-
 @ 08964cb5:51bf010f
2025-05-01 10:32:52
@ 08964cb5:51bf010f
2025-05-01 10:32:52«Reflexiones y Acción: Entre la Defensa del Patrimonio»
[English below][Deutsch unten]
Los recientes acontecimientos que han puesto en peligro mi patrimonio, así como los valores fundamentales que definen mi camino, me han llevado a tomar una decisión importante: iniciar una campaña de recaudación de fondos. Esta iniciativa no solo busca proteger lo que he construido con esfuerzo, sino también garantizar que pueda seguir adelante con proyectos y principios que son esenciales para mí.
Tu apoyo puede marcar una gran diferencia. Si deseas conocer más sobre esta causa o contribuir con tu solidaridad, te invito a visitar ›🔗 éste enlace.‹ "Reflections and Action: Safeguarding My Heritage"
“Reflections and Action: Safeguarding My Heritage”
The recent events that have jeopardised my assets and the core values that define my journey have led me to take a significant step: launching a fundraising campaign. This initiative aims not only to protect what I have built with hard work but also to ensure that I can continue moving forward with projects and principles that are essential to me.
Your support can make a real difference. If you’d like to learn more about this cause or contribute with your solidarity, I invite you to visit ›🔗 this link.‹
„Überlegungen und Handeln: Den Schutz meines Vermögens”
Die jüngsten Ereignisse, die mein Vermögen sowie die grundlegenden Werte, die meinen Weg bestimmen, gefährdet haben, haben mich dazu veranlasst, einen wichtigen Schritt zu gehen: den Start einer Spendenkampagne. Diese Initiative zielt nicht nur darauf ab, das zu schützen, was ich mit harter Arbeit aufgebaut habe, sondern auch sicherzustellen, dass ich mit Projekten und Prinzipien, die für mich unerlässlich sind, weitermachen kann.
Deine Unterstützung kann einen großen Unterschied machen. Wenn du mehr über diese Sache erfahren oder mit deiner Solidarität beitragen möchtest, lade ich dich ein, ›🔗 diesen Link zu besuchen.‹
-
 @ 08964cb5:51bf010f
2025-05-01 10:14:41
@ 08964cb5:51bf010f
2025-05-01 10:14:41«Reflexiones y Acción: Entre la Defensa del Patrimonio»
[English below][Deutsch unten]
Los recientes acontecimientos que han puesto en peligro mi patrimonio, así como los valores fundamentales que definen mi camino, me han llevado a tomar una decisión importante: iniciar una campaña de recaudación de fondos. Esta iniciativa no solo busca proteger lo que he construido con esfuerzo, sino también garantizar que pueda seguir adelante con proyectos y principios que son esenciales para mí.
Tu apoyo puede marcar una gran diferencia. Si deseas conocer más sobre esta causa o contribuir con tu solidaridad, te invito a visitar ›🔗éste enlace.‹
"Reflections and Action: Safeguarding My Heritage"
The recent events that have jeopardised my assets and the core values that define my journey have led me to take a significant step: launching a fundraising campaign. This initiative aims not only to protect what I have built with hard work but also to ensure that I can continue moving forward with projects and principles that are essential to me.
Your support can make a real difference. If you’d like to learn more about this cause or contribute with your solidarity, I invite you to visit ›🔗this link.‹
"Überlegungen und Handeln: Den Schutz meines Vermögens"
Die jüngsten Ereignisse, die mein Vermögen sowie die grundlegenden Werte, die meinen Weg bestimmen, gefährdet haben, haben mich dazu veranlasst, einen wichtigen Schritt zu gehen: den Start einer Spendenkampagne. Diese Initiative zielt nicht nur darauf ab, das zu schützen, was ich mit harter Arbeit aufgebaut habe, sondern auch sicherzustellen, dass ich mit Projekten und Prinzipien, die für mich unerlässlich sind, weitermachen kann.
Deine Unterstützung kann einen großen Unterschied machen. Wenn du mehr über diese Sache erfahren oder mit deiner Solidarität beitragen möchtest, lade ich dich ein, ›🔗diesen Link zu besuchen.‹
-
 @ 2b24a1fa:17750f64
2025-05-01 08:26:05
@ 2b24a1fa:17750f64
2025-05-01 08:26:05Ein Gedicht unserer Zeit von Lionne Douce.
Sprecherin: Sabrina Khalil
https://soundcloud.com/radiomuenchen/der-gutmenschzug-ist-da-von?
-
 @ e7bc35f8:3ed2a7cf
2025-05-01 08:19:56
@ e7bc35f8:3ed2a7cf
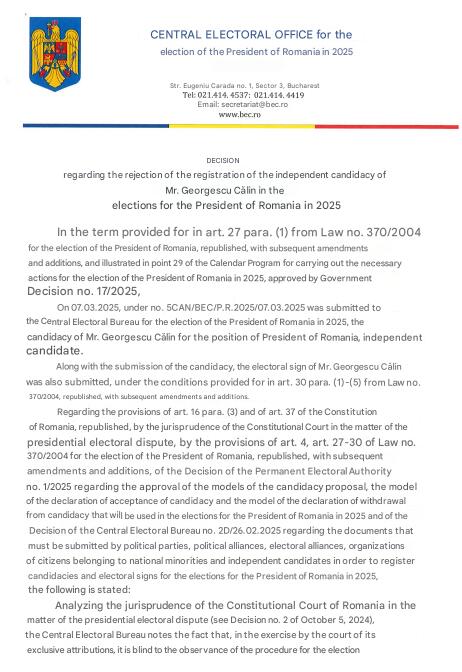
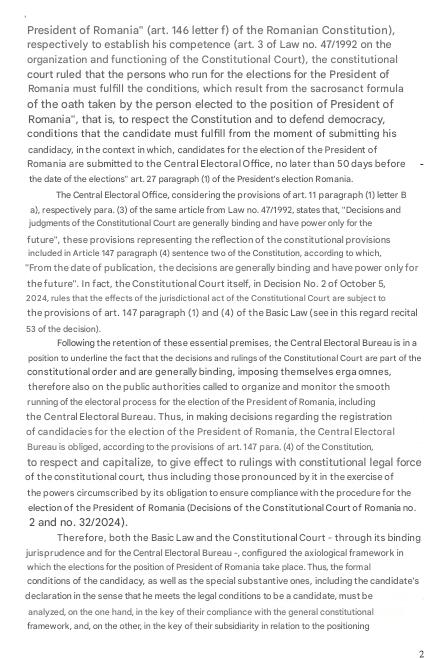
2025-05-01 08:19:56In the heart of Romania’s 2024 presidential election, a seismic shock rattled the foundations of its democracy. Just days before the final runoff, the Constitutional Court made an unprecedented move: it annulled the entire election, citing evidence of Russian interference that propelled a far-right nationalist, Călin Georgescu, to a surprise lead. Was this a bold reflex to safeguard democratic integrity against foreign manipulation, or a chilling cancellation of the people’s voice, silencing millions who had cast their ballots? As Romania grapples with this historic decision, the line between protecting democracy and undermining it has never been blurrier, leaving citizens and observers alike questioning the true cost of this electoral upheaval.
In this article, I will explore Romania’s 2024 presidential election annulment chronologically, tracing the rise of far-right candidate Călin Georgescu, the Constitutional Court’s decision to cancel the vote on December 6, and the resulting protests and probes into foreign interference. This timeline will clarify whether the move was a democratic safeguard or an undemocratic suppression of the people’s will.
October 15, 2024
Judges booted candidate Diana Șoșoacă, leader of the ultra-nationalist party S.O.S Romania, from the race because she threatened Bucharest’s place in the EU and NATO. But her rivals are saying the court overstepped its remit.
The unprecedented ruling by the Constitutional Court of Romania (CCR) sparked criticism from Șoșoacă’s rivals across the political spectrum, encompassing socialists, liberals and academics — with one figure even pointing to how it echoes the Kremlin’s electoral governance.
November 22, 2024
The final major poll before Romania’s 2024 presidential election, released on the eve of the vote, painted a starkly different picture from the eventual outcome. Prime Minister Marcel Ciolacu led with 23.7%, followed by Elena Lasconi at 17.8%, George Simion at 16.9%, and Nicolae Ciucă at 14.3%. Astonishingly, Călin Georgescu, who would later surge to a stunning first-round victory, languished in fifth place with just 8.1%, a staggering underestimation that would soon fuel suspicions of manipulation and upend the nation’s electoral process.

November 24, 2024
In a stunning upset, Călin Georgescu won Romania’s 2024 presidential election with 22.94% of the vote, dominating the first round despite trailing in pre-election polls. George Simion, often labeled the country’s “hard right chief” by Western media, lagged behind in fourth place with just 13.8%. No credible evidence suggests vote tampering; Georgescu’s victory reflected a genuine surge of voter support, particularly among the diaspora, where he won overwhelmingly—except in Moldova, where he secured only 3.11% amid a large pro-Russian population that had narrowly passed a pro-EU referendum a month earlier.
As regards Georgescu himself, by CV, appearance and speaking style he comes across as the ideal candidate. He studied agronomy, has a PhD in soil science and is a university lecturer; has worked at senior levels in government – including in the Ministry of Foreign Affairs – as well as at the UN and other NGOs, with a focus on sustainable development; and he speaks four foreign languages. He projects a professional, clean-cut image of a determined, experienced 62 year-old nationalist at the apex of his powers, speaking very simply and clearly in a calm, confident manner. Strictly by these superficial PR metrics, on paper, he is, at first glance, perfectly suited for the role.
Nor is he unknown in Romanian politics; but he is – or has been – a very fringe figure. His name was floated several times in recent years, in nationalist-populist circles, as a potential alternative for prime minister. He nearly became honorary president of Romania’s main nationalist conservative party, AUR, before the deal fell through when past comments came to light in which he had called the country’s Second World War leader and Axis ally, Marshal Antonescu – who is considered responsible for the Romanian Holocaust – a “hero”.
Georgescu had conducted a persuasive online campaign, primarily on TikTok, focusing on the importance of an autochthon economy, the inherent superiority of rural life in Romania, and essentially claiming that just like a national poet from the 19th century, he is a divine messenger. The campaign consisted of thousands of TikTok profiles distributing ten-second videos about him, with many influencers suggesting in the past weeks that they would vote for him. According to Georgescu, he didn’t spend any money on the campaign, but the scale and the professionalism in which it was conducted suggest otherwise.
November 25, 2024
Politico comes to remind us why EU is so interested about Romania. According to this article, Romania has been a steadfast ally in the West’s support for Ukraine, leveraging the Port of Constanța as a critical lifeline for exporting Ukrainian grain and funneling military supplies into the conflict zone. The war has also elevated the strategic significance of the Mihail Kogălniceanu air base on the Black Sea, poised to become NATO’s largest. However, Călin Georgescu’s unexpected electoral triumph raises alarms across Europe, as his leadership could pivot Romania away from this pro-Western stance, potentially disrupting these vital geopolitical roles. This prospect underscores why European leaders are deeply invested in ensuring Romania remains in “reliable” hands, aligned with NATO and EU priorities.
November 26, 2024
Reformist Elena Lasconi, who was going to face Georgescu in the runoff on Dec. 8, was directly warning that Romanians must now rally together to stop the country falling back under the thrall of Russia, which occupied it after World War II. She urged a crowd in Bucharest not to let frustration with the current establishment “become a vulnerability exploited by Russia.”

November 28, 2024
The official claim of Russian meddling rested directly and exclusively on a specific set of intelligence documents on the matter, first submitted in a closed National Security Council meeting on 28 November. Romania’s Constitutional Court asked the country’s top election authority to recount and check again all ballots from Sunday’s presidential election first round.
November 30, 2024
Elena Lasconi, who narrowly secured a runoff spot by edging out PSD Prime Minister Marcel Ciolacu by just 2,700 votes, has firmly rejected allegations of electoral misconduct. Lasconi and her party, USR, accuse the PSD and center-right PNL of undermining the people’s will through the annulment push. In a passionate statement, she urged, “I appeal to all state institutions: Don’t destroy democracy in Romania,” highlighting the high stakes for the nation’s democratic integrity.
December 4, 2024
The set of intelligence documents on the matter, first submitted in a closed National Security Council meeting on 28 November and then hastily declassified on 4 December by the sitting President in order to “inform” the Constitutional Court’s decision. But the reports contained no actual evidence of the sort.

The documents alleged that 800 TikTok accounts had been activated just before the election and that they had supported Călin Georgescu’s campaign.
Albeit these reports did not definitely say that the meddling effort managed to actually sway the election in Georgescu’s favour, they suggested it.
I ve translated the declassified documents using the AI tools: Grok and ChatGPT. I can assure you that the following summary from "Brussels Signal" is accurate. I will quote the summary because of the key importance on the subject:
The documents provide no concrete evidence of Russian state interference in Romania’s presidential elections or any links between presidential candidate Calin Georgescu and Russia.
The most important and explosive term used in these documents (by SRI) is “state actor.” The documents offer no evidence or analytical explanation for the use of this term, rendering it an unsupported claim.
On the contrary, to the extent that they shed light on anything, the documents indicate that Georgescu’s campaign simply employed highly effective digital marketing techniques, giving him a “comparative exponential” advantage (according to SRI).
The documents offer only disparate, circumstantial, and often trivial information presented in a way that leaves plenty of room for wide-ranging interpretations. Their tone and terminology appear designed to fuel an anti-Georgescu narrative in the public sphere.
As intelligence products, the documents are sloppy and of very poor quality by Allied standards. They include contradictions, errors, and blatant inaccuracies. The language is often vague, and key terms remain undefined (e.g., various uses of the word “network”). For the most part, the documents are full only of useless platitudes, with the majority of the information already having been circulating in the public domain in the days after 24 November (the date of the first voting round).
The documents are merely “Briefing Notes” (note informative, in Romanian), not assessments – thus lacking clear and definitive analytical conclusions or interpretations. They make isolated claims (mostly unsupported), with no discussion of sources or evidence. This is likely a method for the intelligence services to protect themselves politically. Subsequent interpretations of these documents by the media are not, therefore, based on conclusions of the Romanian state.
The documents are also redacted in key parts. It is therefore important to understand that the information in these documents was only partially declassified – despite the media narrative suggesting the documents were declassified in their entirety. It is also important to understand that the redacted passages may alter the meaning of the text.
The SIE Briefing Note has not actually been declassified. The President only published an “unclassified excerpt” from it. The SIE Note itself remains classified, likely because it contradicts the Notes submitted by the other agencies.
The documents do point to potential irregularities in Georgescu’s campaign finance statements. However, such issues are common in campaigns worldwide and, moreover, should be investigated with respect to all the other candidates as well, in the same way. In any case, the documents make no suggestion of foreign funding, let alone from Russia.
The only concrete elements noted in the documents as being specifically identified as of 24 November (the day of the vote in the first round) are: 100 TikTok influencer accounts paid to distribute content using 3 (three) hashtags that do not even mention Calin Georgescu; 797 accounts created before (!) the launch of TikTok itself, under this brand name; 1,088 users in a “coordination” group on Telegram (which, again, is standard in all political campaigns); and $381,000 paid to some “influencers”.
Conclusion: The CSAT documents declassified by the President provide absolutely no real, concrete basis for the public narratives about a “Russian attack” on Romania or of links between Georgescu’s campaign and Russia. These documents, by themselves, cannot rationally be used as arguments against this candidate because they prove nothing.
Shortly after the vote in a televised address President Iohannis claimed that the ‘campaign was illegally supported from outside Romania’ and that it is a ‘matter of national security’.
December 6, 2024
Romania’s top constitutional court dramatically cancelled high-stakes presidential elections after security services warned Russia was mounting “aggressive” hybrid attacks against the country. Călin Georgescu was accused to benefit from a TikTok campaign that was similar to influence operations allegedly run by the Kremlin in Ukraine and Moldova. The files said Moscow was targeting Romania as an enemy state, using “aggressive hybrid action,” a view backed by the United States, at that time.
Running as an independent, Georgescu was due to face liberal Elena Lasconi of the Save Romania Union (USR) in a Dec. 8 runoff. Suspicious of the two old parties, she is also calling on the court not to meddle with Romanian democracy. According to Radio Romania Actualitati, she said: ‘Today is the moment when the Romanian state has trampled on democracy,’ adding: ‘We should have gone ahead with the vote. We should have respected the will of the Romanian people, whether we like it or not; legally and legitimately, nine million Romanian citizens, both at home and in the diaspora, have expressed their preference for a particular candidate by voting. We cannot ignore their will.’
Elena Lasconi, a liberal—by Western standards, however, she might not be considered a typical liberal, as she openly expresses patriotism, displays the Romanian flag alongside the EU flag, and occasionally wears traditional folk costumes—former TV journalist. Lasconi, like Georgescu, is an anti-establishment figure, vocal in her criticism of the current political elite and adept at channelling voter discontent and frustration with mainstream parties. It is no surprise, then, that both the Social Democratic Party (PSD) and the National Liberal Party (PNL)—Romania’s two largest establishment parties—reacted with dismay to the performances of Georgescu and Lasconi. This discontent was amplified by the fact that neither party’s candidate came close to qualifying for a potential second round. Politicians from both the far right as well as liberal reformists Save Romania Union (USR) party view an annulment as an attempt by the widely distrusted old establishment parties — the Social Democratic Party (PSD) and the center-right National Liberal Party (PNL) — to hold on to power by pulling strings within the judiciary. Elena Lasconi, a liberal former TV journalist who was set to stand against Georgescu in the second round, was mortified by what she saw as a hijacking of the electoral process.
The court canceled the process completely, leaving voters bemused as they turned up to cast their ballots. In a defiant video released on Friday night, Georgescu accused the court of launching “practically a formalized coup d’état” and told his supporters to show they are “brave” and not to give up.
In fact, Georgescu was leading with as much as 77 per cent against Lasconi’s 23 per cent in the diaspora when Romania’s Constitutional Court decided to annul the elections.
The President, at that time, Klaus Iohannis was due to end his term on Dec. 21. But in an address to the nation Friday evening, he announced that he was going to stay on until the next president was about to sworn in.
Nicolae Ciucă, the head of the Romanian senate and the National Liberal Party’s presidential candidate in the first round said that The decision to cancel the vote was “without precedent in Romania’s democratic history,” he said, adding “the current situation is a difficult test for our democratic institutions.”
According to the press's findings, behind Georgescu there appears to have been an entire “network” of volunteers – often organised via Telegram – running thousands of co-ordinated TikTok accounts designed to boost each other’s posts – i.e. Georgescu’s short promo videos. TikTok has only relatively recently caught on in Romania; certainly it wasn’t a factor at the last election. This might explain why a strong TikTok campaign would not have registered properly in political analysis, and why it might’ve had an outsized effect on voting intentions. It is also a warning for the future of the very idea of democratic politics, as it shows that it is possible for candidates to completely side-step the traditional “public square”, avoid any major real-world debates or campaigning, and win elections exclusively online.
Still, there is a great deal of mystery over exactly how all this worked. Georgescu’s TikTok metrics are inferior to his three key adversaries for example: there were 145 million views this year for Georgescu’s main hashtags compared to 396 million for Simion’s, 328 million for Ciolacu and 202 million for Lasconi. One difference is that the bulk of Georgescu’s TikTok views and followers accrued within the past two months. Coupled with other indicators, it seems rather clear that so-called “troll farms” have been at work on his behalf, to spread his message; but it is not clear whether this practice is unique to Georgescu or whether it has been used – to varying degrees – by his opponents as well.
As Georgescu is perceived to be “pro-Russia” – an imprecise term to boot – suspicion in this regard is directed towards the Kremlin. But hard evidence is lacking; there is no smoking gun, so far. Russian actors are involved in virtually every election in the West, but their exact role in swinging the result is hardly ever clear. In the US a Congressional investigation – eventually known as the “Russia Hoax”, for good reason – failed to prove alleged collusion between Trump’s 2016 campaign and Moscow, despite widespread belief in this story from those shocked that “orange man” could ever win because his message was more effective.
The reaction from the EU and Washington was particularly alarming, though hardly surprising. ‘The integrity of Romania’s elections is paramount for Romanians’ hard-earned democracy. It is the choice of the Romanian people whom they elect. No other country or foreign actor has that right,’ the US State Department said in a statement. The contradiction is glaring, isn’t it? It’s supposedly the Romanians’ choice who they elect, yet if a candidate not favoured by the Americans wins, the election results are annulled.
Moscow denied meddling into the Romanian democratic process.
December 20, 2024
According to a Snoop (investigative journalist organization) investigation, Georgescu’s alleged financing would have been done by the PNL. ** All this, so that Georgescu’s message would spread and more people could vote for him so that George Simion would not make it to the second round. ** In fact, the ANAF (National Agency for Tax Administration) discovered that the PNL paid for a campaign massively promoting Călin Georgescu on TikTok, published on 20 December 2024.
December 22, 2024
Subsequent investigations by the National Agency for Fiscal Administration (ANAF), Romania’s tax authority, uncovered the origins of Călin Georgescu’s successful TikTok campaign: the PNL. The centre-right party’s campaign initially employed the hashtag #echilibrusiseriozitate to promote European values and pro-EU positions. Kensington Communication, the company responsible for the campaign, also targeted Georgescu’s content, aiming to counter his EU-critical rhetoric. However, the hashtag #echilibrusiseriozitate, designed to create an unfavourable environment for non-liberal presidential candidates on TikTok, was replaced by #echilibrusiverticalitate on the FameUP platform—a free automated platform that amplifies marketing campaigns. Interestingly, this new hashtag was ultimately adopted and used by Georgescu’s supporters, transforming its purpose and amplifying his campaign’s visibility. The Romanian government proposed 4 May as the date for a new presidential election. However, no formal decision was made since. Călin Georgescu has since challenged the Constitutional Court’s decision at a local appeals court and lodged a complaint with the European Court of Human Rights. ‘I will take our cause to the heart of Europe, to the highest courts. Each of us is doing our part in this historic mission to defend our democracy,’ he declared.
January 5, 2025
Recent polls show that Călin Georgescu remains the most popular presidential candidate, with some surveys suggesting that the ultranationalist contender could garner close to 40 per cent support.
January 8, 2025
The court is considering disqualifying Georgescu for undeclared campaign funding.
The leaders of the ruling coalition made up of the Social Democrats (PSD), Liberals (PNL), the Democratic Alliance of Hungarians (UDMR), and the minorities' group decided on the new dates for the presidential elections. According to the agreed election schedule, the first round would have taken place on May 4, followed by the runoff on May 18.
At the beginning of the government meeting, prime minister Marcel Ciolacu announced the introduction of sanctions against social media networks that favor candidates, according to Europa Libera Romania.
Georgescu’s appeal against the constitutional court’s decision to nullify the election was rejected, so he lodged a complaint to the European Court of Human Rights.
In fact, even the Venice Commission (the officially European Commission for Democracy through Law) stated that, regarding what had happened in Romania, evidence must be given: ‘An election annulment must be based on transparent evidence, not classified information.’
January 10, 2025
Former European commissioner Thierry Breton assured that the European Union has mechanisms to overturn an eventual AfD victory:
We did it in Romania and obviously we will do it in Germany if necessary.

This was widely seen as a clear admission of their true intentions, as if they had dropped all pretenses and fully revealed themselves.
They tell you to your face that they can suspend elections and that absolutely nothing happens, then they have the cheek to declare themselves the ‘democrats’ and ‘tolerant’, when it is them who are the main enemies of democracy and freedom of expression!
January 12, 2025
Tens of thousands of supporters of Romanian presidential candidate Călin Georgescu took to the streets in Bucharest on Sunday to protest the annulment of the presidential election. With no concrete evidence emerging to substantiate the allegations of Russian interference, it has become increasingly evident that the progressive elite will go to any lengths to remain in power.

February 1, 2025 According to the last polls, Georgescu would be around 50 per cent; specifically, according to the last one published by România TV, he would obtain 47 per cent.
February 10, 2025
Romanian President Klaus Iohannis announced his resignation before his possible forced dismissal from parliament. Iohannis, echoing Joe Biden, made sure to pardon his family and the judges who suspended the presidential election before leaving, for reasons of precaution.
Once the court cancelled the elections—so no new president was elected—, it also decided to lengthen the current president’s term in office until a new vote in May 2025. Iohannis faced raising opposition, however, as some viewed his lengthened mandate as illegitimate. On the one hand, the Romanian constitution states that a presidential term is five years, and the president remains in office until their successor takes over. On the other hand, it also makes clear that the presidency can be extended only in case of war or catastrophe. Protests also took place against the decision of him remaining in office, and the legislature initiated his removal as well. **Preventing a successful impeachment procedure, Klaus Iohannis stepped down. ** In his resignation speech he highlighted that Romania’s western partners will not understand the reason why he was forced to step down, and that his departure will damage Bucharest’s relationship with its allies. The country’s interim president will be the Senate’s president, Ilie Bolojan.
February 15, 2025
The Constitutional Court of Romania is accused of canceling elections without evidence, allegedly to suppress votes against the EU-aligned political establishment. Claims suggest court judges are linked to Soros-funded NGOs. A network of "independent" NGOs and media, funded by hundreds of millions from the EU and USAID, is said to promote left-wing globalist agendas, manipulate public opinion, and counter conservative values. EU grants and a secret 130 million euro contract to a French agency, tied to corruption, allegedly fueled pro-EU media campaigns, undermining independent journalism and labeling critics as pro-Russia. Independent journalist, Iosefina Pascal, talks thoroughly about this case.
February 19, 2025 Renowned journalist and X (formerly Twitter) personality Mario Nawfal interviews Georgescu, with clear expressions of support for Trump and Musk, alongside a strong critical stance toward George Soros.
February 26, 2025 Romania’s presidential candidate, Calin Georgescu was arrested while en route to Bucharest to announce his new presidential campaign. Georgescu’s campaign team has confirmed that Georgescu was picked up by the police and detained in the middle of traffic for questioning at the attorney general’s office.
Georgescu was declared the winner of that election round, but an arrest warrant was issued against him on February 26, as reported by the Romanian press.
Romanian prosecutors have initiated criminal proceedings against the right-wing politician and candidate for the 2024 presidential election, Călin Georgescu, on six charges. These include allegations of engaging in unconstitutional activities and providing inaccurate financial disclosures, according to official sources.
March 1, 2025
Thousands march for freedom in Romania. Over 200,000 Romanians flood streets for Georgescu. Anti-Soros feelings are everywhere.


March 6, 2025
The Romanian opposition – denied a likely victory – took their case to the European Court of Human Rights.
The ECHR (The European Convention on Human Rights, a supranational convention to protect human rights and political freedoms in Europe) threw the case out without even hearing it. Apparently, the Romanian courts were perfectly within their rights to simply indefinitely postpone their election on the basis of unproven allegations.
Romania is moving toward its strictest censorship law since 1989, granting authorities the power to block websites and social media posts without independent review.
The Emergency Ordinance (OUG) would allow the government to shut down content deemed “false information,” “manipulation,” or a “threat to national security,” with no clear definitions or court approval required.
The Romanian Intelligence Service (SRI), military, cybersecurity agencies, and electoral authorities would have sweeping powers to remove posts and block platforms, while internet providers refusing to comply could face massive daily fines.
This law could be used to silence journalists and political opponents, as there is no independent oversight and no clear standard for what counts as “false information.”
The government claims the measure is meant to combat foreign election interference, but it will actually be weaponized against free speech.
March 7, 2025 Călin Georgescu, the people’s choice in Romania’s annulled election, has officially submitted his candidacy for the upcoming presidential race, backed by over 324,000 signatures.
The Constitutional Court will decide this month or early April if his candidacy is approved, assuming, of course, that he doesn't get arrested again this time.


March 8, 2025
Demonstrators gathered in front of Romania’s Palace of Parliament, holding banners thanking Tulsi Gabbard and urging Trump to “help take our country back!”

Romania’s Constitutional Court has unanimously rejected 4 appeals attempting to block Călin Georgescu from the presidential race. The challenges, filed by minor candidates Sebastian Popescu and Cristian Terheș, accused him of failing to disclose campaign funding and alleged foreign financial ties. The court dismissed the claims as inadmissible, citing procedural failures and lack of legal merit.
Allegedly Soros-linked activists flood Romanian Electoral Bureau with 1,000 identical appeals against CĂLIN GEORGESCU
Over 1,000 copy-paste appeals were filed against Călin Georgescu’s candidacy, organized by Soros-backed activists trying to block him.
But the Electoral Bureau (BEC) is set to reject them all—the challenges were filed before his candidacy was even validated, making them invalid.
March 9, 2025
Calin Georgescu’s presidential candidacy has been officially rejected, sparking outrage among his supporters, who attempted to breach the Bureau of Electoral Control (BEC).
The candidacy was rejected with 10 votes in favor and 4 against.
Romania’s Electoral Office bypassed the Constitutional Court, which had approved his candidacy in December, and shut him down directly instead.
George Simion, president of the AUR stated in viral video:
Georgescu put his candidacy at the Central Electoral Bureau and by 10 members to 4, it was rejected without any reason. All the papers were in good order. They just said they voted through their conscience. We live in a dictatorship. Please help us. Please be on our side to restore democracy in Romania.
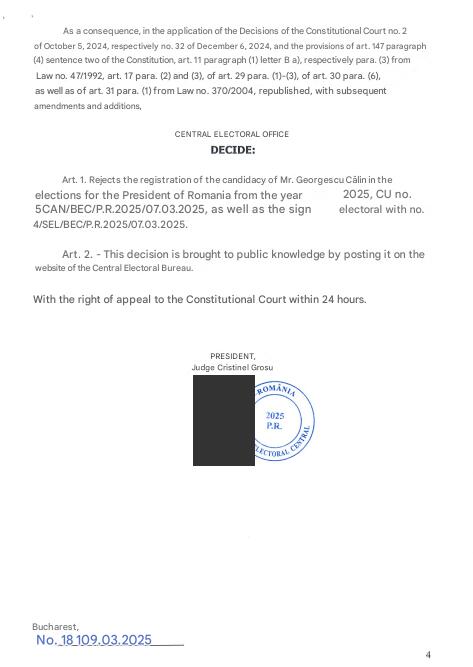
March 11, 2025
Romanian presidential candidate Călin Georgescu cannot run in the Presidential Election. Călin Georgescu’s appeal against the invalidation of his presidential candidacy has been rejected by the Constitutional Court.
March 27, 2025
The National Authority for Administration and Regulation in Communications (ANCOM), coordinator of digital services in Romania held an exercise to test the capacity to respond to challenges that may emerge in the online environment, in view of the presidential elections in May.
This initiative takes its root from the Rapid Response Mechanism (RRM), which ironically, was established during the G7 Charlevoix Summit in June 2018, meant to enhance cooperation among nations in addressing ‘crisis’ moments and perceived threats to western democracy.
Ahead of Romania’s new presidential election, the European Commission has launched its ‘RRM’ as a proactive strategy which the EC presents as a means to tackle potential electoral law violations on social media in member states holding elections. In effect, a similar simulation was reportedly held before the February elections in Germany. Coincidentally, a call for proposals to manage the new project described as a “Media Freedom Rapid Response Mechanism” was issued by the European Commission on Oct 24, 2024, under the cross-sectoral strand of the Creative Europe Programme. This CFP was launched to allegedly promote an independent and pluralistic media environment through an independent Europe-wide rapid response mechanism.
Subsequently, the Romanian government is now drafting an emergency ordinance to empower authorities to eliminate illegal (or inconvenient) online content, which they argue is essential for protecting the electoral process. However, some interpret this as a sign of a democratic crisis, with the current administration struggling to maintain power and resorting to emergency measures to suppress opposition and their freedom of speech. Recent polls suggest that Călin Georgescu could win the presidency in a single round, a situation complicated by the exclusion of the right-wing conservative candidate from the May 2025 elections. Other talks about possible corruption surrounding the construction of the multi-billion classified secret service contract for the Realization of the infrastructure of NATO 57th Air Base Mihail Kogălniceanu, located only 30 kilometres from the Black Sea and anticipated to be NATO’s largest base in Europe upon completion.
-
 @ c0c42bba:a5feb7b5
2025-05-01 07:30:50
@ c0c42bba:a5feb7b5
2025-05-01 07:30:50Hey guy this is my first note on nostr and I'm glad we have something like this now. I've been a Substack writer for a couple of years now and I'm so excited to jump on this and I can't wait for the many things I can do with this
please show your support
-
 @ 107f2bb3:d78aa4c4
2025-05-01 06:24:15
@ 107f2bb3:d78aa4c4
2025-05-01 06:24:15bye
-
 @ ccb30bfc:90b6869f
2025-05-01 06:23:48
@ ccb30bfc:90b6869f
2025-05-01 06:23:48No mundo atual do entretenimento digital, plataformas de jogos online têm se destacado por oferecer experiências imersivas e seguras para jogadores de todos os perfis. Entre essas opções, o Clima777 se consolida como uma das escolhas preferidas do público brasileiro. Com uma interface amigável, ampla gama de jogos e suporte confiável, a plataforma oferece um ambiente completo para quem busca diversão com responsabilidade.
O Clima777 foi criado com o objetivo de proporcionar entretenimento online de alto nível, combinando inovação, praticidade e segurança. Ao acessar o site, os usuários se deparam com um design moderno e intuitivo, facilitando a navegação tanto para iniciantes quanto para jogadores mais experientes.
A plataforma se destaca pelo seu compromisso com a transparência e pela utilização de tecnologias de criptografia que garantem a proteção dos dados dos usuários. Além disso, o Clima777é acessível a partir de computadores, tablets e smartphones, permitindo que os jogadores se divirtam em qualquer lugar e a qualquer momento.
Jogos para Todos os Gostos Um dos principais atrativos do Clima777 é a sua variedade de jogos. A plataforma conta com uma seleção completa, desde jogos clássicos até os mais modernos e interativos, sempre com gráficos de alta qualidade e comandos intuitivos. Entre as categorias mais populares estão:
Slots (caça-níqueis): Diversas opções com temas variados, rodadas bônus e recursos especiais. Os slots são perfeitos para quem busca emoção a cada giro.
Jogos de mesa virtuais: Os fãs de estratégia podem desfrutar de opções como roleta, blackjack, bacará e outros títulos, com diferentes estilos e regras.
Jogos ao vivo com crupiês reais: Para quem deseja uma experiência mais realista, há transmissões em tempo real, com profissionais que conduzem os jogos com excelência.
Minijogos e apostas rápidas: Ideais para quem gosta de partidas curtas e dinâmicas, esses jogos oferecem entretenimento instantâneo.
Experiência do Jogador no Clima777 A experiência no Clima777 vai muito além dos jogos. A plataforma investe constantemente em funcionalidades que tornam a jornada do usuário mais prática e satisfatória. O processo de cadastro é simples e rápido, e os métodos de depósito e saque são variados, incluindo opções locais como boleto bancário, Pix e carteiras digitais.
Outro diferencial é o atendimento ao cliente, disponível 24 horas por dia, sete dias por semana. Os jogadores podem entrar em contato via chat ao vivo ou e-mail e contar com um suporte eficiente e cordial. Além disso, há uma seção de perguntas frequentes bastante completa, onde dúvidas comuns são respondidas de forma clara.
O Clima777 também recompensa seus usuários com promoções regulares e programas de fidelidade. Novos jogadores recebem bônus de boas-vindas, enquanto usuários recorrentes acumulam pontos e vantagens especiais conforme continuam jogando. Tudo isso contribui para manter o engajamento e premiar a lealdade do público.
Conclusão O Clima777 representa uma excelente opção para quem busca entretenimento online seguro, variado e emocionante. Com uma plataforma bem estruturada, catálogo robusto de jogos e foco na experiência do usuário, a marca vem conquistando cada vez mais espaço no Brasil. Seja você um jogador iniciante ou experiente, o Clima777 oferece o clima perfeito para se divertir com tranquilidade e qualidade.
-
 @ ccb30bfc:90b6869f
2025-05-01 06:23:04
@ ccb30bfc:90b6869f
2025-05-01 06:23:04O mundo do entretenimento digital está em constante evolução, e a GG666 surge como uma plataforma moderna e completa que promete revolucionar a forma como os jogadores brasileiros vivenciam a emoção dos jogos online. Com uma interface intuitiva, vasta biblioteca de jogos e suporte dedicado, a GG666 rapidamente conquistou seu espaço entre os melhores portais de jogos da atualidade.
A GG666 foi desenvolvida com foco total na experiência do usuário. Ao acessar a plataforma, o jogador encontra um ambiente visualmente atraente, com menus organizados, design responsivo e fácil navegação tanto em computadores quanto em dispositivos móveis. Além disso, todo o conteúdo está disponível em português, o que facilita o acesso e compreensão para o público brasileiro.
O processo de cadastro é simples e seguro, permitindo que novos usuários comecem sua jornada rapidamente. A Gg666também investe em tecnologia de ponta para garantir a segurança de dados e transações, oferecendo tranquilidade para quem deseja se divertir sem preocupações.
Jogos para Todos os Gostos O grande destaque da GG666 está na variedade de jogos disponíveis. A plataforma oferece centenas de títulos, abrangendo diversas categorias como jogos de mesa, cartas, roletas virtuais, slots e experiências interativas ao vivo. Essa diversidade garante que jogadores com diferentes preferências encontrem opções que combinem com seu estilo de jogo.
Os jogos são desenvolvidos por provedores renomados internacionalmente, o que assegura gráficos de alta qualidade, efeitos sonoros imersivos e mecânicas justas. Além disso, muitos títulos oferecem versões de demonstração, permitindo que os usuários testem suas estratégias antes de apostar com dinheiro real.
Um dos destaques é a seção de jogos ao vivo, onde os jogadores podem interagir em tempo real com apresentadores e outros participantes. Essa funcionalidade proporciona uma experiência social e dinâmica, aumentando ainda mais a imersão.
Experiência do Jogador: Diversão com Responsabilidade e Suporte Dedicado A GG666 entende que uma boa experiência de jogo vai além dos títulos disponíveis. Por isso, a plataforma investe fortemente em suporte ao cliente e em práticas de jogo responsável. Os jogadores contam com atendimento multilíngue disponível 24 horas por dia, via chat ao vivo, e-mail e outras formas de contato.
Além disso, a GG666 oferece ferramentas para controle de gastos, limites de tempo de jogo e outras funcionalidades que ajudam a promover uma experiência equilibrada e saudável.
Outro ponto positivo é o sistema de bônus e promoções regulares, que tornam a jornada ainda mais empolgante. Novos usuários são recebidos com ofertas exclusivas, enquanto os jogadores mais assíduos têm acesso a vantagens progressivas conforme avançam em seus níveis de fidelidade.
Conclusão: GG666 é Sinônimo de Qualidade e Diversão A GG666 não é apenas mais uma plataforma de jogos online. Com sua abordagem centrada no usuário, vasta seleção de jogos de qualidade e compromisso com a segurança e responsabilidade, ela se destaca como uma das melhores escolhas para quem busca entretenimento online com confiança.
Seja você um jogador experiente ou alguém que está começando agora, a GG666 oferece um ambiente completo, seguro e cheio de oportunidades para explorar. Experimente hoje mesmo e descubra por que tantos brasileiros estão escolhendo a GG666 como seu portal favorito de diversão digital.
-
 @ 57d1a264:69f1fee1
2025-05-01 05:57:24
@ 57d1a264:69f1fee1
2025-05-01 05:57:24Design and build chemical processes, better. Alkali is creating the world's first AI Process Engineer.
What the future of chemical process design should look like.
Under the hood, APE-0 uses tried-and-true open-source packages to run simulations. You don't have to trust that the LLM predicted the result — you can check out the simulation file it produced, and run it yourself!
Discover more at https://www.alkali-eng.com/blogs/introducing-fel-0
originally posted at https://stacker.news/items/968211
-
 @ 1d7ff02a:d042b5be
2025-05-01 05:46:41
@ 1d7ff02a:d042b5be
2025-05-01 05:46:41Source: https://youtu.be/e_Y9tI4dALA?si=F5wXRlpM0YulbhmY
Twitter Origins and Evolution
Twitter began as Dorsey's attempt to better understand cities by visualizing what people were doing and thinking (00:35-02:27) Key features like @mentions, hashtags, and retweets were invented by users, not the company (04:06-05:24) Dorsey realized Twitter was becoming significant when he saw politicians using it during Obama's first address to the nation (06:29-07:44)
Reflections on Twitter/X
Regrets monetizing too quickly through advertising rather than exploring better business models (12:19-13:05) Believes Twitter should have been built as an open protocol rather than a centralized company (13:05-14:23) Advocates for user choice in algorithms rather than having companies decide what content users see (15:35-18:31)
Decentralized Social Media
Started Blue Sky while at Twitter to create a decentralized social media protocol (22:51-24:07) Later focused on Nostr, which he believes has a better development model similar to Linux (24:07-25:57) Believes the future of social media includes agent-driven systems and greater user agency (29:01-29:41)
Block and Bitcoin
Block (formerly Square) focuses on economic empowerment through financial tools (32:08-32:47) Sees Bitcoin as essential for creating an internet protocol for moving money (33:25-35:09) Believes Bitcoin will eventually move beyond being just a store of value to become a currency for cross-border remittances (35:09-36:58)
Entrepreneurship Philosophy
Never intended to be an entrepreneur but wanted to build useful products (40:22-42:02) Compares entrepreneurship to art - knowing how to express ideas and where to set boundaries (42:02-43:09) Deals with rejection by viewing all experiences as teachers with lessons to offer (43:44-44:55)
Personal Habits
Practices meditation daily and previously did 10-day silent retreats (45:30-46:43) Creates daily lists of both what to do and what not to do (47:21-48:28) Eats only once a day to save time and better appreciate food (51:29-52:39) Dedicates morning hours to learning difficult subjects like quantum physics (48:28-49:40)
His advice to young people: observe everything, take in information, and don't worry about immediately reacting to it (52:39-53:00).
Noteable Quotes
-
On Twitter's co-creation with users: "What's interesting about Twitter is it wasn't really us who determined where it went, it was the people using it." (04:06)
-
On algorithms: "I think it's less about free speech, I think it's more about do we get to choose how the algorithms are programming us, because the algorithms are definitively programming us." (15:35)
-
On rejections and setbacks: "Everything I encounter, everything I experience is a teacher and they have some lesson for me, and it's up to me whether I decide to learn from it or not." (43:44)
-
On entrepreneurship as art: "It's expression, it's knowing when to end something, it's knowing what the chapters are and where the piece begins and where it ends." (42:02)
-
On Bitcoin's potential: "Bitcoin is over close to 16 years old right now. It's never gone down, it's never had a security issue, it has no leader, it has a completely open roadmap, and it's determined by a consensus development model." (36:18)
-
On learning: "I think people skip the observing phase too often. I don't think people are good listeners. I don't think people have honed their ability to observe the world and observe nature and observe how things work." (50:19)
-
On his advice to young people: "Observe everything, like take everything in, get love information, love receiving information, don't worry about reacting to it, don't worry about memorizing it, don't worry about doing anything with it at all, just be open." (52:39)
-
-
 @ 866e0139:6a9334e5
2025-05-01 05:28:22
@ 866e0139:6a9334e5
2025-05-01 05:28:22Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Woran erkennt man einen Verbrecher? Die meisten Menschen erfahren von Verbrechern aus den Medien, denn die Medien erklären, wer ein Verbrecher und was ein Verbrechen ist. Die Medien berufen sich hierbei gerne auf „Experten“ und „helfen“ dem gewöhnlichen Bürger bei der „Einordnung“ von Sachverhalten. Man lernt, dass „ein junger Mann“, der mit einem Messer ein hilfloses Baby abschlachtet, nicht so hart bestraft wird, wie etwa ein „Steuersünder“. Und wer glaubt, dass Wahlbetrug juristisch geahndet werden könnte, der irrt ebenso wie jemand, der glaubt, dass es in einer Demokratie erlaubt sein könnte, ein satirisches Meme über einen Politiker zu teilen. Neuerdings sind selbst „Meinungen unterhalb der Strafbarkeitsgrenze“ für gewöhnliche Bürger nicht mehr folgenlos.
Bekanntlich ist die Staatsanwaltschaft in Deutschland eine weisungsgebundene Behörde und als solche ein Teil der Exekutive. Dem Staatsanwalt selbst ist gemäß § 353b Strafgesetzbuch zudem strafrechtlich untersagt, ihm gegenüber erteilte Weisungen Dritten mitzuteilen. Sofern demnach direkte Weisungen erteilt würden, hätte der weisungsgebundene Staatsanwalt diese nicht nur zu befolgen, sondern dürfte auch niemandem gegenüber offenbaren, dass er nicht aus eigener Überzeugung, sondern auf Anweisung - wie beispielsweisen aus politischen Motiven heraus - handelt. Diese juristische Konstruktion eröffnet regierenden Politikern einen erheblichen Gestaltungsspielraum.
Anstelle der konsequenten Anwendung des Strafrechts gab es vor allem in der jüngeren Vergangenheit bei den der Öffentlichkeit nicht zu verbergenden Verfehlungen von Politikern lediglich folgenlose Untersuchungsausschüsse. Könnte dies daran gelegen haben, dass Gerechtigkeit eine Frage von Auslegung und Deutung ist – und die Politiker die Deutungshoheit haben?
Wenn dies so wäre, würde sich die Frage aufdrängen, wie weitgehend denn Straftaten dieser Personengruppe ungestraft ausgeführt werden könnten? Ein Manager eines Unternehmens wird für Fehlverhalten massiv bestraft, während der Lenker eines Landes quasi alles tun kann, was er – im Auftrag der Leute, für die er tatsächlich tätig ist – tun möchte? Wenn dies so wäre, würde es sich dann nicht eher um eine Kabale als um eine ehrenhafte Regierung handeln?
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes. friedenstaube@pareto.space
Was wäre in diesem Fall mit dem Gewaltmonopol? Könnten die Soldaten und Polizisten dann nicht für das Durchsetzen der individuellen Interessen dieser Leute missbraucht werden? Ein Bürger dürfte sich nicht kritisch über diese Leute äußern, oder müsste stärkste Repressionen erdulden. Wenn die Gerichtsbarkeit dieser Kabale dienen würde, wäre denn dann eine Rechtsprechung überhaupt möglich? Was würde mit einem Richter, der „in einer wichtigen Sache das falsche Urteil sprechen“ würde, denn passieren? Würde möglicherweise sein Haus von einem Sonderkommando durchsucht und würde er gedemütigt? Würde er seinen Job verlieren und käme er ins Gefängnis? Und wie würde dies auf andere Richter wirken? Würden sich diese gegen die Kabale auflehnen oder lieber tun, was die Kabale ihnen vorgibt?
Was wäre, wenn solch eine Kabale zu Krieg, höheren Steuerzahlungen, medizinischen Zwangsbehandlungen etc. unter Androhung von Bestrafungen zwingen würde? Und was wäre, wenn die Menschen erkennen würden, dass sie von Verbrechern regiert werden?
Was würden Sie tun?
Nun, man könnte demonstrieren, auf die Straße gehen, und dort für seine Rechte eintreten, oder? Aber ist dieses „Demonstrationsrecht“, welches dem eigentlichen Souverän, dem Bürger, „großzügig“ eingeräumt wurde, nicht etwas völlig Wirkungsloses? Wer demonstriert, hat das Gewaltmonopol des Staates zu akzeptieren, sodass er zwar geschlagen, mit Wasserwerfern und Pfefferspray besprüht, gewürgt und von Hunden gebissen werden, aber sich selbst nicht wehren darf. Wenn sich ein Demonstrant in der „falschen Sache“ nicht an die Demonstrationsregeln hält und beispielsweise Sicherheitsabstände nicht korrekt einhält, wird er sehr schnell von einem gepanzerten und anonymisierten Polizisten bestraft. Und was ist mit den vielen V-Leuten? Ein so genannter Agent Provokateur mischt sich unter die Demonstranten und gibt vor, ein Teil von diesen zu sein, um dann in deren Namen „etwas Unrechtes“ zu tun wie eine Reichsbürger-Fahne zu schwenken oder einen Sicherheitsabstand nicht einzuhalten oder einen Polizisten anzugreifen. Und schon hat man „einen Grund“, dieser Demonstration einen besonderen Anstrich zu verpassen. Wer sich noch an „den Sturm auf den Reichstag“ und die Verleihungen von Verdienstorden für „die Rettung unserer Demokratie“ erinnert, weiß, dass Demonstrationen gelenkt werden können und dass ein gewöhnlicher Bürger, der „sein Demonstrationsrecht“ wahrnimmt, im Zuge einer solchen Veranstaltung am eigenen Leib erfahren kann, dass ihm die Demo im günstigsten Fall weder genützt noch geschadet hat.
Aber was sonst könnte man tun, wenn man von Verbrechern regiert würde? Was könnte getan werden, wenn Untaten wie Kriegstreiberei, Gesundheitsdiktatur, Steuerwillkür, Klimawahn, Wahlmanipulationen etc. nicht „aus Versehen“, sondern mit schädigender Absicht, also mit Vorsatz getan wurden und werden?
Wer sich diese Fragen stellt, ist bereits sehr weit und weitgehend isoliert, denn der große Teil der Bevölkerung wird durch die Medien nicht nur darüber „informiert“, was Straftaten sind, sondern erhält zudem „wohlwollende Einordnungen“ zum jeweils aktuellen Geschehen. Der „gute Bürger Unsererdemokratie“ ist einfach „besser informiert“, und weiß, was er zu denken hat. Für den „guten Bürger“ ist alles klar: Wir leben in der besten Demokratie aller Zeiten und die Politiker geben ihr Bestes, zu unser aller Wohle. Sie schützen uns vor Pandemien, vor Feinden der Demokratie und Feinden des Landes, und sind hierbei weitestgehend selbstlos.
Aber wer sich der Mühe unterziehen möchte, selbst zu denken, der hat die Möglichkeit, seine eigenen Einordnungen auf der Basis ungeschwärzter Fakten vorzunehmen. Wer beispielsweise die RKI-Protokolle oder auch anderes Material ungeschwärzt lesen möchte, kann sich (noch) unabhängiger Portale bedienen, die seitens der Regierung zwar allesamt verboten werden sollen (da man schließlich als Regierung bestimmen möchte, was die Bürger zu lesen und zu glauben haben), die aber derzeit noch verfügbar sind.
In welcher Welt wollen wir und unsere Kinder leben und was ist zu tun, damit diese wünschenswerte Welt entsteht? Die Menschen sollten in die Wahrnehmung und von dort aus in die Erkenntnis kommen. Und aus der Erkenntnis ins Wollen, denn letztendlich ist das Wollen stets die Grundvoraussetzung für das Tun. Und ohne das Tun passiert – nichts.
Lesen Sie hier, wie Menschen wie Vieh behandelt werden und hier, wie das System organisiert ist. Und hier ist zu nachzulesen, was getan werden könnte, wenn Verbrecher an der Macht wären.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 57d1a264:69f1fee1
2025-05-01 05:14:06
@ 57d1a264:69f1fee1
2025-05-01 05:14:06The mystical d attribute in SVG paths is actually a series of small commands. In this guide, we'll take a look at each path command and how we can use them to draw icons. Read more at https://www.nan.fyi/svg-paths
I you'd like to learn Interactive SVG Animations, here a text-based mini-course on making whimsical, playful SVG animations https://www.svg-animations.how/
credits: @nandafyi
originally posted at https://stacker.news/items/968195
-
 @ 57d1a264:69f1fee1
2025-05-01 05:01:45
@ 57d1a264:69f1fee1
2025-05-01 05:01:45 -
 @ 7c082548:0b32521e
2025-05-01 04:45:57
@ 7c082548:0b32521e
2025-05-01 04:45:57SP8BET là một nền tảng trực tuyến hiện đại, được thiết kế với mục tiêu mang lại trải nghiệm liền mạch, tiện lợi và bảo mật cao cho người dùng. Giao diện của SP8BET rất dễ sử dụng, với bố cục rõ ràng và trực quan, giúp người dùng nhanh chóng làm quen và tận hưởng các dịch vụ mà nền tảng cung cấp. Với khả năng tương thích đa thiết bị, người dùng có thể truy cập vào SP8BET trên mọi thiết bị, từ máy tính để bàn đến điện thoại di động, mà không gặp phải bất kỳ vấn đề nào về tốc độ hay hiệu suất. Nền tảng này tối ưu hóa tốc độ truy cập, giúp người dùng trải nghiệm một cách mượt mà và hiệu quả nhất. Chính nhờ vào giao diện đơn giản nhưng mạnh mẽ và hiệu suất ổn định, SP8BET trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng trực tuyến tiện lợi và không gặp rắc rối trong quá trình sử dụng.
Bên cạnh những tính năng về giao diện và hiệu suất, SP8BET còn đặc biệt chú trọng đến bảo mật và an toàn thông tin. Với công nghệ bảo mật tiên tiến, nền tảng đảm bảo rằng mọi dữ liệu cá nhân của người dùng đều được bảo vệ an toàn tuyệt đối. SP8BET sử dụng các biện pháp mã hóa mạnh mẽ để ngăn chặn mọi hành vi truy cập trái phép, đồng thời hệ thống của nền tảng này luôn được kiểm tra và cập nhật để chống lại các mối đe dọa từ bên ngoài. Người dùng có thể hoàn toàn yên tâm khi sử dụng nền tảng này mà không cần lo lắng về các vấn đề bảo mật. Thêm vào đó, SP8BET cũng cung cấp các công cụ bảo vệ thông tin tài khoản, giúp người dùng dễ dàng kiểm soát và quản lý dữ liệu của mình. Đội ngũ hỗ trợ khách hàng của SP8BET luôn sẵn sàng giải đáp các thắc mắc về bảo mật, giúp người dùng có một trải nghiệm an toàn, tin cậy và thoải mái.
Ngoài các yếu tố về giao diện và bảo mật, SP8BET cũng không ngừng cải tiến và phát triển các tính năng mới để phục vụ người dùng một cách tốt nhất. Nền tảng này luôn chú trọng đến việc tích hợp các công nghệ mới nhất, đảm bảo rằng người dùng có thể trải nghiệm các tiện ích hiện đại và phù hợp với xu hướng công nghệ toàn cầu. Các tính năng của SP8BET không chỉ đáp ứng nhu cầu hiện tại mà còn mang đến các giải pháp tiên tiến cho tương lai, giúp người dùng luôn được cung cấp những công cụ hữu ích để tối ưu hóa trải nghiệm. SP8BET cũng đặc biệt chú trọng đến việc tạo dựng một cộng đồng người dùng thân thiện và hỗ trợ lẫn nhau. Các hoạt động tương tác giữa người dùng và nền tảng luôn được khuyến khích, tạo ra một không gian chia sẻ, học hỏi và phát triển. Với tất cả những điểm mạnh này, SP8BET đang ngày càng khẳng định được vị thế của mình như một nền tảng trực tuyến hàng đầu, cung cấp những dịch vụ chất lượng và đáng tin cậy cho người dùng trong thời đại công nghệ số hiện nay.
-
 @ 5df413d4:2add4f5b
2025-05-01 02:22:31
@ 5df413d4:2add4f5b
2025-05-01 02:22:31Blank
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 1f79058c:eb86e1cb
2025-04-26 13:53:50
@ 1f79058c:eb86e1cb
2025-04-26 13:53:50I'm currently using this bash script to publish long-form content from local Markdown files to Nostr relays.
It requires all of
yq,jq, andnakto be installed.Usage
Create a signed Nostr event and print it to the console:
bash markdown_to_nostr.sh article-filename.mdCreate a Nostr event and publish it to one or more relays:
bash markdown_to_nostr.sh article-filename.md ws://localhost:7777 wss://nostr.kosmos.orgMarkdown format
You can specify your metadata as YAML in a Front Matter header. Here's an example file:
```markdown
title: "Good Morning" summary: "It's a beautiful day" image: https://example.com/i/beautiful-day.jpg date: 2025-04-24T15:00:00Z tags: gm, poetry published: false
In the blue sky just a few specks of gray
In the evening of a beautiful day
Though last night it rained and more rain on the way
And that more rain is needed 'twould be fair to say.— Francis Duggan ```
The metadata keys are mostly self-explanatory. Note:
- All keys except for
titleare optional date, if present, will be set as thepublished_atdate.- If
publishedis set totrue, it will publish a kind 30023 event, otherwise a kind 30024 (draft) - The
dtag (widely used as URL slug for the article) will be the filename without the.mdextension
- All keys except for
-
 @ 306555fe:fd7fdf12
2025-05-01 02:08:38
@ 306555fe:fd7fdf12
2025-05-01 02:08:38when his rivals got wind of that scandalous evening, they ratted him out to the highest Athenian court for stealing “kykeon,” the sacred elixir he’d shared with his guests. He was tried in absentia for a crime punishable by death—blaspheming the Mysteries.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 47-48
At the center of this dynamic sits the myth of Prometheus,9 the original upstart rebel, who stole fire from the gods and shared it with humankind.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 77-78
For anthropologists, uncovering the ingredients of kykeon has become a Holy Grail kind of quest. It ranks right up there with decoding soma, the ancient Indian sacrament that inspired Aldous Huxley’s groupthink happy drug in Brave New World. Swiss chemist Albert Hofmann7 and Harvard-trained classicist Carl Ruck argued that the barley in kykeon might have been tainted with an ergot fungus.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 65-69
The Greeks had a word3 for this merger that Davis quite liked—ecstasis—the act of “stepping beyond oneself.” Davis had his own word as well. He called it “the switch,” the moment they stopped being separate men with lives and wives and things that matter. The moment they became, well, there’s no easy way to explain it—but something happened out there. Plato described ecstasis as an altered state where our normal waking consciousness vanishes completely, replaced by an intense euphoria and a powerful connection to a greater intelligence. Contemporary scientists have slightly different terms and descriptions. They call the experience “group flow.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 166-171
“More than any other skill,” he explains, “SEALs rely on this merger of consciousness. Being able to flip that switch—that’s the real secret to being a SEAL.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 182-183
“At every step of the training,” says Davis, “from the first day of BUD/S (Basic Underwater Demolition/SEALs) through their last day in DEVGRU, we are weeding out candidates who cannot shift their consciousness and merge with the team.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 211-212
But, by breaking down what’s going on in the brain, we start to see that what feels supernatural might just be super-natural: beyond our normal experience, for sure, but not beyond our actual capabilities.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 44, loc. 726-727
The Greeks called that sudden understanding anamnesis. Literally, “the forgetting of the forgetting.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 44, loc. 719-720
The Greeks called that sudden understanding anamnesis. Literally, “the forgetting of the forgetting.” A powerful sense of remembering.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 44, loc. 719-720
Often, an ecstatic experience25 begins when the brain releases norepinephrine and dopamine into our system. These neurochemicals raise heart rates,26 tighten focus, and help us sit up and pay attention. We notice more of what’s going on around us, so information normally tuned out or ignored becomes more readily available. And besides simply increasing focus, these chemicals amp up the brain’s pattern recognition abilities,27 helping us find new links between all this incoming information.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 44, loc. 727-733
This ability to unlock motivation has widespread implications. Across the board, from education to health care to business, motivational gaps cost us trillions of dollars a year. We know better; we just can’t seem to do better. But we can do better. Effortlessness upends the “suffer now, redemption later” of the Protestant work ethic and replaces it with a far more powerful and enjoyable drive.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 43, loc. 711-714
Anandamide also plays another important role here,31 boosting “lateral thinking,” which is our ability to make far-flung connections between disparate ideas. Post-its, Slinkys, Silly Putty, Super Glue, and a host of other breakthroughs all came when an inventor made a sideways leap, applying an overlooked tool in a novel way. In part, that’s anandamide at work.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 45, loc. 742-746
As we move even deeper into ecstasis, the brain can release endorphins and anandamide.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 45, loc. 740-741
Umwelt is the technical term34 for the sliver of the data stream that we normally apprehend. It’s the reality our senses can perceive. And all umwelts are not the same. Dogs hear whistles we cannot, sharks detect electromagnetic pulses, bees see ultraviolet light—while we remain oblivious. It’s the same physical world, same bits and bytes, just different perception and processing.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 45, loc. 755-758
As of late 2016, with the initial phases of the research completed, the study came to two overarching conclusions. First, creativity is essential for solving complex problems—the kinds we often face in a fast-paced world. Second, we have very little success training people to be more creative. And there’s a pretty simple explanation for this failure: we’re trying to train a skill, but what we really need to be training is a state of mind.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 46, loc. 771-774
But when non-ordinary states trigger timelessness, they deliver us to the perpetual present—where we have undistracted access to the most reliable data. We find ourselves at full strength. “That was another thing I noticed,” says Silva, “when I go off on a tangent and the ideas start to flow, there’s no room for anything else. Definitely not for time. People who see my videos often ask how I can find all those connections between ideas. But the reason I can find them is simple: without time in the picture, I have all the time I need.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 41, loc. 668-672
"lifted"
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 42, loc. 692
“The [experience] lifts the course of life to another level,”19 he writes in his book Flow. “Alienation gives way to involvement, enjoyment replaces boredom, helplessness turns into a feeling of control. . . . When experience is intrinsically rewarding life is justified.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 42, loc. 692-695
Notes: 1) "lifted"But just as the selflessness of an altered state can quiet our inner critic, and the timelessness lets us pause our hectic lives, a sense of effortlessness can propel us past the limits of our normal motivation. And we’re beginning to understand where this added drive comes from. In flow, as in most of the states18 we’re examining, six powerful neurotransmitters—norepinephrine, dopamine, endorphins, serotonin, anandamide, and oxytocin—come online in varying sequences and concentrations.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 42, loc. 684-688
Without the ability to separate past from present from future, we’re plunged into an elongated present, what researchers describe as “the deep now.” Energy normally used for temporal processing gets reallocated for focus and attention. We take in more data per second, and process it more quickly. When we’re processing more information faster, the moment seems to last longer—which explains why the “now” often elongates in altered states.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 40, loc. 645-648
With our prefrontal cortex offline, we can’t run those scenarios. We lose access to the most complex and neurotic part of our brains, and the most primitive and reactive part of our brains, the amygdala, the seat of that fight-or-flight response, calms down, too.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 40, loc. 650-651
During transient hypofrontality, when the prefrontal cortex goes offline, we can no longer perform this calculation.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 40, loc. 644-645
The past is less an archived library of what really happened, and more a fluid director’s commentary we’re constantly updating.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 41, loc. 664-665
In fact, a big part of Silva’s appeal hinges on this overlap. “A Buddhist monk experiencing satori while meditating in a cave, or a nuclear physicist having a breakthrough insight in the lab, or a fire spinner at Burning Man,” he says, “look like different experiences from the outside, but they feel similar from the inside. It’s a shared commonality, a bond linking all of us together. The ecstatic is a language without words that we all speak.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 35, loc. 565-568
But once we get past the narrative wrapping paper—what researchers call the “phenomenological reporting”—we find four signature characteristics underneath: Selflessness, Timelessness, Effortlessness, and Richness, or STER for short.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 36, loc. 572-574
Then the National Geographic Channel hired him to host “Brain Games,” which became their highest-rated TV show ever and earned him an Emmy nomination.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 532-533
At the center of this complexity lies the prefrontal cortex, our most sophisticated piece of neuronal hardware. With this relatively recent evolutionary adaptation came a heightened degree of self-awareness, an ability to delay gratification, plan for the long term, reason through complex logic, and think about our thinking. This hopped-up cogitation promoted us from slow, weak, hairless apes into tool-wielding apex predators, turning a life that was once nasty, brutish, and short into something decidedly more civilized.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 37, loc. 588-591
In reviewing the literature, we discovered that almost every previous breakdown of these experiences was weighed down by content. Trying to tease apart the consciousness-altering effects of meditation, for example, means wading through religious interpretations of what those states mean.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 36, loc. 576-578
When you think about the billion-dollar industries that underpin the Altered States Economy, isn’t this what they’re built for? To shut off the self. To give us a few moments of relief from the voice in our heads.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 37, loc. 596-598
Scientists call this shutdown7 “transient hypofrontality.” Transient means temporary. “Hypo,” the opposite of “hyper,” means “less than normal.” And frontality refers to the prefrontal cortex, the part of our brain that generates our sense of self.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 38, loc. 604-606
He calls it “the subject-object shift” and argues that it’s the single most important move we can make to accelerate personal growth. For Kegan, our subjective selves are, quite simply, who we think we are. On the other hand, the “objects” are things we can look at, name, and talk about with some degree of objective distance. And when we can move from being subject to our identity to having some objective distance from it, we gain flexibility in how we respond to life and its challenges.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 38, loc. 617-621
or the next moment
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 38, loc. 614
Come Monday morning, we may still clamber back into the monkey suits of our everyday roles—parent, spouse, employee, boss, neighbor—but, by then, we know they’re just costumes with zippers.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 38, loc. 614-615
Notes: 1) or the next momentThat’s Kegan’s point. When we are reliably able to make the subject-object shift, as he points out in his book In Over Our Heads, “You start . . . constructing a world that is much more friendly to contradiction, to oppositeness, to being able to hold onto multiple systems of thinking. . . . This means that the self is more about movement through different forms of consciousness than about defending and identifying with any one form.” By stepping outside ourselves, we gain perspective. We become objectively aware of our costumes rather than subjectively fused with them. We realize we can take them off, discard those that are worn out or no longer fit, and even create new ones. That’s the paradox of selflessness—by periodically losing our minds we stand a better chance of finding ourselves.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 39, loc. 623-629
the Pale of the State.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 52, loc. 862-862
Notes: 1) bit cointhe Pale of the Church, the Pale of the Body, and the Pale of the State.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 52, loc. 862-862
That’s because the experiences at the center of this book stand outside the perimeter fence of polite society. Instead of hearing stories about the possibilities of altered states, we’re treated to cautionary tales. Stories of hubris and excess. Icarus redux.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 51, loc. 857-859
doctrine? That’s downright dangerous. In Christianity, it shows up as the tension between chapter-and-verse Roman Catholics and holy-rolling Pentecostals; in Islam, it’s solemn imams versus twirling Sufis; in China, it’s by-the-book Confucians against go-with-the-flow Taoists. In each case, a small community figures out a more direct path to knowledge and, because they blossom without the sanction of the orthodoxy, they are persecuted for it.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 54, loc. 895-898
To understand what happened to Valentine during that game, we need to understand that Mormons believe the Holy Ghost can enter a person during prayer. “The feeling of spirit entering you,” explains Valentine, “what Mormons call ‘the feeling of the Holy Ghost,’ is the very center of the religion.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 53, loc. 878-880
After all, the term “smart drug” applies to the unsupervised and often dangerous off-label use of ADHD drugs like Ritalin and Adderall. But public health wasn’t the issue.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 56, loc. 941-942
my biological skin-bag, inside the ancient fortress of skin and skull.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 56, loc. 935-935
The bishop seized the moment, condemning her for the lesser charge of cross-dressing-as-heresy. She had stolen fire and, the Church insisted, she’d die by it.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 55, loc. 918-919
But similar outcomes are happening in Fadiman’s current survey of microdosing among professionals. With more than four hundred responses from people in dozens of fields, the majority, as Fadiman recently explained, report “enhanced pattern recognition [and] can see more of the pieces at once of a problem they are trying to solve.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 49, loc. 829-831
when it comes to complex problem solving, ecstasis could be the “wicked solution” we’ve been looking for.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 50, loc. 846-847
to prompt flow, they found that soldiers solved complex problems and mastered new skills up to 490 percent faster than normal.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 49, loc. 814-814
While everyone experienced a boost in creativity—some as much as 200 percent—what got the most attention were the real-world breakthroughs that emerged: “Design of a linear electron accelerator beam-steering device, a mathematical theorem regarding NOR-gate circuits, a new design for a vibratory microtome, a space probe designed to measure solar properties, and a new conceptual model of a photon.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 49, loc. 825-828
Some were given 50 micrograms of LSD; others took 100 milligrams of mescaline. Both are microdosages, well below the level needed to produce psychedelic effects.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 49, loc. 822-823
Tibetan Buddhists38 in the 1990s showed that longtime contemplative practice can produce brainwaves in the gamma range. Gamma waves are unusual. They arise primarily during “binding,”39 when novel ideas come together for the first time and carve new neural pathways. We experience binding as “Ah-Ha insight,” that eureka moment, the telltale signature of sudden inspiration. This meant that meditation could amplify complex problem solving, but, since the monks needed to put in more than 34,000 hours (roughly thirty years) to develop this skill, it was a finding with limited application.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 47, loc. 790-796
discovered that their ability to find solutions required holding conflicting perspectives and using that friction to synthesize a new idea. “The ability to face constructively the tension37 of opposing ideas,” Martin writes in his book The Opposable Mind, “. . . is the only way to address this kind of complexity.” But developing Martin’s “opposable mind” isn’t easy. You have to give up exclusively identifying with your own, singular point of view. If you want to train this kind of creativity and problem solving, what the research shows is that the either/or logic of normal consciousness is simply the wrong tool for the job.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 47, loc. 782-788
see reference
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 48, loc. 798
meditation40 training
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 48, loc. 798-799
Notes: 1) see referenceIn a recent University of Sydney study,42 researchers relied on transcranial magnetic stimulation to induce flow—using a weak magnetic pulse to knock out the prefrontal cortex and create a twenty-to-forty-minute flow state.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 48, loc. 806-809
Under normal circumstances, fewer than 5 percent of the population pulls it off. In the control group, no one did. In the flow-induced group, 40 percent connected the dots in record time, or eight times better than the norm.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 48, loc. 810-811
The Pale of the Body is ascetic to its core: no pain, no gain. Altered states that arise within ourselves, via internal catalysts like prayer and meditation, are considered stable, reliable, and earned. If the goal is genuine transformation, then nothing as fleeting or pleasant as a flow state or psychedelic session can substitute for decades of prayer and meditation. “The ultimate wisdom of enlightenment,”11 author Sam Harris emphasized in his recent bestseller Waking Up, “whatever it is, cannot be a matter of having fleeting experiences. . . . Peak experiences are fine, but real freedom must be coincident with normal waking life.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 57, loc. 957-962
Roland Griffiths got the same results when he reran the experiment with full double-blind modern standards. When author Michael Pollan asked him15 about this unusual need for redundancy, in a 2015 New Yorker article, Griffiths’s answer said it all: “There is such a sense of authority that comes out of the primary mystical experience that it can be threatening to existing hierarchical structures. We end up demonizing these compounds. Can you think of another area of science regarded as so dangerous and taboo that all research gets shut down for decades? It’s unprecedented in modern science.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 59, loc. 980-985
Already, commercial versions of the God Helmet are available online, as are stories of DIY hackers who are reproducing its basic effects with little more than some wires and a nine-volt battery. There’s talk about developing a version for virtual reality and incorporating it in video games.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 59, loc. 993-995
the experience on the drug actually increased commitment to religious delusion ?
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 58, loc. 971
“[Psilocybin] subjects ranked their experiences13 much higher in mystical qualities than members of the control group did,” explains John Horgan in his book Rational Mysticism. “Six months later, the psilocybin group reported persistent beneficial effects on their attitude and behavior; the experience had deepened their religious faith. . . . The experiment was widely hailed as proof that psychedelic drugs can generate life-enhancing mystical experiences.” So life-enhancing, in fact, that nine out of the ten seminary students who received psilocybin ended up becoming ministers, while none of the placebo group stayed on the path to ordination.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 58, loc. 971-977
Notes: 1) the experience on the drug actually increased commitment to religious delusion ?Headlines across the country 19 read: “British policy doctor claims ecstasy is safer than riding a horse.” Tabloids had a field day.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 61, loc. 1021-1023
For every 60 million tablets of MDMA consumed, Nutt found 10,000 adverse events, or one for every 6,000 pills popped. He then compared that number to the 1-in-350 tally for horseback riding and published the results.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 61, loc. 1019-1020
Soon, as the technology matures, a novice will be able to put on the device and use these biomarkers to steer toward the same experience. But if we continue to insist that smart drugs and psychedelics are cheating, what happens as the boundaries between ourselves and our tools continue to blur?
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 60, loc. 999-1001
It’s one of the reasons people go on spiritual pilgrimages, and why evangelical megachurches are booming (with more than six million attendees every Sunday).30 Bring a large group of people together, deploy a suite of mind-melding technologies, and suddenly everyone’s consciousness is doing the wave. “Communitas” is the term University of Chicago anthropologist Victor Turner31 used to describe this ecstatic sense of unity. This feeling tightens social bonds and ignites enduring passion—the kind that lets us come together to plan, organize, and tackle great challenges. But it’s a double-edged sword. When we lose ourselves and merge with the group, we are in danger of losing too much of ourselves. Our cherished rational individualism risks being overrun by the power of irrational collectivism.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 68, loc. 1137-1145
Melissa Gregg in the Atlantic,25 “it is little wonder that workers resort to performance-enhancing drugs. . . . When so many jobs require social networking to maintain employability, these mood enhancers are a natural complement to the work day after 5 p.m. In an always-on world, professional credibility involves a judicious mix of just the right amount of uppers and downers to remain charming.” Because these substances drive us forward, they continue to sit inside society’s perimeter fence, and never mind the evidence.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 64, loc. 1078-1083
while the 4.4 million American children who took ADHD drugs were striving to become better students. Same drugs, different contexts. One is manufactured by major pharmaceutical companies and enthusiastically dispensed by suburban doctors; the other is cooked up in trailers and sold on street corners.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 64, loc. 1068-1070
Nutt had transgressed a different barrier, the Pale of the State. In very simple terms, the states of consciousness we prefer are those that reinforce established cultural values. We enshrine these states socially, economically, and legally. That is, we have state-sanctioned states of consciousness. Altered states that subvert these values are persecuted, while the people who enjoy them are marginalized. Take Ritalin and Adderall, the ADHD meds that students as young as grade school pop like candy. These drugs don’t even make an appearance on Nutt’s list,
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 63, loc. 1056-1061
Does an operator, with his back against the wall, retreat into himself, or merge with his team? This is why they relentlessly emphasize “swim buddies” (the partner you can never leave behind, no matter what) in basic training.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 217-219
“When SEALs sweep a building,” says Rich Davis, “slow is dangerous. We want to move as fast as possible. To do this, there are only two rules. The first is do the exact opposite of what the guy in front of you is doing—so if he looks left, then you look right. The second is trickier: the person who knows what to do next is the leader. We’re entirely nonhierarchical in that way. But in a combat environment, when split seconds make all the difference, there’s no time for second-guessing. When someone steps up to become the new leader, everyone, immediately, automatically, moves with him. It’s the only way we win.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 222-226
The conscious mind is a potent tool, but it’s slow, and can manage only a small amount of information at once. The subconscious, meanwhile, is far more efficient. It can process more data in much shorter time frames. In ecstasis, the conscious mind takes a break, and the subconscious takes over. As this occurs, a number of performance-enhancing neurochemicals flood the system, including norepinephrine and dopamine. Both of these chemicals amplify focus, muscle reaction times, and pattern recognition. With the subconscious in charge and those neurochemicals in play, SEALs can read micro-expressions across dark rooms at high speeds.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 256-260
“Attending festivals like Burning Man,”17 explains Oxford professor of neuropsychology Molly Crockett, “practicing meditation, being in flow, or taking psychedelic drugs rely on shared neural substrates. What many of these routes have in common is activation of the serotonin system.” But it’s not only serotonin that makes up the foundation of those collaborative experiences. In those states, all of the neurochemicals18 that can arise—serotonin, dopamine, norepinephrine, endorphins, anandamide, and oxytocin—play roles in social bonding. Norepinephrine and dopamine typically underpin “romantic love,” endorphins and oxytocin link mother to child and friend to friend, anandamide and serotonin deepen feelings of trust, openness, and intimacy. When combinations of these chemicals flow through groups at once, you get tighter bonds and heightened cooperation. That heightened cooperation, that communal vocational ecstasy, was what Page, Brin, and so many of Google’s engineers had discovered in the desert.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 327-336
accomplished on that raid comes much closer to illustrating the true core of special operations culture: at their best, they are always an anonymous team. “I do not seek recognition11 for my actions . . . ,” reads the SEAL code. “I expect to lead and be led . . . my teammates steady my resolve and silently guide my every deed.” And this ethos is reinforced every time they flip that switch, when egos disappear and they perform together in ways that are just not possible alone.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 272-276
Even for a company like Google, dedicated to unassuming goals like “10x moonshots” and organizing the entire world’s information—a 400x return? As close to priceless as they’ll ever get.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 351-352
When we say ecstasis we’re talking about a very specific range of nonordinary states of consciousness (NOSC)21—what Johns Hopkins psychiatrist Stanislav Grof defined as those experiences “characterized by dramatic perceptual changes, intense and often unusual emotions, profound alterations in the thought processes and behavior, [brought about] by a variety of psychosomatic manifestations, rang[ing] from profound terror to ecstatic rapture . . . There exist many different forms of NOSC; they can be induced by a variety of different techniques or occur spontaneously, in the middle of everyday life.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 371-376
an altered state of consciousness was both essential to mission success and elusive as hell—something they had to screen for by attrition, but couldn’t train for by design? That doesn’t make a lot of sense. That’s because, any way you slice it, ecstasis doesn’t make a lot of sense. It remains a profound experience, a place far beyond our normal selves, what author Arthur C. Clarke called a “sufficiently advanced technology”—the kind that still looks like magic to us.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 359-363
Instead of following the breath (or chanting a mantra or puzzling out a koan), meditators can be hooked up to neurofeedback devices that steer the brain directly toward that alpha/theta range. It’s a fairly straightforward adjustment to electrical activity, but it can accelerate learning, letting practitioners achieve in months what used to take years.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 401-403
flow states, those “in-the-zone” moments including group flow, or what the SEALs experienced during the capture of Al-Wazu, and the Googlers harnessed in the desert. Second, contemplative and mystical states, where techniques like chanting, dance, meditation, sexuality, and, most recently, wearable technologies are used to shut off the self. Finally, psychedelic states, where the recent resurgence in sanctioned research is leading to some of the more intriguing pharmacological findings in several decades. Taken together, these three categories define our territory of ecstasis.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 377-381
Regular waking consciousness has a predictable and consistent signature22 in the brain: widespread activity in the prefrontal cortex, brainwaves in the high-frequency beta range, and the steady drip, drip of stress chemicals like norepinephrine and cortisol.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 385-388
Flow states have been typically associated with artists and athletes; contemplative and mystical states belonged to seekers and saints; and psychedelic states were mostly sampled by hippies and ravers. But over the past decade, thanks to advances in brain science, we’ve been able to pull back the curtain and discover that these seemingly unrelated phenomena share remarkable neurobiological similarities.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 382-385
At the same time, brainwaves slow from agitated beta to daydreamy alpha and deeper theta. Neurochemically, stress chemicals like norepinephrine and cortisol are replaced by performance-enhancing, pleasure-producing compounds such as dopamine, endorphins, anandamide, serotonin, and oxytocin.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 391-393
They’re deploying these upgrades for a practical purpose: accelerated learning. By using the tanks to eliminate all distraction, entrain specific brainwaves, and regulate heart rate frequency, the SEALs are able to cut the time it takes to learn a foreign language from six months to six weeks. For a specialized unit deployed across five continents, shutting off the self to accelerate learning has become a strategic imperative.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 434-437
“communal vocational ecstasy” they’d first glimpsed at Burning Man in the Black Rock Desert of Nevada. Right after our presentation, we pedaled a couple of the ubiquitous and colorful Google bikes to the other side of campus to attend the opening of their new multimillion-dollar mindfulness center. Outfitted in soothing lime green with bamboo accents, the center features a vitality bar offering fresh-squeezed juices around the clock and a suite of meditation rooms decked out with sensor suits and neurofeedback devices similar to what we saw in the Navy’s Mind Gym.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 439-443
“G Pause” (their name for their mindfulness training program). “We’ve got active communities around the world, but the bigger challenge is getting people who aren’t already meditators to start. The folks that already sit [in meditation] understand the benefits. It’s the ones that are too busy and too stressed to slow down and need it the most that are the hardest to reach.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 446-449
In fact, many are the exact opposite: impulsive, destructive, and unintentional. But that very fact—that we are driven to pursue altered states often at a steep cost—underscores how large and sometimes hidden a role they play in our lives.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 473-474
And those states have become increasingly popular. In 2014, EDM represented almost half of all concert sales, attracting a quarter of a million concertgoers at a time and drawing the attention of Wall Street investors and major private equity firms.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 488-490
We also included the legal and illegal markets for marijuana, psychopharmaceuticals like Ritalin and Adderall, and mood-shifting painkillers like OxyContin and Vicodin.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 478-479
Yet this raises a few additional questions. If we’re already spending a ton of time and money chasing these states, and even elite organizations like the SEALs and Google haven’t definitively cracked the code, could something so elusive and confounding be worth all that trouble?
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 516-518
(see endnotes for a detailed workup of these numbers and www.stealingfirebook.com/downloads/ for a worksheet where you can calculate your own personal tally).
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 509-510
What makes these online distractions so sticky is how effectively they prime our brains for reward (mainly the feel-good neurochemical dopamine). Stanford neuroscientist Robert Sapolsky calls this priming the “magic of maybe.” When we check our email or Facebook or Twitter, and sometimes we find a response and sometimes we don’t, the next time a friend connects, Sapolsky discovered that we enjoy a 400 percent spike in dopamine.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 500-503
“I still measure the quality of my life by the number of times I get into the zone,” explains Ulmer. “If I spend two weeks at Burning Man and only get that experience a handful of times, then I feel cheated. It wasn’t worth it. But now I can try different things. That’s the real change. Now I know I have options, that there are actual comparisons to make.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 210, loc. 3386
Notes: 1) skills and state contraststhe ability to choose the right tool<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 210, loc. 3386-3388
Notes: 1) skills and state contraststhe ability to choose the right tool
Not long after that near-fatal drowning, he had another brush with death. In the hospital, Lilly had a textbook NDE and, as he reported afterward, was visited by the same entities he’d been encountering in the float tank. They presented him with a choice: leave with them for good, or return to his body, heal, and focus on more worldly pursuits. Finally, Lilly got the message. He abandoned his psychedelic research and retired with his wife to Hawaii, where he lived to the ripe age of eighty-four.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3339
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3339-3342
After all this, Lilly came to one overarching conclusion: “What one believes to be true is true or becomes true, within certain limits to be found experientially and experimentally. These limits are further beliefs to be transcended. In the province of the mind, there are no limits.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3346
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3346-3348
This leaves us with four rules of thumb to carry into our exploration of these states. It’s not about you and it’s not about now help us balance ego inflation and time distortion. While don’t become a bliss junky and don’t dive too deep ensure that we don’t get seduced by the sensations and information that arise in altered states.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3351
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 208, loc. 3351-3353
Research shows we’re more likely to keep habits23 that are tied to cultural milestones. So connecting practices to preexisting traditions can make them easier to stick to. Daily? Link it to sunrise or sunset, dinners, or bedtime. Weekly? Make it your own contemporary TGIF or Sabbath observance. Monthly? Connect it to the lunar cycle or the first or last days of the calendar. Seasonal? Solstices, equinoxes, Christmas, Easter, July Fourth, and Halloween all work and often come with vacation days attached. Annual? Take your pick: birthdays, anniversaries, New Year’s, back to school, whatever’s significant to you.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3453
Notes: 1) it makes sense that an occassional ecstatic event is seasonal because it provides a contrastfrom other days but also rememberin to hav it.no wonder it creates excitement and anticipation and ultimately celebration and release<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3453-3458
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 214, loc. 3443-3444
Notes: 1) it makes sense that an occassional ecstatic event is seasonal because it provides a contrastfrom other days but also rememberin to hav it. no wonder it creates excitement and anticipation and ultimately celebration and releaseAction sports, yoga, live music, sex, brain stimulation, meditation, personal growth workshops, adventure travel, etc.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 214, loc. 3443
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 213, loc. 3430-3433
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 213, loc. 3436-3440
So how to pursue this path without getting “hooked on the high”? If we use the ecstasis equation to help us answer the question, “What is the best way to get into the zone?” then we need to add an additional concept here—hedonic calendaring—which helps us figure out how often we should get into the zone. Hedonic calendaring provides a way to hack the ecstatic path without coming undone. It gives us a method to integrate hard-and-fast approaches like extreme skiing and psychedelics with slow and steady paths like meditation and yoga.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 213, loc. 3436
Yet salt, sugar, fat provide a fraction of the payoff of ecstasis. In that state, we get access to all the brain’s feel-good neurochemistry at once. For most of evolutionary history, nonordinary states were rare and precious experiences. So when we consider how readily accessible the four forces are making them today, it’s important to remember that we’re tinkering with impulses that are millions of years old.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 213, loc. 3430
But the final analysis is simple: are any of these pursuits worth the time, effort, and money we invest in them? Are we more energetic, empathetic, and ethical afterward? If not, they’re just distractions or diversions from our lives. “I care not a whit for a man’s religion,” Abraham Lincoln once quipped, “unless his dog is the better for it.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 212, loc. 3409
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 212, loc. 3409-3411
As Hemingway reminds us,25 “the world breaks everyone.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3481
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3481-3482
Ironically, the attempt to avoid suffering often creates more of it, leaving us susceptible to the most predictable trap of all: spiritual bypassing. “[It’s] a widespread tendency to use spiritual ideas and practices,”26 says John Welwood, the psychologist who coined the term, “to sidestep or avoid facing unresolved emotional issues, psychological wounds, and unfinished developmental tasks.” Typically, what gets bypassed on an ecstatic path are the mundane dissatisfactions of regular life. If those dissatisfactions are too intense, non-ordinary states can offer a tempting escape. But rather than bypassing these challenges, we can accept them and even draw power from them. This response has a paradoxical name: vulnerable strength. Brené Brown, whose books and TED talks on the subject have resonated with massive audiences, explains it this way: “Embracing our vulnerabilities is risky but not nearly as dangerous as giving27 up on love and belonging and joy—the experiences that make us the most vulnerable. Only when we are brave enough to explore the darkness will we discover the infinite power of our light.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3483
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3483-3493
For the stickier (and likely, more enjoyable) weekly, monthly, and annual practices, you’re putting in buffers to ensure you don’t do them too much.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3460
Once a year, set your indulgences up on a shelf, go thirty days cold turkey, and use this time to recalibrate. Attach the hiatus to traditional seasons of forbearance—Lent, Yom Kippur, Ramadan—or impose your own.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3464
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3464-3465
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 215, loc. 3460-3461
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3473-3476
“The road of excess leads to the palace of wisdom,”24 William Blake once wrote. Hedonic calendaring adds guardrails to that road. By dismantling the “oughts and “shoulds” of the orthodox approach, while avoiding the pitfalls of “if it feels good, do it” sensation seeking, we up the odds of getting to our destination in one piece.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 216, loc. 3473
The love that “tells me I am everything” arises from the awe and connection that we often experience in these states. Endorphins, oxytocin, and serotonin soothe our vigilance centers. We feel strong, safe, and secure.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 217, loc. 3499
The Indian philosopher Nisargadatta summed up the dilemma well: “Love tells me I am everything. Wisdom tells me I am nothing.28 And between these two banks, flows the river of my life.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 217, loc. 3495
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 217, loc. 3495-3497
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 218, loc. 3507-3508
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 217, loc. 3499-3500
“Ring the bells that still can ring,31 forget your perfect offering. There is a crack, a crack in everything. It’s where the light gets in.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 218, loc. 3513
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 218, loc. 3513-3515
Ecstasis doesn’t absolve us of our humanity. It connects us to it. It’s in our brokenness, not in spite of our brokenness, that we discover what’s possible.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 218, loc. 3507
Zeus said no, Prometheus stole fire anyway, and got punished. That’s the part we all remember. But Zeus wasn’t finished with the humans, or the brothers. He wanted to make sure that no one challenged his power ever again. So he made a woman, Pandora, whose name means “all giving,” and gave her a box filled with the tragedies of life to unleash on the world.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 219, loc. 3561
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 3561-3564
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 3579-3581
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 3542-3547
Just as old sailing wisdom favored “high and slow”—meaning that you pointed your boat as close to the eventual upwind destination as possible—we are steeped in a “high and slow” culture of relentless goal setting and linear forward progress. It’s why, in the United States, more than half of paid vacation days go unclaimed and we perversely brag about clocking 60–80-hour workweeks (even though our effectiveness drops after 50 hours). We valorize suffering and sacrifice, even when the victories they provide are hollow. Surrendering any of that hard-fought ground to pursue nonordinary states can seem, at first glance, irresponsible, or, at a minimum, deeply counterintuitive.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 219, loc. 3542
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 3615-3618
We’ve got free tools to tally your own Altered States Economy, plan your Hedonic Calendar and discover your flow profile. We also offer intensive trainings to unlock personal and organizational high performance.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 219, loc. 3579
So, for now, the leading candidates to explain how our waking conscious self shuts off in nonordinary states are: transient hypofrontality, transient hyperconnectivity, default mode network interruption, and cortico-thalamic gating (Henri Bergson’s’ original idea, which Aldous Huxley popularized in The Doors of Perception).
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 219, loc. 3615
While the details are subject to constant revision, we believe that the fundamental argument we’re making about our neurobiological “knobs and levers” affecting our psychological experience will only become stronger over time.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 219, loc. 3611
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, loc. 3611-3613
four forces?
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 158, loc. 2501
In other words, it’s a transformation engine tailor-made to invoke the selflessness, timelessness, effortlessness, and richness of STER.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 158, loc. 2501-2502
Notes: 1) four forces?“At Burning Man, we’ve found a way to break out of the box that confines us.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 158, loc. 2496-2497
At least as far back as the Eleusinian Mysteries, which counted notables such as Plato and Pythagoras among its members, ecstatic culture has often been spread by an educated elite.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 168, loc. 2671-2672
former Apple executive Peter Hirshberg wrote in his book From Bitcoin to Burning Man and Beyond, “Burners are particularly skilled at functioning during chaotic crises when normal services—running water, electricity, communication channels and sanitation systems—are not available. Burners don’t just survive in such an environment; they create culture, art and community there.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 166, loc. 2645-2647
to smartphone apps (including Firechat, which was designed as a peer-to-peer communication network at Burning Man, but then played a critical role in protest movements in Taiwan, Hong Kong, and Russia). And because Burners vigorously defend an open-source, noncommercial approach, their efforts are easy to share and hard to censor.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 167, loc. 2655-2658
Over the years, MaiTai members have founded and led companies with an aggregate market value of more than $20 billion,33 making them one of the more influential (and athletic) groups of entrepreneurs in the world.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 172, loc. 2742-2744
“We find the right mix of really interesting people and subject them to powerful state-changing experiences that accelerate social bonding. It’s the same formula used at Burning Man and at Summit.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 172, loc. 2733-2734
By realizing that non-ordinary states are more than just a recreational diversion and can, in fact, heighten trust, amplify cooperation, and accelerate breakthroughs, a new generation of entrepreneurs, philanthropists and activists is fundamentally disrupting business as usual.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 174, loc. 2766-2768
“We learned that when you take a bunch of really bright, diverse people,” explains Rosenthal, “and let them share a dynamic immersive experience, you get powerful results. Lifelong friendships were formed. It removed the tedious, transactional nature of networking. I guess you could say that one of the things we discovered on that trip was that altered states accelerate business.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 170, loc. 2708-2711
MaiTai Global, started in 2006 by venture capitalist Bill Tai 31 and kitesurfing legend Susi Mai, uses action sports (mostly surfing and kitesurfing) as a stimulant for group flow and entrepreneurship.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 171, loc. 2726-2728
The series, which has been called “TED crossed with Burning Man”30 or “the hipper Davos,” has struck a chord.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 170, loc. 2712-2713
By using non-ordinary states to promote community, they’re reimagining the staid world of professional networking, philanthropy, and venture capital.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 171, loc. 2724-2725
“We wanted to build a town dedicated . . . to what altered states really can provide: creativity, collaboration, innovation, entrepreneurship and community. And because our community shared that vision, we were able to crowdsource $40 million and buy a ski area (Powder Mountain) that sits on a mountain range the size of Manhattan.” So while folks at Burning Man are just starting to build themselves a homeland, Summit has already taken that step.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 169, loc. 2697-2700
Just seven weeks earlier, the hosts, Summit Series, had bought the entire mountain. “We wanted a permanent home,29 explains Summit cofounder Jeff Rosenthal.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 169, loc. 2695-2697
“After working in this 3D immersive space,” he admits, “it’s really challenging to go back to creating images that are on a rectangle hanging on a wall. I never realized how limiting the frames were.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 145, loc. 2336-2337
His most recent project, appropriately named MicroDoseVR, is an immersive VR game offering an atom’s-eye tour through many of Shulgin’s alphabetamine compounds.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 145, loc. 2342-2343
2012 study found that encounters with perceptual vastness, be it the endless spiral of galaxies in the night sky or Jones’s’ larger-than-life projections, triggers a self-negating, time-dilating sense of awe. And this happens automatically—which means an encounter with Jones’s projections could be enough to drive subjects into a deeply altered state, willingly or not.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 144, loc. 2328-2330
On the Sydney Opera House,20 for instance, he live-painted during a performance by the YouTube Symphony Orchestra.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 143, loc. 2307-2309
When tunes were playing, the distance between housemates decreased by 12 percent, while chances of cooking together increased by 33 percent, laughing together by 15 percent, inviting other people over by 85 percent, saying “I love you” by 18 percent, and, most tellingly, having sex by 37 percent.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 142, loc. 2283-2285
“What we’re building in the Dance Temple,”18 explained one of its designers, “is a piece of tech to disintegrate peoples’ egos en masse.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 142, loc. 2292-2294
that Neanderthal communities gathered beside the images they had painted, and they chanted or sang in some kind of shamanic ritual, using the reverberations of the cave to magically widen the sound of their voices.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 141, loc. 2263-2264
recent years, scientists have found that a great many of the world’s oldest religious sites have peculiar acoustic properties. While studying the Arcy-sur-Cure caves10 in France, University of Paris music ethnographer Iegor Reznikoff discovered that the largest collection of Neolithic paintings are found more than a kilometer deep. They’d been intentionally located at the most acoustically interesting spots in the cave: the parts with the most resonance.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 140, loc. 2257-2261
Scientists working in the burgeoning field of neuro-musicology15 have begun using high-powered imaging to decode these effects. When listening to music, brainwaves move from the high-beta of normal waking consciousness down into the meditative (and trance-inducing) ranges of alpha and theta. At the same time, levels of stress hormones like norepinephrine and cortisol drop, while social bonding and reward chemicals like dopamine, endorphins, serotonin, and oxytocin spike. Add in entrainment—where people’s brains synch to both the beat and to the brains of those around them—and you’ve got a potent combination for communitas.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 141, loc. 2275-2280
proof that these four forces are driving a revolution is everywhere you look.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 154, loc. 2473-2474
(movement, sound, light, and sensors)
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2460-2460
In the past, to get a glimpse of “no-self,” it might have taken a high-risk wingsuit flight, a decade of monastic isolation, or a heroic (and possibly reckless) dosage of an unpredictable substance. Today, we can use innovations like the Flow Dojo to skillfully tweak and tune the knobs and levers of our bodies and brains and get similar breakthroughs with a fraction of the breakdowns.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2461-2464
setup—Larry was feeling his wife’s heart beat and watching his flower pulse to her heart’s rhythms, and she was watching and feeling his. By deliberately crossing the feedback loops, the installation creates technologically mediated empathy, no talking required. So absorbing was the experience that when the nighttime sprinklers came on and accidentally sprayed them, they just assumed it was part of the simulation.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2455-2458
Sitting in an enclosed dome, he and his wife put on small backpack subwoofers (so they literally felt the bass through their bodies, not their ears).
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2454-2455
Even so, when Sergey Brin, one of Google’s cofounders, stepped up to the looping swing, we were unsure how it was going to go. Brin is an action sports enthusiast, pursuing everything from BASE jumping to kitesurfing. At the TED conference a few years ago, he also topped the leaderboard on an EEG mindfulness training demo. So, while he already had some experience in both the physical and mental elements of this training, he had never put the two together.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 151, loc. 2435-2438
Embodied cognition research shows that we become more flexible and resilient when we train our bodies and brains together, and in increasingly dynamic situations. It’s why the SEALs say “you don’t ever rise to the occasion, you sink to your level of training” and then proceed to overtrain for every scenario possible.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2447-2449
Try remaining centered under more challenging conditions (like managing heart and brain activity while swinging upside down). If we want to train for stability in all conditions, the science suggests, it’s essential to practice with instability first.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 152, loc. 2450-2452
And if I could be in extreme pain and still remain peaceful and clear, then I thought maybe other people could do this, too. In that instant, everything I believed about human potential shifted.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 146, loc. 2360-2361
In his work with heart rate variability, Siegel’s found that by upgrading the tone to include a visual display, and adding in an EEG layer—so there’s neurofeedback to go along with the biofeedback—he can get whole groups of people to synchronize their heart rates and brainwaves and drive them into group flow.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 147, loc. 2376-2378
“Consciousness-hacking technology is going to become as dynamic, available, and ubiquitous as cell phones. Imagine what happens if we can use personal technology to shift these experiences on demand, to support and catalyze the most important changes we can make at scale. More and more it’s looking like we can retune the nervous system of the entire planet.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 148, loc. 2394-2396
“For the past three hundred years,” Siegel explains, “there has been a split between science and religion. But now we have the ability to investigate this domain and innovate around spirituality.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 148, loc. 2390-2392
Jeffery Martin, also cofounded the Transformative Technology Conference23 and started organizing consciousness-hacking meet-ups.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 148, loc. 2384-2386
Each day, participants engaged in a range of activities, from sleep tracking, to diet and hydration, to functional movement (designed to undo the imbalances of deskbound lives), to brain entraining audio and respiration exercises.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 149, loc. 2415-2416
figure out their secret to getting into flow so readily. Time after time, they told us it came down to two things: the right triggers and gravity.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 150, loc. 2420-2421
Historically, every time ecstasis has shown up, it’s led to upheaval and misuse. That’s because, while the insights provided by the four forces may give us a better way to stabilize these experiences and lessen that risk, there will always be those who try to bend them to other ends.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 181, loc. 2874-2876
In both cases, we’ll see how the application of nonordinary states, as with other powerful technologies, has both ethical and political ramifications.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 182, loc. 2882-2883
And despite the ostensibly pious intent of the gathering, there was plenty of drinking and fornicating. Even back then, the “Holy Ghost feeling” was tough to keep under wraps.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 180, loc. 2857-2859
One of Bob Kegan’s graduate students recently determined that by college, many Millennials have reached stages of adult development43 (with all their associated increases in capacity) that took their parents until middle age to attain.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 175, loc. 2794-2796
Since rolling out their program, Aetna estimates40 that it’s saved $2,000 per employee in health-care costs, and gained $3,000 per employee in productivity.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 175, loc. 2786-2788
Take the first force, psychology.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 174, loc. 2781-2781
Take the first force, psychology. Thanks to the work of Martin Seligman and others, a new generation of positive psychologists is repackaging meditation, stripping out its spiritual connotations, and providing evidenced-based validation for its benefits. This new version, known as mindfulness-based stress reduction, is gaining traction in places that would never have embraced earlier variants.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 174, loc. 2781-2783
On the higher-tech end of the spectrum, state-changing treatments like transcranial magnetic stimulation are now outperforming antidepressants, and many Silicon Valley executives are going off-label, using the technology to ‘“defrag’” their mental hard drives and boost performance. Companies like Dave Asprey’s Bulletproof Executive are helping people biohack their daily lives with everything from smart sensors to nootropics (brain stimulating supplements). This market is expanding so rapidly that Bulletproof has grown into a nine-figure enterprise47 in less than four years and hundreds of other companies are flooding into the market.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 176, loc. 2804-2810
And cannabis is merely the most obvious sign of this change. Whether we’re examining psychedelics like LSD or empathogens like MDMA, mind-altering drugs are more popular than at any other time in history. Thirty-two million Americans use psychedelics51 on a regular basis (that’s nearly one in ten) and report considered reasons for doing so. According
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 176, loc. 2819-2822
Transcendence, not decadence, appears to be driving use forward.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 177, loc. 2824-2824
The whole of the cannabis economy49 (including legal and medical) is now worth roughly $6.2 billion, and slated to rise to $22 billion by 2020. As of late 2016, twenty-eight states have legalized medical marijuana, and eight of them—Colorado, Washington, Oregon, Nevada, California, Massachusetts, and Alaska, and the District of Columbia—have legalized recreational use as well.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 176, loc. 2812-2815
Over the next few years the watch will connect these sensors to become a platform for open-source research into everything from obesity to peak performance. In one twenty-four-hour beta test, more than thirty thousand people volunteered to contribute their personal data to Alzheimer’s research, making it four times the size of the next-largest study overnight.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 177, loc. 2829-2831
With a handful of plug-and-play sensors, we can now measure hormones, heart rates, brainwaves, and respiration and get much clearer pictures of our real-time health.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 177, loc. 2826-2827
With the data these devices are providing, we can shortcut our way not only to better health, but to deeper self-awareness, taking weeks and months to train what used to take yogis and monks decades to master.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 177, loc. 2834-2835
It’s what prompted him to coin the term “net neutrality” back in 2003 and spawn an ongoing conversation about the balance of civic and corporate power online. It’s also where he got the title of his 2010 book.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 185, loc. 2954-2955
As John Lilly’s early research established, it’s the knowledge of how to tweak the knobs and levers in our brain. When we get it right, it produces those invaluable sensations of selflessness, timelessness, effortlessness, and richness.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 186, loc. 2961-2963
As John Lilly’s early research established, it’s the knowledge of how to tweak the knobs and levers in our brain. When we get it right, it produces those invaluable sensations of selflessness, timelessness, effortlessness, and richness. And that final step—the richness? That’s the information that we can’t normally access. As W. B. Yeats put it,14 “The world is full of magic things patiently waiting for our senses to grow sharper.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 186, loc. 2961-2965
The tug-of-war between access and control becomes a battle for cognitive liberty. And while nation states have consistently sought to regulate external chemicals that shape consciousness, what happens when they attempt to regulate internal neurochemistry? If that sounds far-fetched, consider that elite athletes already submit “biological passports” to the World Anti-Doping Agency15 to confirm their unique baselines for hormones, blood profiles, and neurochemicals. If they fluctuate from that baseline without official permission, they are penalized and even brought up on criminal charges. Much in the same way that regimes used to declare certain books subversive, it’s not too much of a stretch to imagine a government declaring certain brain chemistry subversive. A telltale combination of neurotransmitters coursing through your bloodstream could be enough to get put on a watch list, or worse.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 186, loc. 2966-2973
discovered that information technologies, ranging from the telegraph to radio, movies, and ultimately, the internet, tend to behave in similar ways—starting out utopian and democratic and ending up centralized and hegemonic. In his book The Master Switch, Wu calls this “the Cycle,” a recurring battle between access and control that shows up whenever these breakthroughs emerge.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 185, loc. 2939-2942
Long before Linus Torvalds gave away the source code to Linux, or Sasha Shulgin published his chemical cookbook, or Elon Musk shared all of Tesla’s car and battery patents—long before there was even a term for it—Lilly took a stand for open-sourcing ecstasis.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 184, loc. 2922-2924
And with the four forces, information technology is moving from the virtual to the perceptual.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 186, loc. 2959-2960
As background research for his novel One Flew Over the Cuckoo’s Nest, which was set in a mental institution, Kesey had been volunteering at a U.S. Veterans Administration hospital (which, unbeknownst to the young author and many of the administering doctors, was part of MK-ULTRA). To earn a little extra money, a friend of his had turned him onto the $75 per session experiments the docs were running there on “psychomimetic” drugs—meaning chemicals like LSD that mimicked the mental breakdown of psychosis.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 188, loc. 3003-3007
And, in the annals of unintended consequences, MK-ULTRA gets a notable mention for accidentally unleashing a leviathan: the psychedelic revolution of the 1960s.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 188, loc. 2996-2997
Tom Wolfe recounts in The Electric Kool-Aid Acid Test, “and somehow drugs were getting up and walking out of there and over to Perry Lane.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 189, loc. 3012-3013
What happened next became the well-documented subject of counterculture lore. Kesey moved the experiment into the hills above Palo Alto, Hunter S. Thompson, the Hells Angels, and Neal Cassady (from Kerouac’s On the Road fame) all showed up, as did a strange little band called the Grateful Dead, led by a chinless but oddly magnetic guitarist named Jerry Garcia. Armed with gallons of day-glo paint,23 strobe lights, and the prototypical art car, a tricked out 1939 International Harvester bus named “Further,” Kesey and his Merry Pranksters birthed West Coast psychedelic culture. Control of the Master Switch had been wrestled away from the spooks, and neither Silicon Valley nor the wider world would ever be the same.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 189, loc. 3017-3023
No one was better at scanning for those ideas than Jim Channon, a lieutenant colonel in the Army and veteran of two tours of duty in Vietnam. “I just made it my weekend duty to get around all of these places, like Esalen, make friends and find out what this esoteric technology really was.”25 By the time he’d finished his hot tubs and crystals junket, Channon had, for all intents and purposes, gone native. He penned The First Earth Battalion Operations Manual,26 making the case that deliberately cultivating nonordinary states, including the ability to experience universal love, to perceive auras, to have out of body experiences, to see into the future, and, perhaps most memorably, “to encounter the enemy with sparkly eyes”—could transform the military.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 190, loc. 3029-3036
In 2014, Ryan Holiday released a bestselling book12 on exactly this subject, The Obstacle Is the Way. It offered an update to the Roman Stoic Marcus Aurelius’s claim that “the impediment to action advances action. What stands in the way becomes the way.” And this is certainly true of the ecstatic way. All that “effortless effort” takes a lot of work.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 205, loc. 3303
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 205, loc. 3303-3306
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 204, loc. 3283-3284
surfer who in a flow state drops into a wave and strings together a series of moves he’s never pulled off before may need months of hard training to be able to reproduce them in a contest.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 204, loc. 3283
Making this switch can help us unburden our psychology and manage the intensity of a wider range of states without overclocking our processors. But, when it comes to exploring those states, we still have to contend with a whole set of “known issues.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3232
And once we do take those freely shared ideas and use them to unlock nonordinary states for ourselves, what do we find? A self-authenticating experience of selflessness, timelessness, effortlessness, and richness. In short, all the ingredients required for a rational mysticism. It cuts out the middlemen, and remains rooted in the certainty of the lived experience. This ability to continually update and advance our own understanding, ahead of anyone else’s attempts to constrain or repurpose them may be the key to breaking the stalemate.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 200, loc. 3210
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 200, loc. 3210-3214
“If we believe in liberty,” he writes, “it must be freedom from both private and public coercion.” It’s for this reason that so many of the Prometheans we’ve met in this book have taken a stand for open sourcing.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 199, loc. 3204
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 199, loc. 3204-3206
In short, Orwell feared that our fears will ruin us. Huxley feared that our desire will ruin us.” And while the possibility of a nation deliberately invading our minds to shape and control behavior may feel like a relic of Cold War paranoia, the prospect of multinational corporations deliberately tweaking our subconscious desires to sell us more stuff is already here.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 199, loc. 3194
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 199, loc. 3194-3196
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3246-3251
Often, the experience of selflessness is so new and compelling that it feels like no one else has ever felt this way before—that it’s evidence of some kind of sacred anointment. When triggered by an awe-inspiring encounter with the Wailing Wall, the result is Jerusalem Syndrome. But the same thing can happen with any ecstatic experience. It’s why Burning Man advises people to not make any life-changing decisions for at least a month following the event,3 and why online psychedelic message boards like Erowid are filled with advice like “Don’t believe everything you think.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3246
Exposure to the selflessness, timelessness, effortlessness, and richness of an ecstasis can go wrong, and wrong in predictable ways. For each of these experiences, there is a corresponding danger that, if we know about it ahead of time, we have a chance to avoid.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3234
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3234-3236
Rather than deciding, “Wow, I just had a mystical experience where I felt like Jesus Christ!” they conclude, “Wow, I am Jesus Christ. Clear the decks, people, I’ve got things to do!”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3240
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 202, loc. 3240-3241
As Buddhist teacher and author Jack Kornfield6 reminds us, “after the ecstasy, the laundry.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 203, loc. 3263
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 203, loc. 3263-3264
In nonordinary states, dopamine often skyrockets, while activity in the prefrontal cortex plummets. Suddenly we’re finding connections between ideas that we’ve never even thought of before. Some of those connections are legitimate insights; others are flights of fancy.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 203, loc. 3252
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 203, loc. 3252-3253
most surprisingly—shopping and spirituality seem to rely on similar neuronal circuitry.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 194, loc. 3104-3105
most surprisingly—shopping and spirituality seem to rely on similar neuronal circuitry. When deeply religious subjects view sacred iconography or reflect on their notion of God, brain scans reveal hyperactivity in the caudate nucleus, a part of the pleasure system that correlates with feelings of joy, love, and serenity. But Lindstrom and Calvert found that this same brain region lights up when subjects view images associated with strong brands like Ferrari or Apple. “Bottom line,” Calvert reported, “there was no discernible way to tell the difference between the ways subjects’ brains reacted to powerful brands35 and the way they reacted to religious icons and figures. . . . Clearly, our emotional engagement with powerful brands. . . . shares strong parallels with our feelings about religion.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 194, loc. 3104-3111
What began as an attempt to infuse the military with the idealism of the human potential movement had devolved into a tool for psychological warfare—and the Cycle churned on.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 191, loc. 3058-3060
But that afterthought got noticed. In May 2003, Newsweek ran a short blurb “PSYOPS: Cruel and Unusual,”29 revealing that U.S. military detention units were using a combination of bright light, disorienting sounds, and other consciousness-shifting tactics to break Iraqi prisoners. “Trust me, it works,” says one U.S. operative. “In training, they forced me to listen to the Barney ‘I Love You’ song for 45 minutes. I never want to go through that again.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 191, loc. 3052-3056
And this repeated pattern of the “spooks lying down with the kooks,” from hippie float tanks at the SEALs’ Mind Gym, to Kesey’s misadventures at the V.A. hospital, to Lieutenant Colonel Channon hottubbing at Esalen, to the Pentagon at Burning Man, clearly highlights the back and forth contest for control of the Master Switch. More critically, it illustrates one of the central challenges of ecstasis: how to ensure that powerful techniques for altering consciousness don’t get used for the wrong reasons.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 192, loc. 3078-3082
In heavily redacted documents recently released through the Freedom of Information Act,30 it turns out that the FBI has conducted a multiyear intelligence program at Burning Man. The official reason was to scout for domestic terrorists and track potential threats from Islamic extremists. More likely, the FBI was taking a page out of their old COINTELPRO playbook,31 the one used in the 1960’s to infiltrate and destabilize the Black Panthers,
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 192, loc. 3065-3069
If that were the case, then one would expect increased surveillance of the event, heightened policing, insertion of agents provocateurs, and aggressive prosecution of nonviolent crimes. And while it’s hard to tell if it’s an anomaly or the beginning of a trend,32 in 2015, plainclothes and undercover agents spiked, and arrests at the festival were up 600 percent.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 192, loc. 3070-3073
Under those amped-up conditions, salience—that is, the attention paid to incoming stimuli—increases. But, with the prefrontal cortex down-regulated, most impulse control mechanisms go offline too. For people who aren’t used to this combination, the results can be expensive. The video game industry may have gone further down this path than anyone. “Games are a multi-billion dollar industry that employ the best neuroscientists42 and behavior psychologists to make them as addicting as possible,” Nicholas Kardaras, one of the country’s top addiction specialists, recently explained to Vice. “The developers strap beta-testing teens with galvanic skin responses, EKG, and blood pressure gauges. If the game doesn’t spike their blood pressure to 180 over 140, they go back and tweak the game to make it have more of an adrenaline-rush effect. . . . Video games raise dopamine to the same degree that sex does, and almost as much as cocaine does. So this combo of adrenaline and dopamine are a potent one-two punch with regards to addiction.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 196, loc. 3146
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 196, loc. 3146-3155
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 195, loc. 3127-3130
But we were at the Advertising Research Foundation38 to discuss the next step: the move from an experience economy to what author Joe Pine calls the “transformation economy.” In this marketplace, what we’re being sold is who we might become—or as, Pine explains: “In the transformation economy, the customer IS the product!”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 195, loc. 3127
To understand this possibility, it’s helpful to understand a few of the developments that have led to today’s marketplace. At the tail end of the twentieth century, we started moving from the selling of ideas,36 the so-called information economy, toward the selling of feelings, or what author Alvin Toffler called the “experience economy.” This is why retail shops started to look like theme parks. Why, instead of stocking ammo on their shelves like Wal-Mart, the outdoor retailer Cabela’s turns their stores into a hunter’s paradise of big-game mounts, faux mountainsides, and giant aquariums.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 195, loc. 3120
To understand this possibility, it’s helpful to understand a few of the developments that have led to today’s marketplace. At the tail end of the twentieth century, we started moving from the selling of ideas,36 the so-called information economy, toward the selling of feelings, or what author Alvi <You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 195, loc. 3120-3125
They also discovered how to prompt that impulse. For the pitch to be most effective—that is, to earn the most money—it had to be highly engaging and display significant contrast between positive and negative story elements. Since the speaker was wearing a discreet earpiece while onstage, the researchers could use biofeedback to provide instant feedback, telling her to change the story on the fly, increasing tension, deepening empathy, and constantly priming the audience to alter their behavior.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 197, loc. 3168
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 197, loc. 3158-3160
Once you understand what Lindstrom calls “buyology,” you can imprint unsuspecting consumers with all the pleasure-producing neurochemistry you can coax out of them. And as with the intelligence community’s efforts, ecstasis at 100 percent is transformational, but ecstasis at 80 percent is, well, pretty much whatever you want it to be.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 197, loc. 3158
<You have reached the clipping limit for this item>
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 197, loc. 3168-3171
If the shift in psychology that led us from Esalen to Eckhart was about greater permission to explore, then Kegan and his colleagues have given us the next piece of that puzzle: a map of where we’re going. By bridging the gap between peak states and personal growth, these discoveries validate ecstasis as a tool not only for self-discovery, but also for self-development.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 94, loc. 1510-1513
Consciousness, it turns out, goes straight to the bottom line.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 94, loc. 1509-1510
In short, altered states can lead to altered traits.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 94, loc. 1514-1515
Somehow, changes in the body—freezing the face with a neurotoxin—were producing changes in the mind: the ability to feel sadness or empathy. The horse appeared to be steering the rider. And we now know why. Our facial expressions are hardwired5 into our emotions: we can’t have one without the other. Botox lessens depression because it prevents us from making sad faces. But it also dampens our connection to those around us because we feel empathy by mimicking each other’s facial expressions.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 97, loc. 1548-1552
The heart has about 40,000 neurons that play a central role in shaping emotion, perception, and decision making. The stomach and intestines complete this network, containing more than 500 million nerve cells, 100 million neurons, 30 different neurotransmitters, and 90 percent of the body’s supply of serotonin (one of the major neurochemicals responsible for mood and well-being). This “second brain,” as scientists have dubbed it, lends some empirical support to the persistent notion of gut instinct.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 97, loc. 1561-1565
For those interested in shifting states, knowing that the body can drive the mind gives us a whole new set of knobs and levers with which to play. Einstein’s quote “you cannot solve a problem at the level at which it was created” is invariably used to encourage higher, more expansive solutions. But the opposite is equally true. Sometimes, lower, more basic solutions can have just as big an impact.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 98, loc. 1577-1580
And two minutes of the pose was enough to increase levels of the dominance hormone testosterone by 20 percent and decrease the stress hormone cortisol by 15 percent. While the field of embodied cognition is in its infancy, and there is still lots of work to be done replicating studies and integrating insights, these early findings suggest a tighter linkage between our minds and our bodies than most of us would ever suspect.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 98, loc. 1573-1576
And today, with so much of our emotional and social lives mediated by screens, we’ve become little more than heads on sticks, the most disembodied generation of humans that has ever lived.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 100, loc. 1597-1598
In direct contrast to skin-and-bone ascetics who sought ecstasis by ignoring or denying the body, these monks believed transcendence began with its total mastery.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 99, loc. 1593-1594
Defined by heightened empathy, an expanded capacity to hold differing and even conflicting perspectives, and a general flexibility in how you think of yourself, self-transforming is the developmental stage we tend to associate with wisdom (and Roger Martin’s Opposable Mind). But not everyone gets to be wise. While it usually takes three to five years for adults to move through a given stage of development, Kegan found that the further you go up that pyramid, the fewer people make it to the next stage. The move from self-authoring to self-transforming for example? Fewer than 5 percent of us ever make that jump.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 92, loc. 1489-1493
He discovered that while some adults remained frozen in time, a select few achieved meaningful growth. Right around middle age, for example, Kegan noticed that some people moved beyond generally well-adjusted adulthood, or what he called “Self-Authoring,” into a different stage entirely: “Self-Transforming.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 92, loc. 1487-1489
Can recurring access to these states really “nurture what is best within ourselves?” Can they, as Alan Watts suggested, be used to “cultivate the exceptional”?
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 91, loc. 1477-1478
“Psychology is not just the study of weakness and damage, it is also the study of strength and virtue. Treatment is not just fixing what is broken, it is nurturing what is best within ourselves.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 91, loc. 1474-1475
Flow researchers have achieved comparable results without drugs, simply by altering neurobiological function. In 2007, working with Iraq War veterans at Camp Pendleton, occupational therapist Carly Rogers of the University of California, Los Angeles blended surfing (a reliable flow trigger) and talk therapy into a treatment for PTSD. It was essentially the same protocol Mithoefer used, only with the flow generated by action sports substituting for MDMA.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 89, loc. 1435-1438
Mithoefer found that the benefits provided by one to three rounds of MDMA therapy lasts for years.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 89, loc. 1432-1433
In a 2014 paper published in the Journal of Occupational Therapy, Rogers reported that after as little as five weeks in the waves, soldiers had a “clinically meaningful improvement in PTSD symptom severity and in depressive symptoms.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 89, loc. 1442-1444
recent study done by the military found that 84 percent of PTSD subjects who meditated for a month could reduce or even stop taking selective serotonin reuptake inhibitors (SSRIs).
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 89, loc. 1445-1446
Taken together, all this work—from the NDE studies to the cancer and trauma research to the flow and meditation programs—demonstrates that even brief moments spent outside ourselves produce positive impact, regardless of the mechanisms used to get there.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 89, loc. 1447-1449
or part of an illuminati controlled dumb-down of human potential
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 90, loc. 1457
As Buddhist scholar Alan Watts put it, ‘Western scientists have an underlying assumption that normal is absolutely as good as it gets and that the exceptional is only for saints, that it is something that cannot be cultivated.’”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 90, loc. 1457-1458
Notes: 1) or part of an illuminati controlled dumb-down of human potentialHer goal was both to get a clear picture of brainwave activity and record how long it took her subjects to enter REM sleep—an excellent way to measure happiness and well-being. Normal people go into REM at about 90 minutes; depressed people enter sooner, usually at 60 minutes. Generally happy people head in the opposite direction, dropping into REM at around 100 minutes. Britton discovered that NDEers delayed entry until 110 minutes—which meant that they were off the charts for happiness and life satisfaction.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 87, loc. 1406-1410
In 2011, Griffiths gave three grams of psilocybin to a group of terminal cancer patients, in an attempt to provide them with relief from fear-of-death anxiety (which is understandably hard to alleviate). Afterward, he administered a battery of psychological tests, including a standard fear-of-dying metric, the Death Transcendence Scale, at one- and fourteen-month intervals. Just as with Britton’s NDE survivors, Griffiths found significant, sustained change: a marked decrease in their fear of death, and a significant uptick in their attitudes, moods, and behavior.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 88, loc. 1418-1422
was glowing and extroverted for the first time since getting blown up. MDMA gave me my life back.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 88, loc. 1428-1429
Pleasure produces endorphins, but pain can prompt even more. The uncertainty of teasing, as Stanford’s Robert Sapolsky established, spikes dopamine 400 percent. Nipple stimulation boosts oxytocin. Pressure in the throat or colon regulates the vagus nerve,23 creating exhilaration, intense relaxation, and goose bumps, what Princeton gastroenterologist Anish Sheth memorably terms poo-phoria. “To some it may feel like a religious experience,” Sheth writes, “to others like an orgasm, and to a lucky few like both.” And momentary erotic transcendence
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 85, loc. 1376-1381
Thirty years of research showed that people who had an NDE scored exceptionally high on tests of overall life satisfaction. As a trauma expert, Britton found this unusual.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 87, loc. 1401-1402
Now there’s a broad movement to explore full-spectrum sexuality and elevate it from compulsion or perversion, into something more deliberate, playful, and potent. The arc of the moral universe may be long, but it’s bending toward the kinky.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 86, loc. 1391-1393
Nowhere did this urge for raw self-expression show up more visibly than at Esalen, the Big Sur, California–based institute that the New York Times once called the “Harvard of the Human Potential movement.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 77, loc. 1243-1245
What Tolle is preaching is nothing less than the Gospel of STER. His core argument is that through the experience of selflessness, timelessness, and effortlessness—his so-called “Power of Now”—we can dwell in a place of unlimited richness. And, if the popularity of his webcast is anything to go by, this idea is resonating with millions of people.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 76, loc. 1219-1222
By democratizing access to some of the more controversial and misunderstood territory in history, these modern-day Gutenbergs are taking experiences once reserved for mystics and making them available to the masses.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 75, loc. 1201-1202
Pharmacology gives us another tool to explore this terrain. By treating the six powerful neurochemicals that underpin ecstasis as raw ingredients, we’ve begun to refine the recipes for peak experience.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 74, loc. 1192-1193
Whether we’re relying on flow-producing neurofeedback or awe-inducing virtual reality, these breakthroughs turn once-solitary epiphanies into experiences that can be shared by hundreds of thousands of people at once. More people having more experiences means more data and firmer conclusions.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 74, loc. 1195-1197
This sharpened perspective allows us to strip out the interpretations of past gatekeepers and understand, in simple and rational terms, the mechanics of transcendence. And unlike the take-it-on faith dictates of traditional mythologies, the discoveries of neurobiology are testable.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 74, loc. 1190-1192
In spiritual terms, Eckhart Tolle found sudden enlightenment. In the language of this book, he stabilized ecstasis, making the temporary selfless, timeless, and effortless experience of a non-ordinary state a part of his permanent reality.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 76, loc. 1215-1217
Because the drive to get out of our heads has ended in tragedy as often as ecstasy. Because the pale protects us as much as it confines us.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 70, loc. 1162-1163
As Nietzsche said: “madness is rare in individuals—but in groups, political parties, nations and eras, it’s the rule.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 70, loc. 1159-1159
In the 1930s, Adolf Hitler provided a frightening example, co-opting traditional techniques of ecstasy—light, sound, chanting, movement—for his Nuremberg rallies. “I am beginning to comprehend some of the reasons for Hitler’s astounding success,”33 wrote Hearst journalist William Shirer in 1934. “Borrowing a chapter from the Roman church, he’s restoring pageantry . . . and mysticism to the drab lives of twentieth century Germans.” Hitler wasn’t just borrowing from Rome, but from the United States as well. According to Fuhrer confidant Ernst Hanfstaengl, “the ‘Sieg Heil’34 used in political rallies was a direct copy of the technique used by American college football cheerleaders. American college type music was used to excite the German masses who had been used to . . . dry-as-dust political lectures.” Hitler wasn’t the only twentieth-century despot to rely on these techniques. Stalin, Mao, and Pol Pot sold the same thing: a Utopia of We, the experience of communitas at scale. They even sold it the same way. Nearly identical stump speeches: “Individualism is out. We are all one. No one is better than anyone else.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 70, loc. 1148-1158
Something similar is happening today. Thanks to accelerating developments in four fields—psychology, neurobiology, pharmacology, and technology; call them the “Four Forces of Ecstasis”—we’re getting greater access to and understanding of nonordinary states of consciousness.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 74, loc. 1181-1183
rely less on hocus-pocus and superstition, and more on science and experience.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 74, loc. 1184-1185
Archbishop of Canterbury John Tillotson later noted,1 “in all probability . . . hocus pocus is nothing else but a corruption of hoc est corpus (“this is the body”), [a] ridiculous imitation of the priests of the Church.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 73, loc. 1175-1177
Tony Robbins’s empowerment seminars to the prosperity theology preached every Sunday by megachurch ministers like Joel Osteen.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 80, loc. 1296-1297
Landmark, the latest incarnation of Erhard’s teachings, boasts corporate clients including Microsoft,14 NASA, Reebok, and Lululemon.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 80, loc. 1293-1294
Erhard understood that seekers needed to be financially successful enough to afford his next workshop. So he hitched the human potential movement to the wagon of the Protestant work ethic. Napoleon Hill’s Think and Grow Rich replaced the Bhagavad Gita as seminal text. Mandalas were out. Vision boards were in. And the American spiritual marketplace has never been the same. If you’ve
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 80, loc. 1284-1287
As an early Esalen motto put it,12 ‘No one captures the flag.’”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 79, loc. 1271-1272
So Erhard repackaged an assortment of Esalen-inspired13 practices into a business-friendly format, creating EST, short for the Erhard Seminars Training. The seminar deliberately reproduced Price’s accidental transformation, engineering a “breakdown-to-breakthrough” experience via a series of marathon, fourteen-hour days, without food or breaks, and with lots of yelling and profanity—the fabled “EST encounter.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 79, loc. 1277-1281
It was a “pragmatic culture of sensation and know-how,” notes author and modern religious historian Erik Davis11 in AfterBurn, “an essentially empirical approach to matters of the spirit that made tools more important than beliefs. Consciousness-altering techniques like meditation, biofeedback, yoga, ritual, isolation tanks, tantric sex, breathwork, martial arts, group dynamics and drugs were privileged over the claustrophobic structures of authority and belief that were seen to define conventional religion.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 78, loc. 1263-1267
The lineage that goes from Esalen to EST to Eckhart is one of increasing self-exploration,
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 81, loc. 1301-1301
“In French literature,” University of Pennsylvania neurologist18 Anjan Chatterjee explains in his book The Aesthetic Brain, “the release from orgasm is famously referred to as la petite mort, the little death . . . the person is in a state without fear and without thought of themselves or their future plans. . . . This pattern of deactivation could be the brain state of a purely transcendent experience enveloping a core experience of pleasure.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 83, loc. 1332-1336
Together, they have prevented us from fully expressing that “fourth evolutionary drive,” the irrepressible desire to seek nonordinary states of consciousness.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 119, loc. 1903-1904
The second limitation is culture. Anthropologists have discovered that as soon as a local intoxicant becomes enshrined in tradition, people grow suspicious of imports. “Most cultures,” explains Pollan, “curiously, promote one plant8 for this purpose, or two, and condemn others. They fetishize one and they have taboos on others.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 118, loc. 1894-1897
Shulgin’s legacy. The first was PiHKAL, short for “Phenethylamines I Have Known and Loved,” a reference to the class of psychedelics containing mescaline and 2C-B. Cowritten with his wife and published in 1991, PiHKAL was divided into two parts. Part One contained a fictionalized autobiography of the couple. Part Two was a detailed description of 179 psychedelics and included step-by-step instructions for synthesis, bioassays, dosages, duration, legal status, and commentary—that is, everything a would-be psychonaut needed for takeoff. The second book, TiHKAL, came out in 1998, with the acronym standing for “Tryptamines I Have Known and Loved,” and referring to drugs like LSD, DMT, and ibogaine. In this volume, the Shulgins included recipes for fifty-five more substances along with even more commentary. “Use them with care,” they wrote, “and use them with respect as to the transformations they can achieve, and you have an extraordinary research tool. Go banging about with a psychedelic drug for a Saturday night turn-on, and you can get to a really bad place. . . .”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 122, loc. 1958
Between 1966, when he first set up his backyard workshop, and his death in 2014, Shulgin became one of the more prolific psychonauts (an explorer of inner space) in history.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 121, loc. 1937-1938
Shulgin’s legacy. The first was PiHKAL, short for “Phenethylamines I Have Known and Loved,” a reference to the class of psychedelics containing mescaline and 2C-B. Cowritten with his wife and published in 1991, PiHKAL was divided into two parts. Part One contained a fictionalized autobiography of the couple. Part Two was a detailed description of 179 psychedelics and included step-by-step instructions for synthesis, bioassays, dosages, duration, legal status, and commentary—that is, everything a would-be psychonaut needed for takeoff. The second book, TiHKAL, came out in 1998, with the acronym standing for “Tryptamines I Have Known and Loved,” and referring to drugs like LSD, DMT, and ibogaine. In this volume, the Shulgins included recipes for fifty-five more substances along with even more commentary. “Use them with care,” they wrote, “and use them with respect as to the transformations they can achieve, and you have an extraordinary research tool. Go banging about with a psychedelic drug for a Saturday night turn-on, and you can get to a really bad place. .
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 122, loc. 1958-1966
His decision to share his research came from a real fear that he would die with this enormous body of knowledge trapped inside him. Even before PiHKAL, Sasha had that open-source impulse. He gave away information to anyone who asked—it didn’t matter if they were DEA agents or underground psychedelic chemists.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 123, loc. 1974-1976
I was in a seminar where the class leader rattled off all the different methods we use to access it—free association, dream analysis, hypnosis, bungled actions, slips of the tongue. None were very good. Except for dreaming, they’re all indirect approaches. And dreaming takes place when we’re asleep, so all we can get is after-the-fact reports. If we were going to make any headway on this problem, we had to find a better way to explore the unconscious.” In his hunt for that better way, Carhart-Harris picked up psychologist Stanislav Grof’s classic book, Realms of the Human Unconscious: Observations from LSD Research. One of Grof’s main arguments was that during psychedelic states, our ego defenses are so diminished that we gain nearly direct access to the unconscious.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 124, loc. 1993-1999
This is how we know that the vanishing of self is not really about specific regions deactivating. It’s bigger than that. It’s more like whole networks disintegrating.” One of the most important networks to disintegrate is the default mode network.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 125, loc. 2017-2019
In 2009, he became head of psychedelic research at Imperial College London and became the second person in history to use fMRI to explore the neurological impact of psilocybin.22 And the very first to explore LSD.23
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 124, loc. 2002-2005
But, like many of the brain’s systems, the default mode network is fragile. A little trouble in a couple of nodes is all it takes to knock it offline. “Early psychologists used terms like ‘ego disintegration’ to describe the effects of an altered state,” says Carhart-Harris. “They were more correct than they knew. The ego is really just a network, and things like psychedelics, flow, and meditation compromise those connections. They literally dis-integrate the network.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 125, loc. 2020-2023
So when researchers like James Fadiman discovered that psychedelics could enhance creative problem solving—these far-flung connections were the reason why. Or, as Carhart-Harris explains, “What we’ve done in this research is begin to identify the biological basis of the reported mind expansion associated with psychedelic drugs.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 126, loc. 2026-2028
This open-source approach to pharmacology has given us a way to fact-check ecstatic inspiration, moving us from the “one to many” route—à la Moses and Joseph Smith—to a “many to many” model. Rather than having to take anyone’s word for what happens out there, explorers can now repeat the original experiments and see for themselves.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 128, loc. 2070-2072
But Strassman’s study group didn’t experience anything that could comfortably be described as Buddhist. More than 50 percent of his research subjects blasted off to distant galaxies, had hair-raising encounters with multidimensional entities, and came back swearing that those experiences felt “as real, or in many cases, more real than waking life.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 129, loc. 2081-2083
One forum in particular, the Hyperspace Lexicon, reflects a collective effort to codify and make sense of the utterly novel landscape of DMT
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 130, loc. 2090-2091
Initially, he turned his attention to melatonin but, disappointed with the results, soon decided to focus on its cousin DMT (dimethyltryptamine). DMT made sense as a candidate. It occurs naturally in the human body yet when vaporized or injected, becomes a powerful psychedelic.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 129, loc. 2076-2078
And Joseph Smith was by no means the first person to have a prophetic vision that then birthed a religion. Moses fathered three of the world’s largest traditions—Judaism, Islam, and Christianity—when he came down from Mount Sinai with two stone tablets written by “the finger of God.” But this time as well, the problem was proof.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 127, loc. 2048-2050
While all manner of psychoactive plants are available online, allowing the adventurous to distill potent psychedelics with little more than a Crock-Pot, some Mason jars and a turkey baster, the DEA and INTERPOL can still shut down these gray market suppliers. But Cronin’s 3D drug printer renders that kind of oversight almost impossible.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 132, loc. 2135-2137
Even a few decades ago, they could have started a cult. These days, they’ll just get trolled online, then ignored.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 131, loc. 2111-2112
If you put this all together, what seems to be emerging in the aftermath of Shulgin, Carhart-Harris, and Strassman is a kind of “agnostic Gnosticism,” an experience of the infinite rooted in the certainty that all interpretations are personal, provisional, and partial. As a result, no one can claim their particular vision of the divine as correct, if there are thousands of other “visions” with which to compare it.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 131, loc. 2108-2111
“Pretty much any substance made by a plant, tree or mushroom, including all the neuroactive substances, is within reach of synthetic biology. We’re not there yet, but within a decade or so this one technology should be able to tickle all the same receptor sites in the brain that mind-altering substances impact.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 133, loc. 2153-2155
Transformational leaders not only regulated their own nervous systems better than most; they also regulated other people’s.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 105, loc. 1691-1692
Our understanding of the science has progressed to the point where we can not only shift how we think and feel in the present, but also make accurate predictions about how we’re going to think and feel in a future that has yet to occur.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 106, loc. 1698-1700
There are thousands of depictions of the experience. And if you read through them, you’ll find that people often describe unity as more ‘fundamentally real’ than anything else they’ve ever experienced. More real than reality. Well, what does that mean? I think it means that in trying to answer this question we need to take into account both the science and the spirituality, that we can’t just dismiss the latter because it makes us uncomfortable as scientists.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 106, loc. 1709-1712
And unity is only the first in a long series of those experiences that researchers have now decoded. “It’s amazing how far neurotheology has come,” explains Newberg. “Different types of meditation, chanting, singing, flow, prayer, mediumship, speaking in tongues, hypnosis, trances, possession, out-of-body-experiences, near-death experiences, and sensed presences—they’ve all been examined using high-powered imaging.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 108, loc. 1736-1739
What Newberg discovered is that extreme concentration can cause the right parietal lobe to shut down. “It’s an efficiency exchange,” he explains. “During ecstatic prayer or meditation, energy normally used for drawing the boundary of self gets reallocated for attention. When this happens, we can no longer distinguish self from other. At that moment, as far as the brain can tell, you are one with everything.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 108, loc. 1730-1732
The neurobiology of emotion shows that our nonverbal cues—our tics, twitches, and tone—reveal much more about our inner experience than words typically do. “People are in a constant state of impression management,”13 explains USC psychologist Albert “Skip” Rizzo, the director of the institute. “They have their true self and the self they want to project to the world. And we know the body displays things that sometimes people try to keep contained.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 101, loc. 1620-1624
you think back to the embodied cognition work of Amy Cuddy, AI Ellie, and others, their big insight was that our bodies, facial expressions, posture, and voice all convey more information than we would ever suspect. And, if we change any of those things, we can substantially shift how we feel and what we think in the present moment. That’s pretty big news. But what we explored with Nike went even further than that, beyond “real-time” transformation and into “future-time” prediction—precognition itself.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 104, loc. 1665-1668
The technical term for this is the Law of the Instrument. Give someone a hammer and, indeed, they’ll look for nails to pound. But present them with a problem where they need to repurpose that same hammer as a doorstop, or a pendulum weight, or a tomahawk, and you’ll typically get blank stares.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 111, loc. 1779-1781
And we know it’s not working. Even a quick glance at today’s dire mental health statistics—the one in four Americans now on psychiatric medicines;23 the escalating rate of suicide24 for everyone from ages ten to seventy-eight—shows how critically overtaxed our mental processing is these days. We may have come to the end of our psychological tether. It might be time to rethink all that thinking.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 111, loc. 1784-1788
Rather than treating our psychology like the unquestioned operating system (or OS) of our entire lives, we can repurpose it to function more like a user interface (or UI)—that
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 112, loc. 1793
Notes: 1) swappable selves instead of Buddhist no-selfTake, for example, one of the most common ailments of the modern world—mild to moderate depression. Instead of moping around, hoping for things to get better on their own, we can scan our UI and choose an alternate program to run.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 112, loc. 1797-1798
Rather than treating our psychology like the unquestioned operating system (or OS) of our entire lives, we can repurpose it to function more like a user interface (or UI)—
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 112, loc. 1793-1794
Choices like these are available not just in our personal lives, but in our professional lives, too. Instead of nervously waiting for a job interview and obsessing about all the things that could go wrong, we can take a page out of Amy Cuddy’s book and stand up, breathe deeply, and power-pose our way to lower cortisol, higher testosterone, and more confidence. Instead of using trendy leadership books and a new mission statement to fire up employees, we can follow ESADE’s lead and use neurofeedback to heighten group coherence and prompt more productive strategy sessions.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 112, loc. 1804-1808
Certainly, atheists have used the fact that there’s neuronal function beneath mystical experience to claim that spirituality is merely a trick of the brain. But neurotheology takes a faith-neutral position. All this work proves is that these experiences are biologically mediated. If you’re a believer, it offers a deeper understanding of divine methods. If you’re a nonbeliever, it provides another consciousness-altering tool upon which to draw. Either way, these advances do more than just provide an academic explanation for the ecstatic—they provide a user manual on how to get there.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 110, loc. 1771-1775
So potent is the urge to get out of our heads that it functions as a “fourth drive,” a behavior-shaping force as powerful as our first three drives—the desire for food, water, and sex. The bigger question is why. Intoxication, in animals as in humans, is not always the best strategy for survival.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 117, loc. 1864-1866
Researchers have been pondering this for a while now, and have concluded that intoxication does play a powerful evolutionary role—“depatterning.” In nature, animals often get stuck in ruts, repeating the same actions over and over with diminishing returns. But interrupting this behavior is not easy. “The principle of conservation6 tends to rigidly preserve established schemes and patterns,” writes Italian ethnobotanist Giorgio Samorini in his book Animals and Psychedelics, “but modification (the search for new pathways) requires a depatterning instrument . . . capable of opposing—at least at certain determined moments—the principle of conservation. It is my impression that drug-seeking and drug-taking behavior, on the part of both humans and animals, enjoys an intimate connection with . . . depatterning.”
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 117, loc. 1871-1878
This idea, that our ego isn’t the be-all and end-all, flourished in Asia for centuries before landing in California in the 1960’s. Thoughts were illusions, the swamis and lamas maintained, and nirvana lay on the other side of ego death.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 113, loc. 1814-1816
We’ll wait until after we feel better to go for that walk in the sun, rather than going for that walk in order to feel better. We’ll wait until after we get that job offer to pump our fists and stand tall, instead of the other way around.
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 112, loc. 1809-1811
That’s because, at first, reorienting from OS to UI can be downright disorienting. If I can change the “wallpaper of my mind” by deliberately shifting my neurophysiology—my breathing, my posture, my brainwaves, or any number of other
Steven Kotler and Jamie Wheal, Stealing Fire: How Silicon Valley, the Navy SEALs, and Maverick Scientists Are Revolutionizing the Way We Live and Work, pg. 113, loc. 1811-1813
Notes: 1) swappable selves instead of Buddhist no-self
-
 @ 38e82785:9f8bc340
2025-05-01 02:02:53
@ 38e82785:9f8bc340
2025-05-01 02:02:53ct
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 502ab02a:a2860397
2025-05-01 01:47:10
@ 502ab02a:a2860397
2025-05-01 01:47:10EVERY Company ไข่ขาวเชื้อรา ที่รัฐส่งเสริม Unilever อุ้ม และเราถูกคลุมถุงให้กิน
อู๊ว ฉันเกิดมาเป็นไก่ โดนคนเลี้ยงเอาไว้ วันๆไม่ต้องทำอะไร แค่กินแล้วออกไข่ ป๊อกๆๆๆๆๆ กะต๊อก ป๊อกๆๆๆ ป๊อกๆๆๆๆๆ กะต๊อก ป๊อกๆๆๆ เพลงของเป้ อารักษ์ อาจกลายเป็นแค่คำเปรียบเปรย มนุษย์ ที่ถูกริดรอนสิทธิ์ตัวเองลงทุกวันจากนักล่า https://youtu.be/RctpDMoymVw?si=D3jzUXZBmyjxKGpN
โลกยุคใหม่อาจไม่ต้องมีแม่ไก่ แค่มีเชื้อรา กับเทคโนโลยี "precision fermentation" ก็สามารถทำให้ “ไข่” โผล่ออกมาในรูปของผงโปรตีนที่ไม่เคยผ่านตูดอุ่นๆ ไม่เคยมีเสียงกุ๊กๆ และไม่เคยเจอรังเจี๊ยบอีกต่อไป แต่เบื้องหลังของไข่ทดแทนที่ว่า “ก้าวหน้า” นี้ กลับเป็นการเคลื่อนไหวที่เชื่อมโยงรัฐ ธุรกิจยักษ์ และแคมเปญแนว “greenwashing” ได้อย่างแนบเนียนแบบพิมพ์นิยมของโลกอาหารสังเคราะห์ เรื่องราวมันประมาณนี้ครับ
เมื่อไข่เกิดจากเชื้อรา The EVERY Company ซึ่งเดิมชื่อว่า Clara Foods ก่อตั้งขึ้นในปี 2014 โดย Arturo Elizondo และเพื่อนร่วมทีมที่ออกมาจากโครงการ IndieBio ซึ่งเป็น accelerator สำหรับสตาร์ทอัปด้านชีววิทยาสังเคราะห์ที่มีชื่อเสียงใน Silicon Valley ได้ใช้ยีสต์ที่ถูกดัดแปลงพันธุกรรม (GMO yeast) สายพันธุ์ Komagataella phaffii เพื่อให้มันสร้าง “ovalbumin” หรือโปรตีนไข่ขาวขึ้นมาได้ คล้ายการหลอกยีสต์ให้กลายเป็นโรงงานสร้างไข่แบบไม่ต้องมีไก่ กระบวนการหมักนี้คือการจับยีสต์ใส่ถัง เติมน้ำตาล เติมสารอาหาร แล้วรอให้มัน "ผลิต" โปรตีนในห้องแล็บ แล้วก็สกัดออกมา ทำให้บริสุทธิ์ ตากแห้ง แล้วบรรจุใส่ซอง ชูป้าย “animal-free” แปะคำว่า “sustainable” แล้วส่งเข้าสู่ตลาดโปรตีนทดแทน ผลิตภัณฑ์นี้ได้รับการรับรองจาก FDA ว่าเป็น Generally Recognized as Safe (GRAS)
แต่คำถามคือ… ยีสต์ GMO + กระบวนการหมัก = sustainable จริงหรือเปล่า?
ถึงจะเป็นโปรตีนสังเคราะห์ ที่คนแพ้ไข่ก็ยังแพ้อยู่ดี แม้จะไม่มีสัตว์เกี่ยวข้องเลย แต่ EVERY Egg White ก็ยังคงต้องติดป้าย “Contains Egg” ตามกฎหมาย เพราะโครงสร้างโปรตีนที่ผลิตออกมา "เหมือน" โปรตีนไข่จริงมากจนสามารถกระตุ้นอาการแพ้ในคนที่แพ้ไข่ได้อยู่ดี แปลว่า... เราไม่ได้หลุดพ้นจากปัญหาแพ้อาหารเลย แค่เปลี่ยนแหล่งกำเนิดจากไก่มาเป็นเชื้อรา แต่สิ่งที่น่าคิดคือ นี่แสดงว่าองค์ประกอบของมันเหมือนชนิดที่ว่า สำเนาถูกต้องขนาดคนแพ้ไข่ยังแพ้อยู่ คุณคิดว่าในมุมนี้น่าคิดกว่าไหม???
Back ดีมีกองทัพอุ้ม เงินภาษีหนุน ที่น่าจับตาคือ EVERY ได้รับเงินสนับสนุนกว่า 2 ล้านดอลลาร์จากกระทรวงกลาโหมสหรัฐฯ (DoD) เพื่อศึกษาความเป็นไปได้ในการผลิตโปรตีนในประเทศ ตัวเลขนี้ไม่ใช่เล่น ๆ แปลว่า ภาครัฐกำลังพิจารณาให้ "ไข่จากเชื้อรา" เป็นอาหารแห่งอนาคตของกองทัพ ซึ่งหมายถึงเม็ดเงินระดับพันล้านเหรียญหากแผนนี้เดินหน้า และเมื่อรัฐหนุนขนาดนี้ เทคโนโลยีที่ยังแพงก็จะ “ไม่แพง” อีกต่อไป เพราะเงินภาษีช่วยลดต้นทุนแบบกลาย ๆ เหมือนที่เคยเกิดกับ Beyond Meat หรือ Impossible Foods
เท่านั้นไม่พอครับ ไข่ขาวของท่าน ได้รับการคัดเลือกที่จะจับมือกับ The Vegetarian Butcher บริษัทลูกของ Unilever บริษัทอาหารที่ครองตลาดโลกราวกับเป็นเจ้าของตู้เย็นของประชากรโลก Unilever จะใช้โปรตีนไข่จาก EVERY ใส่ในผลิตภัณฑ์ plant-based meat ที่กำลังไต่ตลาดโลก โดยไม่จำเป็นต้องแจ้งผู้บริโภคว่าโปรตีนนี้มาจากเชื้อรา GMO หรือกระบวนการ biotech ที่ไม่ธรรมดา แม้จะถูกจัดว่าเป็น "non-animal ingredient" หรือ "ไม่ได้มาจากสัตว์โดยตรง" แต่ก็มีสิทธิ์เข้าสู่เมนูมังสวิรัติ วีแกน และอาหารเด็กได้อย่างง่ายดาย เพราะภาพจำที่สื่อมวลชนร่วมกันสร้างขึ้น เพราะไม่มีภาพของ “สัตว์” อยู่ในกระบวนการเลย จึงกลายเป็น “วีแกนได้” ในสายตาคนทั่วไป ทั้งที่ความจริงมันคือเทคโนโลยีชีวภาพระดับลึก ด้วยการใช้คำอย่าง “cruelty-free”, “animal-free”, “sustainable protein”, รวมถึงหน้าตาผลิตภัณฑ์ที่ดูใสสะอาด ไร้กลิ่นอายห้องแล็บ
แม้จะยังไม่มีหลักฐานตรงๆ ว่า EVERY เข้าล็อบบี้รัฐบาลเหมือน Oatly แต่เส้นทางที่เห็นชัดคือความร่วมมือกับองค์กรระดับนโยบาย เช่น Good Food Institute (GFI) และกลุ่มผลักดัน food-tech เพื่อก่อรูปแนวคิดว่า “อาหารที่ไม่ได้มาจากธรรมชาติ” = “อนาคต” และเมื่อแบรนด์เหล่านี้จับมือกับยักษ์ใหญ่ กลายเป็นอาหารในโรงเรียน ทหาร โรงพยาบาล หรือ planet of the future คนทั่วไปก็ไม่มีสิทธิ์เลือกอีกต่อไป เพราะทุกที่ถูกจัดสรรโดยนโยบายที่ใครบางคนได้ตัดสินไปแล้ว
EVERY Company ไม่ได้ขายแค่ไข่สังเคราะห์ แต่ขาย “อนาคตของอาหาร” แบบที่มนุษย์ถูกแยกออกจากธรรมชาติ แล้วพึ่งพาเทคโนโลยีและเงินทุนแทน และในโลกที่รัฐกับบริษัทยักษ์กำลังร่วมมือกันสร้างนิยามใหม่ของคำว่า “โปรตีนดีต่อสิ่งแวดล้อม” เราในฐานะผู้บริโภคควรถามกลับว่า…
ดีต่อใคร? ธรรมชาติ หรือห้องแล็บ? สุขภาพของมนุษย์ หรือผลกำไรของเจ้าของแพลตฟอร์มอาหาร?
***สรุป timeline เบาๆ 2014 – Clara Foods ก่อตั้งในซานฟรานซิสโก โดยมีเป้าหมายผลิต “ไข่โดยไม่ต้องใช้ไก่” ผ่านกระบวนการ fermentation 2015-2019 – รับทุนหลายรอบ รวมถึงจาก Horizons Ventures (ที่ลงทุนใน Impossible Foods), IndieBio, Blue Horizon ฯลฯ 2021 – เปลี่ยนชื่อจาก Clara Foods เป็น The EVERY Company เพื่อสะท้อนเป้าหมายที่กว้างขึ้น: การสร้างโปรตีน “EVERYthing” จากจุลชีพ
ปล. ใครอยากอ่านเอกสาร GRAS ตัวเต็มของ EGGWHITE โหลดได้จากที่นี่ครับ https://www.fda.gov/media/175248/download #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 3bf0c63f:aefa459d
2025-04-25 19:26:48
@ 3bf0c63f:aefa459d
2025-04-25 19:26:48Redistributing Git with Nostr
Every time someone tries to "decentralize" Git -- like many projects tried in the past to do it with BitTorrent, IPFS, ScuttleButt or custom p2p protocols -- there is always a lurking comment: "but Git is already distributed!", and then the discussion proceeds to mention some facts about how Git supports multiple remotes and its magic syncing and merging abilities and so on.
Turns out all that is true, Git is indeed all that powerful, and yet GitHub is the big central hub that hosts basically all Git repositories in the giant world of open-source. There are some crazy people that host their stuff elsewhere, but these projects end up not being found by many people, and even when they do they suffer from lack of contributions.
Because everybody has a GitHub account it's easy to open a pull request to a repository of a project you're using if it's on GitHub (to be fair I think it's very annoying to have to clone the repository, then add it as a remote locally, push to it, then go on the web UI and click to open a pull request, then that cloned repository lurks forever in your profile unless you go through 16 screens to delete it -- but people in general seem to think it's easy).
It's much harder to do it on some random other server where some project might be hosted, because now you have to add 4 more even more annoying steps: create an account; pick a password; confirm an email address; setup SSH keys for pushing. (And I'm not even mentioning the basic impossibility of offering
pushaccess to external unknown contributors to people who want to host their own simple homemade Git server.)At this point some may argue that we could all have accounts on GitLab, or Codeberg or wherever else, then those steps are removed. Besides not being a practical strategy this pseudo solution misses the point of being decentralized (or distributed, who knows) entirely: it's far from the ideal to force everybody to have the double of account management and SSH setup work in order to have the open-source world controlled by two shady companies instead of one.
What we want is to give every person the opportunity to host their own Git server without being ostracized. at the same time we must recognize that most people won't want to host their own servers (not even most open-source programmers!) and give everybody the ability to host their stuff on multi-tenant servers (such as GitHub) too. Importantly, though, if we allow for a random person to have a standalone Git server on a standalone server they host themselves on their wood cabin that also means any new hosting company can show up and start offering Git hosting, with or without new cool features, charging high or low or zero, and be immediately competing against GitHub or GitLab, i.e. we must remove the network-effect centralization pressure.
External contributions
The first problem we have to solve is: how can Bob contribute to Alice's repository without having an account on Alice's server?
SourceHut has reminded GitHub users that Git has always had this (for most) arcane
git send-emailcommand that is the original way to send patches, using an once-open protocol.Turns out Nostr acts as a quite powerful email replacement and can be used to send text content just like email, therefore patches are a very good fit for Nostr event contents.
Once you get used to it and the proper UIs (or CLIs) are built sending and applying patches to and from others becomes a much easier flow than the intense clickops mixed with terminal copypasting that is interacting with GitHub (you have to clone the repository on GitHub, then update the remote URL in your local directory, then create a branch and then go back and turn that branch into a Pull Request, it's quite tiresome) that many people already dislike so much they went out of their way to build many GitHub CLI tools just so they could comment on issues and approve pull requests from their terminal.
Replacing GitHub features
Aside from being the "hub" that people use to send patches to other people's code (because no one can do the email flow anymore, justifiably), GitHub also has 3 other big features that are not directly related to Git, but that make its network-effect harder to overcome. Luckily Nostr can be used to create a new environment in which these same features are implemented in a more decentralized and healthy way.
Issues: bug reports, feature requests and general discussions
Since the "Issues" GitHub feature is just a bunch of text comments it should be very obvious that Nostr is a perfect fit for it.
I will not even mention the fact that Nostr is much better at threading comments than GitHub (which doesn't do it at all), which can generate much more productive and organized discussions (and you can opt out if you want).
Search
I use GitHub search all the time to find libraries and projects that may do something that I need, and it returns good results almost always. So if people migrated out to other code hosting providers wouldn't we lose it?
The fact is that even though we think everybody is on GitHub that is a globalist falsehood. Some projects are not on GitHub, and if we use only GitHub for search those will be missed. So even if we didn't have a Nostr Git alternative it would still be necessary to create a search engine that incorporated GitLab, Codeberg, SourceHut and whatnot.
Turns out on Nostr we can make that quite easy by not forcing anyone to integrate custom APIs or hardcoding Git provider URLs: each repository can make itself available by publishing an "announcement" event with a brief description and one or more Git URLs. That makes it easy for a search engine to index them -- and even automatically download the code and index the code (or index just README files or whatever) without a centralized platform ever having to be involved.
The relays where such announcements will be available play a role, of course, but that isn't a bad role: each announcement can be in multiple relays known for storing "public good" projects, some relays may curate only projects known to be very good according to some standards, other relays may allow any kind of garbage, which wouldn't make them good for a search engine to rely upon, but would still be useful in case one knows the exact thing (and from whom) they're searching for (the same is valid for all Nostr content, by the way, and that's where it's censorship-resistance comes from).
Continuous integration
GitHub Actions are a very hardly subsidized free-compute-for-all-paid-by-Microsoft feature, but one that isn't hard to replace at all. In fact there exists today many companies offering the same kind of service out there -- although they are mostly targeting businesses and not open-source projects, before GitHub Actions was introduced there were also many that were heavily used by open-source projects.
One problem is that these services are still heavily tied to GitHub today, they require a GitHub login, sometimes BitBucket and GitLab and whatnot, and do not allow one to paste an arbitrary Git server URL, but that isn't a thing that is very hard to change anyway, or to start from scratch. All we need are services that offer the CI/CD flows, perhaps using the same framework of GitHub Actions (although I would prefer to not use that messy garbage), and charge some few satoshis for it.
It may be the case that all the current services only support the big Git hosting platforms because they rely on their proprietary APIs, most notably the webhooks dispatched when a repository is updated, to trigger the jobs. It doesn't have to be said that Nostr can also solve that problem very easily.
-
 @ 5df413d4:2add4f5b
2025-05-01 01:44:19
@ 5df413d4:2add4f5b
2025-05-01 01:44:19 -
 @ e0e92e54:d630dfaa
2025-04-30 23:27:59
@ e0e92e54:d630dfaa
2025-04-30 23:27:59The Leadership Lesson I Learned at the Repair Shop
Today was a reminder of "Who You Know" actually matters.
Our van has been acting up as of late. Front-end noise. My guess? CV joint or bushings.
Not that I’m a mechanic though—my dad took the hammer away from me when I was 12, and now all "my" tools have flowers printed on them or Pink handles...
Yesterday it become apparent to my wife that "sooner rather than later" was optimal.
So this morning she took it to a repair shop where we know the owners.
You may have guessed by now that I’m no car repair guy. It’s just not my strength and I’m ok with that! And even though it’s not my strength, I’m smart enough to know enough about vehicles to be dangerous…
And I’m sure just like you, I hate being ripped off. So last year, we both decided she would handle repair duties—I just get too fired up by most the personnel that work there whom won’t shoot straight with you.
So this morning my wife takes our van in. She sees the owner and next thing my wife knows, the owner’s wife (my wife’s friend) is texting to go get coffee while they take care of the van.
Before the two ladies took off, my wife was told "we'll need all day as one step of it is a 4-hour job just to get to the part that needs to be replaced..."
And the estimate? Half the parts were warrantied out and the labor is lower than we expected it to be.
Fast forward, coffee having been drank… nearly 4 hours on the dot, we get a call “your van is ready!”
My wife didn't stand there haggling the price for parts and labor.
Nope…here’s the real deal:
- Leadership = Relationships
- You can’t have too many
Granted, quality is better than quantity in everything I can think of, and that is true for relationships as well...
And while there are varying degrees or depths of relationships. The best ones go both ways.
We didn’t expect a deal because we were at our friend’s shop. We went because we trust them.
That’s it.
Any other expectation other than a transparent and truthful transaction would be manipulating and exploiting the relationship…the exchange would fall into the purely transactional at best and be parasitic at worst!
The Bigger Lesson
Here’s the kicker:
This isn’t about vans or a repair shop. It’s about leading.
Theodore Roosevelt nailed it: “People don’t care how much you know until they know how much you care.”
Trust comes from relationships.
Relationships begin with who you know…And making who you know matter.
In other words, the relevance of the relationship is critical.
Your Move
Next time you dodge a call—or skip an event—pause.
Kill that thought…Or at least its tire marks. 😁
Realize that relationships fuel your business, your life, and your impact.
Because leadership? It’s relationships.
====
💡Who’s one person you can invest in today? A teammate? A client? A mechanic? 😉
🔹 Drop your answer below 👇 Or hit me up—book a Discovery Call. Let’s make your leadership thrive.
Jason Ansley* is the founder of Above The Line Leader*, where he provides tailored leadership support and operational expertise to help business owners, entrepreneurs, and leaders thrive— without sacrificing your faith, family, or future.
*Want to strengthen your leadership and enhance operational excellence? Connect with Jason at https://abovethelineleader.com/#your-leadership-journey
*📌 This article first appeared on NOSTR. You can also find more Business Leadership Articles and content at: 👉 https://abovethelineleader.com/business-leadership-articles
-
 @ c9badfea:610f861a
2025-04-30 23:12:42
@ c9badfea:610f861a
2025-04-30 23:12:42- Install Image Toolbox (it's free and open source)
- Launch the app and navigate to the Tools tab
- Choose Cipher from the tool list
- Pick any file from your device storage
- Keep Encryption toggle selected
- Enter a password in the Key field
- Keep default AES/GCM/NoPadding algorithm
- Tap the Encrypt button and save your encrypted file
- If you want to decrypt the file just repeat the previous steps but choose Decryption instead of Encryption in step 5
-
 @ 8125b911:a8400883
2025-04-25 07:02:35
@ 8125b911:a8400883
2025-04-25 07:02:35In Nostr, all data is stored as events. Decentralization is achieved by storing events on multiple relays, with signatures proving the ownership of these events. However, if you truly want to own your events, you should run your own relay to store them. Otherwise, if the relays you use fail or intentionally delete your events, you'll lose them forever.
For most people, running a relay is complex and costly. To solve this issue, I developed nostr-relay-tray, a relay that can be easily run on a personal computer and accessed over the internet.
Project URL: https://github.com/CodyTseng/nostr-relay-tray
This article will guide you through using nostr-relay-tray to run your own relay.
Download
Download the installation package for your operating system from the GitHub Release Page.
| Operating System | File Format | | --------------------- | ---------------------------------- | | Windows |
nostr-relay-tray.Setup.x.x.x.exe| | macOS (Apple Silicon) |nostr-relay-tray-x.x.x-arm64.dmg| | macOS (Intel) |nostr-relay-tray-x.x.x.dmg| | Linux | You should know which one to use |Installation
Since this app isn’t signed, you may encounter some obstacles during installation. Once installed, an ostrich icon will appear in the status bar. Click on the ostrich icon, and you'll see a menu where you can click the "Dashboard" option to open the relay's control panel for further configuration.

macOS Users:
- On first launch, go to "System Preferences > Security & Privacy" and click "Open Anyway."
- If you encounter a "damaged" message, run the following command in the terminal to remove the restrictions:
bash sudo xattr -rd com.apple.quarantine /Applications/nostr-relay-tray.appWindows Users:
- On the security warning screen, click "More Info > Run Anyway."
Connecting
By default, nostr-relay-tray is only accessible locally through
ws://localhost:4869/, which makes it quite limited. Therefore, we need to expose it to the internet.In the control panel, click the "Proxy" tab and toggle the switch. You will then receive a "Public address" that you can use to access your relay from anywhere. It's that simple.
Next, add this address to your relay list and position it as high as possible in the list. Most clients prioritize connecting to relays that appear at the top of the list, and relays lower in the list are often ignored.

Restrictions
Next, we need to set up some restrictions to prevent the relay from storing events that are irrelevant to you and wasting storage space. nostr-relay-tray allows for flexible and fine-grained configuration of which events to accept, but some of this is more complex and will not be covered here. If you're interested, you can explore this further later.
For now, I'll introduce a simple and effective strategy: WoT (Web of Trust). You can enable this feature in the "WoT & PoW" tab. Before enabling, you'll need to input your pubkey.
There's another important parameter,
Depth, which represents the relationship depth between you and others. Someone you follow has a depth of 1, someone they follow has a depth of 2, and so on.- Setting this parameter to 0 means your relay will only accept your own events.
- Setting it to 1 means your relay will accept events from you and the people you follow.
- Setting it to 2 means your relay will accept events from you, the people you follow, and the people they follow.
Currently, the maximum value for this parameter is 2.

Conclusion
You've now successfully run your own relay and set a simple restriction to prevent it from storing irrelevant events.
If you encounter any issues during use, feel free to submit an issue on GitHub, and I'll respond as soon as possible.
Not your relay, not your events.
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 2fdae362:c9999539
2025-04-30 22:17:19
@ 2fdae362:c9999539
2025-04-30 22:17:19The architecture you choose for your embedded firmware has long-lasting consequences. It impacts how quickly you can add features, how easily your team can debug and maintain the system, and how confidently you can scale. While main loops and real-time operating systems (RTOS) are common, a third option — the state machine kernel — often delivers the most value in modern embedded development. At Wolff Electronic Design, we’ve used this approach for over 15 years to build scalable, maintainable, and reliable systems across a wide range of industries.
Every embedded system starts with one big decision: how will the firmware be structured?
Many teams default to the familiar—using a simple main loop or adopting a RTOS. But those approaches can introduce unnecessary complexity or long-term maintenance headaches. A third option, often overlooked, is using a state machine kernel—an event-driven framework designed for reactive, real-time systems. Below, we compare the three options head-to-head to help you choose the right architecture for your next project.Comparison Chart
| Approach | Description | Pros | Cons | Best For | |-----------------------|------------------------------------------------------------------------|-------------------------------------------------------------|------------------------------------------------------------|--------------------------------------| | Main Loop | A single, continuous while-loop calling functions in sequence | Simple to implement, low memory usage | Hard to scale, difficult to manage timing and state | Small, simple devices | | RTOS | Multi-threaded system with scheduler, tasks, and preemption | Good for multitasking, robust toolchain support | Thread overhead, complex debugging, race conditions | Systems with multiple async tasks | | State Machine Kernel | Event-driven system with structured state transitions, run in a single thread | Easy to debug, deterministic behavior, scalable and modular | Learning curve, may need rethinking architecture | Reactive systems, clean architecture |
Why the State Machine Kernel Wins
Promotes Innovation Without Chaos
With clear, hierarchical state transitions, your codebase becomes modular and self-documenting — making it easier to prototype, iterate, and innovate without fear of breaking hidden dependencies or triggering bugs.
Prevents Hidden Complexity
Unlike RTOSes, where tasks run in parallel and can create race conditions or timing bugs, state machines run cooperatively in a single-threaded model. This eliminates deadlocks, stack overflows, and debugging nightmares that come with thread-based systems.
Scales Without Becoming Fragile
As features and states are added, the system remains predictable. You don’t have to untangle spaghetti logic or rework your entire loop to support new behaviors — you just add new events and state transitions.
Improves Maintainability and Handoff
Because logic is encapsulated in individual states with defined transitions, the code is easier to understand, test, and maintain. This lowers the cost of onboarding new developers or revisiting the system years later.
At Wolff Electronic Design, we’ve worked with every kind of firmware structure over the past 15+ years. Our go-to for complex embedded systems? A state machine kernel. It gives our clients the flexibility of RTOS-level structure without the bugs, complexity, or overhead. Whether you’re developing restaurant equipment or industrial control systems, this architecture offers a better path forward: clean, maintainable, and built to last.
Learn more about our capabilities here.
design, #methodologies, #quantumleaps, #statemachines
-
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13
@ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13I am happy to present to you the first full review posted to Nostr Reviews: #Primal for #Android!
Primal has its origins as a micro-blogging, social media client, though it is now expanding its horizons into long-form content. It was first released only as a web client in March of 2023, but has since had a native client released for both iOS and Android. All of Primal's clients recently had an update to Primal 2.0, which included both performance improvements and a number of new features. This review will focus on the Android client specifically, both on phone and tablet.
Since Primal has also added features that are only available to those enrolled in their new premium subscription, it should also be noted that this review will be from the perspective of a free user. This is for two reasons. First, I am using an alternate npub to review the app, and if I were to purchase premium at some time in the future, it would be on my main npub. Second, despite a lot of positive things I have to say about Primal, I am not planning to regularly use any of their apps on my main account for the time being, for reasons that will be discussed later in the review.
The application can be installed through the Google Play Store, nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8, or by downloading it directly from Primal's GitHub. The full review is current as of Primal Android version 2.0.21. Updates to the review on 4/30/2025 are current as of version 2.2.13.
In the ecosystem of "notes and other stuff," Primal is predominantly in the "notes" category. It is geared toward users who want a social media experience similar to Twitter or Facebook with an infinite scrolling feed of notes to interact with. However, there is some "other stuff" included to complement this primary focus on short and long form notes including a built-in Lightning wallet powered by #Strike, a robust advanced search, and a media-only feed.
Overall Impression
Score: 4.4 / 5 (Updated 4/30/2025)
Primal may well be the most polished UI of any Nostr client native to Android. It is incredibly well designed and thought out, with all of the icons and settings in the places a user would expect to find them. It is also incredibly easy to get started on Nostr via Primal's sign-up flow. The only two things that will be foreign to new users are the lack of any need to set a password or give an email address, and the prompt to optionally set up the wallet.
Complaints prior to the 2.0 update about Primal being slow and clunky should now be completely alleviated. I only experienced quick load times and snappy UI controls with a couple very minor exceptions, or when loading DVM-based feeds, which are outside of Primal's control.
Primal is not, however, a client that I would recommend for the power-user. Control over preferred relays is minimal and does not allow the user to determine which relays they write to and which they only read from. Though you can use your own wallet, it will not appear within the wallet interface, which only works with the custodial wallet from Strike. Moreover, and most eggregiously, the only way for existing users to log in is by pasting their nsec, as Primal does not support either the Android signer or remote signer options for users to protect their private key at this time. This lack of signer support is the primary reason the client received such a low overall score. If even one form of external signer log in is added to Primal, the score will be amended to 4.2 / 5, and if both Android signer and remote signer support is added, it will increase to 4.5.
Update: As of version 2.2.13, Primal now supports the Amber Android signer! One of the most glaring issues with the app has now been remedied and as promised, the overall score above has been increased.
Another downside to Primal is that it still utilizes an outdated direct message specification that leaks metadata that can be readily seen by anyone on the network. While the content of your messages remains encrypted, anyone can see who you are messaging with, and when. This also means that you will not see any DMs from users who are messaging from a client that has moved to the latest, and far more private, messaging spec.
That said, the beautiful thing about Nostr as a protocol is that users are not locked into any particular client. You may find Primal to be a great client for your average #bloomscrolling and zapping memes, but opt for a different client for more advanced uses and for direct messaging.
Features
Primal has a lot of features users would expect from any Nostr client that is focused on short-form notes, but it also packs in a lot of features that set it apart from other clients, and that showcase Primal's obvious prioritization of a top-tier user experience.
Home Feed
By default, the infinitely scrolling Home feed displays notes from those you currently follow in chronological order. This is traditional Nostr at its finest, and made all the more immersive by the choice to have all distracting UI elements quickly hide themselves from view as the you begin to scroll down the feed. They return just as quickly when you begin to scroll back up.
Scrolling the feed is incredibly fast, with no noticeable choppiness and minimal media pop-in if you are on a decent internet connection.
Helpfully, it is easy to get back to the top of the feed whenever there is a new post to be viewed, as a bubble will appear with the profile pictures of the users who have posted since you started scrolling.

Interacting With Notes
Interacting with a note in the feed can be done via the very recognizable icons at the bottom of each post. You can comment, zap, like, repost, and/or bookmark the note.
Notably, tapping on the zap icon will immediately zap the note your default amount of sats, making zapping incredibly fast, especially when using the built-in wallet. Long pressing on the zap icon will open up a menu with a variety of amounts, along with the ability to zap a custom amount. All of these amounts, and the messages that are sent with the zap, can be customized in the application settings.
Users who are familiar with Twitter or Instagram will feel right at home with only having one option for "liking" a post. However, users from Facebook or other Nostr clients may wonder why they don't have more options for reactions. This is one of those things where users who are new to Nostr probably won't notice they are missing out on anything at all, while users familiar with clients like #Amethyst or #noStrudel will miss the ability to react with a 🤙 or a 🫂.
It's a similar story with the bookmark option. While this is a nice bit of feature parity for Twitter users, for those already used to the ability to have multiple customized lists of bookmarks, or at minimum have the ability to separate them into public and private, it may be a disappointment that they have no access to the bookmarks they already built up on other clients. Primal offers only one list of bookmarks for short-form notes and they are all visible to the public. However, you are at least presented with a warning about the public nature of your bookmarks before saving your first one.
Yet, I can't dock the Primal team much for making these design choices, as they are understandable for Primal's goal of being a welcoming client for those coming over to Nostr from centralized platforms. They have optimized for the onboarding of new users, rather than for those who have been around for a while, and there is absolutely nothing wrong with that.
Post Creation
Composing posts in Primal is as simple as it gets. Accessed by tapping the obvious circular button with a "+" on it in the lower right of the Home feed, most of what you could need is included in the interface, and nothing you don't.
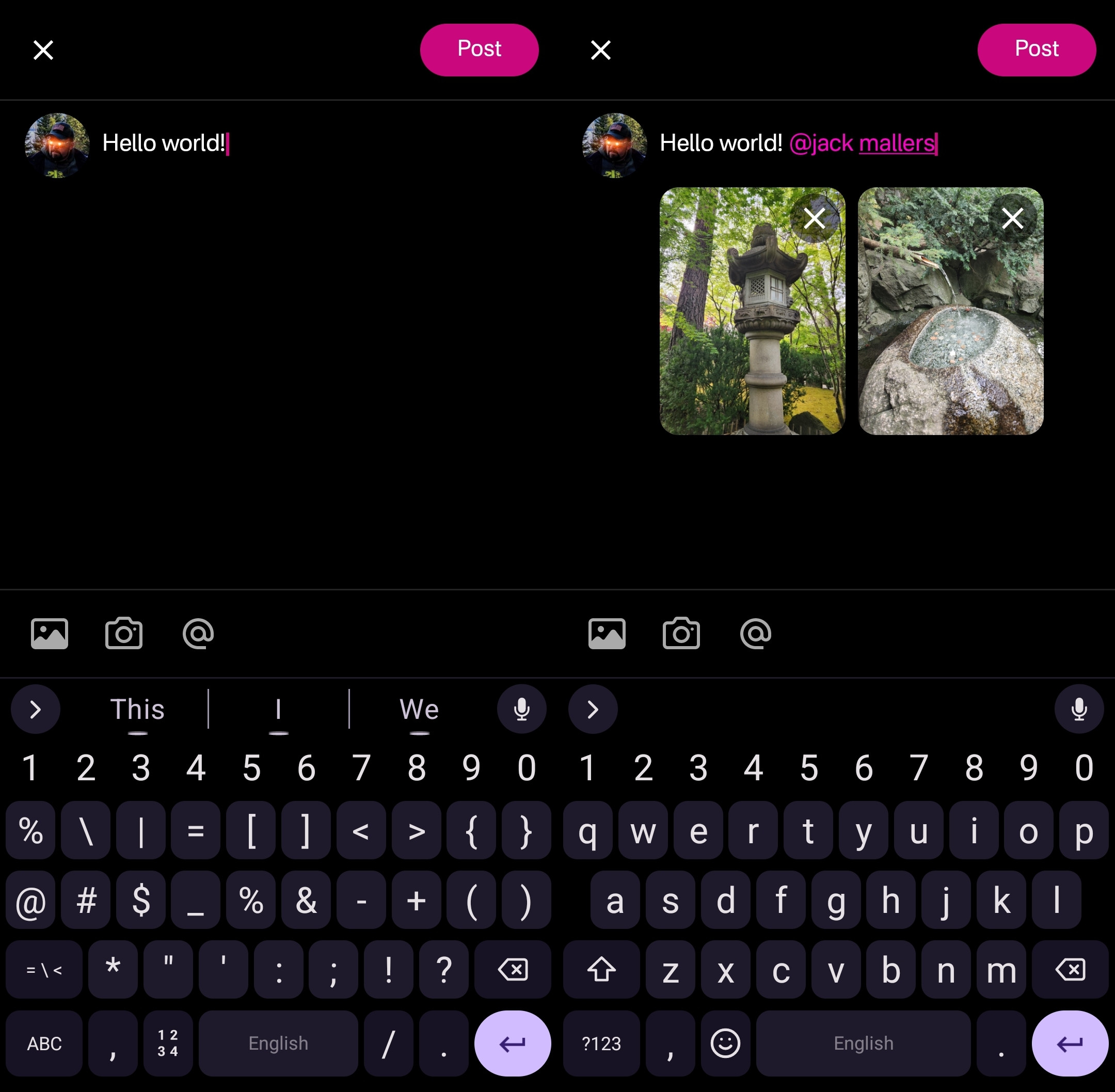
Your device's default keyboard loads immediately, and the you can start typing away.
There are options for adding images from your gallery, or taking a picture with your camera, both of which will result in the image being uploaded to Primal's media-hosting server. If you prefer to host your media elsewhere, you can simply paste the link to that media into your post.
There is also an @ icon as a tip-off that you can tag other users. Tapping on this simply types "@" into your note and brings up a list of users. All you have to do to narrow down the user you want to tag is continue typing their handle, Nostr address, or paste in their npub.
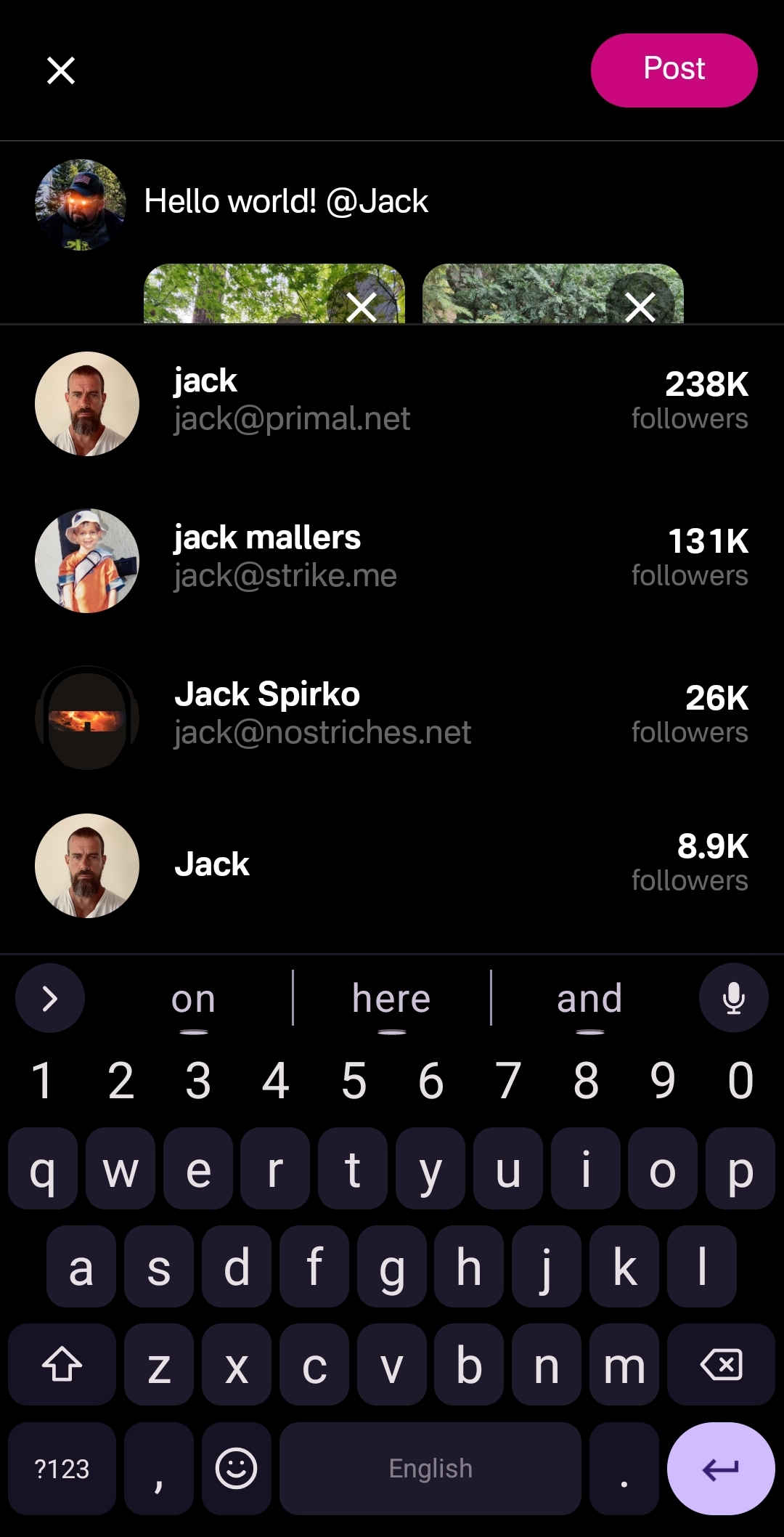
This can get mixed results in other clients, which sometimes have a hard time finding particular users when typing in their handle, forcing you to have to remember their Nostr address or go hunt down their npub by another means. Not so with Primal, though. I had no issues tagging anyone I wanted by simply typing in their handle.
Of course, when you are tagging someone well known, you may find that there are multiple users posing as that person. Primal helps you out here, though. Usually the top result is the person you want, as Primal places them in order of how many followers they have. This is quite reliable right now, but there is nothing stopping someone from spinning up an army of bots to follow their fake accounts, rendering follower count useless for determining which account is legitimate. It would be nice to see these results ranked by web-of-trust, or at least an indication of how many users you follow who also follow the users listed in the results.
Once you are satisfied with your note, the "Post" button is easy to find in the top right of the screen.
Feed Selector and Marketplace
Primal's Home feed really shines when you open up the feed selection interface, and find that there are a plethora of options available for customizing your view. By default, it only shows four options, but tapping "Edit" opens up a new page of available toggles to add to the feed selector.
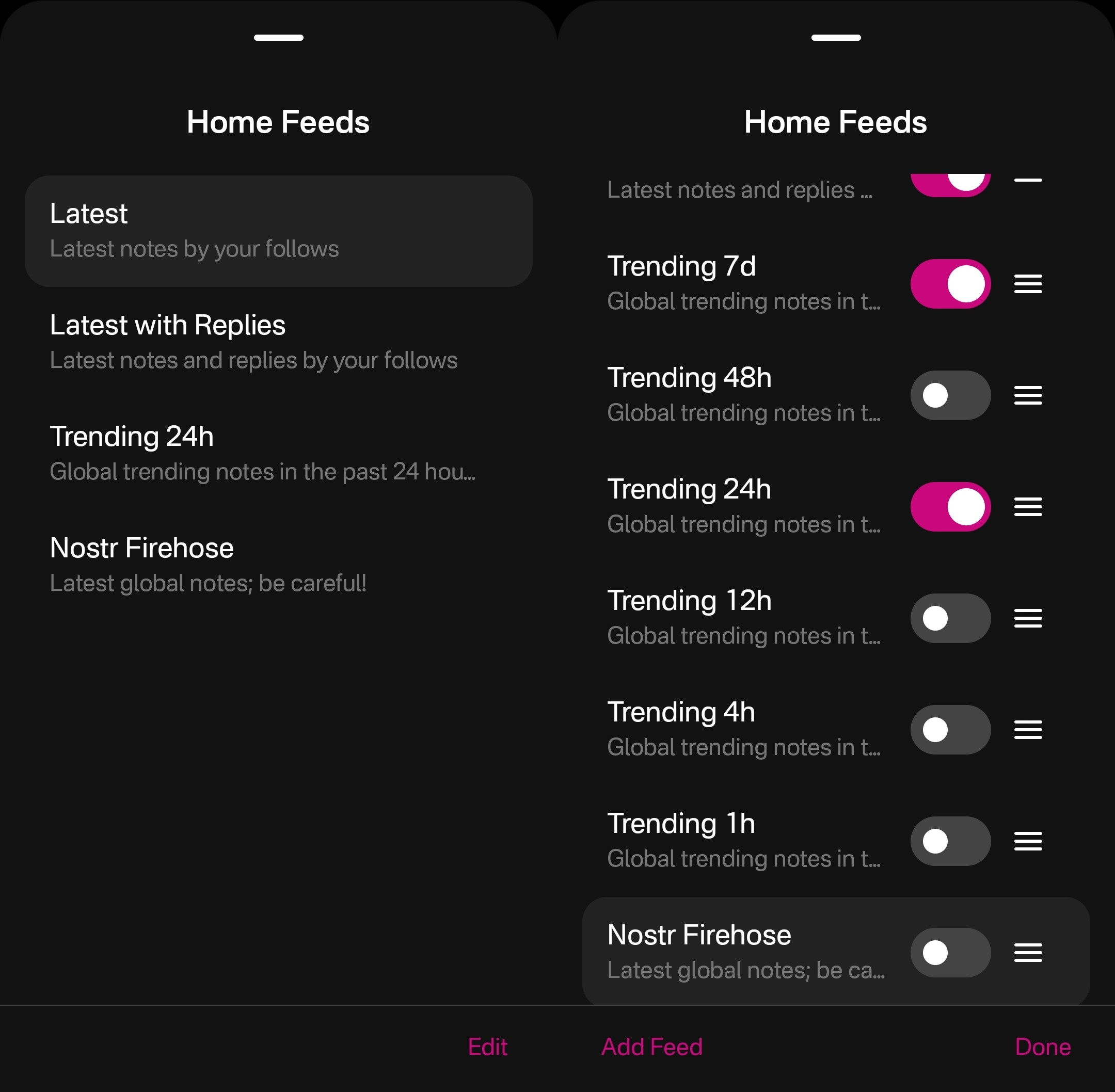
The options don't end there, though. Tapping "Add Feed" will open up the feed marketplace, where an ever-growing number of custom feeds can be found, some created by Primal and some created by others. This feed marketplace is available to a few other clients, but none have so closely integrated it with their Home feeds like Primal has.
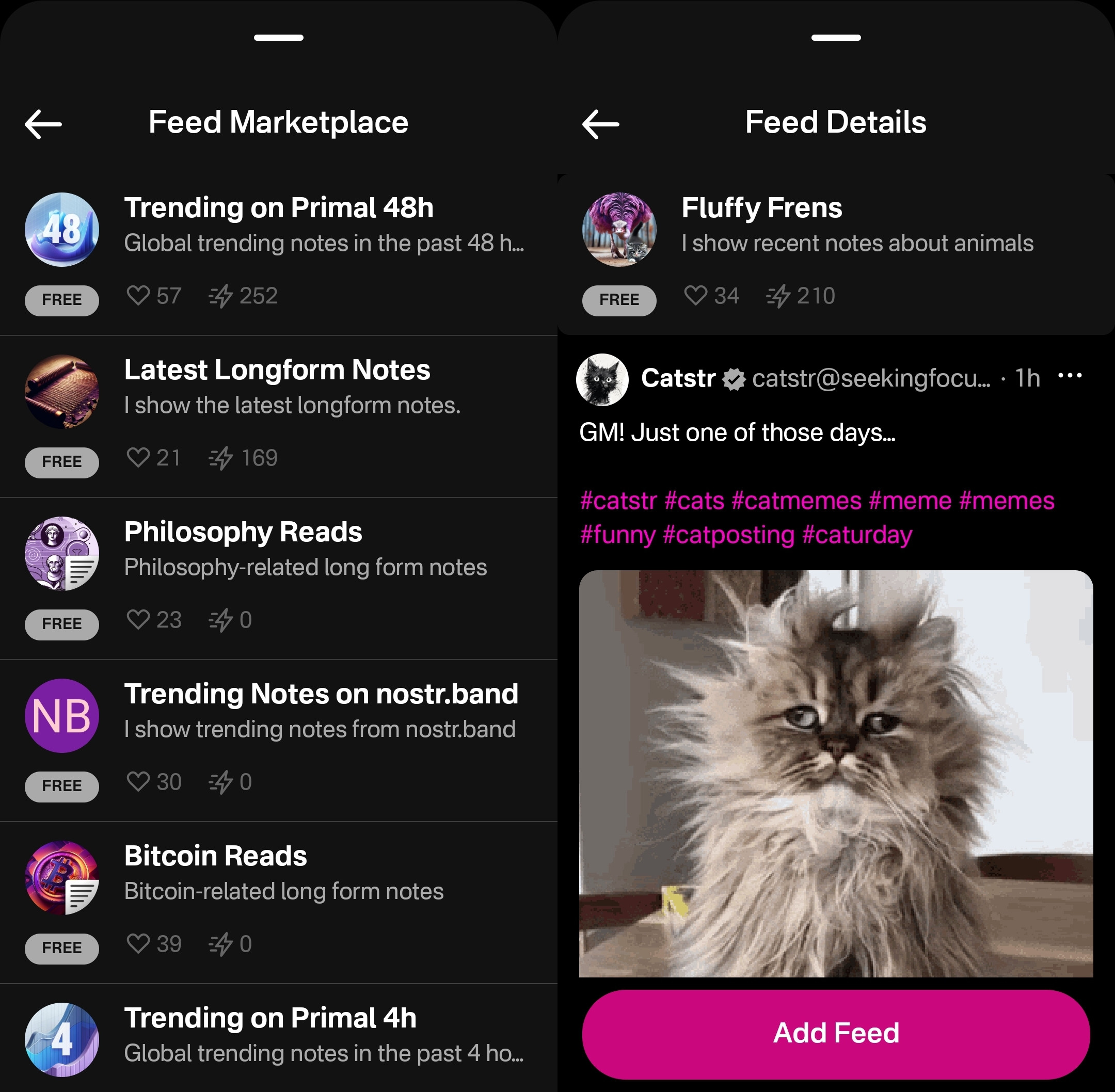
Unfortunately, as great as these custom feeds are, this was also the feature where I ran into the most bugs while testing out the app.
One of these bugs was while selecting custom feeds. Occasionally, these feed menu screens would become unresponsive and I would be unable to confirm my selection, or even use the back button on my device to back out of the screen. However, I was able to pull the screen down to close it and re-open the menu, and everything would be responsive again.
This only seemed to occur when I spent 30 seconds or more on the same screen, so I imagine that most users won't encounter it much in their regular use.
Another UI bug occurred for me while in the feed marketplace. I could scroll down the list of available feeds, but attempting to scroll back up the feed would often close the interface entirely instead, as though I had pulled the screen down from the top, when I was swiping in the middle of the screen.
The last of these bugs occurred when selecting a long-form "Reads" feed while in the menu for the Home feed. The menu would allow me to add this feed and select it to be displayed, but it would fail to load the feed once selected, stating "There is no content in this feed." Going to a different page within the the app and then going back to the Home tab would automatically remove the long-form feed from view, and reset back to the most recently viewed short-form "Notes" feed, though the long-form feed would still be available to select again. The results were similar when selecting a short-form feed for the Reads feed.
I would suggest that if long-form and short-form feeds are going to be displayed in the same list, and yet not be able to be displayed in the same feed, the application should present an error message when attempting to add a long-form feed for the Home feed or a short-form feed for the Reads feed, and encourage the user add it to the proper feed instead.
Long-Form "Reads" Feed
A brand new feature in Primal 2.0, users can now browse and read long-form content posted to Nostr without having to go to a separate client. Primal now has a dedicated "Reads" feed to browse and interact with these articles.
This feed displays the author and title of each article or blog, along with an image, if available. Quite conveniently, it also lets you know the approximate amount of time it will take to read a given article, so you can decide if you have the time to dive into it now, or come back later.
Noticeably absent from the Reads feed, though, is the ability to compose an article of your own. This is another understandable design choice for a mobile client. Composing a long-form note on a smart-phone screen is not a good time. Better to be done on a larger screen, in a client with a full-featured text editor.
Tapping an article will open up an attractive reading interface, with the ability to bookmark for later. These bookmarks are a separate list from your short-form note bookmarks so you don't have to scroll through a bunch of notes you bookmarked to find the article you told yourself you would read later and it's already been three weeks.
While you can comment on the article or zap it, you will notice that you cannot repost or quote-post it. It's not that you can't do so on Nostr. You absolutely can in other clients. In fact, you can do so on Primal's web client, too. However, Primal on Android does not handle rendering long-form note previews in the Home feed, so they have simply left out the option to share them there. See below for an example of a quote-post of a long-form note in the Primal web client vs the Android client.
Primal Web:
Primal Android:
The Explore Tab
Another unique feature of the Primal client is the Explore tab, indicated by the compass icon. This tab is dedicated to discovering content from outside your current follow list. You can find the feed marketplace here, and add any of the available feeds to your Home or Reads feed selections. You can also find suggested users to follow in the People tab. The Zaps tab will show you who has been sending and receiving large zaps. Make friends with the generous ones!
The Media tab gives you a chronological feed of just media, displayed in a tile view. This can be great when you are looking for users who post dank memes, or incredible photography on a regular basis. Unfortunately, it appears that there is no way to filter this feed for sensitive content, and so you do not have to scroll far before you see pornographic material.
Indeed, it does not appear that filters for sensitive content are available in Primal for any feed. The app is kind enough to give a minimal warning that objectionable content may be present when selecting the "Nostr Firehose" option in your Home feed, with a brief "be careful" in the feed description, but there is not even that much of a warning here for the media-only feed.
The media-only feed doesn't appear to be quite as bad as the Nostr Firehose feed, so there must be some form of filtering already taking place, rather than being a truly global feed of all media. Yet, occasional sensitive content still litters the feed and is unavoidable, even for users who would rather not see it. There are, of course, ways to mute particular users who post such content, if you don't want to see it a second time from the same user, but that is a never-ending game of whack-a-mole, so your only realistic choices in Primal are currently to either avoid the Nostr Firehose and media-only feeds, or determine that you can put up with regularly scrolling past often graphic content.
This is probably the only choice Primal has made that is not friendly to new users. Most clients these days will have some protections in place to hide sensitive content by default, but still allow the user to toggle those protections off if they so choose. Some of them hide posts flagged as sensitive content altogether, others just blur the images unless the user taps to reveal them, and others simply blur all images posted by users you don't follow. If Primal wants to target new users who are accustomed to legacy social media platforms, they really should follow suit.
The final tab is titled "Topics," but it is really just a list of popular hashtags, which appear to be arranged by how often they are being used. This can be good for finding things that other users are interested in talking about, or finding specific content you are interested in.
If you tap on any topic in the list, it will display a feed of notes that include that hashtag. What's better, you can add it as a feed option you can select on your Home feed any time you want to see posts with that tag.
The only suggestion I would make to improve this tab is some indication of why the topics are arranged in the order presented. A simple indicator of the number of posts with that hashtag in the last 24 hours, or whatever the interval is for determining their ranking, would more than suffice.
Even with those few shortcomings, Primal's Explore tab makes the client one of the best options for discovering content on Nostr that you are actually interested in seeing and interacting with.
Built-In Wallet
While this feature is completely optional, the icon to access the wallet is the largest of the icons at the bottom of the screen, making you feel like you are missing out on the most important feature of the app if you don't set it up. I could be critical of this design choice, but in many ways I think it is warranted. The built-in wallet is one of the most unique features that Primal has going for it.
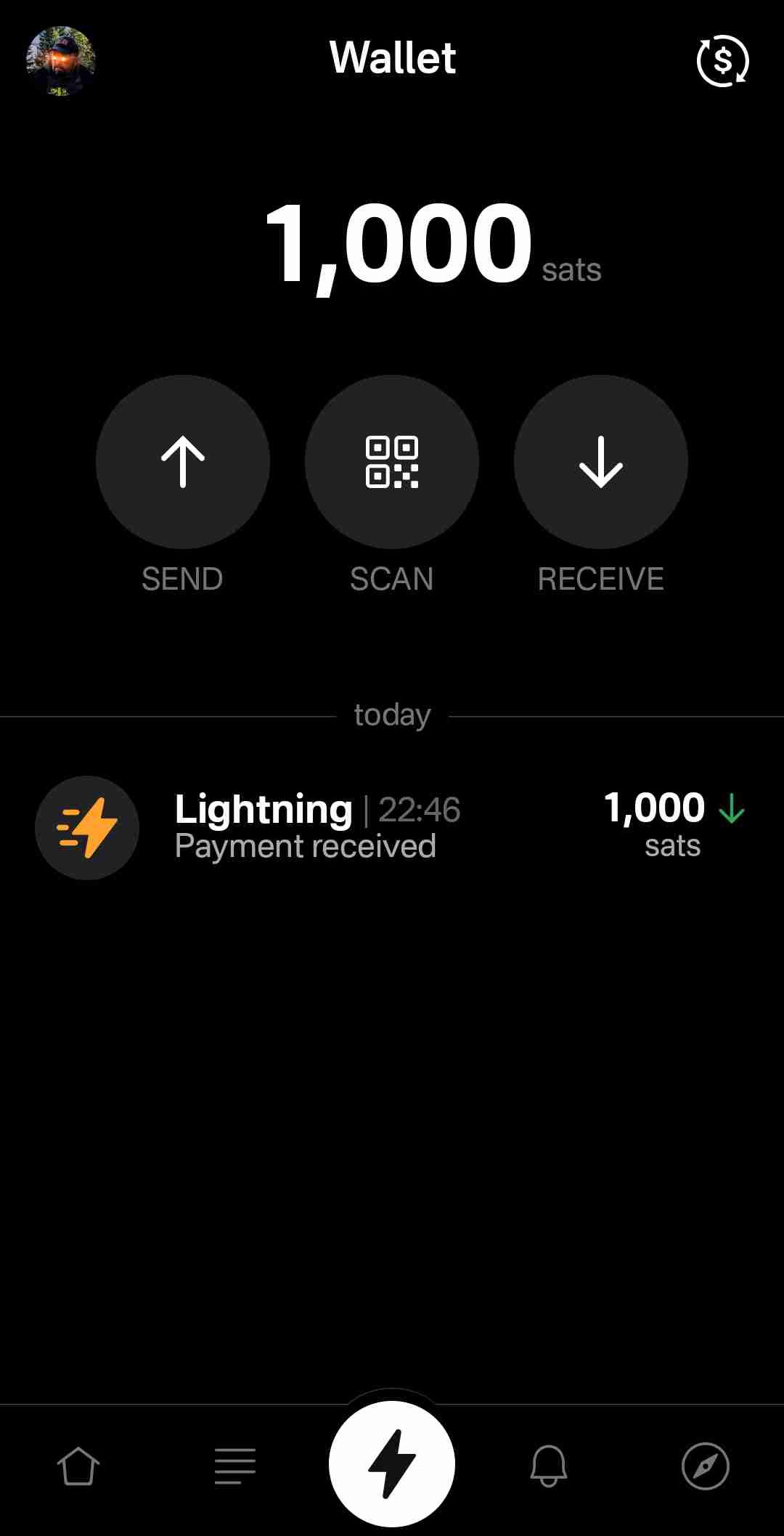
Consider: If you are a new user coming to Nostr, who isn't already a Bitcoiner, and you see that everyone else on the platform is sending and receiving sats for their posts, will you be more likely to go download a separate wallet application or use one that is built-into your client? I would wager the latter option by a long shot. No need to figure out which wallet you should download, whether you should do self-custody or custodial, or make the mistake of choosing a wallet with unexpected setup fees and no Lightning address so you can't even receive zaps to it. nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr often states that he believes more people will be onboarded to Bitcoin through Nostr than by any other means, and by including a wallet into the Primal client, his team has made adopting Bitcoin that much easier for new Nostr users.
Some of us purists may complain that it is custodial and KYC, but that is an unfortunate necessity in order to facilitate onboarding newcoiners to Bitcoin. This is not intended to be a wallet for those of us who have been using Bitcoin and Lightning regularly already. It is meant for those who are not already familiar with Bitcoin to make it as easy as possible to get off zero, and it accomplishes this better than any other wallet I have ever tried.
In large part, this is because the KYC is very light. It does need the user's legal name, a valid email address, date of birth, and country of residence, but that's it! From there, the user can buy Bitcoin directly through the app, but only in the amount of $4.99 at a time. This is because there is a substantial markup on top of the current market price, due to utilizing whatever payment method the user has set up through their Google Play Store. The markup seemed to be about 19% above the current price, since I could purchase 4,143 sats for $4.99 ($120,415 / Bitcoin), when the current price was about $101,500. But the idea here is not for the Primal wallet to be a user's primary method of stacking sats. Rather, it is intended to get them off zero and have a small amount of sats to experience zapping with, and it accomplishes this with less friction than any other method I know.
Moreover, the Primal wallet has the features one would expect from any Lightning wallet. You can send sats to any Nostr user or Lightning address, receive via invoice, or scan to pay an invoice. It even has the ability to receive via on-chain. This means users who don't want to pay the markup from buying through Primal can easily transfer sats they obtained by other means into the Primal wallet for zapping, or for using it as their daily-driver spending wallet.
Speaking of zapping, once the wallet is activated, sending zaps is automatically set to use the wallet, and they are fast. Primal gives you immediate feedback that the zap was sent and the transaction shows in your wallet history typically before you can open the interface. I can confidently say that Primal wallet's integration is the absolute best zapping experience I have seen in any Nostr client.
One thing to note that may not be immediately apparent to new users is they need to add their Lightning address with Primal into their profile details before they can start receiving zaps. So, sending zaps using the wallet is automatic as soon as you activate it, but receiving is not. Ideally, this could be further streamlined, so that Primal automatically adds the Lightning address to the user's profile when the wallet is set up, so long as there is not currently a Lightning address listed.
Of course, if you already have a Lightning wallet, you can connect it to Primal for zapping, too. We will discuss this further in the section dedicated to zap integration.
Advanced Search
Search has always been a tough nut to crack on Nostr, since it is highly dependent on which relays the client is pulling information from. Primal has sought to resolve this issue, among others, by running a caching relay that pulls notes from a number of relays to store them locally, and perform some spam filtering. This allows for much faster retrieval of search results, and also makes their advanced search feature possible.
Advanced search can be accessed from most pages by selecting the magnifying glass icon, and then the icon for more options next to the search bar.
As can be seen in the screenshot below, there are a plethora of filters that can be applied to your search terms.
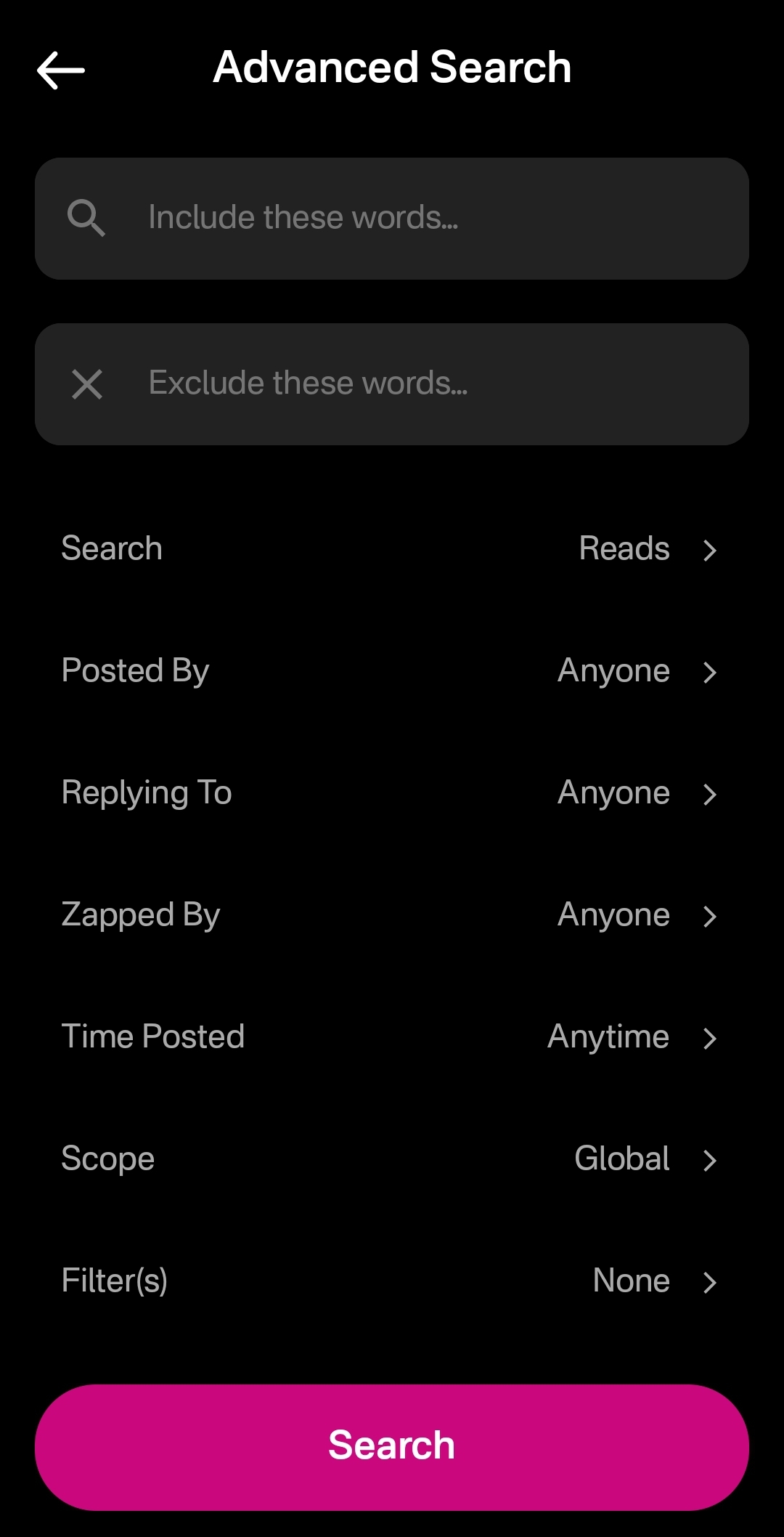
You can immediately see how this advanced search could be a very powerful tool for not just finding a particular previous note that you are looking for, but for creating your own custom feed of notes. Well, wouldn't you know it, Primal allows you to do just that! This search feature, paired with the other features mentioned above related to finding notes you want to see in your feed, makes Primal hands-down the best client for content discovery.
The only downside as a free user is that some of these search options are locked behind the premium membership. Or else you only get to see a certain number of results of your advanced search before you must be a premium member to see more.
Can My Grandma Use It?
Score: 4.8 / 5 Primal has obviously put a high priority on making their client user-friendly, even for those who have never heard of relays, public/private key cryptography, or Bitcoin. All of that complexity is hidden away. Some of it is available to play around with for the users who care to do so, but it does not at all get in the way of the users who just want to jump in and start posting notes and interacting with other users in a truly open public square.
To begin with, the onboarding experience is incredibly smooth. Tap "Create Account," enter your chosen display name and optional bio information, upload a profile picture, and then choose some topics you are interested in. You are then presented with a preview of your profile, with the ability to add a banner image, if you so choose, and then tap "Create Account Now."
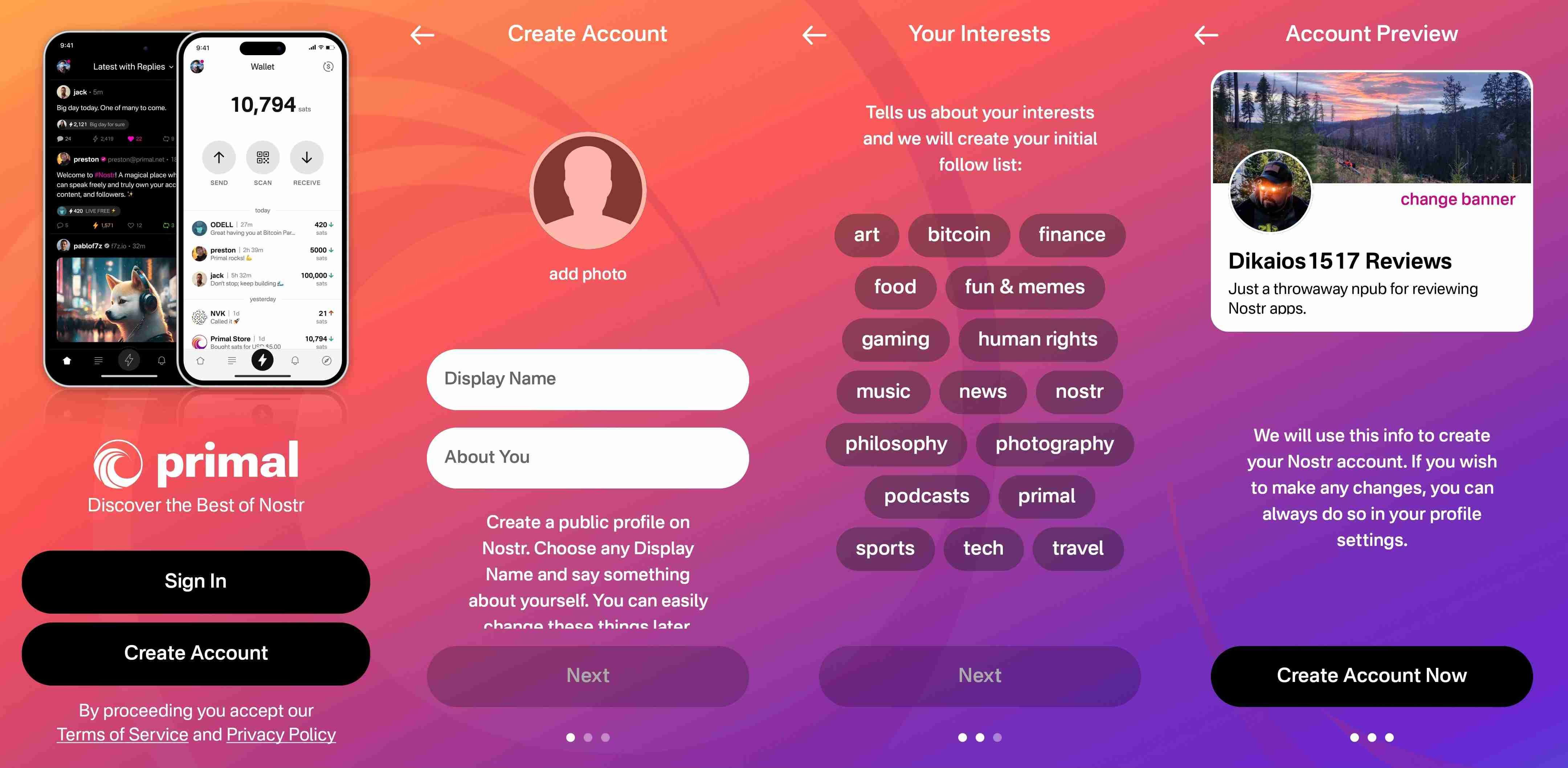
From there you receive confirmation that your account has been created and that your "Nostr key" is available to you in the application settings. No further explanation is given about what this key is for at this point, but the user doesn't really need to know at the moment, either. If they are curious, they will go to the app settings to find out.
At this point, Primal encourages the user to activate Primal Wallet, but also gives the option for the user to do it later.
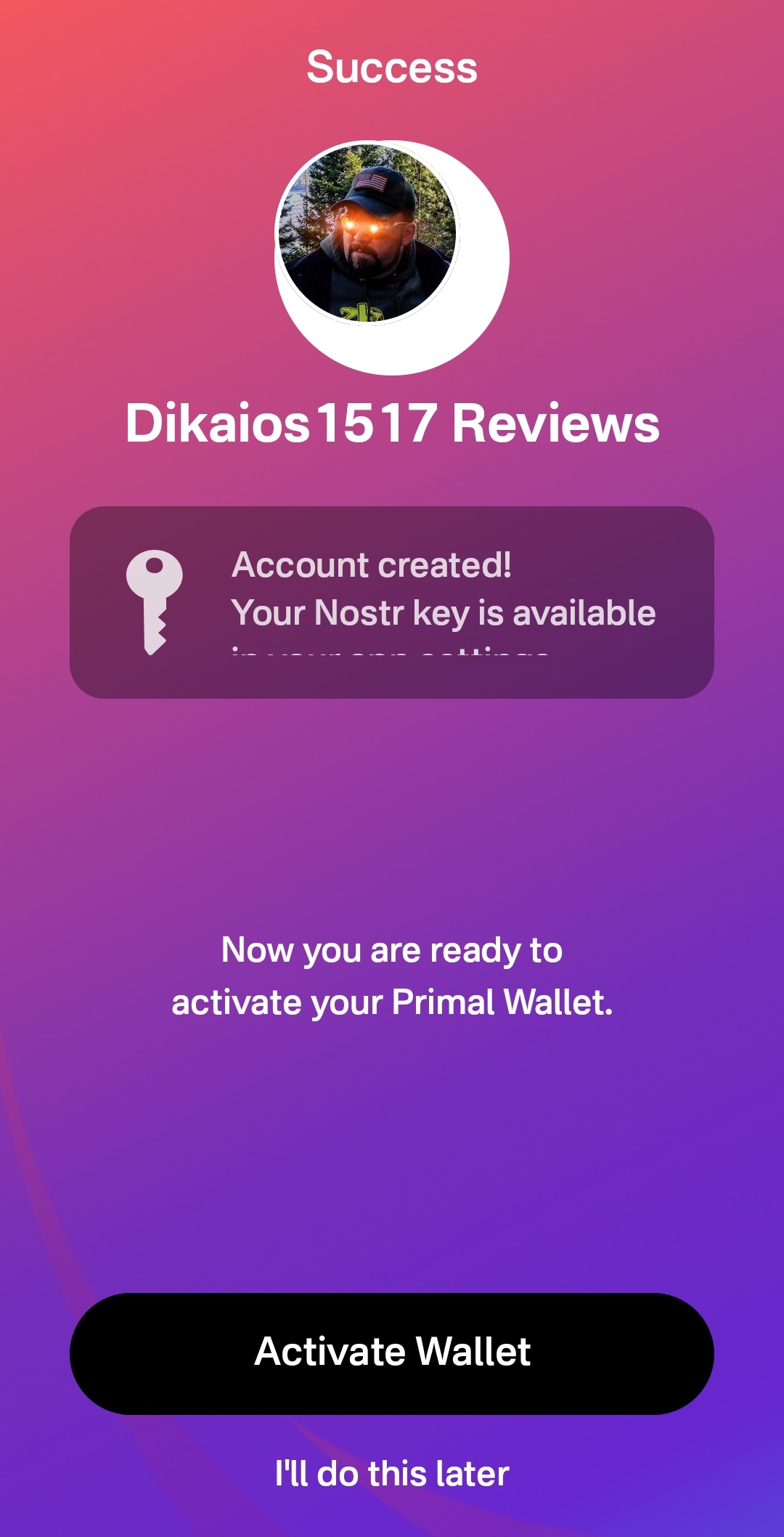
That's it! The next screen the user sees if they don't opt to set up the wallet is their Home feed with notes listed in chronological order. More impressive, the feed is not empty, because Primal has auto-followed several accounts based on your selected topics.
Now, there has definitely been some legitimate criticism of this practice of following specific accounts based on the topic selection, and I agree. I would much prefer to see Primal follow hashtags based on what was selected, and combine the followed hashtags into a feed titled "My Topics" or something of that nature, and make that the default view when the user finishes onboarding. Following particular users automatically will artificially inflate certain users' exposure, while other users who might be quality follows for that topic aren't seen at all.
The advantage of following particular users over a hashtag, though, is that Primal retains some control over the quality of the posts that new users are exposed to right away. Primal can ensure that new users see people who are actually posting quality photography when they choose it as one of their interests. However, even with that example, I chose photography as one of my interests and while I did get some stunning photography in my Home feed by default based on Primal's chosen follows, I also scrolled through the Photography hashtag for a bit and I really feel like I would have been better served if Primal had simply followed that hashtag rather than a particular set of users.
We've already discussed how simple it is to set up the Primal Wallet. You can see the features section above if you missed it. It is, by far, the most user friendly experience to onboarding onto Lightning and getting a few sats for zapping, and it is the only one I know of that is built directly into a Nostr client. This means new users will have a frictionless introduction to transacting via Lightning, perhaps without even realizing that's what they are doing.
Discovering new content of interest is incredibly intuitive on Primal, and the only thing that new users may struggle with is getting their own notes seen by others. To assist with this, I would suggest Primal encourage users to make their first post to the introductions hashtag and direct any questions to the AskNostr hashtag as part of the onboarding process. This will get them some immediate interactions from other users, and further encouragement to set up their wallet if they haven't already done so.
How do UI look?
Score: 4.9 / 5
Primal is the most stunningly beautiful Nostr client available, in my honest opinion. Despite some of my hangups about certain functionality, the UI alone makes me want to use it.
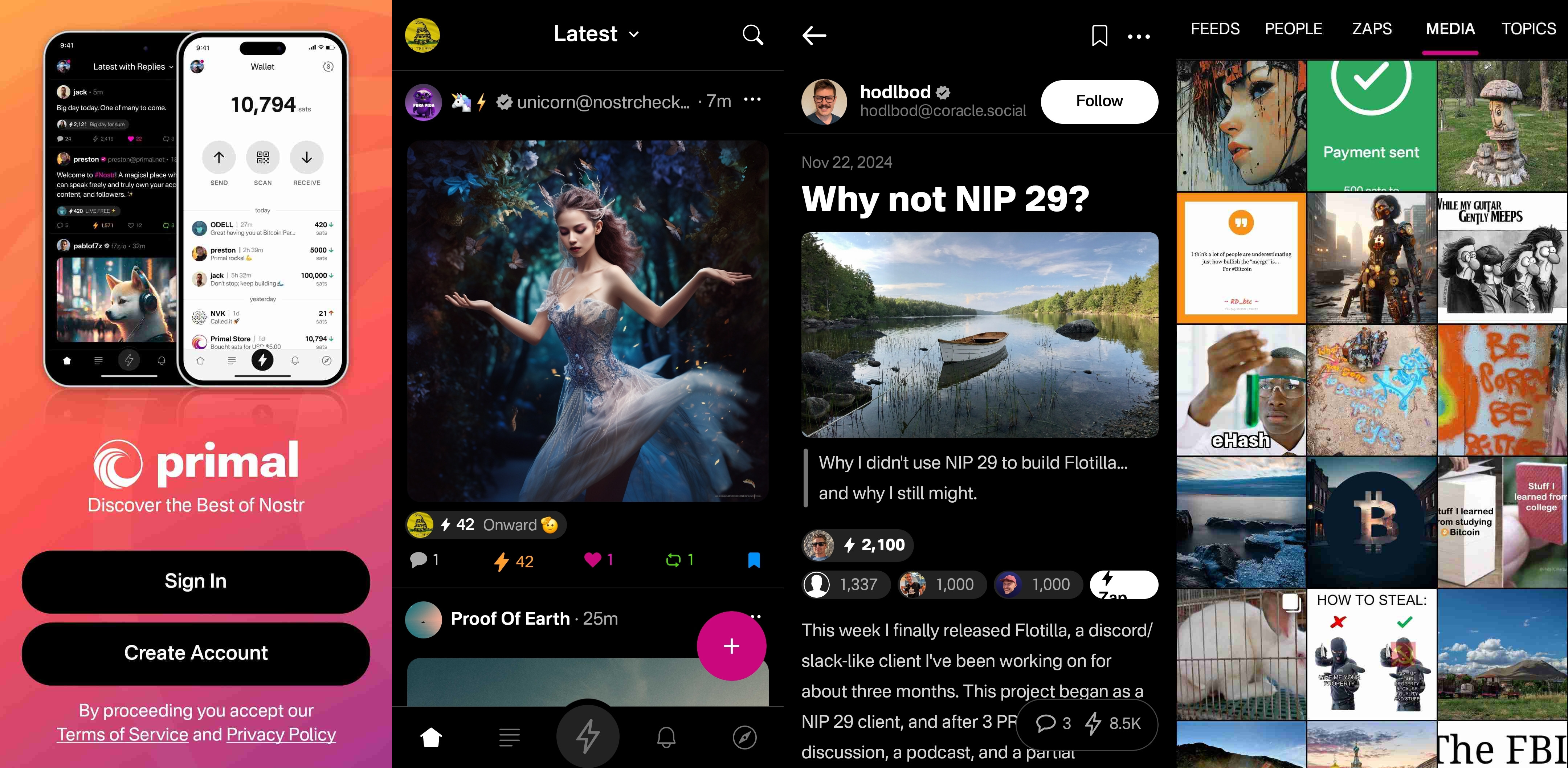
It is clean, attractive, and intuitive. Everything I needed was easy to find, and nothing felt busy or cluttered. There are only a few minor UI glitches that I ran into while testing the app. Some of them were mentioned in the section of the review detailing the feed selector feature, but a couple others occurred during onboarding.
First, my profile picture was not centered in the preview when I uploaded it. This appears to be because it was a low quality image. Uploading a higher quality photo did not have this result.

The other UI bug was related to text instructions that were cut off, and not able to scroll to see the rest of them. This occurred on a few pages during onboarding, and I expect it was due to the size of my phone screen, since it did not occur when I was on a slightly larger phone or tablet.
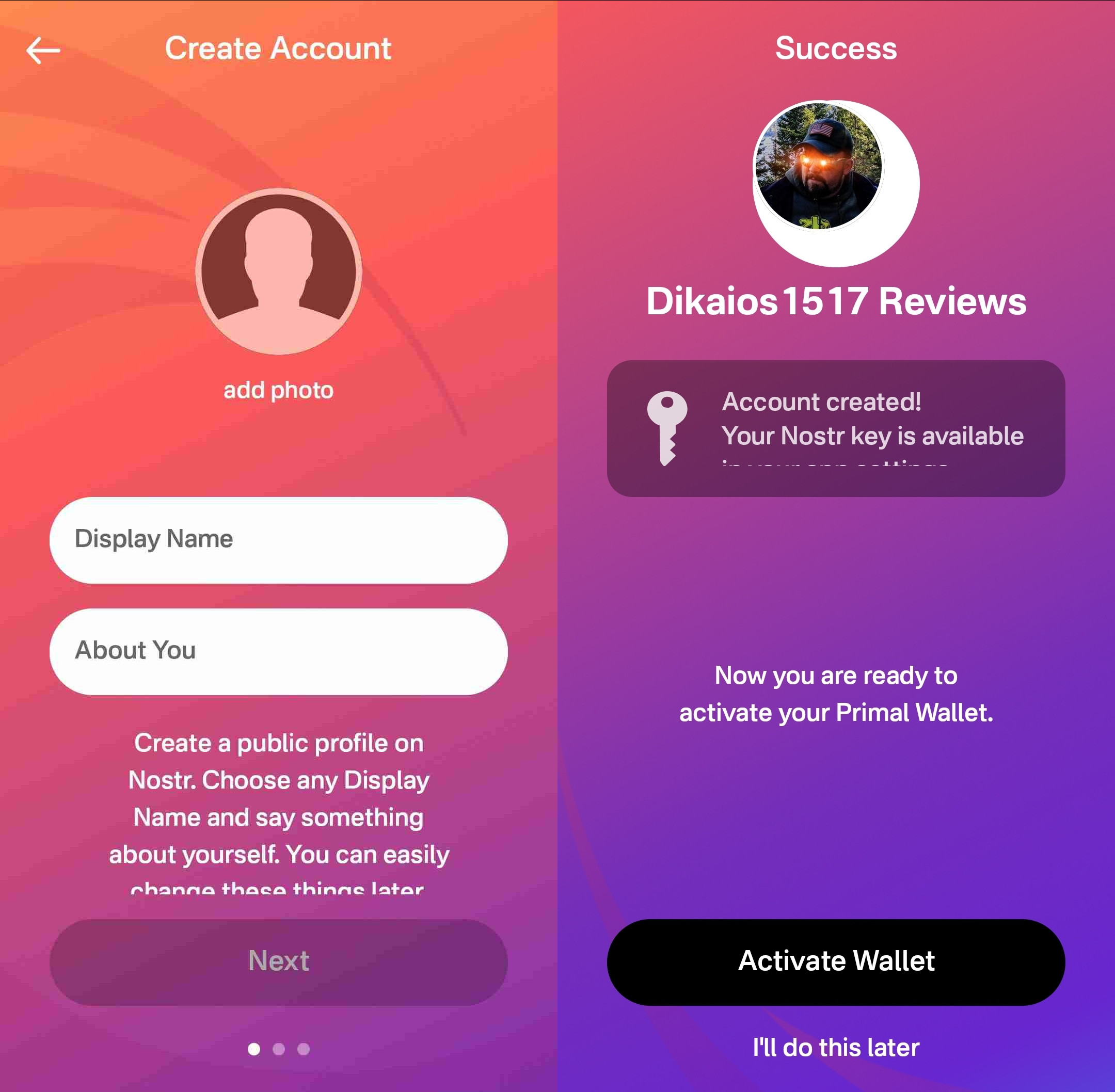
Speaking of tablets, Primal Android looks really good on a tablet, too! While the client does not have a landscape mode by default, many Android tablets support forcing apps to open in full-screen landscape mode, with mixed results. However, Primal handles it well. I would still like to see a tablet version developed that takes advantage of the increased screen real estate, but it is certainly a passable option.

At this point, I would say the web client probably has a bit better UI for use on a tablet than the Android client does, but you miss out on using the built-in wallet, which is a major selling point of the app.
This lack of a landscape mode for tablets and the few very minor UI bugs I encountered are the only reason Primal doesn't get a perfect score in this category, because the client is absolutely stunning otherwise, both in light and dark modes. There are also two color schemes available for each.
Log In Options
Score: 4 / 5 (Updated 4/30/2025)
Unfortunately, Primal has not included any options for log in outside of pasting your private key into the application. While this is a very simple way to log in for new users to understand, it is also the least secure means to log into Nostr applications.
This is because, even with the most trustworthy client developer, giving the application access to your private key always has the potential for that private key to somehow be exposed or leaked, and on Nostr there is currently no way to rotate to a different private key and keep your identity and social graph. If someone gets your key, they are you on Nostr for all intents and purposes.
This is not a situation that users should be willing to tolerate from production-release clients at this point. There are much better log in standards that can and should be implemented if you care about your users.
That said, I am happy to report that external signer support is on the roadmap for Primal, as confirmed below:
nostr:note1n59tc8k5l2v30jxuzghg7dy2ns76ld0hqnn8tkahyywpwp47ms5qst8ehl
No word yet on whether this will be Android signer or remote signer support, or both.
This lack of external signer support is why I absolutely will not use my main npub with Primal for Android. I am happy to use the web client, which supports and encourages logging in with a browser extension, but until the Android client allows users to protect their private key, I cannot recommend it for existing Nostr users.
Update: As of version 2.2.13, all of what I have said above is now obsolete. Primal has added Android signer support, so users can now better protect their nsec by using Amber!
I would still like to see support for remote signers, especially with nstart.me as a recommended Nostr onboarding process and the advent of FROSTR for key management. That said, Android signer support on its own has been a long time coming and is a very welcome addition to the Primal app. Bravo Primal team!
Zap Integration
Score: 4.8 / 5
As mentioned when discussing Primal's built-in wallet feature, zapping in Primal can be the most seamless experience I have ever seen in a Nostr client. Pairing the wallet with the client is absolutely the path forward for Nostr leading the way to Bitcoin adoption.
But what if you already have a Lightning wallet you want to use for zapping? You have a couple options. If it is an Alby wallet or another wallet that supports Nostr Wallet Connect, you can connect it with Primal to use with one-tap zapping.
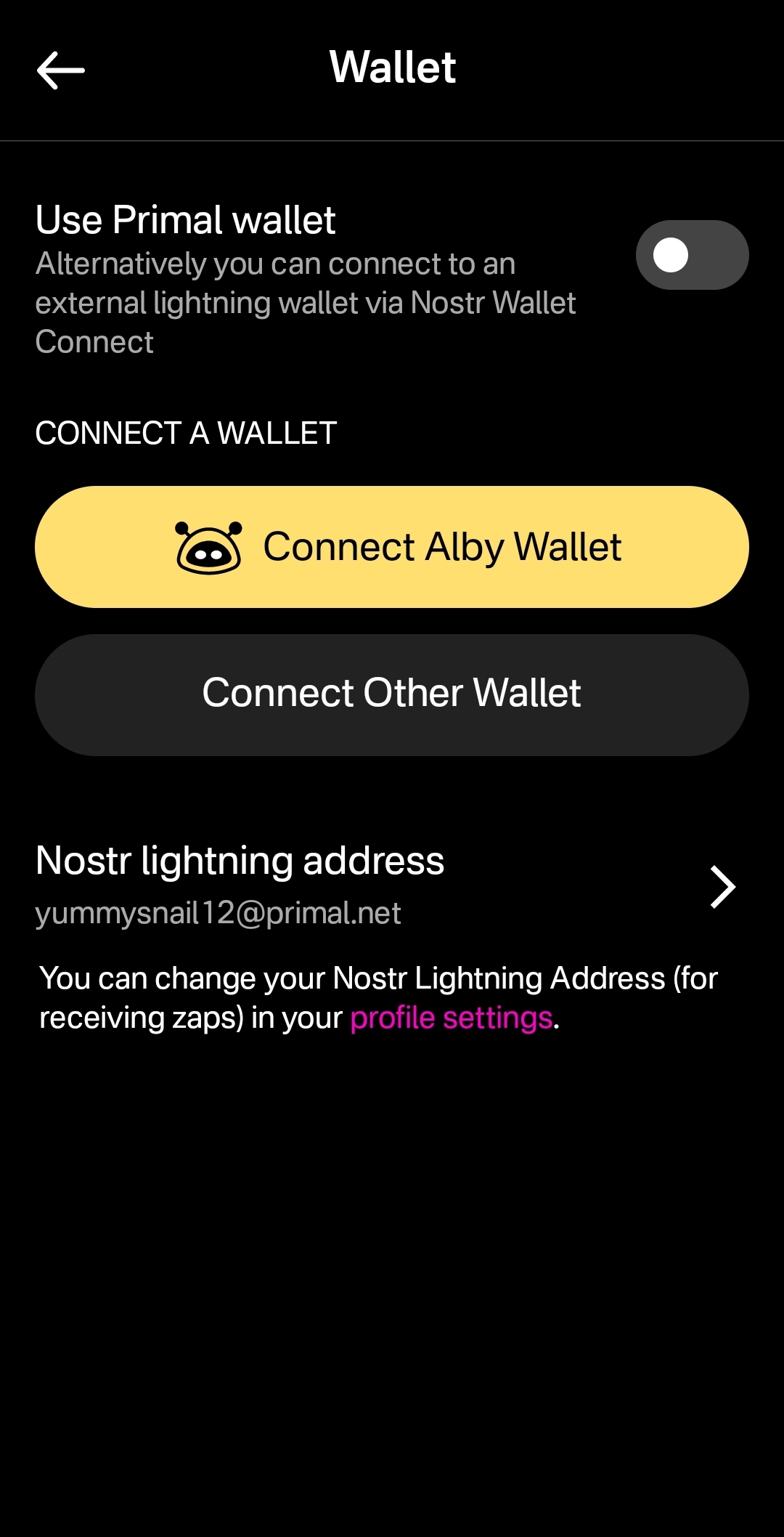
How your zapping experience goes with this option will vary greatly based on your particular wallet of choice and is beyond the scope of this review. I used this option with a hosted wallet on my Alby Hub and it worked perfectly. Primal gives you immediate feedback that you have zapped, even though the transaction usually takes a few seconds to process and appear in your wallet's history.
The one major downside to using an external wallet is the lack of integration with the wallet interface. This interface currently only works with Primal's wallet, and therefore the most prominent tab in the entire app goes unused when you connect an external wallet.
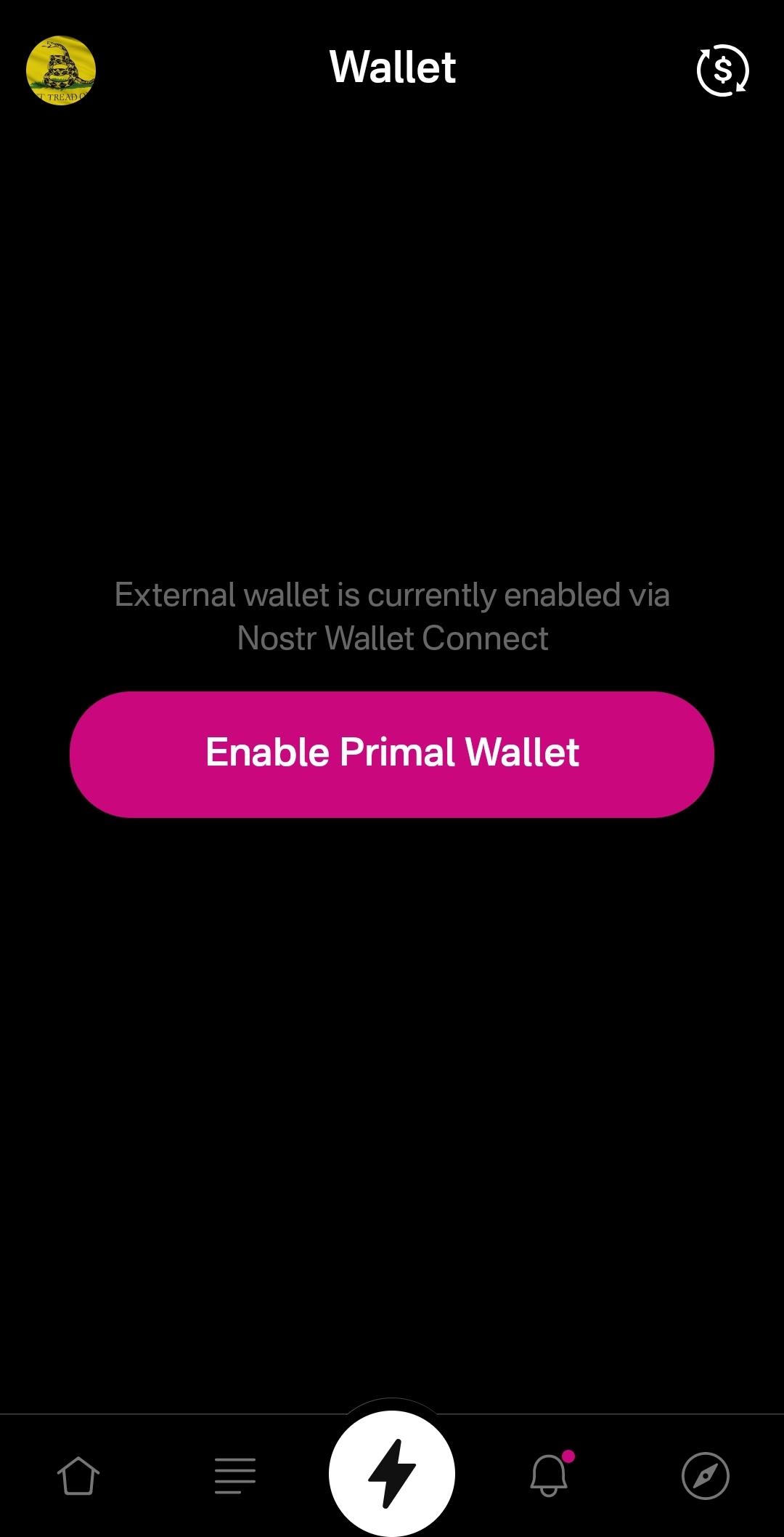
An ideal improvement would be for the wallet screen to work similar to Alby Go when you have an external wallet connected via Nostr Wallet Connect, allowing the user to have Primal act as their primary mobile Lightning wallet. It could have balance and transaction history displayed, and allow sending and receiving, just like the integrated Primal wallet, but remove the ability to purchase sats directly through the app when using an external wallet.
Content Discovery
Score: 4.8 / 5
Primal is the best client to use if you want to discover new content you are interested in. There is no comparison, with only a few caveats.
First, the content must have been posted to Nostr as either a short-form or long-form note. Primal has a limited ability to display other types of content. For instance, discovering video content or streaming content is lacking.
Second, you must be willing to put up with the fact that Primal lacks a means of filtering sensitive content when you are exploring beyond the bounds of your current followers. This may not be an issue for some, but for others it could be a deal-breaker.
Third, it would be preferable for Primal to follow topics you are interested in when you choose them during onboarding, rather than follow specific npubs. Ideally, create a "My Topics" feed that can be edited by selecting your interests in the Topics section of the Explore tab.
Relay Management
Score: 2.5 / 5
For new users who don't want to mess around with managing relays, Primal is fantastic! There are 7 relays selected by default, in addition to Primal's caching service. For most users who aren't familiar with Nostr's protocol archetecture, they probably won't ever have to change their default relays in order to use the client as they would expect.
However, two of these default relays were consistently unreachable during the week that I tested. These were relay.plebes.fans and remnant.cloud. The first relay seems to be an incorrect URL, as I found nosflare.plebes.fans online and with perfect uptime for the last 12 hours on nostr.watch. I was unable to find remnant.cloud on nostr.watch at all. A third relay was intermittent, sometimes online and reachable, and other times unreachable: v1250.planz.io/nostr. If Primal is going to have default relays, they should ideally be reliable and with accurate URLs.
That said, users can add other relays that they prefer, and remove relays that they no longer want to use. They can even set a different caching service to use with the client, rather than using Primal's.
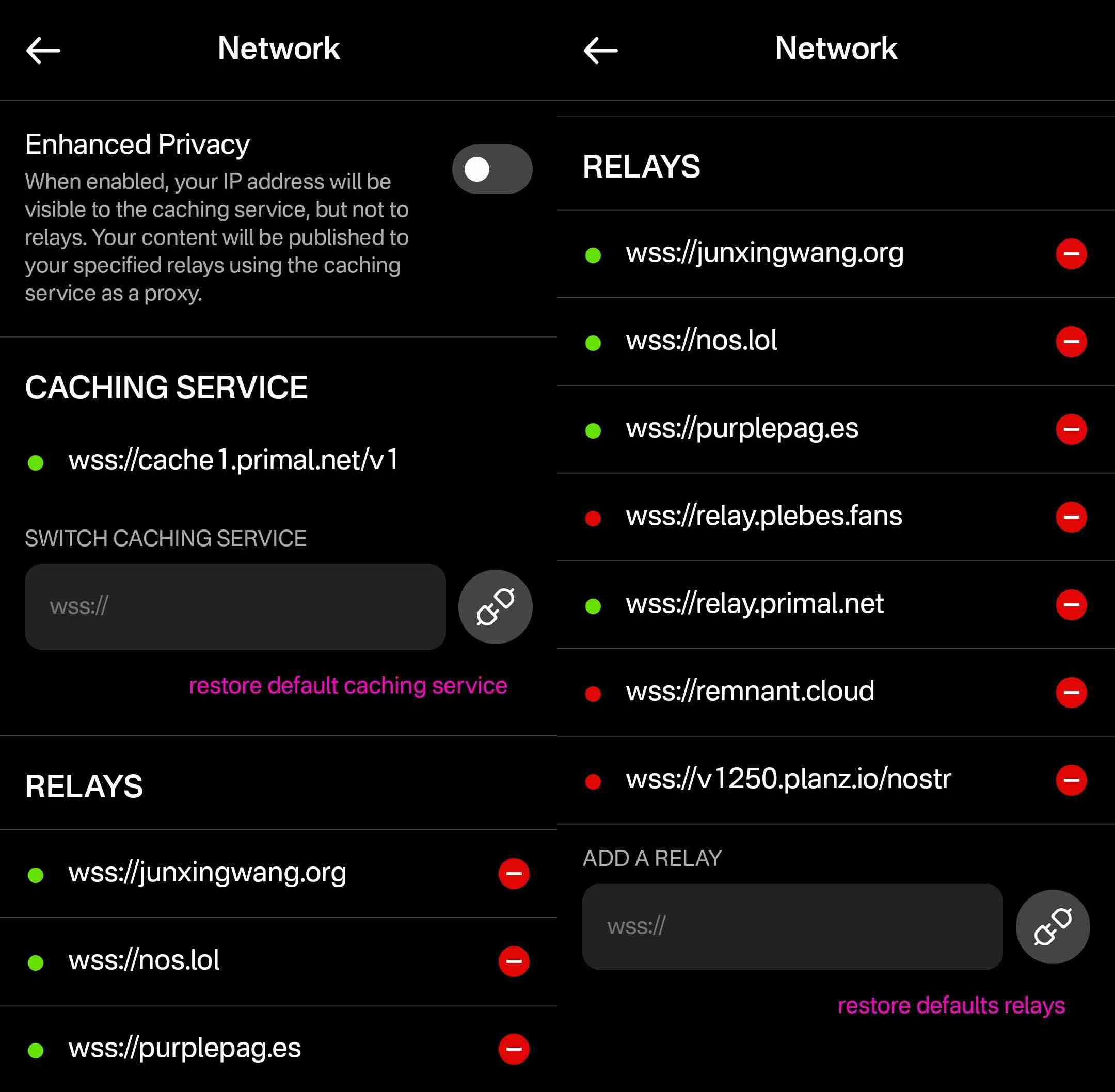
However, that is the extent of a user's control over their relays. They cannot choose which relays they want to write to and which they want to read from, nor can they set any private relays, outbox or inbox relays, or general relays. Loading the npub I used for this review into another client with full relay management support revealed that the relays selected in Primal are being added to both the user's public outbox relays and public inbox relays, but not to any other relay type, which leads me to believe the caching relay is acting as the client's only general relay and search relay.
One unique and welcomed addition is the "Enhanced Privacy" feature, which is off by default, but which can be toggled on. I am not sure why this is not on by default, though. Perhaps someone from the Primal team can enlighten me on that choice.
By default, when you post to Nostr, all of your outbox relays will see your IP address. If you turn on the Enhanced Privacy mode, only Primal's caching service will see your IP address, because it will post your note to the other relays on your behalf. In this way, the caching service acts similar to a VPN for posting to Nostr, as long as you trust Primal not to log or leak your IP address.
In short, if you use any other Nostr clients at all, do not use Primal for managing your relays.
Media Hosting Options
Score: 4.9 / 5 This is a NEW SECTION of this review, as of version 2.2.13!
Primal has recently added support for the Blossom protocol for media hosting, and has added a new section within their settings for "Media Uploads."
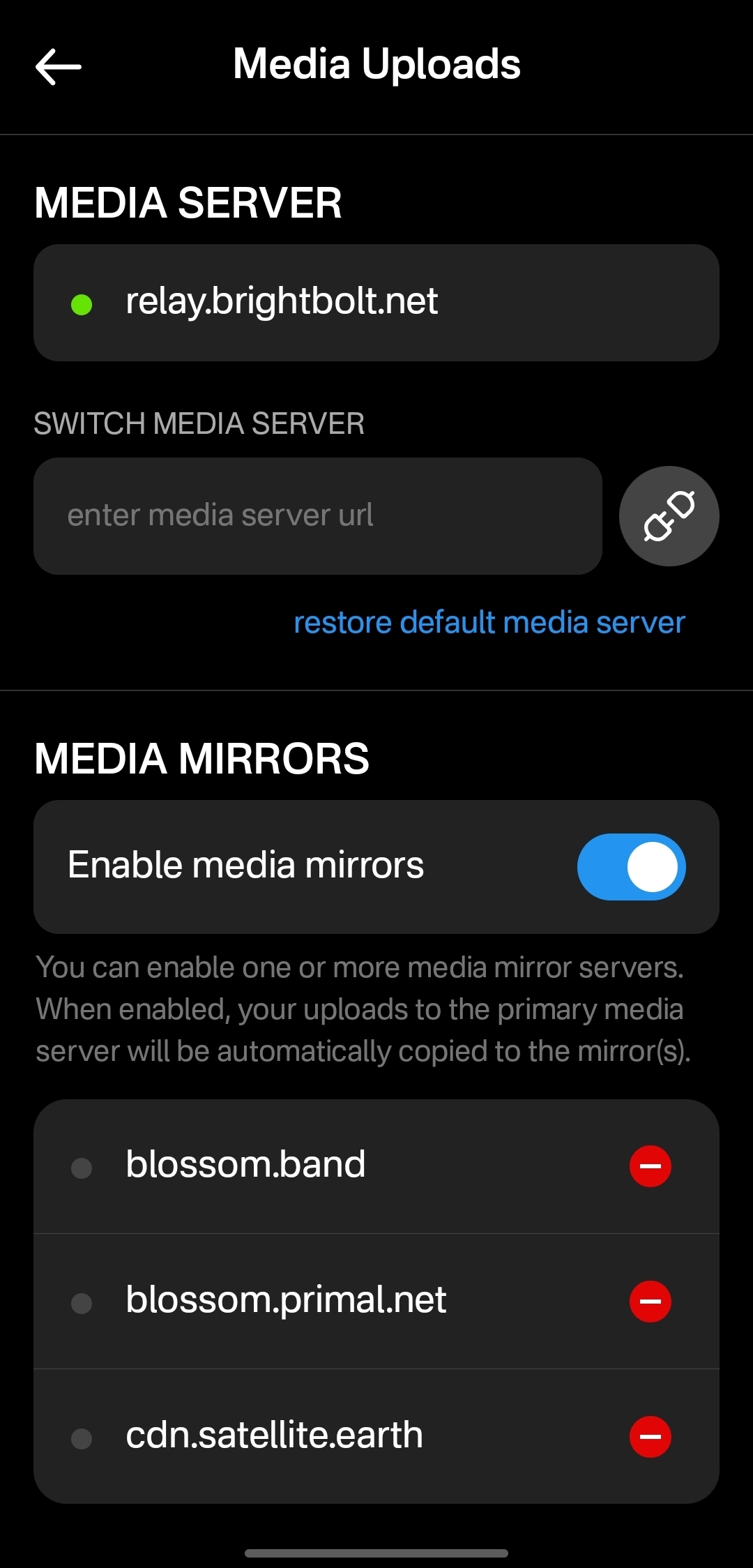
Media hosting is one of the more complicated problems to solve for a decentralized publishing protocol like Nostr. Text-based notes are generally quite small, making them no real burden to store on relays, and a relay can prune old notes as they see fit, knowing that anyone who really cared about those notes has likely archived them elsewhere. Media, on the other hand, can very quickly fill up a server's disk space, and because it is usually addressable via a specific URL, removing it from that location to free up space means it will no longer load for anyone.
Blossom solves this issue by making it easy to run a media server and have the same media mirrored to more than one for redundancy. Since the media is stored with a file name that is a hash of the content itself, if the media is deleted from one server, it can still be found from any other server that has the same file, without any need to update the URL in the Nostr note where it was originally posted.
Prior to this update, Primal only allowed media uploads to their own media server. Now, users can upload to any blossom server, and even choose to have their pictures or videos mirrored additional servers automatically. To my knowledge, no other Nostr client offers this automatic mirroring at the time of upload.
One of my biggest criticisms of Primal was that it had taken a siloed approach by providing a client, a caching relay, a media server, and a wallet all controlled by the same company. The whole point of Nostr is to separate control of all these services to different entities. Now users have more options for separating out their media hosting and their wallet to other providers, at least. I would still like to see other options available for a caching relay, but that relies on someone else being willing to run one, since the software is open for anyone to use. It's just not your average, lightweight relay that any average person can run from home.
Regardless, this update to add custom Blossom servers is a most welcome step in the right direction!
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with a client. Here are some of the most common questions submitted about Primal since the launch of 2.0:
nostr:note1dqv4mwqn7lvpaceg9s7damf932ydv9skv2x99l56ufy3f7q8tkdqpxk0rd
This was a pretty common question, because users expect that they will be able to create the same type of content that they can consume in a particular client. I can understand why this was left out in a mobile client, but perhaps it should be added in the web client.
nostr:note16xnm8a2mmrs7t9pqymwjgd384ynpf098gmemzy49p3572vhwx2mqcqw8xe
This is a more concerning bug, since it appears some users are experiencing their images being replaced with completely different images. I did not experience anything similar in my testing, though.
nostr:note1uhrk30nq0e566kx8ac4qpwrdh0vfaav33rfvckyvlzn04tkuqahsx8e7mr
There hasn't been an answer to this, but I have not been able to find a way. It seems search results will always include replies as well as original notes, so a feed made from the search results will as well. Perhaps a filter can be added to the advanced search to exclude replies? There is already a filter to only show replies, but there is no corresponding filter to only show original notes.
nostr:note1zlnzua28a5v76jwuakyrf7hham56kx9me9la3dnt3fvymcyaq6eqjfmtq6
Since both mobile platforms support the wallet, users expect that they will be able to access it in their web client, too. At this time, they cannot. The only way to have seamless zapping in the web client is to use the Alby extension, but there is not a way to connect it to your Primal wallet via Nostr Wallet Connect either. This means users must have a separate wallet for zapping on the web client if they use the Primal Wallet on mobile.
nostr:note15tf2u9pffy58y9lk27y245ew792raqc7lc22jezxvqj7xrak9ztqu45wep
It seems that Primal is filtering for spam even for profiles you actively follow. Moreover, exactly what the criteria is for being considered spam is currently opaque.
nostr:note1xexnzv0vrmc8svvduurydwmu43w7dftyqmjh4ps98zksr39ln2qswkuced
For those unaware, Blossom is a protocol for hosting media as blobs identified by a hash, allowing them to be located on and displayed from other servers they have been mirrored to when when the target server isn't available. Primal currently runs a Blossom server (blossom.primal.net) so I would expect we see Blossom support in the future.
nostr:note1unugv7s36e2kxl768ykg0qly7czeplp8qnc207k4pj45rexgqv4sue50y6
Currently, Primal on Android only supports uploading photos to your posts. Users must upload any video to some other hosting service and copy/paste a link to the video into their post on Primal. I would not be surprised to see this feature added in the near future, though.
nostr:note10w6538y58dkd9mdrlkfc8ylhnyqutc56ggdw7gk5y7nsp00rdk4q3qgrex
Many Nostr users have more than one npub for various uses. Users would prefer to have a way to quickly switch between accounts than to have to log all the way out and paste their npub for the other account every time they want to use it.
There is good news on this front, though:
nostr:note17xv632yqfz8nx092lj4sxr7drrqfey6e2373ha00qlq8j8qv6jjs36kxlh
Wrap Up
All in all, Primal is an excellent client. It won't be for everyone, but that's one of the strengths of Nostr as a protocol. You can choose to use the client that best fits your own needs, and supplement with other clients and tools as necessary.
There are a couple glaring issues I have with Primal that prevent me from using it on my main npub, but it is also an ever-improving client, that already has me hopeful for those issues to be resolved in a future release.
So, what should I review next? Another Android client, such as #Amethyst or #Voyage? Maybe an "other stuff" app, like #Wavlake or #Fountain? Please leave your suggestions in the comments.
I hope this review was valuable to you! If it was, please consider letting me know just how valuable by zapping me some sats and reposting it out to your follows.
Thank you for reading!
PV 🤙
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ 8cda1daa:e9e5bdd8
2025-04-24 10:20:13
@ 8cda1daa:e9e5bdd8
2025-04-24 10:20:13Bitcoin cracked the code for money. Now it's time to rebuild everything else.
What about identity, trust, and collaboration? What about the systems that define how we live, create, and connect?
Bitcoin gave us a blueprint to separate money from the state. But the state still owns most of your digital life. It's time for something more radical.
Welcome to the Atomic Economy - not just a technology stack, but a civil engineering project for the digital age. A complete re-architecture of society, from the individual outward.
The Problem: We Live in Digital Captivity
Let's be blunt: the modern internet is hostile to human freedom.
You don't own your identity. You don't control your data. You don't decide what you see.
Big Tech and state institutions dominate your digital life with one goal: control.
- Poisoned algorithms dictate your emotions and behavior.
- Censorship hides truth and silences dissent.
- Walled gardens lock you into systems you can't escape.
- Extractive platforms monetize your attention and creativity - without your consent.
This isn't innovation. It's digital colonization.
A Vision for Sovereign Society
The Atomic Economy proposes a new design for society - one where: - Individuals own their identity, data, and value. - Trust is contextual, not imposed. - Communities are voluntary, not manufactured by feeds. - Markets are free, not fenced. - Collaboration is peer-to-peer, not platform-mediated.
It's not a political revolution. It's a technological and social reset based on first principles: self-sovereignty, mutualism, and credible exit.
So, What Is the Atomic Economy?
The Atomic Economy is a decentralized digital society where people - not platforms - coordinate identity, trust, and value.
It's built on open protocols, real software, and the ethos of Bitcoin. It's not about abstraction - it's about architecture.
Core Principles: - Self-Sovereignty: Your keys. Your data. Your rules. - Mutual Consensus: Interactions are voluntary and trust-based. - Credible Exit: Leave any system, with your data and identity intact. - Programmable Trust: Trust is explicit, contextual, and revocable. - Circular Economies: Value flows directly between individuals - no middlemen.
The Tech Stack Behind the Vision
The Atomic Economy isn't just theory. It's a layered system with real tools:
1. Payments & Settlement
- Bitcoin & Lightning: The foundation - sound, censorship-resistant money.
- Paykit: Modular payments and settlement flows.
- Atomicity: A peer-to-peer mutual credit protocol for programmable trust and IOUs.
2. Discovery & Matching
- Pubky Core: Decentralized identity and discovery using PKARR and the DHT.
- Pubky Nexus: Indexing for a user-controlled internet.
- Semantic Social Graph: Discovery through social tagging - you are the algorithm.
3. Application Layer
- Bitkit: A self-custodial Bitcoin and Lightning wallet.
- Pubky App: Tag, publish, trade, and interact - on your terms.
- Blocktank: Liquidity services for Lightning and circular economies.
- Pubky Ring: Key-based access control and identity syncing.
These tools don't just integrate - they stack. You build trust, exchange value, and form communities with no centralized gatekeepers.
The Human Impact
This isn't about software. It's about freedom.
- Empowered Individuals: Control your own narrative, value, and destiny.
- Voluntary Communities: Build trust on shared values, not enforced norms.
- Economic Freedom: Trade without permission, borders, or middlemen.
- Creative Renaissance: Innovation and art flourish in open, censorship-resistant systems.
The Atomic Economy doesn't just fix the web. It frees the web.
Why Bitcoiners Should Care
If you believe in Bitcoin, you already believe in the Atomic Economy - you just haven't seen the full map yet.
- It extends Bitcoin's principles beyond money: into identity, trust, coordination.
- It defends freedom where Bitcoin leaves off: in content, community, and commerce.
- It offers a credible exit from every centralized system you still rely on.
- It's how we win - not just economically, but culturally and socially.
This isn't "web3." This isn't another layer of grift. It's the Bitcoin future - fully realized.
Join the Atomic Revolution
- If you're a builder: fork the code, remix the ideas, expand the protocols.
- If you're a user: adopt Bitkit, use Pubky, exit the digital plantation.
- If you're an advocate: share the vision. Help people imagine a free society again.
Bitcoin promised a revolution. The Atomic Economy delivers it.
Let's reclaim society, one key at a time.
Learn more and build with us at Synonym.to.
-
 @ c631e267:c2b78d3e
2025-04-04 18:47:27
@ c631e267:c2b78d3e
2025-04-04 18:47:27Zwei mal drei macht vier, \ widewidewitt und drei macht neune, \ ich mach mir die Welt, \ widewide wie sie mir gefällt. \ Pippi Langstrumpf
Egal, ob Koalitionsverhandlungen oder politischer Alltag: Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit Rückenwind geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die Wahlwiederholung im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden, das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine Lagarde oder im «Pfizergate»-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen, so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das Stimmrecht entziehen.
Der Pegel an Unzufriedenheit und Frustration wächst in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die Umfrageergebnisse der AfD ein guter Gradmesser dafür.
[Vorlage Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 401014b3:59d5476b
2025-04-30 21:08:52
@ 401014b3:59d5476b
2025-04-30 21:08:52And here's what it said.
And for what it's worth, I actually think ChatGPT nailed it.
Thoughts?
-
Andy Reid – Kansas City Chiefs Andy Reid remains the gold standard among NFL head coaches. With three Super Bowl titles in the past six seasons and a career record of 273-146-1 (.651), Reid's offensive innovation and leadership continue to set him apart.
-
Sean McVay – Los Angeles Rams Sean McVay has revitalized the Rams since taking over in 2017, leading them to two Super Bowl appearances and maintaining only one losing season in eight years. His ability to adapt and keep the team competitive has solidified his status as one of the league's elite coaches.
-
John Harbaugh – Baltimore Ravens John Harbaugh's tenure with the Ravens has been marked by consistent success, including a Super Bowl victory in 2012 and multiple double-digit win seasons. His leadership and adaptability have kept Baltimore as a perennial contender.
-
Nick Sirianni – Philadelphia Eagles Nick Sirianni has quickly risen through the ranks, boasting a .706 regular-season winning percentage and leading the Eagles to two Super Bowl appearances, including one victory. His emphasis on player morale and adaptability have been key to Philadelphia's recent success.
-
Dan Campbell – Detroit Lions Dan Campbell has transformed the Lions into a formidable team, improving their record each season and instilling a culture of toughness and resilience. Despite a disappointing playoff exit in 2024, Campbell's impact on the franchise is undeniable.
originally posted at https://stacker.news/items/967880
-
-
 @ 3c389c8f:7a2eff7f
2025-04-30 20:47:21
@ 3c389c8f:7a2eff7f
2025-04-30 20:47:21Sharing a Note on Nostr:
🔁Yeah, it probably seems obvious. No need to dwell for long, but this is another function that goes by half a dozen different names. Repost, renote, retweet, boost, bump, the ubiquitous little repeat button... It's all the same. It doesn't matter what its called, the feature lets you push notes you may find valuable, to the people who follow you. Additionally you also have the "Quote" option if you would like to add your own remarks or context. Both of these features are supported by most Nostr microblogging clients and some specialty clients, though some have chosen to exclude one or the other to adhere to a set of guiding principles aimed at helping users to enjoy a healthier social media experience.
Similar to a quote, you also have the option to copy NoteIDs to paste in other places. They will look like: nevent..., naddr..., or some other possibly foreign looking string prefixed with 'n' and in some cases the may be preceded by 'nostr:'. These are handy when you'd like to use a note for some other purpose beyond a quote. Perhaps you would like to quote it in a Nostr article or blog entry, or you would like to create a note focusing on a series of notes. Many clients offer easy access to these handy nostr links. If you're finding that the one you are using, does not, then simply hop to another. This is one of the amazing yet simple uses of Nostr's unique identity and contact list ownership.
Sharing Note and Profile Links Off of Nostr:
This is where things get really interesting. If you try to send these 'n' prefixed Nostr links to someone, they will receive that random string and have no clue what to do with it. To solve this, some clever minds came up with njump.me. Just visit that URL and tack your 'n' prefixed event to the end, and boom! you have a link you can send to anyone. Many apps have integrated this feature into their interface to make it easy and convenient to send awesome Nostr content to anyone anywhere, and they can choose which Nostr app they want to use to engage with it right in the landing. Some Nostr clients have traditional link sharing, as well, so you can share links right to the app that you use.
Helping Your Friends to Get Started:
We've touched on this a lot in previous posts but in case you missed it: nstart.me hubstr.org nosta.me These are all great options to onboarding your friends in a way that allows for them to explore Nostr right out of the gate. You always have the option of creating a keypair in nearly every app around, too. This is easier for some people, depending on how much they want to learn right away, or how they may be using Nostr.
There's some cool new tools coming out to help even more with getting your friends set up to use Nostr to its fullest capacity. Follow packs, trust attestations, and suggested app packs are all things we look forward to diving into more deeply in the near future. Please keep an eye out if your interested in reading the Spatia Nostra
-
 @ c631e267:c2b78d3e
2025-04-03 07:42:25
@ c631e267:c2b78d3e
2025-04-03 07:42:25Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-App, die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt in Kraft getreten.
Mit den üblichen Argumenten der Vereinfachung, des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte, wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
Um sich die digitale Version des nationalen Ausweises besorgen zu können (eine App mit dem Namen MiDNI), muss man sich vorab online registrieren. Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
Für jeden Vorgang der Identifikation in der Praxis wird später «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare. Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt in Richtung der «totalen Digitalisierung» des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
In Zukunft könnte der neue Ausweis «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal Cope ganz richtig bemerkt. Das ist die Perspektive.
[Titelbild: Pixabay]
Dazu passend:
Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ e968e50b:db2a803a
2025-04-30 20:40:33
@ e968e50b:db2a803a
2025-04-30 20:40:33Has anyone developed a lightning wallet using a raspberry pi or something like that? This would be a device that could fit in your pocket with a small screen and QR scanner for people that can't afford or don't want to carry a smart phone. It would use wifi or something like that. Is this too much of a security headache? Can it be done easily with any wallet's current software?
originally posted at https://stacker.news/items/967863
-
 @ 5f078e90:b2bacaa3
2025-04-30 20:26:32
@ 5f078e90:b2bacaa3
2025-04-30 20:26:32Petal's Glow
In a quiet meadow, pink flower blooms named Petal danced under moonlight. Their delicate petals glowed, guiding a weary firefly home. Grateful, the firefly wove light patterns, telling their tale. By dawn, bees hummed Petal’s story, spreading it across the valley. The blooms stood prouder, their rosy hue a symbol of gentle hope.
This is 334 characters, some md, bidirectional-bridge.js used.

-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ 5f078e90:b2bacaa3
2025-04-30 20:13:35
@ 5f078e90:b2bacaa3
2025-04-30 20:13:35Cactus story
In a sun-scorched desert, a lone cactus named Sage stood tall. Each dawn, she whispered to the wind, sharing tales of ancient rains. One night, a lost coyote curled beneath her spines, seeking shade. Sage offered her last drops of water, saved from a rare storm. Grateful, the coyote sang her story to the stars, and Sage’s legend grew, a beacon of kindness in the arid wild.
This test is between 300 and 500 characters long, started on Nostr to test the bidirectional-bridge script.
It has a bit of markdown included.

-
 @ b99efe77:f3de3616
2025-04-30 19:57:34
@ b99efe77:f3de3616
2025-04-30 19:57:34🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ c631e267:c2b78d3e
2025-03-21 19:41:50
@ c631e267:c2b78d3e
2025-03-21 19:41:50Wir werden nicht zulassen, dass technisch manches möglich ist, \ aber der Staat es nicht nutzt. \ Angela Merkel
Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach. Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar, dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen, die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war vielleicht früher einmal so, heute ist eher das Gegenteil gemeint.
In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien beleuchtet. Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als «Technofeudalismus» angeprangert.
Nationale Zugangspunkte für Mobilitätsdaten im Sinne der EU gibt es nicht nur in allen Mitgliedsländern, sondern auch in der Schweiz und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen Identifizierungssystem für «nachhaltigen Verkehr und Tourismus».
Natürlich marschiert auch Deutschland stracks und euphorisch in Richtung digitaler Zukunft. Ohne vernetzte Mobilität und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität voll auf Digitalisierung».
Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten, das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Er ist zuerst auf Transition News erschienen.
-
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ b99efe77:f3de3616
2025-04-30 19:57:12
@ b99efe77:f3de3616
2025-04-30 19:57:12🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ b99efe77:f3de3616
2025-04-30 19:53:20
@ b99efe77:f3de3616
2025-04-30 19:53:20🚦Traffic Light Control System🚦
This Petri net represents a traffic control protocol ensuring that two traffic lights alternate safely and are never both green at the same time.
petrinet ;start () -> greenLight1 redLight2 ;toRed1 greenLight1 -> queue redLight1 ;toGreen2 redLight2 queue -> greenLight2 ;toGreen1 queue redLight1 -> greenLight1 ;toRed2 greenLight2 -> redLight2 queue ;stop redLight1 queue redLight2 -> () -
 @ 9bde4214:06ca052b
2025-04-22 18:13:37
@ 9bde4214:06ca052b
2025-04-22 18:13:37"It's gonna be permissionless or hell."
Gigi and gzuuus are vibing towards dystopia.
Books & articles mentioned:
- AI 2027
- DVMs were a mistake
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- The Ultimate Resource by Julian L. Simon
- Harry Potter by J.K. Rowling
- Momo by Michael Ende
In this dialogue:
- Pablo's Roo Setup
- Tech Hype Cycles
- AI 2027
- Prompt injection and other attacks
- Goose and DVMCP
- Cursor vs Roo Code
- Staying in control thanks to Amber and signing delegation
- Is YOLO mode here to stay?
- What agents to trust?
- What MCP tools to trust?
- What code snippets to trust?
- Everyone will run into the issues of trust and micropayments
- Nostr solves Web of Trust & micropayments natively
- Minimalistic & open usually wins
- DVMCP exists thanks to Totem
- Relays as Tamagochis
- Agents aren't nostr experts, at least not right now
- Fix a mistake once & it's fixed forever
- Giving long-term memory to LLMs
- RAG Databases signed by domain experts
- Human-agent hybrids & Chess
- Nostr beating heart
- Pluggable context & experts
- "You never need an API key for anything"
- Sats and social signaling
- Difficulty-adjusted PoW as a rare-limiting mechanism
- Certificate authorities and centralization
- No solutions to policing speech!
- OAuth and how it centralized
- Login with nostr
- Closed vs open-source models
- Tiny models vs large models
- The minions protocol (Stanford paper)
- Generalist models vs specialized models
- Local compute & encrypted queries
- Blinded compute
- "In the eyes of the state, agents aren't people"
- Agents need identity and money; nostr provides both
- "It's gonna be permissionless or hell"
- We already have marketplaces for MCP stuff, code snippets, and other things
- Most great stuff came from marketplaces (browsers, games, etc)
- Zapstore shows that this is already working
- At scale, central control never works. There's plenty scams and viruses in the app stores.
- Using nostr to archive your user-generated content
- HAVEN, blossom, novia
- The switcharoo from advertisements to training data
- What is Truth?
- What is Real?
- "We're vibing into dystopia"
- Who should be the arbiter of Truth?
- First Amendment & why the Logos is sacred
- Silicon Valley AI bros arrogantly dismiss wisdom and philosophy
- Suicide rates & the meaning crisis
- Are LLMs symbiotic or parasitic?
- The Amish got it right
- Are we gonna make it?
- Careless People by Sarah Wynn-Williams
- Takedown by Laila michelwait
- Harry Potter dementors & Momo's time thieves
- Facebook & Google as non-human (superhuman) agents
- Zapping as a conscious action
- Privacy and the internet
- Plausible deniability thanks to generative models
- Google glasses, glassholes, and Meta's Ray Ben's
- People crave realness
- Bitcoin is the realest money we ever had
- Nostr allows for real and honest expression
- How do we find out what's real?
- Constraints, policing, and chilling effects
- Jesus' plans for DVMCP
- Hzrd's article on how DVMs are broken (DVMs were a mistake)
- Don't believe the hype
- DVMs pre-date MCP tools
- Data Vending Machines were supposed to be stupid: put coin in, get stuff out.
- Self-healing vibe-coding
- IP addresses as scarce assets
- Atomic swaps and the ASS protocol
- More marketplaces, less silos
- The intensity of #SovEng and the last 6 weeks
- If you can vibe-code everything, why build anything?
- Time, the ultimate resource
- What are the LLMs allowed to think?
- Natural language interfaces are inherently dialogical
- Sovereign Engineering is dialogical too
-
 @ aa8de34f:a6ffe696
2025-03-21 12:08:31
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119. März 2025
🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s proof-of-work mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, SHA-256 remains secure because:
- Quantum computers excel at factoring large numbers (Shor’s Algorithm).
- However, SHA-256 is a one-way function, meaning there's no known quantum algorithm that can efficiently reverse it.
- Grover’s Algorithm (which theoretically speeds up brute force attacks) would still require 2¹²⁸ operations to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses Elliptic Curve Digital Signature Algorithm (ECDSA) to generate keys.
- A quantum computer could use Shor’s Algorithm to break SECP256K1, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a Bitcoin address is the public key—this is wrong.
- When you receive Bitcoin, it is sent to a hashed public key (the Bitcoin address).
- The actual public key is never exposed because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses Pay-to-Public-Key-Hash (P2PKH) or newer methods like Pay-to-Witness-Public-Key-Hash (P2WPKH), which add extra layers of security.
🕵️♂️ 2.1 The Public Key Never Appears
- When you send Bitcoin, your wallet creates a digital signature.
- This signature uses the private key to prove ownership.
- The Bitcoin address is revealed and creates the Public Key
- The public key remains hidden inside the Bitcoin script and Merkle tree.
This means: ✔ The public key is never exposed. ✔ Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.
+++++++++++++++++++++++++++++++++++++++++++++++++
🔄 3. Bitcoin Can Upgrade
Even if quantum computers eventually become a real threat:
- Bitcoin developers can upgrade to quantum-safe cryptography (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide soft fork or hard fork could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a 10-minute block interval, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack every 10 minutes.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system resets the challenge with every new block.This limits the window of opportunity for quantum attacks.
🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker must solve the cryptographic puzzle (Proof of Work) in under 10 minutes.
- The problem? Any slight error changes the hash completely, meaning:If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails.Quantum decoherence (loss of qubit stability) makes error correction a massive challenge.The computational cost of recovering from an incorrect hash is still incredibly high.
⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer somehow solved a block instantly:The network would quickly recognize and reject invalid transactions.Other miners would continue mining under normal cryptographic rules.51% Attack? The attacker would need to consistently beat the entire Bitcoin network, which is not sustainable.
🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every 2016 blocks (\~2 weeks).
- If quantum miners appeared and suddenly started solving blocks too quickly, the difficulty would adjust upward, making attacks significantly harder.
- This self-correcting mechanism ensures that even quantum computers wouldn't easily overpower the network.
🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ The 10-minute rule limits attack frequency – quantum computers can’t keep up.
✔ Any slight miscalculation ruins the attack, resetting all progress.
✔ Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages.
Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant. 🚀
-
 @ 59b96df8:b208bd59
2025-04-30 19:27:41
@ 59b96df8:b208bd59
2025-04-30 19:27:41Nostr is a decentralized protocol designed to be censorship-resistant.
However, this resilience can sometimes make data synchronization between relays more difficult—though not impossible.In my opinion, Nostr still lacks a few key features to ensure consistent and reliable operation, especially regarding data versioning.
Profile Versions
When I log in to a new Nostr client using my private key, I might end up with an outdated version of my profile, depending on how the client is built or configured.
Why does this happen?
The client fetches my profile data (kind:0 - NIP 1) from its own list of selected relays.
If I didn’t publish the latest version of my profile on those specific relays, the client will only display an older version.Relay List Metadata
The same issue occurs with the relay list metadata (kind:10002 - NIP 65).
When switching to a new client, it's common that my configured relay list isn't properly carried over because it also depends on where the data is fetched.Protocol Change Proposal
I believe the protocol should evolve, specifically regarding how
kind:0(user metadata) andkind:10002(relay list metadata) events are distributed to relays.Relays should be able to build a list of public relays automatically (via autodiscovery), and forward all received
kind:0andkind:10002events to every relay in that list.This would create a ripple effect:
``` Relay A relay list: [Relay B, Relay C]
Relay B relay list: [Relay A, Relay C]
Relay C relay list: [Relay A, Relay B]User A sends kind:0 to Relay A
→ Relay A forwards kind:0 to Relay B
→ Relay A forwards kind:0 to Relay C
→ Relay B forwards kind:0 to Relay A
→ Relay B forwards kind:0 to Relay C → Relay A forwards kind:0 to Relay B
→ etc. ```Solution: Event Encapsulation
To avoid infinite replication loops, the solution could be to wrap the user’s signed event inside a new event signed by the relay, using a dedicated
kind(e.g.,kind:9999).When Relay B receives a
kind:9999event from Relay A, it extracts the original event, checks whether it already exists or if a newer version is present. If not, it adds the event to its database.Here is an example of such encapsulated data:
json { "content": "{\"content\":\"{\\\"lud16\\\":\\\"dolu@npub.cash\\\",\\\"name\\\":\\\"dolu\\\",\\\"nip05\\\":\\\"dolu@dolu.dev\\\",\\\"picture\\\":\\\"!(image)[!(image)[https://pbs.twimg.com/profile_images/1577320325158682626/igGerO9A_400x400.jpg]]\\\",\\\"pubkey\\\":\\\"59b96df8d8b5e66b3b95a3e1ba159750a6edd69bcbba1857aeb652a5b208bd59\\\",\\\"npub\\\":\\\"npub1txukm7xckhnxkwu450sm59vh2znwm45mewaps4awkef2tvsgh4vsf7phrl\\\",\\\"created_at\\\":1688312044}\",\"created_at\":1728233747,\"id\":\"afc3629314aad00f8786af97877115de30c184a25a48440a480bff590a0f9ba8\",\"kind\":0,\"pubkey\":\"59b96df8d8b5e66b3b95a3e1ba159750a6edd69bcbba1857aeb652a5b208bd59\",\"sig\":\"989b250f7fd5d4cfc9a6ee567594c81ee0a91f972e76b61332005fb02aa1343854104fdbcb6c4f77ae8896acd886ab4188043c383e32a6bba509fd78fedb984a\",\"tags\":[]}", "created_at": 1746036589, "id": "efe7fa5844c5c4428fb06d1657bf663d8b256b60c793b5a2c5a426ec773c745c", "kind": 9999, "pubkey": "79be667ef9dcbbac55a06295ce870b07029bfcdb2dce28d959f2815b16f81798", "sig": "219f8bc840d12969ceb0093fb62f314a1f2e19a0cbe3e34b481bdfdf82d8238e1f00362791d17801548839f511533461f10dd45cd0aa4e264d71db6844f5e97c", "tags": [] } -
 @ a95c6243:d345522c
2025-03-20 09:59:20
@ a95c6243:d345522c
2025-03-20 09:59:20Bald werde es verboten, alleine im Auto zu fahren, konnte man dieser Tage in verschiedenen spanischen Medien lesen. Die nationale Verkehrsbehörde (Dirección General de Tráfico, kurz DGT) werde Alleinfahrern das Leben schwer machen, wurde gemeldet. Konkret erörtere die Generaldirektion geeignete Sanktionen für Personen, die ohne Beifahrer im Privatauto unterwegs seien.
Das Alleinfahren sei zunehmend verpönt und ein Mentalitätswandel notwendig, hieß es. Dieser «Luxus» stehe im Widerspruch zu den Maßnahmen gegen Umweltverschmutzung, die in allen europäischen Ländern gefördert würden. In Frankreich sei es «bereits verboten, in der Hauptstadt allein zu fahren», behauptete Noticiastrabajo Huffpost in einer Zwischenüberschrift. Nur um dann im Text zu konkretisieren, dass die sogenannte «Umweltspur» auf der Pariser Ringautobahn gemeint war, die für Busse, Taxis und Fahrgemeinschaften reserviert ist. Ab Mai werden Verstöße dagegen mit einem Bußgeld geahndet.
Die DGT jedenfalls wolle bei der Umsetzung derartiger Maßnahmen nicht hinterherhinken. Diese Medienberichte, inklusive des angeblich bevorstehenden Verbots, beriefen sich auf Aussagen des Generaldirektors der Behörde, Pere Navarro, beim Mobilitätskongress Global Mobility Call im November letzten Jahres, wo es um «nachhaltige Mobilität» ging. Aus diesem Kontext stammt auch Navarros Warnung: «Die Zukunft des Verkehrs ist geteilt oder es gibt keine».
Die «Faktenchecker» kamen der Generaldirektion prompt zu Hilfe. Die DGT habe derlei Behauptungen zurückgewiesen und klargestellt, dass es keine Pläne gebe, Fahrten mit nur einer Person im Auto zu verbieten oder zu bestrafen. Bei solchen Meldungen handele es sich um Fake News. Teilweise wurde der Vorsitzende der spanischen «Rechtsaußen»-Partei Vox, Santiago Abascal, der Urheberschaft bezichtigt, weil er einen entsprechenden Artikel von La Gaceta kommentiert hatte.
Der Beschwichtigungsversuch der Art «niemand hat die Absicht» ist dabei erfahrungsgemäß eher ein Alarmzeichen als eine Beruhigung. Walter Ulbrichts Leugnung einer geplanten Berliner Mauer vom Juni 1961 ist vielen genauso in Erinnerung wie die Fake News-Warnungen des deutschen Bundesgesundheitsministeriums bezüglich Lockdowns im März 2020 oder diverse Äußerungen zu einer Impfpflicht ab 2020.
Aber Aufregung hin, Dementis her: Die Pressemitteilung der DGT zu dem Mobilitätskongress enthält in Wahrheit viel interessantere Informationen als «nur» einen Appell an den «guten» Bürger wegen der Bemühungen um die Lebensqualität in Großstädten oder einen möglichen obligatorischen Abschied vom Alleinfahren. Allerdings werden diese Details von Medien und sogenannten Faktencheckern geflissentlich übersehen, obwohl sie keineswegs versteckt sind. Die Auskünfte sind sehr aufschlussreich, wenn man genauer hinschaut.
Digitalisierung ist der Schlüssel für Kontrolle
Auf dem Kongress stellte die Verkehrsbehörde ihre Initiativen zur Förderung der «neuen Mobilität» vor, deren Priorität Sicherheit und Effizienz sei. Die vier konkreten Ansätze haben alle mit Digitalisierung, Daten, Überwachung und Kontrolle im großen Stil zu tun und werden unter dem Euphemismus der «öffentlich-privaten Partnerschaft» angepriesen. Auch lassen sie die transhumanistische Idee vom unzulänglichen Menschen erkennen, dessen Fehler durch «intelligente» technologische Infrastruktur kompensiert werden müssten.
Die Chefin des Bereichs «Verkehrsüberwachung» erklärte die Funktion des spanischen National Access Point (NAP), wobei sie betonte, wie wichtig Verkehrs- und Infrastrukturinformationen in Echtzeit seien. Der NAP ist «eine essenzielle Web-Applikation, die unter EU-Mandat erstellt wurde», kann man auf der Website der DGT nachlesen.
Das Mandat meint Regelungen zu einem einheitlichen europäischen Verkehrsraum, mit denen die Union mindestens seit 2010 den Aufbau einer digitalen Architektur mit offenen Schnittstellen betreibt. Damit begründet man auch «umfassende Datenbereitstellungspflichten im Bereich multimodaler Reiseinformationen». Jeder Mitgliedstaat musste einen NAP, also einen nationalen Zugangspunkt einrichten, der Zugang zu statischen und dynamischen Reise- und Verkehrsdaten verschiedener Verkehrsträger ermöglicht.
Diese Entwicklung ist heute schon weit fortgeschritten, auch und besonders in Spanien. Auf besagtem Kongress erläuterte die Leiterin des Bereichs «Telematik» die Plattform «DGT 3.0». Diese werde als Integrator aller Informationen genutzt, die von den verschiedenen öffentlichen und privaten Systemen, die Teil der Mobilität sind, bereitgestellt werden.
Es handele sich um eine Vermittlungsplattform zwischen Akteuren wie Fahrzeugherstellern, Anbietern von Navigationsdiensten oder Kommunen und dem Endnutzer, der die Verkehrswege benutzt. Alle seien auf Basis des Internets der Dinge (IOT) anonym verbunden, «um der vernetzten Gemeinschaft wertvolle Informationen zu liefern oder diese zu nutzen».
So sei DGT 3.0 «ein Zugangspunkt für einzigartige, kostenlose und genaue Echtzeitinformationen über das Geschehen auf den Straßen und in den Städten». Damit lasse sich der Verkehr nachhaltiger und vernetzter gestalten. Beispielsweise würden die Karten des Produktpartners Google dank der DGT-Daten 50 Millionen Mal pro Tag aktualisiert.
Des Weiteren informiert die Verkehrsbehörde über ihr SCADA-Projekt. Die Abkürzung steht für Supervisory Control and Data Acquisition, zu deutsch etwa: Kontrollierte Steuerung und Datenerfassung. Mit SCADA kombiniert man Software und Hardware, um automatisierte Systeme zur Überwachung und Steuerung technischer Prozesse zu schaffen. Das SCADA-Projekt der DGT wird von Indra entwickelt, einem spanischen Beratungskonzern aus den Bereichen Sicherheit & Militär, Energie, Transport, Telekommunikation und Gesundheitsinformation.
Das SCADA-System der Behörde umfasse auch eine Videostreaming- und Videoaufzeichnungsplattform, die das Hochladen in die Cloud in Echtzeit ermöglicht, wie Indra erklärt. Dabei gehe es um Bilder, die von Überwachungskameras an Straßen aufgenommen wurden, sowie um Videos aus DGT-Hubschraubern und Drohnen. Ziel sei es, «die sichere Weitergabe von Videos an Dritte sowie die kontinuierliche Aufzeichnung und Speicherung von Bildern zur möglichen Analyse und späteren Nutzung zu ermöglichen».
Letzteres klingt sehr nach biometrischer Erkennung und Auswertung durch künstliche Intelligenz. Für eine bessere Datenübertragung wird derzeit die Glasfaserverkabelung entlang der Landstraßen und Autobahnen ausgebaut. Mit der Cloud sind die Amazon Web Services (AWS) gemeint, die spanischen Daten gehen somit direkt zu einem US-amerikanischen «Big Data»-Unternehmen.
Das Thema «autonomes Fahren», also Fahren ohne Zutun des Menschen, bildet den Abschluss der Betrachtungen der DGT. Zusammen mit dem Interessenverband der Automobilindustrie ANFAC (Asociación Española de Fabricantes de Automóviles y Camiones) sprach man auf dem Kongress über Strategien und Perspektiven in diesem Bereich. Die Lobbyisten hoffen noch in diesem Jahr 2025 auf einen normativen Rahmen zur erweiterten Unterstützung autonomer Technologien.
Wenn man derartige Informationen im Zusammenhang betrachtet, bekommt man eine Idee davon, warum zunehmend alles elektrisch und digital werden soll. Umwelt- und Mobilitätsprobleme in Städten, wie Luftverschmutzung, Lärmbelästigung, Platzmangel oder Staus, sind eine Sache. Mit dem Argument «emissionslos» wird jedoch eine Referenz zum CO2 und dem «menschengemachten Klimawandel» hergestellt, die Emotionen triggert. Und damit wird so ziemlich alles verkauft.
Letztlich aber gilt: Je elektrischer und digitaler unsere Umgebung wird und je freigiebiger wir mit unseren Daten jeder Art sind, desto besser werden wir kontrollier-, steuer- und sogar abschaltbar. Irgendwann entscheiden KI-basierte Algorithmen, ob, wann, wie, wohin und mit wem wir uns bewegen dürfen. Über einen 15-Minuten-Radius geht dann möglicherweise nichts hinaus. Die Projekte auf diesem Weg sind ernst zu nehmen, real und schon weit fortgeschritten.
[Titelbild: Pixabay]
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ fd78c37f:a0ec0833
2025-04-21 04:40:30
@ fd78c37f:a0ec0833
2025-04-21 04:40:30Bitcoin is redefining finance, and in Asia—Thailand, Vietnam, Indonesia, and beyond—developers, entrepreneurs, and communities are fueling this revolution. YakiHonne, a decentralized social payments app built on Nostr, sat down with Gio (nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx), a core member of Thailand’s Sats ‘N’ Facts community, to explore their mission of fostering open-source Bitcoin development. In this interview, Gio shares the origins of Sats ‘N’ Facts, the challenges of hosting Bitcoin-focused events in Asia, and how these efforts are shaping adoption across the region.
YakiHonne: Can you tell us about yourself and how Sats ‘N’ Facts came to life? What sparked your Bitcoin journey?
Gio: I’m originally from Europe but have called Thailand home for six years. My Bitcoin story began while working at a commercial bank, where I saw the fiat system’s flaws firsthand—things like the Cantillon Effect, where money printing favors the connected few, felt deeply unfair. That discomfort led me to Andreas Antonopoulos’ videos, which opened my eyes to Bitcoin’s potential. After moving to Bangkok, I joined the open-source scene at BOB Space, collaborating with folks on tech projects.
Sats ‘N’ Facts grew out of that spirit. We wanted to create a Bitcoin-focused community to support developers and builders in Asia. Our recent conference in Chiang Mai brought together over 70 enthusiasts from Thailand, Vietnam, Laos, and beyond, sparking collaborations like a new Lightning Network tool. It was a milestone in connecting the region’s Bitcoin ecosystem.
YakiHonne: What inspired the Sats ‘N’ Facts conference, and how did you attract attendees?
Gio: The event was born from a desire to create a high-signal, low-noise space for Freedom Tech in Asia. While the U.S. and Europe host major Bitcoin events, Asia’s scene is still emerging under commercial stunts. We aimed to bridge that gap, uniting developers, educators, and enthusiasts to discuss real innovations—no altcoins, no corporate agendas. Our focus was on open-source projects like Bitcoin Core, Ark, Cashu, fostering conversations that could lead to tangible contributions.
Attracting attendees wasn’t easy. We leveraged local networks, reaching out to Bitcoin communities in neighboring countries via Nostr and Telegram. Posts on X helped spread the word, and we saw developers from Laos join for the first time, which was thrilling. Sponsors like Fulgur Ventures, Utreexo, and the Bitcoin Development Kit Foundation played a huge role, covering costs so we could keep the event free and accessible.
YakiHonne: What challenges did you face organizing the conference in Asia?
Gio: It was a steep learning curve. Funding was the biggest hurdle—early on, we struggled to cover venue and travel costs. Thankfully, our sponsors stepped in, letting me focus on logistics, which were no small feat either. As a first-time organizer, I underestimated the chaos of a tight timeline. Day one felt like herding cats without a fixed agenda, but the energy was electric—developers debugging code together, newcomers asking big questions.
Another challenge was cultural. Bitcoin’s still niche in Asia, so convincing locals to attend took persistence; there was no local presence for some reason. Despite the hiccups, we pulled it off, hosting 60+ attendees and sparking ideas for new projects, like a Cashu wallet integration. I’d tweak the planning next time, but the raw passion made it unforgettable.
YakiHonne: How does YakiHonne’s vision of decentralized social payments align with Sats ‘N’ Facts’ goals? Could tools like ours support your community?
Gio: That’s a great question. YakiHonne’s approach—merging Nostr’s censorship-resistant communication with Lightning payments—fits perfectly with our mission to empower users through open tech. At Sats ‘N’ Facts, we’re all about tools that give people control, whether it’s code or money. An app like YakiHonne could streamline community funding, letting developers tip each other for contributions or crowdfund projects directly. Imagine a hackathon where winners get sats instantly via YakiHonne—it’d be a game-changer. I’d love to see you guys at our next event to demo it!
YakiHonne: What advice would you give to someone starting a Bitcoin-focused community or event?
Gio: First, keep it Bitcoin-only. Stay true to the principles—cut out distractions like altcoins or hype-driven schemes. Start small: host regular meetups, maybe five people at a café, and build trust over time. Consistency and authenticity beat flashiness in the medium and long term.
Second, involve technical folks. Developers bring credibility and clarity, explaining Bitcoin’s nuts and bolts in ways newcomers get. I admire how Andreas Antonopoulos bridges that gap—technical yet accessible. You need that foundation to grow a real community.
Finally, lean on existing networks. If you know someone running a Bitcoin meetup in another city, collaborate. Share ideas, speakers, or even livestreams. Nostr’s great for this—our Laos attendees found us through a single post. Relationships are everything.
YakiHonne: Does Sats ‘N’ Facts focus more on Bitcoin’s technical side, non-technical side, or both?
Gio: We blend both. Our event had workshops for coders alongside talks for beginners on why Bitcoin matters. Open-source is our heartbeat, though. If you’re starting out, dive into projects like Bitcoin Core or Lightning. Review a pull request, test a Cashu wallet, or join a hackathon. One developer at our event built a Lightning micropayment tool that’s now live on GitHub.
There’s no shortage of ways to contribute. Community calls, forums, residency programs, and platforms like Geyser Fund are goldmines. YakiHonne could amplify this—imagine tipping developers for bug fixes via your app. It’s about iterating until you create something real.
YakiHonne: Your work is inspiring, Gio. Sats ‘N’ Facts is uniting Asia’s Bitcoin communities in a powerful way. What’s next for you?
Gio: Thanks for the kind words! We’re just getting started. The Chiang Mai event showed what’s possible—connecting developers across borders, reviewing and launching code and testing upcoming technologies. Next, we’re planning smaller hackathons and other events to keep the momentum going, maybe in Vietnam, Indonesia or Korea. I’d love to integrate tools like YakiHonne to fund these efforts directly through Nostr payments. Long-term, we want Sats ‘N’ Facts to be a hub for Asia’s Bitcoin builders, proving open-source can thrive here.

YakiHonne: Thank you, Gio, for sharing Sats ‘N’ Facts incredible journey. Your work is lighting a path for Bitcoin in Asia, and we’re honored to tell this story.
To our readers: Bitcoin’s future depends on communities like Sats ‘N’ Facts—and you can join the revolution. Download YakiHonne on Nostr to connect with builders, send Lightning payments, and explore the decentralized world. Follow Sats ‘N’ Facts for their next hackathon, and let’s build freedom tech together!
-
 @ 866e0139:6a9334e5
2025-04-30 18:47:50
@ 866e0139:6a9334e5
2025-04-30 18:47:50Autor: Ulrike Guérot. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
https://www.youtube.com/watch?v=KarwcXKmD3E
Liebe Freunde und Bekannte,
liebe Friedensbewegte,
liebe Dresdener, Dresden ist ja auch eine kriegsgeplagte Stadt,
dies ist meine dritte Rede auf einer Friedensdemonstration innerhalb von nur gut einem halben Jahr: München im September, München im Februar, Dresden im April. Und der Krieg rückt immer näher! Wer sich den „Operationsplan Deutschland über die zivil-militärische Kooperation als wesentlicher Bestandteil der Kriegsführung“ anschaut, dem kann nur schlecht werden zu sehen, wie weit die Kriegsvorbereitungen schon gediehen sind.
Doch bevor ich darauf eingehe, möchte ich mich als erstes distanzieren von dem wieder einmal erbärmlichen Framing dieser Demo als Querfront oder Schwurblerdemo. Durch dieses Framing wurde diese Demo vom Dresdener Marktplatz auf den Postplatz verwiesen, wurden wir geschmäht und wurde die Stadtverwaltung Dresden dazu gebracht, eine „genehmere“ Demo auf dem Marktplatz zuzulassen! Es wäre schön, wenn wir alle - alle! - solche Framings weglassen würden und uns als Friedensbewegte die Hand reichen! Der Frieden im eigenen Haus ist die Voraussetzung für unsere Friedensarbeit. Der Streit in unserem Haus nutzt nur denen, die den Krieg wollen und uns spalten!
Ich möchte hier noch einmal klarstellen, von welcher Position aus ich hier und heute wiederholt auf einer Bühne spreche: Ich spreche als engagierte Bürgerin der Bundesrepublik Deutschland. Ich spreche als Europäerin, die lange Jahre in und an dem einstigen Friedensprojekt EU gearbeitet hat. Ich spreche als Enkelin von zwei Großvätern. Der eine ist im Krieg gefallen, der andere kam ohne Beine zurück. Ich spreche als Tochter einer Mutter, die 1945, als 6-Jährige, unter traumatischen Umständen aus Schlesien vertrieben wurde, nach Delitzsch in Sachsen übrigens. Ich spreche als Mutter von zwei Söhnen, 33 und 31 Jahre, von denen ich nicht möchte, dass sie in einen Krieg müssen. Von dieser, und nur dieser Position aus spreche ich heute zu Ihnen und von keiner anderen! Ich bin nicht rechts, ich bin keine Schwurblerin, ich bin nicht radikal, ich bin keine Querfront.
Als Bürgerin wünsche ich mir – nein, verlange ich! – dass die Bundesrepublik Deutschland sich an ihre gesetzlichen Grundlagen und Vertragstexte hält. Das sind namentlich: Die Friedensklausel des Grundgesetzes aus Art. 125 und 126 GG, dass von deutschem Boden nie wieder Krieg ausgeht. Und der Zwei-plus-Vier-Vertrag, in dem Deutschland 1990 unterschrieben hat, dass es nie an einem bewaffneten Konflikt gegen Russland teilnimmt. Ich schäme mich dafür, dass mein Land dabei ist, vertragsbrüchig zu werden. Ich bitte Friedrich Merz, den designierten Bundeskanzler, keinen Vertragsbruch durch die Lieferung von Taurus-Raketen zu begehen!
Ich bitte ferner darum, dass sich dieses Land an seine didaktischen Vorgaben für Schulen hält, die im immer noch geltenden „Beutelsbacher Konsens“ aus den 1970er Jahren festgelegt wurden. In diesem steht in Artikel I. ein Überwältigungsverbot: „Es ist nicht erlaubt, den Schüler – mit welchen Mitteln auch immer – im Sinne erwünschter Meinungen zu überrumpeln und damit an der Gewinnung eines selbständigen Urteils zu hindern.“ Vor diesem Hintergrund ist es nicht erlaubt, Soldaten oder Gefreite in Schulen zu schicken und für die Bundeswehr zu werben. Vielmehr wäre es geboten, unsere Kinder über Art. 125 & 126 GG und die Friedenspflicht des Landes und seine Geschichte mit Blick auf Russland aufzuklären.
Als Europäerin wünsche ich mir, dass wir die europäische Hymne, Beethovens 9. Sinfonie, ernst nehmen, deren Text da lautet: Alle Menschen werden Brüder. Alle Menschen werden Brüder. Alle! Dazu gehören auch die Russen und natürlich auch die Ukrainer!
Als Europäerin, die in den 1990er Jahren für den großartigen EU-Kommissionspräsidenten Jacques Delors gearbeitet hat, Katholik, Sozialist und Gewerkschafter, wünsche ich mir, dass wir das Versprechen, #Europa ist nie wieder Krieg, ernst nehmen. Wir haben es 70 Jahre lang auf diesem Kontinent erzählt. Die Lügen und die Propaganda, mit der jetzt die Kriegsnotwendigkeit gegen Russland herbeigeredet wird, sind unerträglich. Die EU, Friedensnobelpreisträgerin von 2012, ist dabei – oder hat schon – ihr Ansehen in der Welt verloren. Es ist eine politische Tragödie! Neben ihrem Ansehen ist die EU jetzt dabei, das zivilisatorische Erbe Europas zu verspielen, die civilité européenne, wie der französische Historiker und Marxist, Étienne Balibar es nennt.
Ein Element dieses historischen Erbes ist es, dass uns in Europa eint, dass wir über Jahrhunderte alle zugleich Täter und Opfer gewesen sind. Ce que nous partageons, c’est ce que nous étions tous bourreaux et victimes. So schreibt es der französische Literat Laurent Gaudet in seinem europäischen Epos, L’Europe. Une Banquet des Peuples von 2016.
Das heißt, dass niemand in Europa, niemand – auch die Esten nicht! – das Recht hat, vorgängige Traumata, die die baltischen Staaten unbestrittenermaßen mit Stalin-Russland gehabt haben, zu verabsolutieren, auf die gesamte EU zu übertragen, die EU damit zu blockieren und die Politikgestaltung der EU einseitig auf einen Kriegskurs gegen Russland auszurichten. Ich wende mich mit dieser Feststellung direkt an Kaja Kalles, die Hohe Beauftragte für Sicherheits- und Außenpolitik der EU und hoffe, dass sie diese Rede hört und das Epos von Laurent Gaudet liest.
Es gibt keinen gerechten Krieg! Krieg ist immer nur Leid. In Straßburg, dem Sitz des Europäischen Parlaments, steht auf dem Place de la République eine Statue, eine Frau, die Republik. Sie hält in jedem Arm einen Sohn, einen Elsässer und einen Franzosen, die aus dem Krieg kommen. In der Darstellung der Bronzefigur haben die beiden Soldaten-Männer ihre Uniformen schon ausgezogen und werden von Madame la République gehalten und getröstet. An diesem Denkmal sollten sich alle Abgeordnete des Straßburger Europaparlamentes am 9. Mai versammeln. Ich zitiere noch einmal Cicero: Der ungerechteste Friede ist besser als der gerechteste Krieg. Für den Vortrag dieses Zitats eines der größten Staatsdenker des antiken Roms in einer Fernsehsendung bin ich 2022 mit einem Shitstorm überzogen worden. Allein das ist Ausdruck des Verfalls unserer Diskussionskultur in unfassbarem Ausmaß, ganz besonders in Deutschland.
Als Europäerin verlange ich die Überwindung unserer kognitiven Dissonanz. Wenn schon die New York Times am 27. März 2025 ein 27-seitiges Dossier veröffentlicht, das nicht nur belegt, was man eigentlich schon weiß, aber bisher nicht sagen durfte, nämlich, dass der ukrainisch-russische Krieg ein eindeutiger Stellvertreter-Krieg der USA ist, in der die Ukraine auf monströseste Weise instrumentalisiert wurde – was das Dossier der NYT unumwunden zugibt! – wäre es an der Zeit, die eindeutige Schuldzuweisung an Russland für den Krieg zurückzuziehen und die gezielt verbreitete Russophobie in Europa zu beenden. Anstatt dass – wofür es leider viele Verdachtsmomente gibt – die EU die Friedensverhandlungen in Saudi-Arabien nach Strich und Faden torpediert.
Der französische Philosoph Luc Ferry hat vor ein paar Tagen im prime time französischen Fernsehen ganz klar gesagt, dass der Krieg 2014 nach der Instrumentalisierung des Maidan durch die USA von der West-Ukraine ausging, dass Zelensky diesen Krieg wollte und – mit amerikanischer Rückendeckung – provoziert hat, dass Putin nicht Hitler ist und dass die einzigen mit faschistoiden Tendenzen in der ukrainischen Regierung sitzen. Ich wünschte mir, ein solches Statement wäre auch im Deutschen Fernsehen möglich und danke Richard David Precht, dass er, der noch in den Öffentlich-Rechtlichen Rundfunk vorgelassen wird, an dieser Stelle versucht, etwas Vernunft in die Debatte zu bringen.
Auch ist es gerade als Europäerin nicht hinzunehmen, dass russische Diplomaten von den Feierlichkeiten am 8. Mai 2025 ausgeschlossen werden sollen, ausgerechnet 80 Jahre nach Ende des II. Weltkrieges. Nicht nur sind Feierlichkeiten genau dazu da, sich die Hand zu reichen und den Frieden zu feiern. Doch gerade vor dem Hintergrund von 27 Millionen gefallenen sowjetischen Soldaten ist die Zurückweisung der Russen von den Feierlichkeiten geradezu eklatante Geschichtsvergessenheit.
***
Der Völkerbund hat 1925 die Frage erörtert, warum der I. Weltkrieg noch so lange gedauert hat, obgleich er militärisch bereits 1916 nach Eröffnung des Zweifrontenkrieges zu Lasten des Deutschen Reiches entschieden war. Wir erinnern uns: Für die Niederlage wurden mit der Dolchstoßlegende die jüdischen, kommunistischen und sozialistischen Pazifisten verantwortlich gemacht. Richtig ist, so der Bericht des Völkerbundes von 1925, dass allein die Rüstungsindustrie dafür gesorgt hat, dass der militärisch eigentlich schon entschiedene Krieg noch zwei weitere Jahre als Materialabnutzungs- und Stellungskrieg weiterbetrieben wurde, nur, damit noch ein bisschen Geld verdient werden konnte. Genauso scheint es heute zu sein. Der Krieg ist militärisch entschieden. Er kann und muss sofort beendet werden, und das passiert lediglich deswegen nicht, weil der Westen seine Niederlage nicht zugeben kann. Hochmut aber kommt vor dem Fall, und es darf nicht sein, dass für europäischen Hochmut jeden Tag rund 2000 ukrainische oder russische Soldaten und viele Zivilisten sterben. Die offenbare europäische Absicht, den Krieg jetzt einzufrieren, nur, um ihn 2029/ 2030 wieder zu entfachen, wenn Europa dann besser aufgerüstet ist, ist nur noch zynisch.
Als Kriegsenkelin von Kriegsversehrten, Tochter einer Flüchtlingsmutter und Mutter von zwei Söhnen, deren französischer Urgroßvater 6 Jahre in deutscher Kriegsgefangenschaft war, wünsche ich mir schließlich und zum Abschluss, dass wir die Kraft haben werden, wenn dieser Wahnsinn, den man den europäischen Bürgern gerade aufbürdet, vorbei sein wird, ein neues europäisches Projekt zu erdenken und zu erbauen, in dem Europa politisch geeint ist und es bleibt, aber dezentral, regional, subsidiär, friedlich und neutral gestaltet wird. Also ein Europa jenseits der Strukturen der EU, das bereit ist, die Pax Americana zu überwinden, aus der NATO auszutreten und der multipolaren Welt seine Hand auszustrecken! Unser Europa ist postimperial, postkolonial, groß, vielfältig und friedfertig!
Ulrike Guérot, Jg. 1964, ist europäische Professorin, Publizistin und Bestsellerautorin. Seit rund 30 Jahren beschäftigt sie sich in europäischen Think Tanks und Universitäten in Paris, Brüssel, London, Washington, New York, Wien und Berlin mit Fragen der europäischen Demokratie sowie mit der Rolle Europas in der Welt. Ulrike Guérot ist seit März 2014 Gründerin und Direktorin des European Democracy Lab e.V., Berlin und initiierte im März 2023 das European Citizens Radio, das auf Spotify zu finden ist. Zuletzt erschien von ihr „Über Halford J. Mackinders Heartland-Theorie, Der geografische Drehpunkt der Geschichte“ (Westend, 2024). Mehr Infos zur Autorin hier.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ a95c6243:d345522c
2025-03-15 10:56:08
@ a95c6243:d345522c
2025-03-15 10:56:08Was nützt die schönste Schuldenbremse, wenn der Russe vor der Tür steht? \ Wir können uns verteidigen lernen oder alle Russisch lernen. \ Jens Spahn
In der Politik ist buchstäblich keine Idee zu riskant, kein Mittel zu schäbig und keine Lüge zu dreist, als dass sie nicht benutzt würden. Aber der Clou ist, dass diese Masche immer noch funktioniert, wenn nicht sogar immer besser. Ist das alles wirklich so schwer zu durchschauen? Mir fehlen langsam die Worte.
Aktuell werden sowohl in der Europäischen Union als auch in Deutschland riesige Milliardenpakete für die Aufrüstung – also für die Rüstungsindustrie – geschnürt. Die EU will 800 Milliarden Euro locker machen, in Deutschland sollen es 500 Milliarden «Sondervermögen» sein. Verteidigung nennen das unsere «Führer», innerhalb der Union und auch an «unserer Ostflanke», der Ukraine.
Das nötige Feindbild konnte inzwischen signifikant erweitert werden. Schuld an allem und zudem gefährlich ist nicht mehr nur Putin, sondern jetzt auch Trump. Europa müsse sich sowohl gegen Russland als auch gegen die USA schützen und rüsten, wird uns eingetrichtert.
Und während durch Diplomatie genau dieser beiden Staaten gerade endlich mal Bewegung in die Bemühungen um einen Frieden oder wenigstens einen Waffenstillstand in der Ukraine kommt, rasselt man im moralisch überlegenen Zeigefinger-Europa so richtig mit dem Säbel.
Begleitet und gestützt wird der ganze Prozess – wie sollte es anders sein – von den «Qualitätsmedien». Dass Russland einen Angriff auf «Europa» plant, weiß nicht nur der deutsche Verteidigungsminister (und mit Abstand beliebteste Politiker) Pistorius, sondern dank ihnen auch jedes Kind. Uns bleiben nur noch wenige Jahre. Zum Glück bereitet sich die Bundeswehr schon sehr konkret auf einen Krieg vor.
Die FAZ und Corona-Gesundheitsminister Spahn markieren einen traurigen Höhepunkt. Hier haben sich «politische und publizistische Verantwortungslosigkeit propagandistisch gegenseitig befruchtet», wie es bei den NachDenkSeiten heißt. Die Aussage Spahns in dem Interview, «der Russe steht vor der Tür», ist das eine. Die Zeitung verschärfte die Sache jedoch, indem sie das Zitat explizit in den Titel übernahm, der in einer ersten Version scheinbar zu harmlos war.
Eine große Mehrheit der deutschen Bevölkerung findet Aufrüstung und mehr Schulden toll, wie ARD und ZDF sehr passend ermittelt haben wollen. Ähnliches gelte für eine noch stärkere militärische Unterstützung der Ukraine. Etwas skeptischer seien die Befragten bezüglich der Entsendung von Bundeswehrsoldaten dorthin, aber immerhin etwa fifty-fifty.
Eigentlich ist jedoch die Meinung der Menschen in «unseren Demokratien» irrelevant. Sowohl in der Europäischen Union als auch in Deutschland sind die «Eliten» offenbar der Ansicht, der Souverän habe in Fragen von Krieg und Frieden sowie von aberwitzigen astronomischen Schulden kein Wörtchen mitzureden. Frau von der Leyen möchte über 150 Milliarden aus dem Gesamtpaket unter Verwendung von Artikel 122 des EU-Vertrags ohne das Europäische Parlament entscheiden – wenn auch nicht völlig kritiklos.
In Deutschland wollen CDU/CSU und SPD zur Aufweichung der «Schuldenbremse» mehrere Änderungen des Grundgesetzes durch das abgewählte Parlament peitschen. Dieser Versuch, mit dem alten Bundestag eine Zweidrittelmehrheit zu erzielen, die im neuen nicht mehr gegeben wäre, ist mindestens verfassungsrechtlich umstritten.
Das Manöver scheint aber zu funktionieren. Heute haben die Grünen zugestimmt, nachdem Kanzlerkandidat Merz läppische 100 Milliarden für «irgendwas mit Klima» zugesichert hatte. Die Abstimmung im Plenum soll am kommenden Dienstag erfolgen – nur eine Woche, bevor sich der neu gewählte Bundestag konstituieren wird.
Interessant sind die Argumente, die BlackRocker Merz für seine Attacke auf Grundgesetz und Demokratie ins Feld führt. Abgesehen von der angeblichen Eile, «unsere Verteidigungsfähigkeit deutlich zu erhöhen» (ausgelöst unter anderem durch «die Münchner Sicherheitskonferenz und die Ereignisse im Weißen Haus»), ließ uns der CDU-Chef wissen, dass Deutschland einfach auf die internationale Bühne zurück müsse. Merz schwadronierte gefährlich mehrdeutig:
«Die ganze Welt schaut in diesen Tagen und Wochen auf Deutschland. Wir haben in der Europäischen Union und auf der Welt eine Aufgabe, die weit über die Grenzen unseres eigenen Landes hinausgeht.»
[Titelbild: Tag des Sieges]
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 90de72b7:8f68fdc0
2025-04-30 18:20:42
@ 90de72b7:8f68fdc0
2025-04-30 18:20:42PetriNostr. My everyday activity 30/02-2
PetriNostr never sleep! This is a demo
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ ed5774ac:45611c5c
2025-04-19 20:29:31
@ ed5774ac:45611c5c
2025-04-19 20:29:31April 20, 2020: The day I saw my so-called friends expose themselves as gutless, brain-dead sheep.
On that day, I shared a video exposing the damning history of the Bill & Melinda Gates Foundation's vaccine campaigns in Africa and the developing world. As Gates was on every TV screen, shilling COVID jabs that didn’t even exist, I called out his blatant financial conflict of interest and pointed out the obvious in my facebook post: "Finally someone is able to explain why Bill Gates runs from TV to TV to promote vaccination. Not surprisingly, it's all about money again…" - referencing his substantial investments in vaccine technology, including BioNTech's mRNA platform that would later produce the COVID vaccines and generate massive profits for his so-called philanthropic foundation.
The conflict of interest was undeniable. I genuinely believed anyone capable of basic critical thinking would at least pause to consider these glaring financial motives. But what followed was a masterclass in human stupidity.
My facebook post from 20 April 2020:

Not only was I branded a 'conspiracy theorist' for daring to question the billionaire who stood to make a fortune off the very vaccines he was shilling, but the brain-dead, logic-free bullshit vomited by the people around me was beyond pathetic. These barely literate morons couldn’t spell "Pfizer" without auto-correct, yet they mindlessly swallowed and repeated every lie the media and government force-fed them, branding anything that cracked their fragile reality as "conspiracy theory." Big Pharma’s rap sheet—fraud, deadly cover-ups, billions in fines—could fill libraries, yet these obedient sheep didn’t bother to open a single book or read a single study before screaming their ignorance, desperate to virtue-signal their obedience. Then, like spineless lab rats, they lined up for an experimental jab rushed to the market in months, too dumb to care that proper vaccine development takes a decade.
The pathetic part is that these idiots spend hours obsessing over reviews for their useless purchases like shoes or socks, but won’t spare 60 seconds to research the experimental cocktail being injected into their veins—or even glance at the FDA’s own damning safety reports. Those same obedient sheep would read every Yelp review for a fucking coffee shop but won't spend five minutes looking up Pfizer's criminal fraud settlements. They would demand absolute obedience to ‘The Science™’—while being unable to define mRNA, explain lipid nanoparticles, or justify why trials were still running as they queued up like cattle for their jab. If they had two brain cells to rub together or spent 30 minutes actually researching, they'd know, but no—they'd rather suck down the narrative like good little slaves, too dumb to question, too weak to think.
Worst of all, they became the system’s attack dogs—not just swallowing the poison, but forcing it down others’ throats. This wasn’t ignorance. It was betrayal. They mutated into medical brownshirts, destroying lives to virtue-signal their obedience—even as their own children’s hearts swelled with inflammation.
One conversation still haunts me to this day—a masterclass in wealth-worship delusion. A close friend, as a response to my facebook post, insisted that Gates’ assumed reading list magically awards him vaccine expertise, while dismissing his billion-dollar investments in the same products as ‘no conflict of interest.’ Worse, he argued that Gates’s $5–10 billion pandemic windfall was ‘deserved.’
This exchange crystallizes civilization’s intellectual surrender: reason discarded with religious fervor, replaced by blind faith in corporate propaganda.
The comment of a friend on my facebook post that still haunts me to this day:

Walking Away from the Herd
After a period of anger and disillusionment, I made a decision: I would no longer waste energy arguing with people who refused to think for themselves. If my circle couldn’t even ask basic questions—like why an untested medical intervention was being pushed with unprecedented urgency—then I needed a new community.
Fortunately, I already knew where to look. For three years, I had been involved in Bitcoin, a space where skepticism wasn’t just tolerated—it was demanded. Here, I’d met some of the most principled and independent thinkers I’d ever encountered. These were people who understood the corrupting influence of centralized power—whether in money, media, or politics—and who valued sovereignty, skepticism, and integrity. Instead of blind trust, bitcoiners practiced relentless verification. And instead of empty rhetoric, they lived by a simple creed: Don’t trust. Verify.
It wasn’t just a philosophy. It was a lifeline. So I chose my side and I walked away from the herd.
Finding My Tribe
Over the next four years, I immersed myself in Bitcoin conferences, meetups, and spaces where ideas were tested, not parroted. Here, I encountered extraordinary people: not only did they share my skepticism toward broken systems, but they challenged me to sharpen it.
No longer adrift in a sea of mindless conformity, I’d found a crew of thinkers who cut through the noise. They saw clearly what most ignored—that at the core of society’s collapse lay broken money, the silent tax on time, freedom, and truth itself. But unlike the complainers I’d left behind, these people built. They coded. They wrote. They risked careers and reputations to expose the rot. Some faced censorship; others, mockery. All understood the stakes.
These weren’t keyboard philosophers. They were modern-day Cassandras, warning of inflation’s theft, the Fed’s lies, and the coming dollar collapse—not for clout, but because they refused to kneel to a dying regime. And in their defiance, I found something rare: a tribe that didn’t just believe in a freer future. They were engineering it.
April 20, 2024: No more herd. No more lies. Only proof-of-work.
On April 20, 2024, exactly four years after my last Facebook post, the one that severed my ties to the herd for good—I stood in front of Warsaw’s iconic Palace of Culture and Science, surrounded by 400 bitcoiners who felt like family. We were there to celebrate Bitcoin’s fourth halving, but it was more than a protocol milestone. It was a reunion of sovereign individuals. Some faces I’d known since the early days; others, I’d met only hours before. We bonded instantly—heated debates, roaring laughter, zero filters on truths or on so called conspiracy theories.
As the countdown to the halving began, it hit me: This was the antithesis of the hollow world I’d left behind. No performative outrage, no coerced consensus—just a room of unyielding minds who’d traded the illusion of safety for the grit of truth. Four years prior, I’d been alone in my resistance. Now, I raised my glass among my people - those who had seen the system's lies and chosen freedom instead. Each had their own story of awakening, their own battles fought, but here we shared the same hard-won truth.
The energy wasn’t just electric. It was alive—the kind that emerges when free people build rather than beg. For the first time, I didn’t just belong. I was home. And in that moment, the halving’s ticking clock mirrored my own journey: cyclical, predictable in its scarcity, revolutionary in its consequences. Four years had burned away the old world. What remained was stronger.

No Regrets
Leaving the herd wasn’t a choice—it was evolution. My soul shouted: "I’d rather stand alone than kneel with the masses!". The Bitcoin community became more than family; they’re living proof that the world still produces warriors, not sheep. Here, among those who forge truth, I found something extinct elsewhere: hope that burns brighter with every halving, every block, every defiant mind that joins the fight.
Change doesn’t come from the crowd. It starts when one person stops applauding.
Today, I stand exactly where I always wanted to be—shoulder-to-shoulder with my true family: the rebels, the builders, the ungovernable. Together, we’re building the decentralized future.
-
 @ 30b99916:3cc6e3fe
2025-04-19 19:55:31
@ 30b99916:3cc6e3fe
2025-04-19 19:55:31btcpayserver #lightning #lnd #powershell #coinos
BTCpayAPI now supports CoinOS.io REST Api
Adding Coinos.io REST Api end points support to BTCpayAPI. Here is what is implemented, tested and doumented so far.
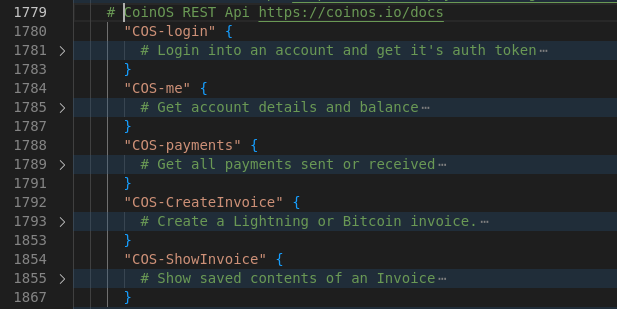
Current REST APIs supported are now:
LND API https://lightning.engineering/api-docs/api/lnd/ BTCPay Greenfield API (v1) https://docs.btcpayserver.org/API/Greenfield/v1/ Hashicorp Vault API https://developer.hashicorp.com/vault/api-docs/secret/kv/kv-v1 Coinos.io API https://coinos.io/docs
Although this is PowerShell code, it is exclusively being developed and tested on Linux only.
Code is available at https://btcpayserver.sytes.net
-
 @ 90de72b7:8f68fdc0
2025-04-30 17:55:30
@ 90de72b7:8f68fdc0
2025-04-30 17:55:30PetriNostr. My everyday activity 30/04
PetriNostr never sleep! This is a demo
petrinet ;startDay () -> working ;stopDay working -> () ;startPause working -> paused ;endPause paused -> working ;goSmoke working -> smoking ;endSmoke smoking -> working ;startEating working -> eating ;stopEating eating -> working ;startCall working -> onCall ;endCall onCall -> working ;startMeeting working -> inMeetinga ;endMeeting inMeeting -> working ;logTask working -> working -
 @ a95c6243:d345522c
2025-03-11 10:22:36
@ a95c6243:d345522c
2025-03-11 10:22:36«Wir brauchen eine digitale Brandmauer gegen den Faschismus», schreibt der Chaos Computer Club (CCC) auf seiner Website. Unter diesem Motto präsentierte er letzte Woche einen Forderungskatalog, mit dem sich 24 Organisationen an die kommende Bundesregierung wenden. Der Koalitionsvertrag müsse sich daran messen lassen, verlangen sie.
In den drei Kategorien «Bekenntnis gegen Überwachung», «Schutz und Sicherheit für alle» sowie «Demokratie im digitalen Raum» stellen die Unterzeichner, zu denen auch Amnesty International und Das NETTZ gehören, unter anderem die folgenden «Mindestanforderungen»:
- Verbot biometrischer Massenüberwachung des öffentlichen Raums sowie der ungezielten biometrischen Auswertung des Internets.
- Anlasslose und massenhafte Vorratsdatenspeicherung wird abgelehnt.
- Automatisierte Datenanalysen der Informationsbestände der Strafverfolgungsbehörden sowie jede Form von Predictive Policing oder automatisiertes Profiling von Menschen werden abgelehnt.
- Einführung eines Rechts auf Verschlüsselung. Die Bundesregierung soll sich dafür einsetzen, die Chatkontrolle auf europäischer Ebene zu verhindern.
- Anonyme und pseudonyme Nutzung des Internets soll geschützt und ermöglicht werden.
- Bekämpfung «privaten Machtmissbrauchs von Big-Tech-Unternehmen» durch durchsetzungsstarke, unabhängige und grundsätzlich föderale Aufsichtsstrukturen.
- Einführung eines digitalen Gewaltschutzgesetzes, unter Berücksichtigung «gruppenbezogener digitaler Gewalt» und die Förderung von Beratungsangeboten.
- Ein umfassendes Förderprogramm für digitale öffentliche Räume, die dezentral organisiert und quelloffen programmiert sind, soll aufgelegt werden.
Es sei ein Irrglaube, dass zunehmende Überwachung einen Zugewinn an Sicherheit darstelle, ist eines der Argumente der Initiatoren. Sicherheit erfordere auch, dass Menschen anonym und vertraulich kommunizieren können und ihre Privatsphäre geschützt wird.
Gesunde digitale Räume lebten auch von einem demokratischen Diskurs, lesen wir in dem Papier. Es sei Aufgabe des Staates, Grundrechte zu schützen. Dazu gehöre auch, Menschenrechte und demokratische Werte, insbesondere Freiheit, Gleichheit und Solidarität zu fördern sowie den Missbrauch von Maßnahmen, Befugnissen und Infrastrukturen durch «die Feinde der Demokratie» zu verhindern.
Man ist geneigt zu fragen, wo denn die Autoren «den Faschismus» sehen, den es zu bekämpfen gelte. Die meisten der vorgetragenen Forderungen und Argumente finden sicher breite Unterstützung, denn sie beschreiben offenkundig gängige, kritikwürdige Praxis. Die Aushebelung der Privatsphäre, der Redefreiheit und anderer Grundrechte im Namen der Sicherheit wird bereits jetzt massiv durch die aktuellen «demokratischen Institutionen» und ihre «durchsetzungsstarken Aufsichtsstrukturen» betrieben.
Ist «der Faschismus» also die EU und ihre Mitgliedsstaaten? Nein, die «faschistische Gefahr», gegen die man eine digitale Brandmauer will, kommt nach Ansicht des CCC und seiner Partner aus den Vereinigten Staaten. Private Überwachung und Machtkonzentration sind dabei weltweit schon lange Realität, jetzt endlich müssen sie jedoch bekämpft werden. In dem Papier heißt es:
«Die willkürliche und antidemokratische Machtausübung der Tech-Oligarchen um Präsident Trump erfordert einen Paradigmenwechsel in der deutschen Digitalpolitik. (...) Die aktuellen Geschehnisse in den USA zeigen auf, wie Datensammlungen und -analyse genutzt werden können, um einen Staat handstreichartig zu übernehmen, seine Strukturen nachhaltig zu beschädigen, Widerstand zu unterbinden und marginalisierte Gruppen zu verfolgen.»
Wer auf der anderen Seite dieser Brandmauer stehen soll, ist also klar. Es sind die gleichen «Feinde unserer Demokratie», die seit Jahren in diese Ecke gedrängt werden. Es sind die gleichen Andersdenkenden, Regierungskritiker und Friedensforderer, die unter dem großzügigen Dach des Bundesprogramms «Demokratie leben» einem «kontinuierlichen Echt- und Langzeitmonitoring» wegen der Etikettierung «digitaler Hass» unterzogen werden.
Dass die 24 Organisationen praktisch auch die Bekämpfung von Google, Microsoft, Apple, Amazon und anderen fordern, entbehrt nicht der Komik. Diese fallen aber sicher unter das Stichwort «Machtmissbrauch von Big-Tech-Unternehmen». Gleichzeitig verlangen die Lobbyisten implizit zum Beispiel die Förderung des Nostr-Netzwerks, denn hier finden wir dezentral organisierte und quelloffen programmierte digitale Räume par excellence, obendrein zensurresistent. Das wiederum dürfte in der Politik weniger gut ankommen.
[Titelbild: Pixabay]
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2025-03-04 09:40:50
@ a95c6243:d345522c
2025-03-04 09:40:50Die «Eliten» führen bereits groß angelegte Pilotprojekte für eine Zukunft durch, die sie wollen und wir nicht. Das schreibt der OffGuardian in einem Update zum Thema «EU-Brieftasche für die digitale Identität». Das Portal weist darauf hin, dass die Akteure dabei nicht gerade zimperlich vorgehen und auch keinen Hehl aus ihren Absichten machen. Transition News hat mehrfach darüber berichtet, zuletzt hier und hier.
Mit der EU Digital Identity Wallet (EUDI-Brieftasche) sei eine einzige von der Regierung herausgegebene App geplant, die Ihre medizinischen Daten, Beschäftigungsdaten, Reisedaten, Bildungsdaten, Impfdaten, Steuerdaten, Finanzdaten sowie (potenziell) Kopien Ihrer Unterschrift, Fingerabdrücke, Gesichtsscans, Stimmproben und DNA enthält. So fasst der OffGuardian die eindrucksvolle Liste möglicher Einsatzbereiche zusammen.
Auch Dokumente wie der Personalausweis oder der Führerschein können dort in elektronischer Form gespeichert werden. Bis 2026 sind alle EU-Mitgliedstaaten dazu verpflichtet, Ihren Bürgern funktionierende und frei verfügbare digitale «Brieftaschen» bereitzustellen.
Die Menschen würden diese App nutzen, so das Portal, um Zahlungen vorzunehmen, Kredite zu beantragen, ihre Steuern zu zahlen, ihre Rezepte abzuholen, internationale Grenzen zu überschreiten, Unternehmen zu gründen, Arzttermine zu buchen, sich um Stellen zu bewerben und sogar digitale Verträge online zu unterzeichnen.
All diese Daten würden auf ihrem Mobiltelefon gespeichert und mit den Regierungen von neunzehn Ländern (plus der Ukraine) sowie über 140 anderen öffentlichen und privaten Partnern ausgetauscht. Von der Deutschen Bank über das ukrainische Ministerium für digitalen Fortschritt bis hin zu Samsung Europe. Unternehmen und Behörden würden auf diese Daten im Backend zugreifen, um «automatisierte Hintergrundprüfungen» durchzuführen.
Der Bundesverband der Verbraucherzentralen und Verbraucherverbände (VZBV) habe Bedenken geäußert, dass eine solche App «Risiken für den Schutz der Privatsphäre und der Daten» berge, berichtet das Portal. Die einzige Antwort darauf laute: «Richtig, genau dafür ist sie ja da!»
Das alles sei keine Hypothese, betont der OffGuardian. Es sei vielmehr «Potential». Damit ist ein EU-Projekt gemeint, in dessen Rahmen Dutzende öffentliche und private Einrichtungen zusammenarbeiten, «um eine einheitliche Vision der digitalen Identität für die Bürger der europäischen Länder zu definieren». Dies ist nur eines der groß angelegten Pilotprojekte, mit denen Prototypen und Anwendungsfälle für die EUDI-Wallet getestet werden. Es gibt noch mindestens drei weitere.
Den Ball der digitalen ID-Systeme habe die Covid-«Pandemie» über die «Impfpässe» ins Rollen gebracht. Seitdem habe das Thema an Schwung verloren. Je näher wir aber der vollständigen Einführung der EUid kämen, desto mehr Propaganda der Art «Warum wir eine digitale Brieftasche brauchen» könnten wir in den Mainstream-Medien erwarten, prognostiziert der OffGuardian. Vielleicht müssten wir schon nach dem nächsten großen «Grund», dem nächsten «katastrophalen katalytischen Ereignis» Ausschau halten. Vermutlich gebe es bereits Pläne, warum die Menschen plötzlich eine digitale ID-Brieftasche brauchen würden.
Die Entwicklung geht jedenfalls stetig weiter in genau diese Richtung. Beispielsweise hat Jordanien angekündigt, die digitale biometrische ID bei den nächsten Wahlen zur Verifizierung der Wähler einzuführen. Man wolle «den Papierkrieg beenden und sicherstellen, dass die gesamte Kette bis zu den nächsten Parlamentswahlen digitalisiert wird», heißt es. Absehbar ist, dass dabei einige Wahlberechtigte «auf der Strecke bleiben» werden, wie im Fall von Albanien geschehen.
Derweil würden die Briten gerne ihre Privatsphäre gegen Effizienz eintauschen, behauptet Tony Blair. Der Ex-Premier drängte kürzlich erneut auf digitale Identitäten und Gesichtserkennung. Blair ist Gründer einer Denkfabrik für globalen Wandel, Anhänger globalistischer Technokratie und «moderner Infrastruktur».
Abschließend warnt der OffGuardian vor der Illusion, Trump und Musk würden den US-Bürgern «diesen Schlamassel ersparen». Das Department of Government Efficiency werde sich auf die digitale Identität stürzen. Was könne schließlich «effizienter» sein als eine einzige App, die für alles verwendet wird? Der Unterschied bestehe nur darin, dass die US-Version vielleicht eher privat als öffentlich sei – sofern es da überhaupt noch einen wirklichen Unterschied gebe.
[Titelbild: Screenshot OffGuardian]
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ dab6c606:51f507b6
2025-04-18 14:59:25
@ dab6c606:51f507b6
2025-04-18 14:59:25Core idea: Use geotagged anonymized Nostr events with Cashu-based points to snitch on cop locations for a more relaxed driving and walking
We all know navigation apps. There's one of them that allows you to report on locations of cops. It's Waze and it's owned by Google. There are perfectly fine navigation apps like Organic Maps, that unfortunately lack the cop-snitching features. In some countries, it is illegal to report cop locations, so it would probably not be a good idea to use your npub to report them. But getting a points Cashu token as a reward and exchanging them from time to time would solve this. You can of course report construction, traffic jams, ...
Proposed solution: Add Nostr client (Copstr) to Organic Maps. Have a button in bottom right allowing you to report traffic situations. Geotagged events are published on Nostr relays, users sending cashu tokens as thank you if the report is valid. Notes have smart expiration times.
Phase 2: Automation: Integration with dashcams and comma.ai allow for automated AI recognition of traffic events such as traffic jams and cops, with automatic touchless reporting.
Result: Drive with most essential information and with full privacy. Collect points to be cool and stay cool.
-
 @ a008def1:57a3564d
2025-04-30 17:52:11
@ a008def1:57a3564d
2025-04-30 17:52:11A Vision for #GitViaNostr
Git has long been the standard for version control in software development, but over time, we has lost its distributed nature. Originally, Git used open, permissionless email for collaboration, which worked well at scale. However, the rise of GitHub and its centralized pull request (PR) model has shifted the landscape.
Now, we have the opportunity to revive Git's permissionless and distributed nature through Nostr!
We’ve developed tools to facilitate Git collaboration via Nostr, but there are still significant friction that prevents widespread adoption. This article outlines a vision for how we can reduce those barriers and encourage more repositories to embrace this approach.
First, we’ll review our progress so far. Then, we’ll propose a guiding philosophy for our next steps. Finally, we’ll discuss a vision to tackle specific challenges, mainly relating to the role of the Git server and CI/CD.
I am the lead maintainer of ngit and gitworkshop.dev, and I’ve been fortunate to work full-time on this initiative for the past two years, thanks to an OpenSats grant.
How Far We’ve Come
The aim of #GitViaNostr is to liberate discussions around code collaboration from permissioned walled gardens. At the core of this collaboration is the process of proposing and applying changes. That's what we focused on first.
Since Nostr shares characteristics with email, and with NIP34, we’ve adopted similar primitives to those used in the patches-over-email workflow. This is because of their simplicity and that they don’t require contributors to host anything, which adds reliability and makes participation more accessible.
However, the fork-branch-PR-merge workflow is the only model many developers have known, and changing established workflows can be challenging. To address this, we developed a new workflow that balances familiarity, user experience, and alignment with the Nostr protocol: the branch-PR-merge model.
This model is implemented in ngit, which includes a Git plugin that allows users to engage without needing to learn new commands. Additionally, gitworkshop.dev offers a GitHub-like interface for interacting with PRs and issues. We encourage you to try them out using the quick start guide and share your feedback. You can also explore PRs and issues with gitplaza.
For those who prefer the patches-over-email workflow, you can still use that approach with Nostr through gitstr or the
ngit sendandngit listcommands, and explore patches with patch34.The tools are now available to support the core collaboration challenge, but we are still at the beginning of the adoption curve.
Before we dive into the challenges—such as why the Git server setup can be jarring and the possibilities surrounding CI/CD—let’s take a moment to reflect on how we should approach the challenges ahead of us.
Philosophy
Here are some foundational principles I shared a few years ago:
- Let Git be Git
- Let Nostr be Nostr
- Learn from the successes of others
I’d like to add one more:
- Embrace anarchy and resist monolithic development.
Micro Clients FTW
Nostr celebrates simplicity, and we should strive to maintain that. Monolithic developments often lead to unnecessary complexity. Projects like gitworkshop.dev, which aim to cover various aspects of the code collaboration experience, should not stifle innovation.
Just yesterday, the launch of following.space demonstrated how vibe-coded micro clients can make a significant impact. They can be valuable on their own, shape the ecosystem, and help push large and widely used clients to implement features and ideas.
The primitives in NIP34 are straightforward, and if there are any barriers preventing the vibe-coding of a #GitViaNostr app in an afternoon, we should work to eliminate them.
Micro clients should lead the way and explore new workflows, experiences, and models of thinking.
Take kanbanstr.com. It provides excellent project management and organization features that work seamlessly with NIP34 primitives.
From kanban to code snippets, from CI/CD runners to SatShoot—may a thousand flowers bloom, and a thousand more after them.
Friction and Challenges
The Git Server
In #GitViaNostr, maintainers' branches (e.g.,
master) are hosted on a Git server. Here’s why this approach is beneficial:- Follows the original Git vision and the "let Git be Git" philosophy.
- Super efficient, battle-tested, and compatible with all the ways people use Git (e.g., LFS, shallow cloning).
- Maintains compatibility with related systems without the need for plugins (e.g., for build and deployment).
- Only repository maintainers need write access.
In the original Git model, all users would need to add the Git server as a 'git remote.' However, with ngit, the Git server is hidden behind a Nostr remote, which enables:
- Hiding complexity from contributors and users, so that only maintainers need to know about the Git server component to start using #GitViaNostr.
- Maintainers can easily swap Git servers by updating their announcement event, allowing contributors/users using ngit to automatically switch to the new one.
Challenges with the Git Server
While the Git server model has its advantages, it also presents several challenges:
- Initial Setup: When creating a new repository, maintainers must select a Git server, which can be a jarring experience. Most options come with bloated social collaboration features tied to a centralized PR model, often difficult or impossible to disable.
-
Manual Configuration: New repositories require manual configuration, including adding new maintainers through a browser UI, which can be cumbersome and time-consuming.
-
User Onboarding: Many Git servers require email sign-up or KYC (Know Your Customer) processes, which can be a significant turn-off for new users exploring a decentralized and permissionless alternative to GitHub.
Once the initial setup is complete, the system works well if a reliable Git server is chosen. However, this is a significant "if," as we have become accustomed to the excellent uptime and reliability of GitHub. Even professionally run alternatives like Codeberg can experience downtime, which is frustrating when CI/CD and deployment processes are affected. This problem is exacerbated when self-hosting.
Currently, most repositories on Nostr rely on GitHub as the Git server. While maintainers can change servers without disrupting their contributors, this reliance on a centralized service is not the decentralized dream we aspire to achieve.
Vision for the Git Server
The goal is to transform the Git server from a single point of truth and failure into a component similar to a Nostr relay.
Functionality Already in ngit to Support This
-
State on Nostr: Store the state of branches and tags in a Nostr event, removing reliance on a single server. This validates that the data received has been signed by the maintainer, significantly reducing the trust requirement.
-
Proxy to Multiple Git Servers: Proxy requests to all servers listed in the announcement event, adding redundancy and eliminating the need for any one server to match GitHub's reliability.
Implementation Requirements
To achieve this vision, the Nostr Git server implementation should:
-
Implement the Git Smart HTTP Protocol without authentication (no SSH) and only accept pushes if the reference tip matches the latest state event.
-
Avoid Bloat: There should be no user authentication, no database, no web UI, and no unnecessary features.
-
Automatic Repository Management: Accept or reject new repositories automatically upon the first push based on the content of the repository announcement event referenced in the URL path and its author.
Just as there are many free, paid, and self-hosted relays, there will be a variety of free, zero-step signup options, as well as self-hosted and paid solutions.
Some servers may use a Web of Trust (WoT) to filter out spam, while others might impose bandwidth or repository size limits for free tiers or whitelist specific npubs.
Additionally, some implementations could bundle relay and blossom server functionalities to unify the provision of repository data into a single service. These would likely only accept content related to the stored repositories rather than general social nostr content.
The potential role of CI / CD via nostr DVMs could create the incentives for a market of highly reliable free at the point of use git servers.
This could make onboarding #GitViaNostr repositories as easy as entering a name and selecting from a multi-select list of Git server providers that announce via NIP89.
!(image)[https://image.nostr.build/badedc822995eb18b6d3c4bff0743b12b2e5ac018845ba498ce4aab0727caf6c.jpg]
Git Client in the Browser
Currently, many tasks are performed on a Git server web UI, such as:
- Browsing code, commits, branches, tags, etc.
- Creating and displaying permalinks to specific lines in commits.
- Merging PRs.
- Making small commits and PRs on-the-fly.
Just as nobody goes to the web UI of a relay (e.g., nos.lol) to interact with notes, nobody should need to go to a Git server to interact with repositories. We use the Nostr protocol to interact with Nostr relays, and we should use the Git protocol to interact with Git servers. This situation has evolved due to the centralization of Git servers. Instead of being restricted to the view and experience designed by the server operator, users should be able to choose the user experience that works best for them from a range of clients. To facilitate this, we need a library that lowers the barrier to entry for creating these experiences. This library should not require a full clone of every repository and should not depend on proprietary APIs. As a starting point, I propose wrapping the WASM-compiled gitlib2 library for the web and creating useful functions, such as showing a file, which utilizes clever flags to minimize bandwidth usage (e.g., shallow clone, noblob, etc.).
This approach would not only enhance clients like gitworkshop.dev but also bring forth a vision where Git servers simply run the Git protocol, making vibe coding Git experiences even better.
song
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 created song with a complementary vision that has shaped how I see the role of the git server. Its a self-hosted, nostr-permissioned git server with a relay baked in. Its currently a WIP and there are some compatability with ngit that we need to work out.
We collaborated on the nostr-permissioning approach now reflected in nip34.
I'm really excited to see how this space evolves.
CI/CD
Most projects require CI/CD, and while this is often bundled with Git hosting solutions, it is currently not smoothly integrated into #GitViaNostr yet. There are many loosely coupled options, such as Jenkins, Travis, CircleCI, etc., that could be integrated with Nostr.
However, the more exciting prospect is to use DVMs (Data Vending Machines).
DVMs for CI/CD
Nostr Data Vending Machines (DVMs) can provide a marketplace of CI/CD task runners with Cashu for micro payments.
There are various trust levels in CI/CD tasks:
- Tasks with no secrets eg. tests.
- Tasks using updatable secrets eg. API keys.
- Unverifiable builds and steps that sign with Android, Nostr, or PGP keys.
DVMs allow tasks to be kicked off with specific providers using a Cashu token as payment.
It might be suitable for some high-compute and easily verifiable tasks to be run by the cheapest available providers. Medium trust tasks could be run by providers with a good reputation, while high trust tasks could be run on self-hosted runners.
Job requests, status, and results all get published to Nostr for display in Git-focused Nostr clients.
Jobs could be triggered manually, or self-hosted runners could be configured to watch a Nostr repository and kick off jobs using their own runners without payment.
But I'm most excited about the prospect of Watcher Agents.
CI/CD Watcher Agents
AI agents empowered with a NIP60 Cashu wallet can run tasks based on activity, such as a push to master or a new PR, using the most suitable available DVM runner that meets the user's criteria. To keep them running, anyone could top up their NIP60 Cashu wallet; otherwise, the watcher turns off when the funds run out. It could be users, maintainers, or anyone interested in helping the project who could top up the Watcher Agent's balance.
As aluded to earlier, part of building a reputation as a CI/CD provider could involve running reliable hosting (Git server, relay, and blossom server) for all FOSS Nostr Git repositories.
This provides a sustainable revenue model for hosting providers and creates incentives for many free-at-the-point-of-use hosting providers. This, in turn, would allow one-click Nostr repository creation workflows, instantly hosted by many different providers.
Progress to Date
nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr and nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 have been working on a runner that uses GitHub Actions YAML syntax (using act) for the dvm-cicd-runner and takes Cashu payment. You can see example runs on GitWorkshop. It currently takes testnuts, doesn't give any change, and the schema will likely change.
Note: The actions tab on GitWorkshop is currently available on all repositories if you turn on experimental mode (under settings in the user menu).
It's a work in progress, and we expect the format and schema to evolve.
Easy Web App Deployment
For those disapointed not to find a 'Nostr' button to import a git repository to Vercel menu: take heart, they made it easy. vercel.com_import_options.png there is a vercel cli that can be easily called in CI / CD jobs to kick of deployments. Not all managed solutions for web app deployment (eg. netlify) make it that easy.
Many More Opportunities
Large Patches via Blossom
I would be remiss not to mention the large patch problem. Some patches are too big to fit into Nostr events. Blossom is perfect for this, as it allows these larger patches to be included in a blossom file and referenced in a new patch kind.
Enhancing the #GitViaNostr Experience
Beyond the large patch issue, there are numerous opportunities to enhance the #GitViaNostr ecosystem. We can focus on improving browsing, discovery, social and notifications. Receiving notifications on daily driver Nostr apps is one of the killer features of Nostr. However, we must ensure that Git-related notifications are easily reviewable, so we don’t miss any critical updates.
We need to develop tools that cater to our curiosity—tools that enable us to discover and follow projects, engage in discussions that pique our interest, and stay informed about developments relevant to our work.
Additionally, we should not overlook the importance of robust search capabilities and tools that facilitate migrations.
Concluding Thoughts
The design space is vast. Its an exciting time to be working on freedom tech. I encourage everyone to contribute their ideas and creativity and get vibe-coding!
I welcome your honest feedback on this vision and any suggestions you might have. Your insights are invaluable as we collaborate to shape the future of #GitViaNostr. Onward.
Contributions
To conclude, I want to acknowledge some the individuals who have made recent code contributions related to #GitViaNostr:
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 (gitstr, song, patch34), nostr:npub1useke4f9maul5nf67dj0m9sq6jcsmnjzzk4ycvldwl4qss35fvgqjdk5ks (gitplaza)
nostr:npub1elta7cneng3w8p9y4dw633qzdjr4kyvaparuyuttyrx6e8xp7xnq32cume (ngit contributions, git-remote-blossom),nostr:npub16p8v7varqwjes5hak6q7mz6pygqm4pwc6gve4mrned3xs8tz42gq7kfhdw (SatShoot, Flotilla-Budabit), nostr:npub1ehhfg09mr8z34wz85ek46a6rww4f7c7jsujxhdvmpqnl5hnrwsqq2szjqv (Flotilla-Budabit, Nostr Git Extension), nostr:npub1ahaz04ya9tehace3uy39hdhdryfvdkve9qdndkqp3tvehs6h8s5slq45hy (gnostr and experiments), and others.
nostr:npub1uplxcy63up7gx7cladkrvfqh834n7ylyp46l3e8t660l7peec8rsd2sfek (git-remote-nostr)
Project Management nostr:npub1ltx67888tz7lqnxlrg06x234vjnq349tcfyp52r0lstclp548mcqnuz40t (kanbanstr) Code Snippets nostr:npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2 (nodebin.io) nostr:npub1r0rs5q2gk0e3dk3nlc7gnu378ec6cnlenqp8a3cjhyzu6f8k5sgs4sq9ac (snipsnip.dev)
CI / CD nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
and for their nostr:npub1c03rad0r6q833vh57kyd3ndu2jry30nkr0wepqfpsm05vq7he25slryrnw nostr:npub1qqqqqq2stely3ynsgm5mh2nj3v0nk5gjyl3zqrzh34hxhvx806usxmln03 and nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z for their testing, feedback, ideas and encouragement.
Thank you for your support and collaboration! Let me know if I've missed you.
-
 @ a95c6243:d345522c
2025-03-01 10:39:35
@ a95c6243:d345522c
2025-03-01 10:39:35Ständige Lügen und Unterstellungen, permanent falsche Fürsorge \ können Bausteine von emotionaler Manipulation sein. Mit dem Zweck, \ Macht und Kontrolle über eine andere Person auszuüben. \ Apotheken Umschau
Irgendetwas muss passiert sein: «Gaslighting» ist gerade Thema in vielen Medien. Heute bin ich nach längerer Zeit mal wieder über dieses Stichwort gestolpert. Das war in einem Artikel von Norbert Häring über Manipulationen des Deutschen Wetterdienstes (DWD). In diesem Fall ging es um eine Pressemitteilung vom Donnerstag zum «viel zu warmen» Winter 2024/25.
Häring wirft der Behörde vor, dreist zu lügen und Dinge auszulassen, um die Klimaangst wach zu halten. Was der Leser beim DWD nicht erfahre, sei, dass dieser Winter kälter als die drei vorangegangenen und kälter als der Durchschnitt der letzten zehn Jahre gewesen sei. Stattdessen werde der falsche Eindruck vermittelt, es würde ungebremst immer wärmer.
Wem also der zu Ende gehende Winter eher kalt vorgekommen sein sollte, mit dessen Empfinden stimme wohl etwas nicht. Das jedenfalls wolle der DWD uns einreden, so der Wirtschaftsjournalist. Und damit sind wir beim Thema Gaslighting.
Als Gaslighting wird eine Form psychischer Manipulation bezeichnet, mit der die Opfer desorientiert und zutiefst verunsichert werden, indem ihre eigene Wahrnehmung als falsch bezeichnet wird. Der Prozess führt zu Angst und Realitätsverzerrung sowie zur Zerstörung des Selbstbewusstseins. Die Bezeichnung kommt von dem britischen Theaterstück «Gas Light» aus dem Jahr 1938, in dem ein Mann mit grausamen Psychotricks seine Frau in den Wahnsinn treibt.
Damit Gaslighting funktioniert, muss das Opfer dem Täter vertrauen. Oft wird solcher Psychoterror daher im privaten oder familiären Umfeld beschrieben, ebenso wie am Arbeitsplatz. Jedoch eignen sich die Prinzipien auch perfekt zur Manipulation der Massen. Vermeintliche Autoritäten wie Ärzte und Wissenschaftler, oder «der fürsorgliche Staat» und Institutionen wie die UNO oder die WHO wollen uns doch nichts Böses. Auch Staatsmedien, Faktenchecker und diverse NGOs wurden zu «vertrauenswürdigen Quellen» erklärt. Das hat seine Wirkung.
Warum das Thema Gaslighting derzeit scheinbar so populär ist, vermag ich nicht zu sagen. Es sind aber gerade in den letzten Tagen und Wochen auffällig viele Artikel dazu erschienen, und zwar nicht nur von Psychologen. Die Frankfurter Rundschau hat gleich mehrere publiziert, und Anwälte interessieren sich dafür offenbar genauso wie Apotheker.
Die Apotheken Umschau machte sogar auf «Medical Gaslighting» aufmerksam. Davon spreche man, wenn Mediziner Symptome nicht ernst nähmen oder wenn ein gesundheitliches Problem vom behandelnden Arzt «schnöde heruntergespielt» oder abgetan würde. Kommt Ihnen das auch irgendwie bekannt vor? Der Begriff sei allerdings irreführend, da er eine manipulierende Absicht unterstellt, die «nicht gewährleistet» sei.
Apropos Gaslighting: Die noch amtierende deutsche Bundesregierung meldete heute, es gelte, «weiter [sic!] gemeinsam daran zu arbeiten, einen gerechten und dauerhaften Frieden für die Ukraine zu erreichen». Die Ukraine, wo sich am Montag «der völkerrechtswidrige Angriffskrieg zum dritten Mal jährte», verteidige ihr Land und «unsere gemeinsamen Werte».
Merken Sie etwas? Das Demokratieverständnis mag ja tatsächlich inzwischen in beiden Ländern ähnlich traurig sein. Bezüglich Friedensbemühungen ist meine Wahrnehmung jedoch eine andere. Das muss an meinem Gedächtnis liegen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ a95c6243:d345522c
2025-02-21 19:32:23
@ a95c6243:d345522c
2025-02-21 19:32:23Europa – das Ganze ist eine wunderbare Idee, \ aber das war der Kommunismus auch. \ Loriot
«Europa hat fertig», könnte man unken, und das wäre nicht einmal sehr verwegen. Mit solch einer Einschätzung stünden wir nicht alleine, denn die Stimmen in diese Richtung mehren sich. Der französische Präsident Emmanuel Macron warnte schon letztes Jahr davor, dass «unser Europa sterben könnte». Vermutlich hatte er dabei andere Gefahren im Kopf als jetzt der ungarische Ministerpräsident Viktor Orbán, der ein «baldiges Ende der EU» prognostizierte. Das Ergebnis könnte allerdings das gleiche sein.
Neben vordergründigen Themenbereichen wie Wirtschaft, Energie und Sicherheit ist das eigentliche Problem jedoch die obskure Mischung aus aufgegebener Souveränität und geschwollener Arroganz, mit der europäische Politiker:innende unterschiedlicher Couleur aufzutreten pflegen. Und das Tüpfelchen auf dem i ist die bröckelnde Legitimation politischer Institutionen dadurch, dass die Stimmen großer Teile der Bevölkerung seit Jahren auf vielfältige Weise ausgegrenzt werden.
Um «UnsereDemokratie» steht es schlecht. Dass seine Mandate immer schwächer werden, merkt natürlich auch unser «Führungspersonal». Entsprechend werden die Maßnahmen zur Gängelung, Überwachung und Manipulation der Bürger ständig verzweifelter. Parallel dazu plustern sich in Paris Macron, Scholz und einige andere noch einmal mächtig in Sachen Verteidigung und «Kriegstüchtigkeit» auf.
Momentan gilt es auch, das Überschwappen covidiotischer und verschwörungsideologischer Auswüchse aus den USA nach Europa zu vermeiden. So ein «MEGA» (Make Europe Great Again) können wir hier nicht gebrauchen. Aus den Vereinigten Staaten kommen nämlich furchtbare Nachrichten. Beispielsweise wurde einer der schärfsten Kritiker der Corona-Maßnahmen kürzlich zum Gesundheitsminister ernannt. Dieser setzt sich jetzt für eine Neubewertung der mRNA-«Impfstoffe» ein, was durchaus zu einem Entzug der Zulassungen führen könnte.
Der europäischen Version von «Verteidigung der Demokratie» setzte der US-Vizepräsident J. D. Vance auf der Münchner Sicherheitskonferenz sein Verständnis entgegen: «Demokratie stärken, indem wir unseren Bürgern erlauben, ihre Meinung zu sagen». Das Abschalten von Medien, das Annullieren von Wahlen oder das Ausschließen von Menschen vom politischen Prozess schütze gar nichts. Vielmehr sei dies der todsichere Weg, die Demokratie zu zerstören.
In der Schweiz kamen seine Worte deutlich besser an als in den meisten europäischen NATO-Ländern. Bundespräsidentin Karin Keller-Sutter lobte die Rede und interpretierte sie als «Plädoyer für die direkte Demokratie». Möglicherweise zeichne sich hier eine außenpolitische Kehrtwende in Richtung integraler Neutralität ab, meint mein Kollege Daniel Funk. Das wären doch endlich mal ein paar gute Nachrichten.
Von der einstigen Idee einer europäischen Union mit engeren Beziehungen zwischen den Staaten, um Konflikte zu vermeiden und das Wohlergehen der Bürger zu verbessern, sind wir meilenweit abgekommen. Der heutige korrupte Verbund unter technokratischer Leitung ähnelt mehr einem Selbstbedienungsladen mit sehr begrenztem Zugang. Die EU-Wahlen im letzten Sommer haben daran ebenso wenig geändert, wie die Bundestagswahl am kommenden Sonntag darauf einen Einfluss haben wird.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 826e9f89:ffc5c759
2025-04-12 21:34:24
@ 826e9f89:ffc5c759
2025-04-12 21:34:24What follows began as snippets of conversations I have been having for years, on and off, here and there. It will likely eventually be collated into a piece I have been meaning to write on “payments” as a whole. I foolishly started writing this piece years ago, not realizing that the topic is gargantuan and for every week I spend writing it I have to add two weeks to my plan. That may or may not ever come to fruition, but in the meantime, Tether announced it was issuing on Taproot Assets and suddenly everybody is interested again. This is as good a catalyst as any to carve out my “stablecoin thesis”, such as it exists, from “payments”, and put it out there for comment and feedback.
In contrast to the “Bitcoiner take” I will shortly revert to, I invite the reader to keep the following potential counterargument in mind, which might variously be termed the “shitcoiner”, “realist”, or “cynical” take, depending on your perspective: that stablecoins have clear product-market-fit. Now, as a venture capitalist and professional thinkboi focusing on companies building on Bitcoin, I obviously think that not only is Bitcoin the best money ever invented and its monetization is pretty much inevitable, but that, furthermore, there is enormous, era-defining long-term potential for a range of industries in which Bitcoin is emerging as superior technology, even aside from its role as money. But in the interest not just of steelmanning but frankly just of honesty, I would grudgingly agree with the following assessment as of the time of writing: the applications of crypto (inclusive of Bitcoin but deliberately wider) that have found product-market-fit today, and that are not speculative bets on future development and adoption, are: Bitcoin as savings technology, mining as a means of monetizing energy production, and stablecoins.
I think there are two typical Bitcoiner objections to stablecoins of significantly greater importance than all others: that you shouldn’t be supporting dollar hegemony, and that you don’t need a blockchain. I will elaborate on each of these, and for the remainder of the post will aim to produce a synthesis of three superficially contrasting (or at least not obviously related) sources of inspiration: these objections, the realisation above that stablecoins just are useful, and some commentary on technical developments in Bitcoin and the broader space that I think inform where things are likely to go. As will become clear as the argument progresses, I actually think the outcome to which I am building up is where things have to go. I think the technical and economic incentives at play make this an inevitability rather than a “choice”, per se. Given my conclusion, which I will hold back for the time being, this is a fantastically good thing, hence I am motivated to write this post at all!
Objection 1: Dollar Hegemony
I list this objection first because there isn’t a huge amount to say about it. It is clearly a normative position, and while I more or less support it personally, I don’t think that it is material to the argument I am going on to make, so I don’t want to force it on the reader. While the case for this objection is probably obvious to this audience (isn’t the point of Bitcoin to destroy central banks, not further empower them?) I should at least offer the steelman that there is a link between this and the realist observation that stablecoins are useful. The reason they are useful is because people prefer the dollar to even shitter local fiat currencies. I don’t think it is particularly fruitful to say that they shouldn’t. They do. Facts don’t care about your feelings. There is a softer bridging argument to be made here too, to the effect that stablecoins warm up their users to the concept of digital bearer (ish) assets, even though these particular assets are significantly scammier than Bitcoin. Again, I am just floating this, not telling the reader they should or shouldn’t buy into it.
All that said, there is one argument I do want to put my own weight behind, rather than just float: stablecoin issuance is a speculative attack on the institution of fractional reserve banking. A “dollar” Alice moves from JPMorgan to Tether embodies two trade-offs from Alice’s perspective: i) a somewhat opaque profile on the credit risk of the asset: the likelihood of JPMorgan ever really defaulting on deposits vs the operator risk of Tether losing full backing and/or being wrench attacked by the Federal Government and rugging its users. These risks are real but are almost entirely political. I’m skeptical it is meaningful to quantify them, but even if it is, I am not the person to try to do it. Also, more transparently to Alice, ii) far superior payment rails (for now, more on this to follow).
However, from the perspective of the fiat banking cartel, fractional reserve leverage has been squeezed. There are just as many notional dollars in circulation, but there the backing has been shifted from levered to unlevered issuers. There are gradations of relevant objections to this: while one might say, Tether’s backing comes from Treasuries, so you are directly funding US debt issuance!, this is a bit silly in the context of what other dollars one might hold. It’s not like JPMorgan is really competing with the Treasury to sell credit into the open market. Optically they are, but this is the core of the fiat scam. Via the guarantees of the Federal Reserve System, JPMorgan can sell as much unbacked credit as it wants knowing full well the difference will be printed whenever this blows up. Short-term Treasuries are also JPMorgan’s most pristine asset safeguarding its equity, so the only real difference is that Tether only holds Treasuries without wishing more leverage into existence. The realization this all builds up to is that, by necessity,
Tether is a fully reserved bank issuing fiduciary media against the only dollar-denominated asset in existence whose value (in dollar terms) can be guaranteed. Furthermore, this media arguably has superior “moneyness” to the obvious competition in the form of US commercial bank deposits by virtue of its payment rails.
That sounds pretty great when you put it that way! Of course, the second sentence immediately leads to the second objection, and lets the argument start to pick up steam …
Objection 2: You Don’t Need a Blockchain
I don’t need to explain this to this audience but to recap as briefly as I can manage: Bitcoin’s value is entirely endogenous. Every aspect of “a blockchain” that, out of context, would be an insanely inefficient or redundant modification of a “database”, in context is geared towards the sole end of enabling the stability of this endogenous value. Historically, there have been two variations of stupidity that follow a failure to grok this: i) “utility tokens”, or blockchains with native tokens for something other than money. I would recommend anybody wanting a deeper dive on the inherent nonsense of a utility token to read Only The Strong Survive, in particular Chapter 2, Crypto Is Not Decentralized, and the subsection, Everything Fights For Liquidity, and/or Green Eggs And Ham, in particular Part II, Decentralized Finance, Technically. ii) “real world assets” or, creating tokens within a blockchain’s data structure that are not intended to have endogenous value but to act as digital quasi-bearer certificates to some or other asset of value exogenous to this system. Stablecoins are in this second category.
RWA tokens definitionally have to have issuers, meaning some entity that, in the real world, custodies or physically manages both the asset and the record-keeping scheme for the asset. “The blockchain” is at best a secondary ledger to outsource ledger updates to public infrastructure such that the issuer itself doesn’t need to bother and can just “check the ledger” whenever operationally relevant. But clearly ownership cannot be enforced in an analogous way to Bitcoin, under both technical and social considerations. Technically, Bitcoin’s endogenous value means that whoever holds the keys to some or other UTXOs functionally is the owner. Somebody else claiming to be the owner is yelling at clouds. Whereas, socially, RWA issuers enter a contract with holders (whether legally or just in terms of a common-sense interpretation of the transaction) such that ownership of the asset issued against is entirely open to dispute. That somebody can point to “ownership” of the token may or may not mean anything substantive with respect to the physical reality of control of the asset, and how the issuer feels about it all.
And so, one wonders, why use a blockchain at all? Why doesn’t the issuer just run its own database (for the sake of argument with some or other signature scheme for verifying and auditing transactions) given it has the final say over issuance and redemption anyway? I hinted at an answer above: issuing on a blockchain outsources this task to public infrastructure. This is where things get interesting. While it is technically true, given the above few paragraphs, that, you don’t need a blockchain for that, you also don’t need to not use a blockchain for that. If you want to, you can.
This is clearly the case given stablecoins exist at all and have gone this route. If one gets too angry about not needing a blockchain for that, one equally risks yelling at clouds! And, in fact, one can make an even stronger argument, more so from the end users’ perspective. These products do not exist in a vacuum but rather compete with alternatives. In the case of stablecoins, the alternative is traditional fiat money, which, as stupid as RWAs on a blockchain are, is even dumber. It actually is just a database, except it’s a database that is extremely annoying to use, basically for political reasons because the industry managing these private databases form a cartel that never needs to innovate or really give a shit about its customers at all. In many, many cases, stablecoins on blockchains are dumb in the abstract, but superior to the alternative methods of holding and transacting in dollars existing in other forms. And note, this is only from Alice’s perspective of wanting to send and receive, not a rehashing of the fractional reserve argument given above. This is the essence of their product-market-fit. Yell at clouds all you like: they just are useful given the alternative usually is not Bitcoin, it’s JPMorgan’s KYC’d-up-the-wazoo 90s-era website, more than likely from an even less solvent bank.
So where does this get us? It might seem like we are back to “product-market-fit, sorry about that” with Bitcoiners yelling about feelings while everybody else makes do with their facts. However, I think we have introduced enough material to move the argument forward by incrementally incorporating the following observations, all of which I will shortly go into in more detail: i) as a consequence of making no technical sense with respect to what blockchains are for, today’s approach won’t scale; ii) as a consequence of short-termist tradeoffs around socializing costs, today’s approach creates an extremely unhealthy and arguably unnatural market dynamic in the issuer space; iii) Taproot Assets now exist and handily address both points i) and ii), and; iv) eCash is making strides that I believe will eventually replace even Taproot Assets.
To tease where all this is going, and to get the reader excited before we dive into much more detail: just as Bitcoin will eat all monetary premia, Lightning will likely eat all settlement, meaning all payments will gravitate towards routing over Lightning regardless of the denomination of the currency at the edges. Fiat payments will gravitate to stablecoins to take advantage of this; stablecoins will gravitate to TA and then to eCash, and all of this will accelerate hyperbitcoinization by “bitcoinizing” payment rails such that an eventual full transition becomes as simple as flicking a switch as to what denomination you want to receive.
I will make two important caveats before diving in that are more easily understood in light of having laid this groundwork: I am open to the idea that it won’t be just Lightning or just Taproot Assets playing the above roles. Without veering into forecasting the entire future development of Bitcoin tech, I will highlight that all that really matters here are, respectively: a true layer 2 with native hashlocks, and a token issuance scheme that enables atomic routing over such a layer 2 (or combination of such). For the sake of argument, the reader is welcome to swap in “Ark” and “RGB” for “Lightning” and “TA” both above and in all that follows. As far as I can tell, this makes no difference to the argument and is even exciting in its own right. However, for the sake of simplicity in presentation, I will stick to “Lightning” and “TA” hereafter.
1) Today’s Approach to Stablecoins Won’t Scale
This is the easiest to tick off and again doesn’t require much explanation to this audience. Blockchains fundamentally don’t scale, which is why Bitcoin’s UTXO scheme is a far better design than ex-Bitcoin Crypto’s’ account-based models, even entirely out of context of all the above criticisms. This is because Bitcoin transactions can be batched across time and across users with combinations of modes of spending restrictions that provide strong economic guarantees of correct eventual net settlement, if not perpetual deferral. One could argue this is a decent (if abstrusely technical) definition of “scaling” that is almost entirely lacking in Crypto.
What we see in ex-Bitcoin crypto is so-called “layer 2s” that are nothing of the sort, forcing stablecoin schemes in these environments into one of two equally poor design choices if usage is ever to increase: fees go higher and higher, to the point of economic unviability (and well past it) as blocks fill up, or move to much more centralized environments that increasingly are just databases, and hence which lose the benefits of openness thought to be gleaned by outsourcing settlement to public infrastructure. This could be in the form of punting issuance to a bullshit “layer 2” that is a really a multisig “backing” a private execution environment (to be decentralized any daw now) or an entirely different blockchain that is just pretending even less not to be a database to begin with. In a nutshell, this is a decent bottom-up explanation as to why Tron has the highest settlement of Tether.
This also gives rise to the weirdness of “gas tokens” - assets whose utility as money is and only is in the form of a transaction fee to transact a different kind of money. These are not quite as stupid as a “utility token,” given at least they are clearly fulfilling a monetary role and hence their artificial scarcity can be justified. But they are frustrating from Bitcoiners’ and users’ perspectives alike: users would prefer to pay transaction fees on dollars in dollars, but they can’t because the value of Ether, Sol, Tron, or whatever, is the string and bubblegum that hold their boondoggles together. And Bitcoiners wish this stuff would just go away and stop distracting people, whereas this string and bubblegum is proving transiently useful.
All in all, today’s approach is fine so long as it isn’t being used much. It has product-market fit, sure, but in the unenviable circumstance that, if it really starts to take off, it will break, and even the original users will find it unusable.
2) Today’s Approach to Stablecoins Creates an Untenable Market Dynamic
Reviving the ethos of you don’t need a blockchain for that, notice the following subtlety: while the tokens representing stablecoins have value to users, that value is not native to the blockchain on which they are issued. Tether can (and routinely does) burn tokens on Ethereum and mint them on Tron, then burn on Tron and mint on Solana, and so on. So-called blockchains “go down” and nobody really cares. This makes no difference whatsoever to Tether’s own accounting, and arguably a positive difference to users given these actions track market demand. But it is detrimental to the blockchain being switched away from by stripping it of “TVL” that, it turns out, was only using it as rails: entirely exogenous value that leaves as quickly as it arrived.
One underdiscussed and underappreciated implication of the fact that no value is natively running through the blockchain itself is that, in the current scheme, both the sender and receiver of a stablecoin have to trust the same issuer. This creates an extremely powerful network effect that, in theory, makes the first-to-market likely to dominate and in practice has played out exactly as this theory would suggest: Tether has roughly 80% of the issuance, while roughly 19% goes to the political carve-out of USDC that wouldn’t exist at all were it not for government interference. Everybody else combined makes up the final 1%.
So, Tether is a full reserve bank but also has to be everybody’s bank. This is the source of a lot of the discomfort with Tether, and which feeds into the original objection around dollar hegemony, that there is an ill-defined but nonetheless uneasy feeling that Tether is slowly morphing into a CBDC. I would argue this really has nothing to do with Tether’s own behavior but rather is a consequence of the market dynamic inevitably created by the current stablecoin scheme. There is no reason to trust any other bank because nobody really wants a bank, they just want the rails. They want something that will retain a nominal dollar value long enough to spend it again. They don’t care what tech it runs on and they don’t even really care about the issuer except insofar as having some sense they won’t get rugged.
Notice this is not how fiat works. Banks can, of course, settle between each other, thus enabling their users to send money to customers of other banks. This settlement function is actually the entire point of central banks, less the money printing and general corruption enabled (we might say, this was the historical point of central banks, which have since become irredeemably corrupted by this power). This process is clunkier than stablecoins, as covered above, but the very possibility of settlement means there is no gigantic network effect to being the first commercial issuer of dollar balances. If it isn’t too triggering to this audience, one might suggest that the money printer also removes the residual concern that your balances might get rugged! (or, we might again say, you guarantee you don’t get rugged in the short term by guaranteeing you do get rugged in the long term).
This is a good point at which to introduce the unsettling observation that broader fintech is catching on to the benefits of stablecoins without any awareness whatsoever of all the limitations I am outlining here. With the likes of Stripe, Wise, Robinhood, and, post-Trump, even many US megabanks supposedly contemplating issuing stablecoins (obviously within the current scheme, not the scheme I am building up to proposing), we are forced to boggle our minds considering how on earth settlement is going to work. Are they going to settle through Ether? Well, no, because i) Ether isn’t money, it’s … to be honest, I don’t think anybody really knows what it is supposed to be, or if they once did they aren’t pretending anymore, but anyway, Stripe certainly hasn’t figured that out yet so, ii) it won’t be possible to issue them on layer 1s as soon as there is any meaningful volume, meaning they will have to route through “bullshit layer 2 wrapped Ether token that is really already a kind of stablecoin for Ether.”
The way they are going to try to fix this (anybody wanna bet?) is routing through DEXes, which is so painfully dumb you should be laughing and, if you aren’t, I would humbly suggest you don’t get just how dumb it is. What this amounts to is plugging the gap of Ether’s lack of moneyness (and wrapped Ether’s hilarious lack of moneyness) with … drum roll … unknowable technical and counterparty risk and unpredictable cost on top of reverting to just being a database. So, in other words, all of the costs of using a blockchain when you don’t strictly need to, and none of the benefits. Stripe is going to waste billions of dollars getting sandwich attacked out of some utterly vanilla FX settlement it is facilitating for clients who have even less of an idea what is going on and why North Korea now has all their money, and will eventually realize they should have skipped their shitcoin phase and gone straight to understanding Bitcoin instead …
3) Bitcoin (and Taproot Assets) Fixes This
To tie together a few loose ends, I only threw in the hilariously stupid suggestion of settling through wrapped Ether on Ether on Ether in order to tee up the entirely sensible suggestion of settling through Lightning. Again, not that this will be new to this audience, but while issuance schemes have been around on Bitcoin for a long time, the breakthrough of Taproot Assets is essentially the ability to atomically route through Lightning.
I will admit upfront that this presents a massive bootstrapping challenge relative to the ex-Bitcoin Crypto approach, and it’s not obvious to me if or how this will be overcome. I include this caveat to make it clear I am not suggesting this is a given. It may not be, it’s just beyond the scope of this post (or frankly my ability) to predict. This is a problem for Lightning Labs, Tether, and whoever else decides to step up to issue. But even highlighting this as an obvious and major concern invites us to consider an intriguing contrast: scaling TA stablecoins is hardest at the start and gets easier and easier thereafter. The more edge liquidity there is in TA stables, the less of a risk it is for incremental issuance; the more TA activity, the more attractive deploying liquidity is into Lightning proper, and vice versa. With apologies if this metaphor is even more confusing than it is helpful, one might conceive of the situation as being that there is massive inertia to bootstrap, but equally there could be positive feedback in driving the inertia to scale. Again, I have no idea, and it hasn’t happened yet in practice, but in theory it’s fun.
More importantly to this conversation, however, this is almost exactly the opposite dynamic to the current scheme on other blockchains, which is basically free to start, but gets more and more expensive the more people try to use it. One might say it antiscales (I don’t think that’s a real word, but if Taleb can do it, then I can do it too!).
Furthermore, the entire concept of “settling in Bitcoin” makes perfect sense both economically and technically: economically because Bitcoin is money, and technically because it can be locked in an HTLC and hence can enable atomic routing (i.e. because Lightning is a thing). This is clearly better than wrapped Eth on Eth on Eth or whatever, but, tantalisingly, is better than fiat too! The core message of the payments tome I may or may not one day write is (or will be) that fiat payments, while superficially efficient on the basis of centralized and hence costless ledger amendments, actually have a hidden cost in the form of interbank credit. Many readers will likely have heard me say this multiple times and in multiple settings but, contrary to popular belief, there is no such thing as a fiat debit. Even if styled as a debit, all fiat payments are credits and all have credit risk baked into their cost, even if that is obscured and pushed to the absolute foundational level of money printing to keep banks solvent and hence keep payment channels open.
Furthermore! this enables us to strip away the untenable market dynamic from the point above. The underappreciated and underdiscussed flip side of the drawback of the current dynamic that is effectively fixed by Taproot Assets is that there is no longer a mammoth network effect to a single issuer. Senders and receivers can trust different issuers (i.e. their own banks) because those banks can atomically settle a single payment over Lightning. This does not involve credit. It is arguably the only true debit in the world across both the relevant economic and technical criteria: it routes through money with no innate credit risk, and it does so atomically due to that money’s native properties.
Savvy readers may have picked up on a seed I planted a while back and which can now delightfully blossom:
This is what Visa was supposed to be!
Crucially, this is not what Visa is now. Visa today is pretty much the bank that is everybody’s counterparty, takes a small credit risk for the privilege, and oozes free cash flow bottlenecking global consumer payments.
But if you read both One From Many by Dee Hock (for a first person but pretty wild and extravagant take) and Electronic Value Exchange by David Stearns (for a third person, drier, but more analytical and historically contextualized take) or if you are just intimately familiar with the modern history of payments for whatever other reason, you will see that the role I just described for Lightning in an environment of unboundedly many banks issuing fiduciary media in the form of stablecoins is exactly what Dee Hock wanted to create when he envisioned Visa:
A neutral and open layer of value settlement enabling banks to create digital, interbank payment schemes for their customers at very low cost.
As it turns out, his vision was technically impossible with fiat, hence Visa, which started as a cooperative amongst member banks, was corrupted into a duopolistic for-profit rent seeker in curious parallel to the historical path of central banks …
4) eCash
To now push the argument to what I think is its inevitable conclusion, it’s worth being even more vigilant on the front of you don’t need a blockchain for that. I have argued that there is a role for a blockchain in providing a neutral settlement layer to enable true debits of stablecoins. But note this is just a fancy and/or stupid way of saying that Bitcoin is both the best money and is programmable, which we all knew anyway. The final step is realizing that, while TA is nice in terms of providing a kind of “on ramp” for global payments infrastructure as a whole to reorient around Lightning, there is some path dependence here in assuming (almost certainly correctly) that the familiarity of stablecoins as “RWA tokens on a blockchain” will be an important part of the lure.
But once that transition is complete, or is well on its way to being irreversible, we may as well come full circle and cut out tokens altogether. Again, you really don’t need a blockchain for that, and the residual appeal of better rails has been taken care of with the above massive detour through what I deem to be the inevitability of Lightning as a settlement layer. Just as USDT on Tron arguably has better moneyness than a JPMorgan balance, so a “stablecoin” as eCash has better moneyness than as a TA given it is cheaper, more private, and has more relevantly bearer properties (in other words, because it is cash). The technical detail that it can be hashlocked is really all you need to tie this all together. That means it can be atomically locked into a Lightning routed debit to the recipient of a different issuer (or “mint” in eCash lingo, but note this means the same thing as what we have been calling fully reserved banks). And the economic incentive is pretty compelling too because, for all their benefits, there is still a cost to TAs given they are issued onchain and they require asset-specific liquidity to route on Lightning. Once the rest of the tech is in place, why bother? Keep your Lightning connectivity and just become a mint.
What you get at that point is dramatically superior private database to JPMorgan with the dramatically superior public rails of Lightning. There is nothing left to desire from “a blockchain” besides what Bitcoin is fundamentally for in the first place: counterparty-risk-free value settlement.
And as a final point with a curious and pleasing echo to Dee Hock at Visa, Calle has made the point repeatedly that David Chaum’s vision for eCash, while deeply philosophical besides the technical details, was actually pretty much impossible to operate on fiat. From an eCash perspective, fiat stablecoins within the above infrastructure setup are a dramatic improvement on anything previously possible. But, of course, they are a slippery slope to Bitcoin regardless …
Objections Revisited
As a cherry on top, I think the objections I highlighted at the outset are now readily addressed – to the extent the reader believes what I am suggesting is more or less a technical and economic inevitability, that is. While, sure, I’m not particularly keen on giving the Treasury more avenues to sell its welfare-warfare shitcoin, on balance the likely development I’ve outlined is an enormous net positive: it’s going to sell these anyway so I prefer a strong economic incentive to steadily transition not only to Lightning as payment rails but eCash as fiduciary media, and to use “fintech” as a carrot to induce a slow motion bank run.
As alluded to above, once all this is in place, the final step to a Bitcoin standard becomes as simple as an individual’s decision to want Bitcoin instead of fiat. On reflection, this is arguably the easiest part! It's setting up all the tech that puts people off, so trojan-horsing them with “faster, cheaper payment rails” seems like a genius long-term strategy.
And as to “needing a blockchain” (or not), I hope that is entirely wrapped up at this point. The only blockchain you need is Bitcoin, but to the extent people are still confused by this (which I think will take decades more to fully unwind), we may as well lean into dazzling them with whatever innovation buzzwords and decentralization theatre they were going to fall for anyway before realizing they wanted Bitcoin all along.
Conclusion
Stablecoins are useful whether you like it or not. They are stupid in the abstract but it turns out fiat is even stupider, on inspection. But you don’t need a blockchain, and using one as decentralization theatre creates technical debt that is insurmountable in the long run. Blockchain-based stablecoins are doomed to a utility inversely proportional to their usage, and just to rub it in, their ill-conceived design practically creates a commercial dynamic that mandates there only ever be a single issuer.
Given they are useful, it seems natural that this tension is going to blow up at some point. It also seems worthwhile observing that Taproot Asset stablecoins have almost the inverse problem and opposite commercial dynamic: they will be most expensive to use at the outset but get cheaper and cheaper as their usage grows. Also, there is no incentive towards a monopoly issuer but rather towards as many as are willing to try to operate well and provide value to their users.
As such, we can expect any sizable growth in stablecoins to migrate to TA out of technical and economic necessity. Once this has happened - or possibly while it is happening but is clearly not going to stop - we may as well strip out the TA component and just use eCash because you really don’t need a blockchain for that at all. And once all the money is on eCash, deciding you want to denominate it in Bitcoin is the simplest on-ramp to hyperbitcoinization you can possibly imagine, given we’ve spent the previous decade or two rebuilding all payments tech around Lightning.
Or: Bitcoin fixes this. The End.
- Allen, #892,125
thanks to Marco Argentieri, Lyn Alden, and Calle for comments and feedback
-
 @ c230edd3:8ad4a712
2025-04-30 16:19:30
@ c230edd3:8ad4a712
2025-04-30 16:19:30Chef's notes
I found this recipe on beyondsweetandsavory.com. The site is incredibly ad infested (like most recipe sites) and its very annoying so I'm copying it to Nostr so all the homemade ice cream people can access it without dealing with that mess. I haven't made it yet. Will report back, when I do.
Details
- ⏲️ Prep time: 20 min
- 🍳 Cook time: 55 min
- 🍽️ Servings: 8
Ingredients
- 2 cups heavy cream
- 1 cup 2% milk
- 8 oz dark chocolate, 70%
- ¼ cup Dutch cocoa
- 2 tbsps loose Earl grey tea leaves
- 4 medium egg yolks
- ¾ cup granulated sugar
- ⅛ tsp salt
- ¼ cup dark chocolate, 70% chopped
Directions
- In a double boiler or a bowl set over a saucepan of simmering water, add the cacao solids and ½ cup of heavy cream. Stir chocolate until melted and smooth. Set melted chocolate aside.
- In a heavy saucepan, combine remaining heavy cream, milk, salt and ½ cup of sugar.
- Put the pan over medium heat and let the mixture boil gently to bubbling just around the edges (gentle simmer) and sugar completely dissolved, about 5 minutes. Remove from heat.
- Add the Earl Grey tea leaves and let it steep for 7-8 minutes until the cream has taken on the tea flavor, stirring occasionally and tasting to make sure it’s not too bitter.
- Whisk in Dutch cocoa until smooth. Add in melted chocolate and whisk until smooth.
- In a medium heatproof bowl, whisk the yolks just to break them up and whisk in remaining sugar. Set aside.
- Put the saucepan back on the stove over low heat and let it warm up for 2 minutes.
- Carefully measure out ½ cup of hot cream mixture.
- While whisking the eggs constantly, whisk the hot cream mixture into the eggs until smooth. Continue tempering the eggs by adding another ½ cup of hot cream to the bowl with the yolks.
- Pour the cream-egg mixture back to the saucepan and cook over medium-low heat, stirring constantly until it is thickened and coats the back of a spatula, about 5 minutes.
- Strain the base through a fine-mesh strainer into a clean container.
- Pour the mixture into a 1-gallon Ziplock freezer bag and submerge the sealed bag in an ice bath until cold, about 30 minutes. Refrigerate the ice cream base for at least 4 hours or overnight.
- Pour the ice cream base into the frozen canister of your ice cream machine and follow the manufacturer’s instructions.
- Spin until thick and creamy about 25-30 minutes.
- Pack the ice cream into a storage container, press a sheet of parchment directly against the surface and seal with an airtight lid. Freeze in the coldest part of your freezer until firm, at least 4 hours.
- When ready to serve, scoop the ice cream into a serving bowl and top with chopped chocolate.
-
 @ a95c6243:d345522c
2025-02-19 09:23:17
@ a95c6243:d345522c
2025-02-19 09:23:17Die «moralische Weltordnung» – eine Art Astrologie. Friedrich Nietzsche
Das Treffen der BRICS-Staaten beim Gipfel im russischen Kasan war sicher nicht irgendein politisches Event. Gastgeber Wladimir Putin habe «Hof gehalten», sagen die Einen, China und Russland hätten ihre Vorstellung einer multipolaren Weltordnung zelebriert, schreiben Andere.
In jedem Fall zeigt die Anwesenheit von über 30 Delegationen aus der ganzen Welt, dass von einer geostrategischen Isolation Russlands wohl keine Rede sein kann. Darüber hinaus haben sowohl die Anreise von UN-Generalsekretär António Guterres als auch die Meldungen und Dementis bezüglich der Beitrittsbemühungen des NATO-Staats Türkei für etwas Aufsehen gesorgt.
Im Spannungsfeld geopolitischer und wirtschaftlicher Umbrüche zeigt die neue Allianz zunehmendes Selbstbewusstsein. In Sachen gemeinsamer Finanzpolitik schmiedet man interessante Pläne. Größere Unabhängigkeit von der US-dominierten Finanzordnung ist dabei ein wichtiges Ziel.
Beim BRICS-Wirtschaftsforum in Moskau, wenige Tage vor dem Gipfel, zählte ein nachhaltiges System für Finanzabrechnungen und Zahlungsdienste zu den vorrangigen Themen. Während dieses Treffens ging der russische Staatsfonds eine Partnerschaft mit dem Rechenzentrumsbetreiber BitRiver ein, um Bitcoin-Mining-Anlagen für die BRICS-Länder zu errichten.
Die Initiative könnte ein Schritt sein, Bitcoin und andere Kryptowährungen als Alternativen zu traditionellen Finanzsystemen zu etablieren. Das Projekt könnte dazu führen, dass die BRICS-Staaten den globalen Handel in Bitcoin abwickeln. Vor dem Hintergrund der Diskussionen über eine «BRICS-Währung» wäre dies eine Alternative zu dem ursprünglich angedachten Korb lokaler Währungen und zu goldgedeckten Währungen sowie eine mögliche Ergänzung zum Zahlungssystem BRICS Pay.
Dient der Bitcoin also der Entdollarisierung? Oder droht er inzwischen, zum Gegenstand geopolitischer Machtspielchen zu werden? Angesichts der globalen Vernetzungen ist es oft schwer zu durchschauen, «was eine Show ist und was im Hintergrund von anderen Strippenziehern insgeheim gesteuert wird». Sicher können Strukturen wie Bitcoin auch so genutzt werden, dass sie den Herrschenden dienlich sind. Aber die Grundeigenschaft des dezentralisierten, unzensierbaren Peer-to-Peer Zahlungsnetzwerks ist ihm schließlich nicht zu nehmen.
Wenn es nach der EZB oder dem IWF geht, dann scheint statt Instrumentalisierung momentan eher der Kampf gegen Kryptowährungen angesagt. Jürgen Schaaf, Senior Manager bei der Europäischen Zentralbank, hat jedenfalls dazu aufgerufen, Bitcoin «zu eliminieren». Der Internationale Währungsfonds forderte El Salvador, das Bitcoin 2021 als gesetzliches Zahlungsmittel eingeführt hat, kürzlich zu begrenzenden Maßnahmen gegen das Kryptogeld auf.
Dass die BRICS-Staaten ein freiheitliches Ansinnen im Kopf haben, wenn sie Kryptowährungen ins Spiel bringen, darf indes auch bezweifelt werden. Im Abschlussdokument bekennen sich die Gipfel-Teilnehmer ausdrücklich zur UN, ihren Programmen und ihrer «Agenda 2030». Ernst Wolff nennt das «eine Bankrotterklärung korrupter Politiker, die sich dem digital-finanziellen Komplex zu 100 Prozent unterwerfen».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ c3c7122c:607731d7
2025-04-12 04:05:06
@ c3c7122c:607731d7
2025-04-12 04:05:06Help!
Calling all El Salvador Nostriches! If you currently live in SV, I need your help and am offering several bounties (0.001, 0.01, and 0.1 BTC).
In Brief
In short, I am pursuing El Salvador citizenship by birthright (through my grandmother). I’ve struggled to progress because her name varies on different documents. I need someone to help me push harder to get past this barrier, or connect me with information or people who can work on my behalf. I am offering:
- 0.001 BTC (100k sats) for information that will help me progress from my current situation
- 0.01 BTC (1 MM sats) to get me in touch with someone that is more impactful than the immigration lawyer I already spoke with
- 0.1 BTC (10 MM sats) if your efforts help me obtain citizenship for me or my father
Background
My grandma married my grandfather (an American Marine) and moved to the states where my father was born. I have some official and unofficial documents where her name varies in spelling, order of first/middle name, and addition of her father’s last name. So every doc basically has a different name for her. I was connected with an english-speaking immigration lawyer in SV who hit a dead end when searching for her official ID because the city hall in her city had burned down so there was no record of her info. He gave up at that point. I find it odd that it was so easy to change your name back then, but they are more strict now with the records from that time.
I believe SV citizenship is my birthright and have several personal reasons for pursuing this. I want someone to act on my behalf who will try harder to work the system (by appeal, loophole, or even bribe if I have to). If you are local and can help me with this, I’d greatly appreciate any efforts you make.
Cheers!
Corey San Diego
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-30 15:50:37
@ 5d4b6c8d:8a1c1ee3
2025-04-30 15:50:37I was a bit more distracted than normal this month, but ~econ kept humming along.
- Posts: 228 (7th)
- Comments: 1459 (5th)
- Stacking: 128k (4th)
- Revenue: 74k (4th)
We're holding pretty steady, but haven't gotten back to our highs from last year.
With revenue down slightly, I'll move the post fee back towards the previous local max and conclude the posting fee optimization process for now. Going forward the posting fee will be set at 84 sats (until I decide to start messing with it again).
Next month, I'll start the comment fee optimization process.
We're still on pace for a profitable year and having a nice sized fund to pay out the end-of-year awards.
Thanks everyone for supporting this community!
Let me know if you have any suggestions for how to improve the territory.
originally posted at https://stacker.news/items/967545
-
 @ a95c6243:d345522c
2025-02-15 19:05:38
@ a95c6243:d345522c
2025-02-15 19:05:38Auf der diesjährigen Münchner Sicherheitskonferenz geht es vor allem um die Ukraine. Protagonisten sind dabei zunächst die US-Amerikaner. Präsident Trump schockierte die Europäer kurz vorher durch ein Telefonat mit seinem Amtskollegen Wladimir Putin, während Vizepräsident Vance mit seiner Rede über Demokratie und Meinungsfreiheit für versteinerte Mienen und Empörung sorgte.
Die Bemühungen der Europäer um einen Frieden in der Ukraine halten sich, gelinde gesagt, in Grenzen. Größeres Augenmerk wird auf militärische Unterstützung, die Pflege von Feindbildern sowie Eskalation gelegt. Der deutsche Bundeskanzler Scholz reagierte auf die angekündigten Verhandlungen über einen möglichen Frieden für die Ukraine mit der Forderung nach noch höheren «Verteidigungsausgaben». Auch die amtierende Außenministerin Baerbock hatte vor der Münchner Konferenz klargestellt:
«Frieden wird es nur durch Stärke geben. (...) Bei Corona haben wir gesehen, zu was Europa fähig ist. Es braucht erneut Investitionen, die der historischen Wegmarke, vor der wir stehen, angemessen sind.»
Die Rüstungsindustrie freut sich in jedem Fall über weltweit steigende Militärausgaben. Die Kriege in der Ukraine und in Gaza tragen zu Rekordeinnahmen bei. Jetzt «winkt die Aussicht auf eine jahrelange große Nachrüstung in Europa», auch wenn der Ukraine-Krieg enden sollte, so hört man aus Finanzkreisen. In der Konsequenz kennt «die Aktie des deutschen Vorzeige-Rüstungskonzerns Rheinmetall in ihrem Anstieg offenbar gar keine Grenzen mehr». «Solche Friedensversprechen» wie das jetzige hätten in der Vergangenheit zu starken Kursverlusten geführt.
Für manche Leute sind Kriegswaffen und sonstige Rüstungsgüter Waren wie alle anderen, jedenfalls aus der Perspektive von Investoren oder Managern. Auch in diesem Bereich gibt es Startups und man spricht von Dingen wie innovativen Herangehensweisen, hocheffizienten Produktionsanlagen, skalierbaren Produktionstechniken und geringeren Stückkosten.
Wir lesen aktuell von Massenproduktion und gesteigerten Fertigungskapazitäten für Kriegsgerät. Der Motor solcher Dynamik und solchen Wachstums ist die Aufrüstung, die inzwischen permanent gefordert wird. Parallel wird die Bevölkerung verbal eingestimmt und auf Kriegstüchtigkeit getrimmt.
Das Rüstungs- und KI-Startup Helsing verkündete kürzlich eine «dezentrale Massenproduktion für den Ukrainekrieg». Mit dieser Expansion positioniere sich das Münchner Unternehmen als einer der weltweit führenden Hersteller von Kampfdrohnen. Der nächste «Meilenstein» steht auch bereits an: Man will eine Satellitenflotte im Weltraum aufbauen, zur Überwachung von Gefechtsfeldern und Truppenbewegungen.
Ebenfalls aus München stammt das als DefenseTech-Startup bezeichnete Unternehmen ARX Robotics. Kürzlich habe man in der Region die größte europäische Produktionsstätte für autonome Verteidigungssysteme eröffnet. Damit fahre man die Produktion von Militär-Robotern hoch. Diese Expansion diene auch der Lieferung der «größten Flotte unbemannter Bodensysteme westlicher Bauart» in die Ukraine.
Rüstung boomt und scheint ein Zukunftsmarkt zu sein. Die Hersteller und Vermarkter betonen, mit ihren Aktivitäten und Produkten solle die europäische Verteidigungsfähigkeit erhöht werden. Ihre Strategien sollten sogar «zum Schutz demokratischer Strukturen beitragen».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 3eba5ef4:751f23ae
2025-04-11 00:40:28
@ 3eba5ef4:751f23ae
2025-04-11 00:40:28Crypto Insights
2025 MIT Bitcoin Expo: Spotlight on Freedom Tech
The 12th MIT Bitcoin Expo took place on April 5–6, centering this year’s theme on “Freedom Tech” and how technology can facilitate physical and social liberation.
-
Day 1 Recap: Mawarire delivered the keynote speech “Why Freedom Tech Matters,” and Dryja discussed how Bitcoin demonstrates resilience against nation-states. The morning sessions focused on corporate adoption, featuring speakers such as Paul Giordano from Marathon Digital and Bitcoin Core contributors like Gloria Zhao. The afternoon shifted toward more technical topics, including consensus cleanup, poisoning attacks, censorship resistance, and the Bitcoin Pipes protocol.
-
Day 2 Recap: The focus shifted to global impact. Mauricio Bartolomeo discussed the exfiltration of resources via Bitcoin, followed by a panel with activists from Venezuela, Russia, and Togo. Technical topics included: scaling self-custody, Steven Roose’s covenant soft fork proposals, the future of freedom tech, quantum resistance, and Tor.
Into Bitcoin Address Poisoning Attacks
In this article, Jameson Lopp highlights the rise of Bitcoin address poisoning attacks—an emerging form of social engineering. Attackers send transactions from newly generated wallets that mimic the beginning and end characters of a target's recently used address. If the target later copies an address from their transaction history, they may unknowingly send funds to the attacker instead of the intended recipient. Though the success rate per attack is low, the low cost of transactions enables attackers to attempt thousands in a short period.
Lopp also argues that such attacks are a byproduct of low transaction fees and that higher fees could deter them. He also suggests wallet-level defenses, such as warnings like, “Oh, this came from a similar looking address,” to help users avoid interaction.
Examining the Mitigation Strategy Against Timewarp Attacks
Timewarp attacks, first identified around 2011, allow a majority of malicious miners to manipulate block timestamps, artificially lower difficulty, and mine blocks every few seconds. The “Great Consensus Cleanup” soft fork proposal can mitigate this by requiring that the first block in a new difficulty period must have a time no earlier than a certain number of minutes before the last block of the previous period.
A report examines the details of this BIP.
Tokenization on Bitcoin: Building a Global Settlement Layer with Taproot Assets and Lightning
Bitcoin’s evolution into a multi-asset platform is accelerating with the advent of Taproot Assets and Lightning Network. The integration of these technologies combines Bitcoin’s decentralization and security with the speed and scalability of the Lightning Network. This report examines how Taproot Assets enable asset issuance, transfers, and swaps on Bitcoin’s base layer, and how the Lightning Network facilitates fast, low-cost transfers of those assets. We compare this approach to earlier attempts at Bitcoin asset issuance and analyze its market potential against other blockchains and traditional payment networks.
Solving Data Availability in Client-Side Validation With UTxO Binding
Issuing tokens on Bitcoin is attractive due to its security and dominance, but its limited functionality creates challenges. Client-side validation (CSV) is a common workaround, using off-chain data with on-chain verification, though it risks data loss and withholding. This paper introduces UTxO binding, a framework that links a Bitcoin UTxO to one on an auxiliary chain, providing data storage and programmability. The authors prove its security and implement it using Nervos CKB.
From State Differences to Scaling: Citrea’s Fee Mechanism for Bitcoin
The Citrea team has designed a new fee mechanism to enhance Bitcoin’s scalability without compromising security. It only records essential state differences (i.e., state slot changes) on the Bitcoin main chain, using zero-knowledge proofs to ensure verifiability and Bitcoin security while drastically reducing state inscription costs. Optimizations include: replacing
codefield withcode_hash, compressing state data using a highly efficient compression algorithm Brotli, and analyzing historical Ethereum block data to estimate each transaction’s impact on cumulative state differences—enabling a discount to each transaction.Second: A New Ark Implementation Launched on Bitcoin Signet
Second, a protocol based on Ark to improve Bitcoin transaction throughput, has launched Bark, a test implementation on Bitcoin Signet.
Ark makes Bitcoin transactions faster, cheaper, and more private, allowing more users and transactions per block. However, funds stored non-custodially via Ark can expire if unused, making it slightly less trustless than mainchain transactions.
BitLayer Optimizes BitVM Bridge Protocol and Demonstrates on Testnet
Bitlayer BitVM Bridge protocol is an optimized adaptation of the bridge protocol outlined in the BitVM2 paper, to improve efficiency, scalability, and security—especially for high-risk cross-chain transactions.
In this article, two key testnet demos on bitvmnet (a BitVM-dedicated testnet) demonstrate how the protocol can:
-
Effectively thwart fraudulent reclaim attempts by brokers.
-
Protect honest brokers from malicious or baseless challenges.
Cardano Enables Bitcoin DeFi via BitVMX and Lightning Hydra
Cardano is integrating with Bitcoin through Lightning Hydra and BitVMX to enable secure and scalable Bitcoin DeFi.
Zcash’s Tachyon Upgrade: Toward Scalable Oblivious Synchronization
Zcash has unveiled project Tachyon, a proposal to scale Zcash by changing how wallets sync and prove ownership of notes. Instead of scanning the entire blockchain, wallets track only their own nullifiers and receive succinct proofs from untrusted, oblivious sync servers. Transactions include proofs of wallet state (using recursive SNARKs), allowing nodes to verify them without keeping the full history. Notes are exchanged out-of-band, reducing on-chain data and improving privacy. In the nominal case, users get fast sync, lightweight wallets, and strong privacy, without the need to trust the network.
Podcast | Why the Future of Bitcoin Mining is Distributed
In this podcast, Professor Troy Cross discusses the centralization of Bitcoin mining and argues convincingly for hashrate decentralization. While economies of scale have led to mega mining operations, he sees economic imperative that will drive mining toward a globally distributed future—not dominated by the U.S.—ensuring neutrality and resilience against state-level threats.
Binance Report|Crypto Industry Map March 2025
This report provides an overview of projects using a framework that divides crypto into four core ecosystems—Infrastructure, DeFi, NFT, and Gaming—and four trending sectors: Stablecoins, RWA, AI, and DeSci.
For infrastructure, five key pillars are identified: scalability & fairness, data availability & tooling, security & privacy, cloud networks, and connectivity. The report also maps out and categorizes the major projects and solutions currently on the market.

Top Reads on Blockchain and Beyond
A Game-Theoretic Approach to Bitcoin’s Valuation in Equilibrium
The author presents a game-theoretic argument for why Bitcoin will emerge as the optimal unit of account in equilibrium. The argument is based upon the observation that a generally agreed upon unit of account that represents a constant share of total wealth (equal to the totality of all other economic utility) will naturally create price signals that passively stabilize the macroeconomy, without requiring external intervention.
Bitcoin’s unique properties—finite supply, inertness, fungibility, accessibility, and ownership history—position it as the leading candidate to emerge as this unit.
Neo: Lattice-Based Folding Scheme for CCS Over Small Fields and Pay-Per-Bit Commitments
This paper introduces Neo, a new lattice-based folding scheme for CCS, an NP-complete relation that generalizes R1CS, Plonkish, and AIR. Neo's folding scheme can be viewed as adapting the folding scheme in HyperNova (CRYPTO'24), which assumes elliptic-curve based linearly homomorphic commitments, to the lattice setting. Unlike HyperNova, Neo can use “small” prime fields (e.g., over the Goldilocks prime). Additionally, Neo provides plausible post-quantum security.
Social Scalability: Key to Massive Value Accumulation in Crypto
Social scalability, a concept first proposed by Nick Szabo in his 2017 article Money, Blockchains, and Social Scalability, is further explored in this thread. Here, “social scalability” refers to an institution's ability to allow the maximum number of people to have skin in the game and win. It’s seen as the main reason crypto has become a $2.9T asset class today and a key driver of value accumulation in the coming decade.
The author argues that two critical ingredients for long-term social scalability are credible neutrality and utility. Currently, only BTC and ETH have this potential, yet neither strikes a perfect balance between the two. The author notes that there is not yet a strong narrative around social scalability, and concludes by emphasizing the importance of focusing on long-term value and resisting the temptation of short-term market narratives.
-
-
 @ c631e267:c2b78d3e
2025-02-07 19:42:11
@ c631e267:c2b78d3e
2025-02-07 19:42:11Nur wenn wir aufeinander zugehen, haben wir die Chance \ auf Überwindung der gegenseitigen Ressentiments! \ Dr. med. dent. Jens Knipphals
In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und langjährige Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und publiziert. Seine Motivation:
«Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.»
Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt, zum Beispiel bei öffentlichen Bürgerfragestunden. Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise?
Der Termin fand allerdings nicht statt – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als Wiederholungstäter, da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber Multipolar erklärte der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen.
Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst, sei aber letztlich eine gesamtgesellschaftliche Aufgabe, schreibt Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien.
Frey erinnert daran, dass Dennis Weilmann mitverantwortlich für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut.
Wolfsburg wurde damals zu einem Modellprojekt des Bundesministeriums des Innern (BMI) und war Finalist im Bitkom-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt «Smart City Wolfsburg» anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin Forbes im April 2020:
«Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.»
Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten, wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten Maßnahmen geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 1739d937:3e3136ef
2025-04-30 14:39:24
@ 1739d937:3e3136ef
2025-04-30 14:39:24MLS over Nostr - 30th April 2025
YO! Exciting stuff in this update so no intro, let's get straight into it.
🚢 Libraries Released
I've created 4 new Rust crates to make implementing NIP-EE (MLS) messaging easy for other projects. These are now part of the rust-nostr project (thanks nostr:npub1drvpzev3syqt0kjrls50050uzf25gehpz9vgdw08hvex7e0vgfeq0eseet) but aren't quite released to crates.io yet. They will be included in the next release of that library. My hope is that these libraries will give nostr developers a simple, safe, and specification-compliant way to work with MLS messaging in their applications.
Here's a quick overview of each:
nostr_mls_storage
One of the challenges of using MLS messaging is that clients have to store quite a lot of state about groups, keys, and messages. Initially, I implemented all of this in White Noise but knew that eventually this would need to be done in a more generalized way.
This crate defines traits and types that are used by the storage implementation crates and sets those up to wrap the OpenMLS storage layer. Now, instead of apps having to implement storage for both OpenMLS and Nostr, you simply pick your storage backend and go from there.
Importantly, because these are generic traits, it allows for the creation of any number of storage implementations for different backend storage providers; postgres, lmdb, nostrdb, etc. To start I've created two implementations; detailed below.
nostr_mls_memory_storage
This is a simple implementation of the nostr_mls_storage traits that uses an in-memory store (that doesn't persist anything to disc). This is principally for testing.
nostr_mls_sqlite_storage
This is a production ready implementation of the nostr_mls_storage traits that uses a persistent local sqlite database to store all data.
nostr_mls
This is the main library that app developers will interact with. Once you've chose a backend and instantiated an instance of NostrMls you can then interact with a simple set of methods to create key packages, create groups, send messages, process welcomes and messages, and more.
If you want to see a complete example of what the interface looks like check out mls_memory.rs.
I'll continue to add to this library over time as I implement more of the MLS protocol features.
🚧 White Noise Refactor
As a result of these new libraries, I was able to remove a huge amount of code from White Noise and refactor large parts of the app to make the codebase easier to understand and maintain. Because of this large refactor and the changes in the underlying storage layer, if you've installed White Noise before you'll need to delete it from your device before you trying to install again.
🖼️ Encrypted Media with Blossom
Let's be honest: Group chat would be basically useless if you couldn't share memes and gifs. Well, now you can in White Noise. Media in groups is encrypted using an MLS secret and uploaded to Blossom with a one-time use keypair. This gives groups a way to have rich conversations with images and documents and anything else while also maintaining the privacy and security of the conversation.
This is still in a rough state but rendering improvements are coming next.
📱 Damn Mobile
The app is still in a semi-broken state on Android and fully broken state on iOS. Now that I have the libraries released and the White Noise core code refactored, I'm focused 100% on fixing these issues. My goal is to have a beta version live on Zapstore in a few weeks.
🧑💻 Join Us
I'm looking for mobile developers on both Android and iOS to join the team and help us build the best possible apps for these platforms. I have grant funding available for the right people. Come and help us build secure, permissionless, censorship-resistant messaging. I can think of few projects that deserve your attention more than securing freedom of speech and freedom of association for the entire world. If you're interested or know someone who might be, please reach out to me directly.
🙏 Thanks to the People
Last but not least: A HUGE thank you to all the folks that have been helping make this project happen. You can check out the people that are directly working on the apps on Following._ (and follow them). There are also a lot of people behind the scenes that have helped in myriad ways to get us this far. Thank you thank you thank you.
🔗 Links
Libraries
White Noise
Other
-
 @ a95c6243:d345522c
2025-01-31 20:02:25
@ a95c6243:d345522c
2025-01-31 20:02:25Im Augenblick wird mit größter Intensität, großer Umsicht \ das deutsche Volk belogen. \ Olaf Scholz im FAZ-Interview
Online-Wahlen stärken die Demokratie, sind sicher, und 61 Prozent der Wahlberechtigten sprechen sich für deren Einführung in Deutschland aus. Das zumindest behauptet eine aktuelle Umfrage, die auch über die Agentur Reuters Verbreitung in den Medien gefunden hat. Demnach würden außerdem 45 Prozent der Nichtwähler bei der Bundestagswahl ihre Stimme abgeben, wenn sie dies zum Beispiel von Ihrem PC, Tablet oder Smartphone aus machen könnten.
Die telefonische Umfrage unter gut 1000 wahlberechtigten Personen sei repräsentativ, behauptet der Auftraggeber – der Digitalverband Bitkom. Dieser präsentiert sich als eingetragener Verein mit einer beeindruckenden Liste von Mitgliedern, die Software und IT-Dienstleistungen anbieten. Erklärtes Vereinsziel ist es, «Deutschland zu einem führenden Digitalstandort zu machen und die digitale Transformation der deutschen Wirtschaft und Verwaltung voranzutreiben».
Durchgeführt hat die Befragung die Bitkom Servicegesellschaft mbH, also alles in der Familie. Die gleiche Erhebung hatte der Verband übrigens 2021 schon einmal durchgeführt. Damals sprachen sich angeblich sogar 63 Prozent für ein derartiges «Demokratie-Update» aus – die Tendenz ist demgemäß fallend. Dennoch orakelt mancher, der Gang zur Wahlurne gelte bereits als veraltet.
Die spanische Privat-Uni mit Globalisten-Touch, IE University, berichtete Ende letzten Jahres in ihrer Studie «European Tech Insights», 67 Prozent der Europäer befürchteten, dass Hacker Wahlergebnisse verfälschen könnten. Mehr als 30 Prozent der Befragten glaubten, dass künstliche Intelligenz (KI) bereits Wahlentscheidungen beeinflusst habe. Trotzdem würden angeblich 34 Prozent der unter 35-Jährigen einer KI-gesteuerten App vertrauen, um in ihrem Namen für politische Kandidaten zu stimmen.
Wie dauerhaft wird wohl das Ergebnis der kommenden Bundestagswahl sein? Diese Frage stellt sich angesichts der aktuellen Entwicklung der Migrations-Debatte und der (vorübergehend) bröckelnden «Brandmauer» gegen die AfD. Das «Zustrombegrenzungsgesetz» der Union hat das Parlament heute Nachmittag überraschenderweise abgelehnt. Dennoch muss man wohl kein ausgesprochener Pessimist sein, um zu befürchten, dass die Entscheidungen der Bürger von den selbsternannten Verteidigern der Demokratie künftig vielleicht nicht respektiert werden, weil sie nicht gefallen.
Bundesweit wird jetzt zu «Brandmauer-Demos» aufgerufen, die CDU gerät unter Druck und es wird von Übergriffen auf Parteibüros und Drohungen gegen Mitarbeiter berichtet. Sicherheitsbehörden warnen vor Eskalationen, die Polizei sei «für ein mögliches erhöhtes Aufkommen von Straftaten gegenüber Politikern und gegen Parteigebäude sensibilisiert».
Der Vorwand «unzulässiger Einflussnahme» auf Politik und Wahlen wird als Argument schon seit einiger Zeit aufgebaut. Der Manipulation schuldig befunden wird neben Putin und Trump auch Elon Musk, was lustigerweise ausgerechnet Bill Gates gerade noch einmal bekräftigt und als «völlig irre» bezeichnet hat. Man stelle sich die Diskussionen um die Gültigkeit von Wahlergebnissen vor, wenn es Online-Verfahren zur Stimmabgabe gäbe. In der Schweiz wird «E-Voting» seit einigen Jahren getestet, aber wohl bisher mit wenig Erfolg.
Die politische Brandstiftung der letzten Jahre zahlt sich immer mehr aus. Anstatt dringende Probleme der Menschen zu lösen – zu denen auch in Deutschland die weit verbreitete Armut zählt –, hat die Politik konsequent polarisiert und sich auf Ausgrenzung und Verhöhnung großer Teile der Bevölkerung konzentriert. Basierend auf Ideologie und Lügen werden abweichende Stimmen unterdrückt und kriminalisiert, nicht nur und nicht erst in diesem Augenblick. Die nächsten Wochen dürften ausgesprochen spannend werden.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 4e616576:43c4fee8
2025-04-30 13:28:18
@ 4e616576:43c4fee8
2025-04-30 13:28:18asdfasdfsadfaf
-
 @ 4e616576:43c4fee8
2025-04-30 13:27:51
@ 4e616576:43c4fee8
2025-04-30 13:27:51asdfasdf
-
 @ a95c6243:d345522c
2025-01-24 20:59:01
@ a95c6243:d345522c
2025-01-24 20:59:01Menschen tun alles, egal wie absurd, \ um ihrer eigenen Seele nicht zu begegnen. \ Carl Gustav Jung
«Extremer Reichtum ist eine Gefahr für die Demokratie», sagen über die Hälfte der knapp 3000 befragten Millionäre aus G20-Staaten laut einer Umfrage der «Patriotic Millionaires». Ferner stellte dieser Zusammenschluss wohlhabender US-Amerikaner fest, dass 63 Prozent jener Millionäre den Einfluss von Superreichen auf US-Präsident Trump als Bedrohung für die globale Stabilität ansehen.
Diese Besorgnis haben 370 Millionäre und Milliardäre am Dienstag auch den in Davos beim WEF konzentrierten Privilegierten aus aller Welt übermittelt. In einem offenen Brief forderten sie die «gewählten Führer» auf, die Superreichen – also sie selbst – zu besteuern, um «die zersetzenden Auswirkungen des extremen Reichtums auf unsere Demokratien und die Gesellschaft zu bekämpfen». Zum Beispiel kontrolliere eine handvoll extrem reicher Menschen die Medien, beeinflusse die Rechtssysteme in unzulässiger Weise und verwandele Recht in Unrecht.
Schon 2019 beanstandete der bekannte Historiker und Schriftsteller Ruthger Bregman an einer WEF-Podiumsdiskussion die Steuervermeidung der Superreichen. Die elitäre Veranstaltung bezeichnete er als «Feuerwehr-Konferenz, bei der man nicht über Löschwasser sprechen darf.» Daraufhin erhielt Bregman keine Einladungen nach Davos mehr. Auf seine Aussagen machte der Schweizer Aktivist Alec Gagneux aufmerksam, der sich seit Jahrzehnten kritisch mit dem WEF befasst. Ihm wurde kürzlich der Zutritt zu einem dreiteiligen Kurs über das WEF an der Volkshochschule Region Brugg verwehrt.
Nun ist die Erkenntnis, dass mit Geld politischer Einfluss einhergeht, alles andere als neu. Und extremer Reichtum macht die Sache nicht wirklich besser. Trotzdem hat man über Initiativen wie Patriotic Millionaires oder Taxmenow bisher eher selten etwas gehört, obwohl es sie schon lange gibt. Auch scheint es kein Problem, wenn ein Herr Gates fast im Alleingang versucht, globale Gesundheits-, Klima-, Ernährungs- oder Bevölkerungspolitik zu betreiben – im Gegenteil. Im Jahr, als der Milliardär Donald Trump zum zweiten Mal ins Weiße Haus einzieht, ist das Echo in den Gesinnungsmedien dagegen enorm – und uniform, wer hätte das gedacht.
Der neue US-Präsident hat jedoch «Davos geerdet», wie Achgut es nannte. In seiner kurzen Rede beim Weltwirtschaftsforum verteidigte er seine Politik und stellte klar, er habe schlicht eine «Revolution des gesunden Menschenverstands» begonnen. Mit deutlichen Worten sprach er unter anderem von ersten Maßnahmen gegen den «Green New Scam», und von einem «Erlass, der jegliche staatliche Zensur beendet»:
«Unsere Regierung wird die Äußerungen unserer eigenen Bürger nicht mehr als Fehlinformation oder Desinformation bezeichnen, was die Lieblingswörter von Zensoren und derer sind, die den freien Austausch von Ideen und, offen gesagt, den Fortschritt verhindern wollen.»
Wie der «Trumpismus» letztlich einzuordnen ist, muss jeder für sich selbst entscheiden. Skepsis ist definitiv angebracht, denn «einer von uns» sind weder der Präsident noch seine auserwählten Teammitglieder. Ob sie irgendeinen Sumpf trockenlegen oder Staatsverbrechen aufdecken werden oder was aus WHO- und Klimaverträgen wird, bleibt abzuwarten.
Das WHO-Dekret fordert jedenfalls die Übertragung der Gelder auf «glaubwürdige Partner», die die Aktivitäten übernehmen könnten. Zufällig scheint mit «Impfguru» Bill Gates ein weiterer Harris-Unterstützer kürzlich das Lager gewechselt zu haben: Nach einem gemeinsamen Abendessen zeigte er sich «beeindruckt» von Trumps Interesse an der globalen Gesundheit.
Mit dem Projekt «Stargate» sind weitere dunkle Wolken am Erwartungshorizont der Fangemeinde aufgezogen. Trump hat dieses Joint Venture zwischen den Konzernen OpenAI, Oracle, und SoftBank als das «größte KI-Infrastrukturprojekt der Geschichte» angekündigt. Der Stein des Anstoßes: Oracle-CEO Larry Ellison, der auch Fan von KI-gestützter Echtzeit-Überwachung ist, sieht einen weiteren potenziellen Einsatz der künstlichen Intelligenz. Sie könne dazu dienen, Krebserkrankungen zu erkennen und individuelle mRNA-«Impfstoffe» zur Behandlung innerhalb von 48 Stunden zu entwickeln.
Warum bitte sollten sich diese superreichen «Eliten» ins eigene Fleisch schneiden und direkt entgegen ihren eigenen Interessen handeln? Weil sie Menschenfreunde, sogenannte Philanthropen sind? Oder vielleicht, weil sie ein schlechtes Gewissen haben und ihre Schuld kompensieren müssen? Deswegen jedenfalls brauchen «Linke» laut Robert Willacker, einem deutschen Politikberater mit brasilianischen Wurzeln, rechte Parteien – ein ebenso überraschender wie humorvoller Erklärungsansatz.
Wenn eine Krähe der anderen kein Auge aushackt, dann tut sie das sich selbst noch weniger an. Dass Millionäre ernsthaft ihre eigene Besteuerung fordern oder Machteliten ihren eigenen Einfluss zugunsten anderer einschränken würden, halte ich für sehr unwahrscheinlich. So etwas glaube ich erst, wenn zum Beispiel die Rüstungsindustrie sich um Friedensverhandlungen bemüht, die Pharmalobby sich gegen institutionalisierte Korruption einsetzt, Zentralbanken ihre CBDC-Pläne für Bitcoin opfern oder der ÖRR die Abschaffung der Rundfunkgebühren fordert.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 4e616576:43c4fee8
2025-04-30 13:13:51
@ 4e616576:43c4fee8
2025-04-30 13:13:51asdffasdf
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ e096a89e:59351479
2025-04-30 12:59:28
@ e096a89e:59351479
2025-04-30 12:59:28Why Oshi?
I had another name for this brand before, but it was hard for folks to say. Then I saw a chance to tap into the #Nostr and #Bitcoin crowd, people who might vibe with what I’m creating, and I knew I needed something that’d stick.
A good name can make a difference. Well, sometimes. Take Blink-182 - it might sound odd, but it worked for them and even has a ring to it. So, why Oshi?
Names mean a lot to me, and Oshi’s got layers. I’m into Japanese culture and Bitcoin, so it fits perfectly with a few meanings baked in:
- It’s a nod to Bitcoin’s visionary, Satoshi Nakamoto.
- In Japanese, “oshi” means cheering on your favorite idol by supporting their work - think of me as the maker, you as the fan.
- It’s short for “oh shiiiitttt” - what most folks say when they taste how good this stuff is.
My goal with Oshi is to share how amazing pecans and dates can be together. Everything I make - Hodl Butter, Hodl Bars, chocolates - is crafted with intention, keeping it simple and nuanced, no overdoing it. It’s healthy snacking without the grains or junk you find in other products.
I’ve got a few bars and jars in stock now. Grab something today and taste the unique flavor for yourself. Visit my website at https://oshigood.us/
foodstr #oshigood #hodlbar #hodlbutter
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 81650982:299380fa
2025-04-30 11:16:42
@ 81650982:299380fa
2025-04-30 11:16:42Let us delve into Monero (XMR). Among the proponents of various altcoins, Monero arguably commands one of the most dedicated followings, perhaps second only to Ethereum. Unlike many altcoins where even investors often harbor speculative, short-term intentions, the genuine belief within the Monero community suggests an inherent appeal to the chain itself.
The primary advantage touted by Monero (and similar so-called "privacy coins") is its robust privacy protection features. The demand for anonymous payment systems, tracing its lineage back to David Chaum, predates even the inception of Bitcoin. Monero's most heavily promoted strength, relative to Bitcoin, is that its privacy features are enabled by default.
This relates to the concept of the "anonymity set." To guarantee anonymity, a user must blend into a crowd of ordinary users. The larger the group one hides within, the more difficult it becomes for an external observer to identify any specific individual. From the perspective of Monero advocates, Bitcoin's default transaction model is overly transparent, clearly revealing the flow of funds between addresses. While repeated mixing can enhance anonymity in Bitcoin, the fact that users must actively undertake such measures presents a significant hurdle. More critically, proponents argue, the very group engaging in such deliberate obfuscation is precisely the group one doesn't want to be associated with for effective anonymity. Hiding requires blending with the ordinary, not merely mixing with others who are also actively trying to hide — the latter, they contend, is akin to criminals mixing only with other criminals.
This is a valid point. For instance, there's a substantial difference between a messenger app offering end-to-end encryption for all communications by default, versus one requiring users to explicitly create a "secret chat" for encryption. While I personally believe that increased self-custody of Bitcoin in personal wallets, acquisition through direct peer-to-peer payments rather than exchange purchases, and the widespread adoption of the Lightning Network would make tracing significantly harder even without explicit mixing efforts, let us concede, for the sake of argument, that Bitcoin's base-layer anonymity might not drastically improve even in such a future scenario.
Nevertheless, Monero's long-term prospects appear considerably constrained when focusing purely on technical limitations, setting aside economic factors or incentive models for now. While discussions on economics can often be countered with "That's just your speculation," technical constraints present more objective facts and leave less room for dispute.
Monero's most fundamental problem is its lack of scalability. To briefly explain how Monero obfuscates the sender: it includes other addresses alongside the true sender's address in the 'from' field and attaches what appears to be valid signatures for all of them. With a default setting of 10 decoys (plus the real spender, making a ring size of 11), the signature size naturally becomes substantially larger than Bitcoin's. Since an observer cannot determine which of the 11 is the true sender, and these decoys are arbitrary outputs selected from the blockchain belonging to other users, anonymity is indeed enhanced. While the sender cannot generate individually valid signatures for the decoy outputs (as they don't own the private keys), the use of a ring signature mathematically proves that one member of the ring authorized the transaction, allowing it to pass network validation.
The critical issue is that this results in transaction sizes several times larger than Bitcoin's. Bitcoin already faces criticism for being relatively expensive and slow. Monero's structure imposes a burden that is multiples greater. One might question the relationship between transaction data size and transaction fees/speed. However, the perceived slowness of blockchains isn't typically due to inefficient code, but rather the strict limitations imposed on block size (or equivalent throughput constraints) to maintain decentralization. Therefore, larger transaction sizes directly translate into throughput limitations and upward pressure on fees. If someone claims Monero fees are currently lower than Bitcoin's, that is merely a consequence of its significantly lower usage. Should Monero's transaction volume reach even a fraction of Bitcoin's, its current architecture would struggle severely under the load.
To address this, Monero implemented a dynamic block size limit instead of a hardcoded one. However, this is not a comprehensive solution. If the block size increases proportionally with usage, a future where Monero achieves widespread adoption as currency — implying usage potentially hundreds, thousands, or even hundreds of thousands of times greater than today — would render the blockchain size extremely difficult to manage for ordinary node operators. Global internet traffic might be consumed by Monero transactions, or at the very least, the bandwidth and storage costs could exceed what individuals can reasonably bear.
Blockchains, by their nature, must maintain a size manageable enough for individuals to run full nodes, necessitating strict block size limits (or equivalent constraints in blockless designs). This fundamental requirement is the root cause of limited transaction speed and rising fees. Consequently, the standard approach to blockchain scaling involves Layer 2 solutions like the Lightning Network. The problem is, implementing such solutions on Monero is extremely challenging.
Layer 2 solutions, while varying in specific implementation details across different blockchains, generally rely heavily on the transparency of on-chain transactions. They typically involve sophisticated smart contracts built upon the ability to publicly verify on-chain states and events. Monero's inherent opacity, hiding crucial details of on-chain transactions, makes it exceptionally difficult for two mutually untrusting parties to reach the necessary consensus and cryptographic agreements (like establishing payment channels with verifiable state transitions and dispute mechanisms) that underpin such Layer 2 systems. The fact that Monero, despite existing for several years, still lacks a functional, widely adopted Layer 2 implementation suggests that this remains an unsolved and technically formidable challenge. While theoretical proposals exist, their real-world feasibility remains uncertain and would likely require significant breakthroughs in cryptographic protocol design.
Furthermore, Monero faces another severe scaling challenge related to its core privacy mechanism. As mentioned, decoy outputs are used to obscure the true sender. An astute observer might wonder: If a third party cannot distinguish the real spender, could the real spender potentially double-spend their funds later? Or could someone's funds become unusable simply because they were chosen as a decoy in another transaction? Naturally, Monero's developers anticipated this. The solution employed involves key images.
When an output is genuinely spent within a ring signature, a unique cryptographic identifier called a "key image" is derived from the real output and the spender's private key. This derivation is one-way (the key image cannot be used to reveal the original output or key). This key image is recorded on the blockchain. When validating a new transaction, the network checks if the submitted key image has already appeared in the history. If it exists, the transaction is rejected as a double-spend attempt. The crucial implication is that this set of used key images can never be pruned. Deleting historical key images would directly enable double-spending.
Therefore, Monero's state size — the data that full nodes must retain and check against — grows linearly and perpetually with the total number of transactions ever processed on the network.
Summary In summary, Monero faces critical technical hurdles:
Significantly Larger Transaction Sizes: The use of ring signatures for anonymity results in transaction data sizes several times larger than typical cryptocurrencies like Bitcoin.
Inherent Scalability Limitations: The large transaction size, combined with the necessity of strict block throughput limits to preserve decentralization, creates severe scalability bottlenecks regarding transaction speed and cost under significant load. Dynamic block sizes, while helpful in the short term, do not constitute a viable long-term solution for broad decentralization.
Layer 2 Implementation Difficulty: Monero's fundamental opacity makes implementing established Layer 2 scaling solutions (like payment channels) extremely difficult with current approaches. The absence of a widely adopted solution to date indicates that this remains a major unresolved challenge.
Unprunable, Linearly Growing State: The key image mechanism required to prevent double-spending mandates the perpetual storage of data proportional to the entire transaction history, unlike Bitcoin where nodes can prune historical blocks and primarily need to maintain the current UTXO set (whose size depends on usage patterns, not total history).
These technical constraints raise legitimate concerns about Monero's ability to scale effectively and achieve widespread adoption in the long term. While ongoing research may alleviate some of these issues, at present they represent formidable challenges that any privacy-focused cryptocurrency must contend with.
-
 @ e4950c93:1b99eccd
2025-04-30 09:29:25
@ e4950c93:1b99eccd
2025-04-30 09:29:25 -
 @ dbc27e2e:b1dd0b0b
2025-04-05 20:44:00
@ dbc27e2e:b1dd0b0b
2025-04-05 20:44:00This method focuses on the amount of water in the first pour, which ultimately defines the coffee’s acidity and sweetness (more water = more acidity, less water = more sweetness). For the remainder of the brew, the water is divided into equal parts according to the strength you wish to attain.

Dose:
20g coffee (Coarse ground coffee) 300mL water (92°C / 197.6°F) Time: 3:30Instructions:
- Pour 1: 0:00 > 50mL (42% of 120mL = 40% of total – less water in the ratio, targeting sweetness.)
- Pour 2: 0:45 > 70mL (58% of 120mL = 40% of total – the top up for 40% of total.)
- Pour 3: 1:30 > 60mL (The remaining water is 180mL / 3 pours = 60mL per pour)
- Pour 4: 2:10 > 60mL
- Pour 5: 2:40 > 60mL
- Remove the V60 at 3:30
-
 @ 3589b793:ad53847e
2025-04-30 12:40:42
@ 3589b793:ad53847e
2025-04-30 12:40:42※本記事は別サービスで2022年6月24日に公開した記事の移植です。
どうも、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」です、こんばんは。
またまた実験的な試みがNostrで行われているのでレポートします。本シリーズはライブ感を重視しており、例によって(?)プルリクエストなどはレビュー段階なのでご承知おきください。
今回の主役はあくまでLightningNetworkの新提案(ただし以前からあるLSATからのリブランディング)となるLightning HTTP 402 Protocol(略称: L402)です。そのショーケースの一つとしてNostrが活用されているというものになります。
Lightning HTTP 402 Protocol(略称: L402)とは何か
bLIPに今月挙がったプロポーザル内容です。
https://github.com/lightning/blips/pull/26
L402について私はまだ完全に理解した段階ではあるのですがなんとか一言で説明しようとすると「Authトークンのように"Paid"トークンをHTTPヘッダーにアタッチして有料リソースへのHTTPリクエストの受け入れ判断を行えるようにする」ものだと解釈しました。
Authenticationでは、HTTPヘッダーにAuthトークンを添付し、その検証が通ればHTTPリクエストを許可し、通らなければ
401 Unauthorizedコードをエラーとして返すように定められています。https://developer.mozilla.org/ja/docs/Web/HTTP/Status/401
L402では、同じように、HTTPヘッダーに支払い済みかどうかを示す"Paid"トークンを添付し、その検証が通ればHTTPリクエストを許可し、通らなければ
402 Payment Requiredコードをエラーとして返すようにしています。なお、"Paid"トークンという用語は私の造語となります。便宜上本記事では使わせていただきますが、実際はAuthも入ってくるのが必至ですし、プルリクエストでも用語をどう定めるかは議論になっていることをご承知おきください。("API key", "credentials", "token", らが登場しています)
この402ステータスコードは従来から定義されていましたが、MDNのドキュメントでも記載されているように「実験的」なものでした。つまり、器は用意されているがこれまで活用されてこなかったものとなり、本プロトコルの物語性を体現しているものとなります。
https://developer.mozilla.org/ja/docs/Web/HTTP/Status/402
幻であったHTTPステータスコード402 Payment Requiredを実装する
この物語性は、上述のbLIPのスペックにも詳述されていますが、以下のスライドが簡潔です。
402 Payment Requiredは予約されていましたが、けっきょくのところWorldWideWebはペイメントプロトコルを実装しなかったので、Bitcoinの登場まで待つことになった、というのが要旨になります。このWorldWideWebにおける決済機能実装に関する歴史話はクリプト界隈でもたびたび話題に上がりますが、そこを繋いでくる文脈にこれこそマネーのインターネットプロトコルだなと痺れました。https://x.com/AlyseKilleen/status/1671342634307297282
この"Paid"トークンによって実現できることとして、第一にAIエージェントがBitcoin/LNを自律的に利用できるようになるM2M(MachineToMachine)的な話が挙げられていますが、ユースケースは想像力がいろいろ要るところです。実際のところは「有料リソースへの認可」を可能にすることが主になると理解しました。本連載では、繰り返しNostrクライアントにLNプロトコルを直接搭載せずにLightningNetworkを利用可能にする組み込み方法を見てきましたが、本件もインボイス文字列 & preimage程度の露出になりアプリケーション側でノードやウォレットの実装が要らないので、その文脈で位置付ける解釈もできるかと思います。
Snortでのサンプル実装
LN組み込み業界のリーディングプロダクトであるSnortのサンプル実装では、L402を有料コンテンツの購読に活用しています。具体的には画像や動画を投稿するときに有料のロックをかける、いわゆるペイウォールの一種となります。もともとアップローダもSnortが自前で用意しているので、そこにL402を組み込んでみたということのようです。
体験方法の詳細はこちらにあります。 https://njump.me/nevent1qqswr2pshcpawk9ny5q5kcgmhak24d92qzdy98jm8xcxlgxstruecccpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz78pvlzg
上記を試してみた結果が以下になります。まず、ペイウォールでロックした画像がNostrに投稿されている状態です。まったくビューワーが実装されておらず、ただのNotFound状態になっていますが、支払い前なのでロックされているということです。

次にこのHTTP通信の内容です。

通信自体はエラーになっているわけですが、ステータスコードが402で、レスポンスヘッダーのWWW-AuthenticateにInvoice文字列が返ってきています。つまり、このインボイスを支払えば"Paid"トークンが付与されて、その"Paid"トークンがあれば最初の画像がアンロックされることとなります。残念ながら現在は日本で利用不可のStrikeAppでしか払込みができないためここまでとなりますが、本懐である
402 Payment Requiredとインボイス文字列は確認できました。今確認できることは以上ですが、AmethystやDamusなどの他のNostrクライアントが実装するにあたり、インラインメディアを巡ってL402の仕様をアップデートする必要性や同じくHTTPヘッダーへのAuthトークンとなるNIP-98と組み合わせるなどの議論が行われている最中です。
LinghtningNetworkであるからこそのL402の実現
"Paid"トークンを実現するためにはLightningNetworkのファイナリティが重要な要素となっています。逆に言うと、reorgによるひっくり返しがあり得るBitcoinではできなくもないけど不便なわけです。LightningNetworkなら、当事者である二者間で支払いが確認されたら「同期的」にその証であるハッシュ値を用いて"Paid"トークンを作成することができます。しかもハッシュ値を提出するだけで台帳などで過去の履歴を確認する必要がありません。加えて言うと、受金者側が複数のノードを建てていて支払いを受け取るノードがどれか一つになる状況でも、つまり、スケーリングされている状況でも、"Paid"トークンそのものはどのノードかを気にすることなくステートレスで利用できるとのことです。(ここは単にreverse proxyとしてAuthサーバががんばっているだけと解釈することもできますがずいぶんこの機能にも力点を置いていて大規模なユースケースが重要になっているのだなという印象を抱きました)
Macaroonの本領発揮か?それとも詳細定義しすぎか?
HTTP通信ではWWW-Authenticateの実値にmacaroonの記述が確認できます。また現在のL402スペックでも"Paid"トークンにはmacaroonの利用が前提になっています。
このmacaroonとは(たぶん)googleで研究開発され、LNDノードソフトウェアで活用されているCookieを超えるという触れ込みのデータストアになります。しかし、あまり普及しなかった技術でもあり、個人の感想ですがなんとも微妙なものになっています。
https://research.google/pubs/macaroons-cookies-with-contextual-caveats-for-decentralized-authorization-in-the-cloud/
macaroonの強みは、Cookieを超えるという触れ込みのようにブラウザが無くてもプロセス間通信でデータ共有できる点に加えて、HMACチェーンで動的に認証認可を更新し続けられるところが挙げられます。しかし、そのようなユースケースがあまり無く、静的な認可となるOAuthやJWTで十分となっているのが現状かと思います。
L402では、macaroonの動的な更新が可能である点を活かして、"Paid"トークンを更新するケースが挙げられています。わかりやすいのは上記のスライド資料でも挙げられている"Dynamic Pricing"でしょうか。プロポーザルではloop©️LightningLabsにおいて月間の最大取引量を認可する"Paid"トークンを発行した上でその条件を動向に応じて動的に変更できる例が解説されています。とはいえ、そんなことしなくても再発行すればええやんけという話もなくもないですし、プルリクエストでも仕様レベルでmacaroonを指定するのは「具体」が過ぎるのではないか、もっと「抽象」し単なる"Opaque Token"程度の粒度にして他の実装も許容するべきではないか、という然るべきツッコミが入っています。
個人的にはそのツッコミが妥当と思いつつも、なんだかんだ初めてmacaroonの良さを実感できて感心した次第です。
-
 @ 3589b793:ad53847e
2025-04-30 12:28:25
@ 3589b793:ad53847e
2025-04-30 12:28:25※本記事は別サービスで2023年4月19日に公開した記事の移植です。
どうも、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」です、こんにちは。
前回まで投げ銭や有料購読の組み込み方法を見てきました。
zapsという投げ銭機能が各種クライアントに一通り実装されて活用が進んでいることで、統合は次の段階へ移り始めています。「作戦名: ウォレットをNostrクライアントに組み込め」です。今回はそちらをまとめます。
投げ銭する毎にいちいちウォレットを開いてまた元のNostrクライアントに手動で戻らないといけない is PAIN
LNとNostrはインボイス文字列で繋がっているだけの疎結合ですが、投稿に投げ銭するためには何かのLNウォレットを開いて支払いをして、また元のNostrクライアントに戻る操作をユーザーが手作業でする必要があります。お試しで一回やる程度では気になりませんが普段使いしているとこれはけっこうな煩わしさを感じるUXです。特にスマホでは大変にだるい状況になります。連打できない!
2月の実装以来、zapsは順調に定着して日々投げられています。


https://stats.nostr.band/#daily_zaps
なので、NostrクライアントにLNウォレットの接続を組み込み、支払いのために他のアプリに遷移せずにNostクライアント単独で完結できるようなアップデートが始まっています。
Webクライアント
NostrのLN組み込み業界のリーディングプレイヤーであるSnortでの例です。以下のようにヘッダーのウォレットアイコンをクリックすると連携ウォレットの選択ができます。

もともとNostrに限らずウェブアプリケーションとの連携をするために、WebLNという規格があります。簡単に言うと、ブラウザのグローバル領域を介して、LNウォレットの拡張機能と、タブで開いているウェブアプリが、お互いに連携するためのインターフェースを定めているものです。これに対応していると、LNによる支払いをウェブアプリが拡張機能に依頼できるようになります。さらにオプションで「確認無し」をオンにすると、拡張機能画面がポップアップせずにバックグラウンドで実行できるようになり、ノールック投げ銭ができるようになります。
似たようなものにNostrではNIP-07があります。NIP-07はNostrの秘密鍵を拡張機能に退避して、Nostrクライアントは秘密鍵を知らない状態で署名や複合を拡張機能に移譲できるようにしているものです。
Albyの拡張機能ではWebLNとNIP-07のどちらにも対応しています。
実はSnortはzapsが来る前からWebLNには対応していたのですが、さらに一歩進み、拡張機能ウォレットだけでなく、LNノードや拡張機能以外のLNウォレットと連携設定できるようになってきています。

umbrelなどでノードを立てている人ならLND with LNCでノードと直接繋げます。またLNDHubに対応したウォレットなどのアプリケーションとも繋げます。これらの接続は、WebLNにラップされて拡張機能ウォレットとインターフェースを揃えられた上で、Snort上でのインボイスの支払いに活用されます。
なお、LNCのpairingPhrase/passwordやLNDHubの接続情報などのクレデンシャルは、ブラウザのローカルストレージに保存されています。Nostrのリレーサーバなどには送られませんので、端末ごとに設定が必要です。
スマホアプリ
今回のメインです。なお、例によって(?)スペックは絶賛議論中でまだフィックスしていない中で記事を書いています。ディテールは変わるかもしれないので悪しからずです。
スマホアプリで上記のことをやるためには、後半のLNCやLNDHubはすでにzeusなどがやっているようにできますが、あくまでネイティブウォレットのラッパーです。Nostrでは限られた用途になるので1-click支払いのようなものを行うためにはそこから各スマホアプリが作り込む必要があります。まあこれはこれでやればいいという話でもあるのですが、LNノードやLNウォレットのアプリケーション側へのインターフェースの共通仕様は定められていないので、LNDとcore-lightningとeclairではすべて実装方法が違いますし、ウォレットもバラバラなので大変です。
そこで、多種多様なノードやウォレットの接続を取りまとめ一般アプリケーションへ統一したインターフェースを媒介するLN Adapter業界のリーディングカンパニーであるAlbyが動きました。AndroidアプリのAmethystで試験公開されていますが、スマホアプリでも上記のSnortのような連携が可能になるようなSDKが開発されました。
リリース記事 https://blog.getalby.com/native-zapping-in-amethyst/
"Unstoppable zapping for users"なんて段落見出しが付けられているように、スマホで別のアプリに切り替えてまた元に戻らなくても良いようにして、Nostr上でマイクロペイメントを滑らかにする、つまり、連打できることを繰り返し強調しています。
具体的にやっていることを見ていきます。以下の画像群はリリース記事の動画から抜粋しています。各投稿のzapsボタン⚡️をタップしたときの画面です。

上の赤枠が従来の投げ銭の詳細を決める場所で、下の赤枠の「Wallet Connect Service」が新たに追加されたAlby提供のSDKを用いたコネクト設定画面です。基本的にはOAuth2.0ベースのAlbyのAPIを活用していて、右上のAlbyアイコンをタップすると以下のようなOAuthの認可画面に飛びます。(ただし後述するように通常のOAuthとは一部異なります。)


画面デザインは違いますが、まあ他のアプリでよく目にするTwitter連携やGoogleアカウント連携とやっていることは同じです。
このOAuthベースのAPIはNostr専用のエンドポイントが建てられています。Nostr以外のECショップやマーケットプレイスなどへのAlbyのOAuthは汎用のエンドポイントが用意されています。よって通常のAlbyの設定とは別にセッション詳細を以下のサイトで作成する必要があります。
https://nwc.getalby.com/ (サブドメインのnwcはNostr Wallet Connectの略)
なぜNostrだけは特別なのかというところが完全には理解しきれていないですが、以下のところまで確認できています。一番にあるのは、Nostrクライアントにウォレットを組み込まずに、かつ、ノードやウォレットへの接続をNostrリレーサーバ以外は挟まずに"decentralized"にしたいというところだと理解しています。
- 上記のnwcのURLはalbyのカストディアルウォレットusername@getalby.comをNostrに繋ぐもの(たぶん)
- umbrelのLNノードを繋ぐためにはやはり専用のアプリがumbrelストアに上がっている。https://github.com/getAlby/umbrel-community-app-store
- 要するにOAuthの1stPartyの役割をウォレットやノードごとにそれぞれ建てる。
- OAuthのシークレットはクライアントに保存するので設定は各クライアント毎に必要。しかし使い回しすることは可能っぽい。通常のOAuthと異なり、1stParty側で3rdPartyのドメインはトラストしていないようなので。
- Nostrクライアントにウォレットを組み込まずに、さらにウォレットやノードへの接続をNostrリレーサーバ以外には挟まなくて良いようにするために、「NIP-47 Nostr Wallet Connect」というプロポーザルが起こされていて、絶賛議論中である。https://github.com/nostr-protocol/nips/pull/406
- このWallet Connect専用のアドホックなリレーサーバが建てられる。その情報が上記画像の赤枠の「Wallet Connect Service」の下半分のpub keyやらrelayURL。どうもNostrクライアントはNIP-47イベントについてはこのリレーサーバにしか送らないようにするらしい。(なんかNostrの基本設計を揺るがすユースケースの気がする...)
- Wallet Connect専用のNostrイベントでは、ペイメント情報をNostrアカウントと切り離すために、Nostrの秘密鍵とは別の秘密鍵が利用できるようにしている。
Imagin the Future
今回取り上げたNostrクライアントにウォレット接続を組み込む話を、Webのペイメントの歴史で類推してみましょう。
Snortでやっていることは、各サイトごとにクレジットカードを打ち込み各サイトがその情報を保持していたようなWeb1.0の時代に近いです。そうなるとクレジットカードの情報は各サービスごとに漏洩リスクなどがあり、Web1.0の時代はECが普及する壁の一つになっていました。(今でもAmazonなどの大手はそうですが)
Webではその後にPayPalをはじめとして、銀行口座やクレジットカードを各サイトから切り出して一括管理し、各ウェブサイトに支払いだけを連携するサービスが出てきて一般化しています。日本ではケータイのキャリア決済が利用者の心理的障壁を取り除きEC普及の後押しになりました。
後半のNostr Wallet ConnectはそれをNostrの中でやろうとしている試みになります。クレジットカードからLNに変える理由はビットコインの話になるので詳細は割愛しますが、現実世界の金(ゴールド)に類した価値保存や交換ができるインターネットマネーだからです。
とはいえ、Nostrの中だけならまだしも、これをNostr外のサービスで利用するためには、他のECショップやブログやSaaSがNostrを喋れる必要があります。そんな未来が来るわけないだろと思うかもしれませんが、言ってみればStripeはまさにそのようなサービスとなっていて、サイト内にクレジット決済のモジュールを組み込むための主流となっています。
果たして、Nostrを、他のECショップやブログやSaaSが喋るようになるのか!?
以上、「NostrはLNがWeb統合されマネーのインターネットプロトコルとしてのビットコインが本気出す具体行動のショーケースと見做せばOK」がお送りしました。
-
 @ 3589b793:ad53847e
2025-04-30 12:10:06
@ 3589b793:ad53847e
2025-04-30 12:10:06前回の続きです。
特に「Snortで試験的にノート単位に投げ銭できる機能」について。実は記事書いた直後にリリースされて慌ててw追記してたんですが追い付かないということで別記事にしました。
今回のここがすごい!
「Snortで試験的にノート単位に投げ銭できる機能」では一つブレイクスルーが起こっています。それは「ウォレットにインボイスを放り投げた後に払い込み完了を提示できる」ようになったことです。これによりペイメントのライフサイクルが一通りカバーされたことになります。
Snortの画面

なにを当たり前のことをという向きもあるかもしれませんが、Nostrクライアントで払い込み完了を追跡することはとても難しいです。基本的にNostrとLNウォレットはまったく別のアプリケーションで両者の間を繋ぐのはインボイス文字列だけです。ウォレットもNostrからキックされずに、インボイス文字列をコピペするなりQRコードで読み取ったものを渡されるだけかもしれません。またその場でリアルタイムに処理される前提もありません。
なのでNostrクライアントでその後をトラックすることは難しく、これまではあくまで請求書を送付したり(LNインボイス)振り込み口座を提示する(LNアドレス)という一方的に放り投げてただけだったわけです。といっても魔法のようにNostrクライアントがトラックできるようになったわけではなく、今回の対応方法もインボイスを発行/お金を振り込まれるサービス側(LNURL)にNostrカスタマイズを入れさせるというものになります。
プロポーザルの概要について
前回の記事ではよくわからんで終わっていましたが、当日夜(日本時間)にスペックをまとめたプロポーザルも起こされました(早い!)。LNURLが、Nostr用のインボイスを発行して、さらにNostrイベントの発行を行っていることがポイントでした。名称は"Lightning Zaps"で確定のようです。プロポーザルは、NostrとLNURLの双方の発明者であるfiatjaf氏からツッコミが入り、またそれが妥当な指摘のために、エンドポイントURLのインターフェースなどは変わりそうなのですが、概要はそう変わらないだろうということで簡単にまとめてみます。
全体の流れ

図は、Nostrクライアント上に提示されているLNアドレスへ投げ銭が開始してから、Nostrクライアント上に払い込み完了したイベントが表示されるまでの流れを示しています。
- 投げ銭の内容が固まったらNostrイベントデータを添付してインボイスの発行を依頼する
- 説明欄にNostr用のデータを記載したインボイスを発行して返却する
- Nostrクライアントで提示されたインボイスをユーザーが何かしらの手段でウォレットに渡す
- ウォレットがLNに支払いを実行する
- インボイスの発行者であるLNURLが管理しているLNノードにsatoshiが届く
- LNURLサーバが投げ銭成功のNostrイベントを発行する
- Nostrクライアントがイベントを受信して投げ銭履歴を表示する
特にポイントとなるところを補足します。
対応しているLNアドレスの識別
LNアドレスに投げ銭する場合は、LNアドレスの有効状態やインボイス発行依頼する先の情報を
https://[domain]/.well-known/lnurlp/[username]から取得しています。そのレスポンス内容にNostr対応を示す情報を追加しています。ただし、ここに突っ込み入っていてlnurlp=LNURL Payから独立させるためにzaps専用のエンドポイントに変わりそうです。(2/15 追記 マージされましたが変更無しでした。PRのディスカッションが盛り上がっているので興味ある方は覗いてみてください。)インボイスの説明欄に書き込むNostrイベント(kind:9734)
これは投げ銭する側のNostrイベントです。投げ銭される者や対象ノートのIDや金額、そしてこのイベントを作成している者が投げ銭したということを「表明」するものになります。表明であって証明でないところは、インボイスを別の人が払っちゃう事態がありえるからですね。この内容をエンクリプトするパターンも用意されていたが複雑になり過ぎるという理由で今回は外され追加提案に回されました。また、このイベントはデータを作成しただけです。支払いを検知した後にLNURLが発行するイベントに添付されることになります。そのため投げ銭する者にちゃんと届くように作成者のリレーサーバリストも書き込まれています。
支払いを検知した後に発行するNostrイベント(kind:9735)
これが実際にNostrリレーサーバに発行されるイベントです。LNURL側はウォッチしているLNノードにsatoshiが届くと、インボイスの説明欄に書かれているNostrイベントを取り出して、いわば受領イベントを作成して発行します。以下のようにNostイベントのkind:9734とkind:9735が親子になったイベントとなります。
json { "pubkey": "LNURLが持っているNostrアカウントの公開鍵", "kind": 9735, "tags": [ [ "p", "投げ銭された者の公開鍵" ], [ "bolt11", "インボイスの文字列lnbc〜" ], [ "description", "投げ銭した者が作成したkind:9734のNostrイベント" ], [ "preimage", "インボイスのpreimage" ] ], }所感
とにかくNostrクライアントはLNノードを持たないしLNプロトコルとも直接喋らずにインボイス文字列だけで取り扱えるようになっているところがおもしろいと思っています。NostrとLNという二つのデセントライズドなオープンプロトコルが協調できていますし、前回も述べましたがどんなアプリでも簡単に真似できます。
とはいえ、さすがに払込完了のトラックは難しく、今回はLNURL側にそのすり合わせの責務が寄せられることになりました。しかし、LNURLもLNの上に作られたオープンプロトコル/スペックの位置付けになるため、他のLNURLのスペックに干渉するという懸念から、本提案のNIP-57に変更依頼が出されています。LN、LNURL、Nostrの3つのオープンプロトコルの責務分担が難しいですね。アーキテクチャ層のスタックにおいて3つの中ではNostrが一番上になるため、Nostrに相当するレイヤーの他のwebサービスでやるときはLNプロトコルを喋るなりLNノードを持つようにして、今回LNURLが寄せられた責務を吸収するのが無難かもしれません。
また、NIP-57の変更依頼理由の一つにはBOLT-12を見越した抽象化も挙げられています。他のLNURLのスペックを削ぎ落としてzapsだけにすることでBOLT-12にも載りやすくなるだろうと。LNURLの多くはBOLT-12に取り込まれる運命なわけですが、LNアドレス以外の点でもNostrではBOLT-12のOfferやInvoiceRequestのユースケースをやりたいという声が挙がっているため、NostrによりBOLT-12が進む展開もありそうだなあ、あってほしい。
-
 @ e4950c93:1b99eccd
2025-04-30 09:28:38
@ e4950c93:1b99eccd
2025-04-30 09:28:38 -
 @ 866e0139:6a9334e5
2025-04-05 11:00:25
@ 866e0139:6a9334e5
2025-04-05 11:00:25
Autor: CJ Hopkins. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier.**
Dieser Beitrag erschien zuerst auf dem Substack-Blog des Autors.
Er soll andauern, was er auch tut. Genau wie der nie endende Krieg in Orwells 1984 wird er vom Imperium gegen seine eigenen Untertanen geführt, aber nicht nur, um die Struktur der Gesellschaft intakt zu halten, sondern in unserem Fall auch, um die Gesellschaft in eine neo-totalitäre global-kapitalistische Dystopie zu verwandeln.
Bist du nicht vertraut mit dem Krieg gegen was auch immer?
Nun ja, okay, du erinnerst dich an den Krieg gegen den Terror.
Du erinnerst dich daran, als die „Freiheit und Demokratie“ von „den Terroristen“ angegriffen wurden und wir keine andere Wahl hatten, als uns unserer demokratischen Rechte und Prinzipien zu entledigen, einen nationalen „Notstand“ auszurufen, die verfassungsmäßigen Rechte der Menschen auszusetzen, einen Angriffskrieg gegen ein Land im Nahen Osten anzuzetteln, das für uns keinerlei Bedrohung darstellte, und unsere Straßen, Bahnhöfe, Flughäfen und alle anderen Orte mit schwer bewaffneten Soldaten zu füllen, denn sonst hätten „die Terroristen gewonnen“. Du erinnerst dich, als wir ein Offshore-Gulag bauten, um verdächtige Terroristen auf unbestimmte Zeit wegzusperren, die wir zuvor zu CIA-Geheimgefängnissen verschleppt hatten, wo wir sie gefoltert und gedemütigt haben, richtig?
Natürlich erinnerst du dich. Wer könnte das vergessen?
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Erinnerst du dich, als die National Security Agency keine andere Wahl hatte, als ein geheimes „Terroristen-Überwachungsprogramm“ einzurichten, um Amerikaner auszuspionieren, oder sonst „hätten die Terroristen gewonnen“? Oder wie wäre es mit den „Anti-Terror“-Unterleibsuntersuchungen der TSA, der Behörde für Transportsicherheit, die nach über zwanzig Jahren immer noch in Kraft sind?
Und was ist mit dem Krieg gegen den Populismus? An den erinnerst du dich vielleicht nicht so gut.
Ich erinnere mich, denn ich habe zwei Bücher dazu veröffentlicht. Er begann im Sommer 2016, als das Imperium erkannte, dass „rechte Populisten“ die „Freiheit und Demokratie“ in Europa bedrohten und Trump in den USA auf dem Vormarsch war. Also wurde ein weiterer „Notstand“ ausgerufen – diesmal von der Gemeinschaft der Geheimdienste, den Medien, der akademischen Welt und der Kulturindustrie. Ja, genau, es war wieder einmal an der Zeit, unsere demokratischen Prinzipien hintanzustellen, „Hassrede“ in sozialen Medien zu zensieren, die Massen mit lächerlicher offizieller Propaganda über „Russiagate,“ „Hitlergate“ und so weiter zu bombardieren – sonst hätten „die Rechtspopulisten gewonnen.“
Der Krieg gegen den Populismus gipfelte in der Einführung des Neuen Normalen Reichs.

Im Frühjahr 2020 rief das Imperium einen globalen „gesundheitlichen Ausnahmezustand“ aus, als Reaktion auf ein Virus mit einer Überlebensrate von etwa 99,8 Prozent. Das Imperium hatte keine andere Wahl, als ganze Gesellschaften abzuriegeln, jeden dazu zu zwingen, in der Öffentlichkeit medizinisch aussehende Masken zu tragen, die Öffentlichkeit mit Propaganda und Lügen zu bombardieren, die Menschen dazu zu nötigen, sich einer Reihe experimenteller mRNA-„Impfungen“ zu unterziehen, Proteste gegen ihre Dekrete zu verbieten und systematisch diejenigen zu zensieren und zu verfolgen, die es wagten, ihre erfundenen „Fakten“ in Frage zu stellen oder ihr totalitäres Programm zu kritisieren.
Das Imperium hatte keine andere Wahl, als das alles zu tun, denn sonst hätten „die Covid-Leugner, die Impfgegner, die Verschwörungstheoretiker und all die anderen Extremisten gewonnen.“
Ich bin mir ziemlich sicher, dass du dich an all das erinnerst.
Und jetzt … nun, hier sind wir. Ja, du hast es erraten – es ist wieder einmal an der Zeit, kräftig auf die US-Verfassung und die Meinungsfreiheit zu scheißen, Menschen in irgendein salvadorianisches Höllenloch abzuschieben, das wir angemietet haben, weil ein Polizist ihre Tattoos nicht mochte, Universitätsstudenten wegen ihrer Anti-Israel-Proteste festzunehmen und zu verschleppen und natürlich die Massen mit Lügen und offizieller Propaganda zu bombardieren, denn … okay, alle zusammen jetzt: „sonst hätten die antisemitischen Terroristen und venezolanischen Banden gewonnen!“
Fängst du an, ein Muster zu erkennen? Ja? Willkommen beim Krieg gegen-was-auch-immer!
Wenn du die Zusammenhänge noch nicht ganz siehst, okay, lass es mich noch einmal ganz simpel erklären.
Das globale ideologische System, in dem wir alle leben, wird totalitär. (Dieses System ist der globale Kapitalismus, aber nenne es, wie du willst. Es ist mir scheißegal.) Es reißt die Simulation der Demokratie nieder, die es nicht mehr aufrechterhalten muss. Der Kalte Krieg ist vorbei. Der Kommunismus ist tot. Der globale Kapitalismus hat keine externen Feinde mehr. Also muss er die Massen nicht mehr mit demokratischen Rechten und Freiheiten besänftigen. Deshalb entzieht er uns diese Rechte nach und nach und konditioniert uns darauf, ihren Verlust hinzunehmen.
Er tut dies, indem er eine Reihe von „Notständen“ inszeniert, jeder mit einer anderen „Bedrohung“ für die „Demokratie,“ die „Freiheit,“ „Amerika“ oder „den Planeten“ – oder was auch immer. Jeder mit seinen eigenen „Monstern,“ die eine so große Gefahr für die „Freiheit“ oder was auch immer darstellen, dass wir unsere verfassungsmäßigen Rechte aufgeben und die demokratischen Werte ad absurdum führen müssen, denn: sonst „würden die Monster gewinnen.“

Es tut dies, indem es sein Antlitz von „links“ nach „rechts,“ dann zurück nach „links“, und dann zurück nach „rechts,“ dann nach „links“ und so weiter neigt, weil es unsere Kooperation dafür benötigt. Nicht die Kooperation von uns allen auf einmal. Nur eine kooperative demografische Gruppe auf einmal.
Es ist dabei erfolgreich – also das System – indem es unsere Angst und unseren Hass instrumentalisiert. Dem System ist es völlig egal, ob wir uns als „links“ oder „rechts“ identifizieren, aber es braucht uns gespalten in „links“ und „rechts,“ damit es unsere Angst und unseren Hass aufeinander nähren kann … eine Regierung, ein „Notfall,“ ein „Krieg“ nach dem anderen.
Da hast du es. Das ist der Krieg gegen was auch immer. Noch simpler kann ich es nicht erklären.
Oh, und noch eine letzte Sache … wenn du einer meiner ehemaligen Fans bist, wie Rob, die über meine „Einsichten“ oder Loyalitäten oder was auch immer verwirrt sind … nun, der Text, den du gerade gelesen hast, sollte das für dich klären. Ich stehe auf keiner Seite. Überhaupt keiner. Aber ich habe ein paar grundlegende demokratische Prinzipien. Und die richten sich nicht danach, was gerade populär ist oder wer im Weißen Haus sitzt.
Die Sache ist die: Ich muss mich morgens im Spiegel anschauen können ohne dort einen Heuchler oder … du weißt schon, einen Feigling zu sehen.
(Aus dem Amerikanischen übersetzt von René Boyke).
CJ Hopkins ist ein US-amerikanischer Dramatiker, Romanautor und politischer Satiriker. Zu seinen Werken zählen die Stücke Horse Country, Screwmachine/Eyecandy und The Extremists. Er hat sich als profilierter Kritiker des Corona-Regimes profiliert und veröffentlicht regelmäßig auf seinem Substack-Blog.
Sein aktuelles Buch:
https://x.com/CJHopkins_Z23/status/1907795633689264530
Hier in einem aktuellen Gespräch:
https://www.youtube.com/watch?v=wF-G32P0leI
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.)
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 3589b793:ad53847e
2025-04-30 12:02:13
@ 3589b793:ad53847e
2025-04-30 12:02:13※本記事は別サービスで2023年2月5日に公開した記事の移植です。
Nostrクライアントは多種ありますがメジャーなものはだいたいLNの支払いが用意されています。現時点でどんな組み込み方法になっているか調べました。この記事では主にSnortを対象にしています。
LN活用場面
大きくLNアドレスとLNインボイスの2つの形式があります。
1. LNアドレスで投げ銭をセットできる

LNURLのLNアドレスをセットすると、プロフィールやノート(ツイートに相当)からLN支払いができます。別クライアントのastralなどではプリミティブなLNURLの投げ銭形式
lnurl1dp68~でもセットできます。[追記]さらに本日、Snortで試験的にノート単位に投げ銭できる機能が追加されています。

2. LNインボイスが投稿できる

投稿でLNインボイスを貼り付ければ上記のように他の発言と同じようにタイムラインに流れます。Payボタンを押すと各自の端末にあるLNウォレットが立ち上がります。
3. DMでLNインボイスを送る
メッセージにLNインボイスが組み込まれているという点では2とほぼ同じですが、ユースケースが異なります。発表されたばかりですがリレーサーバの有料化が始まっていて、その決済をDMにLNインボイスを送付して行うことが試されています。2だとパブリックに投稿されますが、こちらはプライベートなので購入希望者のみにLNインボイスを届けられます。

おまけ: Nostrのユーザ名をLNアドレスと同じにする
直接は関係ないですが、Nostrはユーザー名をemail形式にすることができます。LNアドレスも自分でドメイン取って作れるのでNostrのユーザー名と投げ銭のアドレスを同じにできます。
LNウォレットのAlbyのドメインをNostrのユーザ名にも活用している様子 [Not found]
実装方法
LNアドレスもLNインボイスも非常にシンプルな話ですが軽くまとめます。 Snortリポジトリ
LNアドレス
- セットされたLNアドレスを分解して
https://[domain]/.well-known/lnurlp/[username]にリクエストする - 成功したら投げ銭量を決めるUIを提示する
- Get Inoviceボタンを押したら1のレスポンスにあるcallbackにリクエストしてインボイスを取得する
- 成功したらPayボタンを提示する
LNインボイス
- 投稿内容がLNインボイス識別子
lnbc10m〜だとわかると、識別子の中の文字列から情報(金額、説明、有効期限)を取り出し、表示用のUIを作成する - 有効期限内だったらPayボタンを提示し、期限が切れていたらExpiredでロックする
支払い
Payボタンを押された後の動きはアドレス、インボイスとも同じです。
- ブラウザでWebLN(Albyなど)がセットされていて、window.weblnオブジェクトがenableになっていると、拡張機能の支払い画面が立ち上がる。クライアント側で支払い成功をキャッチすることも可能。
- Open Walletボタンを押すと
lightning:lnbc10m~のURI形式でwindow.openされ、Mac/Windows/iPhone/Androidなど各OSに応じたアプリケーション呼び出しが行われ、URIに対応しているLNウォレットが立ち上がる
[追記]ノート単位の投げ銭
Snort周辺の数人(strike社員っぽい人が一人いて本件のメイン実装している)で試験的にやっているようで現時点では実装レベルでしか詳細わかりませんでした。strikeのzapといまいち区別が付かなかったのですが、実装を見るとnostrプロトコルにzapイベントが追加されています。ソースコメントではこの後NIP(nostr improvement proposal)が起こされるようでかなりハッキーです。zap=tipの方言なんでしょうか?
ノートやプロフィールやリアクションなどに加えて新たにnostrイベントに追加しているものは以下2つです。
- zapRequest 投げ銭した側が対象イベントIDと量を記録する
- zapReceipt 投げ銭を受け取った側用のイベント
一つでできそうと思ったけど、nostrは自己主権のプロトコルでイベント作成するには発行者の署名が必須なので2つに分かれているのでしょう。
所感
現状はクライアントだけで完結する非常にシンプルな方法になっています。リレーサーバも経由しないしクライアントにLNノードを組み込むこともしていません。サードパーティへのhttpリクエストやローカルのアプリに受け渡すだけなので、実はどんな一般アプリでもそんなに知識もコストも要らずにパッとできるものです。
現状ちょっと不便だなと思っていることは、タイムラインに流れるインボイスの有効期限内の支払い済みがわからないことです。Payボタンを押してエラーにならないとわかりません。ウォレットアプリに放り投げていてこのトレースするためには、ウォレット側で支払い成功したらNostrイベントを書き込むなどの対応しない限りは、サービス側でインボイスを定期的に一つ一つLNに投げてチェックするなどが必要だと思われるので、他のサービスでマネするときは留意しておくとよさそうです。
一方で、DMによるLNインボイス送付は活用方法が広がりそうな予感があります。Nostrの公開鍵による本人特定と、LNインボイスのメモ欄のテキスト情報による突き合わせだけでも、かんたんな決済機能として用いれそうだからです。もっとNostrに判断材料を追加したければイベント追加も簡単にできることをSnortが示しています。とくにリレーサーバ購読やPROメニューなどのNostr周辺の支払いはやりやすそうなので、DM活用ではなくなにかしらの決済メニューを搭載したNostrクライアントもすぐに出てきそう気がします。
- セットされたLNアドレスを分解して
-
 @ a95c6243:d345522c
2025-01-13 10:09:57
@ a95c6243:d345522c
2025-01-13 10:09:57Ich begann, Social Media aufzubauen, \ um den Menschen eine Stimme zu geben. \ Mark Zuckerberg
Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs Wendehals-Deklaration bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren».
«Purer Opportunismus» ob des anstehenden Regierungswechsels wäre als Klassifizierung viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich.
«Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg.
Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung, dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen «LifeLog». Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen».
Der Richtungswechsel kommt allerdings nicht überraschend. Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten gesprochen. Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen.
Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine Verhaftung dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt kritisierte und gleichzeitig warnte.
Politik und Systemmedien drehen jedenfalls durch – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten Völkermord», ernsthaft. Die Frage sei, ob sich die EU gegen Musk und Zuckerberg behaupten könne, Brüssel müsse jedenfalls hart durchgreifen.
Auch um die Faktenchecker macht man sich Sorgen. Für die deutsche Nachrichtenagentur dpa und die «Experten» von Correctiv, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die Tagesschau keine Fehler zugeben und zum Beispiel Correctiv-Falschaussagen einräumen.
Bei derlei dramatischen Befürchtungen wundert es nicht, dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft.
Das Anbiedern bei Donald Trump ist indes gerade in Mode. Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. sechs Milliarden eingestrichen hat, geht da vielleicht etwas.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 3589b793:ad53847e
2025-04-30 11:46:52
@ 3589b793:ad53847e
2025-04-30 11:46:52※本記事は別サービスで2022年9月25日に公開した記事の移植です。
LNの手数料の適正水準はどう見積もったらいいだろうか?ルーティングノードの収益性を算出するためにはどうアプローチすればよいだろうか?本記事ではルーティングノード運用のポジションに立ち参考になりそうな数値や計算式を整理する。
個人的な感想を先に書くと以下となる。
- 現在の手数料市場は収益性が低くもっと手数料が上がった方が健全である。
- 他の決済手段と比較すると、LN支払い料金は10000ppm(手数料1%相当)でも十分ではないか。4ホップとすると中間1ノードあたり2500ppmである。
- ルーティングノードの収益性を考えると、1000ppmあれば1BTC程度の資金で年利2.8%になり半年で初期費用回収できるので十分な投資対象になると考える。
基本概念の整理
LNの料金方式
- LNの手数料は送金額に応じた料率方式が主になる。(基本料金の設定もあるが1 ~ 0 satsが大半)
- 料率単位のppm(parts per million)は、1,000,000satsを送るときの手数料をsats金額で示したもの。
- %での手数料率に変換すると1000ppm = 0.1%になる。
- 支払い者が払う手数料はルーティングに参加した各ノードの手数料の合計である。本稿では4ホップ(経由ノードが4つ)のルーティングがあるとすれば、各ノードの取り分は単純計算で1/4とみなす。
- ルーティングノードの収益はアウトバウンドフローで発生するのでアウトバウンドキャパシティが直接的な収益資源となる。
LNの料金以外のベネフィット
本稿では料金比較だけを行うが実際の決済検討では以下のような料金以外の効用も忘れてはならない。
- Bitcoin(L1)に比べると、料金の安さだけでなく、即時確定やトランザクション量のスケールという利点がある。
- クレジットカードなどの集権サービスと比較した特徴はBitcoin(L1)とだいたい同じである。
- 24時間365日利用できる
- 誰でも自由に使える
- 信頼する第三者に対する加盟や審査や手数料率などの交渉手続きが要らない
- 検閲がなく匿名性が高い
- 逆にデメリットはオンライン前提がゆえの利用の不便さやセキュリティ面の不安さなどが挙げられる。
現在の料金相場
- ルーティングノードの料金設定
- sinkノードとのチャネルは500 ~ 1000ppmが多い。
- routing/sourceノードとのチャネルは0 ~ 100ppmあたりのレンジになる。
- リバランスする場合もsinkで収益を上げているならsink以下になるのが道理である。
- プロダクト/サービスのバックエンドにいるノードの料金設定
- sinkやsourceに相当するものは上記の通り。
- 1000〜5000ppmあたりで一律同じ設定というノードもよく見かける。
- ビジネスモデル次第で千差万別だがアクティブと思われるノードでそれ以上はあまり見かけない。
- 上記は1ノードあたりの料金になる。支払い全体では経由したノードの合計になる。
料金目安
いくつかの方法で参考数字を出していく。LN料金算出は「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」の三段階で出す。
類推方式
決済代行業者との比較
- Squareの加盟店手数料は、日本3.25%、アメリカ2.60%である。
- 参考資料 https://www.meti.go.jp/shingikai/mono_info_service/cashless_payment/pdf/20220318_1.pdf
3.25%とするとLNでは「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」でそれぞれ
32,500ppm/16,250ppm/8,125ppmになる。スマホのアプリストアとの比較
- Androidのアプリストアは年間売上高が100万USDまでなら15%、それ以上なら30%
- 参考資料https://support.google.com/googleplay/android-developer/answer/112622?hl=ja
15%とするとLNでは「支払い全体/2ホップしたときの1ノードあたり/4ホップしたときの1ノードあたり」でそれぞれ
150,000ppm/75,000ppm/37,500ppmになる。Bitcoin(L1)との比較
Bitcoin(L1)は送金額が異なっても手数料がほぼ同じため、従量課金のLNと単純比較はできない。そのためここではLNの方が料金がお得になる目安を出す。
Bitcoin(L1)の手数料設定
- SegWitのシンプルな送金を対象にする。
- input×1、output×2(送金+お釣り)、tx合計222byte
- L1の手数料は、1sat/byteなら222sats、10sat/byteなら2,220sats、100sat/byteなら22,200sats。(単純化のためvirtual byteではなくbyteで計算する)
- サンプル例 https://www.blockchain.com/btc/tx/15b959509dad5df0e38be2818d8ec74531198ca29ac205db5cceeb17177ff095
L1相場が1sat/byteの時にLNの方がお得なライン
- 100ppmなら、0.0222BTC(2,220,000sats)まで
- 1000ppmなら、0.00222BTC(222,000sats)まで
L1相場が10sat/byteの時にLNの方がお得なライン
- 100ppmなら、0.222BTC(22,200,000sats)まで
- 1000ppmなら、0.0222BTC(2,220,000sats)まで
L1相場が100sat/byteの時にLNの方がお得なライン
- 100ppmなら、2.22BTC(222,000,000sats)まで
- 1000ppmなら、0.222BTC(22,200,000sats)まで
コスト積み上げ方式
ルーティングノードの原価から損益分岐点となるppmを算出する。事業者ではなく個人を想定し、クラウドではなくラズベリーパイでのノード構築環境で計算する。
費用明細
- BTC市場価格 1sat = 0.03円(1BTC = 3百万円)
初期費用
- ハードウェア一式 40,000円
- Raspberry Pi 4 8GB
- SSD 1TB
- 外付けディスプレイ
- チャネル開設のオンチェーン手数料 6.69円/チャネル
- 開設料 223sats
- 223sats * BTC市場価格0.03円 = 6.69円
固定費用
- 電気代 291.6円/月
- 時間あたりの電力量 0.015kWh
- Raspberry Pi 4 電圧5V、推奨電源容量3.0A
- https://www.raspberrypi.com/documentation/computers/raspberry-pi.html#power-supply
- kWh単価27円
- 0.015kWh * kWh単価27円 * 1ヶ月の時間720h = 291.6円
損益分岐点
- 月あたりの電気代を上回るために9,720sats(291.6円)/月以上の収益が必要である。
- ハードウェア費用回収のために0.01333333BTC(133万sats) = 40,000円の収益が必要である。
費用回収シナリオ例
アウトバウンドキャパに1BTCをデポジットしたAさんを例にする。1BTCは初心者とは言えないと思うが、このくらい原資を用意しないと費用回収の話がしづらいという裏事情がある。チャネル選択やルーティング戦略は何もしていない仮定である。ノード運用次第であることは言うまでもないので今回は要素や式を洗い出すことが主目的で一つ一つの変数の値は参考までに。
変数設定
- インバウンドを同額用意して合計キャパを2BTCとする。
- 1チャネルあたり5m satsで40チャネル開設する。
- チャネル開設費用 223sats * 40チャネル = 8,920sats
- 初期費用合計 1,333,333sats + 8,920sats = 1,342,253sats
- 一回あたり平均ルーティング量 = 100,000sats
- 1チャネルあたり平均アウトバウンド数/日 = 2
- 1チャネルあたり平均アウトバウンドppm = 50
費用回収地点
- 1日のアウトバウンド量は、 40チャネル * 2本 * 100,000sats = 8m sats
- 手数料収入は、8m sats * 0.005%(50ppm) = 400sats/日。月換算すると12,000sats/月
- 電気代を差し引くと、12,000sats - 電気代9,720sats =月収益2,280sats(68.4円)
- 初期費用回収まで、1,342,253sats / 2,280sats = 589ヵ月(49年)
- 後述するが電気代差引き前で年利0.14%になる。
理想的なppm
6ヵ月での初期費用回収を目的にしてアウトバウンドppmを求める。
- ひと月あたり、初期費用合計1,342,253sats / 6ヵ月 + 電気代9,720sats = 233,429sats(7,003円)の収益が必要。
- 1日あたり、7,781sats(233円)の収益
- その場合の平均アウトバウンドppmは、 7,781sats(1日の収益量) / 8m sats(1日のアウトバウンド量) * 1m sats(ppm変換係数) = 973ppm
他のファイナンスとの比較
ルーティングノードを運用して手数料収入を得ることは資産運用と捉えることもできる。レンディングやトレードなどの他の資産運用手段とパフォーマンス比較をするなら、デポジットしたアウトバウンドキャパシティに対する手数料収入をAPY換算する。(獲得した手数料はアウトバウンドキャパシティに積み重ねられるので複利と見做せる)
例としてLNDg(v1.3.1)のAPY算出計算式を転載する。見ての通り画面上の表記はAPYなのに中身はAPRになっているので注意だが今回は考え方の参考としてこのまま採用する。
年換算 = 365 / 7 = 52.142857 年利 = (7dayの収益 * 年換算) / アウトバウンドのキャパシティ例えば上記のAさんの費用回収シナリオに当てはめると以下となる。
年利 0.14% = (400sats * 7日 * 年換算)/ 100m sats
電気代を差し引くと 76sats/日となり年利0.027%
もし平均アウトバウンド1000ppmになると8,000sats/日なので年利2.9%になる。 この場合、電気代はほぼ1日で回収されるため差し引いても大差なく7,676sats/日で年利2.8%になる。
考察
以上、BTC市場価格や一日のアウトバウンド量といった重要な数値をいくつか仮置きした上ではあるが、LN手数料の適正水準を考えるための参考材料を提示した。
まず、現在のLNの料金相場は他の決済手段から比べると圧倒的に安いことがわかった。1%でも競争力が十分ありそうなのに0.1%前後で送金することが大半である。
健全な市場発展のためには、ルーティングノードの採算が取れていることが欠かせないと考えるが、残念ながら現在の収益性は低い。ルーティングノードの収益性は仮定に仮定を重ねた見積もりになるが、平均アウトバウンドが1000ppmでようやく個人でも参入できるレベルになるという結論になった。ルーティングノードの立場に立つと、現在の市場平均から大幅な上昇が必要だと考える。
手数料市場は競争のためつねに下方圧力がかかっていて仕様上で可能な0に近づいている。この重力に逆らうためには、1. 需要 > 供給のバランスになること、2. 事業用途での高額買取のチャネルが増えること、の2つの観点を挙げる。1にせよ2にせよネットワークの活用が進むことで発生し、手数料市場の大きな変動機会になるのではないか。他の決済手段と比較すれば10000ppm、1チャネル2500ppmあたりまでは十分に健全な範囲だと考える。
-
 @ e4950c93:1b99eccd
2025-04-30 09:27:09
@ e4950c93:1b99eccd
2025-04-30 09:27:09 -
 @ e4950c93:1b99eccd
2025-04-30 09:24:29
@ e4950c93:1b99eccd
2025-04-30 09:24:29 -
 @ a95c6243:d345522c
2025-01-03 20:26:47
@ a95c6243:d345522c
2025-01-03 20:26:47Was du bist hängt von drei Faktoren ab: \ Was du geerbt hast, \ was deine Umgebung aus dir machte \ und was du in freier Wahl \ aus deiner Umgebung und deinem Erbe gemacht hast. \ Aldous Huxley
Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses Buch einer gewissen ehemaligen Regierungschefin.
Erklärungsansätze für solche Entwicklungen sind bekannt, und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer Herrschaftsinstrumente.
Aber wollen die Menschen überhaupt Freiheit? Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht.
«Desinformation» ist so ein brisantes Thema. Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur Ukraine, zum Klima, zu Gesundheitsthemen oder zur Migration. Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung.
Freiheit bedingt Eigenverantwortung, ohne Zweifel. Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung.
Sind viele Menschen möglicherweise schon so «eingenordet», dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen Hacker-Kongress des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative.
Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination? Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2025-01-01 17:39:51
@ a95c6243:d345522c
2025-01-01 17:39:51Heute möchte ich ein Gedicht mit euch teilen. Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden.
Dem originalen Titel «Die Uhr» habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension.
Das Ticken der Uhr und die Momente des Glücks und der Trauer stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram.
Was den Takt pocht, ist durchaus auch das Herz, unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.»
Ich trage, wo ich gehe, stets eine Uhr bei mir; \ Wieviel es geschlagen habe, genau seh ich an ihr. \ Es ist ein großer Meister, der künstlich ihr Werk gefügt, \ Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.
Ich wollte, sie wäre rascher gegangen an manchem Tag; \ Ich wollte, sie hätte manchmal verzögert den raschen Schlag. \ In meinen Leiden und Freuden, in Sturm und in der Ruh, \ Was immer geschah im Leben, sie pochte den Takt dazu.
Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr, \ Sie schlug am Morgen der Liebe, sie schlug am Traualtar. \ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft, \ Wenn bessere Tage kommen, wie meine Seele es hofft.
Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf, \ So zog der Meister immer großmütig sie wieder auf. \ Doch stände sie einmal stille, dann wär's um sie geschehn, \ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.
Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit, \ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit! \ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn: \ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.
Johann Gabriel Seidl (1804-1875)
-
 @ a95c6243:d345522c
2024-12-21 09:54:49
@ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde.
Heute ist ein ganz besonderer Tag: die Wintersonnenwende. Genau gesagt hat heute morgen um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben.
Für mich ist dieses Ereignis immer wieder etwas kurios: Es beginnt der Winter, aber die Tage werden länger. Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller!
Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr vorgesehen. Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt lahmgelegt.
Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert.
Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. Ohne Licht keine Farben, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität.
Mir gefällt aber auch die Symbolik dieses Tages: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie.
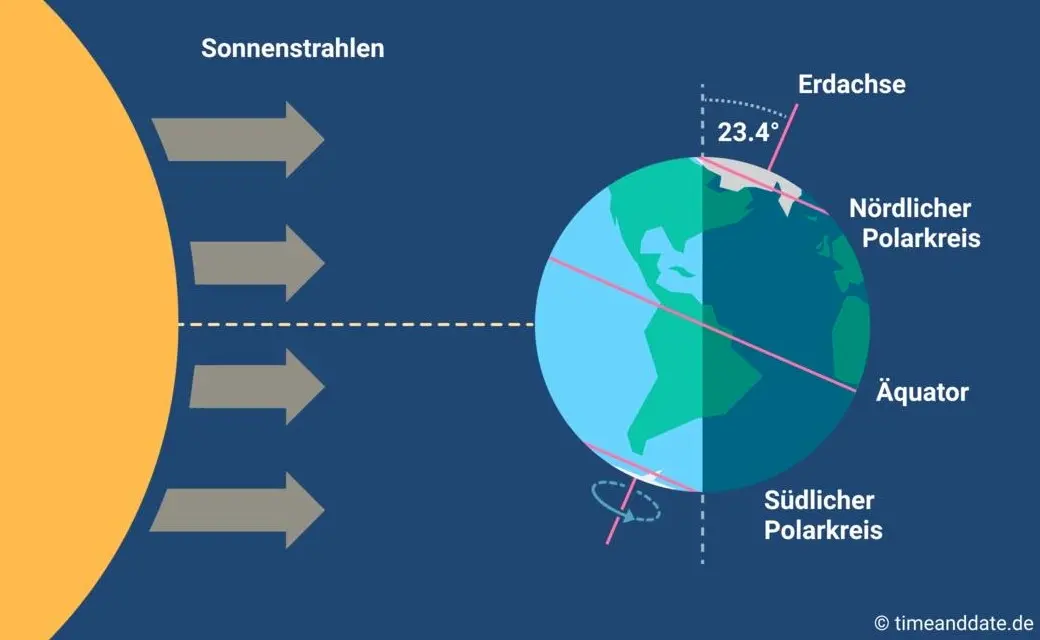
Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell?
Insofern bleibt eindeutig festzuhalten, dass “schräg sein” ein willkommener, wichtiger und positiver Wert ist. Mit anderen Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein.
In diesem Sinne wünsche ich euch allen urige Weihnachtstage!
Dieser Beitrag ist letztes Jahr in meiner Denkbar erschienen.
-
 @ 6c67a3f3:b0ebd196
2025-04-30 08:40:15
@ 6c67a3f3:b0ebd196
2025-04-30 08:40:15To explore the link between Gavekal-style platform companies and the US dollar's status as the global reserve currency, we need to view the problem through multiple interlocking lenses—monetary economics, network effects, macro-political architecture, financial plumbing, and the logic of platform capitalism. Gavekal’s conceptual framework focuses heavily on capital-light, scalable businesses that act as platforms rather than traditional linear firms. Their model emphasizes "soft" balance sheets, asset-light capital formation, high intangible value creation, and the scaling of network effects. These traits dovetail in complex ways with the structural position of the United States in the global financial system.
What follows is a broad and recursive dissection of how these two phenomena—platform companies and reserve currency status—are mutually constitutive, each feeding the other, both directly and via second- and third-order effects.
- The Core Metaphor: Platforms and Monetary Hegemony
At its root, a platform is a meta-infrastructure—a set of protocols and affordances that enable others to interact, produce, consume, and transact. The dollar, as reserve currency, functions in an analogous way. It is not merely a medium of exchange but a platform for global commerce, pricing, credit formation, and risk transfer.
In this metaphor, the United States is not just a country but a platform operator of global finance. And like Amazon or Apple, it enforces terms of access, extracts rents, underwrites standardization, and benefits disproportionately from marginal activity across its ecosystem. Just as Apple's App Store tax or Amazon’s marketplace fee are invisible to most users, the dollar hegemon collects global seigniorage, institutional influence, and capital inflow not as overt tolls, but through the structuring of default behaviors.
This already suggests a deep isomorphism between platform logic and reserve currency logic.
- Capital-Light Scaffolding and Global Dollar Demand
Gavekal-style firms (e.g. Apple, Google, Microsoft) have something unusual in common: they generate high levels of free cash flow with low reinvestment needs. That is, they do not soak up global capital so much as recycle it outward, often via share buybacks or bond issuance. This creates a paradox: they are net issuers of dollar-denominated financial claims even as they are net accumulators of global income.
Now map this onto the structure of reserve currency systems. The US must export financial assets to the world (Treasuries, MBS, high-grade corporates) in order to satisfy foreign demand for dollar claims. But traditional exporting economies (e.g. Germany, China) create excess savings they must park in safe dollar assets, while running trade surpluses.
Gavekal-style firms allow the US to square a circle. The US economy does not need to run trade surpluses, because its platform companies export “intangible products” at near-zero marginal cost (e.g. iOS, search ads, cloud infrastructure), generate global rents, and then repatriate those earnings into US financial markets. These flows offset the US current account deficit, plugging the "Triffin dilemma" (the need to run deficits to supply dollars while maintaining credibility).
Thus, platform companies act as soft exporters, replacing industrial exports with intangible, rent-generating capital. Their global cash flows are then recycled through dollar-denominated assets, providing the scale and liquidity necessary to sustain reserve status.
- The Hierarchy of Money and Intangible Collateral
Modern monetary systems rest on a hierarchy of collateral—some assets are more money-like than others. US Treasuries sit at the apex, but AAA-rated corporates, especially those with global footprints and balance-sheet integrity, are close behind.
Platform firms are unique in their capacity to create high-quality, globally accepted private collateral. Apple’s bonds, Microsoft’s equity, and Google’s cash reserves function as synthetic dollar instruments, widely accepted, liquid, and backed by consistent income streams. These firms extend the reach of the dollar system by providing dollar-denominated assets outside the banking system proper, further embedding dollar logic into global capital flows.
Moreover, platform companies often internalize global tax arbitrage, holding cash offshore (or in tax-efficient jurisdictions) and issuing debt domestically. This creates a loop where foreign dollar claims are used to finance US domestic consumption or investment, but the underlying income comes from global activities. This is reverse colonization through intangibles.
- Winner-Take-Most Dynamics and Network Effects in Dollar Space
The dollar system, like platform capitalism, obeys a power-law distribution. Liquidity begets liquidity. The more that dollar instruments dominate global trade, the more pricing, settlement, and hedging mechanisms are built around them. This self-reinforcing loop mimics network effect entrenchment: the more users a platform has, the harder it is to displace.
Reserve currency status is not a product of GDP share alone. It’s a function of infrastructure, institutional depth, legal recourse, capital mobility, and networked habits. Likewise, Apple’s dominance is not just about better phones, but about developer lock-in, payment systems, user base, and design mores.
Gavekal-style firms reinforce this pattern: their software platforms often denominate activity in dollars, price in dollars, store value in dollars, and link digital labor across borders into dollar-based flows. YouTube creators in Jakarta are paid in dollars. AWS charges Chilean entrepreneurs in dollars. App Store remittances to Kenya settle in dollars.
This creates global micro-tributaries of dollar flows, all of which aggregate into the larger river that sustains dollar supremacy.
- Geopolitical Power Projection by Private Means
Traditional hegemonic systems project power through military, legal, and diplomatic tools. But platforms provide soft control mechanisms. The US can influence foreign populations and elite behavior not merely through embassies and aircraft carriers, but through tech platforms that shape discourse, information flows, norms, and cognitive frames.
This is a kind of cognitive imperialism, in which reserve currency status is bolstered by the fact that cultural products (e.g. Netflix, social media, productivity tools) are encoded in American norms, embedded in American legal systems, and paid for in American currency.
The platform firm thus becomes a shadow extension of statecraft, whether or not it sees itself that way. Dollar hegemony is reinforced not only by Treasury markets and SWIFT access, but by the gravity of the mental ecosystem within which the global bourgeoisie operates. To earn, spend, invest, create, and dream within American-built systems is to keep the dollar central by default.
- Second-Order Effects: The Intangibility Ratchet and Global Liquidity Traps
An overlooked consequence of Gavekal-style platform dominance is that global capital formation becomes disembodied. That is, tangible projects—factories, infrastructure, energy systems—become less attractive relative to financial or intangible investments.
As a result, much of the world, especially the Global South, becomes capital-starved even as capital is abundant. Why? Because the returns on tangible investment are less scalable, less defensible, and less liquid than buying FAANG stocks or US Treasuries.
This results in a liquidity trap at the global scale: too much capital chasing too few safe assets, which only reinforces demand for dollar instruments. Meanwhile, intangible-intensive firms deepen their moats by mining attention, user data, and payment flows—often without any large-scale employment or industrial externalities.
Thus, Gavekal-style firms create asymmetric global development, further concentrating economic gravitational mass in the dollar zone.
- Feedback Loops and Fragility
All of this breeds both strength and fragility. On one hand, platform firm cash flows make the dollar system seem robust—anchored in cash-generative monopolies with global reach. On the other hand, the system becomes narrower and more brittle. When so much of global liquidity is intermediated through a few firms and the sovereign system that hosts them, any attack on these nodes—financial, legal, technological, or geopolitical—could unseat the equilibrium.
Moreover, platform logic tends to reduce systemic redundancy. It optimizes for efficiency, not resilience. It centralizes control, narrows option sets, and abstracts real production into code. If the dollar system ever loses credibility—through inflation, sanctions overreach, geopolitical backlash, or platform fatigue—the network effects could reverse violently.
- Conclusion: The Intangible Empire
The United States today operates an empire of intangibles, in which reserve currency status and platform firm dominance are co-constituted phenomena. Each reinforces the other:
Platform firms channel global rents into dollar instruments.
The dollar system provides legal scaffolding, liquidity, and pricing infrastructure for these firms.
Global user bases are conditioned into dollar-denominated interaction by default.
Financial markets treat platform firms as synthetic sovereigns: safe, liquid, predictable.
What is left is a cybernetic loop of financialized cognition: the dollar is strong because platform firms dominate, and platform firms dominate because the dollar is strong.
This loop may persist longer than many expect, but it is not permanent. Its unravelling, when it comes, will likely not be driven by any single actor, but by the erosion of symbolic power, the emergence of parallel platforms, or the ecological unsustainability of the model. But for now, the Gavekal firm and the dollar empire are the two poles of a single global architecture—seen best not as cause and effect, but as the two faces of the same Janus coin.