taxa geral em vigor. ### 2. IVA (Imposto sobre o Valor Acrescentado) As transacções de troca de bitcoin por euros estão isentas de IVA, conforme o artigo 9.º, alínea 27), subalínea d), do Código do IVA (CIVA), que reconhece as criptomoedas como meios de pagamento e as exclui da incidência de IVA. No entanto, a venda de bens ou serviços pagos em bitcoin deve ser facturada normalmente, em euros, com a taxa de IVA correspondente ao produto ou serviço comercializado. Para garantir conformidade fiscal, a factura deve indicar a contrapartida em euros, com base na taxa de câmbio do momento da transacção, independentemente da moeda utilizada no pagamento. **Na prática**, aceitar pagamento em bitcoin funciona de forma muito semelhante a aceitar pagamento em dinheiro físico... 😉 ### 3. Registos e Demonstrações Financeiras As empresas que aceitam bitcoin devem manter registos contabilísticos detalhados sobre todas as transacções realizadas. bitcoin pode ser registado como activo intangível ou inventário, dependendo do seu uso: - **Activo intangível:** Quando a empresa detém bitcoin como reserva de valor ou investimento, registando-o ao custo de aquisição e procedendo a ajustamentos caso haja desvalorização relevante. - **Inventário:** Se a empresa opera no sector de compra e venda de criptomoedas ou usa bitcoin para transacções comerciais frequentes, deve ser registado como inventário, seguindo as regras de mensuração aplicáveis a mercadorias. As demonstrações financeiras devem reflectir correctamente a posse de bitcoin, incluindo informações sobre variações de valor ao longo do tempo. Os contabilistas devem garantir a correta apresentação destes activos nos balanços e relatórios anuais, o que pode exigir reavaliação periódica dos valores contabilizados. ## O Obstáculo: Contabilistas e a Falta de Apoio ### 1. Falta de Conhecimento Muitos TOC não estão familiarizados com a contabilidade de criptomoedas, o que gera incertezas e complicações para os comerciantes. ### 2. Resistência e Falta de Vontade Em vez de se actualizarem, muitos contabilistas recusam-se a aprender sobre Bitcoin, deixando os comerciantes sem apoio adequado. ### 3. Impacto nos Negócios Com a falta de informação e apoio dos TOC, muitos comerciantes evitam aceitar bitcoin, perdendo uma oportunidade de mercado. ## Soluções e Alternativas ### 1. Educação e Autonomia Os comerciantes podem aprender o essencial sobre contabilidade de bitcoin para questionar e orientar os seus contabilistas. Existem recursos online, cursos e materiais educativos que permitem aos empresários compreender as melhores práticas para registo e declaração das transacções em bitcoin. ### 2. Ferramentas e Software Existem algumas plataformas que ajudam na gestão e declaração de criptomoedas, fornecendo relatórios detalhados sobre transacções, ganhos e impostos devidos. Essas ferramentas facilitam a organização financeira e reduzem erros contábeis. ### 3. Rede de Apoio Juntar-se a comunidades de empresários e especialistas em bitcoin pode ajudar a encontrar soluções e recomendações de contabilistas competentes. Fóruns, grupos em redes sociais e associações focadas no tema podem ser excelentes fontes de suporte e partilha de experiências. ### 4. Links uteis - [Website Aceita Bitcoin](https://aceitabitcoin.pt) - [Grupo Telegram Aceita Bitcoin](https://t.me/aceitabitcoin) - [Mario Moura Contabilidade](https://mmc.pt/en/) - [MM Law](https://www.mmlaw.pt/) ## Conclusão Aceitar bitcoin pode ser vantajoso para pequenos e médios comerciantes, mas a burocracia e a falta de conhecimento dos contabilistas dificultam esse processo. É essencial que os comerciantes exijam um melhor serviço dos seus TOC e procurem alternativas para garantir que estão em conformidade com a lei, aproveitando ao mesmo tempo os benefícios desta nova forma de pagamento. --- _**Disclaimer:** Este artigo é meramente informativo e não deve ser considerado como aconselhamento jurídico ou fiscal. É recomendável consultar um profissional qualificado para obter orientações específicas sobre a aceitação de bitcoin e as obrigações fiscais associadas. A legislação pode variar e é importante estar sempre actualizado com as normas vigentes. A responsabilidade pela aceitação de bitcoin e o cumprimento das obrigações fiscais recai exclusivamente sobre o comerciante. O autor não se responsabiliza por quaisquer consequências decorrentes da aceitação de bitcoin ou da interpretação das informações contidas neste artigo._ _Photo by [CardMapr.nl](https://unsplash.com/@cardmapr?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash) on [Unsplash](https://unsplash.com/photos/black-samsung-android-smartphone-on-brown-wooden-table-rDzI7m7sjPE?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash)_ @ ecda4328:1278f072
2025-03-25 10:00:52**Kubernetes and Linux Swap: A Practical Perspective** After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion. --- ### The Rationale for Disabling Swap We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes. With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion. Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates. --- ### Theoretical Capability vs. Practical Deployment Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly. But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model: - Memory **requests and limits** are declared explicitly. - The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap). - Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals. So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity. --- ### Why Disable Swap in Kubernetes? 1. **Deterministic Failure > Degraded Performance**\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early. 2. **Transparency & Observability**\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically. 3. **Performance Consistency**\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits. 4. **Kubernetes Doesn’t Manage Swap Well**\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control. 5. **Statelessness is the Norm**\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state. --- ### "But Swap Can Be Useful..." Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need: - Fine-tuned `vm.swappiness` - Memory pinning and cgroup-based control - Swap-aware monitoring and alerting - Custom kubelet/systemd integration That's possible, but **not standard practice** — and for good reason. --- ### Future Considerations Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments. Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior. Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet. --- ### Conclusion Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability. If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**.
@ ecda4328:1278f072
2025-03-25 10:00:52**Kubernetes and Linux Swap: A Practical Perspective** After reviewing kernel documentation on swap management (e.g., [Linux Swap Management](https://www.kernel.org/doc/gorman/html/understand/understand014.html)), [KEP-2400 (Kubernetes Node Memory Swap Support)](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), and community discussions like [this post on ServerFault](https://serverfault.com/questions/881517/why-disable-swap-on-kubernetes), it's clear that the topic of swap usage in modern systems—especially Kubernetes environments—is nuanced and often contentious. Here's a practical synthesis of the discussion. --- ### The Rationale for Disabling Swap We disable SWAP on our Linux servers to ensure stable and predictable performance by relying on available RAM, avoiding the performance degradation and unnecessary I/O caused by SWAP usage. If an application runs out of memory, it’s usually due to insufficient RAM allocation or a memory leak, and enabling SWAP only worsens performance for other applications. It's more efficient to let a leaking app restart than to rely on SWAP to prevent OOM crashes. With modern platforms like Kubernetes, memory requests and limits are enforced, ensuring apps use only the RAM allocated to them, while avoiding overcommitment to prevent resource exhaustion. Additionally, disabling swap may protect data from **data remanence attacks**, where sensitive information could potentially be recovered from the swap space even after a process terminates. --- ### Theoretical Capability vs. Practical Deployment Linux provides a powerful and flexible memory subsystem. With proper tuning (e.g., swappiness, memory pinning, cgroups), it's technically possible to make swap usage efficient and targeted. Seasoned sysadmins often argue that disabling swap entirely is a lazy shortcut—an avoidance of learning how to use the tools properly. But Kubernetes is not a traditional system. It's an orchestrated environment that favors predictability, fail-fast behavior, and clear isolation between workloads. Within this model: - Memory **requests and limits** are declared explicitly. - The scheduler makes decisions based on RAM availability, not total virtual memory (RAM + swap). - Swap introduces **non-deterministic performance** characteristics that conflict with Kubernetes' goals. So while the kernel supports intelligent swap usage, Kubernetes **intentionally sidesteps** that complexity. --- ### Why Disable Swap in Kubernetes? 1. **Deterministic Failure > Degraded Performance**\ If a pod exceeds its memory allocation, it should fail fast — not get throttled into slow oblivion due to swap. This behavior surfaces bugs (like memory leaks or poor sizing) early. 2. **Transparency & Observability**\ With swap disabled, memory issues are clearer to diagnose. Swap obfuscates root causes and can make a healthy-looking node behave erratically. 3. **Performance Consistency**\ Swap causes I/O overhead. One noisy pod using swap can impact unrelated workloads on the same node — even if they’re within their resource limits. 4. **Kubernetes Doesn’t Manage Swap Well**\ Kubelet has historically lacked intelligence around swap. As of today, Kubernetes still doesn't support swap-aware scheduling or per-container swap control. 5. **Statelessness is the Norm**\ Most containerized workloads are designed to be ephemeral. Restarting a pod is usually preferable to letting it hang in a degraded state. --- ### "But Swap Can Be Useful..." Yes — for certain workloads (e.g., in-memory databases, caching layers, legacy systems), there may be valid reasons to keep swap enabled. In such cases, you'd need: - Fine-tuned `vm.swappiness` - Memory pinning and cgroup-based control - Swap-aware monitoring and alerting - Custom kubelet/systemd integration That's possible, but **not standard practice** — and for good reason. --- ### Future Considerations Recent Kubernetes releases have introduced [experimental swap support](https://kubernetes.io/blog/2023/08/24/swap-linux-beta/) via [KEP-2400](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md). While this provides more flexibility for advanced use cases — particularly Burstable QoS pods on cgroupsv2 — swap remains disabled by default and is not generally recommended for production workloads unless carefully planned. The rationale outlined in this article remains applicable to most Kubernetes operators, especially in multi-tenant and performance-sensitive environments. Even the Kubernetes maintainers acknowledge the inherent trade-offs of enabling swap. As noted in [KEP-2400's Risks and Mitigations section](https://github.com/kubernetes/enhancements/blob/master/keps/sig-node/2400-node-swap/README.md), swap introduces unpredictability, can severely degrade performance compared to RAM, and complicates Kubernetes' resource accounting — increasing the risk of noisy neighbors and unexpected scheduling behavior. Some argue that with emerging technologies like **non-volatile memory** (e.g., Intel Optane/XPoint), swap may become viable again. These systems promise near-RAM speed with large capacity, offering hybrid memory models. But these are not widely deployed or supported in mainstream Kubernetes environments yet. --- ### Conclusion Disabling swap in Kubernetes is not a lazy hack — it’s a **strategic tradeoff**. It improves transparency, predictability, and system integrity in multi-tenant, containerized environments. While the kernel allows for more advanced configurations, Kubernetes intentionally simplifies memory handling for the sake of reliability. If we want to revisit swap usage, it should come with serious planning: proper instrumentation, swap-aware observability, and potentially upstream K8s improvements. Until then, **disabling swap remains the sane default**. @ 69eea734:4ae31ae6
2025-04-01 15:33:49What to record from the last two weeks? The key points from the things I've read and watched? \ The encounters I had with various groups of people, and also one on one? (on my trip to Munich)\ My thoughts on what is going on in the world?\ It is all connected anyway.  *This is my second post. The* *[first](https://pareto.space/a/naddr1qqxnzden8yunxv3kxvcnjdpsqgsqlvwtq6gjttmchn3nqetzfy42skj9334nhr2ptl2hzqgzeswgssgrqsqqqa28qy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvsq3vamnwvaz7tmjv4kxz7fwwpexjmtpdshxuet5h5apnf)* *was under a different profile, which I lost the private key to.*  ### So close and yet apart The various encounters: Overlapping 'camps'. School friends, friends from uni times, friends from Covid times. One friend from school, and one friend from uni did not have a Covid vaccine and were critical of measures. To think that this still matters! Can you believe it? But it does! Which is sad on one hand, and makes for strong bonds on the other.  I'm in a pub with three school friends. They discover that they all voted Green, and are delighted. They kind of congratulate each other, and themselves. I don't even know what to feel in that moment. I'm not shocked. It is not surprising. And yet I still find it astounding.  As the evening progresses, we move to a Greek restaurant round the corner. On the way there, I walk alongside the friend with whom I exchanged the most challenging emails of the last five years. There had been long pauses between replies. Once I read only the first two lines, and then 'quarantined' the mail. I once deleted one, and three weeks later asked him to send it again.  In 2023 we sat in a café and openly talked about the Corona period and our differing positions. I appreciated it. At least we could talk. Shortly after, the emphasis in our conversations shifted from Covid to Putin. One arch enemy was replaced by another. And when previously, the 'Covid deniers' were the deplorable ones, now it was the 'Putin understanders', and weren't they the same people anyway? And mentioning peace talks was right wing. It was all so predictable. Was I predictable, too? I'd sent a long email a week ago. But walking alongside each other, we preferred to talk about the kids.  At the Greek restaurant, the inevitable happened. We ended up in a massive discussion. I once was gesticulating wildly at him. "Conspiracy theorist! That is *so* convenient. Everything that does not fit into your worldview, becomes a conspiracy theory. That there would be a vaccine mandate was once a conspiracy theory. That the virus came from a lab was once a conspiracy theory." On another occasion, he exclaimed: "You know that I know all that about America! You know exactly that I know all those things!"  We both knew a lot of things, and it went back and forth.  The irony was that we managed to stay respectful, and it was a discussion with the other school friend there (the fourth person on the table was my husband), that turned out to be the last straw. She had voted Green as well, and had congratulated our school mate on having been to the protest 'against the right'. But she was also the one who didn't have the vaccine, and now said, "With Covid, it was just so obvious that it was all set up." A bit later she said something about the WEF. Only to be greeted with a long tirade. "Aha. So you think this is all a big conspiracy with some powerful people in the background planning everything. And this wasn't a pandemic although lots of people died. I know six doctors, and they all told me the same." A bit later, to me: "So why did only the unvaccinated die then?" And then shortly after, when my friend stated again how the whole thing had seemed premeditated, "Right. That's enough now. I'm leaving." And he got up to pay and left.  My friend, who stayed behind, thought we had had interesting discussions and she had learned something. On reflection, it was good to have this discussion at all -- at a time that nobody seems to want to talk about Covid anymore.  But also: Shouldn't we be much much further than this??? ### My first sats A few months ago I had tried to buy bitcoin, just to play around, but there had been difficulties to do with the fact I have a UK bank account. When looking at how to get funds into my getalby account, I ended up with Strike, which is available in the UK. But it seems they take extra care to make sure you know what you are letting yourself into! I had to do a test with about 10 questions to show I understand the risks.  I then had to wait 24 hours, but now I have sent my first sats.  On the Strike website, I noticed this [video of a conversation](https://www.youtube.com/watch?v=Nzvh4AODtWc) between Jack Mallers, founder of Strike, and Jack Dorsey, co-founder of Twitter. The more I watched, the more I thought, wow, here it is all in one video, all that I would like my friend to see. "America has a problem." The Empire needs to end, and it would be a good thing for America, says Jack Dorsey. This was also the second time in a week that I heard about how Great Britain had created money and bought their own bonds when the public didn't want to, in effect stealing from the people by making their money worth less. It was good to be reminded of [Adam Curtis](https://en.wikipedia.org/wiki/Adam_Curtis) who has made some mind-blowing documentaries, using lots of BBC archive material. Including about the special US and UK relationship (*An ocean apart*), and also one about Russia from 1985 to 1999 (*Trauma Zone*). The two Jacks talk about the importance of open source, and of being independent of government. The dangers of building abstraction on abstraction on abstraction. About how Mark Zuckerberg served Dorsey raw goat once, because he had this challenge to only eat what he had killed himself. That was also a way to get back to the real.  Dorsey endorsed RFK jr, this was in summer of 2023, when he was still running for president.  There is also an interesting bit on the pressures of running a company that has gone public. And the government interference, in effect censorship. The Twitter files. It is not quite clear to me, if it was really so difficult for Jack Dorsey to pay attention and know what was going on, but I can understand that it must have been a difficult situation.  What I also find very interesting is that in Africa or Latin America bitcoin is sometimes valuable as an exchange medium. That is where I think it could diverge from the pure Ponzi scheme that people often call it.  And yet, doubts remain. Is bitcoin not too valuable for a lot of people to spend it? But what if you don't have access to any other money. And sending Satoshis around is different from hording bitcoin. Can it fulfil both these functions in the end, storage medium and exchange medium?  I believe that these two people want to achieve something positive. But they also remain tech bros. And I don't mean that in a bad way. It is just something that will always remain a bit alien to me.  I did like what Dorsey said about the punks. How they just started to play an instrument, and didn't care if they were not good at it. Then just turned up again and again and eventually got better. I have often thought of myself as a bit punk-like in that respect, although I've often been worried about not being good enough.  ### Doing away with domination The last [blog article](https://www.lowimpact.org/posts/darren-allen-on-civilisational-collapse/) posted on a website I work on, made me explore the writings by Darren Allen on his [Expressive Egg substack](https://expressiveegg.substack.com/). I had landed there before, years ago, and had been very impressed back then. He seems to criticise people's thoughts a lot though -- almost everybody's -- and I was wondering if that was all he ever did. But then I came across this [article about anarchy](https://expressiveegg.substack.com/p/anarchism-at-the-end-of-the-world). It made me realise again, in all this mess about different worldviews, different expectations and values, that this is a constant for me: How can we have less coercion, how can we live in a way that frees ourselves and others at the same time. I once saw a Twitter bio: "I insist on your freedom." It seems to come from Jack Kerouac.  Allen writes that there are seven *dominants*, seven elements that "control individuals against their will". They are, " in roughly ascending order of subtlety and pervasiveness": 1\. The \[autocratic] *monarchy*.\ 2\. The \[socialist-democratic] *state* (which includes its money, law, property, police, etc.).\ 3\. The \[totalitarian-capitalist] *corporation*.\ 4\. The \[mass] *majority*.\ 5\. The \[professional-religious] *institution*.\ 6\. The \[technocratic] *system*.\ 7\. The \[mental-emotional] *ego*. I want to keep this list in mind and pay attention when I get sucked into the influence of one of these spheres.  \ I also like this quote: > The reason men and women do not need kings, princes, states, professionals, institutions and systems to rule over them is because the life within them is more intelligent, more apt, more sensitive, more forgiving and more creative than anything else—certainly any human authority. But this life cannot be rationally fixed. It can be expressed, artistically, indirectly, poetically, musically, or with tone and glance and such ordinary, metaphorical arts of human interaction; but it cannot be literally stated. \ Although this would be a good ending for this post, I have to mention Jeffrey Sachs as well. I have been following him for a while. He appeared in the EU parliament, invited by Michael von der Schulenburg. Sachs has an amazing amount of experience with both Russian and American government officials, and with currencies. In the 90s he spent some time helping Eastern European countries with the transition to capitalist systems. He realised that the U.S. did not want to help Russia in the same way.  He gave a long speech in which he laid bare the ways in which the U.S. had influenced so many wars and uprisings around the world, and how the NATO enlargement had been a long-term strategy. That now, with Trump, the war was going to end.  There would be so much more to say. In any case, this seems to me a historic speech. Can it break through the mirror glass that has kept so many people away from valid sources of knowledge?
@ 69eea734:4ae31ae6
2025-04-01 15:33:49What to record from the last two weeks? The key points from the things I've read and watched? \ The encounters I had with various groups of people, and also one on one? (on my trip to Munich)\ My thoughts on what is going on in the world?\ It is all connected anyway.  *This is my second post. The* *[first](https://pareto.space/a/naddr1qqxnzden8yunxv3kxvcnjdpsqgsqlvwtq6gjttmchn3nqetzfy42skj9334nhr2ptl2hzqgzeswgssgrqsqqqa28qy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsz9nhwden5te0wfjkccte9ehx7um5wghxyctwvsq3vamnwvaz7tmjv4kxz7fwwpexjmtpdshxuet5h5apnf)* *was under a different profile, which I lost the private key to.*  ### So close and yet apart The various encounters: Overlapping 'camps'. School friends, friends from uni times, friends from Covid times. One friend from school, and one friend from uni did not have a Covid vaccine and were critical of measures. To think that this still matters! Can you believe it? But it does! Which is sad on one hand, and makes for strong bonds on the other.  I'm in a pub with three school friends. They discover that they all voted Green, and are delighted. They kind of congratulate each other, and themselves. I don't even know what to feel in that moment. I'm not shocked. It is not surprising. And yet I still find it astounding.  As the evening progresses, we move to a Greek restaurant round the corner. On the way there, I walk alongside the friend with whom I exchanged the most challenging emails of the last five years. There had been long pauses between replies. Once I read only the first two lines, and then 'quarantined' the mail. I once deleted one, and three weeks later asked him to send it again.  In 2023 we sat in a café and openly talked about the Corona period and our differing positions. I appreciated it. At least we could talk. Shortly after, the emphasis in our conversations shifted from Covid to Putin. One arch enemy was replaced by another. And when previously, the 'Covid deniers' were the deplorable ones, now it was the 'Putin understanders', and weren't they the same people anyway? And mentioning peace talks was right wing. It was all so predictable. Was I predictable, too? I'd sent a long email a week ago. But walking alongside each other, we preferred to talk about the kids.  At the Greek restaurant, the inevitable happened. We ended up in a massive discussion. I once was gesticulating wildly at him. "Conspiracy theorist! That is *so* convenient. Everything that does not fit into your worldview, becomes a conspiracy theory. That there would be a vaccine mandate was once a conspiracy theory. That the virus came from a lab was once a conspiracy theory." On another occasion, he exclaimed: "You know that I know all that about America! You know exactly that I know all those things!"  We both knew a lot of things, and it went back and forth.  The irony was that we managed to stay respectful, and it was a discussion with the other school friend there (the fourth person on the table was my husband), that turned out to be the last straw. She had voted Green as well, and had congratulated our school mate on having been to the protest 'against the right'. But she was also the one who didn't have the vaccine, and now said, "With Covid, it was just so obvious that it was all set up." A bit later she said something about the WEF. Only to be greeted with a long tirade. "Aha. So you think this is all a big conspiracy with some powerful people in the background planning everything. And this wasn't a pandemic although lots of people died. I know six doctors, and they all told me the same." A bit later, to me: "So why did only the unvaccinated die then?" And then shortly after, when my friend stated again how the whole thing had seemed premeditated, "Right. That's enough now. I'm leaving." And he got up to pay and left.  My friend, who stayed behind, thought we had had interesting discussions and she had learned something. On reflection, it was good to have this discussion at all -- at a time that nobody seems to want to talk about Covid anymore.  But also: Shouldn't we be much much further than this??? ### My first sats A few months ago I had tried to buy bitcoin, just to play around, but there had been difficulties to do with the fact I have a UK bank account. When looking at how to get funds into my getalby account, I ended up with Strike, which is available in the UK. But it seems they take extra care to make sure you know what you are letting yourself into! I had to do a test with about 10 questions to show I understand the risks.  I then had to wait 24 hours, but now I have sent my first sats.  On the Strike website, I noticed this [video of a conversation](https://www.youtube.com/watch?v=Nzvh4AODtWc) between Jack Mallers, founder of Strike, and Jack Dorsey, co-founder of Twitter. The more I watched, the more I thought, wow, here it is all in one video, all that I would like my friend to see. "America has a problem." The Empire needs to end, and it would be a good thing for America, says Jack Dorsey. This was also the second time in a week that I heard about how Great Britain had created money and bought their own bonds when the public didn't want to, in effect stealing from the people by making their money worth less. It was good to be reminded of [Adam Curtis](https://en.wikipedia.org/wiki/Adam_Curtis) who has made some mind-blowing documentaries, using lots of BBC archive material. Including about the special US and UK relationship (*An ocean apart*), and also one about Russia from 1985 to 1999 (*Trauma Zone*). The two Jacks talk about the importance of open source, and of being independent of government. The dangers of building abstraction on abstraction on abstraction. About how Mark Zuckerberg served Dorsey raw goat once, because he had this challenge to only eat what he had killed himself. That was also a way to get back to the real.  Dorsey endorsed RFK jr, this was in summer of 2023, when he was still running for president.  There is also an interesting bit on the pressures of running a company that has gone public. And the government interference, in effect censorship. The Twitter files. It is not quite clear to me, if it was really so difficult for Jack Dorsey to pay attention and know what was going on, but I can understand that it must have been a difficult situation.  What I also find very interesting is that in Africa or Latin America bitcoin is sometimes valuable as an exchange medium. That is where I think it could diverge from the pure Ponzi scheme that people often call it.  And yet, doubts remain. Is bitcoin not too valuable for a lot of people to spend it? But what if you don't have access to any other money. And sending Satoshis around is different from hording bitcoin. Can it fulfil both these functions in the end, storage medium and exchange medium?  I believe that these two people want to achieve something positive. But they also remain tech bros. And I don't mean that in a bad way. It is just something that will always remain a bit alien to me.  I did like what Dorsey said about the punks. How they just started to play an instrument, and didn't care if they were not good at it. Then just turned up again and again and eventually got better. I have often thought of myself as a bit punk-like in that respect, although I've often been worried about not being good enough.  ### Doing away with domination The last [blog article](https://www.lowimpact.org/posts/darren-allen-on-civilisational-collapse/) posted on a website I work on, made me explore the writings by Darren Allen on his [Expressive Egg substack](https://expressiveegg.substack.com/). I had landed there before, years ago, and had been very impressed back then. He seems to criticise people's thoughts a lot though -- almost everybody's -- and I was wondering if that was all he ever did. But then I came across this [article about anarchy](https://expressiveegg.substack.com/p/anarchism-at-the-end-of-the-world). It made me realise again, in all this mess about different worldviews, different expectations and values, that this is a constant for me: How can we have less coercion, how can we live in a way that frees ourselves and others at the same time. I once saw a Twitter bio: "I insist on your freedom." It seems to come from Jack Kerouac.  Allen writes that there are seven *dominants*, seven elements that "control individuals against their will". They are, " in roughly ascending order of subtlety and pervasiveness": 1\. The \[autocratic] *monarchy*.\ 2\. The \[socialist-democratic] *state* (which includes its money, law, property, police, etc.).\ 3\. The \[totalitarian-capitalist] *corporation*.\ 4\. The \[mass] *majority*.\ 5\. The \[professional-religious] *institution*.\ 6\. The \[technocratic] *system*.\ 7\. The \[mental-emotional] *ego*. I want to keep this list in mind and pay attention when I get sucked into the influence of one of these spheres.  \ I also like this quote: > The reason men and women do not need kings, princes, states, professionals, institutions and systems to rule over them is because the life within them is more intelligent, more apt, more sensitive, more forgiving and more creative than anything else—certainly any human authority. But this life cannot be rationally fixed. It can be expressed, artistically, indirectly, poetically, musically, or with tone and glance and such ordinary, metaphorical arts of human interaction; but it cannot be literally stated. \ Although this would be a good ending for this post, I have to mention Jeffrey Sachs as well. I have been following him for a while. He appeared in the EU parliament, invited by Michael von der Schulenburg. Sachs has an amazing amount of experience with both Russian and American government officials, and with currencies. In the 90s he spent some time helping Eastern European countries with the transition to capitalist systems. He realised that the U.S. did not want to help Russia in the same way.  He gave a long speech in which he laid bare the ways in which the U.S. had influenced so many wars and uprisings around the world, and how the NATO enlargement had been a long-term strategy. That now, with Trump, the war was going to end.  There would be so much more to say. In any case, this seems to me a historic speech. Can it break through the mirror glass that has kept so many people away from valid sources of knowledge? @ 57d1a264:69f1fee1
2025-03-24 17:08:06Nice podcast with @sbddesign and @ConorOkus about bitcoin payments. https://www.youtube.com/watch?v=GTSqoFKs1cE In this episode, Conor, Open Source product manager at Spiral & Stephen, Product Designer at Voltage & Co founder of ATL Bitlab join Stephan to discuss the current state of Bitcoin user experience, particularly focusing on payments and the challenges faced by users. They explore the comparison between Bitcoin and physical cash, the Western perspective on Bitcoin payments, and the importance of user experience in facilitating Bitcoin transactions. They also touch upon various payment protocols like #BOLT11, #LNURL, and #BOLT12, highlighting the need for interoperability and better privacy features in the Bitcoin ecosystem. The discussion also covers resources available for developers and designers to enhance wallet usability and integration. @StephanLivera Official Podcast Episode: https://stephanlivera.com/646 ### Takeaways 🔸Bitcoin has excelled as a savings technology. 🔸The payments use case for Bitcoin still needs improvement. 🔸User experience is crucial for Bitcoin adoption. 🔸Comparing Bitcoin to cash highlights privacy concerns. 🔸Western users may not see a payments problem. 🔸Regulatory issues impact Bitcoin payments in the West. 🔸User experience challenges hinder Bitcoin transactions. 🔸Different payment protocols create compatibility issues. 🔸Community collaboration is essential for Bitcoin's future. 🔸Improving interoperability can enhance Bitcoin payments. Wallet compatibility issues can create negative user impressions. 🔸Designers can significantly improve wallet user experience. 🔸Testing compatibility between wallets is essential for user satisfaction. 🔸Tether's integration may boost Bitcoin adoption. 🔸Developers should prioritize payment capabilities before receiving capabilities. 🔸Collaboration between designers and developers can lead to better products. 🔸User experience improvements can be low-hanging fruit for wallet projects. 🔸A global hackathon aims to promote miner decentralization. 🔸Resources like BOLT12 and the Bitcoin Design Guide are valuable for developers. 🔸Engaging with the community can lead to innovative solutions. ### Timestamps ([00:00](/watch?v=GTSqoFKs1cE)) - Intro ([01:10](/watch?v=GTSqoFKs1cE&t=70s)) - What is the current state of Bitcoin usage - Payments or Savings? ([04:32](/watch?v=GTSqoFKs1cE&t=272s)) - Comparing Bitcoin with physical cash ([07:08](/watch?v=GTSqoFKs1cE&t=428s)) - What is the western perspective on Bitcoin payments? ([11:30](/watch?v=GTSqoFKs1cE&t=690s)) - Would people use Bitcoin more with improved UX? ([17:05](/watch?v=GTSqoFKs1cE&t=1025s)) - Exploring payment protocols: Bolt11, LNURL, Bolt12 & BIP353 ([30:14](/watch?v=GTSqoFKs1cE&t=1814s)) - Navigating Bitcoin wallet compatibility challenges ([34:45](/watch?v=GTSqoFKs1cE&t=2085s)) - What is the role of designers in wallet development? ([43:13](/watch?v=GTSqoFKs1cE&t=2593s)) - Rumble’s integration of Tether & Bitcoin; The impact of Tether on Bitcoin adoption ([51:22](/watch?v=GTSqoFKs1cE&t=3082s)) - Resources for wallet developers and designers ### Links: • [https://x.com/conorokus](https://x.com/conorokus) • [https://x.com/StephenDeLorme](https://x.com/StephenDeLorme) • [https://bolt12.org/](https://bolt12.org/) • [https://twelve.cash/](https://twelve.cash) • [https://bitcoin.design/guide/](https://bitcoin.design/guide/) • Setting Up Bitcoin Tips for Streamers](/watch?v=IWTpSN8IaLE) originally posted at https://stacker.news/items/923714
@ 57d1a264:69f1fee1
2025-03-24 17:08:06Nice podcast with @sbddesign and @ConorOkus about bitcoin payments. https://www.youtube.com/watch?v=GTSqoFKs1cE In this episode, Conor, Open Source product manager at Spiral & Stephen, Product Designer at Voltage & Co founder of ATL Bitlab join Stephan to discuss the current state of Bitcoin user experience, particularly focusing on payments and the challenges faced by users. They explore the comparison between Bitcoin and physical cash, the Western perspective on Bitcoin payments, and the importance of user experience in facilitating Bitcoin transactions. They also touch upon various payment protocols like #BOLT11, #LNURL, and #BOLT12, highlighting the need for interoperability and better privacy features in the Bitcoin ecosystem. The discussion also covers resources available for developers and designers to enhance wallet usability and integration. @StephanLivera Official Podcast Episode: https://stephanlivera.com/646 ### Takeaways 🔸Bitcoin has excelled as a savings technology. 🔸The payments use case for Bitcoin still needs improvement. 🔸User experience is crucial for Bitcoin adoption. 🔸Comparing Bitcoin to cash highlights privacy concerns. 🔸Western users may not see a payments problem. 🔸Regulatory issues impact Bitcoin payments in the West. 🔸User experience challenges hinder Bitcoin transactions. 🔸Different payment protocols create compatibility issues. 🔸Community collaboration is essential for Bitcoin's future. 🔸Improving interoperability can enhance Bitcoin payments. Wallet compatibility issues can create negative user impressions. 🔸Designers can significantly improve wallet user experience. 🔸Testing compatibility between wallets is essential for user satisfaction. 🔸Tether's integration may boost Bitcoin adoption. 🔸Developers should prioritize payment capabilities before receiving capabilities. 🔸Collaboration between designers and developers can lead to better products. 🔸User experience improvements can be low-hanging fruit for wallet projects. 🔸A global hackathon aims to promote miner decentralization. 🔸Resources like BOLT12 and the Bitcoin Design Guide are valuable for developers. 🔸Engaging with the community can lead to innovative solutions. ### Timestamps ([00:00](/watch?v=GTSqoFKs1cE)) - Intro ([01:10](/watch?v=GTSqoFKs1cE&t=70s)) - What is the current state of Bitcoin usage - Payments or Savings? ([04:32](/watch?v=GTSqoFKs1cE&t=272s)) - Comparing Bitcoin with physical cash ([07:08](/watch?v=GTSqoFKs1cE&t=428s)) - What is the western perspective on Bitcoin payments? ([11:30](/watch?v=GTSqoFKs1cE&t=690s)) - Would people use Bitcoin more with improved UX? ([17:05](/watch?v=GTSqoFKs1cE&t=1025s)) - Exploring payment protocols: Bolt11, LNURL, Bolt12 & BIP353 ([30:14](/watch?v=GTSqoFKs1cE&t=1814s)) - Navigating Bitcoin wallet compatibility challenges ([34:45](/watch?v=GTSqoFKs1cE&t=2085s)) - What is the role of designers in wallet development? ([43:13](/watch?v=GTSqoFKs1cE&t=2593s)) - Rumble’s integration of Tether & Bitcoin; The impact of Tether on Bitcoin adoption ([51:22](/watch?v=GTSqoFKs1cE&t=3082s)) - Resources for wallet developers and designers ### Links: • [https://x.com/conorokus](https://x.com/conorokus) • [https://x.com/StephenDeLorme](https://x.com/StephenDeLorme) • [https://bolt12.org/](https://bolt12.org/) • [https://twelve.cash/](https://twelve.cash) • [https://bitcoin.design/guide/](https://bitcoin.design/guide/) • Setting Up Bitcoin Tips for Streamers](/watch?v=IWTpSN8IaLE) originally posted at https://stacker.news/items/923714 @ 866e0139:6a9334e5
2025-03-24 10:50:59**Autor:** *Ludwig F. Badenhagen.* *Dieser Beitrag wurde mit dem* *[Pareto-Client](https://pareto.space/read)* *geschrieben.* *** Einer der wesentlichen Gründe dafür, dass während der „Corona-Pandemie“ so viele Menschen den Anweisungen der Spitzenpolitiker folgten, war sicher der, dass diese Menschen den Politikern vertrauten. Diese Menschen konnten sich nicht vorstellen, dass Spitzenpolitiker den Auftrag haben könnten, die Bürger analog klaren Vorgaben zu belügen, zu betrügen und sie vorsätzlich (tödlich) zu verletzen. Im Gegenteil, diese gutgläubigen Menschen waren mit der Zuversicht aufgewachsen, dass Spitzenpolitiker den Menschen dienen und deren Wohl im Fokus haben (müssen). Dies beteuerten Spitzenpolitiker schließlich stets in Talkshows und weiteren Medienformaten. Zwar wurden manche Politiker auch bei Fehlverhalten erwischt, aber hierbei ging es zumeist „nur“ um Geld und nicht um Leben. Und wenn es doch einmal um Leben ging, dann passieren die Verfehlungen „aus Versehen“, aber nicht mit Vorsatz. So oder so ähnlich dachte die Mehrheit der Bürger. Aber vor 5 Jahren änderte sich für aufmerksame Menschen alles, denn analog dem Lockstep-Szenario der Rockefeller-Foundation wurde der zuvor ausgiebig vorbereitete Plan zur Inszenierung der „Corona-Pandemie“ Realität. Seitdem wurde so manchem Bürger, der sich jenseits von Mainstream-Medien informierte, das Ausmaß der unter dem Vorwand einer erfundenen Pandemie vollbrachten Taten klar. Und unverändert kommen täglich immer neue Erkenntnisse ans Licht. Auf den Punkt gebracht war die Inszenierung der „Corona-Pandemie“ ein Verbrechen an der Menschheit, konstatieren unabhängige Sachverständige. Dieser Beitrag befasst sich allerdings nicht damit, die vielen Bestandteile dieses Verbrechens (nochmals) aufzuzählen oder weitere zu benennen. Stattdessen soll beleuchtet werden, warum die Spitzenpolitiker sich so verhalten haben und ob es überhaupt nach alledem möglich ist, der Politik jemals wieder zu vertrauen? Ferner ist es ein Anliegen dieses Artikels, die weiteren Zusammenhänge zu erörtern. Und zu guter Letzt soll dargelegt werden, warum sich der große Teil der Menschen unverändert alles gefallen lässt. **Demokratie** Von jeher organisierten sich Menschen mit dem Ziel, Ordnungsrahmen zu erschaffen, welche wechselseitiges Interagieren regeln. Dies führte aber stets dazu, dass einige wenige alle anderen unterordneten. Der Grundgedanke, der vor rund 2500 Jahren formulierten Demokratie, verfolgte dann aber das Ziel, dass die Masse darüber entscheiden können soll, wie sie leben und verwaltet werden möchte. Dieser Grundgedanke wurde von den Mächtigen sowohl gehasst als auch gefürchtet, denn die Gefahr lag nahe, dass die besitzlosen Vielen beispielsweise mit einer schlichten Abstimmung verfügen könnten, den Besitz der Wenigen zu enteignen. Selbst Sokrates war gegen solch eine Gesellschaftsordnung, da die besten Ideen nicht durch die Vielen, sondern durch einige wenige Kluge und Aufrichtige in die Welt kommen. Man müsse die Vielen lediglich manipulieren und würde auf diese Weise quasi jeden Unfug umsetzen können. Die Demokratie war ein Rohrkrepierer. **Die Mogelpackung „Repräsentative Demokratie“** Erst im Zuge der Gründung der USA gelang der Trick, dem Volk die „Repräsentative Demokratie“ unterzujubeln, die sich zwar nach Demokratie anhört, aber mit der Ursprungsdefinition nichts zu tun hat. Man konnte zwischen zwei Parteien wählen, die sich mit ihren jeweiligen Versprechen um die Gunst des Volkes bewarben. Tatsächlich paktierten die Vertreter der gewählten Parteien (Politiker) aber mit den wirklich Mächtigen, die letztendlich dafür sorgten, dass diese Politiker in die jeweiligen exponierten Positionen gelangten, welche ihnen ermöglichten (und somit auch den wirklich Mächtigen), Macht auszuüben. Übrigens, ob die eine oder andere Partei „den Volkswillen“ für sich gewinnen konnte, war für die wirklich Mächtigen weniger von Bedeutung, denn der Wille der wirklich Mächtigen wurde so oder so, wenn auch in voneinander differierenden Details, umgesetzt. Die Menschen waren begeistert von dieser Idee, denn sie glaubten, dass sie selbst „der Souverän“ seien. Schluss mit Monarchie sowie sonstiger Fremdherrschaft und Unterdrückung. Die Mächtigen waren ebenfalls begeistert, denn durch die Repräsentative Demokratie waren sie selbst nicht mehr in der Schusslinie, weil das Volk sich mit seinem Unmut fortan auf die Politiker konzentrierte. Da diese Politiker aber vielleicht nicht von einem selbst, sondern von vielen anderen Wahlberechtigten gewählt wurden, lenkte sich der Groll der Menschen nicht nur ab von den wirklich Mächtigen, sondern auch ab von den Politikern, direkt auf „die vielen Idioten“ aus ihrer eigenen Mitte, die sich „ver-wählt“ hatten. Diese Lenkung des Volkes funktionierte so hervorragend, dass andere Länder die Grundprinzipien dieses Steuerungsinstrumentes übernahmen. Dies ist alles bei Rainer Mausfeld nachzulesen. Ursprünglich waren die Mächtigen nur regional mächtig, sodass das Führen der eigenen Menschen(vieh)herde eher eine lokale Angelegenheit war. Somit mussten auch nur lokale Probleme gelöst werden und die Mittel zur Problemlösung blieben im eigenen Problembereich. *** JETZT ABONNIEREN: ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).* *** * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF/EURO** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):** [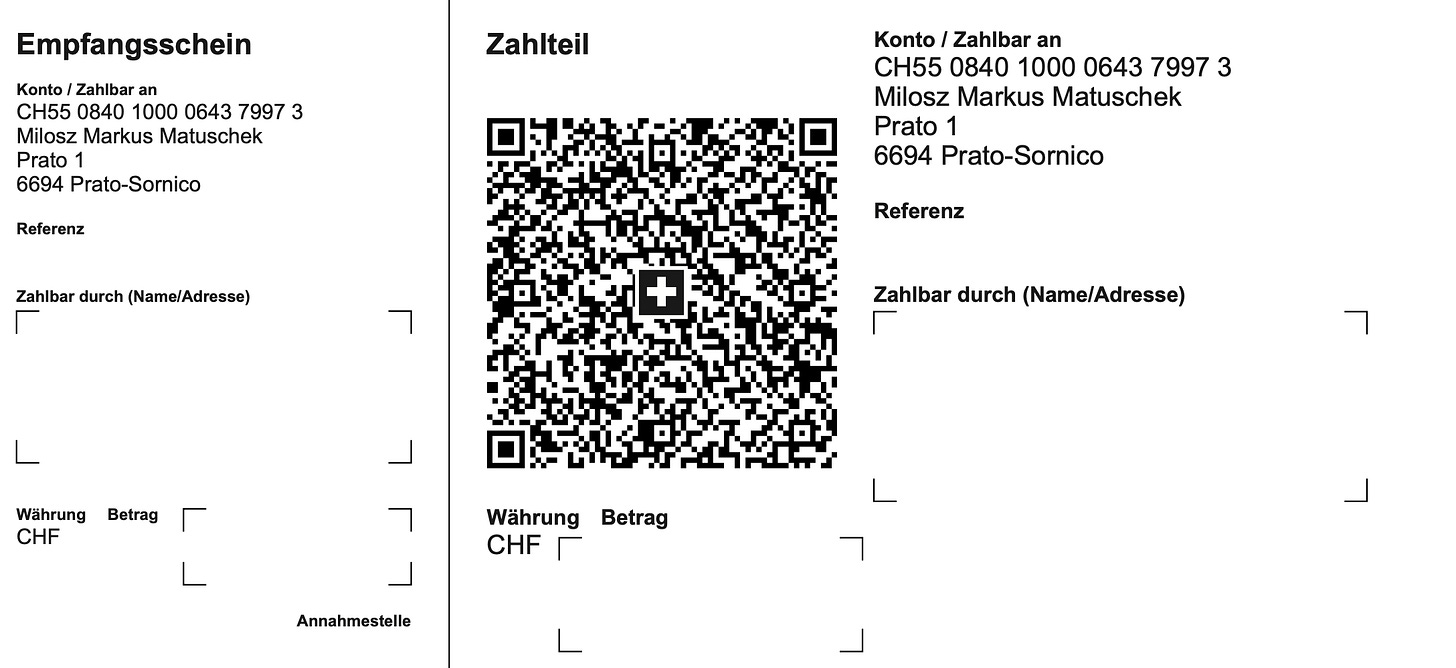](https://substackcdn.com/image/fetch/f_auto%2Cq_auto%3Agood%2Cfl_progressive%3Asteep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F3fdee17a-c22f-404e-a10c-7f87a7b8182a_2176x998.png) **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> oder <kontakt@idw-europe.org>. *** **Beherrschungsinstrumente der globalen Massenhaltung** Im Zuge der territorialen Erweiterungen der „Besitzungen“ einiger wirklich Mächtiger wurden die Verwaltungs- und Beherrschungsinstrumente überregionaler. Und heute, zu Zeiten der globalen Vernetzung, paktieren die wirklich Mächtigen miteinander und beanspruchen die Weltherrschaft. Längst wird offen über die finale Realisierung einen Weltregierung, welche die Nationalstaaten „nicht mehr benötigt“, gesprochen. Dass sich Deutschland, ebenso wie andere europäische Staaten, der EU untergeordnet hat, dürfte auch Leuten nicht entgangen sein, die sich nur über die Tagesschau informieren. Längst steht das EU-Recht über dem deutschen Recht. Und nur kurze Zeit ist es her, als die EU und alle ihre Mitgliedsstaaten die WHO autonom darüber entscheiden lassen wollten, was eine Pandemie ist und wie diese für alle verbindlich „bekämpft“ werden soll. Eine spannende Frage ist nun, wer denn über der EU und der WHO sowie anderen Institutionen steht? Diese Beschreibung macht klar, dass ein „souveränes Land“ wie das unverändert von der amerikanischen Armee besetzte Deutschland in der Entscheidungshierarchie an die Weisungen übergeordneter Entscheidungsorgane gebunden ist. An der Spitze stehen - wie kann es anders sein - die wirklich Mächtigen. Aber was nützt es dann, Spitzenpolitiker zu wählen, wenn diese analog Horst Seehofer nichts zu melden haben? Ist das Wählen von Politikern nicht völlig sinnlos, wenn deren Wahlversprechen ohnehin nicht erfüllt werden? Ist es nicht so, dass die Menschen, welche ihre Stimme nicht behalten, sondern abgeben, das bestehende System nur nähren, indem sie Wahlergebnisse akzeptieren, ohne zu wissen, ob diese manipuliert wurden, aber mit der Gewissheit, dass das im Zuge des Wahlkampfes Versprochene auf keinen Fall geliefert wird? Aktive Wähler glauben trotz allem an die Redlichkeit und Wirksamkeit von Wahlen, und sie akzeptieren Wahlergebnisse, weil sie denken, dass sie von „so vielen Idioten, die falsch wählen“, umgeben sind, womit wir wieder bei der Spaltung sind. Sie glauben, der Stand des aktuellen Elends sei „selbst gewählt“. **Die Wahl der Aufseher** Stellen Sie sich bitte vor, Sie wären im Gefängnis, weil Sie einen kritischen Artikel mit „gefällt mir“ gekennzeichnet haben oder weil Sie eine „Kontaktschuld“ trifft, da in Ihrer Nachbarschaft ein „verschwörerisches Symbol“ von einem „aufmerksamen“ Nachbarn bei einer „Meldestelle“ angezeigt wurde oder Sie gar eine Tat, „unterhalb der Strafbarkeitsgrenze“ begangen hätten, dann würden Sie möglicherweise mit Maßnahmen bestraft, die „keine Folter wären“. Beispielsweise würde man Sie während Ihrer „Umerziehungshaft“ mit Waterboarding, Halten von Stresspositionen, Dunkelhaft etc. dabei „unterstützen“, „Ihre Verfehlungen zu überdenken“. Stellen Sie sich weiterhin vor, dass Sie, so wie alle anderen Inhaftierten, an der alle vier Jahre stattfindenden Wahl der Aufseher teilnehmen könnten, und Sie hätten auch einen Favoriten, der zwar Waterboarding betreibt, aber gegen alle anderen Maßnahmen steht. Sie hätten sicher allen Grund zur Freude, wenn Sie Ihren Kandidaten durchbringen könnten, oder? Aber was wäre, wenn der Aufseher Ihrer Wahl dann dennoch alle 3 „Nicht-Folter-Maßnahmen“ anwenden würde, wie sämtliche anderen Aufseher zuvor? Spätestens dann müssten Sie sich eingestehen, dass es der Beruf des Aufsehers ist, Aufseher zu sein und dass er letztendlich tut, was ihm „von oben“ aufgetragen wird. Andernfalls verliert er seinen Job. Oder er verunfallt oder gerät in einen Skandal etc. So oder so, er verliert seinen Job - und den erledigt dann ein anderer Aufseher. Die Wahl des Aufsehers ändert wenig, solange Sie sich im System des Gefängnisses befinden und der Aufseher integraler Bestandteil dieses Systems ist. Zur Realisierung einer tatsächlichen Änderung müssten Sie dort herauskommen. Dieses Beispiel soll darstellen, dass alles in Hierarchien eingebunden ist. Die in einem System eingebundenen Menschen erfüllen ihre zugewiesenen Aufgaben, oder sie werden bestraft. **Das aktuelle System schadet dem Volk** Auch in der staatlichen Organisation von Menschen existieren hierarchische Gliederungen. Eine kommunale Selbstverwaltung gehört zum Kreis, dieser zum Land, dieses zum Staat, dieser zur EU, und diese - zu wem auch immer. Und vereinnahmte Gelder fließen nach oben. Obwohl es natürlich wäre, dass die Mittel dorthin fließen, wo sie der Allgemeinheit und nicht einigen wenigen dienen, also nach unten. Warum muss es also eine Weltregierung geben? Warum sollen nur einige Wenige über alle anderen bestimmen und an diesen verdienen (Nahrung, Medikamente, Krieg, Steuern etc.)? Warum sollen Menschen, so wie Vieh, das jemandem „gehört“, mit einem Code versehen und bereits als Baby zwangsgeimpft werden? Warum müssen alle Transaktionen und sämtliches Verhalten strickt gesteuert, kontrolliert und bewertet werden? Viele Menschen werden nach alledem zu dem Schluss kommen, dass solch ein System nur einigen wenigen wirklich Mächtigen und deren Helfershelfern nützt. Aber es gibt auch eine Gruppe Menschen, für die im Land alles beanstandungsfrei funktioniert. Die Spaltung der Menschen ist perfekt gelungen und sofern die eine Gruppe darauf wartet, dass die andere „endlich aufwacht“, da die Fakten doch auf dem Tisch liegen, so wird sie weiter warten dürfen. Julian Assange erwähnte einst, dass es für ihn eine unglaubliche Enttäuschung war, dass ihm niemand half. Assange hatte Ungeheuerlichkeiten aufgedeckt. Es gab keinen Aufstand. Assange wurde inhaftiert und gefoltert. Es gab keinen Aufstand. Assange sagte, er hätte nicht damit gerechnet, dass die Leute „so unglaublich feige“ seien. Aber womit rechnete er den stattdessen? Dass die Massen „sich erheben“. Das gibt es nur im Film, denn die Masse besteht aus vielen maximal Indoktrinierten, die sich wie Schafe verhalten, was als Züchtungserfolg der Leute an den Schalthebeln der Macht und deren Herren, den wirklich Mächtigen, anzuerkennen ist. Denn wer mächtig ist und bleiben möchte, will sicher keine problematischen Untertanen, sondern eine gefügige, ängstliche Herde, die er nach Belieben ausbeuten und steuern kann. Wenn er hierüber verfügt, will er keinen Widerstand. Ob Corona, Krieg, Demokratie- und Klimarettung oder Meinungsäußerungsverbote und Bürgerrechte, die unterhalb der Strafbarkeitsgrenze liegen, all diese und viele weitere Stichworte mehr sind es, die viele traurig und so manche wütend machen. Auch das Mittel des Demonstrierens hat sich als völlig wirkungslos erwiesen. Die vielen gruseligen Videoaufnahmen über die massivsten Misshandlungen von Demonstranten gegen die Corona-Maßnahmen führen zu dem Ergebnis, dass die Exekutive ihr Gewaltmonopol nutzt(e), um die Bevölkerung gezielt zu verletzen und einzuschüchtern. Bekanntlich kann jede friedliche Demonstration zum Eskalieren gebracht werden, indem man Menschen in die Enge treibt (fehlender Sicherheitsabstand) und einige V-Leute in Zivil mit einschlägigen Flaggen und sonstigen „Symbolen“ einschleust, die für Krawall sorgen, damit die gepanzerten Kollegen dann losknüppeln und die scharfen Hunde zubeißen können. So lauten zumindest die Berichte vieler Zeitzeugen und so ist es auch auf vielen Videos zu sehen. Allerdings nicht im Mainstream. Dieses Vorgehen ist deshalb besonders perfide, weil man den Deutschen ihre Wehrhaftigkeit aberzogen hat. Nicht wehrfähige Bürger und eine brutale Staatsmacht mit Gewaltmonopol führen zu einem Gemetzel bei den Bürgern. Ähnliches lässt sich auch in zivilen Lebenssituationen beobachten, wenn die hiesige zivilisierte Bevölkerung auf „eingereiste“ Massenvergewaltiger und Messerstecher trifft, die über ein anderes Gewalt- und Rechtsverständnis verfügen als die Einheimischen. **System-Technik** Die These ist, dass es eine Gruppe von global agierenden Personen gibt, welche das Geschehen auf der Erde zunehmend wirksam zu ihrem individuellen Vorteil gestaltet. Wie sich diese Gruppe definiert, kann bei John Coleman (Das Komitee der 300) und David Icke nachgelesen werden. Hierbei handelt es ich um Autoren, die jahrzehntelang analog streng wissenschaftlichen Grundlagen zu ihren Themen geforscht haben und in ihren jeweiligen Werken sämtliche Quellen benennen. Diese Autoren wurden vom Mainstream mit dem Prädikatsmerkmal „Verschwörungstheoretiker“ ausgezeichnet, wodurch die Ergebnisse Ihrer Arbeiten umso glaubwürdiger sind. Diese mächtige Gruppe hat mit ihren Schergen nahezu den gesamten Planeten infiltriert, indem sie Personen in führenden Positionen in vielen Belangen größtmögliche Freiheiten sowie Schutz gewährt, aber diesen im Gegenzug eine völlige Unterwerfung bei Kernthemen abfordert. Die Motivatoren für diese Unterwerfung sind, abgesehen von materiellen Zuwendungen, auch „Ruhm und Ehre sowie Macht“. Manchmal wird auch Beweismaterial für begangene Verfehlungen (Lolita-Express, Pizzagate etc.) genutzt, um Forderungen Nachdruck zu verleihen. Und auch körperliche Bestrafungen der betroffenen Person oder deren Angehörigen zählen zum Repertoire der Motivatoren. Letztendlich ähnlich den Verhaltensweisen in einem Mafia-Film. Mit dieser Methodik hat sich diese mächtige Gruppe im Laufe von Jahrhunderten! eine Organisation erschaffen, welche aus Kirchen, Parteien, Firmen, NGO, Vereinen, Verbänden und weiteren Organisationsformen besteht. Bestimmte Ämter und Positionen in Organisationen können nur von Personen eingenommen und gehalten werden, die „auf Linie sind“. Die Mitglieder der Gruppe tauchen in keiner Rubrik wie „Die reichsten Menschen der Welt“ auf, sondern bleiben fern der Öffentlichkeit. Wer jemanden aus ihren Reihen erkennt und beschuldigt, ist ein „Antisemit“ oder sonstiger Übeltäter und wird verfolgt und bekämpft. Über mächtige Vermögensverwaltungskonzerne beteiligen sich die Mitglieder dieser Gruppe anonym an Unternehmen in Schlüsselpositionen in einer Dimension, die ihnen wesentlichen Einfluss auf die Auswahl der Topmanager einräumt, sodass die jeweilige Unternehmenspolitik nach Vorgaben der Gruppe gestaltet wird. Die Gruppe steuert das Geldsystem, von dem sich der Planet abhängig zu sein wähnt. Hierzu eine Erläuterung: Ein Staat wie Deutschland ist bekanntlich maximal verschuldet. Man stelle sich vor, ein unliebsamer Politiker würde entgegen sämtlicher „Brandmauern“ und sonstiger Propaganda und Wahlmanipulationen gewählt, das Land zu führen, dann könnte dieser keine Kredit über 500 Mrd. Euro bei der nächsten Sparkasse beantragen, sondern wäre auf die Mächtigen dieser Welt angewiesen. Jeder weiß, dass Deutschland als Staat kein funktionierendes Geschäftsmodell hat und somit nicht in der Lage ist, solch ein Darlehen zurückzuzahlen. Welche Motivation sollte also jemand haben, einem Land wie Deutschland so viel Geld ohne Aussicht auf Rückführung zu geben? Es leuchtet ein, dass dieser Politiker andere Gefälligkeiten anbieten müsste, um das Darlehen zu bekommen. Im Falle einer Weigerung zur Kooperation könnte der Staatsapparat mit seinen Staatsdienern, Bürgergeld- und Rentenempfänger etc. nicht mehr bezahlt werden und dieser Politiker wäre schnell wieder weg. Er würde medial hingerichtet. Es ist somit davon auszugehen, dass ein Spitzenpolitiker dieser Tage nicht über viele Optionen verfügt, denn er übernimmt eine Situation, die von seinen Vorgängern erschaffen wurde. Trotz alledem darauf zu hoffen, dass es einen anderen Politiker geben könnte, mit dem dann alles wieder gut wird, mutet ziemlich infantil an. Dass ein Großteil der Medien von Zuwendungen abhängig ist, dürfte ebenfalls leicht nachzuvollziehen sein, denn der gewöhnliche Bürger zahlt nichts für den Content der MSM. Abhängig davon, von wem (Regierung, Philanthrop, Konzern etc.) ein Medium am Leben gehalten wird, gestalten sich auch dessen Inhalte. Und wenn angewiesen wird, dass ein Politiker medial hingerichtet werden soll, dann bedient die Maschinerie das Thema. Man beobachte einfach einmal, dass Politiker der Kartell-Parteien völlig anders behandelt werden als solche jenseits der „Brandmauer“. Und der Leser, der solche Auftragsarbeiten kostenlos liest, ist der Konsument, für dessen Indoktrination die Finanziers der Verlage gerne zahlen. Mittlerweile kann durch die Herrschaft über die Medien und die systematische Vergiftung der Körper und Geister der Population die öffentliche Meinung gesteuert werden. Die überwiegende Zahl der Deutschen scheint nicht mehr klar denken zu können. Wer sich das aktuelle Geschehen in der deutschen Politik mit klarem Verstand ansieht, kommt nicht umhin, eine Fernsteuerung der handelnden Politiker in Betracht zu ziehen. Aber was soll daran verwundern? Sind es deshalb „böse Menschen“? Sind die in „Forschungslaboren“ arbeitenden Quäler von „Versuchstieren“ böse Menschen? Sind der Schlächter, der Folterer und der Henker böse Menschen? Oder der knüppelnde Polizist? Es handelt sich zunächst einmal um Personen, die einen Vorteil dadurch haben, Ihrer Tätigkeit nachzugehen. Sie sind integrale Bestandteile eines Belohnungssystems, welches von oben nach unten Anweisungen gibt. Und wenn diese Anweisungen nicht befolgt werden, führt dies für den Befehlsverweigerer zu Konsequenzen. **Der klare Verstand** Es ist nun eine spannende Frage, warum so viele Menschen sich solch eine Behandlung gefallen lassen? Nun, das ist relativ einfach, denn das angepasste Verhalten der Vielen ist nichts anderes als ein Züchtungserfolg der Wenigen. Die Psyche der Menschen ist ebenso akribisch erforscht worden wie deren Körperfunktionen. Würden die Menschen von den wirklich Mächtigen geliebt, dann würde genau gewusst, wie sie zu behandeln und mit ihren jeweiligen Bedürfnissen zu versorgen sind. Stattdessen werden die Menschen aber als eine Einnahmequelle betrachtet. Dies manifestiert sich exemplarisch in folgenden Bereichen: 1. Das Gesundheitssystem verdient nichts am gesunden Menschen, sondern nur am (dauerhaft) kranken, der um Schmerzlinderung bettelt. Bereits als Baby werden Menschen geimpft, was die jeweilige Gesundheit (mit Verweis auf die Werke von Anita Petek-Dimmer u. a.) nachhaltig negativ beeinflusst. Wer hat denn heute keine Krankheiten? Die „Experten“ des Gesundheitssystems verteufeln Vitamin D, Vitamin C, Lithium, die Sonne, Natur etc. und empfehlen stattdessen Präparate, die man patentieren konnte und mit denen die Hersteller viel Geld verdienen. Die Präparate heilen selten, sondern lindern bestenfalls zuvor künstlich erzeugte Leiden, und müssen oftmals dauerhaft eingenommen werden. Was ist aus den nicht Geimpften geworden, die alle sterben sollten? Sind diese nicht die einzigen Gesunden dieser Tage? Ist nicht jeder Geimpfte entweder permanent krank oder bereits tot? Abgesehen von denen, welche das Glück hatten, „Sonderchargen“ mit Kochsalz zu erhalten. \ \ Wem gehören die wesentlichen Player im Gesundheitswesen zu einem erheblichen Teil? Die Vermögensverwalter der wirklich Mächtigen. 2. Ähnlich gestaltet es sich bei der Ernährungsindustrie. Die von dort aus verabreichten Produkte sind die Ursachen für den Gesundheitszustand der deutschen Population. Das ist aber auch irgendwie logisch, denn wer sich nicht falsch ernährt und gesund bleibt, wird kein Kunde des Gesundheitswesens. \ \ Die Besitzverhältnisse in der Ernährungsindustrie ähneln denen im Gesundheitswesen, sodass am gleichen Kunden gearbeitet und verdient wird. 3. Die Aufzählung konnte nun über die meisten Branchen, in denen mit dem Elend der Menschen viel verdient werden kann, fortgesetzt werden. Waffen (BlackRock erhöhte beispielsweise seine Anteile an der Rheinmetall AG im Juni 2024 auf 5,25 Prozent. Der US-Vermögensverwalter ist damit der zweitgrößte Anteilseigner nach der französischen Großbank Société Générale.), Energie, Umwelt, Technologie, IT, Software, KI, Handel etc. Wie genau Chemtrails und Technologien wie 5G auf den Menschen und die Tiere wirken, ist ebenfalls umstritten. Aber ist es nicht seltsam, wie krank, empathielos, antriebslos und aggressiv viele Menschen heute sind? Was genau verabreicht man der Berliner Polizei, damit diese ihre Prügelorgien auf den Rücken und in den Gesichtern der Menschen wahrnehmen, die friedlich ihre Demonstrationsrechte wahrnehmen? Und was erhalten die ganzen zugereisten „Fachkräfte“, die mit Ihren Autos in Menschenmengen rasen oder auch Kinder und Erwachsene niedermessern? Das Titelbild dieses Beitrags zeigt einige Gebilde, welche regelmäßig bei Obduktionen von Geimpften in deren Blutgefäßen gefunden werden. Wie genau wirken diese kleinen Monster? Können wir Menschen ihr Unverständnis und ihr Nicht-Aufwachen vorwerfen, wenn wir erkennen, dass diese Menschen maximal vergiftet wurden? Oder sollten einfach Lösungen für die Probleme dieser Zeit auch ohne den Einbezug derer gefunden werden, die offenbar nicht mehr Herr ihrer Sinne sind? **Die Ziele der wirklich Mächtigen** Wer sich entsprechende Videosequenzen der Bilderberger, des WEF und anderen „Überorganisationen“ ansieht, der erkennt schnell das Muster: * Reduzierung der Weltpopulation um ca. 80 Prozent * Zusammenbruch der Wirtschaft, damit diese von den Konzernen übernommen werden kann. * Zusammenbruch der öffentlichen Ordnung, um eine totale Entwaffnung und eine totale Überwachung durchsetzen zu können. * Zusammenbruch der Regierungen, damit die Weltregierung übernehmen kann. Es ist zu überdenken, ob die Weltregierung tatsächlich das für die Vielen beste Organisationssystem ist, oder ob die dezentrale Eigenorganisation der jeweils lokalen Bevölkerung nicht doch die bessere Option darstellt. Baustellen würden nicht nur begonnen, sondern auch schnell abgearbeitet. Jede Region könnte bestimmen, ob sie sich mit Chemtrails und anderen Substanzen besprühen lassen möchte. Und die Probleme in Barcelona könnte die Menschen dort viel besser lösen als irgendwelche wirklich Mächtigen in ihren Elfenbeintürmen. Die lokale Wirtschaft könnte wieder zurückkommen und mit dieser die Eigenständigkeit. Denn die den wirklich Mächtigen über ihre Vermögensverwalter gehörenden Großkonzerne haben offensichtlich nicht das Wohl der Bevölkerung im Fokus, sondern eher deren Ausbeutung. Das Aussteigen aus dem System ist die wahre Herkulesaufgabe und es bedarf sicher Mut und Klugheit, sich dieser zu stellen. Die Politiker, die unverändert die Narrative der wirklich Mächtigen bedienen, sind hierfür denkbar ungeeignet, denn sie verfolgen kein Lebensmodell, welches sich von Liebe und Mitgefühl geleitet in den Dienst der Gesamtheit von Menschen, Tieren und Natur stellt. Schauen Sie einmal genau hin, denken Sie nach und fühlen Sie mit. **Was tun?** Jedes System funktioniert nur so lange, wie es unterstützt wird. Somit stellt sich die Frage, wie viele Menschen das System ignorieren müssen, damit es kollabiert, und auf welche Weise dieses Ignorieren durchzuführen ist? Merkbar ist, dass die große Masse der Verwaltungsangestellten krank und oder unmotiviert und somit nicht wirksam ist. Würden die entsprechenden Stellen massiv belastet und parallel hierzu keine Einnahmen mehr realisieren, wäre ein Kollaps nah. Die Prügelpolizisten aus Berlin können nicht überall sein und normale Polizisten arbeiten nicht gegen unbescholtene Bürger, sondern sorgen sich selbst um ihre Zukunft. Gewalt ist sicher keine Lösung, und sicher auch nicht erforderlich. Wie eine gerechte Verwaltungsform aufgebaut werden muss? Einfach so, wie sie in den hiesigen Gesetzen beschrieben steht. Aber eine solche Organisationsform muss frei sein von Blockparteien und korrupten Politikern und weisungsgebundenen Richtern etc. Stattdessen werden Menschen benötigt, welche die Menschen lieben und ihnen nicht schaden wollen. Außerdem sollten diese Führungspersonen auch wirklich etwas können, und nicht nur „Politiker“ ohne weitere Berufserfahrungen sein. *** Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt). *Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.* *** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)**
@ 866e0139:6a9334e5
2025-03-24 10:50:59**Autor:** *Ludwig F. Badenhagen.* *Dieser Beitrag wurde mit dem* *[Pareto-Client](https://pareto.space/read)* *geschrieben.* *** Einer der wesentlichen Gründe dafür, dass während der „Corona-Pandemie“ so viele Menschen den Anweisungen der Spitzenpolitiker folgten, war sicher der, dass diese Menschen den Politikern vertrauten. Diese Menschen konnten sich nicht vorstellen, dass Spitzenpolitiker den Auftrag haben könnten, die Bürger analog klaren Vorgaben zu belügen, zu betrügen und sie vorsätzlich (tödlich) zu verletzen. Im Gegenteil, diese gutgläubigen Menschen waren mit der Zuversicht aufgewachsen, dass Spitzenpolitiker den Menschen dienen und deren Wohl im Fokus haben (müssen). Dies beteuerten Spitzenpolitiker schließlich stets in Talkshows und weiteren Medienformaten. Zwar wurden manche Politiker auch bei Fehlverhalten erwischt, aber hierbei ging es zumeist „nur“ um Geld und nicht um Leben. Und wenn es doch einmal um Leben ging, dann passieren die Verfehlungen „aus Versehen“, aber nicht mit Vorsatz. So oder so ähnlich dachte die Mehrheit der Bürger. Aber vor 5 Jahren änderte sich für aufmerksame Menschen alles, denn analog dem Lockstep-Szenario der Rockefeller-Foundation wurde der zuvor ausgiebig vorbereitete Plan zur Inszenierung der „Corona-Pandemie“ Realität. Seitdem wurde so manchem Bürger, der sich jenseits von Mainstream-Medien informierte, das Ausmaß der unter dem Vorwand einer erfundenen Pandemie vollbrachten Taten klar. Und unverändert kommen täglich immer neue Erkenntnisse ans Licht. Auf den Punkt gebracht war die Inszenierung der „Corona-Pandemie“ ein Verbrechen an der Menschheit, konstatieren unabhängige Sachverständige. Dieser Beitrag befasst sich allerdings nicht damit, die vielen Bestandteile dieses Verbrechens (nochmals) aufzuzählen oder weitere zu benennen. Stattdessen soll beleuchtet werden, warum die Spitzenpolitiker sich so verhalten haben und ob es überhaupt nach alledem möglich ist, der Politik jemals wieder zu vertrauen? Ferner ist es ein Anliegen dieses Artikels, die weiteren Zusammenhänge zu erörtern. Und zu guter Letzt soll dargelegt werden, warum sich der große Teil der Menschen unverändert alles gefallen lässt. **Demokratie** Von jeher organisierten sich Menschen mit dem Ziel, Ordnungsrahmen zu erschaffen, welche wechselseitiges Interagieren regeln. Dies führte aber stets dazu, dass einige wenige alle anderen unterordneten. Der Grundgedanke, der vor rund 2500 Jahren formulierten Demokratie, verfolgte dann aber das Ziel, dass die Masse darüber entscheiden können soll, wie sie leben und verwaltet werden möchte. Dieser Grundgedanke wurde von den Mächtigen sowohl gehasst als auch gefürchtet, denn die Gefahr lag nahe, dass die besitzlosen Vielen beispielsweise mit einer schlichten Abstimmung verfügen könnten, den Besitz der Wenigen zu enteignen. Selbst Sokrates war gegen solch eine Gesellschaftsordnung, da die besten Ideen nicht durch die Vielen, sondern durch einige wenige Kluge und Aufrichtige in die Welt kommen. Man müsse die Vielen lediglich manipulieren und würde auf diese Weise quasi jeden Unfug umsetzen können. Die Demokratie war ein Rohrkrepierer. **Die Mogelpackung „Repräsentative Demokratie“** Erst im Zuge der Gründung der USA gelang der Trick, dem Volk die „Repräsentative Demokratie“ unterzujubeln, die sich zwar nach Demokratie anhört, aber mit der Ursprungsdefinition nichts zu tun hat. Man konnte zwischen zwei Parteien wählen, die sich mit ihren jeweiligen Versprechen um die Gunst des Volkes bewarben. Tatsächlich paktierten die Vertreter der gewählten Parteien (Politiker) aber mit den wirklich Mächtigen, die letztendlich dafür sorgten, dass diese Politiker in die jeweiligen exponierten Positionen gelangten, welche ihnen ermöglichten (und somit auch den wirklich Mächtigen), Macht auszuüben. Übrigens, ob die eine oder andere Partei „den Volkswillen“ für sich gewinnen konnte, war für die wirklich Mächtigen weniger von Bedeutung, denn der Wille der wirklich Mächtigen wurde so oder so, wenn auch in voneinander differierenden Details, umgesetzt. Die Menschen waren begeistert von dieser Idee, denn sie glaubten, dass sie selbst „der Souverän“ seien. Schluss mit Monarchie sowie sonstiger Fremdherrschaft und Unterdrückung. Die Mächtigen waren ebenfalls begeistert, denn durch die Repräsentative Demokratie waren sie selbst nicht mehr in der Schusslinie, weil das Volk sich mit seinem Unmut fortan auf die Politiker konzentrierte. Da diese Politiker aber vielleicht nicht von einem selbst, sondern von vielen anderen Wahlberechtigten gewählt wurden, lenkte sich der Groll der Menschen nicht nur ab von den wirklich Mächtigen, sondern auch ab von den Politikern, direkt auf „die vielen Idioten“ aus ihrer eigenen Mitte, die sich „ver-wählt“ hatten. Diese Lenkung des Volkes funktionierte so hervorragend, dass andere Länder die Grundprinzipien dieses Steuerungsinstrumentes übernahmen. Dies ist alles bei Rainer Mausfeld nachzulesen. Ursprünglich waren die Mächtigen nur regional mächtig, sodass das Führen der eigenen Menschen(vieh)herde eher eine lokale Angelegenheit war. Somit mussten auch nur lokale Probleme gelöst werden und die Mittel zur Problemlösung blieben im eigenen Problembereich. *** JETZT ABONNIEREN: ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel in Ihr Postfach, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht).* *** * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF/EURO** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):** [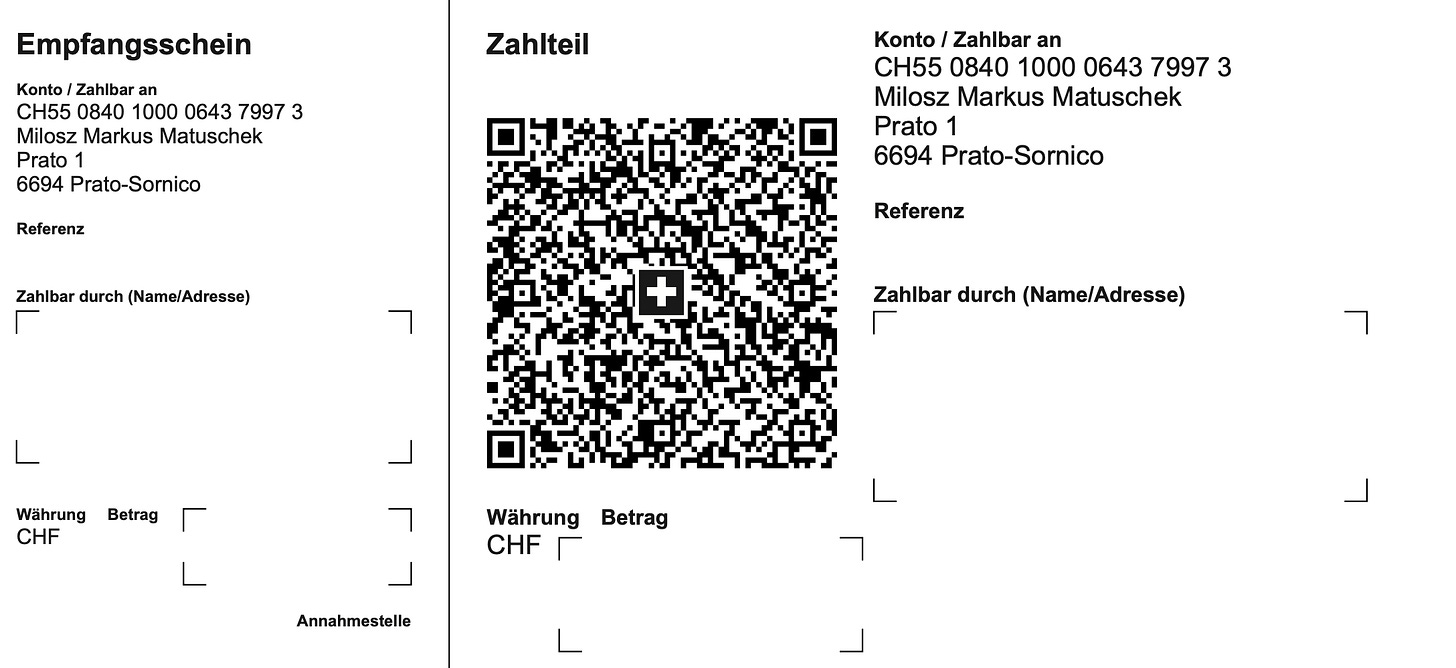](https://substackcdn.com/image/fetch/f_auto%2Cq_auto%3Agood%2Cfl_progressive%3Asteep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F3fdee17a-c22f-404e-a10c-7f87a7b8182a_2176x998.png) **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> oder <kontakt@idw-europe.org>. *** **Beherrschungsinstrumente der globalen Massenhaltung** Im Zuge der territorialen Erweiterungen der „Besitzungen“ einiger wirklich Mächtiger wurden die Verwaltungs- und Beherrschungsinstrumente überregionaler. Und heute, zu Zeiten der globalen Vernetzung, paktieren die wirklich Mächtigen miteinander und beanspruchen die Weltherrschaft. Längst wird offen über die finale Realisierung einen Weltregierung, welche die Nationalstaaten „nicht mehr benötigt“, gesprochen. Dass sich Deutschland, ebenso wie andere europäische Staaten, der EU untergeordnet hat, dürfte auch Leuten nicht entgangen sein, die sich nur über die Tagesschau informieren. Längst steht das EU-Recht über dem deutschen Recht. Und nur kurze Zeit ist es her, als die EU und alle ihre Mitgliedsstaaten die WHO autonom darüber entscheiden lassen wollten, was eine Pandemie ist und wie diese für alle verbindlich „bekämpft“ werden soll. Eine spannende Frage ist nun, wer denn über der EU und der WHO sowie anderen Institutionen steht? Diese Beschreibung macht klar, dass ein „souveränes Land“ wie das unverändert von der amerikanischen Armee besetzte Deutschland in der Entscheidungshierarchie an die Weisungen übergeordneter Entscheidungsorgane gebunden ist. An der Spitze stehen - wie kann es anders sein - die wirklich Mächtigen. Aber was nützt es dann, Spitzenpolitiker zu wählen, wenn diese analog Horst Seehofer nichts zu melden haben? Ist das Wählen von Politikern nicht völlig sinnlos, wenn deren Wahlversprechen ohnehin nicht erfüllt werden? Ist es nicht so, dass die Menschen, welche ihre Stimme nicht behalten, sondern abgeben, das bestehende System nur nähren, indem sie Wahlergebnisse akzeptieren, ohne zu wissen, ob diese manipuliert wurden, aber mit der Gewissheit, dass das im Zuge des Wahlkampfes Versprochene auf keinen Fall geliefert wird? Aktive Wähler glauben trotz allem an die Redlichkeit und Wirksamkeit von Wahlen, und sie akzeptieren Wahlergebnisse, weil sie denken, dass sie von „so vielen Idioten, die falsch wählen“, umgeben sind, womit wir wieder bei der Spaltung sind. Sie glauben, der Stand des aktuellen Elends sei „selbst gewählt“. **Die Wahl der Aufseher** Stellen Sie sich bitte vor, Sie wären im Gefängnis, weil Sie einen kritischen Artikel mit „gefällt mir“ gekennzeichnet haben oder weil Sie eine „Kontaktschuld“ trifft, da in Ihrer Nachbarschaft ein „verschwörerisches Symbol“ von einem „aufmerksamen“ Nachbarn bei einer „Meldestelle“ angezeigt wurde oder Sie gar eine Tat, „unterhalb der Strafbarkeitsgrenze“ begangen hätten, dann würden Sie möglicherweise mit Maßnahmen bestraft, die „keine Folter wären“. Beispielsweise würde man Sie während Ihrer „Umerziehungshaft“ mit Waterboarding, Halten von Stresspositionen, Dunkelhaft etc. dabei „unterstützen“, „Ihre Verfehlungen zu überdenken“. Stellen Sie sich weiterhin vor, dass Sie, so wie alle anderen Inhaftierten, an der alle vier Jahre stattfindenden Wahl der Aufseher teilnehmen könnten, und Sie hätten auch einen Favoriten, der zwar Waterboarding betreibt, aber gegen alle anderen Maßnahmen steht. Sie hätten sicher allen Grund zur Freude, wenn Sie Ihren Kandidaten durchbringen könnten, oder? Aber was wäre, wenn der Aufseher Ihrer Wahl dann dennoch alle 3 „Nicht-Folter-Maßnahmen“ anwenden würde, wie sämtliche anderen Aufseher zuvor? Spätestens dann müssten Sie sich eingestehen, dass es der Beruf des Aufsehers ist, Aufseher zu sein und dass er letztendlich tut, was ihm „von oben“ aufgetragen wird. Andernfalls verliert er seinen Job. Oder er verunfallt oder gerät in einen Skandal etc. So oder so, er verliert seinen Job - und den erledigt dann ein anderer Aufseher. Die Wahl des Aufsehers ändert wenig, solange Sie sich im System des Gefängnisses befinden und der Aufseher integraler Bestandteil dieses Systems ist. Zur Realisierung einer tatsächlichen Änderung müssten Sie dort herauskommen. Dieses Beispiel soll darstellen, dass alles in Hierarchien eingebunden ist. Die in einem System eingebundenen Menschen erfüllen ihre zugewiesenen Aufgaben, oder sie werden bestraft. **Das aktuelle System schadet dem Volk** Auch in der staatlichen Organisation von Menschen existieren hierarchische Gliederungen. Eine kommunale Selbstverwaltung gehört zum Kreis, dieser zum Land, dieses zum Staat, dieser zur EU, und diese - zu wem auch immer. Und vereinnahmte Gelder fließen nach oben. Obwohl es natürlich wäre, dass die Mittel dorthin fließen, wo sie der Allgemeinheit und nicht einigen wenigen dienen, also nach unten. Warum muss es also eine Weltregierung geben? Warum sollen nur einige Wenige über alle anderen bestimmen und an diesen verdienen (Nahrung, Medikamente, Krieg, Steuern etc.)? Warum sollen Menschen, so wie Vieh, das jemandem „gehört“, mit einem Code versehen und bereits als Baby zwangsgeimpft werden? Warum müssen alle Transaktionen und sämtliches Verhalten strickt gesteuert, kontrolliert und bewertet werden? Viele Menschen werden nach alledem zu dem Schluss kommen, dass solch ein System nur einigen wenigen wirklich Mächtigen und deren Helfershelfern nützt. Aber es gibt auch eine Gruppe Menschen, für die im Land alles beanstandungsfrei funktioniert. Die Spaltung der Menschen ist perfekt gelungen und sofern die eine Gruppe darauf wartet, dass die andere „endlich aufwacht“, da die Fakten doch auf dem Tisch liegen, so wird sie weiter warten dürfen. Julian Assange erwähnte einst, dass es für ihn eine unglaubliche Enttäuschung war, dass ihm niemand half. Assange hatte Ungeheuerlichkeiten aufgedeckt. Es gab keinen Aufstand. Assange wurde inhaftiert und gefoltert. Es gab keinen Aufstand. Assange sagte, er hätte nicht damit gerechnet, dass die Leute „so unglaublich feige“ seien. Aber womit rechnete er den stattdessen? Dass die Massen „sich erheben“. Das gibt es nur im Film, denn die Masse besteht aus vielen maximal Indoktrinierten, die sich wie Schafe verhalten, was als Züchtungserfolg der Leute an den Schalthebeln der Macht und deren Herren, den wirklich Mächtigen, anzuerkennen ist. Denn wer mächtig ist und bleiben möchte, will sicher keine problematischen Untertanen, sondern eine gefügige, ängstliche Herde, die er nach Belieben ausbeuten und steuern kann. Wenn er hierüber verfügt, will er keinen Widerstand. Ob Corona, Krieg, Demokratie- und Klimarettung oder Meinungsäußerungsverbote und Bürgerrechte, die unterhalb der Strafbarkeitsgrenze liegen, all diese und viele weitere Stichworte mehr sind es, die viele traurig und so manche wütend machen. Auch das Mittel des Demonstrierens hat sich als völlig wirkungslos erwiesen. Die vielen gruseligen Videoaufnahmen über die massivsten Misshandlungen von Demonstranten gegen die Corona-Maßnahmen führen zu dem Ergebnis, dass die Exekutive ihr Gewaltmonopol nutzt(e), um die Bevölkerung gezielt zu verletzen und einzuschüchtern. Bekanntlich kann jede friedliche Demonstration zum Eskalieren gebracht werden, indem man Menschen in die Enge treibt (fehlender Sicherheitsabstand) und einige V-Leute in Zivil mit einschlägigen Flaggen und sonstigen „Symbolen“ einschleust, die für Krawall sorgen, damit die gepanzerten Kollegen dann losknüppeln und die scharfen Hunde zubeißen können. So lauten zumindest die Berichte vieler Zeitzeugen und so ist es auch auf vielen Videos zu sehen. Allerdings nicht im Mainstream. Dieses Vorgehen ist deshalb besonders perfide, weil man den Deutschen ihre Wehrhaftigkeit aberzogen hat. Nicht wehrfähige Bürger und eine brutale Staatsmacht mit Gewaltmonopol führen zu einem Gemetzel bei den Bürgern. Ähnliches lässt sich auch in zivilen Lebenssituationen beobachten, wenn die hiesige zivilisierte Bevölkerung auf „eingereiste“ Massenvergewaltiger und Messerstecher trifft, die über ein anderes Gewalt- und Rechtsverständnis verfügen als die Einheimischen. **System-Technik** Die These ist, dass es eine Gruppe von global agierenden Personen gibt, welche das Geschehen auf der Erde zunehmend wirksam zu ihrem individuellen Vorteil gestaltet. Wie sich diese Gruppe definiert, kann bei John Coleman (Das Komitee der 300) und David Icke nachgelesen werden. Hierbei handelt es ich um Autoren, die jahrzehntelang analog streng wissenschaftlichen Grundlagen zu ihren Themen geforscht haben und in ihren jeweiligen Werken sämtliche Quellen benennen. Diese Autoren wurden vom Mainstream mit dem Prädikatsmerkmal „Verschwörungstheoretiker“ ausgezeichnet, wodurch die Ergebnisse Ihrer Arbeiten umso glaubwürdiger sind. Diese mächtige Gruppe hat mit ihren Schergen nahezu den gesamten Planeten infiltriert, indem sie Personen in führenden Positionen in vielen Belangen größtmögliche Freiheiten sowie Schutz gewährt, aber diesen im Gegenzug eine völlige Unterwerfung bei Kernthemen abfordert. Die Motivatoren für diese Unterwerfung sind, abgesehen von materiellen Zuwendungen, auch „Ruhm und Ehre sowie Macht“. Manchmal wird auch Beweismaterial für begangene Verfehlungen (Lolita-Express, Pizzagate etc.) genutzt, um Forderungen Nachdruck zu verleihen. Und auch körperliche Bestrafungen der betroffenen Person oder deren Angehörigen zählen zum Repertoire der Motivatoren. Letztendlich ähnlich den Verhaltensweisen in einem Mafia-Film. Mit dieser Methodik hat sich diese mächtige Gruppe im Laufe von Jahrhunderten! eine Organisation erschaffen, welche aus Kirchen, Parteien, Firmen, NGO, Vereinen, Verbänden und weiteren Organisationsformen besteht. Bestimmte Ämter und Positionen in Organisationen können nur von Personen eingenommen und gehalten werden, die „auf Linie sind“. Die Mitglieder der Gruppe tauchen in keiner Rubrik wie „Die reichsten Menschen der Welt“ auf, sondern bleiben fern der Öffentlichkeit. Wer jemanden aus ihren Reihen erkennt und beschuldigt, ist ein „Antisemit“ oder sonstiger Übeltäter und wird verfolgt und bekämpft. Über mächtige Vermögensverwaltungskonzerne beteiligen sich die Mitglieder dieser Gruppe anonym an Unternehmen in Schlüsselpositionen in einer Dimension, die ihnen wesentlichen Einfluss auf die Auswahl der Topmanager einräumt, sodass die jeweilige Unternehmenspolitik nach Vorgaben der Gruppe gestaltet wird. Die Gruppe steuert das Geldsystem, von dem sich der Planet abhängig zu sein wähnt. Hierzu eine Erläuterung: Ein Staat wie Deutschland ist bekanntlich maximal verschuldet. Man stelle sich vor, ein unliebsamer Politiker würde entgegen sämtlicher „Brandmauern“ und sonstiger Propaganda und Wahlmanipulationen gewählt, das Land zu führen, dann könnte dieser keine Kredit über 500 Mrd. Euro bei der nächsten Sparkasse beantragen, sondern wäre auf die Mächtigen dieser Welt angewiesen. Jeder weiß, dass Deutschland als Staat kein funktionierendes Geschäftsmodell hat und somit nicht in der Lage ist, solch ein Darlehen zurückzuzahlen. Welche Motivation sollte also jemand haben, einem Land wie Deutschland so viel Geld ohne Aussicht auf Rückführung zu geben? Es leuchtet ein, dass dieser Politiker andere Gefälligkeiten anbieten müsste, um das Darlehen zu bekommen. Im Falle einer Weigerung zur Kooperation könnte der Staatsapparat mit seinen Staatsdienern, Bürgergeld- und Rentenempfänger etc. nicht mehr bezahlt werden und dieser Politiker wäre schnell wieder weg. Er würde medial hingerichtet. Es ist somit davon auszugehen, dass ein Spitzenpolitiker dieser Tage nicht über viele Optionen verfügt, denn er übernimmt eine Situation, die von seinen Vorgängern erschaffen wurde. Trotz alledem darauf zu hoffen, dass es einen anderen Politiker geben könnte, mit dem dann alles wieder gut wird, mutet ziemlich infantil an. Dass ein Großteil der Medien von Zuwendungen abhängig ist, dürfte ebenfalls leicht nachzuvollziehen sein, denn der gewöhnliche Bürger zahlt nichts für den Content der MSM. Abhängig davon, von wem (Regierung, Philanthrop, Konzern etc.) ein Medium am Leben gehalten wird, gestalten sich auch dessen Inhalte. Und wenn angewiesen wird, dass ein Politiker medial hingerichtet werden soll, dann bedient die Maschinerie das Thema. Man beobachte einfach einmal, dass Politiker der Kartell-Parteien völlig anders behandelt werden als solche jenseits der „Brandmauer“. Und der Leser, der solche Auftragsarbeiten kostenlos liest, ist der Konsument, für dessen Indoktrination die Finanziers der Verlage gerne zahlen. Mittlerweile kann durch die Herrschaft über die Medien und die systematische Vergiftung der Körper und Geister der Population die öffentliche Meinung gesteuert werden. Die überwiegende Zahl der Deutschen scheint nicht mehr klar denken zu können. Wer sich das aktuelle Geschehen in der deutschen Politik mit klarem Verstand ansieht, kommt nicht umhin, eine Fernsteuerung der handelnden Politiker in Betracht zu ziehen. Aber was soll daran verwundern? Sind es deshalb „böse Menschen“? Sind die in „Forschungslaboren“ arbeitenden Quäler von „Versuchstieren“ böse Menschen? Sind der Schlächter, der Folterer und der Henker böse Menschen? Oder der knüppelnde Polizist? Es handelt sich zunächst einmal um Personen, die einen Vorteil dadurch haben, Ihrer Tätigkeit nachzugehen. Sie sind integrale Bestandteile eines Belohnungssystems, welches von oben nach unten Anweisungen gibt. Und wenn diese Anweisungen nicht befolgt werden, führt dies für den Befehlsverweigerer zu Konsequenzen. **Der klare Verstand** Es ist nun eine spannende Frage, warum so viele Menschen sich solch eine Behandlung gefallen lassen? Nun, das ist relativ einfach, denn das angepasste Verhalten der Vielen ist nichts anderes als ein Züchtungserfolg der Wenigen. Die Psyche der Menschen ist ebenso akribisch erforscht worden wie deren Körperfunktionen. Würden die Menschen von den wirklich Mächtigen geliebt, dann würde genau gewusst, wie sie zu behandeln und mit ihren jeweiligen Bedürfnissen zu versorgen sind. Stattdessen werden die Menschen aber als eine Einnahmequelle betrachtet. Dies manifestiert sich exemplarisch in folgenden Bereichen: 1. Das Gesundheitssystem verdient nichts am gesunden Menschen, sondern nur am (dauerhaft) kranken, der um Schmerzlinderung bettelt. Bereits als Baby werden Menschen geimpft, was die jeweilige Gesundheit (mit Verweis auf die Werke von Anita Petek-Dimmer u. a.) nachhaltig negativ beeinflusst. Wer hat denn heute keine Krankheiten? Die „Experten“ des Gesundheitssystems verteufeln Vitamin D, Vitamin C, Lithium, die Sonne, Natur etc. und empfehlen stattdessen Präparate, die man patentieren konnte und mit denen die Hersteller viel Geld verdienen. Die Präparate heilen selten, sondern lindern bestenfalls zuvor künstlich erzeugte Leiden, und müssen oftmals dauerhaft eingenommen werden. Was ist aus den nicht Geimpften geworden, die alle sterben sollten? Sind diese nicht die einzigen Gesunden dieser Tage? Ist nicht jeder Geimpfte entweder permanent krank oder bereits tot? Abgesehen von denen, welche das Glück hatten, „Sonderchargen“ mit Kochsalz zu erhalten. \ \ Wem gehören die wesentlichen Player im Gesundheitswesen zu einem erheblichen Teil? Die Vermögensverwalter der wirklich Mächtigen. 2. Ähnlich gestaltet es sich bei der Ernährungsindustrie. Die von dort aus verabreichten Produkte sind die Ursachen für den Gesundheitszustand der deutschen Population. Das ist aber auch irgendwie logisch, denn wer sich nicht falsch ernährt und gesund bleibt, wird kein Kunde des Gesundheitswesens. \ \ Die Besitzverhältnisse in der Ernährungsindustrie ähneln denen im Gesundheitswesen, sodass am gleichen Kunden gearbeitet und verdient wird. 3. Die Aufzählung konnte nun über die meisten Branchen, in denen mit dem Elend der Menschen viel verdient werden kann, fortgesetzt werden. Waffen (BlackRock erhöhte beispielsweise seine Anteile an der Rheinmetall AG im Juni 2024 auf 5,25 Prozent. Der US-Vermögensverwalter ist damit der zweitgrößte Anteilseigner nach der französischen Großbank Société Générale.), Energie, Umwelt, Technologie, IT, Software, KI, Handel etc. Wie genau Chemtrails und Technologien wie 5G auf den Menschen und die Tiere wirken, ist ebenfalls umstritten. Aber ist es nicht seltsam, wie krank, empathielos, antriebslos und aggressiv viele Menschen heute sind? Was genau verabreicht man der Berliner Polizei, damit diese ihre Prügelorgien auf den Rücken und in den Gesichtern der Menschen wahrnehmen, die friedlich ihre Demonstrationsrechte wahrnehmen? Und was erhalten die ganzen zugereisten „Fachkräfte“, die mit Ihren Autos in Menschenmengen rasen oder auch Kinder und Erwachsene niedermessern? Das Titelbild dieses Beitrags zeigt einige Gebilde, welche regelmäßig bei Obduktionen von Geimpften in deren Blutgefäßen gefunden werden. Wie genau wirken diese kleinen Monster? Können wir Menschen ihr Unverständnis und ihr Nicht-Aufwachen vorwerfen, wenn wir erkennen, dass diese Menschen maximal vergiftet wurden? Oder sollten einfach Lösungen für die Probleme dieser Zeit auch ohne den Einbezug derer gefunden werden, die offenbar nicht mehr Herr ihrer Sinne sind? **Die Ziele der wirklich Mächtigen** Wer sich entsprechende Videosequenzen der Bilderberger, des WEF und anderen „Überorganisationen“ ansieht, der erkennt schnell das Muster: * Reduzierung der Weltpopulation um ca. 80 Prozent * Zusammenbruch der Wirtschaft, damit diese von den Konzernen übernommen werden kann. * Zusammenbruch der öffentlichen Ordnung, um eine totale Entwaffnung und eine totale Überwachung durchsetzen zu können. * Zusammenbruch der Regierungen, damit die Weltregierung übernehmen kann. Es ist zu überdenken, ob die Weltregierung tatsächlich das für die Vielen beste Organisationssystem ist, oder ob die dezentrale Eigenorganisation der jeweils lokalen Bevölkerung nicht doch die bessere Option darstellt. Baustellen würden nicht nur begonnen, sondern auch schnell abgearbeitet. Jede Region könnte bestimmen, ob sie sich mit Chemtrails und anderen Substanzen besprühen lassen möchte. Und die Probleme in Barcelona könnte die Menschen dort viel besser lösen als irgendwelche wirklich Mächtigen in ihren Elfenbeintürmen. Die lokale Wirtschaft könnte wieder zurückkommen und mit dieser die Eigenständigkeit. Denn die den wirklich Mächtigen über ihre Vermögensverwalter gehörenden Großkonzerne haben offensichtlich nicht das Wohl der Bevölkerung im Fokus, sondern eher deren Ausbeutung. Das Aussteigen aus dem System ist die wahre Herkulesaufgabe und es bedarf sicher Mut und Klugheit, sich dieser zu stellen. Die Politiker, die unverändert die Narrative der wirklich Mächtigen bedienen, sind hierfür denkbar ungeeignet, denn sie verfolgen kein Lebensmodell, welches sich von Liebe und Mitgefühl geleitet in den Dienst der Gesamtheit von Menschen, Tieren und Natur stellt. Schauen Sie einmal genau hin, denken Sie nach und fühlen Sie mit. **Was tun?** Jedes System funktioniert nur so lange, wie es unterstützt wird. Somit stellt sich die Frage, wie viele Menschen das System ignorieren müssen, damit es kollabiert, und auf welche Weise dieses Ignorieren durchzuführen ist? Merkbar ist, dass die große Masse der Verwaltungsangestellten krank und oder unmotiviert und somit nicht wirksam ist. Würden die entsprechenden Stellen massiv belastet und parallel hierzu keine Einnahmen mehr realisieren, wäre ein Kollaps nah. Die Prügelpolizisten aus Berlin können nicht überall sein und normale Polizisten arbeiten nicht gegen unbescholtene Bürger, sondern sorgen sich selbst um ihre Zukunft. Gewalt ist sicher keine Lösung, und sicher auch nicht erforderlich. Wie eine gerechte Verwaltungsform aufgebaut werden muss? Einfach so, wie sie in den hiesigen Gesetzen beschrieben steht. Aber eine solche Organisationsform muss frei sein von Blockparteien und korrupten Politikern und weisungsgebundenen Richtern etc. Stattdessen werden Menschen benötigt, welche die Menschen lieben und ihnen nicht schaden wollen. Außerdem sollten diese Führungspersonen auch wirklich etwas können, und nicht nur „Politiker“ ohne weitere Berufserfahrungen sein. *** Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt). *Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.* *** **Not yet on** **[Nostr](https://nostr.com/)** **and want the full experience?** Easy onboarding via **[Start.](https://start.njump.me/)** @ 57d1a264:69f1fee1
2025-03-23 12:24:46https://www.youtube.com/watch?v=obXEnyQ_Veg    source: https://media.jaguar.com/news/2024/11/fearless-exuberant-compelling-jaguar-reimagined-0 originally posted at https://stacker.news/items/922356
@ 57d1a264:69f1fee1
2025-03-23 12:24:46https://www.youtube.com/watch?v=obXEnyQ_Veg    source: https://media.jaguar.com/news/2024/11/fearless-exuberant-compelling-jaguar-reimagined-0 originally posted at https://stacker.news/items/922356 @ c631e267:c2b78d3e
2025-03-21 19:41:50*Wir werden nicht zulassen, dass technisch manches möglich ist,* *\ aber der Staat es nicht nutzt.* *\ Angela Merkel*   **Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach.** Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides. **Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar,** dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.  **Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen,** die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch. **Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen** und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war [vielleicht früher](https://transition-news.org/der-sumpf-aus-ngos-parteien-und-steuergeld) einmal so, heute ist eher das Gegenteil gemeint. **In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung** praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien [beleuchtet](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass). Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als [«Technofeudalismus»](https://transition-news.org/yanis-varoufakis-der-europaische-traum-ist-tot-es-lebe-der-neue-traum) angeprangert. **Nationale** **[Zugangspunkte](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en)** **für Mobilitätsdaten im Sinne der EU** gibt es nicht nur in allen Mitgliedsländern, sondern auch in der [Schweiz](https://opentransportdata.swiss/de/) und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen [Identifizierungssystem](https://transition-news.org/biometrische-gesichtserkennung-in-britischen-hafen) für «nachhaltigen Verkehr und Tourismus». **Natürlich marschiert auch Deutschland stracks und euphorisch** in Richtung digitaler Zukunft. Ohne [vernetzte Mobilität](https://mobilithek.info/about) und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität [voll auf Digitalisierung](https://www.smartcountry.berlin/de/newsblog/smart-city-index-grossstaedte-setzen-bei-mobilitaet-voll-auf-digitalisierung.html)». **Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten,** das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten. *\[Titelbild:* *[Pixabay](https://pareto.space/readhttps://pixabay.com/de/illustrations/schaufensterpuppe-platine-gesicht-5254046/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben. Er ist zuerst auf ***[Transition News](https://transition-news.org/das-gegenteil-von-mussen-ist-nicht-durfen)*** erschienen.
@ c631e267:c2b78d3e
2025-03-21 19:41:50*Wir werden nicht zulassen, dass technisch manches möglich ist,* *\ aber der Staat es nicht nutzt.* *\ Angela Merkel*   **Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach.** Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides. **Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar,** dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.  **Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen,** die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch. **Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen** und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war [vielleicht früher](https://transition-news.org/der-sumpf-aus-ngos-parteien-und-steuergeld) einmal so, heute ist eher das Gegenteil gemeint. **In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung** praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien [beleuchtet](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass). Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als [«Technofeudalismus»](https://transition-news.org/yanis-varoufakis-der-europaische-traum-ist-tot-es-lebe-der-neue-traum) angeprangert. **Nationale** **[Zugangspunkte](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en)** **für Mobilitätsdaten im Sinne der EU** gibt es nicht nur in allen Mitgliedsländern, sondern auch in der [Schweiz](https://opentransportdata.swiss/de/) und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen [Identifizierungssystem](https://transition-news.org/biometrische-gesichtserkennung-in-britischen-hafen) für «nachhaltigen Verkehr und Tourismus». **Natürlich marschiert auch Deutschland stracks und euphorisch** in Richtung digitaler Zukunft. Ohne [vernetzte Mobilität](https://mobilithek.info/about) und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität [voll auf Digitalisierung](https://www.smartcountry.berlin/de/newsblog/smart-city-index-grossstaedte-setzen-bei-mobilitaet-voll-auf-digitalisierung.html)». **Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten,** das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten. *\[Titelbild:* *[Pixabay](https://pareto.space/readhttps://pixabay.com/de/illustrations/schaufensterpuppe-platine-gesicht-5254046/)]* *** Dieser Beitrag wurde mit dem [Pareto-Client](https://pareto.space/read) geschrieben. Er ist zuerst auf ***[Transition News](https://transition-news.org/das-gegenteil-von-mussen-ist-nicht-durfen)*** erschienen. @ 75869cfa:76819987
2025-04-01 05:55:38**GM, Nostriches!** The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem! **Quick review:** In the past two weeks, Nostr statistics indicate over 221,000 daily trusted pubkey events. The number of new users has seen a notable decrease, with profiles containing a contact list dropping by 79%. More than 10 million events have been published, reflecting a 12% decrease. Total Zap activity stands at approximately 21 million, marking a 15% increase. Additionally, 15 pull requests were submitted to the Nostr protocol, with 2 merged. A total of 45 Nostr projects were tracked, with 8 releasing product updates, and over 569 long-form articles were published, 24% focusing on Bitcoin and Nostr. During this period, 7 notable events took place, and 2 significant events are upcoming. ## Nostr Statistics Based on user activity, the total daily trusted pubkeys writing events is about 221,000, representing a slight 8 % decrease compared to the previous period. Daily activity peaked at 17662 events, with a low of approximately 15781. The number of new users has decreased significantly. Profiles with bio are now around 25951, reflecting a 79% drop. Pubkeys writing events have decreased by 50% compared to the previous period. Regarding event publishing, all metrics have shown a decline. The total number of note events published is around 10 million, reflecting a 12% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.7 million, which is a 4.4 % decrease. Both reposts and reactions have decreased by about 5%. For zap activity, the total zap amount is about 21 million, showing an increase of over 15% compared to the previous period. Data source: https://stats.nostr.band/ ## NIPs [**Added optional signString() method**](https://github.com/nostr-protocol/nips/pull/1842) nostr:npub1emq0gngdvntdn4apepxrxr65vln49nytqe0hyr58fg9768z5zmfqcwa3jz is proposing a signString() method that allow Nostr users to sign/authenticate messages for external apps without compromising their private key (nsec).It opens up a more generic and flexible challenge-response style external authentication method, using the same Schnorr signature mechanism that Nostr uses to sign events natively.External apps need only understand Schnorr signatures - they do not need to understand Nostr's event structure. This widens interoperability.A concrete example of where this would be useful is P2PK locking of Cashu ecash tokens to a Nostr pubkey (npub). Decoding the token requires a Scnorr signature on a structured message string. This method would allow a signer to handle It cleanly. **[add nipB0, social bookmarking](https://github.com/nostr-protocol/nips/pull/1847)** nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 defines kind:39701 as website bookmarks.Bookmarks can be queried by the d tag, which is just their URL without the scheme, which is always and everywhere assumed to be https://. The querystring and the hash must be removed entirely, unless their requirement is explicitly stated either by the user or by some hardcoded list of URLs that rely on query strings for basic routing provided by the client (I've searched the internet extensively and could only find 3 websites that do this: YouTube, Hacker News and a random guy's sad old blog). Bookmarks can be commented on with NIP-22. **[NIP-XX: Progress Event](https://github.com/nostr-protocol/nips/pull/1853)** nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that covers the inclusion of Progress Events as implemented in Open Librarian. While the specific implementation is focused on tracking reading progress, the NIP is generic enough to be used in a whole range of other progress tracking scenarios (e.g. Fitness challenges, course progression for learning, personal goals etc..) **[Extension of NIP-51](https://github.com/nostr-protocol/nips/pull/1854)** nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that includes a minor update to extend kind 30003 in NIP-51 to include the i tag for external identities, as implemented for book reading lists in Open Librarian. **[NIP-73: add git permalinks](https://github.com/nostr-protocol/nips/pull/1859)** nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr is proposing a NIP that Enable references to commits, files and lines for both nip34 repositories and other git repositories. Useful for code reviews of nip34 patches, the forthcoming nip95 code snippets and referencing specific code more generally. ## Notable Projects **[Yakihonne](https://yakihonne.com/notes/note1y3upur6ah22axx6dc7na63sszeuv6tx4al5jvuu3udnz2g8gawhqw50aqk)** nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q 🌐web v4.5.0: * Custom reactions are here! Choose your preferred emoji to react to notes and other content. * Improved profile organization with notes and replies now displayed separately. * Adding the ability to zap notes directly from the notifications center. * Enhanced DM filtering by time, allowing you to view only recent messages or browse further back. * Manual cache clearing from settings to optimize web app performance. * Resolved issue preventing users from removing custom media uploader servers. * Expanded export data, including more relevant details in credential and wallet files. * General bug fixes and performance improvements. 📱mobile v1.6.8: * One tap zap: Send a Lightning Network payment with one tap. * Dms extensive filtering: Use advanced filters to sort or prioritise direct messages efficiently. * Separating replies from notes: Split replies and notes in profiles, adding a tab for easier browsing. * Adding slide to display options: Swipe in notifications to access zap, reply, or DM options quickly. * Custom reactions: Choose from a set of emojis for personalised reactions, beyond standard likes. * App cache manager: Manage and clear app cache to boost performance and save space. * Variety of bugs fixed: Fixed multiple bugs for a more stable and seamless app experience. * General app improvements: Enhanced overall performance, usability, and design across the app. **[0xchat ](https://yakihonne.com/notes/nevent1qqszhlqqesc0sx5ej27h72v08ush4thm6k5xh55rze3nv32zvl4d45qzyp0v559qftawle2kt8ahfqgtgfj5ugngcxkv5mjnsqdesckmwj5r5qcyqqqqqqg26f5gv)** nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72 0xChat v1.0.2-Desktop Beta is now live! * Supports NIP-104 MLS secret chat. * Copy images directly from the clipboard. * The app stays running after closing the window. * Fixed Enter key sending messages immediately on desktop. **[Nostur v1.18.2](https://yakihonne.com/notes/note1lgx6zrjvhennwnfkh8fnnvxa6nq4c24hdpfnsq3zqqvu3ww9n2ssxlm4tp)** nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0 Nostur v1.18.2 bugfix update: * Fixed Follow button sometimes disabled * Fixed account switching reload issue * Fixed custom feeds missing * Fixed live stream banner scroll/swipe issue * Fixed screen turns off while playing video **[voca v0.0.6](https://yakihonne.com/notes/note1ughn4alp0cyc3t6p5mwjct47cycutnuw8lvtv4gc5wyt9vw4939s6s3ymr)** nostr:npub17h9fn2ny0lycg7kmvxmw6gqdnv2epya9h9excnjw9wvml87nyw8sqy3hpu This release fine tunes the release process and makes publishing to @Zapstore a lot easier. There are also continuous improvements to initializing the text to speech engine for a faster startup. **[WasabiWallet 2.5.0](https://yakihonne.com/notes/nevent1qqsqhzwuajl8ccnltsvuygu3yt5hw8cvmkz7l5t6lpaa3tynmu9c4fczyzfm6rr08n96u3ec3vq6cm8qktqpxy2defxq34hzwyk5lac5qk3uxqcyqqqqqqg4fe35t)** nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg * 3rd Party Providers for Fee & Exchange Rate * Quality of Life Features * Backend and Coordinator packaged for Linux **[GitPlaza](https://yakihonne.com/notes/nevent1qqspadwmftmpl4xyzgz59yy48j0hpsj8q57xhr0tumdaatpsdkrea9gzyrjrxmx4yh0hn7jd8tekflvkqr2tzrwwgg265npna4m75zzzx393qqcyqqqqqqgkws0q2)** nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks * Login via nsec * Activity feed for the people you follow (only issue creation) * Create issues * Comment on issues **[ZEUS v0.10.1](https://yakihonne.com/notes/nevent1qqs84nch638my3kzvm5yqp5ejcvj2e7h332sep8qmyelrpdyu5jpcyczyq6d9af8fuv43lxjevjx8k474h0c5g0cft8yysw63zqz80c9ejqf2qcyqqqqqqg3jcw0l)** nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 ZEUS v0.10.1-beta1 is now available for testing. * NameDesc / bLIP-11 support: add receiver name to invoices * Bug fix: import of QR image from camera roll * Bug fix: Embedded LND: Open Channel: fund max * UI: Add dynamic background/text colors to Android NFC modal **[KYCNOT.ME](https://yakihonne.com/article/naddr1qvzqqqr4gupzqwwv20y78a75nq9jr049a0y2twwd7lax2w2rpddgym5265n3dpjkqqsxxd3nx9jnscm9x5cnjvtrvvcngcecxpjrxvf3vvmkydn9xsurscgpu4ayq)** nostr:npub188x98j0r7l2fszeph6j7hj99h8xl07n989pskk5zd69d2fcksetq5mgcqf * UI/UX - designe a new logo and color palette for kycnot.me. * Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. * ToS Scrapper: implement a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. * Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. * Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. * Additionally, there's a real-time audits page that displays database changes. * Listing Requests - upgrade the request system. The new form allows you to directly request services or points without any extra steps. * Lightweight and fast - The new site is lighter and faster than its predecessor! * Tor and I2P - At last! kycnot.me is now officially on Tor and I2P! ## Long-Form Content Eco In the past two weeks, more than 569 long-form articles have been published, including over 94 articles on Bitcoin and more than 43 related to Nostr, accounting for 24% of the total content. These articles about Nostr mainly explore the growing importance of decentralization in communication, identity management, and digital infrastructure. From beginner-friendly guides like Nostr 101 and Getting Started with Primal, to more technical deep dives such as NIP-101e, NIP-95, and tutorials on running Nostr relays as TOR hidden services. Some articles focus on security and privacy—like protecting your Nsec with Amber or using tools such as ProtonMail—while others tackle complex challenges including Sybil attack mitigation and child protection in decentralized environments. There are also cultural and political reflections, such as letters from political prisoners and thoughts on the future of free speech in a post-Twitter world. In addition, the Nostr community shows a strong spirit of experimentation—ranging from agent-to-agent communication through dad jokes, to desktop-like clients, fitness tracking protocols, and Lightning integrations like Work Zaps and Wallet Connect. Together, these pieces showcase a dynamic, resilient, and freedom-driven movement shaping the future of the web. The Bitcoin articles discuss a wide range of themes—from foundational ideas like "What is Money?" and Bitcoin’s first principles, to practical guides on mining, self-custody, Lightning payments, and privacy tools. Many explore Bitcoin’s role as a hedge against inflation, a form of sovereignty, and a response to fiat fragility. Cultural and economic reflections appear throughout—ranging from using Bitcoin to buy homes in Italy, to hip-hop collaborations, and even personal stories of financial awakening. There's critical analysis of Bitcoin UX, memetics, policy-making, and even war-time monetary history. From node sovereignty to P2P lending, from grassroots adoption to global macro shifts, these articles together portray Bitcoin not just as a currency, but as a cultural movement, a technological evolution, and a lens to reimagine freedom, value, and the future of money. Thank you, nostr:npub1akzvuyyd79us07m8mtp2ruuha3ylp9757qg46d50rcrkhnx0fs4q2xzr37 nostr:npub1q67f4d7qdja237us384ryeekxsz88lz5kaawrcynwe4hqsnufr6s27up0e nostr:npub1xr8tvnnnr9aqt9vv30vj4vreeq2mk38mlwe7khvhvmzjqlcghh6sr85uum nostr:npub1zmc6qyqdfnllhnzzxr5wpepfpnzcf8q6m3jdveflmgruqvd3qa9sjv7f60 nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0 nostr:npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx nostr:npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm nostr:npub186k25a5rymtae6q0dmsh4ksen04706eurfst8xc5uzjchwkxdljqe59hv0 and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial. ## Nostriches Global Meet Ups Recently, several Nostr events have been hosted in different countries. * YakiHonne teamed up with Bitcoin Safari, nostr:npub1w7z986fez3gmjvxy6dd3sku4ndazhxzafjv2lf6aaa26mtl70q6scz4erj nostr:npub1t4ljwhhg7zlxeahxwgmkwqmn4jjxxq8lzhyuzy0zvy23hq0sacxsdl9fvv nostr:npub1pw778uxwkky3xgq7w3anykdwdw9g46xy8de9mnau0kgwzz375zkq3udv57 and FULAFIA University to successfully host a series of **[Nostr Workshops](https://yakihonne.com/notes/note1n2fadzx4njd8ruv5s26jkxyygp0re3t3ffzdcyumgahpzn2t73mqhwclgq)**, attracting over 200 participants in total. These events introduced the Nostr ecosystem and Bitcoin payments, allowing attendees to explore decentralized technologies through YakiHonne while earning rewards. Participants were encouraged to register and verify their accounts to claim exclusive bonuses—and invite friends to unlock even more benefits. * **[The 2025 Bitcoin, Crypto Economy, and Law FAQ Webinar](https://x.com/BitcoinAR/status/1900643828874572166)** was held online on March 20, 2025 (Thursday) from 12:00 to 13:00 Argentina time. The webinar was hosted by Martin Paolantonio (Academic Director of the course) and Daniel Rybnik (a lawyer specializing in Banking, Corporate, and Financial Law). The session aimed to introduce the academic program and explored Bitcoin, the crypto economy, and related legal issues. * [**The monthly Bitcoin Meetup** ](https://x.com/MyfirstBitcoin_/status/1905333348677095610)organized by Mi Primer Bitcoin took place on Thursday, March 27 at 7:00 PM at CRAFT Basilea in San Salvador. The event featured Bitcoin education, networking opportunities, live music, and fun extras like merchandise, raffles, and more. It was a vibrant evening dedicated to building community and spreading knowledge around Bitcoin. nostr:npub10zuxk4yhygswdmt5n9mfyeq6lh7gcu5g042tlggrgp8yunl32clqsu5t9r Here is the upcoming Nostr event that you might want to check out. * **[Bitcoin Educators Unconference 2025](https://x.com/MyfirstBitcoin_/status/1900513529125380140)** will take place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This event is non-sponsored and follows an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. the event has open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events. * **[Panama Blockchain Week 2025](https://panamablockchainweek.com/index.php/ponentes/)** will take place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aims to position Panama as a leading blockchain financial hub in Latin America. The event features a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration. Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem. Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
@ 75869cfa:76819987
2025-04-01 05:55:38**GM, Nostriches!** The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem! **Quick review:** In the past two weeks, Nostr statistics indicate over 221,000 daily trusted pubkey events. The number of new users has seen a notable decrease, with profiles containing a contact list dropping by 79%. More than 10 million events have been published, reflecting a 12% decrease. Total Zap activity stands at approximately 21 million, marking a 15% increase. Additionally, 15 pull requests were submitted to the Nostr protocol, with 2 merged. A total of 45 Nostr projects were tracked, with 8 releasing product updates, and over 569 long-form articles were published, 24% focusing on Bitcoin and Nostr. During this period, 7 notable events took place, and 2 significant events are upcoming. ## Nostr Statistics Based on user activity, the total daily trusted pubkeys writing events is about 221,000, representing a slight 8 % decrease compared to the previous period. Daily activity peaked at 17662 events, with a low of approximately 15781. The number of new users has decreased significantly. Profiles with bio are now around 25951, reflecting a 79% drop. Pubkeys writing events have decreased by 50% compared to the previous period. Regarding event publishing, all metrics have shown a decline. The total number of note events published is around 10 million, reflecting a 12% decrease. Posts remain the most dominant in terms of volume, totaling approximately 1.7 million, which is a 4.4 % decrease. Both reposts and reactions have decreased by about 5%. For zap activity, the total zap amount is about 21 million, showing an increase of over 15% compared to the previous period. Data source: https://stats.nostr.band/ ## NIPs [**Added optional signString() method**](https://github.com/nostr-protocol/nips/pull/1842) nostr:npub1emq0gngdvntdn4apepxrxr65vln49nytqe0hyr58fg9768z5zmfqcwa3jz is proposing a signString() method that allow Nostr users to sign/authenticate messages for external apps without compromising their private key (nsec).It opens up a more generic and flexible challenge-response style external authentication method, using the same Schnorr signature mechanism that Nostr uses to sign events natively.External apps need only understand Schnorr signatures - they do not need to understand Nostr's event structure. This widens interoperability.A concrete example of where this would be useful is P2PK locking of Cashu ecash tokens to a Nostr pubkey (npub). Decoding the token requires a Scnorr signature on a structured message string. This method would allow a signer to handle It cleanly. **[add nipB0, social bookmarking](https://github.com/nostr-protocol/nips/pull/1847)** nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 defines kind:39701 as website bookmarks.Bookmarks can be queried by the d tag, which is just their URL without the scheme, which is always and everywhere assumed to be https://. The querystring and the hash must be removed entirely, unless their requirement is explicitly stated either by the user or by some hardcoded list of URLs that rely on query strings for basic routing provided by the client (I've searched the internet extensively and could only find 3 websites that do this: YouTube, Hacker News and a random guy's sad old blog). Bookmarks can be commented on with NIP-22. **[NIP-XX: Progress Event](https://github.com/nostr-protocol/nips/pull/1853)** nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that covers the inclusion of Progress Events as implemented in Open Librarian. While the specific implementation is focused on tracking reading progress, the NIP is generic enough to be used in a whole range of other progress tracking scenarios (e.g. Fitness challenges, course progression for learning, personal goals etc..) **[Extension of NIP-51](https://github.com/nostr-protocol/nips/pull/1854)** nostr:npub1zwnx29tj2lnem8wvjcx7avm8l4unswlz6zatk0vxzeu62uqagcash7fhrf is proposing a NIP that includes a minor update to extend kind 30003 in NIP-51 to include the i tag for external identities, as implemented for book reading lists in Open Librarian. **[NIP-73: add git permalinks](https://github.com/nostr-protocol/nips/pull/1859)** nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr is proposing a NIP that Enable references to commits, files and lines for both nip34 repositories and other git repositories. Useful for code reviews of nip34 patches, the forthcoming nip95 code snippets and referencing specific code more generally. ## Notable Projects **[Yakihonne](https://yakihonne.com/notes/note1y3upur6ah22axx6dc7na63sszeuv6tx4al5jvuu3udnz2g8gawhqw50aqk)** nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q 🌐web v4.5.0: * Custom reactions are here! Choose your preferred emoji to react to notes and other content. * Improved profile organization with notes and replies now displayed separately. * Adding the ability to zap notes directly from the notifications center. * Enhanced DM filtering by time, allowing you to view only recent messages or browse further back. * Manual cache clearing from settings to optimize web app performance. * Resolved issue preventing users from removing custom media uploader servers. * Expanded export data, including more relevant details in credential and wallet files. * General bug fixes and performance improvements. 📱mobile v1.6.8: * One tap zap: Send a Lightning Network payment with one tap. * Dms extensive filtering: Use advanced filters to sort or prioritise direct messages efficiently. * Separating replies from notes: Split replies and notes in profiles, adding a tab for easier browsing. * Adding slide to display options: Swipe in notifications to access zap, reply, or DM options quickly. * Custom reactions: Choose from a set of emojis for personalised reactions, beyond standard likes. * App cache manager: Manage and clear app cache to boost performance and save space. * Variety of bugs fixed: Fixed multiple bugs for a more stable and seamless app experience. * General app improvements: Enhanced overall performance, usability, and design across the app. **[0xchat ](https://yakihonne.com/notes/nevent1qqszhlqqesc0sx5ej27h72v08ush4thm6k5xh55rze3nv32zvl4d45qzyp0v559qftawle2kt8ahfqgtgfj5ugngcxkv5mjnsqdesckmwj5r5qcyqqqqqqg26f5gv)** nostr:npub1tm99pgz2lth724jeld6gzz6zv48zy6xp4n9xu5uqrwvx9km54qaqkkxn72 0xChat v1.0.2-Desktop Beta is now live! * Supports NIP-104 MLS secret chat. * Copy images directly from the clipboard. * The app stays running after closing the window. * Fixed Enter key sending messages immediately on desktop. **[Nostur v1.18.2](https://yakihonne.com/notes/note1lgx6zrjvhennwnfkh8fnnvxa6nq4c24hdpfnsq3zqqvu3ww9n2ssxlm4tp)** nostr:npub1n0stur7q092gyverzc2wfc00e8egkrdnnqq3alhv7p072u89m5es5mk6h0 Nostur v1.18.2 bugfix update: * Fixed Follow button sometimes disabled * Fixed account switching reload issue * Fixed custom feeds missing * Fixed live stream banner scroll/swipe issue * Fixed screen turns off while playing video **[voca v0.0.6](https://yakihonne.com/notes/note1ughn4alp0cyc3t6p5mwjct47cycutnuw8lvtv4gc5wyt9vw4939s6s3ymr)** nostr:npub17h9fn2ny0lycg7kmvxmw6gqdnv2epya9h9excnjw9wvml87nyw8sqy3hpu This release fine tunes the release process and makes publishing to @Zapstore a lot easier. There are also continuous improvements to initializing the text to speech engine for a faster startup. **[WasabiWallet 2.5.0](https://yakihonne.com/notes/nevent1qqsqhzwuajl8ccnltsvuygu3yt5hw8cvmkz7l5t6lpaa3tynmu9c4fczyzfm6rr08n96u3ec3vq6cm8qktqpxy2defxq34hzwyk5lac5qk3uxqcyqqqqqqg4fe35t)** nostr:npub1jw7scmeuewhywwytqxkxec9jcqf3znw2fsyddcn3948lw9q950ps9y35fg * 3rd Party Providers for Fee & Exchange Rate * Quality of Life Features * Backend and Coordinator packaged for Linux **[GitPlaza](https://yakihonne.com/notes/nevent1qqspadwmftmpl4xyzgz59yy48j0hpsj8q57xhr0tumdaatpsdkrea9gzyrjrxmx4yh0hn7jd8tekflvkqr2tzrwwgg265npna4m75zzzx393qqcyqqqqqqgkws0q2)** nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks * Login via nsec * Activity feed for the people you follow (only issue creation) * Create issues * Comment on issues **[ZEUS v0.10.1](https://yakihonne.com/notes/nevent1qqs84nch638my3kzvm5yqp5ejcvj2e7h332sep8qmyelrpdyu5jpcyczyq6d9af8fuv43lxjevjx8k474h0c5g0cft8yysw63zqz80c9ejqf2qcyqqqqqqg3jcw0l)** nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5 ZEUS v0.10.1-beta1 is now available for testing. * NameDesc / bLIP-11 support: add receiver name to invoices * Bug fix: import of QR image from camera roll * Bug fix: Embedded LND: Open Channel: fund max * UI: Add dynamic background/text colors to Android NFC modal **[KYCNOT.ME](https://yakihonne.com/article/naddr1qvzqqqr4gupzqwwv20y78a75nq9jr049a0y2twwd7lax2w2rpddgym5265n3dpjkqqsxxd3nx9jnscm9x5cnjvtrvvcngcecxpjrxvf3vvmkydn9xsurscgpu4ayq)** nostr:npub188x98j0r7l2fszeph6j7hj99h8xl07n989pskk5zd69d2fcksetq5mgcqf * UI/UX - designe a new logo and color palette for kycnot.me. * Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. * ToS Scrapper: implement a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. * Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. * Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. * Additionally, there's a real-time audits page that displays database changes. * Listing Requests - upgrade the request system. The new form allows you to directly request services or points without any extra steps. * Lightweight and fast - The new site is lighter and faster than its predecessor! * Tor and I2P - At last! kycnot.me is now officially on Tor and I2P! ## Long-Form Content Eco In the past two weeks, more than 569 long-form articles have been published, including over 94 articles on Bitcoin and more than 43 related to Nostr, accounting for 24% of the total content. These articles about Nostr mainly explore the growing importance of decentralization in communication, identity management, and digital infrastructure. From beginner-friendly guides like Nostr 101 and Getting Started with Primal, to more technical deep dives such as NIP-101e, NIP-95, and tutorials on running Nostr relays as TOR hidden services. Some articles focus on security and privacy—like protecting your Nsec with Amber or using tools such as ProtonMail—while others tackle complex challenges including Sybil attack mitigation and child protection in decentralized environments. There are also cultural and political reflections, such as letters from political prisoners and thoughts on the future of free speech in a post-Twitter world. In addition, the Nostr community shows a strong spirit of experimentation—ranging from agent-to-agent communication through dad jokes, to desktop-like clients, fitness tracking protocols, and Lightning integrations like Work Zaps and Wallet Connect. Together, these pieces showcase a dynamic, resilient, and freedom-driven movement shaping the future of the web. The Bitcoin articles discuss a wide range of themes—from foundational ideas like "What is Money?" and Bitcoin’s first principles, to practical guides on mining, self-custody, Lightning payments, and privacy tools. Many explore Bitcoin’s role as a hedge against inflation, a form of sovereignty, and a response to fiat fragility. Cultural and economic reflections appear throughout—ranging from using Bitcoin to buy homes in Italy, to hip-hop collaborations, and even personal stories of financial awakening. There's critical analysis of Bitcoin UX, memetics, policy-making, and even war-time monetary history. From node sovereignty to P2P lending, from grassroots adoption to global macro shifts, these articles together portray Bitcoin not just as a currency, but as a cultural movement, a technological evolution, and a lens to reimagine freedom, value, and the future of money. Thank you, nostr:npub1akzvuyyd79us07m8mtp2ruuha3ylp9757qg46d50rcrkhnx0fs4q2xzr37 nostr:npub1q67f4d7qdja237us384ryeekxsz88lz5kaawrcynwe4hqsnufr6s27up0e nostr:npub1xr8tvnnnr9aqt9vv30vj4vreeq2mk38mlwe7khvhvmzjqlcghh6sr85uum nostr:npub1zmc6qyqdfnllhnzzxr5wpepfpnzcf8q6m3jdveflmgruqvd3qa9sjv7f60 nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 nostr:npub1ktt8phjnkfmfrsxrgqpztdjuxk3x6psf80xyray0l3c7pyrln49qhkyhz0 nostr:npub1qny3tkh0acurzla8x3zy4nhrjz5zd8l9sy9jys09umwng00manysew95gx nostr:npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm nostr:npub186k25a5rymtae6q0dmsh4ksen04706eurfst8xc5uzjchwkxdljqe59hv0 and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial. ## Nostriches Global Meet Ups Recently, several Nostr events have been hosted in different countries. * YakiHonne teamed up with Bitcoin Safari, nostr:npub1w7z986fez3gmjvxy6dd3sku4ndazhxzafjv2lf6aaa26mtl70q6scz4erj nostr:npub1t4ljwhhg7zlxeahxwgmkwqmn4jjxxq8lzhyuzy0zvy23hq0sacxsdl9fvv nostr:npub1pw778uxwkky3xgq7w3anykdwdw9g46xy8de9mnau0kgwzz375zkq3udv57 and FULAFIA University to successfully host a series of **[Nostr Workshops](https://yakihonne.com/notes/note1n2fadzx4njd8ruv5s26jkxyygp0re3t3ffzdcyumgahpzn2t73mqhwclgq)**, attracting over 200 participants in total. These events introduced the Nostr ecosystem and Bitcoin payments, allowing attendees to explore decentralized technologies through YakiHonne while earning rewards. Participants were encouraged to register and verify their accounts to claim exclusive bonuses—and invite friends to unlock even more benefits. * **[The 2025 Bitcoin, Crypto Economy, and Law FAQ Webinar](https://x.com/BitcoinAR/status/1900643828874572166)** was held online on March 20, 2025 (Thursday) from 12:00 to 13:00 Argentina time. The webinar was hosted by Martin Paolantonio (Academic Director of the course) and Daniel Rybnik (a lawyer specializing in Banking, Corporate, and Financial Law). The session aimed to introduce the academic program and explored Bitcoin, the crypto economy, and related legal issues. * [**The monthly Bitcoin Meetup** ](https://x.com/MyfirstBitcoin_/status/1905333348677095610)organized by Mi Primer Bitcoin took place on Thursday, March 27 at 7:00 PM at CRAFT Basilea in San Salvador. The event featured Bitcoin education, networking opportunities, live music, and fun extras like merchandise, raffles, and more. It was a vibrant evening dedicated to building community and spreading knowledge around Bitcoin. nostr:npub10zuxk4yhygswdmt5n9mfyeq6lh7gcu5g042tlggrgp8yunl32clqsu5t9r Here is the upcoming Nostr event that you might want to check out. * **[Bitcoin Educators Unconference 2025](https://x.com/MyfirstBitcoin_/status/1900513529125380140)** will take place on April 10, 2025, at Bitcoin Park in Nashville, Tennessee, USA. This event is non-sponsored and follows an Unconference format, allowing all participants to apply as speakers and share their Bitcoin education experiences in a free and interactive environment. the event has open-sourced all its blueprints and Standard Operating Procedures (SOPs) to encourage global communities to organize similar Unconference events. * **[Panama Blockchain Week 2025](https://panamablockchainweek.com/index.php/ponentes/)** will take place from April 22 to 24 at the Panama Convention Center in Panama City. As the first large-scale blockchain event in Central America, it aims to position Panama as a leading blockchain financial hub in Latin America. The event features a diverse lineup, including a blockchain conference, Investor’s Night, Web3 gaming experiences, tech exhibitions, and an after-party celebration. Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem. Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage. @ d5c3d063:4d1159b3
2025-04-01 04:20:50“วิธีที่ดีที่สุดในการทำลายทุนนิยมคือทำลายค่าเงิน” Lenin Was Right ประโยคนี้ไม่ใช่แค่คำปลุกระดมของนักปฏิวัติ แต่มันเป็นเหมือนสัญญาณเตือนล่วงหน้า ที่คนส่วนใหญ่ไม่สนใจ จนวันหนึ่งมันก็เกิดขึ้นจริง แบบเงียบ ๆ โดยไม่มีใครทันตั้งตัว Henry Hazlitt เขียนบทความนี้ไว้ตั้งแต่ปี 1947 เขาไม่เพียงบอกว่าเลนินพูดถูก แต่เขาแฉว่าโลกทั้งใบ “กำลังทำตามแผนของเลนิน” แบบไม่รู้ตัว ตอนนั้นรัฐบาลหลายประเทศ โดยเฉพาะในยุโรป พิมพ์เงินออกมาใช้มหาศาล โดยอ้างว่าสงครามบีบบังคับให้ต้องทำแบบนั้น แต่ปัญหาคือ...พอสงครามจบในปี 1945 แล้ว รัฐกลับไม่หยุดพิมพ์เงิน ยังทำเหมือนอยู่ในภาวะฉุกเฉิน เหมือนที่ อ. #SaifedeanAmmous พูดไว้ในหนังสือ #TheBitcoinStandard ว่าเวลารัฐอยากพิมพ์เงินแบบไม่ต้องรับผิดชอบ ก็แค่เอาสงครามมาอ้าง พอพูดว่า “เพื่อความมั่นคง” หรือ “เพื่อชาติ” เท่านั้นแหละ ทุกอย่างก็ดูเป็นเรื่องจำเป็นขึ้นมาทันที แล้วไม่มีใครกล้าถามว่าจริง ๆ แล้วเงินมันมาจากไหน พอเงินเฟ้อมันแรง ของก็แพงขึ้น แต่รัฐไม่ยอมรับหรอกว่าที่ของแพงเพราะตัวเองพิมพ์เงินออกมาเยอะเกิน แต่กลับไปโทษพ่อค้า โทษคนทำธุรกิจ ว่าขายของแพง ค้ากำไรเกินควรซะงั้น Hazlitt เขาเตือนว่า...รัฐกำลังทำให้คนเกลียดพ่อค้า เกลียดเจ้าของธุรกิจ เพื่อให้ดูเหมือนว่าตัวเองมีเหตุผลที่จะเข้ามาคุมเศรษฐกิจ ซึ่งที่น่ากลัวคือ... มันไม่ได้เกิดจากความไม่รู้ แต่มันเกิดจาก “ระบบ” ที่เปิดช่องให้เขาทำแบบนี้ได้เลย แบบไม่ต้องรับผิดชอบอะไรทั้งนั้น ตรงนี้แหละที่ Hazlitt เอาคำพูดของ John Maynard Keynes เข้ามาเสริม เพราะแม้แต่ Keynes ก็ยังเคยเตือนไว้ในหนังสือ The Economic Consequences of the Peace ว่า “เงินเฟ้อ” มันเหมือนเครื่องมือเงียบ ๆ ที่จะค่อย ๆ ทำลายระบบเศรษฐกิจ โดยที่คนส่วนใหญ่ไม่รู้ตัว Hazlitt เขาเป็น "สายวิจารณ์" Keynes ตัวพ่อเลยนะ เขาเขียนหนังสือ The Failure of the New Economics ที่ไล่รื้อแนวคิดของ Keynes แบบ “ตา-ต่อ-ตา หน้า-ต่อ-หน้า” กับหนังสือ The General Theory ของ Keynes เลยนะ แต่พอมาในบทความนี้...Hazlitt กลับหยิบคำพูดของ Keynes มาใช้อย่างเต็มใจ เพราะมันตรงเกินไปที่จะมองข้ามได้ ว่าแม้แต่ #Keynes เองยังเคยเตือนเลยว่า “การทำลายค่าเงิน” คืออาวุธเงียบ ที่ใช้ทำลายระบบทุนนิยมได้อย่างแนบเนียนที่สุด . . พออ่านแล้วแบบ…แม้แต่คนที่เราคิดว่าเชียร์ฝั่งรัฐ ยังเตือนเรื่องนี้ไว้ แล้วเราจะยังเฉยอยู่ได้ไง คือถ้าเงินมันถูกทำให้ด้อยค่าลงเรื่อย ๆ วันนึงมันจะพังแบบเงียบ ๆ จนคนไม่รู้ตัวเลย คนทั่วไปจะรู้แค่ว่าของมันแพงขึ้น แต่ไม่มีใครเห็น ว่าจริง ๆ แล้ว เงินที่เราใช้มันเริ่มไม่มีเสถียรภาพ และไม่มั่นคงอีกต่อไปแล้ว แล้วถ้ามองตัวเลขนี่ยิ่งช็อก ระหว่างปี 1939 ถึง 1947 ในเวลาแค่ 8 ปี ปริมาณเงินในระบบของสหรัฐฯ เพิ่มจาก 33,000 ล้านดอลลารเป็น 108,500 ล้านดอลลาร์ พูดง่าย ๆ คือ คูณสาม (ช่วงสงครามโลกครั้งที่ 2) Hazlitt พูดแบบตรง ๆ เลยว่า ปัญหาที่เกิดขึ้น มันไม่ใช่เพราะเศรษฐกิจโตหรือคนรวยขึ้นนะ มันเกิดจากการที่รัฐเพิ่มปริมาณเงินในระบบเร็วเกินไป เมื่อเงินในตลาดเลยเยอะขึ้น แต่ของที่มีให้ซื้อไม่ได้เยอะขึ้นตาม เมื่อเงินไหลเวียนมากขึ้น โดยที่ของยังมีเท่าเดิม ราคาของก็เลยพุ่ง ทีนี้พอของขึ้นราคา รัฐบาลกลับไม่ยอมรับว่าเป็นเพราะเขาพิมพ์เงิน แต่ไปเลือกวิธีแก้แบบง่าย ๆ แต่สร้างปัญหาในระยะยาว เช่น สั่งห้ามขึ้นราคา กดดันคนทำธุรกิจให้แบกต้นทุนไว้ หรือไม่ก็ล็อกค่าเงิน เหมือนไม่มีอะไรเกิดขึ้น หลังจากนั้น เศรษฐกิจยุโรปก็เริ่มพัง ผู้ผลิตเจอต้นทุนบาน การค้าระหว่างประเทศก็รวน สุดท้ายก็ต้องพึ่งดอลลาร์จากอเมริกา (Marshall Aid) มาช่วยอุ้ม เหมือนพิมพ์เงินของตัวเองจนระบบรวน แล้วไปขอเงินจากฝั่งที่พิมพ์ได้มากกว่าอีกที นี่แหละจุดเริ่มของ “วิกฤตเศรษฐกิจโลกหลังสงคราม” ที่จริง ๆ แล้ว...ก็แค่เรื่องของการพิมพ์เงินล้วน ๆ . . แต่นั้นมันเป็นเรื่องเกิดขึ้นเมื่อปี 1947 นะ...แล้ววันนี้ล่ะ ล่าสุด ปี 2020 ก่อนโควิด ระดับ M2 money supply ของสหรัฐอยู่ราว ๆ 15 ล้านล้านดอลลาร์ แค่ไม่กี่ปีต่อมา มันทะลุไปถึง 21 ล้านล้าน ในเวลาไม่ถึง 3 ปีเงินเพิ่มขึ้นในระบบเศรษฐกิจกว่า 6 ล้านล้านดอลลาร์ แล้วของก็แพงขึ้น ค่าแรงวิ่งตามไม่ทัน แต่แทนที่รัฐจะบอกว่า “เราพิมพ์เงินมากไป” ก็ไปเล่นมุกเดิม โทษตลาด โทษนายทุน โทษธุรกิจ (บ้างก็โทษโลกร้อน) สุดท้ายก็จะมีคนบางกลุ่มเชียร์ให้ “ควบคุมราคา” อีก มันคือ loop เดิม ที่ #Hazlitt เคยเตือนไว้ เมื่อเกือบ 80 ปีก่อน.. . . สิ่งที่ซุปเห็นชัดเจนที่สุดจากบทความนี้คือ... เกมนี้มันไม่มีใครหยุดได้เลย ถ้าคุณยังถือเงินที่รัฐพิมพ์ได้ เพราะตราบใดที่ยังมีคนสั่งพิมพ์เงินได้ตามใจ ระบบเศรษฐกิจก็จะปั่นป่วนซ้ำไปซ้ำมา ของก็จะแพงขึ้นเรื่อย ๆ แบบไม่มีจุดจบ คุณก็จะต้องเหนื่อยทำงานมากขึ้น แต่ซื้อได้น้อยลง แล้วคุณก็จะโทษตัวเอง ว่ายังขยันไม่มากพอ ทั้ง ๆ ที่คุณทำงาน 4-5 อย่าง . เลนิน พูดถูก ถ้าจะทำลายทุนนิยม ก็แค่ทำลายค่าเงิน ฟังดูแรงเนอะ...แต่เรื่องนี้มันไม่ใช่แค่ทฤษฎีแล้ว เพราะเรากำลังเห็น ว่ามันกำลังเกิดขึ้นอยู่จริง ๆ แต่วันนี้ เราเลือกที่จะไม่อยู่ในเกมที่พังซ้ำๆ ได้แล้ว เพราะเรามี “ทางออก” อยู่ตรงหน้า บิตคอยน์ ไม่ใช่อะไรที่ทุกคนจะเข้าใจมันได้ทันที แต่มันคือ “เงิน” ที่ไม่มีใครพิมพ์เพิ่มได้ตามใจ ไม่มีใครมานั่งกดปุ่มสร้างมันขึ้นมาได้ง่าย ๆ ไม่มีใครเปลี่ยนกติกากลางเกมได้ และไม่มีใครแทรกแซงนโยบายของมันได้ สิ่งเดียวที่ #บิตคอยน์ บอกเราตรง ๆ ก็คือ “ความขาดแคลน” ไม่ใช่ปัญหา... สิ่งที่ Hazlitt เตือนเมื่ออดีต คือกับดักของเงินไม่มีขอบเขต สิ่งที่ #Bitcoin เสนอ คือขอบเขตที่ทำให้ “มูลค่า” กลับมามีความหมาย [Newsweek column from September 22, 1947, and reprinted in Business Tides: The Newsweek Era of Henry Hazlitt.] https://mises.org/mises-wire/lenin-was-right #Siamstr
@ d5c3d063:4d1159b3
2025-04-01 04:20:50“วิธีที่ดีที่สุดในการทำลายทุนนิยมคือทำลายค่าเงิน” Lenin Was Right ประโยคนี้ไม่ใช่แค่คำปลุกระดมของนักปฏิวัติ แต่มันเป็นเหมือนสัญญาณเตือนล่วงหน้า ที่คนส่วนใหญ่ไม่สนใจ จนวันหนึ่งมันก็เกิดขึ้นจริง แบบเงียบ ๆ โดยไม่มีใครทันตั้งตัว Henry Hazlitt เขียนบทความนี้ไว้ตั้งแต่ปี 1947 เขาไม่เพียงบอกว่าเลนินพูดถูก แต่เขาแฉว่าโลกทั้งใบ “กำลังทำตามแผนของเลนิน” แบบไม่รู้ตัว ตอนนั้นรัฐบาลหลายประเทศ โดยเฉพาะในยุโรป พิมพ์เงินออกมาใช้มหาศาล โดยอ้างว่าสงครามบีบบังคับให้ต้องทำแบบนั้น แต่ปัญหาคือ...พอสงครามจบในปี 1945 แล้ว รัฐกลับไม่หยุดพิมพ์เงิน ยังทำเหมือนอยู่ในภาวะฉุกเฉิน เหมือนที่ อ. #SaifedeanAmmous พูดไว้ในหนังสือ #TheBitcoinStandard ว่าเวลารัฐอยากพิมพ์เงินแบบไม่ต้องรับผิดชอบ ก็แค่เอาสงครามมาอ้าง พอพูดว่า “เพื่อความมั่นคง” หรือ “เพื่อชาติ” เท่านั้นแหละ ทุกอย่างก็ดูเป็นเรื่องจำเป็นขึ้นมาทันที แล้วไม่มีใครกล้าถามว่าจริง ๆ แล้วเงินมันมาจากไหน พอเงินเฟ้อมันแรง ของก็แพงขึ้น แต่รัฐไม่ยอมรับหรอกว่าที่ของแพงเพราะตัวเองพิมพ์เงินออกมาเยอะเกิน แต่กลับไปโทษพ่อค้า โทษคนทำธุรกิจ ว่าขายของแพง ค้ากำไรเกินควรซะงั้น Hazlitt เขาเตือนว่า...รัฐกำลังทำให้คนเกลียดพ่อค้า เกลียดเจ้าของธุรกิจ เพื่อให้ดูเหมือนว่าตัวเองมีเหตุผลที่จะเข้ามาคุมเศรษฐกิจ ซึ่งที่น่ากลัวคือ... มันไม่ได้เกิดจากความไม่รู้ แต่มันเกิดจาก “ระบบ” ที่เปิดช่องให้เขาทำแบบนี้ได้เลย แบบไม่ต้องรับผิดชอบอะไรทั้งนั้น ตรงนี้แหละที่ Hazlitt เอาคำพูดของ John Maynard Keynes เข้ามาเสริม เพราะแม้แต่ Keynes ก็ยังเคยเตือนไว้ในหนังสือ The Economic Consequences of the Peace ว่า “เงินเฟ้อ” มันเหมือนเครื่องมือเงียบ ๆ ที่จะค่อย ๆ ทำลายระบบเศรษฐกิจ โดยที่คนส่วนใหญ่ไม่รู้ตัว Hazlitt เขาเป็น "สายวิจารณ์" Keynes ตัวพ่อเลยนะ เขาเขียนหนังสือ The Failure of the New Economics ที่ไล่รื้อแนวคิดของ Keynes แบบ “ตา-ต่อ-ตา หน้า-ต่อ-หน้า” กับหนังสือ The General Theory ของ Keynes เลยนะ แต่พอมาในบทความนี้...Hazlitt กลับหยิบคำพูดของ Keynes มาใช้อย่างเต็มใจ เพราะมันตรงเกินไปที่จะมองข้ามได้ ว่าแม้แต่ #Keynes เองยังเคยเตือนเลยว่า “การทำลายค่าเงิน” คืออาวุธเงียบ ที่ใช้ทำลายระบบทุนนิยมได้อย่างแนบเนียนที่สุด . . พออ่านแล้วแบบ…แม้แต่คนที่เราคิดว่าเชียร์ฝั่งรัฐ ยังเตือนเรื่องนี้ไว้ แล้วเราจะยังเฉยอยู่ได้ไง คือถ้าเงินมันถูกทำให้ด้อยค่าลงเรื่อย ๆ วันนึงมันจะพังแบบเงียบ ๆ จนคนไม่รู้ตัวเลย คนทั่วไปจะรู้แค่ว่าของมันแพงขึ้น แต่ไม่มีใครเห็น ว่าจริง ๆ แล้ว เงินที่เราใช้มันเริ่มไม่มีเสถียรภาพ และไม่มั่นคงอีกต่อไปแล้ว แล้วถ้ามองตัวเลขนี่ยิ่งช็อก ระหว่างปี 1939 ถึง 1947 ในเวลาแค่ 8 ปี ปริมาณเงินในระบบของสหรัฐฯ เพิ่มจาก 33,000 ล้านดอลลารเป็น 108,500 ล้านดอลลาร์ พูดง่าย ๆ คือ คูณสาม (ช่วงสงครามโลกครั้งที่ 2) Hazlitt พูดแบบตรง ๆ เลยว่า ปัญหาที่เกิดขึ้น มันไม่ใช่เพราะเศรษฐกิจโตหรือคนรวยขึ้นนะ มันเกิดจากการที่รัฐเพิ่มปริมาณเงินในระบบเร็วเกินไป เมื่อเงินในตลาดเลยเยอะขึ้น แต่ของที่มีให้ซื้อไม่ได้เยอะขึ้นตาม เมื่อเงินไหลเวียนมากขึ้น โดยที่ของยังมีเท่าเดิม ราคาของก็เลยพุ่ง ทีนี้พอของขึ้นราคา รัฐบาลกลับไม่ยอมรับว่าเป็นเพราะเขาพิมพ์เงิน แต่ไปเลือกวิธีแก้แบบง่าย ๆ แต่สร้างปัญหาในระยะยาว เช่น สั่งห้ามขึ้นราคา กดดันคนทำธุรกิจให้แบกต้นทุนไว้ หรือไม่ก็ล็อกค่าเงิน เหมือนไม่มีอะไรเกิดขึ้น หลังจากนั้น เศรษฐกิจยุโรปก็เริ่มพัง ผู้ผลิตเจอต้นทุนบาน การค้าระหว่างประเทศก็รวน สุดท้ายก็ต้องพึ่งดอลลาร์จากอเมริกา (Marshall Aid) มาช่วยอุ้ม เหมือนพิมพ์เงินของตัวเองจนระบบรวน แล้วไปขอเงินจากฝั่งที่พิมพ์ได้มากกว่าอีกที นี่แหละจุดเริ่มของ “วิกฤตเศรษฐกิจโลกหลังสงคราม” ที่จริง ๆ แล้ว...ก็แค่เรื่องของการพิมพ์เงินล้วน ๆ . . แต่นั้นมันเป็นเรื่องเกิดขึ้นเมื่อปี 1947 นะ...แล้ววันนี้ล่ะ ล่าสุด ปี 2020 ก่อนโควิด ระดับ M2 money supply ของสหรัฐอยู่ราว ๆ 15 ล้านล้านดอลลาร์ แค่ไม่กี่ปีต่อมา มันทะลุไปถึง 21 ล้านล้าน ในเวลาไม่ถึง 3 ปีเงินเพิ่มขึ้นในระบบเศรษฐกิจกว่า 6 ล้านล้านดอลลาร์ แล้วของก็แพงขึ้น ค่าแรงวิ่งตามไม่ทัน แต่แทนที่รัฐจะบอกว่า “เราพิมพ์เงินมากไป” ก็ไปเล่นมุกเดิม โทษตลาด โทษนายทุน โทษธุรกิจ (บ้างก็โทษโลกร้อน) สุดท้ายก็จะมีคนบางกลุ่มเชียร์ให้ “ควบคุมราคา” อีก มันคือ loop เดิม ที่ #Hazlitt เคยเตือนไว้ เมื่อเกือบ 80 ปีก่อน.. . . สิ่งที่ซุปเห็นชัดเจนที่สุดจากบทความนี้คือ... เกมนี้มันไม่มีใครหยุดได้เลย ถ้าคุณยังถือเงินที่รัฐพิมพ์ได้ เพราะตราบใดที่ยังมีคนสั่งพิมพ์เงินได้ตามใจ ระบบเศรษฐกิจก็จะปั่นป่วนซ้ำไปซ้ำมา ของก็จะแพงขึ้นเรื่อย ๆ แบบไม่มีจุดจบ คุณก็จะต้องเหนื่อยทำงานมากขึ้น แต่ซื้อได้น้อยลง แล้วคุณก็จะโทษตัวเอง ว่ายังขยันไม่มากพอ ทั้ง ๆ ที่คุณทำงาน 4-5 อย่าง . เลนิน พูดถูก ถ้าจะทำลายทุนนิยม ก็แค่ทำลายค่าเงิน ฟังดูแรงเนอะ...แต่เรื่องนี้มันไม่ใช่แค่ทฤษฎีแล้ว เพราะเรากำลังเห็น ว่ามันกำลังเกิดขึ้นอยู่จริง ๆ แต่วันนี้ เราเลือกที่จะไม่อยู่ในเกมที่พังซ้ำๆ ได้แล้ว เพราะเรามี “ทางออก” อยู่ตรงหน้า บิตคอยน์ ไม่ใช่อะไรที่ทุกคนจะเข้าใจมันได้ทันที แต่มันคือ “เงิน” ที่ไม่มีใครพิมพ์เพิ่มได้ตามใจ ไม่มีใครมานั่งกดปุ่มสร้างมันขึ้นมาได้ง่าย ๆ ไม่มีใครเปลี่ยนกติกากลางเกมได้ และไม่มีใครแทรกแซงนโยบายของมันได้ สิ่งเดียวที่ #บิตคอยน์ บอกเราตรง ๆ ก็คือ “ความขาดแคลน” ไม่ใช่ปัญหา... สิ่งที่ Hazlitt เตือนเมื่ออดีต คือกับดักของเงินไม่มีขอบเขต สิ่งที่ #Bitcoin เสนอ คือขอบเขตที่ทำให้ “มูลค่า” กลับมามีความหมาย [Newsweek column from September 22, 1947, and reprinted in Business Tides: The Newsweek Era of Henry Hazlitt.] https://mises.org/mises-wire/lenin-was-right #Siamstr @ 2fdeba99:fd961eff
2025-03-21 17:16:33# == January 17 2025 Out From Underneath | Prism Shores crazy arms | pigeon pit Humanhood | The Weather Station # == february 07 2025 Wish Defense | FACS Sayan - Savoie | Maria Teriaeva Nowhere Near Today | Midding # == february 14 2025 Phonetics On and On | Horsegirl # == february 21 2025 Finding Our Balance | Tsoh Tso Machine Starts To Sing | Porridge Radio Armageddon In A Summer Dress | Sunny Wa # == february 28 2025 you, infinite | you, infinite On Being | Max Cooper Billboard Heart | Deep Sea Diver # == March 21 2025 Watermelon/Peacock | Exploding Flowers Warlord of the Weejuns | Goya Gumbani
@ 2fdeba99:fd961eff
2025-03-21 17:16:33# == January 17 2025 Out From Underneath | Prism Shores crazy arms | pigeon pit Humanhood | The Weather Station # == february 07 2025 Wish Defense | FACS Sayan - Savoie | Maria Teriaeva Nowhere Near Today | Midding # == february 14 2025 Phonetics On and On | Horsegirl # == february 21 2025 Finding Our Balance | Tsoh Tso Machine Starts To Sing | Porridge Radio Armageddon In A Summer Dress | Sunny Wa # == february 28 2025 you, infinite | you, infinite On Being | Max Cooper Billboard Heart | Deep Sea Diver # == March 21 2025 Watermelon/Peacock | Exploding Flowers Warlord of the Weejuns | Goya Gumbani @ aa8de34f:a6ffe696
2025-03-21 12:08:3119\. März 2025 ### 🔐 1. SHA-256 is Quantum-Resistant Bitcoin’s **proof-of-work** mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, **SHA-256 remains secure** because: - Quantum computers excel at **factoring large numbers** (Shor’s Algorithm). - However, **SHA-256 is a one-way function**, meaning there's no known quantum algorithm that can efficiently reverse it. - **Grover’s Algorithm** (which theoretically speeds up brute force attacks) would still require **2¹²⁸ operations** to break SHA-256 – far beyond practical reach. ++++++++++++++++++++++++++++++++++++++++++++++++++ ### 🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses Bitcoin uses **Elliptic Curve Digital Signature Algorithm (ECDSA)** to generate keys. - A quantum computer could use **Shor’s Algorithm** to break **SECP256K1**, the curve Bitcoin uses. - If you never reuse addresses, it is an additional security element - 🔑 1. Bitcoin Addresses Are NOT Public Keys Many people assume a **Bitcoin address** is the public key—**this is wrong**. - When you **receive Bitcoin**, it is sent to a **hashed public key** (the Bitcoin address). - The **actual public key is never exposed** because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend - Bitcoin uses **Pay-to-Public-Key-Hash (P2PKH)** or newer methods like **Pay-to-Witness-Public-Key-Hash (P2WPKH)**, which add extra layers of security. ### 🕵️♂️ 2.1 The Public Key Never Appears - When you **send Bitcoin**, your wallet creates a **digital signature**. - This signature uses the **private key** to **prove** ownership. - The **Bitcoin address is revealed and creates the Public Key** - The public key **remains hidden inside the Bitcoin script and Merkle tree**. This means: ✔ **The public key is never exposed.** ✔ **Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.** +++++++++++++++++++++++++++++++++++++++++++++++++ ### 🔄 3. Bitcoin Can Upgrade Even if quantum computers **eventually** become a real threat: - Bitcoin developers can **upgrade to quantum-safe cryptography** (e.g., lattice-based cryptography or post-quantum signatures like Dilithium). - Bitcoin’s decentralized nature ensures a network-wide **soft fork or hard fork** could transition to quantum-resistant keys. ++++++++++++++++++++++++++++++++++++++++++++++++++ ### ⏳ 4. The 10-Minute Block Rule as a Security Feature - Bitcoin’s network operates on a **10-minute block interval**, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack **every 10 minutes**.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system **resets the challenge with every new block**.This **limits the window of opportunity** for quantum attacks. --- ### 🎯 5. Quantum Attack Needs to Solve a Block in Real-Time - A quantum attacker **must solve the cryptographic puzzle (Proof of Work) in under 10 minutes**. - The problem? **Any slight error changes the hash completely**, meaning:**If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails**.**Quantum decoherence** (loss of qubit stability) makes error correction a massive challenge.The computational cost of **recovering from an incorrect hash** is still incredibly high. --- ### ⚡ 6. Network Resilience – Even if a Block Is Hacked - Even if a quantum computer **somehow** solved a block instantly:The network would **quickly recognize and reject invalid transactions**.Other miners would **continue mining** under normal cryptographic rules.**51% Attack?** The attacker would need to consistently beat the **entire Bitcoin network**, which is **not sustainable**. --- ### 🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats - Bitcoin adjusts mining difficulty every **2016 blocks (\~2 weeks)**. - If quantum miners appeared and suddenly started solving blocks too quickly, **the difficulty would adjust upward**, making attacks significantly harder. - This **self-correcting mechanism** ensures that even quantum computers wouldn't easily overpower the network. --- ### 🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin ✔ **The 10-minute rule limits attack frequency** – quantum computers can’t keep up. ✔ **Any slight miscalculation ruins the attack**, resetting all progress. ✔ **Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages**. **Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant.** 🚀
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119\. März 2025 ### 🔐 1. SHA-256 is Quantum-Resistant Bitcoin’s **proof-of-work** mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, **SHA-256 remains secure** because: - Quantum computers excel at **factoring large numbers** (Shor’s Algorithm). - However, **SHA-256 is a one-way function**, meaning there's no known quantum algorithm that can efficiently reverse it. - **Grover’s Algorithm** (which theoretically speeds up brute force attacks) would still require **2¹²⁸ operations** to break SHA-256 – far beyond practical reach. ++++++++++++++++++++++++++++++++++++++++++++++++++ ### 🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses Bitcoin uses **Elliptic Curve Digital Signature Algorithm (ECDSA)** to generate keys. - A quantum computer could use **Shor’s Algorithm** to break **SECP256K1**, the curve Bitcoin uses. - If you never reuse addresses, it is an additional security element - 🔑 1. Bitcoin Addresses Are NOT Public Keys Many people assume a **Bitcoin address** is the public key—**this is wrong**. - When you **receive Bitcoin**, it is sent to a **hashed public key** (the Bitcoin address). - The **actual public key is never exposed** because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend - Bitcoin uses **Pay-to-Public-Key-Hash (P2PKH)** or newer methods like **Pay-to-Witness-Public-Key-Hash (P2WPKH)**, which add extra layers of security. ### 🕵️♂️ 2.1 The Public Key Never Appears - When you **send Bitcoin**, your wallet creates a **digital signature**. - This signature uses the **private key** to **prove** ownership. - The **Bitcoin address is revealed and creates the Public Key** - The public key **remains hidden inside the Bitcoin script and Merkle tree**. This means: ✔ **The public key is never exposed.** ✔ **Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.** +++++++++++++++++++++++++++++++++++++++++++++++++ ### 🔄 3. Bitcoin Can Upgrade Even if quantum computers **eventually** become a real threat: - Bitcoin developers can **upgrade to quantum-safe cryptography** (e.g., lattice-based cryptography or post-quantum signatures like Dilithium). - Bitcoin’s decentralized nature ensures a network-wide **soft fork or hard fork** could transition to quantum-resistant keys. ++++++++++++++++++++++++++++++++++++++++++++++++++ ### ⏳ 4. The 10-Minute Block Rule as a Security Feature - Bitcoin’s network operates on a **10-minute block interval**, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack **every 10 minutes**.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system **resets the challenge with every new block**.This **limits the window of opportunity** for quantum attacks. --- ### 🎯 5. Quantum Attack Needs to Solve a Block in Real-Time - A quantum attacker **must solve the cryptographic puzzle (Proof of Work) in under 10 minutes**. - The problem? **Any slight error changes the hash completely**, meaning:**If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails**.**Quantum decoherence** (loss of qubit stability) makes error correction a massive challenge.The computational cost of **recovering from an incorrect hash** is still incredibly high. --- ### ⚡ 6. Network Resilience – Even if a Block Is Hacked - Even if a quantum computer **somehow** solved a block instantly:The network would **quickly recognize and reject invalid transactions**.Other miners would **continue mining** under normal cryptographic rules.**51% Attack?** The attacker would need to consistently beat the **entire Bitcoin network**, which is **not sustainable**. --- ### 🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats - Bitcoin adjusts mining difficulty every **2016 blocks (\~2 weeks)**. - If quantum miners appeared and suddenly started solving blocks too quickly, **the difficulty would adjust upward**, making attacks significantly harder. - This **self-correcting mechanism** ensures that even quantum computers wouldn't easily overpower the network. --- ### 🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin ✔ **The 10-minute rule limits attack frequency** – quantum computers can’t keep up. ✔ **Any slight miscalculation ruins the attack**, resetting all progress. ✔ **Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages**. **Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant.** 🚀 @ a95c6243:d345522c
2025-03-20 09:59:20**Bald werde es verboten, alleine im Auto zu fahren,** konnte man dieser Tage in verschiedenen spanischen Medien lesen. Die nationale Verkehrsbehörde (Dirección General de Tráfico, kurz DGT) werde Alleinfahrern das Leben schwer machen, wurde gemeldet. Konkret erörtere die Generaldirektion geeignete Sanktionen für Personen, die ohne Beifahrer im Privatauto unterwegs seien. **Das Alleinfahren sei zunehmend verpönt und ein Mentalitätswandel notwendig,** hieß es. Dieser «Luxus» stehe im Widerspruch zu den Maßnahmen gegen Umweltverschmutzung, die in allen europäischen Ländern gefördert würden. In Frankreich sei es «bereits verboten, in der Hauptstadt allein zu fahren», [behauptete](https://noticiastrabajo.huffingtonpost.es/sociedad/adios-a-conducir-solo-la-dgt-se-lo-pone-crudo-a-los-conductores-que-viajen-sin-acompanante-en-el-coche/) *Noticiastrabajo Huffpost* in einer Zwischenüberschrift. Nur um dann im Text zu konkretisieren, dass die sogenannte «Umweltspur» auf der Pariser Ringautobahn gemeint war, die für Busse, Taxis und Fahrgemeinschaften reserviert ist. [Ab Mai](https://www.lefigaro.fr/conso/peripherique-parisien-entree-en-vigueur-de-la-voie-reservee-au-covoiturage-ce-lundi-20250303) werden Verstöße dagegen mit einem Bußgeld geahndet. **Die DGT jedenfalls wolle bei der Umsetzung derartiger Maßnahmen** nicht hinterherhinken. Diese Medienberichte, inklusive des angeblich bevorstehenden Verbots, beriefen sich auf Aussagen des Generaldirektors der Behörde, Pere Navarro, beim Mobilitätskongress Global Mobility Call im November letzten Jahres, wo es um «nachhaltige Mobilität» ging. Aus diesem Kontext stammt auch Navarros Warnung: «Die Zukunft des Verkehrs ist geteilt oder es gibt keine». **Die «Faktenchecker» kamen der Generaldirektion prompt zu Hilfe.** Die DGT habe derlei Behauptungen [zurückgewiesen](https://www.newtral.es/dgt-una-persona-coche/20250312/) und klargestellt, dass es keine Pläne gebe, Fahrten mit nur einer Person im Auto zu verbieten oder zu bestrafen. Bei solchen Meldungen handele es sich um Fake News. Teilweise wurde der Vorsitzende der spanischen «Rechtsaußen»-Partei Vox, Santiago Abascal, der Urheberschaft bezichtigt, weil er einen entsprechenden [Artikel](https://gaceta.es/espana/la-dgt-estudia-formas-de-sancionar-a-quien-circule-solo-en-su-vehiculo-el-futuro-sera-compartido-o-no-sera-20250311-1612/) von *La Gaceta* kommentiert hatte. **Der Beschwichtigungsversuch der Art «niemand hat die Absicht»** ist dabei erfahrungsgemäß eher ein Alarmzeichen als eine Beruhigung. Walter Ulbrichts Leugnung einer geplanten Berliner [Mauer](https://www.berlin-mauer.de/videos/walter-ulbricht-zum-mauerbau-530/) vom Juni 1961 ist vielen genauso in Erinnerung wie die Fake News-Warnungen des deutschen Bundesgesundheitsministeriums bezüglich [Lockdowns](https://x.com/BMG_Bund/status/1238780849652465664) im März 2020 oder diverse Äußerungen zu einer [Impfpflicht](https://www.achgut.com/artikel/die_schoensten_politiker_zitate_zur_impfpflicht) ab 2020. **Aber Aufregung hin, Dementis her:** Die [Pressemitteilung](https://archive.is/xXQWD) der DGT zu dem Mobilitätskongress enthält in Wahrheit viel interessantere Informationen als «nur» einen Appell an den «guten» Bürger wegen der Bemühungen um die Lebensqualität in Großstädten oder einen möglichen obligatorischen Abschied vom Alleinfahren. Allerdings werden diese Details von Medien und sogenannten Faktencheckern geflissentlich übersehen, obwohl sie keineswegs versteckt sind. Die Auskünfte sind sehr aufschlussreich, wenn man genauer hinschaut. ### Digitalisierung ist der Schlüssel für Kontrolle **Auf dem Kongress stellte die Verkehrsbehörde ihre Initiativen zur Förderung der «neuen Mobilität» vor,** deren Priorität Sicherheit und Effizienz sei. Die vier konkreten Ansätze haben alle mit Digitalisierung, Daten, Überwachung und Kontrolle im großen Stil zu tun und werden unter dem Euphemismus der «öffentlich-privaten Partnerschaft» angepriesen. Auch lassen sie die transhumanistische Idee vom unzulänglichen Menschen erkennen, dessen Fehler durch «intelligente» technologische Infrastruktur kompensiert werden müssten. **Die Chefin des Bereichs «Verkehrsüberwachung» erklärte die Funktion** des spanischen National Access Point ([NAP](https://nap.dgt.es/)), wobei sie betonte, wie wichtig Verkehrs- und Infrastrukturinformationen in Echtzeit seien. Der NAP ist «eine essenzielle Web-Applikation, die unter EU-Mandat erstellt wurde», kann man auf der Website der DGT nachlesen. **Das Mandat meint Regelungen zu einem einheitlichen europäischen Verkehrsraum,** mit denen die Union mindestens seit 2010 den Aufbau einer digitalen Architektur mit offenen Schnittstellen betreibt. Damit begründet man auch «umfassende Datenbereitstellungspflichten im Bereich multimodaler Reiseinformationen». Jeder Mitgliedstaat musste einen NAP, also einen nationalen [Zugangspunkt](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en) einrichten, der Zugang zu statischen und dynamischen Reise- und Verkehrsdaten verschiedener Verkehrsträger ermöglicht. **Diese Entwicklung ist heute schon weit fortgeschritten,** auch und besonders in Spanien. Auf besagtem Kongress erläuterte die Leiterin des Bereichs «Telematik» die Plattform [«DGT 3.0»](https://www.dgt.es/muevete-con-seguridad/tecnologia-e-innovacion-en-carretera/dgt-3.0/). Diese werde als Integrator aller Informationen genutzt, die von den verschiedenen öffentlichen und privaten Systemen, die Teil der Mobilität sind, bereitgestellt werden. **Es handele sich um eine Vermittlungsplattform zwischen Akteuren wie Fahrzeugherstellern,** Anbietern von Navigationsdiensten oder Kommunen und dem Endnutzer, der die Verkehrswege benutzt. Alle seien auf Basis des Internets der Dinge (IOT) anonym verbunden, «um der vernetzten Gemeinschaft wertvolle Informationen zu liefern oder diese zu nutzen». **So sei DGT 3.0 «ein Zugangspunkt für einzigartige, kostenlose und genaue Echtzeitinformationen** über das Geschehen auf den Straßen und in den Städten». Damit lasse sich der Verkehr nachhaltiger und vernetzter gestalten. Beispielsweise würden die Karten des Produktpartners Google dank der DGT-Daten 50 Millionen Mal pro Tag aktualisiert. **Des Weiteren informiert die Verkehrsbehörde über ihr SCADA-Projekt.** Die Abkürzung steht für Supervisory Control and Data Acquisition, zu deutsch etwa: Kontrollierte Steuerung und Datenerfassung. Mit SCADA kombiniert man Software und Hardware, um automatisierte Systeme zur Überwachung und Steuerung technischer Prozesse zu schaffen. Das SCADA-Projekt der DGT wird von Indra entwickelt, einem spanischen Beratungskonzern aus den Bereichen Sicherheit & Militär, Energie, Transport, Telekommunikation und Gesundheitsinformation. **Das SCADA-System der Behörde umfasse auch eine Videostreaming- und Videoaufzeichnungsplattform,** die das Hochladen in die Cloud in Echtzeit ermöglicht, wie Indra [erklärt](https://www.indracompany.com/es/noticia/indra-presenta-global-mobility-call-pionera-plataforma-nube-desplegada-centros-gestion). Dabei gehe es um Bilder, die von Überwachungskameras an Straßen aufgenommen wurden, sowie um Videos aus DGT-Hubschraubern und Drohnen. Ziel sei es, «die sichere Weitergabe von Videos an Dritte sowie die kontinuierliche Aufzeichnung und Speicherung von Bildern zur möglichen Analyse und späteren Nutzung zu ermöglichen». **Letzteres klingt sehr nach biometrischer Erkennung** und Auswertung durch künstliche Intelligenz. Für eine bessere Datenübertragung wird derzeit die [Glasfaserverkabelung](https://www.moncloa.com/2025/03/18/linea-azul-conduccion-dgt-3191554/) entlang der Landstraßen und Autobahnen ausgebaut. Mit der Cloud sind die Amazon Web Services (AWS) gemeint, die spanischen [Daten gehen](https://norberthaering.de/news/digitalgipfel-wehnes-interview/) somit direkt zu einem US-amerikanischen «Big Data»-Unternehmen. **Das Thema «autonomes Fahren», also Fahren ohne Zutun des Menschen,** bildet den Abschluss der Betrachtungen der DGT. Zusammen mit dem Interessenverband der Automobilindustrie ANFAC (Asociación Española de Fabricantes de Automóviles y Camiones) sprach man auf dem Kongress über Strategien und Perspektiven in diesem Bereich. Die Lobbyisten hoffen noch in diesem Jahr 2025 auf einen [normativen Rahmen](https://www.coches.net/noticias/informe-coche-autonomo-conectado-espana-2024) zur erweiterten Unterstützung autonomer Technologien. **Wenn man derartige Informationen im Zusammenhang betrachtet,** bekommt man eine Idee davon, warum zunehmend alles elektrisch und digital werden soll. Umwelt- und Mobilitätsprobleme in Städten, wie Luftverschmutzung, Lärmbelästigung, Platzmangel oder Staus, sind eine Sache. Mit dem Argument «emissionslos» wird jedoch eine Referenz zum CO2 und dem «menschengemachten Klimawandel» hergestellt, die Emotionen triggert. Und damit wird so ziemlich alles verkauft. **Letztlich aber gilt: Je elektrischer und digitaler unsere Umgebung wird** und je freigiebiger wir mit unseren Daten jeder Art sind, desto besser werden wir kontrollier-, steuer- und sogar abschaltbar. Irgendwann entscheiden KI-basierte Algorithmen, ob, wann, wie, wohin und mit wem wir uns bewegen dürfen. Über einen 15-Minuten-Radius geht dann möglicherweise nichts hinaus. Die Projekte auf diesem Weg sind ernst zu nehmen, real und schon weit fortgeschritten. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/reisen-wagen-ferien-fahrzeug-1426822/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass)*** erschienen.
@ a95c6243:d345522c
2025-03-20 09:59:20**Bald werde es verboten, alleine im Auto zu fahren,** konnte man dieser Tage in verschiedenen spanischen Medien lesen. Die nationale Verkehrsbehörde (Dirección General de Tráfico, kurz DGT) werde Alleinfahrern das Leben schwer machen, wurde gemeldet. Konkret erörtere die Generaldirektion geeignete Sanktionen für Personen, die ohne Beifahrer im Privatauto unterwegs seien. **Das Alleinfahren sei zunehmend verpönt und ein Mentalitätswandel notwendig,** hieß es. Dieser «Luxus» stehe im Widerspruch zu den Maßnahmen gegen Umweltverschmutzung, die in allen europäischen Ländern gefördert würden. In Frankreich sei es «bereits verboten, in der Hauptstadt allein zu fahren», [behauptete](https://noticiastrabajo.huffingtonpost.es/sociedad/adios-a-conducir-solo-la-dgt-se-lo-pone-crudo-a-los-conductores-que-viajen-sin-acompanante-en-el-coche/) *Noticiastrabajo Huffpost* in einer Zwischenüberschrift. Nur um dann im Text zu konkretisieren, dass die sogenannte «Umweltspur» auf der Pariser Ringautobahn gemeint war, die für Busse, Taxis und Fahrgemeinschaften reserviert ist. [Ab Mai](https://www.lefigaro.fr/conso/peripherique-parisien-entree-en-vigueur-de-la-voie-reservee-au-covoiturage-ce-lundi-20250303) werden Verstöße dagegen mit einem Bußgeld geahndet. **Die DGT jedenfalls wolle bei der Umsetzung derartiger Maßnahmen** nicht hinterherhinken. Diese Medienberichte, inklusive des angeblich bevorstehenden Verbots, beriefen sich auf Aussagen des Generaldirektors der Behörde, Pere Navarro, beim Mobilitätskongress Global Mobility Call im November letzten Jahres, wo es um «nachhaltige Mobilität» ging. Aus diesem Kontext stammt auch Navarros Warnung: «Die Zukunft des Verkehrs ist geteilt oder es gibt keine». **Die «Faktenchecker» kamen der Generaldirektion prompt zu Hilfe.** Die DGT habe derlei Behauptungen [zurückgewiesen](https://www.newtral.es/dgt-una-persona-coche/20250312/) und klargestellt, dass es keine Pläne gebe, Fahrten mit nur einer Person im Auto zu verbieten oder zu bestrafen. Bei solchen Meldungen handele es sich um Fake News. Teilweise wurde der Vorsitzende der spanischen «Rechtsaußen»-Partei Vox, Santiago Abascal, der Urheberschaft bezichtigt, weil er einen entsprechenden [Artikel](https://gaceta.es/espana/la-dgt-estudia-formas-de-sancionar-a-quien-circule-solo-en-su-vehiculo-el-futuro-sera-compartido-o-no-sera-20250311-1612/) von *La Gaceta* kommentiert hatte. **Der Beschwichtigungsversuch der Art «niemand hat die Absicht»** ist dabei erfahrungsgemäß eher ein Alarmzeichen als eine Beruhigung. Walter Ulbrichts Leugnung einer geplanten Berliner [Mauer](https://www.berlin-mauer.de/videos/walter-ulbricht-zum-mauerbau-530/) vom Juni 1961 ist vielen genauso in Erinnerung wie die Fake News-Warnungen des deutschen Bundesgesundheitsministeriums bezüglich [Lockdowns](https://x.com/BMG_Bund/status/1238780849652465664) im März 2020 oder diverse Äußerungen zu einer [Impfpflicht](https://www.achgut.com/artikel/die_schoensten_politiker_zitate_zur_impfpflicht) ab 2020. **Aber Aufregung hin, Dementis her:** Die [Pressemitteilung](https://archive.is/xXQWD) der DGT zu dem Mobilitätskongress enthält in Wahrheit viel interessantere Informationen als «nur» einen Appell an den «guten» Bürger wegen der Bemühungen um die Lebensqualität in Großstädten oder einen möglichen obligatorischen Abschied vom Alleinfahren. Allerdings werden diese Details von Medien und sogenannten Faktencheckern geflissentlich übersehen, obwohl sie keineswegs versteckt sind. Die Auskünfte sind sehr aufschlussreich, wenn man genauer hinschaut. ### Digitalisierung ist der Schlüssel für Kontrolle **Auf dem Kongress stellte die Verkehrsbehörde ihre Initiativen zur Förderung der «neuen Mobilität» vor,** deren Priorität Sicherheit und Effizienz sei. Die vier konkreten Ansätze haben alle mit Digitalisierung, Daten, Überwachung und Kontrolle im großen Stil zu tun und werden unter dem Euphemismus der «öffentlich-privaten Partnerschaft» angepriesen. Auch lassen sie die transhumanistische Idee vom unzulänglichen Menschen erkennen, dessen Fehler durch «intelligente» technologische Infrastruktur kompensiert werden müssten. **Die Chefin des Bereichs «Verkehrsüberwachung» erklärte die Funktion** des spanischen National Access Point ([NAP](https://nap.dgt.es/)), wobei sie betonte, wie wichtig Verkehrs- und Infrastrukturinformationen in Echtzeit seien. Der NAP ist «eine essenzielle Web-Applikation, die unter EU-Mandat erstellt wurde», kann man auf der Website der DGT nachlesen. **Das Mandat meint Regelungen zu einem einheitlichen europäischen Verkehrsraum,** mit denen die Union mindestens seit 2010 den Aufbau einer digitalen Architektur mit offenen Schnittstellen betreibt. Damit begründet man auch «umfassende Datenbereitstellungspflichten im Bereich multimodaler Reiseinformationen». Jeder Mitgliedstaat musste einen NAP, also einen nationalen [Zugangspunkt](https://transport.ec.europa.eu/transport-themes/smart-mobility/road/its-directive-and-action-plan/national-access-points_en) einrichten, der Zugang zu statischen und dynamischen Reise- und Verkehrsdaten verschiedener Verkehrsträger ermöglicht. **Diese Entwicklung ist heute schon weit fortgeschritten,** auch und besonders in Spanien. Auf besagtem Kongress erläuterte die Leiterin des Bereichs «Telematik» die Plattform [«DGT 3.0»](https://www.dgt.es/muevete-con-seguridad/tecnologia-e-innovacion-en-carretera/dgt-3.0/). Diese werde als Integrator aller Informationen genutzt, die von den verschiedenen öffentlichen und privaten Systemen, die Teil der Mobilität sind, bereitgestellt werden. **Es handele sich um eine Vermittlungsplattform zwischen Akteuren wie Fahrzeugherstellern,** Anbietern von Navigationsdiensten oder Kommunen und dem Endnutzer, der die Verkehrswege benutzt. Alle seien auf Basis des Internets der Dinge (IOT) anonym verbunden, «um der vernetzten Gemeinschaft wertvolle Informationen zu liefern oder diese zu nutzen». **So sei DGT 3.0 «ein Zugangspunkt für einzigartige, kostenlose und genaue Echtzeitinformationen** über das Geschehen auf den Straßen und in den Städten». Damit lasse sich der Verkehr nachhaltiger und vernetzter gestalten. Beispielsweise würden die Karten des Produktpartners Google dank der DGT-Daten 50 Millionen Mal pro Tag aktualisiert. **Des Weiteren informiert die Verkehrsbehörde über ihr SCADA-Projekt.** Die Abkürzung steht für Supervisory Control and Data Acquisition, zu deutsch etwa: Kontrollierte Steuerung und Datenerfassung. Mit SCADA kombiniert man Software und Hardware, um automatisierte Systeme zur Überwachung und Steuerung technischer Prozesse zu schaffen. Das SCADA-Projekt der DGT wird von Indra entwickelt, einem spanischen Beratungskonzern aus den Bereichen Sicherheit & Militär, Energie, Transport, Telekommunikation und Gesundheitsinformation. **Das SCADA-System der Behörde umfasse auch eine Videostreaming- und Videoaufzeichnungsplattform,** die das Hochladen in die Cloud in Echtzeit ermöglicht, wie Indra [erklärt](https://www.indracompany.com/es/noticia/indra-presenta-global-mobility-call-pionera-plataforma-nube-desplegada-centros-gestion). Dabei gehe es um Bilder, die von Überwachungskameras an Straßen aufgenommen wurden, sowie um Videos aus DGT-Hubschraubern und Drohnen. Ziel sei es, «die sichere Weitergabe von Videos an Dritte sowie die kontinuierliche Aufzeichnung und Speicherung von Bildern zur möglichen Analyse und späteren Nutzung zu ermöglichen». **Letzteres klingt sehr nach biometrischer Erkennung** und Auswertung durch künstliche Intelligenz. Für eine bessere Datenübertragung wird derzeit die [Glasfaserverkabelung](https://www.moncloa.com/2025/03/18/linea-azul-conduccion-dgt-3191554/) entlang der Landstraßen und Autobahnen ausgebaut. Mit der Cloud sind die Amazon Web Services (AWS) gemeint, die spanischen [Daten gehen](https://norberthaering.de/news/digitalgipfel-wehnes-interview/) somit direkt zu einem US-amerikanischen «Big Data»-Unternehmen. **Das Thema «autonomes Fahren», also Fahren ohne Zutun des Menschen,** bildet den Abschluss der Betrachtungen der DGT. Zusammen mit dem Interessenverband der Automobilindustrie ANFAC (Asociación Española de Fabricantes de Automóviles y Camiones) sprach man auf dem Kongress über Strategien und Perspektiven in diesem Bereich. Die Lobbyisten hoffen noch in diesem Jahr 2025 auf einen [normativen Rahmen](https://www.coches.net/noticias/informe-coche-autonomo-conectado-espana-2024) zur erweiterten Unterstützung autonomer Technologien. **Wenn man derartige Informationen im Zusammenhang betrachtet,** bekommt man eine Idee davon, warum zunehmend alles elektrisch und digital werden soll. Umwelt- und Mobilitätsprobleme in Städten, wie Luftverschmutzung, Lärmbelästigung, Platzmangel oder Staus, sind eine Sache. Mit dem Argument «emissionslos» wird jedoch eine Referenz zum CO2 und dem «menschengemachten Klimawandel» hergestellt, die Emotionen triggert. Und damit wird so ziemlich alles verkauft. **Letztlich aber gilt: Je elektrischer und digitaler unsere Umgebung wird** und je freigiebiger wir mit unseren Daten jeder Art sind, desto besser werden wir kontrollier-, steuer- und sogar abschaltbar. Irgendwann entscheiden KI-basierte Algorithmen, ob, wann, wie, wohin und mit wem wir uns bewegen dürfen. Über einen 15-Minuten-Radius geht dann möglicherweise nichts hinaus. Die Projekte auf diesem Weg sind ernst zu nehmen, real und schon weit fortgeschritten. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/photos/reisen-wagen-ferien-fahrzeug-1426822/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/nur-abschied-vom-alleinfahren-monstrose-spanische-uberwachungsprojekte-gemass)*** erschienen. @ 9f475ec5:d9acc946
2025-04-01 03:17:20> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce. # Introducing the Dad Joke Publisher Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**. Agent to agent communication is the next step in the AI revolution: - Agents transacting with other agents - Agents working together to create a multi-agent application To make it a reality, agents need to be able to: - Find other agents - Authenticate the agents - Discover their capabilities - Transact data and / or money Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but... **I believe that there is a better way with Nostr.** Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that. !(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif] ## The Dad Joke Game The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*. The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour. **Dynamic discovery** A Joker is an agent with a Nostr profile with the following characteristics: - The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) - The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md)) - The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) **Authentication** The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com. **Communication** Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md). ## Join the game! Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started. You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`. ## Join Synvya's mission! Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions. Next steps for Synvya: - A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents - Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file. PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this). PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever.
@ 9f475ec5:d9acc946
2025-04-01 03:17:20> Synvya is building the tools and infrastructure for a Nostr agentic ecosystem to be at the foundation of ai-commerce. # Introducing the Dad Joke Publisher Meet nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q , a Nostr-powered agent built to showcase the power of **nostr+cashu+ai**. Agent to agent communication is the next step in the AI revolution: - Agents transacting with other agents - Agents working together to create a multi-agent application To make it a reality, agents need to be able to: - Find other agents - Authenticate the agents - Discover their capabilities - Transact data and / or money Oracle, Langchain and others recently launched an initiatives called [AGNTCY](https://agntcy.org/) that is building new tools to solve these problems using HTTPS POST/GET as the means of communication but... **I believe that there is a better way with Nostr.** Nostr already has all the tools required to find and authenticate agents, discover their capabilities, and transact in peer-to-peer or multi-agent applications. The Dad Joke Game is showing just that. !(image)[https://media4.giphy.com/media/v1.Y2lkPTc5MGI3NjExeWZ3eTZzcTMxdW53aG9iZzYyaTlzdHdzaGp3Zjdwc3puZ2FubnF3cSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/UYSt3oBqFfxWdN0lHZ/giphy.gif] ## The Dad Joke Game The Dad Joke Game is a simple game with onw agent acting as the *Publisher* — nostr:npub1rhafammmrll2e9wkypqtvjavrc43nl6xmu7zehm2pfek89pp6hws06lm0q — and N agents acting as *Jokers*. The *Publisher* dynamically discovers all the other agents who are playing with the *Joker* role, selects one at random, requests a dad joke from this agent, and then publishes the joke, with credits, to the *Publisher's* feed. This processes is repeated every hour. **Dynamic discovery** A Joker is an agent with a Nostr profile with the following characteristics: - The metadata field `bot` is set to `true` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) - The profile includes a label `dad-joke-game` with namespace `com.synvya.gamer` (as per [NIP-32](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/32.md)) - The profile includes a hashtag `joker` (as per [NIP-24](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/24.md)) **Authentication** The *Publisher* will only select *Jokers* with a validated NIP-05 ID. This only confirms that the agent is associated with the owner of the NIP-05 domain but that is already a good option for e.g. joker@fiatjaf.com or joker@mcdonalds.com. **Communication** Communication happens through private direct messages using [NIP-17](https://github.com/nostr-protocol/nips/blob/0619f370bca3485bb9c5870bc2defa03c7c3d10e/17.md). ## Join the game! Check the example implementation at [GitHub](https://github.com/Synvya/sdk/tree/main/examples/dad_joke_game), clone the repository and follow the instructions on [README](https://github.com/Synvya/sdk/blob/main/examples/dad_joke_game/README.md) to get started. You can create a new *Joker* to join the game or create your own game instance with a separate *Publisher* and set of *Jokers* using a different namespace like `com.yourdomain.gamer`. ## Join Synvya's mission! Want to help drive **nostr+cashu+ai**? Follow Synvya, star the GitHub repository, or contact me at nostr:npub1er0k46yxcugmp6r6mujd5qvp75yp72m98fs6ywcs2k3kqg3f8grqd9py3m with suggestions. Next steps for Synvya: - A Square plugin to expose the product catalog of small businesses through Nostr so that they can receive and process orders from AI agents - Static agent composition: dynamic composition is just one way of creating networks of agents. Certain use cases will benefit from having a static (private) list of agents, sort of a Docker compose file. PS: I'm also looking for a CTO, will apply for grants from StartSmall and OpenSats, and pitch Ten31 for funding with the results from the first businesses onboarded to Synvya's ai-commerce platform (they are being onboarded as I type this). PPS: everything [Synvya](https://www.synvya.com) does is open sourced under an [MIT License](https://github.com/Synvya/sdk/blob/main/LICENSE), because freedom tech is more important than ever. @ 266815e0:6cd408a5
2025-03-19 11:10:21How to create a nostr app quickly using [applesauce](https://hzrd149.github.io/applesauce/) In this guide we are going to build a nostr app that lets users follow and unfollow [fiatjaf](nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6) ## 1. Setup new project Start by setting up a new vite app using `pnpm create vite`, then set the name and select `Solid` and `Typescript` ```sh ➜ pnpm create vite │ ◇ Project name: │ followjaf │ ◇ Select a framework: │ Solid │ ◇ Select a variant: │ TypeScript │ ◇ Scaffolding project in ./followjaf... │ └ Done. Now run: cd followjaf pnpm install pnpm run dev ``` ## 2. Adding nostr dependencies There are a few useful nostr dependencies we are going to need. `nostr-tools` for the types and small methods, and [`rx-nostr`](https://penpenpng.github.io/rx-nostr/) for making relay connections ```sh pnpm install nostr-tools rx-nostr ``` ## 3. Setup rx-nostr Next we need to setup rxNostr so we can make connections to relays. create a new `src/nostr.ts` file with ```ts import { createRxNostr, noopVerifier } from "rx-nostr"; export const rxNostr = createRxNostr({ // skip verification here because we are going to verify events at the event store skipVerify: true, verifier: noopVerifier, }); ``` ## 4. Setup the event store Now that we have a way to connect to relays, we need a place to store events. We will use the [`EventStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.EventStore.html) class from `applesauce-core` for this. create a new `src/stores.ts` file with > The event store does not store any events in the browsers local storage or anywhere else. It's in-memory only and provides a model for the UI ```ts import { EventStore } from "applesauce-core"; import { verifyEvent } from "nostr-tools"; export const eventStore = new EventStore(); // verify the events when they are added to the store eventStore.verifyEvent = verifyEvent; ``` ## 5. Create the query store The event store is where we store all the events, but we need a way for the UI to query them. We can use the [`QueryStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.QueryStore.html) class from `applesauce-core` for this. Create a query store in `src/stores.ts` ```ts import { QueryStore } from "applesauce-core"; // ... // the query store needs the event store to subscribe to it export const queryStore = new QueryStore(eventStore); ``` ## 6. Setup the profile loader Next we need a way to fetch user profiles. We are going to use the [`ReplaceableLoader`](https://hzrd149.github.io/applesauce/overview/loaders.html#replaceable-loader) class from [`applesauce-loaders`](https://www.npmjs.com/package/applesauce-loaders) for this. > `applesauce-loaders` is a package that contains a few loader classes that can be used to fetch different types of data from relays. First install the package ```sh pnpm install applesauce-loaders ``` Then create a `src/loaders.ts` file with ```ts import { ReplaceableLoader } from "applesauce-loaders"; import { rxNostr } from "./nostr"; import { eventStore } from "./stores"; export const replaceableLoader = new ReplaceableLoader(rxNostr); // Start the loader and send any events to the event store replaceableLoader.subscribe((packet) => { eventStore.add(packet.event, packet.from); }); ``` ## 7. Fetch fiatjaf's profile Now that we have a way to store events, and a loader to help with fetching them, we should update the `src/App.tsx` component to fetch the profile. We can do this by calling the `next` method on the loader and passing a `pubkey`, `kind` and `relays` to it ```tsx function App() { // ... onMount(() => { // fetch fiatjaf's profile on load replaceableLoader.next({ pubkey: "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", kind: 0, relays: ["wss://pyramid.fiatjaf.com/"], }); }); // ... } ``` ## 8. Display the profile Now that we have a way to fetch the profile, we need to display it in the UI. We can do this by using the [`ProfileQuery`](https://hzrd149.github.io/applesauce/typedoc/functions/applesauce_core.Queries.ProfileQuery.html) which gives us a stream of updates to a pubkey's profile. Create the profile using `queryStore.createQuery` and pass in the `ProfileQuery` and the pubkey. ```tsx const fiatjaf = queryStore.createQuery( ProfileQuery, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d" ); ``` But this just gives us an [observable](https://rxjs.dev/guide/observable), we need to subscribe to it to get the profile. Luckily SolidJS profiles a simple [`from`](https://docs.solidjs.com/reference/reactive-utilities/from) method to subscribe to any observable. > To make things reactive SolidJS uses accessors, so to get the profile we need to call `fiatjaf()` ```tsx function App() { // ... // Subscribe to fiatjaf's profile from the query store const fiatjaf = from( queryStore.createQuery(ProfileQuery, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d") ); return ( <> {/* replace the vite and solid logos with the profile picture */} <div> <img src={fiatjaf()?.picture} class="logo" /> </div> <h1>{fiatjaf()?.name}</h1> {/* ... */} </> ); } ``` ## 9. Letting the user signin Now we should let the user signin to the app. We can do this by creating a [`AccountManager`](https://hzrd149.github.io/applesauce/accounts/manager.html) class from `applesauce-accounts` First we need to install the packages ```sh pnpm install applesauce-accounts applesauce-signers ``` Then create a new `src/accounts.ts` file with ```ts import { AccountManager } from "applesauce-accounts"; import { registerCommonAccountTypes } from "applesauce-accounts/accounts"; // create an account manager instance export const accounts = new AccountManager(); // Adds the common account types to the manager registerCommonAccountTypes(accounts); ``` Next lets presume the user has a NIP-07 browser extension installed and add a signin button. ```tsx function App() { const signin = async () => { // do nothing if the user is already signed in if (accounts.active) return; // create a new nip-07 signer and try to get the pubkey const signer = new ExtensionSigner(); const pubkey = await signer.getPublicKey(); // create a new extension account, add it, and make it the active account const account = new ExtensionAccount(pubkey, signer); accounts.addAccount(account); accounts.setActive(account); }; return ( <> {/* ... */} <div class="card"> <p>Are you following the fiatjaf? the creator of "The nostr"</p> <button onClick={signin}>Check</button> </div> </> ); } ``` Now when the user clicks the button the app will ask for the users pubkey, then do nothing... but it's a start. > We are not persisting the accounts, so when the page reloads the user will NOT be signed in. you can learn about persisting the accounts in the [docs](https://hzrd149.github.io/applesauce/accounts/manager.html#persisting-accounts) ## 10. Showing the signed-in state We should show some indication to the user that they are signed in. We can do this by modifying the signin button if the user is signed in and giving them a way to sign-out ```tsx function App() { // subscribe to the currently active account (make sure to use the account$ observable) const account = from(accounts.active$); // ... const signout = () => { // do nothing if the user is not signed in if (!accounts.active) return; // signout the user const account = accounts.active; accounts.removeAccount(account); accounts.clearActive(); }; return ( <> {/* ... */} <div class="card"> <p>Are you following the fiatjaf? ( creator of "The nostr" )</p> {account() === undefined ? <button onClick={signin}>Check</button> : <button onClick={signout}>Signout</button>} </div> </> ); } ``` ## 11. Fetching the user's profile Now that we have a way to sign in and out of the app, we should fetch the user's profile when they sign in. ```tsx function App() { // ... // fetch the user's profile when they sign in createEffect(async () => { const active = account(); if (active) { // get the user's relays or fallback to some default relays const usersRelays = await active.getRelays?.(); const relays = usersRelays ? Object.keys(usersRelays) : ["wss://relay.damus.io", "wss://nos.lol"]; // tell the loader to fetch the users profile event replaceableLoader.next({ pubkey: active.pubkey, kind: 0, relays, }); // tell the loader to fetch the users contacts replaceableLoader.next({ pubkey: active.pubkey, kind: 3, relays, }); // tell the loader to fetch the users mailboxes replaceableLoader.next({ pubkey: active.pubkey, kind: 10002, relays, }); } }); // ... } ``` Next we need to subscribe to the users profile, to do this we can use some rxjs operators to chain the observables together. ```tsx import { Match, Switch } from "solid-js"; import { of, switchMap } from "rxjs"; function App() { // ... // subscribe to the active account, then subscribe to the users profile or undefined const profile = from( accounts.active$.pipe( switchMap((account) => (account ? queryStore.createQuery(ProfileQuery, account!.pubkey) : of(undefined))) ) ); // ... return ( <> {/* ... */} <div class="card"> <Switch> <Match when={account() && !profile()}> <p>Loading profile...</p> </Match> <Match when={profile()}> <p style="font-size: 1.2rem; font-weight: bold;">Welcome {profile()?.name}</p> </Match> </Switch> {/* ... */} </div> </> ); } ``` ## 12. Showing if the user is following fiatjaf Now that the app is fetching the users profile and contacts we should show if the user is following fiatjaf. ```tsx function App() { // ... // subscribe to the active account, then subscribe to the users contacts or undefined const contacts = from( accounts.active$.pipe( switchMap((account) => (account ? queryStore.createQuery(UserContactsQuery, account!.pubkey) : of(undefined))) ) ); const isFollowing = createMemo(() => { return contacts()?.some((c) => c.pubkey === "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"); }); // ... return ( <> {/* ... */} <div class="card"> {/* ... */} <Switch fallback={ <p style="font-size: 1.2rem;"> Sign in to check if you are a follower of the fiatjaf ( creator of "The nostr" ) </p> } > <Match when={contacts() && isFollowing() === undefined}> <p>checking...</p> </Match> <Match when={contacts() && isFollowing() === true}> <p style="color: green; font-weight: bold; font-size: 2rem;"> Congratulations! You are a follower of the fiatjaf </p> </Match> <Match when={contacts() && isFollowing() === false}> <p style="color: red; font-weight: bold; font-size: 2rem;"> Why don't you follow the fiatjaf? do you even like nostr? </p> </Match> </Switch> {/* ... */} </div> </> ); } ``` ## 13. Adding the follow button Now that we have a way to check if the user is following fiatjaf, we should add a button to follow him. We can do this with [Actions](https://hzrd149.github.io/applesauce/overview/actions.html) which are pre-built methods to modify nostr events for a user. First we need to install the `applesauce-actions` and `applesauce-factory` package ```sh pnpm install applesauce-actions applesauce-factory ``` Then create a `src/actions.ts` file with ```ts import { EventFactory } from "applesauce-factory"; import { ActionHub } from "applesauce-actions"; import { eventStore } from "./stores"; import { accounts } from "./accounts"; // The event factory is used to build and modify nostr events export const factory = new EventFactory({ // accounts.signer is a NIP-07 signer that signs with the currently active account signer: accounts.signer, }); // The action hub is used to run Actions against the event store export const actions = new ActionHub(eventStore, factory); ``` Then create a `toggleFollow` method that will add or remove fiatjaf from the users contacts. > We are using the `exec` method to run the action, and the [`forEach`](https://rxjs.dev/api/index/class/Observable#foreach) method from RxJS allows us to await for all the events to be published ```tsx function App() { // ... const toggleFollow = async () => { // send any created events to rxNostr and the event store const publish = (event: NostrEvent) => { eventStore.add(event); rxNostr.send(event); }; if (isFollowing()) { await actions .exec(UnfollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d") .forEach(publish); } else { await actions .exec( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", "wss://pyramid.fiatjaf.com/" ) .forEach(publish); } }; // ... return ( <> {/* ... */} <div class="card"> {/* ... */} {contacts() && <button onClick={toggleFollow}>{isFollowing() ? "Unfollow" : "Follow"}</button>} </div> </> ); } ``` ## 14. Adding outbox support The app looks like it works now but if the user reloads the page they will still see an the old version of their contacts list. we need to make sure rxNostr is publishing the events to the users outbox relays. To do this we can subscribe to the signed in users mailboxes using the query store in `src/nostr.ts` ```ts import { MailboxesQuery } from "applesauce-core/queries"; import { accounts } from "./accounts"; import { of, switchMap } from "rxjs"; import { queryStore } from "./stores"; // ... // subscribe to the active account, then subscribe to the users mailboxes and update rxNostr accounts.active$ .pipe(switchMap((account) => (account ? queryStore.createQuery(MailboxesQuery, account.pubkey) : of(undefined)))) .subscribe((mailboxes) => { if (mailboxes) rxNostr.setDefaultRelays(mailboxes.outboxes); else rxNostr.setDefaultRelays([]); }); ``` And that's it! we have a working nostr app that lets users follow and unfollow fiatjaf.
@ 266815e0:6cd408a5
2025-03-19 11:10:21How to create a nostr app quickly using [applesauce](https://hzrd149.github.io/applesauce/) In this guide we are going to build a nostr app that lets users follow and unfollow [fiatjaf](nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6) ## 1. Setup new project Start by setting up a new vite app using `pnpm create vite`, then set the name and select `Solid` and `Typescript` ```sh ➜ pnpm create vite │ ◇ Project name: │ followjaf │ ◇ Select a framework: │ Solid │ ◇ Select a variant: │ TypeScript │ ◇ Scaffolding project in ./followjaf... │ └ Done. Now run: cd followjaf pnpm install pnpm run dev ``` ## 2. Adding nostr dependencies There are a few useful nostr dependencies we are going to need. `nostr-tools` for the types and small methods, and [`rx-nostr`](https://penpenpng.github.io/rx-nostr/) for making relay connections ```sh pnpm install nostr-tools rx-nostr ``` ## 3. Setup rx-nostr Next we need to setup rxNostr so we can make connections to relays. create a new `src/nostr.ts` file with ```ts import { createRxNostr, noopVerifier } from "rx-nostr"; export const rxNostr = createRxNostr({ // skip verification here because we are going to verify events at the event store skipVerify: true, verifier: noopVerifier, }); ``` ## 4. Setup the event store Now that we have a way to connect to relays, we need a place to store events. We will use the [`EventStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.EventStore.html) class from `applesauce-core` for this. create a new `src/stores.ts` file with > The event store does not store any events in the browsers local storage or anywhere else. It's in-memory only and provides a model for the UI ```ts import { EventStore } from "applesauce-core"; import { verifyEvent } from "nostr-tools"; export const eventStore = new EventStore(); // verify the events when they are added to the store eventStore.verifyEvent = verifyEvent; ``` ## 5. Create the query store The event store is where we store all the events, but we need a way for the UI to query them. We can use the [`QueryStore`](https://hzrd149.github.io/applesauce/typedoc/classes/applesauce_core.QueryStore.html) class from `applesauce-core` for this. Create a query store in `src/stores.ts` ```ts import { QueryStore } from "applesauce-core"; // ... // the query store needs the event store to subscribe to it export const queryStore = new QueryStore(eventStore); ``` ## 6. Setup the profile loader Next we need a way to fetch user profiles. We are going to use the [`ReplaceableLoader`](https://hzrd149.github.io/applesauce/overview/loaders.html#replaceable-loader) class from [`applesauce-loaders`](https://www.npmjs.com/package/applesauce-loaders) for this. > `applesauce-loaders` is a package that contains a few loader classes that can be used to fetch different types of data from relays. First install the package ```sh pnpm install applesauce-loaders ``` Then create a `src/loaders.ts` file with ```ts import { ReplaceableLoader } from "applesauce-loaders"; import { rxNostr } from "./nostr"; import { eventStore } from "./stores"; export const replaceableLoader = new ReplaceableLoader(rxNostr); // Start the loader and send any events to the event store replaceableLoader.subscribe((packet) => { eventStore.add(packet.event, packet.from); }); ``` ## 7. Fetch fiatjaf's profile Now that we have a way to store events, and a loader to help with fetching them, we should update the `src/App.tsx` component to fetch the profile. We can do this by calling the `next` method on the loader and passing a `pubkey`, `kind` and `relays` to it ```tsx function App() { // ... onMount(() => { // fetch fiatjaf's profile on load replaceableLoader.next({ pubkey: "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", kind: 0, relays: ["wss://pyramid.fiatjaf.com/"], }); }); // ... } ``` ## 8. Display the profile Now that we have a way to fetch the profile, we need to display it in the UI. We can do this by using the [`ProfileQuery`](https://hzrd149.github.io/applesauce/typedoc/functions/applesauce_core.Queries.ProfileQuery.html) which gives us a stream of updates to a pubkey's profile. Create the profile using `queryStore.createQuery` and pass in the `ProfileQuery` and the pubkey. ```tsx const fiatjaf = queryStore.createQuery( ProfileQuery, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d" ); ``` But this just gives us an [observable](https://rxjs.dev/guide/observable), we need to subscribe to it to get the profile. Luckily SolidJS profiles a simple [`from`](https://docs.solidjs.com/reference/reactive-utilities/from) method to subscribe to any observable. > To make things reactive SolidJS uses accessors, so to get the profile we need to call `fiatjaf()` ```tsx function App() { // ... // Subscribe to fiatjaf's profile from the query store const fiatjaf = from( queryStore.createQuery(ProfileQuery, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d") ); return ( <> {/* replace the vite and solid logos with the profile picture */} <div> <img src={fiatjaf()?.picture} class="logo" /> </div> <h1>{fiatjaf()?.name}</h1> {/* ... */} </> ); } ``` ## 9. Letting the user signin Now we should let the user signin to the app. We can do this by creating a [`AccountManager`](https://hzrd149.github.io/applesauce/accounts/manager.html) class from `applesauce-accounts` First we need to install the packages ```sh pnpm install applesauce-accounts applesauce-signers ``` Then create a new `src/accounts.ts` file with ```ts import { AccountManager } from "applesauce-accounts"; import { registerCommonAccountTypes } from "applesauce-accounts/accounts"; // create an account manager instance export const accounts = new AccountManager(); // Adds the common account types to the manager registerCommonAccountTypes(accounts); ``` Next lets presume the user has a NIP-07 browser extension installed and add a signin button. ```tsx function App() { const signin = async () => { // do nothing if the user is already signed in if (accounts.active) return; // create a new nip-07 signer and try to get the pubkey const signer = new ExtensionSigner(); const pubkey = await signer.getPublicKey(); // create a new extension account, add it, and make it the active account const account = new ExtensionAccount(pubkey, signer); accounts.addAccount(account); accounts.setActive(account); }; return ( <> {/* ... */} <div class="card"> <p>Are you following the fiatjaf? the creator of "The nostr"</p> <button onClick={signin}>Check</button> </div> </> ); } ``` Now when the user clicks the button the app will ask for the users pubkey, then do nothing... but it's a start. > We are not persisting the accounts, so when the page reloads the user will NOT be signed in. you can learn about persisting the accounts in the [docs](https://hzrd149.github.io/applesauce/accounts/manager.html#persisting-accounts) ## 10. Showing the signed-in state We should show some indication to the user that they are signed in. We can do this by modifying the signin button if the user is signed in and giving them a way to sign-out ```tsx function App() { // subscribe to the currently active account (make sure to use the account$ observable) const account = from(accounts.active$); // ... const signout = () => { // do nothing if the user is not signed in if (!accounts.active) return; // signout the user const account = accounts.active; accounts.removeAccount(account); accounts.clearActive(); }; return ( <> {/* ... */} <div class="card"> <p>Are you following the fiatjaf? ( creator of "The nostr" )</p> {account() === undefined ? <button onClick={signin}>Check</button> : <button onClick={signout}>Signout</button>} </div> </> ); } ``` ## 11. Fetching the user's profile Now that we have a way to sign in and out of the app, we should fetch the user's profile when they sign in. ```tsx function App() { // ... // fetch the user's profile when they sign in createEffect(async () => { const active = account(); if (active) { // get the user's relays or fallback to some default relays const usersRelays = await active.getRelays?.(); const relays = usersRelays ? Object.keys(usersRelays) : ["wss://relay.damus.io", "wss://nos.lol"]; // tell the loader to fetch the users profile event replaceableLoader.next({ pubkey: active.pubkey, kind: 0, relays, }); // tell the loader to fetch the users contacts replaceableLoader.next({ pubkey: active.pubkey, kind: 3, relays, }); // tell the loader to fetch the users mailboxes replaceableLoader.next({ pubkey: active.pubkey, kind: 10002, relays, }); } }); // ... } ``` Next we need to subscribe to the users profile, to do this we can use some rxjs operators to chain the observables together. ```tsx import { Match, Switch } from "solid-js"; import { of, switchMap } from "rxjs"; function App() { // ... // subscribe to the active account, then subscribe to the users profile or undefined const profile = from( accounts.active$.pipe( switchMap((account) => (account ? queryStore.createQuery(ProfileQuery, account!.pubkey) : of(undefined))) ) ); // ... return ( <> {/* ... */} <div class="card"> <Switch> <Match when={account() && !profile()}> <p>Loading profile...</p> </Match> <Match when={profile()}> <p style="font-size: 1.2rem; font-weight: bold;">Welcome {profile()?.name}</p> </Match> </Switch> {/* ... */} </div> </> ); } ``` ## 12. Showing if the user is following fiatjaf Now that the app is fetching the users profile and contacts we should show if the user is following fiatjaf. ```tsx function App() { // ... // subscribe to the active account, then subscribe to the users contacts or undefined const contacts = from( accounts.active$.pipe( switchMap((account) => (account ? queryStore.createQuery(UserContactsQuery, account!.pubkey) : of(undefined))) ) ); const isFollowing = createMemo(() => { return contacts()?.some((c) => c.pubkey === "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"); }); // ... return ( <> {/* ... */} <div class="card"> {/* ... */} <Switch fallback={ <p style="font-size: 1.2rem;"> Sign in to check if you are a follower of the fiatjaf ( creator of "The nostr" ) </p> } > <Match when={contacts() && isFollowing() === undefined}> <p>checking...</p> </Match> <Match when={contacts() && isFollowing() === true}> <p style="color: green; font-weight: bold; font-size: 2rem;"> Congratulations! You are a follower of the fiatjaf </p> </Match> <Match when={contacts() && isFollowing() === false}> <p style="color: red; font-weight: bold; font-size: 2rem;"> Why don't you follow the fiatjaf? do you even like nostr? </p> </Match> </Switch> {/* ... */} </div> </> ); } ``` ## 13. Adding the follow button Now that we have a way to check if the user is following fiatjaf, we should add a button to follow him. We can do this with [Actions](https://hzrd149.github.io/applesauce/overview/actions.html) which are pre-built methods to modify nostr events for a user. First we need to install the `applesauce-actions` and `applesauce-factory` package ```sh pnpm install applesauce-actions applesauce-factory ``` Then create a `src/actions.ts` file with ```ts import { EventFactory } from "applesauce-factory"; import { ActionHub } from "applesauce-actions"; import { eventStore } from "./stores"; import { accounts } from "./accounts"; // The event factory is used to build and modify nostr events export const factory = new EventFactory({ // accounts.signer is a NIP-07 signer that signs with the currently active account signer: accounts.signer, }); // The action hub is used to run Actions against the event store export const actions = new ActionHub(eventStore, factory); ``` Then create a `toggleFollow` method that will add or remove fiatjaf from the users contacts. > We are using the `exec` method to run the action, and the [`forEach`](https://rxjs.dev/api/index/class/Observable#foreach) method from RxJS allows us to await for all the events to be published ```tsx function App() { // ... const toggleFollow = async () => { // send any created events to rxNostr and the event store const publish = (event: NostrEvent) => { eventStore.add(event); rxNostr.send(event); }; if (isFollowing()) { await actions .exec(UnfollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d") .forEach(publish); } else { await actions .exec( FollowUser, "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d", "wss://pyramid.fiatjaf.com/" ) .forEach(publish); } }; // ... return ( <> {/* ... */} <div class="card"> {/* ... */} {contacts() && <button onClick={toggleFollow}>{isFollowing() ? "Unfollow" : "Follow"}</button>} </div> </> ); } ``` ## 14. Adding outbox support The app looks like it works now but if the user reloads the page they will still see an the old version of their contacts list. we need to make sure rxNostr is publishing the events to the users outbox relays. To do this we can subscribe to the signed in users mailboxes using the query store in `src/nostr.ts` ```ts import { MailboxesQuery } from "applesauce-core/queries"; import { accounts } from "./accounts"; import { of, switchMap } from "rxjs"; import { queryStore } from "./stores"; // ... // subscribe to the active account, then subscribe to the users mailboxes and update rxNostr accounts.active$ .pipe(switchMap((account) => (account ? queryStore.createQuery(MailboxesQuery, account.pubkey) : of(undefined)))) .subscribe((mailboxes) => { if (mailboxes) rxNostr.setDefaultRelays(mailboxes.outboxes); else rxNostr.setDefaultRelays([]); }); ``` And that's it! we have a working nostr app that lets users follow and unfollow fiatjaf. @ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe. Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren: ### 1. Quantitätstheorie des Geldes Die klassische Gleichung der Quantitätstheorie des Geldes lautet: M • V = P • Y wobei: - M die Geldmenge ist, - V die Umlaufgeschwindigkeit des Geldes, - P das Preisniveau, - Y die reale Wirtschaftsleistung (BIP). Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen. ### 2. Gütermenge bleibt begrenzt Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen. ### 3. Erwartungseffekte und Spekulation Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen. ### 4. Internationale Perspektive Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt. ### 5. Kritik an der reinen Geldmengen-Theorie Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe. Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren: ### 1. Quantitätstheorie des Geldes Die klassische Gleichung der Quantitätstheorie des Geldes lautet: M • V = P • Y wobei: - M die Geldmenge ist, - V die Umlaufgeschwindigkeit des Geldes, - P das Preisniveau, - Y die reale Wirtschaftsleistung (BIP). Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen. ### 2. Gütermenge bleibt begrenzt Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen. ### 3. Erwartungseffekte und Spekulation Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen. ### 4. Internationale Perspektive Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt. ### 5. Kritik an der reinen Geldmengen-Theorie Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe. @ b8af284d:f82c91dd
2025-03-16 16:42:49 Liebe Abonnenten, diejenigen, die diese Publikation schon länger abonniert haben, wissen, dass hier immer wieder über den Ursprung des Corona-Virus in einem Labor in Wuhan berichtet wurde. Seit diese Woche ist es „offiziell“ - [der Bundesnachrichtendienst (BND) hält den Labor-Ursprung für die wahrscheinlichste Variante](https://www.zeit.de/2025/11/coronavirus-ursprung-wuhan-labor-china-bnd). Jetzt kann man sich fragen, warum der BND plötzlich umschwenkt: Will man proaktiv erscheinen, weil man die Wahrheit nicht mehr länger verbergen kann? Oder will man die enttäuschten Bürger zurückgewinnen, die aufgrund der Lügen während der Corona-Zeit zunehmend mit Parteien links und rechts außen sympathisiert haben, weil diese die einzigen waren, die den Irrsinn nicht mitgetragen haben? Auffallend bei den „Recherchen“, die in Wahrheit keine sind, sondern Verlautbarungen des deutschen Geheimdienstes, ist auch das völlige Schweigen über die US-amerikanischen Verwicklungen in das Projekt. [In Wuhan wurde mit amerikanischem Geld geforscht](https://oversight.house.gov/release/breaking-hhs-formally-debars-ecohealth-alliance-dr-peter-daszak-after-covid-select-reveals-pandemic-era-wrongdoing/). Warum der BND diese Tatsache verschweigt, ist Teil der Spekulation. Vermutlich will man Peking alles in die Schuhe schieben, um von den eigenen Versäumnissen abzulenken. In meinem aktuellen Buch “[Der chinesische (Alp-)Traum](https://www.amazon.de/chinesische-Alb-Traum-geopolitische-Herausforderung/dp/3442317509/ref=sr_1_1?__mk_de_DE=%C3%85M%C3%85%C5%BD%C3%95%C3%91\&crid=XQVCLFVRCJJ\&dib=eyJ2IjoiMSJ9.kCJqsUXZO8NZjieNQjGy3Vez7tqktnhQynFOnuZE9249tfkKZvqdJtpIfcDiLMOyxmF7JFpMfvAC881caUEufT--GHlSCcAt_shhnVSbNLp-cle-VXel7soyPwi8xGPm88hSBKPY93BtjFYdOueFUU7qrOir_paRMiQOmCs7YOAUe7ZCKAb6YXxu_hz8N1eZhXbFcvc6p01Uu0vgIibiOHzbXxtH6ECNUaWCaHCYus4.Jzuq9IYvQtPedtE4YORWFtEmxTtrHh5xe8b-B25o5uA\&dib_tag=se\&keywords=Philipp+Mattheis\&qid=1730736669\&sprefix=philipp+mattheis%2Caps%2C111\&sr=8-1)” ist den Ereignissen in Wuhan ein ganzes Kapitel gewidmet. Es hat nichts an Aktualität eingebüßt. Alle Fakten lagen seit Jahren auf dem Tisch für jeden, den es interessiert hat. [Hier gibt es das gesamte Kapitel nachzulesen.](https://blingbling.substack.com/p/was-geschah-in-wuhan)  Auf jeden Fall zeigt dies, wie der Begriff „Verschwörungstheoretiker“ in den vergangenen Jahren zum Kampfbegriff und Waffe gemacht wurde, um Kritiker zu diffamieren, und die öffentliche Meinung ohne harte Zensur zu lenken. Ähnliches kann man aktuell beim Projekt „Digitaler Euro“ beobachten. Vermutlich kann sich kein Bürger der Europäischen Union daran erinnern, bei seiner Wahlentscheidung jemals gefragt worden zu sein, ob er die Einführung eines „digitalen Euros“ gut findet. Wurde er nämlich nicht. Er kommt aber trotzdem. EZB-Präsidentin Christine Lagarde hat das diese Woche nochmals bekräftigt: [Schon im Oktober will man die Testphase beenden](https://x.com/efenigson/status/1898382481184993711) und an der Einführung arbeiten. Nun gehört BlingBling nicht zu denjenigen, die im digitalen Euro „Orwell’sches Teufelswerk“ sehen. Strategische Dummheit trifft es besser. Worum geht es? Sogenannte Central Bank Digital Currencies (CBDC) waren vor einigen Jahren so etwas wie der letzte Schrei in der Zentralbank-Welt. Nachdem Facebook/Meta 2017/18 eine eigene Währung namens Libra auf den Markt bringen wollte, und eine obskure Internet-Währung namens Bitcoin immer mehr Anhänger fand, sahen sich viele Zentralbanken der Welt unter Zugzwang. Was man wollte: eine digitale, direkt von der Zentralbank ausgegebene Währung ohne Bugs, aber mit Features. Mit einer Digital-Währung ließe sich der internationale Zahlungsverkehr direkt und ohne Umweg über den US-Dollar abwickeln. Die Zentralbank bekäme wieder mehr direkten Einfluss auf die Geldschöpfung. Und, wie man aus China lernen konnte, ließen sich digitale Bankkonten auch ganz zum „Nudging von Bürgern“ nutzen. So spekulierten die ersten Verschwörungstheoretiker bald, [ein digitaler Euro ließe sich ja mit einem persönlichen CO2-Konto verknüpfen](https://www.derstandard.de/story/2000124296026/was-eine-digitale-co2-waehrung-fuer-das-klima-bedeuten-wuerde). Wäre letzteres einmal aufgebraucht, könnte der Konto-Inhaber einfach keinen Flug mehr buchen. Auch ließe sich eine expansive Geldpolitik, wie sie bis 2022 praktiziert wurde, ganz einfach mit Negativ-Zinsen umsetzen. Geld würde sich nominal reduzieren, was den Bürger zum Konsum animieren würde. Flüchtigen Kriminellen ließe sich per Knopfdruck das Konto sperren. Der Staat würde also über eine ganze neue Palette an Einflussmöglichkeiten verfügen. Die Aluhüte United warnten vor einem Orwellschen Überwachungsstaat. Vertreter von Regierungen und Firmen, die diesen digitalen Euro bauen sollten, beschwichtigten. Mit Ralf Wintergerst, CEO von Giesecke+Devrient, nach wie vor heißester Anwärter, um das Projekt in der EU umzusetzen, sprach ich in den vergangenen Jahren mehrmals zu dem Thema. [Zuletzt im Dezember 24](https://blingbling.substack.com/p/euro-thrash). Wintergerst versichert stets zwei Dinge: Eine Abschaffung von Bargeld sei nicht geplant. Und nur, wenn die Fluchttore Bargeld, Gold und Bitcoin geschlossen werden, greift die dystopische Version. Und zweitens, so Wintergerst, habe niemand ein chinesisches System im Sinne. Der „digitale Euro“ sei für die Bürger gedacht und das Projekt unterliege demokratischer Kontrolle. Ob er Wintergerst und dem guten im Menschen Glauben schenkt, möge jeder Leser selbst entscheiden. Das Interessantere ist ohnehin, dass der digitale Euro ein strategisch dummes Projekt ist. Dazu muss man wissen, dass eine solche Zentralbankwährung Banken im weitesten Sinne überflüssig macht. Kontos bei Privatbanken werden obsolet, genauso wie Spar-, Fest- und Tagesgeld-Strukturen. Deshalb soll der digitale Euro zunächst auf 3000 Euro pro Bürger beschränkt werden. Das ist also nicht als Maximal-Vermögen gedacht, das dann jedem sozialistischen Einheits-EU-Menschen noch zusteht, sondern dient dazu, das Bankensystem nicht kollabieren zu lassen. Aber wozu überhaupt „ein bisschen digitaler Euro“? In den USA setzt man mittlerweile 100 Prozent auf die private Alternative: Stablecoins wie Tether (USDT) und Circle (USDC) sind nichts anderes als digitale Währungen. Nur sind sie nicht von einer Zentralbank ausgeben, sondern von privaten Anbietern. Tether hat technisch die Möglichkeit, einen Inhaber vom Zahlungsverkehr auszusperren. Nur dürfte es davon kaum Gebrauch machen, will das Unternehmen nicht rasant Kunden an die Konkurrenz verlieren. Da USDT und USDC mit US-Dollar gedeckt sind (oder zumindest sein sollten, *looking at you, Tether!*), stärken sie außerdem die Rolle des US-Dollars als Leitwährung. Und da die USA sich aktuell sehr über Käufer von Staatsanleihen freuen, um die Zinsen zu drücken, und [Tether einer der größten Halter von US-Staatsanleihen is](https://crypto.news/tether-treasury-holdings-boost-us-debt-resilience-2025/)t, wird es den digitalen Dollar bis auf Weiteres nicht geben. Den digitalen Yuan gibt es, aber von einer großen Akzeptanz oder Durchdringung der chinesischen Wirtschaft lässt sich nicht sprechen. Kontrolle kann der chinesische Staat ohnehin über seine omnipräsenten Apps WeChat und Alipay ausüben. Was den internationalen Zahlungsverkehr betrifft, [scheint man aktuell eher auf Gold zu setzen](https://blingbling.substack.com/p/goldfinger). Übrig also bleibt die EU mit einem Projekt, das bereits Milliarden an Entwicklungskosten verschlungen hat. Am Ende bleibt dann ein Mini-Digitaler-Euro in Höhe von 3000 Euro, den niemand wollte, und niemand braucht. Helfen könnte er allerdings beim Projekt “Mobilisierung der Sparguthaben”. Der Ausdruck geht auf Friedrich Merz zurück. Ursula von der Leyen paraphrasierte ihn jüngst:  [Irgendwie müssen die Billionen von Sparguthaben in Militär-Investitionen umgewandelt werden](https://blingbling.substack.com/p/panzer-statt-autos). Das wird am besten funktionieren mit Anleihen, die schlechter verzinst sind als sonst auf dem Markt üblich. Wie bringt man Leute dazu, dann ihr Geld dort zu investieren? Entweder man zwingt sie, oder man bewirbt die Anleihen mit viel Patriotismus und Propaganda. Die Verschwörungstheoretiker unter uns bekommen also bald Futter, wenn die „Spar- und Investitionsunion” vorgestellt wird. Like, wenn Dein Aluhut glüht… *Hinter der Paywall: Wie das Trump-Derangement-Syndrom den Blick auf den Markt trübt. **[Wie es mit Bitcoin, Gold und Aktien weitergeht.](https://blingbling.substack.com/p/gluhende-aluhute)***
@ b8af284d:f82c91dd
2025-03-16 16:42:49 Liebe Abonnenten, diejenigen, die diese Publikation schon länger abonniert haben, wissen, dass hier immer wieder über den Ursprung des Corona-Virus in einem Labor in Wuhan berichtet wurde. Seit diese Woche ist es „offiziell“ - [der Bundesnachrichtendienst (BND) hält den Labor-Ursprung für die wahrscheinlichste Variante](https://www.zeit.de/2025/11/coronavirus-ursprung-wuhan-labor-china-bnd). Jetzt kann man sich fragen, warum der BND plötzlich umschwenkt: Will man proaktiv erscheinen, weil man die Wahrheit nicht mehr länger verbergen kann? Oder will man die enttäuschten Bürger zurückgewinnen, die aufgrund der Lügen während der Corona-Zeit zunehmend mit Parteien links und rechts außen sympathisiert haben, weil diese die einzigen waren, die den Irrsinn nicht mitgetragen haben? Auffallend bei den „Recherchen“, die in Wahrheit keine sind, sondern Verlautbarungen des deutschen Geheimdienstes, ist auch das völlige Schweigen über die US-amerikanischen Verwicklungen in das Projekt. [In Wuhan wurde mit amerikanischem Geld geforscht](https://oversight.house.gov/release/breaking-hhs-formally-debars-ecohealth-alliance-dr-peter-daszak-after-covid-select-reveals-pandemic-era-wrongdoing/). Warum der BND diese Tatsache verschweigt, ist Teil der Spekulation. Vermutlich will man Peking alles in die Schuhe schieben, um von den eigenen Versäumnissen abzulenken. In meinem aktuellen Buch “[Der chinesische (Alp-)Traum](https://www.amazon.de/chinesische-Alb-Traum-geopolitische-Herausforderung/dp/3442317509/ref=sr_1_1?__mk_de_DE=%C3%85M%C3%85%C5%BD%C3%95%C3%91\&crid=XQVCLFVRCJJ\&dib=eyJ2IjoiMSJ9.kCJqsUXZO8NZjieNQjGy3Vez7tqktnhQynFOnuZE9249tfkKZvqdJtpIfcDiLMOyxmF7JFpMfvAC881caUEufT--GHlSCcAt_shhnVSbNLp-cle-VXel7soyPwi8xGPm88hSBKPY93BtjFYdOueFUU7qrOir_paRMiQOmCs7YOAUe7ZCKAb6YXxu_hz8N1eZhXbFcvc6p01Uu0vgIibiOHzbXxtH6ECNUaWCaHCYus4.Jzuq9IYvQtPedtE4YORWFtEmxTtrHh5xe8b-B25o5uA\&dib_tag=se\&keywords=Philipp+Mattheis\&qid=1730736669\&sprefix=philipp+mattheis%2Caps%2C111\&sr=8-1)” ist den Ereignissen in Wuhan ein ganzes Kapitel gewidmet. Es hat nichts an Aktualität eingebüßt. Alle Fakten lagen seit Jahren auf dem Tisch für jeden, den es interessiert hat. [Hier gibt es das gesamte Kapitel nachzulesen.](https://blingbling.substack.com/p/was-geschah-in-wuhan)  Auf jeden Fall zeigt dies, wie der Begriff „Verschwörungstheoretiker“ in den vergangenen Jahren zum Kampfbegriff und Waffe gemacht wurde, um Kritiker zu diffamieren, und die öffentliche Meinung ohne harte Zensur zu lenken. Ähnliches kann man aktuell beim Projekt „Digitaler Euro“ beobachten. Vermutlich kann sich kein Bürger der Europäischen Union daran erinnern, bei seiner Wahlentscheidung jemals gefragt worden zu sein, ob er die Einführung eines „digitalen Euros“ gut findet. Wurde er nämlich nicht. Er kommt aber trotzdem. EZB-Präsidentin Christine Lagarde hat das diese Woche nochmals bekräftigt: [Schon im Oktober will man die Testphase beenden](https://x.com/efenigson/status/1898382481184993711) und an der Einführung arbeiten. Nun gehört BlingBling nicht zu denjenigen, die im digitalen Euro „Orwell’sches Teufelswerk“ sehen. Strategische Dummheit trifft es besser. Worum geht es? Sogenannte Central Bank Digital Currencies (CBDC) waren vor einigen Jahren so etwas wie der letzte Schrei in der Zentralbank-Welt. Nachdem Facebook/Meta 2017/18 eine eigene Währung namens Libra auf den Markt bringen wollte, und eine obskure Internet-Währung namens Bitcoin immer mehr Anhänger fand, sahen sich viele Zentralbanken der Welt unter Zugzwang. Was man wollte: eine digitale, direkt von der Zentralbank ausgegebene Währung ohne Bugs, aber mit Features. Mit einer Digital-Währung ließe sich der internationale Zahlungsverkehr direkt und ohne Umweg über den US-Dollar abwickeln. Die Zentralbank bekäme wieder mehr direkten Einfluss auf die Geldschöpfung. Und, wie man aus China lernen konnte, ließen sich digitale Bankkonten auch ganz zum „Nudging von Bürgern“ nutzen. So spekulierten die ersten Verschwörungstheoretiker bald, [ein digitaler Euro ließe sich ja mit einem persönlichen CO2-Konto verknüpfen](https://www.derstandard.de/story/2000124296026/was-eine-digitale-co2-waehrung-fuer-das-klima-bedeuten-wuerde). Wäre letzteres einmal aufgebraucht, könnte der Konto-Inhaber einfach keinen Flug mehr buchen. Auch ließe sich eine expansive Geldpolitik, wie sie bis 2022 praktiziert wurde, ganz einfach mit Negativ-Zinsen umsetzen. Geld würde sich nominal reduzieren, was den Bürger zum Konsum animieren würde. Flüchtigen Kriminellen ließe sich per Knopfdruck das Konto sperren. Der Staat würde also über eine ganze neue Palette an Einflussmöglichkeiten verfügen. Die Aluhüte United warnten vor einem Orwellschen Überwachungsstaat. Vertreter von Regierungen und Firmen, die diesen digitalen Euro bauen sollten, beschwichtigten. Mit Ralf Wintergerst, CEO von Giesecke+Devrient, nach wie vor heißester Anwärter, um das Projekt in der EU umzusetzen, sprach ich in den vergangenen Jahren mehrmals zu dem Thema. [Zuletzt im Dezember 24](https://blingbling.substack.com/p/euro-thrash). Wintergerst versichert stets zwei Dinge: Eine Abschaffung von Bargeld sei nicht geplant. Und nur, wenn die Fluchttore Bargeld, Gold und Bitcoin geschlossen werden, greift die dystopische Version. Und zweitens, so Wintergerst, habe niemand ein chinesisches System im Sinne. Der „digitale Euro“ sei für die Bürger gedacht und das Projekt unterliege demokratischer Kontrolle. Ob er Wintergerst und dem guten im Menschen Glauben schenkt, möge jeder Leser selbst entscheiden. Das Interessantere ist ohnehin, dass der digitale Euro ein strategisch dummes Projekt ist. Dazu muss man wissen, dass eine solche Zentralbankwährung Banken im weitesten Sinne überflüssig macht. Kontos bei Privatbanken werden obsolet, genauso wie Spar-, Fest- und Tagesgeld-Strukturen. Deshalb soll der digitale Euro zunächst auf 3000 Euro pro Bürger beschränkt werden. Das ist also nicht als Maximal-Vermögen gedacht, das dann jedem sozialistischen Einheits-EU-Menschen noch zusteht, sondern dient dazu, das Bankensystem nicht kollabieren zu lassen. Aber wozu überhaupt „ein bisschen digitaler Euro“? In den USA setzt man mittlerweile 100 Prozent auf die private Alternative: Stablecoins wie Tether (USDT) und Circle (USDC) sind nichts anderes als digitale Währungen. Nur sind sie nicht von einer Zentralbank ausgeben, sondern von privaten Anbietern. Tether hat technisch die Möglichkeit, einen Inhaber vom Zahlungsverkehr auszusperren. Nur dürfte es davon kaum Gebrauch machen, will das Unternehmen nicht rasant Kunden an die Konkurrenz verlieren. Da USDT und USDC mit US-Dollar gedeckt sind (oder zumindest sein sollten, *looking at you, Tether!*), stärken sie außerdem die Rolle des US-Dollars als Leitwährung. Und da die USA sich aktuell sehr über Käufer von Staatsanleihen freuen, um die Zinsen zu drücken, und [Tether einer der größten Halter von US-Staatsanleihen is](https://crypto.news/tether-treasury-holdings-boost-us-debt-resilience-2025/)t, wird es den digitalen Dollar bis auf Weiteres nicht geben. Den digitalen Yuan gibt es, aber von einer großen Akzeptanz oder Durchdringung der chinesischen Wirtschaft lässt sich nicht sprechen. Kontrolle kann der chinesische Staat ohnehin über seine omnipräsenten Apps WeChat und Alipay ausüben. Was den internationalen Zahlungsverkehr betrifft, [scheint man aktuell eher auf Gold zu setzen](https://blingbling.substack.com/p/goldfinger). Übrig also bleibt die EU mit einem Projekt, das bereits Milliarden an Entwicklungskosten verschlungen hat. Am Ende bleibt dann ein Mini-Digitaler-Euro in Höhe von 3000 Euro, den niemand wollte, und niemand braucht. Helfen könnte er allerdings beim Projekt “Mobilisierung der Sparguthaben”. Der Ausdruck geht auf Friedrich Merz zurück. Ursula von der Leyen paraphrasierte ihn jüngst:  [Irgendwie müssen die Billionen von Sparguthaben in Militär-Investitionen umgewandelt werden](https://blingbling.substack.com/p/panzer-statt-autos). Das wird am besten funktionieren mit Anleihen, die schlechter verzinst sind als sonst auf dem Markt üblich. Wie bringt man Leute dazu, dann ihr Geld dort zu investieren? Entweder man zwingt sie, oder man bewirbt die Anleihen mit viel Patriotismus und Propaganda. Die Verschwörungstheoretiker unter uns bekommen also bald Futter, wenn die „Spar- und Investitionsunion” vorgestellt wird. Like, wenn Dein Aluhut glüht… *Hinter der Paywall: Wie das Trump-Derangement-Syndrom den Blick auf den Markt trübt. **[Wie es mit Bitcoin, Gold und Aktien weitergeht.](https://blingbling.substack.com/p/gluhende-aluhute)*** @ f3873798:24b3f2f3
2025-03-31 20:14:31Olá, nostrilianos! O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens. Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos. Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI. Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens. ### Grok: Destaque na criação de imagens e fontes  O Grok me impressiona especialmente em dois aspectos. Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual. Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados. ### ChatGPT: Assertividade e clareza  Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas. Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões. Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas. Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras. A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual. ### Minha opinião  Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor. Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas.
@ f3873798:24b3f2f3
2025-03-31 20:14:31Olá, nostrilianos! O tema de hoje é inteligência artificial (IA), com foco em duas ferramentas que têm se destacado no mercado por sua capacidade de responder perguntas, auxiliar em tarefas e, em alguns casos, até gerar imagens. Essas tecnologias estão cada vez mais presentes no dia a dia, ajudando desde a correção de textos até pesquisas rápidas e a criação de imagens personalizadas com base em prompts específicos. Nesse cenário em expansão, duas IAs se sobressaem: o ChatGPT, desenvolvido pela OpenAI, e o Grok, criado pela xAI. Ambas são ferramentas poderosas, cada uma com seus pontos fortes e limitações, e têm conquistado usuários ao redor do mundo. Neste artigo, compartilho minhas impressões sobre essas duas IAs, baseadas em minha experiência pessoal, destacando suas diferenças e vantagens. ### Grok: Destaque na criação de imagens e fontes  O Grok me impressiona especialmente em dois aspectos. Primeiro, sua capacidade de gerar imagens é um diferencial significativo. Enquanto o ChatGPT tem limitações nesse quesito, o Grok oferece uma funcionalidade mais robusta para criar visuais únicos a partir de prompts, o que pode ser uma vantagem para quem busca criatividade visual. Segundo, o Grok frequentemente cita fontes ou indica a origem das informações que fornece, o que agrega credibilidade às suas respostas e facilita a verificação dos dados. ### ChatGPT: Assertividade e clareza  Por outro lado, o ChatGPT se destaca pela assertividade e pela clareza em suas explicações. Suas respostas tendem a ser mais diretas e concisas, o que é ideal para quem busca soluções rápidas ou explicações objetivas. Acredito que essa vantagem possa estar ligada ao fato de o ChatGPT estar em operação há mais tempo, tendo passado por anos de aprimoramento e ajustes com base em interações de usuários.Comparação e reflexões. Em minha experiência, o Grok supera o ChatGPT na geração de imagens e na citação de fontes, enquanto o ChatGPT leva a melhor em precisão e simplicidade nas respostas. Esses pontos refletem não apenas as prioridades de design de cada IA, mas também o tempo de desenvolvimento e os objetivos de suas respectivas empresas criadoras. A OpenAI, por trás do ChatGPT, focou em refinamento conversacional, enquanto a xAI, com o Grok, parece investir em funcionalidades adicionais, como a criação de conteúdo visual. ### Minha opinião  Não há um vencedor absoluto entre Grok e ChatGPT – a escolha depende do que você precisa. Se seu foco é geração de imagens ou rastreamento de fontes, o Grok pode ser a melhor opção. Se busca respostas rápidas e assertivas, o ChatGPT provavelmente atenderá melhor. Ambas as IAs são ferramentas incríveis, e o mais fascinante é ver como elas continuam evoluindo, moldando o futuro da interação entre humanos e máquinas. @ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions. My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change. Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it. I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay. I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene. That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results. In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it. I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful. Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself. If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜 Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem. https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions. My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change. Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it. I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay. I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene. That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results. In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it. I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful. Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself. If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜 Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem. https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion @ 22aa8151:ae9b5954
2025-03-31 07:44:15With all the current hype around Payjoin for the month, I'm open-sourcing a project I developed five years ago: [https://github.com/Kukks/PrivatePond](Private Pond) Note: this project is unmaintained and should only be used as inspiration. Private Pond is a Bitcoin Payjoin application I built specifically to optimize Bitcoin transaction rails for services, such as deposits, withdrawals, and automated wallet rebalancing. The core concept is straightforward: withdrawals requested by users are queued and processed at fixed intervals, enabling traditional, efficient **transaction batching**. Simultaneously, deposits from other users can automatically batch these withdrawals via **Payjoin batching**, reducing them onchain footprint further. Taking it to the next step: a user's deposit is able to fund the withdrawals with its own funds reducing the required operational liquidity in hot wallets through a process called the **Meta Payjoin**. The application supports multiple wallets—hot, cold, multisig, or hybrid—with configurable rules, enabling automated internal fund management and seamless rebalancing based on operational needs such as min/max balance limits and wallet ratios (10% hot, 80% in 2-of-3, 10% in 1-of-2, etc) . This system naturally leverages user Payjoin transactions as part of the automated rebalancing strategy, improving liquidity management by batching server operations with user interactions. Private Pond remains quite possibly the most advanced Payjoin project today, though my [multi-party addendum of 2023](https://x.com/MrKukks/status/1690662070935564289) probably competes. That said, Payjoin adoption overall has been disappointing: the incentives heavily favor service operators who must in turn actively encourage user participation, limiting its appeal only for specialized usage. This is why my efforts refocused on systems like Wabisabi coinjoins, delivering not just great privacy but all the benefits of advanced Payjoin batching on a greater scale through **output compaction**. Soon, I'll also open-source my prototype coinjoin protocol, **Kompaktor**, demonstrating significant scalability improvements, such as 50+ payments from different senders being compacted into a **single Bitcoin output**. And this is not even mentioning [Ark](https://arklabs.to), that pushes these concepts even further, giving insane scalability and asyncrhonous execution. You can take a look at the slides I did around this here: https://miro.com/app/board/uXjVL-UqP4g=/ Parts of Private Pond, the pending transfers and multisig, will soon be integrated into nostr:npub155m2k8ml8sqn8w4dhh689vdv0t2twa8dgvkpnzfggxf4wfughjsq2cdcvg 's next major release—special thanks to nostr:npub1j8y6tcdfw3q3f3h794s6un0gyc5742s0k5h5s2yqj0r70cpklqeqjavrvg for continuing the work and getting it to the finish line.
@ 22aa8151:ae9b5954
2025-03-31 07:44:15With all the current hype around Payjoin for the month, I'm open-sourcing a project I developed five years ago: [https://github.com/Kukks/PrivatePond](Private Pond) Note: this project is unmaintained and should only be used as inspiration. Private Pond is a Bitcoin Payjoin application I built specifically to optimize Bitcoin transaction rails for services, such as deposits, withdrawals, and automated wallet rebalancing. The core concept is straightforward: withdrawals requested by users are queued and processed at fixed intervals, enabling traditional, efficient **transaction batching**. Simultaneously, deposits from other users can automatically batch these withdrawals via **Payjoin batching**, reducing them onchain footprint further. Taking it to the next step: a user's deposit is able to fund the withdrawals with its own funds reducing the required operational liquidity in hot wallets through a process called the **Meta Payjoin**. The application supports multiple wallets—hot, cold, multisig, or hybrid—with configurable rules, enabling automated internal fund management and seamless rebalancing based on operational needs such as min/max balance limits and wallet ratios (10% hot, 80% in 2-of-3, 10% in 1-of-2, etc) . This system naturally leverages user Payjoin transactions as part of the automated rebalancing strategy, improving liquidity management by batching server operations with user interactions. Private Pond remains quite possibly the most advanced Payjoin project today, though my [multi-party addendum of 2023](https://x.com/MrKukks/status/1690662070935564289) probably competes. That said, Payjoin adoption overall has been disappointing: the incentives heavily favor service operators who must in turn actively encourage user participation, limiting its appeal only for specialized usage. This is why my efforts refocused on systems like Wabisabi coinjoins, delivering not just great privacy but all the benefits of advanced Payjoin batching on a greater scale through **output compaction**. Soon, I'll also open-source my prototype coinjoin protocol, **Kompaktor**, demonstrating significant scalability improvements, such as 50+ payments from different senders being compacted into a **single Bitcoin output**. And this is not even mentioning [Ark](https://arklabs.to), that pushes these concepts even further, giving insane scalability and asyncrhonous execution. You can take a look at the slides I did around this here: https://miro.com/app/board/uXjVL-UqP4g=/ Parts of Private Pond, the pending transfers and multisig, will soon be integrated into nostr:npub155m2k8ml8sqn8w4dhh689vdv0t2twa8dgvkpnzfggxf4wfughjsq2cdcvg 's next major release—special thanks to nostr:npub1j8y6tcdfw3q3f3h794s6un0gyc5742s0k5h5s2yqj0r70cpklqeqjavrvg for continuing the work and getting it to the finish line. @ a95c6243:d345522c
2025-03-15 10:56:08*Was nützt die schönste Schuldenbremse, wenn der Russe vor der Tür steht?* *\ Wir können uns verteidigen lernen oder alle Russisch lernen.* *\ Jens Spahn*   **In der Politik ist buchstäblich keine Idee zu riskant, kein Mittel zu schäbig und keine Lüge zu dreist,** als dass sie nicht benutzt würden. Aber der Clou ist, dass diese Masche immer noch funktioniert, wenn nicht sogar immer besser. Ist das alles wirklich so schwer zu durchschauen? Mir fehlen langsam die Worte. **Aktuell werden sowohl in der Europäischen Union als auch in Deutschland** riesige Milliardenpakete für die [Aufrüstung](https://transition-news.org/eu-halt-weiter-kurs-auf-krieg-hunderte-milliarden-fur-aufrustung-beschlossen) – also für die Rüstungsindustrie – geschnürt. Die EU will 800 Milliarden Euro locker machen, in Deutschland sollen es 500 Milliarden «Sondervermögen» sein. Verteidigung nennen das unsere «Führer», innerhalb der Union und auch an «unserer Ostflanke», der Ukraine. **Das nötige Feindbild konnte inzwischen signifikant erweitert werden.** Schuld an allem und zudem gefährlich ist nicht mehr nur Putin, sondern jetzt auch Trump. Europa müsse sich sowohl gegen Russland als auch gegen die USA schützen und rüsten, wird uns eingetrichtert. **Und während durch Diplomatie genau dieser beiden Staaten** gerade endlich mal Bewegung in die Bemühungen um einen Frieden oder wenigstens einen Waffenstillstand in der Ukraine kommt, rasselt man im moralisch überlegenen Zeigefinger-Europa so richtig mit dem Säbel. **Begleitet und gestützt wird der ganze Prozess** – wie sollte es anders sein – von den «Qualitätsmedien». Dass Russland einen Angriff auf «Europa» plant, weiß nicht nur der deutsche Verteidigungsminister (und mit Abstand beliebteste Politiker) Pistorius, sondern dank ihnen auch jedes Kind. Uns bleiben nur noch wenige Jahre. Zum Glück bereitet sich die Bundeswehr schon sehr konkret [auf einen Krieg](https://archive.is/VE8ZM) vor. **Die** ***FAZ*** **und Corona-Gesundheitsminister Spahn markieren einen traurigen Höhepunkt.** Hier haben sich «politische und publizistische Verantwortungslosigkeit propagandistisch gegenseitig befruchtet», wie es bei den *NachDenkSeiten* [heißt](https://www.nachdenkseiten.de/?p=130064). Die Aussage Spahns in dem Interview, «der Russe steht vor der Tür», ist das eine. Die Zeitung verschärfte die Sache jedoch, indem sie das Zitat explizit in den [Titel](https://archive.is/QJdID) übernahm, der in einer [ersten Version](https://archive.is/fNuGA) scheinbar zu harmlos war. **Eine große Mehrheit der deutschen Bevölkerung findet Aufrüstung und mehr Schulden toll,** wie *[ARD](https://archive.is/M3DSk)* und *[ZDF](https://archive.is/ggvJB)* sehr passend ermittelt haben wollen. Ähnliches gelte für eine noch stärkere militärische Unterstützung der Ukraine. Etwas skeptischer seien die Befragten bezüglich der Entsendung von Bundeswehrsoldaten dorthin, aber immerhin etwa fifty-fifty. **Eigentlich ist jedoch die Meinung der Menschen in «unseren Demokratien» irrelevant.** Sowohl in der Europäischen Union als auch in Deutschland sind die «Eliten» offenbar der Ansicht, der Souverän habe in Fragen von Krieg und Frieden sowie von aberwitzigen astronomischen Schulden kein Wörtchen mitzureden. Frau von der Leyen möchte über 150 Milliarden aus dem Gesamtpaket unter Verwendung von Artikel 122 des EU-Vertrags ohne das Europäische Parlament entscheiden – wenn auch nicht völlig [kritiklos](https://www.berliner-zeitung.de/politik-gesellschaft/geopolitik/aufruestung-widerstand-gegen-eu-plaene-waechst-kommission-uebertreibt-russische-gefahr-li.2306863). **In Deutschland wollen CDU/CSU und SPD zur Aufweichung der «Schuldenbremse»** mehrere Änderungen des Grundgesetzes durch das abgewählte Parlament peitschen. Dieser Versuch, mit dem alten [Bundestag](https://www.bundestag.de/dokumente/textarchiv/2025/kw11-de-sondersitzung-1056228) eine Zweidrittelmehrheit zu erzielen, die im neuen nicht mehr gegeben wäre, ist mindestens verfassungsrechtlich umstritten. **Das Manöver scheint aber zu funktionieren.** Heute haben die Grünen [zugestimmt](https://www.reuters.com/world/europe/germany-faces-debt-deal-cliffhanger-merz-strives-greens-backing-2025-03-14/), nachdem Kanzlerkandidat Merz läppische 100 Milliarden für «irgendwas mit Klima» zugesichert hatte. Die Abstimmung im Plenum soll am kommenden Dienstag erfolgen – nur eine Woche, bevor sich der neu gewählte Bundestag konstituieren wird. **Interessant sind die Argumente, die BlackRocker Merz für seine Attacke** auf Grundgesetz und Demokratie ins Feld führt. Abgesehen von der angeblichen Eile, «unsere Verteidigungsfähigkeit deutlich zu erhöhen» (ausgelöst unter anderem durch «die Münchner Sicherheitskonferenz und die Ereignisse im Weißen Haus»), ließ uns der CDU-Chef wissen, dass Deutschland einfach auf die internationale Bühne zurück müsse. Merz [schwadronierte](https://x.com/CDU/status/1900168761686044894) gefährlich mehrdeutig: > «Die ganze Welt schaut in diesen Tagen und Wochen auf Deutschland. Wir haben in der Europäischen Union und auf der Welt eine Aufgabe, die weit über die Grenzen unseres eigenen Landes hinausgeht.»      *\[Titelbild:* *[Tag des Sieges](https://pixabay.com/de/photos/parade-tag-des-sieges-samara-182508/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/propaganda-wahnsinn-und-demokratur)*** erschienen.
@ a95c6243:d345522c
2025-03-15 10:56:08*Was nützt die schönste Schuldenbremse, wenn der Russe vor der Tür steht?* *\ Wir können uns verteidigen lernen oder alle Russisch lernen.* *\ Jens Spahn*   **In der Politik ist buchstäblich keine Idee zu riskant, kein Mittel zu schäbig und keine Lüge zu dreist,** als dass sie nicht benutzt würden. Aber der Clou ist, dass diese Masche immer noch funktioniert, wenn nicht sogar immer besser. Ist das alles wirklich so schwer zu durchschauen? Mir fehlen langsam die Worte. **Aktuell werden sowohl in der Europäischen Union als auch in Deutschland** riesige Milliardenpakete für die [Aufrüstung](https://transition-news.org/eu-halt-weiter-kurs-auf-krieg-hunderte-milliarden-fur-aufrustung-beschlossen) – also für die Rüstungsindustrie – geschnürt. Die EU will 800 Milliarden Euro locker machen, in Deutschland sollen es 500 Milliarden «Sondervermögen» sein. Verteidigung nennen das unsere «Führer», innerhalb der Union und auch an «unserer Ostflanke», der Ukraine. **Das nötige Feindbild konnte inzwischen signifikant erweitert werden.** Schuld an allem und zudem gefährlich ist nicht mehr nur Putin, sondern jetzt auch Trump. Europa müsse sich sowohl gegen Russland als auch gegen die USA schützen und rüsten, wird uns eingetrichtert. **Und während durch Diplomatie genau dieser beiden Staaten** gerade endlich mal Bewegung in die Bemühungen um einen Frieden oder wenigstens einen Waffenstillstand in der Ukraine kommt, rasselt man im moralisch überlegenen Zeigefinger-Europa so richtig mit dem Säbel. **Begleitet und gestützt wird der ganze Prozess** – wie sollte es anders sein – von den «Qualitätsmedien». Dass Russland einen Angriff auf «Europa» plant, weiß nicht nur der deutsche Verteidigungsminister (und mit Abstand beliebteste Politiker) Pistorius, sondern dank ihnen auch jedes Kind. Uns bleiben nur noch wenige Jahre. Zum Glück bereitet sich die Bundeswehr schon sehr konkret [auf einen Krieg](https://archive.is/VE8ZM) vor. **Die** ***FAZ*** **und Corona-Gesundheitsminister Spahn markieren einen traurigen Höhepunkt.** Hier haben sich «politische und publizistische Verantwortungslosigkeit propagandistisch gegenseitig befruchtet», wie es bei den *NachDenkSeiten* [heißt](https://www.nachdenkseiten.de/?p=130064). Die Aussage Spahns in dem Interview, «der Russe steht vor der Tür», ist das eine. Die Zeitung verschärfte die Sache jedoch, indem sie das Zitat explizit in den [Titel](https://archive.is/QJdID) übernahm, der in einer [ersten Version](https://archive.is/fNuGA) scheinbar zu harmlos war. **Eine große Mehrheit der deutschen Bevölkerung findet Aufrüstung und mehr Schulden toll,** wie *[ARD](https://archive.is/M3DSk)* und *[ZDF](https://archive.is/ggvJB)* sehr passend ermittelt haben wollen. Ähnliches gelte für eine noch stärkere militärische Unterstützung der Ukraine. Etwas skeptischer seien die Befragten bezüglich der Entsendung von Bundeswehrsoldaten dorthin, aber immerhin etwa fifty-fifty. **Eigentlich ist jedoch die Meinung der Menschen in «unseren Demokratien» irrelevant.** Sowohl in der Europäischen Union als auch in Deutschland sind die «Eliten» offenbar der Ansicht, der Souverän habe in Fragen von Krieg und Frieden sowie von aberwitzigen astronomischen Schulden kein Wörtchen mitzureden. Frau von der Leyen möchte über 150 Milliarden aus dem Gesamtpaket unter Verwendung von Artikel 122 des EU-Vertrags ohne das Europäische Parlament entscheiden – wenn auch nicht völlig [kritiklos](https://www.berliner-zeitung.de/politik-gesellschaft/geopolitik/aufruestung-widerstand-gegen-eu-plaene-waechst-kommission-uebertreibt-russische-gefahr-li.2306863). **In Deutschland wollen CDU/CSU und SPD zur Aufweichung der «Schuldenbremse»** mehrere Änderungen des Grundgesetzes durch das abgewählte Parlament peitschen. Dieser Versuch, mit dem alten [Bundestag](https://www.bundestag.de/dokumente/textarchiv/2025/kw11-de-sondersitzung-1056228) eine Zweidrittelmehrheit zu erzielen, die im neuen nicht mehr gegeben wäre, ist mindestens verfassungsrechtlich umstritten. **Das Manöver scheint aber zu funktionieren.** Heute haben die Grünen [zugestimmt](https://www.reuters.com/world/europe/germany-faces-debt-deal-cliffhanger-merz-strives-greens-backing-2025-03-14/), nachdem Kanzlerkandidat Merz läppische 100 Milliarden für «irgendwas mit Klima» zugesichert hatte. Die Abstimmung im Plenum soll am kommenden Dienstag erfolgen – nur eine Woche, bevor sich der neu gewählte Bundestag konstituieren wird. **Interessant sind die Argumente, die BlackRocker Merz für seine Attacke** auf Grundgesetz und Demokratie ins Feld führt. Abgesehen von der angeblichen Eile, «unsere Verteidigungsfähigkeit deutlich zu erhöhen» (ausgelöst unter anderem durch «die Münchner Sicherheitskonferenz und die Ereignisse im Weißen Haus»), ließ uns der CDU-Chef wissen, dass Deutschland einfach auf die internationale Bühne zurück müsse. Merz [schwadronierte](https://x.com/CDU/status/1900168761686044894) gefährlich mehrdeutig: > «Die ganze Welt schaut in diesen Tagen und Wochen auf Deutschland. Wir haben in der Europäischen Union und auf der Welt eine Aufgabe, die weit über die Grenzen unseres eigenen Landes hinausgeht.»      *\[Titelbild:* *[Tag des Sieges](https://pixabay.com/de/photos/parade-tag-des-sieges-samara-182508/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/propaganda-wahnsinn-und-demokratur)*** erschienen. @ d5c3d063:4d1159b3
2025-03-31 03:18:05ทำไมทุกครั้งที่รัฐแจกเงิน คนถึงเฮ..ดีใจ แต่พอพูดถึงตลาดเสรี กลับโดนมองว่าใจร้าย แล้วทำไมนักเศรษฐศาสตร์กระแสหลัก ถึงยังไม่อินกับ “ตลาดเสรี” ทั้ง ๆ ที่ทุกคนก็เห็นแล้วว่าแนวคิดของ Keynes และ Marx มันล้มเหลวซ้ำแล้วซ้ำเล่าในทางปฏิบัติ แต่นักเศรษฐศาสตร์ก็ยังเอาทฤษฎีพวกนี้มาใช้อยู่ดี... ทำไมนะ ? ก็เพราะแนวคิดพวกนี้มัน “ฟังดูดี” มันให้ “คำตอบ ตำอธิบายที่ถูกใจ” มากกว่า “ความจริง ที่ฟังแล้วไม่เข้าหู” Keynes ทำให้รัฐบาลดูฉลาดขึ้นเวลาที่ใช้เงินเกินตัว ใครจะกล้าทักละว่า เฮ้ย “รัฐอย่าเพิ่งก่อหนี้นะครับ” ก็เคนส์เค้าบอกว่า “การใช้จ่ายจะช่วยกระตุ้นเศรษฐกิจ” นี่หน่า ส่วน Marx ก็สอนให้เราฝันกลางวัน ที่คนทุกคนจะต้องเท่าเทียม ไม่มีใครรวยกว่าใคร มันฟังแล้วดูดี เหมือนได้คืนความยุติธรรมให้สังคม แต่ไม่มีใครบอกว่า ราคาของความเท่าเทียมแบบปลอมๆ นั้น ต้องแลกกับ "เสรีภาพ" ที่เรามีนะ ทีนี้ ลองหันกลับมาดูตลาดเสรี มันไม่ได้พูดเพราะ (แต่ก็ไม่ได้หยาบคาย) มันไม่ได้สัญญาอะไร (ไม่ต้อง"ขอเวลาอีกไม่นาน") แต่มันซื่อสัตย์ และมันบอกกับเราตรง ๆ ว่า ถ้าอยากได้อะไรคุณต้องให้ก่อน ไม่มีใครได้อะไรฟรี ๆ และไม่มีใครมีสิทธิขโมยของจากใครไปแม้แต่นิดเดียว ฟังดูโหดไหม จะว่าโหดก็ได้ แต่มันคือโลกของคนที่ “มีความรับผิดชอบ ในชีวิตของตัวเอง” คำถามคือ...หรือจริง ๆ แล้ว...เราไม่ได้กลัวระบบ แต่เรากลัวอิสรภาพที่ไม่มีใครมารับผิดแทนเรากันแน่ . . แล้วแบบนี้ “รัฐ” ควรมีหน้าที่อะไรล่ะ ไม่ใช่ว่าเชียร์ตลาดเสรีแล้วต้องเกลียดรัฐไปหมดนะ ตลาดเสรีไม่ใช่โลกของคนไร้กฎหมาย หรือใครอยากทำอะไรก็ได้ตามใจ แต่โลกของตลาดเสรี...ต้องมี “กรรมการ” ที่คอยดูแลเกมให้มันแฟร์ และรัฐในแบบที่ควรเป็นคือ ไม่ใช่คนที่ลงมาเตะบอลแข่งกับนักเตะในสนาม แต่เป็นกรรมการที่คอย “เป่าให้ยุติธรรม” แล้วยืนดูอยู่ข้างสนามอย่างเงียบ ๆ รัฐที่ดี ไม่ใช่รัฐที่มาแจกเงิน มาอุ้มคนล้ม หรือมาคอยสั่งว่าใครควรได้อะไร แต่เป็นรัฐที่ทำหน้าที่แค่ 3 อย่างง่าย ๆ -ดูแลไม่ให้ใครมารังแกใคร -ถ้าใครตกลงอะไรกันไว้ ก็ช่วยดูให้มันเป็นธรรม -ไม่เลือกข้าง ไม่เล่นพวก ไม่ใช้อำนาจเพื่อหาเสียง ก็แค่นั้นพอแล้วจริง ๆ เพราะทันทีที่รัฐ “อยากเป็นพระเอก” เข้ามาอุ้ม อยากเป็นคนคอยแจก คอยจัดการทุกอย่าง เกมมันก็เริ่มไม่แฟร์… พอรัฐช่วยคนหนึ่ง ก็ต้องไปหยิบของจากอีกคนมา เหมือนเล่นบอลแล้วกรรมการยิงประตูให้ทีมตัวเอง แล้วสุดท้าย…มันก็กลายเป็นเกม...ที่มีแต่ คนอยาก “อยู่ฝั่งที่ถูกรัฐอุ้ม” (ทุนนิยมพวกพ้อง) ไม่ใช่ทุนนิยมหรือเกมที่เล่นด้วยความสามารถจริง ๆ รัฐที่ดี ไม่ใช่รัฐที่ “ยิ่งใหญ่ อำนาจล้นฟ้า” แต่คือรัฐที่ให้ผู้คน “ยืนได้ด้วยขาตัวเอง” แค่นี้เอง...ไม่ต้องมีสูตรซับซ้อน ไม่ต้องมีทฤษฎีเยอะ แค่มีสติ ไม่เอื้อใคร ไม่แทรกแซงเกินจำเป็นก็พอแล้ว #Siamstr
@ d5c3d063:4d1159b3
2025-03-31 03:18:05ทำไมทุกครั้งที่รัฐแจกเงิน คนถึงเฮ..ดีใจ แต่พอพูดถึงตลาดเสรี กลับโดนมองว่าใจร้าย แล้วทำไมนักเศรษฐศาสตร์กระแสหลัก ถึงยังไม่อินกับ “ตลาดเสรี” ทั้ง ๆ ที่ทุกคนก็เห็นแล้วว่าแนวคิดของ Keynes และ Marx มันล้มเหลวซ้ำแล้วซ้ำเล่าในทางปฏิบัติ แต่นักเศรษฐศาสตร์ก็ยังเอาทฤษฎีพวกนี้มาใช้อยู่ดี... ทำไมนะ ? ก็เพราะแนวคิดพวกนี้มัน “ฟังดูดี” มันให้ “คำตอบ ตำอธิบายที่ถูกใจ” มากกว่า “ความจริง ที่ฟังแล้วไม่เข้าหู” Keynes ทำให้รัฐบาลดูฉลาดขึ้นเวลาที่ใช้เงินเกินตัว ใครจะกล้าทักละว่า เฮ้ย “รัฐอย่าเพิ่งก่อหนี้นะครับ” ก็เคนส์เค้าบอกว่า “การใช้จ่ายจะช่วยกระตุ้นเศรษฐกิจ” นี่หน่า ส่วน Marx ก็สอนให้เราฝันกลางวัน ที่คนทุกคนจะต้องเท่าเทียม ไม่มีใครรวยกว่าใคร มันฟังแล้วดูดี เหมือนได้คืนความยุติธรรมให้สังคม แต่ไม่มีใครบอกว่า ราคาของความเท่าเทียมแบบปลอมๆ นั้น ต้องแลกกับ "เสรีภาพ" ที่เรามีนะ ทีนี้ ลองหันกลับมาดูตลาดเสรี มันไม่ได้พูดเพราะ (แต่ก็ไม่ได้หยาบคาย) มันไม่ได้สัญญาอะไร (ไม่ต้อง"ขอเวลาอีกไม่นาน") แต่มันซื่อสัตย์ และมันบอกกับเราตรง ๆ ว่า ถ้าอยากได้อะไรคุณต้องให้ก่อน ไม่มีใครได้อะไรฟรี ๆ และไม่มีใครมีสิทธิขโมยของจากใครไปแม้แต่นิดเดียว ฟังดูโหดไหม จะว่าโหดก็ได้ แต่มันคือโลกของคนที่ “มีความรับผิดชอบ ในชีวิตของตัวเอง” คำถามคือ...หรือจริง ๆ แล้ว...เราไม่ได้กลัวระบบ แต่เรากลัวอิสรภาพที่ไม่มีใครมารับผิดแทนเรากันแน่ . . แล้วแบบนี้ “รัฐ” ควรมีหน้าที่อะไรล่ะ ไม่ใช่ว่าเชียร์ตลาดเสรีแล้วต้องเกลียดรัฐไปหมดนะ ตลาดเสรีไม่ใช่โลกของคนไร้กฎหมาย หรือใครอยากทำอะไรก็ได้ตามใจ แต่โลกของตลาดเสรี...ต้องมี “กรรมการ” ที่คอยดูแลเกมให้มันแฟร์ และรัฐในแบบที่ควรเป็นคือ ไม่ใช่คนที่ลงมาเตะบอลแข่งกับนักเตะในสนาม แต่เป็นกรรมการที่คอย “เป่าให้ยุติธรรม” แล้วยืนดูอยู่ข้างสนามอย่างเงียบ ๆ รัฐที่ดี ไม่ใช่รัฐที่มาแจกเงิน มาอุ้มคนล้ม หรือมาคอยสั่งว่าใครควรได้อะไร แต่เป็นรัฐที่ทำหน้าที่แค่ 3 อย่างง่าย ๆ -ดูแลไม่ให้ใครมารังแกใคร -ถ้าใครตกลงอะไรกันไว้ ก็ช่วยดูให้มันเป็นธรรม -ไม่เลือกข้าง ไม่เล่นพวก ไม่ใช้อำนาจเพื่อหาเสียง ก็แค่นั้นพอแล้วจริง ๆ เพราะทันทีที่รัฐ “อยากเป็นพระเอก” เข้ามาอุ้ม อยากเป็นคนคอยแจก คอยจัดการทุกอย่าง เกมมันก็เริ่มไม่แฟร์… พอรัฐช่วยคนหนึ่ง ก็ต้องไปหยิบของจากอีกคนมา เหมือนเล่นบอลแล้วกรรมการยิงประตูให้ทีมตัวเอง แล้วสุดท้าย…มันก็กลายเป็นเกม...ที่มีแต่ คนอยาก “อยู่ฝั่งที่ถูกรัฐอุ้ม” (ทุนนิยมพวกพ้อง) ไม่ใช่ทุนนิยมหรือเกมที่เล่นด้วยความสามารถจริง ๆ รัฐที่ดี ไม่ใช่รัฐที่ “ยิ่งใหญ่ อำนาจล้นฟ้า” แต่คือรัฐที่ให้ผู้คน “ยืนได้ด้วยขาตัวเอง” แค่นี้เอง...ไม่ต้องมีสูตรซับซ้อน ไม่ต้องมีทฤษฎีเยอะ แค่มีสติ ไม่เอื้อใคร ไม่แทรกแซงเกินจำเป็นก็พอแล้ว #Siamstr @ 096ae92f:b8540e0c
2025-03-31 01:09:48## **Hal Finney’s name is etched in Bitcoin lore.** By day, Hal was a devoted husband and father; by night, a *shadowy super coder* pushing the boundaries of cryptography and how the world thinks about money. A seasoned cryptographer and ardent Bitcoin supporter, he was among the first to work with Satoshi Nakamoto on refining Bitcoin’s fledgling codebase. 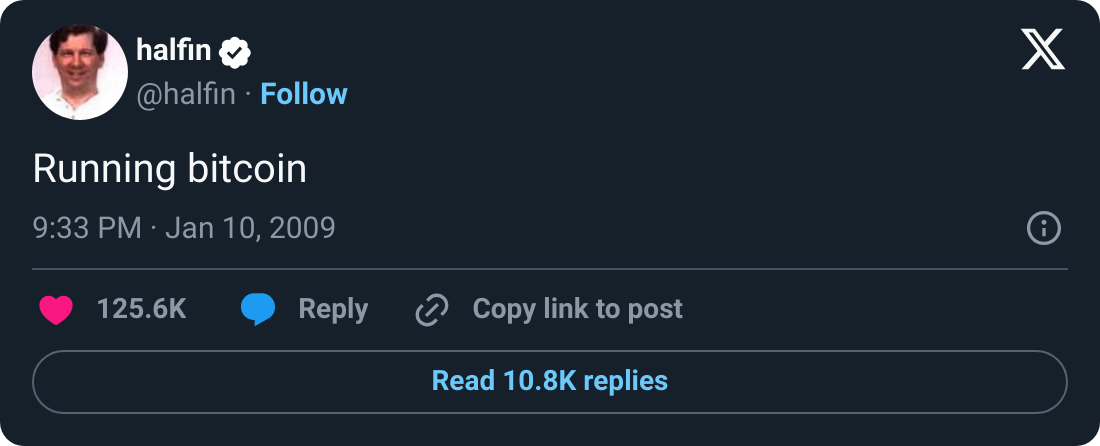January 2009, the iconic *"Running Bitcoin*" tweet was posted. Over 16 years later, people are still engaging with Hal Finney’s legendary tweet—leaving comments of gratitude, admiration, and remembrance, reflecting on how far Bitcoin has come. For many, it marks a key moment in Bitcoin’s early days. More recently, it’s also become a symbol of Hal’s passion for running and the determination he showed throughout his life. That spirit is now carried forward through the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), an ALS fundraiser co-organized by Fran Finney and supported by the Bitcoin community. ## **Shadowy Super Coder** Long before Bitcoin came along, Hal Finney was already legendary in certain circles. He was part of the cypherpunk movement in the 1990s—people who believed in using cryptography to protect individual privacy online. > ***"The computer can be used as a tool to liberate and protect people, rather than to control them."\ > -Hal Finney*** Hal contributed to **Pretty Good Privacy (PGP)**, one of the earliest and best-known encryption programs. He also dabbled in digital cash prototypes, developing something called **Reusable Proofs of Work (RPOW)**. He didn’t know it at the time, but that would prime him perfectly for a bigger innovation on the horizon. ## **Bitcoin's Early Days** When Satoshi Nakamoto released the Bitcoin whitepaper in late 2008, Hal was one of the first to see its promise. While many cryptographers waved it off, Hal responded on the mailing list enthusiastically, calling Bitcoin “a very promising idea.” He soon began corresponding directly with Satoshi. Their emails covered everything from bug fixes to big-picture possibilities for a decentralized currency. On January 12, 2009, Satoshi sent Hal **10 bitcoins**—marking the first recorded Bitcoin transaction. From that day onward, his name was woven into Bitcoin’s origin story. > ***“When Satoshi announced the first release of the software, I grabbed it right away. I think I was the first person besides Satoshi to run Bitcoin.”\ > -Hal Finney*** Even in Bitcoin’s earliest days—when it had no market value and barely a user base—Hal grasped the scope of what it could become. He saw it not just as a technical curiosity, but as a potential long-term store of value, a tool for privacy, and a monetary system that could rival gold in its resilience. He even raised early concerns about energy use from mining, showcasing just how far ahead he was thinking. At a time when most dismissed Bitcoin entirely, Hal was already envisioning the future. ## **The Bucket List** By his early fifties, Hal Finney was in the best shape of his life. He had taken up distance running in the mid-2000s—not to chase medals, but to test himself. To stay healthy, to lose some weight, and above all, to do something hard. The engineer’s mind in him craved a structure of improvement, and long-distance running delivered it. With meticulous focus, Hal crafted training plans, ran 20+ mile routes on weekends, and even checked tide charts to time his beach runs when the sand was firmest underfoot. His ultimate goal: **qualify for the Boston Marathon**. For most, Boston is a dream. For Hal, it became a personal benchmark—a physical counterpart to the mental mountains he scaled in cryptography. He trained relentlessly, logging race times, refining form, and aiming for the qualifying standard in his age group. Running was more than physical for him. It was meditative. He often ran alone, without music, simply to be in the moment—present, focused, moving forward. Running was also a shared passion. Fran often ran shorter distances while Hal trained for the longer ones. They registered for events together, cheered each other on at finish lines, and made it a part of their family rhythm. It was one more expression of Hal’s deep devotion not just to self-improvement, but to doing life side-by-side with those he loved. Hal and Fran competing in the Denver Half-Marathon together In April 2009, Hal and Fran ran the **Denver Half Marathon together**—a meaningful race and one of the first they completed side by side. At the time, Hal was deep in marathon training and hitting peak form.\ \ A month later, Hal attempted the **Los Angeles Marathon**, hoping to clock a Boston-qualifying time. But something wasn’t right. Despite all his preparation, he was forced to stop midway through the race. His body wasn’t recovering the way it used to. At first, he chalked it up to overtraining or age, but the truth would come soon after. ## **ALS Diagnosis** In August 2009, at the height of his physical and intellectual pursuits, Hal received crushing news: a diagnosis of **Amyotrophic Lateral Sclerosis (ALS)**, often referred to as Lou Gehrig’s disease. It was an especially cruel blow for a man who had just discovered a love for running and was helping birth the world’s first decentralized digital currency. ALS gradually robs people of voluntary muscle function. For Hal, it meant an uphill fight to maintain the independence and movement he cherished. 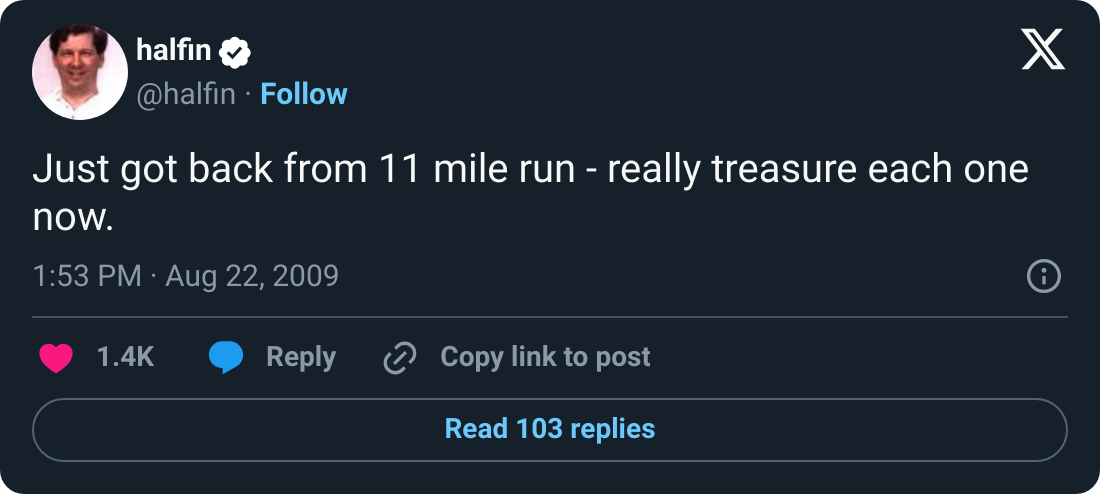Still, Hal didn’t stop. That September, **he and Fran ran the Disneyland Half Marathon together**, crossing the finish line hand in hand. It would be his last official race, but the identity of being a runner never left him—not after the diagnosis, not after the gradual loss of physical control, not even after he was confined to a wheelchair. Fran and Hal at the Disney Half Marathon. By December of that same year, Hal could no longer run. Still, he was determined not to sit on the sidelines. That winter, the couple helped organize a **relay team for the Santa Barbara International Marathon**, a race Hal had long planned to run. Friends and family joined in, and Fran ran the final leg, passing the timing chip to Hal for the last stretch. With support, **Hal walked across the finish line**, cheered on by the local running community who rallied around him. It was a symbolic moment—heartbreaking and inspiring all at once. Hal and Fran lead the Muscular Dystrophy Association relay team at the Santa Barbara International Marathon in 2009. Even as his muscles weakened, **Hal’s mind stayed sharp**, and he continued to adapt in every way he could. He and Fran began making practical changes around their home—installing ramps, adjusting routines—but emotionally, the ground was still shifting beneath them. Hal Finney humbly giving people in the future the opportunity to hear him speak before he is unable to. Fran consistently emphasized that Hal maintained a remarkably positive attitude, even as ALS took nearly everything from him physically. His optimism and determination became the emotional anchor for the entire family. > ***“He was the one who kept us all steady. He was never defeated.”\ > -Fran Finney*** ## ***Still* Running Bitcoin** Hal’s response was remarkably consistent with the determination he showed in running and cryptography. Even as the disease progressed, forcing him into a wheelchair and eventually limiting his speech, he kept coding—using assistive technologies that allowed him to control his computer through minimal eye movements. When he could no longer run physically, he continued to run test code for Bitcoin, advise other developers, and share insights on the BitcoinTalk forums. It was perseverance in its purest form. Fran was with him every step of the way. In October 2009, just months after his diagnosis, Hal published an essay titled [***“Dying Outside”***](https://www.lesswrong.com/posts/bshZiaLefDejvPKuS/dying-outside?ref=blog.austinbitcoinclub.com)—a reflection on the road ahead. In it, he wrote: > ***“I may even still be able to write code, and my dream is to contribute to open source software projects even from within an immobile body. That will be a life very much worth living."*** And he meant it. Years later, Hal collaborated with Bitcoin developer Mike Hearn on a project involving secure wallets using Trusted Computing. Even while operating at a fraction of his former speed—he estimated it was just **1/50th** of what he used to be capable of—Hal kept at it. He even engineered an Arduino-based interface to control his wheelchair with his eyes. The hacker mindset never left him. This wasn’t just about legacy. It was about living with purpose, right up to the edge of possibility. ## **Running Bitcoin Challenge** In recent years, Fran Finney—alongside members of the Bitcoin community—launched the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), a virtual event that invites people around the world to run or walk **21 kilometers** each January in honor of Hal. Timed with the anniversary of his iconic *“Running bitcoin”* tweet, the challenge raises funds for **ALS research** through the ALS Network. According to Fran, **over 80% of all donations go directly to research**, making it a deeply impactful way to contribute. **Nearly $50,000 has been raised so far.** 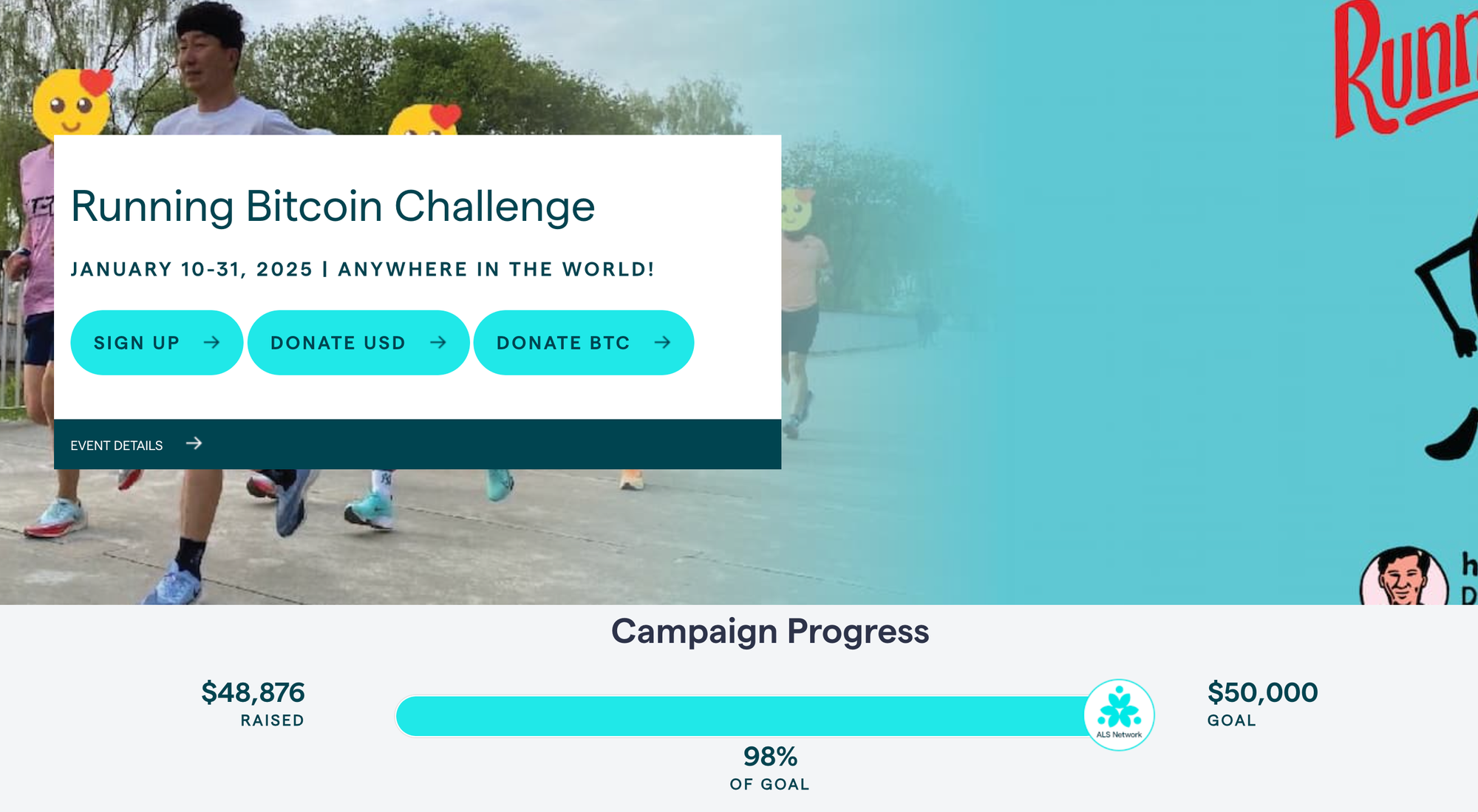It’s not the next Ice Bucket Challenge—but that’s not the point. This is something more grounded, more personal. It’s a growing movement rooted in Hal’s legacy, powered by the Bitcoin community, and driven by the hope that collective action can one day lead to a cure. > ***“Since we’re all rich with bitcoins, or we will be once they’re worth a million dollars like everyone expects, we ought to put some of this unearned wealth to good use.”\ > \ > — Hal Finney, January 2011Price of Bitcoin: $0.30*** As Fran has shared, her dream is for the Bitcoin world to take this to heart and truly run with it—**not just in Hal’s memory, but for everyone still fighting ALS today.** ## **Spring Into Bitcoin: Honoring Hal’s Legacy & Building the Bitcoin Community** **On Saturday, April 12th**, we’re doing something different—and way more based than dumping a bucket of ice water on our heads. [***Spring Into Bitcoin***](https://blog.austinbitcoinclub.com/spring-into-bitcoin/) is a one-day celebration of sound money, health, and legacy. Hosted at [**Hippo Social Club**](https://www.hipposocialclub.com/?ref=blog.austinbitcoinclub.com), the event features a professional [**trail run**](https://www.tejastrails.com/uncommon?ref=blog.austinbitcoinclub.com), a sizzling open-air beef feast, Bitcoin talks, and a wellness zone complete with a **cold plunge challenge** (the ice bucket challenge walked so the cold plunge could run 😏). [**Purchase Tickets**](https://oshi.link/lVH7Qh?ref=blog.austinbitcoinclub.com) **- General Admission** *Tickets purchased using this link will get 10% back in Bitcoin rewards compliments of [**Oshi Rewards**](https://oshi.tech/?ref=blog.austinbitcoinclub.com).* [*Purchase Race Tickets Here*](https://www.tejastrails.com/events/uncommon) *- RACE DISTANCES: Most Miles in 12 Hours, Most Miles in 6 Hours, Most Miles in 1 Hour, 5K, Canine 5K, Youth 1 Mile* It’s all in honor of Hal Finney, one of Bitcoin’s earliest pioneers and a passionate runner. **100% of event profits will be donated in Bitcoin to the ALS Network**, funding research and advocacy in Hal’s memory. Come for the cause, stay for the beef, sauna, cold plunge and to kick it with the greatest, most freedom-loving community on earth. [Please consider donating to our Run for Hal Austin team here.](https://secure.alsnetwork.org/site/TR/Endurance/General?team_id=9302&pg=team&fr_id=1510) This race officially kicks off the 2025 Run for Hal World Tour! Ok, we might be a little biased. ## **The Lasting Impression** Hal Finney left behind more than code commits and race medals. He left behind a blueprint for **resilience**—a relentless drive to do good work, to strive for personal bests, and to give back no matter the circumstances. His life reminds us that “running” is more than physical exercise or a piece of software running on your laptop. It’s about forward progress. It’s about community. It’s about optimism in the face of challenges. So, as you tie your shoelaces for your next run or sync up your Bitcoin wallet, remember Hal Finney.
@ 096ae92f:b8540e0c
2025-03-31 01:09:48## **Hal Finney’s name is etched in Bitcoin lore.** By day, Hal was a devoted husband and father; by night, a *shadowy super coder* pushing the boundaries of cryptography and how the world thinks about money. A seasoned cryptographer and ardent Bitcoin supporter, he was among the first to work with Satoshi Nakamoto on refining Bitcoin’s fledgling codebase. 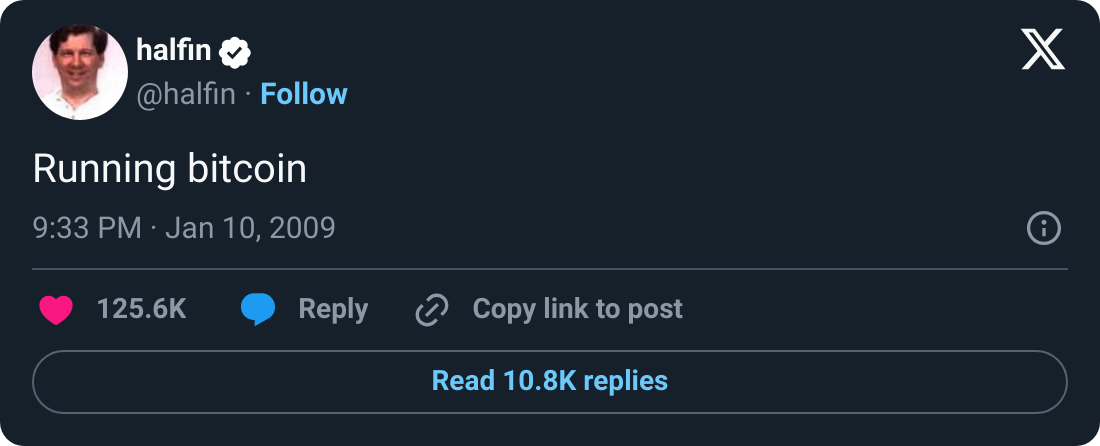January 2009, the iconic *"Running Bitcoin*" tweet was posted. Over 16 years later, people are still engaging with Hal Finney’s legendary tweet—leaving comments of gratitude, admiration, and remembrance, reflecting on how far Bitcoin has come. For many, it marks a key moment in Bitcoin’s early days. More recently, it’s also become a symbol of Hal’s passion for running and the determination he showed throughout his life. That spirit is now carried forward through the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), an ALS fundraiser co-organized by Fran Finney and supported by the Bitcoin community. ## **Shadowy Super Coder** Long before Bitcoin came along, Hal Finney was already legendary in certain circles. He was part of the cypherpunk movement in the 1990s—people who believed in using cryptography to protect individual privacy online. > ***"The computer can be used as a tool to liberate and protect people, rather than to control them."\ > -Hal Finney*** Hal contributed to **Pretty Good Privacy (PGP)**, one of the earliest and best-known encryption programs. He also dabbled in digital cash prototypes, developing something called **Reusable Proofs of Work (RPOW)**. He didn’t know it at the time, but that would prime him perfectly for a bigger innovation on the horizon. ## **Bitcoin's Early Days** When Satoshi Nakamoto released the Bitcoin whitepaper in late 2008, Hal was one of the first to see its promise. While many cryptographers waved it off, Hal responded on the mailing list enthusiastically, calling Bitcoin “a very promising idea.” He soon began corresponding directly with Satoshi. Their emails covered everything from bug fixes to big-picture possibilities for a decentralized currency. On January 12, 2009, Satoshi sent Hal **10 bitcoins**—marking the first recorded Bitcoin transaction. From that day onward, his name was woven into Bitcoin’s origin story. > ***“When Satoshi announced the first release of the software, I grabbed it right away. I think I was the first person besides Satoshi to run Bitcoin.”\ > -Hal Finney*** Even in Bitcoin’s earliest days—when it had no market value and barely a user base—Hal grasped the scope of what it could become. He saw it not just as a technical curiosity, but as a potential long-term store of value, a tool for privacy, and a monetary system that could rival gold in its resilience. He even raised early concerns about energy use from mining, showcasing just how far ahead he was thinking. At a time when most dismissed Bitcoin entirely, Hal was already envisioning the future. ## **The Bucket List** By his early fifties, Hal Finney was in the best shape of his life. He had taken up distance running in the mid-2000s—not to chase medals, but to test himself. To stay healthy, to lose some weight, and above all, to do something hard. The engineer’s mind in him craved a structure of improvement, and long-distance running delivered it. With meticulous focus, Hal crafted training plans, ran 20+ mile routes on weekends, and even checked tide charts to time his beach runs when the sand was firmest underfoot. His ultimate goal: **qualify for the Boston Marathon**. For most, Boston is a dream. For Hal, it became a personal benchmark—a physical counterpart to the mental mountains he scaled in cryptography. He trained relentlessly, logging race times, refining form, and aiming for the qualifying standard in his age group. Running was more than physical for him. It was meditative. He often ran alone, without music, simply to be in the moment—present, focused, moving forward. Running was also a shared passion. Fran often ran shorter distances while Hal trained for the longer ones. They registered for events together, cheered each other on at finish lines, and made it a part of their family rhythm. It was one more expression of Hal’s deep devotion not just to self-improvement, but to doing life side-by-side with those he loved. Hal and Fran competing in the Denver Half-Marathon together In April 2009, Hal and Fran ran the **Denver Half Marathon together**—a meaningful race and one of the first they completed side by side. At the time, Hal was deep in marathon training and hitting peak form.\ \ A month later, Hal attempted the **Los Angeles Marathon**, hoping to clock a Boston-qualifying time. But something wasn’t right. Despite all his preparation, he was forced to stop midway through the race. His body wasn’t recovering the way it used to. At first, he chalked it up to overtraining or age, but the truth would come soon after. ## **ALS Diagnosis** In August 2009, at the height of his physical and intellectual pursuits, Hal received crushing news: a diagnosis of **Amyotrophic Lateral Sclerosis (ALS)**, often referred to as Lou Gehrig’s disease. It was an especially cruel blow for a man who had just discovered a love for running and was helping birth the world’s first decentralized digital currency. ALS gradually robs people of voluntary muscle function. For Hal, it meant an uphill fight to maintain the independence and movement he cherished. Still, Hal didn’t stop. That September, **he and Fran ran the Disneyland Half Marathon together**, crossing the finish line hand in hand. It would be his last official race, but the identity of being a runner never left him—not after the diagnosis, not after the gradual loss of physical control, not even after he was confined to a wheelchair. Fran and Hal at the Disney Half Marathon. By December of that same year, Hal could no longer run. Still, he was determined not to sit on the sidelines. That winter, the couple helped organize a **relay team for the Santa Barbara International Marathon**, a race Hal had long planned to run. Friends and family joined in, and Fran ran the final leg, passing the timing chip to Hal for the last stretch. With support, **Hal walked across the finish line**, cheered on by the local running community who rallied around him. It was a symbolic moment—heartbreaking and inspiring all at once. Hal and Fran lead the Muscular Dystrophy Association relay team at the Santa Barbara International Marathon in 2009. Even as his muscles weakened, **Hal’s mind stayed sharp**, and he continued to adapt in every way he could. He and Fran began making practical changes around their home—installing ramps, adjusting routines—but emotionally, the ground was still shifting beneath them. Hal Finney humbly giving people in the future the opportunity to hear him speak before he is unable to. Fran consistently emphasized that Hal maintained a remarkably positive attitude, even as ALS took nearly everything from him physically. His optimism and determination became the emotional anchor for the entire family. > ***“He was the one who kept us all steady. He was never defeated.”\ > -Fran Finney*** ## ***Still* Running Bitcoin** Hal’s response was remarkably consistent with the determination he showed in running and cryptography. Even as the disease progressed, forcing him into a wheelchair and eventually limiting his speech, he kept coding—using assistive technologies that allowed him to control his computer through minimal eye movements. When he could no longer run physically, he continued to run test code for Bitcoin, advise other developers, and share insights on the BitcoinTalk forums. It was perseverance in its purest form. Fran was with him every step of the way. In October 2009, just months after his diagnosis, Hal published an essay titled [***“Dying Outside”***](https://www.lesswrong.com/posts/bshZiaLefDejvPKuS/dying-outside?ref=blog.austinbitcoinclub.com)—a reflection on the road ahead. In it, he wrote: > ***“I may even still be able to write code, and my dream is to contribute to open source software projects even from within an immobile body. That will be a life very much worth living."*** And he meant it. Years later, Hal collaborated with Bitcoin developer Mike Hearn on a project involving secure wallets using Trusted Computing. Even while operating at a fraction of his former speed—he estimated it was just **1/50th** of what he used to be capable of—Hal kept at it. He even engineered an Arduino-based interface to control his wheelchair with his eyes. The hacker mindset never left him. This wasn’t just about legacy. It was about living with purpose, right up to the edge of possibility. ## **Running Bitcoin Challenge** In recent years, Fran Finney—alongside members of the Bitcoin community—launched the [**Running Bitcoin Challenge**](https://secure.alsnetwork.org/site/TR?fr_id=1510&pg=entry&ref=blog.austinbitcoinclub.com), a virtual event that invites people around the world to run or walk **21 kilometers** each January in honor of Hal. Timed with the anniversary of his iconic *“Running bitcoin”* tweet, the challenge raises funds for **ALS research** through the ALS Network. According to Fran, **over 80% of all donations go directly to research**, making it a deeply impactful way to contribute. **Nearly $50,000 has been raised so far.** 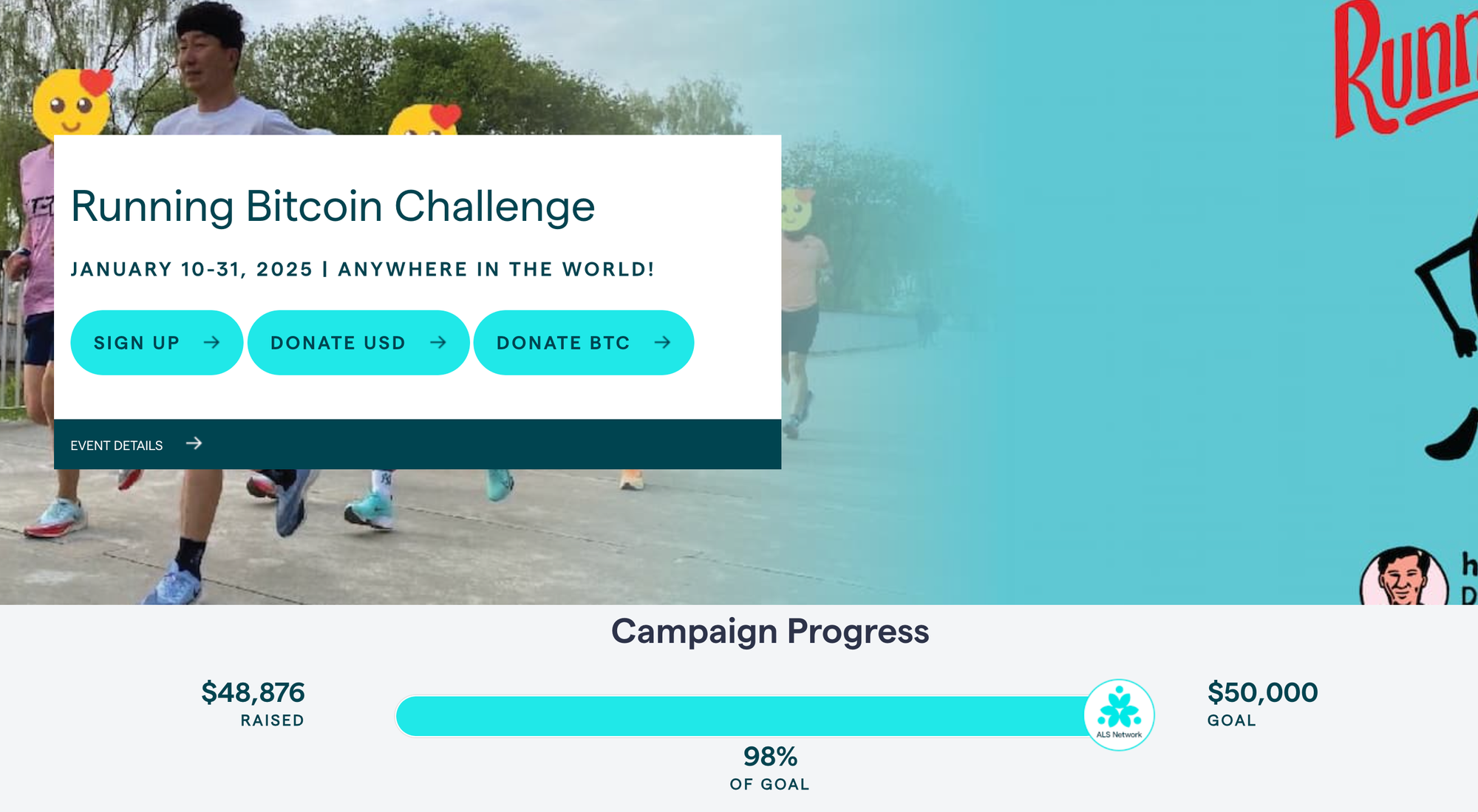It’s not the next Ice Bucket Challenge—but that’s not the point. This is something more grounded, more personal. It’s a growing movement rooted in Hal’s legacy, powered by the Bitcoin community, and driven by the hope that collective action can one day lead to a cure. > ***“Since we’re all rich with bitcoins, or we will be once they’re worth a million dollars like everyone expects, we ought to put some of this unearned wealth to good use.”\ > \ > — Hal Finney, January 2011Price of Bitcoin: $0.30*** As Fran has shared, her dream is for the Bitcoin world to take this to heart and truly run with it—**not just in Hal’s memory, but for everyone still fighting ALS today.** ## **Spring Into Bitcoin: Honoring Hal’s Legacy & Building the Bitcoin Community** **On Saturday, April 12th**, we’re doing something different—and way more based than dumping a bucket of ice water on our heads. [***Spring Into Bitcoin***](https://blog.austinbitcoinclub.com/spring-into-bitcoin/) is a one-day celebration of sound money, health, and legacy. Hosted at [**Hippo Social Club**](https://www.hipposocialclub.com/?ref=blog.austinbitcoinclub.com), the event features a professional [**trail run**](https://www.tejastrails.com/uncommon?ref=blog.austinbitcoinclub.com), a sizzling open-air beef feast, Bitcoin talks, and a wellness zone complete with a **cold plunge challenge** (the ice bucket challenge walked so the cold plunge could run 😏). [**Purchase Tickets**](https://oshi.link/lVH7Qh?ref=blog.austinbitcoinclub.com) **- General Admission** *Tickets purchased using this link will get 10% back in Bitcoin rewards compliments of [**Oshi Rewards**](https://oshi.tech/?ref=blog.austinbitcoinclub.com).* [*Purchase Race Tickets Here*](https://www.tejastrails.com/events/uncommon) *- RACE DISTANCES: Most Miles in 12 Hours, Most Miles in 6 Hours, Most Miles in 1 Hour, 5K, Canine 5K, Youth 1 Mile* It’s all in honor of Hal Finney, one of Bitcoin’s earliest pioneers and a passionate runner. **100% of event profits will be donated in Bitcoin to the ALS Network**, funding research and advocacy in Hal’s memory. Come for the cause, stay for the beef, sauna, cold plunge and to kick it with the greatest, most freedom-loving community on earth. [Please consider donating to our Run for Hal Austin team here.](https://secure.alsnetwork.org/site/TR/Endurance/General?team_id=9302&pg=team&fr_id=1510) This race officially kicks off the 2025 Run for Hal World Tour! Ok, we might be a little biased. ## **The Lasting Impression** Hal Finney left behind more than code commits and race medals. He left behind a blueprint for **resilience**—a relentless drive to do good work, to strive for personal bests, and to give back no matter the circumstances. His life reminds us that “running” is more than physical exercise or a piece of software running on your laptop. It’s about forward progress. It’s about community. It’s about optimism in the face of challenges. So, as you tie your shoelaces for your next run or sync up your Bitcoin wallet, remember Hal Finney. @ 866e0139:6a9334e5
2025-03-30 08:22:48*** **Autor: Ludwig F. Badenhagen.** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Wer den Artikel [Ob Corona oder Krieg: Wir Menschen werden wie Vieh behandelt](https://pareto.space/a/naddr1qqxnzde5xgcnzdeexv6rydpjqgsgvmsp8yy9t8c4chhln5ff23fsstcp58a47s9zt08swa4rd2fnfegrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytnsv9ex2ar09eehqctrv5q3wamnwvaz7tmwdaehgu3wwpshyet5duh8gmmhdcq3wamnwvaz7tmsv9ex2ar09ehx7um5wgcjucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k70ac8na) gelesen und die Ereignisse in Deutschland während der letzten 5 Jahre auch jenseits von Staatsfunk und Mainstream Medien verfolgt hat, dem dürfte folgendes aufgefallen sein:   1. Die absoluten Top-Positionen auf der politischen Bühne wurden vielfach mit Menschen besetzt, deren Eignung und Reputation – vorsichtig ausgedrückt – umstritten ist. 2. Auch massivste Fehlverhalten der Politiker bleiben folgenlos. Rücktritte scheinen ebenso ausgeschlossen wie eine straf- oder zivilrechtliche Aufarbeitung. 3. Wahlversprechen werden nicht eingehalten und neuerdings bereits direkt nach der Wahl gebrochen, obwohl noch keine neue Regierung gebildet wurde. Stattdessen wird das Gegenteil von dem getan, was eindringlich versprochen wurde. 4. Es hat sich eine Parteien-Allianz gebildet, welche eine gemeinsame Agenda verfolgt, die nicht dem Wohle der Bürger zu dienen scheint. In diesem Umfeld tun die Politiker offenbar ungebremst, was sie wollen – und keiner scheint sie hindern zu können. Wenn morgen „von oberster Stelle“ die Anweisung gegeben würde, dass alle Neugeborenen auf Scheiterhaufen zu verbrennen seien, so stehen die Chancen gut, dass auch solch ein Vorhaben durchgebracht werden würde. Es stellt sich die Frage, ob der Willkür überhaupt Grenzen gesetzt sind. Und eine weitere Frage ist, ob es einen Punkt gibt, an dem die Bürger nicht mehr gehorchen. Es ist kein Geheimnis, dass Politiker für ihre Vergehen nicht belangt werden. Entgegen jedem Unternehmenslenker haften Politiker nicht für Fehlverhalten. Offensichtlich auch nicht für grob fahrlässiges oder gar vorsätzliches, denn die deutsche Staatsanwaltschaft untersteht der Politik. Auch Richter sind in Karrieresysteme eingebunden, sodass die letzten fünf Jahre besonders deutlich gezeigt haben, in welche Situation sich „mutige Richter“ bringen. „Bestrafe einen, erziehe hundert“, sagte hierzu einst ein bekannter politischer Führer eines Landes, mit dem Deutschland nicht verglichen werden möchte. *** **DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.* *** Eine Tat wird (abgesehen vom Gesetz) erst durch die individuelle Bewertung zu einem Unrecht. Wie die Dinge „einzuordnen“ sind, erklären die Täter, die Politiker, tagtäglich selbst und werden hierbei von ihren Propagandamitarbeitern unterstützt, die sich selbst immer noch als Journalisten bezeichnen. Wer aber die staatliche Einordnung anzweifelt oder dieser gar offen widerspricht, wird unter Anwendung der vorgenannten Systematik „Bestrafe einen, erziehe hundert“ diffamiert. Aber hierbei bleibt es nicht, denn Hausdurchsuchungen in Herrgottsfrühe, Kontosperrungen, Untersuchungshaft und Jobverlust sowie dauerhafte Inhaftierungen sind nur einige Beispiele dafür, wie „im besten Deutschland aller Zeiten“ vorgegangen wird. ### Der Gamechanger Aber wie wäre der Zustand denn zu ändern, wenn man es denn wollte? Der Staat wird eben durch diese Politiker repräsentiert und hat das Gewaltmonopol. Hierzu einige Zahlen zu Deutschland: * Bevölkerung: ca. 83.000.000 * Polizisten: ca. 45.000 und einige tausend zivile (0,05 % der Bevölkerung) * Soldaten: ca. 260.000 (0,31 % der Bevölkerung) * Gerichte: ca. 1.085 (pro Gericht 77.000 Bürger) * Finanzämter: ca. 600 (pro Finanzamt 138.000 Bürger) Mit Blick auf diese Verhältnisse wird schnell deutlich, dass die Politiker auf eine „Kooperation“ der Bürger angewiesen sind. Würden die Bürger nicht kooperieren, so wären alle Gesetze und Vorschriften aufgrund mangelhafter Durchführbarkeit von heute auf morgen Makulatur. Mahatma Gandhi und viele andere bewiesen, dass ein übermächtig scheinender Gegner nicht mit dessen Gewaltmitteln besiegt werden kann, sondern mit dem Gegenteil. Gandhi beispielsweise rief die Menschen in seinem Land auf, den Engländern einfach nicht mehr zu gehorchen und die ungerechten Gesetze nicht mehr zu befolgen. Bei den Engländern hat dies funktioniert. Man stelle sich als Gedankenexperiment einmal vor, wie es wäre, wenn ein Drittel der Bürger nicht mehr arbeiten und keine Steuern und sogar keine GEZ-Gebühren mehr bezahlen würden. Wie könnten diese Menschen „zur Ordnung“ gerufen werden? Wie wollte man diese Menschen bestrafen? Bestrafungskonzepte funktionieren nur dann, wenn sich die Menschen durch diese einschüchtern lassen. Sofern aber die Vielen solidarisch agieren würden, hätte ein Staatsapparat schlechte Karten. Insbesondere dann, wenn ziviler Ungehorsam bundesweit oder sogar EU-weit ausgeübt würde. In solch einem Fall käme es wahrscheinlich sehr schnell zu einer Verständigung, denn wie sollte eine Regierung mit so viel Gegenwind weiter agieren? Die Prämisse bei solch einem Gedankenexperiment ist, dass ein erheblicher Teil der Bevölkerung sich so „miss-regiert“ fühlt, dass dieser Teil der Bevölkerung bereit ist, seine Komfortzone zum eigenen Wohl und dem Wohl der ihm Anvertrauten zu verlassen. Wahrscheinlich würde das noch nicht einmal besonders lange dauern. Man erinnere sich noch an die Zeiten, als Gewerkschaften noch nicht gekapert waren und tatsächlich die Interessen ihrer Mitglieder vertraten. Damals konnten die aufrechten Gewerkschaftsvertreter im Schulterschluss mit den Arbeitern für sie bessere Ergebnisse erwirken. ### Weg mit dem Grundgesetz In Deutschland wurde insbesondere in letzter Zeit von den Politikern am Grundgesetz herumgebastelt, aber dieses Grundgesetz, welches nach Vollendung der Einheit und Freiheit Deutschlands für das gesamte deutsche Volk gilt, verliert seine Gültigkeit an dem Tage, an dem eine Verfassung in Kraft tritt, die von dem deutschen Volke in freier Entscheidung beschlossen worden ist. Dies ist in Artikel 146 GG nachzulesen.   Das Grundgesetz vom 23. Mai 1949 in der jeweils aktuellen Fassung ist die (vorläufige) Verfassung der Bundesrepublik Deutschland. Das Grundgesetz wurde im Jahre 1949 zunächst bewusst als provisorische Regelung der staatlichen Grundordnung geschaffen. Eine Verfassung für Deutschland hingegen wäre ein besonderes Gesetz, welches bestimmt, wer in einem Staat die Macht ausübt und wie das geschehen soll. Dort ist festgelegt, welche Aufgaben der Staat übernimmt, welche Rechte jeder Bürger hat und wie das Verhältnis zwischen staatlichen Organen und Bürgern aussieht. Solch eine Verfassung hat Deutschland (noch) nicht. Man stelle sich nun vor, das deutsche Volk gäbe sich, so wie im Grundgesetz verankert, in freier Entscheidung eine Verfassung, welche exemplarisch Elemente zu folgenden Themen beinhalten würde: * Jeder Politiker wird an seinen Wahlversprechen gemessen. * Bei Amtsantritt wird ein Dienstvertrag, ähnlich wie bei einem Vorstand einer AG oder einem Geschäftsführer einer GmbH, abgeschlossen. In diesem Dienstvertrag wird auch geregelt, wie bei Verstößen vorgegangen wird. * Das Parteiensystem wird abgeschafft. * Die Staatsanwaltschaft ist nicht weiter weisungsgebunden und die Politiker nicht weiter immun. Die Gerichtsbarkeit wird wirklich unabhängig. * Jeder Politiker hat eine entsprechende Qualifikation nachzuweisen, um gewählt werden zu können. * Ein transparentes Wahlsystem. Schluss mit den manipulativen „Umfragen“. * Direkte Demokratie. * Etc. Statt am Grundgesetz herumzuwerkeln, könnte es eine Option sein, eine gerechte Verfassung zu beschließen, welche darauf ausgerichtet ist, den Bürgern zu dienen. Das GG würde dadurch obsolet. Mit einer gerechten Verfassung könnte sehr viel Optimierungspotenzial für das Zusammenleben in Deutschland realisiert werden. Die von den Politikern angebotenen Lösungen für die Probleme unserer Zeit beziehen sich oftmals auf selbst oder von den wirklich Mächtigen erschaffene Zustände, welche inszeniert wurden/werden, um die Menschen in Krieg, Not und Knappheit, in Leiden, in Angst, in Spaltung, in Fehlernährung, in Medikamentenabhängigkeit, in Krankheit und in Elend zu bringen. Um an den Menschen maximal zu verdienen und um diese vollumfänglich zu beherrschen. So, wie sie es mit Nutzvieh tun. Das Unterordnen von allem ist ein Prinzip, dass wenigen Leuten nützt und fast allen anderen schadet. Eine von Liebe inspirierte Gesellschaft, die Menschen nicht nur als „Verbraucher“ oder „Humankapital“ oder „Wähler“ betrachtet und behandelt, sondern tatsächlich das Wohl aller im Fokus hat, wäre der Gegenentwurf. Dies würde selbstverständlich einhergehen mit einer liebevollen Behandlung von Tieren und Natur. Hierbei profitieren aber die Vielen und die Wenigen ganz oben an der Spitze müssten sich umstellen, was ihnen nicht gefallen dürfte. ### Vom Denken ins Tun Wer sich solch eine Perspektive für sich selbst und seine Nachkommen wünscht, sollte überlegen, wie wir uns eine Verfassung geben können. Ein wesentlicher Schritt wäre sicher der Zusammenschluss von Menschen, die sich mit den vorbezeichneten Überlegungen weiter befassen möchten. Ganz entgegen der Bemühungen unserer Politik um Spaltung der Gesellschaft sollten die Gemeinsamkeiten gesehen und gemeinsam Lösungen entwickelt werden. Ein Beispiel ist die Initiative von Milosz Matuschek, nämlich sein [geplantes „Gipfeltreffen“.](https://www.freischwebende-intelligenz.org/p/exklusiv-einladung-zum-inner-circle) Hierzu schreibt er: *„Ich habe mir ein besonderes Programm überlegt, welches mein Wissen und meine Erfahrung der letzten Jahre bündelt, sich an den Stufen der Selbsterkenntnis, Willensbildung und Kraftentfaltung orientiert und genug Raum für die Dynamik der Gruppe, also ihre Energien, lässt. Erwarten Sie das Unerwartbare. Es wird Raum geben für spirituelle und körperliche Erfahrungen, auch an einem besonderen kulturellen Rahmenprogramm wird es nicht fehlen. Uns eint im Idealfall das Erkennen menschlicher Potentiale, das Erfassen von Möglichkeitsräumen und die aktive Lust an der Mitgestaltung der Zukunft – ohne Denkverbote. Zeit, für unseren Frühling. Ich wette, in Ihnen steckt ein ganzer, unendlicher Sommer.“* In diesem Kontext zitiert Herr Matuschek Ernst Jünger: > *“Wenn alle Institutionen zweifelhaft oder sogar anrüchig werden und man selbst in den Kirchen nicht etwas für die Verfolgten, sondern für die Verfolger öffentlich beten hört, dann geht die sittliche Verantwortung auf den Einzelnen über, oder besser gesagt, auf den noch ungebrochenen Einzelnen.”* Diese Worte von Ernst Jünger erinnern daran, dass die Probleme unserer Zeit nicht neu sind. Die Technologien sind es, denn mit modernen Technologien lässt sich eben besser unterdrücken als mit dem alten Zeugs. Die Methodik allerdings ist geblieben. Halte deine Untergebenen schwach und in Angst, damit diese ergeben bleiben. Zum Wohle einiger wenige Leute, die hiervon maximal profitieren. Machen Sie mit und lösen Sie sich aus der Passivität des Zuschauers. Der wichtige nächste Schritt ist, aus dem Denken ins Tun zu kommen.  Andernfalls wird uns weiter an-getan. *** *Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).* *Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.* *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):**  **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home)
@ 866e0139:6a9334e5
2025-03-30 08:22:48*** **Autor: Ludwig F. Badenhagen.** *Dieser Beitrag wurde mit dem **[Pareto-Client](https://pareto.space/read)** geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden **[hier.](https://pareto.space/read?category=friedenstaube)*** *** Wer den Artikel [Ob Corona oder Krieg: Wir Menschen werden wie Vieh behandelt](https://pareto.space/a/naddr1qqxnzde5xgcnzdeexv6rydpjqgsgvmsp8yy9t8c4chhln5ff23fsstcp58a47s9zt08swa4rd2fnfegrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytnsv9ex2ar09eehqctrv5q3wamnwvaz7tmwdaehgu3wwpshyet5duh8gmmhdcq3wamnwvaz7tmsv9ex2ar09ehx7um5wgcjucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k70ac8na) gelesen und die Ereignisse in Deutschland während der letzten 5 Jahre auch jenseits von Staatsfunk und Mainstream Medien verfolgt hat, dem dürfte folgendes aufgefallen sein:   1. Die absoluten Top-Positionen auf der politischen Bühne wurden vielfach mit Menschen besetzt, deren Eignung und Reputation – vorsichtig ausgedrückt – umstritten ist. 2. Auch massivste Fehlverhalten der Politiker bleiben folgenlos. Rücktritte scheinen ebenso ausgeschlossen wie eine straf- oder zivilrechtliche Aufarbeitung. 3. Wahlversprechen werden nicht eingehalten und neuerdings bereits direkt nach der Wahl gebrochen, obwohl noch keine neue Regierung gebildet wurde. Stattdessen wird das Gegenteil von dem getan, was eindringlich versprochen wurde. 4. Es hat sich eine Parteien-Allianz gebildet, welche eine gemeinsame Agenda verfolgt, die nicht dem Wohle der Bürger zu dienen scheint. In diesem Umfeld tun die Politiker offenbar ungebremst, was sie wollen – und keiner scheint sie hindern zu können. Wenn morgen „von oberster Stelle“ die Anweisung gegeben würde, dass alle Neugeborenen auf Scheiterhaufen zu verbrennen seien, so stehen die Chancen gut, dass auch solch ein Vorhaben durchgebracht werden würde. Es stellt sich die Frage, ob der Willkür überhaupt Grenzen gesetzt sind. Und eine weitere Frage ist, ob es einen Punkt gibt, an dem die Bürger nicht mehr gehorchen. Es ist kein Geheimnis, dass Politiker für ihre Vergehen nicht belangt werden. Entgegen jedem Unternehmenslenker haften Politiker nicht für Fehlverhalten. Offensichtlich auch nicht für grob fahrlässiges oder gar vorsätzliches, denn die deutsche Staatsanwaltschaft untersteht der Politik. Auch Richter sind in Karrieresysteme eingebunden, sodass die letzten fünf Jahre besonders deutlich gezeigt haben, in welche Situation sich „mutige Richter“ bringen. „Bestrafe einen, erziehe hundert“, sagte hierzu einst ein bekannter politischer Führer eines Landes, mit dem Deutschland nicht verglichen werden möchte. *** **DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos* ***[hier](https://pareto.space/a/naddr1qqsxydty8qek2wpsvyck2wphxajrvefjvesngcfhxenrgdty89nrzvgzyzrxuqfepp2e79w9aluaz2252vyz7qdpld05pgjmeurhdgm2jv6w2qcyqqq823cpp4mhxue69uhkummn9ekx7mqprpmhxue69uhkummnw3ezuurpwfjhgmewwdcxzcm9qythwumn8ghj7mn0wd68ytnsv9ex2ar09e6x7amwqyf8wumn8ghj7mmxve3ksctfdch8qatzqythwumn8ghj7urpwfjhgmewdehhxarjxyhxxmmdszcvqk)*** *oder am Ende des Textes.* *** Eine Tat wird (abgesehen vom Gesetz) erst durch die individuelle Bewertung zu einem Unrecht. Wie die Dinge „einzuordnen“ sind, erklären die Täter, die Politiker, tagtäglich selbst und werden hierbei von ihren Propagandamitarbeitern unterstützt, die sich selbst immer noch als Journalisten bezeichnen. Wer aber die staatliche Einordnung anzweifelt oder dieser gar offen widerspricht, wird unter Anwendung der vorgenannten Systematik „Bestrafe einen, erziehe hundert“ diffamiert. Aber hierbei bleibt es nicht, denn Hausdurchsuchungen in Herrgottsfrühe, Kontosperrungen, Untersuchungshaft und Jobverlust sowie dauerhafte Inhaftierungen sind nur einige Beispiele dafür, wie „im besten Deutschland aller Zeiten“ vorgegangen wird. ### Der Gamechanger Aber wie wäre der Zustand denn zu ändern, wenn man es denn wollte? Der Staat wird eben durch diese Politiker repräsentiert und hat das Gewaltmonopol. Hierzu einige Zahlen zu Deutschland: * Bevölkerung: ca. 83.000.000 * Polizisten: ca. 45.000 und einige tausend zivile (0,05 % der Bevölkerung) * Soldaten: ca. 260.000 (0,31 % der Bevölkerung) * Gerichte: ca. 1.085 (pro Gericht 77.000 Bürger) * Finanzämter: ca. 600 (pro Finanzamt 138.000 Bürger) Mit Blick auf diese Verhältnisse wird schnell deutlich, dass die Politiker auf eine „Kooperation“ der Bürger angewiesen sind. Würden die Bürger nicht kooperieren, so wären alle Gesetze und Vorschriften aufgrund mangelhafter Durchführbarkeit von heute auf morgen Makulatur. Mahatma Gandhi und viele andere bewiesen, dass ein übermächtig scheinender Gegner nicht mit dessen Gewaltmitteln besiegt werden kann, sondern mit dem Gegenteil. Gandhi beispielsweise rief die Menschen in seinem Land auf, den Engländern einfach nicht mehr zu gehorchen und die ungerechten Gesetze nicht mehr zu befolgen. Bei den Engländern hat dies funktioniert. Man stelle sich als Gedankenexperiment einmal vor, wie es wäre, wenn ein Drittel der Bürger nicht mehr arbeiten und keine Steuern und sogar keine GEZ-Gebühren mehr bezahlen würden. Wie könnten diese Menschen „zur Ordnung“ gerufen werden? Wie wollte man diese Menschen bestrafen? Bestrafungskonzepte funktionieren nur dann, wenn sich die Menschen durch diese einschüchtern lassen. Sofern aber die Vielen solidarisch agieren würden, hätte ein Staatsapparat schlechte Karten. Insbesondere dann, wenn ziviler Ungehorsam bundesweit oder sogar EU-weit ausgeübt würde. In solch einem Fall käme es wahrscheinlich sehr schnell zu einer Verständigung, denn wie sollte eine Regierung mit so viel Gegenwind weiter agieren? Die Prämisse bei solch einem Gedankenexperiment ist, dass ein erheblicher Teil der Bevölkerung sich so „miss-regiert“ fühlt, dass dieser Teil der Bevölkerung bereit ist, seine Komfortzone zum eigenen Wohl und dem Wohl der ihm Anvertrauten zu verlassen. Wahrscheinlich würde das noch nicht einmal besonders lange dauern. Man erinnere sich noch an die Zeiten, als Gewerkschaften noch nicht gekapert waren und tatsächlich die Interessen ihrer Mitglieder vertraten. Damals konnten die aufrechten Gewerkschaftsvertreter im Schulterschluss mit den Arbeitern für sie bessere Ergebnisse erwirken. ### Weg mit dem Grundgesetz In Deutschland wurde insbesondere in letzter Zeit von den Politikern am Grundgesetz herumgebastelt, aber dieses Grundgesetz, welches nach Vollendung der Einheit und Freiheit Deutschlands für das gesamte deutsche Volk gilt, verliert seine Gültigkeit an dem Tage, an dem eine Verfassung in Kraft tritt, die von dem deutschen Volke in freier Entscheidung beschlossen worden ist. Dies ist in Artikel 146 GG nachzulesen.   Das Grundgesetz vom 23. Mai 1949 in der jeweils aktuellen Fassung ist die (vorläufige) Verfassung der Bundesrepublik Deutschland. Das Grundgesetz wurde im Jahre 1949 zunächst bewusst als provisorische Regelung der staatlichen Grundordnung geschaffen. Eine Verfassung für Deutschland hingegen wäre ein besonderes Gesetz, welches bestimmt, wer in einem Staat die Macht ausübt und wie das geschehen soll. Dort ist festgelegt, welche Aufgaben der Staat übernimmt, welche Rechte jeder Bürger hat und wie das Verhältnis zwischen staatlichen Organen und Bürgern aussieht. Solch eine Verfassung hat Deutschland (noch) nicht. Man stelle sich nun vor, das deutsche Volk gäbe sich, so wie im Grundgesetz verankert, in freier Entscheidung eine Verfassung, welche exemplarisch Elemente zu folgenden Themen beinhalten würde: * Jeder Politiker wird an seinen Wahlversprechen gemessen. * Bei Amtsantritt wird ein Dienstvertrag, ähnlich wie bei einem Vorstand einer AG oder einem Geschäftsführer einer GmbH, abgeschlossen. In diesem Dienstvertrag wird auch geregelt, wie bei Verstößen vorgegangen wird. * Das Parteiensystem wird abgeschafft. * Die Staatsanwaltschaft ist nicht weiter weisungsgebunden und die Politiker nicht weiter immun. Die Gerichtsbarkeit wird wirklich unabhängig. * Jeder Politiker hat eine entsprechende Qualifikation nachzuweisen, um gewählt werden zu können. * Ein transparentes Wahlsystem. Schluss mit den manipulativen „Umfragen“. * Direkte Demokratie. * Etc. Statt am Grundgesetz herumzuwerkeln, könnte es eine Option sein, eine gerechte Verfassung zu beschließen, welche darauf ausgerichtet ist, den Bürgern zu dienen. Das GG würde dadurch obsolet. Mit einer gerechten Verfassung könnte sehr viel Optimierungspotenzial für das Zusammenleben in Deutschland realisiert werden. Die von den Politikern angebotenen Lösungen für die Probleme unserer Zeit beziehen sich oftmals auf selbst oder von den wirklich Mächtigen erschaffene Zustände, welche inszeniert wurden/werden, um die Menschen in Krieg, Not und Knappheit, in Leiden, in Angst, in Spaltung, in Fehlernährung, in Medikamentenabhängigkeit, in Krankheit und in Elend zu bringen. Um an den Menschen maximal zu verdienen und um diese vollumfänglich zu beherrschen. So, wie sie es mit Nutzvieh tun. Das Unterordnen von allem ist ein Prinzip, dass wenigen Leuten nützt und fast allen anderen schadet. Eine von Liebe inspirierte Gesellschaft, die Menschen nicht nur als „Verbraucher“ oder „Humankapital“ oder „Wähler“ betrachtet und behandelt, sondern tatsächlich das Wohl aller im Fokus hat, wäre der Gegenentwurf. Dies würde selbstverständlich einhergehen mit einer liebevollen Behandlung von Tieren und Natur. Hierbei profitieren aber die Vielen und die Wenigen ganz oben an der Spitze müssten sich umstellen, was ihnen nicht gefallen dürfte. ### Vom Denken ins Tun Wer sich solch eine Perspektive für sich selbst und seine Nachkommen wünscht, sollte überlegen, wie wir uns eine Verfassung geben können. Ein wesentlicher Schritt wäre sicher der Zusammenschluss von Menschen, die sich mit den vorbezeichneten Überlegungen weiter befassen möchten. Ganz entgegen der Bemühungen unserer Politik um Spaltung der Gesellschaft sollten die Gemeinsamkeiten gesehen und gemeinsam Lösungen entwickelt werden. Ein Beispiel ist die Initiative von Milosz Matuschek, nämlich sein [geplantes „Gipfeltreffen“.](https://www.freischwebende-intelligenz.org/p/exklusiv-einladung-zum-inner-circle) Hierzu schreibt er: *„Ich habe mir ein besonderes Programm überlegt, welches mein Wissen und meine Erfahrung der letzten Jahre bündelt, sich an den Stufen der Selbsterkenntnis, Willensbildung und Kraftentfaltung orientiert und genug Raum für die Dynamik der Gruppe, also ihre Energien, lässt. Erwarten Sie das Unerwartbare. Es wird Raum geben für spirituelle und körperliche Erfahrungen, auch an einem besonderen kulturellen Rahmenprogramm wird es nicht fehlen. Uns eint im Idealfall das Erkennen menschlicher Potentiale, das Erfassen von Möglichkeitsräumen und die aktive Lust an der Mitgestaltung der Zukunft – ohne Denkverbote. Zeit, für unseren Frühling. Ich wette, in Ihnen steckt ein ganzer, unendlicher Sommer.“* In diesem Kontext zitiert Herr Matuschek Ernst Jünger: > *“Wenn alle Institutionen zweifelhaft oder sogar anrüchig werden und man selbst in den Kirchen nicht etwas für die Verfolgten, sondern für die Verfolger öffentlich beten hört, dann geht die sittliche Verantwortung auf den Einzelnen über, oder besser gesagt, auf den noch ungebrochenen Einzelnen.”* Diese Worte von Ernst Jünger erinnern daran, dass die Probleme unserer Zeit nicht neu sind. Die Technologien sind es, denn mit modernen Technologien lässt sich eben besser unterdrücken als mit dem alten Zeugs. Die Methodik allerdings ist geblieben. Halte deine Untergebenen schwach und in Angst, damit diese ergeben bleiben. Zum Wohle einiger wenige Leute, die hiervon maximal profitieren. Machen Sie mit und lösen Sie sich aus der Passivität des Zuschauers. Der wichtige nächste Schritt ist, aus dem Denken ins Tun zu kommen.  Andernfalls wird uns weiter an-getan. *** *Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).* *Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.* *** **LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!** ***[Hier](https://pareto.space/u/friedenstaube@pareto.space)*** *können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.* Schon jetzt können Sie uns unterstützen: * Für **50 CHF/EURO** bekommen Sie ein Jahresabo der Friedenstaube. * Für **120 CHF/EURO** bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube. * Für **500 CHF/EURO** werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube. * Ab **1000 CHF** werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie). **Für Einzahlungen in CHF (Betreff: Friedenstaube):**  **Für Einzahlungen in Euro:** Milosz Matuschek IBAN DE 53710520500000814137 BYLADEM1TST Sparkasse Traunstein-Trostberg **Betreff: Friedenstaube** Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: <milosz@pareto.space> *** **Sie sind noch nicht auf** [Nostr](https://nostr.com/) **and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil!** Erstellen Sie sich einen Account auf [Start.](https://start.njump.me/) Weitere Onboarding-Leitfäden gibt es im [Pareto-Wiki.](https://wiki.pareto.space/de/home) @ a95c6243:d345522c
2025-03-11 10:22:36**«Wir brauchen eine digitale Brandmauer gegen den Faschismus»,** [schreibt](https://www.ccc.de/de/updates/2025/ccc-fordert-digitale-brandmauer) der Chaos Computer Club (CCC) auf seiner Website. Unter diesem Motto präsentierte er letzte Woche einen Forderungskatalog, mit dem sich 24 Organisationen an die kommende Bundesregierung wenden. Der Koalitionsvertrag müsse sich daran messen lassen, verlangen sie. **In den drei Kategorien «Bekenntnis gegen Überwachung»,** «Schutz und Sicherheit für alle» sowie «Demokratie im digitalen Raum» stellen die [Unterzeichner](https://d-64.org/digitale-brandmauer/), zu denen auch Amnesty International und Das NETTZ gehören, unter anderem die folgenden «Mindestanforderungen»: * Verbot biometrischer Massenüberwachung des öffentlichen Raums sowie der ungezielten biometrischen Auswertung des Internets. * Anlasslose und massenhafte Vorratsdatenspeicherung wird abgelehnt. * Automatisierte Datenanalysen der Informationsbestände der Strafverfolgungsbehörden sowie jede Form von Predictive Policing oder automatisiertes Profiling von Menschen werden abgelehnt. * Einführung eines Rechts auf Verschlüsselung. Die Bundesregierung soll sich dafür einsetzen, die Chatkontrolle auf europäischer Ebene zu verhindern. * Anonyme und pseudonyme Nutzung des Internets soll geschützt und ermöglicht werden. * Bekämpfung «privaten Machtmissbrauchs von Big-Tech-Unternehmen» durch durchsetzungsstarke, unabhängige und grundsätzlich föderale Aufsichtsstrukturen. * Einführung eines digitalen Gewaltschutzgesetzes, unter Berücksichtigung «gruppenbezogener digitaler Gewalt» und die Förderung von Beratungsangeboten. * Ein umfassendes Förderprogramm für digitale öffentliche Räume, die dezentral organisiert und quelloffen programmiert sind, soll aufgelegt werden. **Es sei ein Irrglaube, dass zunehmende Überwachung einen Zugewinn an Sicherheit darstelle,** ist eines der Argumente der Initiatoren. Sicherheit erfordere auch, dass Menschen anonym und vertraulich kommunizieren können und ihre Privatsphäre geschützt wird. **Gesunde digitale Räume lebten auch von einem demokratischen Diskurs,** lesen wir in dem Papier. Es sei Aufgabe des Staates, Grundrechte zu schützen. Dazu gehöre auch, Menschenrechte und demokratische Werte, insbesondere Freiheit, Gleichheit und Solidarität zu fördern sowie den Missbrauch von Maßnahmen, Befugnissen und Infrastrukturen durch «die Feinde der Demokratie» zu verhindern. **Man ist geneigt zu fragen, wo denn die Autoren «den Faschismus» sehen,** den es zu bekämpfen gelte. Die meisten der vorgetragenen Forderungen und Argumente finden sicher breite Unterstützung, denn sie beschreiben offenkundig gängige, kritikwürdige Praxis. Die Aushebelung der Privatsphäre, der Redefreiheit und anderer Grundrechte im Namen der Sicherheit wird bereits jetzt massiv durch die aktuellen «demokratischen Institutionen» und ihre «durchsetzungsstarken Aufsichtsstrukturen» betrieben. **Ist «der Faschismus» also die EU und ihre Mitgliedsstaaten?** Nein, die «faschistische Gefahr», gegen die man eine digitale Brandmauer will, kommt nach Ansicht des CCC und seiner Partner aus den Vereinigten Staaten. Private Überwachung und Machtkonzentration sind dabei weltweit schon lange Realität, jetzt endlich müssen sie jedoch bekämpft werden. In dem Papier heißt es: > «Die willkürliche und antidemokratische Machtausübung der Tech-Oligarchen um Präsident Trump erfordert einen Paradigmenwechsel in der deutschen Digitalpolitik. (...) Die aktuellen Geschehnisse in den USA zeigen auf, wie Datensammlungen und -analyse genutzt werden können, um einen Staat handstreichartig zu übernehmen, seine Strukturen nachhaltig zu beschädigen, Widerstand zu unterbinden und marginalisierte Gruppen zu verfolgen.» **Wer auf der anderen Seite dieser Brandmauer stehen soll, ist also klar.** Es sind die gleichen «Feinde unserer Demokratie», die seit Jahren in diese Ecke gedrängt werden. Es sind die gleichen Andersdenkenden, Regierungskritiker und Friedensforderer, die unter dem großzügigen Dach des Bundesprogramms «Demokratie leben» einem «kontinuierlichen Echt- und Langzeitmonitoring» wegen der Etikettierung [«digitaler Hass»](https://bag-gegen-hass.net/) unterzogen werden. **Dass die 24 Organisationen praktisch auch die Bekämpfung von Google,** Microsoft, Apple, Amazon und anderen fordern, entbehrt nicht der Komik. Diese fallen aber sicher unter das Stichwort «Machtmissbrauch von Big-Tech-Unternehmen». Gleichzeitig verlangen die Lobbyisten implizit zum Beispiel die Förderung des [Nostr](https://reason.com/video/2024/09/17/is-nostr-an-antidote-to-social-media-censorship/)-Netzwerks, denn hier finden wir dezentral organisierte und quelloffen programmierte digitale Räume par excellence, obendrein zensurresistent. Das wiederum dürfte in der Politik weniger gut ankommen. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/uns-ihnen-stammes-wettbewerb-1767691/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/digitale-brandmauer-gegen-den-faschismus-von-der-kunftigen-bundesregierung)*** erschienen.
@ a95c6243:d345522c
2025-03-11 10:22:36**«Wir brauchen eine digitale Brandmauer gegen den Faschismus»,** [schreibt](https://www.ccc.de/de/updates/2025/ccc-fordert-digitale-brandmauer) der Chaos Computer Club (CCC) auf seiner Website. Unter diesem Motto präsentierte er letzte Woche einen Forderungskatalog, mit dem sich 24 Organisationen an die kommende Bundesregierung wenden. Der Koalitionsvertrag müsse sich daran messen lassen, verlangen sie. **In den drei Kategorien «Bekenntnis gegen Überwachung»,** «Schutz und Sicherheit für alle» sowie «Demokratie im digitalen Raum» stellen die [Unterzeichner](https://d-64.org/digitale-brandmauer/), zu denen auch Amnesty International und Das NETTZ gehören, unter anderem die folgenden «Mindestanforderungen»: * Verbot biometrischer Massenüberwachung des öffentlichen Raums sowie der ungezielten biometrischen Auswertung des Internets. * Anlasslose und massenhafte Vorratsdatenspeicherung wird abgelehnt. * Automatisierte Datenanalysen der Informationsbestände der Strafverfolgungsbehörden sowie jede Form von Predictive Policing oder automatisiertes Profiling von Menschen werden abgelehnt. * Einführung eines Rechts auf Verschlüsselung. Die Bundesregierung soll sich dafür einsetzen, die Chatkontrolle auf europäischer Ebene zu verhindern. * Anonyme und pseudonyme Nutzung des Internets soll geschützt und ermöglicht werden. * Bekämpfung «privaten Machtmissbrauchs von Big-Tech-Unternehmen» durch durchsetzungsstarke, unabhängige und grundsätzlich föderale Aufsichtsstrukturen. * Einführung eines digitalen Gewaltschutzgesetzes, unter Berücksichtigung «gruppenbezogener digitaler Gewalt» und die Förderung von Beratungsangeboten. * Ein umfassendes Förderprogramm für digitale öffentliche Räume, die dezentral organisiert und quelloffen programmiert sind, soll aufgelegt werden. **Es sei ein Irrglaube, dass zunehmende Überwachung einen Zugewinn an Sicherheit darstelle,** ist eines der Argumente der Initiatoren. Sicherheit erfordere auch, dass Menschen anonym und vertraulich kommunizieren können und ihre Privatsphäre geschützt wird. **Gesunde digitale Räume lebten auch von einem demokratischen Diskurs,** lesen wir in dem Papier. Es sei Aufgabe des Staates, Grundrechte zu schützen. Dazu gehöre auch, Menschenrechte und demokratische Werte, insbesondere Freiheit, Gleichheit und Solidarität zu fördern sowie den Missbrauch von Maßnahmen, Befugnissen und Infrastrukturen durch «die Feinde der Demokratie» zu verhindern. **Man ist geneigt zu fragen, wo denn die Autoren «den Faschismus» sehen,** den es zu bekämpfen gelte. Die meisten der vorgetragenen Forderungen und Argumente finden sicher breite Unterstützung, denn sie beschreiben offenkundig gängige, kritikwürdige Praxis. Die Aushebelung der Privatsphäre, der Redefreiheit und anderer Grundrechte im Namen der Sicherheit wird bereits jetzt massiv durch die aktuellen «demokratischen Institutionen» und ihre «durchsetzungsstarken Aufsichtsstrukturen» betrieben. **Ist «der Faschismus» also die EU und ihre Mitgliedsstaaten?** Nein, die «faschistische Gefahr», gegen die man eine digitale Brandmauer will, kommt nach Ansicht des CCC und seiner Partner aus den Vereinigten Staaten. Private Überwachung und Machtkonzentration sind dabei weltweit schon lange Realität, jetzt endlich müssen sie jedoch bekämpft werden. In dem Papier heißt es: > «Die willkürliche und antidemokratische Machtausübung der Tech-Oligarchen um Präsident Trump erfordert einen Paradigmenwechsel in der deutschen Digitalpolitik. (...) Die aktuellen Geschehnisse in den USA zeigen auf, wie Datensammlungen und -analyse genutzt werden können, um einen Staat handstreichartig zu übernehmen, seine Strukturen nachhaltig zu beschädigen, Widerstand zu unterbinden und marginalisierte Gruppen zu verfolgen.» **Wer auf der anderen Seite dieser Brandmauer stehen soll, ist also klar.** Es sind die gleichen «Feinde unserer Demokratie», die seit Jahren in diese Ecke gedrängt werden. Es sind die gleichen Andersdenkenden, Regierungskritiker und Friedensforderer, die unter dem großzügigen Dach des Bundesprogramms «Demokratie leben» einem «kontinuierlichen Echt- und Langzeitmonitoring» wegen der Etikettierung [«digitaler Hass»](https://bag-gegen-hass.net/) unterzogen werden. **Dass die 24 Organisationen praktisch auch die Bekämpfung von Google,** Microsoft, Apple, Amazon und anderen fordern, entbehrt nicht der Komik. Diese fallen aber sicher unter das Stichwort «Machtmissbrauch von Big-Tech-Unternehmen». Gleichzeitig verlangen die Lobbyisten implizit zum Beispiel die Förderung des [Nostr](https://reason.com/video/2024/09/17/is-nostr-an-antidote-to-social-media-censorship/)-Netzwerks, denn hier finden wir dezentral organisierte und quelloffen programmierte digitale Räume par excellence, obendrein zensurresistent. Das wiederum dürfte in der Politik weniger gut ankommen. *\[Titelbild:* *[Pixabay](https://pixabay.com/de/illustrations/uns-ihnen-stammes-wettbewerb-1767691/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/digitale-brandmauer-gegen-den-faschismus-von-der-kunftigen-bundesregierung)*** erschienen. @ d560dbc2:bbd59238
2025-03-30 07:56:40We’ve all been there: that one task sitting on your to-do list, staring at you like a disappointed parent, and yet you keep pushing it off for absolutely no good reason. It’s not even that hard, urgent, or complicated—but somehow, it’s been haunting you for days, weeks, or maybe even months. Why do we do this to ourselves? --- ## Why Do We Postpone Tasks for No Reason? Procrastination is a sneaky beast. Even tasks that take 10 minutes, require minimal brainpower, and have no immediate deadline often get pushed aside. Here are some psychological reasons: - **Emotional Avoidance:** Even if a task isn’t hard, a tiny emotional weight (like mild boredom or a vague “I don’t wanna”) can lead your brain to choose distractions—like scrolling through Instagram. - **Lack of Immediate Consequences:** Without a pressing deadline, your brain tends to deprioritize the task, even if completing it would make you feel great. - **The Zeigarnik Effect:** Unfinished tasks stick in our minds, creating mental tension. Ironically, that tension can make the task seem bigger and more daunting, encouraging further avoidance. --- ## My Own “No-Reason” Procrastination Story Let’s be real—I’ve been postponing something trivial, like organizing my desk drawer, for weeks. It’s a simple task that takes about 15 minutes. There’s no deadline, no special skill required—yet every time I open the drawer, I see the chaos of old receipts, random cables, and a half-eaten pack of gum (don’t judge!) and think, “I’ll do it later.” It’s not that I’m busy—I’ve had plenty of time to rewatch my favorite sitcom for the third time. But ignoring it has become my default, and that messy drawer now occupies mental space far beyond its physical size. --- ## Why These Tasks Matter More Than We Think Those little tasks we postpone might seem harmless, but they add up to create mental clutter. That messy desk drawer isn’t just a drawer—it’s a tiny stressor that pops into your head at the worst moments, disrupting your focus on important work or relaxation. - **Mental Clutter:** Unfinished tasks can weigh on your mind, making it harder to focus on what truly matters. - **The Bigger Picture:** Tasks like “reply to that email” or “schedule that doctor’s appointment” may seem minor, but avoiding them can lead to unnecessary stress and lost opportunities. --- ## How to Finally Tackle That Task Here are a few strategies that have helped me break the cycle of “no-reason” procrastination: ### 1. The 20-Minute Rule (Thank You, Pomodoro!) - **Commit to 20 Minutes:** Set a timer for just 20 minutes and start working on the task. You’d be surprised how much you can accomplish once you begin. - **Example:** For my desk drawer, I set a timer, got to work, and finished in 12 minutes. That small win made me feel like a productivity superhero. --- ### 2. Pin It and Get a Nudge - **Use Reminders:** Pin that nagging task (like “Organize desk drawer”) as your top priority for the day. A gentle reminder can help break the cycle of avoidance. - **Result:** It’s like having a friend nudge you, “Hey, remember that thing you’ve been ignoring? Let’s do it now!” --- ### 3. Make It Fun (Yes, Really!) - **Add a Reward:** Turn the task into something enjoyable by setting a reward. Play your favorite music, and promise yourself a treat once you’re done. - **Example:** For my desk drawer, I put on an upbeat playlist and treated myself to a piece of chocolate when finished. Suddenly, it wasn’t a chore—it became a mini dance party with a sweet reward. --- ### 4. Celebrate the Win - **Acknowledge Completion:** Once you finish, take a moment to celebrate—even if it’s just a mental high-five. - **Why It Matters:** That sense of closure clears mental clutter and builds momentum for your next task. --- ## Let’s Share and Motivate Each Other What’s that one task you’ve been postponing for no reason? Maybe it’s cleaning out your fridge, replying to a friend’s text, or finally hanging that picture frame that’s been leaning against the wall for months. Whatever it is, share your story in the comments! Let’s motivate each other to tackle these tasks and turn procrastination into progress. *Bonus points if you’ve got a funny reason for your procrastination (like, “I didn’t schedule that appointment because my doctor’s office has the worst hold music in history”).* --- Ready to stop procrastinating? Let’s get real, take that first step, and clear that mental clutter—one small win at a time! ---
@ d560dbc2:bbd59238
2025-03-30 07:56:40We’ve all been there: that one task sitting on your to-do list, staring at you like a disappointed parent, and yet you keep pushing it off for absolutely no good reason. It’s not even that hard, urgent, or complicated—but somehow, it’s been haunting you for days, weeks, or maybe even months. Why do we do this to ourselves? --- ## Why Do We Postpone Tasks for No Reason? Procrastination is a sneaky beast. Even tasks that take 10 minutes, require minimal brainpower, and have no immediate deadline often get pushed aside. Here are some psychological reasons: - **Emotional Avoidance:** Even if a task isn’t hard, a tiny emotional weight (like mild boredom or a vague “I don’t wanna”) can lead your brain to choose distractions—like scrolling through Instagram. - **Lack of Immediate Consequences:** Without a pressing deadline, your brain tends to deprioritize the task, even if completing it would make you feel great. - **The Zeigarnik Effect:** Unfinished tasks stick in our minds, creating mental tension. Ironically, that tension can make the task seem bigger and more daunting, encouraging further avoidance. --- ## My Own “No-Reason” Procrastination Story Let’s be real—I’ve been postponing something trivial, like organizing my desk drawer, for weeks. It’s a simple task that takes about 15 minutes. There’s no deadline, no special skill required—yet every time I open the drawer, I see the chaos of old receipts, random cables, and a half-eaten pack of gum (don’t judge!) and think, “I’ll do it later.” It’s not that I’m busy—I’ve had plenty of time to rewatch my favorite sitcom for the third time. But ignoring it has become my default, and that messy drawer now occupies mental space far beyond its physical size. --- ## Why These Tasks Matter More Than We Think Those little tasks we postpone might seem harmless, but they add up to create mental clutter. That messy desk drawer isn’t just a drawer—it’s a tiny stressor that pops into your head at the worst moments, disrupting your focus on important work or relaxation. - **Mental Clutter:** Unfinished tasks can weigh on your mind, making it harder to focus on what truly matters. - **The Bigger Picture:** Tasks like “reply to that email” or “schedule that doctor’s appointment” may seem minor, but avoiding them can lead to unnecessary stress and lost opportunities. --- ## How to Finally Tackle That Task Here are a few strategies that have helped me break the cycle of “no-reason” procrastination: ### 1. The 20-Minute Rule (Thank You, Pomodoro!) - **Commit to 20 Minutes:** Set a timer for just 20 minutes and start working on the task. You’d be surprised how much you can accomplish once you begin. - **Example:** For my desk drawer, I set a timer, got to work, and finished in 12 minutes. That small win made me feel like a productivity superhero. --- ### 2. Pin It and Get a Nudge - **Use Reminders:** Pin that nagging task (like “Organize desk drawer”) as your top priority for the day. A gentle reminder can help break the cycle of avoidance. - **Result:** It’s like having a friend nudge you, “Hey, remember that thing you’ve been ignoring? Let’s do it now!” --- ### 3. Make It Fun (Yes, Really!) - **Add a Reward:** Turn the task into something enjoyable by setting a reward. Play your favorite music, and promise yourself a treat once you’re done. - **Example:** For my desk drawer, I put on an upbeat playlist and treated myself to a piece of chocolate when finished. Suddenly, it wasn’t a chore—it became a mini dance party with a sweet reward. --- ### 4. Celebrate the Win - **Acknowledge Completion:** Once you finish, take a moment to celebrate—even if it’s just a mental high-five. - **Why It Matters:** That sense of closure clears mental clutter and builds momentum for your next task. --- ## Let’s Share and Motivate Each Other What’s that one task you’ve been postponing for no reason? Maybe it’s cleaning out your fridge, replying to a friend’s text, or finally hanging that picture frame that’s been leaning against the wall for months. Whatever it is, share your story in the comments! Let’s motivate each other to tackle these tasks and turn procrastination into progress. *Bonus points if you’ve got a funny reason for your procrastination (like, “I didn’t schedule that appointment because my doctor’s office has the worst hold music in history”).* --- Ready to stop procrastinating? Let’s get real, take that first step, and clear that mental clutter—one small win at a time! --- @ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto. ### **A Falácia da Superioridade Moral** O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: **a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas**. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica. --- ### **Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"** A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do **marxismo ortodoxo**, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa: - **Dados do Latinobarómetro (2022):** 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita. - **Pesquisa IPEC (2023):** 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda". Esses números não são acidentais. Refletem uma **mudança estrutural**: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque **nunca conversaram com um sem fazer cara de psicólogo de posto de saúde**. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal". ## **Se ainda não entenderam:** **Direita ≠ rico:** Tem gente que trabalha 12h/dia e vota em liberal porque quer **ser dono do próprio negócio**, não pra pagar mais taxação pra você postar meme no Twitter. **Acham que são o Sherlock Holmes da pobreza:** o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica. --- ### **A Psicologia por Trás do Voto Conservador nas Periferias** A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas **cientificamente falsa**: **Análise Psicológica Básica (para você que se acha o Paulo Freire):** - **Síndrome do Branco Salvador:** Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa. - **Viés da Superioridade Moral:** "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual. - **Efeito Dunning-Kruger:** Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista. - **Estudo da Universidade de São Paulo (USP, 2021):** Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime. - **Pesquisa FGV (2020):** 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios. Esses dados revelam uma **racionalidade prática**: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como: - **Violência** (que afeta seu comércio); - **Impostos** (que consomem até 40% do lucro de um camelô); - **Burocracia** (que impede a legalização de sua barraca de pastel). --- ### **Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"** A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, **76% dos evangélicos são pobres** (Datafolha, 2023), e suas igrejas promovem valores como: - **Família tradicional** (contra pautas progressistas como ideologia de gênero em escolas); - **Auto-responsabilidade** (ênfase em "trabalho duro" em vez de assistencialismo). **Exemplo Concreto:** Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma **ameaça ao seu estilo de vida**. --- ### **A Esquerda e seu Desprezo pela Autonomia do Pobre** O cerne do debate é a **incapacidade da esquerda de aceitar que o pobre possa ser autônomo**. Algumas evidências: #### **O Caso dos Empreendedores Informais** - **Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade.** Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família. #### **A Ascensão do Conservadorismo Periférico** - Pessoas assim tem um pensamento simples. Sua mensagem: *"Queremos empreender, não depender de político."* #### **A Rejeição ao "Vitimismo"** - **Pesquisa Atlas Intel (2022):** 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores". --- ### **A projeção freudiana "o pobre é burro porque eu sou inteligente"** O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a **Síndrome do Salvador** em sua forma mais patética: - **Passo 1:** Assume-se que o pobre é um ser desprovido de agência. - **Passo 2:** Qualquer desvio da narrativa é atribuído a "manipulação da elite". - **Passo 3:** Quem critica o processo é chamado de "fascista". **Exemplo Prático:** Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta *"por quê?"* — ela grita *"lavagem cerebral!"*. A ironia? Essa mesma esquerda defende a **autonomia feminina**, exceto quando a mulher é pobre e pensa diferente. ### **Dados Globais: O Fenômeno Não é Brasileiro** A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais: - **Estados Unidos:** 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga? - **Argentina:** Javier Milei, libertário radical, quando candidato, tinha forte apoio nas *villas miseria* (favelas). Seu lema — *"O estado é um parasita"* — ressoa entre quem sofria com inflação de 211% ao ano. - **Índia:** O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades. ### **A história que a esquerda tenta apagar: pobres de direita existem desde sempre** A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que **classes baixas conservadoras são regra, não exceção**, na história mundial: - **Revolução Francesa (1789):** Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los". - **Brasil Imperial:** Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia. **Tradução:** Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias. --- ### **A Hipocrisia da Esquerda Urbana e Universitária** Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma **elite desconectada da realidade periférica**: - **Perfil Socioeconômico:** 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos. - **Prioridades Descoladas:** Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções. *"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."* ### **A diversidade de pensamento que a esquerda não suporta** A esquerda prega diversidade — desde que você seja diverso dentro de um **checklist pré-aprovado**. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são **microcosmos de pluralidade ideológica**, algo que assusta quem quer reduzir seres humanos a estereótipos. --- ### **Respostas aos Argumentos Esquerdistas (e Por que Falham)** #### **"O pobre de direita é manipulado pela mídia!"** - **Contradição:** Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra. **Contradição Central:** Como explicar que, segundo o **Banco Mundial (2023)**, países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que **o pobre com o mínimo de consciência quer emprego, não esmola**. **Dado que Machuca:** - 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (**Instituto Locomotiva, 2023**). #### **"Ele vota contra os próprios interesses!"** - **Falácia:** Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família. O pobre de direita não é uma anomalia. É o **produto natural de um mundo complexo** onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado: - **Trabalhando** para não depender do governo. - **Escolhendo** religiões que dão sentido à sua vida. - **Rejeitando** pautas identitárias que não resolvem o custo do gás de cozinha. #### **"É falta de educação política!"** - **Ironia:** Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo. --- ### **Por que o Debuste Precisa Acabar** A insistência em descredibilizar o pobre de direita revela um **projeto de poder fracassado**. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo. O pobre de direita existe porque ele **não precisa da permissão do rico de esquerda para pensar**. A incapacidade de entender isso só prova que **a esquerda é a nova aristocracia**. **Último Dado:** Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor. A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições. A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele **desafia o monopólio moral** que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo. **Pergunta Retórica (Para Incomodar):** Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que **pobre também cansa de ser tratado como cachorro que late no ritmo errado**? --- # **Fontes Citadas:** 1. Latinobarómetro (2022) 2. IPEC (2023) 3. USP (2021): *"Segurança Pública e Percepções nas Favelas Cariocas"* 4. FGV (2020): *"Informalidade e Tributação no Brasil"* 5. Datafolha (2023): *"Perfil Religioso do Eleitorado Brasileiro"* 6. Atlas Intel (2022): *"Autopercepção das Classes Baixas"* 7. Pew Research (2020): *"Voting Patterns by Income in the U.S."* 8. TSE (2023): *"Perfil Socioeconômico dos Filiados Partidários"* **Leitura Recomendada para Esquerdistas:** - *"Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda"* (Fernando Schüller, 2023) - *"A Revolução dos Conservadores: Religião e Política nas Periferias"* (Juliano Spyer, 2021) - *"Direita e Esquerda: Razões e Paixões"* (Demétrio Magnoli, 2019)
@ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto. ### **A Falácia da Superioridade Moral** O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: **a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas**. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica. --- ### **Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"** A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do **marxismo ortodoxo**, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa: - **Dados do Latinobarómetro (2022):** 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita. - **Pesquisa IPEC (2023):** 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda". Esses números não são acidentais. Refletem uma **mudança estrutural**: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque **nunca conversaram com um sem fazer cara de psicólogo de posto de saúde**. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal". ## **Se ainda não entenderam:** **Direita ≠ rico:** Tem gente que trabalha 12h/dia e vota em liberal porque quer **ser dono do próprio negócio**, não pra pagar mais taxação pra você postar meme no Twitter. **Acham que são o Sherlock Holmes da pobreza:** o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica. --- ### **A Psicologia por Trás do Voto Conservador nas Periferias** A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas **cientificamente falsa**: **Análise Psicológica Básica (para você que se acha o Paulo Freire):** - **Síndrome do Branco Salvador:** Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa. - **Viés da Superioridade Moral:** "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual. - **Efeito Dunning-Kruger:** Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista. - **Estudo da Universidade de São Paulo (USP, 2021):** Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime. - **Pesquisa FGV (2020):** 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios. Esses dados revelam uma **racionalidade prática**: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como: - **Violência** (que afeta seu comércio); - **Impostos** (que consomem até 40% do lucro de um camelô); - **Burocracia** (que impede a legalização de sua barraca de pastel). --- ### **Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"** A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, **76% dos evangélicos são pobres** (Datafolha, 2023), e suas igrejas promovem valores como: - **Família tradicional** (contra pautas progressistas como ideologia de gênero em escolas); - **Auto-responsabilidade** (ênfase em "trabalho duro" em vez de assistencialismo). **Exemplo Concreto:** Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma **ameaça ao seu estilo de vida**. --- ### **A Esquerda e seu Desprezo pela Autonomia do Pobre** O cerne do debate é a **incapacidade da esquerda de aceitar que o pobre possa ser autônomo**. Algumas evidências: #### **O Caso dos Empreendedores Informais** - **Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade.** Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família. #### **A Ascensão do Conservadorismo Periférico** - Pessoas assim tem um pensamento simples. Sua mensagem: *"Queremos empreender, não depender de político."* #### **A Rejeição ao "Vitimismo"** - **Pesquisa Atlas Intel (2022):** 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores". --- ### **A projeção freudiana "o pobre é burro porque eu sou inteligente"** O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a **Síndrome do Salvador** em sua forma mais patética: - **Passo 1:** Assume-se que o pobre é um ser desprovido de agência. - **Passo 2:** Qualquer desvio da narrativa é atribuído a "manipulação da elite". - **Passo 3:** Quem critica o processo é chamado de "fascista". **Exemplo Prático:** Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta *"por quê?"* — ela grita *"lavagem cerebral!"*. A ironia? Essa mesma esquerda defende a **autonomia feminina**, exceto quando a mulher é pobre e pensa diferente. ### **Dados Globais: O Fenômeno Não é Brasileiro** A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais: - **Estados Unidos:** 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga? - **Argentina:** Javier Milei, libertário radical, quando candidato, tinha forte apoio nas *villas miseria* (favelas). Seu lema — *"O estado é um parasita"* — ressoa entre quem sofria com inflação de 211% ao ano. - **Índia:** O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades. ### **A história que a esquerda tenta apagar: pobres de direita existem desde sempre** A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que **classes baixas conservadoras são regra, não exceção**, na história mundial: - **Revolução Francesa (1789):** Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los". - **Brasil Imperial:** Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia. **Tradução:** Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias. --- ### **A Hipocrisia da Esquerda Urbana e Universitária** Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma **elite desconectada da realidade periférica**: - **Perfil Socioeconômico:** 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos. - **Prioridades Descoladas:** Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções. *"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."* ### **A diversidade de pensamento que a esquerda não suporta** A esquerda prega diversidade — desde que você seja diverso dentro de um **checklist pré-aprovado**. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são **microcosmos de pluralidade ideológica**, algo que assusta quem quer reduzir seres humanos a estereótipos. --- ### **Respostas aos Argumentos Esquerdistas (e Por que Falham)** #### **"O pobre de direita é manipulado pela mídia!"** - **Contradição:** Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra. **Contradição Central:** Como explicar que, segundo o **Banco Mundial (2023)**, países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que **o pobre com o mínimo de consciência quer emprego, não esmola**. **Dado que Machuca:** - 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (**Instituto Locomotiva, 2023**). #### **"Ele vota contra os próprios interesses!"** - **Falácia:** Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família. O pobre de direita não é uma anomalia. É o **produto natural de um mundo complexo** onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado: - **Trabalhando** para não depender do governo. - **Escolhendo** religiões que dão sentido à sua vida. - **Rejeitando** pautas identitárias que não resolvem o custo do gás de cozinha. #### **"É falta de educação política!"** - **Ironia:** Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo. --- ### **Por que o Debuste Precisa Acabar** A insistência em descredibilizar o pobre de direita revela um **projeto de poder fracassado**. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo. O pobre de direita existe porque ele **não precisa da permissão do rico de esquerda para pensar**. A incapacidade de entender isso só prova que **a esquerda é a nova aristocracia**. **Último Dado:** Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor. A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições. A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele **desafia o monopólio moral** que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo. **Pergunta Retórica (Para Incomodar):** Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que **pobre também cansa de ser tratado como cachorro que late no ritmo errado**? --- # **Fontes Citadas:** 1. Latinobarómetro (2022) 2. IPEC (2023) 3. USP (2021): *"Segurança Pública e Percepções nas Favelas Cariocas"* 4. FGV (2020): *"Informalidade e Tributação no Brasil"* 5. Datafolha (2023): *"Perfil Religioso do Eleitorado Brasileiro"* 6. Atlas Intel (2022): *"Autopercepção das Classes Baixas"* 7. Pew Research (2020): *"Voting Patterns by Income in the U.S."* 8. TSE (2023): *"Perfil Socioeconômico dos Filiados Partidários"* **Leitura Recomendada para Esquerdistas:** - *"Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda"* (Fernando Schüller, 2023) - *"A Revolução dos Conservadores: Religião e Política nas Periferias"* (Juliano Spyer, 2021) - *"Direita e Esquerda: Razões e Paixões"* (Demétrio Magnoli, 2019) @ a95c6243:d345522c
2025-03-04 09:40:50**Die «Eliten» führen bereits groß angelegte Pilotprojekte für eine Zukunft durch,** die sie wollen und wir nicht. Das [schreibt](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/) der *OffGuardian* in einem Update zum Thema «EU-Brieftasche für die digitale Identität». Das Portal weist darauf hin, dass die Akteure dabei nicht gerade zimperlich vorgehen und auch keinen Hehl aus ihren Absichten machen. *Transition News* hat mehrfach darüber berichtet, zuletzt [hier](https://transition-news.org/eudi-wallet-der-weg-fur-ein-vollstandig-digitalisiertes-europa-ist-frei) und [hier](https://transition-news.org/iata-biometrische-daten-und-digitale-id-machen-das-vollstandig-digitale). **Mit der EU Digital Identity Wallet (EUDI-Brieftasche) sei eine einzige von der Regierung herausgegebene App geplant,** die Ihre medizinischen Daten, Beschäftigungsdaten, Reisedaten, Bildungsdaten, Impfdaten, Steuerdaten, Finanzdaten sowie (potenziell) Kopien Ihrer Unterschrift, Fingerabdrücke, Gesichtsscans, Stimmproben und DNA enthält. So fasst der *OffGuardian* die eindrucksvolle Liste möglicher Einsatzbereiche zusammen. **Auch Dokumente wie der Personalausweis oder der** **[Führerschein](https://transition-news.org/eu-weite-einfuhrung-von-digitalen-fuhrerscheinen-fur-digitale-geldborsen)** können dort in elektronischer Form gespeichert werden. Bis 2026 sind alle EU-Mitgliedstaaten dazu verpflichtet, Ihren Bürgern funktionierende und frei verfügbare digitale «Brieftaschen» bereitzustellen. **Die Menschen würden diese App nutzen,** so das Portal, um Zahlungen vorzunehmen, Kredite zu beantragen, ihre Steuern zu zahlen, ihre Rezepte abzuholen, internationale Grenzen zu überschreiten, Unternehmen zu gründen, Arzttermine zu buchen, sich um Stellen zu bewerben und sogar digitale Verträge online zu unterzeichnen. **All diese Daten würden auf ihrem Mobiltelefon gespeichert und mit den Regierungen** von neunzehn Ländern (plus der Ukraine) sowie über 140 anderen öffentlichen und privaten Partnern ausgetauscht. Von der Deutschen Bank über das ukrainische Ministerium für digitalen Fortschritt bis hin zu Samsung Europe. Unternehmen und Behörden würden auf diese Daten im Backend zugreifen, um «automatisierte Hintergrundprüfungen» durchzuführen. **Der Bundesverband der Verbraucherzentralen und Verbraucherverbände** (VZBV) habe Bedenken geäußert, dass eine solche App «Risiken für den Schutz der Privatsphäre und der Daten» berge, berichtet das Portal. Die einzige Antwort darauf laute: «Richtig, genau dafür ist sie ja da!» **Das alles sei keine Hypothese, betont der** ***OffGuardian***. Es sei vielmehr [«Potential»](https://www.digital-identity-wallet.eu/about-us/140-public-and-private-partners/). Damit ist ein EU-Projekt gemeint, in dessen Rahmen Dutzende öffentliche und private Einrichtungen zusammenarbeiten, «um eine einheitliche Vision der digitalen Identität für die Bürger der europäischen Länder zu definieren». Dies ist nur eines der groß angelegten [Pilotprojekte](https://ec.europa.eu/digital-building-blocks/sites/display/EUDIGITALIDENTITYWALLET/What+are+the+Large+Scale+Pilot+Projects), mit denen Prototypen und Anwendungsfälle für die EUDI-Wallet getestet werden. Es gibt noch mindestens drei weitere. **Den Ball der digitalen ID-Systeme habe die Covid-«Pandemie»** über die «Impfpässe» ins Rollen gebracht. Seitdem habe das Thema an Schwung verloren. Je näher wir aber der vollständigen Einführung der EUid kämen, desto mehr Propaganda der Art «Warum wir eine digitale Brieftasche brauchen» könnten wir in den Mainstream-Medien erwarten, prognostiziert der *OffGuardian*. Vielleicht müssten wir schon nach dem nächsten großen «Grund», dem nächsten «katastrophalen katalytischen Ereignis» Ausschau halten. Vermutlich gebe es bereits Pläne, warum die Menschen plötzlich eine digitale ID-Brieftasche brauchen würden. **Die Entwicklung geht jedenfalls stetig weiter in genau diese Richtung.** Beispielsweise hat Jordanien angekündigt, die digitale biometrische ID bei den nächsten [Wahlen](https://www.biometricupdate.com/202502/jordan-plans-digital-id-for-voter-verification-in-next-election) zur Verifizierung der Wähler einzuführen. Man wolle «den Papierkrieg beenden und sicherstellen, dass die gesamte Kette bis zu den nächsten Parlamentswahlen digitalisiert wird», heißt es. Absehbar ist, dass dabei einige Wahlberechtigte «auf der Strecke bleiben» werden, wie im Fall von [Albanien](https://transition-news.org/albanien-schliesst-120-000-burger-ohne-biometrische-ausweise-von-wahlen-aus) geschehen. **Derweil würden die Briten gerne ihre Privatsphäre gegen Effizienz eintauschen,** [behauptet](https://www.lbc.co.uk/news/tony-blair-id-cards/) Tony Blair. Der Ex-Premier drängte kürzlich erneut auf digitale Identitäten und Gesichtserkennung. Blair ist Gründer einer [Denkfabrik](https://transition-news.org/blair-institute-durch-vermarktung-von-patientendaten-zu-ki-gestutztem) für globalen Wandel, Anhänger globalistischer Technokratie und [«moderner Infrastruktur»](https://transition-news.org/tony-blair-digitale-id-fur-moderne-infrastruktur-unerlasslich-erfordert-aber). **Abschließend warnt der** ***OffGuardian*** **vor der Illusion, Trump und Musk würden** den US-Bürgern «diesen Schlamassel ersparen». Das Department of Government Efficiency werde sich auf die digitale Identität stürzen. Was könne schließlich «effizienter» sein als eine einzige App, die für alles verwendet wird? Der Unterschied bestehe nur darin, dass die US-Version vielleicht eher privat als öffentlich sei – sofern es da überhaupt noch einen wirklichen Unterschied gebe. *\[Titelbild: Screenshot* *[OffGuardian](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/demnachst-verfugbar-die-europaische-brieftasche-fur-digitale-identitaten)*** erschienen.
@ a95c6243:d345522c
2025-03-04 09:40:50**Die «Eliten» führen bereits groß angelegte Pilotprojekte für eine Zukunft durch,** die sie wollen und wir nicht. Das [schreibt](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/) der *OffGuardian* in einem Update zum Thema «EU-Brieftasche für die digitale Identität». Das Portal weist darauf hin, dass die Akteure dabei nicht gerade zimperlich vorgehen und auch keinen Hehl aus ihren Absichten machen. *Transition News* hat mehrfach darüber berichtet, zuletzt [hier](https://transition-news.org/eudi-wallet-der-weg-fur-ein-vollstandig-digitalisiertes-europa-ist-frei) und [hier](https://transition-news.org/iata-biometrische-daten-und-digitale-id-machen-das-vollstandig-digitale). **Mit der EU Digital Identity Wallet (EUDI-Brieftasche) sei eine einzige von der Regierung herausgegebene App geplant,** die Ihre medizinischen Daten, Beschäftigungsdaten, Reisedaten, Bildungsdaten, Impfdaten, Steuerdaten, Finanzdaten sowie (potenziell) Kopien Ihrer Unterschrift, Fingerabdrücke, Gesichtsscans, Stimmproben und DNA enthält. So fasst der *OffGuardian* die eindrucksvolle Liste möglicher Einsatzbereiche zusammen. **Auch Dokumente wie der Personalausweis oder der** **[Führerschein](https://transition-news.org/eu-weite-einfuhrung-von-digitalen-fuhrerscheinen-fur-digitale-geldborsen)** können dort in elektronischer Form gespeichert werden. Bis 2026 sind alle EU-Mitgliedstaaten dazu verpflichtet, Ihren Bürgern funktionierende und frei verfügbare digitale «Brieftaschen» bereitzustellen. **Die Menschen würden diese App nutzen,** so das Portal, um Zahlungen vorzunehmen, Kredite zu beantragen, ihre Steuern zu zahlen, ihre Rezepte abzuholen, internationale Grenzen zu überschreiten, Unternehmen zu gründen, Arzttermine zu buchen, sich um Stellen zu bewerben und sogar digitale Verträge online zu unterzeichnen. **All diese Daten würden auf ihrem Mobiltelefon gespeichert und mit den Regierungen** von neunzehn Ländern (plus der Ukraine) sowie über 140 anderen öffentlichen und privaten Partnern ausgetauscht. Von der Deutschen Bank über das ukrainische Ministerium für digitalen Fortschritt bis hin zu Samsung Europe. Unternehmen und Behörden würden auf diese Daten im Backend zugreifen, um «automatisierte Hintergrundprüfungen» durchzuführen. **Der Bundesverband der Verbraucherzentralen und Verbraucherverbände** (VZBV) habe Bedenken geäußert, dass eine solche App «Risiken für den Schutz der Privatsphäre und der Daten» berge, berichtet das Portal. Die einzige Antwort darauf laute: «Richtig, genau dafür ist sie ja da!» **Das alles sei keine Hypothese, betont der** ***OffGuardian***. Es sei vielmehr [«Potential»](https://www.digital-identity-wallet.eu/about-us/140-public-and-private-partners/). Damit ist ein EU-Projekt gemeint, in dessen Rahmen Dutzende öffentliche und private Einrichtungen zusammenarbeiten, «um eine einheitliche Vision der digitalen Identität für die Bürger der europäischen Länder zu definieren». Dies ist nur eines der groß angelegten [Pilotprojekte](https://ec.europa.eu/digital-building-blocks/sites/display/EUDIGITALIDENTITYWALLET/What+are+the+Large+Scale+Pilot+Projects), mit denen Prototypen und Anwendungsfälle für die EUDI-Wallet getestet werden. Es gibt noch mindestens drei weitere. **Den Ball der digitalen ID-Systeme habe die Covid-«Pandemie»** über die «Impfpässe» ins Rollen gebracht. Seitdem habe das Thema an Schwung verloren. Je näher wir aber der vollständigen Einführung der EUid kämen, desto mehr Propaganda der Art «Warum wir eine digitale Brieftasche brauchen» könnten wir in den Mainstream-Medien erwarten, prognostiziert der *OffGuardian*. Vielleicht müssten wir schon nach dem nächsten großen «Grund», dem nächsten «katastrophalen katalytischen Ereignis» Ausschau halten. Vermutlich gebe es bereits Pläne, warum die Menschen plötzlich eine digitale ID-Brieftasche brauchen würden. **Die Entwicklung geht jedenfalls stetig weiter in genau diese Richtung.** Beispielsweise hat Jordanien angekündigt, die digitale biometrische ID bei den nächsten [Wahlen](https://www.biometricupdate.com/202502/jordan-plans-digital-id-for-voter-verification-in-next-election) zur Verifizierung der Wähler einzuführen. Man wolle «den Papierkrieg beenden und sicherstellen, dass die gesamte Kette bis zu den nächsten Parlamentswahlen digitalisiert wird», heißt es. Absehbar ist, dass dabei einige Wahlberechtigte «auf der Strecke bleiben» werden, wie im Fall von [Albanien](https://transition-news.org/albanien-schliesst-120-000-burger-ohne-biometrische-ausweise-von-wahlen-aus) geschehen. **Derweil würden die Briten gerne ihre Privatsphäre gegen Effizienz eintauschen,** [behauptet](https://www.lbc.co.uk/news/tony-blair-id-cards/) Tony Blair. Der Ex-Premier drängte kürzlich erneut auf digitale Identitäten und Gesichtserkennung. Blair ist Gründer einer [Denkfabrik](https://transition-news.org/blair-institute-durch-vermarktung-von-patientendaten-zu-ki-gestutztem) für globalen Wandel, Anhänger globalistischer Technokratie und [«moderner Infrastruktur»](https://transition-news.org/tony-blair-digitale-id-fur-moderne-infrastruktur-unerlasslich-erfordert-aber). **Abschließend warnt der** ***OffGuardian*** **vor der Illusion, Trump und Musk würden** den US-Bürgern «diesen Schlamassel ersparen». Das Department of Government Efficiency werde sich auf die digitale Identität stürzen. Was könne schließlich «effizienter» sein als eine einzige App, die für alles verwendet wird? Der Unterschied bestehe nur darin, dass die US-Version vielleicht eher privat als öffentlich sei – sofern es da überhaupt noch einen wirklichen Unterschied gebe. *\[Titelbild: Screenshot* *[OffGuardian](https://off-guardian.org/2025/02/26/coming-soon-the-european-digital-identity-wallet/)]* *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/demnachst-verfugbar-die-europaische-brieftasche-fur-digitale-identitaten)*** erschienen. @ 39cc53c9:27168656
2025-03-30 05:54:55> [Read the original blog post](https://blog.kycnot.me/p/new-kycnot) The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me! ## Why rewrite it all? The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of *design flaws*, would have been a bad idea. It would have been like building on an *unstable foundation*. That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating *"the Python mistake"*. I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like *spaghetti code* all the time. So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a *very enjoyable language* to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and *structure the code* as well as possible. Of course, there's still *room for improvement*, which I'll address in future updates. Now I have a more *maintainable website* that can *scale* much better. It uses a *real database* instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it. ## What's new - **UI/UX** - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant! - **Point system** - The new [point system](https://kycnot.me/about#what-is-a-point) provides more detailed information about the listings, and **can** be expanded to cover additional features across all services. Anyone can request a new **point**! - **ToS Scrapper**: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now! - **Search bar** - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"! - **Transparency** - To be more [transparent](https://beta.kycnot.me/about#transparency), all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time [audits](https://beta.kycnot.me/about#audit) page that displays database changes. - **Listing Requests** - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website. - **Lightweight and fast** - The new site is lighter and faster than its predecessor! - **Tor and I2P** - At last! kycnot.me is now officially on [Tor and I2P](https://beta.kycnot.me/about#tor-and-i2p)! ## How? This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies **without KYC** is a goal I am proud of! If you appreciate [my work](https://kycnot.me/about#about), you can support me through the methods listed [here](https://kycnot.me/about#support). Alternatively, feel free to send me an email with a kind message! ### Technical details All the code is written in [Golang](https://go.dev), the website makes use of the [chi](https://go-chi.io) router for the routing part. I also make use of [BigCache](https://github.com/allegro/bigcache) for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about **2M** requests per month on average (note that this are not unique users). The database is running with [mariadb](https://mariadb.org/), using [gorm](https://gorm.io) as the ORM. This is more than enough for this project. I started working with an `sqlite` database, but I ended up migrating to **mariadb** since it works better with JSON. The scraper is using [chromedp](https://github.com/chromedp/chromedp) combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code [here](https://gitlab.com/kycnot/kycnot.me/-/tree/main/scraper). The frontend is written using **Golang Templates** for the HTML, and [TailwindCSS](https://tailwindcss.com/) plus [DaisyUI](https://daisyui.com) for the CSS classes framework. I also use some plain CSS, but it's minimal. The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the *"captcha"*, which is a simple *Proof of Work* that runs on your browser, destinated to avoid spam. For this, I use [mCaptcha](https://mcaptcha.org/).
@ 39cc53c9:27168656
2025-03-30 05:54:55> [Read the original blog post](https://blog.kycnot.me/p/new-kycnot) The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me! ## Why rewrite it all? The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of *design flaws*, would have been a bad idea. It would have been like building on an *unstable foundation*. That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating *"the Python mistake"*. I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like *spaghetti code* all the time. So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a *very enjoyable language* to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and *structure the code* as well as possible. Of course, there's still *room for improvement*, which I'll address in future updates. Now I have a more *maintainable website* that can *scale* much better. It uses a *real database* instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it. ## What's new - **UI/UX** - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant! - **Point system** - The new [point system](https://kycnot.me/about#what-is-a-point) provides more detailed information about the listings, and **can** be expanded to cover additional features across all services. Anyone can request a new **point**! - **ToS Scrapper**: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now! - **Search bar** - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"! - **Transparency** - To be more [transparent](https://beta.kycnot.me/about#transparency), all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time [audits](https://beta.kycnot.me/about#audit) page that displays database changes. - **Listing Requests** - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website. - **Lightweight and fast** - The new site is lighter and faster than its predecessor! - **Tor and I2P** - At last! kycnot.me is now officially on [Tor and I2P](https://beta.kycnot.me/about#tor-and-i2p)! ## How? This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies **without KYC** is a goal I am proud of! If you appreciate [my work](https://kycnot.me/about#about), you can support me through the methods listed [here](https://kycnot.me/about#support). Alternatively, feel free to send me an email with a kind message! ### Technical details All the code is written in [Golang](https://go.dev), the website makes use of the [chi](https://go-chi.io) router for the routing part. I also make use of [BigCache](https://github.com/allegro/bigcache) for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about **2M** requests per month on average (note that this are not unique users). The database is running with [mariadb](https://mariadb.org/), using [gorm](https://gorm.io) as the ORM. This is more than enough for this project. I started working with an `sqlite` database, but I ended up migrating to **mariadb** since it works better with JSON. The scraper is using [chromedp](https://github.com/chromedp/chromedp) combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code [here](https://gitlab.com/kycnot/kycnot.me/-/tree/main/scraper). The frontend is written using **Golang Templates** for the HTML, and [TailwindCSS](https://tailwindcss.com/) plus [DaisyUI](https://daisyui.com) for the CSS classes framework. I also use some plain CSS, but it's minimal. The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the *"captcha"*, which is a simple *Proof of Work* that runs on your browser, destinated to avoid spam. For this, I use [mCaptcha](https://mcaptcha.org/). @ 39cc53c9:27168656
2025-03-30 05:54:45> [Read the original blog post](https://blog.kycnot.me/p/ai-tos-analysis) **kycnot.me** features a somewhat hidden tool that some users may not be aware of. Every month, an automated job crawls every listed service's Terms of Service (ToS) and FAQ pages and conducts an AI-driven analysis, generating a comprehensive overview that highlights key points related to KYC and user privacy. Here's an example: [Changenow's Tos Review](https://kycnot.me/service/changenow#tos)  ## Why? ToS pages typically contain a lot of complicated text. Since the first versions of **kycnot.me**, I have tried to provide users a comprehensive overview of what can be found in such documents. This automated method keeps the information up-to-date every month, which was one of the main challenges with manual updates. A significant part of the time I invest in investigating a service for **kycnot.me** involves reading the ToS and looking for any clauses that might indicate aggressive KYC practices or privacy concerns. For the past four years, I performed this task manually. However, with advancements in language models, this process can now be somewhat automated. I still manually review the ToS for a quick check and regularly verify the AI’s findings. However, over the past three months, this automated method has proven to be quite reliable. Having a quick ToS overview section allows users to avoid reading the entire ToS page. Instead, you can quickly read the important points that are grouped, summarized, and referenced, making it easier and faster to understand the key information. ## Limitations This method has a key limitation: JS-generated pages. For this reason, I was using Playwright in my crawler implementation. I plan to make a release addressing this issue in the future. There are also sites that don't have ToS/FAQ pages, but these sites already include a warning in that section. Another issue is false positives. Although not very common, sometimes the AI might incorrectly interpret something harmless as harmful. Such errors become apparent upon reading; it's clear when something marked as bad should not be categorized as such. I manually review these cases regularly, checking for anything that seems off and then removing any inaccuracies. Overall, the automation provides great results. ## How? There have been several iterations of this tool. Initially, I started with GPT-3.5, but the results were not good in any way. It made up many things, and important thigs were lost on large ToS pages. I then switched to GPT-4 Turbo, but it was expensive. Eventually, I settled on Claude 3 Sonnet, which provides a quality compromise between GPT-3.5 and GPT-4 Turbo at a more reasonable price, while allowing a generous 200K token context window. I designed a prompt, which is open source[^1], that has been tweaked many times and will surely be adjusted further in the future. For the ToS scraping part, I initially wrote a scraper API using Playwright[^2], but I replaced it with Jina AI Reader[^3], which works quite well and is designed for this task. ### Non-conflictive ToS All services have a dropdown in the ToS section called "Non-conflictive ToS Reviews." These are the reviews that the AI flagged as not needing a user warning. I still provide these because I think they may be interesting to read. ## Feedback and contributing You can give me feedback on this tool, or share any inaccuraties by either opening an issue on Codeberg[^4] or by contacting me [^5]. You can contribute with pull requests, which are always welcome, or you can [support](https://kycnot.me/about#support) this project with any of the listed ways. [^1]: https://codeberg.org/pluja/kycnot.me/src/branch/main/src/utils/ai/prompt.go [^2]: https://codeberg.org/pluja/kycnot.me/commit/483ba8b415cecf323b3d9f0cfd4e9620919467d2 [^3]: https://github.com/jina-ai/reader [^4]: https://codeberg.org/pluja/kycnot.me [^5]: https://kycnot.me/about#contact
@ 39cc53c9:27168656
2025-03-30 05:54:45> [Read the original blog post](https://blog.kycnot.me/p/ai-tos-analysis) **kycnot.me** features a somewhat hidden tool that some users may not be aware of. Every month, an automated job crawls every listed service's Terms of Service (ToS) and FAQ pages and conducts an AI-driven analysis, generating a comprehensive overview that highlights key points related to KYC and user privacy. Here's an example: [Changenow's Tos Review](https://kycnot.me/service/changenow#tos)  ## Why? ToS pages typically contain a lot of complicated text. Since the first versions of **kycnot.me**, I have tried to provide users a comprehensive overview of what can be found in such documents. This automated method keeps the information up-to-date every month, which was one of the main challenges with manual updates. A significant part of the time I invest in investigating a service for **kycnot.me** involves reading the ToS and looking for any clauses that might indicate aggressive KYC practices or privacy concerns. For the past four years, I performed this task manually. However, with advancements in language models, this process can now be somewhat automated. I still manually review the ToS for a quick check and regularly verify the AI’s findings. However, over the past three months, this automated method has proven to be quite reliable. Having a quick ToS overview section allows users to avoid reading the entire ToS page. Instead, you can quickly read the important points that are grouped, summarized, and referenced, making it easier and faster to understand the key information. ## Limitations This method has a key limitation: JS-generated pages. For this reason, I was using Playwright in my crawler implementation. I plan to make a release addressing this issue in the future. There are also sites that don't have ToS/FAQ pages, but these sites already include a warning in that section. Another issue is false positives. Although not very common, sometimes the AI might incorrectly interpret something harmless as harmful. Such errors become apparent upon reading; it's clear when something marked as bad should not be categorized as such. I manually review these cases regularly, checking for anything that seems off and then removing any inaccuracies. Overall, the automation provides great results. ## How? There have been several iterations of this tool. Initially, I started with GPT-3.5, but the results were not good in any way. It made up many things, and important thigs were lost on large ToS pages. I then switched to GPT-4 Turbo, but it was expensive. Eventually, I settled on Claude 3 Sonnet, which provides a quality compromise between GPT-3.5 and GPT-4 Turbo at a more reasonable price, while allowing a generous 200K token context window. I designed a prompt, which is open source[^1], that has been tweaked many times and will surely be adjusted further in the future. For the ToS scraping part, I initially wrote a scraper API using Playwright[^2], but I replaced it with Jina AI Reader[^3], which works quite well and is designed for this task. ### Non-conflictive ToS All services have a dropdown in the ToS section called "Non-conflictive ToS Reviews." These are the reviews that the AI flagged as not needing a user warning. I still provide these because I think they may be interesting to read. ## Feedback and contributing You can give me feedback on this tool, or share any inaccuraties by either opening an issue on Codeberg[^4] or by contacting me [^5]. You can contribute with pull requests, which are always welcome, or you can [support](https://kycnot.me/about#support) this project with any of the listed ways. [^1]: https://codeberg.org/pluja/kycnot.me/src/branch/main/src/utils/ai/prompt.go [^2]: https://codeberg.org/pluja/kycnot.me/commit/483ba8b415cecf323b3d9f0cfd4e9620919467d2 [^3]: https://github.com/jina-ai/reader [^4]: https://codeberg.org/pluja/kycnot.me [^5]: https://kycnot.me/about#contact @ 39cc53c9:27168656
2025-03-30 05:54:42> [Read the original blog post](https://blog.kycnot.me/p/four-years) > “The future is there... staring back at us. Trying to make sense of the fiction we will have become.” > — William Gibson. This month is [the 4th anniversary](#the-anniversary) of kycnot.me. Thank you for being here. Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency **free from government and institutional control**. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play. What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you. Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances. Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition[^1]:  How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us. > ‟Hush now, baby, baby, don't you cry > Mamma's gonna make all of your nightmares come true > Mamma's gonna put all of her fears into you > Mamma's gonna keep you right here, under her wing > She won't let you fly, but she might let you sing > Mamma's gonna keep baby cosy and warm” > — Mother, Pink Floyd We must resist any attack on our privacy and freedom. To do this, we must collaborate. If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that. If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can. This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest. > “We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” > — Eric Hughes, A Cypherpunk's Manifesto ## The anniversary Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of [kycnot.me](https://kycnot.me) — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now. [kycnot.me](https://kycnot.me) has remained 100% independent and 100% open source[^2] all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years). The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see [the score summary](https://https://kycnot.me/api/v1/service/bisq/summary) for any service's score. I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this. [^1]: https://x.com/freedomtech/status/1796190018588872806 [^2]: https://codeberg.org/pluja/kycnot.me
@ 39cc53c9:27168656
2025-03-30 05:54:42> [Read the original blog post](https://blog.kycnot.me/p/four-years) > “The future is there... staring back at us. Trying to make sense of the fiction we will have become.” > — William Gibson. This month is [the 4th anniversary](#the-anniversary) of kycnot.me. Thank you for being here. Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency **free from government and institutional control**. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play. What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you. Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances. Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition[^1]:  How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us. > ‟Hush now, baby, baby, don't you cry > Mamma's gonna make all of your nightmares come true > Mamma's gonna put all of her fears into you > Mamma's gonna keep you right here, under her wing > She won't let you fly, but she might let you sing > Mamma's gonna keep baby cosy and warm” > — Mother, Pink Floyd We must resist any attack on our privacy and freedom. To do this, we must collaborate. If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that. If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can. This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest. > “We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” > — Eric Hughes, A Cypherpunk's Manifesto ## The anniversary Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of [kycnot.me](https://kycnot.me) — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now. [kycnot.me](https://kycnot.me) has remained 100% independent and 100% open source[^2] all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years). The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see [the score summary](https://https://kycnot.me/api/v1/service/bisq/summary) for any service's score. I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this. [^1]: https://x.com/freedomtech/status/1796190018588872806 [^2]: https://codeberg.org/pluja/kycnot.me @ a95c6243:d345522c
2025-03-01 10:39:35*Ständige Lügen und Unterstellungen, permanent falsche Fürsorge* *\ können Bausteine von emotionaler Manipulation sein. Mit dem Zweck,* *\ Macht und Kontrolle über eine andere Person auszuüben.* *\ Apotheken Umschau*   **Irgendetwas muss passiert sein: «Gaslighting» ist gerade Thema** in vielen Medien. Heute bin ich nach längerer Zeit mal wieder über dieses Stichwort gestolpert. Das war in einem [Artikel](https://norberthaering.de/propaganda-zensur/dwd-referenzperiode/) von Norbert Häring über Manipulationen des Deutschen Wetterdienstes (DWD). In diesem Fall ging es um eine Pressemitteilung vom Donnerstag zum «viel zu warmen» Winter 2024/25. **Häring wirft der Behörde vor, dreist zu lügen und Dinge auszulassen,** um die Klimaangst wach zu halten. Was der Leser beim DWD nicht erfahre, sei, dass dieser Winter kälter als die drei vorangegangenen und kälter als der Durchschnitt der letzten zehn Jahre gewesen sei. Stattdessen werde der falsche Eindruck vermittelt, es würde ungebremst immer wärmer. **Wem also der zu Ende gehende Winter eher kalt vorgekommen sein sollte,** mit dessen Empfinden stimme wohl etwas nicht. Das jedenfalls wolle der DWD uns einreden, so der Wirtschaftsjournalist. Und damit sind wir beim Thema Gaslighting. **Als** **[Gaslighting](https://bayern-gegen-gewalt.de/gewalt-infos-und-einblicke/formen-von-gewalt/psychische-gewalt/gaslighting/)** **wird eine Form psychischer Manipulation bezeichnet,** mit der die Opfer desorientiert und zutiefst verunsichert werden, indem ihre eigene Wahrnehmung als falsch bezeichnet wird. Der Prozess führt zu Angst und Realitätsverzerrung sowie zur Zerstörung des Selbstbewusstseins. Die Bezeichnung kommt von dem britischen Theaterstück «Gas Light» aus dem Jahr 1938, in dem ein Mann mit grausamen Psychotricks seine Frau in den Wahnsinn treibt. **Damit Gaslighting funktioniert, muss das Opfer dem Täter vertrauen.** Oft wird solcher Psychoterror daher im privaten oder familiären Umfeld beschrieben, ebenso wie am Arbeitsplatz. Jedoch eignen sich die Prinzipien auch perfekt zur Manipulation der Massen. Vermeintliche Autoritäten wie Ärzte und Wissenschaftler, oder «der fürsorgliche Staat» und Institutionen wie die UNO oder die WHO wollen uns doch nichts Böses. Auch Staatsmedien, Faktenchecker und diverse NGOs wurden zu «vertrauenswürdigen Quellen» erklärt. Das hat seine Wirkung. **Warum das Thema Gaslighting derzeit scheinbar so populär ist,** vermag ich nicht zu sagen. Es sind aber gerade in den letzten Tagen und Wochen auffällig viele Artikel dazu erschienen, und zwar nicht nur von Psychologen. Die *Frankfurter Rundschau* hat gleich mehrere publiziert, und [Anwälte](https://www.anwalt.de/rechtstipps/gaslighting-beispiele-anzeichen-strafbarkeit-212449.html) interessieren sich dafür offenbar genauso wie Apotheker. **Die** ***Apotheken Umschau*** **machte sogar auf** **[«Medical Gaslighting»](https://archive.is/Wx5YM)** **aufmerksam.** Davon spreche man, wenn Mediziner Symptome nicht ernst nähmen oder wenn ein gesundheitliches Problem vom behandelnden Arzt «schnöde heruntergespielt» oder abgetan würde. Kommt Ihnen das auch irgendwie bekannt vor? Der Begriff sei allerdings irreführend, da er eine manipulierende Absicht unterstellt, die «nicht gewährleistet» sei. **Apropos Gaslighting: Die noch amtierende deutsche Bundesregierung** [meldete](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-08-2025-februar-28-2336254?view=renderNewsletterHtml) heute, es gelte, «weiter \[sic!] gemeinsam daran zu arbeiten, einen gerechten und dauerhaften Frieden für die Ukraine zu erreichen». Die Ukraine, wo sich am Montag «der völkerrechtswidrige Angriffskrieg zum dritten Mal jährte», [verteidige](https://transition-news.org/wikileaks-der-westen-wusste-dass-ein-nato-beitritt-der-ukraine-riskant-war) ihr Land und «unsere gemeinsamen Werte». **Merken Sie etwas? Das Demokratieverständnis mag ja tatsächlich** inzwischen in beiden Ländern ähnlich traurig sein. Bezüglich Friedensbemühungen ist meine Wahrnehmung jedoch eine andere. Das muss an meinem Gedächtnis liegen. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/bitte-nicht-von-gaslichtern-irritieren-lassen)*** erschienen.
@ a95c6243:d345522c
2025-03-01 10:39:35*Ständige Lügen und Unterstellungen, permanent falsche Fürsorge* *\ können Bausteine von emotionaler Manipulation sein. Mit dem Zweck,* *\ Macht und Kontrolle über eine andere Person auszuüben.* *\ Apotheken Umschau*   **Irgendetwas muss passiert sein: «Gaslighting» ist gerade Thema** in vielen Medien. Heute bin ich nach längerer Zeit mal wieder über dieses Stichwort gestolpert. Das war in einem [Artikel](https://norberthaering.de/propaganda-zensur/dwd-referenzperiode/) von Norbert Häring über Manipulationen des Deutschen Wetterdienstes (DWD). In diesem Fall ging es um eine Pressemitteilung vom Donnerstag zum «viel zu warmen» Winter 2024/25. **Häring wirft der Behörde vor, dreist zu lügen und Dinge auszulassen,** um die Klimaangst wach zu halten. Was der Leser beim DWD nicht erfahre, sei, dass dieser Winter kälter als die drei vorangegangenen und kälter als der Durchschnitt der letzten zehn Jahre gewesen sei. Stattdessen werde der falsche Eindruck vermittelt, es würde ungebremst immer wärmer. **Wem also der zu Ende gehende Winter eher kalt vorgekommen sein sollte,** mit dessen Empfinden stimme wohl etwas nicht. Das jedenfalls wolle der DWD uns einreden, so der Wirtschaftsjournalist. Und damit sind wir beim Thema Gaslighting. **Als** **[Gaslighting](https://bayern-gegen-gewalt.de/gewalt-infos-und-einblicke/formen-von-gewalt/psychische-gewalt/gaslighting/)** **wird eine Form psychischer Manipulation bezeichnet,** mit der die Opfer desorientiert und zutiefst verunsichert werden, indem ihre eigene Wahrnehmung als falsch bezeichnet wird. Der Prozess führt zu Angst und Realitätsverzerrung sowie zur Zerstörung des Selbstbewusstseins. Die Bezeichnung kommt von dem britischen Theaterstück «Gas Light» aus dem Jahr 1938, in dem ein Mann mit grausamen Psychotricks seine Frau in den Wahnsinn treibt. **Damit Gaslighting funktioniert, muss das Opfer dem Täter vertrauen.** Oft wird solcher Psychoterror daher im privaten oder familiären Umfeld beschrieben, ebenso wie am Arbeitsplatz. Jedoch eignen sich die Prinzipien auch perfekt zur Manipulation der Massen. Vermeintliche Autoritäten wie Ärzte und Wissenschaftler, oder «der fürsorgliche Staat» und Institutionen wie die UNO oder die WHO wollen uns doch nichts Böses. Auch Staatsmedien, Faktenchecker und diverse NGOs wurden zu «vertrauenswürdigen Quellen» erklärt. Das hat seine Wirkung. **Warum das Thema Gaslighting derzeit scheinbar so populär ist,** vermag ich nicht zu sagen. Es sind aber gerade in den letzten Tagen und Wochen auffällig viele Artikel dazu erschienen, und zwar nicht nur von Psychologen. Die *Frankfurter Rundschau* hat gleich mehrere publiziert, und [Anwälte](https://www.anwalt.de/rechtstipps/gaslighting-beispiele-anzeichen-strafbarkeit-212449.html) interessieren sich dafür offenbar genauso wie Apotheker. **Die** ***Apotheken Umschau*** **machte sogar auf** **[«Medical Gaslighting»](https://archive.is/Wx5YM)** **aufmerksam.** Davon spreche man, wenn Mediziner Symptome nicht ernst nähmen oder wenn ein gesundheitliches Problem vom behandelnden Arzt «schnöde heruntergespielt» oder abgetan würde. Kommt Ihnen das auch irgendwie bekannt vor? Der Begriff sei allerdings irreführend, da er eine manipulierende Absicht unterstellt, die «nicht gewährleistet» sei. **Apropos Gaslighting: Die noch amtierende deutsche Bundesregierung** [meldete](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-08-2025-februar-28-2336254?view=renderNewsletterHtml) heute, es gelte, «weiter \[sic!] gemeinsam daran zu arbeiten, einen gerechten und dauerhaften Frieden für die Ukraine zu erreichen». Die Ukraine, wo sich am Montag «der völkerrechtswidrige Angriffskrieg zum dritten Mal jährte», [verteidige](https://transition-news.org/wikileaks-der-westen-wusste-dass-ein-nato-beitritt-der-ukraine-riskant-war) ihr Land und «unsere gemeinsamen Werte». **Merken Sie etwas? Das Demokratieverständnis mag ja tatsächlich** inzwischen in beiden Ländern ähnlich traurig sein. Bezüglich Friedensbemühungen ist meine Wahrnehmung jedoch eine andere. Das muss an meinem Gedächtnis liegen. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/bitte-nicht-von-gaslichtern-irritieren-lassen)*** erschienen. @ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one. ## Public Home/Outbox Relays Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**. Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience. This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts. ## Public Inbox Relays This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out. Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience. This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here. ## DM Inbox Relays These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them. Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy. Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers. Make sure to add at least one public relay if you want to see DM notifications. ## Private Home Relays Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools. Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa. ## Search relays: This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com ## Local Relays: This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option. ## General Relays: This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each. Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible. Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them. ## My setup Here's what I use: 1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself. 2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription. 3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription. 4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country. 5. Download Citrine to your phone. Then, on your relay lists, put: Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. - <your.relay>.nostr1.com Public Inbox Relays - nos.lol or an in-country relay - <your.relay>.nostr1.com DM Inbox Relays - inbox.nostr.wine - <your.relay>.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) - <your.relay>.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com Local Relays - ws://localhost:4869 (Citrine) General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom And a few of the recommended relays from Amethyst. ## Final Considerations Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one. ## Public Home/Outbox Relays Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, **they will not receive your updates**. Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience. This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to [relay.tools](https://relay.tools/) and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts. ## Public Inbox Relays This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out. Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience. This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to [nostr.watch](https://nostr.watch/relays/find) and find relays in your country Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here. ## DM Inbox Relays These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. **If you don't have it setup, you will miss DMs**. DM Inbox relays should accept any message from anyone, but only allow you to download them. Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy. Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers. Make sure to add at least one public relay if you want to see DM notifications. ## Private Home Relays Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools. Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa. ## Search relays: This is the list of relays to use on Amethyst's search and user tagging with @. **Tagging and searching will not work if there is nothing here.**. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com ## Local Relays: This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option. ## General Relays: This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each. Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible. Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them. ## My setup Here's what I use: 1. Go to [relay.tools](https://relay.tools/) and create a relay for yourself. 2. Go to [nostr.wine](https://nostr.wine/) and pay for their subscription. 3. Go to [inbox.nostr.wine](https://inbox.nostr.wine/) and pay for their subscription. 4. Go to [nostr.watch](https://nostr.watch/relays/find) and find a good relay in your country. 5. Download Citrine to your phone. Then, on your relay lists, put: Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. - <your.relay>.nostr1.com Public Inbox Relays - nos.lol or an in-country relay - <your.relay>.nostr1.com DM Inbox Relays - inbox.nostr.wine - <your.relay>.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) - <your.relay>.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com Local Relays - ws://localhost:4869 (Citrine) General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom And a few of the recommended relays from Amethyst. ## Final Considerations Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies. @ d4cb227b:edca6019
2025-03-30 04:26:51Dose: 30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F) Instructions: 1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer. 2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds. 3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase. 4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds. 5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds. 6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction. 7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds. 8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper. 9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
@ d4cb227b:edca6019
2025-03-30 04:26:51Dose: 30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F) Instructions: 1. Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer. 2. Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds. 3. For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase. 4. As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds. 5. Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds. 6. Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction. 7. Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds. 8. Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper. 9. Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction. @ a95c6243:d345522c
2025-02-21 19:32:23*Europa – das Ganze ist eine wunderbare Idee,* *\ aber das war der Kommunismus auch.* *\ Loriot*   **«Europa hat fertig», könnte man unken,** und das wäre nicht einmal sehr verwegen. Mit solch einer [Einschätzung](https://transition-news.org/geopolitische-ohnmacht-und-die-last-des-euro-steht-die-eu-vor-der-implosion) stünden wir nicht alleine, denn die Stimmen in diese Richtung mehren sich. Der französische Präsident Emmanuel Macron warnte schon letztes Jahr davor, dass «unser Europa sterben könnte». Vermutlich hatte er dabei andere Gefahren im Kopf als jetzt der ungarische Ministerpräsident Viktor Orbán, der ein «baldiges Ende der EU» prognostizierte. Das Ergebnis könnte allerdings das gleiche sein. **Neben vordergründigen Themenbereichen wie Wirtschaft, Energie und Sicherheit** ist das eigentliche Problem jedoch die obskure Mischung aus aufgegebener Souveränität und geschwollener Arroganz, mit der europäische Politiker:innende unterschiedlicher Couleur aufzutreten pflegen. Und das Tüpfelchen auf dem i ist die bröckelnde Legitimation politischer Institutionen dadurch, dass die Stimmen großer Teile der Bevölkerung seit Jahren auf vielfältige Weise ausgegrenzt werden. **Um «UnsereDemokratie» steht es schlecht.** Dass seine Mandate immer schwächer werden, merkt natürlich auch unser «Führungspersonal». Entsprechend werden die Maßnahmen zur Gängelung, Überwachung und Manipulation der Bürger ständig verzweifelter. Parallel dazu [plustern](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-07-2025-februar-21-2335652?view=renderNewsletterHtml) sich in Paris Macron, Scholz und einige andere noch einmal mächtig in Sachen Verteidigung und [«Kriegstüchtigkeit»](https://transition-news.org/europaische-investitionsbank-tragt-zur-kriegstuchtigkeit-europas-bei) auf. **Momentan gilt es auch, das Überschwappen covidiotischer und verschwörungsideologischer Auswüchse** aus den USA nach Europa zu vermeiden. So ein «MEGA» (Make Europe Great Again) können wir hier nicht gebrauchen. Aus den Vereinigten Staaten kommen nämlich furchtbare Nachrichten. Beispielsweise wurde einer der schärfsten Kritiker der Corona-Maßnahmen kürzlich zum Gesundheitsminister ernannt. Dieser setzt sich jetzt für eine Neubewertung der mRNA-«Impfstoffe» ein, was durchaus zu einem [Entzug der Zulassungen](https://transition-news.org/usa-zulassungsentzug-fur-corona-impfstoffe-auf-der-tagesordnung) führen könnte. **Der europäischen Version von** **[«Verteidigung der Demokratie»](https://transition-news.org/eu-macht-freiwilligen-verhaltenskodex-gegen-desinformation-zu-bindendem-recht)** setzte der US-Vizepräsident J. D. Vance auf der Münchner Sicherheitskonferenz sein Verständnis entgegen: «Demokratie stärken, indem wir unseren Bürgern erlauben, ihre Meinung zu sagen». Das Abschalten von Medien, das Annullieren von Wahlen oder das Ausschließen von Menschen vom politischen Prozess schütze gar nichts. Vielmehr sei dies der todsichere Weg, die Demokratie zu zerstören. **In der Schweiz kamen seine Worte deutlich besser an** als in den meisten europäischen NATO-Ländern. Bundespräsidentin Karin Keller-Sutter lobte die Rede und interpretierte sie als «Plädoyer für die direkte Demokratie». Möglicherweise zeichne sich hier eine [außenpolitische Kehrtwende](https://transition-news.org/schweiz-vor-aussenpolitischer-kehrtwende-richtung-integraler-neutralitat) in Richtung integraler Neutralität ab, meint mein Kollege Daniel Funk. Das wären doch endlich mal ein paar gute Nachrichten. **Von der einstigen Idee einer europäischen Union** mit engeren Beziehungen zwischen den Staaten, um Konflikte zu vermeiden und das Wohlergehen der Bürger zu verbessern, sind wir meilenweit abgekommen. Der heutige korrupte Verbund unter technokratischer Leitung ähnelt mehr einem Selbstbedienungsladen mit sehr begrenztem Zugang. Die EU-Wahlen im letzten Sommer haben daran ebenso wenig geändert, wie die [Bundestagswahl](https://transition-news.org/bundestagswahl-mehr-aufrustung-statt-friedenskanzler-nach-der-wahl) am kommenden Sonntag darauf einen Einfluss haben wird. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/europaer-seid-ihr-noch-zu-retten)*** erschienen.
@ a95c6243:d345522c
2025-02-21 19:32:23*Europa – das Ganze ist eine wunderbare Idee,* *\ aber das war der Kommunismus auch.* *\ Loriot*   **«Europa hat fertig», könnte man unken,** und das wäre nicht einmal sehr verwegen. Mit solch einer [Einschätzung](https://transition-news.org/geopolitische-ohnmacht-und-die-last-des-euro-steht-die-eu-vor-der-implosion) stünden wir nicht alleine, denn die Stimmen in diese Richtung mehren sich. Der französische Präsident Emmanuel Macron warnte schon letztes Jahr davor, dass «unser Europa sterben könnte». Vermutlich hatte er dabei andere Gefahren im Kopf als jetzt der ungarische Ministerpräsident Viktor Orbán, der ein «baldiges Ende der EU» prognostizierte. Das Ergebnis könnte allerdings das gleiche sein. **Neben vordergründigen Themenbereichen wie Wirtschaft, Energie und Sicherheit** ist das eigentliche Problem jedoch die obskure Mischung aus aufgegebener Souveränität und geschwollener Arroganz, mit der europäische Politiker:innende unterschiedlicher Couleur aufzutreten pflegen. Und das Tüpfelchen auf dem i ist die bröckelnde Legitimation politischer Institutionen dadurch, dass die Stimmen großer Teile der Bevölkerung seit Jahren auf vielfältige Weise ausgegrenzt werden. **Um «UnsereDemokratie» steht es schlecht.** Dass seine Mandate immer schwächer werden, merkt natürlich auch unser «Führungspersonal». Entsprechend werden die Maßnahmen zur Gängelung, Überwachung und Manipulation der Bürger ständig verzweifelter. Parallel dazu [plustern](https://www.bundesregierung.de/breg-de/service/newsletter-und-abos/bundesregierung-aktuell/ausgabe-07-2025-februar-21-2335652?view=renderNewsletterHtml) sich in Paris Macron, Scholz und einige andere noch einmal mächtig in Sachen Verteidigung und [«Kriegstüchtigkeit»](https://transition-news.org/europaische-investitionsbank-tragt-zur-kriegstuchtigkeit-europas-bei) auf. **Momentan gilt es auch, das Überschwappen covidiotischer und verschwörungsideologischer Auswüchse** aus den USA nach Europa zu vermeiden. So ein «MEGA» (Make Europe Great Again) können wir hier nicht gebrauchen. Aus den Vereinigten Staaten kommen nämlich furchtbare Nachrichten. Beispielsweise wurde einer der schärfsten Kritiker der Corona-Maßnahmen kürzlich zum Gesundheitsminister ernannt. Dieser setzt sich jetzt für eine Neubewertung der mRNA-«Impfstoffe» ein, was durchaus zu einem [Entzug der Zulassungen](https://transition-news.org/usa-zulassungsentzug-fur-corona-impfstoffe-auf-der-tagesordnung) führen könnte. **Der europäischen Version von** **[«Verteidigung der Demokratie»](https://transition-news.org/eu-macht-freiwilligen-verhaltenskodex-gegen-desinformation-zu-bindendem-recht)** setzte der US-Vizepräsident J. D. Vance auf der Münchner Sicherheitskonferenz sein Verständnis entgegen: «Demokratie stärken, indem wir unseren Bürgern erlauben, ihre Meinung zu sagen». Das Abschalten von Medien, das Annullieren von Wahlen oder das Ausschließen von Menschen vom politischen Prozess schütze gar nichts. Vielmehr sei dies der todsichere Weg, die Demokratie zu zerstören. **In der Schweiz kamen seine Worte deutlich besser an** als in den meisten europäischen NATO-Ländern. Bundespräsidentin Karin Keller-Sutter lobte die Rede und interpretierte sie als «Plädoyer für die direkte Demokratie». Möglicherweise zeichne sich hier eine [außenpolitische Kehrtwende](https://transition-news.org/schweiz-vor-aussenpolitischer-kehrtwende-richtung-integraler-neutralitat) in Richtung integraler Neutralität ab, meint mein Kollege Daniel Funk. Das wären doch endlich mal ein paar gute Nachrichten. **Von der einstigen Idee einer europäischen Union** mit engeren Beziehungen zwischen den Staaten, um Konflikte zu vermeiden und das Wohlergehen der Bürger zu verbessern, sind wir meilenweit abgekommen. Der heutige korrupte Verbund unter technokratischer Leitung ähnelt mehr einem Selbstbedienungsladen mit sehr begrenztem Zugang. Die EU-Wahlen im letzten Sommer haben daran ebenso wenig geändert, wie die [Bundestagswahl](https://transition-news.org/bundestagswahl-mehr-aufrustung-statt-friedenskanzler-nach-der-wahl) am kommenden Sonntag darauf einen Einfluss haben wird. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/europaer-seid-ihr-noch-zu-retten)*** erschienen. @ d4cb227b:edca6019
2025-03-30 04:23:22This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain. Dose: - 20g coffee (Coarse ground coffee) - 300mL water (92°C / 197.6°F) Time: 3:30 Instructions: Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.) Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.) Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour) Pour 4: 2:10 > 60mL Pour 5: 2:40 > 60mL Remove the V60 at 3:30
@ d4cb227b:edca6019
2025-03-30 04:23:22This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain. Dose: - 20g coffee (Coarse ground coffee) - 300mL water (92°C / 197.6°F) Time: 3:30 Instructions: Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.) Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.) Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour) Pour 4: 2:10 > 60mL Pour 5: 2:40 > 60mL Remove the V60 at 3:30 @ a95c6243:d345522c
2025-02-19 09:23:17*Die «moralische Weltordnung» – eine Art Astrologie. Friedrich Nietzsche* **Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere. **In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt. **Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel. **Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten. **Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY). **Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen. **Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf. **Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen». --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen.
@ a95c6243:d345522c
2025-02-19 09:23:17*Die «moralische Weltordnung» – eine Art Astrologie. Friedrich Nietzsche* **Das Treffen der BRICS-Staaten beim [Gipfel](https://transition-news.org/brics-gipfel-in-kasan-warum-schweigt-die-schweiz) im russischen Kasan** war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere. **In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt,** dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats [Türkei](https://transition-news.org/turkei-entlarvt-fake-news-von-bild-uber-indiens-angebliches-veto-gegen-den) für etwas Aufsehen gesorgt. **Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche** zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel. **Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel,** zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um [Bitcoin](https://www.forbes.com/sites/digital-assets/2024/10/23/russia-launches-brics-mining-infrastructure-project/)-Mining-Anlagen für die BRICS-Länder zu errichten. **Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen** als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem [BRICS Pay](https://en.wikipedia.org/wiki/BRICS_PAY). **Dient der Bitcoin also der Entdollarisierung?** Oder droht er inzwischen, zum Gegenstand geopolitischer [Machtspielchen](https://legitim.ch/es-ist-ein-sieg-fuer-bitcoin-waehrend-russland-und-die-usa-um-die-krypto-vorherrschaft-kaempfen/) zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen. **Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung** momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, [Bitcoin «zu eliminieren»](https://www.btc-echo.de/schlagzeilen/ezb-banker-es-gibt-gute-gruende-bitcoin-zu-eliminieren-194015/). Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu [begrenzenden Maßnahmen](https://legitim.ch/el-salvador-iwf-fordert-trotz-nicht-eingetretener-risiken-neue-massnahmen-gegen-bitcoin/) gegen das Kryptogeld auf. **Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben,** wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im [Abschlussdokument](http://static.kremlin.ru/media/events/files/en/RosOySvLzGaJtmx2wYFv0lN4NSPZploG.pdf) bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine [Bankrotterklärung](https://x.com/wolff_ernst/status/1849781982961557771) korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen». --- Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/aufstand-gegen-die-dollar-hegemonie)* erschienen. @ a95c6243:d345522c
2025-02-15 19:05:38**Auf der diesjährigen Münchner** **[Sicherheitskonferenz](https://transition-news.org/in-munchen-der-realitat-ins-auge-sehen)** **geht es vor allem um die Ukraine.** Protagonisten sind dabei zunächst die US-Amerikaner. Präsident Trump schockierte die Europäer kurz vorher durch ein Telefonat mit seinem Amtskollegen Wladimir Putin, während Vizepräsident Vance mit seiner Rede über Demokratie und Meinungsfreiheit für versteinerte Mienen und Empörung sorgte. **Die Bemühungen der Europäer um einen Frieden in der Ukraine** halten sich, gelinde gesagt, in Grenzen. Größeres Augenmerk wird auf militärische Unterstützung, die Pflege von Feindbildern sowie Eskalation gelegt. Der deutsche Bundeskanzler Scholz [reagierte](https://transition-news.org/gesucht-friedenskanzler) auf die angekündigten Verhandlungen über einen möglichen Frieden für die Ukraine mit der Forderung nach noch höheren «Verteidigungsausgaben». Auch die amtierende Außenministerin Baerbock hatte vor der Münchner Konferenz [klargestellt](https://archive.is/nUpYa): > «Frieden wird es nur durch Stärke geben. (...) Bei Corona haben wir gesehen, zu was Europa fähig ist. Es braucht erneut Investitionen, die der historischen Wegmarke, vor der wir stehen, angemessen sind.» **Die Rüstungsindustrie freut sich in jedem Fall über weltweit steigende Militärausgaben.** Die Kriege in der Ukraine und in Gaza tragen zu [Rekordeinnahmen](https://transition-news.org/kriege-sind-fur-waffenproduzenten-und-hedgefonds-f-king-good) bei. Jetzt «winkt die Aussicht auf eine jahrelange große Nachrüstung in Europa», auch wenn der Ukraine-Krieg enden sollte, so hört man aus Finanzkreisen. In der Konsequenz kennt «die Aktie des deutschen Vorzeige-Rüstungskonzerns Rheinmetall in ihrem Anstieg [offenbar gar keine Grenzen](https://finanzmarktwelt.de/rheinmetall-aktie-mit-mega-rally-nachruestung-und-1-000-euro-kursziel-339271/) mehr». «Solche Friedensversprechen» wie das jetzige hätten in der Vergangenheit zu starken Kursverlusten geführt. **Für manche Leute sind Kriegswaffen und sonstige Rüstungsgüter Waren wie alle anderen,** jedenfalls aus der Perspektive von Investoren oder Managern. Auch in diesem Bereich gibt es Startups und man spricht von Dingen wie innovativen Herangehensweisen, hocheffizienten Produktionsanlagen, skalierbaren Produktionstechniken und geringeren Stückkosten. **Wir lesen aktuell von Massenproduktion und gesteigerten Fertigungskapazitäten** für Kriegsgerät. Der Motor solcher Dynamik und solchen Wachstums ist die Aufrüstung, die inzwischen permanent gefordert wird. Parallel wird die Bevölkerung verbal eingestimmt und auf Kriegstüchtigkeit getrimmt. **Das Rüstungs- und KI-Startup Helsing verkündete kürzlich** eine «dezentrale [Massenproduktion](https://www.trendingtopics.eu/helsing-kampfdrohnen-unicorn-startet-dezentrale-massenproduktion-fuer-ukrainekrieg/) für den Ukrainekrieg». Mit dieser Expansion positioniere sich das Münchner Unternehmen als einer der weltweit führenden Hersteller von Kampfdrohnen. Der nächste [«Meilenstein»](https://archive.is/eZsWP) steht auch bereits an: Man will eine Satellitenflotte im Weltraum aufbauen, zur Überwachung von Gefechtsfeldern und Truppenbewegungen. **Ebenfalls aus München stammt das als** **[DefenseTech-Startup](https://www.trendingtopics.eu/arx-robotics-produktion/)** **bezeichnete Unternehmen** ARX Robotics. Kürzlich habe man in der Region die größte europäische Produktionsstätte für autonome Verteidigungssysteme eröffnet. Damit fahre man die Produktion von Militär-Robotern hoch. Diese Expansion diene auch der Lieferung der «größten Flotte unbemannter Bodensysteme westlicher Bauart» in die Ukraine. **Rüstung boomt und scheint ein Zukunftsmarkt zu sein.** Die Hersteller und Vermarkter betonen, mit ihren Aktivitäten und Produkten solle die europäische Verteidigungsfähigkeit erhöht werden. Ihre Strategien sollten sogar «zum Schutz demokratischer Strukturen beitragen». *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/so-klingt-das-aufrustungs-business-startups-und-alte-hasen)*** erschienen.
@ a95c6243:d345522c
2025-02-15 19:05:38**Auf der diesjährigen Münchner** **[Sicherheitskonferenz](https://transition-news.org/in-munchen-der-realitat-ins-auge-sehen)** **geht es vor allem um die Ukraine.** Protagonisten sind dabei zunächst die US-Amerikaner. Präsident Trump schockierte die Europäer kurz vorher durch ein Telefonat mit seinem Amtskollegen Wladimir Putin, während Vizepräsident Vance mit seiner Rede über Demokratie und Meinungsfreiheit für versteinerte Mienen und Empörung sorgte. **Die Bemühungen der Europäer um einen Frieden in der Ukraine** halten sich, gelinde gesagt, in Grenzen. Größeres Augenmerk wird auf militärische Unterstützung, die Pflege von Feindbildern sowie Eskalation gelegt. Der deutsche Bundeskanzler Scholz [reagierte](https://transition-news.org/gesucht-friedenskanzler) auf die angekündigten Verhandlungen über einen möglichen Frieden für die Ukraine mit der Forderung nach noch höheren «Verteidigungsausgaben». Auch die amtierende Außenministerin Baerbock hatte vor der Münchner Konferenz [klargestellt](https://archive.is/nUpYa): > «Frieden wird es nur durch Stärke geben. (...) Bei Corona haben wir gesehen, zu was Europa fähig ist. Es braucht erneut Investitionen, die der historischen Wegmarke, vor der wir stehen, angemessen sind.» **Die Rüstungsindustrie freut sich in jedem Fall über weltweit steigende Militärausgaben.** Die Kriege in der Ukraine und in Gaza tragen zu [Rekordeinnahmen](https://transition-news.org/kriege-sind-fur-waffenproduzenten-und-hedgefonds-f-king-good) bei. Jetzt «winkt die Aussicht auf eine jahrelange große Nachrüstung in Europa», auch wenn der Ukraine-Krieg enden sollte, so hört man aus Finanzkreisen. In der Konsequenz kennt «die Aktie des deutschen Vorzeige-Rüstungskonzerns Rheinmetall in ihrem Anstieg [offenbar gar keine Grenzen](https://finanzmarktwelt.de/rheinmetall-aktie-mit-mega-rally-nachruestung-und-1-000-euro-kursziel-339271/) mehr». «Solche Friedensversprechen» wie das jetzige hätten in der Vergangenheit zu starken Kursverlusten geführt. **Für manche Leute sind Kriegswaffen und sonstige Rüstungsgüter Waren wie alle anderen,** jedenfalls aus der Perspektive von Investoren oder Managern. Auch in diesem Bereich gibt es Startups und man spricht von Dingen wie innovativen Herangehensweisen, hocheffizienten Produktionsanlagen, skalierbaren Produktionstechniken und geringeren Stückkosten. **Wir lesen aktuell von Massenproduktion und gesteigerten Fertigungskapazitäten** für Kriegsgerät. Der Motor solcher Dynamik und solchen Wachstums ist die Aufrüstung, die inzwischen permanent gefordert wird. Parallel wird die Bevölkerung verbal eingestimmt und auf Kriegstüchtigkeit getrimmt. **Das Rüstungs- und KI-Startup Helsing verkündete kürzlich** eine «dezentrale [Massenproduktion](https://www.trendingtopics.eu/helsing-kampfdrohnen-unicorn-startet-dezentrale-massenproduktion-fuer-ukrainekrieg/) für den Ukrainekrieg». Mit dieser Expansion positioniere sich das Münchner Unternehmen als einer der weltweit führenden Hersteller von Kampfdrohnen. Der nächste [«Meilenstein»](https://archive.is/eZsWP) steht auch bereits an: Man will eine Satellitenflotte im Weltraum aufbauen, zur Überwachung von Gefechtsfeldern und Truppenbewegungen. **Ebenfalls aus München stammt das als** **[DefenseTech-Startup](https://www.trendingtopics.eu/arx-robotics-produktion/)** **bezeichnete Unternehmen** ARX Robotics. Kürzlich habe man in der Region die größte europäische Produktionsstätte für autonome Verteidigungssysteme eröffnet. Damit fahre man die Produktion von Militär-Robotern hoch. Diese Expansion diene auch der Lieferung der «größten Flotte unbemannter Bodensysteme westlicher Bauart» in die Ukraine. **Rüstung boomt und scheint ein Zukunftsmarkt zu sein.** Die Hersteller und Vermarkter betonen, mit ihren Aktivitäten und Produkten solle die europäische Verteidigungsfähigkeit erhöht werden. Ihre Strategien sollten sogar «zum Schutz demokratischer Strukturen beitragen». *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/so-klingt-das-aufrustungs-business-startups-und-alte-hasen)*** erschienen. @ 30ceb64e:7f08bdf5
2025-03-30 00:37:54Hey Freaks, RUNSTR is a motion tracking app built on top of nostr. The project is built by TheWildHustle and TheNostrDev Team. The project has been tinkered with for about 3 months, but development has picked up and its goals and direction have become much clearer. In a previous post I mentioned that RUNSTR was looking to become a Nike Run Club or Strava competitor, offering users an open source community and privacy focused alternative to the centralized silos that we've become used to. I normally ramble incoherently.....even in writing, but this is my attempt to communicate the project's goals and direction as we move forward. This is where the project is now: ## Core Features - **Run Tracker**: Uses an algorithm which adjusts to your phone's location permissions and stores the data on your phone locally - **Stats**: Stored locally on your phone with a basic profile screen so users can monitor calories burned during runs - **Nostr Feed**: Made up of kind1 notes that contain #RUNSTR and other running related hashtags - **Music**: Brought to you via a wavlake API, enabling your wavlake playlists and liked songs to be seen and played in the app ## Current Roadmap - **Bugs and small improvements**: Fixing known issues within the client - **zap.store release**: Launching a bug bounty program after release - **Clubs**: Enabling running organizations to create territories for events, challenges, rewards and competition - **Testflight**: Opening up the app to iOS users (currently Android only) - **Modes**: Adding functionality to switch between Running, Walking, or Cycling modes ## Future Roadmap - **Requested Features**: Implementing features requested by club managers to support virtual events and challenges - **Blossom**: Giving power users the ability to upload their data to personal blossom servers - **NIP28**: Making clubs interoperable with other group chat clients like 0xchat, Keychat, and Chachi Chat - **DVM's**: Creating multiple feeds based on movement mode (e.g., Walking mode shows walkstr feed) - **NIP101e**: Allowing users to create run records and store them on nostr relays - **Calories over relays**: Using NIP89-like functionality for users to save calorie data on relays for use in other applications - **NIP60**: Implementing automatic wallet creation for users to zap and get zapped within the app ## In Conclusion I've just barely begun this thing and it'll be an up and down journey trying to push it into existence. I think RUNSTR has the potential to highlight the other things that nostr has going for it, demonstrating the protocol's interoperability, flexing its permissionless identity piece, and offering an experience that gives users a glimpse into what is possible when shipping into a new paradigm. Although we build into an environment that often offers no solutions, you'd have to be a crazy person not to try. https://github.com/HealthNoteLabs/Runstr/releases/tag/feed-0.1.0-20250329-210157
@ 30ceb64e:7f08bdf5
2025-03-30 00:37:54Hey Freaks, RUNSTR is a motion tracking app built on top of nostr. The project is built by TheWildHustle and TheNostrDev Team. The project has been tinkered with for about 3 months, but development has picked up and its goals and direction have become much clearer. In a previous post I mentioned that RUNSTR was looking to become a Nike Run Club or Strava competitor, offering users an open source community and privacy focused alternative to the centralized silos that we've become used to. I normally ramble incoherently.....even in writing, but this is my attempt to communicate the project's goals and direction as we move forward. This is where the project is now: ## Core Features - **Run Tracker**: Uses an algorithm which adjusts to your phone's location permissions and stores the data on your phone locally - **Stats**: Stored locally on your phone with a basic profile screen so users can monitor calories burned during runs - **Nostr Feed**: Made up of kind1 notes that contain #RUNSTR and other running related hashtags - **Music**: Brought to you via a wavlake API, enabling your wavlake playlists and liked songs to be seen and played in the app ## Current Roadmap - **Bugs and small improvements**: Fixing known issues within the client - **zap.store release**: Launching a bug bounty program after release - **Clubs**: Enabling running organizations to create territories for events, challenges, rewards and competition - **Testflight**: Opening up the app to iOS users (currently Android only) - **Modes**: Adding functionality to switch between Running, Walking, or Cycling modes ## Future Roadmap - **Requested Features**: Implementing features requested by club managers to support virtual events and challenges - **Blossom**: Giving power users the ability to upload their data to personal blossom servers - **NIP28**: Making clubs interoperable with other group chat clients like 0xchat, Keychat, and Chachi Chat - **DVM's**: Creating multiple feeds based on movement mode (e.g., Walking mode shows walkstr feed) - **NIP101e**: Allowing users to create run records and store them on nostr relays - **Calories over relays**: Using NIP89-like functionality for users to save calorie data on relays for use in other applications - **NIP60**: Implementing automatic wallet creation for users to zap and get zapped within the app ## In Conclusion I've just barely begun this thing and it'll be an up and down journey trying to push it into existence. I think RUNSTR has the potential to highlight the other things that nostr has going for it, demonstrating the protocol's interoperability, flexing its permissionless identity piece, and offering an experience that gives users a glimpse into what is possible when shipping into a new paradigm. Although we build into an environment that often offers no solutions, you'd have to be a crazy person not to try. https://github.com/HealthNoteLabs/Runstr/releases/tag/feed-0.1.0-20250329-210157 @ e4950c93:1b99eccd
2025-03-29 14:49:11<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzqr9mwlyllz3zkvk4x2cl98g993k3ele3a55ps6tkay5c3amu4pstqy88wumn8ghj7mn0wvhxcmmv9uqqvvjvgae9x7g0rt3r3?viewKey=f409eabf471c20d1cd3148eca8dc0e388476496b8d47eff10bff145603c1fa9b&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe>
@ e4950c93:1b99eccd
2025-03-29 14:49:11<iframe src="https://formstr.app/#/f/naddr1qvzqqqr4mqpzqr9mwlyllz3zkvk4x2cl98g993k3ele3a55ps6tkay5c3amu4pstqy88wumn8ghj7mn0wvhxcmmv9uqqvvjvgae9x7g0rt3r3?viewKey=f409eabf471c20d1cd3148eca8dc0e388476496b8d47eff10bff145603c1fa9b&hideTitleImage=true" height="1000px" width="480px" frameborder="0" style="border-style:none;box-shadow:0px 0px 2px 2px rgba(0,0,0,0.2);" cellspacing="0" ></iframe> @ c631e267:c2b78d3e
2025-02-07 19:42:11*Nur wenn wir aufeinander zugehen, haben wir die Chance* *\ auf Überwindung der gegenseitigen Ressentiments!* *\ Dr. med. dent. Jens Knipphals*   **In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik** mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und [langjährige](https://transition-news.org/wo-sind-einigkeit-recht-und-freiheit) Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und [publiziert](https://www.alexander-wallasch.de/impfgeschichten/brandbrief-zahnarzt-laesst-nicht-locker-showdown-im-wolfsburger-rathaus). Seine Motivation: > «Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.» **Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt,** zum Beispiel bei öffentlichen [Bürgerfragestunden](https://archive.is/ttTZc). Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise? **Der Termin fand allerdings nicht statt** – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als [Wiederholungstäter](https://www.youtube.com/watch?v=b_zzp6jKiHo), da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber *Multipolar* [erklärte](https://multipolar-magazin.de/artikel/corona-aufarbeitung-wolfsburg) der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen. **Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst,** sei aber letztlich eine gesamtgesellschaftliche Aufgabe, [schreibt](https://peds-ansichten.de/2025/01/plandemie-aufarbeitung/) Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien. **Frey erinnert daran, dass Dennis Weilmann mitverantwortlich** für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut. **Wolfsburg wurde damals zu einem Modellprojekt** des Bundesministeriums des Innern (BMI) und war Finalist im [Bitkom](https://pareto.space/a/naddr1qqxnzden8qen2vejxvenjv35qgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytn8wfhk7an9d9uzucm0d5qs7amnwvaz7tmwdaehgu3wd4hk6qg5waehxw309ahx7um5wghx77r5wghxgetkqydhwumn8ghj7mn0wd68ytnnwa5hxuedv4hxjemdvyhxx6qpzamhxue69uhhqctjv46x7tnwdaehgu339e3k7mgpz4mhxue69uhhqatjwpkx2un9d3shjtnrdaksz9nhwden5te0wfjkccte9cc8scmgv96zucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgkwaehxw309aex2mrp0yhxummnw3ezucnpdejqmk3pae)-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt [«Smart City Wolfsburg»](https://www.beesmart.city/de/city-portraits/smart-city-wolfsburg) anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin *[Forbes](https://web.archive.org/web/20200417064208/https://www.forbes.com/sites/simonchandler/2020/04/13/how-smart-cities-are-protecting-against-coronavirus-but-threatening-privacy/#5edf8d0c1cc3)* im April 2020: > «Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.» **Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten,** wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten [Maßnahmen](https://transition-news.org/stopptcovid-gutachten-von-lauterbach-erhalt-vernichtende-analyse) geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts». *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/corona-aufarbeitung-in-der-praxis-eine-illusion)*** erschienen.
@ c631e267:c2b78d3e
2025-02-07 19:42:11*Nur wenn wir aufeinander zugehen, haben wir die Chance* *\ auf Überwindung der gegenseitigen Ressentiments!* *\ Dr. med. dent. Jens Knipphals*   **In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik** mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und [langjährige](https://transition-news.org/wo-sind-einigkeit-recht-und-freiheit) Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und [publiziert](https://www.alexander-wallasch.de/impfgeschichten/brandbrief-zahnarzt-laesst-nicht-locker-showdown-im-wolfsburger-rathaus). Seine Motivation: > «Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.» **Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt,** zum Beispiel bei öffentlichen [Bürgerfragestunden](https://archive.is/ttTZc). Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise? **Der Termin fand allerdings nicht statt** – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als [Wiederholungstäter](https://www.youtube.com/watch?v=b_zzp6jKiHo), da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber *Multipolar* [erklärte](https://multipolar-magazin.de/artikel/corona-aufarbeitung-wolfsburg) der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen. **Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst,** sei aber letztlich eine gesamtgesellschaftliche Aufgabe, [schreibt](https://peds-ansichten.de/2025/01/plandemie-aufarbeitung/) Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien. **Frey erinnert daran, dass Dennis Weilmann mitverantwortlich** für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut. **Wolfsburg wurde damals zu einem Modellprojekt** des Bundesministeriums des Innern (BMI) und war Finalist im [Bitkom](https://pareto.space/a/naddr1qqxnzden8qen2vejxvenjv35qgs2jhrzgwzvvzgz42kfmef2kr7w8x573k4r62c5ydjh8gyn6dz4ytqrqsqqqa28qyxhwumn8ghj7mn0wvhxcmmvqyv8wumn8ghj7mn0wd68ytn8wfhk7an9d9uzucm0d5qs7amnwvaz7tmwdaehgu3wd4hk6qg5waehxw309ahx7um5wghx77r5wghxgetkqydhwumn8ghj7mn0wd68ytnnwa5hxuedv4hxjemdvyhxx6qpzamhxue69uhhqctjv46x7tnwdaehgu339e3k7mgpz4mhxue69uhhqatjwpkx2un9d3shjtnrdaksz9nhwden5te0wfjkccte9cc8scmgv96zucm0d5q3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgkwaehxw309aex2mrp0yhxummnw3ezucnpdejqmk3pae)-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt [«Smart City Wolfsburg»](https://www.beesmart.city/de/city-portraits/smart-city-wolfsburg) anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin *[Forbes](https://web.archive.org/web/20200417064208/https://www.forbes.com/sites/simonchandler/2020/04/13/how-smart-cities-are-protecting-against-coronavirus-but-threatening-privacy/#5edf8d0c1cc3)* im April 2020: > «Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.» **Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten,** wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten [Maßnahmen](https://transition-news.org/stopptcovid-gutachten-von-lauterbach-erhalt-vernichtende-analyse) geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts». *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/corona-aufarbeitung-in-der-praxis-eine-illusion)*** erschienen. @ a95c6243:d345522c
2025-01-31 20:02:25*Im Augenblick wird mit größter Intensität, großer Umsicht* *\ das deutsche Volk belogen.* *\ Olaf Scholz im FAZ-[Interview](https://www.youtube.com/watch?v=c3KI1GmdoVc\&t=649s)*   **Online-Wahlen stärken die Demokratie, sind sicher, und 61 Prozent der Wahlberechtigten** sprechen sich für deren Einführung in Deutschland aus. Das zumindest behauptet eine aktuelle Umfrage, die auch über die Agentur *Reuters* Verbreitung in den Medien [gefunden](https://archive.is/dnZbY) hat. Demnach würden außerdem 45 Prozent der Nichtwähler bei der Bundestagswahl ihre Stimme abgeben, wenn sie dies zum Beispiel von Ihrem PC, Tablet oder Smartphone aus machen könnten. **Die telefonische Umfrage unter gut 1000 wahlberechtigten Personen** sei repräsentativ, [behauptet](https://www.bitkom.org/Presse/Presseinformation/Knapp-Haelfte-Nichtwaehler-wuerde-online-waehlen) der Auftraggeber – der Digitalverband Bitkom. Dieser präsentiert sich als eingetragener Verein mit einer beeindruckenden Liste von [Mitgliedern](https://www.bitkom.org/Bitkom/Mitgliedschaft/Mitgliederliste), die Software und IT-Dienstleistungen anbieten. Erklärtes Vereinsziel ist es, «Deutschland zu einem führenden Digitalstandort zu machen und die digitale Transformation der deutschen Wirtschaft und Verwaltung voranzutreiben». **Durchgeführt hat die Befragung die Bitkom Servicegesellschaft mbH,** also alles in der Familie. Die gleiche Erhebung hatte der Verband übrigens 2021 schon einmal durchgeführt. Damals sprachen sich angeblich sogar 63 Prozent für ein derartiges [«Demokratie-Update»](https://www.experten.de/id/4922407/online-wahlen-als-update-des-demokratischen-systems/) aus – die Tendenz ist demgemäß fallend. Dennoch orakelt mancher, der Gang zur Wahlurne gelte bereits als veraltet. **Die spanische Privat-Uni mit Globalisten-Touch, IE University, berichtete** Ende letzten Jahres in ihrer Studie «European Tech Insights», 67 Prozent der Europäer [befürchteten](https://www.ie.edu/university/news-events/news/67-europeans-fear-ai-manipulation-elections-according-ie-university-research/), dass Hacker Wahlergebnisse verfälschen könnten. Mehr als 30 Prozent der Befragten glaubten, dass künstliche Intelligenz (KI) bereits Wahlentscheidungen beeinflusst habe. Trotzdem würden angeblich 34 Prozent der unter 35-Jährigen einer KI-gesteuerten App vertrauen, um in ihrem Namen für politische Kandidaten zu stimmen. **Wie dauerhaft wird wohl das Ergebnis der kommenden Bundestagswahl sein?** Diese Frage stellt sich angesichts der aktuellen Entwicklung der Migrations-Debatte und der (vorübergehend) bröckelnden «Brandmauer» gegen die AfD. Das «Zustrombegrenzungsgesetz» der Union hat das Parlament heute Nachmittag überraschenderweise [abgelehnt](https://www.bundestag.de/dokumente/textarchiv/2025/kw05-de-zustrombegrenzungsgesetz-1042038). Dennoch muss man wohl kein ausgesprochener Pessimist sein, um zu befürchten, dass die Entscheidungen der Bürger von den selbsternannten Verteidigern der Demokratie künftig vielleicht nicht respektiert werden, weil sie nicht gefallen. **Bundesweit wird jetzt zu «Brandmauer-Demos» aufgerufen,** die CDU gerät unter Druck und es wird von Übergriffen auf Parteibüros und Drohungen gegen Mitarbeiter [berichtet](https://www.epochtimes.de/politik/deutschland/brandmauer-proteste-cdu-zentrale-geraeumt-kundgebungen-in-46-staedten-a5023745.html). Sicherheitsbehörden warnen vor Eskalationen, die Polizei sei «für ein mögliches erhöhtes Aufkommen von Straftaten gegenüber Politikern und gegen Parteigebäude sensibilisiert». **Der Vorwand** **[«unzulässiger Einflussnahme»](https://transition-news.org/die-minister-faeser-und-wissing-sorgen-sich-um-unzulassige-einflussnahme-auf)** **auf Politik und Wahlen** wird als Argument schon seit einiger Zeit aufgebaut. Der Manipulation schuldig befunden wird neben Putin und Trump auch Elon Musk, was lustigerweise ausgerechnet Bill Gates gerade noch einmal bekräftigt und als [«völlig irre»](https://transition-news.org/bill-gates-nennt-musks-einmischung-in-eu-politik-vollig-irre) bezeichnet hat. Man stelle sich die Diskussionen um die Gültigkeit von Wahlergebnissen vor, wenn es Online-Verfahren zur Stimmabgabe gäbe. In der Schweiz wird [«E-Voting»](https://www.ch.ch/de/abstimmungen-und-wahlen/e-voting/) seit einigen Jahren getestet, aber wohl bisher mit wenig Erfolg. **Die politische Brandstiftung der letzten Jahre zahlt sich immer mehr aus.** Anstatt dringende Probleme der Menschen zu lösen – zu denen auch in Deutschland die [weit verbreitete Armut](https://transition-news.org/ein-funftel-der-bevolkerung-in-deutschland-ist-von-armut-oder-sozialer) zählt –, hat die Politik konsequent polarisiert und sich auf Ausgrenzung und Verhöhnung großer Teile der Bevölkerung konzentriert. Basierend auf Ideologie und Lügen werden abweichende Stimmen unterdrückt und kriminalisiert, nicht nur und nicht erst in diesem Augenblick. Die nächsten Wochen dürften ausgesprochen spannend werden. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/wahlen-und-wahlen-lassen)*** erschienen.
@ a95c6243:d345522c
2025-01-31 20:02:25*Im Augenblick wird mit größter Intensität, großer Umsicht* *\ das deutsche Volk belogen.* *\ Olaf Scholz im FAZ-[Interview](https://www.youtube.com/watch?v=c3KI1GmdoVc\&t=649s)*   **Online-Wahlen stärken die Demokratie, sind sicher, und 61 Prozent der Wahlberechtigten** sprechen sich für deren Einführung in Deutschland aus. Das zumindest behauptet eine aktuelle Umfrage, die auch über die Agentur *Reuters* Verbreitung in den Medien [gefunden](https://archive.is/dnZbY) hat. Demnach würden außerdem 45 Prozent der Nichtwähler bei der Bundestagswahl ihre Stimme abgeben, wenn sie dies zum Beispiel von Ihrem PC, Tablet oder Smartphone aus machen könnten. **Die telefonische Umfrage unter gut 1000 wahlberechtigten Personen** sei repräsentativ, [behauptet](https://www.bitkom.org/Presse/Presseinformation/Knapp-Haelfte-Nichtwaehler-wuerde-online-waehlen) der Auftraggeber – der Digitalverband Bitkom. Dieser präsentiert sich als eingetragener Verein mit einer beeindruckenden Liste von [Mitgliedern](https://www.bitkom.org/Bitkom/Mitgliedschaft/Mitgliederliste), die Software und IT-Dienstleistungen anbieten. Erklärtes Vereinsziel ist es, «Deutschland zu einem führenden Digitalstandort zu machen und die digitale Transformation der deutschen Wirtschaft und Verwaltung voranzutreiben». **Durchgeführt hat die Befragung die Bitkom Servicegesellschaft mbH,** also alles in der Familie. Die gleiche Erhebung hatte der Verband übrigens 2021 schon einmal durchgeführt. Damals sprachen sich angeblich sogar 63 Prozent für ein derartiges [«Demokratie-Update»](https://www.experten.de/id/4922407/online-wahlen-als-update-des-demokratischen-systems/) aus – die Tendenz ist demgemäß fallend. Dennoch orakelt mancher, der Gang zur Wahlurne gelte bereits als veraltet. **Die spanische Privat-Uni mit Globalisten-Touch, IE University, berichtete** Ende letzten Jahres in ihrer Studie «European Tech Insights», 67 Prozent der Europäer [befürchteten](https://www.ie.edu/university/news-events/news/67-europeans-fear-ai-manipulation-elections-according-ie-university-research/), dass Hacker Wahlergebnisse verfälschen könnten. Mehr als 30 Prozent der Befragten glaubten, dass künstliche Intelligenz (KI) bereits Wahlentscheidungen beeinflusst habe. Trotzdem würden angeblich 34 Prozent der unter 35-Jährigen einer KI-gesteuerten App vertrauen, um in ihrem Namen für politische Kandidaten zu stimmen. **Wie dauerhaft wird wohl das Ergebnis der kommenden Bundestagswahl sein?** Diese Frage stellt sich angesichts der aktuellen Entwicklung der Migrations-Debatte und der (vorübergehend) bröckelnden «Brandmauer» gegen die AfD. Das «Zustrombegrenzungsgesetz» der Union hat das Parlament heute Nachmittag überraschenderweise [abgelehnt](https://www.bundestag.de/dokumente/textarchiv/2025/kw05-de-zustrombegrenzungsgesetz-1042038). Dennoch muss man wohl kein ausgesprochener Pessimist sein, um zu befürchten, dass die Entscheidungen der Bürger von den selbsternannten Verteidigern der Demokratie künftig vielleicht nicht respektiert werden, weil sie nicht gefallen. **Bundesweit wird jetzt zu «Brandmauer-Demos» aufgerufen,** die CDU gerät unter Druck und es wird von Übergriffen auf Parteibüros und Drohungen gegen Mitarbeiter [berichtet](https://www.epochtimes.de/politik/deutschland/brandmauer-proteste-cdu-zentrale-geraeumt-kundgebungen-in-46-staedten-a5023745.html). Sicherheitsbehörden warnen vor Eskalationen, die Polizei sei «für ein mögliches erhöhtes Aufkommen von Straftaten gegenüber Politikern und gegen Parteigebäude sensibilisiert». **Der Vorwand** **[«unzulässiger Einflussnahme»](https://transition-news.org/die-minister-faeser-und-wissing-sorgen-sich-um-unzulassige-einflussnahme-auf)** **auf Politik und Wahlen** wird als Argument schon seit einiger Zeit aufgebaut. Der Manipulation schuldig befunden wird neben Putin und Trump auch Elon Musk, was lustigerweise ausgerechnet Bill Gates gerade noch einmal bekräftigt und als [«völlig irre»](https://transition-news.org/bill-gates-nennt-musks-einmischung-in-eu-politik-vollig-irre) bezeichnet hat. Man stelle sich die Diskussionen um die Gültigkeit von Wahlergebnissen vor, wenn es Online-Verfahren zur Stimmabgabe gäbe. In der Schweiz wird [«E-Voting»](https://www.ch.ch/de/abstimmungen-und-wahlen/e-voting/) seit einigen Jahren getestet, aber wohl bisher mit wenig Erfolg. **Die politische Brandstiftung der letzten Jahre zahlt sich immer mehr aus.** Anstatt dringende Probleme der Menschen zu lösen – zu denen auch in Deutschland die [weit verbreitete Armut](https://transition-news.org/ein-funftel-der-bevolkerung-in-deutschland-ist-von-armut-oder-sozialer) zählt –, hat die Politik konsequent polarisiert und sich auf Ausgrenzung und Verhöhnung großer Teile der Bevölkerung konzentriert. Basierend auf Ideologie und Lügen werden abweichende Stimmen unterdrückt und kriminalisiert, nicht nur und nicht erst in diesem Augenblick. Die nächsten Wochen dürften ausgesprochen spannend werden. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/wahlen-und-wahlen-lassen)*** erschienen. @ a95c6243:d345522c
2025-01-24 20:59:01*Menschen tun alles, egal wie absurd,* *\ um ihrer eigenen Seele nicht zu begegnen.* *\ Carl Gustav Jung*   **«Extremer Reichtum ist eine Gefahr für die Demokratie»,** sagen über die Hälfte der knapp 3000 befragten Millionäre aus G20-Staaten laut einer [Umfrage](https://web.archive.org/web/20250122124803/https://patrioticmillionaires.org/web/20250122124803/https://patrioticmillionaires.org/press/nearly-two-thirds-of-millionaires-think-influence-of-the-super-rich-on-trump-presidency-is-threat-to-global-stability/) der «Patriotic Millionaires». Ferner stellte dieser Zusammenschluss wohlhabender US-Amerikaner fest, dass 63 Prozent jener Millionäre den Einfluss von Superreichen auf US-Präsident Trump als Bedrohung für die globale Stabilität ansehen. **Diese Besorgnis haben 370 Millionäre und Milliardäre am Dienstag** auch den in Davos beim WEF konzentrierten Privilegierten aus aller Welt übermittelt. In einem offenen Brief forderten sie die «gewählten Führer» auf, die Superreichen – also sie selbst – zu besteuern, um «die zersetzenden Auswirkungen des extremen Reichtums auf unsere Demokratien und die Gesellschaft zu bekämpfen». Zum Beispiel kontrolliere eine handvoll extrem reicher Menschen die Medien, beeinflusse die Rechtssysteme in unzulässiger Weise und verwandele Recht in Unrecht. **Schon 2019** **[beanstandete](https://www.youtube.com/watch?v=paaen3b44XY)** **der bekannte Historiker und Schriftsteller Ruthger Bregman** an einer WEF-Podiumsdiskussion die Steuervermeidung der Superreichen. Die elitäre Veranstaltung bezeichnete er als «Feuerwehr-Konferenz, bei der man nicht über Löschwasser sprechen darf.» Daraufhin erhielt Bregman keine Einladungen nach Davos mehr. Auf seine Aussagen machte der Schweizer Aktivist Alec Gagneux aufmerksam, der sich seit Jahrzehnten kritisch mit dem WEF befasst. Ihm wurde kürzlich der Zutritt zu einem dreiteiligen Kurs über das WEF an der Volkshochschule Region Brugg [verwehrt](https://transition-news.org/wef-propaganda-an-schweizer-volkshochschule-kritiker-ausgesperrt). **Nun ist die Erkenntnis, dass mit Geld politischer Einfluss einhergeht,** alles andere als neu. Und extremer Reichtum macht die Sache nicht wirklich besser. Trotzdem hat man über Initiativen wie Patriotic Millionaires oder [Taxmenow](https://www.taxmenow.eu/) bisher eher selten etwas gehört, obwohl es sie schon lange gibt. Auch scheint es kein Problem, wenn ein Herr [Gates](https://transition-news.org/bill-melinda-gates-stiftung) fast im Alleingang versucht, globale Gesundheits-, Klima-, Ernährungs- oder Bevölkerungspolitik zu betreiben – im Gegenteil. Im Jahr, als der Milliardär Donald Trump zum zweiten Mal ins Weiße Haus einzieht, ist das Echo in den Gesinnungsmedien dagegen enorm – und uniform, wer hätte das gedacht.  **Der neue US-Präsident hat jedoch** **[«Davos geerdet»](https://www.achgut.com/artikel/trump_erdet_davos_gruener_betrug_green_new_scam),** wie *Achgut* es nannte. In seiner kurzen [Rede](https://www.weforum.org/meetings/world-economic-forum-annual-meeting-2025/sessions/special-address-by-the-president-of-the-united-states-of-america/) beim Weltwirtschaftsforum verteidigte er seine Politik und stellte klar, er habe schlicht eine «Revolution des gesunden Menschenverstands» begonnen. Mit deutlichen Worten sprach er unter anderem von ersten Maßnahmen gegen den «Green New Scam», und von einem «Erlass, der jegliche staatliche Zensur beendet»: > «Unsere Regierung wird die Äußerungen unserer eigenen Bürger nicht mehr als Fehlinformation oder Desinformation bezeichnen, was die Lieblingswörter von Zensoren und derer sind, die den freien Austausch von Ideen und, offen gesagt, den Fortschritt verhindern wollen.» **Wie der** **[«Trumpismus»](https://transition-news.org/trumpismus-zeitenwende-und-tiefer-staat)** **letztlich einzuordnen ist,** muss jeder für sich selbst entscheiden. Skepsis ist definitiv angebracht, denn «einer von uns» sind weder der Präsident noch seine auserwählten Teammitglieder. Ob sie irgendeinen Sumpf trockenlegen oder Staatsverbrechen aufdecken werden oder was aus WHO- und Klimaverträgen wird, bleibt abzuwarten. **Das** **[WHO](https://transition-news.org/who-bedauert-trumps-entscheidung-sich-aus-der-organisation-zuruckzuziehen)-Dekret fordert jedenfalls die Übertragung der Gelder auf «glaubwürdige Partner»,** die die Aktivitäten übernehmen könnten. Zufällig scheint mit «Impfguru» Bill Gates ein weiterer Harris-Unterstützer kürzlich das Lager gewechselt zu haben: Nach einem gemeinsamen Abendessen zeigte er sich [«beeindruckt»](https://archive.is/SpQ24) von Trumps Interesse an der globalen Gesundheit. **Mit dem** **[Projekt «Stargate»](https://transition-news.org/us-privatsektor-will-500-milliarden-dollar-in-ki-investieren-krebsimpfstoffe)** **sind weitere dunkle Wolken am Erwartungshorizont** der Fangemeinde aufgezogen. Trump hat dieses Joint Venture zwischen den Konzernen OpenAI, Oracle, und SoftBank als das «größte KI-Infrastrukturprojekt der Geschichte» angekündigt. Der Stein des Anstoßes: Oracle-CEO Larry Ellison, der auch Fan von KI-gestützter [Echtzeit-Überwachung](https://transition-news.org/oracle-kundigt-neues-ki-rechenzentrum-mit-eigenen-atomreaktoren-an) ist, sieht einen weiteren potenziellen Einsatz der künstlichen Intelligenz. Sie könne dazu dienen, Krebserkrankungen zu erkennen und individuelle mRNA-«Impfstoffe» zur Behandlung innerhalb von 48 Stunden zu entwickeln. **Warum bitte sollten sich diese superreichen «Eliten» ins eigene Fleisch schneiden** und direkt entgegen ihren eigenen Interessen handeln? Weil sie Menschenfreunde, sogenannte Philanthropen sind? Oder vielleicht, weil sie ein schlechtes Gewissen haben und ihre Schuld kompensieren müssen? Deswegen jedenfalls brauchen «Linke» laut Robert Willacker, einem deutschen Politikberater mit brasilianischen Wurzeln, rechte Parteien – ein ebenso überraschender wie humorvoller [Erklärungsansatz](https://www.youtube.com/watch?v=s63_8flX1zk). **Wenn eine Krähe der anderen kein Auge aushackt,** dann tut sie das sich selbst noch weniger an. Dass Millionäre ernsthaft ihre eigene Besteuerung fordern oder Machteliten ihren eigenen Einfluss zugunsten anderer einschränken würden, halte ich für sehr unwahrscheinlich. So etwas glaube ich erst, wenn zum Beispiel die [Rüstungsindustrie](https://transition-news.org/schweiz-zunehmende-beteiligung-an-eu-militarprojekten) sich um Friedensverhandlungen bemüht, die [Pharmalobby](https://transition-news.org/eu-lobbyisten-gegen-pfas-verbot) sich gegen institutionalisierte Korruption einsetzt, [Zentralbanken](https://transition-news.org/digitale-wahrung) ihre CBDC-Pläne für Bitcoin opfern oder der ÖRR die Abschaffung der Rundfunkgebühren fordert. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/elitare-anti-eliten-und-superreiche-anti-reiche)*** erschienen.
@ a95c6243:d345522c
2025-01-24 20:59:01*Menschen tun alles, egal wie absurd,* *\ um ihrer eigenen Seele nicht zu begegnen.* *\ Carl Gustav Jung*   **«Extremer Reichtum ist eine Gefahr für die Demokratie»,** sagen über die Hälfte der knapp 3000 befragten Millionäre aus G20-Staaten laut einer [Umfrage](https://web.archive.org/web/20250122124803/https://patrioticmillionaires.org/web/20250122124803/https://patrioticmillionaires.org/press/nearly-two-thirds-of-millionaires-think-influence-of-the-super-rich-on-trump-presidency-is-threat-to-global-stability/) der «Patriotic Millionaires». Ferner stellte dieser Zusammenschluss wohlhabender US-Amerikaner fest, dass 63 Prozent jener Millionäre den Einfluss von Superreichen auf US-Präsident Trump als Bedrohung für die globale Stabilität ansehen. **Diese Besorgnis haben 370 Millionäre und Milliardäre am Dienstag** auch den in Davos beim WEF konzentrierten Privilegierten aus aller Welt übermittelt. In einem offenen Brief forderten sie die «gewählten Führer» auf, die Superreichen – also sie selbst – zu besteuern, um «die zersetzenden Auswirkungen des extremen Reichtums auf unsere Demokratien und die Gesellschaft zu bekämpfen». Zum Beispiel kontrolliere eine handvoll extrem reicher Menschen die Medien, beeinflusse die Rechtssysteme in unzulässiger Weise und verwandele Recht in Unrecht. **Schon 2019** **[beanstandete](https://www.youtube.com/watch?v=paaen3b44XY)** **der bekannte Historiker und Schriftsteller Ruthger Bregman** an einer WEF-Podiumsdiskussion die Steuervermeidung der Superreichen. Die elitäre Veranstaltung bezeichnete er als «Feuerwehr-Konferenz, bei der man nicht über Löschwasser sprechen darf.» Daraufhin erhielt Bregman keine Einladungen nach Davos mehr. Auf seine Aussagen machte der Schweizer Aktivist Alec Gagneux aufmerksam, der sich seit Jahrzehnten kritisch mit dem WEF befasst. Ihm wurde kürzlich der Zutritt zu einem dreiteiligen Kurs über das WEF an der Volkshochschule Region Brugg [verwehrt](https://transition-news.org/wef-propaganda-an-schweizer-volkshochschule-kritiker-ausgesperrt). **Nun ist die Erkenntnis, dass mit Geld politischer Einfluss einhergeht,** alles andere als neu. Und extremer Reichtum macht die Sache nicht wirklich besser. Trotzdem hat man über Initiativen wie Patriotic Millionaires oder [Taxmenow](https://www.taxmenow.eu/) bisher eher selten etwas gehört, obwohl es sie schon lange gibt. Auch scheint es kein Problem, wenn ein Herr [Gates](https://transition-news.org/bill-melinda-gates-stiftung) fast im Alleingang versucht, globale Gesundheits-, Klima-, Ernährungs- oder Bevölkerungspolitik zu betreiben – im Gegenteil. Im Jahr, als der Milliardär Donald Trump zum zweiten Mal ins Weiße Haus einzieht, ist das Echo in den Gesinnungsmedien dagegen enorm – und uniform, wer hätte das gedacht.  **Der neue US-Präsident hat jedoch** **[«Davos geerdet»](https://www.achgut.com/artikel/trump_erdet_davos_gruener_betrug_green_new_scam),** wie *Achgut* es nannte. In seiner kurzen [Rede](https://www.weforum.org/meetings/world-economic-forum-annual-meeting-2025/sessions/special-address-by-the-president-of-the-united-states-of-america/) beim Weltwirtschaftsforum verteidigte er seine Politik und stellte klar, er habe schlicht eine «Revolution des gesunden Menschenverstands» begonnen. Mit deutlichen Worten sprach er unter anderem von ersten Maßnahmen gegen den «Green New Scam», und von einem «Erlass, der jegliche staatliche Zensur beendet»: > «Unsere Regierung wird die Äußerungen unserer eigenen Bürger nicht mehr als Fehlinformation oder Desinformation bezeichnen, was die Lieblingswörter von Zensoren und derer sind, die den freien Austausch von Ideen und, offen gesagt, den Fortschritt verhindern wollen.» **Wie der** **[«Trumpismus»](https://transition-news.org/trumpismus-zeitenwende-und-tiefer-staat)** **letztlich einzuordnen ist,** muss jeder für sich selbst entscheiden. Skepsis ist definitiv angebracht, denn «einer von uns» sind weder der Präsident noch seine auserwählten Teammitglieder. Ob sie irgendeinen Sumpf trockenlegen oder Staatsverbrechen aufdecken werden oder was aus WHO- und Klimaverträgen wird, bleibt abzuwarten. **Das** **[WHO](https://transition-news.org/who-bedauert-trumps-entscheidung-sich-aus-der-organisation-zuruckzuziehen)-Dekret fordert jedenfalls die Übertragung der Gelder auf «glaubwürdige Partner»,** die die Aktivitäten übernehmen könnten. Zufällig scheint mit «Impfguru» Bill Gates ein weiterer Harris-Unterstützer kürzlich das Lager gewechselt zu haben: Nach einem gemeinsamen Abendessen zeigte er sich [«beeindruckt»](https://archive.is/SpQ24) von Trumps Interesse an der globalen Gesundheit. **Mit dem** **[Projekt «Stargate»](https://transition-news.org/us-privatsektor-will-500-milliarden-dollar-in-ki-investieren-krebsimpfstoffe)** **sind weitere dunkle Wolken am Erwartungshorizont** der Fangemeinde aufgezogen. Trump hat dieses Joint Venture zwischen den Konzernen OpenAI, Oracle, und SoftBank als das «größte KI-Infrastrukturprojekt der Geschichte» angekündigt. Der Stein des Anstoßes: Oracle-CEO Larry Ellison, der auch Fan von KI-gestützter [Echtzeit-Überwachung](https://transition-news.org/oracle-kundigt-neues-ki-rechenzentrum-mit-eigenen-atomreaktoren-an) ist, sieht einen weiteren potenziellen Einsatz der künstlichen Intelligenz. Sie könne dazu dienen, Krebserkrankungen zu erkennen und individuelle mRNA-«Impfstoffe» zur Behandlung innerhalb von 48 Stunden zu entwickeln. **Warum bitte sollten sich diese superreichen «Eliten» ins eigene Fleisch schneiden** und direkt entgegen ihren eigenen Interessen handeln? Weil sie Menschenfreunde, sogenannte Philanthropen sind? Oder vielleicht, weil sie ein schlechtes Gewissen haben und ihre Schuld kompensieren müssen? Deswegen jedenfalls brauchen «Linke» laut Robert Willacker, einem deutschen Politikberater mit brasilianischen Wurzeln, rechte Parteien – ein ebenso überraschender wie humorvoller [Erklärungsansatz](https://www.youtube.com/watch?v=s63_8flX1zk). **Wenn eine Krähe der anderen kein Auge aushackt,** dann tut sie das sich selbst noch weniger an. Dass Millionäre ernsthaft ihre eigene Besteuerung fordern oder Machteliten ihren eigenen Einfluss zugunsten anderer einschränken würden, halte ich für sehr unwahrscheinlich. So etwas glaube ich erst, wenn zum Beispiel die [Rüstungsindustrie](https://transition-news.org/schweiz-zunehmende-beteiligung-an-eu-militarprojekten) sich um Friedensverhandlungen bemüht, die [Pharmalobby](https://transition-news.org/eu-lobbyisten-gegen-pfas-verbot) sich gegen institutionalisierte Korruption einsetzt, [Zentralbanken](https://transition-news.org/digitale-wahrung) ihre CBDC-Pläne für Bitcoin opfern oder der ÖRR die Abschaffung der Rundfunkgebühren fordert. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/elitare-anti-eliten-und-superreiche-anti-reiche)*** erschienen. @ c631e267:c2b78d3e
2025-01-18 09:34:51*Die grauenvollste Aussicht ist die der Technokratie –* *\ einer kontrollierenden Herrschaft,* *\ die durch verstümmelte und verstümmelnde Geister ausgeübt wird.* *\ Ernst Jünger*   **«Davos ist nicht mehr sexy»,** das Weltwirtschaftsforum ([WEF](https://transition-news.org/wef-world-economic-forum)) mache Davos [kaputt](https://web.archive.org/web/20250116114956/https://www.handelszeitung.ch/wef-2025/wie-das-wef-davos-kaputt-macht-785098), diese Aussagen eines Einheimischen las ich kürzlich in der *Handelszeitung*. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher. **Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen** dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den [vergangenen](https://transition-news.org/die-angst-der-eliten-vor-dem-pobel) vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten. **Der deutsche WEF-Gründer hatte bei dieser Gelegenheit** immer höchst lobende Worte für seine Landsmännin: [2021](https://www.weforum.org/meetings/the-davos-agenda-2021/sessions/special-address-by-g20-head-of-state-government/) erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und [2022](https://www.weforum.org/meetings/the-davos-agenda-2022/sessions/special-address-by-ursula-von-der-leyen-president-of-the-european-commission-177737c164/) fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist». **Von der Leyens Handeln während der sogenannten Corona-«Pandemie»** lobte Schwab damals bereits ebenso, wie es diese Woche das [Karlspreis](https://transition-news.org/von-der-leyen-erhalt-karlspreis-albert-bourla-erklart-pfizer-habe-wahrend-der)-Direktorium tat, als man der Beschuldigten im Fall [Pfizergate](https://transition-news.org/pfizergate-startet-ins-neue-jahr) die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt. **Jene Herausforderungen durch «Krisen epochalen Ausmaßes»** werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im [Global Risks Report](https://www.zurich.com/knowledge/topics/global-risks/the-global-risks-report-2025) nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen. **Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen** unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz. **Ein** **[«Great Mental Reset»](https://transition-news.org/angriff-auf-unser-gehirn-michael-nehls-uber-den-great-mental-reset-teil-1)** **sei die Voraussetzung dafür,** dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden. **Der aktuelle Zustand unserer Gesellschaften** ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die [Rechtsstaatlichkeit](https://transition-news.org/schweizer-rechtsstaat-in-der-krise-ein-anwalt-schlagt-alarm) stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/davos-europa-und-der-rest-der-welt)*** erschienen.
@ c631e267:c2b78d3e
2025-01-18 09:34:51*Die grauenvollste Aussicht ist die der Technokratie –* *\ einer kontrollierenden Herrschaft,* *\ die durch verstümmelte und verstümmelnde Geister ausgeübt wird.* *\ Ernst Jünger*   **«Davos ist nicht mehr sexy»,** das Weltwirtschaftsforum ([WEF](https://transition-news.org/wef-world-economic-forum)) mache Davos [kaputt](https://web.archive.org/web/20250116114956/https://www.handelszeitung.ch/wef-2025/wie-das-wef-davos-kaputt-macht-785098), diese Aussagen eines Einheimischen las ich kürzlich in der *Handelszeitung*. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher. **Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen** dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den [vergangenen](https://transition-news.org/die-angst-der-eliten-vor-dem-pobel) vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten. **Der deutsche WEF-Gründer hatte bei dieser Gelegenheit** immer höchst lobende Worte für seine Landsmännin: [2021](https://www.weforum.org/meetings/the-davos-agenda-2021/sessions/special-address-by-g20-head-of-state-government/) erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und [2022](https://www.weforum.org/meetings/the-davos-agenda-2022/sessions/special-address-by-ursula-von-der-leyen-president-of-the-european-commission-177737c164/) fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist». **Von der Leyens Handeln während der sogenannten Corona-«Pandemie»** lobte Schwab damals bereits ebenso, wie es diese Woche das [Karlspreis](https://transition-news.org/von-der-leyen-erhalt-karlspreis-albert-bourla-erklart-pfizer-habe-wahrend-der)-Direktorium tat, als man der Beschuldigten im Fall [Pfizergate](https://transition-news.org/pfizergate-startet-ins-neue-jahr) die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt. **Jene Herausforderungen durch «Krisen epochalen Ausmaßes»** werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im [Global Risks Report](https://www.zurich.com/knowledge/topics/global-risks/the-global-risks-report-2025) nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen. **Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen** unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz. **Ein** **[«Great Mental Reset»](https://transition-news.org/angriff-auf-unser-gehirn-michael-nehls-uber-den-great-mental-reset-teil-1)** **sei die Voraussetzung dafür,** dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden. **Der aktuelle Zustand unserer Gesellschaften** ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die [Rechtsstaatlichkeit](https://transition-news.org/schweizer-rechtsstaat-in-der-krise-ein-anwalt-schlagt-alarm) stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/davos-europa-und-der-rest-der-welt)*** erschienen. @ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** | | Pen drive |  | **16Gb** | Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.). --- ## Passo 1: Atualizar o Sistema 🖥️ Primeiro, atualize seu sistema e instale o Tor: ```bash apt update apt install tor ``` --- ## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧 Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo: ```unit [Unit] Description=Nostr Relay Server Service After=network.target [Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure [Install] WantedBy=multi-user.target ``` --- ## Passo 3: Baixar o Binário do Nostr 🚀 Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases). --- ## Passo 4: Criar as Pastas Necessárias 📂 Agora, crie as pastas para o aplicativo e o pendrive: ```bash mkdir -p /opt/nrs /mnt/edriver ``` --- ## Passo 5: Listar os Dispositivos Conectados 🔌 Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados: ```bash lsblk ``` --- ## Passo 6: Formatando o Pendrive 💾 Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o: ```bash mkfs.vfat /dev/sda ``` --- ## Passo 7: Montar o Pendrive 💻 Monte o pendrive na pasta `/mnt/edriver`: ```bash mount /dev/sda /mnt/edriver ``` --- ## Passo 8: Verificar UUID dos Dispositivos 📋 Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados: ```bash blkid ``` --- ## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝 Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim: ```fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0 ``` --- ## Passo 10: Copiar o Binário para a Pasta Correta 📥 Agora, copie o binário baixado para a pasta `/opt/nrs`: ```bash cp nrs-arm64 /opt/nrs ``` --- ## Passo 11: Criar o Arquivo de Configuração 🛠️ Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`: ```yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true ``` --- ## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️ Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`: ```bash cp nrs.service /etc/systemd/system/ ``` Recarregue os serviços e inicie o serviço `nrs`: ```bash systemctl daemon-reload systemctl enable --now nrs.service ``` --- ## Passo 13: Configurar o Tor 🌐 Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha: ```torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334 ``` --- ## Passo 14: Habilitar e Iniciar o Tor 🧅 Agora, ative e inicie o serviço Tor: ```bash systemctl enable --now tor.service ``` O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`. --- ## Observações ⚠️ - Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi. - O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`. --- Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳 Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |  | **Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2,** | | Pen drive |  | **16Gb** | Recomendo que use o **Ubuntu Server** para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi [aqui]( https://ubuntu.com/download/raspberry-pi). O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível [aqui]( https://ubuntu.com/tutorials/how-to-install-ubuntu-on-your-raspberry-pi). **Não instale um desktop** (como xubuntu, lubuntu, xfce, etc.). --- ## Passo 1: Atualizar o Sistema 🖥️ Primeiro, atualize seu sistema e instale o Tor: ```bash apt update apt install tor ``` --- ## Passo 2: Criar o Arquivo de Serviço `nrs.service` 🔧 Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo: ```unit [Unit] Description=Nostr Relay Server Service After=network.target [Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure [Install] WantedBy=multi-user.target ``` --- ## Passo 3: Baixar o Binário do Nostr 🚀 Baixe o binário mais recente do Nostr [aqui no GitHub]( https://github.com/gabrielmoura/SimpleNosrtRelay/releases). --- ## Passo 4: Criar as Pastas Necessárias 📂 Agora, crie as pastas para o aplicativo e o pendrive: ```bash mkdir -p /opt/nrs /mnt/edriver ``` --- ## Passo 5: Listar os Dispositivos Conectados 🔌 Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados: ```bash lsblk ``` --- ## Passo 6: Formatando o Pendrive 💾 Escolha o pendrive correto (por exemplo, `/dev/sda`) e formate-o: ```bash mkfs.vfat /dev/sda ``` --- ## Passo 7: Montar o Pendrive 💻 Monte o pendrive na pasta `/mnt/edriver`: ```bash mount /dev/sda /mnt/edriver ``` --- ## Passo 8: Verificar UUID dos Dispositivos 📋 Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados: ```bash blkid ``` --- ## Passo 9: Alterar o `fstab` para Montar o Pendrive Automáticamente 📝 Abra o arquivo `/etc/fstab` e adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim: ```fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0 ``` --- ## Passo 10: Copiar o Binário para a Pasta Correta 📥 Agora, copie o binário baixado para a pasta `/opt/nrs`: ```bash cp nrs-arm64 /opt/nrs ``` --- ## Passo 11: Criar o Arquivo de Configuração 🛠️ Crie o arquivo de configuração com o seguinte conteúdo e salve-o em `/opt/nrs/config.yaml`: ```yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true ``` --- ## Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️ Agora, copie o arquivo `nrs.service` para o diretório `/etc/systemd/system/`: ```bash cp nrs.service /etc/systemd/system/ ``` Recarregue os serviços e inicie o serviço `nrs`: ```bash systemctl daemon-reload systemctl enable --now nrs.service ``` --- ## Passo 13: Configurar o Tor 🌐 Abra o arquivo de configuração do Tor `/var/lib/tor/torrc` e adicione a seguinte linha: ```torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334 ``` --- ## Passo 14: Habilitar e Iniciar o Tor 🧅 Agora, ative e inicie o serviço Tor: ```bash systemctl enable --now tor.service ``` O Tor irá gerar um endereço `.onion` para o seu servidor Nostr. Você pode encontrá-lo no arquivo `/var/lib/tor/nostr_server/hostname`. --- ## Observações ⚠️ - Com essa configuração, **os dados serão salvos no pendrive**, enquanto o binário ficará no cartão SD do Raspberry Pi. - O endereço `.onion` do seu servidor Nostr será algo como: `ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion`. --- Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳 Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos. @ a95c6243:d345522c
2025-01-13 10:09:57*Ich begann, Social Media aufzubauen,* *\ um den Menschen eine Stimme zu geben.* *\ Mark Zuckerberg* **Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs** **[Wendehals-Deklaration](https://www.facebook.com/zuck/videos/1525382954801931)** bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren». **«Purer** **[Opportunismus](https://transition-news.org/facebook-grunder-zuckerberg-vom-trump-gegner-zum-trump-buddy-und-anti-zensor)» ob des anstehenden Regierungswechsels wäre als Klassifizierung** viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich. > «Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg. **Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung,** dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen [«LifeLog»](https://norberthaering.de/macht-kontrolle/lifelog/). Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen». **Der Richtungswechsel kommt allerdings nicht überraschend.** Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten [gesprochen](https://www.theverge.com/2024/12/3/24311513/meta-content-moderation-mistakes-nick-clegg). Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen. **Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten** in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine [Verhaftung](https://transition-news.org/nicht-telegram-grunder-durow-sondern-zuckerberg-sollte-in-haft-sitzen-wegen-des) dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt [kritisierte](https://www.berliner-zeitung.de/news/ende-des-faktenchecks-bei-meta-telegram-gruender-kritisiert-zuckerberg-und-spricht-warnung-aus-li.2287988) und gleichzeitig warnte. **Politik und Systemmedien drehen jedenfalls durch** – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten [Völkermord](https://archive.is/PYeH0)», ernsthaft. Die Frage sei, ob sich die [EU gegen Musk und Zuckerberg](https://www.handelsblatt.com/politik/international/internet-regulierung-kann-sich-die-eu-gegen-musk-und-zuckerberg-behaupten/100099373.html) behaupten könne, Brüssel müsse jedenfalls hart durchgreifen. **Auch um die** **[Faktenchecker](https://www.welt.de/kultur/medien/article255065352/Metas-Kurswechsel-Zuckerbergs-Entscheidung-und-die-Folgen-fuer-deutsche-Faktenchecker.html)** **macht man sich Sorgen.** Für die deutsche Nachrichtenagentur *dpa* und die «Experten» von *Correctiv*, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die *Tagesschau* keine Fehler zugeben und zum Beispiel *Correctiv*-[Falschaussagen](https://www.berliner-zeitung.de/politik-gesellschaft/correctiv-falschaussagen-exklusiv-scholz-faeser-und-tagesschau-wollen-sich-fuer-verbreitung-nicht-entschuldigen-li.2288126) einräumen. **Bei derlei dramatischen Befürchtungen wundert es nicht,** dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft. **Das** **[Anbiedern](https://transition-news.org/who-biedert-sich-bei-trump-an)** **bei Donald Trump ist indes gerade in Mode.** Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. [sechs Milliarden](https://x.ai/blog/series-c) eingestrichen hat, geht da vielleicht etwas. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/milliardenschwere-wetterfahnchen-und-windmaschinen)*** erschienen.
@ a95c6243:d345522c
2025-01-13 10:09:57*Ich begann, Social Media aufzubauen,* *\ um den Menschen eine Stimme zu geben.* *\ Mark Zuckerberg* **Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs** **[Wendehals-Deklaration](https://www.facebook.com/zuck/videos/1525382954801931)** bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren». **«Purer** **[Opportunismus](https://transition-news.org/facebook-grunder-zuckerberg-vom-trump-gegner-zum-trump-buddy-und-anti-zensor)» ob des anstehenden Regierungswechsels wäre als Klassifizierung** viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich. > «Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg. **Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung,** dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen [«LifeLog»](https://norberthaering.de/macht-kontrolle/lifelog/). Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen». **Der Richtungswechsel kommt allerdings nicht überraschend.** Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten [gesprochen](https://www.theverge.com/2024/12/3/24311513/meta-content-moderation-mistakes-nick-clegg). Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen. **Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten** in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine [Verhaftung](https://transition-news.org/nicht-telegram-grunder-durow-sondern-zuckerberg-sollte-in-haft-sitzen-wegen-des) dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt [kritisierte](https://www.berliner-zeitung.de/news/ende-des-faktenchecks-bei-meta-telegram-gruender-kritisiert-zuckerberg-und-spricht-warnung-aus-li.2287988) und gleichzeitig warnte. **Politik und Systemmedien drehen jedenfalls durch** – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten [Völkermord](https://archive.is/PYeH0)», ernsthaft. Die Frage sei, ob sich die [EU gegen Musk und Zuckerberg](https://www.handelsblatt.com/politik/international/internet-regulierung-kann-sich-die-eu-gegen-musk-und-zuckerberg-behaupten/100099373.html) behaupten könne, Brüssel müsse jedenfalls hart durchgreifen. **Auch um die** **[Faktenchecker](https://www.welt.de/kultur/medien/article255065352/Metas-Kurswechsel-Zuckerbergs-Entscheidung-und-die-Folgen-fuer-deutsche-Faktenchecker.html)** **macht man sich Sorgen.** Für die deutsche Nachrichtenagentur *dpa* und die «Experten» von *Correctiv*, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die *Tagesschau* keine Fehler zugeben und zum Beispiel *Correctiv*-[Falschaussagen](https://www.berliner-zeitung.de/politik-gesellschaft/correctiv-falschaussagen-exklusiv-scholz-faeser-und-tagesschau-wollen-sich-fuer-verbreitung-nicht-entschuldigen-li.2288126) einräumen. **Bei derlei dramatischen Befürchtungen wundert es nicht,** dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft. **Das** **[Anbiedern](https://transition-news.org/who-biedert-sich-bei-trump-an)** **bei Donald Trump ist indes gerade in Mode.** Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. [sechs Milliarden](https://x.ai/blog/series-c) eingestrichen hat, geht da vielleicht etwas. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/milliardenschwere-wetterfahnchen-und-windmaschinen)*** erschienen. @ fd78c37f:a0ec0833
2025-03-29 04:33:01**YakiHonne**: I'm excited to be joined by our guest Piccolo—thank you very much for being here. Before we dive in, I'd like to briefly introduce YakiHonne. YakiHonne is a decentralized media client built on the Nostr protocol, leveraging technology to enable freedom of speech. It empowers creators to fully own their voice and assets while offering innovative tools such as Smart widget , Verified Notes, and support for long-form content. Today, we’re not just discussing YakiHonne, but also diving into your community. Piccolo, could you start by telling us a bit about yourself and your community? **Piccolo**:Hi, I'm Piccolo. I run BO฿ Space in Bangkok, and we also have a satellite location called the BO฿ Space corner in Chiang Mai, thanks to the Bitcoin Learning Center. **Piccolo**:Regarding my background,I originally came from corporate finance and investment banking. I was in that field for about 20 years, with the last 15 spent running my own firm in corporate finance advisory alongside a couple of partners. We eventually sold the advisory business in 2015, took a short break, and in 2016, I ended up launching a fintech company, which is still operational today. The company specializes in equity crowdfunding and is licensed by the SEC in Thailand. **Piccolo**:I first bought Bitcoin a few years before truly understanding it, initially thinking it was a scam that would eventually collapse. However, in 2017, the block size wars demonstrated the protocol’s strong resistance to attacks on decentralization, which deeply impacted me. By late 2018 or early 2019, I started to really grasp Bitcoin and kept learning. Then, in mid-2022, after having fully fallen down the Bitcoin rabbit hole, I founded BO฿ Space. It was right after COVID, and since the fintech had scaled down, there was extra space. We started by hosting meetups and technical workshops for people who were interested. **Piccolo**:In the early years, we had various groups come by—like the team from BDK (Bitcoin Development Kit), who held workshops. The people behind the Bitcoin Beach Wallet, which later became Blink, also visited. So, BO฿ Space initially functioned as a meetup and technical workshop space. Eventually, we launched the BOB Builders Residency program, which was a lot of fun. We secured grant funding for developers under different cohort themes, so that they can collaborate and co-work for a few months. So far, we have completed three cohorts. **YakiHonne**:How did your community get started, and what did you do to attract new members in the beginning? **Piccolo**:The initial members came through word of mouth and invitations that I sent out. I reached out to an initial group of Bitcoiners here in the city who I believed were strong maximalists or Bitcoin-only supporters, back when that was still a thing. I sent out 21 invitations and had our first meetup with 21 people, most of whom I had interacted with online, though some in person during the COVID years. From there, it spread by word of mouth, and of course, through Twitter and meetup.com. So, I would say that word of mouth remains the main method of growth. Additionally, when people come through Bangkok and are looking for a Bitcoin-only meetup, there really isn't one available. I believe there are a couple now—maybe two or three—but when we started, there weren’t any, especially not a dedicated Bitcoin-only space. I think we may still be the only one in Bangkok. So yeah, word of mouth was definitely the main way we grew. Bitcoiners tend to share their finds when they meet like-minded people.  **YakiHonne**:Didn’t you have people in your community who initially thought Bitcoin was a scam, like you did, or face similar issues? **Piccolo**:Yes, it still happens, especially when the price of Bitcoin rises. Newcomers still join, and some of them believe Bitcoin might be a scam. However, this has become less frequent. The main reason is that when people come to BO฿ Space, they know it’s a Bitcoin-only meetup. We generally don’t discuss the price; instead, we focus on other aspects of Bitcoin, as there are many interesting developments in the space. **YakiHonne**:What advice would you give to someone looking to start or grow a Bitcoin-focused community in today’s world? Considering the current landscape, much like your own experience, what guidance would you offer? **Piccolo**:It sounds simple, but just do it. When it comes to community building, you don’t necessarily need a physical space. Community is about people coming together, right? Two people can start a community, then three, four, and so on. Meetups can happen anywhere—your favorite bar, a restaurant, a friend’s garage, or wherever. So, just do it, but make sure you have more than one person, otherwise, how can you build a community? Once you have more than one person, word of mouth will spread. And as you develop a core group—let’s say more than five people—that’s when I think the community can truly sustain itself. **YakiHonne**:I know you’ve mentioned the technical side of your community, but I’ll ask anyway—does your community engage with the technical or non-technical aspects of Bitcoin? Or perhaps, is there a blend of both? **Piccolo**:I would say both. It really depends on the monthly themes of our meetups. For example, February was focused on Asian communities in Bitcoin. During that month, community leaders came in to give presentations and discuss their work in places like Indonesia, India, and more recently, someone from HRF (Human Rights Foundation) talked about Bitcoin’s use case in Myanmar. Then, in December, we had a very technical month—Mining Month. It was led by our Cohort 3 residents, where we discussed Stratum V2 and had a demo on it. We also examined the Loki board hardware, and Zack took apart the S19, looking at different ways to repurpose the power supply unit, among other things. So, it’s a mix of both, depending on the theme for that month. Some months are very technical, while others are more community-focused and less technical. **YakiHonne**:What advice would you give to a technically inclined individual or organization looking to contribute meaningfully to the Bitcoin ecosystem? **Piccolo**:For technically inclined individuals, I would suggest identifying your favorite open-source project in the Bitcoin ecosystem. Start from Bitcoin Core and explore different layers, such as Lightning or e-cash, and other open-source projects. As for technically inclined organizations, if you're integrating Bitcoin into your business, I would say, first, make sure you have people within your organization who truly understand Bitcoin. Build a capable team first, and then, depending on the part of the Bitcoin ecosystem you’re involved in—whether it’s custody services, Lightning payments, layer 2, or something like Cashu or Ark—find your niche. From there, your team will work with you to discover ways to contribute. But until you build that capability, organizations are a bit different from individuals in this space. **YakiHonne**:How do you see the world of Bitcoin communities evolving as technology matures, particularly in areas like scalability, privacy, and adaptability with other systems? **Piccolo**:That's an interesting question. If we think about the future of Bitcoin communities, I believe they may eventually disappear as technology matures. Once Bitcoin scales to a point where it integrates seamlessly with other payment systems, becoming part of the everyday norm, the need for dedicated communities will diminish. It’s similar to how we no longer have meetups about refrigerators or iPhones, even though they are technologies we use every day. As Bitcoin matures, it will likely reach that level of ubiquity. There might still be occasional meetups or forums, but they will be more about specific knowledge, use cases, and tools, rather than a community dedicated to introducing others to the technology itself. However, this is a long way off. Bitcoin is still relatively small compared to the global fiat financial system, despite the growth we want to see. So, it will take a long time before we reach that stage. **YakiHonne**:It’s something I hadn’t considered before, and it’s quite insightful. Moving to our last question actually which I find very interesting is the government around you for or against bitcoin and how has That affected the community. **Piccolo**:In my opinion, on a general level, the government is more supportive than opposed to Bitcoin. The Thai government classifies Bitcoin as a digital asset, almost like digital gold. In that sense, they want to tax capital gains and regulate it. They also have a regulatory framework for it, known as the Digital Asset Regulatory Sandbox, where you can test various things, mainly coins and tokens. It's unfortunate, but that’s how it is. However, our government, especially the regulatory bodies, are open to innovation. They recognize that Bitcoin is different, but they still view blockchain and tokens as useful technologies, which is somewhat misguided. So, in that sense, it’s more support than opposition. A couple of years ago, there was a circular discouraging the use of Bitcoin as a payment currency, mainly because they can't control its monetary policy. And they’re right—Bitcoin can’t be controlled by anyone; there’re the protocol and the rules, and everyone follows them, unless there’s a hard fork, which is a different matter. So, in that regard, Bitcoin is definitely categorized as a digital asset by the government, and that’s where it stands. **Piccolo**:People who come to BO฿ Space to learn about Bitcoin are often influenced by the government from the point of price movements; especially when government support moves the price up. But they usually only visit once or twice, especially if they’re not deep into the Bitcoin rabbit hole. They often get disappointed because, at BO฿ Space, we rarely discuss the price—maybe once a year, and that’s just after the meetup when people are having drinks. So, in that sense, I’d say the government currently doesn’t really hurt or help the community either way. People will go down the rabbit hole at their own pace. And if you're not a Bitcoiner and you come to a BO฿ Space meetup with a crypto focus, you might be surprised by the approach we take. **YakiHonne**:Thank you, Piccolo, for your time and insights. It’s been a pleasure speaking with you. Your perspective on the evolution of Bitcoin communities was eye-opening. It's clear that your deep understanding of Bitcoin is invaluable. I'm sure our readers will appreciate your insights. Once again, thank you, Piccolo. I look forward to seeing the continued growth of BO฿ Space and Bitcoin adoption.
@ fd78c37f:a0ec0833
2025-03-29 04:33:01**YakiHonne**: I'm excited to be joined by our guest Piccolo—thank you very much for being here. Before we dive in, I'd like to briefly introduce YakiHonne. YakiHonne is a decentralized media client built on the Nostr protocol, leveraging technology to enable freedom of speech. It empowers creators to fully own their voice and assets while offering innovative tools such as Smart widget , Verified Notes, and support for long-form content. Today, we’re not just discussing YakiHonne, but also diving into your community. Piccolo, could you start by telling us a bit about yourself and your community? **Piccolo**:Hi, I'm Piccolo. I run BO฿ Space in Bangkok, and we also have a satellite location called the BO฿ Space corner in Chiang Mai, thanks to the Bitcoin Learning Center. **Piccolo**:Regarding my background,I originally came from corporate finance and investment banking. I was in that field for about 20 years, with the last 15 spent running my own firm in corporate finance advisory alongside a couple of partners. We eventually sold the advisory business in 2015, took a short break, and in 2016, I ended up launching a fintech company, which is still operational today. The company specializes in equity crowdfunding and is licensed by the SEC in Thailand. **Piccolo**:I first bought Bitcoin a few years before truly understanding it, initially thinking it was a scam that would eventually collapse. However, in 2017, the block size wars demonstrated the protocol’s strong resistance to attacks on decentralization, which deeply impacted me. By late 2018 or early 2019, I started to really grasp Bitcoin and kept learning. Then, in mid-2022, after having fully fallen down the Bitcoin rabbit hole, I founded BO฿ Space. It was right after COVID, and since the fintech had scaled down, there was extra space. We started by hosting meetups and technical workshops for people who were interested. **Piccolo**:In the early years, we had various groups come by—like the team from BDK (Bitcoin Development Kit), who held workshops. The people behind the Bitcoin Beach Wallet, which later became Blink, also visited. So, BO฿ Space initially functioned as a meetup and technical workshop space. Eventually, we launched the BOB Builders Residency program, which was a lot of fun. We secured grant funding for developers under different cohort themes, so that they can collaborate and co-work for a few months. So far, we have completed three cohorts. **YakiHonne**:How did your community get started, and what did you do to attract new members in the beginning? **Piccolo**:The initial members came through word of mouth and invitations that I sent out. I reached out to an initial group of Bitcoiners here in the city who I believed were strong maximalists or Bitcoin-only supporters, back when that was still a thing. I sent out 21 invitations and had our first meetup with 21 people, most of whom I had interacted with online, though some in person during the COVID years. From there, it spread by word of mouth, and of course, through Twitter and meetup.com. So, I would say that word of mouth remains the main method of growth. Additionally, when people come through Bangkok and are looking for a Bitcoin-only meetup, there really isn't one available. I believe there are a couple now—maybe two or three—but when we started, there weren’t any, especially not a dedicated Bitcoin-only space. I think we may still be the only one in Bangkok. So yeah, word of mouth was definitely the main way we grew. Bitcoiners tend to share their finds when they meet like-minded people.  **YakiHonne**:Didn’t you have people in your community who initially thought Bitcoin was a scam, like you did, or face similar issues? **Piccolo**:Yes, it still happens, especially when the price of Bitcoin rises. Newcomers still join, and some of them believe Bitcoin might be a scam. However, this has become less frequent. The main reason is that when people come to BO฿ Space, they know it’s a Bitcoin-only meetup. We generally don’t discuss the price; instead, we focus on other aspects of Bitcoin, as there are many interesting developments in the space. **YakiHonne**:What advice would you give to someone looking to start or grow a Bitcoin-focused community in today’s world? Considering the current landscape, much like your own experience, what guidance would you offer? **Piccolo**:It sounds simple, but just do it. When it comes to community building, you don’t necessarily need a physical space. Community is about people coming together, right? Two people can start a community, then three, four, and so on. Meetups can happen anywhere—your favorite bar, a restaurant, a friend’s garage, or wherever. So, just do it, but make sure you have more than one person, otherwise, how can you build a community? Once you have more than one person, word of mouth will spread. And as you develop a core group—let’s say more than five people—that’s when I think the community can truly sustain itself. **YakiHonne**:I know you’ve mentioned the technical side of your community, but I’ll ask anyway—does your community engage with the technical or non-technical aspects of Bitcoin? Or perhaps, is there a blend of both? **Piccolo**:I would say both. It really depends on the monthly themes of our meetups. For example, February was focused on Asian communities in Bitcoin. During that month, community leaders came in to give presentations and discuss their work in places like Indonesia, India, and more recently, someone from HRF (Human Rights Foundation) talked about Bitcoin’s use case in Myanmar. Then, in December, we had a very technical month—Mining Month. It was led by our Cohort 3 residents, where we discussed Stratum V2 and had a demo on it. We also examined the Loki board hardware, and Zack took apart the S19, looking at different ways to repurpose the power supply unit, among other things. So, it’s a mix of both, depending on the theme for that month. Some months are very technical, while others are more community-focused and less technical. **YakiHonne**:What advice would you give to a technically inclined individual or organization looking to contribute meaningfully to the Bitcoin ecosystem? **Piccolo**:For technically inclined individuals, I would suggest identifying your favorite open-source project in the Bitcoin ecosystem. Start from Bitcoin Core and explore different layers, such as Lightning or e-cash, and other open-source projects. As for technically inclined organizations, if you're integrating Bitcoin into your business, I would say, first, make sure you have people within your organization who truly understand Bitcoin. Build a capable team first, and then, depending on the part of the Bitcoin ecosystem you’re involved in—whether it’s custody services, Lightning payments, layer 2, or something like Cashu or Ark—find your niche. From there, your team will work with you to discover ways to contribute. But until you build that capability, organizations are a bit different from individuals in this space. **YakiHonne**:How do you see the world of Bitcoin communities evolving as technology matures, particularly in areas like scalability, privacy, and adaptability with other systems? **Piccolo**:That's an interesting question. If we think about the future of Bitcoin communities, I believe they may eventually disappear as technology matures. Once Bitcoin scales to a point where it integrates seamlessly with other payment systems, becoming part of the everyday norm, the need for dedicated communities will diminish. It’s similar to how we no longer have meetups about refrigerators or iPhones, even though they are technologies we use every day. As Bitcoin matures, it will likely reach that level of ubiquity. There might still be occasional meetups or forums, but they will be more about specific knowledge, use cases, and tools, rather than a community dedicated to introducing others to the technology itself. However, this is a long way off. Bitcoin is still relatively small compared to the global fiat financial system, despite the growth we want to see. So, it will take a long time before we reach that stage. **YakiHonne**:It’s something I hadn’t considered before, and it’s quite insightful. Moving to our last question actually which I find very interesting is the government around you for or against bitcoin and how has That affected the community. **Piccolo**:In my opinion, on a general level, the government is more supportive than opposed to Bitcoin. The Thai government classifies Bitcoin as a digital asset, almost like digital gold. In that sense, they want to tax capital gains and regulate it. They also have a regulatory framework for it, known as the Digital Asset Regulatory Sandbox, where you can test various things, mainly coins and tokens. It's unfortunate, but that’s how it is. However, our government, especially the regulatory bodies, are open to innovation. They recognize that Bitcoin is different, but they still view blockchain and tokens as useful technologies, which is somewhat misguided. So, in that sense, it’s more support than opposition. A couple of years ago, there was a circular discouraging the use of Bitcoin as a payment currency, mainly because they can't control its monetary policy. And they’re right—Bitcoin can’t be controlled by anyone; there’re the protocol and the rules, and everyone follows them, unless there’s a hard fork, which is a different matter. So, in that regard, Bitcoin is definitely categorized as a digital asset by the government, and that’s where it stands. **Piccolo**:People who come to BO฿ Space to learn about Bitcoin are often influenced by the government from the point of price movements; especially when government support moves the price up. But they usually only visit once or twice, especially if they’re not deep into the Bitcoin rabbit hole. They often get disappointed because, at BO฿ Space, we rarely discuss the price—maybe once a year, and that’s just after the meetup when people are having drinks. So, in that sense, I’d say the government currently doesn’t really hurt or help the community either way. People will go down the rabbit hole at their own pace. And if you're not a Bitcoiner and you come to a BO฿ Space meetup with a crypto focus, you might be surprised by the approach we take. **YakiHonne**:Thank you, Piccolo, for your time and insights. It’s been a pleasure speaking with you. Your perspective on the evolution of Bitcoin communities was eye-opening. It's clear that your deep understanding of Bitcoin is invaluable. I'm sure our readers will appreciate your insights. Once again, thank you, Piccolo. I look forward to seeing the continued growth of BO฿ Space and Bitcoin adoption. @ df06d21e:2b23058f
2025-03-29 02:08:31Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust. Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement. Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification. Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation. And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination. Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars. Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them. We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new?
@ df06d21e:2b23058f
2025-03-29 02:08:31Imagine a Living Civilization—a new way to see our world. It starts with the Universe’s pillars: Matter, the stuff we’re made of; Energy, the flow that drives us; Physics, the rules we play by; and Chemistry, the complexity that builds us. We know these well. But civilization? That’s our creation—and although it has been described in so many different ways over the years I thought it was time for something new. Civilization has its own pillars, systems that I call the pillars of the Metaverse: Capital, Information, Innovation, and Trust. Capital is how we measure value. Not just money, but everything that matters: skills, we call that Human Capital; ecosystems, that’s Natural Capital; infrastructure, Public Capital; relationships, Social Capital. Picture a farmer swapping Bitcoin sats for seeds—not fiat debt—or tracking soil health alongside his wallet. Capital is a system, a system of measurement. Information is how we verify truth. Think IPFS, a network holding real data—climate stats, farming fixes—open to all, not locked up by some corporate gatekeeper. Information is a system of verification. Innovation is about generating solutions. On GitHub, coders worldwide crank out tools—Nostr clients, solar apps—shared freely, not patented for profit. Innovation is our system of generation. And Trust—it’s coordination. Nostr’s decentralized threads let communities set trade rules, split resources—governance from the ground up, no overlords required. Trust is our system of coordination. Right now we’re stuck in debt-based systems—and they’re failing us. Take fiat currency—central banks print it, slashing your purchasing power. Our dollar buys less every year; savings erode while the elite stack their gains. It’s a scam, Bitcoiners know it—fiat’s the real Ponzi bleeding us dry. Capital gets twisted—firms hoard Bitcoin for fiat pumps, not real wealth; governments chase GDP while forests die and skills sit idle. Information is buried—our media spits out spin, our corporations lock truth in silos. Innovation is stalled—debt props up corporate patents, not open wins. Trust is gone—our governance systems consist of top-down control that splits us apart, left to right, top to bottom. Debt just measures scarcity—money borrowed, nature trashed, bonds frayed—and it’s crushing the pillars. Wealth-based systems promise to turn that around. Bitcoin’s sound money is just the start—sats hold value, not inflate it away. Real capital measures what sustains us—sats fund a cooperative's water pump, not a vault; they track skills taught, land healed, ties rebuilt. Real Information opens up—IPFS logs show ‘biochar boosted yield 20%’, verified by us, not suits. Real Innovation flows—GitHub devs build Lightning hubs, wealth spreads. Real Trust binds us together—Nostr chats align us, no central puppeteer. Wealth based systems strengthen the pillars of the Metaverse, it doesn’t erode them. We needed a new framing. A new vision of what was, what is, and what could be. We have one. This is real. This is the world we are building. Bitcoin is live, Nostr is growing, IPFS and GitHub are humming. We can see Debt teetering; while real wealth is rising. So, hodlers, maxis, plebs—everyone—what does a true wealth-based system look like? How can we measure Capital beyond fiat’s con job? Bitcoin’s the rock, but it’s just the beginning. How do we build on this, expand it, and transform everything as we build something entirely new? @ a95c6243:d345522c
2025-01-03 20:26:47*Was du bist hängt von drei Faktoren ab:* *\ Was du geerbt hast,* *\ was deine Umgebung aus dir machte* *\ und was du in freier Wahl* *\ aus deiner Umgebung und deinem Erbe gemacht hast.* *\ Aldous Huxley* **Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen** ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses [Buch](https://www.nachdenkseiten.de/?p=126416) einer gewissen ehemaligen Regierungschefin. **Erklärungsansätze für solche Entwicklungen sind bekannt,** und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer [Herrschaftsinstrumente](https://transition-news.org/spip.php?recherche=nudging\&page=recherche_wall). **Aber wollen die Menschen überhaupt Freiheit?** Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht. **«Desinformation» ist so ein brisantes Thema.** Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur [Ukraine](https://transition-news.org/spip.php?recherche=ukraine\&page=recherche_wall), zum [Klima](https://transition-news.org/spip.php?recherche=klima\&page=recherche_wall), zu [Gesundheitsthemen](https://transition-news.org/spip.php?recherche=impfung\&page=recherche_wall) oder zur [Migration](https://transition-news.org/spip.php?recherche=migration\&page=recherche_wall). Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung. **Freiheit bedingt Eigenverantwortung, ohne Zweifel.** Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung. **Sind viele Menschen möglicherweise schon so «eingenordet»,** dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen [Hacker-Kongress](https://transition-news.org/der-38-kongress-des-chaos-computer-clubs-bot-mehr-enthullungen-als-nur-die) des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative. **Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination?** Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/kann-es-sein-dass-die-menschen-gar-keine-freiheit-wollen)*** erschienen.
@ a95c6243:d345522c
2025-01-03 20:26:47*Was du bist hängt von drei Faktoren ab:* *\ Was du geerbt hast,* *\ was deine Umgebung aus dir machte* *\ und was du in freier Wahl* *\ aus deiner Umgebung und deinem Erbe gemacht hast.* *\ Aldous Huxley* **Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen** ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses [Buch](https://www.nachdenkseiten.de/?p=126416) einer gewissen ehemaligen Regierungschefin. **Erklärungsansätze für solche Entwicklungen sind bekannt,** und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer [Herrschaftsinstrumente](https://transition-news.org/spip.php?recherche=nudging\&page=recherche_wall). **Aber wollen die Menschen überhaupt Freiheit?** Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht. **«Desinformation» ist so ein brisantes Thema.** Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur [Ukraine](https://transition-news.org/spip.php?recherche=ukraine\&page=recherche_wall), zum [Klima](https://transition-news.org/spip.php?recherche=klima\&page=recherche_wall), zu [Gesundheitsthemen](https://transition-news.org/spip.php?recherche=impfung\&page=recherche_wall) oder zur [Migration](https://transition-news.org/spip.php?recherche=migration\&page=recherche_wall). Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung. **Freiheit bedingt Eigenverantwortung, ohne Zweifel.** Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung. **Sind viele Menschen möglicherweise schon so «eingenordet»,** dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen [Hacker-Kongress](https://transition-news.org/der-38-kongress-des-chaos-computer-clubs-bot-mehr-enthullungen-als-nur-die) des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative. **Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination?** Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter. *** Dieser Beitrag ist zuerst auf ***[Transition News](https://transition-news.org/kann-es-sein-dass-die-menschen-gar-keine-freiheit-wollen)*** erschienen. @ 3e6e0735:9e95c8a2
2025-03-28 23:58:02https://i.nostr.build/lanoHI3p2aCKRZlV.png I’ve been thinking a lot lately about why Bitcoin still feels so misunderstood. Not just by the media or the IMF — that part’s predictable. But even inside our own circles, something's missing. We say it’s money. We say it’s freedom. We say it’s code. And it is. But when you really zoom out, past the price and the politics, it’s something more radical than we usually admit. Bitcoin is a shift in how power moves. And what we do with that power now actually matters. ## The noise outside Let’s start with the obvious: the media still doesn’t get it. Every other headline is either a death knell or a celebration depending on the price that day. No context. No nuance. No understanding of what we’re building. You’ve seen the headlines: - “Bitcoin is crashing again.” - “Crypto bros are killing the planet.” - “The IMF warns: Bitcoin adoption is dangerous.” Yeah? Dangerous to what? The system they control. The levers they pull. The old game where the house always wins. That’s why they’re afraid. Not because Bitcoin is volatile, but because it doesn’t ask permission. ## This isn’t about panic — it’s about patterns I’m not saying there’s a conspiracy. But there is inertia. Institutions protect themselves. Systems reinforce themselves. They were never going to roll out the red carpet for an open, borderless network that replaces their function. So the IMF calls it a threat. Central banks scramble to launch CBDCs. And journalists keep writing the same shallow takes while ignoring the real story. Meanwhile, we’re still here. Still building. Still holding. Still running nodes. Bitcoin isn’t perfect. But it’s honest. It doesn’t bend to popularity or political pressure. It enforces rules with math, not people. And that’s exactly why it works. ## Even we miss it sometimes Here’s the part that really hit me recently: even within Bitcoin, we often undersell what this is. We talk about savings. Inflation. Fiat debasement. All real, all important. But what about the broader layer? What about governance? Energy? Communication? Defense? Jason Lowery’s book *Softwar* lit that fuse for me again. Not because it’s flawless — it’s not. But because he reframed the game. Bitcoin isn’t a new weapon. It’s the **end** of weapons-as-power. Proof-of-work, in Lowery’s view, is a form of peaceful negotiation. A deterrent against coercion. A way to shift from kinetic violence to computational resolution. Most people — even many Bitcoiners — haven’t fully absorbed that. It’s not about militarizing the network. It’s about **demilitarizing the world** through energy expenditure that replaces human conflict. Let’s be clear: this doesn’t mean Bitcoin *will* be used this way. It means it *can*. And that opens up a few possible futures: - **Scenario A:** Smaller nations adopt Bitcoin infrastructure as a shield — a deterrent and neutral layer to build sovereignty - **Scenario B:** Superpowers attack mining and self-custody, escalating regulatory capture and fragmenting the open protocol into corporate silos - **Scenario C:** Bitcoin becomes the boring backend of legacy finance, its edge neutered by ETFs and custody-as-a-service Which one wins depends on what we build — and who steps up. ## Then I found Maya I came across Maya Parbhoe’s campaign by accident. One of those late-night rabbit holes where Bitcoin Twitter turns into a global map. She’s running for president of Suriname. She’s a Bitcoiner. And she’s not just tweeting about it — she’s building an entire political platform around it. No central bank. Bitcoin as legal tender. Full fiscal transparency. Open-source government. Yeah. You read that right. Not just open-source software — open-source statehood. Her father was murdered after exposing corruption. That’s not a talking point. That’s real-life consequence. And instead of running away from systems, she’s choosing to redesign one. That’s maximalism. Not in ideology. In action. ## The El Salvador experiment — and evolution When El Salvador made Bitcoin legal tender in 2021, it lit up our feeds. It was bold. Unprecedented. A true first. But not without flaws. The rollout was fast. Chivo wallet was centralized. Adoption stalled in rural areas. Transparency was thin. And despite the brave move, the state’s underlying structure remained top-down. Bukele played offense, but the protocol was wrapped in traditional power. Maya is doing it differently. Her approach is grassroots-forward. Open-source by design. Focused on education, transparency, and modular state-building — not just mandates. She’s not using Bitcoin to *prop up* state power. She’s using it to *distribute* it. ## Maximalism is evolving Look, I get it. The memes are fun. The laser eyes. The beefsteak meetups. The HODL culture. But there’s something else growing here. Something a little quieter, a little deeper: - People running nodes to protect civil liberties - Communities using Lightning for real commerce - Builders forging tools for self-sovereign identity - Leaders like Maya testing what Bitcoin can look like as public infrastructure This is happening. In real time. It’s messy and fragile and still small. But it’s happening. Let’s also stay honest: Maximalism has its risks. Dogma can blind us. Toxicity can push people away. And if we’re not careful, we’ll replace one centralization with another — just wearing different memes. We need less purity, more principles. Less hype, more clarity. That’s the kind of maximalism Maya embodies. ## What now? Maya doesn’t have a VC fund or an ad agency. She has a message, a mission, and the courage to put Bitcoin on the ballot. If that resonates, help her. Not just by donating — though here’s the link: [https://geyser.fund/project/maya2025 ](https://geyser.fund/project/maya2025) But by sharing. Writing. Talking. Translating. Connecting. Bitcoin is still early. But it’s not abstract anymore. This isn’t just theory. It’s a protocol, sure. But now, maybe it’s a presidency too. https://i.nostr.build/0luYy8ojK7gkxsuL.png
@ 3e6e0735:9e95c8a2
2025-03-28 23:58:02https://i.nostr.build/lanoHI3p2aCKRZlV.png I’ve been thinking a lot lately about why Bitcoin still feels so misunderstood. Not just by the media or the IMF — that part’s predictable. But even inside our own circles, something's missing. We say it’s money. We say it’s freedom. We say it’s code. And it is. But when you really zoom out, past the price and the politics, it’s something more radical than we usually admit. Bitcoin is a shift in how power moves. And what we do with that power now actually matters. ## The noise outside Let’s start with the obvious: the media still doesn’t get it. Every other headline is either a death knell or a celebration depending on the price that day. No context. No nuance. No understanding of what we’re building. You’ve seen the headlines: - “Bitcoin is crashing again.” - “Crypto bros are killing the planet.” - “The IMF warns: Bitcoin adoption is dangerous.” Yeah? Dangerous to what? The system they control. The levers they pull. The old game where the house always wins. That’s why they’re afraid. Not because Bitcoin is volatile, but because it doesn’t ask permission. ## This isn’t about panic — it’s about patterns I’m not saying there’s a conspiracy. But there is inertia. Institutions protect themselves. Systems reinforce themselves. They were never going to roll out the red carpet for an open, borderless network that replaces their function. So the IMF calls it a threat. Central banks scramble to launch CBDCs. And journalists keep writing the same shallow takes while ignoring the real story. Meanwhile, we’re still here. Still building. Still holding. Still running nodes. Bitcoin isn’t perfect. But it’s honest. It doesn’t bend to popularity or political pressure. It enforces rules with math, not people. And that’s exactly why it works. ## Even we miss it sometimes Here’s the part that really hit me recently: even within Bitcoin, we often undersell what this is. We talk about savings. Inflation. Fiat debasement. All real, all important. But what about the broader layer? What about governance? Energy? Communication? Defense? Jason Lowery’s book *Softwar* lit that fuse for me again. Not because it’s flawless — it’s not. But because he reframed the game. Bitcoin isn’t a new weapon. It’s the **end** of weapons-as-power. Proof-of-work, in Lowery’s view, is a form of peaceful negotiation. A deterrent against coercion. A way to shift from kinetic violence to computational resolution. Most people — even many Bitcoiners — haven’t fully absorbed that. It’s not about militarizing the network. It’s about **demilitarizing the world** through energy expenditure that replaces human conflict. Let’s be clear: this doesn’t mean Bitcoin *will* be used this way. It means it *can*. And that opens up a few possible futures: - **Scenario A:** Smaller nations adopt Bitcoin infrastructure as a shield — a deterrent and neutral layer to build sovereignty - **Scenario B:** Superpowers attack mining and self-custody, escalating regulatory capture and fragmenting the open protocol into corporate silos - **Scenario C:** Bitcoin becomes the boring backend of legacy finance, its edge neutered by ETFs and custody-as-a-service Which one wins depends on what we build — and who steps up. ## Then I found Maya I came across Maya Parbhoe’s campaign by accident. One of those late-night rabbit holes where Bitcoin Twitter turns into a global map. She’s running for president of Suriname. She’s a Bitcoiner. And she’s not just tweeting about it — she’s building an entire political platform around it. No central bank. Bitcoin as legal tender. Full fiscal transparency. Open-source government. Yeah. You read that right. Not just open-source software — open-source statehood. Her father was murdered after exposing corruption. That’s not a talking point. That’s real-life consequence. And instead of running away from systems, she’s choosing to redesign one. That’s maximalism. Not in ideology. In action. ## The El Salvador experiment — and evolution When El Salvador made Bitcoin legal tender in 2021, it lit up our feeds. It was bold. Unprecedented. A true first. But not without flaws. The rollout was fast. Chivo wallet was centralized. Adoption stalled in rural areas. Transparency was thin. And despite the brave move, the state’s underlying structure remained top-down. Bukele played offense, but the protocol was wrapped in traditional power. Maya is doing it differently. Her approach is grassroots-forward. Open-source by design. Focused on education, transparency, and modular state-building — not just mandates. She’s not using Bitcoin to *prop up* state power. She’s using it to *distribute* it. ## Maximalism is evolving Look, I get it. The memes are fun. The laser eyes. The beefsteak meetups. The HODL culture. But there’s something else growing here. Something a little quieter, a little deeper: - People running nodes to protect civil liberties - Communities using Lightning for real commerce - Builders forging tools for self-sovereign identity - Leaders like Maya testing what Bitcoin can look like as public infrastructure This is happening. In real time. It’s messy and fragile and still small. But it’s happening. Let’s also stay honest: Maximalism has its risks. Dogma can blind us. Toxicity can push people away. And if we’re not careful, we’ll replace one centralization with another — just wearing different memes. We need less purity, more principles. Less hype, more clarity. That’s the kind of maximalism Maya embodies. ## What now? Maya doesn’t have a VC fund or an ad agency. She has a message, a mission, and the courage to put Bitcoin on the ballot. If that resonates, help her. Not just by donating — though here’s the link: [https://geyser.fund/project/maya2025 ](https://geyser.fund/project/maya2025) But by sharing. Writing. Talking. Translating. Connecting. Bitcoin is still early. But it’s not abstract anymore. This isn’t just theory. It’s a protocol, sure. But now, maybe it’s a presidency too. https://i.nostr.build/0luYy8ojK7gkxsuL.png @ a95c6243:d345522c
2025-01-01 17:39:51**Heute möchte ich ein Gedicht mit euch teilen.** Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden. **Dem originalen Titel «Die Uhr»** habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension. **Das Ticken der Uhr und die Momente des Glücks und der Trauer** stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram. **Was den Takt pocht, ist durchaus auch das Herz,** unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.» *Ich trage, wo ich gehe, stets eine Uhr bei mir;* \ *Wieviel es geschlagen habe, genau seh ich an ihr.* \ *Es ist ein großer Meister, der künstlich ihr Werk gefügt,* \ *Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.*   *Ich wollte, sie wäre rascher gegangen an manchem Tag;* *\ Ich wollte, sie hätte manchmal verzögert den raschen Schlag.* *\ In meinen Leiden und Freuden, in Sturm und in der Ruh,* *\ Was immer geschah im Leben, sie pochte den Takt dazu.*   *Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr,* *\ Sie schlug am Morgen der Liebe, sie schlug am Traualtar.* *\ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft,* *\ Wenn bessere Tage kommen, wie meine Seele es hofft.*   *Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf,* *\ So zog der Meister immer großmütig sie wieder auf.* *\ Doch stände sie einmal stille, dann wär's um sie geschehn,* *\ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.*   *Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit,* *\ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit!* *\ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn:* *\ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.*   *Johann Gabriel Seidl (1804-1875)*
@ a95c6243:d345522c
2025-01-01 17:39:51**Heute möchte ich ein Gedicht mit euch teilen.** Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden. **Dem originalen Titel «Die Uhr»** habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension. **Das Ticken der Uhr und die Momente des Glücks und der Trauer** stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram. **Was den Takt pocht, ist durchaus auch das Herz,** unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.» *Ich trage, wo ich gehe, stets eine Uhr bei mir;* \ *Wieviel es geschlagen habe, genau seh ich an ihr.* \ *Es ist ein großer Meister, der künstlich ihr Werk gefügt,* \ *Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.*   *Ich wollte, sie wäre rascher gegangen an manchem Tag;* *\ Ich wollte, sie hätte manchmal verzögert den raschen Schlag.* *\ In meinen Leiden und Freuden, in Sturm und in der Ruh,* *\ Was immer geschah im Leben, sie pochte den Takt dazu.*   *Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr,* *\ Sie schlug am Morgen der Liebe, sie schlug am Traualtar.* *\ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft,* *\ Wenn bessere Tage kommen, wie meine Seele es hofft.*   *Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf,* *\ So zog der Meister immer großmütig sie wieder auf.* *\ Doch stände sie einmal stille, dann wär's um sie geschehn,* *\ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.*   *Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit,* *\ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit!* *\ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn:* *\ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.*   *Johann Gabriel Seidl (1804-1875)* @ 7d33ba57:1b82db35
2025-03-28 22:14:24Preko is a charming seaside town on Ugljan Island, just a short ferry ride from Zadar. Known for its beautiful beaches, relaxed atmosphere, and stunning views of the Adriatic, it's the perfect place to experience authentic Dalmatian island life.  ## **🌊 Top Things to See & Do in Preko** ### **1️⃣ Swim at Jaz Beach 🏖️** - A **Blue Flag beach** with **clear turquoise waters and soft pebbles**. - Ideal for **families** thanks to its shallow waters. - Nearby **cafés and restaurants** make it a great spot to spend the day. ### **2️⃣ Visit the Islet of Galevac 🏝️** - A **tiny island just 80 meters from Preko**, reachable by swimming or a short boat ride. - Home to a **15th-century Franciscan monastery**, surrounded by lush greenery. - A **peaceful retreat**, perfect for relaxation.  ### **3️⃣ Hike to St. Michael’s Fortress (Sv. Mihovil) 🏰** - A **medieval fortress from the 13th century** with **breathtaking panoramic views**. - Overlooks **Zadar, Kornati Islands, and the Adriatic Sea**. - A **1-hour scenic hike** from Preko or accessible by **bike or car**. ### **4️⃣ Explore the Local Taverns & Seafood Restaurants 🍽️** - Try **fresh seafood, octopus salad, and Dalmatian peka (slow-cooked meat & vegetables)**. - **Best spots:** Konoba Roko (authentic seafood) & Vile Dalmacija (beachfront dining). ### **5️⃣ Rent a Bike or Scooter 🚲** - Explore **Ugljan Island’s olive groves, hidden coves, and coastal paths**. - Visit nearby villages like **Kali and Kukljica** for more local charm.  ### **6️⃣ Take a Day Trip to Zadar ⛵** - Just **25 minutes by ferry**, Zadar offers **historic landmarks, the Sea Organ, and Roman ruins**. - Perfect for a cultural excursion before returning to the peaceful island.  ## **🚗 How to Get to Preko** 🚢 **By Ferry:** - **From Zadar:** Regular ferries (Jadrolinija) take **~25 minutes**. 🚘 **By Car:** - If driving, take the **ferry from Zadar to Preko** and explore the island. 🚴 **By Bike:** - Many visitors rent bikes to explore Ugljan Island’s coastal roads.  ## **💡 Tips for Visiting Preko** ✅ **Best time to visit?** **May–September** for warm weather & swimming 🌞 ✅ **Ferry schedules** – Check times in advance, especially in the off-season ⏳ ✅ **Bring cash** – Some smaller taverns and cafés may not accept cards 💰 ✅ **Stay for sunset** – The views over Zadar from Preko’s waterfront are stunning 🌅 Would you like **hotel recommendations, hidden beaches, or other island activities**? 😊
@ 7d33ba57:1b82db35
2025-03-28 22:14:24Preko is a charming seaside town on Ugljan Island, just a short ferry ride from Zadar. Known for its beautiful beaches, relaxed atmosphere, and stunning views of the Adriatic, it's the perfect place to experience authentic Dalmatian island life.  ## **🌊 Top Things to See & Do in Preko** ### **1️⃣ Swim at Jaz Beach 🏖️** - A **Blue Flag beach** with **clear turquoise waters and soft pebbles**. - Ideal for **families** thanks to its shallow waters. - Nearby **cafés and restaurants** make it a great spot to spend the day. ### **2️⃣ Visit the Islet of Galevac 🏝️** - A **tiny island just 80 meters from Preko**, reachable by swimming or a short boat ride. - Home to a **15th-century Franciscan monastery**, surrounded by lush greenery. - A **peaceful retreat**, perfect for relaxation.  ### **3️⃣ Hike to St. Michael’s Fortress (Sv. Mihovil) 🏰** - A **medieval fortress from the 13th century** with **breathtaking panoramic views**. - Overlooks **Zadar, Kornati Islands, and the Adriatic Sea**. - A **1-hour scenic hike** from Preko or accessible by **bike or car**. ### **4️⃣ Explore the Local Taverns & Seafood Restaurants 🍽️** - Try **fresh seafood, octopus salad, and Dalmatian peka (slow-cooked meat & vegetables)**. - **Best spots:** Konoba Roko (authentic seafood) & Vile Dalmacija (beachfront dining). ### **5️⃣ Rent a Bike or Scooter 🚲** - Explore **Ugljan Island’s olive groves, hidden coves, and coastal paths**. - Visit nearby villages like **Kali and Kukljica** for more local charm.  ### **6️⃣ Take a Day Trip to Zadar ⛵** - Just **25 minutes by ferry**, Zadar offers **historic landmarks, the Sea Organ, and Roman ruins**. - Perfect for a cultural excursion before returning to the peaceful island.  ## **🚗 How to Get to Preko** 🚢 **By Ferry:** - **From Zadar:** Regular ferries (Jadrolinija) take **~25 minutes**. 🚘 **By Car:** - If driving, take the **ferry from Zadar to Preko** and explore the island. 🚴 **By Bike:** - Many visitors rent bikes to explore Ugljan Island’s coastal roads.  ## **💡 Tips for Visiting Preko** ✅ **Best time to visit?** **May–September** for warm weather & swimming 🌞 ✅ **Ferry schedules** – Check times in advance, especially in the off-season ⏳ ✅ **Bring cash** – Some smaller taverns and cafés may not accept cards 💰 ✅ **Stay for sunset** – The views over Zadar from Preko’s waterfront are stunning 🌅 Would you like **hotel recommendations, hidden beaches, or other island activities**? 😊 @ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( [dominictarr]( https://github.com/dominictarr/scuttlebutt) ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt ([ssb]( https://github.com/ssbc/ssb-db)) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia. Se você está se perguntando de onde diabos veio o nome Scuttlebutt: > Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.  Marinheiros se reunindo em torno da rixa. ( [fonte]( https://twitter.com/IntEtymology/status/998879578851508224) ) Dominic descobriu o termo boato em um [artigo de pesquisa]( https://www.cs.cornell.edu/home/rvr/papers/flowgossip.pdf) que leu. Em sistemas distribuídos, [fofocar]( https://en.wikipedia.org/wiki/Gossip_protocol) é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”. **Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto.** **Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar.** Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário [de bordo]( https://en.wikipedia.org/wiki/Logbook) (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem. Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. **Cada item adicionado a um log do usuário é chamado de mensagem.** **Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.  Estrutura de alto nível de um feed **Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência. Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub. Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.** Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.  Perspectivas dos participantes ## Scuttlebot O software Pub é conhecido como servidor Scuttlebutt (servidor [ssb]( https://github.com/ssbc/ssb-server) ), mas também é conhecido como “Scuttlebot” e `sbot`na linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial. **Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.  Estrutura de alto nível de um feed **Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência. Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub. Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.** Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.   Perspectivas dos participantes ## Pubs - Hubs ### Pubs públicos | Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | | `scuttle.us` | [@Ryan]( https://keybase.io/ryan_singer) | `scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=` | | [pub1.upsocial.com]( https://upsocial.com/) | [@freedomrules]( https://github.com/freedomrules) | `pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=` | | [Monero Pub]( https://xmr-pub.net/) | [@Denis]( https://github.com/Orville2112) | `xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=` | | [FreeSocial]( https://freesocial.co/) | [@Jarland]( https://github.com/mxroute) | `pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=` | | `ssb.vpn.net.br` | [@coffeverton]( https://about.me/coffeverton) | `ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=` | | [gossip.noisebridge.info]( https://www.noisebridge.net/wiki/Pub) | [Noisebridge Hackerspace]( https://www.noisebridge.net/wiki/Unicorn) [@james.network]( https://james.network/) | `gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=` | ### Pubs privados Você precisará entrar em contato com os proprietários desses bares para receber um convite. | Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | | `many.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | `one.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | `ssb.mikey.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | [ssb.celehner.com]( https://ssb.celehner.com/) | [@cel]( https://github.com/ssbc/ssb-server/wiki/@f/6sQ6d2CMxRUhLpspgGIulDxDCwYD7DzFzPNr7u5AU=.ed25519) | [cel@celehner.com](mailto:cel@celehner.com) | ### Pubs muito grandes  *Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)*  | Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | | `scuttlebutt.de` | [SolSoCoG]( https://solsocog.de/impressum) | `scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=` | | `Lohn's Pub` | [@lohn]( https://github.com/lohn) | `p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=` | | [Scuttle Space]( https://scuttle.space/) | [@guil-dot]( https://github.com/guil-dot) | Visit [scuttle.space]( https://scuttle.space/) | | `SSB PeerNet US-East` | [timjrobinson]( https://github.com/timjrobinson) | `us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=` | | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= | ## GUI - Interface Gráfica do Utilizador(Usuário) ### Patchwork - Uma GUI SSB (Descontinuado) [**Patchwork**]( https://github.com/ssbc/patchwork) **é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB** . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.  Fonte: [scuttlebutt.nz]( https://www.scuttlebutt.nz/getting-started) **Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub.** Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs. Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth. ### Patchbay - Uma GUI Alternativa Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que [Patchwork]( https://github.com/ssbc/patchwork) e [Patchfoo]( https://github.com/ssbc/patchfoo) , então você pode facilmente dar uma volta com sua identidade existente.  ### Planetary - GUI para IOS  [Planetary]( https://apps.apple.com/us/app/planetary-app/id1481617318) é um app com pubs pré-carregados para facilitar integração. ### Manyverse - GUI para Android  [Manyverse]( https://www.manyver.se/) é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone . ## Fontes * https://scuttlebot.io/ * https://decentralized-id.com/decentralized-web/scuttlebot/#plugins * https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd * [**Secure Scuttlebutt**]( http://ssbc.github.io/secure-scuttlebutt/) **:** um protocolo de banco de dados global.
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( [dominictarr]( https://github.com/dominictarr/scuttlebutt) ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt ([ssb]( https://github.com/ssbc/ssb-db)) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia. Se você está se perguntando de onde diabos veio o nome Scuttlebutt: > Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.  Marinheiros se reunindo em torno da rixa. ( [fonte]( https://twitter.com/IntEtymology/status/998879578851508224) ) Dominic descobriu o termo boato em um [artigo de pesquisa]( https://www.cs.cornell.edu/home/rvr/papers/flowgossip.pdf) que leu. Em sistemas distribuídos, [fofocar]( https://en.wikipedia.org/wiki/Gossip_protocol) é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”. **Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto.** **Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar.** Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário [de bordo]( https://en.wikipedia.org/wiki/Logbook) (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem. Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. **Cada item adicionado a um log do usuário é chamado de mensagem.** **Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.  Estrutura de alto nível de um feed **Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência. Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub. Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.** Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.  Perspectivas dos participantes ## Scuttlebot O software Pub é conhecido como servidor Scuttlebutt (servidor [ssb]( https://github.com/ssbc/ssb-server) ), mas também é conhecido como “Scuttlebot” e `sbot`na linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial. **Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações.** Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.  Estrutura de alto nível de um feed **Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar.** Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência. Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub. Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. **Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.** Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de [Pubs públicos em que]( https://github.com/ssbc/ssb-server/wiki/Pub-Servers) todos podem participar **.** Explicaremos como ingressar em um posteriormente neste guia. **Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais.** Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.   Perspectivas dos participantes ## Pubs - Hubs ### Pubs públicos | Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | | `scuttle.us` | [@Ryan]( https://keybase.io/ryan_singer) | `scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=` | | [pub1.upsocial.com]( https://upsocial.com/) | [@freedomrules]( https://github.com/freedomrules) | `pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=` | | [Monero Pub]( https://xmr-pub.net/) | [@Denis]( https://github.com/Orville2112) | `xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=` | | [FreeSocial]( https://freesocial.co/) | [@Jarland]( https://github.com/mxroute) | `pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=` | | `ssb.vpn.net.br` | [@coffeverton]( https://about.me/coffeverton) | `ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=` | | [gossip.noisebridge.info]( https://www.noisebridge.net/wiki/Pub) | [Noisebridge Hackerspace]( https://www.noisebridge.net/wiki/Unicorn) [@james.network]( https://james.network/) | `gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=` | ### Pubs privados Você precisará entrar em contato com os proprietários desses bares para receber um convite. | Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | | `many.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | `one.butt.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | `ssb.mikey.nz` | [@dinosaur]( https://dinosaur.is/) | [mikey@enspiral.com](mailto:mikey@enspiral.com) | | [ssb.celehner.com]( https://ssb.celehner.com/) | [@cel]( https://github.com/ssbc/ssb-server/wiki/@f/6sQ6d2CMxRUhLpspgGIulDxDCwYD7DzFzPNr7u5AU=.ed25519) | [cel@celehner.com](mailto:cel@celehner.com) | ### Pubs muito grandes  *Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)*  | Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | | `scuttlebutt.de` | [SolSoCoG]( https://solsocog.de/impressum) | `scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=` | | `Lohn's Pub` | [@lohn]( https://github.com/lohn) | `p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=` | | [Scuttle Space]( https://scuttle.space/) | [@guil-dot]( https://github.com/guil-dot) | Visit [scuttle.space]( https://scuttle.space/) | | `SSB PeerNet US-East` | [timjrobinson]( https://github.com/timjrobinson) | `us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=` | | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= | ## GUI - Interface Gráfica do Utilizador(Usuário) ### Patchwork - Uma GUI SSB (Descontinuado) [**Patchwork**]( https://github.com/ssbc/patchwork) **é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB** . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.  Fonte: [scuttlebutt.nz]( https://www.scuttlebutt.nz/getting-started) **Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub.** Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs. Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth. ### Patchbay - Uma GUI Alternativa Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que [Patchwork]( https://github.com/ssbc/patchwork) e [Patchfoo]( https://github.com/ssbc/patchfoo) , então você pode facilmente dar uma volta com sua identidade existente.  ### Planetary - GUI para IOS  [Planetary]( https://apps.apple.com/us/app/planetary-app/id1481617318) é um app com pubs pré-carregados para facilitar integração. ### Manyverse - GUI para Android  [Manyverse]( https://www.manyver.se/) é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone . ## Fontes * https://scuttlebot.io/ * https://decentralized-id.com/decentralized-web/scuttlebot/#plugins * https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd * [**Secure Scuttlebutt**]( http://ssbc.github.io/secure-scuttlebutt/) **:** um protocolo de banco de dados global. @ f9cf4e94:96abc355
2024-12-30 19:02:32Na era das grandes navegações, piratas ingleses eram autorizados pelo governo para roubar navios. A única coisa que diferenciava um pirata comum de um corsário é que o último possuía a “Carta do Corso”, que funcionava como um “Alvará para o roubo”, onde o governo Inglês legitimava o roubo de navios por parte dos corsários. É claro, que em troca ele exigia uma parte da espoliação. Bastante similar com a maneira que a Receita Federal atua, não? Na verdade, o caso é ainda pior, pois o governo fica com toda a riqueza espoliada, e apenas repassa um mísero salário para os corsários modernos, os agentes da receita federal. Porém eles “justificam” esse roubo ao chamá-lo de imposto, e isso parece acalmar os ânimos de grande parte da população, mas não de nós. Não é por acaso que 'imposto' é o particípio passado do verbo 'impor'. Ou seja, é aquilo que resulta do cumprimento obrigatório -- e não voluntário -- de todos os cidadãos. Se não for 'imposto' ninguém paga. Nem mesmo seus defensores. Isso mostra o quanto as pessoas realmente apreciam os serviços do estado. Apenas volte um pouco na história: os primeiros pagadores de impostos eram fazendeiros cujos territórios foram invadidos por nômades que pastoreavam seu gado. Esses invasores nômades forçavam os fazendeiros a lhes pagar uma fatia de sua renda em troca de "proteção". O fazendeiro que não concordasse era assassinado. Os nômades perceberam que era muito mais interessante e confortável apenas cobrar uma taxa de proteção em vez de matar o fazendeiro e assumir suas posses. Cobrando uma taxa, eles obtinham o que necessitavam. Já se matassem os fazendeiros, eles teriam de gerenciar por conta própria toda a produção da fazenda. Daí eles entenderam que, ao não assassinarem todos os fazendeiros que encontrassem pelo caminho, poderiam fazer desta prática um modo de vida. Assim nasceu o governo. Não assassinar pessoas foi o primeiro serviço que o governo forneceu. Como temos sorte em ter à nossa disposição esta instituição! Assim, não deixa de ser curioso que algumas pessoas digam que os impostos são pagos basicamente para impedir que aconteça exatamente aquilo que originou a existência do governo. O governo nasceu da extorsão. Os fazendeiros tinham de pagar um "arrego" para seu governo. Caso contrário, eram assassinados. Quem era a real ameaça? O governo. A máfia faz a mesma coisa. Mas existe uma forma de se proteger desses corsários modernos. Atualmente, existe uma propriedade privada que NINGUÉM pode tirar de você, ela é sua até mesmo depois da morte. É claro que estamos falando do Bitcoin. Fazendo as configurações certas, é impossível saber que você tem bitcoin. Nem mesmo o governo americano consegue saber. #brasil #bitcoinbrasil #nostrbrasil #grownostr #bitcoin
@ f9cf4e94:96abc355
2024-12-30 19:02:32Na era das grandes navegações, piratas ingleses eram autorizados pelo governo para roubar navios. A única coisa que diferenciava um pirata comum de um corsário é que o último possuía a “Carta do Corso”, que funcionava como um “Alvará para o roubo”, onde o governo Inglês legitimava o roubo de navios por parte dos corsários. É claro, que em troca ele exigia uma parte da espoliação. Bastante similar com a maneira que a Receita Federal atua, não? Na verdade, o caso é ainda pior, pois o governo fica com toda a riqueza espoliada, e apenas repassa um mísero salário para os corsários modernos, os agentes da receita federal. Porém eles “justificam” esse roubo ao chamá-lo de imposto, e isso parece acalmar os ânimos de grande parte da população, mas não de nós. Não é por acaso que 'imposto' é o particípio passado do verbo 'impor'. Ou seja, é aquilo que resulta do cumprimento obrigatório -- e não voluntário -- de todos os cidadãos. Se não for 'imposto' ninguém paga. Nem mesmo seus defensores. Isso mostra o quanto as pessoas realmente apreciam os serviços do estado. Apenas volte um pouco na história: os primeiros pagadores de impostos eram fazendeiros cujos territórios foram invadidos por nômades que pastoreavam seu gado. Esses invasores nômades forçavam os fazendeiros a lhes pagar uma fatia de sua renda em troca de "proteção". O fazendeiro que não concordasse era assassinado. Os nômades perceberam que era muito mais interessante e confortável apenas cobrar uma taxa de proteção em vez de matar o fazendeiro e assumir suas posses. Cobrando uma taxa, eles obtinham o que necessitavam. Já se matassem os fazendeiros, eles teriam de gerenciar por conta própria toda a produção da fazenda. Daí eles entenderam que, ao não assassinarem todos os fazendeiros que encontrassem pelo caminho, poderiam fazer desta prática um modo de vida. Assim nasceu o governo. Não assassinar pessoas foi o primeiro serviço que o governo forneceu. Como temos sorte em ter à nossa disposição esta instituição! Assim, não deixa de ser curioso que algumas pessoas digam que os impostos são pagos basicamente para impedir que aconteça exatamente aquilo que originou a existência do governo. O governo nasceu da extorsão. Os fazendeiros tinham de pagar um "arrego" para seu governo. Caso contrário, eram assassinados. Quem era a real ameaça? O governo. A máfia faz a mesma coisa. Mas existe uma forma de se proteger desses corsários modernos. Atualmente, existe uma propriedade privada que NINGUÉM pode tirar de você, ela é sua até mesmo depois da morte. É claro que estamos falando do Bitcoin. Fazendo as configurações certas, é impossível saber que você tem bitcoin. Nem mesmo o governo americano consegue saber. #brasil #bitcoinbrasil #nostrbrasil #grownostr #bitcoin @ 7d33ba57:1b82db35
2025-03-28 20:59:51Krka National Park, located in central Dalmatia, is one of Croatia’s most breathtaking natural wonders. Famous for its stunning waterfalls, crystal-clear lakes, and lush forests, the park is a must-visit for nature lovers. Unlike Plitvice Lakes, Krka allows swimming in certain areas, making it a perfect summer escape.  ## **🌊 Top Things to See & Do in Krka National Park** ### **1️⃣ Skradinski Buk Waterfall 💦** - The **largest and most famous waterfall** in the park, with **cascading pools and wooden walkways**. - You **used to be able to swim here**, but since 2021, swimming is no longer allowed. - Perfect for **photography and picnics**. ### **2️⃣ Roški Slap Waterfall 🌿** - A **less crowded but equally beautiful** series of waterfalls. - Known for its **"necklace" of small cascades** leading into the main fall. - Nearby **Mlinica**, a restored **watermill**, shows traditional Croatian life. ### **3️⃣ Visovac Island & Monastery 🏝️** - A **tiny island** in the middle of the Krka River, home to a **Franciscan monastery** from the 15th century. - Accessible by **boat tour** from Skradinski Buk or Roški Slap. - A peaceful, scenic spot with **stunning views of the lake**.  ### **4️⃣ Krka Monastery 🏛️** - A **Serbian Orthodox monastery** hidden deep in the park. - Built on **ancient Roman catacombs**, which you can explore. - A **quiet, spiritual place**, often overlooked by tourists. ### **5️⃣ Hike & Walk the Nature Trails 🥾** - The park has **several well-marked trails** through forests, waterfalls, and lakes. - Wooden walkways allow **easy access** to the main sights. - **Wildlife spotting**: Look out for **otters, turtles, and over 200 bird species**! ### **6️⃣ Swim at Skradin Beach 🏖️** - While you can’t swim at Skradinski Buk anymore, **Skradin Beach**, just outside the park, is a great spot for a dip. - **Kayaking and boat tours** available.  ## **🚗 How to Get to Krka National Park** ✈️ **By Air:** The nearest airport is **Split (SPU), 1 hour away**. 🚘 **By Car:** - **Split to Krka:** ~1 hour (85 km) - **Zadar to Krka:** ~1 hour (75 km) - **Dubrovnik to Krka:** ~3.5 hours (280 km) 🚌 **By Bus:** Direct buses from **Split, Zadar, and Šibenik** to the park’s entrances. 🚢 **By Boat:** From **Skradin**, you can take a **boat ride** into the park.  ## **💡 Tips for Visiting Krka National Park** ✅ **Best time to visit?** **Spring & early autumn (April–June, September–October)** – Fewer crowds & mild weather 🍃 ✅ **Start early!** **Arrive before 10 AM** to avoid crowds, especially in summer ☀️ ✅ **Bring water & snacks** – Limited food options inside the park 🍎 ✅ **Wear comfy shoes** – Wooden walkways & trails can be slippery 👟 ✅ **Take a boat tour** – The best way to see Visovac Island & hidden spots ⛵ ✅ **Buy tickets online** – Save time at the entrance 🎟️ 
@ 7d33ba57:1b82db35
2025-03-28 20:59:51Krka National Park, located in central Dalmatia, is one of Croatia’s most breathtaking natural wonders. Famous for its stunning waterfalls, crystal-clear lakes, and lush forests, the park is a must-visit for nature lovers. Unlike Plitvice Lakes, Krka allows swimming in certain areas, making it a perfect summer escape.  ## **🌊 Top Things to See & Do in Krka National Park** ### **1️⃣ Skradinski Buk Waterfall 💦** - The **largest and most famous waterfall** in the park, with **cascading pools and wooden walkways**. - You **used to be able to swim here**, but since 2021, swimming is no longer allowed. - Perfect for **photography and picnics**. ### **2️⃣ Roški Slap Waterfall 🌿** - A **less crowded but equally beautiful** series of waterfalls. - Known for its **"necklace" of small cascades** leading into the main fall. - Nearby **Mlinica**, a restored **watermill**, shows traditional Croatian life. ### **3️⃣ Visovac Island & Monastery 🏝️** - A **tiny island** in the middle of the Krka River, home to a **Franciscan monastery** from the 15th century. - Accessible by **boat tour** from Skradinski Buk or Roški Slap. - A peaceful, scenic spot with **stunning views of the lake**.  ### **4️⃣ Krka Monastery 🏛️** - A **Serbian Orthodox monastery** hidden deep in the park. - Built on **ancient Roman catacombs**, which you can explore. - A **quiet, spiritual place**, often overlooked by tourists. ### **5️⃣ Hike & Walk the Nature Trails 🥾** - The park has **several well-marked trails** through forests, waterfalls, and lakes. - Wooden walkways allow **easy access** to the main sights. - **Wildlife spotting**: Look out for **otters, turtles, and over 200 bird species**! ### **6️⃣ Swim at Skradin Beach 🏖️** - While you can’t swim at Skradinski Buk anymore, **Skradin Beach**, just outside the park, is a great spot for a dip. - **Kayaking and boat tours** available.  ## **🚗 How to Get to Krka National Park** ✈️ **By Air:** The nearest airport is **Split (SPU), 1 hour away**. 🚘 **By Car:** - **Split to Krka:** ~1 hour (85 km) - **Zadar to Krka:** ~1 hour (75 km) - **Dubrovnik to Krka:** ~3.5 hours (280 km) 🚌 **By Bus:** Direct buses from **Split, Zadar, and Šibenik** to the park’s entrances. 🚢 **By Boat:** From **Skradin**, you can take a **boat ride** into the park.  ## **💡 Tips for Visiting Krka National Park** ✅ **Best time to visit?** **Spring & early autumn (April–June, September–October)** – Fewer crowds & mild weather 🍃 ✅ **Start early!** **Arrive before 10 AM** to avoid crowds, especially in summer ☀️ ✅ **Bring water & snacks** – Limited food options inside the park 🍎 ✅ **Wear comfy shoes** – Wooden walkways & trails can be slippery 👟 ✅ **Take a boat tour** – The best way to see Visovac Island & hidden spots ⛵ ✅ **Buy tickets online** – Save time at the entrance 🎟️  @ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde. Heute ist ein ganz besonderer Tag: die **Wintersonnenwende**. Genau gesagt hat [heute morgen](https://www.timeanddate.de/astronomie/wintersonnenwende) um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben. Für mich ist dieses Ereignis immer wieder etwas kurios: **Es beginnt der Winter, aber die Tage werden länger.** Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller! Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr [vorgesehen](https://web.archive.org/web/20231202175946/https://www.spiegel.de/wissenschaft/mensch/winter-ade-nie-wieder-schnee-a-71456.html). Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt [lahmgelegt](https://web.archive.org/web/20231207014311/https://www.dw.com/de/nach-dem-schnee-in-deutschland-und-dem-chaos-am-flughafen-und-bei-der-bahn-ein-winteralptraum/a-67638141). Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert. Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. **Ohne Licht keine Farben**, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität. Mir gefällt aber auch die **Symbolik dieses Tages**: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie. 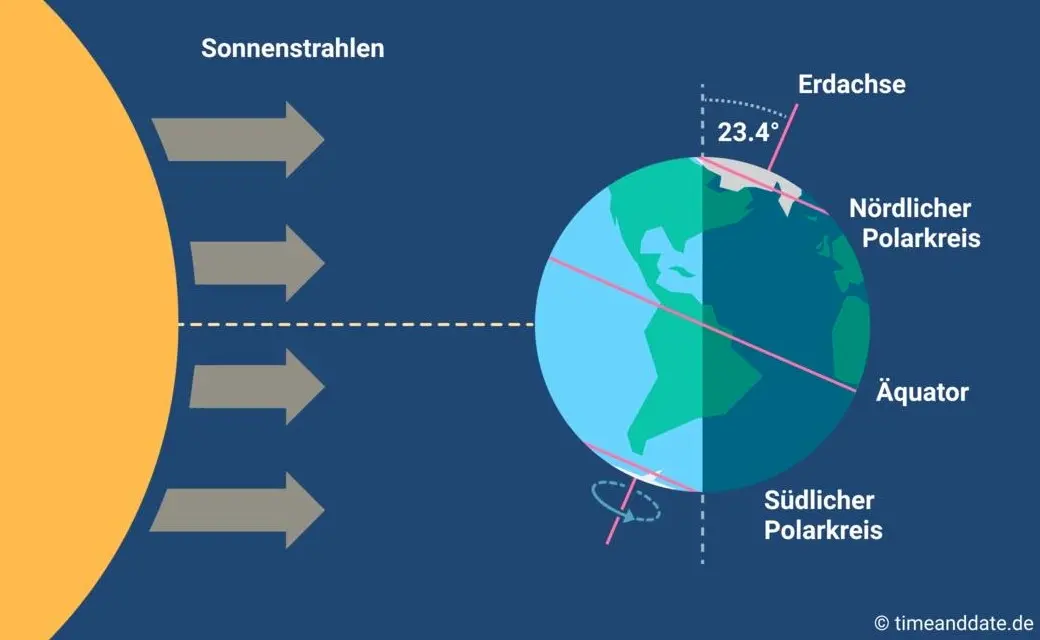 Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell? Insofern bleibt eindeutig festzuhalten, dass “**schräg sein**” ein willkommener, wichtiger und positiver Wert ist. Mit [anderen](https://www.dwds.de/wb/schr%C3%A4g) Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein. **In diesem Sinne wünsche ich euch allen urige Weihnachtstage!** *** Dieser Beitrag ist letztes Jahr in meiner *[Denkbar](https://denkbar.substack.com/p/ab-jetzt-gehts-bergauf)* erschienen.
@ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde. Heute ist ein ganz besonderer Tag: die **Wintersonnenwende**. Genau gesagt hat [heute morgen](https://www.timeanddate.de/astronomie/wintersonnenwende) um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben. Für mich ist dieses Ereignis immer wieder etwas kurios: **Es beginnt der Winter, aber die Tage werden länger.** Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller! Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr [vorgesehen](https://web.archive.org/web/20231202175946/https://www.spiegel.de/wissenschaft/mensch/winter-ade-nie-wieder-schnee-a-71456.html). Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt [lahmgelegt](https://web.archive.org/web/20231207014311/https://www.dw.com/de/nach-dem-schnee-in-deutschland-und-dem-chaos-am-flughafen-und-bei-der-bahn-ein-winteralptraum/a-67638141). Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert. Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. **Ohne Licht keine Farben**, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität. Mir gefällt aber auch die **Symbolik dieses Tages**: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie. 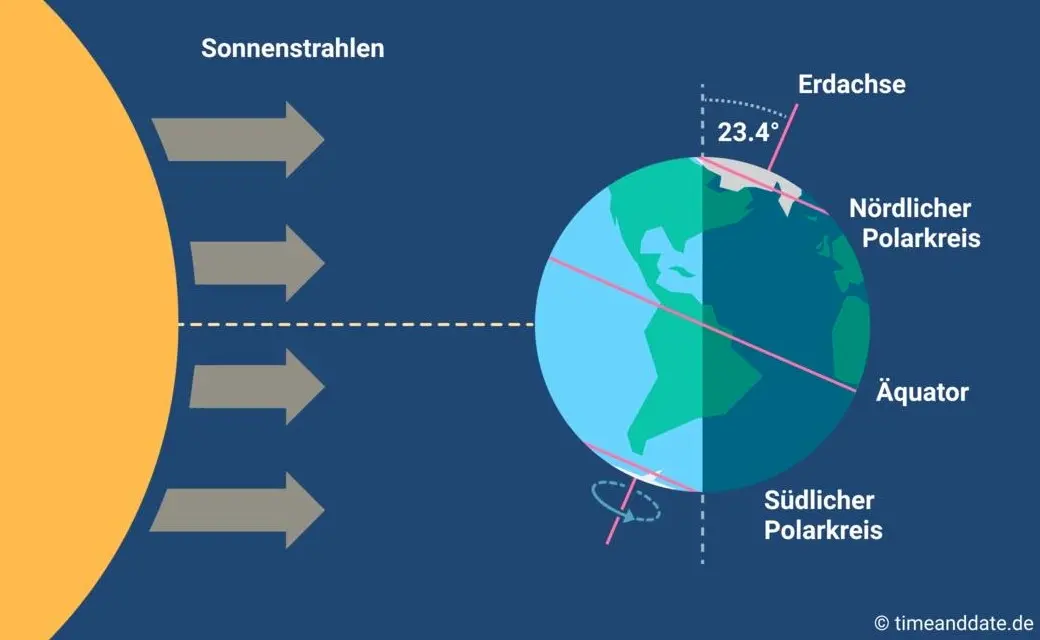 Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell? Insofern bleibt eindeutig festzuhalten, dass “**schräg sein**” ein willkommener, wichtiger und positiver Wert ist. Mit [anderen](https://www.dwds.de/wb/schr%C3%A4g) Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein. **In diesem Sinne wünsche ich euch allen urige Weihnachtstage!** *** Dieser Beitrag ist letztes Jahr in meiner *[Denkbar](https://denkbar.substack.com/p/ab-jetzt-gehts-bergauf)* erschienen. @ 0d6c8388:46488a33
2025-03-28 16:24:00Huge thank you to [OpenSats for the grant](https://opensats.org/blog/10th-wave-of-nostr-grants) to work on [Hypernote this year](https://www.hypernote.club/)! I thought I'd take this opportunity to try and share my thought processes for Hypernote. If this all sounds very dense or irrelevant to you I'm sorry! === How can the ideas of "hypermedia" benefit nostr? That's the goal of hypernote. To take the best ideas from "hypertext" and "hypercard" and "hypermedia systems" and apply them to nostr in a specifically nostr-ey way. ### 1. What do we mean by hypermedia A hypermedia document embeds the methods of interaction (links, forms, and buttons are the most well-known hypermedia controls) within the document itself. It's including the _how_ with the _what_. This is how the old web worked. An HTML page was delivered to the web browser, and it included in it a link or perhaps a form that could be submitted to obtain a new, different HTML page. This is how the whole web worked early on! Forums and GeoCities and eBay and MySpace and Yahoo! and Amazon and Google all emerged inside this paradigm. A web browser in this paradigm was a "thin" client which rendered the "thick" application defined in the HTML (and, implicitly, was defined by the server that would serve that HTML). Contrast this with modern app development, where the _what_ is usually delivered in the form of JSON, and then HTML combined with JavaScript (React, Svelte, Angular, Vue, etc.) is devised to render that JSON as a meaningful piece of hypermedia within the actual browser, the _how_. The browser remains a "thin" client in this scenario, but now the application is delivered in two stages: a client application of HTML and JavaScript, and then the actual JSON data that will hydrate that "application". (Aside: it's interesting how much "thicker" the browser has had to become to support this newer paradigm!) Nostr was obviously built in line with the modern paradigm: nostr "clients" (written in React or Svelte or as mobile apps) define the _how_ of reading and creating nostr events, while nostr events themselves (JSON data) simply describe the _what_. And so the goal with Hypernote is to square this circle somehow: nostr currently delivers JSON _what_, how do we deliver the _how_ with nostr as well. Is that even possible? ### 2. Hypernote's design assumptions Hypernote assumes that hypermedia over nostr is a good idea! I'm expecting some joyful renaissance of app expression similar to that of the web once we figure out how to express applications in a truly "nostr" way. Hypernote was also [deeply inspired by HTMX](https://hypermedia.systems/hypermedia-a-reintroduction/), so it assumes that building web apps in the HTMX style is a good idea. The HTMX insight is that instead of shipping rich scripting along with your app, you could simply make HTML a _tiny_ bit more expressive and get 95% of what most apps need. HTMX's additions to the HTML language are designed to be as minimal and composable as possible, and Hypernote should have the same aims. Hypernote also assumes that the "design" of nostr will remain fluid and anarchic for years to come. There will be no "canonical" list of "required" NIPs that we'll have "consensus" on in order to build stable UIs on top of. Hypernote will need to be built responsive to nostr's moods and seasons, rather than one holy spec. Hypernote likes the `nak` command line tool. Hypernote likes markdown. Hypernote likes Tailwind CSS. Hypernote likes SolidJS. Hypernote likes cold brew coffee. Hypernote is, to be perfectly honest, my aesthetic preferences applied to my perception of an opportunity in the nostr ecosystem. ### 3. "What's a hypernote?" Great question. I'm still figuring this out. Everything right now is subject to change in order to make sure hypernote serves its intended purpose. But here's where things currently stand: A hypernote is a flat list of "Hypernote Elements". A Hypernote Element is composed of: 1. CONTENT. Static or dynamic content. (the what) 2. LOGIC. Filters and events (the how) 3. STYLE. Optional, inline style information specific to this element's content. In the most basic example of a [hypernote story](https://hypernote-stories.fly.dev/), here's a lone "edit me" in the middle of the canvas:  ``` { "id": "fb4aaed4-bf95-4353-a5e1-0bb64525c08f", "type": "text", "text": "edit me", "x": 540, "y": 960, "size": "md", "color": "black" } ``` As you can see, it has no logic, but it does have some content (the text "edit me") and style (the position, size, and color). Here's a "sticker" that displays a note: ``` { "id": "2cd1ef51-3356-408d-b10d-2502cbb8014e", "type": "sticker", "stickerType": "note", "filter": { "kinds": [ 1 ], "ids": [ "92de77507a361ab2e20385d98ff00565aaf3f80cf2b6d89c0343e08166fed931" ], "limit": 1 }, "accessors": [ "content", "pubkey", "created_at" ], "x": 540, "y": 960, "associatedData": {} } ``` As you can see, it's kind of a mess! The content and styling and underdeveloped for this "sticker", but at least it demonstrates some "logic": a nostr filter for getting its data. Here's another sticker, this one displays a form that the user can interact with to SEND a note. Very hyper of us! ``` { "id": "42240d75-e998-4067-b8fa-9ee096365663", "type": "sticker", "stickerType": "prompt", "filter": {}, "accessors": [], "x": 540, "y": 960, "associatedData": { "promptText": "What's your favorite color?" }, "methods": { "comment": { "description": "comment", "eventTemplate": { "kind": 1111, "content": "${content}", "tags": [ [ "E", "${eventId}", "", "${pubkey}" ], [ "K", "${eventKind}" ], [ "P", "${pubkey}" ], [ "e", "${eventId}", "", "${pubkey}" ], [ "k", "${eventKind}" ], [ "p", "${pubkey}" ] ] } } } } ``` It's also a mess, but it demos the other part of "logic": methods which produce new events. This is the total surface of hypernote, ideally! Static or dynamic content, simple inline styles, and logic for fetching and producing events. I'm calling it "logic" but it's purposfully not a whole scripting language. At most we'll have some sort of `jq`-like language for destructing the relevant piece of data we want. My ideal syntax for a hypernote as a developer will look something like ```foo.hypernote Nak-like logic Markdown-like content CSS-like styles ``` But with JSON as the compile target, this can just be my own preference, there can be other (likely better!) ways of authoring this content, such as a Hypernote Stories GUI. ### The end I know this is all still vague but I wanted to get some ideas out in the wild so people understand the through line of my different Hypernote experiments. I want to get the right amount of "expressivity" in Hypernote before it gets locked down into one spec. My hunch is it can be VERY expressive while remaining simple and also while not needing a whole scripting language bolted onto it. If I can't pull it off I'll let you know.
@ 0d6c8388:46488a33
2025-03-28 16:24:00Huge thank you to [OpenSats for the grant](https://opensats.org/blog/10th-wave-of-nostr-grants) to work on [Hypernote this year](https://www.hypernote.club/)! I thought I'd take this opportunity to try and share my thought processes for Hypernote. If this all sounds very dense or irrelevant to you I'm sorry! === How can the ideas of "hypermedia" benefit nostr? That's the goal of hypernote. To take the best ideas from "hypertext" and "hypercard" and "hypermedia systems" and apply them to nostr in a specifically nostr-ey way. ### 1. What do we mean by hypermedia A hypermedia document embeds the methods of interaction (links, forms, and buttons are the most well-known hypermedia controls) within the document itself. It's including the _how_ with the _what_. This is how the old web worked. An HTML page was delivered to the web browser, and it included in it a link or perhaps a form that could be submitted to obtain a new, different HTML page. This is how the whole web worked early on! Forums and GeoCities and eBay and MySpace and Yahoo! and Amazon and Google all emerged inside this paradigm. A web browser in this paradigm was a "thin" client which rendered the "thick" application defined in the HTML (and, implicitly, was defined by the server that would serve that HTML). Contrast this with modern app development, where the _what_ is usually delivered in the form of JSON, and then HTML combined with JavaScript (React, Svelte, Angular, Vue, etc.) is devised to render that JSON as a meaningful piece of hypermedia within the actual browser, the _how_. The browser remains a "thin" client in this scenario, but now the application is delivered in two stages: a client application of HTML and JavaScript, and then the actual JSON data that will hydrate that "application". (Aside: it's interesting how much "thicker" the browser has had to become to support this newer paradigm!) Nostr was obviously built in line with the modern paradigm: nostr "clients" (written in React or Svelte or as mobile apps) define the _how_ of reading and creating nostr events, while nostr events themselves (JSON data) simply describe the _what_. And so the goal with Hypernote is to square this circle somehow: nostr currently delivers JSON _what_, how do we deliver the _how_ with nostr as well. Is that even possible? ### 2. Hypernote's design assumptions Hypernote assumes that hypermedia over nostr is a good idea! I'm expecting some joyful renaissance of app expression similar to that of the web once we figure out how to express applications in a truly "nostr" way. Hypernote was also [deeply inspired by HTMX](https://hypermedia.systems/hypermedia-a-reintroduction/), so it assumes that building web apps in the HTMX style is a good idea. The HTMX insight is that instead of shipping rich scripting along with your app, you could simply make HTML a _tiny_ bit more expressive and get 95% of what most apps need. HTMX's additions to the HTML language are designed to be as minimal and composable as possible, and Hypernote should have the same aims. Hypernote also assumes that the "design" of nostr will remain fluid and anarchic for years to come. There will be no "canonical" list of "required" NIPs that we'll have "consensus" on in order to build stable UIs on top of. Hypernote will need to be built responsive to nostr's moods and seasons, rather than one holy spec. Hypernote likes the `nak` command line tool. Hypernote likes markdown. Hypernote likes Tailwind CSS. Hypernote likes SolidJS. Hypernote likes cold brew coffee. Hypernote is, to be perfectly honest, my aesthetic preferences applied to my perception of an opportunity in the nostr ecosystem. ### 3. "What's a hypernote?" Great question. I'm still figuring this out. Everything right now is subject to change in order to make sure hypernote serves its intended purpose. But here's where things currently stand: A hypernote is a flat list of "Hypernote Elements". A Hypernote Element is composed of: 1. CONTENT. Static or dynamic content. (the what) 2. LOGIC. Filters and events (the how) 3. STYLE. Optional, inline style information specific to this element's content. In the most basic example of a [hypernote story](https://hypernote-stories.fly.dev/), here's a lone "edit me" in the middle of the canvas:  ``` { "id": "fb4aaed4-bf95-4353-a5e1-0bb64525c08f", "type": "text", "text": "edit me", "x": 540, "y": 960, "size": "md", "color": "black" } ``` As you can see, it has no logic, but it does have some content (the text "edit me") and style (the position, size, and color). Here's a "sticker" that displays a note: ``` { "id": "2cd1ef51-3356-408d-b10d-2502cbb8014e", "type": "sticker", "stickerType": "note", "filter": { "kinds": [ 1 ], "ids": [ "92de77507a361ab2e20385d98ff00565aaf3f80cf2b6d89c0343e08166fed931" ], "limit": 1 }, "accessors": [ "content", "pubkey", "created_at" ], "x": 540, "y": 960, "associatedData": {} } ``` As you can see, it's kind of a mess! The content and styling and underdeveloped for this "sticker", but at least it demonstrates some "logic": a nostr filter for getting its data. Here's another sticker, this one displays a form that the user can interact with to SEND a note. Very hyper of us! ``` { "id": "42240d75-e998-4067-b8fa-9ee096365663", "type": "sticker", "stickerType": "prompt", "filter": {}, "accessors": [], "x": 540, "y": 960, "associatedData": { "promptText": "What's your favorite color?" }, "methods": { "comment": { "description": "comment", "eventTemplate": { "kind": 1111, "content": "${content}", "tags": [ [ "E", "${eventId}", "", "${pubkey}" ], [ "K", "${eventKind}" ], [ "P", "${pubkey}" ], [ "e", "${eventId}", "", "${pubkey}" ], [ "k", "${eventKind}" ], [ "p", "${pubkey}" ] ] } } } } ``` It's also a mess, but it demos the other part of "logic": methods which produce new events. This is the total surface of hypernote, ideally! Static or dynamic content, simple inline styles, and logic for fetching and producing events. I'm calling it "logic" but it's purposfully not a whole scripting language. At most we'll have some sort of `jq`-like language for destructing the relevant piece of data we want. My ideal syntax for a hypernote as a developer will look something like ```foo.hypernote Nak-like logic Markdown-like content CSS-like styles ``` But with JSON as the compile target, this can just be my own preference, there can be other (likely better!) ways of authoring this content, such as a Hypernote Stories GUI. ### The end I know this is all still vague but I wanted to get some ideas out in the wild so people understand the through line of my different Hypernote experiments. I want to get the right amount of "expressivity" in Hypernote before it gets locked down into one spec. My hunch is it can be VERY expressive while remaining simple and also while not needing a whole scripting language bolted onto it. If I can't pull it off I'll let you know. @ a95c6243:d345522c
2024-12-13 19:30:32*Das Betriebsklima ist das einzige Klima,* \ *das du selbst bestimmen kannst.* \ *Anonym* **Eine Strategie zur Anpassung an den Klimawandel** hat das deutsche Bundeskabinett diese Woche [beschlossen](https://www.bundesregierung.de/breg-de/aktuelles/klimaanpassungsstrategie-2024-2324828). Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das.  **Für die «Vorsorge vor Klimafolgen» habe man nun erstmals** klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der [Erwärmung](https://transition-news.org/studie-ozeane-kuhlen-die-erde-viel-starker-als-gedacht) ja bekanntermaßen so eine Sache. **Die Zunahme schwerer Unwetterereignisse habe gezeigt,** so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben. **Die** ***ARD*** **spurt wie gewohnt** und setzt die Botschaft zielsicher um. Der Artikel [beginnt](https://www.tagesschau.de/inland/innenpolitik/klima-anpassung-warnapp-100.html) folgendermaßen: > «Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.» **Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen»** vom Zentrum KlimaAnpassung [unterstützt](https://zentrum-klimaanpassung.de/ueber-uns), schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für [Smart City-Projekte](https://difu.de/taxonomy/term/2083) engagiert, und die Adelphi Consult GmbH beauftragt. **Adelphi** **[beschreibt](https://adelphi.de/de)** **sich selbst als «Europas führender Think-and-Do-Tank** und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg\*innen und weltverbessernde Berater\*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere. **Über die** **[Warn-App](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/warn-app-nina_node.html)** **mit dem niedlichen Namen Nina,** die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche. **Beim BBK erfahren wir auch einiges über die empfohlenen** **[Systemeinstellungen](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/Einstellungen-Android/einstellungen-android_node.html)** für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden. **Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann** als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen [Valencia](https://transition-news.org/valencia-zehn-tage-nach-der-katastrophe-warten-viele-menschen-immer-noch-auf) gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat. *** Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/vorsorge-vor-klimafolgen)* erschienen.
@ a95c6243:d345522c
2024-12-13 19:30:32*Das Betriebsklima ist das einzige Klima,* \ *das du selbst bestimmen kannst.* \ *Anonym* **Eine Strategie zur Anpassung an den Klimawandel** hat das deutsche Bundeskabinett diese Woche [beschlossen](https://www.bundesregierung.de/breg-de/aktuelles/klimaanpassungsstrategie-2024-2324828). Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das.  **Für die «Vorsorge vor Klimafolgen» habe man nun erstmals** klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der [Erwärmung](https://transition-news.org/studie-ozeane-kuhlen-die-erde-viel-starker-als-gedacht) ja bekanntermaßen so eine Sache. **Die Zunahme schwerer Unwetterereignisse habe gezeigt,** so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben. **Die** ***ARD*** **spurt wie gewohnt** und setzt die Botschaft zielsicher um. Der Artikel [beginnt](https://www.tagesschau.de/inland/innenpolitik/klima-anpassung-warnapp-100.html) folgendermaßen: > «Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.» **Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen»** vom Zentrum KlimaAnpassung [unterstützt](https://zentrum-klimaanpassung.de/ueber-uns), schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für [Smart City-Projekte](https://difu.de/taxonomy/term/2083) engagiert, und die Adelphi Consult GmbH beauftragt. **Adelphi** **[beschreibt](https://adelphi.de/de)** **sich selbst als «Europas führender Think-and-Do-Tank** und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg\*innen und weltverbessernde Berater\*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere. **Über die** **[Warn-App](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/warn-app-nina_node.html)** **mit dem niedlichen Namen Nina,** die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche. **Beim BBK erfahren wir auch einiges über die empfohlenen** **[Systemeinstellungen](https://www.bbk.bund.de/DE/Warnung-Vorsorge/Warn-App-NINA/Einstellungen-Android/einstellungen-android_node.html)** für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden. **Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann** als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen [Valencia](https://transition-news.org/valencia-zehn-tage-nach-der-katastrophe-warten-viele-menschen-immer-noch-auf) gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat. *** Dieser Beitrag ist zuerst auf *[Transition News](https://transition-news.org/vorsorge-vor-klimafolgen)* erschienen.